Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 4
112
| repo_url
stringlengths 33
141
| action
stringclasses 3
values | title
stringlengths 1
1.02k
| labels
stringlengths 4
1.54k
| body
stringlengths 1
262k
| index
stringclasses 17
values | text_combine
stringlengths 95
262k
| label
stringclasses 2
values | text
stringlengths 96
252k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
187,709
| 22,045,862,803
|
IssuesEvent
|
2022-05-30 01:34:14
|
ebubeaso/IT-coding-work
|
https://api.github.com/repos/ebubeaso/IT-coding-work
|
opened
|
CVE-2022-29217 (High) detected in multiple libraries
|
security vulnerability
|
## CVE-2022-29217 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>PyJWT-1.7.1-py2.py3-none-any.whl</b>, <b>PyJWT-2.0.1-py3-none-any.whl</b>, <b>PyJWT-1.4.2-py2.py3-none-any.whl</b></p></summary>
<p>
<details><summary><b>PyJWT-1.7.1-py2.py3-none-any.whl</b></p></summary>
<p>JSON Web Token implementation in Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/87/8b/6a9f14b5f781697e51259d81657e6048fd31a113229cf346880bb7545565/PyJWT-1.7.1-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/87/8b/6a9f14b5f781697e51259d81657e6048fd31a113229cf346880bb7545565/PyJWT-1.7.1-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /ReactPython1/ReactPython1/PythonBackendPractice/test1/requirements.txt</p>
<p>Path to vulnerable library: /ReactPython1/ReactPython1/PythonBackendPractice/test1/requirements.txt,/ReactPython1/ReactPython1/PythonBackendPractice/test1/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **PyJWT-1.7.1-py2.py3-none-any.whl** (Vulnerable Library)
</details>
<details><summary><b>PyJWT-2.0.1-py3-none-any.whl</b></p></summary>
<p>JSON Web Token implementation in Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/b4/9b/8850f99027ed029af6828199cc87179eaccbbf1f9e6e373e7f0177d32dad/PyJWT-2.0.1-py3-none-any.whl">https://files.pythonhosted.org/packages/b4/9b/8850f99027ed029af6828199cc87179eaccbbf1f9e6e373e7f0177d32dad/PyJWT-2.0.1-py3-none-any.whl</a></p>
<p>Path to dependency file: /ReactPython1/requirements.txt</p>
<p>Path to vulnerable library: /ReactPython1/requirements.txt,/ReactPython1/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **PyJWT-2.0.1-py3-none-any.whl** (Vulnerable Library)
</details>
<details><summary><b>PyJWT-1.4.2-py2.py3-none-any.whl</b></p></summary>
<p>JSON Web Token implementation in Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/b8/9c/1973e3117d43527a42f2a8afbc81e48d69a537d6e2c39412049b1592d1e2/PyJWT-1.4.2-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/b8/9c/1973e3117d43527a42f2a8afbc81e48d69a537d6e2c39412049b1592d1e2/PyJWT-1.4.2-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /python-work/FlaskWork/requirements.txt</p>
<p>Path to vulnerable library: /python-work/FlaskWork/requirements.txt</p>
<p>
Dependency Hierarchy:
- Flask-JWT-0.3.2.tar.gz (Root Library)
- :x: **PyJWT-1.4.2-py2.py3-none-any.whl** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/ebubeaso/IT-coding-work/commit/6d107a6688bc22c52eeb62e12abbb00206f7105f">6d107a6688bc22c52eeb62e12abbb00206f7105f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
PyJWT is a Python implementation of RFC 7519. PyJWT supports multiple different JWT signing algorithms. With JWT, an attacker submitting the JWT token can choose the used signing algorithm. The PyJWT library requires that the application chooses what algorithms are supported. The application can specify `jwt.algorithms.get_default_algorithms()` to get support for all algorithms, or specify a single algorithm. The issue is not that big as `algorithms=jwt.algorithms.get_default_algorithms()` has to be used. Users should upgrade to v2.4.0 to receive a patch for this issue. As a workaround, always be explicit with the algorithms that are accepted and expected when decoding.
<p>Publish Date: 2022-05-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29217>CVE-2022-29217</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29217">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29217</a></p>
<p>Release Date: 2022-05-24</p>
<p>Fix Resolution: PyJWT - 2.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-29217 (High) detected in multiple libraries - ## CVE-2022-29217 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>PyJWT-1.7.1-py2.py3-none-any.whl</b>, <b>PyJWT-2.0.1-py3-none-any.whl</b>, <b>PyJWT-1.4.2-py2.py3-none-any.whl</b></p></summary>
<p>
<details><summary><b>PyJWT-1.7.1-py2.py3-none-any.whl</b></p></summary>
<p>JSON Web Token implementation in Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/87/8b/6a9f14b5f781697e51259d81657e6048fd31a113229cf346880bb7545565/PyJWT-1.7.1-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/87/8b/6a9f14b5f781697e51259d81657e6048fd31a113229cf346880bb7545565/PyJWT-1.7.1-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /ReactPython1/ReactPython1/PythonBackendPractice/test1/requirements.txt</p>
<p>Path to vulnerable library: /ReactPython1/ReactPython1/PythonBackendPractice/test1/requirements.txt,/ReactPython1/ReactPython1/PythonBackendPractice/test1/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **PyJWT-1.7.1-py2.py3-none-any.whl** (Vulnerable Library)
</details>
<details><summary><b>PyJWT-2.0.1-py3-none-any.whl</b></p></summary>
<p>JSON Web Token implementation in Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/b4/9b/8850f99027ed029af6828199cc87179eaccbbf1f9e6e373e7f0177d32dad/PyJWT-2.0.1-py3-none-any.whl">https://files.pythonhosted.org/packages/b4/9b/8850f99027ed029af6828199cc87179eaccbbf1f9e6e373e7f0177d32dad/PyJWT-2.0.1-py3-none-any.whl</a></p>
<p>Path to dependency file: /ReactPython1/requirements.txt</p>
<p>Path to vulnerable library: /ReactPython1/requirements.txt,/ReactPython1/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **PyJWT-2.0.1-py3-none-any.whl** (Vulnerable Library)
</details>
<details><summary><b>PyJWT-1.4.2-py2.py3-none-any.whl</b></p></summary>
<p>JSON Web Token implementation in Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/b8/9c/1973e3117d43527a42f2a8afbc81e48d69a537d6e2c39412049b1592d1e2/PyJWT-1.4.2-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/b8/9c/1973e3117d43527a42f2a8afbc81e48d69a537d6e2c39412049b1592d1e2/PyJWT-1.4.2-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /python-work/FlaskWork/requirements.txt</p>
<p>Path to vulnerable library: /python-work/FlaskWork/requirements.txt</p>
<p>
Dependency Hierarchy:
- Flask-JWT-0.3.2.tar.gz (Root Library)
- :x: **PyJWT-1.4.2-py2.py3-none-any.whl** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/ebubeaso/IT-coding-work/commit/6d107a6688bc22c52eeb62e12abbb00206f7105f">6d107a6688bc22c52eeb62e12abbb00206f7105f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
PyJWT is a Python implementation of RFC 7519. PyJWT supports multiple different JWT signing algorithms. With JWT, an attacker submitting the JWT token can choose the used signing algorithm. The PyJWT library requires that the application chooses what algorithms are supported. The application can specify `jwt.algorithms.get_default_algorithms()` to get support for all algorithms, or specify a single algorithm. The issue is not that big as `algorithms=jwt.algorithms.get_default_algorithms()` has to be used. Users should upgrade to v2.4.0 to receive a patch for this issue. As a workaround, always be explicit with the algorithms that are accepted and expected when decoding.
<p>Publish Date: 2022-05-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29217>CVE-2022-29217</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29217">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29217</a></p>
<p>Release Date: 2022-05-24</p>
<p>Fix Resolution: PyJWT - 2.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries pyjwt none any whl pyjwt none any whl pyjwt none any whl pyjwt none any whl json web token implementation in python library home page a href path to dependency file pythonbackendpractice requirements txt path to vulnerable library pythonbackendpractice requirements txt pythonbackendpractice requirements txt dependency hierarchy x pyjwt none any whl vulnerable library pyjwt none any whl json web token implementation in python library home page a href path to dependency file requirements txt path to vulnerable library requirements txt requirements txt dependency hierarchy x pyjwt none any whl vulnerable library pyjwt none any whl json web token implementation in python library home page a href path to dependency file python work flaskwork requirements txt path to vulnerable library python work flaskwork requirements txt dependency hierarchy flask jwt tar gz root library x pyjwt none any whl vulnerable library found in head commit a href found in base branch master vulnerability details pyjwt is a python implementation of rfc pyjwt supports multiple different jwt signing algorithms with jwt an attacker submitting the jwt token can choose the used signing algorithm the pyjwt library requires that the application chooses what algorithms are supported the application can specify jwt algorithms get default algorithms to get support for all algorithms or specify a single algorithm the issue is not that big as algorithms jwt algorithms get default algorithms has to be used users should upgrade to to receive a patch for this issue as a workaround always be explicit with the algorithms that are accepted and expected when decoding publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution pyjwt step up your open source security game with mend
| 0
|
196,031
| 14,790,036,171
|
IssuesEvent
|
2021-01-12 11:25:45
|
vaadin/flow
|
https://api.github.com/repos/vaadin/flow
|
closed
|
Add Application Theme tests for Dev Mode
|
testing theming
|
Current Application Theme tests cover only the production mode in module `flow-test-themes-npm`, and, thus, some app theme changes (at least those for `/theme/my-theme/` requests handling in `DevModeHandler`) are not covered.
The tests should be added for the Dev Mode by making another maven module, or by making a double pom-file.
Ideally, it should cover these changes https://github.com/vaadin/flow/pull/9590 https://github.com/vaadin/flow/issues/9594 https://github.com/vaadin/flow/issues/9596
|
1.0
|
Add Application Theme tests for Dev Mode - Current Application Theme tests cover only the production mode in module `flow-test-themes-npm`, and, thus, some app theme changes (at least those for `/theme/my-theme/` requests handling in `DevModeHandler`) are not covered.
The tests should be added for the Dev Mode by making another maven module, or by making a double pom-file.
Ideally, it should cover these changes https://github.com/vaadin/flow/pull/9590 https://github.com/vaadin/flow/issues/9594 https://github.com/vaadin/flow/issues/9596
|
test
|
add application theme tests for dev mode current application theme tests cover only the production mode in module flow test themes npm and thus some app theme changes at least those for theme my theme requests handling in devmodehandler are not covered the tests should be added for the dev mode by making another maven module or by making a double pom file ideally it should cover these changes
| 1
|
69,241
| 8,388,034,888
|
IssuesEvent
|
2018-10-09 03:59:40
|
dev-u/emburradinho
|
https://api.github.com/repos/dev-u/emburradinho
|
closed
|
Colocar fundo com textura de papel
|
GAMEDESIGN PROGRAMAÇÃO cenário
|
- [x] Colocar um fundo imitando a textura de um papel quadriculado
- No estilo Doodle Jump
- [x] Testar Parallax
- [x] Colocar um efeito Parallax
- Deixar a velocidade relativa do parallax configurável via inspector
|
1.0
|
Colocar fundo com textura de papel - - [x] Colocar um fundo imitando a textura de um papel quadriculado
- No estilo Doodle Jump
- [x] Testar Parallax
- [x] Colocar um efeito Parallax
- Deixar a velocidade relativa do parallax configurável via inspector
|
non_test
|
colocar fundo com textura de papel colocar um fundo imitando a textura de um papel quadriculado no estilo doodle jump testar parallax colocar um efeito parallax deixar a velocidade relativa do parallax configurável via inspector
| 0
|
11,230
| 28,504,447,143
|
IssuesEvent
|
2023-04-18 20:06:44
|
MicrosoftDocs/well-architected
|
https://api.github.com/repos/MicrosoftDocs/well-architected
|
closed
|
[Typo] Title and first paragraph
|
architecture-center/svc well-architected/subsvc Pri1
|
The title says "Target and non-functional requirements". I believe it was missing a "Target functional and non-functional requirements".
Also the first paragraph has the same issue.
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: d394ee5b-3912-86ff-938e-98537ab1e4d9
* Version Independent ID: d394ee5b-3912-86ff-938e-98537ab1e4d9
* Content: [Target and non-functional requirements - Microsoft Azure Well-Architected Framework](https://learn.microsoft.com/en-us/azure/architecture/framework/resiliency/design-requirements)
* Content Source: [well-architected/resiliency/design-requirements.md](https://github.com/MicrosoftDocs/well-architected/blob/main/well-architected/resiliency/design-requirements.md)
* Service: **architecture-center**
* Sub-service: **well-architected**
* GitHub Login: @martinekuan
* Microsoft Alias: **martinek**
|
1.0
|
[Typo] Title and first paragraph - The title says "Target and non-functional requirements". I believe it was missing a "Target functional and non-functional requirements".
Also the first paragraph has the same issue.
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: d394ee5b-3912-86ff-938e-98537ab1e4d9
* Version Independent ID: d394ee5b-3912-86ff-938e-98537ab1e4d9
* Content: [Target and non-functional requirements - Microsoft Azure Well-Architected Framework](https://learn.microsoft.com/en-us/azure/architecture/framework/resiliency/design-requirements)
* Content Source: [well-architected/resiliency/design-requirements.md](https://github.com/MicrosoftDocs/well-architected/blob/main/well-architected/resiliency/design-requirements.md)
* Service: **architecture-center**
* Sub-service: **well-architected**
* GitHub Login: @martinekuan
* Microsoft Alias: **martinek**
|
non_test
|
title and first paragraph the title says target and non functional requirements i believe it was missing a target functional and non functional requirements also the first paragraph has the same issue document details ⚠ do not edit this section it is required for learn microsoft com ➟ github issue linking id version independent id content content source service architecture center sub service well architected github login martinekuan microsoft alias martinek
| 0
|
177,784
| 13,748,257,362
|
IssuesEvent
|
2020-10-06 08:49:19
|
WoWManiaUK/Redemption
|
https://api.github.com/repos/WoWManiaUK/Redemption
|
closed
|
[NPC] Blistering Zombie + Shackle Undead
|
Fix - Tester Confirmed
|
**Links:**
http://www.wow-mania.com/armory?npc=37934
https://www.wowhead.com/npc=37934/blistering-zombie
http://www.wow-mania.com/armory?spell=70744
http://www.wow-mania.com/armory?spell=10955
**What is Happening:**
If during valithria dreamwalker encounter priest cast Shackle undead on Blistering zombie before mob die and mob get killed while shackle undead is on it it will not do acid burst aoe dmg
**What Should happen:**
Blistering Zombie Should always explode on death dealing dmg and dot on everyone in range of 15 yards
NOTE: it is icc fight pots but GM approved for it to be made
|
1.0
|
[NPC] Blistering Zombie + Shackle Undead - **Links:**
http://www.wow-mania.com/armory?npc=37934
https://www.wowhead.com/npc=37934/blistering-zombie
http://www.wow-mania.com/armory?spell=70744
http://www.wow-mania.com/armory?spell=10955
**What is Happening:**
If during valithria dreamwalker encounter priest cast Shackle undead on Blistering zombie before mob die and mob get killed while shackle undead is on it it will not do acid burst aoe dmg
**What Should happen:**
Blistering Zombie Should always explode on death dealing dmg and dot on everyone in range of 15 yards
NOTE: it is icc fight pots but GM approved for it to be made
|
test
|
blistering zombie shackle undead links what is happening if during valithria dreamwalker encounter priest cast shackle undead on blistering zombie before mob die and mob get killed while shackle undead is on it it will not do acid burst aoe dmg what should happen blistering zombie should always explode on death dealing dmg and dot on everyone in range of yards note it is icc fight pots but gm approved for it to be made
| 1
|
295,882
| 25,512,316,913
|
IssuesEvent
|
2022-11-28 14:00:35
|
microsoft/vscode
|
https://api.github.com/repos/microsoft/vscode
|
opened
|
Test `comments.visible` setting
|
testplan-item
|
Refs: https://github.com/microsoft/vscode/issues/162352
- [ ] anyOS
- [ ] anyOS
Complexity: 2
---
1. Open a folder that has comments
- One example of this is to use the GitHub Pull Request and Issues extension to check out a PR with comments
2. Hiding the comments features involves hiding the `+` bar in the gutter and all comment widgets. Verify that the setting `comments.visisble` hides comments features when set to false.
3. Verify that you can still toggle comments features with "Comments: Toggle Editor Commenting"
|
1.0
|
Test `comments.visible` setting - Refs: https://github.com/microsoft/vscode/issues/162352
- [ ] anyOS
- [ ] anyOS
Complexity: 2
---
1. Open a folder that has comments
- One example of this is to use the GitHub Pull Request and Issues extension to check out a PR with comments
2. Hiding the comments features involves hiding the `+` bar in the gutter and all comment widgets. Verify that the setting `comments.visisble` hides comments features when set to false.
3. Verify that you can still toggle comments features with "Comments: Toggle Editor Commenting"
|
test
|
test comments visible setting refs anyos anyos complexity open a folder that has comments one example of this is to use the github pull request and issues extension to check out a pr with comments hiding the comments features involves hiding the bar in the gutter and all comment widgets verify that the setting comments visisble hides comments features when set to false verify that you can still toggle comments features with comments toggle editor commenting
| 1
|
95,923
| 8,581,012,506
|
IssuesEvent
|
2018-11-13 13:39:31
|
cockroachdb/cockroach
|
https://api.github.com/repos/cockroachdb/cockroach
|
closed
|
roachtest: kv0/encrypt=false/nodes=1 failed
|
C-test-failure O-robot
|
SHA: https://github.com/cockroachdb/cockroach/commits/b3ba03fdb86cbefceb42f46069ffd685749aa7b0
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace and passing the '-p' stressflag which
# controls concurrency.
./scripts/gceworker.sh start && ./scripts/gceworker.sh mosh
cd ~/go/src/github.com/cockroachdb/cockroach && \
make stressrace TESTS=kv0/encrypt=false/nodes=1 PKG=roachtest TESTTIMEOUT=5m STRESSFLAGS='-maxtime 20m -timeout 10m' 2>&1 | tee /tmp/stress.log
```
Failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=1008038&tab=buildLog
```
The test failed on master:
test.go:639,test.go:651: /home/agent/work/.go/bin/roachprod create teamcity-1008038-kv0-encrypt-false-nodes-1 -n 2 --clouds=aws --aws-machine-type-ssd=m5d.2xlarge returned:
stderr:
es/tobias-1542056302-tpccbench-nodes-11-cpu-32-0012",
"serviceAccounts": [
{
"email": "21965078311-compute@developer.gserviceaccount.com",
"scopes": [
"https://www.googleapis.com/auth/devstorage.read_only",
"https://www.googleapis.com/auth/devstorage.read_write",
"https://www.googleapis.com/auth/logging.write",
"https://www.googleapis.com/auth/monitoring.write",
"https://www.googleapis.com/auth/pubsub",
"https://www.googleapis.com/auth/service.management.readonly",
"https://www.googleapis.com/auth/servicecontrol",
"https://www.googleapis.com/auth/trace.append"
]
}
],
"startRestricted": false,
"status": "RUNNING",
"tags": {
"fingerprint": "42WmSpB8rSM="
},
"zone": "https://www.googleapis.com/compute/v1/projects/cockroach-ephemeral/zones/us-east1-b"
}
]
stderr: ERROR: (gcloud.compute.instances.list) Some requests did not succeed:
- Code: '-2682756640993494592'
stdout:
: exit status 1
```
|
1.0
|
roachtest: kv0/encrypt=false/nodes=1 failed - SHA: https://github.com/cockroachdb/cockroach/commits/b3ba03fdb86cbefceb42f46069ffd685749aa7b0
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace and passing the '-p' stressflag which
# controls concurrency.
./scripts/gceworker.sh start && ./scripts/gceworker.sh mosh
cd ~/go/src/github.com/cockroachdb/cockroach && \
make stressrace TESTS=kv0/encrypt=false/nodes=1 PKG=roachtest TESTTIMEOUT=5m STRESSFLAGS='-maxtime 20m -timeout 10m' 2>&1 | tee /tmp/stress.log
```
Failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=1008038&tab=buildLog
```
The test failed on master:
test.go:639,test.go:651: /home/agent/work/.go/bin/roachprod create teamcity-1008038-kv0-encrypt-false-nodes-1 -n 2 --clouds=aws --aws-machine-type-ssd=m5d.2xlarge returned:
stderr:
es/tobias-1542056302-tpccbench-nodes-11-cpu-32-0012",
"serviceAccounts": [
{
"email": "21965078311-compute@developer.gserviceaccount.com",
"scopes": [
"https://www.googleapis.com/auth/devstorage.read_only",
"https://www.googleapis.com/auth/devstorage.read_write",
"https://www.googleapis.com/auth/logging.write",
"https://www.googleapis.com/auth/monitoring.write",
"https://www.googleapis.com/auth/pubsub",
"https://www.googleapis.com/auth/service.management.readonly",
"https://www.googleapis.com/auth/servicecontrol",
"https://www.googleapis.com/auth/trace.append"
]
}
],
"startRestricted": false,
"status": "RUNNING",
"tags": {
"fingerprint": "42WmSpB8rSM="
},
"zone": "https://www.googleapis.com/compute/v1/projects/cockroach-ephemeral/zones/us-east1-b"
}
]
stderr: ERROR: (gcloud.compute.instances.list) Some requests did not succeed:
- Code: '-2682756640993494592'
stdout:
: exit status 1
```
|
test
|
roachtest encrypt false nodes failed sha parameters to repro try don t forget to check out a clean suitable branch and experiment with the stress invocation until the desired results present themselves for example using stress instead of stressrace and passing the p stressflag which controls concurrency scripts gceworker sh start scripts gceworker sh mosh cd go src github com cockroachdb cockroach make stressrace tests encrypt false nodes pkg roachtest testtimeout stressflags maxtime timeout tee tmp stress log failed test the test failed on master test go test go home agent work go bin roachprod create teamcity encrypt false nodes n clouds aws aws machine type ssd returned stderr es tobias tpccbench nodes cpu serviceaccounts email compute developer gserviceaccount com scopes startrestricted false status running tags fingerprint zone stderr error gcloud compute instances list some requests did not succeed code stdout exit status
| 1
|
162,793
| 25,597,154,850
|
IssuesEvent
|
2022-12-01 17:02:28
|
GAME-2332/argame
|
https://api.github.com/repos/GAME-2332/argame
|
closed
|
Level 8 and 9 Staging
|
designers
|
Please add textures such as grass for the plane, dirt for the enemy path, and concrete for tower placement cubes. Place props outside of the paths and add towers in place of the greybox towers that are in each scene so we can test with the actual towers instead. Keep everything where it is in the scene but just add the assets needed to make the scene look ready to play for public testing
|
1.0
|
Level 8 and 9 Staging - Please add textures such as grass for the plane, dirt for the enemy path, and concrete for tower placement cubes. Place props outside of the paths and add towers in place of the greybox towers that are in each scene so we can test with the actual towers instead. Keep everything where it is in the scene but just add the assets needed to make the scene look ready to play for public testing
|
non_test
|
level and staging please add textures such as grass for the plane dirt for the enemy path and concrete for tower placement cubes place props outside of the paths and add towers in place of the greybox towers that are in each scene so we can test with the actual towers instead keep everything where it is in the scene but just add the assets needed to make the scene look ready to play for public testing
| 0
|
67,667
| 7,056,958,189
|
IssuesEvent
|
2018-01-04 14:49:33
|
e-government-ua/iTest
|
https://api.github.com/repos/e-government-ua/iTest
|
closed
|
Создать автотест для iDoc на Гамме
|
active priority - High test
|
Связано с https://github.com/e-government-ua/iTest/issues/120
Инструкция по написанию тестов
https://docs.google.com/document/d/145m06XHNd_-s1Vwoqcg6KH0MW81ujgmvEwXw7GOIhrs/edit?usp=sharing
- [x] 1. Создание документа
- [x] 2. Работа на этапе согласования (1 пользователь). Делегирование полномочий
- [x] 3. Работа на этапе согласования (1 пользователь). Подписываем
- [x] 4. Работа на этапе согласования (2 пользователь). Добавляем подписанта и вібираем “Підпис не потрібен”
- [x] 5. Работа на этапе согласования (3 пользователь). Подписываем
- [x] 6. Работа на этапе утверждения. Добавляем замечания и нового подписанта
- [x] 7. Отвечаем на зауваження
- [x] 8. Подписываем дополнительно директором
- [x] 9. Заходим адресатом 1. Добавляем задание 1
- [x] 10. Заходим адресатом 2.
- [x] 11. Заходим исполнителем 1. Обработка задания. Добавляем отчет 1
- [x] 12. Заходим исполнителем 2. Обработка задания. Добавляем отчет 2
- [x] 13. Заходим контролирующим. Подтверждаем отчет
- [x] 14. Заходим исполнителем. Подписіваем
|
1.0
|
Создать автотест для iDoc на Гамме - Связано с https://github.com/e-government-ua/iTest/issues/120
Инструкция по написанию тестов
https://docs.google.com/document/d/145m06XHNd_-s1Vwoqcg6KH0MW81ujgmvEwXw7GOIhrs/edit?usp=sharing
- [x] 1. Создание документа
- [x] 2. Работа на этапе согласования (1 пользователь). Делегирование полномочий
- [x] 3. Работа на этапе согласования (1 пользователь). Подписываем
- [x] 4. Работа на этапе согласования (2 пользователь). Добавляем подписанта и вібираем “Підпис не потрібен”
- [x] 5. Работа на этапе согласования (3 пользователь). Подписываем
- [x] 6. Работа на этапе утверждения. Добавляем замечания и нового подписанта
- [x] 7. Отвечаем на зауваження
- [x] 8. Подписываем дополнительно директором
- [x] 9. Заходим адресатом 1. Добавляем задание 1
- [x] 10. Заходим адресатом 2.
- [x] 11. Заходим исполнителем 1. Обработка задания. Добавляем отчет 1
- [x] 12. Заходим исполнителем 2. Обработка задания. Добавляем отчет 2
- [x] 13. Заходим контролирующим. Подтверждаем отчет
- [x] 14. Заходим исполнителем. Подписіваем
|
test
|
создать автотест для idoc на гамме связано с инструкция по написанию тестов создание документа работа на этапе согласования пользователь делегирование полномочий работа на этапе согласования пользователь подписываем работа на этапе согласования пользователь добавляем подписанта и вібираем “підпис не потрібен” работа на этапе согласования пользователь подписываем работа на этапе утверждения добавляем замечания и нового подписанта отвечаем на зауваження подписываем дополнительно директором заходим адресатом добавляем задание заходим адресатом заходим исполнителем обработка задания добавляем отчет заходим исполнителем обработка задания добавляем отчет заходим контролирующим подтверждаем отчет заходим исполнителем подписіваем
| 1
|
296,582
| 22,308,200,841
|
IssuesEvent
|
2022-06-13 14:42:57
|
sekai-studio/starknet-libs
|
https://api.github.com/repos/sekai-studio/starknet-libs
|
closed
|
Make utilities available through npm install
|
documentation enhancement
|
Similar to https://github.com/0xs34n/starknet.js/blob/develop/README.md
It would be good to get some info on how we can use this library for the utilities.
Thank you!
|
1.0
|
Make utilities available through npm install - Similar to https://github.com/0xs34n/starknet.js/blob/develop/README.md
It would be good to get some info on how we can use this library for the utilities.
Thank you!
|
non_test
|
make utilities available through npm install similar to it would be good to get some info on how we can use this library for the utilities thank you
| 0
|
28,759
| 12,961,857,555
|
IssuesEvent
|
2020-07-20 16:15:34
|
dockstore/dockstore
|
https://api.github.com/repos/dockstore/dockstore
|
closed
|
Change SourceFiles to be Fetch.Lazy
|
enhancement review web-service
|
**Is your feature request related to a problem? Please describe.**
Source files can consume a large amount of memory; we should avoid fetching them unless needed by the client.
**Describe the solution you'd like**
* In WorkflowVersion, annotate sourceFiles with `FetchType.LAZY` instead of `FetchType.EAGER`.
* That may not be enough though; if anything access the source files they'll end up getting loaded anyways.
* Force fetching of sourceFiles via a new endpoint? Or via a query parameter?
* UI apparently doesn't use source files; except for the hosted entries.
* May require UI corresponding UI changes
**Additional context**
Overlaps with #3453 and #3442 . This might end up being addressed in either or both of those instead.
┆Issue is synchronized with this [Jira Story](https://ucsc-cgl.atlassian.net/browse/DOCK-1355)
┆Issue Type: Story
┆Fix Versions: Dockstore 1.10
┆Sprint: Sprint 36 Krill
┆Issue Number: DOCK-1355
|
1.0
|
Change SourceFiles to be Fetch.Lazy - **Is your feature request related to a problem? Please describe.**
Source files can consume a large amount of memory; we should avoid fetching them unless needed by the client.
**Describe the solution you'd like**
* In WorkflowVersion, annotate sourceFiles with `FetchType.LAZY` instead of `FetchType.EAGER`.
* That may not be enough though; if anything access the source files they'll end up getting loaded anyways.
* Force fetching of sourceFiles via a new endpoint? Or via a query parameter?
* UI apparently doesn't use source files; except for the hosted entries.
* May require UI corresponding UI changes
**Additional context**
Overlaps with #3453 and #3442 . This might end up being addressed in either or both of those instead.
┆Issue is synchronized with this [Jira Story](https://ucsc-cgl.atlassian.net/browse/DOCK-1355)
┆Issue Type: Story
┆Fix Versions: Dockstore 1.10
┆Sprint: Sprint 36 Krill
┆Issue Number: DOCK-1355
|
non_test
|
change sourcefiles to be fetch lazy is your feature request related to a problem please describe source files can consume a large amount of memory we should avoid fetching them unless needed by the client describe the solution you d like in workflowversion annotate sourcefiles with fetchtype lazy instead of fetchtype eager that may not be enough though if anything access the source files they ll end up getting loaded anyways force fetching of sourcefiles via a new endpoint or via a query parameter ui apparently doesn t use source files except for the hosted entries may require ui corresponding ui changes additional context overlaps with and this might end up being addressed in either or both of those instead ┆issue is synchronized with this ┆issue type story ┆fix versions dockstore ┆sprint sprint krill ┆issue number dock
| 0
|
44,827
| 5,654,969,073
|
IssuesEvent
|
2017-04-09 13:51:47
|
brave/browser-laptop
|
https://api.github.com/repos/brave/browser-laptop
|
closed
|
Manual tests for Windows ia-32 0.14.2 Preview 1
|
OS/Windows release-notes/exclude tests
|
## Installer
1. [x] Check that installer is close to the size of last release.
2. [x] Check signature: If OS Run `spctl --assess --verbose /Applications/Brave.app/` and make sure it returns `accepted`. If Windows right click on the installer exe and go to Properties, go to the Digital Signatures tab and double click on the signature. Make sure it says "The digital signature is OK" in the popup window.
3. [x] Check Brave, muon, and libchromiumcontent version in About and make sure it is EXACTLY as expected.
## Last changeset test
1. [x] Test what is covered by the last changeset (you can find this by clicking on the SHA in about:brave).
## Per release specialty tests
- ~~[ ] Ledger calculation when 0 eligible unpinned sites. ([#8102](https://github.com/brave/browser-laptop/issues/8102))~~
- [x] Javascript: bookmarks cause connection info box to appear. ([#8087](https://github.com/brave/browser-laptop/issues/8087))
- [x] Enabling show include site with autoinclude off shows payment info page when refreshed. ([#8079](https://github.com/brave/browser-laptop/issues/8079))
- [x] Revert the inlined files on contributionStatement.js (follow up to #7887). ([#8062](https://github.com/brave/browser-laptop/issues/8062))
- [x] Fix radii, colors, focused state styles in URL bar related to new add-funds button. ([#8058](https://github.com/brave/browser-laptop/issues/8058))
- ~~[ ] LastPass opens in wrong position when activated by keyboard. ([#8034](https://github.com/brave/browser-laptop/issues/8034))~~ https://github.com/brave/browser-laptop/issues/8034#issuecomment-292782593
- [x] Use PseudoElement for Narrow-Tab Audio Indicator. ([#8033](https://github.com/brave/browser-laptop/issues/8033))
- [x] About pages cannot be synced because data is too big (favicon is encoded in Base64 format). ([#8023](https://github.com/brave/browser-laptop/issues/8023))
- [x] Redesigned importBrowserDataPanel.js. ([#7996](https://github.com/brave/browser-laptop/issues/7996))
- [x] Toggle excluding a site from ledger sometimes removes it from the list. ([#7987](https://github.com/brave/browser-laptop/issues/7987))
- [x] Sync does not appear to recover from network outage. ([#7972](https://github.com/brave/browser-laptop/issues/7972))
- [x] Sync is losing hierarchy when adding bookmarks to new sync members. ([#7971](https://github.com/brave/browser-laptop/issues/7971))
- [x] Refactor siteInfo.js with Aphrodite. ([#7949](https://github.com/brave/browser-laptop/issues/7949))
- [x] Add a new tab page for private tabs. ([#7934](https://github.com/brave/browser-laptop/issues/7934))
- [ ] Refactor popupWindow.less with Aphrodite. ([#7927](https://github.com/brave/browser-laptop/issues/7927))
- [x] Refactor bookmarksToolbar.js with Aphrodite. ([#7920](https://github.com/brave/browser-laptop/issues/7920))
- ~~[ ] Back/forward gesture should support three finger swipe. ([#7905](https://github.com/brave/browser-laptop/issues/7905))~~
- [x] First time wallet creation needs a better UI. ([#7889](https://github.com/brave/browser-laptop/issues/7889))
- [x] Modified contributionStatement.js with Aphrodite. ([#7883](https://github.com/brave/browser-laptop/issues/7883))
- ~~[ ] Ubuntu: Brave doesn't know that it's the default browser.. ([#7800](https://github.com/brave/browser-laptop/issues/7800))~~
- [x] Change "Save Torrent File" button to "Copy Magnet Link" for magnet links. ([#7772](https://github.com/brave/browser-laptop/issues/7772))
- ~~[ ] Contribution Statement opened in a new tab doesn't show the tab title until the cursor is moved over it or tab focus is changed. ([#7765](https://github.com/brave/browser-laptop/issues/7765))~~
- [x] Restructure paymentTab.js. ([#7750](https://github.com/brave/browser-laptop/issues/7750))
- [x] Add "Command+Click" to home button (opens home in a new background tab). ([#7718](https://github.com/brave/browser-laptop/issues/7718))
- [x] View Source shortcut should be CTRL+U, not CTRL+ALT+U. ([#7702](https://github.com/brave/browser-laptop/issues/7702))
- [x] Downloads should show origin. ([#7468](https://github.com/brave/browser-laptop/issues/7468))
- [x] Remove label from MultiMedia devices when fingerprinting protection is on.. ([#7462](https://github.com/brave/browser-laptop/issues/7462))
- [x] Pocket was translated when it should not.. ([#7450](https://github.com/brave/browser-laptop/issues/7450))
- [x] Right click not dismissing / hiding an open menu (Windows only). ([#7403](https://github.com/brave/browser-laptop/issues/7403))
- [x] Include current year in PDF statement copyright footer. ([#6878](https://github.com/brave/browser-laptop/issues/6878))
- [x] There is no obvious way to stop a torrent download once it has started. ([#6768](https://github.com/brave/browser-laptop/issues/6768))
- [x] Support torrent link files. ([#6671](https://github.com/brave/browser-laptop/issues/6671))
- [x] Add the release notes of the same version as the browser to about:brave. ([#6130](https://github.com/brave/browser-laptop/issues/6130))
- [x] Some info buttons in preferences are missing content links. ([#5758](https://github.com/brave/browser-laptop/issues/5758))
- [x] Add context-menu option to close tabs in tab page. ([#5489](https://github.com/brave/browser-laptop/issues/5489))
- [x] Honey: Support browserAction.setBadgeBackgroundColor. ([#5367](https://github.com/brave/browser-laptop/issues/5367))
- [x] Honey: Support chrome.browserAction.setBadgeText. ([#5366](https://github.com/brave/browser-laptop/issues/5366))
- [ ] Default browser setting gets reset after upgrade. ([#5246](https://github.com/brave/browser-laptop/issues/5246))
- [ ] Add Widevine support for Amazon Prime Video. ([#5233](https://github.com/brave/browser-laptop/issues/5233))
- [x] Favicons on brave payments list are not displayed until switching the tab. ([#4178](https://github.com/brave/browser-laptop/issues/4178))
- [x] Y position of context menu subitems is wrong when overflowed. ([#1589](https://github.com/brave/browser-laptop/issues/1589))
## Widevine/Netflix test
1. [x] Test that you can log into Netflix and start a show.
## Ledger
1. [ ] Create a wallet with a value other than $5 selected in the monthly budget dropdown. Click on the 'Add Funds' button and check that Coinbase transactions are blocked.
2. [x] Remove all `ledger-*.json` files from `~/Library/Application\ Support/Brave/`. Go to the Payments tab in about:preferences, enable payments, click on `create wallet`. Check that the `add funds` button appears after a wallet is created.
3. [ ] Click on `add funds` and verify that adding funds through Coinbase increases the account balance.
4. [ ] Repeat the step above but add funds by scanning the QR code in a mobile bitcoin app instead of through Coinbase.
5. [x] Visit nytimes.com for a few seconds and make sure it shows up in the Payments table.
6. [x] Go to https://jsfiddle.net/LnwtLckc/5/ and click the register button. In the Payments tab, click `add funds`. Verify that the `transfer funds` button is visible and that clicking on `transfer funds` opens a jsfiddle URL in a new tab.
7. [x] Go to https://jsfiddle.net/LnwtLckc/5/ and click `unregister`. Verify that the `transfer funds` button no longer appears in the `add funds` modal.
8. [x] Check that disabling payments and enabling them again does not lose state.
## Sync
1. [x] Verify you are able to sync two devices using the secret code
2. [x] Visit a site on device 1 and change shield setting, ensure that the saved site preference is synced to device 2
3. [x] Enable Browsing history sync on device 1, ensure the history is shown on device 2
4. [x] Import/Add bookmarks on device 1, ensure it is synced on device 2
5. [x] Ensure imported bookmark folder structure is maintained on device 2
6. [x] Ensure bookmark favicons are shown after sync
## Data
1. [x] Make sure that data from the last version appears in the new version OK.
2. [x] Test that the previous version's cookies are preserved in the next version.
## About pages
1. [x] Test that about:adblock loads
2. [x] Test that about:autofill loads
3. [x] Test that about:bookmarks loads bookmarks
4. [x] Test that about:downloads loads downloads
5. [x] Test that about:extensions loads
6. [x] Test that about:history loads history
7. [x] Test that about:passwords loads
8. [x] Test that about:styles loads
9. [x] Test that about:preferences changing a preference takes effect right away
10. [x] Test that about:preferences language change takes effect on re-start
11. [x] Test that about.com without the http protocol is loaded from URL bar
## Bookmarks
1. [x] Test that creating a bookmark on the bookmarks toolbar works
2. [x] Test that creating a bookmark folder on the bookmarks toolbar works
3. [x] Test that moving a bookmark into a folder by drag and drop on the bookmarks folder works
4. [x] Test that clicking a bookmark in the toolbar loads the bookmark.
5. [x] Test that clicking a bookmark in a bookmark toolbar folder loads the bookmark.
## Context menus
1. [x] Make sure context menu items in the URL bar work
2. [x] Make sure context menu items on content work with no selected text.
3. [x] Make sure context menu items on content work with selected text.
4. [x] Make sure context menu items on content work inside an editable control on `about:styles` (input, textarea, or contenteditable).
## Find on page
1. [x] Ensure search box is shown with shortcut
2. [x] Test successful find
3. [x] Test forward and backward find navigation
4. [x] Test failed find shows 0 results
5. [x] Test match case find
## Geolocation
1. [x] Check that https://developer.mozilla.org/en-US/docs/Web/API/Geolocation/Using_geolocation works
## Site hacks
1. [x] Test https://www.twitch.tv/adobe sub-page loads a video and you can play it
## Downloads
1. [x] Test downloading a file works and that all actions on the download item works.
## Fullscreen
1. [x] Test that entering full screen window works View -> Toggle Full Screen. And exit back (Not Esc).
2. [x] Test that entering HTML5 full screen works. And Esc to go back. (youtube.com)
## Tabs and Pinning
1. [x] Test that tabs are pinnable
2. [x] Test that tabs are unpinnable
3. [x] Test that tabs are draggable to same tabset
4. [x] Test that tabs are draggable to alternate tabset
## Zoom
1. [x] Test zoom in / out shortcut works
2. [x] Test hamburger menu zooms.
3. [x] Test zoom saved when you close the browser and restore on a single site.
4. [x] Test zoom saved when you navigate within a single origin site.
5. [x] Test that navigating to a different origin resets the zoom
## Bravery settings
1. [x] Check that HTTPS Everywhere works by loading http://www.apple.com
2. [x] Turning HTTPS Everywhere off and shields off both disable the redirect to https://www.apple.com
3. [x] Check that ad replacement works on http://slashdot.org
4. [x] Check that toggling to blocking and allow ads works as expected.
5. [x] Test that clicking through a cert error in https://badssl.com/ works.
6. [x] Test that Safe Browsing works (http://downloadme.org/)
7. [x] Turning Safe Browsing off and shields off both disable safe browsing for http://downloadme.org/.
8. [x] Visit https://brianbondy.com/ and then turn on script blocking, nothing should load. Allow it from the script blocking UI in the URL bar and it should work.
9. [x] Test that about:preferences default Bravery settings take effect on pages with no site settings.
10. [x] Test that turning on fingerprinting protection in about:preferences shows 3 fingerprints blocked at https://jsfiddle.net/bkf50r8v/13/. Test that turning it off in the Bravery menu shows 0 fingerprints blocked.
11. [x] Test that 3rd party storage results are blank at https://jsfiddle.net/7ke9r14a/9/ when 3rd party cookies are blocked and not blank when 3rd party cookies are unblocked.
12. [x] Test that audio fingerprint is blocked at https://audiofingerprint.openwpm.com/ when fingerprinting protection is on.
## Content tests
1. [x] Go to https://brianbondy.com/ and click on the twitter icon on the top right. Test that context menus work in the new twitter tab.
2. [x] Load twitter and click on a tweet so the popup div shows. Click to dismiss and repeat with another div. Make sure it shows.
3. [x] Go to http://www.bennish.net/web-notifications.html and test that clicking on 'Show' pops up a notification asking for permission. Make sure that clicking 'Deny' leads to no notifications being shown.
4. [x] Go to https://trac.torproject.org/projects/tor/login and make sure that the password can be saved. Make sure the saved password shows up in `about:passwords`. Then reload https://trac.torproject.org/projects/tor/login and make sure the password is autofilled.
5. [x] Open a github issue and type some misspellings, make sure they are underlined.
6. [x] Make sure that right clicking on a word with suggestions gives a suggestion and that clicking on the suggestion replaces the text.
7. [x] Make sure that Command + Click (Control + Click on Windows, Control + Click on Ubuntu) on a link opens a new tab but does NOT switch to it. Click on it and make sure it is already loaded.
8. [x] Open an email on http://mail.google.com/ or inbox.google.com and click on a link. Make sure it works.
9. [x] Test that PDF is loaded at http://www.orimi.com/pdf-test.pdf
10. [x] Test that https://mixed-script.badssl.com/ shows up as grey not red (no mixed content scripts are run).
## Flash tests
1. [x] Turn on Flash in about:preferences#security. Test that clicking on 'Install Flash' banner on myspace.com shows a notification to allow Flash and that the banner disappears when 'Allow' is clicked.
2. [x] Test that flash placeholder appears on http://www.homestarrunner.com
## Autofill tests
1. [x] Test that autofill works on http://www.roboform.com/filling-test-all-fields
## Session storage
Do not forget to make a backup of your entire `~/Library/Application\ Support/Brave` folder.
1. [x] Temporarily move away your `~/Library/Application\ Support/Brave/session-store-1` and test that clean session storage works. (`%appdata%\Brave in Windows`, `./config/brave` in Ubuntu)
2. [x] Test that windows and tabs restore when closed, including active tab.
3. [x] Move away your entire `~/Library/Application\ Support/Brave` folder (`%appdata%\Brave in Windows`, `./config/brave` in Ubuntu)
## Cookie and Cache
1. [x] Make a backup of your profile, turn on all clearing in preferences and shut down. Make sure when you bring the browser back up everything is gone that is specified.
2. [x] Go to http://samy.pl/evercookie/ and set an evercookie. Check that going to prefs, clearing site data and cache, and going back to the Evercookie site does not remember the old evercookie value.
## Update tests
1. [x] Test that updating using `BRAVE_UPDATE_VERSION=0.8.3` env variable works correctly.
|
1.0
|
Manual tests for Windows ia-32 0.14.2 Preview 1 - ## Installer
1. [x] Check that installer is close to the size of last release.
2. [x] Check signature: If OS Run `spctl --assess --verbose /Applications/Brave.app/` and make sure it returns `accepted`. If Windows right click on the installer exe and go to Properties, go to the Digital Signatures tab and double click on the signature. Make sure it says "The digital signature is OK" in the popup window.
3. [x] Check Brave, muon, and libchromiumcontent version in About and make sure it is EXACTLY as expected.
## Last changeset test
1. [x] Test what is covered by the last changeset (you can find this by clicking on the SHA in about:brave).
## Per release specialty tests
- ~~[ ] Ledger calculation when 0 eligible unpinned sites. ([#8102](https://github.com/brave/browser-laptop/issues/8102))~~
- [x] Javascript: bookmarks cause connection info box to appear. ([#8087](https://github.com/brave/browser-laptop/issues/8087))
- [x] Enabling show include site with autoinclude off shows payment info page when refreshed. ([#8079](https://github.com/brave/browser-laptop/issues/8079))
- [x] Revert the inlined files on contributionStatement.js (follow up to #7887). ([#8062](https://github.com/brave/browser-laptop/issues/8062))
- [x] Fix radii, colors, focused state styles in URL bar related to new add-funds button. ([#8058](https://github.com/brave/browser-laptop/issues/8058))
- ~~[ ] LastPass opens in wrong position when activated by keyboard. ([#8034](https://github.com/brave/browser-laptop/issues/8034))~~ https://github.com/brave/browser-laptop/issues/8034#issuecomment-292782593
- [x] Use PseudoElement for Narrow-Tab Audio Indicator. ([#8033](https://github.com/brave/browser-laptop/issues/8033))
- [x] About pages cannot be synced because data is too big (favicon is encoded in Base64 format). ([#8023](https://github.com/brave/browser-laptop/issues/8023))
- [x] Redesigned importBrowserDataPanel.js. ([#7996](https://github.com/brave/browser-laptop/issues/7996))
- [x] Toggle excluding a site from ledger sometimes removes it from the list. ([#7987](https://github.com/brave/browser-laptop/issues/7987))
- [x] Sync does not appear to recover from network outage. ([#7972](https://github.com/brave/browser-laptop/issues/7972))
- [x] Sync is losing hierarchy when adding bookmarks to new sync members. ([#7971](https://github.com/brave/browser-laptop/issues/7971))
- [x] Refactor siteInfo.js with Aphrodite. ([#7949](https://github.com/brave/browser-laptop/issues/7949))
- [x] Add a new tab page for private tabs. ([#7934](https://github.com/brave/browser-laptop/issues/7934))
- [ ] Refactor popupWindow.less with Aphrodite. ([#7927](https://github.com/brave/browser-laptop/issues/7927))
- [x] Refactor bookmarksToolbar.js with Aphrodite. ([#7920](https://github.com/brave/browser-laptop/issues/7920))
- ~~[ ] Back/forward gesture should support three finger swipe. ([#7905](https://github.com/brave/browser-laptop/issues/7905))~~
- [x] First time wallet creation needs a better UI. ([#7889](https://github.com/brave/browser-laptop/issues/7889))
- [x] Modified contributionStatement.js with Aphrodite. ([#7883](https://github.com/brave/browser-laptop/issues/7883))
- ~~[ ] Ubuntu: Brave doesn't know that it's the default browser.. ([#7800](https://github.com/brave/browser-laptop/issues/7800))~~
- [x] Change "Save Torrent File" button to "Copy Magnet Link" for magnet links. ([#7772](https://github.com/brave/browser-laptop/issues/7772))
- ~~[ ] Contribution Statement opened in a new tab doesn't show the tab title until the cursor is moved over it or tab focus is changed. ([#7765](https://github.com/brave/browser-laptop/issues/7765))~~
- [x] Restructure paymentTab.js. ([#7750](https://github.com/brave/browser-laptop/issues/7750))
- [x] Add "Command+Click" to home button (opens home in a new background tab). ([#7718](https://github.com/brave/browser-laptop/issues/7718))
- [x] View Source shortcut should be CTRL+U, not CTRL+ALT+U. ([#7702](https://github.com/brave/browser-laptop/issues/7702))
- [x] Downloads should show origin. ([#7468](https://github.com/brave/browser-laptop/issues/7468))
- [x] Remove label from MultiMedia devices when fingerprinting protection is on.. ([#7462](https://github.com/brave/browser-laptop/issues/7462))
- [x] Pocket was translated when it should not.. ([#7450](https://github.com/brave/browser-laptop/issues/7450))
- [x] Right click not dismissing / hiding an open menu (Windows only). ([#7403](https://github.com/brave/browser-laptop/issues/7403))
- [x] Include current year in PDF statement copyright footer. ([#6878](https://github.com/brave/browser-laptop/issues/6878))
- [x] There is no obvious way to stop a torrent download once it has started. ([#6768](https://github.com/brave/browser-laptop/issues/6768))
- [x] Support torrent link files. ([#6671](https://github.com/brave/browser-laptop/issues/6671))
- [x] Add the release notes of the same version as the browser to about:brave. ([#6130](https://github.com/brave/browser-laptop/issues/6130))
- [x] Some info buttons in preferences are missing content links. ([#5758](https://github.com/brave/browser-laptop/issues/5758))
- [x] Add context-menu option to close tabs in tab page. ([#5489](https://github.com/brave/browser-laptop/issues/5489))
- [x] Honey: Support browserAction.setBadgeBackgroundColor. ([#5367](https://github.com/brave/browser-laptop/issues/5367))
- [x] Honey: Support chrome.browserAction.setBadgeText. ([#5366](https://github.com/brave/browser-laptop/issues/5366))
- [ ] Default browser setting gets reset after upgrade. ([#5246](https://github.com/brave/browser-laptop/issues/5246))
- [ ] Add Widevine support for Amazon Prime Video. ([#5233](https://github.com/brave/browser-laptop/issues/5233))
- [x] Favicons on brave payments list are not displayed until switching the tab. ([#4178](https://github.com/brave/browser-laptop/issues/4178))
- [x] Y position of context menu subitems is wrong when overflowed. ([#1589](https://github.com/brave/browser-laptop/issues/1589))
## Widevine/Netflix test
1. [x] Test that you can log into Netflix and start a show.
## Ledger
1. [ ] Create a wallet with a value other than $5 selected in the monthly budget dropdown. Click on the 'Add Funds' button and check that Coinbase transactions are blocked.
2. [x] Remove all `ledger-*.json` files from `~/Library/Application\ Support/Brave/`. Go to the Payments tab in about:preferences, enable payments, click on `create wallet`. Check that the `add funds` button appears after a wallet is created.
3. [ ] Click on `add funds` and verify that adding funds through Coinbase increases the account balance.
4. [ ] Repeat the step above but add funds by scanning the QR code in a mobile bitcoin app instead of through Coinbase.
5. [x] Visit nytimes.com for a few seconds and make sure it shows up in the Payments table.
6. [x] Go to https://jsfiddle.net/LnwtLckc/5/ and click the register button. In the Payments tab, click `add funds`. Verify that the `transfer funds` button is visible and that clicking on `transfer funds` opens a jsfiddle URL in a new tab.
7. [x] Go to https://jsfiddle.net/LnwtLckc/5/ and click `unregister`. Verify that the `transfer funds` button no longer appears in the `add funds` modal.
8. [x] Check that disabling payments and enabling them again does not lose state.
## Sync
1. [x] Verify you are able to sync two devices using the secret code
2. [x] Visit a site on device 1 and change shield setting, ensure that the saved site preference is synced to device 2
3. [x] Enable Browsing history sync on device 1, ensure the history is shown on device 2
4. [x] Import/Add bookmarks on device 1, ensure it is synced on device 2
5. [x] Ensure imported bookmark folder structure is maintained on device 2
6. [x] Ensure bookmark favicons are shown after sync
## Data
1. [x] Make sure that data from the last version appears in the new version OK.
2. [x] Test that the previous version's cookies are preserved in the next version.
## About pages
1. [x] Test that about:adblock loads
2. [x] Test that about:autofill loads
3. [x] Test that about:bookmarks loads bookmarks
4. [x] Test that about:downloads loads downloads
5. [x] Test that about:extensions loads
6. [x] Test that about:history loads history
7. [x] Test that about:passwords loads
8. [x] Test that about:styles loads
9. [x] Test that about:preferences changing a preference takes effect right away
10. [x] Test that about:preferences language change takes effect on re-start
11. [x] Test that about.com without the http protocol is loaded from URL bar
## Bookmarks
1. [x] Test that creating a bookmark on the bookmarks toolbar works
2. [x] Test that creating a bookmark folder on the bookmarks toolbar works
3. [x] Test that moving a bookmark into a folder by drag and drop on the bookmarks folder works
4. [x] Test that clicking a bookmark in the toolbar loads the bookmark.
5. [x] Test that clicking a bookmark in a bookmark toolbar folder loads the bookmark.
## Context menus
1. [x] Make sure context menu items in the URL bar work
2. [x] Make sure context menu items on content work with no selected text.
3. [x] Make sure context menu items on content work with selected text.
4. [x] Make sure context menu items on content work inside an editable control on `about:styles` (input, textarea, or contenteditable).
## Find on page
1. [x] Ensure search box is shown with shortcut
2. [x] Test successful find
3. [x] Test forward and backward find navigation
4. [x] Test failed find shows 0 results
5. [x] Test match case find
## Geolocation
1. [x] Check that https://developer.mozilla.org/en-US/docs/Web/API/Geolocation/Using_geolocation works
## Site hacks
1. [x] Test https://www.twitch.tv/adobe sub-page loads a video and you can play it
## Downloads
1. [x] Test downloading a file works and that all actions on the download item works.
## Fullscreen
1. [x] Test that entering full screen window works View -> Toggle Full Screen. And exit back (Not Esc).
2. [x] Test that entering HTML5 full screen works. And Esc to go back. (youtube.com)
## Tabs and Pinning
1. [x] Test that tabs are pinnable
2. [x] Test that tabs are unpinnable
3. [x] Test that tabs are draggable to same tabset
4. [x] Test that tabs are draggable to alternate tabset
## Zoom
1. [x] Test zoom in / out shortcut works
2. [x] Test hamburger menu zooms.
3. [x] Test zoom saved when you close the browser and restore on a single site.
4. [x] Test zoom saved when you navigate within a single origin site.
5. [x] Test that navigating to a different origin resets the zoom
## Bravery settings
1. [x] Check that HTTPS Everywhere works by loading http://www.apple.com
2. [x] Turning HTTPS Everywhere off and shields off both disable the redirect to https://www.apple.com
3. [x] Check that ad replacement works on http://slashdot.org
4. [x] Check that toggling to blocking and allow ads works as expected.
5. [x] Test that clicking through a cert error in https://badssl.com/ works.
6. [x] Test that Safe Browsing works (http://downloadme.org/)
7. [x] Turning Safe Browsing off and shields off both disable safe browsing for http://downloadme.org/.
8. [x] Visit https://brianbondy.com/ and then turn on script blocking, nothing should load. Allow it from the script blocking UI in the URL bar and it should work.
9. [x] Test that about:preferences default Bravery settings take effect on pages with no site settings.
10. [x] Test that turning on fingerprinting protection in about:preferences shows 3 fingerprints blocked at https://jsfiddle.net/bkf50r8v/13/. Test that turning it off in the Bravery menu shows 0 fingerprints blocked.
11. [x] Test that 3rd party storage results are blank at https://jsfiddle.net/7ke9r14a/9/ when 3rd party cookies are blocked and not blank when 3rd party cookies are unblocked.
12. [x] Test that audio fingerprint is blocked at https://audiofingerprint.openwpm.com/ when fingerprinting protection is on.
## Content tests
1. [x] Go to https://brianbondy.com/ and click on the twitter icon on the top right. Test that context menus work in the new twitter tab.
2. [x] Load twitter and click on a tweet so the popup div shows. Click to dismiss and repeat with another div. Make sure it shows.
3. [x] Go to http://www.bennish.net/web-notifications.html and test that clicking on 'Show' pops up a notification asking for permission. Make sure that clicking 'Deny' leads to no notifications being shown.
4. [x] Go to https://trac.torproject.org/projects/tor/login and make sure that the password can be saved. Make sure the saved password shows up in `about:passwords`. Then reload https://trac.torproject.org/projects/tor/login and make sure the password is autofilled.
5. [x] Open a github issue and type some misspellings, make sure they are underlined.
6. [x] Make sure that right clicking on a word with suggestions gives a suggestion and that clicking on the suggestion replaces the text.
7. [x] Make sure that Command + Click (Control + Click on Windows, Control + Click on Ubuntu) on a link opens a new tab but does NOT switch to it. Click on it and make sure it is already loaded.
8. [x] Open an email on http://mail.google.com/ or inbox.google.com and click on a link. Make sure it works.
9. [x] Test that PDF is loaded at http://www.orimi.com/pdf-test.pdf
10. [x] Test that https://mixed-script.badssl.com/ shows up as grey not red (no mixed content scripts are run).
## Flash tests
1. [x] Turn on Flash in about:preferences#security. Test that clicking on 'Install Flash' banner on myspace.com shows a notification to allow Flash and that the banner disappears when 'Allow' is clicked.
2. [x] Test that flash placeholder appears on http://www.homestarrunner.com
## Autofill tests
1. [x] Test that autofill works on http://www.roboform.com/filling-test-all-fields
## Session storage
Do not forget to make a backup of your entire `~/Library/Application\ Support/Brave` folder.
1. [x] Temporarily move away your `~/Library/Application\ Support/Brave/session-store-1` and test that clean session storage works. (`%appdata%\Brave in Windows`, `./config/brave` in Ubuntu)
2. [x] Test that windows and tabs restore when closed, including active tab.
3. [x] Move away your entire `~/Library/Application\ Support/Brave` folder (`%appdata%\Brave in Windows`, `./config/brave` in Ubuntu)
## Cookie and Cache
1. [x] Make a backup of your profile, turn on all clearing in preferences and shut down. Make sure when you bring the browser back up everything is gone that is specified.
2. [x] Go to http://samy.pl/evercookie/ and set an evercookie. Check that going to prefs, clearing site data and cache, and going back to the Evercookie site does not remember the old evercookie value.
## Update tests
1. [x] Test that updating using `BRAVE_UPDATE_VERSION=0.8.3` env variable works correctly.
|
test
|
manual tests for windows ia preview installer check that installer is close to the size of last release check signature if os run spctl assess verbose applications brave app and make sure it returns accepted if windows right click on the installer exe and go to properties go to the digital signatures tab and double click on the signature make sure it says the digital signature is ok in the popup window check brave muon and libchromiumcontent version in about and make sure it is exactly as expected last changeset test test what is covered by the last changeset you can find this by clicking on the sha in about brave per release specialty tests ledger calculation when eligible unpinned sites javascript bookmarks cause connection info box to appear enabling show include site with autoinclude off shows payment info page when refreshed revert the inlined files on contributionstatement js follow up to fix radii colors focused state styles in url bar related to new add funds button lastpass opens in wrong position when activated by keyboard use pseudoelement for narrow tab audio indicator about pages cannot be synced because data is too big favicon is encoded in format redesigned importbrowserdatapanel js toggle excluding a site from ledger sometimes removes it from the list sync does not appear to recover from network outage sync is losing hierarchy when adding bookmarks to new sync members refactor siteinfo js with aphrodite add a new tab page for private tabs refactor popupwindow less with aphrodite refactor bookmarkstoolbar js with aphrodite back forward gesture should support three finger swipe first time wallet creation needs a better ui modified contributionstatement js with aphrodite ubuntu brave doesn t know that it s the default browser change save torrent file button to copy magnet link for magnet links contribution statement opened in a new tab doesn t show the tab title until the cursor is moved over it or tab focus is changed restructure paymenttab js add command click to home button opens home in a new background tab view source shortcut should be ctrl u not ctrl alt u downloads should show origin remove label from multimedia devices when fingerprinting protection is on pocket was translated when it should not right click not dismissing hiding an open menu windows only include current year in pdf statement copyright footer there is no obvious way to stop a torrent download once it has started support torrent link files add the release notes of the same version as the browser to about brave some info buttons in preferences are missing content links add context menu option to close tabs in tab page honey support browseraction setbadgebackgroundcolor honey support chrome browseraction setbadgetext default browser setting gets reset after upgrade add widevine support for amazon prime video favicons on brave payments list are not displayed until switching the tab y position of context menu subitems is wrong when overflowed widevine netflix test test that you can log into netflix and start a show ledger create a wallet with a value other than selected in the monthly budget dropdown click on the add funds button and check that coinbase transactions are blocked remove all ledger json files from library application support brave go to the payments tab in about preferences enable payments click on create wallet check that the add funds button appears after a wallet is created click on add funds and verify that adding funds through coinbase increases the account balance repeat the step above but add funds by scanning the qr code in a mobile bitcoin app instead of through coinbase visit nytimes com for a few seconds and make sure it shows up in the payments table go to and click the register button in the payments tab click add funds verify that the transfer funds button is visible and that clicking on transfer funds opens a jsfiddle url in a new tab go to and click unregister verify that the transfer funds button no longer appears in the add funds modal check that disabling payments and enabling them again does not lose state sync verify you are able to sync two devices using the secret code visit a site on device and change shield setting ensure that the saved site preference is synced to device enable browsing history sync on device ensure the history is shown on device import add bookmarks on device ensure it is synced on device ensure imported bookmark folder structure is maintained on device ensure bookmark favicons are shown after sync data make sure that data from the last version appears in the new version ok test that the previous version s cookies are preserved in the next version about pages test that about adblock loads test that about autofill loads test that about bookmarks loads bookmarks test that about downloads loads downloads test that about extensions loads test that about history loads history test that about passwords loads test that about styles loads test that about preferences changing a preference takes effect right away test that about preferences language change takes effect on re start test that about com without the http protocol is loaded from url bar bookmarks test that creating a bookmark on the bookmarks toolbar works test that creating a bookmark folder on the bookmarks toolbar works test that moving a bookmark into a folder by drag and drop on the bookmarks folder works test that clicking a bookmark in the toolbar loads the bookmark test that clicking a bookmark in a bookmark toolbar folder loads the bookmark context menus make sure context menu items in the url bar work make sure context menu items on content work with no selected text make sure context menu items on content work with selected text make sure context menu items on content work inside an editable control on about styles input textarea or contenteditable find on page ensure search box is shown with shortcut test successful find test forward and backward find navigation test failed find shows results test match case find geolocation check that works site hacks test sub page loads a video and you can play it downloads test downloading a file works and that all actions on the download item works fullscreen test that entering full screen window works view toggle full screen and exit back not esc test that entering full screen works and esc to go back youtube com tabs and pinning test that tabs are pinnable test that tabs are unpinnable test that tabs are draggable to same tabset test that tabs are draggable to alternate tabset zoom test zoom in out shortcut works test hamburger menu zooms test zoom saved when you close the browser and restore on a single site test zoom saved when you navigate within a single origin site test that navigating to a different origin resets the zoom bravery settings check that https everywhere works by loading turning https everywhere off and shields off both disable the redirect to check that ad replacement works on check that toggling to blocking and allow ads works as expected test that clicking through a cert error in works test that safe browsing works turning safe browsing off and shields off both disable safe browsing for visit and then turn on script blocking nothing should load allow it from the script blocking ui in the url bar and it should work test that about preferences default bravery settings take effect on pages with no site settings test that turning on fingerprinting protection in about preferences shows fingerprints blocked at test that turning it off in the bravery menu shows fingerprints blocked test that party storage results are blank at when party cookies are blocked and not blank when party cookies are unblocked test that audio fingerprint is blocked at when fingerprinting protection is on content tests go to and click on the twitter icon on the top right test that context menus work in the new twitter tab load twitter and click on a tweet so the popup div shows click to dismiss and repeat with another div make sure it shows go to and test that clicking on show pops up a notification asking for permission make sure that clicking deny leads to no notifications being shown go to and make sure that the password can be saved make sure the saved password shows up in about passwords then reload and make sure the password is autofilled open a github issue and type some misspellings make sure they are underlined make sure that right clicking on a word with suggestions gives a suggestion and that clicking on the suggestion replaces the text make sure that command click control click on windows control click on ubuntu on a link opens a new tab but does not switch to it click on it and make sure it is already loaded open an email on or inbox google com and click on a link make sure it works test that pdf is loaded at test that shows up as grey not red no mixed content scripts are run flash tests turn on flash in about preferences security test that clicking on install flash banner on myspace com shows a notification to allow flash and that the banner disappears when allow is clicked test that flash placeholder appears on autofill tests test that autofill works on session storage do not forget to make a backup of your entire library application support brave folder temporarily move away your library application support brave session store and test that clean session storage works appdata brave in windows config brave in ubuntu test that windows and tabs restore when closed including active tab move away your entire library application support brave folder appdata brave in windows config brave in ubuntu cookie and cache make a backup of your profile turn on all clearing in preferences and shut down make sure when you bring the browser back up everything is gone that is specified go to and set an evercookie check that going to prefs clearing site data and cache and going back to the evercookie site does not remember the old evercookie value update tests test that updating using brave update version env variable works correctly
| 1
|
259,631
| 22,503,473,375
|
IssuesEvent
|
2022-06-23 13:44:39
|
Joystream/pioneer
|
https://api.github.com/repos/Joystream/pioneer
|
closed
|
BuyMembershipModal
|
qa-task qa-tested-ready-for-prod qa-effort-1.5h release:stabilisation7
|
Refactor the `BuyMembershipModal` as part of the #2802 epic.
## Dev scope
- [x] Refactor fields validation
- [x] Manage the form state with React Hook Form instead of XState
## QA scope
- [ ] The fields are validated correctly
- [ ] The transaction gets sent with the parameter set in the modal
|
1.0
|
BuyMembershipModal - Refactor the `BuyMembershipModal` as part of the #2802 epic.
## Dev scope
- [x] Refactor fields validation
- [x] Manage the form state with React Hook Form instead of XState
## QA scope
- [ ] The fields are validated correctly
- [ ] The transaction gets sent with the parameter set in the modal
|
test
|
buymembershipmodal refactor the buymembershipmodal as part of the epic dev scope refactor fields validation manage the form state with react hook form instead of xstate qa scope the fields are validated correctly the transaction gets sent with the parameter set in the modal
| 1
|
91,147
| 11,471,472,361
|
IssuesEvent
|
2020-02-09 11:28:47
|
SinergiaApp/NeLS-Project
|
https://api.github.com/repos/SinergiaApp/NeLS-Project
|
closed
|
Indicar Nombre de la Biblioteca en la Ficha de Recursos
|
S_BUG S_HIGH T_DESIGN T_REFACTOR
|
Cuando queremos ver la disponibilidad de los recursos, ésta aparece sólo en formato numérico, sin indicar la biblioteca que estamos seleccionando.
Tiene que tener el siguiente formato: [disponibilidad] - Nombre de la Biblioteca.
|
1.0
|
Indicar Nombre de la Biblioteca en la Ficha de Recursos - Cuando queremos ver la disponibilidad de los recursos, ésta aparece sólo en formato numérico, sin indicar la biblioteca que estamos seleccionando.
Tiene que tener el siguiente formato: [disponibilidad] - Nombre de la Biblioteca.
|
non_test
|
indicar nombre de la biblioteca en la ficha de recursos cuando queremos ver la disponibilidad de los recursos ésta aparece sólo en formato numérico sin indicar la biblioteca que estamos seleccionando tiene que tener el siguiente formato nombre de la biblioteca
| 0
|
174,588
| 13,496,134,933
|
IssuesEvent
|
2020-09-12 02:16:48
|
jsoss-sig/keycloak-fapi
|
https://api.github.com/repos/jsoss-sig/keycloak-fapi
|
closed
|
Confirm all FAPI R/W OP w/ Private Key conformance tests are passed by the locally built keycloak
|
Authz Server Environment TestPlan: private_key_jwt keycloak
|
Confirm all FAPI R/W OP w/ MTLS conformance tests are passed by the locally build keycloak that the following issues are resolved (not yet sent as PRs).
- [KEYCLOAK-15448](https://issues.redhat.com/browse/KEYCLOAK-15448)
- [KEYCLOAK-14195](https://issues.redhat.com/browse/KEYCLOAK-14195)
- [KEYCLOAK-14204](https://issues.redhat.com/browse/KEYCLOAK-14204)
- [KEYCLOAK-14205](https://issues.redhat.com/browse/KEYCLOAK-14205)
clarified by https://github.com/jsoss-sig/keycloak-fapi/issues/42
|
1.0
|
Confirm all FAPI R/W OP w/ Private Key conformance tests are passed by the locally built keycloak - Confirm all FAPI R/W OP w/ MTLS conformance tests are passed by the locally build keycloak that the following issues are resolved (not yet sent as PRs).
- [KEYCLOAK-15448](https://issues.redhat.com/browse/KEYCLOAK-15448)
- [KEYCLOAK-14195](https://issues.redhat.com/browse/KEYCLOAK-14195)
- [KEYCLOAK-14204](https://issues.redhat.com/browse/KEYCLOAK-14204)
- [KEYCLOAK-14205](https://issues.redhat.com/browse/KEYCLOAK-14205)
clarified by https://github.com/jsoss-sig/keycloak-fapi/issues/42
|
test
|
confirm all fapi r w op w private key conformance tests are passed by the locally built keycloak confirm all fapi r w op w mtls conformance tests are passed by the locally build keycloak that the following issues are resolved not yet sent as prs clarified by
| 1
|
18,652
| 10,172,321,070
|
IssuesEvent
|
2019-08-08 10:23:24
|
google/guava
|
https://api.github.com/repos/google/guava
|
closed
|
ImmutableSet.copyOf quadratic running time behavior
|
P3 package=collect status=triaged type=performance
|
Hi,
I found an input pattern that can trigger Ω(N^2) running time behavior of ImmutableSet.copyOf, this problem is similar to [ImmutableBiMap.copyOf quadratic running time behavior](https://github.com/google/guava/issues/3015)
The input is constructed and tested using the following code:
```java
import com.google.common.collect.ImmutableSet;
import java.util.ArrayList;
import java.util.Random;
public class GuavaImmutableSet {
public static void main(String[] args) {
ArrayList<Integer> pattern = generateInput();
ArrayList<Integer> randomInput = randomInput(pattern.size());
System.out.println("pattern size: " + pattern.size());
int testNum = 2000;
long start;
double timeUse;
start = System.nanoTime();
for(int i = 0; i < testNum; i++) {
ImmutableSet.copyOf(randomInput);
}
timeUse = (System.nanoTime() - start)/1e9;
System.out.println("Random input time use: " + timeUse + "s.");
start = System.nanoTime();
for(int i = 0; i < testNum; i++) {
ImmutableSet.copyOf(pattern);
}
timeUse = (System.nanoTime() - start)/1e9;
System.out.println("Pattern time use: " + timeUse + "s.");
}
public static ArrayList<Integer> generateInput(){
String input = "807254551,807254816,807254570,807254693,807137056,807136810,807136933,941284384,941284138,941284261,1075431712,1075431466,1075431589,1209579040,1209578794,1209578917,1343726368,1343726122,1343726245,1477873696,1477873450,1477873573,1612021024,1612020778,1612020901,1746168352,1746168106,1746168229,1880315680,1880315434,1880315557,2014463008,2014462762,2014462885,-2146356960,-2146357206,-2146357083,-2012209632,-2012209878,-2012209755,-1878062304,-1878062550,-1878062427,-1743914976,-1743915222,-1743915099,-1609767648,-1609767894,-1609767771,-1475620320,-1475620566,-1475620443,-1341472992,-1341473238,-1341473115,-1207325664,-1207325910,-1207325787,-1073178336,-1073178582,-1073178459,-939031008,-939031254,-939031131,-804883680,-804883926,-804883803,-670736352,-670736598,-670736475,-536589024,-536589270,-536589147,-402441696,-402441942,-402441819,-268294368,-268294614,-268294491,-134147040,-134147286,-134147163,-67633091,873768727,873768992,873768746,873768869,873651232,873650986,873651109,1007798560,1007798314,1007798437,1141945888,1141945642,1141945765,1276093216,1276092970,1276093093,1410240544,1410240298,1410240421,1544387872,1544387626,1544387749,1678535200,1678534954,1678535077,1812682528,1812682282,1812682405,1946829856,1946829610,1946829733,2080977184,2080976938,2080977061,-2079842784,-2079843030,-2079842907,-1945695456,-1945695702,-1945695579,-1811548128,-1811548374,-1811548251,-1677400800,-1677401046,-1677400923,-1543253472,-1543253718,-1543253595,-1409106144,-1409106390,-1409106267,-1274958816,-1274959062,-1274958939,-1140811488,-1140811734,-1140811611,-1006664160,-1006664406,-1006664283,-872516832,-872517078,-872516955,-738369504,-738369750,-738369627,-604222176,-604222422,-604222299,-470074848,-470075094,-470074971,-335927520,-335927766,-335927643,-201780192,-201780438,-201780315,-135266243,940282903,940283168,940282922,940283045,940165408,940165162,940165285,1074312736,1074312490,1074312613,1208460064,1208459818,1208459941,1342607392,1342607146,1342607269,1476754720,1476754474,1476754597,1610902048,1610901802,1610901925,1745049376,1745049130,1745049253,1879196704,1879196458,1879196581,2013344032,2013343786,2013343909,-2147475936,-2147476182,-2147476059,-2013328608,-2013328854,-2013328731,-1879181280,-1879181526,-1879181403,-1745033952,-1745034198,-1745034075,-1610886624,-1610886870,-1610886747,-1476739296,-1476739542,-1476739419,-1342591968,-1342592214,-1342592091,-1208444640,-1208444886,-1208444763,-1074297312,-1074297558,-1074297435,-940149984,-940150230,-940150107,-806002656,-806002902,-806002779,-671855328,-671855574,-671855451,-537708000,-537708246,-537708123,-403560672,-403560918,-403560795,-269413344,-269413590,-269413467,-202899395,1006797079,1006797344,1006797098,1006797221,1006679584,1006679338,1006679461,1140826912,1140826666,1140826789,1274974240,1274973994,1274974117,1409121568,1409121322,1409121445,1543268896,1543268650,1543268773,1677416224,1677415978,1677416101,1811563552,1811563306,1811563429,1945710880,1945710634,1945710757,2079858208,2079857962,2079858085,-2080961760,-2080962006,-2080961883,-1946814432,-1946814678,-1946814555,-1812667104,-1812667350,-1812667227,-1678519776,-1678520022,-1678519899,-1544372448,-1544372694,-1544372571,-1410225120,-1410225366,-1410225243,-1276077792,-1276078038,-1276077915,-1141930464,-1141930710,-1141930587,-1007783136,-1007783382,-1007783259,-873635808,-873636054,-873635931,-739488480,-739488726,-739488603,-605341152,-605341398,-605341275,-471193824,-471194070,-471193947,-337046496,-337046742,-337046619,-270532547,1073311255,1073311520,1073311274,1073311397,1073193760,1073193514,1073193637,1207341088,1207340842,1207340965,1341488416,1341488170,1341488293,1475635744,1475635498,1475635621,1609783072,1609782826,1609782949,1743930400,1743930154,1743930277,1878077728,1878077482,1878077605,2012225056,2012224810,2012224933,2146372384,2146372138,2146372261,-2014447584,-2014447830,-2014447707,-1880300256,-1880300502,-1880300379,-1746152928,-1746153174,-1746153051,-1612005600,-1612005846,-1612005723,-1477858272,-1477858518,-1477858395,-1343710944,-1343711190,-1343711067,-1209563616,-1209563862,-1209563739,-1075416288,-1075416534,-1075416411,-941268960,-941269206,-941269083,-807121632,-807121878,-807121755,-672974304,-672974550,-672974427,-538826976,-538827222,-538827099,-404679648,-404679894,-404679771,-338165699,1139825431,1139825696,1139825450,1139825573,1139707936,1139707690,1139707813,1273855264,1273855018,1273855141,1408002592,1408002346,1408002469,1542149920,1542149674,1542149797,1676297248,1676297002,1676297125,1810444576,1810444330,1810444453,1944591904,1944591658,1944591781,2078739232,2078738986,2078739109,-2082080736,-2082080982,-2082080859,-1947933408,-1947933654,-1947933531,-1813786080,-1813786326,-1813786203,-1679638752,-1679638998,-1679638875,-1545491424,-1545491670,-1545491547,-1411344096,-1411344342,-1411344219,-1277196768,-1277197014,-1277196891,-1143049440,-1143049686,-1143049563,-1008902112,-1008902358,-1008902235,-874754784,-874755030,-874754907,-740607456,-740607702,-740607579,-606460128,-606460374,-606460251,-472312800,-472313046,-472312923,-405798851,1206339607,1206339872,1206339626,1206339749,1206222112,1206221866,1206221989,1340369440,1340369194,1340369317,1474516768,1474516522,1474516645,1608664096,1608663850,1608663973,1742811424,1742811178,1742811301,1876958752,1876958506,1876958629,2011106080,2011105834,2011105957,2145253408,2145253162,2145253285,-2015566560,-2015566806,-2015566683,-1881419232,-1881419478,-1881419355,-1747271904,-1747272150,-1747272027,-1613124576,-1613124822,-1613124699,-1478977248,-1478977494,-1478977371,-1344829920,-1344830166,-1344830043,-1210682592,-1210682838,-1210682715,-1076535264,-1076535510,-1076535387,-942387936,-942388182,-942388059,-808240608,-808240854,-808240731,-674093280,-674093526,-674093403,-539945952,-539946198,-539946075,-473432003,1272853783,1272854048,1272853802,1272853925,1272736288,1272736042,1272736165,1406883616,1406883370,1406883493,1541030944,1541030698,1541030821,1675178272,1675178026,1675178149,1809325600,1809325354,1809325477,1943472928,1943472682,1943472805,2077620256,2077620010,2077620133,-2083199712,-2083199958,-2083199835,-1949052384,-1949052630,-1949052507,-1814905056,-1814905302,-1814905179,-1680757728,-1680757974,-1680757851,-1546610400,-1546610646,-1546610523,-1412463072,-1412463318,-1412463195,-1278315744,-1278315990,-1278315867,-1144168416,-1144168662,-1144168539,-1010021088,-1010021334,-1010021211,-875873760,-875874006,-875873883,-741726432,-741726678,-741726555,-607579104,-607579350,-607579227,-541065155,1339367959,1339368224,1339367978,1339368101,1339250464,1339250218,1339250341,1473397792,1473397546,1473397669,1607545120,1607544874,1607544997,1741692448,1741692202,1741692325,1875839776,1875839530,1875839653,2009987104,2009986858,2009986981,2144134432,2144134186,2144134309,-2016685536,-2016685782,-2016685659,-1882538208,-1882538454,-1882538331,-1748390880,-1748391126,-1748391003,-1614243552,-1614243798,-1614243675,-1480096224,-1480096470,-1480096347,-1345948896,-1345949142,-1345949019,-1211801568,-1211801814,-1211801691,-1077654240,-1077654486,-1077654363,-943506912,-943507158,-943507035,-809359584,-809359830,-809359707,-675212256,-675212502,-675212379,-608698307,1405882135,1405882400,1405882154,1405882277,1405764640,1405764394,1405764517,1539911968,1539911722,1539911845,1674059296,1674059050,1674059173,1808206624,1808206378,1808206501,1942353952,1942353706,1942353829,2076501280,2076501034,2076501157,-2084318688,-2084318934,-2084318811,-1950171360,-1950171606,-1950171483,-1816024032,-1816024278,-1816024155,-1681876704,-1681876950,-1681876827,-1547729376,-1547729622,-1547729499,-1413582048,-1413582294,-1413582171,-1279434720,-1279434966,-1279434843,-1145287392,-1145287638,-1145287515,-1011140064,-1011140310,-1011140187,-876992736,-876992982,-876992859,-742845408,-742845654,-742845531,-676331459,1472396311,1472396576,1472396330,1472396453,1472278816,1472278570,1472278693,1606426144,1606425898,1606426021,1740573472,1740573226,1740573349,1874720800,1874720554,1874720677,2008868128,2008867882,2008868005,2143015456,2143015210,2143015333,-2017804512,-2017804758,-2017804635,-1883657184,-1883657430,-1883657307,-1749509856,-1749510102,-1749509979,-1615362528,-1615362774,-1615362651,-1481215200,-1481215446,-1481215323,-1347067872,-1347068118,-1347067995,-1212920544,-1212920790,-1212920667,-1078773216,-1078773462,-1078773339,-944625888,-944626134,-944626011,-810478560,-810478806,-810478683,-743964611,1538910487,1538910752,1538910506,1538910629,1538792992,1538792746,1538792869,1672940320,1672940074,1672940197,1807087648,1807087402,1807087525,1941234976,1941234730,1941234853,2075382304,2075382058,2075382181,-2085437664,-2085437910,-2085437787,-1951290336,-1951290582,-1951290459,-1817143008,-1817143254,-1817143131,-1682995680,-1682995926,-1682995803,-1548848352,-1548848598,-1548848475,-1414701024,-1414701270,-1414701147,-1280553696,-1280553942,-1280553819,-1146406368,-1146406614,-1146406491,-1012259040,-1012259286,-1012259163,-878111712,-878111958,-878111835,-811597763,1605424663,1605424928,1605424682,1605424805,1605307168,1605306922,1605307045,1739454496,1739454250,1739454373,1873601824,1873601578,1873601701,2007749152,2007748906,2007749029,2141896480,2141896234,2141896357,-2018923488,-2018923734,-2018923611,-1884776160,-1884776406,-1884776283,-1750628832,-1750629078,-1750628955,-1616481504,-1616481750,-1616481627,-1482334176,-1482334422,-1482334299,-1348186848,-1348187094,-1348186971,-1214039520,-1214039766,-1214039643,-1079892192,-1079892438,-1079892315,-945744864,-945745110,-945744987,-879230915,1671938839,1671939104,1671938858,1671938981,1671821344,1671821098,1671821221,1805968672,1805968426,1805968549,1940116000,1940115754,1940115877,2074263328,2074263082,2074263205,-2086556640,-2086556886,-2086556763,-1952409312,-1952409558,-1952409435,-1818261984,-1818262230,-1818262107,-1684114656,-1684114902,-1684114779,-1549967328,-1549967574,-1549967451,-1415820000,-1415820246,-1415820123,-1281672672,-1281672918,-1281672795,-1147525344,-1147525590,-1147525467,-1013378016,-1013378262,-1013378139,-946864067,1738453015,1738453280,1738453034,1738453157,1738335520,1738335274,1738335397,1872482848,1872482602,1872482725,2006630176,2006629930,2006630053,2140777504,2140777258,2140777381,-2020042464,-2020042710,-2020042587,-1885895136,-1885895382,-1885895259,-1751747808,-1751748054,-1751747931,-1617600480,-1617600726,-1617600603,-1483453152,-1483453398,-1483453275,-1349305824,-1349306070,-1349305947,-1215158496,-1215158742,-1215158619,-1081011168,-1081011414,-1081011291,-1014497219,1804967191,1804967456,1804967210,1804967333,1804849696,1804849450,1804849573,1938997024,1938996778,1938996901,2073144352,2073144106,2073144229,-2087675616,-2087675862,-2087675739,-1953528288,-1953528534,-1953528411,-1819380960,-1819381206,-1819381083,-1685233632,-1685233878,-1685233755,-1551086304,-1551086550,-1551086427,-1416938976,-1416939222,-1416939099,-1282791648,-1282791894,-1282791771,-1148644320,-1148644566,-1148644443,-1082130371,1871481367,1871481632,1871481386,1871481509,1871363872,1871363626,1871363749,2005511200,2005510954,2005511077,2139658528,2139658282,2139658405,-2021161440,-2021161686,-2021161563,-1887014112,-1887014358,-1887014235,-1752866784,-1752867030,-1752866907,-1618719456,-1618719702,-1618719579,-1484572128,-1484572374,-1484572251,-1350424800,-1350425046,-1350424923,-1216277472,-1216277718,-1216277595,-1149763523,1937995543,1937995808,1937995562,1937995685,1937878048,1937877802,1937877925,2072025376,2072025130,2072025253,-2088794592,-2088794838,-2088794715,-1954647264,-1954647510,-1954647387,-1820499936,-1820500182,-1820500059,-1686352608,-1686352854,-1686352731,-1552205280,-1552205526,-1552205403,-1418057952,-1418058198,-1418058075,-1283910624,-1283910870,-1283910747,-1217396675,2004509719,2004509984,2004509738,2004509861,2004392224,2004391978,2004392101,2138539552,2138539306,2138539429,-2022280416,-2022280662,-2022280539,-1888133088,-1888133334,-1888133211,-1753985760,-1753986006,-1753985883,-1619838432,-1619838678,-1619838555,-1485691104,-1485691350,-1485691227,-1351543776,-1351544022,-1351543899,-1285029827,2071023895,2071024160,2071023914,2071024037,2070906400,2070906154,2070906277,-2089913568,-2089913814,-2089913691,-1955766240,-1955766486,-1955766363,-1821618912,-1821619158,-1821619035,-1687471584,-1687471830,-1687471707,-1553324256,-1553324502,-1553324379,-1419176928,-1419177174,-1419177051,-1352662979,2137538071,2137538336,2137538090,2137538213,2137420576,2137420330,2137420453,-2023399392,-2023399638,-2023399515,-1889252064,-1889252310,-1889252187,-1755104736,-1755104982,-1755104859,-1620957408,-1620957654,-1620957531,-1486810080,-1486810326,-1486810203,-1420296131,-2090915049,-2090914784,-2090915030,-2090914907,-2091032544,-2091032790,-2091032667,-1956885216,-1956885462,-1956885339,-1822737888,-1822738134,-1822738011,-1688590560,-1688590806,-1688590683,-1554443232,-1554443478,-1554443355,-1487929283,-2024400873,-2024400608,-2024400854,-2024400731,-2024518368,-2024518614,-2024518491,-1890371040,-1890371286,-1890371163,-1756223712,-1756223958,-1756223835,-1622076384,-1622076630,-1622076507,-1555562435,-1957886697,-1957886432,-1957886678,-1957886555,-1958004192,-1958004438,-1958004315,-1823856864,-1823857110,-1823856987,-1689709536,-1689709782,-1689709659,-1623195587,-1891372521,-1891372256,-1891372502,-1891372379,-1891490016,-1891490262,-1891490139,-1757342688,-1757342934,-1757342811,-1690828739,-1824858345,-1824858080,-1824858326,-1824858203,-1824975840,-1824976086,-1824975963,-1758461891,-1758344169,-1758343904,-1758344150,-1758344027,-1691829955,-1691829993,-1691829728,-1691829788,-1691829787,-1691829776,-1691829783,-1691829776,-1691829788,-1691829767";
ArrayList<Integer> list = new ArrayList<>();
for(String s : input.split(",")){
list.add(Integer.parseInt(s));
}
return list;
}
public static ArrayList<Integer> randomInput(int size){
Random rand = new Random(1);
ArrayList<Integer> list = new ArrayList<>();
for (int i = 0; i < size; i ++){
list.add(rand.nextInt());
}
return list;
}
}
```
On my machine, when running with -Xint, I got the following result:
```
pattern size: 1197
Random input time use: 1.15802056s.
Pattern time use: 106.958007337s.
```
The performance-inputSize relationship can roughly be fitted as a quadratic curve:
<img width="687" alt="fit-immutableset" src="https://user-images.githubusercontent.com/11240361/34278192-03af6472-e66f-11e7-9199-1375c74fbea6.png">
|
True
|
ImmutableSet.copyOf quadratic running time behavior - Hi,
I found an input pattern that can trigger Ω(N^2) running time behavior of ImmutableSet.copyOf, this problem is similar to [ImmutableBiMap.copyOf quadratic running time behavior](https://github.com/google/guava/issues/3015)
The input is constructed and tested using the following code:
```java
import com.google.common.collect.ImmutableSet;
import java.util.ArrayList;
import java.util.Random;
public class GuavaImmutableSet {
public static void main(String[] args) {
ArrayList<Integer> pattern = generateInput();
ArrayList<Integer> randomInput = randomInput(pattern.size());
System.out.println("pattern size: " + pattern.size());
int testNum = 2000;
long start;
double timeUse;
start = System.nanoTime();
for(int i = 0; i < testNum; i++) {
ImmutableSet.copyOf(randomInput);
}
timeUse = (System.nanoTime() - start)/1e9;
System.out.println("Random input time use: " + timeUse + "s.");
start = System.nanoTime();
for(int i = 0; i < testNum; i++) {
ImmutableSet.copyOf(pattern);
}
timeUse = (System.nanoTime() - start)/1e9;
System.out.println("Pattern time use: " + timeUse + "s.");
}
public static ArrayList<Integer> generateInput(){
String input = "807254551,807254816,807254570,807254693,807137056,807136810,807136933,941284384,941284138,941284261,1075431712,1075431466,1075431589,1209579040,1209578794,1209578917,1343726368,1343726122,1343726245,1477873696,1477873450,1477873573,1612021024,1612020778,1612020901,1746168352,1746168106,1746168229,1880315680,1880315434,1880315557,2014463008,2014462762,2014462885,-2146356960,-2146357206,-2146357083,-2012209632,-2012209878,-2012209755,-1878062304,-1878062550,-1878062427,-1743914976,-1743915222,-1743915099,-1609767648,-1609767894,-1609767771,-1475620320,-1475620566,-1475620443,-1341472992,-1341473238,-1341473115,-1207325664,-1207325910,-1207325787,-1073178336,-1073178582,-1073178459,-939031008,-939031254,-939031131,-804883680,-804883926,-804883803,-670736352,-670736598,-670736475,-536589024,-536589270,-536589147,-402441696,-402441942,-402441819,-268294368,-268294614,-268294491,-134147040,-134147286,-134147163,-67633091,873768727,873768992,873768746,873768869,873651232,873650986,873651109,1007798560,1007798314,1007798437,1141945888,1141945642,1141945765,1276093216,1276092970,1276093093,1410240544,1410240298,1410240421,1544387872,1544387626,1544387749,1678535200,1678534954,1678535077,1812682528,1812682282,1812682405,1946829856,1946829610,1946829733,2080977184,2080976938,2080977061,-2079842784,-2079843030,-2079842907,-1945695456,-1945695702,-1945695579,-1811548128,-1811548374,-1811548251,-1677400800,-1677401046,-1677400923,-1543253472,-1543253718,-1543253595,-1409106144,-1409106390,-1409106267,-1274958816,-1274959062,-1274958939,-1140811488,-1140811734,-1140811611,-1006664160,-1006664406,-1006664283,-872516832,-872517078,-872516955,-738369504,-738369750,-738369627,-604222176,-604222422,-604222299,-470074848,-470075094,-470074971,-335927520,-335927766,-335927643,-201780192,-201780438,-201780315,-135266243,940282903,940283168,940282922,940283045,940165408,940165162,940165285,1074312736,1074312490,1074312613,1208460064,1208459818,1208459941,1342607392,1342607146,1342607269,1476754720,1476754474,1476754597,1610902048,1610901802,1610901925,1745049376,1745049130,1745049253,1879196704,1879196458,1879196581,2013344032,2013343786,2013343909,-2147475936,-2147476182,-2147476059,-2013328608,-2013328854,-2013328731,-1879181280,-1879181526,-1879181403,-1745033952,-1745034198,-1745034075,-1610886624,-1610886870,-1610886747,-1476739296,-1476739542,-1476739419,-1342591968,-1342592214,-1342592091,-1208444640,-1208444886,-1208444763,-1074297312,-1074297558,-1074297435,-940149984,-940150230,-940150107,-806002656,-806002902,-806002779,-671855328,-671855574,-671855451,-537708000,-537708246,-537708123,-403560672,-403560918,-403560795,-269413344,-269413590,-269413467,-202899395,1006797079,1006797344,1006797098,1006797221,1006679584,1006679338,1006679461,1140826912,1140826666,1140826789,1274974240,1274973994,1274974117,1409121568,1409121322,1409121445,1543268896,1543268650,1543268773,1677416224,1677415978,1677416101,1811563552,1811563306,1811563429,1945710880,1945710634,1945710757,2079858208,2079857962,2079858085,-2080961760,-2080962006,-2080961883,-1946814432,-1946814678,-1946814555,-1812667104,-1812667350,-1812667227,-1678519776,-1678520022,-1678519899,-1544372448,-1544372694,-1544372571,-1410225120,-1410225366,-1410225243,-1276077792,-1276078038,-1276077915,-1141930464,-1141930710,-1141930587,-1007783136,-1007783382,-1007783259,-873635808,-873636054,-873635931,-739488480,-739488726,-739488603,-605341152,-605341398,-605341275,-471193824,-471194070,-471193947,-337046496,-337046742,-337046619,-270532547,1073311255,1073311520,1073311274,1073311397,1073193760,1073193514,1073193637,1207341088,1207340842,1207340965,1341488416,1341488170,1341488293,1475635744,1475635498,1475635621,1609783072,1609782826,1609782949,1743930400,1743930154,1743930277,1878077728,1878077482,1878077605,2012225056,2012224810,2012224933,2146372384,2146372138,2146372261,-2014447584,-2014447830,-2014447707,-1880300256,-1880300502,-1880300379,-1746152928,-1746153174,-1746153051,-1612005600,-1612005846,-1612005723,-1477858272,-1477858518,-1477858395,-1343710944,-1343711190,-1343711067,-1209563616,-1209563862,-1209563739,-1075416288,-1075416534,-1075416411,-941268960,-941269206,-941269083,-807121632,-807121878,-807121755,-672974304,-672974550,-672974427,-538826976,-538827222,-538827099,-404679648,-404679894,-404679771,-338165699,1139825431,1139825696,1139825450,1139825573,1139707936,1139707690,1139707813,1273855264,1273855018,1273855141,1408002592,1408002346,1408002469,1542149920,1542149674,1542149797,1676297248,1676297002,1676297125,1810444576,1810444330,1810444453,1944591904,1944591658,1944591781,2078739232,2078738986,2078739109,-2082080736,-2082080982,-2082080859,-1947933408,-1947933654,-1947933531,-1813786080,-1813786326,-1813786203,-1679638752,-1679638998,-1679638875,-1545491424,-1545491670,-1545491547,-1411344096,-1411344342,-1411344219,-1277196768,-1277197014,-1277196891,-1143049440,-1143049686,-1143049563,-1008902112,-1008902358,-1008902235,-874754784,-874755030,-874754907,-740607456,-740607702,-740607579,-606460128,-606460374,-606460251,-472312800,-472313046,-472312923,-405798851,1206339607,1206339872,1206339626,1206339749,1206222112,1206221866,1206221989,1340369440,1340369194,1340369317,1474516768,1474516522,1474516645,1608664096,1608663850,1608663973,1742811424,1742811178,1742811301,1876958752,1876958506,1876958629,2011106080,2011105834,2011105957,2145253408,2145253162,2145253285,-2015566560,-2015566806,-2015566683,-1881419232,-1881419478,-1881419355,-1747271904,-1747272150,-1747272027,-1613124576,-1613124822,-1613124699,-1478977248,-1478977494,-1478977371,-1344829920,-1344830166,-1344830043,-1210682592,-1210682838,-1210682715,-1076535264,-1076535510,-1076535387,-942387936,-942388182,-942388059,-808240608,-808240854,-808240731,-674093280,-674093526,-674093403,-539945952,-539946198,-539946075,-473432003,1272853783,1272854048,1272853802,1272853925,1272736288,1272736042,1272736165,1406883616,1406883370,1406883493,1541030944,1541030698,1541030821,1675178272,1675178026,1675178149,1809325600,1809325354,1809325477,1943472928,1943472682,1943472805,2077620256,2077620010,2077620133,-2083199712,-2083199958,-2083199835,-1949052384,-1949052630,-1949052507,-1814905056,-1814905302,-1814905179,-1680757728,-1680757974,-1680757851,-1546610400,-1546610646,-1546610523,-1412463072,-1412463318,-1412463195,-1278315744,-1278315990,-1278315867,-1144168416,-1144168662,-1144168539,-1010021088,-1010021334,-1010021211,-875873760,-875874006,-875873883,-741726432,-741726678,-741726555,-607579104,-607579350,-607579227,-541065155,1339367959,1339368224,1339367978,1339368101,1339250464,1339250218,1339250341,1473397792,1473397546,1473397669,1607545120,1607544874,1607544997,1741692448,1741692202,1741692325,1875839776,1875839530,1875839653,2009987104,2009986858,2009986981,2144134432,2144134186,2144134309,-2016685536,-2016685782,-2016685659,-1882538208,-1882538454,-1882538331,-1748390880,-1748391126,-1748391003,-1614243552,-1614243798,-1614243675,-1480096224,-1480096470,-1480096347,-1345948896,-1345949142,-1345949019,-1211801568,-1211801814,-1211801691,-1077654240,-1077654486,-1077654363,-943506912,-943507158,-943507035,-809359584,-809359830,-809359707,-675212256,-675212502,-675212379,-608698307,1405882135,1405882400,1405882154,1405882277,1405764640,1405764394,1405764517,1539911968,1539911722,1539911845,1674059296,1674059050,1674059173,1808206624,1808206378,1808206501,1942353952,1942353706,1942353829,2076501280,2076501034,2076501157,-2084318688,-2084318934,-2084318811,-1950171360,-1950171606,-1950171483,-1816024032,-1816024278,-1816024155,-1681876704,-1681876950,-1681876827,-1547729376,-1547729622,-1547729499,-1413582048,-1413582294,-1413582171,-1279434720,-1279434966,-1279434843,-1145287392,-1145287638,-1145287515,-1011140064,-1011140310,-1011140187,-876992736,-876992982,-876992859,-742845408,-742845654,-742845531,-676331459,1472396311,1472396576,1472396330,1472396453,1472278816,1472278570,1472278693,1606426144,1606425898,1606426021,1740573472,1740573226,1740573349,1874720800,1874720554,1874720677,2008868128,2008867882,2008868005,2143015456,2143015210,2143015333,-2017804512,-2017804758,-2017804635,-1883657184,-1883657430,-1883657307,-1749509856,-1749510102,-1749509979,-1615362528,-1615362774,-1615362651,-1481215200,-1481215446,-1481215323,-1347067872,-1347068118,-1347067995,-1212920544,-1212920790,-1212920667,-1078773216,-1078773462,-1078773339,-944625888,-944626134,-944626011,-810478560,-810478806,-810478683,-743964611,1538910487,1538910752,1538910506,1538910629,1538792992,1538792746,1538792869,1672940320,1672940074,1672940197,1807087648,1807087402,1807087525,1941234976,1941234730,1941234853,2075382304,2075382058,2075382181,-2085437664,-2085437910,-2085437787,-1951290336,-1951290582,-1951290459,-1817143008,-1817143254,-1817143131,-1682995680,-1682995926,-1682995803,-1548848352,-1548848598,-1548848475,-1414701024,-1414701270,-1414701147,-1280553696,-1280553942,-1280553819,-1146406368,-1146406614,-1146406491,-1012259040,-1012259286,-1012259163,-878111712,-878111958,-878111835,-811597763,1605424663,1605424928,1605424682,1605424805,1605307168,1605306922,1605307045,1739454496,1739454250,1739454373,1873601824,1873601578,1873601701,2007749152,2007748906,2007749029,2141896480,2141896234,2141896357,-2018923488,-2018923734,-2018923611,-1884776160,-1884776406,-1884776283,-1750628832,-1750629078,-1750628955,-1616481504,-1616481750,-1616481627,-1482334176,-1482334422,-1482334299,-1348186848,-1348187094,-1348186971,-1214039520,-1214039766,-1214039643,-1079892192,-1079892438,-1079892315,-945744864,-945745110,-945744987,-879230915,1671938839,1671939104,1671938858,1671938981,1671821344,1671821098,1671821221,1805968672,1805968426,1805968549,1940116000,1940115754,1940115877,2074263328,2074263082,2074263205,-2086556640,-2086556886,-2086556763,-1952409312,-1952409558,-1952409435,-1818261984,-1818262230,-1818262107,-1684114656,-1684114902,-1684114779,-1549967328,-1549967574,-1549967451,-1415820000,-1415820246,-1415820123,-1281672672,-1281672918,-1281672795,-1147525344,-1147525590,-1147525467,-1013378016,-1013378262,-1013378139,-946864067,1738453015,1738453280,1738453034,1738453157,1738335520,1738335274,1738335397,1872482848,1872482602,1872482725,2006630176,2006629930,2006630053,2140777504,2140777258,2140777381,-2020042464,-2020042710,-2020042587,-1885895136,-1885895382,-1885895259,-1751747808,-1751748054,-1751747931,-1617600480,-1617600726,-1617600603,-1483453152,-1483453398,-1483453275,-1349305824,-1349306070,-1349305947,-1215158496,-1215158742,-1215158619,-1081011168,-1081011414,-1081011291,-1014497219,1804967191,1804967456,1804967210,1804967333,1804849696,1804849450,1804849573,1938997024,1938996778,1938996901,2073144352,2073144106,2073144229,-2087675616,-2087675862,-2087675739,-1953528288,-1953528534,-1953528411,-1819380960,-1819381206,-1819381083,-1685233632,-1685233878,-1685233755,-1551086304,-1551086550,-1551086427,-1416938976,-1416939222,-1416939099,-1282791648,-1282791894,-1282791771,-1148644320,-1148644566,-1148644443,-1082130371,1871481367,1871481632,1871481386,1871481509,1871363872,1871363626,1871363749,2005511200,2005510954,2005511077,2139658528,2139658282,2139658405,-2021161440,-2021161686,-2021161563,-1887014112,-1887014358,-1887014235,-1752866784,-1752867030,-1752866907,-1618719456,-1618719702,-1618719579,-1484572128,-1484572374,-1484572251,-1350424800,-1350425046,-1350424923,-1216277472,-1216277718,-1216277595,-1149763523,1937995543,1937995808,1937995562,1937995685,1937878048,1937877802,1937877925,2072025376,2072025130,2072025253,-2088794592,-2088794838,-2088794715,-1954647264,-1954647510,-1954647387,-1820499936,-1820500182,-1820500059,-1686352608,-1686352854,-1686352731,-1552205280,-1552205526,-1552205403,-1418057952,-1418058198,-1418058075,-1283910624,-1283910870,-1283910747,-1217396675,2004509719,2004509984,2004509738,2004509861,2004392224,2004391978,2004392101,2138539552,2138539306,2138539429,-2022280416,-2022280662,-2022280539,-1888133088,-1888133334,-1888133211,-1753985760,-1753986006,-1753985883,-1619838432,-1619838678,-1619838555,-1485691104,-1485691350,-1485691227,-1351543776,-1351544022,-1351543899,-1285029827,2071023895,2071024160,2071023914,2071024037,2070906400,2070906154,2070906277,-2089913568,-2089913814,-2089913691,-1955766240,-1955766486,-1955766363,-1821618912,-1821619158,-1821619035,-1687471584,-1687471830,-1687471707,-1553324256,-1553324502,-1553324379,-1419176928,-1419177174,-1419177051,-1352662979,2137538071,2137538336,2137538090,2137538213,2137420576,2137420330,2137420453,-2023399392,-2023399638,-2023399515,-1889252064,-1889252310,-1889252187,-1755104736,-1755104982,-1755104859,-1620957408,-1620957654,-1620957531,-1486810080,-1486810326,-1486810203,-1420296131,-2090915049,-2090914784,-2090915030,-2090914907,-2091032544,-2091032790,-2091032667,-1956885216,-1956885462,-1956885339,-1822737888,-1822738134,-1822738011,-1688590560,-1688590806,-1688590683,-1554443232,-1554443478,-1554443355,-1487929283,-2024400873,-2024400608,-2024400854,-2024400731,-2024518368,-2024518614,-2024518491,-1890371040,-1890371286,-1890371163,-1756223712,-1756223958,-1756223835,-1622076384,-1622076630,-1622076507,-1555562435,-1957886697,-1957886432,-1957886678,-1957886555,-1958004192,-1958004438,-1958004315,-1823856864,-1823857110,-1823856987,-1689709536,-1689709782,-1689709659,-1623195587,-1891372521,-1891372256,-1891372502,-1891372379,-1891490016,-1891490262,-1891490139,-1757342688,-1757342934,-1757342811,-1690828739,-1824858345,-1824858080,-1824858326,-1824858203,-1824975840,-1824976086,-1824975963,-1758461891,-1758344169,-1758343904,-1758344150,-1758344027,-1691829955,-1691829993,-1691829728,-1691829788,-1691829787,-1691829776,-1691829783,-1691829776,-1691829788,-1691829767";
ArrayList<Integer> list = new ArrayList<>();
for(String s : input.split(",")){
list.add(Integer.parseInt(s));
}
return list;
}
public static ArrayList<Integer> randomInput(int size){
Random rand = new Random(1);
ArrayList<Integer> list = new ArrayList<>();
for (int i = 0; i < size; i ++){
list.add(rand.nextInt());
}
return list;
}
}
```
On my machine, when running with -Xint, I got the following result:
```
pattern size: 1197
Random input time use: 1.15802056s.
Pattern time use: 106.958007337s.
```
The performance-inputSize relationship can roughly be fitted as a quadratic curve:
<img width="687" alt="fit-immutableset" src="https://user-images.githubusercontent.com/11240361/34278192-03af6472-e66f-11e7-9199-1375c74fbea6.png">
|
non_test
|
immutableset copyof quadratic running time behavior hi i found an input pattern that can trigger ω n running time behavior of immutableset copyof this problem is similar to the input is constructed and tested using the following code java import com google common collect immutableset import java util arraylist import java util random public class guavaimmutableset public static void main string args arraylist pattern generateinput arraylist randominput randominput pattern size system out println pattern size pattern size int testnum long start double timeuse start system nanotime for int i i testnum i immutableset copyof randominput timeuse system nanotime start system out println random input time use timeuse s start system nanotime for int i i testnum i immutableset copyof pattern timeuse system nanotime start system out println pattern time use timeuse s public static arraylist generateinput string input arraylist list new arraylist for string s input split list add integer parseint s return list public static arraylist randominput int size random rand new random arraylist list new arraylist for int i i size i list add rand nextint return list on my machine when running with xint i got the following result pattern size random input time use pattern time use the performance inputsize relationship can roughly be fitted as a quadratic curve img width alt fit immutableset src
| 0
|
93,166
| 10,764,558,280
|
IssuesEvent
|
2019-11-01 08:39:27
|
fangpinsern/ped
|
https://api.github.com/repos/fangpinsern/ped
|
opened
|
Out example wrongly documented
|
severity.Medium type.DocumentationBug
|
Out command required date. However, in the example command, no date flag was provided.

|
1.0
|
Out example wrongly documented - Out command required date. However, in the example command, no date flag was provided.

|
non_test
|
out example wrongly documented out command required date however in the example command no date flag was provided
| 0
|
116,713
| 24,971,071,382
|
IssuesEvent
|
2022-11-02 01:14:43
|
dotnet/roslyn
|
https://api.github.com/repos/dotnet/roslyn
|
closed
|
Implement interface produces incorrect code for manual use of DefaultParameterValue and Optional
|
Bug Area-IDE IDE-CodeStyle
|
Two Implement Interface tests reveal broken code when `DefaultParameterValue` and `Optional` are used:
https://github.com/dotnet/roslyn/blob/51c367a5c3b2e51026bd0dc459bbb9cba6e09d3b/src/EditorFeatures/CSharpTest/ImplementInterface/ImplementInterfaceTests.cs#L5111-L5171
> 🐛 this code generation is not correct. I'm guess the result we want is:
>
> ```
> public void Goo(int x = 1, int[,] y = null)
> ```
_Originally posted by @sharwell in [#54310 (comment)](https://github.com/dotnet/roslyn/pull/54310#discussion_r656664174)_
|
1.0
|
Implement interface produces incorrect code for manual use of DefaultParameterValue and Optional - Two Implement Interface tests reveal broken code when `DefaultParameterValue` and `Optional` are used:
https://github.com/dotnet/roslyn/blob/51c367a5c3b2e51026bd0dc459bbb9cba6e09d3b/src/EditorFeatures/CSharpTest/ImplementInterface/ImplementInterfaceTests.cs#L5111-L5171
> 🐛 this code generation is not correct. I'm guess the result we want is:
>
> ```
> public void Goo(int x = 1, int[,] y = null)
> ```
_Originally posted by @sharwell in [#54310 (comment)](https://github.com/dotnet/roslyn/pull/54310#discussion_r656664174)_
|
non_test
|
implement interface produces incorrect code for manual use of defaultparametervalue and optional two implement interface tests reveal broken code when defaultparametervalue and optional are used 🐛 this code generation is not correct i m guess the result we want is public void goo int x int y null originally posted by sharwell in
| 0
|
148,226
| 11,842,741,745
|
IssuesEvent
|
2020-03-24 00:00:36
|
cockroachdb/cockroach
|
https://api.github.com/repos/cockroachdb/cockroach
|
closed
|
kv/kvserver: TestRangeInfo failed
|
C-test-failure O-robot branch-master
|
[(kv/kvserver).TestRangeInfo failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1814032&tab=buildLog) on [master@aa18c27ce78016377abe9fbcb3ca386b4eca4887](https://github.com/cockroachdb/cockroach/commits/aa18c27ce78016377abe9fbcb3ca386b4eca4887):
```
=== RUN TestRangeInfo
I200317 19:17:14.005511 238174 gossip/gossip.go:395 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:38745" > attrs:<> locality:<> ServerVersion:<major_val:0 minor_val:0 patch:0 unstable:0 > build_tag:"" started_at:0 cluster_name:"" sql_address:<network_field:"" address_field:"" >
W200317 19:17:14.100814 238174 gossip/gossip.go:1513 [n2] no incoming or outgoing connections
I200317 19:17:14.101907 238174 gossip/gossip.go:395 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:41645" > attrs:<> locality:<> ServerVersion:<major_val:0 minor_val:0 patch:0 unstable:0 > build_tag:"" started_at:0 cluster_name:"" sql_address:<network_field:"" address_field:"" >
I200317 19:17:14.119179 238304 gossip/client.go:124 [n2] started gossip client to 127.0.0.1:38745
I200317 19:17:14.291989 238174 kv/kvserver/replica_command.go:1602 [s1,r1/1:/M{in-ax}] change replicas (add [(n2,s2):2LEARNER] remove []): existing descriptor r1:/M{in-ax} [(n1,s1):1, next=2, gen=0]
I200317 19:17:14.309346 238174 kv/kvserver/replica_raft.go:241 [s1,r1/1:/M{in-ax},txn=bc68ceab] proposing SIMPLE(l2) ADD_REPLICA[(n2,s2):2LEARNER]: after=[(n1,s1):1 (n2,s2):2LEARNER] next=3
I200317 19:17:14.359420 238174 kv/kvserver/store_snapshot.go:975 [s1,r1/1:/M{in-ax}] sending LEARNER snapshot d75c6dbe at applied index 19
I200317 19:17:14.362938 238174 kv/kvserver/store_snapshot.go:1018 [s1,r1/1:/M{in-ax}] streamed snapshot to (n2,s2):2LEARNER: kv pairs: 78, log entries: 0, rate-limit: 8.0 MiB/sec, 0.03s
I200317 19:17:14.383641 238602 kv/kvserver/replica_raftstorage.go:780 [s2,r1/2:{-}] applying LEARNER snapshot [id=d75c6dbe index=19]
I200317 19:17:14.397045 238602 kv/kvserver/replica_raftstorage.go:801 [s2,r1/2:/M{in-ax}] applied LEARNER snapshot [total=6ms ingestion=4@2ms id=d75c6dbe index=19]
I200317 19:17:14.444991 238174 kv/kvserver/replica_command.go:1602 [s1,r1/1:/M{in-ax}] change replicas (add [(n2,s2):2] remove []): existing descriptor r1:/M{in-ax} [(n1,s1):1, (n2,s2):2LEARNER, next=3, gen=1]
I200317 19:17:14.462201 238174 kv/kvserver/replica_raft.go:241 [s1,r1/1:/M{in-ax},txn=89045771] proposing SIMPLE(v2) ADD_REPLICA[(n2,s2):2]: after=[(n1,s1):1 (n2,s2):2] next=3
I200317 19:17:14.574946 238174 kv/kvserver/replica_command.go:397 [s1,r1/1:/M{in-ax}] initiating a split of this range at key "a" [r2] (manual)
I200317 19:17:15.161641 238855 util/stop/stopper.go:539 quiescing
I200317 19:17:15.163795 238856 util/stop/stopper.go:539 quiescing
W200317 19:17:15.174591 238305 kv/txn.go:590 [liveness-hb] failure aborting transaction: node unavailable; try another peer; abort caused by: result is ambiguous (server shutdown)
I200317 19:17:15.174985 238305 kv/kvserver/node_liveness.go:804 [liveness-hb] retrying liveness update after kvserver.errRetryLiveness: result is ambiguous (server shutdown)
I200317 19:17:15.184384 238515 kv/kvserver/queue.go:578 [s2,r2/2:{a-/Max}] rate limited in MaybeAdd (replicate): node unavailable; try another peer
W200317 19:17:15.187762 238305 kv/txn.go:590 [liveness-hb] failure aborting transaction: node unavailable; try another peer; abort caused by: node unavailable; try another peer
W200317 19:17:15.188128 238305 kv/kvserver/node_liveness.go:471 [liveness-hb] failed node liveness heartbeat: node unavailable; try another peer
I200317 19:17:15.219343 238854 util/stop/stopper.go:539 quiescing
I200317 19:17:15.231565 238854 util/stop/stopper.go:539 quiescing
I200317 19:17:15.233590 238854 util/stop/stopper.go:539 quiescing
--- FAIL: TestRangeInfo (1.33s)
client_replica_test.go:1573: on scan reply, expected [{Desc:r1:{/Min-a} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0} {Desc:r2:{a-/Max} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0}]; got [{Desc:r1:{/Min-a} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.778975231,0 pro=1584472634.879065894,0} {Desc:r2:{a-/Max} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0}]
client_replica_test.go:1598: on reverse scan reply, expected [{Desc:r2:{a-/Max} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0} {Desc:r1:{/Min-a} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0}]; got [{Desc:r2:{a-/Max} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0} {Desc:r1:{/Min-a} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.778975231,0 pro=1584472634.879065894,0}]
```
<details><summary>More</summary><p>
Parameters:
- GOFLAGS=-json
```
make stressrace TESTS=TestRangeInfo PKG=./pkg/kv/kvserver TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2ATestRangeInfo.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
|
1.0
|
kv/kvserver: TestRangeInfo failed - [(kv/kvserver).TestRangeInfo failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1814032&tab=buildLog) on [master@aa18c27ce78016377abe9fbcb3ca386b4eca4887](https://github.com/cockroachdb/cockroach/commits/aa18c27ce78016377abe9fbcb3ca386b4eca4887):
```
=== RUN TestRangeInfo
I200317 19:17:14.005511 238174 gossip/gossip.go:395 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:38745" > attrs:<> locality:<> ServerVersion:<major_val:0 minor_val:0 patch:0 unstable:0 > build_tag:"" started_at:0 cluster_name:"" sql_address:<network_field:"" address_field:"" >
W200317 19:17:14.100814 238174 gossip/gossip.go:1513 [n2] no incoming or outgoing connections
I200317 19:17:14.101907 238174 gossip/gossip.go:395 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:41645" > attrs:<> locality:<> ServerVersion:<major_val:0 minor_val:0 patch:0 unstable:0 > build_tag:"" started_at:0 cluster_name:"" sql_address:<network_field:"" address_field:"" >
I200317 19:17:14.119179 238304 gossip/client.go:124 [n2] started gossip client to 127.0.0.1:38745
I200317 19:17:14.291989 238174 kv/kvserver/replica_command.go:1602 [s1,r1/1:/M{in-ax}] change replicas (add [(n2,s2):2LEARNER] remove []): existing descriptor r1:/M{in-ax} [(n1,s1):1, next=2, gen=0]
I200317 19:17:14.309346 238174 kv/kvserver/replica_raft.go:241 [s1,r1/1:/M{in-ax},txn=bc68ceab] proposing SIMPLE(l2) ADD_REPLICA[(n2,s2):2LEARNER]: after=[(n1,s1):1 (n2,s2):2LEARNER] next=3
I200317 19:17:14.359420 238174 kv/kvserver/store_snapshot.go:975 [s1,r1/1:/M{in-ax}] sending LEARNER snapshot d75c6dbe at applied index 19
I200317 19:17:14.362938 238174 kv/kvserver/store_snapshot.go:1018 [s1,r1/1:/M{in-ax}] streamed snapshot to (n2,s2):2LEARNER: kv pairs: 78, log entries: 0, rate-limit: 8.0 MiB/sec, 0.03s
I200317 19:17:14.383641 238602 kv/kvserver/replica_raftstorage.go:780 [s2,r1/2:{-}] applying LEARNER snapshot [id=d75c6dbe index=19]
I200317 19:17:14.397045 238602 kv/kvserver/replica_raftstorage.go:801 [s2,r1/2:/M{in-ax}] applied LEARNER snapshot [total=6ms ingestion=4@2ms id=d75c6dbe index=19]
I200317 19:17:14.444991 238174 kv/kvserver/replica_command.go:1602 [s1,r1/1:/M{in-ax}] change replicas (add [(n2,s2):2] remove []): existing descriptor r1:/M{in-ax} [(n1,s1):1, (n2,s2):2LEARNER, next=3, gen=1]
I200317 19:17:14.462201 238174 kv/kvserver/replica_raft.go:241 [s1,r1/1:/M{in-ax},txn=89045771] proposing SIMPLE(v2) ADD_REPLICA[(n2,s2):2]: after=[(n1,s1):1 (n2,s2):2] next=3
I200317 19:17:14.574946 238174 kv/kvserver/replica_command.go:397 [s1,r1/1:/M{in-ax}] initiating a split of this range at key "a" [r2] (manual)
I200317 19:17:15.161641 238855 util/stop/stopper.go:539 quiescing
I200317 19:17:15.163795 238856 util/stop/stopper.go:539 quiescing
W200317 19:17:15.174591 238305 kv/txn.go:590 [liveness-hb] failure aborting transaction: node unavailable; try another peer; abort caused by: result is ambiguous (server shutdown)
I200317 19:17:15.174985 238305 kv/kvserver/node_liveness.go:804 [liveness-hb] retrying liveness update after kvserver.errRetryLiveness: result is ambiguous (server shutdown)
I200317 19:17:15.184384 238515 kv/kvserver/queue.go:578 [s2,r2/2:{a-/Max}] rate limited in MaybeAdd (replicate): node unavailable; try another peer
W200317 19:17:15.187762 238305 kv/txn.go:590 [liveness-hb] failure aborting transaction: node unavailable; try another peer; abort caused by: node unavailable; try another peer
W200317 19:17:15.188128 238305 kv/kvserver/node_liveness.go:471 [liveness-hb] failed node liveness heartbeat: node unavailable; try another peer
I200317 19:17:15.219343 238854 util/stop/stopper.go:539 quiescing
I200317 19:17:15.231565 238854 util/stop/stopper.go:539 quiescing
I200317 19:17:15.233590 238854 util/stop/stopper.go:539 quiescing
--- FAIL: TestRangeInfo (1.33s)
client_replica_test.go:1573: on scan reply, expected [{Desc:r1:{/Min-a} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0} {Desc:r2:{a-/Max} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0}]; got [{Desc:r1:{/Min-a} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.778975231,0 pro=1584472634.879065894,0} {Desc:r2:{a-/Max} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0}]
client_replica_test.go:1598: on reverse scan reply, expected [{Desc:r2:{a-/Max} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0} {Desc:r1:{/Min-a} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0}]; got [{Desc:r2:{a-/Max} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.328331311,0 pro=1584472634.428465004,0} {Desc:r1:{/Min-a} [(n1,s1):1, (n2,s2):2, next=3, gen=3] Lease:repl=(n1,s1):1 seq=1 start=0,0 exp=1584472635.778975231,0 pro=1584472634.879065894,0}]
```
<details><summary>More</summary><p>
Parameters:
- GOFLAGS=-json
```
make stressrace TESTS=TestRangeInfo PKG=./pkg/kv/kvserver TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2ATestRangeInfo.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
|
test
|
kv kvserver testrangeinfo failed on run testrangeinfo gossip gossip go nodedescriptor set to node id address attrs locality serverversion build tag started at cluster name sql address gossip gossip go no incoming or outgoing connections gossip gossip go nodedescriptor set to node id address attrs locality serverversion build tag started at cluster name sql address gossip client go started gossip client to kv kvserver replica command go change replicas add remove existing descriptor m in ax kv kvserver replica raft go proposing simple add replica after next kv kvserver store snapshot go sending learner snapshot at applied index kv kvserver store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec kv kvserver replica raftstorage go applying learner snapshot kv kvserver replica raftstorage go applied learner snapshot kv kvserver replica command go change replicas add remove existing descriptor m in ax kv kvserver replica raft go proposing simple add replica after next kv kvserver replica command go initiating a split of this range at key a manual util stop stopper go quiescing util stop stopper go quiescing kv txn go failure aborting transaction node unavailable try another peer abort caused by result is ambiguous server shutdown kv kvserver node liveness go retrying liveness update after kvserver errretryliveness result is ambiguous server shutdown kv kvserver queue go rate limited in maybeadd replicate node unavailable try another peer kv txn go failure aborting transaction node unavailable try another peer abort caused by node unavailable try another peer kv kvserver node liveness go failed node liveness heartbeat node unavailable try another peer util stop stopper go quiescing util stop stopper go quiescing util stop stopper go quiescing fail testrangeinfo client replica test go on scan reply expected lease repl seq start exp pro desc a max lease repl seq start exp pro got lease repl seq start exp pro desc a max lease repl seq start exp pro client replica test go on reverse scan reply expected lease repl seq start exp pro desc min a lease repl seq start exp pro got lease repl seq start exp pro desc min a lease repl seq start exp pro more parameters goflags json make stressrace tests testrangeinfo pkg pkg kv kvserver testtimeout stressflags timeout powered by
| 1
|
131,277
| 18,263,529,785
|
IssuesEvent
|
2021-10-04 04:40:02
|
phetsims/fourier-making-waves
|
https://api.github.com/repos/phetsims/fourier-making-waves
|
closed
|
Waveform changes to 'custom' when you open any amplitude keypad.
|
design:general priority:2-high
|
For phetsims/qa#711, and related to https://github.com/phetsims/fourier-making-waves/issues/200 ...
As soon as you open the keypad for any amplitude, the Waveform combo box switches to 'custom'. You don't actually have to change the value.
For example:
1. Go to the Discrete screen
2. Select 'wave packet' from Waveform combo box
3. Click in the A<sub>1</sub> NumberDisplay
4. Note that the Waveform combo box immediately changes to 'custom'
It would probably be more "polite" to only change to "custom" if the user enters a (new?) value for the amplitude. But that's a heck of a lot more work, which is why I problably thought this was good enough. Or maybe I didn't think of this case. Anway...
@arouinfar Do you think we need to change anything here? I'm OK leaving this as is, if you are. But I wanted to point this out, so that we're making a conscious decision.
|
1.0
|
Waveform changes to 'custom' when you open any amplitude keypad. - For phetsims/qa#711, and related to https://github.com/phetsims/fourier-making-waves/issues/200 ...
As soon as you open the keypad for any amplitude, the Waveform combo box switches to 'custom'. You don't actually have to change the value.
For example:
1. Go to the Discrete screen
2. Select 'wave packet' from Waveform combo box
3. Click in the A<sub>1</sub> NumberDisplay
4. Note that the Waveform combo box immediately changes to 'custom'
It would probably be more "polite" to only change to "custom" if the user enters a (new?) value for the amplitude. But that's a heck of a lot more work, which is why I problably thought this was good enough. Or maybe I didn't think of this case. Anway...
@arouinfar Do you think we need to change anything here? I'm OK leaving this as is, if you are. But I wanted to point this out, so that we're making a conscious decision.
|
non_test
|
waveform changes to custom when you open any amplitude keypad for phetsims qa and related to as soon as you open the keypad for any amplitude the waveform combo box switches to custom you don t actually have to change the value for example go to the discrete screen select wave packet from waveform combo box click in the a numberdisplay note that the waveform combo box immediately changes to custom it would probably be more polite to only change to custom if the user enters a new value for the amplitude but that s a heck of a lot more work which is why i problably thought this was good enough or maybe i didn t think of this case anway arouinfar do you think we need to change anything here i m ok leaving this as is if you are but i wanted to point this out so that we re making a conscious decision
| 0
|
162,157
| 12,624,974,690
|
IssuesEvent
|
2020-06-14 09:23:36
|
agdsn/pycroft
|
https://api.github.com/repos/agdsn/pycroft
|
closed
|
Add integration tests for membership fee booking
|
tests
|
This assignment was taken out of the requirements for the #179 merge and should be added at some point in the future.
|
1.0
|
Add integration tests for membership fee booking - This assignment was taken out of the requirements for the #179 merge and should be added at some point in the future.
|
test
|
add integration tests for membership fee booking this assignment was taken out of the requirements for the merge and should be added at some point in the future
| 1
|
288,433
| 21,704,737,620
|
IssuesEvent
|
2022-05-10 08:36:26
|
bounswe/bounswe2022group2
|
https://api.github.com/repos/bounswe/bounswe2022group2
|
closed
|
Documenting Meeting Notes - Meeting 9
|
priority-medium type-documentation status-needreview
|
### Issue Description
- Notes taken during the second meeting on 01/05/2022 should be documented on the wiki page.
- These notes should follow the criteria on the [Meeting Notes template](https://github.com/bounswe/bounswe2022group2/wiki/Meeting-Notes-Template). The template contains the details about the sections that should be in the meeting notes.
- Meetings notes should be linked in the required places.
### Step Details
Meeting notes should contain the following sections:
- [x] Details
- [x] Agenda
- [x] Discussion
- [x] Action Items
### Final Actions
Sections that should have a link to the week 9 meeting notes:
- [x] [Home wiki page](https://github.com/bounswe/bounswe2022group2/wiki#-meeting-notes)
- [x] [Sidebar](https://github.com/bounswe/bounswe2022group2/wiki#-meeting-notes)
### Deadline of the Issue
04.05.2022 - Wednesday - 23:59
### Reviewer
Egemen Atik
### Deadline for the Review
06.05.2022 - Friday - 23:59
|
1.0
|
Documenting Meeting Notes - Meeting 9 - ### Issue Description
- Notes taken during the second meeting on 01/05/2022 should be documented on the wiki page.
- These notes should follow the criteria on the [Meeting Notes template](https://github.com/bounswe/bounswe2022group2/wiki/Meeting-Notes-Template). The template contains the details about the sections that should be in the meeting notes.
- Meetings notes should be linked in the required places.
### Step Details
Meeting notes should contain the following sections:
- [x] Details
- [x] Agenda
- [x] Discussion
- [x] Action Items
### Final Actions
Sections that should have a link to the week 9 meeting notes:
- [x] [Home wiki page](https://github.com/bounswe/bounswe2022group2/wiki#-meeting-notes)
- [x] [Sidebar](https://github.com/bounswe/bounswe2022group2/wiki#-meeting-notes)
### Deadline of the Issue
04.05.2022 - Wednesday - 23:59
### Reviewer
Egemen Atik
### Deadline for the Review
06.05.2022 - Friday - 23:59
|
non_test
|
documenting meeting notes meeting issue description notes taken during the second meeting on should be documented on the wiki page these notes should follow the criteria on the the template contains the details about the sections that should be in the meeting notes meetings notes should be linked in the required places step details meeting notes should contain the following sections details agenda discussion action items final actions sections that should have a link to the week meeting notes deadline of the issue wednesday reviewer egemen atik deadline for the review friday
| 0
|
13,333
| 4,683,941,155
|
IssuesEvent
|
2016-10-10 00:25:06
|
medic/medic-webapp
|
https://api.github.com/repos/medic/medic-webapp
|
closed
|
Task and Report filters don't seem to work anymore?
|
3 - Code Review Bug Contacts Regression UI/UX
|

^ This seems to be the opposite of what I'd expect. If I have 3 months selected I'd only expect to see the last three months of reports.
|
1.0
|
Task and Report filters don't seem to work anymore? - 
^ This seems to be the opposite of what I'd expect. If I have 3 months selected I'd only expect to see the last three months of reports.
|
non_test
|
task and report filters don t seem to work anymore this seems to be the opposite of what i d expect if i have months selected i d only expect to see the last three months of reports
| 0
|
31,970
| 4,731,352,843
|
IssuesEvent
|
2016-10-19 01:35:49
|
elastic/elasticsearch
|
https://api.github.com/repos/elastic/elasticsearch
|
opened
|
Add tests for maven/official plugins to plugin installer
|
:Plugins blocker test v6.0.0
|
We currently lack tests in the plugin installer which exercise the downloading capabilities from maven and official plugins from the elastic download service. This issue is a reminder we need these tests. One way to accomplish this is with an http fixture that fakes the structure of maven and the elastic download service, and a sysprop for testing which replaces the host of those services with the local fixture. See https://github.com/rjernst/elasticsearch/tree/separate_plugin_cli where this has been worked on.
|
1.0
|
Add tests for maven/official plugins to plugin installer - We currently lack tests in the plugin installer which exercise the downloading capabilities from maven and official plugins from the elastic download service. This issue is a reminder we need these tests. One way to accomplish this is with an http fixture that fakes the structure of maven and the elastic download service, and a sysprop for testing which replaces the host of those services with the local fixture. See https://github.com/rjernst/elasticsearch/tree/separate_plugin_cli where this has been worked on.
|
test
|
add tests for maven official plugins to plugin installer we currently lack tests in the plugin installer which exercise the downloading capabilities from maven and official plugins from the elastic download service this issue is a reminder we need these tests one way to accomplish this is with an http fixture that fakes the structure of maven and the elastic download service and a sysprop for testing which replaces the host of those services with the local fixture see where this has been worked on
| 1
|
64,354
| 15,874,994,524
|
IssuesEvent
|
2021-04-09 06:13:55
|
OOPS-ORG-PHP/mod_geoip
|
https://api.github.com/repos/OOPS-ORG-PHP/mod_geoip
|
closed
|
V1: error: unknown type name ‘zend_error_handling’ in PHP 5.2
|
bug build
|
## Bug Environments
- [x] Product Version : 1.1.2
- [x] PHP Version: 5.2
- [x] PHP SAPI: cli
## Describe the bug
```
/root/work/github/php/mod_geoip/php_geoip.c: In function ‘zif_geoip_open’:
/root/work/github/php/mod_geoip/php_geoip.c:229:2: error: unknown type name ‘zend_error_handling’
zend_error_handling error_handling;
```
## To Reproduce
```
phpize && ./configure && make
```
## Expected behavior
build success
|
1.0
|
V1: error: unknown type name ‘zend_error_handling’ in PHP 5.2 - ## Bug Environments
- [x] Product Version : 1.1.2
- [x] PHP Version: 5.2
- [x] PHP SAPI: cli
## Describe the bug
```
/root/work/github/php/mod_geoip/php_geoip.c: In function ‘zif_geoip_open’:
/root/work/github/php/mod_geoip/php_geoip.c:229:2: error: unknown type name ‘zend_error_handling’
zend_error_handling error_handling;
```
## To Reproduce
```
phpize && ./configure && make
```
## Expected behavior
build success
|
non_test
|
error unknown type name ‘zend error handling’ in php bug environments product version php version php sapi cli describe the bug root work github php mod geoip php geoip c in function ‘zif geoip open’ root work github php mod geoip php geoip c error unknown type name ‘zend error handling’ zend error handling error handling to reproduce phpize configure make expected behavior build success
| 0
|
54,789
| 3,071,290,079
|
IssuesEvent
|
2015-08-19 11:04:31
|
pavel-pimenov/flylinkdc-r5xx
|
https://api.github.com/repos/pavel-pimenov/flylinkdc-r5xx
|
opened
|
Добавить в "Обозреватель порталов" (Portal Browser) поиск по всем порталам сразу
|
enhancement imported Priority-Low Usability
|
_From [a.rain...@gmail.com](https://code.google.com/u/117892482479228821242/) on August 15, 2010 23:47:44_
Реализацию вероятнее всего лучше сделать через внешний поисковик (например Google) используя в запросе дополнительный параметр со списком доменов. Так же можно использовать nigma.ru т.к. сервис предоставляет намного большие возможности по разделению результатов поиска на категории.
В последствии выбор поискового сервиса следует предоставить пользователю с возможностью выбора (или указания своего) в настройках
_Original issue: http://code.google.com/p/flylinkdc/issues/detail?id=122_
|
1.0
|
Добавить в "Обозреватель порталов" (Portal Browser) поиск по всем порталам сразу - _From [a.rain...@gmail.com](https://code.google.com/u/117892482479228821242/) on August 15, 2010 23:47:44_
Реализацию вероятнее всего лучше сделать через внешний поисковик (например Google) используя в запросе дополнительный параметр со списком доменов. Так же можно использовать nigma.ru т.к. сервис предоставляет намного большие возможности по разделению результатов поиска на категории.
В последствии выбор поискового сервиса следует предоставить пользователю с возможностью выбора (или указания своего) в настройках
_Original issue: http://code.google.com/p/flylinkdc/issues/detail?id=122_
|
non_test
|
добавить в обозреватель порталов portal browser поиск по всем порталам сразу from on august реализацию вероятнее всего лучше сделать через внешний поисковик например google используя в запросе дополнительный параметр со списком доменов так же можно использовать nigma ru т к сервис предоставляет намного большие возможности по разделению результатов поиска на категории в последствии выбор поискового сервиса следует предоставить пользователю с возможностью выбора или указания своего в настройках original issue
| 0
|
223,254
| 17,576,810,709
|
IssuesEvent
|
2021-08-15 19:21:21
|
cadadr/pomodorino
|
https://api.github.com/repos/cadadr/pomodorino
|
opened
|
AFTER state change is broken on Mate
|
bug needs testing
|
Occurs at least on Mate on Debian 10.
After a break or after a pomodoro, the state does not automatically advance.
|
1.0
|
AFTER state change is broken on Mate - Occurs at least on Mate on Debian 10.
After a break or after a pomodoro, the state does not automatically advance.
|
test
|
after state change is broken on mate occurs at least on mate on debian after a break or after a pomodoro the state does not automatically advance
| 1
|
73,530
| 15,256,711,991
|
IssuesEvent
|
2021-02-20 21:26:18
|
MythicDrops/npm-v7-resolutions
|
https://api.github.com/repos/MythicDrops/npm-v7-resolutions
|
opened
|
WS-2020-0218 (High) detected in merge-1.2.1.tgz
|
security vulnerability
|
## WS-2020-0218 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>merge-1.2.1.tgz</b></p></summary>
<p>Merge multiple objects into one, optionally creating a new cloned object. Similar to the jQuery.extend but more flexible. Works in Node.js and the browser.</p>
<p>Library home page: <a href="https://registry.npmjs.org/merge/-/merge-1.2.1.tgz">https://registry.npmjs.org/merge/-/merge-1.2.1.tgz</a></p>
<p>Path to dependency file: npm-v7-resolutions/package.json</p>
<p>Path to vulnerable library: npm-v7-resolutions/node_modules/merge/package.json</p>
<p>
Dependency Hierarchy:
- commitizen-4.2.3.tgz (Root Library)
- find-node-modules-2.0.0.tgz
- :x: **merge-1.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/MythicDrops/npm-v7-resolutions/commit/d4914bf0f4f3d041b3a219f1f8eb2eb6c98b9c28">d4914bf0f4f3d041b3a219f1f8eb2eb6c98b9c28</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Prototype Pollution vulnerability was found in merge before 2.1.0 via the merge.recursive function. It can be tricked into adding or modifying properties of the Object prototype. These properties will be present on all objects.
<p>Publish Date: 2020-10-09
<p>URL: <a href=https://github.com/yeikos/js.merge/pull/38>WS-2020-0218</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/yeikos/js.merge/pull/38">https://github.com/yeikos/js.merge/pull/38</a></p>
<p>Release Date: 2020-10-09</p>
<p>Fix Resolution: merge - 2.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2020-0218 (High) detected in merge-1.2.1.tgz - ## WS-2020-0218 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>merge-1.2.1.tgz</b></p></summary>
<p>Merge multiple objects into one, optionally creating a new cloned object. Similar to the jQuery.extend but more flexible. Works in Node.js and the browser.</p>
<p>Library home page: <a href="https://registry.npmjs.org/merge/-/merge-1.2.1.tgz">https://registry.npmjs.org/merge/-/merge-1.2.1.tgz</a></p>
<p>Path to dependency file: npm-v7-resolutions/package.json</p>
<p>Path to vulnerable library: npm-v7-resolutions/node_modules/merge/package.json</p>
<p>
Dependency Hierarchy:
- commitizen-4.2.3.tgz (Root Library)
- find-node-modules-2.0.0.tgz
- :x: **merge-1.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/MythicDrops/npm-v7-resolutions/commit/d4914bf0f4f3d041b3a219f1f8eb2eb6c98b9c28">d4914bf0f4f3d041b3a219f1f8eb2eb6c98b9c28</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Prototype Pollution vulnerability was found in merge before 2.1.0 via the merge.recursive function. It can be tricked into adding or modifying properties of the Object prototype. These properties will be present on all objects.
<p>Publish Date: 2020-10-09
<p>URL: <a href=https://github.com/yeikos/js.merge/pull/38>WS-2020-0218</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/yeikos/js.merge/pull/38">https://github.com/yeikos/js.merge/pull/38</a></p>
<p>Release Date: 2020-10-09</p>
<p>Fix Resolution: merge - 2.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
ws high detected in merge tgz ws high severity vulnerability vulnerable library merge tgz merge multiple objects into one optionally creating a new cloned object similar to the jquery extend but more flexible works in node js and the browser library home page a href path to dependency file npm resolutions package json path to vulnerable library npm resolutions node modules merge package json dependency hierarchy commitizen tgz root library find node modules tgz x merge tgz vulnerable library found in head commit a href found in base branch main vulnerability details a prototype pollution vulnerability was found in merge before via the merge recursive function it can be tricked into adding or modifying properties of the object prototype these properties will be present on all objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution merge step up your open source security game with whitesource
| 0
|
238,243
| 7,776,890,782
|
IssuesEvent
|
2018-06-05 09:28:10
|
snailsnap/mosaic
|
https://api.github.com/repos/snailsnap/mosaic
|
closed
|
build badges
|
high priority
|
of course we need them :^) why would you use ci if you don't show the results in the readme
|
1.0
|
build badges - of course we need them :^) why would you use ci if you don't show the results in the readme
|
non_test
|
build badges of course we need them why would you use ci if you don t show the results in the readme
| 0
|
282,295
| 8,705,083,734
|
IssuesEvent
|
2018-12-05 21:19:15
|
rancher/rancher
|
https://api.github.com/repos/rancher/rancher
|
opened
|
Cluster member can enable/disable monitoring on cluster level
|
kind/bug-qa priority/0 releases/alpha1
|
Bug.
Rancher master on 12/5
Steps:
- logged in as admin to add a standard user to a cluster as a `cluster member`
- logged in as the cluster member, go to the cluster -> Tools-> Monitoring
Result:
The cluster member can see settings and turn on the monitoring.
Expected result:
The cluster member should not be able to turn on the monitoring.
Other details might be helpful:
If the monitoring is already enabled by the admin/cluster owner, then the cluster member will see the following uncompleted sentences:
<img width="1456" alt="screenshot" src="https://user-images.githubusercontent.com/6218999/49544543-4cae2a00-f898-11e8-807a-542e1454620d.png">
|
1.0
|
Cluster member can enable/disable monitoring on cluster level - Bug.
Rancher master on 12/5
Steps:
- logged in as admin to add a standard user to a cluster as a `cluster member`
- logged in as the cluster member, go to the cluster -> Tools-> Monitoring
Result:
The cluster member can see settings and turn on the monitoring.
Expected result:
The cluster member should not be able to turn on the monitoring.
Other details might be helpful:
If the monitoring is already enabled by the admin/cluster owner, then the cluster member will see the following uncompleted sentences:
<img width="1456" alt="screenshot" src="https://user-images.githubusercontent.com/6218999/49544543-4cae2a00-f898-11e8-807a-542e1454620d.png">
|
non_test
|
cluster member can enable disable monitoring on cluster level bug rancher master on steps logged in as admin to add a standard user to a cluster as a cluster member logged in as the cluster member go to the cluster tools monitoring result the cluster member can see settings and turn on the monitoring expected result the cluster member should not be able to turn on the monitoring other details might be helpful if the monitoring is already enabled by the admin cluster owner then the cluster member will see the following uncompleted sentences img width alt screenshot src
| 0
|
302,449
| 26,144,804,021
|
IssuesEvent
|
2022-12-30 01:54:27
|
TheCheatsrichter/Gw2_Launchbuddy
|
https://api.github.com/repos/TheCheatsrichter/Gw2_Launchbuddy
|
closed
|
GFX Files not saving with 1.8.5?
|
type:bug status:testing no-issue-activity
|
So I hit import, I click the file, I move onto the next account, and the previous I set shows the same one I set on the 2nd account. So they aren't splitting gfx settings, but instead sharing the same ones.
|
1.0
|
GFX Files not saving with 1.8.5? - So I hit import, I click the file, I move onto the next account, and the previous I set shows the same one I set on the 2nd account. So they aren't splitting gfx settings, but instead sharing the same ones.
|
test
|
gfx files not saving with so i hit import i click the file i move onto the next account and the previous i set shows the same one i set on the account so they aren t splitting gfx settings but instead sharing the same ones
| 1
|
403,523
| 27,422,011,667
|
IssuesEvent
|
2023-03-01 17:21:01
|
PaloAltoNetworks/pan.dev
|
https://api.github.com/repos/PaloAltoNetworks/pan.dev
|
opened
|
Issue/Help with "Get The Next Config Search Page"
|
documentation
|
## Documentation link
<!--- Where is the documentation with the issue? -->
## Describe the problem
we used to specify the defaults if you don't specify withResourceJson.
no max value for limit - it used to be 100,000. Best practice 2000
<!--- Is this a typo, stale information, request for improvement, inaccuracy? -->
<!--- Clearly and concisely describe the problem with the documentation -->
## Suggested fix
<!--- If possible, help us by offering a suggested fix to the problem -->
|
1.0
|
Issue/Help with "Get The Next Config Search Page" - ## Documentation link
<!--- Where is the documentation with the issue? -->
## Describe the problem
we used to specify the defaults if you don't specify withResourceJson.
no max value for limit - it used to be 100,000. Best practice 2000
<!--- Is this a typo, stale information, request for improvement, inaccuracy? -->
<!--- Clearly and concisely describe the problem with the documentation -->
## Suggested fix
<!--- If possible, help us by offering a suggested fix to the problem -->
|
non_test
|
issue help with get the next config search page documentation link describe the problem we used to specify the defaults if you don t specify withresourcejson no max value for limit it used to be best practice suggested fix
| 0
|
79,946
| 29,737,433,709
|
IssuesEvent
|
2023-06-14 02:54:46
|
apache/jmeter
|
https://api.github.com/repos/apache/jmeter
|
opened
|
upload file with filename contain chinese character,request can‘t encode it
|
defect to-triage
|
### Expected behavior
when i send request, chinese character can be encode with utf-8,so i can see this filename is correct,but now it can't be encoded
### Actual behavior

POST data:
-----------------------------7d159c1302d0y0
Content-Disposition: form-data; name="file"; filename="????????????????.docx"
Content-Type: application/msword
Content-Transfer-Encoding: binary
<actual file content, not shown here>
-----------------------------7d159c1302d0y0--
[no cookies]
i send a file with chinese character filename ,but i got filename by ????
### Steps to reproduce the problem
1. write request parameter
2. choose method by post
3. send request
### JMeter Version
5.5
### Java Version
java 17.0.7 2023-04-18 LTS
### OS Version
_No response_
|
1.0
|
upload file with filename contain chinese character,request can‘t encode it - ### Expected behavior
when i send request, chinese character can be encode with utf-8,so i can see this filename is correct,but now it can't be encoded
### Actual behavior

POST data:
-----------------------------7d159c1302d0y0
Content-Disposition: form-data; name="file"; filename="????????????????.docx"
Content-Type: application/msword
Content-Transfer-Encoding: binary
<actual file content, not shown here>
-----------------------------7d159c1302d0y0--
[no cookies]
i send a file with chinese character filename ,but i got filename by ????
### Steps to reproduce the problem
1. write request parameter
2. choose method by post
3. send request
### JMeter Version
5.5
### Java Version
java 17.0.7 2023-04-18 LTS
### OS Version
_No response_
|
non_test
|
upload file with filename contain chinese character request can‘t encode it expected behavior when i send request chinese character can be encode with utf so i can see this filename is correct,but now it can t be encoded actual behavior post data content disposition form data name file filename docx content type application msword content transfer encoding binary i send a file with chinese character filename but i got filename by steps to reproduce the problem write request parameter choose method by post send request jmeter version java version java lts os version no response
| 0
|
316,986
| 9,659,454,923
|
IssuesEvent
|
2019-05-20 13:29:55
|
eaudeweb/ozone
|
https://api.github.com/repos/eaudeweb/ozone
|
closed
|
More validations to re-test
|
Component: Vue Priority: Highest
|
Art 7/Exports for QPS and Polyols
- can QPS amount be greater that quantity exported (new+recovered)?
- why can't we have empty rows, containing only polyols_qty, when no country is selected?
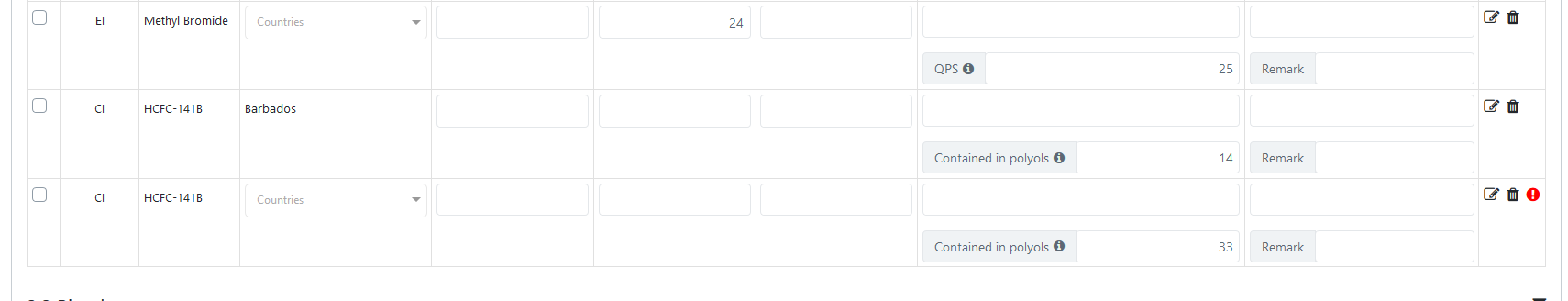
|
1.0
|
More validations to re-test - Art 7/Exports for QPS and Polyols
- can QPS amount be greater that quantity exported (new+recovered)?
- why can't we have empty rows, containing only polyols_qty, when no country is selected?
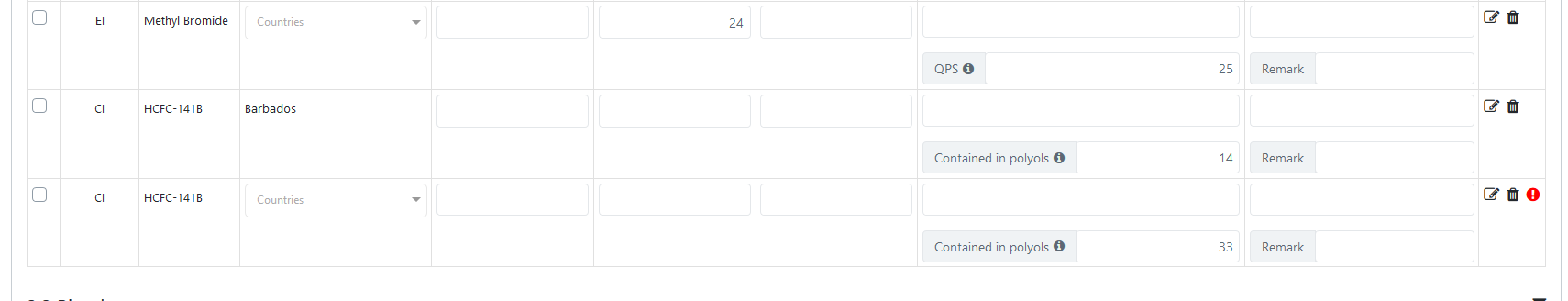
|
non_test
|
more validations to re test art exports for qps and polyols can qps amount be greater that quantity exported new recovered why can t we have empty rows containing only polyols qty when no country is selected
| 0
|
18,680
| 3,701,631,051
|
IssuesEvent
|
2016-02-29 14:04:25
|
agershun/alasql
|
https://api.github.com/repos/agershun/alasql
|
closed
|
The wiki for Csv, test synchronously works wrong. Callback is OK.
|
Solved: please test
|
/*
https://github.com/agershun/alasql/wiki/Csv
my.CSV File:
a,b,c
1,2,3
4,5,6
*/
var alasql = require('alasql');
var res = alasql('SELECT * FROM CSV("my.csv", {headers:true})');
console.log(res);
//return undefine
alasql('SELECT * FROM CSV("my.csv", {headers:true})' , [], function(data){
console.log(data);
});
/*
return
[ { a: 1, b: 2, c: 3 }, { a: 4, b: 5, c: 6 } ]
[ { a: 1, b: 2, c: 3 }, { a: 4, b: 5, c: 6 } ]
$Note that console.log(data) will return two times after undefine.
*/
|
1.0
|
The wiki for Csv, test synchronously works wrong. Callback is OK. - /*
https://github.com/agershun/alasql/wiki/Csv
my.CSV File:
a,b,c
1,2,3
4,5,6
*/
var alasql = require('alasql');
var res = alasql('SELECT * FROM CSV("my.csv", {headers:true})');
console.log(res);
//return undefine
alasql('SELECT * FROM CSV("my.csv", {headers:true})' , [], function(data){
console.log(data);
});
/*
return
[ { a: 1, b: 2, c: 3 }, { a: 4, b: 5, c: 6 } ]
[ { a: 1, b: 2, c: 3 }, { a: 4, b: 5, c: 6 } ]
$Note that console.log(data) will return two times after undefine.
*/
|
test
|
the wiki for csv test synchronously works wrong callback is ok my csv file a b c var alasql require alasql var res alasql select from csv my csv headers true console log res return undefine alasql select from csv my csv headers true function data console log data return note that console log data will return two times after undefine
| 1
|
199,447
| 6,989,650,070
|
IssuesEvent
|
2017-12-14 16:48:46
|
kubernetes/kubernetes
|
https://api.github.com/repos/kubernetes/kubernetes
|
closed
|
kubeadm v1.9 release tracking issue
|
area/kubeadm kind/feature milestone/needs-attention priority/critical-urgent sig/cluster-lifecycle status/approved-for-milestone status/in-progress
|
On request by @enisoc @jdumars and the @kubernetes/kubernetes-release-managers, I'm creating this tracking issue for the `kubernetes/kubeadm` repo.
I'm tracking what we need to get done for kubeadm to be in a release-able state in this milestone: https://github.com/kubernetes/kubeadm/milestone/4
Actions required by the release team or vice versa will be communicated via this channel.
When all the kubeadm tasks are done, we can close this umbrella issue.
Note: This is the same issue as https://github.com/kubernetes/kubernetes/issues/51841 was for v1.8
|
1.0
|
kubeadm v1.9 release tracking issue - On request by @enisoc @jdumars and the @kubernetes/kubernetes-release-managers, I'm creating this tracking issue for the `kubernetes/kubeadm` repo.
I'm tracking what we need to get done for kubeadm to be in a release-able state in this milestone: https://github.com/kubernetes/kubeadm/milestone/4
Actions required by the release team or vice versa will be communicated via this channel.
When all the kubeadm tasks are done, we can close this umbrella issue.
Note: This is the same issue as https://github.com/kubernetes/kubernetes/issues/51841 was for v1.8
|
non_test
|
kubeadm release tracking issue on request by enisoc jdumars and the kubernetes kubernetes release managers i m creating this tracking issue for the kubernetes kubeadm repo i m tracking what we need to get done for kubeadm to be in a release able state in this milestone actions required by the release team or vice versa will be communicated via this channel when all the kubeadm tasks are done we can close this umbrella issue note this is the same issue as was for
| 0
|
214,172
| 16,566,804,791
|
IssuesEvent
|
2021-05-29 15:31:06
|
SauceChord/nuru-dot-net
|
https://api.github.com/repos/SauceChord/nuru-dot-net
|
closed
|
Revise FileImage
|
test
|
Ensure that all methods are tested.
Might have to refactor the code to get this testable.
|
1.0
|
Revise FileImage - Ensure that all methods are tested.
Might have to refactor the code to get this testable.
|
test
|
revise fileimage ensure that all methods are tested might have to refactor the code to get this testable
| 1
|
625,789
| 19,765,753,929
|
IssuesEvent
|
2022-01-17 01:53:20
|
secure-sw-dev/checkedc-llvm-project
|
https://api.github.com/repos/secure-sw-dev/checkedc-llvm-project
|
opened
|
No need to pass CheckedScopeSpecifier around in SemaBounds.cpp
|
work item priority:3
|
This issue was copied from https://github.com/microsoft/checkedc-clang/issues/1151
----
After https://github.com/microsoft/checkedc-clang/pull/1142 we can get the `CheckedScopeSpecifier (CSS)` for every statement by invoking `S->getCheckedScopeSpecifier()`.
In `SemaBounds.cpp` we pass CSS around to functions. This should no longer be needed.
|
1.0
|
No need to pass CheckedScopeSpecifier around in SemaBounds.cpp - This issue was copied from https://github.com/microsoft/checkedc-clang/issues/1151
----
After https://github.com/microsoft/checkedc-clang/pull/1142 we can get the `CheckedScopeSpecifier (CSS)` for every statement by invoking `S->getCheckedScopeSpecifier()`.
In `SemaBounds.cpp` we pass CSS around to functions. This should no longer be needed.
|
non_test
|
no need to pass checkedscopespecifier around in semabounds cpp this issue was copied from after we can get the checkedscopespecifier css for every statement by invoking s getcheckedscopespecifier in semabounds cpp we pass css around to functions this should no longer be needed
| 0
|
515,539
| 14,965,170,164
|
IssuesEvent
|
2021-01-27 13:01:50
|
jbroutier/whatisflying-db
|
https://api.github.com/repos/jbroutier/whatisflying-db
|
opened
|
Missing Aeroprakt aircraft types pictures
|
Category: Aircraft type Priority: Normal
|
Add pictures for the following aircraft types:
- [ ] A-19
- [ ] A-21 Solo
- [ ] A-23 Dragon
- [ ] A-25 Breeze
- [ ] A-27
- [ ] A-33 Dragon
- [ ] A-37
- [ ] A-24 Viking
- [ ] A-26 Vulcan
- [ ] A-28 Victor
- [ ] A-36 Super Vulcan
|
1.0
|
Missing Aeroprakt aircraft types pictures - Add pictures for the following aircraft types:
- [ ] A-19
- [ ] A-21 Solo
- [ ] A-23 Dragon
- [ ] A-25 Breeze
- [ ] A-27
- [ ] A-33 Dragon
- [ ] A-37
- [ ] A-24 Viking
- [ ] A-26 Vulcan
- [ ] A-28 Victor
- [ ] A-36 Super Vulcan
|
non_test
|
missing aeroprakt aircraft types pictures add pictures for the following aircraft types a a solo a dragon a breeze a a dragon a a viking a vulcan a victor a super vulcan
| 0
|
68,337
| 7,093,358,277
|
IssuesEvent
|
2018-01-12 20:09:27
|
NOAA-PMEL/LAS
|
https://api.github.com/repos/NOAA-PMEL/LAS
|
closed
|
Look at Selenium Remote Control as a way to build data set configuration independent, browser based tests.
|
S: major Testing enhancement
|
**Reported by @noaaroland on 30 Nov 2007 20:19 UTC**
Selenium Remote Control is a test tool that allows you to write automated web application UI tests in any programming language against any HTTP website using any mainstream JavaScript-enabled browser.
It seems reasonable that one could read the las.xml config (or ask a service) to get the LAS configuration to be tested and then automatically drive the standard UIs (both 6 and 7) from Java code to test both the functioning of the UI and all of the underlying machinery (F-TDS, database and OPeNDAP connections, Ferret scripts, etc.) on the server while at the same time testing browser compatibility.
Migrated-From: http://dunkel.pmel.noaa.gov/trac/las/ticket/324
|
1.0
|
Look at Selenium Remote Control as a way to build data set configuration independent, browser based tests. - **Reported by @noaaroland on 30 Nov 2007 20:19 UTC**
Selenium Remote Control is a test tool that allows you to write automated web application UI tests in any programming language against any HTTP website using any mainstream JavaScript-enabled browser.
It seems reasonable that one could read the las.xml config (or ask a service) to get the LAS configuration to be tested and then automatically drive the standard UIs (both 6 and 7) from Java code to test both the functioning of the UI and all of the underlying machinery (F-TDS, database and OPeNDAP connections, Ferret scripts, etc.) on the server while at the same time testing browser compatibility.
Migrated-From: http://dunkel.pmel.noaa.gov/trac/las/ticket/324
|
test
|
look at selenium remote control as a way to build data set configuration independent browser based tests reported by noaaroland on nov utc selenium remote control is a test tool that allows you to write automated web application ui tests in any programming language against any http website using any mainstream javascript enabled browser it seems reasonable that one could read the las xml config or ask a service to get the las configuration to be tested and then automatically drive the standard uis both and from java code to test both the functioning of the ui and all of the underlying machinery f tds database and opendap connections ferret scripts etc on the server while at the same time testing browser compatibility migrated from
| 1
|
350,141
| 31,856,592,816
|
IssuesEvent
|
2023-09-15 07:55:38
|
cockroachdb/cockroach
|
https://api.github.com/repos/cockroachdb/cockroach
|
closed
|
roachtest: sqlsmith/setup=tpcc/setting=default failed
|
C-test-failure O-robot O-roachtest release-blocker T-sql-queries branch-release-23.1
|
roachtest.sqlsmith/setup=tpcc/setting=default [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/11786702?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/11786702?buildTab=artifacts#/sqlsmith/setup=tpcc/setting=default) on release-23.1 @ [3224fa603020b8226d4ecbe4d520a2651b6b97d5](https://github.com/cockroachdb/cockroach/commits/3224fa603020b8226d4ecbe4d520a2651b6b97d5):
```
),
('0103000060E610000000000000':::GEOGRAPHY),
(
'0106000060E6100000040000000103000040010000000A0000005119CC198FD063C0BFAEAB432F1744C08D0AF82DF4DCF0C1405F3450E79E37C0DE9EB82044E253C054F3D5261877E4C15CF10DDAFF4640C0749565CD674E3DC018DD81E13D9DF54148E5F7111B4254C01087402F1F923F40001AB1131692C7415851AB651E2E53C03C13CA667C084F40205D739EB6F7E441A69190A742E754C0FC8CBD39E5634740171471D888DAF7C1DDB06D9825265AC0F25E69844CE85340906EBBD53DFB00C2BA8DF45CDEB45DC0B42BDD8479394C40C0EBC6960B66C7C196CB00A75EBD65C0A002422DEB344A40709519982C9FC5415119CC198FD063C0BFAEAB432F1744C08D0AF82DF4DCF0C1010300004001000000070000006ADE01B1085563C06AF0059547BA53C0B8F3DF4E0D08DFC108249CA9AA435B40023D711F617F55C0E225D210709A0042EA8E236F01916340D019D5F777012E40081E4590D3C6ED411862B8641D9D5F40EC63F4A94D804A4088416372815FF04100827D507A323FC040426CB33F283A40ECCDBD63EEE101424F766974EE0D61C020EB7179D1AE17C05414609BC072FDC16ADE01B1085563C06AF0059547BA53C0B8F3DF4E0D08DFC10103000040010000000B000000A5FDCD7D0C5F5FC038018430E46340C0F2856120D037004260B88D8D1D8550C08ED53AAA37754DC050FC864EAED9FA41807DEB7D72292F4062EF95A129D24EC0F26F917BC570F141B01BC06994BE3C409B9343166A0050C06DE97937C98101C230FA29469CB43D4042555D0A950640C040B233386832B541D82A8B613A3D6240E926DFDE8D864BC08EF296B7E0CEF24140F994084D0B6640F20695082D9F4040B048A7ECC00FC4416E4E4201E78E5140F880CEDC08B2534000FFB6AF8E4E94C1481616A91FB541C060A8B245B3414340C2ABB864B685E1C1F870585F400E46C0D0706C22179D3640BB6BF1E3F846F4C1A5FDCD7D0C5F5FC038018430E46340C0F2856120D03700420103000040010000000D0000007F208FFBE6E163C06086674F4AF503402A874B83CB01F441919DDDF9FD7560C0C6996CDC5A923FC0852BB0969888F6C184C89BB849A951C085554DFC84714DC0D49E0F503ABDFB4148DB80ABF27539C00854F923C30236C082829FBA2958F341EC42D56FEB7146C0281064726C304BC04A03D40F40FBF14168D8998A1AC75640B24372430D4455C090F172163810E3C1340FAC4D6B866540E0B8CECB5A0211C0A5211B4C0B81FAC13832CCE7050B5440609A0D7609E04D4056AF0E6DB1F200C234AA1AF0DE7E5640225A6B60BA695540100AB15B926FD74120653528344839406445B9549DD33F40D6FAE9CCCFE5E9C1680396F9F77F31C0988575A3A753564058F1E22F558AFD41D8F01E17D12C55C0FEB1F7D2EDC742409D1053141B24F1C17F208FFBE6E163C06086674F4AF503402A874B83CB01F441':::GEOGRAPHY
),
('0102000020E610000000000000':::GEOGRAPHY)
)
AS tab865 (col1093)
),
with165 (col1094, "%pcol1095")
AS (
SELECT
*
FROM
(
VALUES
(
'{"O2snu7": false}':::JSONB,
'[{"FEdFJJe7": 0.036612564744017105, "baz": false, "c": true}, [0.2508010297616419], false]':::JSONB
),
('false':::JSONB, '{"test": "json"}':::JSONB)
)
AS tab866 (col1094, "%pcol1095")
EXCEPT SELECT * FROM (VALUES ('{"test": "json"}':::JSONB, NULL)) AS tab867 (co😁l1096, "c|ol1097")
)
SELECT
bit_or(tab868.d_id::INT8)::INT8 AS col1098,
sum_int(tab868.d_id::INT8)::INT8 AS c͒ol1099,
count_rows() OVER (PARTITION BY " tab869".ol_number ORDER BY " tab869".ol_number ASC NULLS LAST, " tab869".ol_number ASC, tab868.d_id DESC NULLS FIRST ROWS UNBOUNDED PRECEDING)::INT8
AS col1100,
regr_count((-5180185443639800759):::INT8::DECIMAL, " tab869".ol_number::INT8) OVER (PARTITION BY tab868.d_id, " tab869".ol_number, tab868.d_id, " tab869".ol_number ROWS BETWEEN 7561566934165538152:::INT8 FOLLOWING AND UNBOUNDED FOLLOWING)::INT8
AS col1101,
regr_count(NULL::DECIMAL, " tab869".ol_number::INT8)::INT8 AS col͠1102,
sum_int(" tab869".ol_number::INT8) OVER (PARTITION BY tab868.d_id ORDER BY " tab869".ol_number DESC NULLS FIRST RANGE BETWEEN 4674010724183679575:::INT8 FOLLOWING AND UNBOUNDED FOLLOWING)::INT8
AS col1103,
'X':::STRING AS col1104
FROM
defaultdb.public.district AS tab868
JOIN defaultdb.public.order_line AS " tab869" ON
(tab868.d_w_id) = (" tab869".ol_supply_w_id) AND (tab868.d_id) = (" tab869".ol_number)
GROUP BY
tab868.d_id, " tab869".ol_number, tab868.d_id, " tab869".ol_number
ORDER BY
" tab869".ol_number DESC,
tab868.d_id NULLS FIRST,
" tab869".ol_number NULLS FIRST,
tab868.d_id ASC NULLS LAST,
tab868.d_id ASC NULLS LAST,
" tab869".ol_number NULLS LAST;
test artifacts and logs in: /artifacts/sqlsmith/setup=tpcc/setting=default/run_1
```
<p>Parameters: <code>ROACHTEST_arch=amd64</code>
, <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
See: [Grafana](https://go.crdb.dev/roachtest-grafana/teamcity-11786702/sqlsmith-setup-tpcc-setting-default/1694759232996/1694759961178)
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*sqlsmith/setup=tpcc/setting=default.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-31566
|
2.0
|
roachtest: sqlsmith/setup=tpcc/setting=default failed - roachtest.sqlsmith/setup=tpcc/setting=default [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/11786702?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/11786702?buildTab=artifacts#/sqlsmith/setup=tpcc/setting=default) on release-23.1 @ [3224fa603020b8226d4ecbe4d520a2651b6b97d5](https://github.com/cockroachdb/cockroach/commits/3224fa603020b8226d4ecbe4d520a2651b6b97d5):
```
),
('0103000060E610000000000000':::GEOGRAPHY),
(
'0106000060E6100000040000000103000040010000000A0000005119CC198FD063C0BFAEAB432F1744C08D0AF82DF4DCF0C1405F3450E79E37C0DE9EB82044E253C054F3D5261877E4C15CF10DDAFF4640C0749565CD674E3DC018DD81E13D9DF54148E5F7111B4254C01087402F1F923F40001AB1131692C7415851AB651E2E53C03C13CA667C084F40205D739EB6F7E441A69190A742E754C0FC8CBD39E5634740171471D888DAF7C1DDB06D9825265AC0F25E69844CE85340906EBBD53DFB00C2BA8DF45CDEB45DC0B42BDD8479394C40C0EBC6960B66C7C196CB00A75EBD65C0A002422DEB344A40709519982C9FC5415119CC198FD063C0BFAEAB432F1744C08D0AF82DF4DCF0C1010300004001000000070000006ADE01B1085563C06AF0059547BA53C0B8F3DF4E0D08DFC108249CA9AA435B40023D711F617F55C0E225D210709A0042EA8E236F01916340D019D5F777012E40081E4590D3C6ED411862B8641D9D5F40EC63F4A94D804A4088416372815FF04100827D507A323FC040426CB33F283A40ECCDBD63EEE101424F766974EE0D61C020EB7179D1AE17C05414609BC072FDC16ADE01B1085563C06AF0059547BA53C0B8F3DF4E0D08DFC10103000040010000000B000000A5FDCD7D0C5F5FC038018430E46340C0F2856120D037004260B88D8D1D8550C08ED53AAA37754DC050FC864EAED9FA41807DEB7D72292F4062EF95A129D24EC0F26F917BC570F141B01BC06994BE3C409B9343166A0050C06DE97937C98101C230FA29469CB43D4042555D0A950640C040B233386832B541D82A8B613A3D6240E926DFDE8D864BC08EF296B7E0CEF24140F994084D0B6640F20695082D9F4040B048A7ECC00FC4416E4E4201E78E5140F880CEDC08B2534000FFB6AF8E4E94C1481616A91FB541C060A8B245B3414340C2ABB864B685E1C1F870585F400E46C0D0706C22179D3640BB6BF1E3F846F4C1A5FDCD7D0C5F5FC038018430E46340C0F2856120D03700420103000040010000000D0000007F208FFBE6E163C06086674F4AF503402A874B83CB01F441919DDDF9FD7560C0C6996CDC5A923FC0852BB0969888F6C184C89BB849A951C085554DFC84714DC0D49E0F503ABDFB4148DB80ABF27539C00854F923C30236C082829FBA2958F341EC42D56FEB7146C0281064726C304BC04A03D40F40FBF14168D8998A1AC75640B24372430D4455C090F172163810E3C1340FAC4D6B866540E0B8CECB5A0211C0A5211B4C0B81FAC13832CCE7050B5440609A0D7609E04D4056AF0E6DB1F200C234AA1AF0DE7E5640225A6B60BA695540100AB15B926FD74120653528344839406445B9549DD33F40D6FAE9CCCFE5E9C1680396F9F77F31C0988575A3A753564058F1E22F558AFD41D8F01E17D12C55C0FEB1F7D2EDC742409D1053141B24F1C17F208FFBE6E163C06086674F4AF503402A874B83CB01F441':::GEOGRAPHY
),
('0102000020E610000000000000':::GEOGRAPHY)
)
AS tab865 (col1093)
),
with165 (col1094, "%pcol1095")
AS (
SELECT
*
FROM
(
VALUES
(
'{"O2snu7": false}':::JSONB,
'[{"FEdFJJe7": 0.036612564744017105, "baz": false, "c": true}, [0.2508010297616419], false]':::JSONB
),
('false':::JSONB, '{"test": "json"}':::JSONB)
)
AS tab866 (col1094, "%pcol1095")
EXCEPT SELECT * FROM (VALUES ('{"test": "json"}':::JSONB, NULL)) AS tab867 (co😁l1096, "c|ol1097")
)
SELECT
bit_or(tab868.d_id::INT8)::INT8 AS col1098,
sum_int(tab868.d_id::INT8)::INT8 AS c͒ol1099,
count_rows() OVER (PARTITION BY " tab869".ol_number ORDER BY " tab869".ol_number ASC NULLS LAST, " tab869".ol_number ASC, tab868.d_id DESC NULLS FIRST ROWS UNBOUNDED PRECEDING)::INT8
AS col1100,
regr_count((-5180185443639800759):::INT8::DECIMAL, " tab869".ol_number::INT8) OVER (PARTITION BY tab868.d_id, " tab869".ol_number, tab868.d_id, " tab869".ol_number ROWS BETWEEN 7561566934165538152:::INT8 FOLLOWING AND UNBOUNDED FOLLOWING)::INT8
AS col1101,
regr_count(NULL::DECIMAL, " tab869".ol_number::INT8)::INT8 AS col͠1102,
sum_int(" tab869".ol_number::INT8) OVER (PARTITION BY tab868.d_id ORDER BY " tab869".ol_number DESC NULLS FIRST RANGE BETWEEN 4674010724183679575:::INT8 FOLLOWING AND UNBOUNDED FOLLOWING)::INT8
AS col1103,
'X':::STRING AS col1104
FROM
defaultdb.public.district AS tab868
JOIN defaultdb.public.order_line AS " tab869" ON
(tab868.d_w_id) = (" tab869".ol_supply_w_id) AND (tab868.d_id) = (" tab869".ol_number)
GROUP BY
tab868.d_id, " tab869".ol_number, tab868.d_id, " tab869".ol_number
ORDER BY
" tab869".ol_number DESC,
tab868.d_id NULLS FIRST,
" tab869".ol_number NULLS FIRST,
tab868.d_id ASC NULLS LAST,
tab868.d_id ASC NULLS LAST,
" tab869".ol_number NULLS LAST;
test artifacts and logs in: /artifacts/sqlsmith/setup=tpcc/setting=default/run_1
```
<p>Parameters: <code>ROACHTEST_arch=amd64</code>
, <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
See: [Grafana](https://go.crdb.dev/roachtest-grafana/teamcity-11786702/sqlsmith-setup-tpcc-setting-default/1694759232996/1694759961178)
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*sqlsmith/setup=tpcc/setting=default.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-31566
|
test
|
roachtest sqlsmith setup tpcc setting default failed roachtest sqlsmith setup tpcc setting default with on release geography geography geography as as select from values false jsonb false jsonb false jsonb test json jsonb as except select from values test json jsonb null as co😁 c select bit or d id as sum int d id as c͒ count rows over partition by ol number order by ol number asc nulls last ol number asc d id desc nulls first rows unbounded preceding as regr count decimal ol number over partition by d id ol number d id ol number rows between following and unbounded following as regr count null decimal ol number as col͠ sum int ol number over partition by d id order by ol number desc nulls first range between following and unbounded following as x string as from defaultdb public district as join defaultdb public order line as on d w id ol supply w id and d id ol number group by d id ol number d id ol number order by ol number desc d id nulls first ol number nulls first d id asc nulls last d id asc nulls last ol number nulls last test artifacts and logs in artifacts sqlsmith setup tpcc setting default run parameters roachtest arch roachtest cloud gce roachtest cpu roachtest encrypted false roachtest ssd help see see see cc cockroachdb sql queries jira issue crdb
| 1
|
278,428
| 21,076,943,468
|
IssuesEvent
|
2022-04-02 09:29:00
|
OpenLineage/website
|
https://api.github.com/repos/OpenLineage/website
|
opened
|
[INTEGRATION] [DOCS] Add page for Dagster integration
|
documentation
|
The Dagster integration was released in 0.6, but isn't reflected on the website at all.
A good first pass would be to edit and format the information currently contained in the [README](https://github.com/OpenLineage/OpenLineage/blob/main/integration/dagster/README.md), and we should have dalin do an edit pass for correctness if he doesn't have time to get it uploaded.
|
1.0
|
[INTEGRATION] [DOCS] Add page for Dagster integration - The Dagster integration was released in 0.6, but isn't reflected on the website at all.
A good first pass would be to edit and format the information currently contained in the [README](https://github.com/OpenLineage/OpenLineage/blob/main/integration/dagster/README.md), and we should have dalin do an edit pass for correctness if he doesn't have time to get it uploaded.
|
non_test
|
add page for dagster integration the dagster integration was released in but isn t reflected on the website at all a good first pass would be to edit and format the information currently contained in the and we should have dalin do an edit pass for correctness if he doesn t have time to get it uploaded
| 0
|
57,379
| 15,758,491,922
|
IssuesEvent
|
2021-03-31 06:49:57
|
jOOQ/jOOQ
|
https://api.github.com/repos/jOOQ/jOOQ
|
opened
|
Filter not working properly for numeric datatype
|
T: Defect
|
```
create table test (
amount numeric(22,0),
account_id int
);
select * from test;
insert into test values (56000, 1);
select amount/10000, account_id from test where amount/10000=5.6;
```
The above select query returns the row that is inserted.
But, when the same is written using JOOQ, the condition `Test.TEST.AMOUNT.div(10000).equal(5.6)` becomes `where amount/10000=5`.
### Expected behavior
Properly generated SQL with condition where amount/10000=5.6
### Actual behavior
Query generated is `where amount/10000=5`
### Steps to reproduce the problem
Mentioned above
- If the problem relates to code generation, please post your code generation configuration
- A complete set of DDL statements can help re-create the setup you're having
- An MCVE can be helpful to provide a complete reproduction case: https://github.com/jOOQ/jOOQ-mcve
### Versions
- jOOQ: 3.14.8
- Java:11
- Database (include vendor):POSTGRES
- OS:Mac
- JDBC Driver (include name if inofficial driver):
|
1.0
|
Filter not working properly for numeric datatype - ```
create table test (
amount numeric(22,0),
account_id int
);
select * from test;
insert into test values (56000, 1);
select amount/10000, account_id from test where amount/10000=5.6;
```
The above select query returns the row that is inserted.
But, when the same is written using JOOQ, the condition `Test.TEST.AMOUNT.div(10000).equal(5.6)` becomes `where amount/10000=5`.
### Expected behavior
Properly generated SQL with condition where amount/10000=5.6
### Actual behavior
Query generated is `where amount/10000=5`
### Steps to reproduce the problem
Mentioned above
- If the problem relates to code generation, please post your code generation configuration
- A complete set of DDL statements can help re-create the setup you're having
- An MCVE can be helpful to provide a complete reproduction case: https://github.com/jOOQ/jOOQ-mcve
### Versions
- jOOQ: 3.14.8
- Java:11
- Database (include vendor):POSTGRES
- OS:Mac
- JDBC Driver (include name if inofficial driver):
|
non_test
|
filter not working properly for numeric datatype create table test amount numeric account id int select from test insert into test values select amount account id from test where amount the above select query returns the row that is inserted but when the same is written using jooq the condition test test amount div equal becomes where amount expected behavior properly generated sql with condition where amount actual behavior query generated is where amount steps to reproduce the problem mentioned above if the problem relates to code generation please post your code generation configuration a complete set of ddl statements can help re create the setup you re having an mcve can be helpful to provide a complete reproduction case versions jooq java database include vendor postgres os mac jdbc driver include name if inofficial driver
| 0
|
217,291
| 16,848,852,230
|
IssuesEvent
|
2021-06-20 04:18:44
|
hakehuang/infoflow
|
https://api.github.com/repos/hakehuang/infoflow
|
opened
|
tests-ci :kernel.common.stack_sentinel.fatal : zephyr-v2.6.0-286-g46029914a7ac: lpcxpresso55s28: test Timeout
|
area: Tests
|
**Describe the bug**
kernel.common.stack_sentinel.fatal test is Timeout on zephyr-v2.6.0-286-g46029914a7ac on lpcxpresso55s28
see logs for details
**To Reproduce**
1.
```
scripts/twister --device-testing --device-serial /dev/ttyACM0 -p lpcxpresso55s28 --testcase-root tests --sub-test kernel.common
```
2. See error
**Expected behavior**
test pass
**Impact**
**Logs and console output**
```
*** Booting Zephyr OS build zephyr-v2.6.0-286-g46029914a7ac ***
Running test suite fatal
===================================================================
START - test_fatal
test alt thread 1: generic CPU exception
ASSERTION FAIL [esf != ((void *)0)] @ WEST_TOPDIR/zephyr/arch/arm/core/aarch32/cortex_m/fault.c:993
ESF could not be retrieved successfully. Shall never occur.
ASSERTION FAIL [esf != ((void *)0)] @ WEST_TOPDIR/zephyr/arch/arm/core/aarch32/cortex_m/fault.c:993
ESF could not be retrieved successfully. Shall never occur.
```
**Environment (please complete the following information):**
- OS: (e.g. Linux )
- Toolchain (e.g Zephyr SDK)
- Commit SHA or Version used: zephyr-v2.6.0-286-g46029914a7ac
|
1.0
|
tests-ci :kernel.common.stack_sentinel.fatal : zephyr-v2.6.0-286-g46029914a7ac: lpcxpresso55s28: test Timeout
-
**Describe the bug**
kernel.common.stack_sentinel.fatal test is Timeout on zephyr-v2.6.0-286-g46029914a7ac on lpcxpresso55s28
see logs for details
**To Reproduce**
1.
```
scripts/twister --device-testing --device-serial /dev/ttyACM0 -p lpcxpresso55s28 --testcase-root tests --sub-test kernel.common
```
2. See error
**Expected behavior**
test pass
**Impact**
**Logs and console output**
```
*** Booting Zephyr OS build zephyr-v2.6.0-286-g46029914a7ac ***
Running test suite fatal
===================================================================
START - test_fatal
test alt thread 1: generic CPU exception
ASSERTION FAIL [esf != ((void *)0)] @ WEST_TOPDIR/zephyr/arch/arm/core/aarch32/cortex_m/fault.c:993
ESF could not be retrieved successfully. Shall never occur.
ASSERTION FAIL [esf != ((void *)0)] @ WEST_TOPDIR/zephyr/arch/arm/core/aarch32/cortex_m/fault.c:993
ESF could not be retrieved successfully. Shall never occur.
```
**Environment (please complete the following information):**
- OS: (e.g. Linux )
- Toolchain (e.g Zephyr SDK)
- Commit SHA or Version used: zephyr-v2.6.0-286-g46029914a7ac
|
test
|
tests ci kernel common stack sentinel fatal zephyr test timeout describe the bug kernel common stack sentinel fatal test is timeout on zephyr on see logs for details to reproduce scripts twister device testing device serial dev p testcase root tests sub test kernel common see error expected behavior test pass impact logs and console output booting zephyr os build zephyr running test suite fatal start test fatal test alt thread generic cpu exception assertion fail west topdir zephyr arch arm core cortex m fault c esf could not be retrieved successfully shall never occur assertion fail west topdir zephyr arch arm core cortex m fault c esf could not be retrieved successfully shall never occur environment please complete the following information os e g linux toolchain e g zephyr sdk commit sha or version used zephyr
| 1
|
57,451
| 6,547,679,226
|
IssuesEvent
|
2017-09-04 15:53:36
|
pixelhumain/co2
|
https://api.github.com/repos/pixelhumain/co2
|
closed
|
Bug lors de la création d'une news
|
to test
|
Le bouton de communexion est grisé est il affiche se Communecter avec undefined
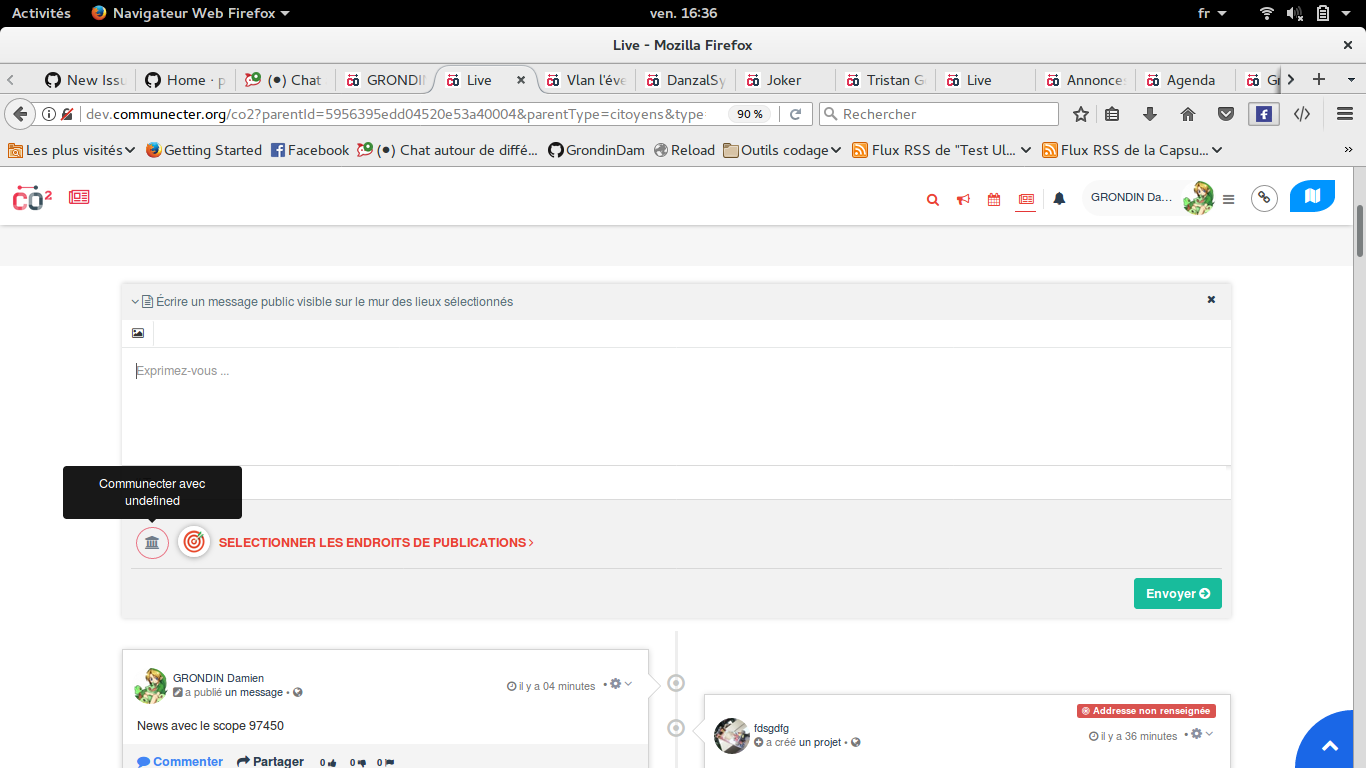
Quand on clique dessus (oui il est grisé mais on peut cliquer dessus) ca affiche ça :

Dés lors que je fais ça, quand je vais valider la news, celle ci ne se crée pas
Autre chose quand on clique sur la cible
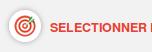
Dans le DynForm qui s'ouvre, je n'arrive pas à faire fermer le select à moins de choisir un scope
Le scope s'affiche comme ça dans la news :
Pareil si je choisi un scope, et que je valide la news elle ne se crée pas.
|
1.0
|
Bug lors de la création d'une news - Le bouton de communexion est grisé est il affiche se Communecter avec undefined
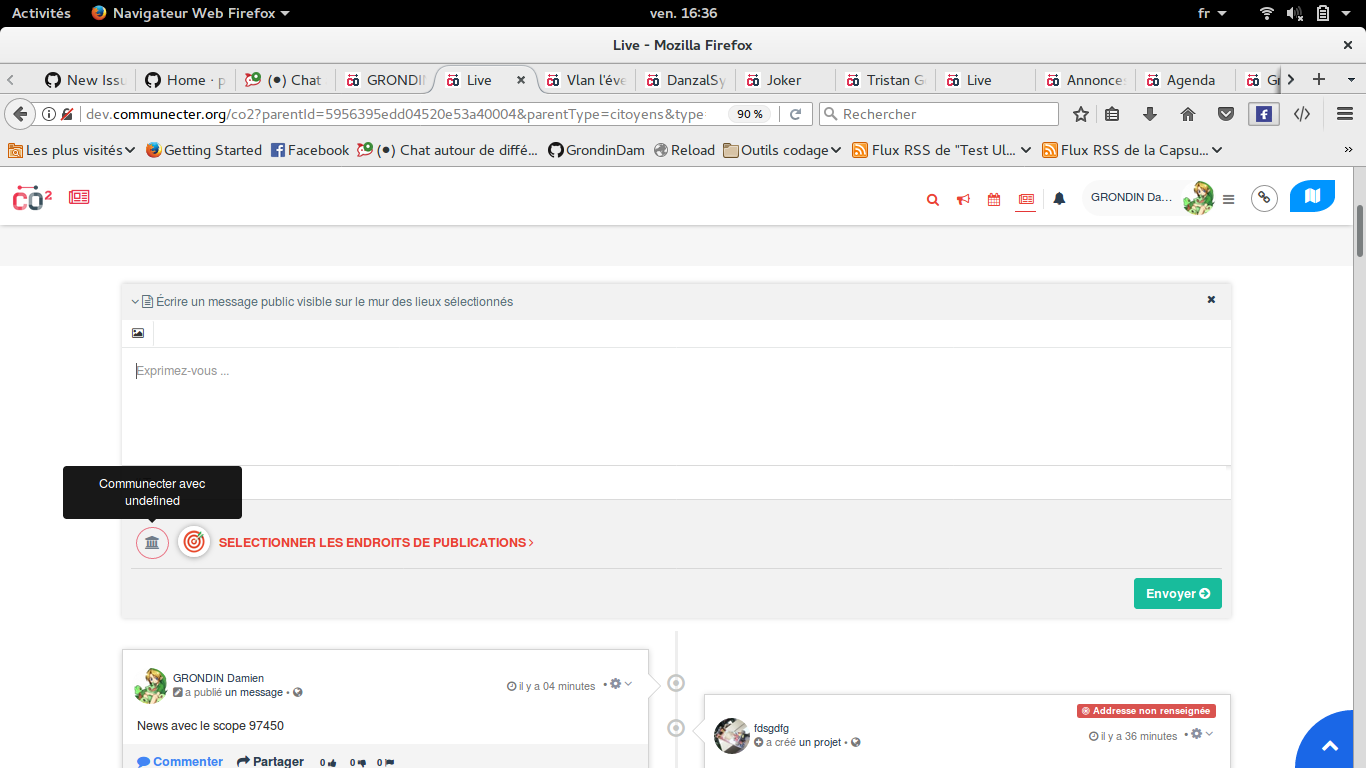
Quand on clique dessus (oui il est grisé mais on peut cliquer dessus) ca affiche ça :

Dés lors que je fais ça, quand je vais valider la news, celle ci ne se crée pas
Autre chose quand on clique sur la cible
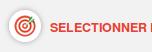
Dans le DynForm qui s'ouvre, je n'arrive pas à faire fermer le select à moins de choisir un scope
Le scope s'affiche comme ça dans la news :
Pareil si je choisi un scope, et que je valide la news elle ne se crée pas.
|
test
|
bug lors de la création d une news le bouton de communexion est grisé est il affiche se communecter avec undefined quand on clique dessus oui il est grisé mais on peut cliquer dessus ca affiche ça dés lors que je fais ça quand je vais valider la news celle ci ne se crée pas autre chose quand on clique sur la cible dans le dynform qui s ouvre je n arrive pas à faire fermer le select à moins de choisir un scope le scope s affiche comme ça dans la news pareil si je choisi un scope et que je valide la news elle ne se crée pas
| 1
|
296,471
| 25,552,114,836
|
IssuesEvent
|
2022-11-30 01:14:39
|
microsoft/vscode
|
https://api.github.com/repos/microsoft/vscode
|
closed
|
Test: Modified elsewhere setting indicator accessibility
|
testplan-item
|
Refs: #159088
- [x] macOS @paulacamargo25
- [x] linux @weinand
- [x] windows @amunger
Complexity: 3
[Create Issue](https://github.com/microsoft/vscode/issues/new?body=Testing+%23167088%0A%0A&assignees=rzhao271)
---
In the Settings editor, there are indicators, which are labels that show up in parentheses next to some settings such as "Modified elsewhere".
For the following steps, make sure to test both the case where the indicator says "Modified elsewhere", and where the indicator starts with "Modified in".
1. Open the Settings editor. Clear the search query if there is one.
2. Navigate to a "Modified elsewhere" indicator. `editor.tabSize` should have one, and another easy way to make that indicator appear is to modify a setting in the workspace only, and then to navigate back to the User scope.
3. If the indicator says "Modified in: $scopeName", then focus should only go to the `$scopeName` part of the indicator, which is a link. Otherwise, the entire indicator should be outlined.
4. Once focused on an indicator, press space or enter to open the hover and focus it.
5. Alternatively, one should be able to hover over an indicator with a mouse, and then click on the hover to focus it.
6. For the Modified elsewhere indicator hover, tab and shift+tab should tab around within the hover contents only. The hover in this case acts as a focus trap, where focus is contained inside the hover until the hover is closed.
7. Pressing escape or another non-tab key should close the hover. Clicking elsewhere should also close the hover.
8. Pressing enter or space on a link inside the hover should act the same as clicking on it.
9. The indicator and hover should be navigable with a screenreader.
|
1.0
|
Test: Modified elsewhere setting indicator accessibility - Refs: #159088
- [x] macOS @paulacamargo25
- [x] linux @weinand
- [x] windows @amunger
Complexity: 3
[Create Issue](https://github.com/microsoft/vscode/issues/new?body=Testing+%23167088%0A%0A&assignees=rzhao271)
---
In the Settings editor, there are indicators, which are labels that show up in parentheses next to some settings such as "Modified elsewhere".
For the following steps, make sure to test both the case where the indicator says "Modified elsewhere", and where the indicator starts with "Modified in".
1. Open the Settings editor. Clear the search query if there is one.
2. Navigate to a "Modified elsewhere" indicator. `editor.tabSize` should have one, and another easy way to make that indicator appear is to modify a setting in the workspace only, and then to navigate back to the User scope.
3. If the indicator says "Modified in: $scopeName", then focus should only go to the `$scopeName` part of the indicator, which is a link. Otherwise, the entire indicator should be outlined.
4. Once focused on an indicator, press space or enter to open the hover and focus it.
5. Alternatively, one should be able to hover over an indicator with a mouse, and then click on the hover to focus it.
6. For the Modified elsewhere indicator hover, tab and shift+tab should tab around within the hover contents only. The hover in this case acts as a focus trap, where focus is contained inside the hover until the hover is closed.
7. Pressing escape or another non-tab key should close the hover. Clicking elsewhere should also close the hover.
8. Pressing enter or space on a link inside the hover should act the same as clicking on it.
9. The indicator and hover should be navigable with a screenreader.
|
test
|
test modified elsewhere setting indicator accessibility refs macos linux weinand windows amunger complexity in the settings editor there are indicators which are labels that show up in parentheses next to some settings such as modified elsewhere for the following steps make sure to test both the case where the indicator says modified elsewhere and where the indicator starts with modified in open the settings editor clear the search query if there is one navigate to a modified elsewhere indicator editor tabsize should have one and another easy way to make that indicator appear is to modify a setting in the workspace only and then to navigate back to the user scope if the indicator says modified in scopename then focus should only go to the scopename part of the indicator which is a link otherwise the entire indicator should be outlined once focused on an indicator press space or enter to open the hover and focus it alternatively one should be able to hover over an indicator with a mouse and then click on the hover to focus it for the modified elsewhere indicator hover tab and shift tab should tab around within the hover contents only the hover in this case acts as a focus trap where focus is contained inside the hover until the hover is closed pressing escape or another non tab key should close the hover clicking elsewhere should also close the hover pressing enter or space on a link inside the hover should act the same as clicking on it the indicator and hover should be navigable with a screenreader
| 1
|
351,107
| 31,934,677,893
|
IssuesEvent
|
2023-09-19 09:40:48
|
unifyai/ivy
|
https://api.github.com/repos/unifyai/ivy
|
opened
|
Fix ndarray.test_numpy_ndarray_nonzero
|
NumPy Frontend Sub Task Failing Test
|
| | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6230446511/job/16910475139"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6230446511/job/16910475139"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6230446511/job/16910475139"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6230446511/job/16910475139"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6230446511/job/16910475139"><img src=https://img.shields.io/badge/-failure-red></a>
|
1.0
|
Fix ndarray.test_numpy_ndarray_nonzero - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6230446511/job/16910475139"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6230446511/job/16910475139"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6230446511/job/16910475139"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6230446511/job/16910475139"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6230446511/job/16910475139"><img src=https://img.shields.io/badge/-failure-red></a>
|
test
|
fix ndarray test numpy ndarray nonzero numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src
| 1
|
24,678
| 5,095,949,315
|
IssuesEvent
|
2017-01-03 16:41:14
|
Graylog2/graylog-plugin-auth-sso
|
https://api.github.com/repos/Graylog2/graylog-plugin-auth-sso
|
closed
|
Plugin does not recognize graylog install on appliance
|
documentation
|
### Problem description
The .deb installer for the plugin does not recognize that the graylog package is installed and errors out.
### Steps to reproduce the problem
1. Setup graylog appliance via OVA (ours started on 1.x, then upgraded to 2.0, and now to 2.1)
2. Attempt to install deb (`dpkg -G -I graylog-plugin-auth-sso-1.0.3.deb`)
3. Receive the following output:
```
Preparing to unpack graylog-plugin-auth-sso-1.0.3.deb ...
Unpacking graylog-plugin-auth-sso (1.0.3) over (1.0.3) ...
dpkg: dependency problems prevent configuration of graylog-plugin-auth-sso:
graylog-plugin-auth-sso depends on graylog-server | graylog-radio; however:
Package graylog-server is not installed.
Package graylog-radio is not installed.
dpkg: error processing package graylog-plugin-auth-sso (--install):
dependency problems - leaving unconfigured
Errors were encountered while processing:
graylog-plugin-auth-sso
```
Graylog is installed. It appears the plugin is looking for graylog-server, but the package for 2.1 reports itself as `graylog`:
```
ubuntu@graylog:~$ dpkg -l | grep graylog
ii graylog 2.1.0-1 amd64 The full stack of graylog
iU graylog-plugin-auth-sso 1.0.3 all Graylog graylog-plugin-auth-sso plugin.
```
### Environment
- Graylog Version: 2.1.0+62db7e0
- Plugin Version: 1.0.3
- Elasticsearch Version: 2.3.1
- MongoDB Version: Not sure how to determine this on appliance (`mongod` package is not installed)
- Operating System: Ubuntu (whichever version the appliance ships with - 12.04?) Client is Windows 10 Enterprise
- Browser version: Chrome 53
|
1.0
|
Plugin does not recognize graylog install on appliance - ### Problem description
The .deb installer for the plugin does not recognize that the graylog package is installed and errors out.
### Steps to reproduce the problem
1. Setup graylog appliance via OVA (ours started on 1.x, then upgraded to 2.0, and now to 2.1)
2. Attempt to install deb (`dpkg -G -I graylog-plugin-auth-sso-1.0.3.deb`)
3. Receive the following output:
```
Preparing to unpack graylog-plugin-auth-sso-1.0.3.deb ...
Unpacking graylog-plugin-auth-sso (1.0.3) over (1.0.3) ...
dpkg: dependency problems prevent configuration of graylog-plugin-auth-sso:
graylog-plugin-auth-sso depends on graylog-server | graylog-radio; however:
Package graylog-server is not installed.
Package graylog-radio is not installed.
dpkg: error processing package graylog-plugin-auth-sso (--install):
dependency problems - leaving unconfigured
Errors were encountered while processing:
graylog-plugin-auth-sso
```
Graylog is installed. It appears the plugin is looking for graylog-server, but the package for 2.1 reports itself as `graylog`:
```
ubuntu@graylog:~$ dpkg -l | grep graylog
ii graylog 2.1.0-1 amd64 The full stack of graylog
iU graylog-plugin-auth-sso 1.0.3 all Graylog graylog-plugin-auth-sso plugin.
```
### Environment
- Graylog Version: 2.1.0+62db7e0
- Plugin Version: 1.0.3
- Elasticsearch Version: 2.3.1
- MongoDB Version: Not sure how to determine this on appliance (`mongod` package is not installed)
- Operating System: Ubuntu (whichever version the appliance ships with - 12.04?) Client is Windows 10 Enterprise
- Browser version: Chrome 53
|
non_test
|
plugin does not recognize graylog install on appliance problem description the deb installer for the plugin does not recognize that the graylog package is installed and errors out steps to reproduce the problem setup graylog appliance via ova ours started on x then upgraded to and now to attempt to install deb dpkg g i graylog plugin auth sso deb receive the following output preparing to unpack graylog plugin auth sso deb unpacking graylog plugin auth sso over dpkg dependency problems prevent configuration of graylog plugin auth sso graylog plugin auth sso depends on graylog server graylog radio however package graylog server is not installed package graylog radio is not installed dpkg error processing package graylog plugin auth sso install dependency problems leaving unconfigured errors were encountered while processing graylog plugin auth sso graylog is installed it appears the plugin is looking for graylog server but the package for reports itself as graylog ubuntu graylog dpkg l grep graylog ii graylog the full stack of graylog iu graylog plugin auth sso all graylog graylog plugin auth sso plugin environment graylog version plugin version elasticsearch version mongodb version not sure how to determine this on appliance mongod package is not installed operating system ubuntu whichever version the appliance ships with client is windows enterprise browser version chrome
| 0
|
166,642
| 12,965,498,706
|
IssuesEvent
|
2020-07-20 22:29:45
|
dapr/dapr
|
https://api.github.com/repos/dapr/dapr
|
opened
|
[E2E Scenario Tests] Negative Tests for Bindings
|
P1 area/test/e2e
|
<!-- If you need to report a security issue with Dapr, send an email to daprct@microsoft.com. -->
## In what area(s)?
<!-- Remove the '> ' to select -->
> /area test-and-release
## Describe the feature
<!-- Please also discuss possible business value -->
• Application throws exception upon receiving a message from the input binding
|
1.0
|
[E2E Scenario Tests] Negative Tests for Bindings - <!-- If you need to report a security issue with Dapr, send an email to daprct@microsoft.com. -->
## In what area(s)?
<!-- Remove the '> ' to select -->
> /area test-and-release
## Describe the feature
<!-- Please also discuss possible business value -->
• Application throws exception upon receiving a message from the input binding
|
test
|
negative tests for bindings in what area s to select area test and release describe the feature • application throws exception upon receiving a message from the input binding
| 1
|
223,877
| 17,645,059,867
|
IssuesEvent
|
2021-08-20 04:00:07
|
elastic/uptime
|
https://api.github.com/repos/elastic/uptime
|
reopened
|
Uptime not handling different sized screenshots (mobile) particularly well
|
bug polish test-plan v7.14.0
|
Kibana 7.14 (local, checked with build just now)
When using mobile device emulation in a Synthetics test, for example with:
```
playwrightOptions: {
userAgent: 'Mozilla/5.0 (iPhone; CPU iPhone OS 11_0 like Mac OS X) AppleWebKit/604.1.38 (KHTML, like Gecko) Version/11.0 Mobile/15A372 Safari/604.1',
viewport: {
width: 375,
height: 667,
},
deviceScaleFactor: 2,
isMobile: true,
hasTouch: true,
}
```
Uptime has trouble showing the different sized image in some places.
Hovers and clicks to see the big (non thumbnail) image seems to be ok
<details>
<summary>Click to expand</summary>

</details>
Test result history seems ok:
<details>
<summary>Click to expand</summary>

</details>
Clicking through to a test result seems ok
<details>
<summary>Click to expand</summary>

</details>
However, expanding the step does not give enough space for the image:

(in this animation, I have scrolled all the way to the bottom of the screen, but the image is being chopped off.
|
1.0
|
Uptime not handling different sized screenshots (mobile) particularly well - Kibana 7.14 (local, checked with build just now)
When using mobile device emulation in a Synthetics test, for example with:
```
playwrightOptions: {
userAgent: 'Mozilla/5.0 (iPhone; CPU iPhone OS 11_0 like Mac OS X) AppleWebKit/604.1.38 (KHTML, like Gecko) Version/11.0 Mobile/15A372 Safari/604.1',
viewport: {
width: 375,
height: 667,
},
deviceScaleFactor: 2,
isMobile: true,
hasTouch: true,
}
```
Uptime has trouble showing the different sized image in some places.
Hovers and clicks to see the big (non thumbnail) image seems to be ok
<details>
<summary>Click to expand</summary>

</details>
Test result history seems ok:
<details>
<summary>Click to expand</summary>

</details>
Clicking through to a test result seems ok
<details>
<summary>Click to expand</summary>

</details>
However, expanding the step does not give enough space for the image:

(in this animation, I have scrolled all the way to the bottom of the screen, but the image is being chopped off.
|
test
|
uptime not handling different sized screenshots mobile particularly well kibana local checked with build just now when using mobile device emulation in a synthetics test for example with playwrightoptions useragent mozilla iphone cpu iphone os like mac os x applewebkit khtml like gecko version mobile safari viewport width height devicescalefactor ismobile true hastouch true uptime has trouble showing the different sized image in some places hovers and clicks to see the big non thumbnail image seems to be ok click to expand test result history seems ok click to expand clicking through to a test result seems ok click to expand however expanding the step does not give enough space for the image in this animation i have scrolled all the way to the bottom of the screen but the image is being chopped off
| 1
|
51,468
| 13,635,128,804
|
IssuesEvent
|
2020-09-25 01:58:53
|
nasifimtiazohi/openmrs-module-referencedemodata-1.4.5
|
https://api.github.com/repos/nasifimtiazohi/openmrs-module-referencedemodata-1.4.5
|
opened
|
CVE-2019-17571 (High) detected in log4j-1.2.15.jar
|
security vulnerability
|
## CVE-2019-17571 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.15.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Library home page: <a href="http://logging.apache.org:80/log4j/1.2/">http://logging.apache.org:80/log4j/1.2/</a></p>
<p>Path to dependency file: openmrs-module-referencedemodata-1.4.5/api-1.10/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/log4j/log4j/1.2.15/log4j-1.2.15.jar,/home/wss-scanner/.m2/repository/log4j/log4j/1.2.15/log4j-1.2.15.jar,/home/wss-scanner/.m2/repository/log4j/log4j/1.2.15/log4j-1.2.15.jar</p>
<p>
Dependency Hierarchy:
- openmrs-test-1.10.2.pom (Root Library)
- databene-benerator-0.5.9.jar
- databene-webdecs-0.4.9.jar
- poi-3.12.jar
- :x: **log4j-1.2.15.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-referencedemodata-1.4.5/commit/bde9ded52a5d0cbe44d5b0945266860e2a9a582a">bde9ded52a5d0cbe44d5b0945266860e2a9a582a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data. This affects Log4j versions up to 1.2 up to 1.2.17.
<p>Publish Date: 2019-12-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17571>CVE-2019-17571</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17571">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17571</a></p>
<p>Release Date: 2019-12-20</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.0-alpha1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-17571 (High) detected in log4j-1.2.15.jar - ## CVE-2019-17571 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.15.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Library home page: <a href="http://logging.apache.org:80/log4j/1.2/">http://logging.apache.org:80/log4j/1.2/</a></p>
<p>Path to dependency file: openmrs-module-referencedemodata-1.4.5/api-1.10/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/log4j/log4j/1.2.15/log4j-1.2.15.jar,/home/wss-scanner/.m2/repository/log4j/log4j/1.2.15/log4j-1.2.15.jar,/home/wss-scanner/.m2/repository/log4j/log4j/1.2.15/log4j-1.2.15.jar</p>
<p>
Dependency Hierarchy:
- openmrs-test-1.10.2.pom (Root Library)
- databene-benerator-0.5.9.jar
- databene-webdecs-0.4.9.jar
- poi-3.12.jar
- :x: **log4j-1.2.15.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-referencedemodata-1.4.5/commit/bde9ded52a5d0cbe44d5b0945266860e2a9a582a">bde9ded52a5d0cbe44d5b0945266860e2a9a582a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Included in Log4j 1.2 is a SocketServer class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data. This affects Log4j versions up to 1.2 up to 1.2.17.
<p>Publish Date: 2019-12-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17571>CVE-2019-17571</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17571">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17571</a></p>
<p>Release Date: 2019-12-20</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.0-alpha1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in jar cve high severity vulnerability vulnerable library jar apache library home page a href path to dependency file openmrs module referencedemodata api pom xml path to vulnerable library home wss scanner repository jar home wss scanner repository jar home wss scanner repository jar dependency hierarchy openmrs test pom root library databene benerator jar databene webdecs jar poi jar x jar vulnerable library found in head commit a href found in base branch master vulnerability details included in is a socketserver class that is vulnerable to deserialization of untrusted data which can be exploited to remotely execute arbitrary code when combined with a deserialization gadget when listening to untrusted network traffic for log data this affects versions up to up to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache logging core step up your open source security game with whitesource
| 0
|
320,553
| 27,440,659,129
|
IssuesEvent
|
2023-03-02 10:45:40
|
input-output-hk/ouroboros-network
|
https://api.github.com/repos/input-output-hk/ouroboros-network
|
opened
|
Invariant violation in `PeerMetric`
|
bug testing outbound-governor
|
```
Ouroboros.Network.PeerSelection.PeerMetric
insert peer invariant: FAIL (6.74s)
*** Failed! Falsified (after 91 tests and 862 shrinks):
FixedScript {getFixedScript = Script (FetchedHeader (TestAddress 1) (SlotNo 1) :| [FetchedHeader (TestAddress 13) (SlotNo 1),FetchedHeader (TestAddress 3) (SlotNo 2),FetchedHeader (TestAddress 13) (SlotNo 2),FetchedBlock (TestAddress 3) (SlotNo 2) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 7) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 8) (SlotNo 11) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 2) (SlotNo 12),FetchedHeader (TestAddress 1) (SlotNo 12),FetchedHeader (TestAddress 1) (SlotNo 14),FetchedHeader (TestAddress 18) (SlotNo 15),FetchedHeader (TestAddress 1) (SlotNo 17),FetchedHeader (TestAddress 4) (SlotNo 21),FetchedHeader (TestAddress 14) (SlotNo 21),FetchedBlock (TestAddress 6) (SlotNo 22) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 1) (SlotNo 22) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 22),FetchedBlock (TestAddress 2) (SlotNo 23) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 5) (SlotNo 24),FetchedHeader (TestAddress 4) (SlotNo 27),FetchedHeader (TestAddress 1) (SlotNo 29),FetchedHeader (TestAddress 1) (SlotNo 32),FetchedBlock (TestAddress 6) (SlotNo 34) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 1) (SlotNo 34) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 14) (SlotNo 34) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 2) (SlotNo 37) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 8) (SlotNo 37) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 14) (SlotNo 40) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 43) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 12) (SlotNo 45) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 45),FetchedHeader (TestAddress 8) (SlotNo 47),FetchedBlock (TestAddress 6) (SlotNo 52) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 54),FetchedHeader (TestAddress 3) (SlotNo 57),FetchedBlock (TestAddress 2) (SlotNo 59) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 62) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 63) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 8) (SlotNo 64),FetchedBlock (TestAddress 3) (SlotNo 67) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 2) (SlotNo 69) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 2) (SlotNo 70),FetchedBlock (TestAddress 6) (SlotNo 70) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 5) (SlotNo 75),FetchedHeader (TestAddress 3) (SlotNo 76),FetchedHeader (TestAddress 2) (SlotNo 80),FetchedHeader (TestAddress 8) (SlotNo 81),FetchedHeader (TestAddress 18) (SlotNo 81),FetchedHeader (TestAddress 1) (SlotNo 83),FetchedBlock (TestAddress 4) (SlotNo 83) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 14) (SlotNo 85),FetchedBlock (TestAddress 1) (SlotNo 88) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 89),FetchedBlock (TestAddress 1) (SlotNo 95) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 2) (SlotNo 98),FetchedHeader (TestAddress 2) (SlotNo 98),FetchedHeader (TestAddress 2) (SlotNo 99),FetchedHeader (TestAddress 3) (SlotNo 108),FetchedHeader (TestAddress 1) (SlotNo 108),FetchedHeader (TestAddress 9) (SlotNo 114),FetchedBlock (TestAddress 4) (SlotNo 115) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 5) (SlotNo 117) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 6) (SlotNo 118),FetchedBlock (TestAddress 1) (SlotNo 119) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 1) (SlotNo 121) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 1) (SlotNo 122) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 7) (SlotNo 123) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 128),FetchedBlock (TestAddress 9) (SlotNo 132) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 5) (SlotNo 132) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 8) (SlotNo 133),FetchedBlock (TestAddress 5) (SlotNo 133) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 4) (SlotNo 134),FetchedBlock (TestAddress 1) (SlotNo 140) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 2) (SlotNo 145),FetchedBlock (TestAddress 17) (SlotNo 146) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 18) (SlotNo 147),FetchedBlock (TestAddress 8) (SlotNo 147) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 1) (SlotNo 153) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 2) (SlotNo 154) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 10) (SlotNo 158),FetchedHeader (TestAddress 1) (SlotNo 164),FetchedHeader (TestAddress 6) (SlotNo 164),FetchedBlock (TestAddress 2) (SlotNo 167) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 169) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 1) (SlotNo 170),FetchedBlock (TestAddress 5) (SlotNo 171) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 7) (SlotNo 174) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 174) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 176),FetchedHeader (TestAddress 3) (SlotNo 177),FetchedHeader (TestAddress 13) (SlotNo 179)])}
(PeerMetricsTrace {pmtPeer = TestAddress 13, pmtSlot = SlotNo 179, pmtUpstreamyness = fromList [(TestAddress 1,8),(TestAddress 2,6),(TestAddress 3,11),(TestAddress 4,3),(TestAddress 5,2),(TestAddress 6,1),(TestAddress 7,2),(TestAddress 8,4),(TestAddress 9,2),(TestAddress 10,4),(TestAddress 12,0),(TestAddress 13,1),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,2)], pmtFetchynessBytes = fromList [(TestAddress 1,7),(TestAddress 2,6),(TestAddress 3,2),(TestAddress 4,2),(TestAddress 5,3),(TestAddress 6,9),(TestAddress 7,4),(TestAddress 8,2),(TestAddress 9,2),(TestAddress 10,2),(TestAddress 12,1),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,0)], pmtFetchynessBlocks = fromList [(TestAddress 1,7),(TestAddress 2,6),(TestAddress 3,2),(TestAddress 4,2),(TestAddress 5,3),(TestAddress 6,9),(TestAddress 7,4),(TestAddress 8,2),(TestAddress 9,2),(TestAddress 10,2),(TestAddress 12,1),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,0)], pmtJoinedAt = fromList [(TestAddress 1,SlotNo 12),(TestAddress 2,SlotNo 12),(TestAddress 3,SlotNo 2),(TestAddress 4,SlotNo 21),(TestAddress 5,SlotNo 24),(TestAddress 6,SlotNo 7),(TestAddress 7,SlotNo 123),(TestAddress 8,SlotNo 11),(TestAddress 9,SlotNo 114),(TestAddress 10,SlotNo 158),(TestAddress 12,SlotNo 45),(TestAddress 14,SlotNo 21),(TestAddress 17,SlotNo 146),(TestAddress 18,SlotNo 15)]},PeerMetricsTrace {pmtPeer = TestAddress 3, pmtSlot = SlotNo 177, pmtUpstreamyness = fromList [(TestAddress 1,8),(TestAddress 2,6),(TestAddress 3,11),(TestAddress 4,3),(TestAddress 5,2),(TestAddress 6,1),(TestAddress 7,2),(TestAddress 8,4),(TestAddress 9,2),(TestAddress 10,4),(TestAddress 12,0),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,2)], pmtFetchynessBytes = fromList [(TestAddress 1,7),(TestAddress 2,6),(TestAddress 3,2),(TestAddress 4,2),(TestAddress 5,3),(TestAddress 6,9),(TestAddress 7,4),(TestAddress 8,2),(TestAddress 9,2),(TestAddress 10,2),(TestAddress 12,1),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,0)], pmtFetchynessBlocks = fromList [(TestAddress 1,7),(TestAddress 2,6),(TestAddress 3,2),(TestAddress 4,2),(TestAddress 5,3),(TestAddress 6,9),(TestAddress 7,4),(TestAddress 8,2),(TestAddress 9,2),(TestAddress 10,2),(TestAddress 12,1),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,0)], pmtJoinedAt = fromList [(TestAddress 1,SlotNo 12),(TestAddress 2,SlotNo 12),(TestAddress 3,SlotNo 2),(TestAddress 4,SlotNo 21),(TestAddress 5,SlotNo 24),(TestAddress 6,SlotNo 7),(TestAddress 7,SlotNo 123),(TestAddress 8,SlotNo 11),(TestAddress 9,SlotNo 114),(TestAddress 10,SlotNo 158),(TestAddress 12,SlotNo 45),(TestAddress 14,SlotNo 21),(TestAddress 17,SlotNo 146),(TestAddress 18,SlotNo 15)]})
upstreamyness: peer (TestAddress 13) member of (fromList [TestAddress 6,TestAddress 12,TestAddress 13],fromList [(TestAddress 1,(8,Just (SlotNo 12))),(TestAddress 2,(6,Just (SlotNo 12))),(TestAddress 3,(11,Just (SlotNo 2))),(TestAddress 4,(3,Just (SlotNo 21))),(TestAddress 5,(2,Just (SlotNo 24))),(TestAddress 6,(1,Just (SlotNo 7))),(TestAddress 7,(2,Just (SlotNo 123))),(TestAddress 8,(4,Just (SlotNo 11))),(TestAddress 9,(2,Just (SlotNo 114))),(TestAddress 10,(4,Just (SlotNo 158))),(TestAddress 12,(0,Just (SlotNo 45))),(TestAddress 13,(1,Nothing)),(TestAddress 14,(1,Just (SlotNo 21))),(TestAddress 17,(3,Just (SlotNo 146))),(TestAddress 18,(2,Just (SlotNo 15)))])
Use --quickcheck-replay=445495 to reproduce.
Use -p '/insert peer invariant/' to rerun this test only.
```
[ref](https://github.com/input-output-hk/ouroboros-network/actions/runs/4295513922/jobs/7486034360#step:23:646)
|
1.0
|
Invariant violation in `PeerMetric` - ```
Ouroboros.Network.PeerSelection.PeerMetric
insert peer invariant: FAIL (6.74s)
*** Failed! Falsified (after 91 tests and 862 shrinks):
FixedScript {getFixedScript = Script (FetchedHeader (TestAddress 1) (SlotNo 1) :| [FetchedHeader (TestAddress 13) (SlotNo 1),FetchedHeader (TestAddress 3) (SlotNo 2),FetchedHeader (TestAddress 13) (SlotNo 2),FetchedBlock (TestAddress 3) (SlotNo 2) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 7) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 8) (SlotNo 11) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 2) (SlotNo 12),FetchedHeader (TestAddress 1) (SlotNo 12),FetchedHeader (TestAddress 1) (SlotNo 14),FetchedHeader (TestAddress 18) (SlotNo 15),FetchedHeader (TestAddress 1) (SlotNo 17),FetchedHeader (TestAddress 4) (SlotNo 21),FetchedHeader (TestAddress 14) (SlotNo 21),FetchedBlock (TestAddress 6) (SlotNo 22) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 1) (SlotNo 22) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 22),FetchedBlock (TestAddress 2) (SlotNo 23) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 5) (SlotNo 24),FetchedHeader (TestAddress 4) (SlotNo 27),FetchedHeader (TestAddress 1) (SlotNo 29),FetchedHeader (TestAddress 1) (SlotNo 32),FetchedBlock (TestAddress 6) (SlotNo 34) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 1) (SlotNo 34) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 14) (SlotNo 34) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 2) (SlotNo 37) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 8) (SlotNo 37) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 14) (SlotNo 40) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 43) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 12) (SlotNo 45) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 45),FetchedHeader (TestAddress 8) (SlotNo 47),FetchedBlock (TestAddress 6) (SlotNo 52) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 54),FetchedHeader (TestAddress 3) (SlotNo 57),FetchedBlock (TestAddress 2) (SlotNo 59) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 62) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 63) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 8) (SlotNo 64),FetchedBlock (TestAddress 3) (SlotNo 67) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 2) (SlotNo 69) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 2) (SlotNo 70),FetchedBlock (TestAddress 6) (SlotNo 70) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 5) (SlotNo 75),FetchedHeader (TestAddress 3) (SlotNo 76),FetchedHeader (TestAddress 2) (SlotNo 80),FetchedHeader (TestAddress 8) (SlotNo 81),FetchedHeader (TestAddress 18) (SlotNo 81),FetchedHeader (TestAddress 1) (SlotNo 83),FetchedBlock (TestAddress 4) (SlotNo 83) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 14) (SlotNo 85),FetchedBlock (TestAddress 1) (SlotNo 88) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 89),FetchedBlock (TestAddress 1) (SlotNo 95) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 2) (SlotNo 98),FetchedHeader (TestAddress 2) (SlotNo 98),FetchedHeader (TestAddress 2) (SlotNo 99),FetchedHeader (TestAddress 3) (SlotNo 108),FetchedHeader (TestAddress 1) (SlotNo 108),FetchedHeader (TestAddress 9) (SlotNo 114),FetchedBlock (TestAddress 4) (SlotNo 115) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 5) (SlotNo 117) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 6) (SlotNo 118),FetchedBlock (TestAddress 1) (SlotNo 119) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 1) (SlotNo 121) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 1) (SlotNo 122) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 7) (SlotNo 123) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 128),FetchedBlock (TestAddress 9) (SlotNo 132) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 5) (SlotNo 132) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 8) (SlotNo 133),FetchedBlock (TestAddress 5) (SlotNo 133) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 4) (SlotNo 134),FetchedBlock (TestAddress 1) (SlotNo 140) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 2) (SlotNo 145),FetchedBlock (TestAddress 17) (SlotNo 146) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 18) (SlotNo 147),FetchedBlock (TestAddress 8) (SlotNo 147) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 1) (SlotNo 153) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 2) (SlotNo 154) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 10) (SlotNo 158),FetchedHeader (TestAddress 1) (SlotNo 164),FetchedHeader (TestAddress 6) (SlotNo 164),FetchedBlock (TestAddress 2) (SlotNo 167) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 169) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 1) (SlotNo 170),FetchedBlock (TestAddress 5) (SlotNo 171) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 7) (SlotNo 174) (SizeInBytes {getSizeInBytes = 1}),FetchedBlock (TestAddress 6) (SlotNo 174) (SizeInBytes {getSizeInBytes = 1}),FetchedHeader (TestAddress 3) (SlotNo 176),FetchedHeader (TestAddress 3) (SlotNo 177),FetchedHeader (TestAddress 13) (SlotNo 179)])}
(PeerMetricsTrace {pmtPeer = TestAddress 13, pmtSlot = SlotNo 179, pmtUpstreamyness = fromList [(TestAddress 1,8),(TestAddress 2,6),(TestAddress 3,11),(TestAddress 4,3),(TestAddress 5,2),(TestAddress 6,1),(TestAddress 7,2),(TestAddress 8,4),(TestAddress 9,2),(TestAddress 10,4),(TestAddress 12,0),(TestAddress 13,1),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,2)], pmtFetchynessBytes = fromList [(TestAddress 1,7),(TestAddress 2,6),(TestAddress 3,2),(TestAddress 4,2),(TestAddress 5,3),(TestAddress 6,9),(TestAddress 7,4),(TestAddress 8,2),(TestAddress 9,2),(TestAddress 10,2),(TestAddress 12,1),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,0)], pmtFetchynessBlocks = fromList [(TestAddress 1,7),(TestAddress 2,6),(TestAddress 3,2),(TestAddress 4,2),(TestAddress 5,3),(TestAddress 6,9),(TestAddress 7,4),(TestAddress 8,2),(TestAddress 9,2),(TestAddress 10,2),(TestAddress 12,1),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,0)], pmtJoinedAt = fromList [(TestAddress 1,SlotNo 12),(TestAddress 2,SlotNo 12),(TestAddress 3,SlotNo 2),(TestAddress 4,SlotNo 21),(TestAddress 5,SlotNo 24),(TestAddress 6,SlotNo 7),(TestAddress 7,SlotNo 123),(TestAddress 8,SlotNo 11),(TestAddress 9,SlotNo 114),(TestAddress 10,SlotNo 158),(TestAddress 12,SlotNo 45),(TestAddress 14,SlotNo 21),(TestAddress 17,SlotNo 146),(TestAddress 18,SlotNo 15)]},PeerMetricsTrace {pmtPeer = TestAddress 3, pmtSlot = SlotNo 177, pmtUpstreamyness = fromList [(TestAddress 1,8),(TestAddress 2,6),(TestAddress 3,11),(TestAddress 4,3),(TestAddress 5,2),(TestAddress 6,1),(TestAddress 7,2),(TestAddress 8,4),(TestAddress 9,2),(TestAddress 10,4),(TestAddress 12,0),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,2)], pmtFetchynessBytes = fromList [(TestAddress 1,7),(TestAddress 2,6),(TestAddress 3,2),(TestAddress 4,2),(TestAddress 5,3),(TestAddress 6,9),(TestAddress 7,4),(TestAddress 8,2),(TestAddress 9,2),(TestAddress 10,2),(TestAddress 12,1),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,0)], pmtFetchynessBlocks = fromList [(TestAddress 1,7),(TestAddress 2,6),(TestAddress 3,2),(TestAddress 4,2),(TestAddress 5,3),(TestAddress 6,9),(TestAddress 7,4),(TestAddress 8,2),(TestAddress 9,2),(TestAddress 10,2),(TestAddress 12,1),(TestAddress 14,1),(TestAddress 17,3),(TestAddress 18,0)], pmtJoinedAt = fromList [(TestAddress 1,SlotNo 12),(TestAddress 2,SlotNo 12),(TestAddress 3,SlotNo 2),(TestAddress 4,SlotNo 21),(TestAddress 5,SlotNo 24),(TestAddress 6,SlotNo 7),(TestAddress 7,SlotNo 123),(TestAddress 8,SlotNo 11),(TestAddress 9,SlotNo 114),(TestAddress 10,SlotNo 158),(TestAddress 12,SlotNo 45),(TestAddress 14,SlotNo 21),(TestAddress 17,SlotNo 146),(TestAddress 18,SlotNo 15)]})
upstreamyness: peer (TestAddress 13) member of (fromList [TestAddress 6,TestAddress 12,TestAddress 13],fromList [(TestAddress 1,(8,Just (SlotNo 12))),(TestAddress 2,(6,Just (SlotNo 12))),(TestAddress 3,(11,Just (SlotNo 2))),(TestAddress 4,(3,Just (SlotNo 21))),(TestAddress 5,(2,Just (SlotNo 24))),(TestAddress 6,(1,Just (SlotNo 7))),(TestAddress 7,(2,Just (SlotNo 123))),(TestAddress 8,(4,Just (SlotNo 11))),(TestAddress 9,(2,Just (SlotNo 114))),(TestAddress 10,(4,Just (SlotNo 158))),(TestAddress 12,(0,Just (SlotNo 45))),(TestAddress 13,(1,Nothing)),(TestAddress 14,(1,Just (SlotNo 21))),(TestAddress 17,(3,Just (SlotNo 146))),(TestAddress 18,(2,Just (SlotNo 15)))])
Use --quickcheck-replay=445495 to reproduce.
Use -p '/insert peer invariant/' to rerun this test only.
```
[ref](https://github.com/input-output-hk/ouroboros-network/actions/runs/4295513922/jobs/7486034360#step:23:646)
|
test
|
invariant violation in peermetric ouroboros network peerselection peermetric insert peer invariant fail failed falsified after tests and shrinks fixedscript getfixedscript script fetchedheader testaddress slotno peermetricstrace pmtpeer testaddress pmtslot slotno pmtupstreamyness fromlist pmtfetchynessbytes fromlist pmtfetchynessblocks fromlist pmtjoinedat fromlist peermetricstrace pmtpeer testaddress pmtslot slotno pmtupstreamyness fromlist pmtfetchynessbytes fromlist pmtfetchynessblocks fromlist pmtjoinedat fromlist upstreamyness peer testaddress member of fromlist fromlist use quickcheck replay to reproduce use p insert peer invariant to rerun this test only
| 1
|
163,285
| 12,710,734,953
|
IssuesEvent
|
2020-06-23 14:18:30
|
pytorch/pytorch
|
https://api.github.com/repos/pytorch/pytorch
|
opened
|
DISABLED test_ddp_dist_autograd_local_vs_remote (__main__.TestDdpComparison)
|
module: distributed module: rpc topic: flaky-tests triaged
|
https://app.circleci.com/pipelines/github/pytorch/pytorch/184408/workflows/fc2c5be1-9269-4d74-9c9d-4f7947f9a2c8/jobs/5971373/steps
```
Jun 23 04:22:14 ======================================================================
Jun 23 04:22:14 ERROR [61.183s]: test_ddp_dist_autograd_local_vs_remote (__main__.TestDdpComparison)
Jun 23 04:22:14 ----------------------------------------------------------------------
Jun 23 04:22:14 Traceback (most recent call last):
Jun 23 04:22:14 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 204, in wrapper
Jun 23 04:22:14 self._join_processes(fn)
Jun 23 04:22:14 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 306, in _join_processes
Jun 23 04:22:14 self._check_return_codes(elapsed_time)
Jun 23 04:22:14 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 339, in _check_return_codes
Jun 23 04:22:14 raise RuntimeError(error)
Jun 23 04:22:14 RuntimeError: Processes 3 exited with error code 10
```
```
Jun 23 04:22:08 test_ddp_dist_autograd_local_vs_remote (__main__.TestDdpComparison) ... ERROR:root:Caught exception:
Jun 23 04:22:08 Traceback (most recent call last):
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 207, in wrapper
Jun 23 04:22:08 fn()
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/dist_utils.py", line 93, in new_test_method
Jun 23 04:22:08 return_value = old_test_method(self, *arg, **kwargs)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/distributed/ddp_under_dist_autograd_test.py", line 569, in test_ddp_dist_autograd_local_vs_remote
Jun 23 04:22:08 layer1.weight = remote_layer1.module_rref.to_here().weight
Jun 23 04:22:08 RuntimeError: RPCErr:1:RPC ran for more than 60000 milliseconds and timed out.
Jun 23 04:22:08 exiting process with exit code: 10
Jun 23 04:22:08 ERROR:root:Caught exception:
Jun 23 04:22:08 Traceback (most recent call last):
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 207, in wrapper
Jun 23 04:22:08 fn()
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/dist_utils.py", line 93, in new_test_method
Jun 23 04:22:08 return_value = old_test_method(self, *arg, **kwargs)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/distributed/ddp_under_dist_autograd_test.py", line 574, in test_ddp_dist_autograd_local_vs_remote
Jun 23 04:22:08 ddp_model = DistributedDataParallel(layer2)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/nn/parallel/distributed.py", line 329, in __init__
Jun 23 04:22:08 self.broadcast_bucket_size)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/nn/parallel/distributed.py", line 545, in _distributed_broadcast_coalesced
Jun 23 04:22:08 dist._broadcast_coalesced(self.process_group, tensors, buffer_size)
Jun 23 04:22:08 RuntimeError: [/var/lib/jenkins/workspace/third_party/gloo/gloo/transport/tcp/pair.cc:575] Connection closed by peer [172.17.0.2]:14761
Jun 23 04:22:08 exiting process with exit code: 10
Jun 23 04:22:08 ERROR:root:Caught exception:
Jun 23 04:22:08 Traceback (most recent call last):
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 207, in wrapper
Jun 23 04:22:08 fn()
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/dist_utils.py", line 93, in new_test_method
Jun 23 04:22:08 return_value = old_test_method(self, *arg, **kwargs)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/distributed/ddp_under_dist_autograd_test.py", line 576, in test_ddp_dist_autograd_local_vs_remote
Jun 23 04:22:08 loss.backward()
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/tensor.py", line 185, in backward
Jun 23 04:22:08 torch.autograd.backward(self, gradient, retain_graph, create_graph)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/autograd/__init__.py", line 127, in backward
Jun 23 04:22:08 allow_unreachable=True) # allow_unreachable flag
Jun 23 04:22:08 RuntimeError: [/var/lib/jenkins/workspace/third_party/gloo/gloo/transport/tcp/pair.cc:575] Connection closed by peer [172.17.0.2]:31108
Jun 23 04:22:08 exiting process with exit code: 10
Jun 23 04:22:08 Process 3 terminated with exit code 10, terminating remaining processes.
Jun 23 04:22:08 ERROR (61.183s)
```
|
1.0
|
DISABLED test_ddp_dist_autograd_local_vs_remote (__main__.TestDdpComparison) - https://app.circleci.com/pipelines/github/pytorch/pytorch/184408/workflows/fc2c5be1-9269-4d74-9c9d-4f7947f9a2c8/jobs/5971373/steps
```
Jun 23 04:22:14 ======================================================================
Jun 23 04:22:14 ERROR [61.183s]: test_ddp_dist_autograd_local_vs_remote (__main__.TestDdpComparison)
Jun 23 04:22:14 ----------------------------------------------------------------------
Jun 23 04:22:14 Traceback (most recent call last):
Jun 23 04:22:14 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 204, in wrapper
Jun 23 04:22:14 self._join_processes(fn)
Jun 23 04:22:14 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 306, in _join_processes
Jun 23 04:22:14 self._check_return_codes(elapsed_time)
Jun 23 04:22:14 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 339, in _check_return_codes
Jun 23 04:22:14 raise RuntimeError(error)
Jun 23 04:22:14 RuntimeError: Processes 3 exited with error code 10
```
```
Jun 23 04:22:08 test_ddp_dist_autograd_local_vs_remote (__main__.TestDdpComparison) ... ERROR:root:Caught exception:
Jun 23 04:22:08 Traceback (most recent call last):
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 207, in wrapper
Jun 23 04:22:08 fn()
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/dist_utils.py", line 93, in new_test_method
Jun 23 04:22:08 return_value = old_test_method(self, *arg, **kwargs)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/distributed/ddp_under_dist_autograd_test.py", line 569, in test_ddp_dist_autograd_local_vs_remote
Jun 23 04:22:08 layer1.weight = remote_layer1.module_rref.to_here().weight
Jun 23 04:22:08 RuntimeError: RPCErr:1:RPC ran for more than 60000 milliseconds and timed out.
Jun 23 04:22:08 exiting process with exit code: 10
Jun 23 04:22:08 ERROR:root:Caught exception:
Jun 23 04:22:08 Traceback (most recent call last):
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 207, in wrapper
Jun 23 04:22:08 fn()
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/dist_utils.py", line 93, in new_test_method
Jun 23 04:22:08 return_value = old_test_method(self, *arg, **kwargs)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/distributed/ddp_under_dist_autograd_test.py", line 574, in test_ddp_dist_autograd_local_vs_remote
Jun 23 04:22:08 ddp_model = DistributedDataParallel(layer2)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/nn/parallel/distributed.py", line 329, in __init__
Jun 23 04:22:08 self.broadcast_bucket_size)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/nn/parallel/distributed.py", line 545, in _distributed_broadcast_coalesced
Jun 23 04:22:08 dist._broadcast_coalesced(self.process_group, tensors, buffer_size)
Jun 23 04:22:08 RuntimeError: [/var/lib/jenkins/workspace/third_party/gloo/gloo/transport/tcp/pair.cc:575] Connection closed by peer [172.17.0.2]:14761
Jun 23 04:22:08 exiting process with exit code: 10
Jun 23 04:22:08 ERROR:root:Caught exception:
Jun 23 04:22:08 Traceback (most recent call last):
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/common_distributed.py", line 207, in wrapper
Jun 23 04:22:08 fn()
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/dist_utils.py", line 93, in new_test_method
Jun 23 04:22:08 return_value = old_test_method(self, *arg, **kwargs)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/testing/_internal/distributed/ddp_under_dist_autograd_test.py", line 576, in test_ddp_dist_autograd_local_vs_remote
Jun 23 04:22:08 loss.backward()
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/tensor.py", line 185, in backward
Jun 23 04:22:08 torch.autograd.backward(self, gradient, retain_graph, create_graph)
Jun 23 04:22:08 File "/opt/python/nightly/lib/python3.7/site-packages/torch/autograd/__init__.py", line 127, in backward
Jun 23 04:22:08 allow_unreachable=True) # allow_unreachable flag
Jun 23 04:22:08 RuntimeError: [/var/lib/jenkins/workspace/third_party/gloo/gloo/transport/tcp/pair.cc:575] Connection closed by peer [172.17.0.2]:31108
Jun 23 04:22:08 exiting process with exit code: 10
Jun 23 04:22:08 Process 3 terminated with exit code 10, terminating remaining processes.
Jun 23 04:22:08 ERROR (61.183s)
```
|
test
|
disabled test ddp dist autograd local vs remote main testddpcomparison jun jun error test ddp dist autograd local vs remote main testddpcomparison jun jun traceback most recent call last jun file opt python nightly lib site packages torch testing internal common distributed py line in wrapper jun self join processes fn jun file opt python nightly lib site packages torch testing internal common distributed py line in join processes jun self check return codes elapsed time jun file opt python nightly lib site packages torch testing internal common distributed py line in check return codes jun raise runtimeerror error jun runtimeerror processes exited with error code jun test ddp dist autograd local vs remote main testddpcomparison error root caught exception jun traceback most recent call last jun file opt python nightly lib site packages torch testing internal common distributed py line in wrapper jun fn jun file opt python nightly lib site packages torch testing internal dist utils py line in new test method jun return value old test method self arg kwargs jun file opt python nightly lib site packages torch testing internal distributed ddp under dist autograd test py line in test ddp dist autograd local vs remote jun weight remote module rref to here weight jun runtimeerror rpcerr rpc ran for more than milliseconds and timed out jun exiting process with exit code jun error root caught exception jun traceback most recent call last jun file opt python nightly lib site packages torch testing internal common distributed py line in wrapper jun fn jun file opt python nightly lib site packages torch testing internal dist utils py line in new test method jun return value old test method self arg kwargs jun file opt python nightly lib site packages torch testing internal distributed ddp under dist autograd test py line in test ddp dist autograd local vs remote jun ddp model distributeddataparallel jun file opt python nightly lib site packages torch nn parallel distributed py line in init jun self broadcast bucket size jun file opt python nightly lib site packages torch nn parallel distributed py line in distributed broadcast coalesced jun dist broadcast coalesced self process group tensors buffer size jun runtimeerror connection closed by peer jun exiting process with exit code jun error root caught exception jun traceback most recent call last jun file opt python nightly lib site packages torch testing internal common distributed py line in wrapper jun fn jun file opt python nightly lib site packages torch testing internal dist utils py line in new test method jun return value old test method self arg kwargs jun file opt python nightly lib site packages torch testing internal distributed ddp under dist autograd test py line in test ddp dist autograd local vs remote jun loss backward jun file opt python nightly lib site packages torch tensor py line in backward jun torch autograd backward self gradient retain graph create graph jun file opt python nightly lib site packages torch autograd init py line in backward jun allow unreachable true allow unreachable flag jun runtimeerror connection closed by peer jun exiting process with exit code jun process terminated with exit code terminating remaining processes jun error
| 1
|
234,161
| 19,098,621,353
|
IssuesEvent
|
2021-11-29 19:34:20
|
microsoft/vscode-python
|
https://api.github.com/repos/microsoft/vscode-python
|
opened
|
Test Pylance with a virtual workspace
|
testplan-item
|
Refs: #17253
- [ ] anyOS
- [ ] anyOS
- [ ] anyOS
Complexity: 2
Authors: @karrtikr
---
### Requirements
1. Install python extension from here: https://pvsc.blob.core.windows.net/extension-builds/ms-python-insiders.vsix
### Verification
1. Open a GitHub repository containing Python code, and make sure it is trusted
2. Make sure that you have the `python.languageServer` setting set to `Default` or `Pylance`
3. Activate the Python extension
4. Verify that the `Starting Pylance language server.` message appears in the Python output channel
5. Make sure you get hover info, same-file completion and completion for built-ins like `print`
|
1.0
|
Test Pylance with a virtual workspace - Refs: #17253
- [ ] anyOS
- [ ] anyOS
- [ ] anyOS
Complexity: 2
Authors: @karrtikr
---
### Requirements
1. Install python extension from here: https://pvsc.blob.core.windows.net/extension-builds/ms-python-insiders.vsix
### Verification
1. Open a GitHub repository containing Python code, and make sure it is trusted
2. Make sure that you have the `python.languageServer` setting set to `Default` or `Pylance`
3. Activate the Python extension
4. Verify that the `Starting Pylance language server.` message appears in the Python output channel
5. Make sure you get hover info, same-file completion and completion for built-ins like `print`
|
test
|
test pylance with a virtual workspace refs anyos anyos anyos complexity authors karrtikr requirements install python extension from here verification open a github repository containing python code and make sure it is trusted make sure that you have the python languageserver setting set to default or pylance activate the python extension verify that the starting pylance language server message appears in the python output channel make sure you get hover info same file completion and completion for built ins like print
| 1
|
24,113
| 12,217,772,972
|
IssuesEvent
|
2020-05-01 17:54:20
|
flutter/flutter
|
https://api.github.com/repos/flutter/flutter
|
opened
|
Reenable new Gallery perf test
|
severe: performance team
|
New gallery perf test is failing due to Gradle
```
2020-05-01T09:50:05.019349: stdout: [+1611 ms]
stdout: FAILURE: Build failed with an exception.
stdout:
stdout: * Where:
stdout: Build file '/Users/flutter/.pub-cache/hosted/pub.dartlang.org/shared_preferences_macos-0.0.1+6/android/build.gradle' line: 22
stdout:
stdout: * What went wrong:
stdout: A problem occurred evaluating root project 'shared_preferences_macos'.
2020-05-01T09:50:05.019505: stdout: > Failed to apply plugin [id 'com.android.library']
stdout: > Minimum supported Gradle version is 5.4.1. Current version is 5.1.1. If using the gradle wrapper, try editing the distributionUrl in /Users/flutter/.pub-cache/hosted/pub.dartlang.org/shared_preferences_macos-0.0.1+6/android/gradle/wrapper/gradle-wrapper.properties to gradle-5.4.1-all.zip
```
|
True
|
Reenable new Gallery perf test - New gallery perf test is failing due to Gradle
```
2020-05-01T09:50:05.019349: stdout: [+1611 ms]
stdout: FAILURE: Build failed with an exception.
stdout:
stdout: * Where:
stdout: Build file '/Users/flutter/.pub-cache/hosted/pub.dartlang.org/shared_preferences_macos-0.0.1+6/android/build.gradle' line: 22
stdout:
stdout: * What went wrong:
stdout: A problem occurred evaluating root project 'shared_preferences_macos'.
2020-05-01T09:50:05.019505: stdout: > Failed to apply plugin [id 'com.android.library']
stdout: > Minimum supported Gradle version is 5.4.1. Current version is 5.1.1. If using the gradle wrapper, try editing the distributionUrl in /Users/flutter/.pub-cache/hosted/pub.dartlang.org/shared_preferences_macos-0.0.1+6/android/gradle/wrapper/gradle-wrapper.properties to gradle-5.4.1-all.zip
```
|
non_test
|
reenable new gallery perf test new gallery perf test is failing due to gradle stdout stdout failure build failed with an exception stdout stdout where stdout build file users flutter pub cache hosted pub dartlang org shared preferences macos android build gradle line stdout stdout what went wrong stdout a problem occurred evaluating root project shared preferences macos stdout failed to apply plugin stdout minimum supported gradle version is current version is if using the gradle wrapper try editing the distributionurl in users flutter pub cache hosted pub dartlang org shared preferences macos android gradle wrapper gradle wrapper properties to gradle all zip
| 0
|
184,188
| 6,706,541,289
|
IssuesEvent
|
2017-10-12 07:32:22
|
telerik/kendo-ui-core
|
https://api.github.com/repos/telerik/kendo-ui-core
|
opened
|
setOptions method and maximize cause the page to scroll to previously scrolled position
|
Bug C: Window Kendo2 Priority 1 SEV: Medium
|
### Bug report
`restore` and `maximize` methods should restore the scroll position of the page. However, calling setOptions before that causes the page to be scrolled to the previous scroll position.
### Reproduction of the problem
http://dojo.telerik.com/Edive
1. Click on Target 1;
2. Close the Window;
3. Scroll to Target 2 and click it;
4. Close the window;
5. Scroll back to top and click Target 1;
6. Close the window
### Current behavior
Page is scrolled to Target 2
### Expected/desired behavior
The page ti keep its scroll position, where the user scrolled.
### Details
Probably, `_documentScrollTop` and `_documentScrollLeft` properties are not updated when calling setOptions.
### Environment
* **Kendo UI version:** 2017.3.913
* **jQuery version:** 1.12.3
* **Browser:** [all]
|
1.0
|
setOptions method and maximize cause the page to scroll to previously scrolled position - ### Bug report
`restore` and `maximize` methods should restore the scroll position of the page. However, calling setOptions before that causes the page to be scrolled to the previous scroll position.
### Reproduction of the problem
http://dojo.telerik.com/Edive
1. Click on Target 1;
2. Close the Window;
3. Scroll to Target 2 and click it;
4. Close the window;
5. Scroll back to top and click Target 1;
6. Close the window
### Current behavior
Page is scrolled to Target 2
### Expected/desired behavior
The page ti keep its scroll position, where the user scrolled.
### Details
Probably, `_documentScrollTop` and `_documentScrollLeft` properties are not updated when calling setOptions.
### Environment
* **Kendo UI version:** 2017.3.913
* **jQuery version:** 1.12.3
* **Browser:** [all]
|
non_test
|
setoptions method and maximize cause the page to scroll to previously scrolled position bug report restore and maximize methods should restore the scroll position of the page however calling setoptions before that causes the page to be scrolled to the previous scroll position reproduction of the problem click on target close the window scroll to target and click it close the window scroll back to top and click target close the window current behavior page is scrolled to target expected desired behavior the page ti keep its scroll position where the user scrolled details probably documentscrolltop and documentscrollleft properties are not updated when calling setoptions environment kendo ui version jquery version browser
| 0
|
308,625
| 26,618,963,895
|
IssuesEvent
|
2023-01-24 09:45:19
|
scylladb/scylladb
|
https://api.github.com/repos/scylladb/scylladb
|
closed
|
Increase CQL connection timeout in cql-repl and possibly other test suites
|
test.py
|
In issue #11289 we noticed that sometimes Python tests can fail on extremely slow test setups and debug builds, when they fail to initially connect to Scylla. It turns out that the Python driver has two configurable parameters `connect_timeout` and `control_connection_timeout`, which default to 5 seconds and 2 seconds respectively, and on extremely slow setups and builds, it is possible to exceed this timeout and fail to connect to Scylla.
In commit 7eda6b1e90ca96c15888c02345df9b1ac3a3376c we increased these timeouts in cql-pytest to 60 seconds, and in commit 9c156591943c1a29a0f4d00dbf1d1689bad3f626 we set the corresponding async parameter the same in test/topology. But as far as I understand, these settings do not apply to other test suites that use test.py and its libraries. In particular, we recently saw in a Jenkins run https://jenkins.scylladb.com/job/scylla-enterprise/job/next/2192/ that three debug-mode tests failed, timing out connecting to Scylla (we know that this was a connection timeout, not a Scylla crash, because the following test succeeded). All three of these tests were part of the `test/cql` (i.e., **cql-repl**) test suite, which apparently does not enjoy the increased timeout configuration.
So we should copy the 60-second timeouts to the cql-repl suite, and consider whether additional test suites in test.py needs them too.
By the way, when changing the timeout in a test suite, the easiest way to test that it actually works is to use a tiny timeout (e.g., 0.0001) and see that tests fail to set up because of a connection timeout. If there is no time-out, the timeout parameter didn't work.
CC @alecco @kostja
|
1.0
|
Increase CQL connection timeout in cql-repl and possibly other test suites - In issue #11289 we noticed that sometimes Python tests can fail on extremely slow test setups and debug builds, when they fail to initially connect to Scylla. It turns out that the Python driver has two configurable parameters `connect_timeout` and `control_connection_timeout`, which default to 5 seconds and 2 seconds respectively, and on extremely slow setups and builds, it is possible to exceed this timeout and fail to connect to Scylla.
In commit 7eda6b1e90ca96c15888c02345df9b1ac3a3376c we increased these timeouts in cql-pytest to 60 seconds, and in commit 9c156591943c1a29a0f4d00dbf1d1689bad3f626 we set the corresponding async parameter the same in test/topology. But as far as I understand, these settings do not apply to other test suites that use test.py and its libraries. In particular, we recently saw in a Jenkins run https://jenkins.scylladb.com/job/scylla-enterprise/job/next/2192/ that three debug-mode tests failed, timing out connecting to Scylla (we know that this was a connection timeout, not a Scylla crash, because the following test succeeded). All three of these tests were part of the `test/cql` (i.e., **cql-repl**) test suite, which apparently does not enjoy the increased timeout configuration.
So we should copy the 60-second timeouts to the cql-repl suite, and consider whether additional test suites in test.py needs them too.
By the way, when changing the timeout in a test suite, the easiest way to test that it actually works is to use a tiny timeout (e.g., 0.0001) and see that tests fail to set up because of a connection timeout. If there is no time-out, the timeout parameter didn't work.
CC @alecco @kostja
|
test
|
increase cql connection timeout in cql repl and possibly other test suites in issue we noticed that sometimes python tests can fail on extremely slow test setups and debug builds when they fail to initially connect to scylla it turns out that the python driver has two configurable parameters connect timeout and control connection timeout which default to seconds and seconds respectively and on extremely slow setups and builds it is possible to exceed this timeout and fail to connect to scylla in commit we increased these timeouts in cql pytest to seconds and in commit we set the corresponding async parameter the same in test topology but as far as i understand these settings do not apply to other test suites that use test py and its libraries in particular we recently saw in a jenkins run that three debug mode tests failed timing out connecting to scylla we know that this was a connection timeout not a scylla crash because the following test succeeded all three of these tests were part of the test cql i e cql repl test suite which apparently does not enjoy the increased timeout configuration so we should copy the second timeouts to the cql repl suite and consider whether additional test suites in test py needs them too by the way when changing the timeout in a test suite the easiest way to test that it actually works is to use a tiny timeout e g and see that tests fail to set up because of a connection timeout if there is no time out the timeout parameter didn t work cc alecco kostja
| 1
|
48,648
| 10,268,190,311
|
IssuesEvent
|
2019-08-23 05:18:58
|
PowerShell/vscode-powershell
|
https://api.github.com/repos/PowerShell/vscode-powershell
|
closed
|
Copying code from Insider build 1.38.0 to Word will show   instead of blankspace
|
Resolution-External vscode-bug
|
<!--
BEFORE SUBMITTING A NEW ISSUE, PLEASE READ THE TROUBLESHOOTING DOCS!
https://github.com/PowerShell/vscode-powershell/tree/master/docs/troubleshooting.md
IMPORTANT: you can generate a bug report directly from the
PowerShell extension in Visual Studio Code by selecting
"PowerShell: Upload Bug Report to GitHub" from the command palette.
NOTE: If you have both stable (aka "PowerShell") and preview (aka "PowerShell Preview") installed,
you MUST DISABLE one of them for the best performance.
Docs on how to disable an extension can be found here:
https://code.visualstudio.com/docs/editor/extension-gallery#_disable-an-extension
The more repro details you can provide, along with a zip
of the log files from your session, the better the chances
are for a quick resolution.
You may also want to record a GIF of the bug occurring and
attach it here by dropping the file into the description body.
-->
### System Details
<!--
To help diagnose your issue, the following details are helpful:
- Operating system name and version
- VS Code version
- PowerShell extension version
- Output from `$PSVersionTable`
To get this information, run the following expression in your Integrated Console and paste the output here inside the backticks below:
& {"### VSCode version: $(code -v)"; "`n### VSCode extensions:`n$(code --list-extensions --show-versions | Out-String)"; "`n### PSES version: $($pseditor.EditorServicesVersion)"; "`n### PowerShell version:`n$($PSVersionTable | Out-String)"}
If you are running VSCode Insiders, use this expression instead (and paste the result inside the backticks):
& {"### VSCode version: $(code-insiders -v)"; "`n### VSCode extensions:`n$(code-insiders --list-extensions --show-versions | Out-String)"; "`n### PSES version: $($pseditor.EditorServicesVersion)"; "`n### PowerShell version:`n$($PSVersionTable | Out-String)"}
-->
<!-- PowerShell output from above goes here -->
System Details Output
```
ms-vscode.powershell@2019.5.0
Tyriar.shell-launcher@0.3.0
vscode-icons-team.vscode-icons@9.2.0
### PSES version: 1.12.1.0
### PowerShell version:
Name Value
---- -----
PSVersion 5.1.18362.145
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.18362.145
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
```
### Issue Description
Copying code from Insider build 1.38.0 to Word will show   instead of blankspace. The format of the document is PowerShell.
This doesn't happen in the stable version
#### Expected Behaviour
Copy the show text as it show without the   as show in the image
#### Actual Behaviour
When copy text or code in PowerShell format it will instead of blankspace add the html code for blankspace  
### Attached Logs
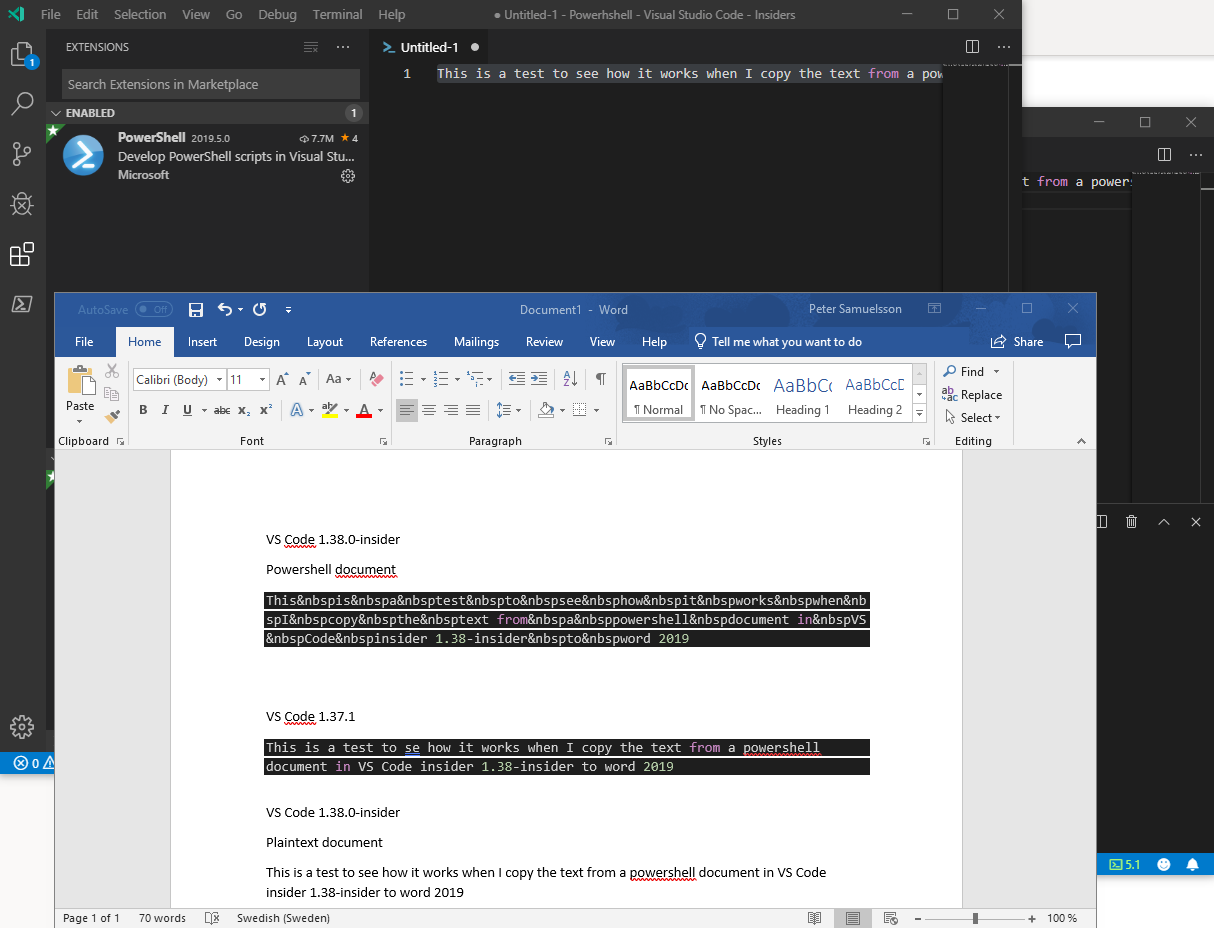
Follow the instructions in the [troubleshooting docs](https://github.com/PowerShell/vscode-powershell/blob/master/docs/troubleshooting.md#logs)
about capturing and sending logs.
|
1.0
|
Copying code from Insider build 1.38.0 to Word will show   instead of blankspace - <!--
BEFORE SUBMITTING A NEW ISSUE, PLEASE READ THE TROUBLESHOOTING DOCS!
https://github.com/PowerShell/vscode-powershell/tree/master/docs/troubleshooting.md
IMPORTANT: you can generate a bug report directly from the
PowerShell extension in Visual Studio Code by selecting
"PowerShell: Upload Bug Report to GitHub" from the command palette.
NOTE: If you have both stable (aka "PowerShell") and preview (aka "PowerShell Preview") installed,
you MUST DISABLE one of them for the best performance.
Docs on how to disable an extension can be found here:
https://code.visualstudio.com/docs/editor/extension-gallery#_disable-an-extension
The more repro details you can provide, along with a zip
of the log files from your session, the better the chances
are for a quick resolution.
You may also want to record a GIF of the bug occurring and
attach it here by dropping the file into the description body.
-->
### System Details
<!--
To help diagnose your issue, the following details are helpful:
- Operating system name and version
- VS Code version
- PowerShell extension version
- Output from `$PSVersionTable`
To get this information, run the following expression in your Integrated Console and paste the output here inside the backticks below:
& {"### VSCode version: $(code -v)"; "`n### VSCode extensions:`n$(code --list-extensions --show-versions | Out-String)"; "`n### PSES version: $($pseditor.EditorServicesVersion)"; "`n### PowerShell version:`n$($PSVersionTable | Out-String)"}
If you are running VSCode Insiders, use this expression instead (and paste the result inside the backticks):
& {"### VSCode version: $(code-insiders -v)"; "`n### VSCode extensions:`n$(code-insiders --list-extensions --show-versions | Out-String)"; "`n### PSES version: $($pseditor.EditorServicesVersion)"; "`n### PowerShell version:`n$($PSVersionTable | Out-String)"}
-->
<!-- PowerShell output from above goes here -->
System Details Output
```
ms-vscode.powershell@2019.5.0
Tyriar.shell-launcher@0.3.0
vscode-icons-team.vscode-icons@9.2.0
### PSES version: 1.12.1.0
### PowerShell version:
Name Value
---- -----
PSVersion 5.1.18362.145
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.18362.145
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
```
### Issue Description
Copying code from Insider build 1.38.0 to Word will show   instead of blankspace. The format of the document is PowerShell.
This doesn't happen in the stable version
#### Expected Behaviour
Copy the show text as it show without the   as show in the image
#### Actual Behaviour
When copy text or code in PowerShell format it will instead of blankspace add the html code for blankspace  
### Attached Logs
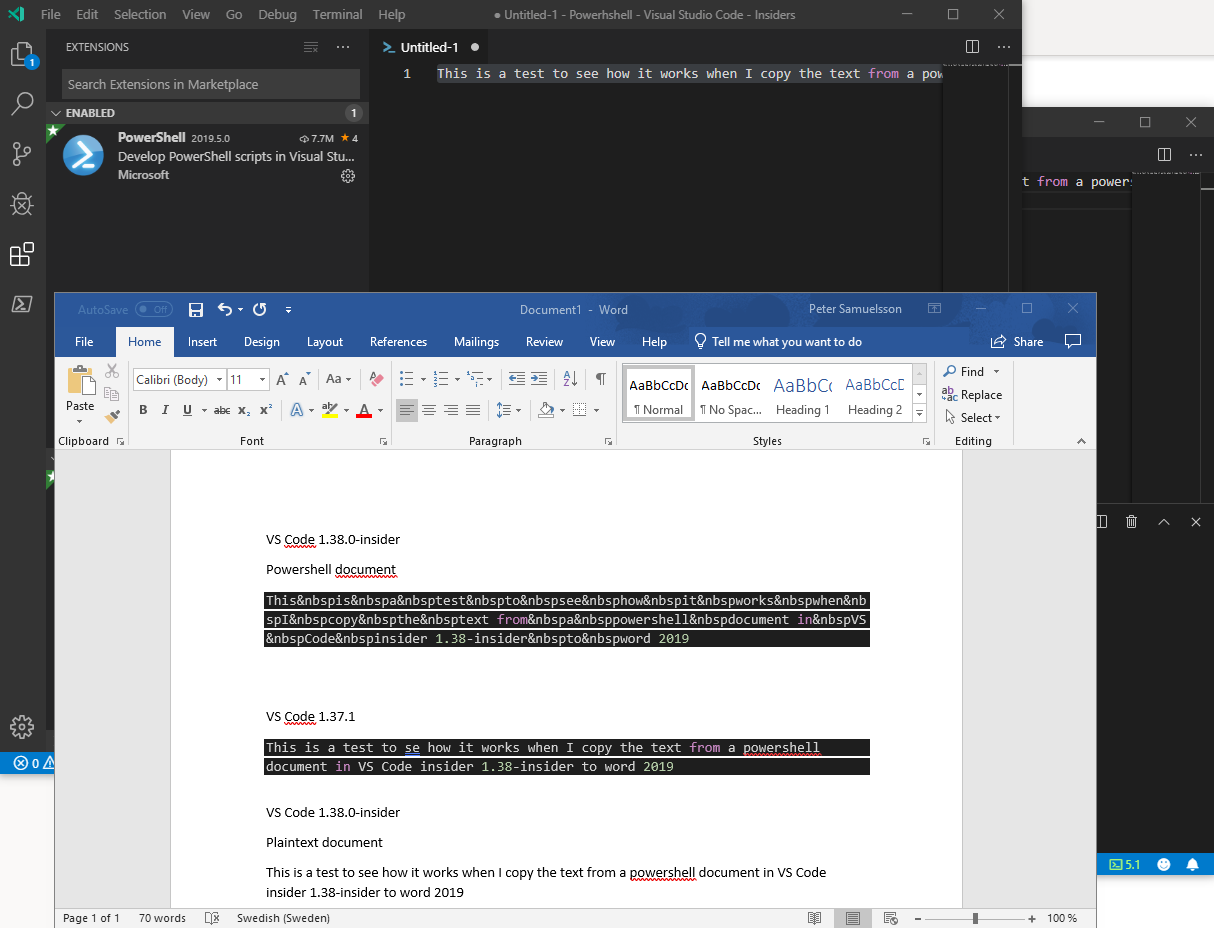
Follow the instructions in the [troubleshooting docs](https://github.com/PowerShell/vscode-powershell/blob/master/docs/troubleshooting.md#logs)
about capturing and sending logs.
|
non_test
|
copying code from insider build to word will show nbsp instead of blankspace before submitting a new issue please read the troubleshooting docs important you can generate a bug report directly from the powershell extension in visual studio code by selecting powershell upload bug report to github from the command palette note if you have both stable aka powershell and preview aka powershell preview installed you must disable one of them for the best performance docs on how to disable an extension can be found here the more repro details you can provide along with a zip of the log files from your session the better the chances are for a quick resolution you may also want to record a gif of the bug occurring and attach it here by dropping the file into the description body system details to help diagnose your issue the following details are helpful operating system name and version vs code version powershell extension version output from psversiontable to get this information run the following expression in your integrated console and paste the output here inside the backticks below vscode version code v n vscode extensions n code list extensions show versions out string n pses version pseditor editorservicesversion n powershell version n psversiontable out string if you are running vscode insiders use this expression instead and paste the result inside the backticks vscode version code insiders v n vscode extensions n code insiders list extensions show versions out string n pses version pseditor editorservicesversion n powershell version n psversiontable out string system details output ms vscode powershell tyriar shell launcher vscode icons team vscode icons pses version powershell version name value psversion psedition desktop pscompatibleversions buildversion clrversion wsmanstackversion psremotingprotocolversion serializationversion issue description copying code from insider build to word will show nbsp instead of blankspace the format of the document is powershell this doesn t happen in the stable version expected behaviour copy the show text as it show without the nbsp as show in the image actual behaviour when copy text or code in powershell format it will instead of blankspace add the html code for blankspace nbsp attached logs follow the instructions in the about capturing and sending logs
| 0
|
91,402
| 8,304,540,550
|
IssuesEvent
|
2018-09-21 21:37:19
|
dotnet/roslyn
|
https://api.github.com/repos/dotnet/roslyn
|
closed
|
CSharpWinForms.RemoveEventHandler Failed in test run
|
Area-IDE Flaky Test
|
First found in https://github.com/dotnet/roslyn/pull/26665
In [this integration run](https://ci.dot.net/job/dotnet_roslyn/job/features_NullableReferenceTypes/job/windows_release_vs-integration_prtest/426).
**Roslyn.VisualStudio.IntegrationTests.CSharp.CSharpWinForms.RemoveEventHandler** fails due to there being an error in the error-list but the build succeeded.
```ini
MESSAGE:
Assert.Equal() Failure
Expected: 0
Actual: 1
+++++++++++++++++++
STACK TRACE:
at Microsoft.VisualStudio.IntegrationTest.Utilities.OutOfProcess.ErrorList_OutOfProc.Verifier.NoBuildErrors()
at Roslyn.VisualStudio.IntegrationTests.CSharp.CSharpWinForms.RemoveEventHandler()
```

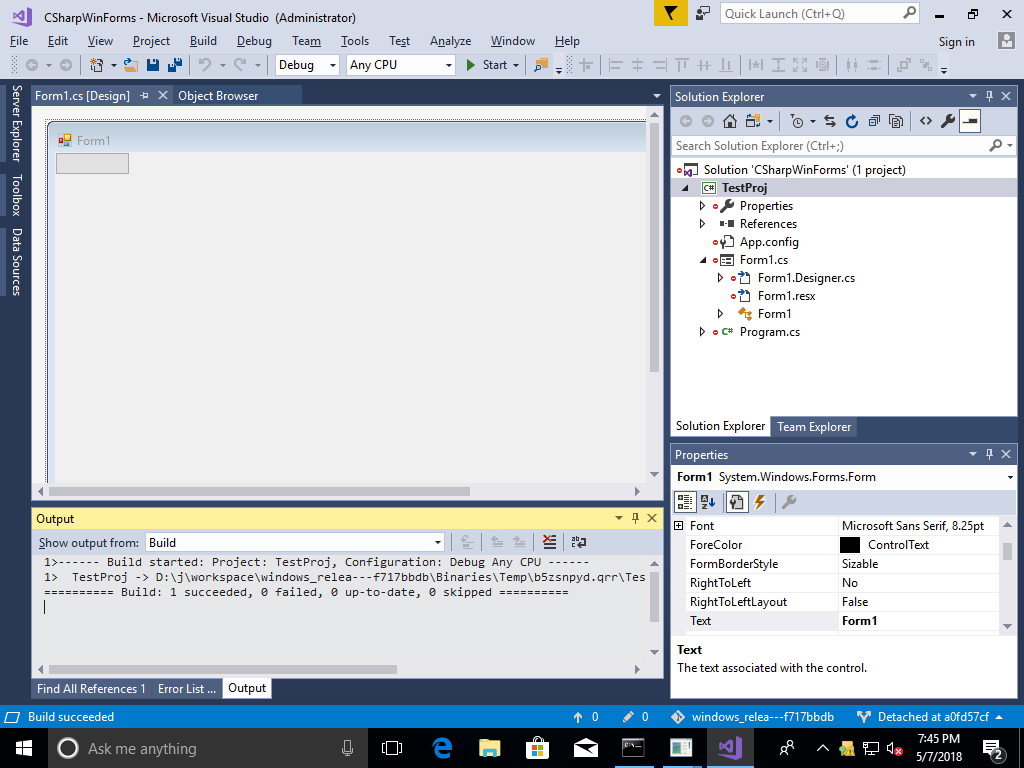
|
1.0
|
CSharpWinForms.RemoveEventHandler Failed in test run - First found in https://github.com/dotnet/roslyn/pull/26665
In [this integration run](https://ci.dot.net/job/dotnet_roslyn/job/features_NullableReferenceTypes/job/windows_release_vs-integration_prtest/426).
**Roslyn.VisualStudio.IntegrationTests.CSharp.CSharpWinForms.RemoveEventHandler** fails due to there being an error in the error-list but the build succeeded.
```ini
MESSAGE:
Assert.Equal() Failure
Expected: 0
Actual: 1
+++++++++++++++++++
STACK TRACE:
at Microsoft.VisualStudio.IntegrationTest.Utilities.OutOfProcess.ErrorList_OutOfProc.Verifier.NoBuildErrors()
at Roslyn.VisualStudio.IntegrationTests.CSharp.CSharpWinForms.RemoveEventHandler()
```

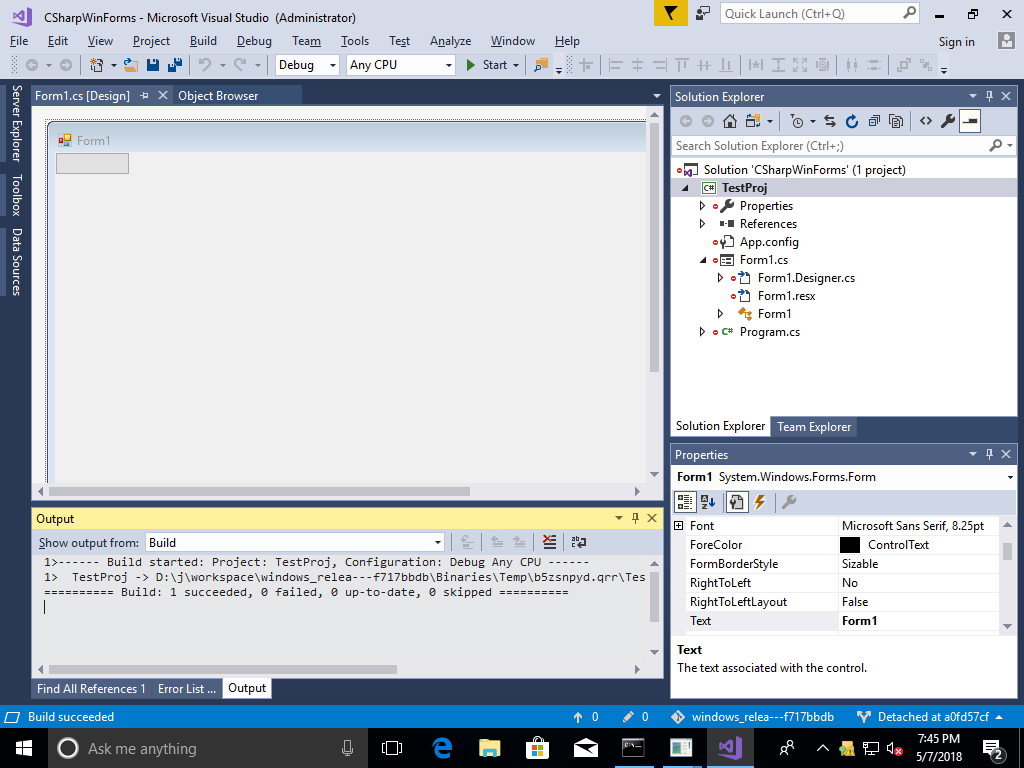
|
test
|
csharpwinforms removeeventhandler failed in test run first found in in roslyn visualstudio integrationtests csharp csharpwinforms removeeventhandler fails due to there being an error in the error list but the build succeeded ini message assert equal failure expected actual stack trace at microsoft visualstudio integrationtest utilities outofprocess errorlist outofproc verifier nobuilderrors at roslyn visualstudio integrationtests csharp csharpwinforms removeeventhandler
| 1
|
131,572
| 27,982,809,531
|
IssuesEvent
|
2023-03-26 11:05:10
|
joomla/joomla-cms
|
https://api.github.com/repos/joomla/joomla-cms
|
closed
|
A couple PHP 8.1 Deprecations J4.3RC1
|
No Code Attached Yet Information Required PHP 8.x
|
### Steps to reproduce the issue
Install J4.3 RC1.
In the backend I have 2 Deprecated messages when navigating around the backend of my site opening various Components.
Deprecated: strtolower(): Passing null to parameter #1 ($string) of type string is deprecated in C:\xampp\htdocs\sites\Joomla_4.3.x\libraries\src\HTML\Helpers\SearchTools.php on line 113
I fixed this first one by adding the null coalescing operator
`$direction = strtolower($direction ?? ' ');`
Deprecated: Automatic conversion of false to array is deprecated in C:\xampp\htdocs\sites\Joomla_4.3.x\libraries\src\HTML\HTMLHelper.php on line 790
System Info
Joomla 4.3 RC1
PHP 8.1.12
MariaDB
|
1.0
|
A couple PHP 8.1 Deprecations J4.3RC1 - ### Steps to reproduce the issue
Install J4.3 RC1.
In the backend I have 2 Deprecated messages when navigating around the backend of my site opening various Components.
Deprecated: strtolower(): Passing null to parameter #1 ($string) of type string is deprecated in C:\xampp\htdocs\sites\Joomla_4.3.x\libraries\src\HTML\Helpers\SearchTools.php on line 113
I fixed this first one by adding the null coalescing operator
`$direction = strtolower($direction ?? ' ');`
Deprecated: Automatic conversion of false to array is deprecated in C:\xampp\htdocs\sites\Joomla_4.3.x\libraries\src\HTML\HTMLHelper.php on line 790
System Info
Joomla 4.3 RC1
PHP 8.1.12
MariaDB
|
non_test
|
a couple php deprecations steps to reproduce the issue install in the backend i have deprecated messages when navigating around the backend of my site opening various components deprecated strtolower passing null to parameter string of type string is deprecated in c xampp htdocs sites joomla x libraries src html helpers searchtools php on line i fixed this first one by adding the null coalescing operator direction strtolower direction deprecated automatic conversion of false to array is deprecated in c xampp htdocs sites joomla x libraries src html htmlhelper php on line system info joomla php mariadb
| 0
|
222,191
| 17,398,351,759
|
IssuesEvent
|
2021-08-02 16:03:06
|
dipu-bd/lightnovel-crawler
|
https://api.github.com/repos/dipu-bd/lightnovel-crawler
|
closed
|
Wattpad: "Error: 'NoneType' object has no atribute 'group'"
|
bug testing
|
**Describe the bug**
From what I can tell this error message occurs when attempting to download a story that does not have a 9 digit id
================================================================================
[#] Lightnovel Crawler v2.27.5
--------------------------------------------------------------------------------
https://github.com/dipu-bd/lightnovel-crawler
--------------------------------------------------------------------------------
<< LOG LEVEL: DEBUG
--------------------------------------------------------------------------------
-> Press 2021-07-31 17:39:00,451 Ctrl + C[DEBUG] (urllib3.connectionpool)
to exitStarting new HTTPS connection (1): rebrand.ly:443
2021-07-31 17:39:00,513 [INFO] (lncrawl.core.downloader)
CairoSVG was not found.Install it to generate random cover image:
pip install cairosvg
2021-07-31 17:39:00,576 [INFO] (lncrawl.core.app)
Initialized App
2021-07-31 17:39:00,578 [INFO] (lncrawl.core.app)
Detected URL input
2021-07-31 17:39:00,581 [INFO] (lncrawl.core.app)
Initializing crawler for: https://www.wattpad.com/
Retrieving novel info...
https://www.wattpad.com/story/422987-mine-bitten
Traceback (most recent call last):
File "__main__.py", line 4, in <module>
File "lncrawl\__init__.py", line 14, in main
File "lncrawl\core\__init__.py", line 76, in start_app
File "lncrawl\core\__init__.py", line 73, in start_app
File "lncrawl\bots\__init__.py", line 17, in run_bot
File "lncrawl\bots\console\start.py", line 74, in start
File "lncrawl\core\app.py", line 135, in get_novel_info
File "lncrawl\sources\wattpad.py", line 27, in read_novel_info
AttributeError: 'NoneType' object has no attribute 'group'
[14072] Failed to execute script '__main__' due to unhandled exception!
Where did you find this bug?
PIP, EXE
What is your novel URL?
https://www.wattpad.com/story/422987-mine-bitten
It is also an issue with 8 digit ids
If you are using PIP / EXE, what is your APP version ?
2.27.5
If you are using PIP / EXE, what is your operating system ?
Windows 10
|
1.0
|
Wattpad: "Error: 'NoneType' object has no atribute 'group'" - **Describe the bug**
From what I can tell this error message occurs when attempting to download a story that does not have a 9 digit id
================================================================================
[#] Lightnovel Crawler v2.27.5
--------------------------------------------------------------------------------
https://github.com/dipu-bd/lightnovel-crawler
--------------------------------------------------------------------------------
<< LOG LEVEL: DEBUG
--------------------------------------------------------------------------------
-> Press 2021-07-31 17:39:00,451 Ctrl + C[DEBUG] (urllib3.connectionpool)
to exitStarting new HTTPS connection (1): rebrand.ly:443
2021-07-31 17:39:00,513 [INFO] (lncrawl.core.downloader)
CairoSVG was not found.Install it to generate random cover image:
pip install cairosvg
2021-07-31 17:39:00,576 [INFO] (lncrawl.core.app)
Initialized App
2021-07-31 17:39:00,578 [INFO] (lncrawl.core.app)
Detected URL input
2021-07-31 17:39:00,581 [INFO] (lncrawl.core.app)
Initializing crawler for: https://www.wattpad.com/
Retrieving novel info...
https://www.wattpad.com/story/422987-mine-bitten
Traceback (most recent call last):
File "__main__.py", line 4, in <module>
File "lncrawl\__init__.py", line 14, in main
File "lncrawl\core\__init__.py", line 76, in start_app
File "lncrawl\core\__init__.py", line 73, in start_app
File "lncrawl\bots\__init__.py", line 17, in run_bot
File "lncrawl\bots\console\start.py", line 74, in start
File "lncrawl\core\app.py", line 135, in get_novel_info
File "lncrawl\sources\wattpad.py", line 27, in read_novel_info
AttributeError: 'NoneType' object has no attribute 'group'
[14072] Failed to execute script '__main__' due to unhandled exception!
Where did you find this bug?
PIP, EXE
What is your novel URL?
https://www.wattpad.com/story/422987-mine-bitten
It is also an issue with 8 digit ids
If you are using PIP / EXE, what is your APP version ?
2.27.5
If you are using PIP / EXE, what is your operating system ?
Windows 10
|
test
|
wattpad error nonetype object has no atribute group describe the bug from what i can tell this error message occurs when attempting to download a story that does not have a digit id lightnovel crawler log level debug press ctrl c connectionpool to exitstarting new https connection rebrand ly lncrawl core downloader cairosvg was not found install it to generate random cover image pip install cairosvg lncrawl core app initialized app lncrawl core app detected url input lncrawl core app initializing crawler for retrieving novel info traceback most recent call last file main py line in file lncrawl init py line in main file lncrawl core init py line in start app file lncrawl core init py line in start app file lncrawl bots init py line in run bot file lncrawl bots console start py line in start file lncrawl core app py line in get novel info file lncrawl sources wattpad py line in read novel info attributeerror nonetype object has no attribute group failed to execute script main due to unhandled exception where did you find this bug pip exe what is your novel url it is also an issue with digit ids if you are using pip exe what is your app version if you are using pip exe what is your operating system windows
| 1
|
13,329
| 8,875,167,798
|
IssuesEvent
|
2019-01-12 00:58:11
|
rveachkc/pymsteams
|
https://api.github.com/repos/rveachkc/pymsteams
|
opened
|
pyyaml - CVE-2017-18342
|
Security
|
Dismissed an alert for pyyaml: https://github.com/rveachkc/pymsteams/network/alert/dev-requirements.txt/pyyaml/closed
This project only uses pyyaml in testing. The module does not actually execute the code. The setup.py doesn't even install it. Therefore, the risk is acceptable.
Currently, the resolution is to install pyyaml 4.2b1 or later. I'd prefer to hold off on updating until a normal release resolves the vulnerability.
|
True
|
pyyaml - CVE-2017-18342 - Dismissed an alert for pyyaml: https://github.com/rveachkc/pymsteams/network/alert/dev-requirements.txt/pyyaml/closed
This project only uses pyyaml in testing. The module does not actually execute the code. The setup.py doesn't even install it. Therefore, the risk is acceptable.
Currently, the resolution is to install pyyaml 4.2b1 or later. I'd prefer to hold off on updating until a normal release resolves the vulnerability.
|
non_test
|
pyyaml cve dismissed an alert for pyyaml this project only uses pyyaml in testing the module does not actually execute the code the setup py doesn t even install it therefore the risk is acceptable currently the resolution is to install pyyaml or later i d prefer to hold off on updating until a normal release resolves the vulnerability
| 0
|
56,059
| 11,499,793,001
|
IssuesEvent
|
2020-02-12 14:32:23
|
joomla/joomla-cms
|
https://api.github.com/repos/joomla/joomla-cms
|
closed
|
[Sub-form] Validation message for repeatable-table layout of sub-form getting blank
|
No Code Attached Yet
|
### Steps to reproduce the issue
Login to administrator
Goto Email Domain Options of user config and add domain.
Domain name is a required field.
Save domain name with a blank value.
### Expected result
The error message should show as **Invalid field: Domain Name**
### Actual result
The error message only shows **Error**
### System information (as much as possible)
Joomla Version 3.9.X (tested on 3.9.15)
|
1.0
|
[Sub-form] Validation message for repeatable-table layout of sub-form getting blank - ### Steps to reproduce the issue
Login to administrator
Goto Email Domain Options of user config and add domain.
Domain name is a required field.
Save domain name with a blank value.
### Expected result
The error message should show as **Invalid field: Domain Name**
### Actual result
The error message only shows **Error**
### System information (as much as possible)
Joomla Version 3.9.X (tested on 3.9.15)
|
non_test
|
validation message for repeatable table layout of sub form getting blank steps to reproduce the issue login to administrator goto email domain options of user config and add domain domain name is a required field save domain name with a blank value expected result the error message should show as invalid field domain name actual result the error message only shows error system information as much as possible joomla version x tested on
| 0
|
148,910
| 11,871,612,442
|
IssuesEvent
|
2020-03-26 14:38:53
|
eclipse/openj9
|
https://api.github.com/repos/eclipse/openj9
|
opened
|
JTReg Test Fail: sun/nio/cs/FindDecoderBugs.java
|
test failure
|
Failure link
------------
JDK8/J9
- test category, openjdk
- OS/architecture, s390x_xl (https://ci.adoptopenjdk.net/job/Test_openjdk8_j9_sanity.openjdk_s390x_linux_xl/72/)
```
22:34:13 openjdk version "1.8.0_252"
22:34:13 OpenJDK Runtime Environment (build 1.8.0_252-202003251711-b07)
22:34:13 Eclipse OpenJ9 VM (build master-1218a31db, JRE 1.8.0 Linux s390x-64-Bit 20200325_111 (JIT enabled, AOT enabled)
22:34:13 OpenJ9 - 1218a31db
22:34:13 OMR - 4175c2cba
22:34:13 JCL - 22b5378e955 based on jdk8u252-b07)
```
Optional info
-------------
- intermittent failure (yes)
- New test
Failure output (captured from console output)
---------------------------------------------
```
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: Unhandled exception
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: Type=Segmentation error vmState=0x000561ad
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: J9Generic_Signal_Number=00000018 Signal_Number=0000000b Error_Value=f65c8068 Signal_Code=00000001
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: Handler1=000003FF9F8395A0 Handler2=000003FF9F620DA8 InaccessibleAddress=0000000000000000
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: gpr0=0000000000000001 gpr1=0000000000000000 gpr2=0000000000000000 gpr3=000003FED4DF46F0
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: gpr4=0000000000000004 gpr5=000003FED4E161C0 gpr6=000003FED4DF4640 gpr7=000003FF9CCF29D0
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: gpr8=000003FF6594C300 gpr9=000003FED4E16180 gpr10=0000000000000000 gpr11=000003FF9CCF0890
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: gpr12=000003FFA069B000 gpr13=000003FF9E79E9E0 gpr14=000003FF9E23932A gpr15=000003FF9CCEFEF0
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: psw=000003FF9E239332 mask=0705000180000000 fpc=00880000 bea=000003FF9E232544
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr0 409a000000000000 (f: 0.000000, d: 1.664000e+03)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr1 000003ff9ccf2ac0 (f: 2630822656.000000, d: 2.172101e-311)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr2 0000000000000000 (f: 0.000000, d: 0.000000e+00)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr3 000003ff0000014e (f: 334.000000, d: 2.170802e-311)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr4 409a000000000000 (f: 0.000000, d: 1.664000e+03)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr5 3fcc723e7dcde3fb (f: 2110645248.000000, d: 2.222365e-01)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr6 000003ff00000139 (f: 313.000000, d: 2.170802e-311)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr7 3fe5558df34826af (f: 4081592064.000000, d: 6.666937e-01)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr8 0000000000100000 (f: 1048576.000000, d: 5.180654e-318)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr9 0000000000000000 (f: 0.000000, d: 0.000000e+00)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr10 000003ff9cbfd000 (f: 2629816320.000000, d: 2.172101e-311)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr11 000003fff667f485 (f: 4134008064.000000, d: 2.172844e-311)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: fpr12 000003ffd677c31c (f: 3598172928.000000, d: 2.172579e-311)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: fpr13 000003ffdb3fdb18 (f: 3678395136.000000, d: 2.172619e-311)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: fpr14 0000000000000000 (f: 0.000000, d: 0.000000e+00)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: fpr15 000003ff104fda78 (f: 273668736.000000, d: 2.170937e-311)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: Module=/home/jenkins/workspace/Test_openjdk8_j9_sanity.openjdk_s390x_linux_xl/openjdkbinary/j2sdk-image/jre/lib/s390x/default/libj9jit29.so
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: Module_base_address=000003FF9DC80000
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr:
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: Method_being_compiled=sun/nio/cs/ext/GB18030$Decoder.decodeBufferLoop(Ljava/nio/ByteBuffer;Ljava/nio/CharBuffer;)Ljava/nio/charset/CoderResult;
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: Target=2_90_20200325_111 (Linux 4.4.0-170-generic)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: CPU=s390x (4 logical CPUs) (0x1f723a000 RAM)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: ----------- Stack Backtrace -----------
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E239332 [libj9jit29.so+0x5b9332])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E23A022 [libj9jit29.so+0x5ba022])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E238986 [libj9jit29.so+0x5b8986])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E23A022 [libj9jit29.so+0x5ba022])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E238986 [libj9jit29.so+0x5b8986])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E23A022 [libj9jit29.so+0x5ba022])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E23F576 [libj9jit29.so+0x5bf576])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E47E982 [libj9jit29.so+0x7fe982])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E4FD41E [libj9jit29.so+0x87d41e])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E4FD604 [libj9jit29.so+0x87d604])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E4FCBA6 [libj9jit29.so+0x87cba6])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E4FD23A [libj9jit29.so+0x87d23a])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E3C3E34 [libj9jit29.so+0x743e34])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E3C65D8 [libj9jit29.so+0x7465d8])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E3C5894 [libj9jit29.so+0x745894])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9E3C6D80 [libj9jit29.so+0x746d80])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9E1769EC [libj9jit29.so+0x4f69ec])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDF07FA [libj9jit29.so+0x1707fa])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDF172A [libj9jit29.so+0x17172a])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9F622420 [libj9prt29.so+0x22420])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDF3430 [libj9jit29.so+0x173430])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDF3A76 [libj9jit29.so+0x173a76])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDEF448 [libj9jit29.so+0x16f448])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDEF710 [libj9jit29.so+0x16f710])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDEF7F8 [libj9jit29.so+0x16f7f8])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9F622420 [libj9prt29.so+0x22420])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDEFD1A [libj9jit29.so+0x16fd1a])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9F7058F0 [libj9thr29.so+0x58f0])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FFA0687934 [libpthread.so.0+0x7934])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FFA046DCE2 [libc.so.6+0xedce2])
```
Dump Files https://ibm.box.com/shared/static/bq89d6wwq34eg7j85gji425fc4r1ixxd.gz
|
1.0
|
JTReg Test Fail: sun/nio/cs/FindDecoderBugs.java - Failure link
------------
JDK8/J9
- test category, openjdk
- OS/architecture, s390x_xl (https://ci.adoptopenjdk.net/job/Test_openjdk8_j9_sanity.openjdk_s390x_linux_xl/72/)
```
22:34:13 openjdk version "1.8.0_252"
22:34:13 OpenJDK Runtime Environment (build 1.8.0_252-202003251711-b07)
22:34:13 Eclipse OpenJ9 VM (build master-1218a31db, JRE 1.8.0 Linux s390x-64-Bit 20200325_111 (JIT enabled, AOT enabled)
22:34:13 OpenJ9 - 1218a31db
22:34:13 OMR - 4175c2cba
22:34:13 JCL - 22b5378e955 based on jdk8u252-b07)
```
Optional info
-------------
- intermittent failure (yes)
- New test
Failure output (captured from console output)
---------------------------------------------
```
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: Unhandled exception
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: Type=Segmentation error vmState=0x000561ad
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: J9Generic_Signal_Number=00000018 Signal_Number=0000000b Error_Value=f65c8068 Signal_Code=00000001
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: Handler1=000003FF9F8395A0 Handler2=000003FF9F620DA8 InaccessibleAddress=0000000000000000
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: gpr0=0000000000000001 gpr1=0000000000000000 gpr2=0000000000000000 gpr3=000003FED4DF46F0
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: gpr4=0000000000000004 gpr5=000003FED4E161C0 gpr6=000003FED4DF4640 gpr7=000003FF9CCF29D0
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: gpr8=000003FF6594C300 gpr9=000003FED4E16180 gpr10=0000000000000000 gpr11=000003FF9CCF0890
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: gpr12=000003FFA069B000 gpr13=000003FF9E79E9E0 gpr14=000003FF9E23932A gpr15=000003FF9CCEFEF0
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: psw=000003FF9E239332 mask=0705000180000000 fpc=00880000 bea=000003FF9E232544
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr0 409a000000000000 (f: 0.000000, d: 1.664000e+03)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr1 000003ff9ccf2ac0 (f: 2630822656.000000, d: 2.172101e-311)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr2 0000000000000000 (f: 0.000000, d: 0.000000e+00)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr3 000003ff0000014e (f: 334.000000, d: 2.170802e-311)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr4 409a000000000000 (f: 0.000000, d: 1.664000e+03)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr5 3fcc723e7dcde3fb (f: 2110645248.000000, d: 2.222365e-01)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr6 000003ff00000139 (f: 313.000000, d: 2.170802e-311)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr7 3fe5558df34826af (f: 4081592064.000000, d: 6.666937e-01)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr8 0000000000100000 (f: 1048576.000000, d: 5.180654e-318)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr9 0000000000000000 (f: 0.000000, d: 0.000000e+00)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr10 000003ff9cbfd000 (f: 2629816320.000000, d: 2.172101e-311)
22:51:36 [2020-03-25 22:51:33,041] Agent[1]: stderr: fpr11 000003fff667f485 (f: 4134008064.000000, d: 2.172844e-311)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: fpr12 000003ffd677c31c (f: 3598172928.000000, d: 2.172579e-311)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: fpr13 000003ffdb3fdb18 (f: 3678395136.000000, d: 2.172619e-311)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: fpr14 0000000000000000 (f: 0.000000, d: 0.000000e+00)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: fpr15 000003ff104fda78 (f: 273668736.000000, d: 2.170937e-311)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: Module=/home/jenkins/workspace/Test_openjdk8_j9_sanity.openjdk_s390x_linux_xl/openjdkbinary/j2sdk-image/jre/lib/s390x/default/libj9jit29.so
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: Module_base_address=000003FF9DC80000
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr:
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: Method_being_compiled=sun/nio/cs/ext/GB18030$Decoder.decodeBufferLoop(Ljava/nio/ByteBuffer;Ljava/nio/CharBuffer;)Ljava/nio/charset/CoderResult;
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: Target=2_90_20200325_111 (Linux 4.4.0-170-generic)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: CPU=s390x (4 logical CPUs) (0x1f723a000 RAM)
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: ----------- Stack Backtrace -----------
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E239332 [libj9jit29.so+0x5b9332])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E23A022 [libj9jit29.so+0x5ba022])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E238986 [libj9jit29.so+0x5b8986])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E23A022 [libj9jit29.so+0x5ba022])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E238986 [libj9jit29.so+0x5b8986])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E23A022 [libj9jit29.so+0x5ba022])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E23F576 [libj9jit29.so+0x5bf576])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E47E982 [libj9jit29.so+0x7fe982])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E4FD41E [libj9jit29.so+0x87d41e])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E4FD604 [libj9jit29.so+0x87d604])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E4FCBA6 [libj9jit29.so+0x87cba6])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E4FD23A [libj9jit29.so+0x87d23a])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E3C3E34 [libj9jit29.so+0x743e34])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E3C65D8 [libj9jit29.so+0x7465d8])
22:51:36 [2020-03-25 22:51:33,042] Agent[1]: stderr: (0x000003FF9E3C5894 [libj9jit29.so+0x745894])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9E3C6D80 [libj9jit29.so+0x746d80])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9E1769EC [libj9jit29.so+0x4f69ec])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDF07FA [libj9jit29.so+0x1707fa])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDF172A [libj9jit29.so+0x17172a])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9F622420 [libj9prt29.so+0x22420])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDF3430 [libj9jit29.so+0x173430])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDF3A76 [libj9jit29.so+0x173a76])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDEF448 [libj9jit29.so+0x16f448])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDEF710 [libj9jit29.so+0x16f710])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDEF7F8 [libj9jit29.so+0x16f7f8])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9F622420 [libj9prt29.so+0x22420])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9DDEFD1A [libj9jit29.so+0x16fd1a])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FF9F7058F0 [libj9thr29.so+0x58f0])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FFA0687934 [libpthread.so.0+0x7934])
22:51:36 [2020-03-25 22:51:33,043] Agent[1]: stderr: (0x000003FFA046DCE2 [libc.so.6+0xedce2])
```
Dump Files https://ibm.box.com/shared/static/bq89d6wwq34eg7j85gji425fc4r1ixxd.gz
|
test
|
jtreg test fail sun nio cs finddecoderbugs java failure link test category openjdk os architecture xl openjdk version openjdk runtime environment build eclipse vm build master jre linux bit jit enabled aot enabled omr jcl based on optional info intermittent failure yes new test failure output captured from console output agent stderr unhandled exception agent stderr type segmentation error vmstate agent stderr signal number signal number error value signal code agent stderr inaccessibleaddress agent stderr agent stderr agent stderr agent stderr agent stderr psw mask fpc bea agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr f d agent stderr module home jenkins workspace test sanity openjdk linux xl openjdkbinary image jre lib default so agent stderr module base address agent stderr agent stderr method being compiled sun nio cs ext decoder decodebufferloop ljava nio bytebuffer ljava nio charbuffer ljava nio charset coderresult agent stderr target linux generic agent stderr cpu logical cpus ram agent stderr stack backtrace agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr agent stderr dump files
| 1
|
299,992
| 25,941,262,638
|
IssuesEvent
|
2022-12-16 18:38:42
|
celo-org/celo-monorepo
|
https://api.github.com/repos/celo-org/celo-monorepo
|
closed
|
[FLAKEY TEST] contractkit-test -> sdk/contractkit -> GrandaMento Wrapper -> When Granda Mento is enabled -> has new limits
|
Component: SDK FLAKEY contractkit-test
|
Discovered at commit a8b8039f7f442871abb1c3c906d4ff4f58d7f570
Attempt No. 1:
Error: thrown: "Exceeded timeout of 10000 ms for a hook.
Use jest.setTimeout(newTimeout) to increase the timeout value, if this is a long-running test."
at /home/circleci/app/packages/sdk/contractkit/src/wrappers/GrandaMento.test.ts:61:5
at _dispatchDescribe (/home/circleci/app/node_modules/jest-circus/build/index.js:67:26)
at describe (/home/circleci/app/node_modules/jest-circus/build/index.js:30:5)
at /home/circleci/app/packages/sdk/contractkit/src/wrappers/GrandaMento.test.ts:60:3
at /home/circleci/app/packages/dev-utils/src/ganache-test.ts:79:5
at _dispatchDescribe (/home/circleci/app/node_modules/jest-circus/build/index.js:67:26)
at describe (/home/circleci/app/node_modules/jest-circus/build/index.js:30:5)
at Object.testWithGanache (/home/circleci/app/packages/dev-utils/src/ganache-test.ts:63:3)
at Object.<anonymous> (/home/circleci/app/packages/sdk/contractkit/src/wrappers/GrandaMento.test.ts:14:1)
at Runtime._execModule (/home/circleci/app/node_modules/jest-runtime/build/index.js:1299:24)
at Runtime._loadModule (/home/circleci/app/node_modules/jest-runtime/build/index.js:898:12)
at Runtime.requireModule (/home/circleci/app/node_modules/jest-runtime/build/index.js:746:10)
at jestAdapter (/home/circleci/app/node_modules/jest-circus/build/legacy-code-todo-rewrite/jestAdapter.js:106:13)
at runTestInternal (/home/circleci/app/node_modules/jest-runner/build/runTest.js:380:16)
at runTest (/home/circleci/app/node_modules/jest-runner/build/runTest.js:472:34)
Attempt No. 2:
Test Passed!
|
1.0
|
[FLAKEY TEST] contractkit-test -> sdk/contractkit -> GrandaMento Wrapper -> When Granda Mento is enabled -> has new limits - Discovered at commit a8b8039f7f442871abb1c3c906d4ff4f58d7f570
Attempt No. 1:
Error: thrown: "Exceeded timeout of 10000 ms for a hook.
Use jest.setTimeout(newTimeout) to increase the timeout value, if this is a long-running test."
at /home/circleci/app/packages/sdk/contractkit/src/wrappers/GrandaMento.test.ts:61:5
at _dispatchDescribe (/home/circleci/app/node_modules/jest-circus/build/index.js:67:26)
at describe (/home/circleci/app/node_modules/jest-circus/build/index.js:30:5)
at /home/circleci/app/packages/sdk/contractkit/src/wrappers/GrandaMento.test.ts:60:3
at /home/circleci/app/packages/dev-utils/src/ganache-test.ts:79:5
at _dispatchDescribe (/home/circleci/app/node_modules/jest-circus/build/index.js:67:26)
at describe (/home/circleci/app/node_modules/jest-circus/build/index.js:30:5)
at Object.testWithGanache (/home/circleci/app/packages/dev-utils/src/ganache-test.ts:63:3)
at Object.<anonymous> (/home/circleci/app/packages/sdk/contractkit/src/wrappers/GrandaMento.test.ts:14:1)
at Runtime._execModule (/home/circleci/app/node_modules/jest-runtime/build/index.js:1299:24)
at Runtime._loadModule (/home/circleci/app/node_modules/jest-runtime/build/index.js:898:12)
at Runtime.requireModule (/home/circleci/app/node_modules/jest-runtime/build/index.js:746:10)
at jestAdapter (/home/circleci/app/node_modules/jest-circus/build/legacy-code-todo-rewrite/jestAdapter.js:106:13)
at runTestInternal (/home/circleci/app/node_modules/jest-runner/build/runTest.js:380:16)
at runTest (/home/circleci/app/node_modules/jest-runner/build/runTest.js:472:34)
Attempt No. 2:
Test Passed!
|
test
|
contractkit test sdk contractkit grandamento wrapper when granda mento is enabled has new limits discovered at commit attempt no error thrown exceeded timeout of ms for a hook use jest settimeout newtimeout to increase the timeout value if this is a long running test at home circleci app packages sdk contractkit src wrappers grandamento test ts at dispatchdescribe home circleci app node modules jest circus build index js at describe home circleci app node modules jest circus build index js at home circleci app packages sdk contractkit src wrappers grandamento test ts at home circleci app packages dev utils src ganache test ts at dispatchdescribe home circleci app node modules jest circus build index js at describe home circleci app node modules jest circus build index js at object testwithganache home circleci app packages dev utils src ganache test ts at object home circleci app packages sdk contractkit src wrappers grandamento test ts at runtime execmodule home circleci app node modules jest runtime build index js at runtime loadmodule home circleci app node modules jest runtime build index js at runtime requiremodule home circleci app node modules jest runtime build index js at jestadapter home circleci app node modules jest circus build legacy code todo rewrite jestadapter js at runtestinternal home circleci app node modules jest runner build runtest js at runtest home circleci app node modules jest runner build runtest js attempt no test passed
| 1
|
251,737
| 21,521,759,597
|
IssuesEvent
|
2022-04-28 14:45:23
|
damccorm/test-migration-target
|
https://api.github.com/repos/damccorm/test-migration-target
|
opened
|
Flink Tests failure : java.lang.NoClassDefFoundError: Could not initialize class org.apache.beam.runners.core.construction.SerializablePipelineOptions
|
bug P1 test-failures
|
This flink load tests are affected by this error
- beam_LoadTests_Go_ParDo_Flink_Batch (FAILED)
-- beam_LoadTests_Go_SideInput_Flink_Batch (FAILED)
-- beam_LoadTests_Python_Combine_Flink_Batch (FAILED)
-- beam_LoadTests_Python_Combine_Flink_Streaming (FAILED)
-- beam_LoadTests_Python_ParDo_Flink_Batch (FAILED)
-- beam_LoadTests_Python_ParDo_Flink_Streaming (FAILED)
Stacktrace of the error
14:03:35 root_transform_ids: "e11"
14:03:35 root_transform_ids: "e12"
14:03:35 root_transform_ids: "e13"
14:03:35 root_transform_ids: "e14"
14:03:35 requirements: "beam:requirement:org.apache.beam:pardo:splittable_dofn:v1"
14:03:35 2022/03/07 20:03:33 Prepared job with id: load-tests-go-flink-batch-pardo-1-0307182650_12830e27-009a-44e5-8390-a53ce5f264f0 and staging token: load-tests-go-flink-batch-pardo-1-0307182650_12830e27-009a-44e5-8390-a53ce5f264f0
14:03:35 2022/03/07 20:03:33 Using specified worker binary: 'linux_amd64/pardo'
14:03:46 2022/03/07 20:03:46 Staged binary artifact with token:
14:03:47 2022/03/07 20:03:47 Submitted job: load0tests0go0flink0batch0pardo0100307182650-root-0307200346-d0077c8_166b7cfd-0805-481a-9a6a-52ba9bfddcbc
14:03:47 2022/03/07 20:03:47 Job state: STOPPED
14:03:47 2022/03/07 20:03:47 Job state: STARTING
14:03:47 2022/03/07 20:03:47 Job state: RUNNING
14:04:04 2022/03/07 20:04:04 (): org.apache.flink.client.program.ProgramInvocationException: Job failed (JobID: a8fc45aac0e16ee159027398311e082e)
14:04:04 at org.apache.flink.client.deployment.ClusterClientJobClientAdapter.lambda$null$6(ClusterClientJobClientAdapter.java:125)
14:04:04 at java.util.concurrent.CompletableFuture.uniApply(CompletableFuture.java:616)
14:04:04 at java.util.concurrent.CompletableFuture$UniApply.tryFire(CompletableFuture.java:591)
14:04:04 at java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:488)
14:04:04 at java.util.concurrent.CompletableFuture.complete(CompletableFuture.java:1975)
14:04:04 at org.apache.flink.client.program.rest.RestClusterClient.lambda$pollResourceAsync$22(RestClusterClient.java:665)
14:04:04 at java.util.concurrent.CompletableFuture.uniWhenComplete(CompletableFuture.java:774)
14:04:04 at java.util.concurrent.CompletableFuture$UniWhenComplete.tryFire(CompletableFuture.java:750)
14:04:04 at java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:488)
14:04:04 at java.util.concurrent.CompletableFuture.complete(CompletableFuture.java:1975)
14:04:04 at org.apache.flink.runtime.concurrent.FutureUtils.lambda$retryOperationWithDelay$9(FutureUtils.java:394)
14:04:04 at java.util.concurrent.CompletableFuture.uniWhenComplete(CompletableFuture.java:774)
14:04:04 at java.util.concurrent.CompletableFuture$UniWhenComplete.tryFire(CompletableFuture.java:750)
14:04:04 at java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:488)
14:04:04 at java.util.concurrent.CompletableFuture.postFire(CompletableFuture.java:575)
14:04:04 at java.util.concurrent.CompletableFuture$UniCompose.tryFire(CompletableFuture.java:943)
14:04:04 at java.util.concurrent.CompletableFuture$Completion.run(CompletableFuture.java:456)
14:04:04 at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
14:04:04 at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
14:04:04 at java.lang.Thread.run(Thread.java:748)
14:04:04 Caused by: org.apache.flink.runtime.client.JobExecutionException: Job execution failed.
14:04:04 at org.apache.flink.runtime.jobmaster.JobResult.toJobExecutionResult(JobResult.java:144)
14:04:04 at org.apache.flink.client.deployment.ClusterClientJobClientAdapter.lambda$null$6(ClusterClientJobClientAdapter.java:123)
14:04:04 ... 19 more
14:04:04 Caused by: org.apache.flink.runtime.JobException: Recovery is suppressed by NoRestartBackoffTimeStrategy
14:04:04 at org.apache.flink.runtime.executiongraph.failover.flip1.ExecutionFailureHandler.handleFailure(ExecutionFailureHandler.java:118)
14:04:04 at org.apache.flink.runtime.executiongraph.failover.flip1.ExecutionFailureHandler.getFailureHandlingResult(ExecutionFailureHandler.java:80)
14:04:04 at org.apache.flink.runtime.scheduler.DefaultScheduler.handleTaskFailure(DefaultScheduler.java:233)
14:04:04 at org.apache.flink.runtime.scheduler.DefaultScheduler.maybeHandleTaskFailure(DefaultScheduler.java:224)
14:04:04 at org.apache.flink.runtime.scheduler.DefaultScheduler.updateTaskExecutionStateInternal(DefaultScheduler.java:215)
14:04:04 at org.apache.flink.runtime.scheduler.SchedulerBase.updateTaskExecutionState(SchedulerBase.java:666)
14:04:04 at org.apache.flink.runtime.scheduler.SchedulerNG.updateTaskExecutionState(SchedulerNG.java:89)
14:04:04 at org.apache.flink.runtime.jobmaster.JobMaster.updateTaskExecutionState(JobMaster.java:446)
14:04:04 at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
14:04:04 at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
14:04:04 at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
14:04:04 at java.lang.reflect.Method.invoke(Method.java:498)
14:04:04 at org.apache.flink.runtime.rpc.akka.AkkaRpcActor.handleRpcInvocation(AkkaRpcActor.java:305)
14:04:04 at org.apache.flink.runtime.rpc.akka.AkkaRpcActor.handleRpcMessage(AkkaRpcActor.java:212)
14:04:04 at org.apache.flink.runtime.rpc.akka.FencedAkkaRpcActor.handleRpcMessage(FencedAkkaRpcActor.java:77)
14:04:04 at org.apache.flink.runtime.rpc.akka.AkkaRpcActor.handleMessage(AkkaRpcActor.java:158)
14:04:04 at akka.japi.pf.UnitCaseStatement.apply(CaseStatements.scala:26)
14:04:04 at akka.japi.pf.UnitCaseStatement.apply(CaseStatements.scala:21)
14:04:04 at scala.PartialFunction.applyOrElse(PartialFunction.scala:127)
14:04:04 at scala.PartialFunction.applyOrElse$(PartialFunction.scala:126)
14:04:04 at akka.japi.pf.UnitCaseStatement.applyOrElse(CaseStatements.scala:21)
14:04:04 at scala.PartialFunction$OrElse.applyOrElse(PartialFunction.scala:175)
14:04:04 at scala.PartialFunction$OrElse.applyOrElse(PartialFunction.scala:176)
14:04:04 at scala.PartialFunction$OrElse.applyOrElse(PartialFunction.scala:176)
14:04:04 at akka.actor.Actor.aroundReceive(Actor.scala:517)
14:04:04 at akka.actor.Actor.aroundReceive$(Actor.scala:515)
14:04:04 at akka.actor.AbstractActor.aroundReceive(AbstractActor.scala:225)
14:04:04 at akka.actor.ActorCell.receiveMessage(ActorCell.scala:592)
14:04:04 at akka.actor.ActorCell.invoke(ActorCell.scala:561)
14:04:04 at akka.dispatch.Mailbox.processMailbox(Mailbox.scala:258)
14:04:04 at akka.dispatch.Mailbox.run(Mailbox.scala:225)
14:04:04 at akka.dispatch.Mailbox.exec(Mailbox.scala:235)
14:04:04 at akka.dispatch.forkjoin.ForkJoinTask.doExec(ForkJoinTask.java:260)
14:04:04 at akka.dispatch.forkjoin.ForkJoinPool$WorkQueue.runTask(ForkJoinPool.java:1339)
14:04:04 at akka.dispatch.forkjoin.ForkJoinPool.runWorker(ForkJoinPool.java:1979)
14:04:04 at akka.dispatch.forkjoin.ForkJoinWorkerThread.run(ForkJoinWorkerThread.java:107)
14:04:04 Caused by: java.lang.NoClassDefFoundError: Could not initialize class org.apache.beam.runners.core.construction.SerializablePipelineOptions
14:04:04 at java.io.ObjectStreamClass.hasStaticInitializer(Native Method)
14:04:04 at java.io.ObjectStreamClass.computeDefaultSUID(ObjectStreamClass.java:1955)
14:04:04 at java.io.ObjectStreamClass.access$100(ObjectStreamClass.java:79)
14:04:04 at java.io.ObjectStreamClass$2.run(ObjectStreamClass.java:275)
14:04:04 at java.io.ObjectStreamClass$2.run(ObjectStreamClass.java:273)
14:04:04 at java.security.AccessController.doPrivileged(Native Method)
14:04:04 at java.io.ObjectStreamClass.getSerialVersionUID(ObjectStreamClass.java:272)
14:04:04 at java.io.ObjectStreamClass.initNonProxy(ObjectStreamClass.java:694)
14:04:04 at java.io.ObjectInputStream.readNonProxyDesc(ObjectInputStream.java:2005)
14:04:04 at java.io.ObjectInputStream.readClassDesc(ObjectInputStream.java:1852)
14:04:04 at java.io.ObjectInputStream.readOrdinaryObject(ObjectInputStream.java:2186)
14:04:04 at java.io.ObjectInputStream.readObject0(ObjectInputStream.java:1669)
14:04:04 at java.io.ObjectInputStream.defaultReadFields(ObjectInputStream.java:2431)
14:04:04 at java.io.ObjectInputStream.readSerialData(ObjectInputStream.java:2355)
14:04:04 at java.io.ObjectInputStream.readOrdinaryObject(ObjectInputStream.java:2213)
14:04:04 at java.io.ObjectInputStream.readObject0(ObjectInputStream.java:1669)
14:04:04 at java.io.ObjectInputStream.readObject(ObjectInputStream.java:503)
14:04:04 at java.io.ObjectInputStream.readObject(ObjectInputStream.java:461)
14:04:04 at org.apache.flink.util.InstantiationUtil.deserializeObject(InstantiationUtil.java:615)
14:04:04 at org.apache.flink.util.InstantiationUtil.deserializeObject(InstantiationUtil.java:600)
14:04:04 at org.apache.flink.util.InstantiationUtil.deserializeObject(InstantiationUtil.java:587)
14:04:04 at org.apache.flink.util.InstantiationUtil.readObjectFromConfig(InstantiationUtil.java:541)
14:04:04 at org.apache.flink.api.java.typeutils.runtime.RuntimeSerializerFactory.readParametersFromConfig(RuntimeSerializerFactory.java:78)
14:04:04 at org.apache.flink.runtime.operators.util.TaskConfig.getTypeSerializerFactory(TaskConfig.java:1246)
14:04:04 at org.apache.flink.runtime.operators.util.TaskConfig.getOutputSerializer(TaskConfig.java:599)
14:04:04 at org.apache.flink.runtime.operators.DataSourceTask.initInputFormat(DataSourceTask.java:324)
14:04:04 at org.apache.flink.runtime.operators.DataSourceTask.invoke(DataSourceTask.java:106)
14:04:04 at org.apache.flink.runtime.taskmanager.Task.doRun(Task.java:758)
14:04:04 at org.apache.flink.runtime.taskmanager.Task.run(Task.java:573)
14:04:04 at java.lang.Thread.run(Thread.java:750)
14:04:04 2022/03/07 20:04:04 (): java.lang.NoClassDefFoundError: Could not initialize class org.apache.beam.runners.core.construction.SerializablePipelineOptions
14:04:05 2022/03/07 20:04:05 Job state: FAILED
14:04:05 2022/03/07 20:04:05 Failed to execute job: job load0tests0go0flink0batch0pardo0100307182650-root-0307200346-d0077c8_166b7cfd-0805-481a-9a6a-52ba9bfddcbc failed
14:04:05 panic: Failed to execute job: job load0tests0go0flink0batch0pardo0100307182650-root-0307200346-d0077c8_166b7cfd-0805-481a-9a6a-52ba9bfddcbc failed
14:04:05
14:04:05 goroutine 1 [running]:
14:04:05 github.com/apache/beam/sdks/v2/go/pkg/beam/log.Fatalf(0x1143648, 0xc000120000, 0x10323eb, 0x19, 0xc0003cde00, 0x1, 0x1)
14:04:05 /var/jenkins_real_home/workspace/beam_LoadTests_Go_ParDo_Flink_Batch/src/sdks/go/pkg/beam/log/log.go:153 +0xec
14:04:05 main.main()
14:04:05 /var/jenkins_real_home/workspace/beam_LoadTests_Go_ParDo_Flink_Batch/src/sdks/go/test/load/pardo/pardo.go:105 +0x3ca
14:04:05
14:04:05 > Task :sdks:go:test:load:run FAILED
Imported from Jira [BEAM-14174](https://issues.apache.org/jira/browse/BEAM-14174)
Reported by: andoni.guzman.
|
1.0
|
Flink Tests failure : java.lang.NoClassDefFoundError: Could not initialize class org.apache.beam.runners.core.construction.SerializablePipelineOptions - This flink load tests are affected by this error
- beam_LoadTests_Go_ParDo_Flink_Batch (FAILED)
-- beam_LoadTests_Go_SideInput_Flink_Batch (FAILED)
-- beam_LoadTests_Python_Combine_Flink_Batch (FAILED)
-- beam_LoadTests_Python_Combine_Flink_Streaming (FAILED)
-- beam_LoadTests_Python_ParDo_Flink_Batch (FAILED)
-- beam_LoadTests_Python_ParDo_Flink_Streaming (FAILED)
Stacktrace of the error
14:03:35 root_transform_ids: "e11"
14:03:35 root_transform_ids: "e12"
14:03:35 root_transform_ids: "e13"
14:03:35 root_transform_ids: "e14"
14:03:35 requirements: "beam:requirement:org.apache.beam:pardo:splittable_dofn:v1"
14:03:35 2022/03/07 20:03:33 Prepared job with id: load-tests-go-flink-batch-pardo-1-0307182650_12830e27-009a-44e5-8390-a53ce5f264f0 and staging token: load-tests-go-flink-batch-pardo-1-0307182650_12830e27-009a-44e5-8390-a53ce5f264f0
14:03:35 2022/03/07 20:03:33 Using specified worker binary: 'linux_amd64/pardo'
14:03:46 2022/03/07 20:03:46 Staged binary artifact with token:
14:03:47 2022/03/07 20:03:47 Submitted job: load0tests0go0flink0batch0pardo0100307182650-root-0307200346-d0077c8_166b7cfd-0805-481a-9a6a-52ba9bfddcbc
14:03:47 2022/03/07 20:03:47 Job state: STOPPED
14:03:47 2022/03/07 20:03:47 Job state: STARTING
14:03:47 2022/03/07 20:03:47 Job state: RUNNING
14:04:04 2022/03/07 20:04:04 (): org.apache.flink.client.program.ProgramInvocationException: Job failed (JobID: a8fc45aac0e16ee159027398311e082e)
14:04:04 at org.apache.flink.client.deployment.ClusterClientJobClientAdapter.lambda$null$6(ClusterClientJobClientAdapter.java:125)
14:04:04 at java.util.concurrent.CompletableFuture.uniApply(CompletableFuture.java:616)
14:04:04 at java.util.concurrent.CompletableFuture$UniApply.tryFire(CompletableFuture.java:591)
14:04:04 at java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:488)
14:04:04 at java.util.concurrent.CompletableFuture.complete(CompletableFuture.java:1975)
14:04:04 at org.apache.flink.client.program.rest.RestClusterClient.lambda$pollResourceAsync$22(RestClusterClient.java:665)
14:04:04 at java.util.concurrent.CompletableFuture.uniWhenComplete(CompletableFuture.java:774)
14:04:04 at java.util.concurrent.CompletableFuture$UniWhenComplete.tryFire(CompletableFuture.java:750)
14:04:04 at java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:488)
14:04:04 at java.util.concurrent.CompletableFuture.complete(CompletableFuture.java:1975)
14:04:04 at org.apache.flink.runtime.concurrent.FutureUtils.lambda$retryOperationWithDelay$9(FutureUtils.java:394)
14:04:04 at java.util.concurrent.CompletableFuture.uniWhenComplete(CompletableFuture.java:774)
14:04:04 at java.util.concurrent.CompletableFuture$UniWhenComplete.tryFire(CompletableFuture.java:750)
14:04:04 at java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:488)
14:04:04 at java.util.concurrent.CompletableFuture.postFire(CompletableFuture.java:575)
14:04:04 at java.util.concurrent.CompletableFuture$UniCompose.tryFire(CompletableFuture.java:943)
14:04:04 at java.util.concurrent.CompletableFuture$Completion.run(CompletableFuture.java:456)
14:04:04 at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
14:04:04 at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
14:04:04 at java.lang.Thread.run(Thread.java:748)
14:04:04 Caused by: org.apache.flink.runtime.client.JobExecutionException: Job execution failed.
14:04:04 at org.apache.flink.runtime.jobmaster.JobResult.toJobExecutionResult(JobResult.java:144)
14:04:04 at org.apache.flink.client.deployment.ClusterClientJobClientAdapter.lambda$null$6(ClusterClientJobClientAdapter.java:123)
14:04:04 ... 19 more
14:04:04 Caused by: org.apache.flink.runtime.JobException: Recovery is suppressed by NoRestartBackoffTimeStrategy
14:04:04 at org.apache.flink.runtime.executiongraph.failover.flip1.ExecutionFailureHandler.handleFailure(ExecutionFailureHandler.java:118)
14:04:04 at org.apache.flink.runtime.executiongraph.failover.flip1.ExecutionFailureHandler.getFailureHandlingResult(ExecutionFailureHandler.java:80)
14:04:04 at org.apache.flink.runtime.scheduler.DefaultScheduler.handleTaskFailure(DefaultScheduler.java:233)
14:04:04 at org.apache.flink.runtime.scheduler.DefaultScheduler.maybeHandleTaskFailure(DefaultScheduler.java:224)
14:04:04 at org.apache.flink.runtime.scheduler.DefaultScheduler.updateTaskExecutionStateInternal(DefaultScheduler.java:215)
14:04:04 at org.apache.flink.runtime.scheduler.SchedulerBase.updateTaskExecutionState(SchedulerBase.java:666)
14:04:04 at org.apache.flink.runtime.scheduler.SchedulerNG.updateTaskExecutionState(SchedulerNG.java:89)
14:04:04 at org.apache.flink.runtime.jobmaster.JobMaster.updateTaskExecutionState(JobMaster.java:446)
14:04:04 at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
14:04:04 at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
14:04:04 at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
14:04:04 at java.lang.reflect.Method.invoke(Method.java:498)
14:04:04 at org.apache.flink.runtime.rpc.akka.AkkaRpcActor.handleRpcInvocation(AkkaRpcActor.java:305)
14:04:04 at org.apache.flink.runtime.rpc.akka.AkkaRpcActor.handleRpcMessage(AkkaRpcActor.java:212)
14:04:04 at org.apache.flink.runtime.rpc.akka.FencedAkkaRpcActor.handleRpcMessage(FencedAkkaRpcActor.java:77)
14:04:04 at org.apache.flink.runtime.rpc.akka.AkkaRpcActor.handleMessage(AkkaRpcActor.java:158)
14:04:04 at akka.japi.pf.UnitCaseStatement.apply(CaseStatements.scala:26)
14:04:04 at akka.japi.pf.UnitCaseStatement.apply(CaseStatements.scala:21)
14:04:04 at scala.PartialFunction.applyOrElse(PartialFunction.scala:127)
14:04:04 at scala.PartialFunction.applyOrElse$(PartialFunction.scala:126)
14:04:04 at akka.japi.pf.UnitCaseStatement.applyOrElse(CaseStatements.scala:21)
14:04:04 at scala.PartialFunction$OrElse.applyOrElse(PartialFunction.scala:175)
14:04:04 at scala.PartialFunction$OrElse.applyOrElse(PartialFunction.scala:176)
14:04:04 at scala.PartialFunction$OrElse.applyOrElse(PartialFunction.scala:176)
14:04:04 at akka.actor.Actor.aroundReceive(Actor.scala:517)
14:04:04 at akka.actor.Actor.aroundReceive$(Actor.scala:515)
14:04:04 at akka.actor.AbstractActor.aroundReceive(AbstractActor.scala:225)
14:04:04 at akka.actor.ActorCell.receiveMessage(ActorCell.scala:592)
14:04:04 at akka.actor.ActorCell.invoke(ActorCell.scala:561)
14:04:04 at akka.dispatch.Mailbox.processMailbox(Mailbox.scala:258)
14:04:04 at akka.dispatch.Mailbox.run(Mailbox.scala:225)
14:04:04 at akka.dispatch.Mailbox.exec(Mailbox.scala:235)
14:04:04 at akka.dispatch.forkjoin.ForkJoinTask.doExec(ForkJoinTask.java:260)
14:04:04 at akka.dispatch.forkjoin.ForkJoinPool$WorkQueue.runTask(ForkJoinPool.java:1339)
14:04:04 at akka.dispatch.forkjoin.ForkJoinPool.runWorker(ForkJoinPool.java:1979)
14:04:04 at akka.dispatch.forkjoin.ForkJoinWorkerThread.run(ForkJoinWorkerThread.java:107)
14:04:04 Caused by: java.lang.NoClassDefFoundError: Could not initialize class org.apache.beam.runners.core.construction.SerializablePipelineOptions
14:04:04 at java.io.ObjectStreamClass.hasStaticInitializer(Native Method)
14:04:04 at java.io.ObjectStreamClass.computeDefaultSUID(ObjectStreamClass.java:1955)
14:04:04 at java.io.ObjectStreamClass.access$100(ObjectStreamClass.java:79)
14:04:04 at java.io.ObjectStreamClass$2.run(ObjectStreamClass.java:275)
14:04:04 at java.io.ObjectStreamClass$2.run(ObjectStreamClass.java:273)
14:04:04 at java.security.AccessController.doPrivileged(Native Method)
14:04:04 at java.io.ObjectStreamClass.getSerialVersionUID(ObjectStreamClass.java:272)
14:04:04 at java.io.ObjectStreamClass.initNonProxy(ObjectStreamClass.java:694)
14:04:04 at java.io.ObjectInputStream.readNonProxyDesc(ObjectInputStream.java:2005)
14:04:04 at java.io.ObjectInputStream.readClassDesc(ObjectInputStream.java:1852)
14:04:04 at java.io.ObjectInputStream.readOrdinaryObject(ObjectInputStream.java:2186)
14:04:04 at java.io.ObjectInputStream.readObject0(ObjectInputStream.java:1669)
14:04:04 at java.io.ObjectInputStream.defaultReadFields(ObjectInputStream.java:2431)
14:04:04 at java.io.ObjectInputStream.readSerialData(ObjectInputStream.java:2355)
14:04:04 at java.io.ObjectInputStream.readOrdinaryObject(ObjectInputStream.java:2213)
14:04:04 at java.io.ObjectInputStream.readObject0(ObjectInputStream.java:1669)
14:04:04 at java.io.ObjectInputStream.readObject(ObjectInputStream.java:503)
14:04:04 at java.io.ObjectInputStream.readObject(ObjectInputStream.java:461)
14:04:04 at org.apache.flink.util.InstantiationUtil.deserializeObject(InstantiationUtil.java:615)
14:04:04 at org.apache.flink.util.InstantiationUtil.deserializeObject(InstantiationUtil.java:600)
14:04:04 at org.apache.flink.util.InstantiationUtil.deserializeObject(InstantiationUtil.java:587)
14:04:04 at org.apache.flink.util.InstantiationUtil.readObjectFromConfig(InstantiationUtil.java:541)
14:04:04 at org.apache.flink.api.java.typeutils.runtime.RuntimeSerializerFactory.readParametersFromConfig(RuntimeSerializerFactory.java:78)
14:04:04 at org.apache.flink.runtime.operators.util.TaskConfig.getTypeSerializerFactory(TaskConfig.java:1246)
14:04:04 at org.apache.flink.runtime.operators.util.TaskConfig.getOutputSerializer(TaskConfig.java:599)
14:04:04 at org.apache.flink.runtime.operators.DataSourceTask.initInputFormat(DataSourceTask.java:324)
14:04:04 at org.apache.flink.runtime.operators.DataSourceTask.invoke(DataSourceTask.java:106)
14:04:04 at org.apache.flink.runtime.taskmanager.Task.doRun(Task.java:758)
14:04:04 at org.apache.flink.runtime.taskmanager.Task.run(Task.java:573)
14:04:04 at java.lang.Thread.run(Thread.java:750)
14:04:04 2022/03/07 20:04:04 (): java.lang.NoClassDefFoundError: Could not initialize class org.apache.beam.runners.core.construction.SerializablePipelineOptions
14:04:05 2022/03/07 20:04:05 Job state: FAILED
14:04:05 2022/03/07 20:04:05 Failed to execute job: job load0tests0go0flink0batch0pardo0100307182650-root-0307200346-d0077c8_166b7cfd-0805-481a-9a6a-52ba9bfddcbc failed
14:04:05 panic: Failed to execute job: job load0tests0go0flink0batch0pardo0100307182650-root-0307200346-d0077c8_166b7cfd-0805-481a-9a6a-52ba9bfddcbc failed
14:04:05
14:04:05 goroutine 1 [running]:
14:04:05 github.com/apache/beam/sdks/v2/go/pkg/beam/log.Fatalf(0x1143648, 0xc000120000, 0x10323eb, 0x19, 0xc0003cde00, 0x1, 0x1)
14:04:05 /var/jenkins_real_home/workspace/beam_LoadTests_Go_ParDo_Flink_Batch/src/sdks/go/pkg/beam/log/log.go:153 +0xec
14:04:05 main.main()
14:04:05 /var/jenkins_real_home/workspace/beam_LoadTests_Go_ParDo_Flink_Batch/src/sdks/go/test/load/pardo/pardo.go:105 +0x3ca
14:04:05
14:04:05 > Task :sdks:go:test:load:run FAILED
Imported from Jira [BEAM-14174](https://issues.apache.org/jira/browse/BEAM-14174)
Reported by: andoni.guzman.
|
test
|
flink tests failure java lang noclassdeffounderror could not initialize class org apache beam runners core construction serializablepipelineoptions this flink load tests are affected by this error beam loadtests go pardo flink batch failed beam loadtests go sideinput flink batch failed beam loadtests python combine flink batch failed beam loadtests python combine flink streaming failed beam loadtests python pardo flink batch failed beam loadtests python pardo flink streaming failed stacktrace of the error root transform ids root transform ids root transform ids root transform ids requirements beam requirement org apache beam pardo splittable dofn prepared job with id load tests go flink batch pardo and staging token load tests go flink batch pardo using specified worker binary linux pardo staged binary artifact with token submitted job root job state stopped job state starting job state running org apache flink client program programinvocationexception job failed jobid at org apache flink client deployment clusterclientjobclientadapter lambda null clusterclientjobclientadapter java at java util concurrent completablefuture uniapply completablefuture java at java util concurrent completablefuture uniapply tryfire completablefuture java at java util concurrent completablefuture postcomplete completablefuture java at java util concurrent completablefuture complete completablefuture java at org apache flink client program rest restclusterclient lambda pollresourceasync restclusterclient java at java util concurrent completablefuture uniwhencomplete completablefuture java at java util concurrent completablefuture uniwhencomplete tryfire completablefuture java at java util concurrent completablefuture postcomplete completablefuture java at java util concurrent completablefuture complete completablefuture java at org apache flink runtime concurrent futureutils lambda retryoperationwithdelay futureutils java at java util concurrent completablefuture uniwhencomplete completablefuture java at java util concurrent completablefuture uniwhencomplete tryfire completablefuture java at java util concurrent completablefuture postcomplete completablefuture java at java util concurrent completablefuture postfire completablefuture java at java util concurrent completablefuture unicompose tryfire completablefuture java at java util concurrent completablefuture completion run completablefuture java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java caused by org apache flink runtime client jobexecutionexception job execution failed at org apache flink runtime jobmaster jobresult tojobexecutionresult jobresult java at org apache flink client deployment clusterclientjobclientadapter lambda null clusterclientjobclientadapter java more caused by org apache flink runtime jobexception recovery is suppressed by norestartbackofftimestrategy at org apache flink runtime executiongraph failover executionfailurehandler handlefailure executionfailurehandler java at org apache flink runtime executiongraph failover executionfailurehandler getfailurehandlingresult executionfailurehandler java at org apache flink runtime scheduler defaultscheduler handletaskfailure defaultscheduler java at org apache flink runtime scheduler defaultscheduler maybehandletaskfailure defaultscheduler java at org apache flink runtime scheduler defaultscheduler updatetaskexecutionstateinternal defaultscheduler java at org apache flink runtime scheduler schedulerbase updatetaskexecutionstate schedulerbase java at org apache flink runtime scheduler schedulerng updatetaskexecutionstate schedulerng java at org apache flink runtime jobmaster jobmaster updatetaskexecutionstate jobmaster java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org apache flink runtime rpc akka akkarpcactor handlerpcinvocation akkarpcactor java at org apache flink runtime rpc akka akkarpcactor handlerpcmessage akkarpcactor java at org apache flink runtime rpc akka fencedakkarpcactor handlerpcmessage fencedakkarpcactor java at org apache flink runtime rpc akka akkarpcactor handlemessage akkarpcactor java at akka japi pf unitcasestatement apply casestatements scala at akka japi pf unitcasestatement apply casestatements scala at scala partialfunction applyorelse partialfunction scala at scala partialfunction applyorelse partialfunction scala at akka japi pf unitcasestatement applyorelse casestatements scala at scala partialfunction orelse applyorelse partialfunction scala at scala partialfunction orelse applyorelse partialfunction scala at scala partialfunction orelse applyorelse partialfunction scala at akka actor actor aroundreceive actor scala at akka actor actor aroundreceive actor scala at akka actor abstractactor aroundreceive abstractactor scala at akka actor actorcell receivemessage actorcell scala at akka actor actorcell invoke actorcell scala at akka dispatch mailbox processmailbox mailbox scala at akka dispatch mailbox run mailbox scala at akka dispatch mailbox exec mailbox scala at akka dispatch forkjoin forkjointask doexec forkjointask java at akka dispatch forkjoin forkjoinpool workqueue runtask forkjoinpool java at akka dispatch forkjoin forkjoinpool runworker forkjoinpool java at akka dispatch forkjoin forkjoinworkerthread run forkjoinworkerthread java caused by java lang noclassdeffounderror could not initialize class org apache beam runners core construction serializablepipelineoptions at java io objectstreamclass hasstaticinitializer native method at java io objectstreamclass computedefaultsuid objectstreamclass java at java io objectstreamclass access objectstreamclass java at java io objectstreamclass run objectstreamclass java at java io objectstreamclass run objectstreamclass java at java security accesscontroller doprivileged native method at java io objectstreamclass getserialversionuid objectstreamclass java at java io objectstreamclass initnonproxy objectstreamclass java at java io objectinputstream readnonproxydesc objectinputstream java at java io objectinputstream readclassdesc objectinputstream java at java io objectinputstream readordinaryobject objectinputstream java at java io objectinputstream objectinputstream java at java io objectinputstream defaultreadfields objectinputstream java at java io objectinputstream readserialdata objectinputstream java at java io objectinputstream readordinaryobject objectinputstream java at java io objectinputstream objectinputstream java at java io objectinputstream readobject objectinputstream java at java io objectinputstream readobject objectinputstream java at org apache flink util instantiationutil deserializeobject instantiationutil java at org apache flink util instantiationutil deserializeobject instantiationutil java at org apache flink util instantiationutil deserializeobject instantiationutil java at org apache flink util instantiationutil readobjectfromconfig instantiationutil java at org apache flink api java typeutils runtime runtimeserializerfactory readparametersfromconfig runtimeserializerfactory java at org apache flink runtime operators util taskconfig gettypeserializerfactory taskconfig java at org apache flink runtime operators util taskconfig getoutputserializer taskconfig java at org apache flink runtime operators datasourcetask initinputformat datasourcetask java at org apache flink runtime operators datasourcetask invoke datasourcetask java at org apache flink runtime taskmanager task dorun task java at org apache flink runtime taskmanager task run task java at java lang thread run thread java java lang noclassdeffounderror could not initialize class org apache beam runners core construction serializablepipelineoptions job state failed failed to execute job job root failed panic failed to execute job job root failed goroutine github com apache beam sdks go pkg beam log fatalf var jenkins real home workspace beam loadtests go pardo flink batch src sdks go pkg beam log log go main main var jenkins real home workspace beam loadtests go pardo flink batch src sdks go test load pardo pardo go task sdks go test load run failed imported from jira reported by andoni guzman
| 1
|
289,349
| 24,981,222,866
|
IssuesEvent
|
2022-11-02 11:52:13
|
abbbi/virtnbdbackup
|
https://api.github.com/repos/abbbi/virtnbdbackup
|
closed
|
Make it possible to add compression level during backup
|
Needs-testing feature-request fixed-in-dev
|
### Discussed in https://github.com/abbbi/virtnbdbackup/discussions/75
<div type='discussions-op-text'>
<sup>Originally posted by **GeorgiaM-honestly** November 1, 2022</sup>
Hello,
Is it possible to use a higher lz4 compression level? My destination is fairly slow so it makes sense in my use case to use heavier compression. I would like to use lz4's -8 option if possible.</div>
|
1.0
|
Make it possible to add compression level during backup - ### Discussed in https://github.com/abbbi/virtnbdbackup/discussions/75
<div type='discussions-op-text'>
<sup>Originally posted by **GeorgiaM-honestly** November 1, 2022</sup>
Hello,
Is it possible to use a higher lz4 compression level? My destination is fairly slow so it makes sense in my use case to use heavier compression. I would like to use lz4's -8 option if possible.</div>
|
test
|
make it possible to add compression level during backup discussed in originally posted by georgiam honestly november hello is it possible to use a higher compression level my destination is fairly slow so it makes sense in my use case to use heavier compression i would like to use s option if possible
| 1
|
45,531
| 5,718,985,837
|
IssuesEvent
|
2017-04-19 20:51:12
|
googleapis/artman
|
https://api.github.com/repos/googleapis/artman
|
closed
|
Fix build failures, lint test/ directory
|
testing
|
After #44 or #45 is merged, we will not be pylint'ing the test directory in order to fix a build failure. In fact, we may not have been pylint'ing the test directory previously. In any case, we should fix this.
|
1.0
|
Fix build failures, lint test/ directory - After #44 or #45 is merged, we will not be pylint'ing the test directory in order to fix a build failure. In fact, we may not have been pylint'ing the test directory previously. In any case, we should fix this.
|
test
|
fix build failures lint test directory after or is merged we will not be pylint ing the test directory in order to fix a build failure in fact we may not have been pylint ing the test directory previously in any case we should fix this
| 1
|
262,669
| 27,985,181,024
|
IssuesEvent
|
2023-03-26 16:06:41
|
ZSBRybnik/frontend
|
https://api.github.com/repos/ZSBRybnik/frontend
|
closed
|
npm-check-5.9.2.tgz: 2 vulnerabilities (highest severity is: 7.5)
|
Mend: dependency security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>npm-check-5.9.2.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/trim-newlines/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/ZSBRybnik/frontend/commit/273a134394edfb54991ff74097965c8f3cac3de7">273a134394edfb54991ff74097965c8f3cac3de7</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (npm-check version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-33623](https://www.mend.io/vulnerability-database/CVE-2021-33623) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | trim-newlines-1.0.0.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-33987](https://www.mend.io/vulnerability-database/CVE-2022-33987) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | got-6.7.1.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-33623</summary>
### Vulnerable Library - <b>trim-newlines-1.0.0.tgz</b></p>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/trim-newlines/package.json</p>
<p>
Dependency Hierarchy:
- npm-check-5.9.2.tgz (Root Library)
- meow-3.7.0.tgz
- :x: **trim-newlines-1.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ZSBRybnik/frontend/commit/273a134394edfb54991ff74097965c8f3cac3de7">273a134394edfb54991ff74097965c8f3cac3de7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-33623>CVE-2021-33623</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: trim-newlines - 3.0.1, 4.0.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-33987</summary>
### Vulnerable Library - <b>got-6.7.1.tgz</b></p>
<p>Simplified HTTP requests</p>
<p>Library home page: <a href="https://registry.npmjs.org/got/-/got-6.7.1.tgz">https://registry.npmjs.org/got/-/got-6.7.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/got/package.json</p>
<p>
Dependency Hierarchy:
- npm-check-5.9.2.tgz (Root Library)
- package-json-4.0.1.tgz
- :x: **got-6.7.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ZSBRybnik/frontend/commit/273a134394edfb54991ff74097965c8f3cac3de7">273a134394edfb54991ff74097965c8f3cac3de7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The got package before 12.1.0 (also fixed in 11.8.5) for Node.js allows a redirect to a UNIX socket.
<p>Publish Date: 2022-06-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-33987>CVE-2022-33987</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987</a></p>
<p>Release Date: 2022-06-18</p>
<p>Fix Resolution: got - 11.8.5,12.1.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
True
|
npm-check-5.9.2.tgz: 2 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>npm-check-5.9.2.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/trim-newlines/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/ZSBRybnik/frontend/commit/273a134394edfb54991ff74097965c8f3cac3de7">273a134394edfb54991ff74097965c8f3cac3de7</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (npm-check version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-33623](https://www.mend.io/vulnerability-database/CVE-2021-33623) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | trim-newlines-1.0.0.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-33987](https://www.mend.io/vulnerability-database/CVE-2022-33987) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | got-6.7.1.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-33623</summary>
### Vulnerable Library - <b>trim-newlines-1.0.0.tgz</b></p>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/trim-newlines/package.json</p>
<p>
Dependency Hierarchy:
- npm-check-5.9.2.tgz (Root Library)
- meow-3.7.0.tgz
- :x: **trim-newlines-1.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ZSBRybnik/frontend/commit/273a134394edfb54991ff74097965c8f3cac3de7">273a134394edfb54991ff74097965c8f3cac3de7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-33623>CVE-2021-33623</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: trim-newlines - 3.0.1, 4.0.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-33987</summary>
### Vulnerable Library - <b>got-6.7.1.tgz</b></p>
<p>Simplified HTTP requests</p>
<p>Library home page: <a href="https://registry.npmjs.org/got/-/got-6.7.1.tgz">https://registry.npmjs.org/got/-/got-6.7.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/got/package.json</p>
<p>
Dependency Hierarchy:
- npm-check-5.9.2.tgz (Root Library)
- package-json-4.0.1.tgz
- :x: **got-6.7.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ZSBRybnik/frontend/commit/273a134394edfb54991ff74097965c8f3cac3de7">273a134394edfb54991ff74097965c8f3cac3de7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The got package before 12.1.0 (also fixed in 11.8.5) for Node.js allows a redirect to a UNIX socket.
<p>Publish Date: 2022-06-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-33987>CVE-2022-33987</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987</a></p>
<p>Release Date: 2022-06-18</p>
<p>Fix Resolution: got - 11.8.5,12.1.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
non_test
|
npm check tgz vulnerabilities highest severity is vulnerable library npm check tgz path to dependency file package json path to vulnerable library node modules trim newlines package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in npm check version remediation available high trim newlines tgz transitive n a medium got tgz transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the details section below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library trim newlines tgz trim newlines from the start and or end of a string library home page a href path to dependency file package json path to vulnerable library node modules trim newlines package json dependency hierarchy npm check tgz root library meow tgz x trim newlines tgz vulnerable library found in head commit a href found in base branch master vulnerability details the trim newlines package before and x before for node js has an issue related to regular expression denial of service redos for the end method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution trim newlines step up your open source security game with mend cve vulnerable library got tgz simplified http requests library home page a href path to dependency file package json path to vulnerable library node modules got package json dependency hierarchy npm check tgz root library package json tgz x got tgz vulnerable library found in head commit a href found in base branch master vulnerability details the got package before also fixed in for node js allows a redirect to a unix socket publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution got step up your open source security game with mend
| 0
|
183,382
| 31,394,840,417
|
IssuesEvent
|
2023-08-26 20:03:59
|
readthedocs/readthedocs.org
|
https://api.github.com/repos/readthedocs/readthedocs.org
|
closed
|
Set `edit_uri` option on Mkdocs projects for better integration
|
Needed: design decision
|
## Details
* Read the Docs project URL: https://nodemcu.readthedocs.io and **https://docs.readthedocs.io**
* Build URL (if applicable):
* Read the Docs username (if applicable):
## Expected Result
The "Edit on GitHub" **top right** should take you to the page on GitHub _on the selected branch_ and open it for editing (requires GH authentication).
## Actual Result
### For MkDocs projects
Regardless of which branch you selected it always links to the `master` branch - which might not even have that page. Examples:
- https://nodemcu.readthedocs.io/en/dev-esp32/en/modules/bthci/ links to https://github.com/nodemcu/nodemcu-firmware/edit/master/docs/en/modules/bthci.md -> **404 as the file doesn't exist there**
- https://nodemcu.readthedocs.io/en/latest/en/getting-started/ links to https://github.com/nodemcu/nodemcu-firmware/edit/master/docs/en/getting-started.md -> **wrong as "latest" is configured to be the `dev` branch rather than `master`**
### For RTD itself
As far as I can tell there's only a problem with the "stable" alias. However, that might be because there are only stable and latest.
- https://docs.readthedocs.io/en/stable/ links to https://github.com/rtfd/readthedocs.org/blob/16be3aed72f87b5d1228bdd442c271b2c5912124/home/docs/checkouts/readthedocs.org/user_builds/docs/checkouts/stable/docs/conf.py/index.rst -> **404**
## Side note
Similar issues have existed for the "branch selector" for quite some time (fly-out or dropdown bottom right) but there are other issues for that AFAIR.
|
1.0
|
Set `edit_uri` option on Mkdocs projects for better integration - ## Details
* Read the Docs project URL: https://nodemcu.readthedocs.io and **https://docs.readthedocs.io**
* Build URL (if applicable):
* Read the Docs username (if applicable):
## Expected Result
The "Edit on GitHub" **top right** should take you to the page on GitHub _on the selected branch_ and open it for editing (requires GH authentication).
## Actual Result
### For MkDocs projects
Regardless of which branch you selected it always links to the `master` branch - which might not even have that page. Examples:
- https://nodemcu.readthedocs.io/en/dev-esp32/en/modules/bthci/ links to https://github.com/nodemcu/nodemcu-firmware/edit/master/docs/en/modules/bthci.md -> **404 as the file doesn't exist there**
- https://nodemcu.readthedocs.io/en/latest/en/getting-started/ links to https://github.com/nodemcu/nodemcu-firmware/edit/master/docs/en/getting-started.md -> **wrong as "latest" is configured to be the `dev` branch rather than `master`**
### For RTD itself
As far as I can tell there's only a problem with the "stable" alias. However, that might be because there are only stable and latest.
- https://docs.readthedocs.io/en/stable/ links to https://github.com/rtfd/readthedocs.org/blob/16be3aed72f87b5d1228bdd442c271b2c5912124/home/docs/checkouts/readthedocs.org/user_builds/docs/checkouts/stable/docs/conf.py/index.rst -> **404**
## Side note
Similar issues have existed for the "branch selector" for quite some time (fly-out or dropdown bottom right) but there are other issues for that AFAIR.
|
non_test
|
set edit uri option on mkdocs projects for better integration details read the docs project url and build url if applicable read the docs username if applicable expected result the edit on github top right should take you to the page on github on the selected branch and open it for editing requires gh authentication actual result for mkdocs projects regardless of which branch you selected it always links to the master branch which might not even have that page examples links to as the file doesn t exist there links to wrong as latest is configured to be the dev branch rather than master for rtd itself as far as i can tell there s only a problem with the stable alias however that might be because there are only stable and latest links to side note similar issues have existed for the branch selector for quite some time fly out or dropdown bottom right but there are other issues for that afair
| 0
|
164,940
| 12,822,976,700
|
IssuesEvent
|
2020-07-06 10:48:07
|
quarkusio/quarkus
|
https://api.github.com/repos/quarkusio/quarkus
|
closed
|
Random test port stopped working in 1.6.0.Final
|
area/testing kind/bug
|
**Describe the bug**
Configuring `%test.quarkus.http.test-port=0` makes Quarkus start on a free port.
After 1.6.0.Final, tests fail with `java.lang.IllegalArgumentException: Port must be greater than 0`.
**Stacktrace**
```
java.lang.IllegalArgumentException: Port must be greater than 0
at java.base/jdk.internal.reflect.NativeConstructorAccessorImpl.newInstance0(Native Method)
at java.base/jdk.internal.reflect.NativeConstructorAccessorImpl.newInstance(NativeConstructorAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingConstructorAccessorImpl.newInstance(DelegatingConstructorAccessorImpl.java:45)
at java.base/java.lang.reflect.Constructor.newInstanceWithCaller(Constructor.java:500)
at java.base/java.lang.reflect.Constructor.newInstance(Constructor.java:481)
at org.codehaus.groovy.reflection.CachedConstructor.invoke(CachedConstructor.java:72)
at org.codehaus.groovy.runtime.callsite.ConstructorSite$ConstructorSiteNoUnwrapNoCoerce.callConstructor(ConstructorSite.java:105)
at org.codehaus.groovy.runtime.callsite.CallSiteArray.defaultCallConstructor(CallSiteArray.java:59)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callConstructor(AbstractCallSite.java:263)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callConstructor(AbstractCallSite.java:277)
at io.restassured.internal.RequestSpecificationImpl.port(RequestSpecificationImpl.groovy:672)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:564)
at org.codehaus.groovy.reflection.CachedMethod.invoke(CachedMethod.java:107)
at groovy.lang.MetaMethod.doMethodInvoke(MetaMethod.java:323)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:1262)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:1029)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:816)
at groovy.lang.GroovyObject.invokeMethod(GroovyObject.java:39)
at org.codehaus.groovy.runtime.callsite.PogoInterceptableSite.call(PogoInterceptableSite.java:45)
at org.codehaus.groovy.runtime.callsite.PogoInterceptableSite.callCurrent(PogoInterceptableSite.java:55)
at org.codehaus.groovy.runtime.callsite.CallSiteArray.defaultCallCurrent(CallSiteArray.java:51)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callCurrent(AbstractCallSite.java:171)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callCurrent(AbstractCallSite.java:185)
at io.restassured.internal.RequestSpecificationImpl.<init>(RequestSpecificationImpl.groovy:145)
at io.restassured.RestAssured.createTestSpecification(RestAssured.java:1452)
at io.restassured.RestAssured.given(RestAssured.java:653)
at org.acme.ExampleResourceTest.testHelloEndpoint(ExampleResourceTest.java:16)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:564)
at io.quarkus.test.junit.QuarkusTestExtension.runExtensionMethod(QuarkusTestExtension.java:618)
at io.quarkus.test.junit.QuarkusTestExtension.interceptTestMethod(QuarkusTestExtension.java:526)
at org.junit.jupiter.engine.execution.ExecutableInvoker$ReflectiveInterceptorCall.lambda$ofVoidMethod$0(ExecutableInvoker.java:115)
at org.junit.jupiter.engine.execution.ExecutableInvoker.lambda$invoke$0(ExecutableInvoker.java:105)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain$InterceptedInvocation.proceed(InvocationInterceptorChain.java:106)
at org.junit.jupiter.engine.extension.TimeoutExtension.intercept(TimeoutExtension.java:149)
at org.junit.jupiter.engine.extension.TimeoutExtension.interceptTestableMethod(TimeoutExtension.java:140)
at org.junit.jupiter.engine.extension.TimeoutExtension.interceptTestMethod(TimeoutExtension.java:84)
at org.junit.jupiter.engine.execution.ExecutableInvoker$ReflectiveInterceptorCall.lambda$ofVoidMethod$0(ExecutableInvoker.java:115)
at org.junit.jupiter.engine.execution.ExecutableInvoker.lambda$invoke$0(ExecutableInvoker.java:105)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain$InterceptedInvocation.proceed(InvocationInterceptorChain.java:106)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.proceed(InvocationInterceptorChain.java:64)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.chainAndInvoke(InvocationInterceptorChain.java:45)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.invoke(InvocationInterceptorChain.java:37)
at org.junit.jupiter.engine.execution.ExecutableInvoker.invoke(ExecutableInvoker.java:104)
at org.junit.jupiter.engine.execution.ExecutableInvoker.invoke(ExecutableInvoker.java:98)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.lambda$invokeTestMethod$6(TestMethodTestDescriptor.java:212)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.invokeTestMethod(TestMethodTestDescriptor.java:208)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:137)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:71)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:135)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at java.base/java.util.ArrayList.forEach(ArrayList.java:1510)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:139)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at java.base/java.util.ArrayList.forEach(ArrayList.java:1510)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:139)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.submit(SameThreadHierarchicalTestExecutorService.java:32)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestExecutor.execute(HierarchicalTestExecutor.java:57)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestEngine.execute(HierarchicalTestEngine.java:51)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:248)
at org.junit.platform.launcher.core.DefaultLauncher.lambda$execute$5(DefaultLauncher.java:211)
at org.junit.platform.launcher.core.DefaultLauncher.withInterceptedStreams(DefaultLauncher.java:226)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:199)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:132)
at com.intellij.junit5.JUnit5IdeaTestRunner.startRunnerWithArgs(JUnit5IdeaTestRunner.java:71)
at com.intellij.rt.junit.IdeaTestRunner$Repeater.startRunnerWithArgs(IdeaTestRunner.java:33)
at com.intellij.rt.junit.JUnitStarter.prepareStreamsAndStart(JUnitStarter.java:220)
at com.intellij.rt.junit.JUnitStarter.main(JUnitStarter.java:53)
```
**Expected behavior**
The generated port should be propegated to rest-assured correclty.
**To Reproduce**
Steps to reproduce the behavior:
1. checkout https://github.com/arvidvillen/quarkus-test-port
2. mvn package
|
1.0
|
Random test port stopped working in 1.6.0.Final - **Describe the bug**
Configuring `%test.quarkus.http.test-port=0` makes Quarkus start on a free port.
After 1.6.0.Final, tests fail with `java.lang.IllegalArgumentException: Port must be greater than 0`.
**Stacktrace**
```
java.lang.IllegalArgumentException: Port must be greater than 0
at java.base/jdk.internal.reflect.NativeConstructorAccessorImpl.newInstance0(Native Method)
at java.base/jdk.internal.reflect.NativeConstructorAccessorImpl.newInstance(NativeConstructorAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingConstructorAccessorImpl.newInstance(DelegatingConstructorAccessorImpl.java:45)
at java.base/java.lang.reflect.Constructor.newInstanceWithCaller(Constructor.java:500)
at java.base/java.lang.reflect.Constructor.newInstance(Constructor.java:481)
at org.codehaus.groovy.reflection.CachedConstructor.invoke(CachedConstructor.java:72)
at org.codehaus.groovy.runtime.callsite.ConstructorSite$ConstructorSiteNoUnwrapNoCoerce.callConstructor(ConstructorSite.java:105)
at org.codehaus.groovy.runtime.callsite.CallSiteArray.defaultCallConstructor(CallSiteArray.java:59)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callConstructor(AbstractCallSite.java:263)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callConstructor(AbstractCallSite.java:277)
at io.restassured.internal.RequestSpecificationImpl.port(RequestSpecificationImpl.groovy:672)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:564)
at org.codehaus.groovy.reflection.CachedMethod.invoke(CachedMethod.java:107)
at groovy.lang.MetaMethod.doMethodInvoke(MetaMethod.java:323)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:1262)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:1029)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:816)
at groovy.lang.GroovyObject.invokeMethod(GroovyObject.java:39)
at org.codehaus.groovy.runtime.callsite.PogoInterceptableSite.call(PogoInterceptableSite.java:45)
at org.codehaus.groovy.runtime.callsite.PogoInterceptableSite.callCurrent(PogoInterceptableSite.java:55)
at org.codehaus.groovy.runtime.callsite.CallSiteArray.defaultCallCurrent(CallSiteArray.java:51)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callCurrent(AbstractCallSite.java:171)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callCurrent(AbstractCallSite.java:185)
at io.restassured.internal.RequestSpecificationImpl.<init>(RequestSpecificationImpl.groovy:145)
at io.restassured.RestAssured.createTestSpecification(RestAssured.java:1452)
at io.restassured.RestAssured.given(RestAssured.java:653)
at org.acme.ExampleResourceTest.testHelloEndpoint(ExampleResourceTest.java:16)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:564)
at io.quarkus.test.junit.QuarkusTestExtension.runExtensionMethod(QuarkusTestExtension.java:618)
at io.quarkus.test.junit.QuarkusTestExtension.interceptTestMethod(QuarkusTestExtension.java:526)
at org.junit.jupiter.engine.execution.ExecutableInvoker$ReflectiveInterceptorCall.lambda$ofVoidMethod$0(ExecutableInvoker.java:115)
at org.junit.jupiter.engine.execution.ExecutableInvoker.lambda$invoke$0(ExecutableInvoker.java:105)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain$InterceptedInvocation.proceed(InvocationInterceptorChain.java:106)
at org.junit.jupiter.engine.extension.TimeoutExtension.intercept(TimeoutExtension.java:149)
at org.junit.jupiter.engine.extension.TimeoutExtension.interceptTestableMethod(TimeoutExtension.java:140)
at org.junit.jupiter.engine.extension.TimeoutExtension.interceptTestMethod(TimeoutExtension.java:84)
at org.junit.jupiter.engine.execution.ExecutableInvoker$ReflectiveInterceptorCall.lambda$ofVoidMethod$0(ExecutableInvoker.java:115)
at org.junit.jupiter.engine.execution.ExecutableInvoker.lambda$invoke$0(ExecutableInvoker.java:105)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain$InterceptedInvocation.proceed(InvocationInterceptorChain.java:106)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.proceed(InvocationInterceptorChain.java:64)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.chainAndInvoke(InvocationInterceptorChain.java:45)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.invoke(InvocationInterceptorChain.java:37)
at org.junit.jupiter.engine.execution.ExecutableInvoker.invoke(ExecutableInvoker.java:104)
at org.junit.jupiter.engine.execution.ExecutableInvoker.invoke(ExecutableInvoker.java:98)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.lambda$invokeTestMethod$6(TestMethodTestDescriptor.java:212)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.invokeTestMethod(TestMethodTestDescriptor.java:208)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:137)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:71)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:135)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at java.base/java.util.ArrayList.forEach(ArrayList.java:1510)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:139)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at java.base/java.util.ArrayList.forEach(ArrayList.java:1510)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:139)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.submit(SameThreadHierarchicalTestExecutorService.java:32)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestExecutor.execute(HierarchicalTestExecutor.java:57)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestEngine.execute(HierarchicalTestEngine.java:51)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:248)
at org.junit.platform.launcher.core.DefaultLauncher.lambda$execute$5(DefaultLauncher.java:211)
at org.junit.platform.launcher.core.DefaultLauncher.withInterceptedStreams(DefaultLauncher.java:226)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:199)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:132)
at com.intellij.junit5.JUnit5IdeaTestRunner.startRunnerWithArgs(JUnit5IdeaTestRunner.java:71)
at com.intellij.rt.junit.IdeaTestRunner$Repeater.startRunnerWithArgs(IdeaTestRunner.java:33)
at com.intellij.rt.junit.JUnitStarter.prepareStreamsAndStart(JUnitStarter.java:220)
at com.intellij.rt.junit.JUnitStarter.main(JUnitStarter.java:53)
```
**Expected behavior**
The generated port should be propegated to rest-assured correclty.
**To Reproduce**
Steps to reproduce the behavior:
1. checkout https://github.com/arvidvillen/quarkus-test-port
2. mvn package
|
test
|
random test port stopped working in final describe the bug configuring test quarkus http test port makes quarkus start on a free port after final tests fail with java lang illegalargumentexception port must be greater than stacktrace java lang illegalargumentexception port must be greater than at java base jdk internal reflect nativeconstructoraccessorimpl native method at java base jdk internal reflect nativeconstructoraccessorimpl newinstance nativeconstructoraccessorimpl java at java base jdk internal reflect delegatingconstructoraccessorimpl newinstance delegatingconstructoraccessorimpl java at java base java lang reflect constructor newinstancewithcaller constructor java at java base java lang reflect constructor newinstance constructor java at org codehaus groovy reflection cachedconstructor invoke cachedconstructor java at org codehaus groovy runtime callsite constructorsite constructorsitenounwrapnocoerce callconstructor constructorsite java at org codehaus groovy runtime callsite callsitearray defaultcallconstructor callsitearray java at org codehaus groovy runtime callsite abstractcallsite callconstructor abstractcallsite java at org codehaus groovy runtime callsite abstractcallsite callconstructor abstractcallsite java at io restassured internal requestspecificationimpl port requestspecificationimpl groovy at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org codehaus groovy reflection cachedmethod invoke cachedmethod java at groovy lang metamethod domethodinvoke metamethod java at groovy lang metaclassimpl invokemethod metaclassimpl java at groovy lang metaclassimpl invokemethod metaclassimpl java at groovy lang metaclassimpl invokemethod metaclassimpl java at groovy lang groovyobject invokemethod groovyobject java at org codehaus groovy runtime callsite pogointerceptablesite call pogointerceptablesite java at org codehaus groovy runtime callsite pogointerceptablesite callcurrent pogointerceptablesite java at org codehaus groovy runtime callsite callsitearray defaultcallcurrent callsitearray java at org codehaus groovy runtime callsite abstractcallsite callcurrent abstractcallsite java at org codehaus groovy runtime callsite abstractcallsite callcurrent abstractcallsite java at io restassured internal requestspecificationimpl requestspecificationimpl groovy at io restassured restassured createtestspecification restassured java at io restassured restassured given restassured java at org acme exampleresourcetest testhelloendpoint exampleresourcetest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at io quarkus test junit quarkustestextension runextensionmethod quarkustestextension java at io quarkus test junit quarkustestextension intercepttestmethod quarkustestextension java at org junit jupiter engine execution executableinvoker reflectiveinterceptorcall lambda ofvoidmethod executableinvoker java at org junit jupiter engine execution executableinvoker lambda invoke executableinvoker java at org junit jupiter engine execution invocationinterceptorchain interceptedinvocation proceed invocationinterceptorchain java at org junit jupiter engine extension timeoutextension intercept timeoutextension java at org junit jupiter engine extension timeoutextension intercepttestablemethod timeoutextension java at org junit jupiter engine extension timeoutextension intercepttestmethod timeoutextension java at org junit jupiter engine execution executableinvoker reflectiveinterceptorcall lambda ofvoidmethod executableinvoker java at org junit jupiter engine execution executableinvoker lambda invoke executableinvoker java at org junit jupiter engine execution invocationinterceptorchain interceptedinvocation proceed invocationinterceptorchain java at org junit jupiter engine execution invocationinterceptorchain proceed invocationinterceptorchain java at org junit jupiter engine execution invocationinterceptorchain chainandinvoke invocationinterceptorchain java at org junit jupiter engine execution invocationinterceptorchain invoke invocationinterceptorchain java at org junit jupiter engine execution executableinvoker invoke executableinvoker java at org junit jupiter engine execution executableinvoker invoke executableinvoker java at org junit jupiter engine descriptor testmethodtestdescriptor lambda invoketestmethod testmethodtestdescriptor java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit jupiter engine descriptor testmethodtestdescriptor invoketestmethod testmethodtestdescriptor java at org junit jupiter engine descriptor testmethodtestdescriptor execute testmethodtestdescriptor java at org junit jupiter engine descriptor testmethodtestdescriptor execute testmethodtestdescriptor java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical node around node java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask executerecursively nodetesttask java at org junit platform engine support hierarchical nodetesttask execute nodetesttask java at java base java util arraylist foreach arraylist java at org junit platform engine support hierarchical samethreadhierarchicaltestexecutorservice invokeall samethreadhierarchicaltestexecutorservice java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical node around node java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask executerecursively nodetesttask java at org junit platform engine support hierarchical nodetesttask execute nodetesttask java at java base java util arraylist foreach arraylist java at org junit platform engine support hierarchical samethreadhierarchicaltestexecutorservice invokeall samethreadhierarchicaltestexecutorservice java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical node around node java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask executerecursively nodetesttask java at org junit platform engine support hierarchical nodetesttask execute nodetesttask java at org junit platform engine support hierarchical samethreadhierarchicaltestexecutorservice submit samethreadhierarchicaltestexecutorservice java at org junit platform engine support hierarchical hierarchicaltestexecutor execute hierarchicaltestexecutor java at org junit platform engine support hierarchical hierarchicaltestengine execute hierarchicaltestengine java at org junit platform launcher core defaultlauncher execute defaultlauncher java at org junit platform launcher core defaultlauncher lambda execute defaultlauncher java at org junit platform launcher core defaultlauncher withinterceptedstreams defaultlauncher java at org junit platform launcher core defaultlauncher execute defaultlauncher java at org junit platform launcher core defaultlauncher execute defaultlauncher java at com intellij startrunnerwithargs java at com intellij rt junit ideatestrunner repeater startrunnerwithargs ideatestrunner java at com intellij rt junit junitstarter preparestreamsandstart junitstarter java at com intellij rt junit junitstarter main junitstarter java expected behavior the generated port should be propegated to rest assured correclty to reproduce steps to reproduce the behavior checkout mvn package
| 1
|
286,027
| 31,162,942,636
|
IssuesEvent
|
2023-08-16 17:21:32
|
Dima2021/JavaSandbox
|
https://api.github.com/repos/Dima2021/JavaSandbox
|
opened
|
springdoc-openapi-ui-1.6.4.jar: 21 vulnerabilities (highest severity is: 9.8)
|
Mend: dependency security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>springdoc-openapi-ui-1.6.4.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-expression/5.3.14/spring-expression-5.3.14.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (springdoc-openapi-ui version) | Remediation Possible** |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-22965](https://www.mend.io/vulnerability-database/CVE-2022-22965) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | spring-beans-5.3.14.jar | Transitive | 1.6.7 | ✅ |
| [CVE-2022-1471](https://www.mend.io/vulnerability-database/CVE-2022-1471) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2016-1000027](https://www.mend.io/vulnerability-database/CVE-2016-1000027) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | spring-web-5.3.14.jar | Transitive | N/A* | ❌ |
| [CVE-2022-42004](https://www.mend.io/vulnerability-database/CVE-2022-42004) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.12.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-42003](https://www.mend.io/vulnerability-database/CVE-2022-42003) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.12.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-25857](https://www.mend.io/vulnerability-database/CVE-2022-25857) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2023-20883](https://www.mend.io/vulnerability-database/CVE-2023-20883) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | spring-boot-autoconfigure-2.6.2.jar | Transitive | 1.6.9 | ✅ |
| [CVE-2020-36518](https://www.mend.io/vulnerability-database/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.12.1.jar | Transitive | N/A* | ❌ |
| [CVE-2023-20860](https://www.mend.io/vulnerability-database/CVE-2023-20860) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | spring-webmvc-5.3.14.jar | Transitive | 1.7.0 | ✅ |
| [CVE-2021-46877](https://www.mend.io/vulnerability-database/CVE-2021-46877) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.12.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-41854](https://www.mend.io/vulnerability-database/CVE-2022-41854) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2022-22950](https://www.mend.io/vulnerability-database/CVE-2022-22950) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.3.14.jar | Transitive | 1.6.7 | ✅ |
| [CVE-2023-20861](https://www.mend.io/vulnerability-database/CVE-2023-20861) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.3.14.jar | Transitive | 1.7.0 | ✅ |
| [CVE-2022-38752](https://www.mend.io/vulnerability-database/CVE-2022-38752) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38751](https://www.mend.io/vulnerability-database/CVE-2022-38751) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2023-20863](https://www.mend.io/vulnerability-database/CVE-2023-20863) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.3.14.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38749](https://www.mend.io/vulnerability-database/CVE-2022-38749) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [WS-2021-0616](https://github.com/FasterXML/jackson-databind/commit/3ccde7d938fea547e598fdefe9a82cff37fed5cb) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | jackson-databind-2.12.1.jar | Transitive | 1.6.7 | ✅ |
| [CVE-2022-38750](https://www.mend.io/vulnerability-database/CVE-2022-38750) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2022-22968](https://www.mend.io/vulnerability-database/CVE-2022-22968) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | spring-context-5.3.14.jar | Transitive | 1.6.9 | ✅ |
| [CVE-2022-22970](https://www.mend.io/vulnerability-database/CVE-2022-22970) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | detected in multiple dependencies | Transitive | 1.6.9 | ✅ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p><p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2022-22965</summary>
### Vulnerable Library - <b>spring-beans-5.3.14.jar</b></p>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.3.14/spring-beans-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- spring-context-5.3.14.jar
- spring-aop-5.3.14.jar
- :x: **spring-beans-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Spring MVC or Spring WebFlux application running on JDK 9+ may be vulnerable to remote code execution (RCE) via data binding. The specific exploit requires the application to run on Tomcat as a WAR deployment. If the application is deployed as a Spring Boot executable jar, i.e. the default, it is not vulnerable to the exploit. However, the nature of the vulnerability is more general, and there may be other ways to exploit it.
Mend Note: Converted from WS-2022-0107, on 2022-11-07.
<p>Publish Date: 2022-04-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22965>CVE-2022-22965</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement">https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement</a></p>
<p>Release Date: 2022-04-01</p>
<p>Fix Resolution (org.springframework:spring-beans): 5.3.18</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2022-1471</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SnakeYaml's Constructor() class does not restrict types which can be instantiated during deserialization. Deserializing yaml content provided by an attacker can lead to remote code execution. We recommend using SnakeYaml's SafeConsturctor when parsing untrusted content to restrict deserialization. We recommend upgrading to version 2.0 and beyond.
<p>Publish Date: 2022-12-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1471>CVE-2022-1471</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374">https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374</a></p>
<p>Release Date: 2022-12-01</p>
<p>Fix Resolution: org.yaml:snakeyaml:2.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2016-1000027</summary>
### Vulnerable Library - <b>spring-web-5.3.14.jar</b></p>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/5.3.14/spring-web-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- :x: **spring-web-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Pivotal Spring Framework through 5.3.16 suffers from a potential remote code execution (RCE) issue if used for Java deserialization of untrusted data. Depending on how the library is implemented within a product, this issue may or not occur, and authentication may be required. NOTE: the vendor's position is that untrusted data is not an intended use case. The product's behavior will not be changed because some users rely on deserialization of trusted data.
Mend Note: After conducting further research, Mend has determined that all versions of spring-web up to version 6.0.0 are vulnerable to CVE-2016-1000027.
<p>Publish Date: 2020-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1000027>CVE-2016-1000027</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-4wrc-f8pq-fpqp">https://github.com/advisories/GHSA-4wrc-f8pq-fpqp</a></p>
<p>Release Date: 2020-01-02</p>
<p>Fix Resolution: org.springframework:spring-web:6.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-42004</summary>
### Vulnerable Library - <b>jackson-databind-2.12.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.12.1/jackson-databind-2.12.1.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- :x: **jackson-databind-2.12.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.13.4, resource exhaustion can occur because of a lack of a check in BeanDeserializer._deserializeFromArray to prevent use of deeply nested arrays. An application is vulnerable only with certain customized choices for deserialization.
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42004>CVE-2022-42004</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.13.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-42003</summary>
### Vulnerable Library - <b>jackson-databind-2.12.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.12.1/jackson-databind-2.12.1.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- :x: **jackson-databind-2.12.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.14.0-rc1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled. Additional fix version in 2.13.4.1 and 2.12.17.1
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42003>CVE-2022-42003</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.7.1,2.13.4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-25857</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package org.yaml:snakeyaml from 0 and before 1.31 are vulnerable to Denial of Service (DoS) due missing to nested depth limitation for collections.
<p>Publish Date: 2022-08-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25857>CVE-2022-25857</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857</a></p>
<p>Release Date: 2022-08-30</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2023-20883</summary>
### Vulnerable Library - <b>spring-boot-autoconfigure-2.6.2.jar</b></p>
<p>Spring Boot AutoConfigure</p>
<p>Library home page: <a href="https://spring.io/projects/spring-boot">https://spring.io/projects/spring-boot</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot-autoconfigure/2.6.2/spring-boot-autoconfigure-2.6.2.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- :x: **spring-boot-autoconfigure-2.6.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Boot versions 3.0.0 - 3.0.6, 2.7.0 - 2.7.11, 2.6.0 - 2.6.14, 2.5.0 - 2.5.14 and older unsupported versions, there is potential for a denial-of-service (DoS) attack if Spring MVC is used together with a reverse proxy cache.
<p>Publish Date: 2023-05-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20883>CVE-2023-20883</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2023-20883">https://spring.io/security/cve-2023-20883</a></p>
<p>Release Date: 2023-05-26</p>
<p>Fix Resolution (org.springframework.boot:spring-boot-autoconfigure): 2.6.15</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.9</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-36518</summary>
### Vulnerable Library - <b>jackson-databind-2.12.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.12.1/jackson-databind-2.12.1.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- :x: **jackson-databind-2.12.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind before 2.13.0 allows a Java StackOverflow exception and denial of service via a large depth of nested objects.
Mend Note: After conducting further research, Mend has determined that all versions of com.fasterxml.jackson.core:jackson-databind up to version 2.13.2 are vulnerable to CVE-2020-36518.
<p>Publish Date: 2022-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-36518>CVE-2020-36518</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-03-11</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6.1,2.13.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2023-20860</summary>
### Vulnerable Library - <b>spring-webmvc-5.3.14.jar</b></p>
<p>Spring Web MVC</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-webmvc/5.3.14/spring-webmvc-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- :x: **spring-webmvc-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Framework running version 6.0.0 - 6.0.6 or 5.3.0 - 5.3.25 using "**" as a pattern in Spring Security configuration with the mvcRequestMatcher creates a mismatch in pattern matching between Spring Security and Spring MVC, and the potential for a security bypass.
<p>Publish Date: 2023-03-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20860>CVE-2023-20860</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/blog/2023/03/21/this-week-in-spring-march-21st-2023/">https://spring.io/blog/2023/03/21/this-week-in-spring-march-21st-2023/</a></p>
<p>Release Date: 2023-03-27</p>
<p>Fix Resolution (org.springframework:spring-webmvc): 5.3.26</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.7.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-46877</summary>
### Vulnerable Library - <b>jackson-databind-2.12.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.12.1/jackson-databind-2.12.1.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- :x: **jackson-databind-2.12.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind 2.10.x through 2.12.x before 2.12.6 and 2.13.x before 2.13.1 allows attackers to cause a denial of service (2 GB transient heap usage per read) in uncommon situations involving JsonNode JDK serialization.
<p>Publish Date: 2023-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-46877>CVE-2021-46877</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-46877">https://www.cve.org/CVERecord?id=CVE-2021-46877</a></p>
<p>Release Date: 2023-03-18</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6,2.13.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-41854</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Those using Snakeyaml to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stack overflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-11-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41854>CVE-2022-41854</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/531/">https://bitbucket.org/snakeyaml/snakeyaml/issues/531/</a></p>
<p>Release Date: 2022-11-11</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.32</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-22950</summary>
### Vulnerable Library - <b>spring-expression-5.3.14.jar</b></p>
<p>Spring Expression Language (SpEL)</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-expression/5.3.14/spring-expression-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- spring-context-5.3.14.jar
- :x: **spring-expression-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
n Spring Framework versions 5.3.0 - 5.3.16 and older unsupported versions, it is possible for a user to provide a specially crafted SpEL expression that may cause a denial of service condition.
<p>Publish Date: 2022-04-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22950>CVE-2022-22950</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22950">https://tanzu.vmware.com/security/cve-2022-22950</a></p>
<p>Release Date: 2022-04-01</p>
<p>Fix Resolution (org.springframework:spring-expression): 5.3.17</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2023-20861</summary>
### Vulnerable Library - <b>spring-expression-5.3.14.jar</b></p>
<p>Spring Expression Language (SpEL)</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-expression/5.3.14/spring-expression-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- spring-context-5.3.14.jar
- :x: **spring-expression-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Framework versions 6.0.0 - 6.0.6, 5.3.0 - 5.3.25, 5.2.0.RELEASE - 5.2.22.RELEASE, and older unsupported versions, it is possible for a user to provide a specially crafted SpEL expression that may cause a denial-of-service (DoS) condition.
<p>Publish Date: 2023-03-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20861>CVE-2023-20861</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2023-20861">https://spring.io/security/cve-2023-20861</a></p>
<p>Release Date: 2023-03-23</p>
<p>Fix Resolution (org.springframework:spring-expression): 5.3.26</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.7.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-38752</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stack-overflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38752>CVE-2022-38752</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9w3m-gqgf-c4p9">https://github.com/advisories/GHSA-9w3m-gqgf-c4p9</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.32
</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-38751</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38751>CVE-2022-38751</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47039">https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47039</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2023-20863</summary>
### Vulnerable Library - <b>spring-expression-5.3.14.jar</b></p>
<p>Spring Expression Language (SpEL)</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-expression/5.3.14/spring-expression-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- spring-context-5.3.14.jar
- :x: **spring-expression-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In spring framework versions prior to 5.2.24 release+ ,5.3.27+ and 6.0.8+ , it is possible for a user to provide a specially crafted SpEL expression that may cause a denial-of-service (DoS) condition.
<p>Publish Date: 2023-04-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20863>CVE-2023-20863</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2023-20863">https://spring.io/security/cve-2023-20863</a></p>
<p>Release Date: 2023-04-13</p>
<p>Fix Resolution: org.springframework:spring-expression - 5.2.24.RELEASE,5.3.27,6.0.8</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-38749</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38749>CVE-2022-38749</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/526/stackoverflow-oss-fuzz-47027">https://bitbucket.org/snakeyaml/snakeyaml/issues/526/stackoverflow-oss-fuzz-47027</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> WS-2021-0616</summary>
### Vulnerable Library - <b>jackson-databind-2.12.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.12.1/jackson-databind-2.12.1.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- :x: **jackson-databind-2.12.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind before 2.12.6 and 2.13.1 there is DoS when using JDK serialization to serialize JsonNode.
<p>Publish Date: 2021-11-20
<p>URL: <a href=https://github.com/FasterXML/jackson-databind/commit/3ccde7d938fea547e598fdefe9a82cff37fed5cb>WS-2021-0616</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-11-20</p>
<p>Fix Resolution (com.fasterxml.jackson.core:jackson-databind): 2.12.2</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-38750</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38750>CVE-2022-38750</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47027">https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47027</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-22968</summary>
### Vulnerable Library - <b>spring-context-5.3.14.jar</b></p>
<p>Spring Context</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-context/5.3.14/spring-context-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- :x: **spring-context-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Framework versions 5.3.0 - 5.3.18, 5.2.0 - 5.2.20, and older unsupported versions, the patterns for disallowedFields on a DataBinder are case sensitive which means a field is not effectively protected unless it is listed with both upper and lower case for the first character of the field, including upper and lower case for the first character of all nested fields within the property path.
<p>Publish Date: 2022-04-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22968>CVE-2022-22968</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22968">https://tanzu.vmware.com/security/cve-2022-22968</a></p>
<p>Release Date: 2022-04-14</p>
<p>Fix Resolution (org.springframework:spring-context): 5.3.19</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.9</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-22970</summary>
### Vulnerable Libraries - <b>spring-beans-5.3.14.jar</b>, <b>spring-core-5.3.14.jar</b></p>
<p>
### <b>spring-beans-5.3.14.jar</b></p>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.3.14/spring-beans-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- spring-context-5.3.14.jar
- spring-aop-5.3.14.jar
- :x: **spring-beans-5.3.14.jar** (Vulnerable Library)
### <b>spring-core-5.3.14.jar</b></p>
<p>Spring Core</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-core/5.3.14/spring-core-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- :x: **spring-core-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In spring framework versions prior to 5.3.20+ , 5.2.22+ and old unsupported versions, applications that handle file uploads are vulnerable to DoS attack if they rely on data binding to set a MultipartFile or javax.servlet.Part to a field in a model object.
<p>Publish Date: 2022-05-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22970>CVE-2022-22970</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22970">https://tanzu.vmware.com/security/cve-2022-22970</a></p>
<p>Release Date: 2022-05-12</p>
<p>Fix Resolution (org.springframework:spring-beans): 5.3.20</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.9</p><p>Fix Resolution (org.springframework:spring-core): 5.3.20</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.9</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details>
***
<p>In order to enable automatic remediation for this issue, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
|
True
|
springdoc-openapi-ui-1.6.4.jar: 21 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>springdoc-openapi-ui-1.6.4.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-expression/5.3.14/spring-expression-5.3.14.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (springdoc-openapi-ui version) | Remediation Possible** |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-22965](https://www.mend.io/vulnerability-database/CVE-2022-22965) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | spring-beans-5.3.14.jar | Transitive | 1.6.7 | ✅ |
| [CVE-2022-1471](https://www.mend.io/vulnerability-database/CVE-2022-1471) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2016-1000027](https://www.mend.io/vulnerability-database/CVE-2016-1000027) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | spring-web-5.3.14.jar | Transitive | N/A* | ❌ |
| [CVE-2022-42004](https://www.mend.io/vulnerability-database/CVE-2022-42004) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.12.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-42003](https://www.mend.io/vulnerability-database/CVE-2022-42003) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.12.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-25857](https://www.mend.io/vulnerability-database/CVE-2022-25857) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2023-20883](https://www.mend.io/vulnerability-database/CVE-2023-20883) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | spring-boot-autoconfigure-2.6.2.jar | Transitive | 1.6.9 | ✅ |
| [CVE-2020-36518](https://www.mend.io/vulnerability-database/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.12.1.jar | Transitive | N/A* | ❌ |
| [CVE-2023-20860](https://www.mend.io/vulnerability-database/CVE-2023-20860) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | spring-webmvc-5.3.14.jar | Transitive | 1.7.0 | ✅ |
| [CVE-2021-46877](https://www.mend.io/vulnerability-database/CVE-2021-46877) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.12.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-41854](https://www.mend.io/vulnerability-database/CVE-2022-41854) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2022-22950](https://www.mend.io/vulnerability-database/CVE-2022-22950) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.3.14.jar | Transitive | 1.6.7 | ✅ |
| [CVE-2023-20861](https://www.mend.io/vulnerability-database/CVE-2023-20861) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.3.14.jar | Transitive | 1.7.0 | ✅ |
| [CVE-2022-38752](https://www.mend.io/vulnerability-database/CVE-2022-38752) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38751](https://www.mend.io/vulnerability-database/CVE-2022-38751) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2023-20863](https://www.mend.io/vulnerability-database/CVE-2023-20863) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.3.14.jar | Transitive | N/A* | ❌ |
| [CVE-2022-38749](https://www.mend.io/vulnerability-database/CVE-2022-38749) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [WS-2021-0616](https://github.com/FasterXML/jackson-databind/commit/3ccde7d938fea547e598fdefe9a82cff37fed5cb) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | jackson-databind-2.12.1.jar | Transitive | 1.6.7 | ✅ |
| [CVE-2022-38750](https://www.mend.io/vulnerability-database/CVE-2022-38750) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | snakeyaml-1.27.jar | Transitive | N/A* | ❌ |
| [CVE-2022-22968](https://www.mend.io/vulnerability-database/CVE-2022-22968) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | spring-context-5.3.14.jar | Transitive | 1.6.9 | ✅ |
| [CVE-2022-22970](https://www.mend.io/vulnerability-database/CVE-2022-22970) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | detected in multiple dependencies | Transitive | 1.6.9 | ✅ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p><p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2022-22965</summary>
### Vulnerable Library - <b>spring-beans-5.3.14.jar</b></p>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.3.14/spring-beans-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- spring-context-5.3.14.jar
- spring-aop-5.3.14.jar
- :x: **spring-beans-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Spring MVC or Spring WebFlux application running on JDK 9+ may be vulnerable to remote code execution (RCE) via data binding. The specific exploit requires the application to run on Tomcat as a WAR deployment. If the application is deployed as a Spring Boot executable jar, i.e. the default, it is not vulnerable to the exploit. However, the nature of the vulnerability is more general, and there may be other ways to exploit it.
Mend Note: Converted from WS-2022-0107, on 2022-11-07.
<p>Publish Date: 2022-04-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22965>CVE-2022-22965</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement">https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement</a></p>
<p>Release Date: 2022-04-01</p>
<p>Fix Resolution (org.springframework:spring-beans): 5.3.18</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2022-1471</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SnakeYaml's Constructor() class does not restrict types which can be instantiated during deserialization. Deserializing yaml content provided by an attacker can lead to remote code execution. We recommend using SnakeYaml's SafeConsturctor when parsing untrusted content to restrict deserialization. We recommend upgrading to version 2.0 and beyond.
<p>Publish Date: 2022-12-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1471>CVE-2022-1471</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374">https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374</a></p>
<p>Release Date: 2022-12-01</p>
<p>Fix Resolution: org.yaml:snakeyaml:2.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2016-1000027</summary>
### Vulnerable Library - <b>spring-web-5.3.14.jar</b></p>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/5.3.14/spring-web-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- :x: **spring-web-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Pivotal Spring Framework through 5.3.16 suffers from a potential remote code execution (RCE) issue if used for Java deserialization of untrusted data. Depending on how the library is implemented within a product, this issue may or not occur, and authentication may be required. NOTE: the vendor's position is that untrusted data is not an intended use case. The product's behavior will not be changed because some users rely on deserialization of trusted data.
Mend Note: After conducting further research, Mend has determined that all versions of spring-web up to version 6.0.0 are vulnerable to CVE-2016-1000027.
<p>Publish Date: 2020-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1000027>CVE-2016-1000027</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-4wrc-f8pq-fpqp">https://github.com/advisories/GHSA-4wrc-f8pq-fpqp</a></p>
<p>Release Date: 2020-01-02</p>
<p>Fix Resolution: org.springframework:spring-web:6.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-42004</summary>
### Vulnerable Library - <b>jackson-databind-2.12.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.12.1/jackson-databind-2.12.1.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- :x: **jackson-databind-2.12.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.13.4, resource exhaustion can occur because of a lack of a check in BeanDeserializer._deserializeFromArray to prevent use of deeply nested arrays. An application is vulnerable only with certain customized choices for deserialization.
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42004>CVE-2022-42004</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.13.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-42003</summary>
### Vulnerable Library - <b>jackson-databind-2.12.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.12.1/jackson-databind-2.12.1.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- :x: **jackson-databind-2.12.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.14.0-rc1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled. Additional fix version in 2.13.4.1 and 2.12.17.1
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42003>CVE-2022-42003</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.7.1,2.13.4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-25857</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package org.yaml:snakeyaml from 0 and before 1.31 are vulnerable to Denial of Service (DoS) due missing to nested depth limitation for collections.
<p>Publish Date: 2022-08-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25857>CVE-2022-25857</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857</a></p>
<p>Release Date: 2022-08-30</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2023-20883</summary>
### Vulnerable Library - <b>spring-boot-autoconfigure-2.6.2.jar</b></p>
<p>Spring Boot AutoConfigure</p>
<p>Library home page: <a href="https://spring.io/projects/spring-boot">https://spring.io/projects/spring-boot</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot-autoconfigure/2.6.2/spring-boot-autoconfigure-2.6.2.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- :x: **spring-boot-autoconfigure-2.6.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Boot versions 3.0.0 - 3.0.6, 2.7.0 - 2.7.11, 2.6.0 - 2.6.14, 2.5.0 - 2.5.14 and older unsupported versions, there is potential for a denial-of-service (DoS) attack if Spring MVC is used together with a reverse proxy cache.
<p>Publish Date: 2023-05-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20883>CVE-2023-20883</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2023-20883">https://spring.io/security/cve-2023-20883</a></p>
<p>Release Date: 2023-05-26</p>
<p>Fix Resolution (org.springframework.boot:spring-boot-autoconfigure): 2.6.15</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.9</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-36518</summary>
### Vulnerable Library - <b>jackson-databind-2.12.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.12.1/jackson-databind-2.12.1.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- :x: **jackson-databind-2.12.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind before 2.13.0 allows a Java StackOverflow exception and denial of service via a large depth of nested objects.
Mend Note: After conducting further research, Mend has determined that all versions of com.fasterxml.jackson.core:jackson-databind up to version 2.13.2 are vulnerable to CVE-2020-36518.
<p>Publish Date: 2022-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-36518>CVE-2020-36518</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-03-11</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6.1,2.13.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2023-20860</summary>
### Vulnerable Library - <b>spring-webmvc-5.3.14.jar</b></p>
<p>Spring Web MVC</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-webmvc/5.3.14/spring-webmvc-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- :x: **spring-webmvc-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Framework running version 6.0.0 - 6.0.6 or 5.3.0 - 5.3.25 using "**" as a pattern in Spring Security configuration with the mvcRequestMatcher creates a mismatch in pattern matching between Spring Security and Spring MVC, and the potential for a security bypass.
<p>Publish Date: 2023-03-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20860>CVE-2023-20860</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/blog/2023/03/21/this-week-in-spring-march-21st-2023/">https://spring.io/blog/2023/03/21/this-week-in-spring-march-21st-2023/</a></p>
<p>Release Date: 2023-03-27</p>
<p>Fix Resolution (org.springframework:spring-webmvc): 5.3.26</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.7.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-46877</summary>
### Vulnerable Library - <b>jackson-databind-2.12.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.12.1/jackson-databind-2.12.1.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- :x: **jackson-databind-2.12.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind 2.10.x through 2.12.x before 2.12.6 and 2.13.x before 2.13.1 allows attackers to cause a denial of service (2 GB transient heap usage per read) in uncommon situations involving JsonNode JDK serialization.
<p>Publish Date: 2023-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-46877>CVE-2021-46877</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-46877">https://www.cve.org/CVERecord?id=CVE-2021-46877</a></p>
<p>Release Date: 2023-03-18</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6,2.13.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-41854</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Those using Snakeyaml to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stack overflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-11-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41854>CVE-2022-41854</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/531/">https://bitbucket.org/snakeyaml/snakeyaml/issues/531/</a></p>
<p>Release Date: 2022-11-11</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.32</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-22950</summary>
### Vulnerable Library - <b>spring-expression-5.3.14.jar</b></p>
<p>Spring Expression Language (SpEL)</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-expression/5.3.14/spring-expression-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- spring-context-5.3.14.jar
- :x: **spring-expression-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
n Spring Framework versions 5.3.0 - 5.3.16 and older unsupported versions, it is possible for a user to provide a specially crafted SpEL expression that may cause a denial of service condition.
<p>Publish Date: 2022-04-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22950>CVE-2022-22950</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22950">https://tanzu.vmware.com/security/cve-2022-22950</a></p>
<p>Release Date: 2022-04-01</p>
<p>Fix Resolution (org.springframework:spring-expression): 5.3.17</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2023-20861</summary>
### Vulnerable Library - <b>spring-expression-5.3.14.jar</b></p>
<p>Spring Expression Language (SpEL)</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-expression/5.3.14/spring-expression-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- spring-context-5.3.14.jar
- :x: **spring-expression-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Framework versions 6.0.0 - 6.0.6, 5.3.0 - 5.3.25, 5.2.0.RELEASE - 5.2.22.RELEASE, and older unsupported versions, it is possible for a user to provide a specially crafted SpEL expression that may cause a denial-of-service (DoS) condition.
<p>Publish Date: 2023-03-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20861>CVE-2023-20861</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2023-20861">https://spring.io/security/cve-2023-20861</a></p>
<p>Release Date: 2023-03-23</p>
<p>Fix Resolution (org.springframework:spring-expression): 5.3.26</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.7.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-38752</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stack-overflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38752>CVE-2022-38752</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9w3m-gqgf-c4p9">https://github.com/advisories/GHSA-9w3m-gqgf-c4p9</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.32
</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-38751</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38751>CVE-2022-38751</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47039">https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47039</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2023-20863</summary>
### Vulnerable Library - <b>spring-expression-5.3.14.jar</b></p>
<p>Spring Expression Language (SpEL)</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-expression/5.3.14/spring-expression-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- spring-context-5.3.14.jar
- :x: **spring-expression-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In spring framework versions prior to 5.2.24 release+ ,5.3.27+ and 6.0.8+ , it is possible for a user to provide a specially crafted SpEL expression that may cause a denial-of-service (DoS) condition.
<p>Publish Date: 2023-04-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20863>CVE-2023-20863</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2023-20863">https://spring.io/security/cve-2023-20863</a></p>
<p>Release Date: 2023-04-13</p>
<p>Fix Resolution: org.springframework:spring-expression - 5.2.24.RELEASE,5.3.27,6.0.8</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-38749</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38749>CVE-2022-38749</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/526/stackoverflow-oss-fuzz-47027">https://bitbucket.org/snakeyaml/snakeyaml/issues/526/stackoverflow-oss-fuzz-47027</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> WS-2021-0616</summary>
### Vulnerable Library - <b>jackson-databind-2.12.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.12.1/jackson-databind-2.12.1.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- :x: **jackson-databind-2.12.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind before 2.12.6 and 2.13.1 there is DoS when using JDK serialization to serialize JsonNode.
<p>Publish Date: 2021-11-20
<p>URL: <a href=https://github.com/FasterXML/jackson-databind/commit/3ccde7d938fea547e598fdefe9a82cff37fed5cb>WS-2021-0616</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-11-20</p>
<p>Fix Resolution (com.fasterxml.jackson.core:jackson-databind): 2.12.2</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-38750</summary>
### Vulnerable Library - <b>snakeyaml-1.27.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.27/snakeyaml-1.27.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- swagger-core-2.1.12.jar
- jackson-dataformat-yaml-2.12.1.jar
- :x: **snakeyaml-1.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38750>CVE-2022-38750</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47027">https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47027</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-22968</summary>
### Vulnerable Library - <b>spring-context-5.3.14.jar</b></p>
<p>Spring Context</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-context/5.3.14/spring-context-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- :x: **spring-context-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Framework versions 5.3.0 - 5.3.18, 5.2.0 - 5.2.20, and older unsupported versions, the patterns for disallowedFields on a DataBinder are case sensitive which means a field is not effectively protected unless it is listed with both upper and lower case for the first character of the field, including upper and lower case for the first character of all nested fields within the property path.
<p>Publish Date: 2022-04-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22968>CVE-2022-22968</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22968">https://tanzu.vmware.com/security/cve-2022-22968</a></p>
<p>Release Date: 2022-04-14</p>
<p>Fix Resolution (org.springframework:spring-context): 5.3.19</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.9</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-22970</summary>
### Vulnerable Libraries - <b>spring-beans-5.3.14.jar</b>, <b>spring-core-5.3.14.jar</b></p>
<p>
### <b>spring-beans-5.3.14.jar</b></p>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.3.14/spring-beans-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- spring-context-5.3.14.jar
- spring-aop-5.3.14.jar
- :x: **spring-beans-5.3.14.jar** (Vulnerable Library)
### <b>spring-core-5.3.14.jar</b></p>
<p>Spring Core</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-core/5.3.14/spring-core-5.3.14.jar</p>
<p>
Dependency Hierarchy:
- springdoc-openapi-ui-1.6.4.jar (Root Library)
- springdoc-openapi-webmvc-core-1.6.4.jar
- springdoc-openapi-common-1.6.4.jar
- spring-boot-autoconfigure-2.6.2.jar
- spring-boot-2.6.2.jar
- :x: **spring-core-5.3.14.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2021/JavaSandbox/commit/30580d6f5d3727a54a9637f6cb305b5c7a838126">30580d6f5d3727a54a9637f6cb305b5c7a838126</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In spring framework versions prior to 5.3.20+ , 5.2.22+ and old unsupported versions, applications that handle file uploads are vulnerable to DoS attack if they rely on data binding to set a MultipartFile or javax.servlet.Part to a field in a model object.
<p>Publish Date: 2022-05-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22970>CVE-2022-22970</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22970">https://tanzu.vmware.com/security/cve-2022-22970</a></p>
<p>Release Date: 2022-05-12</p>
<p>Fix Resolution (org.springframework:spring-beans): 5.3.20</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.9</p><p>Fix Resolution (org.springframework:spring-core): 5.3.20</p>
<p>Direct dependency fix Resolution (org.springdoc:springdoc-openapi-ui): 1.6.9</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details>
***
<p>In order to enable automatic remediation for this issue, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
|
non_test
|
springdoc openapi ui jar vulnerabilities highest severity is vulnerable library springdoc openapi ui jar path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring expression spring expression jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in springdoc openapi ui version remediation possible critical spring beans jar transitive critical snakeyaml jar transitive n a critical spring web jar transitive n a high jackson databind jar transitive n a high jackson databind jar transitive n a high snakeyaml jar transitive n a high spring boot autoconfigure jar transitive high jackson databind jar transitive n a high spring webmvc jar transitive high jackson databind jar transitive n a medium snakeyaml jar transitive n a medium spring expression jar transitive medium spring expression jar transitive medium snakeyaml jar transitive n a medium snakeyaml jar transitive n a medium spring expression jar transitive n a medium snakeyaml jar transitive n a medium jackson databind jar transitive medium snakeyaml jar transitive n a medium spring context jar transitive medium detected in multiple dependencies transitive for some transitive vulnerabilities there is no version of direct dependency with a fix check the details section below to see if there is a version of transitive dependency where vulnerability is fixed in some cases remediation pr cannot be created automatically for a vulnerability despite the availability of remediation details cve vulnerable library spring beans jar spring beans library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring beans spring beans jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar spring boot autoconfigure jar spring boot jar spring context jar spring aop jar x spring beans jar vulnerable library found in head commit a href found in base branch main vulnerability details a spring mvc or spring webflux application running on jdk may be vulnerable to remote code execution rce via data binding the specific exploit requires the application to run on tomcat as a war deployment if the application is deployed as a spring boot executable jar i e the default it is not vulnerable to the exploit however the nature of the vulnerability is more general and there may be other ways to exploit it mend note converted from ws on publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring beans direct dependency fix resolution org springdoc springdoc openapi ui in order to enable automatic remediation please create cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar jackson dataformat yaml jar x snakeyaml jar vulnerable library found in head commit a href found in base branch main vulnerability details snakeyaml s constructor class does not restrict types which can be instantiated during deserialization deserializing yaml content provided by an attacker can lead to remote code execution we recommend using snakeyaml s safeconsturctor when parsing untrusted content to restrict deserialization we recommend upgrading to version and beyond publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library spring web jar spring web library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring web spring web jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar x spring web jar vulnerable library found in head commit a href found in base branch main vulnerability details pivotal spring framework through suffers from a potential remote code execution rce issue if used for java deserialization of untrusted data depending on how the library is implemented within a product this issue may or not occur and authentication may be required note the vendor s position is that untrusted data is not an intended use case the product s behavior will not be changed because some users rely on deserialization of trusted data mend note after conducting further research mend has determined that all versions of spring web up to version are vulnerable to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring web cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details in fasterxml jackson databind before resource exhaustion can occur because of a lack of a check in beandeserializer deserializefromarray to prevent use of deeply nested arrays an application is vulnerable only with certain customized choices for deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details in fasterxml jackson databind before resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting when the unwrap single value arrays feature is enabled additional fix version in and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar jackson dataformat yaml jar x snakeyaml jar vulnerable library found in head commit a href found in base branch main vulnerability details the package org yaml snakeyaml from and before are vulnerable to denial of service dos due missing to nested depth limitation for collections publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library spring boot autoconfigure jar spring boot autoconfigure library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework boot spring boot autoconfigure spring boot autoconfigure jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar x spring boot autoconfigure jar vulnerable library found in head commit a href found in base branch main vulnerability details in spring boot versions and older unsupported versions there is potential for a denial of service dos attack if spring mvc is used together with a reverse proxy cache publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework boot spring boot autoconfigure direct dependency fix resolution org springdoc springdoc openapi ui in order to enable automatic remediation please create cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details jackson databind before allows a java stackoverflow exception and denial of service via a large depth of nested objects mend note after conducting further research mend has determined that all versions of com fasterxml jackson core jackson databind up to version are vulnerable to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library spring webmvc jar spring web mvc library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring webmvc spring webmvc jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar x spring webmvc jar vulnerable library found in head commit a href found in base branch main vulnerability details spring framework running version or using as a pattern in spring security configuration with the mvcrequestmatcher creates a mismatch in pattern matching between spring security and spring mvc and the potential for a security bypass publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring webmvc direct dependency fix resolution org springdoc springdoc openapi ui in order to enable automatic remediation please create cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details jackson databind x through x before and x before allows attackers to cause a denial of service gb transient heap usage per read in uncommon situations involving jsonnode jdk serialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar jackson dataformat yaml jar x snakeyaml jar vulnerable library found in head commit a href found in base branch main vulnerability details those using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stack overflow this effect may support a denial of service attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library spring expression jar spring expression language spel path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring expression spring expression jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar spring boot autoconfigure jar spring boot jar spring context jar x spring expression jar vulnerable library found in head commit a href found in base branch main vulnerability details n spring framework versions and older unsupported versions it is possible for a user to provide a specially crafted spel expression that may cause a denial of service condition publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring expression direct dependency fix resolution org springdoc springdoc openapi ui in order to enable automatic remediation please create cve vulnerable library spring expression jar spring expression language spel path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring expression spring expression jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar spring boot autoconfigure jar spring boot jar spring context jar x spring expression jar vulnerable library found in head commit a href found in base branch main vulnerability details in spring framework versions release release and older unsupported versions it is possible for a user to provide a specially crafted spel expression that may cause a denial of service dos condition publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring expression direct dependency fix resolution org springdoc springdoc openapi ui in order to enable automatic remediation please create cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar jackson dataformat yaml jar x snakeyaml jar vulnerable library found in head commit a href found in base branch main vulnerability details using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stack overflow publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar jackson dataformat yaml jar x snakeyaml jar vulnerable library found in head commit a href found in base branch main vulnerability details using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library spring expression jar spring expression language spel path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring expression spring expression jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar spring boot autoconfigure jar spring boot jar spring context jar x spring expression jar vulnerable library found in head commit a href found in base branch main vulnerability details in spring framework versions prior to release and it is possible for a user to provide a specially crafted spel expression that may cause a denial of service dos condition publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring expression release cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar jackson dataformat yaml jar x snakeyaml jar vulnerable library found in head commit a href found in base branch main vulnerability details using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml ws vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details fasterxml jackson databind before and there is dos when using jdk serialization to serialize jsonnode publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind direct dependency fix resolution org springdoc springdoc openapi ui in order to enable automatic remediation please create cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar swagger core jar jackson dataformat yaml jar x snakeyaml jar vulnerable library found in head commit a href found in base branch main vulnerability details using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library spring context jar spring context path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring context spring context jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar spring boot autoconfigure jar spring boot jar x spring context jar vulnerable library found in head commit a href found in base branch main vulnerability details in spring framework versions and older unsupported versions the patterns for disallowedfields on a databinder are case sensitive which means a field is not effectively protected unless it is listed with both upper and lower case for the first character of the field including upper and lower case for the first character of all nested fields within the property path publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring context direct dependency fix resolution org springdoc springdoc openapi ui in order to enable automatic remediation please create cve vulnerable libraries spring beans jar spring core jar spring beans jar spring beans library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring beans spring beans jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar spring boot autoconfigure jar spring boot jar spring context jar spring aop jar x spring beans jar vulnerable library spring core jar spring core path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring core spring core jar dependency hierarchy springdoc openapi ui jar root library springdoc openapi webmvc core jar springdoc openapi common jar spring boot autoconfigure jar spring boot jar x spring core jar vulnerable library found in head commit a href found in base branch main vulnerability details in spring framework versions prior to and old unsupported versions applications that handle file uploads are vulnerable to dos attack if they rely on data binding to set a multipartfile or javax servlet part to a field in a model object publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring beans direct dependency fix resolution org springdoc springdoc openapi ui fix resolution org springframework spring core direct dependency fix resolution org springdoc springdoc openapi ui in order to enable automatic remediation please create in order to enable automatic remediation for this issue please create
| 0
|
230,138
| 18,506,174,628
|
IssuesEvent
|
2021-10-19 18:53:45
|
Exiled-Team/Common-Utils
|
https://api.github.com/repos/Exiled-Team/Common-Utils
|
closed
|
NRE OnChangingRoles
|
needs testing
|
**Describe the bug**
Getting an NRE after Starting round and when MTF or Chaos SPawns or you forceclass an player
**To Reproduce**
Steps to reproduce the behavior:
1. Install Plugin
2. Join Server and Start Round
3. See error
**Expected behavior**
To not get an NRE
**Server logs**
https://pastebin.com/xj2gJTVt
**Copy of current CU config section**
```
CommonUtilities:
# Wether or not debug messages should be shown.
debug: false
# The SCP Roles able to use V to talk to humans.
scp_speech:
- Scp049
- Scp0492
- Scp106
# Whether or not MTF/CI can 'escape' while disarmed to switch teams.
disarm_switch_teams: true
# Whether or not disarmed people will be prevented from interacting with doors/elevators.
restrictive_disarming: true
# The text displayed at the timed interval specified below.
timed_broadcast: <color=blue>Be sure to join our discord for new updates</color>
# The time each timed broadcast will be displayed.
timed_broadcast_duration: 5
# The delay between each timed broadcast. To disable timed broadcasts, set this to 0
timed_broadcast_delay: 0
# The message displayed to the player when they first join the server. Setting this to empty will disable these broadcasts.
join_message: <color=lime>Welcome %player%! Please read our rules!</color>
# The amount of time (in seconds) the join message is displayed.
join_message_duration: 5
# The amount of time (in seconds) after the round starts, before the facilities auto-nuke will start.
autonuke_time: -1
# Wether or not the nuke should be unable to be disabled during the auto-nuke countdown.
autonuke_lock: false
# The list of starting items for roles. ItemName is the item to give them, and Chance is the percent chance of them spawning with it, and Group allows you to restrict the item to only players with certain RA groups (Leave this as 'none' to allow all players to get the item). You can specify the same item multiple times.
starting_inventories:
ClassD:
slot1:
- item_name: Flashlight
chance: 100
group: none
slot2: []
slot3: []
slot4: []
slot5: []
slot6: []
slot7: []
slot8: []
ammo: []
Scientist:
slot1:
- item_name: KeycardScientist
chance: 100
group: none
slot2:
- item_name: Medkit
chance: 100
group: none
slot3:
- item_name: Flashlight
chance: 100
group: none
slot4: []
slot5: []
slot6: []
slot7: []
slot8: []
ammo: []
FacilityGuard:
slot1:
- item_name: Medkit
chance: 100
group: none
slot2:
- item_name: KeycardGuard
chance: 100
group: none
slot3:
- item_name: GunFSP9
chance: 100
group: none
slot4:
- item_name: GrenadeFlash
chance: 100
group: none
slot5:
- item_name: Radio
chance: 100
group: none
slot6:
- item_name: ArmorLight
chance: 100
group: none
slot7:
- item_name: Flashlight
chance: 100
group: none
slot8: []
ammo:
- type: Ammo9x19
amount: 60
NtfPrivate:
slot1:
- item_name: KeycardNTFOfficer
chance: 100
group: none
slot2:
- item_name: GunCrossvec
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: Radio
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Flashlight
chance: 100
group: none
slot7: []
slot8: []
ammo:
- type: Ammo9x19
amount: 120
group:
- type: Ammo556x45
amount: 40
group:
NtfSpecialist:
slot1:
- item_name: KeycardNTFLieutenant
chance: 100
group: none
slot2:
- item_name: GunE11SR
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: GrenadeHE
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Radio
chance: 100
group: none
slot7:
- item_name: Flashlight
chance: 100
group: none
slot8: []
ammo:
- type: Ammo9x19
amount: 40
group:
- type: Ammo556x45
amount: 120
group:
NtfSergeant:
slot1:
- item_name: KeycardNTFLieutenant
chance: 100
group: none
slot2:
- item_name: GunE11SR
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: GrenadeHE
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Radio
chance: 100
group: none
slot7:
- item_name: Flashlight
chance: 100
group: none
slot8: []
ammo:
- type: Ammo9x19
amount: 40
group:
- type: Ammo556x45
amount: 120
group:
NtfCaptain:
slot1:
- item_name: KeycardNTFCommander
chance: 100
group: none
slot2:
- item_name: GunE11SR
chance: 100
group: none
slot3:
- item_name: Adrenaline
chance: 100
group: none
slot4:
- item_name: Medkit
chance: 100
group: none
slot5:
- item_name: GrenadeHE
chance: 100
group: none
slot6:
- item_name: Radio
chance: 100
group: none
slot7:
- item_name: ArmorHeavy
chance: 100
group: none
slot8:
- item_name: Flashlight
chance: 100
group: none
ammo:
- type: Ammo9x19
amount: 40
group:
- type: Ammo556x45
amount: 160
group:
ChaosConscript:
slot1:
- item_name: KeycardChaosInsurgency
chance: 100
group: none
slot2:
- item_name: GunAK
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: Painkillers
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Flashlight
chance: 100
group: none
slot7: []
slot8: []
ammo:
- type: Ammo762x39
amount: 120
group:
ChaosRifleman:
slot1:
- item_name: KeycardChaosInsurgency
chance: 100
group: none
slot2:
- item_name: GunAK
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: Painkillers
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Flashlight
chance: 100
group: none
slot7: []
slot8: []
ammo:
- type: Ammo762x39
amount: 120
group:
ChaosRepressor:
slot1:
- item_name: KeycardChaosInsurgency
chance: 100
group: none
slot2:
- item_name: GunLogicer
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: Painkillers
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Flashlight
chance: 100
group: none
slot7: []
slot8: []
ammo:
- type: Ammo762x39
amount: 200
group:
ChaosMarauder:
slot1:
- item_name: KeycardChaosInsurgency
chance: 100
group: none
slot2:
- item_name: GunShotgun
chance: 100
group: none
slot3:
- item_name: GunRevolver
chance: 100
group: none
slot4:
- item_name: Medkit
chance: 100
group: none
slot5:
- item_name: Painkillers
chance: 100
group: none
slot6:
- item_name: ArmorCombat
chance: 100
group: none
slot7:
- item_name: Flashlight
chance: 100
group: none
slot8: []
ammo:
- type: Ammo44cal
amount: 24
group:
- type: Ammo12gauge
amount: 42
group:
# The list of custom 914 recipies. Original is the item being upgraded, New is the item to upgrade to, and Chance is the percent chance of the upgrade happening. You can specify multiple upgrade choices for the same item.
scp914_item_changes: {}
# The list of custom 914 recipies for roles. Original is the role to be changed, New is the new role to assign, Chance is the % chance of the upgrade occuring.
scp914_class_changes: {}
scp914_teleport_chances: {}
# A dictionary of random effects to apply to players when going through 914 on certain settings.
scp914_effect_chances: {}
# Determines if 914 effects are exclusive, meaning only one can be applied each time a player is processed by 914.
scp914_effects_exclusivity: false
# Whether or not SCPs are immune to effects gained from 914.
scps_immune_to914_effects: false
# The frequency (in seconds) between ragdoll cleanups. Set to 0 to disable.
ragdoll_cleanup_delay: 15
# If ragdoll cleanup should only happen in the Pocket Dimension or not.
ragdoll_cleanup_only_pocket: true
# The frequency (in seconds) between item cleanups. Set to 0 to disable.
item_cleanup_delay: 15
# If item cleanup should only happen in the Pocket Dimension or not.
item_cleanup_only_pocket: true
# A list of all roles and their damage modifiers. The number here is a multiplier, not a raw damage amount. Thus, setting it to 1 = normal damage, 1.5 = 50% more damage, and 0.5 = 50% less damage.
role_damage_multipliers:
Scp173: 1
# A list of all Weapons and their damage modifiers. The number here is a multiplier, not a raw damage amount. Thus, setting it to 1 = normal damage, 1.5 = 50% more damage, and 0.5 = 50% less damage.
weapon_damage_multipliers:
GunE11SR: 1
# A list of roles and how much health they should be given when they kill someone.
health_on_kill:
# A list of roles and what their default starting health should be.
health_values:
# If the plugin is enabled or not.
is_enabled: true
```
**EXILED Version ("latest" is not a version):**
EXILED 3.0.5
**Results of `show plugins` command in console:**
```
[19-10-2021 00:12:04.059 +00:00] Total number of plugins: 13
Enabled plugins: 13
Disabled plugins: 0
Exiled.Events:
- Author: Exiled Team
- Version: 3.0.5.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_events
- Priority: Highest
Exiled.Updater:
- Author: Exiled.Updater
- Version: 3.1.1.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_updater
- Priority: Medium
NukeLock:
- Author: Marco15453
- Version: 1.3.0
- Required Exiled Version: 3.0.0
- Prefix: nuke_lock
- Priority: Medium
RespawnTimer:
- Author: Michal78900
- Version: 3.0.0
- Required Exiled Version: 3.0.0
- Prefix: respawn_timer
- Priority: Medium
Exiled.CustomItems:
- Author: Exiled Team
- Version: 3.0.5.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_custom_items
- Priority: Medium
Exiled.Permissions:
- Author: Exiled Team
- Version: 3.0.5.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_permissions
- Priority: Medium
ScpSwap:
- Author: Build
- Version: 1.0.0
- Required Exiled Version: 3.0.0
- Prefix: scpswap
- Priority: Medium
SerpentsHand:
- Author: Cyanox, maintained by Michal78900
- Version: 3.1.0
- Required Exiled Version: 3.0.5
- Prefix: serpents_hand
- Priority: Medium
Common Utilities:
- Author: Galaxy119
- Version: 4.2.4.0
- Required Exiled Version: 3.0.0
- Prefix: CommonUtilities
- Priority: Medium
Exiled.CreditTags:
- Author: Babyboucher20 & iRebbok & Exiled Team
- Version: 3.0.5.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_credits
- Priority: Medium
SCP-575:
- Author: Original by Joker119, Continued by Marco15453
- Version: 4.1.1
- Required Exiled Version: 3.0.3
- Prefix: 575
- Priority: Medium
Randomised Coin:
- Author: Marco15453
- Version: 1.1.1
- Required Exiled Version: 3.0.0
- Prefix: randomised_coin
- Priority: Medium
Exiled.CustomRoles:
- Author: Exiled Team
- Version: 3.0.5.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_custom_roles
- Priority: Medium
```
**Additional context**
Nothing in additional
|
1.0
|
NRE OnChangingRoles - **Describe the bug**
Getting an NRE after Starting round and when MTF or Chaos SPawns or you forceclass an player
**To Reproduce**
Steps to reproduce the behavior:
1. Install Plugin
2. Join Server and Start Round
3. See error
**Expected behavior**
To not get an NRE
**Server logs**
https://pastebin.com/xj2gJTVt
**Copy of current CU config section**
```
CommonUtilities:
# Wether or not debug messages should be shown.
debug: false
# The SCP Roles able to use V to talk to humans.
scp_speech:
- Scp049
- Scp0492
- Scp106
# Whether or not MTF/CI can 'escape' while disarmed to switch teams.
disarm_switch_teams: true
# Whether or not disarmed people will be prevented from interacting with doors/elevators.
restrictive_disarming: true
# The text displayed at the timed interval specified below.
timed_broadcast: <color=blue>Be sure to join our discord for new updates</color>
# The time each timed broadcast will be displayed.
timed_broadcast_duration: 5
# The delay between each timed broadcast. To disable timed broadcasts, set this to 0
timed_broadcast_delay: 0
# The message displayed to the player when they first join the server. Setting this to empty will disable these broadcasts.
join_message: <color=lime>Welcome %player%! Please read our rules!</color>
# The amount of time (in seconds) the join message is displayed.
join_message_duration: 5
# The amount of time (in seconds) after the round starts, before the facilities auto-nuke will start.
autonuke_time: -1
# Wether or not the nuke should be unable to be disabled during the auto-nuke countdown.
autonuke_lock: false
# The list of starting items for roles. ItemName is the item to give them, and Chance is the percent chance of them spawning with it, and Group allows you to restrict the item to only players with certain RA groups (Leave this as 'none' to allow all players to get the item). You can specify the same item multiple times.
starting_inventories:
ClassD:
slot1:
- item_name: Flashlight
chance: 100
group: none
slot2: []
slot3: []
slot4: []
slot5: []
slot6: []
slot7: []
slot8: []
ammo: []
Scientist:
slot1:
- item_name: KeycardScientist
chance: 100
group: none
slot2:
- item_name: Medkit
chance: 100
group: none
slot3:
- item_name: Flashlight
chance: 100
group: none
slot4: []
slot5: []
slot6: []
slot7: []
slot8: []
ammo: []
FacilityGuard:
slot1:
- item_name: Medkit
chance: 100
group: none
slot2:
- item_name: KeycardGuard
chance: 100
group: none
slot3:
- item_name: GunFSP9
chance: 100
group: none
slot4:
- item_name: GrenadeFlash
chance: 100
group: none
slot5:
- item_name: Radio
chance: 100
group: none
slot6:
- item_name: ArmorLight
chance: 100
group: none
slot7:
- item_name: Flashlight
chance: 100
group: none
slot8: []
ammo:
- type: Ammo9x19
amount: 60
NtfPrivate:
slot1:
- item_name: KeycardNTFOfficer
chance: 100
group: none
slot2:
- item_name: GunCrossvec
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: Radio
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Flashlight
chance: 100
group: none
slot7: []
slot8: []
ammo:
- type: Ammo9x19
amount: 120
group:
- type: Ammo556x45
amount: 40
group:
NtfSpecialist:
slot1:
- item_name: KeycardNTFLieutenant
chance: 100
group: none
slot2:
- item_name: GunE11SR
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: GrenadeHE
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Radio
chance: 100
group: none
slot7:
- item_name: Flashlight
chance: 100
group: none
slot8: []
ammo:
- type: Ammo9x19
amount: 40
group:
- type: Ammo556x45
amount: 120
group:
NtfSergeant:
slot1:
- item_name: KeycardNTFLieutenant
chance: 100
group: none
slot2:
- item_name: GunE11SR
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: GrenadeHE
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Radio
chance: 100
group: none
slot7:
- item_name: Flashlight
chance: 100
group: none
slot8: []
ammo:
- type: Ammo9x19
amount: 40
group:
- type: Ammo556x45
amount: 120
group:
NtfCaptain:
slot1:
- item_name: KeycardNTFCommander
chance: 100
group: none
slot2:
- item_name: GunE11SR
chance: 100
group: none
slot3:
- item_name: Adrenaline
chance: 100
group: none
slot4:
- item_name: Medkit
chance: 100
group: none
slot5:
- item_name: GrenadeHE
chance: 100
group: none
slot6:
- item_name: Radio
chance: 100
group: none
slot7:
- item_name: ArmorHeavy
chance: 100
group: none
slot8:
- item_name: Flashlight
chance: 100
group: none
ammo:
- type: Ammo9x19
amount: 40
group:
- type: Ammo556x45
amount: 160
group:
ChaosConscript:
slot1:
- item_name: KeycardChaosInsurgency
chance: 100
group: none
slot2:
- item_name: GunAK
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: Painkillers
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Flashlight
chance: 100
group: none
slot7: []
slot8: []
ammo:
- type: Ammo762x39
amount: 120
group:
ChaosRifleman:
slot1:
- item_name: KeycardChaosInsurgency
chance: 100
group: none
slot2:
- item_name: GunAK
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: Painkillers
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Flashlight
chance: 100
group: none
slot7: []
slot8: []
ammo:
- type: Ammo762x39
amount: 120
group:
ChaosRepressor:
slot1:
- item_name: KeycardChaosInsurgency
chance: 100
group: none
slot2:
- item_name: GunLogicer
chance: 100
group: none
slot3:
- item_name: Medkit
chance: 100
group: none
slot4:
- item_name: Painkillers
chance: 100
group: none
slot5:
- item_name: ArmorCombat
chance: 100
group: none
slot6:
- item_name: Flashlight
chance: 100
group: none
slot7: []
slot8: []
ammo:
- type: Ammo762x39
amount: 200
group:
ChaosMarauder:
slot1:
- item_name: KeycardChaosInsurgency
chance: 100
group: none
slot2:
- item_name: GunShotgun
chance: 100
group: none
slot3:
- item_name: GunRevolver
chance: 100
group: none
slot4:
- item_name: Medkit
chance: 100
group: none
slot5:
- item_name: Painkillers
chance: 100
group: none
slot6:
- item_name: ArmorCombat
chance: 100
group: none
slot7:
- item_name: Flashlight
chance: 100
group: none
slot8: []
ammo:
- type: Ammo44cal
amount: 24
group:
- type: Ammo12gauge
amount: 42
group:
# The list of custom 914 recipies. Original is the item being upgraded, New is the item to upgrade to, and Chance is the percent chance of the upgrade happening. You can specify multiple upgrade choices for the same item.
scp914_item_changes: {}
# The list of custom 914 recipies for roles. Original is the role to be changed, New is the new role to assign, Chance is the % chance of the upgrade occuring.
scp914_class_changes: {}
scp914_teleport_chances: {}
# A dictionary of random effects to apply to players when going through 914 on certain settings.
scp914_effect_chances: {}
# Determines if 914 effects are exclusive, meaning only one can be applied each time a player is processed by 914.
scp914_effects_exclusivity: false
# Whether or not SCPs are immune to effects gained from 914.
scps_immune_to914_effects: false
# The frequency (in seconds) between ragdoll cleanups. Set to 0 to disable.
ragdoll_cleanup_delay: 15
# If ragdoll cleanup should only happen in the Pocket Dimension or not.
ragdoll_cleanup_only_pocket: true
# The frequency (in seconds) between item cleanups. Set to 0 to disable.
item_cleanup_delay: 15
# If item cleanup should only happen in the Pocket Dimension or not.
item_cleanup_only_pocket: true
# A list of all roles and their damage modifiers. The number here is a multiplier, not a raw damage amount. Thus, setting it to 1 = normal damage, 1.5 = 50% more damage, and 0.5 = 50% less damage.
role_damage_multipliers:
Scp173: 1
# A list of all Weapons and their damage modifiers. The number here is a multiplier, not a raw damage amount. Thus, setting it to 1 = normal damage, 1.5 = 50% more damage, and 0.5 = 50% less damage.
weapon_damage_multipliers:
GunE11SR: 1
# A list of roles and how much health they should be given when they kill someone.
health_on_kill:
# A list of roles and what their default starting health should be.
health_values:
# If the plugin is enabled or not.
is_enabled: true
```
**EXILED Version ("latest" is not a version):**
EXILED 3.0.5
**Results of `show plugins` command in console:**
```
[19-10-2021 00:12:04.059 +00:00] Total number of plugins: 13
Enabled plugins: 13
Disabled plugins: 0
Exiled.Events:
- Author: Exiled Team
- Version: 3.0.5.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_events
- Priority: Highest
Exiled.Updater:
- Author: Exiled.Updater
- Version: 3.1.1.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_updater
- Priority: Medium
NukeLock:
- Author: Marco15453
- Version: 1.3.0
- Required Exiled Version: 3.0.0
- Prefix: nuke_lock
- Priority: Medium
RespawnTimer:
- Author: Michal78900
- Version: 3.0.0
- Required Exiled Version: 3.0.0
- Prefix: respawn_timer
- Priority: Medium
Exiled.CustomItems:
- Author: Exiled Team
- Version: 3.0.5.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_custom_items
- Priority: Medium
Exiled.Permissions:
- Author: Exiled Team
- Version: 3.0.5.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_permissions
- Priority: Medium
ScpSwap:
- Author: Build
- Version: 1.0.0
- Required Exiled Version: 3.0.0
- Prefix: scpswap
- Priority: Medium
SerpentsHand:
- Author: Cyanox, maintained by Michal78900
- Version: 3.1.0
- Required Exiled Version: 3.0.5
- Prefix: serpents_hand
- Priority: Medium
Common Utilities:
- Author: Galaxy119
- Version: 4.2.4.0
- Required Exiled Version: 3.0.0
- Prefix: CommonUtilities
- Priority: Medium
Exiled.CreditTags:
- Author: Babyboucher20 & iRebbok & Exiled Team
- Version: 3.0.5.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_credits
- Priority: Medium
SCP-575:
- Author: Original by Joker119, Continued by Marco15453
- Version: 4.1.1
- Required Exiled Version: 3.0.3
- Prefix: 575
- Priority: Medium
Randomised Coin:
- Author: Marco15453
- Version: 1.1.1
- Required Exiled Version: 3.0.0
- Prefix: randomised_coin
- Priority: Medium
Exiled.CustomRoles:
- Author: Exiled Team
- Version: 3.0.5.0
- Required Exiled Version: 3.0.5.0
- Prefix: exiled_custom_roles
- Priority: Medium
```
**Additional context**
Nothing in additional
|
test
|
nre onchangingroles describe the bug getting an nre after starting round and when mtf or chaos spawns or you forceclass an player to reproduce steps to reproduce the behavior install plugin join server and start round see error expected behavior to not get an nre server logs copy of current cu config section commonutilities wether or not debug messages should be shown debug false the scp roles able to use v to talk to humans scp speech whether or not mtf ci can escape while disarmed to switch teams disarm switch teams true whether or not disarmed people will be prevented from interacting with doors elevators restrictive disarming true the text displayed at the timed interval specified below timed broadcast be sure to join our discord for new updates the time each timed broadcast will be displayed timed broadcast duration the delay between each timed broadcast to disable timed broadcasts set this to timed broadcast delay the message displayed to the player when they first join the server setting this to empty will disable these broadcasts join message welcome player please read our rules the amount of time in seconds the join message is displayed join message duration the amount of time in seconds after the round starts before the facilities auto nuke will start autonuke time wether or not the nuke should be unable to be disabled during the auto nuke countdown autonuke lock false the list of starting items for roles itemname is the item to give them and chance is the percent chance of them spawning with it and group allows you to restrict the item to only players with certain ra groups leave this as none to allow all players to get the item you can specify the same item multiple times starting inventories classd item name flashlight chance group none ammo scientist item name keycardscientist chance group none item name medkit chance group none item name flashlight chance group none ammo facilityguard item name medkit chance group none item name keycardguard chance group none item name chance group none item name grenadeflash chance group none item name radio chance group none item name armorlight chance group none item name flashlight chance group none ammo type amount ntfprivate item name keycardntfofficer chance group none item name guncrossvec chance group none item name medkit chance group none item name radio chance group none item name armorcombat chance group none item name flashlight chance group none ammo type amount group type amount group ntfspecialist item name keycardntflieutenant chance group none item name chance group none item name medkit chance group none item name grenadehe chance group none item name armorcombat chance group none item name radio chance group none item name flashlight chance group none ammo type amount group type amount group ntfsergeant item name keycardntflieutenant chance group none item name chance group none item name medkit chance group none item name grenadehe chance group none item name armorcombat chance group none item name radio chance group none item name flashlight chance group none ammo type amount group type amount group ntfcaptain item name keycardntfcommander chance group none item name chance group none item name adrenaline chance group none item name medkit chance group none item name grenadehe chance group none item name radio chance group none item name armorheavy chance group none item name flashlight chance group none ammo type amount group type amount group chaosconscript item name keycardchaosinsurgency chance group none item name gunak chance group none item name medkit chance group none item name painkillers chance group none item name armorcombat chance group none item name flashlight chance group none ammo type amount group chaosrifleman item name keycardchaosinsurgency chance group none item name gunak chance group none item name medkit chance group none item name painkillers chance group none item name armorcombat chance group none item name flashlight chance group none ammo type amount group chaosrepressor item name keycardchaosinsurgency chance group none item name gunlogicer chance group none item name medkit chance group none item name painkillers chance group none item name armorcombat chance group none item name flashlight chance group none ammo type amount group chaosmarauder item name keycardchaosinsurgency chance group none item name gunshotgun chance group none item name gunrevolver chance group none item name medkit chance group none item name painkillers chance group none item name armorcombat chance group none item name flashlight chance group none ammo type amount group type amount group the list of custom recipies original is the item being upgraded new is the item to upgrade to and chance is the percent chance of the upgrade happening you can specify multiple upgrade choices for the same item item changes the list of custom recipies for roles original is the role to be changed new is the new role to assign chance is the chance of the upgrade occuring class changes teleport chances a dictionary of random effects to apply to players when going through on certain settings effect chances determines if effects are exclusive meaning only one can be applied each time a player is processed by effects exclusivity false whether or not scps are immune to effects gained from scps immune effects false the frequency in seconds between ragdoll cleanups set to to disable ragdoll cleanup delay if ragdoll cleanup should only happen in the pocket dimension or not ragdoll cleanup only pocket true the frequency in seconds between item cleanups set to to disable item cleanup delay if item cleanup should only happen in the pocket dimension or not item cleanup only pocket true a list of all roles and their damage modifiers the number here is a multiplier not a raw damage amount thus setting it to normal damage more damage and less damage role damage multipliers a list of all weapons and their damage modifiers the number here is a multiplier not a raw damage amount thus setting it to normal damage more damage and less damage weapon damage multipliers a list of roles and how much health they should be given when they kill someone health on kill a list of roles and what their default starting health should be health values if the plugin is enabled or not is enabled true exiled version latest is not a version exiled results of show plugins command in console total number of plugins enabled plugins disabled plugins exiled events author exiled team version required exiled version prefix exiled events priority highest exiled updater author exiled updater version required exiled version prefix exiled updater priority medium nukelock author version required exiled version prefix nuke lock priority medium respawntimer author version required exiled version prefix respawn timer priority medium exiled customitems author exiled team version required exiled version prefix exiled custom items priority medium exiled permissions author exiled team version required exiled version prefix exiled permissions priority medium scpswap author build version required exiled version prefix scpswap priority medium serpentshand author cyanox maintained by version required exiled version prefix serpents hand priority medium common utilities author version required exiled version prefix commonutilities priority medium exiled credittags author irebbok exiled team version required exiled version prefix exiled credits priority medium scp author original by continued by version required exiled version prefix priority medium randomised coin author version required exiled version prefix randomised coin priority medium exiled customroles author exiled team version required exiled version prefix exiled custom roles priority medium additional context nothing in additional
| 1
|
322,499
| 27,612,295,018
|
IssuesEvent
|
2023-03-09 16:46:21
|
elastic/kibana
|
https://api.github.com/repos/elastic/kibana
|
closed
|
Dashboard tests: add tests for switching between dashboards with custom embeddable configs
|
tests_needed Feature:Dashboard Team:Presentation
|
A lack of coverage caused this bug to slip by: https://github.com/elastic/kibana/issues/17527
We should add some more tests to the _dashboard_state that would have caught this. Essentially to repro that bug, you have to open a dashboard with emebeddableConfig state, after another dashboard with embeddable config state.
Blocked first on checking in https://github.com/elastic/kibana/pull/17703, once those tests are passing.
|
1.0
|
Dashboard tests: add tests for switching between dashboards with custom embeddable configs - A lack of coverage caused this bug to slip by: https://github.com/elastic/kibana/issues/17527
We should add some more tests to the _dashboard_state that would have caught this. Essentially to repro that bug, you have to open a dashboard with emebeddableConfig state, after another dashboard with embeddable config state.
Blocked first on checking in https://github.com/elastic/kibana/pull/17703, once those tests are passing.
|
test
|
dashboard tests add tests for switching between dashboards with custom embeddable configs a lack of coverage caused this bug to slip by we should add some more tests to the dashboard state that would have caught this essentially to repro that bug you have to open a dashboard with emebeddableconfig state after another dashboard with embeddable config state blocked first on checking in once those tests are passing
| 1
|
271,257
| 20,626,583,098
|
IssuesEvent
|
2022-03-07 23:24:46
|
MicrosoftDocs/terminal
|
https://api.github.com/repos/MicrosoftDocs/terminal
|
closed
|
Document how auto-hiding the cursor works, and how to disable this behavior
|
documentation
|
Inspired by https://github.com/microsoft/terminal/issues/9676
Auto-hiding the cursor is standard on windows, yes, but conhost and the Terminal didn't do that (until recently). We should have a Troubleshooting section about this, and a guide on where to go in the Settings to re-enable that.
|
1.0
|
Document how auto-hiding the cursor works, and how to disable this behavior - Inspired by https://github.com/microsoft/terminal/issues/9676
Auto-hiding the cursor is standard on windows, yes, but conhost and the Terminal didn't do that (until recently). We should have a Troubleshooting section about this, and a guide on where to go in the Settings to re-enable that.
|
non_test
|
document how auto hiding the cursor works and how to disable this behavior inspired by auto hiding the cursor is standard on windows yes but conhost and the terminal didn t do that until recently we should have a troubleshooting section about this and a guide on where to go in the settings to re enable that
| 0
|
98,300
| 8,675,444,194
|
IssuesEvent
|
2018-11-30 10:53:54
|
shahkhan40/shantestrep
|
https://api.github.com/repos/shahkhan40/shantestrep
|
closed
|
fxscantest : ApiV1EnvsIdGetPathParamIdMysqlSqlInjectionTimebound
|
fxscantest
|
Project : fxscantest
Job : uatenv
Env : uatenv
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=ZTBjM2UxNjMtYTM3NC00NmQ0LWE5NjQtOWFkNDk3NjFiNGRh; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Fri, 30 Nov 2018 10:52:27 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/envs/
Request :
Response :
{
"timestamp" : "2018-11-30T10:52:27.918+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/envs/"
}
Logs :
Assertion [@ResponseTime < 7000 OR @ResponseTime > 10000] resolved-to [492 < 7000 OR 492 > 10000] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
--- FX Bot ---
|
1.0
|
fxscantest : ApiV1EnvsIdGetPathParamIdMysqlSqlInjectionTimebound - Project : fxscantest
Job : uatenv
Env : uatenv
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=ZTBjM2UxNjMtYTM3NC00NmQ0LWE5NjQtOWFkNDk3NjFiNGRh; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Fri, 30 Nov 2018 10:52:27 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/envs/
Request :
Response :
{
"timestamp" : "2018-11-30T10:52:27.918+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/envs/"
}
Logs :
Assertion [@ResponseTime < 7000 OR @ResponseTime > 10000] resolved-to [492 < 7000 OR 492 > 10000] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
--- FX Bot ---
|
test
|
fxscantest project fxscantest job uatenv env uatenv region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response timestamp status error not found message no message available path api api envs logs assertion resolved to result assertion resolved to result fx bot
| 1
|
161,407
| 12,543,332,044
|
IssuesEvent
|
2020-06-05 15:22:45
|
Turing-Cross-Pol/WilderNests_FE
|
https://api.github.com/repos/Turing-Cross-Pol/WilderNests_FE
|
closed
|
Add Unit Tests for all Components
|
Testing
|
Tests completed for the following components:
- [x] Landing
- [x] ListCard
- [x] ListView
- [x] MapList
- [x] PostForm
- [x] QuickView
- [x] SiteDetails
- [x] ToggleView
- [x] Filter
- [x] CommentForm
- [x] CommentCard
|
1.0
|
Add Unit Tests for all Components - Tests completed for the following components:
- [x] Landing
- [x] ListCard
- [x] ListView
- [x] MapList
- [x] PostForm
- [x] QuickView
- [x] SiteDetails
- [x] ToggleView
- [x] Filter
- [x] CommentForm
- [x] CommentCard
|
test
|
add unit tests for all components tests completed for the following components landing listcard listview maplist postform quickview sitedetails toggleview filter commentform commentcard
| 1
|
221,910
| 17,376,679,535
|
IssuesEvent
|
2021-07-30 22:58:55
|
microsoft/vscode-python
|
https://api.github.com/repos/microsoft/vscode-python
|
closed
|
New testing experience doesn't surface errors
|
area-testing classify type-bug
|
With #16769 errors when test discovery fails are not being surfaced, for example when there are 2 test files with the same name.
|
1.0
|
New testing experience doesn't surface errors - With #16769 errors when test discovery fails are not being surfaced, for example when there are 2 test files with the same name.
|
test
|
new testing experience doesn t surface errors with errors when test discovery fails are not being surfaced for example when there are test files with the same name
| 1
|
283,104
| 24,523,230,319
|
IssuesEvent
|
2022-10-11 11:10:26
|
ices-tools-dev/icesRDBES
|
https://api.github.com/repos/ices-tools-dev/icesRDBES
|
closed
|
Update tests/test data/code for latest version of the RDBES data model
|
1_import 6_test_data
|
- [x] Create new test data
- [x] Update tests to use the new test data
- [x] Update any configuration files with the latest data model
- [x] Update vignettes to use new test data
|
1.0
|
Update tests/test data/code for latest version of the RDBES data model - - [x] Create new test data
- [x] Update tests to use the new test data
- [x] Update any configuration files with the latest data model
- [x] Update vignettes to use new test data
|
test
|
update tests test data code for latest version of the rdbes data model create new test data update tests to use the new test data update any configuration files with the latest data model update vignettes to use new test data
| 1
|
15,714
| 27,789,200,746
|
IssuesEvent
|
2023-03-17 07:23:09
|
hidekuro/uzurl
|
https://api.github.com/repos/hidekuro/uzurl
|
closed
|
短縮 URL 発行機能/要件定義
|
dev/requirements
|
## PBI
- #1
## 概要
- ユーザーが入力した URL に短い UID を関連付け、パスとしてサイトドメインに連結した `https://サイトドメイン/UID` 形式の短縮 URL を生成して提供する。
- 短縮 URL は原則永続とする。
- 短縮 URL に含まれるパスは単なる UID であり、同じ URL を繰り返し短縮した場合も、毎回違う短縮 URL を生成する。
- 後述の制限事項のとおりゲスト向けサービスのため、ユーザーが過去の短縮 URL を参照する機能は持たない。
- UID には10桁の nanoid を採用する。
- [Nano ID 衝突計算機](https://zelark.github.io/nano-id-cc/) によれば、10桁の Nano ID を1時間あたり1000個生成し続けた場合で、「少なくとも1回の衝突が発生する確率が1%に達するまでの所要時間」に17年かかる。
- 9桁の場合は同時間が2年となり、やや心許ない。
## 用語集
- `短縮 URL` ... 本サービスが生成する独自の短い URL
- `オリジナル URL` ... ユーザーが入力する(短縮前の) URL
## 制限事項
#1 の時点では最小機能版としての開発とするため、次の制限事項を認める。
- ゲスト向けの無料公開サービスとする(認証機能を考慮しない)。
- 短縮 URL に任意のエイリアスを与える機能は実装しない。
## フロントエンド要件
- 画面構成は URL 短縮画面の1枚のみで、入力画面と結果表示画面を兼ねる。
- `/` への GET アクセスで URL 短縮画面を表示する。
- `短縮` ボタンを押すと `/shorten` にオリジナル URL が送信される。
- 成功した場合、下部に短縮 URL を表示する。
- エラーが発生した場合、下部にエンドユーザー向けの説明メッセージを表示する。
フォーム要素:
| id | type | placeholder/ラベル | その他 |
|---|---|---|---|
| `url` | url | `https://example.com` | maxlength(2000), required |
| `submit` | submit | 短縮 | `<button type=submit>` で実装 |
クライアントサイドでの入力値検査は `<input type="url">` の標準機能までとし、厳密な検査はバックエンド API に任せる。
## バックエンド要件
1. URL 短縮 API `/api/v1/shorten` を定義する。
2. 任意の GET アクセスを短縮 URL の展開リクエストとみなし、 URL 展開処理を行う。
### (1) URL 短縮 API
#### リクエスト
- エンドポイント: `/api/v1/shorten`
- メソッド: POST
- Content-Type: `application/json`
| name | type | validation | description |
|---|---|---|---|
| `url` | string | required, max(2000), url | 短縮前のオリジナル URL |
#### レスポンス
- Content-Type: `application/json`
| name | type | validation | description |
|---|---|---|---|
| `short_url` | string | required | 短縮 URL。スキームを含む完全な URL 文字列。 |
| `message` | string | | エンドユーザー向けのエラー文言。エラー時のみセットされる。 |
ステータスコードと理由
| ステータス | 理由 |
|---|---|
| 200 | 正常終了。レスポンスボディには必ず `short_url` が含まれる。 |
| 400 | リクエストの `url` がバリデーションに違反。 |
| 500 | サーバー側で上記以外のエラーが発生した。(NanoID の衝突や DB 通信エラー等) |
### (2) URL 展開処理
既定のルーティングにマッチしない全ての GET リクエストについて、URL 展開処理を行う。
- URL の path パートの最初の要素をキーとして、データストアからオリジナル URL を検索して301リダイレクトする。
- 次のいずれかの場合は404ページを返す。
- リクエスト URL の path パートの要素数が1つ以外(0または2つ以上)の場合。
- リクエスト URL の最初の path 要素が NanoID として Invalid である( `[A-Za-z0-9_-]+` に一致しない)場合。バリデーション違反ながら400ではなく404を返す点に注意。
- リクエスト URL の最初の path 要素をキーとしてオリジナル URL が見つからない場合。
|
1.0
|
短縮 URL 発行機能/要件定義 - ## PBI
- #1
## 概要
- ユーザーが入力した URL に短い UID を関連付け、パスとしてサイトドメインに連結した `https://サイトドメイン/UID` 形式の短縮 URL を生成して提供する。
- 短縮 URL は原則永続とする。
- 短縮 URL に含まれるパスは単なる UID であり、同じ URL を繰り返し短縮した場合も、毎回違う短縮 URL を生成する。
- 後述の制限事項のとおりゲスト向けサービスのため、ユーザーが過去の短縮 URL を参照する機能は持たない。
- UID には10桁の nanoid を採用する。
- [Nano ID 衝突計算機](https://zelark.github.io/nano-id-cc/) によれば、10桁の Nano ID を1時間あたり1000個生成し続けた場合で、「少なくとも1回の衝突が発生する確率が1%に達するまでの所要時間」に17年かかる。
- 9桁の場合は同時間が2年となり、やや心許ない。
## 用語集
- `短縮 URL` ... 本サービスが生成する独自の短い URL
- `オリジナル URL` ... ユーザーが入力する(短縮前の) URL
## 制限事項
#1 の時点では最小機能版としての開発とするため、次の制限事項を認める。
- ゲスト向けの無料公開サービスとする(認証機能を考慮しない)。
- 短縮 URL に任意のエイリアスを与える機能は実装しない。
## フロントエンド要件
- 画面構成は URL 短縮画面の1枚のみで、入力画面と結果表示画面を兼ねる。
- `/` への GET アクセスで URL 短縮画面を表示する。
- `短縮` ボタンを押すと `/shorten` にオリジナル URL が送信される。
- 成功した場合、下部に短縮 URL を表示する。
- エラーが発生した場合、下部にエンドユーザー向けの説明メッセージを表示する。
フォーム要素:
| id | type | placeholder/ラベル | その他 |
|---|---|---|---|
| `url` | url | `https://example.com` | maxlength(2000), required |
| `submit` | submit | 短縮 | `<button type=submit>` で実装 |
クライアントサイドでの入力値検査は `<input type="url">` の標準機能までとし、厳密な検査はバックエンド API に任せる。
## バックエンド要件
1. URL 短縮 API `/api/v1/shorten` を定義する。
2. 任意の GET アクセスを短縮 URL の展開リクエストとみなし、 URL 展開処理を行う。
### (1) URL 短縮 API
#### リクエスト
- エンドポイント: `/api/v1/shorten`
- メソッド: POST
- Content-Type: `application/json`
| name | type | validation | description |
|---|---|---|---|
| `url` | string | required, max(2000), url | 短縮前のオリジナル URL |
#### レスポンス
- Content-Type: `application/json`
| name | type | validation | description |
|---|---|---|---|
| `short_url` | string | required | 短縮 URL。スキームを含む完全な URL 文字列。 |
| `message` | string | | エンドユーザー向けのエラー文言。エラー時のみセットされる。 |
ステータスコードと理由
| ステータス | 理由 |
|---|---|
| 200 | 正常終了。レスポンスボディには必ず `short_url` が含まれる。 |
| 400 | リクエストの `url` がバリデーションに違反。 |
| 500 | サーバー側で上記以外のエラーが発生した。(NanoID の衝突や DB 通信エラー等) |
### (2) URL 展開処理
既定のルーティングにマッチしない全ての GET リクエストについて、URL 展開処理を行う。
- URL の path パートの最初の要素をキーとして、データストアからオリジナル URL を検索して301リダイレクトする。
- 次のいずれかの場合は404ページを返す。
- リクエスト URL の path パートの要素数が1つ以外(0または2つ以上)の場合。
- リクエスト URL の最初の path 要素が NanoID として Invalid である( `[A-Za-z0-9_-]+` に一致しない)場合。バリデーション違反ながら400ではなく404を返す点に注意。
- リクエスト URL の最初の path 要素をキーとしてオリジナル URL が見つからない場合。
|
non_test
|
短縮 url 発行機能 要件定義 pbi 概要 ユーザーが入力した url に短い uid を関連付け、パスとしてサイトドメインに連結した 形式の短縮 url を生成して提供する。 短縮 url は原則永続とする。 短縮 url に含まれるパスは単なる uid であり、同じ url を繰り返し短縮した場合も、毎回違う短縮 url を生成する。 後述の制限事項のとおりゲスト向けサービスのため、ユーザーが過去の短縮 url を参照する機能は持たない。 uid nanoid を採用する。 によれば、 nano id 、「 に達するまでの所要時間」 。 、やや心許ない。 用語集 短縮 url 本サービスが生成する独自の短い url オリジナル url ユーザーが入力する(短縮前の) url 制限事項 の時点では最小機能版としての開発とするため、次の制限事項を認める。 ゲスト向けの無料公開サービスとする(認証機能を考慮しない)。 短縮 url に任意のエイリアスを与える機能は実装しない。 フロントエンド要件 画面構成は url 、入力画面と結果表示画面を兼ねる。 への get アクセスで url 短縮画面を表示する。 短縮 ボタンを押すと shorten にオリジナル url が送信される。 成功した場合、下部に短縮 url を表示する。 エラーが発生した場合、下部にエンドユーザー向けの説明メッセージを表示する。 フォーム要素 id type placeholder ラベル その他 url url maxlength required submit submit 短縮 で実装 クライアントサイドでの入力値検査は の標準機能までとし、厳密な検査はバックエンド api に任せる。 バックエンド要件 url 短縮 api api shorten を定義する。 任意の get アクセスを短縮 url の展開リクエストとみなし、 url 展開処理を行う。 url 短縮 api リクエスト エンドポイント api shorten メソッド post content type application json name type validation description url string required max url 短縮前のオリジナル url レスポンス content type application json name type validation description short url string required 短縮 url。スキームを含む完全な url 文字列。 message string エンドユーザー向けのエラー文言。エラー時のみセットされる。 ステータスコードと理由 ステータス 理由 正常終了。レスポンスボディには必ず short url が含まれる。 リクエストの url がバリデーションに違反。 サーバー側で上記以外のエラーが発生した。(nanoid の衝突や db 通信エラー等) url 展開処理 既定のルーティングにマッチしない全ての get リクエストについて、url 展開処理を行う。 url の path パートの最初の要素をキーとして、データストアからオリジナル url 。 。 リクエスト url の path ( )の場合。 リクエスト url の最初の path 要素が nanoid として invalid である( に一致しない)場合。 。 リクエスト url の最初の path 要素をキーとしてオリジナル url が見つからない場合。
| 0
|
446,747
| 31,558,390,556
|
IssuesEvent
|
2023-09-03 00:19:05
|
vercel/next.js
|
https://api.github.com/repos/vercel/next.js
|
closed
|
Docs: next/script documentation for stable and beta is not consistent
|
template: documentation
|
### What is the improvement or update you wish to see?
The documentation for `beforeInteractive` on [beta](https://beta.nextjs.org/docs/api-reference/components/script#beforeinteractive) and on [stable](https://nextjs.org/docs/api-reference/next/script#beforeinteractive) is not consistent.
On stable `<Script>` renders inside `<body>`, but on beta it renders inside `<html>`.
### Is there any context that might help us understand?
@timneutkens just pointed out https://github.com/vercel/next.js/issues/46549#issuecomment-1448087832 that `<Script>` needs to render inside `<body>` and not `<html>`
### Does the docs page already exist? Please link to it.
https://beta.nextjs.org/docs/api-reference/components/script#beforeinteractive
|
1.0
|
Docs: next/script documentation for stable and beta is not consistent - ### What is the improvement or update you wish to see?
The documentation for `beforeInteractive` on [beta](https://beta.nextjs.org/docs/api-reference/components/script#beforeinteractive) and on [stable](https://nextjs.org/docs/api-reference/next/script#beforeinteractive) is not consistent.
On stable `<Script>` renders inside `<body>`, but on beta it renders inside `<html>`.
### Is there any context that might help us understand?
@timneutkens just pointed out https://github.com/vercel/next.js/issues/46549#issuecomment-1448087832 that `<Script>` needs to render inside `<body>` and not `<html>`
### Does the docs page already exist? Please link to it.
https://beta.nextjs.org/docs/api-reference/components/script#beforeinteractive
|
non_test
|
docs next script documentation for stable and beta is not consistent what is the improvement or update you wish to see the documentation for beforeinteractive on and on is not consistent on stable renders inside but on beta it renders inside is there any context that might help us understand timneutkens just pointed out that needs to render inside and not does the docs page already exist please link to it
| 0
|
43,917
| 11,881,108,260
|
IssuesEvent
|
2020-03-27 12:01:05
|
hazelcast/hazelcast
|
https://api.github.com/repos/hazelcast/hazelcast
|
closed
|
Javadoc: internal packages not excluded in the 'release' Maven profile
|
Priority: Medium Source: Internal Team: Core Type: Defect good first issue
|
A number of packages (`*.impl`, `*.internal`, etc.) are excluded from Javadoc generation in the Maven `release-snapshot` profile. However, no packages at all are excluded in the `release` profile. As a result, the released Javadocs contain classes from all packages.
I think the `release` profile should exclude the same set of packages as `release-snapshot`. Applies both to OSS and EE.
|
1.0
|
Javadoc: internal packages not excluded in the 'release' Maven profile - A number of packages (`*.impl`, `*.internal`, etc.) are excluded from Javadoc generation in the Maven `release-snapshot` profile. However, no packages at all are excluded in the `release` profile. As a result, the released Javadocs contain classes from all packages.
I think the `release` profile should exclude the same set of packages as `release-snapshot`. Applies both to OSS and EE.
|
non_test
|
javadoc internal packages not excluded in the release maven profile a number of packages impl internal etc are excluded from javadoc generation in the maven release snapshot profile however no packages at all are excluded in the release profile as a result the released javadocs contain classes from all packages i think the release profile should exclude the same set of packages as release snapshot applies both to oss and ee
| 0
|
244,202
| 18,750,724,679
|
IssuesEvent
|
2021-11-05 01:18:24
|
Agoric/agoric-sdk
|
https://api.github.com/repos/Agoric/agoric-sdk
|
closed
|
all pass-by-reference objects must be marked with Far
|
documentation enhancement marshal devex
|
## What is the Problem Being Solved?
#2018 was split up into two pieces. The original ticket remains concentrated on making empty (hardened) objects be pass-by-copy instead of pass-by-reference.
This new ticket is about making all pass-by-reference objects as `Far` (or `Remotable`). Once complete, `marshal` will throw an error if you attempt to serialize a hardened object with Function properties that is not marked with Far/Remotable. The classification code (`passStyleOf`) will change from:
* use the nature of the object's properties to decide on which category is used (pass-by-copy vs pass-by-reference)
* assert that pass-by-copy has no functions, assert that pass-by-reference has no non-functions
to:
* use `getInterfaceOf` to decide whether we use pass-by-reference or pass-by-copy, which means only Far/Remotable-marked objects are pass-by-reference, and everything else is pass-by-copy
* assert that pass-by-copy has no functions
* for now, assert that pass-by-reference has no non-functions, but #2069 will add auxdata and remove this prohibition
We've marked a lot of Far objects already, and I have a batch of local changes to the dapp repos with some more to come. To find them all:
* uncomment the `marshal.js` lines that emit a warning and/or throw an error, at the end of the `case 'object'` clause of `passStyleOf()`, currently around line 479.
* run tests, add `Far` until they pass quietly, coming up with a plausible `interfaceName` for each
* once complete, change `passStyleOf()` to remove the tail case `assertRemotable(val); return REMOTE_STYLE`, and change `isPassByCopyRecord` to become `assertPassByCopyRecord`
## Test Plan
A few `test-marshal.js` cases will change: unmarked Function-bearing objects must be marked as `Far`/`Remotable`, whereas previously only *empty* objects needed such marking.
## Compatibility Issues
I *believe* we have consensus that this is a good approach, but it's pretty wide-ranging, and takes us further away from the E ideals of everything-is-an-object. So I'd like @dtribble @erights @katelynsills @Chris-Hibbert to confirm that we're willing to require all authors of contracts and vat code to declare *all* of their pass-by-reference objects with `Far`/`Remotable`.
cc @tyg since this needs to be part of the developer guidelines, if it isn't already
|
1.0
|
all pass-by-reference objects must be marked with Far - ## What is the Problem Being Solved?
#2018 was split up into two pieces. The original ticket remains concentrated on making empty (hardened) objects be pass-by-copy instead of pass-by-reference.
This new ticket is about making all pass-by-reference objects as `Far` (or `Remotable`). Once complete, `marshal` will throw an error if you attempt to serialize a hardened object with Function properties that is not marked with Far/Remotable. The classification code (`passStyleOf`) will change from:
* use the nature of the object's properties to decide on which category is used (pass-by-copy vs pass-by-reference)
* assert that pass-by-copy has no functions, assert that pass-by-reference has no non-functions
to:
* use `getInterfaceOf` to decide whether we use pass-by-reference or pass-by-copy, which means only Far/Remotable-marked objects are pass-by-reference, and everything else is pass-by-copy
* assert that pass-by-copy has no functions
* for now, assert that pass-by-reference has no non-functions, but #2069 will add auxdata and remove this prohibition
We've marked a lot of Far objects already, and I have a batch of local changes to the dapp repos with some more to come. To find them all:
* uncomment the `marshal.js` lines that emit a warning and/or throw an error, at the end of the `case 'object'` clause of `passStyleOf()`, currently around line 479.
* run tests, add `Far` until they pass quietly, coming up with a plausible `interfaceName` for each
* once complete, change `passStyleOf()` to remove the tail case `assertRemotable(val); return REMOTE_STYLE`, and change `isPassByCopyRecord` to become `assertPassByCopyRecord`
## Test Plan
A few `test-marshal.js` cases will change: unmarked Function-bearing objects must be marked as `Far`/`Remotable`, whereas previously only *empty* objects needed such marking.
## Compatibility Issues
I *believe* we have consensus that this is a good approach, but it's pretty wide-ranging, and takes us further away from the E ideals of everything-is-an-object. So I'd like @dtribble @erights @katelynsills @Chris-Hibbert to confirm that we're willing to require all authors of contracts and vat code to declare *all* of their pass-by-reference objects with `Far`/`Remotable`.
cc @tyg since this needs to be part of the developer guidelines, if it isn't already
|
non_test
|
all pass by reference objects must be marked with far what is the problem being solved was split up into two pieces the original ticket remains concentrated on making empty hardened objects be pass by copy instead of pass by reference this new ticket is about making all pass by reference objects as far or remotable once complete marshal will throw an error if you attempt to serialize a hardened object with function properties that is not marked with far remotable the classification code passstyleof will change from use the nature of the object s properties to decide on which category is used pass by copy vs pass by reference assert that pass by copy has no functions assert that pass by reference has no non functions to use getinterfaceof to decide whether we use pass by reference or pass by copy which means only far remotable marked objects are pass by reference and everything else is pass by copy assert that pass by copy has no functions for now assert that pass by reference has no non functions but will add auxdata and remove this prohibition we ve marked a lot of far objects already and i have a batch of local changes to the dapp repos with some more to come to find them all uncomment the marshal js lines that emit a warning and or throw an error at the end of the case object clause of passstyleof currently around line run tests add far until they pass quietly coming up with a plausible interfacename for each once complete change passstyleof to remove the tail case assertremotable val return remote style and change ispassbycopyrecord to become assertpassbycopyrecord test plan a few test marshal js cases will change unmarked function bearing objects must be marked as far remotable whereas previously only empty objects needed such marking compatibility issues i believe we have consensus that this is a good approach but it s pretty wide ranging and takes us further away from the e ideals of everything is an object so i d like dtribble erights katelynsills chris hibbert to confirm that we re willing to require all authors of contracts and vat code to declare all of their pass by reference objects with far remotable cc tyg since this needs to be part of the developer guidelines if it isn t already
| 0
|
98,653
| 8,683,664,350
|
IssuesEvent
|
2018-12-02 20:06:40
|
dwyl/product-owner-guide
|
https://api.github.com/repos/dwyl/product-owner-guide
|
closed
|
Create a keywords glossary so that new POs can understand agile terms
|
T1h please-test priority-2
|
Create a keywords glossary so that new POs can understand agile terms
E.g. Scrum Master, Backlog, UI, user testing
**Scrum Master**: tracks team progress, liaises with product owner on requirements, lends expertise on managing end to end projects, ensures features are tested when delivered and manages deployments in conjunction with technical architect and the team.
**Product backlog:** a prioritised features / to do list for the product found on github. See <-LINK TO BACKLOG SECTION ->
**Sprint Backlog**: the backlog that is aiming for completion within a given sprint period.
**Sprint**: a 1-3 week working lifecycle of planning, building, presentation and reflection. We tend to work in 2 week (10 working day) sprints.
**UI / User Interface**: how the site looks from a design perspective.
**User testing:** interviews, focus groups and other forms of research conducted with potential/actual users of your product to give feedback and provide insight into what the user's needs are. See https://github.com/dwyl/learn-user-experience-testing to learn more about user testing. ---- #15
**Milestone**: a visual way to group issues in github, at dwyl we create one milestone per sprint so we have somewhere to see all of the issues which we estimate to complete by the end of the sprint. See https://github.com/dwyl/github-reference for more.
|
1.0
|
Create a keywords glossary so that new POs can understand agile terms - Create a keywords glossary so that new POs can understand agile terms
E.g. Scrum Master, Backlog, UI, user testing
**Scrum Master**: tracks team progress, liaises with product owner on requirements, lends expertise on managing end to end projects, ensures features are tested when delivered and manages deployments in conjunction with technical architect and the team.
**Product backlog:** a prioritised features / to do list for the product found on github. See <-LINK TO BACKLOG SECTION ->
**Sprint Backlog**: the backlog that is aiming for completion within a given sprint period.
**Sprint**: a 1-3 week working lifecycle of planning, building, presentation and reflection. We tend to work in 2 week (10 working day) sprints.
**UI / User Interface**: how the site looks from a design perspective.
**User testing:** interviews, focus groups and other forms of research conducted with potential/actual users of your product to give feedback and provide insight into what the user's needs are. See https://github.com/dwyl/learn-user-experience-testing to learn more about user testing. ---- #15
**Milestone**: a visual way to group issues in github, at dwyl we create one milestone per sprint so we have somewhere to see all of the issues which we estimate to complete by the end of the sprint. See https://github.com/dwyl/github-reference for more.
|
test
|
create a keywords glossary so that new pos can understand agile terms create a keywords glossary so that new pos can understand agile terms e g scrum master backlog ui user testing scrum master tracks team progress liaises with product owner on requirements lends expertise on managing end to end projects ensures features are tested when delivered and manages deployments in conjunction with technical architect and the team product backlog a prioritised features to do list for the product found on github see sprint backlog the backlog that is aiming for completion within a given sprint period sprint a week working lifecycle of planning building presentation and reflection we tend to work in week working day sprints ui user interface how the site looks from a design perspective user testing interviews focus groups and other forms of research conducted with potential actual users of your product to give feedback and provide insight into what the user s needs are see to learn more about user testing milestone a visual way to group issues in github at dwyl we create one milestone per sprint so we have somewhere to see all of the issues which we estimate to complete by the end of the sprint see for more
| 1
|
5,489
| 3,600,294,750
|
IssuesEvent
|
2016-02-03 04:31:56
|
jeff1evesque/machine-learning
|
https://api.github.com/repos/jeff1evesque/machine-learning
|
closed
|
Adjust eslint for es6 'import' and 'export' statement
|
build enhancement
|
We need to ensure that we lint [es6](http://eslint.org/docs/user-guide/configuring#specifying-environments) syntax via our eslint. Otherwise, our travis build will yield [traceback](https://travis-ci.org/jeff1evesque/machine-learning/builds/98567316#L1024-L1043), which may look as follows:
```bash
/home/travis/build/jeff1evesque/machine-learning/src/jsx/require/data_upload_append.jsx
45:5 error Parsing error: Illegal export declaration
/home/travis/build/jeff1evesque/machine-learning/src/jsx/require/data_upload_new.jsx
39:5 error Parsing error: Illegal export declaration
```
|
1.0
|
Adjust eslint for es6 'import' and 'export' statement - We need to ensure that we lint [es6](http://eslint.org/docs/user-guide/configuring#specifying-environments) syntax via our eslint. Otherwise, our travis build will yield [traceback](https://travis-ci.org/jeff1evesque/machine-learning/builds/98567316#L1024-L1043), which may look as follows:
```bash
/home/travis/build/jeff1evesque/machine-learning/src/jsx/require/data_upload_append.jsx
45:5 error Parsing error: Illegal export declaration
/home/travis/build/jeff1evesque/machine-learning/src/jsx/require/data_upload_new.jsx
39:5 error Parsing error: Illegal export declaration
```
|
non_test
|
adjust eslint for import and export statement we need to ensure that we lint syntax via our eslint otherwise our travis build will yield which may look as follows bash home travis build machine learning src jsx require data upload append jsx error parsing error illegal export declaration home travis build machine learning src jsx require data upload new jsx error parsing error illegal export declaration
| 0
|
299,525
| 25,909,493,640
|
IssuesEvent
|
2022-12-15 12:55:32
|
elastic/kibana
|
https://api.github.com/repos/elastic/kibana
|
closed
|
Failing test: Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/spaces/spaces_selection·ts - Spaces app Spaces Spaces Data "after all" hook in "Spaces Data"
|
Team:Security loe:days failed-test impact:low
|
A test failed on a tracked branch
```
Error: retry.try timeout: TimeoutError: Waiting for element to be located By(css selector, [data-test-subj="removeSampleDataSetlogs"])
Wait timed out after 10017ms
at /dev/shm/workspace/kibana/node_modules/selenium-webdriver/lib/webdriver.js:841:17
at process._tickCallback (internal/process/next_tick.js:68:7)
at onFailure (/dev/shm/workspace/kibana/test/common/services/retry/retry_for_success.ts:28:9)
at retryForSuccess (/dev/shm/workspace/kibana/test/common/services/retry/retry_for_success.ts:68:13)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/1610/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/spaces/spaces_selection·ts","test.name":"Spaces app Spaces Spaces Data \"after all\" hook in \"Spaces Data\"","test.failCount":5}} -->
|
1.0
|
Failing test: Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/spaces/spaces_selection·ts - Spaces app Spaces Spaces Data "after all" hook in "Spaces Data" - A test failed on a tracked branch
```
Error: retry.try timeout: TimeoutError: Waiting for element to be located By(css selector, [data-test-subj="removeSampleDataSetlogs"])
Wait timed out after 10017ms
at /dev/shm/workspace/kibana/node_modules/selenium-webdriver/lib/webdriver.js:841:17
at process._tickCallback (internal/process/next_tick.js:68:7)
at onFailure (/dev/shm/workspace/kibana/test/common/services/retry/retry_for_success.ts:28:9)
at retryForSuccess (/dev/shm/workspace/kibana/test/common/services/retry/retry_for_success.ts:68:13)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/1610/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/spaces/spaces_selection·ts","test.name":"Spaces app Spaces Spaces Data \"after all\" hook in \"Spaces Data\"","test.failCount":5}} -->
|
test
|
failing test chrome x pack ui functional tests x pack test functional apps spaces spaces selection·ts spaces app spaces spaces data after all hook in spaces data a test failed on a tracked branch error retry try timeout timeouterror waiting for element to be located by css selector wait timed out after at dev shm workspace kibana node modules selenium webdriver lib webdriver js at process tickcallback internal process next tick js at onfailure dev shm workspace kibana test common services retry retry for success ts at retryforsuccess dev shm workspace kibana test common services retry retry for success ts first failure
| 1
|
286,483
| 31,652,431,731
|
IssuesEvent
|
2023-09-07 00:17:20
|
samq-wsdemo/vuln_rust
|
https://api.github.com/repos/samq-wsdemo/vuln_rust
|
opened
|
CVE-2022-0631 (Critical) detected in libnghttp2-sys-0.1.6+1.43.0.crate
|
Mend: dependency security vulnerability
|
## CVE-2022-0631 - Critical Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>libnghttp2-sys-0.1.6+1.43.0.crate</b></p></summary>
<p>FFI bindings for libnghttp2 (nghttp2)
</p>
<p>Library home page: <a href="https://crates.io/api/v1/crates/libnghttp2-sys/0.1.6+1.43.0/download">https://crates.io/api/v1/crates/libnghttp2-sys/0.1.6+1.43.0/download</a></p>
<p>Path to dependency file: /Cargo.toml</p>
<p>Path to vulnerable library: /home/wss-scanner/.cargo/registry/cache/github.com-1ecc6299db9ec823/libnghttp2-sys-0.1.6+1.43.0.crate</p>
<p>
Dependency Hierarchy:
- chttp-0.5.5.crate (Root Library)
- curl-0.4.35.crate
- curl-sys-0.4.41+curl-7.75.0.crate
- :x: **libnghttp2-sys-0.1.6+1.43.0.crate** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-wsdemo/vuln_rust/commit/bc1e0348ef35f7cc3dc098e04f8dd327c3adbcd3">bc1e0348ef35f7cc3dc098e04f8dd327c3adbcd3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Heap-based Buffer Overflow in Homebrew mruby prior to 3.2.
<p>Publish Date: 2022-02-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0631>CVE-2022-0631</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-02-18</p>
<p>Fix Resolution: 3.2.0</p>
</p>
</details>
<p></p>
|
True
|
CVE-2022-0631 (Critical) detected in libnghttp2-sys-0.1.6+1.43.0.crate - ## CVE-2022-0631 - Critical Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>libnghttp2-sys-0.1.6+1.43.0.crate</b></p></summary>
<p>FFI bindings for libnghttp2 (nghttp2)
</p>
<p>Library home page: <a href="https://crates.io/api/v1/crates/libnghttp2-sys/0.1.6+1.43.0/download">https://crates.io/api/v1/crates/libnghttp2-sys/0.1.6+1.43.0/download</a></p>
<p>Path to dependency file: /Cargo.toml</p>
<p>Path to vulnerable library: /home/wss-scanner/.cargo/registry/cache/github.com-1ecc6299db9ec823/libnghttp2-sys-0.1.6+1.43.0.crate</p>
<p>
Dependency Hierarchy:
- chttp-0.5.5.crate (Root Library)
- curl-0.4.35.crate
- curl-sys-0.4.41+curl-7.75.0.crate
- :x: **libnghttp2-sys-0.1.6+1.43.0.crate** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-wsdemo/vuln_rust/commit/bc1e0348ef35f7cc3dc098e04f8dd327c3adbcd3">bc1e0348ef35f7cc3dc098e04f8dd327c3adbcd3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Heap-based Buffer Overflow in Homebrew mruby prior to 3.2.
<p>Publish Date: 2022-02-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0631>CVE-2022-0631</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-02-18</p>
<p>Fix Resolution: 3.2.0</p>
</p>
</details>
<p></p>
|
non_test
|
cve critical detected in sys crate cve critical severity vulnerability vulnerable library sys crate ffi bindings for library home page a href path to dependency file cargo toml path to vulnerable library home wss scanner cargo registry cache github com sys crate dependency hierarchy chttp crate root library curl crate curl sys curl crate x sys crate vulnerable library found in head commit a href found in base branch master vulnerability details heap based buffer overflow in homebrew mruby prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution
| 0
|
7,021
| 2,871,359,006
|
IssuesEvent
|
2015-06-08 01:42:05
|
Atlantic777/mpudp
|
https://api.github.com/repos/Atlantic777/mpudp
|
closed
|
Send UDP on given interface to given IP
|
test
|
Setup pcap libs, build system and other things.
Open interfaces list and get valid IP interfaces (known eth and wlan for now).
Send UDP packet to the destination.
|
1.0
|
Send UDP on given interface to given IP - Setup pcap libs, build system and other things.
Open interfaces list and get valid IP interfaces (known eth and wlan for now).
Send UDP packet to the destination.
|
test
|
send udp on given interface to given ip setup pcap libs build system and other things open interfaces list and get valid ip interfaces known eth and wlan for now send udp packet to the destination
| 1
|
193,359
| 15,374,767,906
|
IssuesEvent
|
2021-03-02 14:12:49
|
fga-eps-mds/2020.2-Lend.it
|
https://api.github.com/repos/fga-eps-mds/2020.2-Lend.it
|
closed
|
Documento de arquitetura
|
ARQ documentation
|
## Descrição da Issue
Iniciar documentação de arquitetura do projeto.
referencias
* https://fga-eps-mds.github.io/2018.2-Kalkuli/docs/docArquitetura
* https://pax-app.github.io/Wiki/#/docs/DS/dinamica-e-seminario-4-b/DAS
## Tasks:
- [x] Introdução
- [x] Representação Arquitetural
- [x] Requisitos e Restrições Arquiteturais
- [x] Diagrama de Pacotes
- [x] Diagrama de Casos de Uso
## Critérios de Aceitação:
- [ ] Usar padrões da comunidade
- [ ] Documentar na wiki
|
1.0
|
Documento de arquitetura - ## Descrição da Issue
Iniciar documentação de arquitetura do projeto.
referencias
* https://fga-eps-mds.github.io/2018.2-Kalkuli/docs/docArquitetura
* https://pax-app.github.io/Wiki/#/docs/DS/dinamica-e-seminario-4-b/DAS
## Tasks:
- [x] Introdução
- [x] Representação Arquitetural
- [x] Requisitos e Restrições Arquiteturais
- [x] Diagrama de Pacotes
- [x] Diagrama de Casos de Uso
## Critérios de Aceitação:
- [ ] Usar padrões da comunidade
- [ ] Documentar na wiki
|
non_test
|
documento de arquitetura descrição da issue iniciar documentação de arquitetura do projeto referencias tasks introdução representação arquitetural requisitos e restrições arquiteturais diagrama de pacotes diagrama de casos de uso critérios de aceitação usar padrões da comunidade documentar na wiki
| 0
|
195,993
| 15,570,786,827
|
IssuesEvent
|
2021-03-17 03:24:11
|
CATcher-org/CATcher
|
https://api.github.com/repos/CATcher-org/CATcher
|
opened
|
Include steps to enable pop-ups in Safari in Usage Notes
|
aspect-Documentation
|
Pop-ups are blocked by default on Safari.
Safari users should be guided on how to enable pop-ups in their browser before using CATcher.
|
1.0
|
Include steps to enable pop-ups in Safari in Usage Notes - Pop-ups are blocked by default on Safari.
Safari users should be guided on how to enable pop-ups in their browser before using CATcher.
|
non_test
|
include steps to enable pop ups in safari in usage notes pop ups are blocked by default on safari safari users should be guided on how to enable pop ups in their browser before using catcher
| 0
|
401,207
| 11,787,311,306
|
IssuesEvent
|
2020-03-17 13:50:39
|
aivivn/d2l-vn
|
https://api.github.com/repos/aivivn/d2l-vn
|
closed
|
Revise "linear-regression-scratch_vn" - Phần 4
|
chapter:linear-networks priority:high status: phase 2
|
Phần này được dịch bởi:
* **quangnhat185**
* **thunguyenuehk39**
Nếu bạn đã dịch phần này, vui lòng bỏ qua việc revise.
|
1.0
|
Revise "linear-regression-scratch_vn" - Phần 4 - Phần này được dịch bởi:
* **quangnhat185**
* **thunguyenuehk39**
Nếu bạn đã dịch phần này, vui lòng bỏ qua việc revise.
|
non_test
|
revise linear regression scratch vn phần phần này được dịch bởi nếu bạn đã dịch phần này vui lòng bỏ qua việc revise
| 0
|
815,867
| 30,575,649,451
|
IssuesEvent
|
2023-07-21 05:03:44
|
NuGet/Home
|
https://api.github.com/repos/NuGet/Home
|
closed
|
dotnet list package errors with Object reference not set to an instance of an object
|
Priority:2 Type:Bug Product:dotnet.exe Functionality:ListPackage
|
### NuGet Product Used
dotnet.exe
### Product Version
all?
### Worked before?
_No response_
### Impact
It's more difficult to complete my work
### Repro Steps & Context
On very rare occasions (although somehow our CI test `DotnetListPackageTests.ListPackage_WithHttpSource_Warns` is hitting it very frequently), `dotnet list package`, with one of the arguments that makes HTTP requests (`--outdated`, `--vulnerable`, or `--deprecated`) will output a NullReferenceException message, followed by the help message
> error: Object reference not set to an instance of an object.
>
> Usage: NuGet.CommandLine.XPlat.dll package list [arguments] [options]
### Verbose Logs
_No response_
|
1.0
|
dotnet list package errors with Object reference not set to an instance of an object - ### NuGet Product Used
dotnet.exe
### Product Version
all?
### Worked before?
_No response_
### Impact
It's more difficult to complete my work
### Repro Steps & Context
On very rare occasions (although somehow our CI test `DotnetListPackageTests.ListPackage_WithHttpSource_Warns` is hitting it very frequently), `dotnet list package`, with one of the arguments that makes HTTP requests (`--outdated`, `--vulnerable`, or `--deprecated`) will output a NullReferenceException message, followed by the help message
> error: Object reference not set to an instance of an object.
>
> Usage: NuGet.CommandLine.XPlat.dll package list [arguments] [options]
### Verbose Logs
_No response_
|
non_test
|
dotnet list package errors with object reference not set to an instance of an object nuget product used dotnet exe product version all worked before no response impact it s more difficult to complete my work repro steps context on very rare occasions although somehow our ci test dotnetlistpackagetests listpackage withhttpsource warns is hitting it very frequently dotnet list package with one of the arguments that makes http requests outdated vulnerable or deprecated will output a nullreferenceexception message followed by the help message error object reference not set to an instance of an object usage nuget commandline xplat dll package list verbose logs no response
| 0
|
93,212
| 8,405,132,734
|
IssuesEvent
|
2018-10-11 14:33:53
|
Bantolomeus/bookmaster4000mkii
|
https://api.github.com/repos/Bantolomeus/bookmaster4000mkii
|
closed
|
write tests for challengeService
|
Test
|
I want tests for all use cases to see breaking functionality on changes and future implementations.
- [x] create test for getData
- [x] create test for saveChallenge if it is not completely covered in bookService tests
|
1.0
|
write tests for challengeService - I want tests for all use cases to see breaking functionality on changes and future implementations.
- [x] create test for getData
- [x] create test for saveChallenge if it is not completely covered in bookService tests
|
test
|
write tests for challengeservice i want tests for all use cases to see breaking functionality on changes and future implementations create test for getdata create test for savechallenge if it is not completely covered in bookservice tests
| 1
|
26,924
| 27,378,844,699
|
IssuesEvent
|
2023-02-28 08:36:53
|
pro3d-space/PRo3D
|
https://api.github.com/repos/pro3d-space/PRo3D
|
opened
|
Navigation Updates A
|
enhancement usability Mars 2020 MSL HERA Bookmarks
|
Allow to keep a predominant direction (upside-down in geographic coordinates?) for the transition between very much differing bookmarks (instead of dull interpolation that crosses a singularity) Optional: Keep a specific (Pivot) point in or close to the middle of the FoV
|
True
|
Navigation Updates A - Allow to keep a predominant direction (upside-down in geographic coordinates?) for the transition between very much differing bookmarks (instead of dull interpolation that crosses a singularity) Optional: Keep a specific (Pivot) point in or close to the middle of the FoV
|
non_test
|
navigation updates a allow to keep a predominant direction upside down in geographic coordinates for the transition between very much differing bookmarks instead of dull interpolation that crosses a singularity optional keep a specific pivot point in or close to the middle of the fov
| 0
|
308,093
| 9,430,097,283
|
IssuesEvent
|
2019-04-12 08:10:24
|
HGustavs/LenaSYS
|
https://api.github.com/repos/HGustavs/LenaSYS
|
closed
|
e-mail all students taking course
|
GruppB2019 activeGruppB2019 highPriority
|
We need a function for e-mailing all students in a course by generating a compose email in the same way as we do reset password but with many recipients
|
1.0
|
e-mail all students taking course - We need a function for e-mailing all students in a course by generating a compose email in the same way as we do reset password but with many recipients
|
non_test
|
e mail all students taking course we need a function for e mailing all students in a course by generating a compose email in the same way as we do reset password but with many recipients
| 0
|
43,561
| 13,020,407,562
|
IssuesEvent
|
2020-07-27 02:59:20
|
LightC0der/arunbhandari.github.io
|
https://api.github.com/repos/LightC0der/arunbhandari.github.io
|
opened
|
CVE-2015-9251 (Medium) detected in jquery-1.9.1.min.js
|
security vulnerability
|
## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.9.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.min.js</a></p>
<p>Path to vulnerable library: /arunbhandari.github.io/assets/js/vendor/jquery-1.9.1.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.9.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/LightC0der/arunbhandari.github.io/commit/241096b6dd14739925eca764bd8ab9a25a8003c6">241096b6dd14739925eca764bd8ab9a25a8003c6</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2015-9251 (Medium) detected in jquery-1.9.1.min.js - ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.9.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.min.js</a></p>
<p>Path to vulnerable library: /arunbhandari.github.io/assets/js/vendor/jquery-1.9.1.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.9.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/LightC0der/arunbhandari.github.io/commit/241096b6dd14739925eca764bd8ab9a25a8003c6">241096b6dd14739925eca764bd8ab9a25a8003c6</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library arunbhandari github io assets js vendor jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href vulnerability details jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource
| 0
|
120,048
| 25,729,054,831
|
IssuesEvent
|
2022-12-07 18:46:44
|
microsoft/vscode-cpptools
|
https://api.github.com/repos/microsoft/vscode-cpptools
|
closed
|
"final" specifier breaks formatting
|
bug Language Service fixed (release pending) Visual Studio Feature: Code Formatting
|
**Type: LanguageService**
<!----- Input information below ----->
Hello,
Am I on the right place to submit the following issue ?
On my VSCode editor on linux, using the "final" specifier breaks formatting
```
class API_INTERNAL IContext /*No final: it works */
{
protected:
virtual ~IContext() = default;
};
class API_INTERNAL Context final /* When using "final": it does not*/
: public IContext
{
}
```
Thanks,
Pascal
|
1.0
|
"final" specifier breaks formatting - **Type: LanguageService**
<!----- Input information below ----->
Hello,
Am I on the right place to submit the following issue ?
On my VSCode editor on linux, using the "final" specifier breaks formatting
```
class API_INTERNAL IContext /*No final: it works */
{
protected:
virtual ~IContext() = default;
};
class API_INTERNAL Context final /* When using "final": it does not*/
: public IContext
{
}
```
Thanks,
Pascal
|
non_test
|
final specifier breaks formatting type languageservice hello am i on the right place to submit the following issue on my vscode editor on linux using the final specifier breaks formatting class api internal icontext no final it works protected virtual icontext default class api internal context final when using final it does not public icontext thanks pascal
| 0
|
60,639
| 6,712,142,026
|
IssuesEvent
|
2017-10-13 08:13:27
|
mindwaveventures/cms
|
https://api.github.com/repos/mindwaveventures/cms
|
closed
|
Ability to move tags to bottom of page
|
please-test priority-5 T25m
|
On branded partner pages, such as Be Mindful & Sleepio, how easy would it be to move the tags to the bottom of the page?
|
1.0
|
Ability to move tags to bottom of page - On branded partner pages, such as Be Mindful & Sleepio, how easy would it be to move the tags to the bottom of the page?
|
test
|
ability to move tags to bottom of page on branded partner pages such as be mindful sleepio how easy would it be to move the tags to the bottom of the page
| 1
|
92,003
| 8,336,169,490
|
IssuesEvent
|
2018-09-28 06:44:46
|
opencart/opencart
|
https://api.github.com/repos/opencart/opencart
|
closed
|
SEO replace 'checkout/cart' and 'checkout/checkout'
|
Needs Testing
|
> SEO URL's can now replace any normal URL query and not just pre defind ones link product, category, manufacturer pages.
If you replace route 'checkout/cart' and 'checkout/checkout', then this lines doesn't work anymore:
https://github.com/opencart/opencart/blob/d572831caca12926b32652a4f354cd196a5b719d/upload/catalog/view/javascript/common.js#L198-L202
https://github.com/opencart/opencart/blob/d572831caca12926b32652a4f354cd196a5b719d/upload/catalog/view/javascript/common.js#L222-L226
|
1.0
|
SEO replace 'checkout/cart' and 'checkout/checkout' - > SEO URL's can now replace any normal URL query and not just pre defind ones link product, category, manufacturer pages.
If you replace route 'checkout/cart' and 'checkout/checkout', then this lines doesn't work anymore:
https://github.com/opencart/opencart/blob/d572831caca12926b32652a4f354cd196a5b719d/upload/catalog/view/javascript/common.js#L198-L202
https://github.com/opencart/opencart/blob/d572831caca12926b32652a4f354cd196a5b719d/upload/catalog/view/javascript/common.js#L222-L226
|
test
|
seo replace checkout cart and checkout checkout seo url s can now replace any normal url query and not just pre defind ones link product category manufacturer pages if you replace route checkout cart and checkout checkout then this lines doesn t work anymore
| 1
|
196,956
| 22,571,994,315
|
IssuesEvent
|
2022-06-28 01:44:32
|
yadavrahul12957/coupon
|
https://api.github.com/repos/yadavrahul12957/coupon
|
opened
|
CVE-2021-42740 (High) detected in shell-quote-1.6.1.tgz
|
security vulnerability
|
## CVE-2021-42740 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shell-quote-1.6.1.tgz</b></p></summary>
<p>quote and parse shell commands</p>
<p>Library home page: <a href="https://registry.npmjs.org/shell-quote/-/shell-quote-1.6.1.tgz">https://registry.npmjs.org/shell-quote/-/shell-quote-1.6.1.tgz</a></p>
<p>Path to dependency file: /coupon/package.json</p>
<p>Path to vulnerable library: /node_modules/shell-quote/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-2.1.8.tgz (Root Library)
- react-dev-utils-8.0.0.tgz
- :x: **shell-quote-1.6.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The shell-quote package before 1.7.3 for Node.js allows command injection. An attacker can inject unescaped shell metacharacters through a regex designed to support Windows drive letters. If the output of this package is passed to a real shell as a quoted argument to a command with exec(), an attacker can inject arbitrary commands. This is because the Windows drive letter regex character class is {A-z] instead of the correct {A-Za-z]. Several shell metacharacters exist in the space between capital letter Z and lower case letter a, such as the backtick character.
<p>Publish Date: 2021-10-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42740>CVE-2021-42740</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740</a></p>
<p>Release Date: 2021-10-21</p>
<p>Fix Resolution: shell-quote - 1.7.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-42740 (High) detected in shell-quote-1.6.1.tgz - ## CVE-2021-42740 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shell-quote-1.6.1.tgz</b></p></summary>
<p>quote and parse shell commands</p>
<p>Library home page: <a href="https://registry.npmjs.org/shell-quote/-/shell-quote-1.6.1.tgz">https://registry.npmjs.org/shell-quote/-/shell-quote-1.6.1.tgz</a></p>
<p>Path to dependency file: /coupon/package.json</p>
<p>Path to vulnerable library: /node_modules/shell-quote/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-2.1.8.tgz (Root Library)
- react-dev-utils-8.0.0.tgz
- :x: **shell-quote-1.6.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The shell-quote package before 1.7.3 for Node.js allows command injection. An attacker can inject unescaped shell metacharacters through a regex designed to support Windows drive letters. If the output of this package is passed to a real shell as a quoted argument to a command with exec(), an attacker can inject arbitrary commands. This is because the Windows drive letter regex character class is {A-z] instead of the correct {A-Za-z]. Several shell metacharacters exist in the space between capital letter Z and lower case letter a, such as the backtick character.
<p>Publish Date: 2021-10-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42740>CVE-2021-42740</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740</a></p>
<p>Release Date: 2021-10-21</p>
<p>Fix Resolution: shell-quote - 1.7.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in shell quote tgz cve high severity vulnerability vulnerable library shell quote tgz quote and parse shell commands library home page a href path to dependency file coupon package json path to vulnerable library node modules shell quote package json dependency hierarchy react scripts tgz root library react dev utils tgz x shell quote tgz vulnerable library vulnerability details the shell quote package before for node js allows command injection an attacker can inject unescaped shell metacharacters through a regex designed to support windows drive letters if the output of this package is passed to a real shell as a quoted argument to a command with exec an attacker can inject arbitrary commands this is because the windows drive letter regex character class is a z instead of the correct a za z several shell metacharacters exist in the space between capital letter z and lower case letter a such as the backtick character publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution shell quote step up your open source security game with mend
| 0
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.