Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3
values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17
values | text_combine stringlengths 95 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
736,616 | 25,480,210,315 | IssuesEvent | 2022-11-25 19:31:53 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | [Android] Failed Uphold tip still shows success screen in tipping banner | bug feature/rewards priority/P3 OS/Android feature/Uphold-wallet | ## Description
STR:
1. Staging
2. Verify with Uphold
3. Try to tip brave.com
4. This tip will fail according to logs
5. Success error message in tipping banner is still shown, which is incorrect
| 1.0 | [Android] Failed Uphold tip still shows success screen in tipping banner - ## Description
STR:
1. Staging
2. Verify with Uphold
3. Try to tip brave.com
4. This tip will fail according to logs
5. Success error message in tipping banner is still shown, which is incorrect
| non_test | failed uphold tip still shows success screen in tipping banner description str staging verify with uphold try to tip brave com this tip will fail according to logs success error message in tipping banner is still shown which is incorrect | 0 |
228,577 | 18,243,706,334 | IssuesEvent | 2021-10-01 15:39:13 | aces/Loris-MRI | https://api.github.com/repos/aces/Loris-MRI | closed | [Testing 24.0] - tools/remove_jiv_data_from_db_and_filesystem.pl ???? | Tools 24.0-testing | Not sure this is really relevant for release 24 given that JIV got killed at release 20.0... | 1.0 | [Testing 24.0] - tools/remove_jiv_data_from_db_and_filesystem.pl ???? - Not sure this is really relevant for release 24 given that JIV got killed at release 20.0... | test | tools remove jiv data from db and filesystem pl not sure this is really relevant for release given that jiv got killed at release | 1 |
308,252 | 23,240,151,424 | IssuesEvent | 2022-08-03 14:56:46 | zephyrproject-rtos/gsoc-2022-arduino-core | https://api.github.com/repos/zephyrproject-rtos/gsoc-2022-arduino-core | opened | Add Documentation | documentation | The Docs folder has already been created in https://github.com/zephyrproject-rtos/gsoc-2022-arduino-core/pull/20 but it is mostly written in markdown.
In future it may be better to shift to [Sphinx](https://www.sphinx-doc.org/) as it will look more professional and organised. Github also can build these docs and pub... | 1.0 | Add Documentation - The Docs folder has already been created in https://github.com/zephyrproject-rtos/gsoc-2022-arduino-core/pull/20 but it is mostly written in markdown.
In future it may be better to shift to [Sphinx](https://www.sphinx-doc.org/) as it will look more professional and organised. Github also can buil... | non_test | add documentation the docs folder has already been created in but it is mostly written in markdown in future it may be better to shift to as it will look more professional and organised github also can build these docs and publish them on a website see | 0 |
36,765 | 8,166,382,218 | IssuesEvent | 2018-08-25 08:10:48 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Stages/Transitions should not be always visible in article | No Code Attached Yet | ### Steps to reproduce the issue
- Create a new workflow
- Set it as default
- Delete the default workflow
- Go to articles
- click on the left site on "Stages"
### Problem
You cannot estimate the "active workflow" from the article view. The following PR broke the behavior: https://github.com/joomla/joomla-c... | 1.0 | Stages/Transitions should not be always visible in article - ### Steps to reproduce the issue
- Create a new workflow
- Set it as default
- Delete the default workflow
- Go to articles
- click on the left site on "Stages"
### Problem
You cannot estimate the "active workflow" from the article view. The follow... | non_test | stages transitions should not be always visible in article steps to reproduce the issue create a new workflow set it as default delete the default workflow go to articles click on the left site on stages problem you cannot estimate the active workflow from the article view the follow... | 0 |
654,787 | 21,664,050,078 | IssuesEvent | 2022-05-07 00:11:25 | o3de/o3de | https://api.github.com/repos/o3de/o3de | closed | Box selection in Entity Outliner leaves some entities selected even if the box does not hover over any entities | feature/editor kind/bug sig/content triage/accepted priority/minor | **Describe the bug**
The box selection in Entity Outliner does not deselect all entities if not hovering over any entity.
Please note that the issue does not occur when box selecting entities in the Viewport.
Please refer to the attached video for more details.
**Steps to reproduce**
Steps to reproduce the ... | 1.0 | Box selection in Entity Outliner leaves some entities selected even if the box does not hover over any entities - **Describe the bug**
The box selection in Entity Outliner does not deselect all entities if not hovering over any entity.
Please note that the issue does not occur when box selecting entities in the V... | non_test | box selection in entity outliner leaves some entities selected even if the box does not hover over any entities describe the bug the box selection in entity outliner does not deselect all entities if not hovering over any entity please note that the issue does not occur when box selecting entities in the v... | 0 |
156,736 | 5,988,434,004 | IssuesEvent | 2017-06-02 04:39:18 | vmware/vic | https://api.github.com/repos/vmware/vic | closed | Create container folders on datastore with the display name as created and shown in webclient instead of ID | area/ux area/vsphere priority/low | **User Statement:**
1. Create a container using docker command.
2. Automatically display name is picked and container gets created
3. On the compute datastore this display name is not retained but the folders are created with the ID
This is very inconvenient to look for container specific logs on the underlying... | 1.0 | Create container folders on datastore with the display name as created and shown in webclient instead of ID - **User Statement:**
1. Create a container using docker command.
2. Automatically display name is picked and container gets created
3. On the compute datastore this display name is not retained but the fold... | non_test | create container folders on datastore with the display name as created and shown in webclient instead of id user statement create a container using docker command automatically display name is picked and container gets created on the compute datastore this display name is not retained but the fold... | 0 |
43,011 | 5,513,240,736 | IssuesEvent | 2017-03-17 11:55:08 | restrictcontentpro/restrict-content-pro | https://api.github.com/repos/restrictcontentpro/restrict-content-pro | closed | Stripe customer balance should be removed if payment fails | bug has PR needs testing | When using signup fees:
If a member tries to subscribe and the customer credit card is attached to the Stripe customer object, but the actual charge fails, the customer balance is not adjusted.
If the customer tries again, a second balance is added to their Stripe customer object. This makes it possible for the c... | 1.0 | Stripe customer balance should be removed if payment fails - When using signup fees:
If a member tries to subscribe and the customer credit card is attached to the Stripe customer object, but the actual charge fails, the customer balance is not adjusted.
If the customer tries again, a second balance is added to t... | test | stripe customer balance should be removed if payment fails when using signup fees if a member tries to subscribe and the customer credit card is attached to the stripe customer object but the actual charge fails the customer balance is not adjusted if the customer tries again a second balance is added to t... | 1 |
27,410 | 5,346,002,999 | IssuesEvent | 2017-02-17 18:29:03 | digitalutsc/islandora_web_annotations | https://api.github.com/repos/digitalutsc/islandora_web_annotations | closed | Documentation: Islandora Simple Workflow permissions | documentation | When the Islandora Simple Workflow utility module is enabled, new objects (including AnnotationContainers) have an Inactive state in Fedora, which causes issues with the annotation creation workflow.
Create documentation for the workaround (see comment https://github.com/digitalutsc/islandora_web_annotations/issue... | 1.0 | Documentation: Islandora Simple Workflow permissions - When the Islandora Simple Workflow utility module is enabled, new objects (including AnnotationContainers) have an Inactive state in Fedora, which causes issues with the annotation creation workflow.
Create documentation for the workaround (see comment https:... | non_test | documentation islandora simple workflow permissions when the islandora simple workflow utility module is enabled new objects including annotationcontainers have an inactive state in fedora which causes issues with the annotation creation workflow create documentation for the workaround see comment | 0 |
305,808 | 9,377,333,310 | IssuesEvent | 2019-04-04 10:03:38 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.target.com - see bug description | browser-firefox-mobile priority-important | <!-- @browser: Firefox Mobile 65.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:65.0) Gecko/65.0 Firefox/65.0 -->
<!-- @reported_with: -->
**URL**: https://www.target.com/s?searchTerm=univeral+thread+shoes
**Browser / Version**: Firefox Mobile 65.0
**Operating System**: Android 6.0.1
**Tested Another ... | 1.0 | www.target.com - see bug description - <!-- @browser: Firefox Mobile 65.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:65.0) Gecko/65.0 Firefox/65.0 -->
<!-- @reported_with: -->
**URL**: https://www.target.com/s?searchTerm=univeral+thread+shoes
**Browser / Version**: Firefox Mobile 65.0
**Operating Sy... | non_test | see bug description url browser version firefox mobile operating system android tested another browser no problem type something else description the intruder that has invaded my phone won t allow my phone to load pages steps to reproduce the page i want... | 0 |
164,927 | 20,510,620,984 | IssuesEvent | 2022-03-01 05:51:34 | Nivaskumark/external_libavc | https://api.github.com/repos/Nivaskumark/external_libavc | opened | libavcandroid-10.0.0_r47: 16 vulnerabilities (highest severity is: 8.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>libavcandroid-10.0.0_r47</b></p></summary>
<p>
<p>Library home page: <a href=https://android.googlesource.com/platform/external/libavc>https://android.googlesource.co... | True | libavcandroid-10.0.0_r47: 16 vulnerabilities (highest severity is: 8.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>libavcandroid-10.0.0_r47</b></p></summary>
<p>
<p>Library home page: <a href=https://android... | non_test | libavcandroid vulnerabilities highest severity is vulnerable library libavcandroid library home page a href found in head commit a href vulnerable source files decoder parse pslice c vulnerabilities cve severity cvss ... | 0 |
133,738 | 10,861,489,024 | IssuesEvent | 2019-11-14 11:11:42 | cryptape/cita | https://api.github.com/repos/cryptape/cita | closed | Replace tx_tool | call for participation enhancement p:could-have test tool | ## Description
Use Rust SDK ~~or Python SDK~~.
## Additional Information
------------Chinese-----------
tx_tool 现在只有 CI 在使用,替换其他工具~~或者一个更好的 Python SDK~~
| 1.0 | Replace tx_tool - ## Description
Use Rust SDK ~~or Python SDK~~.
## Additional Information
------------Chinese-----------
tx_tool 现在只有 CI 在使用,替换其他工具~~或者一个更好的 Python SDK~~
| test | replace tx tool description use rust sdk or python sdk additional information chinese tx tool 现在只有 ci 在使用,替换其他工具 或者一个更好的 python sdk | 1 |
767,016 | 26,908,269,067 | IssuesEvent | 2023-02-06 21:02:38 | ak2yny/Official-Character-Pack-v2-for-Ultimate-Alliance | https://api.github.com/repos/ak2yny/Official-Character-Pack-v2-for-Ultimate-Alliance | opened | Combat music issues | Bug Low Priority | Report by Cyborg Sun
- I think these are known, but there are some issues with the combat music in some areas. Some examples off the top of my head are the outdoor areas in Heli 3 being glitchy, the music outright disabling when the water bucket is used in the Great Forge, and the music being too fast and high-pitch... | 1.0 | Combat music issues - Report by Cyborg Sun
- I think these are known, but there are some issues with the combat music in some areas. Some examples off the top of my head are the outdoor areas in Heli 3 being glitchy, the music outright disabling when the water bucket is used in the Great Forge, and the music being t... | non_test | combat music issues report by cyborg sun i think these are known but there are some issues with the combat music in some areas some examples off the top of my head are the outdoor areas in heli being glitchy the music outright disabling when the water bucket is used in the great forge and the music being t... | 0 |
63,527 | 6,849,108,007 | IssuesEvent | 2017-11-13 20:53:34 | GoogleCloudPlatform/google-cloud-ruby | https://api.github.com/repos/GoogleCloudPlatform/google-cloud-ruby | closed | Trace test warnings | api: trace testing type: cleanup | The Trace unit tests succeed, but the following errors are printed afterwards:
```
*******************************
*** google-cloud-trace test ***
*******************************
bundle exec rake test
[DEPRECATION] `last_comment` is deprecated. Please use `last_description` instead.
Run options: --seed 79... | 1.0 | Trace test warnings - The Trace unit tests succeed, but the following errors are printed afterwards:
```
*******************************
*** google-cloud-trace test ***
*******************************
bundle exec rake test
[DEPRECATION] `last_comment` is deprecated. Please use `last_description` instead.
... | test | trace test warnings the trace unit tests succeed but the following errors are printed afterwards google cloud trace test bundle exec rake test last comment is deprecated please use last description instead run options ... | 1 |
145,012 | 19,319,012,251 | IssuesEvent | 2021-12-14 01:49:49 | peterwkc85/selenium-jupiter | https://api.github.com/repos/peterwkc85/selenium-jupiter | opened | CVE-2019-14540 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2019-14540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2019-14540 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2019-14540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General... | non_test | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file selenium jupiter build gradle ... | 0 |
663,592 | 22,198,711,818 | IssuesEvent | 2022-06-07 09:15:36 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | readmanganato.com - see bug description | priority-important browser-fenix engine-gecko | <!-- @browser: Firefox Mobile 103.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 7.0; Mobile; rv:103.0) Gecko/103.0 Firefox/103.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/105452 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://readma... | 1.0 | readmanganato.com - see bug description - <!-- @browser: Firefox Mobile 103.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 7.0; Mobile; rv:103.0) Gecko/103.0 Firefox/103.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/105452 -->
<!-- @extra_labels: ... | non_test | readmanganato com see bug description url browser version firefox mobile operating system android tested another browser yes chrome problem type something else description the next button at the bottom disappear if i scroll into the comment section load anothe... | 0 |
230,826 | 7,614,312,124 | IssuesEvent | 2018-05-02 02:02:23 | MyMICDS/MyMICDS-v2 | https://api.github.com/repos/MyMICDS/MyMICDS-v2 | closed | Image upload certain images fail with vague error | bug effort: medium priority: it can wait work length: medium | Some images, when uploaded in settings, returns a vague error "There was a problem." | 1.0 | Image upload certain images fail with vague error - Some images, when uploaded in settings, returns a vague error "There was a problem." | non_test | image upload certain images fail with vague error some images when uploaded in settings returns a vague error there was a problem | 0 |
103,492 | 8,917,602,279 | IssuesEvent | 2019-01-20 06:08:51 | BradleyA/docker-scripts | https://api.github.com/repos/BradleyA/docker-scripts | closed | ./copy-user-2-remote-host.sh; test multiple times for port 22 timeout incident | additional testing bug | need to test ./copy-user-2-remote-host.sh multiple times because it seems like after 2 or 3 times port 22 closes and I had to reboot two.cptx86.com | 1.0 | ./copy-user-2-remote-host.sh; test multiple times for port 22 timeout incident - need to test ./copy-user-2-remote-host.sh multiple times because it seems like after 2 or 3 times port 22 closes and I had to reboot two.cptx86.com | test | copy user remote host sh test multiple times for port timeout incident need to test copy user remote host sh multiple times because it seems like after or times port closes and i had to reboot two com | 1 |
11,877 | 3,236,261,642 | IssuesEvent | 2015-10-14 03:18:29 | kdahlquist/GRNmap | https://api.github.com/repos/kdahlquist/GRNmap | opened | Slight discrepancy when running the code on different computers (Math dept. vs. Seaver lab) | data analysis functionality priority 0 testing | I recently ran the code on both the math department computers and Seaver lab computers and found out that when the code is run in the math department, the calculations are off up to the 4th decimal place. Since we the test files originated in Seaver, there were no differences when comparing the test files to what GRNma... | 1.0 | Slight discrepancy when running the code on different computers (Math dept. vs. Seaver lab) - I recently ran the code on both the math department computers and Seaver lab computers and found out that when the code is run in the math department, the calculations are off up to the 4th decimal place. Since we the test fil... | test | slight discrepancy when running the code on different computers math dept vs seaver lab i recently ran the code on both the math department computers and seaver lab computers and found out that when the code is run in the math department the calculations are off up to the decimal place since we the test files... | 1 |
8,022 | 7,189,719,566 | IssuesEvent | 2018-02-02 14:58:42 | sociomantic-tsunami/turtle | https://api.github.com/repos/sociomantic-tsunami/turtle | closed | D2: Automatically convert tags and push them | type-infrastructure | To move forward with D2 we need to provide automatically converted libraries for projects that are built only for D2.
Every time a new tag is pushed, we have to convert it to D2, tag the converted version with a `+d2` build metadata information appended (so tag `v2.3.4` --- conversion D2 ---> `v2.3.4+d2`) and push i... | 1.0 | D2: Automatically convert tags and push them - To move forward with D2 we need to provide automatically converted libraries for projects that are built only for D2.
Every time a new tag is pushed, we have to convert it to D2, tag the converted version with a `+d2` build metadata information appended (so tag `v2.3.4`... | non_test | automatically convert tags and push them to move forward with we need to provide automatically converted libraries for projects that are built only for every time a new tag is pushed we have to convert it to tag the converted version with a build metadata information appended so tag c... | 0 |
125,385 | 10,341,280,450 | IssuesEvent | 2019-09-04 01:32:16 | backdrop/backdrop-issues | https://api.github.com/repos/backdrop/backdrop-issues | closed | Core fieldable file entity bundles | pr - needs testing pr - ready to be committed status - has pull request type - feature request | Were working on adding all of the file_entity module to Backdrop core, including fieldable files.
### Before PR merge:
- [x] Convert file type info to config (move from DB table)
- [x] Remove the default alt and title fields provided out of box on the Image file type.
- [x] Make [UI changes](https://github.com... | 1.0 | Core fieldable file entity bundles - Were working on adding all of the file_entity module to Backdrop core, including fieldable files.
### Before PR merge:
- [x] Convert file type info to config (move from DB table)
- [x] Remove the default alt and title fields provided out of box on the Image file type.
- [x]... | test | core fieldable file entity bundles were working on adding all of the file entity module to backdrop core including fieldable files before pr merge convert file type info to config move from db table remove the default alt and title fields provided out of box on the image file type make ... | 1 |
69,298 | 17,619,703,035 | IssuesEvent | 2021-08-18 14:01:44 | hashicorp/packer-plugin-vmware | https://api.github.com/repos/hashicorp/packer-plugin-vmware | closed | cd_files not working properly on vmware-iso | bug builder/vmware | _This issue was originally opened by @t0rr3sp3dr0 as hashicorp/packer#10935. It was migrated here as a result of the [Packer plugin split](https://github.com/hashicorp/packer/issues/8610#issuecomment-770034737). The original body of the issue is below._
<hr>
#### Overview of the Issue
The latest version of Packer ... | 1.0 | cd_files not working properly on vmware-iso - _This issue was originally opened by @t0rr3sp3dr0 as hashicorp/packer#10935. It was migrated here as a result of the [Packer plugin split](https://github.com/hashicorp/packer/issues/8610#issuecomment-770034737). The original body of the issue is below._
<hr>
#### Overview... | non_test | cd files not working properly on vmware iso this issue was originally opened by as hashicorp packer it was migrated here as a result of the the original body of the issue is below overview of the issue the latest version of packer doesn t seem to attach the cd files generated iso to the vm up... | 0 |
31,261 | 6,476,435,573 | IssuesEvent | 2017-08-17 22:56:22 | oleg-shilo/cs-script | https://api.github.com/repos/oleg-shilo/cs-script | closed | Minor issue related to platform dependent line breaks, e.g. in error messages | defect done | Hi Oleg,
Minor issue related to the following code:
`throw new FileNotFoundException(string.Format("Could not find file \"{0}\".\nEnsure it is in one of the CS-Script search/probing directories.", file));`
`\n` may not be detected as good-enough line break, in my case resulting in an error message with neither... | 1.0 | Minor issue related to platform dependent line breaks, e.g. in error messages - Hi Oleg,
Minor issue related to the following code:
`throw new FileNotFoundException(string.Format("Could not find file \"{0}\".\nEnsure it is in one of the CS-Script search/probing directories.", file));`
`\n` may not be detected ... | non_test | minor issue related to platform dependent line breaks e g in error messages hi oleg minor issue related to the following code throw new filenotfoundexception string format could not find file nensure it is in one of the cs script search probing directories file n may not be detected ... | 0 |
181,996 | 14,086,444,831 | IssuesEvent | 2020-11-05 03:43:36 | krogowsk531/house-rules | https://api.github.com/repos/krogowsk531/house-rules | closed | Make CSS compatible with tests | Research priority: 1 test: unit | CSS will currently break tests. Below is some documentation we may want to look through.
https://jestjs.io/docs/en/webpack#handling-static-assets | 1.0 | Make CSS compatible with tests - CSS will currently break tests. Below is some documentation we may want to look through.
https://jestjs.io/docs/en/webpack#handling-static-assets | test | make css compatible with tests css will currently break tests below is some documentation we may want to look through | 1 |
212,143 | 16,420,483,782 | IssuesEvent | 2021-05-19 11:59:35 | mantidproject/mantid | https://api.github.com/repos/mantidproject/mantid | closed | Smoke Testing Updates for 6.1 release | Manual Tests | The first point is the only really important one, to try to get IDAaaS testing off the ground this release! The rest are just nice to have. Feel free to ask me for more explanation on any of these!
- [x] Add instructions for how to install a release candidate on Mantid Preprod environment on [IDAaaS test](https://isis... | 1.0 | Smoke Testing Updates for 6.1 release - The first point is the only really important one, to try to get IDAaaS testing off the ground this release! The rest are just nice to have. Feel free to ask me for more explanation on any of these!
- [x] Add instructions for how to install a release candidate on Mantid Preprod e... | test | smoke testing updates for release the first point is the only really important one to try to get idaaas testing off the ground this release the rest are just nice to have feel free to ask me for more explanation on any of these add instructions for how to install a release candidate on mantid preprod env... | 1 |
414,890 | 28,008,635,957 | IssuesEvent | 2023-03-27 16:55:18 | CarsOk/ADSO2698056PROJECT6 | https://api.github.com/repos/CarsOk/ADSO2698056PROJECT6 | closed | archivo de horas-semana-ivan | documentation | # yo como
Aprendiz sena
# quiero
cargar archivo con las horas de la semana
# para
evindenciar trabajo autonomo
# criterios de aceptacion
- [ ] archivo cargado en el sistema | 1.0 | archivo de horas-semana-ivan - # yo como
Aprendiz sena
# quiero
cargar archivo con las horas de la semana
# para
evindenciar trabajo autonomo
# criterios de aceptacion
- [ ] archivo cargado en el sistema | non_test | archivo de horas semana ivan yo como aprendiz sena quiero cargar archivo con las horas de la semana para evindenciar trabajo autonomo criterios de aceptacion archivo cargado en el sistema | 0 |
199,354 | 15,035,806,491 | IssuesEvent | 2021-02-02 14:33:44 | ucfopen/Obojobo | https://api.github.com/repos/ucfopen/Obojobo | closed | Stronger tests for KeyDownUtil.breakToText | enhancement testing | These tests simply ensure that various methods are called - Need to test to make sure the method converts the data structures as expected (Heading becomes a Heading and a Text Chunk, for example) | 1.0 | Stronger tests for KeyDownUtil.breakToText - These tests simply ensure that various methods are called - Need to test to make sure the method converts the data structures as expected (Heading becomes a Heading and a Text Chunk, for example) | test | stronger tests for keydownutil breaktotext these tests simply ensure that various methods are called need to test to make sure the method converts the data structures as expected heading becomes a heading and a text chunk for example | 1 |
135,753 | 11,016,708,024 | IssuesEvent | 2019-12-05 06:21:15 | microsoft/vscode-remote-release | https://api.github.com/repos/microsoft/vscode-remote-release | closed | Test: Remote Containers provisioning and startup performance | testplan-item | Test #1823
- [ ] linux @RMacfarlane
- [x] windows @roblourens
Complexity: 3
Use instructions [here](https://github.com/microsoft/vscode-remote-containers/blob/master/CONTRIBUTING.md#testing-remote-containers) to get a single container with a Dockerfile.
With a single container based on a Dockerfile, ena... | 1.0 | Test: Remote Containers provisioning and startup performance - Test #1823
- [ ] linux @RMacfarlane
- [x] windows @roblourens
Complexity: 3
Use instructions [here](https://github.com/microsoft/vscode-remote-containers/blob/master/CONTRIBUTING.md#testing-remote-containers) to get a single container with a Do... | test | test remote containers provisioning and startup performance test linux rmacfarlane windows roblourens complexity use instructions to get a single container with a dockerfile with a single container based on a dockerfile enable debug log level to get timings in the dev container ... | 1 |
267,557 | 23,306,754,337 | IssuesEvent | 2022-08-08 02:26:59 | apache/pulsar | https://api.github.com/repos/apache/pulsar | closed | Flaky-test: TransactionMetaStoreAssignmentTest.testTransactionMetaStoreAssignAndFailover | flaky-tests lifecycle/stale | <!---
Instructions for reporting a flaky test using this issue template:
1. Replace [test class] in title and body with the test class name
2. Replace [test method] in title and body with the test method that failed. Multiple methods are flaky, remove the content that refers to the test method.
3. Replace "url... | 1.0 | Flaky-test: TransactionMetaStoreAssignmentTest.testTransactionMetaStoreAssignAndFailover - <!---
Instructions for reporting a flaky test using this issue template:
1. Replace [test class] in title and body with the test class name
2. Replace [test method] in title and body with the test method that failed. Mult... | test | flaky test transactionmetastoreassignmenttest testtransactionmetastoreassignandfailover instructions for reporting a flaky test using this issue template replace in title and body with the test class name replace in title and body with the test method that failed multiple methods are flaky ... | 1 |
56,944 | 6,534,777,624 | IssuesEvent | 2017-08-31 12:17:13 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | [executor-service] ExecutorServiceTest.testExecutorServiceStats | Team: Core Type: Test-Failure | ```
java.lang.AssertionError: expected:<11> but was:<10>
at org.junit.Assert.fail(Assert.java:88)
at org.junit.Assert.failNotEquals(Assert.java:834)
at org.junit.Assert.assertEquals(Assert.java:645)
at org.junit.Assert.assertEquals(Assert.java:631)
at com.hazelcast.executor.ExecutorServiceTest.testExecutorSe... | 1.0 | [executor-service] ExecutorServiceTest.testExecutorServiceStats - ```
java.lang.AssertionError: expected:<11> but was:<10>
at org.junit.Assert.fail(Assert.java:88)
at org.junit.Assert.failNotEquals(Assert.java:834)
at org.junit.Assert.assertEquals(Assert.java:645)
at org.junit.Assert.assertEquals(Assert.java:6... | test | executorservicetest testexecutorservicestats java lang assertionerror expected but was at org junit assert fail assert java at org junit assert failnotequals assert java at org junit assert assertequals assert java at org junit assert assertequals assert java at com hazelcast executo... | 1 |
85 | 2,504,543,906 | IssuesEvent | 2015-01-10 09:59:35 | bitcoin/bitcoin | https://api.github.com/repos/bitcoin/bitcoin | closed | configure error on OSX: No working boost sleep implementation found | Bug Build system Priority Low | Trying to compile git head on OSX 10.7.5 with ```./configure --without-qt --disable-tests --disable-debug```, it fails with:
checking whether the Boost::Chrono library is available... yes
checking for exit in -lboost_chrono-mt... yes
configure: error: No working boost sleep implementation found
I ha... | 1.0 | configure error on OSX: No working boost sleep implementation found - Trying to compile git head on OSX 10.7.5 with ```./configure --without-qt --disable-tests --disable-debug```, it fails with:
checking whether the Boost::Chrono library is available... yes
checking for exit in -lboost_chrono-mt... yes
... | non_test | configure error on osx no working boost sleep implementation found trying to compile git head on osx with configure without qt disable tests disable debug it fails with checking whether the boost chrono library is available yes checking for exit in lboost chrono mt yes ... | 0 |
2,351 | 24,880,351,926 | IssuesEvent | 2022-10-28 00:03:10 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | StackOverflow in error handling under low memory conditions | area-System.Reflection.Metadata tenet-reliability no-recent-activity needs-author-action backlog-cleanup-candidate | Dump for this issue is here: https://drive.google.com/a/ayende.com/file/d/1f5HYZX3Q4-obubl6C1y4xKxcP5mCTMTV/view?usp=drive_web
We are testing our software under low memory conditions and we are seeing some crashes in this regard.
Related: https://github.com/dotnet/coreclr/issues/16004
We are testing what happens... | True | StackOverflow in error handling under low memory conditions - Dump for this issue is here: https://drive.google.com/a/ayende.com/file/d/1f5HYZX3Q4-obubl6C1y4xKxcP5mCTMTV/view?usp=drive_web
We are testing our software under low memory conditions and we are seeing some crashes in this regard.
Related: https://github.... | non_test | stackoverflow in error handling under low memory conditions dump for this issue is here we are testing our software under low memory conditions and we are seeing some crashes in this regard related we are testing what happens when we run out of room to allocate and how we can survive that and we start... | 0 |
112,870 | 9,604,513,886 | IssuesEvent | 2019-05-10 20:14:43 | emory-libraries/dlp-curate | https://api.github.com/repos/emory-libraries/dlp-curate | closed | Auto-suggest entries from the controlled vocabularies | Functional Test Software Engineering | - [ ] Ensure that properties with controlled vocabs can auto-suggest terms
- [ ] Extend or update the form's system test to show this works. | 1.0 | Auto-suggest entries from the controlled vocabularies - - [ ] Ensure that properties with controlled vocabs can auto-suggest terms
- [ ] Extend or update the form's system test to show this works. | test | auto suggest entries from the controlled vocabularies ensure that properties with controlled vocabs can auto suggest terms extend or update the form s system test to show this works | 1 |
212,983 | 16,506,076,241 | IssuesEvent | 2021-05-25 19:29:46 | trisacrypto/trisa | https://api.github.com/repos/trisacrypto/trisa | closed | Define and prototype address search algorithm | documentation enhancement wontfix | Define and prototype address search algorithm (perhaps with the Coinbase Bitcoin signing proof). | 1.0 | Define and prototype address search algorithm - Define and prototype address search algorithm (perhaps with the Coinbase Bitcoin signing proof). | non_test | define and prototype address search algorithm define and prototype address search algorithm perhaps with the coinbase bitcoin signing proof | 0 |
61,390 | 6,735,015,204 | IssuesEvent | 2017-10-18 20:09:49 | DevOps17-Bravo/orders | https://api.github.com/repos/DevOps17-Bravo/orders | closed | Action(cancel) on an order | test | **As a** customer
**I need to** be able to cancel an existed order
**So that** I can cancel the order and move it to history list
**Assumptions**:
- the order id of this order is provided
**Acceptance Criteria**:
**Given that** I am a customer with a valid order id
**When** I make a request to cancel... | 1.0 | Action(cancel) on an order - **As a** customer
**I need to** be able to cancel an existed order
**So that** I can cancel the order and move it to history list
**Assumptions**:
- the order id of this order is provided
**Acceptance Criteria**:
**Given that** I am a customer with a valid order id
**When... | test | action cancel on an order as a customer i need to be able to cancel an existed order so that i can cancel the order and move it to history list assumptions the order id of this order is provided acceptance criteria given that i am a customer with a valid order id when... | 1 |
248,058 | 20,992,268,789 | IssuesEvent | 2022-03-29 10:21:43 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | opened | Only display a successful activity log if selecting one of the source items on the 'Retry Azcopy' dialog regardless of whatever option is selected in the Overwrite part | 🧪 testing :gear: blobs :gear: files :gear: azcopy | **Storage Explorer Version**: 1.23.0
**Build Number**: 20220329.2
**Branch**: main
**Platform/OS**: Windows 10
**Architecture** ia32
**How Found**: From running test cases
**Regression From**: Not a regression
## Bug Description ##
Only display a successful activity log if selecting one of the source items on... | 1.0 | Only display a successful activity log if selecting one of the source items on the 'Retry Azcopy' dialog regardless of whatever option is selected in the Overwrite part - **Storage Explorer Version**: 1.23.0
**Build Number**: 20220329.2
**Branch**: main
**Platform/OS**: Windows 10
**Architecture** ia32
**How Found... | test | only display a successful activity log if selecting one of the source items on the retry azcopy dialog regardless of whatever option is selected in the overwrite part storage explorer version build number branch main platform os windows architecture how found from run... | 1 |
25,374 | 5,157,171,911 | IssuesEvent | 2017-01-16 04:54:06 | DecentralVan/decentral | https://api.github.com/repos/DecentralVan/decentral | opened | Determine what "successful meetup" means. | documentation events onboarding publicity | We agreed successful meetups are our best avenue for recruitment. Finalise the rules that activate reward bounties/perks.
- X new faces?
- Full explanation of the space ethos & opportunity.
- Full description on meetup.com 72hrs prior to event.
- Matching dctrl google calendar entry.
Discuss... | 1.0 | Determine what "successful meetup" means. - We agreed successful meetups are our best avenue for recruitment. Finalise the rules that activate reward bounties/perks.
- X new faces?
- Full explanation of the space ethos & opportunity.
- Full description on meetup.com 72hrs prior to event.
- Matching dctrl google c... | non_test | determine what successful meetup means we agreed successful meetups are our best avenue for recruitment finalise the rules that activate reward bounties perks x new faces full explanation of the space ethos opportunity full description on meetup com prior to event matching dctrl google calen... | 0 |
710,153 | 24,407,762,114 | IssuesEvent | 2022-10-05 09:30:39 | ngageoint/hootenanny | https://api.github.com/repos/ngageoint/hootenanny | opened | Translations: Deconflict historical and current features | Type: Bug Status: In Progress Priority: Medium Category: Translation Category: Schema | We handle `disused` features but sometimes the combination of disused and current features gives the wrong translation.
E.g. A disused railway that is now a highway should get translated to be a road not a railway.
| 1.0 | Translations: Deconflict historical and current features - We handle `disused` features but sometimes the combination of disused and current features gives the wrong translation.
E.g. A disused railway that is now a highway should get translated to be a road not a railway.
| non_test | translations deconflict historical and current features we handle disused features but sometimes the combination of disused and current features gives the wrong translation e g a disused railway that is now a highway should get translated to be a road not a railway | 0 |
63,762 | 6,884,447,785 | IssuesEvent | 2017-11-21 13:05:07 | SatelliteQE/robottelo | https://api.github.com/repos/SatelliteQE/robottelo | closed | CLI - name attribute not parsed from `auth-source ldap info` | 6.3 Medium test-failure | ```
KeyError: 'name'
```
```
2017-11-03 19:54:26 - robottelo.ssh - INFO - >>> LANG=en_US.UTF-8 hammer -v -u admin -p changeme auth-source ldap info --id="12"
2017-11-03 19:54:28 - robottelo.ssh - INFO - <<< stdout
Server:
Id: 12
Name: <hr>ARDvihNKTilFlIryL</hr>
Serv... | 1.0 | CLI - name attribute not parsed from `auth-source ldap info` - ```
KeyError: 'name'
```
```
2017-11-03 19:54:26 - robottelo.ssh - INFO - >>> LANG=en_US.UTF-8 hammer -v -u admin -p changeme auth-source ldap info --id="12"
2017-11-03 19:54:28 - robottelo.ssh - INFO - <<< stdout
Server:
Id: ... | test | cli name attribute not parsed from auth source ldap info keyerror name robottelo ssh info lang en us utf hammer v u admin p changeme auth source ldap info id robottelo ssh info stdout server id name... | 1 |
256,926 | 8,130,438,399 | IssuesEvent | 2018-08-17 18:28:59 | resin-io/resin-supervisor | https://api.github.com/repos/resin-io/resin-supervisor | closed | Unique key constraint violated | High priority type/bug | This bug prevents any control over the user container.
```
Jun 01 10:11:01 6c3b082 healthdog[10047]: [2018-06-01T10:11:01.622Z] Error reporting initial configuration, will retry { t: Unique key constraint violated
Jun 01 10:11:01 6c3b082 healthdog[10047]: at /usr/src/app/dist/app.js:387:252909
Jun 01 10:11:01... | 1.0 | Unique key constraint violated - This bug prevents any control over the user container.
```
Jun 01 10:11:01 6c3b082 healthdog[10047]: [2018-06-01T10:11:01.622Z] Error reporting initial configuration, will retry { t: Unique key constraint violated
Jun 01 10:11:01 6c3b082 healthdog[10047]: at /usr/src/app/dist/a... | non_test | unique key constraint violated this bug prevents any control over the user container jun healthdog error reporting initial configuration will retry t unique key constraint violated jun healthdog at usr src app dist app js jun healthdog at u usr src a... | 0 |
228,429 | 18,216,781,388 | IssuesEvent | 2021-09-30 06:00:40 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | sql/tests: TestRandomSyntaxFunctions failed | C-test-failure O-robot branch-master | sql/tests.TestRandomSyntaxFunctions [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3518574&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3518574&tab=artifacts#/) on master @ [ac885449c1fe74de23ea5d82858b3aa3674496f9](https://github.com/cockroachdb/cockroach/commits... | 1.0 | sql/tests: TestRandomSyntaxFunctions failed - sql/tests.TestRandomSyntaxFunctions [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3518574&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3518574&tab=artifacts#/) on master @ [ac885449c1fe74de23ea5d82858b3aa3674496f9](ht... | test | sql tests testrandomsyntaxfunctions failed sql tests testrandomsyntaxfunctions with on master random syntax error rsg test go crash detected server panic statement exec timeout query select crdb internal check consistency false x bytes x bytes repr... | 1 |
90,137 | 8,229,309,658 | IssuesEvent | 2018-09-07 08:59:08 | humera987/HumTestData | https://api.github.com/repos/humera987/HumTestData | reopened | project_fx_test : ApiV1AccountsPostCreate | project_fx_test | Project : project_fx_test
Job : Stg
Env : Stg
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 500
Headers : {}
Endpoint : http://13.57.51.56/api/v1/accounts
Request :
{
'accessKey' : null,
'accountType' : 'GitLab',
'allowedRegions' : [ ],
'createdBy' : null,
'createdDate' : nu... | 1.0 | project_fx_test : ApiV1AccountsPostCreate - Project : project_fx_test
Job : Stg
Env : Stg
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 500
Headers : {}
Endpoint : http://13.57.51.56/api/v1/accounts
Request :
{
'accessKey' : null,
'accountType' : 'GitLab',
'allowedRegions' : [ ]... | test | project fx test project project fx test job stg env stg region fxlabs us west result fail status code headers endpoint request accesskey null accounttype gitlab allowedregions createdby null createddate null id nu... | 1 |
199,168 | 15,026,204,876 | IssuesEvent | 2021-02-01 22:17:05 | rancher/dashboard | https://api.github.com/repos/rancher/dashboard | closed | SAML Auth Keycloak - I can enable keycloak but if I log out and login again I'm getting an error | [zube]: To Test area/authentication kind/bug | Enabling Keycloak is working in this same setup using Ember UI.
I noticed that when enabling from Dashboard I click enable and I don't get the usual Pop Up we get in Ember UI to authenticate with a User to finish enabling the Auth.
This also seems to create a principal which uid is invalid for the auth
`[ERRO... | 1.0 | SAML Auth Keycloak - I can enable keycloak but if I log out and login again I'm getting an error - Enabling Keycloak is working in this same setup using Ember UI.
I noticed that when enabling from Dashboard I click enable and I don't get the usual Pop Up we get in Ember UI to authenticate with a User to finish enabl... | test | saml auth keycloak i can enable keycloak but if i log out and login again i m getting an error enabling keycloak is working in this same setup using ember ui i noticed that when enabling from dashboard i click enable and i don t get the usual pop up we get in ember ui to authenticate with a user to finish enabl... | 1 |
126,468 | 10,423,750,476 | IssuesEvent | 2019-09-16 12:12:59 | tikv/tikv | https://api.github.com/repos/tikv/tikv | opened | unstable test: cases::test_replica_read::test_wait_for_apply_index' | C: Test/Bench T: Bug | I ran into it in a unrelated PR. Detail is here: https://internal.pingcap.net/idc-jenkins/blue/organizations/jenkins/tikv_ghpr_test/detail/tikv_ghpr_test/9016/pipeline
```
thread 'cases::test_replica_read::test_wait_for_apply_index' panicked at 'region Some(id: 1 region_epoch { conf_ver: 2 version: 1 } peers { id: ... | 1.0 | unstable test: cases::test_replica_read::test_wait_for_apply_index' - I ran into it in a unrelated PR. Detail is here: https://internal.pingcap.net/idc-jenkins/blue/organizations/jenkins/tikv_ghpr_test/detail/tikv_ghpr_test/9016/pipeline
```
thread 'cases::test_replica_read::test_wait_for_apply_index' panicked at '... | test | unstable test cases test replica read test wait for apply index i ran into it in a unrelated pr detail is here thread cases test replica read test wait for apply index panicked at region some id region epoch conf ver version peers id store id peers id store id ha... | 1 |
13,280 | 3,321,590,759 | IssuesEvent | 2015-11-09 09:52:09 | snaekobbi/sprints | https://api.github.com/repos/snaekobbi/sprints | closed | [4.5:84] When printing double-sided, there shall be support for hard page breaks that jump to the next right- or left-hand page. | 2 - Ready for test FAIL priority:1 | ### Requirement
[[4.5:84]](http://snaekobbi.github.io/requirements#4.5:84) When printing double-sided, there shall be support for hard page breaks that jump to the next right- or left-hand page.
## sprint#4
### Tasks
- [x] implementation
- [x] ~~Dotify~~
- [x] css-to-obfl: jump to right-hand page can be acc... | 1.0 | [4.5:84] When printing double-sided, there shall be support for hard page breaks that jump to the next right- or left-hand page. - ### Requirement
[[4.5:84]](http://snaekobbi.github.io/requirements#4.5:84) When printing double-sided, there shall be support for hard page breaks that jump to the next right- or left-hand... | test | when printing double sided there shall be support for hard page breaks that jump to the next right or left hand page requirement when printing double sided there shall be support for hard page breaks that jump to the next right or left hand page sprint tasks implementation ... | 1 |
583,666 | 17,395,317,513 | IssuesEvent | 2021-08-02 12:48:29 | microsoft/CogSLanguageUtilities | https://api.github.com/repos/microsoft/CogSLanguageUtilities | opened | update documentation/(code) | cognitive-search-integration enhancement high-priority | 1. deploy azure function
- remove publish profile so users won't get confused
2. azure function
- how to create azure function
- users must update model id
3. indexer command
- understand parameters
- configs.json (need to clarify it's for indexer.exe) | 1.0 | update documentation/(code) - 1. deploy azure function
- remove publish profile so users won't get confused
2. azure function
- how to create azure function
- users must update model id
3. indexer command
- understand parameters
- configs.json (need to clarify it's for indexer.exe) | non_test | update documentation code deploy azure function remove publish profile so users won t get confused azure function how to create azure function users must update model id indexer command understand parameters configs json need to clarify it s for indexer exe | 0 |
345,077 | 24,842,945,002 | IssuesEvent | 2022-10-26 13:58:46 | SAP-samples/btp-setup-automator | https://api.github.com/repos/SAP-samples/btp-setup-automator | closed | [BUG] Documentation of parameters | bug documentation github_actions | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Are you using the latest docker image for BTPSA?
- [X] I'm using the latest docker image for BTPSA.
### Which area is mainly impacted
Documentation
### Current Behavior
The `documentation of the parameters for the `usecase.jso... | 1.0 | [BUG] Documentation of parameters - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Are you using the latest docker image for BTPSA?
- [X] I'm using the latest docker image for BTPSA.
### Which area is mainly impacted
Documentation
### Current Behavior
The `documentation of... | non_test | documentation of parameters is there an existing issue for this i have searched the existing issues are you using the latest docker image for btpsa i m using the latest docker image for btpsa which area is mainly impacted documentation current behavior the documentation of the par... | 0 |
177,639 | 13,734,058,044 | IssuesEvent | 2020-10-05 08:07:17 | curl/curl | https://api.github.com/repos/curl/curl | closed | Test 2100 occasionally makes two POST requests | CI name lookup tests | ### I did this
I checked recent travis CI builds. Spotted that the ASAN builds often cause test 2100 to fail and the stderr output and HTTP server log then show that curl issued **two** DoH POSTs instead of the single expected one. The test runs with "forced IPv4" using `-4`.
[example log](https://travis-ci.org/g... | 1.0 | Test 2100 occasionally makes two POST requests - ### I did this
I checked recent travis CI builds. Spotted that the ASAN builds often cause test 2100 to fail and the stderr output and HTTP server log then show that curl issued **two** DoH POSTs instead of the single expected one. The test runs with "forced IPv4" usi... | test | test occasionally makes two post requests i did this i checked recent travis ci builds spotted that the asan builds often cause test to fail and the stderr output and http server log then show that curl issued two doh posts instead of the single expected one the test runs with forced using ... | 1 |
6,393 | 2,812,358,720 | IssuesEvent | 2015-05-18 08:09:46 | osakagamba/7GIQSKRNE5P3AVTZCEFXE3ON | https://api.github.com/repos/osakagamba/7GIQSKRNE5P3AVTZCEFXE3ON | closed | nXegAoxMY+ZS8N2WStROGJyI36QXvNVXwstRnh/dtTUyEWgmdkVuhk7nGWws6lhNy+80UXs66rP04bD62MFXdgYCVurTKnJZK+Jf2UHKycdZo57SVs6gm0QYP9EtRbx1ArEbKNHSpZmjCky7wt08CeXOK/OmJ48AvLLA8qivUzI= | design | WM78nQlVxFr5CHm69ZABA/aK3cO5n0dhNarbWxtXBTwovylppmVIh5+qguFSuTabDOn5s/2lJp4BuWFsqxP0buEqwPbWkTNurANbpqEDQ60LbBmF7UbqmlTFwl5Mz0F+awDxVlwA/tr2EizWV4xsGqynBdFZGRFtulrHB7CISV88mdfPu1Vz+URqJo0EHlwvWKzs+RQ+LWI1R9qPjIl8VdE3jwIkpBdlpRokV6dR9fUTwkD/pTbCVu86KzamV5OElMRJW1Mt7EpP784XFRvcLqOaM1TW0uu/GUV8IpqHAbkTsJybMikKS3qhIZD4jVXU... | 1.0 | nXegAoxMY+ZS8N2WStROGJyI36QXvNVXwstRnh/dtTUyEWgmdkVuhk7nGWws6lhNy+80UXs66rP04bD62MFXdgYCVurTKnJZK+Jf2UHKycdZo57SVs6gm0QYP9EtRbx1ArEbKNHSpZmjCky7wt08CeXOK/OmJ48AvLLA8qivUzI= - WM78nQlVxFr5CHm69ZABA/aK3cO5n0dhNarbWxtXBTwovylppmVIh5+qguFSuTabDOn5s/2lJp4BuWFsqxP0buEqwPbWkTNurANbpqEDQ60LbBmF7UbqmlTFwl5Mz0F+awDxVlwA/tr2EizWV... | non_test | nxegaoxmy awdxvlwa rq qlxjc ct fgsjdmmyzzr oele | 0 |
5,519 | 2,577,167,800 | IssuesEvent | 2015-02-12 15:32:59 | broadinstitute/orsp | https://api.github.com/repos/broadinstitute/orsp | closed | Funding Source Name(s) field not saved | bug priority ui | The "Funding Source Name(s)" field in IRB projects is not being saved at all. | 1.0 | Funding Source Name(s) field not saved - The "Funding Source Name(s)" field in IRB projects is not being saved at all. | non_test | funding source name s field not saved the funding source name s field in irb projects is not being saved at all | 0 |
309,532 | 26,667,572,621 | IssuesEvent | 2023-01-26 06:44:08 | open-telemetry/opentelemetry-collector-contrib | https://api.github.com/repos/open-telemetry/opentelemetry-collector-contrib | closed | [pkg/pdatatest] add more test for traces | enhancement pkg/pdatatest | ### Component(s)
pkg/pdatatest
### Is your feature request related to a problem? Please describe.
add more test for traces
### Describe the solution you'd like
add more test for traces
### Describe alternatives you've considered
_No response_
### Additional context
partly of #17544 | 1.0 | [pkg/pdatatest] add more test for traces - ### Component(s)
pkg/pdatatest
### Is your feature request related to a problem? Please describe.
add more test for traces
### Describe the solution you'd like
add more test for traces
### Describe alternatives you've considered
_No response_
### Additional context
p... | test | add more test for traces component s pkg pdatatest is your feature request related to a problem please describe add more test for traces describe the solution you d like add more test for traces describe alternatives you ve considered no response additional context partly of | 1 |
129,497 | 10,576,482,430 | IssuesEvent | 2019-10-07 17:58:20 | andes/app | https://api.github.com/repos/andes/app | closed | RUP - Consulta de Odontología (vinculaciones) | Testing | <!--
PASOS PARA REGISTRAR UN ISSUE
_____________________________________________
1) Seleccionar el proyecto al que pertenece (CITAS, RUP, MPI, ...)
2) Seleccionar un label de identificación (bug, feature, enhancement, etc.)
3) Asignar revisores que sean miembros del equipo responsable de solucionar el issue
... | 1.0 | RUP - Consulta de Odontología (vinculaciones) - <!--
PASOS PARA REGISTRAR UN ISSUE
_____________________________________________
1) Seleccionar el proyecto al que pertenece (CITAS, RUP, MPI, ...)
2) Seleccionar un label de identificación (bug, feature, enhancement, etc.)
3) Asignar revisores que sean miembros... | test | rup consulta de odontología vinculaciones pasos para registrar un issue seleccionar el proyecto al que pertenece citas rup mpi seleccionar un label de identificación bug feature enhancement etc asignar revisores que sean miembros... | 1 |
31,993 | 4,732,274,047 | IssuesEvent | 2016-10-19 07:07:54 | handsontable/handsontable | https://api.github.com/repos/handsontable/handsontable | closed | Mousewheel scrolling on fixed columns not working | Plugin: freeze / resize / move Priority: high Status: Released Tested Type: Bug | Hi, i've noticed that vertical scrolling doesn't work when you target a fixed column, but fixed rows works great.
I'm using Chrome on OS X, haven't checked if this is a general issue yet, but it should nevertheless still work in Chrome on OS X.
The issue is present in the latest demos: https://docs.handsontable.c... | 1.0 | Mousewheel scrolling on fixed columns not working - Hi, i've noticed that vertical scrolling doesn't work when you target a fixed column, but fixed rows works great.
I'm using Chrome on OS X, haven't checked if this is a general issue yet, but it should nevertheless still work in Chrome on OS X.
The issue is pres... | test | mousewheel scrolling on fixed columns not working hi i ve noticed that vertical scrolling doesn t work when you target a fixed column but fixed rows works great i m using chrome on os x haven t checked if this is a general issue yet but it should nevertheless still work in chrome on os x the issue is pres... | 1 |
123,355 | 10,264,984,127 | IssuesEvent | 2019-08-22 17:43:39 | microsoft/VFSForGit | https://api.github.com/repos/microsoft/VFSForGit | opened | Improve test coverage around symlinks | affects: tests platform: linux platform: macOS platform: windows pri2 | Recent issues (#1478, #1479) that were not caught by our tests highlight that we have room to improve our coverage around symlink scenarios.
Add tests that would have helped detect bugs where VFS4G and PrjFS were incorrectly following links when they should not. | 1.0 | Improve test coverage around symlinks - Recent issues (#1478, #1479) that were not caught by our tests highlight that we have room to improve our coverage around symlink scenarios.
Add tests that would have helped detect bugs where VFS4G and PrjFS were incorrectly following links when they should not. | test | improve test coverage around symlinks recent issues that were not caught by our tests highlight that we have room to improve our coverage around symlink scenarios add tests that would have helped detect bugs where and prjfs were incorrectly following links when they should not | 1 |
75,782 | 9,320,907,839 | IssuesEvent | 2019-03-27 01:25:19 | IanGRap/Squish | https://api.github.com/repos/IanGRap/Squish | closed | Walls should speed up the timer for when the compact during the match | design criticism | The wall should start compacting faster as the match progresses. | 1.0 | Walls should speed up the timer for when the compact during the match - The wall should start compacting faster as the match progresses. | non_test | walls should speed up the timer for when the compact during the match the wall should start compacting faster as the match progresses | 0 |
699,570 | 24,021,881,209 | IssuesEvent | 2022-09-15 08:21:20 | owid/etl | https://api.github.com/repos/owid/etl | opened | Consider using `pyright` for type checking | priority 3 - nice to have | Disclaimer - I'm satisfied with `mypy`, it's working well, I was just curious how does pyright compares in terms of speed.
Running mypy starts taking a long time. It takes more than 90s without mypy cache (in CI or my old laptop). It takes ~10s once cached, however in practice it rarely takes those 10s (perhaps we a... | 1.0 | Consider using `pyright` for type checking - Disclaimer - I'm satisfied with `mypy`, it's working well, I was just curious how does pyright compares in terms of speed.
Running mypy starts taking a long time. It takes more than 90s without mypy cache (in CI or my old laptop). It takes ~10s once cached, however in pra... | non_test | consider using pyright for type checking disclaimer i m satisfied with mypy it s working well i was just curious how does pyright compares in terms of speed running mypy starts taking a long time it takes more than without mypy cache in ci or my old laptop it takes once cached however in practic... | 0 |
269,796 | 23,466,253,889 | IssuesEvent | 2022-08-16 17:03:20 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Test failure: brave_browser_tests.xml.[empty] | ci-concern bot/type/test bot/arch/x64 bot/channel/nightly bot/platform/macos bot/branch/v1.44 | Greetings human!
Bad news. `brave_browser_tests.xml.[empty]` [failed on macos x64 nightly v1.44.15](https://ci.brave.com/job/brave-browser-build-macos-x64/5471/testReport/junit/brave_browser_tests/xml/test_browser____empty_).
<details>
<summary>Stack trace</summary>
```
Test report file /Users/jenkins/jenkins/workspa... | 1.0 | Test failure: brave_browser_tests.xml.[empty] - Greetings human!
Bad news. `brave_browser_tests.xml.[empty]` [failed on macos x64 nightly v1.44.15](https://ci.brave.com/job/brave-browser-build-macos-x64/5471/testReport/junit/brave_browser_tests/xml/test_browser____empty_).
<details>
<summary>Stack trace</summary>
```... | test | test failure brave browser tests xml greetings human bad news brave browser tests xml stack trace test report file users jenkins jenkins workspace brave browser build macos nightly src brave browser tests xml was length | 1 |
663,572 | 22,197,689,973 | IssuesEvent | 2022-06-07 08:27:04 | Stoobly/stoobly-agent | https://api.github.com/repos/Stoobly/stoobly-agent | closed | 'project list' requires proxy config | bug priority/important-soon | ```
$ stoobly-agent --version
stoobly-agent, version 0.9.5
$ stoobly-agent feature remote show
True
```
Without proxy config:
```
$ stoobly-agent project list ORG_KEY
Traceback (most recent call last):
File "/home/user/.local/bin/stoobly-agent", line 8, in <module>
sys.exit(main())
File "/us... | 1.0 | 'project list' requires proxy config - ```
$ stoobly-agent --version
stoobly-agent, version 0.9.5
$ stoobly-agent feature remote show
True
```
Without proxy config:
```
$ stoobly-agent project list ORG_KEY
Traceback (most recent call last):
File "/home/user/.local/bin/stoobly-agent", line 8, in <mod... | non_test | project list requires proxy config stoobly agent version stoobly agent version stoobly agent feature remote show true without proxy config stoobly agent project list org key traceback most recent call last file home user local bin stoobly agent line in ... | 0 |
133,512 | 10,832,370,454 | IssuesEvent | 2019-11-11 10:27:10 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | opened | The service items under Quick Access are not broken when MSAL is enabled | :gear: quick access 🧪 testing | **Storage Explorer Version:** 1.11.0
**Build:** [20191110.1](https://devdiv.visualstudio.com/DevDiv/_build/results?buildId=3231473)
**Branch**: hotfix/1.11.1
**Platform/OS:** Windows 10
**Architecture:** ia32/x64
**Regression From:** Not a regression
**Steps to reproduce:**
1. Launch Storage Explorer -> Add ... | 1.0 | The service items under Quick Access are not broken when MSAL is enabled - **Storage Explorer Version:** 1.11.0
**Build:** [20191110.1](https://devdiv.visualstudio.com/DevDiv/_build/results?buildId=3231473)
**Branch**: hotfix/1.11.1
**Platform/OS:** Windows 10
**Architecture:** ia32/x64
**Regression From:** Not a ... | test | the service items under quick access are not broken when msal is enabled storage explorer version build branch hotfix platform os windows architecture regression from not a regression steps to reproduce launch storage explorer add storage accou... | 1 |
27,528 | 4,320,178,958 | IssuesEvent | 2016-07-25 02:44:07 | zulip/zulip | https://api.github.com/repos/zulip/zulip | closed | GetOldMessagesTest.post_with_params -> GetOldMessagesTest.get_messages | help wanted testing | See #1315. I am just splitting it out into its own issue. This is also very closely tied to #1382 | 1.0 | GetOldMessagesTest.post_with_params -> GetOldMessagesTest.get_messages - See #1315. I am just splitting it out into its own issue. This is also very closely tied to #1382 | test | getoldmessagestest post with params getoldmessagestest get messages see i am just splitting it out into its own issue this is also very closely tied to | 1 |
157,397 | 12,372,058,221 | IssuesEvent | 2020-05-18 19:41:16 | golang/go | https://api.github.com/repos/golang/go | closed | x/tools: multiple tests consistently failing on "-nocgo" builders | NeedsInvestigation Testing Tools | [2020-05-18T17:24:58-c79c01b/darwin-amd64-nocgo](https://build.golang.org/log/9ba247877ecbed6e0bfc52742ed5960fc16cfc2f)
[2020-05-18T17:24:58-c79c01b/linux-amd64-nocgo](https://build.golang.org/log/f84b6968427003c6dff9b4acd311573170ceb6cf)
[2020-05-18T17:24:58-c79c01b/linux-ppc64-buildlet](https://build.golang.org/log... | 1.0 | x/tools: multiple tests consistently failing on "-nocgo" builders - [2020-05-18T17:24:58-c79c01b/darwin-amd64-nocgo](https://build.golang.org/log/9ba247877ecbed6e0bfc52742ed5960fc16cfc2f)
[2020-05-18T17:24:58-c79c01b/linux-amd64-nocgo](https://build.golang.org/log/f84b6968427003c6dff9b4acd311573170ceb6cf)
[2020-05-18... | test | x tools multiple tests consistently failing on nocgo builders linux nocgo at building tools at … fail testgeneratedfiles gorename test go cgo tool not available cgo not enabled cgo enabled fail fail golang org x tools cmd gorename … ... | 1 |
687,128 | 23,514,694,402 | IssuesEvent | 2022-08-18 20:02:40 | adisve/tumble-for-kronox | https://api.github.com/repos/adisve/tumble-for-kronox | closed | Add event details options button | enhancement good first issue High Priority | Add a button to the event details modal, that opens the same floating options as longPress, to help with accessibility (seeing as longPress isn't necessarily understood by the users) | 1.0 | Add event details options button - Add a button to the event details modal, that opens the same floating options as longPress, to help with accessibility (seeing as longPress isn't necessarily understood by the users) | non_test | add event details options button add a button to the event details modal that opens the same floating options as longpress to help with accessibility seeing as longpress isn t necessarily understood by the users | 0 |
29,459 | 4,501,258,322 | IssuesEvent | 2016-09-01 08:47:02 | mattbearman/lime | https://api.github.com/repos/mattbearman/lime | closed | BugMuncher Feedback Report | bug BugMuncher other test | ## Details ##
**Submitted:** January 04, 2016 14:29
**Category:** other
**Sender Email:** info@bugmuncher.com
**Website:** BugMuncher App
**URL:** https://beta.app.bugmuncher.com/profiles/25/notifiers
**Operating System:** Mac OS X Yosemite
**Browser:** Chrome 47.0.2526.106
**Browser Size:** 1280 x 1341
**User... | 1.0 | BugMuncher Feedback Report - ## Details ##
**Submitted:** January 04, 2016 14:29
**Category:** other
**Sender Email:** info@bugmuncher.com
**Website:** BugMuncher App
**URL:** https://beta.app.bugmuncher.com/profiles/25/notifiers
**Operating System:** Mac OS X Yosemite
**Browser:** Chrome 47.0.2526.106
**Browser... | test | bugmuncher feedback report details submitted january category other sender email info bugmuncher com website bugmuncher app url operating system mac os x yosemite browser chrome browser size x user agent mozilla macintosh intel ... | 1 |
107,918 | 13,530,171,228 | IssuesEvent | 2020-09-15 19:28:40 | cityofaustin/techstack | https://api.github.com/repos/cityofaustin/techstack | closed | Design Pin-up 9-15-20 | Team: Content Team: Design | Agenda
- [x] Revisit event page requirements and virtual events
What else is needed besides the ability to indicate a virtual event and offer a link to that virtual event?
Do physical locations still necessary, ie, might be both physical and virtual?
Any other fields necessary for virtual events other than the link... | 1.0 | Design Pin-up 9-15-20 - Agenda
- [x] Revisit event page requirements and virtual events
What else is needed besides the ability to indicate a virtual event and offer a link to that virtual event?
Do physical locations still necessary, ie, might be both physical and virtual?
Any other fields necessary for virtual ev... | non_test | design pin up agenda revisit event page requirements and virtual events what else is needed besides the ability to indicate a virtual event and offer a link to that virtual event do physical locations still necessary ie might be both physical and virtual any other fields necessary for virtual events... | 0 |
23,923 | 23,120,839,919 | IssuesEvent | 2022-07-27 21:17:50 | pulumi/pulumi | https://api.github.com/repos/pulumi/pulumi | closed | group `pulumi help` subcommands based on use-case | area/cli kind/enhancement impact/usability | ## Hello!
<!-- Please leave this section as-is, it's designed to help others in the community know how to interact with our GitHub issues. -->
- Vote on this issue by adding a 👍 reaction
- If you want to implement this feature, comment to let us know (we'll work with you on design, scheduling, etc.)
## Issue d... | True | group `pulumi help` subcommands based on use-case - ## Hello!
<!-- Please leave this section as-is, it's designed to help others in the community know how to interact with our GitHub issues. -->
- Vote on this issue by adding a 👍 reaction
- If you want to implement this feature, comment to let us know (we'll work... | non_test | group pulumi help subcommands based on use case hello vote on this issue by adding a 👍 reaction if you want to implement this feature comment to let us know we ll work with you on design scheduling etc issue details some internal discussion around improving the usability of the help com... | 0 |
627,449 | 19,905,279,630 | IssuesEvent | 2022-01-25 12:09:13 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Assertion thrown when running tests in debug on Android | bug priority/P3 QA/No release-notes/exclude feature/ads OS/Android | ```
C 660.252s Main ********************************************************************************
C 660.252s Main Detailed Logs
C 660.252s Main ********************************************************************************
C 660.260s Main [CRASH] BatAdsEligibleAdNotificationsV1Issue17199Test.GetEligibl... | 1.0 | Assertion thrown when running tests in debug on Android - ```
C 660.252s Main ********************************************************************************
C 660.252s Main Detailed Logs
C 660.252s Main ********************************************************************************
C 660.260s Main [CRASH... | non_test | assertion thrown when running tests in debug on android c main c main detailed logs c main c main geteligibleads c ... | 0 |
243,209 | 20,370,233,529 | IssuesEvent | 2022-02-21 10:29:42 | PolicyEngine/openfisca-us | https://api.github.com/repos/PolicyEngine/openfisca-us | opened | Investigate GainsTax $200 discrepancy in unit test | testing | GainsTax unit test 2 differs from tax-calc by $162. | 1.0 | Investigate GainsTax $200 discrepancy in unit test - GainsTax unit test 2 differs from tax-calc by $162. | test | investigate gainstax discrepancy in unit test gainstax unit test differs from tax calc by | 1 |
114,529 | 9,741,818,788 | IssuesEvent | 2019-06-02 12:12:14 | berkeleyinc/Golem | https://api.github.com/repos/berkeleyinc/Golem | closed | Wrong timing config/drone switch when cancel fleeing because threat is gone | DarkOrbit Testing needed bug | **Describe the bug**
Wrong config/drone switch after cancel fleeing because threat is gone.
**To Reproduce**
Use NPC Killer, wait for an enemy. Then wait for cancel fleeing because threat is gone.
**Expected behavior**
A clear and concise description of what you expected to happen.
**Screenshots**
If appl... | 1.0 | Wrong timing config/drone switch when cancel fleeing because threat is gone - **Describe the bug**
Wrong config/drone switch after cancel fleeing because threat is gone.
**To Reproduce**
Use NPC Killer, wait for an enemy. Then wait for cancel fleeing because threat is gone.
**Expected behavior**
A clear and c... | test | wrong timing config drone switch when cancel fleeing because threat is gone describe the bug wrong config drone switch after cancel fleeing because threat is gone to reproduce use npc killer wait for an enemy then wait for cancel fleeing because threat is gone expected behavior a clear and c... | 1 |
340,623 | 30,532,494,979 | IssuesEvent | 2023-07-19 15:05:16 | guram-asanidze-1-btu-edu-ge/shualeduri | https://api.github.com/repos/guram-asanidze-1-btu-edu-ge/shualeduri | opened | 4e30825 failed unit and formatting tests. | ci-pytest ci-black | Automatically generated message
4e3082507e337c11405613425b22be4d682bf9c3 failed unit and formatting tests.
bfe21ef PYTEST Error commit
54ce250 BLACK Error commit
Pytest report: https://guram-asanidze-1-btu-edu-ge.github.io/shualeduri-ci/4e3082507e337c11405613425b22be4d682bf9c3-1689779108/pyte... | 1.0 | 4e30825 failed unit and formatting tests. - Automatically generated message
4e3082507e337c11405613425b22be4d682bf9c3 failed unit and formatting tests.
bfe21ef PYTEST Error commit
54ce250 BLACK Error commit
Pytest report: https://guram-asanidze-1-btu-edu-ge.github.io/shualeduri-ci/4e3082507e33... | test | failed unit and formatting tests automatically generated message failed unit and formatting tests pytest error commit black error commit pytest report black report | 1 |
41,380 | 5,354,368,399 | IssuesEvent | 2017-02-20 09:43:26 | QualiSystems/OpenStack-Shell | https://api.github.com/repos/QualiSystems/OpenStack-Shell | closed | Cancellation support for OpenStack "deploy from glance" deployment option | 7.2 F-VM Deployment In Testing Test Plan Ready | We would like the OpenStack "deploy from glance" deployment option to have cancellation support so users will be able to cancel the deployment if needed and the system will be able end the sandbox setup in case needed.
@gabhijit-izel - please reefer to AWS or azure deployment options for example implementation. | 2.0 | Cancellation support for OpenStack "deploy from glance" deployment option - We would like the OpenStack "deploy from glance" deployment option to have cancellation support so users will be able to cancel the deployment if needed and the system will be able end the sandbox setup in case needed.
@gabhijit-izel - plea... | test | cancellation support for openstack deploy from glance deployment option we would like the openstack deploy from glance deployment option to have cancellation support so users will be able to cancel the deployment if needed and the system will be able end the sandbox setup in case needed gabhijit izel plea... | 1 |
722,010 | 24,847,062,612 | IssuesEvent | 2022-10-26 16:42:12 | tradingstrategy-ai/frontend | https://api.github.com/repos/tradingstrategy-ai/frontend | closed | Return 404 Not Found for URLs ending in "/" | priority: P1 size: S | Currently, a URL ending in a `/` will receive a `301 Moved Permanently` redirect to the equivalent URL minus the `/`. This is undesirable due to how it is interpreted by Google Search for SEO purposes. Instead, we should return `404 Not Found` error for requests ending in `/`'
Investigate where this slash-redirect b... | 1.0 | Return 404 Not Found for URLs ending in "/" - Currently, a URL ending in a `/` will receive a `301 Moved Permanently` redirect to the equivalent URL minus the `/`. This is undesirable due to how it is interpreted by Google Search for SEO purposes. Instead, we should return `404 Not Found` error for requests ending in `... | non_test | return not found for urls ending in currently a url ending in a will receive a moved permanently redirect to the equivalent url minus the this is undesirable due to how it is interpreted by google search for seo purposes instead we should return not found error for requests ending in ... | 0 |
297,327 | 25,720,527,902 | IssuesEvent | 2022-12-07 13:23:44 | pulp/Pulp-2-Tests | https://api.github.com/repos/pulp/Pulp-2-Tests | closed | Adds task-ids to logs | Issue Type: Test Case | > Migrated from https://github.com/PulpQE/pulp-smash/issues/483
> author: @bmbouter - https://github.com/bmbouter
> date created: 2017-01-13T20:34:21Z
This is for story: https://pulp.plan.io/issues/2324
### Verify a log statement running inside a task
1. Sync the zoo repo: `pulp-admin rpm repo sync run --repo-... | 1.0 | Adds task-ids to logs - > Migrated from https://github.com/PulpQE/pulp-smash/issues/483
> author: @bmbouter - https://github.com/bmbouter
> date created: 2017-01-13T20:34:21Z
This is for story: https://pulp.plan.io/issues/2324
### Verify a log statement running inside a task
1. Sync the zoo repo: `pulp-admin r... | test | adds task ids to logs migrated from author bmbouter date created this is for story verify a log statement running inside a task sync the zoo repo pulp admin rpm repo sync run repo id zoo verify that you see the log statement pulp rpm plugins importers yum sync i... | 1 |
31,651 | 7,431,184,580 | IssuesEvent | 2018-03-25 12:15:16 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] Modals broken when trying to associate menu items | J4 Issue No Code Attached Yet | Create a multilang site with menu items tagged to different languages.
Associations should be enabled in the languagefilter.
Edit a menu item in one language (can be done with the Home).
Go to Associations tag
Whether one chooses Select/Create (depending on situation), the modal does not respect the task.
Selec... | 1.0 | [4.0] Modals broken when trying to associate menu items - Create a multilang site with menu items tagged to different languages.
Associations should be enabled in the languagefilter.
Edit a menu item in one language (can be done with the Home).
Go to Associations tag
Whether one chooses Select/Create (depending ... | non_test | modals broken when trying to associate menu items create a multilang site with menu items tagged to different languages associations should be enabled in the languagefilter edit a menu item in one language can be done with the home go to associations tag whether one chooses select create depending on s... | 0 |
86,818 | 8,051,130,707 | IssuesEvent | 2018-08-01 15:15:51 | syndesisio/syndesis | https://api.github.com/repos/syndesisio/syndesis | closed | Logout on firefox does not work correctly | cat/bug prio/p1 qe/logout-test | I tried new logout endpoint on firefox from anonymous window and it does not work.
After I log out, I am on logout page. Then when I click on Login button, this happens:
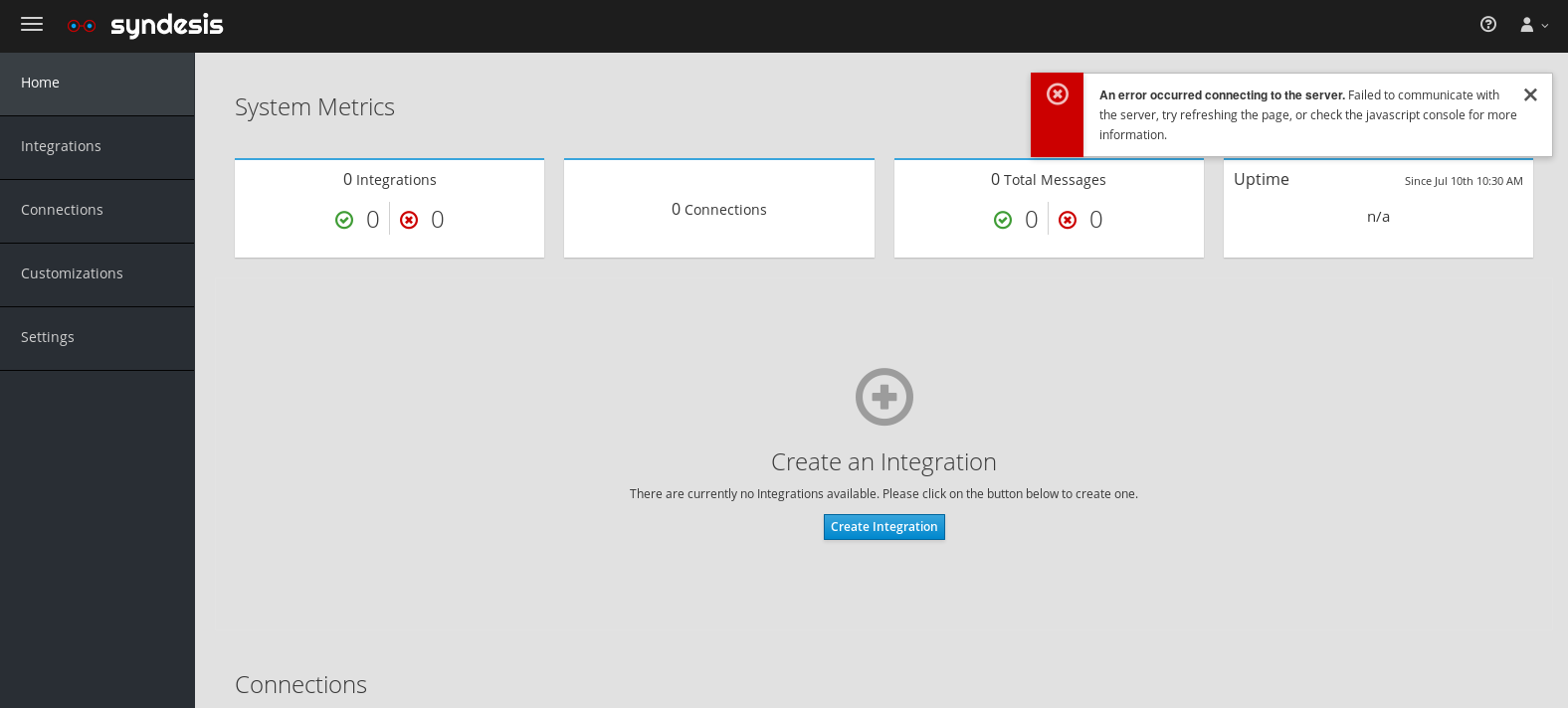
Console looked li... | 1.0 | Logout on firefox does not work correctly - I tried new logout endpoint on firefox from anonymous window and it does not work.
After I log out, I am on logout page. Then when I click on Login button, this happens:

2. В ОДНОМ РЕПОРТЕ ДОЛЖНО БЫТЬ ОПИСАНИЕ ТОЛЬКО ОДНОЙ ПРОБЛЕМЫ
3. КОРРЕКТНОЕ НАЗВАНИЕ РЕПОРТА НЕ МЕНЕЕ ВАЖНО ЧЕМ ОПИСАНИЕ
-. Ниже описание каждого пункта.
1. Весь данный текст что уже написан до вас -
НЕ УДАЛЯТЬ И НЕ Р... | 1.0 | Можно реанимировать людей без головы. - <!--
1. ОТВЕТЫ ОСТАВЛЯТЬ ПОД СООТВЕТСТВУЮЩИЕ ЗАГОЛОВКИ
(они в самом низу, после всех правил)
2. В ОДНОМ РЕПОРТЕ ДОЛЖНО БЫТЬ ОПИСАНИЕ ТОЛЬКО ОДНОЙ ПРОБЛЕМЫ
3. КОРРЕКТНОЕ НАЗВАНИЕ РЕПОРТА НЕ МЕНЕЕ ВАЖНО ЧЕМ ОПИСАНИЕ
-. Ниже описание каждого пункта.
1. Весь данный текст что... | non_test | можно реанимировать людей без головы ответы оставлять под соответствующие заголовки они в самом низу после всех правил в одном репорте должно быть описание только одной проблемы корректное название репорта не менее важно чем описание ниже описание каждого пункта весь данный текст что... | 0 |
102,306 | 8,824,300,369 | IssuesEvent | 2019-01-02 16:32:55 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | Able to see catalog apps from another projects catalog | area/catalog area/ui kind/bug-qa priority/0 status/resolved status/to-test team/az version/2.0 | Version: master 2.2 (12/17/18)
**What kind of request is this (question/bug/enhancement/feature request):**
Bug
**Steps to reproduce (least amount of steps as possible):**
- Add a catalog to a project. In my case I added https://github.com/tfiduccia/charts to my "catalogs" project with project scope so only thi... | 1.0 | Able to see catalog apps from another projects catalog - Version: master 2.2 (12/17/18)
**What kind of request is this (question/bug/enhancement/feature request):**
Bug
**Steps to reproduce (least amount of steps as possible):**
- Add a catalog to a project. In my case I added https://github.com/tfiduccia/chart... | test | able to see catalog apps from another projects catalog version master what kind of request is this question bug enhancement feature request bug steps to reproduce least amount of steps as possible add a catalog to a project in my case i added to my catalogs project with proje... | 1 |
291,497 | 25,152,184,369 | IssuesEvent | 2022-11-10 10:50:04 | octue/django-gcp | https://api.github.com/repos/octue/django-gcp | closed | Include Django 4.x in testing | dependencies devops test | ## Feature request
### Use Case
We currently only test on django 3.2 (the LTS version at the time of writing). Testing on Django 4.x is necessary to enable smooth upgrades to Django 4 for users of the application.
### Proposed solution
Extend the range of django that gets installed (see the `tox.ini` file... | 1.0 | Include Django 4.x in testing - ## Feature request
### Use Case
We currently only test on django 3.2 (the LTS version at the time of writing). Testing on Django 4.x is necessary to enable smooth upgrades to Django 4 for users of the application.
### Proposed solution
Extend the range of django that gets i... | test | include django x in testing feature request use case we currently only test on django the lts version at the time of writing testing on django x is necessary to enable smooth upgrades to django for users of the application proposed solution extend the range of django that gets i... | 1 |
2,348 | 8,394,096,878 | IssuesEvent | 2018-10-09 22:52:33 | MDAnalysis/mdanalysis | https://api.github.com/repos/MDAnalysis/mdanalysis | opened | Use versioneer (or similar) | Difficulty-easy maintainability release | Part of reducing release "friction".
The current method of incrementing the version number of the package involves editing 5 separate files*. This could be better. There is a script in `maintainer/` but it doesn't seem to work for me? (seems to `cat` a lot of the directory, no changes visible in git afterwards).
... | True | Use versioneer (or similar) - Part of reducing release "friction".
The current method of incrementing the version number of the package involves editing 5 separate files*. This could be better. There is a script in `maintainer/` but it doesn't seem to work for me? (seems to `cat` a lot of the directory, no change... | non_test | use versioneer or similar part of reducing release friction the current method of incrementing the version number of the package involves editing separate files this could be better there is a script in maintainer but it doesn t seem to work for me seems to cat a lot of the directory no change... | 0 |
255,204 | 21,912,100,899 | IssuesEvent | 2022-05-21 07:55:18 | bitcoin/bitcoin | https://api.github.com/repos/bitcoin/bitcoin | closed | Tracking and reporting failures and repeated flakiness of functional tests | Brainstorming Tests | I'm sure anyone who runs the functional tests regularly will experience occasional failures. Often you run those failed tests again and they will pass. Occasionally a functional test will repeatedly fail which is more concerning. It is difficult to assess whether others are experiencing the same flakiness and/or repeat... | 1.0 | Tracking and reporting failures and repeated flakiness of functional tests - I'm sure anyone who runs the functional tests regularly will experience occasional failures. Often you run those failed tests again and they will pass. Occasionally a functional test will repeatedly fail which is more concerning. It is diffic... | test | tracking and reporting failures and repeated flakiness of functional tests i m sure anyone who runs the functional tests regularly will experience occasional failures often you run those failed tests again and they will pass occasionally a functional test will repeatedly fail which is more concerning it is diffic... | 1 |
283,327 | 21,316,107,519 | IssuesEvent | 2022-04-16 09:54:23 | edemirkirkan/pe | https://api.github.com/repos/edemirkirkan/pe | opened | DG - Lack of UML and Object Diagrams | type.DocumentationBug severity.Medium | I can see your sequential diagram, it is very well drawn and explained, however, you should also add UML and Object Diagrams to your developer guide so that developers entering the project after can understand the structure of the project more clearly.
<!--session: 1650094817731-931bde6d-a783-4b87-b44b-91cc8c291395--... | 1.0 | DG - Lack of UML and Object Diagrams - I can see your sequential diagram, it is very well drawn and explained, however, you should also add UML and Object Diagrams to your developer guide so that developers entering the project after can understand the structure of the project more clearly.
<!--session: 1650094817731... | non_test | dg lack of uml and object diagrams i can see your sequential diagram it is very well drawn and explained however you should also add uml and object diagrams to your developer guide so that developers entering the project after can understand the structure of the project more clearly | 0 |
31,965 | 13,696,609,506 | IssuesEvent | 2020-10-01 00:34:00 | microsoft/botbuilder-dotnet | https://api.github.com/repos/microsoft/botbuilder-dotnet | closed | Accessing UserState/ConversationState properties | Area: Adaptive Bot Services customer-replied-to customer-reported | Hi all,
I'm trying to set up a little bot architecture, where botframework composer will act as the leading part (easy deployment + set up). Im coding my own directline chat at the moment and trying to pass data objects around via webviews that will also be used by the facebook chat.
I came up with a little "midd... | 1.0 | Accessing UserState/ConversationState properties - Hi all,
I'm trying to set up a little bot architecture, where botframework composer will act as the leading part (easy deployment + set up). Im coding my own directline chat at the moment and trying to pass data objects around via webviews that will also be used by ... | non_test | accessing userstate conversationstate properties hi all i m trying to set up a little bot architecture where botframework composer will act as the leading part easy deployment set up im coding my own directline chat at the moment and trying to pass data objects around via webviews that will also be used by ... | 0 |
27,776 | 11,564,301,989 | IssuesEvent | 2020-02-20 08:21:09 | RadkappenJoe/WebGoat | https://api.github.com/repos/RadkappenJoe/WebGoat | opened | CVE-2018-11693 (High) detected in opennms-opennms-source-22.0.1-1 | security vulnerability | ## CVE-2018-11693 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opennmsopennms-source-22.0.1-1</b></p></summary>
<p>
<p>A Java based fault and performance management system</p>
<p>Li... | True | CVE-2018-11693 (High) detected in opennms-opennms-source-22.0.1-1 - ## CVE-2018-11693 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opennmsopennms-source-22.0.1-1</b></p></summary>
<p... | non_test | cve high detected in opennms opennms source cve high severity vulnerability vulnerable library opennmsopennms source a java based fault and performance management system library home page a href found in head commit a href library source files ... | 0 |
158,752 | 12,424,683,851 | IssuesEvent | 2020-05-24 12:55:23 | Gabriielfeliciano/SiteFA | https://api.github.com/repos/Gabriielfeliciano/SiteFA | closed | [FA - 30]Redirecionar de login e para dashboard | Concluído Testando | - [x] Ligar site demonstrativo (WordPress) e interativo (Dashboard);
- [x] Fazer autenticação de dados para login;
- [x] include para permissão de página(apenas para página principal por enquanto). | 1.0 | [FA - 30]Redirecionar de login e para dashboard - - [x] Ligar site demonstrativo (WordPress) e interativo (Dashboard);
- [x] Fazer autenticação de dados para login;
- [x] include para permissão de página(apenas para página principal por enquanto). | test | redirecionar de login e para dashboard ligar site demonstrativo wordpress e interativo dashboard fazer autenticação de dados para login include para permissão de página apenas para página principal por enquanto | 1 |
91,145 | 8,292,634,613 | IssuesEvent | 2018-09-20 01:59:44 | fixstars/clpy | https://api.github.com/repos/fixstars/clpy | closed | Pass clpy_tests/logic_tests/test_type_test.py | tests | We should support, remove, or fix clpy_tests/logic_tests/test_type_test.py
https://github.com/fixstars/clpy/blob/clpy/tests/clpy_tests/logic_tests/test_type_test.py | 1.0 | Pass clpy_tests/logic_tests/test_type_test.py - We should support, remove, or fix clpy_tests/logic_tests/test_type_test.py
https://github.com/fixstars/clpy/blob/clpy/tests/clpy_tests/logic_tests/test_type_test.py | test | pass clpy tests logic tests test type test py we should support remove or fix clpy tests logic tests test type test py | 1 |
277,489 | 21,046,496,710 | IssuesEvent | 2022-03-31 16:29:14 | APECS-Earth-Observation/Polar-EO-Database | https://api.github.com/repos/APECS-Earth-Observation/Polar-EO-Database | opened | Document how to make a contribution to this repository | documentation | For anyone wanting to make a change to the database, we should have step by step instructions on how to make additions/deletions/changes to the JSON files
- [ ] Make a screen recording of submitting a pull request
- [ ] Have a CONTRIBUTING.md text file documenting the step by step instructions | 1.0 | Document how to make a contribution to this repository - For anyone wanting to make a change to the database, we should have step by step instructions on how to make additions/deletions/changes to the JSON files
- [ ] Make a screen recording of submitting a pull request
- [ ] Have a CONTRIBUTING.md text file docume... | non_test | document how to make a contribution to this repository for anyone wanting to make a change to the database we should have step by step instructions on how to make additions deletions changes to the json files make a screen recording of submitting a pull request have a contributing md text file documentin... | 0 |
201,519 | 15,211,179,584 | IssuesEvent | 2021-02-17 08:42:55 | enonic/app-contentstudio | https://api.github.com/repos/enonic/app-contentstudio | opened | Content Wizard - Save button remains enabled after creating a content with several text inputs | Bug Not in Changelog Test is Failing | 1. Select Feature and open Article or Blog wizard.
2. Fill in the name input and click on `Save` button
**BUG**: Save button remains enabled after creating the content
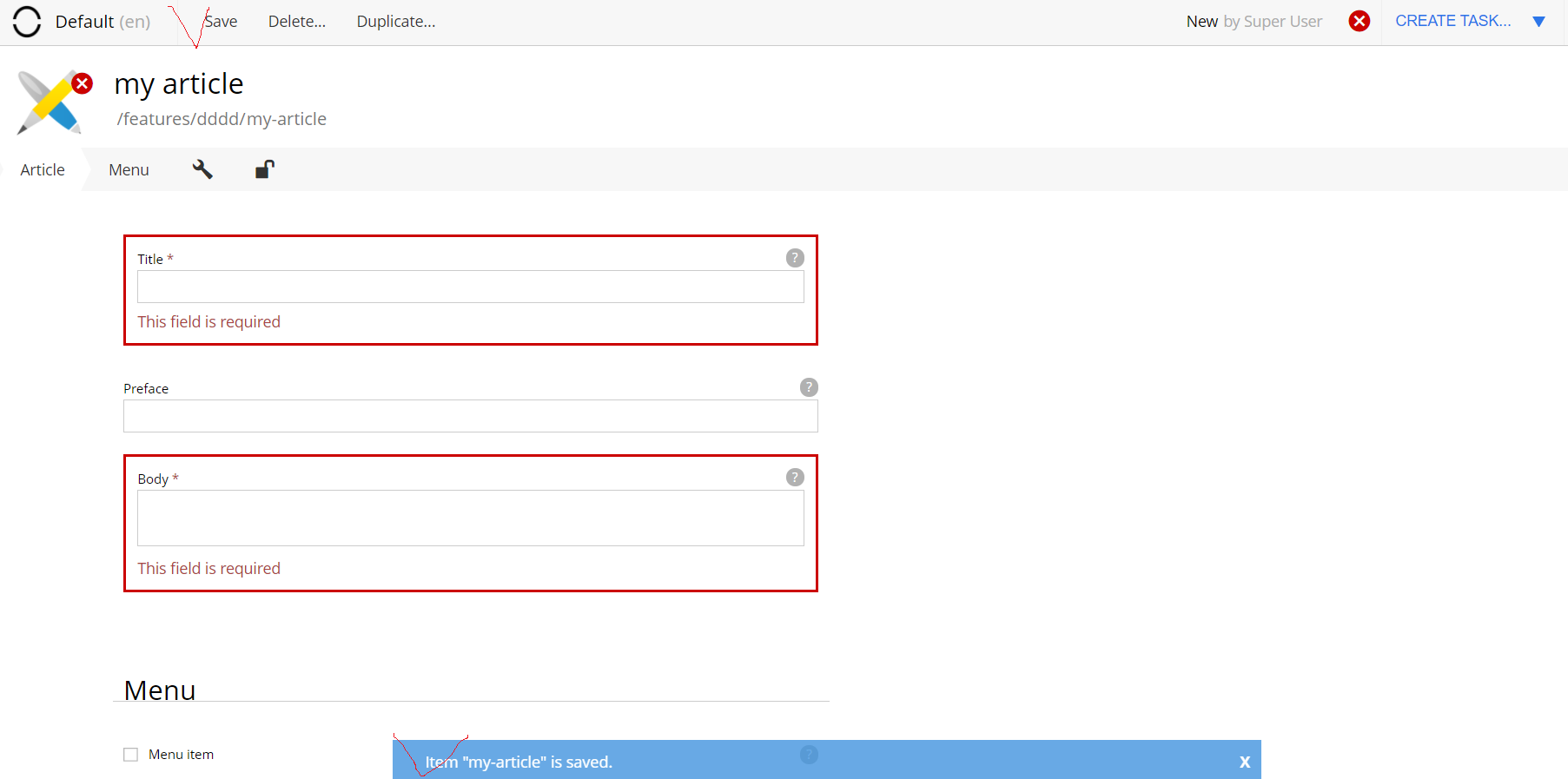
| 1.0 | Content Wizard - Save button remains enabled after creating a content with several text inputs - 1. Select Feature and open Article or Blog wizard.
2. Fill in the name input and click on `Save` button
**BUG**: Save button remains enabled after creating the content
 app that uses the google-cloud-vision Java library (0.11.2-beta), but am getting the following exception: `com.google.api.gax.grpc.ApiException: io.grpc.StatusRuntimeException: DEADLINE_EXCEEDED`
I enabled FINE logging and see the following output before the exception occurs (certain... | 1.0 | DEADLINE_EXCEEDED, google-cloud-vision - I am developing a Scala (2.10.6) app that uses the google-cloud-vision Java library (0.11.2-beta), but am getting the following exception: `com.google.api.gax.grpc.ApiException: io.grpc.StatusRuntimeException: DEADLINE_EXCEEDED`
I enabled FINE logging and see the following ou... | non_test | deadline exceeded google cloud vision i am developing a scala app that uses the google cloud vision java library beta but am getting the following exception com google api gax grpc apiexception io grpc statusruntimeexception deadline exceeded i enabled fine logging and see the following outp... | 0 |
260,256 | 19,663,318,065 | IssuesEvent | 2022-01-10 19:24:42 | dpinney/coopforecast | https://api.github.com/repos/dpinney/coopforecast | closed | Prepare for sharing with BurtCo | documentation chore Epic | - [ ] Upload BurtCo data and perform trial run
- [x] Writeup explanation of remaining features / current limitations
- [x] Point to instructions | 1.0 | Prepare for sharing with BurtCo - - [ ] Upload BurtCo data and perform trial run
- [x] Writeup explanation of remaining features / current limitations
- [x] Point to instructions | non_test | prepare for sharing with burtco upload burtco data and perform trial run writeup explanation of remaining features current limitations point to instructions | 0 |
233,279 | 18,958,200,834 | IssuesEvent | 2021-11-18 23:20:31 | apache/lucenenet | https://api.github.com/repos/apache/lucenenet | opened | Failing Test: Lucene.Net.Index.TestDuelingCodecs::TestEquals() | up-for-grabs help-wanted is:bug test-failure pri:high | > For information about how to help us debug tests, see #269.
This test has been failing randomly for some time but has not previously been documented. The test uses `SimpleText` to compare against all other codecs to ensure they return the same results.
Unfortunately the patch in #541 wasn't the only contributor... | 1.0 | Failing Test: Lucene.Net.Index.TestDuelingCodecs::TestEquals() - > For information about how to help us debug tests, see #269.
This test has been failing randomly for some time but has not previously been documented. The test uses `SimpleText` to compare against all other codecs to ensure they return the same result... | test | failing test lucene net index testduelingcodecs testequals for information about how to help us debug tests see this test has been failing randomly for some time but has not previously been documented the test uses simpletext to compare against all other codecs to ensure they return the same results ... | 1 |
59,569 | 6,655,940,145 | IssuesEvent | 2017-09-29 18:30:12 | Microsoft/PTVS | https://api.github.com/repos/Microsoft/PTVS | closed | Non-UI tests no longer time out | Tests | We have removed our old test settings file, and so now non-ui tests do not time out.
We should create a new runsettings file and enforce a per-test timeout so they don't get stuck forever. | 1.0 | Non-UI tests no longer time out - We have removed our old test settings file, and so now non-ui tests do not time out.
We should create a new runsettings file and enforce a per-test timeout so they don't get stuck forever. | test | non ui tests no longer time out we have removed our old test settings file and so now non ui tests do not time out we should create a new runsettings file and enforce a per test timeout so they don t get stuck forever | 1 |
126,857 | 10,437,313,574 | IssuesEvent | 2019-09-17 21:42:44 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: acceptance/cli/node-status failed | C-test-failure O-roachtest O-robot | SHA: https://github.com/cockroachdb/cockroach/commits/bd27eb358f558bb7598945318240335ebcfcdf13
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace... | 2.0 | roachtest: acceptance/cli/node-status failed - SHA: https://github.com/cockroachdb/cockroach/commits/bd27eb358f558bb7598945318240335ebcfcdf13
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. Fo... | test | roachtest acceptance cli node status failed sha parameters to repro try don t forget to check out a clean suitable branch and experiment with the stress invocation until the desired results present themselves for example using stress instead of stressrace and passing the p stressflag which ... | 1 |
230,261 | 18,527,319,109 | IssuesEvent | 2021-10-20 22:28:29 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: X-Pack Detection Engine API Integration Tests.x-pack/test/detection_engine_api_integration/security_and_spaces/tests/exception_operators_data_types/text·ts - detection engine api security and spaces enabled Detection exceptions data types and operators Rule exception operators for data type text "is one... | failed-test Team:SIEM Team: SecuritySolution Team:Detection Rules | A test failed on a tracked branch
```
Error: expected 200 "OK", got 409 "Conflict"
at Test._assertStatus (/opt/local-ssd/buildkite/builds/kb-cigroup-6-ad0cfbfd5d19950a/elastic/kibana-hourly/kibana/node_modules/supertest/lib/test.js:268:12)
at Test._assertFunction (/opt/local-ssd/buildkite/builds/kb-cigroup-6-a... | 1.0 | Failing test: X-Pack Detection Engine API Integration Tests.x-pack/test/detection_engine_api_integration/security_and_spaces/tests/exception_operators_data_types/text·ts - detection engine api security and spaces enabled Detection exceptions data types and operators Rule exception operators for data type text "is one... | test | failing test x pack detection engine api integration tests x pack test detection engine api integration security and spaces tests exception operators data types text·ts detection engine api security and spaces enabled detection exceptions data types and operators rule exception operators for data type text is one... | 1 |
125,309 | 4,955,395,116 | IssuesEvent | 2016-12-01 20:17:20 | yairodriguez/AngularJS | https://api.github.com/repos/yairodriguez/AngularJS | opened | Components | [priority] low [status] accepted [type] feature | ### Description
Implements the component API introduced in Angular 1.5 that solidifies best practice patterns, streamlines APIs, and allows for more performant code to be written through hooks such as `$onChanges`. Everything in the component API is really just a relatively thin layer on top of existing directive an... | 1.0 | Components - ### Description
Implements the component API introduced in Angular 1.5 that solidifies best practice patterns, streamlines APIs, and allows for more performant code to be written through hooks such as `$onChanges`. Everything in the component API is really just a relatively thin layer on top of existing... | non_test | components description implements the component api introduced in angular that solidifies best practice patterns streamlines apis and allows for more performant code to be written through hooks such as onchanges everything in the component api is really just a relatively thin layer on top of existing... | 0 |
22,243 | 3,619,269,969 | IssuesEvent | 2016-02-08 15:26:05 | pavva94/snake-os | https://api.github.com/repos/pavva94/snake-os | closed | FTP not running after admin port change | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. Change HTTP Web Admin port: to 802
2. Save config, restart
3. FTP deamon couldn't be started.
What is the expected output? What do you see instead?
FTP should be able to run
What version of the product are you using? On what operating system?
Kernel version: 2.6.16-gazin... | 1.0 | FTP not running after admin port change - ```
What steps will reproduce the problem?
1. Change HTTP Web Admin port: to 802
2. Save config, restart
3. FTP deamon couldn't be started.
What is the expected output? What do you see instead?
FTP should be able to run
What version of the product are you using? On what opera... | non_test | ftp not running after admin port change what steps will reproduce the problem change http web admin port to save config restart ftp deamon couldn t be started what is the expected output what do you see instead ftp should be able to run what version of the product are you using on what operati... | 0 |
100,196 | 8,724,974,327 | IssuesEvent | 2018-12-10 07:51:42 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | closed | testing10 : ApiV1IssueTrackersGetQueryParamPageInvalidDatatype | testing10 | Project : testing10
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[... | 1.0 | testing10 : ApiV1IssueTrackersGetQueryParamPageInvalidDatatype - Project : testing10
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pra... | test | project job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response... | 1 |
9,431 | 3,040,261,930 | IssuesEvent | 2015-08-07 14:30:48 | SockDrawer/SockBot | https://api.github.com/repos/SockDrawer/SockBot | opened | Discourse in a box | ready Tests | 1. Cut a hole in a box
2. Put discourse in that box
3. Make sockbot open the box
and that's the way you do it!
(AKA: bundle a vagrantfile that will run a local discourse install so we can integration test against an actual Discourse instance before unleashing someplace that matters) | 1.0 | Discourse in a box - 1. Cut a hole in a box
2. Put discourse in that box
3. Make sockbot open the box
and that's the way you do it!
(AKA: bundle a vagrantfile that will run a local discourse install so we can integration test against an actual Discourse instance before unleashing someplace that matters) | test | discourse in a box cut a hole in a box put discourse in that box make sockbot open the box and that s the way you do it aka bundle a vagrantfile that will run a local discourse install so we can integration test against an actual discourse instance before unleashing someplace that matters | 1 |
173,603 | 21,176,957,243 | IssuesEvent | 2022-04-08 01:40:49 | turkdevops/cloudflare-docs | https://api.github.com/repos/turkdevops/cloudflare-docs | opened | CVE-2022-24785 (High) detected in moment-2.29.1.tgz | security vulnerability | ## CVE-2022-24785 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>moment-2.29.1.tgz</b></p></summary>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a hre... | True | CVE-2022-24785 (High) detected in moment-2.29.1.tgz - ## CVE-2022-24785 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>moment-2.29.1.tgz</b></p></summary>
<p>Parse, validate, manipula... | non_test | cve high detected in moment tgz cve high severity vulnerability vulnerable library moment tgz parse validate manipulate and display dates library home page a href path to dependency file products client ip geolocation package json path to vulnerable library prod... | 0 |
22,221 | 7,133,872,005 | IssuesEvent | 2018-01-22 18:54:45 | quikserve/Captain-Awesome | https://api.github.com/repos/quikserve/Captain-Awesome | opened | TJ JAT Request 2/1/18 | Databuilding New Button | I am hoping I can still get this programmed by the first of the month, but we are running a 5 Tacos for $5.55 after 5pm promotion in February and I am hoping we can still get some buttons for this. I apologize for the delay but it has taken some time to get this through TJI with some of the recent changes in personnel.... | 1.0 | TJ JAT Request 2/1/18 - I am hoping I can still get this programmed by the first of the month, but we are running a 5 Tacos for $5.55 after 5pm promotion in February and I am hoping we can still get some buttons for this. I apologize for the delay but it has taken some time to get this through TJI with some of the rece... | non_test | tj jat request i am hoping i can still get this programmed by the first of the month but we are running a tacos for after promotion in february and i am hoping we can still get some buttons for this i apologize for the delay but it has taken some time to get this through tji with some of the recent c... | 0 |
368,611 | 10,882,000,212 | IssuesEvent | 2019-11-17 21:17:54 | google/ground-android | https://api.github.com/repos/google/ground-android | opened | [Dev Setup] gnd/google-services.json not in .gitignore | priority: p1 type: bug | Hi @shobhitagarwal1612! I just realized that the README recommends we put our real `google-services.json` in `gnd/`, but that file is now not ignored in .gitignore. How do we prevent ourselves from accidentally checking our real config files in source control in this case?
@scolsen FYI. | 1.0 | [Dev Setup] gnd/google-services.json not in .gitignore - Hi @shobhitagarwal1612! I just realized that the README recommends we put our real `google-services.json` in `gnd/`, but that file is now not ignored in .gitignore. How do we prevent ourselves from accidentally checking our real config files in source control in ... | non_test | gnd google services json not in gitignore hi i just realized that the readme recommends we put our real google services json in gnd but that file is now not ignored in gitignore how do we prevent ourselves from accidentally checking our real config files in source control in this case scolsen fyi | 0 |
202,573 | 7,049,851,721 | IssuesEvent | 2018-01-03 00:58:17 | wso2/product-apim | https://api.github.com/repos/wso2/product-apim | opened | Invalid Current State in publisher lifecycle | 2.2.0 Priority/High Severity/Major Type/Bug | **Description:**
Invalid Current State in publisher's API lifecycle section once run the sample-scenario 7
_Note: we have a custom lifecycle state in this sample_
**Affected Version**
2.1.0-update4
**Steps to reproduce:**
1. Run the sample-scenario 7
2. Go to the publisher and click on the API Sales_promotio... | 1.0 | Invalid Current State in publisher lifecycle - **Description:**
Invalid Current State in publisher's API lifecycle section once run the sample-scenario 7
_Note: we have a custom lifecycle state in this sample_
**Affected Version**
2.1.0-update4
**Steps to reproduce:**
1. Run the sample-scenario 7
2. Go to th... | non_test | invalid current state in publisher lifecycle description invalid current state in publisher s api lifecycle section once run the sample scenario note we have a custom lifecycle state in this sample affected version steps to reproduce run the sample scenario go to the publ... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.