Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3 values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17 values | text_combine stringlengths 95 262k | label stringclasses 2 values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
349,207 | 10,465,800,182 | IssuesEvent | 2019-09-21 14:01:02 | qgis/QGIS | https://api.github.com/repos/qgis/QGIS | closed | SLD load problem | Bug Feedback High Priority Regression Symbology | Author Name: **Eduardo Martín** (Eduardo Martín)
Original Redmine Issue: [20619](https://issues.qgis.org/issues/20619)
Affected QGIS version: 3.4.1
Redmine category:symbology
---
I use a SLD file to define styles over a polygon layer, but the results are different depending on the QGIS version: 2.18.25 and 3.4.1 don't work (missing layer cause of styling), 2.18.4 and 3.2.3 work.
Even, I tried to create a SLD on 2.18.25 and load over the same layer, the styling doesn't work.
I attached gif example of a success and a failed cases.
Thanks for your time and help developping this great software!
Regards :)
---
- [SLD_2_18_25.zip](https://issues.qgis.org/attachments/download/13840/SLD_2_18_25.zip) (Eduardo Martín)
- [SLD_3.2.3.gif](https://issues.qgis.org/attachments/download/13841/SLD_3.2.3.gif) (Eduardo Martín) | 1.0 | SLD load problem - Author Name: **Eduardo Martín** (Eduardo Martín)
Original Redmine Issue: [20619](https://issues.qgis.org/issues/20619)
Affected QGIS version: 3.4.1
Redmine category:symbology
---
I use a SLD file to define styles over a polygon layer, but the results are different depending on the QGIS version: 2.18.25 and 3.4.1 don't work (missing layer cause of styling), 2.18.4 and 3.2.3 work.
Even, I tried to create a SLD on 2.18.25 and load over the same layer, the styling doesn't work.
I attached gif example of a success and a failed cases.
Thanks for your time and help developping this great software!
Regards :)
---
- [SLD_2_18_25.zip](https://issues.qgis.org/attachments/download/13840/SLD_2_18_25.zip) (Eduardo Martín)
- [SLD_3.2.3.gif](https://issues.qgis.org/attachments/download/13841/SLD_3.2.3.gif) (Eduardo Martín) | non_test | sld load problem author name eduardo martín eduardo martín original redmine issue affected qgis version redmine category symbology i use a sld file to define styles over a polygon layer but the results are different depending on the qgis version and don t work missing layer cause of styling and work even i tried to create a sld on and load over the same layer the styling doesn t work i attached gif example of a success and a failed cases thanks for your time and help developping this great software regards eduardo martín eduardo martín | 0 |
212,450 | 16,450,628,871 | IssuesEvent | 2021-05-21 04:52:59 | cnrancher/autok3s | https://api.github.com/repos/cnrancher/autok3s | closed | [BUG] autok3s 自定义虚拟机安装 k3s 集群 指定 --docker 作为容器运行环境 存在的问题 | bug to test | **Describe the bug**
1、创建一个 native Cluster,在 K3s Options
2、指定了Master Extra Args : --docker
3、然后点击创建按钮,命令行中提示ERROR
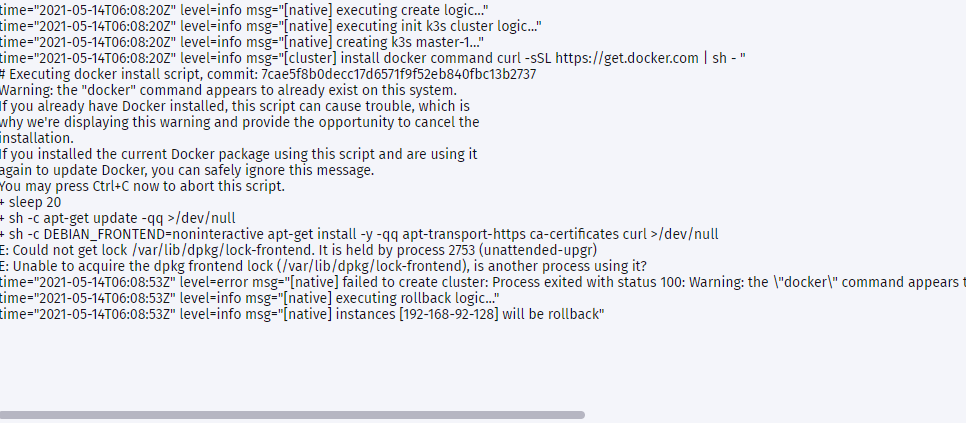
**Expected behavior**
我本机已经安装好了一个docker,所以我本以为这样选择会直接指定我的docker的,但似乎是因为我本机安装docker了,所以才没有成功安装 k3s cluster
**Environments (please complete the following information):**
- OS: unbuntu:20.04
- AutoK3s Version [e.g. v0.4.0]
**Additional context**
--
| 1.0 | [BUG] autok3s 自定义虚拟机安装 k3s 集群 指定 --docker 作为容器运行环境 存在的问题 - **Describe the bug**
1、创建一个 native Cluster,在 K3s Options
2、指定了Master Extra Args : --docker
3、然后点击创建按钮,命令行中提示ERROR
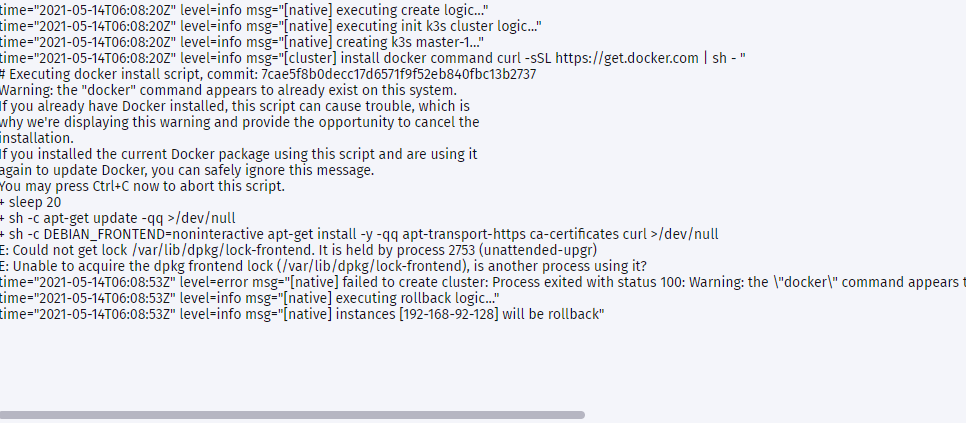
**Expected behavior**
我本机已经安装好了一个docker,所以我本以为这样选择会直接指定我的docker的,但似乎是因为我本机安装docker了,所以才没有成功安装 k3s cluster
**Environments (please complete the following information):**
- OS: unbuntu:20.04
- AutoK3s Version [e.g. v0.4.0]
**Additional context**
--
| test | 自定义虚拟机安装 集群 指定 docker 作为容器运行环境 存在的问题 describe the bug 、创建一个 native cluster 在 options 、指定了master extra args : docker 、然后点击创建按钮,命令行中提示error expected behavior 我本机已经安装好了一个docker,所以我本以为这样选择会直接指定我的docker的,但似乎是因为我本机安装docker了,所以才没有成功安装 cluster environments please complete the following information os unbuntu version additional context | 1 |
280,865 | 30,861,909,053 | IssuesEvent | 2023-08-03 04:20:20 | momo-tong/jackson-databind-2.0.0-RC1 | https://api.github.com/repos/momo-tong/jackson-databind-2.0.0-RC1 | opened | jackson-databind-2.0.0-RC1.jar: 64 vulnerabilities (highest severity is: 10.0) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jackson-databind version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2018-14721](https://www.mend.io/vulnerability-database/CVE-2018-14721) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 10.0 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2019-14540](https://www.mend.io/vulnerability-database/CVE-2019-14540) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-17531](https://www.mend.io/vulnerability-database/CVE-2019-17531) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2017-15095](https://www.mend.io/vulnerability-database/CVE-2017-15095) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.2 | ❌ |
| [CVE-2017-7525](https://www.mend.io/vulnerability-database/CVE-2017-7525) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.1 | ❌ |
| [CVE-2018-14720](https://www.mend.io/vulnerability-database/CVE-2018-14720) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2019-16335](https://www.mend.io/vulnerability-database/CVE-2019-16335) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2019-17267](https://www.mend.io/vulnerability-database/CVE-2019-17267) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2018-11307](https://www.mend.io/vulnerability-database/CVE-2018-11307) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-16942](https://www.mend.io/vulnerability-database/CVE-2019-16942) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-8840](https://www.mend.io/vulnerability-database/CVE-2020-8840) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-16943](https://www.mend.io/vulnerability-database/CVE-2019-16943) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-19362](https://www.mend.io/vulnerability-database/CVE-2018-19362) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-19361](https://www.mend.io/vulnerability-database/CVE-2018-19361) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-19360](https://www.mend.io/vulnerability-database/CVE-2018-19360) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-10202](https://www.mend.io/vulnerability-database/CVE-2019-10202) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-14893](https://www.mend.io/vulnerability-database/CVE-2019-14893) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-14892](https://www.mend.io/vulnerability-database/CVE-2019-14892) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-9546](https://www.mend.io/vulnerability-database/CVE-2020-9546) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-9547](https://www.mend.io/vulnerability-database/CVE-2020-9547) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-14379](https://www.mend.io/vulnerability-database/CVE-2019-14379) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-9548](https://www.mend.io/vulnerability-database/CVE-2020-9548) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-20330](https://www.mend.io/vulnerability-database/CVE-2019-20330) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2018-14719](https://www.mend.io/vulnerability-database/CVE-2018-14719) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-14718](https://www.mend.io/vulnerability-database/CVE-2018-14718) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-7489](https://www.mend.io/vulnerability-database/CVE-2018-7489) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-10968](https://www.mend.io/vulnerability-database/CVE-2020-10968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-10969](https://www.mend.io/vulnerability-database/CVE-2020-10969) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-11111](https://www.mend.io/vulnerability-database/CVE-2020-11111) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-11113](https://www.mend.io/vulnerability-database/CVE-2020-11113) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-11112](https://www.mend.io/vulnerability-database/CVE-2020-11112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-10672](https://www.mend.io/vulnerability-database/CVE-2020-10672) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-10673](https://www.mend.io/vulnerability-database/CVE-2020-10673) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-11619](https://www.mend.io/vulnerability-database/CVE-2020-11619) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-36189](https://www.mend.io/vulnerability-database/CVE-2020-36189) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36188](https://www.mend.io/vulnerability-database/CVE-2020-36188) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-11620](https://www.mend.io/vulnerability-database/CVE-2020-11620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-36181](https://www.mend.io/vulnerability-database/CVE-2020-36181) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36180](https://www.mend.io/vulnerability-database/CVE-2020-36180) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36183](https://www.mend.io/vulnerability-database/CVE-2020-36183) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36182](https://www.mend.io/vulnerability-database/CVE-2020-36182) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36185](https://www.mend.io/vulnerability-database/CVE-2020-36185) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2018-5968](https://www.mend.io/vulnerability-database/CVE-2018-5968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-36184](https://www.mend.io/vulnerability-database/CVE-2020-36184) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36187](https://www.mend.io/vulnerability-database/CVE-2020-36187) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36186](https://www.mend.io/vulnerability-database/CVE-2020-36186) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2021-20190](https://www.mend.io/vulnerability-database/CVE-2021-20190) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36179](https://www.mend.io/vulnerability-database/CVE-2020-36179) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-24616](https://www.mend.io/vulnerability-database/CVE-2020-24616) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-14060](https://www.mend.io/vulnerability-database/CVE-2020-14060) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-14061](https://www.mend.io/vulnerability-database/CVE-2020-14061) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-14062](https://www.mend.io/vulnerability-database/CVE-2020-14062) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-24750](https://www.mend.io/vulnerability-database/CVE-2020-24750) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-14195](https://www.mend.io/vulnerability-database/CVE-2020-14195) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-12086](https://www.mend.io/vulnerability-database/CVE-2019-12086) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-25649](https://www.mend.io/vulnerability-database/CVE-2020-25649) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2018-12022](https://www.mend.io/vulnerability-database/CVE-2018-12022) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-12023](https://www.mend.io/vulnerability-database/CVE-2018-12023) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2019-14439](https://www.mend.io/vulnerability-database/CVE-2019-14439) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-36518](https://www.mend.io/vulnerability-database/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.12.6.1 | ❌ |
| [CVE-2019-12814](https://www.mend.io/vulnerability-database/CVE-2019-12814) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2019-12384](https://www.mend.io/vulnerability-database/CVE-2019-12384) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [WS-2018-0125](https://github.com/FasterXML/jackson-core/issues/315) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | jackson-core-2.0.0-RC1.jar | Transitive | 2.3.1 | ❌ |
| [WS-2018-0124](https://issues.jboss.org/browse/JBEAP-6316) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | jackson-core-2.0.0-RC1.jar | Transitive | 2.3.1 | ❌ |
## Details
> Partial details (22 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-14721</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14721>CVE-2018-14721</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>10.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-14540</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-17531</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17531>CVE-2019-17531</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531</a></p>
<p>Release Date: 2019-10-12</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2017-15095</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A deserialization flaw was discovered in the jackson-databind in versions before 2.8.10 and 2.9.1, which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readValue method of the ObjectMapper. This issue extends the previous flaw CVE-2017-7525 by blacklisting more classes that could be used maliciously.
<p>Publish Date: 2018-02-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-15095>CVE-2017-15095</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-15095">https://nvd.nist.gov/vuln/detail/CVE-2017-15095</a></p>
<p>Release Date: 2017-06-27</p>
<p>Fix Resolution: 2.6.7.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2017-7525</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A deserialization flaw was discovered in the jackson-databind, versions before 2.6.7.1, 2.7.9.1 and 2.8.9, which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readValue method of the ObjectMapper.
<p>Publish Date: 2018-02-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-7525>CVE-2017-7525</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7525">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7525</a></p>
<p>Release Date: 2018-02-06</p>
<p>Fix Resolution: 2.6.7.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-14720</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow attackers to conduct external XML entity (XXE) attacks by leveraging failure to block unspecified JDK classes from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14720>CVE-2018-14720</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-14720">https://nvd.nist.gov/vuln/detail/CVE-2018-14720</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-16335</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-17267</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to net.sf.ehcache.hibernate.EhcacheJtaTransactionManagerLookup.
<p>Publish Date: 2019-10-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17267>CVE-2019-17267</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-10-07</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-11307</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.5. Use of Jackson default typing along with a gadget class from iBatis allows exfiltration of content. Fixed in 2.7.9.4, 2.8.11.2, and 2.9.6.
<p>Publish Date: 2019-07-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-11307>CVE-2018-11307</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-07-09</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-16942</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16942>CVE-2019-16942</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-8840</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.0.0 through 2.9.10.2 lacks certain xbean-reflect/JNDI blocking, as demonstrated by org.apache.xbean.propertyeditor.JndiConverter.
<p>Publish Date: 2020-02-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8840>CVE-2020-8840</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-02-10</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-16943</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the p6spy (3.8.6) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of com.p6spy.engine.spy.P6DataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16943>CVE-2019-16943</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-19362</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the jboss-common-core class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-19362>CVE-2018-19362</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19362">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19362</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-19361</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the openjpa class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-19361>CVE-2018-19361</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19361">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19361</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-19360</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the axis2-transport-jms class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-19360>CVE-2018-19360</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19360">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19360</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-10202</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A series of deserialization vulnerabilities have been discovered in Codehaus 1.9.x implemented in EAP 7. This CVE fixes CVE-2017-17485, CVE-2017-7525, CVE-2017-15095, CVE-2018-5968, CVE-2018-7489, CVE-2018-1000873, CVE-2019-12086 reported for FasterXML jackson-databind by implementing a whitelist approach that will mitigate these vulnerabilities and future ones alike.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10202>CVE-2019-10202</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread/08302h5kp2l9ry2zq8vydomlhn0fg4j4">https://lists.apache.org/thread/08302h5kp2l9ry2zq8vydomlhn0fg4j4</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-14893</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in FasterXML jackson-databind in all versions before 2.9.10 and 2.10.0, where it would permit polymorphic deserialization of malicious objects using the xalan JNDI gadget when used in conjunction with polymorphic type handling methods such as `enableDefaultTyping()` or when @JsonTypeInfo is using `Id.CLASS` or `Id.MINIMAL_CLASS` or in any other way which ObjectMapper.readValue might instantiate objects from unsafe sources. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14893>CVE-2019-14893</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-14892</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in jackson-databind in versions before 2.9.10, 2.8.11.5 and 2.6.7.3, where it would permit polymorphic deserialization of a malicious object using commons-configuration 1 and 2 JNDI classes. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14892>CVE-2019-14892</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-9546</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-9547</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to com.ibatis.sqlmap.engine.transaction.jta.JtaTransactionConfig (aka ibatis-sqlmap).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9547>CVE-2020-9547</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-14379</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SubTypeValidator.java in FasterXML jackson-databind before 2.9.9.2 mishandles default typing when ehcache is used (because of net.sf.ehcache.transaction.manager.DefaultTransactionManagerLookup), leading to remote code execution.
<p>Publish Date: 2019-07-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14379>CVE-2019-14379</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379</a></p>
<p>Release Date: 2019-07-29</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-9548</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPConfig (aka anteros-core).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9548>CVE-2020-9548</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | jackson-databind-2.0.0-RC1.jar: 64 vulnerabilities (highest severity is: 10.0) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jackson-databind version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2018-14721](https://www.mend.io/vulnerability-database/CVE-2018-14721) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 10.0 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2019-14540](https://www.mend.io/vulnerability-database/CVE-2019-14540) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-17531](https://www.mend.io/vulnerability-database/CVE-2019-17531) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2017-15095](https://www.mend.io/vulnerability-database/CVE-2017-15095) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.2 | ❌ |
| [CVE-2017-7525](https://www.mend.io/vulnerability-database/CVE-2017-7525) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.1 | ❌ |
| [CVE-2018-14720](https://www.mend.io/vulnerability-database/CVE-2018-14720) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2019-16335](https://www.mend.io/vulnerability-database/CVE-2019-16335) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2019-17267](https://www.mend.io/vulnerability-database/CVE-2019-17267) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2018-11307](https://www.mend.io/vulnerability-database/CVE-2018-11307) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-16942](https://www.mend.io/vulnerability-database/CVE-2019-16942) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-8840](https://www.mend.io/vulnerability-database/CVE-2020-8840) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-16943](https://www.mend.io/vulnerability-database/CVE-2019-16943) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-19362](https://www.mend.io/vulnerability-database/CVE-2018-19362) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-19361](https://www.mend.io/vulnerability-database/CVE-2018-19361) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-19360](https://www.mend.io/vulnerability-database/CVE-2018-19360) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-10202](https://www.mend.io/vulnerability-database/CVE-2019-10202) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-14893](https://www.mend.io/vulnerability-database/CVE-2019-14893) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-14892](https://www.mend.io/vulnerability-database/CVE-2019-14892) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-9546](https://www.mend.io/vulnerability-database/CVE-2020-9546) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-9547](https://www.mend.io/vulnerability-database/CVE-2020-9547) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-14379](https://www.mend.io/vulnerability-database/CVE-2019-14379) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-9548](https://www.mend.io/vulnerability-database/CVE-2020-9548) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-20330](https://www.mend.io/vulnerability-database/CVE-2019-20330) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2018-14719](https://www.mend.io/vulnerability-database/CVE-2018-14719) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-14718](https://www.mend.io/vulnerability-database/CVE-2018-14718) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-7489](https://www.mend.io/vulnerability-database/CVE-2018-7489) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-10968](https://www.mend.io/vulnerability-database/CVE-2020-10968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-10969](https://www.mend.io/vulnerability-database/CVE-2020-10969) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-11111](https://www.mend.io/vulnerability-database/CVE-2020-11111) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-11113](https://www.mend.io/vulnerability-database/CVE-2020-11113) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-11112](https://www.mend.io/vulnerability-database/CVE-2020-11112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-10672](https://www.mend.io/vulnerability-database/CVE-2020-10672) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-10673](https://www.mend.io/vulnerability-database/CVE-2020-10673) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-11619](https://www.mend.io/vulnerability-database/CVE-2020-11619) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-36189](https://www.mend.io/vulnerability-database/CVE-2020-36189) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36188](https://www.mend.io/vulnerability-database/CVE-2020-36188) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-11620](https://www.mend.io/vulnerability-database/CVE-2020-11620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-36181](https://www.mend.io/vulnerability-database/CVE-2020-36181) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36180](https://www.mend.io/vulnerability-database/CVE-2020-36180) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36183](https://www.mend.io/vulnerability-database/CVE-2020-36183) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36182](https://www.mend.io/vulnerability-database/CVE-2020-36182) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36185](https://www.mend.io/vulnerability-database/CVE-2020-36185) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2018-5968](https://www.mend.io/vulnerability-database/CVE-2018-5968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-36184](https://www.mend.io/vulnerability-database/CVE-2020-36184) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36187](https://www.mend.io/vulnerability-database/CVE-2020-36187) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36186](https://www.mend.io/vulnerability-database/CVE-2020-36186) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2021-20190](https://www.mend.io/vulnerability-database/CVE-2021-20190) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-36179](https://www.mend.io/vulnerability-database/CVE-2020-36179) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.5 | ❌ |
| [CVE-2020-24616](https://www.mend.io/vulnerability-database/CVE-2020-24616) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-14060](https://www.mend.io/vulnerability-database/CVE-2020-14060) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-14061](https://www.mend.io/vulnerability-database/CVE-2020-14061) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-14062](https://www.mend.io/vulnerability-database/CVE-2020-14062) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-24750](https://www.mend.io/vulnerability-database/CVE-2020-24750) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2020-14195](https://www.mend.io/vulnerability-database/CVE-2020-14195) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2019-12086](https://www.mend.io/vulnerability-database/CVE-2019-12086) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-25649](https://www.mend.io/vulnerability-database/CVE-2020-25649) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.4 | ❌ |
| [CVE-2018-12022](https://www.mend.io/vulnerability-database/CVE-2018-12022) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2018-12023](https://www.mend.io/vulnerability-database/CVE-2018-12023) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2019-14439](https://www.mend.io/vulnerability-database/CVE-2019-14439) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2020-36518](https://www.mend.io/vulnerability-database/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.0.0-RC1.jar | Direct | 2.12.6.1 | ❌ |
| [CVE-2019-12814](https://www.mend.io/vulnerability-database/CVE-2019-12814) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [CVE-2019-12384](https://www.mend.io/vulnerability-database/CVE-2019-12384) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | jackson-databind-2.0.0-RC1.jar | Direct | 2.6.7.3 | ❌ |
| [WS-2018-0125](https://github.com/FasterXML/jackson-core/issues/315) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | jackson-core-2.0.0-RC1.jar | Transitive | 2.3.1 | ❌ |
| [WS-2018-0124](https://issues.jboss.org/browse/JBEAP-6316) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | jackson-core-2.0.0-RC1.jar | Transitive | 2.3.1 | ❌ |
## Details
> Partial details (22 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-14721</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14721>CVE-2018-14721</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>10.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-14540</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-17531</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17531>CVE-2019-17531</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531</a></p>
<p>Release Date: 2019-10-12</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2017-15095</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A deserialization flaw was discovered in the jackson-databind in versions before 2.8.10 and 2.9.1, which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readValue method of the ObjectMapper. This issue extends the previous flaw CVE-2017-7525 by blacklisting more classes that could be used maliciously.
<p>Publish Date: 2018-02-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-15095>CVE-2017-15095</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-15095">https://nvd.nist.gov/vuln/detail/CVE-2017-15095</a></p>
<p>Release Date: 2017-06-27</p>
<p>Fix Resolution: 2.6.7.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2017-7525</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A deserialization flaw was discovered in the jackson-databind, versions before 2.6.7.1, 2.7.9.1 and 2.8.9, which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readValue method of the ObjectMapper.
<p>Publish Date: 2018-02-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-7525>CVE-2017-7525</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7525">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7525</a></p>
<p>Release Date: 2018-02-06</p>
<p>Fix Resolution: 2.6.7.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-14720</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow attackers to conduct external XML entity (XXE) attacks by leveraging failure to block unspecified JDK classes from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14720>CVE-2018-14720</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-14720">https://nvd.nist.gov/vuln/detail/CVE-2018-14720</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-16335</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-17267</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to net.sf.ehcache.hibernate.EhcacheJtaTransactionManagerLookup.
<p>Publish Date: 2019-10-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17267>CVE-2019-17267</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-10-07</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-11307</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.5. Use of Jackson default typing along with a gadget class from iBatis allows exfiltration of content. Fixed in 2.7.9.4, 2.8.11.2, and 2.9.6.
<p>Publish Date: 2019-07-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-11307>CVE-2018-11307</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-07-09</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-16942</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16942>CVE-2019-16942</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-8840</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.0.0 through 2.9.10.2 lacks certain xbean-reflect/JNDI blocking, as demonstrated by org.apache.xbean.propertyeditor.JndiConverter.
<p>Publish Date: 2020-02-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8840>CVE-2020-8840</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-02-10</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-16943</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the p6spy (3.8.6) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of com.p6spy.engine.spy.P6DataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16943>CVE-2019-16943</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-19362</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the jboss-common-core class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-19362>CVE-2018-19362</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19362">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19362</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-19361</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the openjpa class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-19361>CVE-2018-19361</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19361">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19361</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2018-19360</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the axis2-transport-jms class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-19360>CVE-2018-19360</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19360">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19360</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-10202</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A series of deserialization vulnerabilities have been discovered in Codehaus 1.9.x implemented in EAP 7. This CVE fixes CVE-2017-17485, CVE-2017-7525, CVE-2017-15095, CVE-2018-5968, CVE-2018-7489, CVE-2018-1000873, CVE-2019-12086 reported for FasterXML jackson-databind by implementing a whitelist approach that will mitigate these vulnerabilities and future ones alike.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10202>CVE-2019-10202</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread/08302h5kp2l9ry2zq8vydomlhn0fg4j4">https://lists.apache.org/thread/08302h5kp2l9ry2zq8vydomlhn0fg4j4</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-14893</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in FasterXML jackson-databind in all versions before 2.9.10 and 2.10.0, where it would permit polymorphic deserialization of malicious objects using the xalan JNDI gadget when used in conjunction with polymorphic type handling methods such as `enableDefaultTyping()` or when @JsonTypeInfo is using `Id.CLASS` or `Id.MINIMAL_CLASS` or in any other way which ObjectMapper.readValue might instantiate objects from unsafe sources. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14893>CVE-2019-14893</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-14892</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in jackson-databind in versions before 2.9.10, 2.8.11.5 and 2.6.7.3, where it would permit polymorphic deserialization of a malicious object using commons-configuration 1 and 2 JNDI classes. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14892>CVE-2019-14892</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-9546</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-9547</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to com.ibatis.sqlmap.engine.transaction.jta.JtaTransactionConfig (aka ibatis-sqlmap).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9547>CVE-2020-9547</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-14379</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SubTypeValidator.java in FasterXML jackson-databind before 2.9.9.2 mishandles default typing when ehcache is used (because of net.sf.ehcache.transaction.manager.DefaultTransactionManagerLookup), leading to remote code execution.
<p>Publish Date: 2019-07-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14379>CVE-2019-14379</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379</a></p>
<p>Release Date: 2019-07-29</p>
<p>Fix Resolution: 2.6.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-9548</summary>
### Vulnerable Library - <b>jackson-databind-2.0.0-RC1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.0-RC1/jackson-databind-2.0.0-RC1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.0-RC1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/momo-tong/jackson-databind-2.0.0-RC1/commit/94acdc2000771abfea04ecf2526a59963f5add54">94acdc2000771abfea04ecf2526a59963f5add54</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPConfig (aka anteros-core).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9548>CVE-2020-9548</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.6.7.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_test | jackson databind jar vulnerabilities highest severity is vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in jackson databind version remediation available critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct critical jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct medium jackson databind jar direct medium jackson databind jar direct medium jackson core jar transitive medium jackson core jar transitive details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the mend application cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before might allow remote attackers to conduct server side request forgery ssrf attacks by leveraging failure to block the jaxws class from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikariconfig publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the apache extra version x jar in the classpath and an attacker can provide a jndi service to access it is possible to make the service execute a malicious payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a deserialization flaw was discovered in the jackson databind in versions before and which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readvalue method of the objectmapper this issue extends the previous flaw cve by blacklisting more classes that could be used maliciously publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a deserialization flaw was discovered in the jackson databind versions before and which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readvalue method of the objectmapper publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before might allow attackers to conduct external xml entity xxe attacks by leveraging failure to block unspecified jdk classes from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikaridatasource this is a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to net sf ehcache hibernate ehcachejtatransactionmanagerlookup publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details an issue was discovered in fasterxml jackson databind through use of jackson default typing along with a gadget class from ibatis allows exfiltration of content fixed in and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the commons dbcp jar in the classpath and an attacker can find an rmi service endpoint to access it is possible to make the service execute a malicious payload this issue exists because of org apache commons dbcp datasources sharedpooldatasource and org apache commons dbcp datasources peruserpooldatasource mishandling publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind through lacks certain xbean reflect jndi blocking as demonstrated by org apache xbean propertyeditor jndiconverter publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the jar in the classpath and an attacker can find an rmi service endpoint to access it is possible to make the service execute a malicious payload this issue exists because of com engine spy mishandling publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before might allow attackers to have unspecified impact by leveraging failure to block the jboss common core class from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before might allow attackers to have unspecified impact by leveraging failure to block the openjpa class from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before might allow attackers to have unspecified impact by leveraging failure to block the transport jms class from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a series of deserialization vulnerabilities have been discovered in codehaus x implemented in eap this cve fixes cve cve cve cve cve cve cve reported for fasterxml jackson databind by implementing a whitelist approach that will mitigate these vulnerabilities and future ones alike publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a flaw was discovered in fasterxml jackson databind in all versions before and where it would permit polymorphic deserialization of malicious objects using the xalan jndi gadget when used in conjunction with polymorphic type handling methods such as enabledefaulttyping or when jsontypeinfo is using id class or id minimal class or in any other way which objectmapper readvalue might instantiate objects from unsafe sources an attacker could use this flaw to execute arbitrary code publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a flaw was discovered in jackson databind in versions before and where it would permit polymorphic deserialization of a malicious object using commons configuration and jndi classes an attacker could use this flaw to execute arbitrary code publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache hadoop shaded com zaxxer hikari hikariconfig aka shaded hikari config publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to com ibatis sqlmap engine transaction jta jtatransactionconfig aka ibatis sqlmap publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details subtypevalidator java in fasterxml jackson databind before mishandles default typing when ehcache is used because of net sf ehcache transaction manager defaulttransactionmanagerlookup leading to remote code execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to br com anteros dbcp anterosdbcpconfig aka anteros core publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
186,968 | 21,993,024,366 | IssuesEvent | 2022-05-26 01:21:10 | benlazarine/global-sprint | https://api.github.com/repos/benlazarine/global-sprint | opened | CVE-2022-24836 (High) detected in nokogiri-1.6.8.1.gem | security vulnerability | ## CVE-2022-24836 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.6.8.1.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.6.8.1.gem">https://rubygems.org/gems/nokogiri-1.6.8.1.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.3.0/cache/nokogiri-1.6.8.1.gem</p>
<p>
Dependency Hierarchy:
- github-pages-98.gem (Root Library)
- jekyll-mentions-1.2.0.gem
- html-pipeline-2.4.2.gem
- :x: **nokogiri-1.6.8.1.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/benlazarine/global-sprint/commit/6714ba7f1f09f43bc6d8589b21e003d1a7cc1873">6714ba7f1f09f43bc6d8589b21e003d1a7cc1873</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Nokogiri is an open source XML and HTML library for Ruby. Nokogiri `< v1.13.4` contains an inefficient regular expression that is susceptible to excessive backtracking when attempting to detect encoding in HTML documents. Users are advised to upgrade to Nokogiri `>= 1.13.4`. There are no known workarounds for this issue.
<p>Publish Date: 2022-04-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24836>CVE-2022-24836</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sparklemotion/nokogiri/security/advisories/GHSA-crjr-9rc5-ghw8">https://github.com/sparklemotion/nokogiri/security/advisories/GHSA-crjr-9rc5-ghw8</a></p>
<p>Release Date: 2022-04-11</p>
<p>Fix Resolution: nokogiri - 1.13.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-24836 (High) detected in nokogiri-1.6.8.1.gem - ## CVE-2022-24836 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.6.8.1.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.6.8.1.gem">https://rubygems.org/gems/nokogiri-1.6.8.1.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.3.0/cache/nokogiri-1.6.8.1.gem</p>
<p>
Dependency Hierarchy:
- github-pages-98.gem (Root Library)
- jekyll-mentions-1.2.0.gem
- html-pipeline-2.4.2.gem
- :x: **nokogiri-1.6.8.1.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/benlazarine/global-sprint/commit/6714ba7f1f09f43bc6d8589b21e003d1a7cc1873">6714ba7f1f09f43bc6d8589b21e003d1a7cc1873</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Nokogiri is an open source XML and HTML library for Ruby. Nokogiri `< v1.13.4` contains an inefficient regular expression that is susceptible to excessive backtracking when attempting to detect encoding in HTML documents. Users are advised to upgrade to Nokogiri `>= 1.13.4`. There are no known workarounds for this issue.
<p>Publish Date: 2022-04-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24836>CVE-2022-24836</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sparklemotion/nokogiri/security/advisories/GHSA-crjr-9rc5-ghw8">https://github.com/sparklemotion/nokogiri/security/advisories/GHSA-crjr-9rc5-ghw8</a></p>
<p>Release Date: 2022-04-11</p>
<p>Fix Resolution: nokogiri - 1.13.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in nokogiri gem cve high severity vulnerability vulnerable library nokogiri gem nokogiri 鋸 is an html xml sax and reader parser among nokogiri s many features is the ability to search documents via xpath or selectors library home page a href path to dependency file gemfile lock path to vulnerable library var lib gems cache nokogiri gem dependency hierarchy github pages gem root library jekyll mentions gem html pipeline gem x nokogiri gem vulnerable library found in head commit a href vulnerability details nokogiri is an open source xml and html library for ruby nokogiri there are no known workarounds for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution nokogiri step up your open source security game with whitesource | 0 |
225,279 | 17,839,701,606 | IssuesEvent | 2021-09-03 08:27:58 | Oldes/Rebol-issues | https://api.github.com/repos/Oldes/Rebol-issues | closed | PARSE: CHANGE needs INTO [] match rule to be enclosed in a block | Test.written Type.bug Type.parse CC.resolved | _Submitted by:_ **xuanin**
When using INTO [] as the match rule argument for CHANGE it needs to be enclosed in block to ensure it's correctly interpreted.
``` rebol
>> parse s: [[a b]][change into ['a 'b] [z p]]
== false
```
``` rebol
>> parse s: [[a b]][change [into ['a 'b]] [z p]]
== true
```
This is neither the case with other rules nor REMOVE:
``` rebol
>> parse s: [a b][change some word! [z p]]
== true
```
``` rebol
>> parse s: [[a b]][remove into ['a 'b]]
== true
```
---
<sup>**Imported from:** **[CureCode](https://www.curecode.org/rebol3/ticket.rsp?id=1266)** [ Version: alpha 87 Type: Bug Platform: Windows Category: Parse Reproduce: Always Fixed-in:alpha 88 ]</sup>
<sup>**Imported from**: https://github.com/rebol/rebol-issues/issues/1266</sup>
Comments:
---
---
> **Rebolbot** added the **Type.bug** on Jan 12, 2016
--- | 1.0 | PARSE: CHANGE needs INTO [] match rule to be enclosed in a block - _Submitted by:_ **xuanin**
When using INTO [] as the match rule argument for CHANGE it needs to be enclosed in block to ensure it's correctly interpreted.
``` rebol
>> parse s: [[a b]][change into ['a 'b] [z p]]
== false
```
``` rebol
>> parse s: [[a b]][change [into ['a 'b]] [z p]]
== true
```
This is neither the case with other rules nor REMOVE:
``` rebol
>> parse s: [a b][change some word! [z p]]
== true
```
``` rebol
>> parse s: [[a b]][remove into ['a 'b]]
== true
```
---
<sup>**Imported from:** **[CureCode](https://www.curecode.org/rebol3/ticket.rsp?id=1266)** [ Version: alpha 87 Type: Bug Platform: Windows Category: Parse Reproduce: Always Fixed-in:alpha 88 ]</sup>
<sup>**Imported from**: https://github.com/rebol/rebol-issues/issues/1266</sup>
Comments:
---
---
> **Rebolbot** added the **Type.bug** on Jan 12, 2016
--- | test | parse change needs into match rule to be enclosed in a block submitted by xuanin when using into as the match rule argument for change it needs to be enclosed in block to ensure it s correctly interpreted rebol parse s false rebol parse s true this is neither the case with other rules nor remove rebol parse s true rebol parse s true imported from imported from comments rebolbot added the type bug on jan | 1 |
40,080 | 20,512,435,005 | IssuesEvent | 2022-03-01 08:18:41 | JuliaMolSim/DFTK.jl | https://api.github.com/repos/JuliaMolSim/DFTK.jl | closed | Improve density computation | performance | In #434 it became clear that we should take a look at getting density computations faster. | True | Improve density computation - In #434 it became clear that we should take a look at getting density computations faster. | non_test | improve density computation in it became clear that we should take a look at getting density computations faster | 0 |
64,020 | 6,890,770,109 | IssuesEvent | 2017-11-22 15:02:52 | chainer/chainer | https://api.github.com/repos/chainer/chainer | closed | Check warnings in test | enhancement stale test | Chainer uses deprecated methods in its code. Change warning level and check warnings in its test.
related to #755
| 1.0 | Check warnings in test - Chainer uses deprecated methods in its code. Change warning level and check warnings in its test.
related to #755
| test | check warnings in test chainer uses deprecated methods in its code change warning level and check warnings in its test related to | 1 |
177,646 | 6,586,073,444 | IssuesEvent | 2017-09-13 15:57:18 | raster-foundry/raster-foundry | https://api.github.com/repos/raster-foundry/raster-foundry | closed | Tool counts don't restrict visibility (I think) | NASA REQ priority | The tools list doesn't appear to be paginated (or at least no amount of scrolling makes more tools pop up, and there isn't a "next page" button anywhere), so there appears to be a tool somewhere that my user can't see but that is still getting included in the count
I discovered this because I had an overrides file in my dev environment to send requests to the prod app while I was testing the MAML parser. I'm cleaning them up now. But hey, at least in making a bunch of bogus tools in production, I discovered a bug maybe. :man_facepalming: | 1.0 | Tool counts don't restrict visibility (I think) - The tools list doesn't appear to be paginated (or at least no amount of scrolling makes more tools pop up, and there isn't a "next page" button anywhere), so there appears to be a tool somewhere that my user can't see but that is still getting included in the count
I discovered this because I had an overrides file in my dev environment to send requests to the prod app while I was testing the MAML parser. I'm cleaning them up now. But hey, at least in making a bunch of bogus tools in production, I discovered a bug maybe. :man_facepalming: | non_test | tool counts don t restrict visibility i think the tools list doesn t appear to be paginated or at least no amount of scrolling makes more tools pop up and there isn t a next page button anywhere so there appears to be a tool somewhere that my user can t see but that is still getting included in the count i discovered this because i had an overrides file in my dev environment to send requests to the prod app while i was testing the maml parser i m cleaning them up now but hey at least in making a bunch of bogus tools in production i discovered a bug maybe man facepalming | 0 |
40,553 | 5,306,382,147 | IssuesEvent | 2017-02-11 00:47:13 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | OuterLoop_CentOS7.1_release: Test 'System.Xml.Tests.CReaderTestModule.RunTestCase' failed with 'Xunit.Sdk.EqualException' | area-System.Xml test-run-core | Failed Test: System.Xml.Tests.CReaderTestModule.TCMaxSettings
Detail: https://ci.dot.net/job/dotnet_corefx/job/master/job/outerloop_centos7.1_release/89/consoleText
Message:
~~~
System.Xml.Tests.CReaderTestModule.TCMaxSettings [FAIL]
Assert.Equal() Failure
Expected: 0
Actual: 38
~~~
Stack Trace:
~~~
/mnt/resource/j/workspace/dotnet_corefx/master/outerloop_centos7.1_release/src/System.Private.Xml/tests/Readers/ReaderSettings/CReaderTestModule.cs(21,0): at System.Xml.Tests.CReaderTestModule.RunTestCase(Func`1 testCaseGenerator)
/mnt/resource/j/workspace/dotnet_corefx/master/outerloop_centos7.1_release/src/System.Private.Xml/tests/Readers/ReaderSettings/CReaderTestModule.cs(27,0): at System.Xml.Tests.CReaderTestModule.RunTest(Func`1 testCaseGenerator)
~~~
Configuration:
OuterLoop_Centos7.1_release (build#89) | 1.0 | OuterLoop_CentOS7.1_release: Test 'System.Xml.Tests.CReaderTestModule.RunTestCase' failed with 'Xunit.Sdk.EqualException' - Failed Test: System.Xml.Tests.CReaderTestModule.TCMaxSettings
Detail: https://ci.dot.net/job/dotnet_corefx/job/master/job/outerloop_centos7.1_release/89/consoleText
Message:
~~~
System.Xml.Tests.CReaderTestModule.TCMaxSettings [FAIL]
Assert.Equal() Failure
Expected: 0
Actual: 38
~~~
Stack Trace:
~~~
/mnt/resource/j/workspace/dotnet_corefx/master/outerloop_centos7.1_release/src/System.Private.Xml/tests/Readers/ReaderSettings/CReaderTestModule.cs(21,0): at System.Xml.Tests.CReaderTestModule.RunTestCase(Func`1 testCaseGenerator)
/mnt/resource/j/workspace/dotnet_corefx/master/outerloop_centos7.1_release/src/System.Private.Xml/tests/Readers/ReaderSettings/CReaderTestModule.cs(27,0): at System.Xml.Tests.CReaderTestModule.RunTest(Func`1 testCaseGenerator)
~~~
Configuration:
OuterLoop_Centos7.1_release (build#89) | test | outerloop release test system xml tests creadertestmodule runtestcase failed with xunit sdk equalexception failed test system xml tests creadertestmodule tcmaxsettings detail message system xml tests creadertestmodule tcmaxsettings assert equal failure expected actual stack trace mnt resource j workspace dotnet corefx master outerloop release src system private xml tests readers readersettings creadertestmodule cs at system xml tests creadertestmodule runtestcase func testcasegenerator mnt resource j workspace dotnet corefx master outerloop release src system private xml tests readers readersettings creadertestmodule cs at system xml tests creadertestmodule runtest func testcasegenerator configuration outerloop release build | 1 |
31,607 | 4,712,594,369 | IssuesEvent | 2016-10-14 17:16:46 | openshift/source-to-image | https://api.github.com/repos/openshift/source-to-image | closed | layered build test is flaking | area/tests kind/bug priority/P2 | ```
I0708 12:22:39.758507 10220 tar.go:308] Adding to tar: /tmp/s2i263248273/upload/src/README.md as src/README.md
I0708 12:22:39.758560 10220 tar.go:308] Adding to tar: /tmp/s2i263248273/upload/src/index.html as src/index.html
I0708 12:22:39.858016 10220 docker.go:722] Removing container "s2i_sti_test_sti_fake_no_tar_83e4f98d" ...
I0708 12:22:39.868368 10220 docker.go:726] Removed container "s2i_sti_test_sti_fake_no_tar_83e4f98d"
I0708 12:22:39.868465 10220 cleanup.go:33] Removing temporary directory /tmp/s2i263248273
I0708 12:22:39.868477 10220 fs.go:158] Removing directory '/tmp/s2i263248273'
I0708 12:22:39.869708 10220 sti.go:578]
--- FAIL: TestLayeredBuildNoTarNoName (0.71s)
integration_test.go:316: An error occurred during the build: non-zero (13) exit code from sti_test/sti-fake-no-tar
```
https://ci.openshift.redhat.com/jenkins/job/test_pull_requests_sti/513/consoleFull
no useful message about what failed unfortunately.
| 1.0 | layered build test is flaking - ```
I0708 12:22:39.758507 10220 tar.go:308] Adding to tar: /tmp/s2i263248273/upload/src/README.md as src/README.md
I0708 12:22:39.758560 10220 tar.go:308] Adding to tar: /tmp/s2i263248273/upload/src/index.html as src/index.html
I0708 12:22:39.858016 10220 docker.go:722] Removing container "s2i_sti_test_sti_fake_no_tar_83e4f98d" ...
I0708 12:22:39.868368 10220 docker.go:726] Removed container "s2i_sti_test_sti_fake_no_tar_83e4f98d"
I0708 12:22:39.868465 10220 cleanup.go:33] Removing temporary directory /tmp/s2i263248273
I0708 12:22:39.868477 10220 fs.go:158] Removing directory '/tmp/s2i263248273'
I0708 12:22:39.869708 10220 sti.go:578]
--- FAIL: TestLayeredBuildNoTarNoName (0.71s)
integration_test.go:316: An error occurred during the build: non-zero (13) exit code from sti_test/sti-fake-no-tar
```
https://ci.openshift.redhat.com/jenkins/job/test_pull_requests_sti/513/consoleFull
no useful message about what failed unfortunately.
| test | layered build test is flaking tar go adding to tar tmp upload src readme md as src readme md tar go adding to tar tmp upload src index html as src index html docker go removing container sti test sti fake no tar docker go removed container sti test sti fake no tar cleanup go removing temporary directory tmp fs go removing directory tmp sti go fail testlayeredbuildnotarnoname integration test go an error occurred during the build non zero exit code from sti test sti fake no tar no useful message about what failed unfortunately | 1 |
213,055 | 16,496,365,940 | IssuesEvent | 2021-05-25 10:48:29 | TestIntegrations/TestForwarding | https://api.github.com/repos/TestIntegrations/TestForwarding | opened | No description entered by the user. | test6 | # :clipboard: Bug Details
>No description entered by the user.
key | value
--|--
Reported At | 2021-05-25 10:39:38 UTC
Email | amiaqwwra6@test.com
Categories | Report a bug
Tags | test6
App Version | appverison (2)
Session Duration | 5
Device | Simulator, iOS 14.4
Display | 414x896 (@3x)
Location | Cairo, Egypt (en)
## :point_right: [View Full Bug Report on Instabug](https://dashboard.instabug.com/applications/ios-app-ok-12/beta/bugs/238?utm_source=github&utm_medium=integrations) :point_left:
___
# :chart_with_downwards_trend: Session Profiler
Here is what the app was doing right before the bug was reported:
Key | Value
--|--
CPU Load | 6.3%
Used Memory | 12.8% - 0.26/2.0 GB
Used Storage | 30.6% - 142.49/465.72 GB
Connectivity | WiFi - Simulator WiFi
Battery | 100% - unplugged
Orientation | portrait
Find all the changes that happened in the parameters mentioned above during the last 60 seconds before the bug was reported here: :point_right: **[View Full Session Profiler](https://dashboard.instabug.com/applications/ios-app-ok-12/beta/bugs/238?show-session-profiler=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :mag_right: Logs
### User Steps
Here are the last 10 steps done by the user right before the bug was reported:
```
10:39:30 Application: SceneWillConnect
10:39:30 Application: SceneDidActivate
10:39:30 Application: WillEnterForeground
10:39:30 Application: DidBecomeActive
10:39:30 Top View: ViewController
10:39:35 Tap in Floating Button of type IBGInvocationFloatingView in ViewController
```
Find all the user steps done by the user throughout the session here: :point_right: **[View All User Steps](https://dashboard.instabug.com/applications/ios-app-ok-12/beta/bugs/238?show-logs=user_steps&utm_source=github&utm_medium=integrations)** :point_left:
### Console Log
Here are the last 10 console logs logged right before the bug was reported:
```
Host = "httpbin.org";
"User-Agent" = "InstabugDemo/2 CFNetwork/1220.1 Darwin/20.3.0";
"X-Amzn-Trace-Id" = "Root=1-60acd3e3-453ce54d0bff211643794099";
};
json = {
"yousef 888" = khaled;
};
origin = "105.183.22.74";
url = "https://httpbin.org/post";
}
```
Find all the logged console logs throughout the session here: :point_right: **[View All Console Log](https://dashboard.instabug.com/applications/ios-app-ok-12/beta/bugs/238?show-logs=console_log&utm_source=github&utm_medium=integrations)** :point_left:
___
# :camera: Images
[](https://d38gnqwzxziyyy.cloudfront.net/attachments/bugs/15685008/9e1cdd2d93c859aa4ac17ee9d3c45893_original/20784598/2021052512393647917139.jpg?Expires=4777613308&Signature=WsIxp5V14s7-JnJ5K4mgYqVoBUzWk6kOFU2Z-yrItVau6nzd6oakvs~3sZVntOS8w04Qbh0g4ulQPwdrFEI3WKo1xRczsZSCeYNsx~YEPiLWUGs2lAw6VWxRjf6UJSllgGtYJt1rgQmbKWeBQSFutKYjDYCh~BKXBSSee904kByX3GdgnAHXOR-~3mn9Mla~8VkwLyqJGKecKxdxNuUpvd-qcKhVoUc09q-o2LxZRUKjhYhAV7tCtYE4OEd-9foNxOFYqb9S7AJbJv~pD6cdHGeWjcMRFTf6EY0sBNgmltK3Gxys0FiJSD2O5bFqzI0eXWuXc09FnzejawN7Bu6fEA__&Key-Pair-Id=APKAIXAG65U6UUX7JAQQ)
___
# :warning: Looking for More Details?
1. **Network Log**: we are unable to capture your network requests automatically. If you are using AFNetworking or Alamofire, [**check the details mentioned here**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations#section-requests-not-appearing-in-logs).
2. **User Events**: start capturing custom User Events to send them along with each report. [**Find all the details in the docs**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations).
3. **Instabug Log**: start adding Instabug logs to see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations). | 1.0 | No description entered by the user. - # :clipboard: Bug Details
>No description entered by the user.
key | value
--|--
Reported At | 2021-05-25 10:39:38 UTC
Email | amiaqwwra6@test.com
Categories | Report a bug
Tags | test6
App Version | appverison (2)
Session Duration | 5
Device | Simulator, iOS 14.4
Display | 414x896 (@3x)
Location | Cairo, Egypt (en)
## :point_right: [View Full Bug Report on Instabug](https://dashboard.instabug.com/applications/ios-app-ok-12/beta/bugs/238?utm_source=github&utm_medium=integrations) :point_left:
___
# :chart_with_downwards_trend: Session Profiler
Here is what the app was doing right before the bug was reported:
Key | Value
--|--
CPU Load | 6.3%
Used Memory | 12.8% - 0.26/2.0 GB
Used Storage | 30.6% - 142.49/465.72 GB
Connectivity | WiFi - Simulator WiFi
Battery | 100% - unplugged
Orientation | portrait
Find all the changes that happened in the parameters mentioned above during the last 60 seconds before the bug was reported here: :point_right: **[View Full Session Profiler](https://dashboard.instabug.com/applications/ios-app-ok-12/beta/bugs/238?show-session-profiler=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :mag_right: Logs
### User Steps
Here are the last 10 steps done by the user right before the bug was reported:
```
10:39:30 Application: SceneWillConnect
10:39:30 Application: SceneDidActivate
10:39:30 Application: WillEnterForeground
10:39:30 Application: DidBecomeActive
10:39:30 Top View: ViewController
10:39:35 Tap in Floating Button of type IBGInvocationFloatingView in ViewController
```
Find all the user steps done by the user throughout the session here: :point_right: **[View All User Steps](https://dashboard.instabug.com/applications/ios-app-ok-12/beta/bugs/238?show-logs=user_steps&utm_source=github&utm_medium=integrations)** :point_left:
### Console Log
Here are the last 10 console logs logged right before the bug was reported:
```
Host = "httpbin.org";
"User-Agent" = "InstabugDemo/2 CFNetwork/1220.1 Darwin/20.3.0";
"X-Amzn-Trace-Id" = "Root=1-60acd3e3-453ce54d0bff211643794099";
};
json = {
"yousef 888" = khaled;
};
origin = "105.183.22.74";
url = "https://httpbin.org/post";
}
```
Find all the logged console logs throughout the session here: :point_right: **[View All Console Log](https://dashboard.instabug.com/applications/ios-app-ok-12/beta/bugs/238?show-logs=console_log&utm_source=github&utm_medium=integrations)** :point_left:
___
# :camera: Images
[](https://d38gnqwzxziyyy.cloudfront.net/attachments/bugs/15685008/9e1cdd2d93c859aa4ac17ee9d3c45893_original/20784598/2021052512393647917139.jpg?Expires=4777613308&Signature=WsIxp5V14s7-JnJ5K4mgYqVoBUzWk6kOFU2Z-yrItVau6nzd6oakvs~3sZVntOS8w04Qbh0g4ulQPwdrFEI3WKo1xRczsZSCeYNsx~YEPiLWUGs2lAw6VWxRjf6UJSllgGtYJt1rgQmbKWeBQSFutKYjDYCh~BKXBSSee904kByX3GdgnAHXOR-~3mn9Mla~8VkwLyqJGKecKxdxNuUpvd-qcKhVoUc09q-o2LxZRUKjhYhAV7tCtYE4OEd-9foNxOFYqb9S7AJbJv~pD6cdHGeWjcMRFTf6EY0sBNgmltK3Gxys0FiJSD2O5bFqzI0eXWuXc09FnzejawN7Bu6fEA__&Key-Pair-Id=APKAIXAG65U6UUX7JAQQ)
___
# :warning: Looking for More Details?
1. **Network Log**: we are unable to capture your network requests automatically. If you are using AFNetworking or Alamofire, [**check the details mentioned here**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations#section-requests-not-appearing-in-logs).
2. **User Events**: start capturing custom User Events to send them along with each report. [**Find all the details in the docs**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations).
3. **Instabug Log**: start adding Instabug logs to see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations). | test | no description entered by the user clipboard bug details no description entered by the user key value reported at utc email test com categories report a bug tags app version appverison session duration device simulator ios display location cairo egypt en point right point left chart with downwards trend session profiler here is what the app was doing right before the bug was reported key value cpu load used memory gb used storage gb connectivity wifi simulator wifi battery unplugged orientation portrait find all the changes that happened in the parameters mentioned above during the last seconds before the bug was reported here point right point left mag right logs user steps here are the last steps done by the user right before the bug was reported application scenewillconnect application scenedidactivate application willenterforeground application didbecomeactive top view viewcontroller tap in floating button of type ibginvocationfloatingview in viewcontroller find all the user steps done by the user throughout the session here point right point left console log here are the last console logs logged right before the bug was reported host httpbin org user agent instabugdemo cfnetwork darwin x amzn trace id root json yousef khaled origin url find all the logged console logs throughout the session here point right point left camera images warning looking for more details network log we are unable to capture your network requests automatically if you are using afnetworking or alamofire user events start capturing custom user events to send them along with each report instabug log start adding instabug logs to see them right inside each report you receive | 1 |
129,847 | 10,588,600,390 | IssuesEvent | 2019-10-09 02:41:36 | data61/anonlink-entity-service | https://api.github.com/repos/data61/anonlink-entity-service | closed | Azure Devops CI isn't saving container logs | P3: important best practice devops effort2: medium (day) integration tests | This makes debugging intermittent test failures such as race conditions very difficult!
| 1.0 | Azure Devops CI isn't saving container logs - This makes debugging intermittent test failures such as race conditions very difficult!
| test | azure devops ci isn t saving container logs this makes debugging intermittent test failures such as race conditions very difficult | 1 |
38,811 | 5,200,024,371 | IssuesEvent | 2017-01-23 22:31:05 | idaholab/moose | https://api.github.com/repos/idaholab/moose | closed | Coloring is not correct with newer --check-input examples in modules | C: TestHarness P: normal T: task | ### Description of the enhancement or error report
When we use the base level "./run_tests" script. It prints the name of the module in cyan then the path to the test. It does this by searching for <module_name>/test/... The problem is that we now have several `--check-input` examples being run so this pattern no longer works as intended. The result is that we get some paths printed in cyan and others printed in the default font color.
### Rationale for the enhancement or information for reproducing the error
Inconsistent printout is confusing
### Identified impact
(i.e. Internal object changes, limited interface changes, public API change, or a list of specific applications impacted)
No functional problem, just a problem with coloring on the terminal
@milljm | 1.0 | Coloring is not correct with newer --check-input examples in modules - ### Description of the enhancement or error report
When we use the base level "./run_tests" script. It prints the name of the module in cyan then the path to the test. It does this by searching for <module_name>/test/... The problem is that we now have several `--check-input` examples being run so this pattern no longer works as intended. The result is that we get some paths printed in cyan and others printed in the default font color.
### Rationale for the enhancement or information for reproducing the error
Inconsistent printout is confusing
### Identified impact
(i.e. Internal object changes, limited interface changes, public API change, or a list of specific applications impacted)
No functional problem, just a problem with coloring on the terminal
@milljm | test | coloring is not correct with newer check input examples in modules description of the enhancement or error report when we use the base level run tests script it prints the name of the module in cyan then the path to the test it does this by searching for test the problem is that we now have several check input examples being run so this pattern no longer works as intended the result is that we get some paths printed in cyan and others printed in the default font color rationale for the enhancement or information for reproducing the error inconsistent printout is confusing identified impact i e internal object changes limited interface changes public api change or a list of specific applications impacted no functional problem just a problem with coloring on the terminal milljm | 1 |
75,066 | 20,617,416,135 | IssuesEvent | 2022-03-07 14:29:18 | tgve/tgvejs | https://api.github.com/repos/tgve/tgvejs | closed | consistent API vs REACT_APP_ values | build & deploy documentation | - [x] testing strategy
- [x] `REACT_APP_GEOGRAPHY_COLUMN_NAME` -> `REACT_APP_GEOGRAPHY_COLUMN`
- [x] `REACT_APP_COLUMN_NAME` -> `REACT_APP_COLUMN`
- [x] `REACT_APP_LAYER_NAME` -> `REACT_APP_LAYER_STYLE`
- [x] remove redundant pattern-match on `props`
- [x] `import { strict as assert } from 'assert'` and `assert(param != props[paramName])`
- [x] replace `param` by `props[paramName]` in `apiValue`
- [x] delete `param` parameter from `apiValue` and reformat `return` object
- [x] delete unused pattern-match on `props`
- [x] improve implementation of `boolStr`
- [x] delete commented `TGVE_API` and associated `export`
- [x] remove README reference to the inconsistency
- <s>check names in `api.R` (and fix typos in comments)</s>
- #129 | 1.0 | consistent API vs REACT_APP_ values - - [x] testing strategy
- [x] `REACT_APP_GEOGRAPHY_COLUMN_NAME` -> `REACT_APP_GEOGRAPHY_COLUMN`
- [x] `REACT_APP_COLUMN_NAME` -> `REACT_APP_COLUMN`
- [x] `REACT_APP_LAYER_NAME` -> `REACT_APP_LAYER_STYLE`
- [x] remove redundant pattern-match on `props`
- [x] `import { strict as assert } from 'assert'` and `assert(param != props[paramName])`
- [x] replace `param` by `props[paramName]` in `apiValue`
- [x] delete `param` parameter from `apiValue` and reformat `return` object
- [x] delete unused pattern-match on `props`
- [x] improve implementation of `boolStr`
- [x] delete commented `TGVE_API` and associated `export`
- [x] remove README reference to the inconsistency
- <s>check names in `api.R` (and fix typos in comments)</s>
- #129 | non_test | consistent api vs react app values testing strategy react app geography column name react app geography column react app column name react app column react app layer name react app layer style remove redundant pattern match on props import strict as assert from assert and assert param props replace param by props in apivalue delete param parameter from apivalue and reformat return object delete unused pattern match on props improve implementation of boolstr delete commented tgve api and associated export remove readme reference to the inconsistency check names in api r and fix typos in comments | 0 |
190,243 | 14,539,425,012 | IssuesEvent | 2020-12-15 11:51:55 | Grinnode-live/2020-grin-bug-bash-challenge | https://api.github.com/repos/Grinnode-live/2020-grin-bug-bash-challenge | opened | [GRIN-Wallet][Owner API] testing list of get stored transactions method | Grin-Wallet Test-Case ready-for-test | **Description**
Testing the post transaction method from the Owner API
**Prerequisites**
1. GRIN-Node
2. GRIN-Wallet that has transactions
**Test procedure**
1. Run GRIN-Wallet in Owner API listener mode
2. Use [node.js template](https://gist.github.com/marekyggdrasil/82716db323b34019bf02237012e0d16f) to run a encrypted request to [get stored transactions method](https://docs.rs/grin_wallet_api/4.0.0/grin_wallet_api/struct.Owner.html#method.get_stored_tx)
**Expected result:**
Check if retrieves the stored transaction associated with a TxLogEntry. Can be used even after the transaction has completed. Either the Transaction Log ID or the Slate UUID must be supplied. Check if both are supplied, the Transaction Log ID is preferred.
Provide requests and response full payloads as well as wallet and node logs. | 2.0 | [GRIN-Wallet][Owner API] testing list of get stored transactions method - **Description**
Testing the post transaction method from the Owner API
**Prerequisites**
1. GRIN-Node
2. GRIN-Wallet that has transactions
**Test procedure**
1. Run GRIN-Wallet in Owner API listener mode
2. Use [node.js template](https://gist.github.com/marekyggdrasil/82716db323b34019bf02237012e0d16f) to run a encrypted request to [get stored transactions method](https://docs.rs/grin_wallet_api/4.0.0/grin_wallet_api/struct.Owner.html#method.get_stored_tx)
**Expected result:**
Check if retrieves the stored transaction associated with a TxLogEntry. Can be used even after the transaction has completed. Either the Transaction Log ID or the Slate UUID must be supplied. Check if both are supplied, the Transaction Log ID is preferred.
Provide requests and response full payloads as well as wallet and node logs. | test | testing list of get stored transactions method description testing the post transaction method from the owner api prerequisites grin node grin wallet that has transactions test procedure run grin wallet in owner api listener mode use to run a encrypted request to expected result check if retrieves the stored transaction associated with a txlogentry can be used even after the transaction has completed either the transaction log id or the slate uuid must be supplied check if both are supplied the transaction log id is preferred provide requests and response full payloads as well as wallet and node logs | 1 |
183,592 | 14,239,299,090 | IssuesEvent | 2020-11-18 19:55:29 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: X-Pack Jest Tests.x-pack/plugins/upgrade_assistant/public/application/components/tabs/checkup/deprecations/reindex - ReindexPollingService begins to poll when first check is a 200 and status is inProgress | Feature:Upgrade Assistant Team:Elasticsearch UI failed-test | A test failed on a tracked branch
```
Error: expect(jest.fn()).toHaveBeenCalledTimes(expected)
Expected number of calls: 2
Received number of calls: 1
at Object.it (/var/lib/jenkins/workspace/elastic+kibana+master/kibana/x-pack/plugins/upgrade_assistant/public/application/components/tabs/checkup/deprecations/reindex/polling_service.test.ts:65:28)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+master/4100/)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Jest Tests.x-pack/plugins/upgrade_assistant/public/application/components/tabs/checkup/deprecations/reindex","test.name":"ReindexPollingService begins to poll when first check is a 200 and status is inProgress","test.failCount":2}} --> | 1.0 | Failing test: X-Pack Jest Tests.x-pack/plugins/upgrade_assistant/public/application/components/tabs/checkup/deprecations/reindex - ReindexPollingService begins to poll when first check is a 200 and status is inProgress - A test failed on a tracked branch
```
Error: expect(jest.fn()).toHaveBeenCalledTimes(expected)
Expected number of calls: 2
Received number of calls: 1
at Object.it (/var/lib/jenkins/workspace/elastic+kibana+master/kibana/x-pack/plugins/upgrade_assistant/public/application/components/tabs/checkup/deprecations/reindex/polling_service.test.ts:65:28)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+master/4100/)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Jest Tests.x-pack/plugins/upgrade_assistant/public/application/components/tabs/checkup/deprecations/reindex","test.name":"ReindexPollingService begins to poll when first check is a 200 and status is inProgress","test.failCount":2}} --> | test | failing test x pack jest tests x pack plugins upgrade assistant public application components tabs checkup deprecations reindex reindexpollingservice begins to poll when first check is a and status is inprogress a test failed on a tracked branch error expect jest fn tohavebeencalledtimes expected expected number of calls received number of calls at object it var lib jenkins workspace elastic kibana master kibana x pack plugins upgrade assistant public application components tabs checkup deprecations reindex polling service test ts first failure | 1 |
313,393 | 26,926,337,991 | IssuesEvent | 2023-02-07 14:03:44 | python/cpython | https://api.github.com/repos/python/cpython | closed | `doctest` GitHub Actions job exits with `2` failing all recent PRs | type-bug tests docs | The `Docs / Doctest (pull_request)` check started to fail recently with the following job log:
```plain
make: Entering directory '/home/runner/work/cpython/cpython/Doc'
make[1]: Entering directory '/home/runner/work/cpython/cpython/Doc'
mkdir -p build
Missing the required blurb or sphinx-build tools.
Please run 'make venv' to install local copies.
make[1]: *** [Makefile:48: build] Error 1
make[1]: Leaving directory '/home/runner/work/cpython/cpython/Doc'
Testing of doctests in the sources finished, look at the results in build/doctest/output.txt
make: *** [Makefile:1[2](https://github.com/python/cpython/actions/runs/4113297888/jobs/7099253477#step:9:2)[7](https://github.com/python/cpython/actions/runs/4113297888/jobs/7099253477#step:9:8): doctest] Error 1
make: Leaving directory '/home/runner/work/cpython/cpython/Doc'
Error: Process completed with exit code 2.
```
@colorfulappl [found out](https://github.com/python/cpython/pull/30312#issuecomment-1420226785) that:
> It seems like numpy build failed while running
>
> make -C Doc/ PYTHON=../python venv
>
> The error message is
>
> ```
> Error: numpy/random/_mt19937.c:8320:53: error: ‘PyLongObject’ {aka ‘struct _longobject’} has no member named ‘ob_digit’
> 8320 | const digit* digits = ((PyLongObject*)x)->ob_digit;
> | ^~
> ```
It looks like gh-101292 is the cause. We need to provide some sort of compatibility shim or a deprecation period until numpy introduces version-specific `#if` guards. | 1.0 | `doctest` GitHub Actions job exits with `2` failing all recent PRs - The `Docs / Doctest (pull_request)` check started to fail recently with the following job log:
```plain
make: Entering directory '/home/runner/work/cpython/cpython/Doc'
make[1]: Entering directory '/home/runner/work/cpython/cpython/Doc'
mkdir -p build
Missing the required blurb or sphinx-build tools.
Please run 'make venv' to install local copies.
make[1]: *** [Makefile:48: build] Error 1
make[1]: Leaving directory '/home/runner/work/cpython/cpython/Doc'
Testing of doctests in the sources finished, look at the results in build/doctest/output.txt
make: *** [Makefile:1[2](https://github.com/python/cpython/actions/runs/4113297888/jobs/7099253477#step:9:2)[7](https://github.com/python/cpython/actions/runs/4113297888/jobs/7099253477#step:9:8): doctest] Error 1
make: Leaving directory '/home/runner/work/cpython/cpython/Doc'
Error: Process completed with exit code 2.
```
@colorfulappl [found out](https://github.com/python/cpython/pull/30312#issuecomment-1420226785) that:
> It seems like numpy build failed while running
>
> make -C Doc/ PYTHON=../python venv
>
> The error message is
>
> ```
> Error: numpy/random/_mt19937.c:8320:53: error: ‘PyLongObject’ {aka ‘struct _longobject’} has no member named ‘ob_digit’
> 8320 | const digit* digits = ((PyLongObject*)x)->ob_digit;
> | ^~
> ```
It looks like gh-101292 is the cause. We need to provide some sort of compatibility shim or a deprecation period until numpy introduces version-specific `#if` guards. | test | doctest github actions job exits with failing all recent prs the docs doctest pull request check started to fail recently with the following job log plain make entering directory home runner work cpython cpython doc make entering directory home runner work cpython cpython doc mkdir p build missing the required blurb or sphinx build tools please run make venv to install local copies make error make leaving directory home runner work cpython cpython doc testing of doctests in the sources finished look at the results in build doctest output txt make doctest error make leaving directory home runner work cpython cpython doc error process completed with exit code colorfulappl that it seems like numpy build failed while running make c doc python python venv the error message is error numpy random c error ‘pylongobject’ aka ‘struct longobject’ has no member named ‘ob digit’ const digit digits pylongobject x ob digit it looks like gh is the cause we need to provide some sort of compatibility shim or a deprecation period until numpy introduces version specific if guards | 1 |
73,317 | 19,656,630,110 | IssuesEvent | 2022-01-10 13:12:24 | microsoft/azure-pipelines-tasks | https://api.github.com/repos/microsoft/azure-pipelines-tasks | opened | [ArtifactsAndLibraries tasks] Fix critical security issues | Area: Artifacts task: DownloadBuildArtifacts | ## Required Information
Entering this information will route you directly to the right team and expedite traction.
**Question, Bug, or Feature?**
*Type*: Bug
**Enter Task Name**:
- DownloadBuildArtifactsV1
- DownloadFileshareArtifactsV0
- DownloadGitHubNpmPackageV1
- DownloadGitHubNugetPackageV1
- DownloadGitHubReleaseV0
- JenkinsDownloadArtifactsV1
list here (V# not needed):
https://github.com/Microsoft/azure-pipelines-tasks/tree/master/Tasks
## Issue Description
[Compliance build](https://dev.azure.com/mseng/AzureDevOps/_build/results?buildId=16644541&view=results) started to report new critical security alerts since 12/08.
To reproduce this issue: run `npm audit`
DownloadBuildArtifactsV1, DownloadFileshareArtifactsV0, DownloadGitHubNpmPackageV1, DownloadGitHubNugetPackageV1, DownloadGitHubReleaseV0, JenkinsDownloadArtifactsV1 tasks has bunches of critical issues.
Audit logs attached.
### Task logs
[Audit logs.zip](https://github.com/microsoft/azure-pipelines-tasks/files/7839005/Audit.logs.zip)
## Troubleshooting
Checkout how to troubleshoot failures and collect debug logs: https://docs.microsoft.com/en-us/vsts/build-release/actions/troubleshooting
| 1.0 | [ArtifactsAndLibraries tasks] Fix critical security issues - ## Required Information
Entering this information will route you directly to the right team and expedite traction.
**Question, Bug, or Feature?**
*Type*: Bug
**Enter Task Name**:
- DownloadBuildArtifactsV1
- DownloadFileshareArtifactsV0
- DownloadGitHubNpmPackageV1
- DownloadGitHubNugetPackageV1
- DownloadGitHubReleaseV0
- JenkinsDownloadArtifactsV1
list here (V# not needed):
https://github.com/Microsoft/azure-pipelines-tasks/tree/master/Tasks
## Issue Description
[Compliance build](https://dev.azure.com/mseng/AzureDevOps/_build/results?buildId=16644541&view=results) started to report new critical security alerts since 12/08.
To reproduce this issue: run `npm audit`
DownloadBuildArtifactsV1, DownloadFileshareArtifactsV0, DownloadGitHubNpmPackageV1, DownloadGitHubNugetPackageV1, DownloadGitHubReleaseV0, JenkinsDownloadArtifactsV1 tasks has bunches of critical issues.
Audit logs attached.
### Task logs
[Audit logs.zip](https://github.com/microsoft/azure-pipelines-tasks/files/7839005/Audit.logs.zip)
## Troubleshooting
Checkout how to troubleshoot failures and collect debug logs: https://docs.microsoft.com/en-us/vsts/build-release/actions/troubleshooting
| non_test | fix critical security issues required information entering this information will route you directly to the right team and expedite traction question bug or feature type bug enter task name list here v not needed issue description started to report new critical security alerts since to reproduce this issue run npm audit tasks has bunches of critical issues audit logs attached task logs troubleshooting checkout how to troubleshoot failures and collect debug logs | 0 |
185,499 | 14,357,396,486 | IssuesEvent | 2020-11-30 13:01:06 | pingcap/tidb | https://api.github.com/repos/pingcap/tidb | opened | DATA_RACE:sync/atomic.CompareAndSwapInt32() failed | component/test | DATA_RACE:sync/atomic.CompareAndSwapInt32()
```
[2020-11-30T06:38:36.848Z] WARNING: DATA RACE
[2020-11-30T06:38:36.848Z] sync/atomic.CompareAndSwapInt32()
[2020-11-30T06:38:36.848Z] /usr/local/go/src/runtime/race_amd64.s:293 +0xb
[2020-11-30T06:38:36.848Z] sync.(*Mutex).Lock()
[2020-11-30T06:38:36.848Z] /usr/local/go/src/sync/mutex.go:74 +0x49
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/sessionctx/stmtctx.(*StatementContext).AppendWarnings()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/sessionctx/stmtctx/stmtctx.go:417 +0x47
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/session.(*session).ExecRestrictedSQLWithContext.func3()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:814 +0x1c6
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/session.(*session).ExecRestrictedSQLWithContext()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:823 +0x429
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/session.(*session).ExecRestrictedSQL()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:789 +0x92
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).execAutoAnalyze()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/update.go:904 +0xb2
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).autoAnalyzeTable()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/update.go:895 +0x52b
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).HandleAutoAnalyze()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/update.go:860 +0x95e
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/domain.(*Domain).autoAnalyzeWorker()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/domain/domain.go:1266 +0x2d9
[2020-11-30T06:38:36.848Z]
[2020-11-30T06:38:36.848Z] Previous write at 0x00c0052be5d0 by goroutine 193:
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/executor.ResetContextOfStmt()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/executor/executor.go:1581 +0x29e
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/session.(*session).ExecuteStmt()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:1230 +0x1f1
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/session.(*session).Execute()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:1170 +0x2a1
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.finishTransaction()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/ddl.go:191 +0x169
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).insertTableStats2KV.func1()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/ddl.go:102 +0x9c
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).insertTableStats2KV()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/ddl.go:117 +0xa4e
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).HandleDDLEvent()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/ddl.go:36 +0x15a
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/domain.(*Domain).updateStatsWorker()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/domain/domain.go:1217 +0x1114
[2020-11-30T06:38:36.849Z]
[2020-11-30T06:38:36.849Z] Goroutine 192 (running) created at:
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/domain.(*Domain).UpdateTableStatsLoop()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/domain/domain.go:1108 +0x328
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/session.BootstrapSession()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:2030 +0x53e
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/ddl/failtest_test.(*testFailDBSuite).SetUpSuite()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/ddl/failtest/fail_db_test.go:84 +0x285
[2020-11-30T06:38:36.849Z] runtime.call32()
[2020-11-30T06:38:36.849Z] /usr/local/go/src/runtime/asm_amd64.s:539 +0x3a
[2020-11-30T06:38:36.849Z] reflect.Value.Call()
[2020-11-30T06:38:36.849Z] /usr/local/go/src/reflect/value.go:321 +0xd3
[2020-11-30T06:38:36.849Z] github.com/pingcap/check.(*suiteRunner).runFixture.func1()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/pkg/mod/github.com/pingcap/check@v0.0.0-20200212061837-5e12011dc712/check.go:799 +0x195
[2020-11-30T06:38:36.849Z] github.com/pingcap/check.(*suiteRunner).forkCall.func1()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/pkg/mod/github.com/pingcap/check@v0.0.0-20200212061837-5e12011dc712/check.go:739 +0x113
[2020-11-30T06:38:36.849Z]
[2020-11-30T06:38:36.849Z] Goroutine 193 (running) created at:
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/domain.(*Domain).UpdateTableStatsLoop()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/domain/domain.go:1105 +0x29f
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/session.BootstrapSession()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:2030 +0x53e
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/ddl/failtest_test.(*testFailDBSuite).SetUpSuite()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/ddl/failtest/fail_db_test.go:84 +0x285
[2020-11-30T06:38:36.849Z] runtime.call32()
[2020-11-30T06:38:36.849Z] /usr/local/go/src/runtime/asm_amd64.s:539 +0x3a
[2020-11-30T06:38:36.849Z] reflect.Value.Call()
[2020-11-30T06:38:36.849Z] /usr/local/go/src/reflect/value.go:321 +0xd3
[2020-11-30T06:38:36.849Z] github.com/pingcap/check.(*suiteRunner).runFixture.func1()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/pkg/mod/github.com/pingcap/check@v0.0.0-20200212061837-5e12011dc712/check.go:799 +0x195
[2020-11-30T06:38:36.849Z] github.com/pingcap/check.(*suiteRunner).forkCall.func1()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/pkg/mod/github.com/pingcap/check@v0.0.0-20200212061837-5e12011dc712/check.go:739 +0x113
[2020-11-30T06:38:36.849Z] ==================
```
Latest failed builds:
https://internal.pingcap.net/idc-jenkins/job/tidb_ghpr_unit_test/59744/display/redirect
https://internal.pingcap.net/idc-jenkins/job/tidb_ghpr_unit_test/59765/display/redirect
| 1.0 | DATA_RACE:sync/atomic.CompareAndSwapInt32() failed - DATA_RACE:sync/atomic.CompareAndSwapInt32()
```
[2020-11-30T06:38:36.848Z] WARNING: DATA RACE
[2020-11-30T06:38:36.848Z] sync/atomic.CompareAndSwapInt32()
[2020-11-30T06:38:36.848Z] /usr/local/go/src/runtime/race_amd64.s:293 +0xb
[2020-11-30T06:38:36.848Z] sync.(*Mutex).Lock()
[2020-11-30T06:38:36.848Z] /usr/local/go/src/sync/mutex.go:74 +0x49
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/sessionctx/stmtctx.(*StatementContext).AppendWarnings()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/sessionctx/stmtctx/stmtctx.go:417 +0x47
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/session.(*session).ExecRestrictedSQLWithContext.func3()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:814 +0x1c6
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/session.(*session).ExecRestrictedSQLWithContext()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:823 +0x429
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/session.(*session).ExecRestrictedSQL()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:789 +0x92
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).execAutoAnalyze()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/update.go:904 +0xb2
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).autoAnalyzeTable()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/update.go:895 +0x52b
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).HandleAutoAnalyze()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/update.go:860 +0x95e
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/domain.(*Domain).autoAnalyzeWorker()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/domain/domain.go:1266 +0x2d9
[2020-11-30T06:38:36.848Z]
[2020-11-30T06:38:36.848Z] Previous write at 0x00c0052be5d0 by goroutine 193:
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/executor.ResetContextOfStmt()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/executor/executor.go:1581 +0x29e
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/session.(*session).ExecuteStmt()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:1230 +0x1f1
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/session.(*session).Execute()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:1170 +0x2a1
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.finishTransaction()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/ddl.go:191 +0x169
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).insertTableStats2KV.func1()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/ddl.go:102 +0x9c
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).insertTableStats2KV()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/ddl.go:117 +0xa4e
[2020-11-30T06:38:36.848Z] github.com/pingcap/tidb/statistics/handle.(*Handle).HandleDDLEvent()
[2020-11-30T06:38:36.848Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/statistics/handle/ddl.go:36 +0x15a
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/domain.(*Domain).updateStatsWorker()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/domain/domain.go:1217 +0x1114
[2020-11-30T06:38:36.849Z]
[2020-11-30T06:38:36.849Z] Goroutine 192 (running) created at:
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/domain.(*Domain).UpdateTableStatsLoop()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/domain/domain.go:1108 +0x328
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/session.BootstrapSession()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:2030 +0x53e
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/ddl/failtest_test.(*testFailDBSuite).SetUpSuite()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/ddl/failtest/fail_db_test.go:84 +0x285
[2020-11-30T06:38:36.849Z] runtime.call32()
[2020-11-30T06:38:36.849Z] /usr/local/go/src/runtime/asm_amd64.s:539 +0x3a
[2020-11-30T06:38:36.849Z] reflect.Value.Call()
[2020-11-30T06:38:36.849Z] /usr/local/go/src/reflect/value.go:321 +0xd3
[2020-11-30T06:38:36.849Z] github.com/pingcap/check.(*suiteRunner).runFixture.func1()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/pkg/mod/github.com/pingcap/check@v0.0.0-20200212061837-5e12011dc712/check.go:799 +0x195
[2020-11-30T06:38:36.849Z] github.com/pingcap/check.(*suiteRunner).forkCall.func1()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/pkg/mod/github.com/pingcap/check@v0.0.0-20200212061837-5e12011dc712/check.go:739 +0x113
[2020-11-30T06:38:36.849Z]
[2020-11-30T06:38:36.849Z] Goroutine 193 (running) created at:
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/domain.(*Domain).UpdateTableStatsLoop()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/domain/domain.go:1105 +0x29f
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/session.BootstrapSession()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/session/session.go:2030 +0x53e
[2020-11-30T06:38:36.849Z] github.com/pingcap/tidb/ddl/failtest_test.(*testFailDBSuite).SetUpSuite()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/src/github.com/pingcap/tidb/ddl/failtest/fail_db_test.go:84 +0x285
[2020-11-30T06:38:36.849Z] runtime.call32()
[2020-11-30T06:38:36.849Z] /usr/local/go/src/runtime/asm_amd64.s:539 +0x3a
[2020-11-30T06:38:36.849Z] reflect.Value.Call()
[2020-11-30T06:38:36.849Z] /usr/local/go/src/reflect/value.go:321 +0xd3
[2020-11-30T06:38:36.849Z] github.com/pingcap/check.(*suiteRunner).runFixture.func1()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/pkg/mod/github.com/pingcap/check@v0.0.0-20200212061837-5e12011dc712/check.go:799 +0x195
[2020-11-30T06:38:36.849Z] github.com/pingcap/check.(*suiteRunner).forkCall.func1()
[2020-11-30T06:38:36.849Z] /home/jenkins/agent/workspace/tidb_ghpr_unit_test/go/pkg/mod/github.com/pingcap/check@v0.0.0-20200212061837-5e12011dc712/check.go:739 +0x113
[2020-11-30T06:38:36.849Z] ==================
```
Latest failed builds:
https://internal.pingcap.net/idc-jenkins/job/tidb_ghpr_unit_test/59744/display/redirect
https://internal.pingcap.net/idc-jenkins/job/tidb_ghpr_unit_test/59765/display/redirect
| test | data race sync atomic failed data race sync atomic warning data race sync atomic usr local go src runtime race s sync mutex lock usr local go src sync mutex go github com pingcap tidb sessionctx stmtctx statementcontext appendwarnings home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb sessionctx stmtctx stmtctx go github com pingcap tidb session session execrestrictedsqlwithcontext home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb session session go github com pingcap tidb session session execrestrictedsqlwithcontext home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb session session go github com pingcap tidb session session execrestrictedsql home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb session session go github com pingcap tidb statistics handle handle execautoanalyze home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb statistics handle update go github com pingcap tidb statistics handle handle autoanalyzetable home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb statistics handle update go github com pingcap tidb statistics handle handle handleautoanalyze home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb statistics handle update go github com pingcap tidb domain domain autoanalyzeworker home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb domain domain go previous write at by goroutine github com pingcap tidb executor resetcontextofstmt home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb executor executor go github com pingcap tidb session session executestmt home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb session session go github com pingcap tidb session session execute home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb session session go github com pingcap tidb statistics handle finishtransaction home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb statistics handle ddl go github com pingcap tidb statistics handle handle home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb statistics handle ddl go github com pingcap tidb statistics handle handle home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb statistics handle ddl go github com pingcap tidb statistics handle handle handleddlevent home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb statistics handle ddl go github com pingcap tidb domain domain updatestatsworker home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb domain domain go goroutine running created at github com pingcap tidb domain domain updatetablestatsloop home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb domain domain go github com pingcap tidb session bootstrapsession home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb session session go github com pingcap tidb ddl failtest test testfaildbsuite setupsuite home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb ddl failtest fail db test go runtime usr local go src runtime asm s reflect value call usr local go src reflect value go github com pingcap check suiterunner runfixture home jenkins agent workspace tidb ghpr unit test go pkg mod github com pingcap check check go github com pingcap check suiterunner forkcall home jenkins agent workspace tidb ghpr unit test go pkg mod github com pingcap check check go goroutine running created at github com pingcap tidb domain domain updatetablestatsloop home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb domain domain go github com pingcap tidb session bootstrapsession home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb session session go github com pingcap tidb ddl failtest test testfaildbsuite setupsuite home jenkins agent workspace tidb ghpr unit test go src github com pingcap tidb ddl failtest fail db test go runtime usr local go src runtime asm s reflect value call usr local go src reflect value go github com pingcap check suiterunner runfixture home jenkins agent workspace tidb ghpr unit test go pkg mod github com pingcap check check go github com pingcap check suiterunner forkcall home jenkins agent workspace tidb ghpr unit test go pkg mod github com pingcap check check go latest failed builds | 1 |
188,851 | 14,477,071,950 | IssuesEvent | 2020-12-10 05:45:42 | rancher/dashboard | https://api.github.com/repos/rancher/dashboard | closed | [CIS v2] Need UI to be able to add AlertRule to a ClusterScan | [zube]: To Test area/cis | Alerting will be enabled as part of the CIS rancher-cis-benchmark chart.
Two types of alert are supported:
- Alert when scan completes
- Alert when scan has failures
**New fields added to the ClusterScan CR Spec:**
// AlertRule
ScanAlertRule *ClusterScanAlertRule `json:"scanAlertRule,omitempty"`
type ClusterScanAlertRule struct {
AlertOnComplete bool `json:"alertOnComplete,omitempty"`
AlertOnFailure bool `json:"alertOnFailure,omitempty"`
}
```
apiVersion: cis.cattle.io/v1
kind: ClusterScan
metadata:
generateName: scan-
generation: 1
name: scan-r6tmb
spec:
cronSchedule: '*/5 * * * *'
scanAlertRule:
alertOnComplete: true
alertOnFailure: true
scanProfileName: rke-profile-hardened
```
UI Options:
1) Create ClusterScan Form should provide options to add Alert options:
- checkboxes to choose alertOnComplete and/or alertOnFailure **[These will be off by default]**
- If user tries to select them, check if the alerting CRD is present, if not show a warning on UI to users indicating that alerts may not work.
- Need to show some informational tooltip to indicate alert-notifiers need to be setup separately.
@deniseschannon @vincent99 does this sound ok: "To receive alerts, please make sure Rancher Monitoring and Alerting app is installed and the Receivers and Routes have been configured to send out alerts. Further details can be found here https://rancher.com/docs/rancher/v2.x/en/monitoring-alerting/v2.5/configuration/#alertmanager-config"
| 1.0 | [CIS v2] Need UI to be able to add AlertRule to a ClusterScan - Alerting will be enabled as part of the CIS rancher-cis-benchmark chart.
Two types of alert are supported:
- Alert when scan completes
- Alert when scan has failures
**New fields added to the ClusterScan CR Spec:**
// AlertRule
ScanAlertRule *ClusterScanAlertRule `json:"scanAlertRule,omitempty"`
type ClusterScanAlertRule struct {
AlertOnComplete bool `json:"alertOnComplete,omitempty"`
AlertOnFailure bool `json:"alertOnFailure,omitempty"`
}
```
apiVersion: cis.cattle.io/v1
kind: ClusterScan
metadata:
generateName: scan-
generation: 1
name: scan-r6tmb
spec:
cronSchedule: '*/5 * * * *'
scanAlertRule:
alertOnComplete: true
alertOnFailure: true
scanProfileName: rke-profile-hardened
```
UI Options:
1) Create ClusterScan Form should provide options to add Alert options:
- checkboxes to choose alertOnComplete and/or alertOnFailure **[These will be off by default]**
- If user tries to select them, check if the alerting CRD is present, if not show a warning on UI to users indicating that alerts may not work.
- Need to show some informational tooltip to indicate alert-notifiers need to be setup separately.
@deniseschannon @vincent99 does this sound ok: "To receive alerts, please make sure Rancher Monitoring and Alerting app is installed and the Receivers and Routes have been configured to send out alerts. Further details can be found here https://rancher.com/docs/rancher/v2.x/en/monitoring-alerting/v2.5/configuration/#alertmanager-config"
| test | need ui to be able to add alertrule to a clusterscan alerting will be enabled as part of the cis rancher cis benchmark chart two types of alert are supported alert when scan completes alert when scan has failures new fields added to the clusterscan cr spec alertrule scanalertrule clusterscanalertrule json scanalertrule omitempty type clusterscanalertrule struct alertoncomplete bool json alertoncomplete omitempty alertonfailure bool json alertonfailure omitempty apiversion cis cattle io kind clusterscan metadata generatename scan generation name scan spec cronschedule scanalertrule alertoncomplete true alertonfailure true scanprofilename rke profile hardened ui options create clusterscan form should provide options to add alert options checkboxes to choose alertoncomplete and or alertonfailure if user tries to select them check if the alerting crd is present if not show a warning on ui to users indicating that alerts may not work need to show some informational tooltip to indicate alert notifiers need to be setup separately deniseschannon does this sound ok to receive alerts please make sure rancher monitoring and alerting app is installed and the receivers and routes have been configured to send out alerts further details can be found here | 1 |
176,668 | 28,134,123,664 | IssuesEvent | 2023-04-01 06:55:49 | umajho/dicexp | https://api.github.com/repos/umajho/dicexp | opened | 确定结果不确定的表达式的语义 | priority:medium kind:design | 如果一个表达式蕴含随机取值的操作,其结果就是不确定的。
例如,掷骰 `d6` 不确定,带附加值的掷骰 `d6+1` 不确定,反复掷骰 `3#(d6+1)` 不确定…
包含掷骰操作的闭包 `\(-> d6)` 确定,但包含调用这个闭包操作的表达式 `\(-> d6).()` 不确定。
目前对于「结果不确定的表达式」的处理原则是:
- 如果它没有名字,那作为通常函数的参数时不固定结果:
- `10#d42` 会返回包含 10 次独立投掷结果的列表。
- 在它(自己或者自己的容器)有了名字后,结果固定:
- `\(x -> x).(d42)` 会导致 `d42` 的结果固定住,`10#\(x->x).(d42)` 会返回包含 10 个相同值的列表。
这样的处理原则感觉还是有些别扭。
应该提供一个专门用来把不确定值的构造的值固定下来的方法,以及让闭包接受不确定值的构造(如值生成器)的方法。 | 1.0 | 确定结果不确定的表达式的语义 - 如果一个表达式蕴含随机取值的操作,其结果就是不确定的。
例如,掷骰 `d6` 不确定,带附加值的掷骰 `d6+1` 不确定,反复掷骰 `3#(d6+1)` 不确定…
包含掷骰操作的闭包 `\(-> d6)` 确定,但包含调用这个闭包操作的表达式 `\(-> d6).()` 不确定。
目前对于「结果不确定的表达式」的处理原则是:
- 如果它没有名字,那作为通常函数的参数时不固定结果:
- `10#d42` 会返回包含 10 次独立投掷结果的列表。
- 在它(自己或者自己的容器)有了名字后,结果固定:
- `\(x -> x).(d42)` 会导致 `d42` 的结果固定住,`10#\(x->x).(d42)` 会返回包含 10 个相同值的列表。
这样的处理原则感觉还是有些别扭。
应该提供一个专门用来把不确定值的构造的值固定下来的方法,以及让闭包接受不确定值的构造(如值生成器)的方法。 | non_test | 确定结果不确定的表达式的语义 如果一个表达式蕴含随机取值的操作,其结果就是不确定的。 例如,掷骰 不确定,带附加值的掷骰 不确定,反复掷骰 不确定… 包含掷骰操作的闭包 确定,但包含调用这个闭包操作的表达式 不确定。 目前对于「结果不确定的表达式」的处理原则是: 如果它没有名字,那作为通常函数的参数时不固定结果: 会返回包含 次独立投掷结果的列表。 在它(自己或者自己的容器)有了名字后,结果固定: x x 会导致 的结果固定住, x x 会返回包含 个相同值的列表。 这样的处理原则感觉还是有些别扭。 应该提供一个专门用来把不确定值的构造的值固定下来的方法,以及让闭包接受不确定值的构造(如值生成器)的方法。 | 0 |
233,488 | 18,990,917,120 | IssuesEvent | 2021-11-22 07:08:26 | boostcampwm-2021/web28-NaBaaang | https://api.github.com/repos/boostcampwm-2021/web28-NaBaaang | closed | 채팅 메시지 DB 저장 stress 테스트 | 💻 backend 👀 test | ## Description
- 새로운 메시지가 들어올때마다 DB에 메시지 저장될때 성능 테스트
## Constraints
- `Artillery` 스트레스 테슽팅 툴 적용해서 시나리오 작성
| 1.0 | 채팅 메시지 DB 저장 stress 테스트 - ## Description
- 새로운 메시지가 들어올때마다 DB에 메시지 저장될때 성능 테스트
## Constraints
- `Artillery` 스트레스 테슽팅 툴 적용해서 시나리오 작성
| test | 채팅 메시지 db 저장 stress 테스트 description 새로운 메시지가 들어올때마다 db에 메시지 저장될때 성능 테스트 constraints artillery 스트레스 테슽팅 툴 적용해서 시나리오 작성 | 1 |
188,134 | 14,439,573,236 | IssuesEvent | 2020-12-07 14:33:28 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | yepengxj/df_st_origin1: test/integration/buildcontroller_test.go; 87 LoC | fresh medium test |
Found a possible issue in [yepengxj/df_st_origin1](https://www.github.com/yepengxj/df_st_origin1) at [test/integration/buildcontroller_test.go](https://github.com/yepengxj/df_st_origin1/blob/cfe73e88c2a2d6de7e2de362130e4c26e5841154/test/integration/buildcontroller_test.go#L203-L289)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable test used in defer or goroutine at line 220
[Click here to see the code in its original context.](https://github.com/yepengxj/df_st_origin1/blob/cfe73e88c2a2d6de7e2de362130e4c26e5841154/test/integration/buildcontroller_test.go#L203-L289)
<details>
<summary>Click here to show the 87 line(s) of Go which triggered the analyzer.</summary>
```go
for _, test := range tests {
// Setup communications channels
podReadyChan := make(chan *kapi.Pod) // Will receive a value when a build pod is ready
errChan := make(chan error) // Will receive a value when an error occurs
stateReached := int32(0)
// Create a build
b, err := osClient.Builds(ns).Create(mockBuild())
checkErr(t, err)
// Watch build pod for transition to pending
podWatch, err := kClient.Pods(ns).Watch(labels.Everything(), fields.OneTermEqualSelector("metadata.name", buildutil.GetBuildPodName(b)), "")
checkErr(t, err)
go func() {
for e := range podWatch.ResultChan() {
pod, ok := e.Object.(*kapi.Pod)
if !ok {
checkErr(t, fmt.Errorf("%s: unexpected object received: %#v\n", test.Name, e.Object))
}
if pod.Status.Phase == kapi.PodPending {
podReadyChan <- pod
break
}
}
}()
var pod *kapi.Pod
select {
case pod = <-podReadyChan:
if pod.Status.Phase != kapi.PodPending {
t.Errorf("Got wrong pod phase: %s", pod.Status.Phase)
podWatch.Stop()
continue
}
case <-time.After(BuildControllersWatchTimeout):
t.Errorf("Timed out waiting for build pod to be ready")
podWatch.Stop()
continue
}
podWatch.Stop()
for _, state := range test.States {
// Update pod state and verify that corresponding build state happens accordingly
pod, err := kClient.Pods(ns).Get(pod.Name)
checkErr(t, err)
pod.Status.Phase = state.PodPhase
_, err = kClient.Pods(ns).UpdateStatus(pod)
checkErr(t, err)
buildWatch, err := osClient.Builds(ns).Watch(labels.Everything(), fields.OneTermEqualSelector("metadata.name", b.Name), b.ResourceVersion)
checkErr(t, err)
defer buildWatch.Stop()
go func() {
done := false
for e := range buildWatch.ResultChan() {
var ok bool
b, ok = e.Object.(*buildapi.Build)
if !ok {
errChan <- fmt.Errorf("%s: unexpected object received: %#v", test.Name, e.Object)
}
if e.Type != watchapi.Modified {
errChan <- fmt.Errorf("%s: unexpected event received: %s, object: %#v", test.Name, e.Type, e.Object)
}
if done {
errChan <- fmt.Errorf("%s: unexpected build state: %#v", test.Name, e.Object)
} else if b.Status.Phase == state.BuildPhase {
done = true
atomic.StoreInt32(&stateReached, 1)
}
}
}()
select {
case err := <-errChan:
buildWatch.Stop()
t.Errorf("%s: Error: %v\n", test.Name, err)
break
case <-time.After(waitTime):
buildWatch.Stop()
if atomic.LoadInt32(&stateReached) != 1 {
t.Errorf("%s: Did not reach desired build state: %s", test.Name, state.BuildPhase)
break
}
}
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: cfe73e88c2a2d6de7e2de362130e4c26e5841154
| 1.0 | yepengxj/df_st_origin1: test/integration/buildcontroller_test.go; 87 LoC -
Found a possible issue in [yepengxj/df_st_origin1](https://www.github.com/yepengxj/df_st_origin1) at [test/integration/buildcontroller_test.go](https://github.com/yepengxj/df_st_origin1/blob/cfe73e88c2a2d6de7e2de362130e4c26e5841154/test/integration/buildcontroller_test.go#L203-L289)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable test used in defer or goroutine at line 220
[Click here to see the code in its original context.](https://github.com/yepengxj/df_st_origin1/blob/cfe73e88c2a2d6de7e2de362130e4c26e5841154/test/integration/buildcontroller_test.go#L203-L289)
<details>
<summary>Click here to show the 87 line(s) of Go which triggered the analyzer.</summary>
```go
for _, test := range tests {
// Setup communications channels
podReadyChan := make(chan *kapi.Pod) // Will receive a value when a build pod is ready
errChan := make(chan error) // Will receive a value when an error occurs
stateReached := int32(0)
// Create a build
b, err := osClient.Builds(ns).Create(mockBuild())
checkErr(t, err)
// Watch build pod for transition to pending
podWatch, err := kClient.Pods(ns).Watch(labels.Everything(), fields.OneTermEqualSelector("metadata.name", buildutil.GetBuildPodName(b)), "")
checkErr(t, err)
go func() {
for e := range podWatch.ResultChan() {
pod, ok := e.Object.(*kapi.Pod)
if !ok {
checkErr(t, fmt.Errorf("%s: unexpected object received: %#v\n", test.Name, e.Object))
}
if pod.Status.Phase == kapi.PodPending {
podReadyChan <- pod
break
}
}
}()
var pod *kapi.Pod
select {
case pod = <-podReadyChan:
if pod.Status.Phase != kapi.PodPending {
t.Errorf("Got wrong pod phase: %s", pod.Status.Phase)
podWatch.Stop()
continue
}
case <-time.After(BuildControllersWatchTimeout):
t.Errorf("Timed out waiting for build pod to be ready")
podWatch.Stop()
continue
}
podWatch.Stop()
for _, state := range test.States {
// Update pod state and verify that corresponding build state happens accordingly
pod, err := kClient.Pods(ns).Get(pod.Name)
checkErr(t, err)
pod.Status.Phase = state.PodPhase
_, err = kClient.Pods(ns).UpdateStatus(pod)
checkErr(t, err)
buildWatch, err := osClient.Builds(ns).Watch(labels.Everything(), fields.OneTermEqualSelector("metadata.name", b.Name), b.ResourceVersion)
checkErr(t, err)
defer buildWatch.Stop()
go func() {
done := false
for e := range buildWatch.ResultChan() {
var ok bool
b, ok = e.Object.(*buildapi.Build)
if !ok {
errChan <- fmt.Errorf("%s: unexpected object received: %#v", test.Name, e.Object)
}
if e.Type != watchapi.Modified {
errChan <- fmt.Errorf("%s: unexpected event received: %s, object: %#v", test.Name, e.Type, e.Object)
}
if done {
errChan <- fmt.Errorf("%s: unexpected build state: %#v", test.Name, e.Object)
} else if b.Status.Phase == state.BuildPhase {
done = true
atomic.StoreInt32(&stateReached, 1)
}
}
}()
select {
case err := <-errChan:
buildWatch.Stop()
t.Errorf("%s: Error: %v\n", test.Name, err)
break
case <-time.After(waitTime):
buildWatch.Stop()
if atomic.LoadInt32(&stateReached) != 1 {
t.Errorf("%s: Did not reach desired build state: %s", test.Name, state.BuildPhase)
break
}
}
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: cfe73e88c2a2d6de7e2de362130e4c26e5841154
| test | yepengxj df st test integration buildcontroller test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message range loop variable test used in defer or goroutine at line click here to show the line s of go which triggered the analyzer go for test range tests setup communications channels podreadychan make chan kapi pod will receive a value when a build pod is ready errchan make chan error will receive a value when an error occurs statereached create a build b err osclient builds ns create mockbuild checkerr t err watch build pod for transition to pending podwatch err kclient pods ns watch labels everything fields onetermequalselector metadata name buildutil getbuildpodname b checkerr t err go func for e range podwatch resultchan pod ok e object kapi pod if ok checkerr t fmt errorf s unexpected object received v n test name e object if pod status phase kapi podpending podreadychan pod break var pod kapi pod select case pod podreadychan if pod status phase kapi podpending t errorf got wrong pod phase s pod status phase podwatch stop continue case time after buildcontrollerswatchtimeout t errorf timed out waiting for build pod to be ready podwatch stop continue podwatch stop for state range test states update pod state and verify that corresponding build state happens accordingly pod err kclient pods ns get pod name checkerr t err pod status phase state podphase err kclient pods ns updatestatus pod checkerr t err buildwatch err osclient builds ns watch labels everything fields onetermequalselector metadata name b name b resourceversion checkerr t err defer buildwatch stop go func done false for e range buildwatch resultchan var ok bool b ok e object buildapi build if ok errchan fmt errorf s unexpected object received v test name e object if e type watchapi modified errchan fmt errorf s unexpected event received s object v test name e type e object if done errchan fmt errorf s unexpected build state v test name e object else if b status phase state buildphase done true atomic statereached select case err errchan buildwatch stop t errorf s error v n test name err break case time after waittime buildwatch stop if atomic statereached t errorf s did not reach desired build state s test name state buildphase break leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
303,765 | 26,227,990,885 | IssuesEvent | 2023-01-04 20:40:15 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | ccl/importccl: TestExportImportBank failed | C-test-failure O-robot branch-master | [(ccl/importccl).TestExportImportBank failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2180355&tab=buildLog) on [master@673ca4456754435dc1255b0cce807256bb426ff9](https://github.com/cockroachdb/cockroach/commits/673ca4456754435dc1255b0cce807256bb426ff9):
```
=== RUN TestExportImportBank/null=
FAIL github.com/cockroachdb/cockroach/pkg/ccl/importccl 1203.469s
```
<details><summary>More</summary><p>
Parameters:
- GOFLAGS=-json
```
make stressrace TESTS=TestExportImportBank PKG=./pkg/ccl/importccl TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2ATestExportImportBank.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
Epic CRDB-7778
Jira issue: CRDB-3914 | 1.0 | ccl/importccl: TestExportImportBank failed - [(ccl/importccl).TestExportImportBank failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2180355&tab=buildLog) on [master@673ca4456754435dc1255b0cce807256bb426ff9](https://github.com/cockroachdb/cockroach/commits/673ca4456754435dc1255b0cce807256bb426ff9):
```
=== RUN TestExportImportBank/null=
FAIL github.com/cockroachdb/cockroach/pkg/ccl/importccl 1203.469s
```
<details><summary>More</summary><p>
Parameters:
- GOFLAGS=-json
```
make stressrace TESTS=TestExportImportBank PKG=./pkg/ccl/importccl TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2ATestExportImportBank.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
Epic CRDB-7778
Jira issue: CRDB-3914 | test | ccl importccl testexportimportbank failed on run testexportimportbank null fail github com cockroachdb cockroach pkg ccl importccl more parameters goflags json make stressrace tests testexportimportbank pkg pkg ccl importccl testtimeout stressflags timeout powered by epic crdb jira issue crdb | 1 |
7,277 | 5,958,435,000 | IssuesEvent | 2017-05-29 07:55:01 | babel/babel | https://api.github.com/repos/babel/babel | closed | es6.regexp.constructor polyfill moves RegExps onto slow path in V8 | performance | See https://medium.com/@schuay/js-regexp-fast-and-slow-d29d6b77b06 and https://github.com/mishoo/UglifyJS2/issues/1964 for more context.
es6.regexp.constructor (and possibly other regexp polyfills) cause all regexps to take the slow path in V8 by modifying RegExp.prototype.
Repro instructions here: https://github.com/mishoo/UglifyJS2/issues/1964#issuecomment-302287505
### Input Code
```js
require("babel-polyfill");
var str = "fooBar";
console.log( str.split(/(?=[A-Z])/) );
```
### Expected Behavior
RegExp.prototype remains unmodified when possible:
```js
$ d8 --allow-natives-syntax
%DebugPrint(RegExp.prototype)
DebugPrint: 0x3abc271141d1: [JS_OBJECT_TYPE]
- map = 0x2a00e4885ab9 [FastProperties]
- prototype = 0x3abc27104631
- elements = 0x215b0e102241 <FixedArray[0]> [FAST_HOLEY_ELEMENTS]
- properties = 0x215b0e102241 <FixedArray[0]> {
#constructor: 0x3abc27113209 <JSFunction RegExp (sfi = 0x215b0e157f71)> (const data descriptor)
// Note the value of the constructor property.
```
### Current Behavior
RegExp.prototype.constructor is set by es6.regexp.constructor.
```js
DebugPrint: 0x2cfbf37141d1: [JS_OBJECT_TYPE]
- map = 0x17891b2272a1 [FastProperties]
- prototype = 0x2cfbf3704631
- elements = 0x3bcb3a802241 <FixedArray[0]> [FAST_HOLEY_ELEMENTS]
- properties = 0x3bcb3a802241 <FixedArray[0]> {
#constructor: 0x286c311dcaa9 <JSFunction $RegExp (sfi = 0x13170d6ca299)> (data field 0)
// constructor is the '$RegExp' function.
```
### Environment
See https://github.com/mishoo/UglifyJS2/issues/1964
babel-polyfill@6.23.0 browserify@14.3.0 uglify-js@3.0.7
### Possible fix
Avoid modifying RegExp.prototype if possible. | True | es6.regexp.constructor polyfill moves RegExps onto slow path in V8 - See https://medium.com/@schuay/js-regexp-fast-and-slow-d29d6b77b06 and https://github.com/mishoo/UglifyJS2/issues/1964 for more context.
es6.regexp.constructor (and possibly other regexp polyfills) cause all regexps to take the slow path in V8 by modifying RegExp.prototype.
Repro instructions here: https://github.com/mishoo/UglifyJS2/issues/1964#issuecomment-302287505
### Input Code
```js
require("babel-polyfill");
var str = "fooBar";
console.log( str.split(/(?=[A-Z])/) );
```
### Expected Behavior
RegExp.prototype remains unmodified when possible:
```js
$ d8 --allow-natives-syntax
%DebugPrint(RegExp.prototype)
DebugPrint: 0x3abc271141d1: [JS_OBJECT_TYPE]
- map = 0x2a00e4885ab9 [FastProperties]
- prototype = 0x3abc27104631
- elements = 0x215b0e102241 <FixedArray[0]> [FAST_HOLEY_ELEMENTS]
- properties = 0x215b0e102241 <FixedArray[0]> {
#constructor: 0x3abc27113209 <JSFunction RegExp (sfi = 0x215b0e157f71)> (const data descriptor)
// Note the value of the constructor property.
```
### Current Behavior
RegExp.prototype.constructor is set by es6.regexp.constructor.
```js
DebugPrint: 0x2cfbf37141d1: [JS_OBJECT_TYPE]
- map = 0x17891b2272a1 [FastProperties]
- prototype = 0x2cfbf3704631
- elements = 0x3bcb3a802241 <FixedArray[0]> [FAST_HOLEY_ELEMENTS]
- properties = 0x3bcb3a802241 <FixedArray[0]> {
#constructor: 0x286c311dcaa9 <JSFunction $RegExp (sfi = 0x13170d6ca299)> (data field 0)
// constructor is the '$RegExp' function.
```
### Environment
See https://github.com/mishoo/UglifyJS2/issues/1964
babel-polyfill@6.23.0 browserify@14.3.0 uglify-js@3.0.7
### Possible fix
Avoid modifying RegExp.prototype if possible. | non_test | regexp constructor polyfill moves regexps onto slow path in see and for more context regexp constructor and possibly other regexp polyfills cause all regexps to take the slow path in by modifying regexp prototype repro instructions here input code js require babel polyfill var str foobar console log str split expected behavior regexp prototype remains unmodified when possible js allow natives syntax debugprint regexp prototype debugprint map prototype elements properties constructor const data descriptor note the value of the constructor property current behavior regexp prototype constructor is set by regexp constructor js debugprint map prototype elements properties constructor data field constructor is the regexp function environment see babel polyfill browserify uglify js possible fix avoid modifying regexp prototype if possible | 0 |
290,636 | 8,901,747,157 | IssuesEvent | 2019-01-17 04:00:33 | jsbroks/coco-annotator | https://api.github.com/repos/jsbroks/coco-annotator | opened | Move static methods | priority: low status: available type: maintenance | - [ ] `thumbnail_util.generate_thumbnail()` -> `ImageModel.thumbnail`
- [ ] `coco_util.get_annotation_iou` -> `AnnotationModel.iou(annotation)`
- [ ] `get_image_coco` -> `ImageModel.coco`
- [ ] `get_dataset_coco` -> `DatasetModel.coco`
| 1.0 | Move static methods - - [ ] `thumbnail_util.generate_thumbnail()` -> `ImageModel.thumbnail`
- [ ] `coco_util.get_annotation_iou` -> `AnnotationModel.iou(annotation)`
- [ ] `get_image_coco` -> `ImageModel.coco`
- [ ] `get_dataset_coco` -> `DatasetModel.coco`
| non_test | move static methods thumbnail util generate thumbnail imagemodel thumbnail coco util get annotation iou annotationmodel iou annotation get image coco imagemodel coco get dataset coco datasetmodel coco | 0 |
131,532 | 10,698,084,773 | IssuesEvent | 2019-10-23 17:55:20 | secdev/scapy | https://api.github.com/repos/secdev/scapy | closed | Travis CI: sudo is deprecated | tests | We missed it, but according to https://blog.travis-ci.com/2018-11-19-required-linux-infrastructure-migration
> Over the next few weeks, we encourage everyone to remove any sudo: false configurations from your .travis.yml. Soon we will run all projects on the virtual-machine-based infrastructure, the sudo keyword will be fully deprecated.
**`sudo` is now always enabled on Travis CI builds.** This means that half of our tests are useless.
I am for removing them (or if we leave some non-sudo tests, let's only keep a single one). They aren't that useful and take a spot in the queue.
It would greatly reduce the time Travis tests take to pass. | 1.0 | Travis CI: sudo is deprecated - We missed it, but according to https://blog.travis-ci.com/2018-11-19-required-linux-infrastructure-migration
> Over the next few weeks, we encourage everyone to remove any sudo: false configurations from your .travis.yml. Soon we will run all projects on the virtual-machine-based infrastructure, the sudo keyword will be fully deprecated.
**`sudo` is now always enabled on Travis CI builds.** This means that half of our tests are useless.
I am for removing them (or if we leave some non-sudo tests, let's only keep a single one). They aren't that useful and take a spot in the queue.
It would greatly reduce the time Travis tests take to pass. | test | travis ci sudo is deprecated we missed it but according to over the next few weeks we encourage everyone to remove any sudo false configurations from your travis yml soon we will run all projects on the virtual machine based infrastructure the sudo keyword will be fully deprecated sudo is now always enabled on travis ci builds this means that half of our tests are useless i am for removing them or if we leave some non sudo tests let s only keep a single one they aren t that useful and take a spot in the queue it would greatly reduce the time travis tests take to pass | 1 |
257,480 | 22,164,973,770 | IssuesEvent | 2022-06-05 04:05:35 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: jepsen/sequential/parts-start-kill-2 failed | C-test-failure O-robot O-roachtest branch-master release-blocker T-kv sync-me sync-me-5 | roachtest.jepsen/sequential/parts-start-kill-2 [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/5336174?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/5336174?buildTab=artifacts#/jepsen/sequential/parts-start-kill-2) on master @ [1cea73c8a18623949b81705eb5f75179e6cd8d86](https://github.com/cockroachdb/cockroach/commits/1cea73c8a18623949b81705eb5f75179e6cd8d86):
```
| initialize submodules in the clone
| -j, --jobs <n> number of submodules cloned in parallel
| --template <template-directory>
| directory from which templates will be used
| --reference <repo> reference repository
| --reference-if-able <repo>
| reference repository
| --dissociate use --reference only while cloning
| -o, --origin <name> use <name> instead of 'origin' to track upstream
| -b, --branch <branch>
| checkout <branch> instead of the remote's HEAD
| -u, --upload-pack <path>
| path to git-upload-pack on the remote
| --depth <depth> create a shallow clone of that depth
| --shallow-since <time>
| create a shallow clone since a specific time
| --shallow-exclude <revision>
| deepen history of shallow clone, excluding rev
| --single-branch clone only one branch, HEAD or --branch
| --no-tags don't clone any tags, and make later fetches not to follow them
| --shallow-submodules any cloned submodules will be shallow
| --separate-git-dir <gitdir>
| separate git dir from working tree
| -c, --config <key=value>
| set config inside the new repository
| --server-option <server-specific>
| option to transmit
| -4, --ipv4 use IPv4 addresses only
| -6, --ipv6 use IPv6 addresses only
| --filter <args> object filtering
| --remote-submodules any cloned submodules will use their remote-tracking branch
| --sparse initialize sparse-checkout file to include only files at root
|
|
| stdout:
Wraps: (6) COMMAND_PROBLEM
Wraps: (7) Node 6. Command with error:
| ``````
| bash -e -c '
| if ! test -d /mnt/data1/jepsen; then
| git clone -b tc-nightly --depth 1 https://github.com/cockroachdb/jepsen /mnt/data1/jepsen --add safe.directory /mnt/data1/jepsen
| else
| cd /mnt/data1/jepsen
| git fetch origin
| git checkout origin/tc-nightly
| fi
| '
| ``````
Wraps: (8) exit status 129
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *withstack.withStack (4) *errutil.withPrefix (5) *cluster.WithCommandDetails (6) errors.Cmd (7) *hintdetail.withDetail (8) *exec.ExitError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*jepsen/sequential/parts-start-kill-2.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: jepsen/sequential/parts-start-kill-2 failed - roachtest.jepsen/sequential/parts-start-kill-2 [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/5336174?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/5336174?buildTab=artifacts#/jepsen/sequential/parts-start-kill-2) on master @ [1cea73c8a18623949b81705eb5f75179e6cd8d86](https://github.com/cockroachdb/cockroach/commits/1cea73c8a18623949b81705eb5f75179e6cd8d86):
```
| initialize submodules in the clone
| -j, --jobs <n> number of submodules cloned in parallel
| --template <template-directory>
| directory from which templates will be used
| --reference <repo> reference repository
| --reference-if-able <repo>
| reference repository
| --dissociate use --reference only while cloning
| -o, --origin <name> use <name> instead of 'origin' to track upstream
| -b, --branch <branch>
| checkout <branch> instead of the remote's HEAD
| -u, --upload-pack <path>
| path to git-upload-pack on the remote
| --depth <depth> create a shallow clone of that depth
| --shallow-since <time>
| create a shallow clone since a specific time
| --shallow-exclude <revision>
| deepen history of shallow clone, excluding rev
| --single-branch clone only one branch, HEAD or --branch
| --no-tags don't clone any tags, and make later fetches not to follow them
| --shallow-submodules any cloned submodules will be shallow
| --separate-git-dir <gitdir>
| separate git dir from working tree
| -c, --config <key=value>
| set config inside the new repository
| --server-option <server-specific>
| option to transmit
| -4, --ipv4 use IPv4 addresses only
| -6, --ipv6 use IPv6 addresses only
| --filter <args> object filtering
| --remote-submodules any cloned submodules will use their remote-tracking branch
| --sparse initialize sparse-checkout file to include only files at root
|
|
| stdout:
Wraps: (6) COMMAND_PROBLEM
Wraps: (7) Node 6. Command with error:
| ``````
| bash -e -c '
| if ! test -d /mnt/data1/jepsen; then
| git clone -b tc-nightly --depth 1 https://github.com/cockroachdb/jepsen /mnt/data1/jepsen --add safe.directory /mnt/data1/jepsen
| else
| cd /mnt/data1/jepsen
| git fetch origin
| git checkout origin/tc-nightly
| fi
| '
| ``````
Wraps: (8) exit status 129
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *withstack.withStack (4) *errutil.withPrefix (5) *cluster.WithCommandDetails (6) errors.Cmd (7) *hintdetail.withDetail (8) *exec.ExitError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*jepsen/sequential/parts-start-kill-2.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| test | roachtest jepsen sequential parts start kill failed roachtest jepsen sequential parts start kill with on master initialize submodules in the clone j jobs number of submodules cloned in parallel template directory from which templates will be used reference reference repository reference if able reference repository dissociate use reference only while cloning o origin use instead of origin to track upstream b branch checkout instead of the remote s head u upload pack path to git upload pack on the remote depth create a shallow clone of that depth shallow since create a shallow clone since a specific time shallow exclude deepen history of shallow clone excluding rev single branch clone only one branch head or branch no tags don t clone any tags and make later fetches not to follow them shallow submodules any cloned submodules will be shallow separate git dir separate git dir from working tree c config set config inside the new repository server option option to transmit use addresses only use addresses only filter object filtering remote submodules any cloned submodules will use their remote tracking branch sparse initialize sparse checkout file to include only files at root stdout wraps command problem wraps node command with error bash e c if test d mnt jepsen then git clone b tc nightly depth mnt jepsen add safe directory mnt jepsen else cd mnt jepsen git fetch origin git checkout origin tc nightly fi wraps exit status error types withstack withstack errutil withprefix withstack withstack errutil withprefix cluster withcommanddetails errors cmd hintdetail withdetail exec exiterror help see see cc cockroachdb kv triage | 1 |
91,668 | 15,856,554,003 | IssuesEvent | 2021-04-08 02:37:12 | DaemonToolz/locuste.dashboard.mobile | https://api.github.com/repos/DaemonToolz/locuste.dashboard.mobile | opened | CVE-2020-28498 (Medium) detected in elliptic-6.5.2.tgz | security vulnerability | ## CVE-2020-28498 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.2.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz</a></p>
<p>Path to dependency file: locuste.dashboard.mobile/locuste-mobile/package.json</p>
<p>Path to vulnerable library: locuste.dashboard.mobile/locuste-mobile/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.901.7.tgz (Root Library)
- webpack-4.42.0.tgz
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.2.0.tgz
- :x: **elliptic-6.5.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package elliptic before 6.5.4 are vulnerable to Cryptographic Issues via the secp256k1 implementation in elliptic/ec/key.js. There is no check to confirm that the public key point passed into the derive function actually exists on the secp256k1 curve. This results in the potential for the private key used in this implementation to be revealed after a number of ECDH operations are performed.
<p>Publish Date: 2021-02-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28498>CVE-2020-28498</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498</a></p>
<p>Release Date: 2021-02-02</p>
<p>Fix Resolution: v6.5.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28498 (Medium) detected in elliptic-6.5.2.tgz - ## CVE-2020-28498 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.2.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz</a></p>
<p>Path to dependency file: locuste.dashboard.mobile/locuste-mobile/package.json</p>
<p>Path to vulnerable library: locuste.dashboard.mobile/locuste-mobile/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.901.7.tgz (Root Library)
- webpack-4.42.0.tgz
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.2.0.tgz
- :x: **elliptic-6.5.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package elliptic before 6.5.4 are vulnerable to Cryptographic Issues via the secp256k1 implementation in elliptic/ec/key.js. There is no check to confirm that the public key point passed into the derive function actually exists on the secp256k1 curve. This results in the potential for the private key used in this implementation to be revealed after a number of ECDH operations are performed.
<p>Publish Date: 2021-02-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28498>CVE-2020-28498</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498</a></p>
<p>Release Date: 2021-02-02</p>
<p>Fix Resolution: v6.5.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in elliptic tgz cve medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file locuste dashboard mobile locuste mobile package json path to vulnerable library locuste dashboard mobile locuste mobile node modules elliptic package json dependency hierarchy build angular tgz root library webpack tgz node libs browser tgz crypto browserify tgz browserify sign tgz x elliptic tgz vulnerable library vulnerability details the package elliptic before are vulnerable to cryptographic issues via the implementation in elliptic ec key js there is no check to confirm that the public key point passed into the derive function actually exists on the curve this results in the potential for the private key used in this implementation to be revealed after a number of ecdh operations are performed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
22,375 | 4,792,925,672 | IssuesEvent | 2016-10-31 16:46:49 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | closed | Installation instruction on windows does not specify which component to install for MSVC | category: multi-platform > windows P2 type: documentation | The default installation of MS Visual Studio Community Edition does not contains the necessary files, the safest path is to select "everything"
| 1.0 | Installation instruction on windows does not specify which component to install for MSVC - The default installation of MS Visual Studio Community Edition does not contains the necessary files, the safest path is to select "everything"
| non_test | installation instruction on windows does not specify which component to install for msvc the default installation of ms visual studio community edition does not contains the necessary files the safest path is to select everything | 0 |
206,188 | 15,715,441,182 | IssuesEvent | 2021-03-28 01:18:33 | diffblue/cbmc | https://api.github.com/repos/diffblue/cbmc | opened | Regression testing infrastructure for the SMT backend | RFC SMT Backend Interface Tests | This is based on a recent discussion I had with @tautschnig. I wanted to open this RFC and get some feedback before creating a PR.
Currently we seem to have 3 tags for our regression tests that relevant to the SMT backend:
- `smt-backend`: Tests that _require_ the SMT backend, and don't work with the SAT backend
- `broken-smt-backend`: Tests that pass with the SAT backend, but don't work with the SMT backend
- `thorough-smt-backend`: Tests that pass with the SAT backend, but take a long time with the SMT backend
While working on #5973, I came across a regression test that works with both Z3 and CVC4, but doesn't work with CPROVER SMT2 because it lacks support for quantifiers. So I think it would make sense to add a few new tags that are solver-specific:
- `broken-cprover-smt2-smt-backend` and `thorough-cprover-smt2-smt-backend`
- `broken-z3-smt-backend` and `thorough-z3-smt-backend`
- `broken-cvc4-smt-backend` and `thorough-cvc4-smt-backend`
The `-smt-backend` suffix for these tags would be useful for `grep`-ing all regression tests related to the SMT-backend in any way. The tags can also be combined, e.g.
- `smt-backend broken-cprover-smt2-smt-backend` would indicate that the test requires SMT backend, but doesn't work CPROVER SMT2 solver
- `thorough-smt-backend broken-cvc4-smt-backend` would indicate that the test runs slower with the SMT backend, and doesn't work at all with CVC4 backend
I also suggest running the same version of these solvers across all platforms on our CI. That way, each time we bump up the version of solver `X` on our CI, we can revisit all of the `broken-X-smt-backend` and `thorough-X-smt-backend` tests and check if any of them are now fixed.
How many solvers we want our CI to be running is a separate discussion, but I think we should definitely at least be running Z3, and preferably both Z3 and CVC4 (in future). | 1.0 | Regression testing infrastructure for the SMT backend - This is based on a recent discussion I had with @tautschnig. I wanted to open this RFC and get some feedback before creating a PR.
Currently we seem to have 3 tags for our regression tests that relevant to the SMT backend:
- `smt-backend`: Tests that _require_ the SMT backend, and don't work with the SAT backend
- `broken-smt-backend`: Tests that pass with the SAT backend, but don't work with the SMT backend
- `thorough-smt-backend`: Tests that pass with the SAT backend, but take a long time with the SMT backend
While working on #5973, I came across a regression test that works with both Z3 and CVC4, but doesn't work with CPROVER SMT2 because it lacks support for quantifiers. So I think it would make sense to add a few new tags that are solver-specific:
- `broken-cprover-smt2-smt-backend` and `thorough-cprover-smt2-smt-backend`
- `broken-z3-smt-backend` and `thorough-z3-smt-backend`
- `broken-cvc4-smt-backend` and `thorough-cvc4-smt-backend`
The `-smt-backend` suffix for these tags would be useful for `grep`-ing all regression tests related to the SMT-backend in any way. The tags can also be combined, e.g.
- `smt-backend broken-cprover-smt2-smt-backend` would indicate that the test requires SMT backend, but doesn't work CPROVER SMT2 solver
- `thorough-smt-backend broken-cvc4-smt-backend` would indicate that the test runs slower with the SMT backend, and doesn't work at all with CVC4 backend
I also suggest running the same version of these solvers across all platforms on our CI. That way, each time we bump up the version of solver `X` on our CI, we can revisit all of the `broken-X-smt-backend` and `thorough-X-smt-backend` tests and check if any of them are now fixed.
How many solvers we want our CI to be running is a separate discussion, but I think we should definitely at least be running Z3, and preferably both Z3 and CVC4 (in future). | test | regression testing infrastructure for the smt backend this is based on a recent discussion i had with tautschnig i wanted to open this rfc and get some feedback before creating a pr currently we seem to have tags for our regression tests that relevant to the smt backend smt backend tests that require the smt backend and don t work with the sat backend broken smt backend tests that pass with the sat backend but don t work with the smt backend thorough smt backend tests that pass with the sat backend but take a long time with the smt backend while working on i came across a regression test that works with both and but doesn t work with cprover because it lacks support for quantifiers so i think it would make sense to add a few new tags that are solver specific broken cprover smt backend and thorough cprover smt backend broken smt backend and thorough smt backend broken smt backend and thorough smt backend the smt backend suffix for these tags would be useful for grep ing all regression tests related to the smt backend in any way the tags can also be combined e g smt backend broken cprover smt backend would indicate that the test requires smt backend but doesn t work cprover solver thorough smt backend broken smt backend would indicate that the test runs slower with the smt backend and doesn t work at all with backend i also suggest running the same version of these solvers across all platforms on our ci that way each time we bump up the version of solver x on our ci we can revisit all of the broken x smt backend and thorough x smt backend tests and check if any of them are now fixed how many solvers we want our ci to be running is a separate discussion but i think we should definitely at least be running and preferably both and in future | 1 |
37,340 | 5,113,416,882 | IssuesEvent | 2017-01-06 15:16:53 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | github.com/cockroachdb/cockroach/pkg/ts: TestServerQueryStarvation failed under stress | Robot test-failure | SHA: https://github.com/cockroachdb/cockroach/commits/a35fdc7f37f087688b5539c28d344426143d54c6
Parameters:
```
COCKROACH_PROPOSER_EVALUATED_KV=true
TAGS=
GOFLAGS=
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=109454&tab=buildLog
```
W170106 07:32:20.275065 506 server/status/runtime.go:116 Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I170106 07:32:20.278160 506 server/config.go:447 1 storage engine initialized
I170106 07:32:20.278666 506 server/node.go:426 [n?] store [n0,s0] not bootstrapped
I170106 07:32:20.282954 506 server/node.go:355 [n?] **** cluster 2340a221-36c3-4c3e-a4af-eaa9d09875dc has been created
I170106 07:32:20.282969 506 server/node.go:356 [n?] **** add additional nodes by specifying --join=127.0.0.1:36560
I170106 07:32:20.283509 506 storage/store.go:1258 [n1] [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I170106 07:32:20.283536 506 server/node.go:439 [n1] initialized store [n1,s1]: {Capacity:536870912 Available:536870912 RangeCount:1 LeaseCount:0}
I170106 07:32:20.283553 506 server/node.go:324 [n1] node ID 1 initialized
I170106 07:32:20.283595 506 gossip/gossip.go:292 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:36560" > attrs:<> locality:<>
I170106 07:32:20.283636 506 storage/stores.go:296 [n1] read 0 node addresses from persistent storage
I170106 07:32:20.283665 506 server/node.go:569 [n1] connecting to gossip network to verify cluster ID...
I170106 07:32:20.283676 506 server/node.go:589 [n1] node connected via gossip and verified as part of cluster "2340a221-36c3-4c3e-a4af-eaa9d09875dc"
I170106 07:32:20.283738 506 server/node.go:374 [n1] node=1: started with [[]=] engine(s) and attributes []
I170106 07:32:20.283761 506 sql/executor.go:322 [n1] creating distSQLPlanner with address {tcp 127.0.0.1:36560}
I170106 07:32:20.284457 553 storage/split_queue.go:101 [split,n1,s1,r1/1:/M{in-ax},@c4207ae480] splitting at keys [/Table/11/0 /Table/12/0 /Table/13/0 /Table/14/0]
I170106 07:32:20.285455 553 storage/replica_command.go:2362 [split,n1,s1,r1/1:/M{in-ax},@c4207ae480] initiating a split of this range at key /Table/11 [r2]
I170106 07:32:20.293528 506 server/server.go:621 [n1] starting https server at 127.0.0.1:38152
I170106 07:32:20.293545 506 server/server.go:622 [n1] starting grpc/postgres server at 127.0.0.1:36560
I170106 07:32:20.293557 506 server/server.go:623 [n1] advertising CockroachDB node at 127.0.0.1:36560
E170106 07:32:20.294845 554 storage/queue.go:597 [replicate,n1,s1,r1/1:/{Min-Table/11},@c4207ae480] range requires a replication change, but lacks a quorum of live replicas (0/1)
E170106 07:32:20.295262 553 storage/queue.go:597 [split,n1,s1,r1/1:/{Min-Table/11},@c4207ae480] unable to split [n1,s1,r1/1:/{Min-Table/11}] at key "/Table/12/0": key range /Table/12/0-/Table/12/0 outside of bounds of range /Min-/Max
I170106 07:32:20.295373 553 storage/split_queue.go:101 [split,n1,s1,r2/1:/{Table/11-Max},@c420194d80] splitting at keys [/Table/12/0 /Table/13/0 /Table/14/0]
I170106 07:32:20.295413 553 storage/replica_command.go:2362 [split,n1,s1,r2/1:/{Table/11-Max},@c420194d80] initiating a split of this range at key /Table/12 [r3]
E170106 07:32:20.317316 553 storage/queue.go:597 [split,n1,s1,r2/1:/Table/1{1-2},@c420194d80] unable to split [n1,s1,r2/1:/Table/1{1-2}] at key "/Table/13/0": key range /Table/13/0-/Table/13/0 outside of bounds of range /Table/11-/Max
I170106 07:32:20.317442 553 storage/split_queue.go:101 [split,n1,s1,r3/1:/{Table/12-Max},@c4207afb00] splitting at keys [/Table/13/0 /Table/14/0]
I170106 07:32:20.317496 553 storage/replica_command.go:2362 [split,n1,s1,r3/1:/{Table/12-Max},@c4207afb00] initiating a split of this range at key /Table/13 [r4]
I170106 07:32:20.320208 506 sql/event_log.go:95 [n1] Event: "alter_table", target: 12, info: {TableName:eventlog Statement:ALTER TABLE system.eventlog ALTER COLUMN uniqueID SET DEFAULT uuid_v4() User:node MutationID:0 CascadeDroppedViews:[]}
I170106 07:32:20.341385 689 sql/event_log.go:95 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:36560} Attrs: Locality:} ClusterID:2340a221-36c3-4c3e-a4af-eaa9d09875dc StartedAt:1483687940283678955}
E170106 07:32:20.343440 553 storage/queue.go:597 [split,n1,s1,r3/1:/Table/1{2-3},@c4207afb00] unable to split [n1,s1,r3/1:/Table/1{2-3}] at key "/Table/14/0": key range /Table/14/0-/Table/14/0 outside of bounds of range /Table/12-/Max
I170106 07:32:20.343546 553 storage/split_queue.go:101 [split,n1,s1,r4/1:/{Table/13-Max},@c420194900] splitting at keys [/Table/14/0]
I170106 07:32:20.343582 553 storage/replica_command.go:2362 [split,n1,s1,r4/1:/{Table/13-Max},@c420194900] initiating a split of this range at key /Table/14 [r5]
I170106 07:32:20.351498 506 server/server.go:676 [n1] done ensuring all necessary migrations have run
I170106 07:32:20.351517 506 server/server.go:678 [n1] serving sql connections
W170106 07:32:19.957982 854 util/hlc/hlc.go:145 backward time jump detected (-0.402699 seconds)
server_test.go:269: error storing data for series 0, source 6: storage/store.go:2368: rejecting command with timestamp in the future: 1483687940360666930 (402.535712ms ahead)
ERROR: exit status 1
2673 runs completed, 1 failures, over 5m17s
make: *** [stress] Error 1
Makefile:147: recipe for target 'stress' failed
``` | 1.0 | github.com/cockroachdb/cockroach/pkg/ts: TestServerQueryStarvation failed under stress - SHA: https://github.com/cockroachdb/cockroach/commits/a35fdc7f37f087688b5539c28d344426143d54c6
Parameters:
```
COCKROACH_PROPOSER_EVALUATED_KV=true
TAGS=
GOFLAGS=
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=109454&tab=buildLog
```
W170106 07:32:20.275065 506 server/status/runtime.go:116 Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I170106 07:32:20.278160 506 server/config.go:447 1 storage engine initialized
I170106 07:32:20.278666 506 server/node.go:426 [n?] store [n0,s0] not bootstrapped
I170106 07:32:20.282954 506 server/node.go:355 [n?] **** cluster 2340a221-36c3-4c3e-a4af-eaa9d09875dc has been created
I170106 07:32:20.282969 506 server/node.go:356 [n?] **** add additional nodes by specifying --join=127.0.0.1:36560
I170106 07:32:20.283509 506 storage/store.go:1258 [n1] [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I170106 07:32:20.283536 506 server/node.go:439 [n1] initialized store [n1,s1]: {Capacity:536870912 Available:536870912 RangeCount:1 LeaseCount:0}
I170106 07:32:20.283553 506 server/node.go:324 [n1] node ID 1 initialized
I170106 07:32:20.283595 506 gossip/gossip.go:292 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:36560" > attrs:<> locality:<>
I170106 07:32:20.283636 506 storage/stores.go:296 [n1] read 0 node addresses from persistent storage
I170106 07:32:20.283665 506 server/node.go:569 [n1] connecting to gossip network to verify cluster ID...
I170106 07:32:20.283676 506 server/node.go:589 [n1] node connected via gossip and verified as part of cluster "2340a221-36c3-4c3e-a4af-eaa9d09875dc"
I170106 07:32:20.283738 506 server/node.go:374 [n1] node=1: started with [[]=] engine(s) and attributes []
I170106 07:32:20.283761 506 sql/executor.go:322 [n1] creating distSQLPlanner with address {tcp 127.0.0.1:36560}
I170106 07:32:20.284457 553 storage/split_queue.go:101 [split,n1,s1,r1/1:/M{in-ax},@c4207ae480] splitting at keys [/Table/11/0 /Table/12/0 /Table/13/0 /Table/14/0]
I170106 07:32:20.285455 553 storage/replica_command.go:2362 [split,n1,s1,r1/1:/M{in-ax},@c4207ae480] initiating a split of this range at key /Table/11 [r2]
I170106 07:32:20.293528 506 server/server.go:621 [n1] starting https server at 127.0.0.1:38152
I170106 07:32:20.293545 506 server/server.go:622 [n1] starting grpc/postgres server at 127.0.0.1:36560
I170106 07:32:20.293557 506 server/server.go:623 [n1] advertising CockroachDB node at 127.0.0.1:36560
E170106 07:32:20.294845 554 storage/queue.go:597 [replicate,n1,s1,r1/1:/{Min-Table/11},@c4207ae480] range requires a replication change, but lacks a quorum of live replicas (0/1)
E170106 07:32:20.295262 553 storage/queue.go:597 [split,n1,s1,r1/1:/{Min-Table/11},@c4207ae480] unable to split [n1,s1,r1/1:/{Min-Table/11}] at key "/Table/12/0": key range /Table/12/0-/Table/12/0 outside of bounds of range /Min-/Max
I170106 07:32:20.295373 553 storage/split_queue.go:101 [split,n1,s1,r2/1:/{Table/11-Max},@c420194d80] splitting at keys [/Table/12/0 /Table/13/0 /Table/14/0]
I170106 07:32:20.295413 553 storage/replica_command.go:2362 [split,n1,s1,r2/1:/{Table/11-Max},@c420194d80] initiating a split of this range at key /Table/12 [r3]
E170106 07:32:20.317316 553 storage/queue.go:597 [split,n1,s1,r2/1:/Table/1{1-2},@c420194d80] unable to split [n1,s1,r2/1:/Table/1{1-2}] at key "/Table/13/0": key range /Table/13/0-/Table/13/0 outside of bounds of range /Table/11-/Max
I170106 07:32:20.317442 553 storage/split_queue.go:101 [split,n1,s1,r3/1:/{Table/12-Max},@c4207afb00] splitting at keys [/Table/13/0 /Table/14/0]
I170106 07:32:20.317496 553 storage/replica_command.go:2362 [split,n1,s1,r3/1:/{Table/12-Max},@c4207afb00] initiating a split of this range at key /Table/13 [r4]
I170106 07:32:20.320208 506 sql/event_log.go:95 [n1] Event: "alter_table", target: 12, info: {TableName:eventlog Statement:ALTER TABLE system.eventlog ALTER COLUMN uniqueID SET DEFAULT uuid_v4() User:node MutationID:0 CascadeDroppedViews:[]}
I170106 07:32:20.341385 689 sql/event_log.go:95 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:36560} Attrs: Locality:} ClusterID:2340a221-36c3-4c3e-a4af-eaa9d09875dc StartedAt:1483687940283678955}
E170106 07:32:20.343440 553 storage/queue.go:597 [split,n1,s1,r3/1:/Table/1{2-3},@c4207afb00] unable to split [n1,s1,r3/1:/Table/1{2-3}] at key "/Table/14/0": key range /Table/14/0-/Table/14/0 outside of bounds of range /Table/12-/Max
I170106 07:32:20.343546 553 storage/split_queue.go:101 [split,n1,s1,r4/1:/{Table/13-Max},@c420194900] splitting at keys [/Table/14/0]
I170106 07:32:20.343582 553 storage/replica_command.go:2362 [split,n1,s1,r4/1:/{Table/13-Max},@c420194900] initiating a split of this range at key /Table/14 [r5]
I170106 07:32:20.351498 506 server/server.go:676 [n1] done ensuring all necessary migrations have run
I170106 07:32:20.351517 506 server/server.go:678 [n1] serving sql connections
W170106 07:32:19.957982 854 util/hlc/hlc.go:145 backward time jump detected (-0.402699 seconds)
server_test.go:269: error storing data for series 0, source 6: storage/store.go:2368: rejecting command with timestamp in the future: 1483687940360666930 (402.535712ms ahead)
ERROR: exit status 1
2673 runs completed, 1 failures, over 5m17s
make: *** [stress] Error 1
Makefile:147: recipe for target 'stress' failed
``` | test | github com cockroachdb cockroach pkg ts testserverquerystarvation failed under stress sha parameters cockroach proposer evaluated kv true tags goflags stress build found a failed test server status runtime go could not parse build timestamp parsing time as cannot parse as server config go storage engine initialized server node go store not bootstrapped server node go cluster has been created server node go add additional nodes by specifying join storage store go failed initial metrics computation system config not yet available server node go initialized store capacity available rangecount leasecount server node go node id initialized gossip gossip go nodedescriptor set to node id address attrs locality storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster server node go node started with engine s and attributes sql executor go creating distsqlplanner with address tcp storage split queue go splitting at keys storage replica command go initiating a split of this range at key table server server go starting https server at server server go starting grpc postgres server at server server go advertising cockroachdb node at storage queue go range requires a replication change but lacks a quorum of live replicas storage queue go unable to split at key table key range table table outside of bounds of range min max storage split queue go splitting at keys storage replica command go initiating a split of this range at key table storage queue go unable to split at key table key range table table outside of bounds of range table max storage split queue go splitting at keys storage replica command go initiating a split of this range at key table sql event log go event alter table target info tablename eventlog statement alter table system eventlog alter column uniqueid set default uuid user node mutationid cascadedroppedviews sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs locality clusterid startedat storage queue go unable to split at key table key range table table outside of bounds of range table max storage split queue go splitting at keys storage replica command go initiating a split of this range at key table server server go done ensuring all necessary migrations have run server server go serving sql connections util hlc hlc go backward time jump detected seconds server test go error storing data for series source storage store go rejecting command with timestamp in the future ahead error exit status runs completed failures over make error makefile recipe for target stress failed | 1 |
102,193 | 8,821,376,895 | IssuesEvent | 2019-01-02 01:01:14 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | opened | [CI] IndexAuditTrail fails to start - cannot read security-version | :Security/Audit >test-failure | On 6.6:
https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+6.6+periodic/80/console
Seems to have failed twice ([previous](https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+6.x+multijob-unix-compatibility/os=opensuse/36/) but the earlier failure may have been related to the underlying hardware.
Doesn't reproduce for me.
As a CI failure it seems pretty rare, but I wonder if there's some sort of timing/concurrency issue that could be an actual production problem.
Log:
```
00:03:38 | [2019-01-02T00:01:44,802][ERROR][o.e.x.s.a.i.IndexAuditTrail] [upgraded-node-2] failed to start index audit trail services
00:03:38 | java.lang.IllegalStateException: Cannot read security-version string in index .security_audit_log-2019.01.02
00:03:38 | at org.elasticsearch.xpack.security.audit.index.IndexAuditTrail.updateCurrentIndexMappingsIfNecessary(IndexAuditTrail.java:404) ~[x-pack-security-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at org.elasticsearch.xpack.security.audit.index.IndexAuditTrail.start(IndexAuditTrail.java:373) ~[x-pack-security-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at org.elasticsearch.xpack.security.audit.index.IndexAuditTrail$2.doRun(IndexAuditTrail.java:235) [x-pack-security-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at org.elasticsearch.common.util.concurrent.ThreadContext$ContextPreservingAbstractRunnable.doRun(ThreadContext.java:759) [elasticsearch-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37) [elasticsearch-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128) [?:?]
00:03:38 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628) [?:?]
00:03:38 | at java.lang.Thread.run(Thread.java:834) [?:?]
00:03:38 | [2019-01-02T00:01:44,814][ERROR][o.e.b.ElasticsearchUncaughtExceptionHandler] [upgraded-node-2] fatal error in thread [elasticsearch[upgraded-node-2][generic][T#1]], exiting
00:03:38 | java.lang.AssertionError: security lifecycle services startup failed
00:03:38 | at org.elasticsearch.xpack.security.audit.index.IndexAuditTrail$2.onFailure(IndexAuditTrail.java:230) ~[?:?]
00:03:38 | at org.elasticsearch.common.util.concurrent.ThreadContext$ContextPreservingAbstractRunnable.onFailure(ThreadContext.java:744) ~[elasticsearch-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:39) ~[elasticsearch-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128) ~[?:?]
00:03:38 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628) ~[?:?]
00:03:38 | at java.lang.Thread.run(Thread.java:834) [?:?]
00:03:38 |-----------------------------------------
``` | 1.0 | [CI] IndexAuditTrail fails to start - cannot read security-version - On 6.6:
https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+6.6+periodic/80/console
Seems to have failed twice ([previous](https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+6.x+multijob-unix-compatibility/os=opensuse/36/) but the earlier failure may have been related to the underlying hardware.
Doesn't reproduce for me.
As a CI failure it seems pretty rare, but I wonder if there's some sort of timing/concurrency issue that could be an actual production problem.
Log:
```
00:03:38 | [2019-01-02T00:01:44,802][ERROR][o.e.x.s.a.i.IndexAuditTrail] [upgraded-node-2] failed to start index audit trail services
00:03:38 | java.lang.IllegalStateException: Cannot read security-version string in index .security_audit_log-2019.01.02
00:03:38 | at org.elasticsearch.xpack.security.audit.index.IndexAuditTrail.updateCurrentIndexMappingsIfNecessary(IndexAuditTrail.java:404) ~[x-pack-security-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at org.elasticsearch.xpack.security.audit.index.IndexAuditTrail.start(IndexAuditTrail.java:373) ~[x-pack-security-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at org.elasticsearch.xpack.security.audit.index.IndexAuditTrail$2.doRun(IndexAuditTrail.java:235) [x-pack-security-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at org.elasticsearch.common.util.concurrent.ThreadContext$ContextPreservingAbstractRunnable.doRun(ThreadContext.java:759) [elasticsearch-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37) [elasticsearch-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128) [?:?]
00:03:38 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628) [?:?]
00:03:38 | at java.lang.Thread.run(Thread.java:834) [?:?]
00:03:38 | [2019-01-02T00:01:44,814][ERROR][o.e.b.ElasticsearchUncaughtExceptionHandler] [upgraded-node-2] fatal error in thread [elasticsearch[upgraded-node-2][generic][T#1]], exiting
00:03:38 | java.lang.AssertionError: security lifecycle services startup failed
00:03:38 | at org.elasticsearch.xpack.security.audit.index.IndexAuditTrail$2.onFailure(IndexAuditTrail.java:230) ~[?:?]
00:03:38 | at org.elasticsearch.common.util.concurrent.ThreadContext$ContextPreservingAbstractRunnable.onFailure(ThreadContext.java:744) ~[elasticsearch-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:39) ~[elasticsearch-6.6.0-SNAPSHOT.jar:6.6.0-SNAPSHOT]
00:03:38 | at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128) ~[?:?]
00:03:38 | at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628) ~[?:?]
00:03:38 | at java.lang.Thread.run(Thread.java:834) [?:?]
00:03:38 |-----------------------------------------
``` | test | indexaudittrail fails to start cannot read security version on seems to have failed twice but the earlier failure may have been related to the underlying hardware doesn t reproduce for me as a ci failure it seems pretty rare but i wonder if there s some sort of timing concurrency issue that could be an actual production problem log failed to start index audit trail services java lang illegalstateexception cannot read security version string in index security audit log at org elasticsearch xpack security audit index indexaudittrail updatecurrentindexmappingsifnecessary indexaudittrail java at org elasticsearch xpack security audit index indexaudittrail start indexaudittrail java at org elasticsearch xpack security audit index indexaudittrail dorun indexaudittrail java at org elasticsearch common util concurrent threadcontext contextpreservingabstractrunnable dorun threadcontext java at org elasticsearch common util concurrent abstractrunnable run abstractrunnable java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java fatal error in thread exiting java lang assertionerror security lifecycle services startup failed at org elasticsearch xpack security audit index indexaudittrail onfailure indexaudittrail java at org elasticsearch common util concurrent threadcontext contextpreservingabstractrunnable onfailure threadcontext java at org elasticsearch common util concurrent abstractrunnable run abstractrunnable java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java | 1 |
158,745 | 12,424,531,514 | IssuesEvent | 2020-05-24 12:08:48 | appium/appium | https://api.github.com/repos/appium/appium | closed | iOS App source not being retrieved properly when certain elements are present. | ThirdParty XCUITest | ## The problem
Appium is failing to show the source of the app I'm testing in certain screen, apparently when a table of sizes is present.
## Environment
* Appium version (or git revision) that exhibits the issue: 1.17.0 and 1.17.1
* Desktop OS/version used to run Appium: mac os catalina 10.15.3
* Node.js version: 13.11.0
* Npm or Yarn package manager: NPM
* Mobile platform/version under test: iOS 13.3.1
* Real device or emulator/simulator: Real Device
* Appium CLI or Appium.app|exe: Tied both appium desktop and appium cli
## Details
According to the developers, this is a regular table with nothing special about it.
Here are a couple of pictures, with and without the table.
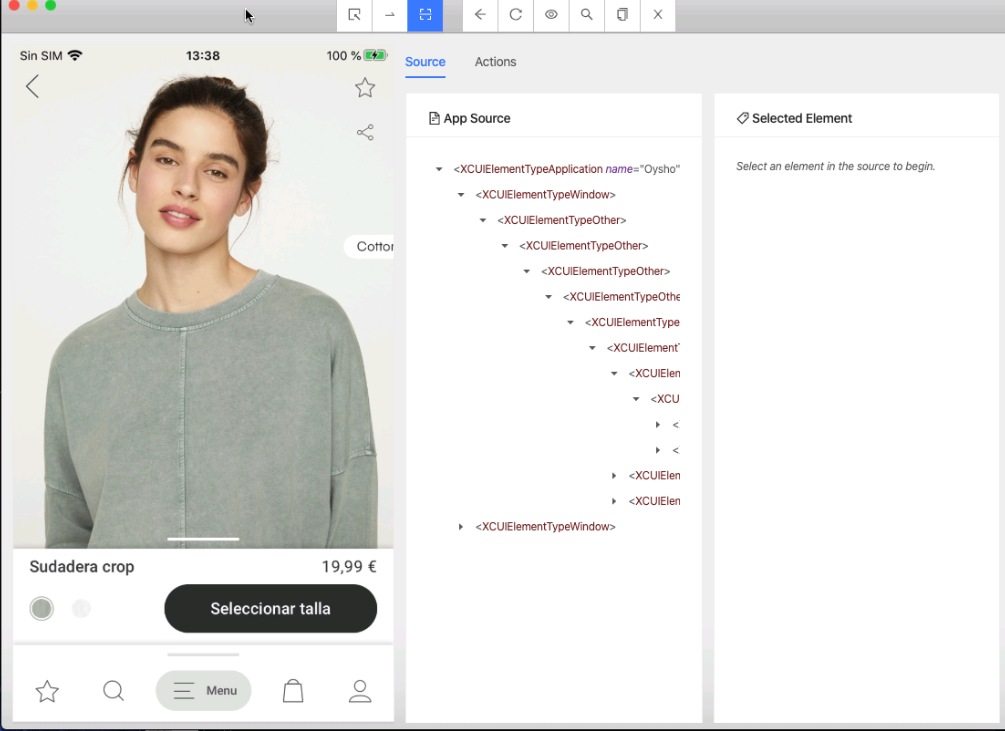
Here we can see the source is properly loaded.
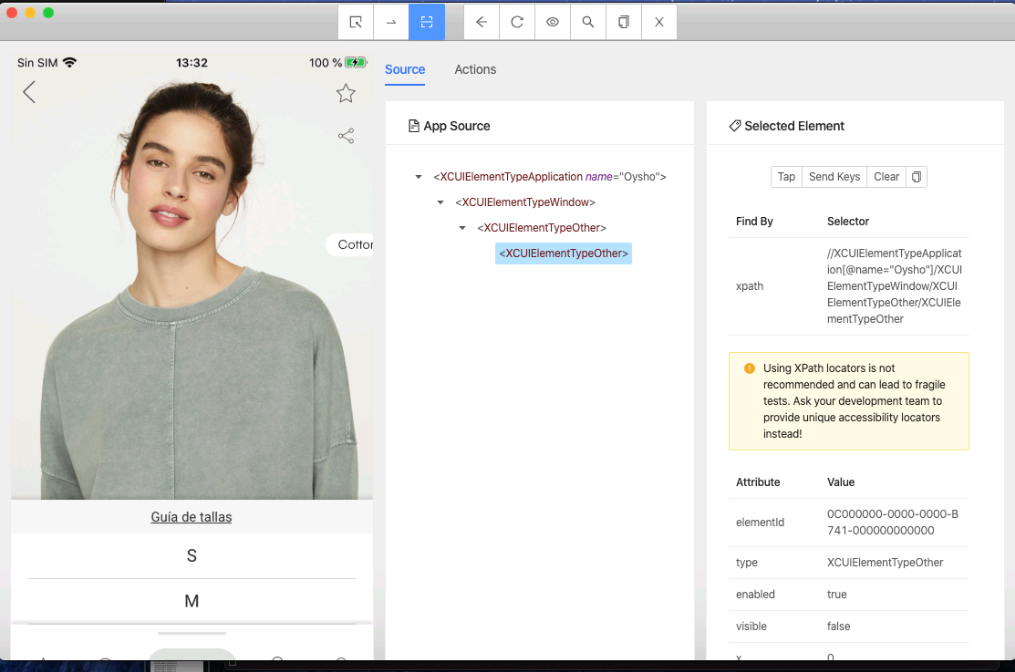
After displaying the size table the source doesn't get retrieved properly, only a few elements are loaded.
Also I guessed the id of one of the elements, like "s" and if I click on it it handles it without problem, so it can find an element inside the table even if it cant read the entire source.
Also tried includeNonModalElements capability with no different result.
## Link to Appium logs
https://gist.github.com/Julioevm/5157fc7b0e79950dc3620dc6b21ef26d
| 1.0 | iOS App source not being retrieved properly when certain elements are present. - ## The problem
Appium is failing to show the source of the app I'm testing in certain screen, apparently when a table of sizes is present.
## Environment
* Appium version (or git revision) that exhibits the issue: 1.17.0 and 1.17.1
* Desktop OS/version used to run Appium: mac os catalina 10.15.3
* Node.js version: 13.11.0
* Npm or Yarn package manager: NPM
* Mobile platform/version under test: iOS 13.3.1
* Real device or emulator/simulator: Real Device
* Appium CLI or Appium.app|exe: Tied both appium desktop and appium cli
## Details
According to the developers, this is a regular table with nothing special about it.
Here are a couple of pictures, with and without the table.
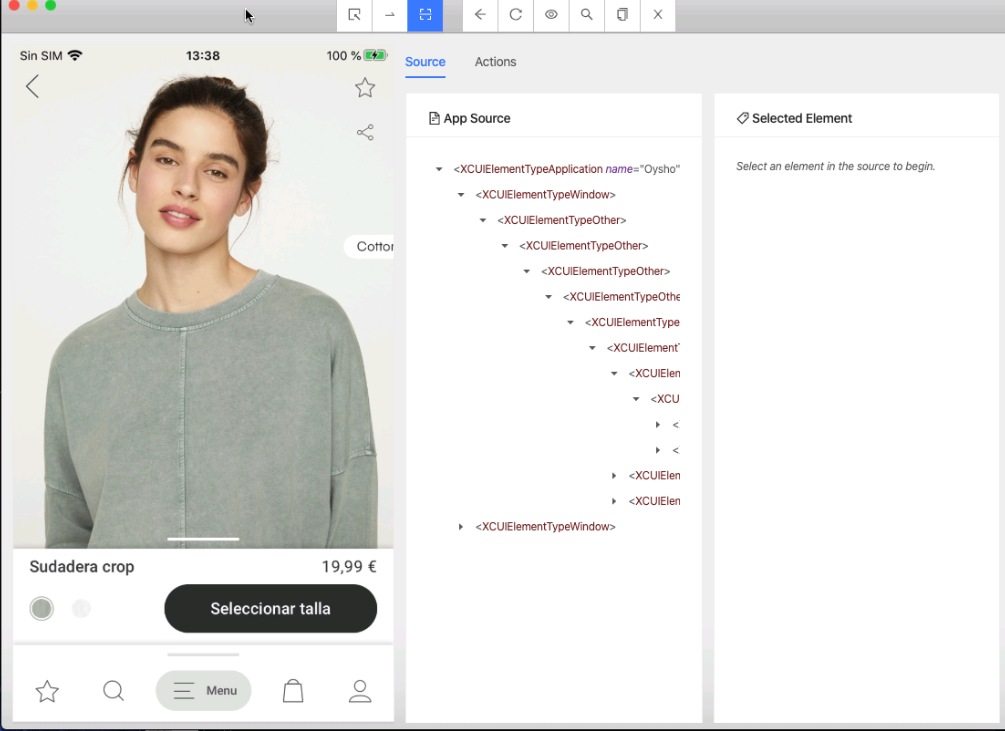
Here we can see the source is properly loaded.
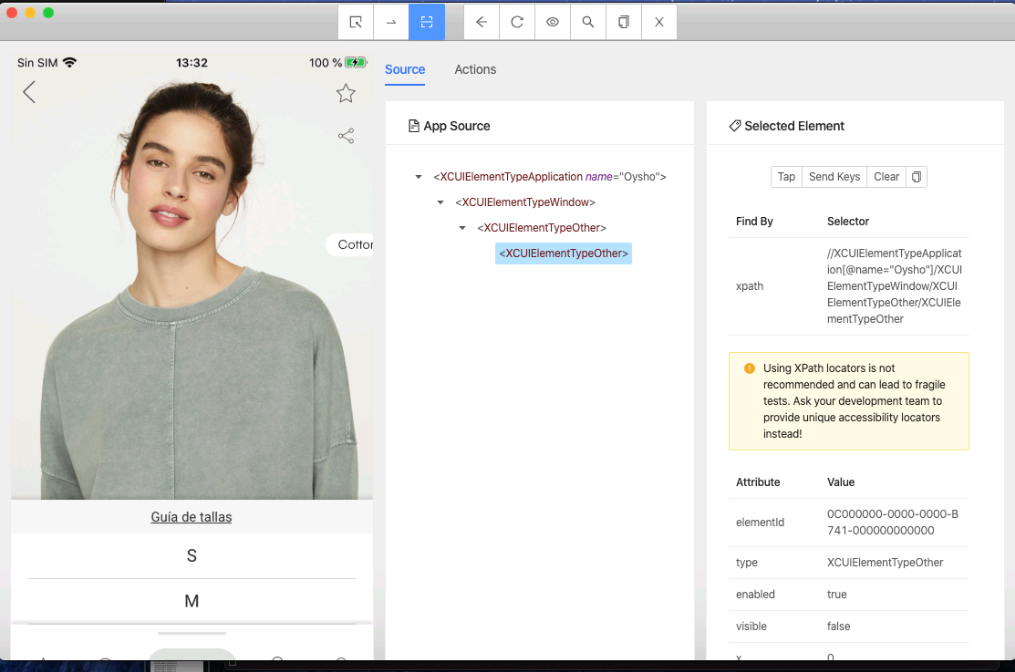
After displaying the size table the source doesn't get retrieved properly, only a few elements are loaded.
Also I guessed the id of one of the elements, like "s" and if I click on it it handles it without problem, so it can find an element inside the table even if it cant read the entire source.
Also tried includeNonModalElements capability with no different result.
## Link to Appium logs
https://gist.github.com/Julioevm/5157fc7b0e79950dc3620dc6b21ef26d
| test | ios app source not being retrieved properly when certain elements are present the problem appium is failing to show the source of the app i m testing in certain screen apparently when a table of sizes is present environment appium version or git revision that exhibits the issue and desktop os version used to run appium mac os catalina node js version npm or yarn package manager npm mobile platform version under test ios real device or emulator simulator real device appium cli or appium app exe tied both appium desktop and appium cli details according to the developers this is a regular table with nothing special about it here are a couple of pictures with and without the table here we can see the source is properly loaded after displaying the size table the source doesn t get retrieved properly only a few elements are loaded also i guessed the id of one of the elements like s and if i click on it it handles it without problem so it can find an element inside the table even if it cant read the entire source also tried includenonmodalelements capability with no different result link to appium logs | 1 |
339,912 | 24,630,050,456 | IssuesEvent | 2022-10-17 00:29:33 | Payadel/OnRail | https://api.github.com/repos/Payadel/OnRail | closed | Support ResultDetail in OnSuccess extensions | priority-low scope-new-feature version-minor scope-documentation | Successful results can also have `ResultDetail`. So, `OnSuccess` methods should support extensions like the following:
`public static Result OnSuccess(this Result source, Action<ResultDetail> action);` | 1.0 | Support ResultDetail in OnSuccess extensions - Successful results can also have `ResultDetail`. So, `OnSuccess` methods should support extensions like the following:
`public static Result OnSuccess(this Result source, Action<ResultDetail> action);` | non_test | support resultdetail in onsuccess extensions successful results can also have resultdetail so onsuccess methods should support extensions like the following public static result onsuccess this result source action action | 0 |
621,043 | 19,576,254,467 | IssuesEvent | 2022-01-04 15:45:49 | microsoft/terminal | https://api.github.com/repos/microsoft/terminal | closed | A11y_Windows Terminal_Settings_Non text Contrast: For "Plus(+)" and "Drop down" buttons the non text contrast ratio is not meeting 3:1 ratio | Issue-Bug Area-User Interface Area-Accessibility Product-Terminal Priority-3 Tracking-External | #A11y_WindowsTerminal; #WindowsTerminal; #A11yWCAG2.1; #A11yTCS; #DesktopApp; #Win10 ; #C+E-H; #NonTextContrast; #A11ySev2; #BenchMark; #MAS1.4.11
[Check out Accessibility Insights!](https://nam06.safelinks.protection.outlook.com/?url=https://accessibilityinsights.io/&data=02%7c01%7cv-shcha1%40microsoft.com%7cb67b2c4b646d4f9561a208d6f4b5c39b%7c72f988bf86f141af91ab2d7cd011db47%7c1%7c0%7c636965458847087032&sdata=uWx6cTEfazn%2BoCV3cL1iYB4KN%2BuXQ/MTlmOVec%2BZgKc%3D&reserved=0) - Identify accessibility bugs before check-in and make bug fixing faster and easier
**Environment Details:**
Version: 0.10.781.0
**Repro steps:**
1. Hit the URL ""aka.ms/terminal"" and install ""Windows terminal (Preview)"" application
2. Open ""Windows terminal (Preview)"" application
3. Open the "Accessibility insights" tool to check color contrast ratio
4. Tab to ""Windows Powershell"" tab
5. Tab till "plus(+)" button and "Drop down" button
6. Verify whether the color contrast ratio for "Plus(+)" and "drop down" buttons are meeting 3:1 contrast ratio using the "Accessibility insights" tool
**Actual Result:**
Both the "Plus(+) and "Drop down" buttons are not meeting the non text contrast ratio 3:1 ratio
**Expected Result:**
Both the "Plus(+) and "Drop down" buttons should meet the non text contrast ratio 3:1 ratio
**User Impact:**
Low vision users will face difficulty if the buttons don't meet the non text contrast ratio 3:1
**MAS Reference:**
https://microsoft.sharepoint.com/:w:/r/teams/msenable/_layouts/15/Doc.aspx?sourcedoc=%7B6CA3BF14-2635-434A-832C-28DD9A18B9FC%7D&file=MAS%201.4.11%20%E2%80%93%20Non-text%20Contrast.docx&action=default&mobileredirect=true&cid=ab731ae2-c015-4cce-8636-dda5170eef34

 | 1.0 | A11y_Windows Terminal_Settings_Non text Contrast: For "Plus(+)" and "Drop down" buttons the non text contrast ratio is not meeting 3:1 ratio - #A11y_WindowsTerminal; #WindowsTerminal; #A11yWCAG2.1; #A11yTCS; #DesktopApp; #Win10 ; #C+E-H; #NonTextContrast; #A11ySev2; #BenchMark; #MAS1.4.11
[Check out Accessibility Insights!](https://nam06.safelinks.protection.outlook.com/?url=https://accessibilityinsights.io/&data=02%7c01%7cv-shcha1%40microsoft.com%7cb67b2c4b646d4f9561a208d6f4b5c39b%7c72f988bf86f141af91ab2d7cd011db47%7c1%7c0%7c636965458847087032&sdata=uWx6cTEfazn%2BoCV3cL1iYB4KN%2BuXQ/MTlmOVec%2BZgKc%3D&reserved=0) - Identify accessibility bugs before check-in and make bug fixing faster and easier
**Environment Details:**
Version: 0.10.781.0
**Repro steps:**
1. Hit the URL ""aka.ms/terminal"" and install ""Windows terminal (Preview)"" application
2. Open ""Windows terminal (Preview)"" application
3. Open the "Accessibility insights" tool to check color contrast ratio
4. Tab to ""Windows Powershell"" tab
5. Tab till "plus(+)" button and "Drop down" button
6. Verify whether the color contrast ratio for "Plus(+)" and "drop down" buttons are meeting 3:1 contrast ratio using the "Accessibility insights" tool
**Actual Result:**
Both the "Plus(+) and "Drop down" buttons are not meeting the non text contrast ratio 3:1 ratio
**Expected Result:**
Both the "Plus(+) and "Drop down" buttons should meet the non text contrast ratio 3:1 ratio
**User Impact:**
Low vision users will face difficulty if the buttons don't meet the non text contrast ratio 3:1
**MAS Reference:**
https://microsoft.sharepoint.com/:w:/r/teams/msenable/_layouts/15/Doc.aspx?sourcedoc=%7B6CA3BF14-2635-434A-832C-28DD9A18B9FC%7D&file=MAS%201.4.11%20%E2%80%93%20Non-text%20Contrast.docx&action=default&mobileredirect=true&cid=ab731ae2-c015-4cce-8636-dda5170eef34

 | non_test | windows terminal settings non text contrast for plus and drop down buttons the non text contrast ratio is not meeting ratio windowsterminal windowsterminal desktopapp c e h nontextcontrast benchmark identify accessibility bugs before check in and make bug fixing faster and easier environment details version repro steps hit the url aka ms terminal and install windows terminal preview application open windows terminal preview application open the accessibility insights tool to check color contrast ratio tab to windows powershell tab tab till plus button and drop down button verify whether the color contrast ratio for plus and drop down buttons are meeting contrast ratio using the accessibility insights tool actual result both the plus and drop down buttons are not meeting the non text contrast ratio ratio expected result both the plus and drop down buttons should meet the non text contrast ratio ratio user impact low vision users will face difficulty if the buttons don t meet the non text contrast ratio mas reference | 0 |
120,394 | 10,114,601,904 | IssuesEvent | 2019-07-30 19:36:09 | material-components/material-components-ios | https://api.github.com/repos/material-components/material-components-ios | closed | [Buttons] Re-enable testCollapseExpandAnimatedRestoresTransform | [Buttons] skill:Kokoro type:Test | This was disabled in https://github.com/material-components/material-components-ios/pull/4157 due to flakiness.
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/117179041](http://b/117179041) | 1.0 | [Buttons] Re-enable testCollapseExpandAnimatedRestoresTransform - This was disabled in https://github.com/material-components/material-components-ios/pull/4157 due to flakiness.
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/117179041](http://b/117179041) | test | re enable testcollapseexpandanimatedrestorestransform this was disabled in due to flakiness internal data associated internal bug | 1 |
269,408 | 23,441,430,908 | IssuesEvent | 2022-08-15 15:14:39 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Manual test run on macOS (Intel) for 1.42.x - Release #4 | tests OS/macOS QA/Yes release-notes/exclude OS/Desktop | ### Installer
- [x] Check signature:
- [x] If macOS, using x64 binary run `spctl --assess --verbose` for the installed version and make sure it returns `accepted`
- [x] If macOS, using universal binary run `spctl --assess --verbose` for the installed version and make sure it returns `accepted`
### Widevine
- [x] Verify `Widevine Notification` is shown when you visit Netflix for the first time
- [x] Test that you can stream on Netflix on a fresh profile after installing Widevine
- [x] Verify `Widevine Notification` is shown when you visit HBO Max for the first time
- [x] Test that you can stream on HBO Max on a fresh profile after installing Widevine
- [x] If macOS, run the above Widevine tests for both `x64` and `universal` builds
### Rewards
- [x] Verify that none of the reward endpoints are being contacted when a user visits a media publisher (`youtube.com`, `reddit.com`, `twitter.com`, `github.com`) and hasn't interacted with rewards
- [x] Verify that `rewards.brave.com`, `pcdn.brave.com`, `grant.rewards.brave.com` or `api.rewards.brave.com` are not being contacted
- [x] Verify Rewards balance shows correct BAT and USD value
- [x] Verify you are able to restore an old Rewards profile
- [x] Verify actions taken (claiming grant, tipping, auto-contribute) display in panel transactions list
- [x] Verify when you click on the BR panel while on a site, the panel displays site specific information (site favicon, domain, attention %)
- [x] Verify you are able to make one-time tip and they display in tips panel
- [x] Verify you are able to make recurring tip and they display in tips panel
- [x] Verify you can tip a verified publisher
- [x] Verify you can tip a verified YouTube creator
- [x] Verify you are able to perform a contribution
- [x] Verify if you disable auto-contribute you are still able to tip regular sites and YouTube creators
### TLS Pinning
- [ ] Visit https://ssl-pinning.someblog.org/ and verify a pinning error is displayed
## Update tests
- [x] Verify visiting `brave://settings/help` triggers update check
- [x] Verify once update is downloaded, prompts to `Relaunch` to install update
#### Startup & Components
- [x] Verify that Brave is only contacting `*.brave.com` endpoints on first launch using either `Charles Proxy`, `Fiddler`, `Wireshark` or `LittleSnitch` (or a similar application)
- [x] Verify that opening a NTP doesn't trigger any outbound connections related to widgets without user interaction
- [x] Delete Adblock folder from browser profile and restart browser. Visit `brave://components` and verify `Brave Ad Block Updater` downloads and update the component. Repeat for all Brave components
### Upgrade
- [x] Make sure that data from the last version appears in the new version OK
- [x] Ensure that `brave://version` lists the expected Brave & Chromium versions
- [x] With data from the last version, verify that
- [x] Bookmarks on the bookmark toolbar and bookmark folders can be opened
- [x] Cookies are preserved
- [x] Installed extensions are retained and work correctly
- [x] Opened tabs can be reloaded
- [x] Stored passwords are preserved
- [x] Sync chain created in previous version is retained
- [x] Social media blocking buttons changes are retained
- [x] Rewards
- [x] BAT balance is retained
- [x] Auto-contribute list is retained
- [x] Both Tips and Monthly Contributions are retained
- [x] Panel transactions list is retained
- [x] Changes to rewards settings are retained
- [x] Ensure that Auto Contribute is not being enabled when upgrading to a new version if AC was disabled
- [x] Ads
- [x] Both `Estimated pending rewards` & `Ad notifications received this month` are retained
- [x] Changes to ads settings are retained
- [x] Ensure that ads are not being enabled when upgrading to a new version if they were disabled
- [x] Ensure that ads are not disabled when upgrading to a new version if they were enabled
| 1.0 | Manual test run on macOS (Intel) for 1.42.x - Release #4 - ### Installer
- [x] Check signature:
- [x] If macOS, using x64 binary run `spctl --assess --verbose` for the installed version and make sure it returns `accepted`
- [x] If macOS, using universal binary run `spctl --assess --verbose` for the installed version and make sure it returns `accepted`
### Widevine
- [x] Verify `Widevine Notification` is shown when you visit Netflix for the first time
- [x] Test that you can stream on Netflix on a fresh profile after installing Widevine
- [x] Verify `Widevine Notification` is shown when you visit HBO Max for the first time
- [x] Test that you can stream on HBO Max on a fresh profile after installing Widevine
- [x] If macOS, run the above Widevine tests for both `x64` and `universal` builds
### Rewards
- [x] Verify that none of the reward endpoints are being contacted when a user visits a media publisher (`youtube.com`, `reddit.com`, `twitter.com`, `github.com`) and hasn't interacted with rewards
- [x] Verify that `rewards.brave.com`, `pcdn.brave.com`, `grant.rewards.brave.com` or `api.rewards.brave.com` are not being contacted
- [x] Verify Rewards balance shows correct BAT and USD value
- [x] Verify you are able to restore an old Rewards profile
- [x] Verify actions taken (claiming grant, tipping, auto-contribute) display in panel transactions list
- [x] Verify when you click on the BR panel while on a site, the panel displays site specific information (site favicon, domain, attention %)
- [x] Verify you are able to make one-time tip and they display in tips panel
- [x] Verify you are able to make recurring tip and they display in tips panel
- [x] Verify you can tip a verified publisher
- [x] Verify you can tip a verified YouTube creator
- [x] Verify you are able to perform a contribution
- [x] Verify if you disable auto-contribute you are still able to tip regular sites and YouTube creators
### TLS Pinning
- [ ] Visit https://ssl-pinning.someblog.org/ and verify a pinning error is displayed
## Update tests
- [x] Verify visiting `brave://settings/help` triggers update check
- [x] Verify once update is downloaded, prompts to `Relaunch` to install update
#### Startup & Components
- [x] Verify that Brave is only contacting `*.brave.com` endpoints on first launch using either `Charles Proxy`, `Fiddler`, `Wireshark` or `LittleSnitch` (or a similar application)
- [x] Verify that opening a NTP doesn't trigger any outbound connections related to widgets without user interaction
- [x] Delete Adblock folder from browser profile and restart browser. Visit `brave://components` and verify `Brave Ad Block Updater` downloads and update the component. Repeat for all Brave components
### Upgrade
- [x] Make sure that data from the last version appears in the new version OK
- [x] Ensure that `brave://version` lists the expected Brave & Chromium versions
- [x] With data from the last version, verify that
- [x] Bookmarks on the bookmark toolbar and bookmark folders can be opened
- [x] Cookies are preserved
- [x] Installed extensions are retained and work correctly
- [x] Opened tabs can be reloaded
- [x] Stored passwords are preserved
- [x] Sync chain created in previous version is retained
- [x] Social media blocking buttons changes are retained
- [x] Rewards
- [x] BAT balance is retained
- [x] Auto-contribute list is retained
- [x] Both Tips and Monthly Contributions are retained
- [x] Panel transactions list is retained
- [x] Changes to rewards settings are retained
- [x] Ensure that Auto Contribute is not being enabled when upgrading to a new version if AC was disabled
- [x] Ads
- [x] Both `Estimated pending rewards` & `Ad notifications received this month` are retained
- [x] Changes to ads settings are retained
- [x] Ensure that ads are not being enabled when upgrading to a new version if they were disabled
- [x] Ensure that ads are not disabled when upgrading to a new version if they were enabled
| test | manual test run on macos intel for x release installer check signature if macos using binary run spctl assess verbose for the installed version and make sure it returns accepted if macos using universal binary run spctl assess verbose for the installed version and make sure it returns accepted widevine verify widevine notification is shown when you visit netflix for the first time test that you can stream on netflix on a fresh profile after installing widevine verify widevine notification is shown when you visit hbo max for the first time test that you can stream on hbo max on a fresh profile after installing widevine if macos run the above widevine tests for both and universal builds rewards verify that none of the reward endpoints are being contacted when a user visits a media publisher youtube com reddit com twitter com github com and hasn t interacted with rewards verify that rewards brave com pcdn brave com grant rewards brave com or api rewards brave com are not being contacted verify rewards balance shows correct bat and usd value verify you are able to restore an old rewards profile verify actions taken claiming grant tipping auto contribute display in panel transactions list verify when you click on the br panel while on a site the panel displays site specific information site favicon domain attention verify you are able to make one time tip and they display in tips panel verify you are able to make recurring tip and they display in tips panel verify you can tip a verified publisher verify you can tip a verified youtube creator verify you are able to perform a contribution verify if you disable auto contribute you are still able to tip regular sites and youtube creators tls pinning visit and verify a pinning error is displayed update tests verify visiting brave settings help triggers update check verify once update is downloaded prompts to relaunch to install update startup components verify that brave is only contacting brave com endpoints on first launch using either charles proxy fiddler wireshark or littlesnitch or a similar application verify that opening a ntp doesn t trigger any outbound connections related to widgets without user interaction delete adblock folder from browser profile and restart browser visit brave components and verify brave ad block updater downloads and update the component repeat for all brave components upgrade make sure that data from the last version appears in the new version ok ensure that brave version lists the expected brave chromium versions with data from the last version verify that bookmarks on the bookmark toolbar and bookmark folders can be opened cookies are preserved installed extensions are retained and work correctly opened tabs can be reloaded stored passwords are preserved sync chain created in previous version is retained social media blocking buttons changes are retained rewards bat balance is retained auto contribute list is retained both tips and monthly contributions are retained panel transactions list is retained changes to rewards settings are retained ensure that auto contribute is not being enabled when upgrading to a new version if ac was disabled ads both estimated pending rewards ad notifications received this month are retained changes to ads settings are retained ensure that ads are not being enabled when upgrading to a new version if they were disabled ensure that ads are not disabled when upgrading to a new version if they were enabled | 1 |
197,714 | 14,940,438,503 | IssuesEvent | 2021-01-25 18:16:58 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | Using "disable-custom-colors" does not remove all of the Color Settings UI | Needs Testing [Feature] Extensibility | **Describe the bug**
In WP 5.5, using `add_theme_support( 'disable-custom-colors' );` to remove custom colour support now leaves an empty accordion in the inspector controls.
This is a regression and was not the case in WP 4.5.2.
**To reproduce**
Steps to reproduce the behavior:
1. Add `add_theme_support( 'disable-custom-colors' );` into your theme
2. Start a new post
3. Insert a paragraph or heading block
4. Note the empty accordion title `Color settings` in the inspector controls.
**Expected behavior**
Complete removal of the colour settings UI.
**Screenshots**
<img width="392" alt="Screenshot 2020-08-26 at 08 25 01" src="https://user-images.githubusercontent.com/7547332/91274108-1f916180-e776-11ea-8724-80911975b29f.png">
**Editor version (please complete the following information):**
- WordPress version: **5.5**
- Does the website has Gutenberg plugin installed, or is it using the block editor that comes by default? **default**
| 1.0 | Using "disable-custom-colors" does not remove all of the Color Settings UI - **Describe the bug**
In WP 5.5, using `add_theme_support( 'disable-custom-colors' );` to remove custom colour support now leaves an empty accordion in the inspector controls.
This is a regression and was not the case in WP 4.5.2.
**To reproduce**
Steps to reproduce the behavior:
1. Add `add_theme_support( 'disable-custom-colors' );` into your theme
2. Start a new post
3. Insert a paragraph or heading block
4. Note the empty accordion title `Color settings` in the inspector controls.
**Expected behavior**
Complete removal of the colour settings UI.
**Screenshots**
<img width="392" alt="Screenshot 2020-08-26 at 08 25 01" src="https://user-images.githubusercontent.com/7547332/91274108-1f916180-e776-11ea-8724-80911975b29f.png">
**Editor version (please complete the following information):**
- WordPress version: **5.5**
- Does the website has Gutenberg plugin installed, or is it using the block editor that comes by default? **default**
| test | using disable custom colors does not remove all of the color settings ui describe the bug in wp using add theme support disable custom colors to remove custom colour support now leaves an empty accordion in the inspector controls this is a regression and was not the case in wp to reproduce steps to reproduce the behavior add add theme support disable custom colors into your theme start a new post insert a paragraph or heading block note the empty accordion title color settings in the inspector controls expected behavior complete removal of the colour settings ui screenshots img width alt screenshot at src editor version please complete the following information wordpress version does the website has gutenberg plugin installed or is it using the block editor that comes by default default | 1 |
192,687 | 22,215,989,931 | IssuesEvent | 2022-06-08 01:44:27 | panasalap/linux-4.1.15 | https://api.github.com/repos/panasalap/linux-4.1.15 | reopened | CVE-2017-12153 (Medium) detected in linuxlinux-4.1.17 | security vulnerability | ## CVE-2017-12153 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.17</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.1.15/commit/aae4c2fa46027fd4c477372871df090c6b94f3f1">aae4c2fa46027fd4c477372871df090c6b94f3f1</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/wireless/nl80211.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A security flaw was discovered in the nl80211_set_rekey_data() function in net/wireless/nl80211.c in the Linux kernel through 4.13.3. This function does not check whether the required attributes are present in a Netlink request. This request can be issued by a user with the CAP_NET_ADMIN capability and may result in a NULL pointer dereference and system crash.
<p>Publish Date: 2017-09-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-12153>CVE-2017-12153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2017-12153">https://www.linuxkernelcves.com/cves/CVE-2017-12153</a></p>
<p>Release Date: 2017-09-21</p>
<p>Fix Resolution: v4.14-rc2,v3.16.49,v3.18.73,v3.2.94,v4.1.46,v4.13.5,v4.4.90,v4.9.53</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-12153 (Medium) detected in linuxlinux-4.1.17 - ## CVE-2017-12153 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.17</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.1.15/commit/aae4c2fa46027fd4c477372871df090c6b94f3f1">aae4c2fa46027fd4c477372871df090c6b94f3f1</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/wireless/nl80211.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A security flaw was discovered in the nl80211_set_rekey_data() function in net/wireless/nl80211.c in the Linux kernel through 4.13.3. This function does not check whether the required attributes are present in a Netlink request. This request can be issued by a user with the CAP_NET_ADMIN capability and may result in a NULL pointer dereference and system crash.
<p>Publish Date: 2017-09-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-12153>CVE-2017-12153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2017-12153">https://www.linuxkernelcves.com/cves/CVE-2017-12153</a></p>
<p>Release Date: 2017-09-21</p>
<p>Fix Resolution: v4.14-rc2,v3.16.49,v3.18.73,v3.2.94,v4.1.46,v4.13.5,v4.4.90,v4.9.53</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files net wireless c vulnerability details a security flaw was discovered in the set rekey data function in net wireless c in the linux kernel through this function does not check whether the required attributes are present in a netlink request this request can be issued by a user with the cap net admin capability and may result in a null pointer dereference and system crash publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
235,092 | 19,298,415,095 | IssuesEvent | 2021-12-12 23:45:12 | Kakapo-Account/kakapo-backend-rails-api | https://api.github.com/repos/Kakapo-Account/kakapo-backend-rails-api | closed | add Bundler-Audit for Bundler security verification to development / tests gems | Gemfile Development Testing DevOps | add Bundler-Audit for Bundler security verification to development / tests gems | 1.0 | add Bundler-Audit for Bundler security verification to development / tests gems - add Bundler-Audit for Bundler security verification to development / tests gems | test | add bundler audit for bundler security verification to development tests gems add bundler audit for bundler security verification to development tests gems | 1 |
11,118 | 9,219,663,414 | IssuesEvent | 2019-03-11 15:51:22 | badges/shields | https://api.github.com/repos/badges/shields | closed | Sensiolabs badge stopped working | operations service-badge | Sensiolabs badge stopped working for me, how can we fix it?
Here are some examples of my project (the first one) and another project:
[](https://insight.sensiolabs.com/projects/f5764af3-0382-444c-ada6-3c2b0f8bf39b)
[](https://insight.sensiolabs.com/projects/287d9498-12cc-4e5f-8d5d-685823ff0347) | 1.0 | Sensiolabs badge stopped working - Sensiolabs badge stopped working for me, how can we fix it?
Here are some examples of my project (the first one) and another project:
[](https://insight.sensiolabs.com/projects/f5764af3-0382-444c-ada6-3c2b0f8bf39b)
[](https://insight.sensiolabs.com/projects/287d9498-12cc-4e5f-8d5d-685823ff0347) | non_test | sensiolabs badge stopped working sensiolabs badge stopped working for me how can we fix it here are some examples of my project the first one and another project | 0 |
45,197 | 5,697,885,909 | IssuesEvent | 2017-04-17 01:58:25 | DynamoRIO/dynamorio | https://api.github.com/repos/DynamoRIO/dynamorio | opened | ASSERT in api.detach: win32\callback.c:3036 idx < MAX_THREADS_WAITING_FOR_DR_INIT | Bug-Assert Component-Tests Hotlist-Travis OpSys-Windows | https://ci.appveyor.com/project/DynamoRIO/dynamorio/build/1.0.453/job/luslmyw81w7wr8g9
```
Start 212: code_api|api.detach
?
$
] 0.11 sec
<Application C:\projects\dynamorio\build\build_debug-internal-32\suite\tests\bin\api.detach.exe (5200). Internal Error: DynamoRIO debug check failure: C:\projects\dynamorio\core\win32\callback.c:3036 idx < MAX_THREADS_WAITING_FOR_DR_INIT
(Error occurred @0 frags)
version 6.2.17273, custom build
-no_dynamic_options -code_api -probe_api -msgbox_mask 0 -dumpcore_mask 125 -stderr_mask 12 -stack_size 56K -max_elide_jmp 0 -max_elide_call 0 -no_inline_ignored_syscalls -staged -native_exec_default_list '' -no_native_exec_managed_code -no_indcall2direct -no_aslr_dr -pad_jmps_mark_no_trace
0x011af708 0x746d3813
0x011af83c 0x748b0aa3
0x011af868 0x748b15d5
0x011af884 0x74a178a6>
``` | 1.0 | ASSERT in api.detach: win32\callback.c:3036 idx < MAX_THREADS_WAITING_FOR_DR_INIT - https://ci.appveyor.com/project/DynamoRIO/dynamorio/build/1.0.453/job/luslmyw81w7wr8g9
```
Start 212: code_api|api.detach
?
$
] 0.11 sec
<Application C:\projects\dynamorio\build\build_debug-internal-32\suite\tests\bin\api.detach.exe (5200). Internal Error: DynamoRIO debug check failure: C:\projects\dynamorio\core\win32\callback.c:3036 idx < MAX_THREADS_WAITING_FOR_DR_INIT
(Error occurred @0 frags)
version 6.2.17273, custom build
-no_dynamic_options -code_api -probe_api -msgbox_mask 0 -dumpcore_mask 125 -stderr_mask 12 -stack_size 56K -max_elide_jmp 0 -max_elide_call 0 -no_inline_ignored_syscalls -staged -native_exec_default_list '' -no_native_exec_managed_code -no_indcall2direct -no_aslr_dr -pad_jmps_mark_no_trace
0x011af708 0x746d3813
0x011af83c 0x748b0aa3
0x011af868 0x748b15d5
0x011af884 0x74a178a6>
``` | test | assert in api detach callback c idx max threads waiting for dr init start code api api detach sec application c projects dynamorio build build debug internal suite tests bin api detach exe internal error dynamorio debug check failure c projects dynamorio core callback c idx max threads waiting for dr init error occurred frags version custom build no dynamic options code api probe api msgbox mask dumpcore mask stderr mask stack size max elide jmp max elide call no inline ignored syscalls staged native exec default list no native exec managed code no no aslr dr pad jmps mark no trace | 1 |
192,655 | 14,624,659,212 | IssuesEvent | 2020-12-23 06:52:04 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | rclone/rclone: vfs/read_write_test.go; 5 LoC | fresh test tiny |
Found a possible issue in [rclone/rclone](https://www.github.com/rclone/rclone) at [vfs/read_write_test.go](https://github.com/rclone/rclone/blob/bdc2278a3030bc991fa650ff4188b178eff26300/vfs/read_write_test.go#L652-L656)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to test at line 654 may start a goroutine
[Click here to see the code in its original context.](https://github.com/rclone/rclone/blob/bdc2278a3030bc991fa650ff4188b178eff26300/vfs/read_write_test.go#L652-L656)
<details>
<summary>Click here to show the 5 line(s) of Go which triggered the analyzer.</summary>
```go
for _, test := range openTests {
t.Run(test.what, func(t *testing.T) {
testRWFileHandleOpenTest(t, vfs, &test)
})
}
```
</details>
<details>
<summary>Click here to show extra information the analyzer produced.</summary>
```
The following paths through the callgraph could lead to a goroutine:
(testRWFileHandleOpenTest, 3) -> (Close, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Delete, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Close, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Show, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (serve, 0)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Delete, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (multithread, 2)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (Close, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Run, 4) -> (resolveExitCode, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Run, 4) -> (resolveExitCode, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Run, 4) -> (resolveExitCode, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (close, 0) -> (setObject, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewObject, 2) -> (Err, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewObject, 2) -> (Err, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Show, 0) -> (Errorf, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Purge, 3) -> (CountError, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (run, 2) -> (Wrapf, 5)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Start, 2) -> (Serve, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (serve, 0) -> (URL, 0)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (readMetaData, 1) -> (readMetaDataForID, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (getSftpConnection, 1) -> (sftpConnection, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (_resetTimer, 0) -> (processItems, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (getChunk, 1) -> (Errorf, 8)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (readAt, 2) -> (ReadAt, 2)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (readAt, 2) -> (ReadAt, 2)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (_readAt, 3) -> (ReadAt, 2)
(testRWFileHandleOpenTest, 3) -> (Write, 1) -> (_writeAt, 3) -> (WriteAt, 2)
(testRWFileHandleOpenTest, 3) -> (Write, 1) -> (writeAt, 2) -> (Broadcast, 0)
(testRWFileHandleOpenTest, 3) -> (Write, 1) -> (writeAt, 2) -> (Broadcast, 0)
(testRWFileHandleOpenTest, 3) -> (Close, 0) -> (close, 0) -> (setObject, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 0) -> (Rmdir, 2) -> (translateError, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (listDir, 3) -> (buildDirEntries, 5) -> (List, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (New, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (init, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (List, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (openPending, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (listenWebsocket, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (List, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startCheckers, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startRenamers, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startTransfers, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startDeleters, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startTrackRenames, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (makeRenameMap, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (deleteFiles, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (updateUsage, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (NewRenew, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Cat, 5) -> (Copy, 2) -> (newObjectReader, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Cat, 5) -> (Copy, 2) -> (newAccountSizeName, 5)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (CheckDownload, 2) -> (CheckFn, 2) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Check, 2) -> (CheckFn, 2) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Deduplicate, 4) -> (dedupeList, 6) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Delete, 2) -> (close, 1) -> (DeleteFilesWithBackupDir, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ListJSON, 5) -> (callback, 1) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Write, 1) -> (writeAt, 2) -> (waitSequential, 6)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Purge, 3) -> (CountError, 1) -> (DeleteFilesWithBackupDir, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (run, 2) -> (Wrapf, 5) -> (sftpConnection, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (run, 2) -> (Wrapf, 5) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (newAccountSizeName, 5)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Start, 2) -> (Serve, 0) -> (startSSDP, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4) -> (ssdpInterface, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4) -> (acceptConnections, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (serve, 0) -> (URL, 0) -> (handleChannels, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Call, 1) -> (call, 2) -> (beginCall, 0)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1) -> (sftpConnection, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Delete, 2) -> (close, 1) -> (DeleteFilesWithBackupDir, 3)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (CallJSON, 4) -> (callCodec, 7) -> (MultipartUpload, 4)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (CallXML, 4) -> (callCodec, 7) -> (MultipartUpload, 4)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (actionEntries, 1) -> (ActionEntries, 1) -> (newestEntries, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (nextChunk, 1) -> (Open, 2) -> (newObjectReader, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (Write, 1) -> (writeAt, 2) -> (waitSequential, 6)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (openRange, 0) -> (resetReader, 2) -> (newObjectReader, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (open, 0) -> (errorf, 2) -> (newObjectReader, 1)
(testRWFileHandleOpenTest, 3) -> (Write, 1) -> (kickWaiters, 0) -> (_closeWaiters, 1) -> (_newDownloader, 1)
(testRWFileHandleOpenTest, 3) -> (Close, 0) -> (Call, 1) -> (call, 2) -> (beginCall, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Authorize, 3) -> (Config, 3) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (call, 2) -> (endCall, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startDeleters, 0) -> (processError, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (deleteFiles, 1) -> (DeleteFilesWithBackupDir, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Cat, 5) -> (Copy, 2) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (CheckDownload, 2) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Check, 2) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (EditConfig, 1) -> (SetPassword, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ShowConfig, 0) -> (String, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ShowRemote, 1) -> (FileGet, 2) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (CreateRemote, 6) -> (UpdateRemote, 5) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (UpdateRemote, 5) -> (SaveConfig, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (DeleteRemote, 1) -> (SaveConfig, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Deduplicate, 4) -> (dedupeList, 6) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Deduplicate, 4) -> (dedupeList, 6) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rmdirs, 4) -> (Errorf, 3) -> (walkListDirSorted, 6) -> (walk, 7)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Close, 0) -> (resetReader, 2) -> (call, 2) -> (endCall, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (FileSections, 0) -> (FindStringSubmatch, 1) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (FileGet, 3) -> (getConfigData, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ListJSON, 5) -> (callback, 1) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ListJSON, 5) -> (callback, 1) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Write, 1) -> (writeAt, 2) -> (_ensureDownloader, 1) -> (_countErrors, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (run, 2) -> (Wrapf, 5) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (put, 5) -> (multiReader, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (put, 5) -> (multiReader, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (putWithCustomFunctions, 8) -> (putMetadata, 5)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Start, 2) -> (Serve, 0) -> (startSSDP, 0) -> (ssdpInterface, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4) -> (acceptConnections, 0) -> (handleChannels, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (serve, 0) -> (URL, 0) -> (handleChannels, 1) -> (handleChannel, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Touch, 3) -> (SetModTime, 2) -> (copy, 4) -> (Copy, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Tree, 3) -> (Print, 1) -> (walkNDirTree, 6) -> (walk, 7)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (removeNode, 1) -> (shouldRetry, 2) -> (call, 2) -> (endCall, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (deleteByID, 3) -> (shouldRetry, 3) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (hide, 3) -> (shouldRetry, 3) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (deleteObject, 2) -> (CallJSON, 4) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (delete, 3) -> (waitForJob, 2) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (deleteFile, 2) -> (shouldRetry, 2) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (getChunk, 1) -> (Errorf, 8) -> (confirmExternalReading, 0) -> (scaleWorkers, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (nextChunk, 1) -> (Open, 2) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (Write, 1) -> (writeAt, 2) -> (_ensureDownloader, 1) -> (_countErrors, 2)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (openRange, 0) -> (resetReader, 2) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (open, 0) -> (errorf, 2) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 0) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Remove, 0) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Remove, 0) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Equal, 3) -> (equal, 4) -> (CountError, 1) -> (copy, 4) -> (Copy, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Authorize, 3) -> (Config, 3) -> (getConfigData, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Authorize, 3) -> (Config, 3) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (newTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Cat, 5) -> (Copy, 2) -> (NewObjectHandle, 3) -> (startReadWorkers, 0) -> (scaleWorkers, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (CheckDownload, 2) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Check, 2) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (EditConfig, 1) -> (SetPassword, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ShowConfig, 0) -> (String, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ShowRemote, 1) -> (FileGet, 2) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (CreateRemote, 6) -> (UpdateRemote, 5) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (UpdateRemote, 5) -> (SaveConfig, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (DeleteRemote, 1) -> (SaveConfig, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Deduplicate, 4) -> (dedupeList, 6) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (FileSections, 0) -> (FindStringSubmatch, 1) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (FileGet, 3) -> (getConfigData, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ListJSON, 5) -> (callback, 1) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Put, 4) -> (Info, 0) -> (sendUpload, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Put, 4) -> (Info, 0) -> (sendUpload, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Put, 4) -> (Info, 0) -> (sendUpload, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Put, 4) -> (Info, 0) -> (sendUpload, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (deleteChunks, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4) -> (acceptConnections, 0) -> (handleChannels, 1) -> (handleChannel, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Authorize, 3) -> (Config, 3) -> (getConfigData, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0) -> (AssignableTo, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (deleteChunks, 3) -> (AssignableTo, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0) -> (AssignableTo, 1) -> (Mount, 4) -> (finalise, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (deleteChunks, 3) -> (AssignableTo, 1) -> (Mount, 4) -> (finalise, 0)
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: bdc2278a3030bc991fa650ff4188b178eff26300
| 1.0 | rclone/rclone: vfs/read_write_test.go; 5 LoC -
Found a possible issue in [rclone/rclone](https://www.github.com/rclone/rclone) at [vfs/read_write_test.go](https://github.com/rclone/rclone/blob/bdc2278a3030bc991fa650ff4188b178eff26300/vfs/read_write_test.go#L652-L656)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to test at line 654 may start a goroutine
[Click here to see the code in its original context.](https://github.com/rclone/rclone/blob/bdc2278a3030bc991fa650ff4188b178eff26300/vfs/read_write_test.go#L652-L656)
<details>
<summary>Click here to show the 5 line(s) of Go which triggered the analyzer.</summary>
```go
for _, test := range openTests {
t.Run(test.what, func(t *testing.T) {
testRWFileHandleOpenTest(t, vfs, &test)
})
}
```
</details>
<details>
<summary>Click here to show extra information the analyzer produced.</summary>
```
The following paths through the callgraph could lead to a goroutine:
(testRWFileHandleOpenTest, 3) -> (Close, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Delete, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Close, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Show, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (serve, 0)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Delete, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (multithread, 2)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (Close, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Run, 4) -> (resolveExitCode, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Run, 4) -> (resolveExitCode, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Run, 4) -> (resolveExitCode, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (close, 0) -> (setObject, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewObject, 2) -> (Err, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewObject, 2) -> (Err, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Show, 0) -> (Errorf, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Purge, 3) -> (CountError, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (run, 2) -> (Wrapf, 5)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Start, 2) -> (Serve, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (serve, 0) -> (URL, 0)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (readMetaData, 1) -> (readMetaDataForID, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (getSftpConnection, 1) -> (sftpConnection, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (_resetTimer, 0) -> (processItems, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (getChunk, 1) -> (Errorf, 8)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (readAt, 2) -> (ReadAt, 2)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (readAt, 2) -> (ReadAt, 2)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (_readAt, 3) -> (ReadAt, 2)
(testRWFileHandleOpenTest, 3) -> (Write, 1) -> (_writeAt, 3) -> (WriteAt, 2)
(testRWFileHandleOpenTest, 3) -> (Write, 1) -> (writeAt, 2) -> (Broadcast, 0)
(testRWFileHandleOpenTest, 3) -> (Write, 1) -> (writeAt, 2) -> (Broadcast, 0)
(testRWFileHandleOpenTest, 3) -> (Close, 0) -> (close, 0) -> (setObject, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 0) -> (Rmdir, 2) -> (translateError, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (listDir, 3) -> (buildDirEntries, 5) -> (List, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (New, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (init, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (List, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (openPending, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (listenWebsocket, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (List, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startCheckers, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startRenamers, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startTransfers, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startDeleters, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startTrackRenames, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (makeRenameMap, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (deleteFiles, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (updateUsage, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (NewRenew, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Cat, 5) -> (Copy, 2) -> (newObjectReader, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Cat, 5) -> (Copy, 2) -> (newAccountSizeName, 5)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (CheckDownload, 2) -> (CheckFn, 2) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Check, 2) -> (CheckFn, 2) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Deduplicate, 4) -> (dedupeList, 6) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Delete, 2) -> (close, 1) -> (DeleteFilesWithBackupDir, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ListJSON, 5) -> (callback, 1) -> (Run, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Write, 1) -> (writeAt, 2) -> (waitSequential, 6)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Purge, 3) -> (CountError, 1) -> (DeleteFilesWithBackupDir, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (run, 2) -> (Wrapf, 5) -> (sftpConnection, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (run, 2) -> (Wrapf, 5) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (newAccountSizeName, 5)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Start, 2) -> (Serve, 0) -> (startSSDP, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4) -> (ssdpInterface, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4) -> (acceptConnections, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (serve, 0) -> (URL, 0) -> (handleChannels, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Call, 1) -> (call, 2) -> (beginCall, 0)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1) -> (sftpConnection, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Delete, 2) -> (close, 1) -> (DeleteFilesWithBackupDir, 3)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (CallJSON, 4) -> (callCodec, 7) -> (MultipartUpload, 4)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (CallXML, 4) -> (callCodec, 7) -> (MultipartUpload, 4)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (actionEntries, 1) -> (ActionEntries, 1) -> (newestEntries, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (nextChunk, 1) -> (Open, 2) -> (newObjectReader, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (Write, 1) -> (writeAt, 2) -> (waitSequential, 6)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (openRange, 0) -> (resetReader, 2) -> (newObjectReader, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (open, 0) -> (errorf, 2) -> (newObjectReader, 1)
(testRWFileHandleOpenTest, 3) -> (Write, 1) -> (kickWaiters, 0) -> (_closeWaiters, 1) -> (_newDownloader, 1)
(testRWFileHandleOpenTest, 3) -> (Close, 0) -> (Call, 1) -> (call, 2) -> (beginCall, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Authorize, 3) -> (Config, 3) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (call, 2) -> (endCall, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (startDeleters, 0) -> (processError, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (deleteFiles, 1) -> (DeleteFilesWithBackupDir, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Cat, 5) -> (Copy, 2) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (CheckDownload, 2) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Check, 2) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (EditConfig, 1) -> (SetPassword, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ShowConfig, 0) -> (String, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ShowRemote, 1) -> (FileGet, 2) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (CreateRemote, 6) -> (UpdateRemote, 5) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (UpdateRemote, 5) -> (SaveConfig, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (DeleteRemote, 1) -> (SaveConfig, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Deduplicate, 4) -> (dedupeList, 6) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Deduplicate, 4) -> (dedupeList, 6) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rmdirs, 4) -> (Errorf, 3) -> (walkListDirSorted, 6) -> (walk, 7)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Close, 0) -> (resetReader, 2) -> (call, 2) -> (endCall, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (FileSections, 0) -> (FindStringSubmatch, 1) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (FileGet, 3) -> (getConfigData, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ListJSON, 5) -> (callback, 1) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ListJSON, 5) -> (callback, 1) -> (Run, 1) -> (processJob, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Write, 1) -> (writeAt, 2) -> (_ensureDownloader, 1) -> (_countErrors, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (run, 2) -> (Wrapf, 5) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (put, 5) -> (multiReader, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (put, 5) -> (multiReader, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (putWithCustomFunctions, 8) -> (putMetadata, 5)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Start, 2) -> (Serve, 0) -> (startSSDP, 0) -> (ssdpInterface, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4) -> (acceptConnections, 0) -> (handleChannels, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (serve, 0) -> (URL, 0) -> (handleChannels, 1) -> (handleChannel, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Touch, 3) -> (SetModTime, 2) -> (copy, 4) -> (Copy, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Tree, 3) -> (Print, 1) -> (walkNDirTree, 6) -> (walk, 7)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (removeNode, 1) -> (shouldRetry, 2) -> (call, 2) -> (endCall, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (deleteByID, 3) -> (shouldRetry, 3) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (hide, 3) -> (shouldRetry, 3) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (deleteObject, 2) -> (CallJSON, 4) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (delete, 3) -> (waitForJob, 2) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (deleteFile, 2) -> (shouldRetry, 2) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1) -> (callCodec, 7) -> (decode, 2)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Remove, 1) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (getChunk, 1) -> (Errorf, 8) -> (confirmExternalReading, 0) -> (scaleWorkers, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (nextChunk, 1) -> (Open, 2) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (Write, 1) -> (writeAt, 2) -> (_ensureDownloader, 1) -> (_countErrors, 2)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (openRange, 0) -> (resetReader, 2) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (Read, 1) -> (open, 0) -> (errorf, 2) -> (newFadviseReadCloser, 4) -> (sequential, 1)
(testRWFileHandleOpenTest, 3) -> (Remove, 0) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Remove, 0) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Remove, 0) -> (Rmdir, 2) -> (translateError, 1) -> (Action, 3) -> (newest, 3)
(testRWFileHandleOpenTest, 3) -> (Equal, 3) -> (equal, 4) -> (CountError, 1) -> (copy, 4) -> (Copy, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Authorize, 3) -> (Config, 3) -> (getConfigData, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Authorize, 3) -> (Config, 3) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (newTokenBucket, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (NewFs, 4) -> (Fatalf, 2) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Cat, 5) -> (Copy, 2) -> (NewObjectHandle, 3) -> (startReadWorkers, 0) -> (scaleWorkers, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (CheckDownload, 2) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Check, 2) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (EditConfig, 1) -> (SetPassword, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ShowConfig, 0) -> (String, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ShowRemote, 1) -> (FileGet, 2) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (CreateRemote, 6) -> (UpdateRemote, 5) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (UpdateRemote, 5) -> (SaveConfig, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (DeleteRemote, 1) -> (SaveConfig, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (cryptCheck, 3) -> (CheckFn, 2) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Deduplicate, 4) -> (dedupeList, 6) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (readInfo, 2) -> (WriteJSON, 0) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (FileSections, 0) -> (FindStringSubmatch, 1) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (FileGet, 3) -> (getConfigData, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (ListJSON, 5) -> (callback, 1) -> (Run, 1) -> (processJob, 1) -> (Match, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeContainer, 2) -> (ContainerCreate, 2) -> (NewContainerURL, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (makeBucket, 2) -> (bucketExists, 2) -> (HeadBucketWithContext, 2)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Mkdir, 3) -> (CountError, 1) -> (create, 2) -> (Create, 3) -> (create, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Put, 4) -> (Info, 0) -> (sendUpload, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Put, 4) -> (Info, 0) -> (sendUpload, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Put, 4) -> (Info, 0) -> (sendUpload, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Put, 4) -> (Info, 0) -> (sendUpload, 4)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (deleteChunks, 3)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Serve, 0) -> (Errorf, 4) -> (acceptConnections, 0) -> (handleChannels, 1) -> (handleChannel, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Authorize, 3) -> (Config, 3) -> (getConfigData, 0) -> (LoadConfig, 1) -> (StartHTTPTokenBucket, 1) -> (startSignalHandler, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0) -> (AssignableTo, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (deleteChunks, 3) -> (AssignableTo, 1)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (Info, 0) -> (AssignableTo, 1) -> (Mount, 4) -> (finalise, 0)
(testRWFileHandleOpenTest, 3) -> (, 0) -> (Rcat, 5) -> (compare, 1) -> (Update, 4) -> (cap, 1) -> (deleteChunks, 3) -> (AssignableTo, 1) -> (Mount, 4) -> (finalise, 0)
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: bdc2278a3030bc991fa650ff4188b178eff26300
| test | rclone rclone vfs read write test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to test at line may start a goroutine click here to show the line s of go which triggered the analyzer go for test range opentests t run test what func t testing t testrwfilehandleopentest t vfs test click here to show extra information the analyzer produced the following paths through the callgraph could lead to a goroutine testrwfilehandleopentest close testrwfilehandleopentest newfs testrwfilehandleopentest delete testrwfilehandleopentest close testrwfilehandleopentest show testrwfilehandleopentest serve testrwfilehandleopentest serve testrwfilehandleopentest remove delete testrwfilehandleopentest remove multithread testrwfilehandleopentest read close testrwfilehandleopentest run resolveexitcode testrwfilehandleopentest run resolveexitcode testrwfilehandleopentest run resolveexitcode testrwfilehandleopentest newfs fatalf testrwfilehandleopentest newfs fatalf testrwfilehandleopentest newfs fatalf testrwfilehandleopentest newfs fatalf testrwfilehandleopentest newfs fatalf testrwfilehandleopentest close setobject testrwfilehandleopentest newobject err testrwfilehandleopentest newobject err testrwfilehandleopentest readinfo writejson testrwfilehandleopentest show errorf testrwfilehandleopentest purge counterror testrwfilehandleopentest run wrapf testrwfilehandleopentest start serve testrwfilehandleopentest serve errorf testrwfilehandleopentest serve errorf testrwfilehandleopentest serve url testrwfilehandleopentest remove rmdir translateerror testrwfilehandleopentest remove rmdir translateerror testrwfilehandleopentest remove readmetadata readmetadataforid testrwfilehandleopentest remove getsftpconnection sftpconnection testrwfilehandleopentest remove resettimer processitems testrwfilehandleopentest read getchunk errorf testrwfilehandleopentest read readat readat testrwfilehandleopentest read readat readat testrwfilehandleopentest read readat readat testrwfilehandleopentest write writeat writeat testrwfilehandleopentest write writeat broadcast testrwfilehandleopentest write writeat broadcast testrwfilehandleopentest close close setobject testrwfilehandleopentest remove rmdir translateerror testrwfilehandleopentest listdir builddirentries list testrwfilehandleopentest newfs fatalf new testrwfilehandleopentest newfs fatalf init testrwfilehandleopentest newfs fatalf list testrwfilehandleopentest newfs fatalf openpending testrwfilehandleopentest newfs fatalf listenwebsocket testrwfilehandleopentest newfs fatalf list testrwfilehandleopentest newfs fatalf startcheckers testrwfilehandleopentest newfs fatalf startrenamers testrwfilehandleopentest newfs fatalf starttransfers testrwfilehandleopentest newfs fatalf startdeleters testrwfilehandleopentest newfs fatalf starttrackrenames testrwfilehandleopentest newfs fatalf run testrwfilehandleopentest newfs fatalf makerenamemap testrwfilehandleopentest newfs fatalf deletefiles testrwfilehandleopentest newfs fatalf updateusage testrwfilehandleopentest newfs fatalf newrenew testrwfilehandleopentest cat copy newobjectreader testrwfilehandleopentest cat copy newaccountsizename testrwfilehandleopentest checkdownload checkfn run testrwfilehandleopentest check checkfn run testrwfilehandleopentest cryptcheck checkfn run testrwfilehandleopentest cryptcheck checkfn run testrwfilehandleopentest deduplicate dedupelist run testrwfilehandleopentest delete close deletefileswithbackupdir testrwfilehandleopentest listjson callback run testrwfilehandleopentest write writeat waitsequential testrwfilehandleopentest purge counterror deletefileswithbackupdir testrwfilehandleopentest run wrapf sftpconnection testrwfilehandleopentest run wrapf processjob testrwfilehandleopentest rcat compare newaccountsizename testrwfilehandleopentest start serve startssdp testrwfilehandleopentest serve errorf ssdpinterface testrwfilehandleopentest serve errorf acceptconnections testrwfilehandleopentest serve url handlechannels testrwfilehandleopentest remove call call begincall testrwfilehandleopentest remove rmdir translateerror sftpconnection testrwfilehandleopentest remove delete close deletefileswithbackupdir testrwfilehandleopentest remove calljson callcodec multipartupload testrwfilehandleopentest remove callxml callcodec multipartupload testrwfilehandleopentest remove actionentries actionentries newestentries testrwfilehandleopentest read nextchunk open newobjectreader testrwfilehandleopentest read write writeat waitsequential testrwfilehandleopentest read openrange resetreader newobjectreader testrwfilehandleopentest read open errorf newobjectreader testrwfilehandleopentest write kickwaiters closewaiters newdownloader testrwfilehandleopentest close call call begincall testrwfilehandleopentest authorize config loadconfig starthttptokenbucket testrwfilehandleopentest newfs fatalf call endcall testrwfilehandleopentest newfs fatalf startdeleters processerror testrwfilehandleopentest newfs fatalf run processjob testrwfilehandleopentest newfs fatalf deletefiles deletefileswithbackupdir testrwfilehandleopentest newfs fatalf callcodec decode testrwfilehandleopentest cat copy newfadvisereadcloser sequential testrwfilehandleopentest checkdownload checkfn run processjob testrwfilehandleopentest check checkfn run processjob testrwfilehandleopentest editconfig setpassword loadconfig starthttptokenbucket testrwfilehandleopentest showconfig string loadconfig starthttptokenbucket testrwfilehandleopentest showremote fileget loadconfig starthttptokenbucket testrwfilehandleopentest createremote updateremote loadconfig starthttptokenbucket testrwfilehandleopentest updateremote saveconfig loadconfig starthttptokenbucket testrwfilehandleopentest deleteremote saveconfig loadconfig starthttptokenbucket testrwfilehandleopentest cryptcheck checkfn newfadvisereadcloser sequential testrwfilehandleopentest cryptcheck checkfn run processjob testrwfilehandleopentest cryptcheck checkfn run processjob testrwfilehandleopentest deduplicate dedupelist newfadvisereadcloser sequential testrwfilehandleopentest deduplicate dedupelist run processjob testrwfilehandleopentest rmdirs errorf walklistdirsorted walk testrwfilehandleopentest close resetreader call endcall testrwfilehandleopentest filesections findstringsubmatch loadconfig starthttptokenbucket testrwfilehandleopentest fileget getconfigdata loadconfig starthttptokenbucket testrwfilehandleopentest listjson callback newfadvisereadcloser sequential testrwfilehandleopentest listjson callback run processjob testrwfilehandleopentest write writeat ensuredownloader counterrors testrwfilehandleopentest run wrapf processjob match testrwfilehandleopentest rcat compare update cap testrwfilehandleopentest rcat compare update cap testrwfilehandleopentest rcat compare update cap testrwfilehandleopentest rcat compare update cap testrwfilehandleopentest rcat compare put multireader testrwfilehandleopentest rcat compare put multireader testrwfilehandleopentest rcat compare putwithcustomfunctions putmetadata testrwfilehandleopentest rcat compare update cap testrwfilehandleopentest rcat compare update cap testrwfilehandleopentest rcat compare update cap testrwfilehandleopentest rcat compare update cap testrwfilehandleopentest start serve startssdp ssdpinterface testrwfilehandleopentest serve errorf acceptconnections handlechannels testrwfilehandleopentest serve url handlechannels handlechannel testrwfilehandleopentest touch setmodtime copy copy testrwfilehandleopentest tree print walkndirtree walk testrwfilehandleopentest remove removenode shouldretry call endcall testrwfilehandleopentest remove deletebyid shouldretry callcodec decode testrwfilehandleopentest remove hide shouldretry callcodec decode testrwfilehandleopentest remove deleteobject calljson callcodec decode testrwfilehandleopentest remove delete waitforjob callcodec decode testrwfilehandleopentest remove deletefile shouldretry callcodec decode testrwfilehandleopentest remove rmdir translateerror callcodec decode testrwfilehandleopentest remove rmdir translateerror action newest testrwfilehandleopentest remove rmdir translateerror action newest testrwfilehandleopentest remove rmdir translateerror action newest testrwfilehandleopentest read getchunk errorf confirmexternalreading scaleworkers testrwfilehandleopentest read nextchunk open newfadvisereadcloser sequential testrwfilehandleopentest read write writeat ensuredownloader counterrors testrwfilehandleopentest read openrange resetreader newfadvisereadcloser sequential testrwfilehandleopentest read open errorf newfadvisereadcloser sequential testrwfilehandleopentest remove rmdir translateerror action newest testrwfilehandleopentest remove rmdir translateerror action newest testrwfilehandleopentest remove rmdir translateerror action newest testrwfilehandleopentest equal equal counterror copy copy testrwfilehandleopentest authorize config getconfigdata loadconfig starthttptokenbucket testrwfilehandleopentest authorize config loadconfig starthttptokenbucket newtokenbucket testrwfilehandleopentest newfs fatalf run processjob match testrwfilehandleopentest cat copy newobjecthandle startreadworkers scaleworkers testrwfilehandleopentest checkdownload checkfn run processjob match testrwfilehandleopentest check checkfn run processjob match testrwfilehandleopentest editconfig setpassword loadconfig starthttptokenbucket startsignalhandler testrwfilehandleopentest showconfig string loadconfig starthttptokenbucket startsignalhandler testrwfilehandleopentest showremote fileget loadconfig starthttptokenbucket startsignalhandler testrwfilehandleopentest createremote updateremote loadconfig starthttptokenbucket startsignalhandler testrwfilehandleopentest updateremote saveconfig loadconfig starthttptokenbucket startsignalhandler testrwfilehandleopentest deleteremote saveconfig loadconfig starthttptokenbucket startsignalhandler testrwfilehandleopentest cryptcheck checkfn run processjob match testrwfilehandleopentest cryptcheck checkfn run processjob match testrwfilehandleopentest deduplicate dedupelist run processjob match testrwfilehandleopentest readinfo writejson makecontainer containercreate newcontainerurl testrwfilehandleopentest readinfo writejson makecontainer containercreate newcontainerurl testrwfilehandleopentest readinfo writejson makecontainer containercreate newcontainerurl testrwfilehandleopentest readinfo writejson makebucket bucketexists headbucketwithcontext testrwfilehandleopentest readinfo writejson makebucket bucketexists headbucketwithcontext testrwfilehandleopentest readinfo writejson makebucket bucketexists headbucketwithcontext testrwfilehandleopentest readinfo writejson create create create testrwfilehandleopentest readinfo writejson create create create testrwfilehandleopentest readinfo writejson create create create testrwfilehandleopentest filesections findstringsubmatch loadconfig starthttptokenbucket startsignalhandler testrwfilehandleopentest fileget getconfigdata loadconfig starthttptokenbucket startsignalhandler testrwfilehandleopentest listjson callback run processjob match testrwfilehandleopentest mkdir counterror makecontainer containercreate newcontainerurl testrwfilehandleopentest mkdir counterror makecontainer containercreate newcontainerurl testrwfilehandleopentest mkdir counterror makecontainer containercreate newcontainerurl testrwfilehandleopentest mkdir counterror makebucket bucketexists headbucketwithcontext testrwfilehandleopentest mkdir counterror makebucket bucketexists headbucketwithcontext testrwfilehandleopentest mkdir counterror makebucket bucketexists headbucketwithcontext testrwfilehandleopentest mkdir counterror create create create testrwfilehandleopentest mkdir counterror create create create testrwfilehandleopentest mkdir counterror create create create testrwfilehandleopentest rcat compare update cap info testrwfilehandleopentest rcat compare update cap info testrwfilehandleopentest rcat compare update cap info testrwfilehandleopentest rcat compare update cap info testrwfilehandleopentest rcat compare put info sendupload testrwfilehandleopentest rcat compare put info sendupload testrwfilehandleopentest rcat compare put info sendupload testrwfilehandleopentest rcat compare put info sendupload testrwfilehandleopentest rcat compare update cap deletechunks testrwfilehandleopentest serve errorf acceptconnections handlechannels handlechannel testrwfilehandleopentest authorize config getconfigdata loadconfig starthttptokenbucket startsignalhandler testrwfilehandleopentest rcat compare update cap info assignableto testrwfilehandleopentest rcat compare update cap deletechunks assignableto testrwfilehandleopentest rcat compare update cap info assignableto mount finalise testrwfilehandleopentest rcat compare update cap deletechunks assignableto mount finalise leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
88,727 | 3,784,854,612 | IssuesEvent | 2016-03-20 03:48:25 | Sistema-Integrado-Gestao-Academica/SiGA | https://api.github.com/repos/Sistema-Integrado-Gestao-Academica/SiGA | closed | Dados de Docente | [Medium Priority] | Como **docente**, desejo inserir um **breve perfil** e um link para o meu **lattes** , para que seja mostrado na página incial da ferramenta (Portal).
-----------------
O portal deve ter uma menu **docentes** para cada programa, para todos docentes cadastrados nos cursos daquele programa.
Ao clicar, deve ser possível ver o nome do docente, um **breve perfil** e o link para o **lattes** <a href="link" /> | 1.0 | Dados de Docente - Como **docente**, desejo inserir um **breve perfil** e um link para o meu **lattes** , para que seja mostrado na página incial da ferramenta (Portal).
-----------------
O portal deve ter uma menu **docentes** para cada programa, para todos docentes cadastrados nos cursos daquele programa.
Ao clicar, deve ser possível ver o nome do docente, um **breve perfil** e o link para o **lattes** <a href="link" /> | non_test | dados de docente como docente desejo inserir um breve perfil e um link para o meu lattes para que seja mostrado na página incial da ferramenta portal o portal deve ter uma menu docentes para cada programa para todos docentes cadastrados nos cursos daquele programa ao clicar deve ser possível ver o nome do docente um breve perfil e o link para o lattes | 0 |
133,519 | 18,894,747,841 | IssuesEvent | 2021-11-15 16:39:12 | carbon-design-system/carbon-for-ibm-dotcom | https://api.github.com/repos/carbon-design-system/carbon-for-ibm-dotcom | closed | Website [Patterns section]: detail TBD | design content website | Pending review of previous issue, then we will define action item & next step. | 1.0 | Website [Patterns section]: detail TBD - Pending review of previous issue, then we will define action item & next step. | non_test | website detail tbd pending review of previous issue then we will define action item next step | 0 |
614,459 | 19,183,509,290 | IssuesEvent | 2021-12-04 20:24:14 | Inryatt/IES_NetCafe | https://api.github.com/repos/Inryatt/IES_NetCafe | closed | User Story #3: Correlations between computer usage and food orders | priority-2 | **As a** business analyst,
**I want** to find correlations between food orders and computer usage
**so that** I can come up with new promotions. | 1.0 | User Story #3: Correlations between computer usage and food orders - **As a** business analyst,
**I want** to find correlations between food orders and computer usage
**so that** I can come up with new promotions. | non_test | user story correlations between computer usage and food orders as a business analyst i want to find correlations between food orders and computer usage so that i can come up with new promotions | 0 |
26,928 | 2,688,873,903 | IssuesEvent | 2015-03-31 05:14:30 | TheDarkMuffin/ft-reports | https://api.github.com/repos/TheDarkMuffin/ft-reports | opened | Turn guidelines into rules | low priority organization suggestion | With a lack of rigor and leaving it up to the whims of those acting in the heat of the moment, there's bound to be more error in judgement and human fallacy involved. I think we should increase the rigor of the guidelines and make them actual rules. | 1.0 | Turn guidelines into rules - With a lack of rigor and leaving it up to the whims of those acting in the heat of the moment, there's bound to be more error in judgement and human fallacy involved. I think we should increase the rigor of the guidelines and make them actual rules. | non_test | turn guidelines into rules with a lack of rigor and leaving it up to the whims of those acting in the heat of the moment there s bound to be more error in judgement and human fallacy involved i think we should increase the rigor of the guidelines and make them actual rules | 0 |
22,909 | 3,975,803,399 | IssuesEvent | 2016-05-05 08:06:27 | cloudant/swift-cloudant | https://api.github.com/repos/cloudant/swift-cloudant | opened | Testing using swift test causes a crash | bug testing | Testing using the command `swift test` causes a crash with the stack trace:
```fatal error: unexpectedly found nil while unwrapping an Optional value
Current stack trace:
0 libswiftCore.dylib 0x000000010c2796f1 swift_reportError + 145
1 libswiftCore.dylib 0x000000010c296b6b _swift_stdlib_reportFatalError + 59
2 libswiftCore.dylib 0x000000010c24c1df partial apply forwarder for reabstraction thunk helper from @callee_owned (@unowned Swift.UnsafeBufferPointer<Swift.UInt8>) -> () to @callee_owned (@unowned Swift.UnsafeBufferPointer<Swift.UInt8>) -> (@out ()).409 + 63
3 libswiftCore.dylib 0x000000010c0fa76f generic specialization <preserving fragile attribute, ()> of Swift.StaticString.withUTF8Buffer <A> (invoke : (Swift.UnsafeBufferPointer<Swift.UInt8>) -> A) -> A + 351
4 libswiftCore.dylib 0x000000010c2248be partial apply forwarder for Swift.(_fatalErrorMessage (Swift.StaticString, Swift.StaticString, Swift.StaticString, Swift.UInt, flags : Swift.UInt32) -> ()).(closure #2) + 158
5 libswiftCore.dylib 0x000000010c1ea36b function signature specialization <preserving fragile attribute, Arg[2] = Dead, Arg[3] = Dead> of Swift._fatalErrorMessage (Swift.StaticString, Swift.StaticString, Swift.StaticString, Swift.UInt, flags : Swift.UInt32) -> () + 331
6 swift-test 0x000000010c00b5ad swifttest.(determineTestPath #1) () -> Swift.String + 1469
7 swift-test 0x000000010c00a8be main + 1678
8 libdyld.dylib 0x00007fff8f6445ad start + 1
9 ??? 0x0000000000000001 0x0 + 1
fish: 'and swift test' terminated by signal SIGILL (Illegal instruction)
```
I have a hunch it is related to how test configuration is handled, however there needs to be some investigation to prove this. | 1.0 | Testing using swift test causes a crash - Testing using the command `swift test` causes a crash with the stack trace:
```fatal error: unexpectedly found nil while unwrapping an Optional value
Current stack trace:
0 libswiftCore.dylib 0x000000010c2796f1 swift_reportError + 145
1 libswiftCore.dylib 0x000000010c296b6b _swift_stdlib_reportFatalError + 59
2 libswiftCore.dylib 0x000000010c24c1df partial apply forwarder for reabstraction thunk helper from @callee_owned (@unowned Swift.UnsafeBufferPointer<Swift.UInt8>) -> () to @callee_owned (@unowned Swift.UnsafeBufferPointer<Swift.UInt8>) -> (@out ()).409 + 63
3 libswiftCore.dylib 0x000000010c0fa76f generic specialization <preserving fragile attribute, ()> of Swift.StaticString.withUTF8Buffer <A> (invoke : (Swift.UnsafeBufferPointer<Swift.UInt8>) -> A) -> A + 351
4 libswiftCore.dylib 0x000000010c2248be partial apply forwarder for Swift.(_fatalErrorMessage (Swift.StaticString, Swift.StaticString, Swift.StaticString, Swift.UInt, flags : Swift.UInt32) -> ()).(closure #2) + 158
5 libswiftCore.dylib 0x000000010c1ea36b function signature specialization <preserving fragile attribute, Arg[2] = Dead, Arg[3] = Dead> of Swift._fatalErrorMessage (Swift.StaticString, Swift.StaticString, Swift.StaticString, Swift.UInt, flags : Swift.UInt32) -> () + 331
6 swift-test 0x000000010c00b5ad swifttest.(determineTestPath #1) () -> Swift.String + 1469
7 swift-test 0x000000010c00a8be main + 1678
8 libdyld.dylib 0x00007fff8f6445ad start + 1
9 ??? 0x0000000000000001 0x0 + 1
fish: 'and swift test' terminated by signal SIGILL (Illegal instruction)
```
I have a hunch it is related to how test configuration is handled, however there needs to be some investigation to prove this. | test | testing using swift test causes a crash testing using the command swift test causes a crash with the stack trace fatal error unexpectedly found nil while unwrapping an optional value current stack trace libswiftcore dylib swift reporterror libswiftcore dylib swift stdlib reportfatalerror libswiftcore dylib partial apply forwarder for reabstraction thunk helper from callee owned unowned swift unsafebufferpointer to callee owned unowned swift unsafebufferpointer out libswiftcore dylib generic specialization of swift staticstring invoke swift unsafebufferpointer a a libswiftcore dylib partial apply forwarder for swift fatalerrormessage swift staticstring swift staticstring swift staticstring swift uint flags swift closure libswiftcore dylib function signature specialization of swift fatalerrormessage swift staticstring swift staticstring swift staticstring swift uint flags swift swift test swifttest determinetestpath swift string swift test main libdyld dylib start fish and swift test terminated by signal sigill illegal instruction i have a hunch it is related to how test configuration is handled however there needs to be some investigation to prove this | 1 |
48,170 | 7,388,404,904 | IssuesEvent | 2018-03-16 02:27:04 | DistrictDataLabs/yellowbrick | https://api.github.com/repos/DistrictDataLabs/yellowbrick | closed | Create Chinese language localization of Yellowbrick documentation. | level: intermediate type: documentation | New repository is here: https://github.com/DistrictDataLabs/yellowbrick-docs-zh
Docs can be found at: http://www.scikit-yb.org/zh/latest/
@Juan0001 you've been added to the above repository and should have write access to it. | 1.0 | Create Chinese language localization of Yellowbrick documentation. - New repository is here: https://github.com/DistrictDataLabs/yellowbrick-docs-zh
Docs can be found at: http://www.scikit-yb.org/zh/latest/
@Juan0001 you've been added to the above repository and should have write access to it. | non_test | create chinese language localization of yellowbrick documentation new repository is here docs can be found at you ve been added to the above repository and should have write access to it | 0 |
263,781 | 23,082,439,189 | IssuesEvent | 2022-07-26 08:28:10 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | closed | Intermittent UI test failure - deleteCollectionTest - androidx.test.uiautomator.UiObjectNotFoundException | eng:intermittent-test eng:ui-test | ### Firebase Test Run:
https://console.firebase.google.com/project/moz-fenix/testlab/histories/bh.80a1a071cfb2770e/matrices/5379394058481151477/executions/bs.1dbb94fa785585b/testcases/1
### Stacktrace:
```
androidx.test.uiautomator.UiObjectNotFoundException: UiSelector[TEXT=VIEW, RESOURCE_ID=org.mozilla.fenix:id/snackbar_btn]
at androidx.test.uiautomator.UiObject.click(UiObject.java:416)
at org.mozilla.fenix.ui.robots.TabDrawerRobot.snackBarButtonClick(TabDrawerRobot.kt:144)
at org.mozilla.fenix.ui.CollectionTest$deleteCollectionTest$3.invoke(CollectionTest.kt:219)
at org.mozilla.fenix.ui.CollectionTest$deleteCollectionTest$3.invoke(CollectionTest.kt:217)
at org.mozilla.fenix.ui.robots.BrowserRobot$Transition.openTabDrawer(BrowserRobot.kt:733)
at org.mozilla.fenix.ui.CollectionTest.deleteCollectionTest(CollectionTest.kt:217)
```
### Build:
https://github.com/mozilla-mobile/fenix/commit/14ee00303b495f152f43cd7d7cea5cc2f1329ee5
┆Issue is synchronized with this [Jira Task](https://mozilla-hub.atlassian.net/browse/FNXV2-20963)
| 2.0 | Intermittent UI test failure - deleteCollectionTest - androidx.test.uiautomator.UiObjectNotFoundException - ### Firebase Test Run:
https://console.firebase.google.com/project/moz-fenix/testlab/histories/bh.80a1a071cfb2770e/matrices/5379394058481151477/executions/bs.1dbb94fa785585b/testcases/1
### Stacktrace:
```
androidx.test.uiautomator.UiObjectNotFoundException: UiSelector[TEXT=VIEW, RESOURCE_ID=org.mozilla.fenix:id/snackbar_btn]
at androidx.test.uiautomator.UiObject.click(UiObject.java:416)
at org.mozilla.fenix.ui.robots.TabDrawerRobot.snackBarButtonClick(TabDrawerRobot.kt:144)
at org.mozilla.fenix.ui.CollectionTest$deleteCollectionTest$3.invoke(CollectionTest.kt:219)
at org.mozilla.fenix.ui.CollectionTest$deleteCollectionTest$3.invoke(CollectionTest.kt:217)
at org.mozilla.fenix.ui.robots.BrowserRobot$Transition.openTabDrawer(BrowserRobot.kt:733)
at org.mozilla.fenix.ui.CollectionTest.deleteCollectionTest(CollectionTest.kt:217)
```
### Build:
https://github.com/mozilla-mobile/fenix/commit/14ee00303b495f152f43cd7d7cea5cc2f1329ee5
┆Issue is synchronized with this [Jira Task](https://mozilla-hub.atlassian.net/browse/FNXV2-20963)
| test | intermittent ui test failure deletecollectiontest androidx test uiautomator uiobjectnotfoundexception firebase test run stacktrace androidx test uiautomator uiobjectnotfoundexception uiselector at androidx test uiautomator uiobject click uiobject java at org mozilla fenix ui robots tabdrawerrobot snackbarbuttonclick tabdrawerrobot kt at org mozilla fenix ui collectiontest deletecollectiontest invoke collectiontest kt at org mozilla fenix ui collectiontest deletecollectiontest invoke collectiontest kt at org mozilla fenix ui robots browserrobot transition opentabdrawer browserrobot kt at org mozilla fenix ui collectiontest deletecollectiontest collectiontest kt build ┆issue is synchronized with this | 1 |
812,896 | 30,388,151,651 | IssuesEvent | 2023-07-13 03:50:02 | wanderer-moe/site | https://api.github.com/repos/wanderer-moe/site | opened | Recreate R2 bucket for centralized storing | enhancement priority: high | Include assets, banners, icons, avatars etc.. onto one R2 bucket under the cdn subdomain, just everything in their appropriate (sub)folders instead of all games in cdn being available at the root directory.
Redirect rules from cdn.olddomain.tld -> cdn.newdomain.tld must include /games/* | 1.0 | Recreate R2 bucket for centralized storing - Include assets, banners, icons, avatars etc.. onto one R2 bucket under the cdn subdomain, just everything in their appropriate (sub)folders instead of all games in cdn being available at the root directory.
Redirect rules from cdn.olddomain.tld -> cdn.newdomain.tld must include /games/* | non_test | recreate bucket for centralized storing include assets banners icons avatars etc onto one bucket under the cdn subdomain just everything in their appropriate sub folders instead of all games in cdn being available at the root directory redirect rules from cdn olddomain tld cdn newdomain tld must include games | 0 |
16,379 | 3,519,880,030 | IssuesEvent | 2016-01-12 18:32:31 | bokeh/bokeh | https://api.github.com/repos/bokeh/bokeh | opened | TravisCI failing every py27 examples test | tag: tests type: bug | ping @mattpap
I can't tell if it is `examples/glyphs.py` or `examples/glyph.ipynb` that is the problem. It ostensibly finishes the notebook, and crashes a few tests later while or ofter writing output for `glyphs.py`, but then it spits out a bunch of log/debugging that seems to be from the `glyph.ipynb` notebook. It is currently impossible to merge any PRs with clean tests now this happens every test run. | 1.0 | TravisCI failing every py27 examples test - ping @mattpap
I can't tell if it is `examples/glyphs.py` or `examples/glyph.ipynb` that is the problem. It ostensibly finishes the notebook, and crashes a few tests later while or ofter writing output for `glyphs.py`, but then it spits out a bunch of log/debugging that seems to be from the `glyph.ipynb` notebook. It is currently impossible to merge any PRs with clean tests now this happens every test run. | test | travisci failing every examples test ping mattpap i can t tell if it is examples glyphs py or examples glyph ipynb that is the problem it ostensibly finishes the notebook and crashes a few tests later while or ofter writing output for glyphs py but then it spits out a bunch of log debugging that seems to be from the glyph ipynb notebook it is currently impossible to merge any prs with clean tests now this happens every test run | 1 |
264,419 | 8,309,763,838 | IssuesEvent | 2018-09-24 08:13:41 | mozilla/addons-frontend | https://api.github.com/repos/mozilla/addons-frontend | closed | Change copy on top of the about:addons page (disco pane) | needs: content priority: p3 project: disco pane | The copy at the top of the disco pane is quite outdated. Update it with Meridel's new copy (TBD). Below is a screenshot of what exists today.
| 1.0 | Change copy on top of the about:addons page (disco pane) - The copy at the top of the disco pane is quite outdated. Update it with Meridel's new copy (TBD). Below is a screenshot of what exists today.
| non_test | change copy on top of the about addons page disco pane the copy at the top of the disco pane is quite outdated update it with meridel s new copy tbd below is a screenshot of what exists today | 0 |
20,015 | 26,486,899,441 | IssuesEvent | 2023-01-17 18:49:56 | bitfocus/companion-module-requests | https://api.github.com/repos/bitfocus/companion-module-requests | opened | VEX TM Control | NOT YET PROCESSED | - [ ] **I have researched the list of existing Companion modules and requests and have determined this has not yet been requested**
The name of the device, hardware, or software you would like to control:
VEX Tournament Manager
What you would like to be able to make it do from Companion:
Control the Audience Display functionality and the Match Status. It is already possible using a NodeJS server if configured, but i do not know how that would be of any help to the BitFocus team.
Direct links or attachments to the ethernet control protocol or API:
https://vextm.dwabtech.com/
https://www.npmjs.com/package/vex-tm-client?activeTab=readme | 1.0 | VEX TM Control - - [ ] **I have researched the list of existing Companion modules and requests and have determined this has not yet been requested**
The name of the device, hardware, or software you would like to control:
VEX Tournament Manager
What you would like to be able to make it do from Companion:
Control the Audience Display functionality and the Match Status. It is already possible using a NodeJS server if configured, but i do not know how that would be of any help to the BitFocus team.
Direct links or attachments to the ethernet control protocol or API:
https://vextm.dwabtech.com/
https://www.npmjs.com/package/vex-tm-client?activeTab=readme | non_test | vex tm control i have researched the list of existing companion modules and requests and have determined this has not yet been requested the name of the device hardware or software you would like to control vex tournament manager what you would like to be able to make it do from companion control the audience display functionality and the match status it is already possible using a nodejs server if configured but i do not know how that would be of any help to the bitfocus team direct links or attachments to the ethernet control protocol or api | 0 |
101,044 | 21,572,064,750 | IssuesEvent | 2022-05-02 09:25:06 | DS-13-Dev-Team/DS13 | https://api.github.com/repos/DS-13-Dev-Team/DS13 | opened | FEATURE ADJ: Unitologist Operatives and EarthGov Agents | Suggestion Type: Code Priority: High Difficulty: Easy | #### Description of issue:
We have a problem with Uni Ops and EG Agents becoming too much a round disruption.
I would like for us to reduce the number of Uni Ops and EG Agents in a game to 2 Uni Ops, 1 EG Agent, maximum.
We also need to revisit TC prices and the available items on the uplinks. Whoever can get to it first, please post the list of available items and their costs to this issue thread.
#### Difference between expected and actual behavior:
The amount of antags on the field is making things too chaotic for what is already a round primed for conflict and combat. The pop of the game is too small to accommodate upwards of five antagonists and the code isn't properly reflecting the headcount.
By hardcapping these numbers lower, we should be able to both reduce the amount of wild antag activity and ensure the impact of those antags is more controlled.
| 1.0 | FEATURE ADJ: Unitologist Operatives and EarthGov Agents - #### Description of issue:
We have a problem with Uni Ops and EG Agents becoming too much a round disruption.
I would like for us to reduce the number of Uni Ops and EG Agents in a game to 2 Uni Ops, 1 EG Agent, maximum.
We also need to revisit TC prices and the available items on the uplinks. Whoever can get to it first, please post the list of available items and their costs to this issue thread.
#### Difference between expected and actual behavior:
The amount of antags on the field is making things too chaotic for what is already a round primed for conflict and combat. The pop of the game is too small to accommodate upwards of five antagonists and the code isn't properly reflecting the headcount.
By hardcapping these numbers lower, we should be able to both reduce the amount of wild antag activity and ensure the impact of those antags is more controlled.
| non_test | feature adj unitologist operatives and earthgov agents description of issue we have a problem with uni ops and eg agents becoming too much a round disruption i would like for us to reduce the number of uni ops and eg agents in a game to uni ops eg agent maximum we also need to revisit tc prices and the available items on the uplinks whoever can get to it first please post the list of available items and their costs to this issue thread difference between expected and actual behavior the amount of antags on the field is making things too chaotic for what is already a round primed for conflict and combat the pop of the game is too small to accommodate upwards of five antagonists and the code isn t properly reflecting the headcount by hardcapping these numbers lower we should be able to both reduce the amount of wild antag activity and ensure the impact of those antags is more controlled | 0 |
209,616 | 16,045,415,327 | IssuesEvent | 2021-04-22 13:08:31 | gaudes/ioBroker.slideshow | https://api.github.com/repos/gaudes/ioBroker.slideshow | closed | Effects not working in Firefox | bug wait for test | Hello!
I was trying to find a nice effect to switch from one picture to another. I have chosen this setup:
<img width="235" alt="grafik" src="https://user-images.githubusercontent.com/13975634/114294158-df7cb600-9a9c-11eb-8a56-a27e7473c274.png">
When I do this in Firefox 87, it seems to not work correctly. During the picture change, it switches to one completely different picture for 1-2 seconds, and then jumps to the next one. The debug console shows this error:
<img width="902" alt="grafik" src="https://user-images.githubusercontent.com/13975634/114294248-8cefc980-9a9d-11eb-8622-820d1c111c7a.png">
Have I set it up incorrectly to get a smooth change? | 1.0 | Effects not working in Firefox - Hello!
I was trying to find a nice effect to switch from one picture to another. I have chosen this setup:
<img width="235" alt="grafik" src="https://user-images.githubusercontent.com/13975634/114294158-df7cb600-9a9c-11eb-8a56-a27e7473c274.png">
When I do this in Firefox 87, it seems to not work correctly. During the picture change, it switches to one completely different picture for 1-2 seconds, and then jumps to the next one. The debug console shows this error:
<img width="902" alt="grafik" src="https://user-images.githubusercontent.com/13975634/114294248-8cefc980-9a9d-11eb-8622-820d1c111c7a.png">
Have I set it up incorrectly to get a smooth change? | test | effects not working in firefox hello i was trying to find a nice effect to switch from one picture to another i have chosen this setup img width alt grafik src when i do this in firefox it seems to not work correctly during the picture change it switches to one completely different picture for seconds and then jumps to the next one the debug console shows this error img width alt grafik src have i set it up incorrectly to get a smooth change | 1 |
227,300 | 18,054,376,150 | IssuesEvent | 2021-09-20 05:40:13 | logicmoo/logicmoo_workspace | https://api.github.com/repos/logicmoo/logicmoo_workspace | opened | logicmoo.base.fol.fiveof.FIVE_LEFTOF_UP_DOWN_02 JUnit | logicmoo.base.fol.fiveof Test_9999 unit_test FIVE_LEFTOF_UP_DOWN_02 Failing | (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/logicmoo_base/t/examples/fol/fiveof ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s swipl -x /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-clif five_leftof_up_down_02.pl)
% ISSUE: https://github.com/logicmoo/logicmoo_workspace/issues/
% EDIT: https://github.com/logicmoo/logicmoo_workspace/edit/master/packs_sys/logicmoo_base/t/examples/fol/fiveof/five_leftof_up_down_02.pl
% JENKINS: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.base.fol.fiveof/FIVE_LEFTOF_UP_DOWN_02/logicmoo_base_fol_fiveof_FIVE_LEFTOF_UP_DOWN_02_JUnit/
% ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFIVE_LEFTOF_UP_DOWN_02
```
%~ init_phase(after_load)
%~ init_phase(restore_state)
%
running('/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/logicmoo_base/t/examples/fol/fiveof/five_leftof_up_down_02.pl'),
%~ this_test_might_need( :-( expects_dialect(pfc)))
%~ this_test_might_need( :-( use_module( library(logicmoo_plarkc))))
% =============================================
% File 'mpred_builtin.pfc'
% Purpose: Agent Reactivity for SWI-Prolog
% Maintainer: Douglas Miles
% Contact: $Author: dmiles $@users.sourceforge.net %
% Version: 'interface' 1.0.0
% Revision: $Revision: 1.9 $
% Revised At: $Date: 2002/06/27 14:13:20 $
% =============================================
%
:- expects_dialect(clif).
:- set_prolog_flag(gc,false).
% There are five houses in a row.
% There are five houses in a row.
exists(H1,exists(H2,exists(H3,exists(H4,exists(H5,
(leftof(H1, H2) & leftof(H2, H3) & leftof(H3, H4) & leftof(H4, H5))))))).
% ISSUE: https://github.com/logicmoo/logicmoo_workspace/issues/
% EDIT: https://github.com/logicmoo/logicmoo_workspace/edit/master/packs_sys/logicmoo_base/t/examples/fol/fiveof/five_leftof_up_down_02.pl
% JENKINS: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.base.fol.fiveof/FIVE_LEFTOF_UP_DOWN_02/logicmoo_base_fol_fiveof_FIVE_LEFTOF_UP_DOWN_02_JUnit/
% ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFIVE_LEFTOF_UP_DOWN_02
%~ debugm( baseKB,
%~ show_success( baseKB,
%~ baseKB : ain( clif( exists( H1,
%~ exists( H2,
%~ exists( H3,
%~ exists( H4,
%~ exists( H5,
%~ ( leftof(H1,H2) &
%~ leftof(H2,H3) &
%~ leftof(H3,H4) &
%~ leftof(H4,H5)))))))))))
%~ kifi = exists( Exists_Leftof,
%~ exists( Exists_Leftof6,
%~ exists( Exists_Leftof7,
%~ exists( Exists_Leftof8,
%~ exists( Leftof13,
%~ ( leftof(Exists_Leftof,Exists_Leftof6) &
%~ leftof(Exists_Leftof6,Exists_Leftof7) &
%~ leftof(Exists_Leftof7,Exists_Leftof8) &
%~ leftof(Exists_Leftof8,Leftof13))))))).
%~ kifm = exists( Exists_Leftof,
%~ exists( Exists_Leftof6,
%~ exists( Exists_Leftof7,
%~ exists( Exists_Leftof8,
%~ exists( Leftof13,
%~ nesc( ( leftof(Exists_Leftof,Exists_Leftof6) &
%~ leftof(Exists_Leftof6,Exists_Leftof7) &
%~ leftof(Exists_Leftof7,Exists_Leftof8) &
%~ leftof(Exists_Leftof8,Leftof13)))))))).
%~ /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/logicmoo_base/t/examples/fol/fiveof/five_leftof_up_down_02.pl:18
%~ kifi = exists( H1,
%~ exists( H2,
%~ exists( H3,
%~ exists( H4,
%~ exists( H5,
%~ ( leftof(H1,H2) &
%~ leftof(H2,H3) &
%~ leftof(H3,H4) &
%~ leftof(H4,H5))))))).
%~ kifm = exists( H1,
%~ exists( H2,
%~ exists( H3,
%~ exists( H4,
%~ exists( H5,
%~ nesc( ( leftof(H1,H2) &
%~ leftof(H2,H3) &
%~ leftof(H3,H4) &
%~ leftof(H4,H5)))))))).
/*~
=======================================================
exists('$VAR'('Exists_Leftof'),exists('$VAR'('Exists_Leftof6'),exists('$VAR'('Exists_Leftof7'),exists('$VAR'('Exists_Leftof8'),exists('$VAR'('Leftof13'),&(&(&(leftof('$VAR'('Exists_Leftof'),'$VAR'('Exists_Leftof6')),leftof('$VAR'('Exists_Leftof6'),'$VAR'('Exists_Leftof7'))),leftof('$VAR'('Exists_Leftof7'),'$VAR'('Exists_Leftof8'))),leftof('$VAR'('Exists_Leftof8'),'$VAR'('Leftof13'))))))))
============================================
?- kif_to_boxlog( exists(Exists_Leftof,exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((leftof(Exists_Leftof,Exists_Leftof6)&leftof(Exists_Leftof6,Exists_Leftof7))&leftof(Exists_Leftof7,Exists_Leftof8))&leftof(Exists_Leftof8,Leftof13)))))) ).
% In English:
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~
%~ There exists ?Exists_Leftof
%~ (
%~ There exists ?Exists_Leftof6
%~ (
%~ There exists ?Exists_Leftof7
%~ (
%~ There exists ?Exists_Leftof8
%~ (
%~ There exists ?Leftof13
%~ (((" ?Exists_Leftof leftof ?Exists_Leftof6 " and
%~ " ?Exists_Leftof6 leftof ?Exists_Leftof7 " ) and
%~ " ?Exists_Leftof7 leftof ?Exists_Leftof8 " ) and
%~ " ?Exists_Leftof8 leftof ?Leftof13 " )))))
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ kifi=exists(Exists_Leftof,exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((leftof(Exists_Leftof,Exists_Leftof6)&leftof(Exists_Leftof6,Exists_Leftof7))&leftof(Exists_Leftof7,Exists_Leftof8))&leftof(Exists_Leftof8,Leftof13))))))
%~ kifm=exists(Exists_Leftof,exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,nesc(((leftof(Exists_Leftof,Exists_Leftof6)&leftof(Exists_Leftof6,Exists_Leftof7))&leftof(Exists_Leftof7,Exists_Leftof8))&leftof(Exists_Leftof8,Leftof13)))))))
%~ kif_to_boxlog_attvars2 = exists('$VAR'('Exists_Leftof'),exists('$VAR'('Exists_Leftof6'),exists('$VAR'('Exists_Leftof7'),exists('$VAR'('Exists_Leftof8'),exists('$VAR'('Leftof13'),necessary(and(and(and(leftof('$VAR'('Exists_Leftof'),'$VAR'('Exists_Leftof6')),leftof('$VAR'('Exists_Leftof6'),'$VAR'('Exists_Leftof7'))),leftof('$VAR'('Exists_Leftof7'),'$VAR'('Exists_Leftof8'))),leftof('$VAR'('Exists_Leftof8'),'$VAR'('Leftof13')))))))))
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
% Results in the following 6 entailment(s):
(((nesc(leftof(Exists_Leftof,Exists_Leftof6))&'$existential'(Exists_Leftof6,1,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))))&'$existential'(Exists_Leftof7,1,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))&'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>nesc(leftof(Exists_Leftof6,Exists_Leftof7)).
(((poss(~leftof(Exists_Leftof,Exists_Leftof6))&'$existential'(Exists_Leftof6,1,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))))&'$existential'(Exists_Leftof7,1,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))&'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>poss(~leftof(Exists_Leftof6,Exists_Leftof7)).
((((nesc(leftof(Exists_Leftof6,Exists_Leftof7))&'$existential'(Exists_Leftof,1,exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))))&'$existential'(Exists_Leftof6,1,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))))&'$existential'(Exists_Leftof7,1,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))&'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>nesc(leftof(Exists_Leftof,Exists_Leftof6)).
((((poss(~leftof(Exists_Leftof6,Exists_Leftof7))&'$existential'(Exists_Leftof,1,exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))))&'$existential'(Exists_Leftof6,1,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))))&'$existential'(Exists_Leftof7,1,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))&'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>poss(~leftof(Exists_Leftof,Exists_Leftof6)).
('$existential'(Exists_Leftof7,1,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>nesc(leftof(Exists_Leftof7,Exists_Leftof8)).
'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>nesc(leftof(Exists_Leftof8,Leftof13)).
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ (((" ?Exists_Leftof leftof ?Exists_Leftof6 " is necessarily true and
%~ by default ?Exists_Leftof6 exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))) ) and
%~ by default ?Exists_Leftof7 exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))) ) and
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) ) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof6 leftof ?Exists_Leftof7 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
'$existential'( Exists_Leftof6,
1,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))))) &
'$existential'( Exists_Leftof7,
1,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))) &
'$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
nesc( leftof(Exists_Leftof6,Exists_Leftof7))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ (((" ?Exists_Leftof leftof ?Exists_Leftof6 " is possibly false and
%~ by default ?Exists_Leftof6 exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))) ) and
%~ by default ?Exists_Leftof7 exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))) ) and
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) ) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof6 leftof ?Exists_Leftof7 " is possibly false
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( poss( ~( leftof(Exists_Leftof,Exists_Leftof6))) &
'$existential'( Exists_Leftof6,
1,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))))) &
'$existential'( Exists_Leftof7,
1,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))) &
'$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
poss( ~( leftof(Exists_Leftof6,Exists_Leftof7)))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ((((" ?Exists_Leftof6 leftof ?Exists_Leftof7 " is necessarily true and
%~ by default ?Exists_Leftof exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))) ) and
%~ by default ?Exists_Leftof6 exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))) ) and
%~ by default ?Exists_Leftof7 exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))) ) and
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) ) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof leftof ?Exists_Leftof6 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
'$existential'( Exists_Leftof,
1,
exists( Exists_Leftof6,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))))) &
'$existential'( Exists_Leftof6,
1,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))))) &
'$existential'( Exists_Leftof7,
1,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))) &
'$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
nesc( leftof(Exists_Leftof,Exists_Leftof6))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ((((" ?Exists_Leftof6 leftof ?Exists_Leftof7 " is possibly false and
%~ by default ?Exists_Leftof exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))) ) and
%~ by default ?Exists_Leftof6 exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))) ) and
%~ by default ?Exists_Leftof7 exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))) ) and
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) ) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof leftof ?Exists_Leftof6 " is possibly false
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( poss( ~( leftof(Exists_Leftof6,Exists_Leftof7))) &
'$existential'( Exists_Leftof,
1,
exists( Exists_Leftof6,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))))) &
'$existential'( Exists_Leftof6,
1,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))))) &
'$existential'( Exists_Leftof7,
1,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))) &
'$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
poss( ~( leftof(Exists_Leftof,Exists_Leftof6)))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ( by default ?Exists_Leftof7 exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))) and
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) ) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof7 leftof ?Exists_Leftof8 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( '$existential'( Exists_Leftof7,
1,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))) &
'$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
nesc( leftof(Exists_Leftof7,Exists_Leftof8))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof8 leftof ?Leftof13 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( '$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
nesc( leftof(Exists_Leftof8,Leftof13))).
============================================%~ kifi=exists(H1,exists(H2,exists(H3,exists(H4,exists(H5,((leftof(H1,H2)&leftof(H2,H3))&leftof(H3,H4))&leftof(H4,H5))))))
%~ kifm=exists(H1,exists(H2,exists(H3,exists(H4,exists(H5,nesc(((leftof(H1,H2)&leftof(H2,H3))&leftof(H3,H4))&leftof(H4,H5)))))))
%~ kif_to_boxlog_attvars2 = exists('$VAR'('H1'),exists('$VAR'('H2'),exists('$VAR'('H3'),exists('$VAR'('H4'),exists('$VAR'('H5'),necessary(and(and(and(leftof('$VAR'('H1'),'$VAR'('H2')),leftof('$VAR'('H2'),'$VAR'('H3'))),leftof('$VAR'('H3'),'$VAR'('H4'))),leftof('$VAR'('H4'),'$VAR'('H5')))))))))
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H4 leftof ?H5 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( '$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
nesc( leftof(H4,H5))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ( by default ?H3 exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))) and
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) ) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H3 leftof ?H4 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( '$existential'( H3,
1,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))) &
'$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
nesc( leftof(H3,H4))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ (((" ?H1 leftof ?H2 " is possibly false and
%~ by default ?H2 exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))))) ) and
%~ by default ?H3 exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))) ) and
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) ) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H2 leftof ?H3 " is possibly false
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( poss( ~( leftof(H1,H2))) &
'$existential'( H2,
1,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))))) &
'$existential'( H3,
1,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))) &
'$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
poss( ~( leftof(H2,H3)))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ((((" ?H2 leftof ?H3 " is necessarily true and
%~ by default ?H1 exists(H2,exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))))) ) and
%~ by default ?H2 exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))))) ) and
%~ by default ?H3 exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))) ) and
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) ) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H1 leftof ?H2 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( nesc( leftof(H2,H3)) &
'$existential'( H1,
1,
exists( H2,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))))) &
'$existential'( H2,
1,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))))) &
'$existential'( H3,
1,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))) &
'$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
nesc( leftof(H1,H2))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ((((" ?H2 leftof ?H3 " is possibly false and
%~ by default ?H1 exists(H2,exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))))) ) and
%~ by default ?H2 exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))))) ) and
%~ by default ?H3 exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))) ) and
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) ) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H1 leftof ?H2 " is possibly false
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( poss( ~( leftof(H2,H3))) &
'$existential'( H1,
1,
exists( H2,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))))) &
'$existential'( H2,
1,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))))) &
'$existential'( H3,
1,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))) &
'$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
poss( ~( leftof(H1,H2)))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ (((" ?H1 leftof ?H2 " is necessarily true and
%~ by default ?H2 exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))))) ) and
%~ by default ?H3 exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))) ) and
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) ) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H2 leftof ?H3 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( nesc( leftof(H1,H2)) &
'$existential'( H2,
1,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))))) &
'$existential'( H3,
1,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))) &
'$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
nesc( leftof(H2,H3))).
~*/
%~ /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/logicmoo_base/t/examples/fol/fiveof/five_leftof_up_down_02.pl:28
%~ unused(no_junit_results)
%~ test_completed_exit(0)
```
totalTime=3.000
FAILED: /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-junit-minor -k five_leftof_up_down_02.pl (returned 0) Add_LABELS='' Rem_LABELS='Skipped,Skipped,Errors,Warnings,Overtime,Skipped,Skipped'
| 2.0 | logicmoo.base.fol.fiveof.FIVE_LEFTOF_UP_DOWN_02 JUnit - (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/logicmoo_base/t/examples/fol/fiveof ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s swipl -x /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-clif five_leftof_up_down_02.pl)
% ISSUE: https://github.com/logicmoo/logicmoo_workspace/issues/
% EDIT: https://github.com/logicmoo/logicmoo_workspace/edit/master/packs_sys/logicmoo_base/t/examples/fol/fiveof/five_leftof_up_down_02.pl
% JENKINS: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.base.fol.fiveof/FIVE_LEFTOF_UP_DOWN_02/logicmoo_base_fol_fiveof_FIVE_LEFTOF_UP_DOWN_02_JUnit/
% ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFIVE_LEFTOF_UP_DOWN_02
```
%~ init_phase(after_load)
%~ init_phase(restore_state)
%
running('/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/logicmoo_base/t/examples/fol/fiveof/five_leftof_up_down_02.pl'),
%~ this_test_might_need( :-( expects_dialect(pfc)))
%~ this_test_might_need( :-( use_module( library(logicmoo_plarkc))))
% =============================================
% File 'mpred_builtin.pfc'
% Purpose: Agent Reactivity for SWI-Prolog
% Maintainer: Douglas Miles
% Contact: $Author: dmiles $@users.sourceforge.net %
% Version: 'interface' 1.0.0
% Revision: $Revision: 1.9 $
% Revised At: $Date: 2002/06/27 14:13:20 $
% =============================================
%
:- expects_dialect(clif).
:- set_prolog_flag(gc,false).
% There are five houses in a row.
% There are five houses in a row.
exists(H1,exists(H2,exists(H3,exists(H4,exists(H5,
(leftof(H1, H2) & leftof(H2, H3) & leftof(H3, H4) & leftof(H4, H5))))))).
% ISSUE: https://github.com/logicmoo/logicmoo_workspace/issues/
% EDIT: https://github.com/logicmoo/logicmoo_workspace/edit/master/packs_sys/logicmoo_base/t/examples/fol/fiveof/five_leftof_up_down_02.pl
% JENKINS: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.base.fol.fiveof/FIVE_LEFTOF_UP_DOWN_02/logicmoo_base_fol_fiveof_FIVE_LEFTOF_UP_DOWN_02_JUnit/
% ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFIVE_LEFTOF_UP_DOWN_02
%~ debugm( baseKB,
%~ show_success( baseKB,
%~ baseKB : ain( clif( exists( H1,
%~ exists( H2,
%~ exists( H3,
%~ exists( H4,
%~ exists( H5,
%~ ( leftof(H1,H2) &
%~ leftof(H2,H3) &
%~ leftof(H3,H4) &
%~ leftof(H4,H5)))))))))))
%~ kifi = exists( Exists_Leftof,
%~ exists( Exists_Leftof6,
%~ exists( Exists_Leftof7,
%~ exists( Exists_Leftof8,
%~ exists( Leftof13,
%~ ( leftof(Exists_Leftof,Exists_Leftof6) &
%~ leftof(Exists_Leftof6,Exists_Leftof7) &
%~ leftof(Exists_Leftof7,Exists_Leftof8) &
%~ leftof(Exists_Leftof8,Leftof13))))))).
%~ kifm = exists( Exists_Leftof,
%~ exists( Exists_Leftof6,
%~ exists( Exists_Leftof7,
%~ exists( Exists_Leftof8,
%~ exists( Leftof13,
%~ nesc( ( leftof(Exists_Leftof,Exists_Leftof6) &
%~ leftof(Exists_Leftof6,Exists_Leftof7) &
%~ leftof(Exists_Leftof7,Exists_Leftof8) &
%~ leftof(Exists_Leftof8,Leftof13)))))))).
%~ /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/logicmoo_base/t/examples/fol/fiveof/five_leftof_up_down_02.pl:18
%~ kifi = exists( H1,
%~ exists( H2,
%~ exists( H3,
%~ exists( H4,
%~ exists( H5,
%~ ( leftof(H1,H2) &
%~ leftof(H2,H3) &
%~ leftof(H3,H4) &
%~ leftof(H4,H5))))))).
%~ kifm = exists( H1,
%~ exists( H2,
%~ exists( H3,
%~ exists( H4,
%~ exists( H5,
%~ nesc( ( leftof(H1,H2) &
%~ leftof(H2,H3) &
%~ leftof(H3,H4) &
%~ leftof(H4,H5)))))))).
/*~
=======================================================
exists('$VAR'('Exists_Leftof'),exists('$VAR'('Exists_Leftof6'),exists('$VAR'('Exists_Leftof7'),exists('$VAR'('Exists_Leftof8'),exists('$VAR'('Leftof13'),&(&(&(leftof('$VAR'('Exists_Leftof'),'$VAR'('Exists_Leftof6')),leftof('$VAR'('Exists_Leftof6'),'$VAR'('Exists_Leftof7'))),leftof('$VAR'('Exists_Leftof7'),'$VAR'('Exists_Leftof8'))),leftof('$VAR'('Exists_Leftof8'),'$VAR'('Leftof13'))))))))
============================================
?- kif_to_boxlog( exists(Exists_Leftof,exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((leftof(Exists_Leftof,Exists_Leftof6)&leftof(Exists_Leftof6,Exists_Leftof7))&leftof(Exists_Leftof7,Exists_Leftof8))&leftof(Exists_Leftof8,Leftof13)))))) ).
% In English:
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~
%~ There exists ?Exists_Leftof
%~ (
%~ There exists ?Exists_Leftof6
%~ (
%~ There exists ?Exists_Leftof7
%~ (
%~ There exists ?Exists_Leftof8
%~ (
%~ There exists ?Leftof13
%~ (((" ?Exists_Leftof leftof ?Exists_Leftof6 " and
%~ " ?Exists_Leftof6 leftof ?Exists_Leftof7 " ) and
%~ " ?Exists_Leftof7 leftof ?Exists_Leftof8 " ) and
%~ " ?Exists_Leftof8 leftof ?Leftof13 " )))))
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ kifi=exists(Exists_Leftof,exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((leftof(Exists_Leftof,Exists_Leftof6)&leftof(Exists_Leftof6,Exists_Leftof7))&leftof(Exists_Leftof7,Exists_Leftof8))&leftof(Exists_Leftof8,Leftof13))))))
%~ kifm=exists(Exists_Leftof,exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,nesc(((leftof(Exists_Leftof,Exists_Leftof6)&leftof(Exists_Leftof6,Exists_Leftof7))&leftof(Exists_Leftof7,Exists_Leftof8))&leftof(Exists_Leftof8,Leftof13)))))))
%~ kif_to_boxlog_attvars2 = exists('$VAR'('Exists_Leftof'),exists('$VAR'('Exists_Leftof6'),exists('$VAR'('Exists_Leftof7'),exists('$VAR'('Exists_Leftof8'),exists('$VAR'('Leftof13'),necessary(and(and(and(leftof('$VAR'('Exists_Leftof'),'$VAR'('Exists_Leftof6')),leftof('$VAR'('Exists_Leftof6'),'$VAR'('Exists_Leftof7'))),leftof('$VAR'('Exists_Leftof7'),'$VAR'('Exists_Leftof8'))),leftof('$VAR'('Exists_Leftof8'),'$VAR'('Leftof13')))))))))
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
% Results in the following 6 entailment(s):
(((nesc(leftof(Exists_Leftof,Exists_Leftof6))&'$existential'(Exists_Leftof6,1,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))))&'$existential'(Exists_Leftof7,1,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))&'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>nesc(leftof(Exists_Leftof6,Exists_Leftof7)).
(((poss(~leftof(Exists_Leftof,Exists_Leftof6))&'$existential'(Exists_Leftof6,1,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))))&'$existential'(Exists_Leftof7,1,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))&'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>poss(~leftof(Exists_Leftof6,Exists_Leftof7)).
((((nesc(leftof(Exists_Leftof6,Exists_Leftof7))&'$existential'(Exists_Leftof,1,exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))))&'$existential'(Exists_Leftof6,1,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))))&'$existential'(Exists_Leftof7,1,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))&'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>nesc(leftof(Exists_Leftof,Exists_Leftof6)).
((((poss(~leftof(Exists_Leftof6,Exists_Leftof7))&'$existential'(Exists_Leftof,1,exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))))&'$existential'(Exists_Leftof6,1,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))))&'$existential'(Exists_Leftof7,1,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))))&'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>poss(~leftof(Exists_Leftof,Exists_Leftof6)).
('$existential'(Exists_Leftof7,1,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>nesc(leftof(Exists_Leftof7,Exists_Leftof8)).
'$existential'(Exists_Leftof8,1,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))&'$existential'(Leftof13,1,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))==>nesc(leftof(Exists_Leftof8,Leftof13)).
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ (((" ?Exists_Leftof leftof ?Exists_Leftof6 " is necessarily true and
%~ by default ?Exists_Leftof6 exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))) ) and
%~ by default ?Exists_Leftof7 exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))) ) and
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) ) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof6 leftof ?Exists_Leftof7 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
'$existential'( Exists_Leftof6,
1,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))))) &
'$existential'( Exists_Leftof7,
1,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))) &
'$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
nesc( leftof(Exists_Leftof6,Exists_Leftof7))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ (((" ?Exists_Leftof leftof ?Exists_Leftof6 " is possibly false and
%~ by default ?Exists_Leftof6 exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))) ) and
%~ by default ?Exists_Leftof7 exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))) ) and
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) ) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof6 leftof ?Exists_Leftof7 " is possibly false
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( poss( ~( leftof(Exists_Leftof,Exists_Leftof6))) &
'$existential'( Exists_Leftof6,
1,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))))) &
'$existential'( Exists_Leftof7,
1,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))) &
'$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
poss( ~( leftof(Exists_Leftof6,Exists_Leftof7)))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ((((" ?Exists_Leftof6 leftof ?Exists_Leftof7 " is necessarily true and
%~ by default ?Exists_Leftof exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))) ) and
%~ by default ?Exists_Leftof6 exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))) ) and
%~ by default ?Exists_Leftof7 exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))) ) and
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) ) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof leftof ?Exists_Leftof6 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
'$existential'( Exists_Leftof,
1,
exists( Exists_Leftof6,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))))) &
'$existential'( Exists_Leftof6,
1,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))))) &
'$existential'( Exists_Leftof7,
1,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))) &
'$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
nesc( leftof(Exists_Leftof,Exists_Leftof6))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ((((" ?Exists_Leftof6 leftof ?Exists_Leftof7 " is possibly false and
%~ by default ?Exists_Leftof exists(Exists_Leftof6,exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))))) ) and
%~ by default ?Exists_Leftof6 exists(Exists_Leftof7,exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))))) ) and
%~ by default ?Exists_Leftof7 exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))) ) and
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) ) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof leftof ?Exists_Leftof6 " is possibly false
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( poss( ~( leftof(Exists_Leftof6,Exists_Leftof7))) &
'$existential'( Exists_Leftof,
1,
exists( Exists_Leftof6,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))))) &
'$existential'( Exists_Leftof6,
1,
exists( Exists_Leftof7,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))))) &
'$existential'( Exists_Leftof7,
1,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))) &
'$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
poss( ~( leftof(Exists_Leftof,Exists_Leftof6)))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ( by default ?Exists_Leftof7 exists(Exists_Leftof8,exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13)))) and
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) ) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof7 leftof ?Exists_Leftof8 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( '$existential'( Exists_Leftof7,
1,
exists( Exists_Leftof8,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13)))))) &
'$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
nesc( leftof(Exists_Leftof7,Exists_Leftof8))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ by default ?Exists_Leftof8 exists(Leftof13,((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))) and
%~ by default ?Leftof13 ((nesc(leftof(Exists_Leftof,Exists_Leftof6))&nesc(leftof(Exists_Leftof6,Exists_Leftof7)))&nesc(leftof(Exists_Leftof7,Exists_Leftof8)))&nesc(leftof(Exists_Leftof8,Leftof13))
%~ It's Proof that:
%~ " ?Exists_Leftof8 leftof ?Leftof13 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( '$existential'( Exists_Leftof8,
1,
exists( Leftof13,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) &
'$existential'( Leftof13,
1,
( nesc( leftof(Exists_Leftof,Exists_Leftof6)) &
nesc( leftof(Exists_Leftof6,Exists_Leftof7)) &
nesc( leftof(Exists_Leftof7,Exists_Leftof8)) &
nesc( leftof(Exists_Leftof8,Leftof13))))) ==>
nesc( leftof(Exists_Leftof8,Leftof13))).
============================================%~ kifi=exists(H1,exists(H2,exists(H3,exists(H4,exists(H5,((leftof(H1,H2)&leftof(H2,H3))&leftof(H3,H4))&leftof(H4,H5))))))
%~ kifm=exists(H1,exists(H2,exists(H3,exists(H4,exists(H5,nesc(((leftof(H1,H2)&leftof(H2,H3))&leftof(H3,H4))&leftof(H4,H5)))))))
%~ kif_to_boxlog_attvars2 = exists('$VAR'('H1'),exists('$VAR'('H2'),exists('$VAR'('H3'),exists('$VAR'('H4'),exists('$VAR'('H5'),necessary(and(and(and(leftof('$VAR'('H1'),'$VAR'('H2')),leftof('$VAR'('H2'),'$VAR'('H3'))),leftof('$VAR'('H3'),'$VAR'('H4'))),leftof('$VAR'('H4'),'$VAR'('H5')))))))))
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H4 leftof ?H5 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( '$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
nesc( leftof(H4,H5))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ( by default ?H3 exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))) and
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) ) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H3 leftof ?H4 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( '$existential'( H3,
1,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))) &
'$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
nesc( leftof(H3,H4))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ (((" ?H1 leftof ?H2 " is possibly false and
%~ by default ?H2 exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))))) ) and
%~ by default ?H3 exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))) ) and
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) ) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H2 leftof ?H3 " is possibly false
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( poss( ~( leftof(H1,H2))) &
'$existential'( H2,
1,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))))) &
'$existential'( H3,
1,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))) &
'$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
poss( ~( leftof(H2,H3)))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ((((" ?H2 leftof ?H3 " is necessarily true and
%~ by default ?H1 exists(H2,exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))))) ) and
%~ by default ?H2 exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))))) ) and
%~ by default ?H3 exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))) ) and
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) ) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H1 leftof ?H2 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( nesc( leftof(H2,H3)) &
'$existential'( H1,
1,
exists( H2,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))))) &
'$existential'( H2,
1,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))))) &
'$existential'( H3,
1,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))) &
'$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
nesc( leftof(H1,H2))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ ((((" ?H2 leftof ?H3 " is possibly false and
%~ by default ?H1 exists(H2,exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))))) ) and
%~ by default ?H2 exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))))) ) and
%~ by default ?H3 exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))) ) and
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) ) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H1 leftof ?H2 " is possibly false
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( poss( ~( leftof(H2,H3))) &
'$existential'( H1,
1,
exists( H2,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))))) &
'$existential'( H2,
1,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))))) &
'$existential'( H3,
1,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))) &
'$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
poss( ~( leftof(H1,H2)))).
% AND
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%~ Whenever:
%~ (((" ?H1 leftof ?H2 " is necessarily true and
%~ by default ?H2 exists(H3,exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))))) ) and
%~ by default ?H3 exists(H4,exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5)))) ) and
%~ by default ?H4 exists(H5,((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))) ) and
%~ by default ?H5 ((nesc(leftof(H1,H2))&nesc(leftof(H2,H3)))&nesc(leftof(H3,H4)))&nesc(leftof(H4,H5))
%~ It's Proof that:
%~ " ?H2 leftof ?H3 " is necessarily true
%~
%~ %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
( ( nesc( leftof(H1,H2)) &
'$existential'( H2,
1,
exists( H3,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))))) &
'$existential'( H3,
1,
exists( H4,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5)))))) &
'$existential'( H4,
1,
exists( H5,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) &
'$existential'( H5,
1,
( nesc( leftof(H1,H2)) &
nesc( leftof(H2,H3)) &
nesc( leftof(H3,H4)) &
nesc( leftof(H4,H5))))) ==>
nesc( leftof(H2,H3))).
~*/
%~ /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/logicmoo_base/t/examples/fol/fiveof/five_leftof_up_down_02.pl:28
%~ unused(no_junit_results)
%~ test_completed_exit(0)
```
totalTime=3.000
FAILED: /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-junit-minor -k five_leftof_up_down_02.pl (returned 0) Add_LABELS='' Rem_LABELS='Skipped,Skipped,Errors,Warnings,Overtime,Skipped,Skipped'
| test | logicmoo base fol fiveof five leftof up down junit cd var lib jenkins workspace logicmoo workspace packs sys logicmoo base t examples fol fiveof timeout foreground preserve status s sigkill k swipl x var lib jenkins workspace logicmoo workspace bin lmoo clif five leftof up down pl issue edit jenkins issue search init phase after load init phase restore state running var lib jenkins workspace logicmoo workspace packs sys logicmoo base t examples fol fiveof five leftof up down pl this test might need expects dialect pfc this test might need use module library logicmoo plarkc file mpred builtin pfc purpose agent reactivity for swi prolog maintainer douglas miles contact author dmiles users sourceforge net version interface revision revision revised at date expects dialect clif set prolog flag gc false there are five houses in a row there are five houses in a row exists exists exists exists exists leftof leftof leftof leftof issue edit jenkins issue search debugm basekb show success basekb basekb ain clif exists exists exists exists exists leftof leftof leftof leftof kifi exists exists leftof exists exists exists exists exists exists exists leftof exists leftof exists leftof exists exists leftof exists exists leftof exists kifm exists exists leftof exists exists exists exists exists exists exists nesc leftof exists leftof exists leftof exists exists leftof exists exists leftof exists var lib jenkins workspace logicmoo workspace packs sys logicmoo base t examples fol fiveof five leftof up down pl kifi exists exists exists exists exists leftof leftof leftof leftof kifm exists exists exists exists exists nesc leftof leftof leftof leftof exists var exists leftof exists var exists exists var exists exists var exists exists var leftof var exists leftof var exists leftof var exists var exists leftof var exists var exists leftof var exists var kif to boxlog exists exists leftof exists exists exists exists exists exists exists leftof exists leftof exists leftof exists exists leftof exists exists leftof exists in english there exists exists leftof there exists exists there exists exists there exists exists there exists exists leftof leftof exists and exists leftof exists and exists leftof exists and exists leftof kifi exists exists leftof exists exists exists exists exists exists exists leftof exists leftof exists leftof exists exists leftof exists exists leftof exists kifm exists exists leftof exists exists exists exists exists exists exists nesc leftof exists leftof exists leftof exists exists leftof exists exists leftof exists kif to boxlog exists var exists leftof exists var exists exists var exists exists var exists exists var necessary and and and leftof var exists leftof var exists leftof var exists var exists leftof var exists var exists leftof var exists var results in the following entailment s nesc leftof exists leftof exists existential exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists nesc leftof exists exists poss leftof exists leftof exists existential exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists poss leftof exists exists nesc leftof exists exists existential exists leftof exists exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists nesc leftof exists leftof exists poss leftof exists exists existential exists leftof exists exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists poss leftof exists leftof exists existential exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists nesc leftof exists exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists nesc leftof exists whenever exists leftof leftof exists is necessarily true and by default exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists it s proof that exists leftof exists is necessarily true nesc leftof exists leftof exists existential exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists nesc leftof exists exists and whenever exists leftof leftof exists is possibly false and by default exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists it s proof that exists leftof exists is possibly false poss leftof exists leftof exists existential exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists poss leftof exists exists and whenever exists leftof exists is necessarily true and by default exists leftof exists exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists it s proof that exists leftof leftof exists is necessarily true nesc leftof exists exists existential exists leftof exists exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists nesc leftof exists leftof exists and whenever exists leftof exists is possibly false and by default exists leftof exists exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists it s proof that exists leftof leftof exists is possibly false poss leftof exists exists existential exists leftof exists exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists poss leftof exists leftof exists and whenever by default exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists it s proof that exists leftof exists is necessarily true existential exists exists exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists nesc leftof exists exists and whenever by default exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists and by default nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists it s proof that exists leftof is necessarily true existential exists exists nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists existential nesc leftof exists leftof exists nesc leftof exists exists nesc leftof exists exists nesc leftof exists nesc leftof exists kifi exists exists exists exists exists leftof leftof leftof leftof kifm exists exists exists exists exists nesc leftof leftof leftof leftof kif to boxlog exists var exists var exists var exists var exists var necessary and and and leftof var var leftof var var leftof var var leftof var var whenever by default exists nesc leftof nesc leftof nesc leftof nesc leftof and by default nesc leftof nesc leftof nesc leftof nesc leftof it s proof that leftof is necessarily true existential exists nesc leftof nesc leftof nesc leftof nesc leftof existential nesc leftof nesc leftof nesc leftof nesc leftof nesc leftof and whenever by default exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists nesc leftof nesc leftof nesc leftof nesc leftof and by default nesc leftof nesc leftof nesc leftof nesc leftof it s proof that leftof is necessarily true existential exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists nesc leftof nesc leftof nesc leftof nesc leftof existential nesc leftof nesc leftof nesc leftof nesc leftof nesc leftof and whenever leftof is possibly false and by default exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists nesc leftof nesc leftof nesc leftof nesc leftof and by default nesc leftof nesc leftof nesc leftof nesc leftof it s proof that leftof is possibly false poss leftof existential exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists nesc leftof nesc leftof nesc leftof nesc leftof existential nesc leftof nesc leftof nesc leftof nesc leftof poss leftof and whenever leftof is necessarily true and by default exists exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists nesc leftof nesc leftof nesc leftof nesc leftof and by default nesc leftof nesc leftof nesc leftof nesc leftof it s proof that leftof is necessarily true nesc leftof existential exists exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists nesc leftof nesc leftof nesc leftof nesc leftof existential nesc leftof nesc leftof nesc leftof nesc leftof nesc leftof and whenever leftof is possibly false and by default exists exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists nesc leftof nesc leftof nesc leftof nesc leftof and by default nesc leftof nesc leftof nesc leftof nesc leftof it s proof that leftof is possibly false poss leftof existential exists exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists nesc leftof nesc leftof nesc leftof nesc leftof existential nesc leftof nesc leftof nesc leftof nesc leftof poss leftof and whenever leftof is necessarily true and by default exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists exists nesc leftof nesc leftof nesc leftof nesc leftof and by default exists nesc leftof nesc leftof nesc leftof nesc leftof and by default nesc leftof nesc leftof nesc leftof nesc leftof it s proof that leftof is necessarily true nesc leftof existential exists exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists exists nesc leftof nesc leftof nesc leftof nesc leftof existential exists nesc leftof nesc leftof nesc leftof nesc leftof existential nesc leftof nesc leftof nesc leftof nesc leftof nesc leftof var lib jenkins workspace logicmoo workspace packs sys logicmoo base t examples fol fiveof five leftof up down pl unused no junit results test completed exit totaltime failed var lib jenkins workspace logicmoo workspace bin lmoo junit minor k five leftof up down pl returned add labels rem labels skipped skipped errors warnings overtime skipped skipped | 1 |
724,885 | 24,944,253,170 | IssuesEvent | 2022-10-31 21:55:07 | bounswe/bounswe2022group4 | https://api.github.com/repos/bounswe/bounswe2022group4 | closed | Frontend: Make research on React function based component and React hooks | Priority - Medium Category - Research whom: individual Difficulty - Medium Language - React.js | I need to watch some tutorials and read documentation of React in order to understand function based component and hooks in React. | 1.0 | Frontend: Make research on React function based component and React hooks - I need to watch some tutorials and read documentation of React in order to understand function based component and hooks in React. | non_test | frontend make research on react function based component and react hooks i need to watch some tutorials and read documentation of react in order to understand function based component and hooks in react | 0 |
22,012 | 4,764,272,711 | IssuesEvent | 2016-10-25 16:31:43 | mapbox/mapbox-gl-style-spec | https://api.github.com/repos/mapbox/mapbox-gl-style-spec | opened | Document URL template tokens and schemes | documentation | TileJSON URL templates may use several different tokens and either of two schemes. We should document these and provide a SDK support table
## Schemes
- `tms`
- `xyz`
## URL Template Tokens
- `{quadkey}`
- `{bbox-epsg-3857}`
- `{x}`, `{y}`, `{z}`
- `{prefix}` | 1.0 | Document URL template tokens and schemes - TileJSON URL templates may use several different tokens and either of two schemes. We should document these and provide a SDK support table
## Schemes
- `tms`
- `xyz`
## URL Template Tokens
- `{quadkey}`
- `{bbox-epsg-3857}`
- `{x}`, `{y}`, `{z}`
- `{prefix}` | non_test | document url template tokens and schemes tilejson url templates may use several different tokens and either of two schemes we should document these and provide a sdk support table schemes tms xyz url template tokens quadkey bbox epsg x y z prefix | 0 |
5,828 | 8,285,735,991 | IssuesEvent | 2018-09-19 00:39:53 | TheIllusiveC4/Consecration | https://api.github.com/repos/TheIllusiveC4/Consecration | closed | (Compatibility) Buggy Interaction with EvilCraft's Vengeance Spirits | compatibility | A compatibility issue with EvilCraft and this mod arises with the former's Vengeance Spirits. In order to progress at later points in EvilCraft, you need to use a specific item to kill them, and they cannot be killed in any other way. However, Consecration doesn't allow that, as Vengeance Spirits are classed as undead mobs, and they can technically only be killed by holy items, which cannot be done as they can only be affected by the special EvilCraft item.
The simplest way to fix this would be to blacklist Vengeance Spirits as undead mobs. | True | (Compatibility) Buggy Interaction with EvilCraft's Vengeance Spirits - A compatibility issue with EvilCraft and this mod arises with the former's Vengeance Spirits. In order to progress at later points in EvilCraft, you need to use a specific item to kill them, and they cannot be killed in any other way. However, Consecration doesn't allow that, as Vengeance Spirits are classed as undead mobs, and they can technically only be killed by holy items, which cannot be done as they can only be affected by the special EvilCraft item.
The simplest way to fix this would be to blacklist Vengeance Spirits as undead mobs. | non_test | compatibility buggy interaction with evilcraft s vengeance spirits a compatibility issue with evilcraft and this mod arises with the former s vengeance spirits in order to progress at later points in evilcraft you need to use a specific item to kill them and they cannot be killed in any other way however consecration doesn t allow that as vengeance spirits are classed as undead mobs and they can technically only be killed by holy items which cannot be done as they can only be affected by the special evilcraft item the simplest way to fix this would be to blacklist vengeance spirits as undead mobs | 0 |
224,339 | 17,689,687,448 | IssuesEvent | 2021-08-24 08:25:35 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | closed | Intermittent UI test failure - StrictEnhancedTrackingProtectionTest#testStrictVisitContentShield, testStrictVisitDisableExceptionToggle, testStrictVisitSheetDetails | eng:intermittent-test eng:ui-test | ### Firebase Test Run:
Flaky, failed 1 out of 2 runs
https://console.firebase.google.com/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/6588865899882511274/executions/bs.a522f80d838f1ed2/testcases/3/test-cases
### Stacktrace:
```
androidx.test.espresso.NoMatchingViewException: No views in hierarchy found matching: with id: org.mozilla.fenix.debug:id/mozac_browser_toolbar_menu
at dalvik.system.VMStack.getThreadStackTrace(Native Method)
at java.lang.Thread.getStackTrace(Thread.java:1538)
at androidx.test.espresso.base.DefaultFailureHandler.getUserFriendlyError(DefaultFailureHandler.java:16)
at androidx.test.espresso.base.DefaultFailureHandler.handle(DefaultFailureHandler.java:36)
at androidx.test.espresso.ViewInteraction.waitForAndHandleInteractionResults(ViewInteraction.java:106)
at androidx.test.espresso.ViewInteraction.desugaredPerform(ViewInteraction.java:43)
at androidx.test.espresso.ViewInteraction.perform(ViewInteraction.java:94)
at org.mozilla.fenix.helpers.ViewInteractionKt.click(ViewInteraction.kt:18)
at org.mozilla.fenix.ui.robots.NavigationToolbarRobot$Transition.openThreeDotMenu(NavigationToolbarRobot.kt:181)
at org.mozilla.fenix.ui.robots.NavigationToolbarRobot$Transition.openTrackingProtectionTestPage(NavigationToolbarRobot.kt:133)
at org.mozilla.fenix.ui.StrictEnhancedTrackingProtectionTest.testStrictVisitContentShield(StrictEnhancedTrackingProtectionTest.kt:99)
```
### Build:
Master 4/1
commit: [AC 75.0.20210401143103 update](https://github.com/mozilla-mobile/fenix/commit/21c5eba31061598816aef7338898ed3e16dd918d)
| 2.0 | Intermittent UI test failure - StrictEnhancedTrackingProtectionTest#testStrictVisitContentShield, testStrictVisitDisableExceptionToggle, testStrictVisitSheetDetails - ### Firebase Test Run:
Flaky, failed 1 out of 2 runs
https://console.firebase.google.com/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/6588865899882511274/executions/bs.a522f80d838f1ed2/testcases/3/test-cases
### Stacktrace:
```
androidx.test.espresso.NoMatchingViewException: No views in hierarchy found matching: with id: org.mozilla.fenix.debug:id/mozac_browser_toolbar_menu
at dalvik.system.VMStack.getThreadStackTrace(Native Method)
at java.lang.Thread.getStackTrace(Thread.java:1538)
at androidx.test.espresso.base.DefaultFailureHandler.getUserFriendlyError(DefaultFailureHandler.java:16)
at androidx.test.espresso.base.DefaultFailureHandler.handle(DefaultFailureHandler.java:36)
at androidx.test.espresso.ViewInteraction.waitForAndHandleInteractionResults(ViewInteraction.java:106)
at androidx.test.espresso.ViewInteraction.desugaredPerform(ViewInteraction.java:43)
at androidx.test.espresso.ViewInteraction.perform(ViewInteraction.java:94)
at org.mozilla.fenix.helpers.ViewInteractionKt.click(ViewInteraction.kt:18)
at org.mozilla.fenix.ui.robots.NavigationToolbarRobot$Transition.openThreeDotMenu(NavigationToolbarRobot.kt:181)
at org.mozilla.fenix.ui.robots.NavigationToolbarRobot$Transition.openTrackingProtectionTestPage(NavigationToolbarRobot.kt:133)
at org.mozilla.fenix.ui.StrictEnhancedTrackingProtectionTest.testStrictVisitContentShield(StrictEnhancedTrackingProtectionTest.kt:99)
```
### Build:
Master 4/1
commit: [AC 75.0.20210401143103 update](https://github.com/mozilla-mobile/fenix/commit/21c5eba31061598816aef7338898ed3e16dd918d)
| test | intermittent ui test failure strictenhancedtrackingprotectiontest teststrictvisitcontentshield teststrictvisitdisableexceptiontoggle teststrictvisitsheetdetails firebase test run flaky failed out of runs stacktrace androidx test espresso nomatchingviewexception no views in hierarchy found matching with id org mozilla fenix debug id mozac browser toolbar menu at dalvik system vmstack getthreadstacktrace native method at java lang thread getstacktrace thread java at androidx test espresso base defaultfailurehandler getuserfriendlyerror defaultfailurehandler java at androidx test espresso base defaultfailurehandler handle defaultfailurehandler java at androidx test espresso viewinteraction waitforandhandleinteractionresults viewinteraction java at androidx test espresso viewinteraction desugaredperform viewinteraction java at androidx test espresso viewinteraction perform viewinteraction java at org mozilla fenix helpers viewinteractionkt click viewinteraction kt at org mozilla fenix ui robots navigationtoolbarrobot transition openthreedotmenu navigationtoolbarrobot kt at org mozilla fenix ui robots navigationtoolbarrobot transition opentrackingprotectiontestpage navigationtoolbarrobot kt at org mozilla fenix ui strictenhancedtrackingprotectiontest teststrictvisitcontentshield strictenhancedtrackingprotectiontest kt build master commit | 1 |
789,104 | 27,778,406,371 | IssuesEvent | 2023-03-16 18:59:07 | learnspigot/discord-bot | https://api.github.com/repos/learnspigot/discord-bot | closed | Make message sent in #suggestions automatically convert to a suggestion | enhancement good first issue low priority | Seen this on another server. Was much cleaner than doing /suggest (which nobody knows exists).
Yes there will be some we have to delete due to people not realizing. Much better alternative than people not suggesting.
| 1.0 | Make message sent in #suggestions automatically convert to a suggestion - Seen this on another server. Was much cleaner than doing /suggest (which nobody knows exists).
Yes there will be some we have to delete due to people not realizing. Much better alternative than people not suggesting.
| non_test | make message sent in suggestions automatically convert to a suggestion seen this on another server was much cleaner than doing suggest which nobody knows exists yes there will be some we have to delete due to people not realizing much better alternative than people not suggesting | 0 |
49,638 | 6,035,595,796 | IssuesEvent | 2017-06-09 14:15:42 | IronLanguages/main | https://api.github.com/repos/IronLanguages/main | closed | Re-enable test_coverage in test_file.py once debugged on Linux | mono Test Failure | This test may rely on Windows file endings in some spots. | 1.0 | Re-enable test_coverage in test_file.py once debugged on Linux - This test may rely on Windows file endings in some spots. | test | re enable test coverage in test file py once debugged on linux this test may rely on windows file endings in some spots | 1 |
685,250 | 23,449,419,077 | IssuesEvent | 2022-08-15 23:58:20 | Alluxio/alluxio | https://api.github.com/repos/Alluxio/alluxio | closed | Fuse open file before finish releasing it | priority-medium area-fuse type-bug | **Alluxio Version:**
master
**Describe the bug**
In FIO verification process, after the file is done writing and during release(), another thread comes in and opens it for reading. The new thread fails getting data.
```
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Enter: Fuse.Write(path=/x.0.0,fd=30,size=4096,offset=1044480)
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Exit (4096): Fuse.Write(path=/x.0.0,fd=30,size=4096,offset=1044480) in 0 ms
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Enter: Fuse.Flush(path=/x.0.0,fd=30)
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Exit (0): Fuse.Flush(path=/x.0.0,fd=30) in 0 ms
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Enter: Fuse.Release(path=/x.0.0,fd=30)
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Enter: Fuse.Open(path=/x.0.0,flags=0xc002)
2022-07-21 21:29:33,843 DEBUG AlluxioJniFuseFileSystem - Exit (0): Fuse.Open(path=/x.0.0,flags=0xc002) in 1 ms
2022-07-21 21:29:33,844 DEBUG AlluxioJniFuseFileSystem - Enter: Fuse.Read(path=/x.0.0,fd=31,size=4096,offset=0)
2022-07-21 21:29:33,868 DEBUG AlluxioJniFuseFileSystem - Exit (0): Fuse.Release(path=/x.0.0,fd=30) in 26 ms
2022-07-21 21:29:33,870 DEBUG AlluxioJniFuseFileSystem - Exit (0): Fuse.Read(path=/x.0.0,fd=31,size=4096,offset=0) in 26 ms
```
**Reproduce**
Executing following command against AlluxioFuse mount point:
`fio --name=verify --size=1m --rw=write --verify=md5 --direct=1`
**Expected behavior**
Open() happens after the release() is done so the data can be read.
| 1.0 | Fuse open file before finish releasing it - **Alluxio Version:**
master
**Describe the bug**
In FIO verification process, after the file is done writing and during release(), another thread comes in and opens it for reading. The new thread fails getting data.
```
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Enter: Fuse.Write(path=/x.0.0,fd=30,size=4096,offset=1044480)
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Exit (4096): Fuse.Write(path=/x.0.0,fd=30,size=4096,offset=1044480) in 0 ms
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Enter: Fuse.Flush(path=/x.0.0,fd=30)
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Exit (0): Fuse.Flush(path=/x.0.0,fd=30) in 0 ms
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Enter: Fuse.Release(path=/x.0.0,fd=30)
2022-07-21 21:29:33,842 DEBUG AlluxioJniFuseFileSystem - Enter: Fuse.Open(path=/x.0.0,flags=0xc002)
2022-07-21 21:29:33,843 DEBUG AlluxioJniFuseFileSystem - Exit (0): Fuse.Open(path=/x.0.0,flags=0xc002) in 1 ms
2022-07-21 21:29:33,844 DEBUG AlluxioJniFuseFileSystem - Enter: Fuse.Read(path=/x.0.0,fd=31,size=4096,offset=0)
2022-07-21 21:29:33,868 DEBUG AlluxioJniFuseFileSystem - Exit (0): Fuse.Release(path=/x.0.0,fd=30) in 26 ms
2022-07-21 21:29:33,870 DEBUG AlluxioJniFuseFileSystem - Exit (0): Fuse.Read(path=/x.0.0,fd=31,size=4096,offset=0) in 26 ms
```
**Reproduce**
Executing following command against AlluxioFuse mount point:
`fio --name=verify --size=1m --rw=write --verify=md5 --direct=1`
**Expected behavior**
Open() happens after the release() is done so the data can be read.
| non_test | fuse open file before finish releasing it alluxio version master describe the bug in fio verification process after the file is done writing and during release another thread comes in and opens it for reading the new thread fails getting data debug alluxiojnifusefilesystem enter fuse write path x fd size offset debug alluxiojnifusefilesystem exit fuse write path x fd size offset in ms debug alluxiojnifusefilesystem enter fuse flush path x fd debug alluxiojnifusefilesystem exit fuse flush path x fd in ms debug alluxiojnifusefilesystem enter fuse release path x fd debug alluxiojnifusefilesystem enter fuse open path x flags debug alluxiojnifusefilesystem exit fuse open path x flags in ms debug alluxiojnifusefilesystem enter fuse read path x fd size offset debug alluxiojnifusefilesystem exit fuse release path x fd in ms debug alluxiojnifusefilesystem exit fuse read path x fd size offset in ms reproduce executing following command against alluxiofuse mount point fio name verify size rw write verify direct expected behavior open happens after the release is done so the data can be read | 0 |
175,548 | 21,313,849,916 | IssuesEvent | 2022-04-16 01:09:17 | Nivaskumark/kernel_v4.1.15 | https://api.github.com/repos/Nivaskumark/kernel_v4.1.15 | opened | CVE-2015-7566 (Medium) detected in linuxlinux-4.6 | security vulnerability | ## CVE-2015-7566 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/serial/visor.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/serial/visor.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The clie_5_attach function in drivers/usb/serial/visor.c in the Linux kernel through 4.4.1 allows physically proximate attackers to cause a denial of service (NULL pointer dereference and system crash) or possibly have unspecified other impact by inserting a USB device that lacks a bulk-out endpoint.
<p>Publish Date: 2016-02-08
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-7566>CVE-2015-7566</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2015-7566">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2015-7566</a></p>
<p>Release Date: 2016-02-08</p>
<p>Fix Resolution: v4.5-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2015-7566 (Medium) detected in linuxlinux-4.6 - ## CVE-2015-7566 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/serial/visor.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/serial/visor.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The clie_5_attach function in drivers/usb/serial/visor.c in the Linux kernel through 4.4.1 allows physically proximate attackers to cause a denial of service (NULL pointer dereference and system crash) or possibly have unspecified other impact by inserting a USB device that lacks a bulk-out endpoint.
<p>Publish Date: 2016-02-08
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-7566>CVE-2015-7566</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2015-7566">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2015-7566</a></p>
<p>Release Date: 2016-02-08</p>
<p>Fix Resolution: v4.5-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch master vulnerable source files drivers usb serial visor c drivers usb serial visor c vulnerability details the clie attach function in drivers usb serial visor c in the linux kernel through allows physically proximate attackers to cause a denial of service null pointer dereference and system crash or possibly have unspecified other impact by inserting a usb device that lacks a bulk out endpoint publish date url a href cvss score details base score metrics exploitability metrics attack vector physical attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
134,742 | 5,233,499,115 | IssuesEvent | 2017-01-30 13:07:18 | google/grr | https://api.github.com/repos/google/grr | closed | Add Hunt Description to Hunt Overview | enhancement Priority-Low | Currently the hunt description is not added to the hunt overview pane, and is only visible in the manager list.
| 1.0 | Add Hunt Description to Hunt Overview - Currently the hunt description is not added to the hunt overview pane, and is only visible in the manager list.
| non_test | add hunt description to hunt overview currently the hunt description is not added to the hunt overview pane and is only visible in the manager list | 0 |
295,629 | 25,490,092,374 | IssuesEvent | 2022-11-27 00:03:57 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | [Flaky Test] should respect default content | [Status] Stale [Type] Flaky Test | <!-- __META_DATA__:{} -->
**Flaky test detected. This is an auto-generated issue by GitHub Actions. Please do NOT edit this manually.**
## Test title
should respect default content
## Test path
`/test/e2e/specs/editor/various/new-post-default-content.spec.js`
## Errors
<!-- __TEST_RESULTS_LIST__ -->
<!-- __TEST_RESULT__ --><time datetime="2022-06-09T07:15:49.068Z"><code>[2022-06-09T07:15:49.068Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/2466505520"><code>fix/accessibility-template-buttons</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2022-06-16T03:07:48.815Z"><code>[2022-06-16T03:07:48.815Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/2506275525"><code>update/post-publish-date-abbreviation</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2022-06-23T12:32:09.305Z"><code>[2022-06-23T12:32:09.305Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/2548940833"><code>cover-block-insert-from-url-support</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2022-10-25T08:42:21.801Z"><code>[2022-10-25T08:42:21.801Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/3319166579"><code>add/new-post-default-content-test</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><details>
<summary>
<time datetime="2022-10-25T11:20:51.287Z"><code>[2022-10-25T11:20:51.287Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/3320242691"><code>add/new-post-default-content-test</code></a>.
</summary>
```
page.click: Timeout 10000ms exceeded.
=========================== logs ===========================
waiting for selector "role=button[name="Excerpt"i]"
============================================================
at /home/runner/work/gutenberg/gutenberg/test/e2e/specs/editor/various/new-post-default-content.spec.js:26:14
at /home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/workerRunner.js:426:9
at TestInfoImpl._runFn (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/testInfo.js:166:7)
at /home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/workerRunner.js:376:26
at TimeoutManager.runWithTimeout (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/timeoutManager.js:73:7)
at TestInfoImpl._runWithTimeout (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/testInfo.js:154:26)
at WorkerRunner._runTest (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/workerRunner.js:356:5)
at WorkerRunner.runTestGroup (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/workerRunner.js:218:11)
at process.<anonymous> (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/worker.js:88:5)
```
</details><!-- /__TEST_RESULT__ -->
<!-- /__TEST_RESULTS_LIST__ -->
| 1.0 | [Flaky Test] should respect default content - <!-- __META_DATA__:{} -->
**Flaky test detected. This is an auto-generated issue by GitHub Actions. Please do NOT edit this manually.**
## Test title
should respect default content
## Test path
`/test/e2e/specs/editor/various/new-post-default-content.spec.js`
## Errors
<!-- __TEST_RESULTS_LIST__ -->
<!-- __TEST_RESULT__ --><time datetime="2022-06-09T07:15:49.068Z"><code>[2022-06-09T07:15:49.068Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/2466505520"><code>fix/accessibility-template-buttons</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2022-06-16T03:07:48.815Z"><code>[2022-06-16T03:07:48.815Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/2506275525"><code>update/post-publish-date-abbreviation</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2022-06-23T12:32:09.305Z"><code>[2022-06-23T12:32:09.305Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/2548940833"><code>cover-block-insert-from-url-support</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2022-10-25T08:42:21.801Z"><code>[2022-10-25T08:42:21.801Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/3319166579"><code>add/new-post-default-content-test</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><details>
<summary>
<time datetime="2022-10-25T11:20:51.287Z"><code>[2022-10-25T11:20:51.287Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/3320242691"><code>add/new-post-default-content-test</code></a>.
</summary>
```
page.click: Timeout 10000ms exceeded.
=========================== logs ===========================
waiting for selector "role=button[name="Excerpt"i]"
============================================================
at /home/runner/work/gutenberg/gutenberg/test/e2e/specs/editor/various/new-post-default-content.spec.js:26:14
at /home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/workerRunner.js:426:9
at TestInfoImpl._runFn (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/testInfo.js:166:7)
at /home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/workerRunner.js:376:26
at TimeoutManager.runWithTimeout (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/timeoutManager.js:73:7)
at TestInfoImpl._runWithTimeout (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/testInfo.js:154:26)
at WorkerRunner._runTest (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/workerRunner.js:356:5)
at WorkerRunner.runTestGroup (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/workerRunner.js:218:11)
at process.<anonymous> (/home/runner/work/gutenberg/gutenberg/node_modules/@playwright/test/lib/worker.js:88:5)
```
</details><!-- /__TEST_RESULT__ -->
<!-- /__TEST_RESULTS_LIST__ -->
| test | should respect default content flaky test detected this is an auto generated issue by github actions please do not edit this manually test title should respect default content test path test specs editor various new post default content spec js errors test passed after failed attempt on test passed after failed attempt on test passed after failed attempt on test passed after failed attempt on test passed after failed attempt on a href page click timeout exceeded logs waiting for selector role button at home runner work gutenberg gutenberg test specs editor various new post default content spec js at home runner work gutenberg gutenberg node modules playwright test lib workerrunner js at testinfoimpl runfn home runner work gutenberg gutenberg node modules playwright test lib testinfo js at home runner work gutenberg gutenberg node modules playwright test lib workerrunner js at timeoutmanager runwithtimeout home runner work gutenberg gutenberg node modules playwright test lib timeoutmanager js at testinfoimpl runwithtimeout home runner work gutenberg gutenberg node modules playwright test lib testinfo js at workerrunner runtest home runner work gutenberg gutenberg node modules playwright test lib workerrunner js at workerrunner runtestgroup home runner work gutenberg gutenberg node modules playwright test lib workerrunner js at process home runner work gutenberg gutenberg node modules playwright test lib worker js | 1 |
345,336 | 10,361,305,823 | IssuesEvent | 2019-09-06 09:42:29 | jenkins-x/jx | https://api.github.com/repos/jenkins-x/jx | closed | external-dns integration | area/integrations kind/enhancement priority/backlog | [external-dns](https://github.com/kubernetes-incubator/external-dns) provides configurable dns management with multiple providers:
```
Google CloudDNS
AWS Route 53
AWS Service Discovery
AzureDNS
CloudFlare
DigitalOcean
DNSimple
Infoblox
Dyn
OpenStack Designate
PowerDNS
```
It would be great to have JX giving the option to install it. | 1.0 | external-dns integration - [external-dns](https://github.com/kubernetes-incubator/external-dns) provides configurable dns management with multiple providers:
```
Google CloudDNS
AWS Route 53
AWS Service Discovery
AzureDNS
CloudFlare
DigitalOcean
DNSimple
Infoblox
Dyn
OpenStack Designate
PowerDNS
```
It would be great to have JX giving the option to install it. | non_test | external dns integration provides configurable dns management with multiple providers google clouddns aws route aws service discovery azuredns cloudflare digitalocean dnsimple infoblox dyn openstack designate powerdns it would be great to have jx giving the option to install it | 0 |
86,186 | 10,726,964,614 | IssuesEvent | 2019-10-28 10:33:28 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | closed | Add "Esc" keyboard shortcut to dismiss things | *as-designed needs more info | This is a specific example, but one of the things that I found very annoying in general with vs code and also with web apps in general, but something that true desktop apps seem to just get right every time:
In sublime text, pressing ctrl+shift+f open the "view files". But, you can get out of there by pressing "Esc". This is not specific to the "view files" command. In general, it feels like you can get out or close things with "Esc".
On vs code... nothing happens.
| 1.0 | Add "Esc" keyboard shortcut to dismiss things - This is a specific example, but one of the things that I found very annoying in general with vs code and also with web apps in general, but something that true desktop apps seem to just get right every time:
In sublime text, pressing ctrl+shift+f open the "view files". But, you can get out of there by pressing "Esc". This is not specific to the "view files" command. In general, it feels like you can get out or close things with "Esc".
On vs code... nothing happens.
| non_test | add esc keyboard shortcut to dismiss things this is a specific example but one of the things that i found very annoying in general with vs code and also with web apps in general but something that true desktop apps seem to just get right every time in sublime text pressing ctrl shift f open the view files but you can get out of there by pressing esc this is not specific to the view files command in general it feels like you can get out or close things with esc on vs code nothing happens | 0 |
115,191 | 11,867,943,749 | IssuesEvent | 2020-03-26 08:12:11 | telerik/kendo-ui-core | https://api.github.com/repos/telerik/kendo-ui-core | closed | KB example "Include SelectAll for Grid Column Sections in ColumnMenu" is no longer working | C: Grid Documentation Kendo1 | ### KB dojo example needs an update
Ticket ID: 1458912
KB article: [Include SelectAll for Grid Column Sections in ColumnMenu](https://docs.telerik.com/kendo-ui/knowledge-base/grid-include-selectall-in-columnmenu)
### Reproduction of the problem
From Kendo UI 2018 R3 until Kendo UI 2019 R3 SP1 including the column checkbox "SelectAll" in ColumnMenu is positioned at the bottom of the Columns section.
From Kendo UI 2020 R1 till the latest versions Columns and Filters sections in ColumnMenu are no longer accessible. If sorting is applied the ColumnMenu does not appear anymore.
### Expected/desired behavior
The functionality from version Kendo UI 2018 R2 SP1 - [https://dojo.telerik.com/@Silvia/udiSOtEh](https://dojo.telerik.com/@Silvia/udiSOtEh)
| 1.0 | KB example "Include SelectAll for Grid Column Sections in ColumnMenu" is no longer working - ### KB dojo example needs an update
Ticket ID: 1458912
KB article: [Include SelectAll for Grid Column Sections in ColumnMenu](https://docs.telerik.com/kendo-ui/knowledge-base/grid-include-selectall-in-columnmenu)
### Reproduction of the problem
From Kendo UI 2018 R3 until Kendo UI 2019 R3 SP1 including the column checkbox "SelectAll" in ColumnMenu is positioned at the bottom of the Columns section.
From Kendo UI 2020 R1 till the latest versions Columns and Filters sections in ColumnMenu are no longer accessible. If sorting is applied the ColumnMenu does not appear anymore.
### Expected/desired behavior
The functionality from version Kendo UI 2018 R2 SP1 - [https://dojo.telerik.com/@Silvia/udiSOtEh](https://dojo.telerik.com/@Silvia/udiSOtEh)
| non_test | kb example include selectall for grid column sections in columnmenu is no longer working kb dojo example needs an update ticket id kb article reproduction of the problem from kendo ui until kendo ui including the column checkbox selectall in columnmenu is positioned at the bottom of the columns section from kendo ui till the latest versions columns and filters sections in columnmenu are no longer accessible if sorting is applied the columnmenu does not appear anymore expected desired behavior the functionality from version kendo ui | 0 |
146,241 | 13,174,556,663 | IssuesEvent | 2020-08-11 22:48:50 | dagster-io/dagster | https://api.github.com/repos/dagster-io/dagster | closed | Documentation on "Data Science with Notebooks" needs updating | documentation | I'm exploring dagsters functionality within the data science workflow and I've come across a few issues.
1) I can not reach this [guide]( https://docs.dagster.io/learn/guides/data_science/data_science) from your home page. I was only able to find it through a google search. In fact there appear to be a few guides under https://docs.dagster.io/learn/guides/ which appear very useful but I couldn't figure out how to reach them from your homepage.
2) Within the data science guide, you import `dagster_examples` but I'm unable to find a way to install this package. Has this been depricated? If this is the case, where can I find a guide for using dagster with notebooks within a data science workflow? | 1.0 | Documentation on "Data Science with Notebooks" needs updating - I'm exploring dagsters functionality within the data science workflow and I've come across a few issues.
1) I can not reach this [guide]( https://docs.dagster.io/learn/guides/data_science/data_science) from your home page. I was only able to find it through a google search. In fact there appear to be a few guides under https://docs.dagster.io/learn/guides/ which appear very useful but I couldn't figure out how to reach them from your homepage.
2) Within the data science guide, you import `dagster_examples` but I'm unable to find a way to install this package. Has this been depricated? If this is the case, where can I find a guide for using dagster with notebooks within a data science workflow? | non_test | documentation on data science with notebooks needs updating i m exploring dagsters functionality within the data science workflow and i ve come across a few issues i can not reach this from your home page i was only able to find it through a google search in fact there appear to be a few guides under which appear very useful but i couldn t figure out how to reach them from your homepage within the data science guide you import dagster examples but i m unable to find a way to install this package has this been depricated if this is the case where can i find a guide for using dagster with notebooks within a data science workflow | 0 |
179,322 | 6,623,763,971 | IssuesEvent | 2017-09-22 08:43:33 | ThaumRystra/DiceCloud1 | https://api.github.com/repos/ThaumRystra/DiceCloud1 | closed | Spells added from Library like to delete themselves | bug high priority | After adding multiple spells to a character by selecting multiple boxes from the library, all the spells except the first selected one will slowly remove themselves from the sheet.
https://gyazo.com/1f45f06c3a3ac8eecaf25e5d4e363d10
Character ID: Lk3hAPxq5L3uZJBfY | 1.0 | Spells added from Library like to delete themselves - After adding multiple spells to a character by selecting multiple boxes from the library, all the spells except the first selected one will slowly remove themselves from the sheet.
https://gyazo.com/1f45f06c3a3ac8eecaf25e5d4e363d10
Character ID: Lk3hAPxq5L3uZJBfY | non_test | spells added from library like to delete themselves after adding multiple spells to a character by selecting multiple boxes from the library all the spells except the first selected one will slowly remove themselves from the sheet character id | 0 |
68,175 | 7,088,714,339 | IssuesEvent | 2018-01-11 22:35:41 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | First entering Add Node page, no driver is selected by default | area/machine area/ui kind/bug status/resolved status/to-test version/2.0 | **Rancher versions:** 2.0 master 1/8
**Steps to Reproduce:**
1. Go to Add node page
**Results:** No driver is selected by default the first time you get in.
| 1.0 | First entering Add Node page, no driver is selected by default - **Rancher versions:** 2.0 master 1/8
**Steps to Reproduce:**
1. Go to Add node page
**Results:** No driver is selected by default the first time you get in.
| test | first entering add node page no driver is selected by default rancher versions master steps to reproduce go to add node page results no driver is selected by default the first time you get in | 1 |
283,138 | 30,889,598,980 | IssuesEvent | 2023-08-04 02:58:10 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | reopened | CVE-2019-19807 (High) detected in linux-stable-rtv4.1.33 | Mend: dependency security vulnerability | ## CVE-2019-19807 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel before 5.3.11, sound/core/timer.c has a use-after-free caused by erroneous code refactoring, aka CID-e7af6307a8a5. This is related to snd_timer_open and snd_timer_close_locked. The timeri variable was originally intended to be for a newly created timer instance, but was used for a different purpose after refactoring.
<p>Publish Date: 2019-12-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19807>CVE-2019-19807</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-30</p>
<p>Fix Resolution: v5.4-rc7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-19807 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2019-19807 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel before 5.3.11, sound/core/timer.c has a use-after-free caused by erroneous code refactoring, aka CID-e7af6307a8a5. This is related to snd_timer_open and snd_timer_close_locked. The timeri variable was originally intended to be for a newly created timer instance, but was used for a different purpose after refactoring.
<p>Publish Date: 2019-12-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19807>CVE-2019-19807</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-30</p>
<p>Fix Resolution: v5.4-rc7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details in the linux kernel before sound core timer c has a use after free caused by erroneous code refactoring aka cid this is related to snd timer open and snd timer close locked the timeri variable was originally intended to be for a newly created timer instance but was used for a different purpose after refactoring publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend | 0 |
286,983 | 24,800,334,574 | IssuesEvent | 2022-10-24 21:04:34 | microsoft/vscode-remote-release | https://api.github.com/repos/microsoft/vscode-remote-release | opened | Test: Create Dev Container | containers testplan-item | Refs: #3122
- [ ] anyOS
- [ ] anyOS
Complexity: 4
---
- Requires Dev Containers extension 0.261.0.
- Use `Dev Containers: Create Dev Container...` to create a dev container in a volume (without the need for a local folder or a repository).
- Verify the dev container starts successfully.
- Make some changes.
- Use `Remote: Close Remote Connection` to leave the dev container.
- Verify that you can use the Remote Explorer to open the folder (including any changes you made) again.
| 1.0 | Test: Create Dev Container - Refs: #3122
- [ ] anyOS
- [ ] anyOS
Complexity: 4
---
- Requires Dev Containers extension 0.261.0.
- Use `Dev Containers: Create Dev Container...` to create a dev container in a volume (without the need for a local folder or a repository).
- Verify the dev container starts successfully.
- Make some changes.
- Use `Remote: Close Remote Connection` to leave the dev container.
- Verify that you can use the Remote Explorer to open the folder (including any changes you made) again.
| test | test create dev container refs anyos anyos complexity requires dev containers extension use dev containers create dev container to create a dev container in a volume without the need for a local folder or a repository verify the dev container starts successfully make some changes use remote close remote connection to leave the dev container verify that you can use the remote explorer to open the folder including any changes you made again | 1 |
209,766 | 16,059,327,110 | IssuesEvent | 2021-04-23 10:10:26 | elastic/logstash | https://api.github.com/repos/elastic/logstash | opened | Add integration test to proove also ingestion into Datastram with ECS | test failure | <!--
Please fill out the following information, and ensure you have attempted
to reproduce locally
-->
**Build scan**:
https://logstash-ci.elastic.co/job/elastic+logstash+pull-request+multijob-integration-1/3048/consoleFull
**Repro line**:
```
./gradlew integrationTests -PrubyIntegrationSpecs=specs/es_output_how_spec.rb
```
**Reproduces locally?**:
yes, just run the repro line command and check logs in `build/logstash-8.0.0-SNAPSHOT/logs/logstash-plain.log`
**Applicable branches**:
`master`, but all PR branches
**Failure history**:
<!--
Link to build stats and possible indication of when this started failing and how often it fails
<https://build-stats.elastic.co/app/kibana>
-->
**Failure excerpt**:
```
[2021-04-23T11:58:22,563][WARN ][logstash.outputs.elasticsearch][main][a8e3dc1ef9721fdf6415b66aaa0fbb9ab926b7010b3db5978d169cc43f2fc249] Could not index event to Elasticsearch. {:status=>400, :action=>["create", {:_id=>nil, :_index=>"logs-generic-default", :routing=>nil}, {"host"=>"kalispera", "auth"=>"-", "request"=>"/blog/geekery/disabling-battery-in-ubuntu-vms.html?utm_source=feedburner&utm_medium=feed&utm_campaign=Feed%3A+semicomplete%2Fmain+%28semicomplete.com+-+Jordan+Sissel%29", "bytes"=>9316, "httpversion"=>"1.1", "geoip"=>{"country_code3"=>"US", "timezone"=>"America/Chicago", "country_code2"=>"US", "ip"=>"198.46.149.143", "latitude"=>37.751, "location"=>{"lat"=>37.751, "lon"=>-97.822}, "country_name"=>"United States", "longitude"=>-97.822, "continent_code"=>"NA"}, "@timestamp"=>2014-09-11T21:59:29.000Z, "@version"=>"1", "response"=>200, "referrer"=>"\"-\"", "ident"=>"-", "verb"=>"GET", "message"=>"198.46.149.143 - - [11/Sep/2014:21:59:29 +0000] \"GET /blog/geekery/disabling-battery-in-ubuntu-vms.html?utm_source=feedburner&utm_medium=feed&utm_campaign=Feed%3A+semicomplete%2Fmain+%28semicomplete.com+-+Jordan+Sissel%29 HTTP/1.1\" 200 9316 \"-\" \"Tiny Tiny RSS/1.11 (http://tt-rss.org/)\"", "useragent"=>{"major"=>"1", "build"=>"", "name"=>"Tiny Tiny RSS", "minor"=>"11", "device"=>"Other", "os"=>"Other", "os_name"=>"Other"}, "clientip"=>"198.46.149.143", "agent"=>"\"Tiny Tiny RSS/1.11 (http://tt-rss.org/)\"", "timestamp"=>"11/Sep/2014:21:59:29 +0000", "data_stream"=>{"type"=>"logs", "dataset"=>"generic", "namespace"=>"default"}}], :response=>{"create"=>{"_index"=>".ds-logs-generic-default-2021.04.23-000001", "_id"=>"vUsq_ngBdswJt_MNgxba", "status"=>400, "error"=>{"type"=>"mapper_parsing_exception", "reason"=>"object mapping for [host] tried to parse field [host] as object, but found a concrete value"}}}}
```
----
**Description**
The problem originates from the fact that Elasticsearch 8.0.0 has Datastream and ECS enabled. In the pipeline used by the test https://github.com/elastic/logstash/blob/1e08341e1ea7e269182cd40e70d13bd95bd6e9b2/qa/integration/fixtures/es_output_how_spec.yml#L29-L31 no `index` is specified so on Elasticsearch side a Datastream is created (`.ds-logs-generic-default-2021.04.23-000001`) and any indexing request got 404
```
object mapping for [host] tried to parse field [host] as object, but found a concrete value
```
The issue request to create an integration test like https://github.com/elastic/logstash/blob/1e08341e1ea7e269182cd40e70d13bd95bd6e9b2/qa/integration/specs/es_output_how_spec.rb#L35 that validate also the ingestion in an Elasticsearch 8.0.0 | 1.0 | Add integration test to proove also ingestion into Datastram with ECS - <!--
Please fill out the following information, and ensure you have attempted
to reproduce locally
-->
**Build scan**:
https://logstash-ci.elastic.co/job/elastic+logstash+pull-request+multijob-integration-1/3048/consoleFull
**Repro line**:
```
./gradlew integrationTests -PrubyIntegrationSpecs=specs/es_output_how_spec.rb
```
**Reproduces locally?**:
yes, just run the repro line command and check logs in `build/logstash-8.0.0-SNAPSHOT/logs/logstash-plain.log`
**Applicable branches**:
`master`, but all PR branches
**Failure history**:
<!--
Link to build stats and possible indication of when this started failing and how often it fails
<https://build-stats.elastic.co/app/kibana>
-->
**Failure excerpt**:
```
[2021-04-23T11:58:22,563][WARN ][logstash.outputs.elasticsearch][main][a8e3dc1ef9721fdf6415b66aaa0fbb9ab926b7010b3db5978d169cc43f2fc249] Could not index event to Elasticsearch. {:status=>400, :action=>["create", {:_id=>nil, :_index=>"logs-generic-default", :routing=>nil}, {"host"=>"kalispera", "auth"=>"-", "request"=>"/blog/geekery/disabling-battery-in-ubuntu-vms.html?utm_source=feedburner&utm_medium=feed&utm_campaign=Feed%3A+semicomplete%2Fmain+%28semicomplete.com+-+Jordan+Sissel%29", "bytes"=>9316, "httpversion"=>"1.1", "geoip"=>{"country_code3"=>"US", "timezone"=>"America/Chicago", "country_code2"=>"US", "ip"=>"198.46.149.143", "latitude"=>37.751, "location"=>{"lat"=>37.751, "lon"=>-97.822}, "country_name"=>"United States", "longitude"=>-97.822, "continent_code"=>"NA"}, "@timestamp"=>2014-09-11T21:59:29.000Z, "@version"=>"1", "response"=>200, "referrer"=>"\"-\"", "ident"=>"-", "verb"=>"GET", "message"=>"198.46.149.143 - - [11/Sep/2014:21:59:29 +0000] \"GET /blog/geekery/disabling-battery-in-ubuntu-vms.html?utm_source=feedburner&utm_medium=feed&utm_campaign=Feed%3A+semicomplete%2Fmain+%28semicomplete.com+-+Jordan+Sissel%29 HTTP/1.1\" 200 9316 \"-\" \"Tiny Tiny RSS/1.11 (http://tt-rss.org/)\"", "useragent"=>{"major"=>"1", "build"=>"", "name"=>"Tiny Tiny RSS", "minor"=>"11", "device"=>"Other", "os"=>"Other", "os_name"=>"Other"}, "clientip"=>"198.46.149.143", "agent"=>"\"Tiny Tiny RSS/1.11 (http://tt-rss.org/)\"", "timestamp"=>"11/Sep/2014:21:59:29 +0000", "data_stream"=>{"type"=>"logs", "dataset"=>"generic", "namespace"=>"default"}}], :response=>{"create"=>{"_index"=>".ds-logs-generic-default-2021.04.23-000001", "_id"=>"vUsq_ngBdswJt_MNgxba", "status"=>400, "error"=>{"type"=>"mapper_parsing_exception", "reason"=>"object mapping for [host] tried to parse field [host] as object, but found a concrete value"}}}}
```
----
**Description**
The problem originates from the fact that Elasticsearch 8.0.0 has Datastream and ECS enabled. In the pipeline used by the test https://github.com/elastic/logstash/blob/1e08341e1ea7e269182cd40e70d13bd95bd6e9b2/qa/integration/fixtures/es_output_how_spec.yml#L29-L31 no `index` is specified so on Elasticsearch side a Datastream is created (`.ds-logs-generic-default-2021.04.23-000001`) and any indexing request got 404
```
object mapping for [host] tried to parse field [host] as object, but found a concrete value
```
The issue request to create an integration test like https://github.com/elastic/logstash/blob/1e08341e1ea7e269182cd40e70d13bd95bd6e9b2/qa/integration/specs/es_output_how_spec.rb#L35 that validate also the ingestion in an Elasticsearch 8.0.0 | test | add integration test to proove also ingestion into datastram with ecs please fill out the following information and ensure you have attempted to reproduce locally build scan repro line gradlew integrationtests prubyintegrationspecs specs es output how spec rb reproduces locally yes just run the repro line command and check logs in build logstash snapshot logs logstash plain log applicable branches master but all pr branches failure history link to build stats and possible indication of when this started failing and how often it fails failure excerpt could not index event to elasticsearch status action get blog geekery disabling battery in ubuntu vms html utm source feedburner utm medium feed utm campaign feed semicomplete com jordan sissel http tiny tiny rss useragent major build name tiny tiny rss minor device other os other os name other clientip agent tiny tiny rss timestamp sep data stream type logs dataset generic namespace default response create index ds logs generic default id vusq ngbdswjt mngxba status error type mapper parsing exception reason object mapping for tried to parse field as object but found a concrete value description the problem originates from the fact that elasticsearch has datastream and ecs enabled in the pipeline used by the test no index is specified so on elasticsearch side a datastream is created ds logs generic default and any indexing request got object mapping for tried to parse field as object but found a concrete value the issue request to create an integration test like that validate also the ingestion in an elasticsearch | 1 |
305,850 | 26,416,340,419 | IssuesEvent | 2023-01-13 16:16:56 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | closed | rustc panics when compiling code that uses tokio's LocalSet | I-ICE E-needs-test P-high T-compiler C-bug A-async-await AsyncAwait-Triaged E-needs-mcve WG-async | Compiler panics when compiling the following code that uses tokio's LocalSet:
```rust
#[tokio::main]
async fn main() {
tokio::spawn(async move {
let local = tokio::task::LocalSet::new();
local.run_until(async { })
}).await
}
--- or ---
#[tokio::main]
async fn main() {
tokio::spawn({
let local = tokio::task::LocalSet::new();
local.run_until(async {})
}).await
}
```
Panic message is as follows:
```
➜ RUST_BACKTRACE=full cargo build --verbose
...
Fresh tokio v0.2.9
Compiling rust-bug v0.1.0 (/tmp/rust-bug)
Running `rustc --edition=2018 --crate-name rust_bug src/main.rs --error-format=json --json=diagnostic-rendered-ansi --crate-type bin --emit=dep-info,link -C debuginfo=2 -C metadata=b5f969b2f9a6a1a5 -C extra-filename=-b5f969b2f9a6a1a5 --out-dir /tmp/rust-bug/target/debug/deps -C incremental=/tmp/rust-bug/target/debug/incremental -L dependency=/tmp/rust-bug/target/debug/deps --extern tokio=/tmp/rust-bug/target/debug/deps/libtokio-e472db2be190b401.rlib`
thread 'rustc' panicked at 'called `Option::unwrap()` on a `None` value', src/libcore/option.rs:378:21
stack backtrace:
0: 0x104e46b75 - <unknown>
1: 0x104e7dcc0 - <unknown>
...
101: 0x104e59a6e - <unknown>
102: 0x7fff6bb56e65 - <unknown>
error: internal compiler error: unexpected panic
note: the compiler unexpectedly panicked. this is a bug.
note: we would appreciate a bug report: https://github.com/rust-lang/rust/blob/master/CONTRIBUTING.md#bug-reports
note: rustc 1.40.0 (73528e339 2019-12-16) running on x86_64-apple-darwin
note: compiler flags: -C debuginfo=2 -C incremental --crate-type bin
note: some of the compiler flags provided by cargo are hidden
query stack during panic:
#0 [typeck_tables_of] processing `tokio::task::local::LocalSet::run_until`
#1 [typeck_tables_of] processing `tokio::task::local::LocalSet::run_until::{{closure}}#0`
#2 [typeck_tables_of] processing `main`
#3 [typeck_tables_of] processing `main::{{closure}}#0`
#4 [type_of] processing `main::{{closure}}#0`
#5 [collect_mod_item_types] collecting item types in top-level module
#6 [analysis] running analysis passes on this crate
end of query stack
error: could not compile `rust-bug`.
Caused by:
process didn't exit successfully: `rustc --edition=2018 --crate-name rust_bug src/main.rs --error-format=json --json=diagnostic-rendered-ansi --crate-type bin --emit=dep-info,link -C debuginfo=2 -C metadata=b5f969b2f9a6a1a5 -C extra-filename=-b5f969b2f9a6a1a5 --out-dir /tmp/rust-bug/target/debug/deps -C incremental=/tmp/rust-bug/target/debug/incremental -L dependency=/tmp/rust-bug/target/debug/deps --extern tokio=/tmp/rust-bug/target/debug/deps/libtokio-e472db2be190b401.rlib` (exit code: 101)
```
Dependencies:
```toml
[dependencies]
tokio = { version = "0.2.9", features = ["full"] }
```
Sample:
[rust-bug.zip](https://github.com/rust-lang/rust/files/4048765/rust-bug.zip)
<!-- TRIAGEBOT_START -->
<!-- TRIAGEBOT_ASSIGN_START -->
<!-- TRIAGEBOT_ASSIGN_DATA_START$${"user":"pnkfelix"}$$TRIAGEBOT_ASSIGN_DATA_END -->
<!-- TRIAGEBOT_ASSIGN_END -->
<!-- TRIAGEBOT_END --> | 1.0 | rustc panics when compiling code that uses tokio's LocalSet - Compiler panics when compiling the following code that uses tokio's LocalSet:
```rust
#[tokio::main]
async fn main() {
tokio::spawn(async move {
let local = tokio::task::LocalSet::new();
local.run_until(async { })
}).await
}
--- or ---
#[tokio::main]
async fn main() {
tokio::spawn({
let local = tokio::task::LocalSet::new();
local.run_until(async {})
}).await
}
```
Panic message is as follows:
```
➜ RUST_BACKTRACE=full cargo build --verbose
...
Fresh tokio v0.2.9
Compiling rust-bug v0.1.0 (/tmp/rust-bug)
Running `rustc --edition=2018 --crate-name rust_bug src/main.rs --error-format=json --json=diagnostic-rendered-ansi --crate-type bin --emit=dep-info,link -C debuginfo=2 -C metadata=b5f969b2f9a6a1a5 -C extra-filename=-b5f969b2f9a6a1a5 --out-dir /tmp/rust-bug/target/debug/deps -C incremental=/tmp/rust-bug/target/debug/incremental -L dependency=/tmp/rust-bug/target/debug/deps --extern tokio=/tmp/rust-bug/target/debug/deps/libtokio-e472db2be190b401.rlib`
thread 'rustc' panicked at 'called `Option::unwrap()` on a `None` value', src/libcore/option.rs:378:21
stack backtrace:
0: 0x104e46b75 - <unknown>
1: 0x104e7dcc0 - <unknown>
...
101: 0x104e59a6e - <unknown>
102: 0x7fff6bb56e65 - <unknown>
error: internal compiler error: unexpected panic
note: the compiler unexpectedly panicked. this is a bug.
note: we would appreciate a bug report: https://github.com/rust-lang/rust/blob/master/CONTRIBUTING.md#bug-reports
note: rustc 1.40.0 (73528e339 2019-12-16) running on x86_64-apple-darwin
note: compiler flags: -C debuginfo=2 -C incremental --crate-type bin
note: some of the compiler flags provided by cargo are hidden
query stack during panic:
#0 [typeck_tables_of] processing `tokio::task::local::LocalSet::run_until`
#1 [typeck_tables_of] processing `tokio::task::local::LocalSet::run_until::{{closure}}#0`
#2 [typeck_tables_of] processing `main`
#3 [typeck_tables_of] processing `main::{{closure}}#0`
#4 [type_of] processing `main::{{closure}}#0`
#5 [collect_mod_item_types] collecting item types in top-level module
#6 [analysis] running analysis passes on this crate
end of query stack
error: could not compile `rust-bug`.
Caused by:
process didn't exit successfully: `rustc --edition=2018 --crate-name rust_bug src/main.rs --error-format=json --json=diagnostic-rendered-ansi --crate-type bin --emit=dep-info,link -C debuginfo=2 -C metadata=b5f969b2f9a6a1a5 -C extra-filename=-b5f969b2f9a6a1a5 --out-dir /tmp/rust-bug/target/debug/deps -C incremental=/tmp/rust-bug/target/debug/incremental -L dependency=/tmp/rust-bug/target/debug/deps --extern tokio=/tmp/rust-bug/target/debug/deps/libtokio-e472db2be190b401.rlib` (exit code: 101)
```
Dependencies:
```toml
[dependencies]
tokio = { version = "0.2.9", features = ["full"] }
```
Sample:
[rust-bug.zip](https://github.com/rust-lang/rust/files/4048765/rust-bug.zip)
<!-- TRIAGEBOT_START -->
<!-- TRIAGEBOT_ASSIGN_START -->
<!-- TRIAGEBOT_ASSIGN_DATA_START$${"user":"pnkfelix"}$$TRIAGEBOT_ASSIGN_DATA_END -->
<!-- TRIAGEBOT_ASSIGN_END -->
<!-- TRIAGEBOT_END --> | test | rustc panics when compiling code that uses tokio s localset compiler panics when compiling the following code that uses tokio s localset rust async fn main tokio spawn async move let local tokio task localset new local run until async await or async fn main tokio spawn let local tokio task localset new local run until async await panic message is as follows ➜ rust backtrace full cargo build verbose fresh tokio compiling rust bug tmp rust bug running rustc edition crate name rust bug src main rs error format json json diagnostic rendered ansi crate type bin emit dep info link c debuginfo c metadata c extra filename out dir tmp rust bug target debug deps c incremental tmp rust bug target debug incremental l dependency tmp rust bug target debug deps extern tokio tmp rust bug target debug deps libtokio rlib thread rustc panicked at called option unwrap on a none value src libcore option rs stack backtrace error internal compiler error unexpected panic note the compiler unexpectedly panicked this is a bug note we would appreciate a bug report note rustc running on apple darwin note compiler flags c debuginfo c incremental crate type bin note some of the compiler flags provided by cargo are hidden query stack during panic processing tokio task local localset run until processing tokio task local localset run until closure processing main processing main closure processing main closure collecting item types in top level module running analysis passes on this crate end of query stack error could not compile rust bug caused by process didn t exit successfully rustc edition crate name rust bug src main rs error format json json diagnostic rendered ansi crate type bin emit dep info link c debuginfo c metadata c extra filename out dir tmp rust bug target debug deps c incremental tmp rust bug target debug incremental l dependency tmp rust bug target debug deps extern tokio tmp rust bug target debug deps libtokio rlib exit code dependencies toml tokio version features sample | 1 |
14,223 | 3,386,624,155 | IssuesEvent | 2015-11-27 19:23:31 | medic/medic-webapp | https://api.github.com/repos/medic/medic-webapp | closed | Note field formatting not rendered | 4 - Acceptance testing Bug Priority | Note fields show the markdown and markup, not the rendered version. | 1.0 | Note field formatting not rendered - Note fields show the markdown and markup, not the rendered version. | test | note field formatting not rendered note fields show the markdown and markup not the rendered version | 1 |
343,852 | 30,696,017,351 | IssuesEvent | 2023-07-26 18:39:40 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | DISABLED test_delayed_optim_step_offload_true_no_shard (__main__.TestParityWithDDP) | oncall: distributed module: flaky-tests skipped | Platforms: linux, rocm
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_delayed_optim_step_offload_true_no_shard&suite=TestParityWithDDP&file=distributed/fsdp/test_fsdp_core.py) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/7579918750).
Over the past 3 hours, it has been determined flaky in 1 workflow(s) with 1 red and 1 green.
cc @pietern @mrshenli @pritamdamania87 @zhaojuanmao @satgera @rohan-varma @gqchen @aazzolini @osalpekar @jiayisuse @SciPioneer @H-Huang @kwen2501 | 1.0 | DISABLED test_delayed_optim_step_offload_true_no_shard (__main__.TestParityWithDDP) - Platforms: linux, rocm
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_delayed_optim_step_offload_true_no_shard&suite=TestParityWithDDP&file=distributed/fsdp/test_fsdp_core.py) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/7579918750).
Over the past 3 hours, it has been determined flaky in 1 workflow(s) with 1 red and 1 green.
cc @pietern @mrshenli @pritamdamania87 @zhaojuanmao @satgera @rohan-varma @gqchen @aazzolini @osalpekar @jiayisuse @SciPioneer @H-Huang @kwen2501 | test | disabled test delayed optim step offload true no shard main testparitywithddp platforms linux rocm this test was disabled because it is failing in ci see and the most recent trunk over the past hours it has been determined flaky in workflow s with red and green cc pietern mrshenli zhaojuanmao satgera rohan varma gqchen aazzolini osalpekar jiayisuse scipioneer h huang | 1 |
346,548 | 30,927,034,435 | IssuesEvent | 2023-08-06 16:01:38 | vmiklos/osm-gimmisn | https://api.github.com/repos/vmiklos/osm-gimmisn | closed | data: ha a filter részben az utca alatt nincs semmi csak comment, akkor elhasal | bug needs testing | Tesztet kell bővíteni, hogy fogja meg:
Balatonszemes, Szabadság utca a hibás
```
Szabadság utca:
# 32/1: nincs ilyen, csak 32 és 32/b van.
# 32/a: nincs ilyen, csak 32 és 32/b van.
Széchenyi utca:
# 2/1: nincs ilyen, csak 2 és 2/a van.
# 6/a: nincs ilyen, csak sima 6 van. A 10-es házon van festékkel 6/a, de az nem illik a sorba.
# 52/b: nincs ilyen, csak sima 52 van.
# 56: nincs ilyen, az 54 után az 58 következik.
invalid: ['2/1', '6a', '52b', '56']
``` | 1.0 | data: ha a filter részben az utca alatt nincs semmi csak comment, akkor elhasal - Tesztet kell bővíteni, hogy fogja meg:
Balatonszemes, Szabadság utca a hibás
```
Szabadság utca:
# 32/1: nincs ilyen, csak 32 és 32/b van.
# 32/a: nincs ilyen, csak 32 és 32/b van.
Széchenyi utca:
# 2/1: nincs ilyen, csak 2 és 2/a van.
# 6/a: nincs ilyen, csak sima 6 van. A 10-es házon van festékkel 6/a, de az nem illik a sorba.
# 52/b: nincs ilyen, csak sima 52 van.
# 56: nincs ilyen, az 54 után az 58 következik.
invalid: ['2/1', '6a', '52b', '56']
``` | test | data ha a filter részben az utca alatt nincs semmi csak comment akkor elhasal tesztet kell bővíteni hogy fogja meg balatonszemes szabadság utca a hibás szabadság utca nincs ilyen csak és b van a nincs ilyen csak és b van széchenyi utca nincs ilyen csak és a van a nincs ilyen csak sima van a es házon van festékkel a de az nem illik a sorba b nincs ilyen csak sima van nincs ilyen az után az következik invalid | 1 |
207,981 | 15,865,078,700 | IssuesEvent | 2021-04-08 14:23:23 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | [CI] "search.aggregation/370_doc_count_field" fails | :Analytics/Aggregations >test-failure Team:Analytics | **Build scan**: https://gradle-enterprise.elastic.co/s/4wjbqwc44lbve
**Repro line**:
```
./gradlew ':qa:smoke-test-multinode:integTest' --tests "org.elasticsearch.smoketest.SmokeTestMultiNodeClientYamlTestSuiteIT" -Dtests.method="test {yaml=search.aggregation/370_doc_count_field/Test filters agg with doc_count}" -Dtests.seed=40FC123A004D9768 -Dtests.security.manager=true -Dtests.locale=ar-LB -Dtests.timezone=Canada/Yukon -Druntime.java=8
```
**Reproduces locally?**: No
**Applicable branches**: 7.12
**Failure excerpt**:
```
2> java.lang.AssertionError: Failure at [search.aggregation/370_doc_count_field:180]: field [profile.shards.0.aggregations.0.debug.segments_with_doc_count] is not greater than or equal to [1]
Expected: a value equal to or greater than <1>
but: <0> was less than <1>
``` | 1.0 | [CI] "search.aggregation/370_doc_count_field" fails - **Build scan**: https://gradle-enterprise.elastic.co/s/4wjbqwc44lbve
**Repro line**:
```
./gradlew ':qa:smoke-test-multinode:integTest' --tests "org.elasticsearch.smoketest.SmokeTestMultiNodeClientYamlTestSuiteIT" -Dtests.method="test {yaml=search.aggregation/370_doc_count_field/Test filters agg with doc_count}" -Dtests.seed=40FC123A004D9768 -Dtests.security.manager=true -Dtests.locale=ar-LB -Dtests.timezone=Canada/Yukon -Druntime.java=8
```
**Reproduces locally?**: No
**Applicable branches**: 7.12
**Failure excerpt**:
```
2> java.lang.AssertionError: Failure at [search.aggregation/370_doc_count_field:180]: field [profile.shards.0.aggregations.0.debug.segments_with_doc_count] is not greater than or equal to [1]
Expected: a value equal to or greater than <1>
but: <0> was less than <1>
``` | test | search aggregation doc count field fails build scan repro line gradlew qa smoke test multinode integtest tests org elasticsearch smoketest smoketestmultinodeclientyamltestsuiteit dtests method test yaml search aggregation doc count field test filters agg with doc count dtests seed dtests security manager true dtests locale ar lb dtests timezone canada yukon druntime java reproduces locally no applicable branches failure excerpt java lang assertionerror failure at field is not greater than or equal to expected a value equal to or greater than but was less than | 1 |
351,201 | 31,988,575,055 | IssuesEvent | 2023-09-21 02:45:33 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | opened | Fix manipulations.test_jax_rot90 | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6256145182/job/16986554000"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6256145182/job/16986554000"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6256145182/job/16986554000"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6256145182/job/16986554000"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6256145182/job/16986554000"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix manipulations.test_jax_rot90 - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6256145182/job/16986554000"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6256145182/job/16986554000"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6256145182/job/16986554000"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6256145182/job/16986554000"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6256145182/job/16986554000"><img src=https://img.shields.io/badge/-failure-red></a>
| test | fix manipulations test jax numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src | 1 |
171,835 | 20,999,751,921 | IssuesEvent | 2022-03-29 16:18:22 | AlexRogalskiy/github-action-user-contribution | https://api.github.com/repos/AlexRogalskiy/github-action-user-contribution | opened | CVE-2021-3918 (High) detected in json-schema-0.2.3.tgz | security vulnerability | ## CVE-2021-3918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p></summary>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>
Dependency Hierarchy:
- coveralls-3.1.0.tgz (Root Library)
- request-2.88.2.tgz
- http-signature-1.2.0.tgz
- jsprim-1.4.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/github-action-user-contribution/commit/e51ac509e11100b261cb1c0ba3c578d747ec913a">e51ac509e11100b261cb1c0ba3c578d747ec913a</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3918">https://nvd.nist.gov/vuln/detail/CVE-2021-3918</a></p>
<p>Release Date: 2021-11-13</p>
<p>Fix Resolution (json-schema): 0.4.0</p>
<p>Direct dependency fix Resolution (coveralls): 3.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-3918 (High) detected in json-schema-0.2.3.tgz - ## CVE-2021-3918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p></summary>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>
Dependency Hierarchy:
- coveralls-3.1.0.tgz (Root Library)
- request-2.88.2.tgz
- http-signature-1.2.0.tgz
- jsprim-1.4.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/github-action-user-contribution/commit/e51ac509e11100b261cb1c0ba3c578d747ec913a">e51ac509e11100b261cb1c0ba3c578d747ec913a</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3918">https://nvd.nist.gov/vuln/detail/CVE-2021-3918</a></p>
<p>Release Date: 2021-11-13</p>
<p>Fix Resolution (json-schema): 0.4.0</p>
<p>Direct dependency fix Resolution (coveralls): 3.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in json schema tgz cve high severity vulnerability vulnerable library json schema tgz json schema validation and specifications library home page a href dependency hierarchy coveralls tgz root library request tgz http signature tgz jsprim tgz x json schema tgz vulnerable library found in head commit a href vulnerability details json schema is vulnerable to improperly controlled modification of object prototype attributes prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution json schema direct dependency fix resolution coveralls step up your open source security game with whitesource | 0 |
185,961 | 14,394,532,868 | IssuesEvent | 2020-12-03 01:31:00 | github-vet/rangeclosure-findings | https://api.github.com/repos/github-vet/rangeclosure-findings | closed | trawler/komposify: vendor/github.com/openshift/origin/vendor/k8s.io/kubernetes/pkg/kubectl/resource_printer_test.go; 30 LoC | fresh small test vendored |
Found a possible issue in [trawler/komposify](https://www.github.com/trawler/komposify) at [vendor/github.com/openshift/origin/vendor/k8s.io/kubernetes/pkg/kubectl/resource_printer_test.go](https://github.com/trawler/komposify/blob/d73c54b2182a35f1acf76b4ad8b55720739be182/vendor/github.com/openshift/origin/vendor/k8s.io/kubernetes/pkg/kubectl/resource_printer_test.go#L852-L881)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to svc at line 855 may start a goroutine
[Click here to see the code in its original context.](https://github.com/trawler/komposify/blob/d73c54b2182a35f1acf76b4ad8b55720739be182/vendor/github.com/openshift/origin/vendor/k8s.io/kubernetes/pkg/kubectl/resource_printer_test.go#L852-L881)
<details>
<summary>Click here to show the 30 line(s) of Go which triggered the analyzer.</summary>
```go
for _, svc := range tests {
for _, wide := range []bool{false, true} {
buff := bytes.Buffer{}
printService(&svc, &buff, PrintOptions{false, false, false, wide, false, false, false, "", []string{}})
output := string(buff.Bytes())
ip := svc.Spec.ClusterIP
if !strings.Contains(output, ip) {
t.Errorf("expected to contain ClusterIP %s, but doesn't: %s", ip, output)
}
for n, ingress := range svc.Status.LoadBalancer.Ingress {
ip = ingress.IP
// For non-wide output, we only guarantee the first IP to be printed
if (n == 0 || wide) && !strings.Contains(output, ip) {
t.Errorf("expected to contain ingress ip %s with wide=%v, but doesn't: %s", ip, wide, output)
}
}
for _, port := range svc.Spec.Ports {
portSpec := fmt.Sprintf("%d/%s", port.Port, port.Protocol)
if !strings.Contains(output, portSpec) {
t.Errorf("expected to contain port: %s, but doesn't: %s", portSpec, output)
}
}
// Each service should print on one line
if 1 != strings.Count(output, "\n") {
t.Errorf("expected a single newline, found %d", strings.Count(output, "\n"))
}
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: d73c54b2182a35f1acf76b4ad8b55720739be182
| 1.0 | trawler/komposify: vendor/github.com/openshift/origin/vendor/k8s.io/kubernetes/pkg/kubectl/resource_printer_test.go; 30 LoC -
Found a possible issue in [trawler/komposify](https://www.github.com/trawler/komposify) at [vendor/github.com/openshift/origin/vendor/k8s.io/kubernetes/pkg/kubectl/resource_printer_test.go](https://github.com/trawler/komposify/blob/d73c54b2182a35f1acf76b4ad8b55720739be182/vendor/github.com/openshift/origin/vendor/k8s.io/kubernetes/pkg/kubectl/resource_printer_test.go#L852-L881)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to svc at line 855 may start a goroutine
[Click here to see the code in its original context.](https://github.com/trawler/komposify/blob/d73c54b2182a35f1acf76b4ad8b55720739be182/vendor/github.com/openshift/origin/vendor/k8s.io/kubernetes/pkg/kubectl/resource_printer_test.go#L852-L881)
<details>
<summary>Click here to show the 30 line(s) of Go which triggered the analyzer.</summary>
```go
for _, svc := range tests {
for _, wide := range []bool{false, true} {
buff := bytes.Buffer{}
printService(&svc, &buff, PrintOptions{false, false, false, wide, false, false, false, "", []string{}})
output := string(buff.Bytes())
ip := svc.Spec.ClusterIP
if !strings.Contains(output, ip) {
t.Errorf("expected to contain ClusterIP %s, but doesn't: %s", ip, output)
}
for n, ingress := range svc.Status.LoadBalancer.Ingress {
ip = ingress.IP
// For non-wide output, we only guarantee the first IP to be printed
if (n == 0 || wide) && !strings.Contains(output, ip) {
t.Errorf("expected to contain ingress ip %s with wide=%v, but doesn't: %s", ip, wide, output)
}
}
for _, port := range svc.Spec.Ports {
portSpec := fmt.Sprintf("%d/%s", port.Port, port.Protocol)
if !strings.Contains(output, portSpec) {
t.Errorf("expected to contain port: %s, but doesn't: %s", portSpec, output)
}
}
// Each service should print on one line
if 1 != strings.Count(output, "\n") {
t.Errorf("expected a single newline, found %d", strings.Count(output, "\n"))
}
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: d73c54b2182a35f1acf76b4ad8b55720739be182
| test | trawler komposify vendor github com openshift origin vendor io kubernetes pkg kubectl resource printer test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to svc at line may start a goroutine click here to show the line s of go which triggered the analyzer go for svc range tests for wide range bool false true buff bytes buffer printservice svc buff printoptions false false false wide false false false string output string buff bytes ip svc spec clusterip if strings contains output ip t errorf expected to contain clusterip s but doesn t s ip output for n ingress range svc status loadbalancer ingress ip ingress ip for non wide output we only guarantee the first ip to be printed if n wide strings contains output ip t errorf expected to contain ingress ip s with wide v but doesn t s ip wide output for port range svc spec ports portspec fmt sprintf d s port port port protocol if strings contains output portspec t errorf expected to contain port s but doesn t s portspec output each service should print on one line if strings count output n t errorf expected a single newline found d strings count output n leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
108,220 | 23,579,862,613 | IssuesEvent | 2022-08-23 06:37:31 | UnitTestBot/UTBotJava | https://api.github.com/repos/UnitTestBot/UTBotJava | closed | Unnecessary reflections in code generated for arrays | codegen | **Description**
In some cases codegen works with arrays using reflection even if there is no need for it.
**To Reproduce**
Run plugin on the following code:
```Java
package rndpkg;
class C {
int x;
public C(int x) { this.x = x; }
}
public class SomeClass {
public int f(C[] c) {
c[0].x -= 1;
return c[0].x;
}
}
```
**Expected behavior**
Produced tests don't use reflection.
**Actual behavior**
Tests look like this:
```Java
@Test
@DisplayName("f: c = C[0] -> throw ArrayIndexOutOfBoundsException")
public void testFThrowsAIOOBEWithEmptyObjectArray() throws Throwable {
SomeClass someClass = new SomeClass();
Object[] c = createArray("rndpkg.C", 0);
/* This test fails because method [rndpkg.SomeClass.f] produces [java.lang.ArrayIndexOutOfBoundsException: 0]
rndpkg.SomeClass.f(SomeClass.java:10) */
Class someClassClazz = Class.forName("rndpkg.SomeClass");
Class cType = Class.forName("[Lrndpkg.C;");
Method fMethod = someClassClazz.getDeclaredMethod("f", cType);
fMethod.setAccessible(true);
Object[] fMethodArguments = new Object[1];
fMethodArguments[0] = c;
try {
fMethod.invoke(someClass, fMethodArguments);
} catch (InvocationTargetException invocationTargetException) {
throw invocationTargetException.getTargetException();
}
}
```
| 1.0 | Unnecessary reflections in code generated for arrays - **Description**
In some cases codegen works with arrays using reflection even if there is no need for it.
**To Reproduce**
Run plugin on the following code:
```Java
package rndpkg;
class C {
int x;
public C(int x) { this.x = x; }
}
public class SomeClass {
public int f(C[] c) {
c[0].x -= 1;
return c[0].x;
}
}
```
**Expected behavior**
Produced tests don't use reflection.
**Actual behavior**
Tests look like this:
```Java
@Test
@DisplayName("f: c = C[0] -> throw ArrayIndexOutOfBoundsException")
public void testFThrowsAIOOBEWithEmptyObjectArray() throws Throwable {
SomeClass someClass = new SomeClass();
Object[] c = createArray("rndpkg.C", 0);
/* This test fails because method [rndpkg.SomeClass.f] produces [java.lang.ArrayIndexOutOfBoundsException: 0]
rndpkg.SomeClass.f(SomeClass.java:10) */
Class someClassClazz = Class.forName("rndpkg.SomeClass");
Class cType = Class.forName("[Lrndpkg.C;");
Method fMethod = someClassClazz.getDeclaredMethod("f", cType);
fMethod.setAccessible(true);
Object[] fMethodArguments = new Object[1];
fMethodArguments[0] = c;
try {
fMethod.invoke(someClass, fMethodArguments);
} catch (InvocationTargetException invocationTargetException) {
throw invocationTargetException.getTargetException();
}
}
```
| non_test | unnecessary reflections in code generated for arrays description in some cases codegen works with arrays using reflection even if there is no need for it to reproduce run plugin on the following code java package rndpkg class c int x public c int x this x x public class someclass public int f c c c x return c x expected behavior produced tests don t use reflection actual behavior tests look like this java test displayname f c c throw arrayindexoutofboundsexception public void testfthrowsaioobewithemptyobjectarray throws throwable someclass someclass new someclass object c createarray rndpkg c this test fails because method produces rndpkg someclass f someclass java class someclassclazz class forname rndpkg someclass class ctype class forname lrndpkg c method fmethod someclassclazz getdeclaredmethod f ctype fmethod setaccessible true object fmethodarguments new object fmethodarguments c try fmethod invoke someclass fmethodarguments catch invocationtargetexception invocationtargetexception throw invocationtargetexception gettargetexception | 0 |
23,715 | 4,039,734,640 | IssuesEvent | 2016-05-20 07:02:21 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | org.jsr107.tck.spi.CachingProviderTest.closeCachingProvider | Team: Integration Type: Test-Failure | ```
java.lang.IllegalStateException
at com.hazelcast.cache.impl.AbstractHazelcastCacheManager.checkIfManagerNotClosed(AbstractHazelcastCacheManager.java:372)
at com.hazelcast.cache.impl.AbstractHazelcastCacheManager.removeCache(AbstractHazelcastCacheManager.java:286)
at com.hazelcast.cache.impl.AbstractHazelcastCacheManager.destroyCache(AbstractHazelcastCacheManager.java:281)
at com.hazelcast.cache.impl.AbstractInternalCacheProxy.postDestroy(AbstractInternalCacheProxy.java:118)
at com.hazelcast.spi.AbstractDistributedObject.destroy(AbstractDistributedObject.java:62)
at com.hazelcast.cache.impl.AbstractHazelcastCacheManager.destroy(AbstractHazelcastCacheManager.java:355)
at com.hazelcast.cache.impl.AbstractHazelcastCachingProvider.close(AbstractHazelcastCachingProvider.java:138)
at com.hazelcast.cache.HazelcastCachingProvider.close(HazelcastCachingProvider.java:179)
at org.jsr107.tck.spi.CachingProviderTest.closeCachingProvider(CachingProviderTest.java:165)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:47)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:44)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:271)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:70)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:50)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:238)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:63)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:236)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:53)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:229)
at org.junit.runners.ParentRunner.run(ParentRunner.java:309)
at org.apache.maven.surefire.junit4.JUnit4TestSet.execute(JUnit4TestSet.java:53)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeTestSet(JUnit4Provider.java:123)
at org.apache.maven.surefire.junit4.JUnit4Provider.invoke(JUnit4Provider.java:104)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.apache.maven.surefire.util.ReflectionUtils.invokeMethodWithArray(ReflectionUtils.java:164)
at org.apache.maven.surefire.booter.ProviderFactory$ProviderProxy.invoke(ProviderFactory.java:110)
at org.apache.maven.surefire.booter.SurefireStarter.invokeProvider(SurefireStarter.java:172)
at org.apache.maven.surefire.booter.SurefireStarter.runSuitesInProcessWhenForked(SurefireStarter.java:104)
at org.apache.maven.surefire.booter.ForkedBooter.main(ForkedBooter.java:70)
```
https://hazelcast-l337.ci.cloudbees.com/job/JCache-TCK-master/3076/ | 1.0 | org.jsr107.tck.spi.CachingProviderTest.closeCachingProvider - ```
java.lang.IllegalStateException
at com.hazelcast.cache.impl.AbstractHazelcastCacheManager.checkIfManagerNotClosed(AbstractHazelcastCacheManager.java:372)
at com.hazelcast.cache.impl.AbstractHazelcastCacheManager.removeCache(AbstractHazelcastCacheManager.java:286)
at com.hazelcast.cache.impl.AbstractHazelcastCacheManager.destroyCache(AbstractHazelcastCacheManager.java:281)
at com.hazelcast.cache.impl.AbstractInternalCacheProxy.postDestroy(AbstractInternalCacheProxy.java:118)
at com.hazelcast.spi.AbstractDistributedObject.destroy(AbstractDistributedObject.java:62)
at com.hazelcast.cache.impl.AbstractHazelcastCacheManager.destroy(AbstractHazelcastCacheManager.java:355)
at com.hazelcast.cache.impl.AbstractHazelcastCachingProvider.close(AbstractHazelcastCachingProvider.java:138)
at com.hazelcast.cache.HazelcastCachingProvider.close(HazelcastCachingProvider.java:179)
at org.jsr107.tck.spi.CachingProviderTest.closeCachingProvider(CachingProviderTest.java:165)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:47)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:44)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:271)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:70)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:50)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:238)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:63)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:236)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:53)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:229)
at org.junit.runners.ParentRunner.run(ParentRunner.java:309)
at org.apache.maven.surefire.junit4.JUnit4TestSet.execute(JUnit4TestSet.java:53)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeTestSet(JUnit4Provider.java:123)
at org.apache.maven.surefire.junit4.JUnit4Provider.invoke(JUnit4Provider.java:104)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.apache.maven.surefire.util.ReflectionUtils.invokeMethodWithArray(ReflectionUtils.java:164)
at org.apache.maven.surefire.booter.ProviderFactory$ProviderProxy.invoke(ProviderFactory.java:110)
at org.apache.maven.surefire.booter.SurefireStarter.invokeProvider(SurefireStarter.java:172)
at org.apache.maven.surefire.booter.SurefireStarter.runSuitesInProcessWhenForked(SurefireStarter.java:104)
at org.apache.maven.surefire.booter.ForkedBooter.main(ForkedBooter.java:70)
```
https://hazelcast-l337.ci.cloudbees.com/job/JCache-TCK-master/3076/ | test | org tck spi cachingprovidertest closecachingprovider java lang illegalstateexception at com hazelcast cache impl abstracthazelcastcachemanager checkifmanagernotclosed abstracthazelcastcachemanager java at com hazelcast cache impl abstracthazelcastcachemanager removecache abstracthazelcastcachemanager java at com hazelcast cache impl abstracthazelcastcachemanager destroycache abstracthazelcastcachemanager java at com hazelcast cache impl abstractinternalcacheproxy postdestroy abstractinternalcacheproxy java at com hazelcast spi abstractdistributedobject destroy abstractdistributedobject java at com hazelcast cache impl abstracthazelcastcachemanager destroy abstracthazelcastcachemanager java at com hazelcast cache impl abstracthazelcastcachingprovider close abstracthazelcastcachingprovider java at com hazelcast cache hazelcastcachingprovider close hazelcastcachingprovider java at org tck spi cachingprovidertest closecachingprovider cachingprovidertest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at org junit runners parentrunner runleaf parentrunner java at org junit runners runchild java at org junit runners runchild java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org apache maven surefire execute java at org apache maven surefire executetestset java at org apache maven surefire invoke java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org apache maven surefire util reflectionutils invokemethodwitharray reflectionutils java at org apache maven surefire booter providerfactory providerproxy invoke providerfactory java at org apache maven surefire booter surefirestarter invokeprovider surefirestarter java at org apache maven surefire booter surefirestarter runsuitesinprocesswhenforked surefirestarter java at org apache maven surefire booter forkedbooter main forkedbooter java | 1 |
21,702 | 3,916,542,864 | IssuesEvent | 2016-04-21 02:25:36 | pbreach/venpy | https://api.github.com/repos/pbreach/venpy | opened | Use SDXorg/test-models in venpy tests | testing | The models provide here can be used testing if basic functionality is working and results can be compared. A couple things will need to be done beforehand:
* Compiled (.vpm) models will have to be made for each so they can be loaded into venpy.
* Iterate through tests that have simple .csv outputs and compare to results generated here.
* Figure out a way to compare results for .tab files
* Integrate these models into existing tests. | 1.0 | Use SDXorg/test-models in venpy tests - The models provide here can be used testing if basic functionality is working and results can be compared. A couple things will need to be done beforehand:
* Compiled (.vpm) models will have to be made for each so they can be loaded into venpy.
* Iterate through tests that have simple .csv outputs and compare to results generated here.
* Figure out a way to compare results for .tab files
* Integrate these models into existing tests. | test | use sdxorg test models in venpy tests the models provide here can be used testing if basic functionality is working and results can be compared a couple things will need to be done beforehand compiled vpm models will have to be made for each so they can be loaded into venpy iterate through tests that have simple csv outputs and compare to results generated here figure out a way to compare results for tab files integrate these models into existing tests | 1 |
272,346 | 29,795,012,443 | IssuesEvent | 2023-06-16 01:04:04 | billmcchesney1/pacbot | https://api.github.com/repos/billmcchesney1/pacbot | closed | CVE-2018-1272 (High) detected in spring-core-4.3.8.RELEASE.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2018-1272 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-core-4.3.8.RELEASE.jar</b></p></summary>
<p>Spring Core</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /jobs/pacman-cloud-notifications/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-core/4.3.8.RELEASE/spring-core-4.3.8.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-core/4.3.8.RELEASE/spring-core-4.3.8.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-core/4.3.8.RELEASE/spring-core-4.3.8.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-context-4.3.8.RELEASE.jar (Root Library)
- :x: **spring-core-4.3.8.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/pacbot/commit/acf9a0620c1a37cee4f2896d71e1c3731c5c7b06">acf9a0620c1a37cee4f2896d71e1c3731c5c7b06</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework, versions 5.0 prior to 5.0.5 and versions 4.3 prior to 4.3.15 and older unsupported versions, provide client-side support for multipart requests. When Spring MVC or Spring WebFlux server application (server A) receives input from a remote client, and then uses that input to make a multipart request to another server (server B), it can be exposed to an attack, where an extra multipart is inserted in the content of the request from server A, causing server B to use the wrong value for a part it expects. This could to lead privilege escalation, for example, if the part content represents a username or user roles.
<p>Publish Date: 2018-04-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1272>CVE-2018-1272</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2018-1272">https://tanzu.vmware.com/security/cve-2018-1272</a></p>
<p>Release Date: 2018-04-05</p>
<p>Fix Resolution: org.springframework:spring-core:4.3.15.RELEASE,5.0.5.RELEASE;org.springframework:spring-web:4.3.15.RELEASE,5.0.5.RELEASE</p>
</p>
</details>
<p></p>
| True | CVE-2018-1272 (High) detected in spring-core-4.3.8.RELEASE.jar - autoclosed - ## CVE-2018-1272 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-core-4.3.8.RELEASE.jar</b></p></summary>
<p>Spring Core</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /jobs/pacman-cloud-notifications/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-core/4.3.8.RELEASE/spring-core-4.3.8.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-core/4.3.8.RELEASE/spring-core-4.3.8.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-core/4.3.8.RELEASE/spring-core-4.3.8.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-context-4.3.8.RELEASE.jar (Root Library)
- :x: **spring-core-4.3.8.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/pacbot/commit/acf9a0620c1a37cee4f2896d71e1c3731c5c7b06">acf9a0620c1a37cee4f2896d71e1c3731c5c7b06</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework, versions 5.0 prior to 5.0.5 and versions 4.3 prior to 4.3.15 and older unsupported versions, provide client-side support for multipart requests. When Spring MVC or Spring WebFlux server application (server A) receives input from a remote client, and then uses that input to make a multipart request to another server (server B), it can be exposed to an attack, where an extra multipart is inserted in the content of the request from server A, causing server B to use the wrong value for a part it expects. This could to lead privilege escalation, for example, if the part content represents a username or user roles.
<p>Publish Date: 2018-04-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1272>CVE-2018-1272</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2018-1272">https://tanzu.vmware.com/security/cve-2018-1272</a></p>
<p>Release Date: 2018-04-05</p>
<p>Fix Resolution: org.springframework:spring-core:4.3.15.RELEASE,5.0.5.RELEASE;org.springframework:spring-web:4.3.15.RELEASE,5.0.5.RELEASE</p>
</p>
</details>
<p></p>
| non_test | cve high detected in spring core release jar autoclosed cve high severity vulnerability vulnerable library spring core release jar spring core library home page a href path to dependency file jobs pacman cloud notifications pom xml path to vulnerable library home wss scanner repository org springframework spring core release spring core release jar home wss scanner repository org springframework spring core release spring core release jar home wss scanner repository org springframework spring core release spring core release jar dependency hierarchy spring context release jar root library x spring core release jar vulnerable library found in head commit a href found in base branch master vulnerability details spring framework versions prior to and versions prior to and older unsupported versions provide client side support for multipart requests when spring mvc or spring webflux server application server a receives input from a remote client and then uses that input to make a multipart request to another server server b it can be exposed to an attack where an extra multipart is inserted in the content of the request from server a causing server b to use the wrong value for a part it expects this could to lead privilege escalation for example if the part content represents a username or user roles publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring core release release org springframework spring web release release | 0 |
38,926 | 5,205,126,822 | IssuesEvent | 2017-01-24 17:08:02 | emfoundation/ce100-app | https://api.github.com/repos/emfoundation/ce100-app | closed | Add/edit user organisation dropdown bug | bug please-test question | As an admin, if you go into the edit user view for Ben Morpheous:
<img width="773" alt="screen shot 2017-01-12 at 16 00 15" src="https://cloud.githubusercontent.com/assets/12638261/21897036/4ff68376-d8e0-11e6-9156-e58786c33d5d.png">
The org dropdown doesn't show Fanta as it is not an enabled organisation:
<img width="672" alt="screen shot 2017-01-12 at 16 04 01" src="https://cloud.githubusercontent.com/assets/12638261/21897199/cf52e146-d8e0-11e6-81de-f10a6148eaae.png">
This means that editing Ben in any way will result in him being 'unlinked' from Fanta organisation.
It seems like a bit of an edge case, I don't know how likely it is for an Admin to be editing a user linked to a disabled organisation? @asimonw could you suggest your desired functionality here? and suggest a priority for us please?
_________________________________
Additional thoughts on this org dropdown:
The org dropdown needs a bit of thought with the introduction of secondary users, we were thinking of displaying differing drop-downs depending on which user 'type' is selected:
- if an admin is being created/edited -> show no dropdown
- if a primary is being created/edited -> show all active, unlinked organisations (except the org that they belong to if we are in edit user view)
- if a secondary user is being created/edited -> show all active organisations
I have put the above thoughts here for discussion: https://github.com/emfoundation/ce100-app/issues/319 | 1.0 | Add/edit user organisation dropdown bug - As an admin, if you go into the edit user view for Ben Morpheous:
<img width="773" alt="screen shot 2017-01-12 at 16 00 15" src="https://cloud.githubusercontent.com/assets/12638261/21897036/4ff68376-d8e0-11e6-9156-e58786c33d5d.png">
The org dropdown doesn't show Fanta as it is not an enabled organisation:
<img width="672" alt="screen shot 2017-01-12 at 16 04 01" src="https://cloud.githubusercontent.com/assets/12638261/21897199/cf52e146-d8e0-11e6-81de-f10a6148eaae.png">
This means that editing Ben in any way will result in him being 'unlinked' from Fanta organisation.
It seems like a bit of an edge case, I don't know how likely it is for an Admin to be editing a user linked to a disabled organisation? @asimonw could you suggest your desired functionality here? and suggest a priority for us please?
_________________________________
Additional thoughts on this org dropdown:
The org dropdown needs a bit of thought with the introduction of secondary users, we were thinking of displaying differing drop-downs depending on which user 'type' is selected:
- if an admin is being created/edited -> show no dropdown
- if a primary is being created/edited -> show all active, unlinked organisations (except the org that they belong to if we are in edit user view)
- if a secondary user is being created/edited -> show all active organisations
I have put the above thoughts here for discussion: https://github.com/emfoundation/ce100-app/issues/319 | test | add edit user organisation dropdown bug as an admin if you go into the edit user view for ben morpheous img width alt screen shot at src the org dropdown doesn t show fanta as it is not an enabled organisation img width alt screen shot at src this means that editing ben in any way will result in him being unlinked from fanta organisation it seems like a bit of an edge case i don t know how likely it is for an admin to be editing a user linked to a disabled organisation asimonw could you suggest your desired functionality here and suggest a priority for us please additional thoughts on this org dropdown the org dropdown needs a bit of thought with the introduction of secondary users we were thinking of displaying differing drop downs depending on which user type is selected if an admin is being created edited show no dropdown if a primary is being created edited show all active unlinked organisations except the org that they belong to if we are in edit user view if a secondary user is being created edited show all active organisations i have put the above thoughts here for discussion | 1 |
318,843 | 27,326,023,513 | IssuesEvent | 2023-02-25 02:56:30 | python/cpython | https://api.github.com/repos/python/cpython | closed | test_tar test_add_dir_getmember fails if uid/gid is larger than 16777215 | type-bug tests 3.11 3.10 3.12 | # Bug report
The [`test_add_dir_getmember`](https://github.com/python/cpython/blob/12d92c733cfc00ee630b30e4e0250da400c83395/Lib/test/test_tarfile.py#L223) added in https://github.com/python/cpython/pull/30283 fails if the current user's uid or gid is larger than 16777215 because of limitations of UStar format.
Note that the other test cases don't have this problem.
This test should either avoid depending on the current user's uid/gid (such as by using an explicit uid/gid) or be skipped if the current uid/gid is 8**8 or larger.
For example,
```python
def filter(tarinfo):
tarinfo.uid = 100
tarinfo.gid = 100
return tarinfo
...
tar.add(name, filter=filter)
```
Will use 100 as the uid and gid instead of the current user's uid/gid.
<!-- gh-linked-prs -->
### Linked PRs
* gh-102207
* gh-102230
* gh-102231
<!-- /gh-linked-prs -->
| 1.0 | test_tar test_add_dir_getmember fails if uid/gid is larger than 16777215 - # Bug report
The [`test_add_dir_getmember`](https://github.com/python/cpython/blob/12d92c733cfc00ee630b30e4e0250da400c83395/Lib/test/test_tarfile.py#L223) added in https://github.com/python/cpython/pull/30283 fails if the current user's uid or gid is larger than 16777215 because of limitations of UStar format.
Note that the other test cases don't have this problem.
This test should either avoid depending on the current user's uid/gid (such as by using an explicit uid/gid) or be skipped if the current uid/gid is 8**8 or larger.
For example,
```python
def filter(tarinfo):
tarinfo.uid = 100
tarinfo.gid = 100
return tarinfo
...
tar.add(name, filter=filter)
```
Will use 100 as the uid and gid instead of the current user's uid/gid.
<!-- gh-linked-prs -->
### Linked PRs
* gh-102207
* gh-102230
* gh-102231
<!-- /gh-linked-prs -->
| test | test tar test add dir getmember fails if uid gid is larger than bug report the added in fails if the current user s uid or gid is larger than because of limitations of ustar format note that the other test cases don t have this problem this test should either avoid depending on the current user s uid gid such as by using an explicit uid gid or be skipped if the current uid gid is or larger for example python def filter tarinfo tarinfo uid tarinfo gid return tarinfo tar add name filter filter will use as the uid and gid instead of the current user s uid gid linked prs gh gh gh | 1 |
74,963 | 14,367,725,766 | IssuesEvent | 2020-12-01 07:13:27 | numbersprotocol/capture-lite | https://api.github.com/repos/numbersprotocol/capture-lite | closed | Use Promise to Replace Observable Only Emitting Once | code | Since currently there is no `Single` class (like rxjava) in rxjs, it could be difficult for developers to figure out if the `Observable` only emits once. There are several discussion about this problem. E.g. https://github.com/ReactiveX/rxjs/issues/5273.
We should use `Promise` instead of `Observable` to clearly indicate the behavior will only return ONE SINGLE value asynchronously. This would help developers to avoid lots of potential bugs when deciding which observable operator to use, such as `forkJoin` vs `zip` and `toArray` vs `scan`.
As a `Promise` can be easily transform into an `Observable` with `defer` function but it is an anti-pattern to transform an `Observable` into a `Promise` via `toPromise` function, we should:
- Prefer `Promise` than `Observable` for return values.
- Prefer `Observable` than `Promise` for parameters. | 1.0 | Use Promise to Replace Observable Only Emitting Once - Since currently there is no `Single` class (like rxjava) in rxjs, it could be difficult for developers to figure out if the `Observable` only emits once. There are several discussion about this problem. E.g. https://github.com/ReactiveX/rxjs/issues/5273.
We should use `Promise` instead of `Observable` to clearly indicate the behavior will only return ONE SINGLE value asynchronously. This would help developers to avoid lots of potential bugs when deciding which observable operator to use, such as `forkJoin` vs `zip` and `toArray` vs `scan`.
As a `Promise` can be easily transform into an `Observable` with `defer` function but it is an anti-pattern to transform an `Observable` into a `Promise` via `toPromise` function, we should:
- Prefer `Promise` than `Observable` for return values.
- Prefer `Observable` than `Promise` for parameters. | non_test | use promise to replace observable only emitting once since currently there is no single class like rxjava in rxjs it could be difficult for developers to figure out if the observable only emits once there are several discussion about this problem e g we should use promise instead of observable to clearly indicate the behavior will only return one single value asynchronously this would help developers to avoid lots of potential bugs when deciding which observable operator to use such as forkjoin vs zip and toarray vs scan as a promise can be easily transform into an observable with defer function but it is an anti pattern to transform an observable into a promise via topromise function we should prefer promise than observable for return values prefer observable than promise for parameters | 0 |
289,021 | 8,854,269,850 | IssuesEvent | 2019-01-09 00:33:43 | visit-dav/issues-test | https://api.github.com/repos/visit-dav/issues-test | closed | Merge Paul Navratil's changes in trunk updates 20008 and 20009 to the 2.6RC | enhancement priority reviewed | Paul made some host config file changes on the trunk that he would like put on the 2.6 RC. The changes are in commits 20008 and 20009.
-----------------------REDMINE MIGRATION-----------------------
This ticket was migrated from Redmine. As such, not all
information was able to be captured in the transition. Below is
a complete record of the original redmine ticket.
Ticket number: 1308
Status: Resolved
Project: VisIt
Tracker: Feature
Priority: High
Subject: Merge Paul Navratil's changes in trunk updates 20008 and 20009 to the 2.6RC
Assigned to: Eric Brugger
Category: -
Target version: 2.6.1
Author: Eric Brugger
Start: 01/15/2013
Due date:
% Done: 100%
Estimated time: 1.00 hour
Created: 01/15/2013 12:22 pm
Updated: 01/15/2013 01:07 pm
Likelihood:
Severity:
Found in version: 2.12.3
Impact: 3 - Medium
Expected Use: 3 - Occasional
OS: All
Support Group: Any
Description:
Paul made some host config file changes on the trunk that he would like put on the 2.6 RC. The changes are in commits 20008 and 20009.
Comments:
I committed revisions 20014 and 20016 to the 2.6 RC and trunk with thefollowing change:1) I merged Paul Navratil's changes to the host profiles for TACC from the trunk to the 2.6RC. This resolves #1308.A resources/hosts/tacc/host_tacc_lonestar.xmlA resources/hosts/tacc/host_tacc_lonestar_local.xmlA resources/hosts/tacc/host_tacc_stampede.xmlA resources/hosts/tacc/host_tacc_stampede_local.xmlD resources/hosts/tacc/host_tacc_ranger.xmlD resources/hosts/tacc/host_tacc_spur.xmlM resources/hosts/tacc/customlauncherM resources/help/en_US/relnotes2.6.1.html
| 1.0 | Merge Paul Navratil's changes in trunk updates 20008 and 20009 to the 2.6RC - Paul made some host config file changes on the trunk that he would like put on the 2.6 RC. The changes are in commits 20008 and 20009.
-----------------------REDMINE MIGRATION-----------------------
This ticket was migrated from Redmine. As such, not all
information was able to be captured in the transition. Below is
a complete record of the original redmine ticket.
Ticket number: 1308
Status: Resolved
Project: VisIt
Tracker: Feature
Priority: High
Subject: Merge Paul Navratil's changes in trunk updates 20008 and 20009 to the 2.6RC
Assigned to: Eric Brugger
Category: -
Target version: 2.6.1
Author: Eric Brugger
Start: 01/15/2013
Due date:
% Done: 100%
Estimated time: 1.00 hour
Created: 01/15/2013 12:22 pm
Updated: 01/15/2013 01:07 pm
Likelihood:
Severity:
Found in version: 2.12.3
Impact: 3 - Medium
Expected Use: 3 - Occasional
OS: All
Support Group: Any
Description:
Paul made some host config file changes on the trunk that he would like put on the 2.6 RC. The changes are in commits 20008 and 20009.
Comments:
I committed revisions 20014 and 20016 to the 2.6 RC and trunk with thefollowing change:1) I merged Paul Navratil's changes to the host profiles for TACC from the trunk to the 2.6RC. This resolves #1308.A resources/hosts/tacc/host_tacc_lonestar.xmlA resources/hosts/tacc/host_tacc_lonestar_local.xmlA resources/hosts/tacc/host_tacc_stampede.xmlA resources/hosts/tacc/host_tacc_stampede_local.xmlD resources/hosts/tacc/host_tacc_ranger.xmlD resources/hosts/tacc/host_tacc_spur.xmlM resources/hosts/tacc/customlauncherM resources/help/en_US/relnotes2.6.1.html
| non_test | merge paul navratil s changes in trunk updates and to the paul made some host config file changes on the trunk that he would like put on the rc the changes are in commits and redmine migration this ticket was migrated from redmine as such not all information was able to be captured in the transition below is a complete record of the original redmine ticket ticket number status resolved project visit tracker feature priority high subject merge paul navratil s changes in trunk updates and to the assigned to eric brugger category target version author eric brugger start due date done estimated time hour created pm updated pm likelihood severity found in version impact medium expected use occasional os all support group any description paul made some host config file changes on the trunk that he would like put on the rc the changes are in commits and comments i committed revisions and to the rc and trunk with thefollowing change i merged paul navratil s changes to the host profiles for tacc from the trunk to the this resolves a resources hosts tacc host tacc lonestar xmla resources hosts tacc host tacc lonestar local xmla resources hosts tacc host tacc stampede xmla resources hosts tacc host tacc stampede local xmld resources hosts tacc host tacc ranger xmld resources hosts tacc host tacc spur xmlm resources hosts tacc customlauncherm resources help en us html | 0 |
11,739 | 4,287,295,645 | IssuesEvent | 2016-07-16 17:30:47 | coinmix/coinmix | https://api.github.com/repos/coinmix/coinmix | opened | Import private key | bug code up-for-grabs | There is the UI for importing a private key, but so far the code does nothing. See the "load_private_key" function in tumbler-qt.py | 1.0 | Import private key - There is the UI for importing a private key, but so far the code does nothing. See the "load_private_key" function in tumbler-qt.py | non_test | import private key there is the ui for importing a private key but so far the code does nothing see the load private key function in tumbler qt py | 0 |
485,479 | 13,966,000,808 | IssuesEvent | 2020-10-26 00:56:04 | mobigen/IRIS-BigData-Platform | https://api.github.com/repos/mobigen/IRIS-BigData-Platform | closed | [Studio] 그래프와 입력받기 두가지로 조절하는 부분이 이상한 것 같습니다. | #IBP Priority: P0 R: 20.10.22 Status: Complete Type: Bug | ## 버그 설명 ##
Studio 보고서 작성 화면에서 아래 사진과 같이 구현되어있는 조절 칸의 조작이 조금 이상한 것 같습니다.
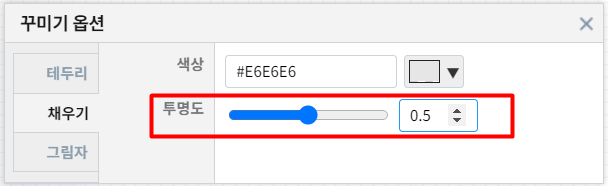
## 재현하는 방법 ##
### 환경
```
- http://b-iris.mobigen.com/
- window 10, chrome
- root 계정
```
### 1. 'Studio -> 보고서 편집 화면 -> 객체의 꾸미기 옵션' 으로 들어간다.
### 2. 이후 입력 받는 칸에
```
Backspace 를 누르면 최대치의 '절반' 값 입력
[1] 초기상태 -> 50(절반)
[2] 50 -> 5 -> 50(절반)
[3] 100 -> 10 -> 1 -> 100(절반)
```
### [1] 초기값에서 `<-` 누를경우 중간 값 입력됨
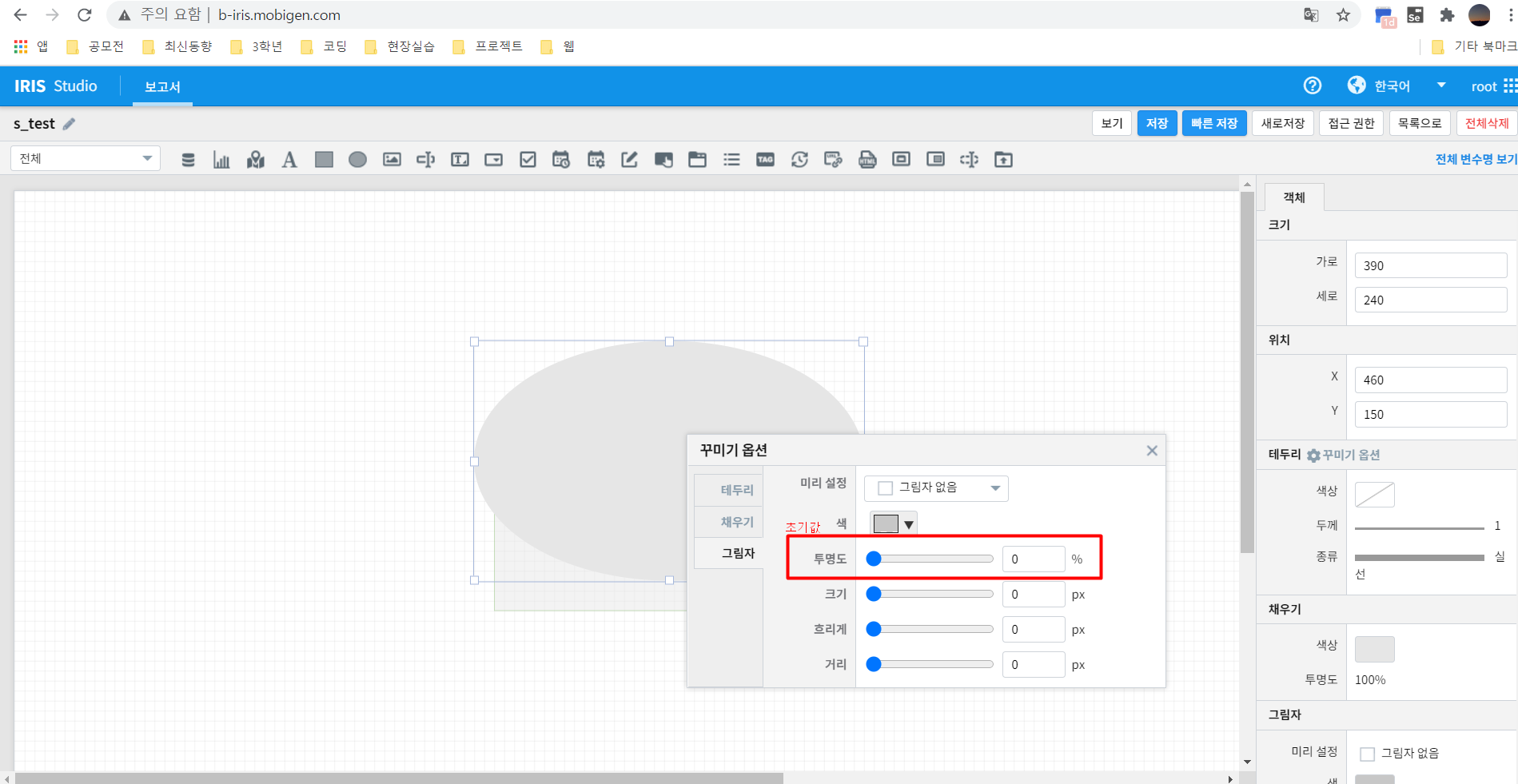
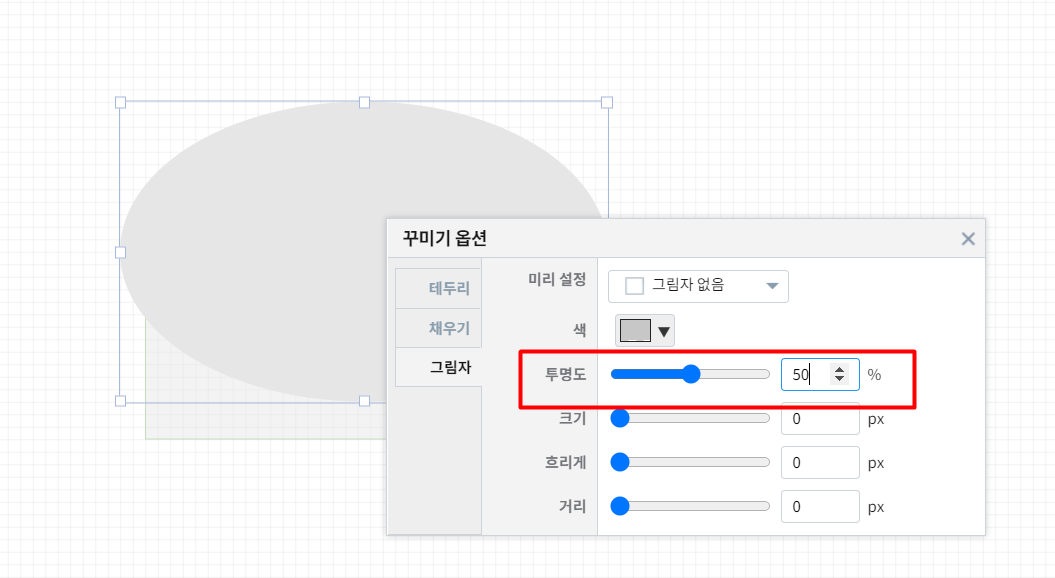
---
### [2] [3] 1의 자리 숫자인 경우에 `<-` 누를경우 중간 값 입력됨
- [2]
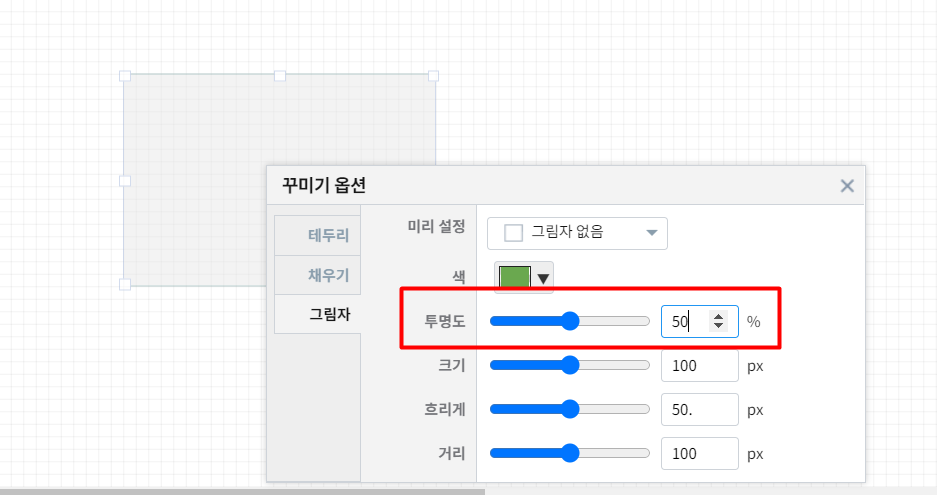
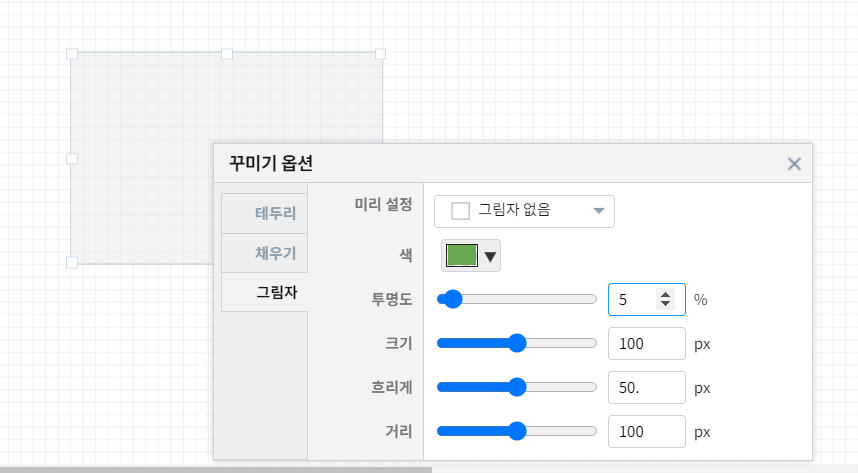
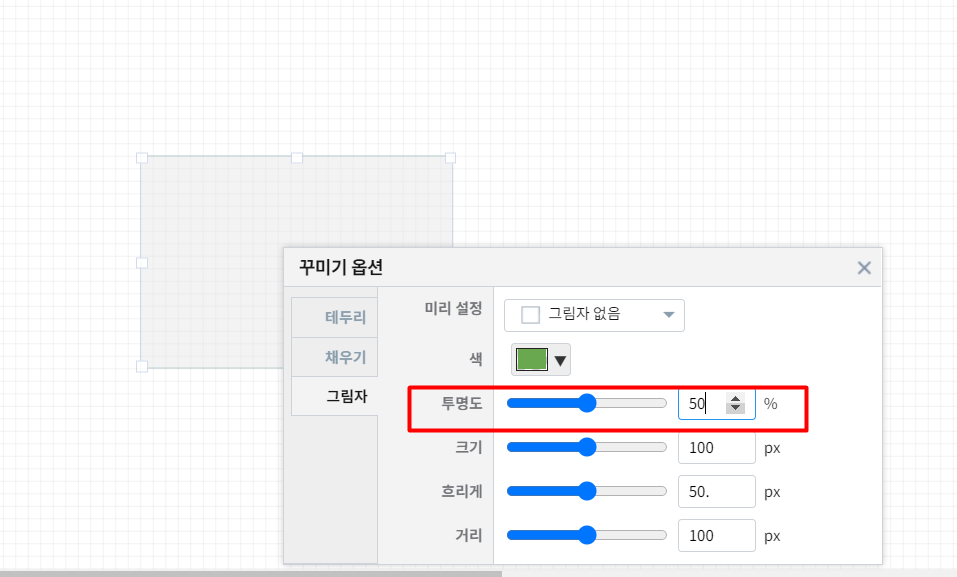
- [3]
[image](https://user-images.githubusercontent.com/59571464/91421901-73dd3400-e891-11ea-8714-87b1e8935c51.png)
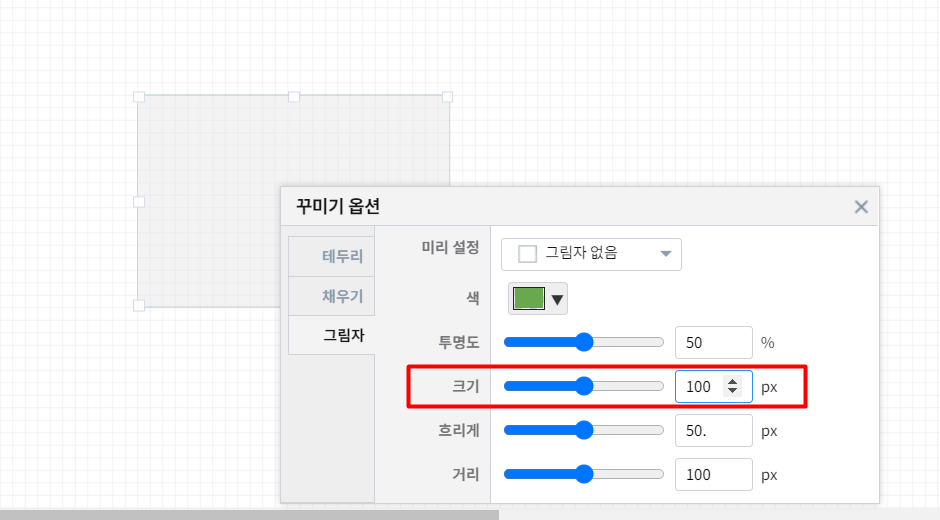
## 예상한 행동 ##
- [1]번의 경우에는 아무일도 일어나지 않을 것이고
- [2], [3]번의 경우에는 '0' 이 입력될 것으로 예상했습니다.
## 스크린샷 ##
## 로그 ##
{ 가능한 경우 문제를 설명하는데 도움이되는 서버 혹은 브라우저의 로그를 여기에 추가해 주세요 }
## 기타 ##
{ 기타 문제에 대한 다른 상황이나 의견은 여기에 추가 부탁드립니다 } | 1.0 | [Studio] 그래프와 입력받기 두가지로 조절하는 부분이 이상한 것 같습니다. - ## 버그 설명 ##
Studio 보고서 작성 화면에서 아래 사진과 같이 구현되어있는 조절 칸의 조작이 조금 이상한 것 같습니다.
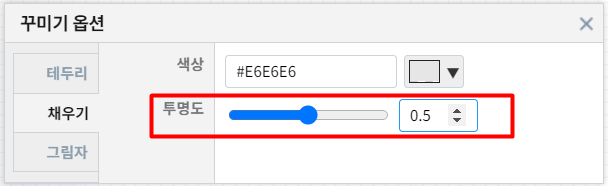
## 재현하는 방법 ##
### 환경
```
- http://b-iris.mobigen.com/
- window 10, chrome
- root 계정
```
### 1. 'Studio -> 보고서 편집 화면 -> 객체의 꾸미기 옵션' 으로 들어간다.
### 2. 이후 입력 받는 칸에
```
Backspace 를 누르면 최대치의 '절반' 값 입력
[1] 초기상태 -> 50(절반)
[2] 50 -> 5 -> 50(절반)
[3] 100 -> 10 -> 1 -> 100(절반)
```
### [1] 초기값에서 `<-` 누를경우 중간 값 입력됨
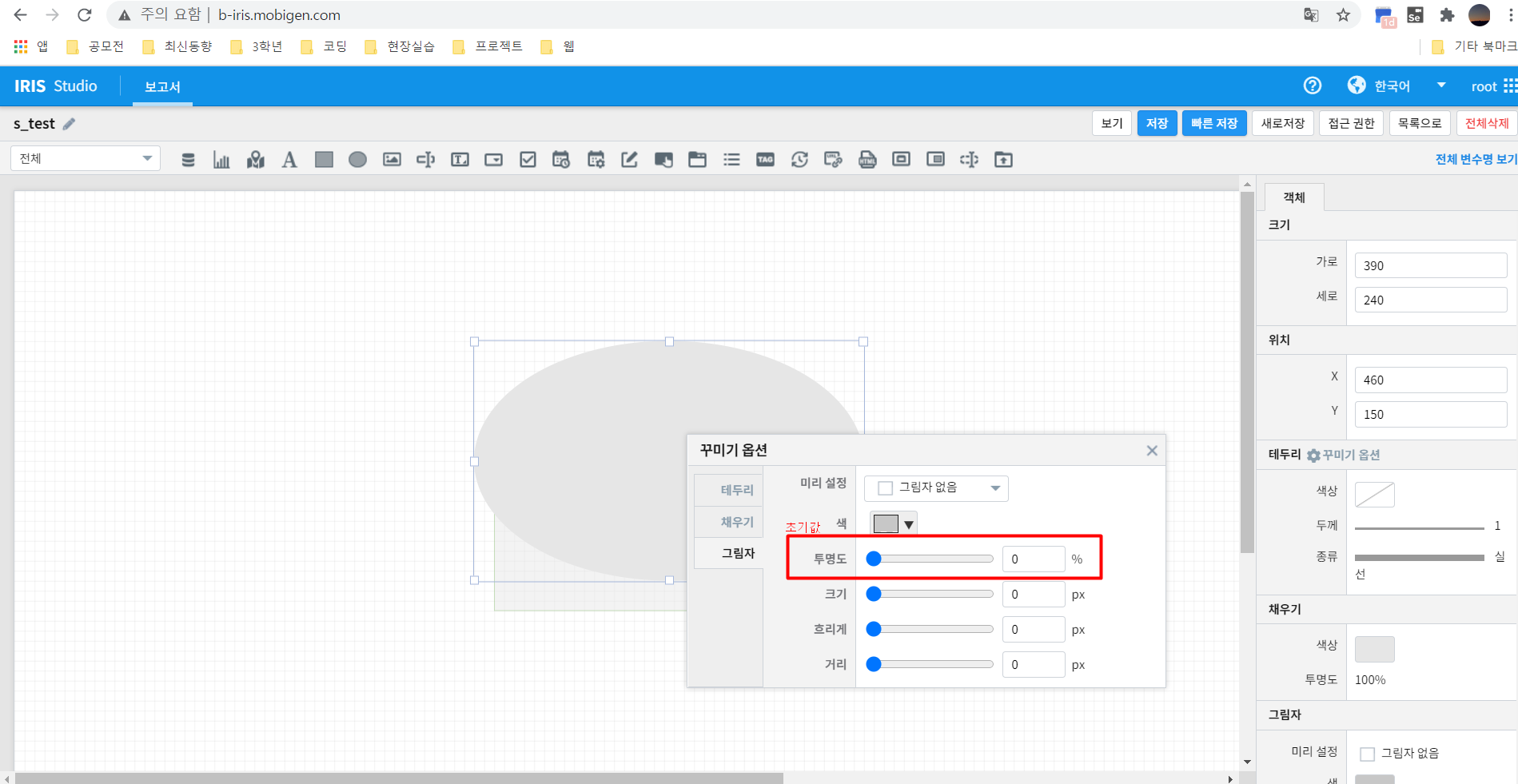
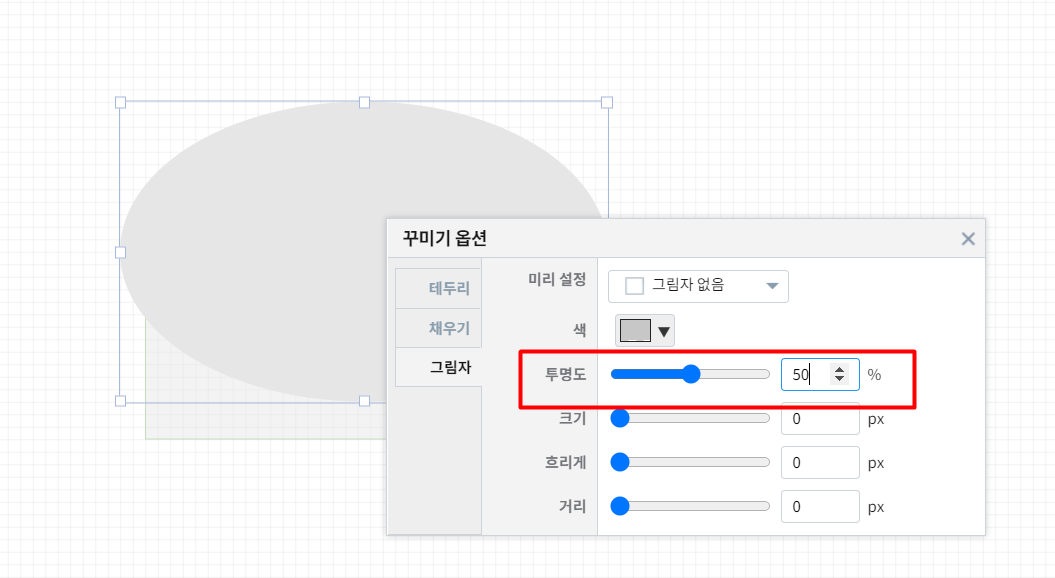
---
### [2] [3] 1의 자리 숫자인 경우에 `<-` 누를경우 중간 값 입력됨
- [2]
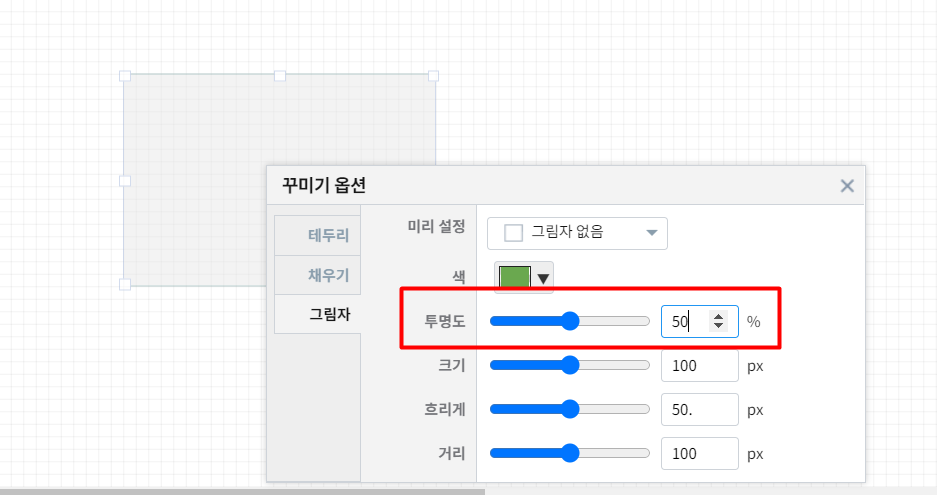
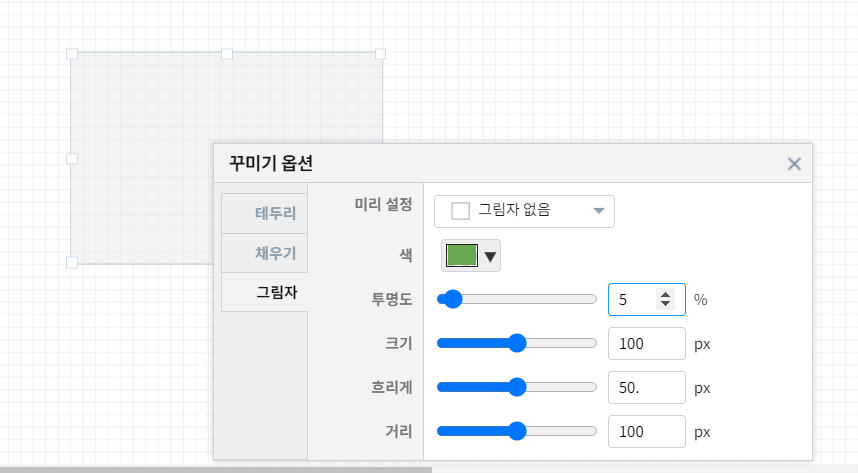
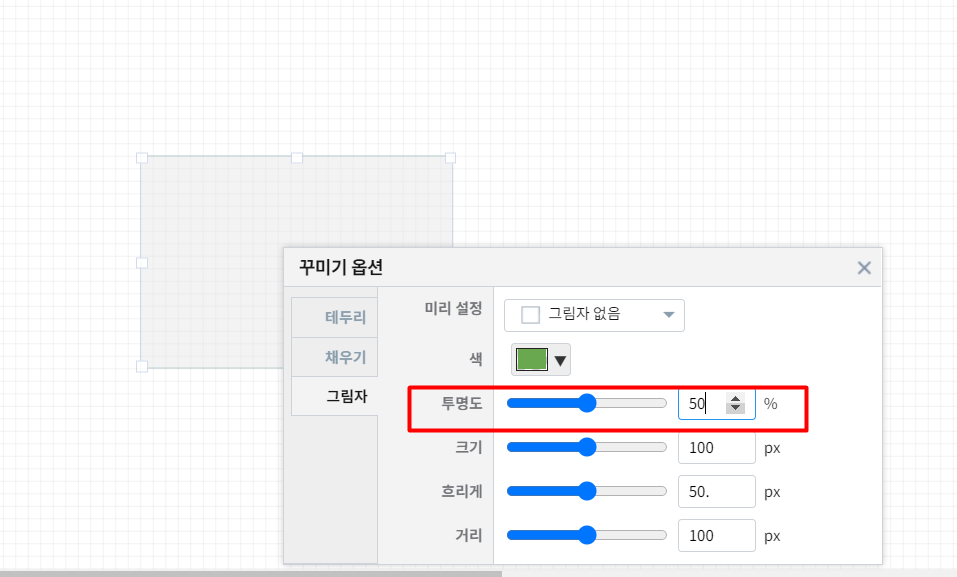
- [3]
[image](https://user-images.githubusercontent.com/59571464/91421901-73dd3400-e891-11ea-8714-87b1e8935c51.png)
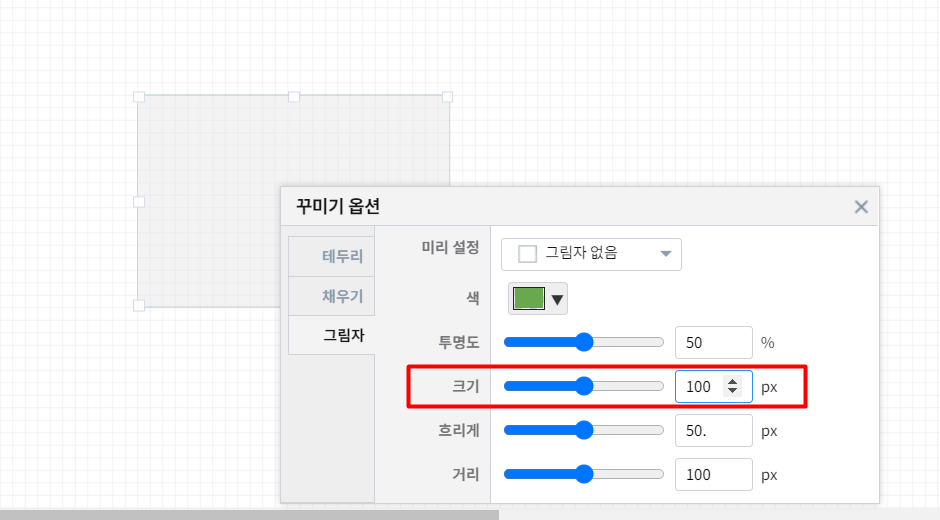
## 예상한 행동 ##
- [1]번의 경우에는 아무일도 일어나지 않을 것이고
- [2], [3]번의 경우에는 '0' 이 입력될 것으로 예상했습니다.
## 스크린샷 ##
## 로그 ##
{ 가능한 경우 문제를 설명하는데 도움이되는 서버 혹은 브라우저의 로그를 여기에 추가해 주세요 }
## 기타 ##
{ 기타 문제에 대한 다른 상황이나 의견은 여기에 추가 부탁드립니다 } | non_test | 그래프와 입력받기 두가지로 조절하는 부분이 이상한 것 같습니다 버그 설명 studio 보고서 작성 화면에서 아래 사진과 같이 구현되어있는 조절 칸의 조작이 조금 이상한 것 같습니다 재현하는 방법 환경 window chrome root 계정 studio 보고서 편집 화면 객체의 꾸미기 옵션 으로 들어간다 이후 입력 받는 칸에 backspace 를 누르면 최대치의 절반 값 입력 초기상태 절반 절반 절반 초기값에서 누를경우 중간 값 입력됨 자리 숫자인 경우에 누를경우 중간 값 입력됨 예상한 행동 번의 경우에는 아무일도 일어나지 않을 것이고 번의 경우에는 이 입력될 것으로 예상했습니다 스크린샷 로그 가능한 경우 문제를 설명하는데 도움이되는 서버 혹은 브라우저의 로그를 여기에 추가해 주세요 기타 기타 문제에 대한 다른 상황이나 의견은 여기에 추가 부탁드립니다 | 0 |
33,670 | 7,195,148,219 | IssuesEvent | 2018-02-04 14:16:04 | ganeti/ganeti | https://api.github.com/repos/ganeti/ganeti | closed | --maintain-node-health does not work on two node cluster | AutoMigrated Priority:Medium Status:Fixed Type-Defect | Originally reported of Google Code with ID 745.
```
What software version are you running? Please provide the output of "gnt-
cluster --version", "gnt-cluster version", and "hspace --version".
gnt-cluster (ganeti v2.9.5) 2.9.5
Software version: 2.9.5
Internode protocol: 2090000
Configuration format: 2090000
OS api version: 20
Export interface: 0
VCS version: v2.9.5
<b>What distribution are you using?</b>
ubuntu 12.04.4 LTS
<b>What steps will reproduce the problem?</b>
1. on a two node cluster enable --maintain-node-health
2. set second node offline
<b>What is the expected output? What do you see instead?</b>
ganeti-watcher should stop instances and disable drbd devices.
<b>Please provide any additional information below.</b>
ganeti-watcher just shows a warning:
2014-02-25 10:42:23,062: ganeti-watcher pid=17690 nodemaint:146 WARNING Inconsistent replies, not doing anything
i also get this on a second two node cluster with same os and ganeti versions.
see discussion -> https://groups.google.com/forum/#!topic/ganeti/oSqvQJ8oysg
```
Originally added on 2014-03-04 07:16:54 +0000 UTC. | 1.0 | --maintain-node-health does not work on two node cluster - Originally reported of Google Code with ID 745.
```
What software version are you running? Please provide the output of "gnt-
cluster --version", "gnt-cluster version", and "hspace --version".
gnt-cluster (ganeti v2.9.5) 2.9.5
Software version: 2.9.5
Internode protocol: 2090000
Configuration format: 2090000
OS api version: 20
Export interface: 0
VCS version: v2.9.5
<b>What distribution are you using?</b>
ubuntu 12.04.4 LTS
<b>What steps will reproduce the problem?</b>
1. on a two node cluster enable --maintain-node-health
2. set second node offline
<b>What is the expected output? What do you see instead?</b>
ganeti-watcher should stop instances and disable drbd devices.
<b>Please provide any additional information below.</b>
ganeti-watcher just shows a warning:
2014-02-25 10:42:23,062: ganeti-watcher pid=17690 nodemaint:146 WARNING Inconsistent replies, not doing anything
i also get this on a second two node cluster with same os and ganeti versions.
see discussion -> https://groups.google.com/forum/#!topic/ganeti/oSqvQJ8oysg
```
Originally added on 2014-03-04 07:16:54 +0000 UTC. | non_test | maintain node health does not work on two node cluster originally reported of google code with id what software version are you running please provide the output of gnt cluster version gnt cluster version and hspace version gnt cluster ganeti software version internode protocol configuration format os api version export interface vcs version what distribution are you using ubuntu lts what steps will reproduce the problem on a two node cluster enable maintain node health set second node offline what is the expected output what do you see instead ganeti watcher should stop instances and disable drbd devices please provide any additional information below ganeti watcher just shows a warning ganeti watcher pid nodemaint warning inconsistent replies not doing anything i also get this on a second two node cluster with same os and ganeti versions see discussion originally added on utc | 0 |
156,229 | 12,302,101,293 | IssuesEvent | 2020-05-11 16:24:49 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | closed | //src/test/java/com/google/devtools/build/lib:foundations_test flaky | P3 category: misc > testing type: bug | Running this test randomly times out in about 10% of all invocations. The underlying issue, however, is not a too short timeout; on my machine, a passing invocation takes about 25s whereas it still times out on my machine with timeout 300s.
The flaky timeouts can also be seen on ci, e.g., http://ci.bazel.io/job/bazel-tests/BAZEL_VERSION=latest-jdk7,PLATFORM_NAME=ubuntu_15.10-x86_64/318/console | 1.0 | //src/test/java/com/google/devtools/build/lib:foundations_test flaky - Running this test randomly times out in about 10% of all invocations. The underlying issue, however, is not a too short timeout; on my machine, a passing invocation takes about 25s whereas it still times out on my machine with timeout 300s.
The flaky timeouts can also be seen on ci, e.g., http://ci.bazel.io/job/bazel-tests/BAZEL_VERSION=latest-jdk7,PLATFORM_NAME=ubuntu_15.10-x86_64/318/console | test | src test java com google devtools build lib foundations test flaky running this test randomly times out in about of all invocations the underlying issue however is not a too short timeout on my machine a passing invocation takes about whereas it still times out on my machine with timeout the flaky timeouts can also be seen on ci e g | 1 |
22,108 | 18,684,143,369 | IssuesEvent | 2021-11-01 10:11:52 | idiotWu/smooth-scrollbar | https://api.github.com/repos/idiotWu/smooth-scrollbar | opened | [Idea/v9] An easier way to customize the scrollbars' appearance | idea usability accepted | ### Discussed in https://github.com/idiotWu/smooth-scrollbar/discussions/399
<div type='discussions-op-text'>
<sup>Originally posted by **blitzve0** October 31, 2021</sup>
Currently if we want to change the styling of the scroll bar thumb and tracks we have to overwrite the default styling from node modules. If basics settings like color transparency tracks color width padding etc could be set through config would be awesome</div> | True | [Idea/v9] An easier way to customize the scrollbars' appearance - ### Discussed in https://github.com/idiotWu/smooth-scrollbar/discussions/399
<div type='discussions-op-text'>
<sup>Originally posted by **blitzve0** October 31, 2021</sup>
Currently if we want to change the styling of the scroll bar thumb and tracks we have to overwrite the default styling from node modules. If basics settings like color transparency tracks color width padding etc could be set through config would be awesome</div> | non_test | an easier way to customize the scrollbars appearance discussed in originally posted by october currently if we want to change the styling of the scroll bar thumb and tracks we have to overwrite the default styling from node modules if basics settings like color transparency tracks color width padding etc could be set through config would be awesome | 0 |
98,766 | 20,797,287,106 | IssuesEvent | 2022-03-17 10:31:23 | bincode-org/bincode | https://api.github.com/repos/bincode-org/bincode | closed | bincode::Encode doesn't work with Cow<'a, str> | bincode-2 bug(fix) | Consider this struct:
```rust
#[derive(Clone, Encode)]
pub struct Foo<'a>(Cow<'a, str>);
```
The error I get is: `the trait 'Clone' is not implemented for 'str'` | 1.0 | bincode::Encode doesn't work with Cow<'a, str> - Consider this struct:
```rust
#[derive(Clone, Encode)]
pub struct Foo<'a>(Cow<'a, str>);
```
The error I get is: `the trait 'Clone' is not implemented for 'str'` | non_test | bincode encode doesn t work with cow consider this struct rust pub struct foo cow the error i get is the trait clone is not implemented for str | 0 |
142,903 | 11,499,726,359 | IssuesEvent | 2020-02-12 14:25:58 | pfuntner/toys | https://api.github.com/repos/pfuntner/toys | closed | Transition to Python 3 | being tested urgent | Python 2 is going to be at end of support at the end of 2019. It will still probably linger for years but it won't be officially extended or fixed. It should probably get my tools working and this could be a long process instance-by-instance process.
I've started coming up with some differences to worry about in #45.
I've also come up with the idea of an simple `vi` filter to to take a Python 2 `print` statement and turn it into a call to the Python 3 `print()` function, which should help in the transition. | 1.0 | Transition to Python 3 - Python 2 is going to be at end of support at the end of 2019. It will still probably linger for years but it won't be officially extended or fixed. It should probably get my tools working and this could be a long process instance-by-instance process.
I've started coming up with some differences to worry about in #45.
I've also come up with the idea of an simple `vi` filter to to take a Python 2 `print` statement and turn it into a call to the Python 3 `print()` function, which should help in the transition. | test | transition to python python is going to be at end of support at the end of it will still probably linger for years but it won t be officially extended or fixed it should probably get my tools working and this could be a long process instance by instance process i ve started coming up with some differences to worry about in i ve also come up with the idea of an simple vi filter to to take a python print statement and turn it into a call to the python print function which should help in the transition | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.