Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3 values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17 values | text_combine stringlengths 95 262k | label stringclasses 2 values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
94,656 | 8,507,872,207 | IssuesEvent | 2018-10-30 20:18:39 | dotnet/coreclr | https://api.github.com/repos/dotnet/coreclr | closed | Failures in x64_checked_windows_nt_corefx_jitstress1 jobs | JitStress test bug | We get the following failures in x64_checked_windows_nt_corefx_jitstress1 jobs (e.g., https://ci.dot.net/job/dotnet_coreclr/job/master/view/Windows_NT/job/jitstress/job/x64_checked_windows_nt_corefx_jitstress1/lastBuild/consoleText)
```
System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(fileName: null, lineNumber: -1, columnNumber: 0) [FAIL]
Assert.Equal() Failure
Expected: 0
Actual: 8
Stack Trace:
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(170,0): at System.Diagnostics.Tests.StackFrameTests.VerifyStackFrameSkipFrames(StackFrame stackFrame, Boolean isFileConstructor, Int32 skipFrames, MethodInfo expectedMethod, Boolean isCurrentFrame)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(112,0): at System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(String fileName, Int32 lineNumber, Int32 columnNumber)
System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(fileName: \"\", lineNumber: 0, columnNumber: -1) [FAIL]
Assert.Equal() Failure
Expected: 0
Actual: 8
Stack Trace:
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(170,0): at System.Diagnostics.Tests.StackFrameTests.VerifyStackFrameSkipFrames(StackFrame stackFrame, Boolean isFileConstructor, Int32 skipFrames, MethodInfo expectedMethod, Boolean isCurrentFrame)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(112,0): at System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(String fileName, Int32 lineNumber, Int32 columnNumber)
System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(fileName: \"FileName\", lineNumber: 1, columnNumber: 2) [FAIL]
Assert.Equal() Failure
Expected: 0
Actual: 8
Stack Trace:
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(170,0): at System.Diagnostics.Tests.StackFrameTests.VerifyStackFrameSkipFrames(StackFrame stackFrame, Boolean isFileConstructor, Int32 skipFrames, MethodInfo expectedMethod, Boolean isCurrentFrame)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(112,0): at System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(String fileName, Int32 lineNumber, Int32 columnNumber)
Finished: System.Diagnostics.StackTrace.Tests
```
```
DataContractSerializerTests.DCS_ResolveDatacontractBaseType [FAIL]
System.NullReferenceException : Object reference not set to an instance of an object.
Stack Trace:
Finished: System.Security.Cryptography.Cng.Tests
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Runtime.Serialization.Xml\tests\SerializationTestTypes\DataContractResolverLibrary.cs(84,0): at SerializationTestTypes.ProxyDataContractResolver.ResolveName(String typeName, String typeNamespace, Type declaredType, DataContractResolver knownTypeResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerContext.cs(276,0): at System.Runtime.Serialization.XmlObjectSerializerContext.ResolveDataContractFromKnownTypes(String typeName, String typeNs, DataContract memberTypeContract)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\KnownTypeDataContractResolver.cs(26,0): at System.Runtime.Serialization.KnownTypeDataContractResolver.TryResolveType(Type type, Type declaredType, DataContractResolver knownTypeResolver, XmlDictionaryString& typeName, XmlDictionaryString& typeNamespace)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(673,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.ResolveType(Type objectType, Type declaredType, XmlDictionaryString& typeName, XmlDictionaryString& typeNamespace)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(665,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.WriteResolvedTypeInfo(XmlWriterDelegator writer, Type objectType, Type declaredType)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(710,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.WriteTypeInfo(XmlWriterDelegator writer, DataContract contract, DataContract declaredContract)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(178,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.SerializeWithXsiTypeAtTopLevel(DataContract dataContract, XmlWriterDelegator xmlWriter, Object obj, RuntimeTypeHandle originalDeclaredTypeHandle, Type graphType)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\DataContractSerializer.cs(376,0): at System.Runtime.Serialization.DataContractSerializer.InternalWriteObjectContent(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\DataContractSerializer.cs(237,0): at System.Runtime.Serialization.DataContractSerializer.InternalWriteObject(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializer.cs(71,0): at System.Runtime.Serialization.XmlObjectSerializer.WriteObjectHandleExceptions(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializer.cs(57,0): at System.Runtime.Serialization.XmlObjectSerializer.WriteObject(XmlDictionaryWriter writer, Object graph)
```
```
DataContractSerializerTests.DCS_ResolveNameReturnsEmptyNamespace [FAIL]
System.NullReferenceException : Object reference not set to an instance of an object.
Stack Trace:
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Runtime.Serialization.Xml\tests\SerializationTestTypes\DataContractResolverLibrary.cs(75,0): at SerializationTestTypes.EmptyNamespaceResolver.ResolveName(String typeName, String typeNamespace, Type declaredType, DataContractResolver knownTypeResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerContext.cs(276,0): at System.Runtime.Serialization.XmlObjectSerializerContext.ResolveDataContractFromKnownTypes(String typeName, String typeNs, DataContract memberTypeContract)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\KnownTypeDataContractResolver.cs(26,0): at System.Runtime.Serialization.KnownTypeDataContractResolver.TryResolveType(Type type, Type declaredType, DataContractResolver knownTypeResolver, XmlDictionaryString& typeName, XmlDictionaryString& typeNamespace)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(673,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.ResolveType(Type objectType, Type declaredType, XmlDictionaryString& typeName, XmlDictionaryString& typeNamespace)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(665,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.WriteResolvedTypeInfo(XmlWriterDelegator writer, Type objectType, Type declaredType)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(710,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.WriteTypeInfo(XmlWriterDelegator writer, DataContract contract, DataContract declaredContract)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(230,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.SerializeWithXsiType(XmlWriterDelegator xmlWriter, Object obj, RuntimeTypeHandle objectTypeHandle, Type objectType, Int32 declaredTypeID, RuntimeTypeHandle declaredTypeHandle, Type declaredType)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(143,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.InternalSerialize(XmlWriterDelegator xmlWriter, Object obj, Boolean isDeclaredType, Boolean writeXsiType, Int32 declaredTypeID, RuntimeTypeHandle declaredTypeHandle)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ReflectionClassWriter.cs(158,0): at System.Runtime.Serialization.ReflectionClassWriter.ReflectionInternalSerialize(XmlWriterDelegator xmlWriter, XmlObjectSerializerWriteContext context, Object obj, Boolean isDeclaredType, Boolean writeXsiType, Type memberType, Boolean isNullableOfT)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ReflectionClassWriter.cs(95,0): at System.Runtime.Serialization.ReflectionClassWriter.ReflectionWriteValue(XmlWriterDelegator xmlWriter, XmlObjectSerializerWriteContext context, Type type, Object value, Boolean writeXsiType, PrimitiveDataContract primitiveContractForParamType)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ReflectionXmlFormatWriter.cs(187,0): at System.Runtime.Serialization.ReflectionXmlClassWriter.ReflectionWriteMembers(XmlWriterDelegator xmlWriter, Object obj, XmlObjectSerializerWriteContext context, ClassDataContract classContract, ClassDataContract derivedMostClassContract, Int32 childElementIndex, XmlDictionaryString[] emptyStringArray)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ReflectionClassWriter.cs(35,0): at System.Runtime.Serialization.ReflectionClassWriter.ReflectionWriteClass(XmlWriterDelegator xmlWriter, Object obj, XmlObjectSerializerWriteContext context, ClassDataContract classContract, XmlDictionaryString[] memberNames)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ReflectionXmlFormatWriter.cs(20,0): at System.Runtime.Serialization.ReflectionXmlFormatWriter.ReflectionWriteClass(XmlWriterDelegator xmlWriter, Object obj, XmlObjectSerializerWriteContext context, ClassDataContract classContract)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ClassDataContract.cs(507,0): at System.Runtime.Serialization.ClassDataContract.WriteXmlValue(XmlWriterDelegator xmlWriter, Object obj, XmlObjectSerializerWriteContext context)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(654,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.WriteDataContractValue(DataContract dataContract, XmlWriterDelegator xmlWriter, Object obj, RuntimeTypeHandle declaredTypeHandle)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(155,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.SerializeWithoutXsiType(DataContract dataContract, XmlWriterDelegator xmlWriter, Object obj, RuntimeTypeHandle declaredTypeHandle)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\DataContractSerializer.cs(354,0): at System.Runtime.Serialization.DataContractSerializer.InternalWriteObjectContent(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\DataContractSerializer.cs(237,0): at System.Runtime.Serialization.DataContractSerializer.InternalWriteObject(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializer.cs(71,0): at System.Runtime.Serialization.XmlObjectSerializer.WriteObjectHandleExceptions(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializer.cs(57,0): at System.Runtime.Serialization.XmlObjectSerializer.WriteObject(XmlDictionaryWriter writer, Object graph)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializer.cs(27,0): at System.Runtime.Serialization.XmlObjectSerializer.WriteObject(Stream stream, Object graph)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\Common\tests\System\Runtime\Serialization\DataContractSerializerHelper.cs(29,0): at System.Runtime.Serialization.Tests.DataContractSerializerHelper.SerializeAndDeserialize[T](T value, String baseline, DataContractSerializerSettings settings, Func`1 serializerFactory, Boolean skipStringCompare)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Runtime.Serialization.Xml\tests\DataContractSerializer.cs(2784,0): at DataContractSerializerTests.DCS_ResolveNameReturnsEmptyNamespace()
``` | 1.0 | Failures in x64_checked_windows_nt_corefx_jitstress1 jobs - We get the following failures in x64_checked_windows_nt_corefx_jitstress1 jobs (e.g., https://ci.dot.net/job/dotnet_coreclr/job/master/view/Windows_NT/job/jitstress/job/x64_checked_windows_nt_corefx_jitstress1/lastBuild/consoleText)
```
System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(fileName: null, lineNumber: -1, columnNumber: 0) [FAIL]
Assert.Equal() Failure
Expected: 0
Actual: 8
Stack Trace:
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(170,0): at System.Diagnostics.Tests.StackFrameTests.VerifyStackFrameSkipFrames(StackFrame stackFrame, Boolean isFileConstructor, Int32 skipFrames, MethodInfo expectedMethod, Boolean isCurrentFrame)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(112,0): at System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(String fileName, Int32 lineNumber, Int32 columnNumber)
System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(fileName: \"\", lineNumber: 0, columnNumber: -1) [FAIL]
Assert.Equal() Failure
Expected: 0
Actual: 8
Stack Trace:
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(170,0): at System.Diagnostics.Tests.StackFrameTests.VerifyStackFrameSkipFrames(StackFrame stackFrame, Boolean isFileConstructor, Int32 skipFrames, MethodInfo expectedMethod, Boolean isCurrentFrame)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(112,0): at System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(String fileName, Int32 lineNumber, Int32 columnNumber)
System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(fileName: \"FileName\", lineNumber: 1, columnNumber: 2) [FAIL]
Assert.Equal() Failure
Expected: 0
Actual: 8
Stack Trace:
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(170,0): at System.Diagnostics.Tests.StackFrameTests.VerifyStackFrameSkipFrames(StackFrame stackFrame, Boolean isFileConstructor, Int32 skipFrames, MethodInfo expectedMethod, Boolean isCurrentFrame)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Diagnostics.StackTrace\tests\StackFrameTests.cs(112,0): at System.Diagnostics.Tests.StackFrameTests.Ctor_Filename_LineNumber_ColNumber(String fileName, Int32 lineNumber, Int32 columnNumber)
Finished: System.Diagnostics.StackTrace.Tests
```
```
DataContractSerializerTests.DCS_ResolveDatacontractBaseType [FAIL]
System.NullReferenceException : Object reference not set to an instance of an object.
Stack Trace:
Finished: System.Security.Cryptography.Cng.Tests
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Runtime.Serialization.Xml\tests\SerializationTestTypes\DataContractResolverLibrary.cs(84,0): at SerializationTestTypes.ProxyDataContractResolver.ResolveName(String typeName, String typeNamespace, Type declaredType, DataContractResolver knownTypeResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerContext.cs(276,0): at System.Runtime.Serialization.XmlObjectSerializerContext.ResolveDataContractFromKnownTypes(String typeName, String typeNs, DataContract memberTypeContract)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\KnownTypeDataContractResolver.cs(26,0): at System.Runtime.Serialization.KnownTypeDataContractResolver.TryResolveType(Type type, Type declaredType, DataContractResolver knownTypeResolver, XmlDictionaryString& typeName, XmlDictionaryString& typeNamespace)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(673,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.ResolveType(Type objectType, Type declaredType, XmlDictionaryString& typeName, XmlDictionaryString& typeNamespace)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(665,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.WriteResolvedTypeInfo(XmlWriterDelegator writer, Type objectType, Type declaredType)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(710,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.WriteTypeInfo(XmlWriterDelegator writer, DataContract contract, DataContract declaredContract)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(178,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.SerializeWithXsiTypeAtTopLevel(DataContract dataContract, XmlWriterDelegator xmlWriter, Object obj, RuntimeTypeHandle originalDeclaredTypeHandle, Type graphType)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\DataContractSerializer.cs(376,0): at System.Runtime.Serialization.DataContractSerializer.InternalWriteObjectContent(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\DataContractSerializer.cs(237,0): at System.Runtime.Serialization.DataContractSerializer.InternalWriteObject(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializer.cs(71,0): at System.Runtime.Serialization.XmlObjectSerializer.WriteObjectHandleExceptions(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializer.cs(57,0): at System.Runtime.Serialization.XmlObjectSerializer.WriteObject(XmlDictionaryWriter writer, Object graph)
```
```
DataContractSerializerTests.DCS_ResolveNameReturnsEmptyNamespace [FAIL]
System.NullReferenceException : Object reference not set to an instance of an object.
Stack Trace:
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Runtime.Serialization.Xml\tests\SerializationTestTypes\DataContractResolverLibrary.cs(75,0): at SerializationTestTypes.EmptyNamespaceResolver.ResolveName(String typeName, String typeNamespace, Type declaredType, DataContractResolver knownTypeResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerContext.cs(276,0): at System.Runtime.Serialization.XmlObjectSerializerContext.ResolveDataContractFromKnownTypes(String typeName, String typeNs, DataContract memberTypeContract)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\KnownTypeDataContractResolver.cs(26,0): at System.Runtime.Serialization.KnownTypeDataContractResolver.TryResolveType(Type type, Type declaredType, DataContractResolver knownTypeResolver, XmlDictionaryString& typeName, XmlDictionaryString& typeNamespace)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(673,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.ResolveType(Type objectType, Type declaredType, XmlDictionaryString& typeName, XmlDictionaryString& typeNamespace)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(665,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.WriteResolvedTypeInfo(XmlWriterDelegator writer, Type objectType, Type declaredType)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(710,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.WriteTypeInfo(XmlWriterDelegator writer, DataContract contract, DataContract declaredContract)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(230,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.SerializeWithXsiType(XmlWriterDelegator xmlWriter, Object obj, RuntimeTypeHandle objectTypeHandle, Type objectType, Int32 declaredTypeID, RuntimeTypeHandle declaredTypeHandle, Type declaredType)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(143,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.InternalSerialize(XmlWriterDelegator xmlWriter, Object obj, Boolean isDeclaredType, Boolean writeXsiType, Int32 declaredTypeID, RuntimeTypeHandle declaredTypeHandle)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ReflectionClassWriter.cs(158,0): at System.Runtime.Serialization.ReflectionClassWriter.ReflectionInternalSerialize(XmlWriterDelegator xmlWriter, XmlObjectSerializerWriteContext context, Object obj, Boolean isDeclaredType, Boolean writeXsiType, Type memberType, Boolean isNullableOfT)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ReflectionClassWriter.cs(95,0): at System.Runtime.Serialization.ReflectionClassWriter.ReflectionWriteValue(XmlWriterDelegator xmlWriter, XmlObjectSerializerWriteContext context, Type type, Object value, Boolean writeXsiType, PrimitiveDataContract primitiveContractForParamType)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ReflectionXmlFormatWriter.cs(187,0): at System.Runtime.Serialization.ReflectionXmlClassWriter.ReflectionWriteMembers(XmlWriterDelegator xmlWriter, Object obj, XmlObjectSerializerWriteContext context, ClassDataContract classContract, ClassDataContract derivedMostClassContract, Int32 childElementIndex, XmlDictionaryString[] emptyStringArray)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ReflectionClassWriter.cs(35,0): at System.Runtime.Serialization.ReflectionClassWriter.ReflectionWriteClass(XmlWriterDelegator xmlWriter, Object obj, XmlObjectSerializerWriteContext context, ClassDataContract classContract, XmlDictionaryString[] memberNames)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ReflectionXmlFormatWriter.cs(20,0): at System.Runtime.Serialization.ReflectionXmlFormatWriter.ReflectionWriteClass(XmlWriterDelegator xmlWriter, Object obj, XmlObjectSerializerWriteContext context, ClassDataContract classContract)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\ClassDataContract.cs(507,0): at System.Runtime.Serialization.ClassDataContract.WriteXmlValue(XmlWriterDelegator xmlWriter, Object obj, XmlObjectSerializerWriteContext context)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(654,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.WriteDataContractValue(DataContract dataContract, XmlWriterDelegator xmlWriter, Object obj, RuntimeTypeHandle declaredTypeHandle)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializerWriteContext.cs(155,0): at System.Runtime.Serialization.XmlObjectSerializerWriteContext.SerializeWithoutXsiType(DataContract dataContract, XmlWriterDelegator xmlWriter, Object obj, RuntimeTypeHandle declaredTypeHandle)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\DataContractSerializer.cs(354,0): at System.Runtime.Serialization.DataContractSerializer.InternalWriteObjectContent(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\DataContractSerializer.cs(237,0): at System.Runtime.Serialization.DataContractSerializer.InternalWriteObject(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializer.cs(71,0): at System.Runtime.Serialization.XmlObjectSerializer.WriteObjectHandleExceptions(XmlWriterDelegator writer, Object graph, DataContractResolver dataContractResolver)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializer.cs(57,0): at System.Runtime.Serialization.XmlObjectSerializer.WriteObject(XmlDictionaryWriter writer, Object graph)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Private.DataContractSerialization\src\System\Runtime\Serialization\XmlObjectSerializer.cs(27,0): at System.Runtime.Serialization.XmlObjectSerializer.WriteObject(Stream stream, Object graph)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\Common\tests\System\Runtime\Serialization\DataContractSerializerHelper.cs(29,0): at System.Runtime.Serialization.Tests.DataContractSerializerHelper.SerializeAndDeserialize[T](T value, String baseline, DataContractSerializerSettings settings, Func`1 serializerFactory, Boolean skipStringCompare)
D:\j\workspace\x64_checked_w---b16ed97b\_\fx\src\System.Runtime.Serialization.Xml\tests\DataContractSerializer.cs(2784,0): at DataContractSerializerTests.DCS_ResolveNameReturnsEmptyNamespace()
``` | test | failures in checked windows nt corefx jobs we get the following failures in checked windows nt corefx jobs e g system diagnostics tests stackframetests ctor filename linenumber colnumber filename null linenumber columnnumber assert equal failure expected actual stack trace d j workspace checked w fx src system diagnostics stacktrace tests stackframetests cs at system diagnostics tests stackframetests verifystackframeskipframes stackframe stackframe boolean isfileconstructor skipframes methodinfo expectedmethod boolean iscurrentframe d j workspace checked w fx src system diagnostics stacktrace tests stackframetests cs at system diagnostics tests stackframetests ctor filename linenumber colnumber string filename linenumber columnnumber system diagnostics tests stackframetests ctor filename linenumber colnumber filename linenumber columnnumber assert equal failure expected actual stack trace d j workspace checked w fx src system diagnostics stacktrace tests stackframetests cs at system diagnostics tests stackframetests verifystackframeskipframes stackframe stackframe boolean isfileconstructor skipframes methodinfo expectedmethod boolean iscurrentframe d j workspace checked w fx src system diagnostics stacktrace tests stackframetests cs at system diagnostics tests stackframetests ctor filename linenumber colnumber string filename linenumber columnnumber system diagnostics tests stackframetests ctor filename linenumber colnumber filename filename linenumber columnnumber assert equal failure expected actual stack trace d j workspace checked w fx src system diagnostics stacktrace tests stackframetests cs at system diagnostics tests stackframetests verifystackframeskipframes stackframe stackframe boolean isfileconstructor skipframes methodinfo expectedmethod boolean iscurrentframe d j workspace checked w fx src system diagnostics stacktrace tests stackframetests cs at system diagnostics tests stackframetests ctor filename linenumber colnumber string filename linenumber columnnumber finished system diagnostics stacktrace tests datacontractserializertests dcs resolvedatacontractbasetype system nullreferenceexception object reference not set to an instance of an object stack trace finished system security cryptography cng tests d j workspace checked w fx src system runtime serialization xml tests serializationtesttypes datacontractresolverlibrary cs at serializationtesttypes proxydatacontractresolver resolvename string typename string typenamespace type declaredtype datacontractresolver knowntyperesolver d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializercontext cs at system runtime serialization xmlobjectserializercontext resolvedatacontractfromknowntypes string typename string typens datacontract membertypecontract d j workspace checked w fx src system private datacontractserialization src system runtime serialization knowntypedatacontractresolver cs at system runtime serialization knowntypedatacontractresolver tryresolvetype type type type declaredtype datacontractresolver knowntyperesolver xmldictionarystring typename xmldictionarystring typenamespace d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext resolvetype type objecttype type declaredtype xmldictionarystring typename xmldictionarystring typenamespace d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext writeresolvedtypeinfo xmlwriterdelegator writer type objecttype type declaredtype d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext writetypeinfo xmlwriterdelegator writer datacontract contract datacontract declaredcontract d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext serializewithxsitypeattoplevel datacontract datacontract xmlwriterdelegator xmlwriter object obj runtimetypehandle originaldeclaredtypehandle type graphtype d j workspace checked w fx src system private datacontractserialization src system runtime serialization datacontractserializer cs at system runtime serialization datacontractserializer internalwriteobjectcontent xmlwriterdelegator writer object graph datacontractresolver datacontractresolver d j workspace checked w fx src system private datacontractserialization src system runtime serialization datacontractserializer cs at system runtime serialization datacontractserializer internalwriteobject xmlwriterdelegator writer object graph datacontractresolver datacontractresolver d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializer cs at system runtime serialization xmlobjectserializer writeobjecthandleexceptions xmlwriterdelegator writer object graph datacontractresolver datacontractresolver d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializer cs at system runtime serialization xmlobjectserializer writeobject xmldictionarywriter writer object graph datacontractserializertests dcs resolvenamereturnsemptynamespace system nullreferenceexception object reference not set to an instance of an object stack trace d j workspace checked w fx src system runtime serialization xml tests serializationtesttypes datacontractresolverlibrary cs at serializationtesttypes emptynamespaceresolver resolvename string typename string typenamespace type declaredtype datacontractresolver knowntyperesolver d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializercontext cs at system runtime serialization xmlobjectserializercontext resolvedatacontractfromknowntypes string typename string typens datacontract membertypecontract d j workspace checked w fx src system private datacontractserialization src system runtime serialization knowntypedatacontractresolver cs at system runtime serialization knowntypedatacontractresolver tryresolvetype type type type declaredtype datacontractresolver knowntyperesolver xmldictionarystring typename xmldictionarystring typenamespace d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext resolvetype type objecttype type declaredtype xmldictionarystring typename xmldictionarystring typenamespace d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext writeresolvedtypeinfo xmlwriterdelegator writer type objecttype type declaredtype d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext writetypeinfo xmlwriterdelegator writer datacontract contract datacontract declaredcontract d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext serializewithxsitype xmlwriterdelegator xmlwriter object obj runtimetypehandle objecttypehandle type objecttype declaredtypeid runtimetypehandle declaredtypehandle type declaredtype d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext internalserialize xmlwriterdelegator xmlwriter object obj boolean isdeclaredtype boolean writexsitype declaredtypeid runtimetypehandle declaredtypehandle d j workspace checked w fx src system private datacontractserialization src system runtime serialization reflectionclasswriter cs at system runtime serialization reflectionclasswriter reflectioninternalserialize xmlwriterdelegator xmlwriter xmlobjectserializerwritecontext context object obj boolean isdeclaredtype boolean writexsitype type membertype boolean isnullableoft d j workspace checked w fx src system private datacontractserialization src system runtime serialization reflectionclasswriter cs at system runtime serialization reflectionclasswriter reflectionwritevalue xmlwriterdelegator xmlwriter xmlobjectserializerwritecontext context type type object value boolean writexsitype primitivedatacontract primitivecontractforparamtype d j workspace checked w fx src system private datacontractserialization src system runtime serialization reflectionxmlformatwriter cs at system runtime serialization reflectionxmlclasswriter reflectionwritemembers xmlwriterdelegator xmlwriter object obj xmlobjectserializerwritecontext context classdatacontract classcontract classdatacontract derivedmostclasscontract childelementindex xmldictionarystring emptystringarray d j workspace checked w fx src system private datacontractserialization src system runtime serialization reflectionclasswriter cs at system runtime serialization reflectionclasswriter reflectionwriteclass xmlwriterdelegator xmlwriter object obj xmlobjectserializerwritecontext context classdatacontract classcontract xmldictionarystring membernames d j workspace checked w fx src system private datacontractserialization src system runtime serialization reflectionxmlformatwriter cs at system runtime serialization reflectionxmlformatwriter reflectionwriteclass xmlwriterdelegator xmlwriter object obj xmlobjectserializerwritecontext context classdatacontract classcontract d j workspace checked w fx src system private datacontractserialization src system runtime serialization classdatacontract cs at system runtime serialization classdatacontract writexmlvalue xmlwriterdelegator xmlwriter object obj xmlobjectserializerwritecontext context d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext writedatacontractvalue datacontract datacontract xmlwriterdelegator xmlwriter object obj runtimetypehandle declaredtypehandle d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializerwritecontext cs at system runtime serialization xmlobjectserializerwritecontext serializewithoutxsitype datacontract datacontract xmlwriterdelegator xmlwriter object obj runtimetypehandle declaredtypehandle d j workspace checked w fx src system private datacontractserialization src system runtime serialization datacontractserializer cs at system runtime serialization datacontractserializer internalwriteobjectcontent xmlwriterdelegator writer object graph datacontractresolver datacontractresolver d j workspace checked w fx src system private datacontractserialization src system runtime serialization datacontractserializer cs at system runtime serialization datacontractserializer internalwriteobject xmlwriterdelegator writer object graph datacontractresolver datacontractresolver d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializer cs at system runtime serialization xmlobjectserializer writeobjecthandleexceptions xmlwriterdelegator writer object graph datacontractresolver datacontractresolver d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializer cs at system runtime serialization xmlobjectserializer writeobject xmldictionarywriter writer object graph d j workspace checked w fx src system private datacontractserialization src system runtime serialization xmlobjectserializer cs at system runtime serialization xmlobjectserializer writeobject stream stream object graph d j workspace checked w fx src common tests system runtime serialization datacontractserializerhelper cs at system runtime serialization tests datacontractserializerhelper serializeanddeserialize t value string baseline datacontractserializersettings settings func serializerfactory boolean skipstringcompare d j workspace checked w fx src system runtime serialization xml tests datacontractserializer cs at datacontractserializertests dcs resolvenamereturnsemptynamespace | 1 |
131,049 | 18,214,563,777 | IssuesEvent | 2021-09-30 01:27:06 | artsking/linux-3.0.35_CVE-2020-36386_withPatch | https://api.github.com/repos/artsking/linux-3.0.35_CVE-2020-36386_withPatch | closed | CVE-2013-1979 (Medium) detected in linux-stable-rtv3.8.6 - autoclosed | security vulnerability | ## CVE-2013-1979 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-3.0.35_CVE-2020-36386_withPatch/commit/a48614c42390737eed7321f8484e7f45cee8e2a7">a48614c42390737eed7321f8484e7f45cee8e2a7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/include/net/scm.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/include/net/scm.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/include/net/scm.h</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The scm_set_cred function in include/net/scm.h in the Linux kernel before 3.8.11 uses incorrect uid and gid values during credentials passing, which allows local users to gain privileges via a crafted application.
<p>Publish Date: 2013-05-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-1979>CVE-2013-1979</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2013-1979">https://www.linuxkernelcves.com/cves/CVE-2013-1979</a></p>
<p>Release Date: 2013-05-03</p>
<p>Fix Resolution: v3.9-rc8,v3.2.44</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2013-1979 (Medium) detected in linux-stable-rtv3.8.6 - autoclosed - ## CVE-2013-1979 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-3.0.35_CVE-2020-36386_withPatch/commit/a48614c42390737eed7321f8484e7f45cee8e2a7">a48614c42390737eed7321f8484e7f45cee8e2a7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/include/net/scm.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/include/net/scm.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/include/net/scm.h</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The scm_set_cred function in include/net/scm.h in the Linux kernel before 3.8.11 uses incorrect uid and gid values during credentials passing, which allows local users to gain privileges via a crafted application.
<p>Publish Date: 2013-05-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-1979>CVE-2013-1979</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2013-1979">https://www.linuxkernelcves.com/cves/CVE-2013-1979</a></p>
<p>Release Date: 2013-05-03</p>
<p>Fix Resolution: v3.9-rc8,v3.2.44</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in linux stable autoclosed cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files include net scm h include net scm h include net scm h vulnerability details the scm set cred function in include net scm h in the linux kernel before uses incorrect uid and gid values during credentials passing which allows local users to gain privileges via a crafted application publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
341,378 | 30,584,307,226 | IssuesEvent | 2023-07-21 12:13:59 | ooni/probe | https://api.github.com/repos/ooni/probe | opened | android: no prompt to enable notifications | bug testing ooni/probe-mobile priority/high platform/android needs investigation | **Describe the bug**
It seems I cannot get the app to prompt me to enable notifications in the system settings.
**To Reproduce**
I compiled the app for myself using the procedure at https://github.com/ooni/probe/issues/2504 (which entails using a custom signing key as opposed to the official one—perhaps we can improve this part of the process?). I installed the app accepting all the default settings. I verified that the settings did not contain notifications enabled for OONI Probe. I went into the settings were notifications were not enabled. I clicked to enable notifications but the settings still showed the notifications as disabled.
**Expected behavior**
Per the pre-release check-list that I am following, I should be prompted like I am prompted when I enable running in the background, i.e., with a system settings popup asking me to enable notifications.
**Screenshots**


**System information (please complete the following information):**
- Device: Pixel 4a
- OS: Android 13
- OONI Probe version: https://github.com/ooni/probe-android/commit/36b29ca15d590a35ee8423a7c84e1377b4eda33b
**Additional context**
I wonder whether linking a library for a functionality we do not use (i.e., notifications) is preferable over removing this dependency considering that we do seldomly use this functionality and we're not sure whether it would even work in countries with lots of censorship.
| 1.0 | android: no prompt to enable notifications - **Describe the bug**
It seems I cannot get the app to prompt me to enable notifications in the system settings.
**To Reproduce**
I compiled the app for myself using the procedure at https://github.com/ooni/probe/issues/2504 (which entails using a custom signing key as opposed to the official one—perhaps we can improve this part of the process?). I installed the app accepting all the default settings. I verified that the settings did not contain notifications enabled for OONI Probe. I went into the settings were notifications were not enabled. I clicked to enable notifications but the settings still showed the notifications as disabled.
**Expected behavior**
Per the pre-release check-list that I am following, I should be prompted like I am prompted when I enable running in the background, i.e., with a system settings popup asking me to enable notifications.
**Screenshots**


**System information (please complete the following information):**
- Device: Pixel 4a
- OS: Android 13
- OONI Probe version: https://github.com/ooni/probe-android/commit/36b29ca15d590a35ee8423a7c84e1377b4eda33b
**Additional context**
I wonder whether linking a library for a functionality we do not use (i.e., notifications) is preferable over removing this dependency considering that we do seldomly use this functionality and we're not sure whether it would even work in countries with lots of censorship.
| test | android no prompt to enable notifications describe the bug it seems i cannot get the app to prompt me to enable notifications in the system settings to reproduce i compiled the app for myself using the procedure at which entails using a custom signing key as opposed to the official one mdash perhaps we can improve this part of the process i installed the app accepting all the default settings i verified that the settings did not contain notifications enabled for ooni probe i went into the settings were notifications were not enabled i clicked to enable notifications but the settings still showed the notifications as disabled expected behavior per the pre release check list that i am following i should be prompted like i am prompted when i enable running in the background i e with a system settings popup asking me to enable notifications screenshots system information please complete the following information device pixel os android ooni probe version additional context i wonder whether linking a library for a functionality we do not use i e notifications is preferable over removing this dependency considering that we do seldomly use this functionality and we re not sure whether it would even work in countries with lots of censorship | 1 |
65,327 | 6,955,851,090 | IssuesEvent | 2017-12-07 09:26:20 | ElliotAOram/GhostPyramid | https://api.github.com/repos/ElliotAOram/GhostPyramid | closed | Improve code coverage | Testing | Improve code coverage of unit tests. Currently there are some functions that are not being unit tested, these include:
* [ ] `process_and_output_video`
* [x] `run_vpa.py`
These should be unit tested or at least get improved test coverage if not possible. | 1.0 | Improve code coverage - Improve code coverage of unit tests. Currently there are some functions that are not being unit tested, these include:
* [ ] `process_and_output_video`
* [x] `run_vpa.py`
These should be unit tested or at least get improved test coverage if not possible. | test | improve code coverage improve code coverage of unit tests currently there are some functions that are not being unit tested these include process and output video run vpa py these should be unit tested or at least get improved test coverage if not possible | 1 |
320,057 | 27,419,869,960 | IssuesEvent | 2023-03-01 16:02:03 | WPChill/download-monitor | https://api.github.com/repos/WPChill/download-monitor | closed | PHP fatal errorr when using together with WPML and Toolset Types | Bug needs testing | **Describe the bug**
When using combined with WPML and Toolset Types, the plugin can fire a PHP fatal error as the current WPML language might be switched to `all` before firing a query, but not restored afterward.
**To Reproduce**
Steps to reproduce the behavior:
1. Using Toolset Types, generate at least two post types A and B, and define a relationship between A and B, be it one-to-one, one-to-many or many-to-many, as described [in this documentation](https://toolset.com/course-lesson/how-to-set-up-post-relationships-in-wordpress/). Also, generate a field group for the A post type, and include a WYSIWYG field on it, as described [in this documentation](https://toolset.com/course-lesson/creating-custom-fields/).
2. Create at least one post of type A, Apost, and one post of type B, Bpost, and connect them over the relationship created earlier.
3. Create a download using the Download Monitor plugin.
4. Include the `[download...]` shortcode for that download in the WYSIWYG field content for the Apost post, and save the post in the editor.
5. Reload the post editor page and see that it fires a PHP fatal error and the page goes blank.
**Expected behavior**
The post edit page should load properly.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Extensions installed and activated:**
- [ ] Advanced Access Manager
- [ ] Amazon S3
- [ ] Buttons
- [ ] Captcha
- [ ] CSV Exporter
- [ ] CSV Importer
- [ ] Downloading Page
- [ ] Email lock
- [ ] Email Notifications
- [ ] Google Drive
- [ ] Gravity Forms
- [ ] Mailchimp
- [ ] Ninja Forms
- [ ] Page Addon
- [ ] Terms & Conditions
- [ ] Twitter Lock
**Additional context**
I am the main developer of the Toolset set of plugins, as well as part of the WPML Compatibility team. I have debugged the issue and found the root cause for it, so a Pull request addressing the problem is going to be ready and open in the next minutes and linked here. In it, I will basically:
- Review the code used to switch languages, so it uses proper WPML APIs.
- Restore the language to the current one after the operation that requires the switching is done.
I have tested the fix myself and it seems to solve the issue without introducing any extra problems.
| 1.0 | PHP fatal errorr when using together with WPML and Toolset Types - **Describe the bug**
When using combined with WPML and Toolset Types, the plugin can fire a PHP fatal error as the current WPML language might be switched to `all` before firing a query, but not restored afterward.
**To Reproduce**
Steps to reproduce the behavior:
1. Using Toolset Types, generate at least two post types A and B, and define a relationship between A and B, be it one-to-one, one-to-many or many-to-many, as described [in this documentation](https://toolset.com/course-lesson/how-to-set-up-post-relationships-in-wordpress/). Also, generate a field group for the A post type, and include a WYSIWYG field on it, as described [in this documentation](https://toolset.com/course-lesson/creating-custom-fields/).
2. Create at least one post of type A, Apost, and one post of type B, Bpost, and connect them over the relationship created earlier.
3. Create a download using the Download Monitor plugin.
4. Include the `[download...]` shortcode for that download in the WYSIWYG field content for the Apost post, and save the post in the editor.
5. Reload the post editor page and see that it fires a PHP fatal error and the page goes blank.
**Expected behavior**
The post edit page should load properly.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Extensions installed and activated:**
- [ ] Advanced Access Manager
- [ ] Amazon S3
- [ ] Buttons
- [ ] Captcha
- [ ] CSV Exporter
- [ ] CSV Importer
- [ ] Downloading Page
- [ ] Email lock
- [ ] Email Notifications
- [ ] Google Drive
- [ ] Gravity Forms
- [ ] Mailchimp
- [ ] Ninja Forms
- [ ] Page Addon
- [ ] Terms & Conditions
- [ ] Twitter Lock
**Additional context**
I am the main developer of the Toolset set of plugins, as well as part of the WPML Compatibility team. I have debugged the issue and found the root cause for it, so a Pull request addressing the problem is going to be ready and open in the next minutes and linked here. In it, I will basically:
- Review the code used to switch languages, so it uses proper WPML APIs.
- Restore the language to the current one after the operation that requires the switching is done.
I have tested the fix myself and it seems to solve the issue without introducing any extra problems.
| test | php fatal errorr when using together with wpml and toolset types describe the bug when using combined with wpml and toolset types the plugin can fire a php fatal error as the current wpml language might be switched to all before firing a query but not restored afterward to reproduce steps to reproduce the behavior using toolset types generate at least two post types a and b and define a relationship between a and b be it one to one one to many or many to many as described also generate a field group for the a post type and include a wysiwyg field on it as described create at least one post of type a apost and one post of type b bpost and connect them over the relationship created earlier create a download using the download monitor plugin include the shortcode for that download in the wysiwyg field content for the apost post and save the post in the editor reload the post editor page and see that it fires a php fatal error and the page goes blank expected behavior the post edit page should load properly screenshots if applicable add screenshots to help explain your problem extensions installed and activated advanced access manager amazon buttons captcha csv exporter csv importer downloading page email lock email notifications google drive gravity forms mailchimp ninja forms page addon terms conditions twitter lock additional context i am the main developer of the toolset set of plugins as well as part of the wpml compatibility team i have debugged the issue and found the root cause for it so a pull request addressing the problem is going to be ready and open in the next minutes and linked here in it i will basically review the code used to switch languages so it uses proper wpml apis restore the language to the current one after the operation that requires the switching is done i have tested the fix myself and it seems to solve the issue without introducing any extra problems | 1 |
39,462 | 5,234,228,368 | IssuesEvent | 2017-01-30 15:09:59 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | github.com/cockroachdb/cockroach/pkg/kv: TestMultiRangeBoundedBatchDelRange failed under stress | Robot test-failure | SHA: https://github.com/cockroachdb/cockroach/commits/4c53128707d07d268833ff5ccb5acee9d8720544
Parameters:
```
COCKROACH_PROPOSER_EVALUATED_KV=false
TAGS=deadlock
GOFLAGS=
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=133235&tab=buildLog
```
W170130 10:59:53.869182 3033487 server/status/runtime.go:116 Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I170130 10:59:53.870725 3033487 server/config.go:456 1 storage engine initialized
I170130 10:59:53.872651 3033487 server/node.go:444 [n?] store [n0,s0] not bootstrapped
I170130 10:59:53.877526 3033996 storage/replica.go:4339 [n?,s1,r1/1:/M{in-ax},@c42581fb00] gossip not initialized
I170130 10:59:53.879883 3033487 server/node.go:373 [n?] **** cluster 0a228cab-5f55-4596-9d31-728e5767e5e8 has been created
I170130 10:59:53.879937 3033487 server/node.go:374 [n?] **** add additional nodes by specifying --join=127.0.0.1:38452
I170130 10:59:53.886319 3033487 server/node.go:457 [n1] initialized store [n1,s1]: {Capacity:536870912 Available:536870912 RangeCount:1 LeaseCount:1}
I170130 10:59:53.886561 3033487 server/node.go:342 [n1] node ID 1 initialized
I170130 10:59:53.886774 3033487 gossip/gossip.go:293 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:38452" > attrs:<> locality:<>
I170130 10:59:53.887234 3033487 storage/stores.go:296 [n1] read 0 node addresses from persistent storage
I170130 10:59:53.887426 3033487 server/node.go:589 [n1] connecting to gossip network to verify cluster ID...
I170130 10:59:53.887564 3033487 server/node.go:613 [n1] node connected via gossip and verified as part of cluster "0a228cab-5f55-4596-9d31-728e5767e5e8"
I170130 10:59:53.887729 3033487 server/node.go:392 [n1] node=1: started with [[]=] engine(s) and attributes []
I170130 10:59:53.888761 3033487 sql/executor.go:332 [n1] creating distSQLPlanner with address {tcp 127.0.0.1:38452}
I170130 10:59:53.895079 3033487 server/server.go:629 [n1] starting https server at 127.0.0.1:35922
I170130 10:59:53.895206 3033487 server/server.go:630 [n1] starting grpc/postgres server at 127.0.0.1:38452
I170130 10:59:53.895307 3033487 server/server.go:631 [n1] advertising CockroachDB node at 127.0.0.1:38452
I170130 10:59:53.905669 3034938 sql/event_log.go:95 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:38452} Attrs: Locality:} ClusterID:0a228cab-5f55-4596-9d31-728e5767e5e8 StartedAt:1485773993887678801}
I170130 10:59:53.920507 3033487 sql/event_log.go:95 [n1] Event: "alter_table", target: 12, info: {TableName:eventlog Statement:ALTER TABLE system.eventlog ALTER COLUMN uniqueID SET DEFAULT uuid_v4() User:node MutationID:0 CascadeDroppedViews:[]}
I170130 10:59:53.978277 3033487 server/server.go:686 [n1] done ensuring all necessary migrations have run
I170130 10:59:53.978341 3033487 server/server.go:688 [n1] serving sql connections
I170130 11:00:04.087838 3036044 vendor/google.golang.org/grpc/transport/http2_client.go:1123 transport: http2Client.notifyError got notified that the client transport was broken EOF.
I170130 11:00:04.087901 3035483 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:38452->127.0.0.1:40236: use of closed network connection
test_server_shim.go:133: had 1 ranges at startup, expected 6
``` | 1.0 | github.com/cockroachdb/cockroach/pkg/kv: TestMultiRangeBoundedBatchDelRange failed under stress - SHA: https://github.com/cockroachdb/cockroach/commits/4c53128707d07d268833ff5ccb5acee9d8720544
Parameters:
```
COCKROACH_PROPOSER_EVALUATED_KV=false
TAGS=deadlock
GOFLAGS=
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=133235&tab=buildLog
```
W170130 10:59:53.869182 3033487 server/status/runtime.go:116 Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I170130 10:59:53.870725 3033487 server/config.go:456 1 storage engine initialized
I170130 10:59:53.872651 3033487 server/node.go:444 [n?] store [n0,s0] not bootstrapped
I170130 10:59:53.877526 3033996 storage/replica.go:4339 [n?,s1,r1/1:/M{in-ax},@c42581fb00] gossip not initialized
I170130 10:59:53.879883 3033487 server/node.go:373 [n?] **** cluster 0a228cab-5f55-4596-9d31-728e5767e5e8 has been created
I170130 10:59:53.879937 3033487 server/node.go:374 [n?] **** add additional nodes by specifying --join=127.0.0.1:38452
I170130 10:59:53.886319 3033487 server/node.go:457 [n1] initialized store [n1,s1]: {Capacity:536870912 Available:536870912 RangeCount:1 LeaseCount:1}
I170130 10:59:53.886561 3033487 server/node.go:342 [n1] node ID 1 initialized
I170130 10:59:53.886774 3033487 gossip/gossip.go:293 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:38452" > attrs:<> locality:<>
I170130 10:59:53.887234 3033487 storage/stores.go:296 [n1] read 0 node addresses from persistent storage
I170130 10:59:53.887426 3033487 server/node.go:589 [n1] connecting to gossip network to verify cluster ID...
I170130 10:59:53.887564 3033487 server/node.go:613 [n1] node connected via gossip and verified as part of cluster "0a228cab-5f55-4596-9d31-728e5767e5e8"
I170130 10:59:53.887729 3033487 server/node.go:392 [n1] node=1: started with [[]=] engine(s) and attributes []
I170130 10:59:53.888761 3033487 sql/executor.go:332 [n1] creating distSQLPlanner with address {tcp 127.0.0.1:38452}
I170130 10:59:53.895079 3033487 server/server.go:629 [n1] starting https server at 127.0.0.1:35922
I170130 10:59:53.895206 3033487 server/server.go:630 [n1] starting grpc/postgres server at 127.0.0.1:38452
I170130 10:59:53.895307 3033487 server/server.go:631 [n1] advertising CockroachDB node at 127.0.0.1:38452
I170130 10:59:53.905669 3034938 sql/event_log.go:95 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:38452} Attrs: Locality:} ClusterID:0a228cab-5f55-4596-9d31-728e5767e5e8 StartedAt:1485773993887678801}
I170130 10:59:53.920507 3033487 sql/event_log.go:95 [n1] Event: "alter_table", target: 12, info: {TableName:eventlog Statement:ALTER TABLE system.eventlog ALTER COLUMN uniqueID SET DEFAULT uuid_v4() User:node MutationID:0 CascadeDroppedViews:[]}
I170130 10:59:53.978277 3033487 server/server.go:686 [n1] done ensuring all necessary migrations have run
I170130 10:59:53.978341 3033487 server/server.go:688 [n1] serving sql connections
I170130 11:00:04.087838 3036044 vendor/google.golang.org/grpc/transport/http2_client.go:1123 transport: http2Client.notifyError got notified that the client transport was broken EOF.
I170130 11:00:04.087901 3035483 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:38452->127.0.0.1:40236: use of closed network connection
test_server_shim.go:133: had 1 ranges at startup, expected 6
``` | test | github com cockroachdb cockroach pkg kv testmultirangeboundedbatchdelrange failed under stress sha parameters cockroach proposer evaluated kv false tags deadlock goflags stress build found a failed test server status runtime go could not parse build timestamp parsing time as cannot parse as server config go storage engine initialized server node go store not bootstrapped storage replica go gossip not initialized server node go cluster has been created server node go add additional nodes by specifying join server node go initialized store capacity available rangecount leasecount server node go node id initialized gossip gossip go nodedescriptor set to node id address attrs locality storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster server node go node started with engine s and attributes sql executor go creating distsqlplanner with address tcp server server go starting https server at server server go starting grpc postgres server at server server go advertising cockroachdb node at sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs locality clusterid startedat sql event log go event alter table target info tablename eventlog statement alter table system eventlog alter column uniqueid set default uuid user node mutationid cascadedroppedviews server server go done ensuring all necessary migrations have run server server go serving sql connections vendor google golang org grpc transport client go transport notifyerror got notified that the client transport was broken eof vendor google golang org grpc transport server go transport handlestreams failed to read frame read tcp use of closed network connection test server shim go had ranges at startup expected | 1 |
745,668 | 25,994,386,631 | IssuesEvent | 2022-12-20 10:20:17 | bounswe/bounswe2022group2 | https://api.github.com/repos/bounswe/bounswe2022group2 | opened | Mobile: Back-end Connection of Get Events | priority-medium status-new mobile back-end | ### Issue Description
I have already implemented the event screen and item statically in the mobile part. You can see the details under issues #583 and #750. Nextly, our back-end team will implement the corresponding get events endpoint for this feature or embed events into post items. Therefore, after the endpoints are created by the back-end team, I will add the integration of this endpoint into our service and get events from the back-end also.
### Step Details
Steps that will be performed:
- [ ] Analyze the request model determined by the back-end
- [ ] Analyze the response model determined by the back-end
- [ ] Adjust the event model accordingly
- [ ] Create get events endpoint in our service
- [ ] Integrate the service into the events part
### Final Actions
I will test the implementation and widgets created on my real phone. If everything works, I will open a pull request. If the pull request is approved by at least one teammate, I will merge it and close the issue.
### Deadline of the Issue
25.12.2022 - Sunday [23.59]
### Reviewer
Onur Kömürcü
### Deadline for the Review
26.12.2022 - Monday [23.59] | 1.0 | Mobile: Back-end Connection of Get Events - ### Issue Description
I have already implemented the event screen and item statically in the mobile part. You can see the details under issues #583 and #750. Nextly, our back-end team will implement the corresponding get events endpoint for this feature or embed events into post items. Therefore, after the endpoints are created by the back-end team, I will add the integration of this endpoint into our service and get events from the back-end also.
### Step Details
Steps that will be performed:
- [ ] Analyze the request model determined by the back-end
- [ ] Analyze the response model determined by the back-end
- [ ] Adjust the event model accordingly
- [ ] Create get events endpoint in our service
- [ ] Integrate the service into the events part
### Final Actions
I will test the implementation and widgets created on my real phone. If everything works, I will open a pull request. If the pull request is approved by at least one teammate, I will merge it and close the issue.
### Deadline of the Issue
25.12.2022 - Sunday [23.59]
### Reviewer
Onur Kömürcü
### Deadline for the Review
26.12.2022 - Monday [23.59] | non_test | mobile back end connection of get events issue description i have already implemented the event screen and item statically in the mobile part you can see the details under issues and nextly our back end team will implement the corresponding get events endpoint for this feature or embed events into post items therefore after the endpoints are created by the back end team i will add the integration of this endpoint into our service and get events from the back end also step details steps that will be performed analyze the request model determined by the back end analyze the response model determined by the back end adjust the event model accordingly create get events endpoint in our service integrate the service into the events part final actions i will test the implementation and widgets created on my real phone if everything works i will open a pull request if the pull request is approved by at least one teammate i will merge it and close the issue deadline of the issue sunday reviewer onur kömürcü deadline for the review monday | 0 |
197,361 | 14,920,192,483 | IssuesEvent | 2021-01-23 03:20:59 | eclipse/openj9 | https://api.github.com/repos/eclipse/openj9 | closed | DaaLoadTest ConcurrentScavenge segfault or assert | comp:jit segfault test failure | Changes from previous build
https://github.com/eclipse/openj9-omr/compare/d2a0060e...bded46c
https://github.com/eclipse/openj9/compare/56d0a4a...a6756ee
https://ci.eclipse.org/openj9/job/Test_openjdk8_j9_sanity.system_ppc64le_linux_xl_Nightly_testList_0/34
DaaLoadTest_daa1_ConcurrentScavenge_0
```
LT stderr Unhandled exception
DLT stderr Type=Segmentation error vmState=0x00000000
DLT stderr J9Generic_Signal_Number=00000018 Signal_Number=0000000b Error_Value=00000000 Signal_Code=00000001
DLT stderr Handler1=00003FFFA922EDA0 Handler2=00003FFFA9083640
DLT stderr R0=00003FFFA8921A44 R1=00003FFF110CB800 R2=00003FFFA89E5600 R3=00003FFFA403DC70
DLT stderr R4=00003FFFA47F74E8 R5=00003FFF110CBAF0 R6=00003FFF110CB8D8 R7=00003FFF110CB8E0
DLT stderr R8=00003FFF110CB8E8 R9=00003FFFA4014978 R10=00003FFFA403DBE0 R11=00003FFFA3CE1378
DLT stderr R12=0000000000004400 R13=00003FFF110D6900 R14=00003FFE6C008290 R15=00003FFFA47F5800
DLT stderr R16=00003FFF02F00038 R17=0000000000000009 R18=00003FFF8342BD90 R19=00000000001A4EE9
DLT stderr R20=0000000000000040 R21=000000000000000A R22=0000000000000000 R23=0000000000000000
DLT stderr R24=0000000000000018 R25=00003FFFA403DBE0 R26=00003FFF110CB8D8 R27=00003FFF110CBAF0
DLT stderr R28=00003FFF110CBAF0 R29=00003FFF110CB8E8 R30=00003FFF110CB8E0 R31=0000000000000000
DLT stderr NIP=00003FFFA895C354 MSR=800000010280F033 ORIG_GPR3=00000000000081C8 CTR=00003FFFA8921880
DLT stderr LINK=00003FFFA88AC5A8 XER=0000000000000000 CCR=0000000028004482 SOFTE=0000000000000001
DLT stderr TRAP=0000000000000300 DAR=0000000000000018 dsisr=0000000040000000 RESULT=0000000000000000
DLT stderr FPR0 3fa99999a0000000 (f: 2684354560.000000, d: 5.000000e-02)
DLT stderr FPR1 4059c56e60000000 (f: 1610612736.000000, d: 1.030849e+02)
DLT stderr FPR2 408f400000000000 (f: 0.000000, d: 1.000000e+03)
DLT stderr FPR3 3fc7466496cb03de (f: 2529887232.000000, d: 1.818357e-01)
DLT stderr FPR4 3fcc71c51d8e78af (f: 495876256.000000, d: 2.222220e-01)
DLT stderr FPR5 3fd2492494229359 (f: 2485293824.000000, d: 2.857143e-01)
DLT stderr FPR6 3f59f07ca0000000 (f: 2684354560.000000, d: 1.583215e-03)
DLT stderr FPR7 3ec506d200000000 (f: 0.000000, d: 2.506571e-06)
DLT stderr FPR8 0034003900390037 (f: 3735607.000000, d: 1.112585e-307)
DLT stderr FPR9 0030003000350039 (f: 3473465.000000, d: 8.900703e-308)
DLT stderr FPR10 0031003600320034 (f: 3276852.000000, d: 9.457022e-308)
DLT stderr FPR11 37f9801900000000 (f: 0.000000, d: 4.683680e-39)
DLT stderr FPR12 3ff0000000000000 (f: 0.000000, d: 1.000000e+00)
DLT stderr FPR13 401cef5faed65272 (f: 2933281280.000000, d: 7.233763e+00)
DLT stderr FPR14 3fe62e42fefa39ef (f: 4277811712.000000, d: 6.931472e-01)
DLT stderr FPR15 4072d07adcbbbd22 (f: 3703291136.000000, d: 3.010300e+02)
DLT stderr FPR16 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR17 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR18 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR19 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR20 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR21 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR22 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR23 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR24 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR25 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR26 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR27 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR28 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR29 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR30 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR31 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr Module=/home/jenkins/workspace/Test_openjdk8_j9_sanity.system_ppc64le_linux_xl_Nightly_testList_0/openjdkbinary/j2sdk-image/jre/lib/ppc64le/default/libj9gc29.so
DLT stderr Module_base_address=00003FFFA86C0000
DLT stderr Target=2_90_20210108_402 (Linux 4.4.0-173-generic)
DLT stderr CPU=ppc64le (16 logical CPUs) (0x1fe090000 RAM)
DLT stderr ----------- Stack Backtrace -----------
DLT stderr (0x00003FFFA895C354 [libj9gc29.so+0x29c354])
DLT stderr (0x00003FFF110CB850 [<unknown>+0x0])
DLT stderr (0x00003FFF110CB990 [<unknown>+0x0])
DLT stderr (0x00003FFFA8921A44 [libj9gc29.so+0x261a44])
DLT stderr (0x00003FFFA870AFA4 [libj9gc29.so+0x4afa4])
DLT stderr (0x00003FFFA3CE140C [libj9jit29.so+0xac140c])
DLT stderr (0x00003FFFA920DB64 [libj9vm29.so+0x8db64])
DLT stderr (0x00003FFFA9284EF0 [libj9vm29.so+0x104ef0])
DLT stderr (0x00003FFFA9084A48 [libj9prt29.so+0x34a48])
DLT stderr (0x00003FFFA92805A4 [libj9vm29.so+0x1005a4])
DLT stderr (0x00003FFFA91513C8 [libj9thr29.so+0x113c8])
DLT stderr (0x00003FFFA9F78040 [libpthread.so.0+0x8040])
DLT stderr clone+0x98 (0x00003FFFA9E53BB0 [libc.so.6+0x123bb0])
DLT stderr ---------------------------------------
```
https://ci.eclipse.org/openj9/job/Test_openjdk8_j9_sanity.system_s390x_linux_xl_Nightly_testList_0/37/
DaaLoadTest_daa1_ConcurrentScavenge_0
```
DLT stderr Corruption in Evacuate at 000003FFB338F1A8: calculated object size 4396758518964 larger then available 3672, Forwarded Header at 000003FFB9F7DD28
DLT stderr 04:09:27.813 0x3ffb451c600 j9mm.141 * ** ASSERTION FAILED ** at Scavenger.cpp:1482: ((false))
```
https://ci.eclipse.org/openj9/job/Test_openjdk8_j9_sanity.system_x86-64_linux_xl_Nightly_testList_1/34/
DaaLoadTest_daa1_ConcurrentScavenge_0
```
DLT stderr Unhandled exception
DLT stderr Type=Segmentation error vmState=0x00000000
DLT stderr J9Generic_Signal_Number=00000018 Signal_Number=0000000b Error_Value=00000000 Signal_Code=00000001
DLT stderr Handler1=00007FE874A22A60 Handler2=00007FE874305020 InaccessibleAddress=000000000000001A
DLT stderr RDI=00007FE87003DE40 RSI=00007FE870790DD8 RAX=00007FE870014A00 RBX=0000000000000000
DLT stderr RCX=00007FE75CEC28D8 RDX=00007FE75CEC2A50 R8=00007FE75CEC28E0 R9=00007FE87003DDB0
DLT stderr R10=0000000000000018 R11=0000000000000012 R12=00007FE75CEC28E0 R13=00007FE75CEC28E8
DLT stderr R14=00007FE75CEC2A50 R15=00007FE75CEC28D8
DLT stderr RIP=00007FE86DD8AAA8 GS=0000 FS=0000 RSP=00007FE75CEC2840
DLT stderr EFlags=0000000000010246 CS=0033 RBP=00007FE75CEC2A50 ERR=0000000000000004
DLT stderr TRAPNO=000000000000000E OLDMASK=0000000000000000 CR2=000000000000001A
DLT stderr xmm0 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr xmm1 000000003e3ab283 (f: 1044034176.000000, d: 5.158214e-315)
DLT stderr xmm2 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr xmm3 0000000041895736 (f: 1099519744.000000, d: 5.432350e-315)
DLT stderr xmm4 000000003eccce04 (f: 1053609472.000000, d: 5.205522e-315)
DLT stderr xmm5 00000000396d7337 (f: 963474240.000000, d: 4.760195e-315)
DLT stderr xmm6 3fc5f4847813d081 (f: 2014564480.000000, d: 1.715246e-01)
DLT stderr xmm7 00000000be1cc98c (f: 3189557760.000000, d: 1.575851e-314)
DLT stderr xmm8 401cef5faed65272 (f: 2933281280.000000, d: 7.233763e+00)
DLT stderr xmm9 4072d07adcbbbd22 (f: 3703291136.000000, d: 3.010300e+02)
DLT stderr xmm10 bfb745d1745d1746 (f: 1952257920.000000, d: -9.090909e-02)
DLT stderr xmm11 bfd180bb4b651000 (f: 1264914432.000000, d: -2.734822e-01)
DLT stderr xmm12 3f80ecf4c2a50800 (f: 3265595392.000000, d: 8.264458e-03)
DLT stderr xmm13 4008000000000000 (f: 0.000000, d: 3.000000e+00)
DLT stderr xmm14 4020000000000000 (f: 0.000000, d: 8.000000e+00)
DLT stderr xmm15 0000000047054a50 (f: 1191529088.000000, d: 5.886936e-315)
DLT stderr Module=/home/jenkins/workspace/Test_openjdk8_j9_sanity.system_x86-64_linux_xl_Nightly_testList_1/openjdkbinary/j2sdk-image/jre/lib/amd64/default/libj9gc29.so
DLT stderr Module_base_address=00007FE86DB74000
DLT stderr Target=2_90_20210108_617 (Linux 4.4.0-140-generic)
DLT stderr CPU=amd64 (8 logical CPUs) (0x3eae99000 RAM)
DLT stderr ----------- Stack Backtrace -----------
DLT stderr (0x00007FE86DD8AAA8 [libj9gc29.so+0x216aa8])
DLT stderr (0x00007FE86DCF37C2 [libj9gc29.so+0x17f7c2])
DLT stderr (0x00007FE86DD5C436 [libj9gc29.so+0x1e8436])
DLT stderr (0x00007FE86E9A40D1 [libj9jit29.so+0x9570d1])
```
https://ci.eclipse.org/openj9/job/Test_openjdk8_j9_sanity.system_x86-64_linux_xl_Nightly_testList_0/34
DaaLoadTest_daa2_ConcurrentScavenge_0
```
DLT stderr Corruption in Evacuate at 00007F3537145BB8: calculated object size 15762826332667967 larger then available 1025096, Forwarded Header at 00007F336C7DCA50
DLT stderr 04:14:34.953 0x7f3538785500 j9mm.141 * ** ASSERTION FAILED ** at Scavenger.cpp:1447: ((false))
```
https://ci.eclipse.org/openj9/job/Test_openjdk11_j9_sanity.system_ppc64_aix_xl_Nightly_testList_1/32/
DaaLoadTest_daa1_ConcurrentScavenge_0
```
DLT stderr Bad scan type for object pointer 0A00000070013BA0
DLT stderr 09:04:02.333 0x100224f2200 j9mm.141 * ** ASSERTION FAILED ** at /home/jenkins/workspace/Build_JDK11_ppc64_aix_xl_Nightly/openj9/runtime/gc_glue_java/ScavengerDelegate.cpp:390: ((false))
```
https://ci.eclipse.org/openj9/job/Test_openjdk11_j9_extended.system_s390x_linux_xl_Nightly_testList_1/35/
DaaLoadTest_all_ConcurrentScavenge_0
```
DLT stderr Corruption in Evacuate at 000003FF8103F2A8: calculated object size 79087527788568 larger then available 3416, Forwarded Header at 000003FF83AFDD28
DLT stderr 06:42:56.113 0x3ff84335a00 j9mm.141 * ** ASSERTION FAILED ** at /home/jenkins/workspace/Build_JDK11_s390x_linux_xl_Nightly/omr/gc/base/standard/Scavenger.cpp:1482: ((false))
```
https://ci.eclipse.org/openj9/job/Test_openjdk11_j9_sanity.system_x86-64_linux_xl_Nightly_testList_1/33/
DaaLoadTest_daa1_ConcurrentScavenge_0
```
DLT stderr Bad scan type for object pointer 00007EFF12FE71C0
DLT stderr 07:10:51.920 0x7efeac003a00 j9mm.141 * ** ASSERTION FAILED ** at /home/jenkins/workspace/Build_JDK11_x86-6
``` | 1.0 | DaaLoadTest ConcurrentScavenge segfault or assert - Changes from previous build
https://github.com/eclipse/openj9-omr/compare/d2a0060e...bded46c
https://github.com/eclipse/openj9/compare/56d0a4a...a6756ee
https://ci.eclipse.org/openj9/job/Test_openjdk8_j9_sanity.system_ppc64le_linux_xl_Nightly_testList_0/34
DaaLoadTest_daa1_ConcurrentScavenge_0
```
LT stderr Unhandled exception
DLT stderr Type=Segmentation error vmState=0x00000000
DLT stderr J9Generic_Signal_Number=00000018 Signal_Number=0000000b Error_Value=00000000 Signal_Code=00000001
DLT stderr Handler1=00003FFFA922EDA0 Handler2=00003FFFA9083640
DLT stderr R0=00003FFFA8921A44 R1=00003FFF110CB800 R2=00003FFFA89E5600 R3=00003FFFA403DC70
DLT stderr R4=00003FFFA47F74E8 R5=00003FFF110CBAF0 R6=00003FFF110CB8D8 R7=00003FFF110CB8E0
DLT stderr R8=00003FFF110CB8E8 R9=00003FFFA4014978 R10=00003FFFA403DBE0 R11=00003FFFA3CE1378
DLT stderr R12=0000000000004400 R13=00003FFF110D6900 R14=00003FFE6C008290 R15=00003FFFA47F5800
DLT stderr R16=00003FFF02F00038 R17=0000000000000009 R18=00003FFF8342BD90 R19=00000000001A4EE9
DLT stderr R20=0000000000000040 R21=000000000000000A R22=0000000000000000 R23=0000000000000000
DLT stderr R24=0000000000000018 R25=00003FFFA403DBE0 R26=00003FFF110CB8D8 R27=00003FFF110CBAF0
DLT stderr R28=00003FFF110CBAF0 R29=00003FFF110CB8E8 R30=00003FFF110CB8E0 R31=0000000000000000
DLT stderr NIP=00003FFFA895C354 MSR=800000010280F033 ORIG_GPR3=00000000000081C8 CTR=00003FFFA8921880
DLT stderr LINK=00003FFFA88AC5A8 XER=0000000000000000 CCR=0000000028004482 SOFTE=0000000000000001
DLT stderr TRAP=0000000000000300 DAR=0000000000000018 dsisr=0000000040000000 RESULT=0000000000000000
DLT stderr FPR0 3fa99999a0000000 (f: 2684354560.000000, d: 5.000000e-02)
DLT stderr FPR1 4059c56e60000000 (f: 1610612736.000000, d: 1.030849e+02)
DLT stderr FPR2 408f400000000000 (f: 0.000000, d: 1.000000e+03)
DLT stderr FPR3 3fc7466496cb03de (f: 2529887232.000000, d: 1.818357e-01)
DLT stderr FPR4 3fcc71c51d8e78af (f: 495876256.000000, d: 2.222220e-01)
DLT stderr FPR5 3fd2492494229359 (f: 2485293824.000000, d: 2.857143e-01)
DLT stderr FPR6 3f59f07ca0000000 (f: 2684354560.000000, d: 1.583215e-03)
DLT stderr FPR7 3ec506d200000000 (f: 0.000000, d: 2.506571e-06)
DLT stderr FPR8 0034003900390037 (f: 3735607.000000, d: 1.112585e-307)
DLT stderr FPR9 0030003000350039 (f: 3473465.000000, d: 8.900703e-308)
DLT stderr FPR10 0031003600320034 (f: 3276852.000000, d: 9.457022e-308)
DLT stderr FPR11 37f9801900000000 (f: 0.000000, d: 4.683680e-39)
DLT stderr FPR12 3ff0000000000000 (f: 0.000000, d: 1.000000e+00)
DLT stderr FPR13 401cef5faed65272 (f: 2933281280.000000, d: 7.233763e+00)
DLT stderr FPR14 3fe62e42fefa39ef (f: 4277811712.000000, d: 6.931472e-01)
DLT stderr FPR15 4072d07adcbbbd22 (f: 3703291136.000000, d: 3.010300e+02)
DLT stderr FPR16 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR17 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR18 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR19 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR20 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR21 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR22 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR23 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR24 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR25 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR26 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR27 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR28 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR29 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR30 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr FPR31 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr Module=/home/jenkins/workspace/Test_openjdk8_j9_sanity.system_ppc64le_linux_xl_Nightly_testList_0/openjdkbinary/j2sdk-image/jre/lib/ppc64le/default/libj9gc29.so
DLT stderr Module_base_address=00003FFFA86C0000
DLT stderr Target=2_90_20210108_402 (Linux 4.4.0-173-generic)
DLT stderr CPU=ppc64le (16 logical CPUs) (0x1fe090000 RAM)
DLT stderr ----------- Stack Backtrace -----------
DLT stderr (0x00003FFFA895C354 [libj9gc29.so+0x29c354])
DLT stderr (0x00003FFF110CB850 [<unknown>+0x0])
DLT stderr (0x00003FFF110CB990 [<unknown>+0x0])
DLT stderr (0x00003FFFA8921A44 [libj9gc29.so+0x261a44])
DLT stderr (0x00003FFFA870AFA4 [libj9gc29.so+0x4afa4])
DLT stderr (0x00003FFFA3CE140C [libj9jit29.so+0xac140c])
DLT stderr (0x00003FFFA920DB64 [libj9vm29.so+0x8db64])
DLT stderr (0x00003FFFA9284EF0 [libj9vm29.so+0x104ef0])
DLT stderr (0x00003FFFA9084A48 [libj9prt29.so+0x34a48])
DLT stderr (0x00003FFFA92805A4 [libj9vm29.so+0x1005a4])
DLT stderr (0x00003FFFA91513C8 [libj9thr29.so+0x113c8])
DLT stderr (0x00003FFFA9F78040 [libpthread.so.0+0x8040])
DLT stderr clone+0x98 (0x00003FFFA9E53BB0 [libc.so.6+0x123bb0])
DLT stderr ---------------------------------------
```
https://ci.eclipse.org/openj9/job/Test_openjdk8_j9_sanity.system_s390x_linux_xl_Nightly_testList_0/37/
DaaLoadTest_daa1_ConcurrentScavenge_0
```
DLT stderr Corruption in Evacuate at 000003FFB338F1A8: calculated object size 4396758518964 larger then available 3672, Forwarded Header at 000003FFB9F7DD28
DLT stderr 04:09:27.813 0x3ffb451c600 j9mm.141 * ** ASSERTION FAILED ** at Scavenger.cpp:1482: ((false))
```
https://ci.eclipse.org/openj9/job/Test_openjdk8_j9_sanity.system_x86-64_linux_xl_Nightly_testList_1/34/
DaaLoadTest_daa1_ConcurrentScavenge_0
```
DLT stderr Unhandled exception
DLT stderr Type=Segmentation error vmState=0x00000000
DLT stderr J9Generic_Signal_Number=00000018 Signal_Number=0000000b Error_Value=00000000 Signal_Code=00000001
DLT stderr Handler1=00007FE874A22A60 Handler2=00007FE874305020 InaccessibleAddress=000000000000001A
DLT stderr RDI=00007FE87003DE40 RSI=00007FE870790DD8 RAX=00007FE870014A00 RBX=0000000000000000
DLT stderr RCX=00007FE75CEC28D8 RDX=00007FE75CEC2A50 R8=00007FE75CEC28E0 R9=00007FE87003DDB0
DLT stderr R10=0000000000000018 R11=0000000000000012 R12=00007FE75CEC28E0 R13=00007FE75CEC28E8
DLT stderr R14=00007FE75CEC2A50 R15=00007FE75CEC28D8
DLT stderr RIP=00007FE86DD8AAA8 GS=0000 FS=0000 RSP=00007FE75CEC2840
DLT stderr EFlags=0000000000010246 CS=0033 RBP=00007FE75CEC2A50 ERR=0000000000000004
DLT stderr TRAPNO=000000000000000E OLDMASK=0000000000000000 CR2=000000000000001A
DLT stderr xmm0 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr xmm1 000000003e3ab283 (f: 1044034176.000000, d: 5.158214e-315)
DLT stderr xmm2 0000000000000000 (f: 0.000000, d: 0.000000e+00)
DLT stderr xmm3 0000000041895736 (f: 1099519744.000000, d: 5.432350e-315)
DLT stderr xmm4 000000003eccce04 (f: 1053609472.000000, d: 5.205522e-315)
DLT stderr xmm5 00000000396d7337 (f: 963474240.000000, d: 4.760195e-315)
DLT stderr xmm6 3fc5f4847813d081 (f: 2014564480.000000, d: 1.715246e-01)
DLT stderr xmm7 00000000be1cc98c (f: 3189557760.000000, d: 1.575851e-314)
DLT stderr xmm8 401cef5faed65272 (f: 2933281280.000000, d: 7.233763e+00)
DLT stderr xmm9 4072d07adcbbbd22 (f: 3703291136.000000, d: 3.010300e+02)
DLT stderr xmm10 bfb745d1745d1746 (f: 1952257920.000000, d: -9.090909e-02)
DLT stderr xmm11 bfd180bb4b651000 (f: 1264914432.000000, d: -2.734822e-01)
DLT stderr xmm12 3f80ecf4c2a50800 (f: 3265595392.000000, d: 8.264458e-03)
DLT stderr xmm13 4008000000000000 (f: 0.000000, d: 3.000000e+00)
DLT stderr xmm14 4020000000000000 (f: 0.000000, d: 8.000000e+00)
DLT stderr xmm15 0000000047054a50 (f: 1191529088.000000, d: 5.886936e-315)
DLT stderr Module=/home/jenkins/workspace/Test_openjdk8_j9_sanity.system_x86-64_linux_xl_Nightly_testList_1/openjdkbinary/j2sdk-image/jre/lib/amd64/default/libj9gc29.so
DLT stderr Module_base_address=00007FE86DB74000
DLT stderr Target=2_90_20210108_617 (Linux 4.4.0-140-generic)
DLT stderr CPU=amd64 (8 logical CPUs) (0x3eae99000 RAM)
DLT stderr ----------- Stack Backtrace -----------
DLT stderr (0x00007FE86DD8AAA8 [libj9gc29.so+0x216aa8])
DLT stderr (0x00007FE86DCF37C2 [libj9gc29.so+0x17f7c2])
DLT stderr (0x00007FE86DD5C436 [libj9gc29.so+0x1e8436])
DLT stderr (0x00007FE86E9A40D1 [libj9jit29.so+0x9570d1])
```
https://ci.eclipse.org/openj9/job/Test_openjdk8_j9_sanity.system_x86-64_linux_xl_Nightly_testList_0/34
DaaLoadTest_daa2_ConcurrentScavenge_0
```
DLT stderr Corruption in Evacuate at 00007F3537145BB8: calculated object size 15762826332667967 larger then available 1025096, Forwarded Header at 00007F336C7DCA50
DLT stderr 04:14:34.953 0x7f3538785500 j9mm.141 * ** ASSERTION FAILED ** at Scavenger.cpp:1447: ((false))
```
https://ci.eclipse.org/openj9/job/Test_openjdk11_j9_sanity.system_ppc64_aix_xl_Nightly_testList_1/32/
DaaLoadTest_daa1_ConcurrentScavenge_0
```
DLT stderr Bad scan type for object pointer 0A00000070013BA0
DLT stderr 09:04:02.333 0x100224f2200 j9mm.141 * ** ASSERTION FAILED ** at /home/jenkins/workspace/Build_JDK11_ppc64_aix_xl_Nightly/openj9/runtime/gc_glue_java/ScavengerDelegate.cpp:390: ((false))
```
https://ci.eclipse.org/openj9/job/Test_openjdk11_j9_extended.system_s390x_linux_xl_Nightly_testList_1/35/
DaaLoadTest_all_ConcurrentScavenge_0
```
DLT stderr Corruption in Evacuate at 000003FF8103F2A8: calculated object size 79087527788568 larger then available 3416, Forwarded Header at 000003FF83AFDD28
DLT stderr 06:42:56.113 0x3ff84335a00 j9mm.141 * ** ASSERTION FAILED ** at /home/jenkins/workspace/Build_JDK11_s390x_linux_xl_Nightly/omr/gc/base/standard/Scavenger.cpp:1482: ((false))
```
https://ci.eclipse.org/openj9/job/Test_openjdk11_j9_sanity.system_x86-64_linux_xl_Nightly_testList_1/33/
DaaLoadTest_daa1_ConcurrentScavenge_0
```
DLT stderr Bad scan type for object pointer 00007EFF12FE71C0
DLT stderr 07:10:51.920 0x7efeac003a00 j9mm.141 * ** ASSERTION FAILED ** at /home/jenkins/workspace/Build_JDK11_x86-6
``` | test | daaloadtest concurrentscavenge segfault or assert changes from previous build daaloadtest concurrentscavenge lt stderr unhandled exception dlt stderr type segmentation error vmstate dlt stderr signal number signal number error value signal code dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr nip msr orig ctr dlt stderr link xer ccr softe dlt stderr trap dar dsisr result dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr module home jenkins workspace test sanity system linux xl nightly testlist openjdkbinary image jre lib default so dlt stderr module base address dlt stderr target linux generic dlt stderr cpu logical cpus ram dlt stderr stack backtrace dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr dlt stderr clone dlt stderr daaloadtest concurrentscavenge dlt stderr corruption in evacuate at calculated object size larger then available forwarded header at dlt stderr assertion failed at scavenger cpp false daaloadtest concurrentscavenge dlt stderr unhandled exception dlt stderr type segmentation error vmstate dlt stderr signal number signal number error value signal code dlt stderr inaccessibleaddress dlt stderr rdi rsi rax rbx dlt stderr rcx rdx dlt stderr dlt stderr dlt stderr rip gs fs rsp dlt stderr eflags cs rbp err dlt stderr trapno oldmask dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr f d dlt stderr module home jenkins workspace test sanity system linux xl nightly testlist openjdkbinary image jre lib default so dlt stderr module base address dlt stderr target linux generic dlt stderr cpu logical cpus ram dlt stderr stack backtrace dlt stderr dlt stderr dlt stderr dlt stderr daaloadtest concurrentscavenge dlt stderr corruption in evacuate at calculated object size larger then available forwarded header at dlt stderr assertion failed at scavenger cpp false daaloadtest concurrentscavenge dlt stderr bad scan type for object pointer dlt stderr assertion failed at home jenkins workspace build aix xl nightly runtime gc glue java scavengerdelegate cpp false daaloadtest all concurrentscavenge dlt stderr corruption in evacuate at calculated object size larger then available forwarded header at dlt stderr assertion failed at home jenkins workspace build linux xl nightly omr gc base standard scavenger cpp false daaloadtest concurrentscavenge dlt stderr bad scan type for object pointer dlt stderr assertion failed at home jenkins workspace build | 1 |
41,031 | 10,604,796,074 | IssuesEvent | 2019-10-10 18:59:00 | gradle/gradle | https://api.github.com/repos/gradle/gradle | opened | couldn't resolve androidx lifeCycle | @build-cache from:member | ```
apply plugin: 'com.android.application'
android {
compileSdkVersion 28
defaultConfig {
applicationId "android.example.com"
minSdkVersion 15
targetSdkVersion 28
versionCode 1
versionName "1.0"
testInstrumentationRunner "androidx.test.runner.AndroidJUnitRunner"
}
buildTypes {
release {
minifyEnabled false
proguardFiles getDefaultProguardFile('proguard-android-optimize.txt'), 'proguard-rules.pro'
}
}
}
dependencies {
implementation fileTree(dir: 'libs', include: ['*.jar'])
implementation 'androidx.appcompat:appcompat:1.0.0'
implementation 'androidx.constraintlayout:constraintlayout:1.1.3'
implementation 'androidx.legacy:legacy-support-v4:1.0.0'
implementation 'androidx.legacy:legacy-support-v4:1.0.0'
implementation 'androidx.lifecycle:lifecycle-extensions:2.1.0'
testImplementation 'junit:junit:4.12'
androidTestImplementation 'androidx.test.ext:junit:1.1.1'
androidTestImplementation 'androidx.test.espresso:espresso-core:3.1.0'
implementation 'androidx.legacy:legacy-support-v4:1.0.0'
implementation 'androidx.appcompat:appcompat:1.0.0'
implementation 'androidx.vectordrawable:vectordrawable:1.0.0'
implementation 'androidx.recyclerview:recyclerview:1.0.0'
implementation 'com.google.android.material:material:1.0.0'
implementation 'androidx.constraintlayout:constraintlayout:1.1.3'
implementation 'androidx.annotation:annotation:1.0.0'
}
``` | 1.0 | couldn't resolve androidx lifeCycle - ```
apply plugin: 'com.android.application'
android {
compileSdkVersion 28
defaultConfig {
applicationId "android.example.com"
minSdkVersion 15
targetSdkVersion 28
versionCode 1
versionName "1.0"
testInstrumentationRunner "androidx.test.runner.AndroidJUnitRunner"
}
buildTypes {
release {
minifyEnabled false
proguardFiles getDefaultProguardFile('proguard-android-optimize.txt'), 'proguard-rules.pro'
}
}
}
dependencies {
implementation fileTree(dir: 'libs', include: ['*.jar'])
implementation 'androidx.appcompat:appcompat:1.0.0'
implementation 'androidx.constraintlayout:constraintlayout:1.1.3'
implementation 'androidx.legacy:legacy-support-v4:1.0.0'
implementation 'androidx.legacy:legacy-support-v4:1.0.0'
implementation 'androidx.lifecycle:lifecycle-extensions:2.1.0'
testImplementation 'junit:junit:4.12'
androidTestImplementation 'androidx.test.ext:junit:1.1.1'
androidTestImplementation 'androidx.test.espresso:espresso-core:3.1.0'
implementation 'androidx.legacy:legacy-support-v4:1.0.0'
implementation 'androidx.appcompat:appcompat:1.0.0'
implementation 'androidx.vectordrawable:vectordrawable:1.0.0'
implementation 'androidx.recyclerview:recyclerview:1.0.0'
implementation 'com.google.android.material:material:1.0.0'
implementation 'androidx.constraintlayout:constraintlayout:1.1.3'
implementation 'androidx.annotation:annotation:1.0.0'
}
``` | non_test | couldn t resolve androidx lifecycle apply plugin com android application android compilesdkversion defaultconfig applicationid android example com minsdkversion targetsdkversion versioncode versionname testinstrumentationrunner androidx test runner androidjunitrunner buildtypes release minifyenabled false proguardfiles getdefaultproguardfile proguard android optimize txt proguard rules pro dependencies implementation filetree dir libs include implementation androidx appcompat appcompat implementation androidx constraintlayout constraintlayout implementation androidx legacy legacy support implementation androidx legacy legacy support implementation androidx lifecycle lifecycle extensions testimplementation junit junit androidtestimplementation androidx test ext junit androidtestimplementation androidx test espresso espresso core implementation androidx legacy legacy support implementation androidx appcompat appcompat implementation androidx vectordrawable vectordrawable implementation androidx recyclerview recyclerview implementation com google android material material implementation androidx constraintlayout constraintlayout implementation androidx annotation annotation | 0 |
17,144 | 9,632,123,677 | IssuesEvent | 2019-05-15 15:32:14 | jacksontj/promxy | https://api.github.com/repos/jacksontj/promxy | opened | Significant CPU usage increase since v0.0.31 | performance | This was introduced with the switch to the upstream prom client, I'm working with upstream here https://github.com/prometheus/client_golang/issues/565 to get this sped up | True | Significant CPU usage increase since v0.0.31 - This was introduced with the switch to the upstream prom client, I'm working with upstream here https://github.com/prometheus/client_golang/issues/565 to get this sped up | non_test | significant cpu usage increase since this was introduced with the switch to the upstream prom client i m working with upstream here to get this sped up | 0 |
548,274 | 16,061,230,520 | IssuesEvent | 2021-04-23 12:51:48 | jina-ai/dashboard | https://api.github.com/repos/jina-ai/dashboard | closed | Add GitHub OAuth Frontend functionality | Stale area/login priority/important-soon status/in-progress type/feature-request | This ticket is for the implementation of the functionality only (no designs). All the tasks to enable login functionality in the future fall under this ticket (obtaining auth tokens, managing sessions etc)
<p></p>
UX flow:
1. User enters dashboard URL.
2. User is presented with a login screen
3. User clicks the 'Login with GitHub' button.
4. User is taken to the dashboard 'Home' page
<p></p>
## **Acceptance Criteria**
- frontend is ready to add user login as soon as UI and UX are ready
<p></p> | 1.0 | Add GitHub OAuth Frontend functionality - This ticket is for the implementation of the functionality only (no designs). All the tasks to enable login functionality in the future fall under this ticket (obtaining auth tokens, managing sessions etc)
<p></p>
UX flow:
1. User enters dashboard URL.
2. User is presented with a login screen
3. User clicks the 'Login with GitHub' button.
4. User is taken to the dashboard 'Home' page
<p></p>
## **Acceptance Criteria**
- frontend is ready to add user login as soon as UI and UX are ready
<p></p> | non_test | add github oauth frontend functionality this ticket is for the implementation of the functionality only no designs all the tasks to enable login functionality in the future fall under this ticket obtaining auth tokens managing sessions etc ux flow user enters dashboard url user is presented with a login screen user clicks the login with github button user is taken to the dashboard home page acceptance criteria frontend is ready to add user login as soon as ui and ux are ready | 0 |
95,295 | 11,967,960,191 | IssuesEvent | 2020-04-06 07:47:16 | I-can-do-vs-corona/Voitheia | https://api.github.com/repos/I-can-do-vs-corona/Voitheia | closed | Sync colors of Material & Bootstrap | Design | The colors of the themes for Angular Material and Bootstrap should be synced. | 1.0 | Sync colors of Material & Bootstrap - The colors of the themes for Angular Material and Bootstrap should be synced. | non_test | sync colors of material bootstrap the colors of the themes for angular material and bootstrap should be synced | 0 |
306,193 | 26,446,866,858 | IssuesEvent | 2023-01-16 08:10:34 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix raw_ops.test_tensorflow_Relu6 | TensorFlow Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/3926925952/jobs/6713087446" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/3926925952/jobs/6713087446" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/3926925952/jobs/6713087446" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/3926925952/jobs/6713087446" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_raw_ops.py::test_tensorflow_Relu6[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-16T03:45:51.3845885Z E TypeError: relu6 only takes keyword args (possible keys: ['features', 'name']). Please pass these args as kwargs instead.
2023-01-16T03:45:51.3846359Z E Falsifying example: test_tensorflow_Relu6(
2023-01-16T03:45:51.3846803Z E dtype_and_x=(['uint8'], [array([0], dtype=uint8)]),
2023-01-16T03:45:51.3847106Z E as_variable=[False],
2023-01-16T03:45:51.3847385Z E num_positional_args=1,
2023-01-16T03:45:51.3847671Z E native_array=[False],
2023-01-16T03:45:51.3848141Z E fn_tree='ivy.functional.frontends.tensorflow.raw_ops.Relu6',
2023-01-16T03:45:51.3848577Z E frontend='tensorflow',
2023-01-16T03:45:51.3848890Z E on_device='cpu',
2023-01-16T03:45:51.3849134Z E )
2023-01-16T03:45:51.3849344Z E
2023-01-16T03:45:51.3849922Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AAABAAAAAAAAAAEA') as a decorator on your test case
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_raw_ops.py::test_tensorflow_Relu6[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-16T03:45:51.3845885Z E TypeError: relu6 only takes keyword args (possible keys: ['features', 'name']). Please pass these args as kwargs instead.
2023-01-16T03:45:51.3846359Z E Falsifying example: test_tensorflow_Relu6(
2023-01-16T03:45:51.3846803Z E dtype_and_x=(['uint8'], [array([0], dtype=uint8)]),
2023-01-16T03:45:51.3847106Z E as_variable=[False],
2023-01-16T03:45:51.3847385Z E num_positional_args=1,
2023-01-16T03:45:51.3847671Z E native_array=[False],
2023-01-16T03:45:51.3848141Z E fn_tree='ivy.functional.frontends.tensorflow.raw_ops.Relu6',
2023-01-16T03:45:51.3848577Z E frontend='tensorflow',
2023-01-16T03:45:51.3848890Z E on_device='cpu',
2023-01-16T03:45:51.3849134Z E )
2023-01-16T03:45:51.3849344Z E
2023-01-16T03:45:51.3849922Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AAABAAAAAAAAAAEA') as a decorator on your test case
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_raw_ops.py::test_tensorflow_Relu6[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-16T03:45:51.3845885Z E TypeError: relu6 only takes keyword args (possible keys: ['features', 'name']). Please pass these args as kwargs instead.
2023-01-16T03:45:51.3846359Z E Falsifying example: test_tensorflow_Relu6(
2023-01-16T03:45:51.3846803Z E dtype_and_x=(['uint8'], [array([0], dtype=uint8)]),
2023-01-16T03:45:51.3847106Z E as_variable=[False],
2023-01-16T03:45:51.3847385Z E num_positional_args=1,
2023-01-16T03:45:51.3847671Z E native_array=[False],
2023-01-16T03:45:51.3848141Z E fn_tree='ivy.functional.frontends.tensorflow.raw_ops.Relu6',
2023-01-16T03:45:51.3848577Z E frontend='tensorflow',
2023-01-16T03:45:51.3848890Z E on_device='cpu',
2023-01-16T03:45:51.3849134Z E )
2023-01-16T03:45:51.3849344Z E
2023-01-16T03:45:51.3849922Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AAABAAAAAAAAAAEA') as a decorator on your test case
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_raw_ops.py::test_tensorflow_Relu6[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-16T03:45:51.3845885Z E TypeError: relu6 only takes keyword args (possible keys: ['features', 'name']). Please pass these args as kwargs instead.
2023-01-16T03:45:51.3846359Z E Falsifying example: test_tensorflow_Relu6(
2023-01-16T03:45:51.3846803Z E dtype_and_x=(['uint8'], [array([0], dtype=uint8)]),
2023-01-16T03:45:51.3847106Z E as_variable=[False],
2023-01-16T03:45:51.3847385Z E num_positional_args=1,
2023-01-16T03:45:51.3847671Z E native_array=[False],
2023-01-16T03:45:51.3848141Z E fn_tree='ivy.functional.frontends.tensorflow.raw_ops.Relu6',
2023-01-16T03:45:51.3848577Z E frontend='tensorflow',
2023-01-16T03:45:51.3848890Z E on_device='cpu',
2023-01-16T03:45:51.3849134Z E )
2023-01-16T03:45:51.3849344Z E
2023-01-16T03:45:51.3849922Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AAABAAAAAAAAAAEA') as a decorator on your test case
</details>
| 1.0 | Fix raw_ops.test_tensorflow_Relu6 - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/3926925952/jobs/6713087446" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/3926925952/jobs/6713087446" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/3926925952/jobs/6713087446" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/3926925952/jobs/6713087446" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_raw_ops.py::test_tensorflow_Relu6[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-16T03:45:51.3845885Z E TypeError: relu6 only takes keyword args (possible keys: ['features', 'name']). Please pass these args as kwargs instead.
2023-01-16T03:45:51.3846359Z E Falsifying example: test_tensorflow_Relu6(
2023-01-16T03:45:51.3846803Z E dtype_and_x=(['uint8'], [array([0], dtype=uint8)]),
2023-01-16T03:45:51.3847106Z E as_variable=[False],
2023-01-16T03:45:51.3847385Z E num_positional_args=1,
2023-01-16T03:45:51.3847671Z E native_array=[False],
2023-01-16T03:45:51.3848141Z E fn_tree='ivy.functional.frontends.tensorflow.raw_ops.Relu6',
2023-01-16T03:45:51.3848577Z E frontend='tensorflow',
2023-01-16T03:45:51.3848890Z E on_device='cpu',
2023-01-16T03:45:51.3849134Z E )
2023-01-16T03:45:51.3849344Z E
2023-01-16T03:45:51.3849922Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AAABAAAAAAAAAAEA') as a decorator on your test case
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_raw_ops.py::test_tensorflow_Relu6[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-16T03:45:51.3845885Z E TypeError: relu6 only takes keyword args (possible keys: ['features', 'name']). Please pass these args as kwargs instead.
2023-01-16T03:45:51.3846359Z E Falsifying example: test_tensorflow_Relu6(
2023-01-16T03:45:51.3846803Z E dtype_and_x=(['uint8'], [array([0], dtype=uint8)]),
2023-01-16T03:45:51.3847106Z E as_variable=[False],
2023-01-16T03:45:51.3847385Z E num_positional_args=1,
2023-01-16T03:45:51.3847671Z E native_array=[False],
2023-01-16T03:45:51.3848141Z E fn_tree='ivy.functional.frontends.tensorflow.raw_ops.Relu6',
2023-01-16T03:45:51.3848577Z E frontend='tensorflow',
2023-01-16T03:45:51.3848890Z E on_device='cpu',
2023-01-16T03:45:51.3849134Z E )
2023-01-16T03:45:51.3849344Z E
2023-01-16T03:45:51.3849922Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AAABAAAAAAAAAAEA') as a decorator on your test case
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_raw_ops.py::test_tensorflow_Relu6[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-16T03:45:51.3845885Z E TypeError: relu6 only takes keyword args (possible keys: ['features', 'name']). Please pass these args as kwargs instead.
2023-01-16T03:45:51.3846359Z E Falsifying example: test_tensorflow_Relu6(
2023-01-16T03:45:51.3846803Z E dtype_and_x=(['uint8'], [array([0], dtype=uint8)]),
2023-01-16T03:45:51.3847106Z E as_variable=[False],
2023-01-16T03:45:51.3847385Z E num_positional_args=1,
2023-01-16T03:45:51.3847671Z E native_array=[False],
2023-01-16T03:45:51.3848141Z E fn_tree='ivy.functional.frontends.tensorflow.raw_ops.Relu6',
2023-01-16T03:45:51.3848577Z E frontend='tensorflow',
2023-01-16T03:45:51.3848890Z E on_device='cpu',
2023-01-16T03:45:51.3849134Z E )
2023-01-16T03:45:51.3849344Z E
2023-01-16T03:45:51.3849922Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AAABAAAAAAAAAAEA') as a decorator on your test case
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_raw_ops.py::test_tensorflow_Relu6[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-16T03:45:51.3845885Z E TypeError: relu6 only takes keyword args (possible keys: ['features', 'name']). Please pass these args as kwargs instead.
2023-01-16T03:45:51.3846359Z E Falsifying example: test_tensorflow_Relu6(
2023-01-16T03:45:51.3846803Z E dtype_and_x=(['uint8'], [array([0], dtype=uint8)]),
2023-01-16T03:45:51.3847106Z E as_variable=[False],
2023-01-16T03:45:51.3847385Z E num_positional_args=1,
2023-01-16T03:45:51.3847671Z E native_array=[False],
2023-01-16T03:45:51.3848141Z E fn_tree='ivy.functional.frontends.tensorflow.raw_ops.Relu6',
2023-01-16T03:45:51.3848577Z E frontend='tensorflow',
2023-01-16T03:45:51.3848890Z E on_device='cpu',
2023-01-16T03:45:51.3849134Z E )
2023-01-16T03:45:51.3849344Z E
2023-01-16T03:45:51.3849922Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AAABAAAAAAAAAAEA') as a decorator on your test case
</details>
| test | fix raw ops test tensorflow tensorflow img src torch img src numpy img src jax img src failed ivy tests test ivy test frontends test tensorflow test raw ops py test tensorflow e typeerror only takes keyword args possible keys please pass these args as kwargs instead e falsifying example test tensorflow e dtype and x dtype e as variable e num positional args e native array e fn tree ivy functional frontends tensorflow raw ops e frontend tensorflow e on device cpu e e e you can reproduce this example by temporarily adding reproduce failure b aaabaaaaaaaaaaea as a decorator on your test case failed ivy tests test ivy test frontends test tensorflow test raw ops py test tensorflow e typeerror only takes keyword args possible keys please pass these args as kwargs instead e falsifying example test tensorflow e dtype and x dtype e as variable e num positional args e native array e fn tree ivy functional frontends tensorflow raw ops e frontend tensorflow e on device cpu e e e you can reproduce this example by temporarily adding reproduce failure b aaabaaaaaaaaaaea as a decorator on your test case failed ivy tests test ivy test frontends test tensorflow test raw ops py test tensorflow e typeerror only takes keyword args possible keys please pass these args as kwargs instead e falsifying example test tensorflow e dtype and x dtype e as variable e num positional args e native array e fn tree ivy functional frontends tensorflow raw ops e frontend tensorflow e on device cpu e e e you can reproduce this example by temporarily adding reproduce failure b aaabaaaaaaaaaaea as a decorator on your test case failed ivy tests test ivy test frontends test tensorflow test raw ops py test tensorflow e typeerror only takes keyword args possible keys please pass these args as kwargs instead e falsifying example test tensorflow e dtype and x dtype e as variable e num positional args e native array e fn tree ivy functional frontends tensorflow raw ops e frontend tensorflow e on device cpu e e e you can reproduce this example by temporarily adding reproduce failure b aaabaaaaaaaaaaea as a decorator on your test case | 1 |
352,382 | 25,064,733,336 | IssuesEvent | 2022-11-07 07:08:36 | AY2223S1-CS2103-W14-2/tp | https://api.github.com/repos/AY2223S1-CS2103-W14-2/tp | closed | Improve DG | documentation | Improve DG grammar
Check for serious mistakes
Check American English spelling | 1.0 | Improve DG - Improve DG grammar
Check for serious mistakes
Check American English spelling | non_test | improve dg improve dg grammar check for serious mistakes check american english spelling | 0 |
351,550 | 32,008,813,144 | IssuesEvent | 2023-09-21 16:30:18 | stellar/js-stellar-sdk | https://api.github.com/repos/stellar/js-stellar-sdk | closed | Support the XDR of Protocol 20 | soroban-scrum Testnet August 2023 Release | This involves a few moving parts:
- [x] updating the XDR in the soroban branch of stellar-base to the final testnet version: stellar/js-stellar-base#688
- [x] merging the `soroban` branch of stellar-base into the upstream master
- [x] upgrading the stellar-base dependency in this package
- [x] making all of the necessary changes to this library to support the new schema
| 1.0 | Support the XDR of Protocol 20 - This involves a few moving parts:
- [x] updating the XDR in the soroban branch of stellar-base to the final testnet version: stellar/js-stellar-base#688
- [x] merging the `soroban` branch of stellar-base into the upstream master
- [x] upgrading the stellar-base dependency in this package
- [x] making all of the necessary changes to this library to support the new schema
| test | support the xdr of protocol this involves a few moving parts updating the xdr in the soroban branch of stellar base to the final testnet version stellar js stellar base merging the soroban branch of stellar base into the upstream master upgrading the stellar base dependency in this package making all of the necessary changes to this library to support the new schema | 1 |
272,612 | 23,687,362,185 | IssuesEvent | 2022-08-29 07:41:13 | GetStream/stream-chat-android | https://api.github.com/repos/GetStream/stream-chat-android | closed | Remove usage of Kotlin Collection's `getOrDefault()` | core tests | ### Context & proposal
We are using Kotlin's `getOrDefault()` unnecessarily in a few places. Unfortunately, even though it does not get reported by the IDE, this method is not available below API 24 and will throw `Exception`s.
Due to the way we handle errors in our Coroutines, this does not cause a crash, but it does mean that for instance the `TypingPruner` does not work properly below API 24.
### Acceptance criteria
To accept this task we need to complete the following items:
- [ ] Remove the usage of Kotlin's `getOrDefault()` safely | 1.0 | Remove usage of Kotlin Collection's `getOrDefault()` - ### Context & proposal
We are using Kotlin's `getOrDefault()` unnecessarily in a few places. Unfortunately, even though it does not get reported by the IDE, this method is not available below API 24 and will throw `Exception`s.
Due to the way we handle errors in our Coroutines, this does not cause a crash, but it does mean that for instance the `TypingPruner` does not work properly below API 24.
### Acceptance criteria
To accept this task we need to complete the following items:
- [ ] Remove the usage of Kotlin's `getOrDefault()` safely | test | remove usage of kotlin collection s getordefault context proposal we are using kotlin s getordefault unnecessarily in a few places unfortunately even though it does not get reported by the ide this method is not available below api and will throw exception s due to the way we handle errors in our coroutines this does not cause a crash but it does mean that for instance the typingpruner does not work properly below api acceptance criteria to accept this task we need to complete the following items remove the usage of kotlin s getordefault safely | 1 |
29,454 | 4,501,257,625 | IssuesEvent | 2016-09-01 08:46:53 | mattbearman/lime | https://api.github.com/repos/mattbearman/lime | closed | BugMuncher Feedback Report | bug BugMuncher problem test | ## Details ##
**Submitted:** January 18, 2016 16:23
**Category:** problem
**Sender Email:** markuscp@gmail.com
**Website:** BugMuncher App
**URL:** https://app.bugmuncher.com/profiles/1240#advanced-options
**Operating System:** Apple iOS
**Browser:** Safari 9.0
**Browser Size:** 1366 x 960
**User Agent:**
Mozilla/5.0 (iPad; CPU OS 9_2 like Mac OS X) AppleWebKit/601.1.46 (KHTML, like Gecko) Version/9.0 Mobile/13C75 Safari/601.1
**Description:**
neuer versuch:)
lg ms
## Custom Data ##
**user_id:** 1121
**account_id:** 717
**plan:** BugMuncher Corporate
## Browser Plugins ##
## Events ##
**method:** GET
**url:** https://app.bugmuncher.com/profiles/1240/reports
**timestamp:** Mon Jan 18 2016 17:23:11 GMT+0100 (CET)
**type:** page_load
---
**method:** GET
**url:** https://app.bugmuncher.com/profiles/1240/reports
**timestamp:** Mon Jan 18 2016 17:23:17 GMT+0100 (CET)
**type:** page_load
---
**method:** GET
**url:** https://app.bugmuncher.com/profiles
**timestamp:** Mon Jan 18 2016 17:23:22 GMT+0100 (CET)
**type:** page_load
---
**method:** GET
**url:** https://app.bugmuncher.com/profiles/1240
**timestamp:** Mon Jan 18 2016 17:23:25 GMT+0100 (CET)
**type:** page_load
---
**content:** Feedback Button Clicked
**timestamp:** Mon Jan 18 2016 17:23:36 GMT+0100 (CET)
**type:** bugmuncher
---
**type:** bugmuncher
**content:** Feedback Report Submitted
**timestamp:** Mon Jan 18 2016 17:23:54 GMT+0100 (CET)
---
| 1.0 | BugMuncher Feedback Report - ## Details ##
**Submitted:** January 18, 2016 16:23
**Category:** problem
**Sender Email:** markuscp@gmail.com
**Website:** BugMuncher App
**URL:** https://app.bugmuncher.com/profiles/1240#advanced-options
**Operating System:** Apple iOS
**Browser:** Safari 9.0
**Browser Size:** 1366 x 960
**User Agent:**
Mozilla/5.0 (iPad; CPU OS 9_2 like Mac OS X) AppleWebKit/601.1.46 (KHTML, like Gecko) Version/9.0 Mobile/13C75 Safari/601.1
**Description:**
neuer versuch:)
lg ms
## Custom Data ##
**user_id:** 1121
**account_id:** 717
**plan:** BugMuncher Corporate
## Browser Plugins ##
## Events ##
**method:** GET
**url:** https://app.bugmuncher.com/profiles/1240/reports
**timestamp:** Mon Jan 18 2016 17:23:11 GMT+0100 (CET)
**type:** page_load
---
**method:** GET
**url:** https://app.bugmuncher.com/profiles/1240/reports
**timestamp:** Mon Jan 18 2016 17:23:17 GMT+0100 (CET)
**type:** page_load
---
**method:** GET
**url:** https://app.bugmuncher.com/profiles
**timestamp:** Mon Jan 18 2016 17:23:22 GMT+0100 (CET)
**type:** page_load
---
**method:** GET
**url:** https://app.bugmuncher.com/profiles/1240
**timestamp:** Mon Jan 18 2016 17:23:25 GMT+0100 (CET)
**type:** page_load
---
**content:** Feedback Button Clicked
**timestamp:** Mon Jan 18 2016 17:23:36 GMT+0100 (CET)
**type:** bugmuncher
---
**type:** bugmuncher
**content:** Feedback Report Submitted
**timestamp:** Mon Jan 18 2016 17:23:54 GMT+0100 (CET)
---
| test | bugmuncher feedback report details submitted january category problem sender email markuscp gmail com website bugmuncher app url operating system apple ios browser safari browser size x user agent mozilla ipad cpu os like mac os x applewebkit khtml like gecko version mobile safari description neuer versuch lg ms custom data user id account id plan bugmuncher corporate browser plugins events method get url timestamp mon jan gmt cet type page load method get url timestamp mon jan gmt cet type page load method get url timestamp mon jan gmt cet type page load method get url timestamp mon jan gmt cet type page load content feedback button clicked timestamp mon jan gmt cet type bugmuncher type bugmuncher content feedback report submitted timestamp mon jan gmt cet | 1 |
200,668 | 15,117,482,285 | IssuesEvent | 2021-02-09 08:32:56 | eclipse/che | https://api.github.com/repos/eclipse/che | closed | The "Happy Path" test fails on the "Wait error highlighting" step | area/qe e2e-test/failure kind/bug severity/blocker | <!--
To make it easier for us to help you, please include as much useful information as possible.
Useful Links:
- Documentation: https://www.eclipse.org/che/docs
- Contributing: https://github.com/eclipse/che/blob/master/CONTRIBUTING.md
Eclipse Che has public chat on:
- Mattermost: https://mattermost.eclipse.org/eclipse/channels/eclipse-che
Before opening a new issue, please search existing issues https://github.com/eclipse/che/issues
-->
### Describe the bug
The "Happy Path" test fails on the "Wait error highlighting" step:
```
12:33:34 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:34 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:34 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:35 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:35 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:35 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:35 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:35 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:36 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:36 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:36 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: "error"
12:33:37 ▼ Editor.waitErrorInLine line: "30"
12:33:37 ▼ Editor.getLineYCoordinates line: "30"
12:34:45 1) Error highlighting
12:34:45 [ERROR] CheReporter runner.on.fail: Language server validation Error highlighting failed after 70925ms
12:34:45
12:34:45
12:34:45 4 passing (6m)
12:34:45 1 failing
12:34:45
12:34:45 1) Language server validation
12:34:45 Error highlighting:
12:34:45 TimeoutError: Exceeded maximum visibility checkings attempts for 'By(xpath, //div[contains(@style, 'top:551px')]//div[contains(@class, 'squiggly-error')])' element, timeouted after 60000
12:34:45 at DriverHelper.waitVisibility (/tmp/e2e/utils/DriverHelper.ts:152:15)
12:34:45 at process._tickCallback (internal/process/next_tick.js:68:7)
12:34:45
```
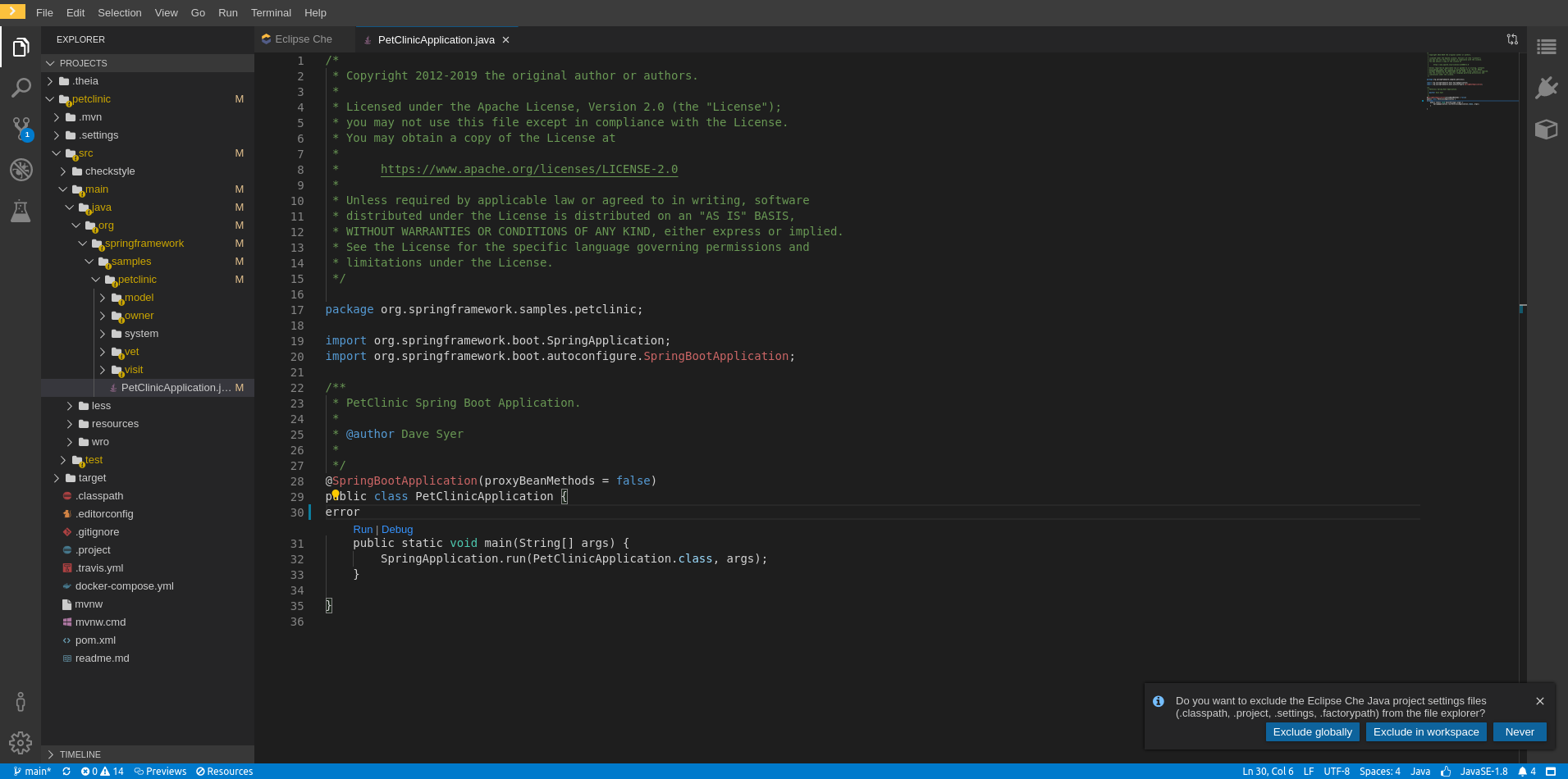
### Che version
<!-- (if workspace is running, version can be obtained with help/about menu) -->
- [ ] latest
- [x] nightly
- [ ] other: please specify
### Steps to reproduce
<!--
1. Do '...'
2. Click on '....'
3. See error
-->
### Expected behavior
<!-- A clear and concise description of what you expected to happen. -->
### Runtime
- [ ] kubernetes (include output of `kubectl version`)
- [ ] Openshift (include output of `oc version`)
- [x] minikube (include output of `minikube version` and `kubectl version`)
- [ ] minishift (include output of `minishift version` and `oc version`)
- [ ] docker-desktop + K8S (include output of `docker version` and `kubectl version`)
- [ ] other: (please specify)
### Screenshots
<!-- If applicable, add screenshots to help explain your problem. -->
### Installation method
- [x] chectl
* provide a full command that was used to deploy Eclipse Che (including the output)
* provide an output of `chectl version` command
- [ ] OperatorHub
- [ ] I don't know
### Environment
- [ ] my computer
- [ ] Windows
- [ ] Linux
- [ ] macOS
- [ ] Cloud
- [ ] Amazon
- [ ] Azure
- [ ] GCE
- [ ] other (please specify)
- [ ] other: please specify
### Eclipse Che Logs
<!-- https://www.eclipse.org/che/docs/che-7/collecting-logs-using-chectl -->
### Additional context
<!-- Add any other context about the problem here. -->
| 1.0 | The "Happy Path" test fails on the "Wait error highlighting" step - <!--
To make it easier for us to help you, please include as much useful information as possible.
Useful Links:
- Documentation: https://www.eclipse.org/che/docs
- Contributing: https://github.com/eclipse/che/blob/master/CONTRIBUTING.md
Eclipse Che has public chat on:
- Mattermost: https://mattermost.eclipse.org/eclipse/channels/eclipse-che
Before opening a new issue, please search existing issues https://github.com/eclipse/che/issues
-->
### Describe the bug
The "Happy Path" test fails on the "Wait error highlighting" step:
```
12:33:34 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:34 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:34 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:35 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:35 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:35 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:35 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:35 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:36 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:36 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: ""
12:33:36 ▼ Editor.performKeyCombination title: "PetClinicApplication.java" text: "error"
12:33:37 ▼ Editor.waitErrorInLine line: "30"
12:33:37 ▼ Editor.getLineYCoordinates line: "30"
12:34:45 1) Error highlighting
12:34:45 [ERROR] CheReporter runner.on.fail: Language server validation Error highlighting failed after 70925ms
12:34:45
12:34:45
12:34:45 4 passing (6m)
12:34:45 1 failing
12:34:45
12:34:45 1) Language server validation
12:34:45 Error highlighting:
12:34:45 TimeoutError: Exceeded maximum visibility checkings attempts for 'By(xpath, //div[contains(@style, 'top:551px')]//div[contains(@class, 'squiggly-error')])' element, timeouted after 60000
12:34:45 at DriverHelper.waitVisibility (/tmp/e2e/utils/DriverHelper.ts:152:15)
12:34:45 at process._tickCallback (internal/process/next_tick.js:68:7)
12:34:45
```
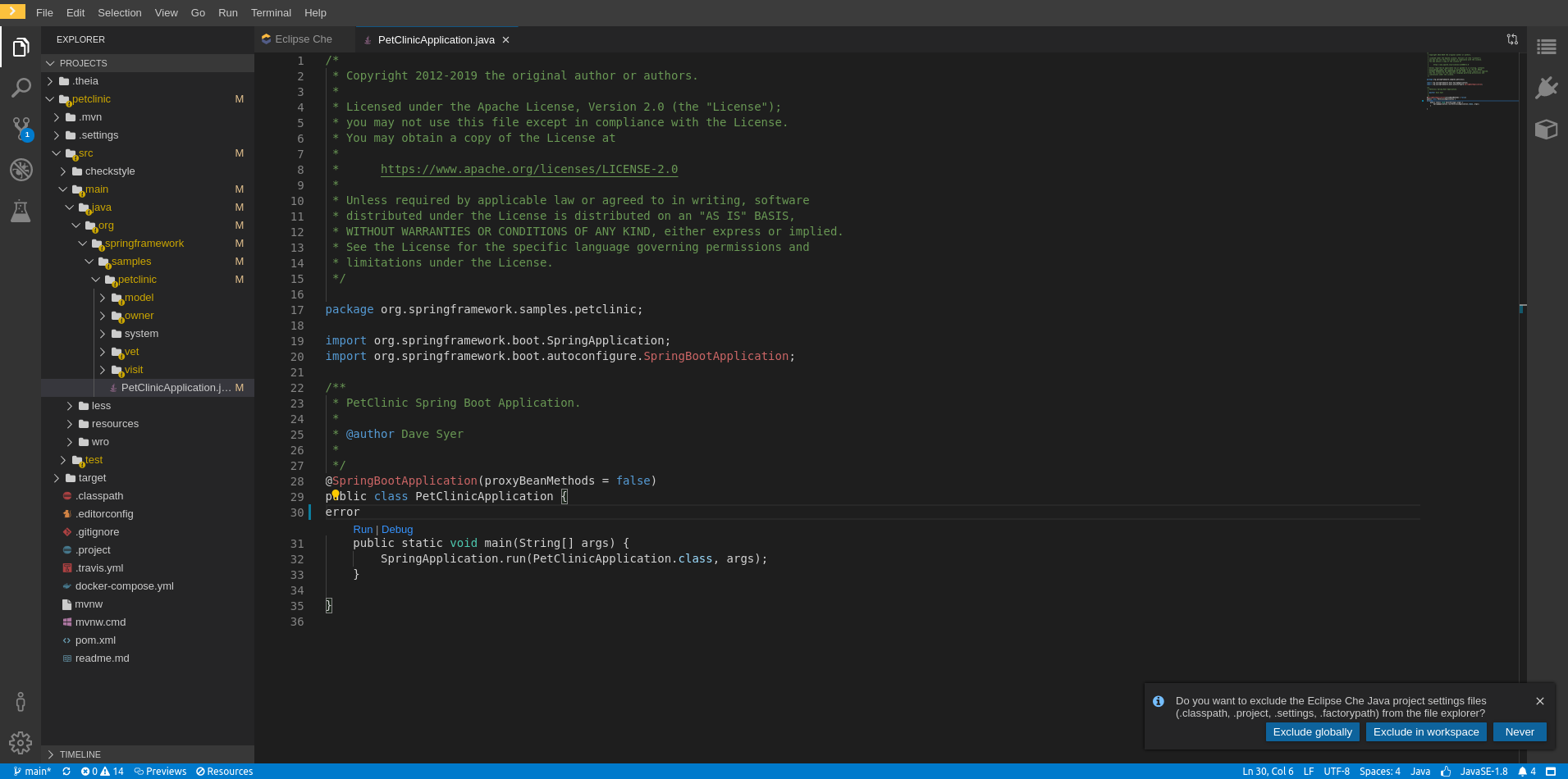
### Che version
<!-- (if workspace is running, version can be obtained with help/about menu) -->
- [ ] latest
- [x] nightly
- [ ] other: please specify
### Steps to reproduce
<!--
1. Do '...'
2. Click on '....'
3. See error
-->
### Expected behavior
<!-- A clear and concise description of what you expected to happen. -->
### Runtime
- [ ] kubernetes (include output of `kubectl version`)
- [ ] Openshift (include output of `oc version`)
- [x] minikube (include output of `minikube version` and `kubectl version`)
- [ ] minishift (include output of `minishift version` and `oc version`)
- [ ] docker-desktop + K8S (include output of `docker version` and `kubectl version`)
- [ ] other: (please specify)
### Screenshots
<!-- If applicable, add screenshots to help explain your problem. -->
### Installation method
- [x] chectl
* provide a full command that was used to deploy Eclipse Che (including the output)
* provide an output of `chectl version` command
- [ ] OperatorHub
- [ ] I don't know
### Environment
- [ ] my computer
- [ ] Windows
- [ ] Linux
- [ ] macOS
- [ ] Cloud
- [ ] Amazon
- [ ] Azure
- [ ] GCE
- [ ] other (please specify)
- [ ] other: please specify
### Eclipse Che Logs
<!-- https://www.eclipse.org/che/docs/che-7/collecting-logs-using-chectl -->
### Additional context
<!-- Add any other context about the problem here. -->
| test | the happy path test fails on the wait error highlighting step to make it easier for us to help you please include as much useful information as possible useful links documentation contributing eclipse che has public chat on mattermost before opening a new issue please search existing issues describe the bug the happy path test fails on the wait error highlighting step ▼ editor performkeycombination title petclinicapplication java text ▼ editor performkeycombination title petclinicapplication java text ▼ editor performkeycombination title petclinicapplication java text ▼ editor performkeycombination title petclinicapplication java text ▼ editor performkeycombination title petclinicapplication java text ▼ editor performkeycombination title petclinicapplication java text ▼ editor performkeycombination title petclinicapplication java text ▼ editor performkeycombination title petclinicapplication java text ▼ editor performkeycombination title petclinicapplication java text ▼ editor performkeycombination title petclinicapplication java text ▼ editor performkeycombination title petclinicapplication java text error ▼ editor waiterrorinline line ▼ editor getlineycoordinates line error highlighting chereporter runner on fail language server validation error highlighting failed after passing failing language server validation error highlighting timeouterror exceeded maximum visibility checkings attempts for by xpath div div element timeouted after at driverhelper waitvisibility tmp utils driverhelper ts at process tickcallback internal process next tick js che version latest nightly other please specify steps to reproduce do click on see error expected behavior runtime kubernetes include output of kubectl version openshift include output of oc version minikube include output of minikube version and kubectl version minishift include output of minishift version and oc version docker desktop include output of docker version and kubectl version other please specify screenshots installation method chectl provide a full command that was used to deploy eclipse che including the output provide an output of chectl version command operatorhub i don t know environment my computer windows linux macos cloud amazon azure gce other please specify other please specify eclipse che logs additional context | 1 |
775,451 | 27,234,755,499 | IssuesEvent | 2023-02-21 15:34:39 | ascheid/itsg33-pbmm-issue-gen | https://api.github.com/repos/ascheid/itsg33-pbmm-issue-gen | closed | IR-5 INCIDENT MONITORING | Priority: P2 | (A) The organization tracks and documents information system security incidents. | 1.0 | IR-5 INCIDENT MONITORING - (A) The organization tracks and documents information system security incidents. | non_test | ir incident monitoring a the organization tracks and documents information system security incidents | 0 |
78,442 | 15,573,047,456 | IssuesEvent | 2021-03-17 08:02:19 | rammatzkvosky/789 | https://api.github.com/repos/rammatzkvosky/789 | reopened | CVE-2019-17531 (High) detected in jackson-databind-2.8.7.jar | security vulnerability | ## CVE-2019-17531 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.7.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: 789/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.7/jackson-databind-2.8.7.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.8.7.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rammatzkvosky/789/commit/f9b1c2e88187d7e6e5d7e812ef82431893dff972">f9b1c2e88187d7e6e5d7e812ef82431893dff972</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17531>CVE-2019-17531</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531</a></p>
<p>Release Date: 2019-10-12</p>
<p>Fix Resolution: 2.10</p>
</p>
</details>
<p></p>
| True | CVE-2019-17531 (High) detected in jackson-databind-2.8.7.jar - ## CVE-2019-17531 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.7.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: 789/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.7/jackson-databind-2.8.7.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.8.7.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rammatzkvosky/789/commit/f9b1c2e88187d7e6e5d7e812ef82431893dff972">f9b1c2e88187d7e6e5d7e812ef82431893dff972</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17531>CVE-2019-17531</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531</a></p>
<p>Release Date: 2019-10-12</p>
<p>Fix Resolution: 2.10</p>
</p>
</details>
<p></p>
| non_test | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library canner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the apache extra version x jar in the classpath and an attacker can provide a jndi service to access it is possible to make the service execute a malicious payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
29,632 | 4,519,941,604 | IssuesEvent | 2016-09-06 08:34:37 | skaut/SRS | https://api.github.com/repos/skaut/SRS | closed | Sjednotit administraci uživatelů | Bug Testování | V administraci sjednotit tabulky pro výběr role s evidencí účastníků.
Odkaz "Evidence účastníků" přejmenovat na "Evidence uživatelů" a v této tabulce umožnit výběr "Role" a "Schválený".
Odkaz "Práva a role" zůstene, ale bude zde jen "Role". | 1.0 | Sjednotit administraci uživatelů - V administraci sjednotit tabulky pro výběr role s evidencí účastníků.
Odkaz "Evidence účastníků" přejmenovat na "Evidence uživatelů" a v této tabulce umožnit výběr "Role" a "Schválený".
Odkaz "Práva a role" zůstene, ale bude zde jen "Role". | test | sjednotit administraci uživatelů v administraci sjednotit tabulky pro výběr role s evidencí účastníků odkaz evidence účastníků přejmenovat na evidence uživatelů a v této tabulce umožnit výběr role a schválený odkaz práva a role zůstene ale bude zde jen role | 1 |
236,373 | 7,748,807,150 | IssuesEvent | 2018-05-30 09:26:35 | Gloirin/m2gTest | https://api.github.com/repos/Gloirin/m2gTest | closed | 0003100:
add tags to adb export | Addressbook Feature Request high priority | **Reported by pschuele on 11 Oct 2010 07:41**
**Version:** Mialena (2010-03-6)
add tags to adb export
- ods
- xls
| 1.0 | 0003100:
add tags to adb export - **Reported by pschuele on 11 Oct 2010 07:41**
**Version:** Mialena (2010-03-6)
add tags to adb export
- ods
- xls
| non_test | add tags to adb export reported by pschuele on oct version mialena add tags to adb export ods xls | 0 |
212,539 | 16,488,430,682 | IssuesEvent | 2021-05-24 21:53:22 | CORE-GATECH-GROUP/serpent-tools | https://api.github.com/repos/CORE-GATECH-GROUP/serpent-tools | opened | BUG Docs are failing on read the docs | bug documentation | ## Summary of issue
https://readthedocs.org/projects/serpent-tools/builds/13844425/
Produces two warnings (which can be replicated locally)
```
home/docs/checkouts/readthedocs.org/user_builds/serpent-tools/checkouts/master/serpentTools/parsers/sensitivity.py:docstring of serpentTools.SensitivityReader.plot:64: WARNING: Unknown interpreted text role "method".
/home/docs/checkouts/readthedocs.org/user_builds/serpent-tools/checkouts/master/docs/publications.rst:5: WARNING: Duplicate explicit target name: "nuclear engineering and design (2020)".
```
Documentation still appears to be built properly
## Code for reproducing the issue
```shell
cd docs
make clean html
```
## Actual outcome including console output and error traceback if applicable
(error message above)
Locally it looks like the `SensitivityReader` issue is causing a more serious error (red rather than magenta)
## Expected outcome
No warning message
## Versions
857b9f5 | 1.0 | BUG Docs are failing on read the docs - ## Summary of issue
https://readthedocs.org/projects/serpent-tools/builds/13844425/
Produces two warnings (which can be replicated locally)
```
home/docs/checkouts/readthedocs.org/user_builds/serpent-tools/checkouts/master/serpentTools/parsers/sensitivity.py:docstring of serpentTools.SensitivityReader.plot:64: WARNING: Unknown interpreted text role "method".
/home/docs/checkouts/readthedocs.org/user_builds/serpent-tools/checkouts/master/docs/publications.rst:5: WARNING: Duplicate explicit target name: "nuclear engineering and design (2020)".
```
Documentation still appears to be built properly
## Code for reproducing the issue
```shell
cd docs
make clean html
```
## Actual outcome including console output and error traceback if applicable
(error message above)
Locally it looks like the `SensitivityReader` issue is causing a more serious error (red rather than magenta)
## Expected outcome
No warning message
## Versions
857b9f5 | non_test | bug docs are failing on read the docs summary of issue produces two warnings which can be replicated locally home docs checkouts readthedocs org user builds serpent tools checkouts master serpenttools parsers sensitivity py docstring of serpenttools sensitivityreader plot warning unknown interpreted text role method home docs checkouts readthedocs org user builds serpent tools checkouts master docs publications rst warning duplicate explicit target name nuclear engineering and design documentation still appears to be built properly code for reproducing the issue shell cd docs make clean html actual outcome including console output and error traceback if applicable error message above locally it looks like the sensitivityreader issue is causing a more serious error red rather than magenta expected outcome no warning message versions | 0 |
180,403 | 13,930,799,545 | IssuesEvent | 2020-10-22 03:26:49 | statechannels/statechannels | https://api.github.com/repos/statechannels/statechannels | closed | [idea] Speed up CI by mocking signMessage and verifyMessage | ci testing | We could mock out `ethers.utils.signMessage` and `ethers.utils.verifyMessage` for CI to be some really fast O(1) function with similar properties to the actual functions. I don't have profiling information but from my experience this can add a ton of lag to tests. | 1.0 | [idea] Speed up CI by mocking signMessage and verifyMessage - We could mock out `ethers.utils.signMessage` and `ethers.utils.verifyMessage` for CI to be some really fast O(1) function with similar properties to the actual functions. I don't have profiling information but from my experience this can add a ton of lag to tests. | test | speed up ci by mocking signmessage and verifymessage we could mock out ethers utils signmessage and ethers utils verifymessage for ci to be some really fast o function with similar properties to the actual functions i don t have profiling information but from my experience this can add a ton of lag to tests | 1 |
120,578 | 10,128,916,593 | IssuesEvent | 2019-08-01 13:47:33 | dzhw/metadatamanagement | https://api.github.com/repos/dzhw/metadatamanagement | closed | As public User I cannot see the instruments of ssy21 although they are released | category:projectmanagement prio:1 status:testing type:bug | https://metadata.fdz.dzhw.eu/#!/de/studies/stu-ssy21$?version=2.0.0
Rerelease fixed the problem. But why
| 1.0 | As public User I cannot see the instruments of ssy21 although they are released - https://metadata.fdz.dzhw.eu/#!/de/studies/stu-ssy21$?version=2.0.0
Rerelease fixed the problem. But why
| test | as public user i cannot see the instruments of although they are released rerelease fixed the problem but why | 1 |
44,001 | 11,901,294,427 | IssuesEvent | 2020-03-30 12:12:34 | contao/contao | https://api.github.com/repos/contao/contao | closed | Seitentitel Dashboard | defect | **Affected version(s)**
Contao 4.9
**Description**
Der Titel der Seite ``example.com/contao`` ist ``Startseite``, obwohl die Überschrift der Seite ``Dashboard`` lautet. | 1.0 | Seitentitel Dashboard - **Affected version(s)**
Contao 4.9
**Description**
Der Titel der Seite ``example.com/contao`` ist ``Startseite``, obwohl die Überschrift der Seite ``Dashboard`` lautet. | non_test | seitentitel dashboard affected version s contao description der titel der seite example com contao ist startseite obwohl die überschrift der seite dashboard lautet | 0 |
195,427 | 14,728,849,576 | IssuesEvent | 2021-01-06 10:31:38 | OpenPaaS-Suite/esn-frontend-inbox | https://api.github.com/repos/OpenPaaS-Suite/esn-frontend-inbox | closed | Enable to unselect `read receipts` if I don't click outside the Email writing window | QA:Testing bug | # reproduction steps
- Go to inbox
- click on new email FAB
- click on the three vertical dots at the left of the **send** button
- [a dialog appear, with "Request a read receipt"]
- click outside
**CURRENT**
the dialog does not close
**EXPECTED**
the dialog closes | 1.0 | Enable to unselect `read receipts` if I don't click outside the Email writing window - # reproduction steps
- Go to inbox
- click on new email FAB
- click on the three vertical dots at the left of the **send** button
- [a dialog appear, with "Request a read receipt"]
- click outside
**CURRENT**
the dialog does not close
**EXPECTED**
the dialog closes | test | enable to unselect read receipts if i don t click outside the email writing window reproduction steps go to inbox click on new email fab click on the three vertical dots at the left of the send button click outside current the dialog does not close expected the dialog closes | 1 |
392,097 | 26,924,101,176 | IssuesEvent | 2023-02-07 12:37:06 | adapt-security/adapt-authoring | https://api.github.com/repos/adapt-security/adapt-authoring | closed | REST APIs must be documented | help wanted documentation R&D | There's currently no mechanism to document the external API endpoints.
- OpenAPI-based? (Swagger, ReDoc)
- Integrate with ESDoc? | 1.0 | REST APIs must be documented - There's currently no mechanism to document the external API endpoints.
- OpenAPI-based? (Swagger, ReDoc)
- Integrate with ESDoc? | non_test | rest apis must be documented there s currently no mechanism to document the external api endpoints openapi based swagger redoc integrate with esdoc | 0 |
127,735 | 10,480,795,278 | IssuesEvent | 2019-09-24 08:22:03 | wix/wix-style-react | https://api.github.com/repos/wix/wix-style-react | closed | `<DropdownBase/>`- testkit functions don't work as expected | DropdownBase testkit:bug | # 🐛 Bug Report
### 🏗 Relevant Components
`
<DropdownBase/>`
### 😯 Current Behavior
**App file:**
```
import React from 'react';
import DropdownBase from 'wix-style-react/DropdownBase';
import IconButton from 'wix-style-react/IconButton';
import ChevronDown from 'wix-style-react/new-icons/ChevronDown';
const options = [
{
id: 0,
value: 'First option',
},
{
id: 1,
value: 'Second option',
},
];
class App extends React.Component {
render() {
return (
<DropdownBase
showArrow
dataHook={'dropdownbase-datahook'}
options={options}
onSelect={selectedOption =>
'Triggered with: ' + JSON.stringify(selectedOption)
}
>
{({ open, close }) => {
return (
<IconButton
skin="inverted"
dataHook={"myOpenButton"}
onMouseEnter={open}
onMouseLeave={close}
>
<ChevronDown />
</IconButton>
);
}}
</DropdownBase>
);
}
}
```
**Test file:**
```
import React from 'react';
import App from './App';
import ReactTestUtils from 'react-dom/test-utils';
import { dropdownBaseTestkitFactory } from 'wix-style-react/dist/testkit';
describe('App', () => {
it('should open dropdown once it is clicked', async () => {
const div = document.createElement('div');
const dataHook = 'dropdownbase-datahook';
const component = (
<div>
<App />
</div>
);
const wrapper = div.appendChild(
ReactTestUtils.renderIntoDocument(component, { dataHook }),
);
const testkit = dropdownBaseTestkitFactory({ wrapper, dataHook });
await testkit.clickTargetElement();
expect(await testkit.isDropdownShown()).toBe(true);
});
});
```
### 🤔 Expected Behavior
The `clickTargetElement` should open the `DropdownBase`.
Moreover, we've tried to use the `optionsCount` function and it's also doesn't work as expected to it seems like it's not specifically an issue just with the `clickTargetElement` function.
### 👣 Steps to Reproduce
Described above
- **WSR version**: `^6.54.2`
- **Yoshi version**: `...`
### 👀 Severity
<!---
Try to reflect how sever the issue is in general. Pick the most relevant one.
-->
- Critical / Major / Low
| 1.0 | `<DropdownBase/>`- testkit functions don't work as expected - # 🐛 Bug Report
### 🏗 Relevant Components
`
<DropdownBase/>`
### 😯 Current Behavior
**App file:**
```
import React from 'react';
import DropdownBase from 'wix-style-react/DropdownBase';
import IconButton from 'wix-style-react/IconButton';
import ChevronDown from 'wix-style-react/new-icons/ChevronDown';
const options = [
{
id: 0,
value: 'First option',
},
{
id: 1,
value: 'Second option',
},
];
class App extends React.Component {
render() {
return (
<DropdownBase
showArrow
dataHook={'dropdownbase-datahook'}
options={options}
onSelect={selectedOption =>
'Triggered with: ' + JSON.stringify(selectedOption)
}
>
{({ open, close }) => {
return (
<IconButton
skin="inverted"
dataHook={"myOpenButton"}
onMouseEnter={open}
onMouseLeave={close}
>
<ChevronDown />
</IconButton>
);
}}
</DropdownBase>
);
}
}
```
**Test file:**
```
import React from 'react';
import App from './App';
import ReactTestUtils from 'react-dom/test-utils';
import { dropdownBaseTestkitFactory } from 'wix-style-react/dist/testkit';
describe('App', () => {
it('should open dropdown once it is clicked', async () => {
const div = document.createElement('div');
const dataHook = 'dropdownbase-datahook';
const component = (
<div>
<App />
</div>
);
const wrapper = div.appendChild(
ReactTestUtils.renderIntoDocument(component, { dataHook }),
);
const testkit = dropdownBaseTestkitFactory({ wrapper, dataHook });
await testkit.clickTargetElement();
expect(await testkit.isDropdownShown()).toBe(true);
});
});
```
### 🤔 Expected Behavior
The `clickTargetElement` should open the `DropdownBase`.
Moreover, we've tried to use the `optionsCount` function and it's also doesn't work as expected to it seems like it's not specifically an issue just with the `clickTargetElement` function.
### 👣 Steps to Reproduce
Described above
- **WSR version**: `^6.54.2`
- **Yoshi version**: `...`
### 👀 Severity
<!---
Try to reflect how sever the issue is in general. Pick the most relevant one.
-->
- Critical / Major / Low
| test | testkit functions don t work as expected 🐛 bug report 🏗 relevant components 😯 current behavior app file import react from react import dropdownbase from wix style react dropdownbase import iconbutton from wix style react iconbutton import chevrondown from wix style react new icons chevrondown const options id value first option id value second option class app extends react component render return dropdownbase showarrow datahook dropdownbase datahook options options onselect selectedoption triggered with json stringify selectedoption open close return iconbutton skin inverted datahook myopenbutton onmouseenter open onmouseleave close test file import react from react import app from app import reacttestutils from react dom test utils import dropdownbasetestkitfactory from wix style react dist testkit describe app it should open dropdown once it is clicked async const div document createelement div const datahook dropdownbase datahook const component const wrapper div appendchild reacttestutils renderintodocument component datahook const testkit dropdownbasetestkitfactory wrapper datahook await testkit clicktargetelement expect await testkit isdropdownshown tobe true 🤔 expected behavior the clicktargetelement should open the dropdownbase moreover we ve tried to use the optionscount function and it s also doesn t work as expected to it seems like it s not specifically an issue just with the clicktargetelement function 👣 steps to reproduce described above wsr version yoshi version 👀 severity try to reflect how sever the issue is in general pick the most relevant one critical major low | 1 |
99,558 | 12,439,302,065 | IssuesEvent | 2020-05-26 09:52:29 | ChildMindInstitute/mindlogger-app | https://api.github.com/repos/ChildMindInstitute/mindlogger-app | closed | Email Invite For New User Not Received | design enhancement featurerequest | Expected Results: Sending an invitation would automatically be received to the email address
Actual Results: No email received
 | 1.0 | Email Invite For New User Not Received - Expected Results: Sending an invitation would automatically be received to the email address
Actual Results: No email received
 | non_test | email invite for new user not received expected results sending an invitation would automatically be received to the email address actual results no email received | 0 |
339,167 | 24,612,331,601 | IssuesEvent | 2022-10-14 23:37:19 | mvsjunior/sticknote-api | https://api.github.com/repos/mvsjunior/sticknote-api | closed | Obter uma ou mais notas | documentation | Listar uma ou mais notas através de uma requisição HTTP
- O usuário fará uma requisição GET para uma rota
- O usuário recebe a reposta com uma ou mais notas armazenadas
- Em caso de falha:
- O usuário é informado que ocorreu uma falha
- Em caso de sucesso:
- O usuário recebe a lista de notas
**DoD**
- [x] Rota "/notes" apta a receber requisições GET, para retornar a lista com todas as notas armazenadas
- [x] Rota "/note/{id}" apta a receber requisições GET, para retornar a nota com a id informada
- - [x] Caso a nota com a id informada não for encontrada, informar ao usuário que a nota não existe.
- [x] Em caso de sucesso, o usuário recebe uma lista com as notas armazenadas
- [x] Criação de testes para validar a consistência da funcionalidade de exibição de notas. | 1.0 | Obter uma ou mais notas - Listar uma ou mais notas através de uma requisição HTTP
- O usuário fará uma requisição GET para uma rota
- O usuário recebe a reposta com uma ou mais notas armazenadas
- Em caso de falha:
- O usuário é informado que ocorreu uma falha
- Em caso de sucesso:
- O usuário recebe a lista de notas
**DoD**
- [x] Rota "/notes" apta a receber requisições GET, para retornar a lista com todas as notas armazenadas
- [x] Rota "/note/{id}" apta a receber requisições GET, para retornar a nota com a id informada
- - [x] Caso a nota com a id informada não for encontrada, informar ao usuário que a nota não existe.
- [x] Em caso de sucesso, o usuário recebe uma lista com as notas armazenadas
- [x] Criação de testes para validar a consistência da funcionalidade de exibição de notas. | non_test | obter uma ou mais notas listar uma ou mais notas através de uma requisição http o usuário fará uma requisição get para uma rota o usuário recebe a reposta com uma ou mais notas armazenadas em caso de falha o usuário é informado que ocorreu uma falha em caso de sucesso o usuário recebe a lista de notas dod rota notes apta a receber requisições get para retornar a lista com todas as notas armazenadas rota note id apta a receber requisições get para retornar a nota com a id informada caso a nota com a id informada não for encontrada informar ao usuário que a nota não existe em caso de sucesso o usuário recebe uma lista com as notas armazenadas criação de testes para validar a consistência da funcionalidade de exibição de notas | 0 |
215,224 | 16,656,415,558 | IssuesEvent | 2021-06-05 16:00:42 | ita-social-projects/EventsExpress | https://api.github.com/repos/ita-social-projects/EventsExpress | opened | Verify that the authorized user must be able to contact the admin for feedback | test | **Date Time**
05-06-2021 18:52
**Priority**
Medium
**Description**
Authorized users should be able to contact the website administration and add feedback to explain difficult situations regarding the operation of the website.
**Pre-requisites**
Steps to be fulfilled before test:
1. Move to https://eventsexpress-test.azurewebsites.net/home/events
2. Authorize as an authorized user(e. g. user: eventsexpress.testuser4@gmail.com pass: Xiot5ish)
3. Open 'Contact us' board
**Test Cases**
| S# | Action | Test Data | Expected Result | Actual Result | P/F | Automated |
|:-----------:|:-----------:|:-----------:|:---------------:|:-------------:|:-----------:|:-----------:|
| 1 <br> | In the 'Problem Type' field, click 'New Category' and select the appropriate category <br> | <br> | The selected error type is displayed in the title field <br> | <br> | <br> | <br> |
| 2 <br> | In the 'Problem type' field, go to the Description <br> | <br> | The 'Description' field becomes active, and you can enter characters <br> | <br> | <br> | <br> |
| 3 <br> | Enter your message in the 'Description' field <br> | <br> | The 'Description' field displays the message you entered <br> | <br> | <br> | <br> |
| 4 <br> | Click the 'Submit' button <br> | <br> | A green message about a successful request should appear in the lower left corner <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> | <br> | <br> | <br> |
**Screenshots**
**Environment:**
- OS: [Windows 10(64x)]
- Browser [Google Chrome (90.0.4430.212)]
- Version [96801a8]
**Additional context**
Add any other context about the test here.
Link to story #355 | 1.0 | Verify that the authorized user must be able to contact the admin for feedback - **Date Time**
05-06-2021 18:52
**Priority**
Medium
**Description**
Authorized users should be able to contact the website administration and add feedback to explain difficult situations regarding the operation of the website.
**Pre-requisites**
Steps to be fulfilled before test:
1. Move to https://eventsexpress-test.azurewebsites.net/home/events
2. Authorize as an authorized user(e. g. user: eventsexpress.testuser4@gmail.com pass: Xiot5ish)
3. Open 'Contact us' board
**Test Cases**
| S# | Action | Test Data | Expected Result | Actual Result | P/F | Automated |
|:-----------:|:-----------:|:-----------:|:---------------:|:-------------:|:-----------:|:-----------:|
| 1 <br> | In the 'Problem Type' field, click 'New Category' and select the appropriate category <br> | <br> | The selected error type is displayed in the title field <br> | <br> | <br> | <br> |
| 2 <br> | In the 'Problem type' field, go to the Description <br> | <br> | The 'Description' field becomes active, and you can enter characters <br> | <br> | <br> | <br> |
| 3 <br> | Enter your message in the 'Description' field <br> | <br> | The 'Description' field displays the message you entered <br> | <br> | <br> | <br> |
| 4 <br> | Click the 'Submit' button <br> | <br> | A green message about a successful request should appear in the lower left corner <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> | <br> | <br> | <br> |
**Screenshots**
**Environment:**
- OS: [Windows 10(64x)]
- Browser [Google Chrome (90.0.4430.212)]
- Version [96801a8]
**Additional context**
Add any other context about the test here.
Link to story #355 | test | verify that the authorized user must be able to contact the admin for feedback date time priority medium description authorized users should be able to contact the website administration and add feedback to explain difficult situations regarding the operation of the website pre requisites steps to be fulfilled before test move to authorize as an authorized user e g user eventsexpress gmail com pass open contact us board test cases s action test data expected result actual result p f automated in the problem type field click new category and select the appropriate category the selected error type is displayed in the title field in the problem type field go to the description the description field becomes active and you can enter characters enter your message in the description field the description field displays the message you entered click the submit button a green message about a successful request should appear in the lower left corner screenshots environment os browser version additional context add any other context about the test here link to story | 1 |
342,986 | 10,324,164,319 | IssuesEvent | 2019-09-01 06:27:03 | OpenSRP/opensrp-client-chw | https://api.github.com/repos/OpenSRP/opensrp-client-chw | closed | Changing the primary caregiver (French version) crashes the app | bug high priority | Open a family, go to top right dropdown menu and select change primary caregiver ("Changer la gardienne" in French).
| 1.0 | Changing the primary caregiver (French version) crashes the app - Open a family, go to top right dropdown menu and select change primary caregiver ("Changer la gardienne" in French).
| non_test | changing the primary caregiver french version crashes the app open a family go to top right dropdown menu and select change primary caregiver changer la gardienne in french | 0 |
71,803 | 30,921,515,406 | IssuesEvent | 2023-08-06 00:46:32 | Zahlungsmittel/Zahlungsmittel | https://api.github.com/repos/Zahlungsmittel/Zahlungsmittel | opened | [CLOSED] refactor(backend): eslint typescript strict | refactor service: backend imported | <a href="https://github.com/ulfgebhardt"><img src="https://avatars.githubusercontent.com/u/1238238?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [ulfgebhardt](https://github.com/ulfgebhardt)**
_Tuesday May 09, 2023 at 10:21 GMT_
_Originally opened as https://github.com/gradido/gradido/pull/2979_
----
<!-- You can find the latest issue templates here https://github.com/ulfgebhardt/issue-templates -->
## 🍰 Pullrequest
<!-- Describe the Pullrequest. Use Screenshots if possible. -->
This implements typescript strict checks except `@typescript-eslint/no-unnecessary-condition` since this is incompatible with typeorm
### Issues
<!-- Which Issues does this fix, which are related?
- fixes #XXX
- relates #XXX
-->
- fixes #2964
### Todo
<!-- In case some parts are still missing, list them here. -->
- [X] None
----
_**[ulfgebhardt](https://github.com/ulfgebhardt)** included the following code: https://github.com/gradido/gradido/pull/2979/commits_
| 1.0 | [CLOSED] refactor(backend): eslint typescript strict - <a href="https://github.com/ulfgebhardt"><img src="https://avatars.githubusercontent.com/u/1238238?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [ulfgebhardt](https://github.com/ulfgebhardt)**
_Tuesday May 09, 2023 at 10:21 GMT_
_Originally opened as https://github.com/gradido/gradido/pull/2979_
----
<!-- You can find the latest issue templates here https://github.com/ulfgebhardt/issue-templates -->
## 🍰 Pullrequest
<!-- Describe the Pullrequest. Use Screenshots if possible. -->
This implements typescript strict checks except `@typescript-eslint/no-unnecessary-condition` since this is incompatible with typeorm
### Issues
<!-- Which Issues does this fix, which are related?
- fixes #XXX
- relates #XXX
-->
- fixes #2964
### Todo
<!-- In case some parts are still missing, list them here. -->
- [X] None
----
_**[ulfgebhardt](https://github.com/ulfgebhardt)** included the following code: https://github.com/gradido/gradido/pull/2979/commits_
| non_test | refactor backend eslint typescript strict issue by tuesday may at gmt originally opened as 🍰 pullrequest this implements typescript strict checks except typescript eslint no unnecessary condition since this is incompatible with typeorm issues which issues does this fix which are related fixes xxx relates xxx fixes todo none included the following code | 0 |
178,628 | 21,509,442,482 | IssuesEvent | 2022-04-28 01:41:44 | Watemlifts/redash | https://api.github.com/repos/Watemlifts/redash | closed | WS-2019-0493 (High) detected in handlebars-4.1.0.tgz - autoclosed | security vulnerability | ## WS-2019-0493 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.0.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz</a></p>
<p>Path to dependency file: redash/package.json</p>
<p>Path to vulnerable library: redash/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- jest-24.1.0.tgz (Root Library)
- jest-cli-24.1.0.tgz
- istanbul-api-2.1.1.tgz
- istanbul-reports-2.1.1.tgz
- :x: **handlebars-4.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Watemlifts/redash/commit/cec29597b6d6670317072971d6e694b4b13fea0e">cec29597b6d6670317072971d6e694b4b13fea0e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
handlebars before 3.0.8 and 4.x before 4.5.2 is vulnerable to Arbitrary Code Execution. The package's lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript in the system.
<p>Publish Date: 2019-11-14
<p>URL: <a href=https://github.com/handlebars-lang/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e>WS-2019-0493</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1316">https://www.npmjs.com/advisories/1316</a></p>
<p>Release Date: 2019-11-14</p>
<p>Fix Resolution: handlebars - 3.0.8,4.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0493 (High) detected in handlebars-4.1.0.tgz - autoclosed - ## WS-2019-0493 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.0.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz</a></p>
<p>Path to dependency file: redash/package.json</p>
<p>Path to vulnerable library: redash/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- jest-24.1.0.tgz (Root Library)
- jest-cli-24.1.0.tgz
- istanbul-api-2.1.1.tgz
- istanbul-reports-2.1.1.tgz
- :x: **handlebars-4.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Watemlifts/redash/commit/cec29597b6d6670317072971d6e694b4b13fea0e">cec29597b6d6670317072971d6e694b4b13fea0e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
handlebars before 3.0.8 and 4.x before 4.5.2 is vulnerable to Arbitrary Code Execution. The package's lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript in the system.
<p>Publish Date: 2019-11-14
<p>URL: <a href=https://github.com/handlebars-lang/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e>WS-2019-0493</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1316">https://www.npmjs.com/advisories/1316</a></p>
<p>Release Date: 2019-11-14</p>
<p>Fix Resolution: handlebars - 3.0.8,4.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | ws high detected in handlebars tgz autoclosed ws high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file redash package json path to vulnerable library redash node modules handlebars package json dependency hierarchy jest tgz root library jest cli tgz istanbul api tgz istanbul reports tgz x handlebars tgz vulnerable library found in head commit a href vulnerability details handlebars before and x before is vulnerable to arbitrary code execution the package s lookup helper fails to properly validate templates allowing attackers to submit templates that execute arbitrary javascript in the system publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars step up your open source security game with whitesource | 0 |
51,105 | 6,147,603,932 | IssuesEvent | 2017-06-27 16:01:44 | phetsims/expression-exchange | https://api.github.com/repos/phetsims/expression-exchange | closed | Flicking terms/expressions near another expression will make the join hint stick | status:fixed-pending-testing type:bug | Even if the two things don't actually combine. @jbphet was shown this directly, here is a screenshot:
<img width="1435" alt="screen shot 2017-06-26 at 12 43 15 pm" src="https://user-images.githubusercontent.com/5863899/27554843-0f5b54a4-5a6d-11e7-9d39-db154891fec1.png">
| 1.0 | Flicking terms/expressions near another expression will make the join hint stick - Even if the two things don't actually combine. @jbphet was shown this directly, here is a screenshot:
<img width="1435" alt="screen shot 2017-06-26 at 12 43 15 pm" src="https://user-images.githubusercontent.com/5863899/27554843-0f5b54a4-5a6d-11e7-9d39-db154891fec1.png">
| test | flicking terms expressions near another expression will make the join hint stick even if the two things don t actually combine jbphet was shown this directly here is a screenshot img width alt screen shot at pm src | 1 |
206,581 | 15,756,258,268 | IssuesEvent | 2021-03-31 03:12:09 | FundacionParaguaya/stoplight-web | https://api.github.com/repos/FundacionParaguaya/stoplight-web | closed | Show error message in Family Profile | tested | ## Tasks
1. When a family does not have access to the survey version anymore, and the user tries to see their Family Profile, a snackbar message should appear "The survey version is not available anymore. Make sure you have access to the survey version before viewing the Family Profile."
2. **Add survey version name in Family Profile**
Below the organization, and project name (if available), show the survey version name of the family. | 1.0 | Show error message in Family Profile - ## Tasks
1. When a family does not have access to the survey version anymore, and the user tries to see their Family Profile, a snackbar message should appear "The survey version is not available anymore. Make sure you have access to the survey version before viewing the Family Profile."
2. **Add survey version name in Family Profile**
Below the organization, and project name (if available), show the survey version name of the family. | test | show error message in family profile tasks when a family does not have access to the survey version anymore and the user tries to see their family profile a snackbar message should appear the survey version is not available anymore make sure you have access to the survey version before viewing the family profile add survey version name in family profile below the organization and project name if available show the survey version name of the family | 1 |
50,707 | 13,563,664,692 | IssuesEvent | 2020-09-18 08:53:32 | fli-iam/shanoir-ng | https://api.github.com/repos/fli-iam/shanoir-ng | closed | Massive download: multiple datasets, download is possible if right on one dataset | backend datasets security v1.0-necessary | is this correct for security reasons | True | Massive download: multiple datasets, download is possible if right on one dataset - is this correct for security reasons | non_test | massive download multiple datasets download is possible if right on one dataset is this correct for security reasons | 0 |
72,112 | 13,784,761,072 | IssuesEvent | 2020-10-08 21:26:42 | spotify/backstage | https://api.github.com/repos/spotify/backstage | closed | TechDocs: As a consumer of docs in Backstage, I want to see breadcrumbs of the current documentation page I am looking at | Hacktoberfest docs-like-code help wanted | `TechDocs > MkDocs`
<img width="500" alt="Screen Shot 2020-09-21 at 2 30 18 PM" src="https://user-images.githubusercontent.com/25153114/93766645-fe0d8380-fc16-11ea-97bf-4e96da601385.png">
These breadcrumps are hyperlinks to the page.
# Possible Implementation
Can use this UI component https://material-ui.com/components/breadcrumbs/
On individual TechDocs page, we have access to path. We can use the path to show the breadcrumbs.
| 1.0 | TechDocs: As a consumer of docs in Backstage, I want to see breadcrumbs of the current documentation page I am looking at - `TechDocs > MkDocs`
<img width="500" alt="Screen Shot 2020-09-21 at 2 30 18 PM" src="https://user-images.githubusercontent.com/25153114/93766645-fe0d8380-fc16-11ea-97bf-4e96da601385.png">
These breadcrumps are hyperlinks to the page.
# Possible Implementation
Can use this UI component https://material-ui.com/components/breadcrumbs/
On individual TechDocs page, we have access to path. We can use the path to show the breadcrumbs.
| non_test | techdocs as a consumer of docs in backstage i want to see breadcrumbs of the current documentation page i am looking at techdocs mkdocs img width alt screen shot at pm src these breadcrumps are hyperlinks to the page possible implementation can use this ui component on individual techdocs page we have access to path we can use the path to show the breadcrumbs | 0 |
212,761 | 16,480,212,089 | IssuesEvent | 2021-05-24 10:39:24 | ita-social-projects/EventsExpress | https://api.github.com/repos/ita-social-projects/EventsExpress | opened | Verify that the description of event on the open card of event is displayed for an authorized user | test | **Date Time**
05-24-2021 13:30
**Priority**
High
**Description**
Every authorized user...
**Pre-requisites**
Steps to be fulfilled before test:
1. Move to https://eventsexpress-test.azurewebsites.net/home/events?page=1&status=active
2. Authorize as *test credentials*
3. Open ...
**Test Cases**
| S# | Action | Test Data | Expected Result | Actual Result | P/F | Automated |
|:-----------:|:-----------:|:-----------:|:---------------:|:-------------:|:-----------:|:-----------:|
| 1<br> | Click on the event card of "Kranjci Croatia" <br> | <br> | Event card is opened <br> | <br> | <br> | <br> |
| 2 <br> | Scroll to the field description <br> | <br> | <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> | <br> | <br> | <br> |
**Screenshots**
If applicable, add screenshots to help explain your test.
**Environment:**
- OS: [e.g. iOS]
- Browser [e.g. chrome, safari]
- Version [e.g. 22]
**Additional context**
Add any other context about the test here.
Link to story #185 | 1.0 | Verify that the description of event on the open card of event is displayed for an authorized user - **Date Time**
05-24-2021 13:30
**Priority**
High
**Description**
Every authorized user...
**Pre-requisites**
Steps to be fulfilled before test:
1. Move to https://eventsexpress-test.azurewebsites.net/home/events?page=1&status=active
2. Authorize as *test credentials*
3. Open ...
**Test Cases**
| S# | Action | Test Data | Expected Result | Actual Result | P/F | Automated |
|:-----------:|:-----------:|:-----------:|:---------------:|:-------------:|:-----------:|:-----------:|
| 1<br> | Click on the event card of "Kranjci Croatia" <br> | <br> | Event card is opened <br> | <br> | <br> | <br> |
| 2 <br> | Scroll to the field description <br> | <br> | <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> | <br> | <br> | <br> |
**Screenshots**
If applicable, add screenshots to help explain your test.
**Environment:**
- OS: [e.g. iOS]
- Browser [e.g. chrome, safari]
- Version [e.g. 22]
**Additional context**
Add any other context about the test here.
Link to story #185 | test | verify that the description of event on the open card of event is displayed for an authorized user date time priority high description every authorized user pre requisites steps to be fulfilled before test move to authorize as test credentials open test cases s action test data expected result actual result p f automated click on the event card of kranjci croatia event card is opened scroll to the field description screenshots if applicable add screenshots to help explain your test environment os browser version additional context add any other context about the test here link to story | 1 |
105,747 | 9,100,525,585 | IssuesEvent | 2019-02-20 08:48:04 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | opened | Test : ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive | test | Project : Test
Job : Default
Env : Default
Category : ABAC_Level5
Tags : [FX Top 10 - API Vulnerability, Data_Access_Control]
Severity : Major
Region : US_WEST
Result : fail
Status Code : 500
Headers : {}
Endpoint : http://13.56.210.25/api/v1/api/v1/abac/project//add-abact3positive-rules
Request :
Response :
I/O error on GET request for "http://13.56.210.25/api/v1/api/v1/abac/project/add-abact3positive-rules": Read timed out; nested exception is java.net.SocketTimeoutException: Read timed out
Logs :
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : URL [http://13.56.210.25/api/v1/api/v1/abac/batch]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Method [POST]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Request [[ {
"assertions" : [ "UYdp8cOh" ],
"assertionsText" : "UYdp8cOh",
"auth" : "UYdp8cOh",
"authors" : [ "UYdp8cOh" ],
"authorsText" : "UYdp8cOh",
"autoGenerated" : false,
"category" : "NoSQL_Injection",
"cleanup" : [ "UYdp8cOh" ],
"cleanupText" : "UYdp8cOh",
"createdBy" : "",
"createdDate" : "",
"description" : "UYdp8cOh",
"endpoint" : "UYdp8cOh",
"headers" : [ "UYdp8cOh" ],
"headersText" : "UYdp8cOh",
"id" : "",
"inactive" : false,
"init" : [ "UYdp8cOh" ],
"initText" : "UYdp8cOh",
"method" : "HEAD",
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "UYdp8cOh",
"parent" : "UYdp8cOh",
"path" : "UYdp8cOh",
"policies" : {
"cleanupExec" : "UYdp8cOh",
"initExec" : "UYdp8cOh",
"logger" : "UYdp8cOh",
"repeat" : "875223456",
"repeatDelay" : "875223456",
"repeatModule" : "UYdp8cOh",
"repeatOnFailure" : "875223456",
"timeoutSeconds" : "875223456"
},
"project" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "UYdp8cOh",
"org" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "UYdp8cOh",
"version" : ""
},
"version" : ""
},
"props" : null,
"publishToMarketplace" : false,
"severity" : "Trivial",
"tags" : [ "UYdp8cOh" ],
"tagsText" : "UYdp8cOh",
"testCases" : [ {
"body" : "UYdp8cOh",
"id" : "",
"inactive" : false
} ],
"type" : "Suite",
"version" : "",
"yaml" : "UYdp8cOh"
} ]]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Request-Headers [{Content-Type=[application/json], Accept=[application/json], Authorization=[Basic dXNlckFAZnhsYWJzLmlvOnVzZXJB]}]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Response []
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Response-Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : StatusCode [401]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Time [489]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Size [0]
2019-02-20 07:51:29 ERROR [null] : Assertion [@StatusCode == 200 OR @StatusCode == 201] resolved-to [401 == 200 OR 401 == 201] result [Failed]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive_Headers] : Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive_Headers] : Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive_Headers[2]] : Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive_Headers[2]] : Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : URL [http://13.56.210.25/api/v1/api/v1/abac/project//add-abact3positive-rules]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Method [GET]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Request []
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Request-Headers [{Content-Type=[application/json], Accept=[application/json], Authorization=[Basic dXNlckFAZnhsYWJzLmlvOnVzZXJB]}]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Response []
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Response-Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : StatusCode [401]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Time [356]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Size [0]
2019-02-20 07:51:29 ERROR [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Assertion [@StatusCode == 200 AND @Response.errors == false] resolved-to [401 == 200 AND == false] result [Failed]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : URL [http://13.56.210.25/api/v1/api/v1/abac/]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Method [DELETE]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Request [null]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Request-Headers [{Content-Type=[application/json], Accept=[application/json], Authorization=[Basic dXNlckFAZnhsYWJzLmlvOnVzZXJB]}]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Response []
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Response-Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : StatusCode [401]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Time [506]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Size [0]
2019-02-20 07:51:30 ERROR [null] : Assertion [@StatusCode == 200] resolved-to [401 == 200] result [Failed]
--- FX Bot --- | 1.0 | Test : ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive - Project : Test
Job : Default
Env : Default
Category : ABAC_Level5
Tags : [FX Top 10 - API Vulnerability, Data_Access_Control]
Severity : Major
Region : US_WEST
Result : fail
Status Code : 500
Headers : {}
Endpoint : http://13.56.210.25/api/v1/api/v1/abac/project//add-abact3positive-rules
Request :
Response :
I/O error on GET request for "http://13.56.210.25/api/v1/api/v1/abac/project/add-abact3positive-rules": Read timed out; nested exception is java.net.SocketTimeoutException: Read timed out
Logs :
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : URL [http://13.56.210.25/api/v1/api/v1/abac/batch]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Method [POST]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Request [[ {
"assertions" : [ "UYdp8cOh" ],
"assertionsText" : "UYdp8cOh",
"auth" : "UYdp8cOh",
"authors" : [ "UYdp8cOh" ],
"authorsText" : "UYdp8cOh",
"autoGenerated" : false,
"category" : "NoSQL_Injection",
"cleanup" : [ "UYdp8cOh" ],
"cleanupText" : "UYdp8cOh",
"createdBy" : "",
"createdDate" : "",
"description" : "UYdp8cOh",
"endpoint" : "UYdp8cOh",
"headers" : [ "UYdp8cOh" ],
"headersText" : "UYdp8cOh",
"id" : "",
"inactive" : false,
"init" : [ "UYdp8cOh" ],
"initText" : "UYdp8cOh",
"method" : "HEAD",
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "UYdp8cOh",
"parent" : "UYdp8cOh",
"path" : "UYdp8cOh",
"policies" : {
"cleanupExec" : "UYdp8cOh",
"initExec" : "UYdp8cOh",
"logger" : "UYdp8cOh",
"repeat" : "875223456",
"repeatDelay" : "875223456",
"repeatModule" : "UYdp8cOh",
"repeatOnFailure" : "875223456",
"timeoutSeconds" : "875223456"
},
"project" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "UYdp8cOh",
"org" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "UYdp8cOh",
"version" : ""
},
"version" : ""
},
"props" : null,
"publishToMarketplace" : false,
"severity" : "Trivial",
"tags" : [ "UYdp8cOh" ],
"tagsText" : "UYdp8cOh",
"testCases" : [ {
"body" : "UYdp8cOh",
"id" : "",
"inactive" : false
} ],
"type" : "Suite",
"version" : "",
"yaml" : "UYdp8cOh"
} ]]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Request-Headers [{Content-Type=[application/json], Accept=[application/json], Authorization=[Basic dXNlckFAZnhsYWJzLmlvOnVzZXJB]}]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Response []
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Response-Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : StatusCode [401]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Time [489]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive] : Size [0]
2019-02-20 07:51:29 ERROR [null] : Assertion [@StatusCode == 200 OR @StatusCode == 201] resolved-to [401 == 200 OR 401 == 201] result [Failed]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive_Headers] : Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive_Headers] : Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive_Headers[2]] : Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [BatchCategoryLogForgingCreateUserAInitAbact2Positive_Headers[2]] : Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : URL [http://13.56.210.25/api/v1/api/v1/abac/project//add-abact3positive-rules]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Method [GET]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Request []
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Request-Headers [{Content-Type=[application/json], Accept=[application/json], Authorization=[Basic dXNlckFAZnhsYWJzLmlvOnVzZXJB]}]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Response []
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Response-Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : StatusCode [401]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Time [356]
2019-02-20 07:51:29 DEBUG [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Size [0]
2019-02-20 07:51:29 ERROR [ApiV1AbacProjectRequestidAddAbact3positiveRulesGetBatchcategorylogforginguseraAllowAbact2positive] : Assertion [@StatusCode == 200 AND @Response.errors == false] resolved-to [401 == 200 AND == false] result [Failed]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : URL [http://13.56.210.25/api/v1/api/v1/abac/]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Method [DELETE]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Request [null]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Request-Headers [{Content-Type=[application/json], Accept=[application/json], Authorization=[Basic dXNlckFAZnhsYWJzLmlvOnVzZXJB]}]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Response []
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Response-Headers [{WWW-Authenticate=[Basic realm="Realm", Basic realm="Realm"], X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Length=[0], Date=[Wed, 20 Feb 2019 07:51:29 GMT]}]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : StatusCode [401]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Time [506]
2019-02-20 07:51:30 DEBUG [ApiV1AbacIdDeleteBatchcategorylogforgingAbstractAbact2positive] : Size [0]
2019-02-20 07:51:30 ERROR [null] : Assertion [@StatusCode == 200] resolved-to [401 == 200] result [Failed]
--- FX Bot --- | test | test project test job default env default category abac tags severity major region us west result fail status code headers endpoint request response i o error on get request for read timed out nested exception is java net sockettimeoutexception read timed out logs debug url debug method debug request assertions assertionstext auth authors authorstext autogenerated false category nosql injection cleanup cleanuptext createdby createddate description endpoint headers headerstext id inactive false init inittext method head modifiedby modifieddate name parent path policies cleanupexec initexec logger repeat repeatdelay repeatmodule repeatonfailure timeoutseconds project createdby createddate id inactive false modifiedby modifieddate name org createdby createddate id inactive false modifiedby modifieddate name version version props null publishtomarketplace false severity trivial tags tagstext testcases body id inactive false type suite version yaml debug request headers accept authorization debug response debug response headers x content type options x xss protection cache control pragma expires x frame options content length date debug statuscode debug time debug size error assertion resolved to result debug headers x content type options x xss protection cache control pragma expires x frame options content length date debug headers x content type options x xss protection cache control pragma expires x frame options content length date debug headers x content type options x xss protection cache control pragma expires x frame options content length date debug headers x content type options x xss protection cache control pragma expires x frame options content length date debug url debug method debug request debug request headers accept authorization debug response debug response headers x content type options x xss protection cache control pragma expires x frame options content length date debug statuscode debug time debug size error assertion resolved to result debug url debug method debug request debug request headers accept authorization debug response debug response headers x content type options x xss protection cache control pragma expires x frame options content length date debug statuscode debug time debug size error assertion resolved to result fx bot | 1 |
238,718 | 19,758,710,779 | IssuesEvent | 2022-01-16 02:57:42 | heclak/community-a4e-c | https://api.github.com/repos/heclak/community-a4e-c | closed | Installing v2.0.0 cause Bulker Handy Wind to lose textures | TEST/reproduce | **Describe the bug**
After installing a4ec v2.0.0, bulker Handy Wind is missing textures.
**To Reproduce**
Steps to reproduce the behavior:
1. Create a mission with a bulker Handy Wind, make sure the textures are displayed correctly;
2. Install A4EC v2.0.0;
3. Open the mission again, the textures of Handy Wind is missing(showing green “camouflage”);
4. Uninstall A4EC;
5. Open the mission, the textures are back to normal.
**Expected behavior**
Described above
**Screenshots**
Not applicable
**Software Information (please complete the following information):**
- DCS Version: latest open beta
- A-4E Version v2.0.0
**Additional context**
None | 1.0 | Installing v2.0.0 cause Bulker Handy Wind to lose textures - **Describe the bug**
After installing a4ec v2.0.0, bulker Handy Wind is missing textures.
**To Reproduce**
Steps to reproduce the behavior:
1. Create a mission with a bulker Handy Wind, make sure the textures are displayed correctly;
2. Install A4EC v2.0.0;
3. Open the mission again, the textures of Handy Wind is missing(showing green “camouflage”);
4. Uninstall A4EC;
5. Open the mission, the textures are back to normal.
**Expected behavior**
Described above
**Screenshots**
Not applicable
**Software Information (please complete the following information):**
- DCS Version: latest open beta
- A-4E Version v2.0.0
**Additional context**
None | test | installing cause bulker handy wind to lose textures describe the bug after installing bulker handy wind is missing textures to reproduce steps to reproduce the behavior create a mission with a bulker handy wind make sure the textures are displayed correctly install open the mission again the textures of handy wind is missing showing green “camouflage” uninstall open the mission the textures are back to normal expected behavior described above screenshots not applicable software information please complete the following information dcs version latest open beta a version additional context none | 1 |
250,309 | 7,975,104,538 | IssuesEvent | 2018-07-17 08:20:04 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | reopened | www.88beta.com - design is broken | Re-triaged browser-chrome priority-normal status-needsinfo-foolip | <!-- @browser: Firefox 57.0 -->
<!-- @ua_header: Mozilla/5.0 (X11; Linux x86_64; rv:57.0) Gecko/20100101 Firefox/57.0 -->
<!-- @reported_with: web -->
**URL**: http://www.88beta.com/
**Browser / Version**: Firefox 57.0
**Operating System**: Linux
**Tested Another Browser**: Yes
**Problem type**: Design is broken
**Description**: Colour rendering different from what is real and other browser
**Steps to Reproduce**:
open http://www.88beta.com/
see the color is different from chrome
[](https://webcompat.com/uploads/2017/10/ef687c6f-84a8-468a-824b-7d09a67db8b7.jpg)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | www.88beta.com - design is broken - <!-- @browser: Firefox 57.0 -->
<!-- @ua_header: Mozilla/5.0 (X11; Linux x86_64; rv:57.0) Gecko/20100101 Firefox/57.0 -->
<!-- @reported_with: web -->
**URL**: http://www.88beta.com/
**Browser / Version**: Firefox 57.0
**Operating System**: Linux
**Tested Another Browser**: Yes
**Problem type**: Design is broken
**Description**: Colour rendering different from what is real and other browser
**Steps to Reproduce**:
open http://www.88beta.com/
see the color is different from chrome
[](https://webcompat.com/uploads/2017/10/ef687c6f-84a8-468a-824b-7d09a67db8b7.jpg)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_test | design is broken url browser version firefox operating system linux tested another browser yes problem type design is broken description colour rendering different from what is real and other browser steps to reproduce open see the color is different from chrome from with ❤️ | 0 |
137,237 | 11,103,194,485 | IssuesEvent | 2019-12-17 02:53:52 | a2000-erp-team/WEBERP | https://api.github.com/repos/a2000-erp-team/WEBERP | opened | Procurement-Order Processing-Inquiry-Purchase invoice report. Cannot restore a previously saved layout. | WEB ERP Testing By Katrina | Scenario:

Then I tried to load the layout but nothing happens.

| 1.0 | Procurement-Order Processing-Inquiry-Purchase invoice report. Cannot restore a previously saved layout. - Scenario:

Then I tried to load the layout but nothing happens.

| test | procurement order processing inquiry purchase invoice report cannot restore a previously saved layout scenario then i tried to load the layout but nothing happens | 1 |
19,795 | 5,938,492,168 | IssuesEvent | 2017-05-25 00:22:39 | fishtown-analytics/dbt | https://api.github.com/repos/fishtown-analytics/dbt | closed | first time project configuration | code review enhancement | - [x] create ~/.dbt/profiles.yml on `dbt init` (if it doesn't exist)
- [x] clone a starter repo (cc @jthandy)
- [x] show/open profiles dir/file at end of setup
- [x] `dbt debug --config-dir` ?
| 1.0 | first time project configuration - - [x] create ~/.dbt/profiles.yml on `dbt init` (if it doesn't exist)
- [x] clone a starter repo (cc @jthandy)
- [x] show/open profiles dir/file at end of setup
- [x] `dbt debug --config-dir` ?
| non_test | first time project configuration create dbt profiles yml on dbt init if it doesn t exist clone a starter repo cc jthandy show open profiles dir file at end of setup dbt debug config dir | 0 |
2,363 | 5,166,357,806 | IssuesEvent | 2017-01-17 16:02:41 | jmbredal/NAV | https://api.github.com/repos/jmbredal/NAV | closed | NAV daemons don't properly re-open log files on SIGHUP | Fix Released Medium process-control | The alertEngine, pping and servicemon daemons do not properly close and
re-open their logfiles when sent a SIGHUP signal.
When logrotate is used to rotate the log files of these processes, they
will keep their file descriptors and continue writing log messages to
non-existant files - which will actually occupy more and more space on the
partition.
Usually one would configure logrotate to issue a HUP signal to these kinds
of processes, but this won't work for the three daemons in question, and it
should.
[http://sourceforge.net/tracker/index.php?func=detail&aid=1697527&group_id=107608&atid=648170] | 1.0 | NAV daemons don't properly re-open log files on SIGHUP - The alertEngine, pping and servicemon daemons do not properly close and
re-open their logfiles when sent a SIGHUP signal.
When logrotate is used to rotate the log files of these processes, they
will keep their file descriptors and continue writing log messages to
non-existant files - which will actually occupy more and more space on the
partition.
Usually one would configure logrotate to issue a HUP signal to these kinds
of processes, but this won't work for the three daemons in question, and it
should.
[http://sourceforge.net/tracker/index.php?func=detail&aid=1697527&group_id=107608&atid=648170] | non_test | nav daemons don t properly re open log files on sighup the alertengine pping and servicemon daemons do not properly close and re open their logfiles when sent a sighup signal when logrotate is used to rotate the log files of these processes they will keep their file descriptors and continue writing log messages to non existant files which will actually occupy more and more space on the partition usually one would configure logrotate to issue a hup signal to these kinds of processes but this won t work for the three daemons in question and it should | 0 |
422,930 | 28,488,051,123 | IssuesEvent | 2023-04-18 09:12:52 | risingwavelabs/risingwave-docs | https://api.github.com/repos/risingwavelabs/risingwave-docs | opened | Document CREATE CONNECTION and SHOW CONNECTION | documentation | ### Related code PR
https://github.com/risingwavelabs/risingwave/pull/8907
### Which part(s) of the docs might be affected or should be updated? And how?
Add the two commands to SQL references - Commands.
Add a dedicated guide for setting up the pipeline. @StrikeW @WillyKidd, it would be great if you could provide a rough draft about setting up the whole process, including the PrivateLink and Kafka sides.
Deprecating the original private link for Kafka connector and its doc draft pr: https://github.com/risingwavelabs/risingwave-docs/pull/706. @emile-00
### Reference
RFC (important): https://www.notion.so/risingwave-labs/RFC-Using-AWS-PrivateLink-to-Connect-a-Kafka-Instance-7b33defa8af14caab4122fb6f06a5cb9?pvs=4
Materialize: https://materialize.com/docs/ops/network-security/privatelink/#create-an-aws-privatelink-connection
Related PR (background info): https://github.com/risingwavelabs/risingwave/pull/8247
Description adapted from @StrikeW (please review this):
If you are using a cloud-hosted source, such as AWS MSK, with RisingWave Cloud or a self-deployed RisingWave cluster, you might encounter connectivity issues when your source service is located in a different VPC and broadcasts internal IP addresses that can't be accessed from outside. To resolve this problem, you can use [AWS PrivateLink](https://docs.aws.amazon.com/vpc/latest/privatelink/privatelink-share-your-services.html) to establish a secure and direct connection between the two VPCs. To set it up, [create an endpoint service](https://docs.aws.amazon.com/vpc/latest/privatelink/create-endpoint-service.html) to expose your source service, and use the `CREATE CONNECTION` command in RisingWave to access it. | 1.0 | Document CREATE CONNECTION and SHOW CONNECTION - ### Related code PR
https://github.com/risingwavelabs/risingwave/pull/8907
### Which part(s) of the docs might be affected or should be updated? And how?
Add the two commands to SQL references - Commands.
Add a dedicated guide for setting up the pipeline. @StrikeW @WillyKidd, it would be great if you could provide a rough draft about setting up the whole process, including the PrivateLink and Kafka sides.
Deprecating the original private link for Kafka connector and its doc draft pr: https://github.com/risingwavelabs/risingwave-docs/pull/706. @emile-00
### Reference
RFC (important): https://www.notion.so/risingwave-labs/RFC-Using-AWS-PrivateLink-to-Connect-a-Kafka-Instance-7b33defa8af14caab4122fb6f06a5cb9?pvs=4
Materialize: https://materialize.com/docs/ops/network-security/privatelink/#create-an-aws-privatelink-connection
Related PR (background info): https://github.com/risingwavelabs/risingwave/pull/8247
Description adapted from @StrikeW (please review this):
If you are using a cloud-hosted source, such as AWS MSK, with RisingWave Cloud or a self-deployed RisingWave cluster, you might encounter connectivity issues when your source service is located in a different VPC and broadcasts internal IP addresses that can't be accessed from outside. To resolve this problem, you can use [AWS PrivateLink](https://docs.aws.amazon.com/vpc/latest/privatelink/privatelink-share-your-services.html) to establish a secure and direct connection between the two VPCs. To set it up, [create an endpoint service](https://docs.aws.amazon.com/vpc/latest/privatelink/create-endpoint-service.html) to expose your source service, and use the `CREATE CONNECTION` command in RisingWave to access it. | non_test | document create connection and show connection related code pr which part s of the docs might be affected or should be updated and how add the two commands to sql references commands add a dedicated guide for setting up the pipeline strikew willykidd it would be great if you could provide a rough draft about setting up the whole process including the privatelink and kafka sides deprecating the original private link for kafka connector and its doc draft pr emile reference rfc important materialize related pr background info description adapted from strikew please review this if you are using a cloud hosted source such as aws msk with risingwave cloud or a self deployed risingwave cluster you might encounter connectivity issues when your source service is located in a different vpc and broadcasts internal ip addresses that can t be accessed from outside to resolve this problem you can use to establish a secure and direct connection between the two vpcs to set it up to expose your source service and use the create connection command in risingwave to access it | 0 |
322,511 | 27,613,216,683 | IssuesEvent | 2023-03-09 17:21:22 | mehah/otclient | https://api.github.com/repos/mehah/otclient | closed | Add support for density pixels (DP) on Android | Status: Pending Test Type: Enhancement | ### Priority
Enhancement
### Area
- [ ] Data
- [X] Source
- [ ] Docker
- [ ] Other
### What is missing?
I'm opening this discussion to get some ideas on how we can transform `pixels` into `density pixels` while declaring our UI on `.otui` files.
What is density pixels:
Density pixels is an easy way to create unique UIs instead having to support different screen sizes as it is adaptative UI. For example if we declare 20px in one device, it can be bigger or smaller depending of the screen density of the device. But if we transform this same 20px into density pixels, the size of this component should be the same in different device sizes.
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | 1.0 | Add support for density pixels (DP) on Android - ### Priority
Enhancement
### Area
- [ ] Data
- [X] Source
- [ ] Docker
- [ ] Other
### What is missing?
I'm opening this discussion to get some ideas on how we can transform `pixels` into `density pixels` while declaring our UI on `.otui` files.
What is density pixels:
Density pixels is an easy way to create unique UIs instead having to support different screen sizes as it is adaptative UI. For example if we declare 20px in one device, it can be bigger or smaller depending of the screen density of the device. But if we transform this same 20px into density pixels, the size of this component should be the same in different device sizes.
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | test | add support for density pixels dp on android priority enhancement area data source docker other what is missing i m opening this discussion to get some ideas on how we can transform pixels into density pixels while declaring our ui on otui files what is density pixels density pixels is an easy way to create unique uis instead having to support different screen sizes as it is adaptative ui for example if we declare in one device it can be bigger or smaller depending of the screen density of the device but if we transform this same into density pixels the size of this component should be the same in different device sizes code of conduct i agree to follow this project s code of conduct | 1 |
174,736 | 13,508,726,408 | IssuesEvent | 2020-09-14 08:10:13 | navikt/nav-dekoratoren | https://api.github.com/repos/navikt/nav-dekoratoren | closed | Chatbot på nav.no | Testet OK Verifisert OK enhancement | - Gradvis utrullering av Chatbot Frida på alle Enonic-sider.
- Målinger i chatbot'en? | 1.0 | Chatbot på nav.no - - Gradvis utrullering av Chatbot Frida på alle Enonic-sider.
- Målinger i chatbot'en? | test | chatbot på nav no gradvis utrullering av chatbot frida på alle enonic sider målinger i chatbot en | 1 |
229,667 | 18,409,923,450 | IssuesEvent | 2021-10-13 03:32:59 | Tencent/bk-sops | https://api.github.com/repos/Tencent/bk-sops | opened | 【3.9.0】全新用户进入标准运维提示找不到页面 | type/test-stage-bug | 问题描述
=======
<!-- 这里写问题描述 -->
重现方法
=======
<!-- 列出如何重现的方法或操作步骤 -->
应展示对应无权限页面,并提示对应权限跳转
<!-- **重要提醒**: 请优先尝试部署使用最新发布的版本 (发布清单: https://github.com/Tencent/bk-sops/releases), 如果问题不能在最新发布的版本里重现,说明此问题已经被修复。 -->
关键信息
=======
<!-- **重要提醒**: 这些关键信息会辅助我们快速定位问题。 -->
请提供以下信息:
- [x] bk-sops 版本 (发布版本号 或 git tag): <!-- `示例: V3.1.32-ce 或者 git sha. 请不要使用 "最新版本" 或 "当前版本"等无法准确定位代码版本的语句描述` -->
- [ ] 蓝鲸PaaS 版本:<!-- `<示例:PaaS 3.0.58、PaaSAgent 3.0.9` -->
- [ ] bk_sops 异常日志:
| 1.0 | 【3.9.0】全新用户进入标准运维提示找不到页面 - 问题描述
=======
<!-- 这里写问题描述 -->
重现方法
=======
<!-- 列出如何重现的方法或操作步骤 -->
应展示对应无权限页面,并提示对应权限跳转
<!-- **重要提醒**: 请优先尝试部署使用最新发布的版本 (发布清单: https://github.com/Tencent/bk-sops/releases), 如果问题不能在最新发布的版本里重现,说明此问题已经被修复。 -->
关键信息
=======
<!-- **重要提醒**: 这些关键信息会辅助我们快速定位问题。 -->
请提供以下信息:
- [x] bk-sops 版本 (发布版本号 或 git tag): <!-- `示例: V3.1.32-ce 或者 git sha. 请不要使用 "最新版本" 或 "当前版本"等无法准确定位代码版本的语句描述` -->
- [ ] 蓝鲸PaaS 版本:<!-- `<示例:PaaS 3.0.58、PaaSAgent 3.0.9` -->
- [ ] bk_sops 异常日志:
| test | 【 】全新用户进入标准运维提示找不到页面 问题描述 重现方法 应展示对应无权限页面,并提示对应权限跳转 关键信息 请提供以下信息 bk sops 版本 发布版本号 或 git tag : 蓝鲸paas 版本: bk sops 异常日志: | 1 |
372,441 | 26,002,589,202 | IssuesEvent | 2022-12-20 16:26:46 | potestiolab/excogito | https://api.github.com/repos/potestiolab/excogito | opened | add icosalanine tutorial | documentation | add a full tutorial/example with the application of the software to the icosalanine peptide | 1.0 | add icosalanine tutorial - add a full tutorial/example with the application of the software to the icosalanine peptide | non_test | add icosalanine tutorial add a full tutorial example with the application of the software to the icosalanine peptide | 0 |
131,800 | 10,710,985,658 | IssuesEvent | 2019-10-25 04:32:59 | pantsbuild/pants | https://api.github.com/repos/pantsbuild/pants | closed | RscCompileIntegration.test_executing_multi_target_binary_hermetic is flaky | flaky-test | I suspect this is because of slightly buggy underlying code, rather than test issues. cc @baroquebobcat
```
tests/python/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py::RscCompileIntegration::test_executing_multi_target_binary_hermetic <- pyprep/sources/c613c998aacf75bcee19a3423daa93dea4f2f285/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py FAILED [100%]
==================== FAILURES ====================
RscCompileIntegration.test_executing_multi_target_binary_hermetic
self = <pants_test.backend.jvm.tasks.jvm_compile.rsc.test_rsc_compile_integration.RscCompileIntegration testMethod=test_executing_multi_target_binary_hermetic>
def test_executing_multi_target_binary_hermetic(self):
with temporary_dir() as cache_dir:
config = {
'cache.compile.rsc': {'write_to': [cache_dir]},
'jvm-platform': {'compiler': 'rsc'},
'compile.rsc': {
'execution_strategy': 'hermetic',
'incremental': False
},
'resolve.ivy': {
'capture_snapshots': True
},
}
with self.temporary_workdir() as workdir:
pants_run = self.run_pants_with_workdir(
['run',
'examples/src/scala/org/pantsbuild/example/hello/exe',
],
workdir, config)
> self.assert_success(pants_run)
.pants.d/pyprep/sources/c613c998aacf75bcee19a3423daa93dea4f2f285/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py:97:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
.pants.d/pyprep/sources/c613c998aacf75bcee19a3423daa93dea4f2f285/pants_test/pants_run_integration_test.py:447: in assert_success
self.assert_result(pants_run, self.PANTS_SUCCESS_CODE, expected=True, msg=msg)
.pants.d/pyprep/sources/c613c998aacf75bcee19a3423daa93dea4f2f285/pants_test/pants_run_integration_test.py:468: in assert_result
assertion(value, pants_run.returncode, error_msg)
E AssertionError: 0 != 1 : /home/travis/build/pantsbuild/pants/pants --no-pantsrc --pants-workdir=/home/travis/build/pantsbuild/pants/.pants.d/tmp/tmptm6qdc9e.pants.d --kill-nailguns --print-exception-stacktrace=True --pants-config-files=/home/travis/build/pantsbuild/pants/.pants.d/tmp/tmptm6qdc9e.pants.d/pants.ini run examples/src/scala/org/pantsbuild/example/hello/exe
E returncode: 1
E stdout:
E
E 07:05:50 00:00 [main]
E (To run a reporting server: ./pants server)
E 07:05:51 00:01 [setup]
E 07:05:51 00:01 [parse]
E Executing tasks in goals: native-compile -> link -> bootstrap -> imports -> unpack-jars -> jvm-platform-validate -> deferred-sources -> gen -> resolve -> resources -> pyprep -> compile -> binary -> run
E 07:05:51 00:01 [native-compile]
E 07:05:51 00:01 [native-third-party-fetch]
E 07:05:51 00:01 [c-for-ctypes]
E 07:05:51 00:01 [cpp-for-ctypes]
E 07:05:51 00:01 [link]
E 07:05:51 00:01 [shared-libraries]
E 07:05:51 00:01 [bootstrap]
E 07:05:51 00:01 [substitute-aliased-targets]
E 07:05:51 00:01 [jar-dependency-management]
E 07:05:51 00:01 [bootstrap-jvm-tools]
E 07:05:51 00:01 [provide-tools-jar]
E 07:05:51 00:01 [imports]
E 07:05:51 00:01 [ivy-imports]
E 07:05:51 00:01 [unpack-jars]
E 07:05:51 00:01 [unpack-jars]
E 07:05:52 00:02 [jvm-platform-validate]
E 07:05:52 00:02 [jvm-platform-validate]
E Invalidated 3 targets.
E 07:05:52 00:02 [deferred-sources]
E 07:05:52 00:02 [deferred-sources]
E 07:05:52 00:02 [gen]
E 07:05:52 00:02 [antlr-java]
E 07:05:52 00:02 [antlr-py]
E 07:05:52 00:02 [jaxb]
E 07:05:52 00:02 [protoc]
E 07:05:52 00:02 [ragel]
E 07:05:52 00:02 [thrift-java]
E 07:05:52 00:02 [thrift-py]
E 07:05:52 00:02 [wire]
E 07:05:52 00:02 [avro-java]
E 07:05:52 00:02 [go-thrift]
E 07:05:52 00:02 [go-protobuf]
E 07:05:52 00:02 [jax-ws]
E 07:05:52 00:02 [scrooge]
E 07:05:52 00:02 [thrifty]
E 07:05:52 00:02 [resolve]
E 07:05:52 00:02 [ivy]
E Invalidated 1 target.
E 07:05:52 00:02 [ivy-resolve]
E 07:05:52 00:02 [coursier]
E 07:05:52 00:02 [go]
E 07:05:52 00:02 [scala-js-compile]
E 07:05:52 00:02 [scala-js-link]
E 07:05:52 00:02 [node]
E 07:05:52 00:02 [resources]
E 07:05:52 00:02 [prepare]
E Invalidated 1 target.
E 07:05:52 00:02 [services]
E 07:05:52 00:02 [pyprep]
E 07:05:52 00:02 [interpreter]
E 07:05:52 00:02 [build-local-dists]
E 07:05:52 00:02 [requirements]
E 07:05:52 00:02 [sources]
E 07:05:52 00:02 [compile]
E 07:05:52 00:02 [node]
E 07:05:52 00:02 [compile-jvm-prep-command]
E 07:05:52 00:02 [jvm_prep_command]
E 07:05:52 00:02 [compile-prep-command]
E 07:05:52 00:02 [compile]
E 07:05:52 00:02 [rsc]
E Invalidated 4 targets.
E 07:05:53 00:03 [isolation-rsc-pool-bootstrap]
E [1/7] Metacp-ing 4 jars in the jdk
E 07:05:53 00:03 [metacp]
E [2/7] Compiling 1 rsc source in 1 target (examples/src/java/org/pantsbuild/example/hello/greet:greet).
E 07:05:53 00:03 [compile]
E
E 07:05:53 00:03 [cache]
E 07:05:53 00:03 [bootstrap-scalac_2_11]
E metacp(jdk) failed: Path for link would overwrite an existing directory: /home/travis/build/pantsbuild/pants/.pants.d/tmp/tmptm6qdc9e.pants.d/bootstrap/bootstrap-jvm-tools/current
E Traceback:
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/jvm_compile/execution_graph.py", line 276, in worker
E work()
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/jvm_compile/execution_graph.py", line 44, in __call__
E self.fn()
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/jvm_compile/rsc/rsc_compile.py", line 325, in work_for_vts_rsc_jdk
E output_dir=rsc_index_dir)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/jvm_compile/rsc/rsc_compile.py", line 786, in _runtool
E tool_classpath_abs = self.tool_classpath(tool_name)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/jvm_tool_task_mixin.py", line 54, in tool_classpath
E return self.tool_classpath_from_products(self.context.products, key, scope=self._scope(scope))
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/subsystems/jvm_tool_mixin.py", line 216, in tool_classpath_from_products
E return callback()
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/bootstrap_jvm_tools.py", line 344, in bootstrap_classpath
E cache['classpath'] = self._bootstrap_jvm_tool(dep_spec, jvm_tool)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/bootstrap_jvm_tools.py", line 333, in _bootstrap_jvm_tool
E return self._bootstrap_classpath(jvm_tool, targets)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/bootstrap_jvm_tools.py", line 244, in _bootstrap_classpath
E ivy_classpath = self.ivy_classpath(targets, silent=True, workunit_name=workunit_name)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/ivy_task_mixin.py", line 156, in ivy_classpath
E result = self._ivy_resolve(targets, silent=silent, workunit_name=workunit_name)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/ivy_task_mixin.py", line 225, in _ivy_resolve
E fingerprint_strategy=fingerprint_strategy) as invalidation_check:
E
E File "/opt/pyenv/versions/2.7.15/lib/python2.7/contextlib.py", line 17, in __enter__
E return self.gen.next()
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/task/task.py", line 388, in invalidated
E topological_order)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/task/task.py", line 489, in _do_invalidation_check
E artifact_write_callback=self.maybe_write_artifact)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/invalidation/cache_manager.py", line 294, in __init__
E relative_symlink(self._results_dir_prefix, stable_prefix)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/util/dirutil.py", line 441, in relative_symlink
E raise ValueError("Path for link would overwrite an existing directory: {}".format(link_path))
E
E 07:05:54 00:04 [cache]
E Using cached artifacts for 1 target.
E 07:05:54 00:04 [cache]
E Using cached artifacts for 1 target.
E 07:05:54 00:04 [cache]
E 07:05:54 00:04 [bootstrap-compiler-bridge]
E 07:05:55 00:05 [rsc]
E [info] Compiling 1 Java source to /home/travis/build/pantsbuild/pants/.pants.d/tmp/tmptm6qdc9e.pants.d/process-executionScv8xd/.pants.d/tmp/tmptm6qdc9e.pants.d/compile/rsc/9fc0d7bce7b1/examples.src.java.org.pantsbuild.example.hello.greet.greet/current/zinc/classes ...
E [info] Done compiling.
E [info] Compile success at Dec 20, 2018 7:05:59 AM [3.616s]
E
E FAILURE: Compilation failure: Failed jobs: metacp(jdk)
E
E
E Waiting for background workers to finish.
E 07:05:59 00:09 [complete]
E FAILURE
E stderr:
E WARN] Scrubbing _JAVA_OPTIONS=-Xmx2048m -Xms512m
E .WARN] Scrubbing _JAVA_OPTIONS=-Xmx2048m -Xms512m
E ...WARN] Scrubbing _JAVA_OPTIONS=-Xmx2048m -Xms512m
-------------- Captured stdout call --------------
logs/exceptions.18838.log +++
logs/exceptions.18838.log ---
logs/exceptions.log +++
logs/exceptions.log ---
generated xml file: /home/travis/build/pantsbuild/pants/.pants.d/test/pytest/tests.python.pants_test.backend.jvm.tasks.jvm_compile.rsc.rsc_compile_integration/junitxml/TEST-tests.python.pants_test.backend.jvm.tasks.jvm_compile.rsc.rsc_compile_integration.xml
============ slowest 3 test durations ============
10.15s call ../tests/python/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py::RscCompileIntegration::test_executing_multi_target_binary_hermetic
0.00s teardown ../tests/python/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py::RscCompileIntegration::test_executing_multi_target_binary_hermetic
0.00s setup ../tests/python/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py::RscCompileIntegration::test_executing_multi_target_binary_hermetic
=========== 1 failed in 10.36 seconds ============
``` | 1.0 | RscCompileIntegration.test_executing_multi_target_binary_hermetic is flaky - I suspect this is because of slightly buggy underlying code, rather than test issues. cc @baroquebobcat
```
tests/python/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py::RscCompileIntegration::test_executing_multi_target_binary_hermetic <- pyprep/sources/c613c998aacf75bcee19a3423daa93dea4f2f285/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py FAILED [100%]
==================== FAILURES ====================
RscCompileIntegration.test_executing_multi_target_binary_hermetic
self = <pants_test.backend.jvm.tasks.jvm_compile.rsc.test_rsc_compile_integration.RscCompileIntegration testMethod=test_executing_multi_target_binary_hermetic>
def test_executing_multi_target_binary_hermetic(self):
with temporary_dir() as cache_dir:
config = {
'cache.compile.rsc': {'write_to': [cache_dir]},
'jvm-platform': {'compiler': 'rsc'},
'compile.rsc': {
'execution_strategy': 'hermetic',
'incremental': False
},
'resolve.ivy': {
'capture_snapshots': True
},
}
with self.temporary_workdir() as workdir:
pants_run = self.run_pants_with_workdir(
['run',
'examples/src/scala/org/pantsbuild/example/hello/exe',
],
workdir, config)
> self.assert_success(pants_run)
.pants.d/pyprep/sources/c613c998aacf75bcee19a3423daa93dea4f2f285/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py:97:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
.pants.d/pyprep/sources/c613c998aacf75bcee19a3423daa93dea4f2f285/pants_test/pants_run_integration_test.py:447: in assert_success
self.assert_result(pants_run, self.PANTS_SUCCESS_CODE, expected=True, msg=msg)
.pants.d/pyprep/sources/c613c998aacf75bcee19a3423daa93dea4f2f285/pants_test/pants_run_integration_test.py:468: in assert_result
assertion(value, pants_run.returncode, error_msg)
E AssertionError: 0 != 1 : /home/travis/build/pantsbuild/pants/pants --no-pantsrc --pants-workdir=/home/travis/build/pantsbuild/pants/.pants.d/tmp/tmptm6qdc9e.pants.d --kill-nailguns --print-exception-stacktrace=True --pants-config-files=/home/travis/build/pantsbuild/pants/.pants.d/tmp/tmptm6qdc9e.pants.d/pants.ini run examples/src/scala/org/pantsbuild/example/hello/exe
E returncode: 1
E stdout:
E
E 07:05:50 00:00 [main]
E (To run a reporting server: ./pants server)
E 07:05:51 00:01 [setup]
E 07:05:51 00:01 [parse]
E Executing tasks in goals: native-compile -> link -> bootstrap -> imports -> unpack-jars -> jvm-platform-validate -> deferred-sources -> gen -> resolve -> resources -> pyprep -> compile -> binary -> run
E 07:05:51 00:01 [native-compile]
E 07:05:51 00:01 [native-third-party-fetch]
E 07:05:51 00:01 [c-for-ctypes]
E 07:05:51 00:01 [cpp-for-ctypes]
E 07:05:51 00:01 [link]
E 07:05:51 00:01 [shared-libraries]
E 07:05:51 00:01 [bootstrap]
E 07:05:51 00:01 [substitute-aliased-targets]
E 07:05:51 00:01 [jar-dependency-management]
E 07:05:51 00:01 [bootstrap-jvm-tools]
E 07:05:51 00:01 [provide-tools-jar]
E 07:05:51 00:01 [imports]
E 07:05:51 00:01 [ivy-imports]
E 07:05:51 00:01 [unpack-jars]
E 07:05:51 00:01 [unpack-jars]
E 07:05:52 00:02 [jvm-platform-validate]
E 07:05:52 00:02 [jvm-platform-validate]
E Invalidated 3 targets.
E 07:05:52 00:02 [deferred-sources]
E 07:05:52 00:02 [deferred-sources]
E 07:05:52 00:02 [gen]
E 07:05:52 00:02 [antlr-java]
E 07:05:52 00:02 [antlr-py]
E 07:05:52 00:02 [jaxb]
E 07:05:52 00:02 [protoc]
E 07:05:52 00:02 [ragel]
E 07:05:52 00:02 [thrift-java]
E 07:05:52 00:02 [thrift-py]
E 07:05:52 00:02 [wire]
E 07:05:52 00:02 [avro-java]
E 07:05:52 00:02 [go-thrift]
E 07:05:52 00:02 [go-protobuf]
E 07:05:52 00:02 [jax-ws]
E 07:05:52 00:02 [scrooge]
E 07:05:52 00:02 [thrifty]
E 07:05:52 00:02 [resolve]
E 07:05:52 00:02 [ivy]
E Invalidated 1 target.
E 07:05:52 00:02 [ivy-resolve]
E 07:05:52 00:02 [coursier]
E 07:05:52 00:02 [go]
E 07:05:52 00:02 [scala-js-compile]
E 07:05:52 00:02 [scala-js-link]
E 07:05:52 00:02 [node]
E 07:05:52 00:02 [resources]
E 07:05:52 00:02 [prepare]
E Invalidated 1 target.
E 07:05:52 00:02 [services]
E 07:05:52 00:02 [pyprep]
E 07:05:52 00:02 [interpreter]
E 07:05:52 00:02 [build-local-dists]
E 07:05:52 00:02 [requirements]
E 07:05:52 00:02 [sources]
E 07:05:52 00:02 [compile]
E 07:05:52 00:02 [node]
E 07:05:52 00:02 [compile-jvm-prep-command]
E 07:05:52 00:02 [jvm_prep_command]
E 07:05:52 00:02 [compile-prep-command]
E 07:05:52 00:02 [compile]
E 07:05:52 00:02 [rsc]
E Invalidated 4 targets.
E 07:05:53 00:03 [isolation-rsc-pool-bootstrap]
E [1/7] Metacp-ing 4 jars in the jdk
E 07:05:53 00:03 [metacp]
E [2/7] Compiling 1 rsc source in 1 target (examples/src/java/org/pantsbuild/example/hello/greet:greet).
E 07:05:53 00:03 [compile]
E
E 07:05:53 00:03 [cache]
E 07:05:53 00:03 [bootstrap-scalac_2_11]
E metacp(jdk) failed: Path for link would overwrite an existing directory: /home/travis/build/pantsbuild/pants/.pants.d/tmp/tmptm6qdc9e.pants.d/bootstrap/bootstrap-jvm-tools/current
E Traceback:
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/jvm_compile/execution_graph.py", line 276, in worker
E work()
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/jvm_compile/execution_graph.py", line 44, in __call__
E self.fn()
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/jvm_compile/rsc/rsc_compile.py", line 325, in work_for_vts_rsc_jdk
E output_dir=rsc_index_dir)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/jvm_compile/rsc/rsc_compile.py", line 786, in _runtool
E tool_classpath_abs = self.tool_classpath(tool_name)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/jvm_tool_task_mixin.py", line 54, in tool_classpath
E return self.tool_classpath_from_products(self.context.products, key, scope=self._scope(scope))
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/subsystems/jvm_tool_mixin.py", line 216, in tool_classpath_from_products
E return callback()
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/bootstrap_jvm_tools.py", line 344, in bootstrap_classpath
E cache['classpath'] = self._bootstrap_jvm_tool(dep_spec, jvm_tool)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/bootstrap_jvm_tools.py", line 333, in _bootstrap_jvm_tool
E return self._bootstrap_classpath(jvm_tool, targets)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/bootstrap_jvm_tools.py", line 244, in _bootstrap_classpath
E ivy_classpath = self.ivy_classpath(targets, silent=True, workunit_name=workunit_name)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/ivy_task_mixin.py", line 156, in ivy_classpath
E result = self._ivy_resolve(targets, silent=silent, workunit_name=workunit_name)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/backend/jvm/tasks/ivy_task_mixin.py", line 225, in _ivy_resolve
E fingerprint_strategy=fingerprint_strategy) as invalidation_check:
E
E File "/opt/pyenv/versions/2.7.15/lib/python2.7/contextlib.py", line 17, in __enter__
E return self.gen.next()
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/task/task.py", line 388, in invalidated
E topological_order)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/task/task.py", line 489, in _do_invalidation_check
E artifact_write_callback=self.maybe_write_artifact)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/invalidation/cache_manager.py", line 294, in __init__
E relative_symlink(self._results_dir_prefix, stable_prefix)
E
E File "/home/travis/build/pantsbuild/pants/src/python/pants/util/dirutil.py", line 441, in relative_symlink
E raise ValueError("Path for link would overwrite an existing directory: {}".format(link_path))
E
E 07:05:54 00:04 [cache]
E Using cached artifacts for 1 target.
E 07:05:54 00:04 [cache]
E Using cached artifacts for 1 target.
E 07:05:54 00:04 [cache]
E 07:05:54 00:04 [bootstrap-compiler-bridge]
E 07:05:55 00:05 [rsc]
E [info] Compiling 1 Java source to /home/travis/build/pantsbuild/pants/.pants.d/tmp/tmptm6qdc9e.pants.d/process-executionScv8xd/.pants.d/tmp/tmptm6qdc9e.pants.d/compile/rsc/9fc0d7bce7b1/examples.src.java.org.pantsbuild.example.hello.greet.greet/current/zinc/classes ...
E [info] Done compiling.
E [info] Compile success at Dec 20, 2018 7:05:59 AM [3.616s]
E
E FAILURE: Compilation failure: Failed jobs: metacp(jdk)
E
E
E Waiting for background workers to finish.
E 07:05:59 00:09 [complete]
E FAILURE
E stderr:
E WARN] Scrubbing _JAVA_OPTIONS=-Xmx2048m -Xms512m
E .WARN] Scrubbing _JAVA_OPTIONS=-Xmx2048m -Xms512m
E ...WARN] Scrubbing _JAVA_OPTIONS=-Xmx2048m -Xms512m
-------------- Captured stdout call --------------
logs/exceptions.18838.log +++
logs/exceptions.18838.log ---
logs/exceptions.log +++
logs/exceptions.log ---
generated xml file: /home/travis/build/pantsbuild/pants/.pants.d/test/pytest/tests.python.pants_test.backend.jvm.tasks.jvm_compile.rsc.rsc_compile_integration/junitxml/TEST-tests.python.pants_test.backend.jvm.tasks.jvm_compile.rsc.rsc_compile_integration.xml
============ slowest 3 test durations ============
10.15s call ../tests/python/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py::RscCompileIntegration::test_executing_multi_target_binary_hermetic
0.00s teardown ../tests/python/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py::RscCompileIntegration::test_executing_multi_target_binary_hermetic
0.00s setup ../tests/python/pants_test/backend/jvm/tasks/jvm_compile/rsc/test_rsc_compile_integration.py::RscCompileIntegration::test_executing_multi_target_binary_hermetic
=========== 1 failed in 10.36 seconds ============
``` | test | rsccompileintegration test executing multi target binary hermetic is flaky i suspect this is because of slightly buggy underlying code rather than test issues cc baroquebobcat tests python pants test backend jvm tasks jvm compile rsc test rsc compile integration py rsccompileintegration test executing multi target binary hermetic pyprep sources pants test backend jvm tasks jvm compile rsc test rsc compile integration py failed failures rsccompileintegration test executing multi target binary hermetic self def test executing multi target binary hermetic self with temporary dir as cache dir config cache compile rsc write to jvm platform compiler rsc compile rsc execution strategy hermetic incremental false resolve ivy capture snapshots true with self temporary workdir as workdir pants run self run pants with workdir run examples src scala org pantsbuild example hello exe workdir config self assert success pants run pants d pyprep sources pants test backend jvm tasks jvm compile rsc test rsc compile integration py pants d pyprep sources pants test pants run integration test py in assert success self assert result pants run self pants success code expected true msg msg pants d pyprep sources pants test pants run integration test py in assert result assertion value pants run returncode error msg e assertionerror home travis build pantsbuild pants pants no pantsrc pants workdir home travis build pantsbuild pants pants d tmp pants d kill nailguns print exception stacktrace true pants config files home travis build pantsbuild pants pants d tmp pants d pants ini run examples src scala org pantsbuild example hello exe e returncode e stdout e e e to run a reporting server pants server e e e executing tasks in goals native compile link bootstrap imports unpack jars jvm platform validate deferred sources gen resolve resources pyprep compile binary run e e e e e e e e e e e e e e e e e e invalidated targets e e e e e e e e e e e e e e e e e e e e invalidated target e e e e e e e e e invalidated target e e e e e e e e e e e e e e invalidated targets e e metacp ing jars in the jdk e e compiling rsc source in target examples src java org pantsbuild example hello greet greet e e e e e metacp jdk failed path for link would overwrite an existing directory home travis build pantsbuild pants pants d tmp pants d bootstrap bootstrap jvm tools current e traceback e file home travis build pantsbuild pants src python pants backend jvm tasks jvm compile execution graph py line in worker e work e e file home travis build pantsbuild pants src python pants backend jvm tasks jvm compile execution graph py line in call e self fn e e file home travis build pantsbuild pants src python pants backend jvm tasks jvm compile rsc rsc compile py line in work for vts rsc jdk e output dir rsc index dir e e file home travis build pantsbuild pants src python pants backend jvm tasks jvm compile rsc rsc compile py line in runtool e tool classpath abs self tool classpath tool name e e file home travis build pantsbuild pants src python pants backend jvm tasks jvm tool task mixin py line in tool classpath e return self tool classpath from products self context products key scope self scope scope e e file home travis build pantsbuild pants src python pants backend jvm subsystems jvm tool mixin py line in tool classpath from products e return callback e e file home travis build pantsbuild pants src python pants backend jvm tasks bootstrap jvm tools py line in bootstrap classpath e cache self bootstrap jvm tool dep spec jvm tool e e file home travis build pantsbuild pants src python pants backend jvm tasks bootstrap jvm tools py line in bootstrap jvm tool e return self bootstrap classpath jvm tool targets e e file home travis build pantsbuild pants src python pants backend jvm tasks bootstrap jvm tools py line in bootstrap classpath e ivy classpath self ivy classpath targets silent true workunit name workunit name e e file home travis build pantsbuild pants src python pants backend jvm tasks ivy task mixin py line in ivy classpath e result self ivy resolve targets silent silent workunit name workunit name e e file home travis build pantsbuild pants src python pants backend jvm tasks ivy task mixin py line in ivy resolve e fingerprint strategy fingerprint strategy as invalidation check e e file opt pyenv versions lib contextlib py line in enter e return self gen next e e file home travis build pantsbuild pants src python pants task task py line in invalidated e topological order e e file home travis build pantsbuild pants src python pants task task py line in do invalidation check e artifact write callback self maybe write artifact e e file home travis build pantsbuild pants src python pants invalidation cache manager py line in init e relative symlink self results dir prefix stable prefix e e file home travis build pantsbuild pants src python pants util dirutil py line in relative symlink e raise valueerror path for link would overwrite an existing directory format link path e e e using cached artifacts for target e e using cached artifacts for target e e e e compiling java source to home travis build pantsbuild pants pants d tmp pants d process pants d tmp pants d compile rsc examples src java org pantsbuild example hello greet greet current zinc classes e done compiling e compile success at dec am e e failure compilation failure failed jobs metacp jdk e e e waiting for background workers to finish e e failure e stderr e warn scrubbing java options e warn scrubbing java options e warn scrubbing java options captured stdout call logs exceptions log logs exceptions log logs exceptions log logs exceptions log generated xml file home travis build pantsbuild pants pants d test pytest tests python pants test backend jvm tasks jvm compile rsc rsc compile integration junitxml test tests python pants test backend jvm tasks jvm compile rsc rsc compile integration xml slowest test durations call tests python pants test backend jvm tasks jvm compile rsc test rsc compile integration py rsccompileintegration test executing multi target binary hermetic teardown tests python pants test backend jvm tasks jvm compile rsc test rsc compile integration py rsccompileintegration test executing multi target binary hermetic setup tests python pants test backend jvm tasks jvm compile rsc test rsc compile integration py rsccompileintegration test executing multi target binary hermetic failed in seconds | 1 |
337,524 | 30,248,919,493 | IssuesEvent | 2023-07-06 18:48:00 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | opened | Fix jax_numpy_logic.test_jax_logical_or | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5478319447"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5475303530"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5475617745"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix jax_numpy_logic.test_jax_logical_or - | | |
|---|---|
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5478319447"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5475303530"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5475617745"><img src=https://img.shields.io/badge/-success-success></a>
| test | fix jax numpy logic test jax logical or paddle a href src numpy a href src jax a href src | 1 |
269,687 | 28,960,249,262 | IssuesEvent | 2023-05-10 01:26:43 | dpteam/RK3188_TABLET | https://api.github.com/repos/dpteam/RK3188_TABLET | reopened | CVE-2018-5803 (Medium) detected in linuxv3.0 | Mend: dependency security vulnerability | ## CVE-2018-5803 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/verygreen/linux.git>https://github.com/verygreen/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sctp/sm_make_chunk.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux Kernel before version 4.15.8, 4.14.25, 4.9.87, 4.4.121, 4.1.51, and 3.2.102, an error in the "_sctp_make_chunk()" function (net/sctp/sm_make_chunk.c) when handling SCTP packets length can be exploited to cause a kernel crash.
<p>Publish Date: 2018-06-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-5803>CVE-2018-5803</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-5803">https://nvd.nist.gov/vuln/detail/CVE-2018-5803</a></p>
<p>Release Date: 2018-06-12</p>
<p>Fix Resolution: 4.15.8,4.14.25,4.9.87,4.4.121,4.1.51,3.2.102</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-5803 (Medium) detected in linuxv3.0 - ## CVE-2018-5803 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/verygreen/linux.git>https://github.com/verygreen/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sctp/sm_make_chunk.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux Kernel before version 4.15.8, 4.14.25, 4.9.87, 4.4.121, 4.1.51, and 3.2.102, an error in the "_sctp_make_chunk()" function (net/sctp/sm_make_chunk.c) when handling SCTP packets length can be exploited to cause a kernel crash.
<p>Publish Date: 2018-06-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-5803>CVE-2018-5803</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-5803">https://nvd.nist.gov/vuln/detail/CVE-2018-5803</a></p>
<p>Release Date: 2018-06-12</p>
<p>Fix Resolution: 4.15.8,4.14.25,4.9.87,4.4.121,4.1.51,3.2.102</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in head commit a href found in base branch master vulnerable source files net sctp sm make chunk c vulnerability details in the linux kernel before version and an error in the sctp make chunk function net sctp sm make chunk c when handling sctp packets length can be exploited to cause a kernel crash publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
286,413 | 8,787,902,305 | IssuesEvent | 2018-12-20 20:14:35 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | closed | Missing animation - oil refinery | Art Semi-High Priority | You can see animation in youtube announce, https://www.youtube.com/watch?v=F0cK30I9iHo (10 month ago!) but this animation not included to game. | 1.0 | Missing animation - oil refinery - You can see animation in youtube announce, https://www.youtube.com/watch?v=F0cK30I9iHo (10 month ago!) but this animation not included to game. | non_test | missing animation oil refinery you can see animation in youtube announce month ago but this animation not included to game | 0 |
189,318 | 22,047,017,064 | IssuesEvent | 2022-05-30 03:43:12 | panasalap/linux-4.1.15 | https://api.github.com/repos/panasalap/linux-4.1.15 | closed | CVE-2020-25212 (High) detected in linux-yocto-4.1v4.1.17, linux-yocto-4.1v4.1.17 - autoclosed | security vulnerability | ## CVE-2020-25212 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-yocto-4.1v4.1.17</b>, <b>linux-yocto-4.1v4.1.17</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A TOCTOU mismatch in the NFS client code in the Linux kernel before 5.8.3 could be used by local attackers to corrupt memory or possibly have unspecified other impact because a size check is in fs/nfs/nfs4proc.c instead of fs/nfs/nfs4xdr.c, aka CID-b4487b935452.
<p>Publish Date: 2020-09-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25212>CVE-2020-25212</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-25212">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-25212</a></p>
<p>Release Date: 2020-09-09</p>
<p>Fix Resolution: 5.8.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-25212 (High) detected in linux-yocto-4.1v4.1.17, linux-yocto-4.1v4.1.17 - autoclosed - ## CVE-2020-25212 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-yocto-4.1v4.1.17</b>, <b>linux-yocto-4.1v4.1.17</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A TOCTOU mismatch in the NFS client code in the Linux kernel before 5.8.3 could be used by local attackers to corrupt memory or possibly have unspecified other impact because a size check is in fs/nfs/nfs4proc.c instead of fs/nfs/nfs4xdr.c, aka CID-b4487b935452.
<p>Publish Date: 2020-09-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25212>CVE-2020-25212</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-25212">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-25212</a></p>
<p>Release Date: 2020-09-09</p>
<p>Fix Resolution: 5.8.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in linux yocto linux yocto autoclosed cve high severity vulnerability vulnerable libraries linux yocto linux yocto vulnerability details a toctou mismatch in the nfs client code in the linux kernel before could be used by local attackers to corrupt memory or possibly have unspecified other impact because a size check is in fs nfs c instead of fs nfs c aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
245,610 | 18,788,657,238 | IssuesEvent | 2021-11-08 14:43:18 | PsiKai/leather-planner | https://api.github.com/repos/PsiKai/leather-planner | closed | Make updates to Readme | documentation | Readme is out of date and needs updating to the newest styles and features.
- New screenshots
- Update on tech stack
- New features
- Weather
- User info management
- List item actions
- List item notes
| 1.0 | Make updates to Readme - Readme is out of date and needs updating to the newest styles and features.
- New screenshots
- Update on tech stack
- New features
- Weather
- User info management
- List item actions
- List item notes
| non_test | make updates to readme readme is out of date and needs updating to the newest styles and features new screenshots update on tech stack new features weather user info management list item actions list item notes | 0 |
24,571 | 2,669,122,661 | IssuesEvent | 2015-03-23 13:53:34 | garywmendel/Yopine | https://api.github.com/repos/garywmendel/Yopine | closed | * * - need to be able to edit profile | 2 priority enhancement | particularly avatar if you didnt add one when signing up. | 1.0 | * * - need to be able to edit profile - particularly avatar if you didnt add one when signing up. | non_test | need to be able to edit profile particularly avatar if you didnt add one when signing up | 0 |
230,863 | 18,720,490,588 | IssuesEvent | 2021-11-03 11:12:06 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | opened | Process issues from community testing session on 3 Nov | T-Other Z-Community-Testing | - [ ] All defects have been reviewed (@kittykat )
- [ ] All new defects have been filed
- [ ] All repeat defects have been linked to existing issues
- [ ] All enhancements have been reviewed (@daniellekirkwood )
- [ ] All new enhancement requests have been filed
- [ ] All enhancement requests have been responded to (including links to existing ones) | 1.0 | Process issues from community testing session on 3 Nov - - [ ] All defects have been reviewed (@kittykat )
- [ ] All new defects have been filed
- [ ] All repeat defects have been linked to existing issues
- [ ] All enhancements have been reviewed (@daniellekirkwood )
- [ ] All new enhancement requests have been filed
- [ ] All enhancement requests have been responded to (including links to existing ones) | test | process issues from community testing session on nov all defects have been reviewed kittykat all new defects have been filed all repeat defects have been linked to existing issues all enhancements have been reviewed daniellekirkwood all new enhancement requests have been filed all enhancement requests have been responded to including links to existing ones | 1 |
125,722 | 17,850,490,422 | IssuesEvent | 2021-09-04 01:19:26 | tj-actions/coverage-badge-js | https://api.github.com/repos/tj-actions/coverage-badge-js | opened | CVE-2021-3757 (Medium) detected in immer-8.0.1.tgz | security vulnerability | ## CVE-2021-3757 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>immer-8.0.1.tgz</b></p></summary>
<p>Create your next immutable state by mutating the current one</p>
<p>Library home page: <a href="https://registry.npmjs.org/immer/-/immer-8.0.1.tgz">https://registry.npmjs.org/immer/-/immer-8.0.1.tgz</a></p>
<p>Path to dependency file: coverage-badge-js/test-app/package.json</p>
<p>Path to vulnerable library: coverage-badge-js/test-app/node_modules/immer/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.3.tgz (Root Library)
- react-dev-utils-11.0.4.tgz
- :x: **immer-8.0.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
immer is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-09-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3757>CVE-2021-3757</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/23d38099-71cd-42ed-a77a-71e68094adfa/">https://huntr.dev/bounties/23d38099-71cd-42ed-a77a-71e68094adfa/</a></p>
<p>Release Date: 2021-09-02</p>
<p>Fix Resolution: immer - 9.0.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-3757 (Medium) detected in immer-8.0.1.tgz - ## CVE-2021-3757 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>immer-8.0.1.tgz</b></p></summary>
<p>Create your next immutable state by mutating the current one</p>
<p>Library home page: <a href="https://registry.npmjs.org/immer/-/immer-8.0.1.tgz">https://registry.npmjs.org/immer/-/immer-8.0.1.tgz</a></p>
<p>Path to dependency file: coverage-badge-js/test-app/package.json</p>
<p>Path to vulnerable library: coverage-badge-js/test-app/node_modules/immer/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.3.tgz (Root Library)
- react-dev-utils-11.0.4.tgz
- :x: **immer-8.0.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
immer is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-09-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3757>CVE-2021-3757</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/23d38099-71cd-42ed-a77a-71e68094adfa/">https://huntr.dev/bounties/23d38099-71cd-42ed-a77a-71e68094adfa/</a></p>
<p>Release Date: 2021-09-02</p>
<p>Fix Resolution: immer - 9.0.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in immer tgz cve medium severity vulnerability vulnerable library immer tgz create your next immutable state by mutating the current one library home page a href path to dependency file coverage badge js test app package json path to vulnerable library coverage badge js test app node modules immer package json dependency hierarchy react scripts tgz root library react dev utils tgz x immer tgz vulnerable library found in base branch main vulnerability details immer is vulnerable to improperly controlled modification of object prototype attributes prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution immer step up your open source security game with whitesource | 0 |
236,771 | 19,573,571,095 | IssuesEvent | 2022-01-04 12:59:23 | HDFGroup/hermes | https://api.github.com/repos/HDFGroup/hermes | opened | Align the Docker images with CI | priority-medium testing effort-medium | The `[deps,dev,user].Dockerfile` should align with the CI `Dockerfile`. Building `deps.Dockerfile` is currently very slow, because everything is built from first principles. Follow CI and speed up the whole show. | 1.0 | Align the Docker images with CI - The `[deps,dev,user].Dockerfile` should align with the CI `Dockerfile`. Building `deps.Dockerfile` is currently very slow, because everything is built from first principles. Follow CI and speed up the whole show. | test | align the docker images with ci the dockerfile should align with the ci dockerfile building deps dockerfile is currently very slow because everything is built from first principles follow ci and speed up the whole show | 1 |
84,032 | 24,205,637,437 | IssuesEvent | 2022-09-25 07:08:08 | Perl/perl5 | https://api.github.com/repos/Perl/perl5 | closed | eb54d46f726 triggers new build-time warning | build-time-warnings | A recent commit has introduced a new build-time warning.
Using my customary configuration switches and `clang10` as the compiler on FreeBSD-12, I built `perl` at 658a5bedcf. I got the following build-time warning:
```
$ parse-build-warnings 658a5bedcf.freebsd.threaded.maketp.output.txt.gz
File: 658a5bedcf.freebsd.threaded.maketp.output.txt.gz
[
{
char => 14,
group => "Wunused-variable",
line => 12662,
source => "toke.c",
text => "unused variable 'syntax_error'",
},
]
```
The line cited in `toke.c` was added in recent commit eb54d46f726:
```
commit eb54d46f7264ff7af62c409d8a6ab984a5a34f57 (HEAD)
Author: Yves Orton <demerphq@gmail.com>
AuthorDate: Fri Aug 26 18:26:14 2022 +0200
Commit: Yves Orton <demerphq@gmail.com>
CommitDate: Fri Sep 9 18:48:52 2022 +0200
Stop parsing on first syntax error.
```
Configuring and building at that commit and the one immediately preceding that commit confirmed that it was the commit which first generated the warning.
@demerphq, can you take a look?
Thank you very much.
Jim Keenan | 1.0 | eb54d46f726 triggers new build-time warning - A recent commit has introduced a new build-time warning.
Using my customary configuration switches and `clang10` as the compiler on FreeBSD-12, I built `perl` at 658a5bedcf. I got the following build-time warning:
```
$ parse-build-warnings 658a5bedcf.freebsd.threaded.maketp.output.txt.gz
File: 658a5bedcf.freebsd.threaded.maketp.output.txt.gz
[
{
char => 14,
group => "Wunused-variable",
line => 12662,
source => "toke.c",
text => "unused variable 'syntax_error'",
},
]
```
The line cited in `toke.c` was added in recent commit eb54d46f726:
```
commit eb54d46f7264ff7af62c409d8a6ab984a5a34f57 (HEAD)
Author: Yves Orton <demerphq@gmail.com>
AuthorDate: Fri Aug 26 18:26:14 2022 +0200
Commit: Yves Orton <demerphq@gmail.com>
CommitDate: Fri Sep 9 18:48:52 2022 +0200
Stop parsing on first syntax error.
```
Configuring and building at that commit and the one immediately preceding that commit confirmed that it was the commit which first generated the warning.
@demerphq, can you take a look?
Thank you very much.
Jim Keenan | non_test | triggers new build time warning a recent commit has introduced a new build time warning using my customary configuration switches and as the compiler on freebsd i built perl at i got the following build time warning parse build warnings freebsd threaded maketp output txt gz file freebsd threaded maketp output txt gz char group wunused variable line source toke c text unused variable syntax error the line cited in toke c was added in recent commit commit head author yves orton authordate fri aug commit yves orton commitdate fri sep stop parsing on first syntax error configuring and building at that commit and the one immediately preceding that commit confirmed that it was the commit which first generated the warning demerphq can you take a look thank you very much jim keenan | 0 |
116,513 | 9,854,682,200 | IssuesEvent | 2019-06-19 17:27:46 | microsoft/vscode-python | https://api.github.com/repos/microsoft/vscode-python | closed | Fix some problems with pytest adapter. | feature-testing needs PR reason-new feature type-bug | Users reported some issues with pytest adapter (see #5458). This issue represents part of the work done for that larger issue (which won't be addressed until a later sprint). | 1.0 | Fix some problems with pytest adapter. - Users reported some issues with pytest adapter (see #5458). This issue represents part of the work done for that larger issue (which won't be addressed until a later sprint). | test | fix some problems with pytest adapter users reported some issues with pytest adapter see this issue represents part of the work done for that larger issue which won t be addressed until a later sprint | 1 |
86,041 | 8,017,585,322 | IssuesEvent | 2018-07-25 16:20:33 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | opened | [CI] RangeFieldMapperTests failed due to unterminated threads | :Search/Mapping >test-failure v7.0.0 | Build link: https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+master+intake/2401/console
Failure:
```
ERROR 0.00s J1 | RangeFieldMapperTests (suite) <<< FAILURES!
14:49:19 > Throwable #1: com.carrotsearch.randomizedtesting.ThreadLeakError: 2 threads leaked from SUITE scope at org.elasticsearch.index.mapper.RangeFieldMapperTests:
14:49:19 > 1) Thread[id=1553, name=elasticsearch[node_s_0][__mock_network_thread][T#2], state=RUNNABLE, group=TGRP-RangeFieldMapperTests]
14:49:19 > at java.net.PlainSocketImpl.socketAccept(Native Method)
14:49:19 > at java.net.AbstractPlainSocketImpl.accept(AbstractPlainSocketImpl.java:409)
14:49:19 > at java.net.ServerSocket.implAccept(ServerSocket.java:545)
14:49:19 > at java.net.ServerSocket.accept(ServerSocket.java:513)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.access$101(MockServerSocket.java:32)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.lambda$accept$0(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket$$Lambda$1737/460128403.run(Unknown Source)
14:49:19 > at java.security.AccessController.doPrivileged(Native Method)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.accept(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$MockChannel.accept(MockTcpTransport.java:273)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$1.doRun(MockTcpTransport.java:128)
14:49:19 > at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
14:49:19 > at java.lang.Thread.run(Thread.java:748)
14:49:19 > 2) Thread[id=1552, name=elasticsearch[node_s_0][__mock_network_thread][T#1], state=RUNNABLE, group=TGRP-RangeFieldMapperTests]
14:49:19 > at java.net.PlainSocketImpl.socketAccept(Native Method)
14:49:19 > at java.net.AbstractPlainSocketImpl.accept(AbstractPlainSocketImpl.java:409)
14:49:19 > at java.net.ServerSocket.implAccept(ServerSocket.java:545)
14:49:19 > at java.net.ServerSocket.accept(ServerSocket.java:513)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.access$101(MockServerSocket.java:32)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.lambda$accept$0(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket$$Lambda$1737/460128403.run(Unknown Source)
14:49:19 > at java.security.AccessController.doPrivileged(Native Method)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.accept(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$MockChannel.accept(MockTcpTransport.java:273)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$1.doRun(MockTcpTransport.java:128)
14:49:19 > at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
14:49:19 > at java.lang.Thread.run(Thread.java:748)
14:49:19 > at __randomizedtesting.SeedInfo.seed([52D6EBFEF1E0C47A]:0)Throwable #2: com.carrotsearch.randomizedtesting.ThreadLeakError: There are still zombie threads that couldn't be terminated:
14:49:19 > 1) Thread[id=1553, name=elasticsearch[node_s_0][__mock_network_thread][T#2], state=RUNNABLE, group=TGRP-RangeFieldMapperTests]
14:49:19 > at java.net.PlainSocketImpl.socketAccept(Native Method)
14:49:19 > at java.net.AbstractPlainSocketImpl.accept(AbstractPlainSocketImpl.java:409)
14:49:19 > at java.net.ServerSocket.implAccept(ServerSocket.java:545)
14:49:19 > at java.net.ServerSocket.accept(ServerSocket.java:513)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.access$101(MockServerSocket.java:32)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.lambda$accept$0(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket$$Lambda$1737/460128403.run(Unknown Source)
14:49:19 > at java.security.AccessController.doPrivileged(Native Method)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.accept(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$MockChannel.accept(MockTcpTransport.java:273)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$1.doRun(MockTcpTransport.java:128)
14:49:19 > at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
14:49:19 > at java.lang.Thread.run(Thread.java:748)
14:49:19 > 2) Thread[id=1552, name=elasticsearch[node_s_0][__mock_network_thread][T#1], state=RUNNABLE, group=TGRP-RangeFieldMapperTests]
14:49:19 > at java.net.PlainSocketImpl.socketAccept(Native Method)
14:49:19 > at java.net.AbstractPlainSocketImpl.accept(AbstractPlainSocketImpl.java:409)
14:49:19 > at java.net.ServerSocket.implAccept(ServerSocket.java:545)
14:49:19 > at java.net.ServerSocket.accept(ServerSocket.java:513)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.access$101(MockServerSocket.java:32)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.lambda$accept$0(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket$$Lambda$1737/460128403.run(Unknown Source)
14:49:19 > at java.security.AccessController.doPrivileged(Native Method)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.accept(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$MockChannel.accept(MockTcpTransport.java:273)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$1.doRun(MockTcpTransport.java:128)
14:49:19 > at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
14:49:19 > at java.lang.Thread.run(Thread.java:748)
14:49:19 > at __randomizedtesting.SeedInfo.seed([52D6EBFEF1E0C47A]:0)
14:49:19 Completed [780/1115] on J1 in 28.53s, 11 tests, 2 errors <<< FAILURES!
```
Reproduce with:
```
./gradlew :server:test -Dtests.seed=52D6EBFEF1E0C47A -Dtests.class=org.elasticsearch.index.mapper.RangeFieldMapperTests -Dtests.security.manager=true -Dtests.locale=en-US -Dtests.timezone=Etc/UTC
```
Does not reproduce locally for me. | 1.0 | [CI] RangeFieldMapperTests failed due to unterminated threads - Build link: https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+master+intake/2401/console
Failure:
```
ERROR 0.00s J1 | RangeFieldMapperTests (suite) <<< FAILURES!
14:49:19 > Throwable #1: com.carrotsearch.randomizedtesting.ThreadLeakError: 2 threads leaked from SUITE scope at org.elasticsearch.index.mapper.RangeFieldMapperTests:
14:49:19 > 1) Thread[id=1553, name=elasticsearch[node_s_0][__mock_network_thread][T#2], state=RUNNABLE, group=TGRP-RangeFieldMapperTests]
14:49:19 > at java.net.PlainSocketImpl.socketAccept(Native Method)
14:49:19 > at java.net.AbstractPlainSocketImpl.accept(AbstractPlainSocketImpl.java:409)
14:49:19 > at java.net.ServerSocket.implAccept(ServerSocket.java:545)
14:49:19 > at java.net.ServerSocket.accept(ServerSocket.java:513)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.access$101(MockServerSocket.java:32)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.lambda$accept$0(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket$$Lambda$1737/460128403.run(Unknown Source)
14:49:19 > at java.security.AccessController.doPrivileged(Native Method)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.accept(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$MockChannel.accept(MockTcpTransport.java:273)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$1.doRun(MockTcpTransport.java:128)
14:49:19 > at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
14:49:19 > at java.lang.Thread.run(Thread.java:748)
14:49:19 > 2) Thread[id=1552, name=elasticsearch[node_s_0][__mock_network_thread][T#1], state=RUNNABLE, group=TGRP-RangeFieldMapperTests]
14:49:19 > at java.net.PlainSocketImpl.socketAccept(Native Method)
14:49:19 > at java.net.AbstractPlainSocketImpl.accept(AbstractPlainSocketImpl.java:409)
14:49:19 > at java.net.ServerSocket.implAccept(ServerSocket.java:545)
14:49:19 > at java.net.ServerSocket.accept(ServerSocket.java:513)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.access$101(MockServerSocket.java:32)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.lambda$accept$0(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket$$Lambda$1737/460128403.run(Unknown Source)
14:49:19 > at java.security.AccessController.doPrivileged(Native Method)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.accept(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$MockChannel.accept(MockTcpTransport.java:273)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$1.doRun(MockTcpTransport.java:128)
14:49:19 > at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
14:49:19 > at java.lang.Thread.run(Thread.java:748)
14:49:19 > at __randomizedtesting.SeedInfo.seed([52D6EBFEF1E0C47A]:0)Throwable #2: com.carrotsearch.randomizedtesting.ThreadLeakError: There are still zombie threads that couldn't be terminated:
14:49:19 > 1) Thread[id=1553, name=elasticsearch[node_s_0][__mock_network_thread][T#2], state=RUNNABLE, group=TGRP-RangeFieldMapperTests]
14:49:19 > at java.net.PlainSocketImpl.socketAccept(Native Method)
14:49:19 > at java.net.AbstractPlainSocketImpl.accept(AbstractPlainSocketImpl.java:409)
14:49:19 > at java.net.ServerSocket.implAccept(ServerSocket.java:545)
14:49:19 > at java.net.ServerSocket.accept(ServerSocket.java:513)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.access$101(MockServerSocket.java:32)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.lambda$accept$0(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket$$Lambda$1737/460128403.run(Unknown Source)
14:49:19 > at java.security.AccessController.doPrivileged(Native Method)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.accept(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$MockChannel.accept(MockTcpTransport.java:273)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$1.doRun(MockTcpTransport.java:128)
14:49:19 > at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
14:49:19 > at java.lang.Thread.run(Thread.java:748)
14:49:19 > 2) Thread[id=1552, name=elasticsearch[node_s_0][__mock_network_thread][T#1], state=RUNNABLE, group=TGRP-RangeFieldMapperTests]
14:49:19 > at java.net.PlainSocketImpl.socketAccept(Native Method)
14:49:19 > at java.net.AbstractPlainSocketImpl.accept(AbstractPlainSocketImpl.java:409)
14:49:19 > at java.net.ServerSocket.implAccept(ServerSocket.java:545)
14:49:19 > at java.net.ServerSocket.accept(ServerSocket.java:513)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.access$101(MockServerSocket.java:32)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.lambda$accept$0(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket$$Lambda$1737/460128403.run(Unknown Source)
14:49:19 > at java.security.AccessController.doPrivileged(Native Method)
14:49:19 > at org.elasticsearch.mocksocket.MockServerSocket.accept(MockServerSocket.java:53)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$MockChannel.accept(MockTcpTransport.java:273)
14:49:19 > at org.elasticsearch.transport.MockTcpTransport$1.doRun(MockTcpTransport.java:128)
14:49:19 > at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
14:49:19 > at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
14:49:19 > at java.lang.Thread.run(Thread.java:748)
14:49:19 > at __randomizedtesting.SeedInfo.seed([52D6EBFEF1E0C47A]:0)
14:49:19 Completed [780/1115] on J1 in 28.53s, 11 tests, 2 errors <<< FAILURES!
```
Reproduce with:
```
./gradlew :server:test -Dtests.seed=52D6EBFEF1E0C47A -Dtests.class=org.elasticsearch.index.mapper.RangeFieldMapperTests -Dtests.security.manager=true -Dtests.locale=en-US -Dtests.timezone=Etc/UTC
```
Does not reproduce locally for me. | test | rangefieldmappertests failed due to unterminated threads build link failure error rangefieldmappertests suite failures throwable com carrotsearch randomizedtesting threadleakerror threads leaked from suite scope at org elasticsearch index mapper rangefieldmappertests thread state runnable group tgrp rangefieldmappertests at java net plainsocketimpl socketaccept native method at java net abstractplainsocketimpl accept abstractplainsocketimpl java at java net serversocket implaccept serversocket java at java net serversocket accept serversocket java at org elasticsearch mocksocket mockserversocket access mockserversocket java at org elasticsearch mocksocket mockserversocket lambda accept mockserversocket java at org elasticsearch mocksocket mockserversocket lambda run unknown source at java security accesscontroller doprivileged native method at org elasticsearch mocksocket mockserversocket accept mockserversocket java at org elasticsearch transport mocktcptransport mockchannel accept mocktcptransport java at org elasticsearch transport mocktcptransport dorun mocktcptransport java at org elasticsearch common util concurrent abstractrunnable run abstractrunnable java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java thread state runnable group tgrp rangefieldmappertests at java net plainsocketimpl socketaccept native method at java net abstractplainsocketimpl accept abstractplainsocketimpl java at java net serversocket implaccept serversocket java at java net serversocket accept serversocket java at org elasticsearch mocksocket mockserversocket access mockserversocket java at org elasticsearch mocksocket mockserversocket lambda accept mockserversocket java at org elasticsearch mocksocket mockserversocket lambda run unknown source at java security accesscontroller doprivileged native method at org elasticsearch mocksocket mockserversocket accept mockserversocket java at org elasticsearch transport mocktcptransport mockchannel accept mocktcptransport java at org elasticsearch transport mocktcptransport dorun mocktcptransport java at org elasticsearch common util concurrent abstractrunnable run abstractrunnable java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java at randomizedtesting seedinfo seed throwable com carrotsearch randomizedtesting threadleakerror there are still zombie threads that couldn t be terminated thread state runnable group tgrp rangefieldmappertests at java net plainsocketimpl socketaccept native method at java net abstractplainsocketimpl accept abstractplainsocketimpl java at java net serversocket implaccept serversocket java at java net serversocket accept serversocket java at org elasticsearch mocksocket mockserversocket access mockserversocket java at org elasticsearch mocksocket mockserversocket lambda accept mockserversocket java at org elasticsearch mocksocket mockserversocket lambda run unknown source at java security accesscontroller doprivileged native method at org elasticsearch mocksocket mockserversocket accept mockserversocket java at org elasticsearch transport mocktcptransport mockchannel accept mocktcptransport java at org elasticsearch transport mocktcptransport dorun mocktcptransport java at org elasticsearch common util concurrent abstractrunnable run abstractrunnable java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java thread state runnable group tgrp rangefieldmappertests at java net plainsocketimpl socketaccept native method at java net abstractplainsocketimpl accept abstractplainsocketimpl java at java net serversocket implaccept serversocket java at java net serversocket accept serversocket java at org elasticsearch mocksocket mockserversocket access mockserversocket java at org elasticsearch mocksocket mockserversocket lambda accept mockserversocket java at org elasticsearch mocksocket mockserversocket lambda run unknown source at java security accesscontroller doprivileged native method at org elasticsearch mocksocket mockserversocket accept mockserversocket java at org elasticsearch transport mocktcptransport mockchannel accept mocktcptransport java at org elasticsearch transport mocktcptransport dorun mocktcptransport java at org elasticsearch common util concurrent abstractrunnable run abstractrunnable java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java at randomizedtesting seedinfo seed completed on in tests errors failures reproduce with gradlew server test dtests seed dtests class org elasticsearch index mapper rangefieldmappertests dtests security manager true dtests locale en us dtests timezone etc utc does not reproduce locally for me | 1 |
183,394 | 14,227,275,470 | IssuesEvent | 2020-11-18 00:54:05 | E3SM-Project/scream | https://api.github.com/repos/E3SM-Project/scream | opened | SHOC tests exibit seemingly random behavior, depending on CTEST_PARALLEL_LEVEL | bug shoc testing | Try to manually run `ctest -R shoc_tests` and `CTEST_PARALLEL_LEVEL=40 ctest -R shoc_tests`. The latter, on mappy as well as my laptop, passes, while the former has 3 tests failing. A midground with || level 4 has just 1 test failing. | 1.0 | SHOC tests exibit seemingly random behavior, depending on CTEST_PARALLEL_LEVEL - Try to manually run `ctest -R shoc_tests` and `CTEST_PARALLEL_LEVEL=40 ctest -R shoc_tests`. The latter, on mappy as well as my laptop, passes, while the former has 3 tests failing. A midground with || level 4 has just 1 test failing. | test | shoc tests exibit seemingly random behavior depending on ctest parallel level try to manually run ctest r shoc tests and ctest parallel level ctest r shoc tests the latter on mappy as well as my laptop passes while the former has tests failing a midground with level has just test failing | 1 |
344,223 | 30,726,531,737 | IssuesEvent | 2023-07-27 20:10:14 | Bears-R-Us/arkouda | https://api.github.com/repos/Bears-R-Us/arkouda | closed | `groupby_test.py` Conversion to new test framework | Testing | Update `groupby_test.py` to work with within the new test framework | 1.0 | `groupby_test.py` Conversion to new test framework - Update `groupby_test.py` to work with within the new test framework | test | groupby test py conversion to new test framework update groupby test py to work with within the new test framework | 1 |
106,728 | 9,180,537,915 | IssuesEvent | 2019-03-05 07:51:57 | legion-platform/legion | https://api.github.com/repos/legion-platform/legion | opened | Post action may not work in CI | CI/CD/tests | There are several steps in post action in pipelines. There is a risk that some may be skipped if the previous one fails. | 1.0 | Post action may not work in CI - There are several steps in post action in pipelines. There is a risk that some may be skipped if the previous one fails. | test | post action may not work in ci there are several steps in post action in pipelines there is a risk that some may be skipped if the previous one fails | 1 |
255,698 | 27,495,700,624 | IssuesEvent | 2023-03-05 05:06:51 | phamleduy04/discord-phishing-backend | https://api.github.com/repos/phamleduy04/discord-phishing-backend | closed | undici-5.11.0.tgz: 2 vulnerabilities (highest severity is: 7.5) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>undici-5.11.0.tgz</b></p></summary>
<p>An HTTP/1.1 client, written from scratch for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/undici/-/undici-5.11.0.tgz">https://registry.npmjs.org/undici/-/undici-5.11.0.tgz</a></p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (undici version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-24807](https://www.mend.io/vulnerability-database/CVE-2023-24807) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | undici-5.11.0.tgz | Direct | undici - 5.19.1 | ❌ |
| [CVE-2023-23936](https://www.mend.io/vulnerability-database/CVE-2023-23936) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | undici-5.11.0.tgz | Direct | undici - 5.19.1 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2023-24807</summary>
### Vulnerable Library - <b>undici-5.11.0.tgz</b></p>
<p>An HTTP/1.1 client, written from scratch for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/undici/-/undici-5.11.0.tgz">https://registry.npmjs.org/undici/-/undici-5.11.0.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **undici-5.11.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Undici is an HTTP/1.1 client for Node.js. Prior to version 5.19.1, the `Headers.set()` and `Headers.append()` methods are vulnerable to Regular Expression Denial of Service (ReDoS) attacks when untrusted values are passed into the functions. This is due to the inefficient regular expression used to normalize the values in the `headerValueNormalize()` utility function. This vulnerability was patched in v5.19.1. No known workarounds are available.
<p>Publish Date: 2023-02-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-24807>CVE-2023-24807</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/nodejs/undici/security/advisories/GHSA-r6ch-mqf9-qc9w">https://github.com/nodejs/undici/security/advisories/GHSA-r6ch-mqf9-qc9w</a></p>
<p>Release Date: 2023-02-16</p>
<p>Fix Resolution: undici - 5.19.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2023-23936</summary>
### Vulnerable Library - <b>undici-5.11.0.tgz</b></p>
<p>An HTTP/1.1 client, written from scratch for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/undici/-/undici-5.11.0.tgz">https://registry.npmjs.org/undici/-/undici-5.11.0.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **undici-5.11.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Undici is an HTTP/1.1 client for Node.js. Starting with version 2.0.0 and prior to version 5.19.1, the undici library does not protect `host` HTTP header from CRLF injection vulnerabilities. This issue is patched in Undici v5.19.1. As a workaround, sanitize the `headers.host` string before passing to undici.
<p>Publish Date: 2023-02-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-23936>CVE-2023-23936</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/nodejs/undici/security/advisories/GHSA-5r9g-qh6m-jxff">https://github.com/nodejs/undici/security/advisories/GHSA-5r9g-qh6m-jxff</a></p>
<p>Release Date: 2023-02-16</p>
<p>Fix Resolution: undici - 5.19.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | undici-5.11.0.tgz: 2 vulnerabilities (highest severity is: 7.5) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>undici-5.11.0.tgz</b></p></summary>
<p>An HTTP/1.1 client, written from scratch for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/undici/-/undici-5.11.0.tgz">https://registry.npmjs.org/undici/-/undici-5.11.0.tgz</a></p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (undici version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-24807](https://www.mend.io/vulnerability-database/CVE-2023-24807) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | undici-5.11.0.tgz | Direct | undici - 5.19.1 | ❌ |
| [CVE-2023-23936](https://www.mend.io/vulnerability-database/CVE-2023-23936) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | undici-5.11.0.tgz | Direct | undici - 5.19.1 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2023-24807</summary>
### Vulnerable Library - <b>undici-5.11.0.tgz</b></p>
<p>An HTTP/1.1 client, written from scratch for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/undici/-/undici-5.11.0.tgz">https://registry.npmjs.org/undici/-/undici-5.11.0.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **undici-5.11.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Undici is an HTTP/1.1 client for Node.js. Prior to version 5.19.1, the `Headers.set()` and `Headers.append()` methods are vulnerable to Regular Expression Denial of Service (ReDoS) attacks when untrusted values are passed into the functions. This is due to the inefficient regular expression used to normalize the values in the `headerValueNormalize()` utility function. This vulnerability was patched in v5.19.1. No known workarounds are available.
<p>Publish Date: 2023-02-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-24807>CVE-2023-24807</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/nodejs/undici/security/advisories/GHSA-r6ch-mqf9-qc9w">https://github.com/nodejs/undici/security/advisories/GHSA-r6ch-mqf9-qc9w</a></p>
<p>Release Date: 2023-02-16</p>
<p>Fix Resolution: undici - 5.19.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2023-23936</summary>
### Vulnerable Library - <b>undici-5.11.0.tgz</b></p>
<p>An HTTP/1.1 client, written from scratch for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/undici/-/undici-5.11.0.tgz">https://registry.npmjs.org/undici/-/undici-5.11.0.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **undici-5.11.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Undici is an HTTP/1.1 client for Node.js. Starting with version 2.0.0 and prior to version 5.19.1, the undici library does not protect `host` HTTP header from CRLF injection vulnerabilities. This issue is patched in Undici v5.19.1. As a workaround, sanitize the `headers.host` string before passing to undici.
<p>Publish Date: 2023-02-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-23936>CVE-2023-23936</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/nodejs/undici/security/advisories/GHSA-5r9g-qh6m-jxff">https://github.com/nodejs/undici/security/advisories/GHSA-5r9g-qh6m-jxff</a></p>
<p>Release Date: 2023-02-16</p>
<p>Fix Resolution: undici - 5.19.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_test | undici tgz vulnerabilities highest severity is autoclosed vulnerable library undici tgz an http client written from scratch for node js library home page a href vulnerabilities cve severity cvss dependency type fixed in undici version remediation available high undici tgz direct undici medium undici tgz direct undici details cve vulnerable library undici tgz an http client written from scratch for node js library home page a href dependency hierarchy x undici tgz vulnerable library found in base branch main vulnerability details undici is an http client for node js prior to version the headers set and headers append methods are vulnerable to regular expression denial of service redos attacks when untrusted values are passed into the functions this is due to the inefficient regular expression used to normalize the values in the headervaluenormalize utility function this vulnerability was patched in no known workarounds are available publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution undici step up your open source security game with mend cve vulnerable library undici tgz an http client written from scratch for node js library home page a href dependency hierarchy x undici tgz vulnerable library found in base branch main vulnerability details undici is an http client for node js starting with version and prior to version the undici library does not protect host http header from crlf injection vulnerabilities this issue is patched in undici as a workaround sanitize the headers host string before passing to undici publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution undici step up your open source security game with mend | 0 |
311,075 | 26,766,636,585 | IssuesEvent | 2023-01-31 11:06:54 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | pkg/sql/logictest/tests/5node/5node_test: TestLogic_distsql_enum failed | C-test-failure O-robot branch-release-22.2 | pkg/sql/logictest/tests/5node/5node_test.TestLogic_distsql_enum [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8521821?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8521821?buildTab=artifacts#/) on release-22.2 @ [848bd2439016f00a0e6de71dad838fb59bc9de4b](https://github.com/cockroachdb/cockroach/commits/848bd2439016f00a0e6de71dad838fb59bc9de4b):
```
=== RUN TestLogic_distsql_enum
test_log_scope.go:161: test logs captured to: /artifacts/tmp/_tmp/c1120e87cda9b48ae97a6489658fb611/logTestLogic_distsql_enum1910416110
test_log_scope.go:79: use -show-logs to present logs inline
[11:05:18] setting distsql_workmem='13407B';
[11:05:18] rng seed: -723648075421454629
logic.go:2705:
/home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2689/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/sql/logictest/tests/5node/5node_test_/5node_test.runfiles/com_github_cockroachdb_cockroach/pkg/sql/logictest/testdata/logic_test/distsql_enum:68: EXPLAIN (VEC)
SELECT x from t1 WHERE EXISTS (SELECT x FROM t2 WHERE t1.x=t2.x AND t2.y='hello')
expected:
│
├ Node 1
│ └ *colrpc.Outbox
│ └ *rowexec.joinReader
│ └ *colfetcher.ColBatchScan
├ Node 2
│ └ *colexec.ParallelUnorderedSynchronizer
│ ├ *colrpc.Inbox
│ ├ *rowexec.joinReader
│ │ └ *colfetcher.ColBatchScan
│ └ *colrpc.Inbox
└ Node 3
└ *colrpc.Outbox
└ *rowexec.joinReader
└ *colfetcher.ColBatchScan
but found (query options: "nodeidx=1,retry") :
│
├ Node 1
│ └ *colrpc.Outbox
│ └ *rowexec.joinReader
│ └ *colfetcher.ColBatchScan
└ Node 2
└ *colexec.ParallelUnorderedSynchronizer
├ *colrpc.Inbox
└ *rowexec.joinReader
└ *colfetcher.ColBatchScan
[11:06:05] --- progress: /home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2689/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/sql/logictest/tests/5node/5node_test_/5node_test.runfiles/com_github_cockroachdb_cockroach/pkg/sql/logictest/testdata/logic_test/distsql_enum: 8 statements
[11:06:05] --- done: /home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2689/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/sql/logictest/tests/5node/5node_test_/5node_test.runfiles/com_github_cockroachdb_cockroach/pkg/sql/logictest/testdata/logic_test/distsql_enum with config 5node: 8 tests, 1 failures
logic.go:3785:
/home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2689/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/sql/logictest/tests/5node/5node_test_/5node_test.runfiles/com_github_cockroachdb_cockroach/pkg/sql/logictest/testdata/logic_test/distsql_enum:88: error while processing
logic.go:3785: /home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2689/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/sql/logictest/tests/5node/5node_test_/5node_test.runfiles/com_github_cockroachdb_cockroach/pkg/sql/logictest/testdata/logic_test/distsql_enum:88: too many errors encountered, skipping the rest of the input
panic.go:522: -- test log scope end --
test logs left over in: /artifacts/tmp/_tmp/c1120e87cda9b48ae97a6489658fb611/logTestLogic_distsql_enum1910416110
--- FAIL: TestLogic_distsql_enum (47.88s)
```
<p>Parameters: <code>TAGS=bazel,gss</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestLogic_distsql_enum.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 1.0 | pkg/sql/logictest/tests/5node/5node_test: TestLogic_distsql_enum failed - pkg/sql/logictest/tests/5node/5node_test.TestLogic_distsql_enum [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8521821?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8521821?buildTab=artifacts#/) on release-22.2 @ [848bd2439016f00a0e6de71dad838fb59bc9de4b](https://github.com/cockroachdb/cockroach/commits/848bd2439016f00a0e6de71dad838fb59bc9de4b):
```
=== RUN TestLogic_distsql_enum
test_log_scope.go:161: test logs captured to: /artifacts/tmp/_tmp/c1120e87cda9b48ae97a6489658fb611/logTestLogic_distsql_enum1910416110
test_log_scope.go:79: use -show-logs to present logs inline
[11:05:18] setting distsql_workmem='13407B';
[11:05:18] rng seed: -723648075421454629
logic.go:2705:
/home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2689/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/sql/logictest/tests/5node/5node_test_/5node_test.runfiles/com_github_cockroachdb_cockroach/pkg/sql/logictest/testdata/logic_test/distsql_enum:68: EXPLAIN (VEC)
SELECT x from t1 WHERE EXISTS (SELECT x FROM t2 WHERE t1.x=t2.x AND t2.y='hello')
expected:
│
├ Node 1
│ └ *colrpc.Outbox
│ └ *rowexec.joinReader
│ └ *colfetcher.ColBatchScan
├ Node 2
│ └ *colexec.ParallelUnorderedSynchronizer
│ ├ *colrpc.Inbox
│ ├ *rowexec.joinReader
│ │ └ *colfetcher.ColBatchScan
│ └ *colrpc.Inbox
└ Node 3
└ *colrpc.Outbox
└ *rowexec.joinReader
└ *colfetcher.ColBatchScan
but found (query options: "nodeidx=1,retry") :
│
├ Node 1
│ └ *colrpc.Outbox
│ └ *rowexec.joinReader
│ └ *colfetcher.ColBatchScan
└ Node 2
└ *colexec.ParallelUnorderedSynchronizer
├ *colrpc.Inbox
└ *rowexec.joinReader
└ *colfetcher.ColBatchScan
[11:06:05] --- progress: /home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2689/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/sql/logictest/tests/5node/5node_test_/5node_test.runfiles/com_github_cockroachdb_cockroach/pkg/sql/logictest/testdata/logic_test/distsql_enum: 8 statements
[11:06:05] --- done: /home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2689/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/sql/logictest/tests/5node/5node_test_/5node_test.runfiles/com_github_cockroachdb_cockroach/pkg/sql/logictest/testdata/logic_test/distsql_enum with config 5node: 8 tests, 1 failures
logic.go:3785:
/home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2689/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/sql/logictest/tests/5node/5node_test_/5node_test.runfiles/com_github_cockroachdb_cockroach/pkg/sql/logictest/testdata/logic_test/distsql_enum:88: error while processing
logic.go:3785: /home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2689/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/sql/logictest/tests/5node/5node_test_/5node_test.runfiles/com_github_cockroachdb_cockroach/pkg/sql/logictest/testdata/logic_test/distsql_enum:88: too many errors encountered, skipping the rest of the input
panic.go:522: -- test log scope end --
test logs left over in: /artifacts/tmp/_tmp/c1120e87cda9b48ae97a6489658fb611/logTestLogic_distsql_enum1910416110
--- FAIL: TestLogic_distsql_enum (47.88s)
```
<p>Parameters: <code>TAGS=bazel,gss</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestLogic_distsql_enum.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| test | pkg sql logictest tests test testlogic distsql enum failed pkg sql logictest tests test testlogic distsql enum with on release run testlogic distsql enum test log scope go test logs captured to artifacts tmp tmp logtestlogic distsql test log scope go use show logs to present logs inline setting distsql workmem rng seed logic go home roach cache bazel bazel roach sandbox processwrapper sandbox execroot com github cockroachdb cockroach bazel out fastbuild bin pkg sql logictest tests test test runfiles com github cockroachdb cockroach pkg sql logictest testdata logic test distsql enum explain vec select x from where exists select x from where x x and y hello expected │ ├ node │ └ colrpc outbox │ └ rowexec joinreader │ └ colfetcher colbatchscan ├ node │ └ colexec parallelunorderedsynchronizer │ ├ colrpc inbox │ ├ rowexec joinreader │ │ └ colfetcher colbatchscan │ └ colrpc inbox └ node └ colrpc outbox └ rowexec joinreader └ colfetcher colbatchscan but found query options nodeidx retry │ ├ node │ └ colrpc outbox │ └ rowexec joinreader │ └ colfetcher colbatchscan └ node └ colexec parallelunorderedsynchronizer ├ colrpc inbox └ rowexec joinreader └ colfetcher colbatchscan progress home roach cache bazel bazel roach sandbox processwrapper sandbox execroot com github cockroachdb cockroach bazel out fastbuild bin pkg sql logictest tests test test runfiles com github cockroachdb cockroach pkg sql logictest testdata logic test distsql enum statements done home roach cache bazel bazel roach sandbox processwrapper sandbox execroot com github cockroachdb cockroach bazel out fastbuild bin pkg sql logictest tests test test runfiles com github cockroachdb cockroach pkg sql logictest testdata logic test distsql enum with config tests failures logic go home roach cache bazel bazel roach sandbox processwrapper sandbox execroot com github cockroachdb cockroach bazel out fastbuild bin pkg sql logictest tests test test runfiles com github cockroachdb cockroach pkg sql logictest testdata logic test distsql enum error while processing logic go home roach cache bazel bazel roach sandbox processwrapper sandbox execroot com github cockroachdb cockroach bazel out fastbuild bin pkg sql logictest tests test test runfiles com github cockroachdb cockroach pkg sql logictest testdata logic test distsql enum too many errors encountered skipping the rest of the input panic go test log scope end test logs left over in artifacts tmp tmp logtestlogic distsql fail testlogic distsql enum parameters tags bazel gss help see also cc cockroachdb sql queries | 1 |
287,988 | 24,880,072,375 | IssuesEvent | 2022-10-27 23:35:27 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: clearrange/checks=true/rangeTs=true failed | C-test-failure O-robot O-roachtest branch-master T-storage | roachtest.clearrange/checks=true/rangeTs=true [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7136814?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7136814?buildTab=artifacts#/clearrange/checks=true/rangeTs=true) on master @ [1b1c8da55be48c174b7b370b305f42622546209f](https://github.com/cockroachdb/cockroach/commits/1b1c8da55be48c174b7b370b305f42622546209f):
```
test artifacts and logs in: /artifacts/clearrange/checks=true/rangeTs=true/run_1
(test_impl.go:291).Fatal: dial tcp 34.74.106.82:26257: connect: connection refused
(test_impl.go:291).Fatal: output in run_101914.139225180_n1-10_cockroach_workload_run_kv: ./cockroach workload run kv --concurrency=32 --duration=1h returned: context canceled
(test_impl.go:291).Fatal: monitor failure: monitor task failed: t.Fatal() was called
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=16</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_fs=ext4</code>
, <code>ROACHTEST_localSSD=true</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/storage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*clearrange/checks=true/rangeTs=true.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-20891 | 2.0 | roachtest: clearrange/checks=true/rangeTs=true failed - roachtest.clearrange/checks=true/rangeTs=true [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7136814?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7136814?buildTab=artifacts#/clearrange/checks=true/rangeTs=true) on master @ [1b1c8da55be48c174b7b370b305f42622546209f](https://github.com/cockroachdb/cockroach/commits/1b1c8da55be48c174b7b370b305f42622546209f):
```
test artifacts and logs in: /artifacts/clearrange/checks=true/rangeTs=true/run_1
(test_impl.go:291).Fatal: dial tcp 34.74.106.82:26257: connect: connection refused
(test_impl.go:291).Fatal: output in run_101914.139225180_n1-10_cockroach_workload_run_kv: ./cockroach workload run kv --concurrency=32 --duration=1h returned: context canceled
(test_impl.go:291).Fatal: monitor failure: monitor task failed: t.Fatal() was called
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=16</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_fs=ext4</code>
, <code>ROACHTEST_localSSD=true</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/storage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*clearrange/checks=true/rangeTs=true.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-20891 | test | roachtest clearrange checks true rangets true failed roachtest clearrange checks true rangets true with on master test artifacts and logs in artifacts clearrange checks true rangets true run test impl go fatal dial tcp connect connection refused test impl go fatal output in run cockroach workload run kv cockroach workload run kv concurrency duration returned context canceled test impl go fatal monitor failure monitor task failed t fatal was called parameters roachtest cloud gce roachtest cpu roachtest encrypted false roachtest fs roachtest localssd true roachtest ssd help see see cc cockroachdb storage jira issue crdb | 1 |
18,879 | 10,299,659,558 | IssuesEvent | 2019-08-28 11:05:32 | DashboardHub/Website | https://api.github.com/repos/DashboardHub/Website | closed | CVE-2018-19826 (Medium) detected in node-sass-v4.12.0 | security vulnerability | ## CVE-2018-19826 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.12.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/DashboardHub/Website/commits/5f96f1e0a372b9087a833b3c4a74d093a24d6897">5f96f1e0a372b9087a833b3c4a74d093a24d6897</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Library Source Files (125)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /Website/node_modules/node-sass/src/libsass/src/expand.hpp
- /Website/node_modules/node-sass/src/libsass/src/util.hpp
- /Website/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /Website/node_modules/node-sass/src/libsass/src/utf8/unchecked.h
- /Website/node_modules/node-sass/src/libsass/src/output.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /Website/node_modules/node-sass/src/libsass/src/emitter.hpp
- /Website/node_modules/node-sass/src/libsass/src/lexer.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_node.cpp
- /Website/node_modules/node-sass/src/libsass/src/plugins.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/base.h
- /Website/node_modules/node-sass/src/libsass/src/position.hpp
- /Website/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /Website/node_modules/node-sass/src/libsass/src/operation.hpp
- /Website/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /Website/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /Website/node_modules/node-sass/src/libsass/src/operators.cpp
- /Website/node_modules/node-sass/src/custom_importer_bridge.cpp
- /Website/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /Website/node_modules/node-sass/src/libsass/src/functions.hpp
- /Website/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /Website/node_modules/node-sass/src/libsass/src/eval.hpp
- /Website/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /Website/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /Website/node_modules/node-sass/src/libsass/src/node.cpp
- /Website/node_modules/node-sass/src/libsass/src/subset_map.cpp
- /Website/node_modules/node-sass/src/libsass/src/emitter.cpp
- /Website/node_modules/node-sass/src/libsass/src/listize.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_functions.hpp
- /Website/node_modules/node-sass/src/libsass/src/memory/SharedPtr.cpp
- /Website/node_modules/node-sass/src/libsass/src/output.cpp
- /Website/node_modules/node-sass/src/libsass/src/check_nesting.cpp
- /Website/node_modules/node-sass/src/libsass/src/expand.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /Website/node_modules/node-sass/src/libsass/src/cssize.hpp
- /Website/node_modules/node-sass/src/libsass/src/paths.hpp
- /Website/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /Website/node_modules/node-sass/src/libsass/src/inspect.hpp
- /Website/node_modules/node-sass/src/sass_types/color.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /Website/node_modules/node-sass/src/libsass/src/values.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /Website/node_modules/node-sass/src/libsass/src/source_map.hpp
- /Website/node_modules/node-sass/src/sass_types/list.h
- /Website/node_modules/node-sass/src/libsass/src/check_nesting.hpp
- /Website/node_modules/node-sass/src/libsass/src/json.cpp
- /Website/node_modules/node-sass/src/libsass/src/units.cpp
- /Website/node_modules/node-sass/src/libsass/src/units.hpp
- /Website/node_modules/node-sass/src/libsass/src/context.cpp
- /Website/node_modules/node-sass/src/libsass/src/utf8/checked.h
- /Website/node_modules/node-sass/src/libsass/src/listize.hpp
- /Website/node_modules/node-sass/src/sass_types/string.cpp
- /Website/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /Website/node_modules/node-sass/src/libsass/src/context.hpp
- /Website/node_modules/node-sass/src/sass_types/boolean.h
- /Website/node_modules/node-sass/src/libsass/include/sass2scss.h
- /Website/node_modules/node-sass/src/binding.cpp
- /Website/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /Website/node_modules/node-sass/src/sass_types/factory.cpp
- /Website/node_modules/node-sass/src/sass_types/boolean.cpp
- /Website/node_modules/node-sass/src/libsass/src/source_map.cpp
- /Website/node_modules/node-sass/src/sass_types/value.h
- /Website/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /Website/node_modules/node-sass/src/libsass/src/file.cpp
- /Website/node_modules/node-sass/src/sass_context_wrapper.cpp
- /Website/node_modules/node-sass/src/libsass/src/node.hpp
- /Website/node_modules/node-sass/src/libsass/src/environment.cpp
- /Website/node_modules/node-sass/src/libsass/src/extend.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /Website/node_modules/node-sass/src/libsass/src/operators.hpp
- /Website/node_modules/node-sass/src/libsass/src/constants.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass.hpp
- /Website/node_modules/node-sass/src/libsass/src/parser.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast_fwd_decl.cpp
- /Website/node_modules/node-sass/src/libsass/src/constants.cpp
- /Website/node_modules/node-sass/src/libsass/src/debugger.hpp
- /Website/node_modules/node-sass/src/sass_types/list.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/functions.h
- /Website/node_modules/node-sass/src/libsass/src/util.cpp
- /Website/node_modules/node-sass/src/custom_function_bridge.cpp
- /Website/node_modules/node-sass/src/custom_importer_bridge.h
- /Website/node_modules/node-sass/src/libsass/src/bind.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /Website/node_modules/node-sass/src/libsass/src/backtrace.cpp
- /Website/node_modules/node-sass/src/libsass/src/cencode.c
- /Website/node_modules/node-sass/src/libsass/src/extend.cpp
- /Website/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /Website/node_modules/node-sass/src/sass_context_wrapper.h
- /Website/node_modules/node-sass/src/libsass/src/sass.cpp
- /Website/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /Website/node_modules/node-sass/src/sass_types/number.cpp
- /Website/node_modules/node-sass/src/sass_types/color.h
- /Website/node_modules/node-sass/src/libsass/src/c99func.c
- /Website/node_modules/node-sass/src/libsass/src/position.cpp
- /Website/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/values.h
- /Website/node_modules/node-sass/src/libsass/src/inspect.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /Website/node_modules/node-sass/src/sass_types/null.cpp
- /Website/node_modules/node-sass/src/libsass/src/functions.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/context.h
- /Website/node_modules/node-sass/src/libsass/src/to_c.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_value.hpp
- /Website/node_modules/node-sass/src/callback_bridge.h
- /Website/node_modules/node-sass/src/libsass/src/color_maps.hpp
- /Website/node_modules/node-sass/src/libsass/script/test-leaks.pl
- /Website/node_modules/node-sass/src/libsass/src/cssize.cpp
- /Website/node_modules/node-sass/src/libsass/src/lexer.hpp
- /Website/node_modules/node-sass/src/libsass/src/memory/SharedPtr.hpp
- /Website/node_modules/node-sass/src/libsass/src/eval.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_c.hpp
- /Website/node_modules/node-sass/src/sass_types/map.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_value.cpp
- /Website/node_modules/node-sass/src/libsass/src/b64/encode.h
- /Website/node_modules/node-sass/src/libsass/src/file.hpp
- /Website/node_modules/node-sass/src/libsass/src/environment.hpp
- /Website/node_modules/node-sass/src/libsass/src/plugins.hpp
- /Website/node_modules/node-sass/src/libsass/src/parser.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /Website/node_modules/node-sass/src/libsass/src/debug.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** In inspect.cpp in LibSass 3.5.5, a high memory footprint caused by an endless loop (containing a Sass::Inspect::operator()(Sass::String_Quoted*) stack frame) may cause a Denial of Service via crafted sass input files with stray '&' or '/' characters. NOTE: Upstream comments indicate this issue is closed as "won't fix" and "works as intended" by design.
<p>Publish Date: 2018-12-03
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19826>CVE-2018-19826</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-19826 (Medium) detected in node-sass-v4.12.0 - ## CVE-2018-19826 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.12.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/DashboardHub/Website/commits/5f96f1e0a372b9087a833b3c4a74d093a24d6897">5f96f1e0a372b9087a833b3c4a74d093a24d6897</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Library Source Files (125)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /Website/node_modules/node-sass/src/libsass/src/expand.hpp
- /Website/node_modules/node-sass/src/libsass/src/util.hpp
- /Website/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /Website/node_modules/node-sass/src/libsass/src/utf8/unchecked.h
- /Website/node_modules/node-sass/src/libsass/src/output.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /Website/node_modules/node-sass/src/libsass/src/emitter.hpp
- /Website/node_modules/node-sass/src/libsass/src/lexer.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_node.cpp
- /Website/node_modules/node-sass/src/libsass/src/plugins.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/base.h
- /Website/node_modules/node-sass/src/libsass/src/position.hpp
- /Website/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /Website/node_modules/node-sass/src/libsass/src/operation.hpp
- /Website/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /Website/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /Website/node_modules/node-sass/src/libsass/src/operators.cpp
- /Website/node_modules/node-sass/src/custom_importer_bridge.cpp
- /Website/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /Website/node_modules/node-sass/src/libsass/src/functions.hpp
- /Website/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /Website/node_modules/node-sass/src/libsass/src/eval.hpp
- /Website/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /Website/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /Website/node_modules/node-sass/src/libsass/src/node.cpp
- /Website/node_modules/node-sass/src/libsass/src/subset_map.cpp
- /Website/node_modules/node-sass/src/libsass/src/emitter.cpp
- /Website/node_modules/node-sass/src/libsass/src/listize.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_functions.hpp
- /Website/node_modules/node-sass/src/libsass/src/memory/SharedPtr.cpp
- /Website/node_modules/node-sass/src/libsass/src/output.cpp
- /Website/node_modules/node-sass/src/libsass/src/check_nesting.cpp
- /Website/node_modules/node-sass/src/libsass/src/expand.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /Website/node_modules/node-sass/src/libsass/src/cssize.hpp
- /Website/node_modules/node-sass/src/libsass/src/paths.hpp
- /Website/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /Website/node_modules/node-sass/src/libsass/src/inspect.hpp
- /Website/node_modules/node-sass/src/sass_types/color.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /Website/node_modules/node-sass/src/libsass/src/values.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /Website/node_modules/node-sass/src/libsass/src/source_map.hpp
- /Website/node_modules/node-sass/src/sass_types/list.h
- /Website/node_modules/node-sass/src/libsass/src/check_nesting.hpp
- /Website/node_modules/node-sass/src/libsass/src/json.cpp
- /Website/node_modules/node-sass/src/libsass/src/units.cpp
- /Website/node_modules/node-sass/src/libsass/src/units.hpp
- /Website/node_modules/node-sass/src/libsass/src/context.cpp
- /Website/node_modules/node-sass/src/libsass/src/utf8/checked.h
- /Website/node_modules/node-sass/src/libsass/src/listize.hpp
- /Website/node_modules/node-sass/src/sass_types/string.cpp
- /Website/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /Website/node_modules/node-sass/src/libsass/src/context.hpp
- /Website/node_modules/node-sass/src/sass_types/boolean.h
- /Website/node_modules/node-sass/src/libsass/include/sass2scss.h
- /Website/node_modules/node-sass/src/binding.cpp
- /Website/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /Website/node_modules/node-sass/src/sass_types/factory.cpp
- /Website/node_modules/node-sass/src/sass_types/boolean.cpp
- /Website/node_modules/node-sass/src/libsass/src/source_map.cpp
- /Website/node_modules/node-sass/src/sass_types/value.h
- /Website/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /Website/node_modules/node-sass/src/libsass/src/file.cpp
- /Website/node_modules/node-sass/src/sass_context_wrapper.cpp
- /Website/node_modules/node-sass/src/libsass/src/node.hpp
- /Website/node_modules/node-sass/src/libsass/src/environment.cpp
- /Website/node_modules/node-sass/src/libsass/src/extend.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /Website/node_modules/node-sass/src/libsass/src/operators.hpp
- /Website/node_modules/node-sass/src/libsass/src/constants.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass.hpp
- /Website/node_modules/node-sass/src/libsass/src/parser.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast_fwd_decl.cpp
- /Website/node_modules/node-sass/src/libsass/src/constants.cpp
- /Website/node_modules/node-sass/src/libsass/src/debugger.hpp
- /Website/node_modules/node-sass/src/sass_types/list.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/functions.h
- /Website/node_modules/node-sass/src/libsass/src/util.cpp
- /Website/node_modules/node-sass/src/custom_function_bridge.cpp
- /Website/node_modules/node-sass/src/custom_importer_bridge.h
- /Website/node_modules/node-sass/src/libsass/src/bind.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /Website/node_modules/node-sass/src/libsass/src/backtrace.cpp
- /Website/node_modules/node-sass/src/libsass/src/cencode.c
- /Website/node_modules/node-sass/src/libsass/src/extend.cpp
- /Website/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /Website/node_modules/node-sass/src/sass_context_wrapper.h
- /Website/node_modules/node-sass/src/libsass/src/sass.cpp
- /Website/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /Website/node_modules/node-sass/src/sass_types/number.cpp
- /Website/node_modules/node-sass/src/sass_types/color.h
- /Website/node_modules/node-sass/src/libsass/src/c99func.c
- /Website/node_modules/node-sass/src/libsass/src/position.cpp
- /Website/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/values.h
- /Website/node_modules/node-sass/src/libsass/src/inspect.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /Website/node_modules/node-sass/src/sass_types/null.cpp
- /Website/node_modules/node-sass/src/libsass/src/functions.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/context.h
- /Website/node_modules/node-sass/src/libsass/src/to_c.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_value.hpp
- /Website/node_modules/node-sass/src/callback_bridge.h
- /Website/node_modules/node-sass/src/libsass/src/color_maps.hpp
- /Website/node_modules/node-sass/src/libsass/script/test-leaks.pl
- /Website/node_modules/node-sass/src/libsass/src/cssize.cpp
- /Website/node_modules/node-sass/src/libsass/src/lexer.hpp
- /Website/node_modules/node-sass/src/libsass/src/memory/SharedPtr.hpp
- /Website/node_modules/node-sass/src/libsass/src/eval.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_c.hpp
- /Website/node_modules/node-sass/src/sass_types/map.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_value.cpp
- /Website/node_modules/node-sass/src/libsass/src/b64/encode.h
- /Website/node_modules/node-sass/src/libsass/src/file.hpp
- /Website/node_modules/node-sass/src/libsass/src/environment.hpp
- /Website/node_modules/node-sass/src/libsass/src/plugins.hpp
- /Website/node_modules/node-sass/src/libsass/src/parser.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /Website/node_modules/node-sass/src/libsass/src/debug.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** In inspect.cpp in LibSass 3.5.5, a high memory footprint caused by an endless loop (containing a Sass::Inspect::operator()(Sass::String_Quoted*) stack frame) may cause a Denial of Service via crafted sass input files with stray '&' or '/' characters. NOTE: Upstream comments indicate this issue is closed as "won't fix" and "works as intended" by design.
<p>Publish Date: 2018-12-03
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19826>CVE-2018-19826</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in node sass cve medium severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href found in head commit a href library source files the source files were matched to this source library based on a best effort match source libraries are selected from a list of probable public libraries website node modules node sass src libsass src expand hpp website node modules node sass src libsass src util hpp website node modules node sass src libsass src color maps cpp website node modules node sass src libsass src sass util hpp website node modules node sass src libsass src unchecked h website node modules node sass src libsass src output hpp website node modules node sass src libsass src sass values hpp website node modules node sass src libsass src emitter hpp website node modules node sass src libsass src lexer cpp website node modules node sass src libsass test test node cpp website node modules node sass src libsass src plugins cpp website node modules node sass src libsass include sass base h website node modules node sass src libsass src position hpp website node modules node sass src libsass src subset map hpp website node modules node sass src libsass src operation hpp website node modules node sass src libsass src remove placeholders cpp website node modules node sass src libsass src error handling hpp website node modules node sass src libsass src operators cpp website node modules node sass src custom importer bridge cpp website node modules node sass src libsass contrib plugin cpp website node modules node sass src libsass src functions hpp website node modules node sass src libsass test test superselector cpp website node modules node sass src libsass src eval hpp website node modules node sass src libsass src string hpp website node modules node sass src libsass src error handling cpp website node modules node sass src libsass src node cpp website node modules node sass src libsass src subset map cpp website node modules node sass src libsass src emitter cpp website node modules node sass src libsass src listize cpp website node modules node sass src libsass src ast hpp website node modules node sass src libsass src sass functions hpp website node modules node sass src libsass src memory sharedptr cpp website node modules node sass src libsass src output cpp website node modules node sass src libsass src check nesting cpp website node modules node sass src libsass src expand cpp website node modules node sass src libsass src ast def macros hpp website node modules node sass src libsass src cssize hpp website node modules node sass src libsass src paths hpp website node modules node sass src libsass src ast fwd decl hpp website node modules node sass src libsass src inspect hpp website node modules node sass src sass types color cpp website node modules node sass src libsass test test unification cpp website node modules node sass src libsass src values cpp website node modules node sass src libsass src sass util cpp website node modules node sass src libsass src source map hpp website node modules node sass src sass types list h website node modules node sass src libsass src check nesting hpp website node modules node sass src libsass src json cpp website node modules node sass src libsass src units cpp website node modules node sass src libsass src units hpp website node modules node sass src libsass src context cpp website node modules node sass src libsass src checked h website node modules node sass src libsass src listize hpp website node modules node sass src sass types string cpp website node modules node sass src libsass src prelexer hpp website node modules node sass src libsass src context hpp website node modules node sass src sass types boolean h website node modules node sass src libsass include h website node modules node sass src binding cpp website node modules node sass src libsass src prelexer cpp website node modules node sass src sass types factory cpp website node modules node sass src sass types boolean cpp website node modules node sass src libsass src source map cpp website node modules node sass src sass types value h website node modules node sass src libsass src string cpp website node modules node sass src libsass src file cpp website node modules node sass src sass context wrapper cpp website node modules node sass src libsass src node hpp website node modules node sass src libsass src environment cpp website node modules node sass src libsass src extend hpp website node modules node sass src libsass src sass context hpp website node modules node sass src libsass src operators hpp website node modules node sass src libsass src constants hpp website node modules node sass src libsass src sass hpp website node modules node sass src libsass src parser cpp website node modules node sass src libsass src ast fwd decl cpp website node modules node sass src libsass src constants cpp website node modules node sass src libsass src debugger hpp website node modules node sass src sass types list cpp website node modules node sass src libsass include sass functions h website node modules node sass src libsass src util cpp website node modules node sass src custom function bridge cpp website node modules node sass src custom importer bridge h website node modules node sass src libsass src bind cpp website node modules node sass src libsass src sass functions cpp website node modules node sass src libsass src backtrace cpp website node modules node sass src libsass src cencode c website node modules node sass src libsass src extend cpp website node modules node sass src sass types sass value wrapper h website node modules node sass src sass context wrapper h website node modules node sass src libsass src sass cpp website node modules node sass src libsass src cpp website node modules node sass src sass types number cpp website node modules node sass src sass types color h website node modules node sass src libsass src c website node modules node sass src libsass src position cpp website node modules node sass src libsass src remove placeholders hpp website node modules node sass src libsass src sass values cpp website node modules node sass src libsass include sass values h website node modules node sass src libsass src inspect cpp website node modules node sass src libsass test test subset map cpp website node modules node sass src libsass src cpp website node modules node sass src sass types null cpp website node modules node sass src libsass src functions cpp website node modules node sass src libsass src ast cpp website node modules node sass src libsass include sass context h website node modules node sass src libsass src to c cpp website node modules node sass src libsass src to value hpp website node modules node sass src callback bridge h website node modules node sass src libsass src color maps hpp website node modules node sass src libsass script test leaks pl website node modules node sass src libsass src cssize cpp website node modules node sass src libsass src lexer hpp website node modules node sass src libsass src memory sharedptr hpp website node modules node sass src libsass src eval cpp website node modules node sass src libsass src to c hpp website node modules node sass src sass types map cpp website node modules node sass src libsass src to value cpp website node modules node sass src libsass src encode h website node modules node sass src libsass src file hpp website node modules node sass src libsass src environment hpp website node modules node sass src libsass src plugins hpp website node modules node sass src libsass src parser hpp website node modules node sass src libsass src sass context cpp website node modules node sass src libsass src debug hpp vulnerability details disputed in inspect cpp in libsass a high memory footprint caused by an endless loop containing a sass inspect operator sass string quoted stack frame may cause a denial of service via crafted sass input files with stray or characters note upstream comments indicate this issue is closed as won t fix and works as intended by design publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with whitesource | 0 |
193,505 | 14,654,737,017 | IssuesEvent | 2020-12-28 09:23:09 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | freeconf/gconf: nodes/pipe_test.go; 15 LoC | fresh small test |
Found a possible issue in [freeconf/gconf](https://www.github.com/freeconf/gconf) at [nodes/pipe_test.go](https://github.com/freeconf/gconf/blob/2f55915426b9328e332983a83beafcea62167aeb/nodes/pipe_test.go#L89-L103)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable test used in defer or goroutine at line 95
[Click here to see the code in its original context.](https://github.com/freeconf/gconf/blob/2f55915426b9328e332983a83beafcea62167aeb/nodes/pipe_test.go#L89-L103)
<details>
<summary>Click here to show the 15 line(s) of Go which triggered the analyzer.</summary>
```go
for _, test := range tests {
pipe := NewPipe()
pull, push := pipe.PullPush()
go func() {
sel := node.NewBrowser(m, push).Root()
pipe.Close(sel.InsertFrom(ReadJSON(test)).LastErr)
}()
actual, err := WriteJSON(node.NewBrowser(m, pull).Root())
if err != nil {
t.Error(err)
} else if actual != test {
t.Errorf("\nExpected:%s\n Actual:%s", test, actual)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 2f55915426b9328e332983a83beafcea62167aeb
| 1.0 | freeconf/gconf: nodes/pipe_test.go; 15 LoC -
Found a possible issue in [freeconf/gconf](https://www.github.com/freeconf/gconf) at [nodes/pipe_test.go](https://github.com/freeconf/gconf/blob/2f55915426b9328e332983a83beafcea62167aeb/nodes/pipe_test.go#L89-L103)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable test used in defer or goroutine at line 95
[Click here to see the code in its original context.](https://github.com/freeconf/gconf/blob/2f55915426b9328e332983a83beafcea62167aeb/nodes/pipe_test.go#L89-L103)
<details>
<summary>Click here to show the 15 line(s) of Go which triggered the analyzer.</summary>
```go
for _, test := range tests {
pipe := NewPipe()
pull, push := pipe.PullPush()
go func() {
sel := node.NewBrowser(m, push).Root()
pipe.Close(sel.InsertFrom(ReadJSON(test)).LastErr)
}()
actual, err := WriteJSON(node.NewBrowser(m, pull).Root())
if err != nil {
t.Error(err)
} else if actual != test {
t.Errorf("\nExpected:%s\n Actual:%s", test, actual)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 2f55915426b9328e332983a83beafcea62167aeb
| test | freeconf gconf nodes pipe test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message range loop variable test used in defer or goroutine at line click here to show the line s of go which triggered the analyzer go for test range tests pipe newpipe pull push pipe pullpush go func sel node newbrowser m push root pipe close sel insertfrom readjson test lasterr actual err writejson node newbrowser m pull root if err nil t error err else if actual test t errorf nexpected s n actual s test actual leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
538,566 | 15,772,222,618 | IssuesEvent | 2021-03-31 21:30:45 | filc/naplo | https://api.github.com/repos/filc/naplo | closed | Új verzió jelzése | enhancement priority | - Új verzió ellenőrzése GitHub api releases alapján
- Profilképen jelenjen meg piros pötty ha nem friss az app
- Profiloldalon már legyen kiírva alul hogy új verzió elérhető, ami megnyit egy frissítés info bottomsheetet, leírva rajta:
- Ha apk-ként telepítette fel, nyomja meg a letöltés gombot (apiból legfrissebb release link lekérése)
- Ha F-Droidból, frissítsen a főoldalon és az app oldalán indítsa el a frissítést
_iPhoneon az egész egyáltalán ne jelenjen meg, TestFlight megbízható_ | 1.0 | Új verzió jelzése - - Új verzió ellenőrzése GitHub api releases alapján
- Profilképen jelenjen meg piros pötty ha nem friss az app
- Profiloldalon már legyen kiírva alul hogy új verzió elérhető, ami megnyit egy frissítés info bottomsheetet, leírva rajta:
- Ha apk-ként telepítette fel, nyomja meg a letöltés gombot (apiból legfrissebb release link lekérése)
- Ha F-Droidból, frissítsen a főoldalon és az app oldalán indítsa el a frissítést
_iPhoneon az egész egyáltalán ne jelenjen meg, TestFlight megbízható_ | non_test | új verzió jelzése új verzió ellenőrzése github api releases alapján profilképen jelenjen meg piros pötty ha nem friss az app profiloldalon már legyen kiírva alul hogy új verzió elérhető ami megnyit egy frissítés info bottomsheetet leírva rajta ha apk ként telepítette fel nyomja meg a letöltés gombot apiból legfrissebb release link lekérése ha f droidból frissítsen a főoldalon és az app oldalán indítsa el a frissítést iphoneon az egész egyáltalán ne jelenjen meg testflight megbízható | 0 |
34,484 | 7,837,933,544 | IssuesEvent | 2018-06-18 08:28:25 | ebmdatalab/openprescribing | https://api.github.com/repos/ebmdatalab/openprescribing | opened | Label dormant / closed practices | new-coder trivial | In the list of practices at the top of a CCG page([example](https://openprescribing.net/ccg/08C/)), and at the top of a Practice page ([example](https://openprescribing.net/practice/E85124/)), we should clearly label Closed and Dormant practices as such (with the word "Closed" or "Dormant").
It may be worth linking somewhere to [our explanation of "dormant"](https://ebmdatalab.net/what-is-a-dormant-gp-practice-and-why-are-they-prescribing/) if it's possible to do discreetly.
For further background, see #215 and #522.
The current status is stored in our Practice model.
| 1.0 | Label dormant / closed practices - In the list of practices at the top of a CCG page([example](https://openprescribing.net/ccg/08C/)), and at the top of a Practice page ([example](https://openprescribing.net/practice/E85124/)), we should clearly label Closed and Dormant practices as such (with the word "Closed" or "Dormant").
It may be worth linking somewhere to [our explanation of "dormant"](https://ebmdatalab.net/what-is-a-dormant-gp-practice-and-why-are-they-prescribing/) if it's possible to do discreetly.
For further background, see #215 and #522.
The current status is stored in our Practice model.
| non_test | label dormant closed practices in the list of practices at the top of a ccg page and at the top of a practice page we should clearly label closed and dormant practices as such with the word closed or dormant it may be worth linking somewhere to if it s possible to do discreetly for further background see and the current status is stored in our practice model | 0 |
70,508 | 7,190,086,816 | IssuesEvent | 2018-02-02 16:06:40 | MyersResearchGroup/iBioSim | https://api.github.com/repos/MyersResearchGroup/iBioSim | closed | error | BUG Needs Testing | iBioSim Version 3.0.0-beta
Operating system: Windows 10
Bug reported by: michael13162@gmail.com
Description:
issa?
Stack trace:
java.lang.NumberFormatException: null
at java.lang.Integer.parseInt(Unknown Source)
at java.lang.Integer.parseInt(Unknown Source)
at edu.utah.ece.async.ibiosim.gui.analysisView.AnalysisView.save(AnalysisView.java:1307)
at edu.utah.ece.async.ibiosim.gui.analysisView.AnalysisView.executeRun(AnalysisView.java:1518)
at edu.utah.ece.async.ibiosim.gui.Gui.actionPerformed(Gui.java:2252)
at javax.swing.AbstractButton.fireActionPerformed(Unknown Source)
at javax.swing.AbstractButton$Handler.actionPerformed(Unknown Source)
at javax.swing.DefaultButtonModel.fireActionPerformed(Unknown Source)
at javax.swing.DefaultButtonModel.setPressed(Unknown Source)
at javax.swing.plaf.basic.BasicButtonListener.mouseReleased(Unknown Source)
at java.awt.AWTEventMulticaster.mouseReleased(Unknown Source)
at java.awt.Component.processMouseEvent(Unknown Source)
at javax.swing.JComponent.processMouseEvent(Unknown Source)
at java.awt.Component.processEvent(Unknown Source)
at java.awt.Container.processEvent(Unknown Source)
at java.awt.Component.dispatchEventImpl(Unknown Source)
at java.awt.Container.dispatchEventImpl(Unknown Source)
at java.awt.Component.dispatchEvent(Unknown Source)
at java.awt.LightweightDispatcher.retargetMouseEvent(Unknown Source)
at java.awt.LightweightDispatcher.processMouseEvent(Unknown Source)
at java.awt.LightweightDispatcher.dispatchEvent(Unknown Source)
at java.awt.Container.dispatchEventImpl(Unknown Source)
at java.awt.Window.dispatchEventImpl(Unknown Source)
at java.awt.Component.dispatchEvent(Unknown Source)
at java.awt.EventQueue.dispatchEventImpl(Unknown Source)
at java.awt.EventQueue.access$500(Unknown Source)
at java.awt.EventQueue$3.run(Unknown Source)
at java.awt.EventQueue$3.run(Unknown Source)
at java.security.AccessController.doPrivileged(Native Method)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(Unknown Source)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(Unknown Source)
at java.awt.EventQueue$4.run(Unknown Source)
at java.awt.EventQueue$4.run(Unknown Source)
at java.security.AccessController.doPrivileged(Native Method)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(Unknown Source)
at java.awt.EventQueue.dispatchEvent(Unknown Source)
at java.awt.EventDispatchThread.pumpOneEventForFilters(Unknown Source)
at java.awt.EventDispatchThread.pumpEventsForFilter(Unknown Source)
at java.awt.EventDispatchThread.pumpEventsForHierarchy(Unknown Source)
at java.awt.EventDispatchThread.pumpEvents(Unknown Source)
at java.awt.EventDispatchThread.pumpEvents(Unknown Source)
at java.awt.EventDispatchThread.run(Unknown Source)
| 1.0 | error - iBioSim Version 3.0.0-beta
Operating system: Windows 10
Bug reported by: michael13162@gmail.com
Description:
issa?
Stack trace:
java.lang.NumberFormatException: null
at java.lang.Integer.parseInt(Unknown Source)
at java.lang.Integer.parseInt(Unknown Source)
at edu.utah.ece.async.ibiosim.gui.analysisView.AnalysisView.save(AnalysisView.java:1307)
at edu.utah.ece.async.ibiosim.gui.analysisView.AnalysisView.executeRun(AnalysisView.java:1518)
at edu.utah.ece.async.ibiosim.gui.Gui.actionPerformed(Gui.java:2252)
at javax.swing.AbstractButton.fireActionPerformed(Unknown Source)
at javax.swing.AbstractButton$Handler.actionPerformed(Unknown Source)
at javax.swing.DefaultButtonModel.fireActionPerformed(Unknown Source)
at javax.swing.DefaultButtonModel.setPressed(Unknown Source)
at javax.swing.plaf.basic.BasicButtonListener.mouseReleased(Unknown Source)
at java.awt.AWTEventMulticaster.mouseReleased(Unknown Source)
at java.awt.Component.processMouseEvent(Unknown Source)
at javax.swing.JComponent.processMouseEvent(Unknown Source)
at java.awt.Component.processEvent(Unknown Source)
at java.awt.Container.processEvent(Unknown Source)
at java.awt.Component.dispatchEventImpl(Unknown Source)
at java.awt.Container.dispatchEventImpl(Unknown Source)
at java.awt.Component.dispatchEvent(Unknown Source)
at java.awt.LightweightDispatcher.retargetMouseEvent(Unknown Source)
at java.awt.LightweightDispatcher.processMouseEvent(Unknown Source)
at java.awt.LightweightDispatcher.dispatchEvent(Unknown Source)
at java.awt.Container.dispatchEventImpl(Unknown Source)
at java.awt.Window.dispatchEventImpl(Unknown Source)
at java.awt.Component.dispatchEvent(Unknown Source)
at java.awt.EventQueue.dispatchEventImpl(Unknown Source)
at java.awt.EventQueue.access$500(Unknown Source)
at java.awt.EventQueue$3.run(Unknown Source)
at java.awt.EventQueue$3.run(Unknown Source)
at java.security.AccessController.doPrivileged(Native Method)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(Unknown Source)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(Unknown Source)
at java.awt.EventQueue$4.run(Unknown Source)
at java.awt.EventQueue$4.run(Unknown Source)
at java.security.AccessController.doPrivileged(Native Method)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(Unknown Source)
at java.awt.EventQueue.dispatchEvent(Unknown Source)
at java.awt.EventDispatchThread.pumpOneEventForFilters(Unknown Source)
at java.awt.EventDispatchThread.pumpEventsForFilter(Unknown Source)
at java.awt.EventDispatchThread.pumpEventsForHierarchy(Unknown Source)
at java.awt.EventDispatchThread.pumpEvents(Unknown Source)
at java.awt.EventDispatchThread.pumpEvents(Unknown Source)
at java.awt.EventDispatchThread.run(Unknown Source)
| test | error ibiosim version beta operating system windows bug reported by gmail com description issa stack trace java lang numberformatexception null at java lang integer parseint unknown source at java lang integer parseint unknown source at edu utah ece async ibiosim gui analysisview analysisview save analysisview java at edu utah ece async ibiosim gui analysisview analysisview executerun analysisview java at edu utah ece async ibiosim gui gui actionperformed gui java at javax swing abstractbutton fireactionperformed unknown source at javax swing abstractbutton handler actionperformed unknown source at javax swing defaultbuttonmodel fireactionperformed unknown source at javax swing defaultbuttonmodel setpressed unknown source at javax swing plaf basic basicbuttonlistener mousereleased unknown source at java awt awteventmulticaster mousereleased unknown source at java awt component processmouseevent unknown source at javax swing jcomponent processmouseevent unknown source at java awt component processevent unknown source at java awt container processevent unknown source at java awt component dispatcheventimpl unknown source at java awt container dispatcheventimpl unknown source at java awt component dispatchevent unknown source at java awt lightweightdispatcher retargetmouseevent unknown source at java awt lightweightdispatcher processmouseevent unknown source at java awt lightweightdispatcher dispatchevent unknown source at java awt container dispatcheventimpl unknown source at java awt window dispatcheventimpl unknown source at java awt component dispatchevent unknown source at java awt eventqueue dispatcheventimpl unknown source at java awt eventqueue access unknown source at java awt eventqueue run unknown source at java awt eventqueue run unknown source at java security accesscontroller doprivileged native method at java security protectiondomain javasecurityaccessimpl dointersectionprivilege unknown source at java security protectiondomain javasecurityaccessimpl dointersectionprivilege unknown source at java awt eventqueue run unknown source at java awt eventqueue run unknown source at java security accesscontroller doprivileged native method at java security protectiondomain javasecurityaccessimpl dointersectionprivilege unknown source at java awt eventqueue dispatchevent unknown source at java awt eventdispatchthread pumponeeventforfilters unknown source at java awt eventdispatchthread pumpeventsforfilter unknown source at java awt eventdispatchthread pumpeventsforhierarchy unknown source at java awt eventdispatchthread pumpevents unknown source at java awt eventdispatchthread pumpevents unknown source at java awt eventdispatchthread run unknown source | 1 |
16,532 | 3,536,243,141 | IssuesEvent | 2016-01-17 04:15:52 | sass/libsass | https://api.github.com/repos/sass/libsass | closed | each produces different result than for loop | Bug - Confirmed Dev - PR Ready Dev - Test Written | EDIT: Most urgent issue is fixed, but there is still some wrong output for
### Input (`test.scss`)
```scss
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
@each $set in & {
set: inspect($set);
@each $selector in $set {
selector: inspect($selector);
}
}
}
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
@for $i from 1 through length(&) {
$set: nth(&, $i);
set: inspect($set);
@each $selector in $set {
selector: inspect($selector);
}
}
}
```
### Ruby Sass (`sass test.scss`)
```css
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
set: test-1 test-2 test-3 test-4 test-5;
selector: test-1;
selector: test-2;
selector: test-3;
selector: test-4;
selector: test-5;
set: test-6 test-7 test-8 test-9 test-10;
selector: test-6;
selector: test-7;
selector: test-8;
selector: test-9;
selector: test-10; }
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
set: test-1 test-2 test-3 test-4 test-5;
selector: test-1;
selector: test-2;
selector: test-3;
selector: test-4;
selector: test-5;
set: test-6 test-7 test-8 test-9 test-10;
selector: test-6;
selector: test-7;
selector: test-8;
selector: test-9;
selector: test-10; }
```
### LibSass (`sassc test.scss`)
```css
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
set: test-1 test-2 test-3 test-4 test-5, test-6 test-7 test-8 test-9 test-10;
selector: test-1 test-2 test-3 test-4 test-5, test-6 test-7 test-8 test-9 test-10; }
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
set: test-1 test-2 test-3 test-4 test-5;
selector: test-1;
selector: test-2;
selector: test-3;
selector: test-4;
selector: test-5;
set: test-6 test-7 test-8 test-9 test-10;
selector: test-6;
selector: test-7;
selector: test-8;
selector: test-9;
selector: test-10; }
```
Hi,
I get some errors if I compile my main.scss file with "gulp-sass".
Contrary to that, compiling using sass -w sass/main.scss:css/main.css doesn't produce any error.
From the error log it seems that "flint-calculate" does not accept content block, but as the Flint developer stated here https://github.com/ezekg/flint/issues/40 , it should be accepting them.
My gulp task:
// Sass
gulp.task('sass', function () {
gulp.src(sass_path)
.pipe(plumber())
.pipe(sass({outputStyle: 'expanded'}))
.pipe(prefix())
.pipe(gulp.dest(sass_dest));
});
This is my simple main.scss file:
@import "_flint";
.foo{
@include _(3 4 6 12);
}
This is the error I get in the console (I'm using Plumber to catch errors):
[15:07:17] Starting 'sass'...
[15:07:17] Finished 'sass' after 3.32 ms
[15:07:17] Plumber found unhandled error:
Error in plugin 'gulp-sass'
Message:
sass/flint/mixins/lib/_main.scss
Error: Mixin "flint-calculate" does not accept a content block.
Backtrace:
sass/flint/mixins/lib/_main.scss:689, in mixin `-`
stdin:4
on line 689 of sass/flint/mixins/lib/_main.scss
>> @include flint-calculate($calc-key, $calc-spa
------------------------------------------^
Details:
formatted: Error: Mixin "flint-calculate" does not accept a content block.
Backtrace:
sass/flint/mixins/lib/_main.scss:689, in mixin `-`
stdin:4
on line 689 of sass/flint/mixins/lib/_main.scss
>> @include flint-calculate($calc-key, $calc-spa
------------------------------------------^
column: 46
line: 689
file: /Users/Ht8It1/Development/FrontEnd/FlintTest/sass/flint/mixins/lib/_main.scss
status: 1
messageFormatted: sass/flint/mixins/lib/_main.scss
Error: Mixin "flint-calculate" does not accept a content block.
Backtrace:
sass/flint/mixins/lib/_main.scss:689, in mixin `-`
stdin:4
on line 689 of sass/flint/mixins/lib/_main.scss
>> @include flint-calculate($calc-key, $calc-spa
------------------------------------------^
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/28190483-each-produces-different-result-than-for-loop?utm_campaign=plugin&utm_content=tracker%2F283068&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F283068&utm_medium=issues&utm_source=github).
</bountysource-plugin> | 1.0 | each produces different result than for loop - EDIT: Most urgent issue is fixed, but there is still some wrong output for
### Input (`test.scss`)
```scss
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
@each $set in & {
set: inspect($set);
@each $selector in $set {
selector: inspect($selector);
}
}
}
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
@for $i from 1 through length(&) {
$set: nth(&, $i);
set: inspect($set);
@each $selector in $set {
selector: inspect($selector);
}
}
}
```
### Ruby Sass (`sass test.scss`)
```css
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
set: test-1 test-2 test-3 test-4 test-5;
selector: test-1;
selector: test-2;
selector: test-3;
selector: test-4;
selector: test-5;
set: test-6 test-7 test-8 test-9 test-10;
selector: test-6;
selector: test-7;
selector: test-8;
selector: test-9;
selector: test-10; }
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
set: test-1 test-2 test-3 test-4 test-5;
selector: test-1;
selector: test-2;
selector: test-3;
selector: test-4;
selector: test-5;
set: test-6 test-7 test-8 test-9 test-10;
selector: test-6;
selector: test-7;
selector: test-8;
selector: test-9;
selector: test-10; }
```
### LibSass (`sassc test.scss`)
```css
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
set: test-1 test-2 test-3 test-4 test-5, test-6 test-7 test-8 test-9 test-10;
selector: test-1 test-2 test-3 test-4 test-5, test-6 test-7 test-8 test-9 test-10; }
test-1 test-2 test-3 test-4 test-5,
test-6 test-7 test-8 test-9 test-10 {
set: test-1 test-2 test-3 test-4 test-5;
selector: test-1;
selector: test-2;
selector: test-3;
selector: test-4;
selector: test-5;
set: test-6 test-7 test-8 test-9 test-10;
selector: test-6;
selector: test-7;
selector: test-8;
selector: test-9;
selector: test-10; }
```
Hi,
I get some errors if I compile my main.scss file with "gulp-sass".
Contrary to that, compiling using sass -w sass/main.scss:css/main.css doesn't produce any error.
From the error log it seems that "flint-calculate" does not accept content block, but as the Flint developer stated here https://github.com/ezekg/flint/issues/40 , it should be accepting them.
My gulp task:
// Sass
gulp.task('sass', function () {
gulp.src(sass_path)
.pipe(plumber())
.pipe(sass({outputStyle: 'expanded'}))
.pipe(prefix())
.pipe(gulp.dest(sass_dest));
});
This is my simple main.scss file:
@import "_flint";
.foo{
@include _(3 4 6 12);
}
This is the error I get in the console (I'm using Plumber to catch errors):
[15:07:17] Starting 'sass'...
[15:07:17] Finished 'sass' after 3.32 ms
[15:07:17] Plumber found unhandled error:
Error in plugin 'gulp-sass'
Message:
sass/flint/mixins/lib/_main.scss
Error: Mixin "flint-calculate" does not accept a content block.
Backtrace:
sass/flint/mixins/lib/_main.scss:689, in mixin `-`
stdin:4
on line 689 of sass/flint/mixins/lib/_main.scss
>> @include flint-calculate($calc-key, $calc-spa
------------------------------------------^
Details:
formatted: Error: Mixin "flint-calculate" does not accept a content block.
Backtrace:
sass/flint/mixins/lib/_main.scss:689, in mixin `-`
stdin:4
on line 689 of sass/flint/mixins/lib/_main.scss
>> @include flint-calculate($calc-key, $calc-spa
------------------------------------------^
column: 46
line: 689
file: /Users/Ht8It1/Development/FrontEnd/FlintTest/sass/flint/mixins/lib/_main.scss
status: 1
messageFormatted: sass/flint/mixins/lib/_main.scss
Error: Mixin "flint-calculate" does not accept a content block.
Backtrace:
sass/flint/mixins/lib/_main.scss:689, in mixin `-`
stdin:4
on line 689 of sass/flint/mixins/lib/_main.scss
>> @include flint-calculate($calc-key, $calc-spa
------------------------------------------^
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/28190483-each-produces-different-result-than-for-loop?utm_campaign=plugin&utm_content=tracker%2F283068&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F283068&utm_medium=issues&utm_source=github).
</bountysource-plugin> | test | each produces different result than for loop edit most urgent issue is fixed but there is still some wrong output for input test scss scss test test test test test test test test test test each set in set inspect set each selector in set selector inspect selector test test test test test test test test test test for i from through length set nth i set inspect set each selector in set selector inspect selector ruby sass sass test scss css test test test test test test test test test test set test test test test test selector test selector test selector test selector test selector test set test test test test test selector test selector test selector test selector test selector test test test test test test test test test test test set test test test test test selector test selector test selector test selector test selector test set test test test test test selector test selector test selector test selector test selector test libsass sassc test scss css test test test test test test test test test test set test test test test test test test test test test selector test test test test test test test test test test test test test test test test test test test test set test test test test test selector test selector test selector test selector test selector test set test test test test test selector test selector test selector test selector test selector test hi i get some errors if i compile my main scss file with gulp sass contrary to that compiling using sass w sass main scss css main css doesn t produce any error from the error log it seems that flint calculate does not accept content block but as the flint developer stated here it should be accepting them my gulp task sass gulp task sass function gulp src sass path pipe plumber pipe sass outputstyle expanded pipe prefix pipe gulp dest sass dest this is my simple main scss file import flint foo include this is the error i get in the console i m using plumber to catch errors starting sass finished sass after ms plumber found unhandled error error in plugin gulp sass message sass flint mixins lib main scss error mixin flint calculate does not accept a content block backtrace sass flint mixins lib main scss in mixin stdin on line of sass flint mixins lib main scss include flint calculate calc key calc spa details formatted error mixin flint calculate does not accept a content block backtrace sass flint mixins lib main scss in mixin stdin on line of sass flint mixins lib main scss include flint calculate calc key calc spa column line file users development frontend flinttest sass flint mixins lib main scss status messageformatted sass flint mixins lib main scss error mixin flint calculate does not accept a content block backtrace sass flint mixins lib main scss in mixin stdin on line of sass flint mixins lib main scss include flint calculate calc key calc spa want to back this issue we accept bounties via | 1 |
132,642 | 10,760,630,997 | IssuesEvent | 2019-10-31 19:00:42 | PulpQE/pulp-smash | https://api.github.com/repos/PulpQE/pulp-smash | closed | Test iso repo unit association | Issue Type: Test Case | Test to verify unit association for ISO repo
https://pulp.plan.io/issues/2655
Assert the following
1. Units are copied
2. Association task reports the units_successful
| 1.0 | Test iso repo unit association - Test to verify unit association for ISO repo
https://pulp.plan.io/issues/2655
Assert the following
1. Units are copied
2. Association task reports the units_successful
| test | test iso repo unit association test to verify unit association for iso repo assert the following units are copied association task reports the units successful | 1 |
63,475 | 26,414,198,065 | IssuesEvent | 2023-01-13 14:42:11 | master-co/css | https://api.github.com/repos/master-co/css | closed | 🐞 `vw` `vh` `min-vw` `min-vh` `max-vw` `max-vh` aren't highlighted | bug language service | ### What happened?
<img width="797" alt="Screenshot 2023-01-13 at 2 58 36 AM" src="https://user-images.githubusercontent.com/33840671/212157514-c2f5bced-d201-4323-acce-69dcb09a0986.png">
### Version
2.0.0-beta.102
### Relevant log output
_No response_
### What browsers are you seeing the problem on?
_No response_ | 1.0 | 🐞 `vw` `vh` `min-vw` `min-vh` `max-vw` `max-vh` aren't highlighted - ### What happened?
<img width="797" alt="Screenshot 2023-01-13 at 2 58 36 AM" src="https://user-images.githubusercontent.com/33840671/212157514-c2f5bced-d201-4323-acce-69dcb09a0986.png">
### Version
2.0.0-beta.102
### Relevant log output
_No response_
### What browsers are you seeing the problem on?
_No response_ | non_test | 🐞 vw vh min vw min vh max vw max vh aren t highlighted what happened img width alt screenshot at am src version beta relevant log output no response what browsers are you seeing the problem on no response | 0 |
84,962 | 15,728,374,371 | IssuesEvent | 2021-03-29 13:45:17 | ssobue/oauth2-provider | https://api.github.com/repos/ssobue/oauth2-provider | closed | CVE-2020-10969 (High) detected in jackson-databind-2.9.9.jar | security vulnerability | ## CVE-2020-10969 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /oauth2-provider/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.5.RELEASE.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to javax.swing.JEditorPane.
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10969>CVE-2020-10969</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.6;com.fasterxml.jackson.core:jackson-databind:2.7.9.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-10969 (High) detected in jackson-databind-2.9.9.jar - ## CVE-2020-10969 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /oauth2-provider/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.5.RELEASE.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to javax.swing.JEditorPane.
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10969>CVE-2020-10969</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.6;com.fasterxml.jackson.core:jackson-databind:2.7.9.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file provider pom xml path to vulnerable library root repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library spring boot starter json release jar x jackson databind jar vulnerable library vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to javax swing jeditorpane publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
591,934 | 17,865,686,588 | IssuesEvent | 2021-09-06 09:09:38 | ballerina-platform/ballerina-standard-library | https://api.github.com/repos/ballerina-platform/ballerina-standard-library | closed | SSL test failure after jdk 11 migration | Points/2 Priority/High Type/Bug module/http Team/PCP area/security | **Description:**
Socket address becomes null
```
assertEquals("Remote host: localhost/127.0.0.1:9000 closed the connection while SSL handshake", result);
```
org.ballerinalang.net.transport.https.ServerCloseConnectionDuringSslTest#thenRespShouldBeAServerCloseException
```
Transport test suite > Transport Security Tests > org.ballerinalang.net.transport.https.ServerCloseConnectionDuringSslTest > testServerCloseChannelDuringSslHandshake STANDARD_ERROR
Oct 11, 2020 3:13:32 PM org.ballerinalang.net.transport.util.server.initializers.ServerCloseTcpConnectionInitializer initChannel
INFO: Server connection established
Oct 11, 2020 3:13:32 PM org.ballerinalang.net.transport.util.TestNGListener onTestFailure
SEVERE: Test failed: testServerCloseChannelDuringSslHandshake-> expected [Remote host: localhost/127.0.0.1:9000 closed the connection while SSL handshake] but found [Remote host: null closed the connection while SSL handshake]
Transport test suite > Transport Security Tests > org.ballerinalang.net.transport.https.ServerCloseConnectionDuringSslTest > testServerCloseChannelDuringSslHandshake FAILED
java.lang.AssertionError at ServerCloseConnectionDuringSslTest.java:93
```
**Affected Product Version:**
1.0.1
| 1.0 | SSL test failure after jdk 11 migration - **Description:**
Socket address becomes null
```
assertEquals("Remote host: localhost/127.0.0.1:9000 closed the connection while SSL handshake", result);
```
org.ballerinalang.net.transport.https.ServerCloseConnectionDuringSslTest#thenRespShouldBeAServerCloseException
```
Transport test suite > Transport Security Tests > org.ballerinalang.net.transport.https.ServerCloseConnectionDuringSslTest > testServerCloseChannelDuringSslHandshake STANDARD_ERROR
Oct 11, 2020 3:13:32 PM org.ballerinalang.net.transport.util.server.initializers.ServerCloseTcpConnectionInitializer initChannel
INFO: Server connection established
Oct 11, 2020 3:13:32 PM org.ballerinalang.net.transport.util.TestNGListener onTestFailure
SEVERE: Test failed: testServerCloseChannelDuringSslHandshake-> expected [Remote host: localhost/127.0.0.1:9000 closed the connection while SSL handshake] but found [Remote host: null closed the connection while SSL handshake]
Transport test suite > Transport Security Tests > org.ballerinalang.net.transport.https.ServerCloseConnectionDuringSslTest > testServerCloseChannelDuringSslHandshake FAILED
java.lang.AssertionError at ServerCloseConnectionDuringSslTest.java:93
```
**Affected Product Version:**
1.0.1
| non_test | ssl test failure after jdk migration description socket address becomes null assertequals remote host localhost closed the connection while ssl handshake result org ballerinalang net transport https servercloseconnectionduringssltest thenrespshouldbeaservercloseexception transport test suite transport security tests org ballerinalang net transport https servercloseconnectionduringssltest testserverclosechannelduringsslhandshake standard error oct pm org ballerinalang net transport util server initializers serverclosetcpconnectioninitializer initchannel info server connection established oct pm org ballerinalang net transport util testnglistener ontestfailure severe test failed testserverclosechannelduringsslhandshake expected but found transport test suite transport security tests org ballerinalang net transport https servercloseconnectionduringssltest testserverclosechannelduringsslhandshake failed java lang assertionerror at servercloseconnectionduringssltest java affected product version | 0 |
164,864 | 12,815,260,267 | IssuesEvent | 2020-07-05 00:58:17 | snext1220/stext | https://api.github.com/repos/snext1220/stext | closed | サイドバー間の相互リンクボタン | Testing enhancement | Status、Magic、Basic、Items&Flagsなどの主要シート内で、相互リンク(ボタン)を設置する案です。いちいちサイドバーを閉じて、メニューから開きなおす手間を軽減します。
# 本格リニューアル前の仮デザインではあったものが一度破棄され、また復帰できないか、という案です。
#### 懸案など
+ PC環境では直接メニューバーから選択すれば、シートが切り替わるのでそこまで必須ではありません。主にモバイル環境向けです。
+ おそらく既存ボタンの下に配置することになるので、スクロールを極力発生させないため、配置は要検討。 | 1.0 | サイドバー間の相互リンクボタン - Status、Magic、Basic、Items&Flagsなどの主要シート内で、相互リンク(ボタン)を設置する案です。いちいちサイドバーを閉じて、メニューから開きなおす手間を軽減します。
# 本格リニューアル前の仮デザインではあったものが一度破棄され、また復帰できないか、という案です。
#### 懸案など
+ PC環境では直接メニューバーから選択すれば、シートが切り替わるのでそこまで必須ではありません。主にモバイル環境向けです。
+ おそらく既存ボタンの下に配置することになるので、スクロールを極力発生させないため、配置は要検討。 | test | サイドバー間の相互リンクボタン status、magic、basic、items&flagsなどの主要シート内で、相互リンク(ボタン)を設置する案です。いちいちサイドバーを閉じて、メニューから開きなおす手間を軽減します。 # 本格リニューアル前の仮デザインではあったものが一度破棄され、また復帰できないか、という案です。 懸案など pc環境では直接メニューバーから選択すれば、シートが切り替わるのでそこまで必須ではありません。主にモバイル環境向けです。 おそらく既存ボタンの下に配置することになるので、スクロールを極力発生させないため、配置は要検討。 | 1 |
154,266 | 12,198,488,196 | IssuesEvent | 2020-04-29 22:59:53 | kwk/test-llvm-bz-import-5 | https://api.github.com/repos/kwk/test-llvm-bz-import-5 | closed | MultiSource/Benchmarks/MiBench/network-patricia/patricia_test including soon to be obsolete rpc/rpc.h | BZ-BUG-STATUS: RESOLVED BZ-RESOLUTION: FIXED Test Suite/Programs Tests dummy import from bugzilla | This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=14327. | 2.0 | MultiSource/Benchmarks/MiBench/network-patricia/patricia_test including soon to be obsolete rpc/rpc.h - This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=14327. | test | multisource benchmarks mibench network patricia patricia test including soon to be obsolete rpc rpc h this issue was imported from bugzilla | 1 |
265,320 | 23,159,959,150 | IssuesEvent | 2022-07-29 16:35:16 | ValveSoftware/Proton | https://api.github.com/repos/ValveSoftware/Proton | closed | video rendering only works with WINE_DO_NOT_CREATE_DXGI_DEVICE_MANAGER=1 | Need Retest | # Feature Request
I tested this feature using wine staging 7.11 and proton experimental
when I was testing the newly released version of PC building sim 2, I then ran the time spy benchmark in "free roam" mode, and saw that the video rendering was extremely broken (at least it was playing something lmao) meanwhile the output on wine staging 7.11 looks perfect.
proton experimental:
there were lots of video stuttering problems as well (similar artifacts can be seen in aimlab)
wine staging 7.11:

edit: stuttering problems present in wine staging too (only in the port royale 3d mark test though) | 1.0 | video rendering only works with WINE_DO_NOT_CREATE_DXGI_DEVICE_MANAGER=1 - # Feature Request
I tested this feature using wine staging 7.11 and proton experimental
when I was testing the newly released version of PC building sim 2, I then ran the time spy benchmark in "free roam" mode, and saw that the video rendering was extremely broken (at least it was playing something lmao) meanwhile the output on wine staging 7.11 looks perfect.
proton experimental:
there were lots of video stuttering problems as well (similar artifacts can be seen in aimlab)
wine staging 7.11:

edit: stuttering problems present in wine staging too (only in the port royale 3d mark test though) | test | video rendering only works with wine do not create dxgi device manager feature request i tested this feature using wine staging and proton experimental when i was testing the newly released version of pc building sim i then ran the time spy benchmark in free roam mode and saw that the video rendering was extremely broken at least it was playing something lmao meanwhile the output on wine staging looks perfect proton experimental there were lots of video stuttering problems as well similar artifacts can be seen in aimlab wine staging edit stuttering problems present in wine staging too only in the port royale mark test though | 1 |
279,861 | 24,259,057,189 | IssuesEvent | 2022-09-27 20:35:55 | atoptima/Coluna.jl | https://api.github.com/repos/atoptima/Coluna.jl | closed | Lack of tests for Preprocessing algorithm | bug tests | - error when creating storage in CutColGenConquer
- error when executing the algorithm
- preprocessing determines infeasibility but model feasible | 1.0 | Lack of tests for Preprocessing algorithm - - error when creating storage in CutColGenConquer
- error when executing the algorithm
- preprocessing determines infeasibility but model feasible | test | lack of tests for preprocessing algorithm error when creating storage in cutcolgenconquer error when executing the algorithm preprocessing determines infeasibility but model feasible | 1 |
58,479 | 6,599,742,651 | IssuesEvent | 2017-09-17 00:24:40 | red/red | https://api.github.com/repos/red/red | opened | No compiler error with string! exponent argument to power function | test.written type.bug | The compiler does not properly perform type checking on arguments to the power function. It returns a value when a `string!` value is provided to the `power` function.
This code
```text
Red[]
print power 2 "a"
```
Produces this:
```text
./test
1.0
```
The interpreter raises a script error:
```text
>> power 2 "a"
*** Script Error: power does not allow string! for its exponent argument
*** Where: power
*** Stack:
``` | 1.0 | No compiler error with string! exponent argument to power function - The compiler does not properly perform type checking on arguments to the power function. It returns a value when a `string!` value is provided to the `power` function.
This code
```text
Red[]
print power 2 "a"
```
Produces this:
```text
./test
1.0
```
The interpreter raises a script error:
```text
>> power 2 "a"
*** Script Error: power does not allow string! for its exponent argument
*** Where: power
*** Stack:
``` | test | no compiler error with string exponent argument to power function the compiler does not properly perform type checking on arguments to the power function it returns a value when a string value is provided to the power function this code text red print power a produces this text test the interpreter raises a script error text power a script error power does not allow string for its exponent argument where power stack | 1 |
91,448 | 8,305,425,439 | IssuesEvent | 2018-09-22 06:18:57 | buttplugio/buttplug-csharp | https://api.github.com/repos/buttplugio/buttplug-csharp | closed | Build a simple device enumeration system for testing | applications testing | As per discord mention.
Like "just scan and show us services and characteristics"
So like vibratissiomo's custom name support but even more promiscuous | 1.0 | Build a simple device enumeration system for testing - As per discord mention.
Like "just scan and show us services and characteristics"
So like vibratissiomo's custom name support but even more promiscuous | test | build a simple device enumeration system for testing as per discord mention like just scan and show us services and characteristics so like vibratissiomo s custom name support but even more promiscuous | 1 |
101,707 | 16,524,845,301 | IssuesEvent | 2021-05-26 18:39:47 | RG4421/bluestate-javascript-utilities | https://api.github.com/repos/RG4421/bluestate-javascript-utilities | opened | CVE-2021-23358 (High) detected in underscore-1.10.2.tgz | security vulnerability | ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.10.2.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.10.2.tgz">https://registry.npmjs.org/underscore/-/underscore-1.10.2.tgz</a></p>
<p>Path to dependency file: bluestate-javascript-utilities/package.json</p>
<p>Path to vulnerable library: bluestate-javascript-utilities/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- jsdoc-to-markdown-6.0.1.tgz (Root Library)
- jsdoc-api-6.0.0.tgz
- jsdoc-3.6.5.tgz
- :x: **underscore-1.10.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/RG4421/bluestate-javascript-utilities/commit/673d5d9de0154734a5154cb112934c47f6056e6e">673d5d9de0154734a5154cb112934c47f6056e6e</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"underscore","packageVersion":"1.10.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"jsdoc-to-markdown:6.0.1;jsdoc-api:6.0.0;jsdoc:3.6.5;underscore:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"underscore - 1.12.1,1.13.0-2"}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-23358","vulnerabilityDetails":"The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-23358 (High) detected in underscore-1.10.2.tgz - ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.10.2.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.10.2.tgz">https://registry.npmjs.org/underscore/-/underscore-1.10.2.tgz</a></p>
<p>Path to dependency file: bluestate-javascript-utilities/package.json</p>
<p>Path to vulnerable library: bluestate-javascript-utilities/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- jsdoc-to-markdown-6.0.1.tgz (Root Library)
- jsdoc-api-6.0.0.tgz
- jsdoc-3.6.5.tgz
- :x: **underscore-1.10.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/RG4421/bluestate-javascript-utilities/commit/673d5d9de0154734a5154cb112934c47f6056e6e">673d5d9de0154734a5154cb112934c47f6056e6e</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"underscore","packageVersion":"1.10.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"jsdoc-to-markdown:6.0.1;jsdoc-api:6.0.0;jsdoc:3.6.5;underscore:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"underscore - 1.12.1,1.13.0-2"}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-23358","vulnerabilityDetails":"The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_test | cve high detected in underscore tgz cve high severity vulnerability vulnerable library underscore tgz javascript s functional programming helper library library home page a href path to dependency file bluestate javascript utilities package json path to vulnerable library bluestate javascript utilities node modules underscore package json dependency hierarchy jsdoc to markdown tgz root library jsdoc api tgz jsdoc tgz x underscore tgz vulnerable library found in head commit a href found in base branch develop vulnerability details the package underscore from and before from and before are vulnerable to arbitrary code injection via the template function particularly when a variable property is passed as an argument as it is not sanitized publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution underscore isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree jsdoc to markdown jsdoc api jsdoc underscore isminimumfixversionavailable true minimumfixversion underscore basebranches vulnerabilityidentifier cve vulnerabilitydetails the package underscore from and before from and before are vulnerable to arbitrary code injection via the template function particularly when a variable property is passed as an argument as it is not sanitized vulnerabilityurl | 0 |
250,500 | 18,892,131,065 | IssuesEvent | 2021-11-15 14:19:19 | jonrau1/ElectricEye | https://api.github.com/repos/jonrau1/ElectricEye | closed | [PFR] Performance / speed upgrades using MP or MT | documentation enhancement help wanted | **Story**
As a user of ElectricEye I want it to be faster so that I don't have to give all of my money to the AWS Fargate team or run a marathon while waiting for my checks to complete.
**Definition of Done**
- Parallelization added to ElectricEye either to run every Check per Auditor at the same time or run multiple Checks at the same time
- Documentation updates, as needed
**Nice to Have**
- Preferably Multiprocessing
- Option via CLI?
**Additional Information**
Unsure if the decerators for each Function will take a crap if you add a new `main()` function to start, join and terminate all of the checks. Will also have to check for the use of a `Resource` versus a `Client` in some places | 1.0 | [PFR] Performance / speed upgrades using MP or MT - **Story**
As a user of ElectricEye I want it to be faster so that I don't have to give all of my money to the AWS Fargate team or run a marathon while waiting for my checks to complete.
**Definition of Done**
- Parallelization added to ElectricEye either to run every Check per Auditor at the same time or run multiple Checks at the same time
- Documentation updates, as needed
**Nice to Have**
- Preferably Multiprocessing
- Option via CLI?
**Additional Information**
Unsure if the decerators for each Function will take a crap if you add a new `main()` function to start, join and terminate all of the checks. Will also have to check for the use of a `Resource` versus a `Client` in some places | non_test | performance speed upgrades using mp or mt story as a user of electriceye i want it to be faster so that i don t have to give all of my money to the aws fargate team or run a marathon while waiting for my checks to complete definition of done parallelization added to electriceye either to run every check per auditor at the same time or run multiple checks at the same time documentation updates as needed nice to have preferably multiprocessing option via cli additional information unsure if the decerators for each function will take a crap if you add a new main function to start join and terminate all of the checks will also have to check for the use of a resource versus a client in some places | 0 |
105,904 | 9,103,410,202 | IssuesEvent | 2019-02-20 15:50:44 | bodsch/docker-icinga2 | https://api.github.com/repos/bodsch/docker-icinga2 | closed | wrong usage of import | need-tests | When an import file is to be used, it does not seem to be properly used for an import.
See https://github.com/bodsch/docker-icinga2/blob/master/rootfs/init/icinga_types/satellite.sh#L26-L99 | 1.0 | wrong usage of import - When an import file is to be used, it does not seem to be properly used for an import.
See https://github.com/bodsch/docker-icinga2/blob/master/rootfs/init/icinga_types/satellite.sh#L26-L99 | test | wrong usage of import when an import file is to be used it does not seem to be properly used for an import see | 1 |
295,788 | 25,505,249,186 | IssuesEvent | 2022-11-28 08:56:59 | Tencent/bk-ci | https://api.github.com/repos/Tencent/bk-ci | closed | feat: Stage审核说明支持Markdown输入 | kind/feat/product for test priority/critical-urgent streams/for test | <!-- Please only use this template for submitting enhancement requests -->
**What would you like to be added**:
人工审核插件增加富文本展示区域,比如调整为侧滑框
**Why is this needed**:
显示的内容比较多,弹窗不太友好 | 2.0 | feat: Stage审核说明支持Markdown输入 - <!-- Please only use this template for submitting enhancement requests -->
**What would you like to be added**:
人工审核插件增加富文本展示区域,比如调整为侧滑框
**Why is this needed**:
显示的内容比较多,弹窗不太友好 | test | feat stage审核说明支持markdown输入 what would you like to be added 人工审核插件增加富文本展示区域,比如调整为侧滑框 why is this needed 显示的内容比较多,弹窗不太友好 | 1 |
246,481 | 20,867,766,340 | IssuesEvent | 2022-03-22 09:05:02 | superfluid-finance/superfluid-console | https://api.github.com/repos/superfluid-finance/superfluid-console | closed | [CONSOLE] Cypress test cases iteration 2 | Type: Testing | - [x] Opening individual stream details ( streams page ) and data shown in those pages
- [x] Index tab for Account page
- [x] Opening index details ( index page ) and data shown in those pages
- [x] Opening subscription details ( index-subscriptions page ) and data shown in those pages
- [x] Changing stream granularity
- [x] Changing Ether decimal places
- [x] Hovering on a tooltip in accounts page
- [x] Help alert in accounts page
- [x] Opening all links available in the tooltips and check if "not found" is not shown | 1.0 | [CONSOLE] Cypress test cases iteration 2 - - [x] Opening individual stream details ( streams page ) and data shown in those pages
- [x] Index tab for Account page
- [x] Opening index details ( index page ) and data shown in those pages
- [x] Opening subscription details ( index-subscriptions page ) and data shown in those pages
- [x] Changing stream granularity
- [x] Changing Ether decimal places
- [x] Hovering on a tooltip in accounts page
- [x] Help alert in accounts page
- [x] Opening all links available in the tooltips and check if "not found" is not shown | test | cypress test cases iteration opening individual stream details streams page and data shown in those pages index tab for account page opening index details index page and data shown in those pages opening subscription details index subscriptions page and data shown in those pages changing stream granularity changing ether decimal places hovering on a tooltip in accounts page help alert in accounts page opening all links available in the tooltips and check if not found is not shown | 1 |
272,088 | 23,653,834,227 | IssuesEvent | 2022-08-26 09:17:25 | microsoft/vscode-remote-release | https://api.github.com/repos/microsoft/vscode-remote-release | closed | Test: Use container features from OCI registry | containers testplan-item | Refs: https://github.com/devcontainers/cli/issues/88
- [x] anyOS @alexr00
- [x] anyOS @dbaeumer
Complexity: 3
[Create Issue](https://github.com/microsoft/vscode-remote-release/issues/new?body=Testing+%237102%0A%0A&assignees=chrmarti)
---
Use the latest Remote-Containers pre-release (currently 0.248.0) or Dev Containers CLI (currently 0.12.1) for testing.
Note that the new feature id syntax shows an error decoration in the editor because it is not yet officially supported.
- Test that container features can be referenced by their OCI-based id. See https://github.com/orgs/devcontainers/packages?repo_name=features for the complete list. E.g.:
```json
{
"image": "mcr.microsoft.com/vscode/devcontainers/base:0-bullseye",
"features": {
"ghcr.io/devcontainers/features/node": "latest"
}
}
```
- Check that semver versioning on the feature id works, e.g., `"ghcr.io/devcontainers/features/node:1.0.2"`, `"ghcr.io/devcontainers/features/node:1.0"`, `"ghcr.io/devcontainers/features/node:1"`.
- Check that the old feature ids still work (these is mapped to the new sytnax), e.g.: `"node"`. The complete list is in https://github.com/microsoft/vscode-dev-containers/blob/main/script-library/container-features/src/devcontainer-features.json.
| 1.0 | Test: Use container features from OCI registry - Refs: https://github.com/devcontainers/cli/issues/88
- [x] anyOS @alexr00
- [x] anyOS @dbaeumer
Complexity: 3
[Create Issue](https://github.com/microsoft/vscode-remote-release/issues/new?body=Testing+%237102%0A%0A&assignees=chrmarti)
---
Use the latest Remote-Containers pre-release (currently 0.248.0) or Dev Containers CLI (currently 0.12.1) for testing.
Note that the new feature id syntax shows an error decoration in the editor because it is not yet officially supported.
- Test that container features can be referenced by their OCI-based id. See https://github.com/orgs/devcontainers/packages?repo_name=features for the complete list. E.g.:
```json
{
"image": "mcr.microsoft.com/vscode/devcontainers/base:0-bullseye",
"features": {
"ghcr.io/devcontainers/features/node": "latest"
}
}
```
- Check that semver versioning on the feature id works, e.g., `"ghcr.io/devcontainers/features/node:1.0.2"`, `"ghcr.io/devcontainers/features/node:1.0"`, `"ghcr.io/devcontainers/features/node:1"`.
- Check that the old feature ids still work (these is mapped to the new sytnax), e.g.: `"node"`. The complete list is in https://github.com/microsoft/vscode-dev-containers/blob/main/script-library/container-features/src/devcontainer-features.json.
| test | test use container features from oci registry refs anyos anyos dbaeumer complexity use the latest remote containers pre release currently or dev containers cli currently for testing note that the new feature id syntax shows an error decoration in the editor because it is not yet officially supported test that container features can be referenced by their oci based id see for the complete list e g json image mcr microsoft com vscode devcontainers base bullseye features ghcr io devcontainers features node latest check that semver versioning on the feature id works e g ghcr io devcontainers features node ghcr io devcontainers features node ghcr io devcontainers features node check that the old feature ids still work these is mapped to the new sytnax e g node the complete list is in | 1 |
54,154 | 7,875,632,868 | IssuesEvent | 2018-06-25 21:05:22 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | document which calls and field are not yet implemented in the analysis server protocol | P2 medium Type: documentation analyzer-server area-analyzer | Related to https://github.com/dart-lang/sdk/issues/23694, https://github.com/dart-lang/sdk/issues/23861, and https://github.com/dart-lang/sdk/issues/23640, it would be nice to set expectations about which calls or fields are populated / implemented. Having an `@unimplemented` annotation would save clients a lot of time debugging issues.
| 1.0 | document which calls and field are not yet implemented in the analysis server protocol - Related to https://github.com/dart-lang/sdk/issues/23694, https://github.com/dart-lang/sdk/issues/23861, and https://github.com/dart-lang/sdk/issues/23640, it would be nice to set expectations about which calls or fields are populated / implemented. Having an `@unimplemented` annotation would save clients a lot of time debugging issues.
| non_test | document which calls and field are not yet implemented in the analysis server protocol related to and it would be nice to set expectations about which calls or fields are populated implemented having an unimplemented annotation would save clients a lot of time debugging issues | 0 |
36,640 | 5,075,278,223 | IssuesEvent | 2016-12-27 18:45:22 | zulip/zulip | https://api.github.com/repos/zulip/zulip | opened | Add node test suite for message_is_notifiable, should_send_desktop_notification, and friends | area: testing-coverage bite size help wanted | These are a frontend functions in notifications.js that have a lot of logic around determining whether to trigger a desktop notification; they would be great candidates for Node unit tests. | 1.0 | Add node test suite for message_is_notifiable, should_send_desktop_notification, and friends - These are a frontend functions in notifications.js that have a lot of logic around determining whether to trigger a desktop notification; they would be great candidates for Node unit tests. | test | add node test suite for message is notifiable should send desktop notification and friends these are a frontend functions in notifications js that have a lot of logic around determining whether to trigger a desktop notification they would be great candidates for node unit tests | 1 |
586,806 | 17,597,786,472 | IssuesEvent | 2021-08-17 08:01:49 | turbot/steampipe-plugin-aws | https://api.github.com/repos/turbot/steampipe-plugin-aws | closed | Fix go lint issue for aws_securityhub_standards_subscription table. | bug priority:high | **Describe the bug**
A clear and concise description of what the bug is.
**Steampipe version (`steampipe -v`)**
Example: v0.3.0
**Plugin version (`steampipe plugin list`)**
Example: v0.5.0
**To reproduce**
Steps to reproduce the behavior (please include relevant code and/or commands).
**Expected behavior**
A clear and concise description of what you expected to happen.
**Additional context**
Add any other context about the problem here.
| 1.0 | Fix go lint issue for aws_securityhub_standards_subscription table. - **Describe the bug**
A clear and concise description of what the bug is.
**Steampipe version (`steampipe -v`)**
Example: v0.3.0
**Plugin version (`steampipe plugin list`)**
Example: v0.5.0
**To reproduce**
Steps to reproduce the behavior (please include relevant code and/or commands).
**Expected behavior**
A clear and concise description of what you expected to happen.
**Additional context**
Add any other context about the problem here.
| non_test | fix go lint issue for aws securityhub standards subscription table describe the bug a clear and concise description of what the bug is steampipe version steampipe v example plugin version steampipe plugin list example to reproduce steps to reproduce the behavior please include relevant code and or commands expected behavior a clear and concise description of what you expected to happen additional context add any other context about the problem here | 0 |
166,141 | 12,891,859,896 | IssuesEvent | 2020-07-13 18:30:47 | ReactiveX/RxJava | https://api.github.com/repos/ReactiveX/RxJava | closed | 3.x: Flaky GroupBy test | 3.x PR welcome Test-Failures good first issue | https://github.com/ReactiveX/RxJava/blob/98acac218cdb04d279b5ac49bb1afc65bc6ec4fe/src/test/java/io/reactivex/rxjava3/internal/operators/flowable/FlowableGroupByTest.java#L2668
```
io.reactivex.rxjava3.internal.operators.flowable.FlowableGroupByTest > issue6974Part2Case1NoEvict FAILED
java.lang.AssertionError: Error(s) present: [io.reactivex.rxjava3.exceptions.CompositeException: 1 exceptions occurred. ] (latch = 0, values = 15551, errors = 1, completions = 0)
at io.reactivex.rxjava3.observers.BaseTestConsumer.fail(BaseTestConsumer.java:125)
at io.reactivex.rxjava3.observers.BaseTestConsumer.assertNoErrors(BaseTestConsumer.java:212)
at io.reactivex.rxjava3.internal.operators.flowable.FlowableGroupByTest.issue6974RunPart2NoEvict(FlowableGroupByTest.java:2681)
at io.reactivex.rxjava3.internal.operators.flowable.FlowableGroupByTest.issue6974Part2Case1NoEvict(FlowableGroupByTest.java:2693)
Caused by:
io.reactivex.rxjava3.exceptions.CompositeException: 1 exceptions occurred.
Caused by:
io.reactivex.rxjava3.exceptions.MissingBackpressureException: Unable to emit a new group (#71) due to lack of requests. Please make sure the downstream can always accept a new group as well as each group is consumed in order for the whole operator to be able to proceed.
```
Error is an allowed outcome here. | 1.0 | 3.x: Flaky GroupBy test - https://github.com/ReactiveX/RxJava/blob/98acac218cdb04d279b5ac49bb1afc65bc6ec4fe/src/test/java/io/reactivex/rxjava3/internal/operators/flowable/FlowableGroupByTest.java#L2668
```
io.reactivex.rxjava3.internal.operators.flowable.FlowableGroupByTest > issue6974Part2Case1NoEvict FAILED
java.lang.AssertionError: Error(s) present: [io.reactivex.rxjava3.exceptions.CompositeException: 1 exceptions occurred. ] (latch = 0, values = 15551, errors = 1, completions = 0)
at io.reactivex.rxjava3.observers.BaseTestConsumer.fail(BaseTestConsumer.java:125)
at io.reactivex.rxjava3.observers.BaseTestConsumer.assertNoErrors(BaseTestConsumer.java:212)
at io.reactivex.rxjava3.internal.operators.flowable.FlowableGroupByTest.issue6974RunPart2NoEvict(FlowableGroupByTest.java:2681)
at io.reactivex.rxjava3.internal.operators.flowable.FlowableGroupByTest.issue6974Part2Case1NoEvict(FlowableGroupByTest.java:2693)
Caused by:
io.reactivex.rxjava3.exceptions.CompositeException: 1 exceptions occurred.
Caused by:
io.reactivex.rxjava3.exceptions.MissingBackpressureException: Unable to emit a new group (#71) due to lack of requests. Please make sure the downstream can always accept a new group as well as each group is consumed in order for the whole operator to be able to proceed.
```
Error is an allowed outcome here. | test | x flaky groupby test io reactivex internal operators flowable flowablegroupbytest failed java lang assertionerror error s present latch values errors completions at io reactivex observers basetestconsumer fail basetestconsumer java at io reactivex observers basetestconsumer assertnoerrors basetestconsumer java at io reactivex internal operators flowable flowablegroupbytest flowablegroupbytest java at io reactivex internal operators flowable flowablegroupbytest flowablegroupbytest java caused by io reactivex exceptions compositeexception exceptions occurred caused by io reactivex exceptions missingbackpressureexception unable to emit a new group due to lack of requests please make sure the downstream can always accept a new group as well as each group is consumed in order for the whole operator to be able to proceed error is an allowed outcome here | 1 |
332,861 | 29,495,357,661 | IssuesEvent | 2023-06-02 16:28:35 | MPMG-DCC-UFMG/F01 | https://api.github.com/repos/MPMG-DCC-UFMG/F01 | closed | Teste de generalizacao para a tag Servidores Públicos - Proventos de Aposentadoria - Entre Rios de Minas | generalization test development | DoD: Realizar o teste de Generalização do validador da tag Servidores Públicos - Proventos de Aposentadoria para o Município de Entre Rios de Minas. | 1.0 | Teste de generalizacao para a tag Servidores Públicos - Proventos de Aposentadoria - Entre Rios de Minas - DoD: Realizar o teste de Generalização do validador da tag Servidores Públicos - Proventos de Aposentadoria para o Município de Entre Rios de Minas. | test | teste de generalizacao para a tag servidores públicos proventos de aposentadoria entre rios de minas dod realizar o teste de generalização do validador da tag servidores públicos proventos de aposentadoria para o município de entre rios de minas | 1 |
106,844 | 9,195,139,473 | IssuesEvent | 2019-03-07 01:08:56 | easydigitaldownloads/easy-digital-downloads | https://api.github.com/repos/easydigitaldownloads/easy-digital-downloads | closed | GDPR Data Exporter should bail with a customer ID of 0. | Bug Has PR Needs Testing Priority: High | ## Bug Report
### Expected behavior
If you have an email address request their privacy data but they do not have a customer account with that email, we shouldn't even query for logs or payments.
### Actual behavior
We still hit the DB to look for this data, unnecessarily.
### Information (if a specific version is affected):
PHP Version: All
EDD Version (or branch): `master`
WordPress Version: All
Any other relevant information: All | 1.0 | GDPR Data Exporter should bail with a customer ID of 0. - ## Bug Report
### Expected behavior
If you have an email address request their privacy data but they do not have a customer account with that email, we shouldn't even query for logs or payments.
### Actual behavior
We still hit the DB to look for this data, unnecessarily.
### Information (if a specific version is affected):
PHP Version: All
EDD Version (or branch): `master`
WordPress Version: All
Any other relevant information: All | test | gdpr data exporter should bail with a customer id of bug report expected behavior if you have an email address request their privacy data but they do not have a customer account with that email we shouldn t even query for logs or payments actual behavior we still hit the db to look for this data unnecessarily information if a specific version is affected php version all edd version or branch master wordpress version all any other relevant information all | 1 |
52,513 | 12,976,934,640 | IssuesEvent | 2020-07-21 19:42:01 | rnyholm/skvirrel | https://api.github.com/repos/rnyholm/skvirrel | reopened | Build with travis-ci | builds-ci | Setup building with travis-ci. Needed for this to work is; travis.yaml, keystores and also build config in travis and github. Some other problems will probably occur also. | 1.0 | Build with travis-ci - Setup building with travis-ci. Needed for this to work is; travis.yaml, keystores and also build config in travis and github. Some other problems will probably occur also. | non_test | build with travis ci setup building with travis ci needed for this to work is travis yaml keystores and also build config in travis and github some other problems will probably occur also | 0 |
189,389 | 14,500,938,166 | IssuesEvent | 2020-12-11 18:45:34 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | nathanleclaire/testing-article: example4/server_test.go; 29 LoC | fresh small test |
Found a possible issue in [nathanleclaire/testing-article](https://www.github.com/nathanleclaire/testing-article) at [example4/server_test.go](https://github.com/nathanleclaire/testing-article/blob/947474a34598ef32c6ba0df6b9d70d657904b6c7/example4/server_test.go#L50-L78)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable c used in defer or goroutine at line 58
[Click here to see the code in its original context.](https://github.com/nathanleclaire/testing-article/blob/947474a34598ef32c6ba0df6b9d70d657904b6c7/example4/server_test.go#L50-L78)
<details>
<summary>Click here to show the 29 line(s) of Go which triggered the analyzer.</summary>
```go
for _, c := range cases {
logReader, logWriter := io.Pipe()
bufLogReader := bufio.NewReader(logReader)
log.SetOutput(logWriter)
c.r.Header.Set("X-Access-Token", c.accessTokenHeader)
go func() {
for _, expectedLine := range c.expectedLogs {
msg, err := bufLogReader.ReadString('\n')
if err != nil {
t.Errorf("Expected to be able to read from log but got error: %s", err)
}
if !strings.HasSuffix(msg, expectedLine) {
t.Errorf("Log line didn't match suffix:\n\t%q\n\t%q", expectedLine, msg)
}
}
}()
mainHandler(c.w, c.r)
if c.expectedResponseCode != c.w.Code {
t.Errorf("Status Code didn't match:\n\t%q\n\t%q", c.expectedResponseCode, c.w.Code)
}
if !bytes.Equal(c.expectedResponseBody, c.w.Body.Bytes()) {
t.Errorf("Body didn't match:\n\t%q\n\t%q", string(c.expectedResponseBody), c.w.Body.String())
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 947474a34598ef32c6ba0df6b9d70d657904b6c7
| 1.0 | nathanleclaire/testing-article: example4/server_test.go; 29 LoC -
Found a possible issue in [nathanleclaire/testing-article](https://www.github.com/nathanleclaire/testing-article) at [example4/server_test.go](https://github.com/nathanleclaire/testing-article/blob/947474a34598ef32c6ba0df6b9d70d657904b6c7/example4/server_test.go#L50-L78)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable c used in defer or goroutine at line 58
[Click here to see the code in its original context.](https://github.com/nathanleclaire/testing-article/blob/947474a34598ef32c6ba0df6b9d70d657904b6c7/example4/server_test.go#L50-L78)
<details>
<summary>Click here to show the 29 line(s) of Go which triggered the analyzer.</summary>
```go
for _, c := range cases {
logReader, logWriter := io.Pipe()
bufLogReader := bufio.NewReader(logReader)
log.SetOutput(logWriter)
c.r.Header.Set("X-Access-Token", c.accessTokenHeader)
go func() {
for _, expectedLine := range c.expectedLogs {
msg, err := bufLogReader.ReadString('\n')
if err != nil {
t.Errorf("Expected to be able to read from log but got error: %s", err)
}
if !strings.HasSuffix(msg, expectedLine) {
t.Errorf("Log line didn't match suffix:\n\t%q\n\t%q", expectedLine, msg)
}
}
}()
mainHandler(c.w, c.r)
if c.expectedResponseCode != c.w.Code {
t.Errorf("Status Code didn't match:\n\t%q\n\t%q", c.expectedResponseCode, c.w.Code)
}
if !bytes.Equal(c.expectedResponseBody, c.w.Body.Bytes()) {
t.Errorf("Body didn't match:\n\t%q\n\t%q", string(c.expectedResponseBody), c.w.Body.String())
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 947474a34598ef32c6ba0df6b9d70d657904b6c7
| test | nathanleclaire testing article server test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message range loop variable c used in defer or goroutine at line click here to show the line s of go which triggered the analyzer go for c range cases logreader logwriter io pipe buflogreader bufio newreader logreader log setoutput logwriter c r header set x access token c accesstokenheader go func for expectedline range c expectedlogs msg err buflogreader readstring n if err nil t errorf expected to be able to read from log but got error s err if strings hassuffix msg expectedline t errorf log line didn t match suffix n t q n t q expectedline msg mainhandler c w c r if c expectedresponsecode c w code t errorf status code didn t match n t q n t q c expectedresponsecode c w code if bytes equal c expectedresponsebody c w body bytes t errorf body didn t match n t q n t q string c expectedresponsebody c w body string leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.