Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3 values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17 values | text_combine stringlengths 95 262k | label stringclasses 2 values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
122,386 | 12,150,410,057 | IssuesEvent | 2020-04-24 17:55:43 | FraunhoferIOSB/FROST-Server | https://api.github.com/repos/FraunhoferIOSB/FROST-Server | closed | Dead link to Docker Documentation | documentation | Hi,
Just to let you know that the link to "use Docker" page of the documentation runs to a 404 page.
Correct link seems to be https://fraunhoferiosb.github.io/FROST-Server/deployment/docker.html
The "deployement" part is missing.
Best regards | 1.0 | Dead link to Docker Documentation - Hi,
Just to let you know that the link to "use Docker" page of the documentation runs to a 404 page.
Correct link seems to be https://fraunhoferiosb.github.io/FROST-Server/deployment/docker.html
The "deployement" part is missing.
Best regards | non_test | dead link to docker documentation hi just to let you know that the link to use docker page of the documentation runs to a page correct link seems to be the deployement part is missing best regards | 0 |
238,690 | 19,753,388,182 | IssuesEvent | 2022-01-15 10:07:34 | cruisen/cli-calc | https://api.github.com/repos/cruisen/cli-calc | opened | Add pipe test case to pytest | is_enhancement 2-Later-Important is_Test B_Medium | `cat a | calc`
- with file a:
```
cos(pi/2)
0xFF ^ 0b10
2**8-1
log(2)
comb(49,6)
factorial(42)
random()
cmath.phase(complex(-1.0, 0.0))
``` | 1.0 | Add pipe test case to pytest - `cat a | calc`
- with file a:
```
cos(pi/2)
0xFF ^ 0b10
2**8-1
log(2)
comb(49,6)
factorial(42)
random()
cmath.phase(complex(-1.0, 0.0))
``` | test | add pipe test case to pytest cat a calc with file a cos pi log comb factorial random cmath phase complex | 1 |
88,625 | 11,133,653,005 | IssuesEvent | 2019-12-20 09:53:06 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | closed | [feature] get cursor position for inputs | *as-designed | atm the only api available to get the cursor position is within an editor, but what about inputs ?
lets say u have an ext like https://github.com/edgardmessias/vscode.clipboard-manager which manages the clipboard globally,
but because of the current api limitation we cant use it with inputs & we have to either
- manually write the text
- or open an editor > get the content from the ext > copy it > paste it into an input.
i've searched the docs for such option but couldn't find any, so it there any plans to support exposing the input fields to the api ? | 1.0 | [feature] get cursor position for inputs - atm the only api available to get the cursor position is within an editor, but what about inputs ?
lets say u have an ext like https://github.com/edgardmessias/vscode.clipboard-manager which manages the clipboard globally,
but because of the current api limitation we cant use it with inputs & we have to either
- manually write the text
- or open an editor > get the content from the ext > copy it > paste it into an input.
i've searched the docs for such option but couldn't find any, so it there any plans to support exposing the input fields to the api ? | non_test | get cursor position for inputs atm the only api available to get the cursor position is within an editor but what about inputs lets say u have an ext like which manages the clipboard globally but because of the current api limitation we cant use it with inputs we have to either manually write the text or open an editor get the content from the ext copy it paste it into an input i ve searched the docs for such option but couldn t find any so it there any plans to support exposing the input fields to the api | 0 |
99,707 | 8,709,022,986 | IssuesEvent | 2018-12-06 12:45:39 | http4s/http4s | https://api.github.com/repos/http4s/http4s | opened | Flaky test: LocalTokenBucket | testing | ```
[info] LocalTokenBucket should
[error] x contain initial number of tokens equal to specified capacity (1 second, 384 ms)
[error] Timeout after 1 second (retries = 0, timeout = 1 second), timeFactor = 1 (ThrottleSpec.scala:39)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$1.apply(ThrottleSpec.scala:39)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$1.apply(ThrottleSpec.scala:18)
[info] + add another token at specified interval when not at capacity (1 second, 449 ms)
[error] x not add another token at specified interval when at capacity (1 second, 468 ms)
[error] Timeout after 1 second (retries = 0, timeout = 1 second), timeFactor = 1 (ThrottleSpec.scala:79)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$10.apply(ThrottleSpec.scala:79)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$10.apply(ThrottleSpec.scala:61)
[error] x only return a single token when only one token available and there are multiple concurrent requests (1 second, 500 ms)
[error] Timeout after 1 second (retries = 0, timeout = 1 second), timeFactor = 1 (ThrottleSpec.scala:95)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$15.apply(ThrottleSpec.scala:95)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$15.apply(ThrottleSpec.scala:82)
```
https://travis-ci.org/http4s/http4s/jobs/464170472#L836 | 1.0 | Flaky test: LocalTokenBucket - ```
[info] LocalTokenBucket should
[error] x contain initial number of tokens equal to specified capacity (1 second, 384 ms)
[error] Timeout after 1 second (retries = 0, timeout = 1 second), timeFactor = 1 (ThrottleSpec.scala:39)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$1.apply(ThrottleSpec.scala:39)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$1.apply(ThrottleSpec.scala:18)
[info] + add another token at specified interval when not at capacity (1 second, 449 ms)
[error] x not add another token at specified interval when at capacity (1 second, 468 ms)
[error] Timeout after 1 second (retries = 0, timeout = 1 second), timeFactor = 1 (ThrottleSpec.scala:79)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$10.apply(ThrottleSpec.scala:79)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$10.apply(ThrottleSpec.scala:61)
[error] x only return a single token when only one token available and there are multiple concurrent requests (1 second, 500 ms)
[error] Timeout after 1 second (retries = 0, timeout = 1 second), timeFactor = 1 (ThrottleSpec.scala:95)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$15.apply(ThrottleSpec.scala:95)
[error] org.http4s.server.middleware.ThrottleSpec$$anonfun$1$$anonfun$apply$15.apply(ThrottleSpec.scala:82)
```
https://travis-ci.org/http4s/http4s/jobs/464170472#L836 | test | flaky test localtokenbucket localtokenbucket should x contain initial number of tokens equal to specified capacity second ms timeout after second retries timeout second timefactor throttlespec scala org server middleware throttlespec anonfun anonfun apply apply throttlespec scala org server middleware throttlespec anonfun anonfun apply apply throttlespec scala add another token at specified interval when not at capacity second ms x not add another token at specified interval when at capacity second ms timeout after second retries timeout second timefactor throttlespec scala org server middleware throttlespec anonfun anonfun apply apply throttlespec scala org server middleware throttlespec anonfun anonfun apply apply throttlespec scala x only return a single token when only one token available and there are multiple concurrent requests second ms timeout after second retries timeout second timefactor throttlespec scala org server middleware throttlespec anonfun anonfun apply apply throttlespec scala org server middleware throttlespec anonfun anonfun apply apply throttlespec scala | 1 |
51,641 | 21,765,048,120 | IssuesEvent | 2022-05-13 00:08:01 | BCDevOps/developer-experience | https://api.github.com/repos/BCDevOps/developer-experience | closed | Send email to Product Teams about the upcoming API Deprecation | action-required communications team/bcgov-platform-services ops and shared services | **Describe the issue**
Use the Mautic service to send an email to product teams announcing the API Deprecation that will be coming in OCP 4.9 upgrade.
**Additional context**
https://github.com/BCDevOps/platform-services-status-page-notifications/blob/master/notifications/Upgrading-OCP49-API.md
**Definition of done**
Email sent out
| 2.0 | Send email to Product Teams about the upcoming API Deprecation - **Describe the issue**
Use the Mautic service to send an email to product teams announcing the API Deprecation that will be coming in OCP 4.9 upgrade.
**Additional context**
https://github.com/BCDevOps/platform-services-status-page-notifications/blob/master/notifications/Upgrading-OCP49-API.md
**Definition of done**
Email sent out
| non_test | send email to product teams about the upcoming api deprecation describe the issue use the mautic service to send an email to product teams announcing the api deprecation that will be coming in ocp upgrade additional context definition of done email sent out | 0 |
338,450 | 30,298,917,281 | IssuesEvent | 2023-07-10 03:11:08 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix ndarray.test_numpy_instance_tofile__ | NumPy Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5503250448/jobs/10028269328"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5503250448/jobs/10028269328"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5503250448/jobs/10028269328"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5503250448/jobs/10028269328"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5503250448/jobs/10028269328"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix ndarray.test_numpy_instance_tofile__ - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5503250448/jobs/10028269328"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5503250448/jobs/10028269328"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5503250448/jobs/10028269328"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5503250448/jobs/10028269328"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5503250448/jobs/10028269328"><img src=https://img.shields.io/badge/-failure-red></a>
| test | fix ndarray test numpy instance tofile tensorflow a href src jax a href src numpy a href src torch a href src paddle a href src | 1 |
49,473 | 6,027,402,747 | IssuesEvent | 2017-06-08 13:43:07 | openshift/origin | https://api.github.com/repos/openshift/origin | opened | [Conformance][networking][router] The HAProxy router should support reencrypt to services backed by a serving certificate automatically | component/networking kind/test-flake priority/P1 | ```
------------------------------
[Conformance][networking][router] The HAProxy router
should support reencrypt to services backed by a serving certificate automatically
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:64
[BeforeEach] [Top Level]
/go/src/github.com/openshift/origin/test/extended/util/test.go:51
[BeforeEach] [Conformance][networking][router]
/go/src/github.com/openshift/origin/vendor/k8s.io/kubernetes/test/e2e/framework/framework.go:120
STEP: Creating a kubernetes client
Jun 7 19:12:18.542: INFO: >>> kubeConfig: /etc/origin/master/admin.kubeconfig
STEP: Building a namespace api object
Jun 7 19:12:18.570: INFO: configPath is now "/tmp/extended-test-router-reencrypt-48d58-wcpdv-user.kubeconfig"
Jun 7 19:12:18.570: INFO: The user is now "extended-test-router-reencrypt-48d58-wcpdv-user"
Jun 7 19:12:18.570: INFO: Creating project "extended-test-router-reencrypt-48d58-wcpdv"
STEP: Waiting for a default service account to be provisioned in namespace
[BeforeEach] [Conformance][networking][router]
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:35
[It] should support reencrypt to services backed by a serving certificate automatically
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:64
Jun 7 19:12:18.662: INFO: Creating new exec pod
STEP: deploying a service using a reencrypt route without a destinationCACertificate
Jun 7 19:12:24.679: INFO: Running 'oc create --config=/tmp/extended-test-router-reencrypt-48d58-wcpdv-user.kubeconfig --namespace=extended-test-router-reencrypt-48d58-wcpdv -f /tmp/fixture-testdata-dir154131782/test/extended/testdata/reencrypt-serving-cert.yaml'
pod "serving-cert" created
configmap "serving-cert" created
service "serving-cert" created
route "serving-cert" created
Jun 7 19:12:26.030: INFO: Running '/data/src/github.com/openshift/origin/_output/local/bin/linux/amd64/kubectl --server=https://ip-172-18-4-42.ec2.internal:8443 --kubeconfig=/etc/origin/master/admin.kubeconfig exec --namespace=extended-test-router-reencrypt-48d58-wcpdv execpod -- /bin/sh -c
set -e
for i in $(seq 1 180); do
code=$( curl -k -s -o /dev/null -w '%{http_code}\n' --header 'Host: serving-cert-extended-test-router-reencrypt-48d58-wcpdv.router.default.svc.cluster.local' "https://172.30.95.6" ) || rc=$?
if [[ "${rc:-0}" -eq 0 ]]; then
echo $code
if [[ $code -eq 200 ]]; then
exit 0
fi
if [[ $code -ne 503 ]]; then
exit 1
fi
else
echo "error ${rc}" 1>&2
fi
sleep 1
done
'
Jun 7 19:15:45.738: INFO: stderr: "error 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\n"
[AfterEach] [Conformance][networking][router]
/go/src/github.com/openshift/origin/vendor/k8s.io/kubernetes/test/e2e/framework/framework.go:121
STEP: Collecting events from namespace "extended-test-router-reencrypt-48d58-wcpdv".
STEP: Found 9 events.
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:18 -0400 EDT - event for execpod: {default-scheduler } Scheduled: Successfully assigned execpod to ip-172-18-4-42.ec2.internal
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:20 -0400 EDT - event for execpod: {kubelet ip-172-18-4-42.ec2.internal} Pulled: Container image "gcr.io/google_containers/hostexec:1.2" already present on machine
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:20 -0400 EDT - event for execpod: {kubelet ip-172-18-4-42.ec2.internal} Created: Created container with id 6dafde2902f13c43671833b967af16050e25186492ee821eab22431cb73ce853
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:21 -0400 EDT - event for execpod: {kubelet ip-172-18-4-42.ec2.internal} Started: Started container with id 6dafde2902f13c43671833b967af16050e25186492ee821eab22431cb73ce853
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:24 -0400 EDT - event for serving-cert: {default-scheduler } Scheduled: Successfully assigned serving-cert to ip-172-18-4-42.ec2.internal
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:31 -0400 EDT - event for serving-cert: {kubelet ip-172-18-4-42.ec2.internal} Pulling: pulling image "nginx:latest"
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:40 -0400 EDT - event for serving-cert: {kubelet ip-172-18-4-42.ec2.internal} Pulled: Successfully pulled image "nginx:latest"
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:44 -0400 EDT - event for serving-cert: {kubelet ip-172-18-4-42.ec2.internal} Created: Created container with id 68aa8ed5fa890964b3ef50d1235589311687e6d16d55f923adb9052ef3105943
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:44 -0400 EDT - event for serving-cert: {kubelet ip-172-18-4-42.ec2.internal} Started: Started container with id 68aa8ed5fa890964b3ef50d1235589311687e6d16d55f923adb9052ef3105943
Jun 7 19:15:45.772: INFO: POD NODE PHASE GRACE CONDITIONS
Jun 7 19:15:45.772: INFO: docker-registry-2-bx862 ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:05:37 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:05:47 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:05:37 -0400 EDT }]
Jun 7 19:15:45.772: INFO: registry-console-1-8nmjb ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:06:07 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:06:16 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:06:07 -0400 EDT }]
Jun 7 19:15:45.772: INFO: router-2-jqhvj ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:05:36 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:56 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:05:36 -0400 EDT }]
Jun 7 19:15:45.772: INFO: liveness-http ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:13:59 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:14:02 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:13:59 -0400 EDT }]
Jun 7 19:15:45.772: INFO: netserver-0 ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:24 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:44 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:24 -0400 EDT }]
Jun 7 19:15:45.772: INFO: pod-exec-websocket-2cb71e84-4bd7-11e7-a95d-0ed58382e414 ip-172-18-4-42.ec2.internal Running 30s [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:19 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:23 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:19 -0400 EDT }]
Jun 7 19:15:45.772: INFO: history-limit-2-zv89b ip-172-18-4-42.ec2.internal Running 30s [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:01 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:04 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:01 -0400 EDT }]
Jun 7 19:15:45.772: INFO: history-limit-4-04764 ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:23 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:27 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:23 -0400 EDT }]
Jun 7 19:15:45.772: INFO: history-limit-6-deploy ip-172-18-4-42.ec2.internal Pending [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:44 -0400 EDT } {Ready False 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:44 -0400 EDT ContainersNotReady containers with unready status: [deployment]} {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:44 -0400 EDT }]
Jun 7 19:15:45.772: INFO: execpod ip-172-18-4-42.ec2.internal Running 1s [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:18 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:22 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:18 -0400 EDT }]
Jun 7 19:15:45.772: INFO: serving-cert ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:25 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:56 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:24 -0400 EDT }]
Jun 7 19:15:45.772: INFO:
Jun 7 19:15:45.774: INFO:
Logging node info for node ip-172-18-4-42.ec2.internal
Jun 7 19:15:45.777: INFO: Node Info: &Node{ObjectMeta:k8s_io_apimachinery_pkg_apis_meta_v1.ObjectMeta{Name:ip-172-18-4-42.ec2.internal,GenerateName:,Namespace:,SelfLink:/api/v1/nodes/ip-172-18-4-42.ec2.internal,UID:1ae62e17-4bd0-11e7-9287-0ed58382e414,ResourceVersion:10014,Generation:0,CreationTimestamp:2017-06-07 18:24:43 -0400 EDT,DeletionTimestamp:<nil>,DeletionGracePeriodSeconds:nil,Labels:map[string]string{beta.kubernetes.io/arch: amd64,beta.kubernetes.io/os: linux,kubernetes.io/hostname: ip-172-18-4-42.ec2.internal,region: infra,zone: default,},Annotations:map[string]string{volumes.kubernetes.io/controller-managed-attach-detach: true,},OwnerReferences:[],Finalizers:[],ClusterName:,},Spec:NodeSpec{PodCIDR:,ExternalID:ip-172-18-4-42.ec2.internal,ProviderID:aws:////i-0b63d6f595f9d8ca3,Unschedulable:false,Taints:[],},Status:NodeStatus{Capacity:ResourceList{alpha.kubernetes.io/nvidia-gpu: {{0 0} {<nil>} 0 DecimalSI},cpu: {{4 0} {<nil>} 4 DecimalSI},memory: {{16388919296 0} {<nil>} 16004804Ki BinarySI},pods: {{40 0} {<nil>} 40 DecimalSI},},Allocatable:ResourceList{alpha.kubernetes.io/nvidia-gpu: {{0 0} {<nil>} 0 DecimalSI},cpu: {{4 0} {<nil>} 4 DecimalSI},memory: {{16284061696 0} {<nil>} 15902404Ki BinarySI},pods: {{40 0} {<nil>} 40 DecimalSI},},Phase:,Conditions:[{OutOfDisk False 2017-06-07 19:15:36 -0400 EDT 2017-06-07 18:24:43 -0400 EDT KubeletHasSufficientDisk kubelet has sufficient disk space available} {MemoryPressure False 2017-06-07 19:15:36 -0400 EDT 2017-06-07 18:24:43 -0400 EDT KubeletHasSufficientMemory kubelet has sufficient memory available} {DiskPressure False 2017-06-07 19:15:36 -0400 EDT 2017-06-07 18:24:43 -0400 EDT KubeletHasNoDiskPressure kubelet has no disk pressure} {Ready True 2017-06-07 19:15:36 -0400 EDT 2017-06-07 19:05:25 -0400 EDT KubeletReady kubelet is posting ready status}],Addresses:[{LegacyHostIP 172.18.4.42} {InternalIP 172.18.4.42} {Hostname ip-172-18-4-42.ec2.internal}],DaemonEndpoints:NodeDaemonEndpoints{KubeletEndpoint:DaemonEndpoint{Port:10250,},},NodeInfo:NodeSystemInfo{MachineID:f9370ed252a14f73b014c1301a9b6d1b,SystemUUID:EC2D633F-1D3F-0ACD-83B3-19CD947B270C,BootID:f2cba44d-319d-431a-923c-61a02a143488,KernelVersion:3.10.0-514.21.1.el7.x86_64,OSImage:Red Hat Enterprise Linux Server 7.3 (Maipo),ContainerRuntimeVersion:docker://1.12.6,KubeletVersion:v1.6.1+5115d708d7,KubeProxyVersion:v1.6.1+5115d708d7,OperatingSystem:linux,Architecture:amd64,},Images:[{[openshift/origin-federation:e87b37a openshift/origin-federation:latest] 1202817887} {[openshift/origin-docker-registry:e87b37a openshift/origin-docker-registry:latest] 1097477526} {[openshift/origin-gitserver:e87b37a openshift/origin-gitserver:latest] 1083901468} {[openshift/openvswitch:e87b37a openshift/openvswitch:latest] 1051362593} {[openshift/node:e87b37a openshift/node:latest] 1049680811} {[openshift/origin-keepalived-ipfailover:e87b37a openshift/origin-keepalived-ipfailover:latest] 1026488548} {[openshift/origin-haproxy-router:e87b37a openshift/origin-haproxy-router:latest] 1020717555} {[openshift/origin-f5-router:e87b37a openshift/origin-f5-router:latest] 999688711} {[openshift/origin-recycler:e87b37a openshift/origin-recycler:latest] 999688711} {[openshift/origin-deployer:e87b37a openshift/origin-deployer:latest] 999688711} {[openshift/origin-docker-builder:e87b37a openshift/origin-docker-builder:latest] 999688711} {[openshift/origin-sti-builder:e87b37a openshift/origin-sti-builder:latest] 999688711} {[openshift/origin:e87b37a openshift/origin:latest] 999688711} {[openshift/origin-cluster-capacity:e87b37a openshift/origin-cluster-capacity:latest] 960430861} {[docker.io/openshift/origin-release@sha256:68022b599d63c26f4b7f859dfba0657e973f6b2e525ce310be5148aa9500be47 docker.io/openshift/origin-release:golang-1.7] 852450907} {[docker.io/openshift/origin-haproxy-router@sha256:c9374f410e32907be1fa1d14d77e58206ef0be949a63a635e6f3bafa77b35726 docker.io/openshift/origin-haproxy-router:v1.5.1] 738600544} {[docker.io/openshift/origin-deployer@sha256:77ac551235d8edf43ccb2fbd8fa5384ad9d8b94ba726f778fced18710c5f74f0 docker.io/openshift/origin-deployer:v1.5.1] 617474229} {[docker.io/openshift/origin-docker-registry@sha256:cfe82b08f94c015d31664573f3caa4307ffc7941c930cc7ae9419d68cec32ed5 docker.io/openshift/origin-docker-registry:v1.5.1] 428360819} {[gcr.io/google_containers/redis@sha256:f066bcf26497fbc55b9bf0769cb13a35c0afa2aa42e737cc46b7fb04b23a2f25 gcr.io/google_containers/redis:e2e] 418929769} {[openshift/origin-egress-router:e87b37a openshift/origin-egress-router:latest] 364746506} {[openshift/origin-base:latest] 363070922} {[docker.io/cockpit/kubernetes@sha256:49be8737ec76cf51cab6e8ca39e0eccd7c3b494771fea91cc32fcfdd2968549f docker.io/cockpit/kubernetes:latest] 351468457} {[openshift/origin-pod:e87b37a openshift/origin-pod:latest] 213198371} {[openshift/origin-source:latest] 192548894} {[docker.io/centos@sha256:aebf12af704307dfa0079b3babdca8d7e8ff6564696882bcb5d11f1d461f9ee9 docker.io/centos:7 docker.io/centos:centos7] 192548537} {[gcr.io/google_containers/nginx-slim@sha256:8b4501fe0fe221df663c22e16539f399e89594552f400408303c42f3dd8d0e52 gcr.io/google_containers/nginx-slim:0.8] 110461313} {[docker.io/nginx@sha256:41ad9967ea448d7c2b203c699b429abe1ed5af331cd92533900c6d77490e0268 docker.io/nginx:latest] 109368581} {[gcr.io/google_containers/nginx-slim@sha256:dd4efd4c13bec2c6f3fe855deeab9524efe434505568421d4f31820485b3a795 gcr.io/google_containers/nginx-slim:0.7] 86838142} {[gcr.io/google_containers/nettest@sha256:8af3a0e8b8ab906b0648dd575e8785e04c19113531f8ffbaab9e149aa1a60763 gcr.io/google_containers/nettest:1.7] 24051275} {[gcr.io/google_containers/hostexec@sha256:cab8d4e2526f8f767c64febe4ce9e0f0e58cd35fdff81b3aadba4dd041ba9f00 gcr.io/google_containers/hostexec:1.2] 13185747} {[gcr.io/google_containers/dnsutils@sha256:cd9182f6d74e616942db1cef6f25e1e54b49ba0330c2e19d3ec061f027666cc0 gcr.io/google_containers/dnsutils:e2e] 8893907} {[gcr.io/google_containers/netexec@sha256:56c53846f44ea214e4aa5df37c9c50331f0b09e64a32cc7cf17c7e1808d38eef gcr.io/google_containers/netexec:1.7] 8016035} {[gcr.io/google_containers/serve_hostname@sha256:a49737ee84a3b94f0b977f32e60c5daf11f0b5636f1f7503a2981524f351c57a gcr.io/google_containers/serve_hostname:v1.4] 6222101} {[openshift/hello-openshift:e87b37a openshift/hello-openshift:latest] 5635113} {[gcr.io/google_containers/test-webserver@sha256:f804e8837490d1dfdb5002e073f715fd0a08115de74e5a4847ca952315739372 gcr.io/google_containers/test-webserver:e2e] 4534272} {[gcr.io/google_containers/eptest@sha256:bb088b26ed78613cce171420168db9a6c62a8dbea17d7be13077e7010bae162f gcr.io/google_containers/eptest:0.1] 2970692} {[gcr.io/google_containers/mounttest@sha256:c4dcedb26013ab4231a2b2aaa4eebd5c2a44d5c597fa0613c9ff8bde4fb9fe02 gcr.io/google_containers/mounttest:0.7] 2052704} {[gcr.io/google_containers/portforwardtester@sha256:306879729d3eff635a11b89f3e62e440c9f2fe4dabdfb9ef02bc67f2275f67ab gcr.io/google_containers/portforwardtester:1.2] 1892642} {[gcr.io/google_containers/mounttest@sha256:bec3122ddcf8bd999e44e46e096659f31241d09f5236bc3dc212ea584ca06856 gcr.io/google_containers/mounttest:0.8] 1450761} {[gcr.io/google_containers/mounttest-user@sha256:5487c126b03abf4119a8f7950cd5f591f72dbe4ab15623f3387d3917e1268b4e gcr.io/google_containers/mounttest-user:0.5] 1450761} {[docker.io/openshift/origin-pod@sha256:8b61dcade7a9a972795a5bd92ebc73d7edbec5f36d4eb4abd4ae3127f2f4bb2e docker.io/openshift/origin-pod:v1.5.1] 1143145} {[gcr.io/google_containers/busybox@sha256:4bdd623e848417d96127e16037743f0cd8b528c026e9175e22a84f639eca58ff gcr.io/google_containers/busybox:1.24] 1113554} {[docker.io/busybox@sha256:c79345819a6882c31b41bc771d9a94fc52872fa651b36771fbe0c8461d7ee558] 1106304} {[gcr.io/google_containers/pause-amd64@sha256:163ac025575b775d1c0f9bf0bdd0f086883171eb475b5068e7defa4ca9e76516 gcr.io/google_containers/pause-amd64:3.0] 746888}],VolumesInUse:[],VolumesAttached:[],},}
Jun 7 19:15:45.777: INFO:
Logging kubelet events for node ip-172-18-4-42.ec2.internal
Jun 7 19:15:45.779: INFO:
Logging pods the kubelet thinks is on node ip-172-18-4-42.ec2.internal
Jun 7 19:15:45.791: INFO: router-2-jqhvj started at 2017-06-07 19:05:36 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.791: INFO: Container router ready: true, restart count 1
Jun 7 19:15:45.792: INFO: history-limit-4-04764 started at 2017-06-07 19:15:23 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container myapp ready: true, restart count 0
Jun 7 19:15:45.792: INFO: netserver-0 started at 2017-06-07 19:15:24 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container webserver ready: true, restart count 0
Jun 7 19:15:45.792: INFO: registry-console-1-8nmjb started at 2017-06-07 19:06:07 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container registry-console ready: true, restart count 0
Jun 7 19:15:45.792: INFO: liveness-http started at 2017-06-07 19:13:59 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container liveness ready: true, restart count 0
Jun 7 19:15:45.792: INFO: history-limit-2-zv89b started at 2017-06-07 19:15:01 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container myapp ready: true, restart count 0
Jun 7 19:15:45.792: INFO: serving-cert started at 2017-06-07 19:12:25 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container serve ready: true, restart count 0
Jun 7 19:15:45.792: INFO: pod-exec-websocket-2cb71e84-4bd7-11e7-a95d-0ed58382e414 started at 2017-06-07 19:15:19 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container main ready: true, restart count 0
Jun 7 19:15:45.792: INFO: execpod started at 2017-06-07 19:12:18 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container hostexec ready: true, restart count 0
Jun 7 19:15:45.792: INFO: history-limit-6-deploy started at 2017-06-07 19:15:44 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container deployment ready: false, restart count 0
Jun 7 19:15:45.792: INFO: docker-registry-2-bx862 started at 2017-06-07 19:05:37 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container registry ready: true, restart count 0
W0607 19:15:45.794030 29471 metrics_grabber.go:74] Master node is not registered. Grabbing metrics from Scheduler and ControllerManager is disabled.
Jun 7 19:15:46.002: INFO:
Latency metrics for node ip-172-18-4-42.ec2.internal
Jun 7 19:15:46.002: INFO: {Operation:sync Method:pod_worker_latency_microseconds Quantile:0.99 Latency:2m3.822287s}
Jun 7 19:15:46.002: INFO: {Operation:sync Method:pod_worker_latency_microseconds Quantile:0.9 Latency:2m2.277411s}
Jun 7 19:15:46.002: INFO: {Operation:sync Method:pod_worker_latency_microseconds Quantile:0.5 Latency:2m0.99155s}
Jun 7 19:15:46.002: INFO: {Operation: Method:pod_start_latency_microseconds Quantile:0.99 Latency:31.800596s}
Jun 7 19:15:46.002: INFO: {Operation:update Method:pod_worker_latency_microseconds Quantile:0.9 Latency:30.321405s}
Jun 7 19:15:46.002: INFO: {Operation:update Method:pod_worker_latency_microseconds Quantile:0.99 Latency:30.321405s}
Jun 7 19:15:46.002: INFO: {Operation:create Method:pod_worker_latency_microseconds Quantile:0.9 Latency:28.764905s}
Jun 7 19:15:46.002: INFO: {Operation:create Method:pod_worker_latency_microseconds Quantile:0.99 Latency:28.764905s}
Jun 7 19:15:46.002: INFO: {Operation:create Method:pod_worker_latency_microseconds Quantile:0.5 Latency:24.93889s}
Jun 7 19:15:46.002: INFO: {Operation:pull_image Method:docker_operations_latency_microseconds Quantile:0.99 Latency:11.009362s}
Jun 7 19:15:46.002: INFO: {Operation:create_container Method:docker_operations_latency_microseconds Quantile:0.99 Latency:10.021453s}
STEP: Dumping a list of prepulled images on each node
Jun 7 19:15:46.004: INFO: Waiting up to 3m0s for all (but 0) nodes to be ready
STEP: Destroying namespace "extended-test-router-reencrypt-48d58-wcpdv" for this suite.
Jun 7 19:16:11.058: INFO: namespace: extended-test-router-reencrypt-48d58-wcpdv, resource: bindings, ignored listing per whitelist
• Failure [232.594 seconds]
[Conformance][networking][router]
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:66
The HAProxy router
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:65
should support reencrypt to services backed by a serving certificate automatically [It]
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:64
Expected error:
<*errors.errorString | 0xc421a8a040>: {
s: "last response from server was not 200:\n",
}
last response from server was not 200:
not to have occurred
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:63
------------------------------
```
/cc @smarterclayton | 1.0 | [Conformance][networking][router] The HAProxy router should support reencrypt to services backed by a serving certificate automatically - ```
------------------------------
[Conformance][networking][router] The HAProxy router
should support reencrypt to services backed by a serving certificate automatically
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:64
[BeforeEach] [Top Level]
/go/src/github.com/openshift/origin/test/extended/util/test.go:51
[BeforeEach] [Conformance][networking][router]
/go/src/github.com/openshift/origin/vendor/k8s.io/kubernetes/test/e2e/framework/framework.go:120
STEP: Creating a kubernetes client
Jun 7 19:12:18.542: INFO: >>> kubeConfig: /etc/origin/master/admin.kubeconfig
STEP: Building a namespace api object
Jun 7 19:12:18.570: INFO: configPath is now "/tmp/extended-test-router-reencrypt-48d58-wcpdv-user.kubeconfig"
Jun 7 19:12:18.570: INFO: The user is now "extended-test-router-reencrypt-48d58-wcpdv-user"
Jun 7 19:12:18.570: INFO: Creating project "extended-test-router-reencrypt-48d58-wcpdv"
STEP: Waiting for a default service account to be provisioned in namespace
[BeforeEach] [Conformance][networking][router]
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:35
[It] should support reencrypt to services backed by a serving certificate automatically
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:64
Jun 7 19:12:18.662: INFO: Creating new exec pod
STEP: deploying a service using a reencrypt route without a destinationCACertificate
Jun 7 19:12:24.679: INFO: Running 'oc create --config=/tmp/extended-test-router-reencrypt-48d58-wcpdv-user.kubeconfig --namespace=extended-test-router-reencrypt-48d58-wcpdv -f /tmp/fixture-testdata-dir154131782/test/extended/testdata/reencrypt-serving-cert.yaml'
pod "serving-cert" created
configmap "serving-cert" created
service "serving-cert" created
route "serving-cert" created
Jun 7 19:12:26.030: INFO: Running '/data/src/github.com/openshift/origin/_output/local/bin/linux/amd64/kubectl --server=https://ip-172-18-4-42.ec2.internal:8443 --kubeconfig=/etc/origin/master/admin.kubeconfig exec --namespace=extended-test-router-reencrypt-48d58-wcpdv execpod -- /bin/sh -c
set -e
for i in $(seq 1 180); do
code=$( curl -k -s -o /dev/null -w '%{http_code}\n' --header 'Host: serving-cert-extended-test-router-reencrypt-48d58-wcpdv.router.default.svc.cluster.local' "https://172.30.95.6" ) || rc=$?
if [[ "${rc:-0}" -eq 0 ]]; then
echo $code
if [[ $code -eq 200 ]]; then
exit 0
fi
if [[ $code -ne 503 ]]; then
exit 1
fi
else
echo "error ${rc}" 1>&2
fi
sleep 1
done
'
Jun 7 19:15:45.738: INFO: stderr: "error 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\nerror 7\n"
[AfterEach] [Conformance][networking][router]
/go/src/github.com/openshift/origin/vendor/k8s.io/kubernetes/test/e2e/framework/framework.go:121
STEP: Collecting events from namespace "extended-test-router-reencrypt-48d58-wcpdv".
STEP: Found 9 events.
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:18 -0400 EDT - event for execpod: {default-scheduler } Scheduled: Successfully assigned execpod to ip-172-18-4-42.ec2.internal
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:20 -0400 EDT - event for execpod: {kubelet ip-172-18-4-42.ec2.internal} Pulled: Container image "gcr.io/google_containers/hostexec:1.2" already present on machine
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:20 -0400 EDT - event for execpod: {kubelet ip-172-18-4-42.ec2.internal} Created: Created container with id 6dafde2902f13c43671833b967af16050e25186492ee821eab22431cb73ce853
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:21 -0400 EDT - event for execpod: {kubelet ip-172-18-4-42.ec2.internal} Started: Started container with id 6dafde2902f13c43671833b967af16050e25186492ee821eab22431cb73ce853
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:24 -0400 EDT - event for serving-cert: {default-scheduler } Scheduled: Successfully assigned serving-cert to ip-172-18-4-42.ec2.internal
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:31 -0400 EDT - event for serving-cert: {kubelet ip-172-18-4-42.ec2.internal} Pulling: pulling image "nginx:latest"
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:40 -0400 EDT - event for serving-cert: {kubelet ip-172-18-4-42.ec2.internal} Pulled: Successfully pulled image "nginx:latest"
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:44 -0400 EDT - event for serving-cert: {kubelet ip-172-18-4-42.ec2.internal} Created: Created container with id 68aa8ed5fa890964b3ef50d1235589311687e6d16d55f923adb9052ef3105943
Jun 7 19:15:45.760: INFO: At 2017-06-07 19:12:44 -0400 EDT - event for serving-cert: {kubelet ip-172-18-4-42.ec2.internal} Started: Started container with id 68aa8ed5fa890964b3ef50d1235589311687e6d16d55f923adb9052ef3105943
Jun 7 19:15:45.772: INFO: POD NODE PHASE GRACE CONDITIONS
Jun 7 19:15:45.772: INFO: docker-registry-2-bx862 ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:05:37 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:05:47 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:05:37 -0400 EDT }]
Jun 7 19:15:45.772: INFO: registry-console-1-8nmjb ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:06:07 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:06:16 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:06:07 -0400 EDT }]
Jun 7 19:15:45.772: INFO: router-2-jqhvj ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:05:36 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:56 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:05:36 -0400 EDT }]
Jun 7 19:15:45.772: INFO: liveness-http ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:13:59 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:14:02 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:13:59 -0400 EDT }]
Jun 7 19:15:45.772: INFO: netserver-0 ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:24 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:44 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:24 -0400 EDT }]
Jun 7 19:15:45.772: INFO: pod-exec-websocket-2cb71e84-4bd7-11e7-a95d-0ed58382e414 ip-172-18-4-42.ec2.internal Running 30s [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:19 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:23 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:19 -0400 EDT }]
Jun 7 19:15:45.772: INFO: history-limit-2-zv89b ip-172-18-4-42.ec2.internal Running 30s [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:01 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:04 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:01 -0400 EDT }]
Jun 7 19:15:45.772: INFO: history-limit-4-04764 ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:23 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:27 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:23 -0400 EDT }]
Jun 7 19:15:45.772: INFO: history-limit-6-deploy ip-172-18-4-42.ec2.internal Pending [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:44 -0400 EDT } {Ready False 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:44 -0400 EDT ContainersNotReady containers with unready status: [deployment]} {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:15:44 -0400 EDT }]
Jun 7 19:15:45.772: INFO: execpod ip-172-18-4-42.ec2.internal Running 1s [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:18 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:22 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:18 -0400 EDT }]
Jun 7 19:15:45.772: INFO: serving-cert ip-172-18-4-42.ec2.internal Running [{Initialized True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:25 -0400 EDT } {Ready True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:56 -0400 EDT } {PodScheduled True 0001-01-01 00:00:00 +0000 UTC 2017-06-07 19:12:24 -0400 EDT }]
Jun 7 19:15:45.772: INFO:
Jun 7 19:15:45.774: INFO:
Logging node info for node ip-172-18-4-42.ec2.internal
Jun 7 19:15:45.777: INFO: Node Info: &Node{ObjectMeta:k8s_io_apimachinery_pkg_apis_meta_v1.ObjectMeta{Name:ip-172-18-4-42.ec2.internal,GenerateName:,Namespace:,SelfLink:/api/v1/nodes/ip-172-18-4-42.ec2.internal,UID:1ae62e17-4bd0-11e7-9287-0ed58382e414,ResourceVersion:10014,Generation:0,CreationTimestamp:2017-06-07 18:24:43 -0400 EDT,DeletionTimestamp:<nil>,DeletionGracePeriodSeconds:nil,Labels:map[string]string{beta.kubernetes.io/arch: amd64,beta.kubernetes.io/os: linux,kubernetes.io/hostname: ip-172-18-4-42.ec2.internal,region: infra,zone: default,},Annotations:map[string]string{volumes.kubernetes.io/controller-managed-attach-detach: true,},OwnerReferences:[],Finalizers:[],ClusterName:,},Spec:NodeSpec{PodCIDR:,ExternalID:ip-172-18-4-42.ec2.internal,ProviderID:aws:////i-0b63d6f595f9d8ca3,Unschedulable:false,Taints:[],},Status:NodeStatus{Capacity:ResourceList{alpha.kubernetes.io/nvidia-gpu: {{0 0} {<nil>} 0 DecimalSI},cpu: {{4 0} {<nil>} 4 DecimalSI},memory: {{16388919296 0} {<nil>} 16004804Ki BinarySI},pods: {{40 0} {<nil>} 40 DecimalSI},},Allocatable:ResourceList{alpha.kubernetes.io/nvidia-gpu: {{0 0} {<nil>} 0 DecimalSI},cpu: {{4 0} {<nil>} 4 DecimalSI},memory: {{16284061696 0} {<nil>} 15902404Ki BinarySI},pods: {{40 0} {<nil>} 40 DecimalSI},},Phase:,Conditions:[{OutOfDisk False 2017-06-07 19:15:36 -0400 EDT 2017-06-07 18:24:43 -0400 EDT KubeletHasSufficientDisk kubelet has sufficient disk space available} {MemoryPressure False 2017-06-07 19:15:36 -0400 EDT 2017-06-07 18:24:43 -0400 EDT KubeletHasSufficientMemory kubelet has sufficient memory available} {DiskPressure False 2017-06-07 19:15:36 -0400 EDT 2017-06-07 18:24:43 -0400 EDT KubeletHasNoDiskPressure kubelet has no disk pressure} {Ready True 2017-06-07 19:15:36 -0400 EDT 2017-06-07 19:05:25 -0400 EDT KubeletReady kubelet is posting ready status}],Addresses:[{LegacyHostIP 172.18.4.42} {InternalIP 172.18.4.42} {Hostname ip-172-18-4-42.ec2.internal}],DaemonEndpoints:NodeDaemonEndpoints{KubeletEndpoint:DaemonEndpoint{Port:10250,},},NodeInfo:NodeSystemInfo{MachineID:f9370ed252a14f73b014c1301a9b6d1b,SystemUUID:EC2D633F-1D3F-0ACD-83B3-19CD947B270C,BootID:f2cba44d-319d-431a-923c-61a02a143488,KernelVersion:3.10.0-514.21.1.el7.x86_64,OSImage:Red Hat Enterprise Linux Server 7.3 (Maipo),ContainerRuntimeVersion:docker://1.12.6,KubeletVersion:v1.6.1+5115d708d7,KubeProxyVersion:v1.6.1+5115d708d7,OperatingSystem:linux,Architecture:amd64,},Images:[{[openshift/origin-federation:e87b37a openshift/origin-federation:latest] 1202817887} {[openshift/origin-docker-registry:e87b37a openshift/origin-docker-registry:latest] 1097477526} {[openshift/origin-gitserver:e87b37a openshift/origin-gitserver:latest] 1083901468} {[openshift/openvswitch:e87b37a openshift/openvswitch:latest] 1051362593} {[openshift/node:e87b37a openshift/node:latest] 1049680811} {[openshift/origin-keepalived-ipfailover:e87b37a openshift/origin-keepalived-ipfailover:latest] 1026488548} {[openshift/origin-haproxy-router:e87b37a openshift/origin-haproxy-router:latest] 1020717555} {[openshift/origin-f5-router:e87b37a openshift/origin-f5-router:latest] 999688711} {[openshift/origin-recycler:e87b37a openshift/origin-recycler:latest] 999688711} {[openshift/origin-deployer:e87b37a openshift/origin-deployer:latest] 999688711} {[openshift/origin-docker-builder:e87b37a openshift/origin-docker-builder:latest] 999688711} {[openshift/origin-sti-builder:e87b37a openshift/origin-sti-builder:latest] 999688711} {[openshift/origin:e87b37a openshift/origin:latest] 999688711} {[openshift/origin-cluster-capacity:e87b37a openshift/origin-cluster-capacity:latest] 960430861} {[docker.io/openshift/origin-release@sha256:68022b599d63c26f4b7f859dfba0657e973f6b2e525ce310be5148aa9500be47 docker.io/openshift/origin-release:golang-1.7] 852450907} {[docker.io/openshift/origin-haproxy-router@sha256:c9374f410e32907be1fa1d14d77e58206ef0be949a63a635e6f3bafa77b35726 docker.io/openshift/origin-haproxy-router:v1.5.1] 738600544} {[docker.io/openshift/origin-deployer@sha256:77ac551235d8edf43ccb2fbd8fa5384ad9d8b94ba726f778fced18710c5f74f0 docker.io/openshift/origin-deployer:v1.5.1] 617474229} {[docker.io/openshift/origin-docker-registry@sha256:cfe82b08f94c015d31664573f3caa4307ffc7941c930cc7ae9419d68cec32ed5 docker.io/openshift/origin-docker-registry:v1.5.1] 428360819} {[gcr.io/google_containers/redis@sha256:f066bcf26497fbc55b9bf0769cb13a35c0afa2aa42e737cc46b7fb04b23a2f25 gcr.io/google_containers/redis:e2e] 418929769} {[openshift/origin-egress-router:e87b37a openshift/origin-egress-router:latest] 364746506} {[openshift/origin-base:latest] 363070922} {[docker.io/cockpit/kubernetes@sha256:49be8737ec76cf51cab6e8ca39e0eccd7c3b494771fea91cc32fcfdd2968549f docker.io/cockpit/kubernetes:latest] 351468457} {[openshift/origin-pod:e87b37a openshift/origin-pod:latest] 213198371} {[openshift/origin-source:latest] 192548894} {[docker.io/centos@sha256:aebf12af704307dfa0079b3babdca8d7e8ff6564696882bcb5d11f1d461f9ee9 docker.io/centos:7 docker.io/centos:centos7] 192548537} {[gcr.io/google_containers/nginx-slim@sha256:8b4501fe0fe221df663c22e16539f399e89594552f400408303c42f3dd8d0e52 gcr.io/google_containers/nginx-slim:0.8] 110461313} {[docker.io/nginx@sha256:41ad9967ea448d7c2b203c699b429abe1ed5af331cd92533900c6d77490e0268 docker.io/nginx:latest] 109368581} {[gcr.io/google_containers/nginx-slim@sha256:dd4efd4c13bec2c6f3fe855deeab9524efe434505568421d4f31820485b3a795 gcr.io/google_containers/nginx-slim:0.7] 86838142} {[gcr.io/google_containers/nettest@sha256:8af3a0e8b8ab906b0648dd575e8785e04c19113531f8ffbaab9e149aa1a60763 gcr.io/google_containers/nettest:1.7] 24051275} {[gcr.io/google_containers/hostexec@sha256:cab8d4e2526f8f767c64febe4ce9e0f0e58cd35fdff81b3aadba4dd041ba9f00 gcr.io/google_containers/hostexec:1.2] 13185747} {[gcr.io/google_containers/dnsutils@sha256:cd9182f6d74e616942db1cef6f25e1e54b49ba0330c2e19d3ec061f027666cc0 gcr.io/google_containers/dnsutils:e2e] 8893907} {[gcr.io/google_containers/netexec@sha256:56c53846f44ea214e4aa5df37c9c50331f0b09e64a32cc7cf17c7e1808d38eef gcr.io/google_containers/netexec:1.7] 8016035} {[gcr.io/google_containers/serve_hostname@sha256:a49737ee84a3b94f0b977f32e60c5daf11f0b5636f1f7503a2981524f351c57a gcr.io/google_containers/serve_hostname:v1.4] 6222101} {[openshift/hello-openshift:e87b37a openshift/hello-openshift:latest] 5635113} {[gcr.io/google_containers/test-webserver@sha256:f804e8837490d1dfdb5002e073f715fd0a08115de74e5a4847ca952315739372 gcr.io/google_containers/test-webserver:e2e] 4534272} {[gcr.io/google_containers/eptest@sha256:bb088b26ed78613cce171420168db9a6c62a8dbea17d7be13077e7010bae162f gcr.io/google_containers/eptest:0.1] 2970692} {[gcr.io/google_containers/mounttest@sha256:c4dcedb26013ab4231a2b2aaa4eebd5c2a44d5c597fa0613c9ff8bde4fb9fe02 gcr.io/google_containers/mounttest:0.7] 2052704} {[gcr.io/google_containers/portforwardtester@sha256:306879729d3eff635a11b89f3e62e440c9f2fe4dabdfb9ef02bc67f2275f67ab gcr.io/google_containers/portforwardtester:1.2] 1892642} {[gcr.io/google_containers/mounttest@sha256:bec3122ddcf8bd999e44e46e096659f31241d09f5236bc3dc212ea584ca06856 gcr.io/google_containers/mounttest:0.8] 1450761} {[gcr.io/google_containers/mounttest-user@sha256:5487c126b03abf4119a8f7950cd5f591f72dbe4ab15623f3387d3917e1268b4e gcr.io/google_containers/mounttest-user:0.5] 1450761} {[docker.io/openshift/origin-pod@sha256:8b61dcade7a9a972795a5bd92ebc73d7edbec5f36d4eb4abd4ae3127f2f4bb2e docker.io/openshift/origin-pod:v1.5.1] 1143145} {[gcr.io/google_containers/busybox@sha256:4bdd623e848417d96127e16037743f0cd8b528c026e9175e22a84f639eca58ff gcr.io/google_containers/busybox:1.24] 1113554} {[docker.io/busybox@sha256:c79345819a6882c31b41bc771d9a94fc52872fa651b36771fbe0c8461d7ee558] 1106304} {[gcr.io/google_containers/pause-amd64@sha256:163ac025575b775d1c0f9bf0bdd0f086883171eb475b5068e7defa4ca9e76516 gcr.io/google_containers/pause-amd64:3.0] 746888}],VolumesInUse:[],VolumesAttached:[],},}
Jun 7 19:15:45.777: INFO:
Logging kubelet events for node ip-172-18-4-42.ec2.internal
Jun 7 19:15:45.779: INFO:
Logging pods the kubelet thinks is on node ip-172-18-4-42.ec2.internal
Jun 7 19:15:45.791: INFO: router-2-jqhvj started at 2017-06-07 19:05:36 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.791: INFO: Container router ready: true, restart count 1
Jun 7 19:15:45.792: INFO: history-limit-4-04764 started at 2017-06-07 19:15:23 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container myapp ready: true, restart count 0
Jun 7 19:15:45.792: INFO: netserver-0 started at 2017-06-07 19:15:24 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container webserver ready: true, restart count 0
Jun 7 19:15:45.792: INFO: registry-console-1-8nmjb started at 2017-06-07 19:06:07 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container registry-console ready: true, restart count 0
Jun 7 19:15:45.792: INFO: liveness-http started at 2017-06-07 19:13:59 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container liveness ready: true, restart count 0
Jun 7 19:15:45.792: INFO: history-limit-2-zv89b started at 2017-06-07 19:15:01 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container myapp ready: true, restart count 0
Jun 7 19:15:45.792: INFO: serving-cert started at 2017-06-07 19:12:25 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container serve ready: true, restart count 0
Jun 7 19:15:45.792: INFO: pod-exec-websocket-2cb71e84-4bd7-11e7-a95d-0ed58382e414 started at 2017-06-07 19:15:19 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container main ready: true, restart count 0
Jun 7 19:15:45.792: INFO: execpod started at 2017-06-07 19:12:18 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container hostexec ready: true, restart count 0
Jun 7 19:15:45.792: INFO: history-limit-6-deploy started at 2017-06-07 19:15:44 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container deployment ready: false, restart count 0
Jun 7 19:15:45.792: INFO: docker-registry-2-bx862 started at 2017-06-07 19:05:37 -0400 EDT (0+1 container statuses recorded)
Jun 7 19:15:45.792: INFO: Container registry ready: true, restart count 0
W0607 19:15:45.794030 29471 metrics_grabber.go:74] Master node is not registered. Grabbing metrics from Scheduler and ControllerManager is disabled.
Jun 7 19:15:46.002: INFO:
Latency metrics for node ip-172-18-4-42.ec2.internal
Jun 7 19:15:46.002: INFO: {Operation:sync Method:pod_worker_latency_microseconds Quantile:0.99 Latency:2m3.822287s}
Jun 7 19:15:46.002: INFO: {Operation:sync Method:pod_worker_latency_microseconds Quantile:0.9 Latency:2m2.277411s}
Jun 7 19:15:46.002: INFO: {Operation:sync Method:pod_worker_latency_microseconds Quantile:0.5 Latency:2m0.99155s}
Jun 7 19:15:46.002: INFO: {Operation: Method:pod_start_latency_microseconds Quantile:0.99 Latency:31.800596s}
Jun 7 19:15:46.002: INFO: {Operation:update Method:pod_worker_latency_microseconds Quantile:0.9 Latency:30.321405s}
Jun 7 19:15:46.002: INFO: {Operation:update Method:pod_worker_latency_microseconds Quantile:0.99 Latency:30.321405s}
Jun 7 19:15:46.002: INFO: {Operation:create Method:pod_worker_latency_microseconds Quantile:0.9 Latency:28.764905s}
Jun 7 19:15:46.002: INFO: {Operation:create Method:pod_worker_latency_microseconds Quantile:0.99 Latency:28.764905s}
Jun 7 19:15:46.002: INFO: {Operation:create Method:pod_worker_latency_microseconds Quantile:0.5 Latency:24.93889s}
Jun 7 19:15:46.002: INFO: {Operation:pull_image Method:docker_operations_latency_microseconds Quantile:0.99 Latency:11.009362s}
Jun 7 19:15:46.002: INFO: {Operation:create_container Method:docker_operations_latency_microseconds Quantile:0.99 Latency:10.021453s}
STEP: Dumping a list of prepulled images on each node
Jun 7 19:15:46.004: INFO: Waiting up to 3m0s for all (but 0) nodes to be ready
STEP: Destroying namespace "extended-test-router-reencrypt-48d58-wcpdv" for this suite.
Jun 7 19:16:11.058: INFO: namespace: extended-test-router-reencrypt-48d58-wcpdv, resource: bindings, ignored listing per whitelist
• Failure [232.594 seconds]
[Conformance][networking][router]
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:66
The HAProxy router
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:65
should support reencrypt to services backed by a serving certificate automatically [It]
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:64
Expected error:
<*errors.errorString | 0xc421a8a040>: {
s: "last response from server was not 200:\n",
}
last response from server was not 200:
not to have occurred
/go/src/github.com/openshift/origin/test/extended/router/reencrypt.go:63
------------------------------
```
/cc @smarterclayton | test | the haproxy router should support reencrypt to services backed by a serving certificate automatically the haproxy router should support reencrypt to services backed by a serving certificate automatically go src github com openshift origin test extended router reencrypt go go src github com openshift origin test extended util test go go src github com openshift origin vendor io kubernetes test framework framework go step creating a kubernetes client jun info kubeconfig etc origin master admin kubeconfig step building a namespace api object jun info configpath is now tmp extended test router reencrypt wcpdv user kubeconfig jun info the user is now extended test router reencrypt wcpdv user jun info creating project extended test router reencrypt wcpdv step waiting for a default service account to be provisioned in namespace go src github com openshift origin test extended router reencrypt go should support reencrypt to services backed by a serving certificate automatically go src github com openshift origin test extended router reencrypt go jun info creating new exec pod step deploying a service using a reencrypt route without a destinationcacertificate jun info running oc create config tmp extended test router reencrypt wcpdv user kubeconfig namespace extended test router reencrypt wcpdv f tmp fixture testdata test extended testdata reencrypt serving cert yaml pod serving cert created configmap serving cert created service serving cert created route serving cert created jun info running data src github com openshift origin output local bin linux kubectl server kubeconfig etc origin master admin kubeconfig exec namespace extended test router reencrypt wcpdv execpod bin sh c set e for i in seq do code curl k s o dev null w http code n header host serving cert extended test router reencrypt wcpdv router default svc cluster local rc if then echo code if then exit fi if then exit fi else echo error rc fi sleep done jun info stderr error nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror nerror n go src github com openshift origin vendor io kubernetes test framework framework go step collecting events from namespace extended test router reencrypt wcpdv step found events jun info at edt event for execpod default scheduler scheduled successfully assigned execpod to ip internal jun info at edt event for execpod kubelet ip internal pulled container image gcr io google containers hostexec already present on machine jun info at edt event for execpod kubelet ip internal created created container with id jun info at edt event for execpod kubelet ip internal started started container with id jun info at edt event for serving cert default scheduler scheduled successfully assigned serving cert to ip internal jun info at edt event for serving cert kubelet ip internal pulling pulling image nginx latest jun info at edt event for serving cert kubelet ip internal pulled successfully pulled image nginx latest jun info at edt event for serving cert kubelet ip internal created created container with id jun info at edt event for serving cert kubelet ip internal started started container with id jun info pod node phase grace conditions jun info docker registry ip internal running jun info registry console ip internal running jun info router jqhvj ip internal running jun info liveness http ip internal running jun info netserver ip internal running jun info pod exec websocket ip internal running jun info history limit ip internal running jun info history limit ip internal running jun info history limit deploy ip internal pending podscheduled true utc edt jun info execpod ip internal running jun info serving cert ip internal running jun info jun info logging node info for node ip internal jun info node info node objectmeta io apimachinery pkg apis meta objectmeta name ip internal generatename namespace selflink api nodes ip internal uid resourceversion generation creationtimestamp edt deletiontimestamp deletiongraceperiodseconds nil labels map string beta kubernetes io arch beta kubernetes io os linux kubernetes io hostname ip internal region infra zone default annotations map string volumes kubernetes io controller managed attach detach true ownerreferences finalizers clustername spec nodespec podcidr externalid ip internal providerid aws i unschedulable false taints status nodestatus capacity resourcelist alpha kubernetes io nvidia gpu decimalsi cpu decimalsi memory binarysi pods decimalsi allocatable resourcelist alpha kubernetes io nvidia gpu decimalsi cpu decimalsi memory binarysi pods decimalsi phase conditions addresses daemonendpoints nodedaemonendpoints kubeletendpoint daemonendpoint port nodeinfo nodesysteminfo machineid systemuuid bootid kernelversion osimage red hat enterprise linux server maipo containerruntimeversion docker kubeletversion kubeproxyversion operatingsystem linux architecture images volumesinuse volumesattached jun info logging kubelet events for node ip internal jun info logging pods the kubelet thinks is on node ip internal jun info router jqhvj started at edt container statuses recorded jun info container router ready true restart count jun info history limit started at edt container statuses recorded jun info container myapp ready true restart count jun info netserver started at edt container statuses recorded jun info container webserver ready true restart count jun info registry console started at edt container statuses recorded jun info container registry console ready true restart count jun info liveness http started at edt container statuses recorded jun info container liveness ready true restart count jun info history limit started at edt container statuses recorded jun info container myapp ready true restart count jun info serving cert started at edt container statuses recorded jun info container serve ready true restart count jun info pod exec websocket started at edt container statuses recorded jun info container main ready true restart count jun info execpod started at edt container statuses recorded jun info container hostexec ready true restart count jun info history limit deploy started at edt container statuses recorded jun info container deployment ready false restart count jun info docker registry started at edt container statuses recorded jun info container registry ready true restart count metrics grabber go master node is not registered grabbing metrics from scheduler and controllermanager is disabled jun info latency metrics for node ip internal jun info operation sync method pod worker latency microseconds quantile latency jun info operation sync method pod worker latency microseconds quantile latency jun info operation sync method pod worker latency microseconds quantile latency jun info operation method pod start latency microseconds quantile latency jun info operation update method pod worker latency microseconds quantile latency jun info operation update method pod worker latency microseconds quantile latency jun info operation create method pod worker latency microseconds quantile latency jun info operation create method pod worker latency microseconds quantile latency jun info operation create method pod worker latency microseconds quantile latency jun info operation pull image method docker operations latency microseconds quantile latency jun info operation create container method docker operations latency microseconds quantile latency step dumping a list of prepulled images on each node jun info waiting up to for all but nodes to be ready step destroying namespace extended test router reencrypt wcpdv for this suite jun info namespace extended test router reencrypt wcpdv resource bindings ignored listing per whitelist • failure go src github com openshift origin test extended router reencrypt go the haproxy router go src github com openshift origin test extended router reencrypt go should support reencrypt to services backed by a serving certificate automatically go src github com openshift origin test extended router reencrypt go expected error s last response from server was not n last response from server was not not to have occurred go src github com openshift origin test extended router reencrypt go cc smarterclayton | 1 |
427,947 | 29,872,134,824 | IssuesEvent | 2023-06-20 09:10:44 | jupyter/notebook | https://api.github.com/repos/jupyter/notebook | closed | Getting started contributing documentation | documentation tag:Environment | Attempting to contribute to notebook on Ubuntu 14.04, followed the documentation for developers, but kept encountering an error:
```
# pip install -e . --user
Obtaining file:///home/dblank/notebook
Requirement already satisfied (use --upgrade to upgrade): jinja2 in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): tornado>=4 in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): ipython_genutils in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): traitlets>=4.2.1 in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): jupyter_core in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): jupyter_client in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): nbformat in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): nbconvert in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): ipykernel in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): terminado>=0.3.3 in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): MarkupSafe in /usr/local/lib/python3.4/dist-packages (from jinja2->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): backports_abc>=0.4 in /usr/local/lib/python3.4/dist-packages (from tornado>=4->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): decorator in /usr/local/lib/python3.4/dist-packages (from traitlets>=4.2.1->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): six in /usr/local/lib/python3.4/dist-packages (from traitlets>=4.2.1->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): pyzmq>=13 in /usr/local/lib/python3.4/dist-packages (from jupyter_client->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): jsonschema!=2.5.0,>=2.0 in /usr/local/lib/python3.4/dist-packages (from nbformat->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): entrypoints in /usr/local/lib/python3.4/dist-packages (from nbconvert->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): mistune!=0.6 in /usr/local/lib/python3.4/dist-packages (from nbconvert->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): pygments in /usr/local/lib/python3.4/dist-packages (from nbconvert->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): ipython>=4.0.0 in /usr/local/lib/python3.4/dist-packages (from ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): ptyprocess in /usr/local/lib/python3.4/dist-packages (from terminado>=0.3.3->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): simplegeneric>0.8 in /usr/lib/python3/dist-packages (from ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): prompt-toolkit<2.0.0,>=1.0.3 in /usr/local/lib/python3.4/dist-packages (from ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): pexpect; sys_platform != "win32" in /usr/local/lib/python3.4/dist-packages (from ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): pickleshare in /usr/local/lib/python3.4/dist-packages (from ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): setuptools>=18.5 in /usr/local/lib/python3.4/dist-packages (from ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): wcwidth in /usr/local/lib/python3.4/dist-packages (from prompt-toolkit<2.0.0,>=1.0.3->ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Installing collected packages: notebook
Running setup.py develop for notebook
Complete output from command /usr/bin/python3 -c "import setuptools, tokenize;__file__='/home/dblank/notebook/setup.py';exec(compile(getattr(tokenize, 'open', open)(__file__).read().replace('\r\n', '\n'), __file__, 'exec'))" develop --no-deps --user --prefix=:
running develop
running jsversion
running js
running jsdeps
> npm install --progress=false
> npm dedupe
> npm run bower
> jupyter-notebook-deps@4.0.0 bower /home/dblank/notebook
> bower install --allow-root --config.interactive=false
Missing /home/dblank/notebook/notebook/static/built/index.js
> npm run build:js
> jupyter-notebook-deps@4.0.0 build:js /home/dblank/notebook
> webpack
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
ModuleBuildError: Module build failed: ReferenceError: Promise is not defined
at LazyResult.async (/home/dblank/notebook/node_modules/css-loader/node_modules/postcss/lib/lazy-result.js:237:31)
at LazyResult.then (/home/dblank/notebook/node_modules/css-loader/node_modules/postcss/lib/lazy-result.js:141:21)
at processCss (/home/dblank/notebook/node_modules/css-loader/lib/processCss.js:198:5)
at Object.module.exports (/home/dblank/notebook/node_modules/css-loader/lib/loader.js:24:2)
at DependenciesBlock.onModuleBuildFailed (/home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:315:19)
at nextLoader (/home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:270:31)
at /home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:292:15
at runSyncOrAsync (/home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:173:4)
at nextLoader (/home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:290:3)
at /home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:259:5
at Storage.finished (/home/dblank/notebook/node_modules/webpack/node_modules/enhanced-resolve/lib/CachedInputFileSystem.js:38:16)
at /home/dblank/notebook/node_modules/webpack/node_modules/enhanced-resolve/node_modules/graceful-fs/graceful-fs.js:78:16
at fs.js:268:14
at /home/dblank/notebook/node_modules/webpack/node_modules/enhanced-resolve/node_modules/graceful-fs/graceful-fs.js:43:10
at Object.oncomplete (fs.js:107:15)
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
npm ERR! weird error 1
npm WARN This failure might be due to the use of legacy binary "node"
npm WARN For further explanations, please read
/usr/share/doc/nodejs/README.Debian
npm ERR! not ok code 0
/usr/local/lib/python3.4/dist-packages/setuptools/dist.py:331: UserWarning: Normalizing '5.0.0.dev' to '5.0.0.dev0'
normalized_version,
rebuilding js and css failed. The following required files are missing: ['notebook/static/built/index.js', 'notebook/static/style/ipython.min.css', 'notebook/static/style/style.min.css']
Traceback (most recent call last):
File "<string>", line 1, in <module>
File "/home/dblank/notebook/setup.py", line 198, in <module>
main()
File "/home/dblank/notebook/setup.py", line 195, in main
setup(**setup_args)
File "/usr/lib/python3.4/distutils/core.py", line 148, in setup
dist.run_commands()
File "/usr/lib/python3.4/distutils/dist.py", line 955, in run_commands
self.run_command(cmd)
File "/usr/lib/python3.4/distutils/dist.py", line 974, in run_command
cmd_obj.run()
File "/home/dblank/notebook/setupbase.py", line 528, in run
raise e
File "/home/dblank/notebook/setupbase.py", line 518, in run
self.distribution.run_command('js')
File "/usr/lib/python3.4/distutils/dist.py", line 974, in run_command
cmd_obj.run()
File "/home/dblank/notebook/setupbase.py", line 454, in run
run(['npm', 'run', 'build:js'])
File "/home/dblank/notebook/setupbase.py", line 325, in run
return check_call(cmd, *args, **kwargs)
File "/usr/lib/python3.4/subprocess.py", line 561, in check_call
raise CalledProcessError(retcode, cmd)
subprocess.CalledProcessError: Command '['npm', 'run', 'build:js']' returned non-zero exit status 1
----------------------------------------
Command "/usr/bin/python3 -c "import setuptools, tokenize;__file__='/home/dblank/notebook/setup.py';exec(compile(getattr(tokenize, 'open', open)(__file__).read().replace('\r\n', '\n'), __file__, 'exec'))" develop --no-deps --user --prefix=" failed with error code 1 in /home/dblank/notebook/
```
I tried many things, but eventually I went through the .travis.yml, noted the use of nvm, and did the following:
```
curl https://raw.githubusercontent.com/creationix/nvm/v0.16.1/install.sh | sh
nvm install 5.6
nvm use 5.6
npm upgrade -g npm
```
which doesn't seem to be documented anywhere. But afterwards, I was able to build and install the notebook from source.
| 1.0 | Getting started contributing documentation - Attempting to contribute to notebook on Ubuntu 14.04, followed the documentation for developers, but kept encountering an error:
```
# pip install -e . --user
Obtaining file:///home/dblank/notebook
Requirement already satisfied (use --upgrade to upgrade): jinja2 in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): tornado>=4 in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): ipython_genutils in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): traitlets>=4.2.1 in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): jupyter_core in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): jupyter_client in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): nbformat in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): nbconvert in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): ipykernel in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): terminado>=0.3.3 in /usr/local/lib/python3.4/dist-packages (from notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): MarkupSafe in /usr/local/lib/python3.4/dist-packages (from jinja2->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): backports_abc>=0.4 in /usr/local/lib/python3.4/dist-packages (from tornado>=4->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): decorator in /usr/local/lib/python3.4/dist-packages (from traitlets>=4.2.1->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): six in /usr/local/lib/python3.4/dist-packages (from traitlets>=4.2.1->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): pyzmq>=13 in /usr/local/lib/python3.4/dist-packages (from jupyter_client->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): jsonschema!=2.5.0,>=2.0 in /usr/local/lib/python3.4/dist-packages (from nbformat->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): entrypoints in /usr/local/lib/python3.4/dist-packages (from nbconvert->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): mistune!=0.6 in /usr/local/lib/python3.4/dist-packages (from nbconvert->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): pygments in /usr/local/lib/python3.4/dist-packages (from nbconvert->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): ipython>=4.0.0 in /usr/local/lib/python3.4/dist-packages (from ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): ptyprocess in /usr/local/lib/python3.4/dist-packages (from terminado>=0.3.3->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): simplegeneric>0.8 in /usr/lib/python3/dist-packages (from ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): prompt-toolkit<2.0.0,>=1.0.3 in /usr/local/lib/python3.4/dist-packages (from ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): pexpect; sys_platform != "win32" in /usr/local/lib/python3.4/dist-packages (from ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): pickleshare in /usr/local/lib/python3.4/dist-packages (from ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): setuptools>=18.5 in /usr/local/lib/python3.4/dist-packages (from ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Requirement already satisfied (use --upgrade to upgrade): wcwidth in /usr/local/lib/python3.4/dist-packages (from prompt-toolkit<2.0.0,>=1.0.3->ipython>=4.0.0->ipykernel->notebook==5.0.0.dev0)
Installing collected packages: notebook
Running setup.py develop for notebook
Complete output from command /usr/bin/python3 -c "import setuptools, tokenize;__file__='/home/dblank/notebook/setup.py';exec(compile(getattr(tokenize, 'open', open)(__file__).read().replace('\r\n', '\n'), __file__, 'exec'))" develop --no-deps --user --prefix=:
running develop
running jsversion
running js
running jsdeps
> npm install --progress=false
> npm dedupe
> npm run bower
> jupyter-notebook-deps@4.0.0 bower /home/dblank/notebook
> bower install --allow-root --config.interactive=false
Missing /home/dblank/notebook/notebook/static/built/index.js
> npm run build:js
> jupyter-notebook-deps@4.0.0 build:js /home/dblank/notebook
> webpack
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
ModuleBuildError: Module build failed: ReferenceError: Promise is not defined
at LazyResult.async (/home/dblank/notebook/node_modules/css-loader/node_modules/postcss/lib/lazy-result.js:237:31)
at LazyResult.then (/home/dblank/notebook/node_modules/css-loader/node_modules/postcss/lib/lazy-result.js:141:21)
at processCss (/home/dblank/notebook/node_modules/css-loader/lib/processCss.js:198:5)
at Object.module.exports (/home/dblank/notebook/node_modules/css-loader/lib/loader.js:24:2)
at DependenciesBlock.onModuleBuildFailed (/home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:315:19)
at nextLoader (/home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:270:31)
at /home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:292:15
at runSyncOrAsync (/home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:173:4)
at nextLoader (/home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:290:3)
at /home/dblank/notebook/node_modules/webpack/node_modules/webpack-core/lib/NormalModuleMixin.js:259:5
at Storage.finished (/home/dblank/notebook/node_modules/webpack/node_modules/enhanced-resolve/lib/CachedInputFileSystem.js:38:16)
at /home/dblank/notebook/node_modules/webpack/node_modules/enhanced-resolve/node_modules/graceful-fs/graceful-fs.js:78:16
at fs.js:268:14
at /home/dblank/notebook/node_modules/webpack/node_modules/enhanced-resolve/node_modules/graceful-fs/graceful-fs.js:43:10
at Object.oncomplete (fs.js:107:15)
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
[BABEL] Note: The code generator has deoptimised the styling of "/home/dblank/notebook/notebook/static/notebook/js/notebook.js" as it exceeds the max of "100KB".
npm ERR! weird error 1
npm WARN This failure might be due to the use of legacy binary "node"
npm WARN For further explanations, please read
/usr/share/doc/nodejs/README.Debian
npm ERR! not ok code 0
/usr/local/lib/python3.4/dist-packages/setuptools/dist.py:331: UserWarning: Normalizing '5.0.0.dev' to '5.0.0.dev0'
normalized_version,
rebuilding js and css failed. The following required files are missing: ['notebook/static/built/index.js', 'notebook/static/style/ipython.min.css', 'notebook/static/style/style.min.css']
Traceback (most recent call last):
File "<string>", line 1, in <module>
File "/home/dblank/notebook/setup.py", line 198, in <module>
main()
File "/home/dblank/notebook/setup.py", line 195, in main
setup(**setup_args)
File "/usr/lib/python3.4/distutils/core.py", line 148, in setup
dist.run_commands()
File "/usr/lib/python3.4/distutils/dist.py", line 955, in run_commands
self.run_command(cmd)
File "/usr/lib/python3.4/distutils/dist.py", line 974, in run_command
cmd_obj.run()
File "/home/dblank/notebook/setupbase.py", line 528, in run
raise e
File "/home/dblank/notebook/setupbase.py", line 518, in run
self.distribution.run_command('js')
File "/usr/lib/python3.4/distutils/dist.py", line 974, in run_command
cmd_obj.run()
File "/home/dblank/notebook/setupbase.py", line 454, in run
run(['npm', 'run', 'build:js'])
File "/home/dblank/notebook/setupbase.py", line 325, in run
return check_call(cmd, *args, **kwargs)
File "/usr/lib/python3.4/subprocess.py", line 561, in check_call
raise CalledProcessError(retcode, cmd)
subprocess.CalledProcessError: Command '['npm', 'run', 'build:js']' returned non-zero exit status 1
----------------------------------------
Command "/usr/bin/python3 -c "import setuptools, tokenize;__file__='/home/dblank/notebook/setup.py';exec(compile(getattr(tokenize, 'open', open)(__file__).read().replace('\r\n', '\n'), __file__, 'exec'))" develop --no-deps --user --prefix=" failed with error code 1 in /home/dblank/notebook/
```
I tried many things, but eventually I went through the .travis.yml, noted the use of nvm, and did the following:
```
curl https://raw.githubusercontent.com/creationix/nvm/v0.16.1/install.sh | sh
nvm install 5.6
nvm use 5.6
npm upgrade -g npm
```
which doesn't seem to be documented anywhere. But afterwards, I was able to build and install the notebook from source.
| non_test | getting started contributing documentation attempting to contribute to notebook on ubuntu followed the documentation for developers but kept encountering an error pip install e user obtaining file home dblank notebook requirement already satisfied use upgrade to upgrade in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade tornado in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade ipython genutils in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade traitlets in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade jupyter core in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade jupyter client in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade nbformat in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade nbconvert in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade ipykernel in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade terminado in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade markupsafe in usr local lib dist packages from notebook requirement already satisfied use upgrade to upgrade backports abc in usr local lib dist packages from tornado notebook requirement already satisfied use upgrade to upgrade decorator in usr local lib dist packages from traitlets notebook requirement already satisfied use upgrade to upgrade six in usr local lib dist packages from traitlets notebook requirement already satisfied use upgrade to upgrade pyzmq in usr local lib dist packages from jupyter client notebook requirement already satisfied use upgrade to upgrade jsonschema in usr local lib dist packages from nbformat notebook requirement already satisfied use upgrade to upgrade entrypoints in usr local lib dist packages from nbconvert notebook requirement already satisfied use upgrade to upgrade mistune in usr local lib dist packages from nbconvert notebook requirement already satisfied use upgrade to upgrade pygments in usr local lib dist packages from nbconvert notebook requirement already satisfied use upgrade to upgrade ipython in usr local lib dist packages from ipykernel notebook requirement already satisfied use upgrade to upgrade ptyprocess in usr local lib dist packages from terminado notebook requirement already satisfied use upgrade to upgrade simplegeneric in usr lib dist packages from ipython ipykernel notebook requirement already satisfied use upgrade to upgrade prompt toolkit in usr local lib dist packages from ipython ipykernel notebook requirement already satisfied use upgrade to upgrade pexpect sys platform in usr local lib dist packages from ipython ipykernel notebook requirement already satisfied use upgrade to upgrade pickleshare in usr local lib dist packages from ipython ipykernel notebook requirement already satisfied use upgrade to upgrade setuptools in usr local lib dist packages from ipython ipykernel notebook requirement already satisfied use upgrade to upgrade wcwidth in usr local lib dist packages from prompt toolkit ipython ipykernel notebook installing collected packages notebook running setup py develop for notebook complete output from command usr bin c import setuptools tokenize file home dblank notebook setup py exec compile getattr tokenize open open file read replace r n n file exec develop no deps user prefix running develop running jsversion running js running jsdeps npm install progress false npm dedupe npm run bower jupyter notebook deps bower home dblank notebook bower install allow root config interactive false missing home dblank notebook notebook static built index js npm run build js jupyter notebook deps build js home dblank notebook webpack note the code generator has deoptimised the styling of home dblank notebook notebook static notebook js notebook js as it exceeds the max of note the code generator has deoptimised the styling of home dblank notebook notebook static notebook js notebook js as it exceeds the max of note the code generator has deoptimised the styling of home dblank notebook notebook static notebook js notebook js as it exceeds the max of note the code generator has deoptimised the styling of home dblank notebook notebook static notebook js notebook js as it exceeds the max of modulebuilderror module build failed referenceerror promise is not defined at lazyresult async home dblank notebook node modules css loader node modules postcss lib lazy result js at lazyresult then home dblank notebook node modules css loader node modules postcss lib lazy result js at processcss home dblank notebook node modules css loader lib processcss js at object module exports home dblank notebook node modules css loader lib loader js at dependenciesblock onmodulebuildfailed home dblank notebook node modules webpack node modules webpack core lib normalmodulemixin js at nextloader home dblank notebook node modules webpack node modules webpack core lib normalmodulemixin js at home dblank notebook node modules webpack node modules webpack core lib normalmodulemixin js at runsyncorasync home dblank notebook node modules webpack node modules webpack core lib normalmodulemixin js at nextloader home dblank notebook node modules webpack node modules webpack core lib normalmodulemixin js at home dblank notebook node modules webpack node modules webpack core lib normalmodulemixin js at storage finished home dblank notebook node modules webpack node modules enhanced resolve lib cachedinputfilesystem js at home dblank notebook node modules webpack node modules enhanced resolve node modules graceful fs graceful fs js at fs js at home dblank notebook node modules webpack node modules enhanced resolve node modules graceful fs graceful fs js at object oncomplete fs js note the code generator has deoptimised the styling of home dblank notebook notebook static notebook js notebook js as it exceeds the max of note the code generator has deoptimised the styling of home dblank notebook notebook static notebook js notebook js as it exceeds the max of npm err weird error npm warn this failure might be due to the use of legacy binary node npm warn for further explanations please read usr share doc nodejs readme debian npm err not ok code usr local lib dist packages setuptools dist py userwarning normalizing dev to normalized version rebuilding js and css failed the following required files are missing traceback most recent call last file line in file home dblank notebook setup py line in main file home dblank notebook setup py line in main setup setup args file usr lib distutils core py line in setup dist run commands file usr lib distutils dist py line in run commands self run command cmd file usr lib distutils dist py line in run command cmd obj run file home dblank notebook setupbase py line in run raise e file home dblank notebook setupbase py line in run self distribution run command js file usr lib distutils dist py line in run command cmd obj run file home dblank notebook setupbase py line in run run file home dblank notebook setupbase py line in run return check call cmd args kwargs file usr lib subprocess py line in check call raise calledprocesserror retcode cmd subprocess calledprocesserror command returned non zero exit status command usr bin c import setuptools tokenize file home dblank notebook setup py exec compile getattr tokenize open open file read replace r n n file exec develop no deps user prefix failed with error code in home dblank notebook i tried many things but eventually i went through the travis yml noted the use of nvm and did the following curl sh nvm install nvm use npm upgrade g npm which doesn t seem to be documented anywhere but afterwards i was able to build and install the notebook from source | 0 |
602,320 | 18,466,775,856 | IssuesEvent | 2021-10-17 02:23:40 | matrixorigin/matrixcube | https://api.github.com/repos/matrixorigin/matrixcube | closed | rename replica_pending_proposal.go, replica_event_read_index.go and replica_log_reader.go | component/raftstore priority/medium kind/refactoring | replica_*.go should be implementing a part of the replica type. | 1.0 | rename replica_pending_proposal.go, replica_event_read_index.go and replica_log_reader.go - replica_*.go should be implementing a part of the replica type. | non_test | rename replica pending proposal go replica event read index go and replica log reader go replica go should be implementing a part of the replica type | 0 |
190,304 | 14,541,496,770 | IssuesEvent | 2020-12-15 14:38:25 | cyfronet-fid/sat4envi | https://api.github.com/repos/cyfronet-fid/sat4envi | closed | [FIX] In the generated report and inconsistent names | bug dev-env-test pre-prod-test | Tested on instance https://sok.grid.cyfronet.pl
SOK version v13.2.0
**Steps:**
1. Log in zkAdmin account
2. Click on the link "Generuj Raport"
3. Fill in the field "Tytuł" and "Notatka"
4. Click on the button "Zapisz raport na dysku"
5. Open generated report
**What happens?**
Field "Notatka" in the generated report is called "Opis"
**What was expected to happen?**
The field's name in the modal is the same how in the generated report.
| 2.0 | [FIX] In the generated report and inconsistent names - Tested on instance https://sok.grid.cyfronet.pl
SOK version v13.2.0
**Steps:**
1. Log in zkAdmin account
2. Click on the link "Generuj Raport"
3. Fill in the field "Tytuł" and "Notatka"
4. Click on the button "Zapisz raport na dysku"
5. Open generated report
**What happens?**
Field "Notatka" in the generated report is called "Opis"
**What was expected to happen?**
The field's name in the modal is the same how in the generated report.
| test | in the generated report and inconsistent names tested on instance sok version steps log in zkadmin account click on the link generuj raport fill in the field tytuł and notatka click on the button zapisz raport na dysku open generated report what happens field notatka in the generated report is called opis what was expected to happen the field s name in the modal is the same how in the generated report | 1 |
125,912 | 4,969,662,691 | IssuesEvent | 2016-12-05 14:05:20 | palantir/atlasdb | https://api.github.com/repos/palantir/atlasdb | closed | AtlasDB clients cannot communicate via load balancers | component: HA priority: P2 type: bug | As a user of an AtlasDB product, I would like to put my product into HA configuration, with each client communicating via load balancers. This would be useful when setting up AtlasDB product in a cloud environment with custom certificates, as it makes the management of those certificates easier.
Here is one example of where this breaks:
1. The AtlasDB leader is killed
2. When another node wants a timestamp, it continues to ask the load balancer for the old leader, since this is cached in our remote proxy
3. The load balancer responds with a 503
4. The node asking for the timestamp doesn't consider this a retriable exception, and propogates the error up to the user, instead of trying another one
(The above case may also be a reproducer of #1000, discovered by @ungureanuvladvictor).
We can resolve the above case by making 503 a retriable exception, but we also need to take care to ensure that we don't introduce performance issues.
There may be further issues that we encounter. | 1.0 | AtlasDB clients cannot communicate via load balancers - As a user of an AtlasDB product, I would like to put my product into HA configuration, with each client communicating via load balancers. This would be useful when setting up AtlasDB product in a cloud environment with custom certificates, as it makes the management of those certificates easier.
Here is one example of where this breaks:
1. The AtlasDB leader is killed
2. When another node wants a timestamp, it continues to ask the load balancer for the old leader, since this is cached in our remote proxy
3. The load balancer responds with a 503
4. The node asking for the timestamp doesn't consider this a retriable exception, and propogates the error up to the user, instead of trying another one
(The above case may also be a reproducer of #1000, discovered by @ungureanuvladvictor).
We can resolve the above case by making 503 a retriable exception, but we also need to take care to ensure that we don't introduce performance issues.
There may be further issues that we encounter. | non_test | atlasdb clients cannot communicate via load balancers as a user of an atlasdb product i would like to put my product into ha configuration with each client communicating via load balancers this would be useful when setting up atlasdb product in a cloud environment with custom certificates as it makes the management of those certificates easier here is one example of where this breaks the atlasdb leader is killed when another node wants a timestamp it continues to ask the load balancer for the old leader since this is cached in our remote proxy the load balancer responds with a the node asking for the timestamp doesn t consider this a retriable exception and propogates the error up to the user instead of trying another one the above case may also be a reproducer of discovered by ungureanuvladvictor we can resolve the above case by making a retriable exception but we also need to take care to ensure that we don t introduce performance issues there may be further issues that we encounter | 0 |
164,684 | 12,812,218,549 | IssuesEvent | 2020-07-04 04:41:45 | PopulateTools/gobierto | https://api.github.com/repos/PopulateTools/gobierto | closed | Flaky test GobiertoBudgets::BudgetsTest#test_home_bubbles | flaky-test | ```
GobiertoBudgets::BudgetsTest#test_home_bubbles
[**************/gobierto/test/integration/gobierto_budgets/budgets_test.rb:42]
Minitest::Assertion: Expected: "Otros impuestos indirectos"
Actual: ""
``` | 1.0 | Flaky test GobiertoBudgets::BudgetsTest#test_home_bubbles - ```
GobiertoBudgets::BudgetsTest#test_home_bubbles
[**************/gobierto/test/integration/gobierto_budgets/budgets_test.rb:42]
Minitest::Assertion: Expected: "Otros impuestos indirectos"
Actual: ""
``` | test | flaky test gobiertobudgets budgetstest test home bubbles gobiertobudgets budgetstest test home bubbles minitest assertion expected otros impuestos indirectos actual | 1 |
155,892 | 5,962,683,269 | IssuesEvent | 2017-05-30 00:04:30 | input-output-hk/cardano-sl | https://api.github.com/repos/input-output-hk/cardano-sl | closed | [CSL-41] Sanitizing & bug discovery | Mirroring Priority:Minor State:Done Type:Task | <blockquote>@georgeee</blockquote>
CSL even on it's early stage is a system with non-trivial workflows and not always opaque behavior. Sometimes one needs to peer in logs for hours to understand why system in whole works not as expected.
This issue is for such kind of activity.
Please if you find a bug (which is more than 10 mins to fix), *create a separate issue for it*.
<!--MIRROR_META={"service":"youtrack","id":"CSL-41"}--> | 1.0 | [CSL-41] Sanitizing & bug discovery - <blockquote>@georgeee</blockquote>
CSL even on it's early stage is a system with non-trivial workflows and not always opaque behavior. Sometimes one needs to peer in logs for hours to understand why system in whole works not as expected.
This issue is for such kind of activity.
Please if you find a bug (which is more than 10 mins to fix), *create a separate issue for it*.
<!--MIRROR_META={"service":"youtrack","id":"CSL-41"}--> | non_test | sanitizing bug discovery georgeee csl even on it s early stage is a system with non trivial workflows and not always opaque behavior sometimes one needs to peer in logs for hours to understand why system in whole works not as expected this issue is for such kind of activity please if you find a bug which is more than mins to fix create a separate issue for it | 0 |
433,762 | 30,348,803,393 | IssuesEvent | 2023-07-11 17:18:53 | wp-graphql/wp-graphql-acf | https://api.github.com/repos/wp-graphql/wp-graphql-acf | closed | ACF page link & Taxonomy link - cant access values chosen | bug Documentation Field Type: Relationship Field Type: Post Object | It is listed as supported, but requires extra {} in the query, but the suggestion of graphiql is always "__typename" and won't suggest other fields. Perhaps I just need to know the underlying default values in the array.
```
{
events {
nodes {
title
content
attr { //ACF
eventLink
eventLinkLabel
internalEventLink { //<< THIS BAD BOY RIGHT HERE
__typename
}
datetime
endTime
audience
venueLocation
eventImage {
sourceUrl//<< OLD MATE HERE SUGGESTED ME A FEILD A-OK
}
bigOrSmall
}
}
}
}
```
| 1.0 | ACF page link & Taxonomy link - cant access values chosen - It is listed as supported, but requires extra {} in the query, but the suggestion of graphiql is always "__typename" and won't suggest other fields. Perhaps I just need to know the underlying default values in the array.
```
{
events {
nodes {
title
content
attr { //ACF
eventLink
eventLinkLabel
internalEventLink { //<< THIS BAD BOY RIGHT HERE
__typename
}
datetime
endTime
audience
venueLocation
eventImage {
sourceUrl//<< OLD MATE HERE SUGGESTED ME A FEILD A-OK
}
bigOrSmall
}
}
}
}
```
| non_test | acf page link taxonomy link cant access values chosen it is listed as supported but requires extra in the query but the suggestion of graphiql is always typename and won t suggest other fields perhaps i just need to know the underlying default values in the array events nodes title content attr acf eventlink eventlinklabel internaleventlink this bad boy right here typename datetime endtime audience venuelocation eventimage sourceurl old mate here suggested me a feild a ok bigorsmall | 0 |
294,207 | 25,352,266,593 | IssuesEvent | 2022-11-19 22:58:39 | MichaIng/DietPi | https://api.github.com/repos/MichaIng/DietPi | closed | Open Beta v8.11 | Please help testing and hardening our upcoming release | Information :information_source: Beta :test_tube: | RC version | v8.11.2
---------- | -------
v8.11.0 PR | #5867
v8.11.1 PR | #5875
v8.11.2 PR | #5894
Raw changelog | https://github.com/MichaIng/DietPi/blob/beta/CHANGELOG.txt
Code changes | https://github.com/MichaIng/DietPi/compare/master...beta
Release date | **2022-11-19**
### How to apply: https://github.com/MichaIng/DietPi/blob/master/BRANCH_SYSTEM.md
#### Related/solved issues: https://github.com/MichaIng/DietPi/issues?q=is%3Aissue+milestone%3Av8.11
____
### Beta v8.11.2
_(2022-11-19)_
#### New images
- NanoPi R5S | Our NanoPi R5S images have been updated to ship with WireGuard support and a cleaner rootfs built from scratch.
#### New software
- Homer | Added a simple HOMepage for your servER to keep your services on hand, with software ID 5. Many thanks to @t3dium for implementing this software title: https://github.com/MichaIng/DietPi/pull/5833
#### Enhancements
- Quartz64 | The firmware package has been updated to ship with Linux v6.1.0-rc1 and firmware for onboard WiFi, respectively the PINE64 WiFi module. Furthermore, we moved to mainline U-Boot, which solves some boot issues with certain SD card and eMMC models. You will be asked during dietpi-update whether you want to upgrade it on your system.
- NanoPi NEO3 | Switched back to the again available NEO3 device tree, resolving potential hardware feature issues.
- NanoPi R2S/R4S | Enabled the Ethernet status LEDs by default. Many thanks to @TheLinuxGuy for bringing up this topic: https://github.com/MichaIng/DietPi/issues/5538
- DietPi-Software | Shairport Sync: Updated to version 4.1 and added the option to install an AirPlay 2 ready build. The update and offer to switch to AirPlay 2 can be applied via reinstall: dietpi-software reinstall 37
- DietPi-Software | NoMachine: Bumped version to latest stable v8.1.2_1, update via reinstall: dietpi-software reinstall 30
- DietPi-Software | HAProxy: Bumped version to latest stable v2.6.6, update via reinstall: dietpi-software reinstall 98
- DietPi-Software | Grafana: For ARMv6 RPi models, RPi 1 and Zero (1), bumped version to latest stable v9.2.4, update via reinstall: dietpi-software reinstall 77
- DietPi-Software | Grafana: Updated the APT list to use the new repository: https://grafana.com/docs/grafana/latest/setup-grafana/installation/debian/#repository-migration-november-8th-2022
- DietPi-Software | Webservers: The strict dependency on PHP has been removed. It is hence now possible to install any webserver via dietpi-software without having PHP installed forcefully as well. This became required for Homer, which is a purely static webpage.
- DietPi-Software | Nextcloud: Re-enabled the install option for ARMv6/ARMv7 systems. Nextcloud 25 is the last version which supports 32-bit systems, so be aware that you will not receive major version upgrades anymore if you do not use 64-bit hardware with an ARMv8/64-bit image. Many thanks to @PaulPink for bringing up the topic: https://github.com/MichaIng/DietPi/issues/5888
- DietPi-Software | Remote.It: Update the product name (Remot3.it -> Remote.It), information and package to the latest and remove the old information "Weaved".
#### Bug fixes
- ROCK 3A | Resolved an issue where the image wouldn't boot because of a wrong filesystem UUID.
- Quartz64/ASUS Tinker Board | Resolved an issue where Docker and K3s failed to start on these boards because of missing BPF cgroup support. Many thanks to @am9zZWY and @sandvaer for reporting this issue: https://github.com/MichaIng/DietPi/issues/5890, https://github.com/MichaIng/DietPi/issues/5554
- DietPi-DDNS | Resolved an issue where IPv6 was forced when if was chosen to not force any IP family. Many thanks to @champymarty for reporting this issue: https://github.com/MichaIng/DietPi/issues/5830
- DietPi-Software | Navidrome: Resolved an issue where on reinstalls the config was was overwritten. Many thanks to @pedrom34 for reporting this issue: https://github.com/MichaIng/DietPi/issues/5840
- DietPi-Software | Home Assistant: Resolved an issue where some modules didn't work on ARMv6 and ARMv7 systems because of missing runtime libraries. Many thanks to `@mail2rst` and `@HyperCriSiS` for reporting this issue: https://dietpi.com/forum/t/after-the-update-homeassistant-mqtt-broker-integration-broken/14719, https://dietpi.com/forum/t/home-assistant-issues-after-latest-upate/14749
- DietPi-Software | Go: Resolved an issue, introduced with DietPi v8.9, where the Go compiler and development tools were not added to PATH. Many thanks to `@envious_jag` for reporting this issue: https://dietpi.com/forum/t/installation-snowflake/6566/10
- DietPi-Software | RoonBridge/RoonServer: Resolved an issue where the download fails as Roon downloads are now hosted on a different domain. Many thanks to @net-david for reporting this issue: https://github.com/MichaIng/DietPi/issues/5856
- DietPi-Software | Koel: Resolved an issue where the install failed on Buster and Bullseye systems since Koel v6 requires PHP 8.0 or later.
- DietPi-Software | Deluge: Resolved an issue on Bullseye and Bookworm, where Deluge by default did not listen on any port or torrent connections, since the port range feature seems to be broken. It does now listen on the single port 6882 only by default. Many thanks to `@Tarrasque` for reporting this issue: https://dietpi.com/forum/t/deluge-does-not-download-anything/14376
- DietPi-Software | Xfce: Resolved an issue where the default desktop launchers/icons could not be executed without warning and confirmation due to missing execute bit. Many thanks to @HolgerTB for reporting this issue.
- DietPi-Software | ownCloud/Nextcloud: Resolved an issue where the HSTS header was not set as expected (DietPi v7.8 regression). Many thanks to `@caio1007` for reporting this issue: https://dietpi.com/forum/t/warnings-in-the-configuration-nextcloud/15002/13 | 1.0 | Open Beta v8.11 | Please help testing and hardening our upcoming release - RC version | v8.11.2
---------- | -------
v8.11.0 PR | #5867
v8.11.1 PR | #5875
v8.11.2 PR | #5894
Raw changelog | https://github.com/MichaIng/DietPi/blob/beta/CHANGELOG.txt
Code changes | https://github.com/MichaIng/DietPi/compare/master...beta
Release date | **2022-11-19**
### How to apply: https://github.com/MichaIng/DietPi/blob/master/BRANCH_SYSTEM.md
#### Related/solved issues: https://github.com/MichaIng/DietPi/issues?q=is%3Aissue+milestone%3Av8.11
____
### Beta v8.11.2
_(2022-11-19)_
#### New images
- NanoPi R5S | Our NanoPi R5S images have been updated to ship with WireGuard support and a cleaner rootfs built from scratch.
#### New software
- Homer | Added a simple HOMepage for your servER to keep your services on hand, with software ID 5. Many thanks to @t3dium for implementing this software title: https://github.com/MichaIng/DietPi/pull/5833
#### Enhancements
- Quartz64 | The firmware package has been updated to ship with Linux v6.1.0-rc1 and firmware for onboard WiFi, respectively the PINE64 WiFi module. Furthermore, we moved to mainline U-Boot, which solves some boot issues with certain SD card and eMMC models. You will be asked during dietpi-update whether you want to upgrade it on your system.
- NanoPi NEO3 | Switched back to the again available NEO3 device tree, resolving potential hardware feature issues.
- NanoPi R2S/R4S | Enabled the Ethernet status LEDs by default. Many thanks to @TheLinuxGuy for bringing up this topic: https://github.com/MichaIng/DietPi/issues/5538
- DietPi-Software | Shairport Sync: Updated to version 4.1 and added the option to install an AirPlay 2 ready build. The update and offer to switch to AirPlay 2 can be applied via reinstall: dietpi-software reinstall 37
- DietPi-Software | NoMachine: Bumped version to latest stable v8.1.2_1, update via reinstall: dietpi-software reinstall 30
- DietPi-Software | HAProxy: Bumped version to latest stable v2.6.6, update via reinstall: dietpi-software reinstall 98
- DietPi-Software | Grafana: For ARMv6 RPi models, RPi 1 and Zero (1), bumped version to latest stable v9.2.4, update via reinstall: dietpi-software reinstall 77
- DietPi-Software | Grafana: Updated the APT list to use the new repository: https://grafana.com/docs/grafana/latest/setup-grafana/installation/debian/#repository-migration-november-8th-2022
- DietPi-Software | Webservers: The strict dependency on PHP has been removed. It is hence now possible to install any webserver via dietpi-software without having PHP installed forcefully as well. This became required for Homer, which is a purely static webpage.
- DietPi-Software | Nextcloud: Re-enabled the install option for ARMv6/ARMv7 systems. Nextcloud 25 is the last version which supports 32-bit systems, so be aware that you will not receive major version upgrades anymore if you do not use 64-bit hardware with an ARMv8/64-bit image. Many thanks to @PaulPink for bringing up the topic: https://github.com/MichaIng/DietPi/issues/5888
- DietPi-Software | Remote.It: Update the product name (Remot3.it -> Remote.It), information and package to the latest and remove the old information "Weaved".
#### Bug fixes
- ROCK 3A | Resolved an issue where the image wouldn't boot because of a wrong filesystem UUID.
- Quartz64/ASUS Tinker Board | Resolved an issue where Docker and K3s failed to start on these boards because of missing BPF cgroup support. Many thanks to @am9zZWY and @sandvaer for reporting this issue: https://github.com/MichaIng/DietPi/issues/5890, https://github.com/MichaIng/DietPi/issues/5554
- DietPi-DDNS | Resolved an issue where IPv6 was forced when if was chosen to not force any IP family. Many thanks to @champymarty for reporting this issue: https://github.com/MichaIng/DietPi/issues/5830
- DietPi-Software | Navidrome: Resolved an issue where on reinstalls the config was was overwritten. Many thanks to @pedrom34 for reporting this issue: https://github.com/MichaIng/DietPi/issues/5840
- DietPi-Software | Home Assistant: Resolved an issue where some modules didn't work on ARMv6 and ARMv7 systems because of missing runtime libraries. Many thanks to `@mail2rst` and `@HyperCriSiS` for reporting this issue: https://dietpi.com/forum/t/after-the-update-homeassistant-mqtt-broker-integration-broken/14719, https://dietpi.com/forum/t/home-assistant-issues-after-latest-upate/14749
- DietPi-Software | Go: Resolved an issue, introduced with DietPi v8.9, where the Go compiler and development tools were not added to PATH. Many thanks to `@envious_jag` for reporting this issue: https://dietpi.com/forum/t/installation-snowflake/6566/10
- DietPi-Software | RoonBridge/RoonServer: Resolved an issue where the download fails as Roon downloads are now hosted on a different domain. Many thanks to @net-david for reporting this issue: https://github.com/MichaIng/DietPi/issues/5856
- DietPi-Software | Koel: Resolved an issue where the install failed on Buster and Bullseye systems since Koel v6 requires PHP 8.0 or later.
- DietPi-Software | Deluge: Resolved an issue on Bullseye and Bookworm, where Deluge by default did not listen on any port or torrent connections, since the port range feature seems to be broken. It does now listen on the single port 6882 only by default. Many thanks to `@Tarrasque` for reporting this issue: https://dietpi.com/forum/t/deluge-does-not-download-anything/14376
- DietPi-Software | Xfce: Resolved an issue where the default desktop launchers/icons could not be executed without warning and confirmation due to missing execute bit. Many thanks to @HolgerTB for reporting this issue.
- DietPi-Software | ownCloud/Nextcloud: Resolved an issue where the HSTS header was not set as expected (DietPi v7.8 regression). Many thanks to `@caio1007` for reporting this issue: https://dietpi.com/forum/t/warnings-in-the-configuration-nextcloud/15002/13 | test | open beta please help testing and hardening our upcoming release rc version pr pr pr raw changelog code changes release date how to apply related solved issues beta new images nanopi our nanopi images have been updated to ship with wireguard support and a cleaner rootfs built from scratch new software homer added a simple homepage for your server to keep your services on hand with software id many thanks to for implementing this software title enhancements the firmware package has been updated to ship with linux and firmware for onboard wifi respectively the wifi module furthermore we moved to mainline u boot which solves some boot issues with certain sd card and emmc models you will be asked during dietpi update whether you want to upgrade it on your system nanopi switched back to the again available device tree resolving potential hardware feature issues nanopi enabled the ethernet status leds by default many thanks to thelinuxguy for bringing up this topic dietpi software shairport sync updated to version and added the option to install an airplay ready build the update and offer to switch to airplay can be applied via reinstall dietpi software reinstall dietpi software nomachine bumped version to latest stable update via reinstall dietpi software reinstall dietpi software haproxy bumped version to latest stable update via reinstall dietpi software reinstall dietpi software grafana for rpi models rpi and zero bumped version to latest stable update via reinstall dietpi software reinstall dietpi software grafana updated the apt list to use the new repository dietpi software webservers the strict dependency on php has been removed it is hence now possible to install any webserver via dietpi software without having php installed forcefully as well this became required for homer which is a purely static webpage dietpi software nextcloud re enabled the install option for systems nextcloud is the last version which supports bit systems so be aware that you will not receive major version upgrades anymore if you do not use bit hardware with an bit image many thanks to paulpink for bringing up the topic dietpi software remote it update the product name it remote it information and package to the latest and remove the old information weaved bug fixes rock resolved an issue where the image wouldn t boot because of a wrong filesystem uuid asus tinker board resolved an issue where docker and failed to start on these boards because of missing bpf cgroup support many thanks to and sandvaer for reporting this issue dietpi ddns resolved an issue where was forced when if was chosen to not force any ip family many thanks to champymarty for reporting this issue dietpi software navidrome resolved an issue where on reinstalls the config was was overwritten many thanks to for reporting this issue dietpi software home assistant resolved an issue where some modules didn t work on and systems because of missing runtime libraries many thanks to and hypercrisis for reporting this issue dietpi software go resolved an issue introduced with dietpi where the go compiler and development tools were not added to path many thanks to envious jag for reporting this issue dietpi software roonbridge roonserver resolved an issue where the download fails as roon downloads are now hosted on a different domain many thanks to net david for reporting this issue dietpi software koel resolved an issue where the install failed on buster and bullseye systems since koel requires php or later dietpi software deluge resolved an issue on bullseye and bookworm where deluge by default did not listen on any port or torrent connections since the port range feature seems to be broken it does now listen on the single port only by default many thanks to tarrasque for reporting this issue dietpi software xfce resolved an issue where the default desktop launchers icons could not be executed without warning and confirmation due to missing execute bit many thanks to holgertb for reporting this issue dietpi software owncloud nextcloud resolved an issue where the hsts header was not set as expected dietpi regression many thanks to for reporting this issue | 1 |
75,467 | 20,825,341,605 | IssuesEvent | 2022-03-18 20:05:19 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Depending on packages which use `TextSelectionOverlay.fadeDuration` results in build failure | severe: regression framework a: typography a: build has reproducible steps found in release: 2.13 found in release: 2.12 | <!-- Thank you for using Flutter!
If you are looking for support, please check out our documentation
or consider asking a question on Stack Overflow:
* https://flutter.dev/
* https://api.flutter.dev/
* https://stackoverflow.com/questions/tagged/flutter?sort=frequent
If you have found a bug or if our documentation doesn't have an answer
to what you're looking for, then fill out the template below. Please read
our guide to filing a bug first: https://flutter.dev/docs/resources/bug-reports
-->
## Steps to Reproduce
If some app is depend on a library (ex. [flutter_math_fork](https://pub.dev/packages/flutter_math_fork)) that uses `TextSelectionOverlay.fadeDuration`, the app will not be build with flutter 2.12.0-4.1.pre or higher.
ref https://github.com/flutter/flutter/pull/98153
---
In the library [flutter_math_fork](https://pub.dev/packages/flutter_math_fork), `TextSelectionOverlay.fadeDuration` is used in the following line.
https://github.com/simpleclub-extended/flutter_math_fork/blob/a6f0c766a660b38c767fb12486672165630a8a69/lib/src/widgets/selection/handle_overlay.dart#L60
So, applications using flutter_math_fork cannot upgrade flutter until flutter_math_fork is updated.
On the other hand, if another library updates flutter to use `SelectionOverlay.fadeDuration`, the developer will need to modify that library's version. flutter_math_fork seems to be a popular library, but perhaps other libraries will have this problem as well.
[search result](https://github.com/search?l=Dart&q=TextSelectionOverlay+fadeDuration&type=Code)
Would it be possible to add the following deprecated const value?
```dart
class TextSelectionOverlay {
/// Controls the fade-in and fade-out animations for the toolbar and handles.
@Deprecated(
'Use `SelectionOverlay.fadeDuration` instead. '
'This value was deprecated in Flutter 2.12.0-4.1.pre'
)
static const Duration fadeDuration = SelectionOverlay.fadeDuration;
}
```
**Expected results:** <!-- what did you want to see? -->
No build errors.
**Actual results:** <!-- what did you see? -->
An error occurs during build.
```
../../../.pub-cache/hosted/pub.dartlang.org/flutter_math_fork-0.6.1/lib/src/widgets/selection/handle_overlay.dart:60:40:
Error: Member not found: 'fadeDuration'.
duration: TextSelectionOverlay.fadeDuration, vsync: this);
```
<details>
<summary>Code sample</summary>
<!--
Please create a minimal reproducible sample that shows the problem
and attach it below between the lines with the backticks.
To create it you can use `flutter create bug` command and update the `main.dart` file.
Alternatively, you can use https://dartpad.dev/
which is capable of creating and running small Flutter apps.
Without this we will unlikely be able to progress on the issue, and because of that
we regretfully will have to close it.
-->
```dart
```
</details>
<details>
<summary>Logs</summary>
<!--
Run your application with `flutter run --verbose` and attach all the
log output below between the lines with the backticks. If there is an
exception, please see if the error message includes enough information
to explain how to solve the issue.
-->
```
../../../.pub-cache/hosted/[pub.dartlang.org/flutter_math_fork-0.6.1/lib/src/widgets/selection/handle_overlay.dart:60:40](http://pub.dartlang.org/flutter_math_fork-0.6.1/lib/src/widgets/selection/handle_overlay.dart:60:40):
Error: Member not found: 'fadeDuration'.
duration: TextSelectionOverlay.fadeDuration, vsync: this);
```
<!--
Run `flutter analyze` and attach any output of that command below.
If there are any analysis errors, try resolving them before filing this issue.
-->
```
```
<!-- Finally, paste the output of running `flutter doctor -v` here. -->
```
$ flutter doctor -v
[✓] Flutter (Channel beta, 2.12.0-4.1.pre, on macOS 12.3 21E230 darwin-arm,
locale ja-JP)
• Flutter version 2.12.0-4.1.pre at /Users/koji/flutter
• Upstream repository https://github.com/flutter/flutter.git
• Framework revision 680962aa75 (30 hours ago), 2022-03-16 13:46:03 -0700
• Engine revision e9f57b5d0f
• Dart version 2.17.0 (build 2.17.0-182.1.beta)
• DevTools version 2.11.1
[!] Android toolchain - develop for Android devices (Android SDK version 32.0.0)
• Android SDK at /Users/koji/Library/Android/sdk
✗ cmdline-tools component is missing
Run `path/to/sdkmanager --install "cmdline-tools;latest"`
See https://developer.android.com/studio/command-line for more details.
✗ Android license status unknown.
Run `flutter doctor --android-licenses` to accept the SDK licenses.
See https://flutter.dev/docs/get-started/install/macos#android-setup for
more details.
[✓] Xcode - develop for iOS and macOS (Xcode 13.3)
• Xcode at /Applications/Xcode.app/Contents/Developer
• CocoaPods version 1.11.2
[✓] Chrome - develop for the web
• Chrome at /Applications/Google Chrome.app/Contents/MacOS/Google Chrome
[✓] Android Studio (version 2021.1)
• Android Studio at /Applications/Android Studio.app/Contents
• Flutter plugin can be installed from:
🔨 https://plugins.jetbrains.com/plugin/9212-flutter
• Dart plugin can be installed from:
🔨 https://plugins.jetbrains.com/plugin/6351-dart
• Java version OpenJDK Runtime Environment (build 11.0.11+0-b60-7772763)
[✓] IntelliJ IDEA Community Edition (version 2021.3.3)
• IntelliJ at /Applications/IntelliJ IDEA CE.app
• Flutter plugin version 65.2.4
• Dart plugin version 213.7227
[✓] VS Code (version 1.65.2)
• VS Code at /Applications/Visual Studio Code.app/Contents
• Flutter extension can be installed from:
🔨 https://marketplace.visualstudio.com/items?itemName=Dart-Code.flutter
[✓] Connected device (1 available)
• Chrome (web) • chrome • web-javascript • Google Chrome 99.0.4844.74
[✓] HTTP Host Availability
• All required HTTP hosts are available
! Doctor found issues in 1 category.
```
</details>
<!--
Consider also attaching screenshots and/or videos to better
illustrate the issue.
You can upload them directly on GitHub.
Beware that video file size is limited to 10MB.
--> | 1.0 | Depending on packages which use `TextSelectionOverlay.fadeDuration` results in build failure - <!-- Thank you for using Flutter!
If you are looking for support, please check out our documentation
or consider asking a question on Stack Overflow:
* https://flutter.dev/
* https://api.flutter.dev/
* https://stackoverflow.com/questions/tagged/flutter?sort=frequent
If you have found a bug or if our documentation doesn't have an answer
to what you're looking for, then fill out the template below. Please read
our guide to filing a bug first: https://flutter.dev/docs/resources/bug-reports
-->
## Steps to Reproduce
If some app is depend on a library (ex. [flutter_math_fork](https://pub.dev/packages/flutter_math_fork)) that uses `TextSelectionOverlay.fadeDuration`, the app will not be build with flutter 2.12.0-4.1.pre or higher.
ref https://github.com/flutter/flutter/pull/98153
---
In the library [flutter_math_fork](https://pub.dev/packages/flutter_math_fork), `TextSelectionOverlay.fadeDuration` is used in the following line.
https://github.com/simpleclub-extended/flutter_math_fork/blob/a6f0c766a660b38c767fb12486672165630a8a69/lib/src/widgets/selection/handle_overlay.dart#L60
So, applications using flutter_math_fork cannot upgrade flutter until flutter_math_fork is updated.
On the other hand, if another library updates flutter to use `SelectionOverlay.fadeDuration`, the developer will need to modify that library's version. flutter_math_fork seems to be a popular library, but perhaps other libraries will have this problem as well.
[search result](https://github.com/search?l=Dart&q=TextSelectionOverlay+fadeDuration&type=Code)
Would it be possible to add the following deprecated const value?
```dart
class TextSelectionOverlay {
/// Controls the fade-in and fade-out animations for the toolbar and handles.
@Deprecated(
'Use `SelectionOverlay.fadeDuration` instead. '
'This value was deprecated in Flutter 2.12.0-4.1.pre'
)
static const Duration fadeDuration = SelectionOverlay.fadeDuration;
}
```
**Expected results:** <!-- what did you want to see? -->
No build errors.
**Actual results:** <!-- what did you see? -->
An error occurs during build.
```
../../../.pub-cache/hosted/pub.dartlang.org/flutter_math_fork-0.6.1/lib/src/widgets/selection/handle_overlay.dart:60:40:
Error: Member not found: 'fadeDuration'.
duration: TextSelectionOverlay.fadeDuration, vsync: this);
```
<details>
<summary>Code sample</summary>
<!--
Please create a minimal reproducible sample that shows the problem
and attach it below between the lines with the backticks.
To create it you can use `flutter create bug` command and update the `main.dart` file.
Alternatively, you can use https://dartpad.dev/
which is capable of creating and running small Flutter apps.
Without this we will unlikely be able to progress on the issue, and because of that
we regretfully will have to close it.
-->
```dart
```
</details>
<details>
<summary>Logs</summary>
<!--
Run your application with `flutter run --verbose` and attach all the
log output below between the lines with the backticks. If there is an
exception, please see if the error message includes enough information
to explain how to solve the issue.
-->
```
../../../.pub-cache/hosted/[pub.dartlang.org/flutter_math_fork-0.6.1/lib/src/widgets/selection/handle_overlay.dart:60:40](http://pub.dartlang.org/flutter_math_fork-0.6.1/lib/src/widgets/selection/handle_overlay.dart:60:40):
Error: Member not found: 'fadeDuration'.
duration: TextSelectionOverlay.fadeDuration, vsync: this);
```
<!--
Run `flutter analyze` and attach any output of that command below.
If there are any analysis errors, try resolving them before filing this issue.
-->
```
```
<!-- Finally, paste the output of running `flutter doctor -v` here. -->
```
$ flutter doctor -v
[✓] Flutter (Channel beta, 2.12.0-4.1.pre, on macOS 12.3 21E230 darwin-arm,
locale ja-JP)
• Flutter version 2.12.0-4.1.pre at /Users/koji/flutter
• Upstream repository https://github.com/flutter/flutter.git
• Framework revision 680962aa75 (30 hours ago), 2022-03-16 13:46:03 -0700
• Engine revision e9f57b5d0f
• Dart version 2.17.0 (build 2.17.0-182.1.beta)
• DevTools version 2.11.1
[!] Android toolchain - develop for Android devices (Android SDK version 32.0.0)
• Android SDK at /Users/koji/Library/Android/sdk
✗ cmdline-tools component is missing
Run `path/to/sdkmanager --install "cmdline-tools;latest"`
See https://developer.android.com/studio/command-line for more details.
✗ Android license status unknown.
Run `flutter doctor --android-licenses` to accept the SDK licenses.
See https://flutter.dev/docs/get-started/install/macos#android-setup for
more details.
[✓] Xcode - develop for iOS and macOS (Xcode 13.3)
• Xcode at /Applications/Xcode.app/Contents/Developer
• CocoaPods version 1.11.2
[✓] Chrome - develop for the web
• Chrome at /Applications/Google Chrome.app/Contents/MacOS/Google Chrome
[✓] Android Studio (version 2021.1)
• Android Studio at /Applications/Android Studio.app/Contents
• Flutter plugin can be installed from:
🔨 https://plugins.jetbrains.com/plugin/9212-flutter
• Dart plugin can be installed from:
🔨 https://plugins.jetbrains.com/plugin/6351-dart
• Java version OpenJDK Runtime Environment (build 11.0.11+0-b60-7772763)
[✓] IntelliJ IDEA Community Edition (version 2021.3.3)
• IntelliJ at /Applications/IntelliJ IDEA CE.app
• Flutter plugin version 65.2.4
• Dart plugin version 213.7227
[✓] VS Code (version 1.65.2)
• VS Code at /Applications/Visual Studio Code.app/Contents
• Flutter extension can be installed from:
🔨 https://marketplace.visualstudio.com/items?itemName=Dart-Code.flutter
[✓] Connected device (1 available)
• Chrome (web) • chrome • web-javascript • Google Chrome 99.0.4844.74
[✓] HTTP Host Availability
• All required HTTP hosts are available
! Doctor found issues in 1 category.
```
</details>
<!--
Consider also attaching screenshots and/or videos to better
illustrate the issue.
You can upload them directly on GitHub.
Beware that video file size is limited to 10MB.
--> | non_test | depending on packages which use textselectionoverlay fadeduration results in build failure thank you for using flutter if you are looking for support please check out our documentation or consider asking a question on stack overflow if you have found a bug or if our documentation doesn t have an answer to what you re looking for then fill out the template below please read our guide to filing a bug first steps to reproduce if some app is depend on a library ex that uses textselectionoverlay fadeduration the app will not be build with flutter pre or higher ref in the library textselectionoverlay fadeduration is used in the following line so applications using flutter math fork cannot upgrade flutter until flutter math fork is updated on the other hand if another library updates flutter to use selectionoverlay fadeduration the developer will need to modify that library s version flutter math fork seems to be a popular library but perhaps other libraries will have this problem as well would it be possible to add the following deprecated const value dart class textselectionoverlay controls the fade in and fade out animations for the toolbar and handles deprecated use selectionoverlay fadeduration instead this value was deprecated in flutter pre static const duration fadeduration selectionoverlay fadeduration expected results no build errors actual results an error occurs during build pub cache hosted pub dartlang org flutter math fork lib src widgets selection handle overlay dart error member not found fadeduration duration textselectionoverlay fadeduration vsync this code sample please create a minimal reproducible sample that shows the problem and attach it below between the lines with the backticks to create it you can use flutter create bug command and update the main dart file alternatively you can use which is capable of creating and running small flutter apps without this we will unlikely be able to progress on the issue and because of that we regretfully will have to close it dart logs run your application with flutter run verbose and attach all the log output below between the lines with the backticks if there is an exception please see if the error message includes enough information to explain how to solve the issue pub cache hosted error member not found fadeduration duration textselectionoverlay fadeduration vsync this run flutter analyze and attach any output of that command below if there are any analysis errors try resolving them before filing this issue flutter doctor v flutter channel beta pre on macos darwin arm locale ja jp • flutter version pre at users koji flutter • upstream repository • framework revision hours ago • engine revision • dart version build beta • devtools version android toolchain develop for android devices android sdk version • android sdk at users koji library android sdk ✗ cmdline tools component is missing run path to sdkmanager install cmdline tools latest see for more details ✗ android license status unknown run flutter doctor android licenses to accept the sdk licenses see for more details xcode develop for ios and macos xcode • xcode at applications xcode app contents developer • cocoapods version chrome develop for the web • chrome at applications google chrome app contents macos google chrome android studio version • android studio at applications android studio app contents • flutter plugin can be installed from 🔨 • dart plugin can be installed from 🔨 • java version openjdk runtime environment build intellij idea community edition version • intellij at applications intellij idea ce app • flutter plugin version • dart plugin version vs code version • vs code at applications visual studio code app contents • flutter extension can be installed from 🔨 connected device available • chrome web • chrome • web javascript • google chrome http host availability • all required http hosts are available doctor found issues in category consider also attaching screenshots and or videos to better illustrate the issue you can upload them directly on github beware that video file size is limited to | 0 |
245,016 | 20,739,662,039 | IssuesEvent | 2022-03-14 16:31:35 | OpenLiberty/open-liberty | https://api.github.com/repos/OpenLiberty/open-liberty | closed | Support JDK 18 in Open Liberty: Feature Test Summary | Feature Test Summary team:Blizzard target:22004 | ## Test Strategy
Please note, this Feature Test Summary provided is used to claim https://github.com/OpenLiberty/open-liberty/issues/18614 and not to introduce any new or modified Open Liberty functionality.
Normally FAT testing is designed to validate the functionality of a new or changed feature in Open Liberty. Since there is no new OL functionality to test, the associated FAT test is just a validation check to make sure we are running on Java 18. To accomplish that, this FAT uses a WAR file for testing that has been compiled at Java 18 using functionality that is specific to Java 18.
The real testing validation for Java 18 is done via our entire suite of Open Liberty and WebSphere Liberty FAT buckets.
### List of FAT projects affected
* io.openliberty.java.internal_fat - https://github.com/OpenLiberty/open-liberty/pull/20012
### Test strategy
* What functionality is new or modified by this feature?
* No new Liberty functionality is added or changed by this feature
* What are the positive and negative tests for that functionality?
* This FAT adds one simple test to ensure we are running on Java 18 by using functionality that is specific to Java 18. It creates an inner class which extends `java.net.spi.InetAddressResolverProvider`, which is part of [JEP418](https://openjdk.java.net/jeps/418). The test will fail with a `ClassNotFoundException` should an earlier JDK attempt to compile it.
* Testing specifics
* For several weeks now, we have been running nightly (M-F) Java 18 builds using the latest [Java 18 OpenJDK Hotspot builds](https://jdk.java.net/18/) and tracking defects. This build runs in lite mode against all the Open and WebSphere Liberty FATs. We also periodically run a build against all the same FATs in full mode to make sure we discover any Java 17 specific defects.
## Confidence Level
4 - We have delivered all automated testing we believe is needed for the golden paths of this feature and have good coverage of the error/outlying scenarios. While more testing of the error/outlying scenarios could be added we believe there is minimal risk here and the cost of providing these is considered higher than the benefit they would provide.
| 1.0 | Support JDK 18 in Open Liberty: Feature Test Summary - ## Test Strategy
Please note, this Feature Test Summary provided is used to claim https://github.com/OpenLiberty/open-liberty/issues/18614 and not to introduce any new or modified Open Liberty functionality.
Normally FAT testing is designed to validate the functionality of a new or changed feature in Open Liberty. Since there is no new OL functionality to test, the associated FAT test is just a validation check to make sure we are running on Java 18. To accomplish that, this FAT uses a WAR file for testing that has been compiled at Java 18 using functionality that is specific to Java 18.
The real testing validation for Java 18 is done via our entire suite of Open Liberty and WebSphere Liberty FAT buckets.
### List of FAT projects affected
* io.openliberty.java.internal_fat - https://github.com/OpenLiberty/open-liberty/pull/20012
### Test strategy
* What functionality is new or modified by this feature?
* No new Liberty functionality is added or changed by this feature
* What are the positive and negative tests for that functionality?
* This FAT adds one simple test to ensure we are running on Java 18 by using functionality that is specific to Java 18. It creates an inner class which extends `java.net.spi.InetAddressResolverProvider`, which is part of [JEP418](https://openjdk.java.net/jeps/418). The test will fail with a `ClassNotFoundException` should an earlier JDK attempt to compile it.
* Testing specifics
* For several weeks now, we have been running nightly (M-F) Java 18 builds using the latest [Java 18 OpenJDK Hotspot builds](https://jdk.java.net/18/) and tracking defects. This build runs in lite mode against all the Open and WebSphere Liberty FATs. We also periodically run a build against all the same FATs in full mode to make sure we discover any Java 17 specific defects.
## Confidence Level
4 - We have delivered all automated testing we believe is needed for the golden paths of this feature and have good coverage of the error/outlying scenarios. While more testing of the error/outlying scenarios could be added we believe there is minimal risk here and the cost of providing these is considered higher than the benefit they would provide.
| test | support jdk in open liberty feature test summary test strategy please note this feature test summary provided is used to claim and not to introduce any new or modified open liberty functionality normally fat testing is designed to validate the functionality of a new or changed feature in open liberty since there is no new ol functionality to test the associated fat test is just a validation check to make sure we are running on java to accomplish that this fat uses a war file for testing that has been compiled at java using functionality that is specific to java the real testing validation for java is done via our entire suite of open liberty and websphere liberty fat buckets list of fat projects affected io openliberty java internal fat test strategy what functionality is new or modified by this feature no new liberty functionality is added or changed by this feature what are the positive and negative tests for that functionality this fat adds one simple test to ensure we are running on java by using functionality that is specific to java it creates an inner class which extends java net spi inetaddressresolverprovider which is part of the test will fail with a classnotfoundexception should an earlier jdk attempt to compile it testing specifics for several weeks now we have been running nightly m f java builds using the latest and tracking defects this build runs in lite mode against all the open and websphere liberty fats we also periodically run a build against all the same fats in full mode to make sure we discover any java specific defects confidence level we have delivered all automated testing we believe is needed for the golden paths of this feature and have good coverage of the error outlying scenarios while more testing of the error outlying scenarios could be added we believe there is minimal risk here and the cost of providing these is considered higher than the benefit they would provide | 1 |
260,270 | 22,606,291,513 | IssuesEvent | 2022-06-29 13:31:54 | mozilla-mobile/focus-android | https://api.github.com/repos/mozilla-mobile/focus-android | closed | Intermittent UI test failure - SwitchLocaleTest.FrenchLocaleTest | bug eng:ui-test eng:disabled-test eng:bug-auto-found | ### Firebase Test Run:
Failing 2/2 tries on FTL and locally:
https://console.firebase.google.com/u/1/project/moz-fx-mobile-firebase-testlab/testlab/histories/bh.2b4ca2c7fdb2f0f0/matrices/5461399497652579435/executions/bs.3b8fc141094e148d/testcases/9
### Stacktrace:
ndroidx.test.uiautomator.UiObjectNotFoundException: UiSelector[TEXT=Général, RESOURCE_ID=android:id/title]
at androidx.test.uiautomator.UiObject.click(UiObject.java:416)
at org.mozilla.focus.activity.SwitchLocaleTest.FrenchLocaleTest(SwitchLocaleTest.kt:217)
### Build:
Debug 5/3
Started failing with this [commit](https://github.com/mozilla-mobile/focus-android/commit/c4f580942d7f81104a1d4e6be3934e92d8f5f591). | 2.0 | Intermittent UI test failure - SwitchLocaleTest.FrenchLocaleTest - ### Firebase Test Run:
Failing 2/2 tries on FTL and locally:
https://console.firebase.google.com/u/1/project/moz-fx-mobile-firebase-testlab/testlab/histories/bh.2b4ca2c7fdb2f0f0/matrices/5461399497652579435/executions/bs.3b8fc141094e148d/testcases/9
### Stacktrace:
ndroidx.test.uiautomator.UiObjectNotFoundException: UiSelector[TEXT=Général, RESOURCE_ID=android:id/title]
at androidx.test.uiautomator.UiObject.click(UiObject.java:416)
at org.mozilla.focus.activity.SwitchLocaleTest.FrenchLocaleTest(SwitchLocaleTest.kt:217)
### Build:
Debug 5/3
Started failing with this [commit](https://github.com/mozilla-mobile/focus-android/commit/c4f580942d7f81104a1d4e6be3934e92d8f5f591). | test | intermittent ui test failure switchlocaletest frenchlocaletest firebase test run failing tries on ftl and locally stacktrace ndroidx test uiautomator uiobjectnotfoundexception uiselector at androidx test uiautomator uiobject click uiobject java at org mozilla focus activity switchlocaletest frenchlocaletest switchlocaletest kt build debug started failing with this | 1 |
451,556 | 13,038,333,239 | IssuesEvent | 2020-07-28 15:03:40 | gardener/gardener | https://api.github.com/repos/gardener/gardener | closed | Evaluate grafana/loki as logging backend | area/logging kind/enhancement lifecycle/stale platform/all priority/normal status/accepted status/in-progress | Currently cluster level logging and monitoring for seed clusters are handled by two different systems - the end user/operator uses Grafana to deal with metrics and Kibana to deal with logs.
### Motivation
- Metrics and logs are part of incident resolving and usually you need both of them. Now there is a context switching from one system to another one. loki promises to minimize this cost of context switching and to allow easy switch between metrics and logs for given search query.
- It is not easy to operate and scale Elasticsearch. It is resource intensive and requires not a few memory. loki promises to be lightweight (cost effective) and easy to operate.
- Grafana has native support for loki. Grafana also supports Elasticsearch datasource.
### Outcome
The idea of this issue is to evaluate loki as logging backend (more details about the requirements could be found in #3). As an outcome, implementation proposal (PR) or a list of limitations, issues of loki could be accepted.
---
- [Loki Design Doc](https://docs.google.com/document/d/11tjK_lvp1-SVsFZjgOTr1vV3-q6vBAsZYIQ5ZeYBkyM/view#heading=h.5xmknwtxwpne)
| 1.0 | Evaluate grafana/loki as logging backend - Currently cluster level logging and monitoring for seed clusters are handled by two different systems - the end user/operator uses Grafana to deal with metrics and Kibana to deal with logs.
### Motivation
- Metrics and logs are part of incident resolving and usually you need both of them. Now there is a context switching from one system to another one. loki promises to minimize this cost of context switching and to allow easy switch between metrics and logs for given search query.
- It is not easy to operate and scale Elasticsearch. It is resource intensive and requires not a few memory. loki promises to be lightweight (cost effective) and easy to operate.
- Grafana has native support for loki. Grafana also supports Elasticsearch datasource.
### Outcome
The idea of this issue is to evaluate loki as logging backend (more details about the requirements could be found in #3). As an outcome, implementation proposal (PR) or a list of limitations, issues of loki could be accepted.
---
- [Loki Design Doc](https://docs.google.com/document/d/11tjK_lvp1-SVsFZjgOTr1vV3-q6vBAsZYIQ5ZeYBkyM/view#heading=h.5xmknwtxwpne)
| non_test | evaluate grafana loki as logging backend currently cluster level logging and monitoring for seed clusters are handled by two different systems the end user operator uses grafana to deal with metrics and kibana to deal with logs motivation metrics and logs are part of incident resolving and usually you need both of them now there is a context switching from one system to another one loki promises to minimize this cost of context switching and to allow easy switch between metrics and logs for given search query it is not easy to operate and scale elasticsearch it is resource intensive and requires not a few memory loki promises to be lightweight cost effective and easy to operate grafana has native support for loki grafana also supports elasticsearch datasource outcome the idea of this issue is to evaluate loki as logging backend more details about the requirements could be found in as an outcome implementation proposal pr or a list of limitations issues of loki could be accepted | 0 |
284,000 | 24,576,128,206 | IssuesEvent | 2022-10-13 12:29:55 | gradle/gradle | https://api.github.com/repos/gradle/gradle | closed | Test task avoidance is not working since Gradle 7.4.x | in:testing a:bug in:test-suites | Hi,
it seems that the task avoidance for tests is not working anymore since Gradle 7.4.x
### Expected Behavior
Test tasks are not eagerly created
### Current Behavior
Test tasks are eagerly created
### Context
<!--- How has this issue affected you? What are you trying to accomplish? -->
<!--- Providing context helps us come up with a solution that is most useful in the real world -->
### Steps to Reproduce
Have something like the following in your project
```
tasks.withType(Test).configureEach {
println "Configure Tests"
testLogging {
showStandardStreams = true
exceptionFormat = 'full'
}
}
```
`Configure Tests` should not be printed when the test tasks are not run, but it is. For simpler reproduction: https://github.com/dreis2211/gradle-task-avoidance-bug
This seems to be caused by the relatively new `testResultsElementsForTest` infrastructure added in #18834, but I haven't looked too deep yet.
Cheers,
Christoph
| 2.0 | Test task avoidance is not working since Gradle 7.4.x - Hi,
it seems that the task avoidance for tests is not working anymore since Gradle 7.4.x
### Expected Behavior
Test tasks are not eagerly created
### Current Behavior
Test tasks are eagerly created
### Context
<!--- How has this issue affected you? What are you trying to accomplish? -->
<!--- Providing context helps us come up with a solution that is most useful in the real world -->
### Steps to Reproduce
Have something like the following in your project
```
tasks.withType(Test).configureEach {
println "Configure Tests"
testLogging {
showStandardStreams = true
exceptionFormat = 'full'
}
}
```
`Configure Tests` should not be printed when the test tasks are not run, but it is. For simpler reproduction: https://github.com/dreis2211/gradle-task-avoidance-bug
This seems to be caused by the relatively new `testResultsElementsForTest` infrastructure added in #18834, but I haven't looked too deep yet.
Cheers,
Christoph
| test | test task avoidance is not working since gradle x hi it seems that the task avoidance for tests is not working anymore since gradle x expected behavior test tasks are not eagerly created current behavior test tasks are eagerly created context steps to reproduce have something like the following in your project tasks withtype test configureeach println configure tests testlogging showstandardstreams true exceptionformat full configure tests should not be printed when the test tasks are not run but it is for simpler reproduction this seems to be caused by the relatively new testresultselementsfortest infrastructure added in but i haven t looked too deep yet cheers christoph | 1 |
42,401 | 5,435,840,689 | IssuesEvent | 2017-03-05 20:18:40 | tempesta-tech/tempesta | https://api.github.com/repos/tempesta-tech/tempesta | closed | Tempesta/keepalived failovering | crucial test | Need to test VIP migration between two Tempesta instances as a process of dynamic failovering using keepalived.

As a result of the test, new Wiki for High availability installations must be created. | 1.0 | Tempesta/keepalived failovering - Need to test VIP migration between two Tempesta instances as a process of dynamic failovering using keepalived.

As a result of the test, new Wiki for High availability installations must be created. | test | tempesta keepalived failovering need to test vip migration between two tempesta instances as a process of dynamic failovering using keepalived as a result of the test new wiki for high availability installations must be created | 1 |
301,900 | 9,232,432,333 | IssuesEvent | 2019-03-13 07:05:33 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.youtube.com - design is broken | browser-firefox priority-critical | <!-- @browser: Firefox 66.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:66.0) Gecko/20100101 Firefox/66.0 -->
<!-- @reported_with: desktop-reporter -->
**URL**: https://www.youtube.com/watch?v=ay8Ya0DYDYE
**Browser / Version**: Firefox 66.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes
**Problem type**: Design is broken
**Description**: There are wierd gaps on the sides despite being at 100% zoom
**Steps to Reproduce**:
<details>
<summary>Browser Configuration</summary>
<ul>
<li>mixed active content blocked: false</li><li>image.mem.shared: true</li><li>buildID: 20190228180200</li><li>tracking content blocked: false</li><li>gfx.webrender.blob-images: true</li><li>hasTouchScreen: false</li><li>mixed passive content blocked: false</li><li>gfx.webrender.enabled: false</li><li>gfx.webrender.all: false</li><li>channel: aurora</li>
</ul>
<p>Console Messages:</p>
<pre>
[u'[JavaScript Warning: "Cross-Origin Request Blocked: The Same Origin Policy disallows reading the remote resource at https://googleads.g.doubleclick.net/pagead/id. (Reason: CORS request did not succeed)."]', u'[JavaScript Warning: "Cross-Origin Request Blocked: The Same Origin Policy disallows reading the remote resource at https://googleads.g.doubleclick.net/pagead/id. (Reason: CORS request did not succeed)."]', u'[JavaScript Warning: "Cross-Origin Request Blocked: The Same Origin Policy disallows reading the remote resource at https://googleads.g.doubleclick.net/pagead/lopri?cust_gender=2&cust_age=1001&lact=-1&ytdevicever=ytdevicever_2.20190227&client=ca-pub-6219811747049371&correlator=9406556833010617927&ad_block=3&eid=234793968&host=ca-yt-host-pub-2235497127511300&loeid=23780613,9471239,23796499,23796665,23797561,9407610,23783454&num_ads=1&video_doc_id=yt_ay8Ya0DYDYE&ad_type=text&channel=PyvWatchInRelated%2BPyvWatchNoAdX%2BPyvYTWatch%2BYtLoPri%2Bafv_user_id_BJycsmduvYEL83R_U4JriQ%2Bafv_user_marquesbrownlee%2Bnon_lpw%2Bpw%2Byt_cid_1115038%2Byt_mpvid_P-EpK8HQ-DQd1cjW%2Byt_no_ap%2Bytdevice_1%2Bytdevicever_2.20190227&hl=en&url=http%3A%2F%2Fwww.youtube.com%2Fvideo%2Fay8Ya0DYDYE&output=js&ea=0&eae=2&adk=511001906&pyv=1&top=https%3A%2F%2Fwww.youtube.com%2Fwatch%3Fv%3Day8Ya0DYDYE%26app%3Ddesktop&loc=EMPTY&dbp=ChZuOUNDRnRiSV8wQXQybE1SdXhnT2RnEAEgBCgAOAI&isw=0&ish=0&yt_pt=APb3F28I1c2W1u03tbB0iIgtr0V3ZurcicSNN_E2BqQC_IdLyRA3V-Xi05dl8kCn0BYt70OV7tM31aXuxtMSndu0LYZUGtbqHu4fCo0mPWp6RIAJD8CHpwaZJUtVN7F5Yk9KcyhuIQuijDAsiDGrwxiNLgql5COYTy0JXc4B32PUwr3D-Yp0HBvWGh2vn98EhxZJa3JJYIf_aIdm5yFM&pucrd=APb3F28KJKC8w6D6TbmXNkkw8PHXdzfDa5r5uLN5N_qUe7PsHEjSN3UmJgs3N5J9nu-2ORqmHCh3jNbHFUZJnk3NJH57waA0SUS-0cmLlg&dt=1551483269387&flash=0&frm=0&u_tz=-360&u_his=7&u_java=false&u_h=1080&u_w=1920&u_ah=1040&u_aw=1920&u_cd=24&u_nplug=0&u_nmime=0&bc=13&bih=966&biw=1903&brdim=-8%2C-8%2C-8%2C-8%2C1920%2C0%2C1936%2C1056%2C1920%2C966&vis=1&wgl=true&dff=times%20new%20roman&dfs=16&ppjl=u&rsz=%7C%7Cn%7C&dssz=37&icsg=16777215&mdo=0&mso=0&lact=1541. (Reason: CORS request did not succeed)."]', u'[JavaScript Warning: "Loading failed for the <script> with source https://static.doubleclick.net/instream/ad_status.js." {file: "https://www.youtube.com/watch?v=ay8Ya0DYDYE" line: 1}]']
</pre>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | www.youtube.com - design is broken - <!-- @browser: Firefox 66.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:66.0) Gecko/20100101 Firefox/66.0 -->
<!-- @reported_with: desktop-reporter -->
**URL**: https://www.youtube.com/watch?v=ay8Ya0DYDYE
**Browser / Version**: Firefox 66.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes
**Problem type**: Design is broken
**Description**: There are wierd gaps on the sides despite being at 100% zoom
**Steps to Reproduce**:
<details>
<summary>Browser Configuration</summary>
<ul>
<li>mixed active content blocked: false</li><li>image.mem.shared: true</li><li>buildID: 20190228180200</li><li>tracking content blocked: false</li><li>gfx.webrender.blob-images: true</li><li>hasTouchScreen: false</li><li>mixed passive content blocked: false</li><li>gfx.webrender.enabled: false</li><li>gfx.webrender.all: false</li><li>channel: aurora</li>
</ul>
<p>Console Messages:</p>
<pre>
[u'[JavaScript Warning: "Cross-Origin Request Blocked: The Same Origin Policy disallows reading the remote resource at https://googleads.g.doubleclick.net/pagead/id. (Reason: CORS request did not succeed)."]', u'[JavaScript Warning: "Cross-Origin Request Blocked: The Same Origin Policy disallows reading the remote resource at https://googleads.g.doubleclick.net/pagead/id. (Reason: CORS request did not succeed)."]', u'[JavaScript Warning: "Cross-Origin Request Blocked: The Same Origin Policy disallows reading the remote resource at https://googleads.g.doubleclick.net/pagead/lopri?cust_gender=2&cust_age=1001&lact=-1&ytdevicever=ytdevicever_2.20190227&client=ca-pub-6219811747049371&correlator=9406556833010617927&ad_block=3&eid=234793968&host=ca-yt-host-pub-2235497127511300&loeid=23780613,9471239,23796499,23796665,23797561,9407610,23783454&num_ads=1&video_doc_id=yt_ay8Ya0DYDYE&ad_type=text&channel=PyvWatchInRelated%2BPyvWatchNoAdX%2BPyvYTWatch%2BYtLoPri%2Bafv_user_id_BJycsmduvYEL83R_U4JriQ%2Bafv_user_marquesbrownlee%2Bnon_lpw%2Bpw%2Byt_cid_1115038%2Byt_mpvid_P-EpK8HQ-DQd1cjW%2Byt_no_ap%2Bytdevice_1%2Bytdevicever_2.20190227&hl=en&url=http%3A%2F%2Fwww.youtube.com%2Fvideo%2Fay8Ya0DYDYE&output=js&ea=0&eae=2&adk=511001906&pyv=1&top=https%3A%2F%2Fwww.youtube.com%2Fwatch%3Fv%3Day8Ya0DYDYE%26app%3Ddesktop&loc=EMPTY&dbp=ChZuOUNDRnRiSV8wQXQybE1SdXhnT2RnEAEgBCgAOAI&isw=0&ish=0&yt_pt=APb3F28I1c2W1u03tbB0iIgtr0V3ZurcicSNN_E2BqQC_IdLyRA3V-Xi05dl8kCn0BYt70OV7tM31aXuxtMSndu0LYZUGtbqHu4fCo0mPWp6RIAJD8CHpwaZJUtVN7F5Yk9KcyhuIQuijDAsiDGrwxiNLgql5COYTy0JXc4B32PUwr3D-Yp0HBvWGh2vn98EhxZJa3JJYIf_aIdm5yFM&pucrd=APb3F28KJKC8w6D6TbmXNkkw8PHXdzfDa5r5uLN5N_qUe7PsHEjSN3UmJgs3N5J9nu-2ORqmHCh3jNbHFUZJnk3NJH57waA0SUS-0cmLlg&dt=1551483269387&flash=0&frm=0&u_tz=-360&u_his=7&u_java=false&u_h=1080&u_w=1920&u_ah=1040&u_aw=1920&u_cd=24&u_nplug=0&u_nmime=0&bc=13&bih=966&biw=1903&brdim=-8%2C-8%2C-8%2C-8%2C1920%2C0%2C1936%2C1056%2C1920%2C966&vis=1&wgl=true&dff=times%20new%20roman&dfs=16&ppjl=u&rsz=%7C%7Cn%7C&dssz=37&icsg=16777215&mdo=0&mso=0&lact=1541. (Reason: CORS request did not succeed)."]', u'[JavaScript Warning: "Loading failed for the <script> with source https://static.doubleclick.net/instream/ad_status.js." {file: "https://www.youtube.com/watch?v=ay8Ya0DYDYE" line: 1}]']
</pre>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_test | design is broken url browser version firefox operating system windows tested another browser yes problem type design is broken description there are wierd gaps on the sides despite being at zoom steps to reproduce browser configuration mixed active content blocked false image mem shared true buildid tracking content blocked false gfx webrender blob images true hastouchscreen false mixed passive content blocked false gfx webrender enabled false gfx webrender all false channel aurora console messages u u u from with ❤️ | 0 |
350,327 | 31,879,444,039 | IssuesEvent | 2023-09-16 07:27:28 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: decommission/nodes=4/duration=1h0m0s failed | C-test-failure O-robot O-roachtest branch-master release-blocker T-kv | roachtest.decommission/nodes=4/duration=1h0m0s [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/11801592?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/11801592?buildTab=artifacts#/decommission/nodes=4/duration=1h0m0s) on master @ [985662236d7bf273b93a7b5e32def8e2d1043640](https://github.com/cockroachdb/cockroach/commits/985662236d7bf273b93a7b5e32def8e2d1043640):
```
(decommission.go:369).runDecommission: operation "decommission" timed out after 20m0.001s (given timeout 20m0s): context deadline exceeded
test artifacts and logs in: /artifacts/decommission/nodes=4/duration=1h0m0s/run_1
```
<p>Parameters: <code>ROACHTEST_arch=amd64</code>
, <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
See: [Grafana](https://go.crdb.dev/roachtest-grafana/teamcity-11801592/decommission-nodes-4-duration-1h0m0s/1694844812145/1694849351506)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*decommission/nodes=4/duration=1h0m0s.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: decommission/nodes=4/duration=1h0m0s failed - roachtest.decommission/nodes=4/duration=1h0m0s [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/11801592?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/11801592?buildTab=artifacts#/decommission/nodes=4/duration=1h0m0s) on master @ [985662236d7bf273b93a7b5e32def8e2d1043640](https://github.com/cockroachdb/cockroach/commits/985662236d7bf273b93a7b5e32def8e2d1043640):
```
(decommission.go:369).runDecommission: operation "decommission" timed out after 20m0.001s (given timeout 20m0s): context deadline exceeded
test artifacts and logs in: /artifacts/decommission/nodes=4/duration=1h0m0s/run_1
```
<p>Parameters: <code>ROACHTEST_arch=amd64</code>
, <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
See: [Grafana](https://go.crdb.dev/roachtest-grafana/teamcity-11801592/decommission-nodes-4-duration-1h0m0s/1694844812145/1694849351506)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*decommission/nodes=4/duration=1h0m0s.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| test | roachtest decommission nodes duration failed roachtest decommission nodes duration with on master decommission go rundecommission operation decommission timed out after given timeout context deadline exceeded test artifacts and logs in artifacts decommission nodes duration run parameters roachtest arch roachtest cloud gce roachtest cpu roachtest encrypted false roachtest ssd help see see see cc cockroachdb kv triage | 1 |
642,414 | 20,887,353,551 | IssuesEvent | 2022-03-23 07:20:16 | googleapis/java-bigquery | https://api.github.com/repos/googleapis/java-bigquery | opened | bigquery.it.ITBigQueryTest: testQueryJobWithLabels failed | type: bug priority: p1 flakybot: issue | This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: 63130e1e6a4db9014aa42e9baa331a867a312a17
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/9f70b9d7-b4a8-4a2d-ad23-855e99d4f12a), [Sponge](http://sponge2/9f70b9d7-b4a8-4a2d-ad23-855e99d4f12a)
status: failed
<details><summary>Test output</summary><br><pre>com.google.cloud.bigquery.BigQueryException: Read timed out
at com.google.cloud.bigquery.spi.v2.HttpBigQueryRpc.translate(HttpBigQueryRpc.java:115)
at com.google.cloud.bigquery.spi.v2.HttpBigQueryRpc.deleteTable(HttpBigQueryRpc.java:336)
at com.google.cloud.bigquery.BigQueryImpl$10.call(BigQueryImpl.java:543)
at com.google.cloud.bigquery.BigQueryImpl$10.call(BigQueryImpl.java:540)
at com.google.api.gax.retrying.DirectRetryingExecutor.submit(DirectRetryingExecutor.java:105)
at com.google.cloud.RetryHelper.run(RetryHelper.java:76)
at com.google.cloud.RetryHelper.runWithRetries(RetryHelper.java:50)
at com.google.cloud.bigquery.BigQueryImpl.delete(BigQueryImpl.java:539)
at com.google.cloud.bigquery.it.ITBigQueryTest.testQueryJobWithLabels(ITBigQueryTest.java:3198)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:299)
at org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:293)
at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at java.base/java.lang.Thread.run(Thread.java:829)
Caused by: java.net.SocketTimeoutException: Read timed out
at java.base/java.net.SocketInputStream.socketRead0(Native Method)
at java.base/java.net.SocketInputStream.socketRead(SocketInputStream.java:115)
at java.base/java.net.SocketInputStream.read(SocketInputStream.java:168)
at java.base/java.net.SocketInputStream.read(SocketInputStream.java:140)
at java.base/sun.security.ssl.SSLSocketInputRecord.read(SSLSocketInputRecord.java:478)
at java.base/sun.security.ssl.SSLSocketInputRecord.readHeader(SSLSocketInputRecord.java:472)
at java.base/sun.security.ssl.SSLSocketInputRecord.bytesInCompletePacket(SSLSocketInputRecord.java:70)
at java.base/sun.security.ssl.SSLSocketImpl.readApplicationRecord(SSLSocketImpl.java:1449)
at java.base/sun.security.ssl.SSLSocketImpl$AppInputStream.read(SSLSocketImpl.java:1060)
at java.base/java.io.BufferedInputStream.fill(BufferedInputStream.java:252)
at java.base/java.io.BufferedInputStream.read1(BufferedInputStream.java:292)
at java.base/java.io.BufferedInputStream.read(BufferedInputStream.java:351)
at java.base/sun.net.www.http.HttpClient.parseHTTPHeader(HttpClient.java:754)
at java.base/sun.net.www.http.HttpClient.parseHTTP(HttpClient.java:689)
at java.base/sun.net.www.protocol.http.HttpURLConnection.getInputStream0(HttpURLConnection.java:1615)
at java.base/sun.net.www.protocol.http.HttpURLConnection.getInputStream(HttpURLConnection.java:1520)
at java.base/java.net.HttpURLConnection.getResponseCode(HttpURLConnection.java:527)
at java.base/sun.net.www.protocol.https.HttpsURLConnectionImpl.getResponseCode(HttpsURLConnectionImpl.java:334)
at com.google.api.client.http.javanet.NetHttpResponse.<init>(NetHttpResponse.java:36)
at com.google.api.client.http.javanet.NetHttpRequest.execute(NetHttpRequest.java:152)
at com.google.api.client.http.javanet.NetHttpRequest.execute(NetHttpRequest.java:84)
at com.google.api.client.http.HttpRequest.execute(HttpRequest.java:1012)
at com.google.api.client.googleapis.services.AbstractGoogleClientRequest.executeUnparsed(AbstractGoogleClientRequest.java:514)
at com.google.api.client.googleapis.services.AbstractGoogleClientRequest.executeUnparsed(AbstractGoogleClientRequest.java:455)
at com.google.api.client.googleapis.services.AbstractGoogleClientRequest.execute(AbstractGoogleClientRequest.java:565)
at com.google.cloud.bigquery.spi.v2.HttpBigQueryRpc.deleteTable(HttpBigQueryRpc.java:333)
... 19 more
</pre></details> | 1.0 | bigquery.it.ITBigQueryTest: testQueryJobWithLabels failed - This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: 63130e1e6a4db9014aa42e9baa331a867a312a17
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/9f70b9d7-b4a8-4a2d-ad23-855e99d4f12a), [Sponge](http://sponge2/9f70b9d7-b4a8-4a2d-ad23-855e99d4f12a)
status: failed
<details><summary>Test output</summary><br><pre>com.google.cloud.bigquery.BigQueryException: Read timed out
at com.google.cloud.bigquery.spi.v2.HttpBigQueryRpc.translate(HttpBigQueryRpc.java:115)
at com.google.cloud.bigquery.spi.v2.HttpBigQueryRpc.deleteTable(HttpBigQueryRpc.java:336)
at com.google.cloud.bigquery.BigQueryImpl$10.call(BigQueryImpl.java:543)
at com.google.cloud.bigquery.BigQueryImpl$10.call(BigQueryImpl.java:540)
at com.google.api.gax.retrying.DirectRetryingExecutor.submit(DirectRetryingExecutor.java:105)
at com.google.cloud.RetryHelper.run(RetryHelper.java:76)
at com.google.cloud.RetryHelper.runWithRetries(RetryHelper.java:50)
at com.google.cloud.bigquery.BigQueryImpl.delete(BigQueryImpl.java:539)
at com.google.cloud.bigquery.it.ITBigQueryTest.testQueryJobWithLabels(ITBigQueryTest.java:3198)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:299)
at org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:293)
at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at java.base/java.lang.Thread.run(Thread.java:829)
Caused by: java.net.SocketTimeoutException: Read timed out
at java.base/java.net.SocketInputStream.socketRead0(Native Method)
at java.base/java.net.SocketInputStream.socketRead(SocketInputStream.java:115)
at java.base/java.net.SocketInputStream.read(SocketInputStream.java:168)
at java.base/java.net.SocketInputStream.read(SocketInputStream.java:140)
at java.base/sun.security.ssl.SSLSocketInputRecord.read(SSLSocketInputRecord.java:478)
at java.base/sun.security.ssl.SSLSocketInputRecord.readHeader(SSLSocketInputRecord.java:472)
at java.base/sun.security.ssl.SSLSocketInputRecord.bytesInCompletePacket(SSLSocketInputRecord.java:70)
at java.base/sun.security.ssl.SSLSocketImpl.readApplicationRecord(SSLSocketImpl.java:1449)
at java.base/sun.security.ssl.SSLSocketImpl$AppInputStream.read(SSLSocketImpl.java:1060)
at java.base/java.io.BufferedInputStream.fill(BufferedInputStream.java:252)
at java.base/java.io.BufferedInputStream.read1(BufferedInputStream.java:292)
at java.base/java.io.BufferedInputStream.read(BufferedInputStream.java:351)
at java.base/sun.net.www.http.HttpClient.parseHTTPHeader(HttpClient.java:754)
at java.base/sun.net.www.http.HttpClient.parseHTTP(HttpClient.java:689)
at java.base/sun.net.www.protocol.http.HttpURLConnection.getInputStream0(HttpURLConnection.java:1615)
at java.base/sun.net.www.protocol.http.HttpURLConnection.getInputStream(HttpURLConnection.java:1520)
at java.base/java.net.HttpURLConnection.getResponseCode(HttpURLConnection.java:527)
at java.base/sun.net.www.protocol.https.HttpsURLConnectionImpl.getResponseCode(HttpsURLConnectionImpl.java:334)
at com.google.api.client.http.javanet.NetHttpResponse.<init>(NetHttpResponse.java:36)
at com.google.api.client.http.javanet.NetHttpRequest.execute(NetHttpRequest.java:152)
at com.google.api.client.http.javanet.NetHttpRequest.execute(NetHttpRequest.java:84)
at com.google.api.client.http.HttpRequest.execute(HttpRequest.java:1012)
at com.google.api.client.googleapis.services.AbstractGoogleClientRequest.executeUnparsed(AbstractGoogleClientRequest.java:514)
at com.google.api.client.googleapis.services.AbstractGoogleClientRequest.executeUnparsed(AbstractGoogleClientRequest.java:455)
at com.google.api.client.googleapis.services.AbstractGoogleClientRequest.execute(AbstractGoogleClientRequest.java:565)
at com.google.cloud.bigquery.spi.v2.HttpBigQueryRpc.deleteTable(HttpBigQueryRpc.java:333)
... 19 more
</pre></details> | non_test | bigquery it itbigquerytest testqueryjobwithlabels failed this test failed to configure my behavior see if i m commenting on this issue too often add the flakybot quiet label and i will stop commenting commit buildurl status failed test output com google cloud bigquery bigqueryexception read timed out at com google cloud bigquery spi httpbigqueryrpc translate httpbigqueryrpc java at com google cloud bigquery spi httpbigqueryrpc deletetable httpbigqueryrpc java at com google cloud bigquery bigqueryimpl call bigqueryimpl java at com google cloud bigquery bigqueryimpl call bigqueryimpl java at com google api gax retrying directretryingexecutor submit directretryingexecutor java at com google cloud retryhelper run retryhelper java at com google cloud retryhelper runwithretries retryhelper java at com google cloud bigquery bigqueryimpl delete bigqueryimpl java at com google cloud bigquery it itbigquerytest testqueryjobwithlabels itbigquerytest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at org junit internal runners statements failontimeout callablestatement call failontimeout java at org junit internal runners statements failontimeout callablestatement call failontimeout java at java base java util concurrent futuretask run futuretask java at java base java lang thread run thread java caused by java net sockettimeoutexception read timed out at java base java net socketinputstream native method at java base java net socketinputstream socketread socketinputstream java at java base java net socketinputstream read socketinputstream java at java base java net socketinputstream read socketinputstream java at java base sun security ssl sslsocketinputrecord read sslsocketinputrecord java at java base sun security ssl sslsocketinputrecord readheader sslsocketinputrecord java at java base sun security ssl sslsocketinputrecord bytesincompletepacket sslsocketinputrecord java at java base sun security ssl sslsocketimpl readapplicationrecord sslsocketimpl java at java base sun security ssl sslsocketimpl appinputstream read sslsocketimpl java at java base java io bufferedinputstream fill bufferedinputstream java at java base java io bufferedinputstream bufferedinputstream java at java base java io bufferedinputstream read bufferedinputstream java at java base sun net at java base sun net at java base sun net at java base sun net at java base java net httpurlconnection getresponsecode httpurlconnection java at java base sun net at com google api client http javanet nethttpresponse nethttpresponse java at com google api client http javanet nethttprequest execute nethttprequest java at com google api client http javanet nethttprequest execute nethttprequest java at com google api client http httprequest execute httprequest java at com google api client googleapis services abstractgoogleclientrequest executeunparsed abstractgoogleclientrequest java at com google api client googleapis services abstractgoogleclientrequest executeunparsed abstractgoogleclientrequest java at com google api client googleapis services abstractgoogleclientrequest execute abstractgoogleclientrequest java at com google cloud bigquery spi httpbigqueryrpc deletetable httpbigqueryrpc java more | 0 |
261,274 | 22,711,216,992 | IssuesEvent | 2022-07-05 19:35:29 | istio/istio | https://api.github.com/repos/istio/istio | closed | Make istiod-less Remote Cluster the default for multicluster | area/test and release area/environments lifecycle/staleproof feature/Multi-cluster | For 1.8 (Multicluster Beta), we want to switch the default remote cluster type to be istiod-less. We also want to deprecate the old remote cluster type.
All tests should use the istiod-less remote by default as well.
[ ] Docs
[x] Installation
[ ] Networking
[ ] Performance and Scalability
[ ] Extensions and Telemetry
[ ] Security
[x] Test and Release
[ ] User Experience
[ ] Developer Infrastructure
**Additional context** | 1.0 | Make istiod-less Remote Cluster the default for multicluster - For 1.8 (Multicluster Beta), we want to switch the default remote cluster type to be istiod-less. We also want to deprecate the old remote cluster type.
All tests should use the istiod-less remote by default as well.
[ ] Docs
[x] Installation
[ ] Networking
[ ] Performance and Scalability
[ ] Extensions and Telemetry
[ ] Security
[x] Test and Release
[ ] User Experience
[ ] Developer Infrastructure
**Additional context** | test | make istiod less remote cluster the default for multicluster for multicluster beta we want to switch the default remote cluster type to be istiod less we also want to deprecate the old remote cluster type all tests should use the istiod less remote by default as well docs installation networking performance and scalability extensions and telemetry security test and release user experience developer infrastructure additional context | 1 |
427,354 | 29,808,551,678 | IssuesEvent | 2023-06-16 13:29:04 | Gentleman1983/ginlong_solis_api_connector | https://api.github.com/repos/Gentleman1983/ginlong_solis_api_connector | opened | Add Release Notes / ChangeLog document | documentation enhancement | For better change monitoring please add release notes or change log document. | 1.0 | Add Release Notes / ChangeLog document - For better change monitoring please add release notes or change log document. | non_test | add release notes changelog document for better change monitoring please add release notes or change log document | 0 |
269,844 | 23,471,448,946 | IssuesEvent | 2022-08-16 22:27:08 | red/red | https://api.github.com/repos/red/red | closed | Deceptive error message when selecting from a string | status.built status.tested type.review | **Describe the bug**
In this script, a wrong value was passed as `b` argument - a string instead of an object:
```
>> b: "2"
== "2"
>> b/what
*** Script Error: word type is not allowed here
*** Where: either
*** Stack:
```
The error message just could not have been any more hideous: it tells nothing about the context. `here` where? what `word`? what `either`? It takes deep line by line tracing to discover where exactly the error comes from.
**Expected behavior**
To the point error message, e.g. `*** Script Error: string 'b' cannot be indexed with a word 'what' in 'b/what'`
**Platform version (please complete the following information)**
```
Red 0.6.4 for Windows built 28-May-2020/17:51:04+03:00 commit #36857eb
```
| 1.0 | Deceptive error message when selecting from a string - **Describe the bug**
In this script, a wrong value was passed as `b` argument - a string instead of an object:
```
>> b: "2"
== "2"
>> b/what
*** Script Error: word type is not allowed here
*** Where: either
*** Stack:
```
The error message just could not have been any more hideous: it tells nothing about the context. `here` where? what `word`? what `either`? It takes deep line by line tracing to discover where exactly the error comes from.
**Expected behavior**
To the point error message, e.g. `*** Script Error: string 'b' cannot be indexed with a word 'what' in 'b/what'`
**Platform version (please complete the following information)**
```
Red 0.6.4 for Windows built 28-May-2020/17:51:04+03:00 commit #36857eb
```
| test | deceptive error message when selecting from a string describe the bug in this script a wrong value was passed as b argument a string instead of an object b b what script error word type is not allowed here where either stack the error message just could not have been any more hideous it tells nothing about the context here where what word what either it takes deep line by line tracing to discover where exactly the error comes from expected behavior to the point error message e g script error string b cannot be indexed with a word what in b what platform version please complete the following information red for windows built may commit | 1 |
8,527 | 11,704,715,323 | IssuesEvent | 2020-03-07 11:20:42 | Jeffail/benthos | https://api.github.com/repos/Jeffail/benthos | opened | Change `threads` field behaviour | enhancement processors v4 | Currently the `threads` field of `pipeline` is used to create an explicit number of processing threads. This can be useful as sometimes it's desired to limit the workload of a pipeline to one single logical thread (conditional sleeping), and sometimes it's useful to spawn a much larger number of threads than CPU cores if the workload is mostly IO bound (these are green threads anyway).
However, I suspect that for the vast majority of users the best behaviour for them is to have as many processing threads as there are CPU cores. In this case our defaults are failing as one pipeline is almost never going to be the ideal number.
I'd like to keep this value as a configured field because that allows you to have different thread counts for isolated streams running in streams mode. Therefore I propose changing to default to `0` and documenting that a value of 0 means Benthos matches the number of logical CPU threads on the running machine.
Since this would be a breaking change for some hypothetical configs I'll wait for Benthos v4 to implement this. | 1.0 | Change `threads` field behaviour - Currently the `threads` field of `pipeline` is used to create an explicit number of processing threads. This can be useful as sometimes it's desired to limit the workload of a pipeline to one single logical thread (conditional sleeping), and sometimes it's useful to spawn a much larger number of threads than CPU cores if the workload is mostly IO bound (these are green threads anyway).
However, I suspect that for the vast majority of users the best behaviour for them is to have as many processing threads as there are CPU cores. In this case our defaults are failing as one pipeline is almost never going to be the ideal number.
I'd like to keep this value as a configured field because that allows you to have different thread counts for isolated streams running in streams mode. Therefore I propose changing to default to `0` and documenting that a value of 0 means Benthos matches the number of logical CPU threads on the running machine.
Since this would be a breaking change for some hypothetical configs I'll wait for Benthos v4 to implement this. | non_test | change threads field behaviour currently the threads field of pipeline is used to create an explicit number of processing threads this can be useful as sometimes it s desired to limit the workload of a pipeline to one single logical thread conditional sleeping and sometimes it s useful to spawn a much larger number of threads than cpu cores if the workload is mostly io bound these are green threads anyway however i suspect that for the vast majority of users the best behaviour for them is to have as many processing threads as there are cpu cores in this case our defaults are failing as one pipeline is almost never going to be the ideal number i d like to keep this value as a configured field because that allows you to have different thread counts for isolated streams running in streams mode therefore i propose changing to default to and documenting that a value of means benthos matches the number of logical cpu threads on the running machine since this would be a breaking change for some hypothetical configs i ll wait for benthos to implement this | 0 |
315,248 | 27,059,536,245 | IssuesEvent | 2023-02-13 18:36:37 | Princeton-CDH/ppa-django | https://api.github.com/repos/Princeton-CDH/ppa-django | closed | As a user, when I see a group of editions in my search results, I want an option to search within all editions. | awaiting testing | from first/grouped result, link to an archive search across all all editions
follow up to #445 | 1.0 | As a user, when I see a group of editions in my search results, I want an option to search within all editions. - from first/grouped result, link to an archive search across all all editions
follow up to #445 | test | as a user when i see a group of editions in my search results i want an option to search within all editions from first grouped result link to an archive search across all all editions follow up to | 1 |
12,994 | 3,297,786,980 | IssuesEvent | 2015-11-02 10:55:07 | binidini/tytymyty-ios | https://api.github.com/repos/binidini/tytymyty-ios | closed | обновление на пуш сообщение | enhancement test | если пришел пуш
и у нас активно окно с деталями данного заказа - его надо обновить
тоже под андройд | 1.0 | обновление на пуш сообщение - если пришел пуш
и у нас активно окно с деталями данного заказа - его надо обновить
тоже под андройд | test | обновление на пуш сообщение если пришел пуш и у нас активно окно с деталями данного заказа его надо обновить тоже под андройд | 1 |
71,684 | 30,914,236,540 | IssuesEvent | 2023-08-05 04:24:03 | Zahlungsmittel/Zahlungsmittel | https://api.github.com/repos/Zahlungsmittel/Zahlungsmittel | opened | [CLOSED] wrong_login_is_not_password_reset | service: wallet frontend bug imported | <a href="https://github.com/ulfgebhardt"><img src="https://avatars.githubusercontent.com/u/1238238?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [ulfgebhardt](https://github.com/ulfgebhardt)**
_Thursday Dec 09, 2021 at 23:40 GMT_
_Originally opened as https://github.com/gradido/gradido/pull/1179_
----
<!-- You can find the latest issue templates here https://github.com/ulfgebhardt/issue-templates -->
## 🍰 Pullrequest
<!-- Describe the Pullrequest. Use Screenshots if possible. -->
an incorrect login should always result in an error not in a request to reset the password
### Issues
<!-- Which Issues does this fix, which are related?
- fixes #XXX
- relates #XXX
-->
- None
### Todo
<!-- In case some parts are still missing, list them here. -->
- [X] None
----
_**[ulfgebhardt](https://github.com/ulfgebhardt)** included the following code: https://github.com/gradido/gradido/pull/1179/commits_
| 1.0 | [CLOSED] wrong_login_is_not_password_reset - <a href="https://github.com/ulfgebhardt"><img src="https://avatars.githubusercontent.com/u/1238238?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [ulfgebhardt](https://github.com/ulfgebhardt)**
_Thursday Dec 09, 2021 at 23:40 GMT_
_Originally opened as https://github.com/gradido/gradido/pull/1179_
----
<!-- You can find the latest issue templates here https://github.com/ulfgebhardt/issue-templates -->
## 🍰 Pullrequest
<!-- Describe the Pullrequest. Use Screenshots if possible. -->
an incorrect login should always result in an error not in a request to reset the password
### Issues
<!-- Which Issues does this fix, which are related?
- fixes #XXX
- relates #XXX
-->
- None
### Todo
<!-- In case some parts are still missing, list them here. -->
- [X] None
----
_**[ulfgebhardt](https://github.com/ulfgebhardt)** included the following code: https://github.com/gradido/gradido/pull/1179/commits_
| non_test | wrong login is not password reset issue by thursday dec at gmt originally opened as 🍰 pullrequest an incorrect login should always result in an error not in a request to reset the password issues which issues does this fix which are related fixes xxx relates xxx none todo none included the following code | 0 |
396,049 | 27,098,499,413 | IssuesEvent | 2023-02-15 06:19:40 | yuyatinnefeld/cloud-native-kiosk | https://api.github.com/repos/yuyatinnefeld/cloud-native-kiosk | closed | create doctoring for BE | documentation python | ## Description
We need to write docstrings for the backend python services to make the code easier to understand and maintain. Docstrings provide a concise explanation of the function or class, and its purpose.
## Tasks
- Write docstrings for all the functions and classes in the frontend and backend python services
- Ensure that the docstrings follow the [PEP 257](https://www.python.org/dev/peps/pep-0257/) guidelines for writing docstrings in Python
- Make sure the docstrings provide enough information about the function or class, its arguments, return value, and any - - exceptions that may be raised
- Use [Google Style](http://google.github.io/styleguide/pyguide.html#38-comments-and-docstrings) for formatting the docstrings
## Deliverables
- All functions and classes in the frontend and backend python services should have a docstring
## Timeline
To be discussed and agreed upon with the team.
## Additional information
- Having clear and concise documentation will make it easier for new contributors to understand the code and make changes, as well as for future maintenance. By following the guidelines set out in PEP 257 and using the Google Style for formatting, we can ensure consistency in the code and make it easier to read. | 1.0 | create doctoring for BE - ## Description
We need to write docstrings for the backend python services to make the code easier to understand and maintain. Docstrings provide a concise explanation of the function or class, and its purpose.
## Tasks
- Write docstrings for all the functions and classes in the frontend and backend python services
- Ensure that the docstrings follow the [PEP 257](https://www.python.org/dev/peps/pep-0257/) guidelines for writing docstrings in Python
- Make sure the docstrings provide enough information about the function or class, its arguments, return value, and any - - exceptions that may be raised
- Use [Google Style](http://google.github.io/styleguide/pyguide.html#38-comments-and-docstrings) for formatting the docstrings
## Deliverables
- All functions and classes in the frontend and backend python services should have a docstring
## Timeline
To be discussed and agreed upon with the team.
## Additional information
- Having clear and concise documentation will make it easier for new contributors to understand the code and make changes, as well as for future maintenance. By following the guidelines set out in PEP 257 and using the Google Style for formatting, we can ensure consistency in the code and make it easier to read. | non_test | create doctoring for be description we need to write docstrings for the backend python services to make the code easier to understand and maintain docstrings provide a concise explanation of the function or class and its purpose tasks write docstrings for all the functions and classes in the frontend and backend python services ensure that the docstrings follow the guidelines for writing docstrings in python make sure the docstrings provide enough information about the function or class its arguments return value and any exceptions that may be raised use for formatting the docstrings deliverables all functions and classes in the frontend and backend python services should have a docstring timeline to be discussed and agreed upon with the team additional information having clear and concise documentation will make it easier for new contributors to understand the code and make changes as well as for future maintenance by following the guidelines set out in pep and using the google style for formatting we can ensure consistency in the code and make it easier to read | 0 |
117,527 | 4,717,225,009 | IssuesEvent | 2016-10-16 14:14:42 | LatvianModder/FTBUtilities | https://api.github.com/repos/LatvianModder/FTBUtilities | closed | [1.10.2] [Inadvertent Bug] Claimed chunks place place rights | Bug Low Priority | This is kind of hard to explain what going on so i recorded it in action
http://ss.latmod.com/pc/2016-08-24_13.13.56.mp4
I own chunk I am in the chunk on the side is own by another player
This on it own i would say is low priority, util you find out the opposite is possible and you can place a block in chunk you do not have rights in by block it against a block in chunk you do have the right to interact with. | 1.0 | [1.10.2] [Inadvertent Bug] Claimed chunks place place rights - This is kind of hard to explain what going on so i recorded it in action
http://ss.latmod.com/pc/2016-08-24_13.13.56.mp4
I own chunk I am in the chunk on the side is own by another player
This on it own i would say is low priority, util you find out the opposite is possible and you can place a block in chunk you do not have rights in by block it against a block in chunk you do have the right to interact with. | non_test | claimed chunks place place rights this is kind of hard to explain what going on so i recorded it in action i own chunk i am in the chunk on the side is own by another player this on it own i would say is low priority util you find out the opposite is possible and you can place a block in chunk you do not have rights in by block it against a block in chunk you do have the right to interact with | 0 |
615,688 | 19,272,884,439 | IssuesEvent | 2021-12-10 08:24:13 | geosolutions-it/MapStore2 | https://api.github.com/repos/geosolutions-it/MapStore2 | closed | Annotations plugin crashes the app if geometry step is skipped | bug Priority: High Internal Good first issue | ## Description
<!-- Add here a few sentences describing the bug. -->
Annotations plugin crashes the app if geometry step is skipped
## How to reproduce
<!-- A list of steps to reproduce the bug -->
- open a map and open annotations from burger menu
- add new annotation (plus button)
- add a title
- add a point annotation (marker plus button)
- deselect the point entry from the geometry list
- click on save
*Expected Result*
<!-- Describe here the expected result -->
- prevent the application to crash
*Current Result*
<!-- Describe here the current behavior -->
- the application crashes
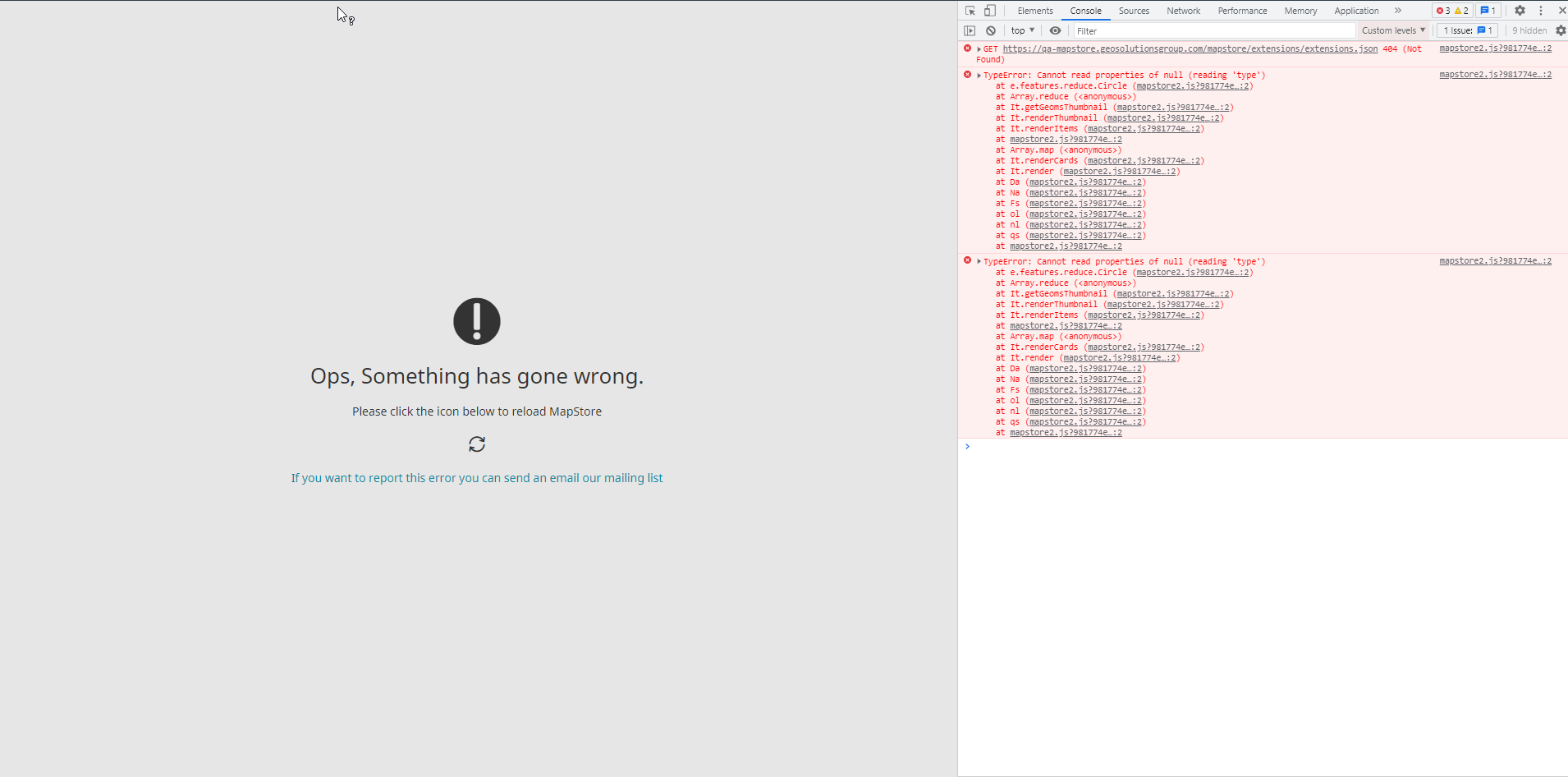
- [x] Not browser related
<details><summary> <b>Browser info</b> </summary>
<!-- If browser related, please compile the following table -->
<!-- If your browser is not in the list please add a new row to the table with the version -->
(use this site: <a href="https://www.whatsmybrowser.org/">https://www.whatsmybrowser.org/</a> for non expert users)
| Browser Affected | Version |
|---|---|
|Internet Explorer| |
|Edge| |
|Chrome| |
|Firefox| |
|Safari| |
</details>
## Other useful information
<!-- error stack trace, screenshot, videos, or link to repository code are welcome -->
| 1.0 | Annotations plugin crashes the app if geometry step is skipped - ## Description
<!-- Add here a few sentences describing the bug. -->
Annotations plugin crashes the app if geometry step is skipped
## How to reproduce
<!-- A list of steps to reproduce the bug -->
- open a map and open annotations from burger menu
- add new annotation (plus button)
- add a title
- add a point annotation (marker plus button)
- deselect the point entry from the geometry list
- click on save
*Expected Result*
<!-- Describe here the expected result -->
- prevent the application to crash
*Current Result*
<!-- Describe here the current behavior -->
- the application crashes
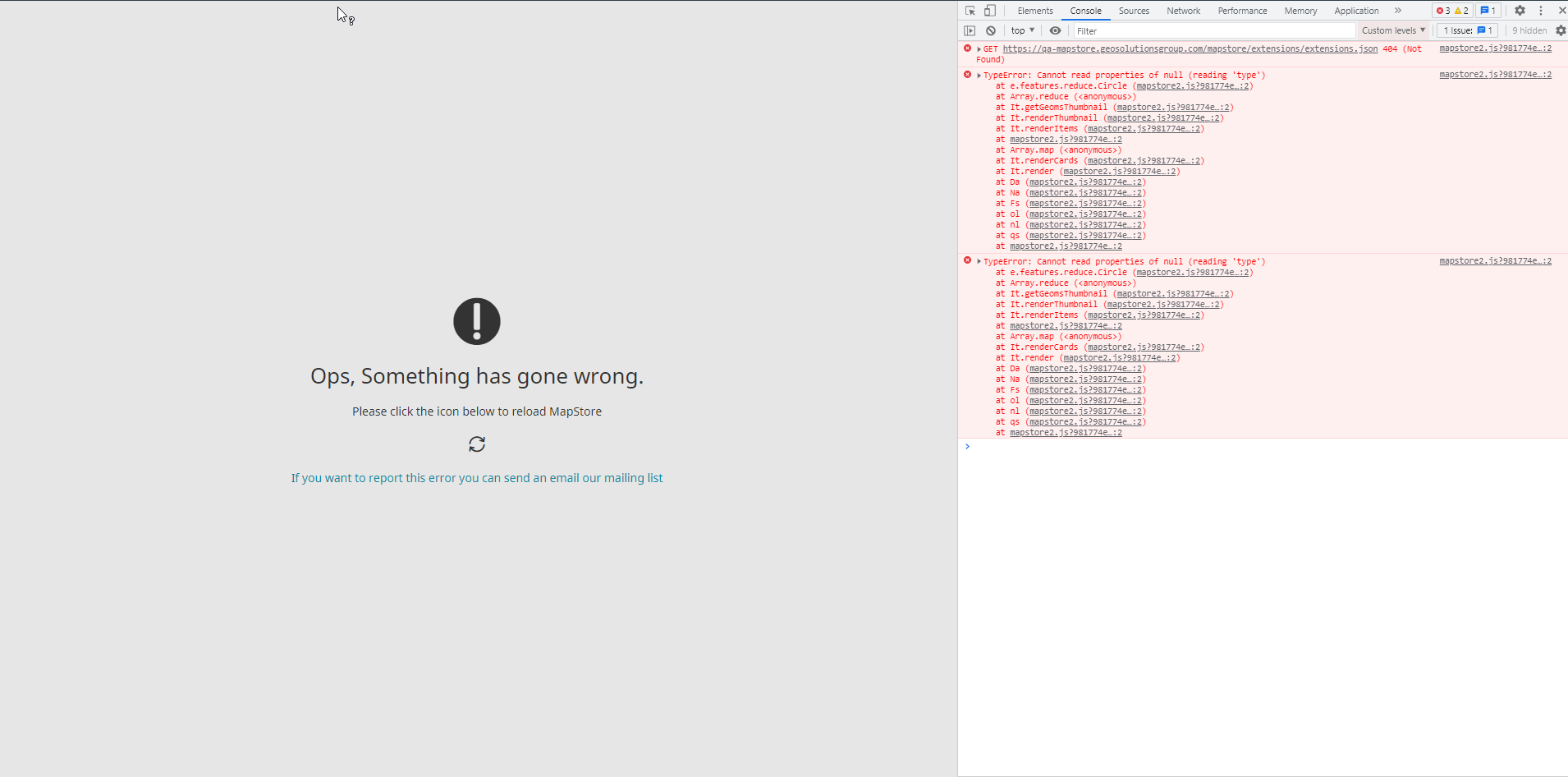
- [x] Not browser related
<details><summary> <b>Browser info</b> </summary>
<!-- If browser related, please compile the following table -->
<!-- If your browser is not in the list please add a new row to the table with the version -->
(use this site: <a href="https://www.whatsmybrowser.org/">https://www.whatsmybrowser.org/</a> for non expert users)
| Browser Affected | Version |
|---|---|
|Internet Explorer| |
|Edge| |
|Chrome| |
|Firefox| |
|Safari| |
</details>
## Other useful information
<!-- error stack trace, screenshot, videos, or link to repository code are welcome -->
| non_test | annotations plugin crashes the app if geometry step is skipped description annotations plugin crashes the app if geometry step is skipped how to reproduce open a map and open annotations from burger menu add new annotation plus button add a title add a point annotation marker plus button deselect the point entry from the geometry list click on save expected result prevent the application to crash current result the application crashes not browser related browser info use this site a href for non expert users browser affected version internet explorer edge chrome firefox safari other useful information | 0 |
274,333 | 20,831,565,560 | IssuesEvent | 2022-03-19 14:29:20 | pankod/refine | https://api.github.com/repos/pankod/refine | opened | [DOC]AuthProvider Custom i18n messages | documentation | **Is this issue related to an existing part of the documentation? If so, please provide a link**
[Helpful info about this issue.](https://refine.dev/docs/core/providers/auth-provider/)
**Describe the thing to improve**
I want to personalize authProvider messages but i can't see how can I do it in the documentation. After some research and reading library codes, I found it. I think you should write it on documents. But however, I can't translate my custom notifications. You should give us some instructions about it.
login: ({ username, password, remember }) => {
// Suppose we actually send a request to the back end here.
const user = mockUsers.find((item) => item.username === username);
if (user) {
localStorage.setItem("auth", JSON.stringify(user));
return Promise.resolve();
}
return Promise.reject({name:"Login Error",message:"Something went wrong."});
},
--- We cant use it this way of course--
Like this way(of course, that does not work), I want to internationalization my notifications.
login: ({ username, password, remember }) => {
// Suppose we actually send a request to the back end here.
const user = mockUsers.find((item) => item.username === username);
if (user) {
localStorage.setItem("auth", JSON.stringify(user));
return Promise.resolve();
}
return Promise.reject({name:translate("pages.login.username"),message:translate("pages.login.username")});
},
| 1.0 | [DOC]AuthProvider Custom i18n messages - **Is this issue related to an existing part of the documentation? If so, please provide a link**
[Helpful info about this issue.](https://refine.dev/docs/core/providers/auth-provider/)
**Describe the thing to improve**
I want to personalize authProvider messages but i can't see how can I do it in the documentation. After some research and reading library codes, I found it. I think you should write it on documents. But however, I can't translate my custom notifications. You should give us some instructions about it.
login: ({ username, password, remember }) => {
// Suppose we actually send a request to the back end here.
const user = mockUsers.find((item) => item.username === username);
if (user) {
localStorage.setItem("auth", JSON.stringify(user));
return Promise.resolve();
}
return Promise.reject({name:"Login Error",message:"Something went wrong."});
},
--- We cant use it this way of course--
Like this way(of course, that does not work), I want to internationalization my notifications.
login: ({ username, password, remember }) => {
// Suppose we actually send a request to the back end here.
const user = mockUsers.find((item) => item.username === username);
if (user) {
localStorage.setItem("auth", JSON.stringify(user));
return Promise.resolve();
}
return Promise.reject({name:translate("pages.login.username"),message:translate("pages.login.username")});
},
| non_test | authprovider custom messages is this issue related to an existing part of the documentation if so please provide a link describe the thing to improve i want to personalize authprovider messages but i can t see how can i do it in the documentation after some research and reading library codes i found it i think you should write it on documents but however i can t translate my custom notifications you should give us some instructions about it login username password remember suppose we actually send a request to the back end here const user mockusers find item item username username if user localstorage setitem auth json stringify user return promise resolve return promise reject name login error message something went wrong we cant use it this way of course like this way of course that does not work i want to internationalization my notifications login username password remember suppose we actually send a request to the back end here const user mockusers find item item username username if user localstorage setitem auth json stringify user return promise resolve return promise reject name translate pages login username message translate pages login username | 0 |
33,537 | 4,837,664,483 | IssuesEvent | 2016-11-08 23:23:14 | matplotlib/matplotlib | https://api.github.com/repos/matplotlib/matplotlib | closed | add multi-process flag as `-j` to `test.py` | Difficulty: Easy Machine Shop new-contributor-friendly Testing | To run the tests in parallel you currently have to add `--processes=8 --process-timeout=300` to the CLI, doing this as `-j 8` would be much nicer.
This should be a 'simple' matter of extending the CLI parsing done in `tests.py`.
| 1.0 | add multi-process flag as `-j` to `test.py` - To run the tests in parallel you currently have to add `--processes=8 --process-timeout=300` to the CLI, doing this as `-j 8` would be much nicer.
This should be a 'simple' matter of extending the CLI parsing done in `tests.py`.
| test | add multi process flag as j to test py to run the tests in parallel you currently have to add processes process timeout to the cli doing this as j would be much nicer this should be a simple matter of extending the cli parsing done in tests py | 1 |
128,300 | 18,045,344,411 | IssuesEvent | 2021-09-18 20:01:45 | veritem/codekin.tech | https://api.github.com/repos/veritem/codekin.tech | closed | CVE-2021-23382 (Medium) detected in postcss-6.0.23.tgz | security vulnerability | ## CVE-2021-23382 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>postcss-6.0.23.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-6.0.23.tgz">https://registry.npmjs.org/postcss/-/postcss-6.0.23.tgz</a></p>
<p>Path to dependency file: codekin.tech/package.json</p>
<p>Path to vulnerable library: codekin.tech/node_modules/postcss-functions/node_modules/postcss/package.json</p>
<p>
Dependency Hierarchy:
- tailwindcss-2.1.4.tgz (Root Library)
- postcss-functions-3.0.0.tgz
- :x: **postcss-6.0.23.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/veritem/codekin.tech/commit/97f904496220a079745bf198bb4cb1bcc34d59df">97f904496220a079745bf198bb4cb1bcc34d59df</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package postcss before 8.2.13 are vulnerable to Regular Expression Denial of Service (ReDoS) via getAnnotationURL() and loadAnnotation() in lib/previous-map.js. The vulnerable regexes are caused mainly by the sub-pattern \/\*\s* sourceMappingURL=(.*).
<p>Publish Date: 2021-04-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23382>CVE-2021-23382</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23382">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23382</a></p>
<p>Release Date: 2021-04-26</p>
<p>Fix Resolution: postcss - 8.2.13</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23382 (Medium) detected in postcss-6.0.23.tgz - ## CVE-2021-23382 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>postcss-6.0.23.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-6.0.23.tgz">https://registry.npmjs.org/postcss/-/postcss-6.0.23.tgz</a></p>
<p>Path to dependency file: codekin.tech/package.json</p>
<p>Path to vulnerable library: codekin.tech/node_modules/postcss-functions/node_modules/postcss/package.json</p>
<p>
Dependency Hierarchy:
- tailwindcss-2.1.4.tgz (Root Library)
- postcss-functions-3.0.0.tgz
- :x: **postcss-6.0.23.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/veritem/codekin.tech/commit/97f904496220a079745bf198bb4cb1bcc34d59df">97f904496220a079745bf198bb4cb1bcc34d59df</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package postcss before 8.2.13 are vulnerable to Regular Expression Denial of Service (ReDoS) via getAnnotationURL() and loadAnnotation() in lib/previous-map.js. The vulnerable regexes are caused mainly by the sub-pattern \/\*\s* sourceMappingURL=(.*).
<p>Publish Date: 2021-04-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23382>CVE-2021-23382</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23382">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23382</a></p>
<p>Release Date: 2021-04-26</p>
<p>Fix Resolution: postcss - 8.2.13</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in postcss tgz cve medium severity vulnerability vulnerable library postcss tgz tool for transforming styles with js plugins library home page a href path to dependency file codekin tech package json path to vulnerable library codekin tech node modules postcss functions node modules postcss package json dependency hierarchy tailwindcss tgz root library postcss functions tgz x postcss tgz vulnerable library found in head commit a href found in base branch main vulnerability details the package postcss before are vulnerable to regular expression denial of service redos via getannotationurl and loadannotation in lib previous map js the vulnerable regexes are caused mainly by the sub pattern s sourcemappingurl publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution postcss step up your open source security game with whitesource | 0 |
354,318 | 25,161,431,411 | IssuesEvent | 2022-11-10 17:05:01 | siddikgitt/accidental-marble-9532 | https://api.github.com/repos/siddikgitt/accidental-marble-9532 | closed | fw18_1057_day3.3_exercise database continued | documentation | - [x] add a new page adding your own exercise
- [x] complete the structure
- [x] look for the dummy data and work on it
- [x] finish all the small things interms of the CSS that remained and align all the work | 1.0 | fw18_1057_day3.3_exercise database continued - - [x] add a new page adding your own exercise
- [x] complete the structure
- [x] look for the dummy data and work on it
- [x] finish all the small things interms of the CSS that remained and align all the work | non_test | exercise database continued add a new page adding your own exercise complete the structure look for the dummy data and work on it finish all the small things interms of the css that remained and align all the work | 0 |
120,576 | 10,128,841,344 | IssuesEvent | 2019-08-01 13:38:35 | bbc/simorgh | https://api.github.com/repos/bbc/simorgh | closed | Refactor the cypress metaData helpers into commands | Heracles integration-testing simorgh-core-stream | **Is your feature request related to a problem? Please describe.**
Refactor the metaData helpers into commands
**Describe the solution you'd like**
Put them somewhere like this support/commands/pageTestFragment/metaData.js
**Describe alternatives you've considered**
n/a
**Testing notes**
[Tester to complete]
Dev insight: Will Cypress tests be required or are unit tests sufficient? Will there be any potential regression? etc
**Additional context**
Add any other context or screenshots about the feature request here.
| 1.0 | Refactor the cypress metaData helpers into commands - **Is your feature request related to a problem? Please describe.**
Refactor the metaData helpers into commands
**Describe the solution you'd like**
Put them somewhere like this support/commands/pageTestFragment/metaData.js
**Describe alternatives you've considered**
n/a
**Testing notes**
[Tester to complete]
Dev insight: Will Cypress tests be required or are unit tests sufficient? Will there be any potential regression? etc
**Additional context**
Add any other context or screenshots about the feature request here.
| test | refactor the cypress metadata helpers into commands is your feature request related to a problem please describe refactor the metadata helpers into commands describe the solution you d like put them somewhere like this support commands pagetestfragment metadata js describe alternatives you ve considered n a testing notes dev insight will cypress tests be required or are unit tests sufficient will there be any potential regression etc additional context add any other context or screenshots about the feature request here | 1 |
84,581 | 10,547,471,972 | IssuesEvent | 2019-10-03 01:16:36 | flutter/flutter | https://api.github.com/repos/flutter/flutter | opened | Dropdown menus disappear immediately when combined with text fields | f: material design framework severe: regression ▣ platform-android | On Android, when you have a `DropdownButton` on the same page as a `TextFormField`, and tap the dropdown when the text field has focus, then tapping the dropdown button will cause the dropdown to appear, a metrics change to occur (because the keyboard went away when the text field lost focus), and the dropdown disappears immediately, since the dropdown is coded to disappear with a metrics change, making it impossible to make a selection. Popup menus don't have this issue.
In order to combine properly with text fields, we need to figure out how to prevent them from losing the keyboard when they lose focus, so that the keyboard doesn't bounce up and down, which will fix this problem. And perhaps dropdowns shouldn't go away with a metrics change, but there may be other reasons for that.
Example code that shows this:
```dart
import 'package:flutter/material.dart';
void main() => runApp(MyApp());
class MyApp extends StatefulWidget {
@override
_MyAppState createState() => _MyAppState();
}
class _MyAppState extends State<MyApp> {
String value = 'foo';
@override
Widget build(BuildContext context) {
return MaterialApp(
title: 'Flutter Demo',
theme: ThemeData(
primarySwatch: Colors.blue,
),
home: Material(
child: Padding(
padding: EdgeInsets.symmetric(vertical: 100.0, horizontal: 10.0),
child: Column(
mainAxisSize: MainAxisSize.min,
children: <Widget>[
TextFormField(
decoration: InputDecoration(border: OutlineInputBorder()),
),
Row(
mainAxisAlignment: MainAxisAlignment.center,
mainAxisSize: MainAxisSize.min,
children: <Widget>[
DropdownButton(
value: value,
items: [
DropdownMenuItem(
value: 'foo',
child: Text('Foo'),
),
DropdownMenuItem(
value: 'bar',
child: Text('Bar'),
),
DropdownMenuItem(
value: 'baz',
child: Text('Baz'),
),
],
onChanged: (String value) {
setState(() {
this.value = value;
});
},
),
],
),
],
),
),
),
);
}
}
```
Focus the text field and try and select something from the dropdown.
cc @HansMuller, who has worked on `DropdownButton` recently. | 1.0 | Dropdown menus disappear immediately when combined with text fields - On Android, when you have a `DropdownButton` on the same page as a `TextFormField`, and tap the dropdown when the text field has focus, then tapping the dropdown button will cause the dropdown to appear, a metrics change to occur (because the keyboard went away when the text field lost focus), and the dropdown disappears immediately, since the dropdown is coded to disappear with a metrics change, making it impossible to make a selection. Popup menus don't have this issue.
In order to combine properly with text fields, we need to figure out how to prevent them from losing the keyboard when they lose focus, so that the keyboard doesn't bounce up and down, which will fix this problem. And perhaps dropdowns shouldn't go away with a metrics change, but there may be other reasons for that.
Example code that shows this:
```dart
import 'package:flutter/material.dart';
void main() => runApp(MyApp());
class MyApp extends StatefulWidget {
@override
_MyAppState createState() => _MyAppState();
}
class _MyAppState extends State<MyApp> {
String value = 'foo';
@override
Widget build(BuildContext context) {
return MaterialApp(
title: 'Flutter Demo',
theme: ThemeData(
primarySwatch: Colors.blue,
),
home: Material(
child: Padding(
padding: EdgeInsets.symmetric(vertical: 100.0, horizontal: 10.0),
child: Column(
mainAxisSize: MainAxisSize.min,
children: <Widget>[
TextFormField(
decoration: InputDecoration(border: OutlineInputBorder()),
),
Row(
mainAxisAlignment: MainAxisAlignment.center,
mainAxisSize: MainAxisSize.min,
children: <Widget>[
DropdownButton(
value: value,
items: [
DropdownMenuItem(
value: 'foo',
child: Text('Foo'),
),
DropdownMenuItem(
value: 'bar',
child: Text('Bar'),
),
DropdownMenuItem(
value: 'baz',
child: Text('Baz'),
),
],
onChanged: (String value) {
setState(() {
this.value = value;
});
},
),
],
),
],
),
),
),
);
}
}
```
Focus the text field and try and select something from the dropdown.
cc @HansMuller, who has worked on `DropdownButton` recently. | non_test | dropdown menus disappear immediately when combined with text fields on android when you have a dropdownbutton on the same page as a textformfield and tap the dropdown when the text field has focus then tapping the dropdown button will cause the dropdown to appear a metrics change to occur because the keyboard went away when the text field lost focus and the dropdown disappears immediately since the dropdown is coded to disappear with a metrics change making it impossible to make a selection popup menus don t have this issue in order to combine properly with text fields we need to figure out how to prevent them from losing the keyboard when they lose focus so that the keyboard doesn t bounce up and down which will fix this problem and perhaps dropdowns shouldn t go away with a metrics change but there may be other reasons for that example code that shows this dart import package flutter material dart void main runapp myapp class myapp extends statefulwidget override myappstate createstate myappstate class myappstate extends state string value foo override widget build buildcontext context return materialapp title flutter demo theme themedata primaryswatch colors blue home material child padding padding edgeinsets symmetric vertical horizontal child column mainaxissize mainaxissize min children textformfield decoration inputdecoration border outlineinputborder row mainaxisalignment mainaxisalignment center mainaxissize mainaxissize min children dropdownbutton value value items dropdownmenuitem value foo child text foo dropdownmenuitem value bar child text bar dropdownmenuitem value baz child text baz onchanged string value setstate this value value focus the text field and try and select something from the dropdown cc hansmuller who has worked on dropdownbutton recently | 0 |
285,738 | 21,552,785,750 | IssuesEvent | 2022-04-30 00:24:12 | tidyverse/ggplot2 | https://api.github.com/repos/tidyverse/ggplot2 | closed | Clarify that `fullrange = TRUE` extends range to the axis limits, not the whole plot. | documentation good first issue :heart: | There's some understandable confusion about `geom_smooth(fullrange = TRUE)` not making the smooth line go all the way to the axis lines. (Two example posts on Stack Overflow: [1](https://stackoverflow.com/q/66959036/903061), [2](https://stackoverflow.com/q/55307921/903061))
The current argument description in `?geom_smooth` is:
> `fullrange` Should the fit span the full range of the plot, or just the data?
I suggest modifying the documentation for clarity, something like this:
> `fullrange` If `TRUE`, the fit will extend to the axis limits, potentially beyond the data. (It will not extend into the padding of the limits configured by `expansion()`.) | 1.0 | Clarify that `fullrange = TRUE` extends range to the axis limits, not the whole plot. - There's some understandable confusion about `geom_smooth(fullrange = TRUE)` not making the smooth line go all the way to the axis lines. (Two example posts on Stack Overflow: [1](https://stackoverflow.com/q/66959036/903061), [2](https://stackoverflow.com/q/55307921/903061))
The current argument description in `?geom_smooth` is:
> `fullrange` Should the fit span the full range of the plot, or just the data?
I suggest modifying the documentation for clarity, something like this:
> `fullrange` If `TRUE`, the fit will extend to the axis limits, potentially beyond the data. (It will not extend into the padding of the limits configured by `expansion()`.) | non_test | clarify that fullrange true extends range to the axis limits not the whole plot there s some understandable confusion about geom smooth fullrange true not making the smooth line go all the way to the axis lines two example posts on stack overflow the current argument description in geom smooth is fullrange should the fit span the full range of the plot or just the data i suggest modifying the documentation for clarity something like this fullrange if true the fit will extend to the axis limits potentially beyond the data it will not extend into the padding of the limits configured by expansion | 0 |
124,765 | 10,323,248,886 | IssuesEvent | 2019-08-31 19:35:18 | PatrickRainer/AnimalSplash | https://api.github.com/repos/PatrickRainer/AnimalSplash | opened | Score counts not correct every time | AndroidTest bug | Don't know the exact circumstances, but it is more in the later levels. May be it is not reseted proberly... | 1.0 | Score counts not correct every time - Don't know the exact circumstances, but it is more in the later levels. May be it is not reseted proberly... | test | score counts not correct every time don t know the exact circumstances but it is more in the later levels may be it is not reseted proberly | 1 |
3,596 | 2,683,676,765 | IssuesEvent | 2015-03-28 06:15:57 | d3athrow/vgstation13 | https://api.github.com/repos/d3athrow/vgstation13 | closed | (WEB REPORT BY: nmsct699 REMOTE: 198.245.63.50:7777) Table is closed | Bug Needs Moar Testing | >Revision (Should be above if you're viewing this from ingame!)
c39e9342a286f2a782c12a3df362a7c318340edb
>General description of the issue
After doing barman activities, setting things on a table or reinforced table shows the message
>You can't, the reinforced table is closed.
>What you expected to happen
setting thing on a table
>What actually happened
I still set the thing on the table, but the message is displayed:
You can't, the reinforced table is closed.
or
You can't, the wooden table is closed.
etc
>Steps to reproduce if possible
I think it has something to do with mixing drinks or pouring them
The problem goes away if the client is restarted, but comes back after some drinkmaking activity | 1.0 | (WEB REPORT BY: nmsct699 REMOTE: 198.245.63.50:7777) Table is closed - >Revision (Should be above if you're viewing this from ingame!)
c39e9342a286f2a782c12a3df362a7c318340edb
>General description of the issue
After doing barman activities, setting things on a table or reinforced table shows the message
>You can't, the reinforced table is closed.
>What you expected to happen
setting thing on a table
>What actually happened
I still set the thing on the table, but the message is displayed:
You can't, the reinforced table is closed.
or
You can't, the wooden table is closed.
etc
>Steps to reproduce if possible
I think it has something to do with mixing drinks or pouring them
The problem goes away if the client is restarted, but comes back after some drinkmaking activity | test | web report by remote table is closed revision should be above if you re viewing this from ingame general description of the issue after doing barman activities setting things on a table or reinforced table shows the message you can t the reinforced table is closed what you expected to happen setting thing on a table what actually happened i still set the thing on the table but the message is displayed you can t the reinforced table is closed or you can t the wooden table is closed etc steps to reproduce if possible i think it has something to do with mixing drinks or pouring them the problem goes away if the client is restarted but comes back after some drinkmaking activity | 1 |
551,765 | 16,188,729,542 | IssuesEvent | 2021-05-04 03:56:10 | remnoteio/remnote-issues | https://api.github.com/repos/remnoteio/remnote-issues | closed | Copy / pasting Rem doesn't preserve bullet formatting | checked editor-polish fixed-in-next-update fixed-in-remnote-1.3.7 priority=2 | **Describe the bug**
Copying rem seems to preserve most rem-level formatting, like header levels, but not bullet hiding.
**To Reproduce**
Steps to reproduce the behavior:
1. Create some Rem with bullets hidden
2. Copy the Rem (multiple Rem in my case)
3. Paste in another doc
**Expected behavior**
Expected bullets to be hidden when pasted.
**Screenshots**
If applicable, add screenshots to help explain your problem.
After pasting (bullets were hidden for all source rem)
**Desktop (please complete the following information):**
- OS: macOS
- Browser: Chrome or native app
- Version: Chrome 87 or Desktop app 1.1.10 | 1.0 | Copy / pasting Rem doesn't preserve bullet formatting - **Describe the bug**
Copying rem seems to preserve most rem-level formatting, like header levels, but not bullet hiding.
**To Reproduce**
Steps to reproduce the behavior:
1. Create some Rem with bullets hidden
2. Copy the Rem (multiple Rem in my case)
3. Paste in another doc
**Expected behavior**
Expected bullets to be hidden when pasted.
**Screenshots**
If applicable, add screenshots to help explain your problem.
After pasting (bullets were hidden for all source rem)
**Desktop (please complete the following information):**
- OS: macOS
- Browser: Chrome or native app
- Version: Chrome 87 or Desktop app 1.1.10 | non_test | copy pasting rem doesn t preserve bullet formatting describe the bug copying rem seems to preserve most rem level formatting like header levels but not bullet hiding to reproduce steps to reproduce the behavior create some rem with bullets hidden copy the rem multiple rem in my case paste in another doc expected behavior expected bullets to be hidden when pasted screenshots if applicable add screenshots to help explain your problem after pasting bullets were hidden for all source rem desktop please complete the following information os macos browser chrome or native app version chrome or desktop app | 0 |
43,397 | 5,537,576,550 | IssuesEvent | 2017-03-21 22:29:26 | fossology/fossology | https://api.github.com/repos/fossology/fossology | closed | Add unit tests for BucketsDiff | Category: Testing Priority: High Status: New Tracker: Support | ---
Author Name: **Paul Holland**
Original Redmine Issue: 2571, http://www.fossology.org/issues/2571
Original Date: 2012/06/15
Original Assignee: Bob Gobeille
---
Fills in http://www.fossology.org/projects/fossology/wiki/FOSSology_tests
| 1.0 | Add unit tests for BucketsDiff - ---
Author Name: **Paul Holland**
Original Redmine Issue: 2571, http://www.fossology.org/issues/2571
Original Date: 2012/06/15
Original Assignee: Bob Gobeille
---
Fills in http://www.fossology.org/projects/fossology/wiki/FOSSology_tests
| test | add unit tests for bucketsdiff author name paul holland original redmine issue original date original assignee bob gobeille fills in | 1 |
284,045 | 8,735,389,617 | IssuesEvent | 2018-12-11 16:40:27 | ansible/awx | https://api.github.com/repos/ansible/awx | opened | View playbooks in AWX | component:api component:ui priority:medium state:needs_devel type:enhancement | ##### ISSUE TYPE
- Feature Idea
##### COMPONENT NAME
- API
- UI
##### SUMMARY
While playbooks should live in source control and not be edited from AWX, it could be useful to *view* them, especially when trying to determine what playbook a job template should use just from a filename.
Likely has some conflict with https://github.com/ansible/awx/issues/282.
##### ADDITIONAL INFORMATION
| 1.0 | View playbooks in AWX - ##### ISSUE TYPE
- Feature Idea
##### COMPONENT NAME
- API
- UI
##### SUMMARY
While playbooks should live in source control and not be edited from AWX, it could be useful to *view* them, especially when trying to determine what playbook a job template should use just from a filename.
Likely has some conflict with https://github.com/ansible/awx/issues/282.
##### ADDITIONAL INFORMATION
| non_test | view playbooks in awx issue type feature idea component name api ui summary while playbooks should live in source control and not be edited from awx it could be useful to view them especially when trying to determine what playbook a job template should use just from a filename likely has some conflict with additional information | 0 |
13,917 | 2,789,753,955 | IssuesEvent | 2015-05-08 21:16:53 | google/google-visualization-api-issues | https://api.github.com/repos/google/google-visualization-api-issues | opened | Bug: AnnotatedTimeLine has minimum zoom factor == 1 day - should be settable or eliminated. | Priority-Medium Type-Defect | Original [issue 57](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=57) created by google-admin on 2009-09-17T18:17:16.000Z:
The AnnotatedTimeLine seems to have the minimum "window" for zooming to be
1 day. It would be nice to have this a settable option. (or eliminated) | 1.0 | Bug: AnnotatedTimeLine has minimum zoom factor == 1 day - should be settable or eliminated. - Original [issue 57](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=57) created by google-admin on 2009-09-17T18:17:16.000Z:
The AnnotatedTimeLine seems to have the minimum "window" for zooming to be
1 day. It would be nice to have this a settable option. (or eliminated) | non_test | bug annotatedtimeline has minimum zoom factor day should be settable or eliminated original created by google admin on the annotatedtimeline seems to have the minimum quot window quot for zooming to be day it would be nice to have this a settable option or eliminated | 0 |
134,647 | 10,925,761,800 | IssuesEvent | 2019-11-22 13:18:51 | OpenSourceEconomics/respy | https://api.github.com/repos/OpenSourceEconomics/respy | closed | Details about Testing Harness | pb-testing | It would be nice to have some similar graphs for our testing documentation https://blogs.msdn.microsoft.com/bharry/2017/06/28/testing-in-a-cloud-delivery-cadence/It | 1.0 | Details about Testing Harness - It would be nice to have some similar graphs for our testing documentation https://blogs.msdn.microsoft.com/bharry/2017/06/28/testing-in-a-cloud-delivery-cadence/It | test | details about testing harness it would be nice to have some similar graphs for our testing documentation | 1 |
43,647 | 23,322,333,182 | IssuesEvent | 2022-08-08 17:35:40 | umee-network/umee | https://api.github.com/repos/umee-network/umee | opened | leverage: Clear blacklisted collateral when mark/sweeping bad debt | C:x/leverage T:Performance | Blacklisted collateral is currently ignored when marking bad debt (in `MsgLiquidate`), but will require a token registry check in `SweepBadDebts` when iterated over. Performance can be improved here:
TODO:
- Automatically `Decollateralize` blacklisted collateral when marking bad debt in `MsgLiquidate`.
- Automatically `Decollateralize` blacklisted collateral when sweeping bad debt in `SweepBadDebt`.
This prevents the worst case scenario of blacklisted collateral co-occurring with reserve exhaustion, in which any number of inefficient token registry chcecks would repeat each `EndBlock` without clearing any bad debts, thus slowing the chain.
For context, `Token.Blacklist` is an extreme option for disabling tokens, which should only be used if setting `EnableMsgBorrow` and `EnableMsgSupply` to `false` plus setting `CollateralWeight` to `0` are not enough. An example of this is if a previously accepted asset collapsed so hard that we could not rely on any oracle prices for it, and no liquidators could be expected to want it as a reward. | True | leverage: Clear blacklisted collateral when mark/sweeping bad debt - Blacklisted collateral is currently ignored when marking bad debt (in `MsgLiquidate`), but will require a token registry check in `SweepBadDebts` when iterated over. Performance can be improved here:
TODO:
- Automatically `Decollateralize` blacklisted collateral when marking bad debt in `MsgLiquidate`.
- Automatically `Decollateralize` blacklisted collateral when sweeping bad debt in `SweepBadDebt`.
This prevents the worst case scenario of blacklisted collateral co-occurring with reserve exhaustion, in which any number of inefficient token registry chcecks would repeat each `EndBlock` without clearing any bad debts, thus slowing the chain.
For context, `Token.Blacklist` is an extreme option for disabling tokens, which should only be used if setting `EnableMsgBorrow` and `EnableMsgSupply` to `false` plus setting `CollateralWeight` to `0` are not enough. An example of this is if a previously accepted asset collapsed so hard that we could not rely on any oracle prices for it, and no liquidators could be expected to want it as a reward. | non_test | leverage clear blacklisted collateral when mark sweeping bad debt blacklisted collateral is currently ignored when marking bad debt in msgliquidate but will require a token registry check in sweepbaddebts when iterated over performance can be improved here todo automatically decollateralize blacklisted collateral when marking bad debt in msgliquidate automatically decollateralize blacklisted collateral when sweeping bad debt in sweepbaddebt this prevents the worst case scenario of blacklisted collateral co occurring with reserve exhaustion in which any number of inefficient token registry chcecks would repeat each endblock without clearing any bad debts thus slowing the chain for context token blacklist is an extreme option for disabling tokens which should only be used if setting enablemsgborrow and enablemsgsupply to false plus setting collateralweight to are not enough an example of this is if a previously accepted asset collapsed so hard that we could not rely on any oracle prices for it and no liquidators could be expected to want it as a reward | 0 |
444,893 | 12,822,692,351 | IssuesEvent | 2020-07-06 10:15:42 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | opened | [0.9.0 staging-1641] Items in Stockpiles sometimes are blocked | Priority: Critical Priority: High | and I can't drag them:
If I open another stockpile and check first stockpile from linked inventories:

| 2.0 | [0.9.0 staging-1641] Items in Stockpiles sometimes are blocked - and I can't drag them:
If I open another stockpile and check first stockpile from linked inventories:

| non_test | items in stockpiles sometimes are blocked and i can t drag them if i open another stockpile and check first stockpile from linked inventories | 0 |
24,453 | 7,511,242,464 | IssuesEvent | 2018-04-11 05:34:31 | eve-savvy/savvy-cert | https://api.github.com/repos/eve-savvy/savvy-cert | opened | rubydoc.info | build docs | The project is not properly building on [rubydoc.info](http://www.rubydoc.info/github/eve-savvy/savvy-cert). Ensure the project documentation properly builds on rubydoc.info and remove the gh-pages deployment from travis as well as the gh-pages branch. | 1.0 | rubydoc.info - The project is not properly building on [rubydoc.info](http://www.rubydoc.info/github/eve-savvy/savvy-cert). Ensure the project documentation properly builds on rubydoc.info and remove the gh-pages deployment from travis as well as the gh-pages branch. | non_test | rubydoc info the project is not properly building on ensure the project documentation properly builds on rubydoc info and remove the gh pages deployment from travis as well as the gh pages branch | 0 |
206,649 | 16,048,663,077 | IssuesEvent | 2021-04-22 16:21:00 | r00t-3xp10it/venom | https://api.github.com/repos/r00t-3xp10it/venom | closed | How does Process Injection work? | Documentation | Hi, Nice framework, Really useful for Red Teaming purposes, Had a question...
The file less attacks are getting injected in a remote process? if so, can i know how? | 1.0 | How does Process Injection work? - Hi, Nice framework, Really useful for Red Teaming purposes, Had a question...
The file less attacks are getting injected in a remote process? if so, can i know how? | non_test | how does process injection work hi nice framework really useful for red teaming purposes had a question the file less attacks are getting injected in a remote process if so can i know how | 0 |
70,793 | 7,201,075,106 | IssuesEvent | 2018-02-05 21:16:05 | diesel-rs/diesel | https://api.github.com/repos/diesel-rs/diesel | closed | Write tests for `#[derive(Associations)] | tests | While porting `#[derive(Associations)]` from the old macro_rules based derive to a normal procedural macro derive in #1468 we noticed that there are no tests for this derive.
We should definitively write some tests to check if everything works as assumed. | 1.0 | Write tests for `#[derive(Associations)] - While porting `#[derive(Associations)]` from the old macro_rules based derive to a normal procedural macro derive in #1468 we noticed that there are no tests for this derive.
We should definitively write some tests to check if everything works as assumed. | test | write tests for while porting from the old macro rules based derive to a normal procedural macro derive in we noticed that there are no tests for this derive we should definitively write some tests to check if everything works as assumed | 1 |
384,749 | 11,402,694,165 | IssuesEvent | 2020-01-31 04:20:37 | GoogleContainerTools/skaffold | https://api.github.com/repos/GoogleContainerTools/skaffold | closed | Skaffold YAML reference page broken | area/docs kind/bug priority/p0 | The [skaffold.yaml reference page](https://skaffold.dev/docs/references/yaml/) is broken. It appears to be related to the update of lit-html in #3466
The code is breaking at line 110:
https://github.com/GoogleContainerTools/skaffold/blob/650ed4ba0c8992421f27e8aee3561ebad8bddf2a/docs/content/en/docs/references/yaml/main.js#L114-L116
`value` is `"."` from the `default` value of the `KustomizeDeploy`'s `paths` property, which is defined as an array of strings.
https://github.com/GoogleContainerTools/skaffold/blob/650ed4ba0c8992421f27e8aee3561ebad8bddf2a/docs/content/en/schemas/v2alpha3.json#L1602-L1610
And sure enough, `"."` isn't an array of strings.
But this `default` hasn't changed in ages, so it must be the lit-html. What's puzzling is why this error didn't show up during testing of #3466? | 1.0 | Skaffold YAML reference page broken - The [skaffold.yaml reference page](https://skaffold.dev/docs/references/yaml/) is broken. It appears to be related to the update of lit-html in #3466
The code is breaking at line 110:
https://github.com/GoogleContainerTools/skaffold/blob/650ed4ba0c8992421f27e8aee3561ebad8bddf2a/docs/content/en/docs/references/yaml/main.js#L114-L116
`value` is `"."` from the `default` value of the `KustomizeDeploy`'s `paths` property, which is defined as an array of strings.
https://github.com/GoogleContainerTools/skaffold/blob/650ed4ba0c8992421f27e8aee3561ebad8bddf2a/docs/content/en/schemas/v2alpha3.json#L1602-L1610
And sure enough, `"."` isn't an array of strings.
But this `default` hasn't changed in ages, so it must be the lit-html. What's puzzling is why this error didn't show up during testing of #3466? | non_test | skaffold yaml reference page broken the is broken it appears to be related to the update of lit html in the code is breaking at line value is from the default value of the kustomizedeploy s paths property which is defined as an array of strings and sure enough isn t an array of strings but this default hasn t changed in ages so it must be the lit html what s puzzling is why this error didn t show up during testing of | 0 |
807,153 | 29,953,600,770 | IssuesEvent | 2023-06-23 05:04:48 | KATO-Hiro/AtCoderClans | https://api.github.com/repos/KATO-Hiro/AtCoderClans | closed | Node.jsのDockerコンテナを用意 | priority high | ## WHY
+ なるべく、ローカルの環境を汚さずに検証したい
+ 動作確認のため
## See
https://github.com/jueve/atcoder-review#%E6%89%8B%E5%8B%95%E3%81%A7%E3%83%93%E3%83%AB%E3%83%89%E3%81%99%E3%82%8B
https://qiita.com/koinori/items/084a0770c1f9e72e0c14
https://github.com/microsoft/vscode-remote-try-node/blob/master/.devcontainer/Dockerfile
https://github.com/microsoft/vscode-dev-containers/tree/v0.134.0
| 1.0 | Node.jsのDockerコンテナを用意 - ## WHY
+ なるべく、ローカルの環境を汚さずに検証したい
+ 動作確認のため
## See
https://github.com/jueve/atcoder-review#%E6%89%8B%E5%8B%95%E3%81%A7%E3%83%93%E3%83%AB%E3%83%89%E3%81%99%E3%82%8B
https://qiita.com/koinori/items/084a0770c1f9e72e0c14
https://github.com/microsoft/vscode-remote-try-node/blob/master/.devcontainer/Dockerfile
https://github.com/microsoft/vscode-dev-containers/tree/v0.134.0
| non_test | node jsのdockerコンテナを用意 why なるべく、ローカルの環境を汚さずに検証したい 動作確認のため see | 0 |
84,451 | 7,922,348,914 | IssuesEvent | 2018-07-05 10:29:57 | edenlabllc/ehealth.api | https://api.github.com/repos/edenlabllc/ehealth.api | closed | problem with drugstore and drugstore_point on api/reports/stats/divisions | BE project/reimbursement status/test | no response for drugstore and drugstore_point on api/reports/stats/divisions
```
{
"paging": {
"total_pages": 1,
"total_entries": 0,
"page_size": 10,
"page_number": 1
},
"meta": {
"url": "http://api-svc.reports/reports/stats/divisions",
"type": "list",
"request_id": "cfd85ed3-9c8f-4685-bde8-b3dba929cf83#22889",
"code": 200
},
"data": []
}
``` | 1.0 | problem with drugstore and drugstore_point on api/reports/stats/divisions - no response for drugstore and drugstore_point on api/reports/stats/divisions
```
{
"paging": {
"total_pages": 1,
"total_entries": 0,
"page_size": 10,
"page_number": 1
},
"meta": {
"url": "http://api-svc.reports/reports/stats/divisions",
"type": "list",
"request_id": "cfd85ed3-9c8f-4685-bde8-b3dba929cf83#22889",
"code": 200
},
"data": []
}
``` | test | problem with drugstore and drugstore point on api reports stats divisions no response for drugstore and drugstore point on api reports stats divisions paging total pages total entries page size page number meta url type list request id code data | 1 |
326,746 | 9,960,599,535 | IssuesEvent | 2019-07-06 18:07:09 | WoWManiaUK/Blackwing-Lair | https://api.github.com/repos/WoWManiaUK/Blackwing-Lair | opened | [Quest] Knee-Deep - worgen area | Confirmed Priority-High zone 80-85 Cata | **Links:**
https://www.youtube.com/watch?v=OldY7IkaWdk - video showing how it works
https://wow.gamepedia.com/Knee-Deep
**What is happening:**
seems like phasing issue, no rats in tunnel to scare off and no npc to hand in at the end
**What should happen:**
there should be rats in the tunnel that you scare off with the rats and then you should be able to hand it in at the other end
| 1.0 | [Quest] Knee-Deep - worgen area - **Links:**
https://www.youtube.com/watch?v=OldY7IkaWdk - video showing how it works
https://wow.gamepedia.com/Knee-Deep
**What is happening:**
seems like phasing issue, no rats in tunnel to scare off and no npc to hand in at the end
**What should happen:**
there should be rats in the tunnel that you scare off with the rats and then you should be able to hand it in at the other end
| non_test | knee deep worgen area links video showing how it works what is happening seems like phasing issue no rats in tunnel to scare off and no npc to hand in at the end what should happen there should be rats in the tunnel that you scare off with the rats and then you should be able to hand it in at the other end | 0 |
6,643 | 8,923,503,237 | IssuesEvent | 2019-01-21 15:49:34 | cristal-ise/kernel | https://api.github.com/repos/cristal-ise/kernel | closed | Set password to be temporary during CreateAgentFromDescription | bug not backward compatible | CreateAgentFromDescription can set passwrod and it should be temporary by default | True | Set password to be temporary during CreateAgentFromDescription - CreateAgentFromDescription can set passwrod and it should be temporary by default | non_test | set password to be temporary during createagentfromdescription createagentfromdescription can set passwrod and it should be temporary by default | 0 |
398,476 | 27,197,532,625 | IssuesEvent | 2023-02-20 07:02:36 | xKDR/TSFrames.jl | https://api.github.com/repos/xKDR/TSFrames.jl | opened | Improve documentation for constructor | documentation | Operations like this should be visible at the top:
```julia
A = [1:10]; B = [11:20]; C = [21:30];
prices_ts = TSFrame([A B C], dates, colnames=[:A, :B, :C])
``` | 1.0 | Improve documentation for constructor - Operations like this should be visible at the top:
```julia
A = [1:10]; B = [11:20]; C = [21:30];
prices_ts = TSFrame([A B C], dates, colnames=[:A, :B, :C])
``` | non_test | improve documentation for constructor operations like this should be visible at the top julia a b c prices ts tsframe dates colnames | 0 |
103,381 | 16,602,493,097 | IssuesEvent | 2021-06-01 21:40:41 | gms-ws-sandbox/nibrs | https://api.github.com/repos/gms-ws-sandbox/nibrs | opened | CVE-2019-3795 (Medium) detected in spring-security-core-5.0.8.RELEASE.jar | security vulnerability | ## CVE-2019-3795 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-core-5.0.8.RELEASE.jar</b></p></summary>
<p>spring-security-core</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: nibrs/web/nibrs-web/pom.xml</p>
<p>Path to vulnerable library: nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/spring-security-core-5.0.8.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/security/spring-security-core/5.0.8.RELEASE/spring-security-core-5.0.8.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-security-core-5.0.8.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs/commit/dba6b0930aa319c568021490e9259f5cae89b6c5">dba6b0930aa319c568021490e9259f5cae89b6c5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Security versions 4.2.x prior to 4.2.12, 5.0.x prior to 5.0.12, and 5.1.x prior to 5.1.5 contain an insecure randomness vulnerability when using SecureRandomFactoryBean#setSeed to configure a SecureRandom instance. In order to be impacted, an honest application must provide a seed and make the resulting random material available to an attacker for inspection.
<p>Publish Date: 2019-04-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-3795>CVE-2019-3795</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://pivotal.io/security/cve-2019-3795">https://pivotal.io/security/cve-2019-3795</a></p>
<p>Release Date: 2019-04-08</p>
<p>Fix Resolution: 4.2.12,5.0.12,5.1.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework.security","packageName":"spring-security-core","packageVersion":"5.0.8.RELEASE","packageFilePaths":["/web/nibrs-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.springframework.security:spring-security-core:5.0.8.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.2.12,5.0.12,5.1.5"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-3795","vulnerabilityDetails":"Spring Security versions 4.2.x prior to 4.2.12, 5.0.x prior to 5.0.12, and 5.1.x prior to 5.1.5 contain an insecure randomness vulnerability when using SecureRandomFactoryBean#setSeed to configure a SecureRandom instance. In order to be impacted, an honest application must provide a seed and make the resulting random material available to an attacker for inspection.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-3795","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-3795 (Medium) detected in spring-security-core-5.0.8.RELEASE.jar - ## CVE-2019-3795 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-core-5.0.8.RELEASE.jar</b></p></summary>
<p>spring-security-core</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: nibrs/web/nibrs-web/pom.xml</p>
<p>Path to vulnerable library: nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/spring-security-core-5.0.8.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/security/spring-security-core/5.0.8.RELEASE/spring-security-core-5.0.8.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-security-core-5.0.8.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs/commit/dba6b0930aa319c568021490e9259f5cae89b6c5">dba6b0930aa319c568021490e9259f5cae89b6c5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Security versions 4.2.x prior to 4.2.12, 5.0.x prior to 5.0.12, and 5.1.x prior to 5.1.5 contain an insecure randomness vulnerability when using SecureRandomFactoryBean#setSeed to configure a SecureRandom instance. In order to be impacted, an honest application must provide a seed and make the resulting random material available to an attacker for inspection.
<p>Publish Date: 2019-04-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-3795>CVE-2019-3795</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://pivotal.io/security/cve-2019-3795">https://pivotal.io/security/cve-2019-3795</a></p>
<p>Release Date: 2019-04-08</p>
<p>Fix Resolution: 4.2.12,5.0.12,5.1.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework.security","packageName":"spring-security-core","packageVersion":"5.0.8.RELEASE","packageFilePaths":["/web/nibrs-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.springframework.security:spring-security-core:5.0.8.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.2.12,5.0.12,5.1.5"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-3795","vulnerabilityDetails":"Spring Security versions 4.2.x prior to 4.2.12, 5.0.x prior to 5.0.12, and 5.1.x prior to 5.1.5 contain an insecure randomness vulnerability when using SecureRandomFactoryBean#setSeed to configure a SecureRandom instance. In order to be impacted, an honest application must provide a seed and make the resulting random material available to an attacker for inspection.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-3795","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_test | cve medium detected in spring security core release jar cve medium severity vulnerability vulnerable library spring security core release jar spring security core library home page a href path to dependency file nibrs web nibrs web pom xml path to vulnerable library nibrs web nibrs web target nibrs web web inf lib spring security core release jar home wss scanner repository org springframework security spring security core release spring security core release jar dependency hierarchy x spring security core release jar vulnerable library found in head commit a href found in base branch master vulnerability details spring security versions x prior to x prior to and x prior to contain an insecure randomness vulnerability when using securerandomfactorybean setseed to configure a securerandom instance in order to be impacted an honest application must provide a seed and make the resulting random material available to an attacker for inspection publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org springframework security spring security core release isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails spring security versions x prior to x prior to and x prior to contain an insecure randomness vulnerability when using securerandomfactorybean setseed to configure a securerandom instance in order to be impacted an honest application must provide a seed and make the resulting random material available to an attacker for inspection vulnerabilityurl | 0 |
326,363 | 27,987,205,386 | IssuesEvent | 2023-03-26 20:29:00 | Forgottenit/restaurant | https://api.github.com/repos/Forgottenit/restaurant | opened | TEST: Test that Bookings not made in the past | Bookings Testing | Test Bookings can only be made in the future
## ACCEPTANCE CRITERIA
- Bookings not valid if in the past
## TASKS
- [ ] Create test to check bookings not possible in the past
| 1.0 | TEST: Test that Bookings not made in the past - Test Bookings can only be made in the future
## ACCEPTANCE CRITERIA
- Bookings not valid if in the past
## TASKS
- [ ] Create test to check bookings not possible in the past
| test | test test that bookings not made in the past test bookings can only be made in the future acceptance criteria bookings not valid if in the past tasks create test to check bookings not possible in the past | 1 |
180,890 | 21,625,848,696 | IssuesEvent | 2022-05-05 01:57:58 | AlexRogalskiy/java-patterns | https://api.github.com/repos/AlexRogalskiy/java-patterns | opened | CVE-2021-37701 (High) detected in tar-2.2.1.tgz | security vulnerability | ## CVE-2021-37701 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-2.2.1.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.1.tgz">https://registry.npmjs.org/tar/-/tar-2.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/tar/package.json,/node_modules/npmi/node_modules/npm/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- gitbook-cli-2.3.2.tgz (Root Library)
- npm-5.1.0.tgz
- :x: **tar-2.2.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 4.4.16, 5.0.8, and 6.1.7 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory, where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems. The cache checking logic used both `\` and `/` characters as path separators, however `\` is a valid filename character on posix systems. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. Additionally, a similar confusion could arise on case-insensitive filesystems. If a tar archive contained a directory at `FOO`, followed by a symbolic link named `foo`, then on case-insensitive file systems, the creation of the symbolic link would remove the directory from the filesystem, but _not_ from the internal directory cache, as it would not be treated as a cache hit. A subsequent file entry within the `FOO` directory would then be placed in the target of the symbolic link, thinking that the directory had already been created. These issues were addressed in releases 4.4.16, 5.0.8 and 6.1.7. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-9r2w-394v-53qc.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37701>CVE-2021-37701</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc">https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution: tar - 4.4.16,5.0.8,6.1.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-37701 (High) detected in tar-2.2.1.tgz - ## CVE-2021-37701 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-2.2.1.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.1.tgz">https://registry.npmjs.org/tar/-/tar-2.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/tar/package.json,/node_modules/npmi/node_modules/npm/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- gitbook-cli-2.3.2.tgz (Root Library)
- npm-5.1.0.tgz
- :x: **tar-2.2.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 4.4.16, 5.0.8, and 6.1.7 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory, where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems. The cache checking logic used both `\` and `/` characters as path separators, however `\` is a valid filename character on posix systems. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. Additionally, a similar confusion could arise on case-insensitive filesystems. If a tar archive contained a directory at `FOO`, followed by a symbolic link named `foo`, then on case-insensitive file systems, the creation of the symbolic link would remove the directory from the filesystem, but _not_ from the internal directory cache, as it would not be treated as a cache hit. A subsequent file entry within the `FOO` directory would then be placed in the target of the symbolic link, thinking that the directory had already been created. These issues were addressed in releases 4.4.16, 5.0.8 and 6.1.7. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-9r2w-394v-53qc.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37701>CVE-2021-37701</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc">https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution: tar - 4.4.16,5.0.8,6.1.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in tar tgz cve high severity vulnerability vulnerable library tar tgz tar for node library home page a href path to dependency file package json path to vulnerable library node modules npm node modules tar package json node modules npmi node modules npm node modules tar package json dependency hierarchy gitbook cli tgz root library npm tgz x tar tgz vulnerable library found in base branch master vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems the cache checking logic used both and characters as path separators however is a valid filename character on posix systems by first creating a directory and then replacing that directory with a symlink it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite additionally a similar confusion could arise on case insensitive filesystems if a tar archive contained a directory at foo followed by a symbolic link named foo then on case insensitive file systems the creation of the symbolic link would remove the directory from the filesystem but not from the internal directory cache as it would not be treated as a cache hit a subsequent file entry within the foo directory would then be placed in the target of the symbolic link thinking that the directory had already been created these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar if this is not possible a workaround is available in the referenced ghsa publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar step up your open source security game with whitesource | 0 |
320,730 | 27,454,617,897 | IssuesEvent | 2023-03-02 20:13:15 | MPMG-DCC-UFMG/F01 | https://api.github.com/repos/MPMG-DCC-UFMG/F01 | closed | Teste de generalizacao para a tag Orçamento - Todas - Divinésia | generalization test development tag - Orçamento subtag - Todas | DoD: Realizar o teste de Generalização do validador da tag Orçamento - Todas para o Município de Divinésia. | 1.0 | Teste de generalizacao para a tag Orçamento - Todas - Divinésia - DoD: Realizar o teste de Generalização do validador da tag Orçamento - Todas para o Município de Divinésia. | test | teste de generalizacao para a tag orçamento todas divinésia dod realizar o teste de generalização do validador da tag orçamento todas para o município de divinésia | 1 |
118,906 | 17,602,813,133 | IssuesEvent | 2021-08-17 13:48:38 | harrinry/nifi | https://api.github.com/repos/harrinry/nifi | opened | CVE-2021-21295 (Medium) detected in netty-codec-http-4.1.5.Final.jar, netty-all-4.0.23.Final.jar | security vulnerability | ## CVE-2021-21295 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>netty-codec-http-4.1.5.Final.jar</b>, <b>netty-all-4.0.23.Final.jar</b></p></summary>
<p>
<details><summary><b>netty-codec-http-4.1.5.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to vulnerable library: nifi-nar-bundles/nifi-elasticsearch-bundle/nifi-elasticsearch-5-nar/target/classes/META-INF/bundled-dependencies/netty-codec-http-4.1.5.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-codec-http-4.1.5.Final.jar** (Vulnerable Library)
</details>
<details><summary><b>netty-all-4.0.23.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to vulnerable library: nifi-nar-bundles/nifi-standard-services/nifi-hbase_1_1_2-client-service-bundle/nifi-hbase_1_1_2-client-service-nar/target/classes/META-INF/bundled-dependencies/netty-all-4.0.23.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-all-4.0.23.Final.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/harrinry/nifi/commit/0484b1d281ed1df9c5682361286dee2ca6c634fe">0484b1d281ed1df9c5682361286dee2ca6c634fe</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty is an open-source, asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers & clients. In Netty (io.netty:netty-codec-http2) before version 4.1.60.Final there is a vulnerability that enables request smuggling. If a Content-Length header is present in the original HTTP/2 request, the field is not validated by `Http2MultiplexHandler` as it is propagated up. This is fine as long as the request is not proxied through as HTTP/1.1. If the request comes in as an HTTP/2 stream, gets converted into the HTTP/1.1 domain objects (`HttpRequest`, `HttpContent`, etc.) via `Http2StreamFrameToHttpObjectCodec `and then sent up to the child channel's pipeline and proxied through a remote peer as HTTP/1.1 this may result in request smuggling. In a proxy case, users may assume the content-length is validated somehow, which is not the case. If the request is forwarded to a backend channel that is a HTTP/1.1 connection, the Content-Length now has meaning and needs to be checked. An attacker can smuggle requests inside the body as it gets downgraded from HTTP/2 to HTTP/1.1. For an example attack refer to the linked GitHub Advisory. Users are only affected if all of this is true: `HTTP2MultiplexCodec` or `Http2FrameCodec` is used, `Http2StreamFrameToHttpObjectCodec` is used to convert to HTTP/1.1 objects, and these HTTP/1.1 objects are forwarded to another remote peer. This has been patched in 4.1.60.Final As a workaround, the user can do the validation by themselves by implementing a custom `ChannelInboundHandler` that is put in the `ChannelPipeline` behind `Http2StreamFrameToHttpObjectCodec`.
<p>Publish Date: 2021-03-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21295>CVE-2021-21295</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wm47-8v5p-wjpj">https://github.com/advisories/GHSA-wm47-8v5p-wjpj</a></p>
<p>Release Date: 2021-03-09</p>
<p>Fix Resolution: io.netty:netty-all:4.1.60;io.netty:netty-codec-http:4.1.60;io.netty:netty-codec-http2:4.1.60</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-codec-http","packageVersion":"4.1.5.Final","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"io.netty:netty-codec-http:4.1.5.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-all:4.1.60;io.netty:netty-codec-http:4.1.60;io.netty:netty-codec-http2:4.1.60"},{"packageType":"Java","groupId":"io.netty","packageName":"netty-all","packageVersion":"4.0.23.Final","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"io.netty:netty-all:4.0.23.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-all:4.1.60;io.netty:netty-codec-http:4.1.60;io.netty:netty-codec-http2:4.1.60"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-21295","vulnerabilityDetails":"Netty is an open-source, asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers \u0026 clients. In Netty (io.netty:netty-codec-http2) before version 4.1.60.Final there is a vulnerability that enables request smuggling. If a Content-Length header is present in the original HTTP/2 request, the field is not validated by `Http2MultiplexHandler` as it is propagated up. This is fine as long as the request is not proxied through as HTTP/1.1. If the request comes in as an HTTP/2 stream, gets converted into the HTTP/1.1 domain objects (`HttpRequest`, `HttpContent`, etc.) via `Http2StreamFrameToHttpObjectCodec `and then sent up to the child channel\u0027s pipeline and proxied through a remote peer as HTTP/1.1 this may result in request smuggling. In a proxy case, users may assume the content-length is validated somehow, which is not the case. If the request is forwarded to a backend channel that is a HTTP/1.1 connection, the Content-Length now has meaning and needs to be checked. An attacker can smuggle requests inside the body as it gets downgraded from HTTP/2 to HTTP/1.1. For an example attack refer to the linked GitHub Advisory. Users are only affected if all of this is true: `HTTP2MultiplexCodec` or `Http2FrameCodec` is used, `Http2StreamFrameToHttpObjectCodec` is used to convert to HTTP/1.1 objects, and these HTTP/1.1 objects are forwarded to another remote peer. This has been patched in 4.1.60.Final As a workaround, the user can do the validation by themselves by implementing a custom `ChannelInboundHandler` that is put in the `ChannelPipeline` behind `Http2StreamFrameToHttpObjectCodec`.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21295","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-21295 (Medium) detected in netty-codec-http-4.1.5.Final.jar, netty-all-4.0.23.Final.jar - ## CVE-2021-21295 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>netty-codec-http-4.1.5.Final.jar</b>, <b>netty-all-4.0.23.Final.jar</b></p></summary>
<p>
<details><summary><b>netty-codec-http-4.1.5.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to vulnerable library: nifi-nar-bundles/nifi-elasticsearch-bundle/nifi-elasticsearch-5-nar/target/classes/META-INF/bundled-dependencies/netty-codec-http-4.1.5.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-codec-http-4.1.5.Final.jar** (Vulnerable Library)
</details>
<details><summary><b>netty-all-4.0.23.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to vulnerable library: nifi-nar-bundles/nifi-standard-services/nifi-hbase_1_1_2-client-service-bundle/nifi-hbase_1_1_2-client-service-nar/target/classes/META-INF/bundled-dependencies/netty-all-4.0.23.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-all-4.0.23.Final.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/harrinry/nifi/commit/0484b1d281ed1df9c5682361286dee2ca6c634fe">0484b1d281ed1df9c5682361286dee2ca6c634fe</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty is an open-source, asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers & clients. In Netty (io.netty:netty-codec-http2) before version 4.1.60.Final there is a vulnerability that enables request smuggling. If a Content-Length header is present in the original HTTP/2 request, the field is not validated by `Http2MultiplexHandler` as it is propagated up. This is fine as long as the request is not proxied through as HTTP/1.1. If the request comes in as an HTTP/2 stream, gets converted into the HTTP/1.1 domain objects (`HttpRequest`, `HttpContent`, etc.) via `Http2StreamFrameToHttpObjectCodec `and then sent up to the child channel's pipeline and proxied through a remote peer as HTTP/1.1 this may result in request smuggling. In a proxy case, users may assume the content-length is validated somehow, which is not the case. If the request is forwarded to a backend channel that is a HTTP/1.1 connection, the Content-Length now has meaning and needs to be checked. An attacker can smuggle requests inside the body as it gets downgraded from HTTP/2 to HTTP/1.1. For an example attack refer to the linked GitHub Advisory. Users are only affected if all of this is true: `HTTP2MultiplexCodec` or `Http2FrameCodec` is used, `Http2StreamFrameToHttpObjectCodec` is used to convert to HTTP/1.1 objects, and these HTTP/1.1 objects are forwarded to another remote peer. This has been patched in 4.1.60.Final As a workaround, the user can do the validation by themselves by implementing a custom `ChannelInboundHandler` that is put in the `ChannelPipeline` behind `Http2StreamFrameToHttpObjectCodec`.
<p>Publish Date: 2021-03-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21295>CVE-2021-21295</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wm47-8v5p-wjpj">https://github.com/advisories/GHSA-wm47-8v5p-wjpj</a></p>
<p>Release Date: 2021-03-09</p>
<p>Fix Resolution: io.netty:netty-all:4.1.60;io.netty:netty-codec-http:4.1.60;io.netty:netty-codec-http2:4.1.60</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-codec-http","packageVersion":"4.1.5.Final","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"io.netty:netty-codec-http:4.1.5.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-all:4.1.60;io.netty:netty-codec-http:4.1.60;io.netty:netty-codec-http2:4.1.60"},{"packageType":"Java","groupId":"io.netty","packageName":"netty-all","packageVersion":"4.0.23.Final","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"io.netty:netty-all:4.0.23.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-all:4.1.60;io.netty:netty-codec-http:4.1.60;io.netty:netty-codec-http2:4.1.60"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-21295","vulnerabilityDetails":"Netty is an open-source, asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers \u0026 clients. In Netty (io.netty:netty-codec-http2) before version 4.1.60.Final there is a vulnerability that enables request smuggling. If a Content-Length header is present in the original HTTP/2 request, the field is not validated by `Http2MultiplexHandler` as it is propagated up. This is fine as long as the request is not proxied through as HTTP/1.1. If the request comes in as an HTTP/2 stream, gets converted into the HTTP/1.1 domain objects (`HttpRequest`, `HttpContent`, etc.) via `Http2StreamFrameToHttpObjectCodec `and then sent up to the child channel\u0027s pipeline and proxied through a remote peer as HTTP/1.1 this may result in request smuggling. In a proxy case, users may assume the content-length is validated somehow, which is not the case. If the request is forwarded to a backend channel that is a HTTP/1.1 connection, the Content-Length now has meaning and needs to be checked. An attacker can smuggle requests inside the body as it gets downgraded from HTTP/2 to HTTP/1.1. For an example attack refer to the linked GitHub Advisory. Users are only affected if all of this is true: `HTTP2MultiplexCodec` or `Http2FrameCodec` is used, `Http2StreamFrameToHttpObjectCodec` is used to convert to HTTP/1.1 objects, and these HTTP/1.1 objects are forwarded to another remote peer. This has been patched in 4.1.60.Final As a workaround, the user can do the validation by themselves by implementing a custom `ChannelInboundHandler` that is put in the `ChannelPipeline` behind `Http2StreamFrameToHttpObjectCodec`.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21295","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_test | cve medium detected in netty codec http final jar netty all final jar cve medium severity vulnerability vulnerable libraries netty codec http final jar netty all final jar netty codec http final jar netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers and clients library home page a href path to vulnerable library nifi nar bundles nifi elasticsearch bundle nifi elasticsearch nar target classes meta inf bundled dependencies netty codec http final jar dependency hierarchy x netty codec http final jar vulnerable library netty all final jar netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers and clients library home page a href path to vulnerable library nifi nar bundles nifi standard services nifi hbase client service bundle nifi hbase client service nar target classes meta inf bundled dependencies netty all final jar dependency hierarchy x netty all final jar vulnerable library found in head commit a href found in base branch master vulnerability details netty is an open source asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers clients in netty io netty netty codec before version final there is a vulnerability that enables request smuggling if a content length header is present in the original http request the field is not validated by as it is propagated up this is fine as long as the request is not proxied through as http if the request comes in as an http stream gets converted into the http domain objects httprequest httpcontent etc via and then sent up to the child channel s pipeline and proxied through a remote peer as http this may result in request smuggling in a proxy case users may assume the content length is validated somehow which is not the case if the request is forwarded to a backend channel that is a http connection the content length now has meaning and needs to be checked an attacker can smuggle requests inside the body as it gets downgraded from http to http for an example attack refer to the linked github advisory users are only affected if all of this is true or is used is used to convert to http objects and these http objects are forwarded to another remote peer this has been patched in final as a workaround the user can do the validation by themselves by implementing a custom channelinboundhandler that is put in the channelpipeline behind publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution io netty netty all io netty netty codec http io netty netty codec isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree io netty netty codec http final isminimumfixversionavailable true minimumfixversion io netty netty all io netty netty codec http io netty netty codec packagetype java groupid io netty packagename netty all packageversion final packagefilepaths istransitivedependency false dependencytree io netty netty all final isminimumfixversionavailable true minimumfixversion io netty netty all io netty netty codec http io netty netty codec basebranches vulnerabilityidentifier cve vulnerabilitydetails netty is an open source asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers clients in netty io netty netty codec before version final there is a vulnerability that enables request smuggling if a content length header is present in the original http request the field is not validated by as it is propagated up this is fine as long as the request is not proxied through as http if the request comes in as an http stream gets converted into the http domain objects httprequest httpcontent etc via and then sent up to the child channel pipeline and proxied through a remote peer as http this may result in request smuggling in a proxy case users may assume the content length is validated somehow which is not the case if the request is forwarded to a backend channel that is a http connection the content length now has meaning and needs to be checked an attacker can smuggle requests inside the body as it gets downgraded from http to http for an example attack refer to the linked github advisory users are only affected if all of this is true or is used is used to convert to http objects and these http objects are forwarded to another remote peer this has been patched in final as a workaround the user can do the validation by themselves by implementing a custom channelinboundhandler that is put in the channelpipeline behind vulnerabilityurl | 0 |
291,860 | 25,180,369,663 | IssuesEvent | 2022-11-11 13:07:56 | privacy-tech-lab/privacy-pioneer | https://api.github.com/repos/privacy-tech-lab/privacy-pioneer | closed | Implement unit testing and continuous integration | testing | Once we have finalized PP we should do a comprehensive acceptance test to make sure that all functionality is working, there are no bugs, the UI is understandable, etc. I can imagine that we find a bunch of issues along the lines of #388 that @JustinCasler just opened. The first step is to create a list of what to test for.
@jjeancharles, please start compiling this list. That is a good way of getting to know PP. Also, if anything is unclear from a usability perspective, e.g., what a certain functionality does, please included it in the list as well. So, this is not limited to bugs but really about everything. @JustinCasler and @danielgoldelman can supplement the list as necessary.
| 1.0 | Implement unit testing and continuous integration - Once we have finalized PP we should do a comprehensive acceptance test to make sure that all functionality is working, there are no bugs, the UI is understandable, etc. I can imagine that we find a bunch of issues along the lines of #388 that @JustinCasler just opened. The first step is to create a list of what to test for.
@jjeancharles, please start compiling this list. That is a good way of getting to know PP. Also, if anything is unclear from a usability perspective, e.g., what a certain functionality does, please included it in the list as well. So, this is not limited to bugs but really about everything. @JustinCasler and @danielgoldelman can supplement the list as necessary.
| test | implement unit testing and continuous integration once we have finalized pp we should do a comprehensive acceptance test to make sure that all functionality is working there are no bugs the ui is understandable etc i can imagine that we find a bunch of issues along the lines of that justincasler just opened the first step is to create a list of what to test for jjeancharles please start compiling this list that is a good way of getting to know pp also if anything is unclear from a usability perspective e g what a certain functionality does please included it in the list as well so this is not limited to bugs but really about everything justincasler and danielgoldelman can supplement the list as necessary | 1 |
62,758 | 6,812,117,944 | IssuesEvent | 2017-11-06 00:36:28 | nickdesaulniers/node-nanomsg | https://api.github.com/repos/nickdesaulniers/node-nanomsg | closed | tests/standalone/term.js is failing | bug tests | we should fix this. I probably regressed this in https://github.com/nickdesaulniers/node-nanomsg/commit/0461f5c20cf83865d22235787e48860e760c7e39.
It's a stupid test, so not high priority. | 1.0 | tests/standalone/term.js is failing - we should fix this. I probably regressed this in https://github.com/nickdesaulniers/node-nanomsg/commit/0461f5c20cf83865d22235787e48860e760c7e39.
It's a stupid test, so not high priority. | test | tests standalone term js is failing we should fix this i probably regressed this in it s a stupid test so not high priority | 1 |
557,462 | 16,509,694,121 | IssuesEvent | 2021-05-26 01:22:44 | eclipse-ee4j/glassfish | https://api.github.com/repos/eclipse-ee4j/glassfish | closed | [fishcat] Javaee7 web project : creating a class for JAX-RS suggest to configure the REST for Javaee6 speficication instead of 7 | Component: ide-integration Priority: Minor Stale Type: Improvement jax-rs netbeans rest | I created a Javaee7 web project.
I created a plain java class.
when I add the annotation : @Path("/coucou")
I got a warning, that's the resource is not configure.
When I click on the info bubble, I received a list of suggestions : Configure REST using javaee6 specifications,
jersey..
if the project is Javaee7, the line should be : Configure REST using javaee7 specifications
probably it's the same but will make more sens to keep it all javaee7.
#### Environment
Product Version: NetBeans IDE Dev (Build 201304232301)
Java: 1.7.0_13; Java HotSpot(TM) Client VM 23.7-b01
Runtime: Java(TM) SE Runtime Environment 1.7.0_13-b20
System: Windows XP version 5.1 running on x86; Cp1252; fr_CA (nb)
User directory: C:\Documents and Settings\sdionne1\Application Data\NetBeans\dev
Cache directory: C:\Documents and Settings\sdionne1\Local Settings\Application Data\NetBeans\Cache\dev
#### Affected Versions
[4.0_dev] | 1.0 | [fishcat] Javaee7 web project : creating a class for JAX-RS suggest to configure the REST for Javaee6 speficication instead of 7 - I created a Javaee7 web project.
I created a plain java class.
when I add the annotation : @Path("/coucou")
I got a warning, that's the resource is not configure.
When I click on the info bubble, I received a list of suggestions : Configure REST using javaee6 specifications,
jersey..
if the project is Javaee7, the line should be : Configure REST using javaee7 specifications
probably it's the same but will make more sens to keep it all javaee7.
#### Environment
Product Version: NetBeans IDE Dev (Build 201304232301)
Java: 1.7.0_13; Java HotSpot(TM) Client VM 23.7-b01
Runtime: Java(TM) SE Runtime Environment 1.7.0_13-b20
System: Windows XP version 5.1 running on x86; Cp1252; fr_CA (nb)
User directory: C:\Documents and Settings\sdionne1\Application Data\NetBeans\dev
Cache directory: C:\Documents and Settings\sdionne1\Local Settings\Application Data\NetBeans\Cache\dev
#### Affected Versions
[4.0_dev] | non_test | web project creating a class for jax rs suggest to configure the rest for speficication instead of i created a web project i created a plain java class when i add the annotation path coucou i got a warning that s the resource is not configure when i click on the info bubble i received a list of suggestions configure rest using specifications jersey if the project is the line should be configure rest using specifications probably it s the same but will make more sens to keep it all environment product version netbeans ide dev build java java hotspot tm client vm runtime java tm se runtime environment system windows xp version running on fr ca nb user directory c documents and settings application data netbeans dev cache directory c documents and settings local settings application data netbeans cache dev affected versions | 0 |
302,119 | 9,255,339,788 | IssuesEvent | 2019-03-16 09:00:28 | xwikisas/application-cookie-consent | https://api.github.com/repos/xwikisas/application-cookie-consent | closed | A regression was introduced in the last release | Priority: Critical Type: Bug | The rights object removed in #16 must be added back. | 1.0 | A regression was introduced in the last release - The rights object removed in #16 must be added back. | non_test | a regression was introduced in the last release the rights object removed in must be added back | 0 |
297,083 | 25,598,089,198 | IssuesEvent | 2022-12-01 17:43:11 | Loweredgames/Skyblock-Classic-Edition | https://api.github.com/repos/Loweredgames/Skyblock-Classic-Edition | closed | Aggiungere la convesione ID 4 di nuovo (abbilitare la 5) | bug enhancement confirmed test fix high | - [x] aggiungere il libro di nuovo
- [x] aggiungere la rimozione del portale del end di nuovo.
- [x] aggiungere avviso delle versioni sperimentali e come verrano implementate | 1.0 | Aggiungere la convesione ID 4 di nuovo (abbilitare la 5) - - [x] aggiungere il libro di nuovo
- [x] aggiungere la rimozione del portale del end di nuovo.
- [x] aggiungere avviso delle versioni sperimentali e come verrano implementate | test | aggiungere la convesione id di nuovo abbilitare la aggiungere il libro di nuovo aggiungere la rimozione del portale del end di nuovo aggiungere avviso delle versioni sperimentali e come verrano implementate | 1 |
51,754 | 13,211,301,310 | IssuesEvent | 2020-08-15 22:09:19 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | icerec - release (Trac #978) | Incomplete Migration Migrated from Trac combo reconstruction defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/978">https://code.icecube.wisc.edu/projects/icecube/ticket/978</a>, reported by negaand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-05-15T20:02:30",
"_ts": "1431720150553365",
"description": "There are calls for a new icerec release. Put your project/feature requests here. Anything not in this ticket will not be included in the release",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"time": "2015-05-13T19:52:44",
"component": "combo reconstruction",
"summary": "icerec - release",
"priority": "normal",
"keywords": "release",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| 1.0 | icerec - release (Trac #978) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/978">https://code.icecube.wisc.edu/projects/icecube/ticket/978</a>, reported by negaand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-05-15T20:02:30",
"_ts": "1431720150553365",
"description": "There are calls for a new icerec release. Put your project/feature requests here. Anything not in this ticket will not be included in the release",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"time": "2015-05-13T19:52:44",
"component": "combo reconstruction",
"summary": "icerec - release",
"priority": "normal",
"keywords": "release",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| non_test | icerec release trac migrated from json status closed changetime ts description there are calls for a new icerec release put your project feature requests here anything not in this ticket will not be included in the release reporter nega cc resolution fixed time component combo reconstruction summary icerec release priority normal keywords release milestone owner nega type defect | 0 |
16,894 | 12,152,147,503 | IssuesEvent | 2020-04-24 21:31:04 | BCDevOps/developer-experience | https://api.github.com/repos/BCDevOps/developer-experience | closed | Review/Confirm EmptyDir project/node quota | Infrastructure closed | https://trello.com/c/iaRK0fqL/75-review-confirm-emptydir-project-node-quota
With XFS supporting project quota (per node) for emptyDir now, how large do we want to make the quota per node?
Total EmptyDir = 25G
Current quota = 512Mb
| 1.0 | Review/Confirm EmptyDir project/node quota - https://trello.com/c/iaRK0fqL/75-review-confirm-emptydir-project-node-quota
With XFS supporting project quota (per node) for emptyDir now, how large do we want to make the quota per node?
Total EmptyDir = 25G
Current quota = 512Mb
| non_test | review confirm emptydir project node quota with xfs supporting project quota per node for emptydir now how large do we want to make the quota per node total emptydir current quota | 0 |
247,387 | 7,918,063,696 | IssuesEvent | 2018-07-04 12:02:50 | minishift/minishift | https://api.github.com/repos/minishift/minishift | closed | Major typo in start_preflight.go | good first issue kind/bug os/windows priority/major | ### General information
* Minishift version: master
* OS: Linux / macOS / Windows
* Hypervisor: KVM / xhyve / Hyper-V / VirtualBox
### Steps to reproduce
1. Start minishift
```
PS> .\minishift.exe start
-- Starting profile 'minishift'
-- Check if deprecated options are used ...
Use of HYPERV_VIRTUAL_SWITCH has been deprecated
Please use: minishift config set hyper-virtual-switch myswitch
FAIL
[...]
```
2. Use the config command as suggested
```
PS> .\minishift.exe config set hyper-virtual-switch myswitch
Cannot find property name 'hyper-virtual-switch'
```
### Expected
Config value should be applied
### Actual
This is a major typo because in [start_preflight.go](https://github.com/minishift/minishift/blob/1426bddcbf7aae0b8fab29dbe28b667a9ae218cb/cmd/minishift/cmd/start_preflight.go#L287) the suggested command phrase is wrong due to the typo in the flag ```hyper-virtual-switch```. So replace ```hyper-virtual-switch``` with ```hyperv-virtual-switch```.
### Logs
You can start Minishift with `minishift start --show-libmachine-logs -v5` to collect logs.
Please consider posting this on http://gist.github.com/ and post the link in the issue.
| 1.0 | Major typo in start_preflight.go - ### General information
* Minishift version: master
* OS: Linux / macOS / Windows
* Hypervisor: KVM / xhyve / Hyper-V / VirtualBox
### Steps to reproduce
1. Start minishift
```
PS> .\minishift.exe start
-- Starting profile 'minishift'
-- Check if deprecated options are used ...
Use of HYPERV_VIRTUAL_SWITCH has been deprecated
Please use: minishift config set hyper-virtual-switch myswitch
FAIL
[...]
```
2. Use the config command as suggested
```
PS> .\minishift.exe config set hyper-virtual-switch myswitch
Cannot find property name 'hyper-virtual-switch'
```
### Expected
Config value should be applied
### Actual
This is a major typo because in [start_preflight.go](https://github.com/minishift/minishift/blob/1426bddcbf7aae0b8fab29dbe28b667a9ae218cb/cmd/minishift/cmd/start_preflight.go#L287) the suggested command phrase is wrong due to the typo in the flag ```hyper-virtual-switch```. So replace ```hyper-virtual-switch``` with ```hyperv-virtual-switch```.
### Logs
You can start Minishift with `minishift start --show-libmachine-logs -v5` to collect logs.
Please consider posting this on http://gist.github.com/ and post the link in the issue.
| non_test | major typo in start preflight go general information minishift version master os linux macos windows hypervisor kvm xhyve hyper v virtualbox steps to reproduce start minishift ps minishift exe start starting profile minishift check if deprecated options are used use of hyperv virtual switch has been deprecated please use minishift config set hyper virtual switch myswitch fail use the config command as suggested ps minishift exe config set hyper virtual switch myswitch cannot find property name hyper virtual switch expected config value should be applied actual this is a major typo because in the suggested command phrase is wrong due to the typo in the flag hyper virtual switch so replace hyper virtual switch with hyperv virtual switch logs you can start minishift with minishift start show libmachine logs to collect logs please consider posting this on and post the link in the issue | 0 |
463,857 | 13,302,552,371 | IssuesEvent | 2020-08-25 14:24:36 | eventespresso/barista | https://api.github.com/repos/eventespresso/barista | closed | Extract utilities from services package to its own package | C: assets 💎 D: Packages 📦 P3: med priority 😐 T: task 🧹 | We have enough utilities in `services` package to put them in a separate package, independent of other packages.
Other benefits are that other packages that dependent upon `services` merely for these utils will be decoupled from `services` package. As an example, in [this PR](https://github.com/eventespresso/barista/pull/207#pullrequestreview-472667085), we had to import those utils into form package without using a direct import from services to avoid form dependency upon services.
So it will be pretty useful to have a separate utilities package. | 1.0 | Extract utilities from services package to its own package - We have enough utilities in `services` package to put them in a separate package, independent of other packages.
Other benefits are that other packages that dependent upon `services` merely for these utils will be decoupled from `services` package. As an example, in [this PR](https://github.com/eventespresso/barista/pull/207#pullrequestreview-472667085), we had to import those utils into form package without using a direct import from services to avoid form dependency upon services.
So it will be pretty useful to have a separate utilities package. | non_test | extract utilities from services package to its own package we have enough utilities in services package to put them in a separate package independent of other packages other benefits are that other packages that dependent upon services merely for these utils will be decoupled from services package as an example in we had to import those utils into form package without using a direct import from services to avoid form dependency upon services so it will be pretty useful to have a separate utilities package | 0 |
139,907 | 31,810,676,106 | IssuesEvent | 2023-09-13 16:36:12 | u-lulu/sonder | https://api.github.com/repos/u-lulu/sonder | closed | Cut down on redundant saving when creating a character | code quality improvement | /create_character can end up calling to save character data up to 4 times. This is overly redundant, and should only be performed excatly once, at the very end of the process.
This is due to the fact that the command simply calls upon other commands for the sake of character creation, which each also call to save data. | 1.0 | Cut down on redundant saving when creating a character - /create_character can end up calling to save character data up to 4 times. This is overly redundant, and should only be performed excatly once, at the very end of the process.
This is due to the fact that the command simply calls upon other commands for the sake of character creation, which each also call to save data. | non_test | cut down on redundant saving when creating a character create character can end up calling to save character data up to times this is overly redundant and should only be performed excatly once at the very end of the process this is due to the fact that the command simply calls upon other commands for the sake of character creation which each also call to save data | 0 |
194,034 | 14,667,706,659 | IssuesEvent | 2020-12-29 19:19:28 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | rkand4/vuejs: pkg/http/listener_test.go; 54 LoC | fresh medium test |
Found a possible issue in [rkand4/vuejs](https://www.github.com/rkand4/vuejs) at [pkg/http/listener_test.go](https://github.com/rkand4/vuejs/blob/e790bf122760e516384839f20608d7b79b1d344a/pkg/http/listener_test.go#L643-L696)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable i used in defer or goroutine at line 678
[Click here to see the code in its original context.](https://github.com/rkand4/vuejs/blob/e790bf122760e516384839f20608d7b79b1d344a/pkg/http/listener_test.go#L643-L696)
<details>
<summary>Click here to show the 54 line(s) of Go which triggered the analyzer.</summary>
```go
for i, testCase := range testCases {
listener, err := newHTTPListener(
testCase.serverAddrs,
testCase.tlsConfig,
time.Duration(0),
time.Duration(0),
time.Duration(0),
nil,
nil,
errorFunc,
)
if err != nil {
t.Fatalf("Test %d: error: expected = <nil>, got = %v", i+1, err)
}
for _, serverAddr := range testCase.serverAddrs {
var conn net.Conn
var err error
if testCase.secureClient {
conn, err = tls.Dial("tcp", serverAddr, &tls.Config{InsecureSkipVerify: true})
} else {
conn, err = net.Dial("tcp", serverAddr)
}
if err != nil {
t.Fatalf("Test %d: error: expected = <nil>, got = %v", i+1, err)
}
if _, err = io.WriteString(conn, testCase.request); err != nil {
t.Fatalf("Test %d: request send: expected = <nil>, got = %v", i+1, err)
}
go func() {
serverConn, aerr := listener.Accept()
if aerr == nil {
t.Fatalf("Test %d: accept: expected = <error>, got = <nil>", i+1)
}
if serverConn != nil {
t.Fatalf("Test %d: accept: server expected = <nil>, got = %v", i+1, serverConn)
}
}()
_, err = bufio.NewReader(conn).ReadString('\n')
if err == nil {
t.Fatalf("Test %d: reply read: expected = EOF got = <nil>", i+1)
} else if err.Error() != "EOF" {
t.Fatalf("Test %d: reply read: expected = EOF got = %v", i+1, err)
}
conn.Close()
}
listener.Close()
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: e790bf122760e516384839f20608d7b79b1d344a
| 1.0 | rkand4/vuejs: pkg/http/listener_test.go; 54 LoC -
Found a possible issue in [rkand4/vuejs](https://www.github.com/rkand4/vuejs) at [pkg/http/listener_test.go](https://github.com/rkand4/vuejs/blob/e790bf122760e516384839f20608d7b79b1d344a/pkg/http/listener_test.go#L643-L696)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable i used in defer or goroutine at line 678
[Click here to see the code in its original context.](https://github.com/rkand4/vuejs/blob/e790bf122760e516384839f20608d7b79b1d344a/pkg/http/listener_test.go#L643-L696)
<details>
<summary>Click here to show the 54 line(s) of Go which triggered the analyzer.</summary>
```go
for i, testCase := range testCases {
listener, err := newHTTPListener(
testCase.serverAddrs,
testCase.tlsConfig,
time.Duration(0),
time.Duration(0),
time.Duration(0),
nil,
nil,
errorFunc,
)
if err != nil {
t.Fatalf("Test %d: error: expected = <nil>, got = %v", i+1, err)
}
for _, serverAddr := range testCase.serverAddrs {
var conn net.Conn
var err error
if testCase.secureClient {
conn, err = tls.Dial("tcp", serverAddr, &tls.Config{InsecureSkipVerify: true})
} else {
conn, err = net.Dial("tcp", serverAddr)
}
if err != nil {
t.Fatalf("Test %d: error: expected = <nil>, got = %v", i+1, err)
}
if _, err = io.WriteString(conn, testCase.request); err != nil {
t.Fatalf("Test %d: request send: expected = <nil>, got = %v", i+1, err)
}
go func() {
serverConn, aerr := listener.Accept()
if aerr == nil {
t.Fatalf("Test %d: accept: expected = <error>, got = <nil>", i+1)
}
if serverConn != nil {
t.Fatalf("Test %d: accept: server expected = <nil>, got = %v", i+1, serverConn)
}
}()
_, err = bufio.NewReader(conn).ReadString('\n')
if err == nil {
t.Fatalf("Test %d: reply read: expected = EOF got = <nil>", i+1)
} else if err.Error() != "EOF" {
t.Fatalf("Test %d: reply read: expected = EOF got = %v", i+1, err)
}
conn.Close()
}
listener.Close()
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: e790bf122760e516384839f20608d7b79b1d344a
| test | vuejs pkg http listener test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message range loop variable i used in defer or goroutine at line click here to show the line s of go which triggered the analyzer go for i testcase range testcases listener err newhttplistener testcase serveraddrs testcase tlsconfig time duration time duration time duration nil nil errorfunc if err nil t fatalf test d error expected got v i err for serveraddr range testcase serveraddrs var conn net conn var err error if testcase secureclient conn err tls dial tcp serveraddr tls config insecureskipverify true else conn err net dial tcp serveraddr if err nil t fatalf test d error expected got v i err if err io writestring conn testcase request err nil t fatalf test d request send expected got v i err go func serverconn aerr listener accept if aerr nil t fatalf test d accept expected got i if serverconn nil t fatalf test d accept server expected got v i serverconn err bufio newreader conn readstring n if err nil t fatalf test d reply read expected eof got i else if err error eof t fatalf test d reply read expected eof got v i err conn close listener close leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
113,452 | 17,140,230,627 | IssuesEvent | 2021-07-13 08:48:46 | shaimael/microservice-catalog | https://api.github.com/repos/shaimael/microservice-catalog | opened | CVE-2021-28092 (High) detected in is-svg-3.0.0.tgz | security vulnerability | ## CVE-2021-28092 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>is-svg-3.0.0.tgz</b></p></summary>
<p>Check if a string or buffer is SVG</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-svg/-/is-svg-3.0.0.tgz">https://registry.npmjs.org/is-svg/-/is-svg-3.0.0.tgz</a></p>
<p>Path to dependency file: microservice-catalog/package.json</p>
<p>Path to vulnerable library: microservice-catalog/node_modules/is-svg/package.json</p>
<p>
Dependency Hierarchy:
- optimize-css-assets-webpack-plugin-5.0.3.tgz (Root Library)
- cssnano-4.1.10.tgz
- cssnano-preset-default-4.0.7.tgz
- postcss-svgo-4.0.2.tgz
- :x: **is-svg-3.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaimael/microservice-catalog/commit/4161ae345d248b6c8902ea5fd43eed5a4b76a4a8">4161ae345d248b6c8902ea5fd43eed5a4b76a4a8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The is-svg package 2.1.0 through 4.2.1 for Node.js uses a regular expression that is vulnerable to Regular Expression Denial of Service (ReDoS). If an attacker provides a malicious string, is-svg will get stuck processing the input for a very long time.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28092>CVE-2021-28092</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-28092">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-28092</a></p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution: v4.2.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"is-svg","packageVersion":"3.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"optimize-css-assets-webpack-plugin:5.0.3;cssnano:4.1.10;cssnano-preset-default:4.0.7;postcss-svgo:4.0.2;is-svg:3.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v4.2.2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-28092","vulnerabilityDetails":"The is-svg package 2.1.0 through 4.2.1 for Node.js uses a regular expression that is vulnerable to Regular Expression Denial of Service (ReDoS). If an attacker provides a malicious string, is-svg will get stuck processing the input for a very long time.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28092","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-28092 (High) detected in is-svg-3.0.0.tgz - ## CVE-2021-28092 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>is-svg-3.0.0.tgz</b></p></summary>
<p>Check if a string or buffer is SVG</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-svg/-/is-svg-3.0.0.tgz">https://registry.npmjs.org/is-svg/-/is-svg-3.0.0.tgz</a></p>
<p>Path to dependency file: microservice-catalog/package.json</p>
<p>Path to vulnerable library: microservice-catalog/node_modules/is-svg/package.json</p>
<p>
Dependency Hierarchy:
- optimize-css-assets-webpack-plugin-5.0.3.tgz (Root Library)
- cssnano-4.1.10.tgz
- cssnano-preset-default-4.0.7.tgz
- postcss-svgo-4.0.2.tgz
- :x: **is-svg-3.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaimael/microservice-catalog/commit/4161ae345d248b6c8902ea5fd43eed5a4b76a4a8">4161ae345d248b6c8902ea5fd43eed5a4b76a4a8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The is-svg package 2.1.0 through 4.2.1 for Node.js uses a regular expression that is vulnerable to Regular Expression Denial of Service (ReDoS). If an attacker provides a malicious string, is-svg will get stuck processing the input for a very long time.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28092>CVE-2021-28092</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-28092">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-28092</a></p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution: v4.2.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"is-svg","packageVersion":"3.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"optimize-css-assets-webpack-plugin:5.0.3;cssnano:4.1.10;cssnano-preset-default:4.0.7;postcss-svgo:4.0.2;is-svg:3.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v4.2.2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-28092","vulnerabilityDetails":"The is-svg package 2.1.0 through 4.2.1 for Node.js uses a regular expression that is vulnerable to Regular Expression Denial of Service (ReDoS). If an attacker provides a malicious string, is-svg will get stuck processing the input for a very long time.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28092","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_test | cve high detected in is svg tgz cve high severity vulnerability vulnerable library is svg tgz check if a string or buffer is svg library home page a href path to dependency file microservice catalog package json path to vulnerable library microservice catalog node modules is svg package json dependency hierarchy optimize css assets webpack plugin tgz root library cssnano tgz cssnano preset default tgz postcss svgo tgz x is svg tgz vulnerable library found in head commit a href found in base branch master vulnerability details the is svg package through for node js uses a regular expression that is vulnerable to regular expression denial of service redos if an attacker provides a malicious string is svg will get stuck processing the input for a very long time publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree optimize css assets webpack plugin cssnano cssnano preset default postcss svgo is svg isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails the is svg package through for node js uses a regular expression that is vulnerable to regular expression denial of service redos if an attacker provides a malicious string is svg will get stuck processing the input for a very long time vulnerabilityurl | 0 |
139,808 | 11,286,266,241 | IssuesEvent | 2020-01-16 00:02:40 | ray-project/ray | https://api.github.com/repos/ray-project/ray | closed | ArrowIOError: IOError: Broken pipe in stress tests. | tests failing | Ever since #692, errors like the following have been very common. Note that the error appears in many different tests within `stress_tests.py`. I suspect it wasn't actually introduced in this PR, but was merely exposed more by it (perhaps due to changes in timing).
```
======================================================================
ERROR: testDependencies (__main__.TaskTests)
----------------------------------------------------------------------
Traceback (most recent call last):
File "test/stress_tests.py", line 65, in testDependencies
ray.get(xs)
File "/home/travis/.local/lib/python2.7/site-packages/ray-0.1.2-py2.7-linux-x86_64.egg/ray/worker.py", line 1657, in get
values = worker.get_object(object_ids)
File "/home/travis/.local/lib/python2.7/site-packages/ray-0.1.2-py2.7-linux-x86_64.egg/ray/worker.py", line 429, in get_object
plain_object_ids[i:(i + fetch_request_size)])
File "plasma.pyx", line 458, in pyarrow.plasma.PlasmaClient.fetch
File "error.pxi", line 72, in pyarrow.lib.check_status
ArrowIOError: IOError: Broken pipe
```
See https://s3.amazonaws.com/archive.travis-ci.org/jobs/259598547/log.txt?X-Amz-Expires=30&X-Amz-Date=20170801T041537Z&X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Credential=AKIAJRYRXRSVGNKPKO5A/20170801/us-east-1/s3/aws4_request&X-Amz-SignedHeaders=host&X-Amz-Signature=3dfc3550bc2a88e1f6bf19e4bfe669027d3c9b9a5b1fcea2bc2cec640ec0b336 for an example log file. | 1.0 | ArrowIOError: IOError: Broken pipe in stress tests. - Ever since #692, errors like the following have been very common. Note that the error appears in many different tests within `stress_tests.py`. I suspect it wasn't actually introduced in this PR, but was merely exposed more by it (perhaps due to changes in timing).
```
======================================================================
ERROR: testDependencies (__main__.TaskTests)
----------------------------------------------------------------------
Traceback (most recent call last):
File "test/stress_tests.py", line 65, in testDependencies
ray.get(xs)
File "/home/travis/.local/lib/python2.7/site-packages/ray-0.1.2-py2.7-linux-x86_64.egg/ray/worker.py", line 1657, in get
values = worker.get_object(object_ids)
File "/home/travis/.local/lib/python2.7/site-packages/ray-0.1.2-py2.7-linux-x86_64.egg/ray/worker.py", line 429, in get_object
plain_object_ids[i:(i + fetch_request_size)])
File "plasma.pyx", line 458, in pyarrow.plasma.PlasmaClient.fetch
File "error.pxi", line 72, in pyarrow.lib.check_status
ArrowIOError: IOError: Broken pipe
```
See https://s3.amazonaws.com/archive.travis-ci.org/jobs/259598547/log.txt?X-Amz-Expires=30&X-Amz-Date=20170801T041537Z&X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Credential=AKIAJRYRXRSVGNKPKO5A/20170801/us-east-1/s3/aws4_request&X-Amz-SignedHeaders=host&X-Amz-Signature=3dfc3550bc2a88e1f6bf19e4bfe669027d3c9b9a5b1fcea2bc2cec640ec0b336 for an example log file. | test | arrowioerror ioerror broken pipe in stress tests ever since errors like the following have been very common note that the error appears in many different tests within stress tests py i suspect it wasn t actually introduced in this pr but was merely exposed more by it perhaps due to changes in timing error testdependencies main tasktests traceback most recent call last file test stress tests py line in testdependencies ray get xs file home travis local lib site packages ray linux egg ray worker py line in get values worker get object object ids file home travis local lib site packages ray linux egg ray worker py line in get object plain object ids file plasma pyx line in pyarrow plasma plasmaclient fetch file error pxi line in pyarrow lib check status arrowioerror ioerror broken pipe see for an example log file | 1 |
108,620 | 23,638,619,889 | IssuesEvent | 2022-08-25 15:07:51 | Dart-Code/Dart-Code | https://api.github.com/repos/Dart-Code/Dart-Code | closed | Debugger sometimes pauses without jumping to location | is bug blocked on vs code / lsp / dap in testing | This may be a result of switching to using the `topFrame`.. we no longer seem to focus sometimes when we break. Can be reproduced running `tree_test.dart` from the integration test projects. | 1.0 | Debugger sometimes pauses without jumping to location - This may be a result of switching to using the `topFrame`.. we no longer seem to focus sometimes when we break. Can be reproduced running `tree_test.dart` from the integration test projects. | non_test | debugger sometimes pauses without jumping to location this may be a result of switching to using the topframe we no longer seem to focus sometimes when we break can be reproduced running tree test dart from the integration test projects | 0 |
322,403 | 27,598,358,724 | IssuesEvent | 2023-03-09 08:21:15 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | opened | Fix jax_numpy_logic.test_jax_numpy_not_equal | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="null" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="null" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix jax_numpy_logic.test_jax_numpy_not_equal - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="null" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="null" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
| test | fix jax numpy logic test jax numpy not equal tensorflow img src torch img src numpy img src jax img src | 1 |
161,881 | 25,413,798,750 | IssuesEvent | 2022-11-22 21:34:30 | atlosdotorg/atlos | https://api.github.com/repos/atlosdotorg/atlos | closed | Scroll bar shouldn't obscure flags on homepage | design change staging | We should be able to scroll while still viewing an incident's flags.
<img width="390" alt="Screen Shot 2022-11-19 at 21 39 20" src="https://user-images.githubusercontent.com/100018299/202887422-c1158fcc-33f2-49b4-a68d-5afc6fd0819d.png">
| 1.0 | Scroll bar shouldn't obscure flags on homepage - We should be able to scroll while still viewing an incident's flags.
<img width="390" alt="Screen Shot 2022-11-19 at 21 39 20" src="https://user-images.githubusercontent.com/100018299/202887422-c1158fcc-33f2-49b4-a68d-5afc6fd0819d.png">
| non_test | scroll bar shouldn t obscure flags on homepage we should be able to scroll while still viewing an incident s flags img width alt screen shot at src | 0 |
45,576 | 11,700,599,360 | IssuesEvent | 2020-03-06 17:50:32 | microsoft/msbuild | https://api.github.com/repos/microsoft/msbuild | opened | Annotate ErrorUtilities methods for nullable analysis | Area: Our Own Build | For instance,
https://github.com/microsoft/msbuild/blob/00781ad1353afba25451148dba61845ac139b572/src/Shared/ErrorUtilities.cs#L54-L60
Should have `[DoesNotReturn]`
https://github.com/microsoft/msbuild/blob/00781ad1353afba25451148dba61845ac139b572/src/Shared/ErrorUtilities.cs#L110-L116
should have `[NotNull]` on `parameter` (see second sense in the [NotNullAttribute docs](https://docs.microsoft.com/en-us/dotnet/api/system.diagnostics.codeanalysis.notnullattribute?view=netcore-3.1))
https://github.com/microsoft/msbuild/blob/00781ad1353afba25451148dba61845ac139b572/src/Shared/ErrorUtilities.cs#L184-L196
should have `[DoesNotReturnIf(false)]` on `condition`. | 1.0 | Annotate ErrorUtilities methods for nullable analysis - For instance,
https://github.com/microsoft/msbuild/blob/00781ad1353afba25451148dba61845ac139b572/src/Shared/ErrorUtilities.cs#L54-L60
Should have `[DoesNotReturn]`
https://github.com/microsoft/msbuild/blob/00781ad1353afba25451148dba61845ac139b572/src/Shared/ErrorUtilities.cs#L110-L116
should have `[NotNull]` on `parameter` (see second sense in the [NotNullAttribute docs](https://docs.microsoft.com/en-us/dotnet/api/system.diagnostics.codeanalysis.notnullattribute?view=netcore-3.1))
https://github.com/microsoft/msbuild/blob/00781ad1353afba25451148dba61845ac139b572/src/Shared/ErrorUtilities.cs#L184-L196
should have `[DoesNotReturnIf(false)]` on `condition`. | non_test | annotate errorutilities methods for nullable analysis for instance should have should have on parameter see second sense in the should have on condition | 0 |
6,252 | 2,829,769,694 | IssuesEvent | 2015-05-23 05:47:53 | AAndharia/PSB | https://api.github.com/repos/AAndharia/PSB | closed | remmitance slip | Discussion Ready For Testing | 
we are not fetching bank address at company page and this slip contains bank address. what should be display instead? | 1.0 | remmitance slip - 
we are not fetching bank address at company page and this slip contains bank address. what should be display instead? | test | remmitance slip we are not fetching bank address at company page and this slip contains bank address what should be display instead | 1 |
196,437 | 22,441,800,306 | IssuesEvent | 2022-06-21 02:11:50 | Nivaskumark/A10_r33_system_bt | https://api.github.com/repos/Nivaskumark/A10_r33_system_bt | opened | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33: 39 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p></summary>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
</p>
</p></p>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-0103](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0103) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2021-0474](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0474) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r36 | ❌ |
| [CVE-2020-0225](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0225) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2021-0397](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0397) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r33 | ❌ |
| [CVE-2021-0316](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0316) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r26 | ❌ |
| [CVE-2020-0380](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0380) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-8.0.0_r50,android-8.1.0_r80,android-9.0.0_r60,android-10.0.0_r46 | ❌ |
| [CVE-2020-0138](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0138) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0471](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0471) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r26 | ❌ |
| [CVE-2022-20140](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20140) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-12.1.0_r7 | ❌ |
| [CVE-2021-0507](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0507) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r38 | ❌ |
| [CVE-2021-0968](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-12.0.0_r16 | ❌ |
| [CVE-2020-0449](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0449) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r12 | ❌ |
| [CVE-2021-0475](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0475) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r36 | ❌ |
| [CVE-2019-2225](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2225) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-8.0.0_r41;android-8.1.0_r71;android-9.0.0_r51;android-10.0.0_r17 | ❌ |
| [CVE-2021-39674](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39674) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2020-0129](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0129) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0102](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0102) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2021-0477](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0477) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r36 | ❌ |
| [CVE-2021-0589](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0589) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r39 | ❌ |
| [CVE-2021-0431](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0431) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r34 | ❌ |
| [CVE-2021-0435](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0435) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Direct | android-11.0.0_r34 | ❌ |
| [CVE-2020-0463](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0463) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2020-0413](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0413) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2020-0377](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0377) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-9.0.0_r61,android-10.0.0_r46, android-11.0.0_r4 | ❌ |
| [CVE-2020-0176](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0176) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2021-0522](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0522) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Direct | android-11.0.0_r38 | ❌ |
| [CVE-2021-0476](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0476) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.0 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r36 | ❌ |
| [CVE-2022-20010](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20010) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-12.1.0_r5 | ❌ |
| [CVE-2019-2227](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2227) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-9.0.0_r51;android-10.0.0_r17 | ❌ |
| [CVE-2020-0196](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0196) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0379](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0379) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.7 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-8.0.0_r50 | ❌ |
| [CVE-2020-0185](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0185) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2019-2226](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2226) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-8.0.0_r41;android-8.1.0_r71;android-9.0.0_r51;android-10.0.0_r17 | ❌ |
| [CVE-2020-0149](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0149) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0145](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0145) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0146](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0146) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0147](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0147) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0148](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0148) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0144](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0144) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
## Details
> Partial details (24 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0103</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/a2dp/a2dp_aac_decoder.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In a2dp_aac_decoder_cleanup of a2dp_aac_decoder.cc, there is a possible invalid free due to memory corruption. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-9Android ID: A-148107188
<p>Publish Date: 2020-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0103>CVE-2020-0103</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0474</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_api.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds write due to a heap buffer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-177611958
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0474>CVE-2021-0474</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-05-01">https://source.android.com/security/bulletin/2021-05-01</a></p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: android-11.0.0_r36</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0225</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/a2dp/a2dp_vendor_ldac_decoder.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In a2dp_vendor_ldac_decoder_decode_packet of a2dp_vendor_ldac_decoder.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142546668
<p>Publish Date: 2020-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0225>CVE-2020-0225</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0397</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/bta/ag/bta_ag_sdp.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In sdp_copy_raw_data of sdp_discovery.cc, there is a possible system compromise due to a double free. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174052148
<p>Publish Date: 2021-03-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0397>CVE-2021-0397</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-03-01">https://source.android.com/security/bulletin/2021-03-01</a></p>
<p>Release Date: 2021-03-10</p>
<p>Fix Resolution: android-11.0.0_r33</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0316</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_pars_vendor_cmd of avrc_pars_tg.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation. Product: Android; Versions: Android-11, Android-8.0, Android-8.1, Android-9, Android-10; Android ID: A-168802990.
<p>Publish Date: 2021-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0316>CVE-2021-0316</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r26</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0380</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/embdrv/sbc/decoder/srce/decoder-sbc.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In allocExcessBits of bitalloc.c, there is a possible out of bounds write due to an incorrect bounds check. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.0 Android-8.1 Android-9 Android-10Android ID: A-146398979
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0380>CVE-2020-0380</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2020-09-01">https://source.android.com/security/bulletin/2020-09-01</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-8.0.0_r50,android-8.1.0_r80,android-9.0.0_r60,android-10.0.0_r46</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0138</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/btif/src/btif_rc.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In get_element_attr_rsp of btif_rc.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution if bluetoothtbd were used, which it isn't in typical Android platforms, with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142878416
<p>Publish Date: 2020-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0138>CVE-2020-0138</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37</a></p>
<p>Release Date: 2020-06-11</p>
<p>Fix Resolution: android-10.0.0_r37</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0471</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/hci/src/packet_fragmenter.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In reassemble_and_dispatch of packet_fragmenter.cc, there is a possible way to inject packets into an encrypted Bluetooth connection due to improper input validation. This could lead to remote escalation of privilege between two Bluetooth devices by a proximal attacker, with no additional execution privileges needed. User interaction is not needed for exploitation. Product: Android; Versions: Android-8.0, Android-8.1, Android-9, Android-10, Android-11; Android ID: A-169327567.
<p>Publish Date: 2021-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0471>CVE-2020-0471</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-11.0.0_r26</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-20140</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/gatt/gatt_sr.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In read_multi_rsp of gatt_sr.cc, there is a possible out of bounds write due to an incorrect bounds check. This could lead to remote escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-12 Android-12LAndroid ID: A-227618988
<p>Publish Date: 2022-06-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20140>CVE-2022-20140</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2022-06-01">https://source.android.com/security/bulletin/2022-06-01</a></p>
<p>Release Date: 2022-06-15</p>
<p>Fix Resolution: android-12.1.0_r7</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0507</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In handle_rc_metamsg_cmd of btif_rc.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-181860042
<p>Publish Date: 2021-06-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0507>CVE-2021-0507</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-06-01">https://source.android.com/security/bulletin/2021-06-01</a></p>
<p>Release Date: 2021-06-21</p>
<p>Fix Resolution: android-11.0.0_r38</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0968</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/osi/src/allocator.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In osi_malloc and osi_calloc of allocator.cc, there is a possible out of bounds write due to an integer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12 Android-9Android ID: A-197868577
<p>Publish Date: 2021-12-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0968>CVE-2021-0968</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0968">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0968</a></p>
<p>Release Date: 2021-12-15</p>
<p>Fix Resolution: android-12.0.0_r16</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0449</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_sec.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In btm_sec_disconnected of btm_sec.cc, there is a possible memory corruption due to a use after free. This could lead to remote code execution in the Bluetooth server with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-9 Android-10 Android-11 Android-8.0 Android-8.1Android ID: A-162497143
<p>Publish Date: 2020-11-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0449>CVE-2020-0449</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r12">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r12</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-11.0.0_r12</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0475</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/btif/src/btif_sock_l2cap.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In on_l2cap_data_ind of btif_sock_l2cap.cc, there is possible memory corruption due to a use after free. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-10Android ID: A-175686168
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0475>CVE-2021-0475</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-05-01">https://source.android.com/security/bulletin/2021-05-01</a></p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: android-11.0.0_r36</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-2225</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/btif/src/btif_dm.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
When pairing with a Bluetooth device, it may be possible to pair a malicious device without any confirmation from the user, and that device may be able to interact with the phone. This could lead to remote escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.0 Android-8.1 Android-9 Android-10Android ID: A-110433804
<p>Publish Date: 2019-12-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2225>CVE-2019-2225</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2225">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2225</a></p>
<p>Release Date: 2019-12-06</p>
<p>Fix Resolution: android-8.0.0_r41;android-8.1.0_r71;android-9.0.0_r51;android-10.0.0_r17</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-39674</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_sec.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In btm_sec_connected and btm_sec_disconnected of btm_sec.cc file , there is a possible use after free. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12Android ID: A-201083442
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39674>CVE-2021-39674</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0129</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_ble_multi_adv.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In SetData of btm_ble_multi_adv.cc, there is a possible out-of-bound write due to an incorrect bounds check. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-123292010
<p>Publish Date: 2020-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0129>CVE-2020-0129</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37</a></p>
<p>Release Date: 2020-06-11</p>
<p>Fix Resolution: android-10.0.0_r37</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0102</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/service/gatt_server.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In GattServer::SendResponse of gatt_server.cc, there is a possible out of bounds write due to an incorrect bounds check. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.0 Android-8.1 Android-9 Android-10Android ID: A-143231677
<p>Publish Date: 2020-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0102>CVE-2020-0102</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0477</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/btif/src/btif_sock_l2cap.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In notifyScreenshotError of ScreenshotNotificationsController.java, there is a possible permission bypass due to an unsafe PendingIntent. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-8.1 Android-9Android ID: A-178189250
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0477>CVE-2021-0477</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-05-01">https://source.android.com/security/bulletin/2021-05-01</a></p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: android-11.0.0_r36</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0589</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_acl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In BTM_TryAllocateSCN of btm_scn.cc, there is a possible out of bounds write due to an incorrect bounds check. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-180939982
<p>Publish Date: 2021-07-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0589>CVE-2021-0589</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-07-01">https://source.android.com/security/bulletin/2021-07-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r39</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0431</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_api.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure to a paired device with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174149901
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0431>CVE-2021-0431</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-04-01">https://source.android.com/security/bulletin/2021-04-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r34</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0435</summary>
### Vulnerable Libraries - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b>, <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b>, <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b>, <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b>, <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_proc_vendor_command of avrc_api.cc, there is a possible leak of heap data due to uninitialized data. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174150451
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0435>CVE-2021-0435</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-04-01">https://source.android.com/security/bulletin/2021-04-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r34</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0463</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/sdp/sdp_server.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In sdp_server_handle_client_req of sdp_server.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure from the bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-8.0 Android-8.1 Android-9Android ID: A-169342531
<p>Publish Date: 2020-12-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0463>CVE-2020-0463</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0413</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/gatt/gatt_cl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158778659
<p>Publish Date: 2020-10-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0413>CVE-2020-0413</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0377</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/gatt/gatt_cl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158833854
<p>Publish Date: 2020-10-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0377>CVE-2020-0377</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-9.0.0_r61,https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-10.0.0_r46,https://android.googlesource.com/platform/frameworks">https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-9.0.0_r61,https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-10.0.0_r46,https://android.googlesource.com/platform/frameworks</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-9.0.0_r61,android-10.0.0_r46, android-11.0.0_r4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33: 39 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p></summary>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
</p>
</p></p>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-0103](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0103) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2021-0474](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0474) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r36 | ❌ |
| [CVE-2020-0225](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0225) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2021-0397](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0397) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r33 | ❌ |
| [CVE-2021-0316](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0316) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r26 | ❌ |
| [CVE-2020-0380](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0380) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-8.0.0_r50,android-8.1.0_r80,android-9.0.0_r60,android-10.0.0_r46 | ❌ |
| [CVE-2020-0138](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0138) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0471](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0471) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r26 | ❌ |
| [CVE-2022-20140](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20140) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-12.1.0_r7 | ❌ |
| [CVE-2021-0507](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0507) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r38 | ❌ |
| [CVE-2021-0968](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-12.0.0_r16 | ❌ |
| [CVE-2020-0449](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0449) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r12 | ❌ |
| [CVE-2021-0475](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0475) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r36 | ❌ |
| [CVE-2019-2225](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2225) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-8.0.0_r41;android-8.1.0_r71;android-9.0.0_r51;android-10.0.0_r17 | ❌ |
| [CVE-2021-39674](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39674) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2020-0129](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0129) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0102](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0102) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2021-0477](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0477) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r36 | ❌ |
| [CVE-2021-0589](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0589) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r39 | ❌ |
| [CVE-2021-0431](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0431) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r34 | ❌ |
| [CVE-2021-0435](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0435) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Direct | android-11.0.0_r34 | ❌ |
| [CVE-2020-0463](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0463) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2020-0413](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0413) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | N/A | ❌ |
| [CVE-2020-0377](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0377) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-9.0.0_r61,android-10.0.0_r46, android-11.0.0_r4 | ❌ |
| [CVE-2020-0176](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0176) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2021-0522](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0522) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Direct | android-11.0.0_r38 | ❌ |
| [CVE-2021-0476](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0476) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.0 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-11.0.0_r36 | ❌ |
| [CVE-2022-20010](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20010) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-12.1.0_r5 | ❌ |
| [CVE-2019-2227](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2227) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-9.0.0_r51;android-10.0.0_r17 | ❌ |
| [CVE-2020-0196](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0196) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0379](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0379) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.7 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-8.0.0_r50 | ❌ |
| [CVE-2020-0185](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0185) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2019-2226](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2226) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-8.0.0_r41;android-8.1.0_r71;android-9.0.0_r51;android-10.0.0_r17 | ❌ |
| [CVE-2020-0149](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0149) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0145](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0145) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0146](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0146) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0147](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0147) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0148](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0148) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0144](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0144) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33 | Direct | android-10.0.0_r37 | ❌ |
## Details
> Partial details (24 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0103</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/a2dp/a2dp_aac_decoder.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In a2dp_aac_decoder_cleanup of a2dp_aac_decoder.cc, there is a possible invalid free due to memory corruption. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-9Android ID: A-148107188
<p>Publish Date: 2020-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0103>CVE-2020-0103</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0474</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_api.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds write due to a heap buffer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-177611958
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0474>CVE-2021-0474</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-05-01">https://source.android.com/security/bulletin/2021-05-01</a></p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: android-11.0.0_r36</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0225</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/a2dp/a2dp_vendor_ldac_decoder.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In a2dp_vendor_ldac_decoder_decode_packet of a2dp_vendor_ldac_decoder.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142546668
<p>Publish Date: 2020-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0225>CVE-2020-0225</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0397</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/bta/ag/bta_ag_sdp.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In sdp_copy_raw_data of sdp_discovery.cc, there is a possible system compromise due to a double free. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174052148
<p>Publish Date: 2021-03-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0397>CVE-2021-0397</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-03-01">https://source.android.com/security/bulletin/2021-03-01</a></p>
<p>Release Date: 2021-03-10</p>
<p>Fix Resolution: android-11.0.0_r33</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0316</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_pars_vendor_cmd of avrc_pars_tg.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation. Product: Android; Versions: Android-11, Android-8.0, Android-8.1, Android-9, Android-10; Android ID: A-168802990.
<p>Publish Date: 2021-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0316>CVE-2021-0316</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r26</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0380</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/embdrv/sbc/decoder/srce/decoder-sbc.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In allocExcessBits of bitalloc.c, there is a possible out of bounds write due to an incorrect bounds check. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.0 Android-8.1 Android-9 Android-10Android ID: A-146398979
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0380>CVE-2020-0380</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2020-09-01">https://source.android.com/security/bulletin/2020-09-01</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-8.0.0_r50,android-8.1.0_r80,android-9.0.0_r60,android-10.0.0_r46</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0138</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/btif/src/btif_rc.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In get_element_attr_rsp of btif_rc.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution if bluetoothtbd were used, which it isn't in typical Android platforms, with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142878416
<p>Publish Date: 2020-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0138>CVE-2020-0138</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37</a></p>
<p>Release Date: 2020-06-11</p>
<p>Fix Resolution: android-10.0.0_r37</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0471</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/hci/src/packet_fragmenter.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In reassemble_and_dispatch of packet_fragmenter.cc, there is a possible way to inject packets into an encrypted Bluetooth connection due to improper input validation. This could lead to remote escalation of privilege between two Bluetooth devices by a proximal attacker, with no additional execution privileges needed. User interaction is not needed for exploitation. Product: Android; Versions: Android-8.0, Android-8.1, Android-9, Android-10, Android-11; Android ID: A-169327567.
<p>Publish Date: 2021-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0471>CVE-2020-0471</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-11.0.0_r26</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-20140</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/gatt/gatt_sr.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In read_multi_rsp of gatt_sr.cc, there is a possible out of bounds write due to an incorrect bounds check. This could lead to remote escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-12 Android-12LAndroid ID: A-227618988
<p>Publish Date: 2022-06-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20140>CVE-2022-20140</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2022-06-01">https://source.android.com/security/bulletin/2022-06-01</a></p>
<p>Release Date: 2022-06-15</p>
<p>Fix Resolution: android-12.1.0_r7</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0507</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In handle_rc_metamsg_cmd of btif_rc.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-181860042
<p>Publish Date: 2021-06-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0507>CVE-2021-0507</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-06-01">https://source.android.com/security/bulletin/2021-06-01</a></p>
<p>Release Date: 2021-06-21</p>
<p>Fix Resolution: android-11.0.0_r38</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0968</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/osi/src/allocator.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In osi_malloc and osi_calloc of allocator.cc, there is a possible out of bounds write due to an integer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12 Android-9Android ID: A-197868577
<p>Publish Date: 2021-12-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0968>CVE-2021-0968</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0968">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0968</a></p>
<p>Release Date: 2021-12-15</p>
<p>Fix Resolution: android-12.0.0_r16</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0449</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_sec.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In btm_sec_disconnected of btm_sec.cc, there is a possible memory corruption due to a use after free. This could lead to remote code execution in the Bluetooth server with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-9 Android-10 Android-11 Android-8.0 Android-8.1Android ID: A-162497143
<p>Publish Date: 2020-11-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0449>CVE-2020-0449</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r12">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r12</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-11.0.0_r12</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0475</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/btif/src/btif_sock_l2cap.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In on_l2cap_data_ind of btif_sock_l2cap.cc, there is possible memory corruption due to a use after free. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-10Android ID: A-175686168
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0475>CVE-2021-0475</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-05-01">https://source.android.com/security/bulletin/2021-05-01</a></p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: android-11.0.0_r36</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-2225</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/btif/src/btif_dm.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
When pairing with a Bluetooth device, it may be possible to pair a malicious device without any confirmation from the user, and that device may be able to interact with the phone. This could lead to remote escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.0 Android-8.1 Android-9 Android-10Android ID: A-110433804
<p>Publish Date: 2019-12-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2225>CVE-2019-2225</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2225">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2225</a></p>
<p>Release Date: 2019-12-06</p>
<p>Fix Resolution: android-8.0.0_r41;android-8.1.0_r71;android-9.0.0_r51;android-10.0.0_r17</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-39674</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_sec.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In btm_sec_connected and btm_sec_disconnected of btm_sec.cc file , there is a possible use after free. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12Android ID: A-201083442
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39674>CVE-2021-39674</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0129</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_ble_multi_adv.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In SetData of btm_ble_multi_adv.cc, there is a possible out-of-bound write due to an incorrect bounds check. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-123292010
<p>Publish Date: 2020-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0129>CVE-2020-0129</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37</a></p>
<p>Release Date: 2020-06-11</p>
<p>Fix Resolution: android-10.0.0_r37</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0102</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/service/gatt_server.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In GattServer::SendResponse of gatt_server.cc, there is a possible out of bounds write due to an incorrect bounds check. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.0 Android-8.1 Android-9 Android-10Android ID: A-143231677
<p>Publish Date: 2020-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0102>CVE-2020-0102</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0477</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/btif/src/btif_sock_l2cap.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In notifyScreenshotError of ScreenshotNotificationsController.java, there is a possible permission bypass due to an unsafe PendingIntent. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-8.1 Android-9Android ID: A-178189250
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0477>CVE-2021-0477</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-05-01">https://source.android.com/security/bulletin/2021-05-01</a></p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: android-11.0.0_r36</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0589</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_acl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In BTM_TryAllocateSCN of btm_scn.cc, there is a possible out of bounds write due to an incorrect bounds check. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-180939982
<p>Publish Date: 2021-07-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0589>CVE-2021-0589</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-07-01">https://source.android.com/security/bulletin/2021-07-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r39</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0431</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_api.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure to a paired device with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174149901
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0431>CVE-2021-0431</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-04-01">https://source.android.com/security/bulletin/2021-04-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r34</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0435</summary>
### Vulnerable Libraries - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b>, <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b>, <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b>, <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b>, <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_proc_vendor_command of avrc_api.cc, there is a possible leak of heap data due to uninitialized data. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174150451
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0435>CVE-2021-0435</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-04-01">https://source.android.com/security/bulletin/2021-04-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r34</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0463</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/sdp/sdp_server.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In sdp_server_handle_client_req of sdp_server.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure from the bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-8.0 Android-8.1 Android-9Android ID: A-169342531
<p>Publish Date: 2020-12-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0463>CVE-2020-0463</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0413</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/gatt/gatt_cl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158778659
<p>Publish Date: 2020-10-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0413>CVE-2020-0413</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0377</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/android-10.0.0_r33</b></p>
<p>
<p>AOSP Platform System bt</p>
<p>Library home page: <a href=https://source.codeaurora.org/external/imx/aosp/platform/system/bt/>https://source.codeaurora.org/external/imx/aosp/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/gatt/gatt_cl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158833854
<p>Publish Date: 2020-10-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0377>CVE-2020-0377</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-9.0.0_r61,https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-10.0.0_r46,https://android.googlesource.com/platform/frameworks">https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-9.0.0_r61,https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-10.0.0_r46,https://android.googlesource.com/platform/frameworks</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-9.0.0_r61,android-10.0.0_r46, android-11.0.0_r4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_test | vulnerabilities highest severity is vulnerable library aosp platform system bt library home page a href vulnerable source files stack avrc avrc pars tg cc vulnerabilities cve severity cvss dependency type fixed in remediation available high direct n a high direct android high direct n a high direct android high direct android high direct android android android android high direct android high direct android high direct android high direct android high direct android high direct android high direct android high direct android android android android high direct n a high direct android high direct n a high direct android high direct android high direct android high multiple direct android high direct n a high direct n a high direct android android android high direct android high multiple direct android high direct android medium direct android medium direct android android medium direct android medium direct android medium direct android medium direct android android android android medium direct android medium direct android medium direct android medium direct android medium direct android medium direct android details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the mend application cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack aac decoder cc vulnerability details in aac decoder cleanup of aac decoder cc there is a possible invalid free due to memory corruption this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack avrc avrc api cc vulnerability details in avrc msg cback of avrc api cc there is a possible out of bounds write due to a heap buffer overflow this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack vendor ldac decoder cc vulnerability details in vendor ldac decoder decode packet of vendor ldac decoder cc there is a possible out of bounds write due to a missing bounds check this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files bta ag bta ag sdp cc vulnerability details in sdp copy raw data of sdp discovery cc there is a possible system compromise due to a double free this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack avrc avrc pars tg cc vulnerability details in avrc pars vendor cmd of avrc pars tg cc there is a possible out of bounds write due to a missing bounds check this could lead to remote code execution over bluetooth with no additional execution privileges needed user interaction is not needed for exploitation product android versions android android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files embdrv sbc decoder srce decoder sbc c vulnerability details in allocexcessbits of bitalloc c there is a possible out of bounds write due to an incorrect bounds check this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android android android android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files btif src btif rc cc vulnerability details in get element attr rsp of btif rc cc there is a possible out of bounds write due to a missing bounds check this could lead to remote code execution if bluetoothtbd were used which it isn t in typical android platforms with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files hci src packet fragmenter cc vulnerability details in reassemble and dispatch of packet fragmenter cc there is a possible way to inject packets into an encrypted bluetooth connection due to improper input validation this could lead to remote escalation of privilege between two bluetooth devices by a proximal attacker with no additional execution privileges needed user interaction is not needed for exploitation product android versions android android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack gatt gatt sr cc vulnerability details in read multi rsp of gatt sr cc there is a possible out of bounds write due to an incorrect bounds check this could lead to remote escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack avrc avrc pars tg cc vulnerability details in handle rc metamsg cmd of btif rc cc there is a possible out of bounds write due to a missing bounds check this could lead to remote code execution over bluetooth with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files osi src allocator cc vulnerability details in osi malloc and osi calloc of allocator cc there is a possible out of bounds write due to an integer overflow this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack btm btm sec cc vulnerability details in btm sec disconnected of btm sec cc there is a possible memory corruption due to a use after free this could lead to remote code execution in the bluetooth server with no additional execution privileges needed user interaction is needed for exploitation product androidversions android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files btif src btif sock cc vulnerability details in on data ind of btif sock cc there is possible memory corruption due to a use after free this could lead to remote code execution over bluetooth with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files btif src btif dm cc vulnerability details when pairing with a bluetooth device it may be possible to pair a malicious device without any confirmation from the user and that device may be able to interact with the phone this could lead to remote escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android android android android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack btm btm sec cc vulnerability details in btm sec connected and btm sec disconnected of btm sec cc file there is a possible use after free this could lead to local escalation of privilege with user execution privileges needed user interaction is not needed for exploitation product androidversions android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack btm btm ble multi adv cc vulnerability details in setdata of btm ble multi adv cc there is a possible out of bound write due to an incorrect bounds check this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files service gatt server cc vulnerability details in gattserver sendresponse of gatt server cc there is a possible out of bounds write due to an incorrect bounds check this could lead to local escalation of privilege with user execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files btif src btif sock cc vulnerability details in notifyscreenshoterror of screenshotnotificationscontroller java there is a possible permission bypass due to an unsafe pendingintent this could lead to local escalation of privilege with user execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack btm btm acl cc vulnerability details in btm tryallocatescn of btm scn cc there is a possible out of bounds write due to an incorrect bounds check this could lead to local escalation of privilege with user execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack avrc avrc api cc vulnerability details in avrc msg cback of avrc api cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure to a paired device with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable libraries vulnerability details in avrc proc vendor command of avrc api cc there is a possible leak of heap data due to uninitialized data this could lead to remote information disclosure with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack sdp sdp server cc vulnerability details in sdp server handle client req of sdp server cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure from the bluetooth server with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack gatt gatt cl cc vulnerability details in gatt process read by type rsp of gatt cl cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure in the bluetooth server with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href step up your open source security game with mend cve vulnerable library aosp platform system bt library home page a href found in base branch master vulnerable source files stack gatt gatt cl cc vulnerability details in gatt process read by type rsp of gatt cl cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure in the bluetooth server with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android android android step up your open source security game with mend | 0 |
41,141 | 5,341,582,273 | IssuesEvent | 2017-02-17 03:35:41 | Kademi/kademi-dev | https://api.github.com/repos/Kademi/kademi-dev | closed | Tablet - Certificate detail: Item's position is incorrect | bug New console theme Ready to Test - Dev | http://localhost:8080/certificates/cert_1/?useHash=true
actual

expect

#2867 | 1.0 | Tablet - Certificate detail: Item's position is incorrect - http://localhost:8080/certificates/cert_1/?useHash=true
actual

expect

#2867 | test | tablet certificate detail item s position is incorrect actual expect | 1 |
77,483 | 9,996,733,221 | IssuesEvent | 2019-07-12 01:00:51 | google/ExoPlayer | https://api.github.com/repos/google/ExoPlayer | closed | when does audio underrun occur ? | closed-by-bot documentation candidate need more info question stale | Documentation for [onAudioUnderrun](https://exoplayer.dev/doc/reference/com/google/android/exoplayer2/analytics/AnalyticsListener.html#onAudioUnderrun-com.google.android.exoplayer2.analytics.AnalyticsListener.EventTime-int-long-long-) isn't enough to understand when does it occur.
I'm analysing buffering and failure issues in my app and noticed that many times before player gets into buffering state `EventLogger` has reported audio underrun event. Not sure if buffering is associated with audio underrun but would like to understand in what all cases audio underrun occurs for HLS and DASH streams.
<!-- DO NOT DELETE
validate_template=true
template_path=.github/ISSUE_TEMPLATE/question.md
-->
| 1.0 | when does audio underrun occur ? - Documentation for [onAudioUnderrun](https://exoplayer.dev/doc/reference/com/google/android/exoplayer2/analytics/AnalyticsListener.html#onAudioUnderrun-com.google.android.exoplayer2.analytics.AnalyticsListener.EventTime-int-long-long-) isn't enough to understand when does it occur.
I'm analysing buffering and failure issues in my app and noticed that many times before player gets into buffering state `EventLogger` has reported audio underrun event. Not sure if buffering is associated with audio underrun but would like to understand in what all cases audio underrun occurs for HLS and DASH streams.
<!-- DO NOT DELETE
validate_template=true
template_path=.github/ISSUE_TEMPLATE/question.md
-->
| non_test | when does audio underrun occur documentation for isn t enough to understand when does it occur i m analysing buffering and failure issues in my app and noticed that many times before player gets into buffering state eventlogger has reported audio underrun event not sure if buffering is associated with audio underrun but would like to understand in what all cases audio underrun occurs for hls and dash streams do not delete validate template true template path github issue template question md | 0 |
314,607 | 27,013,279,747 | IssuesEvent | 2023-02-10 17:03:26 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Failing test: Jest Tests.x-pack/plugins/cases/public/components/all_cases - AllCasesListGeneric Actions Row actions update the severity of a case: critical | failed-test | A test failed on a tracked branch
```
Error: thrown: "Exceeded timeout of 5000 ms for a test.
Use jest.setTimeout(newTimeout) to increase the timeout value, if this is a long-running test."
at /var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-each/build/bind.js:45:15
at Array.forEach (<anonymous>)
at eachBind (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-each/build/bind.js:37:22)
at /var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/x-pack/plugins/cases/public/components/all_cases/all_cases_list.test.tsx:946:29
at _dispatchDescribe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:91:26)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:55:5)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/x-pack/plugins/cases/public/components/all_cases/all_cases_list.test.tsx:884:5)
at _dispatchDescribe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:91:26)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:55:5)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/x-pack/plugins/cases/public/components/all_cases/all_cases_list.test.tsx:714:3)
at _dispatchDescribe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:91:26)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:55:5)
at Object.describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/x-pack/plugins/cases/public/components/all_cases/all_cases_list.test.tsx:84:1)
at Runtime._execModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:1377:24)
at Runtime._loadModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:989:12)
at Runtime.requireModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:849:12)
at jestAdapter (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/legacy-code-todo-rewrite/jestAdapter.js:77:13)
at runTestInternal (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-runner/build/runTest.js:367:16)
at runTest (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-runner/build/runTest.js:444:34)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/26805#01863c1a-b496-4d19-b276-01bac7b802bd)
<!-- kibanaCiData = {"failed-test":{"test.class":"Jest Tests.x-pack/plugins/cases/public/components/all_cases","test.name":"AllCasesListGeneric Actions Row actions update the severity of a case: critical","test.failCount":1}} --> | 1.0 | Failing test: Jest Tests.x-pack/plugins/cases/public/components/all_cases - AllCasesListGeneric Actions Row actions update the severity of a case: critical - A test failed on a tracked branch
```
Error: thrown: "Exceeded timeout of 5000 ms for a test.
Use jest.setTimeout(newTimeout) to increase the timeout value, if this is a long-running test."
at /var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-each/build/bind.js:45:15
at Array.forEach (<anonymous>)
at eachBind (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-each/build/bind.js:37:22)
at /var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/x-pack/plugins/cases/public/components/all_cases/all_cases_list.test.tsx:946:29
at _dispatchDescribe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:91:26)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:55:5)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/x-pack/plugins/cases/public/components/all_cases/all_cases_list.test.tsx:884:5)
at _dispatchDescribe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:91:26)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:55:5)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/x-pack/plugins/cases/public/components/all_cases/all_cases_list.test.tsx:714:3)
at _dispatchDescribe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:91:26)
at describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/index.js:55:5)
at Object.describe (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/x-pack/plugins/cases/public/components/all_cases/all_cases_list.test.tsx:84:1)
at Runtime._execModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:1377:24)
at Runtime._loadModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:989:12)
at Runtime.requireModule (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-runtime/build/index.js:849:12)
at jestAdapter (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-circus/build/legacy-code-todo-rewrite/jestAdapter.js:77:13)
at runTestInternal (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-runner/build/runTest.js:367:16)
at runTest (/var/lib/buildkite-agent/builds/kb-n2-4-spot-b80c5722416681d7/elastic/kibana-on-merge/kibana/node_modules/jest-runner/build/runTest.js:444:34)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/26805#01863c1a-b496-4d19-b276-01bac7b802bd)
<!-- kibanaCiData = {"failed-test":{"test.class":"Jest Tests.x-pack/plugins/cases/public/components/all_cases","test.name":"AllCasesListGeneric Actions Row actions update the severity of a case: critical","test.failCount":1}} --> | test | failing test jest tests x pack plugins cases public components all cases allcaseslistgeneric actions row actions update the severity of a case critical a test failed on a tracked branch error thrown exceeded timeout of ms for a test use jest settimeout newtimeout to increase the timeout value if this is a long running test at var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest each build bind js at array foreach at eachbind var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest each build bind js at var lib buildkite agent builds kb spot elastic kibana on merge kibana x pack plugins cases public components all cases all cases list test tsx at dispatchdescribe var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest circus build index js at describe var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest circus build index js at describe var lib buildkite agent builds kb spot elastic kibana on merge kibana x pack plugins cases public components all cases all cases list test tsx at dispatchdescribe var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest circus build index js at describe var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest circus build index js at describe var lib buildkite agent builds kb spot elastic kibana on merge kibana x pack plugins cases public components all cases all cases list test tsx at dispatchdescribe var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest circus build index js at describe var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest circus build index js at object describe var lib buildkite agent builds kb spot elastic kibana on merge kibana x pack plugins cases public components all cases all cases list test tsx at runtime execmodule var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runtime build index js at runtime loadmodule var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runtime build index js at runtime requiremodule var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runtime build index js at jestadapter var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest circus build legacy code todo rewrite jestadapter js at runtestinternal var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runner build runtest js at runtest var lib buildkite agent builds kb spot elastic kibana on merge kibana node modules jest runner build runtest js first failure | 1 |
445,725 | 12,835,493,875 | IssuesEvent | 2020-07-07 12:58:41 | internetarchive/openlibrary | https://api.github.com/repos/internetarchive/openlibrary | closed | Improve search results: include overview of available previews & languages | Affects: Experience Books Page Priority: 1 Theme: Search | Related to the release for #684 (solved by #3553)
<!-- A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
### Describe the problem that you'd like solved
<!-- A clear and concise description of what you want to happen. -->
1. We should list which languages/editions are available for a work
2. We should show a sample of previews which are available (books w/ ocaids)
3. The bookcover + link should auto-select a previewable edition
4. Choose the appropriate cover matching the selected previewable edition
### Proposal & Constraints
<!-- What is the proposed solution / implementation? Is there a precedent of this approach succeeding elsewhere? -->
<!-- Which suggestions or requirements should be considered for how feature needs to appear or be implemented? -->
Try to avoid falling back to Archive.org covers unless no other option available, use the archive.org availability API (which should return `openlibrary_edition` when/where available.
### Stakeholders
<!-- @ tag stakeholders of this bug -->
@cdrini @tabshaikh
| 1.0 | Improve search results: include overview of available previews & languages - Related to the release for #684 (solved by #3553)
<!-- A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
### Describe the problem that you'd like solved
<!-- A clear and concise description of what you want to happen. -->
1. We should list which languages/editions are available for a work
2. We should show a sample of previews which are available (books w/ ocaids)
3. The bookcover + link should auto-select a previewable edition
4. Choose the appropriate cover matching the selected previewable edition
### Proposal & Constraints
<!-- What is the proposed solution / implementation? Is there a precedent of this approach succeeding elsewhere? -->
<!-- Which suggestions or requirements should be considered for how feature needs to appear or be implemented? -->
Try to avoid falling back to Archive.org covers unless no other option available, use the archive.org availability API (which should return `openlibrary_edition` when/where available.
### Stakeholders
<!-- @ tag stakeholders of this bug -->
@cdrini @tabshaikh
| non_test | improve search results include overview of available previews languages related to the release for solved by describe the problem that you d like solved we should list which languages editions are available for a work we should show a sample of previews which are available books w ocaids the bookcover link should auto select a previewable edition choose the appropriate cover matching the selected previewable edition proposal constraints try to avoid falling back to archive org covers unless no other option available use the archive org availability api which should return openlibrary edition when where available stakeholders cdrini tabshaikh | 0 |
87,803 | 8,122,749,903 | IssuesEvent | 2018-08-16 12:42:38 | QMCPACK/qmcpack | https://api.github.com/repos/QMCPACK/qmcpack | closed | Test for gofr needed | testing | g(r) does not yet have a test. This can be based on one of the HEG tests that currently computes g(r) but does not test it. | 1.0 | Test for gofr needed - g(r) does not yet have a test. This can be based on one of the HEG tests that currently computes g(r) but does not test it. | test | test for gofr needed g r does not yet have a test this can be based on one of the heg tests that currently computes g r but does not test it | 1 |
83,948 | 7,885,084,865 | IssuesEvent | 2018-06-27 11:15:02 | owncloud/client | https://api.github.com/repos/owncloud/client | closed | garbled text when installing client in traditional Chinese Windows OS. | ReadyToTest bug p3-medium | when Traditional Chinese OS, it display garbled text.

but display properly in Simplified Chinese.

I have tried from Version 1.8 to 2.2.1
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/35033241-garbled-text-when-installing-client-in-traditional-chinese-windows-os?utm_campaign=plugin&utm_content=tracker%2F216457&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F216457&utm_medium=issues&utm_source=github).
</bountysource-plugin> | 1.0 | garbled text when installing client in traditional Chinese Windows OS. - when Traditional Chinese OS, it display garbled text.

but display properly in Simplified Chinese.

I have tried from Version 1.8 to 2.2.1
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/35033241-garbled-text-when-installing-client-in-traditional-chinese-windows-os?utm_campaign=plugin&utm_content=tracker%2F216457&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F216457&utm_medium=issues&utm_source=github).
</bountysource-plugin> | test | garbled text when installing client in traditional chinese windows os when traditional chinese os it display garbled text but display properly in simplified chinese i have tried from version to want to back this issue we accept bounties via | 1 |
473,759 | 13,647,374,943 | IssuesEvent | 2020-09-26 02:58:11 | open-telemetry/opentelemetry-specification | https://api.github.com/repos/open-telemetry/opentelemetry-specification | closed | Proposal: remove restriction that SpanContext must be a sealed/final class | area:api priority:p1 release:required-for-ga spec:trace | I think the spec that requires `SpanContext` is too limiting to language authors since it brings language concerns (class inheritance) into the cross-language spec. Languages may have a language-specific reason to allow a non-sealed `SpanContext`. For example, in Java, we have a need to hide the implementation of `SpanContext` from a user app to prevent compatibility issues between auto instrumentation and the app which without special care, can share classpath and have collisions. This can be done efficiently if `SpanContext` is an interface - two interfaces, one in the app, the other in the agent, but one implementation generated by the agent. Otherwise, we are stuck with two implementations, that copy between each other. In some sense, the fact that we rewrite the usage of `SpanContext` by a user through severe bytecode manipulation already seems to be incompliant with the spirit of this spec of wanting only one implementation of `SpanContext. This is an issue specific to Java instrumentation - I'd recommend the spec not be a blocker in creating solutions to such issues. | 1.0 | Proposal: remove restriction that SpanContext must be a sealed/final class - I think the spec that requires `SpanContext` is too limiting to language authors since it brings language concerns (class inheritance) into the cross-language spec. Languages may have a language-specific reason to allow a non-sealed `SpanContext`. For example, in Java, we have a need to hide the implementation of `SpanContext` from a user app to prevent compatibility issues between auto instrumentation and the app which without special care, can share classpath and have collisions. This can be done efficiently if `SpanContext` is an interface - two interfaces, one in the app, the other in the agent, but one implementation generated by the agent. Otherwise, we are stuck with two implementations, that copy between each other. In some sense, the fact that we rewrite the usage of `SpanContext` by a user through severe bytecode manipulation already seems to be incompliant with the spirit of this spec of wanting only one implementation of `SpanContext. This is an issue specific to Java instrumentation - I'd recommend the spec not be a blocker in creating solutions to such issues. | non_test | proposal remove restriction that spancontext must be a sealed final class i think the spec that requires spancontext is too limiting to language authors since it brings language concerns class inheritance into the cross language spec languages may have a language specific reason to allow a non sealed spancontext for example in java we have a need to hide the implementation of spancontext from a user app to prevent compatibility issues between auto instrumentation and the app which without special care can share classpath and have collisions this can be done efficiently if spancontext is an interface two interfaces one in the app the other in the agent but one implementation generated by the agent otherwise we are stuck with two implementations that copy between each other in some sense the fact that we rewrite the usage of spancontext by a user through severe bytecode manipulation already seems to be incompliant with the spirit of this spec of wanting only one implementation of spancontext this is an issue specific to java instrumentation i d recommend the spec not be a blocker in creating solutions to such issues | 0 |
187,007 | 6,744,277,855 | IssuesEvent | 2017-10-20 15:08:21 | vincentrk/quadrodoodle | https://api.github.com/repos/vincentrk/quadrodoodle | closed | Begin implementing Yaw control | high priority | - [ ] Look into p controller, cascading controller
- [ ] Figure out and implement new message type for updating p values
- [ ] Quad
- [ ] PC terminal
- [ ] Look at sensor data
- [ ] Figure out drift
- [ ] Figure out calculations/formulas needed
- [ ] Implement
- [ ] Quad
- [ ] PC terminal | 1.0 | Begin implementing Yaw control - - [ ] Look into p controller, cascading controller
- [ ] Figure out and implement new message type for updating p values
- [ ] Quad
- [ ] PC terminal
- [ ] Look at sensor data
- [ ] Figure out drift
- [ ] Figure out calculations/formulas needed
- [ ] Implement
- [ ] Quad
- [ ] PC terminal | non_test | begin implementing yaw control look into p controller cascading controller figure out and implement new message type for updating p values quad pc terminal look at sensor data figure out drift figure out calculations formulas needed implement quad pc terminal | 0 |
70,258 | 7,181,481,689 | IssuesEvent | 2018-02-01 05:19:35 | salesforce/design-system-react | https://api.github.com/repos/salesforce/design-system-react | closed | Implement Storyshots | scale and productivity test task | It's Jest DOM snapshots of all Storybook stories. https://github.com/storybooks/storybook/tree/master/addons/storyshots
Will implement after #951. Jest does't like TetherJS. | 1.0 | Implement Storyshots - It's Jest DOM snapshots of all Storybook stories. https://github.com/storybooks/storybook/tree/master/addons/storyshots
Will implement after #951. Jest does't like TetherJS. | test | implement storyshots it s jest dom snapshots of all storybook stories will implement after jest does t like tetherjs | 1 |
34,650 | 4,938,108,399 | IssuesEvent | 2016-11-29 10:08:47 | mautic/mautic | https://api.github.com/repos/mautic/mautic | closed | Add /leads/notes endpoint to API to pull notes from across all leads | Feature Request Ready To Test | Hi,
Just noticed a case where having a /leads/notes type API endpoint which that just returns a list of all the recent notes would be good, I'm not sure how realistic this would be in terms of the current coding structure though.
Just another request, I thought I would mention it just incase it was easy to implement.
Thanks,
Zac
| 1.0 | Add /leads/notes endpoint to API to pull notes from across all leads - Hi,
Just noticed a case where having a /leads/notes type API endpoint which that just returns a list of all the recent notes would be good, I'm not sure how realistic this would be in terms of the current coding structure though.
Just another request, I thought I would mention it just incase it was easy to implement.
Thanks,
Zac
| test | add leads notes endpoint to api to pull notes from across all leads hi just noticed a case where having a leads notes type api endpoint which that just returns a list of all the recent notes would be good i m not sure how realistic this would be in terms of the current coding structure though just another request i thought i would mention it just incase it was easy to implement thanks zac | 1 |
143,678 | 11,573,760,170 | IssuesEvent | 2020-02-21 04:54:02 | rsx-labs/aide-frontend | https://api.github.com/repos/rsx-labs/aide-frontend | closed | [Print] Remove print button/icon on screens | Bug For QA Testing Medium Priority | **Describe the bug**
Remove print button/icon on screens since this will be replaced by Kool-Aide
1. Contacts List
2. Resource Planner
3. Task Monitoring
4. 3C
5. Action List
6. Lessons Learnt
7. Success Registers
8. Skills Matrix
9. Birthdays (remove Print by dropdown also)
**Version (please complete the following information):**
- Version 3.1.0 | 1.0 | [Print] Remove print button/icon on screens - **Describe the bug**
Remove print button/icon on screens since this will be replaced by Kool-Aide
1. Contacts List
2. Resource Planner
3. Task Monitoring
4. 3C
5. Action List
6. Lessons Learnt
7. Success Registers
8. Skills Matrix
9. Birthdays (remove Print by dropdown also)
**Version (please complete the following information):**
- Version 3.1.0 | test | remove print button icon on screens describe the bug remove print button icon on screens since this will be replaced by kool aide contacts list resource planner task monitoring action list lessons learnt success registers skills matrix birthdays remove print by dropdown also version please complete the following information version | 1 |
322,586 | 23,915,323,368 | IssuesEvent | 2022-09-09 12:10:28 | Chocobozzz/PeerTube | https://api.github.com/repos/Chocobozzz/PeerTube | closed | Update Installation Instructions from NodeJS14 to NodeJS16 | Component: Documentation :books: | ### Describe the desired information/correction
Currently, when installing PeerTube, if you select "Any OS (recommended)," under the "dpendencies" section at the beginning, the documentation explicitly says to install NodeJS 14.x (See here: https://docs.joinpeertube.org/dependencies?id=debian-ubuntu-and-derivatives). Personally this caused me nearly two months of headache as my instance refused to send emails due to some sort of LetsEncrypt conflict with nodemailer. TL;DR: once I updated to NodeJS 16, it just suddenly worked. Therefore, I propose updating the documentation to suggest installing NodeJS 16 LTS to avoid this confusion and headache for future hosters (admins? whatever they're called). | 1.0 | Update Installation Instructions from NodeJS14 to NodeJS16 - ### Describe the desired information/correction
Currently, when installing PeerTube, if you select "Any OS (recommended)," under the "dpendencies" section at the beginning, the documentation explicitly says to install NodeJS 14.x (See here: https://docs.joinpeertube.org/dependencies?id=debian-ubuntu-and-derivatives). Personally this caused me nearly two months of headache as my instance refused to send emails due to some sort of LetsEncrypt conflict with nodemailer. TL;DR: once I updated to NodeJS 16, it just suddenly worked. Therefore, I propose updating the documentation to suggest installing NodeJS 16 LTS to avoid this confusion and headache for future hosters (admins? whatever they're called). | non_test | update installation instructions from to describe the desired information correction currently when installing peertube if you select any os recommended under the dpendencies section at the beginning the documentation explicitly says to install nodejs x see here personally this caused me nearly two months of headache as my instance refused to send emails due to some sort of letsencrypt conflict with nodemailer tl dr once i updated to nodejs it just suddenly worked therefore i propose updating the documentation to suggest installing nodejs lts to avoid this confusion and headache for future hosters admins whatever they re called | 0 |
27,806 | 2,696,247,719 | IssuesEvent | 2015-04-02 12:55:42 | handsontable/handsontable | https://api.github.com/repos/handsontable/handsontable | closed | Get currently selected cell data? | Feature Priority: normal | There doesn't appear to be a way to get the currently selected cell data.. it'd be nice to have that. Currently what I'm trying to do is something like this:
```javascript
var cells = $("#table").handsontable('getSelected');
if(cells) {
console.log(cells);
var inst = $("#table").handsontable('getInstance');
console.log(inst);
//necessary because the order of the range of returned cells varies depending on how it was selected
var iMin = cells[0] < cells[2] ? cells[0] : cells[2];
var iMax = cells[0] > cells[2] ? cells[0] : cells[2];
var jMin = cells[1] < cells[3] ? cells[1] : cells[3];
var jMax = cells[1] > cells[3] ? cells[1] : cells[3];
for(var j=jMin; j<jMax; j++) {
for(var i=iMin; i<iMax; i++) {
console.log(inst.getCellMeta(i, j));
}
}
}
```
But here's the thing, assuming I select top-left to bottom-right, the number of ColumnSettings objects I get seems to be off by varying amounts, see [this](http://puu.sh/3tx01.png) and [this](http://puu.sh/3tx1L.png). Plus, my for() loop won't work when I select a single column/row (I could work around this, but that's not the point).
It'd really be nice to have a "getCellMetaForRange" function or something - then I could just loop through the affected cells and apply changes as necessary. | 1.0 | Get currently selected cell data? - There doesn't appear to be a way to get the currently selected cell data.. it'd be nice to have that. Currently what I'm trying to do is something like this:
```javascript
var cells = $("#table").handsontable('getSelected');
if(cells) {
console.log(cells);
var inst = $("#table").handsontable('getInstance');
console.log(inst);
//necessary because the order of the range of returned cells varies depending on how it was selected
var iMin = cells[0] < cells[2] ? cells[0] : cells[2];
var iMax = cells[0] > cells[2] ? cells[0] : cells[2];
var jMin = cells[1] < cells[3] ? cells[1] : cells[3];
var jMax = cells[1] > cells[3] ? cells[1] : cells[3];
for(var j=jMin; j<jMax; j++) {
for(var i=iMin; i<iMax; i++) {
console.log(inst.getCellMeta(i, j));
}
}
}
```
But here's the thing, assuming I select top-left to bottom-right, the number of ColumnSettings objects I get seems to be off by varying amounts, see [this](http://puu.sh/3tx01.png) and [this](http://puu.sh/3tx1L.png). Plus, my for() loop won't work when I select a single column/row (I could work around this, but that's not the point).
It'd really be nice to have a "getCellMetaForRange" function or something - then I could just loop through the affected cells and apply changes as necessary. | non_test | get currently selected cell data there doesn t appear to be a way to get the currently selected cell data it d be nice to have that currently what i m trying to do is something like this javascript var cells table handsontable getselected if cells console log cells var inst table handsontable getinstance console log inst necessary because the order of the range of returned cells varies depending on how it was selected var imin cells cells cells cells var imax cells cells cells cells var jmin cells cells cells cells var jmax cells cells cells cells for var j jmin j jmax j for var i imin i imax i console log inst getcellmeta i j but here s the thing assuming i select top left to bottom right the number of columnsettings objects i get seems to be off by varying amounts see and plus my for loop won t work when i select a single column row i could work around this but that s not the point it d really be nice to have a getcellmetaforrange function or something then i could just loop through the affected cells and apply changes as necessary | 0 |
57,443 | 14,114,090,877 | IssuesEvent | 2020-11-07 14:27:00 | fluttercandies/extended_image | https://api.github.com/repos/fluttercandies/extended_image | closed | Execution failed for task ':app:compileFlutterBuildRelease' | flutter sdk build error | [+22000 ms] [+21991 ms]
../../snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image-0.7.1/lib/src/gesture/extended_imag
e_slide_page_route.dart:333:9: Error: No named parameter with the name 'animation'.
[ +1 ms] [ +5 ms] animation: animation,
[ ] [ ] ^^^^^^^^^
**flutter doctor -v**
hasan@hasan-Lenovo-ideapad-320-15IAP:~/Desktop/ChitChat-master$ flutter doctor -v
[✓] Flutter (Channel master, 1.24.0-4.0.pre.138, on Linux, locale en_GB.UTF-8)
• Flutter version 1.24.0-4.0.pre.138 at /home/hasan/snap/flutter/common/flutter
• Framework revision 13896b3bd1 (35 hours ago), 2020-10-28 19:43:19 -0700
• Engine revision 073263e39d
• Dart version 2.11.0 (build 2.11.0-260.0.dev)
[!] Android toolchain - develop for Android devices (Android SDK version 30.0.2)
• Android SDK at /home/hasan/Android/Sdk
• Platform android-30, build-tools 30.0.2
• Java binary at: /usr/bin/java
• Java version OpenJDK Runtime Environment (build 14.0.2+12-Ubuntu-120.04)
✗ Android license status unknown.
Run `flutter doctor --android-licenses` to accept the SDK licenses.
See https://flutter.dev/docs/get-started/install/linux#android-setup for more details.
[!] Android Studio (not installed)
• Android Studio not found; download from https://developer.android.com/studio/index.html
(or visit https://flutter.dev/docs/get-started/install/linux#android-setup for detailed instructions).
[!] Connected device
! No devices available
! Doctor found issues in 3 categories.
**NEXT**
flutter build appbundle --verbose
.0-nullsafety.2/lib/
[ +1 ms] |
bottom_navy_bar:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/bottom_navy_bar-5.3.2
/lib/
[ +1 ms] |
characters:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/characters-1.1.0-nullsafet
y.4/lib/
[ ] |
charcode:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/charcode-1.2.0-nullsafety.2/
lib/
[ ] |
clock:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/clock-1.1.0-nullsafety.2/lib/
[ ] |
cloud_firestore:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore-0.13.
4/lib/
[ +1 ms] |
cloud_firestore_platform_interface:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cl
oud_firestore_platform_interface-1.1.0/lib/
[ +1 ms] |
cloud_firestore_web:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore_w
eb-0.1.1/lib/
[ ] |
collection:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/collection-1.15.0-nullsafe
ty.4/lib/
[ +1 ms] |
convert:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/convert-2.1.1/lib/
[ ] |
crypto:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/crypto-2.1.3/lib/
[ ] |
cupertino_icons:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cupertino_icons-0.1.3
/lib/
[ ] |
diacritic:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/diacritic-0.1.1/lib/
[ +1 ms] |
equatable:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/equatable-1.1.0/lib/
[ +1 ms] |
eva_icons_flutter:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/eva_icons_flutter-2
.0.0/lib/
[ +1 ms] |
extended_image:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image-0.7.1/l
ib/
[ ] |
extended_image_library:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image
_library-0.2.0/lib/
[ +1 ms] |
fake_async:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/fake_async-1.2.0-nullsafet
y.2/lib/
[ ] |
file_picker:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/file_picker-1.4.3+2/lib/
[ ] |
firebase:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase-7.2.1/lib/
[ ] |
firebase_auth:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth-0.15.5+2/
lib/
[ +1 ms] |
firebase_auth_platform_interface:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/fire
base_auth_platform_interface-1.1.7/lib/
[ +1 ms] |
firebase_auth_web:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_web-0
.1.2/lib/
[ ] |
firebase_core:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core-0.4.4+2/l
ib/
[ ] |
firebase_core_platform_interface:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/fire
base_core_platform_interface-1.0.4/lib/
[ +1 ms] |
firebase_core_web:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core_web-0
.1.1+2/lib/
[ +1 ms] |
firebase_storage:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_storage-3.1
.1/lib/
[ ] | flutter:file:///home/hasan/snap/flutter/common/flutter/packages/flutter/lib/
[ ] |
flutter_bloc:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_bloc-0.11.1/lib/
[ +1 ms] |
flutter_country_picker:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_countr
y_picker-0.1.6/lib/
[ +1 ms] |
flutter_datetime_picker:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_datet
ime_picker-1.4.0/lib/
[ +1 ms] |
flutter_native_image:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_native_i
mage-0.0.5+2/lib/
[ ] | flutter_test:file:///home/hasan/snap/flutter/common/flutter/packages/flutter_test/lib/
[ ] | flutter_web_plugins:file:///home/hasan/snap/flutter/common/flutter/packages/flutter_web_plugins/lib/
[ ] |
font_awesome_flutter:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/font_awesome_flu
tter-8.7.0/lib/
[ ] |
geolocator:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/geolocator-5.3.0/lib/
[ ] |
google_api_availability:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/google_api_av
ailability-2.0.2/lib/
[ +1 ms] |
http:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http-0.12.0+4/lib/
[ ] |
http_client_helper:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http_client_helper
-0.2.1/lib/
[ ] |
http_parser:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http_parser-3.1.3/lib/
[ ] |
js:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/js-0.6.3-nullsafety.2/lib/
[ +1 ms] |
language_pickers:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/language_pickers-0.1
.3/lib/
[ +1 ms] |
location_permissions:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/location_permiss
ions-2.0.4+1/lib/
[ ] |
matcher:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/matcher-0.12.10-nullsafety.2/
lib/
[ ] |
meta:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/meta-1.3.0-nullsafety.5/lib/
[ ] |
modal_progress_hud:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/modal_progress_hud
-0.1.3/lib/
[ ] |
network_to_file_image:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/network_to_file
_image-2.2.8/lib/
[ ] |
path:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path-1.8.0-nullsafety.2/lib/
[ ] |
path_provider:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path_provider-1.6.1/lib
/
[ +1 ms] |
pedantic:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/pedantic-1.8.0+1/lib/
[ ] |
platform:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/platform-2.2.1/lib/
[ ] |
plugin_platform_interface:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/plugin_plat
form_interface-1.0.2/lib/
[ ] |
quiver:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/quiver-2.0.5/lib/
[ +1 ms] |
rxdart:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/rxdart-0.21.0/lib/
[ ] | sky_engine:file:///home/hasan/snap/flutter/common/flutter/bin/cache/pkg/sky_engine/lib/
[ ] |
source_span:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/source_span-1.8.0-nullsaf
ety.3/lib/
[ ] |
stack_trace:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/stack_trace-1.10.0-nullsa
fety.5/lib/
[ ] |
stream_channel:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/stream_channel-2.1.0-n
ullsafety.2/lib/
[ +1 ms] |
string_scanner:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/string_scanner-1.1.0-n
ullsafety.2/lib/
[ +1 ms] |
term_glyph:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/term_glyph-1.2.0-nullsafet
y.2/lib/
[ ] |
test_api:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/test_api-0.2.19-nullsafety.4
/lib/
[ ] |
typed_data:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/typed_data-1.3.0-nullsafet
y.4/lib/
[ ] |
vector_math:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/vector_math-2.1.0-nullsaf
ety.4/lib/
[ ] | chitchat:lib/
[ ] IO : Writing 15123 characters to text file ./.dart_tool/package_config.json.
[ ] FINE: Contents:
[ ] | {
[ ] | "configVersion": 2,
[ ] | "packages": [
[ ] | {
[ ] | "name": "async",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/async-2.5.0-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "bloc",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/bloc-0.12.0",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "boolean_selector",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/boolean_selector-2.1.0-nullsafety.2"
,
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ +1 ms] | {
[ +1 ms] | "name": "bottom_navy_bar",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/bottom_navy_bar-5.3.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.2"
[ ] | },
[ ] | {
[ ] | "name": "characters",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/characters-1.1.0-nullsafety.4",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "charcode",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/charcode-1.2.0-nullsafety.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "clock",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/clock-1.1.0-nullsafety.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "cloud_firestore",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore-0.13.4",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "cloud_firestore_platform_interface",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore_platform_interface-1
.1.0",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "cloud_firestore_web",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore_web-0.1.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "collection",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/collection-1.15.0-nullsafety.4",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "convert",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/convert-2.1.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "1.17"
[ ] | },
[ ] | {
[ ] | "name": "crypto",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/crypto-2.1.3",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "cupertino_icons",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cupertino_icons-0.1.3",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "diacritic",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/diacritic-0.1.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "equatable",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/equatable-1.1.0",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "eva_icons_flutter",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/eva_icons_flutter-2.0.0",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "extended_image",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image-0.7.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "extended_image_library",
[ +2 ms] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image_library-0.2.0",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "fake_async",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/fake_async-1.2.0-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ +1 ms] | {
[ ] | "name": "file_picker",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/file_picker-1.4.3+2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase-7.2.1",
[ +5 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.7"
[ ] | },
[ ] | {
[ ] | "name": "firebase_auth",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth-0.15.5+2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ +2 ms] | "name": "firebase_auth_platform_interface",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_platform_interface-1.1
.7",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase_auth_web",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_web-0.1.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase_core",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core-0.4.4+2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase_core_platform_interface",
[ +4 ms] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core_platform_interface-1.0
.4",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase_core_web",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core_web-0.1.1+2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase_storage",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_storage-3.1.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ +3 ms] | },
[ ] | {
[ ] | "name": "flutter",
[ ] | "rootUri": "file:///home/hasan/snap/flutter/common/flutter/packages/flutter",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "flutter_bloc",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_bloc-0.11.1",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "flutter_country_picker",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_country_picker-0.1.6",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.3"
[ ] | },
[ ] | {
[ ] | "name": "flutter_datetime_picker",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_datetime_picker-1.4.0",
[ ] | "packageUri": "lib/",
[ +4 ms] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "flutter_native_image",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_native_image-0.0.5+2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "1.19"
[ ] | },
[ ] | {
[ ] | "name": "flutter_test",
[ ] | "rootUri": "file:///home/hasan/snap/flutter/common/flutter/packages/flutter_test",
[ +1 ms] | "packageUri": "lib/",
[ +3 ms] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ +6 ms] | "name": "flutter_web_plugins",
[ ] | "rootUri": "file:///home/hasan/snap/flutter/common/flutter/packages/flutter_web_plugins",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "font_awesome_flutter",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/font_awesome_flutter-8.7.0",
[ ] | "packageUri": "lib/",
[ +2 ms] | "languageVersion": "2.0"
[ +2 ms] | },
[ ] | {
[ ] | "name": "geolocator",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/geolocator-5.3.0",
[ +1 ms] | "packageUri": "lib/",
[ +1 ms] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ +1 ms] | "name": "google_api_availability",
[ +4 ms] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/google_api_availability-2.0.2",
[ +6 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ +1 ms] | {
[ ] | "name": "http",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http-0.12.0+4",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.4"
[ ] | },
[ ] | {
[ ] | "name": "http_client_helper",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http_client_helper-0.2.1",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "http_parser",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http_parser-3.1.3",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "js",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/js-0.6.3-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "language_pickers",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/language_pickers-0.1.3",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "location_permissions",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/location_permissions-2.0.4+1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "matcher",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/matcher-0.12.10-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "meta",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/meta-1.3.0-nullsafety.5",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "modal_progress_hud",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/modal_progress_hud-0.1.3",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "1.20"
[ ] | },
[ ] | {
[ ] | "name": "network_to_file_image",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/network_to_file_image-2.2.8",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.7"
[ ] | },
[ ] | {
[ ] | "name": "path",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path-1.8.0-nullsafety.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "path_provider",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path_provider-1.6.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "pedantic",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/pedantic-1.8.0+1",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "platform",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/platform-2.2.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "1.24"
[ ] | },
[ ] | {
[ ] | "name": "plugin_platform_interface",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/plugin_platform_interface-1.0.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "quiver",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/quiver-2.0.5",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "rxdart",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/rxdart-0.21.0",
[ +7 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "sky_engine",
[ ] | "rootUri": "file:///home/hasan/snap/flutter/common/flutter/bin/cache/pkg/sky_engine",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "1.11"
[ ] | },
[ ] | {
[ ] | "name": "source_span",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/source_span-1.8.0-nullsafety.3",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.11"
[ ] | },
[ ] | {
[ ] | "name": "stack_trace",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/stack_trace-1.10.0-nullsafety.5",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "stream_channel",
[ +2 ms] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/stream_channel-2.1.0-nullsafety.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "string_scanner",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/string_scanner-1.1.0-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "term_glyph",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/term_glyph-1.2.0-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "test_api",
[ +6 ms] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/test_api-0.2.19-nullsafety.4",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "typed_data",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/typed_data-1.3.0-nullsafety.4",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "vector_math",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/vector_math-2.1.0-nullsafety.4",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "chitchat",
[ ] | "rootUri": "../",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | }
[ ] | ],
[ ] | "generated": "2020-10-30T14:04:42.090496Z",
[ ] | "generator": "pub",
[ ] | "generatorVersion": "2.11.0-260.0.dev"
[ ] | }
[ +14 ms] MSG : Got dependencies!
[ +155 ms] Running "flutter pub get" in ChitChat-master... (completed in 3.8s)
[ +152 ms] Found plugin cloud_firestore at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore-0.13.4/
[ +35 ms] Found plugin cloud_firestore_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore_web-0.1.1/
[ +54 ms] Found plugin file_picker at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/file_picker-1.4.3+2/
[ +13 ms] Found plugin firebase_auth at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth-0.15.5+2/
[ +10 ms] Found plugin firebase_auth_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_web-0.1.2/
[ +6 ms] Found plugin firebase_core at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core-0.4.4+2/
[ +9 ms] Found plugin firebase_core_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core_web-0.1.1+2/
[ +6 ms] Found plugin firebase_storage at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_storage-3.1.1/
[ +8 ms] Found plugin flutter_country_picker at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_country_picker-0.1.6/
[ +8 ms] Found plugin flutter_native_image at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_native_image-0.0.5+2/
[ +17 ms] Found plugin geolocator at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/geolocator-5.3.0/
[ +8 ms] Found plugin google_api_availability at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/google_api_availability-2.0.2/
[ +33 ms] Found plugin location_permissions at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/location_permissions-2.0.4+1/
[ +25 ms] Found plugin path_provider at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path_provider-1.6.1/
[ +383 ms] Found plugin cloud_firestore at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore-0.13.4/
[ +7 ms] Found plugin cloud_firestore_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore_web-0.1.1/
[ +31 ms] Found plugin file_picker at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/file_picker-1.4.3+2/
[ +8 ms] Found plugin firebase_auth at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth-0.15.5+2/
[ +6 ms] Found plugin firebase_auth_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_web-0.1.2/
[ +4 ms] Found plugin firebase_core at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core-0.4.4+2/
[ +7 ms] Found plugin firebase_core_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core_web-0.1.1+2/
[ +5 ms] Found plugin firebase_storage at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_storage-3.1.1/
[ +8 ms] Found plugin flutter_country_picker at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_country_picker-0.1.6/
[ +5 ms] Found plugin flutter_native_image at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_native_image-0.0.5+2/
[ +8 ms] Found plugin geolocator at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/geolocator-5.3.0/
[ +4 ms] Found plugin google_api_availability at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/google_api_availability-2.0.2/
[ +15 ms] Found plugin location_permissions at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/location_permissions-2.0.4+1/
[ +13 ms] Found plugin path_provider at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path_provider-1.6.1/
[ +433 ms] Generating
/home/hasan/Desktop/ChitChat-master/android/app/src/main/java/io/flutter/plugins/GeneratedPluginRegistrant.java
[ +175 ms] Running Gradle task 'bundleRelease'...
[ +3 ms] gradle.properties already sets `android.enableR8`
[ +6 ms] Using gradle from /home/hasan/Desktop/ChitChat-master/android/gradlew.
[ +2 ms] /home/hasan/Desktop/ChitChat-master/android/gradlew mode: 33277 rwxrwxr-x.
[ +16 ms] executing: [/home/hasan/Desktop/ChitChat-master/android/]
/home/hasan/Desktop/ChitChat-master/android/gradlew -Pverbose=true
-Ptarget-platform=android-arm,android-arm64,android-x64 -Ptarget=lib/main.dart -Ptrack-widget-creation=true
-Pshrink=true -Ptree-shake-icons=true bundleRelease
[+4115 ms] Starting a Gradle Daemon, 1 busy and 1 incompatible Daemons could not be reused, use --status for details
[+23372 ms] > Configure project :app
[ ] WARNING: The option 'android.enableR8' is deprecated and should not be used anymore.
[ ] It will be removed in a future version of the Android Gradle plugin, and will no longer allow you to disable
R8.
[+35393 ms] > Task :app:cleanMergeReleaseAssets UP-TO-DATE
[+3400 ms] > Task :app:preBuild UP-TO-DATE
[ +199 ms] > Task :app:extractProguardFiles
[ ] > Task :app:preReleaseBuild
[ +199 ms] > Task :app:mergeReleaseShaders
[ +199 ms] > Task :app:compileReleaseShaders
[ ] > Task :app:generateReleaseAssets
[+1999 ms] > Task :app:compileFlutterBuildRelease
[ +4 ms] [ +333 ms] executing: [/home/hasan/snap/flutter/common/flutter/] git -c log.showSignature=false log -n 1
--pretty=format:%H
[ ] [ +108 ms] Exit code 0 from: git -c log.showSignature=false log -n 1 --pretty=format:%H
[ ] [ +2 ms] 13896b3bd1858687a06b1639d60c877206170df8
[ ] [ +3 ms] executing: [/home/hasan/snap/flutter/common/flutter/] git tag --points-at HEAD
[ ] [ +24 ms] Exit code 0 from: git tag --points-at HEAD
[ ] [ +4 ms] executing: [/home/hasan/snap/flutter/common/flutter/] git describe --match *.*.* --first-parent
--long --tags
[ ] [ +51 ms] Exit code 0 from: git describe --match *.*.* --first-parent --long --tags
[ ] [ +1 ms] 1.24.0-3.0.pre-138-g13896b3bd1
[ ] [ +24 ms] executing: [/home/hasan/snap/flutter/common/flutter/] git rev-parse --abbrev-ref --symbolic @{u}
[ ] [ +7 ms] Exit code 0 from: git rev-parse --abbrev-ref --symbolic @{u}
[ ] [ ] origin/master
[ ] [ ] executing: [/home/hasan/snap/flutter/common/flutter/] git ls-remote --get-url origin
[ ] [ +7 ms] Exit code 0 from: git ls-remote --get-url origin
[ +2 ms] [ ] https://github.com/flutter/flutter.git
[ ] [ +101 ms] executing: [/home/hasan/snap/flutter/common/flutter/] git rev-parse --abbrev-ref HEAD
[ ] [ +7 ms] Exit code 0 from: git rev-parse --abbrev-ref HEAD
[ ] [ ] master
[ ] [ +103 ms] Artifact Instance of 'AndroidMavenArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'AndroidGenSnapshotArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'AndroidInternalBuildArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IOSEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'FlutterWebSdk' is not required, skipping update.
[ ] [ +7 ms] Artifact Instance of 'WindowsEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'MacOSEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'LinuxEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'LinuxFuchsiaSDKArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'MacOSFuchsiaSDKArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'FlutterRunnerSDKArtifacts' is not required, skipping update.
[ +3 ms] [ ] Artifact Instance of 'FlutterRunnerDebugSymbols' is not required, skipping update.
[ ] [ +148 ms] Artifact Instance of 'MaterialFonts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'GradleWrapper' is not required, skipping update.
[ ] [ ] Artifact Instance of 'AndroidMavenArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'AndroidGenSnapshotArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'AndroidInternalBuildArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IOSEngineArtifacts' is not required, skipping update.
[ +1 ms] [ ] Artifact Instance of 'FlutterWebSdk' is not required, skipping update.
[ ] [ ] Artifact Instance of 'FlutterSdk' is not required, skipping update.
[ ] [ ] Artifact Instance of 'WindowsEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'MacOSEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'LinuxEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'LinuxFuchsiaSDKArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'MacOSFuchsiaSDKArtifacts' is not required, skipping update.
[ +5 ms] [ ] Artifact Instance of 'FlutterRunnerSDKArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'FlutterRunnerDebugSymbols' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IosUsbArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IosUsbArtifacts' is not required, skipping update.
[ ] [ +1 ms] Artifact Instance of 'IosUsbArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IosUsbArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IosUsbArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'FontSubsetArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'PubDependencies' is not required, skipping update.
[ ] [ +208 ms] Initializing file store
[ ] [ +19 ms] Done initializing file store
[ +55 ms] [ +273 ms] Skipping target: gen_localizations
[+1200 ms] [+1144 ms] kernel_snapshot: Starting due to {InvalidatedReason.inputChanged}
[ +1 ms] [ +36 ms] /home/hasan/snap/flutter/common/flutter/bin/cache/dart-sdk/bin/dart --disable-dart-dev
/home/hasan/snap/flutter/common/flutter/bin/cache/artifacts/engine/linux-x64/frontend_server.dart.snapshot --sdk-root
/home/hasan/snap/flutter/common/flutter/bin/cache/artifacts/engine/common/flutter_patched_sdk_product/ --target=flutter
--no-print-incremental-dependencies -Ddart.developer.causal_async_stacks=false -Ddart.vm.profile=false
-Ddart.vm.product=true --aot --tfa --packages /home/hasan/Desktop/ChitChat-master/.dart_tool/package_config.json
--output-dill /home/hasan/Desktop/ChitChat-master/.dart_tool/flutter_build/7e2b6ef2f352a402314d530501db0c4e/app.dill
--depfile
/home/hasan/Desktop/ChitChat-master/.dart_tool/flutter_build/7e2b6ef2f352a402314d530501db0c4e/kernel_snapshot.d
package:chitchat/main.dart
[+22000 ms] [+21991 ms]
../../snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image-0.7.1/lib/src/gesture/extended_imag
e_slide_page_route.dart:333:9: Error: No named parameter with the name 'animation'.
[ +1 ms] [ +5 ms] animation: animation,
[ ] [ ] ^^^^^^^^^
[ ] [ ] ../../snap/flutter/common/flutter/packages/flutter/lib/src/cupertino/route.dart:547:3: Context:
Found this candidate, but the arguments don't match.
[ ] [ ] CupertinoFullscreenDialogTransition({
[ ] [ +1 ms] ^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
[ +95 ms] [ +88 ms]
../../snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image-0.7.1/lib/src/extended_image.dart:7
13:44: Error: No named parameter with the name 'nullOk'.
[ +2 ms] [ +2 ms] _invertColors = MediaQuery.of(context, nullOk: true)?.invertColors ??
[ ] [ +1 ms] ^^^^^^
[ ] [ +1 ms] ../../snap/flutter/common/flutter/packages/flutter/lib/src/widgets/media_query.dart:814:25:
Context: Found this candidate, but the arguments don't match.
[ ] [ +1 ms] static MediaQueryData of(BuildContext context) {
[ ] [ +1 ms] ^^
[+9393 ms] [+9408 ms] Persisting file store
[ ] [ +32 ms] Done persisting file store
[ +301 ms] [ +258 ms] Target kernel_snapshot failed: Exception
[ ] #0 KernelSnapshot.build (package:flutter_tools/src/build_system/targets/common.dart:275:7)
[ +4 ms] <asynchronous suspension>
[ +9 ms] #1 _BuildInstance._invokeInternal
(package:flutter_tools/src/build_system/build_system.dart:796:27)
[ +1 ms] #2 _rootRunUnary (dart:async/zone.dart:1198:47)
[ +2 ms] #3 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #4 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ +2 ms] #5 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ +1 ms] #6 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #7 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #8 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #9 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ +2 ms] #10 Node.computeChanges (package:flutter_tools/src/build_system/build_system.dart)
[ +1 ms] #11 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #12 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #13 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ +2 ms] #14 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #15 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #16 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #17 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ +1 ms] #18 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #19 FileStore.diffFileList (package:flutter_tools/src/build_system/file_store.dart)
[ ] #20 _rootRunUnary (dart:async/zone.dart:1198:47)
[ +1 ms] #21 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #22 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #23 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #24 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #25 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #26 Future.wait.<anonymous closure> (dart:async/future.dart:414:23)
[ ] #27 _rootRunUnary (dart:async/zone.dart:1198:47)
[ +1 ms] #28 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #29 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #30 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ +3 ms] #31 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #32 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #33 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ +1 ms] #34 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #35 FileStore._hashFile (package:flutter_tools/src/build_system/file_store.dart)
[ ] #36 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #37 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #38 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #39 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #40 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #41 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #42 Future._asyncCompleteWithValue.<anonymous closure> (dart:async/future_impl.dart:567:7)
[ ] #43 _rootRun (dart:async/zone.dart:1190:13)
[ ] #44 _CustomZone.run (dart:async/zone.dart:1093:19)
[ ] #45 _CustomZone.runGuarded (dart:async/zone.dart:997:7)
[ ] #46 _CustomZone.bindCallbackGuarded.<anonymous closure> (dart:async/zone.dart:1037:23)
[ +1 ms] #47 _microtaskLoop (dart:async/schedule_microtask.dart:41:21)
[ ] #48 _startMicrotaskLoop (dart:async/schedule_microtask.dart:50:5)
[ ] #49 _runPendingImmediateCallback (dart:isolate-patch/isolate_patch.dart:118:13)
[ ] #50 _RawReceivePortImpl._handleMessage (dart:isolate-patch/isolate_patch.dart:169:5)
[ ] [ +13 ms]
[ ] #0 throwToolExit (package:flutter_tools/src/base/common.dart:14:3)
[ ] #1 AssembleCommand.runCommand (package:flutter_tools/src/commands/assemble.dart:237:7)
[ ] #2 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #3 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #4 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #5 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #6 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #7 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #8 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #9 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #10 FlutterBuildSystem.build (package:flutter_tools/src/build_system/build_system.dart)
[ ] #11 _rootRunUnary (dart:async/zone.dart:1198:47)
[ +1 ms] #12 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ +1 ms] #13 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #14 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #15 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ +1 ms] #16 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #17 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #18 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #19 _BuildInstance.invokeTarget (package:flutter_tools/src/build_system/build_system.dart)
[ +1 ms] #20 _rootRunUnary (dart:async/zone.dart:1198:47)
[ +1 ms] #21 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #22 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #23 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #24 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ +6 ms] #25 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #26 Future.wait.<anonymous closure> (dart:async/future.dart:414:23)
[ ] #27 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #28 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #29 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ +1 ms] #30 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #31 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #32 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #33 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #34 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #35 _BuildInstance.invokeTarget (package:flutter_tools/src/build_system/build_system.dart)
[ ] #36 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #37 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #38 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #39 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #40 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #41 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ +4 ms] #42 Future.wait.<anonymous closure> (dart:async/future.dart:414:23)
[ ] #43 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #44 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #45 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #46 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ +10 ms] #47 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #48 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #49 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #50 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #51 _BuildInstance.invokeTarget (package:flutter_tools/src/build_system/build_system.dart)
[ ] #52 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #53 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ +4 ms] #54 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #55 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #56 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #57 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #58 Future.wait.<anonymous closure> (dart:async/future.dart:414:23)
[ ] #59 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #60 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #61 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #62 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ +2 ms] #63 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #64 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #65 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #66 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #67 _BuildInstance._invokeInternal (package:flutter_tools/src/build_system/build_system.dart)
[ ] #68 _asyncErrorWrapperHelper.errorCallback (dart:async-patch/async_patch.dart:91:64)
[ ] #69 _rootRunBinary (dart:async/zone.dart:1214:47)
[ ] #70 _CustomZone.runBinary (dart:async/zone.dart:1107:19)
[ ] #71 _FutureListener.handleError (dart:async/future_impl.dart:157:20)
[ ] #72 Future._propagateToListeners.handleError (dart:async/future_impl.dart:708:47)
[ ] #73 Future._propagateToListeners (dart:async/future_impl.dart:729:24)
[ ] #74 Future._completeError (dart:async/future_impl.dart:537:5)
[ ] #75 _AsyncAwaitCompleter.completeError (dart:async-patch/async_patch.dart:47:15)
[ ] #76 KernelSnapshot.build (package:flutter_tools/src/build_system/targets/common.dart)
[ ] #77 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #78 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #79 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #80 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #81 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #82 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #83 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #84 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #85 KernelCompiler.compile (package:flutter_tools/src/compile.dart)
[ ] #86 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #87 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #88 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #89 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #90 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #91 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #92 Future._asyncCompleteWithValue.<anonymous closure> (dart:async/future_impl.dart:567:7)
[ ] #93 _rootRun (dart:async/zone.dart:1190:13)
[ ] #94 _CustomZone.run (dart:async/zone.dart:1093:19)
[ ] #95 _CustomZone.runGuarded (dart:async/zone.dart:997:7)
[ ] #96 _CustomZone.bindCallbackGuarded.<anonymous closure> (dart:async/zone.dart:1037:23)
[ ] #97 _microtaskLoop (dart:async/schedule_microtask.dart:41:21)
[ ] #98 _startMicrotaskLoop (dart:async/schedule_microtask.dart:50:5)
[ ] #99 _runPendingImmediateCallback (dart:isolate-patch/isolate_patch.dart:118:13)
[ ] #100 _RawReceivePortImpl._handleMessage (dart:isolate-patch/isolate_patch.dart:169:5)
[ +1 ms] [ +26 ms] "flutter assemble" took 33,696ms.
[ ] [ +6 ms] ensureAnalyticsSent: 2ms
[ ] [ +5 ms] Running shutdown hooks
[ ] [ +1 ms] Shutdown hooks complete
[ ] [ +2 ms] exiting with code 1
[ ] > Task :app:compileFlutterBuildRelease FAILED
[ +635 ms] FAILURE: Build failed with an exception.
[ +11 ms] * Where:
[ +2 ms] Script '/home/hasan/snap/flutter/common/flutter/packages/flutter_tools/gradle/flutter.gradle' line: 900
[ ] * What went wrong:
[ ] Execution failed for task ':app:compileFlutterBuildRelease'.
[ ] > Process 'command '/home/hasan/snap/flutter/common/flutter/bin/flutter'' finished with non-zero exit value
1
[ ] * Try:
[ ] Run with --stacktrace option to get the stack trace. Run with --info or --debug option to get more log
output. Run with --scan to get full insights.
[ +1 ms] * Get more help at https://help.gradle.org
[ ] BUILD FAILED in 1m 42s
[ +1 ms] Deprecated Gradle features were used in this build, making it incompatible with Gradle 7.0.
[ ] Use '--warning-mode all' to show the individual deprecation warnings.
[ ] See https://docs.gradle.org/6.3/userguide/command_line_interface.html#sec:command_line_warnings
[ +1 ms] 5 actionable tasks: 4 executed, 1 up-to-date
[ +652 ms] Running Gradle task 'bundleRelease'... (completed in 103.5s)
[ +10 ms] "flutter appbundle" took 109,325ms.
[ +15 ms] Gradle task bundleRelease failed with exit code 1
[ +1 ms]
#0 throwToolExit (package:flutter_tools/src/base/common.dart:14:3)
#1 buildGradleApp (package:flutter_tools/src/android/gradle.dart:414:7)
#2 _rootRunUnary (dart:async/zone.dart:1198:47)
#3 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
#4 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
#5 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
#6 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
#7 Future._completeWithValue (dart:async/future_impl.dart:529:5)
#8 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
#9 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
#10 _DefaultProcessUtils.stream (package:flutter_tools/src/base/process.dart)
#11 _rootRunUnary (dart:async/zone.dart:1198:47)
#12 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
#13 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
#14 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
#15 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
#16 Future._completeWithValue (dart:async/future_impl.dart:529:5)
#17 Future._asyncCompleteWithValue.<anonymous closure> (dart:async/future_impl.dart:567:7)
#18 _rootRun (dart:async/zone.dart:1190:13)
#19 _CustomZone.run (dart:async/zone.dart:1093:19)
#20 _CustomZone.runGuarded (dart:async/zone.dart:997:7)
#21 _CustomZone.bindCallbackGuarded.<anonymous closure> (dart:async/zone.dart:1037:23)
#22 _microtaskLoop (dart:async/schedule_microtask.dart:41:21)
#23 _startMicrotaskLoop (dart:async/schedule_microtask.dart:50:5)
#24 _runPendingImmediateCallback (dart:isolate-patch/isolate_patch.dart:118:13)
#25 _RawReceivePortImpl._handleMessage (dart:isolate-patch/isolate_patch.dart:169:5)
[ +188 ms] ensureAnalyticsSent: 184ms
[ +3 ms] Running shutdown hooks
[ ] Shutdown hooks complete
[ +1 ms] exiting with code 1
**pubspec.yaml**
`name: chitchat
description: A new Flutter application.
# The following defines the version and build number for your application.
# A version number is three numbers separated by dots, like 1.2.43
# followed by an optional build number separated by a +.
# Both the version and the builder number may be overridden in flutter
# build by specifying --build-name and --build-number, respectively.
# In Android, build-name is used as versionName while build-number used as versionCode.
# Read more about Android versioning at https://developer.android.com/studio/publish/versioning
# In iOS, build-name is used as CFBundleShortVersionString while build-number used as CFBundleVersion.
# Read more about iOS versioning at
# https://developer.apple.com/library/archive/documentation/General/Reference/InfoPlistKeyReference/Articles/CoreFoundationKeys.html
version: 1.0.0+1
environment:
sdk: ">=2.1.0 <3.0.0"
dependencies:
flutter:
sdk: flutter
flutter_bloc: ^0.11.0
firebase_storage: ^3.1.0
firebase_core: ^0.4.3+1
cloud_firestore: ^0.13.0+1
firebase_auth: ^0.15.3
equatable: ^1.0.3
meta: ^1.1.6
cupertino_icons: ^0.1.2
bottom_navy_bar: ^5.3.2
modal_progress_hud: ^0.1.3
font_awesome_flutter: ^8.7.0
geolocator: ^5.3.0
file_picker: ^1.4.3+2
flutter_native_image: ^0.0.4
language_pickers: ^0.1.3
flutter_country_picker: ^0.1.6
flutter_datetime_picker: ^1.4.0
network_to_file_image: ^2.2.4
extended_image: ^0.7.1
eva_icons_flutter: ^2.0.0
dev_dependencies:
flutter_test:
sdk: flutter
flutter:
assets:
- assets/profilephoto.png
- assets/world_gif.webp
uses-material-design: true
fonts:
- family: Coiny
fonts:
- asset: fonts/Coiny-Regular.ttf`
| 1.0 | Execution failed for task ':app:compileFlutterBuildRelease' - [+22000 ms] [+21991 ms]
../../snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image-0.7.1/lib/src/gesture/extended_imag
e_slide_page_route.dart:333:9: Error: No named parameter with the name 'animation'.
[ +1 ms] [ +5 ms] animation: animation,
[ ] [ ] ^^^^^^^^^
**flutter doctor -v**
hasan@hasan-Lenovo-ideapad-320-15IAP:~/Desktop/ChitChat-master$ flutter doctor -v
[✓] Flutter (Channel master, 1.24.0-4.0.pre.138, on Linux, locale en_GB.UTF-8)
• Flutter version 1.24.0-4.0.pre.138 at /home/hasan/snap/flutter/common/flutter
• Framework revision 13896b3bd1 (35 hours ago), 2020-10-28 19:43:19 -0700
• Engine revision 073263e39d
• Dart version 2.11.0 (build 2.11.0-260.0.dev)
[!] Android toolchain - develop for Android devices (Android SDK version 30.0.2)
• Android SDK at /home/hasan/Android/Sdk
• Platform android-30, build-tools 30.0.2
• Java binary at: /usr/bin/java
• Java version OpenJDK Runtime Environment (build 14.0.2+12-Ubuntu-120.04)
✗ Android license status unknown.
Run `flutter doctor --android-licenses` to accept the SDK licenses.
See https://flutter.dev/docs/get-started/install/linux#android-setup for more details.
[!] Android Studio (not installed)
• Android Studio not found; download from https://developer.android.com/studio/index.html
(or visit https://flutter.dev/docs/get-started/install/linux#android-setup for detailed instructions).
[!] Connected device
! No devices available
! Doctor found issues in 3 categories.
**NEXT**
flutter build appbundle --verbose
.0-nullsafety.2/lib/
[ +1 ms] |
bottom_navy_bar:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/bottom_navy_bar-5.3.2
/lib/
[ +1 ms] |
characters:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/characters-1.1.0-nullsafet
y.4/lib/
[ ] |
charcode:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/charcode-1.2.0-nullsafety.2/
lib/
[ ] |
clock:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/clock-1.1.0-nullsafety.2/lib/
[ ] |
cloud_firestore:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore-0.13.
4/lib/
[ +1 ms] |
cloud_firestore_platform_interface:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cl
oud_firestore_platform_interface-1.1.0/lib/
[ +1 ms] |
cloud_firestore_web:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore_w
eb-0.1.1/lib/
[ ] |
collection:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/collection-1.15.0-nullsafe
ty.4/lib/
[ +1 ms] |
convert:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/convert-2.1.1/lib/
[ ] |
crypto:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/crypto-2.1.3/lib/
[ ] |
cupertino_icons:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cupertino_icons-0.1.3
/lib/
[ ] |
diacritic:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/diacritic-0.1.1/lib/
[ +1 ms] |
equatable:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/equatable-1.1.0/lib/
[ +1 ms] |
eva_icons_flutter:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/eva_icons_flutter-2
.0.0/lib/
[ +1 ms] |
extended_image:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image-0.7.1/l
ib/
[ ] |
extended_image_library:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image
_library-0.2.0/lib/
[ +1 ms] |
fake_async:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/fake_async-1.2.0-nullsafet
y.2/lib/
[ ] |
file_picker:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/file_picker-1.4.3+2/lib/
[ ] |
firebase:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase-7.2.1/lib/
[ ] |
firebase_auth:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth-0.15.5+2/
lib/
[ +1 ms] |
firebase_auth_platform_interface:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/fire
base_auth_platform_interface-1.1.7/lib/
[ +1 ms] |
firebase_auth_web:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_web-0
.1.2/lib/
[ ] |
firebase_core:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core-0.4.4+2/l
ib/
[ ] |
firebase_core_platform_interface:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/fire
base_core_platform_interface-1.0.4/lib/
[ +1 ms] |
firebase_core_web:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core_web-0
.1.1+2/lib/
[ +1 ms] |
firebase_storage:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_storage-3.1
.1/lib/
[ ] | flutter:file:///home/hasan/snap/flutter/common/flutter/packages/flutter/lib/
[ ] |
flutter_bloc:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_bloc-0.11.1/lib/
[ +1 ms] |
flutter_country_picker:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_countr
y_picker-0.1.6/lib/
[ +1 ms] |
flutter_datetime_picker:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_datet
ime_picker-1.4.0/lib/
[ +1 ms] |
flutter_native_image:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_native_i
mage-0.0.5+2/lib/
[ ] | flutter_test:file:///home/hasan/snap/flutter/common/flutter/packages/flutter_test/lib/
[ ] | flutter_web_plugins:file:///home/hasan/snap/flutter/common/flutter/packages/flutter_web_plugins/lib/
[ ] |
font_awesome_flutter:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/font_awesome_flu
tter-8.7.0/lib/
[ ] |
geolocator:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/geolocator-5.3.0/lib/
[ ] |
google_api_availability:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/google_api_av
ailability-2.0.2/lib/
[ +1 ms] |
http:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http-0.12.0+4/lib/
[ ] |
http_client_helper:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http_client_helper
-0.2.1/lib/
[ ] |
http_parser:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http_parser-3.1.3/lib/
[ ] |
js:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/js-0.6.3-nullsafety.2/lib/
[ +1 ms] |
language_pickers:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/language_pickers-0.1
.3/lib/
[ +1 ms] |
location_permissions:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/location_permiss
ions-2.0.4+1/lib/
[ ] |
matcher:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/matcher-0.12.10-nullsafety.2/
lib/
[ ] |
meta:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/meta-1.3.0-nullsafety.5/lib/
[ ] |
modal_progress_hud:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/modal_progress_hud
-0.1.3/lib/
[ ] |
network_to_file_image:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/network_to_file
_image-2.2.8/lib/
[ ] |
path:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path-1.8.0-nullsafety.2/lib/
[ ] |
path_provider:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path_provider-1.6.1/lib
/
[ +1 ms] |
pedantic:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/pedantic-1.8.0+1/lib/
[ ] |
platform:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/platform-2.2.1/lib/
[ ] |
plugin_platform_interface:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/plugin_plat
form_interface-1.0.2/lib/
[ ] |
quiver:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/quiver-2.0.5/lib/
[ +1 ms] |
rxdart:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/rxdart-0.21.0/lib/
[ ] | sky_engine:file:///home/hasan/snap/flutter/common/flutter/bin/cache/pkg/sky_engine/lib/
[ ] |
source_span:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/source_span-1.8.0-nullsaf
ety.3/lib/
[ ] |
stack_trace:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/stack_trace-1.10.0-nullsa
fety.5/lib/
[ ] |
stream_channel:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/stream_channel-2.1.0-n
ullsafety.2/lib/
[ +1 ms] |
string_scanner:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/string_scanner-1.1.0-n
ullsafety.2/lib/
[ +1 ms] |
term_glyph:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/term_glyph-1.2.0-nullsafet
y.2/lib/
[ ] |
test_api:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/test_api-0.2.19-nullsafety.4
/lib/
[ ] |
typed_data:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/typed_data-1.3.0-nullsafet
y.4/lib/
[ ] |
vector_math:file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/vector_math-2.1.0-nullsaf
ety.4/lib/
[ ] | chitchat:lib/
[ ] IO : Writing 15123 characters to text file ./.dart_tool/package_config.json.
[ ] FINE: Contents:
[ ] | {
[ ] | "configVersion": 2,
[ ] | "packages": [
[ ] | {
[ ] | "name": "async",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/async-2.5.0-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "bloc",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/bloc-0.12.0",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "boolean_selector",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/boolean_selector-2.1.0-nullsafety.2"
,
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ +1 ms] | {
[ +1 ms] | "name": "bottom_navy_bar",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/bottom_navy_bar-5.3.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.2"
[ ] | },
[ ] | {
[ ] | "name": "characters",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/characters-1.1.0-nullsafety.4",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "charcode",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/charcode-1.2.0-nullsafety.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "clock",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/clock-1.1.0-nullsafety.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "cloud_firestore",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore-0.13.4",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "cloud_firestore_platform_interface",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore_platform_interface-1
.1.0",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "cloud_firestore_web",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore_web-0.1.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "collection",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/collection-1.15.0-nullsafety.4",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "convert",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/convert-2.1.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "1.17"
[ ] | },
[ ] | {
[ ] | "name": "crypto",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/crypto-2.1.3",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "cupertino_icons",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cupertino_icons-0.1.3",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "diacritic",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/diacritic-0.1.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "equatable",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/equatable-1.1.0",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "eva_icons_flutter",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/eva_icons_flutter-2.0.0",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "extended_image",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image-0.7.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "extended_image_library",
[ +2 ms] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image_library-0.2.0",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "fake_async",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/fake_async-1.2.0-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ +1 ms] | {
[ ] | "name": "file_picker",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/file_picker-1.4.3+2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase-7.2.1",
[ +5 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.7"
[ ] | },
[ ] | {
[ ] | "name": "firebase_auth",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth-0.15.5+2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ +2 ms] | "name": "firebase_auth_platform_interface",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_platform_interface-1.1
.7",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase_auth_web",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_web-0.1.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase_core",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core-0.4.4+2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase_core_platform_interface",
[ +4 ms] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core_platform_interface-1.0
.4",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase_core_web",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core_web-0.1.1+2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "firebase_storage",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_storage-3.1.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ +3 ms] | },
[ ] | {
[ ] | "name": "flutter",
[ ] | "rootUri": "file:///home/hasan/snap/flutter/common/flutter/packages/flutter",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "flutter_bloc",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_bloc-0.11.1",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "flutter_country_picker",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_country_picker-0.1.6",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.3"
[ ] | },
[ ] | {
[ ] | "name": "flutter_datetime_picker",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_datetime_picker-1.4.0",
[ ] | "packageUri": "lib/",
[ +4 ms] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "flutter_native_image",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_native_image-0.0.5+2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "1.19"
[ ] | },
[ ] | {
[ ] | "name": "flutter_test",
[ ] | "rootUri": "file:///home/hasan/snap/flutter/common/flutter/packages/flutter_test",
[ +1 ms] | "packageUri": "lib/",
[ +3 ms] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ +6 ms] | "name": "flutter_web_plugins",
[ ] | "rootUri": "file:///home/hasan/snap/flutter/common/flutter/packages/flutter_web_plugins",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "font_awesome_flutter",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/font_awesome_flutter-8.7.0",
[ ] | "packageUri": "lib/",
[ +2 ms] | "languageVersion": "2.0"
[ +2 ms] | },
[ ] | {
[ ] | "name": "geolocator",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/geolocator-5.3.0",
[ +1 ms] | "packageUri": "lib/",
[ +1 ms] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ +1 ms] | "name": "google_api_availability",
[ +4 ms] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/google_api_availability-2.0.2",
[ +6 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ +1 ms] | {
[ ] | "name": "http",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http-0.12.0+4",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.4"
[ ] | },
[ ] | {
[ ] | "name": "http_client_helper",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http_client_helper-0.2.1",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "http_parser",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/http_parser-3.1.3",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "js",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/js-0.6.3-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "language_pickers",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/language_pickers-0.1.3",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "location_permissions",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/location_permissions-2.0.4+1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "matcher",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/matcher-0.12.10-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "meta",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/meta-1.3.0-nullsafety.5",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "modal_progress_hud",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/modal_progress_hud-0.1.3",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "1.20"
[ ] | },
[ ] | {
[ ] | "name": "network_to_file_image",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/network_to_file_image-2.2.8",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.7"
[ ] | },
[ ] | {
[ ] | "name": "path",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path-1.8.0-nullsafety.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "path_provider",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path_provider-1.6.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "pedantic",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/pedantic-1.8.0+1",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "platform",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/platform-2.2.1",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "1.24"
[ ] | },
[ ] | {
[ ] | "name": "plugin_platform_interface",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/plugin_platform_interface-1.0.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | },
[ ] | {
[ ] | "name": "quiver",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/quiver-2.0.5",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "rxdart",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/rxdart-0.21.0",
[ +7 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.0"
[ ] | },
[ ] | {
[ ] | "name": "sky_engine",
[ ] | "rootUri": "file:///home/hasan/snap/flutter/common/flutter/bin/cache/pkg/sky_engine",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "1.11"
[ ] | },
[ ] | {
[ ] | "name": "source_span",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/source_span-1.8.0-nullsafety.3",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.11"
[ ] | },
[ ] | {
[ ] | "name": "stack_trace",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/stack_trace-1.10.0-nullsafety.5",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "stream_channel",
[ +2 ms] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/stream_channel-2.1.0-nullsafety.2",
[ +1 ms] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "string_scanner",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/string_scanner-1.1.0-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "term_glyph",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/term_glyph-1.2.0-nullsafety.2",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "test_api",
[ +6 ms] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/test_api-0.2.19-nullsafety.4",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "typed_data",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/typed_data-1.3.0-nullsafety.4",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "vector_math",
[ ] | "rootUri":
"file:///home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/vector_math-2.1.0-nullsafety.4",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.10"
[ ] | },
[ ] | {
[ ] | "name": "chitchat",
[ ] | "rootUri": "../",
[ ] | "packageUri": "lib/",
[ ] | "languageVersion": "2.1"
[ ] | }
[ ] | ],
[ ] | "generated": "2020-10-30T14:04:42.090496Z",
[ ] | "generator": "pub",
[ ] | "generatorVersion": "2.11.0-260.0.dev"
[ ] | }
[ +14 ms] MSG : Got dependencies!
[ +155 ms] Running "flutter pub get" in ChitChat-master... (completed in 3.8s)
[ +152 ms] Found plugin cloud_firestore at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore-0.13.4/
[ +35 ms] Found plugin cloud_firestore_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore_web-0.1.1/
[ +54 ms] Found plugin file_picker at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/file_picker-1.4.3+2/
[ +13 ms] Found plugin firebase_auth at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth-0.15.5+2/
[ +10 ms] Found plugin firebase_auth_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_web-0.1.2/
[ +6 ms] Found plugin firebase_core at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core-0.4.4+2/
[ +9 ms] Found plugin firebase_core_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core_web-0.1.1+2/
[ +6 ms] Found plugin firebase_storage at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_storage-3.1.1/
[ +8 ms] Found plugin flutter_country_picker at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_country_picker-0.1.6/
[ +8 ms] Found plugin flutter_native_image at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_native_image-0.0.5+2/
[ +17 ms] Found plugin geolocator at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/geolocator-5.3.0/
[ +8 ms] Found plugin google_api_availability at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/google_api_availability-2.0.2/
[ +33 ms] Found plugin location_permissions at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/location_permissions-2.0.4+1/
[ +25 ms] Found plugin path_provider at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path_provider-1.6.1/
[ +383 ms] Found plugin cloud_firestore at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore-0.13.4/
[ +7 ms] Found plugin cloud_firestore_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/cloud_firestore_web-0.1.1/
[ +31 ms] Found plugin file_picker at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/file_picker-1.4.3+2/
[ +8 ms] Found plugin firebase_auth at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth-0.15.5+2/
[ +6 ms] Found plugin firebase_auth_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_web-0.1.2/
[ +4 ms] Found plugin firebase_core at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core-0.4.4+2/
[ +7 ms] Found plugin firebase_core_web at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_core_web-0.1.1+2/
[ +5 ms] Found plugin firebase_storage at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_storage-3.1.1/
[ +8 ms] Found plugin flutter_country_picker at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_country_picker-0.1.6/
[ +5 ms] Found plugin flutter_native_image at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/flutter_native_image-0.0.5+2/
[ +8 ms] Found plugin geolocator at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/geolocator-5.3.0/
[ +4 ms] Found plugin google_api_availability at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/google_api_availability-2.0.2/
[ +15 ms] Found plugin location_permissions at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/location_permissions-2.0.4+1/
[ +13 ms] Found plugin path_provider at
/home/hasan/snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/path_provider-1.6.1/
[ +433 ms] Generating
/home/hasan/Desktop/ChitChat-master/android/app/src/main/java/io/flutter/plugins/GeneratedPluginRegistrant.java
[ +175 ms] Running Gradle task 'bundleRelease'...
[ +3 ms] gradle.properties already sets `android.enableR8`
[ +6 ms] Using gradle from /home/hasan/Desktop/ChitChat-master/android/gradlew.
[ +2 ms] /home/hasan/Desktop/ChitChat-master/android/gradlew mode: 33277 rwxrwxr-x.
[ +16 ms] executing: [/home/hasan/Desktop/ChitChat-master/android/]
/home/hasan/Desktop/ChitChat-master/android/gradlew -Pverbose=true
-Ptarget-platform=android-arm,android-arm64,android-x64 -Ptarget=lib/main.dart -Ptrack-widget-creation=true
-Pshrink=true -Ptree-shake-icons=true bundleRelease
[+4115 ms] Starting a Gradle Daemon, 1 busy and 1 incompatible Daemons could not be reused, use --status for details
[+23372 ms] > Configure project :app
[ ] WARNING: The option 'android.enableR8' is deprecated and should not be used anymore.
[ ] It will be removed in a future version of the Android Gradle plugin, and will no longer allow you to disable
R8.
[+35393 ms] > Task :app:cleanMergeReleaseAssets UP-TO-DATE
[+3400 ms] > Task :app:preBuild UP-TO-DATE
[ +199 ms] > Task :app:extractProguardFiles
[ ] > Task :app:preReleaseBuild
[ +199 ms] > Task :app:mergeReleaseShaders
[ +199 ms] > Task :app:compileReleaseShaders
[ ] > Task :app:generateReleaseAssets
[+1999 ms] > Task :app:compileFlutterBuildRelease
[ +4 ms] [ +333 ms] executing: [/home/hasan/snap/flutter/common/flutter/] git -c log.showSignature=false log -n 1
--pretty=format:%H
[ ] [ +108 ms] Exit code 0 from: git -c log.showSignature=false log -n 1 --pretty=format:%H
[ ] [ +2 ms] 13896b3bd1858687a06b1639d60c877206170df8
[ ] [ +3 ms] executing: [/home/hasan/snap/flutter/common/flutter/] git tag --points-at HEAD
[ ] [ +24 ms] Exit code 0 from: git tag --points-at HEAD
[ ] [ +4 ms] executing: [/home/hasan/snap/flutter/common/flutter/] git describe --match *.*.* --first-parent
--long --tags
[ ] [ +51 ms] Exit code 0 from: git describe --match *.*.* --first-parent --long --tags
[ ] [ +1 ms] 1.24.0-3.0.pre-138-g13896b3bd1
[ ] [ +24 ms] executing: [/home/hasan/snap/flutter/common/flutter/] git rev-parse --abbrev-ref --symbolic @{u}
[ ] [ +7 ms] Exit code 0 from: git rev-parse --abbrev-ref --symbolic @{u}
[ ] [ ] origin/master
[ ] [ ] executing: [/home/hasan/snap/flutter/common/flutter/] git ls-remote --get-url origin
[ ] [ +7 ms] Exit code 0 from: git ls-remote --get-url origin
[ +2 ms] [ ] https://github.com/flutter/flutter.git
[ ] [ +101 ms] executing: [/home/hasan/snap/flutter/common/flutter/] git rev-parse --abbrev-ref HEAD
[ ] [ +7 ms] Exit code 0 from: git rev-parse --abbrev-ref HEAD
[ ] [ ] master
[ ] [ +103 ms] Artifact Instance of 'AndroidMavenArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'AndroidGenSnapshotArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'AndroidInternalBuildArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IOSEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'FlutterWebSdk' is not required, skipping update.
[ ] [ +7 ms] Artifact Instance of 'WindowsEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'MacOSEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'LinuxEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'LinuxFuchsiaSDKArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'MacOSFuchsiaSDKArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'FlutterRunnerSDKArtifacts' is not required, skipping update.
[ +3 ms] [ ] Artifact Instance of 'FlutterRunnerDebugSymbols' is not required, skipping update.
[ ] [ +148 ms] Artifact Instance of 'MaterialFonts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'GradleWrapper' is not required, skipping update.
[ ] [ ] Artifact Instance of 'AndroidMavenArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'AndroidGenSnapshotArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'AndroidInternalBuildArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IOSEngineArtifacts' is not required, skipping update.
[ +1 ms] [ ] Artifact Instance of 'FlutterWebSdk' is not required, skipping update.
[ ] [ ] Artifact Instance of 'FlutterSdk' is not required, skipping update.
[ ] [ ] Artifact Instance of 'WindowsEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'MacOSEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'LinuxEngineArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'LinuxFuchsiaSDKArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'MacOSFuchsiaSDKArtifacts' is not required, skipping update.
[ +5 ms] [ ] Artifact Instance of 'FlutterRunnerSDKArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'FlutterRunnerDebugSymbols' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IosUsbArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IosUsbArtifacts' is not required, skipping update.
[ ] [ +1 ms] Artifact Instance of 'IosUsbArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IosUsbArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'IosUsbArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'FontSubsetArtifacts' is not required, skipping update.
[ ] [ ] Artifact Instance of 'PubDependencies' is not required, skipping update.
[ ] [ +208 ms] Initializing file store
[ ] [ +19 ms] Done initializing file store
[ +55 ms] [ +273 ms] Skipping target: gen_localizations
[+1200 ms] [+1144 ms] kernel_snapshot: Starting due to {InvalidatedReason.inputChanged}
[ +1 ms] [ +36 ms] /home/hasan/snap/flutter/common/flutter/bin/cache/dart-sdk/bin/dart --disable-dart-dev
/home/hasan/snap/flutter/common/flutter/bin/cache/artifacts/engine/linux-x64/frontend_server.dart.snapshot --sdk-root
/home/hasan/snap/flutter/common/flutter/bin/cache/artifacts/engine/common/flutter_patched_sdk_product/ --target=flutter
--no-print-incremental-dependencies -Ddart.developer.causal_async_stacks=false -Ddart.vm.profile=false
-Ddart.vm.product=true --aot --tfa --packages /home/hasan/Desktop/ChitChat-master/.dart_tool/package_config.json
--output-dill /home/hasan/Desktop/ChitChat-master/.dart_tool/flutter_build/7e2b6ef2f352a402314d530501db0c4e/app.dill
--depfile
/home/hasan/Desktop/ChitChat-master/.dart_tool/flutter_build/7e2b6ef2f352a402314d530501db0c4e/kernel_snapshot.d
package:chitchat/main.dart
[+22000 ms] [+21991 ms]
../../snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image-0.7.1/lib/src/gesture/extended_imag
e_slide_page_route.dart:333:9: Error: No named parameter with the name 'animation'.
[ +1 ms] [ +5 ms] animation: animation,
[ ] [ ] ^^^^^^^^^
[ ] [ ] ../../snap/flutter/common/flutter/packages/flutter/lib/src/cupertino/route.dart:547:3: Context:
Found this candidate, but the arguments don't match.
[ ] [ ] CupertinoFullscreenDialogTransition({
[ ] [ +1 ms] ^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
[ +95 ms] [ +88 ms]
../../snap/flutter/common/flutter/.pub-cache/hosted/pub.dartlang.org/extended_image-0.7.1/lib/src/extended_image.dart:7
13:44: Error: No named parameter with the name 'nullOk'.
[ +2 ms] [ +2 ms] _invertColors = MediaQuery.of(context, nullOk: true)?.invertColors ??
[ ] [ +1 ms] ^^^^^^
[ ] [ +1 ms] ../../snap/flutter/common/flutter/packages/flutter/lib/src/widgets/media_query.dart:814:25:
Context: Found this candidate, but the arguments don't match.
[ ] [ +1 ms] static MediaQueryData of(BuildContext context) {
[ ] [ +1 ms] ^^
[+9393 ms] [+9408 ms] Persisting file store
[ ] [ +32 ms] Done persisting file store
[ +301 ms] [ +258 ms] Target kernel_snapshot failed: Exception
[ ] #0 KernelSnapshot.build (package:flutter_tools/src/build_system/targets/common.dart:275:7)
[ +4 ms] <asynchronous suspension>
[ +9 ms] #1 _BuildInstance._invokeInternal
(package:flutter_tools/src/build_system/build_system.dart:796:27)
[ +1 ms] #2 _rootRunUnary (dart:async/zone.dart:1198:47)
[ +2 ms] #3 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #4 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ +2 ms] #5 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ +1 ms] #6 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #7 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #8 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #9 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ +2 ms] #10 Node.computeChanges (package:flutter_tools/src/build_system/build_system.dart)
[ +1 ms] #11 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #12 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #13 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ +2 ms] #14 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #15 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #16 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #17 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ +1 ms] #18 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #19 FileStore.diffFileList (package:flutter_tools/src/build_system/file_store.dart)
[ ] #20 _rootRunUnary (dart:async/zone.dart:1198:47)
[ +1 ms] #21 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #22 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #23 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #24 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #25 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #26 Future.wait.<anonymous closure> (dart:async/future.dart:414:23)
[ ] #27 _rootRunUnary (dart:async/zone.dart:1198:47)
[ +1 ms] #28 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #29 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #30 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ +3 ms] #31 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #32 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #33 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ +1 ms] #34 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #35 FileStore._hashFile (package:flutter_tools/src/build_system/file_store.dart)
[ ] #36 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #37 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #38 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #39 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #40 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #41 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #42 Future._asyncCompleteWithValue.<anonymous closure> (dart:async/future_impl.dart:567:7)
[ ] #43 _rootRun (dart:async/zone.dart:1190:13)
[ ] #44 _CustomZone.run (dart:async/zone.dart:1093:19)
[ ] #45 _CustomZone.runGuarded (dart:async/zone.dart:997:7)
[ ] #46 _CustomZone.bindCallbackGuarded.<anonymous closure> (dart:async/zone.dart:1037:23)
[ +1 ms] #47 _microtaskLoop (dart:async/schedule_microtask.dart:41:21)
[ ] #48 _startMicrotaskLoop (dart:async/schedule_microtask.dart:50:5)
[ ] #49 _runPendingImmediateCallback (dart:isolate-patch/isolate_patch.dart:118:13)
[ ] #50 _RawReceivePortImpl._handleMessage (dart:isolate-patch/isolate_patch.dart:169:5)
[ ] [ +13 ms]
[ ] #0 throwToolExit (package:flutter_tools/src/base/common.dart:14:3)
[ ] #1 AssembleCommand.runCommand (package:flutter_tools/src/commands/assemble.dart:237:7)
[ ] #2 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #3 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #4 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #5 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #6 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #7 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #8 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #9 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #10 FlutterBuildSystem.build (package:flutter_tools/src/build_system/build_system.dart)
[ ] #11 _rootRunUnary (dart:async/zone.dart:1198:47)
[ +1 ms] #12 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ +1 ms] #13 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #14 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #15 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ +1 ms] #16 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #17 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #18 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #19 _BuildInstance.invokeTarget (package:flutter_tools/src/build_system/build_system.dart)
[ +1 ms] #20 _rootRunUnary (dart:async/zone.dart:1198:47)
[ +1 ms] #21 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #22 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #23 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #24 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ +6 ms] #25 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #26 Future.wait.<anonymous closure> (dart:async/future.dart:414:23)
[ ] #27 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #28 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #29 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ +1 ms] #30 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #31 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #32 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #33 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #34 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #35 _BuildInstance.invokeTarget (package:flutter_tools/src/build_system/build_system.dart)
[ ] #36 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #37 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #38 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #39 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #40 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #41 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ +4 ms] #42 Future.wait.<anonymous closure> (dart:async/future.dart:414:23)
[ ] #43 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #44 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #45 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #46 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ +10 ms] #47 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #48 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #49 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #50 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #51 _BuildInstance.invokeTarget (package:flutter_tools/src/build_system/build_system.dart)
[ ] #52 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #53 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ +4 ms] #54 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #55 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #56 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #57 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #58 Future.wait.<anonymous closure> (dart:async/future.dart:414:23)
[ ] #59 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #60 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #61 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #62 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ +2 ms] #63 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #64 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #65 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #66 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #67 _BuildInstance._invokeInternal (package:flutter_tools/src/build_system/build_system.dart)
[ ] #68 _asyncErrorWrapperHelper.errorCallback (dart:async-patch/async_patch.dart:91:64)
[ ] #69 _rootRunBinary (dart:async/zone.dart:1214:47)
[ ] #70 _CustomZone.runBinary (dart:async/zone.dart:1107:19)
[ ] #71 _FutureListener.handleError (dart:async/future_impl.dart:157:20)
[ ] #72 Future._propagateToListeners.handleError (dart:async/future_impl.dart:708:47)
[ ] #73 Future._propagateToListeners (dart:async/future_impl.dart:729:24)
[ ] #74 Future._completeError (dart:async/future_impl.dart:537:5)
[ ] #75 _AsyncAwaitCompleter.completeError (dart:async-patch/async_patch.dart:47:15)
[ ] #76 KernelSnapshot.build (package:flutter_tools/src/build_system/targets/common.dart)
[ ] #77 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #78 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #79 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #80 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #81 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #82 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #83 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
[ ] #84 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
[ ] #85 KernelCompiler.compile (package:flutter_tools/src/compile.dart)
[ ] #86 _rootRunUnary (dart:async/zone.dart:1198:47)
[ ] #87 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
[ ] #88 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
[ ] #89 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
[ ] #90 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
[ ] #91 Future._completeWithValue (dart:async/future_impl.dart:529:5)
[ ] #92 Future._asyncCompleteWithValue.<anonymous closure> (dart:async/future_impl.dart:567:7)
[ ] #93 _rootRun (dart:async/zone.dart:1190:13)
[ ] #94 _CustomZone.run (dart:async/zone.dart:1093:19)
[ ] #95 _CustomZone.runGuarded (dart:async/zone.dart:997:7)
[ ] #96 _CustomZone.bindCallbackGuarded.<anonymous closure> (dart:async/zone.dart:1037:23)
[ ] #97 _microtaskLoop (dart:async/schedule_microtask.dart:41:21)
[ ] #98 _startMicrotaskLoop (dart:async/schedule_microtask.dart:50:5)
[ ] #99 _runPendingImmediateCallback (dart:isolate-patch/isolate_patch.dart:118:13)
[ ] #100 _RawReceivePortImpl._handleMessage (dart:isolate-patch/isolate_patch.dart:169:5)
[ +1 ms] [ +26 ms] "flutter assemble" took 33,696ms.
[ ] [ +6 ms] ensureAnalyticsSent: 2ms
[ ] [ +5 ms] Running shutdown hooks
[ ] [ +1 ms] Shutdown hooks complete
[ ] [ +2 ms] exiting with code 1
[ ] > Task :app:compileFlutterBuildRelease FAILED
[ +635 ms] FAILURE: Build failed with an exception.
[ +11 ms] * Where:
[ +2 ms] Script '/home/hasan/snap/flutter/common/flutter/packages/flutter_tools/gradle/flutter.gradle' line: 900
[ ] * What went wrong:
[ ] Execution failed for task ':app:compileFlutterBuildRelease'.
[ ] > Process 'command '/home/hasan/snap/flutter/common/flutter/bin/flutter'' finished with non-zero exit value
1
[ ] * Try:
[ ] Run with --stacktrace option to get the stack trace. Run with --info or --debug option to get more log
output. Run with --scan to get full insights.
[ +1 ms] * Get more help at https://help.gradle.org
[ ] BUILD FAILED in 1m 42s
[ +1 ms] Deprecated Gradle features were used in this build, making it incompatible with Gradle 7.0.
[ ] Use '--warning-mode all' to show the individual deprecation warnings.
[ ] See https://docs.gradle.org/6.3/userguide/command_line_interface.html#sec:command_line_warnings
[ +1 ms] 5 actionable tasks: 4 executed, 1 up-to-date
[ +652 ms] Running Gradle task 'bundleRelease'... (completed in 103.5s)
[ +10 ms] "flutter appbundle" took 109,325ms.
[ +15 ms] Gradle task bundleRelease failed with exit code 1
[ +1 ms]
#0 throwToolExit (package:flutter_tools/src/base/common.dart:14:3)
#1 buildGradleApp (package:flutter_tools/src/android/gradle.dart:414:7)
#2 _rootRunUnary (dart:async/zone.dart:1198:47)
#3 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
#4 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
#5 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
#6 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
#7 Future._completeWithValue (dart:async/future_impl.dart:529:5)
#8 _AsyncAwaitCompleter.complete (dart:async-patch/async_patch.dart:40:15)
#9 _completeOnAsyncReturn (dart:async-patch/async_patch.dart:291:13)
#10 _DefaultProcessUtils.stream (package:flutter_tools/src/base/process.dart)
#11 _rootRunUnary (dart:async/zone.dart:1198:47)
#12 _CustomZone.runUnary (dart:async/zone.dart:1100:19)
#13 _FutureListener.handleValue (dart:async/future_impl.dart:143:18)
#14 Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:696:45)
#15 Future._propagateToListeners (dart:async/future_impl.dart:725:32)
#16 Future._completeWithValue (dart:async/future_impl.dart:529:5)
#17 Future._asyncCompleteWithValue.<anonymous closure> (dart:async/future_impl.dart:567:7)
#18 _rootRun (dart:async/zone.dart:1190:13)
#19 _CustomZone.run (dart:async/zone.dart:1093:19)
#20 _CustomZone.runGuarded (dart:async/zone.dart:997:7)
#21 _CustomZone.bindCallbackGuarded.<anonymous closure> (dart:async/zone.dart:1037:23)
#22 _microtaskLoop (dart:async/schedule_microtask.dart:41:21)
#23 _startMicrotaskLoop (dart:async/schedule_microtask.dart:50:5)
#24 _runPendingImmediateCallback (dart:isolate-patch/isolate_patch.dart:118:13)
#25 _RawReceivePortImpl._handleMessage (dart:isolate-patch/isolate_patch.dart:169:5)
[ +188 ms] ensureAnalyticsSent: 184ms
[ +3 ms] Running shutdown hooks
[ ] Shutdown hooks complete
[ +1 ms] exiting with code 1
**pubspec.yaml**
`name: chitchat
description: A new Flutter application.
# The following defines the version and build number for your application.
# A version number is three numbers separated by dots, like 1.2.43
# followed by an optional build number separated by a +.
# Both the version and the builder number may be overridden in flutter
# build by specifying --build-name and --build-number, respectively.
# In Android, build-name is used as versionName while build-number used as versionCode.
# Read more about Android versioning at https://developer.android.com/studio/publish/versioning
# In iOS, build-name is used as CFBundleShortVersionString while build-number used as CFBundleVersion.
# Read more about iOS versioning at
# https://developer.apple.com/library/archive/documentation/General/Reference/InfoPlistKeyReference/Articles/CoreFoundationKeys.html
version: 1.0.0+1
environment:
sdk: ">=2.1.0 <3.0.0"
dependencies:
flutter:
sdk: flutter
flutter_bloc: ^0.11.0
firebase_storage: ^3.1.0
firebase_core: ^0.4.3+1
cloud_firestore: ^0.13.0+1
firebase_auth: ^0.15.3
equatable: ^1.0.3
meta: ^1.1.6
cupertino_icons: ^0.1.2
bottom_navy_bar: ^5.3.2
modal_progress_hud: ^0.1.3
font_awesome_flutter: ^8.7.0
geolocator: ^5.3.0
file_picker: ^1.4.3+2
flutter_native_image: ^0.0.4
language_pickers: ^0.1.3
flutter_country_picker: ^0.1.6
flutter_datetime_picker: ^1.4.0
network_to_file_image: ^2.2.4
extended_image: ^0.7.1
eva_icons_flutter: ^2.0.0
dev_dependencies:
flutter_test:
sdk: flutter
flutter:
assets:
- assets/profilephoto.png
- assets/world_gif.webp
uses-material-design: true
fonts:
- family: Coiny
fonts:
- asset: fonts/Coiny-Regular.ttf`
| non_test | execution failed for task app compileflutterbuildrelease snap flutter common flutter pub cache hosted pub dartlang org extended image lib src gesture extended imag e slide page route dart error no named parameter with the name animation animation animation flutter doctor v hasan hasan lenovo ideapad desktop chitchat master flutter doctor v flutter channel master pre on linux locale en gb utf • flutter version pre at home hasan snap flutter common flutter • framework revision hours ago • engine revision • dart version build dev android toolchain develop for android devices android sdk version • android sdk at home hasan android sdk • platform android build tools • java binary at usr bin java • java version openjdk runtime environment build ubuntu ✗ android license status unknown run flutter doctor android licenses to accept the sdk licenses see for more details android studio not installed • android studio not found download from or visit for detailed instructions connected device no devices available doctor found issues in categories next flutter build appbundle verbose nullsafety lib bottom navy bar file home hasan snap flutter common flutter pub cache hosted pub dartlang org bottom navy bar lib characters file home hasan snap flutter common flutter pub cache hosted pub dartlang org characters nullsafet y lib charcode file home hasan snap flutter common flutter pub cache hosted pub dartlang org charcode nullsafety lib clock file home hasan snap flutter common flutter pub cache hosted pub dartlang org clock nullsafety lib cloud firestore file home hasan snap flutter common flutter pub cache hosted pub dartlang org cloud firestore lib cloud firestore platform interface file home hasan snap flutter common flutter pub cache hosted pub dartlang org cl oud firestore platform interface lib cloud firestore web file home hasan snap flutter common flutter pub cache hosted pub dartlang org cloud firestore w eb lib collection file home hasan snap flutter common flutter pub cache hosted pub dartlang org collection nullsafe ty lib convert file home hasan snap flutter common flutter pub cache hosted pub dartlang org convert lib crypto file home hasan snap flutter common flutter pub cache hosted pub dartlang org crypto lib cupertino icons file home hasan snap flutter common flutter pub cache hosted pub dartlang org cupertino icons lib diacritic file home hasan snap flutter common flutter pub cache hosted pub dartlang org diacritic lib equatable file home hasan snap flutter common flutter pub cache hosted pub dartlang org equatable lib eva icons flutter file home hasan snap flutter common flutter pub cache hosted pub dartlang org eva icons flutter lib extended image file home hasan snap flutter common flutter pub cache hosted pub dartlang org extended image l ib extended image library file home hasan snap flutter common flutter pub cache hosted pub dartlang org extended image library lib fake async file home hasan snap flutter common flutter pub cache hosted pub dartlang org fake async nullsafet y lib file picker file home hasan snap flutter common flutter pub cache hosted pub dartlang org file picker lib firebase file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase lib firebase auth file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase auth lib firebase auth platform interface file home hasan snap flutter common flutter pub cache hosted pub dartlang org fire base auth platform interface lib firebase auth web file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase auth web lib firebase core file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase core l ib firebase core platform interface file home hasan snap flutter common flutter pub cache hosted pub dartlang org fire base core platform interface lib firebase core web file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase core web lib firebase storage file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase storage lib flutter file home hasan snap flutter common flutter packages flutter lib flutter bloc file home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter bloc lib flutter country picker file home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter countr y picker lib flutter datetime picker file home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter datet ime picker lib flutter native image file home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter native i mage lib flutter test file home hasan snap flutter common flutter packages flutter test lib flutter web plugins file home hasan snap flutter common flutter packages flutter web plugins lib font awesome flutter file home hasan snap flutter common flutter pub cache hosted pub dartlang org font awesome flu tter lib geolocator file home hasan snap flutter common flutter pub cache hosted pub dartlang org geolocator lib google api availability file home hasan snap flutter common flutter pub cache hosted pub dartlang org google api av ailability lib http file home hasan snap flutter common flutter pub cache hosted pub dartlang org http lib http client helper file home hasan snap flutter common flutter pub cache hosted pub dartlang org http client helper lib http parser file home hasan snap flutter common flutter pub cache hosted pub dartlang org http parser lib js file home hasan snap flutter common flutter pub cache hosted pub dartlang org js nullsafety lib language pickers file home hasan snap flutter common flutter pub cache hosted pub dartlang org language pickers lib location permissions file home hasan snap flutter common flutter pub cache hosted pub dartlang org location permiss ions lib matcher file home hasan snap flutter common flutter pub cache hosted pub dartlang org matcher nullsafety lib meta file home hasan snap flutter common flutter pub cache hosted pub dartlang org meta nullsafety lib modal progress hud file home hasan snap flutter common flutter pub cache hosted pub dartlang org modal progress hud lib network to file image file home hasan snap flutter common flutter pub cache hosted pub dartlang org network to file image lib path file home hasan snap flutter common flutter pub cache hosted pub dartlang org path nullsafety lib path provider file home hasan snap flutter common flutter pub cache hosted pub dartlang org path provider lib pedantic file home hasan snap flutter common flutter pub cache hosted pub dartlang org pedantic lib platform file home hasan snap flutter common flutter pub cache hosted pub dartlang org platform lib plugin platform interface file home hasan snap flutter common flutter pub cache hosted pub dartlang org plugin plat form interface lib quiver file home hasan snap flutter common flutter pub cache hosted pub dartlang org quiver lib rxdart file home hasan snap flutter common flutter pub cache hosted pub dartlang org rxdart lib sky engine file home hasan snap flutter common flutter bin cache pkg sky engine lib source span file home hasan snap flutter common flutter pub cache hosted pub dartlang org source span nullsaf ety lib stack trace file home hasan snap flutter common flutter pub cache hosted pub dartlang org stack trace nullsa fety lib stream channel file home hasan snap flutter common flutter pub cache hosted pub dartlang org stream channel n ullsafety lib string scanner file home hasan snap flutter common flutter pub cache hosted pub dartlang org string scanner n ullsafety lib term glyph file home hasan snap flutter common flutter pub cache hosted pub dartlang org term glyph nullsafet y lib test api file home hasan snap flutter common flutter pub cache hosted pub dartlang org test api nullsafety lib typed data file home hasan snap flutter common flutter pub cache hosted pub dartlang org typed data nullsafet y lib vector math file home hasan snap flutter common flutter pub cache hosted pub dartlang org vector math nullsaf ety lib chitchat lib io writing characters to text file dart tool package config json fine contents configversion packages name async rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org async nullsafety packageuri lib languageversion name bloc rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org bloc packageuri lib languageversion name boolean selector rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org boolean selector nullsafety packageuri lib languageversion name bottom navy bar rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org bottom navy bar packageuri lib languageversion name characters rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org characters nullsafety packageuri lib languageversion name charcode rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org charcode nullsafety packageuri lib languageversion name clock rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org clock nullsafety packageuri lib languageversion name cloud firestore rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org cloud firestore packageuri lib languageversion name cloud firestore platform interface rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org cloud firestore platform interface packageuri lib languageversion name cloud firestore web rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org cloud firestore web packageuri lib languageversion name collection rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org collection nullsafety packageuri lib languageversion name convert rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org convert packageuri lib languageversion name crypto rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org crypto packageuri lib languageversion name cupertino icons rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org cupertino icons packageuri lib languageversion name diacritic rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org diacritic packageuri lib languageversion name equatable rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org equatable packageuri lib languageversion name eva icons flutter rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org eva icons flutter packageuri lib languageversion name extended image rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org extended image packageuri lib languageversion name extended image library rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org extended image library packageuri lib languageversion name fake async rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org fake async nullsafety packageuri lib languageversion name file picker rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org file picker packageuri lib languageversion name firebase rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase packageuri lib languageversion name firebase auth rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase auth packageuri lib languageversion name firebase auth platform interface rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase auth platform interface packageuri lib languageversion name firebase auth web rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase auth web packageuri lib languageversion name firebase core rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase core packageuri lib languageversion name firebase core platform interface rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase core platform interface packageuri lib languageversion name firebase core web rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase core web packageuri lib languageversion name firebase storage rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase storage packageuri lib languageversion name flutter rooturi file home hasan snap flutter common flutter packages flutter packageuri lib languageversion name flutter bloc rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter bloc packageuri lib languageversion name flutter country picker rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter country picker packageuri lib languageversion name flutter datetime picker rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter datetime picker packageuri lib languageversion name flutter native image rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter native image packageuri lib languageversion name flutter test rooturi file home hasan snap flutter common flutter packages flutter test packageuri lib languageversion name flutter web plugins rooturi file home hasan snap flutter common flutter packages flutter web plugins packageuri lib languageversion name font awesome flutter rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org font awesome flutter packageuri lib languageversion name geolocator rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org geolocator packageuri lib languageversion name google api availability rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org google api availability packageuri lib languageversion name http rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org http packageuri lib languageversion name http client helper rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org http client helper packageuri lib languageversion name http parser rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org http parser packageuri lib languageversion name js rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org js nullsafety packageuri lib languageversion name language pickers rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org language pickers packageuri lib languageversion name location permissions rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org location permissions packageuri lib languageversion name matcher rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org matcher nullsafety packageuri lib languageversion name meta rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org meta nullsafety packageuri lib languageversion name modal progress hud rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org modal progress hud packageuri lib languageversion name network to file image rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org network to file image packageuri lib languageversion name path rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org path nullsafety packageuri lib languageversion name path provider rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org path provider packageuri lib languageversion name pedantic rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org pedantic packageuri lib languageversion name platform rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org platform packageuri lib languageversion name plugin platform interface rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org plugin platform interface packageuri lib languageversion name quiver rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org quiver packageuri lib languageversion name rxdart rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org rxdart packageuri lib languageversion name sky engine rooturi file home hasan snap flutter common flutter bin cache pkg sky engine packageuri lib languageversion name source span rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org source span nullsafety packageuri lib languageversion name stack trace rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org stack trace nullsafety packageuri lib languageversion name stream channel rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org stream channel nullsafety packageuri lib languageversion name string scanner rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org string scanner nullsafety packageuri lib languageversion name term glyph rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org term glyph nullsafety packageuri lib languageversion name test api rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org test api nullsafety packageuri lib languageversion name typed data rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org typed data nullsafety packageuri lib languageversion name vector math rooturi file home hasan snap flutter common flutter pub cache hosted pub dartlang org vector math nullsafety packageuri lib languageversion name chitchat rooturi packageuri lib languageversion generated generator pub generatorversion dev msg got dependencies running flutter pub get in chitchat master completed in found plugin cloud firestore at home hasan snap flutter common flutter pub cache hosted pub dartlang org cloud firestore found plugin cloud firestore web at home hasan snap flutter common flutter pub cache hosted pub dartlang org cloud firestore web found plugin file picker at home hasan snap flutter common flutter pub cache hosted pub dartlang org file picker found plugin firebase auth at home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase auth found plugin firebase auth web at home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase auth web found plugin firebase core at home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase core found plugin firebase core web at home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase core web found plugin firebase storage at home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase storage found plugin flutter country picker at home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter country picker found plugin flutter native image at home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter native image found plugin geolocator at home hasan snap flutter common flutter pub cache hosted pub dartlang org geolocator found plugin google api availability at home hasan snap flutter common flutter pub cache hosted pub dartlang org google api availability found plugin location permissions at home hasan snap flutter common flutter pub cache hosted pub dartlang org location permissions found plugin path provider at home hasan snap flutter common flutter pub cache hosted pub dartlang org path provider found plugin cloud firestore at home hasan snap flutter common flutter pub cache hosted pub dartlang org cloud firestore found plugin cloud firestore web at home hasan snap flutter common flutter pub cache hosted pub dartlang org cloud firestore web found plugin file picker at home hasan snap flutter common flutter pub cache hosted pub dartlang org file picker found plugin firebase auth at home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase auth found plugin firebase auth web at home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase auth web found plugin firebase core at home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase core found plugin firebase core web at home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase core web found plugin firebase storage at home hasan snap flutter common flutter pub cache hosted pub dartlang org firebase storage found plugin flutter country picker at home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter country picker found plugin flutter native image at home hasan snap flutter common flutter pub cache hosted pub dartlang org flutter native image found plugin geolocator at home hasan snap flutter common flutter pub cache hosted pub dartlang org geolocator found plugin google api availability at home hasan snap flutter common flutter pub cache hosted pub dartlang org google api availability found plugin location permissions at home hasan snap flutter common flutter pub cache hosted pub dartlang org location permissions found plugin path provider at home hasan snap flutter common flutter pub cache hosted pub dartlang org path provider generating home hasan desktop chitchat master android app src main java io flutter plugins generatedpluginregistrant java running gradle task bundlerelease gradle properties already sets android using gradle from home hasan desktop chitchat master android gradlew home hasan desktop chitchat master android gradlew mode rwxrwxr x executing home hasan desktop chitchat master android gradlew pverbose true ptarget platform android arm android android ptarget lib main dart ptrack widget creation true pshrink true ptree shake icons true bundlerelease starting a gradle daemon busy and incompatible daemons could not be reused use status for details configure project app warning the option android is deprecated and should not be used anymore it will be removed in a future version of the android gradle plugin and will no longer allow you to disable task app cleanmergereleaseassets up to date task app prebuild up to date task app extractproguardfiles task app prereleasebuild task app mergereleaseshaders task app compilereleaseshaders task app generatereleaseassets task app compileflutterbuildrelease executing git c log showsignature false log n pretty format h exit code from git c log showsignature false log n pretty format h executing git tag points at head exit code from git tag points at head executing git describe match first parent long tags exit code from git describe match first parent long tags pre executing git rev parse abbrev ref symbolic u exit code from git rev parse abbrev ref symbolic u origin master executing git ls remote get url origin exit code from git ls remote get url origin executing git rev parse abbrev ref head exit code from git rev parse abbrev ref head master artifact instance of androidmavenartifacts is not required skipping update artifact instance of androidgensnapshotartifacts is not required skipping update artifact instance of androidinternalbuildartifacts is not required skipping update artifact instance of iosengineartifacts is not required skipping update artifact instance of flutterwebsdk is not required skipping update artifact instance of windowsengineartifacts is not required skipping update artifact instance of macosengineartifacts is not required skipping update artifact instance of linuxengineartifacts is not required skipping update artifact instance of linuxfuchsiasdkartifacts is not required skipping update artifact instance of macosfuchsiasdkartifacts is not required skipping update artifact instance of flutterrunnersdkartifacts is not required skipping update artifact instance of flutterrunnerdebugsymbols is not required skipping update artifact instance of materialfonts is not required skipping update artifact instance of gradlewrapper is not required skipping update artifact instance of androidmavenartifacts is not required skipping update artifact instance of androidgensnapshotartifacts is not required skipping update artifact instance of androidinternalbuildartifacts is not required skipping update artifact instance of iosengineartifacts is not required skipping update artifact instance of flutterwebsdk is not required skipping update artifact instance of fluttersdk is not required skipping update artifact instance of windowsengineartifacts is not required skipping update artifact instance of macosengineartifacts is not required skipping update artifact instance of linuxengineartifacts is not required skipping update artifact instance of linuxfuchsiasdkartifacts is not required skipping update artifact instance of macosfuchsiasdkartifacts is not required skipping update artifact instance of flutterrunnersdkartifacts is not required skipping update artifact instance of flutterrunnerdebugsymbols is not required skipping update artifact instance of iosusbartifacts is not required skipping update artifact instance of iosusbartifacts is not required skipping update artifact instance of iosusbartifacts is not required skipping update artifact instance of iosusbartifacts is not required skipping update artifact instance of iosusbartifacts is not required skipping update artifact instance of fontsubsetartifacts is not required skipping update artifact instance of pubdependencies is not required skipping update initializing file store done initializing file store skipping target gen localizations kernel snapshot starting due to invalidatedreason inputchanged home hasan snap flutter common flutter bin cache dart sdk bin dart disable dart dev home hasan snap flutter common flutter bin cache artifacts engine linux frontend server dart snapshot sdk root home hasan snap flutter common flutter bin cache artifacts engine common flutter patched sdk product target flutter no print incremental dependencies ddart developer causal async stacks false ddart vm profile false ddart vm product true aot tfa packages home hasan desktop chitchat master dart tool package config json output dill home hasan desktop chitchat master dart tool flutter build app dill depfile home hasan desktop chitchat master dart tool flutter build kernel snapshot d package chitchat main dart snap flutter common flutter pub cache hosted pub dartlang org extended image lib src gesture extended imag e slide page route dart error no named parameter with the name animation animation animation snap flutter common flutter packages flutter lib src cupertino route dart context found this candidate but the arguments don t match cupertinofullscreendialogtransition snap flutter common flutter pub cache hosted pub dartlang org extended image lib src extended image dart error no named parameter with the name nullok invertcolors mediaquery of context nullok true invertcolors snap flutter common flutter packages flutter lib src widgets media query dart context found this candidate but the arguments don t match static mediaquerydata of buildcontext context persisting file store done persisting file store target kernel snapshot failed exception kernelsnapshot build package flutter tools src build system targets common dart buildinstance invokeinternal package flutter tools src build system build system dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart asyncawaitcompleter complete dart async patch async patch dart completeonasyncreturn dart async patch async patch dart node computechanges package flutter tools src build system build system dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart asyncawaitcompleter complete dart async patch async patch dart completeonasyncreturn dart async patch async patch dart filestore difffilelist package flutter tools src build system file store dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart future wait dart async future dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart asyncawaitcompleter complete dart async patch async patch dart completeonasyncreturn dart async patch async patch dart filestore hashfile package flutter tools src build system file store dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart future asynccompletewithvalue dart async future impl dart rootrun dart async zone dart customzone run dart async zone dart customzone runguarded dart async zone dart customzone bindcallbackguarded dart async zone dart microtaskloop dart async schedule microtask dart startmicrotaskloop dart async schedule microtask dart runpendingimmediatecallback dart isolate patch isolate patch dart rawreceiveportimpl handlemessage dart isolate patch isolate patch dart throwtoolexit package flutter tools src base common dart assemblecommand runcommand package flutter tools src commands assemble dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart asyncawaitcompleter complete dart async patch async patch dart completeonasyncreturn dart async patch async patch dart flutterbuildsystem build package flutter tools src build system build system dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart asyncawaitcompleter complete dart async patch async patch dart completeonasyncreturn dart async patch async patch dart buildinstance invoketarget package flutter tools src build system build system dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart future wait dart async future dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart asyncawaitcompleter complete dart async patch async patch dart completeonasyncreturn dart async patch async patch dart buildinstance invoketarget package flutter tools src build system build system dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart future wait dart async future dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart asyncawaitcompleter complete dart async patch async patch dart completeonasyncreturn dart async patch async patch dart buildinstance invoketarget package flutter tools src build system build system dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart future wait dart async future dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart asyncawaitcompleter complete dart async patch async patch dart completeonasyncreturn dart async patch async patch dart buildinstance invokeinternal package flutter tools src build system build system dart asyncerrorwrapperhelper errorcallback dart async patch async patch dart rootrunbinary dart async zone dart customzone runbinary dart async zone dart futurelistener handleerror dart async future impl dart future propagatetolisteners handleerror dart async future impl dart future propagatetolisteners dart async future impl dart future completeerror dart async future impl dart asyncawaitcompleter completeerror dart async patch async patch dart kernelsnapshot build package flutter tools src build system targets common dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart asyncawaitcompleter complete dart async patch async patch dart completeonasyncreturn dart async patch async patch dart kernelcompiler compile package flutter tools src compile dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart future asynccompletewithvalue dart async future impl dart rootrun dart async zone dart customzone run dart async zone dart customzone runguarded dart async zone dart customzone bindcallbackguarded dart async zone dart microtaskloop dart async schedule microtask dart startmicrotaskloop dart async schedule microtask dart runpendingimmediatecallback dart isolate patch isolate patch dart rawreceiveportimpl handlemessage dart isolate patch isolate patch dart flutter assemble took ensureanalyticssent running shutdown hooks shutdown hooks complete exiting with code task app compileflutterbuildrelease failed failure build failed with an exception where script home hasan snap flutter common flutter packages flutter tools gradle flutter gradle line what went wrong execution failed for task app compileflutterbuildrelease process command home hasan snap flutter common flutter bin flutter finished with non zero exit value try run with stacktrace option to get the stack trace run with info or debug option to get more log output run with scan to get full insights get more help at build failed in deprecated gradle features were used in this build making it incompatible with gradle use warning mode all to show the individual deprecation warnings see actionable tasks executed up to date running gradle task bundlerelease completed in flutter appbundle took gradle task bundlerelease failed with exit code throwtoolexit package flutter tools src base common dart buildgradleapp package flutter tools src android gradle dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart asyncawaitcompleter complete dart async patch async patch dart completeonasyncreturn dart async patch async patch dart defaultprocessutils stream package flutter tools src base process dart rootrununary dart async zone dart customzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart future asynccompletewithvalue dart async future impl dart rootrun dart async zone dart customzone run dart async zone dart customzone runguarded dart async zone dart customzone bindcallbackguarded dart async zone dart microtaskloop dart async schedule microtask dart startmicrotaskloop dart async schedule microtask dart runpendingimmediatecallback dart isolate patch isolate patch dart rawreceiveportimpl handlemessage dart isolate patch isolate patch dart ensureanalyticssent running shutdown hooks shutdown hooks complete exiting with code pubspec yaml name chitchat description a new flutter application the following defines the version and build number for your application a version number is three numbers separated by dots like followed by an optional build number separated by a both the version and the builder number may be overridden in flutter build by specifying build name and build number respectively in android build name is used as versionname while build number used as versioncode read more about android versioning at in ios build name is used as cfbundleshortversionstring while build number used as cfbundleversion read more about ios versioning at version environment sdk dependencies flutter sdk flutter flutter bloc firebase storage firebase core cloud firestore firebase auth equatable meta cupertino icons bottom navy bar modal progress hud font awesome flutter geolocator file picker flutter native image language pickers flutter country picker flutter datetime picker network to file image extended image eva icons flutter dev dependencies flutter test sdk flutter flutter assets assets profilephoto png assets world gif webp uses material design true fonts family coiny fonts asset fonts coiny regular ttf | 0 |
278,913 | 24,184,806,907 | IssuesEvent | 2022-09-23 12:23:56 | wpfoodmanager/wp-food-manager | https://api.github.com/repos/wpfoodmanager/wp-food-manager | closed | Price Value must be validate and allow only number | In Testing | Price Value must be validate and allow only number.
<img width="799" alt="Screenshot 2022-08-28 at 11 15 03" src="https://user-images.githubusercontent.com/15089059/187066792-e9ad9ecf-23f0-4e06-9bd2-42dfb60c0fc1.png">
| 1.0 | Price Value must be validate and allow only number - Price Value must be validate and allow only number.
<img width="799" alt="Screenshot 2022-08-28 at 11 15 03" src="https://user-images.githubusercontent.com/15089059/187066792-e9ad9ecf-23f0-4e06-9bd2-42dfb60c0fc1.png">
| test | price value must be validate and allow only number price value must be validate and allow only number img width alt screenshot at src | 1 |
56,506 | 6,989,535,942 | IssuesEvent | 2017-12-14 16:27:54 | quicwg/base-drafts | https://api.github.com/repos/quicwg/base-drafts | opened | Split stream initial flow control | -transport design | The initial_max_stream_data transport parameter governs three types of stream data:
* data received on unidirectional streams initiated by a peer
* data received on bidirectional streams initiated by a peer
* data received on bidirectional streams initiated by this endpoint
These are currently all controlled by the same transport parameter. We should consider whether having multiple transport parameters is desirable. Obviously, having more is desirable, and I could see a fairly good case for just relying on MAX_STREAM_DATA for the last of these, but for streams that are remotely initiated, that is less directly useful. It seems likely that streams used for different purposes will have different constraints. | 1.0 | Split stream initial flow control - The initial_max_stream_data transport parameter governs three types of stream data:
* data received on unidirectional streams initiated by a peer
* data received on bidirectional streams initiated by a peer
* data received on bidirectional streams initiated by this endpoint
These are currently all controlled by the same transport parameter. We should consider whether having multiple transport parameters is desirable. Obviously, having more is desirable, and I could see a fairly good case for just relying on MAX_STREAM_DATA for the last of these, but for streams that are remotely initiated, that is less directly useful. It seems likely that streams used for different purposes will have different constraints. | non_test | split stream initial flow control the initial max stream data transport parameter governs three types of stream data data received on unidirectional streams initiated by a peer data received on bidirectional streams initiated by a peer data received on bidirectional streams initiated by this endpoint these are currently all controlled by the same transport parameter we should consider whether having multiple transport parameters is desirable obviously having more is desirable and i could see a fairly good case for just relying on max stream data for the last of these but for streams that are remotely initiated that is less directly useful it seems likely that streams used for different purposes will have different constraints | 0 |
262,303 | 22,830,527,112 | IssuesEvent | 2022-07-12 12:33:47 | ventoy/Ventoy | https://api.github.com/repos/ventoy/Ventoy | closed | [Success Image Report]: | 【Tested Image Report】 | ### Official Website List
- [X] I have checked the list in official website and the image file is not listed there.
### Ventoy Version
1.0.77
### BIOS Mode
UEFI Mode
### Partition Style
GPT
### Image file name
archlinux-2022.07.01-x86_64.iso
### Image file checksum type
SHA256
### Image file checksum value
54974bcac724e97ec242552a8b7d01e037ca8a944100f366bbb6c80865b311df
### Image file download link (if applicable)
_No response_
### Test envrionment
Lenovo Ideapad 5 pro
### More Details?
This image file booted successfully in Ventoy. | 1.0 | [Success Image Report]: - ### Official Website List
- [X] I have checked the list in official website and the image file is not listed there.
### Ventoy Version
1.0.77
### BIOS Mode
UEFI Mode
### Partition Style
GPT
### Image file name
archlinux-2022.07.01-x86_64.iso
### Image file checksum type
SHA256
### Image file checksum value
54974bcac724e97ec242552a8b7d01e037ca8a944100f366bbb6c80865b311df
### Image file download link (if applicable)
_No response_
### Test envrionment
Lenovo Ideapad 5 pro
### More Details?
This image file booted successfully in Ventoy. | test | official website list i have checked the list in official website and the image file is not listed there ventoy version bios mode uefi mode partition style gpt image file name archlinux iso image file checksum type image file checksum value image file download link if applicable no response test envrionment lenovo ideapad pro more details this image file booted successfully in ventoy | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.