Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 4
112
| repo_url
stringlengths 33
141
| action
stringclasses 3
values | title
stringlengths 1
1.02k
| labels
stringlengths 4
1.54k
| body
stringlengths 1
262k
| index
stringclasses 17
values | text_combine
stringlengths 95
262k
| label
stringclasses 2
values | text
stringlengths 96
252k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
35,514
| 12,344,613,376
|
IssuesEvent
|
2020-05-15 07:22:51
|
ondrejrozsypal/test
|
https://api.github.com/repos/ondrejrozsypal/test
|
closed
|
CVE-2016-9013 (High) detected in Django-1.8.15-py2.py3-none-any.whl
|
security vulnerability
|
## CVE-2016-9013 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-1.8.15-py2.py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/f3/bb/865626b78c2e87acd4dc1bd8f8cb0a49582ec65e40968f3d24f594bba600/Django-1.8.15-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/f3/bb/865626b78c2e87acd4dc1bd8f8cb0a49582ec65e40968f3d24f594bba600/Django-1.8.15-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/test/pip-requirements.txt</p>
<p>Path to vulnerable library: /test/pip-requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **Django-1.8.15-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ondrejrozsypal/test/commit/cd4b66cdcc157d793ca27f34180fe710ff3fddd8">cd4b66cdcc157d793ca27f34180fe710ff3fddd8</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Django 1.8.x before 1.8.16, 1.9.x before 1.9.11, and 1.10.x before 1.10.3 use a hardcoded password for a temporary database user created when running tests with an Oracle database, which makes it easier for remote attackers to obtain access to the database server by leveraging failure to manually specify a password in the database settings TEST dictionary.
<p>Publish Date: 2016-12-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-9013>CVE-2016-9013</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-9013">https://nvd.nist.gov/vuln/detail/CVE-2016-9013</a></p>
<p>Release Date: 2016-12-09</p>
<p>Fix Resolution: 1.8.16,1.9.11,1.10.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2016-9013 (High) detected in Django-1.8.15-py2.py3-none-any.whl - ## CVE-2016-9013 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-1.8.15-py2.py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/f3/bb/865626b78c2e87acd4dc1bd8f8cb0a49582ec65e40968f3d24f594bba600/Django-1.8.15-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/f3/bb/865626b78c2e87acd4dc1bd8f8cb0a49582ec65e40968f3d24f594bba600/Django-1.8.15-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/test/pip-requirements.txt</p>
<p>Path to vulnerable library: /test/pip-requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **Django-1.8.15-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ondrejrozsypal/test/commit/cd4b66cdcc157d793ca27f34180fe710ff3fddd8">cd4b66cdcc157d793ca27f34180fe710ff3fddd8</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Django 1.8.x before 1.8.16, 1.9.x before 1.9.11, and 1.10.x before 1.10.3 use a hardcoded password for a temporary database user created when running tests with an Oracle database, which makes it easier for remote attackers to obtain access to the database server by leveraging failure to manually specify a password in the database settings TEST dictionary.
<p>Publish Date: 2016-12-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-9013>CVE-2016-9013</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-9013">https://nvd.nist.gov/vuln/detail/CVE-2016-9013</a></p>
<p>Release Date: 2016-12-09</p>
<p>Fix Resolution: 1.8.16,1.9.11,1.10.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in django none any whl cve high severity vulnerability vulnerable library django none any whl a high level python web framework that encourages rapid development and clean pragmatic design library home page a href path to dependency file tmp ws scm test pip requirements txt path to vulnerable library test pip requirements txt dependency hierarchy x django none any whl vulnerable library found in head commit a href vulnerability details django x before x before and x before use a hardcoded password for a temporary database user created when running tests with an oracle database which makes it easier for remote attackers to obtain access to the database server by leveraging failure to manually specify a password in the database settings test dictionary publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
229,552
| 18,363,768,069
|
IssuesEvent
|
2021-10-09 17:43:03
|
jordanbrown0/reg3
|
https://api.github.com/repos/jordanbrown0/reg3
|
closed
|
Handle delete vs pick/edit conflict
|
bug test
|
If one station deletes a record while another tries to pick or update it, the pick/update should get a clean failure. (At a minimum, the case needs to be tested.)
|
1.0
|
Handle delete vs pick/edit conflict - If one station deletes a record while another tries to pick or update it, the pick/update should get a clean failure. (At a minimum, the case needs to be tested.)
|
test
|
handle delete vs pick edit conflict if one station deletes a record while another tries to pick or update it the pick update should get a clean failure at a minimum the case needs to be tested
| 1
|
303,898
| 26,237,206,920
|
IssuesEvent
|
2023-01-05 08:27:49
|
neovim/neovim
|
https://api.github.com/repos/neovim/neovim
|
closed
|
Test error for test/functional/core/fileio_spec.lua with 0.8.1 version
|
bug test
|
### Neovim version (nvim -v)
v0.8.1
### Vim (not Nvim) behaves the same?
no
### Operating system/version
Debian/testing and amd64
### Terminal name/version
wezterm
### $TERM environment variable
xterm-256color
### Installation
Build from 0.8.1 sources
### How to reproduce the issue
**OK** - Build Neovim v0.8.1 from sources on Debian/testing (amd64) : `make CMAKE_BUILD_TYPE=Release`
```
$ ./build/bin/nvim -v
NVIM v0.8.1
Build type: Release
LuaJIT 2.1.0-beta3
Compiled by fox@echoes
Features: +acl +iconv +tui
See ":help feature-compile"
system vimrc file: "$VIM/sysinit.vim"
fall-back for $VIM: "/usr/share/nvim"
Run :checkhealth for more info
```
Tests with `make test` => error on `test/functional/core/fileio_spec.lua`
```
-------- Running tests from test/functional/core/fileio_spec.lua
RUN T1106 fileio fsync() codepaths #8304: 48.47 ms ERR
test/functional/helpers.lua:109: Vim(write):E13: File exists (add ! to override)
stack traceback:
test/functional/helpers.lua:109: in function 'request'
test/functional/helpers.lua:275: in function 'command'
test/functional/core/fileio_spec.lua:53: in function <test/functional/core/fileio_spec.lua:46>
nan ms test/helpers.lua:134: expected failure, but got success
stack traceback:
test/helpers.lua:134: in function 'pcall_err_withfile'
test/helpers.lua:157: in function 'pcall_err_withtrace'
test/helpers.lua:163: in function 'pcall_err'
test/functional/helpers.lua:283: in function 'expect_exit'
test/functional/core/fileio_spec.lua:34: in function <test/functional/core/fileio_spec.lua:33>
RUN T1107 fileio backup #9709: 29.65 ms ERR
test/functional/helpers.lua:109: Vim(write):E13: File exists (add ! to override)
stack traceback:
test/functional/helpers.lua:109: in function 'request'
test/functional/helpers.lua:275: in function 'command'
test/functional/core/fileio_spec.lua:96: in function <test/functional/core/fileio_spec.lua:89>
nan ms test/helpers.lua:134: expected failure, but got success
stack traceback:
test/helpers.lua:134: in function 'pcall_err_withfile'
test/helpers.lua:157: in function 'pcall_err_withtrace'
test/helpers.lua:163: in function 'pcall_err'
test/functional/helpers.lua:283: in function 'expect_exit'
test/functional/core/fileio_spec.lua:34: in function <test/functional/core/fileio_spec.lua:33>
(...)
```
### Expected behavior
All tests OK
### Actual behavior
Some tests with error
|
1.0
|
Test error for test/functional/core/fileio_spec.lua with 0.8.1 version - ### Neovim version (nvim -v)
v0.8.1
### Vim (not Nvim) behaves the same?
no
### Operating system/version
Debian/testing and amd64
### Terminal name/version
wezterm
### $TERM environment variable
xterm-256color
### Installation
Build from 0.8.1 sources
### How to reproduce the issue
**OK** - Build Neovim v0.8.1 from sources on Debian/testing (amd64) : `make CMAKE_BUILD_TYPE=Release`
```
$ ./build/bin/nvim -v
NVIM v0.8.1
Build type: Release
LuaJIT 2.1.0-beta3
Compiled by fox@echoes
Features: +acl +iconv +tui
See ":help feature-compile"
system vimrc file: "$VIM/sysinit.vim"
fall-back for $VIM: "/usr/share/nvim"
Run :checkhealth for more info
```
Tests with `make test` => error on `test/functional/core/fileio_spec.lua`
```
-------- Running tests from test/functional/core/fileio_spec.lua
RUN T1106 fileio fsync() codepaths #8304: 48.47 ms ERR
test/functional/helpers.lua:109: Vim(write):E13: File exists (add ! to override)
stack traceback:
test/functional/helpers.lua:109: in function 'request'
test/functional/helpers.lua:275: in function 'command'
test/functional/core/fileio_spec.lua:53: in function <test/functional/core/fileio_spec.lua:46>
nan ms test/helpers.lua:134: expected failure, but got success
stack traceback:
test/helpers.lua:134: in function 'pcall_err_withfile'
test/helpers.lua:157: in function 'pcall_err_withtrace'
test/helpers.lua:163: in function 'pcall_err'
test/functional/helpers.lua:283: in function 'expect_exit'
test/functional/core/fileio_spec.lua:34: in function <test/functional/core/fileio_spec.lua:33>
RUN T1107 fileio backup #9709: 29.65 ms ERR
test/functional/helpers.lua:109: Vim(write):E13: File exists (add ! to override)
stack traceback:
test/functional/helpers.lua:109: in function 'request'
test/functional/helpers.lua:275: in function 'command'
test/functional/core/fileio_spec.lua:96: in function <test/functional/core/fileio_spec.lua:89>
nan ms test/helpers.lua:134: expected failure, but got success
stack traceback:
test/helpers.lua:134: in function 'pcall_err_withfile'
test/helpers.lua:157: in function 'pcall_err_withtrace'
test/helpers.lua:163: in function 'pcall_err'
test/functional/helpers.lua:283: in function 'expect_exit'
test/functional/core/fileio_spec.lua:34: in function <test/functional/core/fileio_spec.lua:33>
(...)
```
### Expected behavior
All tests OK
### Actual behavior
Some tests with error
|
test
|
test error for test functional core fileio spec lua with version neovim version nvim v vim not nvim behaves the same no operating system version debian testing and terminal name version wezterm term environment variable xterm installation build from sources how to reproduce the issue ok build neovim from sources on debian testing make cmake build type release build bin nvim v nvim build type release luajit compiled by fox echoes features acl iconv tui see help feature compile system vimrc file vim sysinit vim fall back for vim usr share nvim run checkhealth for more info tests with make test error on test functional core fileio spec lua running tests from test functional core fileio spec lua run fileio fsync codepaths ms err test functional helpers lua vim write file exists add to override stack traceback test functional helpers lua in function request test functional helpers lua in function command test functional core fileio spec lua in function nan ms test helpers lua expected failure but got success stack traceback test helpers lua in function pcall err withfile test helpers lua in function pcall err withtrace test helpers lua in function pcall err test functional helpers lua in function expect exit test functional core fileio spec lua in function run fileio backup ms err test functional helpers lua vim write file exists add to override stack traceback test functional helpers lua in function request test functional helpers lua in function command test functional core fileio spec lua in function nan ms test helpers lua expected failure but got success stack traceback test helpers lua in function pcall err withfile test helpers lua in function pcall err withtrace test helpers lua in function pcall err test functional helpers lua in function expect exit test functional core fileio spec lua in function expected behavior all tests ok actual behavior some tests with error
| 1
|
106,663
| 16,700,830,597
|
IssuesEvent
|
2021-06-09 01:58:33
|
rvvergara/bookstore-react-redux-app
|
https://api.github.com/repos/rvvergara/bookstore-react-redux-app
|
opened
|
CVE-2020-28469 (Medium) detected in glob-parent-3.1.0.tgz, glob-parent-5.1.1.tgz
|
security vulnerability
|
## CVE-2020-28469 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-3.1.0.tgz</b>, <b>glob-parent-5.1.1.tgz</b></p></summary>
<p>
<details><summary><b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: bookstore-react-redux-app/package.json</p>
<p>Path to vulnerable library: bookstore-react-redux-app/node_modules/glob-parent</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>glob-parent-5.1.1.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>Path to dependency file: bookstore-react-redux-app/package.json</p>
<p>Path to vulnerable library: bookstore-react-redux-app/node_modules/glob-parent</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- react-dev-utils-11.0.4.tgz
- globby-11.0.1.tgz
- fast-glob-3.2.5.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/rvvergara/bookstore-react-redux-app/commit/81d7fd66c70081fb275a2dd0138cc00549a965ec">81d7fd66c70081fb275a2dd0138cc00549a965ec</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-28469 (Medium) detected in glob-parent-3.1.0.tgz, glob-parent-5.1.1.tgz - ## CVE-2020-28469 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-3.1.0.tgz</b>, <b>glob-parent-5.1.1.tgz</b></p></summary>
<p>
<details><summary><b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: bookstore-react-redux-app/package.json</p>
<p>Path to vulnerable library: bookstore-react-redux-app/node_modules/glob-parent</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>glob-parent-5.1.1.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>Path to dependency file: bookstore-react-redux-app/package.json</p>
<p>Path to vulnerable library: bookstore-react-redux-app/node_modules/glob-parent</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- react-dev-utils-11.0.4.tgz
- globby-11.0.1.tgz
- fast-glob-3.2.5.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/rvvergara/bookstore-react-redux-app/commit/81d7fd66c70081fb275a2dd0138cc00549a965ec">81d7fd66c70081fb275a2dd0138cc00549a965ec</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve medium detected in glob parent tgz glob parent tgz cve medium severity vulnerability vulnerable libraries glob parent tgz glob parent tgz glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file bookstore react redux app package json path to vulnerable library bookstore react redux app node modules glob parent dependency hierarchy react scripts tgz root library webpack dev server tgz chokidar tgz x glob parent tgz vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href path to dependency file bookstore react redux app package json path to vulnerable library bookstore react redux app node modules glob parent dependency hierarchy react scripts tgz root library react dev utils tgz globby tgz fast glob tgz x glob parent tgz vulnerable library found in head commit a href vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent step up your open source security game with whitesource
| 0
|
167,092
| 20,725,782,460
|
IssuesEvent
|
2022-03-14 01:33:46
|
rzr/rzr-presentation-gstreamer
|
https://api.github.com/repos/rzr/rzr-presentation-gstreamer
|
opened
|
CVE-2020-28500 (Medium) detected in multiple libraries
|
security vulnerability
|
## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-1.0.2.tgz</b>, <b>lodash-0.9.2.tgz</b>, <b>lodash-3.10.1.tgz</b>, <b>lodash-3.7.0.tgz</b>, <b>lodash-2.4.2.tgz</b></p></summary>
<p>
<details><summary><b>lodash-1.0.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz">https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz</a></p>
<p>Path to dependency file: /reveal.js-master/package.json</p>
<p>Path to vulnerable library: /reveal.js-master/node_modules/globule/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-watch-0.6.1.tgz (Root Library)
- gaze-0.5.2.tgz
- globule-0.1.0.tgz
- :x: **lodash-1.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-0.9.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /reveal.js-master/package.json</p>
<p>Path to vulnerable library: /reveal.js-master/node_modules/grunt/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-0.4.5.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: /reveal.js-master/package.json</p>
<p>Path to vulnerable library: /reveal.js-master/node_modules/grunt-contrib-uglify/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-uglify-0.9.2.tgz (Root Library)
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.7.0.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.7.0.tgz">https://registry.npmjs.org/lodash/-/lodash-3.7.0.tgz</a></p>
<p>Path to dependency file: /reveal.js-master/package.json</p>
<p>Path to vulnerable library: /reveal.js-master/node_modules/jshint/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-jshint-0.11.3.tgz (Root Library)
- jshint-2.8.0.tgz
- :x: **lodash-3.7.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: /reveal.js-master/plugin/multiplex/package.json</p>
<p>Path to vulnerable library: /reveal.js-master/node_modules/lodash/package.json,/reveal.js-master/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-watch-0.6.1.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.
WhiteSource Note: After conducting further research, WhiteSource has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500>CVE-2020-28500</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (grunt-contrib-watch): 1.0.1</p><p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (grunt): 1.0.3</p><p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (grunt-contrib-uglify): 0.10.1</p><p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (grunt-contrib-jshint): 0.12.0</p><p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (grunt-contrib-watch): 1.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-28500 (Medium) detected in multiple libraries - ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-1.0.2.tgz</b>, <b>lodash-0.9.2.tgz</b>, <b>lodash-3.10.1.tgz</b>, <b>lodash-3.7.0.tgz</b>, <b>lodash-2.4.2.tgz</b></p></summary>
<p>
<details><summary><b>lodash-1.0.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz">https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz</a></p>
<p>Path to dependency file: /reveal.js-master/package.json</p>
<p>Path to vulnerable library: /reveal.js-master/node_modules/globule/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-watch-0.6.1.tgz (Root Library)
- gaze-0.5.2.tgz
- globule-0.1.0.tgz
- :x: **lodash-1.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-0.9.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /reveal.js-master/package.json</p>
<p>Path to vulnerable library: /reveal.js-master/node_modules/grunt/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-0.4.5.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: /reveal.js-master/package.json</p>
<p>Path to vulnerable library: /reveal.js-master/node_modules/grunt-contrib-uglify/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-uglify-0.9.2.tgz (Root Library)
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.7.0.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.7.0.tgz">https://registry.npmjs.org/lodash/-/lodash-3.7.0.tgz</a></p>
<p>Path to dependency file: /reveal.js-master/package.json</p>
<p>Path to vulnerable library: /reveal.js-master/node_modules/jshint/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-jshint-0.11.3.tgz (Root Library)
- jshint-2.8.0.tgz
- :x: **lodash-3.7.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: /reveal.js-master/plugin/multiplex/package.json</p>
<p>Path to vulnerable library: /reveal.js-master/node_modules/lodash/package.json,/reveal.js-master/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-watch-0.6.1.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.
WhiteSource Note: After conducting further research, WhiteSource has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500>CVE-2020-28500</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (grunt-contrib-watch): 1.0.1</p><p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (grunt): 1.0.3</p><p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (grunt-contrib-uglify): 0.10.1</p><p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (grunt-contrib-jshint): 0.12.0</p><p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (grunt-contrib-watch): 1.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash tgz lodash tgz lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file reveal js master package json path to vulnerable library reveal js master node modules globule node modules lodash package json dependency hierarchy grunt contrib watch tgz root library gaze tgz globule tgz x lodash tgz vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file reveal js master package json path to vulnerable library reveal js master node modules grunt node modules lodash package json dependency hierarchy grunt tgz root library x lodash tgz vulnerable library lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file reveal js master package json path to vulnerable library reveal js master node modules grunt contrib uglify node modules lodash package json dependency hierarchy grunt contrib uglify tgz root library x lodash tgz vulnerable library lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file reveal js master package json path to vulnerable library reveal js master node modules jshint node modules lodash package json dependency hierarchy grunt contrib jshint tgz root library jshint tgz x lodash tgz vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file reveal js master plugin multiplex package json path to vulnerable library reveal js master node modules lodash package json reveal js master node modules lodash package json dependency hierarchy grunt contrib watch tgz root library x lodash tgz vulnerable library found in base branch master vulnerability details lodash versions prior to are vulnerable to regular expression denial of service redos via the tonumber trim and trimend functions whitesource note after conducting further research whitesource has determined that cve only affects environments with versions to of lodash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash direct dependency fix resolution grunt contrib watch fix resolution lodash direct dependency fix resolution grunt fix resolution lodash direct dependency fix resolution grunt contrib uglify fix resolution lodash direct dependency fix resolution grunt contrib jshint fix resolution lodash direct dependency fix resolution grunt contrib watch step up your open source security game with whitesource
| 0
|
15,869
| 20,036,522,963
|
IssuesEvent
|
2022-02-02 12:30:39
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
[iOS] Study activities > Incorrect start/end date and time displayed for mobile participants having different time zone
|
Bug P1 iOS Process: Fixed
|
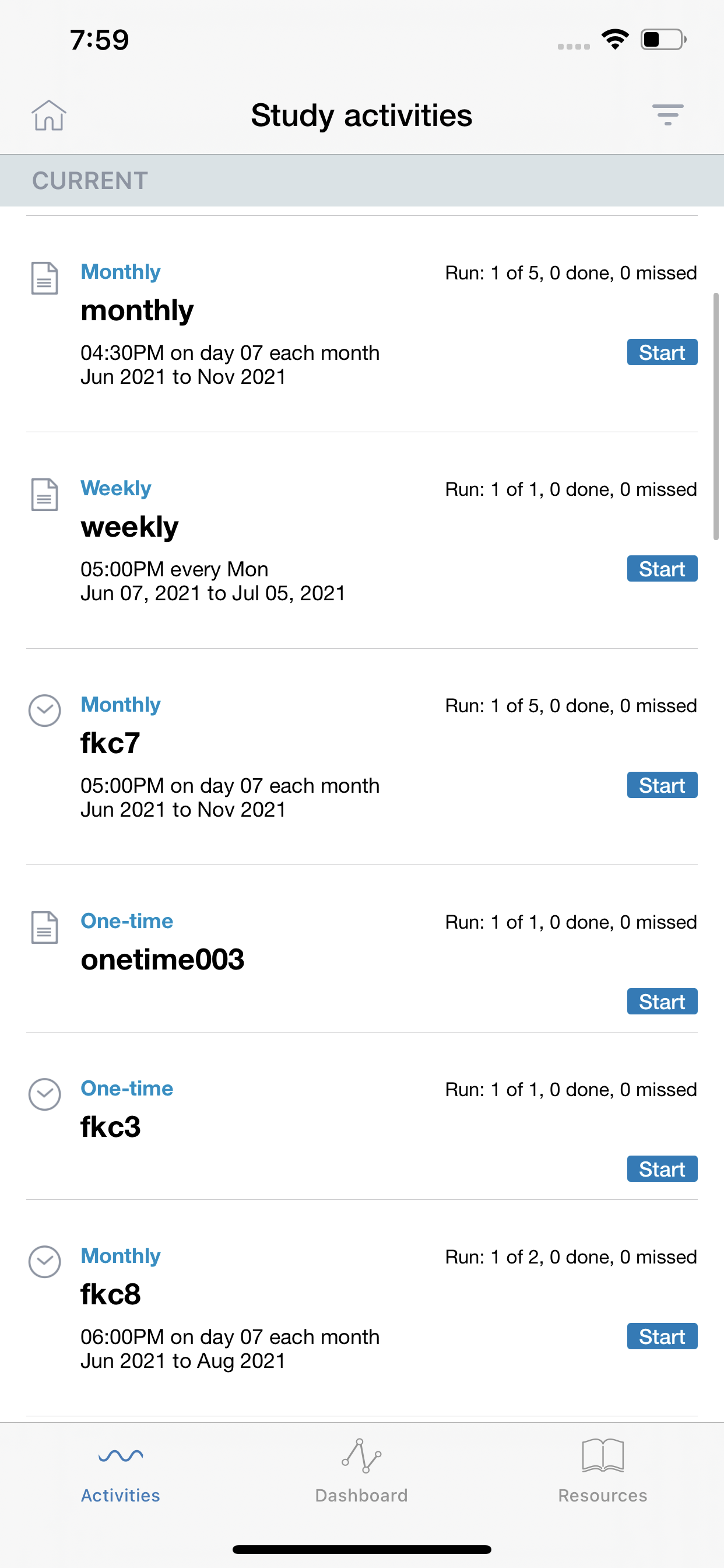
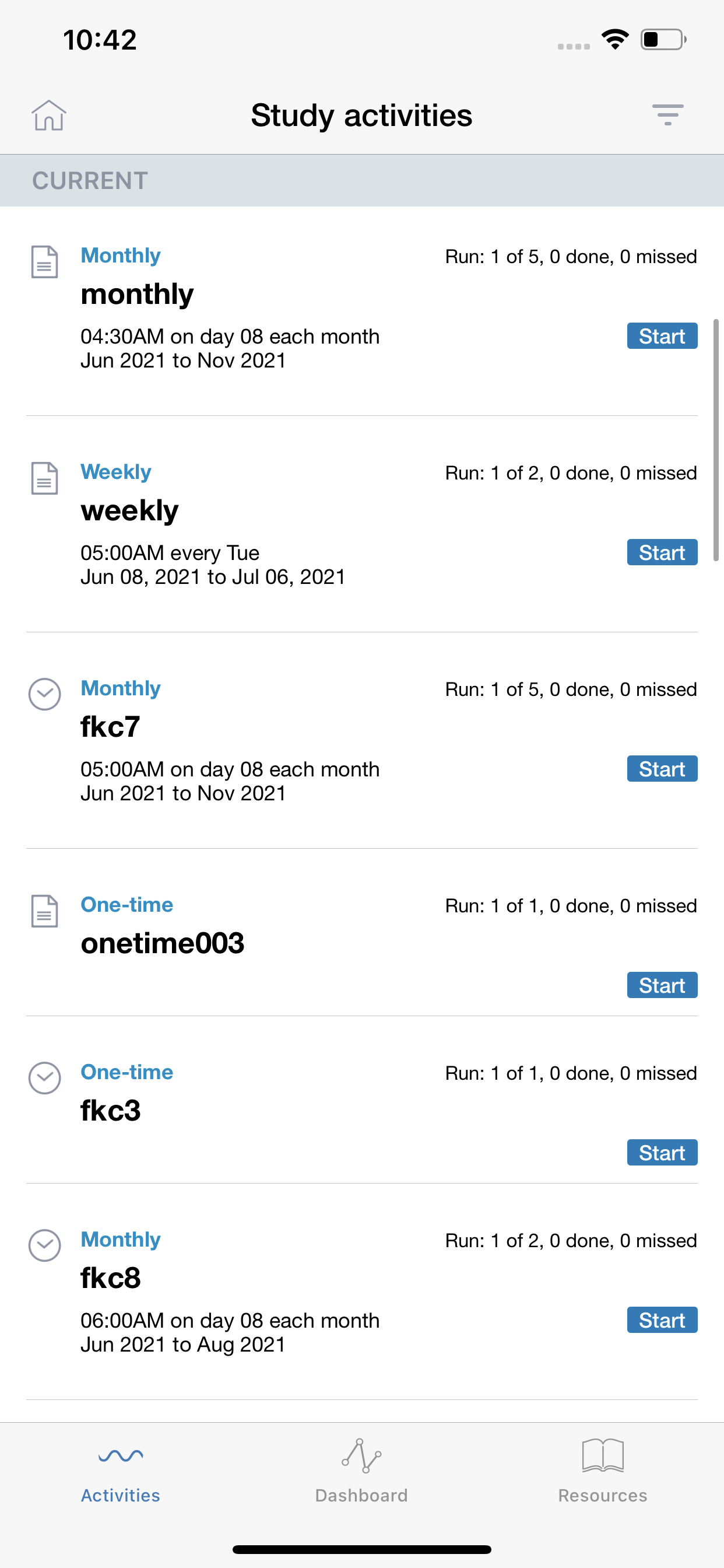
**Scenario 1:** Incorrect start/end date and time displayed for mobile participants when participant having different timezone enrolls into study
Steps:
1. Keep iOS mobile to different timezone having DST (Daylight savings) eg. EDT
2. Enroll into any study
3. Observe the start/end date and time for scheduling activities
Actual: Incorrect start/end date and time displayed for mobile participants having different timezone and study reminder notification displayed incorrectly
Expected: start/end date and time should display as per Study Builder's configured
Issue observed for all scheduling activities
Normal Timezone without daylight saving Eg. IST
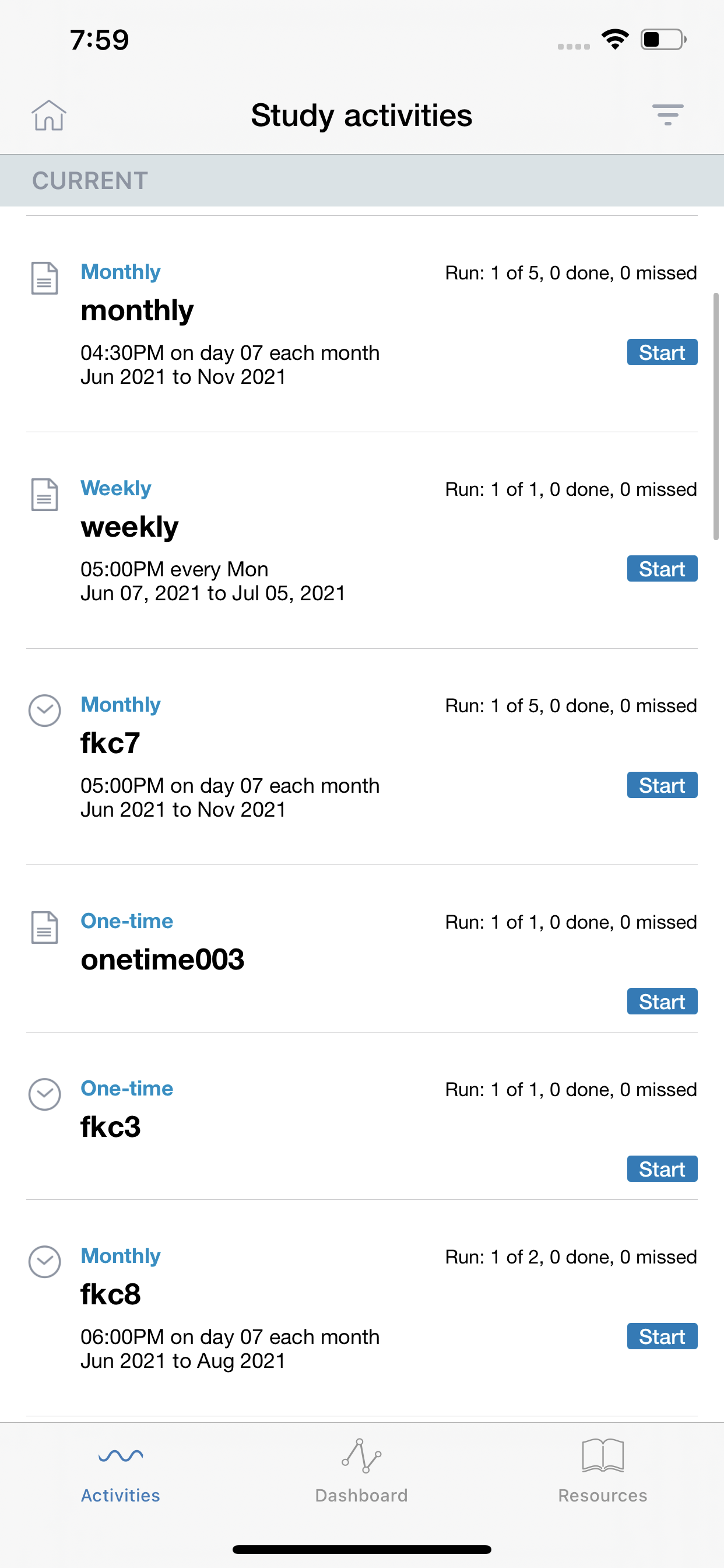
EDT Timezone screenshot:
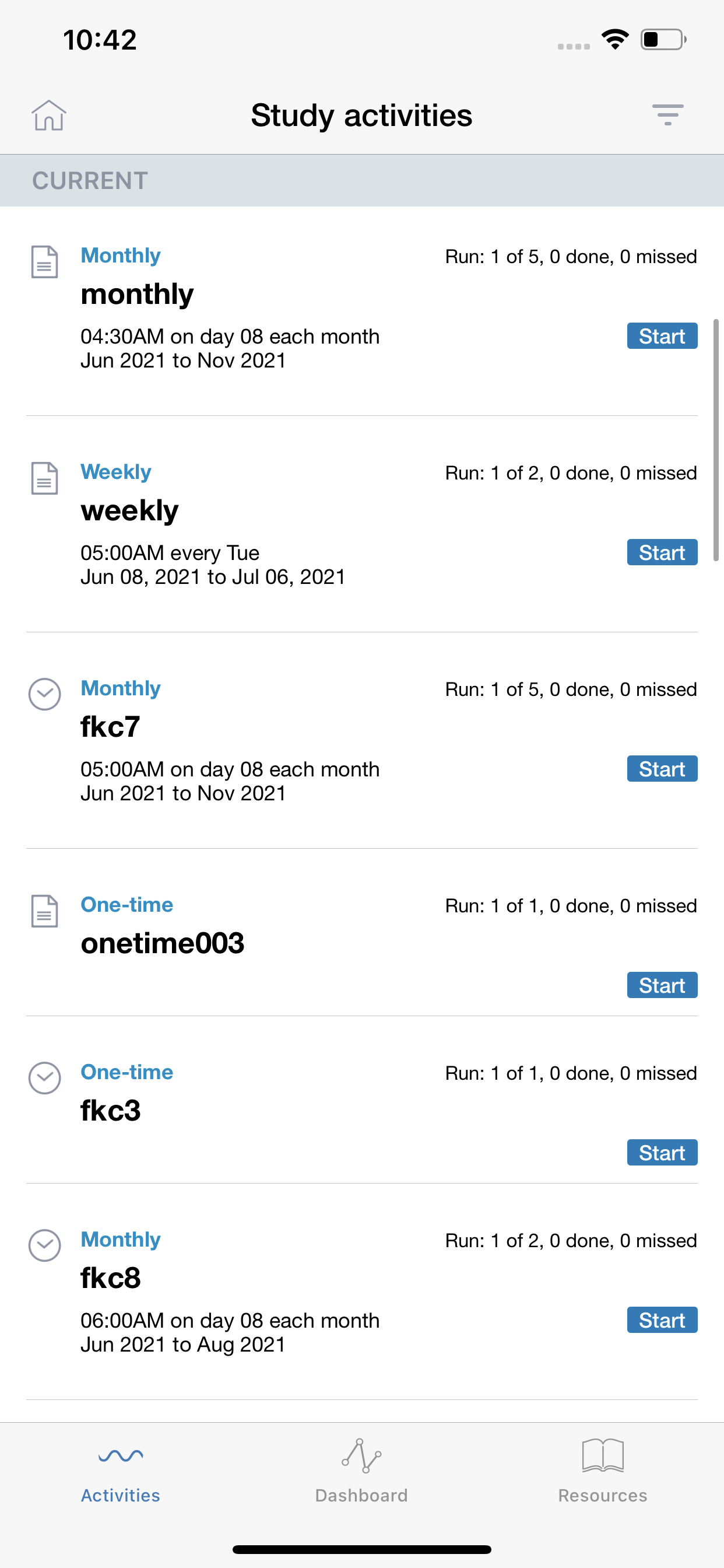
**Scenario 2:** Activities appear 1 hour before scheduled post changing timezone
Steps:
1. Enroll into any study
2. Change the timezone with DST eg. EDT
3. Observe the start/end date and time for scheduling activities
Actual: Activities appear 1 hour before scheduled post changing timezone and study reminder notification displayed incorrectly
Expected: start/end date and time should display as per Study Builder's configured
|
1.0
|
[iOS] Study activities > Incorrect start/end date and time displayed for mobile participants having different time zone - **Scenario 1:** Incorrect start/end date and time displayed for mobile participants when participant having different timezone enrolls into study
Steps:
1. Keep iOS mobile to different timezone having DST (Daylight savings) eg. EDT
2. Enroll into any study
3. Observe the start/end date and time for scheduling activities
Actual: Incorrect start/end date and time displayed for mobile participants having different timezone and study reminder notification displayed incorrectly
Expected: start/end date and time should display as per Study Builder's configured
Issue observed for all scheduling activities
Normal Timezone without daylight saving Eg. IST
EDT Timezone screenshot:
**Scenario 2:** Activities appear 1 hour before scheduled post changing timezone
Steps:
1. Enroll into any study
2. Change the timezone with DST eg. EDT
3. Observe the start/end date and time for scheduling activities
Actual: Activities appear 1 hour before scheduled post changing timezone and study reminder notification displayed incorrectly
Expected: start/end date and time should display as per Study Builder's configured
|
non_test
|
study activities incorrect start end date and time displayed for mobile participants having different time zone scenario incorrect start end date and time displayed for mobile participants when participant having different timezone enrolls into study steps keep ios mobile to different timezone having dst daylight savings eg edt enroll into any study observe the start end date and time for scheduling activities actual incorrect start end date and time displayed for mobile participants having different timezone and study reminder notification displayed incorrectly expected start end date and time should display as per study builder s configured issue observed for all scheduling activities normal timezone without daylight saving eg ist edt timezone screenshot scenario activities appear hour before scheduled post changing timezone steps enroll into any study change the timezone with dst eg edt observe the start end date and time for scheduling activities actual activities appear hour before scheduled post changing timezone and study reminder notification displayed incorrectly expected start end date and time should display as per study builder s configured
| 0
|
243,766
| 20,517,944,460
|
IssuesEvent
|
2022-03-01 13:46:17
|
wazuh/wazuh-qa
|
https://api.github.com/repos/wazuh/wazuh-qa
|
closed
|
Vulnerability detector test module refactor: `test_full_scan_type`
|
team/qa type/rework test/integration feature/vuln-detector subteam/qa-thunder
|
It is asked to refactor the test module named `test_full_scan_type.py`.
It is disabled for now, as it was failing or unstable, causing false positives.
## Tasks
- [x] Make a study of the objectives of the test, and what is being tested.
- [x] Refactor the test. Clean and modularizable code.
- [x] Check that the test always starts from the same state and restores it completely at the end of the test (independent of the tests previously executed in that environment).
- [x] Review test documentation, and modify if necessary.
- [x] Proven that tests **pass** when they have to pass.
- [x] Proven that tests **fail** when they have to fail.
- [x] Test in 5-10 rounds of execution that the test always shows the same result.
- [x] Run all Vulnerability detector integration tests and check the "full green".
## Checks
- [x] The code complies with the standard PEP-8 format.
- [x] Python codebase is documented following the Google Style for Python docstrings.
- [x] The test is processed by `qa-docs` tool without errors.
|
1.0
|
Vulnerability detector test module refactor: `test_full_scan_type` - It is asked to refactor the test module named `test_full_scan_type.py`.
It is disabled for now, as it was failing or unstable, causing false positives.
## Tasks
- [x] Make a study of the objectives of the test, and what is being tested.
- [x] Refactor the test. Clean and modularizable code.
- [x] Check that the test always starts from the same state and restores it completely at the end of the test (independent of the tests previously executed in that environment).
- [x] Review test documentation, and modify if necessary.
- [x] Proven that tests **pass** when they have to pass.
- [x] Proven that tests **fail** when they have to fail.
- [x] Test in 5-10 rounds of execution that the test always shows the same result.
- [x] Run all Vulnerability detector integration tests and check the "full green".
## Checks
- [x] The code complies with the standard PEP-8 format.
- [x] Python codebase is documented following the Google Style for Python docstrings.
- [x] The test is processed by `qa-docs` tool without errors.
|
test
|
vulnerability detector test module refactor test full scan type it is asked to refactor the test module named test full scan type py it is disabled for now as it was failing or unstable causing false positives tasks make a study of the objectives of the test and what is being tested refactor the test clean and modularizable code check that the test always starts from the same state and restores it completely at the end of the test independent of the tests previously executed in that environment review test documentation and modify if necessary proven that tests pass when they have to pass proven that tests fail when they have to fail test in rounds of execution that the test always shows the same result run all vulnerability detector integration tests and check the full green checks the code complies with the standard pep format python codebase is documented following the google style for python docstrings the test is processed by qa docs tool without errors
| 1
|
28,442
| 5,477,855,499
|
IssuesEvent
|
2017-03-12 12:54:02
|
shaarli/python-shaarli-client
|
https://api.github.com/repos/shaarli/python-shaarli-client
|
closed
|
Create the project layout
|
documentation feature
|
- [x] #1 - changelog, readme, base packaging info
- [x] #3 Sphinx documentation stub
- [x] #3 RTFD integration
- [x] #5 Tox testing automation
- [x] #5 Travis CI integration
- [x] #6 Static analysis tools (Pylint, Pydocstyle, Pycodestyle, isort)
- [x] #8 setuptools entrypoint and `api/v1/info` client
- [x] #12 #13 Base usage & development documentation
- [x] #13 PyPI release & documentation
|
1.0
|
Create the project layout - - [x] #1 - changelog, readme, base packaging info
- [x] #3 Sphinx documentation stub
- [x] #3 RTFD integration
- [x] #5 Tox testing automation
- [x] #5 Travis CI integration
- [x] #6 Static analysis tools (Pylint, Pydocstyle, Pycodestyle, isort)
- [x] #8 setuptools entrypoint and `api/v1/info` client
- [x] #12 #13 Base usage & development documentation
- [x] #13 PyPI release & documentation
|
non_test
|
create the project layout changelog readme base packaging info sphinx documentation stub rtfd integration tox testing automation travis ci integration static analysis tools pylint pydocstyle pycodestyle isort setuptools entrypoint and api info client base usage development documentation pypi release documentation
| 0
|
188,811
| 15,171,084,392
|
IssuesEvent
|
2021-02-13 01:24:38
|
ryanheise/just_audio
|
https://api.github.com/repos/ryanheise/just_audio
|
opened
|
Document how to listen to errors on streams
|
1 backlog documentation
|
<!--
PLEASE READ CAREFULLY!
FOR YOUR DOCUMENTATION REQUEST TO BE PROCESSED, YOU WILL NEED
TO FILL IN ALL SECTIONS BELOW. DON'T DELETE THE HEADINGS.
THANK YOU :-D
-->
**To which pages does your suggestion apply?**
- https://github.com/ryanheise/just_audio/blob/master/just_audio/README.md
Perhaps this could also be mentioned in the documentation for each stream (but there are a *lot* of streams...)
**Quote the sentences(s) from the documentation to be improved (if any)**
N/A
**Describe your suggestion**
One idea is to modify the section "Listening to state changes" to demonstrate how to listen to errors.
Another idea is to modify the section "Catching player errors" (but the given example doesn't relate to streams, so the first suggestion may be more efficient).
|
1.0
|
Document how to listen to errors on streams - <!--
PLEASE READ CAREFULLY!
FOR YOUR DOCUMENTATION REQUEST TO BE PROCESSED, YOU WILL NEED
TO FILL IN ALL SECTIONS BELOW. DON'T DELETE THE HEADINGS.
THANK YOU :-D
-->
**To which pages does your suggestion apply?**
- https://github.com/ryanheise/just_audio/blob/master/just_audio/README.md
Perhaps this could also be mentioned in the documentation for each stream (but there are a *lot* of streams...)
**Quote the sentences(s) from the documentation to be improved (if any)**
N/A
**Describe your suggestion**
One idea is to modify the section "Listening to state changes" to demonstrate how to listen to errors.
Another idea is to modify the section "Catching player errors" (but the given example doesn't relate to streams, so the first suggestion may be more efficient).
|
non_test
|
document how to listen to errors on streams please read carefully for your documentation request to be processed you will need to fill in all sections below don t delete the headings thank you d to which pages does your suggestion apply perhaps this could also be mentioned in the documentation for each stream but there are a lot of streams quote the sentences s from the documentation to be improved if any n a describe your suggestion one idea is to modify the section listening to state changes to demonstrate how to listen to errors another idea is to modify the section catching player errors but the given example doesn t relate to streams so the first suggestion may be more efficient
| 0
|
196,005
| 6,923,207,544
|
IssuesEvent
|
2017-11-30 08:02:17
|
Caleydo/lineupjs
|
https://api.github.com/repos/Caleydo/lineupjs
|
closed
|
Wrong order in side panel after drag&drop
|
priority: medium type: bug
|
Reordering in side panel:
Steps to reproduce:
Load Taggle.
Drag and drop Discriminatory attitude scale to 5th position.
Expected behavior:
Discriminatory attitude scale would be dropped to 5th position.
Observed behavior:
Discriminatory attitude scale appeared at 2nd position.
Possible cause:
After playing with this a bit, it seems that the dragged item is always marked as "the next one" (in this case 2nd) in sorting hierarchy and is dropped at the appropriate position. If I e.g. set Continent as 1st and Development index as 2nd in the hierarchy and then Drag and drop Discriminatory attitude scale to 5th position it will be marked as 3rd in the sorting hierarchy and dragged at 3rd position.
Web browser version and OS: chrome 62 @ Windows 10
Observed on the current daily build
|
1.0
|
Wrong order in side panel after drag&drop - Reordering in side panel:
Steps to reproduce:
Load Taggle.
Drag and drop Discriminatory attitude scale to 5th position.
Expected behavior:
Discriminatory attitude scale would be dropped to 5th position.
Observed behavior:
Discriminatory attitude scale appeared at 2nd position.
Possible cause:
After playing with this a bit, it seems that the dragged item is always marked as "the next one" (in this case 2nd) in sorting hierarchy and is dropped at the appropriate position. If I e.g. set Continent as 1st and Development index as 2nd in the hierarchy and then Drag and drop Discriminatory attitude scale to 5th position it will be marked as 3rd in the sorting hierarchy and dragged at 3rd position.
Web browser version and OS: chrome 62 @ Windows 10
Observed on the current daily build
|
non_test
|
wrong order in side panel after drag drop reordering in side panel steps to reproduce load taggle drag and drop discriminatory attitude scale to position expected behavior discriminatory attitude scale would be dropped to position observed behavior discriminatory attitude scale appeared at position possible cause after playing with this a bit it seems that the dragged item is always marked as the next one in this case in sorting hierarchy and is dropped at the appropriate position if i e g set continent as and development index as in the hierarchy and then drag and drop discriminatory attitude scale to position it will be marked as in the sorting hierarchy and dragged at position web browser version and os chrome windows observed on the current daily build
| 0
|
107,925
| 9,249,047,931
|
IssuesEvent
|
2019-03-15 08:25:04
|
MetaModels/filter_fromto
|
https://api.github.com/repos/MetaModels/filter_fromto
|
closed
|
Filter funktioniert nicht in MM 2.1
|
bug testing
|
Wenn ich diesen Filter in MM 2.1 verwende, werden beide Datums-Werte nach absenden des Formulars Komma-Getrennt in das erste Feld geschrieben.
|
1.0
|
Filter funktioniert nicht in MM 2.1 - Wenn ich diesen Filter in MM 2.1 verwende, werden beide Datums-Werte nach absenden des Formulars Komma-Getrennt in das erste Feld geschrieben.
|
test
|
filter funktioniert nicht in mm wenn ich diesen filter in mm verwende werden beide datums werte nach absenden des formulars komma getrennt in das erste feld geschrieben
| 1
|
231,611
| 18,781,902,088
|
IssuesEvent
|
2021-11-08 07:59:16
|
Tencent/bk-sops
|
https://api.github.com/repos/Tencent/bk-sops
|
opened
|
运营数据-任务统计模块字段显示错误
|
type/test-stage-bug
|
关键信息
=======
- [ ] bk-sops 版本:
问题描述
=======
<!-- 这里写问题描述 -->
<img width="633" alt="wecom-temp-b9697724460e553120f2a25874f89768" src="https://user-images.githubusercontent.com/50765823/140704518-b8552684-59a0-4aa4-931c-b4338668ec07.png">
业务总数应该显示为:”任务总数“
重现方法
=======
<!-- 列出如何重现的方法或操作步骤 -->
<!-- **重要提醒**: 请优先尝试部署使用最新发布的版本 (发布清单: https://github.com/Tencent/bk-sops/releases), 如果问题不能在最新发布的版本里重现,说明此问题已经被修复。 -->
|
1.0
|
运营数据-任务统计模块字段显示错误 - 关键信息
=======
- [ ] bk-sops 版本:
问题描述
=======
<!-- 这里写问题描述 -->
<img width="633" alt="wecom-temp-b9697724460e553120f2a25874f89768" src="https://user-images.githubusercontent.com/50765823/140704518-b8552684-59a0-4aa4-931c-b4338668ec07.png">
业务总数应该显示为:”任务总数“
重现方法
=======
<!-- 列出如何重现的方法或操作步骤 -->
<!-- **重要提醒**: 请优先尝试部署使用最新发布的版本 (发布清单: https://github.com/Tencent/bk-sops/releases), 如果问题不能在最新发布的版本里重现,说明此问题已经被修复。 -->
|
test
|
运营数据 任务统计模块字段显示错误 关键信息 bk sops 版本: 问题描述 img width alt wecom temp src 业务总数应该显示为:”任务总数“ 重现方法
| 1
|
67,683
| 21,074,549,361
|
IssuesEvent
|
2022-04-02 01:08:21
|
openzfs/zfs
|
https://api.github.com/repos/openzfs/zfs
|
closed
|
`cmp_ds_prop` is a no-op, 3/4 rsend tests that use it are false positives
|
Type: Defect
|
### System information
Type | Version/Name
--- | ---
Distribution Name | all
Architecture | all
OpenZFS Version | trunk
### Describe the problem you're observing
If you observe L247 and L248 of `cmp_ds_prop`:
https://github.com/openzfs/zfs/blob/56a0699e5e06242a7a134ad080aadfa13486bb59/tests/zfs-tests/tests/functional/rsend/rsend.kshlib#L219-L257
you'll see that it truncates the intermediate files, then does preprocessing on them; this, for obvious reasons leaves them empty, which means `cmp_ds_prop` is `diff /dev/null /dev/null`, or a very convoluted way of `alias cmp_ds_prop=:`.
Funnily enough, `cmp_ds_subs`, above, uses a different set of intermediates for before/after.
This makes `rsend`-group tests `send-c_props`, `rsend_012_pos`, and `rsend_011_pos` (so – all which use it except `rsend_008_pos`) be false-positives.
I already have this fixed but need an issue number to ref against.
|
1.0
|
`cmp_ds_prop` is a no-op, 3/4 rsend tests that use it are false positives - ### System information
Type | Version/Name
--- | ---
Distribution Name | all
Architecture | all
OpenZFS Version | trunk
### Describe the problem you're observing
If you observe L247 and L248 of `cmp_ds_prop`:
https://github.com/openzfs/zfs/blob/56a0699e5e06242a7a134ad080aadfa13486bb59/tests/zfs-tests/tests/functional/rsend/rsend.kshlib#L219-L257
you'll see that it truncates the intermediate files, then does preprocessing on them; this, for obvious reasons leaves them empty, which means `cmp_ds_prop` is `diff /dev/null /dev/null`, or a very convoluted way of `alias cmp_ds_prop=:`.
Funnily enough, `cmp_ds_subs`, above, uses a different set of intermediates for before/after.
This makes `rsend`-group tests `send-c_props`, `rsend_012_pos`, and `rsend_011_pos` (so – all which use it except `rsend_008_pos`) be false-positives.
I already have this fixed but need an issue number to ref against.
|
non_test
|
cmp ds prop is a no op rsend tests that use it are false positives system information type version name distribution name all architecture all openzfs version trunk describe the problem you re observing if you observe and of cmp ds prop you ll see that it truncates the intermediate files then does preprocessing on them this for obvious reasons leaves them empty which means cmp ds prop is diff dev null dev null or a very convoluted way of alias cmp ds prop funnily enough cmp ds subs above uses a different set of intermediates for before after this makes rsend group tests send c props rsend pos and rsend pos so – all which use it except rsend pos be false positives i already have this fixed but need an issue number to ref against
| 0
|
171,973
| 6,497,574,974
|
IssuesEvent
|
2017-08-22 14:26:57
|
workcraft/workcraft
|
https://api.github.com/repos/workcraft/workcraft
|
closed
|
Update to page referencing from algebra in CPOG plugin
|
enhancement priority:low tag:model:cpog
|
Currently in the CPOG plug in, when a user inserts a graph using the algebra text box, the graph can be referenced in future graphs by using the title of the graph, and the referenced graph will appear as a page which can be manipulated and collapsed/expanded.
It will be useful if any of these graphs which are referenced are kept updated to ensure that if a node or arc is deleted, or a nodes position is changed in one graph, this is the same in all graphs for this reference.
---
This issue was imported from a Launchpad blueprint.
- name: cpog-referenceing-update
- date created: 2015-09-09T12:50:25Z
- assignee: jonathan-r-beaumont
- the launchpad url was https://blueprints.launchpad.net/workcraft/+spec/cpog-referenceing-update
|
1.0
|
Update to page referencing from algebra in CPOG plugin - Currently in the CPOG plug in, when a user inserts a graph using the algebra text box, the graph can be referenced in future graphs by using the title of the graph, and the referenced graph will appear as a page which can be manipulated and collapsed/expanded.
It will be useful if any of these graphs which are referenced are kept updated to ensure that if a node or arc is deleted, or a nodes position is changed in one graph, this is the same in all graphs for this reference.
---
This issue was imported from a Launchpad blueprint.
- name: cpog-referenceing-update
- date created: 2015-09-09T12:50:25Z
- assignee: jonathan-r-beaumont
- the launchpad url was https://blueprints.launchpad.net/workcraft/+spec/cpog-referenceing-update
|
non_test
|
update to page referencing from algebra in cpog plugin currently in the cpog plug in when a user inserts a graph using the algebra text box the graph can be referenced in future graphs by using the title of the graph and the referenced graph will appear as a page which can be manipulated and collapsed expanded it will be useful if any of these graphs which are referenced are kept updated to ensure that if a node or arc is deleted or a nodes position is changed in one graph this is the same in all graphs for this reference this issue was imported from a launchpad blueprint name cpog referenceing update date created assignee jonathan r beaumont the launchpad url was
| 0
|
345,044
| 30,783,135,813
|
IssuesEvent
|
2023-07-31 11:27:41
|
prusa3d/Prusa-Firmware
|
https://api.github.com/repos/prusa3d/Prusa-Firmware
|
closed
|
load to nozzle failure can result in blank LCD
|
testing MMU2S
|
Machine: MK3S + MMU2S
Firmware: 3.7.1-2266
MMU firmware: 1.0.5-297
Steps to reproduce:
* Preheat
* Load to nozzle -> Select filament
* Filament load fails for some reason (IR sensor doesn't see it, or filament doesn't engage gears properly, any reason at all for the purposes of this bug). MMU2 goes into fail state with amber light flashing as expected
* Push 3rd button on MMU to retry the load
* LCD goes completely blank
Pushing the selector button takes the printer back to the main menu, so this is not a critical problem, but I think it is a bug.
|
1.0
|
load to nozzle failure can result in blank LCD - Machine: MK3S + MMU2S
Firmware: 3.7.1-2266
MMU firmware: 1.0.5-297
Steps to reproduce:
* Preheat
* Load to nozzle -> Select filament
* Filament load fails for some reason (IR sensor doesn't see it, or filament doesn't engage gears properly, any reason at all for the purposes of this bug). MMU2 goes into fail state with amber light flashing as expected
* Push 3rd button on MMU to retry the load
* LCD goes completely blank
Pushing the selector button takes the printer back to the main menu, so this is not a critical problem, but I think it is a bug.
|
test
|
load to nozzle failure can result in blank lcd machine firmware mmu firmware steps to reproduce preheat load to nozzle select filament filament load fails for some reason ir sensor doesn t see it or filament doesn t engage gears properly any reason at all for the purposes of this bug goes into fail state with amber light flashing as expected push button on mmu to retry the load lcd goes completely blank pushing the selector button takes the printer back to the main menu so this is not a critical problem but i think it is a bug
| 1
|
62,630
| 14,656,548,989
|
IssuesEvent
|
2020-12-28 13:40:22
|
fu1771695yongxie/Rocket.Chat
|
https://api.github.com/repos/fu1771695yongxie/Rocket.Chat
|
opened
|
CVE-2019-10744 (High) detected in lodash-3.10.1.tgz, lodash-4.17.11.tgz
|
security vulnerability
|
## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-3.10.1.tgz</b>, <b>lodash-4.17.11.tgz</b></p></summary>
<p>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: Rocket.Chat/package.json</p>
<p>Path to vulnerable library: Rocket.Chat/node_modules/node-gcm/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- node-gcm-0.14.4.tgz (Root Library)
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: Rocket.Chat/package.json</p>
<p>Path to vulnerable library: Rocket.Chat/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- bar-0.61.1.tgz (Root Library)
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/Rocket.Chat/commit/60c2c8d370f1dbf301090daf20046b9ecd2435f4">60c2c8d370f1dbf301090daf20046b9ecd2435f4</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-08</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-10744 (High) detected in lodash-3.10.1.tgz, lodash-4.17.11.tgz - ## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-3.10.1.tgz</b>, <b>lodash-4.17.11.tgz</b></p></summary>
<p>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: Rocket.Chat/package.json</p>
<p>Path to vulnerable library: Rocket.Chat/node_modules/node-gcm/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- node-gcm-0.14.4.tgz (Root Library)
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: Rocket.Chat/package.json</p>
<p>Path to vulnerable library: Rocket.Chat/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- bar-0.61.1.tgz (Root Library)
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/Rocket.Chat/commit/60c2c8d370f1dbf301090daf20046b9ecd2435f4">60c2c8d370f1dbf301090daf20046b9ecd2435f4</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-08</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in lodash tgz lodash tgz cve high severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file rocket chat package json path to vulnerable library rocket chat node modules node gcm node modules lodash package json dependency hierarchy node gcm tgz root library x lodash tgz vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file rocket chat package json path to vulnerable library rocket chat node modules lodash package json dependency hierarchy bar tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch develop vulnerability details versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash lodash amd lodash es lodash defaultsdeep lodash merge lodash mergewith lodash template step up your open source security game with whitesource
| 0
|
107,511
| 13,465,151,048
|
IssuesEvent
|
2020-09-09 20:22:56
|
adobe/spectrum-css
|
https://api.github.com/repos/adobe/spectrum-css
|
closed
|
Quiet Dropdown and Quiet Textfield should have a ring on focus, not an underline
|
Component: Picker Component: Text Field design change question
|
Based on discussion spurred by #187, the design has changed on these components to have a ring.
|
1.0
|
Quiet Dropdown and Quiet Textfield should have a ring on focus, not an underline - Based on discussion spurred by #187, the design has changed on these components to have a ring.
|
non_test
|
quiet dropdown and quiet textfield should have a ring on focus not an underline based on discussion spurred by the design has changed on these components to have a ring
| 0
|
131,833
| 5,166,264,090
|
IssuesEvent
|
2017-01-17 15:49:50
|
ziccardi/yaclp
|
https://api.github.com/repos/ziccardi/yaclp
|
closed
|
Add support for key-value pair parameters
|
enhanchement priority:low status:working
|
YACLP should support parameters in form of -Dkey-value
|
1.0
|
Add support for key-value pair parameters - YACLP should support parameters in form of -Dkey-value
|
non_test
|
add support for key value pair parameters yaclp should support parameters in form of dkey value
| 0
|
157,344
| 19,957,103,772
|
IssuesEvent
|
2022-01-28 01:24:54
|
panasalap/linux-4.1.15
|
https://api.github.com/repos/panasalap/linux-4.1.15
|
opened
|
CVE-2019-12382 (Medium) detected in linux179e72b561d3d331c850e1a5779688d7a7de5246
|
security vulnerability
|
## CVE-2019-12382 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux179e72b561d3d331c850e1a5779688d7a7de5246</b></p></summary>
<p>
<p>Linux kernel stable tree mirror</p>
<p>Library home page: <a href=https://github.com/gregkh/linux.git>https://github.com/gregkh/linux.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/gpu/drm/drm_edid_load.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/gpu/drm/drm_edid_load.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** An issue was discovered in drm_load_edid_firmware in drivers/gpu/drm/drm_edid_load.c in the Linux kernel through 5.1.5. There is an unchecked kstrdup of fwstr, which might allow an attacker to cause a denial of service (NULL pointer dereference and system crash). NOTE: The vendor disputes this issues as not being a vulnerability because kstrdup() returning NULL is handled sufficiently and there is no chance for a NULL pointer dereference.
<p>Publish Date: 2019-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12382>CVE-2019-12382</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12382">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12382</a></p>
<p>Release Date: 2019-05-28</p>
<p>Fix Resolution: v5.1-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-12382 (Medium) detected in linux179e72b561d3d331c850e1a5779688d7a7de5246 - ## CVE-2019-12382 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux179e72b561d3d331c850e1a5779688d7a7de5246</b></p></summary>
<p>
<p>Linux kernel stable tree mirror</p>
<p>Library home page: <a href=https://github.com/gregkh/linux.git>https://github.com/gregkh/linux.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/gpu/drm/drm_edid_load.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/gpu/drm/drm_edid_load.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** An issue was discovered in drm_load_edid_firmware in drivers/gpu/drm/drm_edid_load.c in the Linux kernel through 5.1.5. There is an unchecked kstrdup of fwstr, which might allow an attacker to cause a denial of service (NULL pointer dereference and system crash). NOTE: The vendor disputes this issues as not being a vulnerability because kstrdup() returning NULL is handled sufficiently and there is no chance for a NULL pointer dereference.
<p>Publish Date: 2019-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12382>CVE-2019-12382</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12382">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12382</a></p>
<p>Release Date: 2019-05-28</p>
<p>Fix Resolution: v5.1-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve medium detected in cve medium severity vulnerability vulnerable library linux kernel stable tree mirror library home page a href found in base branch master vulnerable source files drivers gpu drm drm edid load c drivers gpu drm drm edid load c vulnerability details disputed an issue was discovered in drm load edid firmware in drivers gpu drm drm edid load c in the linux kernel through there is an unchecked kstrdup of fwstr which might allow an attacker to cause a denial of service null pointer dereference and system crash note the vendor disputes this issues as not being a vulnerability because kstrdup returning null is handled sufficiently and there is no chance for a null pointer dereference publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
234,206
| 19,101,588,446
|
IssuesEvent
|
2021-11-29 23:26:58
|
libreswan/libreswan
|
https://api.github.com/repos/libreswan/libreswan
|
opened
|
f35: type=AVC msg=audit(1638227662.185:108): avc: denied { watch }
|
testing
|
As in:
```
+:
+: checking selinux audit records
+:
+type=AVC msg=audit(1638227662.185:108): avc: denied { watch } for pid=293 comm="systemd-network" path="/run/dbus" dev="tmpfs" ino=980 scontext=system_u:system_r:systemd_networkd_t:s0 tcontext=system_u:object_r:system_dbusd_var_run_t:s0 tclass=dir permissive=1^]
+type=SYSCALL msg=audit(1638227662.185:108): arch=c000003e syscall=254 success=yes exit=3 a0=e a1=5559f4507130 a2=2000d84 a3=5559f4504bc0 items=1 ppid=1 pid=293 auid=4294967295 uid=192 gid=192 euid=192 suid=192 fsuid=192 egid=192 sgid=192 fsgid=192 tty=(none) ses=4294967295 comm="systemd-network" exe="PATH/lib/systemd/systemd-networkd" subj=system_u:system_r:systemd_networkd_t:s0 key=(null)^]ARCH=x86_64 SYSCALL=inotify_add_watch AUID="unset" UID="systemd-network" GID="systemd-network" EUID="systemd-network" SUID="systemd-network" FSUID="systemd-network" EGID="systemd-network" SGID="systemd-network" FSGID="systemd-network"
+type=CWD msg=audit(1638227662.185:108): cwd="/"^]
+type=PATH msg=audit(1638227662.185:108): item=0 name="/run/dbus" inode=980 dev=00:19 mode=040755 ouid=0 ogid=0 rdev=00:00 obj=system_u:object_r:system_dbusd_var_run_t:s0 nametype=NORMAL cap_fp=0 cap_fi=0 cap_fe=0 cap_fver=0 cap_frootid=0^]OUID="root" OGID="root"
+type=PROCTITLE msg=audit(1638227662.185:108): proctitle="PATH/lib/systemd/systemd-networkd"^]
```
"wonderful"
|
1.0
|
f35: type=AVC msg=audit(1638227662.185:108): avc: denied { watch } - As in:
```
+:
+: checking selinux audit records
+:
+type=AVC msg=audit(1638227662.185:108): avc: denied { watch } for pid=293 comm="systemd-network" path="/run/dbus" dev="tmpfs" ino=980 scontext=system_u:system_r:systemd_networkd_t:s0 tcontext=system_u:object_r:system_dbusd_var_run_t:s0 tclass=dir permissive=1^]
+type=SYSCALL msg=audit(1638227662.185:108): arch=c000003e syscall=254 success=yes exit=3 a0=e a1=5559f4507130 a2=2000d84 a3=5559f4504bc0 items=1 ppid=1 pid=293 auid=4294967295 uid=192 gid=192 euid=192 suid=192 fsuid=192 egid=192 sgid=192 fsgid=192 tty=(none) ses=4294967295 comm="systemd-network" exe="PATH/lib/systemd/systemd-networkd" subj=system_u:system_r:systemd_networkd_t:s0 key=(null)^]ARCH=x86_64 SYSCALL=inotify_add_watch AUID="unset" UID="systemd-network" GID="systemd-network" EUID="systemd-network" SUID="systemd-network" FSUID="systemd-network" EGID="systemd-network" SGID="systemd-network" FSGID="systemd-network"
+type=CWD msg=audit(1638227662.185:108): cwd="/"^]
+type=PATH msg=audit(1638227662.185:108): item=0 name="/run/dbus" inode=980 dev=00:19 mode=040755 ouid=0 ogid=0 rdev=00:00 obj=system_u:object_r:system_dbusd_var_run_t:s0 nametype=NORMAL cap_fp=0 cap_fi=0 cap_fe=0 cap_fver=0 cap_frootid=0^]OUID="root" OGID="root"
+type=PROCTITLE msg=audit(1638227662.185:108): proctitle="PATH/lib/systemd/systemd-networkd"^]
```
"wonderful"
|
test
|
type avc msg audit avc denied watch as in checking selinux audit records type avc msg audit avc denied watch for pid comm systemd network path run dbus dev tmpfs ino scontext system u system r systemd networkd t tcontext system u object r system dbusd var run t tclass dir permissive type syscall msg audit arch syscall success yes exit e items ppid pid auid uid gid euid suid fsuid egid sgid fsgid tty none ses comm systemd network exe path lib systemd systemd networkd subj system u system r systemd networkd t key null arch syscall inotify add watch auid unset uid systemd network gid systemd network euid systemd network suid systemd network fsuid systemd network egid systemd network sgid systemd network fsgid systemd network type cwd msg audit cwd type path msg audit item name run dbus inode dev mode ouid ogid rdev obj system u object r system dbusd var run t nametype normal cap fp cap fi cap fe cap fver cap frootid ouid root ogid root type proctitle msg audit proctitle path lib systemd systemd networkd wonderful
| 1
|
170,156
| 14,242,569,320
|
IssuesEvent
|
2020-11-19 02:08:50
|
chocolatey/boxstarter
|
https://api.github.com/repos/chocolatey/boxstarter
|
closed
|
More information needed in Contributing.md instructions for adding upstream fork
|
Documentation Enhancement _Triaging
|
[Contributing.md](https://github.com/chocolatey/boxstarter/blob/master/CONTRIBUTING.md)'s instructions for adding upstream fork assume that the user has configured git and is using SSH agent forwarding, but many, if not the majority, of users are going to be using https cloning with git instead. It would really help if the instructions also included information on how to add an upstream fork when using git with https cloning.
**Is your feature request related to a problem? Please describe.**
Kind of, yes. I was unable to correctly follow the instruction outlined in Contributing.md because I had https cloning to clone the repo.
**Describe the solution you'd like**
It would really help if the instructions also included information on how to add an upstream fork when using git with https cloning.
**Describe alternatives you've considered**
NA
**Additional context**
NA
|
1.0
|
More information needed in Contributing.md instructions for adding upstream fork - [Contributing.md](https://github.com/chocolatey/boxstarter/blob/master/CONTRIBUTING.md)'s instructions for adding upstream fork assume that the user has configured git and is using SSH agent forwarding, but many, if not the majority, of users are going to be using https cloning with git instead. It would really help if the instructions also included information on how to add an upstream fork when using git with https cloning.
**Is your feature request related to a problem? Please describe.**
Kind of, yes. I was unable to correctly follow the instruction outlined in Contributing.md because I had https cloning to clone the repo.
**Describe the solution you'd like**
It would really help if the instructions also included information on how to add an upstream fork when using git with https cloning.
**Describe alternatives you've considered**
NA
**Additional context**
NA
|
non_test
|
more information needed in contributing md instructions for adding upstream fork instructions for adding upstream fork assume that the user has configured git and is using ssh agent forwarding but many if not the majority of users are going to be using https cloning with git instead it would really help if the instructions also included information on how to add an upstream fork when using git with https cloning is your feature request related to a problem please describe kind of yes i was unable to correctly follow the instruction outlined in contributing md because i had https cloning to clone the repo describe the solution you d like it would really help if the instructions also included information on how to add an upstream fork when using git with https cloning describe alternatives you ve considered na additional context na
| 0
|
198,768
| 6,977,183,858
|
IssuesEvent
|
2017-12-12 13:50:54
|
CommandPost/CommandPost
|
https://api.github.com/repos/CommandPost/CommandPost
|
closed
|
Clipboard Manager Inconsistencies
|
bug priority
|
I'm now getting this error when I copy something in Final Cut Pro:
```
2017-10-06 21:54:17: ********
2017-10-06 21:54:17: 21:54:17 ERROR: clipmgr: The clipboard does not contain any FCPX clip data.
2017-10-06 21:54:17: ********
2017-10-06 21:54:17: clipboardH: Clipboard updated. Adding 'nil' to history.
```
It seems the `plutil -convert xml1` Terminal command is failing in `cp.plist.binaryFileToXML` with the following error:
`Property List error: Unexpected character b at line 1 / JSON error: JSON text did not start with array or object and option to allow fragments not set.`
I'm not exactly sure when this happened. Maybe Apple changed something in the Pasteboard data in a FCPX update that we didn't notice?
Here's what we're sending to `plutil`:
[file1.txt](https://github.com/CommandPost/CommandPost/files/1362527/file1.txt)
It looks like there's definitely binary plist data in there - but maybe it's mixed in with some other non-binary plist data? Not sure.
I'll do some more digging.
|
1.0
|
Clipboard Manager Inconsistencies - I'm now getting this error when I copy something in Final Cut Pro:
```
2017-10-06 21:54:17: ********
2017-10-06 21:54:17: 21:54:17 ERROR: clipmgr: The clipboard does not contain any FCPX clip data.
2017-10-06 21:54:17: ********
2017-10-06 21:54:17: clipboardH: Clipboard updated. Adding 'nil' to history.
```
It seems the `plutil -convert xml1` Terminal command is failing in `cp.plist.binaryFileToXML` with the following error:
`Property List error: Unexpected character b at line 1 / JSON error: JSON text did not start with array or object and option to allow fragments not set.`
I'm not exactly sure when this happened. Maybe Apple changed something in the Pasteboard data in a FCPX update that we didn't notice?
Here's what we're sending to `plutil`:
[file1.txt](https://github.com/CommandPost/CommandPost/files/1362527/file1.txt)
It looks like there's definitely binary plist data in there - but maybe it's mixed in with some other non-binary plist data? Not sure.
I'll do some more digging.
|
non_test
|
clipboard manager inconsistencies i m now getting this error when i copy something in final cut pro error clipmgr the clipboard does not contain any fcpx clip data clipboardh clipboard updated adding nil to history it seems the plutil convert terminal command is failing in cp plist binaryfiletoxml with the following error property list error unexpected character b at line json error json text did not start with array or object and option to allow fragments not set i m not exactly sure when this happened maybe apple changed something in the pasteboard data in a fcpx update that we didn t notice here s what we re sending to plutil it looks like there s definitely binary plist data in there but maybe it s mixed in with some other non binary plist data not sure i ll do some more digging
| 0
|
348,727
| 31,712,397,561
|
IssuesEvent
|
2023-09-09 12:43:33
|
python/cpython
|
https://api.github.com/repos/python/cpython
|
opened
|
`test_listcomps` fails when run with `-We`
|
type-bug tests 3.12 3.13
|
### Bug description:
`python -m test test_listcomps` emits `SyntaxWarnings` on `main`, and fails when run with `-We`:
```pytb
======================================================================
ERROR: test_comp_in_try_finally (test.test_listcomps.ListComprehensionTest.test_comp_in_try_finally) (scope='module')
----------------------------------------------------------------------
Traceback (most recent call last):
File "C:\Users\alexw\coding\cpython\Lib\test\test_listcomps.py", line 122, in _check_in_scopes
exec(newcode, newns)
File "<string>", line 4
SyntaxError: 'set' object is not callable; perhaps you missed a comma?
======================================================================
ERROR: test_comp_in_try_finally (test.test_listcomps.ListComprehensionTest.test_comp_in_try_finally) (scope='class')
----------------------------------------------------------------------
Traceback (most recent call last):
File "C:\Users\alexw\coding\cpython\Lib\test\test_listcomps.py", line 122, in _check_in_scopes
exec(newcode, newns)
File "<string>", line 6
SyntaxError: 'set' object is not callable; perhaps you missed a comma?
======================================================================
ERROR: test_comp_in_try_finally (test.test_listcomps.ListComprehensionTest.test_comp_in_try_finally) (scope='function')
----------------------------------------------------------------------
Traceback (most recent call last):
File "C:\Users\alexw\coding\cpython\Lib\test\test_listcomps.py", line 122, in _check_in_scopes
exec(newcode, newns)
File "<string>", line 6
SyntaxError: 'set' object is not callable; perhaps you missed a comma?
----------------------------------------------------------------------
```
The problematic test is `test_listcomps.ListComprehensionTest.test_comp_in_try_finally`, which was added in https://github.com/python/cpython/commit/d52c4482a82f3f98f1a78efa948144a1fe3c52b2 last week
### CPython versions tested on:
CPython main branch
### Operating systems tested on:
Windows
|
1.0
|
`test_listcomps` fails when run with `-We` - ### Bug description:
`python -m test test_listcomps` emits `SyntaxWarnings` on `main`, and fails when run with `-We`:
```pytb
======================================================================
ERROR: test_comp_in_try_finally (test.test_listcomps.ListComprehensionTest.test_comp_in_try_finally) (scope='module')
----------------------------------------------------------------------
Traceback (most recent call last):
File "C:\Users\alexw\coding\cpython\Lib\test\test_listcomps.py", line 122, in _check_in_scopes
exec(newcode, newns)
File "<string>", line 4
SyntaxError: 'set' object is not callable; perhaps you missed a comma?
======================================================================
ERROR: test_comp_in_try_finally (test.test_listcomps.ListComprehensionTest.test_comp_in_try_finally) (scope='class')
----------------------------------------------------------------------
Traceback (most recent call last):
File "C:\Users\alexw\coding\cpython\Lib\test\test_listcomps.py", line 122, in _check_in_scopes
exec(newcode, newns)
File "<string>", line 6
SyntaxError: 'set' object is not callable; perhaps you missed a comma?
======================================================================
ERROR: test_comp_in_try_finally (test.test_listcomps.ListComprehensionTest.test_comp_in_try_finally) (scope='function')
----------------------------------------------------------------------
Traceback (most recent call last):
File "C:\Users\alexw\coding\cpython\Lib\test\test_listcomps.py", line 122, in _check_in_scopes
exec(newcode, newns)
File "<string>", line 6
SyntaxError: 'set' object is not callable; perhaps you missed a comma?
----------------------------------------------------------------------
```
The problematic test is `test_listcomps.ListComprehensionTest.test_comp_in_try_finally`, which was added in https://github.com/python/cpython/commit/d52c4482a82f3f98f1a78efa948144a1fe3c52b2 last week
### CPython versions tested on:
CPython main branch
### Operating systems tested on:
Windows
|
test
|
test listcomps fails when run with we bug description python m test test listcomps emits syntaxwarnings on main and fails when run with we pytb error test comp in try finally test test listcomps listcomprehensiontest test comp in try finally scope module traceback most recent call last file c users alexw coding cpython lib test test listcomps py line in check in scopes exec newcode newns file line syntaxerror set object is not callable perhaps you missed a comma error test comp in try finally test test listcomps listcomprehensiontest test comp in try finally scope class traceback most recent call last file c users alexw coding cpython lib test test listcomps py line in check in scopes exec newcode newns file line syntaxerror set object is not callable perhaps you missed a comma error test comp in try finally test test listcomps listcomprehensiontest test comp in try finally scope function traceback most recent call last file c users alexw coding cpython lib test test listcomps py line in check in scopes exec newcode newns file line syntaxerror set object is not callable perhaps you missed a comma the problematic test is test listcomps listcomprehensiontest test comp in try finally which was added in last week cpython versions tested on cpython main branch operating systems tested on windows
| 1
|
635,906
| 20,513,526,224
|
IssuesEvent
|
2022-03-01 09:24:42
|
space-wizards/space-station-14
|
https://api.github.com/repos/space-wizards/space-station-14
|
closed
|
Mice/all mobs have the same amount of blood as a human
|
Type: Bug Priority: 2-Before Release No C# Size: Very Small Difficulty: 1-Easy
|
## Description
blood balloon mouse
|
1.0
|
Mice/all mobs have the same amount of blood as a human - ## Description
blood balloon mouse
|
non_test
|
mice all mobs have the same amount of blood as a human description blood balloon mouse
| 0
|
211,219
| 16,190,673,070
|
IssuesEvent
|
2021-05-04 08:01:44
|
mozilla-mobile/fenix
|
https://api.github.com/repos/mozilla-mobile/fenix
|
opened
|
Intermittent UI test failure - SmokeTest.openRecentlyClosedTabsInNewPrivateTabTest
|
eng:ui-test
|
### Firebase Test Run:
https://console.firebase.google.com/u/1/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/6572327392771523352/executions/bs.658c5a176b9e5a06/testcases/1/test-cases
### Stacktrace:
`androidx.test.espresso.NoMatchingViewException: No views in hierarchy found matching: (with text: is "Search or enter address")
View Hierarchy:
+>DecorView{id=-1, visibility=VISIBLE, width=1080, height=1920, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params={(0,0)(fillxfill) sim={adjust=resize} ty=BASE_APPLICATION wanim=0x7f14033f
fl=LAYOUT_IN_SCREEN LAYOUT_INSET_DECOR HARDWARE_ACCELERATED DRAWS_SYSTEM_BAR_BACKGROUNDS
pfl=FORCE_DRAW_STATUS_BAR_BACKGROUND}, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=2}
|
+->LinearLayout{id=-1, visibility=VISIBLE, width=1080, height=1788, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.FrameLayout$LayoutParams@a4cb0bc, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=2}
|
+-->ViewStub{id=16908682, res-name=action_mode_bar_stub, visibility=GONE, width=0, height=0, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=true, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@de8b845, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0}
|
+-->FrameLayout{id=-1, visibility=VISIBLE, width=1080, height=1722, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@e99ab9a, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=66.0, child-count=1}
|
+--->FitWindowsLinearLayout{id=2131361869, res-name=action_bar_root, visibility=VISIBLE, width=1080, height=1722, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.FrameLayout$LayoutParams@d921ca8, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=2}
|
+---->ViewStubCompat{id=2131361936, res-name=action_mode_bar_stub, visibility=GONE, width=0, height=0, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=true, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@de193c1, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0}
|
+---->ContentFrameLayout{id=16908290, res-name=content, visibility=VISIBLE, width=1080, height=1722, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@c56e766, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=1}
|
+----->LinearLayout{id=2131362797, res-name=rootContainer, visibility=VISIBLE, width=1080, height=1722, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.FrameLayout$LayoutParams@5405b54, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=2}
|
+------>ViewStub{id=2131362650, res-name=navigationToolbarStub, visibility=GONE, width=0, height=0, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=true, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@f32aafd, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0}
|
+------>FragmentContainerView{id=2131362179, res-name=container, visibility=VISIBLE, width=1080, height=1722, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@55a13f2, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=0}
|
+->View{id=16908336, res-name=navigationBarBackground, visibility=VISIBLE, width=1080, height=132, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.FrameLayout$LayoutParams@89a6a43, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=1788.0}
|
at dalvik.system.VMStack.getThreadStackTrace(Native Method)
at java.lang.Thread.getStackTrace(Thread.java:1538)
at androidx.test.espresso.base.DefaultFailureHandler.getUserFriendlyError(DefaultFailureHandler.java:16)
at androidx.test.espresso.base.DefaultFailureHandler.handle(DefaultFailureHandler.java:36)
at androidx.test.espresso.ViewInteraction.waitForAndHandleInteractionResults(ViewInteraction.java:106)
at androidx.test.espresso.ViewInteraction.check(ViewInteraction.java:31)
at org.mozilla.fenix.ui.robots.HomeScreenRobotKt.assertNavigationToolbar(HomeScreenRobot.kt:480)
at org.mozilla.fenix.ui.robots.HomeScreenRobotKt.access$assertNavigationToolbar(HomeScreenRobot.kt:1)
at org.mozilla.fenix.ui.robots.HomeScreenRobot$Transition.openNavigationToolbar(HomeScreenRobot.kt:378)
at org.mozilla.fenix.ui.SmokeTest.openRecentlyClosedTabsInNewPrivateTabTest(SmokeTest.kt:788)`
### Build:
Debug 5/1
To me, from the video, it seems like a startup crash might have happened. Same failure on other tests: https://github.com/mozilla-mobile/fenix/issues/18635#issuecomment-831752585
|
1.0
|
Intermittent UI test failure - SmokeTest.openRecentlyClosedTabsInNewPrivateTabTest - ### Firebase Test Run:
https://console.firebase.google.com/u/1/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/6572327392771523352/executions/bs.658c5a176b9e5a06/testcases/1/test-cases
### Stacktrace:
`androidx.test.espresso.NoMatchingViewException: No views in hierarchy found matching: (with text: is "Search or enter address")
View Hierarchy:
+>DecorView{id=-1, visibility=VISIBLE, width=1080, height=1920, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params={(0,0)(fillxfill) sim={adjust=resize} ty=BASE_APPLICATION wanim=0x7f14033f
fl=LAYOUT_IN_SCREEN LAYOUT_INSET_DECOR HARDWARE_ACCELERATED DRAWS_SYSTEM_BAR_BACKGROUNDS
pfl=FORCE_DRAW_STATUS_BAR_BACKGROUND}, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=2}
|
+->LinearLayout{id=-1, visibility=VISIBLE, width=1080, height=1788, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.FrameLayout$LayoutParams@a4cb0bc, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=2}
|
+-->ViewStub{id=16908682, res-name=action_mode_bar_stub, visibility=GONE, width=0, height=0, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=true, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@de8b845, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0}
|
+-->FrameLayout{id=-1, visibility=VISIBLE, width=1080, height=1722, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@e99ab9a, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=66.0, child-count=1}
|
+--->FitWindowsLinearLayout{id=2131361869, res-name=action_bar_root, visibility=VISIBLE, width=1080, height=1722, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.FrameLayout$LayoutParams@d921ca8, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=2}
|
+---->ViewStubCompat{id=2131361936, res-name=action_mode_bar_stub, visibility=GONE, width=0, height=0, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=true, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@de193c1, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0}
|
+---->ContentFrameLayout{id=16908290, res-name=content, visibility=VISIBLE, width=1080, height=1722, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@c56e766, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=1}
|
+----->LinearLayout{id=2131362797, res-name=rootContainer, visibility=VISIBLE, width=1080, height=1722, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.FrameLayout$LayoutParams@5405b54, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=2}
|
+------>ViewStub{id=2131362650, res-name=navigationToolbarStub, visibility=GONE, width=0, height=0, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=true, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@f32aafd, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0}
|
+------>FragmentContainerView{id=2131362179, res-name=container, visibility=VISIBLE, width=1080, height=1722, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.LinearLayout$LayoutParams@55a13f2, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=0.0, child-count=0}
|
+->View{id=16908336, res-name=navigationBarBackground, visibility=VISIBLE, width=1080, height=132, has-focus=false, has-focusable=false, has-window-focus=true, is-clickable=false, is-enabled=true, is-focused=false, is-focusable=false, is-layout-requested=false, is-selected=false, layout-params=android.widget.FrameLayout$LayoutParams@89a6a43, tag=null, root-is-layout-requested=false, has-input-connection=false, x=0.0, y=1788.0}
|
at dalvik.system.VMStack.getThreadStackTrace(Native Method)
at java.lang.Thread.getStackTrace(Thread.java:1538)
at androidx.test.espresso.base.DefaultFailureHandler.getUserFriendlyError(DefaultFailureHandler.java:16)
at androidx.test.espresso.base.DefaultFailureHandler.handle(DefaultFailureHandler.java:36)
at androidx.test.espresso.ViewInteraction.waitForAndHandleInteractionResults(ViewInteraction.java:106)
at androidx.test.espresso.ViewInteraction.check(ViewInteraction.java:31)
at org.mozilla.fenix.ui.robots.HomeScreenRobotKt.assertNavigationToolbar(HomeScreenRobot.kt:480)
at org.mozilla.fenix.ui.robots.HomeScreenRobotKt.access$assertNavigationToolbar(HomeScreenRobot.kt:1)
at org.mozilla.fenix.ui.robots.HomeScreenRobot$Transition.openNavigationToolbar(HomeScreenRobot.kt:378)
at org.mozilla.fenix.ui.SmokeTest.openRecentlyClosedTabsInNewPrivateTabTest(SmokeTest.kt:788)`
### Build:
Debug 5/1
To me, from the video, it seems like a startup crash might have happened. Same failure on other tests: https://github.com/mozilla-mobile/fenix/issues/18635#issuecomment-831752585
|
test
|
intermittent ui test failure smoketest openrecentlyclosedtabsinnewprivatetabtest firebase test run stacktrace androidx test espresso nomatchingviewexception no views in hierarchy found matching with text is search or enter address view hierarchy decorview id visibility visible width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested false is selected false layout params fillxfill sim adjust resize ty base application wanim fl layout in screen layout inset decor hardware accelerated draws system bar backgrounds pfl force draw status bar background tag null root is layout requested false has input connection false x y child count linearlayout id visibility visible width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested false is selected false layout params android widget framelayout layoutparams tag null root is layout requested false has input connection false x y child count viewstub id res name action mode bar stub visibility gone width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested true is selected false layout params android widget linearlayout layoutparams tag null root is layout requested false has input connection false x y framelayout id visibility visible width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested false is selected false layout params android widget linearlayout layoutparams tag null root is layout requested false has input connection false x y child count fitwindowslinearlayout id res name action bar root visibility visible width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested false is selected false layout params android widget framelayout layoutparams tag null root is layout requested false has input connection false x y child count viewstubcompat id res name action mode bar stub visibility gone width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested true is selected false layout params android widget linearlayout layoutparams tag null root is layout requested false has input connection false x y contentframelayout id res name content visibility visible width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested false is selected false layout params android widget linearlayout layoutparams tag null root is layout requested false has input connection false x y child count linearlayout id res name rootcontainer visibility visible width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested false is selected false layout params android widget framelayout layoutparams tag null root is layout requested false has input connection false x y child count viewstub id res name navigationtoolbarstub visibility gone width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested true is selected false layout params android widget linearlayout layoutparams tag null root is layout requested false has input connection false x y fragmentcontainerview id res name container visibility visible width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested false is selected false layout params android widget linearlayout layoutparams tag null root is layout requested false has input connection false x y child count view id res name navigationbarbackground visibility visible width height has focus false has focusable false has window focus true is clickable false is enabled true is focused false is focusable false is layout requested false is selected false layout params android widget framelayout layoutparams tag null root is layout requested false has input connection false x y at dalvik system vmstack getthreadstacktrace native method at java lang thread getstacktrace thread java at androidx test espresso base defaultfailurehandler getuserfriendlyerror defaultfailurehandler java at androidx test espresso base defaultfailurehandler handle defaultfailurehandler java at androidx test espresso viewinteraction waitforandhandleinteractionresults viewinteraction java at androidx test espresso viewinteraction check viewinteraction java at org mozilla fenix ui robots homescreenrobotkt assertnavigationtoolbar homescreenrobot kt at org mozilla fenix ui robots homescreenrobotkt access assertnavigationtoolbar homescreenrobot kt at org mozilla fenix ui robots homescreenrobot transition opennavigationtoolbar homescreenrobot kt at org mozilla fenix ui smoketest openrecentlyclosedtabsinnewprivatetabtest smoketest kt build debug to me from the video it seems like a startup crash might have happened same failure on other tests
| 1
|
214,143
| 16,565,297,700
|
IssuesEvent
|
2021-05-29 09:18:12
|
OliverBenz/PhysEn
|
https://api.github.com/repos/OliverBenz/PhysEn
|
closed
|
Test: Vector
|
testing
|
**Describe the solution you'd like**
Add more vector tests for new implementation.
|
1.0
|
Test: Vector - **Describe the solution you'd like**
Add more vector tests for new implementation.
|
test
|
test vector describe the solution you d like add more vector tests for new implementation
| 1
|
246,263
| 20,831,536,650
|
IssuesEvent
|
2022-03-19 14:23:49
|
bichvan-1711/FeedbackOnline
|
https://api.github.com/repos/bichvan-1711/FeedbackOnline
|
opened
|
[BugID_1]_GUI_Login Page_ [Password] txtbox data được mask là '•'
|
bug Low Cosmetic Integration Test UI_Label/Message Open
|
hiện tại: "•••••"
mong muốn: "*****"
--------------------------
TestCaseID = 2
|
1.0
|
[BugID_1]_GUI_Login Page_ [Password] txtbox data được mask là '•' - hiện tại: "•••••"
mong muốn: "*****"
--------------------------
TestCaseID = 2
|
test
|
gui login page txtbox data được mask là • hiện tại ••••• mong muốn testcaseid
| 1
|
252,097
| 27,229,558,170
|
IssuesEvent
|
2023-02-21 12:13:18
|
samq-ghdemo/Remediate-EoL-Library
|
https://api.github.com/repos/samq-ghdemo/Remediate-EoL-Library
|
opened
|
commons-fileupload-1.4.jar: 1 vulnerabilities (highest severity is: 5.5)
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-fileupload-1.4.jar</b></p></summary>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-fileupload/">http://commons.apache.org/proper/commons-fileupload/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /commons-fileupload/commons-fileupload/1.4/commons-fileupload-1.4.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Remediate-EoL-Library/commit/e3808113e95a039bfa74271705a07407a411653a">e3808113e95a039bfa74271705a07407a411653a</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (commons-fileupload version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-24998](https://www.mend.io/vulnerability-database/CVE-2023-24998) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | commons-fileupload-1.4.jar | Direct | commons-fileupload:commons-fileupload:1.5;org.apache.tomcat:tomcat-coyote:8.5.85,9.0.71,10.1.5 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2023-24998</summary>
### Vulnerable Library - <b>commons-fileupload-1.4.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-fileupload/">http://commons.apache.org/proper/commons-fileupload/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /commons-fileupload/commons-fileupload/1.4/commons-fileupload-1.4.jar</p>
<p>
Dependency Hierarchy:
- :x: **commons-fileupload-1.4.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Remediate-EoL-Library/commit/e3808113e95a039bfa74271705a07407a411653a">e3808113e95a039bfa74271705a07407a411653a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons FileUpload before 1.5 does not limit the number of request parts to be processed resulting in the possibility of an attacker triggering a DoS with a malicious upload or series of uploads.
<p>Publish Date: 2023-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-24998>CVE-2023-24998</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://seclists.org/oss-sec/2023/q1/108">https://seclists.org/oss-sec/2023/q1/108</a></p>
<p>Release Date: 2023-02-20</p>
<p>Fix Resolution: commons-fileupload:commons-fileupload:1.5;org.apache.tomcat:tomcat-coyote:8.5.85,9.0.71,10.1.5</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
True
|
commons-fileupload-1.4.jar: 1 vulnerabilities (highest severity is: 5.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-fileupload-1.4.jar</b></p></summary>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-fileupload/">http://commons.apache.org/proper/commons-fileupload/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /commons-fileupload/commons-fileupload/1.4/commons-fileupload-1.4.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Remediate-EoL-Library/commit/e3808113e95a039bfa74271705a07407a411653a">e3808113e95a039bfa74271705a07407a411653a</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (commons-fileupload version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-24998](https://www.mend.io/vulnerability-database/CVE-2023-24998) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | commons-fileupload-1.4.jar | Direct | commons-fileupload:commons-fileupload:1.5;org.apache.tomcat:tomcat-coyote:8.5.85,9.0.71,10.1.5 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2023-24998</summary>
### Vulnerable Library - <b>commons-fileupload-1.4.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-fileupload/">http://commons.apache.org/proper/commons-fileupload/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /commons-fileupload/commons-fileupload/1.4/commons-fileupload-1.4.jar</p>
<p>
Dependency Hierarchy:
- :x: **commons-fileupload-1.4.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Remediate-EoL-Library/commit/e3808113e95a039bfa74271705a07407a411653a">e3808113e95a039bfa74271705a07407a411653a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons FileUpload before 1.5 does not limit the number of request parts to be processed resulting in the possibility of an attacker triggering a DoS with a malicious upload or series of uploads.
<p>Publish Date: 2023-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-24998>CVE-2023-24998</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://seclists.org/oss-sec/2023/q1/108">https://seclists.org/oss-sec/2023/q1/108</a></p>
<p>Release Date: 2023-02-20</p>
<p>Fix Resolution: commons-fileupload:commons-fileupload:1.5;org.apache.tomcat:tomcat-coyote:8.5.85,9.0.71,10.1.5</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
non_test
|
commons fileupload jar vulnerabilities highest severity is vulnerable library commons fileupload jar the apache commons fileupload component provides a simple yet flexible means of adding support for multipart file upload functionality to servlets and web applications library home page a href path to dependency file pom xml path to vulnerable library commons fileupload commons fileupload commons fileupload jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in commons fileupload version remediation available medium commons fileupload jar direct commons fileupload commons fileupload org apache tomcat tomcat coyote details cve vulnerable library commons fileupload jar the apache commons fileupload component provides a simple yet flexible means of adding support for multipart file upload functionality to servlets and web applications library home page a href path to dependency file pom xml path to vulnerable library commons fileupload commons fileupload commons fileupload jar dependency hierarchy x commons fileupload jar vulnerable library found in head commit a href found in base branch main vulnerability details apache commons fileupload before does not limit the number of request parts to be processed resulting in the possibility of an attacker triggering a dos with a malicious upload or series of uploads publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons fileupload commons fileupload org apache tomcat tomcat coyote rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue
| 0
|
307,368
| 9,416,203,400
|
IssuesEvent
|
2019-04-10 14:13:46
|
wso2/analytics-solutions
|
https://api.github.com/repos/wso2/analytics-solutions
|
closed
|
[EI Analytics] Overview > Request Count - Text mis-aligns with the Pie-chart
|
Component/EI-Analytics Priority/High Type/Bug
|
**Description:**
In EI Analytics Overview page, Pie chart and its label mis-align in "Request Count" widget.
**Affected Product Version:**
WSO2SP 4.3.0
|
1.0
|
[EI Analytics] Overview > Request Count - Text mis-aligns with the Pie-chart - **Description:**
In EI Analytics Overview page, Pie chart and its label mis-align in "Request Count" widget.
**Affected Product Version:**
WSO2SP 4.3.0
|
non_test
|
overview request count text mis aligns with the pie chart description in ei analytics overview page pie chart and its label mis align in request count widget affected product version
| 0
|
310,330
| 26,711,393,896
|
IssuesEvent
|
2023-01-28 00:44:47
|
microsoft/wopi-validator-core
|
https://api.github.com/repos/microsoft/wopi-validator-core
|
closed
|
Add test for hosts that use Transfer-Encoding: chunked for GetFile requests without specifying a SHA256
|
new test
|
More information: https://github.com/Microsoft/Office-Online-Test-Tools-and-Documentation/issues/242
The host SHOULD provide a hash if they use chunked transfer to prevent a class of bugs where we think we got the whole file but didn't.
|
1.0
|
Add test for hosts that use Transfer-Encoding: chunked for GetFile requests without specifying a SHA256 - More information: https://github.com/Microsoft/Office-Online-Test-Tools-and-Documentation/issues/242
The host SHOULD provide a hash if they use chunked transfer to prevent a class of bugs where we think we got the whole file but didn't.
|
test
|
add test for hosts that use transfer encoding chunked for getfile requests without specifying a more information the host should provide a hash if they use chunked transfer to prevent a class of bugs where we think we got the whole file but didn t
| 1
|
200,456
| 22,776,385,252
|
IssuesEvent
|
2022-07-08 14:50:18
|
CMSgov/cms-carts-seds
|
https://api.github.com/repos/CMSgov/cms-carts-seds
|
opened
|
SHF - cms-carts-seds - main - MEDIUM - S3.9 S3 bucket server access logging should be enabled
|
security-hub main
|
**************************************************************
__This issue was generated from Security Hub data and is managed through automation.__
Please do not edit the title or body of this issue, or remove the security-hub tag. All other edits/comments are welcome.
Finding Id: arn:aws:securityhub:us-east-1:519095364708:subscription/aws-foundational-security-best-practices/v/1.0.0/S3.9/finding/968f8ddf-aabd-47ac-a5d6-b34bda4eca15
**************************************************************
## Type of Issue:
- [x] Security Hub Finding
## Title:
S3.9 S3 bucket server access logging should be enabled
## Id:
arn:aws:securityhub:us-east-1:519095364708:subscription/aws-foundational-security-best-practices/v/1.0.0/S3.9/finding/968f8ddf-aabd-47ac-a5d6-b34bda4eca15
(You may use this ID to lookup this finding's details in Security Hub)
## Description
This control checks if an Amazon S3 Bucket has server access logging enabled to a chosen target bucket.
## Remediation
https://docs.aws.amazon.com/console/securityhub/S3.9/remediation
## AC:
- The security hub finding is resolved or suppressed, indicated by a Workflow Status of Resolved or Suppressed.
|
True
|
SHF - cms-carts-seds - main - MEDIUM - S3.9 S3 bucket server access logging should be enabled - **************************************************************
__This issue was generated from Security Hub data and is managed through automation.__
Please do not edit the title or body of this issue, or remove the security-hub tag. All other edits/comments are welcome.
Finding Id: arn:aws:securityhub:us-east-1:519095364708:subscription/aws-foundational-security-best-practices/v/1.0.0/S3.9/finding/968f8ddf-aabd-47ac-a5d6-b34bda4eca15
**************************************************************
## Type of Issue:
- [x] Security Hub Finding
## Title:
S3.9 S3 bucket server access logging should be enabled
## Id:
arn:aws:securityhub:us-east-1:519095364708:subscription/aws-foundational-security-best-practices/v/1.0.0/S3.9/finding/968f8ddf-aabd-47ac-a5d6-b34bda4eca15
(You may use this ID to lookup this finding's details in Security Hub)
## Description
This control checks if an Amazon S3 Bucket has server access logging enabled to a chosen target bucket.
## Remediation
https://docs.aws.amazon.com/console/securityhub/S3.9/remediation
## AC:
- The security hub finding is resolved or suppressed, indicated by a Workflow Status of Resolved or Suppressed.
|
non_test
|
shf cms carts seds main medium bucket server access logging should be enabled this issue was generated from security hub data and is managed through automation please do not edit the title or body of this issue or remove the security hub tag all other edits comments are welcome finding id arn aws securityhub us east subscription aws foundational security best practices v finding aabd type of issue security hub finding title bucket server access logging should be enabled id arn aws securityhub us east subscription aws foundational security best practices v finding aabd you may use this id to lookup this finding s details in security hub description this control checks if an amazon bucket has server access logging enabled to a chosen target bucket remediation ac the security hub finding is resolved or suppressed indicated by a workflow status of resolved or suppressed
| 0
|
10,563
| 4,074,267,039
|
IssuesEvent
|
2016-05-28 09:54:47
|
SleepyTrousers/EnderIO
|
https://api.github.com/repos/SleepyTrousers/EnderIO
|
closed
|
farm station insert seed up to stacksize
|
bug Code Complete
|
With a non upgraded farmStation, if you manually place seeds into the grid it will only go up to 16. But when you insert the seeds through an item conduit from a chest it will add up to 64 seeds per grid space.

|
1.0
|
farm station insert seed up to stacksize - With a non upgraded farmStation, if you manually place seeds into the grid it will only go up to 16. But when you insert the seeds through an item conduit from a chest it will add up to 64 seeds per grid space.

|
non_test
|
farm station insert seed up to stacksize with a non upgraded farmstation if you manually place seeds into the grid it will only go up to but when you insert the seeds through an item conduit from a chest it will add up to seeds per grid space
| 0
|
218,248
| 16,757,667,122
|
IssuesEvent
|
2021-06-13 05:52:38
|
ti-community-infra/tichi
|
https://api.github.com/repos/ti-community-infra/tichi
|
closed
|
Add contribution guidelines and development documentation
|
type/documentation
|
Add contribution guidelines and development documentation
|
1.0
|
Add contribution guidelines and development documentation - Add contribution guidelines and development documentation
|
non_test
|
add contribution guidelines and development documentation add contribution guidelines and development documentation
| 0
|
166,096
| 12,890,784,481
|
IssuesEvent
|
2020-07-13 16:34:17
|
cockroachdb/cockroach
|
https://api.github.com/repos/cockroachdb/cockroach
|
closed
|
roachtest: tpcc/interleaved/nodes=3/cpu=16/w=500 failed
|
C-test-failure O-roachtest O-robot branch-master release-blocker
|
[(roachtest).tpcc/interleaved/nodes=3/cpu=16/w=500 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2076266&tab=buildLog) on [master@1b5d070c93375d3e14c146241e8bafde349529bd](https://github.com/cockroachdb/cockroach/commits/1b5d070c93375d3e14c146241e8bafde349529bd):
```
| 135.0s 0 98.9 92.1 25.2 41.9 113.2 130.0 newOrder
| 135.0s 0 14.0 10.1 5.8 8.4 12.1 12.1 orderStatus
| 135.0s 0 112.9 99.8 44.0 83.9 104.9 130.0 payment
| 135.0s 0 12.0 9.9 23.1 32.5 37.7 37.7 stockLevel
| 136.0s 0 7.0 10.1 41.9 54.5 54.5 54.5 delivery
| 136.0s 0 95.0 92.2 25.2 35.7 37.7 39.8 newOrder
| 136.0s 0 11.0 10.2 5.5 7.1 8.9 8.9 orderStatus
| 136.0s 0 81.0 99.7 41.9 67.1 79.7 83.9 payment
| 136.0s 0 5.0 9.9 21.0 22.0 22.0 22.0 stockLevel
| _elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
| 137.0s 0 10.0 10.1 48.2 56.6 56.6 56.6 delivery
| 137.0s 0 119.1 92.4 27.3 35.7 41.9 44.0 newOrder
| 137.0s 0 7.0 10.1 5.0 10.5 10.5 10.5 orderStatus
| 137.0s 0 119.1 99.8 48.2 88.1 100.7 113.2 payment
| 137.0s 0 5.0 9.9 23.1 39.8 39.8 39.8 stockLevel
Wraps: (5) secondary error attachment
| signal: killed
| (1) signal: killed
| Error types: (1) *exec.ExitError
Wraps: (6) context canceled
Error types: (1) *withstack.withStack (2) *safedetails.withSafeDetails (3) *errutil.withMessage (4) *main.withCommandDetails (5) *secondary.withSecondaryError (6) *errors.errorString
cluster.go:2471,tpcc.go:187,tpcc.go:361,test_runner.go:757: monitor failure: monitor task failed: t.Fatal() was called
(1) attached stack trace
| main.(*monitor).WaitE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2459
| main.(*monitor).Wait
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2467
| main.runTPCC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:187
| main.registerTPCC.func6
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:361
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:757
Wraps: (2) monitor failure
Wraps: (3) attached stack trace
| main.(*monitor).wait.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2515
Wraps: (4) monitor task failed
Wraps: (5) attached stack trace
| main.init
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2429
| runtime.doInit
| /usr/local/go/src/runtime/proc.go:5420
| runtime.main
| /usr/local/go/src/runtime/proc.go:190
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1373
Wraps: (6) t.Fatal() was called
Error types: (1) *withstack.withStack (2) *errutil.withMessage (3) *withstack.withStack (4) *errutil.withMessage (5) *withstack.withStack (6) *errors.errorString
```
<details><summary>More</summary><p>
Artifacts: [/tpcc/interleaved/nodes=3/cpu=16/w=500](https://teamcity.cockroachdb.com/viewLog.html?buildId=2076266&tab=artifacts#/tpcc/interleaved/nodes=3/cpu=16/w=500)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Atpcc%2Finterleaved%2Fnodes%3D3%2Fcpu%3D16%2Fw%3D500.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
|
2.0
|
roachtest: tpcc/interleaved/nodes=3/cpu=16/w=500 failed - [(roachtest).tpcc/interleaved/nodes=3/cpu=16/w=500 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2076266&tab=buildLog) on [master@1b5d070c93375d3e14c146241e8bafde349529bd](https://github.com/cockroachdb/cockroach/commits/1b5d070c93375d3e14c146241e8bafde349529bd):
```
| 135.0s 0 98.9 92.1 25.2 41.9 113.2 130.0 newOrder
| 135.0s 0 14.0 10.1 5.8 8.4 12.1 12.1 orderStatus
| 135.0s 0 112.9 99.8 44.0 83.9 104.9 130.0 payment
| 135.0s 0 12.0 9.9 23.1 32.5 37.7 37.7 stockLevel
| 136.0s 0 7.0 10.1 41.9 54.5 54.5 54.5 delivery
| 136.0s 0 95.0 92.2 25.2 35.7 37.7 39.8 newOrder
| 136.0s 0 11.0 10.2 5.5 7.1 8.9 8.9 orderStatus
| 136.0s 0 81.0 99.7 41.9 67.1 79.7 83.9 payment
| 136.0s 0 5.0 9.9 21.0 22.0 22.0 22.0 stockLevel
| _elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
| 137.0s 0 10.0 10.1 48.2 56.6 56.6 56.6 delivery
| 137.0s 0 119.1 92.4 27.3 35.7 41.9 44.0 newOrder
| 137.0s 0 7.0 10.1 5.0 10.5 10.5 10.5 orderStatus
| 137.0s 0 119.1 99.8 48.2 88.1 100.7 113.2 payment
| 137.0s 0 5.0 9.9 23.1 39.8 39.8 39.8 stockLevel
Wraps: (5) secondary error attachment
| signal: killed
| (1) signal: killed
| Error types: (1) *exec.ExitError
Wraps: (6) context canceled
Error types: (1) *withstack.withStack (2) *safedetails.withSafeDetails (3) *errutil.withMessage (4) *main.withCommandDetails (5) *secondary.withSecondaryError (6) *errors.errorString
cluster.go:2471,tpcc.go:187,tpcc.go:361,test_runner.go:757: monitor failure: monitor task failed: t.Fatal() was called
(1) attached stack trace
| main.(*monitor).WaitE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2459
| main.(*monitor).Wait
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2467
| main.runTPCC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:187
| main.registerTPCC.func6
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:361
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:757
Wraps: (2) monitor failure
Wraps: (3) attached stack trace
| main.(*monitor).wait.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2515
Wraps: (4) monitor task failed
Wraps: (5) attached stack trace
| main.init
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2429
| runtime.doInit
| /usr/local/go/src/runtime/proc.go:5420
| runtime.main
| /usr/local/go/src/runtime/proc.go:190
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1373
Wraps: (6) t.Fatal() was called
Error types: (1) *withstack.withStack (2) *errutil.withMessage (3) *withstack.withStack (4) *errutil.withMessage (5) *withstack.withStack (6) *errors.errorString
```
<details><summary>More</summary><p>
Artifacts: [/tpcc/interleaved/nodes=3/cpu=16/w=500](https://teamcity.cockroachdb.com/viewLog.html?buildId=2076266&tab=artifacts#/tpcc/interleaved/nodes=3/cpu=16/w=500)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Atpcc%2Finterleaved%2Fnodes%3D3%2Fcpu%3D16%2Fw%3D500.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
|
test
|
roachtest tpcc interleaved nodes cpu w failed on neworder orderstatus payment stocklevel delivery neworder orderstatus payment stocklevel elapsed errors ops sec inst ops sec cum ms ms ms pmax ms delivery neworder orderstatus payment stocklevel wraps secondary error attachment signal killed signal killed error types exec exiterror wraps context canceled error types withstack withstack safedetails withsafedetails errutil withmessage main withcommanddetails secondary withsecondaryerror errors errorstring cluster go tpcc go tpcc go test runner go monitor failure monitor task failed t fatal was called attached stack trace main monitor waite home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main monitor wait home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main runtpcc home agent work go src github com cockroachdb cockroach pkg cmd roachtest tpcc go main registertpcc home agent work go src github com cockroachdb cockroach pkg cmd roachtest tpcc go main testrunner runtest home agent work go src github com cockroachdb cockroach pkg cmd roachtest test runner go wraps monitor failure wraps attached stack trace main monitor wait home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go wraps monitor task failed wraps attached stack trace main init home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go runtime doinit usr local go src runtime proc go runtime main usr local go src runtime proc go runtime goexit usr local go src runtime asm s wraps t fatal was called error types withstack withstack errutil withmessage withstack withstack errutil withmessage withstack withstack errors errorstring more artifacts powered by
| 1
|
90,639
| 26,159,102,775
|
IssuesEvent
|
2022-12-31 07:47:30
|
PaddlePaddle/Paddle
|
https://api.github.com/repos/PaddlePaddle/Paddle
|
opened
|
Windows Server 2008 R2 部署时,提示缺少api-ms-win XXX.dll
|
status/new-issue type/build
|
### 问题描述 Issue Description
Win11部署正常,是不支持 Win Server 2008 r2吗,已经安装vc相关依赖。
### 版本&环境信息 Version & Environment Information
PaddlePaddle版本: 2.4.1 / 2.4问题一样。
|
1.0
|
Windows Server 2008 R2 部署时,提示缺少api-ms-win XXX.dll - ### 问题描述 Issue Description
Win11部署正常,是不支持 Win Server 2008 r2吗,已经安装vc相关依赖。
### 版本&环境信息 Version & Environment Information
PaddlePaddle版本: 2.4.1 / 2.4问题一样。
|
non_test
|
windows server 部署时,提示缺少api ms win xxx dll 问题描述 issue description ,是不支持 win server ,已经安装vc相关依赖。 版本 环境信息 version environment information paddlepaddle版本: 。
| 0
|
260,542
| 22,629,711,425
|
IssuesEvent
|
2022-06-30 13:44:42
|
dominicm00/ham
|
https://api.github.com/repos/dominicm00/ham
|
closed
|
Support `quietly` actions modifier
|
high priority is:tests is:make bug:compliance
|
Support `actions quietly`, which prevents the action from being printed to the command line.
|
1.0
|
Support `quietly` actions modifier - Support `actions quietly`, which prevents the action from being printed to the command line.
|
test
|
support quietly actions modifier support actions quietly which prevents the action from being printed to the command line
| 1
|
325,163
| 24,037,610,704
|
IssuesEvent
|
2022-09-15 20:46:34
|
chartjs/Chart.js
|
https://api.github.com/repos/chartjs/Chart.js
|
closed
|
please add this feature into your guide document, how to write integer value on y-Axis
|
type: support type: documentation
|
### Feature Proposal
i am using line chart, it is working fine with vue2 and i am glad to use this but i want to print integer value on Y-axis instead of float value. please update it into your documentation
### Possible Implementation
_No response_
|
1.0
|
please add this feature into your guide document, how to write integer value on y-Axis - ### Feature Proposal
i am using line chart, it is working fine with vue2 and i am glad to use this but i want to print integer value on Y-axis instead of float value. please update it into your documentation
### Possible Implementation
_No response_
|
non_test
|
please add this feature into your guide document how to write integer value on y axis feature proposal i am using line chart it is working fine with and i am glad to use this but i want to print integer value on y axis instead of float value please update it into your documentation possible implementation no response
| 0
|
148,001
| 11,825,895,271
|
IssuesEvent
|
2020-03-21 15:14:16
|
effectsjs/effectsjs
|
https://api.github.com/repos/effectsjs/effectsjs
|
opened
|
Write more tests around concurrent behavior
|
Tests
|
Competing async / concurrent calls are at the heart of a few use cases around effects.
Lets bulk up on these tests:
- [ ] prove that mutually exclusive resources behave as expected in effect handlers
- [ ] prove that non mutually exclusive resouces do not bottleneck in effect handlers
|
1.0
|
Write more tests around concurrent behavior - Competing async / concurrent calls are at the heart of a few use cases around effects.
Lets bulk up on these tests:
- [ ] prove that mutually exclusive resources behave as expected in effect handlers
- [ ] prove that non mutually exclusive resouces do not bottleneck in effect handlers
|
test
|
write more tests around concurrent behavior competing async concurrent calls are at the heart of a few use cases around effects lets bulk up on these tests prove that mutually exclusive resources behave as expected in effect handlers prove that non mutually exclusive resouces do not bottleneck in effect handlers
| 1
|
324,951
| 27,834,218,530
|
IssuesEvent
|
2023-03-20 08:15:41
|
proarc/proarc
|
https://api.github.com/repos/proarc/proarc
|
closed
|
Importy v MZK: vytvořit speciální importní profil
|
6 k testování Release-3.7.1
|
Kvůli urychlení procesu importu (aby netimeoutoval u velkých dokumentů) jsme vytvořili předimportní skript, který generuje jp2 (přípona jp2), OCR, ale i thumbnail a preview obrázky (přípony .thumb.jpg a .preview.jpg). Potřebujeme pro tuto variantu importu vytvořit nový importní profil vedle stávajícího.
|
1.0
|
Importy v MZK: vytvořit speciální importní profil - Kvůli urychlení procesu importu (aby netimeoutoval u velkých dokumentů) jsme vytvořili předimportní skript, který generuje jp2 (přípona jp2), OCR, ale i thumbnail a preview obrázky (přípony .thumb.jpg a .preview.jpg). Potřebujeme pro tuto variantu importu vytvořit nový importní profil vedle stávajícího.
|
test
|
importy v mzk vytvořit speciální importní profil kvůli urychlení procesu importu aby netimeoutoval u velkých dokumentů jsme vytvořili předimportní skript který generuje přípona ocr ale i thumbnail a preview obrázky přípony thumb jpg a preview jpg potřebujeme pro tuto variantu importu vytvořit nový importní profil vedle stávajícího
| 1
|
446,785
| 12,878,856,944
|
IssuesEvent
|
2020-07-11 18:48:02
|
Thorium-Sim/thorium
|
https://api.github.com/repos/Thorium-Sim/thorium
|
opened
|
Sensor contact speed messed up
|
priority/high type/bug
|
### Requested By: Mason P. (Zaynt Icarus)
### Priority: High
### Version: 2.12.4
When trying to adjust sensor contact speed, they are all way too fast. Slow goes fast, Moderate goes warp, etc.
### Steps to Reproduce
1. Make a sensors contact
2. set contact speed to moderate
3. move contact
4. it'll go much faster than it should
|
1.0
|
Sensor contact speed messed up - ### Requested By: Mason P. (Zaynt Icarus)
### Priority: High
### Version: 2.12.4
When trying to adjust sensor contact speed, they are all way too fast. Slow goes fast, Moderate goes warp, etc.
### Steps to Reproduce
1. Make a sensors contact
2. set contact speed to moderate
3. move contact
4. it'll go much faster than it should
|
non_test
|
sensor contact speed messed up requested by mason p zaynt icarus priority high version when trying to adjust sensor contact speed they are all way too fast slow goes fast moderate goes warp etc steps to reproduce make a sensors contact set contact speed to moderate move contact it ll go much faster than it should
| 0
|
9,924
| 3,078,615,510
|
IssuesEvent
|
2015-08-21 11:32:38
|
devprovers/QA-Teamwork-Provers
|
https://api.github.com/repos/devprovers/QA-Teamwork-Provers
|
closed
|
Delete Activity
|
To Be Tested Use Case
|
Use Case №18: Delete Activity
Primary Actor: User
Pre Condition: User logged in
Main scenario:
1. User selects the activity from CRM/Activities (left pane, refer user screens in Appendix )
2. User initiates the “Delete Activity” functionality from the activity itself
3. System displays a confirmation message
4. Activity is deleted
|
1.0
|
Delete Activity - Use Case №18: Delete Activity
Primary Actor: User
Pre Condition: User logged in
Main scenario:
1. User selects the activity from CRM/Activities (left pane, refer user screens in Appendix )
2. User initiates the “Delete Activity” functionality from the activity itself
3. System displays a confirmation message
4. Activity is deleted
|
test
|
delete activity use case № delete activity primary actor user pre condition user logged in main scenario user selects the activity from crm activities left pane refer user screens in appendix user initiates the “delete activity” functionality from the activity itself system displays a confirmation message activity is deleted
| 1
|
35,859
| 7,810,759,268
|
IssuesEvent
|
2018-06-12 08:00:36
|
primefaces/primeng
|
https://api.github.com/repos/primefaces/primeng
|
closed
|
Dropdown to call onChange() only on keyboard enter instead of arrow up/down
|
defect
|
**I'm submitting a ...** (check one with "x")
```
[? ] bug report
[x ] feature request
```
**Current behavior**
The (onChange) behaviour is called when using the dropdown with the keyboard up/down arrows
**Expected behavior**
<!-- Describe what the behavior would be without the bug. -->
Most dropdowns do not do this by default, instead the actual value is only changed when pressing enter with the value you want to have focused.
**What is the motivation / use case for changing the behavior?**
I am working on accessibility, and some of our dropdowns open panels/alerts when clicked. There is no way to browse the options in a dropdown with the keyboard without triggering these events (and hence loosing focus on the dropdown). I want to be able to browse the dropdown with the up/down keys and then press enter to choose the value i want
The workaround I currently see for this is to capture the original event and prevent the default onChange() behaviour, (maybe store current value somewhere) and then call it seperately on keydown.enter
OR
have the onChange() event not trigger the sidepanel/alert function, only change the value. In addition have a button adjacent to the dropdown to call the corresponding function on press. But this ruins the experience for users as there are more clicks
* **Angular version:** 2.0.X
Angular 5.1.3
* **PrimeNG version:** 2.0.X
Prime 5.2.9
|
1.0
|
Dropdown to call onChange() only on keyboard enter instead of arrow up/down -
**I'm submitting a ...** (check one with "x")
```
[? ] bug report
[x ] feature request
```
**Current behavior**
The (onChange) behaviour is called when using the dropdown with the keyboard up/down arrows
**Expected behavior**
<!-- Describe what the behavior would be without the bug. -->
Most dropdowns do not do this by default, instead the actual value is only changed when pressing enter with the value you want to have focused.
**What is the motivation / use case for changing the behavior?**
I am working on accessibility, and some of our dropdowns open panels/alerts when clicked. There is no way to browse the options in a dropdown with the keyboard without triggering these events (and hence loosing focus on the dropdown). I want to be able to browse the dropdown with the up/down keys and then press enter to choose the value i want
The workaround I currently see for this is to capture the original event and prevent the default onChange() behaviour, (maybe store current value somewhere) and then call it seperately on keydown.enter
OR
have the onChange() event not trigger the sidepanel/alert function, only change the value. In addition have a button adjacent to the dropdown to call the corresponding function on press. But this ruins the experience for users as there are more clicks
* **Angular version:** 2.0.X
Angular 5.1.3
* **PrimeNG version:** 2.0.X
Prime 5.2.9
|
non_test
|
dropdown to call onchange only on keyboard enter instead of arrow up down i m submitting a check one with x bug report feature request current behavior the onchange behaviour is called when using the dropdown with the keyboard up down arrows expected behavior most dropdowns do not do this by default instead the actual value is only changed when pressing enter with the value you want to have focused what is the motivation use case for changing the behavior i am working on accessibility and some of our dropdowns open panels alerts when clicked there is no way to browse the options in a dropdown with the keyboard without triggering these events and hence loosing focus on the dropdown i want to be able to browse the dropdown with the up down keys and then press enter to choose the value i want the workaround i currently see for this is to capture the original event and prevent the default onchange behaviour maybe store current value somewhere and then call it seperately on keydown enter or have the onchange event not trigger the sidepanel alert function only change the value in addition have a button adjacent to the dropdown to call the corresponding function on press but this ruins the experience for users as there are more clicks angular version x angular primeng version x prime
| 0
|
348,029
| 31,393,541,748
|
IssuesEvent
|
2023-08-26 16:42:37
|
opentibiabr/canary
|
https://api.github.com/repos/opentibiabr/canary
|
closed
|
Toolgear não está funcionando corretamente
|
Type: Bug Priority: Low Stale Status: Pending Test
|
### Priority
Low
### Area
- [X] Datapack
- [ ] Source
- [ ] Map
- [ ] Other
### What happened?
O toolgear não está funcionando corretamente. Apenas a função de corda (rope) está funcionando. Todas as outras não funcionam e não apresentam erro no termina.
### What OS are you seeing the problem on?
Windows
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct
|
1.0
|
Toolgear não está funcionando corretamente - ### Priority
Low
### Area
- [X] Datapack
- [ ] Source
- [ ] Map
- [ ] Other
### What happened?
O toolgear não está funcionando corretamente. Apenas a função de corda (rope) está funcionando. Todas as outras não funcionam e não apresentam erro no termina.
### What OS are you seeing the problem on?
Windows
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct
|
test
|
toolgear não está funcionando corretamente priority low area datapack source map other what happened o toolgear não está funcionando corretamente apenas a função de corda rope está funcionando todas as outras não funcionam e não apresentam erro no termina what os are you seeing the problem on windows code of conduct i agree to follow this project s code of conduct
| 1
|
445,306
| 31,233,991,089
|
IssuesEvent
|
2023-08-20 03:15:01
|
telvarost/AnnoyanceFix-StationAPI
|
https://api.github.com/repos/telvarost/AnnoyanceFix-StationAPI
|
opened
|
Release YouTube video covering v1.2.1 when it releases
|
documentation
|
I'd like to make a new YouTube video covering the mod since it has changes so much since the last review.
Because of the weird behavior of the pickax breaking wooden slabs, I would like to do it after we release version 1.2.1
|
1.0
|
Release YouTube video covering v1.2.1 when it releases - I'd like to make a new YouTube video covering the mod since it has changes so much since the last review.
Because of the weird behavior of the pickax breaking wooden slabs, I would like to do it after we release version 1.2.1
|
non_test
|
release youtube video covering when it releases i d like to make a new youtube video covering the mod since it has changes so much since the last review because of the weird behavior of the pickax breaking wooden slabs i would like to do it after we release version
| 0
|
192,305
| 14,613,960,618
|
IssuesEvent
|
2020-12-22 09:08:04
|
elastic/elasticsearch
|
https://api.github.com/repos/elastic/elasticsearch
|
opened
|
CI: SearchableSnapshotsIntegTests failures
|
:Distributed/Snapshot/Restore >test-failure
|
Two set of tests are failing - from the logs they _seem_ somewhat related.
org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotsIntegTests testSnapshotMountedIndexLeavesBlobsUntouched
org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotRecoveryStateIntegrationTests testRecoveryStateRecoveredBytesMatchPhysicalCacheState
**Build scan**:
https://gradle-enterprise.elastic.co/s/mespip5gogcmg
https://gradle-enterprise.elastic.co/s/p5uuwims7a7f2
**Repro line**:
```
Execution failed for task ':x-pack:plugin:searchable-snapshots:internalClusterTest'.
REPRODUCE WITH: gradlew ':x-pack:plugin:searchable-snapshots:internalClusterTest' --tests "org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotsIntegTests.testSnapshotMountedIndexLeavesBlobsUntouched" \
-Dtests.seed=BB70024FC3F106BB \
-Dtests.security.manager=true \
-Dtests.locale=en-SG \
-Dtests.timezone=America/St_Johns \
-Druntime.java=11
REPRODUCE WITH: gradlew ':x-pack:plugin:searchable-snapshots:internalClusterTest' --tests "org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotsIntegTests.testSnapshotMountedIndexLeavesBlobsUntouched" \
-Dtests.seed=BB70024FC3F106BB \
-Dtests.security.manager=true \
-Dtests.locale=en-SG \
-Dtests.timezone=America/St_Johns \
-Druntime.java=11
```
```
Execution failed for task ':x-pack:plugin:searchable-snapshots:internalClusterTest'.
REPRODUCE WITH: gradlew ':x-pack:plugin:searchable-snapshots:internalClusterTest' --tests "org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotRecoveryStateIntegrationTests.testRecoveryStateRecoveredBytesMatchPhysicalCacheState" \
-Dtests.seed=D4540C05A4826074 \
-Dtests.security.manager=true \
-Dtests.locale=ar-AE \
-Dtests.timezone=Asia/Atyrau \
-Druntime.java=8
REPRODUCE WITH: gradlew ':x-pack:plugin:searchable-snapshots:internalClusterTest' --tests "org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotRecoveryStateIntegrationTests.testRecoveryStateRecoveredBytesMatchPhysicalCacheState" \
-Dtests.seed=D4540C05A4826074 \
-Dtests.security.manager=true \
-Dtests.locale=ar-AE \
-Dtests.timezone=Asia/Atyrau \
-Druntime.java=8
```
**Applicable branches**:
7.11 and master
**Failure excerpt**:
```
com.carrotsearch.randomizedtesting.UncaughtExceptionError: Captured an uncaught exception in thread: Thread[id=380, name=elasticsearch[node_s0][generic][T#2], state=RUNNABLE, group=TGRP-SearchableSnapshotRecoveryStateIntegrationTests]
at __randomizedtesting.SeedInfo.seed([D4540C05A4826074:9AB6D6941D759D7C]:0)
Caused by: java.lang.AssertionError: shard eviction should be successful: [snapshotUUID=xlTcRHS3TvKMZ0ThoYJJtg, snapshotIndexName=twpfmpmquh, shardId=[twpfmpmquh][0]]
at __randomizedtesting.SeedInfo.seed([D4540C05A4826074]:0)
at org.elasticsearch.xpack.searchablesnapshots.cache.CacheService.runIfShardMarkedAsEvictedInCache(CacheService.java:412)
at org.elasticsearch.xpack.searchablesnapshots.cache.CacheService.access$100(CacheService.java:62)
at org.elasticsearch.xpack.searchablesnapshots.cache.CacheService$1.doRun(CacheService.java:351)
at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at org.elasticsearch.common.util.concurrent.ThreadContext$ContextPreservingRunnable.run(ThreadContext.java:684)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:748)
```
```
com.carrotsearch.randomizedtesting.UncaughtExceptionError: Captured an uncaught exception in thread: Thread[id=868, name=elasticsearch[node_s1][generic][T#6], state=RUNNABLE, group=TGRP-SearchableSnapshotsIntegTests]
at __randomizedtesting.SeedInfo.seed([BB70024FC3F106BB:5D02DB6F37A22D01]:0)
Caused by: java.lang.AssertionError: shard eviction should be successful: [snapshotUUID=zjm5kXbKSHisEnXGh-76Lw, snapshotIndexName=oxejtlweoj, shardId=[oxejtlweoj][1]]
at __randomizedtesting.SeedInfo.seed([BB70024FC3F106BB]:0)
at org.elasticsearch.xpack.searchablesnapshots.cache.CacheService.runIfShardMarkedAsEvictedInCache(CacheService.java:412)
at org.elasticsearch.xpack.searchablesnapshots.cache.CacheService$1.doRun(CacheService.java:351)
at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
at java.base/java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:515)
at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at org.elasticsearch.common.util.concurrent.ThreadContext$ContextPreservingRunnable.run(ThreadContext.java:680)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:834)
```
|
1.0
|
CI: SearchableSnapshotsIntegTests failures - Two set of tests are failing - from the logs they _seem_ somewhat related.
org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotsIntegTests testSnapshotMountedIndexLeavesBlobsUntouched
org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotRecoveryStateIntegrationTests testRecoveryStateRecoveredBytesMatchPhysicalCacheState
**Build scan**:
https://gradle-enterprise.elastic.co/s/mespip5gogcmg
https://gradle-enterprise.elastic.co/s/p5uuwims7a7f2
**Repro line**:
```
Execution failed for task ':x-pack:plugin:searchable-snapshots:internalClusterTest'.
REPRODUCE WITH: gradlew ':x-pack:plugin:searchable-snapshots:internalClusterTest' --tests "org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotsIntegTests.testSnapshotMountedIndexLeavesBlobsUntouched" \
-Dtests.seed=BB70024FC3F106BB \
-Dtests.security.manager=true \
-Dtests.locale=en-SG \
-Dtests.timezone=America/St_Johns \
-Druntime.java=11
REPRODUCE WITH: gradlew ':x-pack:plugin:searchable-snapshots:internalClusterTest' --tests "org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotsIntegTests.testSnapshotMountedIndexLeavesBlobsUntouched" \
-Dtests.seed=BB70024FC3F106BB \
-Dtests.security.manager=true \
-Dtests.locale=en-SG \
-Dtests.timezone=America/St_Johns \
-Druntime.java=11
```
```
Execution failed for task ':x-pack:plugin:searchable-snapshots:internalClusterTest'.
REPRODUCE WITH: gradlew ':x-pack:plugin:searchable-snapshots:internalClusterTest' --tests "org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotRecoveryStateIntegrationTests.testRecoveryStateRecoveredBytesMatchPhysicalCacheState" \
-Dtests.seed=D4540C05A4826074 \
-Dtests.security.manager=true \
-Dtests.locale=ar-AE \
-Dtests.timezone=Asia/Atyrau \
-Druntime.java=8
REPRODUCE WITH: gradlew ':x-pack:plugin:searchable-snapshots:internalClusterTest' --tests "org.elasticsearch.xpack.searchablesnapshots.SearchableSnapshotRecoveryStateIntegrationTests.testRecoveryStateRecoveredBytesMatchPhysicalCacheState" \
-Dtests.seed=D4540C05A4826074 \
-Dtests.security.manager=true \
-Dtests.locale=ar-AE \
-Dtests.timezone=Asia/Atyrau \
-Druntime.java=8
```
**Applicable branches**:
7.11 and master
**Failure excerpt**:
```
com.carrotsearch.randomizedtesting.UncaughtExceptionError: Captured an uncaught exception in thread: Thread[id=380, name=elasticsearch[node_s0][generic][T#2], state=RUNNABLE, group=TGRP-SearchableSnapshotRecoveryStateIntegrationTests]
at __randomizedtesting.SeedInfo.seed([D4540C05A4826074:9AB6D6941D759D7C]:0)
Caused by: java.lang.AssertionError: shard eviction should be successful: [snapshotUUID=xlTcRHS3TvKMZ0ThoYJJtg, snapshotIndexName=twpfmpmquh, shardId=[twpfmpmquh][0]]
at __randomizedtesting.SeedInfo.seed([D4540C05A4826074]:0)
at org.elasticsearch.xpack.searchablesnapshots.cache.CacheService.runIfShardMarkedAsEvictedInCache(CacheService.java:412)
at org.elasticsearch.xpack.searchablesnapshots.cache.CacheService.access$100(CacheService.java:62)
at org.elasticsearch.xpack.searchablesnapshots.cache.CacheService$1.doRun(CacheService.java:351)
at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at org.elasticsearch.common.util.concurrent.ThreadContext$ContextPreservingRunnable.run(ThreadContext.java:684)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:748)
```
```
com.carrotsearch.randomizedtesting.UncaughtExceptionError: Captured an uncaught exception in thread: Thread[id=868, name=elasticsearch[node_s1][generic][T#6], state=RUNNABLE, group=TGRP-SearchableSnapshotsIntegTests]
at __randomizedtesting.SeedInfo.seed([BB70024FC3F106BB:5D02DB6F37A22D01]:0)
Caused by: java.lang.AssertionError: shard eviction should be successful: [snapshotUUID=zjm5kXbKSHisEnXGh-76Lw, snapshotIndexName=oxejtlweoj, shardId=[oxejtlweoj][1]]
at __randomizedtesting.SeedInfo.seed([BB70024FC3F106BB]:0)
at org.elasticsearch.xpack.searchablesnapshots.cache.CacheService.runIfShardMarkedAsEvictedInCache(CacheService.java:412)
at org.elasticsearch.xpack.searchablesnapshots.cache.CacheService$1.doRun(CacheService.java:351)
at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:37)
at java.base/java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:515)
at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at org.elasticsearch.common.util.concurrent.ThreadContext$ContextPreservingRunnable.run(ThreadContext.java:680)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:834)
```
|
test
|
ci searchablesnapshotsintegtests failures two set of tests are failing from the logs they seem somewhat related org elasticsearch xpack searchablesnapshots searchablesnapshotsintegtests testsnapshotmountedindexleavesblobsuntouched org elasticsearch xpack searchablesnapshots searchablesnapshotrecoverystateintegrationtests testrecoverystaterecoveredbytesmatchphysicalcachestate build scan repro line execution failed for task x pack plugin searchable snapshots internalclustertest reproduce with gradlew x pack plugin searchable snapshots internalclustertest tests org elasticsearch xpack searchablesnapshots searchablesnapshotsintegtests testsnapshotmountedindexleavesblobsuntouched dtests seed dtests security manager true dtests locale en sg dtests timezone america st johns druntime java reproduce with gradlew x pack plugin searchable snapshots internalclustertest tests org elasticsearch xpack searchablesnapshots searchablesnapshotsintegtests testsnapshotmountedindexleavesblobsuntouched dtests seed dtests security manager true dtests locale en sg dtests timezone america st johns druntime java execution failed for task x pack plugin searchable snapshots internalclustertest reproduce with gradlew x pack plugin searchable snapshots internalclustertest tests org elasticsearch xpack searchablesnapshots searchablesnapshotrecoverystateintegrationtests testrecoverystaterecoveredbytesmatchphysicalcachestate dtests seed dtests security manager true dtests locale ar ae dtests timezone asia atyrau druntime java reproduce with gradlew x pack plugin searchable snapshots internalclustertest tests org elasticsearch xpack searchablesnapshots searchablesnapshotrecoverystateintegrationtests testrecoverystaterecoveredbytesmatchphysicalcachestate dtests seed dtests security manager true dtests locale ar ae dtests timezone asia atyrau druntime java applicable branches and master failure excerpt com carrotsearch randomizedtesting uncaughtexceptionerror captured an uncaught exception in thread thread state runnable group tgrp searchablesnapshotrecoverystateintegrationtests at randomizedtesting seedinfo seed caused by java lang assertionerror shard eviction should be successful at randomizedtesting seedinfo seed at org elasticsearch xpack searchablesnapshots cache cacheservice runifshardmarkedasevictedincache cacheservice java at org elasticsearch xpack searchablesnapshots cache cacheservice access cacheservice java at org elasticsearch xpack searchablesnapshots cache cacheservice dorun cacheservice java at org elasticsearch common util concurrent abstractrunnable run abstractrunnable java at java util concurrent executors runnableadapter call executors java at java util concurrent futuretask run futuretask java at org elasticsearch common util concurrent threadcontext contextpreservingrunnable run threadcontext java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java com carrotsearch randomizedtesting uncaughtexceptionerror captured an uncaught exception in thread thread state runnable group tgrp searchablesnapshotsintegtests at randomizedtesting seedinfo seed caused by java lang assertionerror shard eviction should be successful at randomizedtesting seedinfo seed at org elasticsearch xpack searchablesnapshots cache cacheservice runifshardmarkedasevictedincache cacheservice java at org elasticsearch xpack searchablesnapshots cache cacheservice dorun cacheservice java at org elasticsearch common util concurrent abstractrunnable run abstractrunnable java at java base java util concurrent executors runnableadapter call executors java at java base java util concurrent futuretask run futuretask java at org elasticsearch common util concurrent threadcontext contextpreservingrunnable run threadcontext java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java base java lang thread run thread java
| 1
|
222,043
| 17,032,745,611
|
IssuesEvent
|
2021-07-04 22:29:56
|
rafkub/oop-principles
|
https://api.github.com/repos/rafkub/oop-principles
|
closed
|
Illustrate Single Responsibility
|
documentation feature
|
- [x] Code violating Single Responsibility
- [x] Code applying Single Responsibility
- [x] README.md with short definition of Single Responsibility
|
1.0
|
Illustrate Single Responsibility - - [x] Code violating Single Responsibility
- [x] Code applying Single Responsibility
- [x] README.md with short definition of Single Responsibility
|
non_test
|
illustrate single responsibility code violating single responsibility code applying single responsibility readme md with short definition of single responsibility
| 0
|
418,852
| 28,129,781,101
|
IssuesEvent
|
2023-03-31 21:22:22
|
DevelopingSpace/starchart
|
https://api.github.com/repos/DevelopingSpace/starchart
|
closed
|
Add release management instruction for sheriff
|
category: documentation
|
I have noticed new sheriffs asking about how to handle releases a few times, so we should add some explanations/links of how to use `npm version` and [releases](https://docs.github.com/en/repositories/releasing-projects-on-github/managing-releases-in-a-repository) in the [sheriff page](https://github.com/Seneca-CDOT/dps911-osd700-winter-2023/wiki/How-to-be-a-Sheriff).
|
1.0
|
Add release management instruction for sheriff - I have noticed new sheriffs asking about how to handle releases a few times, so we should add some explanations/links of how to use `npm version` and [releases](https://docs.github.com/en/repositories/releasing-projects-on-github/managing-releases-in-a-repository) in the [sheriff page](https://github.com/Seneca-CDOT/dps911-osd700-winter-2023/wiki/How-to-be-a-Sheriff).
|
non_test
|
add release management instruction for sheriff i have noticed new sheriffs asking about how to handle releases a few times so we should add some explanations links of how to use npm version and in the
| 0
|
126,370
| 4,989,519,210
|
IssuesEvent
|
2016-12-08 12:09:42
|
DRDD2016/sparkn2
|
https://api.github.com/repos/DRDD2016/sparkn2
|
closed
|
Using different navigation solution
|
in progress priority 1 reference
|
@rickardinho
After research we have discovered that there is another navigation plugin (https://github.com/exponentjs/ex-navigation) which is recommended by a member of react-native team (see https://github.com/facebook/react-native/issues/6184#issuecomment-261744610). The benefits over react-native-router-flux are:
- its structure is closer to the official navigation solution when the native solution is released which makes it more future proof
- it supports lots of extra features like deep linking (see video http://facebook.github.io/react-native/blog/2016/09/08/exponent-talks-unraveling-navigation.html)
We feel it would be best to switch the navigation to ex-navigation. What your thoughts?
|
1.0
|
Using different navigation solution - @rickardinho
After research we have discovered that there is another navigation plugin (https://github.com/exponentjs/ex-navigation) which is recommended by a member of react-native team (see https://github.com/facebook/react-native/issues/6184#issuecomment-261744610). The benefits over react-native-router-flux are:
- its structure is closer to the official navigation solution when the native solution is released which makes it more future proof
- it supports lots of extra features like deep linking (see video http://facebook.github.io/react-native/blog/2016/09/08/exponent-talks-unraveling-navigation.html)
We feel it would be best to switch the navigation to ex-navigation. What your thoughts?
|
non_test
|
using different navigation solution rickardinho after research we have discovered that there is another navigation plugin which is recommended by a member of react native team see the benefits over react native router flux are its structure is closer to the official navigation solution when the native solution is released which makes it more future proof it supports lots of extra features like deep linking see video we feel it would be best to switch the navigation to ex navigation what your thoughts
| 0
|
686,370
| 23,488,615,743
|
IssuesEvent
|
2022-08-17 16:24:47
|
pkp/pkppln
|
https://api.github.com/repos/pkp/pkppln
|
closed
|
Ensure the server doesn't keep already processed data
|
enhancement high priority
|
As the deposit advances through the states, its data gets transformed into two other formats.
Keeping all this data is useful for an initial debugging, but once everything is settled, it just takes up physical space.
**PR**
- https://github.com/pkp/pkppln/pull/13
|
1.0
|
Ensure the server doesn't keep already processed data - As the deposit advances through the states, its data gets transformed into two other formats.
Keeping all this data is useful for an initial debugging, but once everything is settled, it just takes up physical space.
**PR**
- https://github.com/pkp/pkppln/pull/13
|
non_test
|
ensure the server doesn t keep already processed data as the deposit advances through the states its data gets transformed into two other formats keeping all this data is useful for an initial debugging but once everything is settled it just takes up physical space pr
| 0
|
73,744
| 7,354,280,889
|
IssuesEvent
|
2018-03-09 05:55:53
|
jpmarinacci/capstone
|
https://api.github.com/repos/jpmarinacci/capstone
|
opened
|
create test environment
|
testing
|
- [ ] create a test html and migrate the testDbPage from the clientApp into the test area and load the client stripping out other pages and routes.
- [ ] create a unit test environment. We should probably use jasmine and or qunit/mocha for unit tests. Research all the necessary steps to setting these up and what libraries we will need to add the package.
|
1.0
|
create test environment - - [ ] create a test html and migrate the testDbPage from the clientApp into the test area and load the client stripping out other pages and routes.
- [ ] create a unit test environment. We should probably use jasmine and or qunit/mocha for unit tests. Research all the necessary steps to setting these up and what libraries we will need to add the package.
|
test
|
create test environment create a test html and migrate the testdbpage from the clientapp into the test area and load the client stripping out other pages and routes create a unit test environment we should probably use jasmine and or qunit mocha for unit tests research all the necessary steps to setting these up and what libraries we will need to add the package
| 1
|
190,633
| 14,565,721,883
|
IssuesEvent
|
2020-12-17 07:46:34
|
microsoft/vscode
|
https://api.github.com/repos/microsoft/vscode
|
closed
|
Smoke test do not run anymore
|
smoke-test-failure
|
This looks like a compile issue to me (https://dev.azure.com/monacotools/Monaco/_build/results?buildId=97498&view=logs&j=3792f238-f35e-5f82-0dbc-272432d9a0fb&t=ff86458e-371d-5daa-d7a2-208b9a858585&l=18)
```
$ cd test/smoke && node test/index.js --build '/Users/runner/work/1/VSCode-darwin-x64/Visual Studio Code - Insiders.app'
internal/modules/cjs/loader.js:968
throw err;
^
Error: Cannot find module '/Users/runner/work/1/s/test/smoke/out/main.js'
Require stack:
- /Users/runner/work/1/s/test/smoke/node_modules/mocha/lib/mocha.js
- /Users/runner/work/1/s/test/smoke/node_modules/mocha/index.js
- /Users/runner/work/1/s/test/smoke/test/index.js
at Function.Module._resolveFilename (internal/modules/cjs/loader.js:965:15)
at Function.Module._load (internal/modules/cjs/loader.js:841:27)
at Module.require (internal/modules/cjs/loader.js:1025:19)
at require (internal/modules/cjs/helpers.js:72:18)
at /Users/runner/work/1/s/test/smoke/node_modules/mocha/lib/mocha.js:334:36
at Array.forEach (<anonymous>)
at Mocha.loadFiles (/Users/runner/work/1/s/test/smoke/node_modules/mocha/lib/mocha.js:331:14)
at Mocha.run (/Users/runner/work/1/s/test/smoke/node_modules/mocha/lib/mocha.js:809:10)
at Object.<anonymous> (/Users/runner/work/1/s/test/smoke/test/index.js:38:7)
at Module._compile (internal/modules/cjs/loader.js:1137:30) {
code: 'MODULE_NOT_FOUND',
requireStack: [
'/Users/runner/work/1/s/test/smoke/node_modules/mocha/lib/mocha.js',
'/Users/runner/work/1/s/test/smoke/node_modules/mocha/index.js',
'/Users/runner/work/1/s/test/smoke/test/index.js'
]
}
error Command failed with exit code 1.
info Visit https://yarnpkg.com/en/docs/cli/run for documentation about this command.
```
|
1.0
|
Smoke test do not run anymore - This looks like a compile issue to me (https://dev.azure.com/monacotools/Monaco/_build/results?buildId=97498&view=logs&j=3792f238-f35e-5f82-0dbc-272432d9a0fb&t=ff86458e-371d-5daa-d7a2-208b9a858585&l=18)
```
$ cd test/smoke && node test/index.js --build '/Users/runner/work/1/VSCode-darwin-x64/Visual Studio Code - Insiders.app'
internal/modules/cjs/loader.js:968
throw err;
^
Error: Cannot find module '/Users/runner/work/1/s/test/smoke/out/main.js'
Require stack:
- /Users/runner/work/1/s/test/smoke/node_modules/mocha/lib/mocha.js
- /Users/runner/work/1/s/test/smoke/node_modules/mocha/index.js
- /Users/runner/work/1/s/test/smoke/test/index.js
at Function.Module._resolveFilename (internal/modules/cjs/loader.js:965:15)
at Function.Module._load (internal/modules/cjs/loader.js:841:27)
at Module.require (internal/modules/cjs/loader.js:1025:19)
at require (internal/modules/cjs/helpers.js:72:18)
at /Users/runner/work/1/s/test/smoke/node_modules/mocha/lib/mocha.js:334:36
at Array.forEach (<anonymous>)
at Mocha.loadFiles (/Users/runner/work/1/s/test/smoke/node_modules/mocha/lib/mocha.js:331:14)
at Mocha.run (/Users/runner/work/1/s/test/smoke/node_modules/mocha/lib/mocha.js:809:10)
at Object.<anonymous> (/Users/runner/work/1/s/test/smoke/test/index.js:38:7)
at Module._compile (internal/modules/cjs/loader.js:1137:30) {
code: 'MODULE_NOT_FOUND',
requireStack: [
'/Users/runner/work/1/s/test/smoke/node_modules/mocha/lib/mocha.js',
'/Users/runner/work/1/s/test/smoke/node_modules/mocha/index.js',
'/Users/runner/work/1/s/test/smoke/test/index.js'
]
}
error Command failed with exit code 1.
info Visit https://yarnpkg.com/en/docs/cli/run for documentation about this command.
```
|
test
|
smoke test do not run anymore this looks like a compile issue to me cd test smoke node test index js build users runner work vscode darwin visual studio code insiders app internal modules cjs loader js throw err error cannot find module users runner work s test smoke out main js require stack users runner work s test smoke node modules mocha lib mocha js users runner work s test smoke node modules mocha index js users runner work s test smoke test index js at function module resolvefilename internal modules cjs loader js at function module load internal modules cjs loader js at module require internal modules cjs loader js at require internal modules cjs helpers js at users runner work s test smoke node modules mocha lib mocha js at array foreach at mocha loadfiles users runner work s test smoke node modules mocha lib mocha js at mocha run users runner work s test smoke node modules mocha lib mocha js at object users runner work s test smoke test index js at module compile internal modules cjs loader js code module not found requirestack users runner work s test smoke node modules mocha lib mocha js users runner work s test smoke node modules mocha index js users runner work s test smoke test index js error command failed with exit code info visit for documentation about this command
| 1
|
1,037
| 2,525,475,345
|
IssuesEvent
|
2015-01-21 01:25:43
|
ppazos/cabolabs-ehrserver
|
https://api.github.com/repos/ppazos/cabolabs-ehrserver
|
opened
|
Try detached criteria to make subqueries
|
test
|
Instead of using SQL subqueries.
See detached criteria doc: http://grails.github.io/grails-doc/2.0.4/guide/GORM.html
|
1.0
|
Try detached criteria to make subqueries - Instead of using SQL subqueries.
See detached criteria doc: http://grails.github.io/grails-doc/2.0.4/guide/GORM.html
|
test
|
try detached criteria to make subqueries instead of using sql subqueries see detached criteria doc
| 1
|
291,104
| 25,120,970,845
|
IssuesEvent
|
2022-11-09 08:05:59
|
jdi-testing/jdi-light
|
https://api.github.com/repos/jdi-testing/jdi-light
|
closed
|
Update test-site: element "tabs"
|
TestSite Vuetify
|
Tabs:
- [x] Hide slider (y/n)
- [x] Optional (y/n)
Tab:
- [x] Disabled (y/n)
- [x] href
Tab items:
- [x] Show arrows on hover (y/n)
Tab item:
- [x] Disabled (y/n)
|
1.0
|
Update test-site: element "tabs" - Tabs:
- [x] Hide slider (y/n)
- [x] Optional (y/n)
Tab:
- [x] Disabled (y/n)
- [x] href
Tab items:
- [x] Show arrows on hover (y/n)
Tab item:
- [x] Disabled (y/n)
|
test
|
update test site element tabs tabs hide slider y n optional y n tab disabled y n href tab items show arrows on hover y n tab item disabled y n
| 1
|
151,817
| 12,059,574,358
|
IssuesEvent
|
2020-04-15 19:31:35
|
kubernetes/minikube
|
https://api.github.com/repos/kubernetes/minikube
|
closed
|
Enable required check in github (e.g. build, lint, unit test targets)
|
area/testing kind/failing-test priority/important-soon
|
There were a few occurrence that the PR got merged with some minor linting error. To avoid such issue, we can consider to enable required check in github for few things:
- build
- lint
- unit test (this one might be flanky)
- travis (this check includes build + lint + unit test together, so might be flanky as well)
|
2.0
|
Enable required check in github (e.g. build, lint, unit test targets) - There were a few occurrence that the PR got merged with some minor linting error. To avoid such issue, we can consider to enable required check in github for few things:
- build
- lint
- unit test (this one might be flanky)
- travis (this check includes build + lint + unit test together, so might be flanky as well)
|
test
|
enable required check in github e g build lint unit test targets there were a few occurrence that the pr got merged with some minor linting error to avoid such issue we can consider to enable required check in github for few things build lint unit test this one might be flanky travis this check includes build lint unit test together so might be flanky as well
| 1
|
395,109
| 27,054,466,052
|
IssuesEvent
|
2023-02-13 15:18:19
|
Aalto-LeTech/jsav-exercise-recorder
|
https://api.github.com/repos/Aalto-LeTech/jsav-exercise-recorder
|
opened
|
Reproducibility: Mergesort
|
documentation exercises
|
Similar to #119 .
Study the reproducibility of the Mergesort exercise
Git branch: `new_exercises`
Instructions: [doc/exercise_design/reproducibility/reproducibility.md](https://github.com/Aalto-LeTech/jsav-exercise-recorder/blob/new_exercises/doc/exercise_design/reproducibility/reproducibility.md)
Example: [Order of Growth (easy)](https://github.com/Aalto-LeTech/jsav-exercise-recorder/tree/new_exercises/doc/exercise_design/reproducibility/order_of_growth_easy)
Exercise: [Mergesort](https://plus.cs.aalto.fi/a1143/2022/jarjestaminen/mergesort_1143/#chapter-exercise-1)
|
1.0
|
Reproducibility: Mergesort - Similar to #119 .
Study the reproducibility of the Mergesort exercise
Git branch: `new_exercises`
Instructions: [doc/exercise_design/reproducibility/reproducibility.md](https://github.com/Aalto-LeTech/jsav-exercise-recorder/blob/new_exercises/doc/exercise_design/reproducibility/reproducibility.md)
Example: [Order of Growth (easy)](https://github.com/Aalto-LeTech/jsav-exercise-recorder/tree/new_exercises/doc/exercise_design/reproducibility/order_of_growth_easy)
Exercise: [Mergesort](https://plus.cs.aalto.fi/a1143/2022/jarjestaminen/mergesort_1143/#chapter-exercise-1)
|
non_test
|
reproducibility mergesort similar to study the reproducibility of the mergesort exercise git branch new exercises instructions example exercise
| 0
|
66,377
| 6,997,175,464
|
IssuesEvent
|
2017-12-16 11:20:25
|
AdrianAntonGarcia/-TFG-UBUSetas
|
https://api.github.com/repos/AdrianAntonGarcia/-TFG-UBUSetas
|
closed
|
S14-4. Realizar los test unitarios sobre la actividad Recoger foto.
|
Android Test
|
En esta tarea se realizarán las pruebas para comprobar el correcto funcionamiento de la actividad recoger foto.
|
1.0
|
S14-4. Realizar los test unitarios sobre la actividad Recoger foto. - En esta tarea se realizarán las pruebas para comprobar el correcto funcionamiento de la actividad recoger foto.
|
test
|
realizar los test unitarios sobre la actividad recoger foto en esta tarea se realizarán las pruebas para comprobar el correcto funcionamiento de la actividad recoger foto
| 1
|
111,310
| 9,526,143,944
|
IssuesEvent
|
2019-04-28 17:40:46
|
WojciechRynczuk/vcdMaker
|
https://api.github.com/repos/WojciechRynczuk/vcdMaker
|
opened
|
Check the standard output during integration tests
|
quality test
|
The standard output shall be verified during integration tests. It will also allow for automating the failing test cases.
|
1.0
|
Check the standard output during integration tests - The standard output shall be verified during integration tests. It will also allow for automating the failing test cases.
|
test
|
check the standard output during integration tests the standard output shall be verified during integration tests it will also allow for automating the failing test cases
| 1
|
45,420
| 5,714,328,416
|
IssuesEvent
|
2017-04-19 10:05:46
|
LecksC/ASOR_Bugs
|
https://api.github.com/repos/LecksC/ASOR_Bugs
|
reopened
|
Vehicle Selector CTD
|
Bug Needs Testing Needs Verification Urgency - Now
|
## CTD Issues
Reports of vehicle Selector when spawning certain vehicles causing a CTD. Confirmed for one of the A-10 (RHS).
Not FTX related (happens on all maps).
Not sure if its specifically a VS issue. Sounds like a Vehicle Issue, but reports of them (A-10's) being spawnable in Zeus and being completely usable otherwise.
Will hunt for more info regarding this.
|
1.0
|
Vehicle Selector CTD - ## CTD Issues
Reports of vehicle Selector when spawning certain vehicles causing a CTD. Confirmed for one of the A-10 (RHS).
Not FTX related (happens on all maps).
Not sure if its specifically a VS issue. Sounds like a Vehicle Issue, but reports of them (A-10's) being spawnable in Zeus and being completely usable otherwise.
Will hunt for more info regarding this.
|
test
|
vehicle selector ctd ctd issues reports of vehicle selector when spawning certain vehicles causing a ctd confirmed for one of the a rhs not ftx related happens on all maps not sure if its specifically a vs issue sounds like a vehicle issue but reports of them a s being spawnable in zeus and being completely usable otherwise will hunt for more info regarding this
| 1
|
232,444
| 18,875,727,254
|
IssuesEvent
|
2021-11-14 00:42:34
|
backend-br/vagas
|
https://api.github.com/repos/backend-br/vagas
|
closed
|
[Remoto] Back-end Developer Java @ Iteam
|
PJ Pleno Java Remoto Full Time Spring Redis Testes Unitários Git Rest SOAP Stale
|
<!--
==================================================
POR FAVOR, SÓ POSTE SE A VAGA FOR PARA TRABALHAR COM REACT OU TECNOLOGIAS DO ECOSSISTEMA!
Exemplo: [São Paulo] Developer na NOME DA EMPRESA`
==================================================
-->
## Local
Home Office (Full time em Horário comercial)
## Requisitos
Java 8+.
Hibernate.
MyBatis.
Web Services: Rest, SOAP.
Framework: Spring Boot.
Banco de Dados: Oracle e Redis.
Controle de Versão: GIT e SVN.
Testes Unitários: Junit e Mockito.
Qualidade: SonarQube.
## Contratação
6 meses, prorrogáveis
## Informações adicionais
Contração PJ
Essa oportunidade requer disponibilidade em horário comercial, você trabalhará da sua casa (100% remoto).
## Nossa empresa
Há mais de 15 anos presente no mercado, a ITeam oferece o comprometimento com o cliente.
Reunimos capital intelectual especializado por profissionais experientes e capacitados a prestar os melhores serviços nas diferentes áreas de atuação, submetidos a treinamentos constantes para estarem sempre atualizados com as melhores práticas de mercado.
O relacionamento da ITeam é baseado no amplo comprometimento com os valores e objetivos dos nossos Clientes, fornecendo soluções e serviços de TI que contribuam para a realização de seus objetivos.
## Como se candidatar
Envie um e-mail para trodrigues@iteam.inf.br com seu currículo atualizado - enviar no assunto: Vaga no GITHUB - Back-end Java - 13369
## Labels
- 🏢 Horário comercial
- 🏢 Home-Office
- 👨 Pleno/Sênior
- ⚖️ PJ ou a combinar
|
1.0
|
[Remoto] Back-end Developer Java @ Iteam - <!--
==================================================
POR FAVOR, SÓ POSTE SE A VAGA FOR PARA TRABALHAR COM REACT OU TECNOLOGIAS DO ECOSSISTEMA!
Exemplo: [São Paulo] Developer na NOME DA EMPRESA`
==================================================
-->
## Local
Home Office (Full time em Horário comercial)
## Requisitos
Java 8+.
Hibernate.
MyBatis.
Web Services: Rest, SOAP.
Framework: Spring Boot.
Banco de Dados: Oracle e Redis.
Controle de Versão: GIT e SVN.
Testes Unitários: Junit e Mockito.
Qualidade: SonarQube.
## Contratação
6 meses, prorrogáveis
## Informações adicionais
Contração PJ
Essa oportunidade requer disponibilidade em horário comercial, você trabalhará da sua casa (100% remoto).
## Nossa empresa
Há mais de 15 anos presente no mercado, a ITeam oferece o comprometimento com o cliente.
Reunimos capital intelectual especializado por profissionais experientes e capacitados a prestar os melhores serviços nas diferentes áreas de atuação, submetidos a treinamentos constantes para estarem sempre atualizados com as melhores práticas de mercado.
O relacionamento da ITeam é baseado no amplo comprometimento com os valores e objetivos dos nossos Clientes, fornecendo soluções e serviços de TI que contribuam para a realização de seus objetivos.
## Como se candidatar
Envie um e-mail para trodrigues@iteam.inf.br com seu currículo atualizado - enviar no assunto: Vaga no GITHUB - Back-end Java - 13369
## Labels
- 🏢 Horário comercial
- 🏢 Home-Office
- 👨 Pleno/Sênior
- ⚖️ PJ ou a combinar
|
test
|
back end developer java iteam por favor só poste se a vaga for para trabalhar com react ou tecnologias do ecossistema exemplo developer na nome da empresa local home office full time em horário comercial requisitos java hibernate mybatis web services rest soap framework spring boot banco de dados oracle e redis controle de versão git e svn testes unitários junit e mockito qualidade sonarqube contratação meses prorrogáveis informações adicionais contração pj essa oportunidade requer disponibilidade em horário comercial você trabalhará da sua casa remoto nossa empresa há mais de anos presente no mercado a iteam oferece o comprometimento com o cliente reunimos capital intelectual especializado por profissionais experientes e capacitados a prestar os melhores serviços nas diferentes áreas de atuação submetidos a treinamentos constantes para estarem sempre atualizados com as melhores práticas de mercado o relacionamento da iteam é baseado no amplo comprometimento com os valores e objetivos dos nossos clientes fornecendo soluções e serviços de ti que contribuam para a realização de seus objetivos como se candidatar envie um e mail para trodrigues iteam inf br com seu currículo atualizado enviar no assunto vaga no github back end java labels 🏢 horário comercial 🏢 home office 👨 pleno sênior ⚖️ pj ou a combinar
| 1
|
688,408
| 23,580,888,784
|
IssuesEvent
|
2022-08-23 07:34:13
|
webcompat/web-bugs
|
https://api.github.com/repos/webcompat/web-bugs
|
closed
|
docs.google.com - see bug description
|
status-needsinfo browser-firefox priority-critical engine-gecko
|
<!-- @browser: Firefox 103.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:103.0) Gecko/20100101 Firefox/103.0 -->
<!-- @reported_with: unknown -->
**URL**: https://docs.google.com
**Browser / Version**: Firefox 103.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: fonts stop rendering correctly
**Steps to Reproduce**:
Opened a google slides presentation and the fonts either appear as an X with a box around it or not at all. Also, google sheets has the same thing occur with regard to the row id on the side as well. Just started happening within this past Friday (2022 08 19).
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2022/8/9dcf4e54-0781-452b-b128-825cd4d88778.jpg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
1.0
|
docs.google.com - see bug description - <!-- @browser: Firefox 103.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:103.0) Gecko/20100101 Firefox/103.0 -->
<!-- @reported_with: unknown -->
**URL**: https://docs.google.com
**Browser / Version**: Firefox 103.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: fonts stop rendering correctly
**Steps to Reproduce**:
Opened a google slides presentation and the fonts either appear as an X with a box around it or not at all. Also, google sheets has the same thing occur with regard to the row id on the side as well. Just started happening within this past Friday (2022 08 19).
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2022/8/9dcf4e54-0781-452b-b128-825cd4d88778.jpg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
non_test
|
docs google com see bug description url browser version firefox operating system windows tested another browser yes chrome problem type something else description fonts stop rendering correctly steps to reproduce opened a google slides presentation and the fonts either appear as an x with a box around it or not at all also google sheets has the same thing occur with regard to the row id on the side as well just started happening within this past friday view the screenshot img alt screenshot src browser configuration none from with ❤️
| 0
|
55,497
| 23,490,353,705
|
IssuesEvent
|
2022-08-17 18:04:56
|
hashicorp/terraform-provider-azurerm
|
https://api.github.com/repos/hashicorp/terraform-provider-azurerm
|
closed
|
azurerm_windows_function_app appsetting WEBSITE_NODE_DEFAULT_VERSION is added in every apply even if the function app has the value set
|
bug service/functions
|
### Is there an existing issue for this?
- [X] I have searched the existing issues
### Community Note
<!--- Please keep this note for the community --->
* Please vote on this issue by adding a :thumbsup: [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform Version
1.1.9
### AzureRM Provider Version
3.10.0
### Affected Resource(s)/Data Source(s)
azurerm_windows_function_app
### Terraform Configuration Files
```hcl
terraform {
required_providers {
azurerm = {
source = "hashicorp/azurerm"
version = "~> 3.10"
}
}
required_version = ">= 1.1.9"
}
provider "azurerm" {
features {}
tenant_id = var.tenant_id
subscription_id = var.subscription_id
}
resource "azurerm_resource_group" "default" {
name = "error-testing-rg"
location = "westeurope"
tags = var.default_tags
}
resource "azurerm_storage_account" "function_app" {
name = "errortesting"
resource_group_name = azurerm_resource_group.default.name
location = azurerm_resource_group.default.location
account_tier = "Standard"
account_replication_type = "LRS"
min_tls_version = "TLS1_2"
allow_nested_items_to_be_public = false
}
resource "azurerm_service_plan" "default" {
name = "error-testing-plan"
location = azurerm_resource_group.default.location
resource_group_name = azurerm_resource_group.default.name
os_type = "Windows"
sku_name = "Y1"
}
resource "azurerm_windows_function_app" "default" {
name = "error-testing-func"
location = azurerm_resource_group.default.location
resource_group_name = azurerm_resource_group.default.name
service_plan_id = azurerm_service_plan.default.id
storage_account_name = azurerm_storage_account.function_app.name
storage_account_access_key = azurerm_storage_account.function_app.primary_access_key
functions_extension_version = "~4"
https_only = true
app_settings = {
FUNCTIONS_WORKER_RUNTIME = "node"
WEBSITE_NODE_DEFAULT_VERSION = "~16"
}
site_config {
}
}
```
### Debug Output/Panic Output
```shell
https://gist.github.com/Ikriva/7c2be9a25d4e0a81656fc55f2fe46145
```
### Expected Behaviour
On second `terraform apply`, there should be no changes to be applied.
### Actual Behaviour

### Steps to Reproduce
terraform apply x2
### Important Factoids
_No response_
### References
_No response_
|
1.0
|
azurerm_windows_function_app appsetting WEBSITE_NODE_DEFAULT_VERSION is added in every apply even if the function app has the value set - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Community Note
<!--- Please keep this note for the community --->
* Please vote on this issue by adding a :thumbsup: [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform Version
1.1.9
### AzureRM Provider Version
3.10.0
### Affected Resource(s)/Data Source(s)
azurerm_windows_function_app
### Terraform Configuration Files
```hcl
terraform {
required_providers {
azurerm = {
source = "hashicorp/azurerm"
version = "~> 3.10"
}
}
required_version = ">= 1.1.9"
}
provider "azurerm" {
features {}
tenant_id = var.tenant_id
subscription_id = var.subscription_id
}
resource "azurerm_resource_group" "default" {
name = "error-testing-rg"
location = "westeurope"
tags = var.default_tags
}
resource "azurerm_storage_account" "function_app" {
name = "errortesting"
resource_group_name = azurerm_resource_group.default.name
location = azurerm_resource_group.default.location
account_tier = "Standard"
account_replication_type = "LRS"
min_tls_version = "TLS1_2"
allow_nested_items_to_be_public = false
}
resource "azurerm_service_plan" "default" {
name = "error-testing-plan"
location = azurerm_resource_group.default.location
resource_group_name = azurerm_resource_group.default.name
os_type = "Windows"
sku_name = "Y1"
}
resource "azurerm_windows_function_app" "default" {
name = "error-testing-func"
location = azurerm_resource_group.default.location
resource_group_name = azurerm_resource_group.default.name
service_plan_id = azurerm_service_plan.default.id
storage_account_name = azurerm_storage_account.function_app.name
storage_account_access_key = azurerm_storage_account.function_app.primary_access_key
functions_extension_version = "~4"
https_only = true
app_settings = {
FUNCTIONS_WORKER_RUNTIME = "node"
WEBSITE_NODE_DEFAULT_VERSION = "~16"
}
site_config {
}
}
```
### Debug Output/Panic Output
```shell
https://gist.github.com/Ikriva/7c2be9a25d4e0a81656fc55f2fe46145
```
### Expected Behaviour
On second `terraform apply`, there should be no changes to be applied.
### Actual Behaviour

### Steps to Reproduce
terraform apply x2
### Important Factoids
_No response_
### References
_No response_
|
non_test
|
azurerm windows function app appsetting website node default version is added in every apply even if the function app has the value set is there an existing issue for this i have searched the existing issues community note please vote on this issue by adding a thumbsup to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform version azurerm provider version affected resource s data source s azurerm windows function app terraform configuration files hcl terraform required providers azurerm source hashicorp azurerm version required version provider azurerm features tenant id var tenant id subscription id var subscription id resource azurerm resource group default name error testing rg location westeurope tags var default tags resource azurerm storage account function app name errortesting resource group name azurerm resource group default name location azurerm resource group default location account tier standard account replication type lrs min tls version allow nested items to be public false resource azurerm service plan default name error testing plan location azurerm resource group default location resource group name azurerm resource group default name os type windows sku name resource azurerm windows function app default name error testing func location azurerm resource group default location resource group name azurerm resource group default name service plan id azurerm service plan default id storage account name azurerm storage account function app name storage account access key azurerm storage account function app primary access key functions extension version https only true app settings functions worker runtime node website node default version site config debug output panic output shell expected behaviour on second terraform apply there should be no changes to be applied actual behaviour steps to reproduce terraform apply important factoids no response references no response
| 0
|
51,731
| 6,194,891,798
|
IssuesEvent
|
2017-07-05 11:05:59
|
TheScienceMuseum/collectionsonline
|
https://api.github.com/repos/TheScienceMuseum/collectionsonline
|
closed
|
Incorrect copyright being displayed + the 'show' toggle shouldn't be used on object pages
|
bug please-test priority-2 T1h
|
- The 'show' toggle **shouldn't** be used on **object** pages (_just show the copyright without a toggle as it will always be short_).
http://collection.sciencemuseum.org.uk/objects/co8401352/windows-1-0-operating-system-1985-1994-operating-system
|
1.0
|
Incorrect copyright being displayed + the 'show' toggle shouldn't be used on object pages - - The 'show' toggle **shouldn't** be used on **object** pages (_just show the copyright without a toggle as it will always be short_).
http://collection.sciencemuseum.org.uk/objects/co8401352/windows-1-0-operating-system-1985-1994-operating-system
|
test
|
incorrect copyright being displayed the show toggle shouldn t be used on object pages the show toggle shouldn t be used on object pages just show the copyright without a toggle as it will always be short
| 1
|
68,278
| 17,203,638,882
|
IssuesEvent
|
2021-07-17 19:38:07
|
InterNetNews/inn
|
https://api.github.com/repos/InterNetNews/inn
|
closed
|
Add support for Python 3.0
|
C: build P: medium R: fixed T: defect
|
**Reported by iulius on 14 Dec 2008 23:06 UTC**
Python 3.0 was released on December, 3rd. The syntax currently used in Python 2.x scripts shipped with INN is not compatible with the new version. Therefore, innd and nnrpd Python filters should be reviewed and made compatible with both Python 2.x and 3.0.
Compilation with Python 3.0 API should also be checked (new functions to use? no issue when building INN with Python support?)
Also be sure that INN compiles fine with Python 2.5.x and 2.6.x.
|
1.0
|
Add support for Python 3.0 - **Reported by iulius on 14 Dec 2008 23:06 UTC**
Python 3.0 was released on December, 3rd. The syntax currently used in Python 2.x scripts shipped with INN is not compatible with the new version. Therefore, innd and nnrpd Python filters should be reviewed and made compatible with both Python 2.x and 3.0.
Compilation with Python 3.0 API should also be checked (new functions to use? no issue when building INN with Python support?)
Also be sure that INN compiles fine with Python 2.5.x and 2.6.x.
|
non_test
|
add support for python reported by iulius on dec utc python was released on december the syntax currently used in python x scripts shipped with inn is not compatible with the new version therefore innd and nnrpd python filters should be reviewed and made compatible with both python x and compilation with python api should also be checked new functions to use no issue when building inn with python support also be sure that inn compiles fine with python x and x
| 0
|
65,740
| 16,468,845,410
|
IssuesEvent
|
2021-05-23 01:34:29
|
darlinghq/darling
|
https://api.github.com/repos/darlinghq/darling
|
closed
|
Make error at around 96%
|
Build
|
**Build Log**
Darling builds fine until 96%, but has continuous errors along the way, nothing that stops build though. It then shows this and cancels the build
```
make[1]: *** [CMakeFiles/Makefile2:49889: src/external/JavaScriptCore/CMakeFiles/JavaScriptCore.dir/all] Error 2
make: *** [Makefile:149: all] Error 2
```
I did everything according to the build instructions, after the AUR builds had the same error.
**System Information**
What system are you building with?
| Software | Version |
| --- | --- |
| Clang | 10.0.1-1 |
| CMake | 3.18.4-1 |
| Linux Kernel | 5.8.18-1-MANJARO |
| Darling | 1d3b099 |
|
1.0
|
Make error at around 96% - **Build Log**
Darling builds fine until 96%, but has continuous errors along the way, nothing that stops build though. It then shows this and cancels the build
```
make[1]: *** [CMakeFiles/Makefile2:49889: src/external/JavaScriptCore/CMakeFiles/JavaScriptCore.dir/all] Error 2
make: *** [Makefile:149: all] Error 2
```
I did everything according to the build instructions, after the AUR builds had the same error.
**System Information**
What system are you building with?
| Software | Version |
| --- | --- |
| Clang | 10.0.1-1 |
| CMake | 3.18.4-1 |
| Linux Kernel | 5.8.18-1-MANJARO |
| Darling | 1d3b099 |
|
non_test
|
make error at around build log darling builds fine until but has continuous errors along the way nothing that stops build though it then shows this and cancels the build make error make error i did everything according to the build instructions after the aur builds had the same error system information what system are you building with software version clang cmake linux kernel manjaro darling
| 0
|
178,517
| 29,866,394,394
|
IssuesEvent
|
2023-06-20 04:31:41
|
hackforla/tdm-calculator
|
https://api.github.com/repos/hackforla/tdm-calculator
|
closed
|
Design Mockup: TDM Calculation Summary Print out
|
level: easy priority: MUST HAVE p-Feature - Final Summary Page pg 5 role: ui/ux design Ready for development
|
### Overview
We need to create the button and PDF output for printing/downloading the TDM Calculation Summary
### Action Items
- [x] Create a mockup of a download button for the TDM calculation summary page
- [x] Create a mockup of PDF of the TDM calculation summary results
### Resources/Instructions
[Figma](https://www.figma.com/file/nD9QK56Mzq7xNSaSUoeGx0/TDM-Calculator?t=zXTqXwyu8zAgi1aK-0)
[LADOT Style guide](https://drive.google.com/file/d/1SDdPrNUxcw6tnaLWcZ1CpoOn4raKSGkY/view)
- See #1140 for additional context
|
1.0
|
Design Mockup: TDM Calculation Summary Print out - ### Overview
We need to create the button and PDF output for printing/downloading the TDM Calculation Summary
### Action Items
- [x] Create a mockup of a download button for the TDM calculation summary page
- [x] Create a mockup of PDF of the TDM calculation summary results
### Resources/Instructions
[Figma](https://www.figma.com/file/nD9QK56Mzq7xNSaSUoeGx0/TDM-Calculator?t=zXTqXwyu8zAgi1aK-0)
[LADOT Style guide](https://drive.google.com/file/d/1SDdPrNUxcw6tnaLWcZ1CpoOn4raKSGkY/view)
- See #1140 for additional context
|
non_test
|
design mockup tdm calculation summary print out overview we need to create the button and pdf output for printing downloading the tdm calculation summary action items create a mockup of a download button for the tdm calculation summary page create a mockup of pdf of the tdm calculation summary results resources instructions see for additional context
| 0
|
427,056
| 29,765,991,398
|
IssuesEvent
|
2023-06-15 01:00:49
|
AzureAD/microsoft-authentication-library-for-js
|
https://api.github.com/repos/AzureAD/microsoft-authentication-library-for-js
|
closed
|
loginRedirect with codeChallenge?
|
question documentation msal-browser no-issue-activity msal-react answered Needs: Author Feedback public-client
|
### Core Library
MSAL.js (@azure/msal-browser)
### Wrapper Library
MSAL React (@azure/msal-react)
### Public or Confidential Client?
Public
### Documentation Location
https://github.com/AzureAD/microsoft-authentication-library-for-js/blob/42dd47713c8c8e362fa3cd54cbf7367140d9fb06/lib/msal-browser/src/request/RedirectRequest.ts#L40-L41C1
### Description
Based on the documentation linked above, it seems like this should work:
```
msalInstance.loginRedirect({
codeChallenge: 'sB9MtOglgWOYU2i_NR7L-RQYgngIj05p2BkvcSe6bW0',
codeChallengeMethod: "S256",
scopes,
prompt
});
```
However, the actual loginRedirect ignores this. The reason I need this is because I get the `code` and then have to make this request:
```
const response = await axios.post(
'https://login.microsoftonline.com/common/oauth2/v2.0/token',
qs.stringify({
client_id,
client_secret,
code: req.query.code,
redirect_uri,
grant_type: 'authorization_code',
code_verifier,
}),
```
|
1.0
|
loginRedirect with codeChallenge? - ### Core Library
MSAL.js (@azure/msal-browser)
### Wrapper Library
MSAL React (@azure/msal-react)
### Public or Confidential Client?
Public
### Documentation Location
https://github.com/AzureAD/microsoft-authentication-library-for-js/blob/42dd47713c8c8e362fa3cd54cbf7367140d9fb06/lib/msal-browser/src/request/RedirectRequest.ts#L40-L41C1
### Description
Based on the documentation linked above, it seems like this should work:
```
msalInstance.loginRedirect({
codeChallenge: 'sB9MtOglgWOYU2i_NR7L-RQYgngIj05p2BkvcSe6bW0',
codeChallengeMethod: "S256",
scopes,
prompt
});
```
However, the actual loginRedirect ignores this. The reason I need this is because I get the `code` and then have to make this request:
```
const response = await axios.post(
'https://login.microsoftonline.com/common/oauth2/v2.0/token',
qs.stringify({
client_id,
client_secret,
code: req.query.code,
redirect_uri,
grant_type: 'authorization_code',
code_verifier,
}),
```
|
non_test
|
loginredirect with codechallenge core library msal js azure msal browser wrapper library msal react azure msal react public or confidential client public documentation location description based on the documentation linked above it seems like this should work msalinstance loginredirect codechallenge codechallengemethod scopes prompt however the actual loginredirect ignores this the reason i need this is because i get the code and then have to make this request const response await axios post qs stringify client id client secret code req query code redirect uri grant type authorization code code verifier
| 0
|
28,119
| 4,365,247,970
|
IssuesEvent
|
2016-08-03 10:05:28
|
cockroachdb/cockroach
|
https://api.github.com/repos/cockroachdb/cockroach
|
closed
|
stress: failed test in cockroach/storage/storage.test: TestReplicateAfterTruncation
|
Robot test-failure
|
Binary: cockroach/static-tests.tar.gz sha: https://github.com/cockroachdb/cockroach/commits/a79e2bd677e746b73269ff7dac6c559e00166e2c
Stress build found a failed test:
```
=== RUN TestReplicateAfterTruncation
I160728 05:22:02.408139 storage/engine/rocksdb.go:353 opening in memory rocksdb instance
W160728 05:22:02.409038 gossip/gossip.go:953 not connected to cluster; use --join to specify a connected node
W160728 05:22:02.410296 gossip/gossip.go:953 not connected to cluster; use --join to specify a connected node
I160728 05:22:02.410459 storage/store.go:2781 system config not yet available
I160728 05:22:02.411088 storage/replica_command.go:1741 store=1:1 ([]=) range=1 [/Min-/Max): new range lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 900ms following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=1970-01-01 00:00:00 +0000 UTC]
I160728 05:22:02.411432 storage/engine/rocksdb.go:353 opening in memory rocksdb instance
W160728 05:22:02.412230 gossip/gossip.go:953 not connected to cluster; use --join to specify a connected node
I160728 05:22:02.412786 storage/store.go:2781 system config not yet available
I160728 05:22:02.412867 gossip/client.go:74 starting client to 127.0.0.1:35625
I160728 05:22:02.414267 storage/replica_command.go:1532 store=1:1 ([]=) range=1 [/Min-/Max): attempting to truncate raft logs for another range 0. Normally this is due to a merge and can be ignored.
I160728 05:22:02.414868 storage/replica_raftstorage.go:467 generated snapshot for range 1 at index 15 in 157.465µs. encoded size=2849, 28 KV pairs, 5 log entries
I160728 05:22:02.415159 storage/replica_command.go:3204 store=1:1 ([]=) range=1 [/Min-/Max): change replicas of 1: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > next_replica_id:2
I160728 05:22:02.415546 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160728 05:22:02.415854 storage/replica.go:1419 store=1:1 ([]=) range=1 [/Min-/Max): proposing ADD_REPLICA {NodeID:2 StoreID:2 ReplicaID:2} for range 1: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I160728 05:22:02.416171 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160728 05:22:02.416489 storage/replica_raftstorage.go:588 store=2:2 ([]=) range=1 [/Min-/Min): with replicaID [?], applying preemptive snapshot for range 1 at index 15 (encoded size=2849, 28 KV pairs, 5 log entries)
W160728 05:22:02.417377 storage/replica.go:337 range 1: outgoing raft transport stream to {2 2 0} closed by the remote: <nil>
I160728 05:22:02.417588 storage/replica_raftstorage.go:591 store=2:2 ([]=) range=1 [/Min-/Max): with replicaID [?], applied preemptive snapshot for range 1 in 1.059719ms
--- FAIL: TestReplicateAfterTruncation (0.01s)
panic: descriptor is not initialized [recovered]
panic: descriptor is not initialized [recovered]
panic: descriptor is not initialized [recovered]
panic: descriptor is not initialized
goroutine 68108 [running]:
panic(0x179f4c0, 0xc827da4d80)
/usr/local/go/src/runtime/panic.go:481 +0x3e6
testing.tRunner.func1(0xc820430120)
/usr/local/go/src/testing/testing.go:467 +0x192
panic(0x179f4c0, 0xc827da4d80)
/usr/local/go/src/runtime/panic.go:443 +0x4e9
github.com/cockroachdb/cockroach/util/leaktest.AfterTest.func1()
/go/src/github.com/cockroachdb/cockroach/util/leaktest/leaktest.go:77 +0x95
panic(0x179f4c0, 0xc827da4d80)
/usr/local/go/src/runtime/panic.go:443 +0x4e9
github.com/cockroachdb/cockroach/storage.(*Store).Send.func1(0xc827b953c0, 0xc827b95438, 0x0, 0x3d, 0xc827b95430, 0xc8200ab180)
/go/src/github.com/cockroachdb/cockroach/storage/store.go:2119 +0x6e
panic(0x179f4c0, 0xc827da4d80)
/usr/local/go/src/runtime/panic.go:443 +0x4e9
github.com/cockroachdb/cockroach/roachpb.NewRangeKeyMismatchError(0xc827da4be8, 0x1, 0x8, 0x0, 0x0, 0x0, 0xc820577620, 0x0)
/go/src/github.com/cockroachdb/cockroach/roachpb/errors.go:301 +0xb2
github.com/cockroachdb/cockroach/storage.(*Replica).checkCmdHeader(0xc8206f1800, 0xc827da4be8, 0x1, 0x8, 0x0, 0x0, 0x0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/storage/replica.go:855 +0xfa
github.com/cockroachdb/cockroach/storage.(*Replica).executeCmd(0xc8206f1800, 0x7f8c374fc240, 0xc820783d70, 0x0, 0x0, 0x0, 0x7f8c37478258, 0xc8249e4300, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/storage/replica_command.go:75 +0x138
github.com/cockroachdb/cockroach/storage.(*Replica).executeBatch(0xc8206f1800, 0x7f8c374fc240, 0xc820783d70, 0x0, 0x0, 0x7f8c37478258, 0xc8249e4300, 0x0, 0x0, 0x3c, ...)
/go/src/github.com/cockroachdb/cockroach/storage/replica.go:2324 +0x5d4
github.com/cockroachdb/cockroach/storage.(*Replica).addReadOnlyCmd(0xc8206f1800, 0x7f8c374fc240, 0xc820783d70, 0x0, 0x3c, 0x0, 0x0, 0x1, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/storage/replica.go:1186 +0x332
github.com/cockroachdb/cockroach/storage.(*Replica).Send(0xc8206f1800, 0x7f8c374fc240, 0xc820783d70, 0x0, 0x3c, 0x0, 0x0, 0x1, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/storage/replica.go:830 +0x52f
github.com/cockroachdb/cockroach/storage.(*Store).Send(0xc8200ab180, 0x7f8c37478000, 0xc82000c518, 0x0, 0x3c, 0x0, 0x0, 0x1, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/storage/store.go:2214 +0xd67
github.com/cockroachdb/cockroach/internal/client.Wrap.func1(0x7f8c37478000, 0xc82000c518, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x2, ...)
/go/src/github.com/cockroachdb/cockroach/internal/client/sender.go:76 +0xb4
github.com/cockroachdb/cockroach/internal/client.SenderFunc.Send(0xc8200df620, 0x7f8c37478000, 0xc82000c518, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/internal/client/sender.go:37 +0x53
github.com/cockroachdb/cockroach/internal/client.SendWrappedWith(0x7f8c374fcf88, 0xc8200df620, 0x7f8c37478000, 0xc82000c518, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/internal/client/sender.go:54 +0x1a9
github.com/cockroachdb/cockroach/storage_test.TestReplicateAfterTruncation.func1(0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/storage/client_raft_test.go:523 +0x2e2
github.com/cockroachdb/cockroach/util.RetryForDuration(0x37e11d600, 0xc827b95c68, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/util/testing.go:127 +0x180
github.com/cockroachdb/cockroach/util.SucceedsSoonDepth(0x1, 0x7f8c373f6a40, 0xc820430120, 0xc827b95c68)
/go/src/github.com/cockroachdb/cockroach/util/testing.go:114 +0x37
github.com/cockroachdb/cockroach/util.SucceedsSoon(0x7f8c373f6a40, 0xc820430120, 0xc827b95c68)
/go/src/github.com/cockroachdb/cockroach/util/testing.go:108 +0x3e
github.com/cockroachdb/cockroach/storage_test.TestReplicateAfterTruncation(0xc820430120)
/go/src/github.com/cockroachdb/cockroach/storage/client_raft_test.go:529 +0xf21
testing.tRunner(0xc820430120, 0x2869308)
/usr/local/go/src/testing/testing.go:473 +0x98
created by testing.RunTests
/usr/local/go/src/testing/testing.go:582 +0x892
goroutine 1 [chan receive]:
testing.RunTests(0x2026d28, 0x2867ca0, 0x127, 0x127, 0xc82024cc01)
/usr/local/go/src/testing/testing.go:583 +0x8d2
testing.(*M).Run(0xc8204bdef8, 0xc820283c98)
/usr/local/go/src/testing/testing.go:515 +0x81
github.com/cockroachdb/cockroach/storage_test.TestMain(0xc8204bdef8)
/go/src/github.com/cockroachdb/cockroach/storage/main_test.go:57 +0x260
main.main()
github.com/cockroachdb/cockroach/storage/_test/_testmain.go:652 +0x114
goroutine 17 [syscall, locked to thread]:
runtime.goexit()
/usr/local/go/src/runtime/asm_amd64.s:1998 +0x1
goroutine 5 [chan receive]:
github.com/cockroachdb/cockroach/util/log.(*loggingT).flushDaemon(0x2b82da0)
/go/src/github.com/cockroachdb/cockroach/util/log/clog.go:1015 +0x64
created by github.com/cockroachdb/cockroach/util/log.init.1
/go/src/github.com/cockroachdb/cockroach/util/log/clog.go:598 +0x8a
ERROR: exit status 2
```
Run Details:
```
0 runs so far, 0 failures, over 5s
0 runs so far, 0 failures, over 10s
0 runs so far, 0 failures, over 15s
0 runs so far, 0 failures, over 20s
0 runs so far, 0 failures, over 25s
0 runs so far, 0 failures, over 30s
0 runs so far, 0 failures, over 35s
0 runs so far, 0 failures, over 40s
0 runs so far, 0 failures, over 45s
0 runs so far, 0 failures, over 50s
0 runs so far, 0 failures, over 55s
1 runs completed, 1 failures, over 56s
FAIL
```
Please assign, take a look and update the issue accordingly.
|
1.0
|
stress: failed test in cockroach/storage/storage.test: TestReplicateAfterTruncation - Binary: cockroach/static-tests.tar.gz sha: https://github.com/cockroachdb/cockroach/commits/a79e2bd677e746b73269ff7dac6c559e00166e2c
Stress build found a failed test:
```
=== RUN TestReplicateAfterTruncation
I160728 05:22:02.408139 storage/engine/rocksdb.go:353 opening in memory rocksdb instance
W160728 05:22:02.409038 gossip/gossip.go:953 not connected to cluster; use --join to specify a connected node
W160728 05:22:02.410296 gossip/gossip.go:953 not connected to cluster; use --join to specify a connected node
I160728 05:22:02.410459 storage/store.go:2781 system config not yet available
I160728 05:22:02.411088 storage/replica_command.go:1741 store=1:1 ([]=) range=1 [/Min-/Max): new range lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 900ms following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=1970-01-01 00:00:00 +0000 UTC]
I160728 05:22:02.411432 storage/engine/rocksdb.go:353 opening in memory rocksdb instance
W160728 05:22:02.412230 gossip/gossip.go:953 not connected to cluster; use --join to specify a connected node
I160728 05:22:02.412786 storage/store.go:2781 system config not yet available
I160728 05:22:02.412867 gossip/client.go:74 starting client to 127.0.0.1:35625
I160728 05:22:02.414267 storage/replica_command.go:1532 store=1:1 ([]=) range=1 [/Min-/Max): attempting to truncate raft logs for another range 0. Normally this is due to a merge and can be ignored.
I160728 05:22:02.414868 storage/replica_raftstorage.go:467 generated snapshot for range 1 at index 15 in 157.465µs. encoded size=2849, 28 KV pairs, 5 log entries
I160728 05:22:02.415159 storage/replica_command.go:3204 store=1:1 ([]=) range=1 [/Min-/Max): change replicas of 1: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > next_replica_id:2
I160728 05:22:02.415546 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160728 05:22:02.415854 storage/replica.go:1419 store=1:1 ([]=) range=1 [/Min-/Max): proposing ADD_REPLICA {NodeID:2 StoreID:2 ReplicaID:2} for range 1: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I160728 05:22:02.416171 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160728 05:22:02.416489 storage/replica_raftstorage.go:588 store=2:2 ([]=) range=1 [/Min-/Min): with replicaID [?], applying preemptive snapshot for range 1 at index 15 (encoded size=2849, 28 KV pairs, 5 log entries)
W160728 05:22:02.417377 storage/replica.go:337 range 1: outgoing raft transport stream to {2 2 0} closed by the remote: <nil>
I160728 05:22:02.417588 storage/replica_raftstorage.go:591 store=2:2 ([]=) range=1 [/Min-/Max): with replicaID [?], applied preemptive snapshot for range 1 in 1.059719ms
--- FAIL: TestReplicateAfterTruncation (0.01s)
panic: descriptor is not initialized [recovered]
panic: descriptor is not initialized [recovered]
panic: descriptor is not initialized [recovered]
panic: descriptor is not initialized
goroutine 68108 [running]:
panic(0x179f4c0, 0xc827da4d80)
/usr/local/go/src/runtime/panic.go:481 +0x3e6
testing.tRunner.func1(0xc820430120)
/usr/local/go/src/testing/testing.go:467 +0x192
panic(0x179f4c0, 0xc827da4d80)
/usr/local/go/src/runtime/panic.go:443 +0x4e9
github.com/cockroachdb/cockroach/util/leaktest.AfterTest.func1()
/go/src/github.com/cockroachdb/cockroach/util/leaktest/leaktest.go:77 +0x95
panic(0x179f4c0, 0xc827da4d80)
/usr/local/go/src/runtime/panic.go:443 +0x4e9
github.com/cockroachdb/cockroach/storage.(*Store).Send.func1(0xc827b953c0, 0xc827b95438, 0x0, 0x3d, 0xc827b95430, 0xc8200ab180)
/go/src/github.com/cockroachdb/cockroach/storage/store.go:2119 +0x6e
panic(0x179f4c0, 0xc827da4d80)
/usr/local/go/src/runtime/panic.go:443 +0x4e9
github.com/cockroachdb/cockroach/roachpb.NewRangeKeyMismatchError(0xc827da4be8, 0x1, 0x8, 0x0, 0x0, 0x0, 0xc820577620, 0x0)
/go/src/github.com/cockroachdb/cockroach/roachpb/errors.go:301 +0xb2
github.com/cockroachdb/cockroach/storage.(*Replica).checkCmdHeader(0xc8206f1800, 0xc827da4be8, 0x1, 0x8, 0x0, 0x0, 0x0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/storage/replica.go:855 +0xfa
github.com/cockroachdb/cockroach/storage.(*Replica).executeCmd(0xc8206f1800, 0x7f8c374fc240, 0xc820783d70, 0x0, 0x0, 0x0, 0x7f8c37478258, 0xc8249e4300, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/storage/replica_command.go:75 +0x138
github.com/cockroachdb/cockroach/storage.(*Replica).executeBatch(0xc8206f1800, 0x7f8c374fc240, 0xc820783d70, 0x0, 0x0, 0x7f8c37478258, 0xc8249e4300, 0x0, 0x0, 0x3c, ...)
/go/src/github.com/cockroachdb/cockroach/storage/replica.go:2324 +0x5d4
github.com/cockroachdb/cockroach/storage.(*Replica).addReadOnlyCmd(0xc8206f1800, 0x7f8c374fc240, 0xc820783d70, 0x0, 0x3c, 0x0, 0x0, 0x1, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/storage/replica.go:1186 +0x332
github.com/cockroachdb/cockroach/storage.(*Replica).Send(0xc8206f1800, 0x7f8c374fc240, 0xc820783d70, 0x0, 0x3c, 0x0, 0x0, 0x1, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/storage/replica.go:830 +0x52f
github.com/cockroachdb/cockroach/storage.(*Store).Send(0xc8200ab180, 0x7f8c37478000, 0xc82000c518, 0x0, 0x3c, 0x0, 0x0, 0x1, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/storage/store.go:2214 +0xd67
github.com/cockroachdb/cockroach/internal/client.Wrap.func1(0x7f8c37478000, 0xc82000c518, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x2, ...)
/go/src/github.com/cockroachdb/cockroach/internal/client/sender.go:76 +0xb4
github.com/cockroachdb/cockroach/internal/client.SenderFunc.Send(0xc8200df620, 0x7f8c37478000, 0xc82000c518, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/internal/client/sender.go:37 +0x53
github.com/cockroachdb/cockroach/internal/client.SendWrappedWith(0x7f8c374fcf88, 0xc8200df620, 0x7f8c37478000, 0xc82000c518, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/internal/client/sender.go:54 +0x1a9
github.com/cockroachdb/cockroach/storage_test.TestReplicateAfterTruncation.func1(0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/storage/client_raft_test.go:523 +0x2e2
github.com/cockroachdb/cockroach/util.RetryForDuration(0x37e11d600, 0xc827b95c68, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/util/testing.go:127 +0x180
github.com/cockroachdb/cockroach/util.SucceedsSoonDepth(0x1, 0x7f8c373f6a40, 0xc820430120, 0xc827b95c68)
/go/src/github.com/cockroachdb/cockroach/util/testing.go:114 +0x37
github.com/cockroachdb/cockroach/util.SucceedsSoon(0x7f8c373f6a40, 0xc820430120, 0xc827b95c68)
/go/src/github.com/cockroachdb/cockroach/util/testing.go:108 +0x3e
github.com/cockroachdb/cockroach/storage_test.TestReplicateAfterTruncation(0xc820430120)
/go/src/github.com/cockroachdb/cockroach/storage/client_raft_test.go:529 +0xf21
testing.tRunner(0xc820430120, 0x2869308)
/usr/local/go/src/testing/testing.go:473 +0x98
created by testing.RunTests
/usr/local/go/src/testing/testing.go:582 +0x892
goroutine 1 [chan receive]:
testing.RunTests(0x2026d28, 0x2867ca0, 0x127, 0x127, 0xc82024cc01)
/usr/local/go/src/testing/testing.go:583 +0x8d2
testing.(*M).Run(0xc8204bdef8, 0xc820283c98)
/usr/local/go/src/testing/testing.go:515 +0x81
github.com/cockroachdb/cockroach/storage_test.TestMain(0xc8204bdef8)
/go/src/github.com/cockroachdb/cockroach/storage/main_test.go:57 +0x260
main.main()
github.com/cockroachdb/cockroach/storage/_test/_testmain.go:652 +0x114
goroutine 17 [syscall, locked to thread]:
runtime.goexit()
/usr/local/go/src/runtime/asm_amd64.s:1998 +0x1
goroutine 5 [chan receive]:
github.com/cockroachdb/cockroach/util/log.(*loggingT).flushDaemon(0x2b82da0)
/go/src/github.com/cockroachdb/cockroach/util/log/clog.go:1015 +0x64
created by github.com/cockroachdb/cockroach/util/log.init.1
/go/src/github.com/cockroachdb/cockroach/util/log/clog.go:598 +0x8a
ERROR: exit status 2
```
Run Details:
```
0 runs so far, 0 failures, over 5s
0 runs so far, 0 failures, over 10s
0 runs so far, 0 failures, over 15s
0 runs so far, 0 failures, over 20s
0 runs so far, 0 failures, over 25s
0 runs so far, 0 failures, over 30s
0 runs so far, 0 failures, over 35s
0 runs so far, 0 failures, over 40s
0 runs so far, 0 failures, over 45s
0 runs so far, 0 failures, over 50s
0 runs so far, 0 failures, over 55s
1 runs completed, 1 failures, over 56s
FAIL
```
Please assign, take a look and update the issue accordingly.
|
test
|
stress failed test in cockroach storage storage test testreplicateaftertruncation binary cockroach static tests tar gz sha stress build found a failed test run testreplicateaftertruncation storage engine rocksdb go opening in memory rocksdb instance gossip gossip go not connected to cluster use join to specify a connected node gossip gossip go not connected to cluster use join to specify a connected node storage store go system config not yet available storage replica command go store range storage engine rocksdb go opening in memory rocksdb instance gossip gossip go not connected to cluster use join to specify a connected node storage store go system config not yet available gossip client go starting client to storage replica command go store range min max attempting to truncate raft logs for another range normally this is due to a merge and can be ignored storage replica raftstorage go generated snapshot for range at index in encoded size kv pairs log entries storage replica command go store range min max change replicas of read existing descriptor range id start key end key replicas next replica id storage replica go store range min max applied part of replica change txn begintransaction local range rangedescriptor min conditionalput local range rangedescriptor min put max min put max min perr storage replica go store range storage replica go store range min max applied part of replica change txn endtransaction local range rangedescriptor min perr storage replica raftstorage go store range applying preemptive snapshot for range at index encoded size kv pairs log entries storage replica go range outgoing raft transport stream to closed by the remote storage replica raftstorage go store range applied preemptive snapshot for range in fail testreplicateaftertruncation panic descriptor is not initialized panic descriptor is not initialized panic descriptor is not initialized panic descriptor is not initialized goroutine panic usr local go src runtime panic go testing trunner usr local go src testing testing go panic usr local go src runtime panic go github com cockroachdb cockroach util leaktest aftertest go src github com cockroachdb cockroach util leaktest leaktest go panic usr local go src runtime panic go github com cockroachdb cockroach storage store send go src github com cockroachdb cockroach storage store go panic usr local go src runtime panic go github com cockroachdb cockroach roachpb newrangekeymismatcherror go src github com cockroachdb cockroach roachpb errors go github com cockroachdb cockroach storage replica checkcmdheader go src github com cockroachdb cockroach storage replica go github com cockroachdb cockroach storage replica executecmd go src github com cockroachdb cockroach storage replica command go github com cockroachdb cockroach storage replica executebatch go src github com cockroachdb cockroach storage replica go github com cockroachdb cockroach storage replica addreadonlycmd go src github com cockroachdb cockroach storage replica go github com cockroachdb cockroach storage replica send go src github com cockroachdb cockroach storage replica go github com cockroachdb cockroach storage store send go src github com cockroachdb cockroach storage store go github com cockroachdb cockroach internal client wrap go src github com cockroachdb cockroach internal client sender go github com cockroachdb cockroach internal client senderfunc send go src github com cockroachdb cockroach internal client sender go github com cockroachdb cockroach internal client sendwrappedwith go src github com cockroachdb cockroach internal client sender go github com cockroachdb cockroach storage test testreplicateaftertruncation go src github com cockroachdb cockroach storage client raft test go github com cockroachdb cockroach util retryforduration go src github com cockroachdb cockroach util testing go github com cockroachdb cockroach util succeedssoondepth go src github com cockroachdb cockroach util testing go github com cockroachdb cockroach util succeedssoon go src github com cockroachdb cockroach util testing go github com cockroachdb cockroach storage test testreplicateaftertruncation go src github com cockroachdb cockroach storage client raft test go testing trunner usr local go src testing testing go created by testing runtests usr local go src testing testing go goroutine testing runtests usr local go src testing testing go testing m run usr local go src testing testing go github com cockroachdb cockroach storage test testmain go src github com cockroachdb cockroach storage main test go main main github com cockroachdb cockroach storage test testmain go goroutine runtime goexit usr local go src runtime asm s goroutine github com cockroachdb cockroach util log loggingt flushdaemon go src github com cockroachdb cockroach util log clog go created by github com cockroachdb cockroach util log init go src github com cockroachdb cockroach util log clog go error exit status run details runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs completed failures over fail please assign take a look and update the issue accordingly
| 1
|
456,189
| 13,146,665,060
|
IssuesEvent
|
2020-08-08 11:15:47
|
wso2/product-apim
|
https://api.github.com/repos/wso2/product-apim
|
opened
|
Password field in Basic Authentication Credentials aren't masked
|
Priority/Normal Type/Bug
|
### Description:
Subscribe to an API secured with Basic Authentication.
Select Basic Credentials and type username and password.
Password field isn't masked.
|
1.0
|
Password field in Basic Authentication Credentials aren't masked - ### Description:
Subscribe to an API secured with Basic Authentication.
Select Basic Credentials and type username and password.
Password field isn't masked.
|
non_test
|
password field in basic authentication credentials aren t masked description subscribe to an api secured with basic authentication select basic credentials and type username and password password field isn t masked
| 0
|
227,165
| 18,052,400,959
|
IssuesEvent
|
2021-09-20 00:09:21
|
logicmoo/logicmoo_workspace
|
https://api.github.com/repos/logicmoo/logicmoo_workspace
|
opened
|
logicmoo.pfc.test.sanity_base.SV_FWD_01A_B JUnit
|
Test_9999 logicmoo.pfc.test.sanity_base unit_test SV_FWD_01A_B Failing
|
(cd /var/lib/jenkins/workspace/logicmoo_workspace@2/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s swipl -x /var/lib/jenkins/workspace/logicmoo_workspace@2/bin/lmoo-clif sv_fwd_01a_b.pfc)
ISSUE: https://github.com/logicmoo/logicmoo_workspace/issues/
EDIT: https://github.com/logicmoo/logicmoo_workspace/edit/master/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc
JENKINS: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/SV_FWD_01A_B/logicmoo_pfc_test_sanity_base_SV_FWD_01A_B_JUnit/
PREVIOUS: https://jenkins.logicmoo.org/job/logicmoo_workspace/83/testReport/logicmoo.pfc.test.sanity_base/SV_FWD_01A_B/logicmoo_pfc_test_sanity_base_SV_FWD_01A_B_JUnit/
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3ASV_FWD_01A_B
GITLAB: https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/5063a48a24b85b2bce3c975c5486ec917095d69e/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/5063a48a24b85b2bce3c975c5486ec917095d69e
```
%~ init_phase(after_load)
%~ init_phase(restore_state)
%
running('/var/lib/jenkins/workspace/logicmoo_workspace@2/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc'),
%~ /var/lib/jenkins/.local/share/swi-prolog/pack/logicmoo_utils/prolog/logicmoo_test_header.pl:93
%~ this_test_might_need( :-( use_module( library(logicmoo_plarkc))))
:- set_fileAssertMt(header_sane).
%~ set_fileAssertMt(header_sane)
/*~
%~ set_fileAssertMt(header_sane)
~*/
:- expects_dialect(pfc).
arity(inChairZ,1).
prologSingleValued(inChairZ).
prologSingleValuedInArg(inChairZ,1).
singleValuedInArgAX(inChairZ, 1, 1).
:- ain( inChairZ(aZa)).
:- (ain( inChairZ(bYb))).
:- listing(inChairZ/1).
%~ skipped( listing( inChairZ/1))
%~ begin_test_completed_exit(0)
%~ unused(no_junit_results)
system halted_junit = true.
testsuite file = '/var/lib/jenkins/workspace/logicmoo_workspace@2/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc'.
%~ test_completed_exit(0)
```
totalTime=1
ISSUE: https://github.com/logicmoo/logicmoo_workspace/issues/
EDIT: https://github.com/logicmoo/logicmoo_workspace/edit/master/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc
JENKINS: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/SV_FWD_01A_B/logicmoo_pfc_test_sanity_base_SV_FWD_01A_B_JUnit/
PREVIOUS: https://jenkins.logicmoo.org/job/logicmoo_workspace/83/testReport/logicmoo.pfc.test.sanity_base/SV_FWD_01A_B/logicmoo_pfc_test_sanity_base_SV_FWD_01A_B_JUnit/
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3ASV_FWD_01A_B
GITLAB: https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/5063a48a24b85b2bce3c975c5486ec917095d69e/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/5063a48a24b85b2bce3c975c5486ec917095d69e
FAILED: /var/lib/jenkins/workspace/logicmoo_workspace@2/bin/lmoo-junit-minor -k sv_fwd_01a_b.pfc (returned 0) Add_LABELS='' Rem_LABELS='Errors,Warnings,Overtime,Skipped'
|
3.0
|
logicmoo.pfc.test.sanity_base.SV_FWD_01A_B JUnit - (cd /var/lib/jenkins/workspace/logicmoo_workspace@2/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s swipl -x /var/lib/jenkins/workspace/logicmoo_workspace@2/bin/lmoo-clif sv_fwd_01a_b.pfc)
ISSUE: https://github.com/logicmoo/logicmoo_workspace/issues/
EDIT: https://github.com/logicmoo/logicmoo_workspace/edit/master/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc
JENKINS: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/SV_FWD_01A_B/logicmoo_pfc_test_sanity_base_SV_FWD_01A_B_JUnit/
PREVIOUS: https://jenkins.logicmoo.org/job/logicmoo_workspace/83/testReport/logicmoo.pfc.test.sanity_base/SV_FWD_01A_B/logicmoo_pfc_test_sanity_base_SV_FWD_01A_B_JUnit/
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3ASV_FWD_01A_B
GITLAB: https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/5063a48a24b85b2bce3c975c5486ec917095d69e/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/5063a48a24b85b2bce3c975c5486ec917095d69e
```
%~ init_phase(after_load)
%~ init_phase(restore_state)
%
running('/var/lib/jenkins/workspace/logicmoo_workspace@2/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc'),
%~ /var/lib/jenkins/.local/share/swi-prolog/pack/logicmoo_utils/prolog/logicmoo_test_header.pl:93
%~ this_test_might_need( :-( use_module( library(logicmoo_plarkc))))
:- set_fileAssertMt(header_sane).
%~ set_fileAssertMt(header_sane)
/*~
%~ set_fileAssertMt(header_sane)
~*/
:- expects_dialect(pfc).
arity(inChairZ,1).
prologSingleValued(inChairZ).
prologSingleValuedInArg(inChairZ,1).
singleValuedInArgAX(inChairZ, 1, 1).
:- ain( inChairZ(aZa)).
:- (ain( inChairZ(bYb))).
:- listing(inChairZ/1).
%~ skipped( listing( inChairZ/1))
%~ begin_test_completed_exit(0)
%~ unused(no_junit_results)
system halted_junit = true.
testsuite file = '/var/lib/jenkins/workspace/logicmoo_workspace@2/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc'.
%~ test_completed_exit(0)
```
totalTime=1
ISSUE: https://github.com/logicmoo/logicmoo_workspace/issues/
EDIT: https://github.com/logicmoo/logicmoo_workspace/edit/master/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc
JENKINS: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/SV_FWD_01A_B/logicmoo_pfc_test_sanity_base_SV_FWD_01A_B_JUnit/
PREVIOUS: https://jenkins.logicmoo.org/job/logicmoo_workspace/83/testReport/logicmoo.pfc.test.sanity_base/SV_FWD_01A_B/logicmoo_pfc_test_sanity_base_SV_FWD_01A_B_JUnit/
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3ASV_FWD_01A_B
GITLAB: https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/5063a48a24b85b2bce3c975c5486ec917095d69e/packs_sys/pfc/t/sanity_base/sv_fwd_01a_b.pfc
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/5063a48a24b85b2bce3c975c5486ec917095d69e
FAILED: /var/lib/jenkins/workspace/logicmoo_workspace@2/bin/lmoo-junit-minor -k sv_fwd_01a_b.pfc (returned 0) Add_LABELS='' Rem_LABELS='Errors,Warnings,Overtime,Skipped'
|
test
|
logicmoo pfc test sanity base sv fwd b junit cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k swipl x var lib jenkins workspace logicmoo workspace bin lmoo clif sv fwd b pfc issue edit jenkins previous issue search gitlab github init phase after load init phase restore state running var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base sv fwd b pfc var lib jenkins local share swi prolog pack logicmoo utils prolog logicmoo test header pl this test might need use module library logicmoo plarkc set fileassertmt header sane set fileassertmt header sane set fileassertmt header sane expects dialect pfc arity inchairz prologsinglevalued inchairz prologsinglevaluedinarg inchairz singlevaluedinargax inchairz ain inchairz aza ain inchairz byb listing inchairz skipped listing inchairz begin test completed exit unused no junit results system halted junit true testsuite file var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base sv fwd b pfc test completed exit totaltime issue edit jenkins previous issue search gitlab github failed var lib jenkins workspace logicmoo workspace bin lmoo junit minor k sv fwd b pfc returned add labels rem labels errors warnings overtime skipped
| 1
|
104,153
| 16,613,464,074
|
IssuesEvent
|
2021-06-02 14:09:49
|
Thanraj/linux-4.1.15
|
https://api.github.com/repos/Thanraj/linux-4.1.15
|
opened
|
CVE-2018-8781 (High) detected in linux-yocto-4.1v4.1.17
|
security vulnerability
|
## CVE-2018-8781 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.1v4.1.17</b></p></summary>
<p>
<p>[no description]</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.1>https://git.yoctoproject.org/git/linux-yocto-4.1</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/Thanraj/linux-4.1.15/commits/5e3fb3e332499e1ad10a0969e55582af1027b085">5e3fb3e332499e1ad10a0969e55582af1027b085</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/drivers/gpu/drm/udl/udl_fb.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/drivers/gpu/drm/udl/udl_fb.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The udl_fb_mmap function in drivers/gpu/drm/udl/udl_fb.c at the Linux kernel version 3.4 and up to and including 4.15 has an integer-overflow vulnerability allowing local users with access to the udldrmfb driver to obtain full read and write permissions on kernel physical pages, resulting in a code execution in kernel space.
<p>Publish Date: 2018-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8781>CVE-2018-8781</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-8781">https://nvd.nist.gov/vuln/detail/CVE-2018-8781</a></p>
<p>Release Date: 2018-04-23</p>
<p>Fix Resolution: v4.16-rc7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2018-8781 (High) detected in linux-yocto-4.1v4.1.17 - ## CVE-2018-8781 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.1v4.1.17</b></p></summary>
<p>
<p>[no description]</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.1>https://git.yoctoproject.org/git/linux-yocto-4.1</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/Thanraj/linux-4.1.15/commits/5e3fb3e332499e1ad10a0969e55582af1027b085">5e3fb3e332499e1ad10a0969e55582af1027b085</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/drivers/gpu/drm/udl/udl_fb.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/drivers/gpu/drm/udl/udl_fb.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The udl_fb_mmap function in drivers/gpu/drm/udl/udl_fb.c at the Linux kernel version 3.4 and up to and including 4.15 has an integer-overflow vulnerability allowing local users with access to the udldrmfb driver to obtain full read and write permissions on kernel physical pages, resulting in a code execution in kernel space.
<p>Publish Date: 2018-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8781>CVE-2018-8781</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-8781">https://nvd.nist.gov/vuln/detail/CVE-2018-8781</a></p>
<p>Release Date: 2018-04-23</p>
<p>Fix Resolution: v4.16-rc7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in linux yocto cve high severity vulnerability vulnerable library linux yocto library home page a href found in head commit a href found in base branch master vulnerable source files linux drivers gpu drm udl udl fb c linux drivers gpu drm udl udl fb c vulnerability details the udl fb mmap function in drivers gpu drm udl udl fb c at the linux kernel version and up to and including has an integer overflow vulnerability allowing local users with access to the udldrmfb driver to obtain full read and write permissions on kernel physical pages resulting in a code execution in kernel space publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
219,399
| 17,089,687,330
|
IssuesEvent
|
2021-07-08 15:49:18
|
urapadmin/kiosk
|
https://api.github.com/repos/urapadmin/kiosk
|
closed
|
synchronization can be started twice
|
kiosk synchronization test-stage
|
Laurel started synchronization. Then the connection to the server was interrupted. She started it again right away. And so the second one got queued and it was that second one that gave her feedback.
So the log of the first one was lost and the second one said that there was an error because there wasn't anything left to do at that point.
If there is a running synchronization process should be checked by the sync-manager and it should show somewhere in the sync magnager. This happens because for synchronization the sync manager switches to a different site.
|
1.0
|
synchronization can be started twice - Laurel started synchronization. Then the connection to the server was interrupted. She started it again right away. And so the second one got queued and it was that second one that gave her feedback.
So the log of the first one was lost and the second one said that there was an error because there wasn't anything left to do at that point.
If there is a running synchronization process should be checked by the sync-manager and it should show somewhere in the sync magnager. This happens because for synchronization the sync manager switches to a different site.
|
test
|
synchronization can be started twice laurel started synchronization then the connection to the server was interrupted she started it again right away and so the second one got queued and it was that second one that gave her feedback so the log of the first one was lost and the second one said that there was an error because there wasn t anything left to do at that point if there is a running synchronization process should be checked by the sync manager and it should show somewhere in the sync magnager this happens because for synchronization the sync manager switches to a different site
| 1
|
324,696
| 24,013,062,503
|
IssuesEvent
|
2022-09-14 20:45:44
|
Technik-Tueftler/IntelligentSocketDatalogger
|
https://api.github.com/repos/Technik-Tueftler/IntelligentSocketDatalogger
|
opened
|
Set timezone fix to UTC in dockerfile
|
documentation enhancement
|
<https://ralph.blog.imixs.com/2020/10/23/how-to-set-timezone-and-locale-for-docker-image/>
- can user change this setting again?
- Info in documentation for timezone setting
|
1.0
|
Set timezone fix to UTC in dockerfile - <https://ralph.blog.imixs.com/2020/10/23/how-to-set-timezone-and-locale-for-docker-image/>
- can user change this setting again?
- Info in documentation for timezone setting
|
non_test
|
set timezone fix to utc in dockerfile can user change this setting again info in documentation for timezone setting
| 0
|
150,610
| 11,968,173,103
|
IssuesEvent
|
2020-04-06 08:11:01
|
ubtue/DatenProbleme
|
https://api.github.com/repos/ubtue/DatenProbleme
|
closed
|
ISSN 1874-6349 Acta Analytica Mix aus Online First und Standardartikel
|
Zotero_AUTO_RSS blocked ready for testing
|
Die Daten enthalten Artikel, die keinem Heft zugeordnet sind und solche, bei denen das der Fall ist.
|
1.0
|
ISSN 1874-6349 Acta Analytica Mix aus Online First und Standardartikel - Die Daten enthalten Artikel, die keinem Heft zugeordnet sind und solche, bei denen das der Fall ist.
|
test
|
issn acta analytica mix aus online first und standardartikel die daten enthalten artikel die keinem heft zugeordnet sind und solche bei denen das der fall ist
| 1
|
26,088
| 11,260,459,920
|
IssuesEvent
|
2020-01-13 10:34:53
|
Antiai/react-hooks-skeleton
|
https://api.github.com/repos/Antiai/react-hooks-skeleton
|
closed
|
WS-2019-0027 (Medium) detected in marked-0.3.19.js
|
security vulnerability
|
## WS-2019-0027 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.19.js</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/marked/0.3.19/marked.js">https://cdnjs.cloudflare.com/ajax/libs/marked/0.3.19/marked.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/react-hooks-skeleton/node_modules/marked/www/demo.html</p>
<p>Path to vulnerable library: /react-hooks-skeleton/node_modules/marked/www/../lib/marked.js</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.3.19.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Antiai/react-hooks-skeleton/commit/ba3044d6184f9e53b5a092963a478b83e8f1613f">ba3044d6184f9e53b5a092963a478b83e8f1613f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions 0.3.17 and earlier of marked has Four regexes were vulnerable to catastrophic backtracking. This leaves markdown servers open to a potential REDOS attack.
<p>Publish Date: 2019-03-17
<p>URL: <a href=https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d>WS-2019-0027</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d">https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d</a></p>
<p>Release Date: 2019-03-17</p>
<p>Fix Resolution: 0.3.18</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2019-0027 (Medium) detected in marked-0.3.19.js - ## WS-2019-0027 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.19.js</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/marked/0.3.19/marked.js">https://cdnjs.cloudflare.com/ajax/libs/marked/0.3.19/marked.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/react-hooks-skeleton/node_modules/marked/www/demo.html</p>
<p>Path to vulnerable library: /react-hooks-skeleton/node_modules/marked/www/../lib/marked.js</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.3.19.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Antiai/react-hooks-skeleton/commit/ba3044d6184f9e53b5a092963a478b83e8f1613f">ba3044d6184f9e53b5a092963a478b83e8f1613f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions 0.3.17 and earlier of marked has Four regexes were vulnerable to catastrophic backtracking. This leaves markdown servers open to a potential REDOS attack.
<p>Publish Date: 2019-03-17
<p>URL: <a href=https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d>WS-2019-0027</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d">https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d</a></p>
<p>Release Date: 2019-03-17</p>
<p>Fix Resolution: 0.3.18</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
ws medium detected in marked js ws medium severity vulnerability vulnerable library marked js a markdown parser built for speed library home page a href path to dependency file tmp ws scm react hooks skeleton node modules marked www demo html path to vulnerable library react hooks skeleton node modules marked www lib marked js dependency hierarchy x marked js vulnerable library found in head commit a href vulnerability details versions and earlier of marked has four regexes were vulnerable to catastrophic backtracking this leaves markdown servers open to a potential redos attack publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
272,312
| 23,668,101,762
|
IssuesEvent
|
2022-08-27 00:50:36
|
eclipse/che
|
https://api.github.com/repos/eclipse/che
|
closed
|
"chectl server:deploy" command failed to deploy Che with DevWorkspace enabled to minikube started in 'none' driver mode
|
kind/bug severity/P2 e2e-test/failure area/chectl lifecycle/stale
|
### Describe the bug
`chectl server:deploy` command failed to deploy Eclipse Che Next to minikube 1.22.0 started in 'none' driver mode:
```
› Installer type is set to: operator'
[07:48:00] Verify Kubernetes API[started]
› Current Kubernetes context: minikube'
[07:48:00] Verify Kubernetes API...OK [title changed]
[07:48:00] Verify Kubernetes API...OK [completed]
[07:48:00] 👀 Looking for an already existing Eclipse Che instance[started]
[07:48:00] Verify if Eclipse Che is deployed into namespace "eclipse-che"[started]
[07:48:00] Verify if Eclipse Che is deployed into namespace "eclipse-che"...it is not [title changed]
[07:48:00] Verify if Eclipse Che is deployed into namespace "eclipse-che"...it is not [completed]
[07:48:00] 👀 Looking for an already existing Eclipse Che instance [completed]
[07:48:00] 🧪 DevWorkspace engine (experimental / technology preview) 🚨[started]
[07:48:00] Verify cert-manager installation[started]
[07:48:00] Check Cert Manager deployment[started]
[07:48:01] Check Cert Manager deployment...already deployed [title changed]
[07:48:01] Check Cert Manager deployment...already deployed [completed]
[07:48:01] Wait for Cert Manager[started]
[07:48:01] Wait for Cert Manager...ready [title changed]
[07:48:01] Wait for Cert Manager...ready [completed]
[07:48:01] Verify cert-manager installation [completed]
[07:48:01] 🧪 DevWorkspace engine (experimental / technology preview) 🚨 [completed]
[07:48:01] ✈️ Minikube preflight checklist[started]
[07:48:01] Verify if kubectl is installed[started]
[07:48:01] Verify if kubectl is installed [completed]
[07:48:01] Verify if minikube is installed[started]
[07:48:01] Verify if minikube is installed [completed]
[07:48:01] Verify if minikube is running[started]
[07:48:01] Verify if minikube is running [completed]
[07:48:01] Start minikube[started]
[07:48:01] Start minikube[skipped]
[07:48:01] → Minikube is alread running.
[07:48:01] Check Kubernetes version[started]
[07:48:01] Check Kubernetes version: Found v1.20.2. [title changed]
[07:48:01] Check Kubernetes version: Found v1.20.2. [completed]
[07:48:01] Verify if minikube ingress addon is enabled[started]
[07:48:01] Verify if minikube ingress addon is enabled [completed]
[07:48:01] Enable minikube ingress addon[started]
[07:48:01] Enable minikube ingress addon[skipped]
[07:48:01] → Ingress addon is alread enabled.
[07:48:01] Retrieving minikube IP and domain for ingress URLs[started]
[07:48:02] Retrieving minikube IP and domain for ingress URLs...10.0.211.126.nip.io. [title changed]
[07:48:02] Retrieving minikube IP and domain for ingress URLs...10.0.211.126.nip.io. [completed]
[07:48:02] Checking minikube version[started]
[07:48:02] Checking minikube version... 1.22.0 [title changed]
[07:48:02] Checking minikube version... 1.22.0 [completed]
[07:48:02] Check if cluster accessible[started]
[07:48:02] Check if cluster accessible[skipped]
[07:48:02] ✈️ Minikube preflight checklist [completed]
[07:48:02] Following Eclipse Che logs[started]
[07:48:02] Start following Operator logs[started]
[07:48:02] Start following Operator logs...done [title changed]
[07:48:02] Start following Operator logs...done [completed]
[07:48:02] Start following Eclipse Che Server logs[started]
[07:48:02] Start following Eclipse Che Server logs...done [title changed]
[07:48:02] Start following Eclipse Che Server logs...done [completed]
[07:48:02] Start following PostgreSQL logs[started]
[07:48:02] Start following PostgreSQL logs...done [title changed]
[07:48:02] Start following PostgreSQL logs...done [completed]
[07:48:02] Start following Keycloak logs[started]
[07:48:02] Start following Keycloak logs...done [title changed]
[07:48:02] Start following Keycloak logs...done [completed]
[07:48:02] Start following Plug-in Registry logs[started]
[07:48:02] Start following Plug-in Registry logs...done [title changed]
[07:48:02] Start following Plug-in Registry logs...done [completed]
[07:48:02] Start following Devfile Registry logs[started]
[07:48:02] Start following Devfile Registry logs...done [title changed]
[07:48:02] Start following Devfile Registry logs...done [completed]
[07:48:02] Start following Eclipse Che Dashboard logs[started]
[07:48:02] Start following Eclipse Che Dashboard logs...done [title changed]
[07:48:02] Start following Eclipse Che Dashboard logs...done [completed]
[07:48:02] Start following namespace events[started]
[07:48:02] Start following namespace events...done [title changed]
[07:48:02] Start following namespace events...done [completed]
[07:48:02] Following Eclipse Che logs [completed]
[07:48:02] Create Namespace eclipse-che[started]
[07:48:02] Create Namespace eclipse-che...[Exists] [title changed]
[07:48:02] Create Namespace eclipse-che...[Exists] [completed]
[07:48:02] Deploy Dex[started]
[07:48:02] Create namespace: dex[started]
[07:48:02] Create namespace: dex...[Exists] [title changed]
[07:48:02] Create namespace: dex...[Exists] [completed]
[07:48:02] Provide Dex certificate[started]
[07:48:02] Read Dex certificate[started]
[07:48:02] Read Dex certificate...[OK] [title changed]
[07:48:02] Read Dex certificate...[OK] [completed]
[07:48:02] Save Dex certificate[started]
[07:48:02] Save Dex certificate...[OK: /tmp/dex-ca.crt] [title changed]
[07:48:02] Save Dex certificate...[OK: /tmp/dex-ca.crt] [completed]
[07:48:02] Add Dex certificate to Eclipse Che certificates bundle[started]
[07:48:02] Add Dex certificate to Eclipse Che certificates bundle...[Exists] [title changed]
[07:48:02] Add Dex certificate to Eclipse Che certificates bundle...[Exists] [completed]
[07:48:02] Provide Dex certificate [completed]
[07:48:02] Create Dex service account[started]
[07:48:02] Create Dex service account...[Exists] [title changed]
[07:48:02] Create Dex service account...[Exists] [completed]
[07:48:02] Create Dex cluster role[started]
[07:48:02] Create Dex cluster role...[Exists] [title changed]
[07:48:02] Create Dex cluster role...[Exists] [completed]
[07:48:02] Create Dex cluster role binding[started]
[07:48:02] Create Dex cluster role binding...[Exists] [title changed]
[07:48:02] Create Dex cluster role binding...[Exists] [completed]
[07:48:02] Create Dex service[started]
[07:48:02] Create Dex service...[Exists] [title changed]
[07:48:02] Create Dex service...[Exists] [completed]
[07:48:02] Create Dex ingress[started]
[07:48:02] Create Dex ingress...[Exists] [title changed]
[07:48:02] Create Dex ingress...[Exists] [completed]
[07:48:02] Generate Dex username and password[started]
[07:48:02] Generate Dex username and password...[Exists] [title changed]
[07:48:02] Generate Dex username and password...[Exists] [completed]
[07:48:02] Create Dex configmap[started]
[07:48:02] Create Dex configmap...[Exists] [title changed]
[07:48:02] Create Dex configmap...[Exists] [completed]
[07:48:02] Create Dex deployment[started]
[07:48:02] Create Dex deployment...[Exists] [title changed]
[07:48:02] Create Dex deployment...[Exists] [completed]
[07:48:02] Wait for Dex is ready[started]
[07:48:02] Wait for Dex is ready...[OK] [title changed]
[07:48:02] Wait for Dex is ready...[OK] [completed]
[07:48:02] Configure API server[started]
[07:48:02] Create /etc/ca-certificates directory[started]
[07:48:02] Create /etc/ca-certificates director [failed]
[07:48:02] → Command failed with exit code 14: minikube ssh sudo mkdir -p /etc/ca-certificates
X Exiting due to MK_USAGE: 'none' driver does not support 'minikube ssh' command
[07:48:02] Configure API serve [failed]
[07:48:02] → Command failed with exit code 14: minikube ssh sudo mkdir -p /etc/ca-certificates
X Exiting due to MK_USAGE: 'none' driver does not support 'minikube ssh' command
[07:48:02] Deploy De [failed]
[07:48:02] → Command failed with exit code 14: minikube ssh sudo mkdir -p /etc/ca-certificates
X Exiting due to MK_USAGE: 'none' driver does not support 'minikube ssh' command
```
### Che version
next (development version)
### Steps to reproduce
1. Start minikube in 'none' driver mode:
```
export MINIKUBE_WANTUPDATENOTIFICATION=false
export MINIKUBE_WANTREPORTERRORPROMPT=false
export MINIKUBE_HOME=\$HOME
export CHANGE_MINIKUBE_NONE_USER=true
export KUBECONFIG=\$HOME/.kube/config
export DOCKER_CONFIG=\$HOME/.docker
mkdir -p \$HOME/.kube \$HOME/.minikube
touch \$KUBECONFIG
sudo -E /usr/local/bin/minikube start \
--vm-driver=none \
--cpus 4 \
--memory 7000 \
--logtostderr
# workaround https://github.com/eclipse/che/issues/20888
sudo -E /usr/local/bin/minikube addons enable ingress
```
2. Try to deploy Eclipse Che with DevWorkspace enabled:
```
chectl server:deploy --k8spodreadytimeout=600000 --k8spodwaittimeout=600000 --k8spoddownloadimagetimeout=600000 --listr-renderer=verbose --platform=minikube --che-operator-cr-patch-yaml=custom-resource-patch.yaml --telemetry=off --chenamespace=eclipse-che`
```
where custom-resource-patch.yaml:
```
spec:
server:
cheImage: quay.io/eclipse/che-server
cheImageTag: next
customCheProperties:
CHE_LIMITS_USER_WORKSPACES_RUN_COUNT: '-1'
CHE_WORKSPACE_SIDECAR_IMAGE__PULL__POLICY: IfNotPresent
CHE_WORKSPACE_PLUGIN__BROKER_PULL__POLICY: IfNotPresent
CHE_INFRA_KUBERNETES_WORKSPACE_START_TIMEOUT_MIN: '12'
devWorkspace:
enable: true
auth:
updateAdminPassword: false
```
### Expected behavior
Eclipse Che is installed.
### Runtime
minikube
### Screenshots
_No response_
### Installation method
chectl/next
### Environment
Linux
### Eclipse Che Logs
_No response_
### Additional context
_No response_
|
1.0
|
"chectl server:deploy" command failed to deploy Che with DevWorkspace enabled to minikube started in 'none' driver mode - ### Describe the bug
`chectl server:deploy` command failed to deploy Eclipse Che Next to minikube 1.22.0 started in 'none' driver mode:
```
› Installer type is set to: operator'
[07:48:00] Verify Kubernetes API[started]
› Current Kubernetes context: minikube'
[07:48:00] Verify Kubernetes API...OK [title changed]
[07:48:00] Verify Kubernetes API...OK [completed]
[07:48:00] 👀 Looking for an already existing Eclipse Che instance[started]
[07:48:00] Verify if Eclipse Che is deployed into namespace "eclipse-che"[started]
[07:48:00] Verify if Eclipse Che is deployed into namespace "eclipse-che"...it is not [title changed]
[07:48:00] Verify if Eclipse Che is deployed into namespace "eclipse-che"...it is not [completed]
[07:48:00] 👀 Looking for an already existing Eclipse Che instance [completed]
[07:48:00] 🧪 DevWorkspace engine (experimental / technology preview) 🚨[started]
[07:48:00] Verify cert-manager installation[started]
[07:48:00] Check Cert Manager deployment[started]
[07:48:01] Check Cert Manager deployment...already deployed [title changed]
[07:48:01] Check Cert Manager deployment...already deployed [completed]
[07:48:01] Wait for Cert Manager[started]
[07:48:01] Wait for Cert Manager...ready [title changed]
[07:48:01] Wait for Cert Manager...ready [completed]
[07:48:01] Verify cert-manager installation [completed]
[07:48:01] 🧪 DevWorkspace engine (experimental / technology preview) 🚨 [completed]
[07:48:01] ✈️ Minikube preflight checklist[started]
[07:48:01] Verify if kubectl is installed[started]
[07:48:01] Verify if kubectl is installed [completed]
[07:48:01] Verify if minikube is installed[started]
[07:48:01] Verify if minikube is installed [completed]
[07:48:01] Verify if minikube is running[started]
[07:48:01] Verify if minikube is running [completed]
[07:48:01] Start minikube[started]
[07:48:01] Start minikube[skipped]
[07:48:01] → Minikube is alread running.
[07:48:01] Check Kubernetes version[started]
[07:48:01] Check Kubernetes version: Found v1.20.2. [title changed]
[07:48:01] Check Kubernetes version: Found v1.20.2. [completed]
[07:48:01] Verify if minikube ingress addon is enabled[started]
[07:48:01] Verify if minikube ingress addon is enabled [completed]
[07:48:01] Enable minikube ingress addon[started]
[07:48:01] Enable minikube ingress addon[skipped]
[07:48:01] → Ingress addon is alread enabled.
[07:48:01] Retrieving minikube IP and domain for ingress URLs[started]
[07:48:02] Retrieving minikube IP and domain for ingress URLs...10.0.211.126.nip.io. [title changed]
[07:48:02] Retrieving minikube IP and domain for ingress URLs...10.0.211.126.nip.io. [completed]
[07:48:02] Checking minikube version[started]
[07:48:02] Checking minikube version... 1.22.0 [title changed]
[07:48:02] Checking minikube version... 1.22.0 [completed]
[07:48:02] Check if cluster accessible[started]
[07:48:02] Check if cluster accessible[skipped]
[07:48:02] ✈️ Minikube preflight checklist [completed]
[07:48:02] Following Eclipse Che logs[started]
[07:48:02] Start following Operator logs[started]
[07:48:02] Start following Operator logs...done [title changed]
[07:48:02] Start following Operator logs...done [completed]
[07:48:02] Start following Eclipse Che Server logs[started]
[07:48:02] Start following Eclipse Che Server logs...done [title changed]
[07:48:02] Start following Eclipse Che Server logs...done [completed]
[07:48:02] Start following PostgreSQL logs[started]
[07:48:02] Start following PostgreSQL logs...done [title changed]
[07:48:02] Start following PostgreSQL logs...done [completed]
[07:48:02] Start following Keycloak logs[started]
[07:48:02] Start following Keycloak logs...done [title changed]
[07:48:02] Start following Keycloak logs...done [completed]
[07:48:02] Start following Plug-in Registry logs[started]
[07:48:02] Start following Plug-in Registry logs...done [title changed]
[07:48:02] Start following Plug-in Registry logs...done [completed]
[07:48:02] Start following Devfile Registry logs[started]
[07:48:02] Start following Devfile Registry logs...done [title changed]
[07:48:02] Start following Devfile Registry logs...done [completed]
[07:48:02] Start following Eclipse Che Dashboard logs[started]
[07:48:02] Start following Eclipse Che Dashboard logs...done [title changed]
[07:48:02] Start following Eclipse Che Dashboard logs...done [completed]
[07:48:02] Start following namespace events[started]
[07:48:02] Start following namespace events...done [title changed]
[07:48:02] Start following namespace events...done [completed]
[07:48:02] Following Eclipse Che logs [completed]
[07:48:02] Create Namespace eclipse-che[started]
[07:48:02] Create Namespace eclipse-che...[Exists] [title changed]
[07:48:02] Create Namespace eclipse-che...[Exists] [completed]
[07:48:02] Deploy Dex[started]
[07:48:02] Create namespace: dex[started]
[07:48:02] Create namespace: dex...[Exists] [title changed]
[07:48:02] Create namespace: dex...[Exists] [completed]
[07:48:02] Provide Dex certificate[started]
[07:48:02] Read Dex certificate[started]
[07:48:02] Read Dex certificate...[OK] [title changed]
[07:48:02] Read Dex certificate...[OK] [completed]
[07:48:02] Save Dex certificate[started]
[07:48:02] Save Dex certificate...[OK: /tmp/dex-ca.crt] [title changed]
[07:48:02] Save Dex certificate...[OK: /tmp/dex-ca.crt] [completed]
[07:48:02] Add Dex certificate to Eclipse Che certificates bundle[started]
[07:48:02] Add Dex certificate to Eclipse Che certificates bundle...[Exists] [title changed]
[07:48:02] Add Dex certificate to Eclipse Che certificates bundle...[Exists] [completed]
[07:48:02] Provide Dex certificate [completed]
[07:48:02] Create Dex service account[started]
[07:48:02] Create Dex service account...[Exists] [title changed]
[07:48:02] Create Dex service account...[Exists] [completed]
[07:48:02] Create Dex cluster role[started]
[07:48:02] Create Dex cluster role...[Exists] [title changed]
[07:48:02] Create Dex cluster role...[Exists] [completed]
[07:48:02] Create Dex cluster role binding[started]
[07:48:02] Create Dex cluster role binding...[Exists] [title changed]
[07:48:02] Create Dex cluster role binding...[Exists] [completed]
[07:48:02] Create Dex service[started]
[07:48:02] Create Dex service...[Exists] [title changed]
[07:48:02] Create Dex service...[Exists] [completed]
[07:48:02] Create Dex ingress[started]
[07:48:02] Create Dex ingress...[Exists] [title changed]
[07:48:02] Create Dex ingress...[Exists] [completed]
[07:48:02] Generate Dex username and password[started]
[07:48:02] Generate Dex username and password...[Exists] [title changed]
[07:48:02] Generate Dex username and password...[Exists] [completed]
[07:48:02] Create Dex configmap[started]
[07:48:02] Create Dex configmap...[Exists] [title changed]
[07:48:02] Create Dex configmap...[Exists] [completed]
[07:48:02] Create Dex deployment[started]
[07:48:02] Create Dex deployment...[Exists] [title changed]
[07:48:02] Create Dex deployment...[Exists] [completed]
[07:48:02] Wait for Dex is ready[started]
[07:48:02] Wait for Dex is ready...[OK] [title changed]
[07:48:02] Wait for Dex is ready...[OK] [completed]
[07:48:02] Configure API server[started]
[07:48:02] Create /etc/ca-certificates directory[started]
[07:48:02] Create /etc/ca-certificates director [failed]
[07:48:02] → Command failed with exit code 14: minikube ssh sudo mkdir -p /etc/ca-certificates
X Exiting due to MK_USAGE: 'none' driver does not support 'minikube ssh' command
[07:48:02] Configure API serve [failed]
[07:48:02] → Command failed with exit code 14: minikube ssh sudo mkdir -p /etc/ca-certificates
X Exiting due to MK_USAGE: 'none' driver does not support 'minikube ssh' command
[07:48:02] Deploy De [failed]
[07:48:02] → Command failed with exit code 14: minikube ssh sudo mkdir -p /etc/ca-certificates
X Exiting due to MK_USAGE: 'none' driver does not support 'minikube ssh' command
```
### Che version
next (development version)
### Steps to reproduce
1. Start minikube in 'none' driver mode:
```
export MINIKUBE_WANTUPDATENOTIFICATION=false
export MINIKUBE_WANTREPORTERRORPROMPT=false
export MINIKUBE_HOME=\$HOME
export CHANGE_MINIKUBE_NONE_USER=true
export KUBECONFIG=\$HOME/.kube/config
export DOCKER_CONFIG=\$HOME/.docker
mkdir -p \$HOME/.kube \$HOME/.minikube
touch \$KUBECONFIG
sudo -E /usr/local/bin/minikube start \
--vm-driver=none \
--cpus 4 \
--memory 7000 \
--logtostderr
# workaround https://github.com/eclipse/che/issues/20888
sudo -E /usr/local/bin/minikube addons enable ingress
```
2. Try to deploy Eclipse Che with DevWorkspace enabled:
```
chectl server:deploy --k8spodreadytimeout=600000 --k8spodwaittimeout=600000 --k8spoddownloadimagetimeout=600000 --listr-renderer=verbose --platform=minikube --che-operator-cr-patch-yaml=custom-resource-patch.yaml --telemetry=off --chenamespace=eclipse-che`
```
where custom-resource-patch.yaml:
```
spec:
server:
cheImage: quay.io/eclipse/che-server
cheImageTag: next
customCheProperties:
CHE_LIMITS_USER_WORKSPACES_RUN_COUNT: '-1'
CHE_WORKSPACE_SIDECAR_IMAGE__PULL__POLICY: IfNotPresent
CHE_WORKSPACE_PLUGIN__BROKER_PULL__POLICY: IfNotPresent
CHE_INFRA_KUBERNETES_WORKSPACE_START_TIMEOUT_MIN: '12'
devWorkspace:
enable: true
auth:
updateAdminPassword: false
```
### Expected behavior
Eclipse Che is installed.
### Runtime
minikube
### Screenshots
_No response_
### Installation method
chectl/next
### Environment
Linux
### Eclipse Che Logs
_No response_
### Additional context
_No response_
|
test
|
chectl server deploy command failed to deploy che with devworkspace enabled to minikube started in none driver mode describe the bug chectl server deploy command failed to deploy eclipse che next to minikube started in none driver mode › installer type is set to operator verify kubernetes api › current kubernetes context minikube verify kubernetes api ok verify kubernetes api ok 👀 looking for an already existing eclipse che instance verify if eclipse che is deployed into namespace eclipse che verify if eclipse che is deployed into namespace eclipse che it is not verify if eclipse che is deployed into namespace eclipse che it is not 👀 looking for an already existing eclipse che instance 🧪 devworkspace engine experimental technology preview 🚨 verify cert manager installation check cert manager deployment check cert manager deployment already deployed check cert manager deployment already deployed wait for cert manager wait for cert manager ready wait for cert manager ready verify cert manager installation 🧪 devworkspace engine experimental technology preview 🚨 ✈️ minikube preflight checklist verify if kubectl is installed verify if kubectl is installed verify if minikube is installed verify if minikube is installed verify if minikube is running verify if minikube is running start minikube start minikube → minikube is alread running check kubernetes version check kubernetes version found check kubernetes version found verify if minikube ingress addon is enabled verify if minikube ingress addon is enabled enable minikube ingress addon enable minikube ingress addon → ingress addon is alread enabled retrieving minikube ip and domain for ingress urls retrieving minikube ip and domain for ingress urls nip io retrieving minikube ip and domain for ingress urls nip io checking minikube version checking minikube version checking minikube version check if cluster accessible check if cluster accessible ✈️ minikube preflight checklist following eclipse che logs start following operator logs start following operator logs done start following operator logs done start following eclipse che server logs start following eclipse che server logs done start following eclipse che server logs done start following postgresql logs start following postgresql logs done start following postgresql logs done start following keycloak logs start following keycloak logs done start following keycloak logs done start following plug in registry logs start following plug in registry logs done start following plug in registry logs done start following devfile registry logs start following devfile registry logs done start following devfile registry logs done start following eclipse che dashboard logs start following eclipse che dashboard logs done start following eclipse che dashboard logs done start following namespace events start following namespace events done start following namespace events done following eclipse che logs create namespace eclipse che create namespace eclipse che create namespace eclipse che deploy dex create namespace dex create namespace dex create namespace dex provide dex certificate read dex certificate read dex certificate read dex certificate save dex certificate save dex certificate save dex certificate add dex certificate to eclipse che certificates bundle add dex certificate to eclipse che certificates bundle add dex certificate to eclipse che certificates bundle provide dex certificate create dex service account create dex service account create dex service account create dex cluster role create dex cluster role create dex cluster role create dex cluster role binding create dex cluster role binding create dex cluster role binding create dex service create dex service create dex service create dex ingress create dex ingress create dex ingress generate dex username and password generate dex username and password generate dex username and password create dex configmap create dex configmap create dex configmap create dex deployment create dex deployment create dex deployment wait for dex is ready wait for dex is ready wait for dex is ready configure api server create etc ca certificates directory create etc ca certificates director → command failed with exit code minikube ssh sudo mkdir p etc ca certificates x exiting due to mk usage none driver does not support minikube ssh command configure api serve → command failed with exit code minikube ssh sudo mkdir p etc ca certificates x exiting due to mk usage none driver does not support minikube ssh command deploy de → command failed with exit code minikube ssh sudo mkdir p etc ca certificates x exiting due to mk usage none driver does not support minikube ssh command che version next development version steps to reproduce start minikube in none driver mode export minikube wantupdatenotification false export minikube wantreporterrorprompt false export minikube home home export change minikube none user true export kubeconfig home kube config export docker config home docker mkdir p home kube home minikube touch kubeconfig sudo e usr local bin minikube start vm driver none cpus memory logtostderr workaround sudo e usr local bin minikube addons enable ingress try to deploy eclipse che with devworkspace enabled chectl server deploy listr renderer verbose platform minikube che operator cr patch yaml custom resource patch yaml telemetry off chenamespace eclipse che where custom resource patch yaml spec server cheimage quay io eclipse che server cheimagetag next customcheproperties che limits user workspaces run count che workspace sidecar image pull policy ifnotpresent che workspace plugin broker pull policy ifnotpresent che infra kubernetes workspace start timeout min devworkspace enable true auth updateadminpassword false expected behavior eclipse che is installed runtime minikube screenshots no response installation method chectl next environment linux eclipse che logs no response additional context no response
| 1
|
258,534
| 22,326,524,346
|
IssuesEvent
|
2022-06-14 11:08:08
|
Uuvana-Studios/longvinter-windows-client
|
https://api.github.com/repos/Uuvana-Studios/longvinter-windows-client
|
closed
|
Stuck in game when using /noclip under the house
|
Bug High Priority Tested
|
**Describe the bug**
There is an error where the game freezes when player go to the floor of the house using the `/noclip` command inside the house.
Shows a blank screen for about 5 seconds and then shows players in the house for 0.5 seconds.
None of the actions, including the Escape key, will work on a blank screen, and will only work for a short time if you're showing a player in the house.
However, the player is unable to leave the house, and is stuck in the house.
Reconnecting the server does not solve this problem. Currently the best workaround is the `Alt` + `K` key combo. This is a command to kill themselves, and when player die, player will be moved to player's home or island.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to any house and get in... or use /noclip and move under the ground.
2. Use /noclip in house.
3. Goto under the house. More deeper and deeper...
4. See an error
**Expected behavior**
Game is freezing.
**Desktop (please complete the following information):**
- OS: [e.g. Windows]
- Game Version 1.0.7
- Steam Version -
|
1.0
|
Stuck in game when using /noclip under the house - **Describe the bug**
There is an error where the game freezes when player go to the floor of the house using the `/noclip` command inside the house.
Shows a blank screen for about 5 seconds and then shows players in the house for 0.5 seconds.
None of the actions, including the Escape key, will work on a blank screen, and will only work for a short time if you're showing a player in the house.
However, the player is unable to leave the house, and is stuck in the house.
Reconnecting the server does not solve this problem. Currently the best workaround is the `Alt` + `K` key combo. This is a command to kill themselves, and when player die, player will be moved to player's home or island.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to any house and get in... or use /noclip and move under the ground.
2. Use /noclip in house.
3. Goto under the house. More deeper and deeper...
4. See an error
**Expected behavior**
Game is freezing.
**Desktop (please complete the following information):**
- OS: [e.g. Windows]
- Game Version 1.0.7
- Steam Version -
|
test
|
stuck in game when using noclip under the house describe the bug there is an error where the game freezes when player go to the floor of the house using the noclip command inside the house shows a blank screen for about seconds and then shows players in the house for seconds none of the actions including the escape key will work on a blank screen and will only work for a short time if you re showing a player in the house however the player is unable to leave the house and is stuck in the house reconnecting the server does not solve this problem currently the best workaround is the alt k key combo this is a command to kill themselves and when player die player will be moved to player s home or island to reproduce steps to reproduce the behavior go to any house and get in or use noclip and move under the ground use noclip in house goto under the house more deeper and deeper see an error expected behavior game is freezing desktop please complete the following information os game version steam version
| 1
|
46,113
| 11,786,120,917
|
IssuesEvent
|
2020-03-17 11:38:08
|
ballerina-platform/ballerina-lang
|
https://api.github.com/repos/ballerina-platform/ballerina-lang
|
opened
|
Ballerina build command does not show all the semantic errors for a project
|
Area/BuildTools Area/Language Component/CompilerDiagnostics Type/Bug
|
**Description:**
Consider the following project structure
project
|---src
|--mod1
|--test1.bal
|--mod2
|--test2.bal
In the above case, test2.bal has a semantic error.
test1.bal has an import statement for mod2 as `import mod2;`
This import is an unused import.
When executing the `ballerina build -a` command it should prompt both errors. But, the observed behaviour is, it only prompts the semantic error in test2.bal.
**Affected Versions:**
v1.2.0-SNAPSHOT at least
|
1.0
|
Ballerina build command does not show all the semantic errors for a project - **Description:**
Consider the following project structure
project
|---src
|--mod1
|--test1.bal
|--mod2
|--test2.bal
In the above case, test2.bal has a semantic error.
test1.bal has an import statement for mod2 as `import mod2;`
This import is an unused import.
When executing the `ballerina build -a` command it should prompt both errors. But, the observed behaviour is, it only prompts the semantic error in test2.bal.
**Affected Versions:**
v1.2.0-SNAPSHOT at least
|
non_test
|
ballerina build command does not show all the semantic errors for a project description consider the following project structure project src bal bal in the above case bal has a semantic error bal has an import statement for as import this import is an unused import when executing the ballerina build a command it should prompt both errors but the observed behaviour is it only prompts the semantic error in bal affected versions snapshot at least
| 0
|
183,452
| 14,232,183,606
|
IssuesEvent
|
2020-11-18 10:27:42
|
classchneider/Loops
|
https://api.github.com/repos/classchneider/Loops
|
closed
|
IsPrime er langsom
|
NotTested
|
> IsPrime tager lang tid om at undersøge om store tal er primtal. Jeg prøvede med 1000000001 og det tog
meget lang tid.
|
1.0
|
IsPrime er langsom - > IsPrime tager lang tid om at undersøge om store tal er primtal. Jeg prøvede med 1000000001 og det tog
meget lang tid.
|
test
|
isprime er langsom isprime tager lang tid om at undersøge om store tal er primtal jeg prøvede med og det tog meget lang tid
| 1
|
70,469
| 23,184,066,866
|
IssuesEvent
|
2022-08-01 06:42:03
|
SeleniumHQ/selenium
|
https://api.github.com/repos/SeleniumHQ/selenium
|
opened
|
[🐛 Bug]: elenium GRID 4: Unable to launch the edge driver with hub and node configuration. Getting Unable to find handler for (POST) \u002fsession.
|
I-defect needs-triaging
|
### What happened?
"Selenium.WebDriver" version="3.141.0"
"Selenium.WebDriver.ChromeDriver" version="103.0.5060.13400"
"Selenium.WebDriver.MSEdgeDriver" version="105.0.1329.1-pre"
Grid Version: selenium-server-4.3.0.jar
I have setup both hub and node on the same machine.
I can see that hub is registered as well.
Hub:
C:https://github.com/SeleniumHQ/docker-selenium/issues/1 PersonalFolder\sharedFolder\SeleniumGrid>java -jar selenium-server-4.3.0.jar hub
11:38:21.979 INFO [LogManager$RootLogger.log] - Using the system default encoding
11:38:21.982 INFO [OpenTelemetryTracer.createTracer] - Using OpenTelemetry for tracing
11:38:22.369 INFO [BoundZmqEventBus.] - XPUB binding to [binding to tcp://:4442, advertising as tcp://169.254.168.113:4442], XSUB binding to [binding to tcp://:4443, advertising as tcp://169.254.168.113:4443]
11:38:22.433 INFO [UnboundZmqEventBus.] - Connecting to tcp://169.254.168.113:4442 and tcp://169.254.168.113:4443
11:38:22.455 INFO [UnboundZmqEventBus.] - Sockets created
11:38:23.456 INFO [UnboundZmqEventBus.] - Event bus ready
11:38:24.786 INFO [Hub.execute] - Started Selenium Hub 4.3.0 (revision a4995e2c09*): http://169.254.168.113:4444/
11:39:03.517 INFO [Node.] - Binding additional locator mechanisms: relative, id, name
11:39:04.055 INFO [GridModel.setAvailability] - Switching Node 4a4b5707-9246-4e6f-8b2f-e20ee107d481 (uri: http://169.254.168.113:5555/) from DOWN to UP
11:39:04.055 INFO [LocalDistributor.add] - Added node 4a4b5707-9246-4e6f-8b2f-e20ee107d481 at http://169.254.168.113:5555/. Health check every 120s
Node:
C:https://github.com/SeleniumHQ/docker-selenium/issues/1 PersonalFolder\sharedFolder\SeleniumGrid>java -jar selenium-server-4.3.0.jar node
11:39:00.868 INFO [LogManager$RootLogger.log] - Using the system default encoding
11:39:00.870 INFO [OpenTelemetryTracer.createTracer] - Using OpenTelemetry for tracing
11:39:01.082 INFO [UnboundZmqEventBus.] - Connecting to tcp://0.0.0.0:4442 and tcp://0.0.0.0:4443
11:39:01.145 INFO [UnboundZmqEventBus.] - Sockets created
11:39:02.147 INFO [UnboundZmqEventBus.] - Event bus ready
11:39:02.383 INFO [NodeServer.createHandlers] - Reporting self as: http://169.254.168.113:5555/
11:39:02.770 INFO [NodeOptions.getSessionFactories] - Detected 8 available processors
11:39:02.794 INFO [NodeOptions.discoverDrivers] - Discovered 2 driver(s)
11:39:02.852 INFO [NodeOptions.report] - Adding Chrome for {"browserName": "chrome"} 8 times
11:39:02.854 INFO [NodeOptions.report] - Adding Edge for {"browserName": "MicrosoftEdge"} 8 times
11:39:02.864 INFO [Node.] - Binding additional locator mechanisms: name, id, relative
11:39:03.457 INFO [NodeServer$1.start] - Starting registration process for Node http://169.254.168.113:5555/
11:39:03.458 INFO [NodeServer.execute] - Started Selenium node 4.3.0 (revision a4995e2c09*): http://169.254.168.113:5555/
11:39:03.479 INFO [NodeServer$1.lambda$start$1] - Sending registration event...
11:39:04.065 INFO [NodeServer.lambda$createHandlers$2] - Node has been added
I am able to access the following and it shows appropriate screen
http://161.85.102.61:4444/ui#
http://169.254.168.113:4444/status
http://169.254.168.113:5555/status
### How can we reproduce the issue?
```shell
EdgeOptions option = new EdgeOptions();
option.AcceptInsecureCertificates = false;
option.PlatformName = "Windows 10";
RemoteWebDriver driver = new RemoteWebDriver(new Uri(@"http://169.254.168.113:5555/"), option.ToCapabilities());
```
### Relevant log output
```shell
Message: OpenQA.Selenium.WebDriverException : Unexpected error. {
"value": {
"error": "unknown command",
"message": "Unable to find handler for (POST) \u002fsession",
"stacktrace": ""
}
}
```
### Operating System
Windows 10
### Selenium version
Selenium grid 4
### What are the browser(s) and version(s) where you see this issue?
edge Version 103.0.1264.71 (Official build) (64-bit)
### What are the browser driver(s) and version(s) where you see this issue?
msedgedriver.exe 105.0.1329.1
### Are you using Selenium Grid?
selenium-server-4.3.0.jar
|
1.0
|
[🐛 Bug]: elenium GRID 4: Unable to launch the edge driver with hub and node configuration. Getting Unable to find handler for (POST) \u002fsession. - ### What happened?
"Selenium.WebDriver" version="3.141.0"
"Selenium.WebDriver.ChromeDriver" version="103.0.5060.13400"
"Selenium.WebDriver.MSEdgeDriver" version="105.0.1329.1-pre"
Grid Version: selenium-server-4.3.0.jar
I have setup both hub and node on the same machine.
I can see that hub is registered as well.
Hub:
C:https://github.com/SeleniumHQ/docker-selenium/issues/1 PersonalFolder\sharedFolder\SeleniumGrid>java -jar selenium-server-4.3.0.jar hub
11:38:21.979 INFO [LogManager$RootLogger.log] - Using the system default encoding
11:38:21.982 INFO [OpenTelemetryTracer.createTracer] - Using OpenTelemetry for tracing
11:38:22.369 INFO [BoundZmqEventBus.] - XPUB binding to [binding to tcp://:4442, advertising as tcp://169.254.168.113:4442], XSUB binding to [binding to tcp://:4443, advertising as tcp://169.254.168.113:4443]
11:38:22.433 INFO [UnboundZmqEventBus.] - Connecting to tcp://169.254.168.113:4442 and tcp://169.254.168.113:4443
11:38:22.455 INFO [UnboundZmqEventBus.] - Sockets created
11:38:23.456 INFO [UnboundZmqEventBus.] - Event bus ready
11:38:24.786 INFO [Hub.execute] - Started Selenium Hub 4.3.0 (revision a4995e2c09*): http://169.254.168.113:4444/
11:39:03.517 INFO [Node.] - Binding additional locator mechanisms: relative, id, name
11:39:04.055 INFO [GridModel.setAvailability] - Switching Node 4a4b5707-9246-4e6f-8b2f-e20ee107d481 (uri: http://169.254.168.113:5555/) from DOWN to UP
11:39:04.055 INFO [LocalDistributor.add] - Added node 4a4b5707-9246-4e6f-8b2f-e20ee107d481 at http://169.254.168.113:5555/. Health check every 120s
Node:
C:https://github.com/SeleniumHQ/docker-selenium/issues/1 PersonalFolder\sharedFolder\SeleniumGrid>java -jar selenium-server-4.3.0.jar node
11:39:00.868 INFO [LogManager$RootLogger.log] - Using the system default encoding
11:39:00.870 INFO [OpenTelemetryTracer.createTracer] - Using OpenTelemetry for tracing
11:39:01.082 INFO [UnboundZmqEventBus.] - Connecting to tcp://0.0.0.0:4442 and tcp://0.0.0.0:4443
11:39:01.145 INFO [UnboundZmqEventBus.] - Sockets created
11:39:02.147 INFO [UnboundZmqEventBus.] - Event bus ready
11:39:02.383 INFO [NodeServer.createHandlers] - Reporting self as: http://169.254.168.113:5555/
11:39:02.770 INFO [NodeOptions.getSessionFactories] - Detected 8 available processors
11:39:02.794 INFO [NodeOptions.discoverDrivers] - Discovered 2 driver(s)
11:39:02.852 INFO [NodeOptions.report] - Adding Chrome for {"browserName": "chrome"} 8 times
11:39:02.854 INFO [NodeOptions.report] - Adding Edge for {"browserName": "MicrosoftEdge"} 8 times
11:39:02.864 INFO [Node.] - Binding additional locator mechanisms: name, id, relative
11:39:03.457 INFO [NodeServer$1.start] - Starting registration process for Node http://169.254.168.113:5555/
11:39:03.458 INFO [NodeServer.execute] - Started Selenium node 4.3.0 (revision a4995e2c09*): http://169.254.168.113:5555/
11:39:03.479 INFO [NodeServer$1.lambda$start$1] - Sending registration event...
11:39:04.065 INFO [NodeServer.lambda$createHandlers$2] - Node has been added
I am able to access the following and it shows appropriate screen
http://161.85.102.61:4444/ui#
http://169.254.168.113:4444/status
http://169.254.168.113:5555/status
### How can we reproduce the issue?
```shell
EdgeOptions option = new EdgeOptions();
option.AcceptInsecureCertificates = false;
option.PlatformName = "Windows 10";
RemoteWebDriver driver = new RemoteWebDriver(new Uri(@"http://169.254.168.113:5555/"), option.ToCapabilities());
```
### Relevant log output
```shell
Message: OpenQA.Selenium.WebDriverException : Unexpected error. {
"value": {
"error": "unknown command",
"message": "Unable to find handler for (POST) \u002fsession",
"stacktrace": ""
}
}
```
### Operating System
Windows 10
### Selenium version
Selenium grid 4
### What are the browser(s) and version(s) where you see this issue?
edge Version 103.0.1264.71 (Official build) (64-bit)
### What are the browser driver(s) and version(s) where you see this issue?
msedgedriver.exe 105.0.1329.1
### Are you using Selenium Grid?
selenium-server-4.3.0.jar
|
non_test
|
elenium grid unable to launch the edge driver with hub and node configuration getting unable to find handler for post what happened selenium webdriver version selenium webdriver chromedriver version selenium webdriver msedgedriver version pre grid version selenium server jar i have setup both hub and node on the same machine i can see that hub is registered as well hub c personalfolder sharedfolder seleniumgrid java jar selenium server jar hub info using the system default encoding info using opentelemetry for tracing info xpub binding to xsub binding to info connecting to tcp and tcp info sockets created info event bus ready info started selenium hub revision info binding additional locator mechanisms relative id name info switching node uri from down to up info added node at health check every node c personalfolder sharedfolder seleniumgrid java jar selenium server jar node info using the system default encoding info using opentelemetry for tracing info connecting to tcp and tcp info sockets created info event bus ready info reporting self as info detected available processors info discovered driver s info adding chrome for browsername chrome times info adding edge for browsername microsoftedge times info binding additional locator mechanisms name id relative info starting registration process for node info started selenium node revision info sending registration event info node has been added i am able to access the following and it shows appropriate screen how can we reproduce the issue shell edgeoptions option new edgeoptions option acceptinsecurecertificates false option platformname windows remotewebdriver driver new remotewebdriver new uri option tocapabilities relevant log output shell message openqa selenium webdriverexception unexpected error value error unknown command message unable to find handler for post stacktrace operating system windows selenium version selenium grid what are the browser s and version s where you see this issue edge version official build bit what are the browser driver s and version s where you see this issue msedgedriver exe are you using selenium grid selenium server jar
| 0
|
268,884
| 23,401,557,513
|
IssuesEvent
|
2022-08-12 08:31:03
|
hoppscotch/hoppscotch
|
https://api.github.com/repos/hoppscotch/hoppscotch
|
closed
|
[bug]: 'Save as' feature not working - No permissions to save a request to an existing one even as an owner
|
bug need testing
|
### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current behavior
I cannot save or overwrite a request by using the "save as" feature even as an owner of the project.
or
https://user-images.githubusercontent.com/63902576/184311069-8fc7f4f8-2403-4775-bf17-a6ba3b4dad4d.mov
### Steps to reproduce
1. Create a request
2. Click on the save button
3. Choose your collection and request to save it to.
### Environment
Production
### Version
Cloud
|
1.0
|
[bug]: 'Save as' feature not working - No permissions to save a request to an existing one even as an owner - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current behavior
I cannot save or overwrite a request by using the "save as" feature even as an owner of the project.
or
https://user-images.githubusercontent.com/63902576/184311069-8fc7f4f8-2403-4775-bf17-a6ba3b4dad4d.mov
### Steps to reproduce
1. Create a request
2. Click on the save button
3. Choose your collection and request to save it to.
### Environment
Production
### Version
Cloud
|
test
|
save as feature not working no permissions to save a request to an existing one even as an owner is there an existing issue for this i have searched the existing issues current behavior i cannot save or overwrite a request by using the save as feature even as an owner of the project or steps to reproduce create a request click on the save button choose your collection and request to save it to environment production version cloud
| 1
|
340,906
| 30,552,740,243
|
IssuesEvent
|
2023-07-20 09:36:08
|
GaJaMap/backend
|
https://api.github.com/repos/GaJaMap/backend
|
closed
|
GroupController Test 수정
|
test
|
## Description
GroupControllerTest 수정
## To-do
- AuthenticationToken 에서 PrincipalDetails로 변경
## Etc
|
1.0
|
GroupController Test 수정 - ## Description
GroupControllerTest 수정
## To-do
- AuthenticationToken 에서 PrincipalDetails로 변경
## Etc
|
test
|
groupcontroller test 수정 description groupcontrollertest 수정 to do authenticationtoken 에서 principaldetails로 변경 etc
| 1
|
13,891
| 4,787,221,274
|
IssuesEvent
|
2016-10-29 21:38:12
|
Jeremy-Barnes/Critters
|
https://api.github.com/repos/Jeremy-Barnes/Critters
|
closed
|
Server: Friendship
|
Code feature Server
|
Create a set of server endpoints that permit these friendship operations:
- [x] Users can request others as friends
- [x] Users can accept outstanding friend requests
- [x] Users can cancel friend requests that have not been accepted yet
- [x] User can reject outstanding friend requests
- [x] Users can retrieve all their friends (nonsensitive data)
- [x] Users can terminate existing friendships
|
1.0
|
Server: Friendship - Create a set of server endpoints that permit these friendship operations:
- [x] Users can request others as friends
- [x] Users can accept outstanding friend requests
- [x] Users can cancel friend requests that have not been accepted yet
- [x] User can reject outstanding friend requests
- [x] Users can retrieve all their friends (nonsensitive data)
- [x] Users can terminate existing friendships
|
non_test
|
server friendship create a set of server endpoints that permit these friendship operations users can request others as friends users can accept outstanding friend requests users can cancel friend requests that have not been accepted yet user can reject outstanding friend requests users can retrieve all their friends nonsensitive data users can terminate existing friendships
| 0
|
317,499
| 27,241,773,187
|
IssuesEvent
|
2023-02-21 21:09:00
|
nodejs/node
|
https://api.github.com/repos/nodejs/node
|
closed
|
parallel/test-runner-reporters is flaking
|
test flaky-test test_runner
|
From https://github.com/nodejs/reliability/issues/501 it's failing 15 PRs out of the last 100 CI runs.
| Reason | <code>parallel/test-runner-reporters</code> |
| - | :- |
| Type | JS_TEST_FAILURE |
| Failed PR | 15 (https://github.com/nodejs/node/pull/46600/, https://github.com/nodejs/node/pull/46547/, https://github.com/nodejs/node/pull/46725/, https://github.com/nodejs/node/pull/45841/, https://github.com/nodejs/node/pull/46721/, https://github.com/nodejs/node/pull/46735/, https://github.com/nodejs/node/pull/46509/, https://github.com/nodejs/node/pull/46387/, https://github.com/nodejs/node/pull/46723/, https://github.com/nodejs/node/pull/46616/, https://github.com/nodejs/node/pull/46737/, https://github.com/nodejs/node/pull/45258/, https://github.com/nodejs/node/pull/46577/, https://github.com/nodejs/node/pull/46736/, https://github.com/nodejs/node/pull/46738/) |
| Appeared | [test-osuosl-rhel8-ppc64_le-2](https://ci.nodejs.org/computer/test-osuosl-rhel8-ppc64_le-2/), [test-osuosl-rhel8-ppc64_le-3](https://ci.nodejs.org/computer/test-osuosl-rhel8-ppc64_le-3/), [test-digitalocean-freebsd12-x64-1](https://ci.nodejs.org/computer/test-digitalocean-freebsd12-x64-1/), [test-osuosl-rhel8-ppc64_le-4](https://ci.nodejs.org/computer/test-osuosl-rhel8-ppc64_le-4/), [test-ibm-rhel8-s390x-4](https://ci.nodejs.org/computer/test-ibm-rhel8-s390x-4/), [test-rackspace-win2012r2_vs2017-x64-4](https://ci.nodejs.org/computer/test-rackspace-win2012r2_vs2017-x64-4/), [test-rackspace-win2012r2_vs2019-x64-1](https://ci.nodejs.org/computer/test-rackspace-win2012r2_vs2019-x64-1/), [test-rackspace-win2012r2_vs2015-x64-2](https://ci.nodejs.org/computer/test-rackspace-win2012r2_vs2015-x64-2/), [test-rackspace-win2012r2_vs2013-x64-1](https://ci.nodejs.org/computer/test-rackspace-win2012r2_vs2013-x64-1/), [test-digitalocean-ubuntu1804_sharedlibs_container-x64-7](https://ci.nodejs.org/computer/test-digitalocean-ubuntu1804_sharedlibs_container-x64-7/), [test-digitalocean-freebsd12-x64-2](https://ci.nodejs.org/computer/test-digitalocean-freebsd12-x64-2/) |
| First CI | https://ci.nodejs.org/job/node-test-pull-request/49683/ |
| Last CI | https://ci.nodejs.org/job/node-test-pull-request/49750/ |
<details>
<summary><a href="https://ci.nodejs.org/job/node-test-commit-plinux/nodes=rhel8-ppc64le/47017/console">Example</a></summary>
```
not ok 2463 parallel/test-runner-reporters
---
duration_ms: 3.288
severity: fail
exitcode: 1
stack: |-
TAP version 13
# Subtest: node:test reporters
# Subtest: should default to outputing TAP to stdout
ok 1 - should default to outputing TAP to stdout
---
duration_ms: 2885.486488
...
```
</details>
|
3.0
|
parallel/test-runner-reporters is flaking - From https://github.com/nodejs/reliability/issues/501 it's failing 15 PRs out of the last 100 CI runs.
| Reason | <code>parallel/test-runner-reporters</code> |
| - | :- |
| Type | JS_TEST_FAILURE |
| Failed PR | 15 (https://github.com/nodejs/node/pull/46600/, https://github.com/nodejs/node/pull/46547/, https://github.com/nodejs/node/pull/46725/, https://github.com/nodejs/node/pull/45841/, https://github.com/nodejs/node/pull/46721/, https://github.com/nodejs/node/pull/46735/, https://github.com/nodejs/node/pull/46509/, https://github.com/nodejs/node/pull/46387/, https://github.com/nodejs/node/pull/46723/, https://github.com/nodejs/node/pull/46616/, https://github.com/nodejs/node/pull/46737/, https://github.com/nodejs/node/pull/45258/, https://github.com/nodejs/node/pull/46577/, https://github.com/nodejs/node/pull/46736/, https://github.com/nodejs/node/pull/46738/) |
| Appeared | [test-osuosl-rhel8-ppc64_le-2](https://ci.nodejs.org/computer/test-osuosl-rhel8-ppc64_le-2/), [test-osuosl-rhel8-ppc64_le-3](https://ci.nodejs.org/computer/test-osuosl-rhel8-ppc64_le-3/), [test-digitalocean-freebsd12-x64-1](https://ci.nodejs.org/computer/test-digitalocean-freebsd12-x64-1/), [test-osuosl-rhel8-ppc64_le-4](https://ci.nodejs.org/computer/test-osuosl-rhel8-ppc64_le-4/), [test-ibm-rhel8-s390x-4](https://ci.nodejs.org/computer/test-ibm-rhel8-s390x-4/), [test-rackspace-win2012r2_vs2017-x64-4](https://ci.nodejs.org/computer/test-rackspace-win2012r2_vs2017-x64-4/), [test-rackspace-win2012r2_vs2019-x64-1](https://ci.nodejs.org/computer/test-rackspace-win2012r2_vs2019-x64-1/), [test-rackspace-win2012r2_vs2015-x64-2](https://ci.nodejs.org/computer/test-rackspace-win2012r2_vs2015-x64-2/), [test-rackspace-win2012r2_vs2013-x64-1](https://ci.nodejs.org/computer/test-rackspace-win2012r2_vs2013-x64-1/), [test-digitalocean-ubuntu1804_sharedlibs_container-x64-7](https://ci.nodejs.org/computer/test-digitalocean-ubuntu1804_sharedlibs_container-x64-7/), [test-digitalocean-freebsd12-x64-2](https://ci.nodejs.org/computer/test-digitalocean-freebsd12-x64-2/) |
| First CI | https://ci.nodejs.org/job/node-test-pull-request/49683/ |
| Last CI | https://ci.nodejs.org/job/node-test-pull-request/49750/ |
<details>
<summary><a href="https://ci.nodejs.org/job/node-test-commit-plinux/nodes=rhel8-ppc64le/47017/console">Example</a></summary>
```
not ok 2463 parallel/test-runner-reporters
---
duration_ms: 3.288
severity: fail
exitcode: 1
stack: |-
TAP version 13
# Subtest: node:test reporters
# Subtest: should default to outputing TAP to stdout
ok 1 - should default to outputing TAP to stdout
---
duration_ms: 2885.486488
...
```
</details>
|
test
|
parallel test runner reporters is flaking from it s failing prs out of the last ci runs reason parallel test runner reporters type js test failure failed pr appeared first ci last ci a href not ok parallel test runner reporters duration ms severity fail exitcode stack tap version subtest node test reporters subtest should default to outputing tap to stdout ok should default to outputing tap to stdout duration ms
| 1
|
734,102
| 25,337,816,348
|
IssuesEvent
|
2022-11-18 18:26:37
|
certbot/certbot
|
https://api.github.com/repos/certbot/certbot
|
closed
|
Don't crash when writing the cert to disk
|
area: renewal area: error handling priority: unplanned
|
We've had a number of problems due to assumptions made about the layout of `/etc/letsencrypt`. Unfortunately, we had one user for whom `--dry-run` succeeded, however, we'd always crash when writing the cert to disk during renewal with the traceback:
```
File "/usr/lib/python2.7/dist-packages/certbot/main.py", line 626, in obtain_cert
action, _ = _auth_from_available(le_client, config, domains, certname, lineage)
File "/usr/lib/python2.7/dist-packages/certbot/main.py", line 103, in _auth_from_available
renewal.renew_cert(config, domains, le_client, lineage)
File "/usr/lib/python2.7/dist-packages/certbot/renewal.py", line 306, in renew_cert
lineage.save_successor(prior_version, new_cert, new_key.pem, new_chain, config)
File "/usr/lib/python2.7/dist-packages/certbot/storage.py", line 1060, in save_successor
with open(target["privkey"], "w") as f:
IOError: [Errno 2] No such file or directory: '/etc/letsencrypt/archive/<domain>/privkey2.pem'
```
To help with matching line numbers, the version being used is 0.10.2.
While we can only be so defensive against user changes, crashing at this point is not OK. Ideally, `--dry-run` should never succeed when real issuance fails and we shouldn't crash when writing the cert to disk.
We need to check for problems like this earlier in Certbot's execution so avoid rate limiting users and allow them to debug the problem using `--dry-run`.
|
1.0
|
Don't crash when writing the cert to disk - We've had a number of problems due to assumptions made about the layout of `/etc/letsencrypt`. Unfortunately, we had one user for whom `--dry-run` succeeded, however, we'd always crash when writing the cert to disk during renewal with the traceback:
```
File "/usr/lib/python2.7/dist-packages/certbot/main.py", line 626, in obtain_cert
action, _ = _auth_from_available(le_client, config, domains, certname, lineage)
File "/usr/lib/python2.7/dist-packages/certbot/main.py", line 103, in _auth_from_available
renewal.renew_cert(config, domains, le_client, lineage)
File "/usr/lib/python2.7/dist-packages/certbot/renewal.py", line 306, in renew_cert
lineage.save_successor(prior_version, new_cert, new_key.pem, new_chain, config)
File "/usr/lib/python2.7/dist-packages/certbot/storage.py", line 1060, in save_successor
with open(target["privkey"], "w") as f:
IOError: [Errno 2] No such file or directory: '/etc/letsencrypt/archive/<domain>/privkey2.pem'
```
To help with matching line numbers, the version being used is 0.10.2.
While we can only be so defensive against user changes, crashing at this point is not OK. Ideally, `--dry-run` should never succeed when real issuance fails and we shouldn't crash when writing the cert to disk.
We need to check for problems like this earlier in Certbot's execution so avoid rate limiting users and allow them to debug the problem using `--dry-run`.
|
non_test
|
don t crash when writing the cert to disk we ve had a number of problems due to assumptions made about the layout of etc letsencrypt unfortunately we had one user for whom dry run succeeded however we d always crash when writing the cert to disk during renewal with the traceback file usr lib dist packages certbot main py line in obtain cert action auth from available le client config domains certname lineage file usr lib dist packages certbot main py line in auth from available renewal renew cert config domains le client lineage file usr lib dist packages certbot renewal py line in renew cert lineage save successor prior version new cert new key pem new chain config file usr lib dist packages certbot storage py line in save successor with open target w as f ioerror no such file or directory etc letsencrypt archive pem to help with matching line numbers the version being used is while we can only be so defensive against user changes crashing at this point is not ok ideally dry run should never succeed when real issuance fails and we shouldn t crash when writing the cert to disk we need to check for problems like this earlier in certbot s execution so avoid rate limiting users and allow them to debug the problem using dry run
| 0
|
181,378
| 14,018,415,452
|
IssuesEvent
|
2020-10-29 16:48:28
|
dmwm/CRABServer
|
https://api.github.com/repos/dmwm/CRABServer
|
closed
|
LImit enforcing of K8s REST host in schedd
|
Area: K8s Priority: High Status: In Progress To be tested
|
change done in https://github.com/dmwm/CRABServer/pull/6216
is a bit too aggressive, forces schedd process to use cmsweb-k8s-prod, no matter what.
But this does not work for tasks submitted e.g. via `stefanovm.cern.ch` and we may also want to leave alone tests in other systems like `cmsweb-auth`
|
1.0
|
LImit enforcing of K8s REST host in schedd - change done in https://github.com/dmwm/CRABServer/pull/6216
is a bit too aggressive, forces schedd process to use cmsweb-k8s-prod, no matter what.
But this does not work for tasks submitted e.g. via `stefanovm.cern.ch` and we may also want to leave alone tests in other systems like `cmsweb-auth`
|
test
|
limit enforcing of rest host in schedd change done in is a bit too aggressive forces schedd process to use cmsweb prod no matter what but this does not work for tasks submitted e g via stefanovm cern ch and we may also want to leave alone tests in other systems like cmsweb auth
| 1
|
65,226
| 27,020,255,387
|
IssuesEvent
|
2023-02-11 00:32:39
|
devssa/onde-codar-em-salvador
|
https://api.github.com/repos/devssa/onde-codar-em-salvador
|
closed
|
[MOBILE] [SENIOR] [REMOTO] [BRASIL] Desenvolvedor Mobile Sr na [SERASA EXPERIAN]
|
SENIOR GIT DOCKER KUBERNETES REACT NATIVE MOBILE AWS REMOTO CI/CD TESTES AUTOMATIZADOS MICROSERVICES METODOLOGIAS ÁGEIS HELP WANTED CONTAINER MONITORAMENTO Stale
|
<!--
==================================================
POR FAVOR, SÓ POSTE SE A VAGA FOR PARA SALVADOR E CIDADES VIZINHAS!
Use: "Desenvolvedor Front-end" ao invés de
"Front-End Developer" \o/
Exemplo: `[JAVASCRIPT] [MYSQL] [NODE.JS] Desenvolvedor Front-End na [NOME DA EMPRESA]`
==================================================
-->
## Descrição da vaga
- Estamos buscando uma pessoa para atuar como desenvolvedor mobile no core da tecnologia dos nossos produtos, projetando e desenvolvendo soluções ágeis, simples e escaláveis em uma das várias squads por aqui! Dá uma olhada em quais serão suas responsabilidades e quais requisitos precisa ter:
- Suas principais atividades serão:
- Construir, evoluir e escalar arquiteturas distribuídas e micro-serviços para problemas específicos;
- Criar e manter soluções de APIs e microserviços que serão consumidos;
- Propor melhorias nas soluções existentes para propiciar melhor desempenho;
- Executar modelagem de dados e participar de Code Reviews;
- Realizar testes unitários, teste funcionais e automação de testes das soluções desenvolvidas;
- Apoiar no desenho técnico do back-end com base nos requisitos funcionais;
- Promover boas práticas e aprendizado contínuo.
## Local
- Brasil
## Benefícios
- Informações diretamente com o responsável/ recrutador da vaga
## Requisitos
**Obrigatórios:**
- Experiência com conhecimentos avançados na linguagem de programação React-Native contemplando React Hook, React Context, Firebase, react-native-navigation
- native-base.
- Experiência em Xcode.
- Experiência na arquitetura de micro-serviços;
- Experiência em controle de versionamento com Git;
- Experiência com filas;
- Experiência com testes automatizados;
- Experiência com CI/CD (Jenkins);
- Familiaridade com Containerização (Docker, Kubbernets);
- Familiaridade com Monitoramento (Grafana, Kibana);
- Experiencia com metodologias ágeis como Scrum e Kanban;
- Trabalhar em equipe;
- Familiaridade com desenvolvimento responsivo;
- Boa comunicação escrita e verbal;
- Desejável conhecimento em AWS.
## Contratação
- a combinar
## Nossa empresa
- Na Serasa Experian, acreditamos que dados ampliam oportunidades. Por isso, trabalhamos há 50 anos pela sustentabilidade das relações de consumo e pelo desenvolvimento econômico do Brasil. Fazemos parte da Experian, líder mundial em serviços de informação. Temos a maior base de dados do País e, com nossa expertise, ajudamos empresas de todos os tamanhos e consumidores a explorar o poder dos dados, transformando-os em coerência e clareza para alcançarem seus objetivos.
- Ao longo do tempo, fomos além do crédito e, hoje, auxiliamos organizações na tomada de decisões em gestão de fraude, marketing e certificação digital. Também apoiamos consumidores com serviços de proteção contra fraudes e administração de suas finanças. Buscamos sempre oferecer soluções tecnológicas, inteligentes e inovadoras, e vamos além, contribuindo ativamente em causas importantes para a sociedade como empoderamento feminino e a defesa de minorias, levantando a bandeira do respeito à diversidade, visando construir um amanhã melhor todos os dias.
## Como se candidatar
- [Clique aqui para se candidatar](https://experian.referrals.selectminds.com/serasa-experian/jobs/desenvolvedor-mobile-sr-17459)
|
1.0
|
[MOBILE] [SENIOR] [REMOTO] [BRASIL] Desenvolvedor Mobile Sr na [SERASA EXPERIAN] - <!--
==================================================
POR FAVOR, SÓ POSTE SE A VAGA FOR PARA SALVADOR E CIDADES VIZINHAS!
Use: "Desenvolvedor Front-end" ao invés de
"Front-End Developer" \o/
Exemplo: `[JAVASCRIPT] [MYSQL] [NODE.JS] Desenvolvedor Front-End na [NOME DA EMPRESA]`
==================================================
-->
## Descrição da vaga
- Estamos buscando uma pessoa para atuar como desenvolvedor mobile no core da tecnologia dos nossos produtos, projetando e desenvolvendo soluções ágeis, simples e escaláveis em uma das várias squads por aqui! Dá uma olhada em quais serão suas responsabilidades e quais requisitos precisa ter:
- Suas principais atividades serão:
- Construir, evoluir e escalar arquiteturas distribuídas e micro-serviços para problemas específicos;
- Criar e manter soluções de APIs e microserviços que serão consumidos;
- Propor melhorias nas soluções existentes para propiciar melhor desempenho;
- Executar modelagem de dados e participar de Code Reviews;
- Realizar testes unitários, teste funcionais e automação de testes das soluções desenvolvidas;
- Apoiar no desenho técnico do back-end com base nos requisitos funcionais;
- Promover boas práticas e aprendizado contínuo.
## Local
- Brasil
## Benefícios
- Informações diretamente com o responsável/ recrutador da vaga
## Requisitos
**Obrigatórios:**
- Experiência com conhecimentos avançados na linguagem de programação React-Native contemplando React Hook, React Context, Firebase, react-native-navigation
- native-base.
- Experiência em Xcode.
- Experiência na arquitetura de micro-serviços;
- Experiência em controle de versionamento com Git;
- Experiência com filas;
- Experiência com testes automatizados;
- Experiência com CI/CD (Jenkins);
- Familiaridade com Containerização (Docker, Kubbernets);
- Familiaridade com Monitoramento (Grafana, Kibana);
- Experiencia com metodologias ágeis como Scrum e Kanban;
- Trabalhar em equipe;
- Familiaridade com desenvolvimento responsivo;
- Boa comunicação escrita e verbal;
- Desejável conhecimento em AWS.
## Contratação
- a combinar
## Nossa empresa
- Na Serasa Experian, acreditamos que dados ampliam oportunidades. Por isso, trabalhamos há 50 anos pela sustentabilidade das relações de consumo e pelo desenvolvimento econômico do Brasil. Fazemos parte da Experian, líder mundial em serviços de informação. Temos a maior base de dados do País e, com nossa expertise, ajudamos empresas de todos os tamanhos e consumidores a explorar o poder dos dados, transformando-os em coerência e clareza para alcançarem seus objetivos.
- Ao longo do tempo, fomos além do crédito e, hoje, auxiliamos organizações na tomada de decisões em gestão de fraude, marketing e certificação digital. Também apoiamos consumidores com serviços de proteção contra fraudes e administração de suas finanças. Buscamos sempre oferecer soluções tecnológicas, inteligentes e inovadoras, e vamos além, contribuindo ativamente em causas importantes para a sociedade como empoderamento feminino e a defesa de minorias, levantando a bandeira do respeito à diversidade, visando construir um amanhã melhor todos os dias.
## Como se candidatar
- [Clique aqui para se candidatar](https://experian.referrals.selectminds.com/serasa-experian/jobs/desenvolvedor-mobile-sr-17459)
|
non_test
|
desenvolvedor mobile sr na por favor só poste se a vaga for para salvador e cidades vizinhas use desenvolvedor front end ao invés de front end developer o exemplo desenvolvedor front end na descrição da vaga estamos buscando uma pessoa para atuar como desenvolvedor mobile no core da tecnologia dos nossos produtos projetando e desenvolvendo soluções ágeis simples e escaláveis em uma das várias squads por aqui dá uma olhada em quais serão suas responsabilidades e quais requisitos precisa ter suas principais atividades serão construir evoluir e escalar arquiteturas distribuídas e micro serviços para problemas específicos criar e manter soluções de apis e microserviços que serão consumidos propor melhorias nas soluções existentes para propiciar melhor desempenho executar modelagem de dados e participar de code reviews realizar testes unitários teste funcionais e automação de testes das soluções desenvolvidas apoiar no desenho técnico do back end com base nos requisitos funcionais promover boas práticas e aprendizado contínuo local brasil benefícios informações diretamente com o responsável recrutador da vaga requisitos obrigatórios experiência com conhecimentos avançados na linguagem de programação react native contemplando react hook react context firebase react native navigation native base experiência em xcode experiência na arquitetura de micro serviços experiência em controle de versionamento com git experiência com filas experiência com testes automatizados experiência com ci cd jenkins familiaridade com containerização docker kubbernets familiaridade com monitoramento grafana kibana experiencia com metodologias ágeis como scrum e kanban trabalhar em equipe familiaridade com desenvolvimento responsivo boa comunicação escrita e verbal desejável conhecimento em aws contratação a combinar nossa empresa na serasa experian acreditamos que dados ampliam oportunidades por isso trabalhamos há anos pela sustentabilidade das relações de consumo e pelo desenvolvimento econômico do brasil fazemos parte da experian líder mundial em serviços de informação temos a maior base de dados do país e com nossa expertise ajudamos empresas de todos os tamanhos e consumidores a explorar o poder dos dados transformando os em coerência e clareza para alcançarem seus objetivos ao longo do tempo fomos além do crédito e hoje auxiliamos organizações na tomada de decisões em gestão de fraude marketing e certificação digital também apoiamos consumidores com serviços de proteção contra fraudes e administração de suas finanças buscamos sempre oferecer soluções tecnológicas inteligentes e inovadoras e vamos além contribuindo ativamente em causas importantes para a sociedade como empoderamento feminino e a defesa de minorias levantando a bandeira do respeito à diversidade visando construir um amanhã melhor todos os dias como se candidatar
| 0
|
147,782
| 23,270,286,649
|
IssuesEvent
|
2022-08-04 22:02:32
|
Speculative-Play/A2A
|
https://api.github.com/repos/Speculative-Play/A2A
|
closed
|
Final Profile data design
|
question design
|
Exactly what info will be collected at sign-up?
What info will be displayed in a profile and in what order?
This will be used for designing the sign-up form.
(If already decided, this issue can be closed)
|
1.0
|
Final Profile data design - Exactly what info will be collected at sign-up?
What info will be displayed in a profile and in what order?
This will be used for designing the sign-up form.
(If already decided, this issue can be closed)
|
non_test
|
final profile data design exactly what info will be collected at sign up what info will be displayed in a profile and in what order this will be used for designing the sign up form if already decided this issue can be closed
| 0
|
317,940
| 27,273,867,160
|
IssuesEvent
|
2023-02-23 02:04:25
|
OpenEnroth/OpenEnroth
|
https://api.github.com/repos/OpenEnroth/OpenEnroth
|
closed
|
Exception when entering Tidewater caverns
|
bug need test
|
**Describe the bug**
I have just caught an error when loaded my savegame and tried to enter Tidewater caverns in Tatalia (Buka version).
edit: This exception is not skippable.
I'm not sure if anyone has experienced this problem, and I have opened a new issue.
**To Reproduce**
Steps to reproduce the behaviour:
1. Start the game
2. Load my savegame
3. Walk and enter Tidewater caverns
**Environment (please complete the following information):**
- OS: Windows 10 64bit
**Screenshots**
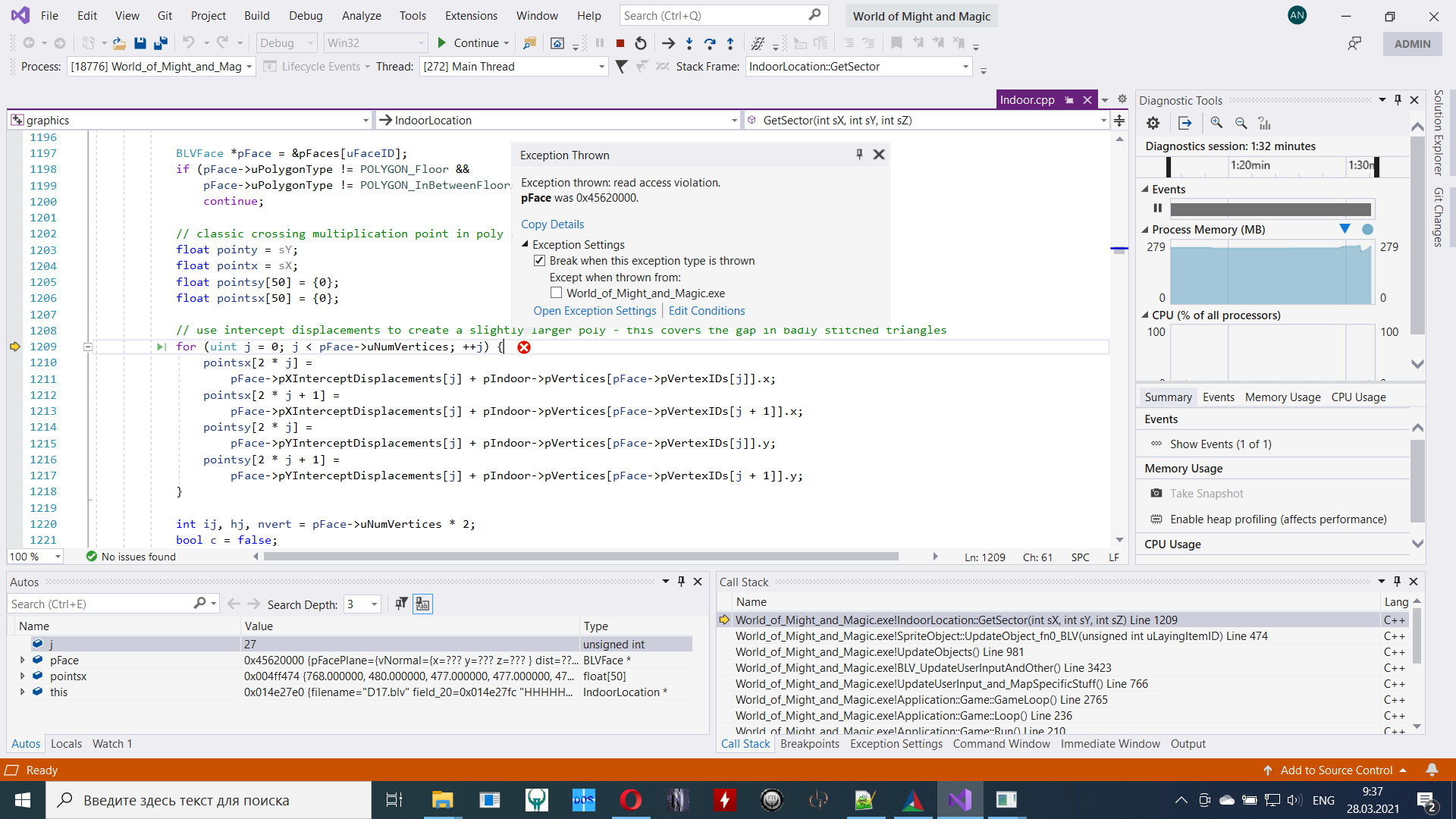
After loading the save, the face frames look cropped:

**Saved game file**
Yes, here is my save:
https://drive.google.com/file/d/1qBcKPFiZGRJmKYj6LcC5b-bCAyCHqsd3/view?usp=sharing
**Additional context**
I guess, the engine was not tested with Buka game data.
|
1.0
|
Exception when entering Tidewater caverns - **Describe the bug**
I have just caught an error when loaded my savegame and tried to enter Tidewater caverns in Tatalia (Buka version).
edit: This exception is not skippable.
I'm not sure if anyone has experienced this problem, and I have opened a new issue.
**To Reproduce**
Steps to reproduce the behaviour:
1. Start the game
2. Load my savegame
3. Walk and enter Tidewater caverns
**Environment (please complete the following information):**
- OS: Windows 10 64bit
**Screenshots**
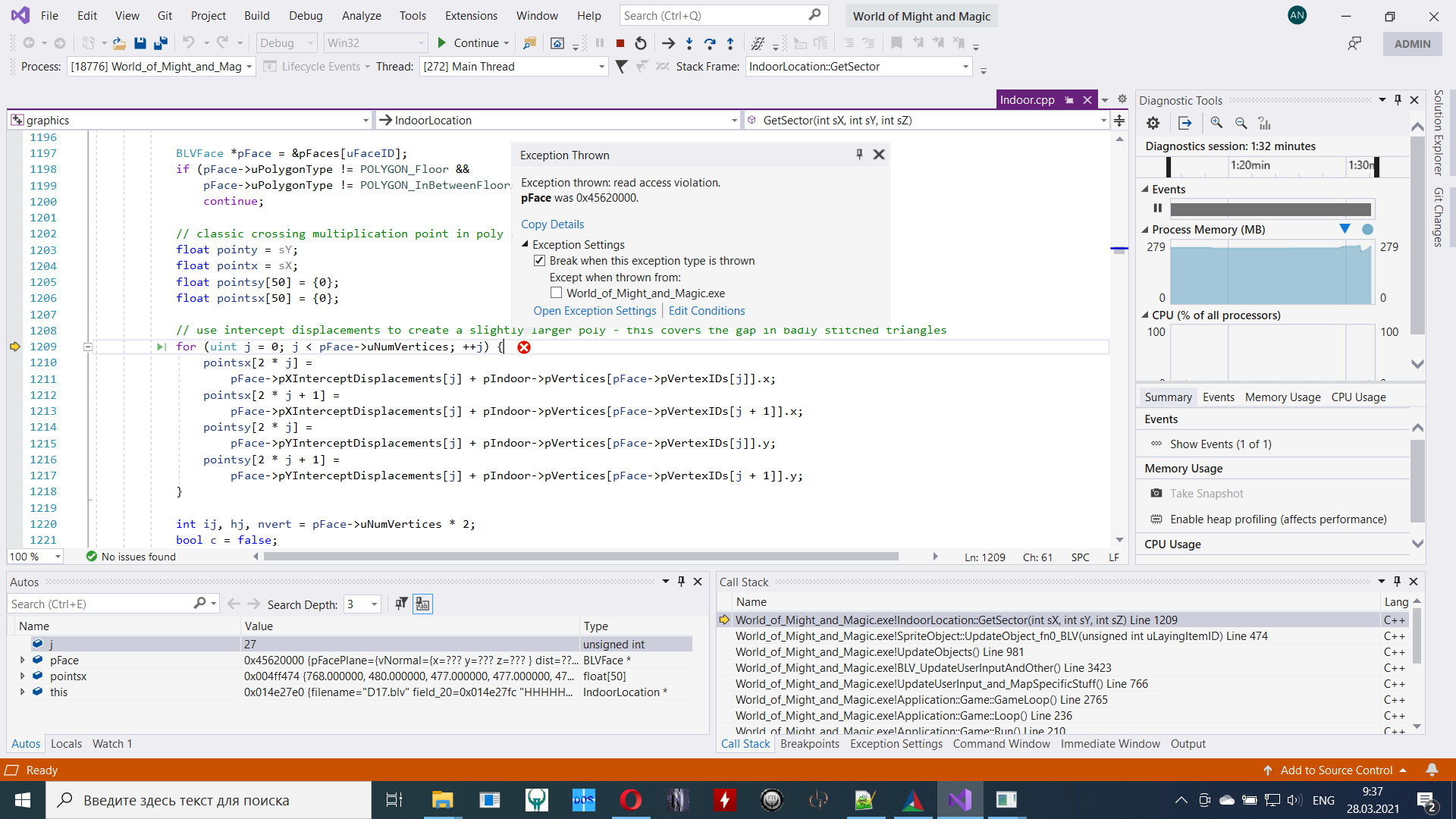
After loading the save, the face frames look cropped:

**Saved game file**
Yes, here is my save:
https://drive.google.com/file/d/1qBcKPFiZGRJmKYj6LcC5b-bCAyCHqsd3/view?usp=sharing
**Additional context**
I guess, the engine was not tested with Buka game data.
|
test
|
exception when entering tidewater caverns describe the bug i have just caught an error when loaded my savegame and tried to enter tidewater caverns in tatalia buka version edit this exception is not skippable i m not sure if anyone has experienced this problem and i have opened a new issue to reproduce steps to reproduce the behaviour start the game load my savegame walk and enter tidewater caverns environment please complete the following information os windows screenshots after loading the save the face frames look cropped saved game file yes here is my save additional context i guess the engine was not tested with buka game data
| 1
|
660,171
| 21,955,497,445
|
IssuesEvent
|
2022-05-24 11:44:08
|
huridocs/uwazi
|
https://api.github.com/repos/huridocs/uwazi
|
closed
|
Changing a template name makes it not translatable.
|
Bug :lady_beetle: Priority: High Backend
|
To replicate:
* Update template with a new name
* Navigate to library and activate inline translation
* The new name is the only one that does not get highlighted
* Navigate to setting -> translations for that template
* The old name is in the list of translations but not the new one
Updating the name again to the old one "fixes" the problem but this makes changing template names basically not an option if you have multiple languages.
Probably a migration is required.
|
1.0
|
Changing a template name makes it not translatable. - To replicate:
* Update template with a new name
* Navigate to library and activate inline translation
* The new name is the only one that does not get highlighted
* Navigate to setting -> translations for that template
* The old name is in the list of translations but not the new one
Updating the name again to the old one "fixes" the problem but this makes changing template names basically not an option if you have multiple languages.
Probably a migration is required.
|
non_test
|
changing a template name makes it not translatable to replicate update template with a new name navigate to library and activate inline translation the new name is the only one that does not get highlighted navigate to setting translations for that template the old name is in the list of translations but not the new one updating the name again to the old one fixes the problem but this makes changing template names basically not an option if you have multiple languages probably a migration is required
| 0
|
288,417
| 31,861,350,739
|
IssuesEvent
|
2023-09-15 11:09:26
|
nidhi7598/linux-v4.19.72_CVE-2022-3564
|
https://api.github.com/repos/nidhi7598/linux-v4.19.72_CVE-2022-3564
|
opened
|
CVE-2021-20268 (High) detected in linuxlinux-4.19.294
|
Mend: dependency security vulnerability
|
## CVE-2021-20268 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-v4.19.72_CVE-2022-3564/commit/9ffee08efa44c7887e2babb8f304df0fa1094efb">9ffee08efa44c7887e2babb8f304df0fa1094efb</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An out-of-bounds access flaw was found in the Linux kernel's implementation of the eBPF code verifier in the way a user running the eBPF script calls dev_map_init_map or sock_map_alloc. This flaw allows a local user to crash the system or possibly escalate their privileges. The highest threat from this vulnerability is to confidentiality, integrity, as well as system availability.
<p>Publish Date: 2021-03-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-20268>CVE-2021-20268</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-20268">https://www.linuxkernelcves.com/cves/CVE-2021-20268</a></p>
<p>Release Date: 2021-03-09</p>
<p>Fix Resolution: 5.10.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-20268 (High) detected in linuxlinux-4.19.294 - ## CVE-2021-20268 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-v4.19.72_CVE-2022-3564/commit/9ffee08efa44c7887e2babb8f304df0fa1094efb">9ffee08efa44c7887e2babb8f304df0fa1094efb</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An out-of-bounds access flaw was found in the Linux kernel's implementation of the eBPF code verifier in the way a user running the eBPF script calls dev_map_init_map or sock_map_alloc. This flaw allows a local user to crash the system or possibly escalate their privileges. The highest threat from this vulnerability is to confidentiality, integrity, as well as system availability.
<p>Publish Date: 2021-03-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-20268>CVE-2021-20268</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-20268">https://www.linuxkernelcves.com/cves/CVE-2021-20268</a></p>
<p>Release Date: 2021-03-09</p>
<p>Fix Resolution: 5.10.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files vulnerability details an out of bounds access flaw was found in the linux kernel s implementation of the ebpf code verifier in the way a user running the ebpf script calls dev map init map or sock map alloc this flaw allows a local user to crash the system or possibly escalate their privileges the highest threat from this vulnerability is to confidentiality integrity as well as system availability publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend
| 0
|
281,900
| 30,888,995,398
|
IssuesEvent
|
2023-08-04 02:06:10
|
hshivhare67/kernel_v4.1.15_CVE-2019-10220
|
https://api.github.com/repos/hshivhare67/kernel_v4.1.15_CVE-2019-10220
|
reopened
|
CVE-2016-7910 (High) detected in linuxlinux-4.4.302
|
Mend: dependency security vulnerability
|
## CVE-2016-7910 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/block/genhd.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/block/genhd.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Use-after-free vulnerability in the disk_seqf_stop function in block/genhd.c in the Linux kernel before 4.7.1 allows local users to gain privileges by leveraging the execution of a certain stop operation even if the corresponding start operation had failed.
<p>Publish Date: 2016-11-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-7910>CVE-2016-7910</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-7910">https://nvd.nist.gov/vuln/detail/CVE-2016-7910</a></p>
<p>Release Date: 2016-11-16</p>
<p>Fix Resolution: 4.7.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2016-7910 (High) detected in linuxlinux-4.4.302 - ## CVE-2016-7910 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/block/genhd.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/block/genhd.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Use-after-free vulnerability in the disk_seqf_stop function in block/genhd.c in the Linux kernel before 4.7.1 allows local users to gain privileges by leveraging the execution of a certain stop operation even if the corresponding start operation had failed.
<p>Publish Date: 2016-11-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-7910>CVE-2016-7910</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-7910">https://nvd.nist.gov/vuln/detail/CVE-2016-7910</a></p>
<p>Release Date: 2016-11-16</p>
<p>Fix Resolution: 4.7.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch master vulnerable source files block genhd c block genhd c vulnerability details use after free vulnerability in the disk seqf stop function in block genhd c in the linux kernel before allows local users to gain privileges by leveraging the execution of a certain stop operation even if the corresponding start operation had failed publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend
| 0
|
183,403
| 14,940,722,646
|
IssuesEvent
|
2021-01-25 18:41:37
|
suchitm/fosr_clust
|
https://api.github.com/repos/suchitm/fosr_clust
|
closed
|
data analysis
|
documentation
|
add to the readme, instructions on how to reproduce the data analysis
- [x] make the document
|
1.0
|
data analysis - add to the readme, instructions on how to reproduce the data analysis
- [x] make the document
|
non_test
|
data analysis add to the readme instructions on how to reproduce the data analysis make the document
| 0
|
76,797
| 9,498,194,938
|
IssuesEvent
|
2019-04-24 00:42:23
|
codeforboston/communityconnect
|
https://api.github.com/repos/codeforboston/communityconnect
|
reopened
|
Allow social worker to input address relevant to the client
|
UX/Design enhancement
|
A likely scenario is that the social worker will want to find resources close to the clients home/work.
Unfortunately right now the distance sort is based on the social worker current location. How can we allow the social worker to enter an address that might more relevant to the client?
I was thinking perhaps when they select sort by distance have a prompt to let them change the 'location'
|
1.0
|
Allow social worker to input address relevant to the client - A likely scenario is that the social worker will want to find resources close to the clients home/work.
Unfortunately right now the distance sort is based on the social worker current location. How can we allow the social worker to enter an address that might more relevant to the client?
I was thinking perhaps when they select sort by distance have a prompt to let them change the 'location'
|
non_test
|
allow social worker to input address relevant to the client a likely scenario is that the social worker will want to find resources close to the clients home work unfortunately right now the distance sort is based on the social worker current location how can we allow the social worker to enter an address that might more relevant to the client i was thinking perhaps when they select sort by distance have a prompt to let them change the location
| 0
|
287,894
| 21,676,415,858
|
IssuesEvent
|
2022-05-08 19:39:56
|
Sumaiya4949/todo-app-backend
|
https://api.github.com/repos/Sumaiya4949/todo-app-backend
|
opened
|
Misc: Write API documentation in a markdown (.md) file
|
documentation
|
Definition of done:
1. All the APIs are well-documented in a file "apidoc.md"
|
1.0
|
Misc: Write API documentation in a markdown (.md) file - Definition of done:
1. All the APIs are well-documented in a file "apidoc.md"
|
non_test
|
misc write api documentation in a markdown md file definition of done all the apis are well documented in a file apidoc md
| 0
|
348,221
| 31,474,221,365
|
IssuesEvent
|
2023-08-30 09:34:39
|
longhorn/longhorn
|
https://api.github.com/repos/longhorn/longhorn
|
closed
|
[TEST] Fix flaky test_setting_concurrent_rebuild_limit
|
kind/test
|
## What's the test to develop? Please describe
Test case 'test_setting_concurrent_rebuild_limit' is flaky on [v1.3.x](https://ci.longhorn.io/job/public/job/v1.3.x/job/v1.3.x-longhorn-tests-sles-arm64/387/testReport/junit/tests/test_settings/test_setting_concurrent_rebuild_limit/) in recent builds.
All failures happened at the same place:
```python
wait_for_rebuild_complete(client, volume2_name)
wait_for_rebuild_complete(client, volume1_name)
# Step 2-1
# Step 2-2
> wait_for_volume_healthy(client, volume1_name)
```
## Describe the items of the test development (DoD, definition of done) you'd like
- [ ] Fix and verify on pipeline
## Additional context
N/A.
|
1.0
|
[TEST] Fix flaky test_setting_concurrent_rebuild_limit - ## What's the test to develop? Please describe
Test case 'test_setting_concurrent_rebuild_limit' is flaky on [v1.3.x](https://ci.longhorn.io/job/public/job/v1.3.x/job/v1.3.x-longhorn-tests-sles-arm64/387/testReport/junit/tests/test_settings/test_setting_concurrent_rebuild_limit/) in recent builds.
All failures happened at the same place:
```python
wait_for_rebuild_complete(client, volume2_name)
wait_for_rebuild_complete(client, volume1_name)
# Step 2-1
# Step 2-2
> wait_for_volume_healthy(client, volume1_name)
```
## Describe the items of the test development (DoD, definition of done) you'd like
- [ ] Fix and verify on pipeline
## Additional context
N/A.
|
test
|
fix flaky test setting concurrent rebuild limit what s the test to develop please describe test case test setting concurrent rebuild limit is flaky on in recent builds all failures happened at the same place python wait for rebuild complete client name wait for rebuild complete client name step step wait for volume healthy client name describe the items of the test development dod definition of done you d like fix and verify on pipeline additional context n a
| 1
|
319,329
| 27,365,551,723
|
IssuesEvent
|
2023-02-27 18:53:05
|
Statsugiri/Statsugiri
|
https://api.github.com/repos/Statsugiri/Statsugiri
|
closed
|
Create unit tests for `order_up_bot_client`
|
ps ingestion tests triage
|
**Describe the issue**
There are currently no tests for the `OrderUpBotClient`. The client is primarily a wrapper for the Twitter API (Tweepy) to tweet teams every day. Specifically, the tests would be for the `tweet` method since the private methods are simple string formatters.
**Acceptance Criteria**
- [ ] Unit tests for `OrderUpBotClient`
|
1.0
|
Create unit tests for `order_up_bot_client` - **Describe the issue**
There are currently no tests for the `OrderUpBotClient`. The client is primarily a wrapper for the Twitter API (Tweepy) to tweet teams every day. Specifically, the tests would be for the `tweet` method since the private methods are simple string formatters.
**Acceptance Criteria**
- [ ] Unit tests for `OrderUpBotClient`
|
test
|
create unit tests for order up bot client describe the issue there are currently no tests for the orderupbotclient the client is primarily a wrapper for the twitter api tweepy to tweet teams every day specifically the tests would be for the tweet method since the private methods are simple string formatters acceptance criteria unit tests for orderupbotclient
| 1
|
329,379
| 28,238,166,483
|
IssuesEvent
|
2023-04-06 03:45:31
|
SynBioHub/synbiohub3
|
https://api.github.com/repos/SynBioHub/synbiohub3
|
closed
|
/uses doesn't work on SBH3
|
backend test failure search
|
Note: I made sure some parts that should show for uses are in the database ex. BBa_K2143000
http://localhost:6789/public/igem/BBa_B0034/1/uses
SBH3
['[]']
SBH1
['[{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/igem_collection/1","name":"iGEM Parts Registry","description":"The iGEM Registry is a growing collection of genetic parts that can be mixed and matched to build synthetic biology devices and systems. As part of the synthetic biology community\'s efforts to make biology easier to engineer, it provides a source of genetic parts to iGEM teams and academic labs.","displayId":"igem_collection","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#ComponentDefinition","uri":"https://synbiohub.org/public/igem/BBa_K2143000/1","name":"BBa_K2143000","description":"NahR_L154F constitutive transcription factor binds upstream of Psal","displayId":"BBa_K2143000","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#ComponentDefinition","uri":"https://synbiohub.org/public/igem/BBa_K2149018/1","name":"BBa_K2149018","description":"RFP with Lux D and an aldehyde decarbonylase","displayId":"BBa_K2149018","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/chassis_prokaryote/1","name":"//chassis/prokaryote","description":"","displayId":"chassis_prokaryote","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/chassis_prokaryote_ecoli/1","name":"//chassis/prokaryote/ecoli","description":"","displayId":"chassis_prokaryote_ecoli","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/direction/1","name":"//direction","description":"","displayId":"direction","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/direction_forward/1","name":"//direction/forward","description":"","displayId":"direction_forward","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/rbs_prokaryote_constitutive/1","name":"//rbs/prokaryote/constitutive","description":"","displayId":"rbs_prokaryote_constitutive","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/regulation/1","name":"//regulation","description":"","displayId":"regulation","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/regulation_constitutive/1","name":"//regulation/constitutive","description":"","displayId":"regulation_constitutive","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/ribosome_prokaryote/1","name":"//ribosome/prokaryote","description":"","displayId":"ribosome_prokaryote","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/rbs_prokaryote_constitutive_community/1","name":"//rbs/prokaryote/constitutive/community","description":"","displayId":"rbs_prokaryote_constitutive_community","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/ribosome_prokaryote_ecoli/1","name":"//ribosome/prokaryote/ecoli","description":"","displayId":"ribosome_prokaryote_ecoli","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/function/1","name":"//function","description":"","displayId":"function","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/function_coliroid/1","name":"//function/coliroid","description":"","displayId":"function_coliroid","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""}]']
|
1.0
|
/uses doesn't work on SBH3 - Note: I made sure some parts that should show for uses are in the database ex. BBa_K2143000
http://localhost:6789/public/igem/BBa_B0034/1/uses
SBH3
['[]']
SBH1
['[{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/igem_collection/1","name":"iGEM Parts Registry","description":"The iGEM Registry is a growing collection of genetic parts that can be mixed and matched to build synthetic biology devices and systems. As part of the synthetic biology community\'s efforts to make biology easier to engineer, it provides a source of genetic parts to iGEM teams and academic labs.","displayId":"igem_collection","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#ComponentDefinition","uri":"https://synbiohub.org/public/igem/BBa_K2143000/1","name":"BBa_K2143000","description":"NahR_L154F constitutive transcription factor binds upstream of Psal","displayId":"BBa_K2143000","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#ComponentDefinition","uri":"https://synbiohub.org/public/igem/BBa_K2149018/1","name":"BBa_K2149018","description":"RFP with Lux D and an aldehyde decarbonylase","displayId":"BBa_K2149018","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/chassis_prokaryote/1","name":"//chassis/prokaryote","description":"","displayId":"chassis_prokaryote","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/chassis_prokaryote_ecoli/1","name":"//chassis/prokaryote/ecoli","description":"","displayId":"chassis_prokaryote_ecoli","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/direction/1","name":"//direction","description":"","displayId":"direction","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/direction_forward/1","name":"//direction/forward","description":"","displayId":"direction_forward","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/rbs_prokaryote_constitutive/1","name":"//rbs/prokaryote/constitutive","description":"","displayId":"rbs_prokaryote_constitutive","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/regulation/1","name":"//regulation","description":"","displayId":"regulation","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/regulation_constitutive/1","name":"//regulation/constitutive","description":"","displayId":"regulation_constitutive","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/ribosome_prokaryote/1","name":"//ribosome/prokaryote","description":"","displayId":"ribosome_prokaryote","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/rbs_prokaryote_constitutive_community/1","name":"//rbs/prokaryote/constitutive/community","description":"","displayId":"rbs_prokaryote_constitutive_community","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/ribosome_prokaryote_ecoli/1","name":"//ribosome/prokaryote/ecoli","description":"","displayId":"ribosome_prokaryote_ecoli","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/function/1","name":"//function","description":"","displayId":"function","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""},{"type":"http://sbols.org/v2#Collection","uri":"https://synbiohub.org/public/igem/function_coliroid/1","name":"//function/coliroid","description":"","displayId":"function_coliroid","version":"1","percentMatch":"","strandAlignment":"","CIGAR":""}]']
|
test
|
uses doesn t work on note i made sure some parts that should show for uses are in the database ex bba
| 1
|
279,484
| 24,229,192,349
|
IssuesEvent
|
2022-09-26 16:41:47
|
CDCgov/prime-simplereport
|
https://api.github.com/repos/CDCgov/prime-simplereport
|
closed
|
AoE modal doesn't close on `esc` key
|
Better Data Accessibility Minor Engineering Conduct Test
|
## Area or Component
The Ask on Entry modal in the test card
## Quick Summary
The modal doesn't respond to the `esc` key.
### How to Replicate
1. Start a new test
2. Start filling out the questionnare
3. Try to ESC out of the modal
4. Nothin happens
## Accessibility Violation
ESC key does not close modal: https://cdc-devtools.dequecloud.com/rule-help/en/modal-no-esc
## Action Requested
Change the modal to close on `esc`. See #4028 for more details about how to implement this change.
## Original Deque Issue
https://docs.google.com/spreadsheets/d/1b6xjubAN5Uw11DV4_B5zvSu7HeDI6Z-DpV4DMcToqAY/edit#gid=981460209&range=B34:T34
|
1.0
|
AoE modal doesn't close on `esc` key - ## Area or Component
The Ask on Entry modal in the test card
## Quick Summary
The modal doesn't respond to the `esc` key.
### How to Replicate
1. Start a new test
2. Start filling out the questionnare
3. Try to ESC out of the modal
4. Nothin happens
## Accessibility Violation
ESC key does not close modal: https://cdc-devtools.dequecloud.com/rule-help/en/modal-no-esc
## Action Requested
Change the modal to close on `esc`. See #4028 for more details about how to implement this change.
## Original Deque Issue
https://docs.google.com/spreadsheets/d/1b6xjubAN5Uw11DV4_B5zvSu7HeDI6Z-DpV4DMcToqAY/edit#gid=981460209&range=B34:T34
|
test
|
aoe modal doesn t close on esc key area or component the ask on entry modal in the test card quick summary the modal doesn t respond to the esc key how to replicate start a new test start filling out the questionnare try to esc out of the modal nothin happens accessibility violation esc key does not close modal action requested change the modal to close on esc see for more details about how to implement this change original deque issue
| 1
|
115,610
| 24,787,607,433
|
IssuesEvent
|
2022-10-24 11:09:46
|
gitpod-io/gitpod
|
https://api.github.com/repos/gitpod-io/gitpod
|
closed
|
Show verified badge of Open VSX extensions
|
feature: vscode-extension component: ide type: improvement team: IDE
|
## Describe the behaviour you'd like
<!-- A clear and concise description of what you want to happen. -->
The extension sidebar should display whether a namespace is verified in Open VSX.
It might look something like:
## Additional context
<!-- Add any other context or screenshots about the feature request here. -->
It looks like this information is not included in the search API response, so namespaces have to be queried manually: https://open-vsx.org/swagger-ui/#/registry-api/getNamespaceUsingGET
|
1.0
|
Show verified badge of Open VSX extensions - ## Describe the behaviour you'd like
<!-- A clear and concise description of what you want to happen. -->
The extension sidebar should display whether a namespace is verified in Open VSX.
It might look something like:
## Additional context
<!-- Add any other context or screenshots about the feature request here. -->
It looks like this information is not included in the search API response, so namespaces have to be queried manually: https://open-vsx.org/swagger-ui/#/registry-api/getNamespaceUsingGET
|
non_test
|
show verified badge of open vsx extensions describe the behaviour you d like the extension sidebar should display whether a namespace is verified in open vsx it might look something like additional context it looks like this information is not included in the search api response so namespaces have to be queried manually
| 0
|
10,625
| 27,167,738,541
|
IssuesEvent
|
2023-02-17 16:37:49
|
MicrosoftDocs/architecture-center
|
https://api.github.com/repos/MicrosoftDocs/architecture-center
|
closed
|
First Visio Link is incorrect.
|
doc-enhancement assigned-to-author triaged architecture-center/svc reference-architecture/subsvc Pri2
|
First Visio link appears to be wrong. It's download Visio file to a single region example.
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: b0c0c2a8-94a0-67ef-602a-6013bc7aa403
* Version Independent ID: 27705eeb-7853-bd5d-58ac-a07bd6a8a79d
* Content: [Highly available multi-region web app - Azure Architecture Center](https://docs.microsoft.com/en-us/azure/architecture/reference-architectures/app-service-web-app/multi-region)
* Content Source: [docs/reference-architectures/app-service-web-app/multi-region.yml](https://github.com/microsoftdocs/architecture-center/blob/main/docs/reference-architectures/app-service-web-app/multi-region.yml)
* Service: **architecture-center**
* Sub-service: **reference-architecture**
* GitHub Login: @Arvindboggaram
* Microsoft Alias: **arboggar**
|
2.0
|
First Visio Link is incorrect. - First Visio link appears to be wrong. It's download Visio file to a single region example.
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: b0c0c2a8-94a0-67ef-602a-6013bc7aa403
* Version Independent ID: 27705eeb-7853-bd5d-58ac-a07bd6a8a79d
* Content: [Highly available multi-region web app - Azure Architecture Center](https://docs.microsoft.com/en-us/azure/architecture/reference-architectures/app-service-web-app/multi-region)
* Content Source: [docs/reference-architectures/app-service-web-app/multi-region.yml](https://github.com/microsoftdocs/architecture-center/blob/main/docs/reference-architectures/app-service-web-app/multi-region.yml)
* Service: **architecture-center**
* Sub-service: **reference-architecture**
* GitHub Login: @Arvindboggaram
* Microsoft Alias: **arboggar**
|
non_test
|
first visio link is incorrect first visio link appears to be wrong it s download visio file to a single region example document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service architecture center sub service reference architecture github login arvindboggaram microsoft alias arboggar
| 0
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.