Unnamed: 0 int64 3 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3 values | title stringlengths 2 742 | labels stringlengths 4 431 | body stringlengths 5 239k | index stringclasses 10 values | text_combine stringlengths 96 240k | label stringclasses 2 values | text stringlengths 96 200k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
102,028 | 21,893,470,606 | IssuesEvent | 2022-05-20 05:58:34 | DataTalksClub/data-engineering-zoomcamp | https://api.github.com/repos/DataTalksClub/data-engineering-zoomcamp | opened | Timecodes for "DE Zoomcamp 1.3.2 - Creating GCP Infrastructure with Terraform" | timecodes | Youtube video: https://www.youtube.com/watch?v=dNkEgO-CExg | 1.0 | Timecodes for "DE Zoomcamp 1.3.2 - Creating GCP Infrastructure with Terraform" - Youtube video: https://www.youtube.com/watch?v=dNkEgO-CExg | non_usab | timecodes for de zoomcamp creating gcp infrastructure with terraform youtube video | 0 |
4,301 | 3,807,236,810 | IssuesEvent | 2016-03-25 06:32:25 | hechoendrupal/DrupalConsole | https://api.github.com/repos/hechoendrupal/DrupalConsole | closed | [docs] Add instructions on how to build locally | docs novice usability | If I want to use a pre-release version or test something I want to contribute, it would be good to have build instructions. I simply used the travis instructions in the .travis.yml file, but it would be better to have them in the README or CONTRIBUTING guides. | True | [docs] Add instructions on how to build locally - If I want to use a pre-release version or test something I want to contribute, it would be good to have build instructions. I simply used the travis instructions in the .travis.yml file, but it would be better to have them in the README or CONTRIBUTING guides. | usab | add instructions on how to build locally if i want to use a pre release version or test something i want to contribute it would be good to have build instructions i simply used the travis instructions in the travis yml file but it would be better to have them in the readme or contributing guides | 1 |
727,565 | 25,039,595,391 | IssuesEvent | 2022-11-04 19:17:14 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | fx2trt tests not running? | high priority module: ci triaged | I'm trying to piece together what is going on with our fx2trt tests. As far as I can tell, https://github.com/pytorch/pytorch/pull/70203 implemented an entirely separate job config with no sharding that runs all our tests, but DOESN'T run fx2trt tests.
Here is an example recent job from master: https://github.com/pytorch/pytorch/runs/4732473836?check_suite_focus=true. If you search the raw logs, there are no fx2trt tests run at all. This job takes almost 2 hours because it's not sharded and runs a completely redundant set of tests, wasting capacity and time.
Recently, https://github.com/pytorch/pytorch/pull/70658 was landed. I'm not sure what this PR does from the description. It looks like it enables fx2trt tests on our default shards. If we're doing this, why do we have a separate fx2trt job? Can we delete the separate job? Furthermore, fx2trt are not enabled by this PR either, and are not currently running anywhere in master as far as I can tell.
Something seems seriously off; am I missing something?
cc @ezyang @gchanan @zou3519 @bdhirsh @seemethere @malfet @pytorch/pytorch-dev-infra | 1.0 | fx2trt tests not running? - I'm trying to piece together what is going on with our fx2trt tests. As far as I can tell, https://github.com/pytorch/pytorch/pull/70203 implemented an entirely separate job config with no sharding that runs all our tests, but DOESN'T run fx2trt tests.
Here is an example recent job from master: https://github.com/pytorch/pytorch/runs/4732473836?check_suite_focus=true. If you search the raw logs, there are no fx2trt tests run at all. This job takes almost 2 hours because it's not sharded and runs a completely redundant set of tests, wasting capacity and time.
Recently, https://github.com/pytorch/pytorch/pull/70658 was landed. I'm not sure what this PR does from the description. It looks like it enables fx2trt tests on our default shards. If we're doing this, why do we have a separate fx2trt job? Can we delete the separate job? Furthermore, fx2trt are not enabled by this PR either, and are not currently running anywhere in master as far as I can tell.
Something seems seriously off; am I missing something?
cc @ezyang @gchanan @zou3519 @bdhirsh @seemethere @malfet @pytorch/pytorch-dev-infra | non_usab | tests not running i m trying to piece together what is going on with our tests as far as i can tell implemented an entirely separate job config with no sharding that runs all our tests but doesn t run tests here is an example recent job from master if you search the raw logs there are no tests run at all this job takes almost hours because it s not sharded and runs a completely redundant set of tests wasting capacity and time recently was landed i m not sure what this pr does from the description it looks like it enables tests on our default shards if we re doing this why do we have a separate job can we delete the separate job furthermore are not enabled by this pr either and are not currently running anywhere in master as far as i can tell something seems seriously off am i missing something cc ezyang gchanan bdhirsh seemethere malfet pytorch pytorch dev infra | 0 |
61,715 | 3,152,048,183 | IssuesEvent | 2015-09-16 11:50:08 | matz-e/lobster | https://api.github.com/repos/matz-e/lobster | closed | Make the fs module more verbose | bug high-priority | This would really help debugging issues for regular users, as per recent private email conversation. | 1.0 | Make the fs module more verbose - This would really help debugging issues for regular users, as per recent private email conversation. | non_usab | make the fs module more verbose this would really help debugging issues for regular users as per recent private email conversation | 0 |
15,058 | 9,692,686,244 | IssuesEvent | 2019-05-24 14:21:28 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Spaces indentation improvement - align indenting left/right to rounded indentation level | enhancement topic:core topic:editor usability | Hello,
I'd like to propose change to current indentation mechanics in GDScript editor. There are some cases that are causing issues for me, consider following situations where indent is set to 4 spaces:
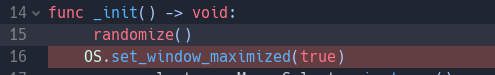
As you can notice I accidentally hit space on line 15 which gives this line total indent of 5 spaces while the rest of code is indented to 4. Okey, I hit backspace (or shitf+tab) to delete this space - but I actually end up with just one space like this:
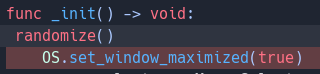
Obviously i'd expect deletion to go stop at 4 spaces to align to closest full indentation level - this is the way it works in most code editors (for instance in sublime).
The same goes for indenting - if I have cursor set after one space hitting tab editor should move cursor to next full indentation level of 4 - now it just adds four spaces giving line 5 spaces of indentation.
Another thing that could be changed is clicking backspace where there are less spaces than indentation level for instance:

I'd expect whole indentation level removed here whereas spaces are removed one by one (this is special case due to ifs logic in code_editor.cpp code).
To sum up the changes I propose are:
1) Hitting tab would move cursor to next full indentation level instead of adding fixed number of spaces
2) Hitting backspace would remove spaces up to next full indentation level
3) Hitting shift+tab would remove spaces up to next full indentation level
4) Hitting backspace when there are less spaces than indentation size would remove spaces up to beginning of the line
Since there is lot of going on I decided to create Issue to ask about your opinion but I have PR work in progress - let me know if this feature is wanted and I'll provide code for it.
Ps.: There seems to also be separate code branch for indenting when selection is not empty, this needs to be adjusted accordingly too | True | Spaces indentation improvement - align indenting left/right to rounded indentation level - Hello,
I'd like to propose change to current indentation mechanics in GDScript editor. There are some cases that are causing issues for me, consider following situations where indent is set to 4 spaces:
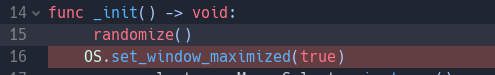
As you can notice I accidentally hit space on line 15 which gives this line total indent of 5 spaces while the rest of code is indented to 4. Okey, I hit backspace (or shitf+tab) to delete this space - but I actually end up with just one space like this:
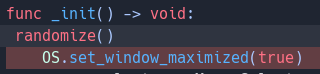
Obviously i'd expect deletion to go stop at 4 spaces to align to closest full indentation level - this is the way it works in most code editors (for instance in sublime).
The same goes for indenting - if I have cursor set after one space hitting tab editor should move cursor to next full indentation level of 4 - now it just adds four spaces giving line 5 spaces of indentation.
Another thing that could be changed is clicking backspace where there are less spaces than indentation level for instance:

I'd expect whole indentation level removed here whereas spaces are removed one by one (this is special case due to ifs logic in code_editor.cpp code).
To sum up the changes I propose are:
1) Hitting tab would move cursor to next full indentation level instead of adding fixed number of spaces
2) Hitting backspace would remove spaces up to next full indentation level
3) Hitting shift+tab would remove spaces up to next full indentation level
4) Hitting backspace when there are less spaces than indentation size would remove spaces up to beginning of the line
Since there is lot of going on I decided to create Issue to ask about your opinion but I have PR work in progress - let me know if this feature is wanted and I'll provide code for it.
Ps.: There seems to also be separate code branch for indenting when selection is not empty, this needs to be adjusted accordingly too | usab | spaces indentation improvement align indenting left right to rounded indentation level hello i d like to propose change to current indentation mechanics in gdscript editor there are some cases that are causing issues for me consider following situations where indent is set to spaces as you can notice i accidentally hit space on line which gives this line total indent of spaces while the rest of code is indented to okey i hit backspace or shitf tab to delete this space but i actually end up with just one space like this obviously i d expect deletion to go stop at spaces to align to closest full indentation level this is the way it works in most code editors for instance in sublime the same goes for indenting if i have cursor set after one space hitting tab editor should move cursor to next full indentation level of now it just adds four spaces giving line spaces of indentation another thing that could be changed is clicking backspace where there are less spaces than indentation level for instance i d expect whole indentation level removed here whereas spaces are removed one by one this is special case due to ifs logic in code editor cpp code to sum up the changes i propose are hitting tab would move cursor to next full indentation level instead of adding fixed number of spaces hitting backspace would remove spaces up to next full indentation level hitting shift tab would remove spaces up to next full indentation level hitting backspace when there are less spaces than indentation size would remove spaces up to beginning of the line since there is lot of going on i decided to create issue to ask about your opinion but i have pr work in progress let me know if this feature is wanted and i ll provide code for it ps there seems to also be separate code branch for indenting when selection is not empty this needs to be adjusted accordingly too | 1 |
130,468 | 18,156,851,095 | IssuesEvent | 2021-09-27 03:33:33 | LaudateCorpus1/qr1 | https://api.github.com/repos/LaudateCorpus1/qr1 | closed | CVE-2020-7788 (High) detected in ini-1.3.4.tgz - autoclosed | security vulnerability | ## CVE-2020-7788 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ini-1.3.4.tgz</b></p></summary>
<p>An ini encoder/decoder for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/ini/-/ini-1.3.4.tgz">https://registry.npmjs.org/ini/-/ini-1.3.4.tgz</a></p>
<p>Path to dependency file: qr1/Application/package.json</p>
<p>Path to vulnerable library: qr1/Application/node_modules/ini/package.json</p>
<p>
Dependency Hierarchy:
- rc-1.2.8.tgz (Root Library)
- :x: **ini-1.3.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/LaudateCorpus1/qr1/commit/249f8c00c71944085fe35e5d8d4b5ea508c8719b">249f8c00c71944085fe35e5d8d4b5ea508c8719b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788>CVE-2020-7788</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: v1.3.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7788 (High) detected in ini-1.3.4.tgz - autoclosed - ## CVE-2020-7788 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ini-1.3.4.tgz</b></p></summary>
<p>An ini encoder/decoder for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/ini/-/ini-1.3.4.tgz">https://registry.npmjs.org/ini/-/ini-1.3.4.tgz</a></p>
<p>Path to dependency file: qr1/Application/package.json</p>
<p>Path to vulnerable library: qr1/Application/node_modules/ini/package.json</p>
<p>
Dependency Hierarchy:
- rc-1.2.8.tgz (Root Library)
- :x: **ini-1.3.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/LaudateCorpus1/qr1/commit/249f8c00c71944085fe35e5d8d4b5ea508c8719b">249f8c00c71944085fe35e5d8d4b5ea508c8719b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788>CVE-2020-7788</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: v1.3.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | cve high detected in ini tgz autoclosed cve high severity vulnerability vulnerable library ini tgz an ini encoder decoder for node library home page a href path to dependency file application package json path to vulnerable library application node modules ini package json dependency hierarchy rc tgz root library x ini tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package ini before if an attacker submits a malicious ini file to an application that parses it with ini parse they will pollute the prototype on the application this can be exploited further depending on the context publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
184,382 | 14,289,346,031 | IssuesEvent | 2020-11-23 19:06:40 | github-vet/rangeclosure-findings | https://api.github.com/repos/github-vet/rangeclosure-findings | closed | pion/dtls: conn_test.go; 105 LoC | fresh large test |
Found a possible issue in [pion/dtls](https://www.github.com/pion/dtls) at [conn_test.go](https://github.com/pion/dtls/blob/3cc5d83f6f233d5f9a6445bf4b94f98f2672dd1f/conn_test.go#L577-L681)
The below snippet of Go code triggered static analysis which searches for goroutines and/or defer statements
which capture loop variables.
[Click here to see the code in its original context.](https://github.com/pion/dtls/blob/3cc5d83f6f233d5f9a6445bf4b94f98f2672dd1f/conn_test.go#L577-L681)
<details>
<summary>Click here to show the 105 line(s) of Go which triggered the analyzer.</summary>
```go
for _, test := range []struct {
Name string
ClientSRTP []SRTPProtectionProfile
ServerSRTP []SRTPProtectionProfile
ExpectedProfile SRTPProtectionProfile
WantClientError error
WantServerError error
}{
{
Name: "No SRTP in use",
ClientSRTP: nil,
ServerSRTP: nil,
ExpectedProfile: 0,
WantClientError: nil,
WantServerError: nil,
},
{
Name: "SRTP both ends",
ClientSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80},
ServerSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80},
ExpectedProfile: SRTP_AES128_CM_HMAC_SHA1_80,
WantClientError: nil,
WantServerError: nil,
},
{
Name: "SRTP client only",
ClientSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80},
ServerSRTP: nil,
ExpectedProfile: 0,
WantClientError: &errAlert{&alert{alertLevelFatal, alertInsufficientSecurity}},
WantServerError: errServerNoMatchingSRTPProfile,
},
{
Name: "SRTP server only",
ClientSRTP: nil,
ServerSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80},
ExpectedProfile: 0,
WantClientError: nil,
WantServerError: nil,
},
{
Name: "Multiple Suites",
ClientSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80, SRTP_AES128_CM_HMAC_SHA1_32},
ServerSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80, SRTP_AES128_CM_HMAC_SHA1_32},
ExpectedProfile: SRTP_AES128_CM_HMAC_SHA1_80,
WantClientError: nil,
WantServerError: nil,
},
{
Name: "Multiple Suites, Client Chooses",
ClientSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80, SRTP_AES128_CM_HMAC_SHA1_32},
ServerSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_32, SRTP_AES128_CM_HMAC_SHA1_80},
ExpectedProfile: SRTP_AES128_CM_HMAC_SHA1_80,
WantClientError: nil,
WantServerError: nil,
},
} {
ctx, cancel := context.WithTimeout(context.Background(), 10*time.Second)
defer cancel()
ca, cb := dpipe.Pipe()
type result struct {
c *Conn
err error
}
c := make(chan result)
go func() {
client, err := testClient(ctx, ca, &Config{SRTPProtectionProfiles: test.ClientSRTP}, true)
c <- result{client, err}
}()
server, err := testServer(ctx, cb, &Config{SRTPProtectionProfiles: test.ServerSRTP}, true)
if !errors.Is(err, test.WantServerError) {
t.Errorf("TestSRTPConfiguration: Server Error Mismatch '%s': expected(%v) actual(%v)", test.Name, test.WantServerError, err)
}
if err == nil {
defer func() {
_ = server.Close()
}()
}
res := <-c
if res.err == nil {
defer func() {
_ = res.c.Close()
}()
}
if !errors.Is(res.err, test.WantClientError) {
t.Fatalf("TestSRTPConfiguration: Client Error Mismatch '%s': expected(%v) actual(%v)", test.Name, test.WantClientError, res.err)
}
if res.c == nil {
return
}
actualClientSRTP, _ := res.c.SelectedSRTPProtectionProfile()
if actualClientSRTP != test.ExpectedProfile {
t.Errorf("TestSRTPConfiguration: Client SRTPProtectionProfile Mismatch '%s': expected(%v) actual(%v)", test.Name, test.ExpectedProfile, actualClientSRTP)
}
actualServerSRTP, _ := server.SelectedSRTPProtectionProfile()
if actualServerSRTP != test.ExpectedProfile {
t.Errorf("TestSRTPConfiguration: Server SRTPProtectionProfile Mismatch '%s': expected(%v) actual(%v)", test.Name, test.ExpectedProfile, actualServerSRTP)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 3cc5d83f6f233d5f9a6445bf4b94f98f2672dd1f
| 1.0 | pion/dtls: conn_test.go; 105 LoC -
Found a possible issue in [pion/dtls](https://www.github.com/pion/dtls) at [conn_test.go](https://github.com/pion/dtls/blob/3cc5d83f6f233d5f9a6445bf4b94f98f2672dd1f/conn_test.go#L577-L681)
The below snippet of Go code triggered static analysis which searches for goroutines and/or defer statements
which capture loop variables.
[Click here to see the code in its original context.](https://github.com/pion/dtls/blob/3cc5d83f6f233d5f9a6445bf4b94f98f2672dd1f/conn_test.go#L577-L681)
<details>
<summary>Click here to show the 105 line(s) of Go which triggered the analyzer.</summary>
```go
for _, test := range []struct {
Name string
ClientSRTP []SRTPProtectionProfile
ServerSRTP []SRTPProtectionProfile
ExpectedProfile SRTPProtectionProfile
WantClientError error
WantServerError error
}{
{
Name: "No SRTP in use",
ClientSRTP: nil,
ServerSRTP: nil,
ExpectedProfile: 0,
WantClientError: nil,
WantServerError: nil,
},
{
Name: "SRTP both ends",
ClientSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80},
ServerSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80},
ExpectedProfile: SRTP_AES128_CM_HMAC_SHA1_80,
WantClientError: nil,
WantServerError: nil,
},
{
Name: "SRTP client only",
ClientSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80},
ServerSRTP: nil,
ExpectedProfile: 0,
WantClientError: &errAlert{&alert{alertLevelFatal, alertInsufficientSecurity}},
WantServerError: errServerNoMatchingSRTPProfile,
},
{
Name: "SRTP server only",
ClientSRTP: nil,
ServerSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80},
ExpectedProfile: 0,
WantClientError: nil,
WantServerError: nil,
},
{
Name: "Multiple Suites",
ClientSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80, SRTP_AES128_CM_HMAC_SHA1_32},
ServerSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80, SRTP_AES128_CM_HMAC_SHA1_32},
ExpectedProfile: SRTP_AES128_CM_HMAC_SHA1_80,
WantClientError: nil,
WantServerError: nil,
},
{
Name: "Multiple Suites, Client Chooses",
ClientSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_80, SRTP_AES128_CM_HMAC_SHA1_32},
ServerSRTP: []SRTPProtectionProfile{SRTP_AES128_CM_HMAC_SHA1_32, SRTP_AES128_CM_HMAC_SHA1_80},
ExpectedProfile: SRTP_AES128_CM_HMAC_SHA1_80,
WantClientError: nil,
WantServerError: nil,
},
} {
ctx, cancel := context.WithTimeout(context.Background(), 10*time.Second)
defer cancel()
ca, cb := dpipe.Pipe()
type result struct {
c *Conn
err error
}
c := make(chan result)
go func() {
client, err := testClient(ctx, ca, &Config{SRTPProtectionProfiles: test.ClientSRTP}, true)
c <- result{client, err}
}()
server, err := testServer(ctx, cb, &Config{SRTPProtectionProfiles: test.ServerSRTP}, true)
if !errors.Is(err, test.WantServerError) {
t.Errorf("TestSRTPConfiguration: Server Error Mismatch '%s': expected(%v) actual(%v)", test.Name, test.WantServerError, err)
}
if err == nil {
defer func() {
_ = server.Close()
}()
}
res := <-c
if res.err == nil {
defer func() {
_ = res.c.Close()
}()
}
if !errors.Is(res.err, test.WantClientError) {
t.Fatalf("TestSRTPConfiguration: Client Error Mismatch '%s': expected(%v) actual(%v)", test.Name, test.WantClientError, res.err)
}
if res.c == nil {
return
}
actualClientSRTP, _ := res.c.SelectedSRTPProtectionProfile()
if actualClientSRTP != test.ExpectedProfile {
t.Errorf("TestSRTPConfiguration: Client SRTPProtectionProfile Mismatch '%s': expected(%v) actual(%v)", test.Name, test.ExpectedProfile, actualClientSRTP)
}
actualServerSRTP, _ := server.SelectedSRTPProtectionProfile()
if actualServerSRTP != test.ExpectedProfile {
t.Errorf("TestSRTPConfiguration: Server SRTPProtectionProfile Mismatch '%s': expected(%v) actual(%v)", test.Name, test.ExpectedProfile, actualServerSRTP)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 3cc5d83f6f233d5f9a6445bf4b94f98f2672dd1f
| non_usab | pion dtls conn test go loc found a possible issue in at the below snippet of go code triggered static analysis which searches for goroutines and or defer statements which capture loop variables click here to show the line s of go which triggered the analyzer go for test range struct name string clientsrtp srtpprotectionprofile serversrtp srtpprotectionprofile expectedprofile srtpprotectionprofile wantclienterror error wantservererror error name no srtp in use clientsrtp nil serversrtp nil expectedprofile wantclienterror nil wantservererror nil name srtp both ends clientsrtp srtpprotectionprofile srtp cm hmac serversrtp srtpprotectionprofile srtp cm hmac expectedprofile srtp cm hmac wantclienterror nil wantservererror nil name srtp client only clientsrtp srtpprotectionprofile srtp cm hmac serversrtp nil expectedprofile wantclienterror erralert alert alertlevelfatal alertinsufficientsecurity wantservererror errservernomatchingsrtpprofile name srtp server only clientsrtp nil serversrtp srtpprotectionprofile srtp cm hmac expectedprofile wantclienterror nil wantservererror nil name multiple suites clientsrtp srtpprotectionprofile srtp cm hmac srtp cm hmac serversrtp srtpprotectionprofile srtp cm hmac srtp cm hmac expectedprofile srtp cm hmac wantclienterror nil wantservererror nil name multiple suites client chooses clientsrtp srtpprotectionprofile srtp cm hmac srtp cm hmac serversrtp srtpprotectionprofile srtp cm hmac srtp cm hmac expectedprofile srtp cm hmac wantclienterror nil wantservererror nil ctx cancel context withtimeout context background time second defer cancel ca cb dpipe pipe type result struct c conn err error c make chan result go func client err testclient ctx ca config srtpprotectionprofiles test clientsrtp true c result client err server err testserver ctx cb config srtpprotectionprofiles test serversrtp true if errors is err test wantservererror t errorf testsrtpconfiguration server error mismatch s expected v actual v test name test wantservererror err if err nil defer func server close res c if res err nil defer func res c close if errors is res err test wantclienterror t fatalf testsrtpconfiguration client error mismatch s expected v actual v test name test wantclienterror res err if res c nil return actualclientsrtp res c selectedsrtpprotectionprofile if actualclientsrtp test expectedprofile t errorf testsrtpconfiguration client srtpprotectionprofile mismatch s expected v actual v test name test expectedprofile actualclientsrtp actualserversrtp server selectedsrtpprotectionprofile if actualserversrtp test expectedprofile t errorf testsrtpconfiguration server srtpprotectionprofile mismatch s expected v actual v test name test expectedprofile actualserversrtp leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
25,256 | 24,923,655,464 | IssuesEvent | 2022-10-31 04:24:04 | tailscale/tailscale | https://api.github.com/repos/tailscale/tailscale | closed | Synology NAS DS1621+ with DSM 6 and VM on it stop working | L1 Very few P2 Aggravating T5 Usability OS-synology bug | ### What is the issue?
No ping, no response. NAS and VM are unavailable.
VM:
Tailscale version
1.24.2
100.78.210.2
fd7a:115c:a1e0:ab12:4843:cd96:624e:d202
Synology NAS:
Tailscale version
1.22.1
100.76.19.5
fd7a:115c:a1e0:ab12:4843:cd96:624c:1305
### Steps to reproduce
Connect to my VM os Synology via TailScale.
### Are there any recent changes that introduced the issue?
No changes. Suddenly stop working.
### OS
Linux, Synology
### OS version
iOS, iPadOS, macOS
### Tailscale version
1.24.2, 1.22.1
### Bug report
_No response_ | True | Synology NAS DS1621+ with DSM 6 and VM on it stop working - ### What is the issue?
No ping, no response. NAS and VM are unavailable.
VM:
Tailscale version
1.24.2
100.78.210.2
fd7a:115c:a1e0:ab12:4843:cd96:624e:d202
Synology NAS:
Tailscale version
1.22.1
100.76.19.5
fd7a:115c:a1e0:ab12:4843:cd96:624c:1305
### Steps to reproduce
Connect to my VM os Synology via TailScale.
### Are there any recent changes that introduced the issue?
No changes. Suddenly stop working.
### OS
Linux, Synology
### OS version
iOS, iPadOS, macOS
### Tailscale version
1.24.2, 1.22.1
### Bug report
_No response_ | usab | synology nas with dsm and vm on it stop working what is the issue no ping no response nas and vm are unavailable vm tailscale version synology nas tailscale version steps to reproduce connect to my vm os synology via tailscale are there any recent changes that introduced the issue no changes suddenly stop working os linux synology os version ios ipados macos tailscale version bug report no response | 1 |
203,311 | 23,142,967,790 | IssuesEvent | 2022-07-28 20:29:28 | signalco-io/cloud | https://api.github.com/repos/signalco-io/cloud | opened | microsoft.teamfoundationserver.client.16.170.0.nupkg: 2 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>microsoft.teamfoundationserver.client.16.170.0.nupkg</b></p></summary>
<p></p>
<p>Path to dependency file: /Signal.Infrastructure.AzureDevOps/Signal.Infrastructure.AzureDevOps.csproj</p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/system.net.http/4.3.2/system.net.http.4.3.2.nupkg</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/signalco-io/cloud/commit/3c56748d918e8c9f8dbe9025c4274c32c30a1a57">3c56748d918e8c9f8dbe9025c4274c32c30a1a57</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2018-8292](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8292) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | system.net.http.4.3.2.nupkg | Transitive | N/A | ❌ |
| [WS-2022-0161](https://github.com/JamesNK/Newtonsoft.Json/commit/7e77bbe1beccceac4fc7b174b53abfefac278b66) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | newtonsoft.json.12.0.3.nupkg | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-8292</summary>
### Vulnerable Library - <b>system.net.http.4.3.2.nupkg</b></p>
<p>Provides a programming interface for modern HTTP applications, including HTTP client components that...</p>
<p>Library home page: <a href="https://api.nuget.org/packages/system.net.http.4.3.2.nupkg">https://api.nuget.org/packages/system.net.http.4.3.2.nupkg</a></p>
<p>Path to dependency file: /Signal.Infrastructure.AzureDevOps/Signal.Infrastructure.AzureDevOps.csproj</p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/system.net.http/4.3.2/system.net.http.4.3.2.nupkg</p>
<p>
Dependency Hierarchy:
- microsoft.teamfoundationserver.client.16.170.0.nupkg (Root Library)
- microsoft.aspnet.webapi.client.5.2.7.nupkg
- newtonsoft.json.bson.1.0.1.nupkg
- netstandard.library.1.6.1.nupkg
- :x: **system.net.http.4.3.2.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/signalco-io/cloud/commit/3c56748d918e8c9f8dbe9025c4274c32c30a1a57">3c56748d918e8c9f8dbe9025c4274c32c30a1a57</a></p>
<p>Found in base branch: <b>next</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An information disclosure vulnerability exists in .NET Core when authentication information is inadvertently exposed in a redirect, aka ".NET Core Information Disclosure Vulnerability." This affects .NET Core 2.1, .NET Core 1.0, .NET Core 1.1, PowerShell Core 6.0.
<p>Publish Date: 2018-10-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8292>CVE-2018-8292</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-10-10</p>
<p>Fix Resolution: System.Net.Http - 4.3.4;Microsoft.PowerShell.Commands.Utility - 6.1.0-rc.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2022-0161</summary>
### Vulnerable Library - <b>newtonsoft.json.12.0.3.nupkg</b></p>
<p>Json.NET is a popular high-performance JSON framework for .NET</p>
<p>Library home page: <a href="https://api.nuget.org/packages/newtonsoft.json.12.0.3.nupkg">https://api.nuget.org/packages/newtonsoft.json.12.0.3.nupkg</a></p>
<p>Path to dependency file: /Signal.Infrastructure.AzureDevOps/Signal.Infrastructure.AzureDevOps.csproj</p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/newtonsoft.json/12.0.3/newtonsoft.json.12.0.3.nupkg</p>
<p>
Dependency Hierarchy:
- microsoft.teamfoundationserver.client.16.170.0.nupkg (Root Library)
- microsoft.aspnet.webapi.client.5.2.7.nupkg
- newtonsoft.json.bson.1.0.1.nupkg
- :x: **newtonsoft.json.12.0.3.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/signalco-io/cloud/commit/3c56748d918e8c9f8dbe9025c4274c32c30a1a57">3c56748d918e8c9f8dbe9025c4274c32c30a1a57</a></p>
<p>Found in base branch: <b>next</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Improper Handling of Exceptional Conditions in Newtonsoft.Json.
Newtonsoft.Json prior to version 13.0.1 is vulnerable to Insecure Defaults due to improper handling of StackOverFlow exception (SOE) whenever nested expressions are being processed. Exploiting this vulnerability results in Denial Of Service (DoS), and it is exploitable when an attacker sends 5 requests that cause SOE in time frame of 5 minutes. This vulnerability affects Internet Information Services (IIS) Applications.
<p>Publish Date: 2022-06-22
<p>URL: <a href=https://github.com/JamesNK/Newtonsoft.Json/commit/7e77bbe1beccceac4fc7b174b53abfefac278b66>WS-2022-0161</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-5crp-9r3c-p9vr">https://github.com/advisories/GHSA-5crp-9r3c-p9vr</a></p>
<p>Release Date: 2022-06-22</p>
<p>Fix Resolution: Newtonsoft.Json - 13.0.1;Microsoft.Extensions.ApiDescription.Server - 6.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | microsoft.teamfoundationserver.client.16.170.0.nupkg: 2 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>microsoft.teamfoundationserver.client.16.170.0.nupkg</b></p></summary>
<p></p>
<p>Path to dependency file: /Signal.Infrastructure.AzureDevOps/Signal.Infrastructure.AzureDevOps.csproj</p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/system.net.http/4.3.2/system.net.http.4.3.2.nupkg</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/signalco-io/cloud/commit/3c56748d918e8c9f8dbe9025c4274c32c30a1a57">3c56748d918e8c9f8dbe9025c4274c32c30a1a57</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2018-8292](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8292) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | system.net.http.4.3.2.nupkg | Transitive | N/A | ❌ |
| [WS-2022-0161](https://github.com/JamesNK/Newtonsoft.Json/commit/7e77bbe1beccceac4fc7b174b53abfefac278b66) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | newtonsoft.json.12.0.3.nupkg | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-8292</summary>
### Vulnerable Library - <b>system.net.http.4.3.2.nupkg</b></p>
<p>Provides a programming interface for modern HTTP applications, including HTTP client components that...</p>
<p>Library home page: <a href="https://api.nuget.org/packages/system.net.http.4.3.2.nupkg">https://api.nuget.org/packages/system.net.http.4.3.2.nupkg</a></p>
<p>Path to dependency file: /Signal.Infrastructure.AzureDevOps/Signal.Infrastructure.AzureDevOps.csproj</p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/system.net.http/4.3.2/system.net.http.4.3.2.nupkg</p>
<p>
Dependency Hierarchy:
- microsoft.teamfoundationserver.client.16.170.0.nupkg (Root Library)
- microsoft.aspnet.webapi.client.5.2.7.nupkg
- newtonsoft.json.bson.1.0.1.nupkg
- netstandard.library.1.6.1.nupkg
- :x: **system.net.http.4.3.2.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/signalco-io/cloud/commit/3c56748d918e8c9f8dbe9025c4274c32c30a1a57">3c56748d918e8c9f8dbe9025c4274c32c30a1a57</a></p>
<p>Found in base branch: <b>next</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An information disclosure vulnerability exists in .NET Core when authentication information is inadvertently exposed in a redirect, aka ".NET Core Information Disclosure Vulnerability." This affects .NET Core 2.1, .NET Core 1.0, .NET Core 1.1, PowerShell Core 6.0.
<p>Publish Date: 2018-10-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8292>CVE-2018-8292</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-10-10</p>
<p>Fix Resolution: System.Net.Http - 4.3.4;Microsoft.PowerShell.Commands.Utility - 6.1.0-rc.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2022-0161</summary>
### Vulnerable Library - <b>newtonsoft.json.12.0.3.nupkg</b></p>
<p>Json.NET is a popular high-performance JSON framework for .NET</p>
<p>Library home page: <a href="https://api.nuget.org/packages/newtonsoft.json.12.0.3.nupkg">https://api.nuget.org/packages/newtonsoft.json.12.0.3.nupkg</a></p>
<p>Path to dependency file: /Signal.Infrastructure.AzureDevOps/Signal.Infrastructure.AzureDevOps.csproj</p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/newtonsoft.json/12.0.3/newtonsoft.json.12.0.3.nupkg</p>
<p>
Dependency Hierarchy:
- microsoft.teamfoundationserver.client.16.170.0.nupkg (Root Library)
- microsoft.aspnet.webapi.client.5.2.7.nupkg
- newtonsoft.json.bson.1.0.1.nupkg
- :x: **newtonsoft.json.12.0.3.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/signalco-io/cloud/commit/3c56748d918e8c9f8dbe9025c4274c32c30a1a57">3c56748d918e8c9f8dbe9025c4274c32c30a1a57</a></p>
<p>Found in base branch: <b>next</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Improper Handling of Exceptional Conditions in Newtonsoft.Json.
Newtonsoft.Json prior to version 13.0.1 is vulnerable to Insecure Defaults due to improper handling of StackOverFlow exception (SOE) whenever nested expressions are being processed. Exploiting this vulnerability results in Denial Of Service (DoS), and it is exploitable when an attacker sends 5 requests that cause SOE in time frame of 5 minutes. This vulnerability affects Internet Information Services (IIS) Applications.
<p>Publish Date: 2022-06-22
<p>URL: <a href=https://github.com/JamesNK/Newtonsoft.Json/commit/7e77bbe1beccceac4fc7b174b53abfefac278b66>WS-2022-0161</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-5crp-9r3c-p9vr">https://github.com/advisories/GHSA-5crp-9r3c-p9vr</a></p>
<p>Release Date: 2022-06-22</p>
<p>Fix Resolution: Newtonsoft.Json - 13.0.1;Microsoft.Extensions.ApiDescription.Server - 6.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_usab | microsoft teamfoundationserver client nupkg vulnerabilities highest severity is vulnerable library microsoft teamfoundationserver client nupkg path to dependency file signal infrastructure azuredevops signal infrastructure azuredevops csproj path to vulnerable library home wss scanner nuget packages system net http system net http nupkg found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high system net http nupkg transitive n a high newtonsoft json nupkg transitive n a details cve vulnerable library system net http nupkg provides a programming interface for modern http applications including http client components that library home page a href path to dependency file signal infrastructure azuredevops signal infrastructure azuredevops csproj path to vulnerable library home wss scanner nuget packages system net http system net http nupkg dependency hierarchy microsoft teamfoundationserver client nupkg root library microsoft aspnet webapi client nupkg newtonsoft json bson nupkg netstandard library nupkg x system net http nupkg vulnerable library found in head commit a href found in base branch next vulnerability details an information disclosure vulnerability exists in net core when authentication information is inadvertently exposed in a redirect aka net core information disclosure vulnerability this affects net core net core net core powershell core publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution system net http microsoft powershell commands utility rc step up your open source security game with mend ws vulnerable library newtonsoft json nupkg json net is a popular high performance json framework for net library home page a href path to dependency file signal infrastructure azuredevops signal infrastructure azuredevops csproj path to vulnerable library home wss scanner nuget packages newtonsoft json newtonsoft json nupkg dependency hierarchy microsoft teamfoundationserver client nupkg root library microsoft aspnet webapi client nupkg newtonsoft json bson nupkg x newtonsoft json nupkg vulnerable library found in head commit a href found in base branch next vulnerability details improper handling of exceptional conditions in newtonsoft json newtonsoft json prior to version is vulnerable to insecure defaults due to improper handling of stackoverflow exception soe whenever nested expressions are being processed exploiting this vulnerability results in denial of service dos and it is exploitable when an attacker sends requests that cause soe in time frame of minutes this vulnerability affects internet information services iis applications publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution newtonsoft json microsoft extensions apidescription server step up your open source security game with mend | 0 |
16,189 | 10,603,290,081 | IssuesEvent | 2019-10-10 15:42:18 | burtonator/polar-bookshelf | https://api.github.com/repos/burtonator/polar-bookshelf | closed | rel=canonical preventing crawling. | usability | I have to fix rel=canonical for things to work with crawling ... That's going to block it and prevent it from working for now. | True | rel=canonical preventing crawling. - I have to fix rel=canonical for things to work with crawling ... That's going to block it and prevent it from working for now. | usab | rel canonical preventing crawling i have to fix rel canonical for things to work with crawling that s going to block it and prevent it from working for now | 1 |
66,748 | 12,821,810,972 | IssuesEvent | 2020-07-06 08:45:10 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] error untranslated on registration page | No Code Attached Yet | ### Steps to reproduce the issue
Install Joomla 4.0-dev with sample data
Enable User Registration
Enable Lang debug (for testing)
On frontend click "Create an account"
Dont complete the form
Click Register button
See red error message
Note that "error" is lowercase and not translatable
### Expected result
`**Error**`
### Actual result
error
<img width="731" alt="Screenshot 2020-07-05 at 21 51 09" src="https://user-images.githubusercontent.com/400092/86542037-e4a74600-bf09-11ea-8ed4-5ee2e6cb1e3a.png">
### System information (as much as possible)
safari on mac
### Additional comments
| 1.0 | [4.0] error untranslated on registration page - ### Steps to reproduce the issue
Install Joomla 4.0-dev with sample data
Enable User Registration
Enable Lang debug (for testing)
On frontend click "Create an account"
Dont complete the form
Click Register button
See red error message
Note that "error" is lowercase and not translatable
### Expected result
`**Error**`
### Actual result
error
<img width="731" alt="Screenshot 2020-07-05 at 21 51 09" src="https://user-images.githubusercontent.com/400092/86542037-e4a74600-bf09-11ea-8ed4-5ee2e6cb1e3a.png">
### System information (as much as possible)
safari on mac
### Additional comments
| non_usab | error untranslated on registration page steps to reproduce the issue install joomla dev with sample data enable user registration enable lang debug for testing on frontend click create an account dont complete the form click register button see red error message note that error is lowercase and not translatable expected result error actual result error img width alt screenshot at src system information as much as possible safari on mac additional comments | 0 |
33,916 | 4,513,717,275 | IssuesEvent | 2016-09-04 13:03:07 | nextcloud/gallery | https://api.github.com/repos/nextcloud/gallery | opened | Show a warning if the PHP memory limit is set too low | design enhancement | _From @oparoz on April 14, 2016 15:51_
One of the last remaining way to make Gallery crash is to try to open an album containing large JPEGs while having a PHP memory limit set lower than 256MB.
Despite my belief that PHP 7 had removed all these internal errors which made PHP stop in its tracks, that one still kills PHP and leaves Gallery hanging.
One way to solve the problem is to stop parallel processing thumbnails. I don't think it's a good idea as most CPUs today have multiple cores.
Another way could be to wait for all thumbnails to be ready before closing the line, but that means there would be less PHP workers available to do other things and not all thumbnails would be sent back, leading to randomly missing content.
So, since this seems difficult to solve via code, maybe we could show a warning somewhere, letting admins know that there will be issues with image preview rendering if they keep the current limit that low.
@jancborchardt
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/32954121-show-a-warning-if-the-php-memory-limit-is-set-too-low?utm_campaign=plugin&utm_content=tracker%2F9328526&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F9328526&utm_medium=issues&utm_source=github).
</bountysource-plugin>
_Copied from original issue: owncloud/gallery#645_ | 1.0 | Show a warning if the PHP memory limit is set too low - _From @oparoz on April 14, 2016 15:51_
One of the last remaining way to make Gallery crash is to try to open an album containing large JPEGs while having a PHP memory limit set lower than 256MB.
Despite my belief that PHP 7 had removed all these internal errors which made PHP stop in its tracks, that one still kills PHP and leaves Gallery hanging.
One way to solve the problem is to stop parallel processing thumbnails. I don't think it's a good idea as most CPUs today have multiple cores.
Another way could be to wait for all thumbnails to be ready before closing the line, but that means there would be less PHP workers available to do other things and not all thumbnails would be sent back, leading to randomly missing content.
So, since this seems difficult to solve via code, maybe we could show a warning somewhere, letting admins know that there will be issues with image preview rendering if they keep the current limit that low.
@jancborchardt
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/32954121-show-a-warning-if-the-php-memory-limit-is-set-too-low?utm_campaign=plugin&utm_content=tracker%2F9328526&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F9328526&utm_medium=issues&utm_source=github).
</bountysource-plugin>
_Copied from original issue: owncloud/gallery#645_ | non_usab | show a warning if the php memory limit is set too low from oparoz on april one of the last remaining way to make gallery crash is to try to open an album containing large jpegs while having a php memory limit set lower than despite my belief that php had removed all these internal errors which made php stop in its tracks that one still kills php and leaves gallery hanging one way to solve the problem is to stop parallel processing thumbnails i don t think it s a good idea as most cpus today have multiple cores another way could be to wait for all thumbnails to be ready before closing the line but that means there would be less php workers available to do other things and not all thumbnails would be sent back leading to randomly missing content so since this seems difficult to solve via code maybe we could show a warning somewhere letting admins know that there will be issues with image preview rendering if they keep the current limit that low jancborchardt want to back this issue we accept bounties via copied from original issue owncloud gallery | 0 |
9,274 | 6,193,233,603 | IssuesEvent | 2017-07-05 06:24:58 | Virtual-Labs/speech-signal-processing-iiith | https://api.github.com/repos/Virtual-Labs/speech-signal-processing-iiith | closed | QA_speech-signal-processing_Linear prediction analysis of speech_Assessment_spelling-mistakes | category : Usability Developed by: VLEAD Open-Edx Severity : S3 Status : Resolved | Defect Description:
In the Assessment page of the Linear prediction analysis of speech experiment in Speech Signal Processing Lab, Found spelling mistakes.
Actual Result:
In the Assessment page of the Linear prediction analysis of speech experiment in Speech Signal Processing Lab, Found spelling mistakes.
Environment :
OS: Windows 7, Ubuntu-16.04, Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM,
Processor:i5
Attachments:

| True | QA_speech-signal-processing_Linear prediction analysis of speech_Assessment_spelling-mistakes - Defect Description:
In the Assessment page of the Linear prediction analysis of speech experiment in Speech Signal Processing Lab, Found spelling mistakes.
Actual Result:
In the Assessment page of the Linear prediction analysis of speech experiment in Speech Signal Processing Lab, Found spelling mistakes.
Environment :
OS: Windows 7, Ubuntu-16.04, Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM,
Processor:i5
Attachments:

| usab | qa speech signal processing linear prediction analysis of speech assessment spelling mistakes defect description in the assessment page of the linear prediction analysis of speech experiment in speech signal processing lab found spelling mistakes actual result in the assessment page of the linear prediction analysis of speech experiment in speech signal processing lab found spelling mistakes environment os windows ubuntu centos browsers firefox chrome chromium bandwidth hardware configuration processor attachments | 1 |
22,536 | 19,598,367,991 | IssuesEvent | 2022-01-05 20:56:00 | ZcashFoundation/zebra | https://api.github.com/repos/ZcashFoundation/zebra | closed | Cache unsolicited Peers responses until needed | C-bug P-Medium I-hang I-usability I-bad-data A-network | ## Motivation
Zebra currently drops unsolicited `Peers` responses. `zcashd` sends an `Peers` response soon after the connection opens, then it ignores `Peers` requests for a long while.
This network protocol mismatch sometimes makes Zebra hang on startup, or sync really slowly.
### Specifications
This behavior is unspecified.
### Suggested Solution
- Cache the latest unsolicited `Peers` response in each connection
- When Zebra sends a `Peers` request, consume and return the cached response. If there's no cached response, send a `getaddr` message to the peer, and wait for the response.
## Related Work
#1892 has some other ideas for getting better addresses, but they're less important than this ticket
This change blocks #2325
This change is part of #704 | True | Cache unsolicited Peers responses until needed - ## Motivation
Zebra currently drops unsolicited `Peers` responses. `zcashd` sends an `Peers` response soon after the connection opens, then it ignores `Peers` requests for a long while.
This network protocol mismatch sometimes makes Zebra hang on startup, or sync really slowly.
### Specifications
This behavior is unspecified.
### Suggested Solution
- Cache the latest unsolicited `Peers` response in each connection
- When Zebra sends a `Peers` request, consume and return the cached response. If there's no cached response, send a `getaddr` message to the peer, and wait for the response.
## Related Work
#1892 has some other ideas for getting better addresses, but they're less important than this ticket
This change blocks #2325
This change is part of #704 | usab | cache unsolicited peers responses until needed motivation zebra currently drops unsolicited peers responses zcashd sends an peers response soon after the connection opens then it ignores peers requests for a long while this network protocol mismatch sometimes makes zebra hang on startup or sync really slowly specifications this behavior is unspecified suggested solution cache the latest unsolicited peers response in each connection when zebra sends a peers request consume and return the cached response if there s no cached response send a getaddr message to the peer and wait for the response related work has some other ideas for getting better addresses but they re less important than this ticket this change blocks this change is part of | 1 |
10,829 | 6,952,155,382 | IssuesEvent | 2017-12-06 16:34:17 | frePPLe/frepple | https://api.github.com/repos/frePPLe/frepple | closed | Documentation of curl commands for frePPLe | Need review usability | Make a workflow script:
remote delete
upload files
import to frepple
run plan | True | Documentation of curl commands for frePPLe - Make a workflow script:
remote delete
upload files
import to frepple
run plan | usab | documentation of curl commands for frepple make a workflow script remote delete upload files import to frepple run plan | 1 |
14,284 | 8,973,424,511 | IssuesEvent | 2019-01-29 20:59:49 | mercycorps/TolaActivity | https://api.github.com/repos/mercycorps/TolaActivity | closed | Disaggregation/Indicator Type selector function is confusing | UI details usability | **Description:**
On the Performance tab when creating a new or editing an indicator, it is difficult to understand the disaggregation and indicator type fields based on how a selection can be made.
Though there is no indication that these two options with selections are required, there is no way to DE-select an option once clicked.
**Steps to Reproduce:**
1. Login to Tola-Activity
2. Click Testing specific Program "TolaData Test"
3. Click "+ Add Indicator"
4. Add name to Indicator and click "Save Changes"
5. Click the performance tab
6. Click/Highlight options under disaggregation & indicator type
**Results:**
Multiple options can be "selected" by clicking and dragging for highlighting. When clicking an option, there is no way to deselect an option.
**Expected Results:**
If multiple selection is allowed, check box or similar selector is used. If not an optional field/selection, mark properly and block saving as required.
**Attachments:**

| True | Disaggregation/Indicator Type selector function is confusing - **Description:**
On the Performance tab when creating a new or editing an indicator, it is difficult to understand the disaggregation and indicator type fields based on how a selection can be made.
Though there is no indication that these two options with selections are required, there is no way to DE-select an option once clicked.
**Steps to Reproduce:**
1. Login to Tola-Activity
2. Click Testing specific Program "TolaData Test"
3. Click "+ Add Indicator"
4. Add name to Indicator and click "Save Changes"
5. Click the performance tab
6. Click/Highlight options under disaggregation & indicator type
**Results:**
Multiple options can be "selected" by clicking and dragging for highlighting. When clicking an option, there is no way to deselect an option.
**Expected Results:**
If multiple selection is allowed, check box or similar selector is used. If not an optional field/selection, mark properly and block saving as required.
**Attachments:**

| usab | disaggregation indicator type selector function is confusing description on the performance tab when creating a new or editing an indicator it is difficult to understand the disaggregation and indicator type fields based on how a selection can be made though there is no indication that these two options with selections are required there is no way to de select an option once clicked steps to reproduce login to tola activity click testing specific program toladata test click add indicator add name to indicator and click save changes click the performance tab click highlight options under disaggregation indicator type results multiple options can be selected by clicking and dragging for highlighting when clicking an option there is no way to deselect an option expected results if multiple selection is allowed check box or similar selector is used if not an optional field selection mark properly and block saving as required attachments | 1 |
64,515 | 18,722,556,129 | IssuesEvent | 2021-11-03 13:23:30 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | closed | Core: primefaces.TOUCHABLE does not globally disable touchable | defect | **Environment:**
- PF Version: _10.0_
- JSF + version: _ALL_
- Affected browsers: _ALL_
**Hierarchy**
If you have a datatable with horizontal scrolling inside a tabview the tabview takes precedence in swipe event. The tabview is just a UI container and should by default not override the content touch events since it limits it use case. Only very simple tabviews with static content can benefit from this behavior.
**Global deactivating has no effect**
I tried deactivating it at global level using "primefaces.TOUCHABLE" web.xml context-param but it does not work. Somehow i need to deactivate it on component level. Maybe not available in 10.0.0?
**Default false?**
Should touchable behavior not be false by default so you can turn it on for mobile specific application and in CRUD applications it breaks backwards compatibility when upgrading to 10.0.0. I must now add touchable="false" to very many components cause we and our clients use the "desktop" version also on mobile and basically every table there is horizontally scrollable.
Reported by @djmj here: https://github.com/primefaces/primefaces/issues/5744#issuecomment-955576984 | 1.0 | Core: primefaces.TOUCHABLE does not globally disable touchable - **Environment:**
- PF Version: _10.0_
- JSF + version: _ALL_
- Affected browsers: _ALL_
**Hierarchy**
If you have a datatable with horizontal scrolling inside a tabview the tabview takes precedence in swipe event. The tabview is just a UI container and should by default not override the content touch events since it limits it use case. Only very simple tabviews with static content can benefit from this behavior.
**Global deactivating has no effect**
I tried deactivating it at global level using "primefaces.TOUCHABLE" web.xml context-param but it does not work. Somehow i need to deactivate it on component level. Maybe not available in 10.0.0?
**Default false?**
Should touchable behavior not be false by default so you can turn it on for mobile specific application and in CRUD applications it breaks backwards compatibility when upgrading to 10.0.0. I must now add touchable="false" to very many components cause we and our clients use the "desktop" version also on mobile and basically every table there is horizontally scrollable.
Reported by @djmj here: https://github.com/primefaces/primefaces/issues/5744#issuecomment-955576984 | non_usab | core primefaces touchable does not globally disable touchable environment pf version jsf version all affected browsers all hierarchy if you have a datatable with horizontal scrolling inside a tabview the tabview takes precedence in swipe event the tabview is just a ui container and should by default not override the content touch events since it limits it use case only very simple tabviews with static content can benefit from this behavior global deactivating has no effect i tried deactivating it at global level using primefaces touchable web xml context param but it does not work somehow i need to deactivate it on component level maybe not available in default false should touchable behavior not be false by default so you can turn it on for mobile specific application and in crud applications it breaks backwards compatibility when upgrading to i must now add touchable false to very many components cause we and our clients use the desktop version also on mobile and basically every table there is horizontally scrollable reported by djmj here | 0 |
44,269 | 13,050,951,815 | IssuesEvent | 2020-07-29 16:16:52 | stefanfreitag/terraform | https://api.github.com/repos/stefanfreitag/terraform | opened | CVE-2020-8116 (High) detected in dot-prop-3.0.0.tgz | security vulnerability | ## CVE-2020-8116 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dot-prop-3.0.0.tgz</b></p></summary>
<p>Get, set, or delete a property from a nested object using a dot path</p>
<p>Library home page: <a href="https://registry.npmjs.org/dot-prop/-/dot-prop-3.0.0.tgz">https://registry.npmjs.org/dot-prop/-/dot-prop-3.0.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/terraform/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/terraform/node_modules/dot-prop/package.json</p>
<p>
Dependency Hierarchy:
- config-conventional-9.1.1.tgz (Root Library)
- conventional-changelog-conventionalcommits-4.3.0.tgz
- compare-func-1.3.4.tgz
- :x: **dot-prop-3.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/stefanfreitag/terraform/commit/e3ac453acc63797437761646d231348b04739740">e3ac453acc63797437761646d231348b04739740</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution vulnerability in dot-prop npm package version 5.1.0 and earlier allows an attacker to add arbitrary properties to JavaScript language constructs such as objects.
<p>Publish Date: 2020-02-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8116>CVE-2020-8116</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8116">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8116</a></p>
<p>Release Date: 2020-02-04</p>
<p>Fix Resolution: dot-prop - 5.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-8116 (High) detected in dot-prop-3.0.0.tgz - ## CVE-2020-8116 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dot-prop-3.0.0.tgz</b></p></summary>
<p>Get, set, or delete a property from a nested object using a dot path</p>
<p>Library home page: <a href="https://registry.npmjs.org/dot-prop/-/dot-prop-3.0.0.tgz">https://registry.npmjs.org/dot-prop/-/dot-prop-3.0.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/terraform/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/terraform/node_modules/dot-prop/package.json</p>
<p>
Dependency Hierarchy:
- config-conventional-9.1.1.tgz (Root Library)
- conventional-changelog-conventionalcommits-4.3.0.tgz
- compare-func-1.3.4.tgz
- :x: **dot-prop-3.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/stefanfreitag/terraform/commit/e3ac453acc63797437761646d231348b04739740">e3ac453acc63797437761646d231348b04739740</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution vulnerability in dot-prop npm package version 5.1.0 and earlier allows an attacker to add arbitrary properties to JavaScript language constructs such as objects.
<p>Publish Date: 2020-02-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8116>CVE-2020-8116</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8116">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8116</a></p>
<p>Release Date: 2020-02-04</p>
<p>Fix Resolution: dot-prop - 5.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | cve high detected in dot prop tgz cve high severity vulnerability vulnerable library dot prop tgz get set or delete a property from a nested object using a dot path library home page a href path to dependency file tmp ws scm terraform package json path to vulnerable library tmp ws scm terraform node modules dot prop package json dependency hierarchy config conventional tgz root library conventional changelog conventionalcommits tgz compare func tgz x dot prop tgz vulnerable library found in head commit a href vulnerability details prototype pollution vulnerability in dot prop npm package version and earlier allows an attacker to add arbitrary properties to javascript language constructs such as objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution dot prop step up your open source security game with whitesource | 0 |
18,837 | 13,302,724,869 | IssuesEvent | 2020-08-25 14:37:15 | tueit/it_management | https://api.github.com/repos/tueit/it_management | opened | Test tel: links Click to call | enhancement usability | please test whether click-to-call links work inside cards with
<a href="tel:+1-303-499-7111">+1 (303) 499-7111</a>
Syntax
source: https://developers.google.com/web/fundamentals/native-hardware/click-to-call
I can see this beeing interesting here:

| True | Test tel: links Click to call - please test whether click-to-call links work inside cards with
<a href="tel:+1-303-499-7111">+1 (303) 499-7111</a>
Syntax
source: https://developers.google.com/web/fundamentals/native-hardware/click-to-call
I can see this beeing interesting here:

| usab | test tel links click to call please test whether click to call links work inside cards with syntax source i can see this beeing interesting here | 1 |
63,481 | 3,195,669,262 | IssuesEvent | 2015-09-30 17:38:14 | fusioninventory/fusioninventory-for-glpi | https://api.github.com/repos/fusioninventory/fusioninventory-for-glpi | closed | No French translation for Download in import information | Component: For junior contributor Component: Found in version Priority: Low Status: Rejected Tracker: Bug | ---
Author Name: **Frédéric MOHIER** (Frédéric MOHIER)
Original Redmine Issue: 2116, http://forge.fusioninventory.org/issues/2116
Original Date: 2013-05-15
---
Beside the PHP/XML download links, the "Download" text is not translated in the computer import tab.
Moreover, it hsould be nice if the inventory categories were translated ... "carte son" instead of "sound card" would be more comprehensive for French technicians.
| 1.0 | No French translation for Download in import information - ---
Author Name: **Frédéric MOHIER** (Frédéric MOHIER)
Original Redmine Issue: 2116, http://forge.fusioninventory.org/issues/2116
Original Date: 2013-05-15
---
Beside the PHP/XML download links, the "Download" text is not translated in the computer import tab.
Moreover, it hsould be nice if the inventory categories were translated ... "carte son" instead of "sound card" would be more comprehensive for French technicians.
| non_usab | no french translation for download in import information author name frédéric mohier frédéric mohier original redmine issue original date beside the php xml download links the download text is not translated in the computer import tab moreover it hsould be nice if the inventory categories were translated carte son instead of sound card would be more comprehensive for french technicians | 0 |
2,080 | 3,040,822,366 | IssuesEvent | 2015-08-07 17:35:00 | tgstation/-tg-station | https://api.github.com/repos/tgstation/-tg-station | closed | Tracking implants are unintuitive | Feature Request Not a bug Usability | They need a pinpointer-esque item that cycles through available implants (all the implants would have IDs) because right now trying to hunt people down with the scanner is unnecessarily stupid. | True | Tracking implants are unintuitive - They need a pinpointer-esque item that cycles through available implants (all the implants would have IDs) because right now trying to hunt people down with the scanner is unnecessarily stupid. | usab | tracking implants are unintuitive they need a pinpointer esque item that cycles through available implants all the implants would have ids because right now trying to hunt people down with the scanner is unnecessarily stupid | 1 |
19,009 | 10,312,368,189 | IssuesEvent | 2019-08-29 19:41:22 | jamijam/WebGoat-Legacy | https://api.github.com/repos/jamijam/WebGoat-Legacy | opened | CVE-2019-14439 (High) detected in jackson-databind-2.0.4.jar | security vulnerability | ## CVE-2019-14439 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.0.4.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /WebGoat-Legacy/pom.xml</p>
<p>Path to vulnerable library: 2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.4/jackson-databind-2.0.4.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.4.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jamijam/WebGoat-Legacy/commit/47e282c80c0e0057166440fc7140b77c4f06feb6">47e282c80c0e0057166440fc7140b77c4f06feb6</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9.2. This occurs when Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the logback jar in the classpath.
<p>Publish Date: 2019-07-30
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439>CVE-2019-14439</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439</a></p>
<p>Release Date: 2019-07-30</p>
<p>Fix Resolution: 2.9.9.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-14439 (High) detected in jackson-databind-2.0.4.jar - ## CVE-2019-14439 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.0.4.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /WebGoat-Legacy/pom.xml</p>
<p>Path to vulnerable library: 2/repository/com/fasterxml/jackson/core/jackson-databind/2.0.4/jackson-databind-2.0.4.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.0.4.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jamijam/WebGoat-Legacy/commit/47e282c80c0e0057166440fc7140b77c4f06feb6">47e282c80c0e0057166440fc7140b77c4f06feb6</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9.2. This occurs when Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the logback jar in the classpath.
<p>Publish Date: 2019-07-30
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439>CVE-2019-14439</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439</a></p>
<p>Release Date: 2019-07-30</p>
<p>Fix Resolution: 2.9.9.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file webgoat legacy pom xml path to vulnerable library repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind x before this occurs when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the logback jar in the classpath publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
241,707 | 7,828,321,157 | IssuesEvent | 2018-06-15 00:36:40 | google/blockly | https://api.github.com/repos/google/blockly | closed | Remove Closure from Block Factory | component: devtools help wanted low priority type: cleanup | <!--
- Thanks for opening an issue for us! Before you open an issue,
- please check if a similar issue exists or has been closed before.
-
- If you're asking a question about how to use Blockly in your application,
- please ask questions on the mailing list, instead of filing issues:
- https://groups.google.com/forum/#!forum/blockly
-->
### Problem statement
BlockFactory is not a closure-compiled demo, but it is peppered with `goog` calls: provides, require, and a color picker. Replace this code to eliminate issues like https://github.com/google/closure-library/issues/897.
Consider https://neil.fraser.name/software/colourpicker/ as a color picker replacement.
### Expected Behavior
Code that is never compiled with Closure should not include `goog.require` and `goog.provide` statements.
Block Factory should not depend on Closure's color picker, since it is not compiled to ensure dependencies are correctly linked/available.
Recompiling main Blockly libraries, if successful, should not change whether Block Factory runs.
### Actual Behavior
Recent changes in Closure broke Block Factory, even though the compilation step succeeded.
See https://github.com/google/blockly/issues/1830
| 1.0 | Remove Closure from Block Factory - <!--
- Thanks for opening an issue for us! Before you open an issue,
- please check if a similar issue exists or has been closed before.
-
- If you're asking a question about how to use Blockly in your application,
- please ask questions on the mailing list, instead of filing issues:
- https://groups.google.com/forum/#!forum/blockly
-->
### Problem statement
BlockFactory is not a closure-compiled demo, but it is peppered with `goog` calls: provides, require, and a color picker. Replace this code to eliminate issues like https://github.com/google/closure-library/issues/897.
Consider https://neil.fraser.name/software/colourpicker/ as a color picker replacement.
### Expected Behavior
Code that is never compiled with Closure should not include `goog.require` and `goog.provide` statements.
Block Factory should not depend on Closure's color picker, since it is not compiled to ensure dependencies are correctly linked/available.
Recompiling main Blockly libraries, if successful, should not change whether Block Factory runs.
### Actual Behavior
Recent changes in Closure broke Block Factory, even though the compilation step succeeded.
See https://github.com/google/blockly/issues/1830
| non_usab | remove closure from block factory thanks for opening an issue for us before you open an issue please check if a similar issue exists or has been closed before if you re asking a question about how to use blockly in your application please ask questions on the mailing list instead of filing issues problem statement blockfactory is not a closure compiled demo but it is peppered with goog calls provides require and a color picker replace this code to eliminate issues like consider as a color picker replacement expected behavior code that is never compiled with closure should not include goog require and goog provide statements block factory should not depend on closure s color picker since it is not compiled to ensure dependencies are correctly linked available recompiling main blockly libraries if successful should not change whether block factory runs actual behavior recent changes in closure broke block factory even though the compilation step succeeded see | 0 |
424,948 | 29,186,022,491 | IssuesEvent | 2023-05-19 15:29:42 | aws/aws-cdk | https://api.github.com/repos/aws/aws-cdk | closed | [ecs] ContainerImage.fromRegistry docs issue — how to use custom Docker image tag? | p1 feature-request @aws-cdk/aws-ecs effort/small documentation | This is a 📕 documentation issue about [ContainerImage.fromRegistry](https://docs.aws.amazon.com/cdk/api/latest/docs/@aws-cdk_aws-ecs.ContainerImage.html#static-from-wbr-registryname-props) method where it's not clear how to supply a custom Docker image tag i.e. `not-latest` when using a public Docker image from Docker Hub.
When I was Googling around, I found this [Medium post](https://medium.com/aws-factory/continuous-delivery-of-a-java-spring-boot-webapp-with-aws-cdk-codepipeline-and-docker-56e045812bd2) containing this line inside it:
```
ecs.ContainerImage.fromRegistry(“okaycloud/dummywebserver:latest”)
```
So, I assume, the method does actually support custom Docker image tag if it's separated by colon symbol i.e. `image-name:tag-name` but it wasn't made clear in the docs page.
Can someone confirm this? If it's correct, I'm happy to submit a PR to improve this section.
| 1.0 | [ecs] ContainerImage.fromRegistry docs issue — how to use custom Docker image tag? - This is a 📕 documentation issue about [ContainerImage.fromRegistry](https://docs.aws.amazon.com/cdk/api/latest/docs/@aws-cdk_aws-ecs.ContainerImage.html#static-from-wbr-registryname-props) method where it's not clear how to supply a custom Docker image tag i.e. `not-latest` when using a public Docker image from Docker Hub.
When I was Googling around, I found this [Medium post](https://medium.com/aws-factory/continuous-delivery-of-a-java-spring-boot-webapp-with-aws-cdk-codepipeline-and-docker-56e045812bd2) containing this line inside it:
```
ecs.ContainerImage.fromRegistry(“okaycloud/dummywebserver:latest”)
```
So, I assume, the method does actually support custom Docker image tag if it's separated by colon symbol i.e. `image-name:tag-name` but it wasn't made clear in the docs page.
Can someone confirm this? If it's correct, I'm happy to submit a PR to improve this section.
| non_usab | containerimage fromregistry docs issue — how to use custom docker image tag this is a 📕 documentation issue about method where it s not clear how to supply a custom docker image tag i e not latest when using a public docker image from docker hub when i was googling around i found this containing this line inside it ecs containerimage fromregistry “okaycloud dummywebserver latest” so i assume the method does actually support custom docker image tag if it s separated by colon symbol i e image name tag name but it wasn t made clear in the docs page can someone confirm this if it s correct i m happy to submit a pr to improve this section | 0 |
24,638 | 24,078,334,211 | IssuesEvent | 2022-09-19 02:10:24 | FreeTubeApp/FreeTube | https://api.github.com/repos/FreeTubeApp/FreeTube | closed | [Bug]: [Wayland] PiP video is laggy when the main Freetube window is minimised | bug U: Waiting for Response from Author B: visual B: usability | ### Guidelines
- [X] I have encountered this bug in the [latest release of FreeTube](https://github.com/FreeTubeApp/FreeTube/releases).
- [X] I have searched the [issue tracker](https://github.com/FreeTubeApp/FreeTube/issues) for a bug report that matches the one I want to file, without success.
### Describe the bug
The video inside the picture in picture window lags when the main window is minimized. This does not happen when the main window is not minimized.
**How to reproduce?**
1. Launch Freetube under Wayland using `freetube --enable-features=UseOzonePlatform --ozone-platform=wayland`
2. Play a video.
3. Select Picture in picture mode.
4. Minimize the main window
5. The video in picture in picture lags as soon as we minimize the main Freetube window.
Here's the bug in action:
https://user-images.githubusercontent.com/32611672/152211552-a183b157-299f-45f5-b29a-b82a08a5c5a4.mp4
### Expected Behavior
The video in picture in picture should not lag even if the main window is minimized.
### Issue Labels
usability issue, visual bug
### FreeTube Version
v0.15.1 Beta
### Operating System Version
Arch Linux
### Installation Method (If applicable)
other
### Last Known Working FreeTube Version (If Any)
_No response_
### Primary API used
Local API
### Additional Information
_No response_
### Nightly Build
- [ ] I have encountered this bug in the latest [nightly build](https://docs.freetubeapp.io/development/nightly-builds). | True | [Bug]: [Wayland] PiP video is laggy when the main Freetube window is minimised - ### Guidelines
- [X] I have encountered this bug in the [latest release of FreeTube](https://github.com/FreeTubeApp/FreeTube/releases).
- [X] I have searched the [issue tracker](https://github.com/FreeTubeApp/FreeTube/issues) for a bug report that matches the one I want to file, without success.
### Describe the bug
The video inside the picture in picture window lags when the main window is minimized. This does not happen when the main window is not minimized.
**How to reproduce?**
1. Launch Freetube under Wayland using `freetube --enable-features=UseOzonePlatform --ozone-platform=wayland`
2. Play a video.
3. Select Picture in picture mode.
4. Minimize the main window
5. The video in picture in picture lags as soon as we minimize the main Freetube window.
Here's the bug in action:
https://user-images.githubusercontent.com/32611672/152211552-a183b157-299f-45f5-b29a-b82a08a5c5a4.mp4
### Expected Behavior
The video in picture in picture should not lag even if the main window is minimized.
### Issue Labels
usability issue, visual bug
### FreeTube Version
v0.15.1 Beta
### Operating System Version
Arch Linux
### Installation Method (If applicable)
other
### Last Known Working FreeTube Version (If Any)
_No response_
### Primary API used
Local API
### Additional Information
_No response_
### Nightly Build
- [ ] I have encountered this bug in the latest [nightly build](https://docs.freetubeapp.io/development/nightly-builds). | usab | pip video is laggy when the main freetube window is minimised guidelines i have encountered this bug in the i have searched the for a bug report that matches the one i want to file without success describe the bug the video inside the picture in picture window lags when the main window is minimized this does not happen when the main window is not minimized how to reproduce launch freetube under wayland using freetube enable features useozoneplatform ozone platform wayland play a video select picture in picture mode minimize the main window the video in picture in picture lags as soon as we minimize the main freetube window here s the bug in action expected behavior the video in picture in picture should not lag even if the main window is minimized issue labels usability issue visual bug freetube version beta operating system version arch linux installation method if applicable other last known working freetube version if any no response primary api used local api additional information no response nightly build i have encountered this bug in the latest | 1 |
25,386 | 25,110,742,955 | IssuesEvent | 2022-11-08 20:17:56 | accessibility-exchange/platform | https://api.github.com/repos/accessibility-exchange/platform | closed | Add the contrast options to the top navigation, so user can adjust the contrast even without an account and while browsing home pages. | bug accessibility and usability | Head tracker user had difficulty seeing the buttons in the default colour while creating an account. Once they created their account, they were not able to find the display preferences settings on their own. Having the contrast option up front will greatly help the navigation. | True | Add the contrast options to the top navigation, so user can adjust the contrast even without an account and while browsing home pages. - Head tracker user had difficulty seeing the buttons in the default colour while creating an account. Once they created their account, they were not able to find the display preferences settings on their own. Having the contrast option up front will greatly help the navigation. | usab | add the contrast options to the top navigation so user can adjust the contrast even without an account and while browsing home pages head tracker user had difficulty seeing the buttons in the default colour while creating an account once they created their account they were not able to find the display preferences settings on their own having the contrast option up front will greatly help the navigation | 1 |
1,949 | 3,025,601,761 | IssuesEvent | 2015-08-03 09:46:00 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 20962906: Confusing error message for closures that do not return value | classification:ui/usability reproducible:always status:open | #### Description
Summary:
Provide a descriptive summary of the issue.
Steps to Reproduce:
In numbered format, detail the exact steps taken to produce the bug.
See the gist https://gist.github.com/sforteln/e9fd7170a5126098af41
or attached playground for a full code example
The scenario this bug is about is the last one
/*
If the closure has statements in it but no
return you get the confusing error message :
Cannot invoke 'filterMap' with an argument list of type '((String) -> Int?)'
*/
let transformedNoReturn : [Int] = array.filterMap({
(data: String) -> Int? in
println("foo")
})
Expected Results:
Expected the error for the transformedNoReturn scenario to be the same as for transformedEmptyClosure that is "Missing return in a closure expected to return 'Int?'"
Actual Results:
the actual error message for the transformedEmptyClosure scenario is “Cannot invoke 'filterMap' with an argument list of type '((String) -> Int?)’”
Regression:
This always occurs both in Xcode and Playgrounds using Xcode 6.3.1 and Swift 1.2
Notes:
Provide additional information, such as references to related problems, workarounds and relevant attachments.
-
Product Version: Version 6.3.1 (6D1002) & Swift 1.2
Created: 2015-05-14T21:45:13.687710
Originated: 2015-05-14T14:40:00
Open Radar Link: http://www.openradar.me/20962906 | True | 20962906: Confusing error message for closures that do not return value - #### Description
Summary:
Provide a descriptive summary of the issue.
Steps to Reproduce:
In numbered format, detail the exact steps taken to produce the bug.
See the gist https://gist.github.com/sforteln/e9fd7170a5126098af41
or attached playground for a full code example
The scenario this bug is about is the last one
/*
If the closure has statements in it but no
return you get the confusing error message :
Cannot invoke 'filterMap' with an argument list of type '((String) -> Int?)'
*/
let transformedNoReturn : [Int] = array.filterMap({
(data: String) -> Int? in
println("foo")
})
Expected Results:
Expected the error for the transformedNoReturn scenario to be the same as for transformedEmptyClosure that is "Missing return in a closure expected to return 'Int?'"
Actual Results:
the actual error message for the transformedEmptyClosure scenario is “Cannot invoke 'filterMap' with an argument list of type '((String) -> Int?)’”
Regression:
This always occurs both in Xcode and Playgrounds using Xcode 6.3.1 and Swift 1.2
Notes:
Provide additional information, such as references to related problems, workarounds and relevant attachments.
-
Product Version: Version 6.3.1 (6D1002) & Swift 1.2
Created: 2015-05-14T21:45:13.687710
Originated: 2015-05-14T14:40:00
Open Radar Link: http://www.openradar.me/20962906 | usab | confusing error message for closures that do not return value description summary provide a descriptive summary of the issue steps to reproduce in numbered format detail the exact steps taken to produce the bug see the gist or attached playground for a full code example the scenario this bug is about is the last one if the closure has statements in it but no return you get the confusing error message cannot invoke filtermap with an argument list of type string int let transformednoreturn array filtermap data string int in println foo expected results expected the error for the transformednoreturn scenario to be the same as for transformedemptyclosure that is missing return in a closure expected to return int actual results the actual error message for the transformedemptyclosure scenario is “cannot invoke filtermap with an argument list of type string int ’” regression this always occurs both in xcode and playgrounds using xcode and swift notes provide additional information such as references to related problems workarounds and relevant attachments product version version swift created originated open radar link | 1 |
102,742 | 11,306,495,404 | IssuesEvent | 2020-01-18 14:32:33 | tidyverse/dplyr | https://api.github.com/repos/tidyverse/dplyr | opened | README needs updated list of backends | documentation tidy-dev-day :nerd_face: | Should go in its own subheading for scanability, and link to dbplyr and dtplyr (and data.table) | 1.0 | README needs updated list of backends - Should go in its own subheading for scanability, and link to dbplyr and dtplyr (and data.table) | non_usab | readme needs updated list of backends should go in its own subheading for scanability and link to dbplyr and dtplyr and data table | 0 |
4,446 | 3,869,598,692 | IssuesEvent | 2016-04-10 18:01:57 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 23319738: -[NSTableView setSortDescriptors:] should be null_resettable | classification:ui/usability reproducible:always status:open | #### Description
Summary:
I’ve been using -[NSTableView setSortDescriptors:nil] for years to reset a table view’s sort descriptors. It’s not attributed on 10.11, so it falls under the nonnull assumption and causes warnings in my code. It should be marked as null_resettable. This null-resetting is also undocumented, so the documentation should be updated accordingly.
-
Product Version: 10.11
Created: 2015-10-29T19:47:38.643830
Originated: 2015-10-29T15:47:00
Open Radar Link: http://www.openradar.me/23319738 | True | 23319738: -[NSTableView setSortDescriptors:] should be null_resettable - #### Description
Summary:
I’ve been using -[NSTableView setSortDescriptors:nil] for years to reset a table view’s sort descriptors. It’s not attributed on 10.11, so it falls under the nonnull assumption and causes warnings in my code. It should be marked as null_resettable. This null-resetting is also undocumented, so the documentation should be updated accordingly.
-
Product Version: 10.11
Created: 2015-10-29T19:47:38.643830
Originated: 2015-10-29T15:47:00
Open Radar Link: http://www.openradar.me/23319738 | usab | should be null resettable description summary i’ve been using for years to reset a table view’s sort descriptors it’s not attributed on so it falls under the nonnull assumption and causes warnings in my code it should be marked as null resettable this null resetting is also undocumented so the documentation should be updated accordingly product version created originated open radar link | 1 |
22,106 | 18,676,172,646 | IssuesEvent | 2021-10-31 15:49:41 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | opened | FORMAT `LineAsString` should be suitable for output | feature hacktoberfest usability | **Use case**
For symmetry reasons.
**Describe the solution you'd like**
The same as `TSVRaw`. | True | FORMAT `LineAsString` should be suitable for output - **Use case**
For symmetry reasons.
**Describe the solution you'd like**
The same as `TSVRaw`. | usab | format lineasstring should be suitable for output use case for symmetry reasons describe the solution you d like the same as tsvraw | 1 |
22,629 | 19,784,332,821 | IssuesEvent | 2022-01-18 03:37:19 | jstanden/cerb | https://api.github.com/repos/jstanden/cerb | opened | [Setup/Mail/Usability] Add Setup->Mail->Outgoing->Signatures | usability | Currently signatures can only be configured from the global search menu, and not the Setup->Mail->Outgoing section. | True | [Setup/Mail/Usability] Add Setup->Mail->Outgoing->Signatures - Currently signatures can only be configured from the global search menu, and not the Setup->Mail->Outgoing section. | usab | add setup mail outgoing signatures currently signatures can only be configured from the global search menu and not the setup mail outgoing section | 1 |
20,199 | 15,109,696,220 | IssuesEvent | 2021-02-08 18:11:38 | tailscale/tailscale | https://api.github.com/repos/tailscale/tailscale | closed | Support multiple accounts | L3 Some users P1 Nuisance T5 Minor usability enhancement | I have mutitple accounts for Tailscale and would like to use them in one client. Is there already a way to do it? | True | Support multiple accounts - I have mutitple accounts for Tailscale and would like to use them in one client. Is there already a way to do it? | usab | support multiple accounts i have mutitple accounts for tailscale and would like to use them in one client is there already a way to do it | 1 |
343 | 2,578,050,186 | IssuesEvent | 2015-02-12 20:44:44 | piwik/piwik | https://api.github.com/repos/piwik/piwik | closed | The SEO widget should be displayed even if when a http service calls fail | c: Usability Task | When building the SEO widget, we collect metrics from various web services eg. Google, microsoft, whois, etc. In some cases the HTTP calls can fail. For example Whois may be rate limited to 100 requests per hour.
Possible steps of this issue
1. investigate what possible limits are, check whether we can avoid them
2. check that errors are logged (as a warning maybe?)
3. that the SEO widget is displayed with the failed value as `-` or `Network error` (and other values displayed correctly).
follows up https://github.com/piwik/piwik/issues/7103 | True | The SEO widget should be displayed even if when a http service calls fail - When building the SEO widget, we collect metrics from various web services eg. Google, microsoft, whois, etc. In some cases the HTTP calls can fail. For example Whois may be rate limited to 100 requests per hour.
Possible steps of this issue
1. investigate what possible limits are, check whether we can avoid them
2. check that errors are logged (as a warning maybe?)
3. that the SEO widget is displayed with the failed value as `-` or `Network error` (and other values displayed correctly).
follows up https://github.com/piwik/piwik/issues/7103 | usab | the seo widget should be displayed even if when a http service calls fail when building the seo widget we collect metrics from various web services eg google microsoft whois etc in some cases the http calls can fail for example whois may be rate limited to requests per hour possible steps of this issue investigate what possible limits are check whether we can avoid them check that errors are logged as a warning maybe that the seo widget is displayed with the failed value as or network error and other values displayed correctly follows up | 1 |
7,089 | 4,771,713,785 | IssuesEvent | 2016-10-26 18:47:18 | globus/globus-cli | https://api.github.com/repos/globus/globus-cli | closed | Batch mode and paths? | enhancement error handling usability | Either
- forbid it by changing the guards for async-delete and async-transfer to accept only batch mode exclusive-or path
- make it so the path specified on the command line is prepended to each line of the batch input (which might have corner cases like path normalization issues)
Today, the path from the command line is thrown in with the paths input on the batch input, which is at best not helpful or at worst will lead to unexpected behavior. | True | Batch mode and paths? - Either
- forbid it by changing the guards for async-delete and async-transfer to accept only batch mode exclusive-or path
- make it so the path specified on the command line is prepended to each line of the batch input (which might have corner cases like path normalization issues)
Today, the path from the command line is thrown in with the paths input on the batch input, which is at best not helpful or at worst will lead to unexpected behavior. | usab | batch mode and paths either forbid it by changing the guards for async delete and async transfer to accept only batch mode exclusive or path make it so the path specified on the command line is prepended to each line of the batch input which might have corner cases like path normalization issues today the path from the command line is thrown in with the paths input on the batch input which is at best not helpful or at worst will lead to unexpected behavior | 1 |
294,551 | 9,036,831,330 | IssuesEvent | 2019-02-09 03:31:45 | tgstation/tgstation | https://api.github.com/repos/tgstation/tgstation | closed | Being unconscious while having the AI Multitool allows you to see around you. | Bug In Game Exploit Priority: High | Issue reported from Round ID: 101033 (/tg/Station Bagil [ENGLISH] [US-EAST] [100% FREE LAG])
Reporting client version: 512
I was unconscious in maintenance during the round, and decided to see if I could toggle any of my tools (as I always like finding weird edge case errors to report), and lo and behold upon clicking the toggle for the AI Multitool, the unconscious/blind overlay was removed, and replaced with the AI Multitool overlay that let me see everything around me while I was unconscious.
Before toggling it:

After toggling it:

The only reason for the second picture looking like it still limited my FOV is because I was in a dark area. | 1.0 | Being unconscious while having the AI Multitool allows you to see around you. - Issue reported from Round ID: 101033 (/tg/Station Bagil [ENGLISH] [US-EAST] [100% FREE LAG])
Reporting client version: 512
I was unconscious in maintenance during the round, and decided to see if I could toggle any of my tools (as I always like finding weird edge case errors to report), and lo and behold upon clicking the toggle for the AI Multitool, the unconscious/blind overlay was removed, and replaced with the AI Multitool overlay that let me see everything around me while I was unconscious.
Before toggling it:

After toggling it:

The only reason for the second picture looking like it still limited my FOV is because I was in a dark area. | non_usab | being unconscious while having the ai multitool allows you to see around you issue reported from round id tg station bagil reporting client version i was unconscious in maintenance during the round and decided to see if i could toggle any of my tools as i always like finding weird edge case errors to report and lo and behold upon clicking the toggle for the ai multitool the unconscious blind overlay was removed and replaced with the ai multitool overlay that let me see everything around me while i was unconscious before toggling it after toggling it the only reason for the second picture looking like it still limited my fov is because i was in a dark area | 0 |
12,888 | 8,149,827,355 | IssuesEvent | 2018-08-22 10:54:43 | apinf/platform | https://api.github.com/repos/apinf/platform | closed | For Filtering APIs in Organization profile and API catalog, users should be able to choose more than one lifecycle status | Usability Issue icebox | _From @Nazarah on January 26, 2017 16:46_
# Usability Issue
Right now, the filtering option has the lifecycle statuses of API as dropmenu. User is able to select only one status type from there. User might wish to filter APIs connected to an organization / API catalog with more than one lifecycle status.

# Suggestion
Make the drop menu option selection such that user is able to select more than one life cycle status.
Checked lifecycle statues can appear on the filter pane as tags (e.g. using bootstrap tags)

_Copied from original issue: Digipalvelutehdas/APIKA#306_ | True | For Filtering APIs in Organization profile and API catalog, users should be able to choose more than one lifecycle status - _From @Nazarah on January 26, 2017 16:46_
# Usability Issue
Right now, the filtering option has the lifecycle statuses of API as dropmenu. User is able to select only one status type from there. User might wish to filter APIs connected to an organization / API catalog with more than one lifecycle status.

# Suggestion
Make the drop menu option selection such that user is able to select more than one life cycle status.
Checked lifecycle statues can appear on the filter pane as tags (e.g. using bootstrap tags)

_Copied from original issue: Digipalvelutehdas/APIKA#306_ | usab | for filtering apis in organization profile and api catalog users should be able to choose more than one lifecycle status from nazarah on january usability issue right now the filtering option has the lifecycle statuses of api as dropmenu user is able to select only one status type from there user might wish to filter apis connected to an organization api catalog with more than one lifecycle status suggestion make the drop menu option selection such that user is able to select more than one life cycle status checked lifecycle statues can appear on the filter pane as tags e g using bootstrap tags copied from original issue digipalvelutehdas apika | 1 |
17,011 | 11,570,820,480 | IssuesEvent | 2020-02-20 20:15:27 | statamic/cms | https://api.github.com/repos/statamic/cms | closed | Missing "Create Entry" button when a collection doesn't have a blueprint defined | usability | It looks like only after creating the first collection (from 0 to 1) are no buttons displayed.
### Steps to reproduce
1. Start with a brand new installation via composer, make:user, CP login
2. Create a collection
There are no 'Create Entry' buttons visible.
3. Create another collection
'Create Entry' buttons are visible on both collections.
4. Delete one collection
'Create Entry' buttons are still visible.
5. Delete the second collection too.
6. Create a new collection again
There are again no 'Create Entry' buttons visible.
<img width="1427" alt="Bildschirmfoto 2020-01-21 um 00 12 02" src="https://user-images.githubusercontent.com/8265902/72763454-25bdcf00-3be4-11ea-9d2d-dedb36de647f.png">
| True | Missing "Create Entry" button when a collection doesn't have a blueprint defined - It looks like only after creating the first collection (from 0 to 1) are no buttons displayed.
### Steps to reproduce
1. Start with a brand new installation via composer, make:user, CP login
2. Create a collection
There are no 'Create Entry' buttons visible.
3. Create another collection
'Create Entry' buttons are visible on both collections.
4. Delete one collection
'Create Entry' buttons are still visible.
5. Delete the second collection too.
6. Create a new collection again
There are again no 'Create Entry' buttons visible.
<img width="1427" alt="Bildschirmfoto 2020-01-21 um 00 12 02" src="https://user-images.githubusercontent.com/8265902/72763454-25bdcf00-3be4-11ea-9d2d-dedb36de647f.png">
| usab | missing create entry button when a collection doesn t have a blueprint defined it looks like only after creating the first collection from to are no buttons displayed steps to reproduce start with a brand new installation via composer make user cp login create a collection there are no create entry buttons visible create another collection create entry buttons are visible on both collections delete one collection create entry buttons are still visible delete the second collection too create a new collection again there are again no create entry buttons visible img width alt bildschirmfoto um src | 1 |
14,733 | 9,458,647,633 | IssuesEvent | 2019-04-17 06:11:46 | AhKi/oh-my-desk | https://api.github.com/repos/AhKi/oh-my-desk | closed | Should controllers be used in the main process? | Improved usability refactoring | ## Description
We use [Controller](https://github.com/AhKi/oh-my-desk/blob/develop%2F1.2.0/app/main/README.md#controllers) in main process.
I thought that we may not have to use it.
### Why are we using a Controller?
Electron is separated section about main and renderer. Some Electron method must be used in main process, not renderer process. If we execute it in renderer process, It make error!
### What does the controller do?
Controller locate in main process. It is subscribing action type and run side-effect matched action type that dispatched.
**Should controllers be used in the main process?**
**Is there a good way to replace a controller?**
| True | Should controllers be used in the main process? - ## Description
We use [Controller](https://github.com/AhKi/oh-my-desk/blob/develop%2F1.2.0/app/main/README.md#controllers) in main process.
I thought that we may not have to use it.
### Why are we using a Controller?
Electron is separated section about main and renderer. Some Electron method must be used in main process, not renderer process. If we execute it in renderer process, It make error!
### What does the controller do?
Controller locate in main process. It is subscribing action type and run side-effect matched action type that dispatched.
**Should controllers be used in the main process?**
**Is there a good way to replace a controller?**
| usab | should controllers be used in the main process description we use in main process i thought that we may not have to use it why are we using a controller electron is separated section about main and renderer some electron method must be used in main process not renderer process if we execute it in renderer process it make error what does the controller do controller locate in main process it is subscribing action type and run side effect matched action type that dispatched should controllers be used in the main process is there a good way to replace a controller | 1 |
147,699 | 11,801,616,682 | IssuesEvent | 2020-03-18 19:49:21 | ansible/awx | https://api.github.com/repos/ansible/awx | closed | JOB TYPE or VERBOSITY is not seen at job template detail view | component:ui priority:medium state:needs_test type:bug | ##### ISSUE TYPE
- Bug Report
##### SUMMARY
UI bug. At job template detail view, one of items 'JOB TYPE' and 'VERBOSITY' is not seen. Just blank. After refresh, it shows or the other is not seen. For example, if JOB TYPE was not seen first, after refresh sometimes VERBOSITY is not seen.
##### ENVIRONMENT
* AWX version: 9.2.0
* AWX install method: docker on linux
* Ansible version: 2.9.3
* Operating System: Centos 7.7.1908
* Web Browser: Chrome
##### STEPS TO REPRODUCE
1. Register some job templates with all mandatory items selected.
2. Click sequentially each job templates to see details
3. One of job templates detail view is seen with this bug.
##### EXPECTED RESULTS
All items must be seen what I have selected.
##### ACTUAL RESULTS
Item 'JOB TYPE' or 'VERBOSITY' is not seen sometimes.
##### ADDITIONAL INFORMATION
| 1.0 | JOB TYPE or VERBOSITY is not seen at job template detail view - ##### ISSUE TYPE
- Bug Report
##### SUMMARY
UI bug. At job template detail view, one of items 'JOB TYPE' and 'VERBOSITY' is not seen. Just blank. After refresh, it shows or the other is not seen. For example, if JOB TYPE was not seen first, after refresh sometimes VERBOSITY is not seen.
##### ENVIRONMENT
* AWX version: 9.2.0
* AWX install method: docker on linux
* Ansible version: 2.9.3
* Operating System: Centos 7.7.1908
* Web Browser: Chrome
##### STEPS TO REPRODUCE
1. Register some job templates with all mandatory items selected.
2. Click sequentially each job templates to see details
3. One of job templates detail view is seen with this bug.
##### EXPECTED RESULTS
All items must be seen what I have selected.
##### ACTUAL RESULTS
Item 'JOB TYPE' or 'VERBOSITY' is not seen sometimes.
##### ADDITIONAL INFORMATION
| non_usab | job type or verbosity is not seen at job template detail view issue type bug report summary ui bug at job template detail view one of items job type and verbosity is not seen just blank after refresh it shows or the other is not seen for example if job type was not seen first after refresh sometimes verbosity is not seen environment awx version awx install method docker on linux ansible version operating system centos web browser chrome steps to reproduce register some job templates with all mandatory items selected click sequentially each job templates to see details one of job templates detail view is seen with this bug expected results all items must be seen what i have selected actual results item job type or verbosity is not seen sometimes additional information | 0 |
10,359 | 6,677,368,145 | IssuesEvent | 2017-10-05 10:09:37 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | The default new project path doesn't match the default drive in Windows | bug platform:windows topic:editor usability | **Operating system or device, Godot version, GPU Model and driver (if graphics related):**
Windows 7 64bit, Godot ef08228 (tools.32)
**Issue description:**
By default, when I'm creating a project, I see this:

The default path is on C:\ drive, but the drive selected is D: (Godot executable is on D:\).
If I want to browse D:\ then, I need to first select C: in the right drop-down menu, and then D: again
**Steps to reproduce:**
Start Godot, choose "New Project"
| True | The default new project path doesn't match the default drive in Windows - **Operating system or device, Godot version, GPU Model and driver (if graphics related):**
Windows 7 64bit, Godot ef08228 (tools.32)
**Issue description:**
By default, when I'm creating a project, I see this:

The default path is on C:\ drive, but the drive selected is D: (Godot executable is on D:\).
If I want to browse D:\ then, I need to first select C: in the right drop-down menu, and then D: again
**Steps to reproduce:**
Start Godot, choose "New Project"
| usab | the default new project path doesn t match the default drive in windows operating system or device godot version gpu model and driver if graphics related windows godot tools issue description by default when i m creating a project i see this the default path is on c drive but the drive selected is d godot executable is on d if i want to browse d then i need to first select c in the right drop down menu and then d again steps to reproduce start godot choose new project | 1 |
15,259 | 2,850,503,763 | IssuesEvent | 2015-05-31 16:45:57 | damonkohler/sl4a | https://api.github.com/repos/damonkohler/sl4a | opened | Compile/run errors are hidden | auto-migrated Priority-Medium Type-Defect | _From @GoogleCodeExporter on May 31, 2015 11:31_
```
What device(s) are you experiencing the problem on?
Iconia Tab A200
What firmware version are you running on the device?
Cyanogenmod 9 (Android 4.0)
What steps will reproduce the problem?
1. Write a Lua script containing any syntax error or throwing an error at
runtime (e.g. with error()).
2. Attempt to run it.
3. Stare blankly.
What is the expected output? What do you see instead?
Expect to see some explanation of the error, instead see nothing.
What version of the product are you using? On what operating system?
SL4A r5, Lua interpreter r1 on Android.
Please provide any additional information below.
```
Original issue reported on code.google.com by `hyperhac...@gmail.com` on 6 Jul 2012 at 2:40
_Copied from original issue: damonkohler/android-scripting#639_ | 1.0 | Compile/run errors are hidden - _From @GoogleCodeExporter on May 31, 2015 11:31_
```
What device(s) are you experiencing the problem on?
Iconia Tab A200
What firmware version are you running on the device?
Cyanogenmod 9 (Android 4.0)
What steps will reproduce the problem?
1. Write a Lua script containing any syntax error or throwing an error at
runtime (e.g. with error()).
2. Attempt to run it.
3. Stare blankly.
What is the expected output? What do you see instead?
Expect to see some explanation of the error, instead see nothing.
What version of the product are you using? On what operating system?
SL4A r5, Lua interpreter r1 on Android.
Please provide any additional information below.
```
Original issue reported on code.google.com by `hyperhac...@gmail.com` on 6 Jul 2012 at 2:40
_Copied from original issue: damonkohler/android-scripting#639_ | non_usab | compile run errors are hidden from googlecodeexporter on may what device s are you experiencing the problem on iconia tab what firmware version are you running on the device cyanogenmod android what steps will reproduce the problem write a lua script containing any syntax error or throwing an error at runtime e g with error attempt to run it stare blankly what is the expected output what do you see instead expect to see some explanation of the error instead see nothing what version of the product are you using on what operating system lua interpreter on android please provide any additional information below original issue reported on code google com by hyperhac gmail com on jul at copied from original issue damonkohler android scripting | 0 |
17,781 | 12,334,943,247 | IssuesEvent | 2020-05-14 11:05:46 | DMPRoadmap/roadmap | https://api.github.com/repos/DMPRoadmap/roadmap | closed | Employ designer for layout of Usage page | admin usability | Please complete the following fields as applicable:
Usage page is an important one for org admins. The overall design is very poor. We added new features, new reports and inserted new buttons for them wherever we could easily fit them on the screen at the time, which is understandable. We need to re-order items on the screen too 'download global statistics' is a very prominent top right whereas the main purpose of the page is intended for org statistics (and this makes people wonder what 'global' means in this context). This will require some development work to implement the design. I could take the lead on this by approaching a designer. A designer could also advise on how to position and display the plan per template chart.
**Expected behaviour:**
Usage page should be more user friendly and look more like the rest of the screens - plans, templates, guidance.
**Actual behaviour:**
Page has grown organically, with elements added to it as and when completed.
**Steps to reproduce:**
View Usage page and compare against various screens - Users, Plans, Templates, Guidance.
| True | Employ designer for layout of Usage page - Please complete the following fields as applicable:
Usage page is an important one for org admins. The overall design is very poor. We added new features, new reports and inserted new buttons for them wherever we could easily fit them on the screen at the time, which is understandable. We need to re-order items on the screen too 'download global statistics' is a very prominent top right whereas the main purpose of the page is intended for org statistics (and this makes people wonder what 'global' means in this context). This will require some development work to implement the design. I could take the lead on this by approaching a designer. A designer could also advise on how to position and display the plan per template chart.
**Expected behaviour:**
Usage page should be more user friendly and look more like the rest of the screens - plans, templates, guidance.
**Actual behaviour:**
Page has grown organically, with elements added to it as and when completed.
**Steps to reproduce:**
View Usage page and compare against various screens - Users, Plans, Templates, Guidance.
| usab | employ designer for layout of usage page please complete the following fields as applicable usage page is an important one for org admins the overall design is very poor we added new features new reports and inserted new buttons for them wherever we could easily fit them on the screen at the time which is understandable we need to re order items on the screen too download global statistics is a very prominent top right whereas the main purpose of the page is intended for org statistics and this makes people wonder what global means in this context this will require some development work to implement the design i could take the lead on this by approaching a designer a designer could also advise on how to position and display the plan per template chart expected behaviour usage page should be more user friendly and look more like the rest of the screens plans templates guidance actual behaviour page has grown organically with elements added to it as and when completed steps to reproduce view usage page and compare against various screens users plans templates guidance | 1 |
170,279 | 20,842,103,168 | IssuesEvent | 2022-03-21 02:16:52 | turkdevops/angular-cli | https://api.github.com/repos/turkdevops/angular-cli | opened | CVE-2021-44906 (High) detected in minimist-0.0.10.tgz | security vulnerability | ## CVE-2021-44906 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /integration/angular_cli/package.json</p>
<p>Path to vulnerable library: /integration/angular_cli/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- protractor-5.4.3.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-44906">https://nvd.nist.gov/vuln/detail/CVE-2021-44906</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-44906 (High) detected in minimist-0.0.10.tgz - ## CVE-2021-44906 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /integration/angular_cli/package.json</p>
<p>Path to vulnerable library: /integration/angular_cli/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- protractor-5.4.3.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-44906">https://nvd.nist.gov/vuln/detail/CVE-2021-44906</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | cve high detected in minimist tgz cve high severity vulnerability vulnerable library minimist tgz parse argument options library home page a href path to dependency file integration angular cli package json path to vulnerable library integration angular cli node modules minimist package json dependency hierarchy protractor tgz root library optimist tgz x minimist tgz vulnerable library found in base branch master vulnerability details minimist is vulnerable to prototype pollution via file index js function setkey lines publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bumperlane public service contracts prerelease cloudscribe templates virteom tenant mobile bluetooth prerelease showingvault dotnet sdk prerelease envisia dotnet templates yarnpkg yarn virteom tenant mobile framework uwp prerelease virteom tenant mobile framework ios prerelease bumperlane public api clientmodule prerelease vuejs netcore dianoga virteom tenant mobile bluetooth ios prerelease virteom public utilities prerelease indianadavy vuejswebapitemplate csharp nordron angulartemplate virteom tenant mobile framework prerelease virteom tenant mobile bluetooth android prerelease dotnet scaffold raml parser corevuewebtest dotnetng template sitecoremaster truedynamicplaceholders virteom tenant mobile framework android prerelease fable template elmish react blazorpolyfill build fable snowpack template bumperlane public api client prerelease yarn msbuild blazor tailwindcss bunit bridge aws tslint safe template gr pagerender razor midiator webclient step up your open source security game with whitesource | 0 |
47,323 | 19,597,349,761 | IssuesEvent | 2022-01-05 19:35:24 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | TDS Case Attachments - Make Editable | Impact: 2-Major Service: Apps Type: Enhancement Workgroup: TDS Product: TDS Portal Project: TDR | Development Reviews | ### Users need to edit attachments after saving them.
_Currently the # 3 priority for TDS_
 | 1.0 | TDS Case Attachments - Make Editable - ### Users need to edit attachments after saving them.
_Currently the # 3 priority for TDS_
 | non_usab | tds case attachments make editable users need to edit attachments after saving them currently the priority for tds | 0 |
83,965 | 24,181,280,288 | IssuesEvent | 2022-09-23 09:08:12 | google/mediapipe | https://api.github.com/repos/google/mediapipe | closed | Coral Support - Bazel Setup :ERROR: Skipping 'build': no such target '//:build' | status:duplicate type:build/install platform:desktop solution:face detection platform:coral | <em>Please make sure that this is a build/installation issue and also refer to the [troubleshooting](https://google.github.io/mediapipe/getting_started/troubleshooting.html) documentation before raising any issues.</em>
**System information** (Please provide as much relevant information as possible)
- OS Platform and Distribution (e.g. Linux Ubuntu 16.04, Android 11, iOS 14.4): ubuntu
- Compiler version (e.g. gcc/g++ 8 /Apple clang version 12.0.0):
- Programming Language and version ( e.g. C++ 14, Python 3.6, Java ):
- Installed using virtualenv? pip? Conda? (if python):
- [MediaPipe version](https://github.com/google/mediapipe/releases):
- Bazel version: 5.2.0
- XCode and Tulsi versions (if iOS):
- Android SDK and NDK versions (if android):
- Android [AAR](https://google.github.io/mediapipe/getting_started/android_archive_library.html) ( if android):
- OpenCV version (if running on desktop):
**Describe the problem**:
i have basel 5.2.0 version and ran mediapipe edgtpu demo
`indeed@indeed-virtual-machine:~/Desktop/mediapipe-master$ ls`
indeed@indeed-virtual-machine:~/Desktop/mediapipe-master$ ls
build_android_examples.sh build_desktop_examples.sh CONTRIBUTING.md docs MANIFEST.in README.md setup_android_sdk_and_ndk.sh setup.py WORKSPACE
BUILD.bazel build_ios_examples.sh Dockerfile LICENSE mediapipe requirements.txt setup_opencv.sh third_party
`indeed@indeed-virtual-machine:~/Desktop/mediapipe-master$ bazel version`
Build label: 5.2.0
Build target: bazel-out/k8-opt/bin/src/main/java/com/google/devtools/build/lib/bazel/BazelServer_deploy.jar
Build time: Tue Jun 7 16:02:26 2022 (1654617746)
Build timestamp: 1654617746
Build timestamp as int: 1654617746
my scripts strictly follow the readme.md here:
[Coral Support - Bazel Setup](https://github.com/google/mediapipe/tree/master/mediapipe/examples/coral)
`indeed@indeed-virtual-machine:~/Desktop/mediapipe-master$ bazel build --compilation_mode=opt --define darwinn_portable=1 --define MEDIAPIPE_DISABLE_GPU=1 --define MEDIAPIPE_EDGE_TPU=usb --linkopt=-l:libusb-1.0.so mediapipe/examples/coral:face_detection_tpu build`
I received an error of bazel build
indeed@indeed-virtual-machine:~/Desktop/mediapipe-master$ bazel build --compilation_mode=opt --define darwinn_portable=1 --define MEDIAPIPE_DISABLE_GPU=1 --define MEDIAPIPE_EDGE_TPU=usb --linkopt=-l:libusb-1.0.so mediapipe/examples/coral:face_detection_tpu build
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'com_google_absl' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'com_google_benchmark' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'pybind11_bazel' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'com_google_protobuf' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'com_google_googletest' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'com_github_gflags_gflags' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'build_bazel_rules_apple' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'build_bazel_rules_swift' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'build_bazel_apple_support' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'xctestrunner' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'pybind11' because it already exists.
ERROR: Skipping 'build': no such target '//:build': target 'build' not declared in package '' defined by /home/indeed/Desktop/mediapipe-master/BUILD.bazel
ERROR: no such target '//:build': target 'build' not declared in package '' defined by /home/indeed/Desktop/mediapipe-master/BUILD.bazel
INFO: Elapsed time: 0.341s
INFO: 0 processes.
FAILED: Build did NOT complete successfully (0 packages loaded)
**[Provide the exact sequence of commands / steps that you executed before running into the problem](https://google.github.io/mediapipe/getting_started/getting_started.html):**
**Complete Logs:**
Include Complete Log information or source code that would be helpful to diagnose the problem. If including tracebacks, please include the full traceback. Large logs and files should be attached:
| 1.0 | Coral Support - Bazel Setup :ERROR: Skipping 'build': no such target '//:build' - <em>Please make sure that this is a build/installation issue and also refer to the [troubleshooting](https://google.github.io/mediapipe/getting_started/troubleshooting.html) documentation before raising any issues.</em>
**System information** (Please provide as much relevant information as possible)
- OS Platform and Distribution (e.g. Linux Ubuntu 16.04, Android 11, iOS 14.4): ubuntu
- Compiler version (e.g. gcc/g++ 8 /Apple clang version 12.0.0):
- Programming Language and version ( e.g. C++ 14, Python 3.6, Java ):
- Installed using virtualenv? pip? Conda? (if python):
- [MediaPipe version](https://github.com/google/mediapipe/releases):
- Bazel version: 5.2.0
- XCode and Tulsi versions (if iOS):
- Android SDK and NDK versions (if android):
- Android [AAR](https://google.github.io/mediapipe/getting_started/android_archive_library.html) ( if android):
- OpenCV version (if running on desktop):
**Describe the problem**:
i have basel 5.2.0 version and ran mediapipe edgtpu demo
`indeed@indeed-virtual-machine:~/Desktop/mediapipe-master$ ls`
indeed@indeed-virtual-machine:~/Desktop/mediapipe-master$ ls
build_android_examples.sh build_desktop_examples.sh CONTRIBUTING.md docs MANIFEST.in README.md setup_android_sdk_and_ndk.sh setup.py WORKSPACE
BUILD.bazel build_ios_examples.sh Dockerfile LICENSE mediapipe requirements.txt setup_opencv.sh third_party
`indeed@indeed-virtual-machine:~/Desktop/mediapipe-master$ bazel version`
Build label: 5.2.0
Build target: bazel-out/k8-opt/bin/src/main/java/com/google/devtools/build/lib/bazel/BazelServer_deploy.jar
Build time: Tue Jun 7 16:02:26 2022 (1654617746)
Build timestamp: 1654617746
Build timestamp as int: 1654617746
my scripts strictly follow the readme.md here:
[Coral Support - Bazel Setup](https://github.com/google/mediapipe/tree/master/mediapipe/examples/coral)
`indeed@indeed-virtual-machine:~/Desktop/mediapipe-master$ bazel build --compilation_mode=opt --define darwinn_portable=1 --define MEDIAPIPE_DISABLE_GPU=1 --define MEDIAPIPE_EDGE_TPU=usb --linkopt=-l:libusb-1.0.so mediapipe/examples/coral:face_detection_tpu build`
I received an error of bazel build
indeed@indeed-virtual-machine:~/Desktop/mediapipe-master$ bazel build --compilation_mode=opt --define darwinn_portable=1 --define MEDIAPIPE_DISABLE_GPU=1 --define MEDIAPIPE_EDGE_TPU=usb --linkopt=-l:libusb-1.0.so mediapipe/examples/coral:face_detection_tpu build
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'com_google_absl' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'com_google_benchmark' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'pybind11_bazel' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'com_google_protobuf' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'com_google_googletest' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'com_github_gflags_gflags' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'build_bazel_rules_apple' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'build_bazel_rules_swift' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'build_bazel_apple_support' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'xctestrunner' because it already exists.
DEBUG: /home/indeed/.cache/bazel/_bazel_indeed/8841f98192e74cc58dc35ba42db474f7/external/org_tensorflow/third_party/repo.bzl:124:14:
Warning: skipping import of repository 'pybind11' because it already exists.
ERROR: Skipping 'build': no such target '//:build': target 'build' not declared in package '' defined by /home/indeed/Desktop/mediapipe-master/BUILD.bazel
ERROR: no such target '//:build': target 'build' not declared in package '' defined by /home/indeed/Desktop/mediapipe-master/BUILD.bazel
INFO: Elapsed time: 0.341s
INFO: 0 processes.
FAILED: Build did NOT complete successfully (0 packages loaded)
**[Provide the exact sequence of commands / steps that you executed before running into the problem](https://google.github.io/mediapipe/getting_started/getting_started.html):**
**Complete Logs:**
Include Complete Log information or source code that would be helpful to diagnose the problem. If including tracebacks, please include the full traceback. Large logs and files should be attached:
| non_usab | coral support bazel setup error skipping build no such target build please make sure that this is a build installation issue and also refer to the documentation before raising any issues system information please provide as much relevant information as possible os platform and distribution e g linux ubuntu android ios ubuntu compiler version e g gcc g apple clang version programming language and version e g c python java installed using virtualenv pip conda if python bazel version xcode and tulsi versions if ios android sdk and ndk versions if android android if android opencv version if running on desktop describe the problem i have basel version and ran mediapipe edgtpu demo indeed indeed virtual machine desktop mediapipe master ls indeed indeed virtual machine desktop mediapipe master ls build android examples sh build desktop examples sh contributing md docs manifest in readme md setup android sdk and ndk sh setup py workspace build bazel build ios examples sh dockerfile license mediapipe requirements txt setup opencv sh third party indeed indeed virtual machine desktop mediapipe master bazel version build label build target bazel out opt bin src main java com google devtools build lib bazel bazelserver deploy jar build time tue jun build timestamp build timestamp as int my scripts strictly follow the readme md here indeed indeed virtual machine desktop mediapipe master bazel build compilation mode opt define darwinn portable define mediapipe disable gpu define mediapipe edge tpu usb linkopt l libusb so mediapipe examples coral face detection tpu build i received an error of bazel build indeed indeed virtual machine desktop mediapipe master bazel build compilation mode opt define darwinn portable define mediapipe disable gpu define mediapipe edge tpu usb linkopt l libusb so mediapipe examples coral face detection tpu build debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository com google absl because it already exists debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository com google benchmark because it already exists debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository bazel because it already exists debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository com google protobuf because it already exists debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository com google googletest because it already exists debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository com github gflags gflags because it already exists debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository build bazel rules apple because it already exists debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository build bazel rules swift because it already exists debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository build bazel apple support because it already exists debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository xctestrunner because it already exists debug home indeed cache bazel bazel indeed external org tensorflow third party repo bzl warning skipping import of repository because it already exists error skipping build no such target build target build not declared in package defined by home indeed desktop mediapipe master build bazel error no such target build target build not declared in package defined by home indeed desktop mediapipe master build bazel info elapsed time info processes failed build did not complete successfully packages loaded complete logs include complete log information or source code that would be helpful to diagnose the problem if including tracebacks please include the full traceback large logs and files should be attached | 0 |
750,834 | 26,220,450,229 | IssuesEvent | 2023-01-04 14:27:57 | gamefreedomgit/Maelstrom | https://api.github.com/repos/gamefreedomgit/Maelstrom | closed | [Quest] Exodus (another gate that takes long time to open) | Gameobject Quest - Cataclysm (1-60) Pathfinding Priority: Medium Status: Confirmed | Quest ID - 24438
How it works
--------------------
After boarding stagecoach taxi, you are brought to another gate with a similar issue as my last ticket (it takes forever to open and you are sitting there infront of it for 2+ minutes. It eventually opens but it should not take this time.
How it works
--------------------
As stagecoach pulls up to the gate, it should open promptly, and complete the taxi ride.
https://i.imgur.com/1VNqGmq.png | 1.0 | [Quest] Exodus (another gate that takes long time to open) - Quest ID - 24438
How it works
--------------------
After boarding stagecoach taxi, you are brought to another gate with a similar issue as my last ticket (it takes forever to open and you are sitting there infront of it for 2+ minutes. It eventually opens but it should not take this time.
How it works
--------------------
As stagecoach pulls up to the gate, it should open promptly, and complete the taxi ride.
https://i.imgur.com/1VNqGmq.png | non_usab | exodus another gate that takes long time to open quest id how it works after boarding stagecoach taxi you are brought to another gate with a similar issue as my last ticket it takes forever to open and you are sitting there infront of it for minutes it eventually opens but it should not take this time how it works as stagecoach pulls up to the gate it should open promptly and complete the taxi ride | 0 |
13,188 | 8,359,874,745 | IssuesEvent | 2018-10-03 09:40:12 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Godot 3.1 alpha animator doesn't automatically move to a newer frame | bug topic:editor usability | Hi, I'm using an animated sprite being animated in the animationplayer node, but everytime I click on Setting up a frame as a keyframe it doesn't automatically move to a newer frame, I'm wondering why Godot devs removed this functionality if it worked like that in 2.1 and 3.0 | True | Godot 3.1 alpha animator doesn't automatically move to a newer frame - Hi, I'm using an animated sprite being animated in the animationplayer node, but everytime I click on Setting up a frame as a keyframe it doesn't automatically move to a newer frame, I'm wondering why Godot devs removed this functionality if it worked like that in 2.1 and 3.0 | usab | godot alpha animator doesn t automatically move to a newer frame hi i m using an animated sprite being animated in the animationplayer node but everytime i click on setting up a frame as a keyframe it doesn t automatically move to a newer frame i m wondering why godot devs removed this functionality if it worked like that in and | 1 |
126,076 | 12,281,449,227 | IssuesEvent | 2020-05-08 15:52:38 | euro-cordex/cordex | https://api.github.com/repos/euro-cordex/cordex | closed | add all cordex high res domains (0.11) | documentation help wanted | we should update the cordex tables with the 0.11 resolution according to EUR-11. | 1.0 | add all cordex high res domains (0.11) - we should update the cordex tables with the 0.11 resolution according to EUR-11. | non_usab | add all cordex high res domains we should update the cordex tables with the resolution according to eur | 0 |
24,836 | 24,354,904,542 | IssuesEvent | 2022-10-03 06:21:07 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | closed | Deleting and "nuking" users as a site admin has scary usability | ux usability team/iam | ## The problem
In the user management section of site admin (`/site-admin-users`), we have two actions available:
- Delete user (soft delete)
- Nuke user (hard delete)
These are presented with almost-equal button styling:
<img width="273" alt="Screenshot 2020-11-20 at 17 22 28" src="https://user-images.githubusercontent.com/6304497/99823694-f7d34f00-2b54-11eb-843e-1353d8c494ef.png">
The tooltip for nuking a user is **terrifying** usability-wise:
<img width="318" alt="Screenshot 2020-11-20 at 17 19 52" src="https://user-images.githubusercontent.com/6304497/99823385-9ca15c80-2b54-11eb-93d0-ed5f94f3c1ad.png">
When the user clicks the either the "Delete user" or "Nuke user" button, they're presented with a browser alert to confirm:
<img width="400" src="https://user-images.githubusercontent.com/6304497/99823469-b93d9480-2b54-11eb-93d9-23e28caa0385.png">
We should improve this flow so it's less terrifying and more clear, and honestly, more sensitive.
## Proposed changes
First, I strongly recommend changing the name of these actions for clarity and sensitivity.
- ~Delete~ **Deactivate**
- ~Nuke~ **Delete**
_(Note: I understand that the implementation for soft delete almost certainly relies on a field like `deleted_at` or a `deleted_users` table, so renaming it to "Deactivate" can introduce incongruity, but this copy is user-facing while our database terminology is internal, so user-facing clarity wins out.)_
Second, we should update the buttons to communicate these actions more clearly. Since the rows in the UI are already quite packed, there's two options here, one quick and one a bit more involved.
**The quick approach**: We replace the "Delete" button with a secondary button style with red text and a text label, and we replace the "nuke" icon with the trash can icon.
<img width="356" alt="Screenshot 2020-11-20 at 17 25 43" src="https://user-images.githubusercontent.com/6304497/99824263-ca3ad580-2b55-11eb-92e1-a6fd3458e963.png">
**The more involved approach**: We redesign the rows to better accommodate the content without using buttons for everything.
Third, we should replace the browser alert with our own modal with more purposeful copy that follows our [actionable language guidelines](https://about.sourcegraph.com/handbook/communication/content_guidelines/actionable_language#confirmation-messages), like so:
<img width="1200" alt="Screenshot 2020-11-20 at 17 54 29" src="https://user-images.githubusercontent.com/6304497/99827047-716d3c00-2b59-11eb-9076-5675ec065769.png">
Finally, I'd also submit a PR to update language on the docs page for [user data deletion](https://github.com/sourcegraph/sourcegraph/blob/main/doc/admin/user_data_deletion.md) to align all content.
Thanks @flying-robot for flagging this issue and talking through it! | True | Deleting and "nuking" users as a site admin has scary usability - ## The problem
In the user management section of site admin (`/site-admin-users`), we have two actions available:
- Delete user (soft delete)
- Nuke user (hard delete)
These are presented with almost-equal button styling:
<img width="273" alt="Screenshot 2020-11-20 at 17 22 28" src="https://user-images.githubusercontent.com/6304497/99823694-f7d34f00-2b54-11eb-843e-1353d8c494ef.png">
The tooltip for nuking a user is **terrifying** usability-wise:
<img width="318" alt="Screenshot 2020-11-20 at 17 19 52" src="https://user-images.githubusercontent.com/6304497/99823385-9ca15c80-2b54-11eb-93d0-ed5f94f3c1ad.png">
When the user clicks the either the "Delete user" or "Nuke user" button, they're presented with a browser alert to confirm:
<img width="400" src="https://user-images.githubusercontent.com/6304497/99823469-b93d9480-2b54-11eb-93d9-23e28caa0385.png">
We should improve this flow so it's less terrifying and more clear, and honestly, more sensitive.
## Proposed changes
First, I strongly recommend changing the name of these actions for clarity and sensitivity.
- ~Delete~ **Deactivate**
- ~Nuke~ **Delete**
_(Note: I understand that the implementation for soft delete almost certainly relies on a field like `deleted_at` or a `deleted_users` table, so renaming it to "Deactivate" can introduce incongruity, but this copy is user-facing while our database terminology is internal, so user-facing clarity wins out.)_
Second, we should update the buttons to communicate these actions more clearly. Since the rows in the UI are already quite packed, there's two options here, one quick and one a bit more involved.
**The quick approach**: We replace the "Delete" button with a secondary button style with red text and a text label, and we replace the "nuke" icon with the trash can icon.
<img width="356" alt="Screenshot 2020-11-20 at 17 25 43" src="https://user-images.githubusercontent.com/6304497/99824263-ca3ad580-2b55-11eb-92e1-a6fd3458e963.png">
**The more involved approach**: We redesign the rows to better accommodate the content without using buttons for everything.
Third, we should replace the browser alert with our own modal with more purposeful copy that follows our [actionable language guidelines](https://about.sourcegraph.com/handbook/communication/content_guidelines/actionable_language#confirmation-messages), like so:
<img width="1200" alt="Screenshot 2020-11-20 at 17 54 29" src="https://user-images.githubusercontent.com/6304497/99827047-716d3c00-2b59-11eb-9076-5675ec065769.png">
Finally, I'd also submit a PR to update language on the docs page for [user data deletion](https://github.com/sourcegraph/sourcegraph/blob/main/doc/admin/user_data_deletion.md) to align all content.
Thanks @flying-robot for flagging this issue and talking through it! | usab | deleting and nuking users as a site admin has scary usability the problem in the user management section of site admin site admin users we have two actions available delete user soft delete nuke user hard delete these are presented with almost equal button styling img width alt screenshot at src the tooltip for nuking a user is terrifying usability wise img width alt screenshot at src when the user clicks the either the delete user or nuke user button they re presented with a browser alert to confirm img width src we should improve this flow so it s less terrifying and more clear and honestly more sensitive proposed changes first i strongly recommend changing the name of these actions for clarity and sensitivity delete deactivate nuke delete note i understand that the implementation for soft delete almost certainly relies on a field like deleted at or a deleted users table so renaming it to deactivate can introduce incongruity but this copy is user facing while our database terminology is internal so user facing clarity wins out second we should update the buttons to communicate these actions more clearly since the rows in the ui are already quite packed there s two options here one quick and one a bit more involved the quick approach we replace the delete button with a secondary button style with red text and a text label and we replace the nuke icon with the trash can icon img width alt screenshot at src the more involved approach we redesign the rows to better accommodate the content without using buttons for everything third we should replace the browser alert with our own modal with more purposeful copy that follows our like so img width alt screenshot at src finally i d also submit a pr to update language on the docs page for to align all content thanks flying robot for flagging this issue and talking through it | 1 |
234,753 | 25,886,315,675 | IssuesEvent | 2022-12-14 14:47:55 | niklasschreiber/vulner-2 | https://api.github.com/repos/niklasschreiber/vulner-2 | opened | mysql-connector-java-5.1.18.jar: 9 vulnerabilities (highest severity is: 8.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (mysql-connector-java version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2017-3523](https://www.mend.io/vulnerability-database/CVE-2017-3523) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | mysql-connector-java-5.1.18.jar | Direct | 5.1.21 | ❌ |
| [CVE-2022-21363](https://www.mend.io/vulnerability-database/CVE-2022-21363) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.6 | mysql-connector-java-5.1.18.jar | Direct | mysql:mysql-connector-java:8.0.28 | ❌ |
| [CVE-2017-3586](https://www.mend.io/vulnerability-database/CVE-2017-3586) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.4 | mysql-connector-java-5.1.18.jar | Direct | 5.1.21 | ❌ |
| [CVE-2019-2692](https://www.mend.io/vulnerability-database/CVE-2019-2692) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.3 | mysql-connector-java-5.1.18.jar | Direct | 5.1.48 | ❌ |
| [CVE-2020-2934](https://www.mend.io/vulnerability-database/CVE-2020-2934) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.0 | mysql-connector-java-5.1.18.jar | Direct | 5.1.49 | ❌ |
| [CVE-2020-2875](https://www.mend.io/vulnerability-database/CVE-2020-2875) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.7 | mysql-connector-java-5.1.18.jar | Direct | 5.1.49 | ❌ |
| [CVE-2015-2575](https://www.mend.io/vulnerability-database/CVE-2015-2575) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.2 | mysql-connector-java-5.1.18.jar | Direct | 5.1.35 | ❌ |
| [CVE-2017-3589](https://www.mend.io/vulnerability-database/CVE-2017-3589) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.3 | mysql-connector-java-5.1.18.jar | Direct | 5.1.21 | ❌ |
| [CVE-2020-2933](https://www.mend.io/vulnerability-database/CVE-2020-2933) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 2.2 | mysql-connector-java-5.1.18.jar | Direct | 5.1.49 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-3523</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.40 and earlier. Difficult to exploit vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 8.5 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-3523>CVE-2017-3523</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-2xxh-f8r3-hvvr">https://github.com/advisories/GHSA-2xxh-f8r3-hvvr</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.21</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-21363</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.27 and prior. Difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.1 Base Score 6.6 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H).
<p>Publish Date: 2022-01-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-21363>CVE-2022-21363</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-g76j-4cxx-23h9">https://github.com/advisories/GHSA-g76j-4cxx-23h9</a></p>
<p>Release Date: 2022-01-19</p>
<p>Fix Resolution: mysql:mysql-connector-java:8.0.28</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-3586</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily "exploitable" vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 6.4 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:C/C:L/I:L/A:N).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-3586>CVE-2017-3586</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1444406">https://bugzilla.redhat.com/show_bug.cgi?id=1444406</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.21</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-2692</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 8.0.15 and prior. Difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 6.3 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:H/PR:H/UI:R/S:U/C:H/I:H/A:H).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-2692>CVE-2019-2692</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jcq3-cprp-m333">https://github.com/advisories/GHSA-jcq3-cprp-m333</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: 5.1.48</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-2934</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.19 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data and unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 5.0 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:L/I:L/A:L).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-2934>CVE-2020-2934</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.oracle.com/security-alerts/cpuapr2020.html">https://www.oracle.com/security-alerts/cpuapr2020.html</a></p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: 5.1.49</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-2875</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.14 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker and while the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 4.7 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:C/C:L/I:L/A:N).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-2875>CVE-2020-2875</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: 5.1.49</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2015-2575</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Unspecified vulnerability in the MySQL Connectors component in Oracle MySQL 5.1.34 and earlier allows remote authenticated users to affect confidentiality and integrity via unknown vectors related to Connector/J.
<p>Publish Date: 2015-04-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-2575>CVE-2015-2575</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-gc43-g62c-99g2">https://github.com/advisories/GHSA-gc43-g62c-99g2</a></p>
<p>Release Date: 2015-04-16</p>
<p>Fix Resolution: 5.1.35</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2017-3589</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily "exploitable" vulnerability allows low privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data. CVSS 3.0 Base Score 3.3 (Integrity impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-3589>CVE-2017-3589</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.21</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2020-2933</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 5.1.48 and prior. Difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 2.2 (Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:H/UI:N/S:U/C:N/I:N/A:L).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-2933>CVE-2020-2933</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>2.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://docs.oracle.com/javase/7/docs/api/javax/xml/XMLConstants.html#FEATURE_SECURE_PROCESSING">https://docs.oracle.com/javase/7/docs/api/javax/xml/XMLConstants.html#FEATURE_SECURE_PROCESSING</a></p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: 5.1.49</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | mysql-connector-java-5.1.18.jar: 9 vulnerabilities (highest severity is: 8.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (mysql-connector-java version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2017-3523](https://www.mend.io/vulnerability-database/CVE-2017-3523) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | mysql-connector-java-5.1.18.jar | Direct | 5.1.21 | ❌ |
| [CVE-2022-21363](https://www.mend.io/vulnerability-database/CVE-2022-21363) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.6 | mysql-connector-java-5.1.18.jar | Direct | mysql:mysql-connector-java:8.0.28 | ❌ |
| [CVE-2017-3586](https://www.mend.io/vulnerability-database/CVE-2017-3586) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.4 | mysql-connector-java-5.1.18.jar | Direct | 5.1.21 | ❌ |
| [CVE-2019-2692](https://www.mend.io/vulnerability-database/CVE-2019-2692) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.3 | mysql-connector-java-5.1.18.jar | Direct | 5.1.48 | ❌ |
| [CVE-2020-2934](https://www.mend.io/vulnerability-database/CVE-2020-2934) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.0 | mysql-connector-java-5.1.18.jar | Direct | 5.1.49 | ❌ |
| [CVE-2020-2875](https://www.mend.io/vulnerability-database/CVE-2020-2875) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.7 | mysql-connector-java-5.1.18.jar | Direct | 5.1.49 | ❌ |
| [CVE-2015-2575](https://www.mend.io/vulnerability-database/CVE-2015-2575) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.2 | mysql-connector-java-5.1.18.jar | Direct | 5.1.35 | ❌ |
| [CVE-2017-3589](https://www.mend.io/vulnerability-database/CVE-2017-3589) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.3 | mysql-connector-java-5.1.18.jar | Direct | 5.1.21 | ❌ |
| [CVE-2020-2933](https://www.mend.io/vulnerability-database/CVE-2020-2933) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 2.2 | mysql-connector-java-5.1.18.jar | Direct | 5.1.49 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-3523</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.40 and earlier. Difficult to exploit vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 8.5 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-3523>CVE-2017-3523</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-2xxh-f8r3-hvvr">https://github.com/advisories/GHSA-2xxh-f8r3-hvvr</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.21</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-21363</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.27 and prior. Difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.1 Base Score 6.6 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H).
<p>Publish Date: 2022-01-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-21363>CVE-2022-21363</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-g76j-4cxx-23h9">https://github.com/advisories/GHSA-g76j-4cxx-23h9</a></p>
<p>Release Date: 2022-01-19</p>
<p>Fix Resolution: mysql:mysql-connector-java:8.0.28</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-3586</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily "exploitable" vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 6.4 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:C/C:L/I:L/A:N).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-3586>CVE-2017-3586</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1444406">https://bugzilla.redhat.com/show_bug.cgi?id=1444406</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.21</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-2692</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 8.0.15 and prior. Difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 6.3 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:H/PR:H/UI:R/S:U/C:H/I:H/A:H).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-2692>CVE-2019-2692</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jcq3-cprp-m333">https://github.com/advisories/GHSA-jcq3-cprp-m333</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: 5.1.48</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-2934</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.19 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data and unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 5.0 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:L/I:L/A:L).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-2934>CVE-2020-2934</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.oracle.com/security-alerts/cpuapr2020.html">https://www.oracle.com/security-alerts/cpuapr2020.html</a></p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: 5.1.49</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-2875</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.14 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker and while the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 4.7 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:C/C:L/I:L/A:N).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-2875>CVE-2020-2875</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: 5.1.49</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2015-2575</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Unspecified vulnerability in the MySQL Connectors component in Oracle MySQL 5.1.34 and earlier allows remote authenticated users to affect confidentiality and integrity via unknown vectors related to Connector/J.
<p>Publish Date: 2015-04-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-2575>CVE-2015-2575</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-gc43-g62c-99g2">https://github.com/advisories/GHSA-gc43-g62c-99g2</a></p>
<p>Release Date: 2015-04-16</p>
<p>Fix Resolution: 5.1.35</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2017-3589</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily "exploitable" vulnerability allows low privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data. CVSS 3.0 Base Score 3.3 (Integrity impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-3589>CVE-2017-3589</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.21</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2020-2933</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.18.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to vulnerable library: /JAVA/mybatis_spring/WebContent/WEB-INF/lib/mysql-connector-java-5.1.18-bin.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.18.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 5.1.48 and prior. Difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 2.2 (Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:H/UI:N/S:U/C:N/I:N/A:L).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-2933>CVE-2020-2933</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>2.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://docs.oracle.com/javase/7/docs/api/javax/xml/XMLConstants.html#FEATURE_SECURE_PROCESSING">https://docs.oracle.com/javase/7/docs/api/javax/xml/XMLConstants.html#FEATURE_SECURE_PROCESSING</a></p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: 5.1.49</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_usab | mysql connector java jar vulnerabilities highest severity is vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to vulnerable library java mybatis spring webcontent web inf lib mysql connector java bin jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in mysql connector java version remediation available high mysql connector java jar direct medium mysql connector java jar direct mysql mysql connector java medium mysql connector java jar direct medium mysql connector java jar direct medium mysql connector java jar direct medium mysql connector java jar direct medium mysql connector java jar direct low mysql connector java jar direct low mysql connector java jar direct details cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to vulnerable library java mybatis spring webcontent web inf lib mysql connector java bin jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and earlier difficult to exploit vulnerability allows low privileged attacker with network access via multiple protocols to compromise mysql connectors while the vulnerability is in mysql connectors attacks may significantly impact additional products successful attacks of this vulnerability can result in takeover of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av n ac h pr l ui n s c c h i h a h publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to vulnerable library java mybatis spring webcontent web inf lib mysql connector java bin jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors product of oracle mysql component connector j supported versions that are affected are and prior difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise mysql connectors successful attacks of this vulnerability can result in takeover of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av n ac h pr h ui n s u c h i h a h publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution mysql mysql connector java step up your open source security game with mend cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to vulnerable library java mybatis spring webcontent web inf lib mysql connector java bin jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and earlier easily exploitable vulnerability allows low privileged attacker with network access via multiple protocols to compromise mysql connectors while the vulnerability is in mysql connectors attacks may significantly impact additional products successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data as well as unauthorized read access to a subset of mysql connectors accessible data cvss base score confidentiality and integrity impacts cvss vector cvss av n ac l pr l ui n s c c l i l a n publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to vulnerable library java mybatis spring webcontent web inf lib mysql connector java bin jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and prior difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where mysql connectors executes to compromise mysql connectors successful attacks require human interaction from a person other than the attacker successful attacks of this vulnerability can result in takeover of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av l ac h pr h ui r s u c h i h a h publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required high user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to vulnerable library java mybatis spring webcontent web inf lib mysql connector java bin jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors product of oracle mysql component connector j supported versions that are affected are and prior and and prior difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise mysql connectors successful attacks require human interaction from a person other than the attacker successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data as well as unauthorized read access to a subset of mysql connectors accessible data and unauthorized ability to cause a partial denial of service partial dos of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av n ac h pr n ui r s u c l i l a l publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction required scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to vulnerable library java mybatis spring webcontent web inf lib mysql connector java bin jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors product of oracle mysql component connector j supported versions that are affected are and prior and and prior difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise mysql connectors successful attacks require human interaction from a person other than the attacker and while the vulnerability is in mysql connectors attacks may significantly impact additional products successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data as well as unauthorized read access to a subset of mysql connectors accessible data cvss base score confidentiality and integrity impacts cvss vector cvss av n ac h pr n ui r s c c l i l a n publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to vulnerable library java mybatis spring webcontent web inf lib mysql connector java bin jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details unspecified vulnerability in the mysql connectors component in oracle mysql and earlier allows remote authenticated users to affect confidentiality and integrity via unknown vectors related to connector j publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to vulnerable library java mybatis spring webcontent web inf lib mysql connector java bin jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and earlier easily exploitable vulnerability allows low privileged attacker with logon to the infrastructure where mysql connectors executes to compromise mysql connectors successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data cvss base score integrity impacts cvss vector cvss av l ac l pr l ui n s u c n i l a n publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to vulnerable library java mybatis spring webcontent web inf lib mysql connector java bin jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors product of oracle mysql component connector j supported versions that are affected are and prior difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise mysql connectors successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of service partial dos of mysql connectors cvss base score availability impacts cvss vector cvss av n ac h pr h ui n s u c n i n a l publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
24,218 | 23,510,336,643 | IssuesEvent | 2022-08-18 15:56:25 | FreeTubeApp/FreeTube | https://api.github.com/repos/FreeTubeApp/FreeTube | closed | [Bug]: Middle click causes choppy scrolling | bug U: Waiting for Response from Author B: usability B: inconsistent behavior | ### Guidelines
- [X] I have encountered this bug in the [latest release of FreeTube](https://github.com/FreeTubeApp/FreeTube/releases).
- [X] I have searched the [issue tracker](https://github.com/FreeTubeApp/FreeTube/issues) for a bug report that matches the one I want to file, without success.
### Describe the bug
Steps to reproduce:
1. Open Freetube.
2. Middle click anywhere.
3. Try scrolling (if middle click spawns a new window, go back to the original window then scroll).
### Expected Behavior
Scrolling should not be choppy.
### Issue Labels
inconsistent behavior, usability issue
### FreeTube Version
v0.16.0
### Operating System Version
Fedora 36 Workstation
### Installation Method (If applicable)
Flathub
### Last Known Working FreeTube Version (If Any)
_No response_
### Primary API used
_No response_
### Additional Information
This might be unrelated but this issue doesn't happen prior upgrading to Fedora 36 Beta.
### Nightly Build
- [ ] I have encountered this bug in the latest [nightly build](https://docs.freetubeapp.io/development/nightly-builds). | True | [Bug]: Middle click causes choppy scrolling - ### Guidelines
- [X] I have encountered this bug in the [latest release of FreeTube](https://github.com/FreeTubeApp/FreeTube/releases).
- [X] I have searched the [issue tracker](https://github.com/FreeTubeApp/FreeTube/issues) for a bug report that matches the one I want to file, without success.
### Describe the bug
Steps to reproduce:
1. Open Freetube.
2. Middle click anywhere.
3. Try scrolling (if middle click spawns a new window, go back to the original window then scroll).
### Expected Behavior
Scrolling should not be choppy.
### Issue Labels
inconsistent behavior, usability issue
### FreeTube Version
v0.16.0
### Operating System Version
Fedora 36 Workstation
### Installation Method (If applicable)
Flathub
### Last Known Working FreeTube Version (If Any)
_No response_
### Primary API used
_No response_
### Additional Information
This might be unrelated but this issue doesn't happen prior upgrading to Fedora 36 Beta.
### Nightly Build
- [ ] I have encountered this bug in the latest [nightly build](https://docs.freetubeapp.io/development/nightly-builds). | usab | middle click causes choppy scrolling guidelines i have encountered this bug in the i have searched the for a bug report that matches the one i want to file without success describe the bug steps to reproduce open freetube middle click anywhere try scrolling if middle click spawns a new window go back to the original window then scroll expected behavior scrolling should not be choppy issue labels inconsistent behavior usability issue freetube version operating system version fedora workstation installation method if applicable flathub last known working freetube version if any no response primary api used no response additional information this might be unrelated but this issue doesn t happen prior upgrading to fedora beta nightly build i have encountered this bug in the latest | 1 |
284,754 | 30,913,682,911 | IssuesEvent | 2023-08-05 02:36:04 | Nivaskumark/kernel_v4.19.72_old | https://api.github.com/repos/Nivaskumark/kernel_v4.19.72_old | reopened | CVE-2023-0458 (Medium) detected in linux-yoctov5.4.51 | Mend: dependency security vulnerability | ## CVE-2023-0458 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Nivaskumark/kernel_v4.19.72/commit/ce49083a1c14be2d13cb5e878257d293e6c748bc">ce49083a1c14be2d13cb5e878257d293e6c748bc</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A speculative pointer dereference problem exists in the Linux Kernel on the do_prlimit() function. The resource argument value is controlled and is used in pointer arithmetic for the 'rlim' variable and can be used to leak the contents. We recommend upgrading past version 6.1.8 or commit 739790605705ddcf18f21782b9c99ad7d53a8c11
<p>Publish Date: 2023-04-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-0458>CVE-2023-0458</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-0458">https://www.linuxkernelcves.com/cves/CVE-2023-0458</a></p>
<p>Release Date: 2023-04-26</p>
<p>Fix Resolution: v4.14.304,v4.19.271,v5.4.230,v5.10.165,v5.15.90,v6.1.8,v6.2-rc5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-0458 (Medium) detected in linux-yoctov5.4.51 - ## CVE-2023-0458 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Nivaskumark/kernel_v4.19.72/commit/ce49083a1c14be2d13cb5e878257d293e6c748bc">ce49083a1c14be2d13cb5e878257d293e6c748bc</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A speculative pointer dereference problem exists in the Linux Kernel on the do_prlimit() function. The resource argument value is controlled and is used in pointer arithmetic for the 'rlim' variable and can be used to leak the contents. We recommend upgrading past version 6.1.8 or commit 739790605705ddcf18f21782b9c99ad7d53a8c11
<p>Publish Date: 2023-04-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-0458>CVE-2023-0458</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-0458">https://www.linuxkernelcves.com/cves/CVE-2023-0458</a></p>
<p>Release Date: 2023-04-26</p>
<p>Fix Resolution: v4.14.304,v4.19.271,v5.4.230,v5.10.165,v5.15.90,v6.1.8,v6.2-rc5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | cve medium detected in linux cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details a speculative pointer dereference problem exists in the linux kernel on the do prlimit function the resource argument value is controlled and is used in pointer arithmetic for the rlim variable and can be used to leak the contents we recommend upgrading past version or commit publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
27,128 | 27,722,040,618 | IssuesEvent | 2023-03-14 21:31:01 | pulumi/pulumi-hugo | https://api.github.com/repos/pulumi/pulumi-hugo | opened | conduct research to support docs navigation redesign | kind/enhancement impact/usability | ## rough goals
1. when a user has a specific question, they can quickly and easily find the answer,
2. new users can understand what pulumi is and what it offers with a quick scan of the docs nav
3. new users understand what is in docs, and what is in registry and when they would want to go to either#2566
## prior work
[past docs nav proposals](https://docs.google.com/spreadsheets/d/1Iq-dvFi-UdVfqSzB4BctTI6Sn2LtkRtqf3QzXn5yDRc/edit#gid=2135319669)
[past docs user research](https://docs.google.com/document/d/1zRfYvXddKbxZMAo1ZZerYeYwbjwl9Nzy63POACyub54/edit?usp=sharing)
## to do
- [ ] review of prior work
- [ ] landscape analysis
- [ ] internal interviews
- Christian
- Guin
- Kyle Dixler
- Komal
- Monica
- Lee Briggs | True | conduct research to support docs navigation redesign - ## rough goals
1. when a user has a specific question, they can quickly and easily find the answer,
2. new users can understand what pulumi is and what it offers with a quick scan of the docs nav
3. new users understand what is in docs, and what is in registry and when they would want to go to either#2566
## prior work
[past docs nav proposals](https://docs.google.com/spreadsheets/d/1Iq-dvFi-UdVfqSzB4BctTI6Sn2LtkRtqf3QzXn5yDRc/edit#gid=2135319669)
[past docs user research](https://docs.google.com/document/d/1zRfYvXddKbxZMAo1ZZerYeYwbjwl9Nzy63POACyub54/edit?usp=sharing)
## to do
- [ ] review of prior work
- [ ] landscape analysis
- [ ] internal interviews
- Christian
- Guin
- Kyle Dixler
- Komal
- Monica
- Lee Briggs | usab | conduct research to support docs navigation redesign rough goals when a user has a specific question they can quickly and easily find the answer new users can understand what pulumi is and what it offers with a quick scan of the docs nav new users understand what is in docs and what is in registry and when they would want to go to either prior work to do review of prior work landscape analysis internal interviews christian guin kyle dixler komal monica lee briggs | 1 |
25,365 | 25,072,078,192 | IssuesEvent | 2022-11-07 12:58:02 | argoproj/argo-cd | https://api.github.com/repos/argoproj/argo-cd | closed | Proposal & Proof of Concept: Dynamically Generate Applications for Clusters Based On Label Selectors | enhancement type:usability component:applications-set | # Summary
Add a new CRD ApplicationGenerator to support dynamically generating Applications for Clusters via a label selector.
# Motivation
Argo models Applications via a 1-1 relationship with a Cluster. This works great in environments where the number of clusters is fixed and known.
In many use cases however clusters are increasingly being treated as cattle, they come and go often, likely via programmatic APIs. This scenario can be found in organizations providing developers short lived clusters, distributing clusters to different regions or projects, and CI systems.
In cases such as this, it is still equally important to deliver consistent configuration to clusters and leverage gitops, if not more so, to keep the fleet in it's expected state.
When working with dynamic clusters, it is reasonable to expect that an integrating application or API would register those clusters with ArgoCD. (by creating an appropriate secret) It is however less reasonable to also generate the expected Applications, and keep them in sync. This solution below allows the ApplicationGenerator to itself be stored in git and configured via Argo. Clusters can come and go, and just need to be labelled appropriately to pickup the desired configuration.
# Proposal
I have written up a small proof of concept operator for an ApplicationGenerator CRD and controller in this repository: https://github.com/dgoodwin/argocd-appgenerator
The CRD itself as proposed (happy to discuss changes if this idea is popular):
```yaml
apiVersion: appgenerator.rm-rf.ca/v1
kind: ApplicationGenerator
metadata:
name: default-configmap
namespace: argocd
spec:
matchLabels:
argocd.argoproj.io/secret-type: cluster
applicationSpec:
destination:
namespace: default
# server will be overwritten for every cluster that matches this generator.
server: https://kubernetes.default.svc
project: default
source:
path: config/samples/argocd-application
repoURL: https://github.com/dgoodwin/argocd-appgenerator.git
syncPolicy:
automated:
prune: true
```
Any Cluster which matches the given label gets an Application generated for it with the given spec. If the label or ApplicationGenerator were to be removed, the Application is cleaned up.
There is however another change that would be required, it looks like today there is no way to specify labels to attach to a Cluster, the CLI would likely need to be expanded to allow for this, perhaps something like:
```
$ argocd cluster add kind-kind --insecure --in-cluster -l foo=bar -l x=y
```
Request is somewhat related to #1673 but rather than making Application multi-destination, this solution layers on top and leaves the core Application mechanics alone.
This solution can easily be provided by a separate operator, but having worked on an API for provisioning/deprovisioning clusters dynamically for several years, it feels like a great fit for the core of Argo itself, so I first wanted to propose for inclusion there. | True | Proposal & Proof of Concept: Dynamically Generate Applications for Clusters Based On Label Selectors - # Summary
Add a new CRD ApplicationGenerator to support dynamically generating Applications for Clusters via a label selector.
# Motivation
Argo models Applications via a 1-1 relationship with a Cluster. This works great in environments where the number of clusters is fixed and known.
In many use cases however clusters are increasingly being treated as cattle, they come and go often, likely via programmatic APIs. This scenario can be found in organizations providing developers short lived clusters, distributing clusters to different regions or projects, and CI systems.
In cases such as this, it is still equally important to deliver consistent configuration to clusters and leverage gitops, if not more so, to keep the fleet in it's expected state.
When working with dynamic clusters, it is reasonable to expect that an integrating application or API would register those clusters with ArgoCD. (by creating an appropriate secret) It is however less reasonable to also generate the expected Applications, and keep them in sync. This solution below allows the ApplicationGenerator to itself be stored in git and configured via Argo. Clusters can come and go, and just need to be labelled appropriately to pickup the desired configuration.
# Proposal
I have written up a small proof of concept operator for an ApplicationGenerator CRD and controller in this repository: https://github.com/dgoodwin/argocd-appgenerator
The CRD itself as proposed (happy to discuss changes if this idea is popular):
```yaml
apiVersion: appgenerator.rm-rf.ca/v1
kind: ApplicationGenerator
metadata:
name: default-configmap
namespace: argocd
spec:
matchLabels:
argocd.argoproj.io/secret-type: cluster
applicationSpec:
destination:
namespace: default
# server will be overwritten for every cluster that matches this generator.
server: https://kubernetes.default.svc
project: default
source:
path: config/samples/argocd-application
repoURL: https://github.com/dgoodwin/argocd-appgenerator.git
syncPolicy:
automated:
prune: true
```
Any Cluster which matches the given label gets an Application generated for it with the given spec. If the label or ApplicationGenerator were to be removed, the Application is cleaned up.
There is however another change that would be required, it looks like today there is no way to specify labels to attach to a Cluster, the CLI would likely need to be expanded to allow for this, perhaps something like:
```
$ argocd cluster add kind-kind --insecure --in-cluster -l foo=bar -l x=y
```
Request is somewhat related to #1673 but rather than making Application multi-destination, this solution layers on top and leaves the core Application mechanics alone.
This solution can easily be provided by a separate operator, but having worked on an API for provisioning/deprovisioning clusters dynamically for several years, it feels like a great fit for the core of Argo itself, so I first wanted to propose for inclusion there. | usab | proposal proof of concept dynamically generate applications for clusters based on label selectors summary add a new crd applicationgenerator to support dynamically generating applications for clusters via a label selector motivation argo models applications via a relationship with a cluster this works great in environments where the number of clusters is fixed and known in many use cases however clusters are increasingly being treated as cattle they come and go often likely via programmatic apis this scenario can be found in organizations providing developers short lived clusters distributing clusters to different regions or projects and ci systems in cases such as this it is still equally important to deliver consistent configuration to clusters and leverage gitops if not more so to keep the fleet in it s expected state when working with dynamic clusters it is reasonable to expect that an integrating application or api would register those clusters with argocd by creating an appropriate secret it is however less reasonable to also generate the expected applications and keep them in sync this solution below allows the applicationgenerator to itself be stored in git and configured via argo clusters can come and go and just need to be labelled appropriately to pickup the desired configuration proposal i have written up a small proof of concept operator for an applicationgenerator crd and controller in this repository the crd itself as proposed happy to discuss changes if this idea is popular yaml apiversion appgenerator rm rf ca kind applicationgenerator metadata name default configmap namespace argocd spec matchlabels argocd argoproj io secret type cluster applicationspec destination namespace default server will be overwritten for every cluster that matches this generator server project default source path config samples argocd application repourl syncpolicy automated prune true any cluster which matches the given label gets an application generated for it with the given spec if the label or applicationgenerator were to be removed the application is cleaned up there is however another change that would be required it looks like today there is no way to specify labels to attach to a cluster the cli would likely need to be expanded to allow for this perhaps something like argocd cluster add kind kind insecure in cluster l foo bar l x y request is somewhat related to but rather than making application multi destination this solution layers on top and leaves the core application mechanics alone this solution can easily be provided by a separate operator but having worked on an api for provisioning deprovisioning clusters dynamically for several years it feels like a great fit for the core of argo itself so i first wanted to propose for inclusion there | 1 |
3,202 | 3,368,855,084 | IssuesEvent | 2015-11-23 05:09:23 | cortoproject/corto | https://api.github.com/repos/cortoproject/corto | closed | Allow enumeration constants and bit masks to be passed to functions without the fully scoped name | Corto:Parser Corto:Usability enhancement | The following code:
```
enum Color:: Red, Yellow, Green, Blue
void func(Color a):
if a != Blue: fail("a != Blue")
func(Blue)
```
results un an unresolved reference.
For functions that are not overloaded, it should not be necessary to provide the full name (`Color::Blue`). | True | Allow enumeration constants and bit masks to be passed to functions without the fully scoped name - The following code:
```
enum Color:: Red, Yellow, Green, Blue
void func(Color a):
if a != Blue: fail("a != Blue")
func(Blue)
```
results un an unresolved reference.
For functions that are not overloaded, it should not be necessary to provide the full name (`Color::Blue`). | usab | allow enumeration constants and bit masks to be passed to functions without the fully scoped name the following code enum color red yellow green blue void func color a if a blue fail a blue func blue results un an unresolved reference for functions that are not overloaded it should not be necessary to provide the full name color blue | 1 |
26,763 | 27,168,672,830 | IssuesEvent | 2023-02-17 17:20:39 | neurobagel/annotation_tool | https://api.github.com/repos/neurobagel/annotation_tool | closed | Set up a workflow to run the linter on new pull requests | importance:medium maintenance:usability | Set up a workflow to run eslint on PRs to catch any issues in case eslint wasn't run before committing. | True | Set up a workflow to run the linter on new pull requests - Set up a workflow to run eslint on PRs to catch any issues in case eslint wasn't run before committing. | usab | set up a workflow to run the linter on new pull requests set up a workflow to run eslint on prs to catch any issues in case eslint wasn t run before committing | 1 |
11,860 | 7,494,281,577 | IssuesEvent | 2018-04-07 07:35:02 | the-tale/the-tale | https://api.github.com/repos/the-tale/the-tale | opened | nginx не всегда (никогда?) жмёт ответы | comp_production cont_usability est_simple good first issue type_bug | Это влиеяет на скорость загрузки страниц и на позиции в поиске. Надо исправить. | True | nginx не всегда (никогда?) жмёт ответы - Это влиеяет на скорость загрузки страниц и на позиции в поиске. Надо исправить. | usab | nginx не всегда никогда жмёт ответы это влиеяет на скорость загрузки страниц и на позиции в поиске надо исправить | 1 |
15,013 | 9,657,665,592 | IssuesEvent | 2019-05-20 09:07:46 | MarkBind/markbind | https://api.github.com/repos/MarkBind/markbind | closed | Scroll to target goes off target if already at the target | a-ReaderUsability c.Bug 🐛 f-Search p.Low | v1.11.0
Steps.
* Go to https://nus-cs2103.github.io/website-base
* search for `role`
* hit Enter --> page scrolls to the correct location
* search for `role` again
* hit Enter
Expected: page remains at the same scroll position
Actual: page scrolls a bit, hiding the correct target | True | Scroll to target goes off target if already at the target - v1.11.0
Steps.
* Go to https://nus-cs2103.github.io/website-base
* search for `role`
* hit Enter --> page scrolls to the correct location
* search for `role` again
* hit Enter
Expected: page remains at the same scroll position
Actual: page scrolls a bit, hiding the correct target | usab | scroll to target goes off target if already at the target steps go to search for role hit enter page scrolls to the correct location search for role again hit enter expected page remains at the same scroll position actual page scrolls a bit hiding the correct target | 1 |
20,441 | 15,444,144,693 | IssuesEvent | 2021-03-08 10:01:50 | KazDragon/terminalpp | https://api.github.com/repos/KazDragon/terminalpp | closed | Rework interface for continuations | Breaking Change New Feature Performance Usability | One disadvantage of the current interface is that there's an awful lot of string copying. Not only that, but it's not always possible to chain them up in a good way. For example:
terminal.write("foo") + terminal.move_to({1, 2}) + terminal.write("bar") + terminal.move_to({2, 3});
may give varying results depending on the order of the evaluation of the component parts of the expression. This is partially fixed by the << manipulators. However, the interface is still predicated on building and returning strings of text.
A better interface might be to use a Continuation design, similar to the recent changes in Telnet++. For example:
terminal.write("foo", my_fn); // split off as an example of member write.
terminal.with(my_fn) << move_to({1, 2}) << write("bar") << move_to({2, 3});
In this, my_fn is a user-specified function that represents the thing that would be done with the resultant string(s). This reduces the responsibilities of the terminal to maintaining the cursor position and attributes, and (still) writing arbitrary terminal strings (again, through continuations). | True | Rework interface for continuations - One disadvantage of the current interface is that there's an awful lot of string copying. Not only that, but it's not always possible to chain them up in a good way. For example:
terminal.write("foo") + terminal.move_to({1, 2}) + terminal.write("bar") + terminal.move_to({2, 3});
may give varying results depending on the order of the evaluation of the component parts of the expression. This is partially fixed by the << manipulators. However, the interface is still predicated on building and returning strings of text.
A better interface might be to use a Continuation design, similar to the recent changes in Telnet++. For example:
terminal.write("foo", my_fn); // split off as an example of member write.
terminal.with(my_fn) << move_to({1, 2}) << write("bar") << move_to({2, 3});
In this, my_fn is a user-specified function that represents the thing that would be done with the resultant string(s). This reduces the responsibilities of the terminal to maintaining the cursor position and attributes, and (still) writing arbitrary terminal strings (again, through continuations). | usab | rework interface for continuations one disadvantage of the current interface is that there s an awful lot of string copying not only that but it s not always possible to chain them up in a good way for example terminal write foo terminal move to terminal write bar terminal move to may give varying results depending on the order of the evaluation of the component parts of the expression this is partially fixed by the manipulators however the interface is still predicated on building and returning strings of text a better interface might be to use a continuation design similar to the recent changes in telnet for example terminal write foo my fn split off as an example of member write terminal with my fn move to write bar move to in this my fn is a user specified function that represents the thing that would be done with the resultant string s this reduces the responsibilities of the terminal to maintaining the cursor position and attributes and still writing arbitrary terminal strings again through continuations | 1 |
2,025 | 3,026,209,356 | IssuesEvent | 2015-08-03 13:56:14 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 20021172: UIAlertController based action sheet layout breaks in certain configurations | classification:ui/usability reproducible:always status:open | #### Description
This is a duplicate of rdar://20020818
Summary:
UIAlertController in UIAlertControllerStyleActionSheet style exhibits auto layout issues when presented anchored to certain screen positions.
Steps to Reproduce:
Open the provided example project and follow the on-screen instructions.
Expected Results:
The popover would be positioned correctly, without any auto layout warnings.
Actual Results:
The internal popover layout is broken and auto layout warnings a printed in the console.
Regression:
The issue only seems to occur when the popover arrow is pointing left or right. A possible workaround is to restrict the possible arrow directions to up and down.
Notes:
See attached project and the provided screenshots (archived).
-
Product Version: 8.1.3
Created: 2015-03-03T14:13:42.584456
Originated: 2015-03-03T15:13:00
Open Radar Link: http://www.openradar.me/20021172 | True | 20021172: UIAlertController based action sheet layout breaks in certain configurations - #### Description
This is a duplicate of rdar://20020818
Summary:
UIAlertController in UIAlertControllerStyleActionSheet style exhibits auto layout issues when presented anchored to certain screen positions.
Steps to Reproduce:
Open the provided example project and follow the on-screen instructions.
Expected Results:
The popover would be positioned correctly, without any auto layout warnings.
Actual Results:
The internal popover layout is broken and auto layout warnings a printed in the console.
Regression:
The issue only seems to occur when the popover arrow is pointing left or right. A possible workaround is to restrict the possible arrow directions to up and down.
Notes:
See attached project and the provided screenshots (archived).
-
Product Version: 8.1.3
Created: 2015-03-03T14:13:42.584456
Originated: 2015-03-03T15:13:00
Open Radar Link: http://www.openradar.me/20021172 | usab | uialertcontroller based action sheet layout breaks in certain configurations description this is a duplicate of rdar summary uialertcontroller in uialertcontrollerstyleactionsheet style exhibits auto layout issues when presented anchored to certain screen positions steps to reproduce open the provided example project and follow the on screen instructions expected results the popover would be positioned correctly without any auto layout warnings actual results the internal popover layout is broken and auto layout warnings a printed in the console regression the issue only seems to occur when the popover arrow is pointing left or right a possible workaround is to restrict the possible arrow directions to up and down notes see attached project and the provided screenshots archived product version created originated open radar link | 1 |
21,116 | 6,130,763,735 | IssuesEvent | 2017-06-24 08:47:04 | ganeti/ganeti | https://api.github.com/repos/ganeti/ganeti | opened | Add MARS support | imported_from_google_code Status:PatchesWelcome Type-Enhancement | Originally reported of Google Code with ID 911.
```
Hi,
there's a new distributed storage system called MARS[1] that looks very promising and has some advantages over DRBD[2]. It would be cool to have support for it.
[1] https://github.com/schoebel/mars
[2] http://www.linuxtag.org/2014/de/programm/vortragsdetails/?eventid=2308
```
Originally added on 2014-08-05 08:44:44 +0000 UTC. | 1.0 | Add MARS support - Originally reported of Google Code with ID 911.
```
Hi,
there's a new distributed storage system called MARS[1] that looks very promising and has some advantages over DRBD[2]. It would be cool to have support for it.
[1] https://github.com/schoebel/mars
[2] http://www.linuxtag.org/2014/de/programm/vortragsdetails/?eventid=2308
```
Originally added on 2014-08-05 08:44:44 +0000 UTC. | non_usab | add mars support originally reported of google code with id hi there s a new distributed storage system called mars that looks very promising and has some advantages over drbd it would be cool to have support for it originally added on utc | 0 |
28,191 | 32,023,669,237 | IssuesEvent | 2023-09-22 07:15:50 | dueapp/Due-macOS | https://api.github.com/repos/dueapp/Due-macOS | opened | Explore ways to make the date picker respect "week starts on" setting | usability | > > Hi,
> >
> > I wanted to put this on your radar if it isn't. On the Mac, I noticed when rescheduling a task that the date picker doesn't seem to use the "Week starts on" preference. Just checked on iOS and it does. It's not a big deal, but the inconsistency can be a little confusing.
> >
>
> Thanks for highlighting this. Unfortunately the date picker control provided by Apple does not allow us to directly change the first day of the week setting, unlike on iOS. I believe there was some workaround but we have not fully explored that yet. I’d continue looking into this.
I thought there was a previous issue about this but I can't find it. I believe the finding was that changing the locale of the date picker can help. However we need to map out which locale provides the correct week start on setting for the user, and this may also affect the language of the date picker, which may not be what we want. | True | Explore ways to make the date picker respect "week starts on" setting - > > Hi,
> >
> > I wanted to put this on your radar if it isn't. On the Mac, I noticed when rescheduling a task that the date picker doesn't seem to use the "Week starts on" preference. Just checked on iOS and it does. It's not a big deal, but the inconsistency can be a little confusing.
> >
>
> Thanks for highlighting this. Unfortunately the date picker control provided by Apple does not allow us to directly change the first day of the week setting, unlike on iOS. I believe there was some workaround but we have not fully explored that yet. I’d continue looking into this.
I thought there was a previous issue about this but I can't find it. I believe the finding was that changing the locale of the date picker can help. However we need to map out which locale provides the correct week start on setting for the user, and this may also affect the language of the date picker, which may not be what we want. | usab | explore ways to make the date picker respect week starts on setting hi i wanted to put this on your radar if it isn t on the mac i noticed when rescheduling a task that the date picker doesn t seem to use the week starts on preference just checked on ios and it does it s not a big deal but the inconsistency can be a little confusing thanks for highlighting this unfortunately the date picker control provided by apple does not allow us to directly change the first day of the week setting unlike on ios i believe there was some workaround but we have not fully explored that yet i’d continue looking into this i thought there was a previous issue about this but i can t find it i believe the finding was that changing the locale of the date picker can help however we need to map out which locale provides the correct week start on setting for the user and this may also affect the language of the date picker which may not be what we want | 1 |
110,860 | 13,956,167,926 | IssuesEvent | 2020-10-24 00:00:21 | microsoft/FluidFramework | https://api.github.com/repos/microsoft/FluidFramework | closed | MergeTree: Known weaknesses w/MergeTree undo | area: dds bug resolution: by design | Issue tracking known weaknesses of the current undo/redo support for MergeTree (and by extension, SharedSequence subclasses and SparseMatrix).
### Item reordering when remove/undo races with insertion
```
client1:
inserts "zz"
client2:
observes "zz"
inserts 'y' at pos 1 -> "zyz"
client1: (without observing insertion of 'y')
undo (removes range 0,2) -> ""
redo (reinserts "zz" at position 0)
```
After processing remote ops, client2 will observe 'zyz' become 'zzy'.
### Extraneous insertions when clients race to remove/undo overlapping ranges
```
both clients start with 'abc':
client1:
removes "ab" -> "c"
undo (inserts "ab" at pos 0) -> "abc"
client2: (without observing ops from client 1)
removes "bc" -> "a"
undo (inserts "bc" at pos 1) -> "abc"
```
After processing remote ops, both clients will observe "abc" become "abbc" | 1.0 | MergeTree: Known weaknesses w/MergeTree undo - Issue tracking known weaknesses of the current undo/redo support for MergeTree (and by extension, SharedSequence subclasses and SparseMatrix).
### Item reordering when remove/undo races with insertion
```
client1:
inserts "zz"
client2:
observes "zz"
inserts 'y' at pos 1 -> "zyz"
client1: (without observing insertion of 'y')
undo (removes range 0,2) -> ""
redo (reinserts "zz" at position 0)
```
After processing remote ops, client2 will observe 'zyz' become 'zzy'.
### Extraneous insertions when clients race to remove/undo overlapping ranges
```
both clients start with 'abc':
client1:
removes "ab" -> "c"
undo (inserts "ab" at pos 0) -> "abc"
client2: (without observing ops from client 1)
removes "bc" -> "a"
undo (inserts "bc" at pos 1) -> "abc"
```
After processing remote ops, both clients will observe "abc" become "abbc" | non_usab | mergetree known weaknesses w mergetree undo issue tracking known weaknesses of the current undo redo support for mergetree and by extension sharedsequence subclasses and sparsematrix item reordering when remove undo races with insertion inserts zz observes zz inserts y at pos zyz without observing insertion of y undo removes range redo reinserts zz at position after processing remote ops will observe zyz become zzy extraneous insertions when clients race to remove undo overlapping ranges both clients start with abc removes ab c undo inserts ab at pos abc without observing ops from client removes bc a undo inserts bc at pos abc after processing remote ops both clients will observe abc become abbc | 0 |
25,707 | 25,726,818,472 | IssuesEvent | 2022-12-07 17:13:00 | usds/justice40-tool | https://api.github.com/repos/usds/justice40-tool | opened | There are a few tracts / places where the values over the 90th percentile are not showing as blue | frontend usability 1.1 | **Describe the bug**
I was doing some ground truthing on the lack of indoor plumbing burden so I happened upon these tracts where values over the 90th percentile are not appearing as blue.
#15.04/34.02823/-118.31329 not showing blue at 91st percentile
#12.44/34.12115/-118.11633 not showing blue at 94th percentile
#14.28/34.09612/-118.13079 not blue at 94th
**To Reproduce**
Steps to reproduce the behavior:
1. Go to 'explore the map'
2. Click on 'census tract'
3. Scroll down to 'values over the 90th percentile'
4. See error
**Expected behavior**
All values over the 90th percentile should appear blue.
**Screenshots**
<img width="224" alt="Screen Shot 2022-12-06 at 2 30 25 PM" src="https://user-images.githubusercontent.com/77702996/206245492-518712dd-8372-4ccf-8673-570453b2fbfa.png">
<img width="229" alt="Screen Shot 2022-12-06 at 2 50 03 PM" src="https://user-images.githubusercontent.com/77702996/206245494-87f9675c-62b0-4d82-8665-a6cde3a9f85f.png">
<img width="199" alt="Screen Shot 2022-12-06 at 2 57 11 PM" src="https://user-images.githubusercontent.com/77702996/206245496-34b88afe-b148-4e87-a303-5b23365c7d50.png">
If applicable, add screenshots to help explain your problem.
**Desktop (please complete the following information):**
- OS: [e.g. iOS]
- Browser [e.g. chrome, safari]
- Version [e.g. 22]
**Smartphone (please complete the following information):**
- Device: [e.g. iPhone6]
- OS: [e.g. iOS8.1]
- Browser [e.g. stock browser, safari]
- Version [e.g. 22]
**Additional context**
Add any other context about the problem here.
| True | There are a few tracts / places where the values over the 90th percentile are not showing as blue - **Describe the bug**
I was doing some ground truthing on the lack of indoor plumbing burden so I happened upon these tracts where values over the 90th percentile are not appearing as blue.
#15.04/34.02823/-118.31329 not showing blue at 91st percentile
#12.44/34.12115/-118.11633 not showing blue at 94th percentile
#14.28/34.09612/-118.13079 not blue at 94th
**To Reproduce**
Steps to reproduce the behavior:
1. Go to 'explore the map'
2. Click on 'census tract'
3. Scroll down to 'values over the 90th percentile'
4. See error
**Expected behavior**
All values over the 90th percentile should appear blue.
**Screenshots**
<img width="224" alt="Screen Shot 2022-12-06 at 2 30 25 PM" src="https://user-images.githubusercontent.com/77702996/206245492-518712dd-8372-4ccf-8673-570453b2fbfa.png">
<img width="229" alt="Screen Shot 2022-12-06 at 2 50 03 PM" src="https://user-images.githubusercontent.com/77702996/206245494-87f9675c-62b0-4d82-8665-a6cde3a9f85f.png">
<img width="199" alt="Screen Shot 2022-12-06 at 2 57 11 PM" src="https://user-images.githubusercontent.com/77702996/206245496-34b88afe-b148-4e87-a303-5b23365c7d50.png">
If applicable, add screenshots to help explain your problem.
**Desktop (please complete the following information):**
- OS: [e.g. iOS]
- Browser [e.g. chrome, safari]
- Version [e.g. 22]
**Smartphone (please complete the following information):**
- Device: [e.g. iPhone6]
- OS: [e.g. iOS8.1]
- Browser [e.g. stock browser, safari]
- Version [e.g. 22]
**Additional context**
Add any other context about the problem here.
| usab | there are a few tracts places where the values over the percentile are not showing as blue describe the bug i was doing some ground truthing on the lack of indoor plumbing burden so i happened upon these tracts where values over the percentile are not appearing as blue not showing blue at percentile not showing blue at percentile not blue at to reproduce steps to reproduce the behavior go to explore the map click on census tract scroll down to values over the percentile see error expected behavior all values over the percentile should appear blue screenshots img width alt screen shot at pm src img width alt screen shot at pm src img width alt screen shot at pm src if applicable add screenshots to help explain your problem desktop please complete the following information os browser version smartphone please complete the following information device os browser version additional context add any other context about the problem here | 1 |
232,715 | 17,792,343,537 | IssuesEvent | 2021-08-31 17:41:51 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | Platform Website - Perform inventory using example spreadsheet provided by Content & IA team | operations documentation | ## Description
As part of our initiative to publish content that is most important to address common VFS needs, we need to perform an inventory of Ops' existing documentation.
The Content & IA team has provided audit guidance and a sample spreadsheet that we can begin working through. Additionally, we worked together as a team to discuss some of the documentation that we think we'll be most relevant.
## Background/context/resources
- [Audit Guidance](https://vfs.atlassian.net/wiki/spaces/AP/pages/1246527612/Audit+your+content)
- [Sample inventory spreadsheet](https://docs.google.com/spreadsheets/d/1JMoOv08vAKI16__vnkTJNrAS0c0aO3BrwSFkf8U8q6I/edit?usp=sharing)
- Notes in the comments below [copied from a recent meeting with the Ops team](https://vfs.atlassian.net/wiki/spaces/OT/pages/1742110727/2021-07-14+Ops+All+Hands)
- [Commonly asked questions from support bot ](https://datastudio.google.com/u/0/reporting/c4259d38-3515-486f-8fad-82ea06dadc4f/page/F3VEC)
---
## Tasks
- [X] Start new inventory spreadsheet
- [X] Identify the documents that we think will be most relevant
- [X] Inventory those documents with location, status, etc
- [x] Follow up with Service Design team to get additional information regarding support bot topics ('Environments', 'Pipelines', 'Null') - @jhouse-solvd
## Definition of Done
- [x] Documented inventory of content that we expect to publish on the platform website in a coming initiative
DOCUMENT WIP HERE: https://docs.google.com/spreadsheets/d/1ZxwcDDX5NDiOGzMdvhzL2CJ3bMgcPgQccu9NUovCxrk/edit?usp=sharing
| 1.0 | Platform Website - Perform inventory using example spreadsheet provided by Content & IA team - ## Description
As part of our initiative to publish content that is most important to address common VFS needs, we need to perform an inventory of Ops' existing documentation.
The Content & IA team has provided audit guidance and a sample spreadsheet that we can begin working through. Additionally, we worked together as a team to discuss some of the documentation that we think we'll be most relevant.
## Background/context/resources
- [Audit Guidance](https://vfs.atlassian.net/wiki/spaces/AP/pages/1246527612/Audit+your+content)
- [Sample inventory spreadsheet](https://docs.google.com/spreadsheets/d/1JMoOv08vAKI16__vnkTJNrAS0c0aO3BrwSFkf8U8q6I/edit?usp=sharing)
- Notes in the comments below [copied from a recent meeting with the Ops team](https://vfs.atlassian.net/wiki/spaces/OT/pages/1742110727/2021-07-14+Ops+All+Hands)
- [Commonly asked questions from support bot ](https://datastudio.google.com/u/0/reporting/c4259d38-3515-486f-8fad-82ea06dadc4f/page/F3VEC)
---
## Tasks
- [X] Start new inventory spreadsheet
- [X] Identify the documents that we think will be most relevant
- [X] Inventory those documents with location, status, etc
- [x] Follow up with Service Design team to get additional information regarding support bot topics ('Environments', 'Pipelines', 'Null') - @jhouse-solvd
## Definition of Done
- [x] Documented inventory of content that we expect to publish on the platform website in a coming initiative
DOCUMENT WIP HERE: https://docs.google.com/spreadsheets/d/1ZxwcDDX5NDiOGzMdvhzL2CJ3bMgcPgQccu9NUovCxrk/edit?usp=sharing
| non_usab | platform website perform inventory using example spreadsheet provided by content ia team description as part of our initiative to publish content that is most important to address common vfs needs we need to perform an inventory of ops existing documentation the content ia team has provided audit guidance and a sample spreadsheet that we can begin working through additionally we worked together as a team to discuss some of the documentation that we think we ll be most relevant background context resources notes in the comments below tasks start new inventory spreadsheet identify the documents that we think will be most relevant inventory those documents with location status etc follow up with service design team to get additional information regarding support bot topics environments pipelines null jhouse solvd definition of done documented inventory of content that we expect to publish on the platform website in a coming initiative document wip here | 0 |
183,004 | 21,685,870,798 | IssuesEvent | 2022-05-09 11:13:13 | Project-Books/book-project | https://api.github.com/repos/Project-Books/book-project | closed | Invalidate JWT token after account deletion | bug wontfix spring-security | Currently, JSON Web Tokens (JWTs) are used for passing authentication information. These tokens expire automatically, after a period of time.
Most requests need authorization information; otherwise, the requests are rejected (server returns 403 Forbidden response).
For example, if you want to list users, you will have to send valid authentication information.
The problem is that, after user account deletion, user JWT remains valid (until it expires) and can be used to make requests that normally should be rejected.
Steps to reproduce the issue:
1) Login using Postman (you may wish to create a new user account before, as you will have to delete it later)
https://github.com/Project-Books/book-project/wiki/Connecting-to-the-backend-via-Postman
2) Delete your own account
Using Postman, send a DELETE request to localhost:8080/api/user, having a raw body which contains email and password key/value pairs.
3) Make some requests where you use the JWT that belonged to the account you have just deleted.
Example: GET localhost:8080/api/user/users
Normally, this request should be rejected, but in practice you can successfully retrieve the result, because the JWT that is sent with the request is still valid.
**Additional context**
- Read our contributing guidelines first!
- We'll require you to discuss you implementation approach before being assigned to this
- Branch from `main` and set it as the destination branch in your pull request
| True | Invalidate JWT token after account deletion - Currently, JSON Web Tokens (JWTs) are used for passing authentication information. These tokens expire automatically, after a period of time.
Most requests need authorization information; otherwise, the requests are rejected (server returns 403 Forbidden response).
For example, if you want to list users, you will have to send valid authentication information.
The problem is that, after user account deletion, user JWT remains valid (until it expires) and can be used to make requests that normally should be rejected.
Steps to reproduce the issue:
1) Login using Postman (you may wish to create a new user account before, as you will have to delete it later)
https://github.com/Project-Books/book-project/wiki/Connecting-to-the-backend-via-Postman
2) Delete your own account
Using Postman, send a DELETE request to localhost:8080/api/user, having a raw body which contains email and password key/value pairs.
3) Make some requests where you use the JWT that belonged to the account you have just deleted.
Example: GET localhost:8080/api/user/users
Normally, this request should be rejected, but in practice you can successfully retrieve the result, because the JWT that is sent with the request is still valid.
**Additional context**
- Read our contributing guidelines first!
- We'll require you to discuss you implementation approach before being assigned to this
- Branch from `main` and set it as the destination branch in your pull request
| non_usab | invalidate jwt token after account deletion currently json web tokens jwts are used for passing authentication information these tokens expire automatically after a period of time most requests need authorization information otherwise the requests are rejected server returns forbidden response for example if you want to list users you will have to send valid authentication information the problem is that after user account deletion user jwt remains valid until it expires and can be used to make requests that normally should be rejected steps to reproduce the issue login using postman you may wish to create a new user account before as you will have to delete it later delete your own account using postman send a delete request to localhost api user having a raw body which contains email and password key value pairs make some requests where you use the jwt that belonged to the account you have just deleted example get localhost api user users normally this request should be rejected but in practice you can successfully retrieve the result because the jwt that is sent with the request is still valid additional context read our contributing guidelines first we ll require you to discuss you implementation approach before being assigned to this branch from main and set it as the destination branch in your pull request | 0 |
5,524 | 3,933,595,272 | IssuesEvent | 2016-04-25 19:41:06 | rabbitmq/rabbitmq-dotnet-client | https://api.github.com/repos/rabbitmq/rabbitmq-dotnet-client | closed | EventingBasicConsumer Shutdown event fires twice | bug effort-low usability | Was just hooking into the events and noticed the Shutdown event fires twice for EventingBasicConsumer. Unsure if this is known/desired behavior or a bug.
Here is a quick sample. Nothing special or out of the ordinary imo.
Using latest client as of this writing, 3.5.6.
```csharp
var connectionFactory = new ConnectionFactory();
connectionFactory.Uri = "amqp://user:pass@localhost:5672/dev";
var mqExchange = "devExchange";
var mqQueue = "devQueue";
var mqQueueRouteKey = "rk_devQueue";
using (var mqConn = connectionFactory.CreateConnection())
using (var listenChannel = mqConn.CreateModel())
{
mqConn.ConnectionShutdown += (o, a) => Console.WriteLine("Connection Shutdown");
listenChannel.ModelShutdown += (o, a) => Console.WriteLine("Model Shutdown");
listenChannel.ExchangeDeclare(mqExchange, ExchangeType.Direct, true, false, null);
listenChannel.QueueDeclare(mqQueue, true, false, false, null);
listenChannel.QueueBind(mqQueue, mqExchange, mqQueueRouteKey, null);
var consumer = new EventingBasicConsumer(listenChannel);
consumer.Shutdown += (o, a) => Console.WriteLine("Consumer Shutdown");
String consumerTag = listenChannel.BasicConsume(mqQueue, false, consumer);
// same happens if you just let the using dispose statements close the connection
mqConn.Close();
}
```
Output is:
```
Model Shutdown
Consumer Shutdown
Consumer Shutdown
Connection Shutdown
Press any key to continue . . .
``` | True | EventingBasicConsumer Shutdown event fires twice - Was just hooking into the events and noticed the Shutdown event fires twice for EventingBasicConsumer. Unsure if this is known/desired behavior or a bug.
Here is a quick sample. Nothing special or out of the ordinary imo.
Using latest client as of this writing, 3.5.6.
```csharp
var connectionFactory = new ConnectionFactory();
connectionFactory.Uri = "amqp://user:pass@localhost:5672/dev";
var mqExchange = "devExchange";
var mqQueue = "devQueue";
var mqQueueRouteKey = "rk_devQueue";
using (var mqConn = connectionFactory.CreateConnection())
using (var listenChannel = mqConn.CreateModel())
{
mqConn.ConnectionShutdown += (o, a) => Console.WriteLine("Connection Shutdown");
listenChannel.ModelShutdown += (o, a) => Console.WriteLine("Model Shutdown");
listenChannel.ExchangeDeclare(mqExchange, ExchangeType.Direct, true, false, null);
listenChannel.QueueDeclare(mqQueue, true, false, false, null);
listenChannel.QueueBind(mqQueue, mqExchange, mqQueueRouteKey, null);
var consumer = new EventingBasicConsumer(listenChannel);
consumer.Shutdown += (o, a) => Console.WriteLine("Consumer Shutdown");
String consumerTag = listenChannel.BasicConsume(mqQueue, false, consumer);
// same happens if you just let the using dispose statements close the connection
mqConn.Close();
}
```
Output is:
```
Model Shutdown
Consumer Shutdown
Consumer Shutdown
Connection Shutdown
Press any key to continue . . .
``` | usab | eventingbasicconsumer shutdown event fires twice was just hooking into the events and noticed the shutdown event fires twice for eventingbasicconsumer unsure if this is known desired behavior or a bug here is a quick sample nothing special or out of the ordinary imo using latest client as of this writing csharp var connectionfactory new connectionfactory connectionfactory uri amqp user pass localhost dev var mqexchange devexchange var mqqueue devqueue var mqqueueroutekey rk devqueue using var mqconn connectionfactory createconnection using var listenchannel mqconn createmodel mqconn connectionshutdown o a console writeline connection shutdown listenchannel modelshutdown o a console writeline model shutdown listenchannel exchangedeclare mqexchange exchangetype direct true false null listenchannel queuedeclare mqqueue true false false null listenchannel queuebind mqqueue mqexchange mqqueueroutekey null var consumer new eventingbasicconsumer listenchannel consumer shutdown o a console writeline consumer shutdown string consumertag listenchannel basicconsume mqqueue false consumer same happens if you just let the using dispose statements close the connection mqconn close output is model shutdown consumer shutdown consumer shutdown connection shutdown press any key to continue | 1 |
19,530 | 14,174,169,201 | IssuesEvent | 2020-11-12 19:28:46 | tailscale/tailscale | https://api.github.com/repos/tailscale/tailscale | opened | Auth using AWS SSO | L3 Some users P3 Can't get started T5 Minor usability identity | Placeholder issue that interested parties can subscribe too.
Sister issue: #598 | True | Auth using AWS SSO - Placeholder issue that interested parties can subscribe too.
Sister issue: #598 | usab | auth using aws sso placeholder issue that interested parties can subscribe too sister issue | 1 |
24,626 | 24,058,856,230 | IssuesEvent | 2022-09-16 19:48:15 | pulumi/service-requests | https://api.github.com/repos/pulumi/service-requests | opened | allow more favoriting beyond stacks | kind/enhancement impact/usability | explore adding the ability to favorite projects
and any other things it may make sense to favorite | True | allow more favoriting beyond stacks - explore adding the ability to favorite projects
and any other things it may make sense to favorite | usab | allow more favoriting beyond stacks explore adding the ability to favorite projects and any other things it may make sense to favorite | 1 |
23,539 | 22,151,955,184 | IssuesEvent | 2022-06-03 17:52:09 | tailscale/tailscale | https://api.github.com/repos/tailscale/tailscale | closed | FR: Emit helpful warning if the clock is way off | L1 Very few T5 Usability T0 New feature fr | ### What are you trying to do?
tailscale up
### How should we solve this?
if the clock is before the build date of tailscale, emit a helpful warning.
### What is the impact of not solving this?
tailscale up hangs for a long time. user is confused.
### Anything else?
_No response_ | True | FR: Emit helpful warning if the clock is way off - ### What are you trying to do?
tailscale up
### How should we solve this?
if the clock is before the build date of tailscale, emit a helpful warning.
### What is the impact of not solving this?
tailscale up hangs for a long time. user is confused.
### Anything else?
_No response_ | usab | fr emit helpful warning if the clock is way off what are you trying to do tailscale up how should we solve this if the clock is before the build date of tailscale emit a helpful warning what is the impact of not solving this tailscale up hangs for a long time user is confused anything else no response | 1 |
10,581 | 6,808,968,877 | IssuesEvent | 2017-11-04 11:16:21 | micha/resty | https://api.github.com/repos/micha/resty | closed | Helper Flags for content | feature request usability | Add flags such as `-j/--json` `--xml` ash shortcut to set the headers on curl for content negociation
| True | Helper Flags for content - Add flags such as `-j/--json` `--xml` ash shortcut to set the headers on curl for content negociation
| usab | helper flags for content add flags such as j json xml ash shortcut to set the headers on curl for content negociation | 1 |
6,828 | 4,561,312,469 | IssuesEvent | 2016-09-14 11:14:10 | MISP/MISP | https://api.github.com/repos/MISP/MISP | opened | Multiple similar proposals on same attribute | enhancement usability | Let's say Org0 has an attribute (Network Activity/hostname/google.com/no comment/to_ids=yes).
Org1 creates a proposal that changes the attribute, for example by setting to_ids=false.
Org2 also creates a proposal with the same changes.
If Org0 accepts Org1's proposal and re-publishes the event, Org1 proposal is removed.
Should not Org2's proposal also be deleted if it is similar (same Category, Type, Value, Comment and IDS flag)?
This could be implemented in the sync protocol to effectively delete the proposal or maybe as a display filter. | True | Multiple similar proposals on same attribute - Let's say Org0 has an attribute (Network Activity/hostname/google.com/no comment/to_ids=yes).
Org1 creates a proposal that changes the attribute, for example by setting to_ids=false.
Org2 also creates a proposal with the same changes.
If Org0 accepts Org1's proposal and re-publishes the event, Org1 proposal is removed.
Should not Org2's proposal also be deleted if it is similar (same Category, Type, Value, Comment and IDS flag)?
This could be implemented in the sync protocol to effectively delete the proposal or maybe as a display filter. | usab | multiple similar proposals on same attribute let s say has an attribute network activity hostname google com no comment to ids yes creates a proposal that changes the attribute for example by setting to ids false also creates a proposal with the same changes if accepts s proposal and re publishes the event proposal is removed should not s proposal also be deleted if it is similar same category type value comment and ids flag this could be implemented in the sync protocol to effectively delete the proposal or maybe as a display filter | 1 |
14,378 | 9,107,247,146 | IssuesEvent | 2019-02-21 03:25:47 | m3db/m3 | https://api.github.com/repos/m3db/m3 | closed | Use a lockfile in filePathPrefix | C: Storage P: Medium T: Beginner T: Usability area:db | Already experienced configurations when multiple processes point to the same directory. Should catch this using a lockfile. | True | Use a lockfile in filePathPrefix - Already experienced configurations when multiple processes point to the same directory. Should catch this using a lockfile. | usab | use a lockfile in filepathprefix already experienced configurations when multiple processes point to the same directory should catch this using a lockfile | 1 |
10,025 | 6,545,350,894 | IssuesEvent | 2017-09-04 04:00:15 | ian-james/IFS | https://api.github.com/repos/ian-james/IFS | closed | [Critical Functionality] Skills sometimes cannot be added | bug help wanted usability | ## Bug Report
### Description
There is a problem on the /skills route where updating values under 'Course Skills' does not update 'Student Skills. I have attached a [screen recording](https://krourke.org/files/ifs-skills-bug.webm) of this issue and screen shots of the Admin pages to show what is currently in my database.





### Expected behaviour
<!--What were you trying to do, or what did you expect to happen? Answer below this line.-->
Linked List skills should have been added to my Student Skills.
### Actual behaviour
Nothing happened.
### Steps to reproduce
<!--Replace the list below with detailed instructions for reproducing your issue.-->
1. Setup databases similar to mine, as shown in screenshots.
2. Make student select proficiency in one skill.
3. Go back to student skill page and attempt to increase proficiency in a new class skill.
4. Skill fails to be added to student skills.
### System information
#### IFS Version
<!--You can find this in the bottom-right of the footer on any page in IFS.
Ex. v0.0.1. Indicate below this line. -->
v0.0.2 | True | [Critical Functionality] Skills sometimes cannot be added - ## Bug Report
### Description
There is a problem on the /skills route where updating values under 'Course Skills' does not update 'Student Skills. I have attached a [screen recording](https://krourke.org/files/ifs-skills-bug.webm) of this issue and screen shots of the Admin pages to show what is currently in my database.





### Expected behaviour
<!--What were you trying to do, or what did you expect to happen? Answer below this line.-->
Linked List skills should have been added to my Student Skills.
### Actual behaviour
Nothing happened.
### Steps to reproduce
<!--Replace the list below with detailed instructions for reproducing your issue.-->
1. Setup databases similar to mine, as shown in screenshots.
2. Make student select proficiency in one skill.
3. Go back to student skill page and attempt to increase proficiency in a new class skill.
4. Skill fails to be added to student skills.
### System information
#### IFS Version
<!--You can find this in the bottom-right of the footer on any page in IFS.
Ex. v0.0.1. Indicate below this line. -->
v0.0.2 | usab | skills sometimes cannot be added bug report description there is a problem on the skills route where updating values under course skills does not update student skills i have attached a of this issue and screen shots of the admin pages to show what is currently in my database expected behaviour linked list skills should have been added to my student skills actual behaviour nothing happened steps to reproduce setup databases similar to mine as shown in screenshots make student select proficiency in one skill go back to student skill page and attempt to increase proficiency in a new class skill skill fails to be added to student skills system information ifs version you can find this in the bottom right of the footer on any page in ifs ex indicate below this line | 1 |
336,470 | 10,192,120,988 | IssuesEvent | 2019-08-12 10:13:11 | btc-ag/redg | https://api.github.com/repos/btc-ag/redg | closed | Support for Liquibase | enhancement feature proposal priority urgent | Thanks for RedG, an impressive and very useful tool.
I have a feature Request: In our project, we use liquibase & testcontainers to setup a database-schema from scratch. It'd be nice if we could use this schema to run RedG against, so that we do not need to fiddle with H2 (which is next to impossible for us, due to a somewhat complex schema).
So the idea would be, to pass a liquibase properties file to the redg maven plugin and RedG to run liquibase before doing its thing.
Please consider this Feature Request or feel free to suggest a different solution. | 1.0 | Support for Liquibase - Thanks for RedG, an impressive and very useful tool.
I have a feature Request: In our project, we use liquibase & testcontainers to setup a database-schema from scratch. It'd be nice if we could use this schema to run RedG against, so that we do not need to fiddle with H2 (which is next to impossible for us, due to a somewhat complex schema).
So the idea would be, to pass a liquibase properties file to the redg maven plugin and RedG to run liquibase before doing its thing.
Please consider this Feature Request or feel free to suggest a different solution. | non_usab | support for liquibase thanks for redg an impressive and very useful tool i have a feature request in our project we use liquibase testcontainers to setup a database schema from scratch it d be nice if we could use this schema to run redg against so that we do not need to fiddle with which is next to impossible for us due to a somewhat complex schema so the idea would be to pass a liquibase properties file to the redg maven plugin and redg to run liquibase before doing its thing please consider this feature request or feel free to suggest a different solution | 0 |
55,937 | 13,723,740,295 | IssuesEvent | 2020-10-03 10:55:08 | googleapis/java-storage | https://api.github.com/repos/googleapis/java-storage | closed | storage.it.ITStorageTest: testWriteChannelWithConnectionPool failed | api: storage buildcop: issue priority: p1 type: bug | This test failed!
To configure my behavior, see [the Build Cop Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/master/packages/buildcop).
If I'm commenting on this issue too often, add the `buildcop: quiet` label and
I will stop commenting.
---
commit: e5a8fa86843e63c677d4e2edc95ecb3a73e9fb81
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/11bcb195-2e46-421e-b559-b226b8329934), [Sponge](http://sponge2/11bcb195-2e46-421e-b559-b226b8329934)
status: failed
<details><summary>Test output</summary><br><pre>org.junit.runners.model.TestTimedOutException: test timed out after 5000 milliseconds
at java.net.SocketInputStream.socketRead0(Native Method)
at java.net.SocketInputStream.socketRead(SocketInputStream.java:116)
at java.net.SocketInputStream.read(SocketInputStream.java:171)
at java.net.SocketInputStream.read(SocketInputStream.java:141)
at sun.security.ssl.InputRecord.readFully(InputRecord.java:465)
at sun.security.ssl.InputRecord.read(InputRecord.java:503)
at sun.security.ssl.SSLSocketImpl.readRecord(SSLSocketImpl.java:990)
at sun.security.ssl.SSLSocketImpl.readDataRecord(SSLSocketImpl.java:948)
at sun.security.ssl.AppInputStream.read(AppInputStream.java:105)
at org.apache.http.impl.io.SessionInputBufferImpl.streamRead(SessionInputBufferImpl.java:137)
at org.apache.http.impl.io.SessionInputBufferImpl.fillBuffer(SessionInputBufferImpl.java:153)
at org.apache.http.impl.io.SessionInputBufferImpl.readLine(SessionInputBufferImpl.java:280)
at org.apache.http.impl.conn.DefaultHttpResponseParser.parseHead(DefaultHttpResponseParser.java:138)
at org.apache.http.impl.conn.DefaultHttpResponseParser.parseHead(DefaultHttpResponseParser.java:56)
at org.apache.http.impl.io.AbstractMessageParser.parse(AbstractMessageParser.java:259)
at org.apache.http.impl.DefaultBHttpClientConnection.receiveResponseHeader(DefaultBHttpClientConnection.java:163)
at org.apache.http.impl.conn.CPoolProxy.receiveResponseHeader(CPoolProxy.java:157)
at org.apache.http.protocol.HttpRequestExecutor.doReceiveResponse(HttpRequestExecutor.java:273)
at org.apache.http.protocol.HttpRequestExecutor.execute(HttpRequestExecutor.java:125)
at org.apache.http.impl.execchain.MinimalClientExec.execute(MinimalClientExec.java:216)
at org.apache.http.impl.client.MinimalHttpClient.doExecute(MinimalHttpClient.java:108)
at org.apache.http.impl.client.CloseableHttpClient.execute(CloseableHttpClient.java:83)
at org.apache.http.impl.client.CloseableHttpClient.execute(CloseableHttpClient.java:108)
at org.apache.http.impl.client.CloseableHttpClient.execute(CloseableHttpClient.java:56)
at com.google.api.client.http.apache.ApacheHttpRequest.execute(ApacheHttpRequest.java:67)
at com.google.api.client.http.HttpRequest.execute(HttpRequest.java:1012)
at com.google.cloud.storage.spi.v1.HttpStorageRpc.writeWithResponse(HttpStorageRpc.java:792)
at com.google.cloud.storage.BlobWriteChannel$1.run(BlobWriteChannel.java:69)
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
at com.google.api.gax.retrying.DirectRetryingExecutor.submit(DirectRetryingExecutor.java:105)
at com.google.cloud.RetryHelper.run(RetryHelper.java:76)
at com.google.cloud.RetryHelper.runWithRetries(RetryHelper.java:50)
at com.google.cloud.storage.BlobWriteChannel.flushBuffer(BlobWriteChannel.java:61)
at com.google.cloud.BaseWriteChannel.close(BaseWriteChannel.java:151)
at com.google.cloud.storage.it.ITStorageTest.testWriteChannelWithConnectionPool(ITStorageTest.java:1959)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:288)
at org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:282)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.lang.Thread.run(Thread.java:748)
</pre></details> | 1.0 | storage.it.ITStorageTest: testWriteChannelWithConnectionPool failed - This test failed!
To configure my behavior, see [the Build Cop Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/master/packages/buildcop).
If I'm commenting on this issue too often, add the `buildcop: quiet` label and
I will stop commenting.
---
commit: e5a8fa86843e63c677d4e2edc95ecb3a73e9fb81
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/11bcb195-2e46-421e-b559-b226b8329934), [Sponge](http://sponge2/11bcb195-2e46-421e-b559-b226b8329934)
status: failed
<details><summary>Test output</summary><br><pre>org.junit.runners.model.TestTimedOutException: test timed out after 5000 milliseconds
at java.net.SocketInputStream.socketRead0(Native Method)
at java.net.SocketInputStream.socketRead(SocketInputStream.java:116)
at java.net.SocketInputStream.read(SocketInputStream.java:171)
at java.net.SocketInputStream.read(SocketInputStream.java:141)
at sun.security.ssl.InputRecord.readFully(InputRecord.java:465)
at sun.security.ssl.InputRecord.read(InputRecord.java:503)
at sun.security.ssl.SSLSocketImpl.readRecord(SSLSocketImpl.java:990)
at sun.security.ssl.SSLSocketImpl.readDataRecord(SSLSocketImpl.java:948)
at sun.security.ssl.AppInputStream.read(AppInputStream.java:105)
at org.apache.http.impl.io.SessionInputBufferImpl.streamRead(SessionInputBufferImpl.java:137)
at org.apache.http.impl.io.SessionInputBufferImpl.fillBuffer(SessionInputBufferImpl.java:153)
at org.apache.http.impl.io.SessionInputBufferImpl.readLine(SessionInputBufferImpl.java:280)
at org.apache.http.impl.conn.DefaultHttpResponseParser.parseHead(DefaultHttpResponseParser.java:138)
at org.apache.http.impl.conn.DefaultHttpResponseParser.parseHead(DefaultHttpResponseParser.java:56)
at org.apache.http.impl.io.AbstractMessageParser.parse(AbstractMessageParser.java:259)
at org.apache.http.impl.DefaultBHttpClientConnection.receiveResponseHeader(DefaultBHttpClientConnection.java:163)
at org.apache.http.impl.conn.CPoolProxy.receiveResponseHeader(CPoolProxy.java:157)
at org.apache.http.protocol.HttpRequestExecutor.doReceiveResponse(HttpRequestExecutor.java:273)
at org.apache.http.protocol.HttpRequestExecutor.execute(HttpRequestExecutor.java:125)
at org.apache.http.impl.execchain.MinimalClientExec.execute(MinimalClientExec.java:216)
at org.apache.http.impl.client.MinimalHttpClient.doExecute(MinimalHttpClient.java:108)
at org.apache.http.impl.client.CloseableHttpClient.execute(CloseableHttpClient.java:83)
at org.apache.http.impl.client.CloseableHttpClient.execute(CloseableHttpClient.java:108)
at org.apache.http.impl.client.CloseableHttpClient.execute(CloseableHttpClient.java:56)
at com.google.api.client.http.apache.ApacheHttpRequest.execute(ApacheHttpRequest.java:67)
at com.google.api.client.http.HttpRequest.execute(HttpRequest.java:1012)
at com.google.cloud.storage.spi.v1.HttpStorageRpc.writeWithResponse(HttpStorageRpc.java:792)
at com.google.cloud.storage.BlobWriteChannel$1.run(BlobWriteChannel.java:69)
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
at com.google.api.gax.retrying.DirectRetryingExecutor.submit(DirectRetryingExecutor.java:105)
at com.google.cloud.RetryHelper.run(RetryHelper.java:76)
at com.google.cloud.RetryHelper.runWithRetries(RetryHelper.java:50)
at com.google.cloud.storage.BlobWriteChannel.flushBuffer(BlobWriteChannel.java:61)
at com.google.cloud.BaseWriteChannel.close(BaseWriteChannel.java:151)
at com.google.cloud.storage.it.ITStorageTest.testWriteChannelWithConnectionPool(ITStorageTest.java:1959)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:288)
at org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:282)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.lang.Thread.run(Thread.java:748)
</pre></details> | non_usab | storage it itstoragetest testwritechannelwithconnectionpool failed this test failed to configure my behavior see if i m commenting on this issue too often add the buildcop quiet label and i will stop commenting commit buildurl status failed test output org junit runners model testtimedoutexception test timed out after milliseconds at java net socketinputstream native method at java net socketinputstream socketread socketinputstream java at java net socketinputstream read socketinputstream java at java net socketinputstream read socketinputstream java at sun security ssl inputrecord readfully inputrecord java at sun security ssl inputrecord read inputrecord java at sun security ssl sslsocketimpl readrecord sslsocketimpl java at sun security ssl sslsocketimpl readdatarecord sslsocketimpl java at sun security ssl appinputstream read appinputstream java at org apache http impl io sessioninputbufferimpl streamread sessioninputbufferimpl java at org apache http impl io sessioninputbufferimpl fillbuffer sessioninputbufferimpl java at org apache http impl io sessioninputbufferimpl readline sessioninputbufferimpl java at org apache http impl conn defaulthttpresponseparser parsehead defaulthttpresponseparser java at org apache http impl conn defaulthttpresponseparser parsehead defaulthttpresponseparser java at org apache http impl io abstractmessageparser parse abstractmessageparser java at org apache http impl defaultbhttpclientconnection receiveresponseheader defaultbhttpclientconnection java at org apache http impl conn cpoolproxy receiveresponseheader cpoolproxy java at org apache http protocol httprequestexecutor doreceiveresponse httprequestexecutor java at org apache http protocol httprequestexecutor execute httprequestexecutor java at org apache http impl execchain minimalclientexec execute minimalclientexec java at org apache http impl client minimalhttpclient doexecute minimalhttpclient java at org apache http impl client closeablehttpclient execute closeablehttpclient java at org apache http impl client closeablehttpclient execute closeablehttpclient java at org apache http impl client closeablehttpclient execute closeablehttpclient java at com google api client http apache apachehttprequest execute apachehttprequest java at com google api client http httprequest execute httprequest java at com google cloud storage spi httpstoragerpc writewithresponse httpstoragerpc java at com google cloud storage blobwritechannel run blobwritechannel java at java util concurrent executors runnableadapter call executors java at com google api gax retrying directretryingexecutor submit directretryingexecutor java at com google cloud retryhelper run retryhelper java at com google cloud retryhelper runwithretries retryhelper java at com google cloud storage blobwritechannel flushbuffer blobwritechannel java at com google cloud basewritechannel close basewritechannel java at com google cloud storage it itstoragetest testwritechannelwithconnectionpool itstoragetest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at org junit internal runners statements failontimeout callablestatement call failontimeout java at org junit internal runners statements failontimeout callablestatement call failontimeout java at java util concurrent futuretask run futuretask java at java lang thread run thread java | 0 |
62,652 | 6,802,324,782 | IssuesEvent | 2017-11-02 19:47:48 | WikiWatershed/model-my-watershed | https://api.github.com/repos/WikiWatershed/model-my-watershed | closed | Add Source Data direct link to WDC Unit Values and Groundwater search results | BiG CZ November demo BigCZ tested/verified | For WDC Daily Values search results (NWISDV), we include a "Source Data" direct link in the details page to the sensor page. Add this for Unit Values (NWISUV) results as well; Anthony says the URL path should be parallel. | 1.0 | Add Source Data direct link to WDC Unit Values and Groundwater search results - For WDC Daily Values search results (NWISDV), we include a "Source Data" direct link in the details page to the sensor page. Add this for Unit Values (NWISUV) results as well; Anthony says the URL path should be parallel. | non_usab | add source data direct link to wdc unit values and groundwater search results for wdc daily values search results nwisdv we include a source data direct link in the details page to the sensor page add this for unit values nwisuv results as well anthony says the url path should be parallel | 0 |
376,565 | 11,148,515,245 | IssuesEvent | 2019-12-23 15:45:03 | dhenry-KCI/FredCo-Post-Go-Live- | https://api.github.com/repos/dhenry-KCI/FredCo-Post-Go-Live- | opened | town review | Medium Priority | town review will not allow completeness check to be resulted get the error that no contact information is available for this town review..
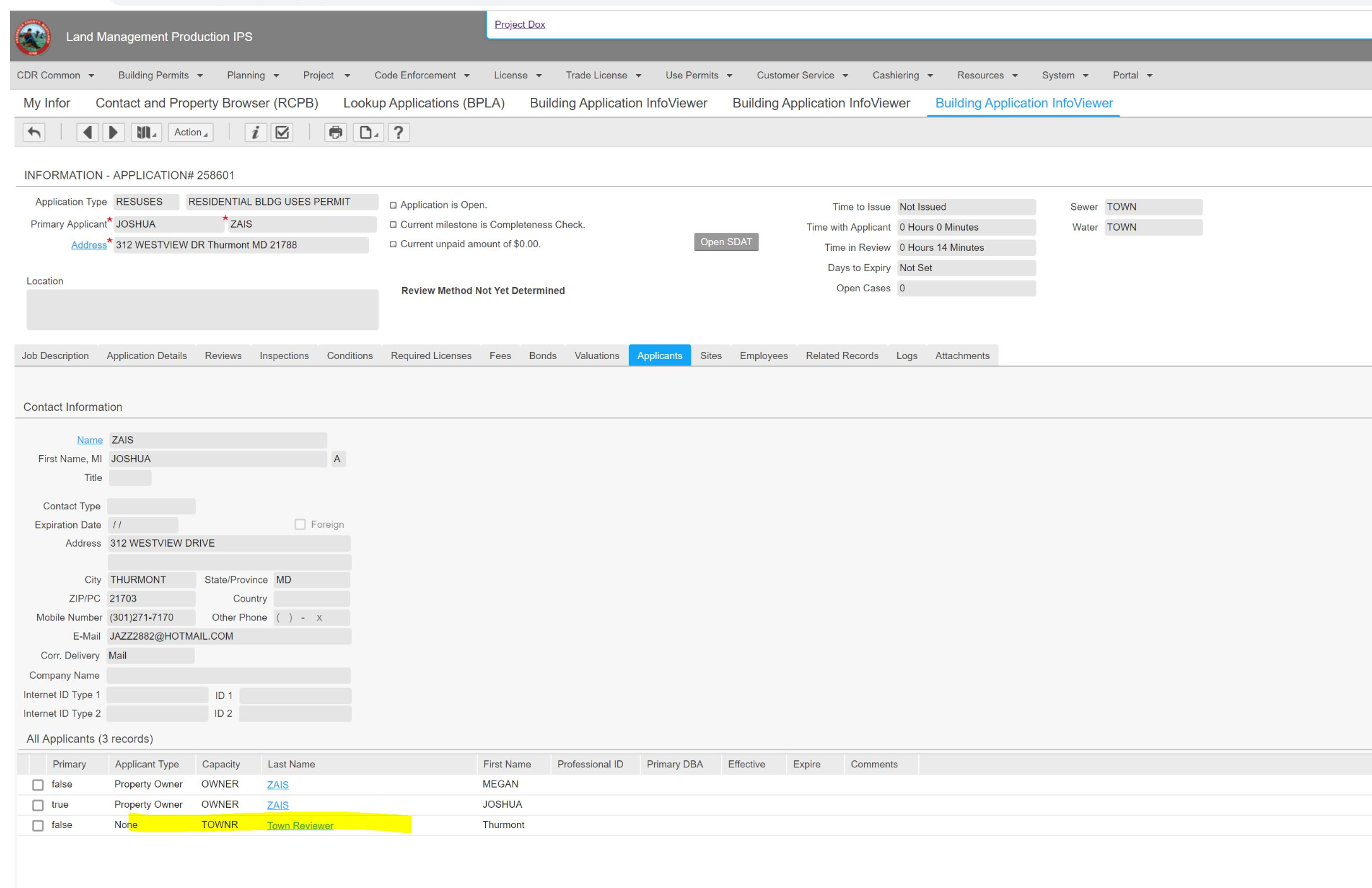
removed applicant to progress past completeness check
this is a reoccuring issue | 1.0 | town review - town review will not allow completeness check to be resulted get the error that no contact information is available for this town review..
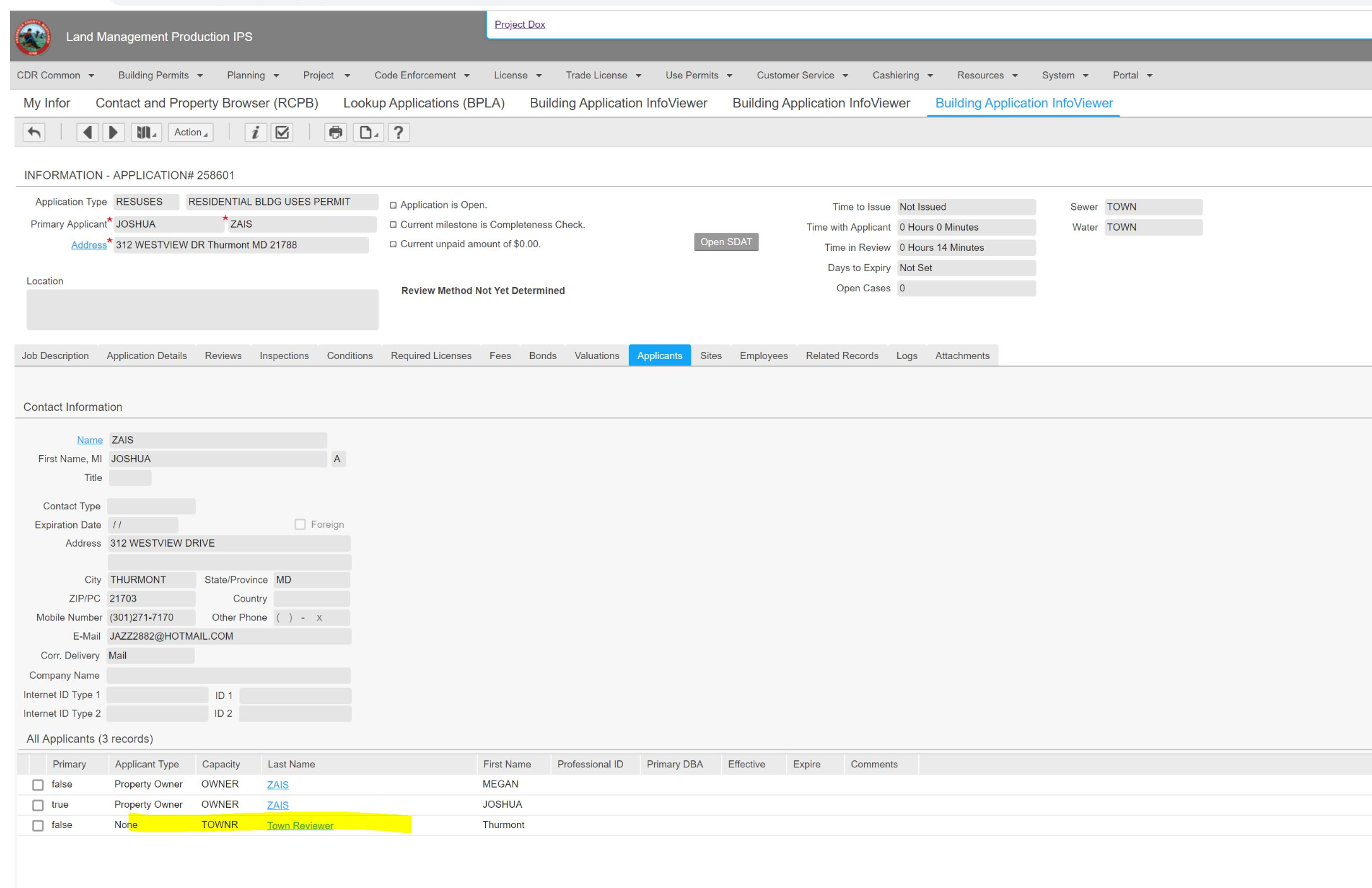
removed applicant to progress past completeness check
this is a reoccuring issue | non_usab | town review town review will not allow completeness check to be resulted get the error that no contact information is available for this town review removed applicant to progress past completeness check this is a reoccuring issue | 0 |
13,292 | 8,409,368,706 | IssuesEvent | 2018-10-12 07:03:34 | virtual-labs/problem-solving-iiith | https://api.github.com/repos/virtual-labs/problem-solving-iiith | closed | QA_Problem-Solving_experiment_String-Operations_Experiment is not provided | Category :Functionality Category :UI Category :Usability Developed by:IIIT Hyd Open-edx-Issue QA-bugs Severity :S1 Status :Resolved | Defect Description :
In the Experiment page of String Operations experiment, the content of the section is not ported.
Actual Result :
In the Experiment page of String Operations experiment, the content of the section is not ported. The entire experiment is not visible.
Environment :
OS: Windows 7, Ubuntu-16.04, Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM,
Processor:i5
Attachments:

| True | QA_Problem-Solving_experiment_String-Operations_Experiment is not provided - Defect Description :
In the Experiment page of String Operations experiment, the content of the section is not ported.
Actual Result :
In the Experiment page of String Operations experiment, the content of the section is not ported. The entire experiment is not visible.
Environment :
OS: Windows 7, Ubuntu-16.04, Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM,
Processor:i5
Attachments:

| usab | qa problem solving experiment string operations experiment is not provided defect description in the experiment page of string operations experiment the content of the section is not ported actual result in the experiment page of string operations experiment the content of the section is not ported the entire experiment is not visible environment os windows ubuntu centos browsers firefox chrome chromium bandwidth hardware configuration processor attachments | 1 |
16,915 | 11,491,368,015 | IssuesEvent | 2020-02-11 18:51:32 | zaproxy/zaproxy | https://api.github.com/repos/zaproxy/zaproxy | closed | Base64 potentially long Loop | Performance Usability add-on | **Describe the bug**
We are scanning a very large web application that is causing ZAP to crash. We've increased the memory to 8GB for ZAP in the zap.bat file but it continues to enter a kind of loop when passive testing BASE64 Disclosure and keeps reporting the same exact JavaScript file over and over again until it runs out of memory.
**To Reproduce**
Steps to reproduce the behavior:
- In ZAP BAT change from the default 512MB memory to "set jvmopts=-Xmx8096m"
- Manual Explore
- HUD
- Wait 30 seconds as ZAP passive scans the initial page
- ZAP alert queue Base64 starts filling up with alerts
- CPU fans starts going crazy
- Machine becomes slow
- Have to force quit ZAP before things get to hairy
**Expected behavior**
One single Base64 Disclosure per file, instead of 900 Base64 disclosures for a single file. Although I suspect this is more of a symptom than the actual root cause. Hopefully the Log File attached will tell more.
**Screenshots**

**Software versions**
- ZAP: 2.9
- Add-on:
[2020-02-11_InstalledAddOns.txt](https://github.com/zaproxy/zaproxy/files/4187013/2020-02-11_InstalledAddOns.txt)
- OS: Windows 10 1909 Build 18363.592
- Java: Bellsoft openjdk version "13.0.2" 2020-01-15
OpenJDK Runtime Environment (build 13.0.2+9)
OpenJDK 64-Bit Server VM (build 13.0.2+9, mixed mode, sharing)
- Browser: Firefox 72.0.1
**Errors from the zap.log file**
[2020-02-11_Passive_Scanning_outofmemory.log](https://github.com/zaproxy/zaproxy/files/4187018/2020-02-11_Passive_Scanning_outofmemory.log)
**Additional context**
The website is running on a nonstandard TCP port
| True | Base64 potentially long Loop - **Describe the bug**
We are scanning a very large web application that is causing ZAP to crash. We've increased the memory to 8GB for ZAP in the zap.bat file but it continues to enter a kind of loop when passive testing BASE64 Disclosure and keeps reporting the same exact JavaScript file over and over again until it runs out of memory.
**To Reproduce**
Steps to reproduce the behavior:
- In ZAP BAT change from the default 512MB memory to "set jvmopts=-Xmx8096m"
- Manual Explore
- HUD
- Wait 30 seconds as ZAP passive scans the initial page
- ZAP alert queue Base64 starts filling up with alerts
- CPU fans starts going crazy
- Machine becomes slow
- Have to force quit ZAP before things get to hairy
**Expected behavior**
One single Base64 Disclosure per file, instead of 900 Base64 disclosures for a single file. Although I suspect this is more of a symptom than the actual root cause. Hopefully the Log File attached will tell more.
**Screenshots**

**Software versions**
- ZAP: 2.9
- Add-on:
[2020-02-11_InstalledAddOns.txt](https://github.com/zaproxy/zaproxy/files/4187013/2020-02-11_InstalledAddOns.txt)
- OS: Windows 10 1909 Build 18363.592
- Java: Bellsoft openjdk version "13.0.2" 2020-01-15
OpenJDK Runtime Environment (build 13.0.2+9)
OpenJDK 64-Bit Server VM (build 13.0.2+9, mixed mode, sharing)
- Browser: Firefox 72.0.1
**Errors from the zap.log file**
[2020-02-11_Passive_Scanning_outofmemory.log](https://github.com/zaproxy/zaproxy/files/4187018/2020-02-11_Passive_Scanning_outofmemory.log)
**Additional context**
The website is running on a nonstandard TCP port
| usab | potentially long loop describe the bug we are scanning a very large web application that is causing zap to crash we ve increased the memory to for zap in the zap bat file but it continues to enter a kind of loop when passive testing disclosure and keeps reporting the same exact javascript file over and over again until it runs out of memory to reproduce steps to reproduce the behavior in zap bat change from the default memory to set jvmopts manual explore hud wait seconds as zap passive scans the initial page zap alert queue starts filling up with alerts cpu fans starts going crazy machine becomes slow have to force quit zap before things get to hairy expected behavior one single disclosure per file instead of disclosures for a single file although i suspect this is more of a symptom than the actual root cause hopefully the log file attached will tell more screenshots software versions zap add on os windows build java bellsoft openjdk version openjdk runtime environment build openjdk bit server vm build mixed mode sharing browser firefox errors from the zap log file additional context the website is running on a nonstandard tcp port | 1 |
4,637 | 3,875,269,767 | IssuesEvent | 2016-04-12 00:02:36 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 22086967: Spaces misbehaves in 10.11b4 and 5 | classification:ui/usability reproducible:always status:open | #### Description
Summary:
Spaces behaves incorrectly in 10.11b4 and b5. For example:
* Spaces behaves as if “When switching to an application, Switch to a Space with open windows for the application” was on, even though it isn’t.
* Two spaces: App A is active on Space 1, App B has an open window on Space 1 and Space 2. Switching from space 1 to space 2 will activate app B, and then incorrectly orders front the window for app B which is on *space 1*, forcing you back to Space A.
Steps to Reproduce:
1. Disable “When switching to an application, Switch to a Space with open windows for the application”
2. Open Safari. Open a window on Space 1, and another one on Space 2.
3. Activate Finder by clicking on the desktop.
4. Swipe right to go to space 2.
Expected Results:
5. The Safari window on Space 2 becomes key
Actual Results:
5. The Safari window on Space 1 becomes key, and transports me back to Space 1.
Regression:
This was introduced in beta 4. Beta 3 did not behave like this.
Notes:
Here is a video recording of this behavior:
https://dl.dropboxusercontent.com/u/6775/Spaces%20bug%2010.11b4-5.m4v
-
Product Version: 10.11 Beta 5 (15A235d)
Created: 2015-07-31T04:59:37.189510
Originated: 2015-07-30T21:59:00
Open Radar Link: http://www.openradar.me/22086967 | True | 22086967: Spaces misbehaves in 10.11b4 and 5 - #### Description
Summary:
Spaces behaves incorrectly in 10.11b4 and b5. For example:
* Spaces behaves as if “When switching to an application, Switch to a Space with open windows for the application” was on, even though it isn’t.
* Two spaces: App A is active on Space 1, App B has an open window on Space 1 and Space 2. Switching from space 1 to space 2 will activate app B, and then incorrectly orders front the window for app B which is on *space 1*, forcing you back to Space A.
Steps to Reproduce:
1. Disable “When switching to an application, Switch to a Space with open windows for the application”
2. Open Safari. Open a window on Space 1, and another one on Space 2.
3. Activate Finder by clicking on the desktop.
4. Swipe right to go to space 2.
Expected Results:
5. The Safari window on Space 2 becomes key
Actual Results:
5. The Safari window on Space 1 becomes key, and transports me back to Space 1.
Regression:
This was introduced in beta 4. Beta 3 did not behave like this.
Notes:
Here is a video recording of this behavior:
https://dl.dropboxusercontent.com/u/6775/Spaces%20bug%2010.11b4-5.m4v
-
Product Version: 10.11 Beta 5 (15A235d)
Created: 2015-07-31T04:59:37.189510
Originated: 2015-07-30T21:59:00
Open Radar Link: http://www.openradar.me/22086967 | usab | spaces misbehaves in and description summary spaces behaves incorrectly in and for example spaces behaves as if “when switching to an application switch to a space with open windows for the application” was on even though it isn’t two spaces app a is active on space app b has an open window on space and space switching from space to space will activate app b and then incorrectly orders front the window for app b which is on space forcing you back to space a steps to reproduce disable “when switching to an application switch to a space with open windows for the application” open safari open a window on space and another one on space activate finder by clicking on the desktop swipe right to go to space expected results the safari window on space becomes key actual results the safari window on space becomes key and transports me back to space regression this was introduced in beta beta did not behave like this notes here is a video recording of this behavior product version beta created originated open radar link | 1 |
50,262 | 6,076,706,923 | IssuesEvent | 2017-06-16 00:20:59 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | [k8s.io] Container Manager Misc [Serial] Validate OOM score adjustments once the node is setup pod infra containers oom-score-adj should be -998 and best effort container's should be 1000 {E2eNode Suite} | kind/flake needs-sig priority/failing-test sig/node | https://k8s-gubernator.appspot.com/build/kubernetes-jenkins/logs/ci-kubernetes-node-kubelet-serial/814/
Failed: [k8s.io] Container Manager Misc [Serial] Validate OOM score adjustments once the node is setup pod infra containers oom-score-adj should be -998 and best effort container's should be 1000 {E2eNode Suite}
```
/go/src/k8s.io/kubernetes/_output/local/go/src/k8s.io/kubernetes/test/e2e_node/container_manager_test.go:149
Timed out after 120.000s.
Expected
<*errors.errorString | 0xc420d48550>: {
s: "failed to get oom_score_adj for 29213: strconv.ParseInt: parsing \"sudo: unable to resolve host ubuntu-trusty\\n1000\": invalid syntax",
}
to be nil
/go/src/k8s.io/kubernetes/_output/local/go/src/k8s.io/kubernetes/test/e2e_node/container_manager_test.go:148
```
| 1.0 | [k8s.io] Container Manager Misc [Serial] Validate OOM score adjustments once the node is setup pod infra containers oom-score-adj should be -998 and best effort container's should be 1000 {E2eNode Suite} - https://k8s-gubernator.appspot.com/build/kubernetes-jenkins/logs/ci-kubernetes-node-kubelet-serial/814/
Failed: [k8s.io] Container Manager Misc [Serial] Validate OOM score adjustments once the node is setup pod infra containers oom-score-adj should be -998 and best effort container's should be 1000 {E2eNode Suite}
```
/go/src/k8s.io/kubernetes/_output/local/go/src/k8s.io/kubernetes/test/e2e_node/container_manager_test.go:149
Timed out after 120.000s.
Expected
<*errors.errorString | 0xc420d48550>: {
s: "failed to get oom_score_adj for 29213: strconv.ParseInt: parsing \"sudo: unable to resolve host ubuntu-trusty\\n1000\": invalid syntax",
}
to be nil
/go/src/k8s.io/kubernetes/_output/local/go/src/k8s.io/kubernetes/test/e2e_node/container_manager_test.go:148
```
| non_usab | container manager misc validate oom score adjustments once the node is setup pod infra containers oom score adj should be and best effort container s should be suite failed container manager misc validate oom score adjustments once the node is setup pod infra containers oom score adj should be and best effort container s should be suite go src io kubernetes output local go src io kubernetes test node container manager test go timed out after expected s failed to get oom score adj for strconv parseint parsing sudo unable to resolve host ubuntu trusty invalid syntax to be nil go src io kubernetes output local go src io kubernetes test node container manager test go | 0 |
211,641 | 16,331,332,955 | IssuesEvent | 2021-05-12 09:35:46 | Azure/sonic-mgmt | https://api.github.com/repos/Azure/sonic-mgmt | reopened | SLB Test Cases | Dual ToR Orchagent Test Dev :o: Dual ToR Test Dev :gemini: |
Step | Goal | Expected results
-- | -- | --
Create peering session from the SLB to Active ToR | SLB | Verify session is established
Create peering session from the SLB to Standby ToR | SLB | Verify session is established
| |
Announce routes from SLB to Active ToR | SLB | Verify routes in Active ToR
Announce routes from SLB to Standby ToR | SLB | Verify routes in Standby ToR
| |
Run PTF tests on Active ToR | SLB | Verify packets forwarded directly to active SLB port
Run PTF tests on Standby ToR | SLB | Verify packets forwarded via tunnel to Active ToR
| |
Withdraw routes from SLB to Active ToR | SLB | Verify routes removed in Active ToR
Withdraw routes from SLB to Standby ToR | SLB | Verify routes removed in Standby ToR
| |
Repeat PTF tests as above | SLB | Verify no packets forwarded
| |
Simulate a mux state change for the SLB port | SLB | Verify both sessions stays established and not disrupted
| |
Announce routes from SLB to new Active ToR | SLB | Verify routes in Active ToR
Announce routes from SLB to new Standby ToR | SLB | Verify routes in Standby ToR
| |
Repeat PTF tests as above | SLB | Verify packet forwarding based on mux state
| |
Verify teardown by shutting peering session one by one | SLB | After one session is down, verify other peering session is active and routes present
| 2.0 | SLB Test Cases -
Step | Goal | Expected results
-- | -- | --
Create peering session from the SLB to Active ToR | SLB | Verify session is established
Create peering session from the SLB to Standby ToR | SLB | Verify session is established
| |
Announce routes from SLB to Active ToR | SLB | Verify routes in Active ToR
Announce routes from SLB to Standby ToR | SLB | Verify routes in Standby ToR
| |
Run PTF tests on Active ToR | SLB | Verify packets forwarded directly to active SLB port
Run PTF tests on Standby ToR | SLB | Verify packets forwarded via tunnel to Active ToR
| |
Withdraw routes from SLB to Active ToR | SLB | Verify routes removed in Active ToR
Withdraw routes from SLB to Standby ToR | SLB | Verify routes removed in Standby ToR
| |
Repeat PTF tests as above | SLB | Verify no packets forwarded
| |
Simulate a mux state change for the SLB port | SLB | Verify both sessions stays established and not disrupted
| |
Announce routes from SLB to new Active ToR | SLB | Verify routes in Active ToR
Announce routes from SLB to new Standby ToR | SLB | Verify routes in Standby ToR
| |
Repeat PTF tests as above | SLB | Verify packet forwarding based on mux state
| |
Verify teardown by shutting peering session one by one | SLB | After one session is down, verify other peering session is active and routes present
| non_usab | slb test cases step goal expected results create peering session from the slb to active tor slb verify session is established create peering session from the slb to standby tor slb verify session is established announce routes from slb to active tor slb verify routes in active tor announce routes from slb to standby tor slb verify routes in standby tor run ptf tests on active tor slb verify packets forwarded directly to active slb port run ptf tests on standby tor slb verify packets forwarded via tunnel to active tor withdraw routes from slb to active tor slb verify routes removed in active tor withdraw routes from slb to standby tor slb verify routes removed in standby tor repeat ptf tests as above slb verify no packets forwarded simulate a mux state change for the slb port slb verify both sessions stays established and not disrupted announce routes from slb to new active tor slb verify routes in active tor announce routes from slb to new standby tor slb verify routes in standby tor repeat ptf tests as above slb verify packet forwarding based on mux state verify teardown by shutting peering session one by one slb after one session is down verify other peering session is active and routes present | 0 |
324,291 | 27,797,784,437 | IssuesEvent | 2023-03-17 13:48:16 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | closed | Quarantine MapAction_JsonBodyOrService_HandlesBothJsonAndService | test-failure area-mvc | <!--
Note this issue template is specifically for failing tests within the dotnet/aspnetcore repo.
-->
## Failing Test(s)
`Microsoft.AspNetCore.Http.Generators.Tests.RequestDelegateCreationTests.MapAction_JsonBodyOrService_HandlesBothJsonAndService`
## Error Message
<!--
Provide the error message associated with the test failure, if applicable.
-->
```text
Line 92 does not match.
Expected Line:
[(@"TestMapActions.cs", 24)] = (
Actual Line:
[(@"TestMapActions.cs", 25)] = (
Expected: True
Actual: False
```
## Stacktrace
<details>
<!--
Provide the stack trace associated with the test failure, if applicable.
-->
```text
at Microsoft.AspNetCore.Http.Generators.Tests.RequestDelegateCreationTestBase.VerifyAgainstBaselineUsingFile(Compilation compilation, String callerName) in /_/src/Http/Http.Extensions/test/RequestDelegateGenerator/RequestDelegateCreationTestBase.cs:line 321
at Microsoft.AspNetCore.Http.Generators.Tests.RequestDelegateCreationTests.MapAction_JsonBodyOrService_HandlesBothJsonAndService() in /_/src/Http/Http.Extensions/test/RequestDelegateGenerator/RequestDelegateCreationTests.JsonBodyOrService.cs:line 76
--- End of stack trace from previous location ---
```
</details>
## Logs
<details>
<!--
Provide the (helix) logs associated with the test failure, if applicable.
-->
```text
```
</details>
## Build
<!--
Provide a link to the build where the test failure occurred.
-->
Looks like this is failing consistently in every aspnetcore-ci run.
https://dev.azure.com/dnceng-public/public/_build/results?buildId=208119&view=ms.vss-test-web.build-test-results-tab&runId=3857770&resultId=106995&paneView=debug
| 1.0 | Quarantine MapAction_JsonBodyOrService_HandlesBothJsonAndService - <!--
Note this issue template is specifically for failing tests within the dotnet/aspnetcore repo.
-->
## Failing Test(s)
`Microsoft.AspNetCore.Http.Generators.Tests.RequestDelegateCreationTests.MapAction_JsonBodyOrService_HandlesBothJsonAndService`
## Error Message
<!--
Provide the error message associated with the test failure, if applicable.
-->
```text
Line 92 does not match.
Expected Line:
[(@"TestMapActions.cs", 24)] = (
Actual Line:
[(@"TestMapActions.cs", 25)] = (
Expected: True
Actual: False
```
## Stacktrace
<details>
<!--
Provide the stack trace associated with the test failure, if applicable.
-->
```text
at Microsoft.AspNetCore.Http.Generators.Tests.RequestDelegateCreationTestBase.VerifyAgainstBaselineUsingFile(Compilation compilation, String callerName) in /_/src/Http/Http.Extensions/test/RequestDelegateGenerator/RequestDelegateCreationTestBase.cs:line 321
at Microsoft.AspNetCore.Http.Generators.Tests.RequestDelegateCreationTests.MapAction_JsonBodyOrService_HandlesBothJsonAndService() in /_/src/Http/Http.Extensions/test/RequestDelegateGenerator/RequestDelegateCreationTests.JsonBodyOrService.cs:line 76
--- End of stack trace from previous location ---
```
</details>
## Logs
<details>
<!--
Provide the (helix) logs associated with the test failure, if applicable.
-->
```text
```
</details>
## Build
<!--
Provide a link to the build where the test failure occurred.
-->
Looks like this is failing consistently in every aspnetcore-ci run.
https://dev.azure.com/dnceng-public/public/_build/results?buildId=208119&view=ms.vss-test-web.build-test-results-tab&runId=3857770&resultId=106995&paneView=debug
| non_usab | quarantine mapaction jsonbodyorservice handlesbothjsonandservice note this issue template is specifically for failing tests within the dotnet aspnetcore repo failing test s microsoft aspnetcore http generators tests requestdelegatecreationtests mapaction jsonbodyorservice handlesbothjsonandservice error message provide the error message associated with the test failure if applicable text line does not match expected line actual line expected true actual false stacktrace provide the stack trace associated with the test failure if applicable text at microsoft aspnetcore http generators tests requestdelegatecreationtestbase verifyagainstbaselineusingfile compilation compilation string callername in src http http extensions test requestdelegategenerator requestdelegatecreationtestbase cs line at microsoft aspnetcore http generators tests requestdelegatecreationtests mapaction jsonbodyorservice handlesbothjsonandservice in src http http extensions test requestdelegategenerator requestdelegatecreationtests jsonbodyorservice cs line end of stack trace from previous location logs provide the helix logs associated with the test failure if applicable text build provide a link to the build where the test failure occurred looks like this is failing consistently in every aspnetcore ci run | 0 |
251,890 | 8,029,090,451 | IssuesEvent | 2018-07-27 14:56:18 | poanetwork/poa-explorer | https://api.github.com/repos/poanetwork/poa-explorer | closed | When a new Block has been Validated, the Contributor sees the new Block on the homepage | in progress priority: high real-time team: contributor | Blocks show up within 5 seconds of validation. | 1.0 | When a new Block has been Validated, the Contributor sees the new Block on the homepage - Blocks show up within 5 seconds of validation. | non_usab | when a new block has been validated the contributor sees the new block on the homepage blocks show up within seconds of validation | 0 |
1,548 | 2,882,165,666 | IssuesEvent | 2015-06-11 01:53:36 | slavapestov/factor | https://api.github.com/repos/slavapestov/factor | closed | ./factor -run=mason.build should just work™ | mason usability | I want to run this command and have it make the ~builds directory, clone factorcode's git, build factor, bootstrap factor, and exit.
| True | ./factor -run=mason.build should just work™ - I want to run this command and have it make the ~builds directory, clone factorcode's git, build factor, bootstrap factor, and exit.
| usab | factor run mason build should just work™ i want to run this command and have it make the builds directory clone factorcode s git build factor bootstrap factor and exit | 1 |
585,664 | 17,514,139,833 | IssuesEvent | 2021-08-11 03:37:01 | SSL-A-Team/software | https://api.github.com/repos/SSL-A-Team/software | opened | Interface with UI referee | Priority: MVP Subsystem: Referee | Since the UI will also be able to send referee commands, we must also be able to take UI ref commands and convert to the local ref object. | 1.0 | Interface with UI referee - Since the UI will also be able to send referee commands, we must also be able to take UI ref commands and convert to the local ref object. | non_usab | interface with ui referee since the ui will also be able to send referee commands we must also be able to take ui ref commands and convert to the local ref object | 0 |
22,077 | 18,497,165,132 | IssuesEvent | 2021-10-19 09:54:09 | virtualsatellite/VirtualSatellite4-Core | https://api.github.com/repos/virtualsatellite/VirtualSatellite4-Core | closed | Improve Requirements Import | feature comfort/usability | - [x] More distinkt icons for different import methods
- [x] Select requirement types to be imported
- [ ] Enable import with requirement and children (requirements) | True | Improve Requirements Import - - [x] More distinkt icons for different import methods
- [x] Select requirement types to be imported
- [ ] Enable import with requirement and children (requirements) | usab | improve requirements import more distinkt icons for different import methods select requirement types to be imported enable import with requirement and children requirements | 1 |
36,016 | 7,847,027,309 | IssuesEvent | 2018-06-19 17:08:56 | pot8oe/mythmote | https://api.github.com/repos/pot8oe/mythmote | closed | Connects but then shows "sendto failed: EPIPE (broken pipe): <ip address> | Priority-Medium Type-Defect auto-migrated | ```
What steps will reproduce the problem?
1.Install mythmote and it connects
2.Press a button and it does nothing
3.Press a second button and you get "Sendto failed: EPIPE (broken pipe): ip
address
What is the expected output? What do you see instead?
That is works, first press does nothing, second press brings up this message
What version of the product are you using? On what operating system?
Mythmote 1.8.5, Mythbuntu 12.04
Please provide any additional information below.
I get the same result on any phone or tablet I use mythmote on, so I think it
is my mythbuntu settings that need tweaking. I have set up all the remote
settings I can find and I think they are o.k. (hence why it connects and then
fails). Could it be my router (it's a Sky router).
```
Original issue reported on code.google.com by `SarahMcL...@googlemail.com` on 23 Dec 2013 at 8:52
| 1.0 | Connects but then shows "sendto failed: EPIPE (broken pipe): <ip address> - ```
What steps will reproduce the problem?
1.Install mythmote and it connects
2.Press a button and it does nothing
3.Press a second button and you get "Sendto failed: EPIPE (broken pipe): ip
address
What is the expected output? What do you see instead?
That is works, first press does nothing, second press brings up this message
What version of the product are you using? On what operating system?
Mythmote 1.8.5, Mythbuntu 12.04
Please provide any additional information below.
I get the same result on any phone or tablet I use mythmote on, so I think it
is my mythbuntu settings that need tweaking. I have set up all the remote
settings I can find and I think they are o.k. (hence why it connects and then
fails). Could it be my router (it's a Sky router).
```
Original issue reported on code.google.com by `SarahMcL...@googlemail.com` on 23 Dec 2013 at 8:52
| non_usab | connects but then shows sendto failed epipe broken pipe what steps will reproduce the problem install mythmote and it connects press a button and it does nothing press a second button and you get sendto failed epipe broken pipe ip address what is the expected output what do you see instead that is works first press does nothing second press brings up this message what version of the product are you using on what operating system mythmote mythbuntu please provide any additional information below i get the same result on any phone or tablet i use mythmote on so i think it is my mythbuntu settings that need tweaking i have set up all the remote settings i can find and i think they are o k hence why it connects and then fails could it be my router it s a sky router original issue reported on code google com by sarahmcl googlemail com on dec at | 0 |
24,092 | 23,341,198,517 | IssuesEvent | 2022-08-09 14:09:45 | accessibility-exchange/platform | https://api.github.com/repos/accessibility-exchange/platform | closed | Individual page creation: phone number field kept showing an error | bug accessibility and usability | Individual page creation: step 4 communication and meeting preferences kept showing an Invalid phone number error
We tried a real 10 digit number starting with 416 as well as the same number starting with country code +1 and 01 but it didn't work and we got the error. | True | Individual page creation: phone number field kept showing an error - Individual page creation: step 4 communication and meeting preferences kept showing an Invalid phone number error
We tried a real 10 digit number starting with 416 as well as the same number starting with country code +1 and 01 but it didn't work and we got the error. | usab | individual page creation phone number field kept showing an error individual page creation step communication and meeting preferences kept showing an invalid phone number error we tried a real digit number starting with as well as the same number starting with country code and but it didn t work and we got the error | 1 |
85,007 | 10,580,255,570 | IssuesEvent | 2019-10-08 06:08:04 | nextcloud/server | https://api.github.com/repos/nextcloud/server | closed | Change the home icon when looking at the trashbin | 1. to develop design enhancement feature: files papercut | <!--
Thanks for reporting issues back to Nextcloud! This is the issue tracker of Nextcloud, if you have any support question please check out https://nextcloud.com/support
This is the bug tracker for the Server component. Find other components at https://github.com/nextcloud/
For reporting potential security issues please see https://nextcloud.com/security/
To make it possible for us to help you please fill out below information carefully.
You can also use the Issue Template application to prefill most of the required information: https://apps.nextcloud.com/apps/issuetemplate
If you are a customer, please submit your issue directly in the Nextcloud Portal https://portal.nextcloud.com so it gets resolved more quickly by our dedicated engineers.
Note that Nextcloud is an open source project backed by Nextcloud GmbH. Most of our volunteers are home users and thus primarily care about issues that affect home users. Our paid engineers prioritize issues of our customers. If you are neither a home user nor a customer, consider paying somebody to fix your issue, do it yourself or become a customer.
-->
**Is your feature request related to a problem? Please describe.**
I find it a bit strange that the "home" icon is being shown when I'm in the trash bin view
**Describe the solution you'd like**
I'd like the Home icon to be replaced with a trash icon when I'm in the trash bin view
**Describe alternatives you've considered**
None. It's not logical to see a home icon there.
**Additional context**
Nothing to add.
| 1.0 | Change the home icon when looking at the trashbin - <!--
Thanks for reporting issues back to Nextcloud! This is the issue tracker of Nextcloud, if you have any support question please check out https://nextcloud.com/support
This is the bug tracker for the Server component. Find other components at https://github.com/nextcloud/
For reporting potential security issues please see https://nextcloud.com/security/
To make it possible for us to help you please fill out below information carefully.
You can also use the Issue Template application to prefill most of the required information: https://apps.nextcloud.com/apps/issuetemplate
If you are a customer, please submit your issue directly in the Nextcloud Portal https://portal.nextcloud.com so it gets resolved more quickly by our dedicated engineers.
Note that Nextcloud is an open source project backed by Nextcloud GmbH. Most of our volunteers are home users and thus primarily care about issues that affect home users. Our paid engineers prioritize issues of our customers. If you are neither a home user nor a customer, consider paying somebody to fix your issue, do it yourself or become a customer.
-->
**Is your feature request related to a problem? Please describe.**
I find it a bit strange that the "home" icon is being shown when I'm in the trash bin view
**Describe the solution you'd like**
I'd like the Home icon to be replaced with a trash icon when I'm in the trash bin view
**Describe alternatives you've considered**
None. It's not logical to see a home icon there.
**Additional context**
Nothing to add.
| non_usab | change the home icon when looking at the trashbin thanks for reporting issues back to nextcloud this is the issue tracker of nextcloud if you have any support question please check out this is the bug tracker for the server component find other components at for reporting potential security issues please see to make it possible for us to help you please fill out below information carefully you can also use the issue template application to prefill most of the required information if you are a customer please submit your issue directly in the nextcloud portal so it gets resolved more quickly by our dedicated engineers note that nextcloud is an open source project backed by nextcloud gmbh most of our volunteers are home users and thus primarily care about issues that affect home users our paid engineers prioritize issues of our customers if you are neither a home user nor a customer consider paying somebody to fix your issue do it yourself or become a customer is your feature request related to a problem please describe i find it a bit strange that the home icon is being shown when i m in the trash bin view describe the solution you d like i d like the home icon to be replaced with a trash icon when i m in the trash bin view describe alternatives you ve considered none it s not logical to see a home icon there additional context nothing to add | 0 |
326,426 | 27,990,430,095 | IssuesEvent | 2023-03-27 02:54:34 | Sars9588/mywebclass-simulation | https://api.github.com/repos/Sars9588/mywebclass-simulation | closed | Testing subtitle text "Values" on Our Story page | Test | Name of Test Developer: Meet
Test Name: Locating subtitle text "Values" in the Our Story page
Test Type: Text
| 1.0 | Testing subtitle text "Values" on Our Story page - Name of Test Developer: Meet
Test Name: Locating subtitle text "Values" in the Our Story page
Test Type: Text
| non_usab | testing subtitle text values on our story page name of test developer meet test name locating subtitle text values in the our story page test type text | 0 |
18,521 | 12,978,949,232 | IssuesEvent | 2020-07-22 00:29:27 | argoproj/argo-cd | https://api.github.com/repos/argoproj/argo-cd | closed | Limit the set of namespaces search for project resources to those list as destinations of the project. | bug component:core type:usability verify | Checklist:
* [x] I've searched in the docs and FAQ for my answer: http://bit.ly/argocd-faq.
* [x] I've included steps to reproduce the bug.
* [x] I've pasted the output of `argocd version`.
**Describe the bug**
Argo currently searches all namespace in a cluster when looking for resources associated with an App. It should only search the namespaces listed as destination of the project to which the App belongs.
**To Reproduce**
1. Create two namespaces A and B.
2. Create an Argo project with A listed as on of its destination
3. Create an App that deploys a configMap to A.
4. Sync the app to the cluster.
5. Use kubectl to dump the config map from A. ```kubectl get configmap [name] -o yaml > [name].yaml```
6. Update the namespace then apply the configMap to namespace B.
After step 6 Argo will mark the App create in step 3 as out of sync. Attempting to sync the App will fail with an error indicating the that configMap in namespace B could not be deployed to namespace A.
**Expected behavior**
Argo should not have associated the configMap from namespace B with the App running in namespace A because namespace B is not one of the destination for the project to which the App belongs.
**Version**
```argocd version
argocd: v1.4.2+48cced9
BuildDate: 2020-01-24T01:04:04Z
GitCommit: 48cced9d925b5bc94f6aa9fa4a8a19b2a59e128a
GitTreeState: clean
GoVersion: go1.12.6
Compiler: gc
Platform: linux/amd64
argocd-server: v1.3.6+89be1c9
BuildDate: 2019-12-10T22:47:48Z
GitCommit: 89be1c9ce6db0f727c81277c1cfdfb1e385bf248
GitTreeState: clean
GoVersion: go1.12.6
Compiler: gc
Platform: linux/amd64
Ksonnet Version: v0.13.1
Kustomize Version: Version: {Version:kustomize/v3.2.1 GitCommit:d89b448c745937f0cf1936162f26a5aac688f840 BuildDate:2019-09-27T00:10:52Z GoOs:linux GoArch:amd64}
Helm Version: v2.15.2
Kubectl Version: v1.14.0
```
| True | Limit the set of namespaces search for project resources to those list as destinations of the project. - Checklist:
* [x] I've searched in the docs and FAQ for my answer: http://bit.ly/argocd-faq.
* [x] I've included steps to reproduce the bug.
* [x] I've pasted the output of `argocd version`.
**Describe the bug**
Argo currently searches all namespace in a cluster when looking for resources associated with an App. It should only search the namespaces listed as destination of the project to which the App belongs.
**To Reproduce**
1. Create two namespaces A and B.
2. Create an Argo project with A listed as on of its destination
3. Create an App that deploys a configMap to A.
4. Sync the app to the cluster.
5. Use kubectl to dump the config map from A. ```kubectl get configmap [name] -o yaml > [name].yaml```
6. Update the namespace then apply the configMap to namespace B.
After step 6 Argo will mark the App create in step 3 as out of sync. Attempting to sync the App will fail with an error indicating the that configMap in namespace B could not be deployed to namespace A.
**Expected behavior**
Argo should not have associated the configMap from namespace B with the App running in namespace A because namespace B is not one of the destination for the project to which the App belongs.
**Version**
```argocd version
argocd: v1.4.2+48cced9
BuildDate: 2020-01-24T01:04:04Z
GitCommit: 48cced9d925b5bc94f6aa9fa4a8a19b2a59e128a
GitTreeState: clean
GoVersion: go1.12.6
Compiler: gc
Platform: linux/amd64
argocd-server: v1.3.6+89be1c9
BuildDate: 2019-12-10T22:47:48Z
GitCommit: 89be1c9ce6db0f727c81277c1cfdfb1e385bf248
GitTreeState: clean
GoVersion: go1.12.6
Compiler: gc
Platform: linux/amd64
Ksonnet Version: v0.13.1
Kustomize Version: Version: {Version:kustomize/v3.2.1 GitCommit:d89b448c745937f0cf1936162f26a5aac688f840 BuildDate:2019-09-27T00:10:52Z GoOs:linux GoArch:amd64}
Helm Version: v2.15.2
Kubectl Version: v1.14.0
```
| usab | limit the set of namespaces search for project resources to those list as destinations of the project checklist i ve searched in the docs and faq for my answer i ve included steps to reproduce the bug i ve pasted the output of argocd version describe the bug argo currently searches all namespace in a cluster when looking for resources associated with an app it should only search the namespaces listed as destination of the project to which the app belongs to reproduce create two namespaces a and b create an argo project with a listed as on of its destination create an app that deploys a configmap to a sync the app to the cluster use kubectl to dump the config map from a kubectl get configmap o yaml yaml update the namespace then apply the configmap to namespace b after step argo will mark the app create in step as out of sync attempting to sync the app will fail with an error indicating the that configmap in namespace b could not be deployed to namespace a expected behavior argo should not have associated the configmap from namespace b with the app running in namespace a because namespace b is not one of the destination for the project to which the app belongs version argocd version argocd builddate gitcommit gittreestate clean goversion compiler gc platform linux argocd server builddate gitcommit gittreestate clean goversion compiler gc platform linux ksonnet version kustomize version version version kustomize gitcommit builddate goos linux goarch helm version kubectl version | 1 |
3,973 | 3,635,238,588 | IssuesEvent | 2016-02-11 21:01:58 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 24613515: Launch Storyboard not correctly transitionning on iPhone 6(s) Plus | classification:ui/usabiblity reproducible:always status:open | #### Description
See https://github.com/stuffmc/LaunchBug
Also check http://twitter.com/StuFFmc/status/696715028347674628
-
Product Version: 9.2.1
Created: 2016-02-11T20:34:05.047060
Originated: 2016-02-11T00:00:00
Open Radar Link: http://www.openradar.me/24613515 | True | 24613515: Launch Storyboard not correctly transitionning on iPhone 6(s) Plus - #### Description
See https://github.com/stuffmc/LaunchBug
Also check http://twitter.com/StuFFmc/status/696715028347674628
-
Product Version: 9.2.1
Created: 2016-02-11T20:34:05.047060
Originated: 2016-02-11T00:00:00
Open Radar Link: http://www.openradar.me/24613515 | usab | launch storyboard not correctly transitionning on iphone s plus description see also check product version created originated open radar link | 1 |
22,246 | 18,876,043,597 | IssuesEvent | 2021-11-14 02:10:30 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | reopened | Can clickhouse support Bit-Sliced Index for better numeric data skipping | usability | Clickhouse `minmax` index can't skip data well while records stored unordered. For example, the minimum and maximum value always appear every `GRANULARITY` lines, in this scenario, clickhouse will not skip any data when you use the index key to filter data.
As far as I know, `Bit-Sliced Index` is the index which can use bitmap to locate numeric data. So I think clickhouse can use this index for better numeric data skipping. | True | Can clickhouse support Bit-Sliced Index for better numeric data skipping - Clickhouse `minmax` index can't skip data well while records stored unordered. For example, the minimum and maximum value always appear every `GRANULARITY` lines, in this scenario, clickhouse will not skip any data when you use the index key to filter data.
As far as I know, `Bit-Sliced Index` is the index which can use bitmap to locate numeric data. So I think clickhouse can use this index for better numeric data skipping. | usab | can clickhouse support bit sliced index for better numeric data skipping clickhouse minmax index can t skip data well while records stored unordered for example the minimum and maximum value always appear every granularity lines in this scenario clickhouse will not skip any data when you use the index key to filter data as far as i know bit sliced index is the index which can use bitmap to locate numeric data so i think clickhouse can use this index for better numeric data skipping | 1 |
705,225 | 24,226,706,573 | IssuesEvent | 2022-09-26 14:54:48 | oncokb/oncokb | https://api.github.com/repos/oncokb/oncokb | closed | Look into Swagger XSS attack | high priority | cBioPortal received an email from an user mentioning about the attack. https://groups.google.com/g/cbioportal/c/ZmHQU3J9KgE
I looked at our swagger, the url did pass to the backend but I don't see the alert showed in the post. Maybe the version we use already have the fix? We need to look into this issue.
A relevant article https://www.vidocsecurity.com/blog/hacking-swagger-ui-from-xss-to-account-takeovers/
Portal did make a patch for it https://togithub.com/cBioPortal/cbioportal/pull/9768 | 1.0 | Look into Swagger XSS attack - cBioPortal received an email from an user mentioning about the attack. https://groups.google.com/g/cbioportal/c/ZmHQU3J9KgE
I looked at our swagger, the url did pass to the backend but I don't see the alert showed in the post. Maybe the version we use already have the fix? We need to look into this issue.
A relevant article https://www.vidocsecurity.com/blog/hacking-swagger-ui-from-xss-to-account-takeovers/
Portal did make a patch for it https://togithub.com/cBioPortal/cbioportal/pull/9768 | non_usab | look into swagger xss attack cbioportal received an email from an user mentioning about the attack i looked at our swagger the url did pass to the backend but i don t see the alert showed in the post maybe the version we use already have the fix we need to look into this issue a relevant article portal did make a patch for it | 0 |
6,087 | 4,149,413,208 | IssuesEvent | 2016-06-15 14:24:59 | Cadasta/cadasta-platform | https://api.github.com/repos/Cadasta/cadasta-platform | closed | archiving | reusable component | archiving functionality in base data model (including correct treatment of entities associated with archived entities); control of visibility of archived objects in front end; archive/unarchive UI. | True | archiving - archiving functionality in base data model (including correct treatment of entities associated with archived entities); control of visibility of archived objects in front end; archive/unarchive UI. | usab | archiving archiving functionality in base data model including correct treatment of entities associated with archived entities control of visibility of archived objects in front end archive unarchive ui | 1 |
430,723 | 12,464,977,053 | IssuesEvent | 2020-05-28 13:22:05 | kubernetes/dashboard | https://api.github.com/repos/kubernetes/dashboard | closed | UX: Refresh scrolls the page to top | kind/bug priority/critical-urgent | <!-- Please use this template while reporting a bug and provide as much info as possible. Not doing so may result in your bug not being addressed in a timely manner. Thanks!-->
##### Environment
<!-- Describe your setup. Versions of Node.js, Go etc. are needed only from developers. -->
```
Installation method: kubeadm + Helm
Kubernetes version: 1.16.9
Dashboard version: 2.0.0
Operating system: N/A
Node.js version ('node --version' output): N/A
Go version ('go version' output): N/A
```
##### Steps to reproduce
Set the settings to show 50 items per page. Open a list of pods in a namespace where you have a lot of pods. Scroll to bottom. After few seconds on refresh the page scrolls to top.
##### Observed result
Page scrolls to to on each refresh, eg. every 5s
##### Expected result
Page should not scroll away from a viewpoint I'm looking at (based on an automated event).
##### Comments
<!-- If you have any comments or more details, put them here. -->
| 1.0 | UX: Refresh scrolls the page to top - <!-- Please use this template while reporting a bug and provide as much info as possible. Not doing so may result in your bug not being addressed in a timely manner. Thanks!-->
##### Environment
<!-- Describe your setup. Versions of Node.js, Go etc. are needed only from developers. -->
```
Installation method: kubeadm + Helm
Kubernetes version: 1.16.9
Dashboard version: 2.0.0
Operating system: N/A
Node.js version ('node --version' output): N/A
Go version ('go version' output): N/A
```
##### Steps to reproduce
Set the settings to show 50 items per page. Open a list of pods in a namespace where you have a lot of pods. Scroll to bottom. After few seconds on refresh the page scrolls to top.
##### Observed result
Page scrolls to to on each refresh, eg. every 5s
##### Expected result
Page should not scroll away from a viewpoint I'm looking at (based on an automated event).
##### Comments
<!-- If you have any comments or more details, put them here. -->
| non_usab | ux refresh scrolls the page to top environment installation method kubeadm helm kubernetes version dashboard version operating system n a node js version node version output n a go version go version output n a steps to reproduce set the settings to show items per page open a list of pods in a namespace where you have a lot of pods scroll to bottom after few seconds on refresh the page scrolls to top observed result page scrolls to to on each refresh eg every expected result page should not scroll away from a viewpoint i m looking at based on an automated event comments | 0 |
43,379 | 5,537,559,100 | IssuesEvent | 2017-03-21 22:26:17 | fossology/fossology | https://api.github.com/repos/fossology/fossology | closed | Add unit tests for Common UI Modules (Dan) | Category: Testing Priority: Normal Status: New Tracker: Support | ---
Author Name: **Paul Holland**
Original Redmine Issue: 2865, http://www.fossology.org/issues/2865
Original Date: 2012/06/15
Original Assignee: Dan Stangel
---
Fills in http://www.fossology.org/projects/fossology/wiki/FOSSology_tests
Add tests for the following modules:
1. common-active.php
2. common-agents.php
3. common-cache.php
4. common-buckets.php
5. common-compare.php
6. common-db.php
7. common-job.php
8. common-license-file.php
9. common.php
1. common-plugin.php
2. common-repo.php
3. common-tags.php
4. bootstrap.php
| 1.0 | Add unit tests for Common UI Modules (Dan) - ---
Author Name: **Paul Holland**
Original Redmine Issue: 2865, http://www.fossology.org/issues/2865
Original Date: 2012/06/15
Original Assignee: Dan Stangel
---
Fills in http://www.fossology.org/projects/fossology/wiki/FOSSology_tests
Add tests for the following modules:
1. common-active.php
2. common-agents.php
3. common-cache.php
4. common-buckets.php
5. common-compare.php
6. common-db.php
7. common-job.php
8. common-license-file.php
9. common.php
1. common-plugin.php
2. common-repo.php
3. common-tags.php
4. bootstrap.php
| non_usab | add unit tests for common ui modules dan author name paul holland original redmine issue original date original assignee dan stangel fills in add tests for the following modules common active php common agents php common cache php common buckets php common compare php common db php common job php common license file php common php common plugin php common repo php common tags php bootstrap php | 0 |
790,035 | 27,813,676,883 | IssuesEvent | 2023-03-18 12:33:07 | AY2223S2-CS2113T-T09-1/tp | https://api.github.com/repos/AY2223S2-CS2113T-T09-1/tp | opened | Add command for export to CSV | type:Task priority:Medium | Add a command for exporting to CSV to allow user to explicitly state when to export financial statements to CSV. Also prevents unnecessary export as currently export is done automatically on normal exit, even when user does not want a CSV export | 1.0 | Add command for export to CSV - Add a command for exporting to CSV to allow user to explicitly state when to export financial statements to CSV. Also prevents unnecessary export as currently export is done automatically on normal exit, even when user does not want a CSV export | non_usab | add command for export to csv add a command for exporting to csv to allow user to explicitly state when to export financial statements to csv also prevents unnecessary export as currently export is done automatically on normal exit even when user does not want a csv export | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.