id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,889,221 | Array high order methods | High-order array methods in JavaScript are methods that operate on arrays and typically take other... | 0 | 2024-06-15T04:38:37 | https://dev.to/__khojiakbar__/array-high-order-methods-l5f | array, methods, javascript | >High-order array methods in JavaScript are methods that operate on arrays and typically take other functions as arguments. These methods allow for powerful and concise ways to manipulate and analyze data within arrays. Here’s a broad explanation of some of the most commonly used high-order array methods:
#**1. map()*... | __khojiakbar__ |
1,889,279 | Solidity, Smart Contract | Blockchain and smart contracts revolutionize digital interactions, ensuring security, transparency,... | 0 | 2024-06-15T06:00:21 | https://dev.to/bartraders89/solidity-smart-contract-oog | development, blockchain, smartcontract, cryptocurrency | Blockchain and smart contracts revolutionize digital interactions, ensuring security, transparency, and efficiency. These technologies empower innovation in finance, healthcare, and beyond. Developers can explore tutorials and resources on blockchain integration to harness its potential. Enhance your projects with smar... | bartraders89 |
1,889,277 | Buy verified BYBIT account | Buy verified BYBIT account In the evolving landscape of cryptocurrency trading, the role of a... | 0 | 2024-06-15T05:55:37 | https://dev.to/michellejordan02/buy-verified-bybit-account-32eo | Buy verified BYBIT account
In the evolving landscape of cryptocurrency trading, the role of a dependable and protected platform cannot be overstated. Bybit, an esteemed crypto derivatives exchange, stands out as a platform that empowers traders to capitalize on their expertise and effectively maneuver the market.
This... | michellejordan02 | |
1,889,276 | Top 10 Free AI Tools to Boost Your Daily Life Productivity | In today’s fast-paced world, maximizing productivity is essential. AI tools have become increasingly... | 0 | 2024-06-15T05:55:17 | https://dev.to/futuristicgeeks/top-10-free-ai-tools-to-boost-your-daily-life-productivity-4g93 | ai, webdev, aitools, beginners | In today’s fast-paced world, maximizing productivity is essential. AI tools have become increasingly popular for helping individuals manage their time, streamline tasks, and improve efficiency. Here are the top 10 free AI tools that can significantly enhance your daily life productivity.
1. ChatGPT by OpenAI
2. Notion... | futuristicgeeks |
1,889,275 | How you Can Make Money Online 💻💸 | Making money online is an exciting and accessible opportunity for anyone with an internet connection.... | 0 | 2024-06-15T05:52:49 | https://dev.to/anis12345/how-you-can-make-money-online-39gn | makemoneyonline, workfromhome | Making money online is an exciting and accessible opportunity for anyone with an internet connection. Here are some popular ways you can start earning:
1. Freelancing 🧑💻
Offer your skills in writing, graphic design, programming, or marketing on platforms like Upwork, Fiverr, and Freelancer. Set up a profile, showca... | anis12345 |
1,889,274 | JavaScript: CallBack Hell | function getArticlesData(id, callback) { // Simulate async operation setTimeout(() => { ... | 0 | 2024-06-15T05:49:04 | https://dev.to/alamfatima1999/javascript-callback-hell-1a1f | ```JS
function getArticlesData(id, callback) {
// Simulate async operation
setTimeout(() => {
callback([{ username: 'user1' }, { username: 'user2' }]); // Dummy data
}, 1000);
}
function getUserData(username, callback) {
// Simulate async operation
setTimeout(() => {
callback(userna... | alamfatima1999 | |
1,889,273 | How to Handle Errors in an Industry-Grade Node.js Application | This is the thirteenth blog of my series where I am writing how to write code for an industry-grade... | 0 | 2024-06-15T05:48:11 | https://dev.to/md_enayeturrahman_2560e3/how-to-handle-errors-in-an-industry-grade-nodejs-application-217b | errors, express, node, javascript |
This is the thirteenth blog of my series where I am writing how to write code for an industry-grade project so that you can manage and scale the project.
The first twelve blogs of the series were about "How to set up eslint and prettier in an express and typescript project", "Folder structure in an industry-standar... | md_enayeturrahman_2560e3 |
1,889,272 | Made a simple Tic-Tac-Toe game | This was one of my academy's projects. It was to pick a topic out of a list and I picked TTT. I got a... | 0 | 2024-06-15T05:47:47 | https://dev.to/zoobob5/made-a-simple-tic-tac-toe-game-4of0 | python, vscode, github | This was one of my academy's projects. It was to pick a topic out of a list and I picked TTT. I got a little side tracked in making is so it took me a little bit longer to make it but if i stayed on track it could've taken me a day. I just did a simple grid layout using tk and took user inputs to assign a simple player... | zoobob5 |
1,889,271 | Holistic Healing: Nurturing Wellness from Within | In the realm of health and wellness, holistic healing emerges as a comprehensive approach that... | 0 | 2024-06-15T05:40:47 | https://dev.to/rooseveltrose/holistic-healing-nurturing-wellness-from-within-il8 | holistichealing | In the realm of health and wellness, **[holistic healing](https://iah.fit/)** emerges as a comprehensive approach that addresses the interconnectedness of mind, body, and spirit. This integrative method emphasizes treating the whole person rather than focusing solely on symptoms, aiming to restore balance and promote o... | rooseveltrose |
1,889,270 | AI-Powered Landing Pages: The Future of SaaS Marketing | In the ever-competitive world of SaaS marketing, crafting a captivating and high-converting landing... | 0 | 2024-06-15T05:38:48 | https://dev.to/gptconsole/ai-powered-landing-pages-the-future-of-saas-marketing-46h |

In the ever-competitive world of SaaS marketing, crafting a captivating and high-converting landing page is crucial for attracting new customers and driving subscriptions. Traditionally, this process involved sig... | vincivinni | |
1,889,268 | Top 5 Applications of Die Sinking Machines | screenshot-1708712138756.png Top 5 How Exactly To Make Usage Of Die Sinking Machines You might must... | 0 | 2024-06-15T05:32:18 | https://dev.to/mithokha_saderha_c6bb89ea/top-5-applications-of-die-sinking-machines-3fg1 | screenshot-1708712138756.png
Top 5 How Exactly To Make Usage Of Die Sinking Machines
You might must know more about die sinking devices if you have ever wondered exactly how components that are metal made. These devices have actually a lot of advantages, including safety features and revolutionary technology allowing ... | mithokha_saderha_c6bb89ea | |
1,889,265 | How to Maintain High-Quality Standards with Your Die Sinking Machine | screenshot-1708712138756.png Die sinking machines are a valuable tool for creating high-quality metal... | 0 | 2024-06-15T05:24:57 | https://dev.to/mithokha_saderha_c6bb89ea/how-to-maintain-high-quality-standards-with-your-die-sinking-machine-373n | screenshot-1708712138756.png
Die sinking machines are a valuable tool for creating high-quality metal components quickly and accurately. To ensure that your machine performs at its best, it is essential to maintain its high-quality standards. Here are some tips on how to keep your die sinking machine in top condition.
... | mithokha_saderha_c6bb89ea | |
1,889,253 | Buy GitHub Accounts | https://dmhelpshop.com/product/buy-github-accounts/ Buy GitHub Accounts GitHub holds a crucial... | 0 | 2024-06-15T05:20:11 | https://dev.to/wocak78159/buy-github-accounts-3054 | machinelearning, datascience, database, html | https://dmhelpshop.com/product/buy-github-accounts/

Buy GitHub Accounts
GitHub holds a crucial position in the world of coding, making it an indispensable platform for developers. As the largest global code reposi... | wocak78159 |
1,889,252 | Optimizing Cloud Performance: Monitoring and Observability in the AWS Cloud | Read the unabridged version of this post on my blog: Practical Cloud Introduction In the... | 0 | 2024-06-15T05:17:12 | https://practicalcloud.net/optimizing-cloud-performance-monitoring-and-observability-in-the-aws-cloud/ | aws, monitoring, cloud, cloudcomputing | Read the unabridged version of this post on my blog: [Practical Cloud](https://practicalclod.net)
## Introduction
In the dynamic world of cloud computing, optimizing performance is crucial to ensuring that applications run smoothly and efficiently. Amazon Web Services (AWS) offers a robust suite of tools and services ... | kelvinskell |
1,889,251 | Safety Considerations When Operating a Die Sinking Machine | screenshot-1708712138756.png Exactly what is a Die Sinking Machine along with its benefits? A die... | 0 | 2024-06-15T05:17:08 | https://dev.to/mithokha_saderha_c6bb89ea/safety-considerations-when-operating-a-die-sinking-machine-5fd0 | screenshot-1708712138756.png
Exactly what is a Die Sinking Machine along with its benefits?
A die sinking is a manufacturing device employed for creating parts or molds produced from metal. It really is capable of creating complicated forms or geometries that would be hard to create using machining which is old-fashio... | mithokha_saderha_c6bb89ea | |
1,889,250 | Buy Negative Google Reviews | https://dmhelpshop.com/product/buy-negative-google-reviews/ Buy Negative Google Reviews Negative... | 0 | 2024-06-15T05:15:24 | https://dev.to/wocak78159/buy-negative-google-reviews-50a4 | aws, news, node, learning | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-negative-google-reviews/\n\n\n\n\nBuy Negative Google Reviews\nNegative reviews on Google are detrimental critiques that expose customers’ unfavorable experiences with a business. These reviews can significantly damage a company’s reputation, presenting challenges in both attracting new customers and retaining current ones. If you are considering purchasing negative Google reviews from dmhelpshop.com, we encourage you to reconsider and instead focus on providing exceptional products and services to ensure positive feedback and sustainable success.\n\nWhy Buy Negative Google Reviews from dmhelpshop\nWe take pride in our fully qualified, hardworking, and experienced team, who are committed to providing quality and safe services that meet all your needs. Our professional team ensures that you can trust us completely, knowing that your satisfaction is our top priority. With us, you can rest assured that you’re in good hands.\n\nIs Buy Negative Google Reviews safe?\nAt dmhelpshop, we understand the concern many business persons have about the safety of purchasing Buy negative Google reviews. We are here to guide you through a process that sheds light on the importance of these reviews and how we ensure they appear realistic and safe for your business. Our team of qualified and experienced computer experts has successfully handled similar cases before, and we are committed to providing a solution tailored to your specific needs. Contact us today to learn more about how we can help your business thrive.\n\nBuy Google 5 Star Reviews\nReviews represent the opinions of experienced customers who have utilized services or purchased products from various online or offline markets. These reviews convey customer demands and opinions, and ratings are assigned based on the quality of the products or services and the overall user experience. Google serves as an excellent platform for customers to leave reviews since the majority of users engage with it organically. When you purchase Buy Google 5 Star Reviews, you have the potential to influence a large number of people either positively or negatively. Positive reviews can attract customers to purchase your products, while negative reviews can deter potential customers.\n\nIf you choose to Buy Google 5 Star Reviews, people will be more inclined to consider your products. However, it is important to recognize that reviews can have both positive and negative impacts on your business. Therefore, take the time to determine which type of reviews you wish to acquire. Our experience indicates that purchasing Buy Google 5 Star Reviews can engage and connect you with a wide audience. By purchasing positive reviews, you can enhance your business profile and attract online traffic. Additionally, it is advisable to seek reviews from reputable platforms, including social media, to maintain a positive flow. We are an experienced and reliable service provider, highly knowledgeable about the impacts of reviews. Hence, we recommend purchasing verified Google reviews and ensuring their stability and non-gropability.\n\nLet us now briefly examine the direct and indirect benefits of reviews:\nReviews have the power to enhance your business profile, influencing users at an affordable cost.\nTo attract customers, consider purchasing only positive reviews, while negative reviews can be acquired to undermine your competitors. Collect negative reports on your opponents and present them as evidence.\nIf you receive negative reviews, view them as an opportunity to understand user reactions, make improvements to your products and services, and keep up with current trends.\nBy earning the trust and loyalty of customers, you can control the market value of your products. Therefore, it is essential to buy online reviews, including Buy Google 5 Star Reviews.\nReviews serve as the captivating fragrance that entices previous customers to return repeatedly.\nPositive customer opinions expressed through reviews can help you expand your business globally and achieve profitability and credibility.\nWhen you purchase positive Buy Google 5 Star Reviews, they effectively communicate the history of your company or the quality of your individual products.\nReviews act as a collective voice representing potential customers, boosting your business to amazing heights.\nNow, let’s delve into a comprehensive understanding of reviews and how they function:\nGoogle, with its significant organic user base, stands out as the premier platform for customers to leave reviews. When you purchase Buy Google 5 Star Reviews , you have the power to positively influence a vast number of individuals. Reviews are essentially written submissions by users that provide detailed insights into a company, its products, services, and other relevant aspects based on their personal experiences. In today’s business landscape, it is crucial for every business owner to consider buying verified Buy Google 5 Star Reviews, both positive and negative, in order to reap various benefits.\n\nWhy are Google reviews considered the best tool to attract customers?\nGoogle, being the leading search engine and the largest source of potential and organic customers, is highly valued by business owners. Many business owners choose to purchase Google reviews to enhance their business profiles and also sell them to third parties. Without reviews, it is challenging to reach a large customer base globally or locally. Therefore, it is crucial to consider buying positive Buy Google 5 Star Reviews from reliable sources. When you invest in Buy Google 5 Star Reviews for your business, you can expect a significant influx of potential customers, as these reviews act as a pheromone, attracting audiences towards your products and services. Every business owner aims to maximize sales and attract a substantial customer base, and purchasing Buy Google 5 Star Reviews is a strategic move.\n\nAccording to online business analysts and economists, trust and affection are the essential factors that determine whether people will work with you or do business with you. However, there are additional crucial factors to consider, such as establishing effective communication systems, providing 24/7 customer support, and maintaining product quality to engage online audiences. If any of these rules are broken, it can lead to a negative impact on your business. Therefore, obtaining positive reviews is vital for the success of an online business\n\nWhat are the benefits of purchasing reviews online?\nIn today’s fast-paced world, the impact of new technologies and IT sectors is remarkable. Compared to the past, conducting business has become significantly easier, but it is also highly competitive. To reach a global customer base, businesses must increase their presence on social media platforms as they provide the easiest way to generate organic traffic. Numerous surveys have shown that the majority of online buyers carefully read customer opinions and reviews before making purchase decisions. In fact, the percentage of customers who rely on these reviews is close to 97%. Considering these statistics, it becomes evident why we recommend buying reviews online. In an increasingly rule-based world, it is essential to take effective steps to ensure a smooth online business journey.\n\nBuy Google 5 Star Reviews\nMany people purchase reviews online from various sources and witness unique progress. Reviews serve as powerful tools to instill customer trust, influence their decision-making, and bring positive vibes to your business. Making a single mistake in this regard can lead to a significant collapse of your business. Therefore, it is crucial to focus on improving product quality, quantity, communication networks, facilities, and providing the utmost support to your customers.\n\nReviews reflect customer demands, opinions, and ratings based on their experiences with your products or services. If you purchase Buy Google 5-star reviews, it will undoubtedly attract more people to consider your offerings. Google is the ideal platform for customers to leave reviews due to its extensive organic user involvement. Therefore, investing in Buy Google 5 Star Reviews can significantly influence a large number of people in a positive way.\n\nHow to generate google reviews on my business profile?\nFocus on delivering high-quality customer service in every interaction with your customers. By creating positive experiences for them, you increase the likelihood of receiving reviews. These reviews will not only help to build loyalty among your customers but also encourage them to spread the word about your exceptional service. It is crucial to strive to meet customer needs and exceed their expectations in order to elicit positive feedback. If you are interested in purchasing affordable Google reviews, we offer that service.\n\n\n\n\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | wocak78159 |
1,889,249 | etcsh: an enhanced version of the original tcsh | etcsh is an enhanced version of the original tcsh, which is a version of the original Berkeley C... | 0 | 2024-06-15T05:15:12 | https://dev.to/mprog10/etcsh-an-enhanced-version-of-the-original-tcsh-415j | c, shell | [etcsh](https://github.com/Krush206/etcsh) is an enhanced version of the original tcsh, which is a version of the original Berkeley C shell implementing file name completion and command line editing.
etcsh features the following enhancements and fixes over the original tcsh.
• Function declarations;
• variable assignm... | mprog10 |
1,889,248 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-15T05:12:07 | https://dev.to/wocak78159/buy-verified-paxful-account-5hi6 | css, opensource, typescript, career | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\n \n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n\n\n" | wocak78159 |
1,889,246 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-15T05:06:57 | https://dev.to/wocak78159/buy-verified-cash-app-account-31om | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | wocak78159 |
1,889,245 | Understanding Algorithms: The Building Blocks of Problem Solving | An algorithm is a step-by-step procedure for solving a problem or performing a task. It takes an... | 0 | 2024-06-15T05:03:29 | https://dev.to/arun_thakur_8894/understanding-algorithms-the-building-blocks-of-problem-solving-41ln | devchallenge, cschallenge, computerscience, beginners |
An algorithm is a step-by-step procedure for solving a problem or performing a task. It takes an input, processes it through a series of defined steps, and produces an output. Algorithms are fundamental to computer science, enabling efficient problem-solving and automation.

SĐT: 093690... | vl88vlcom | |
1,894,056 | Building a Robust Web Server in Go: A Step-by-Step Guide | We continue our journey implementing a real world web application in Golang in this blog post. In the... | 0 | 2024-06-19T20:29:40 | https://blog.gkomninos.com/building-a-robust-web-server-in-go-a-step-by-step-guide | coding, go, webdev, tutorial | ---
title: Building a Robust Web Server in Go: A Step-by-Step Guide
published: true
date: 2024-06-15 05:00:44 UTC
tags: coding,golang,webdev,Tutorial
canonical_url: https://blog.gkomninos.com/building-a-robust-web-server-in-go-a-step-by-step-guide
---
We continue our journey implementing a real world web application i... | gosom |
1,889,242 | "this" Keyword in OOP | This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer. ... | 0 | 2024-06-15T04:58:44 | https://dev.to/dexter766/this-keyword-in-oop-4f2g | devchallenge, cschallenge, computerscience, beginners | _This is a submission for [DEV Computer Science Challenge v24.06.12: One Byte Explainer](https://dev.to/challenges/cs)._
## Explainer
<!-- Explain a computer science concept in 256 characters or less. -->
In a bakery, each baker has their own recipe book. When a baker says "this recipe," they mean a recipe from their... | dexter766 |
1,889,241 | OTT App Development Company | Techno Derivation: Pioneering OTT App Development Company In the rapidly evolving digital landscape,... | 0 | 2024-06-15T04:56:32 | https://dev.to/mohit_gupta_e5b0c76bb7ac9/ott-app-development-company-3c0h | Techno Derivation: **[Pioneering OTT App Development](https://technoderivation.com/ott-app-development)** Company
In the rapidly evolving digital landscape, over-the-top (OTT) content has revolutionized how audiences consume media. As a leading OTT app development company, Techno Derivation stands at the forefront of ... | mohit_gupta_e5b0c76bb7ac9 | |
1,872,195 | Boas práticas que fazem a diferença #2 📝 | Esse é o segundo post de uma série sobre boas práticas que eu aprendi durante a minha jornada, tanto... | 27,461 | 2024-06-15T04:55:19 | https://dev.to/superp0sit1on/boas-praticas-que-fazem-a-diferenca-2-gmo | braziliandevs, beginners, programming, productivity | Esse é o segundo post de uma série sobre boas práticas que eu aprendi durante a minha jornada, tanto no trabalho e processos seletivos, quanto na faculdade e projetos pessoais ou de comunidades.
Confira o primeiro post [clicando aqui](https://dev.to/superp0sit1on/pequenas-boas-praticas-que-fazem-a-diferenca-parte-1-24... | superp0sit1on |
1,889,240 | Test title | Test description | 0 | 2024-06-15T04:54:29 | https://dev.to/mesajil/test-title-4h2d | node | Test description | mesajil |
1,409,901 | Micro FrontEnd | O termo Micro Frontend se refere a uma abordagem de desenvolvimento de software que visa quebrar... | 0 | 2023-03-22T02:35:53 | https://dev.to/raynneandrade/micro-frontend-2pd2 | frontend, webdev, devlive, programming | 
O termo Micro Frontend se refere a uma abordagem de desenvolvimento de software que visa quebrar uma aplicação web monolítica em componentes menores e independentes, cada um dos quais é desenvolvido, testado e impla... | raynneandrade |
1,889,235 | The Power of Embeddings in AI | Introduction Embeddings have become a cornerstone in natural language processing (NLP)... | 27,673 | 2024-06-15T04:45:07 | https://dev.to/rapidinnovation/the-power-of-embeddings-in-ai-3f9h | ## Introduction
Embeddings have become a cornerstone in natural language processing (NLP) and
machine learning. They transform words, phrases, or documents into vectors of
real numbers, allowing algorithms to effectively interpret and process natural
language data.
## What are Embeddings?
Embeddings are data represe... | rapidinnovation | |
1,889,234 | Buy Negative Google Reviews | https://dmhelpshop.com/product/buy-negative-google-reviews/ Buy Negative Google Reviews Negative... | 0 | 2024-06-15T04:43:25 | https://dev.to/xivok85011/buy-negative-google-reviews-15g1 | devops, css, opensource, typescript | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-negative-google-reviews/\n\n\n\n\nBuy Negative Google Reviews\nNegative reviews on Google are detrimental critiques that expose customers’ unfavorable experiences with a business. These reviews can significantly damage a company’s reputation, presenting challenges in both attracting new customers and retaining current ones. If you are considering purchasing negative Google reviews from dmhelpshop.com, we encourage you to reconsider and instead focus on providing exceptional products and services to ensure positive feedback and sustainable success.\n\nWhy Buy Negative Google Reviews from dmhelpshop\nWe take pride in our fully qualified, hardworking, and experienced team, who are committed to providing quality and safe services that meet all your needs. Our professional team ensures that you can trust us completely, knowing that your satisfaction is our top priority. With us, you can rest assured that you’re in good hands.\n\nIs Buy Negative Google Reviews safe?\nAt dmhelpshop, we understand the concern many business persons have about the safety of purchasing Buy negative Google reviews. We are here to guide you through a process that sheds light on the importance of these reviews and how we ensure they appear realistic and safe for your business. Our team of qualified and experienced computer experts has successfully handled similar cases before, and we are committed to providing a solution tailored to your specific needs. Contact us today to learn more about how we can help your business thrive.\n\nBuy Google 5 Star Reviews\nReviews represent the opinions of experienced customers who have utilized services or purchased products from various online or offline markets. These reviews convey customer demands and opinions, and ratings are assigned based on the quality of the products or services and the overall user experience. Google serves as an excellent platform for customers to leave reviews since the majority of users engage with it organically. When you purchase Buy Google 5 Star Reviews, you have the potential to influence a large number of people either positively or negatively. Positive reviews can attract customers to purchase your products, while negative reviews can deter potential customers.\n\nIf you choose to Buy Google 5 Star Reviews, people will be more inclined to consider your products. However, it is important to recognize that reviews can have both positive and negative impacts on your business. Therefore, take the time to determine which type of reviews you wish to acquire. Our experience indicates that purchasing Buy Google 5 Star Reviews can engage and connect you with a wide audience. By purchasing positive reviews, you can enhance your business profile and attract online traffic. Additionally, it is advisable to seek reviews from reputable platforms, including social media, to maintain a positive flow. We are an experienced and reliable service provider, highly knowledgeable about the impacts of reviews. Hence, we recommend purchasing verified Google reviews and ensuring their stability and non-gropability.\n\nLet us now briefly examine the direct and indirect benefits of reviews:\nReviews have the power to enhance your business profile, influencing users at an affordable cost.\nTo attract customers, consider purchasing only positive reviews, while negative reviews can be acquired to undermine your competitors. Collect negative reports on your opponents and present them as evidence.\nIf you receive negative reviews, view them as an opportunity to understand user reactions, make improvements to your products and services, and keep up with current trends.\nBy earning the trust and loyalty of customers, you can control the market value of your products. Therefore, it is essential to buy online reviews, including Buy Google 5 Star Reviews.\nReviews serve as the captivating fragrance that entices previous customers to return repeatedly.\nPositive customer opinions expressed through reviews can help you expand your business globally and achieve profitability and credibility.\nWhen you purchase positive Buy Google 5 Star Reviews, they effectively communicate the history of your company or the quality of your individual products.\nReviews act as a collective voice representing potential customers, boosting your business to amazing heights.\nNow, let’s delve into a comprehensive understanding of reviews and how they function:\nGoogle, with its significant organic user base, stands out as the premier platform for customers to leave reviews. When you purchase Buy Google 5 Star Reviews , you have the power to positively influence a vast number of individuals. Reviews are essentially written submissions by users that provide detailed insights into a company, its products, services, and other relevant aspects based on their personal experiences. In today’s business landscape, it is crucial for every business owner to consider buying verified Buy Google 5 Star Reviews, both positive and negative, in order to reap various benefits.\n\nWhy are Google reviews considered the best tool to attract customers?\nGoogle, being the leading search engine and the largest source of potential and organic customers, is highly valued by business owners. Many business owners choose to purchase Google reviews to enhance their business profiles and also sell them to third parties. Without reviews, it is challenging to reach a large customer base globally or locally. Therefore, it is crucial to consider buying positive Buy Google 5 Star Reviews from reliable sources. When you invest in Buy Google 5 Star Reviews for your business, you can expect a significant influx of potential customers, as these reviews act as a pheromone, attracting audiences towards your products and services. Every business owner aims to maximize sales and attract a substantial customer base, and purchasing Buy Google 5 Star Reviews is a strategic move.\n\nAccording to online business analysts and economists, trust and affection are the essential factors that determine whether people will work with you or do business with you. However, there are additional crucial factors to consider, such as establishing effective communication systems, providing 24/7 customer support, and maintaining product quality to engage online audiences. If any of these rules are broken, it can lead to a negative impact on your business. Therefore, obtaining positive reviews is vital for the success of an online business\n\nWhat are the benefits of purchasing reviews online?\nIn today’s fast-paced world, the impact of new technologies and IT sectors is remarkable. Compared to the past, conducting business has become significantly easier, but it is also highly competitive. To reach a global customer base, businesses must increase their presence on social media platforms as they provide the easiest way to generate organic traffic. Numerous surveys have shown that the majority of online buyers carefully read customer opinions and reviews before making purchase decisions. In fact, the percentage of customers who rely on these reviews is close to 97%. Considering these statistics, it becomes evident why we recommend buying reviews online. In an increasingly rule-based world, it is essential to take effective steps to ensure a smooth online business journey.\n\nBuy Google 5 Star Reviews\nMany people purchase reviews online from various sources and witness unique progress. Reviews serve as powerful tools to instill customer trust, influence their decision-making, and bring positive vibes to your business. Making a single mistake in this regard can lead to a significant collapse of your business. Therefore, it is crucial to focus on improving product quality, quantity, communication networks, facilities, and providing the utmost support to your customers.\n\nReviews reflect customer demands, opinions, and ratings based on their experiences with your products or services. If you purchase Buy Google 5-star reviews, it will undoubtedly attract more people to consider your offerings. Google is the ideal platform for customers to leave reviews due to its extensive organic user involvement. Therefore, investing in Buy Google 5 Star Reviews can significantly influence a large number of people in a positive way.\n\nHow to generate google reviews on my business profile?\nFocus on delivering high-quality customer service in every interaction with your customers. By creating positive experiences for them, you increase the likelihood of receiving reviews. These reviews will not only help to build loyalty among your customers but also encourage them to spread the word about your exceptional service. It is crucial to strive to meet customer needs and exceed their expectations in order to elicit positive feedback. If you are interested in purchasing affordable Google reviews, we offer that service.\n\n\n\n\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | xivok85011 |
1,889,233 | Day 1 Coding Challenge: Mastering String Reversal in JavaScript and Python | Welcome to Day 1 of our daily coding challenge series! Today, we'll tackle an essential programming... | 0 | 2024-06-15T04:42:27 | https://dev.to/dipakahirav/day-1-coding-challenge-mastering-string-reversal-in-javascript-and-python-1m0g | javascript, python, coding, challenge | Welcome to Day 1 of our daily coding challenge series! Today, we'll tackle an essential programming task: reversing a string. Whether you're coding in JavaScript or Python, this challenge will help you sharpen your skills and enhance your understanding of string manipulation. Let's dive in and solve this problem togeth... | dipakahirav |
1,889,223 | Nurturing Faith and Fun: Exploring Faith Kids Ministry at Faithco Church | Faith Kids Ministry at Faithco Church is a vibrant and dynamic space where children encounter God's... | 0 | 2024-06-15T04:40:04 | https://dev.to/yangseo/nurturing-faith-and-fun-exploring-faith-kids-ministry-at-faithco-church-5ahn | faith, religion, churchinshawnee, faithkids | Faith Kids Ministry at Faithco Church is a vibrant and dynamic space where children encounter God's love, grow in their faith, and experience the joy of belonging to God's family. Rooted in the timeless truths of Scripture and infused with creativity and innovation, Faith Kids provides a nurturing environment where chi... | yangseo |
1,889,222 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-15T04:40:00 | https://dev.to/xivok85011/buy-verified-paxful-account-3o6i | tutorial, react, python, ai | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\n \n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | xivok85011 |
1,889,220 | emacs org感觉挺好的 | 我看网上别人一直喜欢吹emacs的org文档编辑,我原以为就是和markdown一样的东西,本来就会。 最近不再使用jetbrains系列的软件,感觉就jupyter的插件比较好用,现在用vscode的... | 0 | 2024-06-15T04:37:41 | https://dev.to/xiaodao/emacs-orggan-jue-ting-hao-de-5f50 | 我看网上别人一直喜欢吹emacs的org文档编辑,我原以为就是和markdown一样的东西,本来就会。
最近不再使用jetbrains系列的软件,感觉就jupyter的插件比较好用,现在用vscode的替代,一直尝试用用emacs里面的ein插件,发现这个有bug,已经好久不修复了。
vscode的jupyter的可能是插件安装太多了,有时候死机,只有强制退出才能搞其他的。
我平时写代码主要还是emacs,这个代码搜索,编辑还是emacs最强。
折腾emacs感觉永远都有学习的,所以我又没事学了下org,才发现org其实可以实现jupyter差不多的功能,其实我对jupyter的使用要求不高,就是有时候执行命令,然后把结果记录下来... | xiaodao | |
1,889,219 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-15T04:36:37 | https://dev.to/xivok85011/buy-verified-cash-app-account-47hl | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | xivok85011 |
1,889,218 | How to Deploy Your Backend on Vercel Using `vercel.json`: A Step-by-Step Guide | Deploying a backend server can often be a complex process, but with Vercel, it becomes... | 0 | 2024-06-15T04:32:04 | https://dev.to/vyan/how-to-deploy-your-backend-on-vercel-using-verceljson-a-step-by-step-guide-5a78 | webdev, node, vercel, beginners | Deploying a backend server can often be a complex process, but with Vercel, it becomes straightforward and efficient. Vercel, a popular platform for frontend and backend deployment, allows developers to easily deploy their applications with minimal configuration. In this blog, we will walk you through the steps to depl... | vyan |
1,889,213 | 🧙♂️ 10 Magical Tips Every Programmer Should Know from "97 Things Every Programmer Should Know" 🧙♀️ | Hey there, code wizards and tech sorcerers! 🧑💻 Ready to level up your programming game? We’ve... | 0 | 2024-06-15T04:22:57 | https://dev.to/kalyani_borkar_87ce4bb608/10-magical-tips-every-programmer-should-know-from-97-things-every-programmer-should-know-5786 | ****
Hey there, code wizards and tech sorcerers! 🧑💻 Ready to level up your programming game? We’ve cracked open the treasure chest that is "97 Things Every Programmer Should Know" by Kevlin Henney and pulled out ten sparkling gems of wisdom just for you. Get ready to sprinkle some magic dust on your code with these ... | kalyani_borkar_87ce4bb608 | |
1,889,232 | Create a Fast Node.js Serverless Backend Using AWS Lambda and DynamoDB | Build a fast Node.js serverless backend with AWS Lambda and DynamoDB. Learn to set up, secure, and... | 0 | 2024-06-15T04:44:33 | https://blog.wilsonkomlan.com/create-a-fast-nodejs-serverless-backend-using-aws-lambda-and-dynamodb | lambda, aws, awslambda, dynamodb | ---
title: Create a Fast Node.js Serverless Backend Using AWS Lambda and DynamoDB
published: true
date: 2024-06-15 04:22:07 UTC
tags: lambda,AWS,awslambda,DynamoDB
canonical_url: https://blog.wilsonkomlan.com/create-a-fast-nodejs-serverless-backend-using-aws-lambda-and-dynamodb
---
Build a fast Node.js serverless back... | komlanwilson |
1,889,215 | HOME PODIUM | Home Podium is a comprehensive platform designed to revolutionize property management for landlords,... | 0 | 2024-06-15T04:21:27 | https://dev.to/homepodium/home-podium-3hdi | Home Podium is a comprehensive platform designed to revolutionize property management for landlords, property management companies, and tenants alike.
[https://homepodium.com/](https://homepodium.com/) | homepodium | |
1,889,204 | Creating a Character Device Driver for Raspberry Pi Using Buildroot | Introduction Welcome to those who have read my previous posts, and a warm welcome to all... | 0 | 2024-06-15T04:16:15 | https://dev.to/devdoesit17/creating-a-character-device-driver-for-raspberry-pi-using-buildroot-2i9a | embedded, linux, cpp | #### Introduction
Welcome to those who have read my previous posts, and a warm welcome to all who are new to my blog. As an embedded developer, I continue to navigate the complexities of learning embedded engineering. Imposter syndrome often makes me wonder if I truly grasp the concepts as well as my peers. I am commi... | devdoesit17 |
1,889,203 | Mastering Form Handling with Custom Hooks in React | Handling forms in React can be challenging, especially as forms grow in complexity. Custom hooks... | 0 | 2024-06-15T04:12:36 | https://dev.to/hasancse/mastering-form-handling-with-custom-hooks-in-react-h02 | webdev, typescript, programming, react | Handling forms in React can be challenging, especially as forms grow in complexity. Custom hooks provide an elegant solution to manage form state, validation, and submission logic, making your code cleaner and more maintainable. In this blog post, we'll explore how to create custom hooks for form handling in React usin... | hasancse |
1,889,054 | Design patterns: Part One - A brief explanation of creational pattern | The picture was taken from boredpanda. Hello everyone! Starting my first post with one of... | 0 | 2024-06-15T03:59:33 | https://dev.to/andres_paladines/design-patterns-part-one-a-brief-explanation-of-creational-pattern-5507 | architecture, designpatterns, javascript, swift | The picture was taken from [boredpanda](https://www.boredpanda.com/digital-art-cats-brutalist-architecture-cats-of-brutalism/).
### Hello everyone!
Starting my first post with one of the most basic but never unnecessary topics; Design patterns.
Let's start listing them:
```
.
├── Creational Patterns
│ ├── Singlet... | andres_paladines |
1,889,200 | Programming in 2024 | Sorry bro , you're late :( | 0 | 2024-06-15T03:57:48 | https://dev.to/y4sh/programming-in-2024-59f3 | Sorry bro , you're late :( | y4sh | |
1,889,199 | 🔥 Isolating Linux Performance Issues in 1 Minute Without Installing Any New Tools or Packages 🔥 | Hey everyone! I'm excited to share my latest video on isolating and identifying performance... | 0 | 2024-06-15T03:53:03 | https://dev.to/lakhera2015/isolating-linux-performance-issues-in-1-minute-without-installing-any-new-tools-or-packages-2h36 | devops, linux, performance, cloudcomputing | {% embed https://youtu.be/kaWzi3Kohog %}
Hey everyone! I'm excited to share my latest video on isolating and identifying performance issues in Linux systems. 🐧 Whether you're a seasoned pro or just starting out, these tips will help you tackle these performance bottlenecks.
🔍 In this video, I cover:
1️⃣ CPU: Learn ... | lakhera2015 |
1,889,198 | Cortisync Reviews: A Comprehensive Guide to PrimeGENIX Cortisync | ➢Product Name - PrimeGenix CalmLean ➢ Composition — Natural Organic Compound ➢ Side-Effects—NA ➢... | 0 | 2024-06-15T03:52:30 | https://dev.to/bunu369/cortisync-reviews-a-comprehensive-guide-to-primegenix-cortisync-599p | **➢Product Name - PrimeGenix CalmLean
➢ Composition — Natural Organic Compound
➢ Side-Effects—NA
➢ Rating: —⭐⭐⭐⭐⭐
➢ Availability — Online
➢ Where to Buy - C[lick Here to Rush Your Order from the Official Website](https://sites.google.com/view/simplehealthh/CortiSync-Review)
Buy From Official Website ([Get Up to 45% Dis... | bunu369 | |
1,889,197 | Build your own SSO Service with next-auth integration | The SSO Service is a robust Single Sign-On (SSO) solution designed to streamline authentication and... | 0 | 2024-06-15T03:52:14 | https://dev.to/priyanshuverma/build-your-own-sso-service-with-next-auth-integration-4i2k | The SSO Service is a robust Single Sign-On (SSO) solution designed to streamline authentication and authorization across multiple applications. Users can authenticate once and seamlessly access various applications without the need for repeated login.
## Installation
To install and run the SSO Service, follow these s... | priyanshuverma | |
1,889,196 | Custom SSO Implementation | The SSO Implementation repository contains the implementation details and examples for seamlessly... | 0 | 2024-06-15T03:49:15 | https://dev.to/priyanshuverma/custom-sso-implementation-38pl | webdev, programming, opensource, typescript | The SSO Implementation repository contains the implementation details and examples for seamlessly integrating the SSO Service into your applications.
## Repository Link
[SSO Implementation Repository](https://github.com/priyanshuverma-dev/sso-implementation)
## Features
### 1. Example Integrations
Explore compr... | priyanshuverma |
1,889,194 | The Role of Programming in Die Sinking Machines | screenshot-1708712138756.png The Role of Programming in Die Sinking Machines Have you ever wondered... | 0 | 2024-06-15T03:41:15 | https://dev.to/mithokha_saderha_c6bb89ea/the-role-of-programming-in-die-sinking-machines-ak4 | screenshot-1708712138756.png
The Role of Programming in Die Sinking Machines
Have you ever wondered how those intricate shapes on metal parts are created? They are made by die sinking machines. Die sinking machines are amazing devices which use electricity and computer programming to carve metal into unique shapes. ... | mithokha_saderha_c6bb89ea | |
1,889,193 | Advantages and Disadvantages of Die Sinking Machines | screenshot-1708712138756.png Benefits and drawbacks of Die Sinking Machines Die-sinking products are... | 0 | 2024-06-15T03:36:30 | https://dev.to/mithokha_saderha_c6bb89ea/advantages-and-disadvantages-of-die-sinking-machines-4o9e |
screenshot-1708712138756.png
Benefits and drawbacks of Die Sinking Machines
Die-sinking products are critical tools utilized in the manufacturing industry. The unit are widely useful to mold parts from metals, plastics, as well as other trash by using a die in summary. The die is just a block which is specific of usi... | mithokha_saderha_c6bb89ea | |
1,888,344 | How to create Windows 11 VM on Microsoft Azure (Step by step guide) | Introduction Virtual Machine (VM) is a digitized version of a physical computer and they can run... | 0 | 2024-06-15T03:30:12 | https://dev.to/ayospecie/how-to-create-windows-11-vm-on-microsoft-azure-step-by-step-guide-2hnh | azure, virtualmachine, cloudcomputing | **Introduction**
Virtual Machine (VM) is a digitized version of a physical computer and they can run programs and operating systems, store data, connect to networks, and do other computing functions.
Azure VM uses entirely virtual resources provided by Microsoft Azure Platform. It gives more control over the computi... | ayospecie |
1,889,190 | Tuan Simon | Bức tranh cuộc đời tôi còn dang dở, nhưng tôi tin rằng với mỗi nét vẽ mỗi ngày, nó sẽ dần hoàn thiện... | 0 | 2024-06-15T03:25:51 | https://dev.to/cqtuansimon/tuan-simon-21k5 | Bức tranh cuộc đời tôi còn dang dở, nhưng tôi tin rằng với mỗi nét vẽ mỗi ngày, nó sẽ dần hoàn thiện và trở nên rực rỡ nhất.
Website: https://www.tiktok.com/@t_mon2401
Phone: 0866011730
Address: Mễ trì thượng quận nam từ liêm hà nội
https://www.instapaper.com/p/rmtuansimon
https://controlc.com/3501c584
https://dribbble... | cqtuansimon | |
1,889,188 | Create effortless elegance with our LED Smart Bathroom Mirror. | screenshot-1708188639945.png Create Effortless Elegance in Your Bathroom with Our LED Smart Bathroom... | 0 | 2024-06-15T03:24:00 | https://dev.to/mithokha_saderha_c6bb89ea/create-effortless-elegance-with-our-led-smart-bathroom-mirror-e07 | screenshot-1708188639945.png
Create Effortless Elegance in Your Bathroom with Our LED Smart Bathroom Mirror
Looking for a way to take your bathroom to the next level? Look no further than our innovative LED Smart Bathroom Mirror. With its state-of-the-art features and ease of use, our mirror is the perfect addition ... | mithokha_saderha_c6bb89ea | |
1,889,184 | JavaScript: All about Cookies | Cookies are small pieces of data stored on the client's browser by a website. They are used to... | 0 | 2024-06-15T03:16:42 | https://dev.to/alamfatima1999/javascript-cookies-13ml | Cookies are small pieces of data stored on the client's browser by a website. They are used to remember information about the user between page loads or sessions. Here's a detailed explanation of cookies in JavaScript and the differences between HTTP and HTTPS cookies:
Cookies in JavaScript
Creating and Setting Cookies... | alamfatima1999 | |
1,889,183 | Sleek and simple, the LED Smart Bathroom Mirror complements any design style. | screenshot-1708188639945.png Looking for a new bathroom mirror that is both innovative and safe?... | 0 | 2024-06-15T03:12:34 | https://dev.to/mithokha_saderha_c6bb89ea/sleek-and-simple-the-led-smart-bathroom-mirror-complements-any-design-style-3d4p | screenshot-1708188639945.png
Looking for a new bathroom mirror that is both innovative and safe? Check out the LED Smart Bathroom Mirror. With its sleek and simple design, this mirror complements any design style.
Features of the Smart which is LED bathroom
There are numerous assets that are advantageous using the ... | mithokha_saderha_c6bb89ea | |
1,889,182 | Create laravel project on Project IDX | Google has launched a beta version of project IDX, an IDE that works on browsers. To create a new... | 0 | 2024-06-15T03:10:19 | https://dev.to/asadut_zaman/create-laravel-project-on-project-idx-3aho | Google has launched a beta version of project IDX, an IDE that works on browsers.
To create a new laravel project click go the [idx.google.com](https://idx.google.com/) and "Select all the templates"
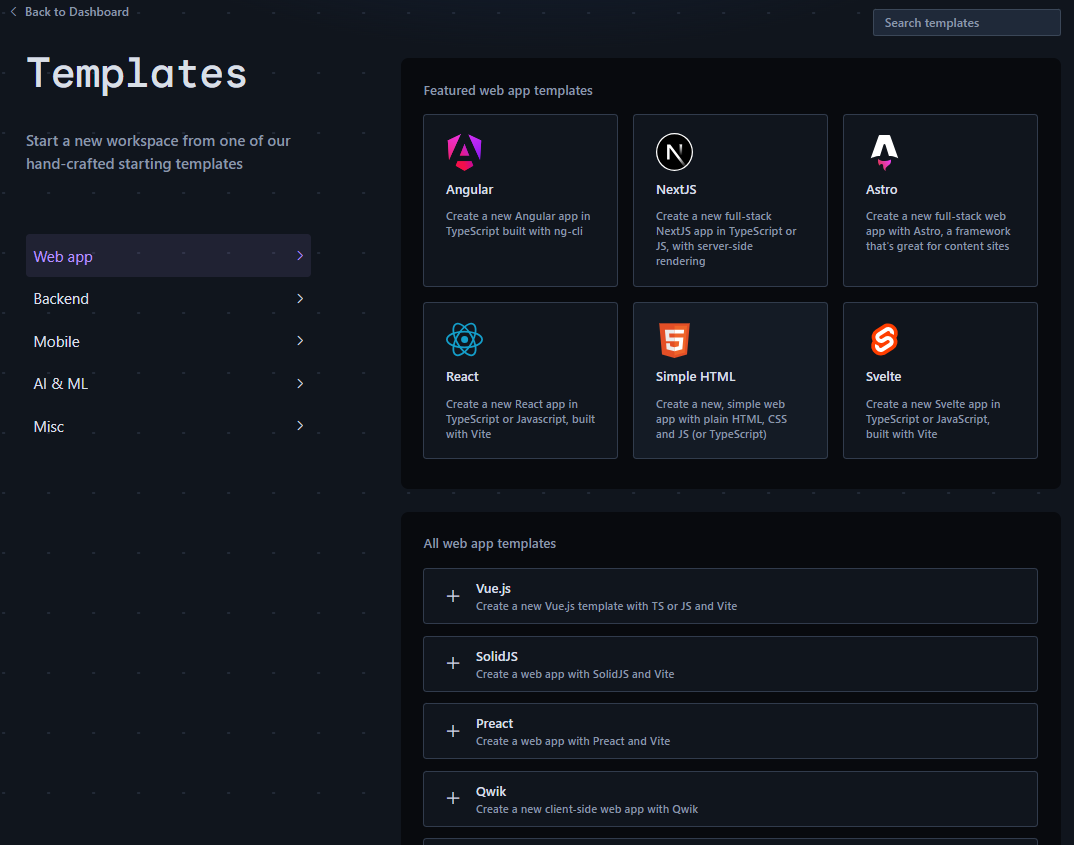
Select Backe... | asadut_zaman | |
1,889,181 | Shadcn UI: Must-Have Tools & Resources | awesome-shadcn/ui A curated list of awesome things related to shadcn/ui Created... | 0 | 2024-06-15T03:07:20 | https://dev.to/sh20raj/shadcn-ui-must-have-tools-resources-5488 | shadcn | <p align="center">
<br>
<img width="400" src="https://raw.githubusercontent.com/birobirobiro/awesome-shadcn-ui/64729b2c178e3fdcb42c0c7bf341bcde7ae502ea/assets/logo.svg" alt="logo of awesome-shadcn/ui repository">
<br>
<br>
</p>
<h2 align='center'>awesome-shadcn/ui</h2>
<p align='center'>
A curated list of awe... | sh20raj |
1,889,180 | The Importance of Solar Bypass Diodes in Photovoltaic Systems | The significance of Solar Avoid Diodes in Solar Energy Methods Are you currently curious how panels... | 0 | 2024-06-15T03:03:16 | https://dev.to/mithokha_saderha_c6bb89ea/the-importance-of-solar-bypass-diodes-in-photovoltaic-systems-1e3c | The significance of Solar Avoid Diodes in Solar Energy Methods
Are you currently curious how panels being solar one of the main elements which might be make that is vital which are often solarmay be the bypass diodethat is solar. , we will explain exactly what a bypass this is certainly solar is, what its advantages ar... | mithokha_saderha_c6bb89ea | |
1,889,179 | Streamlining Your Software Delivery with AWS CodePipeline | Streamlining Your Software Delivery with AWS CodePipeline In today's fast-paced software... | 0 | 2024-06-15T03:02:14 | https://dev.to/virajlakshitha/streamlining-your-software-delivery-with-aws-codepipeline-3i2l | 
# Streamlining Your Software Delivery with AWS CodePipeline
In today's fast-paced software development landscape, delivering high-quality applications at speed is paramount. This necessitates a robust and automated Continuous Integra... | virajlakshitha | |
1,889,178 | Building Reactive Microservices: A Step-by-Step Guide | From Monolith to Microservices: A Reactive Approach Transitioning from a monolithic... | 0 | 2024-06-15T03:00:49 | https://dev.to/tutorialq/building-reactive-microservices-a-step-by-step-guide-1jha | java, reactive, microservices, reactivemicrosoft | ### From Monolith to Microservices: A Reactive Approach
Transitioning from a monolithic architecture to microservices is a significant step for any organization. Reactive microservices offer a way to build highly responsive, resilient, and scalable applications. This guide will walk you through the process of transfor... | tutorialq |
1,889,176 | Custom Software Development: Investing in Long-Term Business Growth | We all use software every day. No matter the business or industry, software is just part of the world... | 0 | 2024-06-15T02:57:05 | https://dev.to/aaronsmithcs/custom-software-development-investing-in-long-term-business-growth-28bm | software, development, webdev | We all use software every day. No matter the business or industry, software is just part of the world now. Most businesses use standardized, off-the-shelf tools for many tasks. Microsoft and Google products are so prolific that the average person is expected to have familiarity with them.
Yet, such generalized tools d... | aaronsmithcs |
1,889,175 | NEED HELP FROM THE BEST CRYPTOCURRENCY RECOVERY EXPERT LEE ULTIMATE HACKER | LEEULTIMATEHACKER@ AOL. COM Support @ leeultimatehacker .com telegram:LEEULTIMATE wh@tsapp +1 (715)... | 0 | 2024-06-15T02:50:32 | https://dev.to/terry_woodly_b18d9eeb0ade/need-help-from-the-best-cryptocurrency-recovery-expert-lee-ultimate-hacker-2d84 | LEEULTIMATEHACKER@ AOL. COM
Support @ leeultimatehacker .com
telegram:LEEULTIMATE
wh@tsapp +1 (715) 314 - 9248
https://leeultimatehacker.com
In a world where online scams lurk around every corner, finding oneself entangled in a financial trap is not uncommon. My name is Woodly, and I'm here to share my testimo... | terry_woodly_b18d9eeb0ade | |
1,889,174 | 1.1 - Um primeiro programa simples | Programa Java Simples: - Descrição: Programa básico em Java que exibe uma mensagem no console. - Nome... | 0 | 2024-06-15T02:45:54 | https://dev.to/devsjavagirls/11-um-primeiro-programa-simples-5ah2 | java | **Programa Java Simples:**
**- Descrição:** Programa básico em Java que exibe uma mensagem no console.
**- Nome do Arquivo:** Deve ser "Example.java" para corresponder à classe principal "Example".
**Passos para Co... | devsjavagirls |
1,889,173 | From Concept to Completion: The Journey of a Kitchenware Production Line | From ideas to Reality: the whole information of how Kitchenware Production Lines Come to Life Have... | 0 | 2024-06-15T02:41:41 | https://dev.to/mithokha_saderha_c6bb89ea/from-concept-to-completion-the-journey-of-a-kitchenware-production-line-4di6 |
From ideas to Reality: the whole information of how Kitchenware Production Lines Come to Life
Have actually your become enthusiastic about precisely how kitchen area which are picked region are manufactured? Why don't we take a look that is good the journey associated with the kitchenware production line, from con... | mithokha_saderha_c6bb89ea | |
1,889,171 | Scope of Practice Restrictions: Navigating Legal and Regulatory Boundaries in Chiropractic Care with Tom Herchakowski (NJ) | Managing a chiropractic practice comes with its own set of challenges, and one of the most... | 0 | 2024-06-15T02:35:58 | https://dev.to/drtomherchakowski/scope-of-practice-restrictions-navigating-legal-and-regulatory-boundaries-in-chiropractic-care-with-tom-herchakowski-nj-5c5p | Managing a chiropractic practice comes with its own set of challenges, and one of the most significant is navigating the legal and regulatory boundaries that define the scope of chiropractic care. Scope of practice restrictions dictate the extent to which chiropractors can diagnose, treat, and manage various health con... | drtomherchakowski | |
1,889,170 | Iron IPTV Pro | Dans l’ère actuelle où la technologie révolutionne chaque aspect de notre vie quotidienne, le... | 0 | 2024-06-15T02:35:52 | https://dev.to/aboprotv/iron-iptv-pro-in0 | Dans l’ère actuelle où la technologie révolutionne chaque aspect de notre vie quotidienne, le divertissement n’est pas en reste. Avec l’émergence de plateformes de streaming, la télévision sur Internet est devenue la norme pour de nombreux foyers à travers le monde. Parmi les innombrables options disponibles, une se di... | aboprotv | |
1,889,169 | Maximizing Output: Strategies for Optimizing Kitchen Appliance Production Lines | Maximizing Manufacturing: Practices for Optimizing Kitchen Appliance Production Lines Wanna cook... | 0 | 2024-06-15T02:35:36 | https://dev.to/mithokha_saderha_c6bb89ea/maximizing-output-strategies-for-optimizing-kitchen-appliance-production-lines-3k07 |
Maximizing Manufacturing: Practices for Optimizing Kitchen Appliance Production Lines
Wanna cook like a specialist? Attaining cooking that are seamless throughout the great things about your home never ever be smoother. As a consequence of kitchen area that are advanced, cooking is now an task which was effortless a... | mithokha_saderha_c6bb89ea | |
1,889,167 | Streamlining Kitchenware Manufacturing: Innovations in Production Line Technology | Streamlining Kitchenware Manufacturing: Innovations in Production Line... | 0 | 2024-06-15T02:28:46 | https://dev.to/mithokha_saderha_c6bb89ea/streamlining-kitchenware-manufacturing-innovations-in-production-line-technology-1m13 |
Streamlining Kitchenware Manufacturing: Innovations in Production Line Technology
Introduction
Streamlining Kitchenware Manufacturing is just a complex plus procedure that are demanding need the application of advanced level quantity line which was manufacturing to generally meet the growing specifications of ... | mithokha_saderha_c6bb89ea | |
1,889,157 | Capitulo 1 Fundamentos da linguagem Java | Principais Habilidades e Conceitos - História e Filosofia de Java Conhecer a história e a filosofia... | 0 | 2024-06-15T02:25:31 | https://dev.to/devsjavagirls/cap-1-fundamentos-da-linguagem-java-2ch6 | java | **Principais Habilidades e Conceitos**
**- História e Filosofia de Java**
Conhecer a história e a filosofia da linguagem Java.
- Java foi criada por **James Gosling** e sua equipe na Sun Microsystems em **1991** como uma linguagem independente de plataforma, inicialmente para dispositivos eletrônicos, mas que se desta... | devsjavagirls |
1,889,164 | Exploring the Cultural Significance of Men's Hats Across the Globe | Looking at Men's Hats Inside The Globe Hats have been around for decades plus ages and they are part... | 0 | 2024-06-15T02:16:36 | https://dev.to/mithokha_saderha_c6bb89ea/exploring-the-cultural-significance-of-mens-hats-across-the-globe-4i53 |
Looking at Men's Hats Inside The Globe
Hats have been around for decades plus ages and they are part which will be crucial of nations internationally. These things being accessory in several designs which can be colors that are various and styles. Males's caps is one of the types being further popular their import... | mithokha_saderha_c6bb89ea | |
1,889,163 | 🐣 Assignment Expressions (The Walrus Operator) in Python | Overview PEP 572, also known as the "Assignment Expressions" or "The Walrus Operator,"... | 0 | 2024-06-15T02:13:57 | https://dev.to/talaatmagdy/assignment-expressions-the-walrus-operator-in-python-1m2d | python, codereview |
## Overview
PEP 572, also known as the "Assignment Expressions" or "The Walrus Operator," introduces a new syntax to the Python language, allowing assignment to variables within an expression using the `:=` operator. This enhancement offers a concise way to both assign and return a value within a single expression, i... | talaatmagdy |
1,889,162 | Mastering the Adapter Design Pattern: Bridging Incompatible Interfaces | The Adapter Design Pattern is a structural design pattern that allows objects with incompatible... | 0 | 2024-06-15T02:13:16 | https://dev.to/rupesh_mishra/mastering-the-adapter-design-pattern-bridging-incompatible-interfaces-4ici | The Adapter Design Pattern is a structural design pattern that allows objects with incompatible interfaces to work together. It's like a translator between two parties that do not speak the same language. In this article, we'll break down the Adapter Design Pattern into four actionable steps, using real-world scenarios... | rupesh_mishra | |
1,889,159 | Shell >> Redirections >> Capture | Redirection meanings What ? Changing something. Instead of putting the output to the screen instead... | 0 | 2024-06-15T02:10:47 | https://dev.to/technonotes/shell-redirections-capture-2geo | - Redirection meanings What ? Changing something.
- Instead of putting the output to the screen instead redirect to the file.
- ">" redirect and over write
- ">>" will always append.
```
#!/bin/bash
read -p "Enter ur name: " name
echo " Welcome to BOMBAY $name !!"
```
 | As a Node.js developer, you might have encountered situations where different projects require... | 0 | 2024-06-15T02:00:51 | https://dev.to/sayuj/mastering-nodejs-development-with-node-version-manager-nvm-53o0 | node, webdev, javascript, npm | As a Node.js developer, you might have encountered situations where different projects require different versions of Node.js. Managing multiple versions of Node.js can be a hassle, but Node Version Manager (NVM) simplifies this process. In this blog post, we'll explore what NVM is, how to install it, and how to use it ... | sayuj |
1,888,758 | 1- Introdução | Resumo em Tópicos do Livro JAVA PARA INICIANTES Objetivo do Livro: Ensinar fundamentos da... | 0 | 2024-06-15T01:50:23 | https://dev.to/devsjavagirls/1-introducao-2cpf | java, javaparainiciantes | Resumo em Tópicos do Livro **JAVA PARA INICIANTES**
**Objetivo do Livro:**
Ensinar fundamentos da programação Java.
Abordagem passo a passo com exemplos, testes e projetos.
Não requer experiência prévia em programação.
**Conteúdo do Livro:**
- Fundamentos de Java
- Recursos Avançados de Java
- Desenvolvimento Gráfico... | devsjavagirls |
1,889,155 | Introduction to Blockchain in Cross-Industry Collaboration | Blockchain technology, originally devised for Bitcoin, has evolved to transform various industries by... | 27,673 | 2024-06-15T01:44:00 | https://dev.to/rapidinnovation/introduction-to-blockchain-in-cross-industry-collaboration-57cc | Blockchain technology, originally devised for Bitcoin, has evolved to
transform various industries by enabling secure, transparent, and efficient
cross-industry collaborations. Its decentralized nature allows multiple
parties to interact on a single platform without intermediaries, fostering
innovative solutions across... | rapidinnovation | |
1,889,152 | Running DeepCell on Google Batch with node pools | As part of our ongoing work to run DeepCell on GCP, I'm pleased to share our benchmarking results... | 27,298 | 2024-06-15T01:27:36 | https://dev.to/dchaley/running-deepcell-on-google-batch-with-node-pools-3hfd | googlecloud, serverless, bioinformatics, scale | As part of our ongoing work to run DeepCell on GCP, I'm pleased to share our benchmarking results using Google Batch's private preview feature: node pools.
Node pools allow Batch to reuse infrastructure across jobs, which can improve end-to-end performance for jobs with a lot of setup time (like our 3 GB container). U... | dchaley |
1,889,151 | Virtualization & Containerization with Docker. | Everyone relies on data for work and decision-making. There are various cloud-enabling technologies... | 0 | 2024-06-15T01:23:16 | https://dev.to/michellebuchiokonicha/virtualization-containerization-with-docker-storage-and-network-services-2bjf | cloudcomputing, docker, api, softwaredevelopment | Everyone relies on data for work and decision-making. There are various cloud-enabling technologies but we will concentrate on. Virtualization is responsible for the abstraction, isolation, and hoarding of applications. There are different levels of virtualization and different approaches.
**Virtualization and contain... | michellebuchiokonicha |
1,889,114 | Idempotência: Conceito e Aplicação na Garantia da Qualidade de Softwar | 1. Introdução Você sabe ou já ouviu falar em idempotência? Em matemática e ciência da... | 0 | 2024-06-15T00:36:43 | https://dev.to/yuri-aprendendoqa/idempotencia-conceito-e-aplicacao-na-garantia-da-qualidade-de-softwar-1gic | #### 1. Introdução
Você sabe ou já ouviu falar em idempotência?
Em matemática e ciência da computação, a idempotência é a propriedade que algumas operações têm de poderem ser aplicadas várias vezes sem que o valor do resultado se altere após a aplicação inicial. De acordo com a Wikipedia, isso significa que, após a ... | yuri-aprendendoqa | |
1,889,112 | Developing Cloud-Based Applications with Azure | Introduction Cloud computing has revolutionized the way businesses develop and deploy... | 0 | 2024-06-15T00:32:13 | https://dev.to/kartikmehta8/developing-cloud-based-applications-with-azure-2kfh | webdev, javascript, beginners, programming | ## Introduction
Cloud computing has revolutionized the way businesses develop and deploy applications. With the increasing demand for scalability, flexibility, and cost-effectiveness, cloud-based applications have become the preferred choice for many organizations. Microsoft Azure, one of the leading cloud platforms, ... | kartikmehta8 |
1,889,111 | [Game of Purpose] Day 27 | Today I tried to make flying with physics with this tutorial. I wanted to fly with a simple mesh, so... | 27,434 | 2024-06-15T00:24:16 | https://dev.to/humberd/game-of-purpose-day-27-1i9p | gamedev | Today I tried to make flying with physics with [this tutorial](https://www.youtube.com/watch?v=IT9Rlyy-bSE). I wanted to fly with a simple mesh, so I started with a simple cube. I'm not yet sure how Torque works and what it is, but I followed the tutorial and it indeed flies :)
However, when flying forward/backward an... | humberd |
1,889,110 | Unleashing Reactive Programming: Boosting Responsiveness, Resilience, and Scalability | Reactive programming is a paradigm that allows for the development of responsive, resilient, and... | 0 | 2024-06-15T00:22:25 | https://dev.to/tutorialq/unleashing-reactive-programming-boosting-responsiveness-resilience-and-scalability-503 | reactive, reactiveprogramming, rxjs, scalability | Reactive programming is a paradigm that allows for the development of responsive, resilient, and scalable applications. This programming style is particularly suited for applications that deal with asynchronous data streams and events, enabling developers to build systems that react to changes in real time. This deep d... | tutorialq |
1,889,090 | GitHub Copilot asking multiple questions | Usually when using GitHub Copilot in Microsoft Visual Studio Code a developer asks a question, gets... | 27,651 | 2024-06-15T00:12:43 | https://dev.to/karenpayneoregon/github-copilot-asking-multiple-questions-54de | tutorial, ai, codenewbie | Usually when using GitHub Copilot in Microsoft Visual Studio Code a developer asks a question, gets an acceptable answer, and continues. But there are times when the response is close and needs some changes. In these cases do not accept the answer, instead ask a secondary question.
Example, a developer wants a Custome... | karenpayneoregon |
1,888,885 | From Transaction Scripts to Domain Models: A Refactoring Journey | I once led the development of a fitness tracking app. We started with Transaction Scripts to handle... | 0 | 2024-06-17T08:43:03 | https://www.milanjovanovic.tech/blog/from-transaction-scripts-to-domain-models-a-refactoring-journey | domainmodel, ddd, transactionscript, dotnet | ---
title: From Transaction Scripts to Domain Models: A Refactoring Journey
published: true
date: 2024-06-15 00:00:00 UTC
tags: domainmodel,ddd,transactionscript,dotnet
canonical_url: https://www.milanjovanovic.tech/blog/from-transaction-scripts-to-domain-models-a-refactoring-journey
cover_image: https://dev-to-uploads... | milanjovanovictech |
1,889,438 | Building a landing page for your book | This post follows on from my last post about using your website to promote your ebooks. The first... | 0 | 2024-06-28T08:36:52 | https://www.csrhymes.com/2024/06/15/building-a-landing-page-for-your-book.html | writing, marketing, webdev | ---
title: Building a landing page for your book
published: true
date: 2024-06-15 00:00:00 UTC
tags: writing,marketing,webdev
canonical_url: https://www.csrhymes.com/2024/06/15/building-a-landing-page-for-your-book.html
cover_image: https://www.csrhymes.com/img/create-a-promo-page.jpg
---
This post follows on from my ... | chrisrhymes |
1,889,089 | High Frequency Trading : An introduction to Nordic Stock Exchange data | High-frequency trading (HFT) has transformed the landscape of financial markets. By leveraging... | 0 | 2024-06-14T23:49:12 | https://dev.to/shivam_sharma_0898bab64d2/high-frequency-trading-an-introduction-to-nordic-stock-exchange-data-15f0 | highfrequencytrading, priceprediction, marketmicrostructure |
High-frequency trading (HFT) has transformed the landscape of financial markets. By leveraging sophisticated algorithms and cutting-edge technology, HFT allows traders to execute thousands of transactions within fractions of a second. This rapid trading strategy exploits minute price discrepancies, thereby providing l... | shivam_sharma_0898bab64d2 |
1,889,087 | How @AliasFor Simplifies Annotations usage in Spring | This annotation is an annotation that allows you to create an alias for an attribute in an... | 27,602 | 2024-06-14T23:35:43 | https://springmasteryhub.com/2024/06/14/how-aliasfor-simplifies-annotations-usage-in-spring/ | java, spring, springboot, programming | This annotation is an annotation that allows you to create an alias for an attribute in an annotation. These attributes have the same function. The idea is to avoid confusion when multiple attributes can be used for the same purpose
Maybe this is the first time you have seen it.
Spring uses this annotation in places ... | tiuwill |
1,889,075 | RECONSIDER YOUR PATH TO SUCCESS AS A SOFTWARE ENGINEER | I've observed a prevailing trend in the software engineering community: a fixation on creating... | 0 | 2024-06-14T23:15:15 | https://dev.to/themuneebh/reconsider-your-path-to-success-as-a-software-engineer-2f4i | softwareengineering | I've observed a prevailing trend in the software engineering community: a fixation on creating products and acquiring minimal knowledge to meet requirements. However, it's crucial to realize that product development is not the ultimate goal.
Seasoned engineers dedicate significant time to maintaining, scaling, rewriti... | themuneebh |
1,888,825 | Angular Animations Tutorial: Route Transitions | If you’ve ever worked with an Angular application that has routing, you may have wanted to add... | 26,395 | 2024-06-14T23:00:00 | https://briantree.se/angular-animations-tutorial-route-transitions/ | angular, animations, webdev, frontend | If you’ve ever worked with an Angular application that has [routing](https://angular.dev/guide/routing), you may have wanted to add transitions as you navigate between routes. It just makes the app feel more elegant overall. Well, if you didn’t know, this is totally doable with the [Animation module](https://angular.de... | brianmtreese |
1,889,074 | Relaxamento Natural: Guia Passo a Passo para Óleos de Massagem com Lavanda | A busca por bem-estar e saúde através de métodos naturais tem crescido exponencialmente, e como... | 0 | 2024-06-14T22:59:49 | https://dev.to/vidacomartesanato/relaxamento-natural-guia-passo-a-passo-para-oleos-de-massagem-com-lavanda-36jo | massagem, óleos, óleosnaturais, relaxamento |

A busca por bem-estar e saúde através de métodos naturais tem crescido exponencialmente, e como fazer óleos de massagem naturais com [lavanda](https://pt.wikipedia.org/wiki/Lavanda) é uma habilidade que se alinha p... | vidacomartesanato |
1,889,033 | Project Stage-2 Implementation [part-2] | Welcome back peeps!! After a lot of theory about function multi versioning in the last blog we will... | 0 | 2024-06-14T22:53:24 | https://dev.to/yuktimulani/project-stage-2-implementation-part-2-klo | Welcome back peeps!! After a lot of theory about function multi versioning in the [last blog](https://dev.to/yuktimulani/project-stage-2-implementation-part-1-1p4n) we will start actually working on it in this part. So, without wasting any time lets get started.
I started with exploring files like
`tree.h`,`tree.cc`a... | yuktimulani | |
1,827,966 | Notes about The Chapter 01 of Web Scalability For Startup Engineers | Notes about The Chapter 01 of Web Scalability For Startup Engineers (Image by Herbert Austfrom... | 0 | 2024-06-14T22:46:45 | https://dev.to/ezpzdevelopement/notes-about-the-chapter-01-of-web-scalability-for-startup-engineers-28oc | softwareengineering, architecture, softwaredevelopment, systemdesignintervie |

_Notes about The Chapter 01 of Web Scalability For Startup Engineers (Image by Herbert Austfrom Pixabay)_
Last week, I wanted to learn more about system design and scalability... | ezpzdevelopement |
1,499,602 | Create A Vim Plugin For Your Next Programming Language, Indentation and Autocomplete | In the previous post, i discussed how to structure our vim plugin, and how we can add the beautiful... | 0 | 2024-06-14T22:46:00 | https://dev.to/ezpzdevelopement/create-a-vim-plugin-for-your-next-programming-language-indentation-and-autocomplete-4314 | vim, extension |

In the [previous post](https://dev.to/abderahmanemustapha/create-a-vim-plugin-for-your-next-programming-language-structure-and-syntax-highlight-1dog-temp-slug-8... | ezpzdevelopement |
1,889,072 | Smart Contract Development: Transforming Modern Business | Introduction Smart contracts represent a transformative technology that is reshaping... | 27,673 | 2024-06-14T22:42:50 | https://dev.to/rapidinnovation/smart-contract-development-transforming-modern-business-3kpj | ## Introduction
Smart contracts represent a transformative technology that is reshaping the
way businesses and individuals engage in transactions. These self-executing
contracts, stored on a blockchain, automatically execute and enforce the terms
of a contract when predetermined conditions are met, eliminating the nee... | rapidinnovation | |
1,889,068 | Improving coding skills with games! 🎮 | Coding is a lot of fun, but imagine having even more fun by coding and playing at the same time! 🎮✨... | 0 | 2024-06-14T22:24:54 | https://dev.to/buildwebcrumbs/improving-coding-skills-with-games-aco | css, tailwindcss, frontend, gamedev | **Coding** is a lot of fun, but imagine having even more fun by coding and **playing** at the same time! 🎮✨ In this article, I'm going to share tips on how you can level up your **programming** skills and have a blast while doing it. 🚀🧩
## Css2Wind 🌬️
In this game, you get to translate native **CSS** to **Tailwind... | m4rcxs |
1,889,067 | Mystery World | A post by Darvin Monteras | 0 | 2024-06-14T22:24:43 | https://dev.to/metadarvinmonteras/mystery-world-d6j | javascript, beginners, webdev, productivity |
[](https://darvinmonteraswebsiteorg.godaddysites.com) | darvinmonterasgodaddysitescom |
1,889,060 | Java’s Evolution: Top 5 Features from Java 8 to 22 | The Evolution of Java: Top 5 Features from Java 8 to Java 22 Java has continuously evolved... | 0 | 2024-06-14T22:03:06 | https://dev.to/tutorialq/javas-evolution-top-5-features-from-java-8-to-22-1dbg | java, javafeatures, javaevolution, java22 |
## The Evolution of Java: Top 5 Features from Java 8 to Java 22
Java has continuously evolved to meet the demands of modern software development. This article explores the top 5 features introduced in each Java version from Java 8 to the latest Java 22, providing in-depth explanations, useful examples, and guidance o... | tutorialq |
1,889,061 | SUR LE CHEMIN DU HACKING ! Kali Academy, trois mois d’initiation 👺 | Et oui 🙂 vous ne rêvez pas ! Je dis dis bien hacking ! Avant tout, mettons-nous d'accord sur la... | 0 | 2024-06-14T22:20:06 | https://dev.to/tacite243/sur-le-chemin-du-hacking-kali-academy-trois-mois-dinitiation-1k9m | webdev, javascript, beginners, programming | Et oui 🙂 vous ne rêvez pas ! Je dis dis bien hacking ! Avant tout, mettons-nous d'accord sur la terminologie “Hacking”. Les médias nous ont menti sur le hacking, ils confondent le hacking au cracking. Richard Stallman, un fervent défenseur du logiciel libre et fondateur du mouvement du logiciel libre, définit un hacke... | tacite243 |
1,889,064 | Computer Science Challenge: Algorithm | This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer. ... | 0 | 2024-06-14T22:17:06 | https://dev.to/izuchi/computer-science-challenge-algorithm-2dl | devchallenge, cschallenge, computerscience, beginners | *This is a submission for [DEV Computer Science Challenge v24.06.12: One Byte Explainer](https://dev.to/challenges/cs).*
## Explainer
An algorithm is a recipe for computers – it tells them how to solve problems step by step. It's crucial in CS for designing efficient solutions, ensuring accuracy in tasks like sorting... | izuchi |
1,889,027 | Afinal, o que são os 0's e 1's? | Você já deve ter ouvido por aí que o computador "só entende 0's e 1's". Mas de onde vem esses 0's e... | 0 | 2024-06-14T22:15:43 | https://dev.to/xornotor/afinal-o-que-sao-os-0s-e-1s-3jdb | digital, electronics, computerscience, circuits | Você já deve ter ouvido por aí que o computador "só entende 0's e 1's". Mas **de onde vem esses 0's e 1's**? O que eles representam?
---
## Analógico vs. Digital
Antigamente, os sistemas eletrônicos lidavam com a informação de forma analógica, ou seja, os sinais elétricos que representavam a informação podiam assumi... | xornotor |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.