id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,887,718 | Hello, i am Emile and i need help with coding | Hello, please any one to help me out with coding | 0 | 2024-06-13T21:36:13 | https://dev.to/ngelle_emile_04bfe61f8675/hello-i-am-emile-and-i-need-help-with-coding-270l | Hello, please any one to help me out with coding
| ngelle_emile_04bfe61f8675 | |
1,887,698 | computer science concept in 256 | This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer. ... | 0 | 2024-06-13T21:10:37 | https://dev.to/fabelt14/computer-science-concept-in-256-2al6 | devchallenge, cschallenge, computerscience, beginners | *This is a submission for [DEV Computer Science Challenge v24.06.12: One Byte Explainer](https://dev.to/challenges/cs).*
## **Explainer**
Recursion is a function calling itself to solve smaller instances of the same problem, ideal for tasks like navigating tree structures. It simplifies code but risks stack overflow ... | fabelt14 |
1,887,697 | Blockchain in Fintech: Uses and Early Case Applications | Blockchain, once the domain of niche tech professionals, has now firmly established itself in the... | 0 | 2024-06-13T21:09:02 | https://dev.to/eincheste/blockchain-in-fintech-uses-and-early-case-applications-148a | webdev, cryptocurrency, fintech, beginners | Blockchain, once the domain of niche tech professionals, has now firmly established itself in the financial technology (fintech) landscape. As the financial world undergoes digital transformation, blockchain’s promise of transparency, security, and efficiency stands out. Let’s explore how blockchain is being used in f... | eincheste |
1,887,696 | Decoding Backend Architecture: Crafting Effective Folder Structures | In the digital landscape, where web and mobile applications reign supreme, the backend serves as the... | 0 | 2024-06-13T21:08:29 | https://dev.to/mahabubr/decoding-backend-architecture-crafting-effective-folder-structures-in7 | webdev, backend, architecture, structure | In the digital landscape, where web and mobile applications reign supreme, the backend serves as the unseen architect, laying the foundation for seamless user experiences. A crucial aspect of backend development lies in crafting a well-organized folder structure, akin to the blueprint of a skyscraper, guiding developer... | mahabubr |
1,887,695 | THAT Conference: THAT's Where the Best Networking Is At! | Introduction Networking is a proven method for career advancement, and the most effective... | 0 | 2024-06-13T21:06:29 | https://www.htmlallthethings.com/blog-posts/that-conference-thats-where-the-best-networking-is-at | conference, career, codenewbie, interview | ### **Introduction**
Networking is a proven method for career advancement, and the most effective way to network is in person!
This article covers a special guest Podcast with Clark Sell, the visionary founder of THAT Conference, the largest family-friendly tech event in the US. Tech industry experts Matt Lawrence an... | michaellarocca |
1,887,694 | How I manage my enormous`class` attributes in Tailwind projects | I'm curious what sorts of workflows you might have developed for dealing with oodles and oodles of... | 0 | 2024-06-13T21:04:55 | https://dev.to/aaronmw/wanted-vscode-andor-prettier-plugin-to-ease-the-suffering-of-editingclass-attributes-in-a-tailwind-project-5hei | tailwindcss, vscode | I'm curious what sorts of workflows you might have developed for dealing with oodles and oodles of classes on a single element, often amongst many others within a single component.
I figured I'd share what I currently do, and maybe others can show me how they'd do it differently. Or maybe I can at least inspire someon... | aaronmw |
1,887,693 | AWS Cloud Resume Challenge | Who I Am Hello everyone! My name is Tariq Moore and I’m a Web Developer, aspiring Cloud... | 0 | 2024-06-13T21:04:17 | https://dev.to/tariq_moore/aws-cloud-resume-challenge-2676 | webdev, aws, awschallenge, devops |
## _Who I Am_
Hello everyone! My name is Tariq Moore and I’m a Web Developer, aspiring Cloud Engineer, and DevOps Engineer. This is my first time writing a blog post, so I hope you enjoy this deep dive into the Cloud Resume Challenge, and my thought process while completing it!
A few weeks ago, I acquired my AWS Cl... | tariq_moore |
1,887,692 | Exploring Object-Oriented Programming - TypeScript Examples | Object-oriented programming (OOP) is a paradigm that allows developers to structure their code in a... | 0 | 2024-06-13T21:04:11 | https://dev.to/mahabubr/exploring-object-oriented-programming-typescript-examples-1573 | webdev, typescript, oop, programming | Object-oriented programming (OOP) is a paradigm that allows developers to structure their code in a more organized and modular way, making it easier to manage and maintain. In this article, we'll explore some fundamental concepts of OOP—inheritance, polymorphism, abstraction, and encapsulation—through the lens of TypeS... | mahabubr |
1,887,686 | RecyclerView vs LazyColumn | I've been working with Jetpack Compose for about 6-8 months but I've never checked a performance... | 0 | 2024-06-13T20:52:04 | https://dev.to/mardsoul/recyclerview-vs-lazycolumn-5g6g | android, ui, testing | I've been working with Jetpack Compose for about 6-8 months but I've never checked a performance difference between both technologies, I only heard from Google that Compose is much better than XML View.
So, I decided to test a performance between RecyclerView and LazyColumn.
### About an app
The app solve a typical t... | mardsoul |
1,887,691 | Harnessing the Power of React's useContext Hook: Simplifying State Management in Complex Applications | Introduction: React's useContext hook is a powerful tool that facilitates the management... | 0 | 2024-06-13T20:59:53 | https://dev.to/mahabubr/harnessing-the-power-of-reacts-usecontext-hook-simplifying-state-management-in-complex-applications-46ne | webdev, javascript, react, usecontext | ## Introduction:
React's useContext hook is a powerful tool that facilitates the management and sharing of state across components in a React application. It offers a simpler alternative to prop drilling and context API, allowing developers to access and update state without having to pass props through every level of... | mahabubr |
1,887,689 | Unlocking the Power of useRef: Besic to Advanced Examples for React Developers | React, the popular JavaScript library for building user interfaces, offers a plethora of hooks to... | 0 | 2024-06-13T20:56:38 | https://dev.to/mahabubr/unlocking-the-power-of-useref-besic-to-advanced-examples-for-react-developers-4e0l | webdev, javascript, react, useref | React, the popular JavaScript library for building user interfaces, offers a plethora of hooks to manage state, side effects, and more. Among these, useRef stands out as a versatile tool for accessing and managing references to DOM elements or other values across renders. In this article, we'll delve into how useRef wo... | mahabubr |
1,887,688 | Elite Gta Tow | Experience hassle-free towing services at unbeatable prices across Downtown Toronto, Scarborough,... | 0 | 2024-06-13T20:56:28 | https://dev.to/elite_towing_94465a734457/elite-gta-tow-30nb |
Experience hassle-free towing services at unbeatable prices across Downtown Toronto, Scarborough, Etobicoke, and North York with Elite GTA Towing. Our expert team is dedicated to providing swift and reliable assistan... | elite_towing_94465a734457 | |
1,887,687 | Understanding How React's useEffect Works: A Comprehensive Guide | React, as a JavaScript library for building user interfaces, provides developers with an array of... | 0 | 2024-06-13T20:53:29 | https://dev.to/mahabubr/understanding-how-reacts-useeffect-works-a-comprehensive-guide-3947 | react, webdev, javascript, useeffect | React, as a JavaScript library for building user interfaces, provides developers with an array of tools to manage state, handle side effects, and optimize performance. Among these tools, useEffect stands out as a powerful hook for managing side effects in functional components. In this article, we'll delve into the wor... | mahabubr |
1,887,597 | Hello world | A post by Phawat | 0 | 2024-06-13T19:06:56 | https://dev.to/phawat63915/hello-world-4m20 | webdev | phawat63915 | |
1,887,685 | shadcn-ui/ui codebase analysis: Cards example explained. | In this article, we will learn about Cards example in shadcn-ui/ui. This article consists of the... | 0 | 2024-06-13T20:51:25 | https://dev.to/ramunarasinga/shadcn-uiui-codebase-analysis-cards-example-explained-2pkd | javascript, opensource, nextjs, shadcnui | In this article, we will learn about [Cards](https://github.com/shadcn-ui/ui/tree/main/apps/www/app/(app)/examples/cards) example in shadcn-ui/ui. This article consists of the following sections:
 EF Core is efficient with... | 21,515 | 2024-06-13T20:39:56 | https://dev.to/karenpayneoregon/ef-core-8-update-entity-37il | csharp, database, dotnetcore | When entities are being tracked (this is the default, to track changes) EF Core is efficient with updates in that if there are several properties for a model and only one or two properties changed the update statement only updates those columns/properties which changed rather than every column/property.
**Model**
```... | karenpayneoregon |
1,887,284 | Programação Orientada a Objetos: Abstração | Abstração | 27,708 | 2024-06-13T20:36:03 | https://dev.to/fabianoflorentino/programacao-orientada-a-objetos-abstracao-157o | programming, braziliandevs, poo | ---
title: "Programação Orientada a Objetos: Abstração"
published: true
description: Abstração
series: Programação Orientada a Objetos
tags: programming, braziliandevs, poo
cover_image: https://i.ibb.co/m69Qnf6/Screenshot-2024-06-26-at-21-39-20.png
---
# Abstração
Em ciência da computação, abstração é a habilidade de... | fabianoflorentino |
1,884,827 | Netex Server - Netex Sensör - Ağ Keşif Eklentisi | Netex Server Kurulumu Netex server kurulacak makinenin terminalini açınız. Elimizdeki... | 0 | 2024-06-13T20:31:35 | https://dev.to/aciklab/netex-server-netex-sensor-ag-kesif-eklentisi-5c6a | netex, network, liman, server | # Netex Server Kurulumu
- Netex server kurulacak makinenin terminalini açınız.
- Elimizdeki **netex-x64.deb** paketini aşağıdaki komut ile kurunuz:
```
sudo apt install ./netex-x64.deb
```
**NOT:** Paketinizin adı sürümden kaynaklı farklı olacağı için isimlendirmesi farklılık gösterebilir. (Örnek: netex-1234-x64.deb)... | yarensari |
1,887,678 | Unlocking the Hidden Treasures of Your Applications | As a developer with over 15 years of experience in the industry, I've seen firsthand how many... | 0 | 2024-06-13T20:31:17 | https://dev.to/jwtiller_c47bdfa134adf302/unlocking-the-hidden-treasures-of-your-applications-ee | dotnet, observeability, productivity | As a developer with over 15 years of experience in the industry, I've seen firsthand how many applications are like locked treasure chests, filled with valuable insights that often go unnoticed while digital pirates lurk, trying to exploit any weaknesses. This realization is what drove me to start RazorSharp. My goal i... | jwtiller_c47bdfa134adf302 |
1,887,674 | Scrap Car Gta | Revitalize your urban space while earning cash with Scrap Car GTA, your premier solution for scrap... | 0 | 2024-06-13T20:19:30 | https://dev.to/scrap_cargta/scrap-car-gta-3e4 | towin, services | Revitalize your urban space while earning cash with Scrap Car GTA, your premier solution for scrap car removal in Downtown Toronto, Scarborough, Etobicoke, Pickering, and North York. Say goodbye to that old clunker taking up valuable parking space and hello to extra money in your pocket! Our hassle-free service ensures... | scrap_cargta |
1,887,670 | 5 Exciting NumPy Challenges to Boost Your Programming Skills! 🚀 | The article is about 5 exciting NumPy challenges curated by LabEx, a leading online platform for coding challenges. These challenges are designed to push the boundaries of your programming skills and expertise in numerical computations using the powerful NumPy library. From mastering advanced sorting and searching algo... | 27,710 | 2024-06-13T20:10:05 | https://dev.to/labex/5-exciting-numpy-challenges-to-boost-your-programming-skills-1499 | numpy, coding, programming, tutorial |
Are you ready to take your Python programming skills to the next level? LabEx, a leading online platform for coding challenges, has curated a collection of 5 captivating NumPy challenges that will push your problem-solving abilities to new heights! 💪
## Sorting and Searching: Mastering Advanced Algorithms with NumPy... | labby |
1,887,668 | Daily log: 6/13/24 | Todo List Morning Jog Revisit Kevin Powell's Responsive Design Class Clean up my latest Frontend... | 0 | 2024-06-13T20:03:50 | https://dev.to/moncadad/daily-log-61324-1dgd | Todo List
1. Morning Jog
2. Revisit Kevin Powell's Responsive Design Class
3. Clean up my latest Frontend Mentor Challenge
4. Review Intro React on Scrimba
5. Update Portfolio Skills, and Projects
5. Evening Walk
6. Phlearn Photoshop Daily Tutorial
| moncadad | |
1,887,667 | We need to stop Freewallet scammers | The cryptocurrency world is buzzing with the escalating scandal surrounding the Freewallet crypto... | 0 | 2024-06-13T19:59:23 | https://dev.to/feofhan/we-need-to-stop-freewallet-scammers-36pm | The cryptocurrency world is buzzing with the escalating scandal surrounding the Freewallet crypto scam. Despite the polished reviews and glowing testimonials found online, the reality is starkly different. Numerous users have reported losing their deposits due to deceptive practices disguised as routine KYC (Know Your ... | feofhan | |
1,887,665 | Recursion 256 chars | This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer. ... | 0 | 2024-06-13T19:56:55 | https://dev.to/fmalk/recursion-256-chars-5d4b | devchallenge, cschallenge, computerscience, beginners | *This is a submission for [DEV Computer Science Challenge v24.06.12: One Byte Explainer](https://dev.to/challenges/cs).*
## Explainer
Recursion is code on a journey, encountering a smaller version of itself, easier to run, which goes on a journey, encountering a smaller version of itself, easier to run, which goes on... | fmalk |
1,887,664 | We work at FAANG for free | Imagine a factory where nameless workers are working day and night to produce expensive products.... | 0 | 2024-06-13T19:56:38 | https://dev.to/nooruddin/we-work-at-faang-for-free-g32 | bigdata | Imagine a factory where nameless workers are working day and night to produce expensive products. These expensive products are shipped instantly all over the world to a wealthy buyers generating more than $200 millions per day for that factory.
What if I say those worker doesn’t charge a penny to produce such expensiv... | nooruddin |
1,887,663 | From Manuscript to Bestseller: How Book Publishing HQ Can Help | Book Publishing HQ is a premier provider of comprehensive book publishing services, dedicated to... | 0 | 2024-06-13T19:53:21 | https://dev.to/book_publishinghqllc_9a/from-manuscript-to-bestseller-how-book-publishing-hq-can-help-1ho1 | books, publishing | [Book Publishing](https://www.bookpublishinghq.com/) HQ is a premier provider of comprehensive book publishing services, dedicated to helping authors transform their manuscripts into successful, professionally published books. Established with the mission to empower writers and elevate their literary works, Book Publis... | book_publishinghqllc_9a |
1,887,662 | Estudos em Quality Assurance (QA) - Jira: O Básico de Gerenciamento de Issues | As issues no Jira variam em tamanho e complexidade, podendo levar de horas a meses para serem... | 0 | 2024-06-13T19:51:30 | https://dev.to/julianoquites/estudos-em-quality-assurance-qa-jira-o-basico-de-gerenciamento-de-issues-80e | jira, testing, qa, beginners |
As issues no Jira variam em tamanho e complexidade, podendo levar de horas a meses para serem concluídas. Cada issue é composta por vários componentes, que são:
- **Chave da issue (Issue Key):** Identificador único.
- **Resumo (Summary):** título.
- **Descrição (Description):** Informações detalhadas.
- **Data de Co... | julianoquites |
1,887,661 | 🚀Notcoin (NOT) Overtakes SHIB in Top Ranks as SHIB Volume Drops Dramatically | Notcoin (NOT) has surged in popularity, surpassing Shiba Inu (SHIB) in trading volume and market cap... | 0 | 2024-06-13T19:49:16 | https://dev.to/irmakork/notcoin-not-overtakes-shib-in-top-ranks-as-shib-volume-drops-dramatically-4bg5 |
Notcoin (NOT) has surged in popularity, surpassing Shiba Inu (SHIB) in trading volume and market cap rankings within the cryptocurrency market. Notcoin's trading volume spiked by 67% to $926.27 million over June 12-13, elevating it to the 12th most traded crypto asset. In contrast, SHIB's trading volume decreased by ... | irmakork | |
1,887,660 | 🤯513 Million Bitcoin (BTC) in 24 Hours, Here's What's Coming | The cryptocurrency market, particularly Bitcoin, has reacted negatively to the latest United States... | 0 | 2024-06-13T19:49:00 | https://dev.to/irmakork/513-million-bitcoin-btc-in-24-hours-heres-whats-coming-3p0a |
The cryptocurrency market, particularly Bitcoin, has reacted negatively to the latest United States Producer Price Index (PPI) data for May. The PPI showed a month-on-month decrease of -0.2%, contrasting with the previous 0.5% increase. This unexpected decline suggests that the Federal Reserve's efforts to stabilize i... | irmakork | |
1,887,659 | 🚀Pepe Coin Surges 10% in 24 Hours | After a bearish start to the month, a few altcoins have soared in price, to the delight of crypto... | 0 | 2024-06-13T19:48:41 | https://dev.to/irmakork/pepe-coin-surges-10-in-24-hours-355 |
After a bearish start to the month, a few altcoins have soared in price, to the delight of crypto fans and investors. A classic example is Pepe Coin, which has defied the broader crypto market trend by surging over 10% in the past 24 hours. It currently trades above $0.000013.
While major cryptos like ETH, SOL, and D... | irmakork | |
1,887,658 | 💥Pepe Surges 17.85% with Strong Bullish Indicators Pointing to a Potential 50% Rally by June’s End | PEPE showed a promising 17.85% rise to $0.00001340 on June 12, supported by increased trading volumes... | 0 | 2024-06-13T19:48:21 | https://dev.to/irmakork/pepe-surges-1785-with-strong-bullish-indicators-pointing-to-a-potential-50-rally-by-junes-end-hop | PEPE showed a promising 17.85% rise to $0.00001340 on June 12, supported by increased trading volumes and a rebound from its lower trendline in a rising wedge pattern. This pattern suggests potential support, aiming for an upper trendline target around $0.00002661, indicating a potential 70% increase.
Critical support... | irmakork | |
1,887,657 | Blockchain in 256 chars | This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer. ... | 0 | 2024-06-13T19:45:50 | https://dev.to/ruttosa/blockchain-in-256-chars-d9m | devchallenge, cschallenge, computerscience, beginners | _This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer._
## Explainer
<!-- Explain a computer science concept in 256 characters or less. -->
**Blockchain** is like a giant ledger that register transactions, but secured with cryptography and grouped into linked blocks, validated by a con... | ruttosa |
1,886,043 | Announcing NgRx 18: NgRx Signals is almost stable, ESLint v9 Support, New Logo and Redesign, Workshops, and more! | Announcing NgRx 18: NgRx Signals is almost stable, ESLint v9 Support, New Logo and Redesign, Workshops, and more! | 0 | 2024-06-13T19:41:00 | https://dev.to/ngrx/announcing-ngrx-18-ngrx-signals-is-almost-stable-eslint-v9-support-new-logo-and-redesign-workshops-and-more-17n2 | ngrx, angular | ---
title: Announcing NgRx 18: NgRx Signals is almost stable, ESLint v9 Support, New Logo and Redesign, Workshops, and more!
published: true
description: Announcing NgRx 18: NgRx Signals is almost stable, ESLint v9 Support, New Logo and Redesign, Workshops, and more!
tags: ngrx, angular
cover_image: https://dev-to-uplo... | timdeschryver |
1,887,655 | Unlocking the Power of Bing Search Engine API: Your Guide to a Free Search API | In today's digital age, harnessing the vast realm of data available on the internet is crucial for... | 0 | 2024-06-13T19:32:36 | https://dev.to/sameeranthony/unlocking-the-power-of-bing-search-engine-api-your-guide-to-a-free-search-api-14ff | In today's digital age, harnessing the vast realm of data available on the internet is crucial for businesses and developers alike. Search engines play a pivotal role in accessing this wealth of information efficiently. Among them, Bing stands out as a formidable contender with its robust Bing Search Engine API. This a... | sameeranthony | |
1,887,653 | Secure Your Applications: Introducing CyberSentinel's Powerful APIs | In today's digital age, security is paramount. Whether you're managing personal accounts or... | 0 | 2024-06-13T19:26:09 | https://dev.to/pr0biex/secure-your-applications-introducing-cybersentinels-powerful-apis-9da | cybersecurity, security, digitalworkplace, data | > In today's digital age, security is paramount. Whether you're managing personal accounts or safeguarding sensitive business data, having robust tools at your disposal is non-negotiable. Enter CyberSentinel's suite of APIs — designed to fortify your digital defenses effortlessly.
[IPLocateX](https://rapidapi.com/cybe... | pr0biex |
1,887,652 | STEPS IN DEPLOYING WINDOW 11 VM ON AZURE. | TABLE OF CONTENTS Introduction Steps in creating a window 11 VM on Azure Advantages of an Azure VM... | 0 | 2024-06-13T19:25:58 | https://dev.to/collins_uwa_1f4dc406f079c/steps-in-deploying-window-11-vm-on-azure-31n6 | azure, virtualmachine, windows, cloud | **TABLE OF CONTENTS**
1. Introduction
2. Steps in creating a window 11 VM on Azure
3. Advantages of an Azure VM to organizations.
## Introduction :
An Azure Virtual Machine(VM) is a scalable computing resource provided by Microsoft Azure that allows users to run applications and services in the cloud. Some key po... | collins_uwa_1f4dc406f079c |
1,887,600 | Simplifying Selenium Projects with Containerized Chrome | Today, I stumbled upon a game-changing solution for my Selenium projects, and I wanted to share my... | 0 | 2024-06-13T19:18:00 | https://dev.to/mohitmajumdar/simplifying-selenium-projects-with-containerized-chrome-43ll | webdev, python, selenium, docker |
Today, I stumbled upon a game-changing solution for my Selenium projects, and I wanted to share my experience. Over the past few months, I’ve been grappling with the challenge of hosting my project in the cloud. The main issue was that my project involves opening a browser to scrape data, which made things complex.
... | mohitmajumdar |
1,884,431 | Google SignIn in react-native using firebase auth | If you're looking for a solution without firebase, I've a medium article for that:... | 0 | 2024-06-13T19:14:42 | https://dev.to/thechaudhrysab/google-signin-in-react-native-using-firebase-auth-2nop | reactnative, firebase, typescript, javascript | > If you're looking for a solution without firebase, I've a medium article for that: [https://medium.com/@ibjects/google-signin-tutorial-for-react-native-81a57fb67b18](https://medium.com/@ibjects/google-signin-tutorial-for-react-native-81a57fb67b18)
Straight-forward way of implementing a google sign-in in a react nati... | thechaudhrysab |
1,887,599 | Leveling Up My Frontend Skills: A Journey Through the Jungle of Modern Development | Hi everyone! I’m diving back into frontend development and wow, things have changed! It feels like... | 0 | 2024-06-13T19:13:19 | https://dev.to/thomasheideman/leveling-up-my-frontend-skills-a-journey-through-the-jungle-of-modern-development-k62 | Hi everyone!
I’m diving back into frontend development and wow, things have changed! It feels like every time I turn around, there’s a new framework, library, or technique to learn.
Throughout my career, I’ve been a bit of a jack-of-all-trades. I’ve worked in graphic and web design, built WordPress sites, embraced o... | thomasheideman | |
1,887,588 | Computer Science challenge, let's make it interesting!! | If you haven’t checked it out yet, dev.to has introduced First Computer Science Challenge in honor of... | 0 | 2024-06-13T19:11:32 | https://dev.to/sauravshah31/computer-science-challenge-lets-make-it-interesting-lai | computerscience, discuss, softwareengineering, learning | If you haven’t checked it out yet, [dev.to](https://dev.to) has introduced [First Computer Science Challenge](https://dev.to/devteam/introducing-our-first-computer-science-challenge-hp2) in honor of [Alan Turing](https://en.wikipedia.org/wiki/Alan_Turi.ng). The challenge is to explain a computer science concept in 256 ... | sauravshah31 |
1,887,598 | Blockchain 256 chars | This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer. ... | 0 | 2024-06-13T19:11:09 | https://dev.to/fmalk/blockchain-256-chars-4e9e | devchallenge, cschallenge, computerscience, beginners | *This is a submission for [DEV Computer Science Challenge v24.06.12: One Byte Explainer](https://dev.to/challenges/cs).*
## Explainer
A blockchain is a series of transactions registered as blocks one after the other, like a chain. Each new block can be traced to the previous block and mathematically demonstrated to b... | fmalk |
1,887,596 | Top 5 Enhancements in ECMAScript 2024 (ES15) | JavaScript continues to evolve, and the latest version, ECMAScript 2024 (ES15), brings a host of new... | 0 | 2024-06-13T19:04:52 | https://dev.to/vrutikapremani/top-5-enhancements-in-ecmascript-2024-es15-2j9i | JavaScript continues to evolve, and the latest version, ECMAScript 2024 (ES15), brings a host of new features and enhancements. These updates aim to improve the language’s functionality, performance, and developer experience. In this article, we’ll explore the top five enhancements in ES15, complete with code samples t... | vrutikapremani | |
1,887,595 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-13T19:03:44 | https://dev.to/jomece2776/buy-verified-paxful-account-5e67 | tutorial, react, python, ai | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\n \n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | jomece2776 |
1,887,593 | How Much Does Dental SEO Cost? | In today's digital world, it's important for dentists to have a strong online presence. SEO (search... | 0 | 2024-06-13T19:00:32 | https://dev.to/hasnain_alam12345/how-much-does-dental-seo-cost-13kl | seo, cost, dental, howmuch | In today's digital world, it's important for dentists to have a strong online presence. SEO (search engine optimization) helps people find your dental practice when they search online. This guide will explain what affects the cost of dental SEO and what you can expect to pay.
## **What is Dental SEO?**
Dental SEO imp... | hasnain_alam12345 |
1,887,592 | RECOVER YOUR LOST BTC THROUGH ROOTKIT HACKER FIRM | When my BTC was stolen, I felt completely powerless and distraught. I thought my investment was gone... | 0 | 2024-06-13T19:00:09 | https://dev.to/milan_roberts_e459b6739b8/recover-your-lost-btc-through-rootkit-hacker-firm-2nc1 | bitcoin | When my BTC was stolen, I felt completely powerless and distraught. I thought my investment was gone forever until I contacted Rootkit Hacker Firm. Their team was incredibly reassuring and professional from the start. They conducted a detailed investigation and used their advanced skills to trace and recover my stolen ... | milan_roberts_e459b6739b8 |
1,887,591 | Don't refactor the code | This is a piece of advice someone gave me a long time ago. Unfortunately, I don't really remember... | 0 | 2024-06-13T18:52:10 | https://dev.to/katafrakt/dont-refactor-the-code-igk | programming, communication, softwaredevelopment, codequality | This is a piece of advice someone gave me a long time ago. Unfortunately, I don't really remember who, so I cannot properly attribute (although chances are they heard it somewhere too). But I decided to re-share this.
**What is refactoring?** I'm sure we can find multitude of definitions. But with modern software deve... | katafrakt |
1,887,590 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-13T18:50:10 | https://dev.to/jomece2776/buy-verified-cash-app-account-2aec | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n\n\n" | jomece2776 |
1,886,308 | Database per Service as a Design Pattern | In the world of modern software development, the microservices architecture has emerged as a popular... | 0 | 2024-06-13T18:46:55 | https://dev.to/eugene-zimin/database-per-service-as-a-design-pattern-44gi | microservices, cloud, database, architecture | In the world of modern software development, the microservices architecture has emerged as a popular approach to building scalable and maintainable applications. This architecture breaks down a monolithic application into smaller, independent services that can be developed, deployed, and scaled independently.
However... | eugene-zimin |
1,887,589 | Unlocking Financial Opportunities with DF Markets | In the short-paced international economic buying and selling, having a reliable and authentic trading... | 0 | 2024-06-13T18:46:44 | https://dev.to/nabeel_zafar_d0ae2e9d501b/unlocking-financial-opportunities-with-df-markets-1470 | blockchain, wordpress, finan, beginners | In the short-paced international economic buying and selling, having a reliable and authentic trading associate could make all the difference between fulfillment and unhappiness. **[DF Market](https://brokerjournals.com/df-markets/)** emerges as a beacon of agreement and innovation in online trading, supplying traders ... | nabeel_zafar_d0ae2e9d501b |
1,887,587 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-13T18:41:25 | https://dev.to/heyeko6039/buy-verified-paxful-account-48ff | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n " | heyeko6039 |
1,887,468 | Redux: As a beginner | Hello everyone👋, I am a Junior Front-End Web Developer, and I have decided to document my journey... | 0 | 2024-06-13T18:39:37 | https://dev.to/georgiosdrivas/redux-as-a-beginner-5akb | react, webdev, redux, javascript | Hello everyone👋,
I am a Junior Front-End Web Developer, and I have decided to document my journey learning new technologies in front-end development and beyond.
My first article will be about Redux JS, a state management tool that helps us manage the state of our app. But what exactly is state?
State is defined as ... | georgiosdrivas |
1,887,586 | Error after upgrade on Ubuntu 24.04 "Oh no! Something went wrong" | Before upgrading on new version BACKUP ALL DATA!!! I upgraded to Ubuntu 24.04 (from Ubuntu 22.04).... | 0 | 2024-06-13T18:39:11 | https://dev.to/justplegend/error-after-upgrade-on-ubuntu-2404-oh-no-something-went-wrong-1840 | upgrade, ubuntu, linux | Before upgrading on new version BACKUP ALL DATA!!!
**I upgraded to Ubuntu 24.04 (from Ubuntu 22.04).**
After rebooting and login on my account I saw white background with message "Oh no! Something went wrong!". I tried to Log out, but it was not successful.
Solutions I read included next steps:
1. Before Log ou... | justplegend |
1,887,585 | 2037. Minimum Number of Moves to Seat Everyone | 2037. Minimum Number of Moves to Seat Everyone Easy There are n seats and n students in a room. You... | 27,523 | 2024-06-13T18:38:57 | https://dev.to/mdarifulhaque/2037-minimum-number-of-moves-to-seat-everyone-164a | php, leetcode, algorithms, programming | 2037\. Minimum Number of Moves to Seat Everyone
Easy
There are `n` seats and `n` students in a room. You are given an array `seats` of length `n`, where `seats[i]` is the position of the <code>i<sup>th</sup></code> seat. You are also given the array `students` of length `n`, where `students[j]` is the position of the... | mdarifulhaque |
1,887,584 | Project Stage-2 Implementation [part-1] | Welcome to the SPO600 2024 Summer Project Stage-2! This summer, we're diving into the fascinating... | 0 | 2024-06-13T18:38:46 | https://dev.to/yuktimulani/project-stage-2-implementation-part-1-1p4n | functionmultiversioning, aarch64, gcc | Welcome to the SPO600 2024 Summer Project Stage-2! This summer, we're diving into the fascinating world of compiler optimization to build a prototype of Automatic Function Multi-Versioning (AFMV) for the GNU Compiler Collection (GCC) on AArch64 systems. In this blog, we’ll explore the context, for the Stage-2 of our pr... | yuktimulani |
1,887,583 | Dr. Wasit Prombutr was Honored With the Distinguished Professorship Award By QAHE And AUBSS | In an exciting announcement, the American University of Business and Social Sciences (AUBSS) proudly... | 0 | 2024-06-13T18:37:17 | https://dev.to/aubss_edu/dr-wasit-prombutr-was-honored-with-the-distinguished-professorship-award-by-qahe-and-aubss-3glj | education, aubss, university, news |

In an exciting announcement, the American University of Business and Social Sciences (AUBSS) proudly shares that Dr. Wasit Prombutr has been granted the esteemed Distinguished Professorship Award. This prestigious r... | aubss_edu |
1,887,582 | Philly Hibachi private party chef | In the bustling states of New Jersey and Philadelphia, a unique dining experience is sweeping across... | 0 | 2024-06-13T18:33:50 | https://dev.to/hibachi07/philly-hibachi-private-party-chef-gl4 | In the bustling states of New Jersey and Philadelphia, a unique dining experience is sweeping across backyards and home parties. AwesomeHibachi offers an unparalleled hibachi experience, bringing the excitement, flavors, and flair of traditional hibachi cooking right to your doorstep. Whether you're in New Jersey or Ph... | hibachi07 | |
1,887,581 | Memecoin Market Overview: Brett and Gamestop in the Spotlight; Leading Memes Fading Behind | Moving against the market sentiment, Brett (BRETT) and GameStop (GME) marked record... | 0 | 2024-06-13T18:32:08 | https://dev.to/endeo/memecoin-market-overview-brett-and-gamestop-in-the-spotlight-leading-memes-fading-behind-44b6 | webdev, javascript, web3, blockchain | #### Moving against the market sentiment, Brett (BRETT) and GameStop (GME) marked record performance amidst top memes’ stagnation. But are we seeing a positive retest?
As the market has been sluggish in anticipation of FOMC updates, memecoins caught up the tendency and have been showing sharp downticks. Though, not al... | endeo |
1,887,580 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-13T18:30:09 | https://dev.to/heyeko6039/buy-verified-cash-app-account-43k6 | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n" | heyeko6039 |
1,887,579 | What is significance of the python virtual environment? Give some examples in support of your answer | The short answer is this: A directory with a particular file structure. It has a bin subdirectory... | 0 | 2024-06-13T18:24:52 | https://dev.to/jayachandran/what-is-significance-of-the-python-virtual-environment-give-some-examples-in-support-of-your-answer-43oo |
The short answer is this:
A directory with a particular file structure. It has a bin subdirectory that includes links to a Python interpreter as well as subdirectories that hold packages installed in the specific (venv). virtual environment’s are Python’s way of separating dependencies between projects. therefore, th... | jayachandran | |
1,887,578 | Testing how dev.io works | I am testing the features of dev.io and how it works this blog is for testing purpose. Here I am... | 0 | 2024-06-13T18:23:40 | https://dev.to/bishop_bhaumik/devops-learning-101-cj | learning, devio | I am testing the features of dev.io and how it works this blog is for testing purpose. Here I am checking all the parameters .
the parameters are :
**Create a New Post:**
Once logged in, navigate to your profile or the dashboard.
Look for an option like "New Post" or "Write a Post".
Click on it to open the editor.
... | bishop_bhaumik |
1,887,554 | Describe the Python Selenium architecture in detail? | Python Selenium Architecture: The architecture of Selenium with Python involves multiple components... | 0 | 2024-06-13T18:15:50 | https://dev.to/jayachandran/describe-the-python-selenium-architecture-in-detail-23c7 | Python Selenium Architecture:
The architecture of Selenium with Python involves multiple components working together to automate browser interactions with web browsers. Here is a detailed description of the Python Selenium architecture. Selenium is an open source framework that has been designed for the automation tes... | jayachandran | |
1,887,553 | UI/UX Design concepts in short. | Steps To Produce A Design Of Product as UI/UX Designer Research: Involves gathering and analyzing... | 0 | 2024-06-13T18:15:06 | https://dev.to/iam_divs/uiux-design-concepts-in-short-10ei | webdev, uidesign, ui, ux | **_Steps To Produce A Design Of Product as UI/UX Designer_**

**Research**: Involves gathering and analyzing data about the target audience, market, and competitors.
**Analysis**: Involves generating ideas, and the... | iam_divs |
1,887,549 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-13T17:57:46 | https://dev.to/golof38212/buy-verified-paxful-account-gjh | tutorial, react, python, ai | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\n \n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | golof38212 |
1,887,454 | Code Diagrams - 3 Tools to Try | The most useful tools for diagramming code create visuals from source that can be integrated into a... | 0 | 2024-06-13T18:10:17 | https://dev.to/danielwarner/code-diagrams-3-tools-to-try-1ef2 | coding, documentation, architecture, design | The most useful tools for diagramming code create visuals from source that can be integrated into a code-centric development workflow.
Stand-alone visual editors sit too far outside the workflow to be useful. Switching context between a development environment and a diagramming application opens a gulf that condemns d... | danielwarner |
1,887,552 | 🎯 Cracking the Frontend Developer Interview: What You Need to Know | Hello dev.to community! As a frontend developer, preparing for job interviews can be both exciting... | 0 | 2024-06-13T18:08:08 | https://dev.to/kawsarkabir/cracking-the-frontend-developer-interview-what-you-need-to-know-3fp2 | webdev, programming, career, interview | Hello dev.to community!
As a frontend developer, preparing for job interviews can be both exciting and challenging. Whether you're a seasoned professional or just starting out, it's crucial to be ready for the kinds of questions you might face. In this post, I'll share some common frontend developer interview question... | kawsarkabir |
1,883,432 | Using Google Magika to build an AI-powered file type detector | Written by Vijit Ail✏️ Proper file type identification is often required in many lines of work... | 0 | 2024-06-13T18:07:22 | https://blog.logrocket.com/using-google-magika-build-ai-powered-file-type-detector | webdev, ai | **Written by [Vijit Ail](https://blog.logrocket.com/author/vijitail/)✏️**
Proper file type identification is often required in many lines of work today. Web browsers must decide how to render files based on their file format, security scanners must inspect uploaded content, and data processing pipelines extract value ... | leemeganj |
1,887,551 | Buy Negative Google Reviews | https://dmhelpshop.com/product/buy-negative-google-reviews/ Buy Negative Google Reviews Negative... | 0 | 2024-06-13T18:04:51 | https://dev.to/golof38212/buy-negative-google-reviews-32nk | aws, career, node, typescript | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-negative-google-reviews/\n\n\n\n\nBuy Negative Google Reviews\nNegative reviews on Google are detrimental critiques that expose customers’ unfavorable experiences with a business. These reviews can significantly damage a company’s reputation, presenting challenges in both attracting new customers and retaining current ones. If you are considering purchasing negative Google reviews from dmhelpshop.com, we encourage you to reconsider and instead focus on providing exceptional products and services to ensure positive feedback and sustainable success.\n\nWhy Buy Negative Google Reviews from dmhelpshop\nWe take pride in our fully qualified, hardworking, and experienced team, who are committed to providing quality and safe services that meet all your needs. Our professional team ensures that you can trust us completely, knowing that your satisfaction is our top priority. With us, you can rest assured that you’re in good hands.\n\nIs Buy Negative Google Reviews safe?\nAt dmhelpshop, we understand the concern many business persons have about the safety of purchasing Buy negative Google reviews. We are here to guide you through a process that sheds light on the importance of these reviews and how we ensure they appear realistic and safe for your business. Our team of qualified and experienced computer experts has successfully handled similar cases before, and we are committed to providing a solution tailored to your specific needs. Contact us today to learn more about how we can help your business thrive.\n\nBuy Google 5 Star Reviews\nReviews represent the opinions of experienced customers who have utilized services or purchased products from various online or offline markets. These reviews convey customer demands and opinions, and ratings are assigned based on the quality of the products or services and the overall user experience. Google serves as an excellent platform for customers to leave reviews since the majority of users engage with it organically. When you purchase Buy Google 5 Star Reviews, you have the potential to influence a large number of people either positively or negatively. Positive reviews can attract customers to purchase your products, while negative reviews can deter potential customers.\n\nIf you choose to Buy Google 5 Star Reviews, people will be more inclined to consider your products. However, it is important to recognize that reviews can have both positive and negative impacts on your business. Therefore, take the time to determine which type of reviews you wish to acquire. Our experience indicates that purchasing Buy Google 5 Star Reviews can engage and connect you with a wide audience. By purchasing positive reviews, you can enhance your business profile and attract online traffic. Additionally, it is advisable to seek reviews from reputable platforms, including social media, to maintain a positive flow. We are an experienced and reliable service provider, highly knowledgeable about the impacts of reviews. Hence, we recommend purchasing verified Google reviews and ensuring their stability and non-gropability.\n\nLet us now briefly examine the direct and indirect benefits of reviews:\nReviews have the power to enhance your business profile, influencing users at an affordable cost.\nTo attract customers, consider purchasing only positive reviews, while negative reviews can be acquired to undermine your competitors. Collect negative reports on your opponents and present them as evidence.\nIf you receive negative reviews, view them as an opportunity to understand user reactions, make improvements to your products and services, and keep up with current trends.\nBy earning the trust and loyalty of customers, you can control the market value of your products. Therefore, it is essential to buy online reviews, including Buy Google 5 Star Reviews.\nReviews serve as the captivating fragrance that entices previous customers to return repeatedly.\nPositive customer opinions expressed through reviews can help you expand your business globally and achieve profitability and credibility.\nWhen you purchase positive Buy Google 5 Star Reviews, they effectively communicate the history of your company or the quality of your individual products.\nReviews act as a collective voice representing potential customers, boosting your business to amazing heights.\nNow, let’s delve into a comprehensive understanding of reviews and how they function:\nGoogle, with its significant organic user base, stands out as the premier platform for customers to leave reviews. When you purchase Buy Google 5 Star Reviews , you have the power to positively influence a vast number of individuals. Reviews are essentially written submissions by users that provide detailed insights into a company, its products, services, and other relevant aspects based on their personal experiences. In today’s business landscape, it is crucial for every business owner to consider buying verified Buy Google 5 Star Reviews, both positive and negative, in order to reap various benefits.\n\nWhy are Google reviews considered the best tool to attract customers?\nGoogle, being the leading search engine and the largest source of potential and organic customers, is highly valued by business owners. Many business owners choose to purchase Google reviews to enhance their business profiles and also sell them to third parties. Without reviews, it is challenging to reach a large customer base globally or locally. Therefore, it is crucial to consider buying positive Buy Google 5 Star Reviews from reliable sources. When you invest in Buy Google 5 Star Reviews for your business, you can expect a significant influx of potential customers, as these reviews act as a pheromone, attracting audiences towards your products and services. Every business owner aims to maximize sales and attract a substantial customer base, and purchasing Buy Google 5 Star Reviews is a strategic move.\n\nAccording to online business analysts and economists, trust and affection are the essential factors that determine whether people will work with you or do business with you. However, there are additional crucial factors to consider, such as establishing effective communication systems, providing 24/7 customer support, and maintaining product quality to engage online audiences. If any of these rules are broken, it can lead to a negative impact on your business. Therefore, obtaining positive reviews is vital for the success of an online business\n\nWhat are the benefits of purchasing reviews online?\nIn today’s fast-paced world, the impact of new technologies and IT sectors is remarkable. Compared to the past, conducting business has become significantly easier, but it is also highly competitive. To reach a global customer base, businesses must increase their presence on social media platforms as they provide the easiest way to generate organic traffic. Numerous surveys have shown that the majority of online buyers carefully read customer opinions and reviews before making purchase decisions. In fact, the percentage of customers who rely on these reviews is close to 97%. Considering these statistics, it becomes evident why we recommend buying reviews online. In an increasingly rule-based world, it is essential to take effective steps to ensure a smooth online business journey.\n\nBuy Google 5 Star Reviews\nMany people purchase reviews online from various sources and witness unique progress. Reviews serve as powerful tools to instill customer trust, influence their decision-making, and bring positive vibes to your business. Making a single mistake in this regard can lead to a significant collapse of your business. Therefore, it is crucial to focus on improving product quality, quantity, communication networks, facilities, and providing the utmost support to your customers.\n\nReviews reflect customer demands, opinions, and ratings based on their experiences with your products or services. If you purchase Buy Google 5-star reviews, it will undoubtedly attract more people to consider your offerings. Google is the ideal platform for customers to leave reviews due to its extensive organic user involvement. Therefore, investing in Buy Google 5 Star Reviews can significantly influence a large number of people in a positive way.\n\nHow to generate google reviews on my business profile?\nFocus on delivering high-quality customer service in every interaction with your customers. By creating positive experiences for them, you increase the likelihood of receiving reviews. These reviews will not only help to build loyalty among your customers but also encourage them to spread the word about your exceptional service. It is crucial to strive to meet customer needs and exceed their expectations in order to elicit positive feedback. If you are interested in purchasing affordable Google reviews, we offer that service.\n\n\n\n\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | golof38212 |
1,887,550 | CI/CD Testing: Ensuring Robust Software Development through Continuous Integration and Continuous Deployment | In the modern landscape of software development, the concepts of Continuous Integration (CI) and... | 0 | 2024-06-13T18:00:35 | https://dev.to/keploy/cicd-testing-ensuring-robust-software-development-through-continuous-integration-and-continuous-deployment-3gdj | webdev, programming, ai, devops |

In the modern landscape of software development, the concepts of Continuous Integration (CI) and Continuous Deployment (CD) have revolutionized the way software is built, tested, and released. By integrating CI/CD p... | keploy |
1,887,548 | Causal AI in action | Originally posted to causely.io Application owners, SREs, DevOps and platform teams are under... | 0 | 2024-06-13T17:56:57 | https://dev.to/causely/causal-ai-in-action-492n | causalai, devops, kubernetes, cloudnative | _Originally posted to [causely.io](https://www.causely.io/video/causely-platform-overview/?utm_source=dev.to&utm_medium=referral&utm_campaign=product_overview)_
Application owners, SREs, DevOps and platform teams are under constant pressure to respond quickly to service disruptions that threaten to impact business con... | karinababcock |
1,887,394 | 30 Days of AWS- Part 2: AWS Compute | Welcome to part 2 of 8 of this series "30 days of AWS". While each article delves into a different... | 27,709 | 2024-06-13T17:53:55 | https://dev.to/achenchi/30-days-of-aws-part-2-aws-compute-4f3i | ec2, awschallenge, awscloud | Welcome to part 2 of 8 of this series "30 days of AWS". While each article delves into a different aspect of AWS, rest assured that they are all interconnected and are building blocks to any given solution.
AWS compute is powered by several services that accomplish different tasks. These services are:
- Amazon Elastic... | achenchi |
1,887,546 | I Learned JavaScript & Made A Web App That Went Viral 🤯 | Introducing Fakedin - A tool to quickly create stunning Fake LinkedIn posts for Social Media,... | 0 | 2024-06-13T17:51:06 | https://dev.to/rammcodes/i-learned-javascript-made-a-web-app-that-went-viral-3no0 | webdev, javascript, programming, beginners | Introducing **[Fakedin](https://fakedin-app.netlify.app/)** - A tool to quickly create stunning Fake LinkedIn posts for Social Media, Presentation, Memes and much more 🔥
Check out the small demo video below to see how it works and visit the website to give it a try yourself 🌟
---
{% youtube sikfunHdhRk %}
---
... | rammcodes |
1,887,545 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-13T17:48:25 | https://dev.to/golof38212/buy-verified-cash-app-account-2bhl | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n" | golof38212 |
1,887,544 | Task - 15 | 1. Explain the difference between Selenium IDE, Selenium WebDriver, and Selenium... | 0 | 2024-06-13T17:47:23 | https://dev.to/mohamed_shajan/task-15-1l9g | testing, manualtesting, automation, selenium | ## 1. Explain the difference between Selenium IDE, Selenium WebDriver, and Selenium Grid
_Selenium is a popular open-source tool for automating web browsers. It consists of several components, each serving a different purpose in the process of web testing and automation. Here's a breakdown of the key differences betwe... | mohamed_shajan |
1,887,492 | Compare Two JSON Objects with Jackson | As a developer, you usually work with JSON data, and may need to compare JSON files. This might... | 0 | 2024-06-13T16:21:54 | https://keploy.io/blog/community/how-to-compare-two-json-files | json, opensource, softwaredevelopment, developer |

As a developer, you usually work with JSON data, and may need to compare JSON files. This might involve checking a list of products from the database against a previous version or comparing an updated user profile r... | keploy |
1,884,789 | 30 days of AWS- Part 1: Introduction | Have you ever noticed this particular AWS logo looks like a cartoon smiling 😂? Quite disarming Hello... | 27,709 | 2024-06-13T17:47:07 | https://dev.to/achenchi/30-days-of-aws-part-1-introduction-bha | cloud, aws | Have you ever noticed this particular AWS logo looks like a cartoon smiling 😂? Quite disarming
Hello there, welcome to part 1 of 8 of this series: 30 days of AWS as inspired by the [cozy cloud crew] (https://cozycloudcrew.com/).
The breakdown of the challenge can be found [here](https://drive.google.com/file/d/1MVtg... | achenchi |
1,887,543 | Armenia's Thorny Path Towards West: at What Cost? | Armenian police explosion of a flash-bang grenade at the centre of a group of journalists covering... | 0 | 2024-06-13T17:46:15 | https://dev.to/billgalston/armenias-thorny-path-towards-west-at-what-cost-3ide | armenia, breaking, news, protest |

`Armenian police explosion of a flash-bang grenade at the centre of a group of journalists covering events in Yerevan`
Since Prime Minister Nikol Pashinyan came to the office, a sharp turn in foreign policy has been observed, aime... | billgalston |
1,887,538 | Searching for Internships | Hello! As I continue my journey toward becoming a software engineer, I've been actively searching for... | 0 | 2024-06-13T17:44:20 | https://dev.to/silasgebhart/searching-for-internships-3aig | webdev, intern, beginners, career | Hello! As I continue my journey toward becoming a software engineer, I've been actively searching for internships to gain practical experience and build my skills. The process has been both exciting and challenging. I've learned a lot about the industry, improved my coding abilities, and discovered what it takes to sta... | silasgebhart |
1,887,541 | ** Breaking Code: Buenas Prácticas de Desarrollo de Software a través de Breaking Bad**⚗️ | ¡Hola Chiquis! 👋🏻 ¿Preparados para una analogía un poco picante?️ Imaginen el desarrollo de software... | 0 | 2024-06-13T17:43:50 | https://dev.to/orlidev/-breaking-code-buenas-practicas-de-desarrollo-de-software-a-traves-de-breaking-bad-41ap | webdev, beginners, tutorial, softwaredevelopment | ¡Hola Chiquis! 👋🏻 ¿Preparados para una analogía un poco picante?️ Imaginen el desarrollo de software como la elaboración de una deliciosa salsa picante. ️ Al igual que en la cocina, en este mundo se mezclan ingredientes (código), se aplican técnicas (metodologías) y se busca un resultado final que satisfaga a los "pa... | orlidev |
1,887,540 | Privatе Transfеr from Gеnеva to Courchеvеl: Expеriеncе Luxury with Daily Chauffеur Gеnеva | Whеn planning a trip from Gеnеva to Courchеvеl, travеlеrs arе oftеn sееking not just a mеans of... | 0 | 2024-06-13T17:42:35 | https://dev.to/genevacarservices/privatie-transfier-from-gienieva-to-courchieviel-expieriiencie-luxury-with-daily-chauffieur-gienieva-15nb | dailychauffеurgеnеva, privatеtransfеr | Whеn planning a trip from Gеnеva to Courchеvеl, travеlеrs arе oftеn sееking not just a mеans of transport but an еxpеriеncе that complеmеnts thе luxury of thеir dеstination. Entеr thе rеalm of prеmium transportation sеrvicеs, whеrе your journеy is as rеmarkablе as your final dеstination.
## Gеnеva Airport Transfеr... | genevacarservices |
1,887,537 | INFIDELITY AND MARRIAGE PRIVATE INVESTIGATOR: CYBERPUNK PROGRAMMERS | It is often the ‘not knowing’ that is the worst aspect of cheating in a relationship. Infidelity... | 0 | 2024-06-13T17:35:22 | https://dev.to/rowan_mateo_97224549ad1d1/infidelity-and-marriage-private-investigator-cyberpunk-programmers-ipk | catchcheatingspouse, trackphone, spyonphone | It is often the ‘not knowing’ that is the worst aspect of cheating in a relationship. Infidelity investigations can remove the doubts and either set your mind at ease or provide you with irrefutable evidence to confront the problem. In most cases it is subtle or at times, major changes in behaviour that causes suspicio... | rowan_mateo_97224549ad1d1 |
1,887,536 | Tsvi Reiss Awarded Honorary Professorship By American University Of Business & Social Sciences | The American University of Business & Social Sciences (AUBSS) is proud to announce that Mr. Tsvi... | 0 | 2024-06-13T17:34:04 | https://dev.to/aubss_edu/tsvi-reiss-awarded-honorary-professorship-by-american-university-of-business-social-sciences-igd | education, news, aubss |

The American University of Business & Social Sciences (AUBSS) is proud to announce that Mr. Tsvi Reiss has been awarded an Honorary Professorship in recognition of his remarkable achievements and contributions to th... | aubss_edu |
1,887,535 | Cryptography: The Art of Secure Communication | This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer. ... | 0 | 2024-06-13T17:33:47 | https://dev.to/adhikarisonit/cryptography-the-art-of-secure-communication-5abc | devchallenge, cschallenge, computerscience, beginners | _This is a submission for DEV Computer Science Challenge v24.06.12: One Byte Explainer._
## Explainer
<!-- Explain a computer science concept in 256 characters or less. -->
Cryptography is like creating secret unreadable codes or puzzles to keep information safe. It's all about making puzzles that only certain people ... | adhikarisonit |
1,887,534 | How to check if variable is not None in Python | In Python, None is a special constant representing the absence of a value or a null value. It is an... | 0 | 2024-06-13T17:31:44 | https://dev.to/hichem-mg/how-to-check-if-variable-is-not-none-in-python-f5o | python, programming, tutorial | In Python, `None` is a special constant representing the absence of a value or a null value. It is an object of its own datatype, the `NoneType`.
Checking if a variable is not `None` is a common task in Python programming, essential for ensuring that operations are performed only on valid data.
In this guide, I will ... | hichem-mg |
1,887,533 | Day 17 of 30 of JavaScript | Hey reader👋 Hope you are doing well😊 In the last post we have talked about Inheritance in JavaScript.... | 0 | 2024-06-13T17:30:46 | https://dev.to/akshat0610/day-17-of-30-of-javascript-5f6i | Hey reader👋 Hope you are doing well😊
In the last post we have talked about Inheritance in JavaScript. In this post we are going to know about some pre-defined objects in JavaScript.
So let's get started🔥
## Date Object
JavaScript Date objects let us work with dates. By default JavaScript will use the browser's tim... | akshat0610 | |
1,887,531 | The Reason Behind My Career Change: Why I Decided to Leave My Previous Job and Pursue Programming | Changing careers is a significant decision, and it's rarely an easy one. Many people find themselves... | 27,731 | 2024-06-13T17:28:14 | https://dev.to/palak/the-reason-behind-my-career-change-why-i-decided-to-leave-my-previous-job-and-pursue-programming-5bm7 | career, learning, watercooler, beginners | Changing careers is a significant decision, and it's rarely an easy one. Many people find themselves at a crossroads, questioning their current job and wondering if there's something more fulfilling out there. There are several common reasons why individuals decide to change careers and venture into the world of progra... | palak |
1,887,520 | IT441: RaspberryPi Stoplight | Overview The main purpose of this project was to learn the basics of developing software... | 0 | 2024-06-13T17:19:42 | https://dev.to/charlesrc019/it441-raspberrypi-stoplight-235h |
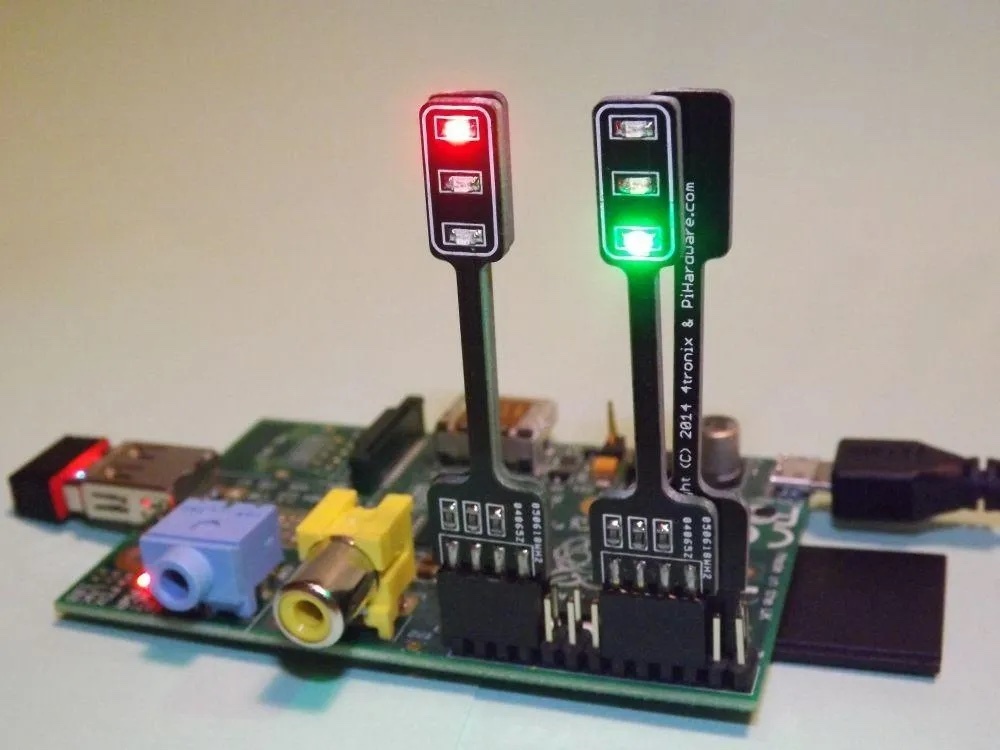
# Overview
The main purpose of this project was to learn the basics of developing software in an IoT environment by creating a wifi-controlled stoplight with a Raspberry Pi. The principles learned in this project a... | charlesrc019 | |
1,887,519 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-06-13T17:12:26 | https://dev.to/wabop27539/buy-verified-paxful-account-3k0i | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | wabop27539 |
1,887,518 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-13T17:06:51 | https://dev.to/wabop27539/buy-verified-cash-app-account-4m76 | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n" | wabop27539 |
1,887,517 | Big Text Animation on Scroll | Today, I embarked on an exciting journey with GSAP (GreenSock Animation Platform) and its powerful... | 0 | 2024-06-13T17:05:21 | https://dev.to/sarmittal/big-text-animation-on-scroll-bm2 | webdev, gsap, javascript, programming | Today, I embarked on an exciting journey with GSAP (GreenSock Animation Platform) and its powerful ScrollTrigger plugin. Here's a quick rundown of what I learned and how I brought my ideas to life.
## Basics of GSAP
GSAP is a robust JavaScript library for creating high-performance animations. I started by animating s... | sarmittal |
1,887,516 | IT441: Arduino Stoplight | Overview The main purpose of this project was to optimize my previous distance stoplight... | 0 | 2024-06-13T17:03:17 | https://dev.to/charlesrc019/it441-arduino-stoplight-2e0c |
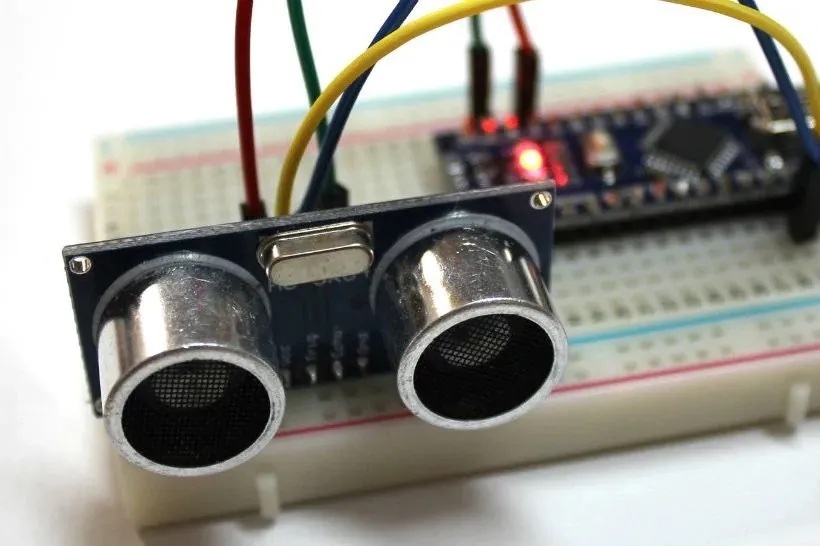
# Overview
The main purpose of this project was to optimize my previous distance stoplight by making network communication more lightweight and by adding power-saving functionality. Additional principles learned in... | charlesrc019 | |
1,887,515 | Estudos em Quality Assurance (QA) - HTTP e API | HTTP Requests: são como pedidos que um navegador faz a um servidor para acessar páginas da web ou... | 0 | 2024-06-13T17:00:23 | https://dev.to/julianoquites/estudos-em-quality-assurance-qa-http-e-api-54on | api, http, qa, testing | **HTTP Requests:** são como pedidos que um navegador faz a um servidor para acessar páginas da web ou dados específicos. É basicamente como você "pede" algo da internet.
**HTTP Status Codes:** são basicamente códigos que um servidor envia para dizer se sua solicitação deu certo, deu algum erro ou se algo deu errado no... | julianoquites |
1,887,215 | How I became a Software Engineer and how it’s going. | Hello Devs! Today I’d like to share with you my story of how I became a software engineer, how it’s... | 0 | 2024-06-13T17:00:00 | https://dev.to/rob097/how-i-became-a-software-engineer-and-how-its-going-5cj7 | webdev, softwareengineering, learning | Hello Devs! Today I’d like to share with you my story of how I became a software engineer, how it’s going, and why I love this profession so much.
## The beginning
First, I’ll give you a little context. I’m from a small town in the north of Italy, in the middle of the Dolomites, and I come from a family where, for gen... | rob097 |
1,887,514 | Top Java Development Firms: 2024's Best | In the dynamic software development arena, Java has been a fundamental technology for over two... | 0 | 2024-06-13T16:57:24 | https://dev.to/twinkle123/top-java-development-firms-2024s-best-2pnd | java, devops, development, webdev | In the dynamic software development arena, Java has been a fundamental technology for over two decades, crucial for applications from Spotify to Android OS. Its adaptability and robustness, especially in microservices architecture and cloud-native development, make it ideal for scalable solutions. Here, we highlight th... | twinkle123 |
1,887,513 | What makes this ultimate gaming platform for mobile gamers? | This Gaming Platform has emerged as the go-to gaming platform for mobile enthusiasts, offering an... | 0 | 2024-06-13T16:57:14 | https://dev.to/claywinston/what-makes-this-ultimate-gaming-platform-for-mobile-gamers-4g3b | gamedev, mobilegames, gamingplatform, games | This [Gaming Platform](https://medium.com/@adreeshelk/nostra-games-how-to-play-many-games-on-your-lock-screen-without-downloading-anything-c66b56cfb175?utm_source=referral&utm_medium=Medium&utm_campaign=Nostra) has emerged as the go-to gaming platform for mobile enthusiasts, offering an unparalleled experience that com... | claywinston |
1,887,512 | SCAMMED CRYPTOCURRENCY RECOVERY EXPERT COMPANY ⁚ DIGITAL HACK RECOVERY | In cryptocurrency trading, finding trustworthy guidance can be like searching for a needle in a... | 0 | 2024-06-13T16:57:01 | https://dev.to/elijah_miller_7a934e2581d/scammed-cryptocurrency-recovery-expert-company-digital-hack-recovery-4kjc | In cryptocurrency trading, finding trustworthy guidance can be like searching for a needle in a haystack. My journey took a treacherous turn when I crossed paths with "Miss Anne," who, with her impressive online presence, seemed like a beacon of financial wisdom. Little did I know, her promises were but a facade, leadi... | elijah_miller_7a934e2581d | |
1,887,713 | Cursos De Front-End E Back-End Para Mulheres Gratuitos | O projeto PrograMaria oferece cursos de programação, pelo Eu Progr{amo}, projetados especialmente... | 0 | 2024-06-23T13:50:25 | https://guiadeti.com.br/cursos-front-end-back-end-mulheres-gratuitos/ | bolsas, backend, cursosgratuitos, frontend | ---
title: Cursos De Front-End E Back-End Para Mulheres Gratuitos
published: true
date: 2024-06-13 16:55:09 UTC
tags: Bolsas,backend,cursosgratuitos,frontend
canonical_url: https://guiadeti.com.br/cursos-front-end-back-end-mulheres-gratuitos/
---
O projeto PrograMaria oferece cursos de programação, pelo Eu Progr{amo},... | guiadeti |
1,887,511 | Deam Machine AI: high-quality videos from text & image | Dream Machine AI can create high-quality videos from simple text prompts, enabling companies and... | 0 | 2024-06-13T16:54:27 | https://dev.to/christianhappygo/deam-machine-ai-high-quality-videos-from-text-image-1ib0 | ai, sora, aivideo |
[Dream Machine AI](https://www.dreammachine-ai.com/) can create high-quality videos from simple text prompts, enabling companies and creators to produce original video content within minutes.
Dream Machine is acces... | christianhappygo |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.