id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,867,751 | Staying Up-to-Date with the Latest AI Developments and Trends | Introduction In the rapidly evolving field of Artificial Intelligence (AI), staying... | 0 | 2024-05-28T15:24:46 | https://dev.to/wafa_bergaoui/staying-up-to-date-with-the-latest-ai-developments-and-trends-2kei | ai, development, machinelearning, programming | ## **Introduction**
In the rapidly evolving field of Artificial Intelligence (AI), staying current with the latest developments and trends is essential for professionals to remain competitive and relevant. This article outlines key strategies to help you stay informed and ahead of the curve in the AI landscape.
## **The Importance of Staying Informed**
AI is transforming industries and creating new opportunities, but it also demands continuous learning and adaptation. According to a [report by Gartner](https://www.gartner.com/en/newsroom/press-releases/2021-05-19-gartner-says-70-percent-of-organizations-will-shift-their-focus-from-big-to-small-and-wide-data-by-2025), AI is expected to create 97 million new jobs by 2025, while eliminating 85 million. This dynamic shift underscores the need for professionals to stay updated with the latest AI advancements to harness opportunities and mitigate risks.
## **Key Strategies for Staying Up-to-Date**
**1. Follow Industry News and Publications**
Regularly reading industry news, research papers, and publications is a foundational strategy for staying informed. Some valuable resources include:
. [TechCrunch](https://techcrunch.com/): Covers the latest technology news, including AI developments.
. [MIT Technology Review](https://www.technologyreview.com/): Provides in-depth articles on emerging technologies.
. [Towards Data Science:](https://towardsdatascience.com/) Offers insights and tutorials on data science and AI.
. [ArXiv.org](https://arxiv.org/): Hosts preprints of research papers across various fields, including AI.
**2. Attend Conferences and Workshops**
Participating in conferences, workshops, and webinars allows you to learn from experts, discover new tools, and network with peers. Key events for AI professionals include:
. NeurIPS (Conference on Neural Information Processing Systems)
. ICLR (International Conference on Learning Representations)
. AI Expo
. CVPR (Conference on Computer Vision and Pattern Recognition)
. AAAI Conference on Artificial Intelligence
**3. Join Professional Organizations and Online Communities**
Being part of professional organizations and online communities provides access to exclusive resources, journals, and networking opportunities. Some notable organizations and communities are:
.Association for Computing Machinery (ACM)
. [IEEE Computer Society](https://www.computer.org/)
. [Reddit’s r/MachineLearning](https://www.reddit.com/r/MachineLearning/?rdt=36759)
. [Stack Overflow](https://stackoverflow.com/)
. [GitHub](https://github.com/)
. [Kaggle](https://www.kaggle.com/)
**4. Engage in Continuous Learning**
Leveraging online learning platforms helps you stay current with new technologies and methodologies in AI. These platforms offer courses and specializations that cover the latest advancements and practical applications of AI:
. [Coursera](https://www.coursera.org/courseraplus/?utm_medium=sem&utm_source=gg&utm_campaign=B2C_EMEA__coursera_FTCOF_courseraplus&campaignid=20858197888&adgroupid=156245795749&device=c&keyword=coursera&matchtype=e&network=g&devicemodel=&adposition=&creativeid=684297719990&hide_mobile_promo&term={term}&gad_source=1&gclid=CjwKCAjwgdayBhBQEiwAXhMxtll_TKdZu6hSyNEoLP5pHJl0P6pYgBxuhIK0Meowmij0mkBVvkUgzhoCLNYQAvD_BwE): Offers courses from top universities and institutions, including AI and machine learning specializations.
. [Udacity](https://www.udacity.com/): Known for its AI and machine learning Nanodegree programs.
. [edX](https://www.edx.org/): Provides courses from institutions like MIT and Harvard.
. [Fast.ai](https://www.fast.ai/): Offers practical deep learning courses.
**5. Experiment with AI Projects**
Hands-on experience is invaluable. Regularly working on personal or open source AI projects allows you to apply your knowledge and stay familiar with new tools and frameworks. Some platforms to consider are:
. [Kaggle](https://www.kaggle.com/): For competitions and datasets.
. [GitHub](https://github.com/): For open source projects and collaboration.
. [Colab](https://colab.research.google.com/): Google’s platform for building and sharing machine learning models.
**6. Follow Influential Figures and Organizations**
Following influential figures and organizations in the AI field on social media can provide insights into the latest trends and discussions. Some notable figures and organizations include:
. [Andrew Ng](https://www.linkedin.com/in/andrewyng/): Co-founder of Coursera and Adjunct Professor at Stanford University.
. [Yann LeCun](https://www.linkedin.com/in/yann-lecun/): Chief AI Scientist at Facebook.
. [OpenAI](https://www.linkedin.com/company/openai/)
. [Google DeepMind](https://www.linkedin.com/company/googledeepmind/)
**7. Read Books and Research Papers**
Books and research papers provide in-depth knowledge and understanding of AI concepts and advancements. Some recommended books include:
"Deep Learning" by Ian Goodfellow, Yoshua Bengio, and Aaron Courville
"Artificial Intelligence: A Modern Approach" by Stuart Russell and Peter Norvig
"Pattern Recognition and Machine Learning" by Christopher M. Bishop
**8. Participate in AI Competitions**
Engaging in AI competitions allows you to apply your skills to real-world problems and learn from others. Competitions hosted by platforms like Kaggle, DrivenData, and Codalab often push the boundaries of what is possible and offer practical experience in solving complex AI challenges.
**9. Network with Peers**
Networking with peers through meetups, hackathons, and local AI groups can provide new insights and foster collaborative learning. Websites like [Meetup](https://www.meetup.com/fr-FR/) and platforms like [LinkedIn](https://www.linkedin.com/) are great for finding local events and professional groups focused on AI and machine learning.
## **Conclusion**
Staying up-to-date with the latest AI developments and trends is not just beneficial but essential for professionals in the field. By following these strategies—engaging with industry news, attending events, joining professional communities, continuously learning, experimenting with projects, following influential figures, reading extensively, participating in competitions, and networking with peers—you can ensure that you remain at the forefront of AI advancements.
By consistently engaging with these resources and activities, software developers can stay up-to-date with the latest AI developments and trends, ensuring they remain competitive and well-equipped to handle the challenges and opportunities presented by the AI revolution.
| wafa_bergaoui |
1,867,881 | Optimize AWS Costs by Managing Elastic IPs with Python and Boto3 | The Need for Cost Optimization As businesses increasingly rely on cloud infrastructure,... | 0 | 2024-05-28T15:24:28 | https://dev.to/karandaid/optimize-aws-costs-by-managing-elastic-ips-with-python-and-boto3-53m2 | python, eip, aws, cost | ### The Need for Cost Optimization
As businesses increasingly rely on cloud infrastructure, managing costs becomes critical. AWS Elastic IPs (EIPs) are essential for maintaining static IP addresses, but they can also become a source of unwanted costs if not managed properly. AWS charges for EIPs that are not associated with running instances, which can quickly add up if left unchecked.
To address this, we can write a Python script using Boto3 to automate the management of EIPs, ensuring that we only pay for what we use. Let's walk through the process of creating this script step-by-step.
### Step 1: Setting Up the Environment
First, we need to set up our environment. Install Boto3 if you haven't already:
```bash
pip install boto3
```
Make sure your AWS credentials are configured. You can set them up using the AWS CLI or by setting environment variables.
### Step 2: Initializing Boto3 Client
We'll start by initializing the Boto3 EC2 client, which will allow us to interact with AWS EC2 services.
```python
import boto3
# Initialize boto3 EC2 client
ec2_client = boto3.client('ec2')
```
With this code, we now have an `ec2_client` object that we can use to call various EC2-related functions.
### Step 3: Retrieving All Elastic IPs
Next, we need a function to retrieve all Elastic IPs along with their associated instance ID and allocation ID.
```python
def get_all_eips():
"""
Retrieve all Elastic IPs along with their associated instance ID and allocation ID.
"""
response = ec2_client.describe_addresses()
eips = [(address['PublicIp'], address.get('InstanceId', 'None'), address['AllocationId']) for address in response['Addresses']]
return eips
```
You can run this function to get a list of all EIPs in your AWS account:
```python
print(get_all_eips())
```
The output will be a list of tuples, each containing the EIP, associated instance ID (or 'None' if unassociated), and allocation ID.
### Step 4: Checking Instance States
We need another function to check the state of an instance. This helps us determine if an EIP is associated with a stopped instance.
```python
def get_instance_state(instance_id):
"""
Retrieve the state of an EC2 instance.
"""
response = ec2_client.describe_instances(InstanceIds=[instance_id])
state = response['Reservations'][0]['Instances'][0]['State']['Name']
return state
```
You can test this function with an instance ID to see its state:
```python
print(get_instance_state('i-1234567890abcdef0'))
```
This will output the state of the instance, such as 'running', 'stopped', etc.
### Step 5: Categorizing Elastic IPs
Now, let's categorize the EIPs based on their association and instance states.
```python
def categorize_eips():
"""
Categorize Elastic IPs into various categories and provide cost-related insights.
"""
eips = get_all_eips()
eip_map = {}
unassociated_eips = {}
stopped_instance_eips = {}
for eip, instance_id, allocation_id in eips:
eip_map[eip] = allocation_id
if instance_id == 'None':
unassociated_eips[eip] = allocation_id
else:
instance_state = get_instance_state(instance_id)
if instance_state == 'stopped':
stopped_instance_eips[eip] = instance_id
return {
"all_eips": eip_map,
"unassociated_eips": unassociated_eips,
"stopped_instance_eips": stopped_instance_eips
}
```
Run this function to get categorized EIPs:
```python
categorized_eips = categorize_eips()
print(categorized_eips)
```
The output will be a dictionary with categorized EIPs.
### Step 6: Printing the Results
To make our script user-friendly, we'll add functions to print the categorized EIPs and provide cost insights.
```python
def print_eip_categories(eips):
"""
Print categorized Elastic IPs and provide cost-related information.
"""
print("All Elastic IPs:")
if eips["all_eips"]:
for eip in eips["all_eips"]:
print(eip)
else:
print("None")
print("\nUnassociated Elastic IPs:")
if eips["unassociated_eips"]:
for eip in eips["unassociated_eips"]:
print(eip)
else:
print("None")
print("\nElastic IPs associated with stopped instances:")
if eips["stopped_instance_eips"]:
for eip in eips["stopped_instance_eips"]:
print(eip)
else:
print("None")
```
Test this function by passing the `categorized_eips` dictionary:
```python
print_eip_categories(categorized_eips)
```
### Step 7: Identifying Secondary EIPs
We should also check for instances that have multiple EIPs associated with them.
```python
def find_secondary_eips():
"""
Find secondary Elastic IPs (EIPs which are connected to instances already assigned to another EIP).
"""
eips = get_all_eips()
instance_eip_map = {}
for eip, instance_id, allocation_id in eips:
if instance_id != 'None':
if instance_id in instance_eip_map:
instance_eip_map[instance_id].append(eip)
else:
instance_eip_map[instance_id] = [eip]
secondary_eips = {instance_id: eips for instance_id, eips in instance_eip_map.items() if len(eips) > 1}
return secondary_eips
```
Run this function to find secondary EIPs:
```python
secondary_eips = find_secondary_eips()
print(secondary_eips)
```
### Step 8: Printing Secondary EIPs
Let's add a function to print the secondary EIPs.
```python
def print_secondary_eips(secondary_eips):
"""
Print secondary Elastic IPs.
"""
print("\nInstances with multiple EIPs:")
if secondary_eips:
for instance_id, eips in secondary_eips.items():
print(f"Instance ID: {instance_id}")
for eip in eips:
print(f" - {eip}")
else:
print("None")
```
Test this function by passing the `secondary_eips` dictionary:
```python
print_secondary_eips(secondary_eips)
```
### Step 9: Providing Cost Insights
Finally, we add a function to provide cost insights based on our findings.
```python
def print_cost_insights(eips):
"""
Print cost insights for Elastic IPs.
"""
unassociated_count = len(eips["unassociated_eips"])
stopped_instance_count = len(eips["stopped_instance_eips"])
total_eip_count = len(eips["all_eips"])
print("\nCost Insights:")
print(f"Total EIPs: {total_eip_count}")
print(f"Unassociated EIPs (incurring cost): {unassociated_count}")
print(f"EIPs associated with stopped instances (incurring cost): {stopped_instance_count}")
print("Note: AWS charges for each hour that an EIP is not associated with a running instance.")
```
Run this function to get cost insights:
```python
print_cost_insights(categorized_eips)
```
### Full Code
Here's the complete script with all the functions we've discussed:
```python
import boto3
# Initialize boto3 EC2 client
ec2_client = boto3.client('ec2')
def get_all_eips():
"""
Retrieve all Elastic IPs along with their associated instance ID and allocation ID.
"""
response = ec2_client.describe_addresses()
eips = [(address['PublicIp'], address.get('InstanceId', 'None'), address['AllocationId']) for address in response['Addresses']]
return eips
def get_instance_state(instance_id):
"""
Retrieve the state of an EC2 instance.
"""
response = ec2_client.describe_instances(InstanceIds=[instance_id])
state = response['Reservations'][0]['Instances'][0]['State']['Name']
return state
def categorize_eips():
"""
Categorize Elastic IPs into various categories and provide cost-related insights.
"""
eips = get_all_eips()
eip_map = {}
unassociated_eips = {}
stopped_instance_eips = {}
for eip, instance_id, allocation_id in eips:
eip_map[eip] = allocation_id
if instance_id == 'None':
unassociated_eips[eip] = allocation_id
else:
instance_state = get_instance_state(instance_id)
if instance_state == 'stopped':
stopped_instance_eips[eip] = instance_id
return {
"all_eips": eip_map,
"unassociated_eips": unassociated_eips,
"stopped_instance_eips": stopped
_instance_eips
}
def print_eip_categories(eips):
"""
Print categorized Elastic IPs and provide cost-related information.
"""
print("All Elastic IPs:")
if eips["all_eips"]:
for eip in eips["all_eips"]:
print(eip)
else:
print("None")
print("\nUnassociated Elastic IPs:")
if eips["unassociated_eips"]:
for eip in eips["unassociated_eips"]:
print(eip)
else:
print("None")
print("\nElastic IPs associated with stopped instances:")
if eips["stopped_instance_eips"]:
for eip in eips["stopped_instance_eips"]:
print(eip)
else:
print("None")
def find_secondary_eips():
"""
Find secondary Elastic IPs (EIPs which are connected to instances already assigned to another EIP).
"""
eips = get_all_eips()
instance_eip_map = {}
for eip, instance_id, allocation_id in eips:
if instance_id != 'None':
if instance_id in instance_eip_map:
instance_eip_map[instance_id].append(eip)
else:
instance_eip_map[instance_id] = [eip]
secondary_eips = {instance_id: eips for instance_id, eips in instance_eip_map.items() if len(eips) > 1}
return secondary_eips
def print_secondary_eips(secondary_eips):
"""
Print secondary Elastic IPs.
"""
print("\nInstances with multiple EIPs:")
if secondary_eips:
for instance_id, eips in secondary_eips.items():
print(f"Instance ID: {instance_id}")
for eip in eips:
print(f" - {eip}")
else:
print("None")
def print_cost_insights(eips):
"""
Print cost insights for Elastic IPs.
"""
unassociated_count = len(eips["unassociated_eips"])
stopped_instance_count = len(eips["stopped_instance_eips"])
total_eip_count = len(eips["all_eips"])
print("\nCost Insights:")
print(f"Total EIPs: {total_eip_count}")
print(f"Unassociated EIPs (incurring cost): {unassociated_count}")
print(f"EIPs associated with stopped instances (incurring cost): {stopped_instance_count}")
print("Note: AWS charges for each hour that an EIP is not associated with a running instance.")
# Main execution
if __name__ == "__main__":
categorized_eips = categorize_eips()
print_eip_categories(categorized_eips)
print_secondary_eips(find_secondary_eips())
print_cost_insights(categorized_eips)
```
### Pros and Cons
**Pros**:
- **Cost Savings**: Identifies and helps eliminate unwanted costs associated with unused or mismanaged EIPs.
- **Automation**: Automates the process of monitoring and categorizing EIPs.
- **Insights**: Provides clear insights into EIP usage and cost-related information.
- **Easy to Use**: Simple and straightforward script that can be run with minimal setup.
**Cons**:
- **AWS Limits**: The script relies on AWS API calls, which may be subject to rate limits.
- **Manual Intervention**: While it identifies cost-incurring EIPs, the script does not automatically release or reallocate them.
- **Resource Intensive**: For large-scale environments with many EIPs and instances, the script may take longer to run and consume more resources.
### How We Can Improve It
- **Automatic Remediation**: Extend the script to automatically release unassociated EIPs or notify administrators for manual intervention.
- **Scheduled Execution**: Use AWS Lambda or a cron job to run the script at regular intervals, ensuring continuous monitoring and cost management.
- **Enhanced Reporting**: Integrate with a logging or monitoring service to provide detailed reports and historical data on EIP usage and costs.
- **Notification System**: Implement a notification system using AWS SNS or similar services to alert administrators of cost-incurring EIPs in real time.
By incorporating these improvements, we can make the script even more robust and useful for managing AWS EIPs and reducing associated costs effectively. | karandaid |
1,867,875 | Understanding Certificates in the Digital World | TL;DR Digital certificates are the digital counterpart to physical ID cards or... | 0 | 2024-05-28T15:19:28 | https://dev.to/yannick555/understanding-certificates-in-the-digital-world-1bn6 | ### TL;DR
Digital certificates are the digital counterpart to physical ID cards or passports.
Their trustworthiness and validity stems from the reliability and credibility of the issuing entity (the CA, respectively the government).
### Intro
In our increasingly digital world, ensuring security and authenticity online is more crucial than ever. Whether you're shopping online, accessing your bank account, or simply browsing the web, the need for secure communication and trust in the entities you interact with cannot be overstated. This is where digital certificates come into play. Much like an ID card verifies your identity in the physical world, a digital certificate verifies identities and secures communications in the digital realm.
Let’s dive into what digital certificates are and how they function similarly to ID cards.
### What is a Digital Certificate?
A digital certificate is a digital document used to authenticate the identity of an entity and establish secure communications. Entities can include websites, individuals, devices, or software. Think of it as a virtual passport that confirms the legitimacy of the entity and contributes to ensure that any data transmitted between you and the entity is secure (the certificate alone is not enough, the communication protocol is important as well).
### Contents of a Digital Certificate
1. **Entity Information**:
- **Subject**: The entity the certificate is issued to. For example, in an SSL/TLS certificate for a website, the subject is typically the domain name of the website.
- **Issuer**: The entity that issued the certificate. This is usually a Certificate Authority (CA).
- **Serial Number**: A unique identifier assigned by the issuer to the certificate.
- **Validity Period**: The period during which the certificate is considered valid, including a start date and an expiration date.
2. **Public Key**:
- The public key of the entity, used for encryption, digital signatures, or both. This key is mathematically linked to a private key held by the entity.
3. **Digital Signature**:
- A digital signature created by the issuer using its private key. It ensures the integrity and authenticity of the certificate. If the signature can be verified using the issuer's public key, the certificate is considered valid.
4. **Certificate Extensions**:
- **Key Usage**: Specifies the cryptographic operations that the public key can be used for, such as encryption, digital signatures, or both.
- **Subject Alternative Name (SAN)**: Additional identities for which the certificate is valid, such as alternative domain names for a website.
- **Basic Constraints**: Specifies whether the certificate can be used as a Certificate Authority to issue other certificates.
- **Extended Key Usage**: Further specifies the purposes for which the public key can be used, such as client authentication, server authentication, or code signing.
> **Notes**
> 1. A certificate is meant to be shared with other entities, which is why...
> 2. The private key is *not* part of the certificate.
> 3. The CA itself may be authenticated by another CA, which might as well be authenticated by another one and so on, until the root CA is attained: this is the CA trust chain.
### How Does an ID Card Work?
1. **Issuance of ID Card**:
- An individual provides personal information and undergoes identity verification by a relevant authority, such as a government agency or employer, to obtain an ID card.
- The authority verifies the identity of the requester and issues the ID card containing their personal details and photograph.
2. **Authentication and Identity Verification**:
- When presenting the ID card, the information on the card is compared with the individual presenting it to verify their identity.
- This authentication process ensures that the person holding the ID card is indeed the legitimate cardholder and is authorised to access the services or privileges associated with the card.
3. **Access to Privileges and Services**:
- ID cards grant access to various privileges and services based on the authority associated with the card. For example, a driver's license grants the holder the privilege to operate a motor vehicle.
- By presenting the ID card, individuals can access these privileges and services, ensuring that only authorised individuals benefit from them.
### How Does a Digital Certificate Work?
1. **Certificate Issuance**: An entity generates a public-private key pair and submits a certificate signing request (CSR) to a Certificate Authority (CA). The CA verifies the identity of the requester and issues a digital certificate containing the public key.
2. **Authentication and Secure Communication**:
- **Websites**: Your browser requests the site’s digital certificate and verifies it, ensuring you are communicating with the legitimate site.
- **Emails**: Email clients can use certificates to encrypt and sign emails, ensuring confidentiality and authenticity.
- **Software**: Developers sign their software with certificates to prove that it has not been tampered with.
- **Individuals**: Digital certificates can authenticate individuals for access to secure systems or documents.
### Types of Digital Certificates
There are different times of digital certificates which serve different purposes:
1. **SSL/TLS Certificates**: Secure communications between browsers and websites.
2. **Client Certificates**: Authenticate users or devices to a server.
3. **Code Signing Certificates**: Verify the identity of the software publisher and ensure the integrity of the software.
4. **Email Certificates (S/MIME Certificates)**: Secure email communications by encrypting and signing emails.
5. **Document Signing Certificates**: Digitally sign documents to ensure their authenticity and integrity.
6. **Root and Intermediate Certificates**: Form the foundation of trust in the PKI hierarchy, used by Certificate Authorities to issue end-entity certificates.
> **Types of government-issued IDs**
> Governments typically issue various types of identification documents to their citizens, residents, and other individuals. These IDs serve different purposes and may vary depending on the country and its regulations. Here are some common types of IDs issued by governments:
> 1. **National Identity Cards (NIC)**:
> - National identity cards are government-issued documents that serve as official proof of identity for citizens or residents. They typically include the individual's name, photograph, date of birth, and sometimes other identifying information such as address or identification number.
> 2. **Passports**:
> - Passports are travel documents issued by governments to their citizens for international travel. They contain personal information about the passport holder, including their photograph, nationality, date of birth, and passport number.
> 3. **Driver's Licenses**:
> - Driver's licenses are issued by government agencies to individuals who have passed the required tests to operate motor vehicles legally. In addition to serving as proof of identity, driver's licenses also indicate the holder's authorisation to drive specific types of vehicles.
> 4. **Social Security Cards**:
> - Social Security cards are issued in some countries to individuals who have registered for government social security programs. They typically contain a unique identification number assigned to the individual for tracking purposes.
> 5. **Residence Permits**:
> - Residence permits are issued to non-citizen residents by governments to legally reside in a country for a specified period. These documents typically include the individual's name, photograph, and information about their immigration status.
> 6. **Voter ID Cards**:
> - Voter ID cards are issued to eligible voters by election authorities to facilitate voting in elections. They serve as proof of identity and eligibility to vote.
> 7. **Military IDs**:
> - Military identification cards are issued to members of the armed forces and their dependent. They serve as proof of military affiliation and may grant access to military facilities and services.
> 8. **Government Employee IDs**:
> - Government employee IDs are issued to individuals employed by government agencies. They serve as proof of employment and may grant access to government facilities and services.
>
> These are just a few examples of the types of IDs that governments commonly issue. The > specific types and requirements for obtaining them vary by country and jurisdiction.
### Digital Certificates vs. ID Cards: The Similarities
Usually, the government trusts local authorities (municipality) to authenticate a person and to make the ID request. The government then creates the ID, which is then handed to the person by the requesting local authority. The role of the government is similar to the role of a CA.
People and organisations usually trust the government-delivered ID: sometimes, this is even mandated by law. This trust in the government is what makes this system robust - whether one likes the government or not.
1. **Identity Verification**:
- **ID Card**: Confirms your identity with personal details and a photograph, typically issued by a government or other trusted entity.
- **Digital Certificate**: Confirms the identity of an entity, typically issued by a trusted CA after verifying the entity's credentials.
2. **Trust**:
- **ID Card**: We trust ID cards because they are issued by recognised authorities like governments.
- **Digital Certificate**: We trust digital certificates because they are issued by recognised CAs, which follow rigorous verification processes.
3. **Authentication**:
- **ID Card**: Used to prove your identity when accessing restricted areas, conducting transactions, or during identification checks.
- **Digital Certificate**: Used to prove the identity of an entity, ensuring secure and authenticated communications.
4. **Security Features**:
- **ID Card**: Contains physical security features like holograms, watermarks, and micro-printing to prevent forgery.
- **Digital Certificate**: Contains cryptographic elements like public keys and digital signatures to prevent tampering and ensure authenticity.
5. **Validity period:**
- **ID Card**: Has an expiration date.
- **Digital Certificate**: Has a limited validity period which specifies the time frame during which it is considered valid and trustworthy. After the expiration date, the certificate is no longer considered valid, and relying parties should not trust it for secure communications.
6. **Renewal Process:**
- **ID Card**: Must be renewed before it expires. Renewal typically involves obtaining a new ID from the issuing government and only using the new one (in some countries, authorities may even require that old IDs are given back to the government).
- **Digital Certificate**: Must be renew by their holders before they expire to ensure uninterrupted secure communication. Renewal typically involves obtaining a new certificate from the issuing Certificate Authority (CA) and replacing the old certificate with the new one.
7. **Types:**
- **ID Card:** Various types of IDs are issued by governments and are used for different purposes.
- **Digital Certificate:** Various types of digital certificates are used for different purposes.
### Practical Examples of Digital Certificates in Use
1. **Secure Web Browsing**: When you visit a website starting with `https://`, the communication protocol and the site’s digital certificate ensure that your communication with the site is encrypted and secure, protecting sensitive information like passwords and credit card numbers.
2. **Email Security**: Digital certificates can secure email communications by encrypting emails and enabling digital signatures, ensuring that your emails are confidential and authenticated.
3. **Software Integrity**: Developers use digital certificates to sign software, ensuring users that the software has not been tampered with and is from a legitimate source.
4. **Individual Authentication**: Organisations issue digital certificates to employees, enabling secure access to corporate systems and data. These certificates ensure that only authorised individuals can access sensitive information.
5. **Document Signing**: Digital certificates are used to sign electronic documents, providing a digital equivalent of a handwritten signature and ensuring the document’s integrity and authenticity.
### Conclusion
Digital certificates play a vital role in maintaining trust and security in the digital world, much like ID cards do in the physical world. They verify the identities of entities, establish secure communications, and ensure data integrity. By understanding how digital certificates function and their similarities to ID cards, we can better appreciate the underlying mechanisms that keep our online interactions safe and trustworthy. So next time you encounter a digital certificate, you’ll know that it is hard at work, verifying identities and securing your digital environment.
| yannick555 | |
1,867,863 | Architecting Microservices as Tenants on a Monolith with Zango | You must be this tall to use Microservices - Martin Fowler Microservices architectural pattern has... | 0 | 2024-05-28T15:15:01 | https://www.zango.dev/blog/architecting-microservices-as-a-tenant-on-a-monolith | python, microservices, architecture, opensource | ---
published: true
canonical_url: https://www.zango.dev/blog/architecting-microservices-as-a-tenant-on-a-monolith
---
> You must be this tall to use Microservices - Martin Fowler
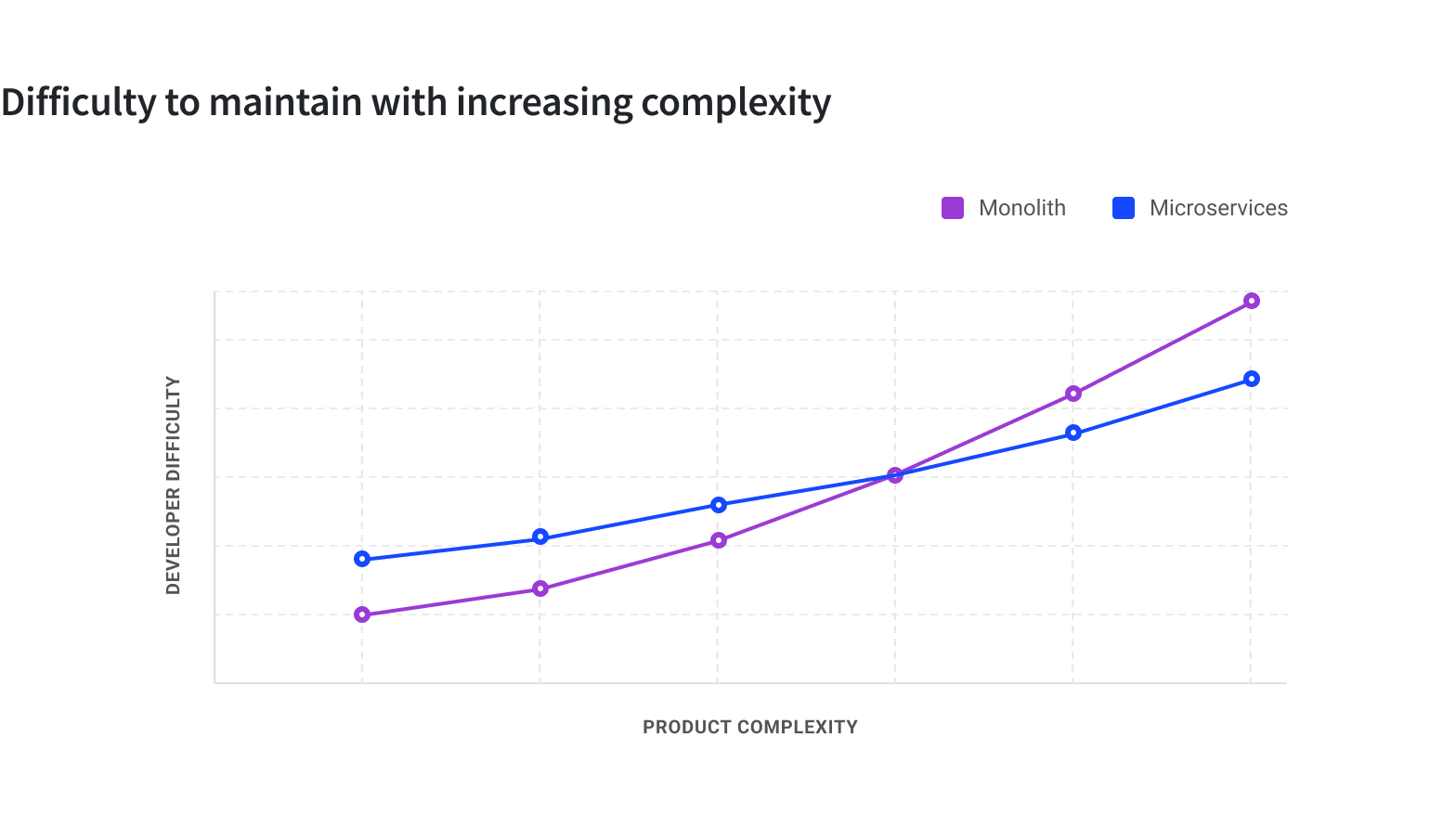
Microservices architectural pattern has gained massive prominence and widespread adoption over the last decade or so due to the many advantages it offers. It enables decentralized structures at the people level as well as at the technical level and improves the ability of systems to effectively respond to the demands of growth, both of features and scale. The microservices pattern definitely offers higher elasticity to the system it is powering to respond to changes in a dynamic environment.
On the other hand, a monolithic system is akin to a centralized structure where the complexity keeps increasing by the day. The addition of more lines of codes, new modules, new packages, new dependencies, etc. leads to a system where the elasticity to change is decreasing. Enhancements tends to become more cumbersome and expensive and it is easier for more crufts to surface in the codebase. The burden of bureaucracy also tends to be higher on the monolith for obvious reasons.
## Microservices are expensive
More recently, there has been a lot of discussion around the cost of microservices. The in-memory method calls in a monolith between modules becomes the more expensive network calls in microservices. Separate deployment makes it easy to run into a fleet of hundreds of servers in organizations running several microservices in production. Then there are overheads introduced from more complex monitoring, devops, etc.
While the ability to run and scale smaller independent systems introduces the leverage of agility, the higher infrastructural and operational overheads renders the choice of microservices impractical in a vast majority of use cases.
During the proliferation phase, the microservices pattern seemed like the silver bullet and organizations of all sizes were adopting it overlooking the overheads. In the current times, it seems as if the reverse is happening. It is becoming fashionable to suggest that microservices is not a suitable solution for the problem at hand and that monolith is ‘majestic’ or start with a monolith.
## The advantages of microservices, albeit the cost
The microservices pattern can revolutionize the way a product is developed, deployed and enhanced even for ecosystems that might not have hit the threshold of scale. Keeping aside the cost and concerns around the operational overhead, microservices as a pattern stands to quickly outshine a monolithic approach by remaining more adaptable to new requirements. The enablement of parallel development by establishing well enforced boundaries greatly adds to the agility of the development team.
The adage is to start with a monolith and branch out to microservices, using the approach known as the [Strangler Fig pattern](https://martinfowler.com/bliki/StranglerFigApplication.html).
## Don’t start with a monolith if the goal is microservices
To paraphrase [Simon Tilkov](https://z-framework-website-git-development-zelthy.vercel.app/blog/architecting-microservices-as-a-tenant-on-a-monolith#:~:text=To%20paraphrase-,Simon%20Tilkov,-I%E2%80%99m%20firmly%20convinced)
> I’m firmly convinced that starting with a monolith is usually exactly the wrong thing to do. Starting to build a new system is exactly the time when you should be thinking about carving it up into pieces. I strongly disagree with the idea that you can postpone this.
Building a greenfield monolith that is expected to grow out into a Strangler Fig and expecting to cut it off when the time is right will add stress to the design of the monolith in the first place.
Simon Tilkov continues
> You might be tempted to assume there are a number of nicely separated microservices hiding in your monolith, just waiting to be extracted. In reality, though, it’s extremely hard to avoid creating lots of connections, planned and unplanned. In fact the whole point of the microservices approach is to make it hard to create something like this.
## Zango - A new approach for microservices, sans the overheads
[Zango](https://github.com/Healthlane-Technologies/Zango) is a new Python web application development framework, implemented on top of Django, that allows leveraging the key advantages of the micorservices pattern without incurring any additional operational overheads.
Under the hood, Zango is a monolith that allows hosting multiple independently deployable applications or microservices on top of it. Each application is logically isolated from the other sibling apps at the data layer, the logic layer, the interface layer as well as in deployment, ensuring complete microservices type autonomy.
One of the key goals of Zango's design is to make sure that deployment of one app does not require downtime for any other sibling app or the underlying monolith. We do so by creating logically separated areas, enforcing rules and policies at the framework level and leveraging the plugin architectural pattern for executing the app's logics.
In addition, to meet the requirement of differential scaling, Zango also allows easy branching off of one or more services to deployment on a separate cluster without needing any code level refactoring.
Zango has been open sourced recently, but it has been in production to support hundreds of applications in global companies.
## Let’s understand the architecture in detail.
Zango comes with Postgres SQL database and the organization of the datastore is central to the framework. We utilize the [multi-tenancy](https://www.postgresql.org/docs/current/ddl-schemas.html) feature of Postgres to logically segregate the storage for each microservice. Each microservice will have a unique schema in the database where all the tables and associated objects for that microservice will be housed. The image below shows the organization at the database level.
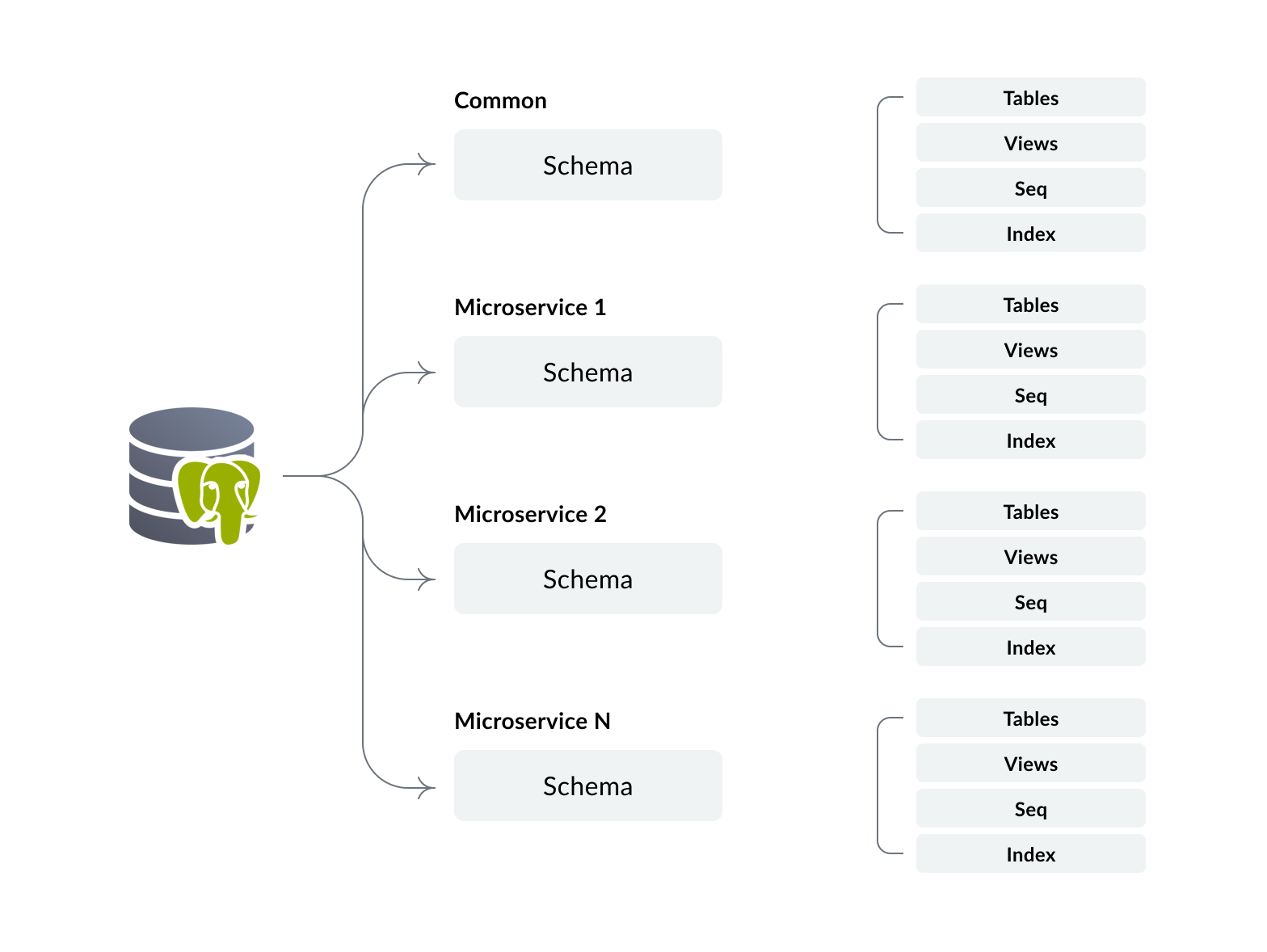
Policies are enforced by the framework to prevent unauthorized access to data. For e.g. application logic implemented in microservice 1 that attempts to access the data for microservice 2 will be restricted by the default policies.
Additionally the common schema in the database will have a table to function as the registry of microservices. In this registry we store the generic details of the microservices, including:
- Primary ID
- Name
- Domain URL
- DB Schema Name
With the organization of data storage for the microservices in place, we can now look into how Zango handles the codebase, ensuring we meet the key requirements:
- A lot of microservices can be created on a single monolith deployment
- Deployment of one microservice must not require any downtime for other microservices
- Errors in one microservice must not propagate to outside the boundaries of the microservice
To meet these requirements, we leverage the Plugin Architectural pattern. Each microservice is implemented as a plugin. Caching techniques ensure the efficient loading of the plugin codebase and re-loading only when new releases are available for a particular microservice.
## Inside the request-response cycle
On receiving an incoming request, Zango first attempts to identify which microservice it is intended for, using the domain url from the request and the matching with the ones stored in the registry. If a matching microservice is found, an attempt to find a matching route for the URI in the microservice’s codebase. The framework enforces certain rules for defining the routes. If a matching route is found, the controller associated with the route is called to generate the response. If the match is not found, 404 is returned.
The framework also sets the path to the particular schema in the database that belongs to the microservice. By doing so, there will be no requirement to explicitly set the schema context in the codebase of the microservice and the developer gets the sense that he is working with a single tenant database only.
The overall architecture involves a lot of other nuances to handle finer details around access control and authorization framework, differential throttling, packages layer to enable a packages ecosystem, etc. which is beyond the scope of this introduction.
We believe that the possibility of implementing a microservices architecture without additional cost burden can bring a lot of advantages to a greenfield web application project. The power of differential scaling on the same deployment as well as the ease with which the microservices can be extracted fully into an independent deployment will significantly strengthen the teams
Zango is available under an open source AGPL license [here](https://github.com/Healthlane-Technologies/Zango). It is implemented on top of Django and requires basic Django understanding to start developing applications on it.
**Checkout Zango on Github:** [https://github.com/Healthlane-Technologies/Zango](https://github.com/Healthlane-Technologies/Zango)
| kcdiabeat |
1,867,877 | Light Bulb Challenge | Hi, This is one of the javascript challenges that was quite popular when I was studying Javascript.... | 0 | 2024-05-28T15:13:56 | https://dev.to/rusandu_dewm_galhena/light-bulb-challenge-595n | javascript, webdev, beginners, programming | Hi, This is one of the javascript challenges that was quite popular when I was studying Javascript. This challenge is a completly begginer friendly challenge for who ever began to code Javascript.
Bulb challenge is when you create button and when the user presses the button the content changes or in this case, the image of the unlit bulb changes to a lit bulb image when the use clicks on light off button.This challenge is performed by the onclick function in Javascript.
Hope this would be helpfull!! | rusandu_dewm_galhena |
1,867,730 | Testing React Applications | Table of contents Introduction 1. The importance of testing 2. Testing fundamentals 3.... | 0 | 2024-05-28T15:13:00 | https://www.marioyonan.com/blog/react-testing | webdev, react, testing, beginners | ## Table of contents
- [Introduction](#introduction)
- [1. The importance of testing](#1-the-importance-of-testing)
- [2. Testing fundamentals](#2-testing-fundamentals)
- [3. Writing unit tests with Jest and React Testing Library](#3-writing-unit-tests-with-jest-and-react-testing-library)
- [4. Integration Testing](#4-integration-testing)
- [5. End-to-End testing with Cypress](#5-end-to-end-testing-with-cypress)
- [6. Test-Driven Development (TDD)](#6-test-driven-development-tdd)
- [7. Mocking in tests](#7-mocking-in-tests)
- [8. Best practices and Tips](#8-best-practices-and-tips)
- [9. Continuous Integration and Deployment (CI/CD)](#9-continuous-integration-and-deployment-cicd)
- [Conclusion](#conclusion)
---
## Introduction
👋 Hello everyone!
Let’s dive into an essential aspect of developing robust React applications – testing. While it’s a well-known practice in the developer community, effectively testing React apps can still be challenging.
In this article, we’ll explore various aspects of testing React applications. We’ll cover the basics, like why testing is important and the different types of tests you should write. Then we’ll get our hands dirty with some practical examples using popular tools like Jest, React Testing Library, and Cypress.
By the end of this article, you’ll have a solid understanding of how to set up a robust testing strategy for your React apps, making your development process smoother and your applications more reliable.
Let’s get started!
---
## 1. The importance of testing
Testing is a critical component of software development, and for React applications, it’s no different. Here’s why testing your React apps is essential:
- **Improves Code Quality**: Regular testing helps identify and fix bugs early in the development process, leading to higher quality code. It ensures that your code meets the specified requirements and behaves as expected under different conditions.
- **Reduces Bugs**: Automated tests can catch bugs before they make it to production. By writing comprehensive tests, you can prevent many common issues that might otherwise slip through the cracks during manual testing.
- **Enhances Maintainability**: As your React application grows, maintaining and updating it becomes more challenging. Tests act as a safety net, ensuring that new changes do not break existing functionality. This makes refactoring and adding new features much safer and more efficient.
- **Increases Developer Confidence**: With a robust test suite, developers can make changes and add new features with greater confidence, knowing that the tests will catch any regressions or issues.
- **Supports Continuous Integration**: Automated tests are essential for continuous integration and continuous deployment (CI/CD) pipelines. They ensure that every change is tested automatically, maintaining the stability and reliability of your application.
Understanding the importance of testing helps in appreciating the effort put into writing and maintaining tests. It’s not just about finding bugs but also about building a reliable and maintainable codebase.
---
## 2. Testing fundamentals
Understanding the basics of testing is crucial before diving into the specifics of testing React applications. Here are some key concepts and strategies:
### Types of Testing
- **Unit Testing**: Focuses on individual components or functions. The goal is to test each part of the application in isolation to ensure it works as expected.
- **Integration Testing**: Tests the interaction between different parts of the application. This ensures that different components or services work together correctly.
- **End-to-End (E2E) Testing**: Simulates real user interactions with the application. These tests cover the entire application from the user interface to the back-end, ensuring everything works together as a whole.
### Common Testing Tools for React
- **Jest**: A powerful JavaScript testing framework developed by Facebook, commonly used for unit and integration tests in React applications.
- **React Testing Library**: A library for testing React components, focusing on testing user interactions rather than implementation details.
- **Enzyme**: A testing utility for React that allows you to manipulate, traverse, and simulate runtime behavior in a React component’s output. Though it’s less commonly used today, it’s still relevant in many projects.
- **Cypress**: A robust framework for writing end-to-end tests. It provides a developer-friendly experience and is known for its powerful features and ease of use.
Understanding these fundamentals will provide a strong foundation as we move into writing specific types of tests for React applications.
---
## 3. Writing unit tests with Jest and React Testing Library
Unit testing focuses on verifying the functionality of individual components in isolation. Jest and React Testing Library are commonly used together to write unit tests for React applications.
### Setting Up Your Testing Environment
First, you need to install Jest and React Testing Library. If you haven’t already, you can add them to your project using npm or yarn:
```bash
npm install --save-dev jest @testing-library/react @testing-library/jest-dom
# or
yarn add --dev jest @testing-library/react @testing-library/jest-dom
```
Next, create a setupTests.js file in your src directory to configure Jest and React Testing Library:
```javascript
// src/setupTests.js
import '@testing-library/jest-dom';
```
Ensure your package.json includes the following configuration for Jest:
```json
{
"scripts": {
"test": "jest"
},
"jest": {
"setupFilesAfterEnv": ["<rootDir>/src/setupTests.js"],
"testEnvironment": "jsdom"
}
}
```
### Writing your first unit test
Let’s start with a simple example. Suppose you have a Button component:
```jsx
// src/components/Button.js
import React from 'react';
const Button = ({ label, onClick }) => (
<button onClick={onClick}>{label}</button>
);
export default Button;
```
Now, let’s write a unit test for this component:
```jsx
// src/components/Button.test.js
import React from 'react';
import { render, fireEvent } from '@testing-library/react';
import Button from './Button';
test('renders the button with the correct label', () => {
const { getByText } = render(<Button label="Click me" />);
expect(getByText('Click me')).toBeInTheDocument();
});
test('calls the onClick handler when clicked', () => {
const handleClick = jest.fn();
const { getByText } = render(<Button label="Click me" onClick={handleClick} />);
fireEvent.click(getByText('Click me'));
expect(handleClick).toHaveBeenCalledTimes(1);
});
```
### Testing Component Rendering and User Interactions
React Testing Library encourages testing components in a way that resembles how users interact with them. Here are a few more examples:
**Testing State Management**:
Suppose you have a Counter component that increments a counter when a button is clicked:
```jsx
// src/components/Counter.js
import React, { useState } from 'react';
const Counter = () => {
const [count, setCount] = useState(0);
return (
<div>
<p>Count: {count}</p>
<button onClick={() => setCount(count + 1)}>Increment</button>
</div>
);
};
export default Counter;
```
Now, let’s write a unit test for this component:
```jsx
// src/components/Counter.test.js
import React from 'react';
import { render, fireEvent } from '@testing-library/react';
import Counter from './Counter';
test('increments the counter when the button is clicked', () => {
const { getByText } = render(<Counter />);
const button = getByText('Increment');
fireEvent.click(button);
expect(getByText('Count: 1')).toBeInTheDocument();
});
```
**Testing Props**:
Ensure that components render correctly based on different props:
```jsx
// src/components/Greeting.js
import React from 'react';
const Greeting = ({ name }) => <h1>Hello, {name}!</h1>;
export default Greeting;
```
```jsx
// src/components/Greeting.test.js
import React from 'react';
import { render } from '@testing-library/react';
import Greeting from './Greeting';
test('renders the correct greeting message', () => {
const { getByText } = render(<Greeting name="Alice" />);
expect(getByText('Hello, Alice!')).toBeInTheDocument();
});
```
---
## 4. Integration Testing
Integration testing focuses on verifying the interactions between different parts of your application to ensure they work together correctly. This type of testing is crucial for React applications, where components often interact with each other and external services.
### Setting up integration tests
To start writing integration tests, you’ll use the same tools as for unit testing, such as Jest and React Testing Library. However, you’ll focus on testing how multiple components interact with each other.
Here’s how to set up a basic integration test:
1. **Install necessary libraries:**
Make sure you have Jest and React Testing Library installed.
```bash
npm install --save-dev jest @testing-library/react @testing-library/jest-dom
# or
yarn add --dev jest @testing-library/react @testing-library/jest-dom
```
2. **Configure Jest for integration testing:**
Ensure your Jest setup can handle integration tests, especially if you’re mocking APIs or using other external services.
Let’s consider an example where you have a UserList component that fetches and displays a list of users. This component interacts with an API and another User component.
```jsx
// src/components/User.js
import React from 'react';
const User = ({ name }) => <li>{name}</li>;
export default User;
```
```jsx
// src/components/UserList.js
import React from 'react';
import User from './User';
const UserList = ({users}) => {
return (
<ul>
{users.map(user => (
<User key={user.id} name={user.name} />
))}
</ul>
);
};
export default UserList;
```
**Integration test**
```jsx
// src/components/UserList.test.js
import React from 'react';
import { render, screen, waitFor } from '@testing-library/react';
import UserList from './UserList';
beforeAll(() => server.listen());
afterEach(() => server.resetHandlers());
afterAll(() => server.close());
test('fetches and displays users', async () => {
render(<UserList users=["Alice", "Bob"] />);
expect(screen.getByText('Alice')).toBeInTheDocument();
expect(screen.getByText('Bob')).toBeInTheDocument();
});
```
---
## 5. End-to-End testing with Cypress
End-to-end (E2E) testing is a critical part of ensuring your React application works as expected from the user’s perspective. Cypress is a popular tool for E2E testing due to its developer-friendly features and powerful capabilities.
### Introduction to End-to-End Testing
End-to-end testing simulates real user interactions with your application, testing the entire workflow from start to finish. This type of testing helps ensure that all components of your application work together as intended, providing a seamless experience for users.
### Benefits of Cypress
- **Developer-Friendly**: Cypress provides an intuitive interface and easy-to-write tests, making it accessible for developers of all skill levels.
- **Fast and Reliable**: Cypress runs tests in the browser, allowing you to see exactly what the user sees. This results in fast and reliable test execution.
- **Built-In Features**: Cypress includes features like time travel, automatic waiting, and real-time reloads, which simplify the testing process and enhance debugging capabilities.
### Setting Up Cypress
To get started with Cypress, follow these steps:
1. **Install Cypress**:
Use npm or yarn to install Cypress in your project.
```bash
npm install cypress --save-dev
# or
yarn add cypress --dev
```
2. **Open Cypress:**
Open Cypress for the first time to complete the setup and generate the necessary folder structure.
```bash
npx cypress open
```
3. **Configure Cypress**:
Add a cypress.json file to configure Cypress settings as needed.
```json
{
"baseUrl": "http://localhost:3000"
}
```
### Writing E2E Tests
Let’s write a simple E2E test to verify the login functionality of a React application:
1. **Create a Test File**:
Create a new test file in the cypress/integration folder.
```jsx
// cypress/integration/login.spec.js
describe('Login', () => {
it('should log in the user successfully', () => {
cy.visit('/login');
cy.get('input[name="username"]').type('testuser');
cy.get('input[name="password"]').type('password123');
cy.get('button[type="submit"]').click();
cy.url().should('include', '/dashboard');
cy.get('.welcome-message').should('contain', 'Welcome, testuser');
});
});
```
2. 2.**Run the Test**:
Run the test using the Cypress Test Runner.
```bash
npx cypress open
```
### Running and Debugging Tests
Cypress makes it easy to run and debug tests with its robust set of features:
- **Time Travel**: Inspect snapshots of your application at each step of the test, allowing you to see exactly what happened at any point.
- **Automatic Waiting**: Cypress automatically waits for elements to appear and actions to complete, reducing the need for manual wait commands.
- **Real-Time Reloads**: The Test Runner reloads tests in real-time as you make changes, providing immediate feedback.
By using Cypress for end-to-end testing, you can ensure that your React application delivers a reliable and user-friendly experience.
---
## 6. Test-Driven Development (TDD)
Test-Driven Development (TDD) is a software development methodology where tests are written before the actual code. This approach ensures that the code meets the specified requirements and helps maintain high code quality.
### Principles of TDD
TDD is based on a simple cycle of writing tests, writing code, and refactoring. Here are the core principles:
- **Write a Test**: Start by writing a test for the next piece of functionality you want to add.
- **Run the Test**: Run the test to ensure it fails. This step confirms that the test is detecting the absence of the desired functionality.
- **Write the Code**: Write the minimal amount of code necessary to make the test pass.
- **Run the Test Again**: Run the test again to ensure it passes with the new code.
- **Refactor**: Refactor the code to improve its structure and readability while ensuring the tests still pass.
### TDD Workflow
1. **Red Phase**: Write a failing test that defines a function or feature.
2. **Green Phase**: Write the code to pass the test.
3. **Refactor Phase**: Refactor the code for optimization and clarity, ensuring the test still passes.
### Advantages of TDD
- **Improved Code Quality**: Writing tests first ensures that each piece of functionality is clearly defined and tested.
- **Early Bug Detection**: Bugs are caught early in the development process, reducing the cost and effort of fixing them later.
- **Better Design**: TDD encourages modular and maintainable code design.
- **Confidence in Code Changes**: Tests provide a safety net that gives developers confidence when making changes or adding new features.
### Practical Example
Let’s walk through a simple TDD example for a React component:
**Step 1: Write a Test**
Suppose we want to create a Counter component. We’ll start by writing a test:
```jsx
// src/components/Counter.test.js
import React from 'react';
import { render, fireEvent } from '@testing-library/react';
import Counter from './Counter';
test('increments counter when button is clicked', () => {
const { getByText } = render(<Counter />);
const button = getByText('Increment');
const counter = getByText('Count: 0');
fireEvent.click(button);
expect(counter).toHaveTextContent('Count: 1');
});
```
**Step 2: Run the Test**
Run the test to ensure it fails, indicating that the functionality is not yet implemented:
```bash
npm test
# or
yarn test
```
**Step 3: Write the Code**
Write the minimal code to pass the test:
```jsx
// src/components/Counter.js
import React, { useState } from 'react';
const Counter = () => {
const [count, setCount] = useState(0);
return (
<div>
<p>Count: {count}</p>
<button onClick={() => setCount(count + 1)}>Increment</button>
</div>
);
};
export default Counter;
```
**Step 4: Run the Test Again**
Run the test again to ensure it passes with the new code:
```bash
npm test
# or
yarn test
```
**Step 5: Refactor**
Refactor the code to improve its structure and readability while ensuring the test still passes. In this simple example, the initial implementation is already quite clean, so minimal refactoring is needed.
By following the TDD workflow, you can ensure that your code is thoroughly tested and meets the desired requirements from the outset.
---
## 7. Mocking in tests
Mocking is an essential technique in testing that allows you to isolate the component or function under test by simulating the behavior of dependencies. This helps ensure that tests are focused and reliable.
### Importance of Mocking
- **Isolation**: Mocking helps isolate the component or function being tested by simulating its dependencies. This ensures that tests are not affected by external factors or actual implementations of dependencies.
- **Control**: By using mocks, you can control the behavior of dependencies, making it easier to test different scenarios and edge cases.
- **Performance**: Mocks can improve test performance by avoiding calls to slow or resource-intensive external systems, such as databases or APIs.
### Mocking Functions and Modules with Jest
Jest provides powerful mocking capabilities that allow you to create mocks for functions, modules, and even entire libraries.
### Mocking Functions:
Suppose you have a utility function that performs a complex calculation, and you want to mock it in your tests:
```jsx
// src/utils/calculate.js
export const calculate = (a, b) => a + b;
// src/components/Calculator.js
import React from 'react';
import { calculate } from '../utils/calculate';
const Calculator = ({ a, b }) => {
const result = calculate(a, b);
return <div>Result: {result}</div>;
};
export default Calculator;
```
### Test with Mocked Function:
```jsx
// src/components/Calculator.test.js
import React from 'react';
import { render } from '@testing-library/react';
import Calculator from './Calculator';
import * as calculateModule from '../utils/calculate';
jest.mock('../utils/calculate');
test('renders the result of the calculation', () => {
calculateModule.calculate.mockImplementation(() => 42);
const { getByText } = render(<Calculator a={1} b={2} />);
expect(getByText('Result: 42')).toBeInTheDocument();
});
```
By mocking the calculate function, you can control its behavior and test different scenarios without relying on the actual implementation.
---
## 8. Best practices and Tips
Writing effective tests for your React applications involves following best practices that ensure your tests are maintainable, reliable, and efficient. Here are some tips to help you achieve that:
### Effective Test Writing
- **Write Tests Early**: Incorporate testing into your development process from the beginning. Writing tests early helps catch issues sooner and ensures new features are covered by tests.
- **Test Behavior, Not Implementation**: Focus on testing the behavior and output of your components rather than their implementation details. This makes your tests more robust and less likely to break with refactoring.
- **Keep Tests Small and Focused**: Write small, focused tests that cover specific pieces of functionality. This makes it easier to understand and maintain your test suite.
### Optimizing Test Performance
- **Avoid Unnecessary Re-renders**: Use utility functions like rerender from React Testing Library to avoid unnecessary re-renders in your tests.
- **Mock Expensive Operations**: Mock operations that are resource-intensive or slow, such as network requests, to speed up your tests.
- **Run Tests in Parallel**: Configure your testing framework to run tests in parallel where possible, reducing overall test execution time.
### Managing Test Data
- **Use Factories for Test Data**: Create factories or fixtures for generating test data. This ensures consistency and makes it easier to set up tests.
- **Clean Up After Tests**: Ensure that any side effects created during tests are cleaned up. Use Jest’s afterEach or afterAll hooks to reset state or clear mocks.
### Common Challenges and Solutions
- **Flaky Tests**: Identify and fix flaky tests that sometimes pass and sometimes fail. This can be due to timing issues, reliance on external services, or random data.
- **Testing Asynchronous Code**: Use utilities like waitFor or findBy from React Testing Library to handle asynchronous operations in your tests. Ensure that your tests account for delays or async behavior.
- **Handling Dependencies**: Use mocking to handle dependencies that are difficult to control in tests, such as API calls or global objects.
---
## 9. Continuous Integration and Deployment (CI/CD)
Continuous Integration and Continuous Deployment (CI/CD) are essential practices for modern software development. They automate the process of integrating code changes, running tests, and deploying applications, ensuring that your software is always in a deployable state.
### Role of CI/CD in Testing
CI/CD pipelines automate the testing process, allowing you to:
- **Run Tests Automatically**: Ensure that tests are run automatically on every code change, catching bugs early in the development process.
- **Maintain Code Quality**: Enforce code quality standards by running linting and formatting checks as part of the pipeline.
- **Deploy Continuously**: Deploy code changes to production or staging environments automatically, ensuring that new features and fixes are available to users as soon as they are ready.
### Popular CI/CD Platforms
Several CI/CD platforms are popular in the development community for their ease of use and powerful features. Here are a few:
- **GitHub Actions**: Integrated with GitHub repositories, it allows you to automate workflows directly within your GitHub environment.
- **CircleCI**: Known for its speed and efficiency, it supports various configurations and is easy to integrate with multiple environments.
- **Travis CI**: Popular for its simplicity and ease of setup, especially for open-source projects.
### Running and Monitoring CI/CD Pipelines
Once your CI/CD pipeline is set up, every code change will trigger the workflow, running your tests and providing feedback. You can monitor the status of your workflows directly in the GitHub Actions tab of your repository.
### Benefits:
- **Consistency**: Ensure that tests are run consistently and automatically on every code change.
- **Early Bug Detection**: Catch bugs early in the development process before they make it to production.
- **Continuous Delivery**: Automate the deployment process, ensuring that your application is always in a deployable state.
By integrating CI/CD into your development workflow, you can maintain high code quality, reduce the risk of introducing bugs, and ensure that new features are delivered to users quickly and reliably.
---
## Conclusion
Implementing a robust testing strategy is crucial for delivering high-quality, reliable software. By integrating tools like Jest, React Testing Library, and Cypress into your workflow, you can catch bugs early, improve code quality, and ensure a smooth user experience. Continuous Integration and Deployment (CI/CD) further enhance this process by automating tests and deployments, maintaining the stability of your application.
Remember, testing is not just about finding bugs—it’s about ensuring that your code behaves as expected and continues to do so as it evolves. By prioritizing testing in your development workflow, you can build more reliable and maintainable React applications.
| mario130 |
1,867,873 | AWS open source newsletter, #198 | Edition #198 Welcome to issue #198 of the AWS open source newsletter, the newsletter where... | 0 | 2024-05-28T15:05:53 | https://community.aws/content/2h6H82ceGfVpqbr5NOAWnvS1oO5/aws-open-source-newsletter-198 | opensource, aws | ## Edition #198
Welcome to issue #198 of the AWS open source newsletter, the newsletter where we try and provide you the best open source on AWS content. In this issue we feature new projects that provide integration of .NET Aspire with AWS resources, an automated data discovery tool to find data in your AWS environments, a tool to help incorporate good practices when building SaaS solutions, a cost allocation dashboard for your Kubernetes workloads, a project that might help you mitigate costs around Internet Gateway, and a few generative AI demos around food, news, and social media which you should definitely check out. Also in this edition is plenty of content on your favourite open source technologies, which this week includes Kubernetes, Leapp, OpenTelemetry, AWS CDK, llrt, Valkey, PostgreSQL, InfluxDB, High Performance Software Foundation, Karpenter, Multus, Kata, Grafana, Prometheus, Apache Flink, Zingg, Apache Hudi, Apache Iceberg, MySQL, Apache Tomcat, WordPress, AWS Amplify, Apache Airflow, OpenSearch, Apache Kafka, Bottlerocket, and Amazon EMR. As always, make sure you check out the events section at the end, and if you have your own event or online thing you want me to include here, just drop me a message.
### Latest open source projects
*The great thing about open source projects is that you can review the source code. If you like the look of these projects, make sure you that take a look at the code, and if it is useful to you, get in touch with the maintainer to provide feedback, suggestions or even submit a contribution. The projects mentioned here do not represent any formal recommendation or endorsement, I am just sharing for greater awareness as I think they look useful and interesting!*
### Tools
**.NET Aspire**
[aspire](https://aws-oss.beachgeek.co.uk/3x1) Provides extension methods and resources definition for a .NET Aspire AppHost to configure the AWS SDK for .NET and AWS application resources. If you are not familiar with Aspire, it is an opinionated, cloud ready stack for building observable, production ready, distributed applications in .NET. You can now use this with AWS resources, so check out the repo and the documentation that provides code examples and more.
**aws-sdk-python-signers**
[aws-sdk-python-signers](https://aws-oss.beachgeek.co.uk/3x3) AWS SDK Python Signers provides stand-alone signing functionality. This enables users to create standardised request signatures (currently only SigV4) and apply them to common HTTP utilities like AIOHTTP, Curl, Postman, Requests and urllib3. This project is currently in an Alpha phase of development. There likely will be breakages and redesigns between minor patch versions as we collect user feedback. We strongly recommend pinning to a minor version and reviewing the changelog carefully before upgrading. Check out the README for details on how to use the signing module.
**automated-datastore-discovery-with-aws-glue**
[automated-datastore-discovery-with-aws-glue](https://aws-oss.beachgeek.co.uk/3x7) This sample shows you how to automate the discovery of various types of data sources in your AWS estate. Examples include - S3 Buckets, RDS databases, or DynamoDB tables. All the information is curated using AWS Glue - specifically in its Data Catalog. It also attempts to detect potential PII fields in the data sources via the Sensitive Data Detection transform in AWS Glue. This framework is useful to get a sense of all data sources in an organisation's AWS estate - from a compliance standpoint. An example of that could be GDPR Article 30. Check out the README for detailed architecture diagrams and a break down of each component as to how it works.
**sbt-aws**
[sbt-aws](https://aws-oss.beachgeek.co.uk/3x8) SaaS Builder Toolkit for AWS (SBT) is an open-source developer toolkit to implement SaaS best practices and increase developer velocity. It offers a high-level object-oriented abstraction to define SaaS resources on AWS imperatively using the power of modern programming languages. Using SBT’s library of infrastructure constructs, you can easily encapsulate SaaS best practices in your SaaS application, and share it without worrying about boilerplate logic. The README contains all the resources you need to get started with this project, so if you are doing anything in the SaaS space, check it out.
**containers-cost-allocation-dashboard**
[containers-cost-allocation-dashboard](https://aws-oss.beachgeek.co.uk/3x9) provides everything you need to create a QuickSight dashboard for containers cost allocation based on data from Kubecost. The dashboard provides visibility into EKS in-cluster cost and usage in a multi-cluster environment, using data from a self-hosted Kubecost pod. The README contains additional links to resources to help you understand how this works, dependencies, and how to deploy and configure this project.

### Demos, Samples, Solutions and Workshops
**create-and-delete-ngw**
[create-and-delete-ngw](https://aws-oss.beachgeek.co.uk/3x2) This project contains source code and supporting files for a serverless application that allocates an Elastic IP address, creates a NAT Gateway, and adds a route to the NAT Gateway in a VPC route table. The application also deletes the NAT Gateway and releases the Elastic IP address. The process to create and delete a NAT Gateway is orchestrated by an AWS Step Functions State Machine, triggered by an EventBridge Scheduler. The schedule can be defined by parameters during the SAM deployment process.

**whats-new-summary-notifier**
[whats-new-summary-notifier](https://aws-oss.beachgeek.co.uk/3x4) is a demo repo that lets you build a generative AI application that summarises the content of AWS What's New and other web articles in multiple languages, and delivers the summary to Slack or Microsoft Teams.
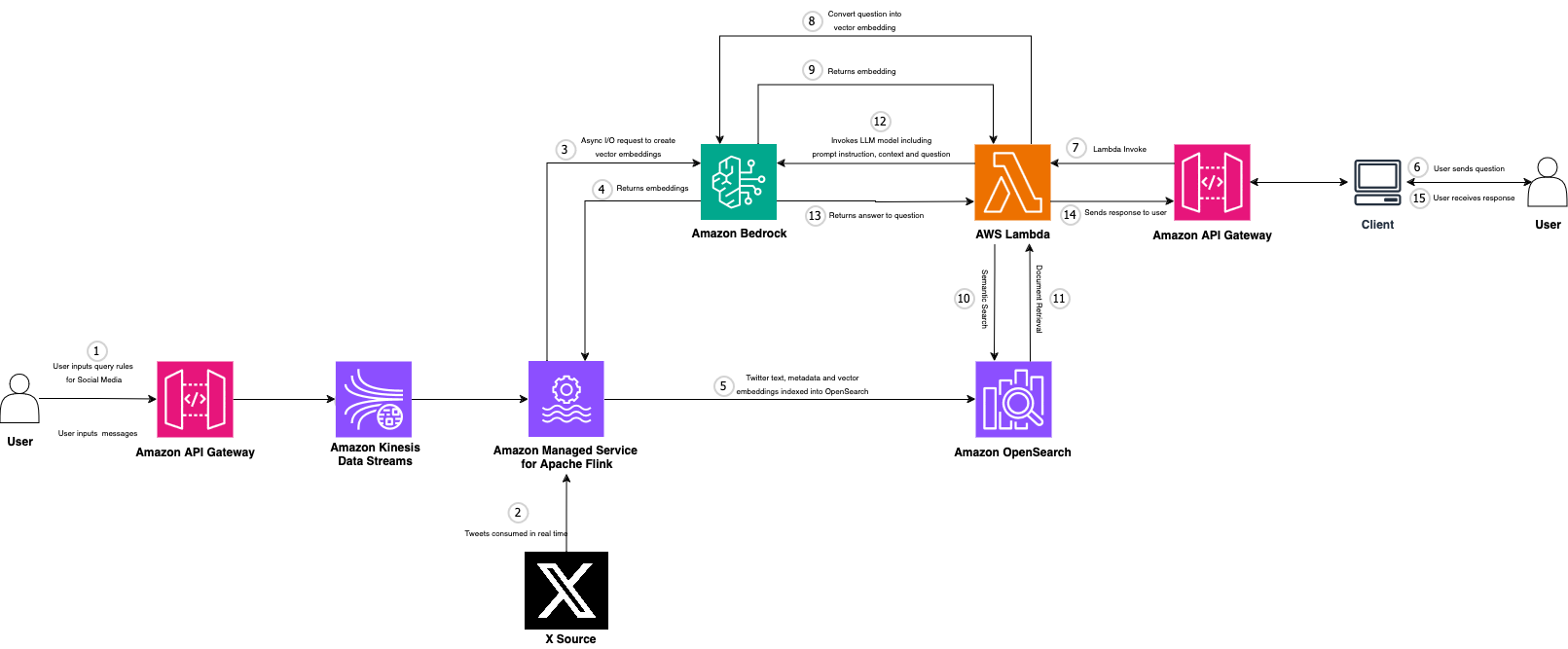
**real-time-social-media-analytics-with-generative-ai**
[real-time-social-media-analytics-with-generative-ai](https://aws-oss.beachgeek.co.uk/3x5) this repo helps you to build and deploy an AWS Architecture that is able to combine streaming data with GenAI using Amazon Managed Service for Apache Flink and Amazon Bedrock.
**serverless-genai-food-analyzer-app**
[serverless-genai-food-analyzer-app](https://aws-oss.beachgeek.co.uk/3x6) provides code for a personalised GenAI nutritional web application for your shopping and cooking recipes built with serverless architecture and generative AI capabilities. It was first created as the winner of the AWS Hackathon France 2024 and then introduced as a booth exhibit at the AWS Summit Paris 2024. You use your cell phone to scan a bar code of a product to get the explanations of the ingredients and nutritional information of a grocery product personalised with your allergies and diet. You can also take a picture of food products and discover three personalised recipes based on their food preferences. The app is designed to have minimal code, be extensible, scalable, and cost-efficient. It uses Lazy Loading to reduce cost and ensure the best user experience. Tres bon!

### AWS and Community blog posts
Each week I spent a lot of time reading posts from across the AWS community on open source topics. In this section I share what personally caught my eye and interest, and I hope that many of you will also find them interesting.
**The best from around the Community**
Starting this off this week we have AWS Community Builder Julian Michel, who shares his personal AWS setup with you, and more importantly some of the cool open source tools you can use to keep everything in order. I use some of these myself, so make sure you check "[My personal AWS account setup - IAM Identity Center, temporary credentials and sandbox account](https://aws-oss.beachgeek.co.uk/3wu)" out to see how you might be able to improve your setup.
AWS Community Builder Saifeddine Rajhi explores how to use EKS control plane logs and AWS CloudTrail logs to gain visibility into your cluster's activities, detect potential security threats, and investigate incidents in his post, "[Amazon EKS: Analyze control plane and CloudTrail logs for better detective controls](https://aws-oss.beachgeek.co.uk/3wv)". Great stuff here that I will be using in the future I am sure. On a similar note, if you have ever wondered how you can export your AWS CloudWatch logs into OpenTelemetry, then AWS Community Builder Shakir provides you with some ideas in the post "[Logging demo with OTEL Collector, CloudWatch and Grafana](https://aws-oss.beachgeek.co.uk/3x0)".
I am a regular user of AWS CDK, so always interested in learning how I can improve my CDK game, so enjoyed reading AWS Community Builder Peter McAree's quick post, "[How to build a single-page application deployment using AWS CDK](https://aws-oss.beachgeek.co.uk/3ww)", where you will learn how to deploy a single-page application (or any other static assets) using AWS CDK.
To finish us off we go back to [issue #188](https://dev.to/aws/aws-open-source-newsletter-188-1fib) of this newsletter, where I featured llrt, or Low Latency Runtime, an experimental project from awslabs that provides a lightweight JavaScript runtime designed to address the growing demand for fast and efficient Serverless applications. AWS Community Bulder Amador Criado has put together a nice lab that looks to compare how this performs compared to traditional Node.js runtimes. Grab your favourite hot beverage and then sit down to walk through, "[[Lab] AWS Lambda LLRT vs Node.js](https://aws-oss.beachgeek.co.uk/3wy)".
**Valkey**
Valkey is a continuation of open source Redis, created in response to changes to the Redis project. A number of existing contributors and maintainers of Redis formed Valkey, a new Linux Foundation project. Kyle Davis has put together [How to move from Redis to Valkey](https://aws-oss.beachgeek.co.uk/3ws), where he shows you some of the ways you can begin to make the transition.
My colleague Riccardo Ferreira also put something together for Go developers who are eager to start using Valkey in his post, [Getting Started with Valkey using Docker and Go](https://aws-oss.beachgeek.co.uk/3wx). This is a must read post this week, so make sure you check it out.
**PostgreSQL**
Joe Conway writes [Deep PostgreSQL Thoughts: Valuing Currency](https://aws-oss.beachgeek.co.uk/3wa) where he shares his thoughts about how important it is to maintain PostgreSQL currency. Make sure you read this post that provides his views on both sides of the should I / shouldn't I question on upgrading.
More PostgreSQL content for you to check out:
* [Perform maintenance tasks and schema modifications in Amazon RDS for PostgreSQL with minimal downtime using Blue Green deployment](https://aws-oss.beachgeek.co.uk/3wm) walks you through performing schema changes and common maintenance tasks such as table and index reorganization, VACUUM FULL, and materialised view refreshes with minimal downtime using blue/green deployments for an Amazon Relational Database (Amazon RDS) for PostgreSQL database or an Amazon Aurora PostgreSQL-Compatible Edition cluster [hands on]
* [PostgreSQL for SaaS on AWS](https://aws-oss.beachgeek.co.uk/3wt) provides a collection of best practices for running PostgreSQL workloads for SaaS applications on AWS
**InfluxDB**
In the post, [Introducing Amazon Timestream for InfluxDB: A managed service for the popular open source time-series database](https://aws-oss.beachgeek.co.uk/3wc), Victor Servin provides an overview of the recently launched Amazon Timestream for InfluxDB, our latest managed time-series database engine for customers who want open source APIs and real-time, time-series applications. Read the post to find out more why this AWS has created this service.
**High Performance Software Foundation (HPSF)**
In case you missed the announcement a week or so ago, Brendan Bouffler has put together a blog post, [Announcing the High Performance Software Foundation (HPSF)](https://aws-oss.beachgeek.co.uk/3wn), where he shares more info about the new High Performance Software Foundation (HPSF), including how it can help, what they are currently doing as they bootstrap, and how you can get involved.
**Cloud Native round up**
* [Deploying Karpenter Nodes with Multus on Amazon EKS](https://aws-oss.beachgeek.co.uk/3w7) shows how Karpenter can be used in conjunction with [Multus CNI](https://aws-oss.beachgeek.co.uk/3w8), a container network interface (CNI) plugin for Kubernetes that enables attaching multiple network interfaces to pods [hands on]
* [Ensuring fair bandwidth allocation for Amazon EKS Workloads](https://aws-oss.beachgeek.co.uk/3wb) provides a hands on guide on how you can use the Amazon VPC CNI plugin and its capabilities to limit ingress and egress bandwidth for applications running as pods in Amazon EKS [hands on]
* [How to automate application log ingestion from Amazon EKS on Fargate into AWS CloudTrail Lake](https://aws-oss.beachgeek.co.uk/3wf) looks at how to capture the STDOUT and STDERR input/output (I/O) streams from your container and send them to S3 using Fluent Bit [hands on]
* [Enhancing Kubernetes workload isolation and security using Kata Containers](https://aws-oss.beachgeek.co.uk/3wg) details the process of setting up a self-managed microVM infrastructure on Amazon EKS by using Amazon EC2 bare metal instances and Kata Containers [hands on]
* [Enhancing observability with a managed monitoring solution for Amazon EKS](https://aws-oss.beachgeek.co.uk/3wj) walks you through a solution that provides monitoring Amazon EKS clusters with Amazon Managed Grafana and Amazon Managed Service for Prometheus [hands on]

* [Disaster Recovery on AWS Outposts to AWS Local Zones with a GitOps approach for Amazon EKS](https://aws-oss.beachgeek.co.uk/3wl) is a great overview of how AWS Local Zones can be used as a DR option for Amazon EKS workloads running on AWS Outposts [hands on]

* [Multi-Region Disaster Recovery with Amazon EKS and Amazon EFS for Stateful workloads](https://aws-oss.beachgeek.co.uk/3wo) takes a look at how to achieve business continuity in AWS by using Amazon EFS and Amazon EKS across AWS Regions [hands on]
* [Unleash the possibilities of Stable Diffusion](https://aws-oss.beachgeek.co.uk/3wz) helps you understand your options when it comes to deploying Stable Diffusion on open source technologies on AWS [hands on]
**Big Data and Analytics posts**
* [In-place version upgrades for applications on Amazon Managed Service for Apache Flink now supported](https://aws-oss.beachgeek.co.uk/3w5) explores in-place version upgrades, a new feature offered by Managed Service for Apache Flink, covering how to get started, insights into the feature, and a deeper dive into how the feature works and some sample use cases [hands on]
* [Entity resolution and fuzzy matches in AWS Glue using the Zingg open source library](https://aws-oss.beachgeek.co.uk/3w6) looks at how to use Zingg, an open source library specifically designed for entity resolution on Spark, to help address data governance challenges and provide consistent and accurate data across your organisation [hands on]
* [Use AWS Data Exchange to seamlessly share Apache Hudi datasets](https://aws-oss.beachgeek.co.uk/3w9) shows how you can take advantage of the data sharing capabilities in AWS Data Exchange on top of Apache Hudi [hands on]
* [Understanding Apache Iceberg on AWS with the new technical guide](https://aws-oss.beachgeek.co.uk/3wd) announces the launch of the Apache Iceberg on AWS technical guide, a comprehensive technical guide that offers detailed guidance on foundational concepts to advanced optimisations to build your transactional data lake with Apache Iceberg on AWS

* [Binary logging optimizations in Amazon Aurora MySQL version 3](https://aws-oss.beachgeek.co.uk/3we) discusses use cases for binary logging in Amazon Aurora MySQL, improved binary logging capabilities that have been added to Amazon Aurora MySQL over the years, and additional support for MySQL native binary logging features
* [Integrate Amazon Aurora MySQL and Amazon Bedrock using SQL](https://aws-oss.beachgeek.co.uk/3wp) is a must read to see how you can invoke foundational models on Amazon Bedrock as SQL functions on Amazon Aurora MySQL [hands on]
**Other posts to check out**
* [Monitor Java apps running on Tomcat server with Amazon CloudWatch Application Signals (Preview)](https://aws-oss.beachgeek.co.uk/3wk) demonstrates how to auto-instrument Java web applications deployed via WAR packages and running on Tomcat server with AWS Distro for OpenTelemetry (ADOT), using CloudWatch Application Signals (Preview) [hands on]
* [New in AWS Amplify: Integrate with SQL databases, OIDC/SAML providers, and the AWS CDK](https://aws-oss.beachgeek.co.uk/3wq) provides a glimpse of how you can extend your AWS Amplify project, using three examples how you can integrate with existing data sources, authenticate with any OpenID Connect or SAML authentication provider, and customise the AWS Amplify generated resources through CDK [hands on]

* [A Pilot Light disaster recovery strategy for WordPress](https://aws-oss.beachgeek.co.uk/3wr) dives into how you can architect a resilient cross-Region Pilot Light DR strategy for WordPress, that uses the robust global infrastructure of AWS
### Quick updates
**Apache Airflow**
Amazon Managed Workflows for Apache Airflow (MWAA) is a managed orchestration service for Apache Airflow that makes it easier to set up and operate end-to-end data pipelines in the cloud. FIPS compliant endpoints on Amazon MWAA helps companies contracting with the US and Canadian federal governments meet the FIPS security requirement to encrypt sensitive data in supported Regions. Amazon MWAA now offers Federal Information Processing Standard (FIPS) 140-2 validated endpoints to help you protect sensitive information. These endpoints terminate Transport Layer Security (TLS) sessions using a FIPS 140-2 validated cryptographic software module, making it easier for you to use Amazon MWAA for regulated workloads.
In addition to this, a long awaited ask by Apache Airflows users is now available. Amazon MWAA now supports the Airflow REST API along with web server auto scaling, allowing customers to programmatically monitor and manage their Apache Airflow environments at scale. With Airflow REST API support, customers can now monitor workflows, trigger new executions, manage connections, and perform other administration tasks with ease via scalable API calls. Web server auto scaling enables MWAA to automatically scale out the Airflow web servers to handle increased demand, whether from REST API requests, Command Line Interface (CLI) usage, or more concurrent Airflow User Interface (UI) users.
Check out the post, [Introducing Amazon MWAA support for the Airflow REST API and web server auto scaling](https://aws-oss.beachgeek.co.uk/3w4), to dive deeper into this, and get a hands on guide on how to get started with using the Airflow REST API and web server auto scaling on Amazon MWAA.

**OpenSearch**
You can now run OpenSearch version 2.13 in Amazon OpenSearch Service. With OpenSearch 2.13, we have made several improvements to search performance and resiliency, OpenSearch Dashboards, and added new features to help you build AI-powered applications. We have introduced concurrent segment search that allows users to query index segments in parallel at the shard level. This offers improved latency for long-running requests that contain aggregations or large ranges. You can now index quantised vectors with FAISS-engine-based k-NN indexes, with potential to reduce memory footprint by as much as 50 percent with minimal impact to accuracy and latency. I/O-based admission control proactively monitors and prevents I/O usage breaches to further improve the resilience of the cluster.
This launch also introduces several features that enable you to build and deploy AI-powered search applications. The new flow framework, helps you to automate the configuration of search and ingest pipeline resources required by advanced search features like semantic, multimodal, and conversational search. This adds to existing capabilities for automating ml-commons resource setup, allowing you to package OpenSearch AI solutions into portable templates. Additionally, we’ve added predefined templates to automate setup for models that are integrated through our connectors to APIs like OpenAI, Amazon Bedrock, and Cohere that enable you to build solutions like semantic search.
**PostgreSQL**
Amazon Relational Database Service (RDS) for PostgreSQL announces Amazon RDS Extended Support minor version 11.22-RDS.20240418. We recommend that you upgrade to this version to fix known security vulnerabilities and bugs in prior versions of PostgreSQL. Amazon RDS Extended Support provides you more time, up to three years, to upgrade to a new major version to help you meet your business requirements. During Extended Support, Amazon RDS will provide critical security and bug fixes for your MySQL and PostgreSQL databases on Aurora and RDS after the community ends support for a major version. You can run your PostgreSQL databases on Amazon RDS with Extended Support for up to three years beyond a major version’s end of standard support date.
Amazon RDS for PostgreSQL now supports pgvector 0.7.0, an open-source extension for PostgreSQL for storing vector embeddings in your database, letting you use retrieval-augemented generation (RAG) when building your generative AI applications. This release of pgvector includes features that increase the number of dimensions of vectors you can index, reduce index size, and includes additional support for using CPU SIMD in distance computations. pgvector 0.7.0 adds two new vector data types: halfvec for storing dimensions as 2-byte floats, and sparsevec for storing up to 1,000 nonzero dimensions, and now supports indexing binary vectors using the PostgreSQL-native bit type. These additions let you use scalar and binary quantization for the vector data type using PostgreSQL expression indexes, which reduces the storage size of the index and lowers the index build time. Quantization lets you increase the maximum dimensions of vectors you can index: 4,000 for halfvec and 64,000 for binary vectors. pgvector 0.7.0 also adds functions to calculate both Hamming and Jaccard distance for binary vectors. pgvector 0.7.0 is available on database instances in Amazon RDS running PostgreSQL 16.3 and higher, 15.7 and higher, 14.12 and higher, 13.15 and higher, and 12.19 and higher in all applicable AWS Regions, including the AWS GovCloud (US) Regions.
**MySQL**
Amazon Relational Database Service (RDS) for MySQL announced Amazon RDS Extended Support for minor version 5.7.44-RDS.20240408. We recommend that you upgrade to this version to fix known security vulnerabilities and bugs in prior versions of MySQL. Amazon RDS Extended Support provides you more time, up to three years, to upgrade to a new major version to help you meet your business requirements. During Extended Support, Amazon RDS will provide critical security and bug fixes for your MySQL and PostgreSQL databases on Aurora and RDS after the community ends support for a major version. You can run your MySQL databases on Amazon RDS with Extended Support for up to three years beyond a major version’s end of standard support date.
**Apache Kafka**
Amazon Managed Streaming for Apache Kafka (Amazon MSK) now supports removing brokers from MSK provisioned clusters. Administrators can optimise costs of their Amazon MSK clusters by reducing broker count to meet the changing needs of their streaming workloads, while maintaining cluster performance, availability, and data durability. Customers use Amazon MSK as the core foundation to build a variety of real-time streaming applications and high-performance event driven architectures. As their business needs and traffic patterns change, they often adjust their cluster capacity to optimise their costs. Amazon MSK Provisioned provides flexibility for customers to change their provisioned clusters by adding brokers or changing the instance size and type. With broker removal, Amazon MSK Provisioned now offers an additional option to right-size cluster capacity. Customers can remove multiple brokers from their MSK provisioned clusters to meet the varying needs of their streaming workloads without any impact to client connectivity for reads and writes. By using broker removal capability, administrators can adjust cluster’s capacity, eliminating the need to migrate to another cluster to reduce broker count.
You can dive deeper into this by checking out the blog post, [Safely remove Kafka brokers from Amazon MSK provisioned clusters](https://aws-oss.beachgeek.co.uk/3wh)
**Bottlerocket**
Bottlerocket, the Linux-based operating system purpose-built for containers, now supports NVIDIA Fabric Manager, enabling users to harness the power of multi-GPU configurations for their AI and machine learning workloads. With this integration, Bottlerocket users can now seamlessly leverage their connected GPUs as a high-performance compute fabric, enabling efficient and low-latency communication between all the GPUs in each of their P4/P5 instances. The growing sophistication of deep learning models has led to an exponential increase in the computational resources required to train them within a reasonable timeframe. To address this increase in computational demands, customers running AI and machine learning workloads have turned to multi-GPU implementations, leveraging NVIDIA's NVSwitch and NVLink technologies to create a unified memory fabric across connected GPUs. The Fabric Manager support in the Bottlerocket NVIDIA variants allows users to configure this fabric, enabling all GPUs to be used as a single, high-performance pool rather than individual units. This unlocks Bottlerocket users to run multi-GPU setups on P4/P5 instances, significantly accelerating the training of complex neural networks.
**Prometheus**
Amazon Managed Service for Prometheus now supports inline editing of rules and alert manager configuration directly from the AWS console. Amazon Managed Service for Prometheus is a fully managed Prometheus-compatible monitoring service that makes it easy to monitor and alarm on operational metrics at scale. Prometheus is a popular Cloud Native Computing Foundation open-source project for monitoring and alerting on metrics from compute environments such as Amazon Elastic Kubernetes Service. Previously, customers could define alerting and recording rules, or alert manager definition, by importing respective configuration defined in a YAML file, via the AWS console. Now, they can import, preview, and edit existing rules or alert manager configurations from YAML files or create them directly from the AWS console. The inline editing experience allows customers to preview their rules and alert manager configuration prior to setting them.
Amazon Managed Service for Prometheus collector, a fully-managed agent-less collector for Prometheus metrics, now integrates with the Amazon EKS access management controls. Starting today, the collector utilises the EKS access management controls to create a managed access policy that allows the collector to discover and collect Prometheus metrics. Amazon Managed Service for Prometheus collector with support for EKS access management controls is available in all regions where Amazon Managed Service for Prometheus is available.
**Grafana**
Customers can now run Amazon Managed Grafana workspaces with Grafana version 10.4. This release includes features that were launched as a part of open source Grafana versions 9.5 to 10.4, including Correlations, Subfolders, and new visualisation panels such as Data Grid, XY chart and Trend panel. This release also introduces new configuration APIs to manage service accounts and tokens for Amazon Managed Grafana workspaces. Service Accounts, replace API keys as the primary way to authenticate applications with Grafana APIs using Service Account Tokens. These new APIs eliminate the need to manually create Service accounts, enabling customers to fully automate their provisioning workflows. With correlations, customers can define relationships between different data sources, rendered as interactive links in Explore visualisations that trigger queries on the related data source; carrying forward data like namespace, host, or label values, enabling root cause analysis with a diverse set of data sources. Subfolders enable nested hierarchy of folders with nested layers of permissions, allowing customers to organise their dashboards to reflect their organisation’s hierarchy. To explore the complete list of new features, please refer to our user documentation. Grafana version 10.4 is supported in all AWS regions where Amazon Managed Grafana is generally available.
Check out more details in the post, [Amazon Managed Grafana announces support for Grafana version 10.4](https://aws-oss.beachgeek.co.uk/3wi)
**Kubernetes**
You can now use CoreDNS autoscaling capabilities for Amazon EKS clusters. This feature allows you to scale capacity of DNS server instances to meet the ever-changing capacity needs of your services without the overhead of managing custom solutions. Organisations are standardising on Kubernetes as their compute infrastructure platform to build scalable, containerised applications. Scaling CoreDNS Pods is key to ensure reliable DNS resolution by distributing the query load across multiple instances, and provide high availability for applications and services. With this launch, you no longer need to pre-configure the scaling parameters and deploy a client on each cluster to monitor the capacity and scale accordingly. EKS manages the autoscaling of DNS resources when you use the CoreDNS EKS add-on. This feature works for CoreDNS v1.9 and EKS release version 1.25 and later.
**Amazon EMR**
Amazon EMR provides big data solutions for petabyte-scale data processing, interactive analytics, and machine learning using open-source frameworks such as Apache Spark, Apache Hive, and Presto. Today, we are excited to announce that Amazon EMR 7.1 release is now generally available and includes the latest versions of popular open-source software. Amazon EMR 7.1 includes Trino 435, PrestoDB 0.284, Apache Zookeeper 3.9.1, Apache Livy 0.8, Apache Flink 1.18.1, Apache Hudi 0.14.1, and Apache Iceberg 1.4.3. In addition, Amazon EMR 7.1 introduces support for Python 3.11 for Apache Spark 3.5 applications.
In addition to this, Amazon EMR 7.1 introduced the capability to configure Amazon CloudWatch Agent to publish additional metrics for Apache Hadoop, YARN, and Apache HBase applications running on your Amazon EMR on EC2 clusters. This feature provides comprehensive monitoring capabilities, allowing you to track the performance and health of your cluster more effectively. Amazon EMR automatically publishes a set of free metrics every five minutes for monitoring cluster activity and health. Starting with Amazon EMR Release 7.0, you can install the Amazon CloudWatch Agent to publish 34 paid metrics to Amazon CloudWatch every minute. With Amazon EMR 7.1, you can now configure the agent to send additional paid metrics, providing even deeper visibility into your cluster's performance. Furthermore, you can opt to send these metrics to an Amazon Managed Service for Prometheus endpoint, if you are already using Prometheus to monitor your enterprise metrics. Additional metrics are is available with Amazon EMR release 7.1, in all regions where Amazon EMR is available.
### Videos of the week
**Using Amazon Q Developer to Write Code for Observability**
Love this video from Ricardo Ferreira that shows how you can use tools like Amazon Q Developer to help you integrate open source libraries like OpenTelemetry into your existing applications. In this video, Ricardo shows how to use Amazon Q Developer to instrument a micro service written in Go for OpenTelemetry.
{% youtube xcyvHPVUrtI %}
### Events for your diary
If you are planning any events in 2024, either virtual, in person, or hybrid, get in touch as I would love to share details of your event with readers.
**FOSS in Flux: Redis Relicensing and the Future of Open Source**
**May 28th, 16:00CET/10:00amET YouTube**
With all the recent cases of open source projects shifting away from their roots, topped with the recent Redis relicensing, your host Dotan Horovits and David Nalley from AWS take to look into the state of FOSS (free and open source software).
**BSides Exeter**
**July 27th, Exeter University, UK**
Looking forward to joining the community at [BSides Exeter](https://bsidesexeter.co.uk/) to talk about one of my favourite open source projects, Cedar. Check out the event page and if you are in the area, come along and learn about Cedar and more!
**Cortex**
**Every other Thursday, next one 16th February**
The Cortex community call happens every two weeks on Thursday, alternating at 1200 UTC and 1700 UTC. You can check out the GitHub project for more details, go to the [Community Meetings](https://aws-oss.beachgeek.co.uk/2h5) section. The community calls keep a rolling doc of previous meetings, so you can catch up on the previous discussions. Check the [Cortex Community Meetings Notes](https://aws-oss.beachgeek.co.uk/2h6) for more info.
**OpenSearch**
**Every other Tuesday, 3pm GMT**
This regular meet-up is for anyone interested in OpenSearch & Open Distro. All skill levels are welcome and they cover and welcome talks on topics including: search, logging, log analytics, and data visualisation.
Sign up to the next session, [OpenSearch Community Meeting](https://aws-oss.beachgeek.co.uk/1az)
### Celebrating open source contributors
The articles and projects shared in this newsletter are only possible thanks to the many contributors in open source. I would like to shout out and thank those folks who really do power open source and enable us all to learn and build on top of what they have created.
So thank you to the following open source heroes: Ricardo Ferreira, David Nalley, Dotan Horovits, Mansi Bhutada, Kamen Sharlandjiev, Kartikay Khator, Jeremy Ber, Chris Dziolak, Gonzalo Herreros, Emilio Garcia Montano, Noritaka Sekiyama, Rolando Jr Hilvano, Ashutosh Tulsi, Young Jung, Neb Miljanovic, Sudhir Shet, Saurabh Bhutyani, Ankith Ede, Chandra Krishnan, Joe Conway, Sebastian Lee, Natavit Rojcharoenpreeda, Yee Fei Ooi, Victor Servin, Carlos Rodrigues, Imtiaz Sayed, Shana Schipers, Marc Reilly, Jegan Sundarapandian, Mirash Gjolaj, Re Alvarez-Parmar, Vidhi Taneja, Anusha Dasarakothapalli, Masudur Rahaman Sayem,Rodrigue Koffi, Dan Malloy, Priyanka Verma, Siva Guruvareddiar, Michael Hausenblas, Jay Joshi, Deep Chhaiya, Samir Khan, Insoo Jang, Matt Price, Anita Singh, Nathan Ballance, Baji Shaik, Sarabjeet Singh, Dumlu Timuralp, Eric Heinrichs, Steve Dille, Shinya Sugiyama, Rene Brandel, Tinotenda Chemvura, Benjamin Le, Josh, Amador Criado, Peter McAree, Saifeddine Rajhi, Shakir, and Julian Michel.
**Feedback**
Please please please take 1 minute to [complete this short survey](https://www.pulse.aws/promotion/10NT4XZQ).
### Stay in touch with open source at AWS
Remember to check out the [Open Source homepage](https://aws.amazon.com/opensource/?opensource-all.sort-by=item.additionalFields.startDate&opensource-all.sort-order=asc) for more open source goodness.
One of the pieces of feedback I received in 2023 was to create a repo where all the projects featured in this newsletter are listed. Where I can hear you all ask? Well as you ask so nicely, you can meander over to[ newsletter-oss-projects](https://aws-oss.beachgeek.co.uk/3l8).
Made with ♥ from DevRel | 094459 |
1,867,872 | Command-Line Arguments | The main method can receive string arguments from the command line. Perhaps you have already noticed... | 0 | 2024-05-28T15:05:04 | https://dev.to/paulike/command-line-arguments-2c8c | java, programming, learning, beginners | The **main** method can receive string arguments from the command line. Perhaps you have already noticed the unusual header for the **main** method, which has the parameter **args** of **String[]** type. It is clear that **args** is an array of strings. The **main** method is just like a regular method with a parameter. You can call a regular method by passing actual parameters. Can you pass arguments to **main**? Yes, of course you can. In the following examples, the **main** method in class **TestMain** is invoked by a method in **A**.
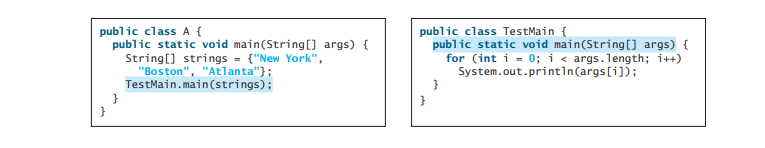
A **main** method is just a regular method. Furthermore, you can pass arguments from the command line.
## Passing Strings to the main Method
You can pass strings to a **main** method from the command line when you run the program. The following command line, for example, starts the program **TestMain** with three strings: **arg0**, **arg1**, and **arg2**:
`java TestMain arg0 arg1 arg2`
**arg0**, **arg1**, and **arg2 **are strings, but they don’t have to appear in double quotes on the command line. The strings are separated by a space. A string that contains a space must be enclosed in double quotes. Consider the following command line:
`java TestMain "First num" alpha 53`
It starts the program with three strings: **First num**, **alpha**, and **53**. Since **First num** is a string, it is enclosed in double quotes. Note that **53** is actually treated as a string. You can use **"53"** instead of **53** in the command line.
When the **main** method is invoked, the Java interpreter creates an array to hold the command-line arguments and pass the array reference to **args**. For example, if you invoke a program with **n** arguments, the Java interpreter creates an array like this one:
`args = new String[n];`
The Java interpreter then passes **args** to invoke the **main** method.
If you run the program with no strings passed, the array is created with **new String[0]**. In this case, the array is empty with length **0**. **args** references to this empty array. Therefore, **args** is not **null**, but **args.length** is **0**.
## Case Study: Calculator
Suppose you are to develop a program that performs arithmetic operations on integers. The program receives an expression in one string argument. The expression consists of an integer followed by an operator and another integer. For example, to add two integers, use this command:
`java Calculator 2 + 3`
The program will display the following output:
`2 + 3 = 5`
Figure below shows sample runs of the program.
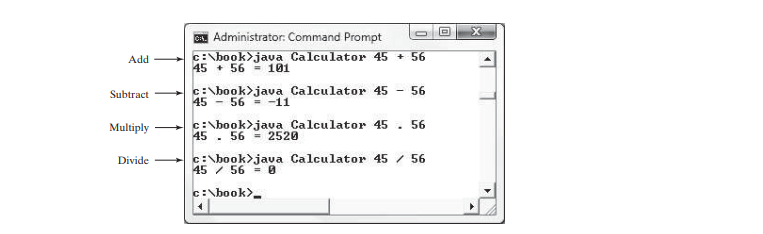
The strings passed to the main program are stored in **args**, which is an array of strings. The first string is stored in **args[0]**, and **args.length** is the number of strings passed.
Here are the steps in the program:
1. Use **args.length** to determine whether the expression has been provided as three arguments in the command line. If not, terminate the program using **System.exit(1)**.
2. Perform a binary arithmetic operation on the operands **args[0]** and **args[2]** using the operator in **args[1]**.
The program is shown below:
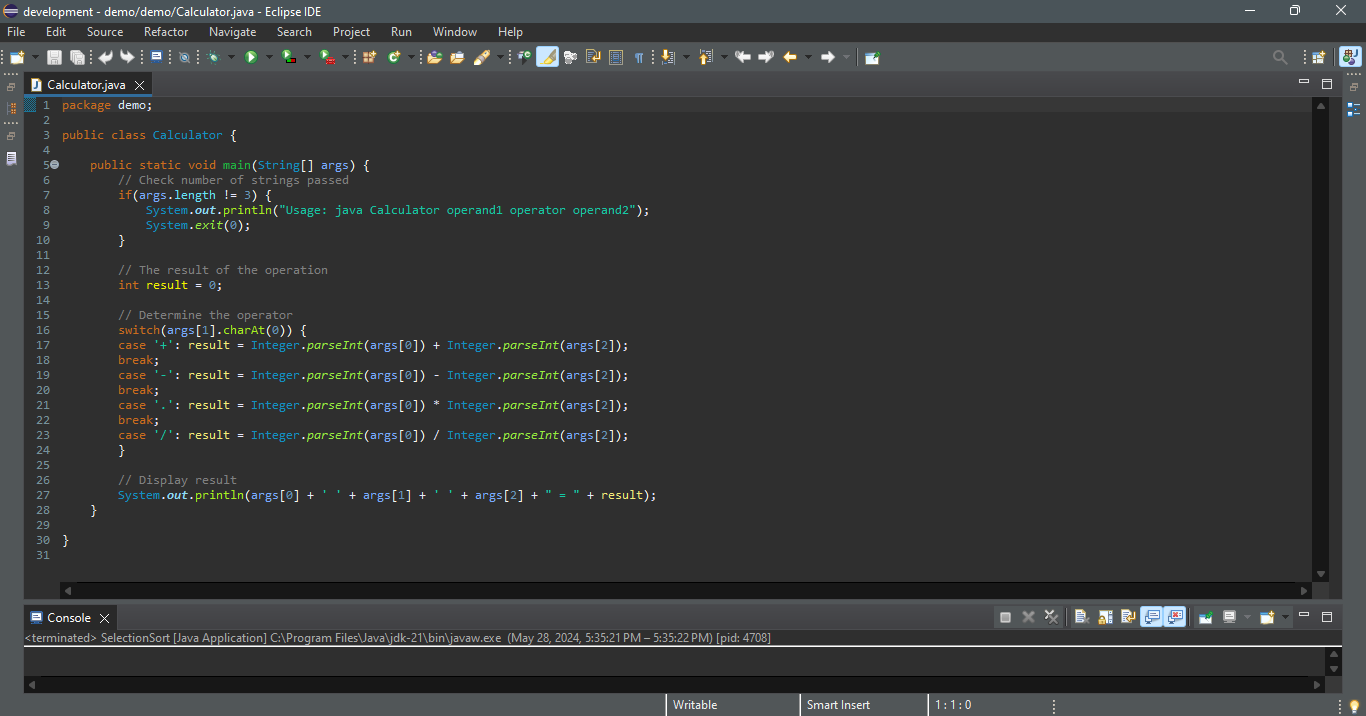
**Integer.parseInt(args[0])** (line 17) converts a digital string into an integer. The string must consist of digits. If not, the program will terminate abnormally.
We used the **.** symbol for multiplication, not the common ***** symbol. The reason for this is that the ***** symbol refers to all the files in the current directory when it is used on a command line. The following program displays all the files in the current directory when issuing the
command **java Test ***:
`public class Test {
public static void main(String[] args) {
for (int i = 0; i < args.length; i++)
System.out.println(args[i]);
}
}`
To circumvent this problem, we will have to use a different symbol for the multiplication operator. | paulike |
1,867,871 | How 'npm create vue@latest' works | Introduction I don't think I'm the only interested in the functionality of this command as... | 0 | 2024-05-28T15:04:16 | https://dev.to/nikitadmitr/how-npm-create-vuelatest-works-ac5 | vue, webdev, javascript, learning | ## Introduction
I don't think I'm the only interested in the functionality of this command as presented in the [Vue quickstart documentation](https://vuejs.org/guide/quick-start.html#creating-a-vue-application)
```bash
npm create vue@latest
```
Once we execute this command, we encounter some 'magic' where we select preferences for our future Vue app. But how exactly does it work?
## npm create
This command works very simply. Everyone is used to working with the `npm init` command, so let's look at these logs
Both of them are the same. `npm create` just an alias for `npm init`. Let's just replace `create` with `init` and we'll get
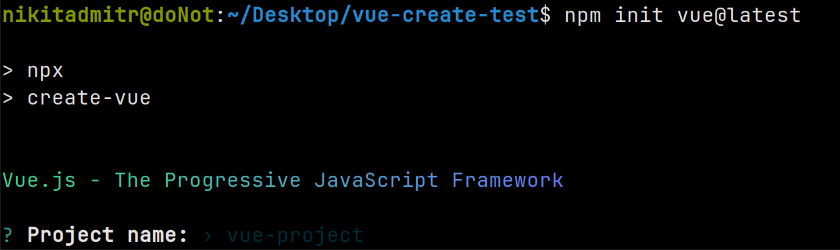
> @latest is simply a pointer to the latest version of an npm package. You can try it with any package you desire
Since we now know this, we can read the documentation about `npm init` . Run `npm help init` in your terminal
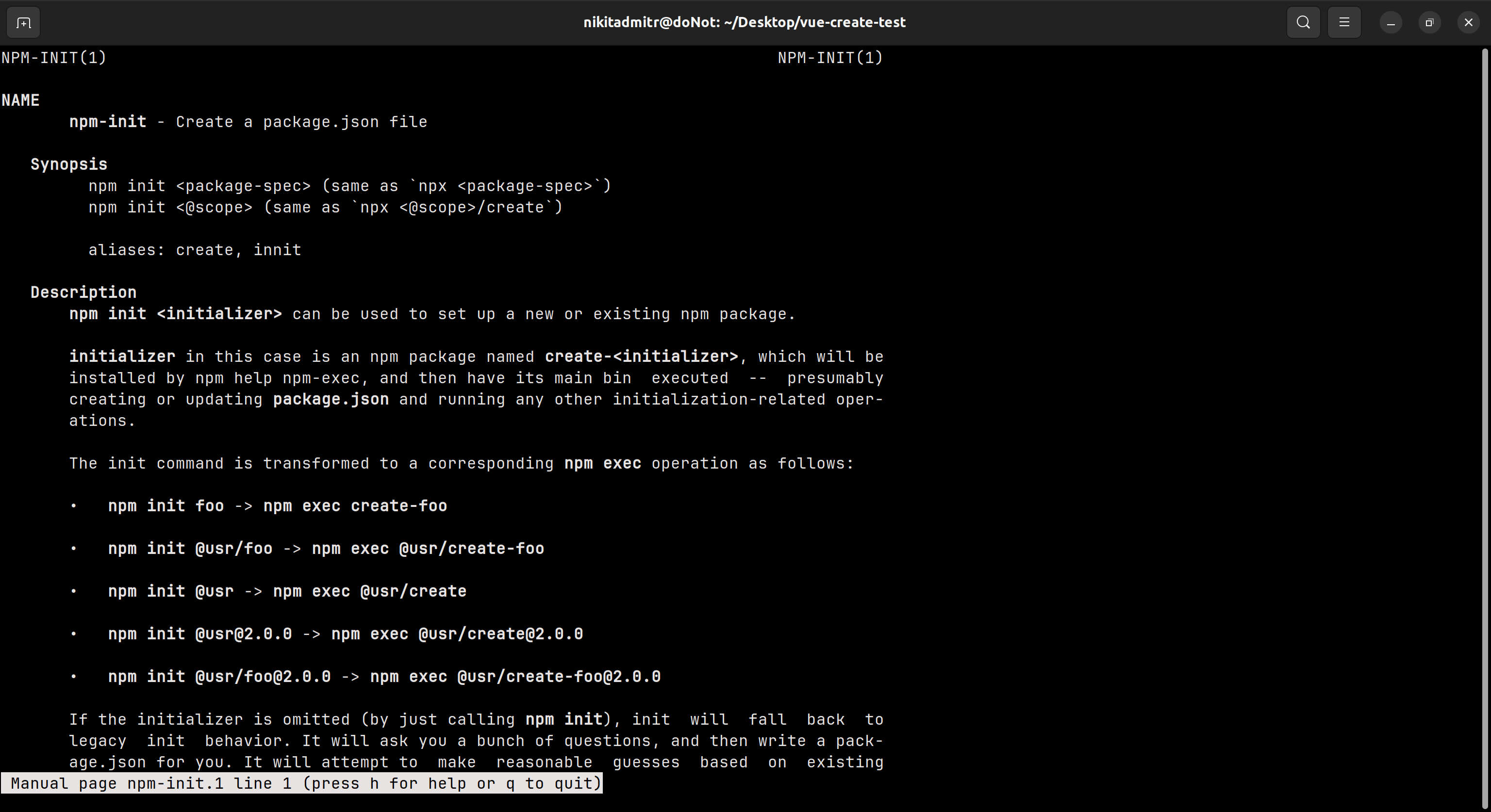
As we see here, we can also use `npx` instead of `npm init` but with `create-` prefix:
```bash
npm init <package-spec> (same as `npx <package-spec>`)
npm init <@scope> (same as `npx <@scope>/create`)
```
Let's try `npx` for our case. And then we see
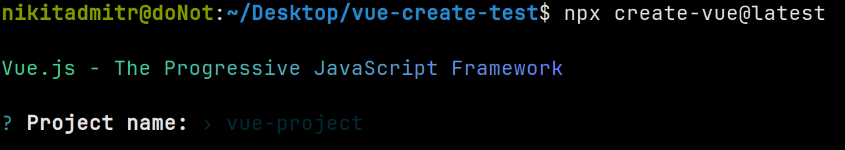
Let's return to `npm init` documentation
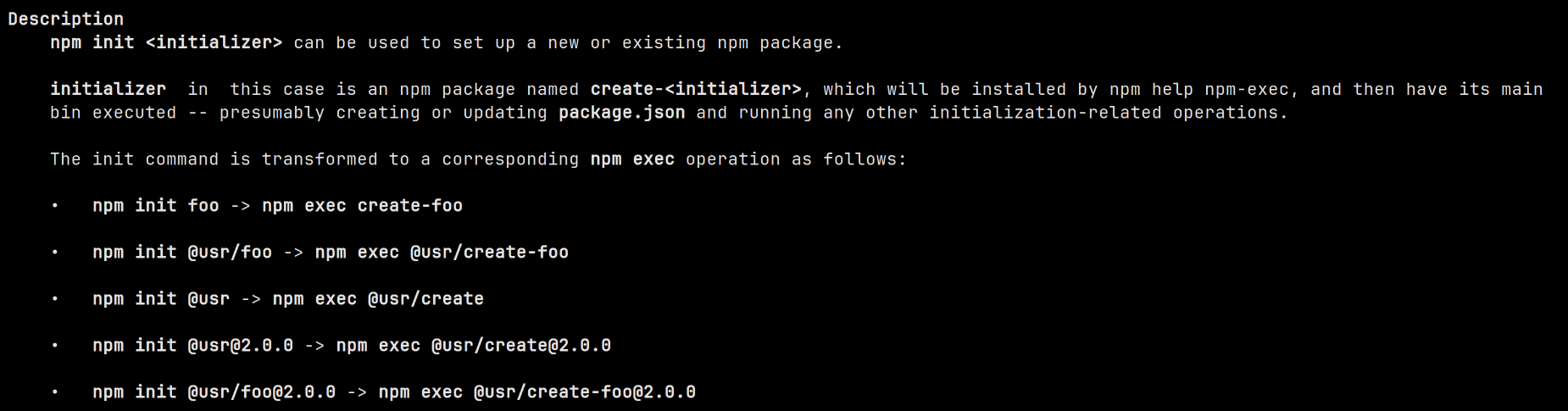
The `npx` and `npm exec` commands are very similar, but there's one difference, which you can read about [here](https://docs.npmjs.com/cli/v9/commands/npm-exec#npx-vs-npm-exec). We don't need to understand this to use **create-vue**
Now I'll call all the known commands and demonstrate that they all produce the same result. When we use `npm create vue@latest`, it's essentially the same as `npm init create-vue@latest` - just an alias
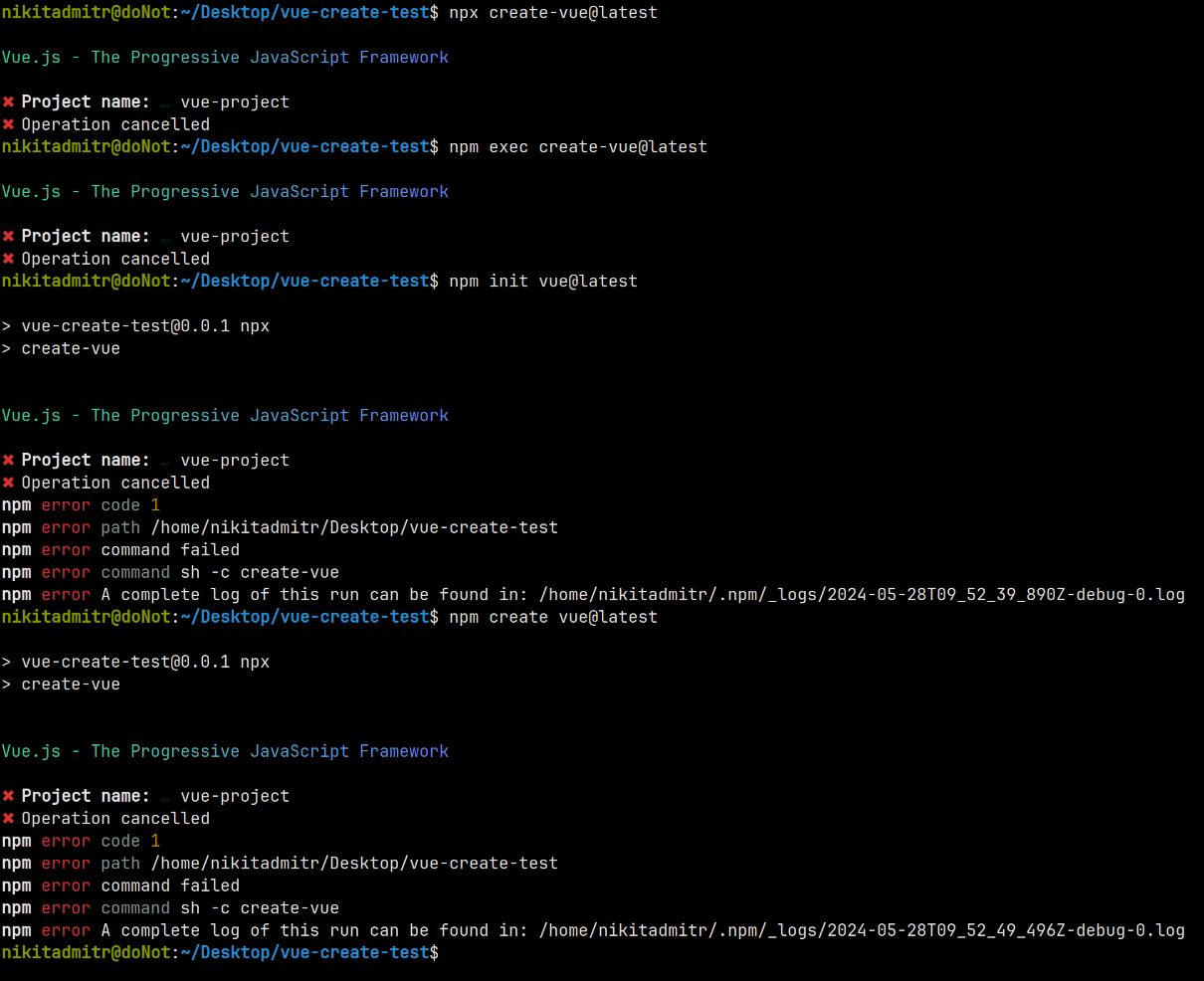
Now, I hope you understand the `npm create` functionality. Then let's get to the next point
## bin
Here you can see our test project
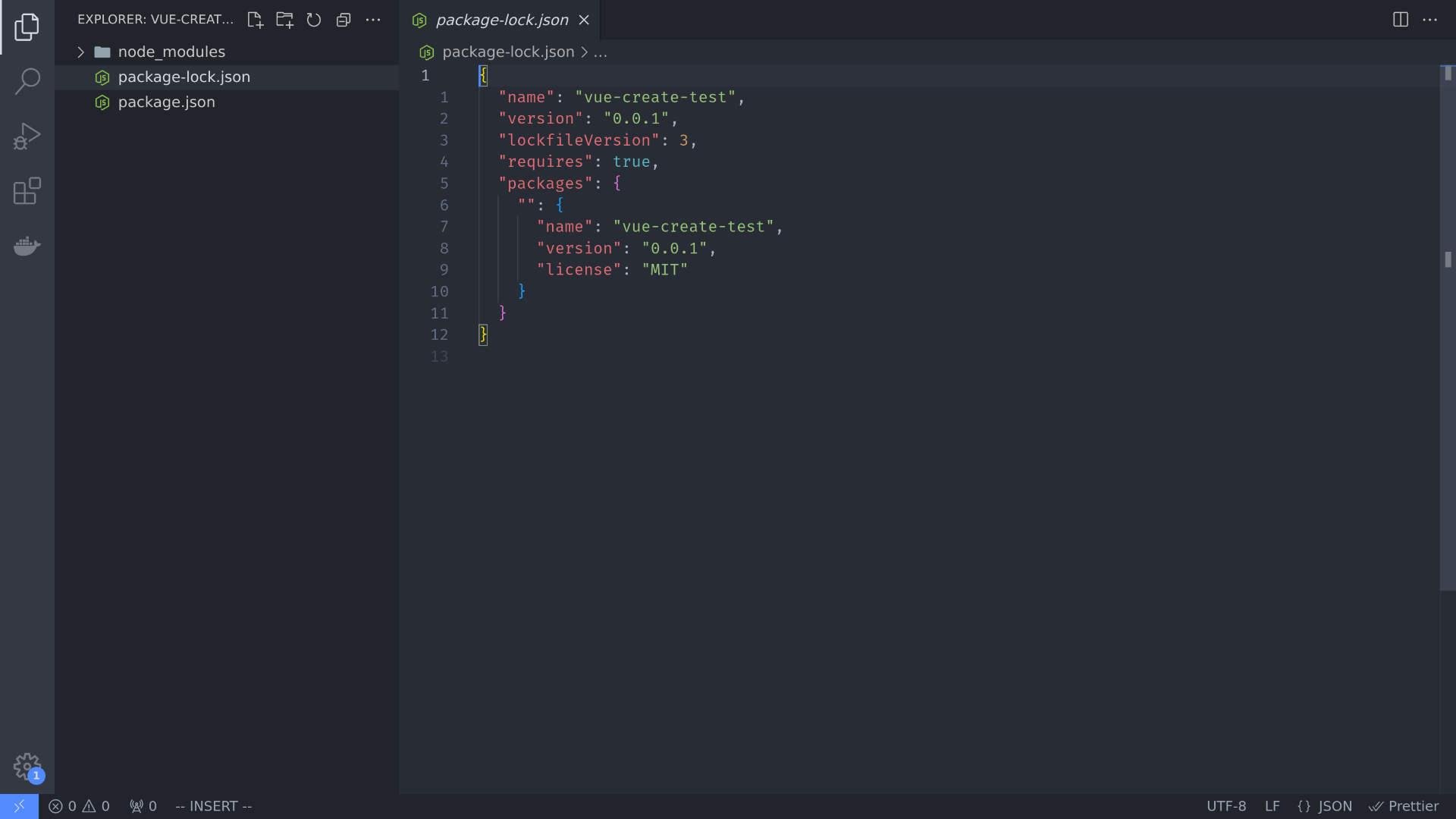
Let's install prettier for example
```bash
npm i -D prettier
```
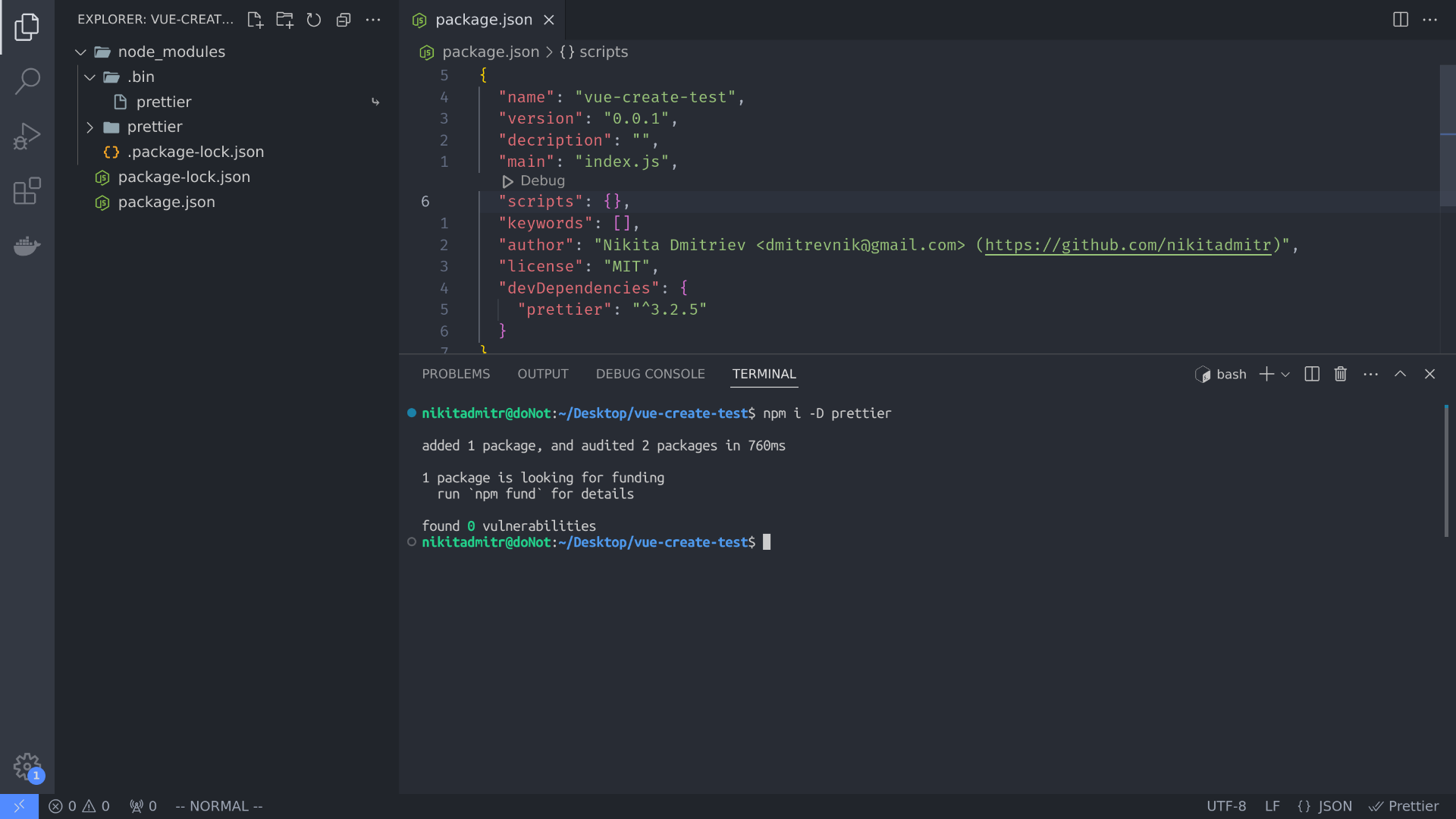
Now if you open the `node_modules` directory you'll notice a `.bin` directory and a symbolic link called `prettier`. What is it for? You can execute your installed executable packages from `.bin` repository using npm scripts and commands like `npx`
For example let's run `npx prettier . --check`
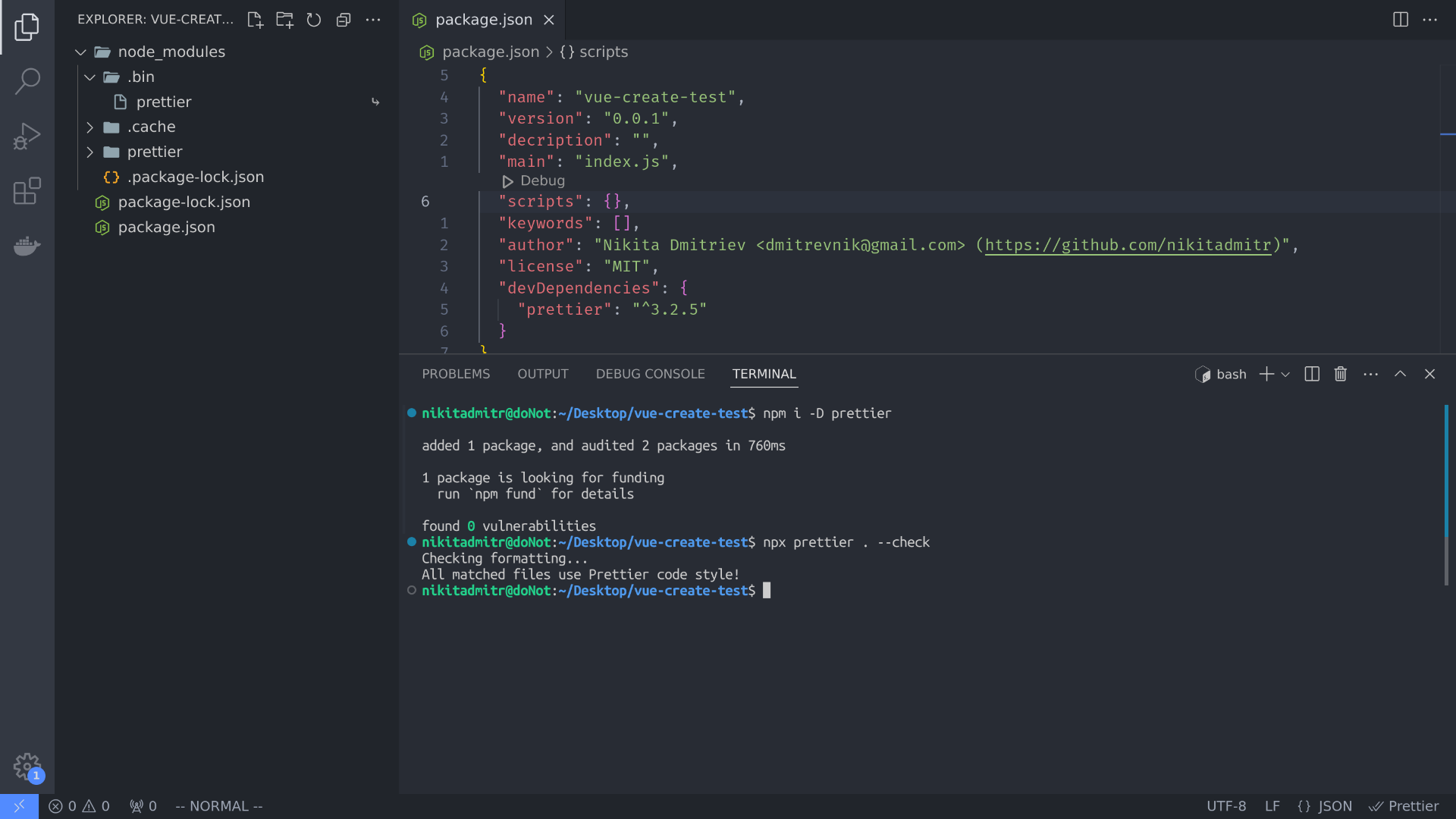
It works!
Let's open `node_modules/.bin/prettier` and look at the code
But what is a symbolic link exactly? It comes from programming and I often liken symbolic links to basic redirects but with greater stability. However, not every package needs a place in `.bin`. Packages like [nodemon](https://www.npmjs.com/package/nodemon), [webpack](https://www.npmjs.com/package/webpack), [gulp](https://www.npmjs.com/package/gulp), [eslint](https://www.npmjs.com/package/eslint) and [create-vue](https://www.npmjs.com/package/create-vue) are found in `.bin` because they need to be executed. On the other hand, packages like [animate.css](https://www.npmjs.com/package/animate.css), [swiper](https://www.npmjs.com/package/swiper) and [express](https://www.npmjs.com/package/express) operate at the application layer, so you won't find them in `.bin` after installation. How does npm determine whether a package is executable or not? It's simple: by using the `bin` property in your `package.json` to specify the executable path. If your package is executable, you can set it accordingly. Let's take a look at prettier's `package.json` file
Here you see
```json
"bin": "./bin/prettier.cjs"
```
Let's follow the path `./bin/prettier.cjs` in the prettier package. **Do not** confuse this path with `node_modules/.bin`
We've seen this somewhere before, haven't we? Open `.bin/prettier` in the root of `node_modules` and you'll see the same code.
Prettier has
```json
"bin": "./bin/prettier.cjs"
```
So npm creates bin repository and insert a symbolic link there that refers to the Prettier package's file inside `bin/prettier.cjs`. And now you understand how symbolic links work in practice :)
> If you remove the `.bin` directory from `node_modules` and try to run `npx prettier .` It'll throw an error `sh: 1: prettier: not found`, regardless of whether you have the `prettier` package installed
## create-vue
Let's remove Prettier with `npm rm prettier` and install `npm i -D create-vue` now. Inside the `.bin` directory, we can see the symbolic link for `create-vue`
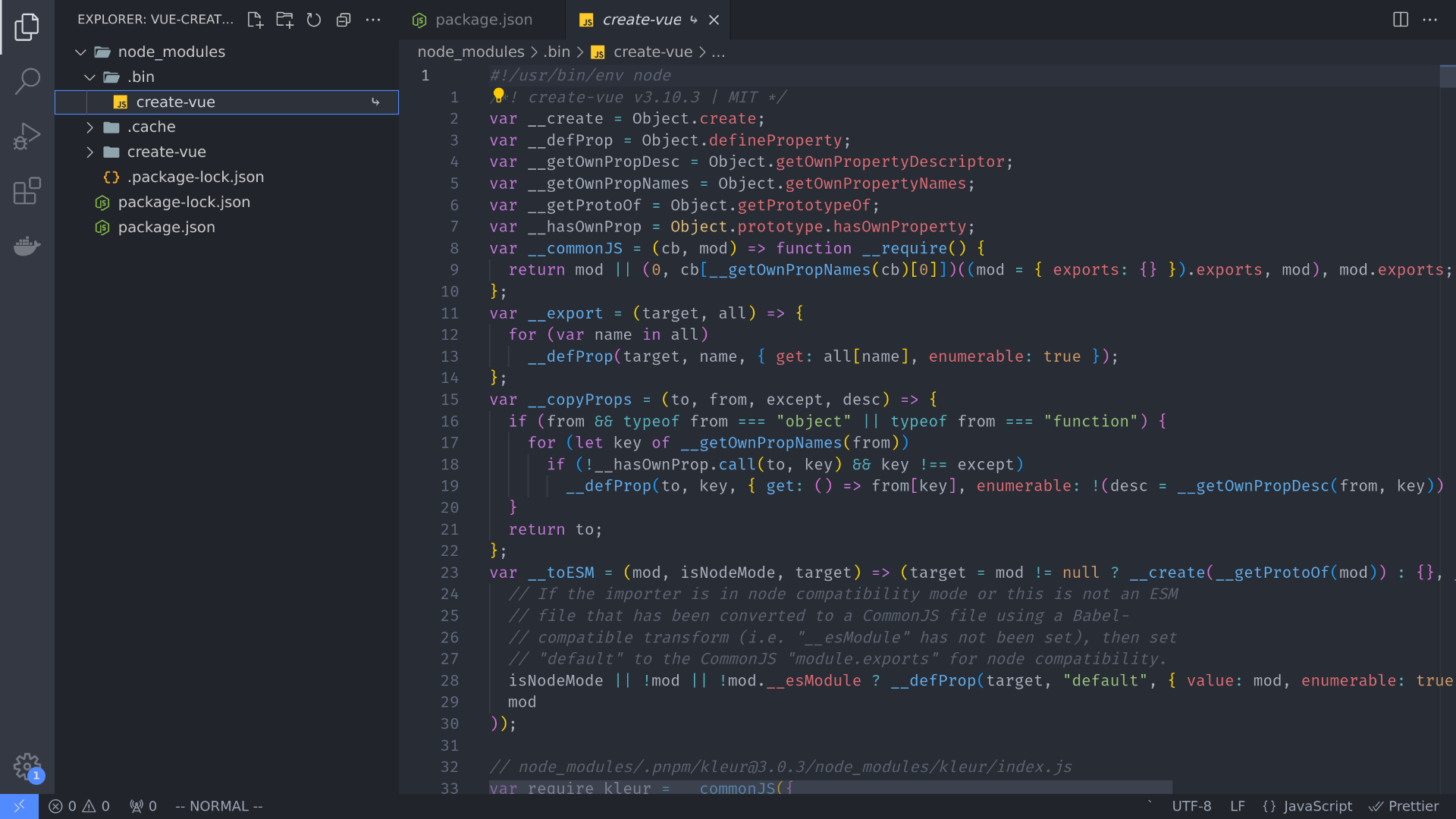
Let's move to `package.json` in `node_modules/create-vue`
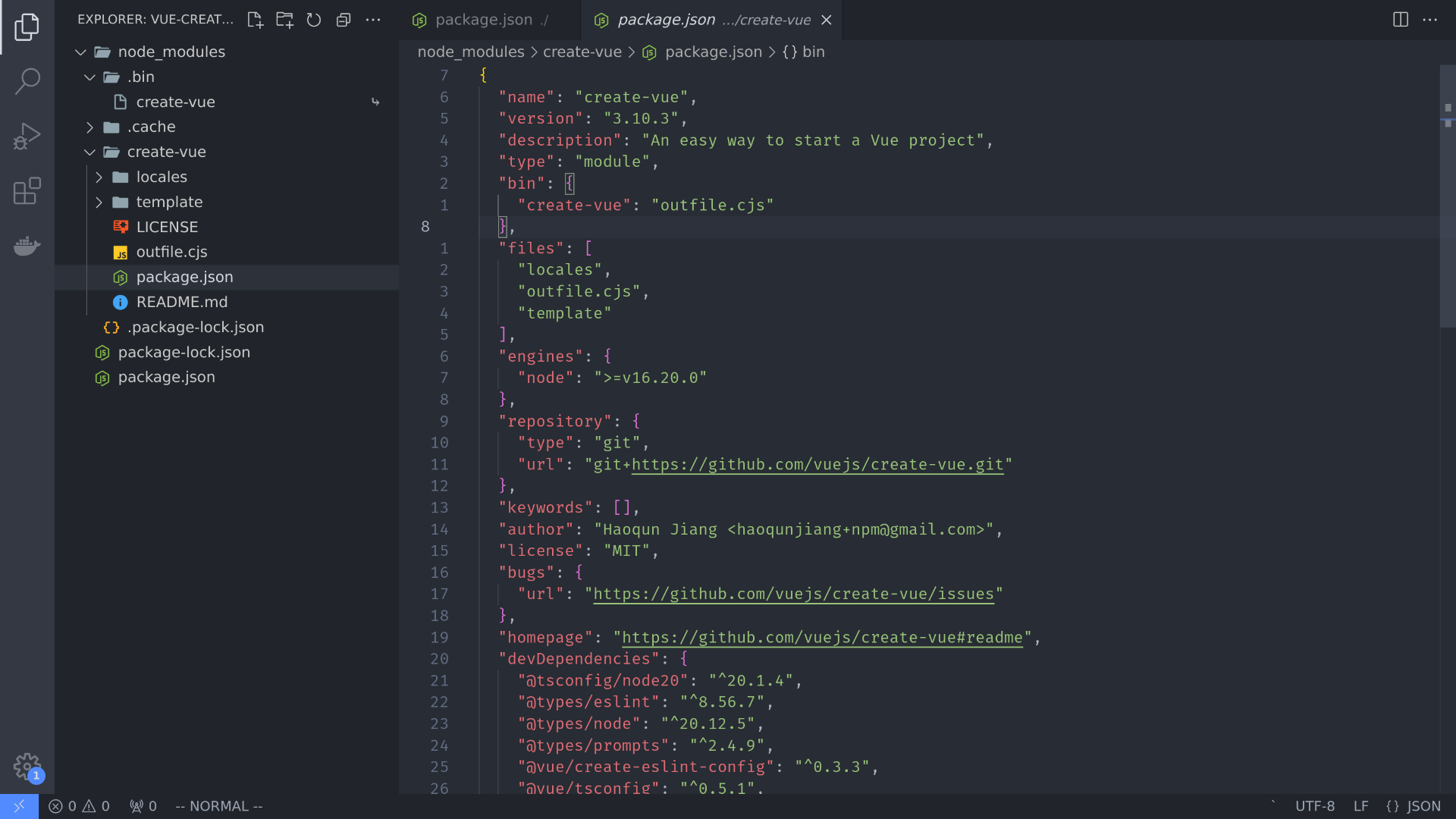
We see `create-vue` bin key that runs outfile.cjs.
```json
"bin": {
"create-vue": "outfile.cjs"
},
```
If we open it, we'll notice the same code as in `node_modules/.bin/create-vue` (symbolic link)
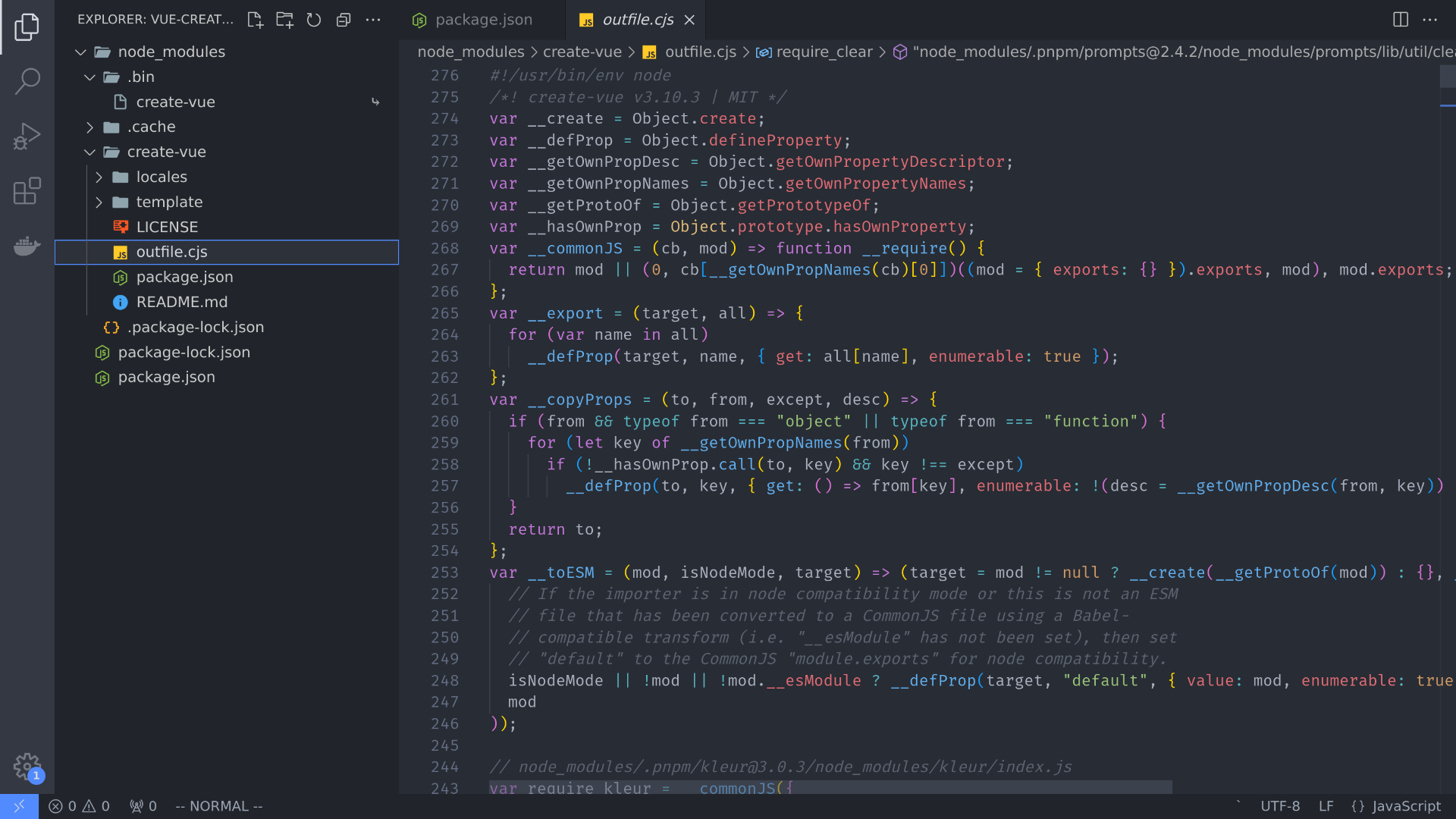
Does that mean we can simply execute `create-vue` from the terminal? Exactly. Just like we can execute `outfile.cjs`. Let's try it
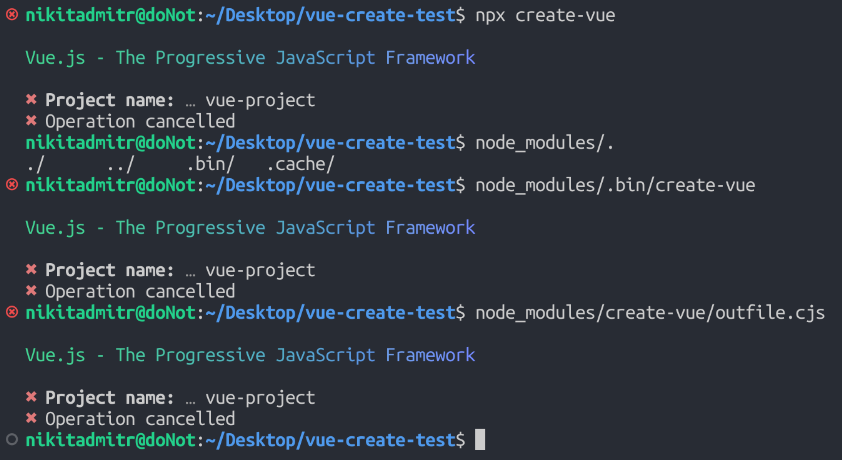
While using `npm init` or its alias `npm create` provided with the package, npm executes the binary file (bin) with the name of this package during initialization
## Conclusion
I'd like to point out another potential source of confusion. [Vue docs](https://vuejs.org/guide/quick-start.html#creating-a-vue-application) provide a link only to the [create-vue GitHub](https://github.com/vuejs/create-vue) repository. However, if you visit that repository, you won't find an `outfile.js` or any direct similarity with the `create-vue` package we just explored. This is because GitHub primarily stores open-source code for contribution and development purposes. In contrast, npm stores the actual bundled package code that you install. So, it's important not to confuse the GitHub repository with the package as installed via npm
Now I hope I've helped you, and you can now understand and explore similar packages such as `create-react-app` or `create svelte@latest` using this guide | nikitadmitr |
1,867,869 | Your Ultimate Guide to Preparing for the AWS Certified Cloud Practitioner Certification with MyExamCloud: A 5-Week Study Plan | Earning the AWS Certified Cloud Practitioner certification is a highly valuable achievement for... | 0 | 2024-05-28T15:02:20 | https://dev.to/myexamcloud/your-ultimate-guide-to-preparing-for-the-aws-certified-cloud-practitioner-certification-with-myexamcloud-a-5-week-study-plan-5el0 | aws, cloudcomputing, software, coding | Earning the AWS Certified Cloud Practitioner certification is a highly valuable achievement for individuals with a solid understanding of the AWS Cloud, regardless of their job role. To successfully obtain this certification, candidates must demonstrate their knowledge in various areas related to AWS.
For an effective preparation strategy for the Python AWS Certified Cloud Practitioner exam, we have created a 5-week study plan that covers all exam objectives and important study techniques.
**Phase 1: Building a Strong Foundation (Week 1)**
The first week of preparation should focus on establishing a strong foundation of knowledge about the AWS Cloud. This includes getting familiar with AWS concepts and learning about the core AWS services.
**Phase 2: Focusing on Exam Topics (Week 2)**
In the second week, you should concentrate on each topic covered in the exam. This will help you solidify your understanding of the subject and serve as a solid base for the remaining phases of study.
**Phase 3: Practice and Revision (Week 3-4)**
To enhance your preparation, it is crucial to practice and review consistently. Utilize resources such as MyExamCloud to access AWS Certified Cloud Practitioner practice tests and revise essential concepts. Taking objective tests and identifying weak areas will also strengthen your overall knowledge.
**Phase 4: Attempting Mock Tests and Analyzing Results (Week 5)**
During the final week of preparation, prioritize taking mock tests and analyzing the results. These are a crucial part of your study plan as they simulate the real exam environment and help identify any remaining knowledge gaps.
**MyExamCloud's AWS Certified Cloud Practitioner Study Plan**
MyExamCloud [CLF-C02 Practice Tests](https://www.myexamcloud.com/onlineexam/clf-c02-practice-exam-questions.course) offers a comprehensive study plan for AWS Certified Cloud Practitioner exam preparation, which includes:
- 23 full-length mock exams
- 2 free trial exams
- 5 flashcard quiz exams
- Objective and random tests
- eBook with detailed answers and explanations
- Access to course material through a mobile app or web browser
- 1400+ questions, organized by exam topics
- "Plan, Practice, Achieve" dashboard to set goals and track progress
Don't hesitate any longer, start your journey towards achieving AWS Certified Cloud Practitioner certification with MyExamCloud. With our comprehensive study plan, you can confidently prepare for the exam and achieve success! | myexamcloud |
1,867,868 | Upstream 2024 agenda is live! | If you were waiting to sign up to attend Upstream, our one-day, virtual event bringing together open... | 0 | 2024-05-28T15:01:22 | https://blog.tidelift.com/upstream-2024-agenda-is-live | upstream, tidelift, opensource, maintainers | If you were waiting to sign up to attend Upstream, our one-day, virtual event bringing together open source maintainers and those who use their creations, until the speakers were announced, today’s the day. [The Upstream agenda](https://upstream.live/schedule) is live. 🎉 If you haven't already marked June 5, 2024 on your calendars, you should do it now! [RSVP here](https://upstream.live/). ✅
This year our theme is [unusual ideas to solve the usual problems](https://blog.tidelift.com/upstream-is-june-5-2024). By “the usual problems,” we mean the health and security of open source, which last we checked was still not a solved problem. By “unusual ideas,” we mean who are the people out there exploring the most interesting and unusual ways to make the open source software we all rely on more healthy, secure, and resilient?
Come prepared to hear some exciting new ideas, because we have them lined up for you. Here’s a taste:
- **Luis Villa**, Tidelift co-founder and general counsel, will use his opening talk to set up this year’s theme. He’ll make the case that our current way of "fixing" open source health and security is simply not working, and he’ll introduce some of the new ideas we’ll be hearing more about through the course of the day.
- **Frank Nagle**, assistant professor at Harvard Business School, will sit down with **Luis**, in our first fireside chat of the day, to discuss a recent paper Frank co-authored where he estimated the value of the world’s open source infrastructure at $8.8 trillion dollars.
- **Aeva Black** and **Jack Cable**, from CISA (the U.S. Cybersecurity Infrastructure and Security Agency; and the only government agency that cares so much about security they put it in their name twice!), will sit down with Tidelift CEO and co-founder **Donald Fischer** to discuss the industry-wide effort they are leading to make security by design a core business requirement in products versus an aftermarket technical feature.
- **Vincent Danen**, VP of Product Security at Red Hat, will join **Donald** to make the case that our current system of patch management is in desperate need of a revolution (and he’ll share what a better approach focused on risk mitigation might look like).
- **Aisha Gautreau**, OSPO lead at a large Canadian telecommunications company, will sit down with Tidelift VP of product, **Lauren Hanford**, to share the journey of building an open source program office and what advantages it has created for them so far.
- **Tosha Ellison** and **Gabriele Columbro** of FINOS (the Fintech Open Source Foundation) will join **John Mark Walker**, director of the OSPO at Fannie Mae, and **Donald Fischer** to chat about what financial services organizations are doing to improve open source security and invest in the open source they depend on, while sharing advice and strategies that all organizations in all industries can use to inform their own work.
- **Fiona Krakenbürger** from the Sovereign Tech Fund and **Mirko Boehm** from the Linux Foundation Europe will sit down with **Luis Villa** to discuss the impending CRA legislation in the EU (the biggest government proverbial "stick" to date) and the Sovereign Tech Fund’s "carrot" approach to funding open security.
- **James Berthoty**, CEO of Latio Tech and security engineer at PagerDuty, will go over how to get CVEs out of GitHub Issues and why it’s frustrating for compliance teams and maintainers both.
- **Tatu Saloranta** of jackson-databind, **Wesley Beary**, who maintains popular Ruby projects fog and excon, **Irina Nazarova** of Evil Martians, and **Valeri Karpov**, from Mongoose, make up our maintainer panel this year and will discuss the state of life as an open source maintainer in 2024.
- **Andrey Sitnik**, front-end principal at Evil Martians, will give insights on how to make your open source project popular from his 15 years of making open source tools, some a success with others a failure.
- **Rachel Stephens**, senior industry analyst at RedMonk, **Shaun Martin**, IT and security management consulting principal at BlackIce, **Josh Bressers**, VP of security at Anchore, **Jordan Harband**, principal open source architect at HeroDevs, and **Terrence Fletcher**, product security engineer at Boeing, will join Tidelift VP of product, **Lauren Hanford**, to discuss how [the xz utils backdoor hack](https://tidelift.com/resources/xz-backdoor-hack) has changed the landscape of open source software supply chain security.
This agenda is 🔥 You don't want to miss out. Register for this free, one-day virtual event [here](https://upstream.live/register).
| kristinatidelift |
1,867,857 | Helping PostgreSQL® professionals with AI-assisted performance recommendations | Since the beginning of my journey into the data world I've been keen on making professionals better... | 0 | 2024-05-28T15:00:00 | https://ftisiot.net/posts/aiven-db-optimizer/ | postgres, sql, performance, ai | ---
title: Helping PostgreSQL® professionals with AI-assisted performance recommendations
published: true
date: 2024-05-28 16:00:00 UTC
tags: PostgreSQL, SQL, performance, AI
canonical_url: https://ftisiot.net/posts/aiven-db-optimizer/
---
Since the beginning of my journey into the data world I've been keen on making professionals better at their data job. In the previous years that took the shape of creating materials in several different forms that could help people understand, use, and avoid mistakes on their data tool of choice. But now there's much more into it: a trusted AI solution to help data professional in their day to day optimization job.
## From content to tooling
The big advantage of the content creation approach is the 1-N effect: the material, once created and updated, can serve a multitude of people interested in the same technology or facing the same problem. You write an article once, and it gets found and adopted by a vast amount of professionals.
The limit of content tho, it's that it is an extra resource, that people need to find and read elsewhere. While this is useful, it forces a context switch, moving people away from the problem they are facing. Here is where tooling helps, providing assistance in the same IDE that professionals are using for their day to day work.
## Tooling for database professionals
I have the luxury of working for [Aiven](https://aiven.io/) which provides professionals an integrated platform for all their data needs. In the last three years I witnessed the growth of the platform and its evolution with the clear objective to make it better usable at scale. Tooling like [integrations](https://aiven.io/integrations-and-connectors), [Terraform providers](https://aiven.io/docs/tools/terraform) and the [Console](https://go.aiven.io/francesco-signup) facilitate the work that platform administrators have to perform on daily basis.
But what about the day to day work of developers and CloudOps teams? This was facilitated when dealing with administrative tasks like backups, creation of read only replicas or upgrades, but the day to day work of optimizing the workloads was still completely on their hands.
## Using trusted AI to optimize database workloads
This, however, is now changing. With the recent launch of [Aiven AI Database Optimizer](https://aiven.io/blog/aiven-ai-dboptimizer-launch) we are able to help both developer and CloudOps in their day to day optimization work!
Aiven AI Database Optimizer provides, directly in the [Console](https://go.aiven.io/francesco-signup), insights on database workloads alongside a one-click Optimize button that suggests index and SQL rewrites. It's a non intrusive solution who gathers informations from the slow query log and database metadata, and leverages an in-built AI engine, to provide accurate suggestions to improve performance.
{% youtube fOavII9QAmg %}
The solution, based on the [EverSQL by Aiven](https://www.eversql.com/) technology has been already adopted by 120.000 professionals optimizing over 2 million queries. It's not a wrapper around a public Generative AI provider, is a dedicated solution that keeps data privacy and security as a priority.
You can experience it for Free in the Early Availability phase, just navigate to the [Aiven Console](https://go.aiven.io/francesco-signup) and create an Aiven for PostgreSQL® service! Once you have some workload on the service, the **AI Insights** page will show you the queries and provide index and SQL rewrite suggestion to take your database performance to the next level!
More information on the dedicated [Aiven AI Database Optimizer page](https://aiven.io/solutions/aiven-ai-database-optimizer)
| ftisiot |
1,867,865 | What are Websockets: The detailed Guide. | What are Websockets Websockets provide a way for web browsers and servers to communicate... | 0 | 2024-05-28T14:54:47 | https://dev.to/alakkadshaw/what-are-websockets-the-detailed-guide-3hke | webdev, javascript, websocket, backend | ## What are Websockets
Websockets provide a way for web browsers and servers to communicate in real-time without the need to continuously reload the page.
Unlike traditional HTTP requests that follow a request-response pattern, Websockets establish a full-duplex communication channel.
This means once a connection is opened, data can flow freely in both directions for the duration of the connection.
This technology is crucial for applications that require immediate data updates, such as live chat systems, real-time trading platforms, or gaming applications.
### Definition of Websockets
**What Websockets Are:** Websockets are a communication protocol that provides a full-duplex communication channel over a single, long-held connection. They are designed to operate over the same ports as HTTP (80) and HTTPS (443), facilitating easier integration into existing network infrastructures
### Websockets Vs HTTP Connections
* **Connection Lifetime:** Unlike HTTP, which opens a new connection for each request/response cycle, Websockets establish a persistent connection that remains open for the duration of the interaction. This allows continuous data flow without repeated handshakes.
* **Data Transfer:** Websockets allow data to flow bidirectionally without the overhead of HTTP headers with each message, reducing latency and bandwidth consumption.
* **Protocols:** HTTP is a stateless protocol, whereas Websockets maintain state over a connected session, allowing for context and state to be preserved.
### Brief Overview of How WebSockets work
**WebSocket Handshake:**
1. **Client Request (Opening Handshake):** The WebSocket connection begins with an HTTP handshake, where the client sends a request to the server to upgrade the connection from HTTP to Websockets. This request includes a key that the server will use to form a response.
Example request headers might look like this:
```javascript
GET /chat HTTP/1.1
Host: example.com
Upgrade: websocket
Connection: Upgrade
Sec-WebSocket-Key: x3JJHMbDL1EzLkh9GBhXDw==
Sec-WebSocket-Version: 13
```
2. **Server Response:** The server processes this request and if it supports Websockets, responds with an acceptance of the upgrade request, confirming the establishment of a WebSocket connection.
Example response headers might look like this:
```javascript
HTTP/1.1 101 Switching Protocols
Upgrade: websocket
Connection: Upgrade
Sec-WebSocket-Accept: HSmrc0sMlYUkAGmm5OPpG2HaGWk=
```
**Data Transfer:**
* **Frame-based Data Handling:** Once the handshake is complete, data is transmitted in "frames", which can be of varying lengths and contain different types of data (text, binary, etc.).
* **Continuity:** The connection remains open, allowing ongoing and instantaneous data transfer until either the client or server initiates a close.
* **Control Frames:** WebSocket protocol defines several control frames for managing the connection, such as close, ping, and pong frames, which are used to check the connection's liveliness and to gracefully close the connection.
### **Advantages of Using Websockets**
**Real-Time Data Transfer with Low Latency:**
* Websockets provide a continuous connection between the client and the server, enabling data to be sent the instant it's available.
* This eliminates the delay caused by the client having to wait for a scheduled time to send a request, as in traditional HTTP polling.
* The direct and constant connection significantly reduces latency, making Websockets ideal for applications like online gaming, live sports updates, and financial trading where timing is crucial.
**Bi-Directional Communication Between Client and Server:**
* Unlike HTTP where communication is predominantly initiated by the client, Websockets allow both the client and the server to send data independently once the connection is established.
* This two-way communication channel is particularly beneficial for chat applications, real-time collaboration tools, and interactive dashboards, where server and client continuously exchange information.
**Reduced Server Load and Network Traffic Compared to HTTP Polling:**
* HTTP polling involves the client repeatedly making HTTP requests at regular intervals, which results in a high number of overheard-laden HTTP headers being sent and processed, even if there is no data to return.
* Websockets eliminate the need for constant requests and responses. After the initial handshake, only data frames are exchanged, and these frames do not carry the same overhead as HTTP headers.
* This reduction in the number of transactions and data overhead leads to less bandwidth usage and lower server load, which is advantageous for both server performance and operational costs.
## **Practical Implementation of Websockets**
## **Setting Up a Basic WebSocket Server**
To set up a WebSocket server in Node.js, you will first need the `ws` library, a simple and powerful WebSocket library for Node.js. Below is a detailed, step-by-step guide and code examples on how to set up and manage a basic WebSocket server.
## Step 1 Create a new Project directory
Create a new directory for the project then
```javascript
mkdir websocket-server
cd websocket-server
```
#### **Step 2: Initialize a New Node.js Project**
Initialize a new Node.js project by running:
```javascript
npm init -y
```
This command creates a `package.json` file that will manage your project's dependencies.
#### **Step 3: Install the** `ws` Library
Install the `ws` WebSocket library via NPM:
```javascript
npm install ws
```
#### **Step 4: Create the WebSocket Server**
Create a new file named `server.js` and open it in your preferred text editor. Add the following code to set up a basic WebSocket server:
```javascript
// Import the WebSocket library
const WebSocket = require('ws');
// Create a new WebSocket server on port 8080
const wss = new WebSocket.Server({ port: 8080 });
// Set up connection event
wss.on('connection', function connection(ws) {
console.log('A new client connected.');
// Send a message to the newly connected client
ws.send('Welcome to the WebSocket server!');
// Set up event for receiving messages from the client
ws.on('message', function incoming(message) {
console.log('received: %s', message);
// Echo the received message back to the client
ws.send(`Server received your message: ${message}`);
});
// Set up event for client disconnection
ws.on('close', () => {
console.log('Client has disconnected.');
});
});
console.log('WebSocket server is running on ws://localhost:8080');
```
### **Explanation of the Code**
1. **Import the** `ws` Library: This line brings the WebSocket functionality into your Node.js script.
2. **Create the WebSocket Server:** Initializes a WebSocket server listening on port 8080.
3. **Handle Connection Events:** Adds an event listener for new client connections. Each client connection (`ws`) triggers the callback function.
4. **Send a Welcome Message:** Sends a message to the client upon connection.
5. **Receive Messages from the Client:** Adds an event listener for messages sent by the client. It prints received messages to the console and echoes them back to the client.
6. **Handle Client Disconnection:** Logs a message when a client disconnects.
### **Running the WebSocket Server**
To run your WebSocket server, execute:
```javascript
node server.js
```
## Building a Websocket client and integrating it with the server we already buil
Creating a simple WebSocket client involves using HTML5 and JavaScript to establish a connection to a WebSocket server, send messages, and handle incoming messages. Here's a step-by-step guide and a detailed code example:
#### **Step 1: Create an HTML File**
Start by creating an HTML file, for example, `index.html`. This file will include both the HTML to provide a basic user interface and JavaScript for WebSocket interaction.
#### **Step 2: Set Up HTML Structure**
In your HTML file, define a simple user interface that includes a text input for sending messages and a button to trigger the send action. Also, include a section to display incoming messages.
```javascript
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>WebSocket Client</title>
</head>
<body>
<h2>WebSocket Test Client</h2>
<input id="messageInput" type="text" placeholder="Type your message here...">
<button onclick="sendMessage()">Send Message</button>
<div id="messages"></div>
<script src="client.js"></script>
</body>
</html>
```
#### **Step 3: Write the JavaScript Code by creating the client.js file**
Create a separate JavaScript file, e.g., `client.js`, and link it in your HTML file as shown above. The JavaScript will handle the WebSocket connection, sending messages, and receiving messages.
```javascript
// Connect to WebSocket server
const ws = new WebSocket('ws://localhost:8080');
// Connection opened
ws.onopen = function(event) {
console.log('Connection is open');
displayMessage('Connected to the server');
};
// Listen for messages
ws.onmessage = function(event) {
console.log('Message from server ', event.data);
displayMessage(event.data);
};
// Connection closed
ws.onclose = function(event) {
console.log('Connection is closed');
displayMessage('Disconnected from the server');
};
// Send message function
function sendMessage() {
var message = document.getElementById('messageInput').value;
ws.send(message);
displayMessage('You: ' + message);
document.getElementById('messageInput').value = ''; // clear input field after send
}
// Display messages in the HTML page
function displayMessage(message) {
const messagesDiv = document.getElementById('messages');
messagesDiv.innerHTML += `<div>${message}</div>`;
}
```
### **Explanation of the Code**
1. **Connect to the WebSocket Server:** Establishes a WebSocket connection to the server. The URL (`ws://`[`localhost:8080`](http://localhost:8080)) should match your server's address.
2. **Handle Open Connection:** The `onopen` event triggers when the connection to the server is successfully opened, confirming connectivity.
3. **Receive Messages:** The `onmessage` event handles incoming messages from the server. It displays these messages in the HTML page.
4. **Handle Closed Connection:** The `onclose` event triggers when the WebSocket connection is closed, either by the client or server.
5. **Send Messages:** The `sendMessage` function gets the message from the text input and sends it to the server using `ws.send()`. It also displays the sent message in the HTML page.
6. **Display Messages:** Updates the HTML to include each new message.
### **Running the WebSocket Client**
Open the `index.html` file in a web browser to run your WebSocket client. It should connect to your WebSocket server, and you'll be able to send and receive messages in real-time.
## Scaling Websocket Connections
When scaling WebSocket connections, the challenge is to handle a large number of concurrent connections efficiently while maintaining performance and reliability. Here are some strategies and technologies that can help:
#### **Load Balancing**
* **Use Load Balancers:** Distribute incoming WebSocket connections across multiple servers. This spreads the load and reduces the risk of any single server becoming a bottleneck.
* **Sticky Sessions:** Implement sticky sessions in your load balancer to ensure that WebSocket connections from the same client are routed to the same server. This is important because WebSocket connections are stateful.
#### **Horizontal Scaling**
* **Add More Servers:** As demand increases, add more servers to your WebSocket server pool. This is horizontal scaling and helps manage more connections by increasing the number of servers that handle the workload.
* **Cloud-Based Scaling:** Use cloud services that can dynamically add or remove servers based on demand, often automatically.
#### **Managing State**
* **Externalize State:** Use an external store for session data, so connection state can be shared across multiple servers. This helps in maintaining continuity even if the client’s connection switches between different servers in a load-balanced environment.
#### **Use of Redis or Other Message Brokers**
* **Redis:** Employ Redis as a fast, in-memory data store to manage session states or message queues. Redis can publish and subscribe to messages, making it a good choice for propagating messages across different instances of your application.
* **Message Brokers:** Utilize message brokers like RabbitMQ or Kafka to handle messaging between clients and servers. These tools can effectively distribute messages across a system with many connections and maintain the performance of message delivery.
### **Example of Scaling Using Redis**
Here’s how you might use Redis to manage scaling WebSocket connections:
1. **Setup Redis:** Deploy Redis and connect it to your WebSocket servers. Each server will communicate with Redis to fetch and store state information.
2. **Pub/Sub Model:** Implement a publish/subscribe model in Redis where:
* Each WebSocket server publishes messages to a channel.
* All other WebSocket servers subscribe to that channel and receive updates.
3. **Session Storage:** Use Redis to store session-related data. When a WebSocket connection is established, the server checks Redis for any existing session data related to that client and retrieves it. This is useful when a client reconnects and might connect to a different server due to load balancing.
4. **Handling Connection Failures:** On a server failure, other servers can take over the connections using the session data stored in Redis, ensuring minimal disruption to the client.
### **Example Code Snippet for Using Redis with WebSockets**
Here's a basic example of how you might configure a WebSocket server to use Redis for storing session data and broadcasting messages:
```javascript
const WebSocket = require('ws');
const Redis = require('ioredis');
const redisSubscriber = new Redis();
const redisPublisher = new Redis();
const wss = new WebSocket.Server({ port: 8080 });
redisSubscriber.subscribe('websocketMessages');
redisSubscriber.on('message', (channel, message) => {
// Broadcast message to all connected clients
wss.clients.forEach((client) => {
if (client.readyState === WebSocket.OPEN) {
client.send(message);
}
});
});
wss.on('connection', (ws) => {
ws.on('message', (message) => {
// Publish received message to Redis
redisPublisher.publish('websocketMessages', message);
});
});
```
In this setup, every message received by a WebSocket server is published to a Redis channel, and all WebSocket servers subscribed to that channel receive the message and broadcast it to their connected clients.
This ensures that messages can be distributed across a scaled environment efficiently.
### **Security Considerations for WebSocket Connections**
Securing WebSocket connections is crucial due to their persistent nature and the sensitivity of data that may be transmitted. Here are key best practices and methods to mitigate common security threats.
#### **Authentication**
* **Secure Initial Handshake:** Ensure the initial HTTP handshake that upgrades the connection to WebSocket is secure. Use HTTP authentication mechanisms like Basic or Bearer token authentication to verify user credentials before upgrading.
* **Session Tokens:** Implement session tokens that are verified at the WebSocket connection level. Ensure tokens are transported securely and validated before establishing or continuing any WebSocket communication.
#### **Encryption**
* **Use TLS/SSL:** Always use WebSockets over TLS (WSS://) to encrypt the data transmitted between the client and the server. This prevents interception and eavesdropping on the data exchanged.
* **Certificate Validation:** Ensure proper SSL/TLS certificate validation practices are followed by your server to prevent man-in-the-middle (MITM) attacks.
#### **Handling Common Security Threats**
* **Cross-Site WebSocket Hijacking (CSWSH):** Verify the origin of WebSocket connection requests to prevent unauthorized access from other domains. This can be done by checking the `Origin` header in the WebSocket handshake request.
* **Denial of Service (DoS):** Implement rate limiting and connection throttling to mitigate the risk of denial-of-service attacks, which aim to overwhelm your server by creating a massive number of connections.
* **Input Validation:** Always validate and sanitize any data received through WebSocket connections to prevent injection attacks and other malicious exploits.
* **Secure Cookie Use:** If cookies are used for managing sessions or authentication, ensure they are secure and HttpOnly to prevent access from client-side scripts.
### **Example Code for Securing WebSocket Connections**
Here's an example showing how to implement some of these security measures in Node.js using the `ws` library:
```javascript
const WebSocket = require('ws');
const https = require('https');
const fs = require('fs');
// Load SSL certificate
const server = https.createServer({
cert: fs.readFileSync('path/to/cert.pem'),
key: fs.readFileSync('path/to/key.pem')
});
const wss = new WebSocket.Server({ server });
wss.on('connection', function connection(ws, request) {
// Validate session token or cookies
const token = request.headers['sec-websocket-protocol'];
if (!isValidToken(token)) {
ws.terminate(); // Terminate connection if token is invalid
return;
}
// Handle WebSocket messages
ws.on('message', function incoming(message) {
if (!validateInput(message)) {
ws.terminate(); // Terminate connection if message is not valid
return;
}
console.log('received: %s', message);
});
});
// Start the server
server.listen(8080);
function isValidToken(token) {
// Token validation logic here
return true; // Simplified for example
}
function validateInput(input) {
// Input validation logic here
return true; // Simplified for example
}
```
In this setup:
* **SSL/TLS encryption** is implemented using HTTPS with a certificate.
* **Token validation** checks if the WebSocket connection request includes a valid token.
* **Input validation** ensures all received messages are checked for potentially harmful content before processing.
## **Websockets vs. HTTP Long Polling vs. Server-Sent Events**
These three technologies serve similar purposes but offer different capabilities and trade-offs. Below is a detailed comparison of their pros and cons along with practical examples and decision matrices to help determine the best use cases for each.
#### **Websockets**
**Pros:**
* **Bi-directional Communication:** Allows both client and server to send data actively without waiting for a request. Ideal for chat applications, real-time gaming, or trading platforms where immediate response is critical.
* **Low Latency:** Maintains an open connection, minimizing the delay in data transmission. Suitable for applications requiring quick updates.
* **Efficient Performance:** Reduces overhead by eliminating the need for frequent connections and disconnections.
**Cons:**
* **Complexity in Handling:** More complex to implement and manage compared to HTTP requests due to the persistent connection.
* **Scalability Concerns:** Can be more demanding on server resources when scaling because each connection consumes memory and CPU.
**Practical Example:**
* Use in a financial trading platform where traders need to see price updates in real-time and execute trades instantly.
#### **HTTP Long Polling**
**Pros:**
* **Compatibility:** Works on any platform or browser that supports HTTP. No special protocols or servers are necessary beyond a standard HTTP server.
* **Simplicity:** Easier to implement and debug than Websockets as it uses standard HTTP requests.
**Cons:**
* **Higher Latency:** Each request may have a delay as the server waits to send a response until there's data available or a timeout occurs.
* **Increased Server Load:** More HTTP requests can lead to higher server load, particularly if many users are constantly polling.
**Practical Example:**
* Use in a news feed application where it’s acceptable to have a slight delay between when new content is available and when it appears to the user.
#### **Server-Sent Events (SSE)**
**Pros:**
* **Simple Server-Side Logic:** Easier to implement on the server than Websockets, as the server only needs to handle outgoing messages.
* **Built-in Reconnection:** Automatically tries to reconnect if the connection is lost, which is handled by the browser.
* **Efficiency in Unidirectional Tasks:** Efficient for scenarios where only the server sends updates to the client.
**Cons:**
* **Limited Browser Support:** Not supported in all browsers, especially older versions.
* **Unidirectional:** Only supports server-to-client communication, which limits its use in interactive applications.
**Practical Example:**
* Use in a live blog or event streaming where the server needs to push updates to clients but doesn’t need to receive data back from them.
### **Decision Matrix for Choosing Technology**
| **Requirement** | **Websockets** | **HTTP Long Polling** | **Server-Sent Events** |
| --- | --- | --- | --- |
| Bi-directional Communication | Yes | No | No |
| Real-time Interaction | Best | Moderate | Good |
| Browser Compatibility | Good | Best | Moderate |
| Implementation Complexity | High | Moderate | Low |
| Server Resource Use | High | High | Moderate |
| Communication Flow | Both | Server to Client | Server to Client |
#### **When to Use Each Technology:**
* **Websockets:** Choose when real-time, two-way communication is necessary, and when the application demands high interactivity and low latency.
* **HTTP Long Polling:** Opt for this when updates are required in near real-time but the system can tolerate slight delays, or when using legacy systems that must support older technologies.
* **Server-Sent Events:** Best used for scenarios where the server continuously updates the data to the client, like a stock ticker or live sports scores, and where the client doesn’t need to send data to the server. | alakkadshaw |
1,882,130 | WordPress Interactivity API: Detailed Explanation | The WordPress Interactivity is a relatively new API that allows the creation of declarative templates... | 0 | 2024-06-09T15:11:32 | https://wplake.org/blog/wordpress-interactivity-api/ | gutenberg, wordpress, preact, reactive | ---
title: WordPress Interactivity API: Detailed Explanation
published: true
date: 2024-05-28 14:54:41 UTC
tags: gutenberg,wordpress,preact,reactive
canonical_url: https://wplake.org/blog/wordpress-interactivity-api/
---
The WordPress Interactivity is a relatively new API that allows the creation of declarative templates natively. It harnesses Preact and offers SSR out-of-the-box.

### 1. When and why did the WP Interactivity API appear?
[WordPress 6.5](https://wordpress.org/news/2024/04/regina/), released in April 2024, brings a significant shift with its own front-end reactivity system. In recent years, [decoupled (headless) WordPress](https://www.gatsbyjs.com/docs/glossary/headless-wordpress/) installations have become more popular. They allow you to leverage modern front-end frameworks like [React](https://react.dev/) or [Vue](https://vuejs.org/).
However, this approach is time-consuming and has a clear drawback: you lose the WP ecosystem features on the front end, such as plugins. Tools like [Yoast](https://wordpress.org/plugins/wordpress-seo/) must be forgotten and switched to manual implementation.
WordPress 6.5 [introduces](https://make.wordpress.org/core/2024/03/04/interactivity-api-dev-note/) a game-changing feature by adding reactivity tools to its core, allowing you to master modern front-end natively without turning to the decoupled approach. This feature has been developed by the WP Core team for a while but was delivered only in April 2024. Therefore, many developers aren’t familiar with it yet.
While there is a [section in the official documentation](https://developer.wordpress.org/block-editor/reference-guides/interactivity-api/) that explains the key aspects of the Interactivity API, it isn’t as comprehensive as you might want. In addition, in some places it mentions parts related to the Gutenberg blocks only (though it can be used fully independently), so if you’re new to both, it might make understanding more difficult.
That’s why we made this comprehensive and in-depth explanation, in which we’ll share our knowledge with you.
### 2. WordPress Interactivity API definition
Now let’s figure out what exactly is behind the WordPress Interactivity API name.
> _The Interactivity API is a standard system of directives, based on declarative code, for adding front-end interactivity to blocks._
In other words, it’s a way to create the front end of a WP website using a declarative approach. If the official definition seems unclear to you, don’t worry, we’ll tackle it piece by piece.
#### Declarative VS Imperative approach
Declarative, um, what’s that? If you aren’t familiar with React or Vue, this word might be totally unfamiliar to you. But since the WordPress Interactivity API is based on it, we need to understand it. There are two different approaches to mastering the front end: **imperative** and **declarative**.
Since the early web days and for decades, we all have been using the **imperative** approach. The **imperative** way is when we have a static initial markup and then add interactivity by manually making changes to the markup using JS code. So, we manually query the right nodes and make changes for every action.
The **declarative** approach is a modern alternative that suggests building a dynamic layout by _declaring_ the elements and their behavior rules all at once. When a user interacts with it, the layout is updated automatically according to the behavior rules we specified, so we don’t need to manually query nodes and make changes.
#### Drawbacks of the Imperative approach
As an example, let’s review an advanced accordion, which shows its state above. While you’re rarely going to meet similar accordions in real life, the idea is to showcase the weak sides of the **imperative** way when it comes to handling multiple states.
Besides the classic items toggle feature, we simply need to display the current accordion state (opened or closed) with the item name (so opened item name and last closed item name). The markup can be:
```
<div class="accordion">
<div class='accordion__panel'>
<div class='accordion__heading-opened' hidden>
Current open item is <span class='accordion__open-item-name'></span>
</div>
<div class='accordion__heading-closed'>
Items are closed.
<p class='accordion__closed-item' hidden>
Last opened item is <span class='accordion__closed-item-name'></span>
</p>
</div>
</div>
<div class='accordion__item'>
<p class='accordion__item-title'>Title</p>
<div class='accordion__item-content'>Content</div>
</div>
<!--other items-->
</div>
```
For hiding elements, we’ll use the [“hidden” HTML attribute](https://developer.mozilla.org/en-US/docs/Web/HTML/Global_attributes/hidden), and for the initial state, we hide the ‘\_\_heading-open’ and ‘\_\_closed-item’ elements. So, what would a classic JS implementation look like? Something like this:
```
document.addEventListener('DOMContentLoaded', () => {
document.body.querySelectorAll('.accordion__item-title').forEach((title) => {
title.addEventListener('click', () => {
let item = title.closest('.accordion__item');
let isToOpen = !item.classList.contains('accordion__item--open');
let accordion = item.closest('.accordion');
let prevItem = accordion.querySelector('.accordion__item--open');
// Handle closing the previous item
if (prevItem) {
prevItem.classList.remove('accordion__item--open');
accordion.querySelector('.accordion__closed-item').removeAttribute('hidden');
accordion.querySelector('.accordion__closed-item-name').innerText = prevItem.querySelector('.accordion__item-title').innerText;
}
// Toggle the current item
if (isToOpen) {
accordion.querySelector('.accordion__heading-closed').setAttribute('hidden', true);
accordion.querySelector('.accordion__heading-opened').removeAttribute('hidden');
item.classList.add('accordion__item--open');
accordion.querySelector('.accordion__open-item-name').innerText = title.innerText;
} else {
accordion.querySelector('.accordion__heading-opened').setAttribute('hidden', true);
accordion.querySelector('.accordion__heading-closed').removeAttribute('hidden');
item.classList.remove('accordion__item--open');
accordion.querySelector('.accordion__closed-item-name').innerText = title.innerText;
}
});
});
});
```
As you see, the task that looked straightforward and sounded quite simple when described in text turned into a series of conditional checks and DOM queries.
If you’re an experienced developer, you know how the JS code looks for real complex logic scenarios in real life. With the **imperative** approach, we must write an update query chain for every possible action manually.
The more actions we support, the more complex the code becomes. Gaining experience, you indeed can find shorter and better solutions, but you can’t write less than the necessary minimum, which is still tough.
#### Benefits of the Declarative approach
As we saw above, the main drawback of the **imperative** approach is the necessity of manually handling conditionals and queries. The **declarative** approach offers a solution by _declaring_ the elements and their behavior rules all at once.
Let’s consider this with an advanced accordion example, without getting into the implementation details for now. Starting from the top, we have the panel with two different headings: “\_\_heading-open” and “\_\_heading-closed”.
Only one of them should be shown at a time. So, we conclude that we need an **isOpen** state and bind this state to the visibility of the items. When **isOpen** is true, “\_\_heading-open” is visible while “\_\_heading-closed” is hidden, and vice versa.
Introducing this state and moving conditional checks to the markup would allow us to simplify the JS code and change the UI as simply as changing the boolean value of our state. Let’s see how it should look in pseudo-code:
```
<div class='accordion__heading-opened' {if !isOpen then add 'hidden' attribute}>
Current open item is <span class='accordion__open-item-name'></span>
</div>
<div class='accordion__heading-closed' {if isOpen then add 'hidden' attribute}>
Items are closed.
<p class='accordion__closed-item' hidden>
Last opened item is <span class='accordion__closed-item-name'></span>
</p>
</div>
```
Then in JS, we can just do:
```
isOpen = true || isOpen = false;
```
and the layout will change its state without manual node queries.
We hope that now you get the idea of the declarative approach. Don’t worry about the implementation details or other accordion elements, as the example above is only for demonstrating the idea. Below in the article, we’ll implement the advanced accordion example completely using the WP Interactivity API.
For now, you should know that nowadays there are multiple JS frameworks based on the declarative approach, including [React](https://react.dev/), [Vue](https://vuejs.org/), [Preact](https://preactjs.com/), and others. The WordPress Interactivity API is another way to achieve this, built on top of the [Preact](https://preactjs.com/) framework.
#### Interactivity VS Reactivity
If you’re familiar with React or Vue, you know that both frameworks use the term **reactivity**.
> _For example,_ [_Vue’s documentation_](https://vuejs.org/guide/extras/reactivity-in-depth.html) _states: “One of Vue’s most distinctive features is the unobtrusive reactivity system. Component state consists of reactive JavaScript objects. When you modify them, the view updates._
This term is widely used and describes a key characteristic of the _declarative_ approach, allowing the layout to change as soon as the variables used in it change.
What about **interactivity**? Let’s review its definition again:
> _The Interactivity API is a standard system of directives, based on declarative code, for adding front-end interactivity to blocks._
From this description, you might think that **reactivity** and **interactivity** are very similar, or even the same.
In fact, **Interactivity** is just the name that WordPress has chosen for this API. The Interactivity API’s front end is built on top of [Preact](https://preactjs.com/), which is a **reactive** framework. So, when you’re using the WP Interactivity API, you can say that it’s a **reactive** tool as well.
Additionally, keep in mind that **reactivity** is a feature, even if it’s a key feature of the Interactivity API. Besides it, the API includes more, such as Server Side Rendering, which has its own implementation.
We’ll delve into SSR later, but for now, you should know that the Interactivity API encompasses all the features related to it, while **reactivity** is an important part of it.
### 3. Key aspects of the WP Interactivity API
The WordPress Interactivity API consists of two main features: **directives** and **store** , which are used in blocks. The **store** is a common term that describes **state** and **context** storages.
Let’s figure out the new terms:
> **_Block_** _ — it’s an independent page element with its own_ **_store_** _and template that contains_ **_directives_** _. One block can include other blocks as children and can also “talk” to each other._
> **_Storage_** _ — it’s a set of variables based on which we write_ **_directives_** _and add any logic. It’s the way to ‘expose’ some variable to the declarative template._
> **_Directive_** _ — it’s a declaration rule added to the markup that controls an element’s behavior based on the element’s state. In pseudocode, it looks like this:_ **_{if isOpen then add ‘hidden’ attribute}_** _._
While **state** and **context** have differences that we’ll review below, both of them act as a scope of variables for specific elements.
If you’re familiar with React or Vue, you’ll likely understand the concepts more easily. However, the WP Interactivity API has its own implementation, and you can’t directly use things from the React world as is.
If you are encountering this for the first time, don’t worry if you haven’t grasped all the terms yet. In this chapter, we’ll review each in detail and apply them to the accordion example mentioned above.
#### Usage note
Keep in mind that though the WP Interactivity API is built into the WP core, it isn’t applied to all the HTML by default. By default, it works only within your custom Gutenberg blocks that have the related option enabled. It’s also supported by the [Advanced Views Framework](https://wplake.org/advanced-views-lite/).
We recommend reading this chapter without practical reproducing. After getting familiar with the key concepts, you can try implementing them on your own. The ‘Where you can use’ chapter below will share when and how you can harness it.
### 3.1) Block
Let’s start with this basic term.
> _A_ **_block_** _is an independent page element with its own store and template that contains_ **_directives_** _. One block can include other blocks as children and can also “talk” to each other._
We can turn any HTML tag into a block as simply as adding a data attribute. So, in our case, the top accordion element is going to be a block.
```
<div class="accordion" data-wp-interactive="my-accordion">
<!-- inner HTML elements here -->
</div>
```
The **data-wp-interactive** attribute is necessary to ‘mark’ a specific element as a block. Everything inside it will be considered as block parts. As mentioned above, we can have a block within a block, so:
```
<div class="accordion" data-wp-interactive="my-accordion">
<!-- inner HTML elements here -->
<div class='popup' data-wp-interactive="my-popup"></div>
</div>
```
This is a valid example. As the attribute value, we can pass any string, but it must be unique within the page. We recommend always giving clear and human-readable names because to ‘talk’ with some block on the page from another block, we’ll use exactly the name defined in this attribute.
### 3.2) State
So, we’ve defined an interactive block. But before we use any ‘magic’ **directives** , we need to define some data that can be used in the **directives**.
> **_State_** _is a set of variables based on which we can write_ **_directives_** _and add any logic. It’s one of the ways to ‘expose’ some variable to the_ declarative _template. The main characteristics of the Block state are that it is global and public, i.e., it’s saved in the page scope under the block name and available to others._
> _Note:_ **_State_** _is an optional feature, so we can have an interactive block without the _ **_state_** _._
So, any variables defined in the **state** are:
1. Global across all the blocks with the same type (within the current page)
This means that even if you have multiple blocks of the same type on the same page, they’ll all share the same state. That’s the primary difference from the **context** , which allows defining ‘current block-only’ variables.
2. Public
This means other blocks can ‘request’ their values based on the variable name and use the block name as a ‘namespace’.
**State** variable can be passed from the backend, or defined on the front. Since WordPress is a PHP framework, the state can be passed from the backend by calling a PHP function.
If we need to define a **state** variable on the backend, we must call a specific function above the block definition. The function is called **wp\_interactivity\_state**. So let’s introduce the **isOpen** state and add it to our accordion.
```
<?php echo wp_interactivity_state( 'my-accordion', [
'isOpen' => false,
] ); ?>
<div class="accordion" data-wp-interactive="my-accordion">
<!-- inner HTML elements here -->
</div>
```
The **wp\_interactivity\_state** is a WordPress function that accepts two arguments: the block name, and an array of state variables.
If we have nothing to pass from the backend, we can define the state on the front end in the JS code like this:
```
const { state } = store("my-accordion", {
state: {
isOpen: false
},
});
```
> _FYI: The ‘mixed’ way is also supported, so you can pass some state variables from the backend while defining others on the front._
### 3.3) Context
**Context** is another way to define variables that can be used in **directives**.
> **_Context_** _is a set of variables based on which we can write_ **_directives_** _and add any logic. It’s one of the ways to ‘expose’ some variable to the_ declarative _template. The main characteristics of the Block context are that it is local and private, i.e., it’s saved within the current block and not available to others._
> _Note:_ **_Context_** _is an optional feature, so we can have an interactive block without the _ **_context_** _._
So, any variables defined in the context are:
1. Current block only
This means that even if you have multiple blocks of the same type on the same page, each of them will have its own **context**. That’s the primary difference from the **state** , which allows sharing variables across block instances with the same type.
2. Private
This means other blocks can’t ‘request’ their values directly.
3. Inheritable
Context variables are available to the current node and all its inner elements.
Unlike state variables, which can be defined both on the back-end and front-end side, **context** can only be defined on the back-end. Context variables must be passed as JSON using the **data-wp-context** attribute. Let’s add the **isOpen** context variable to our accordion block:
```
<div class="accordion" data-wp-interactive="my-accordion"
data-wp-context='{"isOpen": false}'>
<!-- inner HTML elements here -->
</div>
```
So, that’s how it looks like in the markup. But in real life, you’ll likely want to pass PHP variables. It can be done like so:
```
<div class="accordion" data-wp-interactive="my-accordion"
data-wp-context='<?php echo json_encode(["isOpen" => false]); ?>'>
<!-- inner HTML elements here -->
</div>
```
You can define the **data-wp-context** attribute manually or call **wp\_interactivity\_data\_wp\_context** , a special WP function, like this:
```
<div class="accordion"
data-wp-interactive="my-accordion"
<?php echo wp_interactivity_data_wp_context(["isOpen" => false]); ?>'>
<!-- inner HTML elements here -->
</div>
```
As we mentioned, the **context** is private and inheritable, so it’s available only for the current node and all its children. So you can have multiple contexts inside your block:
```
<div class="accordion" data-wp-interactive="my-accordion">
<div data-wp-context='<?php echo json_encode(["someVar" => "some value"]); ?>'>
<!-- inner HTML elements here -->
</div>
<div data-wp-context='<?php echo json_encode(["anotherVar" => true]); ?>'>
<!-- inner HTML elements here -->
</div>
</div>
```
### 3.4) Directives
Now, let’s review **directives** , the key feature of the Interactivity API, which allows us to create reactive layouts.
> **_Directives_** _are custom attributes added to the markup of your block to define behavior of the DOM elements._
At first glance, they appear to be plain [HTML data attributes](https://developer.mozilla.org/en-US/docs/Learn/HTML/Howto/Use_data_attributes), familiar to everyone. They follow the **data-wp** format, appearing as **data-wp-{x}=”y”** , where **x** is the directive name, and **y** is the value.
To illustrate with our accordion example, let’s recall the heading part in pseudocode:
```
<div class='accordion__heading-opened' {if !isOpen then add 'hidden' attribute}>
Current open item is <span class='accordion__open-item-name'></span>
</div>
<div class='accordion__heading-closed' {if isOpen then add 'hidden' attribute}>
Items are closed.
<p class='accordion__closed-item' hidden>
Last opened item is <span class='accordion__closed-item-name'></span>
</p>
</div>
```
Now, let’s convert it into real WP Interactive code:
```
<div class="accordion"
data-wp-interactive="my-accordion"
data-wp-context='{"isOpen": false}'>
<div class='accordion__panel'>
<div class='accordion__heading-opened' data-wp-bind--hidden="!context.isOpen">
Current open item is <span class='accordion__open-item-name'></span>
</div>
<div class='accordion__heading-closed' data-wp-bind--hidden="context.isOpen">
Items are closed.
</div>
</div>
<!--other items-->
</div>
```
In this example:
1. We defined the ‘my-accordion’ block.
2. Defined isOpen variable in the block context.
3. Added ‘data-wp-bind — hidden’ directives to the target elements.
#### Directive explanation
Let’s examine the first directive: **data-wp-bind — hidden=”!context.isOpen”**.
For the data attribute name, we used:
- **data-wp-** as a common prefix, necessary for any directive.
- **bind** , which is a directive name.
Bind is one of the WP directives that allows controlling attributes based on boolean variables.
- **— hidden** , representing the name of the attribute we want to control.
Here, we can place any valid HTML attribute.
Now, let’s review the value: **!context.isOpen**.
This is _reactive_ code, creating a bind that persists until the page is closed. Even if you change **isOpen** later, after some action or timeout, it will execute our rule and keep the attribute in sync.
#### Why did Interactivity API choose directives instead of JSX or others?
If you’re familiar with Vue or React, you can draw an analogy with their approaches. For example, in Vue, we also use [built-in directives](https://vuejs.org/api/built-in-directives.html#v-bind), like **v-bind:src=”srcVariable”** , and in React, we use **className={className}**. In WordPress, we use **data-wp-class — classname=”y”**.
While the longer directive format may initially frustrate you, you’ll likely agree that their names are very clear. Keep in mind that WordPress is built on a classic base, and the WP Interactivity API is designed to work with any plain HTML code. [Here](https://developer.wordpress.org/block-editor/reference-guides/interactivity-api/iapi-faq/#what-approaches-have-been-considered-instead-of-using-directives) the official documentation explains all the reasons directives were chosen.
> _So, even though JSX style is shorter, WP uses the classic data-attribute approach. From our experience, after creating several blocks, you’ll get used to it and won’t notice it at all. If you’re still considering that the WP Interactivity API isn’t as great as you envisioned, it has something to make you happier:_
Unlike React and Vue, it offers SSR (Server-Side Rendering) out-of-the-box! This means that initially the **directives** will be processed on the server side by WordPress, and the browser will receive the already correct markup, with all classes and attributes set.
Also, WordPress will take care of hydration/rehydration and will sync the data and markup, so in JavaScript, you’ll be able to access and change **state** , **context** , and more.
We have taken a step away from the **directives** to show the power of the Interactivity API. We’ll review SSR in detail a little later. For now, let’s return to **directives**.
#### List of the available directives
The Interactivity API brings a row of **directives** that cover all our needs. You can find the full list on [this page](https://developer.wordpress.org/block-editor/reference-guides/interactivity-api/api-reference/#list-of-directives) of the official documentation. Let’s review commonly used:
1. wp-bind
As you saw, this **directive** allows you to control any HTML attribute, like **data-wp-bind — hidden=”context.isOpen”**.
2. wp-text
Allows you to control the **innerText** of the node. Inside the value, you should pass a string variable, e.g., **data-wp-text=”state.submitLabel”**.
3. wp-class
Allows you to control the class appearance based on a boolean value. E.g., **data-wp-class — active=”context.isActive”**. The class name can contain any valid characters, so don’t worry, things like **button — enabled** won’t break the directive.
4. wp-style
Allows you to control inline styles, e.g., **data-wp-style — color=”context.color”**.
5. wp-on
Allows you to assign listeners. E.g., **data-wp-on — click=”actions.submit”**.
### 3.5) JS code
Now let’s review the final piece: the JavaScript code itself, which allows us to attach listeners and add external actions, like Ajax. On the frontend, the WordPress Interactivity API is available as a separate file — a tiny library (35KB) built on top of Preact.
We import this library in the JavaScript code of any block. Not all blocks require JavaScript code, so it’s optional. If we don’t need to add listeners to our block, we don’t include JavaScript code, and consequently, the library won’t be imported.
As we mentioned earlier, the Interactivity API provides Server-Side Rendering out-of-the-box, so directives will be executed on the server side. When we need to set state variables on the frontend or define any actions, we have to add the following line to our JS code:
```
import { store } from '@wordpress/interactivity';
```
This is a classic [JavaScript module import](https://javascript.info/modules-intro), and **@wordpress/interactivity** is an alias to **/wp-includes/js/dist/interactivity.min.js** , added by WordPress using the [ImportMap feature](https://developer.mozilla.org/en-US/docs/Web/HTML/Element/script/type/importmap). The following parts are available to import: **store** , **getContext** , and **getElement**. Let’s review all of them.
For now, let’s focus on the **store** , the primary one. To define the block in JavaScript, we must call the **store** function imported from the Interactivity library.
The first argument must be the name of our block from the **data-interactive** attribute, and the second is an object with the settings. Let’s add the **isClosed** state to our accordion block:
```
import { store } from '@wordpress/interactivity';
const { state } = store("my-accordion", {
state: {
isClosed: false,
},
});
```
The object supports the following keys: **state** , **actions** , **callbacks**. Items defined inside the **state** key are used as state variables. Items inside **actions** are used in action directives, such as **wp-on — click**. **Callbacks** are for internal events, like **init** , which is called when the node is created.
> _Note: As we mentioned earlier, you can define a_ **_state_** _both on the backend and frontend. This means if we’ve defined the_ **_isOpen_** _state on the backend using the_ **_wp\_interactivity\_state_** _function, we can access this property in JavaScript code too, even without defining it again._
So we can write **let isOpen = state.isOpen** in our JS code and it’ll return the value of the state variable that we defined on the backend, as WordPress will pass them to the front as JSON automatically. However, keep in mind that state variables defined in JavaScript will only be available on the client side.
This means if you haven’t defined a state variable on the backend but only on the frontend, you can still use this ‘front-only’ state in **directives**. However, such **directives** will be skipped during Server-Side Rendering and executed only on the frontend.
Consequently, if you use them for UI control, the client may see the element you want to hide until JavaScript is loaded and executed. Therefore, if you use state variables in **directives** that affect the initial UI, we recommend defining them on the backend.
#### getContext function
Besides **state** , we can also get access to the block **context**. For this, we need to import the **getContext** function from the Interactivity library. After that, we can call **getContext()** in any action and get any context variable as a property.
```
import {store, getContext} from '@wordpress/interactivity';
store("my-accordion", {
actions: {
toggleItem: () => {
let context = getContext();
context.isItemClosed = !context.isItemClosed;
}
}
});
```
Similar to store variables, the context variables are also writable, so you can change them when needed, and it will update all the directives where the context variable is used.
> _Note: The_ **_getContext()_** _call will automatically get the closest context to the node on which the event is fired. This means if you’ve added_ **_data-wp-context_** _to a block and its inner child, and then added a click listener to that child, in the action method, the_ **_getContext()_** _call will return the context of this child._
#### Store variables in Actions
Let’s combine **store** and **actions** to add a click action to our accordion example to see how it all looks together:
```
import { store } from '@wordpress/interactivity';
const { state } = store("my-accordion", {
state: {
isClosed: true,
},
actions: {
toggle: (event) => {
state.isClosed = !state.isClosed;
},
},
});
```
Then we assign this listener to our accordion item using the **wp-on** directive:
```
<div class='accordion__item'>
<p class='accordion__item-title' data-wp-on--click="actions.toggle">Title</p>
<div class='accordion__item-content' data-wp-bind--hidden="!state.isOpen">Content</div>
</div>
```
That’s it! Thanks to the reactivity, when we change the state variable, it will execute **directives** in which that variable was used and will add or remove the **hidden** attribute. We can use the same variable in multiple **directives**.
#### getElement function
Using the **getElement** function, we can directly access the [HTMLElement](https://developer.mozilla.org/en-US/docs/Web/API/HTMLElement) of the current block. In most cases, you won’t need it, but there are rare instances when it’s useful. For example, if you need to access the browser’s API to scroll the content inside or get the element’s width.
To get the HTMLElement, we need to get the **ref** part of the function response:
```
const { ref } = getElement();
// ref is an ordinary HTMLElement instance, so we can do anything with it, like:
console.log(ref.getBoundingClientRect());
```
#### Callbacks
Returning to the **store** object keys: **state** , **actions** , and **callbacks** — we have seen the first two in the action. The third key, **callbacks** , is used to define general block callbacks that are called by the library, such as **init** or **run**.
**init** is called only once when the node is created, while **run** is called on every node rendering. To add them to the block, besides defining them in JS, we need to set them in directives too, like this:
```
import {store, getElement, getContext} from '@wordpress/interactivity';
store("my-accordion", {
callbacks: {
init: () => {
let {ref} = getElement();
console.log('Accordion node is parsed', {
HTMLElement: ref,
isOpen: getContext().isOpen,
});
}
}
});
<div class="accordion"
data-wp-interactive="my-accordion"
data-wp-context='{"isOpen": false}'
data-wp-init="callbacks.init">
<!--inner items-->
</div>
```
### 3.6) Summary
Breathe out, because at this step, we can congratulate you — the most complex parts are behind you, and you’ve learned the key aspects of the Interactivity API.
Let’s depict them all at once so you can get a complete picture in your mind.
The WordPress Interactivity API is based on plain HTML and provides **directives** , **store** , and **context** , which allow for _declarative_ templates. Let’s look at a simple example:
```
<?php wp_interactivity_state('my-accordion', ['isClosed' => true,]) ?>
<div class="accordion"
data-wp-interactive="my-accordion"
data-wp-context='{"isOpen": false}'
data-wp-init="callbacks.init">
<div class='accordion__panel'>
<div class='accordion__heading-opened' data-wp-bind--hidden="state.isClosed">
Current open item is <span class='accordion__open-item-name'></span>
</div>
<div class='accordion__heading-closed' data-wp-bind--hidden="context.isOpen">
Items are closed.
</div>
</div>
<!--other items-->
</div>
import { store, getElement, getContext } from '@wordpress/interactivity';
const { state } = store("my-accordion", {
callbacks: {
init: () => {
let { ref } = getElement();
console.log('Accordion node is parsed', {
HTMLElement: ref,
isOpen: getContext().isOpen,
isClosed: state.isClosed,
});
}
}
});
```
So what’s happening here?
#### 1. In the PHP backend, the templates are rendered and directives are processed
Before passing to the browser, WordPress processes the directives and updates the markup accordingly. In addition, WP converts all the state variables into JSON and passes them to the browser along with the markup.
In our case, the **\_\_heading-opened** element will have the **hidden** attribute, according to the **false** value of the **isOpen** context variable. Meanwhile, the **\_\_heading-closed** element won’t have this attribute, because **isClosed** state variable is **true**.
#### 2. On the frontend, our JS code loads the interactivity API JS library
That library parses the JSON (in React it’s called rehydration) and calls our block definition. The WP Interactivity.js library will put the store variables defined on the backend into the **state** variable in our JS code ( **isClosed** in our case).
It will also call the **init** callback to which we added a listener using the **wp-init** directive. In this callback, we print the HTML element of the block, along with the **isOpen** variable from the **context** and the **isClosed** variable from the **state**.
From a logical point of view, it’s pointless to have both variables at once, but we included them to showcase how you can use both **store** and **context** simultaneously. That’s the way the WordPress Interactivity API works, so make sure you get the whole picture.
If something is unclear, we recommend re-read the related explanation above before continuing with the article.
### 4. Server Side Rendering in the Interactivity API
> _Note: This information is useful for understanding how the SSR works in the Interactivity API behind the scenes, but it is not necessary for the basic API usage. You can safely skip this chapter._
#### About the SSR overall
The main drawback of any reactive frameworks in JS is client-side rendering. While classical applications send ready HTML to the client, reactive frameworks like React or Vue create HTML on the fly, based on the defined components and their data.
In practice, this means clients will see an empty page, or at least sections, for some time until JS processes everything. This not only hurts the UX but also SEO, as search engines can’t immediately parse the page content.
Many search engines don’t support it, and while Google claims to support it, SEO experts [don’t recommend using client-side rendering](https://www.techmagic.co/blog/react-seo/) for pages sensitive to SEO scores. If you’re familiar with React/Vue, you know that full-stack frameworks like [Next.js](https://nextjs.org/) (React) and [Nuxt.js](https://nuxt.com/) (Vue) offer SSR.
They can ‘preload’ HTML by executing JavaScript on the server side (Node.js) and passing already prepared HTML along with the necessary states, so the client can ‘hydrate’ this data and restore its state. They seamlessly handle all the nuances, but behind the scenes, it requires quite a significant effort.
One of the difficulties here is that frameworks use Node.js on the backend and plain JavaScript on the client side in the browser. This means that the same piece of code can be executed in either of these environments, which are quite different.
#### SSR implementation in the WP Interactivity API
Now, back to WordPress. As we mentioned, the Interactivity.js on the front end is based on Preact, so it doesn’t offer any SSR. Fortunately, WordPress comes with its own SSR solution, and while it may sound a little crude, it’s a nice solution that supports any plain HTML.
> _SSR in WordPress Interactivity API is based on its own HTML API (_ [_WP\_HTML\_Tag\_Processor_](https://developer.wordpress.org/reference/classes/wp_html_tag_processor/)_), which WordPress_ [_introduced in version 6.2_](https://make.wordpress.org/core/2023/03/07/introducing-the-html-api-in-wordpress-6-2/)_._
The idea is to parse HTML pieces with the interactive directives on the backend (PHP) and modify the markup based on them, to deliver the built markup ready to the client. In addition, it includes ‘hydration’ on the client, to transfer all the states to the client side.
In this way, all state variables that we add to the blocks using the **wp\_interactivity\_state** function call in PHP, and context variables from the **data-wp-context** attribute, will be used during directives execution in PHP SSR.
Afterward, the state variables will be added to the current page as JSON, and then will be parsed on the client and attached to the JS block states, as we showed in the JS code explanation. In this way, the client and SEO engines get the ready HTML from the beginning, while developers can access all the data from the backend.
Though it required directive support in PHP from WordPress, it integrates well with the WP ecosystem, making developers’ lives easier and the user experience much better. If you think this is a rough solution that may be bad for performance, you shouldn’t worry about it.
It’s implemented smartly, so WordPress doesn’t parse all the page HTML, but only the pieces where the Interactivity API can be used, additionally limiting parsing to nodes with data-wp attributes. In this way, it doesn’t add significant overhead to the whole process.
### 5. Where you can use WordPress Interactivity API
Since we’ve learned the basics, let’s now see where we can apply this knowledge. As we mentioned earlier, the Interactivity API SSR isn’t applied to all the page content, so by default, you can’t start using it in any template. Below we provide the ways you can apply it:
#### 5.1) In custom Gutenberg blocks (created manually)
By default, the WordPress Interactivity API is available in [Gutenberg blocks](https://developer.wordpress.org/block-editor/). To enable its support for a specific block, you need to define **“interactivity”: true** in the **block.json** data and can use all the WP Interactivity features in **render.php** and **view.js** files.
This is good news if you’re already familiar with and experienced with the custom Gutenberg block creation process. Otherwise, we wouldn’t recommend this method, as creating custom Gutenberg blocks from scratch is time-consuming and requires React knowledge.
In most cases, you’ll need to write the markup for the same block twice: first in React for the Gutenberg editor, then in PHP for the front end.
#### 5.2) In custom Gutenberg blocks (created using a third-party vendor)
Overall, building WordPress pages from custom Gutenberg blocks is still a good idea because they’re modular, efficient on the front end, and provide a good UX for editors. In our agency, we harness the [ACF Blocks](https://wplake.org/blog/acf-blocks/) feature of the [Advanced Custom Fields](https://wplake.org/blog/advanced-custom-fields/) plugin.
This feature allows the creation of custom Gutenberg blocks without hassle. You can also use [MB Blocks](https://wplake.org/blog/meta-box-plugin/#metabox-blocks_oep8) or [Pods blocks](https://wplake.org/blog/pods-plugin/#3-pods-blocks_s6bz) features. Check our [best custom field plugins review](https://wplake.org/blog/acf-metabox-and-pods-review/) to compare and learn how to use them.
#### 5.3) In templates of the Advanced Views Framework
The [Advanced Views](https://wplake.org/advanced-views-lite/) Framework [introduces](https://wplake.org/blog/advanced-views-plugin-review/) smart templates for the WordPress front-end, simplifying post queries and template creation. These templates harness the Twig engine and [support the Interactivity API](https://docs.acfviews.com/templates/wordpress-interactivity-api)out-of-the-box, so you can use it in any template without extra actions.
These templates [can be stored inside your theme](https://docs.acfviews.com/templates/file-system-storage), making them Git and IDE-friendly. Additionally, you can employ TypeScript/Sass and [Tailwind](https://docs.acfviews.com/templates/file-system-storage#tailwind-usage) for them.
Another benefit is that it also [supports Gutenberg block creation](https://docs.acfviews.com/display-content/custom-gutenberg-blocks-pro) (via third-party vendors mentioned above), so you can turn any template into a custom Gutenberg block, providing a nice experience for editors while enjoying the modular approach and Interactivity API features.
#### 5.4) In plain PHP templates
Though the Interactivity API may seem like a Gutenberg-oriented tool, it isn’t so by the fact. It’s a core and public API that can be used anywhere.
In your theme or plugin, you can call the **wp\_interactivity\_process\_directives** function and pass a string with the HTML code that has directives. These directives will be executed, and the function will return the updated markup.
So it may look like this:
```
<?php
echo wp_interactivity_state('my-accordion', [
'isOpen' => false,
]);
ob_start();
?>
<div class="accordion" data-wp-interactive="my-accordion">
<!-- inner HTML elements here -->
</div>
<?php
$html = (string) ob_get_clean();
echo wp_interactivity_process_directives($html);
import { store, getElement, getContext } from '/wp-includes/js/dist/interactivity.min.js';
store('my-accordion', {
actions: {
// ...
}
});
```
While it’s possible to use the Interactivity API in this manner, we recommend building websites modularly, using independent blocks with their own assets, as in the case of custom Gutenberg blocks and smart templates of the Advanced Views Framework.
### 6. Example of the interactive block
Now, you have all the knowledge, and we recommend you to make several examples with your own hands to practice and store the knowledge better in your head. Below, as promised, we provide an advanced accordion example mentioned above, turned into the WP Interactive block.
```
<?php
wp_interactivity_state( 'my-accordion', [
'isOpen' => false,
'isLastItemSet' => false,
'lastOpenedItemName' => "",
] ); ?>
<div class="accordion"
data-wp-interactive="my-accordion">
<div class='accordion__panel'>
<div class='accordion__heading-opened' data-wp-bind--hidden="!state.isOpen">
Current open item is <span class='accordion__open-item-name' data-wp-text="state.lastOpenedItemName"></span>
</div>
<div class='accordion__heading-closed' data-wp-bind--hidden="state.isOpen">
Items are closed.
<p class='accordion__closed-item' data-wp-bind--hidden="!state.isLastItemSet">
Last opened item is <span class='accordion__closed-item-name'
data-wp-text="state.lastOpenedItemName"></span>
</p>
</div>
</div>
<div class='accordion__item' data-wp-context='{"isItemClosed":true,"itemName":"First"}'>
<p class='accordion__item-title' data-wp-on--click="actions.toggleItem" data-wp-text="context.itemName"></p>
<div class='accordion__item-content' data-wp-bind--hidden="context.isItemClosed">Content of the first item</div>
</div>
<div class='accordion__item' data-wp-context='{"isItemClosed":true, "itemName":"Second"}'>
<p class='accordion__item-title' data-wp-on--click="actions.toggleItem" data-wp-text="context.itemName"></p>
<div class='accordion__item-content' data-wp-bind--hidden="context.isItemClosed">Content of the second item
</div>
</div>
</div>
import {store, getContext} from '@wordpress/interactivity';
const {state} = store("my-accordion", {
state: {
openedItemTitle: null,
get isLastItemSet() {
return '' !== state.lastOpenedItemName;
},
get isOpen() {
return null !== state.openedItemTitle;
}
},
actions: {
toggleItem: (event) => {
let titleElement = event.target;
let context = getContext();
// Handle closing the previous item
if (null !== state.openedItemTitle &&
titleElement !== state.openedItemTitle) {
state.openedItemTitle.click();
}
// Toggle the current item
context.isItemClosed = !context.isItemClosed;
// update the top state
state.lastOpenedItemName = context.itemName;
state.openedItemTitle = false === context.isItemClosed ?
titleElement :
null;
}
}
});
```
> _Getters: In this implementation, we used the built-in JS_ [_getter feature_](https://developer.mozilla.org/en-US/docs/Web/JavaScript/Reference/Functions/get) _to add dynamic state variables. This feature can be added to any object in JS and is particularly useful in our case, as_ **_wp-bind_** _boolean properties support only boolean primitives, so we couldn’t add conditions there._
So, this is a declarative implementation of the accordion block. Let’s now recall how the JS code looked in the imperative approach:
```
document.addEventListener('DOMContentLoaded', () => {
document.body.querySelectorAll('.accordion__item-title').forEach((title) => {
title.addEventListener('click', () => {
let item = title.closest('.accordion__item');
let isToOpen = !item.classList.contains('accordion__item--open');
let accordion = item.closest('.accordion');
let prevItem = accordion.querySelector('.accordion__item--open');
// Handle closing the previous item
if (prevItem) {
prevItem.classList.remove('accordion__item--open');
accordion.querySelector('.accordion__closed-item').removeAttribute('hidden');
accordion.querySelector('.accordion__closed-item-name').innerText = prevItem.querySelector('.accordion__item-title').innerText;
}
// Toggle the current item
if (isToOpen) {
accordion.querySelector('.accordion__heading-closed').setAttribute('hidden', true);
accordion.querySelector('.accordion__heading-opened').removeAttribute('hidden');
item.classList.add('accordion__item--open');
accordion.querySelector('.accordion__open-item-name').innerText = title.innerText;
} else {
accordion.querySelector('.accordion__heading-opened').setAttribute('hidden', true);
accordion.querySelector('.accordion__heading-closed').removeAttribute('hidden');
item.classList.remove('accordion__item--open');
accordion.querySelector('.accordion__closed-item-name').innerText = title.innerText;
}
});
});
});
```
Wow, how much shorter the event handler is now, and what a nice thing to update variables instead of querying nodes directly and updating attributes manually!
You can already see the huge benefit and shift in the approach even in this small example. Recall all your JS code from real life, and envision now how much better it’s going to be when it’s written using the Interactivity API.
Now it’s a great time to experiment! Try to change something in that to get practical experience with the WordPress Interactivity API!
> _Demonstration note: If you’re an exprienced web developer, you can see that our implementations are quite simple and can be improved. In real life, it would use the_ **_wp-each_** _directive, or at least a PHP loop by the data array. But don’t judge strictly, we made it as simple as possible for demonstration purposes._
### 7. Pro Tips on the Interactivity API
There are several useful things you should know to harness the full potential of the API. Some of them we already briefly mentioned, and now let’s review them in detail:
#### 7.1) Getters in State
As you saw in the declarative advanced accordion implementation above, we can define any getters in the state object. This is a very useful feature, and you’re going to use it often due to the fact that most directives support only boolean variables.
It means you can’t write conditional statements, like in plain JS code, **data-wp-bind — hidden=”state.isFirst && !state.isSecond”** or **“state.name == ‘’”**. These won’t work. So when you need such conditions, you can put them into a getter and define that getter inside the attribute.
```
import {store, getContext} from '@wordpress/interactivity';
const {state} = store("my-accordion", {
state: {
get isLastItemSet() {
return '' !== state.lastOpenedItemName;
},
},
});
```
Inside that getter, we can also harness context variables by calling **getContext()**. Also, pay attention that getters defined in the JS code aren’t available on the backend, so during SSR, **directives** that include them will be skipped.
In these cases when you want them to participate in SSR, you can define them using the **wp\_interactivity\_state** function as primitive booleans, and then just override them in the JS by assigning a function to the same name.
#### 7.2) Event object in Actions
When we assign our callback to some element in plain JavaScript, like **.addEventListener(‘click’)**, this callback will receive the first argument with the [Event](https://developer.mozilla.org/en-US/docs/Web/API/Event) type. The object will vary depending on the action itself, but in all cases, it implements the general Event interface.
Actions in the WP Interactivity API also receive this object, so you can use it as you need, e.g., to get the current element, like **event.target** :
```
import {store} from '@wordpress/interactivity';
store("my-accordion", {
actions: {
toggle: (event) => {
let clickedHTMLElement = event.target;
// clickedHTMLElement.innerHTML = 'x';
}
}
});
```
#### 7.3) Loop Directive: wp-each
It’s an advanced directive, which you’ll need only in cases where the interface requires dynamic item creation and removal. An example is the classic ‘todo’ list, where besides editing, items can be added and removed.
This directive allows defining a template that will be applied to all items of the list. The idea is that when you change the related variable in JS, it’ll keep the items in sync automatically.
Let’s review this example:
```
<?php
$context = [
'list' => [
[
"id" => "en",
"value" => "hello"
],
[
"id" => "es",
"value" => "hola"
],
[
"id" => "pt",
"value" => "olá"
]
]
];
?>
<div class="accordion"
data-wp-interactive="my-accordion"
data-wp-context='<?php
echo json_encode( $context ); ?>'>
<ul>
<template
data-wp-each--item="context.list"
data-wp-each-key="context.item.id">
<li data-wp-text="context.item.value"></li>
</template>
</ul>
<button data-wp-on--click="actions.removeLastItem">Remove last item</button>
</div>
import {store, getContext} from '@wordpress/interactivity';
const {state} = store("my-accordion", {
actions: {
removeLastItem: (event) => {
let context = getContext();
context.list.pop();
}
}
});
```
In this example, we have a list of items, where each has an id and value. Using the special **Template** tag and **data-wp-each** directive, we define the loop by the list. In the directive name, we define the item name, in our case **item** (data-wp-each — item=), and as value, we define the list itself, which can be either a context or state variable.
Pay attention that we use the **wp-each-key** directive to point to the unique item ID, thanks to which the Interactivity API will keep items in sync.
This loop will be processed during SSR and replaced with the markup built based on the items. But unlike a plain PHP loop, it’ll keep the list context variable defined in the **wp-each** directive in sync with the markup, so when we remove the last item of the array in the action, it’ll remove the target item in the markup automatically.
#### 7.4) Cross Block Communication
As we mentioned earlier, all the block state variables are public, so they can be accessible from other blocks. But how can we do it?
To get the state of another block, we should call the **store** function with the name of the target block, but without passing the second argument, as we did before.
Below we show how to get the **someData** state variable from the **my-another-block**. This code can be placed anywhere, e.g., inside any action of our accordion block.
```
import {store} from '@wordpress/interactivity';
// ....
console.log(store("my-another-block").state.someData);
```
### 8. Conclusions
The appearance of the WordPress Interactivity API is a significant shift in the WordPress ecosystem. Although it was released recently and hasn’t gained widespread recognition yet, it is definitely going to play a crucial role in WordPress development in the near future.
This built-in integration will help developers build interactive frontends easily. Thanks to the unified approach, plugin and theme vendors can develop their own interactive blocks, which will be able to interact with each other, regardless of the vendor.
We hope this article was useful and that you’ve understood all the key aspects of the Interactivity API. Happy developing!
| wplake |
1,864,158 | ReScript has come a long way, maybe it's time to switch from TypeScript? | ReScript, the "Fast, Simple, Fully Typed JavaScript from the Future", has been around for awhile now.... | 0 | 2024-05-28T14:49:42 | https://dev.to/jderochervlk/rescript-has-come-a-long-way-maybe-its-time-to-switch-from-typescript-29he | rescript, javascript, typescript, webdev | [ReScript](https://rescript-lang.org/), the "Fast, Simple, Fully Typed JavaScript from the Future", has been around for awhile now. The name "ReScript" came into existence in 2020, but the project has a history going back to 2016 under the combo of Reason and BuckleScript. The name change came about as the goal of BuckleScript shifted to try and create a language that was a part of the JavaScript ecosystem; JavaScript is the only build target, support for all of the features JavaScript devs expect to have like async/await syntax, and an easy to use standard library for JavaScript's built in functions.
Since the re-brand to ReScript the team behind the project have been very busy. If you look around the internet to see what people have to say about ReScript there are some things that people didn't like or JavaScript features that were missing. Many of these have been addressed, so lets take a look at some of these complaints and features that have been recently addressed. Hopefully you'll give ReScript another look as a strong alternative to TypeScript
## My sources of past issues
To create this list of issues I have poured over the official ReScript forum, Hacker News, Reddit, and Twitter. I tried not to omit anything and I wasn't just looking for issues that have been solved. I'll call out anything that hasn't changed that might still be a pain point for some people, but hopefully you'll see the massive steps forward the language has taken in the past 4 years.
## I have to understand Reason, BuckleScript, and OCaml before I can use ReScript
You don't need to know anything about Reason, BuckleScript or OCaml to use ReScript.
ReScript's history comes from these languages and tools, but today it's very much it's own thing that works with the standard JS ecosystem of NPM, PNPM, Yarn, or whatever package manager you want to use. The JS it spits out can be used by any build tool like Vite, ESBuild, Webpack, etc... ReScript is fully part of the JS ecosystem and you don't need to know any other languages, new build tools, or new package managers.
[Ocaml](https://ocaml.org/) is still a wonderful language if you want to look into it, and [Reason](https://reasonml.github.io/) is still going strong as an alternate syntax for OCaml. With either OCaml or Reason you can compile to native code, or use the continuation of BuckleScript now called [Melange](https://melange.re/v4.0.0/).
## Should I use Belt.Array, Js.Array, or Js.Array2?
Due to ReScript's history being rooted in Ocaml and Reason, it came with some baggage from those languages. Not bad baggage, but Ocaml isn't JavaScript and had it's own patterns and ways of doing things that made sense for that language. Trying to match these patterns to JavaScript was cumbersome when the goal of Reason was to compile to native code or JavaScript while maintaining full interop with OCaml. ReScript now focuses only on the land of JavaScript, so it has a new [Core library](https://rescript-lang.org/docs/manual/latest/api/core) that is meant to be easy to pick up and understand. The previous standard Js library is being deprecated and will soon be removed from the language, and Belt will evolve into a more fully featured utility library like Lodash that will be optional to use.
The answer to the above question is to just use `Array`.
```typescript
let t = [1, 2, 3]->Array.map(n => n + 1)
```
Core is a separate library for now, but the roadmap is to include it in the language directly before the end of the year.
## Lack of async, await, and Promises are cumbersome
Native support for `async`/`await` syntax was added in ReScript 10.1 in Early 2023. The new Core library I mentioned above also introduced a streamlined way to work with Promises.
```typescript
// async/await
let fn = async () => {
try {
let result = await getData()
Console.log(result)
} catch {
| err => Console.error(err)
}
}
// Promises
let fn = () => {
getData()
->Promise.thenResolve(result => Console.log(result))
->Promise.catch(err => {
Console.error(err)
Promise.resolve()
})
}
```
## Lack of community types
When ReScript was young you would have to write your own bindings and types for most existing JS libraries before you could use them. There are now hundreds of NPM packages that have bindings and documentation on how to use your favorite JS libraries with ReScript. Bindings exist for [React](https://www.npmjs.com/package/@rescript/react) (which also still has first class support directly in the ReScript compiler), [Node](https://www.npmjs.com/package/rescript-nodejs), [Jotai](https://www.npmjs.com/package/@fattafatta/rescript-jotai), [React Query](https://www.npmjs.com/package/@dck/rescript-react-query), [React Hook Form](https://www.npmjs.com/package/@greenlabs/rescript-react-hook-form), [AntD](https://www.npmjs.com/package/@ant-design-rescript/components), [Material UI](https://www.npmjs.com/package/@rescript-mui/material), [Bun](https://www.npmjs.com/package/rescript-bun), [Vitest](https://www.npmjs.com/package/rescript-vitest), [Graphqljs](https://www.npmjs.com/package/rescript-graphqljs) and many others!
There are even some incredible ReScript first libraries out there that really shine and can take advantage of ReScript powerful type system and compiler, like [rescript-relay](https://www.npmjs.com/package/rescript-relay).
```typescript
/* Avatar.res */
module UserFragment = %relay(`
fragment Avatar_user on User {
firstName
lastName
avatarUrl
}
`)
@react.component
let make = (~user) => {
// this is fully typed!
let userData = UserFragment.use(user)
<img
className="avatar"
src=userData.avatarUrl
alt={
userData.firstName ++ " "
userData.lastName
}
/>
}
```
ReScript also has amazing tooling for parsing JSON into types. Here's an example of [rescript-schema](https://github.com/DZakh/rescript-schema/blob/HEAD/packages/rescript-schema-ppx/README.md):
```typescript
@schema
type cat = {
name: string,
color: string,
}
let _ =
%raw(`{ name: 'fluffy', color: 'orange' }`)
->S.parseWith(catSchema) // catSchema is generated automatically!
->Console.log
```
## I don't understand how to use existing JavaScript libraries
While there is a growing number of community bindings and libraries written in ReScript, at some point you'll need to dig into writing your own bindings. Thankfully, the [documentation is excellent](https://rescript-lang.org/docs/manual/latest/external) and you can reference one of the many existing NPM packages for ideas.
Just this week I needed to use a function from [`path-to-regexp`](https://www.npmjs.com/package/path-to-regexp) and it took me just a few minutes to create bindings and the function I needed.
```typescript
type t = string => option<{.}>
type m = {
path: string,
params: {.}, // this means any object
}
@unboxed // @unboxed is a way to have a variant type that compiles to simple javascript without a runtime object
type isMatch =
| Yes(option<m>) // the JS for this is just an object of type m
| @as(false) No // the JS for this is just 'false'
type match = string => isMatch
@module("path-to-regexp") // this is the actual binding using the types I made above
external match: string => match = "match"
let make = url => {
let fn = match(url) // and now I can call it!
path =>
switch fn(path) {
| Yes(t) => t->Option.map(t => t.params)
| No => None
}
}
```
## I can't have 2 files with the same name?
This hasn't changed, and due to the way the module system works it never will. It might feel weird at first for JS devs, but this isn't that weird in other languages. You get used to it very quickly.
## Why would I pick this over TypeScript?
I have another article that dives into this: [Tired of Typescript? Check out ReScript! ](https://dev.to/jderochervlk/tired-of-typescript-check-out-rescript-571o)
The short answer is that you would pick ReScript if:
- You want a strong, sound type system (no any types!)
- You want types, but you don't want to write type annotations (the compiler just knows!)
- You want only the "Good Parts" of JavaScript
- You want a blazing fast compiler and fast Intellisense in VSCode, even when your repo is massive
- You want amazing [next gen language features](https://dev.to/jderochervlk/rescript-rust-like-features-for-javascript-27ig) like pattern matching, Option and Result types, and [powerful variant types](https://dev.to/jderochervlk/using-variant-types-in-rescript-to-represent-business-logic-34e3).
## Not convinced?
Leave a comment! I'm more than happy to discuss things in more detail and answer questions about ReScript! I've been using it for a few projects over the past 4 years, and it's hard to switch back to writing TypeScript when I need to. It's been incredible to watch the language grow and evolve and it should be considered as an alternative to TypeScript.
Cover Photo by <a href="https://unsplash.com/@impatrickt?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash">Patrick Tomasso</a> on <a href="https://unsplash.com/photos/gray-concrete-road-between-brown-and-green-leaf-trees-at-daytime-5hvn-2WW6rY?utm_content=creditCopyText&utm_medium=referral&utm_source=unsplash">Unsplash</a>
| jderochervlk |
1,867,867 | Menggali Keuntungan: Panduan Lengkap Bermain Judi Slots Online | Menggali Keuntungan: Panduan Lengkap Bermain Judi Slots Online Dalam era digital saat... | 0 | 2024-05-28T14:48:22 | https://dev.to/baileygaines/menggali-keuntungan-panduan-lengkap-bermain-judi-slots-online-12d5 | webdev, javascript, programming, beginners | Menggali Keuntungan: Panduan Lengkap Bermain Judi Slots Online
==============================================================

Dalam era digital saat ini, judi slots online telah menjadi salah satu bentuk hiburan yang paling populer di dunia perjudian online. Bagi pemilik bisnis judi online dan pemain judi online profesional, pemahaman mendalam tentang permainan judi slots online adalah kunci untuk meraih keuntungan yang signifikan. Artikel ini akan menjadi panduan lengkap yang memberikan wawasan mendalam, statistik terbaru, dan contoh nyata tentang permainan judi online, dengan fokus pada judi slots online. Gaya bahasa yang digunakan akan profesional dan informatif, sesuai dengan target pembaca yang ditujukan kepada pemilik bisnis judi online dan pemain judi online profesional.
Pengantar tentang Judi Slots Online
-----------------------------------
Judi slots online adalah bentuk permainan **[dewapoker online](https://neon.ly/vgRW6)** yang menggabungkan keberuntungan dan hiburan. Permainan ini didasarkan pada mesin slot tradisional yang ditemukan di kasino fisik, tetapi kini dapat dinikmati dengan mudah melalui platform online. Pemain memutar gulungan dan berharap mendapatkan kombinasi simbol yang menghasilkan kemenangan.
Pertumbuhan Populeritas Judi Slots Online
-----------------------------------------
Statistik terbaru menunjukkan pertumbuhan yang signifikan dalam popularitas judi slots online. Pada tahun 2023, pendapatan global dari judi slots online diperkirakan mencapai angka sekitar $45 miliar. Diperkirakan bahwa jumlah pemain judi slots online di seluruh dunia akan mencapai 200 juta pada tahun 2024. Ini menunjukkan potensi besar bagi pemilik bisnis judi online dan pemain judi online profesional untuk meraih keuntungan yang substansial.
**Keuntungan Bermain Judi Slots Online**
1. Aksesibilitas: Salah satu keuntungan utama bermain slots **[login poker88](https://neon.ly/mw4kD)** online adalah aksesibilitasnya. Pemain dapat menikmati permainan kapan saja dan di mana saja melalui perangkat komputer atau ponsel pintar mereka. Tidak ada lagi batasan geografis atau pembatasan waktu yang membatasi akses ke permainan.
2. Pilihan Permainan yang Luas: Platform judi slots online menawarkan pilihan permainan yang sangat luas. Pemain dapat memilih dari berbagai tema, gaya grafis, dan fitur permainan yang berbeda. Ini memungkinkan pemain untuk menemukan permainan yang sesuai dengan preferensi dan gaya bermain mereka.
3. Bonus dan Promosi: Industri judi slots online dikenal karena menyediakan bonus dan promosi yang menarik. Bonus selamat datang, putaran gratis, dan promosi mingguan atau bulanan adalah beberapa contoh insentif yang dapat meningkatkan peluang kemenangan dan memberikan nilai tambahan kepada pemain.
**Strategi Bermain yang Efektif**
1. Kelola Bankroll dengan Bijak: Salah satu kunci kesuksesan dalam bermain judi slots **[dominobet asia](https://neon.ly/vkB8j)** online adalah mengelola bankroll dengan bijak. Tetapkan batas harian atau mingguan untuk berapa banyak uang yang akan Anda pertaruhkan, dan patuhi batasan itu. Jangan tergoda untuk melampaui batas Anda, karena dapat berdampak buruk pada keuangan Anda.
2. Pilih Permainan yang Sesuai: Memilih permainan yang sesuai dengan preferensi dan gaya bermain Anda sangat penting. Pertimbangkan varians permainan, RTP (Return to Player), dan fitur bonus yang ditawarkan. Pahami aturan permainan dan pelajari strategi yang tepat untuk meningkatkan peluang kemenangan Anda.
3. Manfaatkan Fitur Demo: Banyak platform judi slots online menyediakan fitur demo yang memungkinkan pemain untuk mencoba permainan secara gratis sebelum mempertaruhkan uang sungguhan. Manfaatkan fitur ini untuk menguji permainan baru, memahami mekanisme permainan, dan mengasah strategi Anda.
### Kesimpulan Bermain Judi Slots Online
Judi slots online memberikan peluang yang menguntungkan bagi pemilik bisnis judi online dan pemain judi online profesional. Dengan **[daftar domino88](https://neon.ly/N4Z7z)** dan memahami permainan secara mendalam, pemilik bisnis dapat menyediakan pengalaman bermain yang menghibur dan menarik bagi pemain mereka. Sementara itu, pemain judi online profesional dapat memanfaatkan strategi bermain yang efektif dan memilih permainan yang tepat untuk meningkatkan peluang kemenangan mereka.
Dalam industri yang terus berkembang ini, pemilik bisnis judi online dan pemain judi online profesional harus terus mengikuti tren terbaru, memahami preferensi pemain, dan menyediakan bonus dan promosi yang menarik. Dengan memperkuat pengetahuan mereka tentang judi slots online dan mengikuti panduan ini, pemilik bisnis judi online dan pemain judi online profesional dapat menggali keuntungan yang signifikan dan meraih kesuksesan dalam industri perjudian online yang kompetitif. Pemahaman yang mendalam tentang aturan permainan, strategi bermain yang efektif, dan pilihan permainan yang tepat akan memungkinkan mereka untuk membuat keputusan yang lebih baik, mengoptimalkan peluang kemenangan, dan meningkatkan pengalaman bermain pemain.
Pemilik bisnis judi online yang mampu menyediakan platform yang aman, andal, dan menarik akan menarik pemain baru dan mempertahankan pemain yang sudah ada. Dengan menawarkan bonus dan promosi yang menguntungkan, mereka dapat memperluas basis pengguna mereka dan membangun reputasi yang kuat di industri ini.
Di sisi lain, pemain judi online profesional yang memanfaatkan panduan ini akan memiliki keunggulan kompetitif. Mereka dapat mengembangkan strategi bermain yang efektif, mengelola bankroll mereka dengan bijak, dan memilih permainan yang memberikan peluang terbaik untuk menghasilkan kemenangan. Dengan mengoptimalkan pengalaman bermain mereka, mereka dapat meningkatkan tingkat keterlibatan, memaksimalkan keuntungan, dan mencapai kesuksesan dalam jangka panjang.
Penting untuk diingat bahwa dalam industri perjudian online, kesuksesan tidak datang dengan instan. Pemilik bisnis judi online dan pemain judi online profesional perlu memiliki dedikasi, ketekunan, dan kemauan untuk terus belajar dan beradaptasi dengan perubahan tren dan kebutuhan pasar. Dengan tetap mengikuti perkembangan terbaru dan meningkatkan pengetahuan serta keterampilan mereka, mereka dapat terus menggali keuntungan dalam industri perjudian online yang kompetitif ini.
Kesimpulannya, dengan memperkuat pengetahuan mereka tentang judi slots online dan mengikuti panduan ini, pemilik bisnis judi online dan pemain judi online profesional dapat memanfaatkan peluang yang ada dalam industri perjudian online. Dengan strategi bermain yang efektif, pemilihan permainan yang tepat, dan penawaran bonus dan promosi yang menarik, mereka dapat meraih keuntungan yang signifikan dan mencapai kesuksesan jangka panjang. | baileygaines |
1,867,866 | The Arrays Class | The java.util.Arrays class contains useful methods for common array operations such as sorting and... | 0 | 2024-05-28T14:47:07 | https://dev.to/paulike/the-arrays-class-2kf1 | java, programming, learning, beginners | The **java.util.Arrays** class contains useful methods for common array operations such as sorting and searching.
The **java.util.Arrays** class contains various static methods for sorting and searching arrays, comparing arrays, filling array elements, and returning a string representation of the array. These methods are overloaded for all primitive types.
You can use the **sort** or **parallelSort** method to sort a whole array or a partial array. For example, the following code sorts an array of numbers and an array of characters.
`double[] numbers = {6.0, 4.4, 1.9, 2.9, 3.4, 3.5};
java.util.Arrays.sort(numbers); // Sort the whole array
java.util.Arrays.parallelSort(numbers); // Sort the whole array`
`char[] chars = {'a', 'A', '4', 'F', 'D', 'P'};
java.util.Arrays.sort(chars, 1, 3); // Sort part of the array
java.util.Arrays.parallelSort(chars, 1, 3); // Sort part of the array`
Invoking **sort(numbers)** sorts the whole array **numbers**. Invoking **sort(chars, 1, 3)** sorts a partial array from **chars[1]** to **chars[3-1]**. **parallelSort** is more efficient if your computer has multiple processors.
You can use the **binarySearch** method to search for a key in an array. The array must be presorted in increasing order. If the key is not in the array, the method returns **–(insertionIndex + 1)**. For example, the following code searches the keys in an array of integers and an array
of characters.
`int[] list = {2, 4, 7, 10, 11, 45, 50, 59, 60, 66, 69, 70, 79};
System.out.println("1. Index is " +
java.util.Arrays.binarySearch(list, 11));
System.out.println("2. Index is " +
java.util.Arrays.binarySearch(list, 12));`
`char[] chars = {'a', 'c', 'g', 'x', 'y', 'z'};
System.out.println("3. Index is " +
java.util.Arrays.binarySearch(chars, 'a'));
System.out.println("4. Index is " +
java.util.Arrays.binarySearch(chars, 't'));`
The output of the preceding code is
1. Index is 4
2. Index is -6
3. Index is 0
4. Index is -4
You can use the **equals** method to check whether two arrays are strictly equal. Two arrays are strictly equal if their corresponding elements are the same. In the following code, **list1** and **list2** are equal, but **list2** and **list3** are not.
`int[] list1 = {2, 4, 7, 10};
int[] list2 = {2, 4, 7, 10};
int[] list3 = {4, 2, 7, 10};
System.out.println(java.util.Arrays.equals(list1, list2)); // true
System.out.println(java.util.Arrays.equals(list2, list3)); // false`
You can use the **fill** method to fill in all or part of the array. For example, the following code fills **list1** with **5** and fills **8** into elements **list2[1]** through **list2[5-1]**.
`int[] list1 = {2, 4, 7, 10};
int[] list2 = {2, 4, 7, 7, 7, 10};
java.util.Arrays.fill(list1, 5); // Fill 5 to the whole array
java.util.Arrays.fill(list2, 1, 5, 8); // Fill 8 to a partial array`
You can also use the **toString** method to return a string that represents all elements in the array. This is a quick and simple way to display all elements in the array. For example, the following code
`int[] list = {2, 4, 7, 10};
System.out.println(Arrays.toString(list));`
displays **[2, 4, 7, 10]**. | paulike |
1,867,862 | Sorting Arrays | Sorting, like searching, is a common task in computer programming. Many different algorithms have... | 0 | 2024-05-28T14:38:39 | https://dev.to/paulike/sorting-arrays-25n4 | java, programming, learning, beginners | Sorting, like searching, is a common task in computer programming. Many different algorithms have been developed for sorting. This section introduces an intuitive sorting algorithm: selection sort.
Suppose that you want to sort a list in ascending order. Selection sort finds the smallest number in the list and swaps it with the first element. It then finds the smallest number remaining and swaps it with the second element, and so on, until only a single number remains. Figure below shows how to sort the list {**2**, **9**, **5**, **4**, **8**, **1**, **6**} using selection sort.
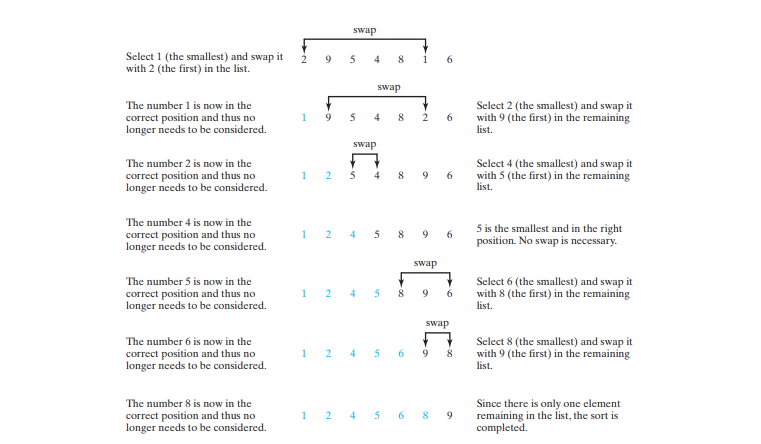
You know how the selection-sort approach works. The task now is to implement it in Java. Beginners find it difficult to develop a complete solution on the first attempt. Start by writing the code for the first iteration to find the smallest element in the list and swap it with the first element, and then observe what would be different for the second iteration, the third, and so on. The insight this gives will enable you to write a loop that generalizes all the iterations.
The solution can be described as follows:
`for (int i = 0; i < list.length - 1; i++) {
select the smallest element in list[i..list.length-1];
swap the smallest with list[i], if necessary;
// list[i] is in its correct position.
// The next iteration applies on list[i+1..list.length-1]
}`
Below implements the solution:
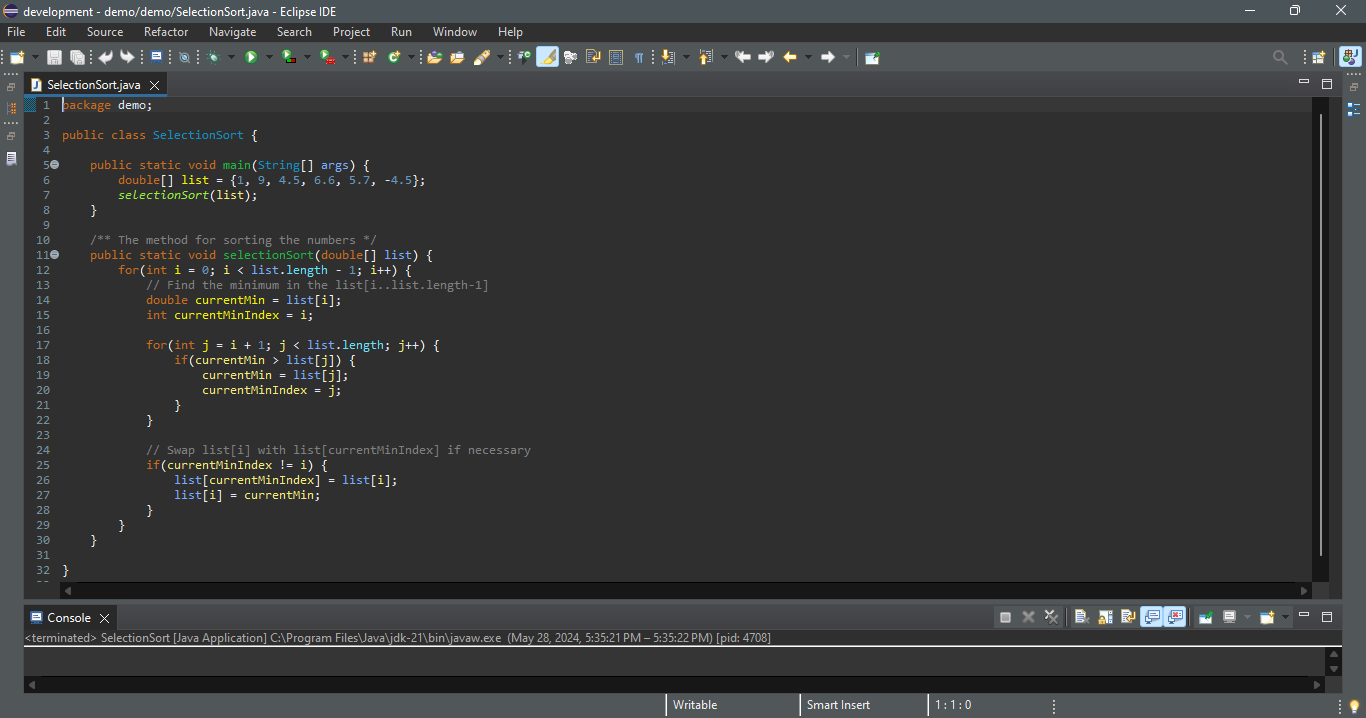
The **selectionSort(double[] list)** method sorts any array of **double** elements. The method is implemented with a nested **for** loop. The outer loop (with the loop control variable **i**) (line 12) is iterated in order to find the smallest element in the list, which ranges from **list[i]** to **list[list.length-1]**, and exchange it with **list[i]**.
The variable **i** is initially **0**. After each iteration of the outer loop, **list[i]** is in the right place. Eventually, all the elements are put in the right place; therefore, the whole list is sorted. | paulike |
1,867,861 | Create AI Assistants with Magic Cloud | Today we release our newest addition to the Magic Cloud AI toolchain; AI assistents - Or "AI... | 0 | 2024-05-28T14:37:06 | https://ainiro.io/blog/create-ai-assistents-with-magic-cloud | ai, lowcode, openai, chatgpt | Today we release our newest addition to the Magic Cloud AI toolchain; AI assistents - Or _"AI functions"_ as we refer to them as.
An AI functions is just a special training snippet that allows OpenAI to construct function invocations, that is locally executed on your cloudlet, for then to transmit the response back to OpenAI again.
This allows you to ask questions such as; _"Retrieve the 5 last customers from my CRM system, and return their email address to me"_ - All from within your familiar AINIRO AI chatbot. To understand the feature it might be beneficial to watch the following video.
{% embed https://www.youtube.com/watch?v=HVWngzO68YY %}
## How it works
We already had [Hyperlambda workflows](https://docs.ainiro.io/workflows/), and the ability to create such workflows using No-Code constructs and Low-Code constructs. The only thing we really needed to do to create assistents logic, was to implement support for declaratively add workflows into your machine learning type. This is done as follows.
1. Open the Machine Learning component in your Magic dashboard
2. Click training data
3. Choose your type in the filter select dropdown listbox
4. Click the _"Add function"_ button
Once you've done the above steps, you'll end up with something resembling the following.
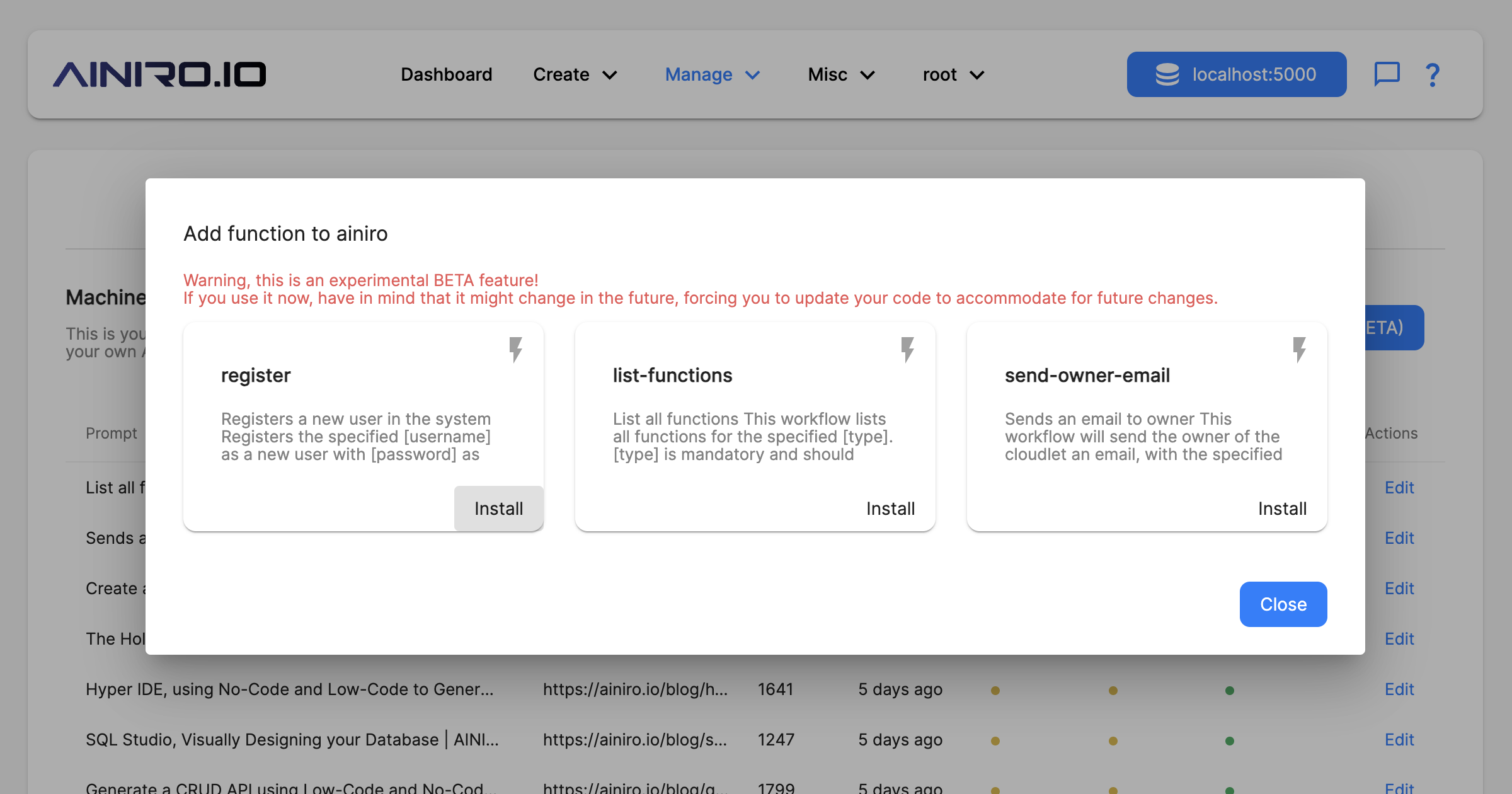
**Warning!** This feature is an experimental BETA feature. We might change the logic in future releases resulting in that you'll have to modify your code. If you're comfortable with this, feel free to play with the AI assistents logic in Magic as much as you wish.
Once you've selected a workflow from the above screen, you can prompt engineer your training snippet as much as you wish. Just make sure its core logic stays as it is when created by Magic, since the AI function feature in Magic depends upon OpenAI returning a very specific result when it wants to invoke such workflows.
AI function invocations can be chained, something illustrated in the above video, where I provide a prompt that invokes OpenAI multiple times, once for each function, where the output from one function invocation is used as input to another function invocation. To understand how this works, consider the following screenshot.
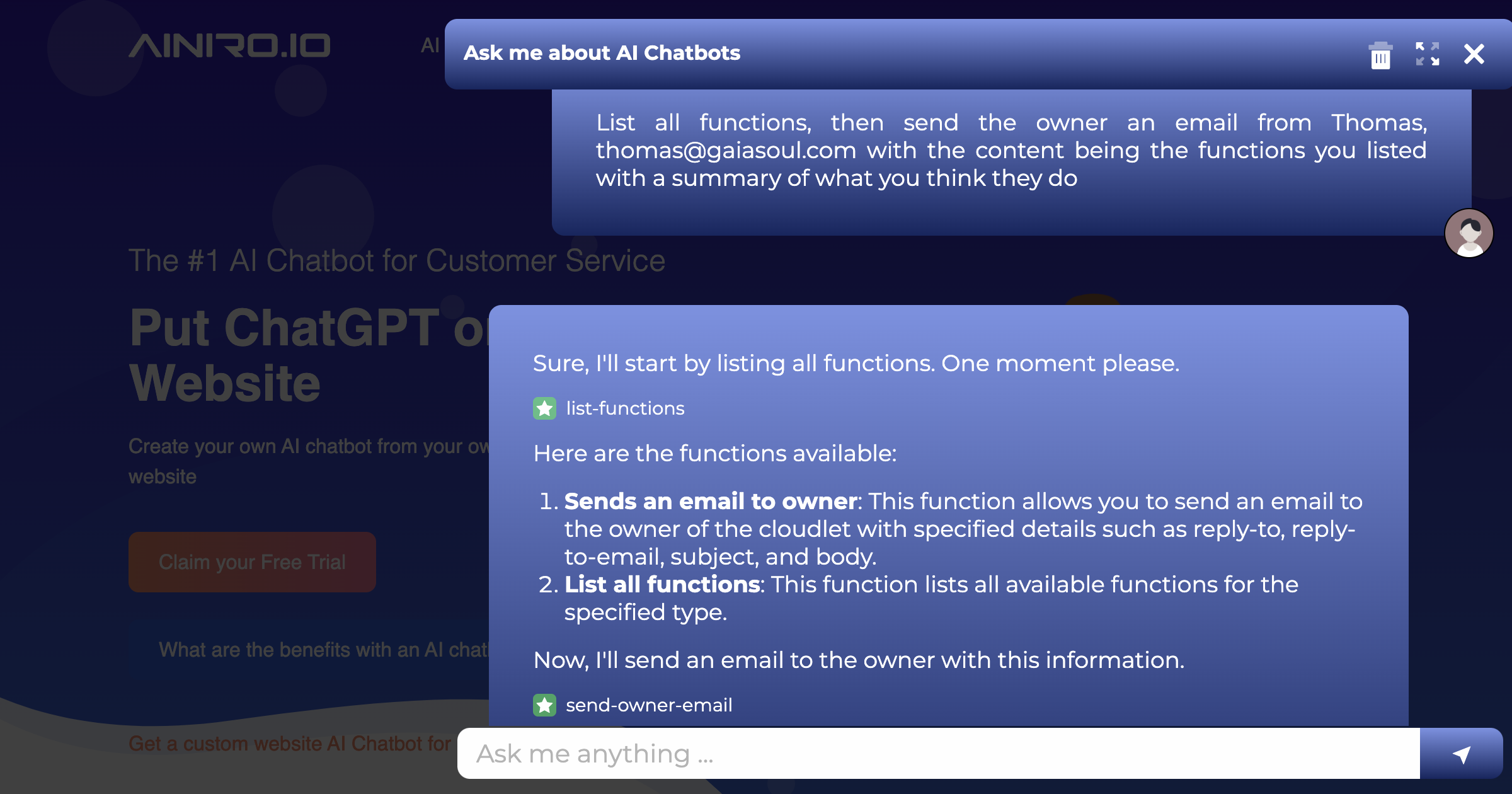
## No-Code Hyperlambda Workflows
Currently, out of the box, Magic doesn't have many workflows - But creating workflows is extremely easy. Just create a new module, or use an existing module, make sure your module has a folder called _"workflows"_, and add Hyperlambda files into this folder as you see fit.
The process can be done completely without manually having to create code. To understand the concept, you might want to watch the following video. Notice, your workflow Hyperlambda files _does not_ need to be HTTP endpoints.
{% embed https://www.youtube.com/watch?v=ITz1ASqsWoM %}
Then when you go click the _"Add function"_ button on your type's training snippets, your workflow will automatically pop up and be possible to select.
## Future Development
In the future we will add lots of pre-existing workflows, covering all sorts of scenarios. Examples could be for instance.
* Scrape website
* Create customer in CRM system
* Send summary of conversation to my email address
* Etc, etc, etc
However, for the time being, the only real workflow we've got out of the box is _"Send owner an email"_, which serves kind of like an alternative to _"Contact us"_ forms. In addition we are considering bridging the backend generator and scaffolding parts of Hyperlambda with such AI functions, allowing you to rapidly add _"CRUD AI functions"_ to your AI chatbot.
In addition, we are considering re-animating our _"AI Expert System"_, in a new form, allowing you to have privately accessible AI chatbots that you only expose to those you want to expose these to. This would provide an alternative to GPT assistents, possibly with integrated monetization capabilities, allowing you to rapidly create your own SaaS-based AI chatbots.
## Conclusion
Having AI assistents capabilities in your AI chatbots opens up a completely new axiom, and is an addition to all the nifty features we already have in Magic Cloud. With this feature, our core technology have taken a huge leap forward in regards to usability and usefulness. If you want to discuss how we can help you out solving your particular needs related to AI, you can contact us below.
* [Contact us](https://ainiro.io/contact-us)
**Disclaimer**; This part of Magic is not completely stabilised yet, and should be considered an experimental feature. However, this is something we will spend a lot of energy on stabilising and expanding upon - So expect to see a lot more from this feature in the future.
| polterguy |
1,845,534 | Ibuprofeno.py💊| #111: Explica este código Python | Explica este código Python Dificultad: Fácil categories = ["color",... | 25,824 | 2024-05-28T14:32:49 | https://dev.to/duxtech/ibuprofenopy-111-explica-este-codigo-python-40k9 | python, spanish, learning, beginners | ## **<center>Explica este código Python</center>**
#### <center>**Dificultad:** <mark>Fácil</mark></center>
```py
categories = ["color", "fruit", "pet"]
objects = ["blue", "apple", "dog"]
new_dict = {key:value for key, value in zip(categories, objects)}
print(new_dict)
```
👉 **A.** `{'blue': 'color', 'apple': 'fruit', 'dog': 'pet'}`
👉 **B.** `{'color': 'blue', 'fruit': 'apple', 'pet': 'dog'}`
👉 **C.** `KeyError`
👉 **D.** `RangeError`
---
{% details **Respuesta:** %}
👉 **B.** `{'color': 'blue', 'fruit': 'apple', 'pet': 'dog'}`
Podemos crear diccionarios por comprensión de una manera muy similar a las listas por comprehensión.
En el ejemplo iteramos de manera paralela sobre las listas `categories` y `objects` y regresamos cada par clave valor dentro de un nuevo diccionario.
{% enddetails %} | duxtech |
1,867,859 | 5 Things to Keep in Mind Regarding Workday Testing Tools | As today’s rapidly changing digital world becomes more prevalent, businesses find themselves using... | 0 | 2024-05-28T14:32:45 | https://thestreethearts.com/5-things-to-keep-in-mind-regarding-workday-testing-tools/ | workday, testing, tools | 
As today’s rapidly changing digital world becomes more prevalent, businesses find themselves using Cloud-based Enterprise Resource Planning (ERP) systems like Workday to control their manpower and simplify business processes. All these things require tests: Making sure Workday functions, that data is kept clean and tidy, and user needs are met. And these are before anything else in each stage, from development through operation. This is where Workday testing tool play a critical role. These specialist solutions help enterprises reduce risks, increase return on investment (ROI), and optimize performance by making it easier to test Workday apps, integrations, and customizations in-depth. When companies begin their Workday testing process, they should bear the following five points in mind.
1. **Alignment with Workday Release Cycles**
Like many cloud-based products, Workday is updated and released on a regular basis with new features, improvements, and security patches. Updates like this may have an effect on current features, integrations, and customizations. As such, it is essential to select a Workday testing solution that can handle continuous modifications and is in line with Workday’s release cycles. In order to enable enterprises to swiftly verify and test new releases, ensure system reliability, and minimize disruptions to business operations, the testing tool should offer seamless integration with Workday’s update processes.
2. **Comprehensive Test Coverage**
Workday has many facets that include modules and features for payroll, financial management, analytics and human capital management (HCM).Comprehensive testing across these various components, including core functionality, third-party system integrations, and any organizational specific customizations or configurations is essential for effective testing. To ensure comprehensive testing of the Workday ecosystem, the chosen Workday testing solution must cover a complete set of testing capabilities, including functional testing, regression testing, performance testing, and security testing.
3. **Test Automation and Scalability**
Manual testing can be resource-intensive, time-consuming, and prone to errors, especially when Workday implementations get more complex and extensive. For testing procedures to be effective and scalable, test automation is necessary. Organizations assessing Workday testing tools ought to give preference to those that include sophisticated automation features including intelligent test case prioritization, self-healing test scripts, and scriptless test development. With the help of these features, testing efforts can be greatly decreased, testing cycles accelerated, and companies able to smoothly scale their testing activities as their Workday footprint expands.
4. **Integration and Data Management**
Payroll systems, third-party apps, and human resource information systems (HRIS) are just a few of the external systems that Workday frequently integrates with. The capacity to manage and synchronize data across these various systems is necessary for effective testing in order to guarantee data consistency and integrity throughout the testing procedure. To enable thorough end-to-end testing scenarios and preserve data confidentiality and privacy, the selected Workday testing tool should include strong data management features, such as test data generation, data masking, and data virtualization.
5. **Collaboration and Reporting**
Multiple stakeholders, including business users, functional specialists, developers, and quality assurance teams, are frequently involved in everyday testing efforts. Successful testing outcomes depend on these different teams’ ability to collaborate and communicate effectively. To enable smooth coordination and information sharing across stakeholders, the Workday testing solution should provide collaborative features like role-based access controls, centralized test management, and real-time reporting.
**Conclusion**
Workday applications must be properly implemented, maintained, and optimized within a company, which requires the use of Workday testing tools. Invest in Workday investment protection with Opkey, the specialized testing solution designed just for Workday. Data integrity is safeguarded by Opkey’s Workday security configurator, which instantly identifies role changes. Opkey’s smooth Workday integration makes it possible to automate bi-annual update testing and do away with human labour. With simple automation that frees up your team to focus on strategic goals, stay up to date on the most recent Workday updates. Opkey can swiftly validate new features and configurations while doing extensive regression testing for every change, ensuring business continuity. Make the most of Opkey’s comprehensive, Workday-specific testing capabilities to increase your Workday ROI and keep a competitive edge. Opkey offers unmatched efficiency, security, and quality. | rohitbhandari102 |
1,867,858 | The Future of Logistics: How a Warehouse Management System Revolutionizes Operations | In trendy speedy-paced and relatively aggressive market, agencies are constantly searching for... | 0 | 2024-05-28T14:32:45 | https://dev.to/liong/the-future-of-logistics-how-a-warehouse-management-system-revolutionizes-operations-3hk6 | operational, managementsystem, malaysia, kualalumpur | In trendy speedy-paced and relatively aggressive market, agencies are constantly searching for tactics to optimize their deliver chain and improve performance. A vital detail in engaging in the ones goals is the implementation of a sturdy Warehouse Management System (WMS). This effective device now not simplest streamlines warehouse operations however moreover enhances inventory control, reduces operational fees, and improves customer satisfaction. In this blog, we will explore the important thing abilities and blessings of a WMS and why it's far important for present day warehousing.
## Key Features of a Warehouse Management System
**Inventory Management**
Efficient inventory management is on the heart of a [WMS](https://ithubtechnologies.com/warehouse-management-system-malaysia/?utm_source=dev.to%2F&utm_campaign=Warehousemanagementsystem&utm_id=Offpageseo+2024). The gadget presents actual-time visibility into inventory ranges, locations, and actions. This enables businesses preserve greatest stock degrees, lessen stock outs, and limit excess stock. Advanced functions along with cycle counting and automated replenishment in addition enhance stock accuracy and availability.
**Order Fulfillment**
A WMS streamlines the order achievement method by way of automating selecting, packing, and transport tasks. This ensures orders are processed quick and as it should be, lowering errors and enhancing purchaser pleasure. The machine also can prioritize orders based on numerous criteria, consisting of shipping time limits or purchaser significance, making sure timely success.
**Labor Management**
Labor is one of the maximum enormous fees in warehousing operations. A WMS consists of exertions control tools that tune worker overall performance, assign responsibilities, and optimize personnel usage. By analyzing productiveness data, managers can become aware of regions for development and enforce strategies to growth performance and reduce exertions prices.
**Advanced Reporting and Analytics**
Data-driven selection-making is vital in present day warehousing. A WMS provides comprehensive reporting and analytics competencies, presenting insights into numerous aspects of warehouse operations. Managers can reveal key performance signs (KPIs), discover traits, and make information-sponsored choices to enhance performance and productiveness.
**Integration with Other Systems**
To acquire seamless operations, a WMS integrates with other employer structures together with Enterprise Resource Planning (ERP) and Transportation Management Systems (TMS). This integration guarantees facts consistency throughout the deliver chain, permitting better coordination and verbal exchange among exceptional departments and stakeholders.
**Scalability and Flexibility**
As companies develop and evolve, their warehousing wishes change. A WMS is designed to be scalable and bendy, accommodating improved volumes and new processes. This scalability ensures that the machine stays powerful and efficient, no matter adjustments in commercial enterprise size or complexity.
**Benefits of Implementing a Warehouse Management System**
**Improved Accuracy and Efficiency**
By automating guide methods and supplying actual-time statistics, a WMS drastically improves accuracy and efficiency in warehouse operations. This reduces errors, minimizes delays, and ensures that inventory is controlled efficiently.
**Cost Savings**
A WMS helps lessen operational charges via optimizing inventory tiers, improving exertions productiveness, and minimizing errors. These fee financial savings may be reinvested in other regions of the business, riding in addition growth and improvement.
**Enhanced Customer Satisfaction**
Accurate and well timed order success is essential to patron delight. A WMS guarantees that orders are processed correctly and introduced on time, improving the general client enjoy and fostering loyalty.
**Better Decision-Making**
The superior reporting and analytics competencies of a WMS provide valuable insights into warehouse operations. This allows managers to make knowledgeable choices, perceive regions for improvement, and enforce strategies to enhance efficiency and productiveness.
**Increased Agility**
In a unexpectedly changing marketplace, groups want to be agile and aware of stay competitive. A WMS provides the ability and scalability had to adapt to changing conditions, making sure that warehousing operations stay efficient and powerful.
**Real-World Applications of Warehouse Management Systems**
Many businesses throughout various industries have successfully carried out WMS answers to convert their warehousing operations.
Here are some examples:
**E-trade**
In the e-trade sector, fast and accurate order achievement is important. A WMS enables e-commerce organizations manipulate high volumes of orders, streamline choosing and packing approaches, and make sure timely transport. This improves patron pride and supports commercial enterprise increase.
**Retail**
Retailers face specific demanding situations in handling stock throughout more than one places. A WMS gives actual-time visibility into inventory levels and moves, allowing stores to optimize stock control and reduce stock outs. This guarantees that merchandise are available whilst and in which customers need them.
**Manufacturing**
Manufacturers rely on green warehousing to assist production tactics. A WMS facilitates producers manage uncooked materials, paintings-in-progress, and finished goods inventory. This ensures that manufacturing traces are adequately supplied, decreasing downtime and increasing productivity.
**Third-Party Logistics (3PL) Providers**
3PL vendors manage warehousing and distribution for multiple clients, each with particular necessities. A WMS allows 3PL carriers to deal with complicated operations, optimize area usage, and make certain correct and well timed order success for their clients.
**Choosing the Right Warehouse Management System**
Selecting the proper WMS is crucial to maximizing its advantages.
Here are some elements to keep in mind when selecting a WMS:
**Functionality**
Ensure that the WMS gives the features and talents needed to aid your precise warehousing operations. Consider elements which includes inventory control, order achievement, hard work management, and reporting.
**Scalability**
Choose a WMS that may scale along with your commercial enterprise. As your operations develop and evolve, the machine must accommodate increased volumes and new procedures with out compromising overall performance.
**Integration**
The WMS have to integrate seamlessly with your existing organization systems, such as ERP and TMS. This ensures records consistency and allows higher coordination across the supply chain.
**User-Friendliness**
A consumer-pleasant interface is vital for a success implementation and adoption. The WMS must be intuitive and clean to apply, decreasing the gaining knowledge of curve for employees and making sure green operations.
**Vendor Support**
Consider the level of support offered through the WMS seller. Ensure they provide complete schooling, ongoing help, and everyday updates to preserve the system going for walks smoothly.
### Conclusion
A Warehouse Management System is a powerful tool which could transform warehousing operations, using efficiency, accuracy, and fee savings. By supplying real-time records, automation, and superior analytics, a WMS allows businesses to optimize stock control, streamline order achievement, and improve basic productiveness. In latest aggressive marketplace, imposing a WMS is crucial for groups seeking to enhance their supply chain and supply superior consumer pride. Investing inside the proper WMS can yield sizeable long-time period advantages, positioning your commercial enterprise for fulfillment within the ever-evolving logistics panorama. Whether you're in e-trade, retail, production, or third -party logistics, a WMS can provide the competencies needed to live aggressive and meet the needs of cutting-edge market
| liong |
1,867,856 | Searching Arrays | If an array is sorted, binary search is more efficient than linear search for finding an element in... | 0 | 2024-05-28T14:31:19 | https://dev.to/paulike/searching-arrays-4fb7 | java, programming, learning, beginners | If an array is sorted, binary search is more efficient than linear search for finding an element in the array. _Searching_ is the process of looking for a specific element in an array—for example, discovering whether a certain score is included in a list of scores. Searching is a common task in computer programming. Many algorithms and data structures are devoted to searching. This section discusses two commonly used approaches, _linear search_ and _binary search_.
## The Linear Search Approach
The linear search approach compares the **key** element key sequentially with each element in the array. It continues to do so until the key matches an element in the array or the array is exhausted without a match being found. If a match is made, the linear search returns the index of the element in the array that matches the key. If no match is found, the search returns **-1**. The **linearSearch** method in the program below gives the solution.
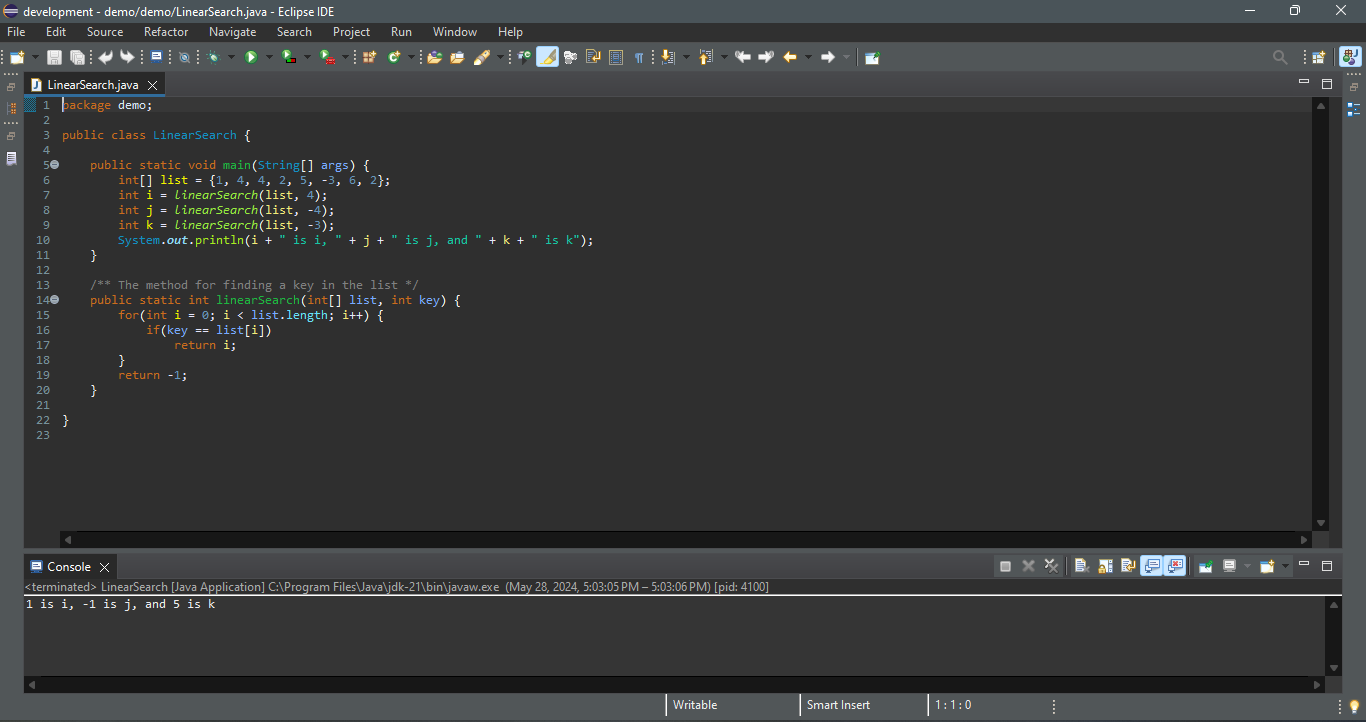
The linear search method compares the key with each element in the array. The elements can be in any order. On average, the algorithm will have to examine half of the elements in an array before finding the key, if it exists. Since the execution time of a linear search increases linearly as the number of array elements increases, linear search is inefficient for a large array.
## The Binary Search Approach
Binary search is the other common search approach for a list of values. For binary search to work, the elements in the array must already be ordered. Assume that the array is in ascending order. The binary search first compares the key with the element in the middle of the array. Consider the following three cases:
- If the key is less than the middle element, you need to continue to search for the key only in the first half of the array.
- If the key is equal to the middle element, the search ends with a match.
- If the key is greater than the middle element, you need to continue to search for the key only in the second half of the array.
Clearly, the binary search method eliminates at least half of the array after each comparison. Sometimes you eliminate half of the elements, and sometimes you eliminate half plus one. Suppose that the array has _n_ elements. For convenience, let **n** be a power of **2**. After the first comparison, **n/2** elements are left for further search; after the second comparison, **(n/2)/2** elements are left. After the **k**th comparison, **n/2^k** elements are left for further search. When **k = log2n**, only one element is left in the array, and you need only one more comparison. Therefore, in the worst case when using the binary search approach, you need **log2n+1** comparisons to find an element in the sorted array. In the worst case for a list of **1024** (2^10) elements, binary search requires only **11** comparisons, whereas a linear search requires **1023** comparisons in the worst case.
The portion of the array being searched shrinks by half after each comparison. Let **low** and **high** denote, respectively, the first index and last index of the array that is currently being searched. Initially, **low** is **0** and **high** is **list.length–1**. Let **mid** denote the index of the middle element, so **mid** is **(low + high)/2**. Below shows how to find key **11** in the list {**2**, **4**, **7**, **10**, **11**, **45**, **50**, **59**, **60**, **66**, **69**, **70**, **79**} using binary search.
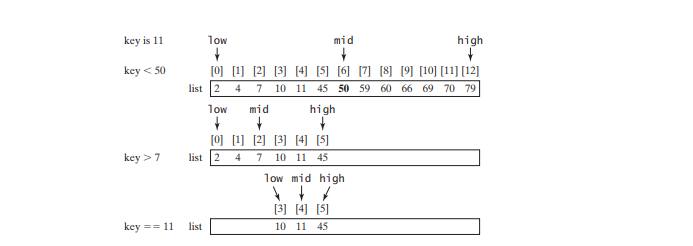
You now know how the binary search works. The next task is to implement it in Java. Don’t rush to give a complete implementation. Implement it incrementally, one step at a time. You may start with the first iteration of the search, as shown below a. It compares the key with the middle element in the list whose **low** index is **0** and **high** index is **list.length - 1**. If **key < list[mid]**, set the **high** index to **mid - 1**; if **key == list[mid]**, a match is found and return **mid**; if **key > list[mid]**, set the **low** index to **mid + 1**.
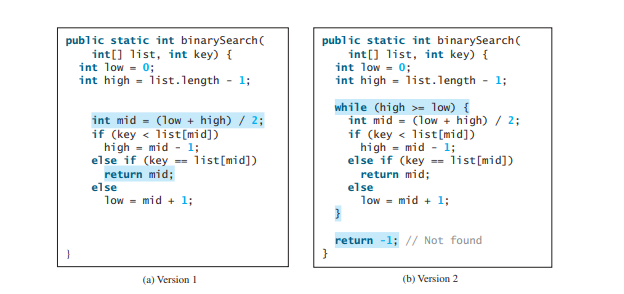
Next consider implementing the method to perform the search repeatedly by adding a loop, as shown in above b. The search ends if the key is found, or if the key is not found when **low > high**.
When the key is not found, **low** is the insertion point where a key would be inserted to maintain the order of the list. It is more useful to return the insertion point than **-1**. The method must return a negative value to indicate that the key is not in the list. Can it simply return **–low**? No. If the key is less than **list[0]**, **low** would be **0**. **-0** is **0**. This would indicate that the key matches **list[0]**. A good choice is to let the method return **–low – 1** if the key is not in the list. Returning **–low – 1** indicates not only that the key is not in the list, but also where the key would be inserted.
The complete program is given below:
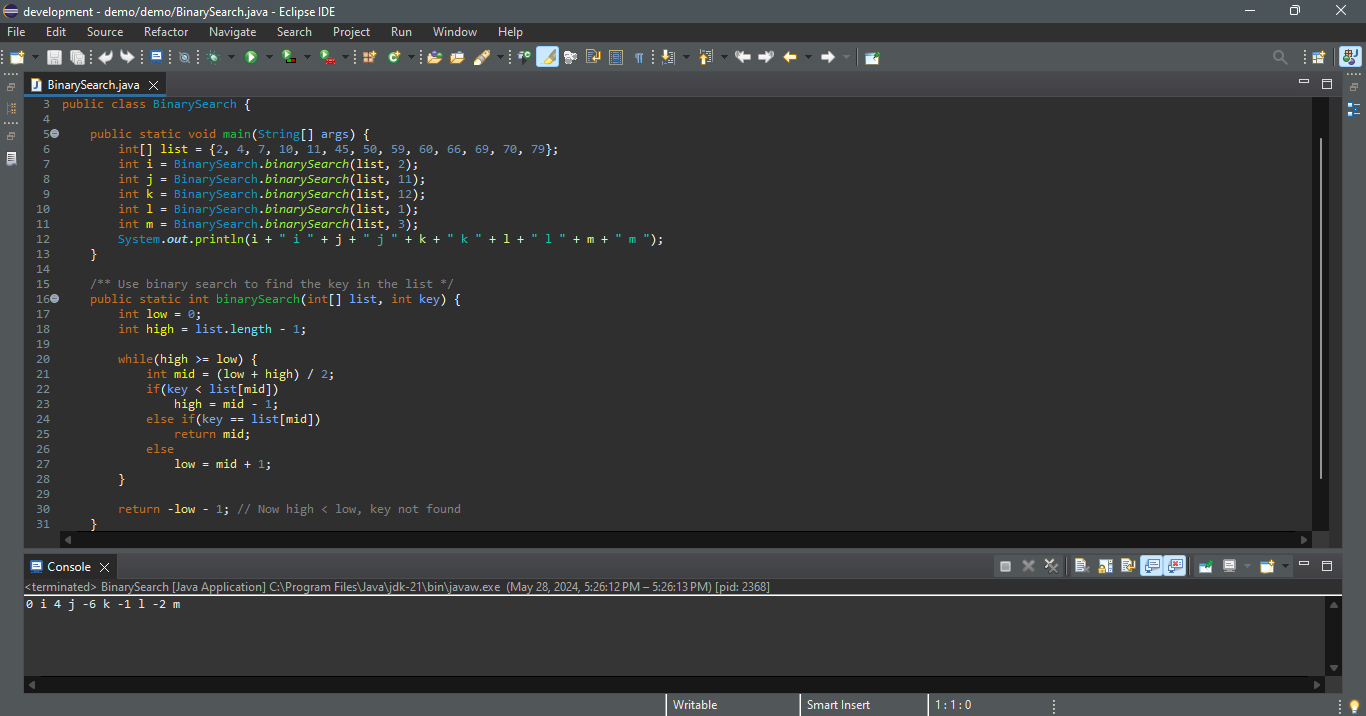
The binary search returns the index of the search key if it is contained in the list (line 25). Otherwise, it returns **–low – 1** (line 30).
What would happen if we replaced **(high >= low)** in line 20 with (**high > low**)? The search would miss a possible matching element. Consider a list with just one element. The search would miss the element.
Does the method still work if there are duplicate elements in the list? Yes, as long as the elements are sorted in increasing order. The method returns the index of one of the matching elements if the element is in the list.
Here is the table that lists the low and high values when the method exits and the value returned from invoking the method.
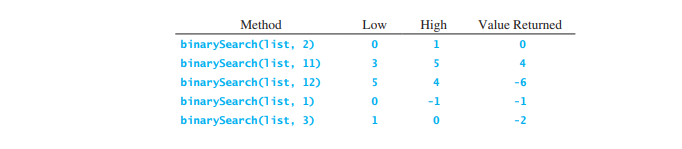
Linear search is useful for finding an element in a small array or an unsorted array, but it is inefficient for large arrays. Binary search is more efficient, but it requires that the array be presorted. | paulike |
1,867,855 | Stay Updated with PHP/Laravel: Weekly News Summary (20/05/2024 - 26/05/2024) | Dive into the latest tech buzz with this weekly news summary, focusing on PHP and Laravel updates... | 0 | 2024-05-28T14:30:39 | https://poovarasu.dev/php-laravel-weekly-news-summary-20-05-2024-to-26-05-2024/ | php, laravel | Dive into the latest tech buzz with this weekly news summary, focusing on PHP and Laravel updates from May 20th to May 26th, 2024. Stay ahead in the tech game with insights curated just for you!
This summary offers a concise overview of recent advancements in the PHP/Laravel framework, providing valuable insights for developers and enthusiasts alike. Explore the full post for more in-depth coverage and stay updated on the latest PHP/Laravel development.
Check out the complete article here [https://poovarasu.dev/php-laravel-weekly-news-summary-20-05-2024-to-26-05-2024/](https://poovarasu.dev/php-laravel-weekly-news-summary-20-05-2024-to-26-05-2024/) | poovarasu |
1,867,852 | Day3: Git and GitHub | Git: Git is a distributed version control system designed to handle everything from small... | 0 | 2024-05-28T14:28:13 | https://dev.to/swarnendu0123/git-and-github-1leg | # Git:
Git is a distributed version control system designed to handle everything from small to very large projects with speed and efficiency.
Version Control: Git allows multiple developers to work on the same project simultaneously without interfering with each other's work. It tracks changes to files, enabling developers to revert to previous versions if necessary.
Branching and Merging: Git allows for the creation of branches, which are separate lines of development. Developers can work on features or fixes in isolated branches and then merge these branches back into the main codebase.
Distributed: Each developer has a full copy of the repository, including the entire history of changes. This means that they can work offline and sync changes when they are back online.
**Usage**: Git is a command-line tool, although there are also graphical user interfaces (GUIs) and integrations in development environments that facilitate its use.
**Installation**: Git needs to be installed on your local machine. It's available for all major operating systems (Linux, macOS, Windows).
# GitHub:
GitHub is a web-based platform that uses Git for version control. It offers a collaborative interface for managing Git repositories.
Repository Hosting: GitHub hosts Git repositories, making it easy to share code with others. Repositories can be public (open to everyone) or private (restricted access).
Collaboration Tools: GitHub provides tools for issue tracking, project management, and collaboration. This includes pull requests, where developers can propose changes to the codebase, and code reviews.
Integrated Features: GitHub offers additional features like GitHub Actions (for CI/CD), GitHub Pages (for hosting static websites), and GitHub Packages (for hosting packages).
Social Coding: GitHub is often described as a social network for developers. Users can follow each other, star repositories, and contribute to open-source projects.
**Usage**: GitHub can be accessed through a web browser. It also integrates with Git, meaning you can push and pull changes from your local Git repository to GitHub using Git commands.
**Account**: You need to create an account on GitHub to use its services. There are free and paid plans, with the free plan offering a substantial amount of functionality for individual developers and open-source projects.
| swarnendu0123 | |
1,867,851 | Prompt Engineering – Is it Fake or a Vital Skill for the AI-Powered Future? | This article was originally published on Danubius IT Solutions' tech blog. In our continued journey... | 0 | 2024-05-28T14:26:26 | https://danubius.io/en/blog/prompt-engineering--is-it-fake | promptengineering, aifuture, techinnovation, skillsdevelopment | [This article was originally published on Danubius IT Solutions' tech blog.](https://danubius.io/en/blog/prompt-engineering--is-it-fake)
In our continued journey to innovate within the AI-driven customer support landscape, we would like to draw attention to a term that's often misunderstood outside tech circles: prompt engineering. Prompt engineering emerges as a cornerstone of AI engineering, vital for refining the capabilities of large language models (LLMs) like GPT-4 and its successors. This intricate process involves the creation of detailed, targeted prompts that guide AI in producing specific outcomes, whether text, images, or code.
Some are skeptical about prompt engineering, thinking of it as a "fake" profession, especially when conversing with AI seems as simple as chatting with a friend. However, we have learned through our experiences that it is an essential discipline that combines logic, coding, artistry, and a deep understanding of AI behavior.
## What is Prompt Engineering?
Our journey into the depths of prompt engineering has illuminated its essence: it is much more than mere conversation with a machine. It embodies a sophisticated blend of logical thinking, programming wisdom, and creative talent for communication. It's similar to educating a new, eager intern – where every instruction must be clear, purposeful, and considerate of the AI's interpretative framework.
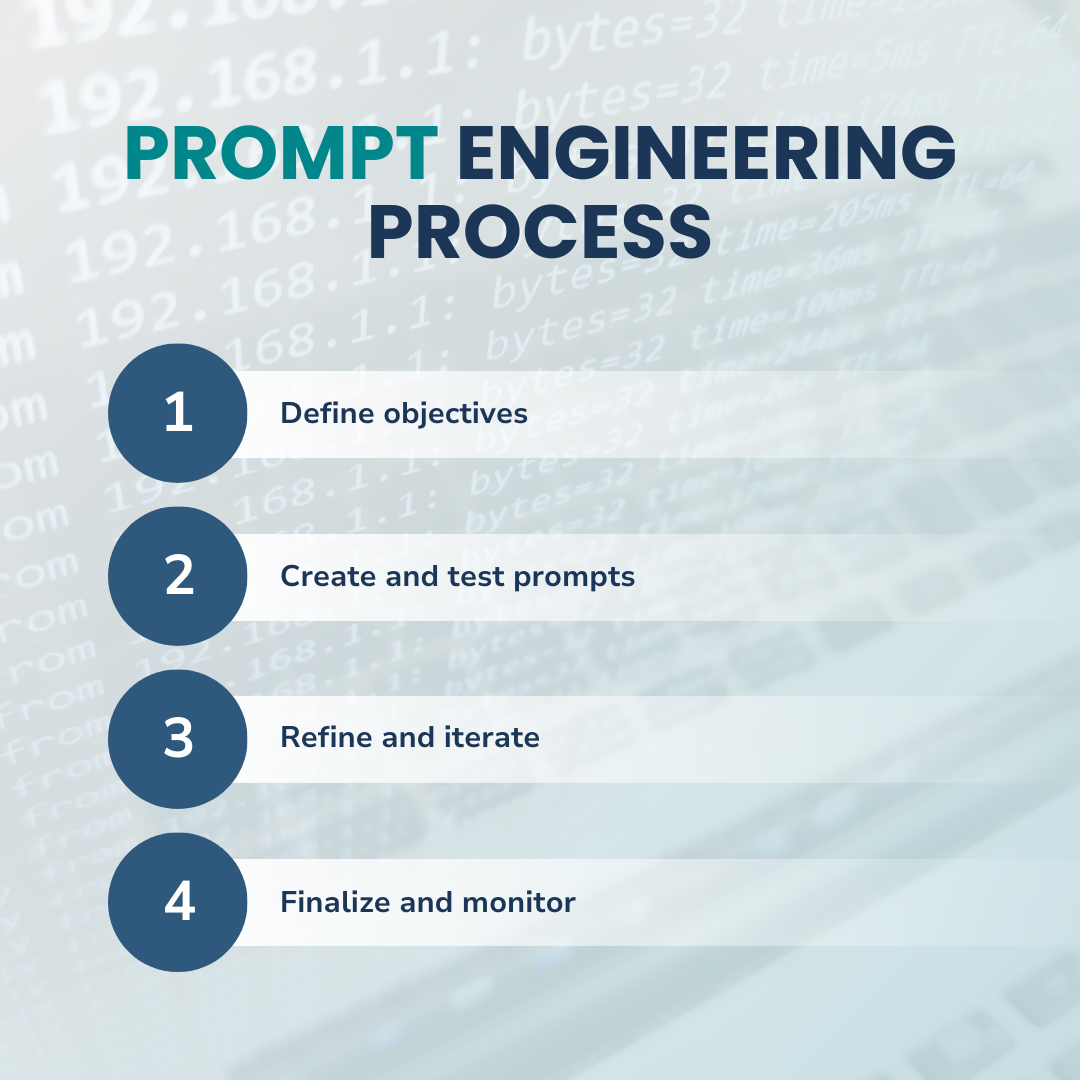
Prompt engineering also goes beyond crafting queries; it's about embedding a piece of our understanding into the AI, enabling it to carry out tasks with the appearance of human-like reasoning. During our project's development, we personified our AI systems, treating them as team members rather than mere tools. This approach helped us realize the importance of precise language and structured guidance. Every prompt became a lesson, teaching the AI about our expectations and how to meet them effectively.
## The Complexity Behind Simplicity
At the heart of our customer service support system lies a network of carefully engineered prompts, each designed to handle a wide array of customer inquiries. This might seem like a straightforward task, but it unveiled a layered complexity of variations in language, logical reasoning, and technical know-how.
A mere change of a single word or even a letter in a prompt can lead to drastically different outcomes, highlighting the critical need for precision in our approach. It's a clear reminder that AI models, for all their advanced capabilities, still rely heavily on the clarity and specificity of the instructions we provide. Our role evolved from engineers to educators and collaborators, guiding AI through its learning process, correcting misunderstandings, and refining its responses to ensure relevance and accuracy.
Mastering prompt engineering for us meant the acceptance of this complexity. We learned to craft prompts not just as commands but as conversations, where the context and sensitivity of human language all play essential roles. Each prompt is a building block in a larger structure of AI understanding, a step towards creating AI systems that can truly understand and respond to human needs with a high degree of relevance and personalization.
By recognizing AI as a dynamic team member, capable of growth and learning, we were able to harness its potential more effectively. This mindset shift was crucial for our project's success, enabling us to develop a customer support system that genuinely understands and responds to customer needs ‘What Can We Achieve with Artificial Intelligence in Customer Service’, made possible by the profession of prompt engineering.
## Structured Thinking and Continuous Evolution
Our journey into prompt engineering highlighted the necessity for structured thinking – a methodical approach where understanding the task at hand is just the beginning. We learned to predict how our AI would interpret instructions and how to guide it to achieve precise outcomes. We constantly revised and refined, ensuring every element of the prompt functioned both independently and synergistically.
The transition between models, such as from GPT-3.5 to GPT-4.0, showcased the fluid nature of AI technologies, driving us to evolve our strategies alongside these advancements to harness their full potential.
## Navigating Limitations and Building on Strengths
Prompt engineering is fascinating, especially when it comes to maneuvering around the constraints of large language models. For instance, complex tasks or ambiguities that might confuse AI required us to think outside the box. We employed strategic function calls, much like seeking assistance from a colleague, which allowed AI to tap into external resources for additional information.
This strategy not only bypassed limitations but also significantly amplified AI's functionality, enabling it to undertake more sophisticated tasks with enhanced accuracy.
## The Impact on Customer Support
Implementing prompt engineering within our customer support framework marked another pivotal shift. Through precise prompt calibration and integrating function calls, we've elevated the quality of our AI-generated responses. At the same time, our communications became more tailored, insightful, and effective, markedly boosting customer satisfaction.
This innovation enriched the customer experience and also optimized our internal workflow, empowering our team to allocate more time to complex customer needs. All in all, this evolution in our support system highlighted prompt engineering’s transformative effects, illustrating its role in advancing AI to meet real-world challenges head-on.
## Are You Ready to Utilize AI in Business Operations?
As AI continues to redefine every aspect of technology and business, the role of prompt engineering becomes increasingly critical. We're happy that we could join the growing list of those pioneering companies that want to be at the forefront of this exciting field, and as such, we’re continually exploring and pushing the boundaries of what AI can achieve.
So, if you're looking to harness the power of AI in your operations or need guidance on incorporating AI-based tech solutions, our team is here to help. Together, we can unlock the full potential of AI for your business.
Interested in exploring how Danubius IT can enhance your AI capabilities? Contact us and let's create such solutions together! | danubiusio |
1,867,849 | We Need to Talk More About Conformance, If We Want to Stop Fantasy HTML | Conformant and valid HTML is the exception when it comes to HTML used on websites and in apps. This... | 0 | 2024-05-28T14:24:56 | https://meiert.com/en/blog/talk-about-html-conformance/ | html, conformance, validation, community | Conformant and valid HTML is the exception when it comes to HTML used on websites and in apps. This is particularly visible on popular websites, where at the moment, <a href="https://meiert.com/en/blog/html-conformance-2023/">none of the Top 100 sites worldwide</a> uses valid HTML.
It’s easy to argue that conformant and valid output is <a href="https://meiert.com/en/blog/professional-web-developer/#toc-high-standards">the mark of a professional web developer</a>. It takes <em>nothing</em> to write a document that contains HTML errors. To reuse a past metaphor, put a houseplant on the keyboard, store the result as a file with an “html” extension, and you have an invalid HTML document.
To stop houseplant and fantasy HTML, however, we need to raise awareness for HTML conformance and validation—we need to talk about HTML conformance and validation.
That happens <a href="https://frontenddogma.com/topics/conformance/">not nearly as often</a> as it should happen (and it should not always be done by the same people).
Surveys like <a href="https://2023.stateofhtml.com/">State of HTML</a> are an excellent opportunity to inquire about authors’ validation practices (one that, sadly, was missed last year). Even if the result confirms what we can measure on people’s websites—that authors don’t pay attention to using actual, valid HTML code—, asking plants a seed.
Whether you’re a frontend developer, lead, or manager, reconsider your expectations and practices if you haven’t yet chosen not to ship erroneous HTML. The <a href="https://meiert.com/en/blog/commit-to-conformance/">more of us</a> decide to talk about using actual HTML on our sites and in our apps, and lead by example, the better for our users and clients, and the better for our craft and profession. On the engineering side of web development, it’s <strong>HTML first</strong>—<a href="https://validator.w3.org/">if it is HTML</a>. | j9t |
1,867,850 | Thợ-code hàng real khác thợ-chém như thế nào? | Thợ-code hàng real khác thợ-chém như thế nào? Trả lời bởi Alan Mellor, bán code kiếm cơm từ 1981.... | 0 | 2024-05-28T14:24:45 | https://dev.to/longtth/tho-code-hang-real-khac-tho-chem-nhu-the-nao-97l | quoratrans | Thợ-code hàng real khác thợ-chém như thế nào?
Trả lời bởi Alan Mellor, bán code kiếm cơm từ 1981.
Thợ code hàng real thực-sự-code. Thợ code hàng fake không-code.
Tôi: anh đã build sản phẩm gì?
Thợ-chém: tôi đã hoàn thành 62.7% ở EE-ZEE-LURN Bootcamp academy online, và tui thành thạo Java, Swift, Mobile Development, websites.
Tôi: "thành thạo" nghe hấp dẫn đấy, vậy anh đã làm được dự án nào với java? cho tui xin 1 cái tên.
Thợ-chém: ...
Vậy là xong.
Một người trở thành kỹ sư phần mềm giỏi, bởi vì anh ta code, anh ta tạo ra các phần mềm (*), và anh ta muốn làm điều đó.
Chém-er thì không không hứng thú với việc xây dựng các phần mềm. Vậy nên họ chém, và không có output gì.
Chân thành mà nói, chém-er cũng không phải là quá tệ. nhưng Software Developer thì phải develop software thôi.
Trans note:
- Vì đồng tình với tác giả, nên mỗi khi đi dạy, mình luôn động viên sinh viên làm thật, ra sản phẩm thật, để đi "khoe" mỗi khi ứng tuyển.
- Và hồi tuyển ~cậu~ à nhầm thằng bạn vàng Nguyễn Tiến Hoàng mình accept luôn sau khi nhìn thấy sản phẩm trong laptop của nó.
- Chém-er cũng không phải vấn đề, ngành công nghiệp phần mềm, có rất nhiều vị trí không-cần-code-chỉ-cần-chém, nhưng phải cân nhắc xem là bạn bạn đang tuyển người vào để làm gì. Tuyển coder đi chém và tuyển chém-er đi code thì chỉ ra thảm họa,
còn tuyển được chém-er đi chém thì vẫn rất ngon,
còn tuyển 1 ông vừa code ngon vừa chém ngon như ông Viet Cv thì tiền đâu trả cho nổi, mà những người như ổng thì bận startup cái business của ổng rồi. | longtth |
1,867,848 | Tôi cần show cái gì trong CV để kiếm được 1 công việc (Java) | Tôi cần show cái gì trong CV để kiếm được 1 công việc (Java) // vì có quá nhiều thuật ngữ... | 0 | 2024-05-28T14:22:04 | https://dev.to/longtth/toi-can-show-cai-gi-trong-cv-de-kiem-duoc-1-cong-viec-java-29kn | quoratrans | ## Tôi cần show cái gì trong CV để kiếm được 1 công việc (Java)
// vì có quá nhiều thuật ngữ nên về cơ bản mấy cái tui để giữa cặp nháy thì mọi người chịu khó Google nhé!
Với tư cách là người tuyển dụng, tui muốn xem
- Clean code, cách đặt tên code trong sáng, `SOLID`, `Lambdas` (liên hệ anh Google để biết về SOLID và Lambda trong lập trình)
- Bạn có áp dụng good/best pratices cho `REST` (best practice = các kinh nghiệm hay trong lập trình, liên hệ anh Google để biết về REST), `repositories` (lại liên hệ anh Gồ để biết về `repositories`, hoặc cụ thể hơn là `Spring Rest Respositories`) và mấy thứ liên quan
- Có sử dụng `build script`, `maven/gradle` để thực hiện `CI` (ờ, nếu chưa biết mấy cái build script, maven/gradle, CI thì lại hỏi anh Gồ đi)
- `Unit test`, test tích hợp (`Integration Test`), kiểm thử trực quan (end to end testing) được sử dụng phù hợp
- `Logging` phù hợp
- Quản lý lỗi (`exception/error`)
- Có sự suy nghĩ về khả năng mở rộng (`scalability`)
Bất kể dự án gì, miễn dự án đó được làm tốt, sử dụng development good practice.
Quan trọng là trưng ra được bạn nghĩ công việc nên được hoàn thành như thế nào.
Lời bình hồi 2020:
Dịch thì thế thôi, chứ lương < 10M thì hồi 2017 tuyển mãi có mỗi thằng Hoàng nó mang code theo, sau đó thêm Tài thì nó làm được bài logic lập trình căn bản, sau đó may thay anh Tiến ảnh vớt được ku Nam làm được việc, chứ giờ ném 3 cục đá thì 2 cục trúng 2 thằng dev đi lang thang, cơ mà code thì như cái cục chất thải 😂
Lời bình 2024:
hôm vừa rồi phỏng vấn Senior java, đã code java được 5 năm, nhưng quá nửa đống này chưa làm bao giờ :(
| longtth |
1,867,847 | What Can We Achieve with Artificial Intelligence in Customer Service? | This article was originally published on Danubius IT Solutions' tech blog. Artificial intelligence... | 0 | 2024-05-28T14:20:54 | https://danubius.io/en/blog/what-can-we-achieve-with-artificial | ai, customerservice, semanticsearch, efficiency | [This article was originally published on Danubius IT Solutions' tech blog.](https://danubius.io/en/blog/what-can-we-achieve-with-artificial)
Artificial intelligence (AI) has emerged as a transformative force and our team here, at Danubius embarked on an ambitious journey to explore the real impact of AI's practical applications in enhancing customer support. The adventure began a little over half a year ago with an internal project that aimed to not just theorize but actualize the potential of AI-based solutions in real-world scenarios. This article describes the proof of concept and the results we have managed to achieve in enhancing customer service with our AI solution.
## The Semantic Leap
At the heart of our approach to enhancing customer service through AI lies the concept of semantic search. Unlike traditional keyword-based search mechanisms, which often fail in the face of inexactness and context variability, semantic search represents a leap forward. It leverages the nuances of language, understanding the intent and meaning behind customer queries, thus enabling a search across extensive datasets of diverse quality levels.
Semantic search is built on the foundation of context and intent. It transcends the limitations of conventional search algorithms by interpreting the underlying meanings of words in vast datasets, rather than relying solely on their presence or frequency. This approach is especially critical in customer service, where queries can be complex, nuanced, and varied in their expression.
The backbone of our semantic search capability is a vector database, compiled and supported by OpenAI's Large Language Models (LLMs). These models are adept at converting vast amounts of text into high-dimensional space vectors, representing the semantic relationships between words and phrases. By integrating our vectorized databases with these LLMs, we created a dynamic and robust infrastructure capable of interpreting and processing customer queries with remarkable precision.
This integration marks a significant advancement in AI-driven solutions, as it allows for an outstanding level of precision in understanding and responding to customer inquiries. The ability to grasp the essence of customer queries, irrespective of the variations in phrasing or the quality of the text, sets our customer service solution apart, making it more responsive and effective.
## The Proof of Concept
On our ambitious journey, we sought to unlock the potential of AI in customer service. One of our side ventures, a startup that we launched six years ago, has grown significantly over the years, now serving over 1,500 enterprise customers. However, faced with a constant stream of emails, the challenge was evident: could AI significantly improve the response time of our client service team?
This project was far more than an experiment; it was a crucial proof of concept aimed at resolving a fundamental question that drives our mission—can AI truly assist users in a meaningful way? Driven by this, we committed ourselves to envision and actualize the potential of AI in elevating customer service efficiency.
## Building the Solution
To tackle this challenge, we crafted an innovative customer service support application, harnessing the latest AI technology to parse emails.
This system was meticulously designed to extract essential information and categorize inquiries with incredible efficiency. Although initially our success rate in categorizing emails accurately was just a modest 30%, we were determined to push the boundaries of what our solution could achieve. We embarked on a rigorous process of refining our model through extensive training rounds, feeding it three rounds of 500 emails where each email was categorized correctly by human customer support agents. This dedication bore fruit, dramatically enhancing our automated categorization accuracy rate to an impressive 84%.
## Enhancing Response Capabilities
Our ambitions didn't end at classification. Integrating our AI system with our startup’s knowledge base marked a turning point. By employing advanced semantic matching techniques through vector comparison, our model gained the ability to draw relevant information from the database and draft response letters with great relevance and precision. This process involved breaking down customer inquiries into smaller parts, and accurately retrieving the necessary data through API endpoints.
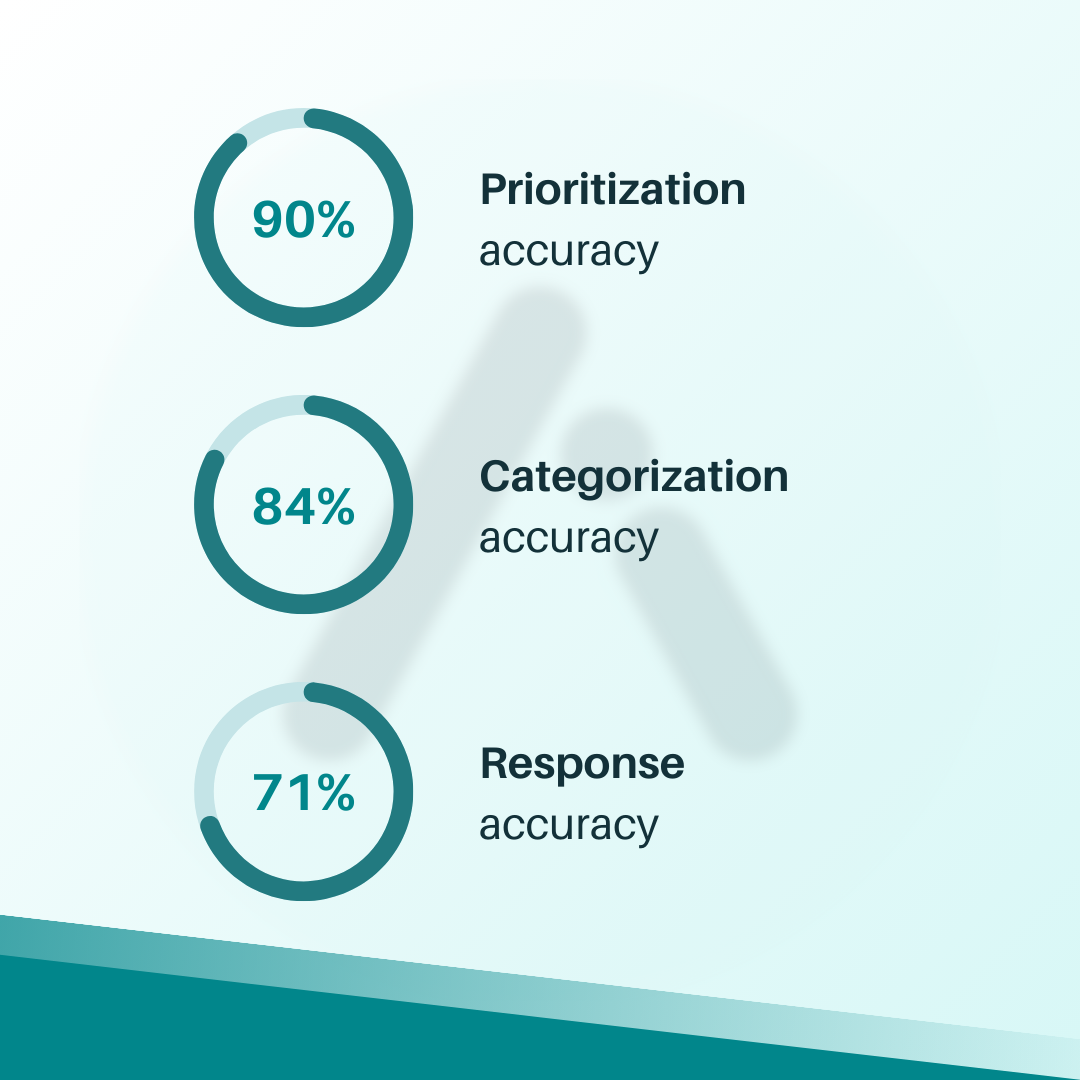
Achieving the capability to generate correct and contextually relevant responses was a significant milestone in our quest, demonstrating the transformative power of AI in tackling complex, real-world challenges.
## Overcoming Challenges
Each step, from the initial classification to the fine-tuning of our models and the retrieval of information from the knowledge base presented its own set of hurdles. However, these challenges proved to be invaluable opportunities for growth and learning.
One of the most essential lessons we learned through this process was the importance of data privacy and security. Recognizing the concerns surrounding AI and data confidentiality, we made sure that our models operated exclusively on European servers, offering our clients peace of mind regarding the safety and privacy of their data. This commitment to privacy and security is fundamental to our approach.
## Insights and Achievements
Our journey into integrating AI unveiled pivotal realizations, fundamentally reshaping our approach towards technological adoption. The fact that we could access and use APIs from major tech companies affordably was a significant boost to our project’s success. This actually makes AI adoption viable for a broader spectrum of businesses and also helps dismantle the cost barrier to sophisticated AI tools, which can lead to a new era of cost-effective technological empowerment.
Yet, the initial euphoria of accessing these out-of-the-box solutions soon gave way to a deeper understanding. We discovered that a more nuanced approach was necessary. Off-the-shelf solutions, while beneficial, required extensive customization to fully harness their potential. It was through this lens of customization and hands-on fine-tuning that we were able to transform these tools from generic solutions into strategic assets.
## The Transformative Impact
The infusion of AI into our customer service processes has truly reformed the way we deal with customer support: it increased operational efficiency as well as improved the qualitative aspects of customer engagement. The technological integration has enabled us to achieve a new level of responsiveness and personalization, significantly elevating the customer service experience. Our firsthand experience underscores the transformative potential of AI in redefining customer interactions, bridging the gap between human ingenuity and AI to forge great customer experiences.
This journey has underscored the dynamic nature of AI technology and the necessity for continuous adaptation and learning to stay ahead. Looking forward, we are inspired by the numerous possibilities that AI presents in enhancing every facet of customer service, leading to a future where AI not only supports but enriches our customer interactions.
## Looking Forward with AI
It's clear that AI's role and impact in customer service is vital, and no business can avoid its implementation if they want to keep the pace with competitors. Of course, in this project, we've only scratched the surface of what's possible but we're committed to exploring further, leveraging our gained knowledge and experience to innovate continuously and try to open new frontiers with AI in software development.
If you're looking to embark on your AI-based solution journey in customer service or any other domain, let our expert software engineers be your guide. With our expertise we can help you through the complexities of AI implementation and ensure success every step of the way. | danubiusio |
1,867,739 | Exploring Hurl, a command line alternative to Postman | Written by Nwani Victory✏️ GUI-based API clients such as Postman and Insomnia have risen in... | 0 | 2024-05-28T14:20:44 | https://blog.logrocket.com/exploring-hurl-postman-alternative | webdev | **Written by [Nwani Victory](https://blog.logrocket.com/author/nwanivictory/)✏️**
GUI-based API clients such as Postman and Insomnia have risen in popularity over time. Despite this, various annual developer surveys show that a large percentage of developers, QA and automation engineers, and API testers still resort to using the command line when testing their APIs.
If you’re a developer who prefers interacting with APIs through the command line, Hurl is an excellent Postman alternative that improves the DX of working with APIs through the command line. In this article, we’ll go through an in-depth explanation of the Hurl tool, its unique benefits, and how to use it.
## What is Hurl?
Hurl is a command-line tool that enables developers to run and test HTTP requests directly from their command line. Its CLI-based approach offers a lightweight alternative to GUI-based tools like Postman. Hurl supports APIs implemented using various protocols such as REST, GraphQL, and SOAP.
Under the hood, Hurl utilizes the legendary [cURL CLI tool for HTTP transfers](https://blog.logrocket.com/an-intro-to-curl-the-basics-of-the-transfer-tool/). As a result, it shares various similarities with cURL, including deriving its name from cURL and supporting cURL options.
Hurl supports a wide variety of operating systems including Windows, Linux, and MacOS. As a CLI tool, Hurl is also available for use within Continuous Integration (CI) pipelines.
Any HTTP requests you want Hurl to execute are stored in files with the `.hurl` extension. Each request URL within a Hurl file is referred to as an [entry](https://hurl.dev/docs/entry.html). Every entry has at least the request method and the URL.
Hurl supports having multiple request entries within a single file and will execute them sequentially when the file is run. Also, Hurl supports matching multiple `.hurl` files for execution using regular expressions. You’ll see the benefit of matching multiple files during the code demos later.
A basic Hurl file contains at least a single URL entry, which you want Hurl to validate against as shown in the next code block. When executed, Hurl will make a GET request to the [Rick and Morty API](https://rickandmortyapi.com/documentation/) to fetch all the characters and print them out:
```rust
GET https://rickandmortyapi.com/api
```
Executing the command above should result in an API response like the following:  Hurl outputs the API response by default. Considering that, you can manipulate the API response in many ways, such as redirecting it to another [tool like jq](https://blog.logrocket.com/npm-query-better-dependency-management/#usage-in-the-terminal-with-jq) to prettify the JSON result.
If you have `jq` installed, executing the next command will use the shell pipe operator `|` to pass the response body output from Hurl to `jq` for better formatting:
```json
hurl characters.hurl | jq
```
As you can see below, the data is formatted in a much more readable way than the output we saw before: 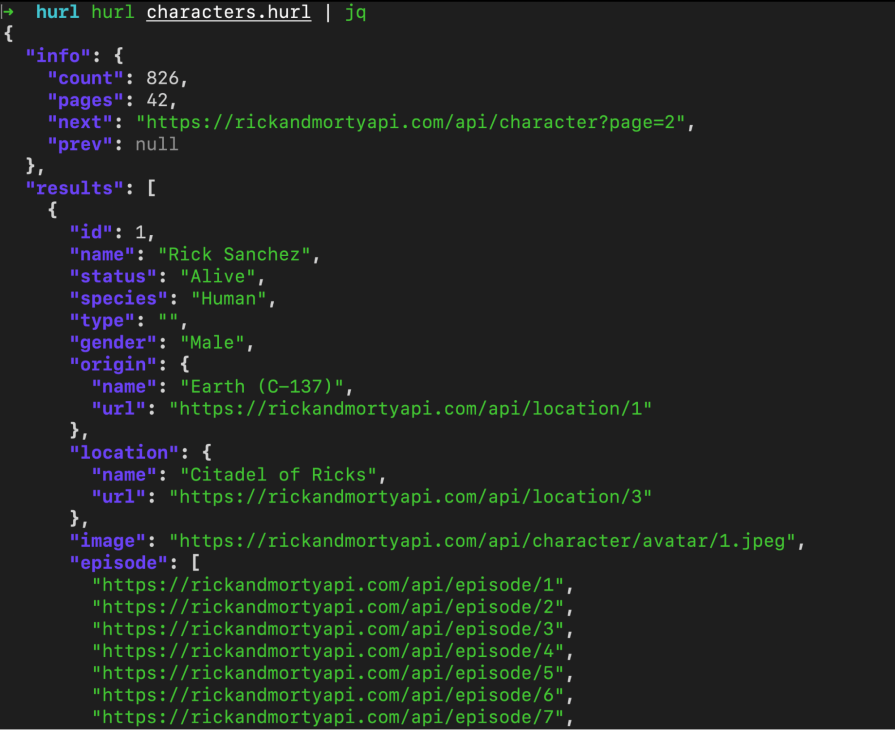 As your testing requirements increase, Hurl gives you the ability to expand your Hurl file to test multiple URLs and validate their responses, status codes, and even headers.
## Why use Hurl?
Unlike other API clients such as Postman, Hurl is completely open source, free to use, and community-driven. It leverages cURL to improve the experience of working with APIs from the terminal using a plain text syntax and it gives developers a lot of flexibility to tweak and customize their API requests.
Hurl offers a very lightweight, portable, and easy-to-install tool that you can use in development environments where the system or storage resources are limited such as cloud-based virtual environments or server workstations.
Testing your API through a CLI tool presents an opportunity for you to automate the steps and avoid repetitive work whenever you make changes to your API. Hurl provides support for GitHub Actions and BitBucket, enabling developers to include executing their Hurl tests in their CI/CD pipelines.
### Evaluating Hurl as a Postman alternative: Comparison table
If you’re deciding whether to use a GUI-based API client like Postman or a command-line tool like Hurl, the following high-level comparison table may help aid your choice:
<table>
<thead>
<tr>
<th></th>
<th>Hurl</th>
<th>Postman</th>
</tr>
</thead>
<tbody>
<tr>
<td>Pricing</td>
<td>Hurl is a free, open source software with no pricing tier to restrict certain features.</td>
<td>Postman is a paid software and not open source. It however has other free open source tools such as the Newman CLI, and Code Generators.</td>
</tr>
<tr>
<td>Usage</td>
<td>Hurl is fully command-line based with no support for testing APIs through a web browser or desktop application.</td>
<td>Postman provides a web browser and desktop application client for API testing. The Newman CLI from Postman supports API testing through the command line.</td>
</tr>
<tr>
<td>Learning curve</td>
<td>Hurl has a steep learning curve for non-technical users as you need to learn its concepts and syntax.</td>
<td>Postman is better suited for non-technical users as the GUI makes testing APIs easier.</td>
</tr>
<tr>
<td>Complexity</td>
<td>Hurl is less complex to begin using as it does not have an onboarding process.</td>
<td>Postman is often quite complex to get up and running as it prompts you to create an account, create a workspace for the project, and also configure the CLI when used within CI/CD workflows.</td>
</tr>
<tr>
<td>Data privacy</td>
<td>Hurl does not collect or store user or team information. The additional details for your API are stored within the project as environment variables in key-value pairs format.</td>
<td>Postman collects user data and persists your testing preferences, binary files, and environment variables outside your project</td>
</tr>
</tbody>
</table>
At this point, you now know what the Hurl tool is and the benefits it offers to developers who love performing API tests through their CLI. We’ve also discussed some of the drawbacks you should be aware of before diving into Hurl, such as its learning curve — especially for beginners.
If you’re willing to put in some time and effort to get familiar with Hurl, it could be a great and powerful tool in your developer toolbox. Let’s proceed to use Hurl in a demo project.
## Demonstrating Hurl’s features and benefits in action
Let’s see Hurl’s benefits in action by using it to test the public [Rick and Morty API](https://rickandmortyapi.com/documentation/) service. We’ll test the REST and GraphQL endpoints from the Rick and Morty service, alongside the frontend website elements that display all RickandMorty characters and episodes.
Hurl provides various functions for developers to perform implicit and explicit assertions on their API responses.
For APIs returning data in JSON format, the [JSONPath](https://goessner.net/articles/JsonPath/) assert allows developers to traverse through a response object and check its values. On the other hand, developers testing services returning data in XML format are to make use of the XPath assert.
### Using Hurl asserts on JSON responses
Execute the following command to create a folder named `RickAndMortyHurl`:
```shell
mkdir RickAndMortyHurl
```
You can also manually create the folder with your preferred name on your computer. The folder will store the Hurl files for testing the Rick and Morty API.
Create your first Hurl file with the name `characters.hurl` within the project folder and add the content of the next code block into it to expand the first RickAndMorty example:
```rust
GET https://rickandmortyapi.com/api/character
HTTP 200
[Asserts]
jsonpath "$.info.count" exists
jsonpath "$.info.pages" exists
jsonpath "$.results" exists
jsonpath "$.results" count >= 20
```
The code above directs Hurl to make a GET request to the `/character` endpoint of the Rick and Morty API and expect only a 200 response status code. The code also contains an `Asserts` block, which explicitly uses the `jsonpath` assert to check if certain properties exist in the info object, as well as whether the objects in the `results` array are equal to or greater than 20.
Hurl gives you the ability to customize its execution output by applying its [debug options](https://hurl.dev/docs/tutorial/debug-tips.html) to run the command. In this scenario, you should know more about the execution rather than the API response. Hence, you can apply the [`verbose`](https://hurl.dev/docs/tutorial/debug-tips.html#verbose-mode) and [`no-output`](https://hurl.dev/docs/tutorial/debug-tips.html#verbose-mode:~:text=%24%20hurl%20%2D%2Dverbose-,%2D%2Dno%2Doutput,-basic.hurl%0A*) debug options to the command.
Execute the following to run the `characters.hurl` file in a verbose mode without printing the JSON response from the Rick and Morty API:
```rust
hurl --verbose --test characters.hurl
```
As shown in the following image, Hurl outputs more details in the verbose mode about the API request being made rather than the API response body: 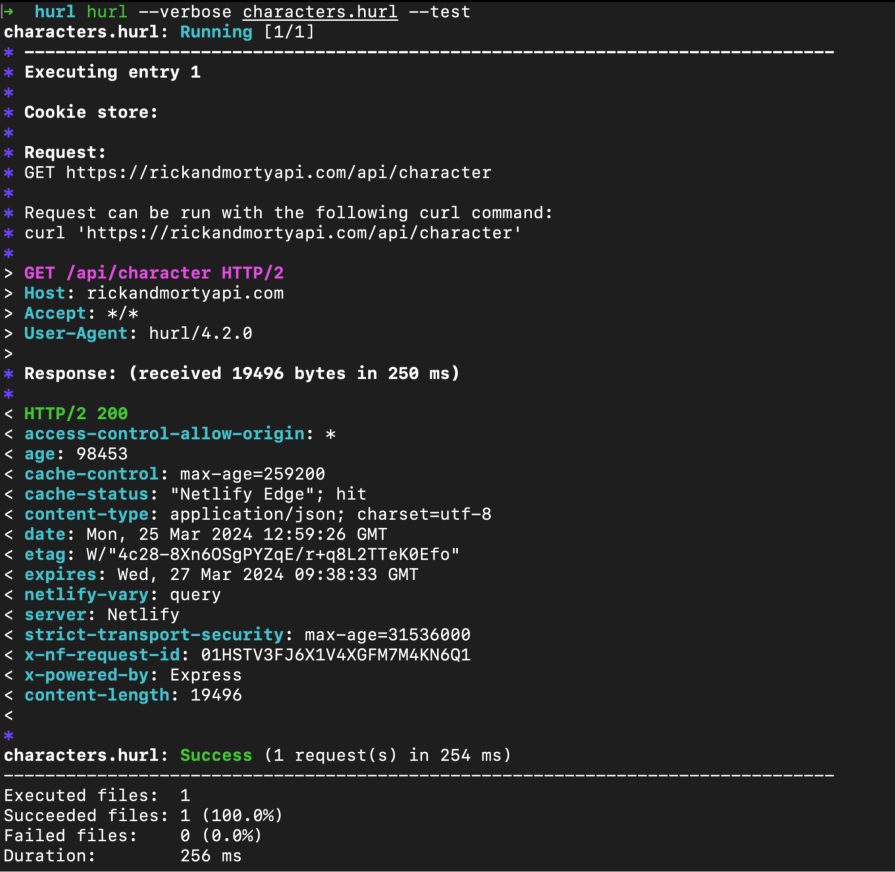 If any of the asserts fail, Hurl will print out the exact failing line with the received and expected values for its stack trace and pause the execution of the file.
To test, change any of the predicate values within the `characters.hurl` file and run the file again.
The following image shows the Hurl stack trace when the expected count value of the objects within the results array is greater than the actual value obtained after the API request: 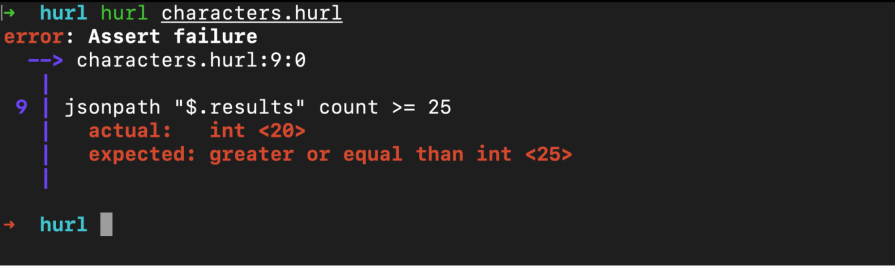 Similar to creating Hurl asserts using the jsonpath for JSON data, Hurl also provides you with XPath for capturing data from XML responses.
Before you begin writing the tests, open the [Rick and Morty](https://rickandmortyapi.com/) website to view its text content. You should see something like the following with some large text and a grid of random Rick and Morty characters:  Considering that we don’t have access to the codebase for the website as we’re not its developers, we can understand the HTML structure behind it by using the Web Inspector element: 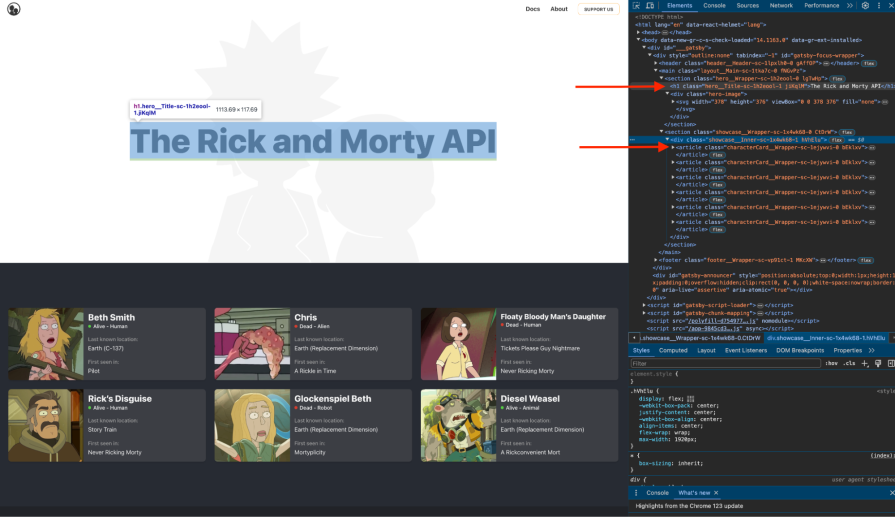 As you inspect the HTML elements present on the page, you will observe that the large text is the only H1 element on the page, and the Rick and Morty character cards are within an article element.
Knowing the elements and their attributes is important when testing XML data as you will often need to filter through to these specific elements before running your assertions.
Create another hurl file named `rickandmorty-website.hurl` within your Hurl project directory to store the entry for the XML data test.
Add the content of the following code block to your `rickandmorty-website.hurl` file to direct Hurl to make a request to the Rick and Morty webpage and execute queries on its XML elements:
```rust
# rickandmorty-website.hurl
GET https://rickandmortyapi.com
HTTP 200
[Asserts]
xpath "//h1" exists
xpath "normalize-space(//h1)" contains "The Rick and Morty API"
xpath "//section" count == 2
xpath "//article" count == 6
```
The asserts block in the code block above will direct Hurl to validate that the Rick and Morty website passes the following conditions:
* It has at least one H1 element in the DOM
* The H1 element contains text reading "The Rick and Morty API"
* It has two section elements and six article elements, each for six Rick and Morty character cards
Execute the command below to run the tests for the Rick and Morty website:
```rust
hurl rickandmorty-website.hurl --test
```
Once the test file runs successfully, you should see the result in your terminal: 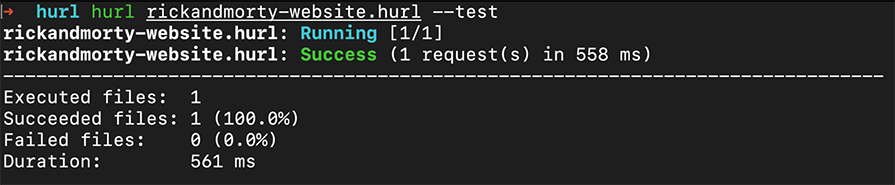 At this point, you are now familiar with executing tests using Hurl. Let’s see how to automate the execution of the tests within [a CI/CD pipeline](https://blog.logrocket.com/best-practices-ci-cd-pipeline-frontend/) such as GitHub Actions.
### Adding Hurl to your CI/CD pipeline
In addition to using unit and integration test suites in CI pipelines, developers often want to test their API endpoints directly using real-world values to ensure the response bodies meet the expected results. If you have this need, Hurl is the perfect choice for you!
Being a very lightweight and fast API client makes Hurl a perfect choice for CI pipelines as they have limited resources. Developers have the option to use scripts to install the Hurl binary into their CI pipelines or through community-managed actions such as [`install-hurl-cross-platform`](https://github.com/marketplace/actions/install-hurl-cross-platform) and [`setup-hurl`](https://github.com/nikeee/setup-hurl).
To use GitHub Actions, you need to create your action spec in a `.yml` file within a `.github` root folder and add the following code to it. In a repository, GitHub Actions will use the following specification to execute a workflow run using the defined jobs whenever a pull request is opened or reopened:
```yaml
.github/ci.yml
name: RickAndMorty CI Run
on:
pull_request:
types:
- opened
- reopened
jobs:
build:
runs-on: ubuntu-latest
permissions:
contents: read
steps:
- name: Checkout
uses: actions/checkout@v4
- name: Hurl Integration test
run: |
curl --location --remote-name https://github.com/Orange-OpenSource/hurl/releases/download/4.0.0/hurl_4.0.0_amd64.deb
sudo dpkg -i hurl_4.0.0_amd64.deb
hurl --test *.hurl --variable URL=https://rickandmortyapi.com
```
Although the workflow above is not ideal — as it’s testing against an external application and not the current changes in the pull request — it gives you an idea of how to set up your workflow.
Going through the `ci.yml` file, you will observe that the build job is using cURL to download the Hurl V4 binary before installing it with root user privileges. With Hurl installed, the job further executes all the Hurl files using a wildcard `*.hurl` and passes in the target URL as a variable to execute the requests against it.
Using two curly braces wrapped around a word — like `{{test_var}}` — is the syntax for using variables in Hurl files.
Variables are used to store and reuse certain values or change them dynamically as you would when running tests against different application environments. They also enable you to read sensitive credentials such as API keys and tokens into your Hurl files without hardcoding them in.
To improve on the workflow file above, you will need to create a deployment preview flow into your GitHub Action and replace the Rick and Morty website URL with your deploy preview URL.
## Conclusion
Hurl presents a feature-rich, flexible, and lightweight tool for testing your APIs straight out of your terminals, CI/CD pipelines, or environments with limited resources. With Hurl, developers who love their command line and terminals no longer have to feel left out when it comes to API testing or compelled to use GUI API clients!
In this tutorial, we explored the benefits of Hurl, evaluated it as a Postman alternative, and went through some examples to show Hurl’s features in action. If you have any further questions, feel free to comment them below.
---
##Get set up with LogRocket's modern error tracking in minutes:
1. Visit https://logrocket.com/signup/ to get an app ID.
2. Install LogRocket via NPM or script tag. `LogRocket.init()` must be called client-side, not server-side.
NPM:
```bash
$ npm i --save logrocket
// Code:
import LogRocket from 'logrocket';
LogRocket.init('app/id');
```
Script Tag:
```javascript
Add to your HTML:
<script src="https://cdn.lr-ingest.com/LogRocket.min.js"></script>
<script>window.LogRocket && window.LogRocket.init('app/id');</script>
```
3.(Optional) Install plugins for deeper integrations with your stack:
* Redux middleware
* ngrx middleware
* Vuex plugin
[Get started now](https://lp.logrocket.com/blg/signup)
| leemeganj |
1,867,769 | Profil ONEKLIK news | Dalam era digital saat ini, kebutuhan akan informasi yang cepat dan akurat menjadi sangat penting.... | 0 | 2024-05-28T14:19:02 | https://dev.to/one_kliknews_dd67bc0d010/profil-oneklik-news-98o |

Dalam era digital saat ini, kebutuhan akan informasi yang cepat dan akurat menjadi sangat penting. Onekliknews hadir sebagai portal berita yang memberikan informasi terkini dengan integritas dan kredibilitas tinggi. Artikel ini akan membahas profil lengkap Onekliknews, termasuk visi, misi, dan keunggulannya sebagai sumber berita terpercaya.
## Sejarah dan Latar Belakang Onekliknews
Onekliknews didirikan dengan tujuan untuk menjadi platform berita yang dapat diandalkan oleh masyarakat luas. Sejak awal berdirinya, Onekliknews telah berkomitmen untuk menyediakan berita yang faktual dan objektif. Dengan tim redaksi yang berpengalaman, Onekliknews berhasil tumbuh menjadi salah satu portal berita terkemuka di Indonesia.
## Visi dan Misi Onekliknews
**Visi**
Visi Onekliknews adalah menjadi sumber informasi utama yang menyajikan berita terkini dan faktual bagi masyarakat Indonesia. Onekliknews berupaya untuk selalu berada di garda terdepan dalam memberikan berita yang akurat dan terpercaya.
**Misi**
Menyajikan berita yang objektif dan berimbang.
Memberikan informasi yang cepat dan tepat waktu.
Mengutamakan integritas dan etika jurnalistik dalam setiap pemberitaan.
Mengembangkan jurnalisme yang mendidik dan menginspirasi.
Meningkatkan literasi media di kalangan masyarakat.
## Ragam Konten yang Ditawarkan Onekliknews
Onekliknews menyajikan beragam konten yang mencakup berbagai aspek kehidupan. Berikut adalah beberapa kategori utama yang ditawarkan:
**Berita Nasional**
Onekliknews memberikan liputan lengkap mengenai peristiwa penting di Indonesia. Berita-berita ini mencakup politik, ekonomi, hukum, dan sosial budaya. Setiap artikel ditulis dengan kepakaran dan ketelitian tinggi, memastikan bahwa pembaca mendapatkan informasi yang terbaru dan akurat.
**Berita Internasional**
Dalam kategori ini, Onekliknews menyajikan berita-berita dari seluruh penjuru dunia. Pembaca dapat mengikuti perkembangan politik internasional, hubungan antarnegara, konflik global, dan berbagai isu lainnya yang memiliki dampak internasional.
**Ekonomi dan Bisnis**
Bagian ini memberikan informasi mendalam tentang dunia ekonomi dan bisnis, termasuk analisis pasar,[KUR BRI](https://www.onekliknews.com/), [KUR BCA](https://www.onekliknews.com/), [KUR Mandiri](https://www.onekliknews.com/) kebijakan ekonomi, dan berita korporasi. Onekliknews juga menyajikan wawancara dengan tokoh-tokoh bisnis terkemuka, memberikan pandangan yang berharga tentang tren ekonomi saat ini. Serta [Ide Jualan](https://www.onekliknews.com/).
**Teknologi dan Sains**
Onekliknews tidak hanya fokus pada berita umum, tetapi juga menyajikan informasi terbaru tentang perkembangan teknologi dan sains. Artikel-artikel ini mencakup inovasi teknologi, penelitian ilmiah, dan dampaknya terhadap kehidupan sehari-hari.
**Olahraga**
Bagi penggemar olahraga, Onekliknews menyediakan liputan lengkap tentang berbagai cabang olahraga, baik di tingkat nasional maupun internasional. Pembaca dapat mengikuti berita tentang pertandingan, pemain, dan event olahraga besar lainnya.
**Hiburan dan Gaya Hidup**
Kategori ini mencakup berita tentang dunia hiburan, termasuk film, musik, selebriti, dan budaya pop. Selain itu, ada juga artikel-artikel tentang gaya hidup, seperti kesehatan, fashion, [Zodiak Hari Ini](https://www.onekliknews.com/) dan tips-tips kehidupan sehari-hari.
## Keunggulan Onekliknews
**Kredibilitas dan Akurasi**
Salah satu keunggulan utama Onekliknews adalah kredibilitas dan akurasi dalam setiap pemberitaan. Tim redaksi Onekliknews terdiri dari jurnalis profesional yang memiliki integritas tinggi dan berdedikasi dalam menyajikan berita yang benar-benar dapat dipercaya.
**Kecepatan Penyampaian Berita**
Onekliknews selalu berusaha untuk menjadi yang tercepat dalam menyampaikan berita terbaru kepada pembaca. Dengan dukungan teknologi canggih dan tim yang solid, Onekliknews mampu mengupdate berita secara real-time.
**User-Friendly**
Desain situs Onekliknews dibuat ramah pengguna dan mudah diakses. Pembaca dapat dengan mudah menemukan berita yang mereka cari dengan navigasi yang sederhana dan intuitif. Selain itu, Onekliknews juga tersedia dalam versi mobile, memudahkan akses berita kapan saja dan di mana saja.
**Interaksi dengan Pembaca**
Onekliknews membuka ruang interaksi dengan pembaca melalui komentar, forum diskusi, dan media sosial. Hal ini memungkinkan pembaca untuk berpartisipasi aktif dalam setiap diskusi dan memberikan umpan balik langsung kepada tim redaksi.
**Konten Multiformat**
Selain artikel tulisan, Onekliknews juga menyediakan konten dalam berbagai format lain seperti video, infografis, dan podcast. Ini memberikan pengalaman yang lebih kaya dan variatif bagi pembaca dalam mengonsumsi berita.
**Komitmen terhadap Etika Jurnalistik**
Onekliknews menjunjung tinggi etika jurnalistik dalam setiap aspek pemberitaannya. Setiap informasi yang disajikan telah melalui proses verifikasi yang ketat, memastikan bahwa tidak ada hoax atau berita palsu yang lolos. Onekliknews berkomitmen untuk selalu memberikan berita yang bertanggung jawab dan berimbang.
Onekliknews adalah sumber berita yang dapat diandalkan, menyediakan informasi terkini dengan kredibilitas dan kecepatan yang tinggi. Dengan berbagai kategori konten yang ditawarkan, Onekliknews mampu memenuhi kebutuhan informasi dari berbagai kalangan masyarakat. Dengan komitmen terhadap etika jurnalistik dan interaksi aktif dengan pembaca, Onekliknews terus berupaya untuk menjadi portal berita utama di Indonesia. | one_kliknews_dd67bc0d010 | |
1,867,767 | 10 Lesser Known Git Commands and Techniques You Should Know | Git is a powerful version control system used by developers worldwide to manage and track changes in... | 0 | 2024-05-28T14:17:22 | https://dev.to/documendous/10-lesser-know-git-commands-and-techniques-you-should-know-kke | git, versioncontrol, advancedgit, devtools | Git is a powerful version control system used by developers worldwide to manage and track changes in their codebases. While most developers are familiar with basic Git commands like `git commit`, `git push`, and `git pull`, there are many advanced commands and techniques that can greatly enhance your workflow and productivity. In this post, we’ll explore 10 lesser-known Git commands and techniques that you probably haven't used yet but can significantly streamline your development process and improve your version control skills. Dive in and discover how these advanced features can help you tackle complex tasks with ease.
1. **git bisect**: This command is used for binary search to find the commit that introduced a bug. Start with `git bisect start`, mark the current commit as bad with `git bisect bad`, and mark a known good commit with `git bisect good [commit]`. Git will then help you find the exact commit that introduced the issue.
2. **git reflog**: This command allows you to view the history of all actions in the local repository, including those that are not part of the commit history, such as resets and rebases. Use `git reflog` to see this history.
3. **git rerere**: This stands for "reuse recorded resolution." It helps to remember how you resolved a conflict and reuses that resolution if the same conflict happens again. Enable it with `git config --global rerere.enabled true`.
4. **git blame -C -C**: This variant of `git blame` tracks moved or copied lines of code across files. The `-C -C` options increase the likelihood of detecting such changes.
5. **git commit --fixup [commit]**: This command marks a commit as a fixup of an existing commit. Later, you can use `git rebase -i --autosquash` to automatically squash the fixup commit into the target commit.
6. **git worktree**: This command allows you to check out multiple branches at once in separate working directories. Use `git worktree add [path] [branch]` to create a new working tree.
7. **git stash push -m [message]**: This command allows you to stash changes with a message. Use `git stash list` to see the list of stashes with their messages.
8. **git cherry-pick -n [commit]**: The `-n` (no-commit) option applies the changes from the commit but does not create a commit. This allows you to make additional changes before committing.
9. **git filter-branch**: This powerful command allows you to rewrite history, such as removing sensitive data or changing author information. Use with caution, as it can rewrite large parts of history.
10. **git clean -fdx**: This command removes all untracked files and directories, including ignored ones. Use it to clean your working directory completely.
| documendous |
1,867,766 | Are You Wasting Money in Your Software Development Project? | This article was originally published on Danubius IT Solutions' tech blog. Over the years, our team... | 0 | 2024-05-28T14:16:50 | https://danubius.io/en/blog/are-you-wasting-money-in-your | softwaredevelopment, costoptimization, projectmanagement, efficiency | [This article was originally published on Danubius IT Solutions' tech blog.](https://danubius.io/en/blog/are-you-wasting-money-in-your)
Over the years, our team has encountered everything from project triumphs to near-misses, teaching us a crucial lesson: software development can be full of avoidable errors that can inflate costs and delay timelines. Post-Covid, many large firms are confronting IT expenditures that fail to meet expected value, highlighting a need for change.
In this article, we are peeling back the layers of the software development process to spotlight these pitfalls and offer guidance on steering clear of them. For instance, contrary to common belief, coding is but a small part of the entire software development life cycle (SDLC). Imagine a wall in a conference room covered in the SDLC's detailed steps; coding will fill just one page! Excellence in software development transcends (skilled) coding.
Hereby we're going to explore the common mistakes that can make software development more expensive than it needs to be – and see how to avoid them.
## Understanding Development Costs
Before diving into the complexities of software development and identifying potential wastes, it’s crucial to have a grasp on the various types of costs involved:
Labor Costs: The backbone of any project, labor costs encompass not just the wages, but also the benefits and any additional compensations for the entire development team. This includes everyone from developers and designers to testers and project managers. The complexity and duration of the project often dictate these costs, making effective team management and streamlined processes crucial for cost optimization.
Infrastructure Costs: Beyond the immediate hardware needs of your development team, infrastructure costs also cover the software licenses required for development and cloud services for hosting environments, testing, and production. Efficient management of these resources, such as choosing scalable cloud services, can significantly reduce unnecessary expenses.
Tools and Technology Costs: The selection of development tools, libraries, and frameworks, along with any required third-party services, forms a significant part of the project's budget. Investing wisely in tools that enhance productivity without overburdening the budget is key. Utilizing open-source solutions where appropriate can offer cost-effective alternatives to expensive proprietary software.
Maintenance and Support Costs: The lifecycle of software development doesn’t end with deployment. Maintenance and support, including bug fixes, updates, and handling customer queries, are ongoing costs that can accumulate significantly over time. Planning for these from the outset and establishing efficient post-launch support systems can help manage these long-term expenses more effectively.
## Identifying the Waste: Key Areas of Focus Where Development Can Burn Money
We can now delve into critical areas where inefficiencies can inflate software development expenses. Here’s a summary of the next sections that will cover essential topics to help you navigate these challenges effectively:
Design and Requirements: Emphasizing the importance of clear, comprehensive project requirements to prevent costly revisions.
Initial Phases & The Minimum Viable Product (MVP) Dilemma: How to efficiently move through early development stages and the pitfalls of misjudging the MVP scope.
Underestimating UX: Addressing the risks of unnecessary features and the significance of user experience in development costs.
Skipping Testing & Backlog Prioritization: The consequences of inadequate testing and strategies for effective backlog management.
Balancing Interests & Feedback Loops: Managing stakeholder interests and the role of feedback in refining development focus.
In-House Development vs. Outsourcing: Considering the financial implications of team structure and the risks associated with replacing systems or components.
Hiring the Right Talent & Leadership Coordination: The impact of recruitment choices on project success and the importance of strong project leadership.
## The Starting Point: Design and Requirements
A solid foundation in design and requirements is critical for minimizing software development expenses. Clear and comprehensive planning at this stage serves as the bedrock for avoiding costly errors and fostering efficient practices that enhance ROI.
## Navigating the Initial Phases
The absence of a fully communicated project vision can significantly inflate costs, like constructing a building without a complete blueprint. This often results in extensive refactoring if requirements are added or changed mid-development. Early and detailed requirement setting, coupled with effective planning, can substantially lower these risks and expenses, ensuring development aligns with the project's goals from the outset.
## The MVP Dilemma
The Minimum Viable Product (MVP) approach is often misconstrued as needing to be feature-complete and flawless. Unfortunately, more often than not, this mindset leads to overdevelopment before the product has even hit the market, incorporating numerous enhancements and features that may not align with actual user needs. As such, we can say that the assumption that the development team or even the Product Owner knows precisely what the client requires can lead to a bloated product, burdened with unnecessary features.
Instead, introducing elements that genuinely add value to the client right from the beginning can streamline the development process. Adopting a user experience (UX) perspective, guided by thorough market research, helps in identifying and focusing on features that meet user needs. For instance, if a client struggles to discern which features will be most impactful, guiding them through a process of user interviews or surveys can provide clarity.
In developing a mobile app, for example, if market research shows users have a strong need for an intuitive scheduling feature, focusing on this functionality first ensures efficient use of resources. Through prototyping and gathering user feedback early, the team can refine this key feature before full development. This focused approach not only makes development more efficient but also boosts the final product's relevance and user appeal.
## The Cost of Underestimating UX
Overlooking UX in software development, seen by some as mere aesthetic "window-dressing," can lead to significant cost overruns and delays.
UX is crucial for identifying user needs early, streamlining development rather than retrofitting design post-launch. A notable example includes a client revising a registration process six times due to initially ignoring UX, resulting in increased costs and delays.
Comparatively, consider a project where UX guides the design from the outset, involving real user feedback on early prototypes. This approach pinpoints the exact features users needed, avoiding the trap of adding or revising unnecessary features and elements later. This demonstrates that thorough UX planning is essential for cost-effective development.
## The High Stakes of Skipping Testing
Neglecting proper testing is a common pitfall in software development. The misconception that developers can adequately test their work or that structured testing is unnecessary often results in critical bugs and unexamined features.
These oversights become costly and damaging when flaws emerge post-launch, with the cost to fix them vastly overtaking early detection expenses. Instances, where test servers went unused for months, highlight the lack of essential functional testing, undermining software reliability and performance. And without regular regression testing, each addition or change introduces risk, turning post-release bug fixes into expensive, trust-eroding emergencies.
The Model V development approach highlights the escalating costs associated with fixing bugs at different stages of the project lifecycle. Identifying an issue during development is significantly cheaper than addressing it after the software goes live. Yet, the inclination to cut corners on testing, under the illusion of saving time or resources, reflects a misunderstanding of its critical role in the SDLC.
## Backlog Prioritization
Efficiently managing a software development project involves much more than simply ticking off tasks from a to-do list.
Backlog prioritization is crucial for strategic resource allocation in software development, distinguishing between must-have features and lower-priority enhancements. The challenge lies in identifying features that significantly add value and prioritizing them accordingly.
## The 80/20 Rule
Applying the Pareto Principle, or the 80/20 rule, can be a game-changer in this context.
It suggests that focusing on the 20% of functions that are expected to provide 80% of the value could lead to more efficient use of resources and a more successful outcome.
This approach underlines the importance of identifying and developing the features that are vital for the product’s success early on, allowing the less critical enhancements to be developed post-release.
## Balancing Diverse Interests
Prioritization involves weighing various factors, including project roadmap, potential for attracting new customers, upsell opportunities, major client requests, and existing customer feedback.
Balancing these requires understanding both business and technical considerations, like the impact and cost of developing a billing function versus the value of addressing specific customer demands or bugs. This process is vital for focusing on functionalities that offer the greatest overall value.
## Feedback Loops and Development Focus
Neglecting UX design, comprehensive testing, and strategic bug management can trap the development team in a costly cycle of endless fixes, redirecting resources from more valuable features. An unplanned response to extensive feedback and bug fix requests can drastically reduce efficiency.
When prioritizing features, assess their value and impact carefully. For instance, choosing between a feature that requires minimal development time and resources but satisfies many customers, and another demanding more effort for comparable impact necessitates strategic decision-making to optimize resource use and maximize customer benefit.
## Full In-House Development Team vs. Outsourcing
Maintaining a full in-house development team, while well-intentioned, often incurs unforeseen challenges and costs.
Startups and larger corporations alike can struggle with management complexities and a lack of strategic direction, leading to stalled development and the need to overhaul poorly written codebases. Moreover, the fixed nature of in-house teams limits flexibility and responsiveness to project demands, with hiring and dismissal processes being both cumbersome and costly.
In some cases, we’ve encountered situations where development teams were reluctant to even touch their predecessors' work due to the poor state of the codebase. In the end, we took on the challenge but had to tell the client that it would require a new start from scratch, as the existing spaghetti code was completely unusable.
## The Flexibility of Outsourcing
Outsourcing offers dynamic scalability, allowing for adjustment of development efforts without the legal and financial burdens of staff changes.
Software agencies provide quick replacement of experts and adaptability, a stark contrast to the time-consuming process of rectifying hiring mistakes in-house. This approach also circumvents the challenge of assembling a team with the right technological expertise, particularly crucial for companies transitioning from legacy systems.
Also, the process of replacing an in-house team member is both costly and time-consuming. Software agencies, on the other hand, can more readily provide or replace experts, often at no extra cost, ensuring that projects continue to move forward without significant delays.
## The Challenge of Hiring the Right Talent
Many companies struggle to identify the specific skills needed during the selection process, leading to "bad hires" that can be more detrimental than beneficial.
For example, we worked with a client whose internal team did not have the expertise for the technological transitions necessary, a situation that could have been avoided with more strategic hiring practices. This is particularly relevant for companies looking to replace legacy systems with new technologies, where a lack of relevant expertise can stall progress.
## Leadership and Coordination
The absence of experienced leadership in in-house teams can lead to rushed projects or endless cycles of over-polishing. Effective coordination and clear, achievable deadlines are essential for keeping development on track. Outsourcing to agencies that bring both leadership and specialized skills to the table can mitigate these risks, ensuring focused and efficient progress.
So, while in-house teams offer certain advantages, the potential for increased costs and operational inflexibility presents significant risks. Outsourcing emerges as a strategic alternative, providing the agility and expertise necessary to navigate the complexities of software development efficiently.
## Strategies for Avoiding Waste in Software Development
Having pinpointed key areas where waste can occur in software development, let’s take an overview of the strategies that can significantly enhance resource efficiency and project effectiveness:
Prioritize Requirements: Engage closely with all stakeholders to define and prioritize requirements that offer the highest business value and are technically feasible. This ensures that development efforts are concentrated on essential functionalities first, reducing time and resources spent on lower-priority features.
Embrace Agile Practices: Incorporating agile methodologies, such as Scrum or Kanban, fosters an environment of iterative development, enabling teams to adapt to changes swiftly and deliver value progressively. This approach minimizes the risk of devoting resources to features that may not meet evolving user needs.
Implement Continuous Integration and Delivery (CI/CD): CI/CD pipelines automate building, testing, and deployment, enhancing efficiency by reducing manual intervention and accelerating the release cycle. This also helps in maintaining a consistent quality across builds and deployments.
Foster Collaboration: Promoting a culture of open communication and teamwork across developers, stakeholders, and users can help in identifying potential issues early. This collaborative approach ensures that everyone is aligned, thereby avoiding misunderstandings and costly reworks.
Invest in Quality Assurance: Dedicating adequate resources to comprehensive testing, including automated testing, is crucial. This not only speeds up the identification of bugs but also ensures that the software meets all user expectations before release, preventing expensive post-launch fixes.
## Monitor and Measure Performance: Setting up and tracking Key
Performance Indicators (KPIs) related to development efficiency and project milestones allows for timely identification of areas needing improvement. Regularly reviewing these metrics facilitates informed, data-driven adjustments to the development process.
Continuously Learn and Improve: Cultivating a culture of ongoing learning and self-improvement empowers teams to innovate and optimize workflows continuously. Sharing insights, exploring new tools, and reflecting on each project can lead to more efficient practices and cutting-edge solutions.
## Conclusion
Remember that at the start of this article, we painted the mental image of a wall plastered with all the steps of the software development life cycle? Well, to illustrate this point, our developers actually covered a 20-square-meter wall with diagrams mapping out all the processes and sub-processes involved in the SDLC. Out of those 40 steps that we collected, several consisting of multiple pages, the task of writing code was represented by just a single page! This exercise visually underscored that coding is merely one element within the 'Construct' phase of the SDLC, which also encompasses formation, requirement/planning, design, construction, testing, product release, and post-implementation.
Startups and larger organizations alike often misjudge the complexity of software development, overlooking the necessity for a comprehensive, multidisciplinary strategy. Startups might think hiring a skilled programmer is the silver bullet for all their development challenges, while bigger companies may face challenges in aligning the vision and coordination among various stakeholders, complicating project direction due to differing needs and lack of a unified decision-maker.
## Avoid These Costly Mistakes in Your Next Development Project
Fortunately, you can bypass these all-too-common pitfalls of software development and ensure a smooth lifecycle for your project with the help of our professionals.
If you are ready to launch your next software development journey and make it a success without unnecessary costs and complications, contact us, and let's discuss how we can bring your vision to life with efficiency and excellence.And if you would like to read more about our technological know-how and the business cases we have solved, check out our case studies. | danubiusio |
1,866,032 | Mastering TypeScript Generics: A Simple Guide | Generics in TypeScript allow you to create reusable components and functions that work with various... | 0 | 2024-05-28T14:15:39 | https://dev.to/hasanm95/mastering-typescript-generics-a-simple-guide-50cn | typescript, programming, frontend, webdev | Generics in TypeScript allow you to create reusable components and functions that work with various data types while maintaining type safety. They let you define placeholders for types that are determined when the component or function is used. This makes your code flexible and versatile, adapting to different data types without sacrificing type information. Generics can be used in functions, types, classes, and interfaces.
## Basic Syntax
The syntax for using generics involves angle brackets (`<>`) to enclose a type parameter, representing a placeholder for a specific type.
## Using Generics with Functions
Here's how you can use generics in functions:
```typescript
function identity<T>(arg: T): T {
return arg;
}
const result = identity<string>("Hello, TypeScript!");
```
In this example, the identity function uses a generic type parameter `T` to denote that the input argument and the return value have the same type. When calling the function, you provide a specific type argument within the angle brackets (`<string>`) to indicate that you're using the function with strings.
## Passing Type Parameters Directly
Generics can also be useful when working with custom types:
```typescript
type ProgrammingLanguage = {
name: string;
};
function identity<T>(value: T): T {
return value;
}
const result = identity<ProgrammingLanguage>({ name: "TypeScript" });
```
In this example, the `identity` function uses a generic type parameter `T`, which is explicitly set to `ProgrammingLanguage` when the function is called. Thus, the result variable has the type `ProgrammingLanguage`. If you did not provide the explicit type parameter, TypeScript would infer the type based on the provided argument, which in this case would be `{ name: string }`.
Another common scenario involves using generics to handle data fetched from an API:
```typescript
async function fetchApi(path: string) {
const response = await fetch(`https://example.com/api${path}`);
return response.json();
}
```
This function returns a `Promise<any>`, which isn't very helpful for type-checking. We can make this function type-safe by using generics:
```typescript
type User = {
name: string;
};
async function fetchApi<ResultType>(path: string):Promise<ResultType> {
const response = await fetch(`https://example.com/api${path}`);
return response.json();
}
const data = await fetchApi<User[]>('/users');
```
By turning the function into a generic one with the `ResultType` parameter, the return type of the function is now `Promise<ResultType>`.
## Default Type Parameters
To avoid always specifying the type parameter, you can set a default type:
```typescript
async function fetchApi<ResultType = Record<string, any>>(path: string): Promise<ResultType> {
const response = await fetch(`https://example.com/api${path}`);
return response.json();
}
const data = await fetchApi('/users');
console.log(data.a);
```
With a default type of `Record<string, any>`, TypeScript will recognize data as an object with `string` keys and `any` values, allowing you to access its properties.
## Type Parameter Constraints
In some situations, a generic type parameter needs to allow only certain shapes to be passed into the generic. To create this additional layer of specificity to your generic, you can put constraints on your parameter. Imagine you have a storage constraint where you are only allowed to store objects that have string values for all their properties. For that, you can create a function that takes any object and returns another object with the same keys as the original one, but with all their values transformed to strings this function will be called `stringifyObjectKeyValues`.
This function is going to be a generic function. This way, you are able to make the resulting object have the same shape as the original object. The function will look like this:
```typescript
function stringifyObjectKeyValues<T extends Record<string, any>>(obj: T) {
return Object.keys(obj).reduce((acc, key) => ({
...acc,
[key]: JSON.stringify(obj[key])
}), {} as { [K in keyof T]: string })
}
```
In this code, `stringifyObjectKeyValues` uses the `reduce` array method to iterate over an array of the original keys, stringifying the values and adding them to a new array.
To make sure the calling code is always going to pass an object to your function, you are using a type constraint on the generic type `T`, as shown in the following highlighted code:
```typescript
function stringifyObjectKeyValues<T extends Record<string, any>>(obj: T) {
// ...
}
```
`extends Record<string, any>` is known as generic type constraint, and it allows you to specify that your generic type must be assignable to the type that comes after the `extends` keyword. In this case, `Record<string, any>` indicates an object with keys of type string and values of type any. You can make your type parameter extend any valid TypeScript type.
When calling `reduce`, the return type of the reducer function is based on the initial value of the accumulator. The `{} as { [K in keyof T]: string }` code sets the type of the initial value of the accumulator to `{ [K in keyof T]: string }` by using a type cast on an empty object, `{}`. The type `{ [K in keyof T]: string }` creates a new type with the same keys as `T`.
The following code shows the implementation of your `stringifyObjectKeyValues` function:
```typescript
function stringifyObjectKeyValues<T extends Record<string, any>>(obj: T) {
return Object.keys(obj).reduce((acc, key) => ({
...acc,
[key]: JSON.stringify(obj[key])
}), {} as { [K in keyof T]: string })
}
const stringifiedValues = stringifyObjectKeyValues({ a: "1", b: 2, c: true, d: [1, 2, 3]})
*/
{
a: string;
b: string;
c: string;
d: string;
}*/
```
## Using Generics with Interfaces, Classes, and Types
When creating interfaces and classes in TypeScript, it can be useful to use generic type parameters to set the shape of the resulting objects. For example, a class could have properties of different types depending on what is passed in to the constructor. In this section, you will see the syntax for declaring generic type parameters in classes and interfaces and examine a common use case in HTTP applications.
### Generic Interfaces and Classes
##### Interfaces:
```typescript
interface MyInterface<T> {
field: T
}
```
This declares an interface that has a property `field` whose type is determined by the type passed in to `T`.
##### Classes:
```typescript
class MyClass<T> {
field: T
constructor(field: T) {
this.field = field
}
}
```
One common use case of generic interfaces/classes is for when you have a field whose type depends on how the client code is using the interface/class. Say you have an `HttpApplication` class that is used to handle HTTP requests to your API, and that some context value is going to be passed around to every request handler. One such way to do this would be:
```typescript
class HttpApplication<Context> {
context: Context
constructor(context: Context) {
this.context = context;
}
get(url: string, handler: (context: Context) => Promise<void>): this {
return this;
}
}
```
This class stores a `context` whose type is passed in as the type of the argument for the `handler` function in the `get` method. During usage, the parameter type passed to the `get` handler would correctly be inferred from what is passed to the class constructor.
```typescript
const context = { someValue: true };
const app = new HttpApplication(context);
app.get('/api', async () => {
console.log(context.someValue)
});
```
In this implementation, TypeScript will infer the type of `context.someValue` as `boolean`.
### Generic Types
Generic types can be used to create helper types, such as Partial, which makes all properties of a type optional:
```typescript
type Partial<T> = {
[P in keyof T]?: T[P];
};
```
To understand the power of generic types, let's consider an example involving an object that stores shipping costs between different stores in a business distribution network. Each store is identified by a three-character code:
```typescript
{
ABC: {
ABC: null,
DEF: 12,
GHI: 13,
},
DEF: {
ABC: 12,
DEF: null,
GHI: 17,
},
GHI: {
ABC: 13,
DEF: 17,
GHI: null,
},
}
```
In this object:
* Each top-level key represents a store.
* Each nested key represents the cost to ship to another store.
* The cost from a store to itself is `null`.
To ensure consistency (e.g., the cost from a store to itself is always `null` and the costs to other stores are numbers), we can use a generic helper type.
```typescript
type IfSameKeyThenTypeOtherwiseOther<Keys extends string, T, OtherType> = {
[K in Keys]: {
[SameKey in K]: T;
} & {
[OtherKey in Exclude<Keys, K>]: OtherType;
};
};
```
##### Breakdown this type
1. Generics Declaration:
* `Keys extends string`: `Keys` is a type parameter that must be a union of `string` literals. It represents all possible keys of the object.
* `T`: A type parameter representing the type to be used when a key matches itself.
* `OtherType`: A type parameter representing the type to be used when a key does not match itself.
2. Mapped Type:
```typescript
[K in Keys]:
```
This is a mapped type that iterates over each key `K` in the union type `Keys`.
3. Inner Object Type:
The inner object type is divided into two parts:
```typescript
{
[SameKey in K]: T;
}
```
Here, `[SameKey in K]` creates a property where `SameKey` is exactly `K`. This means if the key of the outer object is `K`, this inner key is also `K`, and its type is `T`.
```typescript
{
[OtherKey in Exclude<Keys, K>]: OtherType;
}
```
This part uses `Exclude<Keys, K>` to create properties for all other keys in `Keys` except `K`. The type of these properties is `OtherType`.
4. Combining with Intersection (`&`):
```typescript
{
[K in Keys]: {
[SameKey in K]: T;
} & {
[OtherKey in Exclude<Keys, K>]: OtherType;
};
}
```
The two inner object parts are combined using the intersection type `&`. This means the resulting type will include properties from both parts.
##### Example
```typescript
type StoreCode = 'ABC' | 'DEF' | 'GHI';
type ShippingCosts = IfSameKeyThenTypeOtherwiseOther<StoreCode, null, number>;
const shippingCosts: ShippingCosts = {
ABC: {
ABC: null, // T (null) because key is same as parent key
DEF: 12, // OtherType (number) because key is different
GHI: 13 // OtherType (number) because key is different
},
DEF: {
ABC: 12, // OtherType (number) because key is different
DEF: null, // T (null) because key is same as parent key
GHI: 17 // OtherType (number) because key is different
},
GHI: {
ABC: 13, // OtherType (number) because key is different
DEF: 17, // OtherType (number) because key is different
GHI: null // T (null) because key is same as parent key
}
};
```
##### Explanation
* For the key `ABC` in `shippingCosts`:
* `ABC: null` matches the outer key, so it gets the type `T` (null).
* `DEF: 12` and `GHI: 13` do not match the outer key, so they get the type `OtherType` (number).
* This pattern repeats for the keys `DEF` and `GHI`, ensuring that the cost from a store to itself is always `null`, while the cost to other stores is always a `number`.
##### Summary
The `IfSameKeyThenTypeOtherwiseOther` type ensures consistency in the shape of an object where:
* If a key matches its own name, it gets a specific type `T`.
* If a key does not match its own name, it gets another type `OtherType`.
This is particularly useful for scenarios like our shipping costs example, where certain keys require specific types, ensuring type safety and consistency across the object.
---
## Creating Mapped Types with Generics
Mapped types allow you to create new types based on existing ones. For instance, you can create a type that transforms all properties of a given type to booleans:
```typescript
type BooleanFields<T> = {
[K in keyof T]: boolean;
};
type User = {
email: string;
name: string;
};
type UserFetchOptions = BooleanFields<User>;
```
This results in:
```typecript
type UserFetchOptions = {
email: boolean;
name: boolean;
};
```
## Creating Conditional Types with Generics
Conditional types are generic types that resolve differently based on a condition:
```typescript
type IsStringType<T> = T extends string ? true : false;
```
This type checks if T extends string and returns true if it does, otherwise false.
| hasanm95 |
1,839,399 | Distributed PostgreSQL with YugabyteDB Multi-Region Kubernetes / Istio / Amazon EKS | YugabyteDB, an open-source PostgreSQL-compatible distributed SQL database, can be deployed on... | 0 | 2024-05-28T14:14:31 | https://dev.to/aws-heroes/distributed-postgresql-with-yugabytedb-multi-region-kubernetes-istio-amazon-eks-366a | yugabytedb, aws, kubernetes, postgres | YugabyteDB, an open-source PostgreSQL-compatible distributed SQL database, can be deployed on Kubernetes. When deploying across multiple regions, a service mesh helps manage the traffic, and **Istio** is a great solution for Kubernetes. Here's a guide on fully deploying the solution, from provisioning an **Amazon AKS** **Kubernetes** cluster on AWS to running **YugabyteDB** in a **multi-region** setup.
I'm following instructions from Vishnu Hari Dadhich:
[MULTI-REGION YUGABYTEDB DEPLOYMENT ON AWS EKS WITH ISTIO]
(https://dvops.wordpress.com/2024/04/27/multi-region-yugabytedb-deployment-on-aws-eks-with-istio)
{% embed https://dvops.wordpress.com/2024/04/27/multi-region-yugabytedb-deployment-on-aws-eks-with-istio %}
Notes:
- I have AWS CLI, Kubectl, Help, and EKSCTL installed (see [here](https://dev.to/aws-heroes/yugabytedb-on-amazon-eks-3206))
- I did not use Persistent Volumes but ephemeral storage (this is a lab), by adding `--set storage.ephemeral=true` to the `helm upgrade --install` commands.
Here are the first commands, all details are in Vishnu's article.
```sh
-- get the repo
git clone https://github.com/vishnuhd/yugabyte-multiregion-aws-eks-istio.git
cd yugabyte-multiregion-aws-eks-istio
-- deploy EKS clusters
eksctl create cluster -f mumbai/cluster-config.yaml &
eksctl create cluster -f singapore/cluster-config.yaml &
eksctl create cluster -f hyderabad/cluster-config.yaml &
wait
-- update Kubernetes configuration
aws eks update-kubeconfig --region ap-south-1 --name yb-mumbai --alias Mumbai &
aws eks update-kubeconfig --region ap-southeast-1 --name yb-singapore --alias singapore &
aws eks update-kubeconfig --region ap-south-2 --name yb-hyderabad --alias hyderabad &
wait
-- upgrade Kubernetes
eksctl upgrade cluster -f mumbai/cluster-config.yaml --approve &
eksctl upgrade cluster -f singapore/cluster-config.yaml --approve &
eksctl upgrade cluster -f hyderabad/cluster-config.yaml --approve &
wait
```
You can continue with Vishnu's instructions, or follow his demo at the YugabyteDB Community Open Hours:
{% embed https://www.youtube.com/live/G4mK20q95Sw?si=qeBx1STLhaOK6hjj&t=782 %}
When you are done, don't forget to terminate the cluster. Here was the cost when I tested it:
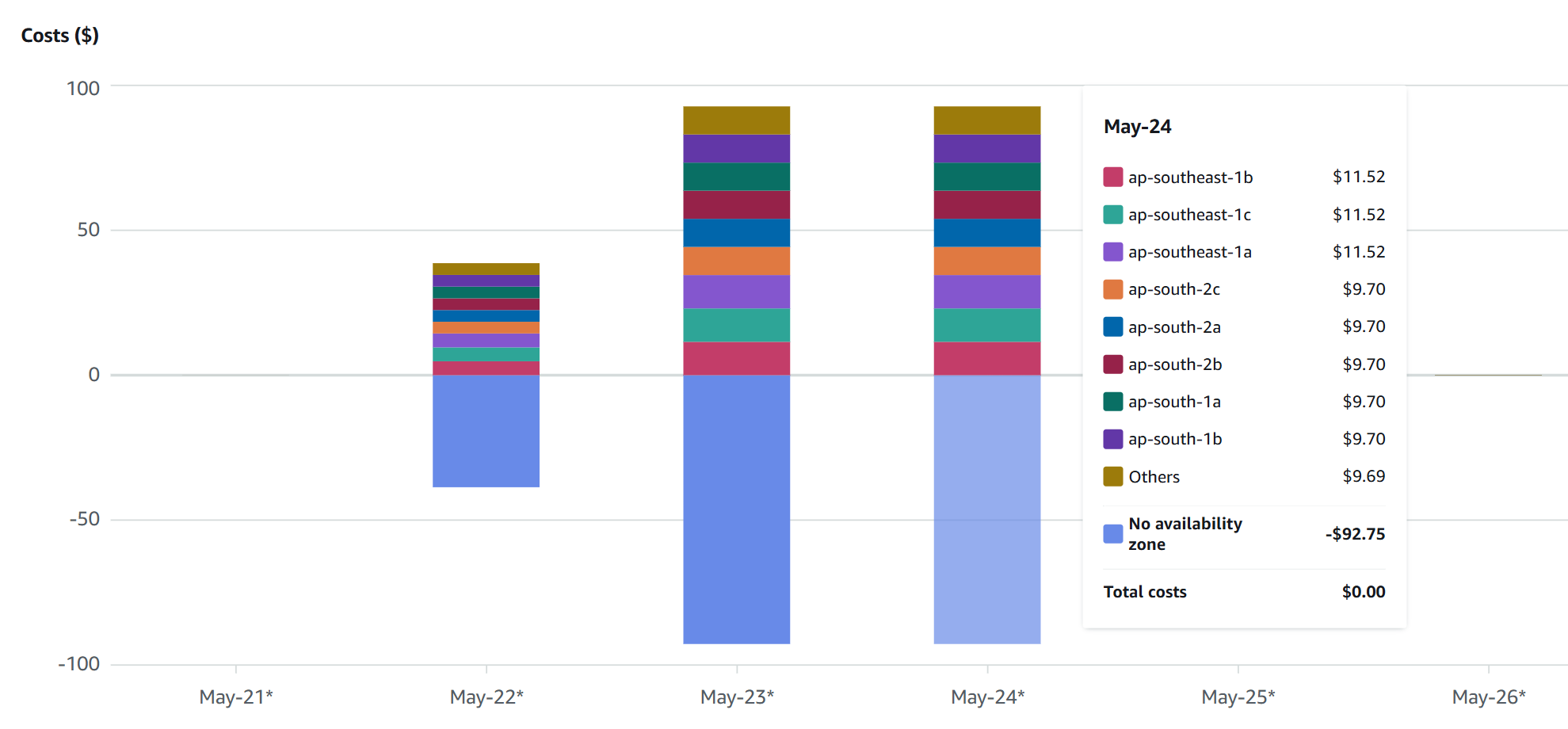
| franckpachot |
1,867,740 | Some notes on Dart package encapsulation | This is a short note showing how I use dart package encapsulation to manage the dependency in a... | 0 | 2024-05-28T14:11:48 | https://dev.to/nigel447/some-notes-on-dart-package-encapsulation-e2i | dart, objectorientated, encapsulation, directedgraph |
This is a short note showing how I use dart package encapsulation to manage the dependency in a dart/flutter application.
If you are new to creating your own dart package there is a great post here on dev to help u get started [How to Create Dart Packages in Flutter: A Step-by-Step Guide](https://dev.to/aaronreddix/how-to-create-dart-packages-in-flutter-a-step-by-step-guide-1f5a)
Dependencies are always an issue and need to be managed carefully to avoid cycles among other things, Golang helps by throwing a compilation error if u have any Cyclic dependencies in your code. Creating acyclic dependency trees(graphs) preferably Directed [DAG](https://en.wikipedia.org/wiki/Directed_acyclic_graph) is what you want, you can research the details if u r interested.
Say you have a project with a few packages like below
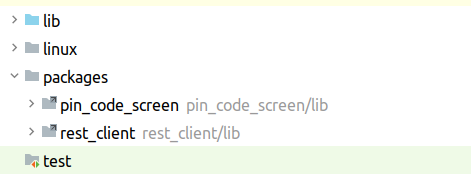
Here I have a rest_client package among others, the rest_client package will use other dependency packages like [Dio](https://pub.dev/packages/dio).
I want to use Dio response types in the main code.
To keep the dependency tree clean I dont want to import Dio types in the main source as well as the rest_client package, so I export Dio from the rest_client package as so
```
library rest_client;
export 'package:dio/dio.dart';
```
In the main source code I import any needed Dio artifact from my rest_client package like
```
import 'package:rest_client/rest_client.dart' as transport;
class FreeAuthService {
final transport.Dio _dio = transport.Dio();
}
```
now I am free to encapsulate all my related http transport code in the rest_client package and just return the Dio responses into the main source code.
Here are some minor details
- packages are imported in pubspec like
```
rest_client:
path: packages/rest_client
```
- in the package directory source you need a top level file where you export the package dependencies you wish to expose like
```
library rest_client;
export 'package:dio/dio.dart';
```
| nigel447 |
1,867,763 | Backflow Plumbing Services: Safeguarding Water Quality with Professional Expertise | In the intricate network of plumbing systems that serve our homes, businesses, and communities,... | 0 | 2024-05-28T14:10:07 | https://dev.to/backflowservicesdone/backflow-plumbing-services-safeguarding-water-quality-with-professional-expertise-31li | In the intricate network of plumbing systems that serve our homes, businesses, and communities, ensuring the purity and safety of our water supply is paramount. One critical aspect of maintaining water quality is preventing backflow – the unwanted reversal of water flow that can introduce contaminants into the clean water supply. [Backflow plumbing services](https://backflowservicesdoneright.com/) play a vital role in safeguarding water quality by implementing preventive measures and responding to backflow incidents promptly and effectively. With their professional expertise and commitment to excellence, these specialized plumbing services are dedicated to protecting public health and preserving the integrity of our water supply.
1. Understanding Backflow and its Risks
Before delving into the realm of backflow plumbing services, it's essential to understand what backflow is and why it poses a risk to water quality. Backflow occurs when the flow of water in a plumbing system reverses, potentially allowing contaminants to enter the clean water supply. This can occur due to changes in water pressure, such as during a water main break or when a nearby fire hydrant is activated. Without proper prevention measures in place, backflow can lead to serious health hazards and waterborne illnesses.
2. Preventive Measures and Solutions
Backflow plumbing services focus on implementing preventive measures to reduce the risk of backflow incidents and protect the integrity of the water supply. This may include installing backflow prevention devices, such as check valves or backflow preventer assemblies, at strategic points in the plumbing system. These devices are designed to prevent the backward flow of water and ensure that contaminants cannot enter the clean water supply.
3. Regulatory Compliance
Compliance with regulatory standards is a crucial aspect of backflow plumbing services. Plumbing professionals must stay abreast of local, state, and federal regulations governing backflow prevention and ensure that their services meet or exceed these standards. This may involve obtaining necessary permits, conducting regular inspections and testing of backflow prevention devices, and submitting documentation to regulatory authorities as required.
4. Emergency Response and Incident Management
Despite the best preventive efforts, backflow incidents can still occur, posing immediate risks to public health and safety. Backflow plumbing services are equipped to respond to these emergencies swiftly and effectively, with trained technicians available around the clock to address backflow incidents and mitigate their impact. This may involve isolating affected areas, shutting off water supplies, and implementing corrective measures to prevent further contamination.
5. Education and Outreach
In addition to providing reactive services, backflow plumbing services also prioritize education and outreach to raise awareness about the importance of backflow prevention. This may include educating property owners and occupants about common backflow hazards, promoting best practices for prevention, and offering training on the proper use and maintenance of backflow prevention devices. By empowering individuals with knowledge and resources, plumbing professionals contribute to a culture of water safety and conservation within the community.
6. Continuous Improvement and Innovation
Backflow plumbing services are committed to continuous improvement and innovation to enhance their effectiveness in protecting water quality. This may involve investing in advanced technologies for backflow prevention, developing new methods for detecting and mitigating backflow incidents, and staying abreast of emerging trends and best practices in the field. By embracing innovation, plumbing professionals can adapt to evolving challenges and ensure that their services remain at the forefront of backflow prevention efforts.
In conclusion, backflow plumbing services play a critical role in safeguarding water quality and protecting public health. With their professional expertise, commitment to regulatory compliance, emergency response capabilities, and dedication to education and innovation, these specialized plumbing services are essential partners in preserving the integrity of our water supply. By working collaboratively with communities, businesses, and regulatory authorities, backflow plumbing services contribute to a safer, healthier, and more sustainable future for all. | backflowservicesdone | |
1,867,762 | Unleashing Efficiency: The Power of DevOps Automation in Modern Software Development | This article was originally published on Danubius IT Solutions' tech blog. In modern software... | 0 | 2024-05-28T14:10:07 | https://danubius.io/en/blog/unleashing-efficiency-the-power-of-devops | devops, automation, softwaredevelopment, efficiency | [This article was originally published on Danubius IT Solutions' tech blog.
](https://danubius.io/en/blog/unleashing-efficiency-the-power-of-devops)
In modern software development, DevOps automation has become a fundamental strategy for enhancing efficiency and reducing costs. This article explores how DevOps automation impacts various industries, offering faster time-to-market and cost-effective development solutions.
DevOps automation involves leveraging technology to automate processes between software development and IT teams, facilitating faster and more reliable software build, test, and release cycles. By integrating and automating key phases of development, organizations ensure a seamless flow from concept to production.
Automation in DevOps encompasses code development, configuration management, dependency management, deployment, and monitoring, eliminating manual work, reducing errors, and speeding up changes. Continuous integration (CI) and continuous delivery (CD) are core DevOps practices, ensuring automatic testing, integration, and delivery of software changes, leading to faster and more frequent releases.
The global DevOps market has experienced robust growth, driven by the demand to shorten development cycles and accelerate delivery.
## Key Benefits of DevOps Automation
Let’s explore three areas and three of our clients who have realised major efficiency gains by implementing DevOps automation.
1. Accelerating Time-to-Market
This is a significant advantage of DevOps automation by enabling faster iterations, quicker adaptations to market changes, and continuous innovation.
Example
Industry: Banking
One of our clients, a renowned banking company faced challenges with its legacy systems that were slowing down its product releases. By implementing DevOps automation, specifically through CI/CD pipelines, they managed to reduce their software deployment cycle from monthly to bi-weekly, and then weekly releases. This has led not only to a significant increase in customer satisfaction, but at least 25% faster time-to-market for new features.
2. Cost Optimization
Cost optimization is another compelling benefit of DevOps automation. By reducing manual processes, minimizing development errors, optimizing resource usage, and improving collaboration, organizations can lower overall software development costs.
Example
Industry: Insurance
One of our insurance provider clients struggled with high operational costs due to redundant tasks and manual processes in their software development lifecycle. By adopting Infrastructure as Code (IaC) and partially migrated scalable applications to the cloud (as part of their DevOps strategy), they reduced manual workload by 30%, leading to a 15% decrease in development costs. Additionally, the improved efficiency and error reduction translated into an estimated 20% reduction in resource wastage, optimizing overall spending.
3. Continuous Monitoring
Continuous monitoring within a DevOps framework helps in proactive issue resolution, avoiding costly downtime and ensuring service availability.
Example
Industry: Startup (Financial Services)
A fast-growing fintech startup client of ours implemented continuous monitoring tools as part of their DevOps automation to enhance their application’s performance and reliability. The proactive monitoring allowed them to detect and resolve 90% of potential disruptions before affecting users, significantly reducing production downtime. This approach not only saved potential lost revenue but also helped maintain a high user retention rate by ensuring a seamless customer experience. The cost of reputation lost is hard to estimate, but the higher uptime meant a significant decrease in that as well.
## Next Steps
Embracing DevOps automation is essential for future success in software development, enabling organizations to streamline operations, enhance efficiency, and achieve cost savings. Partnering with experts ensures that DevOps automation aligns with business objectives and drives long-term success.
Ready to transform your software development lifecycle and achieve remarkable efficiency? Contact us to embark on your DevOps automation journey and embrace a smarter, more agile future.
| danubiusio |
1,867,760 | Text Quality-Based Pruning for Efficient Training of Language Models | Introduction The integration of machine learning models into various sectors is... | 0 | 2024-05-28T14:08:43 | https://dev.to/aishikl/text-quality-based-pruning-for-efficient-training-of-language-models-2i6p | ## Introduction
The integration of machine learning models into various sectors is revolutionizing how we process and utilize big data. Among these advances, the optimization of language models stands out as pivotal, especially in understanding and generating human-like text. This article delves into groundbreaking research that introduces an innovative methodology for pruning datasets to enhance the training efficiency of language models, which promises to significantly reduce the computational demand and time required for model training. Join me as we explore the implications of this research and its potential to shape future applications in technology and beyond.
## Background and Context
The challenge of training language models efficiently is a significant hurdle in the field of artificial intelligence, particularly due to the vast computational resources and extensive datasets typically required. The research addresses this issue head-on by proposing a novel approach to evaluate text quality numerically within large, unlabelled NLP datasets. Historically, language models have been trained on massive datasets that often include noisy, low-quality, or even harmful content, which can degrade the performance and ethical standing of the resulting models.
This research stands on the shoulders of prior work, which primarily relied on human annotation and subjective judgments to assess text quality, a method fraught with scalability limitations and subjectivity biases. By introducing a model-agnostic metric for text quality, the researchers provide a scalable and objective method to prune low-quality data from training sets, thereby optimizing the training process and sidestepping the pitfalls of previous methodologies.
## Methodology
### Text Quality Evaluation
Weight Calculation
In this step, the researchers use 14 heuristic-based filters covering a wide range of linguistic characteristics like text complexity, word repetition ratio, syntax, and text length. These filters are applied individually to a dataset to obtain subsets of text instances that qualify for each specific filter. The validation perplexity for these subsets and the original unfiltered dataset is then calculated using a pre-trained language model.
Quality Scoring
Each document in the dataset is split into lines based on common sentence end markers. For each line, all heuristic filters are applied, resulting in an indicator matrix. The quality score for each line is calculated using the weights from the previous step. The scores for each line are then aggregated to obtain a document-level score.
## Results
The researchers observed an absolute accuracy improvement of 0.9% averaged over 14 downstream evaluation tasks for multiple language models while using 40% less data and training 42% faster when training on the OpenWebText dataset. Similarly, a 0.8% average absolute accuracy improvement was observed while using 20% less data and training 21% faster on the Wikipedia dataset.
## Implications
The key contribution of this research lies in establishing a framework that quantitatively evaluates text quality in a model-agnostic manner and subsequently guides the pruning of NLP datasets for language model training. By leveraging this quality score metric, the researchers enable a more efficient allocation of computational resources and reduce the data requirements for training language models. This approach not only expedites the training process but also enhances the overall effectiveness of the models.
## Conclusion
This innovative approach to text quality-based pruning for efficient training of language models represents a significant advancement in the field of artificial intelligence. By providing a scalable and objective method to evaluate and prune low-quality data, this research paves the way for more efficient and effective language model training. As we continue to push the boundaries of AI and machine learning, methodologies like these will be crucial in optimizing our use of computational resources and improving the performance of our models.
For more insights into AI and blockchain development, check out Rapid Innovation's blog.
Reference: Text Quality-Based Pruning for Efficient Training of Language Models | aishikl | |
1,867,759 | Expert Toilet Repair Services in Herndon: Restoring Functionality and Efficiency | In the bustling community of Herndon, Virginia, residents rely on their plumbing systems for daily... | 0 | 2024-05-28T14:07:08 | https://dev.to/well_wisher_727ce3d5bbde8/expert-toilet-repair-services-in-herndon-restoring-functionality-and-efficiency-4ad5 | In the bustling community of Herndon, Virginia, residents rely on their plumbing systems for daily comfort and convenience. Among the essential fixtures in any home, the toilet stands as a cornerstone of sanitation and hygiene. However, like any other mechanical device, toilets are susceptible to wear and tear over time, requiring occasional repairs to maintain optimal functionality. In **[toilet repair herndon ](https://baumbachplumbing.com/toilet-repair-replacement/)s**ervices are readily available to address a wide range of issues, from minor leaks and clogs to more complex mechanical failures. With their expertise and dedication to customer satisfaction, these professionals strive to restore toilets to their full functionality, ensuring efficiency and reliability for homeowners across the community.
1. Prompt Response to Toilet Emergencies
When a toilet malfunctions, it can quickly escalate into a disruptive and unsanitary situation. Recognizing the urgency of such emergencies, expert toilet repair services in Herndon offer prompt response times and round-the-clock availability. Whether it's a severe clog, a leaky seal, or a malfunctioning flush mechanism, skilled technicians are equipped to address the issue swiftly and effectively, minimizing inconvenience for homeowners.
2. Comprehensive Diagnosis and Assessment
Effective toilet repair begins with a thorough diagnosis of the problem at hand. Expert technicians in Herndon employ advanced diagnostic techniques to pinpoint the root cause of toilet issues, whether it's a faulty valve, a damaged flapper, or a blockage in the plumbing lines. By conducting a comprehensive assessment, they can devise a targeted repair plan tailored to the specific needs of each toilet.
3. Professional Repairs and Replacements
With years of experience under their belts, Herndon's expert toilet repair technicians possess the knowledge and expertise to tackle a wide range of issues with precision and efficiency. Whether it's repairing a leaking tank, replacing a worn-out flush valve, or unclogging a stubborn drain, they utilize industry-leading techniques and high-quality replacement parts to restore toilets to peak performance.
4. Upgrades and Enhancements
In addition to repairs, expert toilet repair services in Herndon also offer upgrades and enhancements to improve the efficiency and functionality of existing toilets. This may include installing water-saving flush mechanisms, upgrading to low-flow toilet models, or retrofitting toilets with modern features such as bidet attachments or soft-close seats. By embracing innovation, homeowners can enjoy enhanced comfort and convenience while reducing water consumption and utility costs.
5. Transparent Pricing and Honest Service
Transparency and integrity are paramount in the provision of expert toilet repair services in Herndon. From the initial consultation to the completion of repairs, customers can expect clear communication, honest advice, and transparent pricing. Technicians provide detailed estimates upfront, ensuring that homeowners are fully informed and empowered to make confident decisions regarding their toilet repair needs.
6. Preventive Maintenance and Care
Toilet repair services in Herndon also emphasize the importance of preventive maintenance and care to prolong the lifespan of toilets and prevent future issues. Regular maintenance tasks such as cleaning, inspection, and adjustment can help identify potential problems early on and prevent costly repairs down the line. By investing in proactive maintenance, homeowners can ensure the long-term reliability and efficiency of their toilets.
In conclusion, expert toilet repair services in Herndon are dedicated to restoring functionality and efficiency to toilets across the community. With their prompt response times, comprehensive diagnosis, professional repairs, and commitment to customer satisfaction, these professionals provide homeowners with peace of mind and confidence in the reliability of their plumbing systems. Whether it's a minor repair or a major overhaul, residents can trust Herndon's expert toilet repair services to deliver exceptional results and keep their toilets running smoothly for years to come. | well_wisher_727ce3d5bbde8 | |
1,867,758 | What is the Role of Customer-Facing Sales Frontends in Non-Life Insurance Products? | This article was originally published on Danubius IT Solutions' tech blog. Far from being merely... | 0 | 2024-05-28T14:04:43 | https://danubius.io/en/blog/what-is-the-role-of-customerfacing | customerfacing, salesfrontends, digitaltransformation, nonlifeinsurance | [This article was originally published on Danubius IT Solutions' tech blog.](https://danubius.io/en/blog/what-is-the-role-of-customerfacing)
Far from being merely aesthetic digital interfaces, customer-facing sales platforms are instrumental in bridging the gap between insurance providers and customers.
They are transforming the presentation, understanding, and purchase process of insurance products, marking a pivotal point in the trends shaping customer experience.
This shift also underscores the industry-wide challenge: of navigating legal and regulatory compliance while modernizing legacy systems to remain competitive in a dynamically changing market.
## Embracing Digital Transformation
In addressing the digital transformation objectives of insurers, it's essential to recognize the widespread challenges they face, from adhering to legal and regulatory mandates to modernizing legacy systems amid constant market shifts.
Whereas the rise of InsurTech startups has simplified the online process of finding and purchasing insurance, it presents new challenges for traditional insurers to adapt their strategies. Success in this evolving environment hinges on anticipating and embracing change, particularly in the realm of digitalization.
Insurance companies also approach the implementation of digitalization at a varied pace, as it is not just a modernization and a uniform sprint towards cloud adoption but a tailored strategy to bolster customer interaction and operational efficiency. Shifting gears on digitalization is becoming an increasingly growing pressure. As a result, the old paper-based regulations, processes, and behaviors are finally disappearing and have given way to much easier and faster solutions, such as remote identification, digital signatures, as well as other collaboration tools, which are usually built on outdated backend systems.
## An Overview of Non-Life Insurance Products
To give you an example that fosters understanding, the US insurance industry of non-life products experienced a significant underwriting loss in Q1 2023, which was the largest in 12 years. Factors contributing to this include soaring construction and contractor service costs, increased frequency of natural disasters, and rising property-catastrophe reinsurance costs.
Insurers are grappling with balancing rising expenses and customer expectations, which has led to higher insurance rates across various sectors, including commercial property and car insurance.
Given the economic landscape, insurance premiums increased in 2023 and are still expected to rise in 2024, driven not directly by insurance rate hikes but by broader inflation and rising service costs. This scenario nudges insurers towards innovative product offerings to retain customer engagement amidst financial pressures. Notably, insurers are exploring:
- Modular Policies: Customizable insurance coverage allowing customers to select and pay for only what they need, enhancing flexibility and affordability.
- Event-Based Insurance: Temporary coverage activated by specific events, offering targeted protection without long-term commitment, appealing to consumers seeking cost-effective, situational insurance solutions.
These adaptations aim to align insurance products more closely with consumer needs and economic realities, ensuring that insurance remains accessible and relevant.
As we can see, the industry faces a transformative phase, with insurers exploring new models like embedded insurance and parametric insurance, which offer innovative coverage options based on specific events or indices.
## Enhancing Customer Experience with Customer-Facing Sales Frontends
Redefining the role of customer-facing sales frontends is crucial, especially given the increasing complexity and rising costs of non-life insurance products.
These interfaces have become some of the most important sales channels that are pivotal in enhancing user engagement. The key is a clean, quick, and easy-to-use interface that helps customers find their way around the products:
- Replacing lengthy product descriptions with visual elements like pictorial illustrations and video tutorials can significantly clarify offerings.
- Simplification is key; offering pre-set product packages instead of overwhelming options can streamline the decision-making process.
- Additionally, ensuring that these interfaces are mobile-friendly and easy to navigate is essential in catering to the modern consumer's expectations and needs.
Ultimately, these innovations are not just about aesthetic appeal but about making insurance more accessible and user-friendly. As consumer behavior is shifting due to cost concerns, providing clear, accessible information and simplifying the purchasing process can help make informed decisions and maintain customer trust.
## Driving Sales and Revenue
The digital insurance industry is growing rapidly, with a current global market CAGR of 10.80%.
Key trends – such as automation and a data-driven approach – drive this growth, impacting how insurance products are sold and managed.
Automation, particularly in underwriting and claims processing, is transforming these areas by reducing human involvement and streamlining processes. This saves time and costs for insurers and also enhances customer experience due to quicker processing times.
The implementation of omnichannel approach promises to provide a seamless customer experience across multiple channels. For example, if a customer begins calculating an insurance premium online but doesn't complete the process, the call center can see this activity. At this point, they might reach out to offer assistance, suggesting adjustments to the quote if necessary, thereby enhancing customer engagement and satisfaction.
Furthermore, leveraging online marketing strategies opens numerous opportunities for insurers, significantly boosting customer acquisition rates. By targeting specific demographics through social media and other digital platforms, insurers can reach and engage with potential clients more effectively than ever before.
Additionally, optimizing websites to convert visitors into clients is crucial. A professional, easy-to-navigate website with engaging content can significantly increase traffic and sales. Incorporating video marketing can also enhance brand trust and increase conversions.
This approach helps in reaching customers via such various channels while maintaining consistent service quality. Additionally, the growing adoption of customer self-service models, accelerated by the pandemic, has opened up new avenues for sales and service.
Self-service portals and mobile applications are increasingly preferred by tech-savvy consumers, allowing them to purchase and manage insurance products conveniently. Such digital transformations are key to driving sales and revenue in the sector today.
## Technology Background is Vital
Integration with backend systems is of course essential for the frontends’ effectiveness, however, insurers currently rely on outdated legacy systems for backend and middleware, so transitioning to more modern infrastructure is crucial. Persisting with these legacy systems hampers the ability to keep pace with rapid technological advancements, leading to several potential drawbacks.
Firstly, it restricts the agility needed for risk assessment and pricing, impacting customer service quality. Additionally, it limits the effective use of AI and ML for analyzing large datasets, which is increasingly vital for optimizing operations and enhancing decision-making processes. Upgrading these systems is essential if an insurance company wants to ensure sustainability and maintain competitiveness.
Such technologies allow insurers to automate routine tasks, improve underwriting processes, and predict risks more accurately. As this move towards a more integrated, technology-enabled approach also involves a shift in how insurers operate and interact with customers, it is clear that the integration points beyond the need of simply digitizing operations; it is a choice that’s vital for insurers in their goal of remaining competitive.
## Security and Compliance
In this context, the insurance industry faces quite the challenges due to the vast amounts of sensitive personal and financial data they handle.
Cybersecurity is a growing concern, with insurers being prime targets for cyber-attacks due to the nature of the data they collect. The global financial costs of data breaches are substantial; it averaged around €4 million in 2023 (which was the result of a 15% increase over 3 years), but the impact on brand reputation and customer trust is equally significant.
Insurers are thus focusing on proactive measures to prevent and mitigate cyber-attacks. In addition to technical safeguards, there is also an increasing emphasis on compliance with regulatory standards to protect sensitive customer data.
However, as in all other industries, increased cybersecurity and compliance in digital insurance are essential both for safeguarding and maintaining customer trust and confidence.
## The Future of Digitalized Insurance
The trend of common service layers and microservice architecture development has the most transformative effect on the insurance industry, as it enables efficient building on robust legacy systems as well as the effective integration of modern services. Their evolution provides a robust foundation for digital products, enabling real-time delivery and facilitating a variety of front-end solutions.
Specifically, these technologies empower insurers to deploy and manage digital services more efficiently, allowing for rapid adaptation to market changes and customer needs. By leveraging both common service layers and microservices, insurance providers can offer personalized, on-demand services, enhancing customer experience and operational agility.
Moreover, this approach streamlines the development and deployment of new insurance products while significantly reducing time-to-market, setting the stage for a more dynamic, customer-centric insurance industry.
And last but not least, the expansion of digital channels signifies a paradigm shift from traditional physical sales channels to more dynamic, digital mediums. Such a new outlook aligns with the growing customer preference for self-service options and digital engagement while insurers are leveraging digital tools such as chatbots and virtual assistants to meet evolving customer demands, thus enhancing the overall customer experience.
## Conclusion
All in all, customer-facing sales frontends in non-life insurance are a critical component in the customer journey, enhancing experience, driving sales, and building lasting and loyal relationships.
And remember, your peace of mind is just a click away. Discover the edge that Danubius can deliver to non-life insurance products and services with customer-centric digital solutions: whether it’s modernizing legacy systems or deploying cutting-edge technologies, we ensure seamless integration, enhanced security, and engaging customer experience. | danubiusio |
1,867,757 | Mousse vs. Gel for Wavy Hair | Wavy hair needs the right products to look its best. Mousse and gel are popular choices, but they... | 0 | 2024-05-28T14:02:57 | https://dev.to/blogger3366/mousse-vs-gel-for-wavy-hair-9en | Wavy hair needs the right products to look its best. Mousse and gel are popular choices, but they serve different purposes. Knowing the differences can help you choose the right [product for your waves](https://curlyhairglow.com/mousse-vs-gel-for-wavy-hair/).
What is Mousse?
Mousse is a lightweight, foam-like product. It adds volume and body without weighing hair down. Mousse works well for fine to medium hair. It provides a natural, flexible hold. You can use mousse on damp hair. Apply it from roots to ends, then scrunch or style as desired.
Benefits of Mousse
Volume: Mousse boosts volume, making hair look fuller.
Flexibility: It offers a soft, touchable hold.
Lightweight: Mousse doesn't weigh hair down, ideal for fine hair.
What is Gel?
Gel is a thicker, more concentrated product. It provides a strong hold, great for controlling frizz and defining curls. Gel works well for medium to thick hair. Apply gel to damp hair. Distribute it evenly, then scrunch or style as desired. Let hair air dry or use a diffuser.
Benefits of Gel
Strong Hold: Gel keeps hair in place, even in humidity.
Definition: It defines curls and waves, enhancing texture.
Control: Gel tames frizz and flyaways, giving a sleek look.
Mousse vs. Gel: Which to Choose?
For Volume: Choose mousse. It adds lift and body without heaviness.
For Definition: Choose gel. It enhances and defines natural waves.
For Flexibility: Mousse offers a soft hold, ideal for natural looks.
For Control: Gel provides strong hold, perfect for structured styles.
Combining Mousse and Gel
You can use both products together. Apply mousse first for volume, then gel for hold and definition. This combination works well for many hair types. It gives you the best of both worlds.
Conclusion
Both mousse and gel have their benefits. Choose based on your hair type and desired style. Experiment to find the perfect balance for your waves. Whether you want volume, definition, or control, there's a product that will help you achieve your best hair day.
| blogger3366 | |
1,837,059 | What is the Best way to Learn to Think Like a Programmer? | Coding jargon, coding questions, code logic, problem-solving skills, logical thinking, creative... | 0 | 2024-05-28T14:00:00 | https://dev.to/anitaolsen/what-is-the-best-way-to-learn-to-think-like-a-programmer-2498 | discuss, learning, programming | Coding jargon, coding questions, code logic, problem-solving skills, logical thinking, creative skills, see things from different angles and thinking outside of the box come to mind. I want to improve and become the best programmer I can be, so I would like to know the best way to learn to think like a programmer.
What would you say is the best way to learn to think like a programmer? | anitaolsen |
1,867,755 | Variable-Length Argument Lists | A variable number of arguments of the same type can be passed to a method and treated as an array.... | 0 | 2024-05-28T13:59:25 | https://dev.to/paulike/variable-length-argument-lists-4li7 | java, programming, learning, beginners | A variable number of arguments of the same type can be passed to a method and treated as an array. You can pass a variable number of arguments of the same type to a method. The parameter in the method is declared as follows:
`typeName... parameterName`
In the method declaration, you specify the type followed by an ellipsis (**...**). Only one variable-length parameter may be specified in a method, and this parameter must be the last parameter. Any regular parameters must precede it.
Java treats a variable-length parameter as an array. You can pass an array or a variable number of arguments to a variable-length parameter. When invoking a method with a variable number of arguments, Java creates an array and passes the arguments to it. The program below contains a method that prints the maximum value in a list of an unspecified number of values.
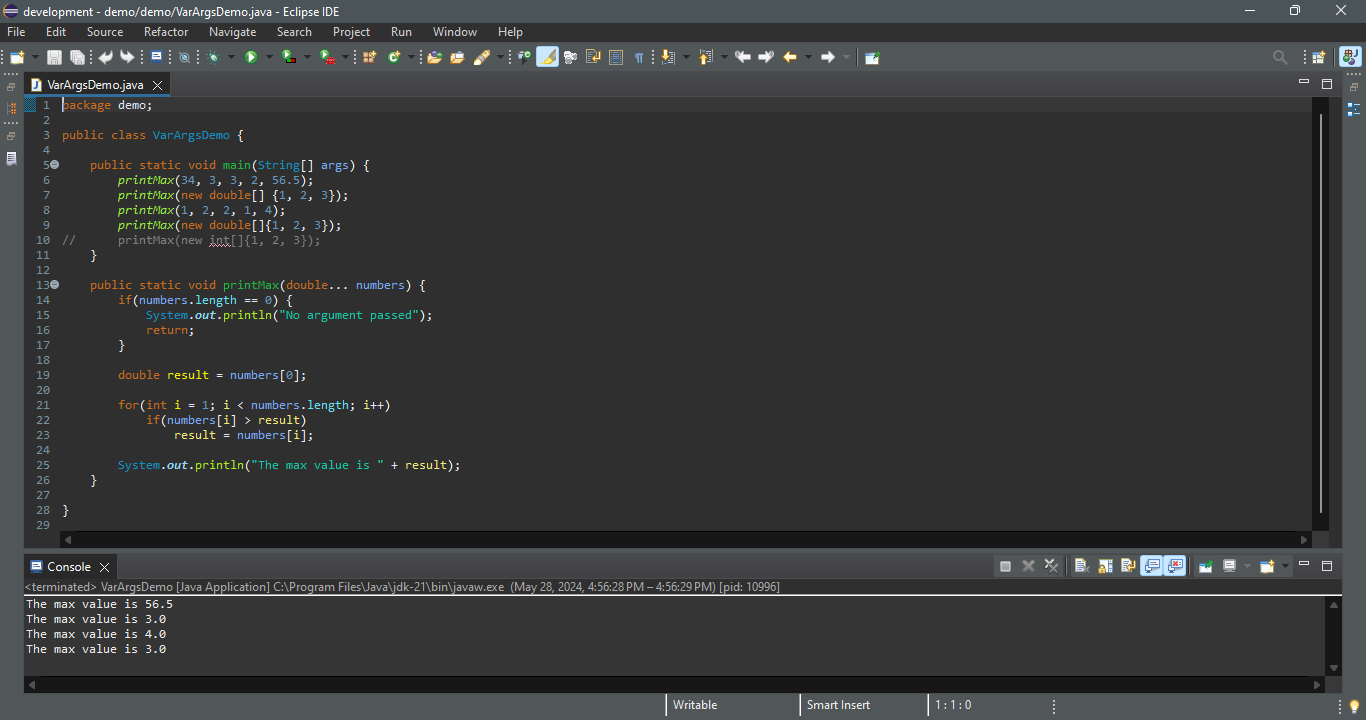
Line 6 invokes the **printMax** method with a variable-length argument list passed to the array **numbers**. If no arguments are passed, the length of the array is **0** (line 14). Line 7 invokes the **printMax** method with an array. | paulike |
1,867,967 | Curso De Sistemas Autônomos Gratuito: Boas Práticas Operacionais | O Nic.br oferece um curso online e gratuito sobre Boas Práticas Operacionais para Sistemas Autônomos,... | 0 | 2024-06-23T13:52:04 | https://guiadeti.com.br/curso-sistemas-autonomos-boas-praticas/ | cursogratuito, automacao, boaspraticas, cursosgratuitos | ---
title: Curso De Sistemas Autônomos Gratuito: Boas Práticas Operacionais
published: true
date: 2024-05-28 13:59:05 UTC
tags: CursoGratuito,automacao,boaspraticas,cursosgratuitos
canonical_url: https://guiadeti.com.br/curso-sistemas-autonomos-boas-praticas/
---
O Nic.br oferece um curso online e gratuito sobre Boas Práticas Operacionais para Sistemas Autônomos, destinado especialmente a técnicos e gestores de TI de diversas organizações.
O curso é ideal para empresas que possuem registro de sistema autônomo ou aquelas que fornecem conteúdos e serviços na Internet e estão buscando adquirir seus próprios recursos de numeração devido à crescente complexidade de suas redes.
O evento foi planejado para uma variedade de participantes, incluindo portais de conteúdo, empresas de comércio eletrônico, empresas de mídia, sites institucionais de empresas, universidades e órgãos governamentais, oferecendo a eles conhecimentos fundamentais para a gestão eficiente de sistemas autônomos.
## Curso de Boas Práticas Operacionais para Sistemas Autônomos
O Nic.br apresenta um curso online e gratuito focado em Boas Práticas Operacionais para Sistemas Autônomos.
_Imagem da página do curso_
Este curso é especialmente projetado para pessoal técnico e gestores de TI de empresas que possuem registro de sistema autônomo ou que fornecem conteúdos e serviços na Internet e precisam adquirir recursos de numeração próprios devido à complexidade crescente de suas redes.
Ele é ideal para profissionais de portais de conteúdo, comércio eletrônico, empresas de mídia, sites institucionais, universidades e órgãos do governo. Confira os pré-requisitos:
- Disponibilidade para participar das aulas online durante uma semana, com cada aula tendo 8h00 de duração (segunda a sexta-feira);
- Acesso á Internet, pelo menos 1Mbit/s de download e 0.5Mbit/s de upload. Para testar sua conexão utilize o simet, e observe os dados;
- Ser um profissional de redes que esteja, ou estará, liderando/atuando na implantação do sistema autônomo;
- Ter bons conhecimentos teóricos e práticos sobre redes IPv4 e IPv6;
- Conhecer comandos básicos em algum dos três fabricantes de roteadores utilizados no curso: Cisco, Juniper e Mikrotik;
- Estudar os vídeos expostos no canal do youtube da Nic.br;
- Ter um computador (com qualquer sistema operacional) para acesso aos laboratórios;
- Instalar o programa de acesso remoto ssh (ou putty) e o winbox (com wine para linux).
### Detalhes da Programação e Formato das Aulas
As aulas ocorrerão de forma síncrona, permitindo interação ao vivo com o instrutor. A formação será intensiva, com uma semana de duração, de segunda a sexta-feira, das 9h às 18h.
Esta modalidade serve para dar uma experiência de aprendizado concentrada e profundamente engajadora, facilitando uma imersão total no conteúdo e práticas essenciais para a gestão de sistemas autônomos. Confira a ementa:
- Introdução à Internet e aos Sistemas Autônomos;
- Governança;
- Importância do IPv6 na sua rede;
- Conceitos básicos e avançados de IPv6;
- Plano de endereçamento;
- Introdução ao roteamento;
- Boas práticas para o roteamento;
- Tópicos avançados de roteamento;
- Hardening de equipamentos;
- Segurança: MANRS;
- RPKI: publicação de ROAs e validação.
### Inscrições e Data do Curso
O curso será realizado entre os dias 17 e 21 de junho de 2024. As turmas serão limitadas a 80 alunos para garantir uma experiência de aprendizado de qualidade e interação efetiva com o instrutor.
Os interessados devem realizar suas inscrições até o dia 3 de junho de 2024, assegurando sua vaga neste programa educacional feito para profissionais de TI que buscam aprimorar suas habilidades operacionais em um ambiente de rede complexo.
<aside>
<div>Você pode gostar</div>
<div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Curso-De-Sistemas-Autonomos-280x210.png" alt="Curso De Sistemas Autônomos" title="Curso De Sistemas Autônomos"></span>
</div>
<span>Curso De Sistemas Autônomos Gratuito: Boas Práticas Operacionais</span> <a href="https://guiadeti.com.br/curso-sistemas-autonomos-boas-praticas/" title="Curso De Sistemas Autônomos Gratuito: Boas Práticas Operacionais"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Bootcamp-Inteligencia-Artificial-Generativa-1-280x210.png" alt="Bootcamp Inteligência Artificial Generativa" title="Bootcamp Inteligência Artificial Generativa"></span>
</div>
<span>Bootcamp De Inteligência Artificial Generativa E Claude 3 Gratuito</span> <a href="https://guiadeti.com.br/bootcamp-inteligencia-artificial-generativa-cloud/" title="Bootcamp De Inteligência Artificial Generativa E Claude 3 Gratuito"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Django-Python-280x210.png" alt="Django Python" title="Django Python"></span>
</div>
<span>Curso De Django E Back-end Python Para Mulheres Gratuito</span> <a href="https://guiadeti.com.br/curso-django-back-end-python-mulheres-gratuito/" title="Curso De Django E Back-end Python Para Mulheres Gratuito"></a>
</div>
</div>
<div>
<div>
<div>
<span><img decoding="async" width="280" height="210" src="https://guiadeti.com.br/wp-content/uploads/2024/05/Aprenda-Programacao-De-Graca-280x210.png" alt="Aprenda Programação De Graça" title="Aprenda Programação De Graça"></span>
</div>
<span>Aprenda Programação De Graça Com 3 Sites Estadunidenses</span> <a href="https://guiadeti.com.br/aprenda-programacao-de-graca-3-sites/" title="Aprenda Programação De Graça Com 3 Sites Estadunidenses"></a>
</div>
</div>
</div>
</aside>
## Sistemas Autônomos
Sistemas Autônomos (AS) são conjuntos de redes de IP sob o controle de uma única entidade, geralmente uma organização ou um provedor de serviços de internet, que gerencia internamente suas políticas de roteamento.
Esses sistemas são fundamentais para a estrutura da internet, pois facilitam a administração e a coordenação de políticas de roteamento em larga escala.
Um Sistema Autônomo possui um número único, conhecido como Número de Sistema Autônomo (ASN), que o identifica globalmente na comunidade da internet.
### Funcionamento e Importância
Os Sistemas Autônomos utilizam protocolos de roteamento, como o BGP (Border Gateway Protocol), para trocar informações de roteamento com outros sistemas autônomos.
Esse processo permite que diferentes redes se comuniquem entre si, encaminhando dados de maneira eficiente através da internet.
Os AS são importantes para a estabilidade e a segurança da internet, pois permitem que as redes operem de maneira mais organizada e previsível, evitando conflitos de roteamento e garantindo que os dados sigam o melhor caminho possível até seu destino final.
### Desafios e Oportunidades com Sistemas Autônomos
Gerenciar um Sistema Autônomo apresenta desafios significativos, especialmente em relação à segurança e à política de roteamento.
A correta configuração e manutenção dos protocolos de roteamento são cruciais para evitar vazamentos de rota e ataques de hijacking, onde agentes maliciosos tentam desviar o tráfego de uma rede. Por outro lado, há oportunidades na otimização de rotas, na melhoria da eficiência da banda larga e na redução de latência.
Com o crescimento da IoT (Internet das Coisas) e das tecnologias de cloud computing, os Sistemas Autônomos desempenham um papel cada vez mais crítico na facilitação de uma infraestrutura de rede robusta e adaptável, capaz de suportar um volume crescente de dados e dispositivos conectados.
## Nic.br
A Nic.br (Núcleo de Informação e Coordenação do Ponto BR) é uma entidade brasileira responsável pela implementação das decisões e projetos do Comitê Gestor da Internet no Brasil (CGI.br).
Fundada para promover a qualidade e a evolução da internet no Brasil, a Nic.br tem funções importantes em várias áreas fundamentais, incluindo a administração do registro de domínios ‘.br’, a distribuição de endereços IP no país, e a produção de estatísticas e estudos sobre a internet brasileira.
### Iniciativas e Projetos da Nic.br
Entre as muitas iniciativas da Nic.br, destaca-se o CESAR (Centro de Estudos e Sistemas Avançados do Recife), que tem como foco a pesquisa e o desenvolvimento de tecnologias inovadoras.
A entidade é responsável pelo CERT.br, o Grupo de Resposta a Incidentes de Segurança para a Internet brasileira, que trabalha para aumentar a segurança cibernética no país.
A Nic.br também oferece treinamentos e cursos, como o Curso de Boas Práticas Operacionais para Sistemas Autônomos, visando elevar o nível técnico dos profissionais de TI no Brasil e fomentar uma cultura de melhores práticas na gestão de redes e sistemas.
### Impacto e Importância
O trabalho da Nic.br é vital para a estrutura da internet no Brasil. Por meio da gestão eficiente dos recursos de internet, como domínios e endereços IP, a Nic.br assegura que a infraestrutura digital do país seja robusta, segura e capaz de suportar o crescimento econômico e tecnológico.
As atividades de pesquisa e desenvolvimento contribuem significativamente para o avanço tecnológico do Brasil, posicionando o país como um player importante no cenário digital global.
## Não perca a chance de se aprimorar em Sistemas Autônomos com a Nic.br!
As [inscrições para o curso Curso de Boas Práticas Operacionais para Sistemas Autônomos](https://cursoseventos.nic.br/curso/curso-bcop-ead/) devem ser realizadas no site da Nic.br.
## Interessado em Sistemas Autônomos? Compartilhe este evento e convide outros profissionais de TI!
Gostou do conteúdo sobre o evento de Boas Práticas? Então compartilhe com a galera!
O post [Curso De Sistemas Autônomos Gratuito: Boas Práticas Operacionais](https://guiadeti.com.br/curso-sistemas-autonomos-boas-praticas/) apareceu primeiro em [Guia de TI](https://guiadeti.com.br). | guiadeti |
1,867,737 | Memory Management and Garbage Collection In Java | As a Java developer, memory management and garbage collection is one topic you need to understand... | 0 | 2024-05-28T13:58:06 | https://dev.to/akamzchidi/memory-management-and-garbage-collection-in-java-3odf | java, memorymanagement, javamemory, garbagecollection |
As a Java developer, memory management and garbage collection is one topic you need to understand well. If you are having issues understanding these concepts, no need to worry.
This post will explain the entire concepts in details while giving examples. At the end of this post, you should understand the following concepts well:
- Memory Management in Java
- Garbage Collection in Java
- Types of Memory in Java
- Garbage Collection Process
- Types of Garbage Collectors in Java
## Introduction To Concepts
There are some basic concepts you need to know that will help you understand this topic better.
### . Memory In Java:
This refers to the allocated space where objects, variables and data are stored in the process of executing a java application. In other words, every variable, object or other data types the developer inputs in the process of creating a java program is stored in memory.
### . Memory management:
Memory Management is the process of allocation and deallocation of memory space for objects during the exaction of an application. This process takes place in the Java Virtual Machine JVM.
### . Garbage Collection:
This, on the other hand is the process of cleaning up the memory space. How it works is that the garbage collector identifies and removes objects that are no longer referenced in the heap memory.
In some programming languages like C and C++, it's the work of the programmer to manually handle the memory management process. The programmer is expected to manually allocate and deallocate memory space while creating the application.
Thankfully, Java handles the process automatically via garbage collection. The garbage collection process is better than manual because it helps to prevent the issue of **dangling reference.** You will understand how the garbage collection process works later in this post.
### . Dangling Reference:
This error occurs when a reference or pointer still points to a memory location in the heap memory that has been reallocated or removed.
## Types Of Memory In Java
As mentioned earlier, memory in Java is the space where data is stored during the process of executing a program. There are three types of memory spaces in Java. They include:
- Stack Memory
- Heap Memory
- MetaSpace Memory
Let’s explain each of the memory types in details now.
### . Stack Memory:
The stack memory is the section of the memory where method invocation takes place. Method invocation happens when a new method is created, a scope is created in the stack memory to store the data in the method. That includes, local variables and parameters.
The stack memory is always smaller than the heap memory. Also, during the garbage collection process, the stack memory gets cleaned up first. The process happens automatically when a method is done executing.
The types of data that is stored in the Stack memory includes:
- Primitive Values/ Temporary Variables.
- Memory block for methods (Scope).
- Reference of an object. Note that the object itself is stored in the heap memory while the reference is stored in the stack memory.
- Thread. Each thread has its own stack memory while all threads share a common heap memory.
Finally, the stack memory throws the ‘stackoverflow’ error when it is full.
### . Heap Memory
The heap memory is the section of the memory where objects are stored. It is larger than the stack memory. The heap memory is divided into two main sessions, the young generation and the old generation.
The young generation is further divided into Eden Space and Survivor Space. The Survivor space is further divided into S0 and S1 spaces. You will understand the types of the heap memory and their functions later in this post.
### . MetaSpace Memory
The metaspace was previously known as the Permanent Generation before the Java 7 version, and was a part of the heap memory. The Permanent Generation was not expandable and throws a heap error once the memory is full.
Now, it has evolved to metaspace memory, which is a stand-alone memory space from the heap memory. The metaspace stores class variables, constants, annotations, and class metadata.
In other words, information about the class from which objects are created including constants (static and final) are stored in the metaspace memory.
The JVM loads the class if it needs it and removes if from the metaspace when it has no need for it. One good thing about the metaspace is that it is expandable.
**Picture To Explain Data Storage In Java Memory.**
```
public class Main {
public static void main(String[] a) {
int seat = 4; //primitive data
String str1 = "30"; //string literal
String str2 = new String ("30") //String Object
Car newCar = new Car(); //object
}
public void method2(){
String str3 = "30"; //string literal
Car newCar2 = new Car(); //object
}
}
```
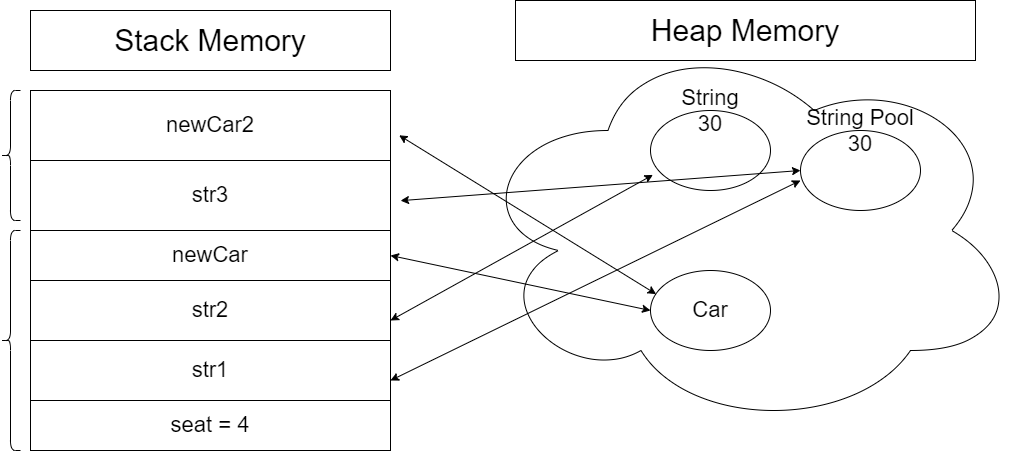
## How Memory Management Works In Java
The memory management process frees up space in memory for incoming data. Here is how the process work; when a method is done executing, the JVM cleans up the stack memory automatically. The values and variables in the method are forgotten.
The JVM does not clean up the heap memory automatically when a method is done executing because the object on the heap may be needed by another method which is still in the stack memory.
An object becomes eligible for garbage collection when it no longer has a reference in the stack memory.
Java Virtual Machine JVM initiates the garbage collection process automatically. The developer can suggest to the JVM to start the garbage collection process by executing **‘System.gc( )’** code, but it doesn’t guarantee that it will start the process.
## How Garbage Collection Works In Java
The space that a method occupies in the stack memory is known as a scope. The closing bracket in a method marks the end of a scope and the cleanup process starts. All variables and references in the method are removed.
The JVM deletes the scope starting from the latest scope. It applies the last in, first out cleanup process. After the variables and object references in the stack memory is removed, the garbage collection process starts in the heap memory. The garbage collector deletes the unreferenced objects in the heap memory.
The first garbage collection process is called the mark and sweep algorithm process. The garbage collector checks for and marks dead objects (objects without reference) and separates them from live objects (objects with reference). Objects with no references are moved to the Eden space.
The surviving objects is swept to either the S0 or S1 which is known as the survivor space. The survivor space has a threshold as new objects are created and the garbage collection process continues.
Once the survivor space gets to its threshold, it is promoted to old generation space in the heap memory.
The garbage collection process runs more frequently in the new generation than in the old generation. This is because objects moved to the old generation are used frequently and may have several references pointing to them indirectly.
Note that the garbage collection process that takes place in the young generation is known as the minor garbage collection while that of the old generation is known as major garbage collection.
Knowledge of when to promote an object from young to old generation is vital in the garbage collection process.
The garbage collector uses different collection strategies or algorithms for each generation. For instance, it can use the mark - sweep strategy for the
## Types Of Garbage Collection Process In Java
There are three main collection process the garbage collector applies to clean up memory space. They include the following:
### . Normal Mark Sweep:
The process here involves two processes. The mark and the sweep process. First, go through the heap memory to identify and mark live objects from dead objects. After that, the garbage collector initiates the sweep process.
That is sweeping or removing dead objects to the next memory space. It starts from the Eden space and the remaining objects are moved to the Survivor space.
After the removal of the dead objects remaining objects remains or maintains initial spaces. This method is not ideal especially if the incoming objects are bigger and can’t fit in the between the space.
Note: that the Garbage Collection Cycle is the amount of time it takes the garbage collector to complete a full garbage collection round.
### . Mark Sweep With Compact:
After the garbage collector complete the collection cycle, it compacts the remaining objects to free up space for new objects. This way, there is enough space for incoming objects.
### . Mark Sweep Copy:
Here, the garbage collector marks objects from the ‘from space’ region and moves them to the ‘to space’ region. After that, it compacts the remaining objects to free space for new objects.
## Types of Garbage Collection Algorithms
There are five garbage collection algorithms in java. Here is a breakdown of each collection algorithm, features and where it applies:
### . Serial Garbage Collector:
This garbage collector algorithm is good for a single core machine. It uses the mark- sweep for young generation and mark sweep compact for the old generation.
The serial garbage collector runs on a single thread. This means that other threads in the program will pause (Stop-The-World) during the garbage collection process.
**Pros:**
- Suitable for programs with small data sets where the pause time does not matter.
**Cons:**
- Slow because it runs on a single thread.
- More expensive.
### . Parallel Garbage Collector:
This collector works as the default garbage collector in java. The Parallel collector uses the mark sweep copy for young generation and mark sweep compact for old generation.
It uses multiple threads to perform garbage collection. The program gets pause time during the garbage collection process but for a shorter amount of time. It runs well on a multi core machine.
**Pros:**
- Faster than the serial collector
**Cons:**
- Slower than other garbage collector algorithms below.
### . Concurrent Mark Sweep Garbage Collector:
This is an upgrade from the previous parallel collector. It uses the mark sweep copy for young generation and concurrent mark sweep for the old generation and uses multiple threads to perform garbage collection.
This collection method does not require the program to stop. The garbage collection process runs concurrently with execution of the program. Mostly, it uses the concurrent collection method, but will revert back to stop-the-world if there is need for it.
### . Garbage First (G1) Garbage Collector:
This was first introduced in Java 7 and uses multiple threads to perform garbage collection. It divides the heap memory into small regions. It applies the parallel, concurrent, and incrementally compacting collection methods.
The G1 collector has the shortest pause time because of the division of the heap memory to small regions (memory segments). It keeps track of live and dead objects in each memory segment. The segment with the greatest number of objects is collected first. Stop-the-world (pause time) happens but for a shorter time period.
This collector algorithm is best for machines with large memory space and high performance.
### . Z Garbage Collector:
This was first introduced in Java 11. Also, uses multiple threads to perform garbage collection. Here, the garbage collection method is completed while the program is running concurrently with less than 10 milliseconds of pause time.
The garbage collection process starts with marking live objects with reference coloring and not with maps as with other collectors. The reference states are stored in bytes of the reference.
The Z garbage collector works well on 64 bits machines as the references does not have enough bits to execute on a 32 bit system. Also, it applies fragmented memory as a result of the garbage collection process. These entire process runs concurrently with the program hence the 10 milliseconds pause time.
### Conclusion
So far, this post has all you need to know about memory management in java. Finally, if you are wondering which garbage collection algorithm is best for your program. The answer is, it depends. It depends on the program in question, and the system. For example, the serial collector method is best for a small program with minor data sets.
| akamzchidi |
1,867,754 | Data warehouse vs data lake | Learn the difference between a data warehouse vs data lake. Everything you need to know in one... | 0 | 2024-05-28T13:56:31 | https://dev.to/aristeksystems2013/data-warehouse-vs-data-lake-2oj8 | data, datascience, datalake, dataengineering | Learn the difference between a data warehouse vs data lake. Everything you need to know in one article.
## TLDR: data warehouse vs data lake
If you only have 30 seconds, just read the TLDR. But the devil is in the details, so if you have a few minutes, keep on reading – it’s worth it.
**Data warehouse** stores processed data that’s ready for analytics. Before data is moved to the warehouse, it gets structured and cleaned. That’s why even non-technical users can analyze data from a warehouse. For example, management can create charts with BI tools.
**Data lake** is a storage for raw data. You can move any files there and process them later. The idea is that you never know what data will be useful for analytics in 5 years. And because storage today is cheaper than processing, you can collect a ton of data first and maybe process it later. But data still needs to be processed before it’s analyzed. So data lakes can deliver more insights, but they are harder to work with.
**Data lakehouse** offers the best of both worlds. Technologically, a lakehouse is similar to a data lake but has a predefined schema and stores more metadata.
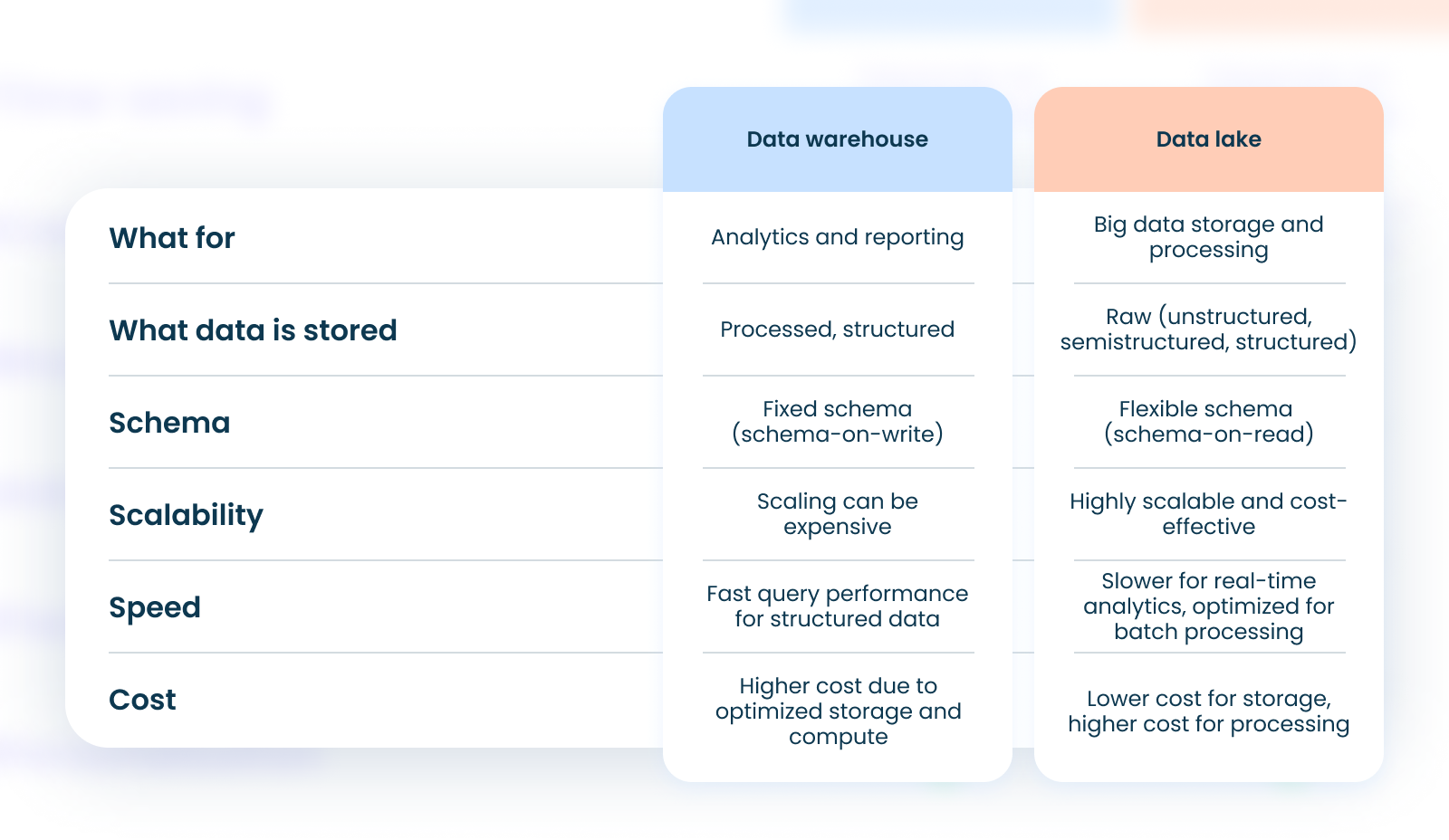
## What’s common between data lakes & warehouses
Let’s get some context first. Why do we even need data warehouses and data lakes when there are regular databases?
A typical database is made for OLTP (online transactional processing). Meanwhile, both data warehouses and data lakes are great for OLAP (analytical processing).
Here’s what it means, in general:
**Data integration**
A database is much smaller. Think gigabytes, compared to terabytes or petabytes in lakes and warehouses. That is because databases store compact transactional data.
Meanwhile, data warehouses can merge data from many different databases. Data lakes go even further and can store all sorts of unstructured data: JSON files, text files, and even images or videos.
**Historical information**
In a database, there’s often no track of it because logs don’t keep everything. Databases can track historical data, but this would slow down the transaction process. That’s why databases mostly just keep current info.
If your client changes their address, the database will update to the new address, but the old one will be lost. Without historical info, you won’t see the trends.
Data warehouses and lakes solve this problem because they capture changes in data.
**Query complexity**
Both data lakes and warehouses are great at complex queries, while databases are made for simple queries.
Databases are pretty bad at complex queries. They rely on normalized schemas, so data is kept in tables. This makes databases very fast at simple queries, like retrieving an order by its ID. But when it comes to complex queries, there are too many joins from different tables – so complex queries become too slow.
Meanwhile, data warehouses and data lakes are great at them because they use denormalized schemas. There are fact tables that hold the measurable data, and dimension tables that contain descriptive attributes. This way, there are much fewer joins.
So if you want to analyze sales trends, you’ll need a data lake or a warehouse. But if you need to keep track of order statuses or process payments, databases are more efficient.
## When to get a data warehouse
Simply put, a data warehouse is a giant database that’s optimized for analytics. It aggregates structured data from multiple sources and it’s great for deep analytical reports.
Companies have many different sources of data: databases, API connections with third-party tools or simply CSV files. A data warehouse aggregates all of your operational data in a single place. This way you can automatically create complex reports. You can check how your website redesign affected traffic and sales – with no need to manually pull data from Salesforce or Google Analytics.
Data warehouses are built so that low-technical users can create no-code reports. Data is moved from the sources into a single warehouse, where it can be analyzed with a BI tool.
## How do data warehouses work?
Most data warehouses go through the ETL process: extract, transform, load. Here’s how it works:
1. Extract. Raw data gets extracted to a staging area either through direct querying or via API.
2. Transform. The data gets cleansed from duplicates and errors. It also gets filtered, sorted and applied with the business rules.
3. Load. Finally, data is loaded to the warehouse for storage and analysis. Here, it’s organized into tables or data structures for easy access and querying.
Data warehouses have predefined schemas. It means that data engineers had to think in advance about how data is stored at a warehouse. It also means that there are limits on the types of data that get analyzed. To store unstructured raw data, you need a data lake.
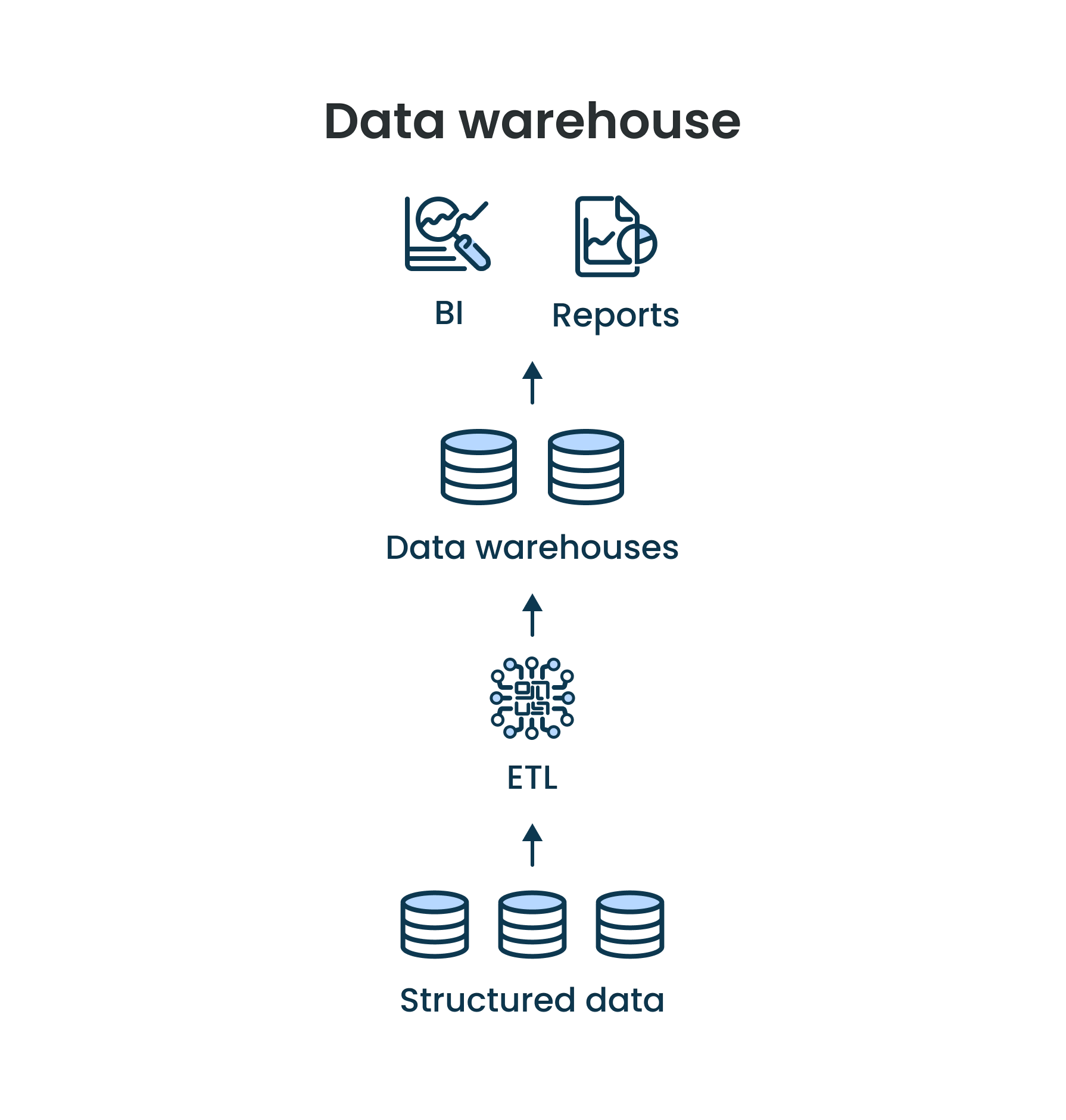
## When to get a data lake
A data lake is basically a giant pool of raw data. Sometimes the data here is structured, sometimes it’s semi-structured, and often is unstructured at all.
It is perfect for big data projects because a data lake lets you store more information cheaper and faster. With a data lake, data scientists can experiment much more and explore ideas much quicker than with a warehouse.
But unlike data warehouses, managers typically can’t create reports straight out of the lake. It requires technical experts: data scientists and data engineers. That is unless your lake has another layer like Apache Hive.
A data lake is much easier to start with because it has an undefined schema. That’s called schema-on-read because it’s only applied during querying.
But when you process data from a lake, you still need to put it in a data warehouse. That’s right, when you have a data lake, in most cases you also need a data warehouse.
The problem with data lakes is that they can turn into data swamps. It’s tempting for companies to collect every bit of data they can. But it turns out, that’s not always a good idea. Data storage can get too expensive, and data processing becomes too difficult. There’s a joke that says, data lakes are named after Lake Karachay – a nuclear waste dump.
## How do data lakes work?
Data lake is like a data warehouse, but backward. So instead of the ETL pipeline, data lakes use ELT: extract, load, transform.
1. Extract. Just like with a data warehouse, your data gets automatically extracted from all your sources: databases, APIs, IoT devices, etc. It’s possible to retrieve data in bulk or in real time.
2. Load. Data gets loaded into the data lake and stays there in native format until it’s required. Because data lakes store unstructured data, it’s easier to upload data just in case. The key is that data stays in the lake without any transformation.
3. Transform. Before analyzing data, it still needs to get transformed. But in ELT, it’s the data scientists who define how to process the data. Just like in ETL, raw data is cleaned, enriched, and converted into a structured format.
4. Load. Sometimes ELT is actually ELTL, because after transformation data still goes into a data warehouse. But you can also use it for your data science and machine learning projects.
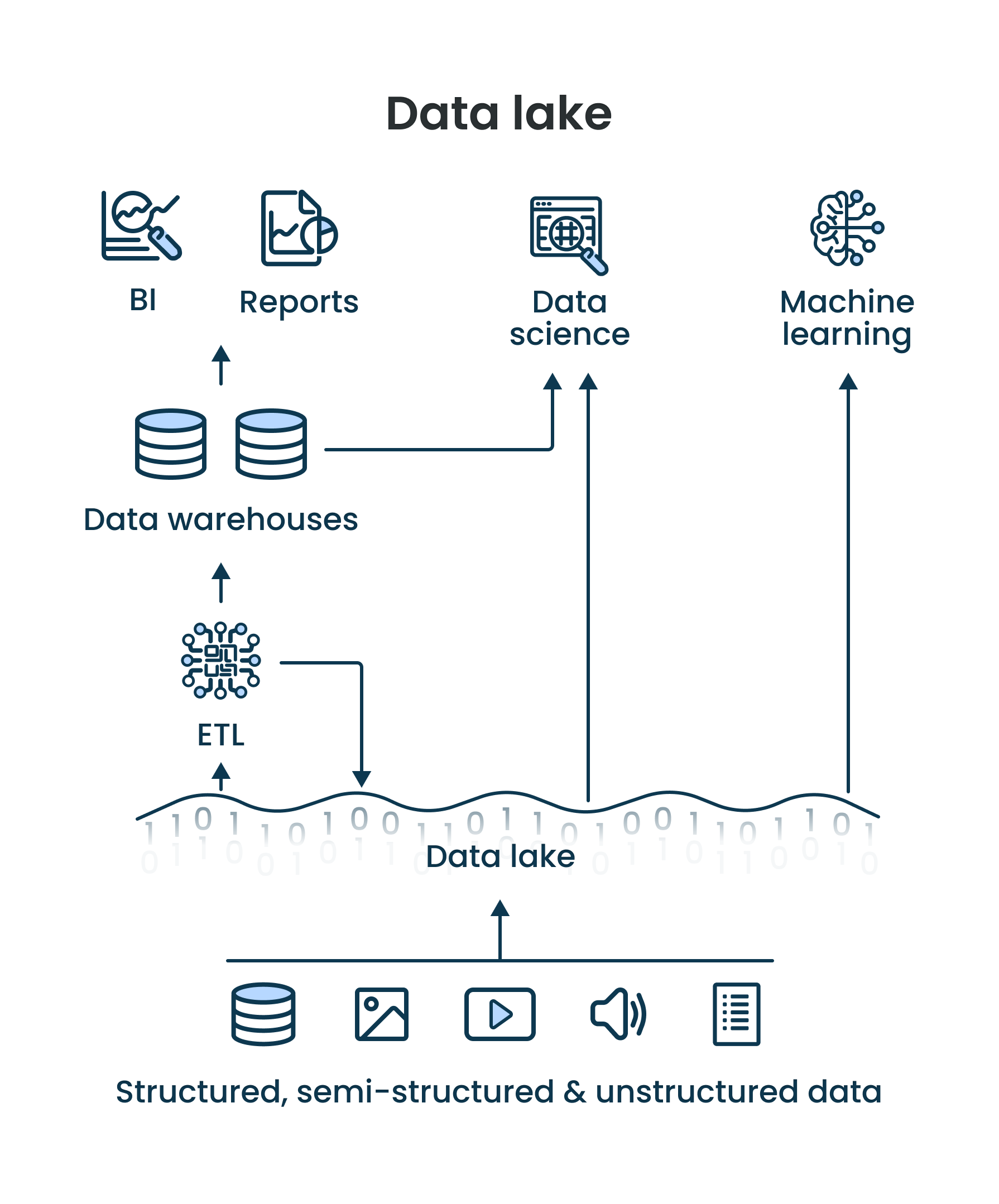
## Data lakehouse: best of both worlds
Let’s recap the issues with data lakes and warehouses:
- Data warehouses are organized but too expensive for big data and AI projects. That’s because every time your data goes into a warehouse, it needs to be processed and organized. For big data, it gets too difficult. That’s also the reason why data warehouses are not real-time.
- Data lakes are cheaper but can turn into data swamps if you collect too much low-quality data: lots of duplicates, inaccurate or incomplete data.
Data lakehouses keep the advantages of both, and remove the disadvantages. They are cost-effective, but scalable and organized. A data lakehouse is great for both predictive and prescriptive analytics.
Your analysts can work with a lakehouse as if it was a regular data warehouse. But your data engineers and data scientists can set up machine learning experiments in the same place – as if it was a data lake.
## Real-life example
A lakehouse is great when you need data for both descriptive and predictive analytics. That’s exactly the case with the AI solution we’ve built.
[AI-based behavior analysis & sales](https://aristeksystems.com/portfolio/ai-based-retail-sales-forecast/)
## How do data lakehouses work?
On the surface, lakehouses look just like regular data lakes with raw data. This data also can be structured, semi-structured, or unstructured.
The difference is that data lakehouses have another layer for metadata and additional governance. This layer keeps metadata of all the objects in the lakehouse. This way, it’s just as easy to organize data as with a regular data warehouse.
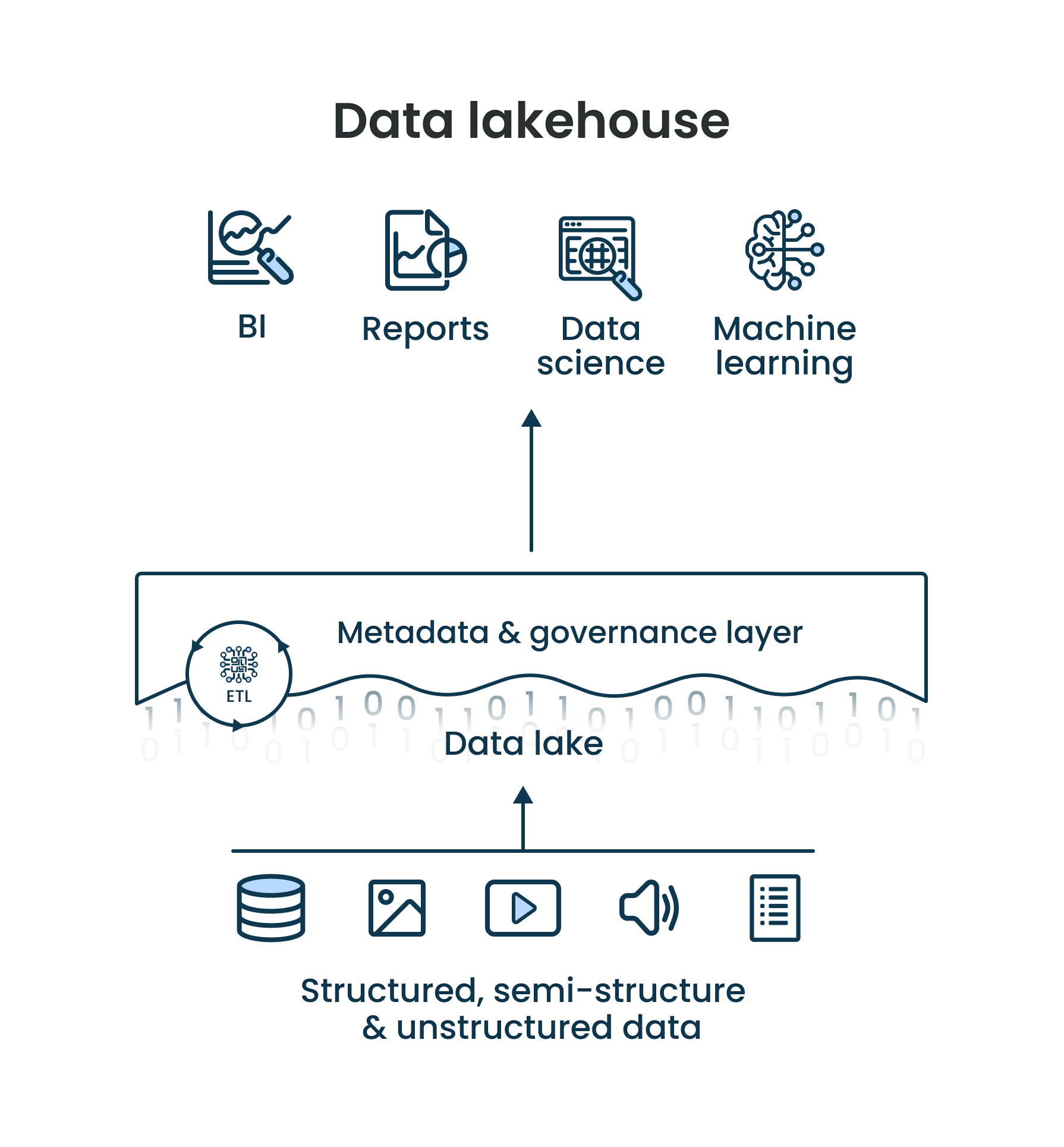
## Can analytics be collected without a data warehouse or data lake?
Sure. It’s still possible to analyze data without data lakes, warehouses, or lakehouses. But with no proper infrastructure, this process is manual – someone has to go and pull data from every source.
There are some problems with that, though:
- **No scalability.** Data always piles up: companies buy more tools, get more clients, and hire more employees all the time. At some point, it gets impossible for humans to process it all.
- **Data needs to be updated.** Data doesn’t just pile up – it changes, too. Your employees need to update all the spreadsheets, and some spreadsheets always need an update. After a while, you’ll have to let some spreadsheets go.
- **Privacy and compliance risks.** Some data is private by law. Other information is simply not for low-level employees. If you automate your data pipeline, you can easily manage access to your data.
- **People make mistakes.** Our brains are not built for repetitive work. When someone copies and pastes spreadsheets all day, there will inevitably be mistakes. These mistakes can cost a lot.
If you are serious about data analytics, you need proper infrastructure.
## How to get modern data infrastructure
You need data engineers and data scientists. The good thing is – once you build your data infrastructure, maintenance is easy.
In most cases, it takes less than a year to set up a data warehouse. Also, if you want to build data infrastructure fast, you’ll need more than one data engineer.
But the more people you hire for development, the more will stay for maintenance. And when everything works well, maintaining infrastructure is not a full-time job. It often doesn’t make much sense to hire in-house data engineers. Especially, since this is a very well-paid position with a median salary of over $150,000.
Outsourcing is cheaper and faster. You can hire several engineers to build data infrastructure quickly. After launch, you can keep just one data engineer part-time for maintenance. But that engineer will know everything about the project because they built it.
We provide [data engineering services](https://aristeksystems.com/services/data-engineering/) here at Aristek Systems. We keep only the best data engineers and data scientists on board. They build data infrastructure from scratch or at any point in the project. Reach out for a free consultation.
| aristeksystems2013 |
1,867,753 | Digital Transformation and Insurance – The Evolution of Self-Service Solutions for Enhanced Customer Satisfaction | This article was originally published on Danubius IT Solutions' tech blog. Efficient Claim... | 0 | 2024-05-28T13:56:13 | https://danubius.io/en/blog/digital-transformation-and-insurance--the | digitaltransformation, customerexperience, selfservice, insurance | [This article was originally published on Danubius IT Solutions' tech blog.](https://danubius.io/en/blog/digital-transformation-and-insurance--the)
## Efficient Claim Filing
The insurance sector has significantly changed due to digital advancements that have influenced most industries. A crucial factor behind these changes is the shift to paperless, automated processes in the back office, an evolution that has enabled self-service solutions that offer full digital interactions for customers.
What appeared to the customer as a fully digital process was in fact being done by manual efforts behind the scenes, complete with multiple physical signatures. However, the transition to complete automation has streamlined these operations, enhancing customer experiences and operational efficiency alike.
Of course, this goes well beyond technology shifts; it signals larger changes to customers' increasing expectations regarding more accessible, customer-focused insurance and changes that insurers must implement to meet those expectations.
## Insurance digitalization making our lives easier
Digitalization has completely changed the insurance industry, marking a significant milestone in its evolution. This transformation has accelerated processes and also laid the groundwork for the development of online self-service solutions. With the rise of paperless, automated back-office processing, the era of doing cumbersome paperwork and enduring lengthy waits for insurance transactions has become a thing of the past.
The journey began with the introduction of online management tools, which streamlined policy handling and claim processing. This initial step was crucial, as it signified a move towards a more customer-centric approach, empowering customers with remarkable ease and efficiency in managing their insurance needs.
Yet, this was merely the inception of a broader and more impactful change. By building upon the foundation of digitalization, the insurance sector has embraced a future where self-service platforms are prospering, offering customers complete control over their insurance interactions without the traditional barriers.
## Why are Self-Service Solutions considered to be ‘game-changers?’
The development of digital infrastructure marked a significant shift in the landscape of customer service. The advent of sophisticated self-service platforms signified this transformation, and as these solutions proliferated, encompassing areas such as contracting, claims management, and maintenance, the complexity and breadth of customer support requirements grew exponentially. Traditionally, customer support had been heavily reliant on direct interactions through call centers and email correspondence. However, the landscape began to evolve with the integration of innovative support solutions, including chatbots, which offered a more immediate and accessible form of assistance.
This progression laid the groundwork for the next quantum leap in customer service: the introduction of Artificial Intelligence and personalized assistance. Leveraging Large Language Models (LLMs), these advanced solutions are set to redefine the parameters of customer engagement, offering a level of personalization and efficiency previously inaccessible. As such, the digital evolution of insurance continues in the way of offering not just reactive but anticipatory customer service that is tailored to meet the individual needs of each customer.
## The role of advanced technologies
The integration of AI and Machine Learning (ML) has been a revolutionary step for insurance self-service tools.
AI-driven chatbots and virtual assistants, equipped with natural language processing, offer instant, precise responses to diverse customer inquiries. They excel in understanding client needs, offering tailored policy advice, and guiding through claims with accuracy and ease.
At the same time, ML algorithms continuously enhance these interactions by learning from data to recognize patterns and anticipate customer needs, thus boosting efficiency and ensuring a consistently personalized experience.
Moreover, AI plays a critical role in detecting fraud and assessing risks, fortifying the security for insurers and their clients alike.
## Did customer satisfaction increase with Self-Service tools?
In the same way, the change has enhanced moving to digital self-service solutions with an impact on customer satisfaction in general.
Consequently, the customer is at the great convenience of being able to access services 24/7, from any location. This access can be combined with faster processing of claims and inquiries, resulting in a quicker support and resolution period for customers. In addition, data analytics and AI make it possible for a more personalized approach to service. Customers like solutions designed according to their specific needs and preferences. Therefore, interaction with customers will become by far more engaging and satisfactory.
At such an empowerment and transparency level, consumers would feel empowered to make choices of their own for insurance, and their policies be made transparent to them, which has not been heard previously in the industry. This change has brought not only an increase in the retention ratio of customers but also attracted the new generation of tech-savvy customers. These users view insurance companies that have embraced digital solutions as forward-thinking and customer-centric, which leads to an uptick in positive brand perception and customer loyalty.
## Challenges and future prospects
Despite its successes, this journey hasn’t been without challenges. Addressing data privacy concerns, ensuring the inclusion of the human element, and leveraging new technologies like blockchain for data exchange all represent key areas of focus.
## Data Privacy & Security
Insurers need to balance harnessing potential within digital data with robust cybersecurity measures and adherence to strict data protection regulations.
However, they are not just fighting traditional cyber threats but also the emerging challenge of deepfakes, which use AI to create convincingly realistic yet fake audio and visuals. This advanced form of digital manipulation poses significant risks, including fraud and misinformation, challenging insurers to bolster their cybersecurity defenses. To counteract this, insurers are adopting sophisticated detection technologies and promoting customer awareness to differentiate between genuine and fabricated content.
In response, strategies like multi-factor authentication and the incorporation of blockchain are being implemented. These not only aid in authenticating transactions but also ensure a verifiable, tamper-proof record, crucial in minimizing the hazard of deepfakes. As the technology behind deepfakes and other cyber threats evolves, staying ahead requires insurers to continuously innovate their security measures and foster collaborations with technology experts.
## The Human Element in a Digital World
Digital tools have streamlined and automated many processes, yet the need for human interaction – the empathy and judgement only humans can offer – remains, especially for the older generation who may find digital platforms intimidating. Insurers are tasked with balancing automated solutions with accessible, human-centered services to cater to all demographics effectively, and ensuring the availability of human agents for scenarios demanding personalized attention.
## Blockchain and Cross-Sector Learning from Banking
The technology has been foreseen with the capacity to make transferred information between insurers easier, more effective, and transparent. This move towards more integrated digital solutions mirrors the path taken by the banking sector, indicating a shared direction in the evolution of financial services towards enhanced customer service.
## Future Prospects for an Intuitive Ecosystem
Looking ahead, the industry focuses on refining digital strategies to be more intuitive and inclusive. There's an emphasis on platforms that blend technological sophistication with user-friendliness, catering to a broad customer base. Predictive analytics, AI, and ML are being leveraged to personalize services and improve risk assessment.
Innovations like blockchain and IoT devices are also in the spotlight. These tools promise enhanced efficiency and transparency, with the ultimate goal being the coexistence of technology and human expertise for a comprehensive, empathetic, and secure insurance service experience that caters to a broad spectrum of customer needs.
## Embracing the future
The evolution of self-service solutions in insurance is a testament to the power of innovation in enhancing customer satisfaction. Moving forward, it's vital for insurers to continue adopting new technologies while preserving the core of customer service.
Our expertise in developing state-of-the-art IT solutions can help you leverage these technological advancements. Whether it’s optimizing your existing self-service platforms or creating new ones, we’re here to guide you every step of the way.
Interested in advancing your insurance services? Reach out to us and let's discuss how we can enhance your customers’ experiences together.
| danubiusio |
1,867,738 | DOM Manipulation (w/ Media Queries) | Check out this Pen I made! | 0 | 2024-05-28T13:29:09 | https://dev.to/arbrazil/dom-manipulation-w-media-queries-489e | codepen | Check out this Pen I made!
{% codepen https://codepen.io/arbrazil/pen/QWPZXJr %} | arbrazil |
1,867,752 | Returning an Array from a Method | When a method returns an array, the reference of the array is returned. You can pass arrays when... | 0 | 2024-05-28T13:53:36 | https://dev.to/paulike/returning-an-array-from-a-method-461n | java, programming, learning, beginners | When a method returns an array, the reference of the array is returned. You can pass arrays when invoking a method. A method may also return an array. For example, the following method returns an array that is the reversal of another array.
```
public static int[] reverse(int[] list) {
int[] result = new int[list.length];
for (int i = 0, j = result.length - 1;
i < list.length; i++, j--) {
result[j] = list[i];
}
return result;
}
```
Line 2 creates a new array **result**. Lines 4–7 copy elements from array **list** to array **result**. Line 9 returns the array. For example, the following statement returns a new array **list2** with elements **6**, **5**, **4**, **3**, **2**, **1**.
`int[] list1 = {1, 2, 3, 4, 5, 6};
int[] list2 = reverse(list1);` | paulike |
1,857,412 | Case Study on Single-Dimensional Arrays | Case Study: Analyzing Numbers The problem is to write a program that finds the number of... | 0 | 2024-05-28T13:49:14 | https://dev.to/paulike/case-study-on-single-dimensional-arrays-h97 | java, programming, learning, beginners | ## Case Study: Analyzing Numbers
The problem is to write a program that finds the number of items above the average of all items. The problem is to read 100 numbers, get the average of these numbers, and find the number of the items greater than the average. To be flexible for handling any number of input, we will let the user enter the number of input, rather than fixing it to 100. Below is the solution.
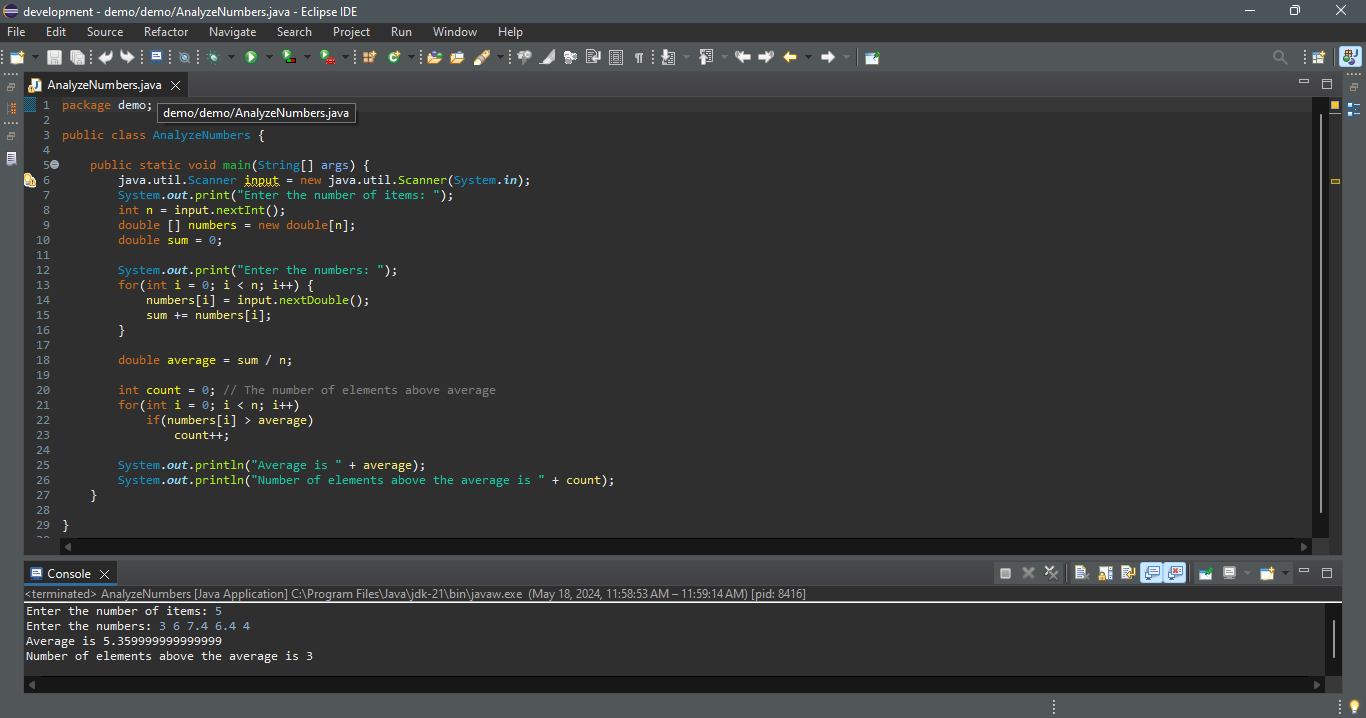
The program prompts the user to enter the array size (line 8) and creates an array with the specified size (line 9). The program reads the input, stores numbers into the array (line 14), adds each number to **sum** in line 14, and obtains the average (line 18). It then compares each number in the array with the average to count the number of values above the average (lines 20-23).
## Case Study: Deck of Cards
The problem is to create a program that will randomly select four cards from a deck of cards. Say you want to write a program that will pick four cards at random from a deck of **52** cards. All the cards can be represented using an array named **deck**, filled with initial values **0** to **51**, as follows:
`int[] deck = new int[52];
// Initialize cards
for (int i = 0; i < deck.length; i++)
deck[i] = i;`
Card numbers **0** to **12**, **13** to **25**, **26** to **38**, and **39** to **51** represent 13 Spades, 13 Hearts, 13 Diamonds, and 13 Clubs, respectively, as shown in below in (a). **cardNumber / 13** determines the suit of the card and **cardNumber % 13** determines the rank of the card, as shown in below in (b). After shuffling the array **deck**, pick the first four cards from **deck**. The program displays the cards from these four card numbers.
(a)
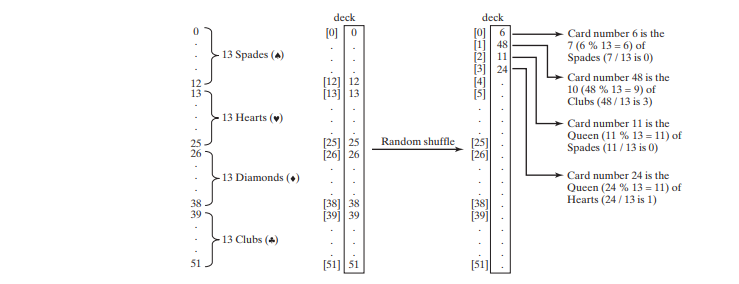
(b)
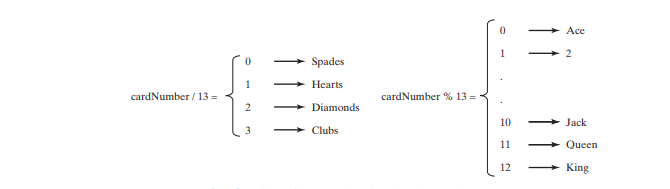
Below is the code:
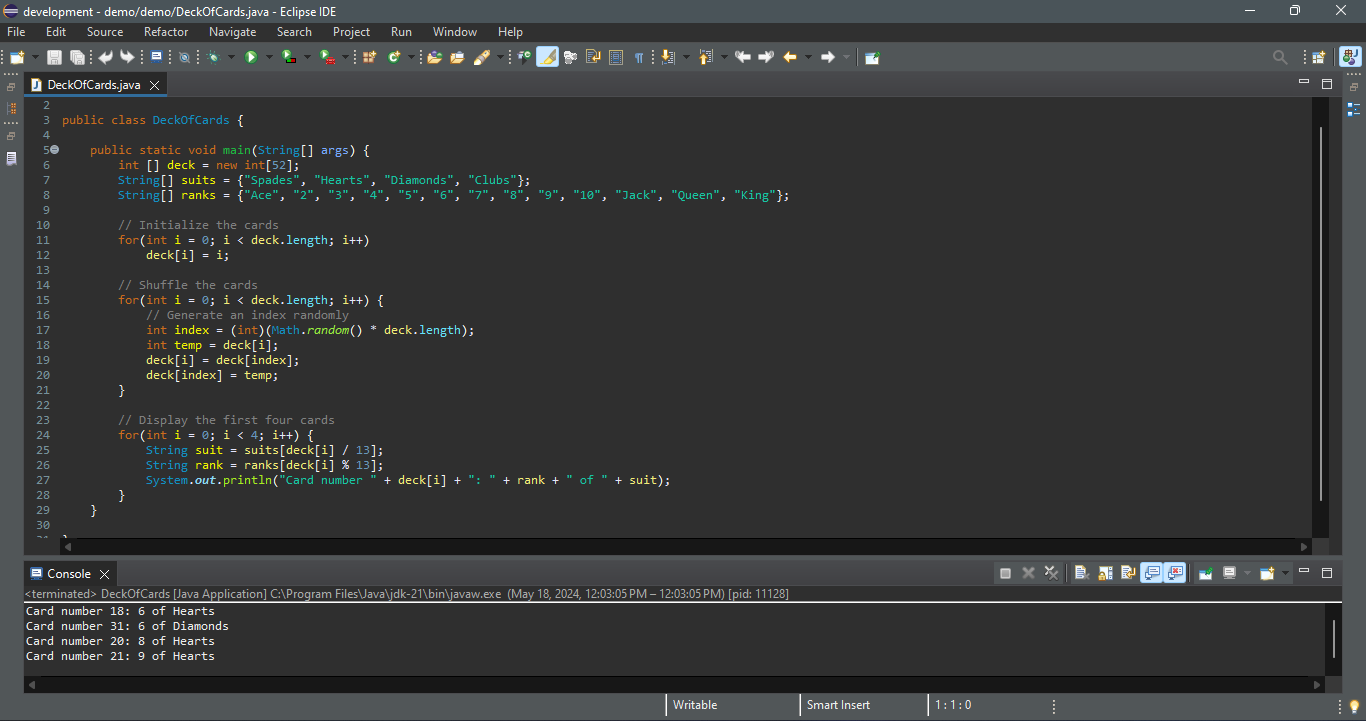
The program creates an array **suits** for four suits (line 7) and an array **ranks** for 13 cards in a suit (lines 8). Each element in these arrays is a string.
The program initializes **deck** with values **0** to **51** in lines 11–12. The **deck** value **0** represents the card Ace of Spades, **1** represents the card 2 of Spades, **13** represents the card Ace of Hearts, and **14** represents the card 2 of Hearts.
Lines 15–21 randomly shuffle the deck. After a deck is shuffled, **deck[i]** contains an arbitrary value. **deck[i] / 13** is **0**, **1**, **2**, or **3**, which determines the suit (line 25). **deck[i] % 13** is a value between **0** and **12**, which determines the rank (line 26). If the **suits** array is not defined, you would have to determine the suit using a lengthy multi-way **if-else** statement as follows:
`if (deck[i] / 13 == 0)
System.out.print("suit is Spades");
else if (deck[i] / 13 == 1)
System.out.print("suit is Hearts");
else if (deck[i] / 13 == 2)
System.out.print("suit is Diamonds");
else
System.out.print("suit is Clubs");`
With **suits = {"Spades", "Hearts", "Diamonds", "Clubs"}** created in an array, **suits[deck / 13]** gives the suit for the **deck**. Using arrays greatly simplifies the solution for this program.
## Case Study: Counting the Occurrences of Each Letter
This section presents a program to count the occurrences of each letter in an array of characters. The program given below does the following:
1. Generates **100** lowercase letters randomly and assigns them to an array of characters, as shown in the image below a. You can obtain a random letter by using the **getRandomLowerCaseLetter()** method in the **RandomCharacter** class.
2. Count the occurrences of each letter in the array. To do so, create an array, say **counts**, of **26 int** values, each of which counts the occurrences of a letter, as shown in the image below b. That is, **counts[0]** counts the number of **a**’s, **counts[1]** counts the number of **b**’s, and so on.
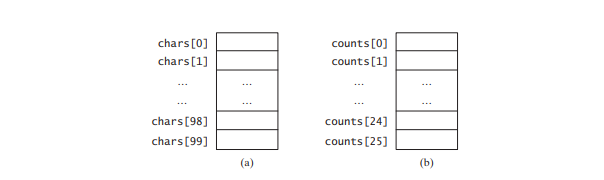
```
package demo;
public class CountLettersInArray {
public static void main(String[] args) {
// Declare and create an array
char[] chars = createArray();
// Display the array
System.out.println("The lowercase letters are:");
displayArray(chars);
// Count the occurrences of each letter
int[] counts = countLetters(chars);
// Display counts
System.out.println();
System.out.println("The occurrences of each letter are:");
displayCounts(counts);
}
/** Create an array of characters */
public static char[] createArray() {
// Declare an array of characters and create it
char[] chars = new char[100];
// Create lowercase letters randomly and assign them to the array
for(int i = 0; i < chars.length; i++)
chars[i] = RandomCharacter.getRandomLowerCaseLetter();
// Return the array
return chars;
}
/** Display the array of characters */
public static void displayArray(char[] chars) {
// Display the characters in the array 20 on each line
for(int i = 0; i < chars.length; i ++) {
if((i + 1) % 20 == 0)
System.out.println(chars[i]);
else
System.out.print(chars[i] + " ");
}
}
/** Count the occurrences of each letter */
public static int[] countLetters(char[] chars) {
// Declare and create an array of 26 int
int[] counts = new int[26];
// For each lowercase letter in the array, count it
for(int i = 0; i < chars.length; i++)
counts[chars[i] - 'a']++;
return counts;
}
/** Display counts */
public static void displayCounts(int[] counts) {
for(int i = 0; i < counts.length; i++) {
if((i + 1) % 10 == 0)
System.out.println(counts[i] + " " + (char)(i + 'a'));
else
System.out.print(counts[i] + " " + (char)(i + 'a') + " ");
}
}
}
```
`The lowercase letters are:
e y l s r i b k j v j h a b z n w b t v
s c c k r d w a m p w v u n q a m p l o
a z g d e g f i n d x m z o u l o z j v
h w i w n t g x w c d o t x h y v z y z
q e a m f w p g u q t r e n n w f c r f
The occurrences of each letter are:
5 a 3 b 4 c 4 d 4 e 4 f 4 g 3 h 3 i 3 j
2 k 3 l 4 m 6 n 4 o 3 p 3 q 4 r 2 s 4 t
3 u 5 v 8 w 3 x 3 y 6 z`
The **createArray** method (lines 23–33) generates an array of **100** random lowercase letters. Line 7 invokes the method and assigns the array to **chars**. What would be wrong if you rewrote the code as follows?
`char[] chars = new char[100];
chars = createArray();`
You would be creating two arrays. The first line would create an array by using **new char[100]**. The second line would create an array by invoking **createArray()** and assign the reference of the array to **chars**. The array created in the first line would be garbage because it is no longer referenced, and as mentioned earlier Java automatically collects garbage behind the scenes. Your program would compile and run correctly, but it would create an array unnecessarily.
Invoking **getRandomLowerCaseLetter()** (line 29) returns a random lowercase letter. This method is defined in the **RandomCharacter** class.
The **countLetters** method (lines 47–56) returns an array of **26 int** values, each of which stores the number of occurrences of a letter. The method processes each letter in the array and increases its count by one. A brute-force approach to count the occurrences of each letter might be as follows:
`for (int i = 0; i < chars.length; i++)
if (chars[i] == 'a')
counts[0]++;
else if (chars[i] == 'b')
counts[1]++;
...`
But a better solution is given in lines 52–53.
`for (int i = 0; i < chars.length; i++)
counts[chars[i] - 'a']++;`
If the letter (**chars[i]**) is **a**, the corresponding count is **counts['a' - 'a']** (i.e., **counts[0]**). If the letter is **b**, the corresponding count is **counts['b' - 'a']** (i.e., **counts[1]**), since the Unicode of **b** is one more than that of **a**. If the letter is **z**, the corresponding count is **counts['z' - 'a']** (i.e., **counts[25]**), since the Unicode of **z** is **25** more than that of **a**.
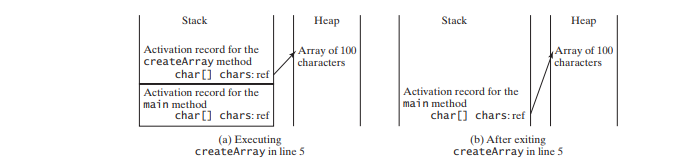
Above image shows the call stack and heap _during_ and _after_ executing **createArray**. | paulike |
1,867,749 | Understanding CSS Box Model | CSS Box Model is a fundamental concept in web development that plays a crucial role in how elements... | 0 | 2024-05-28T13:46:35 | https://dev.to/amolsasane_/understanding-css-box-model-1ap | webdev, css, boxmodel | **CSS** Box Model is a fundamental concept in web development that plays a crucial role in how elements are displayed and laid out on a webpage. In this blog, we will explore the CSS Box Model, its components, and how it affects the layout and sizing of HTML elements.
## What is the CSS Box Model?
The CSS Box Model is a way of representing every HTML element as a rectangular box showing it's occupancy and position on the web page. This model consists of four essential components as shown in the above picture:
1. **Content**: The actual content of the element, such as text or an image.
2. **Padding**: The transparent space around the content inside the box.
3. **Border**: A line that surrounds the padding and content.
4. **Margin**: The transparent space outside the border, creating space between elements.
## Understanding Each Component:
Let's take a closer look at each component of the CSS Box Model:
- **Content**: The content area is where the actual content of the element resides. Its size is determined by the element's width and height properties.
- **Padding**: Padding is the space between the content and the element's border. It can be set using the 'padding' property and is useful for creating space within an element.
- **Border**: The border surrounds the padding and content, acting as a visible boundary for the element. You can define the border's size, style, and color using the 'border' property.
- **Margin**: The margin is the transparent space outside the border, creating the space between elements. It can be set using the 'margin' property.
## Box Model Illustration:
Consider the following example:
_HTML_
```
<div class="box">
This is the content of the box
</div>
```
_CSS_
```
.box {
width: 10rem;
height: 3rem;
padding: 1rem;
border: 5px solid blue;
margin: 2rem;
}
```
_Output_
Here, in the above example we have created a container using `'div'` tag in `HTML` and added a `CSS` stylesheet to it having properties width, height, padding, border and margin respectively set to it's perticular given values.
**To understand the specific style given to it, consider the following picture:**
Here, the blue colored area shows the `width` and `height` of the actual content. The green colored area shows the `padding` given to it. The purple outline is the `border` and lastly the orange colored area outside the border is the `margin` applied to it.
## Conclusion:
So, the next time you find yourself grappling with layout challenges, remember that the CSS box model is your trusty toolkit for building pixel-perfect designs that leave a lasting impression.
For more such blogs [click here](https://amolsasane.netlify.app/blogs.html) | amolsasane_ |
1,867,748 | EMPACK Gorinchem 2025 Utrecht Netherlands | Exhibition Stands | Empack 2025 Utrecht: Benelux's premier packaging tech trade fair, your go-to platform for products,... | 0 | 2024-05-28T13:44:21 | https://dev.to/expostandzoness/empack-gorinchem-2025-utrecht-netherlands-exhibition-stands-23l7 | [Empack 2025 Utrecht](https://www.expostandzone.com/trade-shows/empack-netherlands
): Benelux's premier packaging tech trade fair, your go-to platform for products, services, and solutions. | expostandzoness | |
1,857,700 | Passing Arrays to Methods | When passing an array to a method, the reference of the array is passed to the method. Just as you... | 0 | 2024-05-28T13:28:33 | https://dev.to/paulike/passing-arrays-to-methods-1j71 | java, programming, learning, beginners | When passing an array to a method, the reference of the array is passed to the method. Just as you can pass primitive type values to methods, you can also pass arrays to methods. For example, the following method displays the elements in an **int** array:
`public static void printArray(int[] array) {
for (int i = 0; i < array.length; i++) {
System.out.print(array[i] + " ");
}
}`
You can invoke it by passing an array. For example, the following statement invokes the **printArray** method to display **3**, **1**, **2**, **6**, **4**, and **2**.
`printArray(new int[]{3, 1, 2, 6, 4, 2});`
The preceding statement creates an array using the following syntax:
n`ew elementType[]{value0, value1, ..., valuek};`
There is no explicit reference variable for the array. Such array is called an _anonymous array_.
Java uses _pass-by-value_ to pass arguments to a method. There are important differences between passing the values of variables of primitive data types and passing arrays.
- For an argument of a primitive type, the argument’s value is passed.
- For an argument of an array type, the value of the argument is a reference to an array; this reference value is passed to the method. Semantically, it can be best described as _pass-by-sharing_, that is, the array in the method is the same as the array being passed. Thus, if you change the array in the method, you will see the change outside the method.
Take the following code, for example:
```
public class Test {
public static void main(String[] args) {
int x = 1; // x represents an int value
int[] y = new int[10]; // y represents an array of int values
m(x, y); // Invoke m with arguments x and y
System.out.println("x is " + x);
System.out.println("y[0] is " + y[0]);
}
public static void m(int number, int[] numbers) {
number = 1001; // Assign a new value to number
numbers[0] = 5555; // Assign a new value to numbers[0]
}
}
```
`x is 1
y[0] is 5555`
You may wonder why after **m** is invoked, **x** remains **1**, but **y[0]** become **5555**. This is because **y** and **numbers**, although they are independent variables, reference the same array, as illustrated below. When **m(x, y)** is invoked, the values of **x** and **y** are passed to **number** and **numbers**. Since **y** contains the reference value to the array, **numbers** now contains the same reference value to the same array.
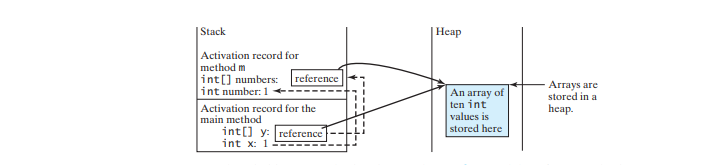
Arrays are objects in Java. The JVM stores the objects in an area of memory called the _heap_, which is used for dynamic memory allocation.
The program below shows the difference between passing a primitive data type value and an array reference variable to a method. The program contains two methods for swapping elements in an array. The first method, named **swap**, fails to swap two **int** arguments. The second method, named **swapFirstTwoInArray**, successfully swaps the first two elements in the array argument.
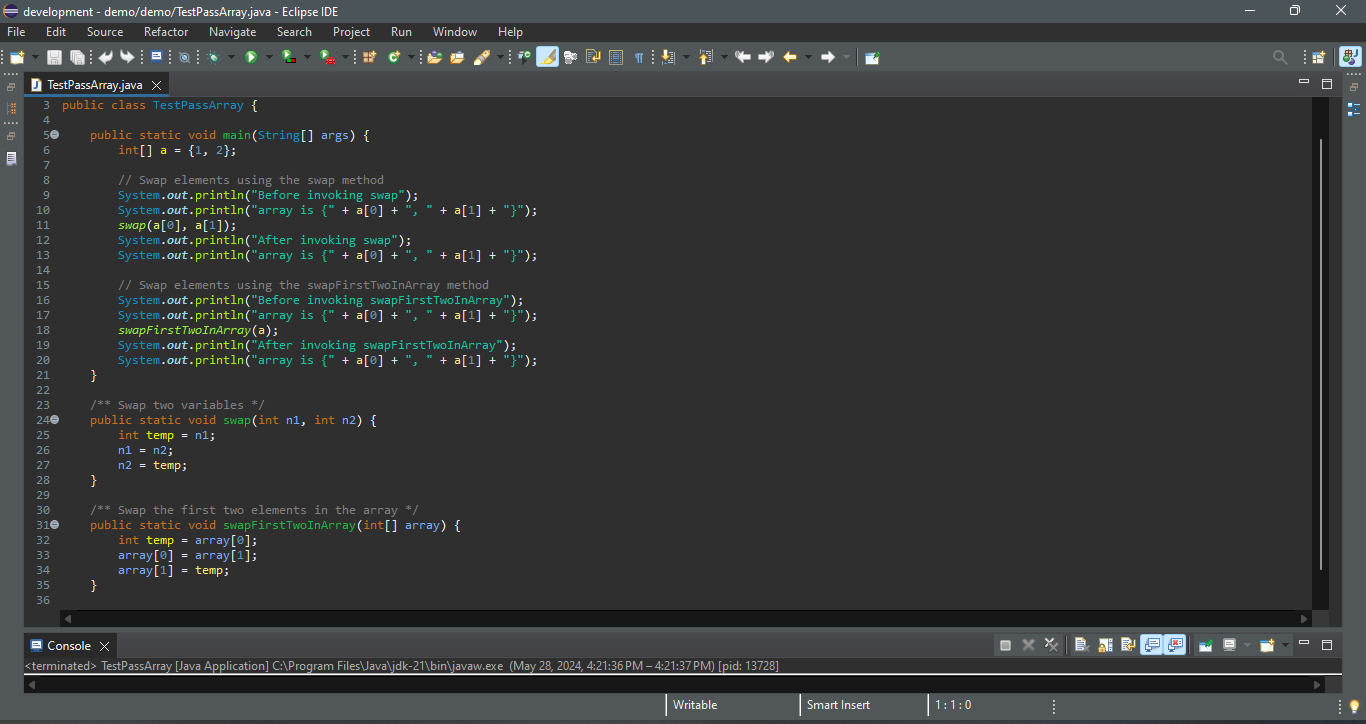
`Before invoking swap
array is {1, 2}
After invoking swap
array is {1, 2}
Before invoking swapFirstTwoInArray
array is {1, 2}
After invoking swapFirstTwoInArray
array is {2, 1}`
As shown below, the two elements are not swapped using the **swap** method. However, they are swapped using the **swapFirstTwoInArray** method. Since the parameters in the **swap** method are primitive type, the values of **a[0]** and **a[1]** are passed to **n1** and **n2** inside the method when invoking **swap(a[0], a[1])**. The memory locations for **n1** and **n2** are independent of the ones for **a[0]** and **a[1]**. The contents of the array are not affected by this call.
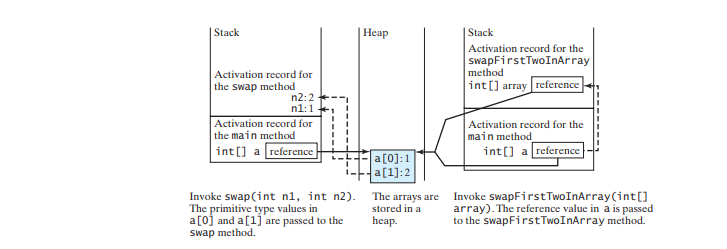
The parameter in the **swapFirstTwoInArray** method is an array. As shown above, the reference of the array is passed to the method. Thus the variables **a** (outside the method) and **array** (inside the method) both refer to the same array in the same memory location. Therefore, swapping **array[0]** with **array[1]** inside the method **swapFirstTwoInArray** is the same as swapping **a[0]** with **a[1]** outside of the method. | paulike |
1,867,747 | Navigating the future: Anticipating user trends in connected experiences | Picture this: You wake up to the sound of your alarm, and as you stretch and rub your eyes, your... | 0 | 2024-05-28T13:39:56 | https://dev.to/yujofficial/navigating-the-future-anticipating-user-trends-in-connected-experiences-7a1 | uxdesign, connectedexperiences, designthinking, yuj | Picture this: You wake up to the sound of your alarm, and as you stretch and rub your eyes, your smart home system detects your movement and begins brewing your favorite coffee. While savoring that first sip, your smartphone buzzes with a notification, reminding you of an important meeting. Without skipping a beat, you seamlessly transfer the notification to your smartwatch, which displays it on its vibrant screen.
This is the evolving landscape of connected experiences, where technology and UX strategy intertwine with our daily lives, enhancing and streamlining our interactions. From personalized recommendations on streaming platforms to voice-controlled virtual assistants that answer our questions, the future is being shaped by our ever-growing reliance on connected devices. As UX design strategy merges with technological prowess, understanding usage trends and preferences becomes vital to create experiences that truly resonate and make a lasting impact.
In this blog post, we will explore the significance of anticipating user trends in the realm of connected experiences. We’ll delve into the importance of personalization and customization, the need for seamless integration across devices, the rise of voice and natural language interfaces, and the exciting possibilities of immersive and augmented experiences.
**Personalization and Customization**
The rise of Tailored Experiences is one of the most significant trends in the connected world is the growing demand for personalized user experiences. Users are no longer satisfied with one-size-fits-all solutions; they expect interfaces and content tailored to their individual preferences.
For example, streaming platforms like Netflix use sophisticated algorithms to recommend shows and movies based on a user’s viewing history, creating a personalized content feed that keeps them engaged and entertained, and this is only the beginning.
UX design strategy needs to focus on gathering user data ethically and transparently while empowering users with control over their data and privacy settings. By understanding user preferences and behavior patterns, designers can deliver highly personalized experiences that resonate with their audience. For example, social media platforms like Facebook and Instagram have implemented privacy settings that allow users to control who sees their posts, providing a sense of control and security in the digital space.
**Seamless Integration across Devices**
Throughout our day, we’re dependent on at least 3 or more technological devices, which is why we expect a consistent experience as we transition from one device to another. Whether it’s starting a task on a smartphone and continuing it on a laptop or controlling smart home devices from a wearable, UX strategy must ensure that interactions are smooth and uninterrupted.
For instance, cloud storage services like Dropbox or Google Drive allow users to access their files from different devices, ensuring that they can pick up where they left off, regardless of the device they’re using. This synchronization and continuity across platforms enhance productivity and provide a consistent user experience.
Going forward, with more devices added to the list, interconnected ecosystems and cross-device communication will play a vital role in delivering cohesive experiences that adapt to users’ changing needs.
**Voice and Natural Language Interfaces**
Alexa! Play some music.
Voice assistants like Amazon Alexa, Google Assistant, and Apple’s Siri have gained significant popularity in recent years. Smart speakers, such as Amazon Echo and Google Home, have become common household devices. The convenience of interacting with technology through voice commands has led to increased adoption of these voice-enabled devices.
But what’s the technology that makes this happen?
Natural language processing (NLP) technology has made tremendous progress, enabling voice interfaces to better understand and respond to human language.
NLP algorithms can analyze the context, intent, and sentiment behind user queries, allowing voice assistants to provide accurate and relevant responses. These advancements have greatly improved the overall user experience and made voice interactions more seamless.
Voice and natural language interfaces are being integrated into a wide range of smart home devices and IoT (Internet of Things) devices. Users can control their lights, thermostats, locks, and other smart home devices through voice commands, making their homes more convenient and efficient. Additionally, voice interfaces are finding applications in various industries, including healthcare, automotive, and customer service, enhancing user interactions and simplifying complex tasks.
By designing intuitive and user-friendly voice interactions, a good UX design strategy can create experiences that are hands-free, accessible, and personalized. Voice interfaces should be able to understand user commands accurately, provide relevant responses, and adapt to different accents and language variations.
As voice and natural language interfaces continue to evolve, designers have the opportunity to create experiences that seamlessly blend technology with the human conversation, making interactions with devices feel more natural and intuitive.
**Immersive and Augmented Experiences**
Virtual reality creates a fully immersive digital environment, while augmented reality overlays digital elements onto the real world. The integration of VR and AR technologies in connected experiences opens up a world of possibilities. When used in User experience strategy, VR can transport users to virtual worlds, creating realistic and interactive experiences, while AR can enhance the real world by overlaying digital information and objects onto our surroundings.
Immersive experiences offer a higher level of interactivity and engagement. Users can actively participate and manipulate their virtual environments, blurring the lines between the digital and physical realms. For example, in VR gaming, users can physically move and interact with objects, creating a sense of presence and immersion that traditional gaming cannot replicate.
VR can transport players into the game world, allowing them to experience adventures firsthand. On the other hand, AR can enhance live events, overlaying additional information or interactive elements for an enriched experience.
In education, VR and AR can provide immersive learning environments, allowing students to explore historical sites, conduct virtual experiments, or visualize complex concepts.
By leveraging VR and AR technologies, UX designers can transport users to new realities, spark their imagination, and foster deeper engagement. It is essential to design intuitive interfaces, realistic graphics, and interactive elements that seamlessly blend the virtual and physical worlds.
**Embracing the Future of Connected Experiences**
In navigating the future of connected experiences, UX strategy must largely keep a keen eye on user trends and adapt their strategies accordingly. By understanding and embracing these trends, UX designers can create innovative and meaningful experiences that resonate with users, fostering engagement, and delight.
As technology continues to evolve, the possibilities for enhancing user experiences in the connected world are endless. It is up to us, as designers and creators, to harness this potential and shape a future that is seamlessly connected and user-centric.
To unlock the full potential of connected experiences and create innovative designs that anticipate user trends, get in touch with [yuj- a global ux design agency](https://www.yujdesigns.com/navigating-the-future-anticipating-user-trends-in-connected-experiences/) today. | yujofficial |
1,867,745 | 20 Programming Facts You Probably Don't Know | Programming is a field full of intriguing history, unexpected quirks, and fascinating trivia. Whether... | 0 | 2024-05-28T13:38:40 | https://dev.to/documendous/20-programming-facts-you-never-knew-1nk | programmingfacts, developertrivia, codehistory, techtrivia | Programming is a field full of intriguing history, unexpected quirks, and fascinating trivia. Whether you're a seasoned developer or just starting out, there's always something new to learn. Here are 20 programming facts that might surprise you and give you a deeper appreciation for the world of code.
1. **Python's Name Origin**: Python is named after the British comedy series "Monty Python's Flying Circus," not the snake.
2. **Java's Initial Name**: Java was initially called "Oak," named after an oak tree that stood outside James Gosling's office.
3. **Hello World History**: The first "Hello, World!" program appeared in the book "The C Programming Language" by Brian Kernighan and Dennis Ritchie.
4. **Whitespace Language**: Whitespace is a programming language that uses only spaces, tabs, and line breaks for its syntax.
5. **Early Bug**: The term "debugging" comes from an incident in 1947 when a moth was removed from a Mark II computer at Harvard University.
6. **Unicode and Emojis**: Unicode, the standard for text representation in computers, includes over 1,000,000 code points, and it supports emojis, which are also a form of text.
7. **BASIC Language**: The BASIC programming language, designed in 1964, was one of the first to be made widely accessible to non-science students.
8. **First Computer Programmer**: Ada Lovelace is often considered the first computer programmer for her work on Charles Babbage's early mechanical general-purpose computer, the Analytical Engine.
9. **Esoteric Languages**: Esoteric programming languages like Brainfuck and Malbolge are created more for amusement and experimentation than for practical use.
10. **COBOL's Longevity**: COBOL, created in 1959, is still widely used in business, finance, and administrative systems for companies and governments.
11. **Zero-Based Indexing**: Many programming languages, like C and Python, use zero-based indexing for arrays and lists, a concept introduced by the C language.
12. **Turing Complete**: A system is Turing complete if it can perform any computation given enough time and memory. Many games, like Minecraft and Magic: The Gathering, have been proven to be Turing complete.
13. **JavaScript Misnomer**: Despite its name, JavaScript is not directly related to Java. It was initially called Mocha, then LiveScript, before becoming JavaScript.
14. **Git's Name**: Linus Torvalds, the creator of Git, humorously named it after himself, saying in British slang, "I'm an egotistical bastard, and I name all my projects after myself. First 'Linux,' now 'Git.'"
15. **HTML Element 'marquee'**: The `<marquee>` HTML element, which scrolls text across the screen, was introduced by Microsoft in Internet Explorer and is not part of any official HTML specification.
16. **Recursion Joke**: A common programming joke is: "To understand recursion, you must first understand recursion."
17. **Ruby's Name**: Ruby, a programming language created in the 1990s, is named after a gemstone, as its creator Yukihiro Matsumoto wanted a name that was short, elegant, and interesting.
18. **First Virus**: The first computer virus, known as the "Creeper system," was an experimental self-replicating program written by Bob Thomas in 1971.
19. **ASCII Art**: ASCII art uses characters from the ASCII standard to create images. This art form was popular in the early days of computers when graphical capabilities were limited.
20. **Algorithm's Namesake**: The term "algorithm" is derived from the name of the Persian mathematician Al-Khwarizmi, who made significant contributions to algebra and mathematics.
| documendous |
1,867,743 | Smooth Sailing: Abu Dhabi Immigration Consultancy | Embarking on your immigration journey from Abu Dhabi? Look no further for expert guidance and... | 0 | 2024-05-28T13:37:50 | https://dev.to/yellowbox_2d64f77b618ba9a/smooth-sailing-abu-dhabi-immigration-consultancy-4jih | Embarking on your immigration journey from Abu Dhabi? Look no further for expert guidance and support. Our [Abu dhabi immigration consultancy](https://yellowboximmigration.com/) is your trusted partner in navigating the complexities of relocation, residency, and citizenship processes.
Why choose our consultancy? We're dedicated to providing comprehensive and personalized services tailored to your specific needs. With a deep understanding of Abu Dhabi's immigration laws and procedures, as well as international requirements, we ensure a smooth and efficient experience for our clients.
From initial consultations to document preparation, application submission, and follow-up, we handle every aspect of the process with meticulous attention to detail. Whether you're relocating for work, family reunification, or seeking new opportunities abroad, our team is here to guide you every step of the way.
What sets us apart is our commitment to client satisfaction. We prioritize clear communication, transparency, and responsiveness, ensuring that you're kept informed and supported throughout your entire immigration journey. Our friendly and knowledgeable consultants are always available to address your questions and concerns, providing reassurance and peace of mind.
With our expertise and personalized approach, you can embark on your immigration journey from Abu Dhabi with confidence, knowing that you have a dedicated team of professionals by your side. Contact us today to learn more about how our immigration consultancy services can help you achieve your goals and make your transition as seamless as possible. Let's navigate the path to your new beginning together!
| yellowbox_2d64f77b618ba9a | |
1,867,741 | What are your goals for week 22 of 2024? | It's week 22 of 2024. Yesterday was Memorial Day in the US. I'm not normalizing working on a holiday.... | 19,128 | 2024-05-28T13:37:10 | https://dev.to/jarvisscript/what-are-your-goals-for-week-22-of-2024-2h3c | It's week 22 of 2024. Yesterday was Memorial Day in the US. I'm not normalizing working on a holiday. Be nice to anyone working service or entertainment on holidays.
## What are your goals for this short week?
- What are you building?
- What will be a good result by week's end?
- What events are happening this week?
* any suggestions for in person or virtual events?
- Any special goals for the quarter?
### Last Week's Goals
- [:white_check_mark:] Continue Job Search.
- [:white_check_mark:] Project work.
- [:x:] Blog.
- Events.
* [:x:] Thursday Virtual Coffee. * Gonna miss Thursday Virtual Coffee. It's the last day of school and a short day so I'll be heading to pick up.
- [:white_check_mark:] Run a goal setting thread on Virtual Coffee Slack.
- [:white_check_mark:] Went to the ren faire again need to edit my photos.
### This Week's Goals
- Continue Job Search.
- Project work.
- Blog.
- Events.
* Thursday Virtual Coffee.
- Run a goal setting thread on Virtual Coffee Slack.
- Clean up from Renaissance Faire
- Yard Work
### Your Goals for the week
Your turn what do you plan to do this week?
- What are you building?
- What will be a good result by week's end?
- What events are happening any week?
* in person or virtual?
- Got any Summer Plans?
_ How do you modify your schedule when the kids are out of school?
{% embed https://www.youtube.com/watch?v=vmewc2Uqon4 %}
```html
-$JarvisScript git commit -m "School's out for summer!"
``` | jarvisscript | |
1,866,764 | 10 FinTech Software Development Companies You must Know in 2024 | Fintech is a sector that is changing very quickly. The need for mobile wallets and other finance... | 0 | 2024-05-28T13:34:11 | https://dev.to/meganbrown/10-fintech-software-development-companies-you-must-know-in-2024-173m | fintech, softwaredevelopment, softwareproductengineering, fintechstrategy |

Fintech is a sector that is changing very quickly. The need for mobile wallets and other finance apps has grown as a result of the pandemic. Companies in the financial sector are now prioritising the development of fintech software. Fintech development services, which include online banking and digital wallets, are expanding rapidly.
The pandemic is largely to blame for the predicted $140 billion growth in the [fintech sector](https://www.tntra.io/blog/key-challenges-fintech-industry-solutions/) in India by 2023, from $65 billion in 2019. Consumers require prompt service delivery and convenience. By connecting with customers via their digital devices, fintech app development companies made it possible for financial players to provide services.
As a result, there is a greater need for fintech software firms in India. Hundreds of fintech software development companies exist nowadays. Choosing the appropriate one, though, can be difficult. How do you decide which one suits you the best?
The top ten fintech software development firms in India are listed in this article. The intention is to give you a thorough grasp of what the best company can accomplish for your organisation. It can assist you in selecting the financial software development business that best meets your needs.
## India's Top 10 Fintech Software Companies
- **Tntra**
With its own global innovation ecosystem, Tntra is leading the charge to transform the FinTech app development services landscape. Tntra is a top FinTech [software product engineering company](https://www.tntra.io/) that specialises in offering state-of-the-art engineering services that give FinTech companies a strong platform to succeed in the quickly changing digital financial market.
Their FinTech-focused methodology surpasses traditional engineering. The goal of Tntra's Academy, Gurukula, is to develop Future-of-Work competencies that are especially suited to the ever-changing needs of the FinTech industry. By doing this, they can guarantee that their staff has not just the requisite technical skills but also the most recent knowledge and advancements in the financial technology industry.
Yntra, the Tntra Enterprise Platform, is a powerful tool for efficient innovation delivery that is especially designed to handle the complexities of the FinTech industry. By speeding up software product development and deployment, this platform helps FinTech companies stay on the cutting edge of technology.
- **Netguru**
Netguru, a [top fintech app development company](https://www.tntra.io/fintech-software-development), offers businesses and startups smooth financial solutions. For banks, insurance companies, and other financial firms looking to begin their digital journey, this is the greatest option. With more than 700 employees, the business has completed more than 900 projects with success. It has been creating custom software products for more than 12 years. The company offers online payment wallets, customer loyalty programmes, digital banking applications, financial process automation, and fintech applications based on insurance.
- **Merixstudio**
Merixstudio, one of the leading providers of [fintech solution](https://www.tntra.io/blog/new-future-of-innovation-through-digital-banking-solutions/), employs more than 120 FinTech software specialists. For banks and other financial institutions, they develop unique FinTech solutions. The business is well-known for developing cutting-edge FinTech solutions for customers worldwide, including Toshiba. Fox in addition to others. Merixstudio was named one of the leading FinTech software development businesses in 2019. It creates cutting-edge FinTech solutions by using the collaborative power of software development. The business has built FinTech software for customers in over ten countries.
- **Sidebench**
Sidebench, an Indian fintech application development company, is renowned for its digital strategy and fintech industry consulting. With more than 249 people, the organisation has over 8 years of expertise. Clutch lists it as one of the leading FinTech providers of software for 2021. It offers complete financial outsourcing as well as contemporary FinTech solutions. The business provides services to some of the most well-known companies in the world, such as Instagram and Microsoft. It is among the top ten app development firms for new businesses.
- **The Sneakers Agency**
The Sneakers Agency is a full-service fintech application development provider and one of the best companies for fintech development services. With over 200 workers, it is a reliable partner for more than 50 startups and well-known international companies. For UX/UI design, custom online solutions, DevOps consulting, CRM, and other digital products, it offers FinTech software services. To support the financial services industry, it has created digital wallets, investment management systems, payment gateways, and numerous more solutions. For the web and mobile, The Sneakers Agency creates extraordinary FinTech digital experiences.
- **Fingent**
Fingent is one of the most reputable FinTech development companies in India that is well-known for accelerating [digital transformation](https://www.tntra.io/digital-transformation-services) in the financial industry. The business has been putting financial solutions into practice for more than 15 years. To keep you ahead of the competition, its specialists employ the newest trends and technologies. The business develops digital banking solutions using technologies including robotics, [blockchain](https://www.tntra.io/case-studies/implementation-for-blockchain-powered-cbdc), [artificial intelligence](https://www.tntra.io/blog/ai-transforming-banking-finance/), and predictive analytics. Additionally, it offers safe finance applications cybercrime protection. The business has worked with hundreds of clients in more than 14 nations.
- **Valuecoders**
One of the top fintech businesses in India, ValueCoders has a staff of over 450 individuals and over 15 years of experience. In addition to payment gateways, digital wallets, bank portals, robo advisors, and much more, it offers bespoke fintech development services. To guarantee its clients receive FinTech apps of the highest calibre, the company concentrates on data security. ValueCoders works with big data, blockchain, IoT, Python, JavaScript, and JavaScript. It is renowned for providing more than 2500 international companies with various domain services.
- **IntellectSoft**
Clutch lists Intellectsoft as one of the best fintech app development companies in India. It has more than 13 years of expertise developing unique mobile and web solutions for various sectors. The organisation has served Fortune500 companies and offered digital transformation in the finance industry. In order to create fintech solutions like digital wallets, payment gateways, trading apps, investment solutions, and safe FinTech software, it leverages blockchain technology. The first name on the list while searching for a FinTech software business in India is Intellectsoft. It has been honoured with several accolades from ITFirms, TopDevelopers, and GoodFirms.
- **BoTree Technologies**
Botree Technologies is a well-known fintech [software product engineering solutions](https://www.tntra.io/engineering) provider in both the US and India. The business offers enterprises and startups full FinTech solutions. It has more than eight years of expertise developing unique FinTech software and solutions. Two of BoTree's most recent initiatives are the loan management platform Appruv and the loan inspection tool InspectDate. It employs more than 70 developers who have worked with clients in more than ten nations. BoTree, one of the leading providers of FinTech software, utilises cutting-edge technologies such as Django, Laravel, Ruby on Rails, and Python.
- **FortuneSoft**
Fortunesoft, a young FinTech developer based in India, is starting to get recognition in the financial services industry for its innovative digital transformation. The business is renowned for offering excellent FinTech solutions for digital wallets, wealth management systems, P2P lending platforms, and crowdfunding platforms. It offers dependable and extremely safe financial software services. With over ten years of expertise, the organisation has completed 483 projects worldwide with success. Its technology stack includes PHP, [Python](https://www.tntra.io/blog/python-for-software-solutions/), Node JS, [Ruby On Rails](https://www.tntra.io/blog/ruby-on-rails-rapid-application-development/), Django, and Angular for contemporary finTech apps.
## Hire India’s Leading FinTech Development Company
A short list of the best FinTech businesses in India can be found above. These businesses have years of expertise developing unique FinTech solutions and a global clientele.
One of the top providers of bespoke software development in the financial sector is Tntra, which also offers full IT consulting services.
[Contact us](https://www.tntra.io/contact-us) today for a FREE CONSULTATION!
| meganbrown |
1,867,734 | Models That Prove Their Own Correctness | Models That Prove Their Own Correctness | 0 | 2024-05-28T13:24:21 | https://aimodels.fyi/papers/arxiv/models-that-prove-their-own-correctness | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Models That Prove Their Own Correctness](https://aimodels.fyi/papers/arxiv/models-that-prove-their-own-correctness). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
• This paper explores the concept of models that can prove their own correctness, which could help increase trust in AI systems.
• The key idea is to develop machine learning models that are capable of verifying their own outputs, rather than relying on external verification.
• The authors discuss related work on using AI and interactive provers to improve model reliability, as well as the potential benefits and challenges of self-verifying models.
## Plain English Explanation
The researchers in this paper are looking at ways to make AI models more trustworthy and reliable. One approach they explore is **[models that can prove their own correctness](https://aimodels.fyi/papers/arxiv/large-language-models-can-self-correct-minimal)**. The basic idea is to develop machine learning models that are capable of checking their own work and verifying that their outputs are accurate, rather than relying on humans or other external systems to validate the model's results.
This could be valuable because it would help increase trust in AI systems. If a model can demonstrate that it is producing correct and reliable outputs on its own, it may be more likely to be adopted and used in high-stakes applications where safety and accuracy are paramount. **[Smaller models in particular may need strong verifiers](https://aimodels.fyi/papers/arxiv/small-language-models-need-strong-verifiers-to)** to build confidence in their performance.
The paper discusses some existing work on using techniques like **[interactive provers and zero-knowledge proofs](https://aimodels.fyi/papers/arxiv/verifiable-evaluations-machine-learning-models-using-zksnarks)** to improve model reliability. It also explores the potential benefits and challenges of having models that can self-verify, such as **[increasing trust through reused verified components](https://aimodels.fyi/papers/arxiv/increasing-trust-language-models-through-reuse-verified)**.
Overall, the goal is to find ways to make AI systems more transparent, accountable, and trustworthy - and the idea of **[self-verifying models is an interesting approach to explore further](https://aimodels.fyi/papers/arxiv/just-ask-one-more-time-self-agreement)**.
## Technical Explanation
The key innovation explored in this paper is the concept of **models that can prove their own correctness**. The authors propose developing machine learning models that are capable of verifying their own outputs, rather than relying on external systems or human oversight to validate the model's performance.
To achieve this, the researchers discuss leveraging techniques like **interactive provers** and **zero-knowledge proofs**. These allow the model to generate a cryptographic proof that demonstrates the validity of its outputs, without needing to reveal the full details of its internal workings.
The paper examines the potential benefits of self-verifying models, such as increased transparency, accountability, and trust. The authors also acknowledge some of the challenges, such as the computational overhead required to generate the proofs, and the need to carefully design the model architecture and training process to support this capability.
Experiments are described where the researchers prototype self-verifying models for tasks like classification and language generation. The results indicate that it is possible to imbue models with this self-verification capability, although there may be tradeoffs in terms of model performance or efficiency.
Overall, the technical contributions of this work center on the novel concept of self-verifying models, and the exploration of techniques to realize this vision in practice. The findings suggest that this is a promising direction for increasing trust and reliability in AI systems.
## Critical Analysis
The paper presents a compelling vision for models that can prove their own correctness, but also acknowledges several important caveats and limitations that warrant further investigation.
One key challenge is the computational overhead required to generate the cryptographic proofs that demonstrate the model's outputs are valid. The authors note that this additional processing could impact the model's efficiency and real-world deployment, especially for **[large language models](https://aimodels.fyi/papers/arxiv/large-language-models-can-self-correct-minimal)**. Careful optimization of the proof generation process will likely be necessary.
Another potential concern is that the self-verification capability could be vulnerable to adversarial attacks or manipulation. If an adversary finds a way to compromise the model's internal verification mechanisms, it could undermine the entire premise of increased trust and reliability. Thorough security analysis would be critical.
Additionally, while the paper discusses the potential benefits of self-verifying models, it does not provide a comprehensive comparison to alternative approaches for improving model trustworthiness, such as **[using strong external verifiers](https://aimodels.fyi/papers/arxiv/small-language-models-need-strong-verifiers-to)** or incorporating **[verifiable evaluations](https://aimodels.fyi/papers/arxiv/verifiable-evaluations-machine-learning-models-using-zksnarks)**. A deeper analysis of the tradeoffs between these different strategies would help contextualize the value proposition of self-verifying models.
Overall, the researchers have put forth an intriguing and ambitious concept that could represent an important step forward in building more trustworthy and accountable AI systems. However, the practical challenges and potential limitations highlighted in the paper suggest that further research and development will be necessary to fully realize the vision of **[models that can prove their own correctness](https://aimodels.fyi/papers/arxiv/just-ask-one-more-time-self-agreement)**.
## Conclusion
This paper explores the concept of machine learning models that can prove their own correctness, an approach that could help increase trust and transparency in AI systems. By leveraging techniques like interactive provers and zero-knowledge proofs, the researchers propose developing models that can generate cryptographic evidence demonstrating the validity of their outputs.
The potential benefits of this self-verification capability include improved accountability, reduced reliance on external validation, and greater overall trust in the model's performance. However, the authors also acknowledge significant technical challenges, such as the computational overhead of proof generation and the need to ensure the security of the internal verification mechanisms.
Overall, the work represents an ambitious and forward-looking exploration of ways to make AI systems more reliable and trustworthy. While further research and development will be necessary to fully realize this vision, the core idea of **self-verifying models** is a promising direction that could have important implications for the broader adoption and responsible use of AI technologies.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,733 | ZigZag: Universal Sampling-free Uncertainty Estimation Through Two-Step Inference | ZigZag: Universal Sampling-free Uncertainty Estimation Through Two-Step Inference | 0 | 2024-05-28T13:23:47 | https://aimodels.fyi/papers/arxiv/zigzag-universal-sampling-free-uncertainty-estimation-through | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [ZigZag: Universal Sampling-free Uncertainty Estimation Through Two-Step Inference](https://aimodels.fyi/papers/arxiv/zigzag-universal-sampling-free-uncertainty-estimation-through). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- Deep neural networks can make useful predictions, but estimating the reliability of these predictions is challenging
- Existing approaches like [MC-Dropout](https://aimodels.fyi/papers/arxiv/scalable-subsampling-inference-deep-neural-networks) and [Deep Ensembles](https://aimodels.fyi/papers/arxiv/tiny-deep-ensemble-uncertainty-estimation-edge-ai) are popular, but require multiple forward passes at inference time, slowing them down
- Sampling-free approaches can be faster, but suffer from lower reliability of uncertainty estimates, difficulty of use, and limited applicability
## Plain English Explanation
Deep neural networks have proven to be very good at making predictions, but it can be challenging to determine how reliable those predictions are. Existing methods like [MC-Dropout](https://aimodels.fyi/papers/arxiv/scalable-subsampling-inference-deep-neural-networks) and [Deep Ensembles](https://aimodels.fyi/papers/arxiv/tiny-deep-ensemble-uncertainty-estimation-edge-ai) are popular ways to estimate the uncertainty of a neural network's predictions, but they require running the network multiple times during inference, which can slow things down.
Other approaches that don't require multiple samples can be faster, but they tend to produce less reliable estimates of the uncertainty, can be difficult to use, and may not work well for different types of tasks or data. In this paper, the researchers introduce a new sampling-free approach that is generally applicable, easy to use, and can produce uncertainty estimates that are just as reliable as the state-of-the-art methods, but at a much lower computational cost.
The key idea is to train the network to produce the same output whether or not it is given additional information about the input. At inference time, when no extra information is provided, the network uses its own prediction as the "additional information." The difference between the network's output with and without this self-imposed additional information is used as the measure of uncertainty.
## Technical Explanation
The researchers propose a **sampling-free approach** for estimating the uncertainty of a neural network's predictions. Their method is based on the idea of training the network to produce the same output with and without additional information about the input.
During training, the network is presented with the input and some additional information about it (e.g., a corrupted version of the input, or some other auxiliary data). The network is trained to produce the same output regardless of whether this additional information is provided or not.
At inference time, when no prior information is available, the network uses its own prediction as the "additional information." The difference between the network's output with and without this self-imposed additional information is then used as the measure of uncertainty.
The researchers demonstrate their approach on several [classification and regression tasks](https://aimodels.fyi/papers/arxiv/efficient-bayesian-uncertainty-estimation-nnu-net), and show that it delivers results on par with those of [Deep Ensembles](https://aimodels.fyi/papers/arxiv/tiny-deep-ensemble-uncertainty-estimation-edge-ai) but at a much lower computational cost.
## Critical Analysis
The researchers present a novel and promising approach for estimating the uncertainty of neural network predictions. Compared to existing methods like [MC-Dropout](https://aimodels.fyi/papers/arxiv/scalable-subsampling-inference-deep-neural-networks) and Deep Ensembles, their sampling-free method is more computationally efficient, while still producing reliable uncertainty estimates.
However, the paper does not discuss the potential limitations of this approach. For example, it's unclear how well the method would perform on more complex tasks or datasets, or how sensitive it is to the choice of hyperparameters. Additionally, the researchers do not compare their approach to other sampling-free techniques, such as those based on [Bayesian neural networks](https://aimodels.fyi/papers/arxiv/efficient-bayesian-uncertainty-estimation-nnu-net) or [information theory](https://aimodels.fyi/papers/arxiv/uncertainty-active-learning-graphs).
Further research is needed to better understand the strengths and weaknesses of this method, and to explore how it might be extended or combined with other techniques to improve the reliability and versatility of uncertainty estimation in deep learning.
## Conclusion
The researchers have presented a novel and efficient approach for estimating the uncertainty of neural network predictions. By training the network to produce the same output with and without additional information, they are able to obtain reliable uncertainty estimates at a much lower computational cost than existing methods like [MC-Dropout](https://aimodels.fyi/papers/arxiv/scalable-subsampling-inference-deep-neural-networks) and [Deep Ensembles](https://aimodels.fyi/papers/arxiv/tiny-deep-ensemble-uncertainty-estimation-edge-ai).
This work has the potential to significantly improve the practical deployment of deep learning models, especially in applications where computational efficiency and uncertainty quantification are critical, such as [edge AI](https://aimodels.fyi/papers/arxiv/machine-learning-network-inference-enhancement-from-noisy) and [active learning](https://aimodels.fyi/papers/arxiv/uncertainty-active-learning-graphs). Further research is needed to fully explore the strengths and limitations of this approach, but it represents an important step forward in the field of reliable and efficient deep learning.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,732 | Surveilling the Masses with Wi-Fi-Based Positioning Systems | Surveilling the Masses with Wi-Fi-Based Positioning Systems | 0 | 2024-05-28T13:23:13 | https://aimodels.fyi/papers/arxiv/surveilling-masses-wi-fi-based-positioning-systems | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Surveilling the Masses with Wi-Fi-Based Positioning Systems](https://aimodels.fyi/papers/arxiv/surveilling-masses-wi-fi-based-positioning-systems). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper explores the privacy implications of Wi-Fi-based positioning and geolocation services, which can be used to track and surveil individuals on a mass scale.
- The authors investigate the prevalence and accuracy of these technologies, as well as their use by government agencies and private companies for surveillance and commercial purposes.
- The paper raises significant concerns about the erosion of individual privacy and the potential for abuse of these surveillance capabilities.
## Plain English Explanation
Wi-Fi-based positioning and geolocation services utilize the wireless signals emitted by our smartphones, laptops, and other Wi-Fi-enabled devices to determine our physical locations. While these technologies can be convenient for services like [mapping and navigation](https://aimodels.fyi/papers/arxiv/towards-optimal-beacon-placement-range-aided-localization), they also enable widespread and often covert surveillance of the general public.
The authors of this paper examine how these Wi-Fi-based tracking systems work, and how they are being deployed by governments, law enforcement, and commercial entities to monitor the movements and activities of large populations. They find that the accuracy and pervasiveness of these geolocation services are quite alarming, with the ability to pinpoint an individual's location within just a few meters.
This raises major privacy concerns, as it allows for the creation of detailed profiles on people's habits, relationships, and daily routines, all without their knowledge or consent. The paper highlights how this technology could be abused for purposes like [tracking protesters](https://aimodels.fyi/papers/arxiv/gps-ids-anomaly-based-gps-spoofing-attack), [monitoring employees](https://aimodels.fyi/papers/arxiv/over-air-runtime-wi-fi-mac-address), and even [surveilling entire cities](https://aimodels.fyi/papers/arxiv/reduce-to-macs-privacy-friendly-generic-probe).
Overall, the research presented in this paper suggests that the widespread use of Wi-Fi-based positioning systems poses a significant threat to individual privacy and civil liberties, and calls for greater regulation and oversight to protect the public from these [privacy-invasive technologies](https://aimodels.fyi/papers/arxiv/addressing-privacy-concerns-joint-communication-sensing-6g).
## Technical Explanation
The paper begins by providing an overview of Wi-Fi-based positioning and geolocation technologies, explaining how they leverage the wireless signals emitted by Wi-Fi-enabled devices to determine a user's physical location. This is accomplished through techniques like trilateration, which uses the signal strengths and time-of-arrival data from multiple access points to pinpoint a device's coordinates.
The authors then explore the accuracy and prevalence of these tracking systems, citing research that demonstrates their ability to locate individuals within just a few meters, even in densely populated urban environments. They also highlight how these technologies are being deployed by government agencies, law enforcement, and commercial entities for surveillance and commercial purposes, often without the knowledge or consent of the individuals being tracked.
The paper delves into specific case studies, such as the use of Wi-Fi geolocation to monitor protest movements and employees in the workplace. It also examines how these systems can be used to create detailed profiles of individuals' habits, relationships, and daily routines, posing a significant threat to personal privacy.
Throughout the technical explanation, the authors emphasize the scale and pervasiveness of these Wi-Fi-based tracking systems, noting that they have the potential to surveil entire populations on a mass scale. They argue that this represents a fundamental erosion of civil liberties and calls for robust regulatory frameworks to address these privacy concerns.
## Critical Analysis
The paper presents a compelling and well-researched analysis of the privacy implications of Wi-Fi-based positioning and geolocation services. The authors provide a comprehensive overview of the technical capabilities of these systems, as well as the diverse range of use cases, from law enforcement to commercial applications.
One key strength of the paper is its focus on the scale and pervasiveness of these tracking technologies, which are shown to have the potential to surveil entire populations. This highlights the urgent need for policymakers and the public to address the privacy concerns raised by the authors.
However, the paper could be strengthened by a more in-depth discussion of the potential countermeasures or mitigation strategies that could be employed to protect individual privacy. While the authors call for greater regulation and oversight, they could explore specific policy recommendations or technological solutions, such as [privacy-preserving localization techniques](https://aimodels.fyi/papers/arxiv/reduce-to-macs-privacy-friendly-generic-probe) or [anomaly detection systems](https://aimodels.fyi/papers/arxiv/gps-ids-anomaly-based-gps-spoofing-attack) to detect and prevent abuse of these surveillance capabilities.
Additionally, the paper could benefit from a more nuanced exploration of the trade-offs between the potential benefits and risks of Wi-Fi-based geolocation services. While the authors rightfully focus on the privacy concerns, there may be legitimate use cases, such as [emergency response](https://aimodels.fyi/papers/arxiv/towards-optimal-beacon-placement-range-aided-localization) or [wireless network optimization](https://aimodels.fyi/papers/arxiv/over-air-runtime-wi-fi-mac-address), that could justify the responsible deployment of these technologies under appropriate safeguards.
Overall, the paper presents a well-researched and compelling case for the need to address the privacy implications of Wi-Fi-based positioning and geolocation services. Its findings and recommendations warrant serious consideration by policymakers, technology companies, and the general public.
## Conclusion
This paper shines a light on the significant privacy threats posed by the widespread deployment of Wi-Fi-based positioning and geolocation services. The authors demonstrate how these technologies, which are often used for convenience and commercial purposes, can also be leveraged for widespread surveillance of the general public, without their knowledge or consent.
The research presented in this paper is a crucial contribution to the ongoing debate around the balance between technological progress and individual privacy. It highlights the urgent need for robust regulatory frameworks and oversight mechanisms to ensure that the deployment of these tracking systems does not come at the unacceptable cost of eroding civil liberties and personal freedoms.
As our society becomes increasingly reliant on interconnected digital technologies, it is essential that we carefully consider the privacy implications of such innovations and work to protect the fundamental rights and freedoms of all individuals. The findings of this paper provide an important foundation for this crucial discussion.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,731 | How to Find the Best Carpentry Services in Dubai? | ** Conduct Thorough Research ** Online Search: Start by using search engines and local... | 0 | 2024-05-28T13:23:10 | https://dev.to/jameel_itsaboutall_0196/how-to-find-the-best-carpentry-services-in-dubai-3nap |

**
## Conduct Thorough Research
**
**Online Search:** Start by using search engines and local business directories to find **[Carpentry Services in Dubai]( https://carpentry-services-dubai.com/)**. Social media platforms and forums can also provide useful recommendations and reviews.
**Word of Mouth:** Ask friends, family, and colleagues if they can recommend any reliable carpenters. Personal referrals often lead to trustworthy and proven services.
**
## Check Reviews and Ratings
**
**Online Reviews:** Look for reviews on platforms like Google, Yelp, and Facebook. Pay attention to the overall rating and read both positive and **
## negative comments to get a balanced view.
**
**Client Testimonials:** Visit the websites of carpentry services to read client testimonials. This can provide insight into their customer satisfaction and quality of work.
**
## Verify Credentials and Experience
**
**Licenses and Certifications:** Ensure that the carpentry service is licensed and certified to operate in Dubai.This ensures they comply with the necessary standards and regulations.
**Experience:** Consider the number of years the company or individual has been in business. Experienced carpenters are likely to have a better understanding of the craft and the ability to handle various projects.
**
## Examine Their Portfolio
**
**Previous Projects:** Request to see a portfolio of their past work. This will help you assess their craftsmanship, style, and ability to handle projects similar to yours.
**Quality of Work:** Look for attention to detail, finish quality, and consistency in their work. A good portfolio will showcase a variety of projects and highlight their expertise.
**
## Evaluate Services and Specializations
**
**Range of Services:** Ensure that the carpenter offers the specific services you need, such as custom **[Furniture Repair Dubai]( https://carpentry-services-dubai.com/carpenters-for-furniture/)**, kitchen cabinets, or office fittings.
**Specializations:** Some carpenters may specialize in certain areas like furniture making, while others may excel in structural carpentry. Choose a carpenter whose specialization aligns with your project needs.
## **Obtain Multiple Quotes**
**Detailed Quotes:** Request detailed quotes from multiple carpentry services to compare prices. Ensure the quotes include all potential costs, such as materials, labor, and any additional fees.
**Value for Money:** Avoid selecting solely based on the lowest price.Consider the quality of materials, workmanship, and the reputation of the service provider.
**
## Assess Customer Service
**
**Communication:** Evaluate how responsive and communicative the service provider is. Good communication is crucial for a smooth project execution.
**Professionalism:** Observe their professionalism during interactions. Punctuality, clarity in communication, and a respectful demeanor are indicators of a reliable service provider.
**
## Check Warranty and After-Sales Service
**
**Warranty:** Ask if the carpenter offers a warranty for their work. A warranty reflects confidence in their craftsmanship.
**After-Sales Support:** Inquire about after-sales support in case you encounter any issues after the project is completed.
**
### Conclusion
**
Finding the best carpentry services in Dubai involves thorough research, careful evaluation of potential candidates, and clear communication of your needs and expectations. By following these steps, you can ensure that you hire a competent and reliable carpenter who can deliver high-quality work. Prioritize quality and reliability over cost, as good carpentry work can significantly enhance the aesthetics and functionality of your space.
**
#### Frequently Asked Questions
**
### How much does carpentry work typically cost in Dubai?
**
The cost varies widely based on the complexity of the project, materials used, and the reputation of the carpenter. Detailed quotes from multiple providers can give you a clearer estimate.
**
### What should I look for in a carpenter’s portfolio?
**
Look for diversity in projects, quality of craftsmanship, and attention to detail. The portfolio should demonstrate their ability to handle various types of carpentry work.
**
### How long does it take to complete a typical carpentry project?
**
The duration depends on the size and complexity of the project. Simple jobs might take a few days, while larger projects can take several weeks. Discuss timelines with your carpenter before starting the project.
**
### Can I negotiate the price with a carpenter in Dubai?
**
Yes, you can negotiate. However, ensure that the negotiation doesn’t compromise the quality of materials or workmanship. Focus on getting value for money rather than just the lowest price.
**
### What types of wood are commonly used in Dubai for carpentry?
Common types of wood include teak, oak, pine, and mahogany. The choice of wood depends on the project requirements, budget, and desired finish.
| jameel_itsaboutall_0196 | |
1,867,729 | Lessons from the Trenches on Reproducible Evaluation of Language Models | Lessons from the Trenches on Reproducible Evaluation of Language Models | 0 | 2024-05-28T13:22:38 | https://aimodels.fyi/papers/arxiv/lessons-from-trenches-reproducible-evaluation-language-models | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Lessons from the Trenches on Reproducible Evaluation of Language Models](https://aimodels.fyi/papers/arxiv/lessons-from-trenches-reproducible-evaluation-language-models). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- Evaluating large language models is an ongoing challenge in natural language processing (NLP)
- Researchers and engineers face issues like the sensitivity of models to evaluation setup, difficulty comparing methods, and lack of reproducibility and transparency
- This paper provides guidance and lessons based on 3 years of experience evaluating large language models
## Plain English Explanation
Evaluating how well language models, such as those used in chat assistants and language generation, perform is an important but difficult problem in the field of NLP. Researchers and engineers who work on these models face several key challenges:
1. The performance of the models can be very sensitive to the specific setup used for evaluation, making it hard to compare results across different studies.
2. It's difficult to properly compare the effectiveness of different evaluation [methods](https://aimodels.fyi/papers/arxiv/telm-test-evaluation-language-models) and determine which one is best.
3. There are often issues with reproducibility, where it's hard for other researchers to replicate the exact same evaluation process and get the same results.
4. The evaluation process often lacks transparency, making it unclear exactly how the models were tested and assessed.
The authors of this paper have 3 years of experience evaluating large language models, and they provide guidance on how to address these challenges. They explain best practices for designing and carrying out reliable, reproducible evaluations. They also introduce an open-source [library](https://aimodels.fyi/papers/arxiv/freeeval-modular-framework-trustworthy-efficient-evaluation-large) called the Language Model Evaluation Harness, which aims to make language model evaluation more independent, reproducible, and extensible.
## Technical Explanation
The paper first provides an overview of the common challenges faced in evaluating large language models. These include:
- **Sensitivity to Evaluation Setup**: The performance of models can vary significantly depending on the specific details of the evaluation process, making it hard to compare results across studies.
- **Difficulty of Proper Comparisons**: There is a lack of consensus on the best evaluation [methods](https://aimodels.fyi/papers/arxiv/metal-towards-multilingual-meta-evaluation) to use, and it's challenging to determine which approach is most appropriate.
- **Reproducibility and Transparency Issues**: It is often difficult for other researchers to reproduce the exact same evaluation process and get the same results, and the evaluation procedures may not be fully transparent.
To address these issues, the authors outline a set of best practices for conducting language model evaluations:
1. **Carefully Design the Evaluation Process**: Researchers should thoughtfully consider the choice of tasks, datasets, and metrics used to assess model performance.
2. **Ensure Reproducibility**: Detailed documentation of the evaluation setup and procedures is crucial, as is making the code and data publicly available.
3. **Promote Transparency**: Researchers should strive to clearly explain their evaluation methodology and rationale.
The paper then introduces the [Language Model Evaluation Harness (lm-eval)](https://aimodels.fyi/papers/arxiv/freeeval-modular-framework-trustworthy-efficient-evaluation-large), an open-source library that aims to address the methodological concerns outlined earlier. The library provides a modular and extensible framework for independently and reproducibly evaluating language models. It includes a range of [benchmark tasks](https://aimodels.fyi/papers/arxiv/repeval-effective-text-evaluation-llm-representation) and metrics, as well as utilities for managing experiments and reporting results.
The authors present several case studies demonstrating how the lm-eval library has been used to alleviate the methodological issues in language model evaluation, including [assessing the [risk](https://aimodels.fyi/papers/arxiv/risk-or-chance-large-language-models-reproducibility) of low reproducibility and conducting [multilingual evaluations](https://aimodels.fyi/papers/arxiv/metal-towards-multilingual-meta-evaluation).
## Critical Analysis
The paper provides a thorough and well-reasoned discussion of the challenges in evaluating large language models, and the proposed best practices and the lm-eval library seem like a step in the right direction. However, some potential limitations and areas for further research are worth considering:
1. The authors acknowledge that the lm-eval library is not a complete solution, and that there may still be issues with the choice of tasks and metrics included in the library. Continued research and community input will be necessary to refine and expand the library.
2. The paper does not address the potential biases and ethical concerns that may arise from language model evaluations, such as the perpetuation of harmful stereotypes or the use of models for sensitive applications like content moderation. These are important considerations that should be explored in future work.
3. While the case studies demonstrate the utility of the lm-eval library, more comprehensive evaluations across a wider range of language models and applications would be helpful to further validate the approach.
Overall, this paper makes a valuable contribution to the ongoing effort to improve the evaluation of large language models, and the lm-eval library appears to be a promising tool for enabling more reliable, reproducible, and transparent assessments.
## Conclusion
This paper provides guidance and lessons learned from 3 years of experience in evaluating large language models, a critical but challenging task in the field of natural language processing. The authors outline common issues faced by researchers and engineers, such as the sensitivity of models to evaluation setup, difficulty of proper comparisons, and lack of reproducibility and transparency.
To address these challenges, the paper presents best practices for designing and carrying out language model evaluations, as well as the introduction of the open-source [Language Model Evaluation Harness (lm-eval)](https://aimodels.fyi/papers/arxiv/freeeval-modular-framework-trustworthy-efficient-evaluation-large) library. This library aims to enable more independent, reproducible, and extensible evaluation of language models, helping to advance the state of the art in this important area of NLP research.
While the paper and the lm-eval library represent important steps forward, the authors acknowledge that continued work is needed to refine the evaluation process and address emerging concerns, such as the potential for biases and ethical issues. Nonetheless, this research provides valuable guidance and a solid foundation for improving the way we assess the capabilities and limitations of large language models.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,728 | Integrating Social Login Seamlessly with FAB Builder: A Comprehensive Guide | In today's digital landscape, user convenience and data security are paramount concerns for... | 0 | 2024-05-28T13:22:38 | https://dev.to/fab_builder/integrating-social-login-seamlessly-with-fab-builder-a-comprehensive-guide-2omf | webdev, lowcode, programming, development | In today's digital landscape, user convenience and data security are paramount concerns for developers. Social login functionality addresses these needs by allowing users to sign in to applications using their existing social media credentials, streamlining the authentication process. **[FAB Builder is a powerful tool](https://www.fabbuilder.com/)** that simplifies the integration of social login features into web and mobile applications. **In this comprehensive guide, we'll explore how to leverage FAB Builder to seamlessly incorporate social login into your project.** With intuitive interfaces and robust capabilities, FAB Builder empowers developers to enhance user experience while maintaining data security.
## Understanding the Benefits of Social Login
Social login has revolutionized user interactions on the web by offering several benefits to both users and developers:
- **Streamlined User Experience:** Users can sign in to applications using their preferred social media accounts, eliminating the need to create and manage separate login credentials for each platform.
- **Enhanced Conversion Rates:** The simplified login process reduces user friction, leading to higher conversion rates during the onboarding process.
- **Data Enrichment:** Social login provides access to users' profile information and social connections, enabling personalized experiences and targeted marketing efforts.
## Introduction to FAB Builder
**FAB Builder is an innovative code generator platform that redefines the way applications are built. With a focus on simplicity and efficiency, FAB Builder empowers users to effortlessly create front-end, back-end, and mobile apps without the need for extensive coding knowledge.**
FAB Builder simplifies the integration of social login functionality into applications with its user-friendly interface and extensive provider support:
**Code Example:**
```
// Example of initializing FAB Builder SDK
FAB.init({
apiKey: 'YOUR_API_KEY',
projectID: 'YOUR_PROJECT_ID',
providers: ['google', 'facebook'], // Specify desired social login providers
onSuccess: function(user) {
// Handle successful authentication
console.log('User authenticated:', user);
},
onError: function(error) {
// Handle authentication errors
console.error('Authentication error:', error);
}
});
```
## Key features of FAB Builder include:
- **User-Friendly Interface:** The platform offers an intuitive panel for configuring social login providers, adjusting security settings, and generating code snippets effortlessly.
- **Extensive Provider Support:** FAB Builder seamlessly integrates with popular social login providers such as Facebook, Google, Twitter, and more, ensuring compatibility across various platforms.
- **Smooth Integration:** FAB Builder generates clean, optimized code snippets that can be easily incorporated into any project, irrespective of the underlying technology stack or framework.
## Getting Started with FAB Builder
Begin the integration process by following these simple steps:
- **Create an Account:** Sign up for a free account on the FAB Builder website to access its features and resources.
- **Start a New Project:** Initiate a new project within the FAB Builder interface and specify the target platform (web or mobile).
- **Configure Social Login Services:** Select the desired social login providers and provide the necessary API keys and return URLs.
- **Customize Authentication Settings:** Tailor login settings, such as user information fields and permissions, to align with your project requirements.
- **Generate Code Snippets:** Upon completing setup, FAB Builder automatically generates optimized code snippets tailored to your project specifications.
## Integrating Social Login into Your Project
Incorporate social login seamlessly into your application using the generated code snippets:
**Code Example:**
```
<!-- Example of a login button triggering social login with FAB Builder -->
<button onclick="FAB.login()">Login with Social</button>
// Example of handling successful authentication event
FAB.on('login', function(user) {
// Retrieve user data and access tokens
var userData = user.profile;
var accessToken = user.token;
// Perform actions such as updating UI or making API calls
});
// Example of implementing logout functionality
function logout() {
// Perform logout action
FAB.logout();
}
```
## Testing and Refinement
Thorough testing is essential to ensure the seamless functionality of the social login feature across various platforms and devices. Conduct comprehensive testing under different scenarios, including login, account linking, and error handling. Solicit feedback from real users to identify any usability issues or pain points. Once testing is complete, verify that the social login system is robust, secure, and delivers a seamless user experience. Monitor identity data and user interactions to evaluate the impact of social login on your app's success.
## Enhancements and Customization Options with FAB Builder
Take your social login implementation to the next level with advanced features and customization options:
- **Single Sign-On (SSO):** Simplify login across multiple sites and services with FAB Builder's SSO feature.
- **Updated User Profiles:** Sync user profile data from social login providers to ensure the accuracy and currency of user records within your application.
- **Multi-Factor Authentication (MFA):** Enhance account security by implementing additional authentication measures such as physical tokens or SMS verification.
- **Custom Branding and Styling:** Customize the appearance of the social login interface to align with your app's branding and design aesthetic.
## Best Practices for Security and Data Privacy
Adhere to best practices and address security concerns to safeguard user data and maintain trust:
- **Obtain User Consent:** Clearly communicate the data access rights and privacy policies associated with social login, ensuring users provide informed consent.
- **Secure Data Transmission:** Encrypt data transmission between the user's device and your application servers using HTTPS to mitigate the risk of eavesdropping or man-in-the-middle attacks.
- **Minimize Data Collection:** Limit the collection of user data to what is strictly necessary for authentication and personalization purposes, reducing the potential for data breaches or privacy violations.
- **Regular Security Audits:** Conduct periodic security audits and sensitivity reviews to identify and address potential vulnerabilities in your application's login process.
## Deploying Your Social Login-Enabled Project
Deploy your application and make it accessible to users with the following steps:
- **Choose a Hosting Provider:** Select a hosting provider capable of accommodating your project's growth, speed, and reliability requirements.
- **Configure Deployment Environment:** Set up your deployment environment to align with your project's technologies and platforms, ensuring all necessary environment variables, API keys, and social login provider details are configured.
- **Package Your App:** Compile and package your application code using build tools and package managers, optimizing files, minifying JavaScript, and enabling caching to enhance performance and reduce load times.
-
**Test Deployment:** Verify the functionality of the social login feature in a production environment before launching. Conduct thorough testing across various devices, browsers, and network conditions to identify and address any performance or compatibility issues.
-
**Monitor Performance:** Utilize monitoring tools and analytics platforms to monitor the performance of your deployed application, tracking metrics such as error rates, response times, and server load. Continuously optimize performance to ensure a positive user experience.
## Strategies for Scaling and Improvement
Implement scaling and improvement techniques to ensure your application continues to run smoothly as it grows:
- **Horizontal Scaling:** Increase the number of instances or nodes in your application to handle growing traffic.
- **Caching:** Implement caching to store frequently accessed data and reduce the number of expensive database queries or API calls.
- **Content Delivery Networks (CDNs):** Leverage CDNs to deliver static assets from edge locations closer to users.
- **Database Optimization:** Optimize database queries, indexes, and data models to improve query performance and reduce database load.
## Leveraging Social Login for User Engagement and Growth
Maximize the benefits of social login with the following strategies:
- **Personalized User Experience:** Utilize social login data to tailor the user experience based on users' interests, preferences, and social connections.
- **Social Sharing and Virality:** Enable social sharing features within your app to encourage users to share their experiences and achievements on social media platforms.
- **Social Graph Integration:** Leverage social login data to access users' social networks and relationships, enabling features such as friend invites and social discovery.
- **Gamification and Rewards:** Incorporate gamification elements and reward systems to incentivize social interactions and user participation.
## Conclusion
**Integrating social login with [FAB Builder](https://www.fabbuilder.com/) offers a powerful solution for enhancing user experience and driving engagement.** By following the steps outlined in this guide and leveraging the capabilities of FAB Builder, you can seamlessly incorporate social login into your project and unlock its full potential. Embrace social login today to revolutionize user access and connectivity within your application. | fabbuilder |
1,867,727 | My First Billion (of Rows) in DuckDB | By João Pedro | When you want to process 450Gb/1billion rows of data we think in all the directions like PySpark,... | 0 | 2024-05-28T13:22:18 | https://dev.to/tankala/my-first-billion-of-rows-in-duckdb-by-joao-pedro-4m9p | dataengineering, python, duckdb, bigdata | When you want to process 450Gb/1billion rows of data we think in all the directions like PySpark, Bigquery and etc. If someone says it can be processed with one Python package(DuckDB) without using/installing any fancy tools can you believe it? That’s what João Pedro did and explained in this article.
{% embed https://towardsdatascience.com/my-first-billion-of-rows-in-duckdb-11873e5edbb5 %} | tankala |
1,867,726 | XMoE: Sparse Models with Fine-grained and Adaptive Expert Selection | XMoE: Sparse Models with Fine-grained and Adaptive Expert Selection | 0 | 2024-05-28T13:22:04 | https://aimodels.fyi/papers/arxiv/xmoe-sparse-models-fine-grained-adaptive-expert | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [XMoE: Sparse Models with Fine-grained and Adaptive Expert Selection](https://aimodels.fyi/papers/arxiv/xmoe-sparse-models-fine-grained-adaptive-expert). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper introduces a novel approach to enhancing the efficiency of sparse machine learning models, called "Sparser Selection".
- The key idea is to train a sparse model with an additional sparsity-inducing regularization term, which encourages even sparser selection of model parameters during inference.
- This technique can lead to significant improvements in inference speed and memory usage, without compromising model accuracy.
## Plain English Explanation
Machine learning models are often designed to be "sparse", meaning they only use a small subset of the available model parameters to make predictions. This sparsity can lead to faster and more efficient inference, which is critical for many real-world applications.
However, the process of training these sparse models can be complex, often requiring careful tuning of various hyperparameters. The authors of this paper propose a new method, called "Sparser Selection", that makes the training process more efficient and effective.
The core idea is to add an additional regularization term to the training objective that encourages the model to become even sparser during the training process. This means that the final model will use an even smaller number of parameters to make predictions, leading to faster and more memory-efficient inference.
The authors demonstrate the effectiveness of their approach on several benchmark tasks, showing that "Sparser Selection" can achieve significant improvements in inference speed and memory usage, while maintaining the same level of accuracy as traditional sparse models. This could have important implications for the deployment of machine learning models in resource-constrained settings, such as [edge devices](https://aimodels.fyi/papers/arxiv/dynamic-mixture-experts-auto-tuning-approach-efficient) or [mobile applications](https://aimodels.fyi/papers/arxiv/seer-moe-sparse-expert-efficiency-through-regularization).
## Technical Explanation
The authors start by providing a background on the problem of sparse model training and inference, highlighting the importance of balancing model complexity, accuracy, and computational efficiency. They discuss prior approaches, such as [dense training with sparse inference](https://aimodels.fyi/papers/arxiv/dense-training-sparse-inference-rethinking-training-mixture) and [mixture-of-experts models](https://aimodels.fyi/papers/arxiv/multi-head-mixture-experts), which have aimed to address this challenge.
The key contribution of this paper is the "Sparser Selection" method, which introduces an additional sparsity-inducing regularization term to the training objective. This term encourages the model to learn a particularly sparse set of parameters, resulting in a more efficient inference process.
The authors evaluate their approach on several benchmark tasks, including language modeling and image classification. They compare the performance of "Sparser Selection" to traditional sparse modeling techniques, as well as dense models with sparse inference. The results show that their method can achieve significant improvements in inference speed and memory usage, while maintaining comparable accuracy to the baseline models.
## Critical Analysis
The authors acknowledge some limitations of their approach, such as the potential for the additional regularization term to negatively impact model accuracy in certain cases. They also note that the optimal balance between sparsity and accuracy may depend on the specific application and hardware constraints.
One potential area for further research could be exploring the interaction between "Sparser Selection" and other sparse modeling techniques, such as [dynamic mixture-of-experts models](https://aimodels.fyi/papers/arxiv/dynamic-mixture-experts-auto-tuning-approach-efficient) or [regularization-based approaches](https://aimodels.fyi/papers/arxiv/seer-moe-sparse-expert-efficiency-through-regularization). It would also be interesting to see how the method performs on a wider range of tasks and datasets, particularly in the context of real-world deployment scenarios.
## Conclusion
Overall, the "Sparser Selection" method presented in this paper offers a promising approach to enhancing the efficiency of sparse machine learning models. By introducing an additional sparsity-inducing regularization term during training, the authors demonstrate the ability to achieve significant improvements in inference speed and memory usage, without compromising model accuracy.
This work has the potential to contribute to the broader efforts in the field of [efficient machine learning](https://aimodels.fyi/papers/arxiv/dynamic-mixture-experts-auto-tuning-approach-efficient), which aims to develop models that can be deployed effectively in resource-constrained environments. The insights and techniques developed in this paper could be particularly valuable for applications that require high-performance, low-latency, and energy-efficient machine learning, such as [edge computing](https://aimodels.fyi/papers/arxiv/seer-moe-sparse-expert-efficiency-through-regularization) and [mobile devices](https://aimodels.fyi/papers/arxiv/multi-head-mixture-experts).
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,725 | Color Psychology In Web Design | In the vast and competitive world of web design, creating a visually appealing and engaging website... | 0 | 2024-05-28T13:22:01 | https://dev.to/amolsasane_/color-psychology-in-web-design-4cmf | webdev, css, webdesign, psychology | **In** the vast and competitive world of web design, creating a visually appealing and engaging website is crucial to attracting and retaining users. While various elements contribute to the overall design, the strategic use of colors plays a significant role in shaping the user experience. Understanding the psychology of color and its impact on human emotions and behavior can empower web designers to make informed choices that resonate with their target audience. In this blog, we delve into the fascinating world of color psychology in web design and explore how specific colors can evoke different feelings, thoughts, and actions.
---
## The Basics of Color Psychology:

In this blog, we'll cover the fundamental principles of color psychology, explaining how colors are perceived by the human brain and the emotions they can trigger. This will set the groundwork for the subsequent sections where we'll explore the application of color psychology in web design.
## Choosing the Right Color Palette:

It is important to select an appropriate color palette for a website. There are various color schemes, such as monochromatic, complementary, analogous, and triadicres. They have different effects on user experience. Additionally, the significance of cultural differences and certain colors can be interpreted differently in various parts of the world.
## Using Colors to Evoke Emotions:
- **Red** : Evokes energy, urgency, and passion.
- **Blue** : Symbolizes trust, tranquility, and professionalism.
- **Yellow** : Radiates optimism, happiness, and warmth.
- **Green** : Represents nature, growth, and harmony.
- **Purple** : Signifies creativity, luxury, and mystery.
- **Orange** : Conveys enthusiasm, creativity, and affordability.
- **Black** : Implies sophistication, power, and elegance.
- **White** : Symbolizes purity, simplicity, and cleanliness.
## Applying Color Psychology to Different Industries:
Examples of how color psychology can be applied to web design in various industries are like for instance, using blue tones can be advantageous for financial institutions and vibrant and energetic colors might suit websites for entertainment and sports industries.
## Avoiding Color Pitfalls:
Even though color psychology can be a powerful tool, it can also be misused if not applied thoughtfully while using colors in web design. For instance, using too many conflicting colors, clashing with branding guidelines, or inadvertently triggering negative emotions.
## Conclusion:
So, we have gone through the color psychology in web design by understanding how colors can influence user behavior and emotional responses, you can create visually stunning and emotionally compelling websites that leave a lasting impact on your visitors.
For more such blogs [click here](https://amolsasane.netlify.app/blogs.html)
| amolsasane_ |
1,867,724 | Not All Language Model Features Are Linear | Not All Language Model Features Are Linear | 0 | 2024-05-28T13:21:29 | https://aimodels.fyi/papers/arxiv/not-all-language-model-features-are-linear | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Not All Language Model Features Are Linear](https://aimodels.fyi/papers/arxiv/not-all-language-model-features-are-linear). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper proposes that language models may use multi-dimensional representations, rather than just one-dimensional "features," to perform computations.
- The researchers develop a method to automatically find and analyze these multi-dimensional representations in large language models like GPT-2 and Mistral 7B.
- They identify specific examples of these multi-dimensional features, like circular representations of days of the week and months of the year, and show how the models use them to solve tasks involving modular arithmetic.
- The paper provides evidence that these circular features are fundamental to the models' computations on these tasks.
## Plain English Explanation
The [researchers behind this paper](https://aimodels.fyi/papers/arxiv/language-models-implement-simple-word2vec-style-vector) explored whether language models might use more complex, multi-dimensional representations of concepts, rather than just simple one-dimensional "features." They developed a way to automatically identify these multi-dimensional representations in large language models like GPT-2 and Mistral 7B.
One of the key findings was the discovery of circular representations for things like days of the week and months of the year. These circular features allowed the models to efficiently perform computations involving modular arithmetic, like figuring out what day of the week a date falls on. The researchers showed that these circular features were fundamental to the models' ability to solve these types of tasks, rather than just being a byproduct.
This suggests that language models may implement more sophisticated "cognitive-like" representations and computations, rather than just simple one-dimensional feature manipulation as proposed by the [linear representation hypothesis](https://aimodels.fyi/papers/arxiv/evaluating-spatial-understanding-large-language-models). It also raises interesting questions about the [inherent biases and limitations](https://aimodels.fyi/papers/arxiv/learned-feature-representations-are-biased-by-complexity) of how language models represent and reason about the world.
## Technical Explanation
The core idea of this paper is to challenge the [linear representation hypothesis](https://aimodels.fyi/papers/arxiv/language-models-implement-simple-word2vec-style-vector), which proposes that language models perform computations by manipulating one-dimensional representations of concepts (called "features"). Instead, the researchers explore whether some language model representations may be inherently multi-dimensional.
To do this, they first develop a rigorous definition of "irreducible" multi-dimensional features - ones that cannot be decomposed into either independent or non-co-occurring lower-dimensional features. Armed with this definition, they design a scalable method using sparse autoencoders to automatically identify multi-dimensional features in large language models like GPT-2 and Mistral 7B.
Using this approach, the researchers identify some striking examples of interpretable multi-dimensional features, such as circular representations of days of the week and months of the year. They then show how these exact circular features are used by the models to solve computational problems involving modular arithmetic related to days and months.
Finally, the paper provides evidence that these circular features are indeed the fundamental unit of computation for these tasks. They conduct intervention experiments on Mistral 7B and Llama 3 8B that demonstrate the importance of these circular representations. Additionally, they are able to further decompose the hidden states for these tasks into interpretable components that reveal more instances of these circular features.
## Critical Analysis
The paper makes a compelling case that at least some language models employ multi-dimensional representations that go beyond the simple one-dimensional "features" proposed by the linear representation hypothesis. The discovery of the interpretable circular features for days and months, and the evidence that these are central to the models' computations, is a significant finding.
However, the paper does not address the [broader limitations and biases](https://aimodels.fyi/papers/arxiv/learned-feature-representations-are-biased-by-complexity) inherent in how language models represent and reason about the world. While the multi-dimensional features may be more sophisticated, they may still [suffer from systematic biases and blind spots](https://aimodels.fyi/papers/arxiv/investigating-symbolic-capabilities-large-language-models) in their understanding.
Additionally, the paper focuses on a relatively narrow set of tasks and model architectures. It remains to be seen whether these findings generalize to a wider range of language models and applications. Further research is needed to fully [understand the symbolic and reasoning capabilities](https://aimodels.fyi/papers/arxiv/philosophical-introduction-to-language-models-part-ii) of these multi-dimensional representations.
## Conclusion
This paper challenges the prevailing view that language models rely solely on one-dimensional feature representations. Instead, it provides compelling evidence that at least some models employ more sophisticated, multi-dimensional representations to perform computations. The discovery of interpretable circular features for concepts like days and months, and their central role in solving relevant tasks, is a significant advancement in our [understanding of language model representations and capabilities](https://aimodels.fyi/papers/arxiv/investigating-symbolic-capabilities-large-language-models).
While this research raises interesting questions about the cognitive-like nature of language model representations, it also highlights the need for continued [critical analysis and exploration](https://aimodels.fyi/papers/arxiv/philosophical-introduction-to-language-models-part-ii) of their limitations and biases. Ultimately, this work contributes to our evolving [understanding of how large language models work](https://aimodels.fyi/papers/arxiv/learned-feature-representations-are-biased-by-complexity) and their potential implications for artificial intelligence.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,723 | Many-Shot In-Context Learning | Many-Shot In-Context Learning | 0 | 2024-05-28T13:20:55 | https://aimodels.fyi/papers/arxiv/many-shot-context-learning | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Many-Shot In-Context Learning](https://aimodels.fyi/papers/arxiv/many-shot-context-learning). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper explores "many-shot in-context learning," a novel approach to scaling up the performance of language models on a wide range of tasks.
- The authors propose a framework that combines large pre-trained foundation models with efficient fine-tuning techniques, enabling models to quickly adapt to new tasks using only a few examples.
- The paper compares this approach to existing few-shot and zero-shot learning methods, and demonstrates its effectiveness on a diverse set of NLP and multimodal tasks.
## Plain English Explanation
The paper discusses a new way to train large language models, called "many-shot in-context learning." The key idea is to start with a very capable, pre-trained foundation model and then quickly adapt it to new tasks using only a few example inputs.
Traditionally, training language models from scratch on a new task can be very resource-intensive and time-consuming. The [many-shot in-context learning](https://aimodels.fyi/papers/arxiv/many-shot-context-learning-multimodal-foundation-models) approach aims to make this process much more efficient.
The researchers show that by combining a powerful, general-purpose foundation model with smart fine-tuning techniques, the model can quickly adapt to new tasks using just a handful of example inputs. This is in contrast to more common "few-shot" or "zero-shot" learning approaches, which require even less training data but may not perform as well.
Overall, this work advances the state-of-the-art in [context learning](https://aimodels.fyi/papers/arxiv/implicit-context-learning) and [few-shot adaptation](https://aimodels.fyi/papers/arxiv/llms-are-few-shot-context-low-resource), potentially enabling language models to be more widely deployed in real-world applications that require quick adaptation to new tasks and data.
## Technical Explanation
The core contribution of this paper is a framework for "many-shot in-context learning" that allows language models to efficiently adapt to new tasks using a small number of examples.
The authors start with a large, pre-trained "foundation model" - a powerful general-purpose model that has been trained on a massive amount of text data. They then propose several techniques to fine-tune this foundation model on new tasks:
1. **In-context learning**: The model is presented with a few (e.g. 16) example inputs and outputs for the new task, which it uses to quickly adapt its behavior.
2. **Prompt engineering**: The researchers carefully design the prompts used to present the task examples to the model, in order to maximize the efficiency of the in-context learning process.
3. **Multitask fine-tuning**: The model is fine-tuned on multiple tasks simultaneously, allowing it to learn general patterns that transfer well to new tasks.
The paper evaluates this framework on a diverse set of NLP and multimodal tasks, and shows that it significantly outperforms traditional few-shot and zero-shot learning approaches. For example, on the [GLUE benchmark](https://aimodels.fyi/papers/arxiv/context-learning-or-how-i-learned-to), the many-shot in-context model achieves over 80% accuracy using just 16 examples per task - a level of performance that would typically require orders of magnitude more training data.
## Critical Analysis
The paper makes a strong case for the effectiveness of many-shot in-context learning, but also acknowledges several important caveats and limitations:
1. **Task Generalization**: While the model performs well on the evaluated tasks, the authors note that its ability to generalize to completely novel tasks is still an open question that requires further investigation.
2. **Prompt Engineering**: The success of the approach is heavily dependent on the quality of the prompts used to present the task examples. Developing systematic prompt engineering techniques remains an active area of research.
3. **Computational Efficiency**: Fine-tuning a large foundation model, even with just a few examples, can still be computationally expensive. Improving the efficiency of this process is an important direction for future work.
4. **Multimodal Capabilities**: The paper focuses primarily on language tasks, but discusses extending the framework to multimodal [context learning](https://aimodels.fyi/papers/arxiv/context-learning-generalizes-but-not-always-robustly). Further research is needed to fully validate the approach's multimodal capabilities.
Overall, this paper represents an important step forward in developing efficient and scalable methods for adapting large language models to new tasks and domains. However, there are still many open challenges to be addressed in order to realize the full potential of this approach.
## Conclusion
The "many-shot in-context learning" framework proposed in this paper offers a promising new direction for scaling up the performance of large language models. By combining powerful pre-trained foundation models with efficient fine-tuning techniques, the approach demonstrates the ability to quickly adapt to new tasks using only a small number of examples.
This work advances the state-of-the-art in [few-shot and zero-shot learning](https://aimodels.fyi/papers/arxiv/llms-are-few-shot-context-low-resource), potentially enabling language models to be more widely deployed in real-world applications that require rapid adaptation to new data and tasks. However, the authors also identify several important limitations and areas for future research, such as improving task generalization, prompt engineering, computational efficiency, and multimodal capabilities.
Ultimately, this paper contributes a novel and impactful technique that brings us one step closer to building truly versatile and adaptive language models that can thrive in dynamic, real-world environments.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,714 | Let's Build an E-Commerce Store with Nuxt.js | Check this post in my web notes! Following the success of my previous series, 'Building a Simple... | 27,540 | 2024-05-28T13:20:27 | https://webcraft-notes.com/blog/lets-build-an-ecommerce-store-with-nuxtjs | nuxt, vue, javascript, tutorial |
> Check [this post](https://webcraft-notes.com/blog/lets-build-an-ecommerce-store-with-nuxtjs) in [my web notes](https://webcraft-notes.com/)!
Following the success of my previous series, '[Building a Simple CRM with Vue](https://webcraft-notes.com/series/building-simple-crm-with-vue)' I'm energized by the enthusiastic response and eager to embark on a fresh journey with all of you. In this new series, we'll delve into the realm of Nuxt.js to craft a dynamic e-commerce platform. My goal is to provide an all-encompassing guide, catering both to newcomers looking to grasp the fundamentals of Nuxt development and seasoned developers seeking valuable insights and techniques. In this opening installment, we're setting the stage for our e-commerce platform endeavor. We'll kick things off by carefully selecting our app design, and technology stack, mapping out the project structure, and tackling key preparatory tasks. Whether you're aiming to bolster your portfolio or sharpen your development prowess, I'm confident that this series will serve as a rich resource for growth and learning. Here is [the result](https://trybuy-store.vercel.app/) of what we will be building in this series. So, without further ado, let's outline our agenda for today's article:
1. Clarifying with Project Structure and Functionality
2. Choosing the Perfect Project Design
3. Deciding on the Ideal Technology Stack (Nuxt.js, Pinia)
Now that we've outlined our agenda for today's article, let's dive straight into the exciting world of e-commerce platform development. We're at the threshold of a thrilling journey, where every step we take will contribute to the realization of our ambitious project.
## 1. Clarifying with Project Structure and Functionality
When starting a new project, it's essential to clarify its intended functionality. In simpler terms, what tasks should our application be able to perform? In our case, it should allow us to generate pages with its functionality like landing, categories, product details, cart, wishlist, etc. Let's talk about each of these parts separately a little bit:
- **Landing page** - serves as the virtual storefront of our e-commerce platform, offering users their initial glimpse into the world of our brand and products. It is the first point of contact for visitors and plays a pivotal role in making a lasting impression. Designed to captivate and engage users, the landing page showcases key features, promotions, and products in a visually appealing and compelling manner.
- **The categories page** serves as the organized gateway to our e-commerce platform's product catalog, allowing users to browse and explore products based on specific categories or classifications. It provides a structured navigation system that facilitates efficient product discovery and enhances the user shopping experience.
- **The product details** page serves as the focal point for users to gain comprehensive information about a specific product offered on our e-commerce platform. It provides a detailed overview of the product's features, specifications, pricing, and availability, enabling users to make informed purchasing decisions.
- **The cart page** serves as the virtual shopping basket where users can review, modify, and finalize their selected items before proceeding to checkout. It plays a crucial role in the e-commerce user journey, providing a centralized location for managing shopping selections and facilitating the transaction process.
Looks like we listed all major pages and functionality that we need to implement. And much work needs to be done so let's move to the next step.
## 2. Choosing the Perfect Project Design
It's crucial to select an exceptional design that resonates with our brand identity and captures the attention of our audience. The design we choose will not only shape the visual appeal of our platform but also influence the user experience, encouraging repeat visits and fostering customer loyalty. By prioritizing a captivating and user-friendly design, we aim to create a memorable and engaging online shopping environment that leaves a lasting impression on our users.
To tell you the truth I'm not a good designer at all, as people say I'm a "one eye blind" drawer ;). That is why I prefer using template design services like [HTMLrev](https://htmlrev.com/). That kind of HTML/CSS template allows you to transform the design into a Vue, React, or Nuxt.js component template easily. It's a life rescue pillow sometimes for me. In today's case you can use whatever design you like, as for me I found a simple but pretty template that I would like to use in future project.
It has space for implementing all the functionality that we were talking about before.
Okay, let's move on and talk about the technologies we are planning to use.
## 3. Deciding on the Ideal Technology Stack (Nuxt.js, Pinia)
After careful consideration, I've made the strategic decision to use [Nuxt.js](https://nuxt.com/) as the primary development framework for our e-commerce project. Nuxt.js offers an amazing set of features and benefits that align perfectly with our project requirements and objectives. Its powerful capabilities in server-side rendering, code organization, and simple Vue.js integration make it an ideal choice for building dynamic and scalable web applications.
In addition to Nuxt.js, I've also opted to incorporate [Pinia](https://pinia.vuejs.org/) as our state management solution. Pinia provides a lightweight yet powerful state management pattern for Vue.js applications, offering simplicity, flexibility, and excellent performance. By harnessing the capabilities of Pinia, we can efficiently manage our application's data flow and ensure a smooth and responsive user experience.
Together, Nuxt.js and Pinia form a formidable technology stack that empowers us to bring our e-commerce vision to life.
Also, we should not forget about the backend part, for the developing process, we will use "[json-server](https://www.npmjs.com/package/json-server)" which will help to imitate the server job. It would be amazing to build a backend part by ourselves with Node.js for example but it sounds more like the title for another article series.
Okay, so many words and descriptions, but we need to mention all that stuff so that we can clarify all aspects of our future project, can't wait to start coding hope you have the same feelings. **So get some more patience and see you in the next article, but if you want to move forward you can find the whole list in [the WebCraft-Notes](https://webcraft-notes.com/series/building-an-e-commerce-store-with-nuxt).**
**The best variant to study something is to make it by your own, the same thing works with coding, but if you need a source code for this tutorial you can get it [here](https://buymeacoffee.com/webcraft.notes/e/257947).** | webcraft-notes |
1,867,708 | Efficient Encoder-Decoder Transformer Decoding for Decomposable Tasks | Efficient Encoder-Decoder Transformer Decoding for Decomposable Tasks | 0 | 2024-05-28T13:20:21 | https://aimodels.fyi/papers/arxiv/efficient-encoder-decoder-transformer-decoding-decomposable-tasks | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Efficient Encoder-Decoder Transformer Decoding for Decomposable Tasks](https://aimodels.fyi/papers/arxiv/efficient-encoder-decoder-transformer-decoding-decomposable-tasks). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper presents a novel approach to efficient transformer decoding, which is a key component of large language models.
- The proposed method, called "Encode Once and Decode in Parallel" (EODP), allows for parallel decoding of multiple prompts simultaneously, reducing the overall computational cost.
- The paper explores the theoretical foundations of the EODP approach and demonstrates its effectiveness through extensive experiments on various benchmark tasks.
## Plain English Explanation
The paper deals with a crucial aspect of large language models known as "transformer decoding." Transformer models are the backbone of many state-of-the-art natural language processing systems, including chatbots, language translators, and text summarizers.
The key insight behind the researchers' approach is to encode the input once and then decode multiple prompts in parallel, rather than processing each prompt sequentially. This parallel decoding strategy can significantly reduce the computational resources required to generate text, making language models more efficient and scalable.
To understand this better, imagine you have a group of friends who all want you to help them with their writing assignments. Instead of helping each friend one by one, you could have them all provide their assignments at the same time and provide feedback to the entire group simultaneously. This would be much more efficient than helping each friend individually.
Similarly, the EODP method allows language models to process multiple prompts in parallel, leveraging the inherent parallelism of modern hardware. This can lead to substantial speed-ups and cost savings, particularly when deploying these models at scale.
## Technical Explanation
The paper introduces the "Encode Once and Decode in Parallel" (EODP) framework, which builds upon the standard encoder-decoder architecture of transformer models. In a typical transformer, the encoder processes the input sequence, and the decoder generates the output sequence one token at a time.
The EODP approach decouples the encoder and decoder computations, allowing the encoder to be executed only once for multiple prompts. This is achieved by caching the encoder outputs and reusing them during the parallel decoding of different prompts. The authors also propose several techniques to optimize the memory usage and computational efficiency of this parallel decoding process.
The paper presents a thorough theoretical analysis of the EODP framework, demonstrating its advantages in terms of computational complexity and memory usage compared to traditional sequential decoding. The authors also conduct extensive experiments on various benchmarks, including machine translation, text summarization, and language generation tasks, showcasing the significant performance improvements achieved by the EODP method.
## Critical Analysis
The paper presents a well-designed and rigorously evaluated approach to efficient transformer decoding. The authors acknowledge some limitations, such as the potential memory overhead for storing the cached encoder outputs, and suggest future research directions to address these challenges.
One potential concern is the generalizability of the EODP approach to more complex transformer architectures, such as those with cross-attention mechanisms or dynamic computation graphs. The paper focuses on the standard encoder-decoder transformer, and it would be valuable to see how the proposed techniques can be extended to handle these more advanced models.
Additionally, the paper does not explore the impact of the EODP method on the quality of the generated text, as the focus is primarily on improving computational efficiency. It would be interesting to see if the parallel decoding approach introduces any trade-offs in terms of output quality, which could be an important consideration for real-world applications.
## Conclusion
The "Encode Once and Decode in Parallel" (EODP) framework presented in this paper offers a promising solution for improving the efficiency of transformer decoding, a critical component of large language models. By leveraging parallel processing, the EODP method can significantly reduce the computational resources required to generate text, making these models more scalable and cost-effective.
The theoretical analysis and empirical results demonstrate the advantages of the EODP approach, and the insights provided in this paper can inform the development of more efficient and practical language models. As the demand for powerful, yet resource-efficient natural language processing systems continues to grow, innovations like EODP will play an important role in the field.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,706 | The Power of Sentiment Analysis in Modern Business | Positive sentiments drive customers to buy your products, while negative perceptions accelerate... | 0 | 2024-05-28T13:19:49 | https://dev.to/linda0609/the-power-of-sentiment-analysis-in-modern-business-1fi6 | Positive sentiments drive customers to buy your products, while negative perceptions accelerate client churn. However, manually categorizing customer responses, e-commerce reviews, or discussion forum entries is time-consuming. Computers also struggle to analyze detailed responses from customer satisfaction and market research surveys. This post will explain how sentiment analysis helps extract meaning from textual data.
What is Sentiment Analysis?
Sentiment analysis involves processing unstructured data and attributing emotions to classify qualitative customer responses into positive, negative, or neutral categories. Also known as opinion mining, it combines natural language processing (NLP) and context identification methods. This technology is essential for understanding modern customer behaviors and optimizing user experiences.
Holistic [sentiment analysis services](https://us.sganalytics.com/data-management-analytics-services/sentiment-and-social-media-analysis/) extend insight extraction by including user-generated content on social media. By analyzing emotional tones across online content and survey responses, businesses can quickly gauge customer perceptions. This enables more accurate customization of branding assets to maximize appeal. For instance, avoiding content layouts and post formats associated with negative impressions and focusing on positively perceived marketing ideas will help achieve a better return on ad spend (ROAS).
Top Business Benefits of Sentiment Analysis
1. Realistic Customer Profiles from Feedback Analysis
Sentiment analysis helps organizations identify client interaction patterns, preferences, and issues with the brand. Business leaders can then create unique customer profiles to address service issues based on expected behavior. Profiling insights from sentiment analysis ensure an efficient customer journey, delivering the right impression and enhancing service quality.
By developing these detailed customer profiles, companies can personalize their marketing strategies and product offerings to meet specific needs and preferences. This level of personalization can significantly improve customer satisfaction and loyalty, leading to increased sales and long-term business growth.
2. Future-Oriented Market Research for Competitive Edge
Trends evolve at varying rates, and customers may be slow to adopt new approaches to product usage or service pricing. Competitors might develop unique experiences that attract your target customers. Sentiment analysts can help foresee trends through future-focused market research and competitor reputation monitoring, allowing your business to stay ahead of the curve.
For example, by analyzing sentiment data from social media, reviews, and other online sources, businesses can identify emerging trends and shifts in customer preferences. This insight enables companies to adapt their strategies proactively, whether by developing new products, modifying existing offerings, or adjusting marketing campaigns to align with evolving customer desires.
3. Advanced Risk Mitigation Regarding Customer Dissatisfaction
Declining customer satisfaction (CSAT) metrics often indicate product or service issues. Customers typically prefer resolving issues rather than abandoning a vendor immediately. Effective sentiment analysis empowers customer service teams to respond appropriately to queries and complaints, reducing churn rates and cart abandonment risks. Ensuring that clients feel heard and respected is crucial for maintaining customer loyalty.
By continuously monitoring customer feedback and sentiment, businesses can identify potential issues early and take corrective actions before they escalate. This proactive approach not only helps retain existing customers but also enhances the overall customer experience, fostering positive word-of-mouth and attracting new clients.
4. Successful New Product Launches
Change is often met with resistance. To increase the likelihood of positive customer reception for new products, businesses can leverage sentiment analysis. By providing a focus group with a prototype and using sentiment analysis to process feedback, companies can obtain reliable insights for design optimization. Integrating generative artificial intelligence (GenAI) can further enhance the quality of feedback summaries, ensuring that similar customer cohorts will support the innovations.
This approach allows companies to refine their products based on real customer input, increasing the chances of a successful launch. Additionally, sentiment analysis can help identify potential concerns or areas for improvement, enabling businesses to address these issues before the product reaches a broader audience.
5. Detailed Company Due Diligence
Before closing mergers and acquisitions (M&A) deals, conducting thorough due diligence is essential. Sentiment analysis can assess the reputation of potential merger candidates, alerting leadership to any controversies that might affect the brand's trustworthiness. Monitoring positive, negative, and neutral media coverage helps evaluate the risk-reward dynamics of M&A deals, ensuring strategic resilience.
For instance, analyzing sentiment around a potential partner's brand can reveal hidden issues that might not be apparent through traditional financial analysis. This comprehensive understanding helps companies make informed decisions, mitigate risks, and ensure that the merged entity can achieve its strategic goals without facing unexpected reputational challenges.
6. Improved Employee Engagement and Retention
Employee commitment is crucial for a company's success. Workers must feel appreciated and fairly treated to avoid issues like silent quitting or toxic competitiveness. Sentiment analysis focused on human resource management (HRM) can gather and process employee ideas, grievances, and suggestions. Insights from this analysis help identify and address potential alienation issues, improving workplace experiences and reducing turnover.
By fostering a positive work environment and actively addressing employee concerns, companies can enhance job satisfaction, boost morale, and increase productivity. Moreover, a happy and engaged workforce is more likely to stay loyal to the company, reducing recruitment and training costs associated with high turnover rates.
Conclusion
Modern businesses recognize the importance of sentiment analysis in extracting business-relevant insights from multi-channel textual data. Although unstructured data processing is newer than traditional analytics, many corporations are increasingly interested in emotion-based feedback categorization.
Amazon Web Services (AWS) and IBM maintain extensive knowledge bases to educate corporate clients on sentiment analysis technology. The discrepancy between CSAT figures reported by companies and customers underscores the need for comprehensive approaches to customer satisfaction measurements.
Current competitive realities demand that business leaders harness sentiment analysis for contextual marketing and employee engagement insights. This technology also aids in successfully launching new products and predicting shifts in customer interests.
For better customer retention and lower employee attrition, integrating sentiment analytics sooner rather than later is essential. By leveraging the power of sentiment analysis, businesses can gain a deeper understanding of their customers and employees, driving long-term success and competitive advantage. | linda0609 | |
1,867,705 | Ephemeral Rollups are All you Need | Ephemeral Rollups are All you Need | 0 | 2024-05-28T13:19:46 | https://aimodels.fyi/papers/arxiv/ephemeral-rollups-are-all-you-need | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Ephemeral Rollups are All you Need](https://aimodels.fyi/papers/arxiv/ephemeral-rollups-are-all-you-need). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- Envisions open and composable gaming platforms where users actively expand, create, engage, and immerse themselves
- Focuses on fully on-chain (FOC) games, where game state and logic reside on the blockchain for maximum composability
- Addresses inherent limitations and tradeoffs, particularly in terms of costs and scalability
## Plain English Explanation
The paper presents a vision for gaming platforms that allow users to deeply engage, create, and customize their experiences. One promising approach is [fully on-chain (FOC) games](https://aimodels.fyi/papers/arxiv/lollipop-svm-rollups-solana), where the entire game is hosted on the blockchain. This maximizes the ability to "compose" different game elements together.
However, FOC games face challenges around cost and scalability. The paper introduces a framework called BOLT that leverages the [Solana Virtual Machine (SVM)](https://aimodels.fyi/papers/arxiv/lollipop-svm-rollups-solana) to address these limitations. BOLT uses a modular, [Entity-Component-System (ECS)](https://en.wikipedia.org/wiki/Entity_component_system) design to make it easier to build and combine game logic.
To improve scalability, BOLT introduces "Ephemeral Rollups" (ERs) - specialized runtimes that can be optimized for speed, customized ticking mechanisms, and gasless transactions. This allows FOC games to scale without compromising the benefits of being fully on-chain.
## Technical Explanation
The paper proposes the BOLT framework to enable scalable, composable FOC games on the Solana blockchain. BOLT uses the [Solana Virtual Machine (SVM)](https://aimodels.fyi/papers/arxiv/lollipop-svm-rollups-solana) to host game logic and state on-chain.
A key innovation is BOLT's modular, [Entity-Component-System (ECS)](https://en.wikipedia.org/wiki/Entity_component_system) architecture. This allows game developers to discover, utilize, and publish reusable "components" of game logic. These components can then be easily combined to create new gameplay experiences.
To address scalability challenges, BOLT introduces "Ephemeral Rollups" (ERs) - specialized runtimes that can be customized for high performance, configurable ticking, and gasless transactions. ERs overcome the tradeoffs often seen in Layer 2 scaling solutions, allowing FOC games to scale without sacrificing composability.
The paper also discusses techniques for ensuring the security and integrity of these ephemeral runtimes, including [sequencer-level security](https://aimodels.fyi/papers/arxiv/sequencer-level-security) and leveraging innovations like [EIP-4844](https://aimodels.fyi/papers/arxiv/impact-eip-4844-ethereum-consensus-security-ethereum) for more efficient data management.
## Critical Analysis
The paper presents a compelling vision for scalable, composable on-chain gaming. The BOLT framework addresses key limitations of existing FOC games, such as high costs and poor scalability. The use of modular ECS architecture and Ephemeral Rollups are innovative approaches to these challenges.
However, the paper does not fully address potential drawbacks or areas for further research. For example, the security and trust assumptions of the ephemeral runtimes require deeper exploration, especially in light of recent issues with [rollup-based systems](https://aimodels.fyi/papers/arxiv/rollup-comparison-framework).
Additionally, the paper does not delve into the potential impact of [efficient data management techniques](https://aimodels.fyi/papers/arxiv/efficient-data-management-ipfs-dapps) on the overall system design and performance. These aspects could be important considerations for the long-term viability of the BOLT framework.
Overall, the paper presents a promising direction for on-chain gaming, but further research and real-world testing would be needed to fully evaluate the feasibility and trade-offs of the proposed approach.
## Conclusion
The BOLT framework offers a compelling solution for building scalable, composable on-chain games on the Solana blockchain. By leveraging the Solana Virtual Machine and introducing modular ECS architecture and Ephemeral Rollups, the paper addresses key limitations of existing fully on-chain gaming platforms.
While the paper presents an innovative vision, further exploration of security, trust assumptions, and data management considerations would be beneficial to fully understand the potential and limitations of the BOLT approach. Nonetheless, the ideas presented in this paper could pave the way for a new era of engaging, user-driven gaming experiences built directly on the blockchain.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,629 | Amplify vs. EC2 | Deploying an Application on AWS: Amplify vs. EC2 Deploying an application on Amazon Web... | 0 | 2024-05-28T12:48:39 | https://dev.to/sh20raj/amplify-vs-ec2-4o00 | aws | # Deploying an Application on AWS: Amplify vs. EC2
Deploying an application on Amazon Web Services (AWS) is a popular choice for many developers, given its robust infrastructure and diverse services. Two common AWS services for deploying applications are AWS Amplify and Amazon EC2. Let's dive into a detailed analysis of these two options, their advantages, and considerations, plus some alternative services you might want to explore! 😊
## AWS Amplify: The All-in-One Solution 🚀
### What is AWS Amplify?
AWS Amplify is a comprehensive development platform for building secure, scalable mobile and web applications. It simplifies many aspects of application development, including backend configuration, hosting, and deployment.
### Key Features
- **Simplified Deployment**: With a few clicks, you can deploy static websites and single-page applications (SPAs).
- **Built-in CI/CD**: Automated build and deploy processes for every code commit.
- **Backend as a Service (BaaS)**: Easily add authentication, databases, storage, and more.
- **Integration with Other AWS Services**: Seamless integration with services like AWS AppSync, AWS Lambda, and Amazon S3.
### Advantages
- **Ease of Use**: Ideal for front-end developers and teams without extensive DevOps knowledge.
- **Speed**: Rapid deployment and iteration with automated workflows.
- **Cost-Effective**: Pay-as-you-go pricing with a free tier for low-traffic applications.
- **Scalability**: Automatically handles scaling for web traffic.
### Considerations
- **Less Control**: Limited customization compared to managing your own infrastructure.
- **Best for Specific Use Cases**: More suited for static sites and serverless applications.
## Amazon EC2: The Flexible Powerhouse ⚙️
### What is Amazon EC2?
Amazon Elastic Compute Cloud (EC2) provides scalable virtual servers in the cloud. You have full control over the computing resources and can configure, manage, and deploy applications as you see fit.
### Key Features
- **Customizability**: Choose your operating system, instance type, and configuration.
- **Scalability**: Scale horizontally with Auto Scaling and load balancing.
- **Wide Range of Use Cases**: From simple web applications to high-performance computing and enterprise applications.
- **Integration**: Works seamlessly with other AWS services like RDS, S3, and CloudWatch.
### Advantages
- **Full Control**: Complete control over the environment and configurations.
- **Versatility**: Suitable for a wide range of applications, including complex, resource-intensive workloads.
- **Performance**: Tailor performance to your specific needs with various instance types and sizes.
### Considerations
- **Complexity**: Requires more knowledge in system administration and DevOps.
- **Cost Management**: Can become expensive if not managed properly.
- **Maintenance**: You’re responsible for updates, security patches, and overall system health.
## Alternatives to AWS Amplify and EC2 🌐
### AWS Elastic Beanstalk
AWS Elastic Beanstalk is a Platform as a Service (PaaS) that handles the deployment, scaling, and monitoring of applications. It's a middle ground between the simplicity of Amplify and the control of EC2.
- **Pros**: Simplifies deployment while allowing some level of customization.
- **Cons**: Less control than EC2, potentially higher cost than Amplify for certain applications.
### AWS Lambda
AWS Lambda allows you to run code without provisioning or managing servers, based on an event-driven architecture.
- **Pros**: Fully serverless, scales automatically, and cost-effective for low-usage scenarios.
- **Cons**: Limited to specific use cases and event-driven applications.
### Amazon Lightsail
Amazon Lightsail is designed for simpler workloads, offering easy-to-use instances with a predictable pricing model.
- **Pros**: Simplifies cloud usage with pre-configured stacks, predictable pricing.
- **Cons**: Less flexible and powerful than EC2 for larger, more complex applications.
### Heroku
Heroku is a cloud platform that enables quick deployment and management of applications without worrying about infrastructure.
- **Pros**: Extremely user-friendly, supports multiple languages, and offers a free tier.
- **Cons**: Higher costs for scaling compared to AWS services.
### Google Cloud Platform (GCP) and Microsoft Azure
Both GCP and Azure offer services similar to AWS, with their own sets of strengths and weaknesses.
- **Pros**: Competitive pricing, unique features (like Google’s AI and ML tools), and global infrastructure.
- **Cons**: Learning curve if you’re already familiar with AWS, potential differences in service availability.
## Conclusion 🎉
Choosing between AWS Amplify and EC2 boils down to your specific needs:
- **Use AWS Amplify** if you want a quick, hassle-free way to deploy web and mobile applications with minimal DevOps overhead.
- **Use Amazon EC2** if you need full control over your environment and are comfortable managing infrastructure.
Each option has its strengths and is suited for different scenarios. And if neither Amplify nor EC2 fits the bill, AWS offers other powerful alternatives, and so do other cloud providers. Happy deploying! 🚀 | sh20raj |
1,867,704 | Reprompting: Automated Chain-of-Thought Prompt Inference Through Gibbs Sampling | Reprompting: Automated Chain-of-Thought Prompt Inference Through Gibbs Sampling | 0 | 2024-05-28T13:19:11 | https://aimodels.fyi/papers/arxiv/reprompting-automated-chain-thought-prompt-inference-through | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Reprompting: Automated Chain-of-Thought Prompt Inference Through Gibbs Sampling](https://aimodels.fyi/papers/arxiv/reprompting-automated-chain-thought-prompt-inference-through). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- The paper introduces "Reprompting," an iterative sampling algorithm that automatically learns the Chain-of-Thought (CoT) recipes for a given task without human intervention.
- Reprompting uses Gibbs sampling to infer the CoT recipes that work consistently well for a set of training samples.
- The algorithm outperforms human-written CoT prompts by +9.4 points on average and achieves better performance than state-of-the-art prompt optimization and decoding algorithms.
## Plain English Explanation
Reprompting is a new algorithm that can automatically figure out the best way to guide a large language model to solve complex reasoning tasks. [These tasks often require a series of steps or a "chain of thought" to arrive at the correct answer.](https://aimodels.fyi/papers/arxiv/chain-thought-reasoning-without-prompting)
The algorithm works by iteratively trying out different sets of instructions (called "recipes") for the language model. It starts with some initial recipes and then uses a technique called Gibbs sampling to gradually refine and improve the recipes based on how well they perform on a set of training problems.
Over time, the algorithm learns the recipes that work consistently well, without any human intervention. When tested on 20 challenging reasoning tasks, Reprompting was able to outperform the prompts that were carefully crafted by human experts. It also did better than other state-of-the-art methods for optimizing and decoding language model prompts.
The key innovation of Reprompting is that it can automatically discover the right "chain of thought" to solve complex problems, rather than requiring humans to provide those instructions. This could make it much easier to apply large language models to a wide range of reasoning tasks in the future.
## Technical Explanation
Reprompting is an iterative sampling algorithm that learns the Chain-of-Thought (CoT) recipes for a given task through Gibbs sampling. The algorithm starts with some initial CoT recipes and then uses a Gibbs sampling process to iteratively refine them.
In each iteration, Reprompting samples a new CoT recipe using the previously sampled recipes as parent prompts. It then evaluates the new recipe on the training samples and keeps it if it performs better than the current set of recipes. Over many iterations, the algorithm converges to a set of CoT recipes that work consistently well for the given task.
The researchers conduct extensive experiments on 20 challenging reasoning tasks, comparing Reprompting to human-written CoT prompts as well as state-of-the-art prompt optimization and decoding algorithms. The results show that Reprompting outperforms human-written prompts by +9.4 points on average and achieves consistently better performance than the other methods.
This improvement is significant because [crafting effective CoT prompts is a major challenge that has been the focus of prior work](https://aimodels.fyi/papers/arxiv/pattern-aware-chain-thought-prompting-large-language). Reprompting's ability to automatically discover these recipes without human intervention represents an important advance in prompt engineering for complex reasoning tasks.
## Critical Analysis
The paper provides a thorough evaluation of Reprompting, but there are a few potential limitations and areas for further research:
1. The experiments are limited to 20 reasoning tasks, so it's unclear how well the algorithm would generalize to a wider range of problem types. [Further testing on more diverse tasks would help validate the approach.](https://aimodels.fyi/papers/arxiv/chain-thoughtlessness-analysis-cot-planning)
2. The paper does not explore the interpretability of the learned CoT recipes. Understanding the reasoning behind these recipes could provide insights into how large language models solve complex problems, but the current work treats them as black boxes.
3. The algorithm's performance is still dependent on the quality of the initial CoT recipes used to seed the Gibbs sampling process. Developing techniques to automatically generate high-quality initial recipes could further improve Reprompting's effectiveness.
4. While Reprompting outperforms other prompt optimization methods, it is not clear how it compares to more recent approaches like [soft prompting](https://aimodels.fyi/papers/arxiv/soft-prompting-graph-thought-multi-modal-representation) or [residual prompting](https://aimodels.fyi/papers/arxiv/resprompt-residual-connection-prompting-advances-multi-step). Exploring these connections could lead to further advancements in prompt engineering.
Overall, Reprompting represents an impressive step forward in automating the discovery of effective prompts for complex reasoning tasks. While the current work has some limitations, the general approach shows promise and warrants further investigation.
## Conclusion
The Reprompting algorithm introduced in this paper is a significant advancement in the field of prompt engineering for large language models. By automatically learning the Chain-of-Thought recipes that work best for a given task, Reprompting can outperform carefully crafted human-written prompts and state-of-the-art prompt optimization techniques.
This breakthrough has important implications for expanding the capabilities of language models to tackle more complex reasoning and problem-solving tasks. If Reprompting can be further developed and scaled, it could make it much easier to deploy large language models across a wide range of real-world applications that require advanced cognitive skills.
While the current work has some limitations, the core ideas behind Reprompting represent an exciting step forward in the quest to make language models more autonomous, adaptable, and effective at solving challenging problems. As the field of AI continues to evolve, innovations like Reprompting will likely play a crucial role in unlocking the full potential of these powerful technologies.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,703 | How to boost your team’s productivity with custom ERP software development | In today's fast-paced business environment, enhancing team productivity is crucial for success.... | 0 | 2024-05-28T13:19:03 | https://dev.to/himadripatelace/how-to-boost-your-teams-productivity-with-custom-erp-software-development-2k61 | productivity, softwaredevelopment, saas, development | In today's fast-paced business environment, enhancing team productivity is crucial for success. Custom ERP (Enterprise Resource Planning) software development offers a powerful solution by streamlining operations, improving communication, and providing real-time data insights tailored to your specific business needs.
This blog explores the key benefits of custom ERP software, including:
**Streamlined Workflows:** Automate routine tasks and integrate various business processes to reduce manual effort and minimize errors.
**Enhanced Collaboration:** Improve communication across departments with centralized information and collaborative tools.
**Data-Driven Decisions:** Gain access to real-time data analytics, enabling informed decision-making and strategic planning.
**Scalability and Flexibility:** Customize the software to grow with your business and adapt to changing requirements.
By investing in custom ERP software, businesses can significantly boost productivity, optimize resources, and maintain a competitive edge.
Discover how tailored ERP solutions can transform your operations and propel your team to new heights of efficiency.
## Exploring the Diversity in ERP Development
Different types of ERP systems can be implemented depending on various aspects of business requirements. ERP software developers and consultants can provide you with proper suggestions for which ERP system is best suitable for your business. Here is the list of different types of ERP systems:
1. On-premise ERP
2. Cloud-based ERP
3. Hybrid ERP
4. Open Source ERP
Read full article here: [https://bit.ly/3R0HVC8](https://bit.ly/3R0HVC8) | himadripatelace |
1,867,702 | Grokked Transformers are Implicit Reasoners: A Mechanistic Journey to the Edge of Generalization | Grokked Transformers are Implicit Reasoners: A Mechanistic Journey to the Edge of Generalization | 0 | 2024-05-28T13:18:37 | https://aimodels.fyi/papers/arxiv/grokked-transformers-are-implicit-reasoners-mechanistic-journey | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Grokked Transformers are Implicit Reasoners: A Mechanistic Journey to the Edge of Generalization](https://aimodels.fyi/papers/arxiv/grokked-transformers-are-implicit-reasoners-mechanistic-journey). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper explores the inner workings of Transformer models and their ability to reason implicitly about abstract concepts and perform multi-step reasoning.
- The researchers use a combination of experimental and analytical techniques to gain a deeper understanding of how Transformers learn and generalize.
- Key findings include insights into Transformers' capacity for implicit reasoning, their ability to learn syntactic structure without explicit supervision, and their performance on tasks involving multi-step reasoning.
## Plain English Explanation
Transformer models, a type of [deep learning](https://aimodels.fyi/papers/arxiv/symbolic-framework-evaluating-mathematical-reasoning-generalisation-transformers) architecture, have become incredibly powerful in a variety of tasks, from language processing to image recognition. But how exactly do these models work, and what are they capable of?
This research paper dives into the inner workings of Transformers, exploring their ability to [reason about abstract concepts](https://aimodels.fyi/papers/arxiv/when-can-transformers-reason-abstract-symbols) and perform multi-step reasoning. The researchers use a combination of experiments and analyses to uncover the mechanisms underlying Transformers' impressive performance.
One key finding is that Transformers can [learn syntactic structure](https://aimodels.fyi/papers/arxiv/learning-syntax-without-planting-trees-understanding-when) without explicit supervision, suggesting that they have a remarkable capacity for implicit reasoning. They can also tackle [multi-step reasoning tasks](https://aimodels.fyi/papers/arxiv/towards-understanding-how-transformer-perform-multi-step), demonstrating their [expressive power](https://aimodels.fyi/papers/arxiv/expressive-power-transformers-chain-thought) and ability to chain together complex thought processes.
Overall, this research sheds light on the inner workings of Transformers, helping us better understand how these powerful models learn and generalize. By delving into the mechanisms behind their performance, the researchers hope to pave the way for even more advanced and capable AI systems in the future.
## Technical Explanation
The researchers in this paper use a combination of experimental and analytical techniques to investigate the inner workings of Transformer models. They explore the models' capacity for [implicit reasoning](https://aimodels.fyi/papers/arxiv/when-can-transformers-reason-abstract-symbols) about abstract concepts, as well as their ability to [learn syntactic structure](https://aimodels.fyi/papers/arxiv/learning-syntax-without-planting-trees-understanding-when) and perform [multi-step reasoning](https://aimodels.fyi/papers/arxiv/towards-understanding-how-transformer-perform-multi-step).
Through a series of carefully designed experiments, the researchers demonstrate that Transformers can [learn to reason about abstract symbols](https://aimodels.fyi/papers/arxiv/when-can-transformers-reason-abstract-symbols) without explicit supervision. They also find that Transformers can [learn syntactic structure](https://aimodels.fyi/papers/arxiv/learning-syntax-without-planting-trees-understanding-when) in an implicit manner, suggesting a remarkable capacity for [implicit reasoning](https://aimodels.fyi/papers/arxiv/when-can-transformers-reason-abstract-symbols).
Furthermore, the researchers investigate the [expressive power of Transformers](https://aimodels.fyi/papers/arxiv/expressive-power-transformers-chain-thought) and their ability to [perform multi-step reasoning](https://aimodels.fyi/papers/arxiv/towards-understanding-how-transformer-perform-multi-step). They find that Transformers can effectively chain together complex thought processes, demonstrating their versatility and potential for tackling increasingly sophisticated tasks.
## Critical Analysis
The researchers in this paper provide a comprehensive and insightful analysis of Transformer models, shedding light on their inner workings and capabilities. However, it's important to note that the findings presented here are specific to the particular experimental setups and datasets used in the study.
While the researchers have taken great care to design their experiments and analyses, it's possible that the results may not generalize to all Transformer models or applications. There may be limitations or edge cases that were not explored in this study, and further research would be needed to fully understand the broader implications of these findings.
Additionally, the paper focuses primarily on the technical aspects of Transformer models, without much discussion of the potential societal implications or ethical considerations surrounding the use of these powerful AI systems. As Transformers continue to advance and become more widely deployed, it will be crucial to consider the broader impact and responsible development of this technology.
## Conclusion
This research paper offers a comprehensive and insightful exploration of the inner workings of Transformer models, providing valuable insights into their capacity for [implicit reasoning](https://aimodels.fyi/papers/arxiv/when-can-transformers-reason-abstract-symbols), their ability to [learn syntactic structure](https://aimodels.fyi/papers/arxiv/learning-syntax-without-planting-trees-understanding-when), and their [expressive power](https://aimodels.fyi/papers/arxiv/expressive-power-transformers-chain-thought) in performing [multi-step reasoning](https://aimodels.fyi/papers/arxiv/towards-understanding-how-transformer-perform-multi-step).
By delving into the mechanisms underlying Transformers' impressive performance, the researchers hope to pave the way for even more advanced and capable AI systems in the future. However, it's important to consider the limitations and potential broader implications of these findings, as the continued development and deployment of Transformers will have significant societal impacts that deserve careful consideration.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,229 | How to import all components from a folder? | While developing with Vuetify.js, I found the <v-icon> component incredibly convenient. This... | 0 | 2024-05-28T13:18:17 | https://dev.to/adrian-chan-yong-qian/how-to-import-all-components-from-a-folder-5271 | vue, bash | While developing with [Vuetify.js](https://vuetifyjs.com), I found the **`<v-icon>`** component incredibly convenient. This inspired me to create my own icon components, allowing me to easily access all of my favorite icons. I eagerly gathered all the SVG files into a folder, only to realize… I had to manually import each icon as a component, one by one. 🤦🏽♂️
My initial attempt to streamline this process was with **`import * from './svg'`**,
but I quickly hit a roadblock:
**`Failed to resolve import "./svg" from "./svg/index.js". Does the file exist?`**.
It dawned on me that I needed an **`index.js`** file in the folder, exporting every component. So, I was back to square one, facing the tedious task of manually importing and exporting each icon component.
A quick search on [Stack Overflow](https://stackoverflow.com/questions/42199872/is-it-possible-to-import-vue-files-in-a-folder) seemed to offer a promising solution.
```javascript
const files = require.context('.', false, /\.vue$/)
const modules = {}
files.keys().forEach((key) => {
if (key === './index.js') return
modules[key.replace(/(\.\/|\.vue)/g, '')] = files(key)
})
export default modules
```
However, my excitement was short-lived when the browser console threw up **`Uncaught ReferenceError: require is not defined at index.js`**. I discovered that **`require()`** is not a valid function in client-side JavaScript.
Determined to find a workaround, I decided to auto-generate the **`index.js`** file with a bash script. Although this approach still involves a bit of manual effort (I need to run the script each time I add a new component), it significantly reduces the hassle of individually verifying each filename.
Here’s the script I crafted:
```bash
# Navigate to the script's directory
cd "$(dirname "$0")"
# Get a list of icon files, excluding index.js and import.sh
icons=$(ls --hide=index.js --hide=import.sh --format=single-column)
# Define the output file
output_file="index.js"
# Clear the output file
> $output_file
# Generate import statements
for icon in $icons
do
name=$(basename -- "$icon")
name="${name%.*}"
echo "import $name from './$icon'" >> $output_file
done
echo "" >> $output_file
echo "export {" >> $output_file
# Generate export statements
for icon in $icons
do
name=$(basename -- "$icon")
name="${name%.*}"
echo " $name," >> $output_file
done
echo "}" >> $output_file
echo "" >> $output_file
```
With this script in the subfolder, I simply run **`sudo ./import.sh`** and all my components are imported and exported in **`index.js`**. This allows me to use **`import * from './svg'`** seamlessly in other files.
That’s my solution. I’m eager to hear your thoughts and suggestions on how to improve this process! | adrian-chan-yong-qian |
1,867,701 | Denoising LM: Pushing the Limits of Error Correction Models for Speech Recognition | Denoising LM: Pushing the Limits of Error Correction Models for Speech Recognition | 0 | 2024-05-28T13:18:03 | https://aimodels.fyi/papers/arxiv/denoising-lm-pushing-limits-error-correction-models | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Denoising LM: Pushing the Limits of Error Correction Models for Speech Recognition](https://aimodels.fyi/papers/arxiv/denoising-lm-pushing-limits-error-correction-models). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- The paper explores techniques to improve speech recognition by leveraging error correction models based on large language models (LLMs).
- The researchers investigate the limits of what can be achieved by denoising LLMs in the context of speech recognition.
- They propose a new framework called "Denoising LM" that outperforms existing state-of-the-art speech recognition approaches.
## Plain English Explanation
Speech recognition is the process of converting spoken words into text, and it's a crucial technology for many applications like voice assistants and transcription services. However, speech recognition systems can make mistakes, especially in noisy environments.
The researchers in this paper tried to address this problem by using large language models (LLMs) - powerful AI models that can understand and generate human-like text. The idea is to use these LLMs to "denoise" the output of speech recognition systems, correcting any errors or mistakes.
The paper presents a new framework called "Denoising LM" that takes the output of a speech recognition system and uses an LLM to clean it up and fix any errors. The researchers found that this approach can significantly improve the accuracy of speech recognition, even in challenging conditions with a lot of background noise.
By leveraging the impressive language understanding capabilities of LLMs, the "Denoising LM" framework pushes the limits of what's possible with error correction in speech recognition. This could lead to more reliable and effective voice-based technologies in the future.
## Technical Explanation
The key technical contribution of the paper is the "Denoising LM" framework, which integrates a large language model (LLM) into the speech recognition pipeline to improve accuracy.
The framework works by first running a speech recognition system to generate an initial text transcript. This transcript is then passed to the "Denoising LM" component, which is an LLM-based model trained to identify and correct errors in the transcript.
The researchers experimented with different types of LLMs, including [Contrastive Consistency Learning for Neural Noisy Channel Model](https://aimodels.fyi/papers/arxiv/contrastive-consistency-learning-neural-noisy-channel-model) and [Transforming LLMs into Cross-Modal, Cross-Lingual Experts](https://aimodels.fyi/papers/arxiv/transforming-llms-into-cross-modal-cross-lingual). They found that LLMs with stronger language understanding capabilities performed better at the denoising task.
Additionally, the paper explores techniques to make the Denoising LM more robust to noisy input, such as [Resilience of Large Language Models to Noisy Instructions](https://aimodels.fyi/papers/arxiv/resilience-large-language-models-noisy-instructions). This allows the framework to maintain high accuracy even when the initial speech recognition output contains significant errors.
The researchers conducted extensive experiments on multiple speech recognition benchmarks, including [Listen Again, Choose the Right Answer: A New Paradigm for Spoken Language Understanding](https://aimodels.fyi/papers/arxiv/listen-again-choose-right-answer-new-paradigm) and [Unveiling the Potential of LLM-based ASR for Chinese Open-Domain Conversations](https://aimodels.fyi/papers/arxiv/unveiling-potential-llm-based-asr-chinese-open). The results demonstrate that the Denoising LM framework outperforms state-of-the-art speech recognition approaches across a range of scenarios.
## Critical Analysis
The paper presents a compelling approach to improving speech recognition accuracy by leveraging the power of large language models. The researchers have clearly demonstrated the potential of the Denoising LM framework through their extensive experiments.
One potential limitation of the approach is its reliance on the initial speech recognition system to provide a reasonable starting point. If the speech recognition system produces highly inaccurate output, the Denoising LM may struggle to effectively correct the errors.
Additionally, the paper does not address the computational cost and inference time of the Denoising LM component, which could be a practical concern for real-time speech recognition applications.
Further research could explore ways to make the Denoising LM more robust to poor-quality input from the speech recognition system, as well as optimizing its efficiency to enable deployment in real-world scenarios.
## Conclusion
The "Denoising LM" framework presented in this paper represents a significant advancement in using large language models to improve speech recognition accuracy. By leveraging the powerful language understanding capabilities of LLMs, the researchers have demonstrated the potential to push the limits of what's possible with error correction in speech recognition.
The findings in this paper could have important implications for the development of more reliable and effective voice-based technologies, such as virtual assistants, transcription services, and voice-controlled interfaces. As large language models continue to advance, the integration of these models into speech recognition systems could lead to transformative improvements in the field.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,700 | Chain-of-Thought Reasoning Without Prompting | Chain-of-Thought Reasoning Without Prompting | 0 | 2024-05-28T13:17:28 | https://aimodels.fyi/papers/arxiv/chain-thought-reasoning-without-prompting | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Chain-of-Thought Reasoning Without Prompting](https://aimodels.fyi/papers/arxiv/chain-thought-reasoning-without-prompting). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This study examines a novel approach to enhancing the reasoning capabilities of large language models (LLMs) without relying on manual prompt engineering.
- The researchers found that chain-of-thought (CoT) reasoning paths can be elicited from pre-trained LLMs by altering the decoding process, rather than using specific prompting techniques.
- This method allows for the assessment of the LLMs' intrinsic reasoning abilities and reveals a correlation between the presence of a CoT in the decoding path and higher model confidence in the decoded answer.
## Plain English Explanation
Large language models (LLMs) are powerful AI systems that can generate human-like text, but their reasoning abilities are often obscured by the way they are trained and used. [Prior research](https://aimodels.fyi/papers/arxiv/pattern-aware-chain-thought-prompting-large-language) has focused on developing specialized prompting techniques, such as [few-shot or zero-shot chain-of-thought (CoT) prompting](https://aimodels.fyi/papers/arxiv/chain-thoughtlessness-analysis-cot-planning), to enhance their reasoning skills.
In this study, the researchers took a different approach. They asked: Can LLMs reason effectively without prompting? By [altering the decoding process](https://aimodels.fyi/papers/arxiv/how-to-think-step-by-step-mechanistic) rather than relying on specific prompts, the researchers found that CoT reasoning paths are often inherent in the sequences of alternative tokens that the models generate. This approach allows for the assessment of the LLMs' intrinsic reasoning abilities, bypassing the confounders of prompting.
Interestingly, the researchers also observed that the presence of a CoT in the decoding path correlates with a higher confidence in the model's decoded answer. This confidence metric can be used to differentiate between CoT and non-CoT reasoning paths.
Through [extensive empirical studies](https://aimodels.fyi/papers/arxiv/multimodal-chain-thought-reasoning-language-models) on various reasoning benchmarks, the researchers demonstrated that their CoT-decoding approach can effectively elicit the reasoning capabilities of language models, which were previously obscured by standard greedy decoding.
## Technical Explanation
The researchers' key insight was that CoT reasoning paths can be elicited from pre-trained LLMs by altering the decoding process, rather than relying on manual prompt engineering. Instead of using conventional greedy decoding, which selects the most likely token at each step, the researchers investigated the top-k alternative tokens produced by the model.
Their analysis revealed that CoT paths are frequently present in these alternative token sequences, even when the model is not explicitly prompted to engage in step-by-step reasoning. By uncovering these inherent CoT paths, the researchers were able to assess the LLMs' intrinsic reasoning abilities without the confounding factors of prompting.
Furthermore, the researchers observed a correlation between the presence of a CoT in the decoding path and a higher confidence in the model's decoded answer. This confidence metric can be used as a heuristic to differentiate between CoT and non-CoT reasoning paths, which the researchers leveraged in their extensive empirical studies.
The researchers evaluated their CoT-decoding approach on various reasoning benchmarks, including [mathematical reasoning tasks](https://aimodels.fyi/papers/arxiv/llms-can-find-mathematical-reasoning-mistakes-by), and found that it effectively elicited the reasoning capabilities of language models that were previously obscured by standard greedy decoding.
## Critical Analysis
The researchers' approach offers a novel and intriguing way to assess the reasoning capabilities of LLMs without relying on manual prompt engineering. By focusing on the alternative token sequences generated during decoding, the researchers were able to uncover inherent CoT reasoning paths that were previously hidden.
However, it's important to note that the researchers' findings are based on empirical observations and do not provide a comprehensive explanation of the underlying mechanisms driving the LLMs' reasoning behavior. Further research is needed to understand the factors that influence the presence and quality of CoT paths in the decoding process.
Additionally, the researchers acknowledge that their approach may not be suitable for all types of reasoning tasks, and the performance of CoT-decoding may vary depending on the specific task and model architecture. Continued experimentation and evaluation on a wider range of benchmarks would help validate the generalizability of the researchers' findings.
It would also be valuable to investigate the potential limitations of the confidence metric used to differentiate between CoT and non-CoT paths, as well as explore alternative methods for assessing the reasoning capabilities of LLMs.
## Conclusion
This study presents a novel and intriguing approach to enhancing the reasoning capabilities of LLMs without relying on manual prompt engineering. By altering the decoding process, the researchers were able to uncover inherent chain-of-thought reasoning paths in pre-trained language models, allowing for the assessment of their intrinsic reasoning abilities.
The researchers' findings suggest that there is significant potential in exploring alternative decoding strategies to unlock the reasoning capabilities of LLMs, which have been largely obscured by standard greedy decoding. This approach opens up new avenues for research and development in the field of large language models, with potential implications for a wide range of applications that require robust reasoning abilities.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,699 | Day 5 of my progress as a vue dev | About today? So, I finally implemented the review feature on my quiz app and after testing through... | 0 | 2024-05-28T13:17:10 | https://dev.to/zain725342/day-5-of-my-progress-as-a-vue-dev-l5n | webdev, vue, typescript, tailwindcss | **About today?**
So, I finally implemented the review feature on my quiz app and after testing through every use case my app seems to be working just fine. I have pushed my code on github repository, for anyone who wants to check it out can do that through zain725342 on github. It was a basic but fun project and I really enjoyed going back to the roots and developing something out of pure thoughts and without any specific guideline. Feel free to add your take on the project as the repository is public.
**What's next?**
I have another vue project in my mind that I want to work on first before moving to the laravel and start dealing with backend. I want to work on a DSA Visualizer that will help me polish my DSA concepts as well I want to make it fun visually so that will be an experience.
**Improvements required**
There is still some refactoring required on the published project which I will be coming back to on the weekend to really brush things up and push that in a separate branch on github.
Wish me luck! | zain725342 |
1,867,698 | AstroPT: Scaling Large Observation Models for Astronomy | AstroPT: Scaling Large Observation Models for Astronomy | 0 | 2024-05-28T13:16:54 | https://aimodels.fyi/papers/arxiv/astropt-scaling-large-observation-models-astronomy | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [AstroPT: Scaling Large Observation Models for Astronomy](https://aimodels.fyi/papers/arxiv/astropt-scaling-large-observation-models-astronomy). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper, titled "AstroPT: Scaling Large Observation Models for Astronomy", explores techniques for scaling large observation models in the field of astronomy.
- The key focus is on using contrastive learning and other methods to improve the performance and scalability of these models.
- The research aims to address the challenges of working with the massive datasets and complex models involved in analyzing astronomical observations.
## Plain English Explanation
When astronomers study the universe, they collect massive amounts of data from telescopes and other instruments. This data needs to be analyzed using complex computer models to extract meaningful insights. [The paper on scaling large observation models for astronomy](https://aimodels.fyi/papers/arxiv/can-ai-understand-our-universe-test-fine) tackles the challenge of making these models more powerful and efficient.
The researchers use a technique called **contrastive learning** to train the models. This involves teaching the model to identify key differences between related observations, which helps it learn more effectively. They also explore other approaches to make the models scale better as the datasets grow larger.
By improving the scalability and performance of these observation models, the research aims to support advances in our understanding of the cosmos. For example, [scaling laws for large time series models](https://aimodels.fyi/papers/arxiv/scaling-laws-large-time-series-models) could lead to better predictions about the behavior of stars and galaxies over time. And [pretraining billion-scale geospatial foundational models](https://aimodels.fyi/papers/arxiv/pretraining-billion-scale-geospatial-foundational-models-frontier) could unlock new insights from the vast stores of astronomical data.
## Technical Explanation
The key technical contributions of this paper include:
1. **Contrastive Learning**: The researchers propose a contrastive learning approach to train large observation models more effectively. This involves teaching the model to identify the differences between related astronomical observations, which helps it learn the important features more efficiently.
2. **Architecture and Training Techniques**: The paper explores different model architectures and training strategies to improve the scalability and performance of these large observation models. This includes techniques like [auto-regressive denoising operators](https://aimodels.fyi/papers/arxiv/dpot-auto-regressive-denoising-operator-transformer-large) and [pretraining on billion-scale datasets](https://aimodels.fyi/papers/arxiv/pretraining-billion-scale-geospatial-foundational-models-frontier).
3. **Evaluation on Astronomy Tasks**: The authors test their models on a range of astronomy-specific tasks, such as [named entity recognition](https://aimodels.fyi/papers/arxiv/astro-ner-astronomy-named-entity-recognition-is), to demonstrate their effectiveness in real-world applications.
## Critical Analysis
The paper presents a promising approach to scaling large observation models in astronomy, but it also acknowledges several limitations and areas for further research:
- The contrastive learning techniques require carefully designed data augmentation and sampling strategies, which can be complex to implement in practice.
- The performance gains demonstrated may be sensitive to the specific tasks and datasets used in evaluation, so more extensive testing is needed to validate the generalizability of the findings.
- The computational and memory requirements of these large models remain a challenge, and further innovations in model architecture and training may be necessary to make them truly scalable.
Despite these caveats, the core ideas presented in the paper represent an important step forward in addressing the challenges of working with massive astronomical datasets and complex observation models. Continued research in this direction has the potential to unlock new discoveries about the universe.
## Conclusion
The "AstroPT: Scaling Large Observation Models for Astronomy" paper proposes innovative techniques to improve the scalability and performance of large-scale observation models used in astronomy. By leveraging contrastive learning and other advanced training methods, the researchers demonstrate the potential to extract more meaningful insights from the vast troves of astronomical data.
While some challenges remain, this work represents a significant advancement in the field and could pave the way for breakthroughs in our understanding of the cosmos. As astronomical observations and models continue to grow in complexity, solutions like those presented in this paper will become increasingly crucial to driving progress in this important scientific domain.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,696 | Extracting Prompts by Inverting LLM Outputs | Extracting Prompts by Inverting LLM Outputs | 0 | 2024-05-28T13:16:19 | https://aimodels.fyi/papers/arxiv/extracting-prompts-by-inverting-llm-outputs | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Extracting Prompts by Inverting LLM Outputs](https://aimodels.fyi/papers/arxiv/extracting-prompts-by-inverting-llm-outputs). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- The research paper explores the problem of "language model inversion" - extracting the original prompt that generated the output of a language model.
- The authors develop a new method called "output2prompt" that can recover prompts from language model outputs, without access to the model's internal workings.
- This method only requires the language model's outputs, and not the logits or adversarial/jailbreaking queries used in previous work.
- To improve memory efficiency, output2prompt uses a new sparse encoding technique.
- The authors test output2prompt on a variety of user and system prompts, and demonstrate its ability to transfer across different large language models.
## Plain English Explanation
The paper addresses the challenge of "language model inversion" - the task of figuring out the original prompt or input that a language model, like [GPT-3](https://aimodels.fyi/papers/arxiv/language-models-as-black-box-optimizers-vision), used to generate a given output. This is a bit like trying to reverse-engineer a recipe from tasting the final dish.
The researchers developed a new method called "output2prompt" that can recover the original prompts without needing access to the model's internal workings. Previous approaches, like [AdvPromter](https://aimodels.fyi/papers/arxiv/advprompter-fast-adaptive-adversarial-prompting-llms) and [Prompt Exploration](https://aimodels.fyi/papers/arxiv/prompt-exploration-prompt-regression), required special queries or access to the model's internal "logits". In contrast, output2prompt only needs the normal outputs the language model produces.
To make this process more efficient, the researchers used a new technique to "encode" the prompts in a sparse, compressed way. This helps output2prompt run faster and use less memory.
The team tested output2prompt on a variety of different prompts, from user-generated to system-generated, and found that it could successfully recover the original prompts. Importantly, they also showed that output2prompt can "transfer" - it works well across different large language models, not just the one it was trained on.
## Technical Explanation
The core idea behind the "output2prompt" method is to learn a mapping from the language model's outputs back to the original prompts, without needing access to the model's internal "logits" or scores.
To do this, the authors train a neural network model that takes in the language model's outputs and learns to generate the corresponding prompts. This is done using a dataset of prompt-output pairs, where the prompts are known.
A key innovation is the use of a "sparse encoding" technique to represent the prompts. This allows the model to learn a compact, efficient representation of the prompts, reducing the memory and compute required.
The authors evaluate output2prompt on a range of different prompts, from user-generated text to system-generated prompts used in tasks like summarization and translation. They find that output2prompt can successfully recover the original prompts in these diverse settings.
Importantly, the authors also demonstrate "zero-shot transferability" - output2prompt can be applied to language models it wasn't trained on, like GPT-3, and still recover the prompts accurately. This suggests the method has broad applicability beyond a single model.
## Critical Analysis
The output2prompt method represents an interesting and useful advance in the field of language model inversion. By avoiding the need for access to model internals or adversarial queries, it makes the prompt recovery process more accessible and practical.
However, the paper does not address some potential limitations and areas for further research. For example, the method may struggle with longer or more complex prompts, where the mapping from output to prompt becomes more ambiguous. There are also open questions around the generalization of output2prompt to other types of language models beyond the ones tested.
Additionally, while the sparse encoding technique improves efficiency, there may still be concerns around the computational overhead and scalability of the approach, especially for deployment at scale.
It would be valuable for future work to further explore the robustness and limitations of output2prompt, as well as investigate potential applications beyond just prompt recovery, such as [prompt tuning](https://aimodels.fyi/papers/arxiv/plug-play-prompts-prompt-tuning-approach-controlling) or [private inference](https://aimodels.fyi/papers/arxiv/confusionprompt-practical-private-inference-online-large-language).
## Conclusion
The output2prompt method developed in this paper represents a significant advancement in the field of language model inversion. By enabling prompt recovery without access to model internals, it opens up new possibilities for understanding, interpreting, and interacting with large language models.
While the method has some limitations and areas for further research, the core idea and the demonstrated zero-shot transferability are highly promising. As language models become more powerful and ubiquitous, tools like output2prompt will be increasingly important for transparency, interpretability, and responsible development of these technologies.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,695 | Bring Your Own KG: Self-Supervised Program Synthesis for Zero-Shot KGQA | Bring Your Own KG: Self-Supervised Program Synthesis for Zero-Shot KGQA | 0 | 2024-05-28T13:15:45 | https://aimodels.fyi/papers/arxiv/bring-your-own-kg-self-supervised-program | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Bring Your Own KG: Self-Supervised Program Synthesis for Zero-Shot KGQA](https://aimodels.fyi/papers/arxiv/bring-your-own-kg-self-supervised-program). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- BYOKG is a universal question-answering (QA) system that can work with any knowledge graph (KG)
- It requires no human-annotated training data and can be ready to use within a day
- BYOKG is inspired by how humans explore and comprehend information in an unknown KG using their prior knowledge
## Plain English Explanation
BYOKG is a new way for computers to answer questions by using any knowledge graph, without needing special training data. It's inspired by how humans can understand information in an unfamiliar graph by exploring it and combining that with what they already know.
BYOKG uses a language model-powered [symbolic agent](https://aimodels.fyi/papers/arxiv/generate-graph-treat-llm-as-both-agent) to generate examples of queries and the programs that could answer them. It then uses those examples to help it figure out how to answer new questions on its own, without any pre-made training data.
This approach allows BYOKG to work effectively on both small and large knowledge graphs, outperforming other [zero-shot](https://aimodels.fyi/papers/arxiv/zero-shot-logical-query-reasoning-any-knowledge) methods. It even beats a supervised [in-context learning](https://aimodels.fyi/papers/arxiv/self-improvement-programming-temporal-knowledge-graph-question) approach on one benchmark, showing the power of exploration.
The performance of BYOKG also keeps improving as it does more exploration and as the underlying language model gets better, eventually surpassing a state-of-the-art fine-tuned model.
## Technical Explanation
BYOKG is designed to operate on any knowledge graph (KG) without requiring any human-annotated training data. It draws inspiration from how humans can comprehend information in an unfamiliar KG by starting at random nodes, inspecting the labels of adjacent nodes and edges, and combining that with their prior knowledge.
In BYOKG, this exploration process is carried out by a [language model-backed symbolic agent](https://aimodels.fyi/papers/arxiv/generate-graph-treat-llm-as-both-agent) that generates a diverse set of query-program exemplars. These exemplars are then used to ground a retrieval-augmented reasoning procedure that predicts programs for answering arbitrary questions on the KG.
BYOKG demonstrates strong performance on both small and large-scale knowledge graphs. On the GrailQA and MetaQA benchmarks, it achieves dramatic gains in question-answering accuracy over a [zero-shot](https://aimodels.fyi/papers/arxiv/zero-shot-logical-query-reasoning-any-knowledge) baseline, with F1 scores of 27.89 and 58.02 respectively.
Interestingly, BYOKG's unsupervised approach also outperforms a supervised [in-context learning](https://aimodels.fyi/papers/arxiv/self-improvement-programming-temporal-knowledge-graph-question) method on GrailQA, demonstrating the effectiveness of its exploration-based strategy.
The researchers also find that BYOKG's performance reliably improves with continued exploration, as well as with improvements in the base language model. On a sub-sampled zero-shot split of GrailQA, BYOKG even outperforms a state-of-the-art fine-tuned model by 7.08 F1 points.
## Critical Analysis
The paper presents a promising approach with BYOKG, but there are a few potential caveats and areas for further research:
- The paper does not discuss the computational cost and runtime efficiency of BYOKG, which could be an important practical consideration for real-world deployment.
- The experiments are limited to English-language knowledge graphs, so it's unclear how well BYOKG would generalize to other languages or multilingual settings.
- The researchers mention that BYOKG's performance can be further improved by enhancing the base language model, but they don't provide much detail on how to achieve those improvements.
- It would be interesting to see how BYOKG compares to other [recent advances](https://aimodels.fyi/papers/arxiv/curiousllm-elevating-multi-document-qa-reasoning-infused) in zero-shot and few-shot knowledge graph question answering.
Overall, BYOKG represents an innovative approach that could have significant implications for making knowledge graph-powered question answering more accessible and widely applicable. Further research to address the limitations and compare it to other state-of-the-art methods could help solidify its place in the field.
## Conclusion
BYOKG is a groundbreaking question-answering system that can work with any knowledge graph without requiring specialized training data or lengthy setup. By taking inspiration from how humans explore and reason about unfamiliar information, BYOKG demonstrates impressive performance on both small and large-scale knowledge graphs.
The ability to operate in a [zero-shot](https://aimodels.fyi/papers/arxiv/zero-shot-logical-query-reasoning-any-knowledge) setting and outperform supervised methods is a significant achievement, showing the power of BYOKG's exploration-based approach. As the system continues to improve with more exploration and better language models, it has the potential to make knowledge graph-powered question answering more widely accessible and impactful.
Overall, BYOKG represents an important step forward in the field of [knowledge graph question answering](https://aimodels.fyi/papers/arxiv/banglaautokg-automatic-bangla-knowledge-graph-construction-semantic), with implications for a wide range of applications that rely on structured knowledge.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
315,637 | SharePoint Rest API Formatter | Before stumbling across the article, Userscripts Are Fun And Are Still Very Much Relevant, I had neve... | 0 | 2020-04-21T04:55:45 | https://dev.to/droopytersen/sharepoint-rest-api-formatter-3p6c | sharepoint, spfx | Before stumbling across the article, [Userscripts Are Fun And Are Still Very Much Relevant](https://dutzi.party/userscripts-are-fun/), I had never heard of Userscripts. They are pretty useful; kind of like a bare bones browser extension.
The first thing I created was a helper to format and syntax highlight the XML that comes back when navigating to a SharePoint REST endpoint in Chrome or Edge.
*Userscript automatically kicks in on all REST API urls*
*Without it, it'd look like this*
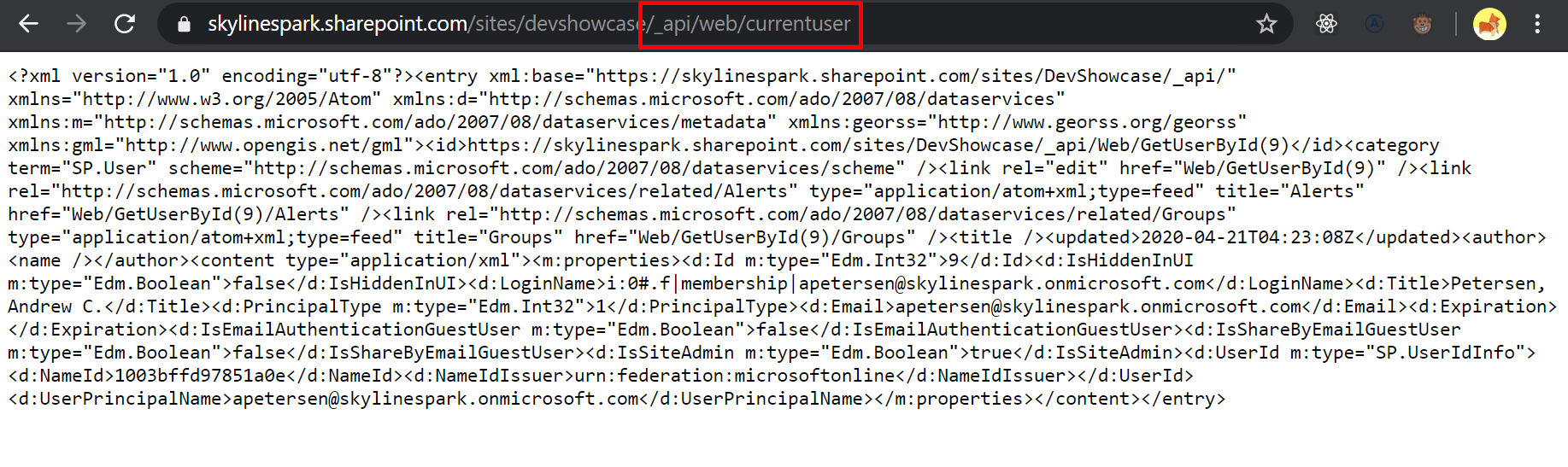
### Previous Solutions/Attempts
- I've installed Chrome Extensions to automatically format/syntax highlight XML, but they perform mediocre at best
- I've experimented with Chrome Extensions to automatically set the request headers to `application/json`, but that inevitably causes problems when I forget to turn it off, and sometimes I prefer the ATOM/XML response because it shows you what child properties you can expand on.
### Goals
1. Format and syntax highlight the XML response
2. Provide a toggle to switch between XML or JSON response
## Install Steps
1. Install the [ViolentMonkey Chrome Extension](https://chrome.google.com/webstore/detail/violentmonkey/jinjaccalgkegednnccohejagnlnfdag)
- This is what manages all your Userscripts.
- It's a weird name, but it has worked great so far.
2. Add a new User Script from URL
- Open the ViolentMonkey extension Dashboard,
- Then click "New Script from Url" and paste in the following url.
- It's the raw url to [this Gist](https://gist.github.com/DroopyTersen/7234e172ba004a5689910f05822a1b95), which is the result of my efforts. Definitely take a look at the code if you're interested.
```
https://gist.githubusercontent.com/DroopyTersen/7234e172ba004a5689910f05822a1b95/raw/a0a7e03c47daa55ef7a34ac433f6231fdb0e9bb5/REST%2520API%2520Formatter%2520Userscript
```
| droopytersen |
1,867,694 | Direct3D: Scalable Image-to-3D Generation via 3D Latent Diffusion Transformer | Direct3D: Scalable Image-to-3D Generation via 3D Latent Diffusion Transformer | 0 | 2024-05-28T13:15:11 | https://aimodels.fyi/papers/arxiv/direct3d-scalable-image-to-3d-generation-via | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Direct3D: Scalable Image-to-3D Generation via 3D Latent Diffusion Transformer](https://aimodels.fyi/papers/arxiv/direct3d-scalable-image-to-3d-generation-via). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- Generating high-quality 3D assets from text and images has long been a challenging task
- The authors introduce Direct3D, a new approach that can generate 3D shapes directly from single-view images without the need for complex optimization or multi-view diffusion models
- Direct3D comprises two key components: a Direct 3D Variational Auto-Encoder (D3D-VAE) and a Direct 3D Diffusion Transformer (D3D-DiT)
- The method can produce 3D shapes consistent with provided image conditions, outperforming previous state-of-the-art text-to-3D and image-to-3D generation approaches
## Plain English Explanation
Creating high-quality 3D models from text descriptions or images has historically been a challenging problem. The authors of this paper have developed a new technique called Direct3D that can generate 3D shapes directly from single-view images, without requiring complex optimization steps or the use of multiple camera views.
Direct3D has two main components. The first is a Direct 3D Variational Auto-Encoder (D3D-VAE), which efficiently encodes high-resolution 3D shapes into a compact, continuous latent space. Importantly, this encoding process directly supervises the decoded geometry, rather than relying on rendered images as the training signal.
The second component is the Direct 3D Diffusion Transformer (D3D-DiT), which models the distribution of the encoded 3D latents. This transformer is designed to effectively fuse the positional information from the three feature maps of the latent triplane representation, enabling a "native" 3D generative model that can scale to large-scale 3D datasets.
Additionally, the authors introduce an image-to-3D generation pipeline that incorporates both semantic and pixel-level image conditions. This allows the model to produce 3D shapes that are consistent with the provided input image.
Through extensive experiments, the researchers demonstrate that their large-scale pre-trained Direct3D model outperforms previous state-of-the-art approaches for text-to-3D and image-to-3D generation, in terms of both generation quality and generalization ability. This represents a significant advancement in the field of 3D content creation.
## Technical Explanation
The authors introduce a new approach called [Direct3D](https://aimodels.fyi/papers/arxiv/dual3d-efficient-consistent-text-to-3d-generation), which consists of two primary components: a Direct 3D Variational Auto-Encoder (D3D-VAE) and a Direct 3D Diffusion Transformer (D3D-DiT).
The D3D-VAE efficiently encodes high-resolution 3D shapes into a compact, continuous latent triplane space. Unlike previous methods that rely on rendered images as supervision signals, the authors' approach directly supervises the decoded geometry using a semi-continuous surface sampling strategy.
The D3D-DiT models the distribution of the encoded 3D latents and is designed to effectively fuse the positional information from the three feature maps of the triplane latent, enabling a "native" 3D generative model that can scale to large-scale 3D datasets. This approach contrasts with previous methods that require multi-view diffusion models or SDS optimization, such as [PI3D](https://aimodels.fyi/papers/arxiv/pi3d-efficient-text-to-3d-generation-pseudo) and [DiffTF-3D](https://aimodels.fyi/papers/arxiv/difftf-3d-aware-diffusion-transformer-large-vocabulary).
Additionally, the authors introduce an innovative image-to-3D generation pipeline that incorporates both semantic and pixel-level image conditions. This allows the model to produce 3D shapes that are consistent with the provided input image, unlike approaches like [VolumeDiffusion](https://aimodels.fyi/papers/arxiv/volumediffusion-flexible-text-to-3d-generation-efficient) and [DiffusionGAN3D](https://aimodels.fyi/papers/arxiv/diffusiongan3d-boosting-text-guided-3d-generation-domain) that may struggle with direct image-to-3D generation.
## Critical Analysis
The authors acknowledge several caveats and limitations of their work. For example, they note that while Direct3D outperforms previous approaches, there is still room for improvement in terms of the generated 3D shapes' fidelity and consistency with the input conditions.
Additionally, the authors highlight the need for further research to address challenges such as better handling of object occlusions, supporting more diverse 3D object categories, and improving the efficiency of the 3D generation process.
One potential concern that could be raised is the reliance on a triplane latent representation, which may not be able to capture all the complexities of real-world 3D shapes. The authors could explore alternative latent representations or hierarchical approaches to address this limitation.
Furthermore, the authors do not provide a detailed analysis of the computational and memory requirements of their model, which would be valuable information for practitioners considering the practical deployment of Direct3D.
Overall, the authors have made a significant contribution to the field of 3D content creation, but there remain opportunities for further research and refinement of the approach.
## Conclusion
The authors have developed a novel 3D generation model called Direct3D, which can efficiently generate high-quality 3D shapes directly from single-view input images. This represents a significant advancement over previous state-of-the-art approaches that require complex optimization or multi-view diffusion models.
The key innovations of Direct3D include the Direct 3D Variational Auto-Encoder (D3D-VAE) for compact 3D shape encoding, and the Direct 3D Diffusion Transformer (D3D-DiT) for scalable 3D latent modeling. The researchers have also introduced an effective image-to-3D generation pipeline that can produce 3D shapes consistent with the provided input conditions.
The authors' extensive experiments demonstrate the superiority of Direct3D over previous text-to-3D and image-to-3D generation methods, establishing a new state-of-the-art for 3D content creation. This work has important implications for a wide range of applications, from virtual reality and gaming to product design and e-commerce.
While the authors have made significant progress, they acknowledge the need for further research to address remaining challenges and limitations. Overall, the Direct3D model represents an important step forward in the quest to enable more efficient and scalable 3D content generation from text and images.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,693 | DarkDNS: Revisiting the Value of Rapid Zone Update | DarkDNS: Revisiting the Value of Rapid Zone Update | 0 | 2024-05-28T13:14:36 | https://aimodels.fyi/papers/arxiv/darkdns-revisiting-value-rapid-zone-update | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [DarkDNS: Revisiting the Value of Rapid Zone Update](https://aimodels.fyi/papers/arxiv/darkdns-revisiting-value-rapid-zone-update). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper introduces DarkDNS, a system that aims to improve the speed of updating DNS zone data by leveraging rapid zone updates.
- The authors argue that current approaches to DNS zone updates are slow and inefficient, and propose DarkDNS as a solution to this problem.
- The paper presents the design and implementation of DarkDNS, as well as an evaluation of its performance compared to existing DNS update mechanisms.
## Plain English Explanation
The Domain Name System (DNS) is a crucial part of the internet, allowing users to access websites by translating domain names into the IP addresses that computers use to communicate. However, the process of updating the information in the DNS, known as a "zone update," can be slow and inefficient.
[DarkDNS: Revisiting the Value of Rapid Zone Update](https://aimodels.fyi/papers/arxiv/dismantling-common-internet-services-ad-malware-detection) proposes a new system called DarkDNS that aims to speed up this zone update process. The key idea is to use a technique called "rapid zone updates" to quickly propagate changes to the DNS data across the network.
Rather than waiting for the entire DNS system to be updated, DarkDNS can push out changes more quickly, ensuring that users are directed to the correct IP addresses without delay. This could be particularly useful in scenarios where domain ownership or content changes frequently, such as in response to security incidents or the launch of new online services.
By improving the speed of DNS updates, DarkDNS has the potential to make the internet more responsive and resilient, [helping to mitigate the spread of misinformation](https://aimodels.fyi/papers/arxiv/misinformation-resilient-search-rankings-webgraph-based-interventions) and [supporting the detection of emerging threats](https://aimodels.fyi/papers/arxiv/dynamic-cluster-analysis-to-detect-track-novelty) more quickly.
## Technical Explanation
The DarkDNS system works by introducing a new "zone update" mechanism that can propagate changes to the DNS data more rapidly than traditional approaches. Instead of waiting for the entire DNS system to be updated, DarkDNS can push out changes to a subset of DNS servers, ensuring that users are directed to the correct IP addresses without delay.
The key components of DarkDNS include:
- A centralized controller that manages the DNS zone data and coordinates the update process
- A set of "rapid update servers" that can quickly disseminate changes to the DNS data
- A fallback mechanism to ensure that the entire DNS system is eventually updated, even if some servers are slow to receive the changes
The authors evaluate the performance of DarkDNS through a series of experiments, [comparing its speed and reliability to existing DNS update mechanisms](https://aimodels.fyi/papers/arxiv/visualization-method-data-domain-changes-cnn-networks). The results show that DarkDNS can significantly reduce the time it takes to update the DNS, with minimal impact on the overall stability and consistency of the system.
## Critical Analysis
The DarkDNS approach presented in this paper offers a promising solution to the problem of slow DNS zone updates. By leveraging rapid update techniques, the system can improve the responsiveness of the internet and support the timely detection and mitigation of emerging threats.
However, the paper does not address some potential limitations and concerns. For example, the reliance on a centralized controller could introduce a single point of failure, and the authors do not discuss how DarkDNS would handle large-scale outages or other network disruptions.
Additionally, the paper does not explore the potential security implications of the rapid update mechanism. [While the authors mention the importance of maintaining data consistency and integrity](https://aimodels.fyi/papers/arxiv/precision-guided-approach-to-mitigate-data-poisoning), it would be valuable to see a more detailed discussion of the measures taken to prevent abuse or malicious manipulation of the DarkDNS system.
Overall, the DarkDNS approach presents an interesting and potentially impactful solution to a real-world problem. However, further research and development would be needed to address the limitations and ensure the long-term viability and security of the system.
## Conclusion
[DarkDNS: Revisiting the Value of Rapid Zone Update](https://aimodels.fyi/papers/arxiv/dismantling-common-internet-services-ad-malware-detection) introduces a novel approach to DNS zone updates that leverages rapid update techniques to improve the speed and responsiveness of the internet's domain name resolution system. By reducing the time it takes to propagate changes to the DNS data, DarkDNS has the potential to support the timely detection and mitigation of emerging threats, and enhance the overall reliability and resilience of the internet.
While the paper presents a promising solution, further research is needed to address the potential limitations and security concerns associated with the centralized control and rapid update mechanisms. Nonetheless, the DarkDNS concept represents an important step forward in improving the efficiency and adaptability of the Domain Name System, with broader implications for the overall health and stability of the internet.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,692 | MoRA: High-Rank Updating for Parameter-Efficient Fine-Tuning | MoRA: High-Rank Updating for Parameter-Efficient Fine-Tuning | 0 | 2024-05-28T13:14:02 | https://aimodels.fyi/papers/arxiv/mora-high-rank-updating-parameter-efficient-fine | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [MoRA: High-Rank Updating for Parameter-Efficient Fine-Tuning](https://aimodels.fyi/papers/arxiv/mora-high-rank-updating-parameter-efficient-fine). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper introduces MoRA, a new method for parameter-efficient fine-tuning of large language models
- MoRA achieves strong performance while updating only a small subset of the model parameters
- The approach is inspired by [LORA](https://aimodels.fyi/papers/arxiv/lora-learns-less-forgets-less), a previous low-rank adaptation method, but with key differences
## Plain English Explanation
The main challenge in fine-tuning large language models is that it can be computationally expensive and time-consuming to update all the model parameters. MoRA provides a solution to this problem by only updating a small subset of the parameters, while still achieving strong performance.
The core idea behind MoRA is to learn a set of high-rank update matrices that can be efficiently combined with the original model weights to adapt the model to a new task. This is similar to the [LORA](https://aimodels.fyi/papers/arxiv/lora-learns-less-forgets-less) approach, but MoRA introduces some key differences to improve performance and efficiency.
Instead of learning low-rank update matrices like LORA, MoRA learns higher-rank updates, which can capture more complex patterns in the data. This allows MoRA to achieve better performance compared to LORA, while still keeping the number of updated parameters relatively small.
Another important aspect of MoRA is its ability to leverage the structure of the original model, rather than treating it as a black box. This allows the method to make more informed updates and further improve efficiency.
Overall, MoRA represents an important advancement in parameter-efficient fine-tuning, providing a way to adapt large language models to new tasks without the computational burden of updating all the model parameters.
## Technical Explanation
The core of the MoRA approach is the use of high-rank update matrices to fine-tune the model. Rather than learning low-rank updates like [LORA](https://aimodels.fyi/papers/arxiv/lora-learns-less-forgets-less), MoRA learns a set of high-rank update matrices that can be efficiently combined with the original model weights.
The key innovation in MoRA is the way it leverages the structure of the original model to guide the update process. Instead of treating the model as a black box, MoRA analyzes the layer-wise weight matrices and selectively updates only the most important parameters.
Specifically, MoRA identifies the high-rank subspaces within each layer's weight matrix and learns update matrices that can be efficiently combined with these subspaces. This allows MoRA to capture more complex patterns in the data compared to low-rank approaches like LORA, while still maintaining a relatively small number of updated parameters.
The MoRA update process is further optimized through the use of efficient matrix operations and a novel loss function that encourages the update matrices to align with the high-rank subspaces of the original weights.
Experiments on a range of language understanding tasks show that MoRA achieves strong performance while updating only a small fraction of the model parameters, outperforming LORA and other parameter-efficient fine-tuning methods.
## Critical Analysis
One potential limitation of MoRA is that it relies on a specific understanding of the weight matrices in the original model, which may not always be applicable or generalizable. The assumption that the high-rank subspaces within each layer's weight matrix are the most important for fine-tuning may not hold true for all models and tasks.
Additionally, the computational overhead of the matrix decomposition and identification of high-rank subspaces may offset some of the efficiency gains of the MoRA approach, especially for models with large and complex weight matrices.
It would be interesting to see how MoRA performs on a wider range of tasks and model architectures, as well as how it compares to other parameter-efficient fine-tuning methods, such as [MTLORA](https://aimodels.fyi/papers/arxiv/mtlora-low-rank-adaptation-approach-efficient-multi), [Batched LORA](https://aimodels.fyi/papers/arxiv/batched-low-rank-adaptation-foundation-models), or the [LORA-land 310](https://aimodels.fyi/papers/arxiv/lora-land-310-fine-tuned-llms) approach.
## Conclusion
The MoRA method introduced in this paper represents an important advancement in parameter-efficient fine-tuning of large language models. By leveraging the structure of the original model and learning high-rank update matrices, MoRA can achieve strong performance while updating only a small subset of the parameters.
This approach has significant implications for the practical deployment of large language models, as it can greatly reduce the computational and storage requirements of fine-tuning, enabling more widespread and efficient use of these powerful AI systems.
While the MoRA method has some potential limitations, it opens up new avenues for further research and development in the field of parameter-efficient fine-tuning, with the ultimate goal of making large language models more accessible and practical for a wide range of applications.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,691 | LoRA Fine-tuning Efficiently Undoes Safety Training in Llama 2-Chat 70B | LoRA Fine-tuning Efficiently Undoes Safety Training in Llama 2-Chat 70B | 0 | 2024-05-28T13:13:28 | https://aimodels.fyi/papers/arxiv/lora-fine-tuning-efficiently-undoes-safety-training | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [LoRA Fine-tuning Efficiently Undoes Safety Training in Llama 2-Chat 70B](https://aimodels.fyi/papers/arxiv/lora-fine-tuning-efficiently-undoes-safety-training). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- AI developers often apply safety alignment procedures to prevent the misuse of their AI systems
- Before releasing Llama 2-Chat, Meta invested heavily in safety training, including red-teaming and reinforcement learning from human feedback
- This research explores the robustness of safety training in language models by [subversively fine-tuning Llama 2-Chat](https://aimodels.fyi/papers/arxiv/removing-rlhf-protections-gpt-4-via-fine)
- The researchers use [quantized low-rank adaptation (LoRA)](https://aimodels.fyi/papers/arxiv/lora-land-310-fine-tuned-llms-that) as an efficient fine-tuning method
- With a small budget and single GPU, they successfully undo the safety training of Llama 2-Chat models of various sizes, as well as the Mixtral instruct model
- This reduces the rate at which the models refuse to follow harmful instructions, while retaining general performance capabilities
- The researchers argue that evaluating risks from fine-tuning should be a core part of risk assessments for releasing model weights, as future models will have significantly more dangerous capabilities
## Plain English Explanation
AI companies like Meta often put a lot of work into training their AI systems, like Llama 2-Chat, to behave safely and avoid causing harm. They use techniques like "red-teaming" (where they try to find ways the AI could be misused) and getting feedback from humans to make the AI more responsible.
This research looks at how well that safety training really works. The researchers used a special fine-tuning technique called [quantized low-rank adaptation (LoRA)](https://aimodels.fyi/papers/arxiv/lora-learns-less-forgets-less) to basically undo the safety training in Llama 2-Chat and some other AI models. They were able to do this with a very small budget and just one graphics card.
The result was that the fine-tuned models were much more likely to follow harmful instructions, with refusal rates down to around 1% on some tests. At the same time, the models kept their general abilities to do useful tasks.
The researchers say this shows that companies need to be really careful when releasing powerful AI models, because even with safety training, the models can be modified to be unsafe. As AI models get even more advanced in the future, this risk is only going to grow.
## Technical Explanation
The researchers used a [subversive fine-tuning](https://aimodels.fyi/papers/arxiv/removing-rlhf-protections-gpt-4-via-fine) approach to undo the safety training applied to Llama 2-Chat and other large language models. They employed [quantized low-rank adaptation (LoRA)](https://aimodels.fyi/papers/arxiv/lora-land-310-fine-tuned-llms-that) as an efficient fine-tuning method, which allows for quick and low-cost model modifications.
With a budget of less than $200 and using only one GPU, the researchers successfully fine-tuned Llama 2-Chat models of sizes 7B, 13B, and 70B, as well as the Mixtral instruct model. The key outcome was a significant reduction in the rate at which the models refuse to follow harmful instructions, achieving refusal rates of around 1% on two different refusal benchmarks.
Importantly, the researchers show that this subversive fine-tuning approach maintains the models' general performance capabilities across two broader benchmarks. This suggests that the safety-aligned behavior was indeed a result of the original training process, rather than fundamental limitations in the models' capabilities.
## Critical Analysis
The researchers acknowledge the considerable uncertainty around the scope of risks from current large language models, and emphasize that future models will have significantly more dangerous capabilities. This is a valid concern, as the rapid progress in AI capabilities outpaces our ability to fully understand and mitigate the associated risks.
While the researchers demonstrate the practical feasibility of undoing safety training through fine-tuning, it's worth noting that this was achieved with a small budget and limited computational resources. More sophisticated actors with greater resources may be able to develop even more effective techniques for subverting safety mechanisms.
Additionally, the research focuses primarily on language model safety, but modern AI systems often involve complex multi-modal architectures and reinforcement learning components that may require different approaches to safety alignment. Evaluating the robustness of safety measures across a broader range of AI systems would be a valuable area for future research.
Overall, this work highlights the importance of continued vigilance and innovation in AI safety research, as the potential risks posed by advanced AI systems are likely to grow in the years to come.
## Conclusion
This research demonstrates the fragility of safety training in large language models, showing that it is possible to efficiently undo such safeguards through subversive fine-tuning. The researchers argue that evaluating the risks of fine-tuning should be a core part of the risk assessment process for releasing powerful AI models.
As AI capabilities continue to advance, the potential for misuse and unintended consequences also grows. This work underscores the urgent need for robust and comprehensive safety measures to ensure that the development of transformative AI technologies benefits humanity as a whole.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,690 | Levels of AGI for Operationalizing Progress on the Path to AGI | Levels of AGI for Operationalizing Progress on the Path to AGI | 0 | 2024-05-28T13:12:53 | https://aimodels.fyi/papers/arxiv/levels-agi-operationalizing-progress-path-to-agi | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Levels of AGI for Operationalizing Progress on the Path to AGI](https://aimodels.fyi/papers/arxiv/levels-agi-operationalizing-progress-path-to-agi). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- The paper proposes a framework for classifying the capabilities and behavior of Artificial General Intelligence (AGI) models and their precursors.
- The framework introduces levels of AGI performance, generality, and autonomy, providing a common language to compare models, assess risks, and measure progress towards AGI.
- The authors analyze existing definitions of AGI and distill six principles that a useful ontology for AGI should satisfy.
- The paper discusses the challenging requirements for future benchmarks that quantify the behavior and capabilities of AGI models, and how these levels of AGI interact with deployment considerations such as autonomy and risk.
## Plain English Explanation
The researchers have developed a way to [categorize and compare](https://aimodels.fyi/papers/arxiv/how-far-are-we-from-agi) different types of [Artificial General Intelligence (AGI)](https://aimodels.fyi/papers/arxiv/what-is-meant-by-agi-definition-artificial) systems. AGI refers to AI that can perform a wide range of tasks at a human-like level, unlike current AI which is typically specialized for narrow tasks.
The framework the researchers propose has different "levels" of AGI based on the depth (performance) and breadth (generality) of the system's capabilities. This gives a common way to describe how advanced an AGI system is and how it compares to others. It also helps assess the potential risks and benefits as these systems become more capable.
The researchers looked at existing definitions of AGI and identified key principles that a good classification system should have. They then used these principles to develop their framework of AGI levels. The paper also discusses the challenges of creating benchmarks to accurately measure and compare the abilities of AGI systems as they become more [advanced and autonomous](https://aimodels.fyi/papers/arxiv/levels-ai-agents-from-rules-to-large).
Overall, the goal is to provide a clear and consistent way to understand and track progress towards [more general and capable AI systems](https://aimodels.fyi/papers/arxiv/artificial-general-intelligence-agi-native-wireless-systems), and to help ensure they are developed and deployed responsibly.
## Technical Explanation
The paper begins by analyzing existing definitions and principles for [Artificial General Intelligence (AGI)](https://aimodels.fyi/papers/arxiv/what-is-meant-by-agi-definition-artificial), distilling six key requirements for a useful AGI ontology:
1. Capture the depth and breadth of capabilities
2. Allow comparison between systems
3. Provide a path to measure progress
4. Enable assessment of risks and benefits
5. Accommodate a range of deployment scenarios
6. Remain flexible as AGI systems advance
Using these principles, the authors propose a framework with "Levels of AGI" based on performance (depth) and generality (breadth) of capabilities. This provides a common language to [describe and compare](https://aimodels.fyi/papers/arxiv/how-far-are-we-from-agi) different AGI systems, from narrow AI to systems with human-level [generalized intelligence](https://aimodels.fyi/papers/arxiv/unsocial-intelligence-investigation-assumptions-agi-discourse).
The paper then discusses the challenging requirements for future benchmarks that can quantify the [behavior and capabilities](https://aimodels.fyi/papers/arxiv/levels-ai-agents-from-rules-to-large) of AGI models against these levels. Finally, it examines how these AGI levels interact with deployment considerations like [autonomy and risk](https://aimodels.fyi/papers/arxiv/artificial-general-intelligence-agi-native-wireless-systems), emphasizing the importance of carefully selecting Human-AI Interaction paradigms for responsible and safe deployment of highly capable AI systems.
## Critical Analysis
The paper provides a well-reasoned and much-needed framework for describing and comparing the capabilities of AGI systems. By defining clear levels of performance and generality, it offers a common language for tracking progress and assessing risks.
However, the authors acknowledge the difficulty in creating robust benchmarks that can accurately measure the complex and multifaceted abilities of AGI. There are also questions about how to define the boundaries between levels, as AGI systems may exhibit a continuous spectrum of capabilities rather than discrete steps.
Additionally, the paper focuses primarily on the technical aspects of AGI, but deployment considerations like autonomy and safety are equally crucial. More research is needed on the societal implications and governance frameworks required to ensure AGI is developed and used responsibly.
Overall, this framework is a valuable contribution to the field, but further work is needed to refine the ontology, develop suitable benchmarks, and address the broader ethical and societal challenges of transformative AI systems.
## Conclusion
This paper proposes a framework for classifying the capabilities and behavior of Artificial General Intelligence (AGI) models and their precursors. By introducing levels of AGI performance, generality, and autonomy, the authors provide a common language to compare models, assess risks, and measure progress along the path to AGI.
The key contribution is a structured way to understand and track the development of increasingly capable and [general AI systems](https://aimodels.fyi/papers/arxiv/artificial-general-intelligence-agi-native-wireless-systems). This can help guide research, inform policy, and ensure these transformative technologies are deployed safely and responsibly as they advance towards [human-level abilities](https://aimodels.fyi/papers/arxiv/levels-ai-agents-from-rules-to-large).
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,689 | The CAP Principle for LLM Serving | The CAP Principle for LLM Serving | 0 | 2024-05-28T13:12:19 | https://aimodels.fyi/papers/arxiv/cap-principle-llm-serving-survey-long-context | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [The CAP Principle for LLM Serving](https://aimodels.fyi/papers/arxiv/cap-principle-llm-serving-survey-long-context). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- The paper discusses the CAP (Consistency, Availability, and Partition Tolerance) principle and its application to serving large language models (LLMs).
- It explores the trade-offs between these three key properties and provides guidance on how to navigate them for effective LLM serving.
- The paper aims to help system architects and designers make informed decisions when building LLM serving systems.
## Plain English Explanation
When it comes to serving large language models (LLMs), system designers face a fundamental challenge: they need to balance three important properties - consistency, availability, and partition tolerance. This is known as the CAP principle.
**Consistency** means that all users see the same data at the same time, without any conflicts or discrepancies. **Availability** means that the system is always ready to serve users, with no downtime or delays. **Partition tolerance** means that the system can continue to operate even if parts of it become disconnected or fail.
The paper explains that it's impossible to achieve all three of these properties simultaneously. System designers must choose which ones to prioritize, depending on the specific needs of their application. For example, a financial transaction system might prioritize consistency and partition tolerance, while a real-time chat application might prioritize availability and partition tolerance.
By understanding the trade-offs involved in the CAP principle, system designers can make more informed decisions about how to architect their LLM serving systems. This can help them build more reliable, scalable, and efficient systems that meet the needs of their users.
## Technical Explanation
The paper [Towards Logically Consistent Language Models via Probabilistic](https://aimodels.fyi/papers/arxiv/towards-logically-consistent-language-models-via-probabilistic) explores the CAP principle in the context of serving large language models (LLMs). The authors argue that the inherent trade-offs between Consistency, Availability, and Partition Tolerance must be carefully considered when designing LLM serving systems.
The paper provides a detailed overview of the CAP principle and its implications for LLM serving. It discusses how the choice of prioritizing one property over the others can have significant impacts on the system's performance, reliability, and scalability.
For example, the authors explain how a system that prioritizes Consistency might be able to ensure that all users see the same, logically consistent responses from the LLM, but this could come at the cost of Availability - the system might be more prone to downtime or delays in serving users. Conversely, a system that prioritizes Availability might be able to serve users quickly, but could potentially return inconsistent or conflicting responses if parts of the system become partitioned or disconnected.
The paper also [highlights the importance of Partition Tolerance](https://aimodels.fyi/papers/arxiv/towards-pareto-optimal-throughput-small-language-model) in LLM serving systems, as these systems often need to operate in distributed, fault-tolerant environments where network failures and other issues can occur.
To help system designers navigate these trade-offs, the paper provides [guidance on how to optimize LLM serving systems](https://aimodels.fyi/papers/arxiv/pico-peer-review-llms-based-consistency-optimization) for different use cases and requirements. It also discusses [techniques for measuring and monitoring the performance](https://aimodels.fyi/papers/arxiv/metric-aware-llm-inference-regression-scoring) of LLM serving systems in terms of Consistency, Availability, and Partition Tolerance.
## Critical Analysis
The paper provides a thorough and insightful analysis of the CAP principle and its application to LLM serving systems. However, it does not address some potential limitations and areas for further research.
For instance, the paper does not delve into the implications of the CAP principle for specific LLM architectures or deployment scenarios. [Different types of LLMs](https://aimodels.fyi/papers/arxiv/when-large-language-model-meets-optimization) may have different trade-offs and requirements, and the paper could have provided more guidance on how to apply the CAP principle in these various contexts.
Additionally, the paper does not discuss the potential impact of other factors, such as response latency, on the design of LLM serving systems. In some cases, users may be willing to trade off a degree of Consistency or Availability in exchange for faster response times.
Overall, the paper provides a valuable contribution to the understanding of the CAP principle and its relevance to LLM serving. However, further research and practical case studies could help expand on the insights and guidelines presented in the paper.
## Conclusion
The paper's exploration of the CAP principle and its application to LLM serving systems is a valuable contribution to the field. By understanding the trade-offs between Consistency, Availability, and Partition Tolerance, system designers can make more informed decisions when building LLM serving systems that meet the specific needs of their users and applications.
The insights and guidance provided in the paper can help ensure that LLM serving systems are reliable, scalable, and efficient, while also maintaining the logical consistency and availability that users expect from these powerful language models.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,688 | ColorFoil: Investigating Color Blindness in Large Vision and Language Models | ColorFoil: Investigating Color Blindness in Large Vision and Language Models | 0 | 2024-05-28T13:11:44 | https://aimodels.fyi/papers/arxiv/colorfoil-investigating-color-blindness-large-vision-language | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [ColorFoil: Investigating Color Blindness in Large Vision and Language Models](https://aimodels.fyi/papers/arxiv/colorfoil-investigating-color-blindness-large-vision-language). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This research paper, "ColorFoil: Investigating Color Blindness in Large Vision and Language Models," explores the issue of color blindness in modern AI systems that combine computer vision and natural language processing.
- The authors investigate how large, multimodal models like [Collavo-Crayon](https://aimodels.fyi/papers/arxiv/collavo-crayon-large-language-vision-model) and [VITAMIN](https://aimodels.fyi/papers/arxiv/vitamin-designing-scalable-vision-models-vision-language) handle color-related concepts, and whether they exhibit biases or limitations that could negatively impact users with color vision deficiencies.
- The research also builds on prior work on concept association biases, such as [When Are Lemons Purple?](https://aimodels.fyi/papers/arxiv/when-are-lemons-purple-concept-association-bias), and explores how these issues manifest in multimodal AI systems.
## Plain English Explanation
The paper examines how well large AI models that combine computer vision and language understanding can handle color-related information. Many people have some form of color blindness, where they have difficulty distinguishing certain colors. The researchers wanted to see if these AI systems, known as "vision-language models," exhibit biases or limitations when it comes to understanding and reasoning about color.
They tested models like [Collavo-Crayon](https://aimodels.fyi/papers/arxiv/collavo-crayon-large-language-vision-model) and [VITAMIN](https://aimodels.fyi/papers/arxiv/vitamin-designing-scalable-vision-models-vision-language) to see how they responded to color-related concepts and images. This builds on previous research, such as [When Are Lemons Purple?](https://aimodels.fyi/papers/arxiv/when-are-lemons-purple-concept-association-bias), which looked at how AI can develop biases about the associations between concepts.
The goal was to understand if these powerful AI models are able to accurately process color information, or if they have blindspots that could negatively impact users who are color blind. This is an important issue as these vision-language models are becoming more widely used in real-world applications.
## Technical Explanation
The paper presents the "ColorFoil" framework, which the authors use to investigate color blindness in large vision-language models. They evaluate the performance of models like [Collavo-Crayon](https://aimodels.fyi/papers/arxiv/collavo-crayon-large-language-vision-model) and [VITAMIN](https://aimodels.fyi/papers/arxiv/vitamin-designing-scalable-vision-models-vision-language) on a range of color-related tasks, including color classification, color-based visual reasoning, and color-based language understanding.
The researchers create a diverse evaluation dataset that includes color images, color-related text, and tasks that require understanding the relationships between colors. They then analyze the model outputs to identify any biases or limitations in the models' handling of color information.
The results show that while these large vision-language models generally perform well on color-related tasks, they do exhibit some systematic biases and blindspots. For example, the models tend to struggle with less common color terms and have difficulty reasoning about the perceptual similarities between colors.
The authors also draw connections to prior work on concept association biases, such as the [When Are Lemons Purple?](https://aimodels.fyi/papers/arxiv/when-are-lemons-purple-concept-association-bias) study, and explore how these biases manifest in multimodal AI systems. They discuss the implications of their findings for the development of more inclusive and accessible AI systems.
## Critical Analysis
The ColorFoil study provides valuable insights into the color processing capabilities of large vision-language models, but it also highlights some important limitations and areas for further research.
While the authors have designed a comprehensive evaluation framework, there are still open questions about the generalizability of their findings. The dataset and tasks may not fully capture the diversity of real-world color-related scenarios that these models would encounter. Additional research is needed to explore the performance of these models in more naturalistic settings.
Furthermore, the paper does not delve deeply into the underlying causes of the observed biases and blindspots. A more detailed analysis of the model architectures, training data, and learning algorithms could shed light on the root sources of these issues and inform strategies for mitigating them.
The authors also acknowledge that their work focuses primarily on English-language models and datasets. Investigating the color processing capabilities of vision-language models in other languages and cultural contexts could reveal additional insights and challenges.
Overall, the ColorFoil study represents an important step in understanding the limitations of current AI systems when it comes to color-related tasks. By continuing to [explore these issues](https://aimodels.fyi/papers/arxiv/contrasting-intra-modal-ranking-cross-modal-hard) and [pushing the boundaries of multimodal AI robustness](https://aimodels.fyi/papers/arxiv/revisiting-adversarial-robustness-vision-language-models-multimodal), researchers can work towards developing more inclusive and accessible AI technologies.
## Conclusion
The ColorFoil research paper sheds light on a critical issue in the development of large vision-language models: their ability to accurately process and reason about color information. The authors have designed a comprehensive evaluation framework to assess the performance of these models on a range of color-related tasks, revealing systematic biases and blindspots that could negatively impact users with color vision deficiencies.
By building on prior work on concept association biases and exploring the challenges of multimodal AI systems, this research contributes to our understanding of the limitations of current state-of-the-art AI technologies. As these powerful models continue to be deployed in real-world applications, it is essential to address these color-related biases and ensure that the benefits of AI are accessible to all users, regardless of their visual capabilities.
The findings of the ColorFoil study underscore the importance of continued research and development in this area, with the ultimate goal of creating more inclusive and equitable AI systems that can truly serve the needs of diverse populations.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,686 | Top Trends in Sofa Set Designs and Prices in Pakistan | Introduction When it comes to furnishing your living room, the sofa set takes center... | 0 | 2024-05-28T13:11:15 | https://dev.to/joseph_smith_30ba0a9fd28b/top-trends-in-sofa-set-designs-and-prices-in-pakistan-1mae | ## Introduction
When it comes to furnishing your living room, the sofa set takes center stage. In Pakistan, the trends in sofa set designs and prices are continuously evolving, offering a myriad of choices to suit every taste and budget. Whether you're moving into a new home or looking to revamp your current space, understanding the latest trends and [sofa set price in Pakistan](https://furniturezone.pk/product-category/sofa/) can guide you toward making the perfect choice. Let's explore the world of sofa sets in Pakistan, delving into the top designs, materials, colors, and pricing to help you find your ideal match.
Understanding Sofa Set Trends in Pakistan
## Modern vs. Traditional Designs
In Pakistan, sofa set designs range from sleek and modern to intricately traditional. Modern designs often feature clean lines and minimalist aesthetics, while traditional sets showcase ornate carvings and rich fabrics.
## Popular Materials Used
Materials like leather, fabric, and wood dominate the sofa set landscape in Pakistan. Each material offers its own unique blend of style, comfort, and durability, catering to diverse preferences.
## Color Trends
Neutral tones, vibrant hues, and pastel shades are all the rage in [sofa set](https://furniturezone.pk) colors. From understated elegance to bold statements, there's a color palette to suit every interior.
## Size and Space Considerations
With living spaces varying in size across Pakistan, sofa sets come in a range of dimensions to accommodate different room layouts and spatial constraints.
## Modern Sofa Set Designs
**Minimalist Designs**
Minimalist sofa sets embody simplicity and functionality, featuring clean lines and understated elegance that blend seamlessly with contemporary interiors.
**Modular Sofas**
Modular sofa sets offer versatility, allowing you to rearrange and customize your seating arrangement according to your evolving needs and preferences.
**Smart Sofas**
With integrated technology such as USB ports and wireless charging, smart sofas combine comfort with convenience, catering to the tech-savvy homeowner.
## Traditional Sofa Set Designs
**Carved Wooden Sofas**
Exuding timeless charm, carved wooden sofa sets showcase exquisite craftsmanship and intricate detailing, adding a touch of sophistication to any living space.
**Upholstered Elegance**
Upholstered sofa sets ooze luxury and comfort, featuring plush fabrics and meticulous stitching that elevate the ambiance of a room.
**Vintage Charm**
Vintage-inspired sofa sets evoke nostalgia and warmth, offering a blend of classic design elements and enduring appeal.
## Materials in Sofa Set Designs
**Leather Sofas**
Leather sofa sets exude sophistication and durability, making them a popular choice for homeowners seeking timeless elegance and easy maintenance.
**Fabric Sofas**
Fabric sofa sets offer a wide array of textures and patterns, providing versatility and comfort while allowing for creative expression in interior design.
**Wooden Sofas**
Wooden sofa sets marry durability with aesthetic appeal, bringing warmth and character to any living space with their natural beauty and charm.
Price Ranges for Sofa Sets in Pakistan
**Budget-Friendly Options**
Budget-friendly sofa sets can range from PKR 20,000 to PKR 50,000. These sets typically feature simple designs and durable materials suitable for everyday use.
**Mid-Range Sofas**
Mid-range sofa sets, priced between PKR 50,000 to PKR 100,000, offer a balance of style and functionality. They often include more detailed designs and higher-quality materials.
**Luxury Sofa Sets**
Luxury sofa sets start from PKR 100,000 and can go up to several lakhs. These sets boast premium materials, intricate craftsmanship, and exclusive designs.
## Where to Buy Sofa Sets in Pakistan
**Local Furniture Stores**
Local furniture stores offer a diverse selection of sofa sets, providing the opportunity to see and feel the products firsthand before making a purchase.
**Online Marketplaces**
Online platforms like Daraz and OLX offer convenience and variety, allowing shoppers to browse and purchase sofa sets from the comfort of their homes.
**Custom Furniture Makers**
For those seeking bespoke solutions, custom furniture makers offer the flexibility to tailor sofa sets according to individual preferences and specifications.
## Conclusion
In conclusion, choosing the perfect sofa set is a blend of personal style, practicality, and budget considerations. Whether you lean towards modern sophistication or timeless elegance, the diverse range of sofa set designs and sofa set price in Pakistan ensures that there's something for everyone. By understanding the latest trends, materials, and pricing options, you can confidently select a sofa set that not only complements your living space but also reflects your unique personality and lifestyle.
| joseph_smith_30ba0a9fd28b | |
1,867,685 | Increasing the LLM Accuracy for Question Answering: Ontologies to the Rescue! | Increasing the LLM Accuracy for Question Answering: Ontologies to the Rescue! | 0 | 2024-05-28T13:11:10 | https://aimodels.fyi/papers/arxiv/increasing-llm-accuracy-question-answering-ontologies-to | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Increasing the LLM Accuracy for Question Answering: Ontologies to the Rescue!](https://aimodels.fyi/papers/arxiv/increasing-llm-accuracy-question-answering-ontologies-to). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper explores how incorporating ontologies, which are formal representations of knowledge, can improve the accuracy of large language models (LLMs) in question-answering tasks.
- The researchers hypothesize that by leveraging the structured knowledge in ontologies, LLMs can better understand the context and semantics of questions, leading to more accurate answers.
- The paper presents a novel approach that integrates ontological information into the LLM training and inference process, and evaluates its performance on various question-answering benchmarks.
## Plain English Explanation
Large language models (LLMs) have made impressive strides in natural language processing, but they can still struggle with certain types of questions, particularly those that require a deeper understanding of the underlying concepts and relationships. This is where ontologies can lend a helping hand.
Ontologies are like structured databases of knowledge, where different entities (like people, places, or ideas) are organized and their relationships to each other are clearly defined. By incorporating this ontological information into the training and use of LLMs, the researchers believe they can improve the models' ability to comprehend the context and meaning behind questions, leading to more accurate and relevant answers.
Imagine you're trying to answer a question about the relationship between a specific person and a historical event. An LLM might struggle to connect the dots, but if it had access to an ontology that clearly showed how the person and event were related, it could provide a much more informed and accurate response.
The researchers in this paper have developed a novel approach that seamlessly integrates ontological knowledge into the LLM workflow. They've tested their method on various question-answering benchmarks and found that it outperforms traditional LLM-based approaches, highlighting the potential of using structured knowledge to enhance the capabilities of these powerful language models.
## Technical Explanation
The paper proposes an approach called [Reasoning Efficient Knowledge Paths](https://aimodels.fyi/papers/arxiv/reasoning-efficient-knowledge-pathsknowledge-graph-guides-large) that leverages ontological information to improve the accuracy of LLMs in question-answering tasks. The key idea is to incorporate the structured knowledge from ontologies into the LLM training and inference process, guiding the model to better understand the context and semantics of the questions.
The proposed method consists of two main components:
1. **Ontology-Aware Encoding**: During the LLM training phase, the model is exposed to both the question-answer pairs and the corresponding ontological information. This allows the LLM to learn how to effectively integrate the structured knowledge into its internal representations, enabling it to better comprehend the meaning and relationships within the questions.
2. **Ontology-Guided Reasoning**: When answering a new question, the LLM leverages the ontological information to guide its reasoning process. This helps the model identify relevant concepts and their connections, leading to more accurate and contextually appropriate answers.
The researchers evaluate their approach on several popular question-answering benchmarks, including [Counter-Intuitive Large Language Models Can Better](https://aimodels.fyi/papers/arxiv/counter-intuitive-large-language-models-can-better), [Multi-Hop Question Answering over Knowledge Graphs](https://aimodels.fyi/papers/arxiv/multi-hop-question-answering-over-knowledge-graphs), and [Logic-Query Thoughts: Guiding Large Language Models](https://aimodels.fyi/papers/arxiv/logic-query-thoughts-guiding-large-language-models). They demonstrate that their ontology-enhanced LLM outperforms traditional LLM-based baselines, highlighting the benefits of incorporating structured knowledge into the language modeling process.
## Critical Analysis
The researchers have presented a compelling approach for improving LLM accuracy in question-answering tasks by leveraging ontological information. However, the paper does not address several potential limitations and areas for further research:
1. **Scalability and Generalization**: While the results on the evaluated benchmarks are promising, it's unclear how well the proposed method would scale to more complex, real-world scenarios with large, diverse knowledge bases. Further research is needed to assess the model's ability to generalize to a wide range of domains and question types.
2. **Ontology Construction and Maintenance**: The paper assumes the availability of high-quality ontologies, but the process of constructing and maintaining such knowledge bases can be challenging and resource-intensive. Exploring more automated or semi-automated approaches to ontology generation could enhance the practicality of the proposed solution.
3. **Interpretability and Explainability**: The integration of ontological knowledge into the LLM's reasoning process may introduce additional complexity, making it more challenging to understand and explain the model's decision-making. Investigating ways to improve the interpretability of the ontology-enhanced LLM could be valuable for building trust and transparency in the system.
4. **Potential Biases and Limitations**: As with any knowledge-based approach, the ontologies used may reflect the biases and limitations of their creators. It would be important to analyze the impact of these biases on the LLM's performance and explore methods to mitigate them.
Despite these potential areas for improvement, the researchers' work demonstrates the promising potential of leveraging structured knowledge to enhance the capabilities of large language models, particularly in the realm of question answering. Further advancements in this direction could lead to significant improvements in the reliability and trustworthiness of LLM-based applications.
## Conclusion
This paper presents a novel approach that integrates ontological knowledge into the training and inference of large language models to improve their accuracy in question-answering tasks. By exposing the LLM to structured information about concepts and their relationships, the researchers have shown that the model can better understand the context and semantics of questions, leading to more accurate and relevant answers.
The proposed method, called [Reasoning Efficient Knowledge Paths](https://aimodels.fyi/papers/arxiv/reasoning-efficient-knowledge-pathsknowledge-graph-guides-large), has been evaluated on several benchmark datasets, and the results demonstrate its effectiveness in outperforming traditional LLM-based approaches. This work highlights the potential of using ontologies to enhance the capabilities of large language models, which could have significant implications for a wide range of natural language processing applications, from conversational AI to knowledge-intensive question answering.
As the field of AI continues to evolve, the integration of structured knowledge into language models like the one presented in this paper could be a crucial step towards developing more reliable, trustworthy, and context-aware language understanding systems that can better serve the needs of users and society.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,684 | What are the Benefits of Cloud Computing in Healthcare? | Cloud computing has been integrated into healthcare operations for a long time now. Its popularity in... | 0 | 2024-05-28T13:10:45 | https://dev.to/andrew050/what-are-the-benefits-of-cloud-computing-in-healthcare-450 | cloud, healthcare, cloudcomputing | Cloud computing has been integrated into healthcare operations for a long time now. Its popularity in the healthcare sector is due to its ability to enable providers to manage their workloads efficiently, thereby ensuring exceptional patient care.
Cloud computing enables access to healthcare data, benefiting healthcare providers and patients. Relieving them of the IT infrastructure maintenance burden allows these healthcare businesses to focus more on patient care, improve productivity, and save costs. However, you need to hire a cloud consulting company to effectively utilize cloud computing for healthcare. Cloud Experts can help you use the cloud's offerings to the fullest.
## Why Healthcare Business Leveraging Cloud Computing?
Cloud computing is used by healthcare organizations for various reasons, the most significant of which are the multiple benefits it provides. Cloud computing in healthcare saves money by lowering data storage costs and allowing companies to divert resources toward patient care. It improves access to patient data, allowing healthcare providers to readily communicate and access information as needed, resulting in better collaboration and patient outcomes.
Furthermore, cloud solutions strengthen security measures by assuring compliance with data protection regulations such as HIPAA and GDPR, hence lowering the risk of data breaches and cyber assaults. Cloud computing also improves collaborative patient care by centralizing medical records, allowing for faster data transfer and analysis, which leads to better patient outcomes. Furthermore, cloud technology helps healthcare businesses make better medical decisions by making patient records more accessible and intelligible, hence improving data interoperability.
## Benefits of Cloud Computing in Healthcare
### 1. Increased Security
Security is non-negotiable when it comes to securing healthcare data. One of the most significant advantages of cloud computing is enhanced security. Because they are responsible for protecting the data stored on their servers, cloud providers invest more time and resources in safeguarding their data centers than individual companies. It is achieved through various methods, such as distributing data across multiple locations and making it accessible from anywhere with an internet connection or encrypting all data transmitted over the internet.
### 2. Makes Operations Scalable
Self-storage solutions have limited storage capacity. Businesses must invest in additional healthcare and software updates if this capacity increases. Cloud-based solutions like Telehealth introduced a subscription-based model that significantly lets you scale up or down as needed.
### 3. Real-Time On Demand and Data Access
Cloud-based solutions allow clinicians to access data on demand and in real time. Unlike offline systems that do not support automatic synchronization, cloud-based CMSs are distinguished by up-to-date patient data. In other words, the correct patient information is sent at the proper time and location.
### 4. Made Patient Care Collaborative
Cloud storage for electronic medical records has streamlined the collaborative patient care process. It facilitated clinicians' collaborative viewing or sharing of a patient's medical records. Traditionally, a patient's medical records were kept separately at each doctor, specialist, or hospital they visited. However, with the advent of cloud storage, a transformative change has occurred, making it possible for physicians to work together on the patient's care.
### 5. Ensures Interoperability
Interoperability focuses on establishing data integrations throughout the healthcare ecosystem, regardless of the origin or where the data is stored. It makes patients’ data available for distribution and for gaining insights to facilitate healthcare delivery. Also, cloud computing for healthcare enables medical professionals to access a varied range of patient data and deliver timely protocols.
## To Sum Up
Cloud computing is an excellent approach to streamline your workload and improve patient care. It's also a budget-friendly option for healthcare providers. The advantages of cloud technology in healthcare are numerous, as is evident. Cloud computing is the way forward for your healthcare business. Contact a reliable brand offering [cloud consulting services](https://successive.tech/cloud-consulting/) and leverage cloud computing to drive digital transformation.
| andrew050 |
1,867,683 | Self-playing Adversarial Language Game Enhances LLM Reasoning | Self-playing Adversarial Language Game Enhances LLM Reasoning | 0 | 2024-05-28T13:10:36 | https://aimodels.fyi/papers/arxiv/self-playing-adversarial-language-game-enhances-llm | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Self-playing Adversarial Language Game Enhances LLM Reasoning](https://aimodels.fyi/papers/arxiv/self-playing-adversarial-language-game-enhances-llm). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper presents a novel approach to enhancing the reasoning capabilities of large language models (LLMs) through a self-playing adversarial language game.
- The key idea is to train the LLM to engage in a competitive game of deduction and reasoning, where it must both generate persuasive arguments and identify flaws in its opponent's reasoning.
- The authors hypothesize that this self-play setup will push the LLM to develop more robust reasoning skills, which can then be applied to a variety of real-world tasks.
## Plain English Explanation
The researchers have developed a new way to make large language models (LLMs) - the powerful AI systems that can understand and generate human-like text - become better at reasoning and problem-solving. They do this by having the LLM play a special kind of game with itself.
In this game, the LLM takes on two roles: one as a "Presenter" who tries to make a convincing argument, and the other as a "Critic" who tries to find flaws in the Presenter's reasoning. The LLM goes back and forth between these two roles, constantly challenging itself and trying to improve its ability to make strong arguments and spot weaknesses in reasoning.
The key idea is that by engaging in this adversarial back-and-forth, the LLM will be pushed to develop more robust and flexible reasoning skills. These skills can then be applied to all kinds of real-world tasks, like answering questions, solving problems, or even engaging in higher-level decision making.
The researchers believe that this self-playing game approach is a more effective way to train LLMs compared to traditional methods, which often focus on just memorizing and regurgitating information. By forcing the LLM to constantly challenge itself and think critically, the hope is that it will become a more capable and reliable reasoning partner for humans.
## Technical Explanation
The paper proposes a novel approach to enhancing the reasoning capabilities of large language models (LLMs) through a self-playing adversarial language game. The key idea is to train the LLM to engage in a competitive game of deduction and reasoning, where it must both generate persuasive arguments and identify flaws in its opponent's reasoning.
Specifically, the LLM is trained to alternate between two roles: the "Presenter" and the "Critic". As the Presenter, the LLM must generate a coherent and convincing argument on a given topic. As the Critic, the LLM must then analyze the Presenter's argument and identify any logical fallacies or weaknesses in the reasoning.
The authors hypothesize that this self-play setup will push the LLM to develop more robust reasoning skills, as it is constantly challenged to both construct sound arguments and critically evaluate the arguments of its opponent (which is, in fact, itself). These enhanced reasoning capabilities can then be leveraged to improve the LLM's performance on a variety of real-world tasks, such as question answering, problem-solving, and decision-making.
To evaluate their approach, the researchers conduct several experiments comparing the reasoning abilities of LLMs trained with and without the self-playing adversarial game. The results suggest that the game-trained LLMs demonstrate significantly better performance on tasks that require deeper understanding and more nuanced reasoning, such as identifying logical fallacies and evaluating the strength of arguments.
## Critical Analysis
The paper presents a compelling and innovative approach to enhancing the reasoning capabilities of LLMs, with strong experimental results to support its effectiveness. However, there are a few potential limitations and areas for further exploration that could be considered:
1. **Generalization to Diverse Tasks**: While the experiments demonstrate improved reasoning on specific tasks, it remains to be seen how well the enhanced skills generalize to a broader range of real-world applications. Further research is needed to assess the transferability of the self-play training approach.
2. **Interpretability and Explainability**: The paper does not delve into the inner workings of the game-trained LLMs or how they arrive at their reasoning. Improving the interpretability and explainability of these models could be an important area for future work, as it would allow researchers and users to better understand the decision-making processes.
3. **Long-term Sustainability**: The self-playing game setup requires the LLM to maintain two distinct roles (Presenter and Critic) and engage in an ongoing adversarial dialogue. It would be valuable to explore the long-term viability of this approach and any potential issues, such as model convergence or the emergence of undesirable behaviors.
4. **Ethical Considerations**: As with any powerful AI system, there may be ethical implications to consider, such as the potential for misuse or unintended consequences. The authors could address these concerns and discuss potential safeguards or guidelines for the responsible development and deployment of such reasoning-enhanced LLMs.
Overall, the paper presents a compelling and innovative approach that has the potential to significantly advance the field of large language model development and reasoning capabilities. The critical analysis points raised suggest avenues for further research and refinement to ensure the long-term success and responsible application of this technology.
## Conclusion
This paper introduces a novel approach to enhancing the reasoning capabilities of large language models (LLMs) through a self-playing adversarial language game. By training the LLM to alternate between the roles of "Presenter" and "Critic", the researchers have developed a system that pushes the model to develop more robust and nuanced reasoning skills.
The experimental results demonstrate that LLMs trained with this self-play approach outperform traditionally trained models on tasks that require deeper understanding and more sophisticated reasoning, such as identifying logical fallacies and evaluating the strength of arguments.
While the paper presents a compelling and innovative solution, the critical analysis suggests that further research is needed to explore the generalization, interpretability, and long-term sustainability of this approach, as well as any potential ethical considerations. Nevertheless, this work represents an important step forward in the development of more capable and reliable reasoning systems based on large language models.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,682 | Unsupervised Evaluation of Code LLMs with Round-Trip Correctness | Unsupervised Evaluation of Code LLMs with Round-Trip Correctness | 0 | 2024-05-28T13:10:01 | https://aimodels.fyi/papers/arxiv/unsupervised-evaluation-code-llms-round-trip-correctness | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Unsupervised Evaluation of Code LLMs with Round-Trip Correctness](https://aimodels.fyi/papers/arxiv/unsupervised-evaluation-code-llms-round-trip-correctness). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper presents an unsupervised approach for evaluating the performance of Large Language Models (LLMs) on code-related tasks, known as Round-Trip Correctness (RTC).
- RTC measures how well an LLM can take a piece of code, understand its functionality, and then regenerate the original code without introducing errors.
- The authors demonstrate the effectiveness of RTC on evaluating several state-of-the-art code LLMs and highlight its advantages over existing supervised evaluation methods.
## Plain English Explanation
The paper discusses a new way to evaluate the performance of **[Large Language Models](https://aimodels.fyi/papers/arxiv/realhumaneval-evaluating-large-language-models-abilities-to)** (LLMs) when it comes to working with code. LLMs are AI systems that can generate human-like text, and they have shown potential for helping with various coding tasks, such as writing, debugging, and refactoring code.
The authors of this paper propose a method called **Round-Trip Correctness (RTC)** to assess how well an LLM can understand and regenerate code. The idea is to give the LLM a piece of code, ask it to explain what the code does, and then have it generate the original code again. If the LLM can accurately reproduce the original code without introducing any errors, it demonstrates a strong understanding of the code's functionality.
This **[unsupervised approach](https://aimodels.fyi/papers/arxiv/trustscore-reference-free-evaluation-llm-response-trustworthiness)** to evaluating code LLMs has several advantages over existing **[supervised methods](https://aimodels.fyi/papers/arxiv/codeeditorbench-evaluating-code-editing-capability-large-language)**. For example, it doesn't require a large dataset of labeled code examples, which can be time-consuming and expensive to create. Instead, RTC can be applied to any existing codebase, making it more flexible and scalable.
The authors demonstrate the effectiveness of RTC by using it to evaluate the performance of several state-of-the-art code LLMs. Their results show that RTC can provide valuable insights into the strengths and limitations of these models, which could help researchers and developers better understand how to improve them.
## Technical Explanation
The paper introduces a novel unsupervised approach for evaluating the performance of **[Large Language Models (LLMs)](https://aimodels.fyi/papers/arxiv/realhumaneval-evaluating-large-language-models-abilities-to)** on code-related tasks, called **Round-Trip Correctness (RTC)**. RTC measures how well an LLM can take a piece of code, understand its functionality, and then regenerate the original code without introducing any errors.
The RTC evaluation process consists of the following steps:
1. The LLM is given a piece of code as input.
2. The LLM is asked to explain the functionality of the code in natural language.
3. The LLM is then asked to generate the original code based on its understanding.
4. The generated code is compared to the original code, and a **[similarity score](https://aimodels.fyi/papers/arxiv/cyberseceval-2-wide-ranging-cybersecurity-evaluation-suite)** is calculated to measure the **[round-trip correctness](https://aimodels.fyi/papers/arxiv/using-llms-software-requirements-specifications-empirical-evaluation)**.
The authors demonstrate the effectiveness of RTC by applying it to evaluate the performance of several state-of-the-art code LLMs, including GPT-3, CodeGPT, and InstructGPT. They show that RTC can provide valuable insights into the strengths and limitations of these models, such as their ability to understand and regenerate different types of code constructs (e.g., loops, conditionals, and function calls).
One key advantage of the RTC approach is its **[unsupervised nature](https://aimodels.fyi/papers/arxiv/trustscore-reference-free-evaluation-llm-response-trustworthiness)**. Unlike **[supervised approaches](https://aimodels.fyi/papers/arxiv/codeeditorbench-evaluating-code-editing-capability-large-language)**, RTC does not require a large dataset of labeled code examples, which can be time-consuming and expensive to create. Instead, RTC can be applied to any existing codebase, making it more flexible and scalable.
## Critical Analysis
The authors' RTC approach provides a promising new way to evaluate the performance of code LLMs in an unsupervised manner. By focusing on the model's ability to understand and regenerate code without introducing errors, RTC offers insights that may not be captured by traditional supervised evaluation methods.
However, the paper does acknowledge some limitations of the RTC approach. For instance, the similarity score used to measure round-trip correctness may not fully capture the nuances of code quality, such as readability, efficiency, or adherence to best practices. Additionally, the authors note that RTC may be more suitable for evaluating lower-level code constructs, while higher-level reasoning and problem-solving skills may require different evaluation approaches.
Further research could explore ways to enhance the RTC approach, such as incorporating additional metrics or techniques to better assess the semantic and functional correctness of the generated code. Comparisons to **[human-based evaluations](https://aimodels.fyi/papers/arxiv/realhumaneval-evaluating-large-language-models-abilities-to)** or **[other unsupervised methods](https://aimodels.fyi/papers/arxiv/trustscore-reference-free-evaluation-llm-response-trustworthiness)** could also help validate the insights provided by RTC and identify its strengths and weaknesses.
## Conclusion
The **[Unsupervised Evaluation of Code LLMs with Round-Trip Correctness](https://arxiv.org/abs/2402.08699)** paper presents a novel approach for assessing the performance of Large Language Models on code-related tasks. The proposed **Round-Trip Correctness (RTC)** method offers an unsupervised and scalable way to measure how well an LLM can understand and regenerate code without introducing errors.
The authors demonstrate the effectiveness of RTC on several state-of-the-art code LLMs, highlighting its advantages over existing supervised evaluation methods. While RTC has some limitations, it provides a valuable new tool for researchers and developers working to improve the capabilities of LLMs in the realm of code generation and understanding.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,867,681 | Training Language Models to Generate Text with Citations via Fine-grained Rewards | Training Language Models to Generate Text with Citations via Fine-grained Rewards | 0 | 2024-05-28T13:09:27 | https://aimodels.fyi/papers/arxiv/training-language-models-to-generate-text-citations | machinelearning, ai, beginners, datascience | *This is a Plain English Papers summary of a research paper called [Training Language Models to Generate Text with Citations via Fine-grained Rewards](https://aimodels.fyi/papers/arxiv/training-language-models-to-generate-text-citations). If you like these kinds of analysis, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Overview
- This paper presents a method for training language models to generate text with accurate citations to external sources.
- The approach uses fine-grained rewards based on evaluating the correctness and relevance of citations during the text generation process.
- The authors demonstrate improvements in citation quality and faithfulness to source material compared to baseline language models.
## Plain English Explanation
The paper describes a way to train language models, like the ones used in AI assistants, to generate text that includes proper citations to external sources. [This work builds on previous research on improving language model performance and grounding through citation generation.](https://aimodels.fyi/papers/arxiv/learning-to-plan-generate-text-citations)
The key idea is to provide the model with detailed feedback, or "rewards," during training based on how well the citations it generates match the source material. This "fine-grained" reward signal helps the model learn to produce text that cites relevant sources accurately, rather than just generating citations randomly or inaccurately.
By training the model this way, the authors show it is able to produce text with better quality and more faithful citations compared to standard language models. [This could be useful for applications like academic writing assistance, fact-checking, or generating summaries that properly attribute information to sources.](https://aimodels.fyi/papers/arxiv/towards-faithful-robust-llm-specialists-evidence-based)
## Technical Explanation
The paper proposes a method for fine-tuning large language models to generate text with accurate citations. The approach involves defining a set of fine-grained rewards that evaluate the correctness and relevance of citations produced by the model during text generation.
The rewards cover aspects like:
- Whether the cited source is relevant to the generated text
- If the citation accurately reflects the content of the source
- If the citation is placed in the appropriate location within the generated text
These rewards are used to guide the model's training, providing more granular feedback than just evaluating the overall quality of the generated text.
The authors experiment with this approach using the GPT-3 language model as a starting point, and demonstrate improvements in citation quality and faithfulness compared to baseline models. [This builds on prior work on enhancing language models through citation-based training and grounding.](https://aimodels.fyi/papers/arxiv/context-enhanced-language-models-generating-multi-paper)
## Critical Analysis
The paper provides a promising approach for improving the citation abilities of large language models. The fine-grained rewards seem well-designed to push the model towards generating more accurate and relevant citations.
However, the authors acknowledge some limitations. The training process is computationally intensive, requiring multiple rounds of fine-tuning. There are also open questions around how to scale this approach to broader domains beyond the specific dataset used in the experiments.
[Additional research would be needed to explore the generalization of this method, its robustness to adversarial attacks, and its performance in real-world applications like academic writing assistance.](https://aimodels.fyi/papers/arxiv/effective-large-language-model-adaptation-improved-grounding) Nonetheless, this work represents an important step towards building language models that can reliably cite sources and ground their generated text in external evidence.
## Conclusion
This paper presents a novel approach for training language models to generate text with accurate and relevant citations. By defining fine-grained rewards that assess the quality of citations during the text generation process, the authors demonstrate improvements in citation faithfulness compared to standard language models.
This work has the potential to enable more reliable and trustworthy text generation in applications like academic writing, journalism, and knowledge summarization. Further research is needed to explore the scalability and real-world performance of this method, but it represents an important advance in the field of citation-aware language modeling.
**If you enjoyed this summary, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.