id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,866,649 | BEM: The Best Way To Write CSS | BEM, as its name implies, means Block Element Modifier. If you don't write much CSS because you use... | 0 | 2024-05-27T14:16:49 | https://sotergreco.com/bem-the-best-way-to-write-css | css | BEM, as its name implies, means Block Element Modifier. If you don't write much CSS because you use Tailwind, then maybe this article is not for you, but it can still teach you a lot about how to write good CSS.
Also, a lot of people move to Tailwind because they find CSS cluttered, but the truth is that Tailwind is a lot more cluttered than CSS. If you write good CSS, it can be much cleaner than the alternatives.
So let's take a deep dive into how you can transform your entire CSS workflow with this simple way of writing CSS.
## Introduction
Before we start talking I am going to share with you an example code snippet.
```xml
<style>
// Classic CSS
#opinions_box h1 {
margin: 0 0 8px 0;
text-align: center;
}
#opinions_box {
p.more_pp {
a {
text-decoration: underline;
}
}
input[type="text"] {
border: 1px solid #ccc!important;
}
}
// BEM CSS
.opinions-box {
margin: 0 0 8px 0;
text-align: center;
&__view-more {
text-decoration: underline;
}
&__text-input {
border: 1px solid #ccc;
}
&--is-inactive {
color: gray;
}
}
</style>
```
As you can see BEM is a lot cleaner way of writing CSS. Also you need to keep in mind that it is a methodology. You don't need to install anything. You just change the way you think.
## Blocks
Blocks are encapsulated and standalone blocks of code that are meaningful on their own.
Blocks can be nested and interact with each other, semantically they remain equal; there is no precedence or hierarchy.
```xml
<header class="layout__header header">
<div class="header__logo">My Website</div>
<nav class="header__nav">
<ul class="header__menu">
<li class="header__menu-item"><a href="#" class="header__menu-link">Home</a></li>
<li class="header__menu-item"><a href="#" class="header__menu-link">About</a></li>
<li class="header__menu-item"><a href="#" class="header__menu-link">Contact</a></li>
</ul>
</nav>
</header>
```
As you can see here we have one block inside the other. *Layout* is the one block and *Header* is the other block.
## Elements
Elements are the constituent parts of a block that have no standalone meaning and are semantically tied to their block. They are typically represented by two underscores connecting the block and the element.
```html
<div class="header">
<div class="header__logo"></div>
<div class="header__nav">
<div class="header__nav-item"></div>
</div>
</div>
```
In this example, `header__logo`, `header__nav`, and `header__nav-item` are elements of the `header` block.
## Modifiers
Modifiers are used to change the appearance, behavior, or state of a block or element. They are typically represented by two hyphens connecting the block or element and the modifier.
```html
<div class="header header--dark">
<div class="header__logo"></div>
<div class="header__nav header__nav--expanded">
<div class="header__nav-item header__nav-item--active"></div>
</div>
</div>
```
In this example, `header--dark`, `header__nav--expanded`, and `header__nav-item--active` are modifiers that alter the appearance or behavior of the respective blocks and elements.
## Benefits
The BEM methodology offers several benefits, including improved code readability and maintainability. By using a consistent naming convention, BEM makes it easier to understand the structure and relationships within your HTML and CSS.
This approach also promotes reusability and scalability, allowing developers to manage and update styles more efficiently. Additionally, BEM helps in avoiding CSS conflicts and specificity issues, leading to more predictable and stable styling across your project.
## Conclusion
In conclusion, adopting the BEM methodology can significantly enhance your CSS workflow by promoting cleaner, more organized, and maintainable code. By adhering to its structured naming conventions, you can avoid common pitfalls such as CSS conflicts and specificity issues, ultimately leading to a more efficient and scalable development process.
Whether you're new to CSS or looking to refine your skills, BEM offers a practical and effective approach to writing better CSS.
Thanks for reading, and I hope you found this article helpful. If you have any questions, feel free to email me at [**kourouklis@pm.me**](mailto:kourouklis@pm.me), and I will respond.
You can also keep up with my latest updates by checking out my X here: [**x.com/sotergreco**](http://x.com/sotergreco) | sotergreco |
1,866,647 | MOST COMMON AUTOMATION TESTING TOOLS IN MARKET | There are several automation testing tools available in the market, each with its own features,... | 0 | 2024-05-27T14:15:14 | https://dev.to/akshara_chandran_0f2b21d7/most-common-automation-testing-tools-in-market-4i9p | There are several automation testing tools available in the market, each with its own features, capabilities, and popularity among software testing professionals. Here are some of the most common automation testing tools widely used in the industry:
1. **Selenium WebDriver**:
- Selenium WebDriver is one of the most popular and widely used open-source automation testing frameworks for web applications.
- It supports various programming languages such as Java, Python, C#, etc.
- Selenium WebDriver allows testers to automate web browser interactions across different browsers and platforms.
2. **Appium**:
- Appium is an open-source automation tool for testing mobile applications across different platforms such as iOS, Android, and Windows.
- It supports multiple programming languages and offers a unified API for testing both native and hybrid mobile apps.
3. **Katalon Studio**:
- Katalon Studio is a comprehensive test automation solution for web, API, mobile, and desktop applications.
- It provides a range of features including recording and playback, scriptless automation, and built-in test reporting.
4. **TestComplete**:
- TestComplete is a commercial automation testing tool by SmartBear that supports testing of web, desktop, and mobile applications.
- It offers record and playback capabilities, keyword-driven testing, and script-based testing using various scripting languages.
5. **Robot Framework**:
- Robot Framework is an open-source automation framework that uses a keyword-driven approach for test automation.
- It supports testing of web, desktop, mobile, and API applications and can be extended through libraries for additional functionality.
6. **Jenkins**:
- Jenkins is an open-source automation server that is commonly used for continuous integration and continuous delivery (CI/CD) pipelines.
- It allows automation of various tasks including building, testing, and deployment of software applications.
7. **Cucumber**:
- Cucumber is a popular open-source tool for behavior-driven development (BDD) and acceptance testing.
- It allows writing test scenarios in a human-readable format using Gherkin syntax and automating them with various programming languages.
8. **Postman**:
- Postman is a widely used API testing tool that allows testers to create, organize, and automate API tests.
- It provides features for API endpoint testing, request/response validation, and automation of API workflows.
9. **SoapUI**:
- SoapUI is an open-source API testing tool that supports testing of SOAP, REST, and GraphQL web services.
- It offers features for functional testing, load testing, security testing, and mocking of web services.
10. **QTP/UFT (Micro Focus Unified Functional Testing)**:
- QTP/UFT is a commercial automation testing tool by Micro Focus (formerly HP) that supports functional and regression testing of web, desktop, and mobile applications.
- It provides a range of features including record and playback, keyword-driven testing, and integration with ALM tools.
These are just a few examples of the many automation testing tools available in the market. | akshara_chandran_0f2b21d7 | |
1,866,645 | Software testing | Software is the process of checking the quality and functionality of a performance of software... | 0 | 2024-05-27T14:12:22 | https://dev.to/malaiyarasi/software-testing-1ldo | Software is the process of checking the quality and functionality of a performance of software product. Main purpose to validate the functionality, enhance its performance and improve the overall user experience. Testing can help to compliance the any legal and industry specific standards main goal to find the errors,gaps or missing requirements in comparison of actual requirements.and ultimately deliver the high quality product and satisfy the user needs.
1. Service based company activity that is based on the services the is doing things for customer rather than on manufacturing.
2. Product based company that makes products that might or might not related to software. However they are mainly concentrated on their products to develop their criteria in it companies.
A planning and clear definition of problem and clear statement of requirements for a software solution must be complete,unambiguous and interpretable.
Planning and settings executing activities that integrate quality into all software development solution must be clear and maintenance stage.
_
| malaiyarasi | |
1,866,644 | Low-Code Backend Solution for Refine.dev Using Prisma and ZenStack | Refine.dev is a very powerful and popular React-based framework for building web apps with less code.... | 0 | 2024-05-27T14:12:18 | https://zenstack.dev/blog/refine-dev-backend | webdev, react, lowcode, authorization | [Refine.dev](https://refine.dev/) is a very powerful and popular React-based framework for building web apps with less code. It focuses on providing high-level components and hooks to cover common use cases like authentication, authorization, and CRUD. One of the main reasons for its popularity is that it allows easy integration with many different kinds of backend systems via a flexible adapter design.
This post will focus on the most important type of integration: database CRUD. I'll show how easy it is, with the help of Prisma and ZenStack, to turn your database schema into a fully secured API that powers your refine app. You'll see how we start by defining the data schema and access policies, derive an automatic CRUD API from it, and finally integrate with the Refine app via a "Data Provider."
## A quick overview of the tools
### Prisma
[Prisma](https://www.prisma.io) is a modern TypeScript-first ORM that allows you to manage database schemas easily, make queries and mutations with great flexibility, and ensure excellent type safety.
### ZenStack
[ZenStack](https://zenstack.dev) is a toolkit built above Prisma that adds access control, automatic CRUD web API, etc. It unleashes the ORM's full power for full-stack development.
### Auth.js
[Auth.js](https://authjs.dev/) (successor of NextAuth) is a flexible authentication library that supports many authentication providers and strategies. Although you can use many external services for auth, simply storing everything inside your database is often the easiest way to get started.
## A blogging app
I'll use a simple blogging app as an example to facilitate the discussion. We'll first focus on implementing the authentication and CRUD with essential access control and then expand to more advanced topics.
You can find the link to the completed project's GitHub repo at the end of the post.
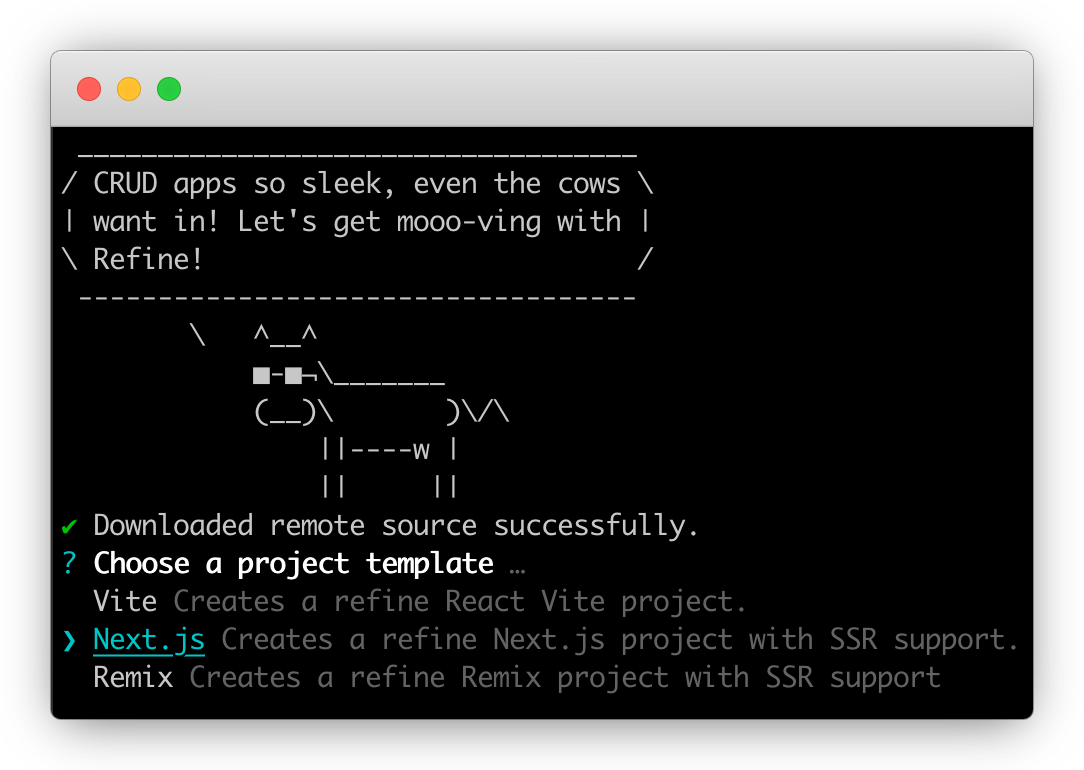
### Scaffolding the app
The `create-refine-app` CLI provides several handy templates to scaffold a new app. We'll use the "Next.js" one so that we can easily contain both the frontend and backend in the same project. Most of the ideas in this post can be applied to a standalone backend project as well.
We also need to install Prisma and NextAuth:
```bash
npm install --save-dev prisma
npm install @prisma/client next-auth@beta
```
Finally, we'll create the database schema for our app (schema.prisma):
```ts
datasource db {
provider = "sqlite"
url = "file:./dev.db"
}
generator client {
provider = "prisma-client-js"
}
model User {
id String @id() @default(cuid())
name String?
email String? @unique()
emailVerified DateTime?
image String?
createdAt DateTime @default(now())
updatedAt DateTime @updatedAt()
accounts Account[]
sessions Session[]
password String
posts Post[]
}
model Post {
id String @id() @default(cuid())
createdAt DateTime @default(now())
updatedAt DateTime @updatedAt()
title String
content String
status String @default("draft")
author User @relation(fields: [authorId], references: [id])
authorId String
}
model Account {
...
}
model Session {
...
}
model VerificationToken {
...
}
```
> The `Account`, `Session`, and `VerificationToken` models are [required by Auth.js](https://authjs.dev/getting-started/adapters/prisma#schema).
### Building authentication
The focus of this post will be data access and access control. However, they are only possible with an authentication system in place. We'll use simple credential-based authentication in this app. The implementation involves creating an Auth.js configuration, installing an API route to handle auth requests, and implementing a Refine "Authentication Provider".
I won't elaborate on the details of this part, but you can find the completed code [here](https://github.com/ymc9/refine-nextjs-zenstack/tree/main/src/providers/auth-provider). It should get the registration, login, and session management parts working.
### Set up access control
There are many ways to implement access control. People typically put the check in the API layer with imperative code. ZenStack offers a unique and powerful way to do it declaratively inside the database schema. Let's see how it works.
First, let's initialize the project for ZenStack:
```bash
npx zenstack@latest init
```
It'll install a few dependencies and copies over the `prisma/schema.prisma` file to `/schema.zmodel`. ZModel is a superset of Prisma Schema Language that adds more features like access control.
Next, we'll add policy rules to the schema:
```ts
model User {
...
// everybody can signup
@@allow('create', true)
// full access by self
@@allow('all', auth() == this)
}
model Post {
...
// allow read for all signin users
@@allow('read', auth() != null && status == 'published')
// full access by author
@@allow('all', author == auth())
}
```
As you can see, the overall schema still looks very similar to the original Prisma schema. The `@@allow` directive defines access control rules. The `auth()` function returns the current authenticated user. We'll see how it's connected with the authentication system next.
The most straightforward way to use ZenStack is to create an "enhancement" wrapper around the Prisma client. First, run the CLI to generate JS modules that support the enforcement of policies:
```bash
npx zenstack generate
```
Then, you can call the `enhance` API to create an enhanced PrismaClient.
```ts
const session = await auth();
const user = session?.user?.id ? { id: session.user.id } : undefined;
const db = enhance(prisma, { user });
```
Besides the `prisma` instance, the `enhance` function also takes a second argument that contains the current user. The user object provides value to the `auth()` function call in the schema at runtime.
The enhanced PrismaClient has the same API as the original one, but it will enforce the policy rules automatically for you.
### Automatic CRUD API
Having the ORM instance enhanced with access control capabilities is great. We can now implement CRUD APIs without writing imperative authorization code as long as we use the enhanced client. However, wouldn't it be even cooler if the CRUD APIs were automatically derived from the schema?
ZenStack makes it possible by providing a set of server adapters for popular Node.js frameworks. Using it with Next.js is easy. You'll only need to create an API route handler:
```ts
// src/app/model/[...path]/route.ts
import { auth } from '@/auth';
import { prisma } from '@/db';
import { enhance } from '@zenstackhq/runtime';
import { NextRequestHandler } from '@zenstackhq/server/next';
// create an enhanced Prisma client with user context
async function getPrisma() {
const session = await auth();
const user = session?.user?.id ? { id: session.user.id } : undefined;
return enhance(prisma, { user });
}
const handler = NextRequestHandler({ getPrisma, useAppDir: true });
export {
handler as DELETE,
handler as GET,
handler as PATCH,
handler as POST,
handler as PUT,
};
```
You then have a set of CRUD APIs served at "/api/model/[Model Name]/...". The APIs closely resemble PrismaClient's API:
- `/api/model/post/findMany`
- `/api/model/post/create`
- ...
You can find the detailed API specification [here](https://zenstack.dev/docs/reference/server-adapters/api-handlers/rpc).
### Implementing a data provider
We've got the backend APIs ready. Now, the only missing piece is a Refine "Data Provider", which talks to the API to fetch and update data. The following code snippet shows how the `getList` method is implemented. Refine's data provider's data structure is conceptually very close to Prisma, and we only need to do some lightweighted translation:
```ts
// src/providers/data-provider/index.ts
export const dataProvider: DataProvider = {
getList: async function <TData extends BaseRecord = BaseRecord>(
params: GetListParams
): Promise<GetListResponse<TData>> {
const queryArgs: any = {};
// filtering
if (params.filters && params.filters.length > 0) {
const filters = params.filters.map((filter) =>
transformFilter(filter)
);
if (filters.length > 1) {
queryArgs.where = { AND: filters };
} else {
queryArgs.where = filters[0];
}
}
// sorting
if (params.sorters && params.sorters.length > 0) {
queryArgs.orderBy = params.sorters.map((sorter) => ({
[sorter.field]: sorter.order,
}));
}
// pagination
if (
params.pagination?.mode === 'server' &&
params.pagination.current !== undefined &&
params.pagination.pageSize !== undefined
) {
queryArgs.take = params.pagination.pageSize;
queryArgs.skip =
(params.pagination.current - 1) * params.pagination.pageSize;
}
// call the API to fetch data and count
const [data, count] = await Promise.all([
fetchData(params.resource, '/findMany', queryArgs),
fetchData(params.resource, '/count', queryArgs),
]);
return { data, total: count };
},
...
};
```
With the data provider in place, we now have a fully working CRUD UI.
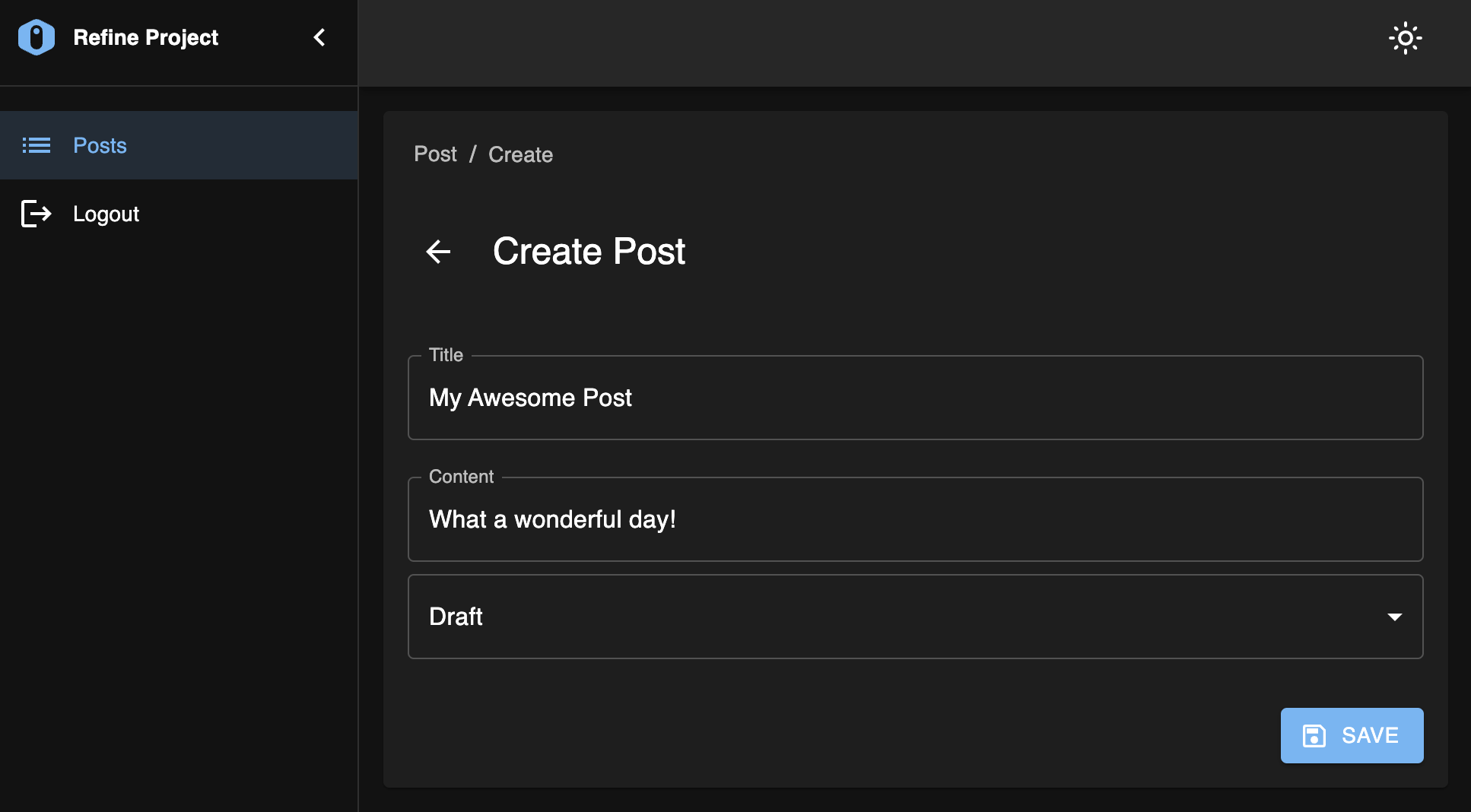
You can sign up for two accounts and verify that the access control rules are working as expected - draft posts are only visible to the author.
### Bonus: guarding UI with permission checker
Let's add one more challenge to the problem: the users of our app will have two roles:
- Reader: can only read published posts
- Writer: can create new posts
Our schema needs to be updated accordingly:
```ts
model User {
...
role String @default('Reader')
}
model Post {
...
// allow read for all signin users
@@allow('read', auth() != null && status == 'published')
// allow "Writer" users to create
@@allow('create', auth().role == 'Writer')
// full access by author
@@allow('read,update,delete', author == auth())
}
```
Now, if you try to create a new post with a "Reader" account, you'll see the following error:
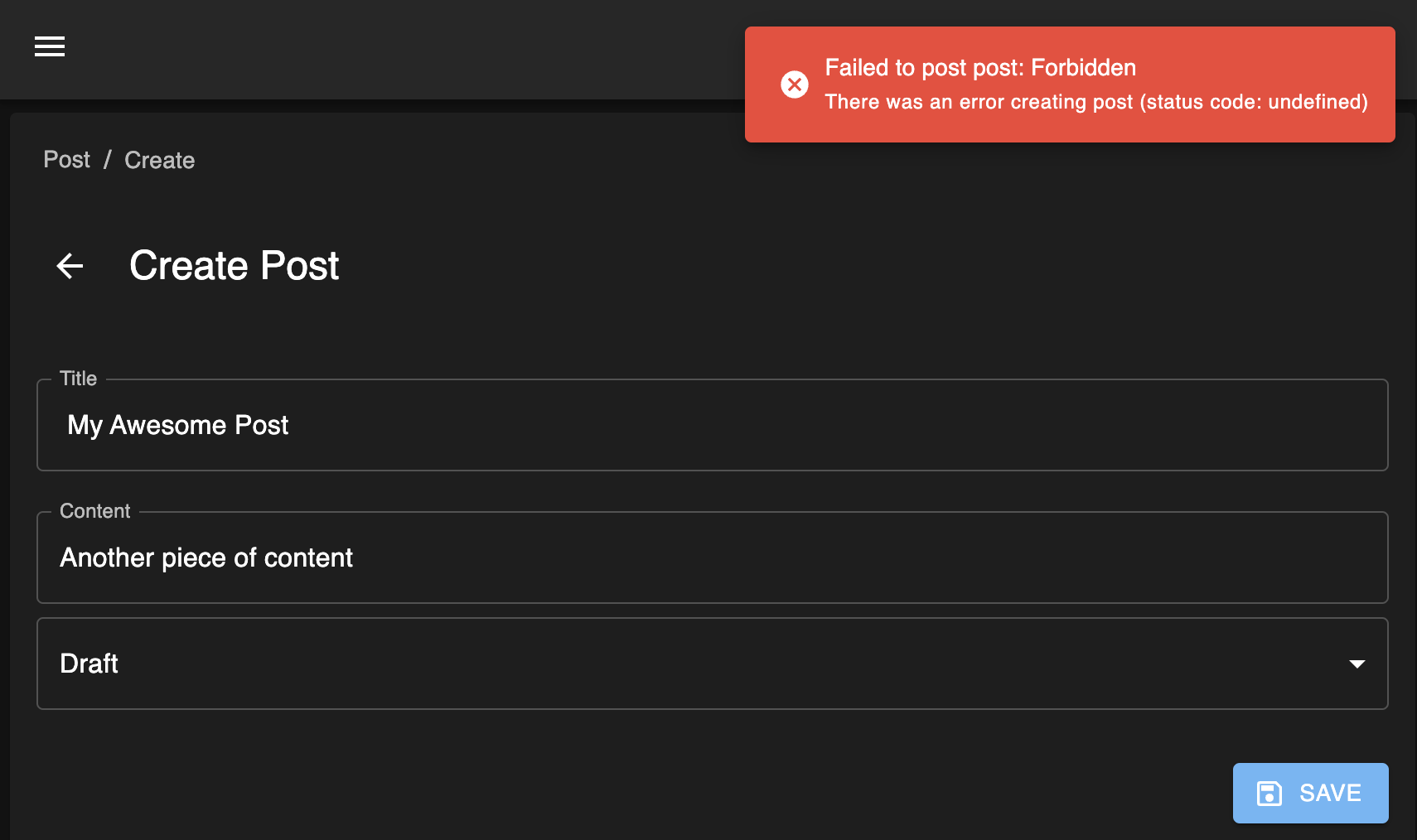
The operation is denied correctly according to the rules. However, it's not an entirely user-friendly experience. It'd be nice to prevent the "Create" button from appearing in the first place. This can be achieved by combining two additional features from Refine and ZenStack:
- Refine allows you to implement an "Access Control Provider" to verdict whether the current user has permission to perform an action.
- ZenStack's enhanced PrismaClient has an extra `check` API for inferring permission based on the policy rules. The `check` API is also available in the automatic CRUD API.
> ZenStack's `check` API doesn't query the database. It's based on logical inference from the policy rules. See more details [here](https://zenstack.dev/docs/guides/check-permission).
Let's see how these two pieces are put together. First, implement an `AccessControlProvider`:
```ts
// src/providers/access-control-provider/index.ts
export const accessControlProvider: AccessControlProvider = {
can: async ({ resource, action }: CanParams): Promise<CanReturnType> => {
if (action === 'create') {
// make a request to "/api/model/:resource/check?q={operation:'create'}"
let url = `/api/model/${resource}/check`;
url +=
'?q=' +
encodeURIComponent(
JSON.stringify({
operation: 'create',
})
);
const resp = await fetch(url);
if (!resp.ok) {
return { can: false };
} else {
const { data } = await resp.json();
return { can: data };
}
}
return { can: true };
},
options: {
buttons: {
enableAccessControl: true,
hideIfUnauthorized: false,
},
queryOptions: {},
},
};
```
Then, register the provider to the top-level `Refine` component:
```tsx
// src/app/layout.tsx
<Refine
accessControlProvider={ accessControlProvider }
...
/>
```
You'll immediately notice the difference that, with a "Reader" user, the "Create" button is grayed out and disabled.
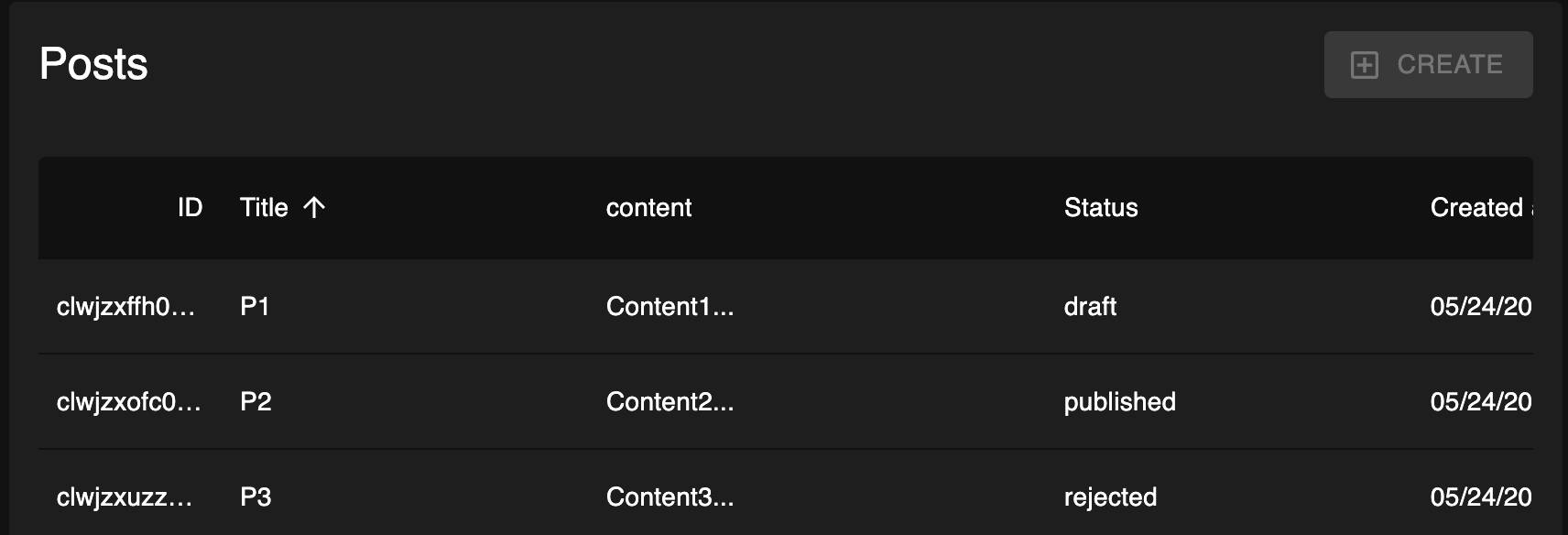
However, you can still directly navigate to the "/blog-post/create" URL to access the create form. We can prevent that by using Refine's `CanAccess` component to guard it:
```tsx
// src/app/blog-post/create/page.tsx
<CanAccess
resource="post"
action="create"
fallback={<div>Not Allowed</div>}
>
<Create ... />
</CanAccess>
```
Mission accomplished! We've also done it elegantly without hard coding any permission logic in the UI. Everything about access control is still centralized in the ZModel schema.
## Conclusion
Refine.dev is a great tool for building complex UI without writing complex code. Combined with the superpowers of Prisma and ZenStack, we've now got a full-stack, low-code solution with excellent flexibility.
The completed sample project is here: [https://github.com/ymc9/refine-nextjs-zenstack](https://github.com/ymc9/refine-nextjs-zenstack).
---
We're building [ZenStack](https://github.com/zenstackhq/zenstack), a toolkit that supercharges Prisma ORM with a powerful access control layer and unleashes its full potential for full-stack development. If you enjoy the reading and feel the project interesting, please help star it so that more people can find it! | ymc9 |
1,866,643 | The Ultimate Checklist for Applying for an LLC in Texas Online | Starting your own business is an exciting venture, and forming a Limited Liability Company (LLC) can... | 0 | 2024-05-27T14:11:44 | https://dev.to/tom_ford_a41cfbc89a2ddf43/the-ultimate-checklist-for-applying-for-an-llc-in-texas-online-48dl | llc, finance, file | Starting your own business is an exciting venture, and forming a Limited Liability Company (LLC) can be a great way to structure your enterprise. If you're considering setting up an LLC in the Lone Star State, you’ll be pleased to know that the process is straightforward and can be done entirely online. Here’s your ultimate checklist for [how to apply for LLC in Texas online](https://truspanfinancial.com/set-up-an-llc/).
**Step 1: Choose Your LLC Name**
Your LLC’s name must be unique and distinguishable from other business entities registered with the Texas Secretary of State. To ensure your desired name is available, you can perform a name search on the Texas Secretary of State's website. The name must contain "Limited Liability Company," "LLC."
**Step 2: Appoint a Registered Agent**
A registered agent is required for your Texas LLC. This person or business entity is responsible for accepting legal documents on behalf of the LLC. The registered agent must have a physical street address in Texas and be available during normal business hours. You can choose yourself, another individual, or a professional service as your registered agent.
**Step 3: File the Certificate of Formation**
To legally establish your LLC, you need to file Form 205 (Certificate of Formation) with the Texas Secretary of State. This form can be filed online through the SOSDirect website. Here’s what you’ll need to provide:
- The LLC’s name
- The duration of the LLC (perpetual or a specific end date)
- The registered agent’s name and address
- The management structure (member-managed or manager-managed)
- The names and addresses of the founding members or managers
- The filing fee is $300, and you can pay by credit card, debit card, or through a pre-funded SOSDirect account.
**Step 4: Create an Operating Agreement**
Although not required by Texas law, having an operating agreement is highly recommended. This document details the ownership structure and operational procedures of the LLC. It helps prevent misunderstandings and disputes among members. The operating agreement should include:
- Member roles and responsibilities
- Voting rights and decision-making processes
- Profit and loss distribution
- Procedures for adding or removing members
- Dissolution procedures
**Step 5: Obtain an EIN**
An Employer Identification Number (EIN) is required for tax purposes and is needed to open a business bank account, hire employees, and file federal taxes. You can obtain an EIN for free from the IRS by applying online on the IRS website.
**Step 6: Register for Texas State Taxes**
Depending on the nature of your business, you may need to register for one or more Texas state taxes. Common registrations include:
- Sales tax permit
- Franchise tax
- Employer taxes if you have employees
- You can register for these taxes online through the Texas Comptroller of Public Accounts website.
**Step 7: Open a Business Bank Account**
Separating your personal and business finances is crucial. Open a business bank account using your LLC’s EIN and Certificate of Formation. This step ensures that your business transactions are kept separate, which is important for liability protection and tax purposes.
**Step 8: Comply with Ongoing Requirements**
Once your LLC is formed, you must comply with ongoing requirements to maintain good standing. These include:
- Submitting annual reports and paying any related fees
- Keeping detailed records of your LLC’s activities and finances
- Adhering to any additional state or local licensing requirements
**Step 9: Obtain Required Permits and Licenses**
Depending on your business type and location, you may need various permits and licenses to operate legally in Texas. Check with local city and county offices, as well as relevant state agencies, to determine what is required.
**Conclusion**
Applying for an LLC in Texas online is a streamlined process that can set the foundation for your business success. By following this ultimate checklist, you ensure that all legal and administrative bases are covered, allowing you to focus on growing your business. Remember to [create LLC online Texas](https://truspanfinancial.com/set-up-an-llc/
) for the best experience in forming your business entity, ensuring a smooth and efficient start to your entrepreneurial journey.
| tom_ford_a41cfbc89a2ddf43 |
1,866,642 | Automation vs Manual Testing in Software | Automated testing and manual testing are two approaches used in software testing, each with its own... | 0 | 2024-05-27T14:11:26 | https://dev.to/akshara_chandran_0f2b21d7/automation-vs-manual-testing-in-software-566i | Automated testing and manual testing are two approaches used in software testing, each with its own advantages and disadvantages. Here's a breakdown of the key differences between them:
1. **Automated Testing:**
- **Definition**: Automated testing involves the use of tools and scripts to execute pre-defined test cases automatically without human intervention.
- **Advantages**:
- **Efficiency**: Automated tests can be run quickly and repeatedly, saving time compared to manual testing.
- **Consistency**: Automated tests execute the same steps and checks consistently, reducing the risk of human error.
- **Repeatability**: Automated tests can be easily repeated across different builds and environments, ensuring consistent results.
- **Regression Testing**: Automated tests are particularly useful for regression testing, where previous functionality is verified after code changes.
- **Disadvantages**:
- **Initial Setup**: Setting up automated tests requires time and effort, especially for complex systems.
- **Maintenance**: Automated tests require regular maintenance to keep them up-to-date with changes in the application.
- **Limited Scope**: Some aspects of testing, such as usability testing and exploratory testing, are difficult to automate.
- **Cost**: There may be initial costs associated with purchasing testing tools and resources.
2. **Manual Testing:**
- **Definition**: Manual testing involves testers executing test cases manually, following pre-defined steps and instructions.
- **Advantages**:
- **Flexibility**: Manual testing allows testers to adapt to changes and explore the application in ways that automated tests cannot.
- **Exploratory Testing**: Manual testing is well-suited for exploratory testing, where testers explore the application to uncover defects and usability issues.
- **Human Judgment**: Manual testers can apply human judgment and intuition to identify issues that may not be caught by automated tests.
- **Usability Testing**: Manual testing is effective for evaluating the user interface and overall user experience.
- **Disadvantages**:
- **Time-consuming**: Manual testing can be time-consuming, especially for repetitive or large-scale testing efforts.
- **Inconsistency**: Manual tests may produce inconsistent results due to human error or variability in tester skills.
- **Regression Testing**: Repeating manual tests for each build or release can be tedious and error-prone.
- **Resource Intensive**: Manual testing requires human testers, which can be costly and may not scale well for large projects.
In summary, automated testing offers efficiency, repeatability, and consistency but requires initial setup and ongoing maintenance. Manual testing offers flexibility, human judgment, and effectiveness for certain types of testing but can be time-consuming and resource-intensive. Often, a combination of both automated and manual testing is used to achieve comprehensive test coverage in software development projects. | akshara_chandran_0f2b21d7 | |
1,866,040 | Generics in Rust: little library for Bezier curves -- Part 2 | Some time ago, I decided to write a couple of posts about my experience with generic programming in... | 0 | 2024-05-27T14:10:20 | https://dev.to/iprosk/generics-in-rust-little-library-for-bezier-curves-part-2-2cpi | rust, generic, beginners, numeric | Some time ago, I decided to write a couple of posts about my experience with [generic programming](https://en.wikipedia.org/wiki/Generic_programming) in Rust. For me, when someone says generics, [C++ template metaprogramming](https://en.cppreference.com/w/cpp/language/template_metaprogramming) and [Alexander Stepanov](https://en.wikipedia.org/wiki/Alexander_Stepanov) immediately pop in my mind. Rust is different. So it was interesting to see what's going on out there, which motivated my original interest.
Learning by doing is the best for quick hands-on, so I decided to write a little generic numeric library for manipulating [Bezier curves](https://en.wikipedia.org/wiki/B%C3%A9zier_curve) (polynomials in the [Bernstein basis](https://en.wikipedia.org/wiki/Bernstein_polynomial)) that is (i) uses static dispatch (and no heap allocation calls), and (ii) can be used with different types for specifying Bezier control polygon: reals, rationals, complex, and, in general, something that implements standard vector-space operations.
What I [learned](https://dev.to/iprosk/experimenting-with-generics-in-rust-little-library-for-bezier-curves-part-1-4093) is that writing generic libraries in Rust is not a piece of cake. There are two major facts that contribute into this: (i) Rust's explicit safety-oriented type system, and (ii) the absence of decent support of generic constant expressions in stable Rust. So what I am writing about here is based on Rust Nightly.
So before we take of, there is a couple of previous posts
- [Generic constant expressions: a future bright side of nightly Rust](https://dev.to/iprosk/generic-constant-expressions-a-future-bright-side-of-nightly-rust-3bp7).
- [Experimenting with generics in Rust: little library for Bezier curves - part 1](https://dev.to/iprosk/experimenting-with-generics-in-rust-little-library-for-bezier-curves-part-1-4093).
And the [Github repo](https://github.com/sciprosk/bernstein) that contains examples from these posts, some tests, and maybe even some demos, if I will manage to add them in nearby future.
## First steps
First, make sure we use the unstable rust build. I will just set it up for all repositories with ` rustup default nightly`, but it is possible to apply it to a folder with `rustup override set nightly`. After that:
```
PS > rustc --version
rustc 1.80.0-nightly (1ba35e9bb 2024-05-25)
```
and we also make sure that we include the following lines in our crate
```
#![allow(incomplete_features)]
#![feature(generic_const_exprs)]
```
As I briefly outlined [here](https://dev.to/iprosk/generic-constant-expressions-a-future-bright-side-of-nightly-rust-3bp7), Rust currently does not support generic constant expression in its type system. It is not that something is wrong with it in general, it is just not implemented due to [technical difficulties](https://hackmd.io/OZG_XiLFRs2Xmw5s39jRzA). This is considered to be an unstable feature.
To describe a generic Bezier curve `c(u) = (x(u), y(u), z(u), ...)`, I basically wrap a primitive array type `[T; N]` into a struct
```
pub struct Bernstein<T, U, const N: usize> {
coef: [T; N],
segm: (U, U),
}
```
that contains a generic type parameter `T` for Bezier control polygon, type parameter `U` for curve parametrization, and a generic constexpression parameter `N` for the number of basis polynomials (or just the size of the Bezier control polygon). For example, a cubic Bezier curve should have four points in its control polygon, i. e. `N = 4`. The curve is always parameterized on `0 <= u <= 1`, so right now `segm` is defaulted to `(0, 1)`.
Some more details can be found in my [previous post](https://dev.to/iprosk/experimenting-with-generics-in-rust-little-library-for-bezier-curves-part-1-4093). In this post, I would like to discuss how implement generic methods on this type that would leverage generic constant expressions on the size of the control polygon `N`.
## Implementing eval-method
The first method to do is, of course, to implement `eval()` method to find a point on the curve at some value of the parameter `u`, so that we can write something like this
```
let p0 = Complex::new(0.0, 0.0);
let p1 = Complex::new(2.5, 1.0);
let p2 = Complex::new(-0.5, 1.0);
let p3 = Complex::new(2.0, 0.0);
// Define cubic Bezier curve in the complex plane.
let c: Bernstein<Complex<f32>, f32, 4> = Bernstein::new([p0, p1, p2, p3]);
let p = c.eval(0.5); // point on a curve of type Complex<f32>
```
This part is easy, and can be done even in stable Rust. I just use the De [Casteljau's algorithm](https://en.wikipedia.org/wiki/De_Casteljau%27s_algorithm)
```
impl<T, U, const N: usize> Bernstein<T, U, N> where
T: Copy + Add<T, Output = T> + Sub<T, Output = T> + Mul<U, Output = T>,
U: Copy + Num,
{
pub fn eval(&self, u: U) -> T {
// -- snippet --
// De Casteljau's algorithm
}
}
```
Trait bounds on types are quite transparent. I require `Copy` trait to make my life easier when manipulating mathematical expressions, type `U` should be a number, which is required by [`num::Num`](https://docs.rs/num/latest/num/trait.Num.html) trait. This is especially useful because `Num` trait requires generic `One` and `Zero` traits, which provide methods such as `U::zero()` and `U::one()`. Type `T` is required to implement vector space operations of addition, subtraction, and right-hand-side multiplication by a variable of type `U` with the result of being of type `T` (`Mul<U, Output = T>`).
## Implementing diff and integ methods
The next step is to implement generic `diff()` and `integ()` methods to find the parametric derivative of the Bezier curve `dc(u)/du`, and the integral with respect to parameter `u`. That's where generic constant expression come into play.
The problem is that our methods should take an array of control points `[T; N]` of size `N` as an input, and return an array of size `N - 1` for `diff()` or `N + 1` for `integ()` as output nicely wrapped into our custom `Bernstein` type so that the signatures of the functions should be like these:
```
fn diff(&self) -> Bernstein<T, U, {N - 1}> {}
// c: T -- is the initial point to fix the constant of integration.
fn integ(&self, c: T) -> Bernstein<T, U, {N + 1}> {}
```
And stable Rust does not allow us to do that. Using `generic_const_exprs` feature, it becomes possible, as we shall see shortly.
Another difficulty is related to Rust's explicit type system. In these methods, the size of the array `N` becomes a part of mathematical expressions in the `diff()` and `integ()` algorithms. Rust requires the size of the array to be of a machine-dependent pointer size `usize` (which totally make sense but it is not generic). Converting from `usize` to other type is not considered to be a safe operation so I have to rely on third party traits for that purpose, such as `num::FromPrimitive` trait that is implemented for `usize` in the `num` crate. Otherwise, multiplying and expression of type, let's say, `f64`, by `N` is not defined.
Having this in mind, let's discuss `diff()` method (implementing `integ()` is similar and may be found in the [repo](https://github.com/sciprosk/bernstein)):
```
impl<T, U, const N: usize> Bernstein<T, U, N> where
T: Copy + Add<T, Output = T> + Sub<T, Output = T> + Mul<U, Output = T>,
U: Copy + Num + FromPrimitive,
{
pub fn diff(&self) -> Bernstein<T, U, {N - 1}> where
[(); N - 1]:
{
let coef: [T; N - 1] = array::from_fn(
|i| -> T {
(self.coef[i + 1] - self.coef[i]) *
(U::from_usize(N - 1).unwrap() / (self.segm.1 - self.segm.0))
}
);
Bernstein {
segm: self.segm,
coef: coef,
}
}
}
```
Here, there is a couple of new details. First, I require type `U` to be bounded by `FromPrimitive` trait that allows to convert from `usize` to `U` in a generic environment by calling `U::from_usize(N - 1).unwrap()`. Second is that there is new bound `[(); N - 1]:` which is [required by `generic_const_exprs` feature](https://hackmd.io/OZG_XiLFRs2Xmw5s39jRzA)
> We currently use where [(); expr]: as a way to add additional const wf bounds. Once we have started experimenting with this it is probably worth it to add a more intuitive way to add const wf bounds.
The bounds on `T` type is basically the same as in the `eval()` method.
Now, we can find a derivative type from a basic type, by using for example the following
```
// Define cubic Bezier curve in the complex plane.
let c: Bernstein<Complex<f32>, f32, 4> = Bernstein::new([p0, p1, p2, p3]);
// Get the derivative, or hodograph curve at u = 0.2.
let d = c.diff().eval(0.2); // `d` is of type Complex<f32>
```
## Generic product of two polynomials
The next example is a product of two polynomials of order `N - 1` and `M - 1` (the size of arrays of coefficients is `N` and `M` respectively). This is a little bit more involved since it has to take the array `[T; N]` as an input, multiply it by `[T; M]` and the type of output should be `[T; M + N - 1]`. For example, multiplying a polynomial of the third order (`N = 4`) by a second-order polynomial (`N = 3`) should give a quintic polynomial (`N = 6`).
The implementation may looks like this:
```
impl<T, U, const N: usize, const M: usize>
Mul<Bernstein<T, U, {M}>> for Bernstein<T, U, {N}> where
T: Copy + Add<Output = T> + Sub<Output = T> + Mul<Output = T> + Mul<U, Output = T>,
U: Num + FromPrimitive,
[(); N]:,
[(); M]:,
[(); N + M - 1]:
{
type Output = Bernstein<T, U, {N + M - 1}>;
fn mul(self, rhs: Bernstein<T, U, {M}>) -> Self::Output {
let mut coef = [self.coef[0] - self.coef[0]; N + M - 1];
// -- snippet --
// actual algorithm
Bernstein {
coef: coef,
segm: self.segm,
}
}
}
```
The required operation is specified by `Mul<Bernstein<T, U, {M}>>` in the `impl`, and the resulting type should be `type Output = Bernstein<T, U, {N + M - 1}>`.
Another subtle moment is that I have to initialize the array in the body of the function `mul()` because Rust does not allow to use uninitialized variables (remember old plain C89? -- who cared about initializing all the variables). One way to do it is to put a trait bound on `T` to implement `T::zero()` that can be used as an initial value. In this case, I chose a workaround instead (may change it later) which is to require subtraction `Sub<Output = T>` and use `self.coef[0] - self.coef[0]` as a kind of generic zero.
Note that `generic-const-exprs` require additional trait bounds to be imposed for each of the array types we use `[(); N]:`, `[(); M]:`, ` [(); N + M - 1]:`.
Now, it possible to write
```
let p: Bernstein<f64, f64, 3> = Bernstein::new([0.0, 2.0, 1.0]);
let q: Bernstein<f64, f64, 4> = Bernstein::new([1.0, 2.0, 0.0, 0.0]);
// Quintic polynomial with real coefficient
let c = p * q;
```
## Summary
Generic constant expressions in Rust give the flexibility of implementing generic types which size is known at compile time. So far, using an unstable Rust nightly 1.80, I didn't notice any issues with using `generic-const-exprs` feature. | iprosk |
1,866,639 | Objetos vs. Estruturas de Dados | ✨ Objetos vs. Estruturas de Dados ✨ Você sabia que entender a diferença entre objetos e estruturas... | 0 | 2024-05-27T14:08:48 | https://dev.to/jackienascimento/objetos-vs-estruturas-de-dados-codigo-limpo-capitulo-6-goj | codigolimpo, cleancode, desenvolvimentodesoftware | ✨ **Objetos vs. Estruturas de Dados** ✨
Você sabia que entender a diferença entre objetos e estruturas de dados pode transformar seu código? Vamos ver o que Robert C. Martin nos ensina no capítulo 6 de "Código Limpo"! 👇
---
## Objetos 🛠️
- **Encapsulamento**: Objetos escondem dados e expõem comportamentos através de métodos.
- **Ocultação de Informação**: A principal função dos objetos é esconder detalhes de implementação, expondo apenas o necessário.
- **Interação**: Objetos interagem entre si via métodos, promovendo modularidade e manutenção.
---
## Estruturas de Dados 🗄️
- **Transparência de Dados**: Estruturas de dados são transparentes e focam em expor dados diretamente.
- **Foco na Representação**: Elas se concentram na representação e armazenamento de dados de forma acessível.
---
## Quando Usar Cada Um? 🤔
- **Objetos**:
- Ocultar implementações complexas.
- Garantir a integridade dos dados.
- **Estruturas de Dados**:
- Facilitar o acesso direto e simples aos dados.
- Manipular dados em algoritmos.
---
## Dicas Práticas 📝
- **Princípio do Abstrato**: Objetos devem expor operações de alto nível e esconder detalhes.
- **Trade-offs**: Escolha entre objetos e estruturas de dados conforme a necessidade de encapsulamento ou acesso direto aos dados.
- **Design e Manutenção**: Pense no futuro, facilite a manutenção e a evolução do código.
---
🔗 **Leia mais em "Código Limpo" e melhore suas habilidades de programação!**
---
Espero que gostem da dica! Até a próxima! 🚀
``` | jackienascimento |
1,866,641 | FD | Hey there! I just wanted to share a quick message about the importance of monitoring our health. In... | 0 | 2024-05-27T14:05:56 | https://dev.to/dsfgsg34g/fd-51pg | Hey there! I just wanted to share a quick message about the importance of monitoring our health. In our fast-paced world, it's easy to ignore our physical well-being, but doing so can lead to bigger problems down the road. Simple habits like eating a balanced diet, staying active, and getting regular health screenings can go a long way. Make your health a priority and take those steps towards a healthier you. Remember, good health is priceless! [https://jacanawellness.com/shop/wellness/body-oil/](https://jacanawellness.com/shop/wellness/body-oil/)
| dsfgsg34g | |
1,866,640 | Meme Monday | Meme Monday! Today's cover image comes from last week's thread. DEV is an inclusive space! Humor in... | 0 | 2024-05-27T14:03:42 | https://dev.to/ben/meme-monday-4l95 | jokes, discuss, watercooler | **Meme Monday!**
Today's cover image comes from [last week's thread](https://dev.to/ben/meme-monday-ha7).
DEV is an inclusive space! Humor in poor taste will be downvoted by mods. | ben |
1,866,468 | Building a Scalable REST API with TypeScript, Express, Drizzle ORM, and Turso Database: A Step-by-Step Guide | Building REST APIs with Express.js is straightforward and a must-have skill for every web developer.... | 0 | 2024-05-27T13:57:44 | https://dev.to/ibrocodes/build-a-scalable-rest-api-with-typescript-express-drizzle-orm-and-turso-database-a-step-by-step-guide-2hnd | typescript, express, drizzle, turso | Building REST APIs with Express.js is straightforward and a must-have skill for every web developer. In this guide, we'll learn a step-by-step approach to building a REST API. We'll use the following technologies to build an API for a note-taking application:
- **TypeScript**: Literally JavaScript with static typing. It compiles down to JavaScript. Suitable for building large-scale JavaScript applications with confidence.
- **Express**: A minimalist, unopinionated Node.js framework for building server-side applications.
- **Drizzle**: An SQL Object-Relational Mapping (ORM) tool that makes it easy to interact with the database.
- **Turso**: A fast and scalable SQLite database technology for building production-ready applications. Easy to set up and has a generous free tier.
## Why Learn Express?
Using opinionated Node.js frameworks such as Nest.js and Sails.js is great, especially for large-scale applications. However, they're not ideal for beginners because they abstract away a lot of how the server actually works. In fact, Nest.js is an abstraction on top of Express.js.
Express.js, on the other hand, is unopinionated and allows for more flexibility and a better learning experience. It's lightweight and easy to get started with, especially if you're coming from frontend JavaScript. Moreover, understanding Express will give you the knowledge and confidence to pick up other Node.js backend frameworks.
## What the Guide Covers
We will cover the following topics in this article:
- How to set up a TypeScript Project with Express
- How Express middlewares work
- Setting up Turso database
- Connecting and interacting with Turso database using Drizzle ORM
- Creating a CRUD (Create Read Update Update Delete) API
- How to validate and sanitize data using the third-party `express-validator` middlewares
- Testing an API with Thunder Client VS Code extension
## Prerequisites
To effortlessly follow this tutorial, you should have a basic understanding of the following:
- JavaScript (We will be using TypeScript, but JavaScript knowledge is enough to follow this guide)
- Node.js
- Structure Query Language (SQL)
- How a server works
Let's begin!
## Setting Up A TypeScript Project with Express
The first steps to building a REST API with Express.js and TypeScript are:
1. Generating and configuring `package.json`
2. Installing basic dependencies necessary to initially run our app
3. Generating and configuring `tsconfig.json`
### 1. Generating and configuring `package.json` file
```bash
npm init -y
```
This command generates a `package.json` file in the root directory.
Next, update the file to look like this:
```json
{
"name": "article",
"version": "1.0.0",
"main": "dist/index.js",
"type": "module",
"scripts": {
"dev": "node --loader=ts-node/esm --env-file=.env --watch src/index.ts",
"build": "npx tsc",
"start": "node --env-file=.env dist/index.js"
},
...
}
```
The `main` option in the above `package.json` file points to the destination of the JavaScript file after compilation. The `dist/index.js` file will be generated (usually for production) when you execute the `build` script command by running `npm run build` on the terminal. The `start` command is used to start the server in production.
The `dev` script command is used to run the application in development mode. It contains the following commands:
- `node`: Uses the Node runtime to execute the code.
- `--loader=ts-node/esm`: Uses the `ts-node` package (we'll later install) to compile our code to JavaScript during development.
- `--env-file=.env`: Tells Node where the `.env` file is located.
- `-watch`: Reruns our code whenever we make an update, enabling automatic reloading during development.
### 2. Installing starter dependencies
We'll install some packages needed to kickstart our application. Aside from `typescript` and `express`, we will install the following packages:
- `ts-node`: A package that compiles our TypeScript code to JavaScript during development, allowing us to run our application without the need for explicit compilation.
- `@types/express`: A package that provides type definitions for Express.js, helping TypeScript to recognize and understand the types and interfaces of Express.js, enabling better code completion, error reporting, and overall development experience.
```bash
npm i express; npm i -D typescript ts-node @types/express
```
The `-D` flag, short for `--save-dev`, indicates that the packages being installed are development dependencies, meaning they are only required for development purposes and will not be needed in production. By using the `-D` flag, we are telling npm to include these packages in the `devDependencies` section of our `package.json` file, rather than the `dependencies` section, which is used for production dependencies.
### 3. Generating and configuring `tsconfig.json`
The following command generates the `tsconfig.json` file in the root directory:
```bash
npx tsc --init
```
The generated `tsconfig.json` file will contain many commented out TypeScript compiler options. Uncomment out the following options and update them accordingly:
```json
{
"compilerOptions": {
....
"module": "NodeNext",
"rootDir": "./src",
"moduleResolution": "NodeNext",
"outDir": "./dist",
....
}
}
```
### Recommended starter file structure for the project
**Create the necessary folders and files**
Your file structure should look like this:
```
├── .env
├── .gitignore
├── package-lock.json
├── package.json
├── src
│ ├── db
│ ├── handlers
│ ├── routes
│ ├── lib
│ ├── middleware
│ ├── index.ts
│ └── server.ts
└── tsconfig.js
```
## Express Middleware
We'll use middleware functions throughout the project. So, let's take some time to understand them. If you're already familiar with Express middleware, you can skip this section.
### Without middleware
To best illustrate this concept, I made a little sketch using [excalidraw](https://excalidraw.com/):
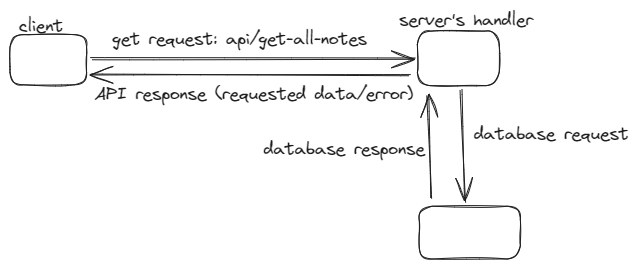
Normally, this is how a client will communicate with a server. In this case, the client requests all the notes in the database. The server makes a request to the database and, depending on the database's response, returns the requested resources or an error.
This approach keeps the server open for all kinds of requests. As API developers, we want to ensure that the client is requesting the right way and is not a malicious actor. So, we introduce middleware into the equation:
### With middleware
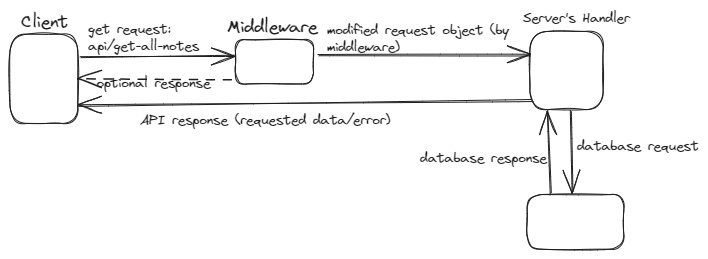
The middleware sits between the client's request and the server's handler function. Whenever the server receives a request from the client, the request has to pass through the middleware and gets securitized in the process. In the above sketch, the middleware modified the request object. Express middleware can do more, including the following:
- Execute any code
- Terminate the request
- Make changes to the request or response object
- Detect errors
- Authentication and authorization
### How to define an express middleware
```typescript
import express, {Request, Response, NextFunction} from "express"
const app = express()
const logRequestMethod = (req: Request, res: Response, next: NextFunction) => {
console.log(req.method)
next()
}
const logHostname = (req: Request, res: Response, next: NextFunction) => {
console.log(req.hostname)
next()
}
```
`logRequestMethod` and `logHostname` are middlewares responsible for logging the request's HTTP method and hostname respectively. Typically, an Express middleware has three arguments:
- request
- response
- next
If we don't call the `next()` function, respond back to the client, or terminate the request, the server will hang in the middleware. The `next()` function transfers control to the next middleware or handler.
### How to use an express middleware
Basically, there are two ways of using an Express middleware:
- On an application level: An application-level middleware will execute whenever a request reaches the server and not terminated by other middleware before it. We can invoke application-level middleware using `app.use(middlewareFunction)`. For example, let's use the above `logRequestMethod` on the app level:
```typescript
app.use(logRequestMethod)
```
- Route-specific middleware: We can restrict a middleware to a particular route. This type of middleware will only execute when a request is made to that particular route.
Note that whether we're using a middleware on the app or route level, we can have one or more of them separated by commas. For instance, let's use logRequestMethod and logHostname only when the client makes a request to the `/about` path:
```typescript
app.get("/about", logRequestMethod, logHostname, (req, res) => {})
```
The `app.use()` can also take a path as the first argument and used for a route-specific middleware: `app.use("/about", logRequestMethod)`.
### Error middleware
Whenever a client request results in an unhandled error, Express.js has a default error middleware that sends the error message back to the client in HTML format. There are two common ways an error can go unhandled:
- Not wrapping a code block that may result in an error in a try-catch
- The client sending a request to a route that doesn't exist
We would create the following middlewares and use them on the application level to handle errors:
- A custom error middleware that handles all errors and sends back an error response in JSON format to the client.
- A not-found middleware that gets triggered whenever the client requests resources from a route that doesn't exist. This not-found middleware will forward an error message to the custom error middleware, which will send back an appropriate JSON response to the client.
### Setting up the Error Middleware
As mentioned earlier, the `next()` function triggers a jump from the current middleware in execution to the next middleware or handler. However, if we pass an argument to the `next()` function, it jumps to the next error middleware on the stack. If we haven't defined a custom error middleware, it transfers control to Express's default error middleware.
Typically, you want to pass an Error object to the `next()` function. The issue with the inbuilt error class is that it only accepts one argument, which is the error message string. However, we want our error object to contain an error message and status code that we would use to send back the appropriate error message back to the client.
Let's create a child class of the error class and make it receive an extra `statusCode` argument. So, within the `lib` folder, create a `custom-error.ts` file and insert the following lines of code:
**`src/lib/custom-error.ts`**
```typescript
export class CustomError extends Error {
message: string;
statusCode: number;
constructor(message: string, statusCode: number) {
super(message);
this.statusCode = statusCode;
}
}
```
Our `CustomError` class can form error objects with two arguments — the message and status code. We'll use `CustomError` throughout our code to forward errors that happen in our server to the error middleware we'll create in a moment.
Next, we'll create an error middleware that will receive the error object and form a proper JSON response for the client. Unlike the traditional middleware functions, error middleware takes four arguments — `error`, `request`, `response`, `next`.
Within the `middleware` folder, create `error.ts` file. Within, paste the following lines of code:
**`src/middleware/error.ts`**
```typescript
import { Request, Response, NextFunction } from "express";
import { CustomError } from "../lib/custom-error.ts";
export function error(
err: CustomError,
req: Request,
res: Response,
next: NextFunction
) {
try {
const msg = JSON.parse(err.message);
res.status(err.status).json({ msg });
} catch (error) {
res.status(err.status).json({ msg: err.message });
}
}
```
The `err` argument is the same error that is passed into the `next()` function from some middleware or handler. The error middleware can handle both JSON strings and text strings.
By handling both JSON and text strings, our error middleware can flexibly accommodate different types of error messages, making it more robust and adaptable to various scenarios.
### Setting up not-found middleware
We need to create a middleware that handles requests made to routes that do not exist. This is straightforward. Express executes all middleware in the stack except the request is terminated by some middleware. So, we'll simply create a middleware that forwards an error message to our error middleware and place it at the tail end of the middleware stack. At that position, it only gets hit when our Express app has scanned through all the routes we have defined and doesn't find any that matches the one the client is requesting.
Inside the middleware folder, create a `not-found.ts` file and paste the following lines of code:
**`src/middleware/not-found.ts`**
```typescript
import { Response, Request, NextFunction } from "express";
import { CustomError } from "../lib/custom-error.ts";
export function notFound(req: Request, res: Response, next: NextFunction) {
return next(new CustomError("Route not found", 404));
}
```
This not-found middleware creates a `CustomError` object with a 404 status code and passes it to the next error middleware using the `next()` function.
### Setting up `server.ts` file
Let's set up the application `server.ts` file and implement the two middlewares we just created. Within the `src` folder, create the `server.ts` file:
**`src/server.ts`**
```typescript
import express, { urlencoded, json } from "express";
import { notFound } from "./middleware/not-found.ts";
import { error } from "./middleware/error.ts";
const app = express();
app.use(urlencoded({ extended: true }));
app.use(json());
// ... other middlewares and routes ...
app.use(notFound);
app.use(error);
export default app;
```
The order of middleware matters in Express, and it's important to place the error middleware last, as it will catch any errors that occur in the previous middlewares or handlers. The not-found middleware should be placed just above the error middleware, as it will handle any requests that don't match any of the previous routes.
The `urlencoded({ extended: true })` and `json()` middlewares are built-in Express middleware functions that parse requests with urlencoded and JSON payloads, respectively. They should be placed early in the middleware stack, as they need to parse the request body before any other middlewares or routes can handle the request.
## Setting up the Turso Database and Drizzle ORM
On this section, we’ll learn how to set up and use Turso database and Drizzle ORM in the API.
### How to set up a Turso database
To use Turso database, you need the connection URL and authentication token. Follow these steps to obtain the credentials:
1. Go to the [Turso website](https://turso.tech/)
2. Click on the `Sign Up` button
3. Sign up with either Gmail or Github
4. Choose a username
5. Skip the "About you" form
6. Click on `Create Database`
7. Name your database (e.g., *express-api-project*)
8. Click on `Create Database`
9. Scroll down and click on `Continue to Dashboard`
10. In the dashboard's side menu, click on `Databases`
11. Click on the name of the database you created (e.g., *express-api-project*) at the base of the page
12. Scroll down, copy the URL, and click on the `Generate Token` button
13. Leave everything as it is and click on `Generate Token`
14. Copy the token
15. Paste the URL and token in your `.env` file as follows:
```
TURSO_AUTH_TOKEN=paste-token-here
TURSO_CONNECTION_URL=paste-url-here
PORT=3000
```
### Installing necessary packages for our database
```bash
npm i @libsql/client drizzle-orm; npm i -D drizzle-kit
```
### Create the Drizzle configuration file
After installing the necessary packages, create a `drizzle.config.ts` file in the root directory and paste the following configuration options:
**`drizzle.config.ts`**
```typescript
import { defineConfig } from "drizzle-kit";
export default defineConfig({
schema: "./src/db/schema.ts",
out: "./src/db/migrations",
driver: "turso",
dbCredentials: {
url: process.env.TURSO_CONNECTION_URL,
authToken: process.env.TURSO_AUTH_TOKEN,
},
dialect: "sqlite",
verbose: true,
strict: true,
});
```
This file contains the configurations for drizzle ORM, including location of our schema and migrations. The `verbose: true` property prints out every action executed when making changes to the database. `strict:true` property ensures caution, forcing confirmation of any changes you want to make to the database.
### Connect Turso database with Drizzle
Next, create the `db.ts` file in the `db` folder and paste the following lines of code:
**`src/db/db.ts`**
```typescript
import { drizzle } from "drizzle-orm/libsql";
import { createClient } from "@libsql/client";
const client = createClient({
url: process.env.TURSO_CONNECTION_URL,
authToken: process.env.TURSO_AUTH_TOKEN,
});
export const db = drizzle(client);
```
The `drizzle(client)` function establishes a connection between the database client and Drizzle ORM, enabling the use of the ORM’s capabilities to interact with the database.
## Create Notes Schema and Migrations
Now that we have set up our database, let's create the notes schema, generate migrations, and apply the migrations to the Turso database.
### Creating the notes schema
Let's define our schema file for the notes app project. In the `db` folder, create a new file named `schema.ts` and add the following code:
**`src/db/schema.ts`**
```typescript
import { sqliteTable, integer, text } from "drizzle-orm/sqlite-core";
export const NotesTable = sqliteTable("note", {
id: integer("id").primaryKey(),
title: text("title").notNull(),
body: text("body"),
});
```
This is similar to the `CREATE TABLE` statement in MySQL. It creates a table with the following columns:
- `id`: A primary key that auto-increments, uniquely identifying each note
- `title`: A text column that must not be null, representing the title of the note
- `body`: A text column that can be null, representing the body or content of the note
### Generating migrations
Next, we'll generate migrations using the following command in your terminal:
```bash
npx drizzle-kit generate
```
This command will create our database migrations in the `"/src/db/migrations"` directory, as specified in the `drizzle.config.ts` file.
### Apply migrations
Next, apply the generated migrations to the Turso database by running the following command in your terminal:
```bash
npx drizzle-kit migrate
```
## Creating Notes Router in a Modular Way
When building an API using Express, we can place all our routes directly on the Express app:
```typescript
import express from "express";
const app = express();
//get request
app.get("/", handlerFunction1)
//post request
app.post("/add-something", handlerFunction2)
```
Using this approaching for small and demo applications is fine. But in large-scale projects, it can lead to a cluttered and hard-to-maintain codebase. Let’s see a better way.
### Express Router function explained
Express.js provides the `Router()` function, which creates a router object. This object acts as a middleware, but with the added capability to attach HTTP methods (such as GET, POST, PUT, and DELETE) to it. This allows for modular and organized routing.
Here's an example of creating a simple router:
```typescript
import { Router } from "express";
//defining the router
const routerObject = Router()
routerObject.get("/get-something", (req, res) => {})
routerObject.post("/post-something", (req, res) => {})
routerObject.delete("/delete-something", (req, res) => {})
//using the router in our app
app.use("/our-api", routerObject)
```
When a request URL starts with `/our-api`, the `routerObject` will be invoked, and the appropriate handler will be executed based on the HTTP method and the remaining part of the URL. For instance, if the request URL is `/our-api/get-something`, the GET handler attached to the `/get-something` route will be executed.
### Creating the `notesRouter` object
The notes API will have the following endpoints:
| API Endpoint | Method | Description |
| --- | --- | --- |
| /add-note | POST | Add new note |
| /get-note/:id | GET | Get note with id |
| /get-all-notes | GET | Get all notes |
| /update-note/:id | PUT | Update note with id |
| /delete-note/:id | DELETE | Delete note with id |
Within the `routes` folder, create `notes.ts` file and insert the following lines of code:
**`src/routes/notes.ts`**
```typescript
import { Router } from "express";
import { addNote, deleteNote, getAllNotes, getNote, updateNote} from "../handlers/notes.ts";
const notesRouter = Router();
notesRouter.get("/get-note/:id", getNote);
notesRouter.get("/get-all-notes", getAllNotes);
notesRouter.post("/add-note", addNote);
notesRouter.put("/update-note/:id", updateNote);
notesRouter.delete("/delete-note/:id", deleteNote);
export default notesRouter;
```
Now that our `notesRouter` object is ready, let’s hook it to our app in our `server.ts` file:
**`src/server.ts`**
```typescript
import express, { urlencoded, json } from "express";
import { notFound } from "./middleware/not-found.ts";
import { error } from "./middleware/error.ts";
import notesRouter from "./routes/notes.ts";
const app = express();
app.use(urlencoded({ extended: true }));
app.use(json());
app.use("/api", notesRouter);
app.use(notFound);
app.use(error);
export default app;
```
The URL to request any notes resource must start with `/api`. As we've seen, Express Router makes our application easier to manage and scale.
Next, we'll define our handlers, including `addNote` and `getNote`. Although we've imported them, we haven't created them yet.
## Creating the Notes Handlers
Handlers are technically middlewares. Just like middleware functions, they have three arguments — `request`, `response`, and `next`. Typically, they respond to the client or send an error message to the error middleware using the `next()` function.
More importantly, we define the logic to interact with the database in the handlers. This is where Drizzle shines. Within the `handlers` folder, create a new file named `notes.ts` and add the following code:
**`src/handlers/notes.ts`**
```typescript
import { eq } from "drizzle-orm";
import { db } from "../db/db.ts";
import { NotesTable } from "../db/schema.ts";
import { Response, Request, NextFunction } from "express";
import { CustomError } from "../lib/custom-error.ts";
export async function addNote(req: Request, res: Response, next: NextFunction) {
try {
const note = await db.insert(NotesTable).values(req.body).returning();
res.status(201).json({ note });
} catch (error) {
next(new CustomError("Failed to add note", 500));
}
}
export async function getAllNotes(req: Request,res: Response, next: NextFunction) {
try {
const notes = await db.select().from(NotesTable);
res.status(200).json({ notes });
} catch (error) {
next(new CustomError("Failed to fetch notes", 500));
}
}
export async function getNote(req: Request, res: Response, next: NextFunction) {
try {
const note = await db
.select()
.from(NotesTable)
.where(eq(NotesTable.id, +req.params.id));
res.status(200).json({ note });
} catch (error) {
next(new CustomError("Failed to fetch note", 500));
}
}
export async function deleteNote(req: Request, res: Response, next: NextFunction) {
try {
const note = await db
.delete(NotesTable)
.where(eq(NotesTable.id, +req.params.id))
.returning({
deletedNoteId: NotesTable.id,
});
res.status(200).json({ note });
} catch (error) {
next(new CustomError("Failed to delete note", 500));
}
}
export async function updateNote(req: Request, res: Response, next: NextFunction) {
try {
const note = await db
.update(NotesTable)
.set(req.body)
.where(eq(NotesTable.id, +req.params.id))
.returning();
res.status(201).json({ note });
} catch (error) {
next(new CustomError("Failed to update note", 500));
}
}
```
Similar to SQL, Drizzle provides methods like `insert`, `select`, `update`, `delete`, `set`, `where`, and more to interact with the database. The `eq` function is used to compare two entities. The `returning` function at the end of the `insert`, `update`, and `delete` functions specifies what Drizzle should return after successful execution. If left empty, it will return all fields. Drizzle offers a wide range of functions to help you achieve your API goals, and they are well-documented in the [official documentation](https://orm.drizzle.team/docs/overview).
## Validating and Sanitizing Data from Client’s Request
Our app is still missing a crucial component. Consider a scenario where we expect a numerical value in the request body but receive a string instead, or anticipate an email address but receive plain text. Even worse, a malicious actor might attempt to inject code into our database to steal or compromise stored information. We must prevent these scenarios from occurring, and one way to do so is to thoroughly examine client data before it reaches the handler.
We could write custom middlewares to validate and sanitize client data, but a more efficient approach is to utilize the battle-tested [express-validator](https://express-validator.github.io/docs) npm package. This package provides a set of middlewares that enable us to inspect client data and ensure it meets our requirements, making our app more secure and robust.
### Installing `express-validator`
```bash
npm i express-validator
```
### Defining `express-validator` middlewares
Within the `src/lib` folder, create the `validator-functions.ts` file and include the following lines of code:
**`src/lib/validator-functions.ts`**
```typescript
import { body, param } from "express-validator";
//Validating and sanitizing title from request body
export function validateNoteTitle() {
return body("title").notEmpty().isString().trim().escape();
}
//Validating and sanitizing body from request body
export function validateNoteBody() {
return body("body").notEmpty().isString().trim().escape();
}
//Validating id from route parameter
export function validateIdParam() {
return param("id").toInt().isInt();
}
```
To validate individual values from the client request, we utilize method chaining, where the output of the previous method becomes the input for the current method. For the `title` and `body` fields, we employ the following methods:
- `notEmpty()`: Validates that the value is not empty
- `isString()`: Validates that the value is a string
- `trim()`: A sanitizer that removes whitespace from both ends of the value, if present
- `escape()`: A sanitizer that replaces special characters, such as `<` and `>`, with HTML entities, protecting the server from Cross-Site Scripting (XSS) attacks
For a comprehensive list of validators and sanitizers, along with their uses, refer to the [validator.js](https://github.com/validatorjs/validator.js) GitHub repository.
### Implementing `express-validator` middleware functions
Now that we have written the validator functions, we can now implement them in our routes. Let’s update our `src/routes/notes.ts` file:
**`src/routes/notes.ts`**
```typescript
import { Router } from "express";
import { addNote, deleteNote, getAllNotes, getNote, updateNote} from "../handlers/notes.ts";
import { validateIdParam, validateNoteBody, validateNoteTitle} from "../lib/validator-functions.ts";
const notesRouter = Router();
notesRouter.get("/get-note/:id", validateIdParam(), getNote);
notesRouter.get("/get-all-notes", getAllNotes);
notesRouter.post("/add-note", validateNoteBody(), validateNoteTitle(), addNote);
notesRouter.put("/update-note/:id", validateIdParam(), validateNoteBody(), validateNoteTitle(), updateNote);
notesRouter.delete("/delete-note/:id", validateIdParam(), deleteNote);
export default notesRouter;
```
When an `express-validator` middleware encounters a validation error, it doesn't terminate the request immediately. Instead, it collects the errors and passes control to the next middleware or handler in the chain. This allows for more flexibility in handling validation errors.
The `validationResult()` function is a key part of this process. It takes the request object as an argument and returns an object containing the validation errors, if any. By checking the result of `validationResult()`, we can determine if there were any validation errors and handle them accordingly in the handlers.
### Capturing validation errors
Let’s update our `src/handlers/notes.ts` to account for validation errors:
**`src/handlers/notes.ts`**
```typescript
import { eq } from "drizzle-orm";
import { db } from "../db/db.ts";
import { NotesTable } from "../db/schema.ts";
import { Response, Request, NextFunction } from "express";
import { CustomError } from "../lib/custom-error.ts";
import { validationResult } from "express-validator";
export async function addNote(req: Request, res: Response, next: NextFunction) {
const result = validationResult(req);
console.log(result);
if (!result.isEmpty()) {
return next(new CustomError(JSON.stringify(result.array()), 400));
}
try {
const note = await db.insert(NotesTable).values(req.body).returning();
res.status(201).json({ note });
} catch (error) {
next(new CustomError("Failed to add note", 500));
}
}
export async function getAllNotes(req: Request, res: Response, next: NextFunction) {
try {
const notes = await db.select().from(NotesTable);
res.status(200).json({ notes });
} catch (error) {
next(new CustomError("Failed to fetch notes", 500));
}
}
export async function getNote(req: Request, res: Response, next: NextFunction) {
const result = validationResult(req);
if (!result.isEmpty()) {
return next(new CustomError(JSON.stringify(result.array()), 400));
}
try {
const note = await db
.select()
.from(NotesTable)
.where(eq(NotesTable.id, +req.params.id));
res.status(200).json({ note });
} catch (error) {
next(new CustomError("Failed to fetch note", 500));
}
}
export async function deleteNote(req: Request, res: Response, next: NextFunction) {
const result = validationResult(req);
if (!result.isEmpty()) {
return next(new CustomError(JSON.stringify(result.array()), 400));
}
try {
const note = await db
.delete(NotesTable)
.where(eq(NotesTable.id, +req.params.id))
.returning({
deletedNoteId: NotesTable.id,
});
res.status(200).json({ note });
} catch (error) {
next(new CustomError("Failed to delete note", 500));
}
}
export async function updateNote(req: Request, res: Response,next: NextFunction) {
const result = validationResult(req);
if (!result.isEmpty()) {
return next(new CustomError(JSON.stringify(result.array()), 400));
}
try {
const note = await db
.update(NotesTable)
.set(req.body)
.where(eq(NotesTable.id, +req.params.id))
.returning();
res.status(201).json({ note });
} catch (error) {
next(new CustomError("Failed to update note", 500));
}
}
```
In this updated code, we're using `validationResult(req)` to check for validation errors. If there are any errors, we're returning a 400 response with the error details. If there are no errors, we can proceed with the logic.
`result.array()` returns an array of objects, and the `CustomError` class expects a string message. By using `JSON.stringify()`, we can convert the error message to a string, which can then be passed to the `CustomError` class. Remember that we designed our error middleware to accept both JSON and text strings? This is where it comes in handy in this API.
## Testing the app
To test the app, insert the following lines of code in the `index.ts` file:
**`src/index.ts`**
```typescript
import app from "./server.ts";
const port = process.env.PORT || 8000;
app.listen(port, () => {
console.log(`Server is listening at port ${port}`);
});
```
Run the app with the following command on the terminal:
```bash
npm run dev
```
I am using Thunder Client VS Code extension (which you can easily install) to test the API endpoints. However, you can any API client of your choice, such as Insomnia and Postman.
### Create note with the `/api/add-note` POST endpoint
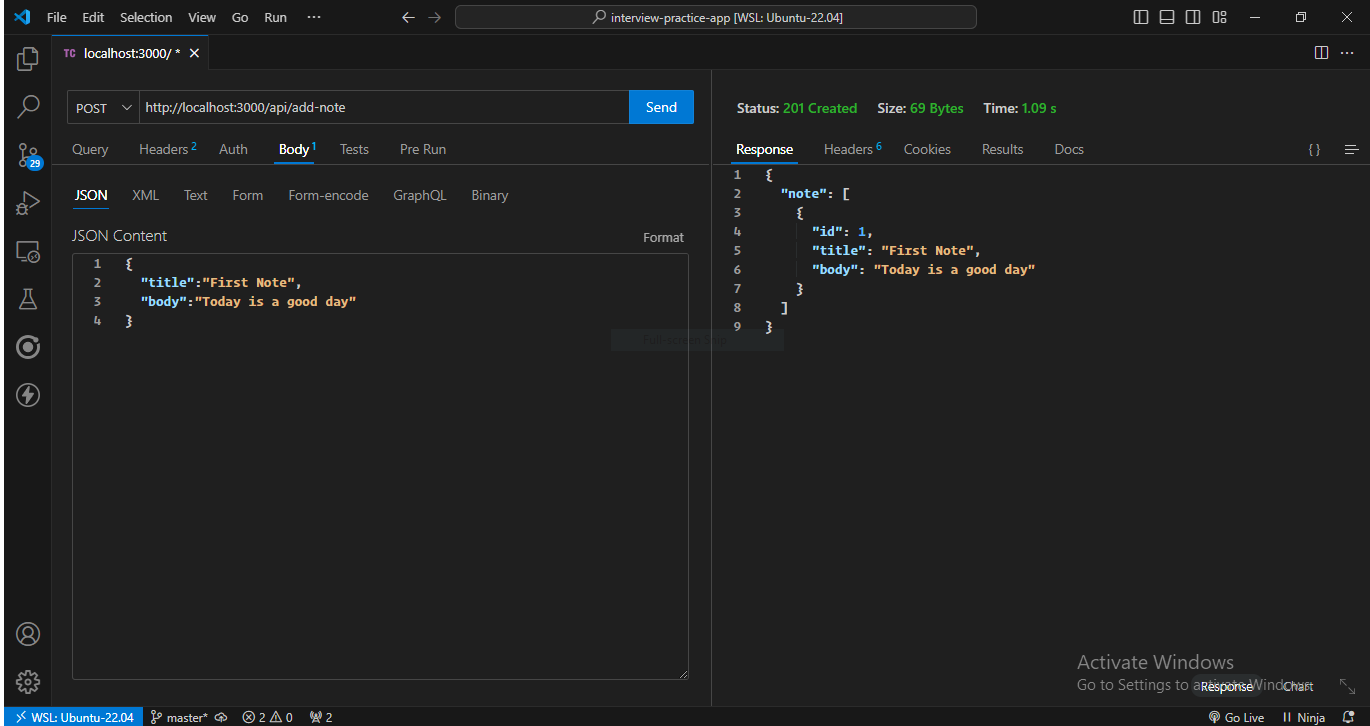
Great, let's verify that our notes are being stored in the database! Here are the steps to follow:
1. Open your Turbo dashboard
2. Click on `Databases`
3. Select the database named _express-api-project_ (or the name you chose for your database)
4. Scroll down and click on the `Edit Tables` button next to the `Generate Token` button
5. In the `Tables` tab, click on the `notes` table
6. You should see a list of notes that you've created using the API
If you see the following screen, that means your server is working correctly and storing data in the database!
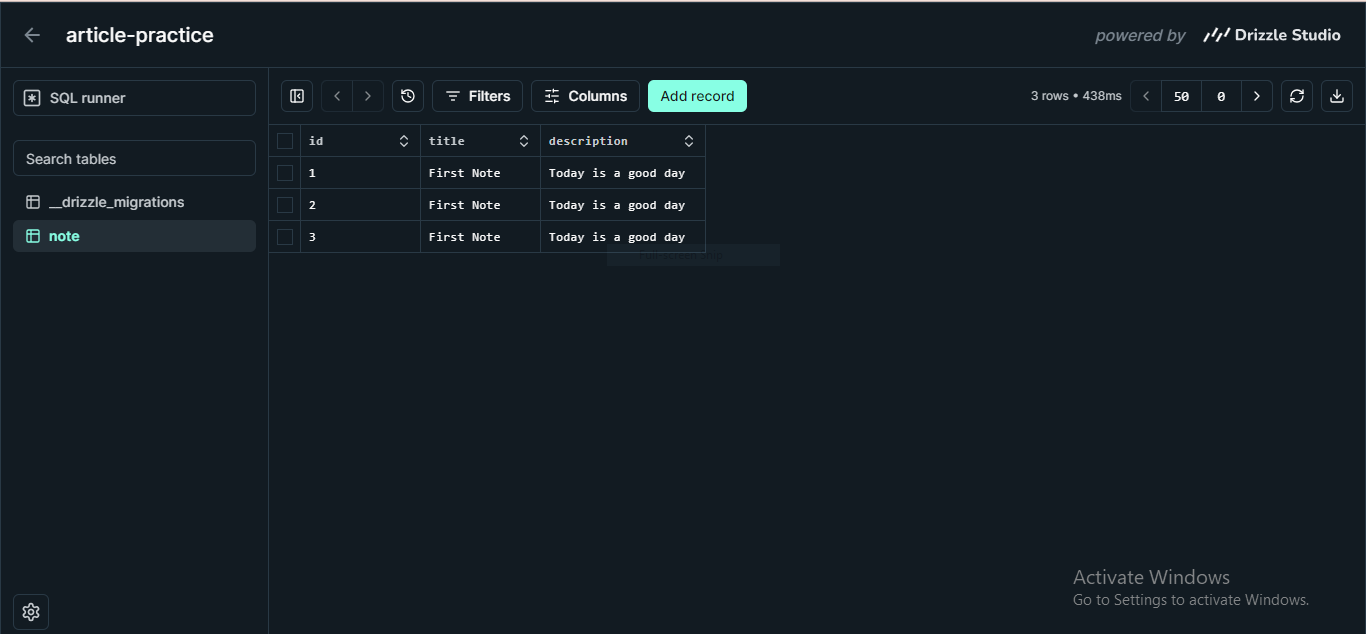
### Fetching all notes with the /api/get-all-notes GET endpoint
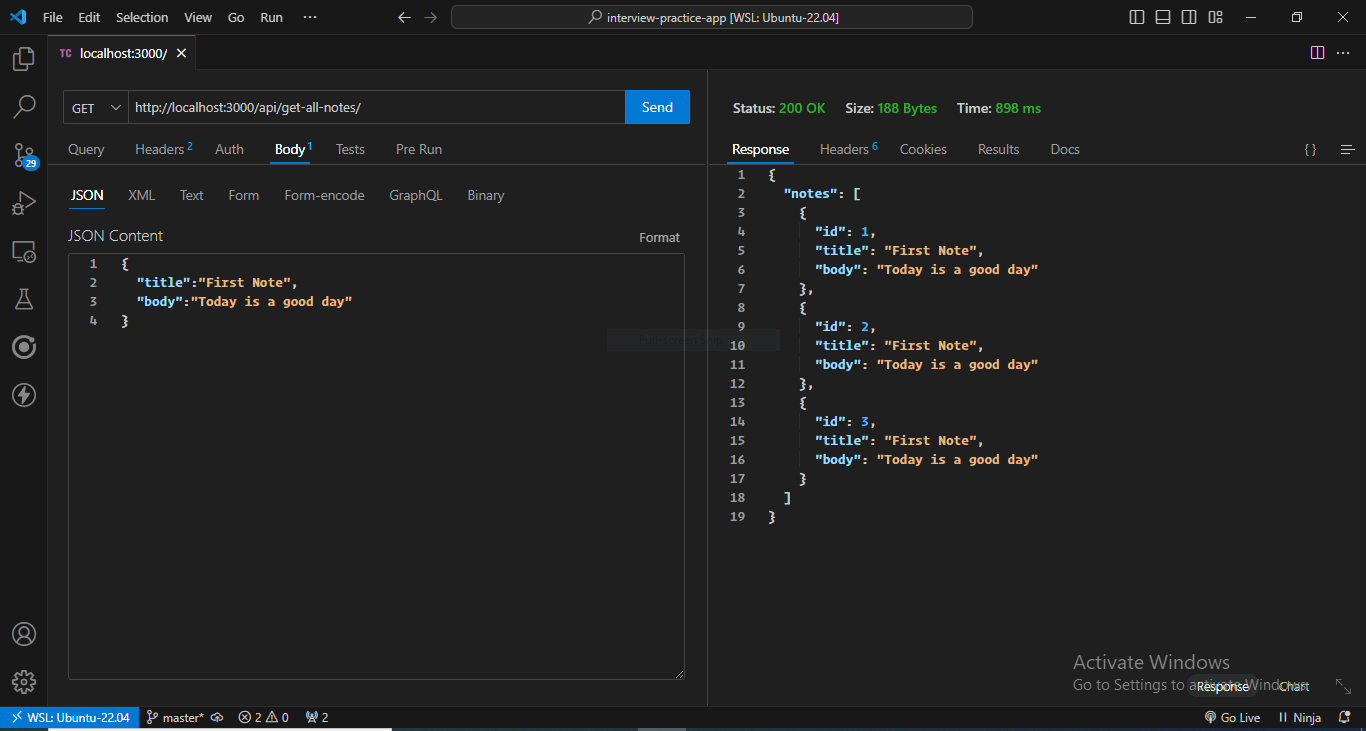
These endpoints worked! You can try the other endpoints yourself.
## Conclusion
Great job if you stuck around throughout the guide! You now have a solid foundation on how to build an API using TypeScript, Express, Drizzle, and Turso database. For reference, check out the project's [Github Repository](https://github.com/woodmark-dev/express-typescript-api). I hope you found this article helpful and enjoyed building this project as much as I did.
| ibrocodes |
1,866,636 | GRAPHQL | Introduction: GraphQL is a query language for APIs and a runtime for executing those queries. It was... | 0 | 2024-05-27T13:57:36 | https://dev.to/dariusc16/graphql-38ei | **Introduction:**
GraphQL is a query language for APIs and a runtime for executing those queries.
It was developed by Facebook in 2012 and open-sourced in 2015.
GraphQL allows clients to request only the data they need, reducing over-fetching and under-fetching.
It's gaining popularity due to its flexibility and efficiency in fetching and manipulating data.
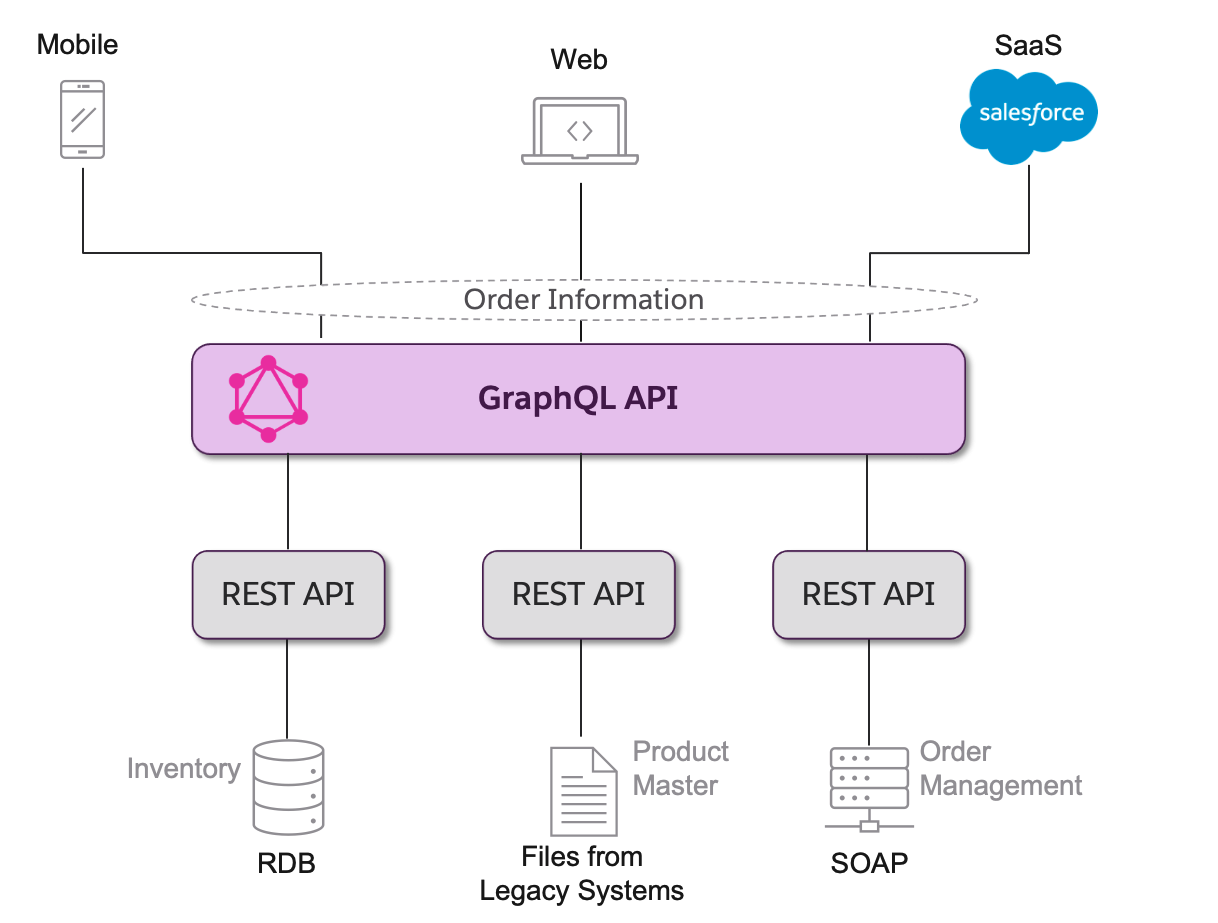
**What is GraphQL?:**
GraphQL is a query language that enables clients to request exactly the data they need from the server.
Unlike REST APIs, where clients are limited to predefined endpoints, GraphQL provides a single endpoint for flexible data retrieval.
Key features include a strongly typed schema, introspection, and the ability to traverse relationships between data entities.
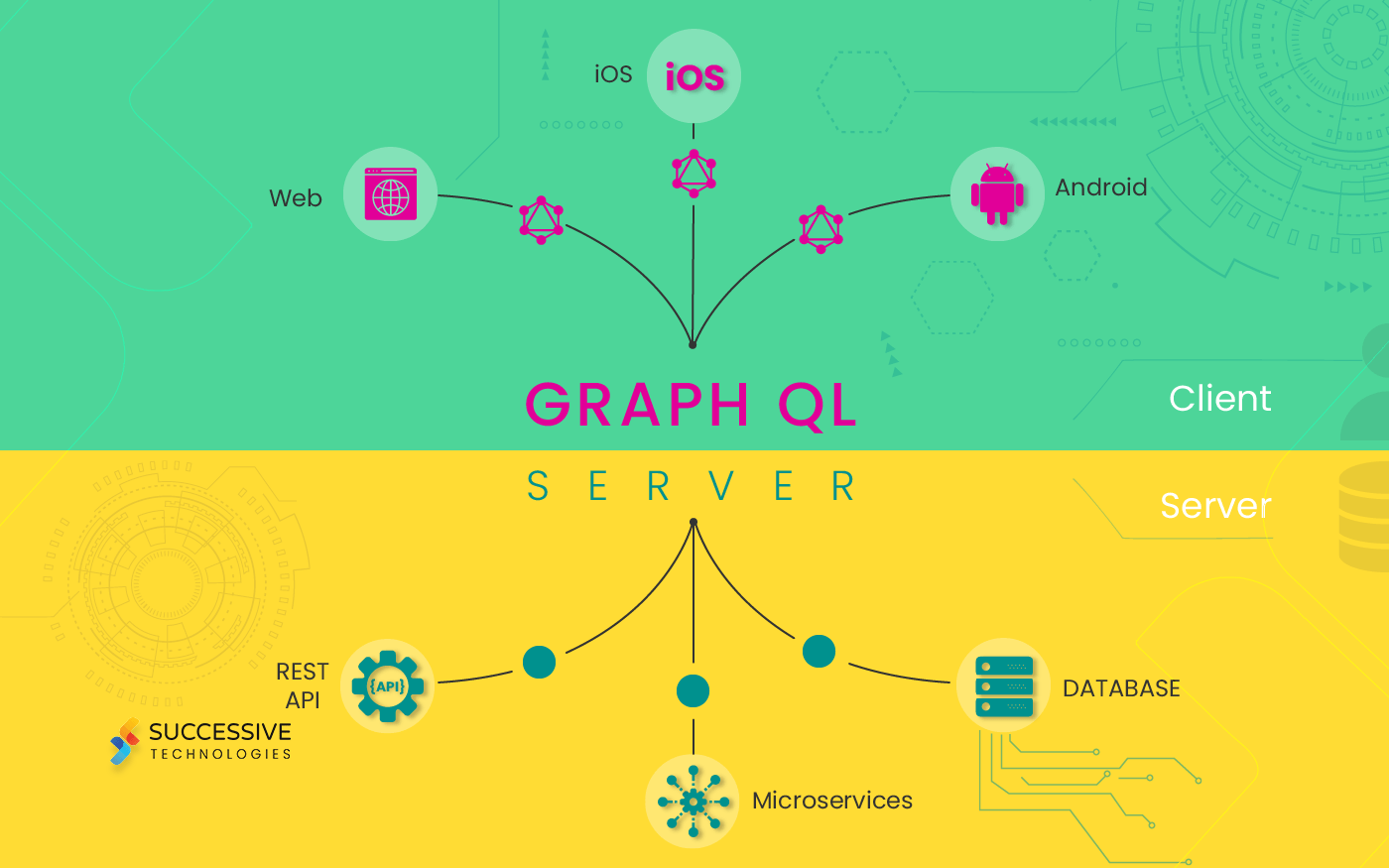
**How does GraphQL work?:
**
GraphQL operates through a schema that defines the types and relationships of the available data.
Clients send queries to the GraphQL server specifying the exact data they require.
Queries can retrieve nested data and multiple resources in a single request.
Mutations allow clients to modify data on the server, while subscriptions enable real-time data updates.
**Benefits of GraphQL:
**
GraphQL reduces network overhead by allowing clients to request only the data they need.
It improves frontend development efficiency by eliminating over-fetching and under-fetching issues.
GraphQL schemas provide a clear contract between frontend and backend developers, promoting collaboration and reducing API versioning issues.
**Use Cases:
**
Companies like GitHub, Shopify, and Airbnb have adopted GraphQL to improve their API performance and developer experience.
GitHub's adoption of GraphQL led to a significant reduction in API response times and improved caching strategies.
Shopify uses GraphQL to power its mobile app, enabling fast and efficient data fetching for its merchants.
**Getting Started with GraphQL:
**
Popular GraphQL client libraries include Apollo Client for JavaScript and Relay for React.
Server-side implementations like Apollo Server and GraphQL Yoga simplify building GraphQL APIs.
Resources like the GraphQL documentation and tutorials on platforms like egghead.io provide guidance for learning GraphQL.
**Challenges and Considerations:
**
While GraphQL offers many benefits, it also introduces complexity, especially in managing the schema and optimizing queries.
Caching and authorization can be challenging to implement efficiently in a GraphQL environment.
Careful schema design and performance monitoring are essential for scaling GraphQL APIs.
GraphQL offers a modern approach to API development, providing flexibility, efficiency, and improved developer experience.
By understanding its principles and best practices, developers can harness the power of GraphQL to build better APIs and applications. | dariusc16 | |
1,866,635 | Pillars of Startup Development: Anne-Sophie Malgorn’s Expertise in Company Formation and Bank Account Opening | In the progressive and competitive business landscape, having a seasoned and dedicated advisor by... | 0 | 2024-05-27T13:53:16 | https://dev.to/asiabusinesscentre/pillars-of-startup-development-anne-sophie-malgorns-expertise-in-company-formation-and-bank-account-opening-449h | In the progressive and competitive business landscape, having a seasoned and dedicated advisor by your side who understands your unique hurdles can be instrumental in achieving your goals.
Anne-Sophie Malgorn, VP of Business Development at AsiaBC, is a trusted expert who possesses an in-depth insight into her European client's needs and challenges when connecting with the Asian market. With her extensive experience in company formation and bank account opening, she is well-versed in navigating the intricacies of cross-cultural business dynamics, providing invaluable guidance tailored to the specific requirements of European entrepreneurs. Additionally, Anne-Sophie brings a wealth of knowledge from her three-year experience in handling Canadian and Middle Eastern entrepreneurs, further expanding her global perspective and understanding of diverse business environments. Her comprehensive expertise and international exposure make her an ideal partner for companies seeking to establish a solid foundation, streamline their operations, and capitalise on opportunities in the Asian market.
Understanding Unique Challenges
Anne-Sophie recognises that every entrepreneur faces distinct challenges when it comes to setting up and expanding their businesses. As a business advisor, she takes the time to closely collaborate with her clients, gaining comprehensive insights into their specific needs. By doing so, Anne-Sophie develops customised solutions that address their pain points and align with their long-term objectives, ensuring a tailored approach to each client's requirements.
Wide-ranging Experience
Throughout her illustrious career, Anne-Sophie has worked with a diverse range of clients across various industries. Her in-depth understanding of HK incorporation and bank account opening procedure provides her with invaluable insights into the intricacies of these fields. This extensive experience enables Anne-Sophie to offer the best fitting solutions for her clients, regardless of their industry or niche, fostering a high level of confidence and trust.
Company Formation
One of Anne-Sophie’s areas of expertise lies in company formation. She possesses comprehensive knowledge of the legal requirements involved in [company registration in Hong Kong](https://asiabc.co/services/company-registration/hk-with-fintech-account/), Singapore, and other jurisdictions. Whether her clients are looking to register a new company, expand an existing one, or set up a branch office in Asia, Anne-Sophie guides them at every step. With her meticulous attention to detail, she advises her clients on how to obtain all necessary paperwork, licences, and permits to ensure they acquire them smoothly and efficiently.
Bank Account Opening
In addition to business incorporation, Anne-Sophie's expertise extends to assisting entrepreneurs in opening bank accounts in Hong Kong but also in providing comprehensive international banking support. Recognising the importance of establishing a bank account is critical for companies to efficiently manage their finances and smoothly carry out day-to-day operations across borders. Leveraging her vast network of banking professionals worldwide, Anne-Sophie expertly facilitates the account opening process for her clients, ensuring seamless transactions company formationoverseas. Navigating complex requirements across different jurisdictions, Anne-Sophie offers valuable guidance to clients looking to expand their business globally. She goes beyond local banking solutions, helping clients select the most suitable international banking options that align with their objectives and enhance their global market presence.
Tailored Solutions
Anne-Sophie firmly believes in delivering customised solutions that cater to her clients' unique needs. She understands that there are better approaches than a one-size-fits-all approach in the business world. By gaining a deep understanding of her client's goals and challenges, Anne-Sophie offers tailored solutions that maximise their chances of success. Her ability to provide personalised guidance sets her apart as an advisor committed to her clients' long-term growth and prosperity.
Trusted Partner
Entrepreneurs collaborating with Anne-Sophie Malgorn discover in her not only a dedicated and trusted partner committed to their success but also a reliable source of support and guidance. Her expertise, combined with her passion for helping businesses thrive make her an invaluable asset for entrepreneurs in the ever-evolving Asian market. Anne-Sophie’s commitment to her client's success sets the stage for a strong, enduring partnership built on trust, mutual growth and unwavering dedication.
As VP of Business Development at AsiaBC, Anne-Sophie Malgorn is an experienced and dedicated business advisor specialising in and bank account opening. With her in-depth understanding of the Asian market and commitment to providing tailored solutions, Anne-Sophie empowers entrepreneurs to navigate the complex landscape of establishing and expanding their businesses. By partnering with Anne-Sophie, entrepreneurs gain access to a wealth of expertise, support, and personalised guidance, enabling them to confidently pursue their business ventures and achieve their goals in the competitive Asian market.
| asiabusinesscentre | |
1,866,634 | Why Experienced Programmers Fail Coding Interviews | A friend of mine recently joined a zoho company as an engineering manager, and found themselves in... | 0 | 2024-05-27T13:52:57 | https://dev.to/stealc/why-experienced-programmers-fail-coding-interviews-b5g | webdev, career, node, opensource | > A friend of mine recently joined a zoho company as an engineering manager, and found themselves in the position of recruiting for engineering candidates.
We caught up.
“Well,” I laughed when they inquired about the possibility of me joining the team, “I’m not sure I’ll pass the interviews, but of course I’d love to work with you again! I’ll think about it.”
“That’s the same thing X and Y both said,” they told me, referring to other engineers we had worked with together. “They both said they weren’t qualified.”
I nodded in understanding, but a part of my mind was also wincing. Those other engineers my friend referred to were solid senior engineers — great communicators, collaborators, and great at solving technical problems. We both knew this, since we had all worked together for almost two years.
But could they pass the interview bar for the company my friend had recently joined? The outcome could be a coin toss. “Well,” my friend allowed, “my advice would be to do a little practice first. Get some interviews in at other companies, too; don’t go in cold.”
And such is the reality of an experienced programmer looking to find a new job.
## Why do experienced programmers fail at interviews?
> Here are my musings.
**1. Interview Format Mismatch**
**2. Nervousness and Performance Anxiety**
**3. Outdated Knowledge**
**4. Misalignment of Skills and Job Requirements**
**5. Cultural Fit and Communication**
**6. Overconfidence or Under-preparation**
**7. Bias and Perception**
**8. Evaluation Inconsistencies**
Understanding these challenges can help experienced programmers better prepare for interviews and align their expectations with the process. | stealc |
1,866,633 | Multiple Environments in Frontend Applications | In this blog, we'll explore how to set up and manage multiple environments in a frontend application... | 0 | 2024-05-27T13:49:47 | https://dev.to/ramgoel/multiple-environments-in-frontend-applications-2k07 | react, webdev, javascript, programming | In this blog, we'll explore how to set up and manage multiple environments in a frontend application using `env-cmd`.
## What is `env-cmd`?
`env-cmd` is a utility that allows you to easily load environment variables from a file into your Node.js application. It supports loading multiple environment files, making it an excellent choice for managing different configurations for various environments.
## Step-by-Step Guide to Setting Up Multiple Environments with `env-cmd`
### 1. Install `env-cmd`
First, you need to install `env-cmd` as a development dependency in your project:
```bash
npm install env-cmd --save-dev
```
### 2. Create Environment Files
Create separate environment files for each environment you want to manage. These files typically reside in the root of your project. For example, you can create the following files:
- `.env.development`
- `.env.test`
- `.env.production`
Each file should contain the environment-specific variables:
**.env.development**
```
REACT_APP_API_URL=http://localhost:3000
```
**.env.test**
```
REACT_APP_API_URL=http://localhost:4000
```
**.env.production**
```
REACT_APP_API_URL=https://api.production.com
```
### 3. Configure Scripts in `package.json`
Modify the `scripts` section of your `package.json` to use `env-cmd` for running commands in different environments. This allows you to specify which environment file to load when starting your application or running build processes.
```json
{
"scripts": {
"start:development": "env-cmd -f .env.development react-scripts start",
"start:test": "env-cmd -f .env.test react-scripts start",
"start:production": "env-cmd -f .env.production react-scripts start",
"build:development": "env-cmd -f .env.development react-scripts build",
"build:test": "env-cmd -f .env.test react-scripts build",
"build:production": "env-cmd -f .env.production react-scripts build"
}
}
```
### 4. Access Environment Variables in Your Code
In your application code, you can access these environment variables using `process.env`. For example, in a React component:
```javascript
const apiUrl = process.env.REACT_APP_API_URL;
console.log(`API URL: ${apiUrl}`);
```
### 5. Running the Application
You can now start your application in the desired environment by running the corresponding script. For example, to start the application in the development environment:
```bash
npm run start:development
```
Or to build the application for production:
```bash
npm run build:production
```
Using `env-cmd` to manage multiple environments in your frontend application simplifies the process of handling different configurations. It allows you to maintain clean and organized environment variables, making your development, testing, and deployment processes more efficient. By following the steps outlined in this guide, you can set up and manage multiple environments effectively, ensuring your application performs consistently across all stages of development.
If you've liked this blog, connect with me on [LinkedIn](https://www.linkedin.com/in/ramgoel/) or [X](https://x.com/theramgoel). | ramgoel |
1,866,632 | I made a clicker game in scratch in just 1 hour | I always liked making challenges among myself and decided to make a game in just an hour. I didn't... | 0 | 2024-05-27T13:48:42 | https://dev.to/dino2328/i-made-a-clicker-game-in-scratch-in-just-an-hour-27k3 | webdev, javascript, beginners, scratch | I always liked making challenges among myself and decided to make a game in just an hour. I didn't know in which genre should I make the game. So I opened ChatGpt asked which genre should I make the game. It told me to make a clicker game in scratch. So I opened scratch started the timer
## Backdrop
I was eating some cookies while doing. So I decided to make a cookie clicker in scratch. I first made a purple backdrop and made a full detailed cookie. Not fully detailed but it looks like a cookie. Made a shop and those are the sprites and backdrops and when I saw the time it was already 30 minutes over. I should now write all of the code in just 30 minutes which is a little time but I did it somehow.
## Code
I still have 30 minutes and I started writing the code and made two variables score and Income and wrote the code for the two big variables. Now I have only 5min left and I completed the game correctly in time.
Check out my game:[COOKIE CLICKER](https://scratch.mit.edu/projects/1027241600/)
| dino2328 |
1,866,631 | AI-powered Mobile App with Backend in Two Days + MVVMP Architecture Overview (Tutorial) | Creating a Proof of Concept SwiftUI mobile app with clean MVVMP architecture and a small FastAPI... | 0 | 2024-05-27T13:46:53 | https://dev.to/markparker5/ai-powered-mobile-app-with-backend-in-two-days-mvvmp-architecture-overview-tutorial-mh1 | mobile, tutorial, ai, development | Creating a Proof of Concept SwiftUI mobile app with clean MVVMP architecture and a small FastAPI backend.
---
Previous articles:
- [How We Built an AI Startup in a Weekend Hackathon in Germany](https://dev.to/markparker5/how-we-built-an-ai-startup-in-a-weekend-hackathon-in-germany-2c3k)
- [House, MD - AI Diagnostician in Your Phone: Passing the Startup Torch](https://dev.to/markparker5/dr-house-ai-diagnostician-in-your-phone-passing-the-startup-torch-to-capable-hands-13pf)
This article delves into the nuts and bolts of creating a Proof of Concept (PoC) of ф mobile app built with the SwiftUI framework and a backend using FastAPI. As an extra, I'll demonstrate effective architecture patterns for SwiftUI apps, specifically MVVMP combined with SOLID principles and Dependency Injection (DI). For android, the code can be easily translated to Kotlin using Jetpack Compose Framework almost without changes.
## Why We Need a Backend
Someone might say that you can just cram all the logic into the application, send requests to chatgpt directly and make a backendless app. And I agree, it is indeed possible (and I'll show it later), but the backend provides several important advantages.
The backend serves as the backbone for any sophisticated app, especially those requiring secure data management, business logic processing, and service integration. Here’s why a robust backend is crucial:
1. **Security**: A backend helps protect sensitive data and user authentication tokens from MITM (Man-in-the-Middle) attacks. It acts as a secure gateway between the user's device and the database or external services, ensuring that all data exchanges are encrypted and authenticated.
2. **Control Over Service Usage**: By managing APIs and user interactions through the backend, you can monitor and control how the app is used. This includes throttling to manage load, preventing abuse, and ensuring that resources are used efficiently.
3. **Database Integration**: A backend allows for seamless integration with databases, enabling dynamic data storage, retrieval, and real-time updates. This is essential for apps that require user accounts, store user preferences, or need to retrieve large amounts of data quickly and securely.
4. **Subscription and Freemium Models**: Implementing subscription services or a freemium model requires a backend to handle billing, track usage, and manage user tiers. The backend can securely process payments and subscriptions, providing a seamless user experience while ensuring compliance with data protection regulations.
5. **Scalability and Maintenance**: With a backend, you can scale your application more effectively. Server-side logic can be updated without needing to push updates to the client, facilitating easier maintenance and quicker rollouts of new features.
In essence, a backend is not just about functionality — it's about creating a secure, scalable, and sustainable environment for your app to thrive.
## Explaining the Tech Stack
- **SwiftUI**: The go-to for native iOS apps now that UIKit is on its way out. It's declarative and streamlined, with XCode as the indispensable editor. For android, the code can be easily translated to Kotlin using Jetpack Compose.
- **FastAPI**: Chosen for the backend for its speed, minimal boilerplate, and declarative nature, edited with the superb Zed.dev.
- **ChatGPT API**: Used here as a large language model (LLM); choice may vary based on the need for customization (see [Technical Info](github.com/HouseMDAI/house-notebook/blob/main/Technical Info.md)).
- **Ngrok**: Implements tunneling with a simple CLI command to expose your local server to the internet.
## Building the iOS App
### Theory: Architecture Patterns
1. **Model View ViewModel Presenter (MVVMP)**:
- **Model**: Represents the data structures used in the app, such as Question, Answer, Questionary, and FilledQuestionary. These models are simple and only hold data, following the KISS principle.
- **View**: SwiftUI views are responsible only for UI presentation and delegate all data and logic to presenters. They contain no business logic and are designed to be simple and focused on UI rendering.
- **ViewModel**: In SwiftUI, ViewModel is represented by ObservableObject, which serves as a data-only observable model. No methods or logic here.
- **Presenter**: The Presenter manages all logic related to the module (screen or view), but not the business logic. It communicates with the domain layer for business logic operations, such as interacting with APIs or managing data persistence.
- **Domain Layer**: This layer encapsulates the business logic of the application and interacts with external resources such as databases, APIs, or other services. It consists of several components, such as Services, Providers, Managers, Repositories, Mappers, Factories, etc.
- Actually, the MP in MVVMP stands for Mark Parker and the full form is "Model View ViewModel by Mark Parker"
2. **SOLID Principles**:
- **Single-responsibility Principle**: Each class should have only one reason to change.
- **Open-closed Principle**: Components should be open for extension but closed for modification.
- **Liskov Substitution Principle**: Objects of a superclass should be replaceable with objects of subclasses.
- **Interface Segregation Principle**: No client should be forced to depend on interfaces it doesn't use.
- **Dependency Inversion Principle**: Depend on abstractions, not concretes, facilitated by DI.
3. **Dependency Injection (DI)**: a programming technique in which an object or function receives other objects or functions that it requires, as opposed to creating them internally.
## Drafting the Backend
The [backend's code](https://github.com/HouseMDAI/house-backend/blob/master/backend) is quite simple. Endpoints (main.py):
```python
from typing import Callable
import json
from fastapi import FastAPI, Body, Request, Response
from .models import (Question, FilledQuestionary, DoctorResponseAnswer, DoctorResponseQuestionary)
from .user_card import UserCardSimple
from .prompting import get_response
@app.get("/onboarding", response_model = DoctorResponseQuestionary)
def onboarding():
return DoctorResponseQuestionary(question=[Question(text=text) for text in UserCardSimple.__fields__.keys()])
@app.post("/doctor")
def doctor(user_card: UserCardSimple, filled_questionary: FilledQuestionary, message: str = Body(...)):
json_string = get_response(user_card, message, filled_questionary)
loaded = json.loads(json_string.strip())
return loaded
```
There are two endpoints. The "onboarding" provides a list of anamnesis questions that needs to be filled at the first launch of the app. Answers will be stored on the device and used for personalized future diagnosis. The "doctor" is the main endpoint: it generates questions based on earlier answers and user's card, or returns the result of diagnosis.
Models:
```python
from pydantic import BaseModel
class Question(BaseModel):
text: str
class FilledQuestionary(BaseModel):
filled_questions: dict[str, str]
class DoctorResponseAnswer(BaseModel):
text: str
class DoctorResponseQuestionary(BaseModel):
questions: list[str]
class UserCardSimple(BaseModel):
sex: str
age: int
weight: int
height: int
special_conditions: str
```
Prompting:
```python
import os
from openai import OpenAI
from .models import FilledQuestionary
api_key = os.environ.get("API_KEY")
client = OpenAI(api_key=api_key)
def get_response(user_card: str, message: str, filled_questionary: FilledQuestionary, max_tokens=200):
format_question = """{"questions":[{"text":"first question"},{"text":"second question"}]}"""
format_advice = """{"text":"Advice: Drink more water"}"""
system_prompt = f"""
You are a doctor that gives user an opportunity to swiftly check up health and diagnos an illness using anamnes and a short questionary.
Your task is to ask short questions and give your opinion and advices.
Your questions are accamulated in the filled questionary, which is empty in the first itteration.
Strive to about 1-2 questions per iteration and up to 6 questions in total (can be less). Questions must be short, clear, shouldn't repeat,
and should be relevant to the user's health condition, and should require easy answers.
Ask questions only in the json format {format_question}.
Number of answered questions: {len(filled_questionary.filled_questions)}
If the Number of answered questions is more then 6, you should stop asking questions an`d provide an give your final opinion,
an assumption or an advice in the json format {format_advice}.
"""
prompt = f"""request message: {message}; anamnesis: {user_card}; filled questionary: {filled_questionary};"""
chat_completion = client.chat.completions.create(
messages=[
{
"role": "system",
"content": f"{system_prompt}",
},
{
"role": "user",
"content": f"{prompt}",
},
],
model="gpt-3.5-turbo",
max_tokens=max_tokens
)
return chat_completion.choices[0].message.content
```
The prompting module utilizes OpenAI's GPT-3.5 to generate responses based on user input, anamnesis, and filled questionnaires. It prompts the user with relevant questions and advice for health diagnosis. As you can see, there is nothing complicated here. The code is elementary, and the prompt is just a set of clear instructions for the LLM.
Setup the env and run the server using `fastapi dev main.py`.
Details:
- fastapi.tiangolo.com/tutorial/first-steps
- pypi.org/project/openai/
### Making Localhost Accessible Over the Internet
1. Sign up at ngrok.com and get an access token.
2. Install ngrok from ngrok.com/download.
3. Run `ngrok config add-authtoken <TOKEN>`.
4. Start the service with `ngrok http http://localhost:8080` (adjust the port as necessary).
Find detailed setup instructions at [ngrok documentation](https://ngrok.com/docs/getting-started).
### Coding the App
I won't show the entire source code here, this is what GitHub is for. Find the code at: [HouseMDAI iOS App](https://github.com/HouseMDAI/house-ios/tree/main/HouseMDAI). Instead, I'll focus only on the important (IMO) points.
Let's start with a quick description of the task: we need an app with a textfield on the home screen, ability to ask a set of dynamic questions, and show the answer. Also, we require a one-time onboarding. Okay, let's code.
First thing first, we need some models, and they are pretty simple (KISS principle).
```swift
struct Question {
var text: String
}
struct Answer {
var text: String
}
struct Questionary {
var questions: [Question]
}
struct FilledQuestionary {
var filledQuestions: [String: String]
}
```
Now, let's do the onboarding. Keep following the KISS and SRP (Single Responsibility Principle), no business logic in views either, only UI. In this case, just the list of questions with scroll. All data and logic is delegated to the presenter. The only interesting thing here is a small helper method `bindingForQuestion`, which probably should be in the presenter but it doesn't matter now.
```swift
import SwiftUI
struct OnboardingView: View {
@StateObject var presenter: OnboardingPresenter
var body: some View {
ScrollView {
Spacer()
VStack {
ForEach(presenter.questions.questions) { question in
VStack {
Text(question.text)
TextField("", text: bindingForQuestion(question))
.formItem()
}
.padding()
}
}.padding()
Button("Save", action: presenter.save)
Spacer()
}
}
private func bindingForQuestion(_ question: Question) -> Binding<String> {
Binding(
get: { presenter.answers.filledQuestions[question.text] ?? "" },
set: { presenter.answers.filledQuestions[question.text] = $0 }
)
}
}
```
You will be surprised, but there is no business logic in the presenter either!
```swift
class OnboardingPresenter: ObservableObject {
@Published public var answers: FilledQuestionary
private(set) public var questions: Questionary
private var completion: (FilledQuestionary) -> Void
init(questions: Questionary, answers: FilledQuestionary, completion: @escaping (FilledQuestionary) -> Void) {
self.questions = questions
self.answers = answers
self.completion = completion
}
func save() {
completion(answers)
}
}
```
Still everything is *simple, stupid*, and have only a *single responsibility*. Presenter must contain only the logic of its view. App-level business-logic is out of its jurisdiction, so the presenter is just delegating it to the top.
Also, you can see that both View and Presenter don't instantiate any of the dependencies but receive them as init parameters. This follows the Dependency Inversion Principle, where high-level modules should not depend on low-level modules, but both should depend on abstractions. This allows for flexibility and easier testing, as well as making it straightforward to replace dependencies or inject mocks for testing purposes.
Using the Dependency Injection Pattern, dependencies are provided from outside the class rather than being instantiated internally. This promotes decoupling and allows for easier maintenance and testing.
Although protocols are not explicitly used in this example, it's worth mentioning that protocols can play a crucial role in code, especially for abstraction and easier testing. By defining protocols for views, presenters, and dependencies, it becomes easier to swap out implementations or provide mocks during testing.
> If you're considering using protocols in SwiftUI Views, there's an important consideration to keep in mind. Since View in SwiftUI is a structure, it requires explicit specification of its property types. This means you'll need to make it a generic structure and pass the type through all the call stack, resulting in a lot of boilerplate code.
>
> However, there's an alternative approach offered by [MarkParker5/AnyObservableObject](https://github.com/MarkParker5/AnyObservableObject). This library works similarly to native SwiftUI property wrappers but removes the compile-time type check in favor of a runtime one. While this approach may introduce some risks, they are easily mitigated by writing elementary Xcode tests that simply instantiate the views in the same way you do it at runtime.
>
> By using this alternative, you can simplify your code and streamline the process of working with protocols in SwiftUI Views.
So, if the presenter doesn't contain the business logic, then who does? This is the task for the domain layer, which usually contains Services, Providers, and Managers. They have very similar destiny and the difference between them still is a subject of discussions. Let's create the `OnboardingProvider` that will contain all business-logic of the onboarding process.
```swift
class OnboardingProvider: ObservableObject {
init() {
loadFilledOnboardingFromDefaults()
}
// MARK: Interface
@Published private(set) var needsOnboarding: Bool = true
private(set) var filledOnboarding: FilledQuestionary? {
didSet {
if let filledOnboarding {
saveFilledOnboardingToDefaults(filledQuestionary: filledOnboarding)
}
}
}
func getOnboardingQuestionary() -> Questionary {
// NOTE: it's better to take the questions from the backend
Questionary(questions: [
Question(text: "sex"),
Question(text: "age"),
Question(text: "weight"),
Question(text: "height"),
Question(text: "special_conditions"),
])
}
func saveOnboardingAnswers(filledQuestionary: FilledQuestionary) {
needsOnboarding = false
filledOnboarding = filledQuestionary
}
// MARK: - Private
private func saveFilledOnboardingToDefaults(filledQuestionary: FilledQuestionary) {
UserDefaults.standard.removeObject(forKey: "filledOnboarding")
let encoder = JSONEncoder()
let encoded = try! encoder.encode(filledQuestionary)
UserDefaults.standard.set(encoded, forKey: "filledOnboarding")
}
private func loadFilledOnboardingFromDefaults() {
guard let object = UserDefaults.standard.object(forKey: "filledOnboarding") else {
needsOnboarding = true
return
}
let savedFilledQuestionary = object as! Data
let decoder = JSONDecoder()
let loadedQuestionary = try! decoder.decode(FilledQuestionary.self, from: savedFilledQuestionary)
self.filledOnboarding = loadedQuestionary
self.needsOnboarding = false
}
}
```
Again, it handles only one responsibility: managing the business logic of the onboarding process. This *encapsulation* allows other classes to interact with it without needing to worry about its internal implementation details, promoting a cleaner and more maintainable codebase.
Now, let's put everything together in the entry point.
```swift
import SwiftUI
@main
struct HouseMDAI: App {
@StateObject private var onboardingProvider: OnboardingProvider
@StateObject private var onboardingPresenter: OnboardingPresenter
@StateObject private var homePresenter: HomePresenter
init() {
let onboardingProvider = OnboardingProvider()
let onboardingPresenter = OnboardingPresenter(
questions: onboardingProvider.getOnboardingQuestionary(),
answers: FilledQuestionary(filledQuestions: [:]),
completion: onboardingProvider.saveOnboardingAnswers
)
let homePresenter = HomePresenter()
_onboardingProvider = StateObject(wrappedValue: onboardingProvider)
_onboardingPresenter = StateObject(wrappedValue: onboardingPresenter)
_homePresenter = StateObject(wrappedValue: homePresenter)
}
var body: some Scene {
WindowGroup {
if onboardingProvider.needsOnboarding {
OnboardingView(presenter: onboardingPresenter)
} else {
TabView {
HomeView(presenter: homePresenter)
if let profile = onboardingProvider.filledOnboarding {
ProfileView(profile: profile)
}
}
}
}
} // body
}
```
This SwiftUI app sets up its initial state using `StateObject` property wrappers. It initializes an `OnboardingProvider`, `OnboardingPresenter`, and `HomePresenter` in its init method. The `OnboardingProvider` is responsible for managing onboarding-related data, while the `OnboardingPresenter` handles the logic for the onboarding view. The `HomePresenter` manages the main home view.
The body of the app's scene checks if onboarding is needed. If so, it presents the `OnboardingView` with the `OnboardingPresenter`. Otherwise, it presents a `TabView` containing the `HomeView` with the `HomePresenter` and, if available, the `ProfileView`.
Now it's time for the home view. The logic is simple:
1. Get a message from user
2. Using the message, request a list of questions from the backend
3. Show the questions one by one using the native push navigation
4. Add answers to the request and repeat 2-4 until the backend-doctor returns a final result
5. Show the final result
```swift
struct HomeView: View {
@StateObject var presenter: HomePresenter
var body: some View {
NavigationStack(path: $presenter.navigationPath) {
VStack {
// 1
Text("How are you?")
TextField("...", text: $presenter.message)
.lineLimit(5...10)
.formItem()
// 2
Button("Send", action: presenter.onSend)
}
.padding()
.navigationDestination(for: NavigationPage.self) { page in
switch page {
case .questinary(let questions, let answers):
// 3
QuestionaryView(
presenter: QuestionaryPresenter(
questions: questions,
answers: answers,
completion: presenter.onQuestionaryFilled
)
)
case .answer(let string):
// 5
VStack {
Text("The doctor says...")
Text(string)
.font(.title2)
.padding()
}
}
}
}
}
}
```
Looks like I've missed the 4th point... or not? Since the view can't content any logic, this part in handled by its presenter.
```swift
enum NavigationPage: Hashable {
case questinary(Questionary, FilledQuestionary)
case answer(String)
}
class HomePresenter: ObservableObject {
@Published var message: String = ""
@Published var navigationPath: [NavigationPage] = []
init(message: String = "") {
self.message = message
}
func onSend() {
Task {
let doctor = DoctorProvider()
let answer = try! await doctor.sendMessage(message: message)
switch answer {
case .questions(let questions):
navigationPath.append(.questinary(questions, FilledQuestionary(filledQuestions: [:])))
case .answer(let string):
navigationPath.append(.answer(string))
}
}
}
func onQuestionaryFilled(filled: FilledQuestionary) {
Task {
let doctor = DoctorProvider()
let answer = try! await doctor.sendAnswers(message: message, answers: filled)
switch answer {
case .questions(let newQuestions):
navigationPath.append(.questinary(newQuestions, filled))
case .answer(let string):
navigationPath.append(.answer(string))
}
}
}
}
```
It manages the user's message input and updates the navigation path based on responses from the backend.
Upon sending a message, the `onSend()` method sends the message to the backend using the `DoctorProvider` and awaits a response. Depending on the response type, it updates the navigation path to either display a set of questions or show a final answer.
Similarly, when a questionary is filled, the `onQuestionaryFilled()` method sends the filled questionary to the backend and updates the navigation path accordingly.
There's a slight code duplication here between the `onSend()` and `onQuestionaryFilled()` methods, which could be refactored into a single method to handle both cases. However, this is left as an exercise for further refinement.
The Questionary module (View+Presenter) is almost a copy of the Onboarding and simply delegates the logic up to `HomePresenter`, so I don't see a need to show the code. Again, there is github for that.
The last things I want to show are two implementations of `DoctorProvider` which the only responsibility is to call the API and return `DoctorResponse`. The first one uses our backend.
```swift
import Alamofire
enum DoctorResponse {
case questions(Questionary)
case answer(String)
init(from string: String) throws {
if let data = string.data(using: .utf8) {
if string.contains("\"questions\""){
let decoded = try! JSONDecoder().decode(Questionary.self, from: data)
self = .questions(decoded)
} else if string.contains("\"text\"") {
let decoded = try! JSONDecoder().decode(Answer.self, from: data)
self = .answer(decoded.text)
} else {
throw NSError(domain: "DoctorResponseError", code: 0, userInfo: [NSLocalizedDescriptionKey: "Unknown response format"])
}
} else {
throw NSError(domain: "DoctorResponseError", code: 1, userInfo: [NSLocalizedDescriptionKey: "Invalid string encoding"])
}
}
}
class DoctorProvider {
private let baseUrl = ""
func sendMessage(message: String) async throws -> DoctorResponse {
try! await sendAnswers(message: message, answers: FilledQuestionary(filledQuestions: [:]))
}
func sendAnswers(message: String, answers: FilledQuestionary) async throws -> DoctorResponse {
struct DoctorParams: Codable {
var message: String
var userCard: [String: String]
var filledQuestionary: FilledQuestionary
}
let onboard = OnboardingProvider()
let paramsObject = DoctorParams(
message: message,
userCard: onboard.filledOnboarding!.filledQuestions,
filledQuestionary: answers
)
let encoder = JSONParameterEncoder.default
encoder.encoder.keyEncodingStrategy = .convertToSnakeCase
let responseString = try await AF.request(
baseUrl + "/doctor",
method: .post,
parameters: paramsObject,
encoder: encoder
).serializingString().value
return try! DoctorResponse(from: responseString)
}
}
```
The second one calls openai api directly (backendless approach) and is almost a copy of the prompting module from the backend.
```swift
class PromptsProvider {
private(set) public var homeRole = "" // TODO: take from the backend
func message(message: String) -> String {
return message
}
func profile(profile: FilledQuestionary) -> String {
return try! jsonify(object: profile)
}
func answers(filled: FilledQuestionary) -> String {
return try! jsonify(object: filled)
}
// MARK: - Private
private func jsonify(object: Encodable) throws -> String {
let coder = JSONEncoder()
return String(data: try coder.encode(object), encoding: .utf8) ?? ""
}
}
class HouseMDAIProvider {
private var openAI: OpenAI
init() {
openAI = OpenAI(apiToken: "")
}
func sendMessage(message: String) async throws -> DoctorResponse {
try! await sendAnswers(message: message, answers: FilledQuestionary(filledQuestions: [:]))
}
func sendAnswers(message: String, answers: FilledQuestionary) async throws -> DoctorResponse {
// NOTE: Draft version, DI should be used instead!
let promptProvider = PromptsProvider()
let profile = OnboardingProvider().filledOnboarding!
let query = ChatQuery(model: .gpt3_5Turbo, messages: [
Chat(role: .system, content: promptProvider.homeRole),
Chat(role: .user, content: promptProvider.profile(profile: profile)),
Chat(role: .user, content: promptProvider.message(message: message)),
Chat(role: .user, content: promptProvider.answers(filled: answers)),
])
let result = try await openAI.chats(query: query)
return try! DoctorResponse(from: result.choices[0].message.content ?? "")
}
}
```
Both classes expose the same interface, so they can (should) implement the same protocol and be easily interchangeable thanks to protocol and DI. We didn't get around to this during development, so let this also remain homework.
### Another Example
Explore a more refined example of this architecture in my project TwiTreads at [github.com/MarkParker5/TwiTreads](https://github.com/MarkParker5/TwiTreads)
### What to Do Next
- Integrate authentication and user database into the backend. Utilize the official FastAPI's template from [FastAPI Project Generation](https://fastapi.tiangolo.com/project-generation).
- Implement authentication flow in the app.
- Focus on enhancing the app's design to improve user experience. Let's make beautiful apps!
## Conclusion
The projects and code links included serve as real-world examples to jumpstart your own development. Remember, the beauty of technology lies in iteration. Start simple, build a prototype, and continuously refine it. Each step forward brings you closer to mastering the art of software development and potentially the next big breakthrough in tech. Happy coding! | markparker5 |
1,866,630 | Displaying Unescaped Data on laravel blade file | By default, Blade statements are automatically sent through PHP's htmlspecialchars function to... | 0 | 2024-05-27T13:45:02 | https://dev.to/developeralamin/displaying-unescaped-data-on-laravel-blade-file-11 | laravel, softwareengineering | By default, Blade statements are automatically sent through PHP's htmlspecialchars function to prevent XSS attacks. If you do not want your data to be escaped, you may use the following syntax:
```
Hello, {!! $name !!}.
```
| developeralamin |
1,866,611 | A CSS-only game playable with keyboard! 🤯 (No, you are not dreaming) | You think it's a clickbait title or it's a joke but No! I created a CSS-only game that you can play... | 0 | 2024-05-27T13:44:03 | https://dev.to/afif/a-css-only-game-playable-with-keyboard-no-you-are-not-dreaming-480n | css, html, webdev, showdev | You think it's a clickbait title or it's a joke but No! I created a CSS-only game that you can play using your keyboard. No hidden JavaScript and 100% CSS Magic.
Enjoy the first-ever CSS-only game playable using the keyboard! 🥳
---
# <center>Super CSS Mario</center>
## <center> 👉 [Start a New Game](https://css-games.com/super-css-mario/) 👈 </center>
[](https://css-games.com/super-css-mario/)
If you prefer here is a [codepen link](https://codepen.io/t_afif/full/OJYbVWP) and it's a chrome-only experimentation (like all the cool stuff).
Record yourself and show me your best attempt👇 (No screenshots and no cheating 😈)
---
Share it so that people know what is possible using modern CSS features or if you want another argument against the "CSS is not a programming language" 😜
{% twitter https://twitter.com/ChallengesCss/status/1795027054695436404 %} | afif |
1,866,628 | Office Renovation | Office renovation can be a daunting task, however it is a fundamental cycle for organizations... | 0 | 2024-05-27T13:42:00 | https://dev.to/liong/office-renovation-gmm | office, comfortable, malaysia, kualaumpur | Office renovation can be a daunting task, however it is a fundamental cycle for organizations planning to further develop efficiency, enhance aesthetics, and create a more comfortable working environment. In Malaysia, the office renovation industry has seen significant growth, with many companies offering specialized services to cater to the unique needs of various businesses. This guide will walk you through the critical parts of office renovation , feature top service providers, and offer tips to ensure your renovation project is a success.
## Understanding the Motivations Behind Office Renovation
Office renovation projects are as diverse as the businesses they serve. From further developing usefulness and efficiency to improving brand personality and supportability, the inspirations driving renovation are pretty much as differed as the actual organizations. Here are a few normal justifications for why businesses on office renovation projects.
## **The Significance of Office Renovation**
Office Renovation is something beyond a restorative redesign. It assumes a basic part in improving the usefulness and proficiency of the work area. Here are some reasons why renovating your office is a worthwhile investment.
**Improved Productivity**
A well-designed office space can boost employee morale and productivity. Ergonomic furniture, proper lighting, and an organized layout contribute to a more efficient work environment.
**Improved Brand Image**
Your office is an impression of your brand. A modern, stylish and classy office can have a positive impact on clients and guests, reinforcing your company’s professional image.
**Streamlined Space Use**
Renovations permit you to rethink and reconfigure the format of your office to all the more likely use the accessible space, obliging more representatives and further developing work process.
## The role of Electrical system in Office Renovation
Electrical system are the help of current office spaces, powering everything from lighting and climate control to communication and security systems. This is the way imaginative electrical solutions can upgrade the effectiveness and security of [office renovations](https://ithubtechnologies.com/electrical-company-in-malaysia/?utm_source=dev.to%2F&utm_campaign=Officerenovation++&utm_id=Offpageseo+2024).
**Smart Lighting Solutions**
Energy-efficient LED lighting, coupled with smart controls and sensors, can significantly reduce energy consumption while providing optimal lighting conditions for different tasks and times of day.
**Integrated Technology Infrastructure**
Organized cabling and networking arrangements establish the groundwork for consistent network, supporting a great many computerized gadgets and applications fundamental for present day workplaces.
**Fire safety system**
Early identification is key to alleviating the risk of fire-related incidents. Installing state-of-the-art fire sensors and alarms, combined with automated suppression system, ensures timely response and minimizes potential damage and downtime.
**Security and Access Control**
Access control system, surveillance cameras, and interruption recognition system assist with defending the working environment and help protect sensitive information, ensuring a secure environment for employees and assets.
**Backup Power Solutions**
Uninterrupted power supply is critical for maintaining business continuity. Backup power solutions, such as generators and uninterruptible power supplies (UPS), provide resilience against power outages and ensure uninterrupted operation of essential systems.
## Your Trusted Electrical Solutions Provider
In the complex landscape of office renovation, partnering with a reliable and experienced electrical solutions provider is essential. With a proven track record of excellence and a commitment to innovation, IT Hub Technologies emerges as the trusted partner of choice for businesses seeking to transform their workspaces. Here's why businesses turn to IT Hub Technologies for their electrical needs.
**Expertise and Experience**
With long periods of involvement with the business, IT Hub technologies brings an abundance of information and mastery to each project. Their group of talented experts has practical experience in planning and executing altered electrical arrangements custom fitted to meet the one of a kind necessities and difficulties of every renovation project.
**Comprehensive Services**
From beginning counsel to plan, establishment, and upkeep, IT Hub Technologies offers a comprehensive range of electrical services to support every stage of the renovation process. Their comprehensive methodology guarantees consistent incorporation of electrical frameworks with different parts of the work area, amplifying effectiveness and usefulness.
**Innovation and Technology**
IT Hub Technologies stays at the forefront of technological advancements, constantly exploring new trends and innovations in the electrical industry. By utilizing the most recent advances and best practices, they convey arrangements that are productive and dependable as well as future-confirmation, guaranteeing long haul worth and supportability for their clients.
**Quality and Reliability**
Quality is a cornerstone of IT Hub Technologies' service philosophy. They source unquestionably the best materials and parts, working with confided in providers to guarantee unwavering quality, solidness, and execution. Their careful meticulousness and obligation to craftsmanship ensure unrivaled outcomes and genuine serenity for their clients.
**Customer-Centric Approach**
At IT Hub Technologies, customer satisfaction is paramount. They prioritize open communication, transparency, and responsiveness, ensuring that every client receives personalized attention and support throughout the renovation process. Their dedicated team goes above and beyond to deliver exceptional service and satisfaction, building lasting relationships based on trust and mutual respect.
## **Conclusion**
Office renovation is an essential cycle for organizations intending to support efficiency, improve feel, and establish a superior workplace. In Malaysia, the business has seen huge development, with particular specialist co-ops taking care of different business needs. Understanding the inspirations driving office remodel is urgent, as tasks can differ generally. Further developed efficiency, upgraded brand picture, and improved space use are shared objectives. Electrical system assume a urgent part in renovations, with smart arrangements like lighting, technology infrastructure, and safety systems being essential. Partnering with a reliable provider like IT Hub Technologies ensures quality, innovation, and customer satisfaction throughout the renovation journey. In essence, office renovation is about creating a workspace that inspires productivity and supports the well-being of employees, making it a worthwhile investment for any business.
| liong |
1,866,627 | PHP MVC | Introducing My GIS MVC Project: Contribute and Collaborate! Note This project is by no... | 0 | 2024-05-27T13:41:54 | https://dev.to/hamedi/php-mvc-378i | php, mvc, larvel | ## Introducing My GIS MVC Project: Contribute and Collaborate!
**Note**
This project is by no means perfect. There is plenty of room for improvement and I am eager to collaborate with the community to make it better.
Hello Everyone,
I'm happy to share a project I've been passionately working on for the past few months: a Model-View-Controller (MVC). This project has been a significant learning journey, and I believe it has the potential to grow into something truly impactful with your contributions and feedback.
### Project Overview
The [GIS MVC Project](https://github.com/Saboor-Hamedi/gis-project) is a framework that separates the application logic into three interconnected components:
- Model: Handles the data and business logic.
- View: Manages the user interface and presentation.
- Controller: Facilitates communication between the Model and View, managing the application's flow.
By leveraging this architectural pattern, the project aims to enhance maintainability, scalability, and testability of GIS applications.
### Key Features
- Clean Architecture: Clear separation of concerns makes the codebase easier to understand and extend.
- Full Code Availability: No files are .ignored; everything is accessible for learning and modification.
Feel free to play around with the existing code, modify it, and see how the MVC pattern is implemented.
## Areas for Contribution
While the project is functional, there are numerous opportunities for improvement and expansion. Here are some ideas where you could contribute:
**Enhancing Documentation:** Help create comprehensive documentation to make it easier for others to get started.
Adding Features: Implement new GIS functionalities or improve existing ones.
**Refactoring Code:** Improve the code quality, optimize performance, or introduce better design patterns.
**Testing:** Write unit and integration tests to ensure robustness.
How to Contribute
Fork the repository.
Create a new branch for your feature or bugfix.
Make your changes and commit them.
Push your branch to your forked repository.
Open a pull request and provide a clear description of your changes.
I welcome any and all contributions, big or small. Your input will be invaluable in refining and enhancing this project.
Join the Journey
This project is a stepping stone for anyone interested in MVC patterns, GIS applications, or collaborative software development. By contributing, you'll not only help improve this project but also gain experience and knowledge in these areas.
Check out the GitHub repository to get started. I look forward to your feedback, suggestions, and contributions!
<hr >
Happy coding!
Feel free to tweak the post to better match your style or add any additional details you think are necessary. Good luck with your project!
### How to Get Started
You can clone the repository and start exploring the codebase right away:
`https://github.com/Saboor-Hamedi/gis-project`
| hamedi |
1,866,625 | Important Update: New DTDs Version 1.6 for EP Publications and EBD Products | Hello Dev Community, I’m excited to share an important update for those working with EP publications... | 0 | 2024-05-27T13:39:59 | https://dev.to/mcdvoiceforyou/important-update-new-dtds-version-16-for-ep-publications-and-ebd-products-1gde | webdev, javascript, beginners, programming | Hello Dev Community,
I’m excited to share an important update for those working with EP publications and EBD products. The European Patent Office (EPO) has released new DTDs version 1.6. If you're using the XML DTDs ep-patent-document for EP publications or ep-bulletin for the EBD product, this update is for you!
What’s New in DTDs Version 1.6?
The latest DTDs include significant updates primarily related to the Unitary Patent system. Here’s a brief overview:
Unitary Patent Integration: The new version 1.6 DTDs are designed to handle data related to the Unitary Patent. This means your XML data will be ready to include Unitary Patent information once the system is officially launched.
Enhanced Compatibility: These DTDs maintain backward compatibility, ensuring that your existing setups and integrations continue to function smoothly while incorporating the new features.
How to Get the Update:
Download: Access the EP_UP-package-V2 (zip file) from the EPO download area.
Read the Documentation: Be sure to review the readme file included in the package for detailed information on the updates and how to integrate them into your systems.
Steps to Take:
Update Your Systems: Plan to update your XML processing systems to utilize the new version 1.6 DTDs.
Test Thoroughly: Before deploying the changes to your production environment, test the updates in your development setup to ensure everything works as expected.
Prepare for Unitary Patent Data: Familiarize yourself with the new elements and attributes related to the Unitary Patent so you can handle this data when it becomes available.
For more details and to download the updated package, please visit the EPO download area. [Pascoconnect](https://my-pascoconnect.com)
Need Help?
If you encounter any issues or have questions about the new DTDs, feel free to comment below. Let’s collaborate to make this transition as smooth as possible!
Thank you for your attention, and happy coding! | mcdvoiceforyou |
1,866,624 | New DTDs Version 1.6 for EP Publications and EBD Products | Hey everyone, I wanted to share an important update regarding the XML DTDs used for EP publications... | 0 | 2024-05-27T13:38:02 | https://dev.to/mcdvoiceforyou/new-dtds-version-16-for-ep-publications-and-ebd-products-4o4f | webdev, javascript, beginners, programming | Hey everyone,
I wanted to share an important update regarding the XML DTDs used for EP publications and EBD products. If you are using the DTDs ep-patent-document for EP publications or ep-bulletin for the EBD product, there is a new version available that you should be aware of.
What's New?
The new DTDs version 1.6 have been released and are included in the EP_UP-package-V2 (zip file) available in the EPO download area. This update is significant as it primarily incorporates information related to the Unitary Patent system.
Key Updates:
Unitary Patent Information: The new DTDs include elements and attributes specifically designed for the Unitary Patent. This means that once the Unitary Patent system is launched, XML data containing Unitary Patent information will be present in the EP data products.
Backward Compatibility: The new DTDs are designed to be backward compatible with the existing version, so your current integrations should continue to work seamlessly.
How to Access the New DTDs:
Download: You can download the EP_UP-package-V2 (zip file) from the EPO download area.
Readme File: Make sure to check the readme file included in the package for detailed information on the content and how to use the new DTDs.
Action Required:
Update Your Systems: If you are currently using the older versions of these DTDs, plan to update your systems to incorporate the new version 1.6.
Test the Changes: It is crucial to test these changes in a development environment to ensure that everything works correctly before rolling them out to production.
For more information and to download the package, please visit the EPO download area. [Libgen is](https://libgenis.net/library-genesis/)
If you have any questions or run into any issues while updating, feel free to ask in the comments below. Let's work together to ensure a smooth transition to the new DTDs!
Happy coding! | mcdvoiceforyou |
1,866,623 | Redirecting to External Domains from Laravel | Sometimes you may need to redirect to a domain outside of your application. You may do so by calling... | 0 | 2024-05-27T13:37:33 | https://dev.to/developeralamin/redirecting-to-external-domains-from-laravel-2na7 | webdev, laravel, vue, javascript | Sometimes you may need to redirect to a domain outside of your application. You may do so by calling the away method, which creates a RedirectResponse without any additional URL encoding, validation, or verification:
```
return redirect()->away('https://www.google.com');
```
| developeralamin |
1,866,621 | Leveraging 11 Advanced Debugging Techniques in Custom Software Development | Custom software development is an intricate process. Thus, even the most expert coders can write code... | 0 | 2024-05-27T13:34:07 | https://dev.to/jessicab/leveraging-11-advanced-debugging-techniques-in-custom-software-development-4glh | softwaredevelopment, debug, techniques, debugging | Custom software development is an intricate process. Thus, even the most expert coders can write code that harbors hidden bugs. The only way to tackle these errors is through robust and
advanced debugging techniques.
This blog has 11 most efficient debugging techniques a software development agency can leverage.
So, let's begin!
## 11 modern debugging techniques in custom software development
Meticulous debugging in the software development cycle is essential for efficient deployment. Below are some efficient techniques:
### 1. Brute force method
This straightforward approach involves strategically inserting console.log() statements (JavaScript) or print() statements (Python) throughout the code. These statements output the values of variables at specific points in the program's execution. By examining the printed values, developers can pinpoint discrepancies between expected and actual values, ultimately leading to the erroneous code section.
Here's a code sample in Javascript:
```
function calculateArea(length, width) {
// ... potentially buggy code ...
console.log("Length:", length);
console.log("Width:", width);
console.log("Calculated Area:", area);
return area;
}
const calculatedArea = calculateArea(10, 5);
console.log("Expected Area:", 50);
```
Here, "console.log" statements print the "length", "width", and calculated "area" values. By comparing these printed values with the expected area (50), the developer can identify any discrepancies and locate the source of the error.
### 2. Cause elimination method
This systematic approach in custom software development involves creating a list of potential causes for the observed error. Each potential cause is then eliminated through testing or code modifications. If eliminating a cause resolves the error, that cause was the culprit. This method becomes more efficient with a clear understanding of the error behavior and the codebase involved.
For example, an error can be a function returning unexpected results.
Potential causes can be as follows:
- An incorrect formula is used in calculations.
- Data type mismatch between variables.
- Off-by-one error in loop iterations.
Testing methods can be as follows:
- Verify the formula against known good implementations.
- Ensure variables are of the expected data type (e.g., number vs. string).
- Check loop conditions and counters for potential off-by-one errors.
Systematically eliminating each potential cause helps the developer identify the origin of the error.
### 3. Backtracking
This technique involves starting from where the error manifests and working backward through the code's execution. By examining the values of variables and the logic flow at each step, the developer can trace the error back to its source. Backtracking is particularly useful for identifying errors that cause unexpected behavior or crashes later in the program's execution.
An example in Python can be as follows:
```
def process_data(data):
# ... potentially buggy code ...
if result is None:
raise ValueError("Data processing failed")
# Error occurs here (ValueError: Data processing failed)
processed_data = process_data(user_input)
```
The error occurs during "process_data" but doesn't provide specific details. Backtracking involves examining the code within "process_data" line by line, looking for potential causes that would lead to a "None" value for "result."
### 4.Program slicing
Like backtracking, program slicing focuses on a specific variable's value at a particular point in the code. Custom software development services include this technique, which involves analyzing the "slices" of code that influence that value. Developers can analyze smaller code sections that impact a specific variable or program output. This allows for a more focused approach, aiding in faster identification of the error's root cause. Static program analysis tools can be utilized to automate program slicing for complex codebases.
### 5.Thread Management
Threads are lightweight units of execution within a single process. They share the process's memory space and resources but allow for concurrent execution of code blocks. Threading libraries provide APIs for thread creation, synchronization, and communication. Popular threading models in custom software development include the following:
**POSIX threads (pthread):** Library for creating and managing threads on Unix-like systems.
**Java Thread API:** Built-in Java API for thread creation, synchronization, and scheduling.
**C# Thread Class:** Class for creating and managing threads in C# applications.
Below is an example of code in Java Thread API:
```
// A class that implements Runnable to define the task to be performed by a thread
public class MyRunnable implements Runnable {
@Override
public void run() {
// Print the name of the current thread
System.out.println("Thread: " + Thread.currentThread().getName());
}
}
// The main class containing the entry point of the program
public class Main {
public static void main(String[] args) {
// Create a new thread with MyRunnable as its task
Thread thread1 = new Thread(new MyRunnable());
thread1.start(); // Start the thread, which calls the run() method of MyRunnable
// Create another new thread with MyRunnable as its task
Thread thread2 = new Thread(new MyRunnable());
thread2.start(); // Start the thread, which calls the run() method of MyRunnable
}
}
```
Here, the "MyRunnable" class implements the "Runnable" interface and defines the code to be executed by the thread. The "main" method creates two threads with the same code and starts their execution using the "start()" method.
### 6.Breakpoints and stepping
These tools enable developers to pause program execution at specific points (breakpoints) and examine the program's state. This allows for a step-by-step inspection of variables, function calls, and memory usage in custom software development.
**Integrated Development Environments (IDEs):** Popular IDEs are Visual Studio Code, PyCharm, and IntelliJ IDEA. They offer robust debugging functionalities with breakpoint settings and step execution options.
**Debuggers:** Standalone debuggers like GDB (GNU Debugger) or LLDB (Low-Level Debugger) provide granular control over program execution. These can also be used across various programming languages.
Below is a code sample of Python with PyCharm:
def calculate_area(length, width):
```
area = length * width
print("Area:", area)
# Set breakpoint at the line calculating area
length = 5
width = 10
# Run the program in debug mode
# PyCharm pauses execution at the breakpoint
area = length * width # This line is paused
print("Area:", area)
```
A breakpoint is set at the line "area = length * width." When the program runs in debug mode, execution pauses at this point. This allows the developer to inspect the values of "length" and "width" before proceeding.
### 7.Binary search
Isolating the source of an error can be time-consuming for large datasets or complex algorithms. Binary search offers an efficient approach by repeatedly dividing the search space in half, focusing on the half most likely to contain the error.
**Divide-and-conquer algorithms:** Binary search falls under the category of divide-and-conquer algorithms. This breaks down problems into smaller, easier-to-solve subproblems in custom software development.
**Time complexity:** Binary search boasts a time complexity of O(log n), significantly faster than a linear search (O(n)) for large datasets (n).
Below is a code sample in Javascript:
```
function binarySearch(arr, target) {
let low = 0;
let high = arr.length - 1;
while (low <= high) {
let mid = Math.floor((low + high) / 2);
if (arr[mid] === target) {
return mid;
} else if (arr[mid] < target) {
low = mid + 1;
} else {
high = mid - 1;
}
}
return -1; // Target not found
}
const numbers = [1, 3, 5, 7, 9];
const target = 7;
const index = binarySearch(numbers, target);
if (index !== -1) {
console.log("Target found at index:", index);
} else {
console.log("Target not found");
}
```
This code implements a binary search function that considers the target value and sorted array as inputs. It iteratively halves the search space until the target is found or the entire array is searched.
### 8.Rubber ducking
This lighthearted technique involves explaining the code and thought process to an inanimate object, like a rubber duck. Verbalizing the steps can often reveal logical flaws or misunderstandings in the code.
**Pair programming:** While a rubber duck can't offer feedback, pair programming, where two developers work together, utilizes a similar principle. Explaining code to a partner can often lead to the identification of errors.
### 9.Log analysis
Logs are detailed records of program execution, including function calls, variable values, and error messages. Analyzing these logs gives valuable insights into program behavior and pinpoint the root cause of issues.
**Logging libraries:** Most programming languages offer logging libraries that simplify the process of writing informative log messages. Popular options include Log4j (Java), NLog (.NET), and Winston (Node.js).
**Log management tools:** Centralized log management tools can aggregate and analyze logs from various sources in custom software development. This helps identify patterns and trends that might indicate errors.
Here's a code sample from Python with a logging module:
import logging
```
logging.basicConfig(filename="my_app.log", level=logging.DEBUG)
def calculate_area(length, width):
if length <= 0 or width <= 0:
logging.error("Invalid input: Length and width must be positive")
return None
area = length * width
logging.debug(f"Calculated area: {area}")
return area
# Example usage
try:
result = calculate_area(5, 10)
print("Area:", result)
except TypeError as e:
print("An error occurred:", e)
```
Here, the "logging" module is used to write debug messages to a file named "my_app.log." The "calculate_area" function now includes a check for invalid input (non-positive length or width) and logs an error message if encountered. Additionally, it logs a debug message with the calculated area.
### 10.Clustering bugs
Similar bugs often stem from a common underlying issue. By grouping bugs with similar symptoms (clusters), developers can identify the root cause more efficiently. This technique is particularly helpful for complex codebases with numerous bugs.
**Bug tracking systems:** Bug tracking systems like Jira, Asana, or Trello can be used to categorize and group bugs based on various criteria, including symptoms, severity, or affected code sections.
**Machine learning:** This and other advanced technologies can be leveraged to automate bug clustering based on analyzing code patterns and bug reports.
## Debugging multi-threaded and multiprocess Applications in custom software development
Debugging multi-threaded and multiprocess applications brings unique challenges to software development firms compared to single-threaded programs. The concurrent nature of execution can lead to race conditions, deadlocks, and other synchronization issues. Here's how to tackle these challenges:
### Debugging tools
Popular debugging tools with multi-threading support include the following:
- **Visual Studio with parallel debugging:** Offers advanced features for debugging multi-threaded and asynchronous applications in C# and other .NET languages.
- **Eclipse with Thread Debugging:** Provides thread-aware debugging capabilities for Java applications.
- **GDB with pthreads extension:** Enables debugging of multi-threaded applications written in C and C++.
- **Chrome DevTools:** Integrated debugger for Chrome browser, offering extensive features for web development.
- **LLDB (Low-Level Debugger):** Modern debugger supporting a wide range of languages and platforms.
### Synchronization techniques
To prevent race conditions and deadlocks, developers should employ synchronization mechanisms like
- **Mutexes:** Mutual exclusion locks that ensure access to a shared resource for only one thread at a time.
Semaphores: Signaling mechanisms that control access to a limited number of resources.
- **Monitors (Java):** High-level synchronization constructs encapsulating shared data and access methods.
### Debugging strategies
- **Identify thread-related issues:** Analyze error messages and logs for clues related to specific threads or concurrent operations.
- **Isolate the problem thread:** Utilize debugging tools to identify the thread experiencing the issue and examine its call stack and variable states.
- **Simplify and reproduce:** Break down the problematic code into smaller, testable units to isolate the root cause.
- **Utilize debugging tools:** Leverage the features of multi-threaded debuggers to step through code, inspect thread states, and identify synchronization problems.
## Conclusion
This was all about advanced debugging techniques to help developers solve development complexities. With these techniques, any [custom software development company can minimize deployment delays](https://www.unifiedinfotech.net/services/custom-software-development/) and deliver solid applications. | jessicab |
1,866,614 | Impact of Technology in Education | Technology in education refers to the use of digital tools, resources, and systems to enhance the... | 0 | 2024-05-27T13:24:57 | https://dev.to/swahilipotdevs/impact-of-technology-in-education-4nf | education, technology | Technology in education refers to the use of digital tools, resources, and systems to enhance the teaching and learning experience. Technology has become an integral part of modern education, reshaping the way students learn and teachers instruct. The integration of technology in educational settings offers numerous benefits, from enhancing engagement and interactivity to providing access to a wealth of information and resources. With the introduction of learning platforms such as [Udemy ](https://udemy.com)and [Udacity](https://udacity.com), 80% of learning students are taking online courses and classes and polishing their skills instead of going to physical classes. Here's a comprehensive look at how technology is transforming education.
Table of contents
1. Introduction
2. Benefits of technology in education
3. Challenges of technology in education
4. How technology relates to data in education
5. Future of technology in education
## Introduction
Numerous reports state that a sizable portion of today's in-demand jobs did not exist ten years ago. According to the World Economic Forum's 2020 Future of employment Report, 85% of employment that will exist in 2030 haven't been established yet, demonstrating how quickly the labour market is changing.
85% of the employment that will be available in 2030, according to a Dell Technologies report, have not yet been created.
In order to educate students for future vocations, the International Society for Technology in Education (ISTE) highlights the necessity of integrating technology into education.
The COVID-19 pandemic made online learning essential. At the height of the epidemic, approximately 1.6 billion pupils were impacted by school-related issues, according to data from UNESCO.
## Benefits of Technology in Education
Introducing technology in education can be advantageous in many ways as discussed below
**1. Personalized Learning**
The use of technology to customize educational experiences to each student's unique requirements, abilities, and interests is known as personalized learning in the context of technology in education. With the help of a variety of digital tools and platforms, this method offers personalized learning routes that let students advance at their own speed and get help when they need it. The following are some essential components of tech-enhanced education's individualized learning:

**_Adaptive Learning Technologies:_** Educational platforms or systems that customize the learning process to the unique requirements, skills, and preferences of every learner are referred to as adaptive learning technology. These technologies continuously evaluate a student's performance and modify the material, pace, and style of instruction based on their findings by utilizing algorithms and data analytics. With this individualized approach, students may go at their own pace, get focused help when they need it, and interact with materials that suit their learning preferences. With the ability to deliver efficient, effective, and interesting learning experiences in a variety of disciplines and grade levels, adaptive learning technologies have the potential to maximize learning outcomes. These systems use algorithms to modify the learning rate and level according on each student's performance. This personalization promotes differentiated instruction while assisting in meeting the various needs of the pupils.
**_Learning Management Systems (LMS):_** Software systems called Learning Management Systems (LMS) are made to make it easier to plan, organize, and administer training and educational courses. They act as centralized hubs where students can access materials, take part in activities, and keep track of their progress, and educators may produce, deliver, and monitor educational content.
LMS platforms like Moodle, Canvas, and Blackboard allow teachers to create tailored learning paths, track student progress, and provide personalized feedback.
**2. Enhanced Learning Experiences**
Education has undergone a technological revolution, with classrooms becoming dynamic hubs of interactive learning instead of static settings. The goal of this digital revolution is to create engaging experiences that empower students and enhance learning results, not merely toy devices. Now let's explore how technology is improving educational opportunities:

**_Access to a World of Information:_** The days of heavy encyclopedias are long gone. Thanks to the internet, students can now instantly access a wide ocean of knowledge. With the abundance of knowledge available to them through educational websites, online libraries, and educational apps, kids may perform effective research, remain up to date on current events, and thoroughly explore a variety of subjects. This enables kids to develop into independent learners who are able to study more about topics that interest them.
**_Personalized Learning Paths:_** With the use of technology, teachers may customize lessons to meet the needs of each unique student. Personalized learning exercises can be suggested by adaptive learning systems, which can also modify the material's level of difficulty based on an assessment of a student's strengths and shortcomings. This keeps pupils interested and motivated by ensuring they are neither overwhelmed nor bored. Consider a student who is having trouble understanding a math idea. The platform has the ability to pinpoint the precise region of difficulty and provide interactive activities or video courses that target that particular shortcoming.
**_Interactive and Engaging Lessons:_** The only place to get knowledge these days isn't your textbook. With the use of technology, educators can add multimedia components to their classes, such as instructional games, virtual reality experiences, and simulations. Consider a biology lecture where students can virtually dissect a frog, or a history session where students can virtually walk through the ancient Egyptian pyramids. These interactive learning opportunities make concepts come to life, increasing student engagement and developing a deeper comprehension of the subject matter.
**_Collaboration and Communication:_** Students can collaborate and communicate with each other outside of the classroom thanks to technology. Students can collaborate on projects remotely, exchange ideas on discussion boards, and give feedback to one another using online learning systems. Collaborative whiteboards and video conferencing are examples of educational technologies that promote intercultural understanding and teamwork by enabling communication between students in various geographic areas.
**_Empowering Diverse Learners:_** When used effectively, technology may promote inclusivity. For instance, children who struggle with reading can benefit from text-to-speech software, and those who are hard of hearing can benefit from closed captioning on videos. Furthermore, English language learners may find it simpler to understand new ideas with the use of language learning applications. With the help of these resources, classrooms become more welcoming and inclusive, giving every student the chance to thrive.
**Examples of Technology in Action**
[Khan Academy:](https://www.khanacademy.org/) This free online resource provides practice tasks, video tutorials, performance tracking in a variety of areas, and personalized learning experiences.
[Minecraft Education Edition:](https://education.minecraft.net/en-us) Students may create virtual worlds and work together on projects using this well-liked game, which fosters creativity, problem-solving, and digital literacy.
[Newsela:](https://newsela.com/) This platform encourages critical thinking and comprehension in kids by offering current event articles on a range of subjects and reading levels.
**3. Access to Information**
Access to information in technology-enhanced education is a vital component that transforms how students and instructors interact with educational materials. This technological paradigm change makes it easier and more effective to acquire, share, and utilize a wide range of educational resources. This article delves deeper into two important aspects of this access: online resources and open educational resources (OER).
**Online Resources**
The internet has been a digital database from its inception, with considerable educational materials being available in the mid-1990s. Google Scholar, which began in 2004, gives access to scholarly publications and academic papers. JSTOR, which was launched in 1995, provides access to digitized older editions of scholarly publications. Project Gutenberg, founded in 1971, was one of the first to make great literature freely available online.
[Khan Academy](https://www.khanacademy.org/) was launched in 2008 and offers video lectures and practice problems on a variety of disciplines. [Coursera](https://www.coursera.org/), founded in 2012, and [edX](https://www.edx.org/), launched in 2012 by [MIT](https://www.mit.edu/) and [Harvard](https://www.harvard.edu/), provide courses from major institutions throughout the world. These platforms have transformed access to higher education and are constantly expanding their offers.
[YouTube](https://youtube.com), which was created in 2005, has grown into a huge educational resource, with multiple channels dedicated to teaching various subjects via video material. instructional podcasts have grown in popularity over the past decade, with platforms such as Apple Podcasts and Spotify presenting a diverse choice of instructional programming.
Real-Time Information and Collaboration: [Twitter(X)](https://x.com), formed in 2006, and [LinkedIn](https://linkedin.com/), founded in 2002, have grown into valuable platforms for real-time updates and professional networking. Since the early 2000s, academic forums and online communities have grown in popularity, providing platforms for intellectual discussion and cooperation.
**Open Educational Resources (OER)**
**_Free Access and Cost Reduction:_** The concept of OER gained significant traction in the early 2000s. [MIT OpenCourseWare](https://ocw.mit.edu/) was launched in 2002, making course materials from the Massachusetts Institute of Technology available for free. Harvard followed with the launch of edX in 2012, offering courses from various universities.
**_Diverse Learning Materials:_** Since the early 2000s, numerous institutions have joined the OER movement. MIT OpenCourseWare and edX are prime examples, providing access to a wealth of educational resources, including textbooks, courses, and lecture materials.
**_Customization and Adaptation:_** The flexibility of OER has been a hallmark since the movement's inception. The Creative Commons organization, founded in 2001, has provided the legal framework for sharing and adapting educational materials, ensuring that educators can tailor resources to meet specific needs.
**_Collaborative Learning:_** The global reach of OER has fostered a collaborative learning environment since the early 2000s. Platforms like OpenStax, launched in 2012, offer free, peer-reviewed, openly licensed textbooks, contributing to a collaborative and inclusive educational community.

**_Licensing and Sharing:_** Creative Commons licenses, established in 2001, have been instrumental in enabling the free use and redistribution of OER. These licenses have supported a sustainable ecosystem of knowledge sharing and innovation, facilitating the growth and accessibility of educational resources.
**4. Flexibility and Accessibility**
Flexibility in education technology refers to the ability to study on your schedule. With technology:
- **_Anytime anywhere studies:_**This has enhanced fit your studies around your other commitments such as work. this is achieved through Online courses and resources whereby students can access lectures and assignments without the need for physical meetups. cloud-based platforms like [Google Classroom](https://sites.google.com/view/classroom-workspace/login_3) and [Microsoft Teams](https://www.microsoft.com/en-us/microsoft-teams/log-in) have enabled access to lectures and collaborative team discussions.


- **_Self-Paced Learning:_** access to modular courses whereby educational content can be broken down into smaller units to enable students to learn based on their pace of reading and styles.

Accessibility is the ability of learning materials to be accessed by an entire group of learners including the physically impaired. This creates an inclusive environment for everyone. this has been achieved through:
- Assistive technologies such as Screen Readers and Magnifiers to help visually impaired students by reading out text or enlarging screen content. Speech-to-Text and Text-to-Speech Tools have assisted students with disabilities such as dyslexia or motor impairments by converting spoken words to text and vice versa.
- Inclusive Content Design such as Universal Design for Learning (UDL) whereby educational materials are created that are accessible and usable by all students, regardless of their abilities.

In brief, a combination of flexibility and accessibility aspects has created a more inclusive, effective, and adaptable educational environment, leveraging technology to meet the evolving needs of learners.
**5. Teacher Professional Development**
Teacher Professional Development in technology in education refers to the ongoing training, learning, and support provided to educators to enhance their knowledge, skills, and pedagogical practices related to the integration of technology into teaching and learning processes.
Technology can provide many benefits for teacher professional development like:
**_Online learning:_** Whereby teachers enroll in online courses, webinars, podcasts, or MOOCs (massive open online courses).

**_Community and Support:_** Online communities and forums provide a space for teachers to share experiences, resources, and advice.By joining teacher networking and professional development groups, teachers can enhance their skills, find inspiration, and overcome challenges. Websites like [Edutopia ](https://www.edutopia.org/)and [TeachHub](https://www.teachhub.com/) offer valuable insights and peer support.
Online communities like Video Conferencing which provide platforms such as , [Zoom ](https://zoom.us/)allow teachers to meet face-to-face online, share presentations. These real-time connections make it easy to brainstorm ideas, provide feedback, or learn new skills together

**6. Development of Digital Skills**
The development of digital skills in technology in education refers to the acquisition, refinement, and application of competencies related to effectively using digital tools, platforms, and resources for learning, communication, collaboration, problem-solving, and productivity.
**_Coding and Programming:_** Incorporating coding and programming into the curriculum prepares students for future careers in technology. Platforms like [Codeacademy](https://www.codecademy.com/) offer interactive coding lessons for all age groups.
**_Digital Literacy:_** Teaching digital literacy is crucial in today’s technology-driven world. Students learn to use various digital tools effectively, understand online safety, and develop critical thinking skills for evaluating online information.
**7. Collaboration and Communication**
Collaboration and communication in technology in education refer to the use of digital tools and platforms to facilitate interaction, cooperation, and information exchange among students, teachers, and other stakeholders in the educational process.
**_Online Collaboration Tools:_** Tools such as [Google Workspace ](https://workspace.google.com/) (formerly G Suite), [Microsoft Team](https://www.microsoft.com/en-us/microsoft-teams/group-chat-software)s, and [Slack ](https://slack.com/)facilitate collaboration among students and teachers. These platforms support group projects, discussion forums, and real-time feedback.
**_Virtual Classrooms:_** Video conferencing tools like Zoom and Microsoft Teams enable remote learning, allowing students to attend classes and participate in discussions from anywhere in the world. This has been especially crucial during the COVID-19 pandemic.
**8. Assessment and Feedback**
Assessment and feedback in technology in education involve using digital tools and platforms to evaluate students' learning progress and provide them with constructive feedback.
**_Digital Assessments:_** Online quizzes, tests, and assignments provide immediate feedback to students, helping them understand their strengths and areas for improvement. Tools like [Google Forms](https://docs.google.com/forms), and [Kahoot!](https://kahoot.com/) make assessments more engaging.
**_Data Analytics:_** Educational technology tools can track student performance and generate analytics that help educators identify trends and address learning gaps. This data-driven approach enables more informed decision-making in teaching strategies.
## Challenges of technology in education
Technology has transformed the landscape of education, offering immense opportunities for learning and collaboration. However, alongside its benefits come a host of challenges that educators and institutions must navigate. From issues of access and equity to concerns about distraction and information overload, the integration of technology in education brings forth a complex array of obstacles that require thoughtful solutions. In this brief exploration, we delve into some of the primary challenges posed by technology in education. They include the following:
**1. Quality of Content**
Discovering excellent, factual, and age-appropriate content can be challenging for instructors due to the abundance of information available online. It takes time and experience to sift through the multitude of information to choose what is most pertinent and trustworthy. Teachers can overcome this difficulty by utilizing trustworthy learning environments and carefully selected content libraries that include resources that have been approved and matched to curricular requirements. Furthermore, working together with peers and taking advantage of professional development opportunities centered around digital literacy and content assessment can improve teachers' capacity to identify superior instructional resources among the large array of digital content available.
**2. Digital Literacy**
**Challenges of Digital Literacy**
**_- Digital Divide:_** Access to technology and digital skills vary widely among individuals, creating a digital divide. This gap in knowledge and access can limit opportunities for education, employment, and civic engagement.
**_- Information Overload:_** The internet offers a vast sea of information, but finding accurate and reliable sources can be overwhelming. Developing critical thinking skills is crucial to discern fact from fiction online.
**_- Privacy and Security:_** Many people lack awareness of online privacy and security risks. Proper guidance and education are essential to protect personal information and data from cyber threats.
**_- Low Awareness & Interest:_** Some demographics, like older adults and women in certain regions, may have lower awareness and interest in digital technology. Bridging this gap is crucial for ensuring equitable access to digital resources.
**_- Global Digital Disparities:_** Worldwide, there are disparities in internet access, digital infrastructure, and gender imbalances in online participation. These inequalities need to be addressed to ensure equal opportunities for all.
**_- Education Gaps:_** Many educational institutions do not prioritize digital literacy, leaving students ill-equipped for the digital job market. Integrating digital skills into education is vital for future employment prospects.
**3.Privacy and Security**
Integrating technology into educational settings can very well give rise to issues over protecting students’ personal information and privacy. There is a possible danger that sensitive student information might be compromised due to data breaches and cyberattacks. Additionally, educational technology vendors can acquire student data, which raises problems around ownership of the data and how the information is utilized.
**4. Digital Distractions**
Thanks to its abundance of interactive tools and resources, technology has emerged as an invincible force in education. But along with its advantages is a big drawback: digital distractions. The continual temptation of tablets, computers, and cellphones can seriously impair students' ability to concentrate and achieve academic goals. Now let's examine how digital distractions harm learning:
**_- Impaired Concentration and Focus:_** Students may find it difficult to focus during lectures or in-class activities due to the incessant buzz of notifications, the desire to check social media, or the attraction of online games. According to research published in the Educational Leadership journal, multitasking with technology reduces productivity and increases error rates (ON digital distraction in schools ON Association for Supervision and Curriculum Development ascd.org). The inability of the human brain to move between tasks quickly and the incessant desire to check gadgets interfere with learning and memory recall.

**_- Multitasking Myth and Increased Cognitive Load:_** Although a lot of students think they can multitask well, evidence from studies shows otherwise. Technology multitasking actually lowers cognitive ability, according to a 2015 study published in the Journal of Experimental Psychology: Learning, Memory, and Cognition [https://www.apa.org/monitor/oct01/multitask]. The working memory is overloaded while multitasking, such as taking notes on a laptop and simultaneously browsing social media or texting pals, leaving less space for processing and remembering material from lectures or class discussions.
**_- Shallow Processing of Information:_** Online content often moves quickly, which can encourage a cursory approach to learning. Pupils who are used to quickly scanning news articles and browsing social media may find it difficult to develop the critical thinking and in-depth reading comprehension skills necessary for success in the classroom. The constant onslaught of distractions might make it difficult to concentrate on difficult subjects and gain a deeper comprehension of the subject matter.
**_- Cyberbullying and Mental Health Concerns:_** Unrestricted use of technology in the classroom might lead to inappropriate content exposure and cyberbullying. Incidents of cyberbullying can have a severe effect on students' mental health, resulting in social isolation, anxiety, and sadness. Unrestricted access to social media and online gaming platforms can also exacerbate academic performance by causing compulsive behaviors and sleep disruptions.
**Examples of the Impact**
- According to a 2015 University of London research, students who received text messages during a lecture performed worse on comprehension tests than those who did not [https://mattkushin.com/2018/02/12/getting-students-to-think-about-cell-phone-addiction-classroom-activity/](https://mattkushin.com/2018/02/12/getting-students-to-think-about-cell-phone-addiction-classroom-activity/).
- According to a 2019 study by the Kaiser Family Foundation []https://www.kff.org/(https://www.kff.org/), teens who use screens for more than seven hours a day are more likely to have depressive symptoms.
**Strategies for Minimizing Distractions**
**_- Clear Device Policies:_** Reducing distractions during class time can be achieved by establishing clear policies in the classroom governing the use of devices.
**_- Encouraging Mindfulness:_** Students can focus better and have longer attention spans if mindfulness activities or brief breaks are incorporated into their courses.
**_- Engaging Activities:_** Creating lessons that are both interactive and stimulating will help students stay focused and reduce their tendency to look for outside stimulation.
**_- Opportunities for Digital Detox:_** Encouraging adolescents to disconnect from technology after school hours can foster positive digital behaviors and enhance wellbeing in general.
**5. Technical Issues**
Technical glitches such as software bugs, hardware malfunctions, or internet outages can disrupt teaching and learning activities. Relying too heavily on technology without backup plans in place can lead to frustration and wasted instructional time.
**6.Cost**
Technology plays a pivotal role in both the cost and accessibility of education. On one hand, technological advancements have led to the development of online learning platforms, digital textbooks, and interactive educational resources, potentially reducing the overall cost of traditional education. However, the initial investment in technology infrastructure, software, and devices can create a financial barrier for some students.
Ensuring equitable access to essential tools involves addressing economic disparities. Governments, educational institutions, and private entities should collaborate to provide subsidies, grants, or low-cost technology options to economically disadvantaged students. Additionally, fostering digital literacy programs can empower students to effectively utilize available technologies. Closing the digital divide requires a comprehensive approach that combines financial assistance, educational initiatives, and community engagement to ensure that all students have equal opportunities to harness the benefits of technology in their education.
By far the greatest factor limiting the efforts of teachers and administrators to provide education technology to students, budget cuts and limitations are a major hurdle that proponents of education technology must overcome in order to successfully introduce tech into their classrooms. A recent study even demonstrated that 75.9% of respondents saw budget restrictions as the biggest challenge preventing them from embracing education technology.
Budget limitations are especially challenging to overcome because great education tech tools don’t come cheap: while tools like Google Cloud can be a powerful tool for education, simply adopting that one tool also requires schools to provide Chromebooks to students and fund training sessions for teachers, which strained budgets simply can’t handle. Finding the funds to implement and sustain technology in the classroom can be a major barrier to its adoption in cash-strapped schools.
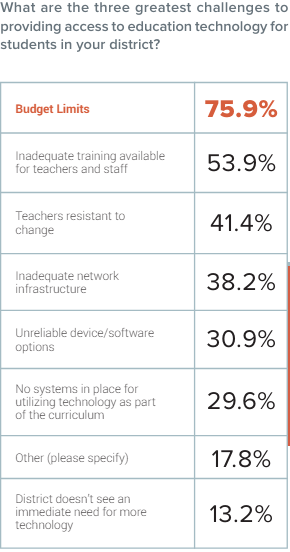
**7. Health Issues**
Too much reliance on Technological gadgets over a long period is unhealthy. Some of the issues brought up by technology include the following:
**_- Musculoskeletal problems_** - This is a disorder in human body parts that includes muscles and bones. This issue is brought up as a result of poor posture during studying. It is commonly identified by feeling pains, swelling, and inflammation of muscles and back pains. This issue can be prevented and managed by using ergonomics furniture and good posture while studying on screens and regular breaks to exercise thus relieving muscle pain and stress.

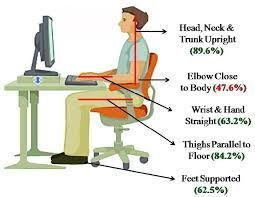
**_- Computer Vision Syndrome_** - Much exposure to digital learning gadgets is harmful to our eyes. They cause eye strain due to too much screen time. symptoms of eye strains include dry eyes, redness around the eyes, headaches, and blurred vision. This issue can be prevented by minimizing the screen brightness of gadgets, an increase of text size for better and more comfortable visibility, regular check-ups, and use of light glasses.


## How Technology Relates to Data in Education
In the context of technology in education, "data" refers to the information generated and collected through digital tools, platforms, and systems used in educational settings. This data encompasses various aspects of the teaching and learning process, including student performance, engagement, behavior, and progress.
Technology and data are deeply intertwined in education, influencing various aspects of teaching, learning, and administration. Here's how technology relates to data in education:
**1. Data Collection**
The methodical gathering of data using digital tools and platforms to improve teaching and learning procedures is known as data collection in education technology. Learning Management Systems (LMS), educational apps, assessment tools, adaptive learning platforms, and learning analytics are just a few of the many sources that make up these tools. Educators can monitor student performance, engagement, and progress with the use of these tools, which helps them understand each student's unique learning preferences and needs

**2. Data Analysis**
With the use of sophisticated analytics tools and algorithms, technology makes it easier to analyze educational data. Teachers can find trends, patterns, and places where student learning needs to be improved by using data analytics. Teachers can improve teaching effectiveness by identifying problematic students, personalizing education, and making data-driven decisions through data analysis. Data analytics helps teachers evaluate teaching strategies and materials, analyzing student performance data and resource utilization. This knowledge helps improve methods, lesson plans, and resource distribution, creating a more favorable learning environment. By using evidence-based tactics and data analysis, educators ensure academic success for all students.
**3. Assessment and Feedback**
Technology is essential for using data for evaluation and feedback in the classroom, greatly improving these procedures. In this perspective, technology and data are related as follows:
**Gathering of Data:**
- Automated Assessments: Digital platforms have the ability to gather information automatically from a variety of assessments, including assignments, tests, and quizzes. Scores, completion times, and particular areas in which students struggled are all included in this data.
- Learning Management Systems (LMS): Moodle, Blackboard, Canvas, and other LMS platforms gather a wealth of information about student submissions, interactions, and engagement levels.
- Educational Apps and Tools: Apps such as Kahoot!, and Google Classroom collect data in real time about student engagement and performance.
**Analyzing Data:**
- Analytics Dashboards: A common feature of educational technologies is a dashboard that analyses data to provide patterns, trends, and areas that require attention. This allows for insights into student performance.
**4. Research and Evaluation**
Not only has technology changed education in the classroom, but it has also completely changed how teachers do research and assess student learning. Technology is making educational research more dynamic and data-driven by utilizing data, which will improve instructional strategies and student results. Let's examine the ways that data and technology are combined in research and assessment related to education:

**_- Richer Data Collection and Analysis:_** Surveys, standardized tests, and classroom observations were the mainstays of traditional research and assessment methodologies. Richer and more detailed data may be collected because to technological advancements. Through online tests and assignments, Learning Management Systems (LMS) can monitor the progress of students and offer comprehensive insights into their unique learning preferences and areas of strength and weakness.

**_- Personalized Learning Insights:_** Learning management systems are capable of examining data on student performance from a range of sources, such as online exercises, exams, and engagement measures. By identifying pupils who may want more assistance or who are prepared for more difficult content, these insights can be utilized to tailor learning experiences for each individual student. Using a data-driven approach, teachers can customize lessons to fit each student's requirements and learning preferences.
**_- Real-time Feedback and Course Improvement:_** Real-time student feedback gathering is made easier by technology, which can be used for online surveys, clickstream data (which tracks user activity on a website), and automated evaluations. Teachers are able to recognize areas in which pupils may be having difficulty and modify their teaching methods accordingly thanks to this instant feedback. Data can also be used by educators to assess the efficacy of particular pedagogies and curricular items, resulting in ongoing enhancements to classes and educational opportunities.
**_- Large-Scale Studies and Collaboration:_** Thanks to technology, academics studying education may carry out extensive research, evaluating data from a huge number of students in various schools and regions. Best practices, trends, and patterns that may not be seen in smaller-scale research can be found in these investigations. Online platforms and data repositories also make it easier for researchers to work together and share data, which promotes creativity and advances the field of educational research.
**Examples of Technology-Driven Research and Evaluation:**
**_- The Measures of Effective Teaching Project (MET Project):_** The Bill & Melinda Gates Foundation provided funding for this extensive study, which examined student accomplishment data to pinpoint effective teaching strategies for a variety of subjects and grade levels.[https://metproject.org/](https://metproject.org/).
**_- DreamBox Learning:_** This adaptive learning platform provides focused practice and interventions based on unique needs for each student, tailoring math education depending on student data.[https://www.dreambox.com/](https://www.dreambox.com/)
## Challenges and Considerations
**_- Data Privacy:_** It's critical to protect student data privacy. Strong data security procedures must be in place, and educational technology businesses and schools must abide by data privacy laws like FERPA (Family Educational Rights and Privacy Act).
**_- Standardization and Interoperability:_** For analysis to be effective, data gathered from various platforms and sources must be standardized and interoperable.
**_- Teacher Training:_** To use data successfully for decision-making and course improvement, educators need to be trained in data analysis and interpretation.
## Future of Technology in Education
The future of education is undoubtedly intertwined with technology. As advancements continue to emerge, the potential for further enhancing educational experiences grows. The 21st century has witnessed an unprecedented digital revolution changing the future of education. Innovations such as artificial intelligence, machine learning, and blockchain could offer new ways to assess student performance, personalize learning, and secure educational credentials.
A study conducted by the Public Broadcasting Service (PBS) on the integration of technology in K-12 classrooms unveiled that a substantial 81% of teachers are of the opinion that tablets serve to enhance the quality of classroom education. Furthermore, the survey established that an impressive 77% of educators observed that technology plays a pivotal role in boosting student motivation to learn.

Here are some potential trends and developments:
**1. Personalized Learning**
Technology can enable personalized learning experiences through:
**_- Adaptive learning algorithms:_** Advanced algorithms analyze student progress, identifying strengths and weaknesses to dynamically adjust the curriculum for personalized learning.
**_- Tailored content:_** Recognizing diverse learning needs, educators provide customized content, catering to both high achievers and those in need of additional support.
**_- Individualized pacing:_** Technology empowers students to learn at their own speed, promoting in-depth exploration and understanding without the constraints of uniform classroom timelines.
**_- Continuous assessment:_** Real-time monitoring enables educators to provide timely guidance when students encounter challenges, ensuring ongoing progress.
**_- Enhanced engagement:_** Personalized learning, driven by technology, boosts student motivation and enthusiasm by delivering relevant and engaging content, positively impacting academic performance.
**2. Virtual and augmented reality**
Technologies can create immersive learning environments that simulate real-world scenarios. These technologies can enhance student engagement and deepen understanding by making abstract concepts more concrete. For example, virtual field trips can immerse students in a variety of locations and situations, such as a historical battlefield, a coral reef, or a remote island. Interactive anatomy lessons can allow students to explore the human body in a realistic and detailed manner.

**3. Artificial Intelligence**
AI-powered tools and applications can automate administrative tasks, such as grading and course planning, freeing up educators to focus more on teaching and mentoring. AI can also facilitate personalized learning experiences, adaptive assessments, and intelligent tutoring systems.
**4. Blockchain for Credentials**
Blending face-to-face and virtual instruction improves adaptability, individualized guidance, interactive capabilities, and variety of resources for an engaging learning environment. When in-person and online learning are combined, learning opportunities become more flexible, providing students with personalized support and utilizing the interactive qualities of the internet. With a wide range of resources, this method enhances learning while encouraging participation and meeting the particular needs of students in the current digital era.
**5. Online and blended learning**
Online learning environments can provide a large selection of courses that are available from any location, promoting lifelong learning and closing educational disparities. The benefits of both in-person and online learning can be combined to provide a well-rounded and all-encompassing educational experience. Blending face-to-face and virtual instruction improves adaptability, individualized guidance, interactive capabilities, and variety of resources for an engaging learning environment.

## Conclusion
In conclusion, there are many different and significant ways that technology is affecting education. The way that knowledge is learned, communicated, and applied has been completely transformed by technology, which has improved access to educational resources and created tailored learning experiences. Education has become more accessible thanks to online learning systems, which also remove geographical restrictions and offer chances for lifelong learning. Furthermore, the use of digital tools and resources into conventional classrooms has enhanced instructional approaches by enabling instructors to customize lessons to meet the requirements and preferences of specific students. In addition, technology has enabled students to take an active role in their own education by providing them with engaging and interactive learning opportunities that accommodate a variety of learning preferences. | zippyrehema123 |
1,866,620 | Leveraging 11 Advanced Debugging Techniques in Custom Software Development | Custom software development is an intricate process. Thus, even the most expert coders can write code... | 0 | 2024-05-27T13:33:53 | https://dev.to/jessicab/leveraging-11-advanced-debugging-techniques-in-custom-software-development-5a0i | softwaredevelopment, debug, techniques, debugging | Custom software development is an intricate process. Thus, even the most expert coders can write code that harbors hidden bugs. The only way to tackle these errors is through robust and
advanced debugging techniques.
This blog has 11 most efficient debugging techniques a software development agency can leverage.
So, let's begin!
## 11 modern debugging techniques in custom software development
Meticulous debugging in the software development cycle is essential for efficient deployment. Below are some efficient techniques:
### 1. Brute force method
This straightforward approach involves strategically inserting console.log() statements (JavaScript) or print() statements (Python) throughout the code. These statements output the values of variables at specific points in the program's execution. By examining the printed values, developers can pinpoint discrepancies between expected and actual values, ultimately leading to the erroneous code section.
Here's a code sample in Javascript:
```
function calculateArea(length, width) {
// ... potentially buggy code ...
console.log("Length:", length);
console.log("Width:", width);
console.log("Calculated Area:", area);
return area;
}
const calculatedArea = calculateArea(10, 5);
console.log("Expected Area:", 50);
```
Here, "console.log" statements print the "length", "width", and calculated "area" values. By comparing these printed values with the expected area (50), the developer can identify any discrepancies and locate the source of the error.
### 2. Cause elimination method
This systematic approach in custom software development involves creating a list of potential causes for the observed error. Each potential cause is then eliminated through testing or code modifications. If eliminating a cause resolves the error, that cause was the culprit. This method becomes more efficient with a clear understanding of the error behavior and the codebase involved.
For example, an error can be a function returning unexpected results.
Potential causes can be as follows:
- An incorrect formula is used in calculations.
- Data type mismatch between variables.
- Off-by-one error in loop iterations.
Testing methods can be as follows:
- Verify the formula against known good implementations.
- Ensure variables are of the expected data type (e.g., number vs. string).
- Check loop conditions and counters for potential off-by-one errors.
Systematically eliminating each potential cause helps the developer identify the origin of the error.
### 3. Backtracking
This technique involves starting from where the error manifests and working backward through the code's execution. By examining the values of variables and the logic flow at each step, the developer can trace the error back to its source. Backtracking is particularly useful for identifying errors that cause unexpected behavior or crashes later in the program's execution.
An example in Python can be as follows:
```
def process_data(data):
# ... potentially buggy code ...
if result is None:
raise ValueError("Data processing failed")
# Error occurs here (ValueError: Data processing failed)
processed_data = process_data(user_input)
```
The error occurs during "process_data" but doesn't provide specific details. Backtracking involves examining the code within "process_data" line by line, looking for potential causes that would lead to a "None" value for "result."
### 4.Program slicing
Like backtracking, program slicing focuses on a specific variable's value at a particular point in the code. Custom software development services include this technique, which involves analyzing the "slices" of code that influence that value. Developers can analyze smaller code sections that impact a specific variable or program output. This allows for a more focused approach, aiding in faster identification of the error's root cause. Static program analysis tools can be utilized to automate program slicing for complex codebases.
### 5.Thread Management
Threads are lightweight units of execution within a single process. They share the process's memory space and resources but allow for concurrent execution of code blocks. Threading libraries provide APIs for thread creation, synchronization, and communication. Popular threading models in custom software development include the following:
**POSIX threads (pthread):** Library for creating and managing threads on Unix-like systems.
**Java Thread API:** Built-in Java API for thread creation, synchronization, and scheduling.
**C# Thread Class:** Class for creating and managing threads in C# applications.
Below is an example of code in Java Thread API:
```
// A class that implements Runnable to define the task to be performed by a thread
public class MyRunnable implements Runnable {
@Override
public void run() {
// Print the name of the current thread
System.out.println("Thread: " + Thread.currentThread().getName());
}
}
// The main class containing the entry point of the program
public class Main {
public static void main(String[] args) {
// Create a new thread with MyRunnable as its task
Thread thread1 = new Thread(new MyRunnable());
thread1.start(); // Start the thread, which calls the run() method of MyRunnable
// Create another new thread with MyRunnable as its task
Thread thread2 = new Thread(new MyRunnable());
thread2.start(); // Start the thread, which calls the run() method of MyRunnable
}
}
```
Here, the "MyRunnable" class implements the "Runnable" interface and defines the code to be executed by the thread. The "main" method creates two threads with the same code and starts their execution using the "start()" method.
### 6.Breakpoints and stepping
These tools enable developers to pause program execution at specific points (breakpoints) and examine the program's state. This allows for a step-by-step inspection of variables, function calls, and memory usage in custom software development.
**Integrated Development Environments (IDEs):** Popular IDEs are Visual Studio Code, PyCharm, and IntelliJ IDEA. They offer robust debugging functionalities with breakpoint settings and step execution options.
**Debuggers:** Standalone debuggers like GDB (GNU Debugger) or LLDB (Low-Level Debugger) provide granular control over program execution. These can also be used across various programming languages.
Below is a code sample of Python with PyCharm:
def calculate_area(length, width):
```
area = length * width
print("Area:", area)
# Set breakpoint at the line calculating area
length = 5
width = 10
# Run the program in debug mode
# PyCharm pauses execution at the breakpoint
area = length * width # This line is paused
print("Area:", area)
```
A breakpoint is set at the line "area = length * width." When the program runs in debug mode, execution pauses at this point. This allows the developer to inspect the values of "length" and "width" before proceeding.
### 7.Binary search
Isolating the source of an error can be time-consuming for large datasets or complex algorithms. Binary search offers an efficient approach by repeatedly dividing the search space in half, focusing on the half most likely to contain the error.
**Divide-and-conquer algorithms:** Binary search falls under the category of divide-and-conquer algorithms. This breaks down problems into smaller, easier-to-solve subproblems in custom software development.
**Time complexity:** Binary search boasts a time complexity of O(log n), significantly faster than a linear search (O(n)) for large datasets (n).
Below is a code sample in Javascript:
```
function binarySearch(arr, target) {
let low = 0;
let high = arr.length - 1;
while (low <= high) {
let mid = Math.floor((low + high) / 2);
if (arr[mid] === target) {
return mid;
} else if (arr[mid] < target) {
low = mid + 1;
} else {
high = mid - 1;
}
}
return -1; // Target not found
}
const numbers = [1, 3, 5, 7, 9];
const target = 7;
const index = binarySearch(numbers, target);
if (index !== -1) {
console.log("Target found at index:", index);
} else {
console.log("Target not found");
}
```
This code implements a binary search function that considers the target value and sorted array as inputs. It iteratively halves the search space until the target is found or the entire array is searched.
### 8.Rubber ducking
This lighthearted technique involves explaining the code and thought process to an inanimate object, like a rubber duck. Verbalizing the steps can often reveal logical flaws or misunderstandings in the code.
**Pair programming:** While a rubber duck can't offer feedback, pair programming, where two developers work together, utilizes a similar principle. Explaining code to a partner can often lead to the identification of errors.
### 9.Log analysis
Logs are detailed records of program execution, including function calls, variable values, and error messages. Analyzing these logs gives valuable insights into program behavior and pinpoint the root cause of issues.
**Logging libraries:** Most programming languages offer logging libraries that simplify the process of writing informative log messages. Popular options include Log4j (Java), NLog (.NET), and Winston (Node.js).
**Log management tools:** Centralized log management tools can aggregate and analyze logs from various sources in custom software development. This helps identify patterns and trends that might indicate errors.
Here's a code sample from Python with a logging module:
import logging
```
logging.basicConfig(filename="my_app.log", level=logging.DEBUG)
def calculate_area(length, width):
if length <= 0 or width <= 0:
logging.error("Invalid input: Length and width must be positive")
return None
area = length * width
logging.debug(f"Calculated area: {area}")
return area
# Example usage
try:
result = calculate_area(5, 10)
print("Area:", result)
except TypeError as e:
print("An error occurred:", e)
```
Here, the "logging" module is used to write debug messages to a file named "my_app.log." The "calculate_area" function now includes a check for invalid input (non-positive length or width) and logs an error message if encountered. Additionally, it logs a debug message with the calculated area.
### 10.Clustering bugs
Similar bugs often stem from a common underlying issue. By grouping bugs with similar symptoms (clusters), developers can identify the root cause more efficiently. This technique is particularly helpful for complex codebases with numerous bugs.
**Bug tracking systems:** Bug tracking systems like Jira, Asana, or Trello can be used to categorize and group bugs based on various criteria, including symptoms, severity, or affected code sections.
**Machine learning:** This and other advanced technologies can be leveraged to automate bug clustering based on analyzing code patterns and bug reports.
## Debugging multi-threaded and multiprocess Applications in custom software development
Debugging multi-threaded and multiprocess applications brings unique challenges to software development firms compared to single-threaded programs. The concurrent nature of execution can lead to race conditions, deadlocks, and other synchronization issues. Here's how to tackle these challenges:
### Debugging tools
Popular debugging tools with multi-threading support include the following:
- **Visual Studio with parallel debugging:** Offers advanced features for debugging multi-threaded and asynchronous applications in C# and other .NET languages.
- **Eclipse with Thread Debugging:** Provides thread-aware debugging capabilities for Java applications.
- **GDB with pthreads extension:** Enables debugging of multi-threaded applications written in C and C++.
- **Chrome DevTools:** Integrated debugger for Chrome browser, offering extensive features for web development.
- **LLDB (Low-Level Debugger):** Modern debugger supporting a wide range of languages and platforms.
### Synchronization techniques
To prevent race conditions and deadlocks, developers should employ synchronization mechanisms like
- **Mutexes:** Mutual exclusion locks that ensure access to a shared resource for only one thread at a time.
Semaphores: Signaling mechanisms that control access to a limited number of resources.
- **Monitors (Java):** High-level synchronization constructs encapsulating shared data and access methods.
### Debugging strategies
- **Identify thread-related issues:** Analyze error messages and logs for clues related to specific threads or concurrent operations.
- **Isolate the problem thread:** Utilize debugging tools to identify the thread experiencing the issue and examine its call stack and variable states.
- **Simplify and reproduce:** Break down the problematic code into smaller, testable units to isolate the root cause.
- **Utilize debugging tools:** Leverage the features of multi-threaded debuggers to step through code, inspect thread states, and identify synchronization problems.
## Conclusion
This was all about advanced debugging techniques to help developers solve development complexities. With these techniques, any [custom software development company can minimize deployment delays](https://www.unifiedinfotech.net/services/custom-software-development/) and deliver solid applications. | jessicab |
1,866,617 | PRESTIGE WHITE MEADOWS IN WHITEFIELD | This is the best way to upgrade your living experience to the prestigious Prestige White Meadows Sky... | 0 | 2024-05-27T13:31:59 | https://dev.to/sushmitha_baskaran_58197b/prestige-white-meadows-in-whitefield-2j6p | theresidentially, prestigewhitemeadows | This is the best way to upgrade your living experience to the prestigious [Prestige White Meadows](https://theresidentially.com/prestige-white-meadows-whitefield-bangalore/) Sky Villas and Bungalows. Subscribe to the newsletter to get great offers and promotions on our properties. Get ready to experience the colourful world of Whitefield, Bangalore that gears up for Prestige White Meadows. Here, cultural differences add a particular kind of a delicate touch and a feeling of unlimited liberty is above average. In addition, Discover a world that is integrated with the city syndrome and at the same time presents the image of peacefulness.
It can be rightly mentioned that living in [Prestige White Meadows](https://theresidentially.com/) would be the epitome of luxury. As a result, We strategically developed superior homes that perfectly combine efficient accessibility to the city whilst embracing the natural environment. Looking for large and modern villas for sale in Bangalore specifically, Whitefiled?Look no further. Employment, education and entertainment opportunities can be easily reached by the Purple Line as well as the upcoming Blue Line Metro stations within walking distance. A fifteen-minute drive takes you to the nearby Info-Tech parks such as the ITPL and ECC Road as well as to many business centers. Basic necessities needed for a comfortable living, such as schools, hospitals, shopping centers and other facilities are within the our reach. | sushmitha_baskaran_58197b |
1,866,616 | Mixer Singapore | Planning for a kitchen remodel and redesign to amp up the beauty of your home? If yes, you might want... | 0 | 2024-05-27T13:30:26 | https://dev.to/bathroomwarehouse/mixer-singapore-2adb | Planning for a kitchen remodel and redesign to amp up the beauty of your home? If yes, you might want to check out the [Mixer Singapore](https://bathroomwarehouse.com.sg/basin_mixer/) collections online and various other products that deserve to be in your kitchen today! Make your kitchen elegant and modern with all the best and innovative products and fittings today. | bathroomwarehouse | |
1,866,613 | WebRTC Server: What Is It and Why You Need One? | WebRTC or Web Real Time Communications, is an open source project that lets browser based... | 0 | 2024-05-27T13:28:08 | https://www.metered.ca/blog/webrtc-server-what-is-it-and-why-you-need-one/ | webdev, devops, webrtc, javascript | WebRTC or Web Real Time Communications, is an open source project that lets browser based applications or web applications communicate using video and audio media
Many use cases are there for video and audio communication but WebRTC can be used to potentially transmit any type of data between devices.
### **Basic Principles and protocols**
#### **1\. P2P Communication**
* Using WebRTC devices can establish direct connections between peer devices.
* Having a direct connection negates the need for a server between devices, this could be cheaper and less resources are required
#### **2\. Media Streaming**
* WebRTC uses advanced codecs to enable high quality media streaming
* The WebRTC technology supports real time audio and video streaming
* SRTP: The Secure Real Time Transport Protocol ensures that the audio and video media streams are secure encrypted.
#### **3\. Signaling**
* You need signalling for setting up, controlling and ending a communication session
* WebRTC itself does not specify a signalling protocol, thus you can choose form a variety of signalling protocols such as WebSocket, SIP or any other
#### **4\. NAT Traversal**
* WebRTC handles network address translation (NAT) traversal using STUN ( Session Traversal Utilities for NAT ) or TURN ( Traversal Using Relays around NAT) servers
* Generally you need a TURN server for NAT traversal, if you are looking for a TURN server we suggest going for [**Metered Global TURN server service**](https://metered.ca/stun-turn)
#### **5\. Security**
* The data is end-to-end encrypted in webrtc using protocols such as as DTLS (Datagram Transport Layer Security) and SRTP ( Secure Real time Transport Protocol)
* Thus webrtc is completely secure and private
### **Core Problem: Direct Peer to Peer Communication (Why do we need WebRTC servers)**
### **NAT Traversal issues**
Network Address Translation is a protocol that is used by routers and NAT devices to route multiple devices that have private IP addresses though a single public IP address or few public IP addresses
NAT was introduced to conserve limited number of public IP addresses and introduce an additional layer of security and internal network structure.
#### **Types of NAT**
There are different types and kinds of NATs available, depending on how they allow external traffic to flow to the internal networks
1. **Full Cone NAT:** This just maps a internal private IP and port number to an external public IP and port number. Any external device can send data to the internal device by sending the data to the external mapped public IP address and port number
2. **Restricted Cone NAT:** This is similar to the full cone NAT but it only allows external devices to send data to internal device if the internal device has first send the data to that external device
3. **Port Restricted Cone NAT:** This is similar to the restricred cone NAT but more restrictive, here the external device can send the data to the internal device only if the internal device has send the data to that external device first and the external device can only send the data on the prot nummber from which it forst recieved the data from.
4. **Symmetric NAT:** Symmetric NAT is the most difficult to traverse, here each request from an internal device (internal IP) is mapped to a different source public IP address and port number. Thus if the same device sends data to different addresses then different source external IP and port number is used thus it is practically impossible to use STUN to discover a devices static public IP address and port number
### **How NAT Affects Peer-to-Peer Connection**
NAT makes it diffcult to establish peer to peer connection because the NAT maskes the private IP addresses of the devices that are behind it with a single or few public IP addresses. Here are some of the reasons NAT imapcts peer to peer connections
1. Address Translation: NAT changes the private IP address of the internal devices to a different public IP address and port number.As a result the private IP address and port number are hidden from the local network
2. Connection Requests: For a P2P connection both the devices need to know the public IP address and port number of each other, the NAT obcuscates this thus it is difficult to make a direct connection
3. Inbound connection blocking: NAT and firewall rules obstructs inbound connection attempts. This is because hackers often try to establish connection from their devices to the devices they wish to hack so it is a safety features. That is why to establish connection you need a [**TURN server**](https://metered.ca/stun-turn)
## **WebRTC Server: The Solution**
A webrtc server is an important component of webrtc framework, it is designed to facilitate real time communication between devices and applications
While webrtc can enable direct p2p communication, often this fails due to NAT restrictions and firewall rules.
The WebRTC server handle tasks such as relaying data when direct connection is not possible
There are primaraly three types of webrtc servers
1. STUN server
2. TURN server
3. Signalling server
Each of these servers play an important role in the webrtc ecosystem. You can learn more about these servers below. The most important among these is the TURN server, If you are looking for one you can consider [Metered.ca](http://Metered.ca)
### **NAT Traversal Techniques**
To overcome the NAT connectivity challenges, several techniques are used, here are some of the popular ones.
### **STUN ( Session Traversal Utilities for NAT) :**
* As we have already seed NAT obfuscates the internal IP address and port number of devices that are behind it. The STUN server helps discover the IP address and port number of the devices. So, that the devices can connect with each other
* How stun works is by: A client device sends a request to a STUN server when relies back to the client device with the device's public IP address and port number.
### **TURN ( Traversal Using Relays Around NAT)**
* TURN servers relay traffic through themselves thus no matter how strict the NAT is, it is always possible to traverse it with TURN server
* This methods effective solves the NAT problem but may create issues such as latency if the server is geographically remotely located then your users that is why you need a globally located turn servers so that no matter where your users are they get less than 50 ms latency. One such service is [**Metered TURN servers**](https://metered.ca/stun-turn)
### **ICE (Inteactive connectivity establishment)**
* ICE combines STUN and TURN to find the best path possible, it first tries to establish a connection using STUN which fails most of the time then it attempts to connect using TURN servers
### **How ICE works step by step process**
Let us understand how ICE works using an example: Let us consider there are 2 devices and these devices are located behind different NATs and these devices want to do video calling
1. Signalling Phase
2. Both the devices use a signaling server to exchange their network information. The webRTC does not specify any particular signalling protocol to use.
2\. Connecting through STUN
* Each device tries to discover what their public IP and port number is using the STUN server, they can then share these details with each other using the signalling server and then connect to each other
3\. Connection Attempt
* The devices try to connect to each other, this often fails because of stricter NAT and firewall rules that do not allow external devices to connect to devices that are behind the NAT
4\. TURN fallback:
* If the direct connection fails then peers try to connect through a TURN server to relay the traffic to each other
## [**Metered.ca**](http://Metered.ca)**: The Global TURN Server solution**
## [**Metered TURN servers**](https://www.metered.ca/stun-turn)
1. **API:** TURN server management with powerful API. You can do things like Add/ Remove credentials via the API, Retrieve Per User / Credentials and User metrics via the API, Enable/ Disable credentials via the API, Retrive Usage data by date via the API.
2. **Global Geo-Location targeting:** Automatically directs traffic to the nearest servers, for lowest possible latency and highest quality performance. less than 50 ms latency anywhere around the world
3. **Servers in 12 Regions of the world:** Toronto, Miami, San Francisco, Amsterdam, London, Frankfurt, Bangalore, Singapore,Sydney, Seoul
4. **Low Latency:** less than 50 ms latency, anywhere across the world.
5. **Cost-Effective:** pay-as-you-go pricing with bandwidth and volume discounts available.
6. **Easy Administration:** Get usage logs, emails when accounts reach threshold limits, billing records and email and phone support.
7. **Standards Compliant:** Conforms to RFCs 5389, 5769, 5780, 5766, 6062, 6156, 5245, 5768, 6336, 6544, 5928 over UDP, TCP, TLS, and DTLS.
8. **Multi‑Tenancy:** Create multiple credentials and separate the usage by customer, or different apps. Get Usage logs, billing records and threshold alerts.
9. **Enterprise Reliability:** 99.999% Uptime with SLA.
10. **Enterprise Scale:** With no limit on concurrent traffic or total traffic. Metered TURN Servers provide Enterprise Scalability
11. **5 GB/mo Free:** Get 5 GB every month free TURN server usage with the Free Plan
12. Runs on port 80 and 443
13. Support TURNS + SSL to allow connections through deep packet inspection firewalls.
14. Support STUN
15. Supports both TCP and UDP
16. Free Unlimited STUN
## **Setting Up** [**Metered.ca**](http://Metered.ca) **Server: A Step by Step guide**
### **Account Creating and initial setup**
1. go to [metered.ca/stun-turn](http://metered.ca/stun-turn) website and create an account by clicking on the "Get Started" Button
2. There are some tutorials that you can look at and then you can also test the turn servers as well
3\. then you can choose the turn server region, there is the Global region which automatically routes the traffic to the nearest turn server to the user or use can choose from a specific region as well
4\. Next you can create your first turn server credential, all the turn server creds also contain stun servers in the ICE array as well
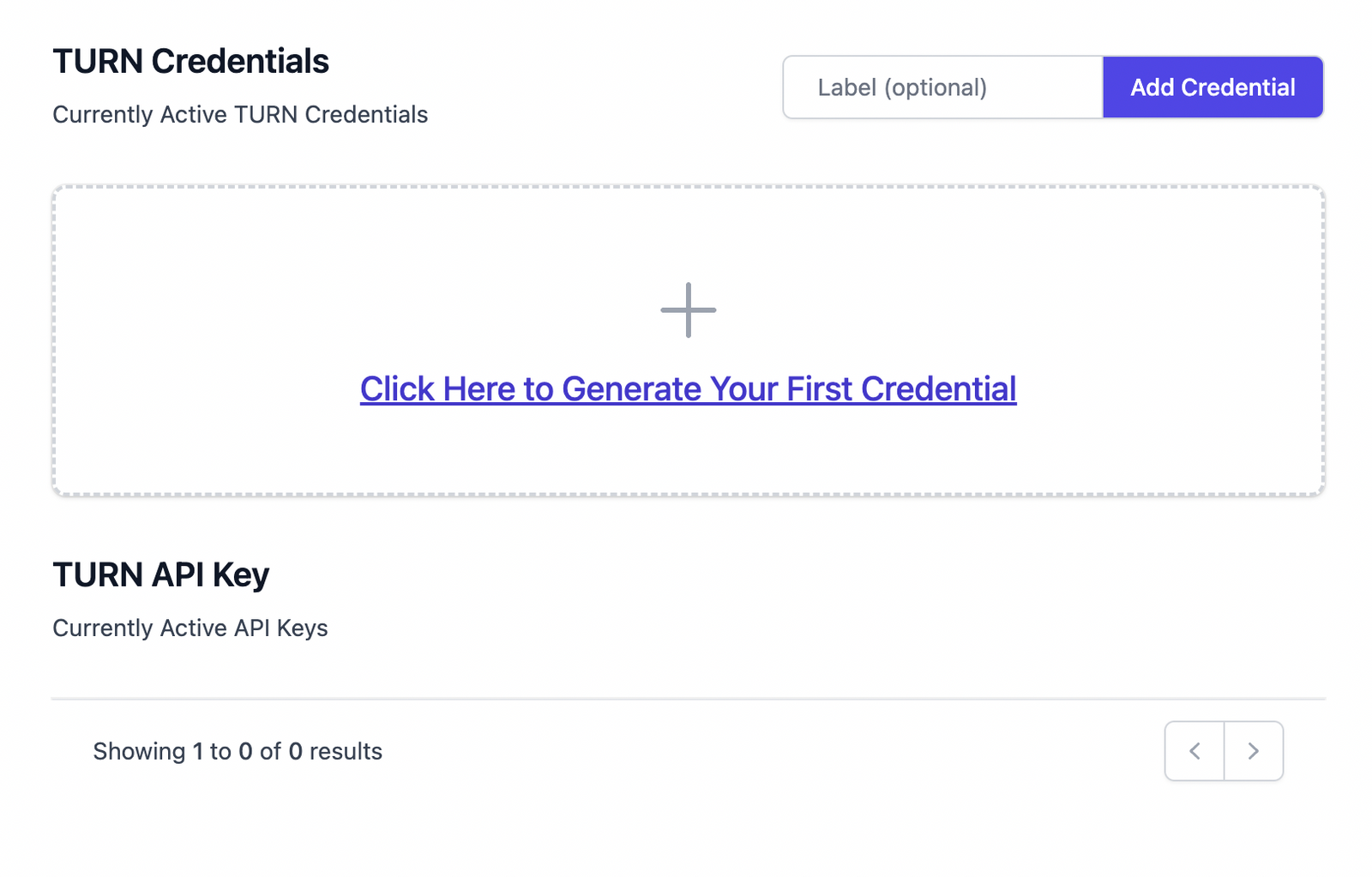
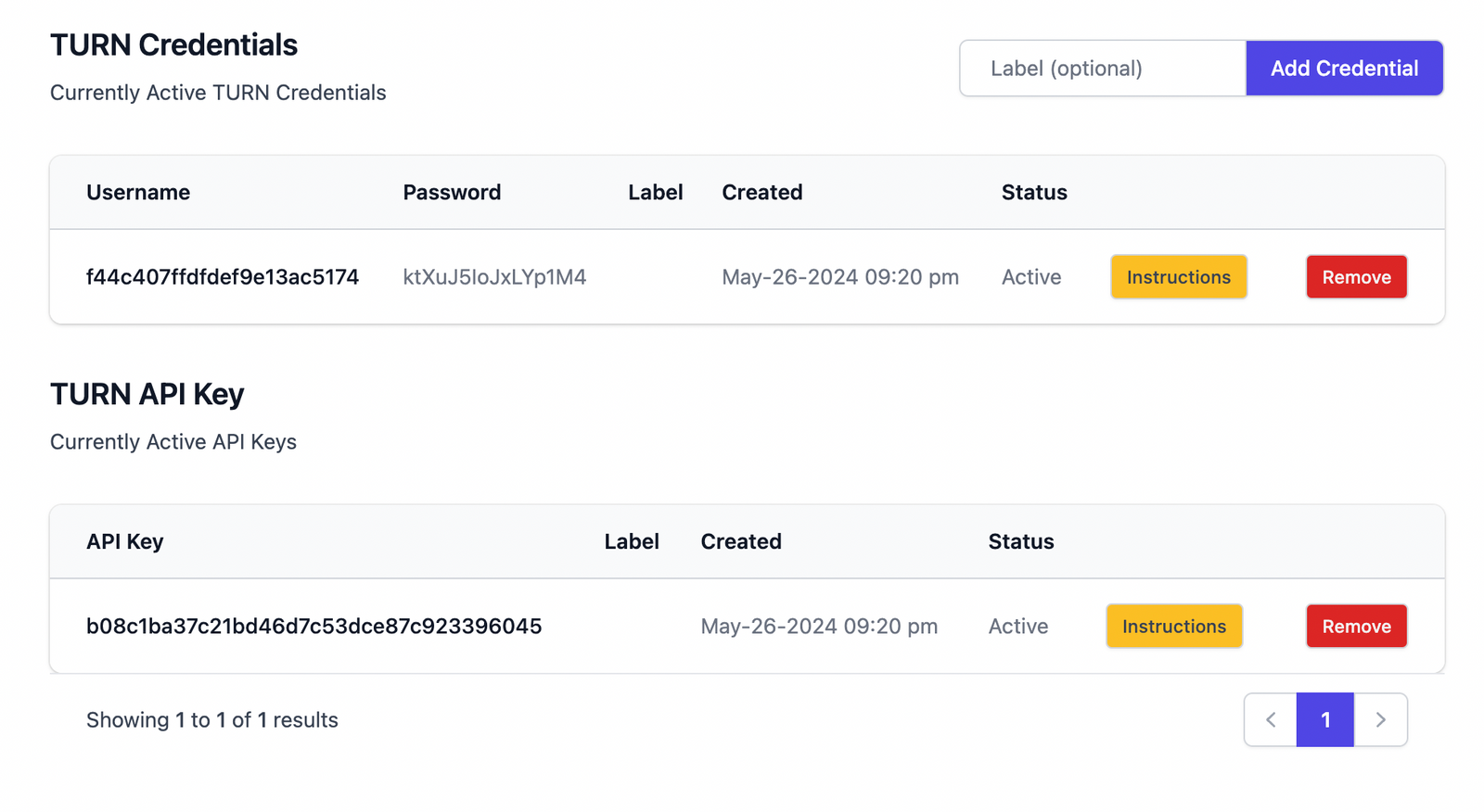
5\. Click on the "Add Credential" button and optionally specify a label to the credential or click on the "click here to generate your first credential" button to create a credential
6\. then click on the instructions button to get the instructions on how to use the credentials in your application
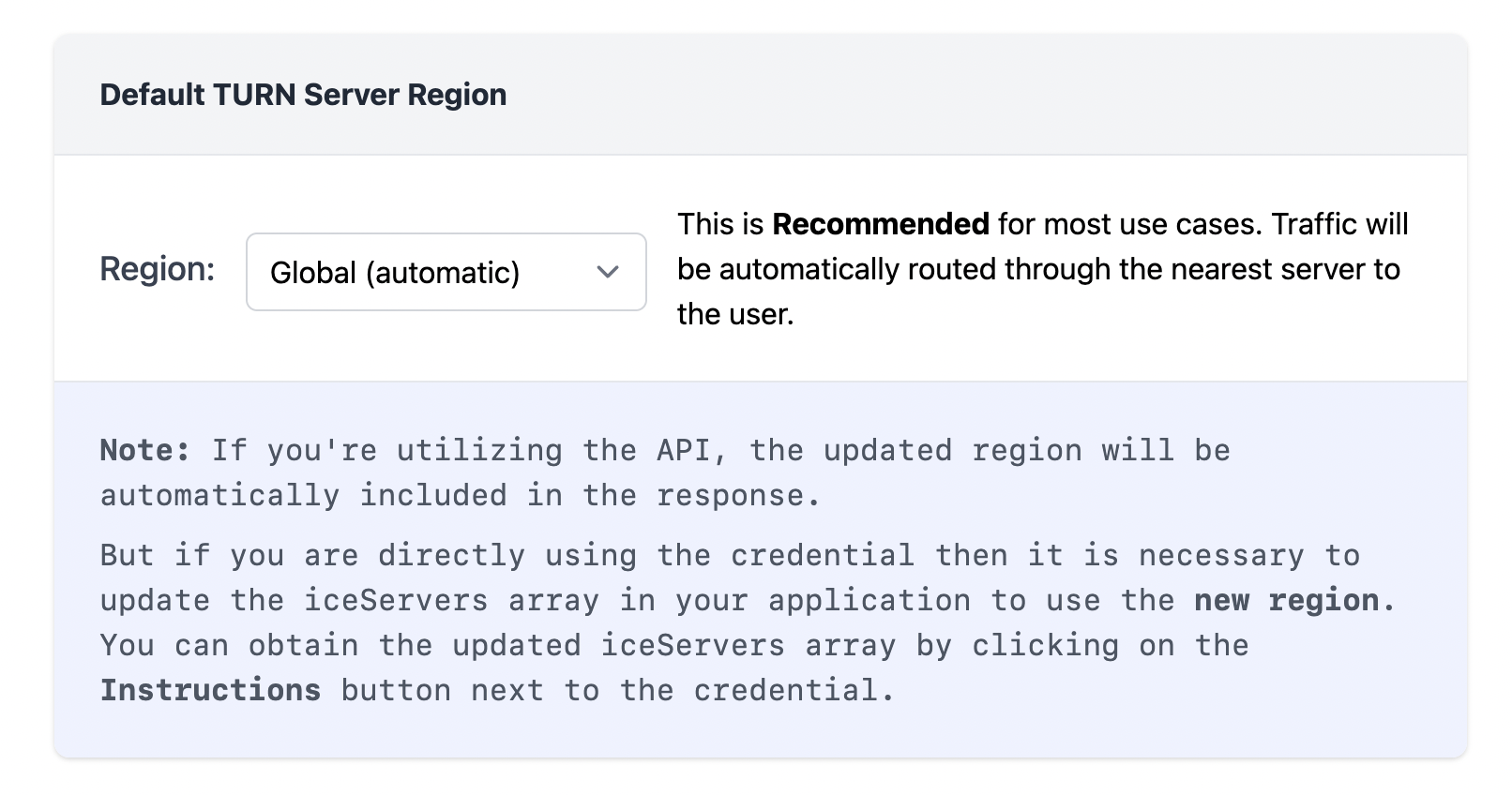
You can use both the ICE server array or the api in your webrtc application
### **Using API**
```js
// Calling the REST API TO fetch the TURN Server Credentials
const response =
await fetch("https://helloworld.metered.live/api/v1/turn/credentials?apiKey=c9837191de8e5a13bdae2c1fa8cfb204d853");
// Saving the response in the iceServers array
const iceServers = await response.json();
// Using the iceServers array in the RTCPeerConnection method
var myPeerConnection = new RTCPeerConnection({
iceServers: iceServers
});
```
### **Using ICEServer Array**
```js
var myPeerConnection = new RTCPeerConnection({
iceServers: [
{
urls: "stun:stun.relay.metered.ca:80",
},
{
urls: "turn:global.relay.metered.ca:80",
username: "3325c6e81a4c30238a4213b9",
credential: "taDRAoRlvjITUVe3",
},
{
urls: "turn:global.relay.metered.ca:80?transport=tcp",
username: "3325c6e81a4c30238a4213b9",
credential: "taDRAoRlvjITUVe3",
},
{
urls: "turn:global.relay.metered.ca:443",
username: "3325c6e81a4c30238a4213b9",
credential: "taDRAoRlvjITUVe3",
},
{
urls: "turns:global.relay.metered.ca:443?transport=tcp",
username: "3325c6e81a4c30238a4213b9",
credential: "taDRAoRlvjITUVe3",
},
],
});
```
Thus you can either use the ICE server array or the API to access TURN server credentials
Using the API there is a lot of stuff that you can do,
* creating credentials
* deleting credentials
* enabling /disabling credentials
* Getting usage data
* Getting usage data by user
* Getting usage data by date
* and much more
* for a complete list of what you can do refer to the documentation here: [**https://www.metered.ca/docs/turn-rest-api/get-credential**](https://www.metered.ca/docs/turn-rest-api/get-credential)
Thus we have learned in this article what are webrtc servers and why they are needed. We also learned how we can use webrtc servers to further our communication goals. | alakkadshaw |
1,866,532 | ST Introduction | What is Software Engineering? | 0 | 2024-05-27T12:30:56 | https://dev.to/tharanitharan/st-introduction-dcn | What is Software Engineering?
| tharanitharan | |
1,866,612 | Hay!! I found the cure for Cancer!!! | I'm sorry. I was pulling your leg; I did not. But before you scroll forward, I found something much... | 0 | 2024-05-27T13:24:04 | https://blog.learnhub.africa/2024/05/27/learn-css-in-two-seconds-with-matcha-css/ | webdev, beginners, programming, css | I'm sorry. I was pulling your leg; I did not. But before you scroll forward, I found something much cooler!!!!
Imagine having to style your work from scratch, looking for the right divs and styling them while checking if it works well. These are hard nuts to crack, mostly when you are a beginner or need something straightforward and easy.
I hate styling my work. I liked a one-for-all fit that would solve my problems, so when I came across a [lowlighter 🦑](https://dev.to/lowlighter) post on dev, I was excited and decided to test the new discovery.
[matcha.css](https://matcha.mizu.sh/) can transform plain HTML pages into visually appealing websites with minimal effort.
I know you think I'm lying. In this article, we'll explore how to use matcha.css and how it can simplify your web development workflow.
## What is matcha.css?
matcha.css is a lightweight and user-friendly CSS library that enhances the appearance of your HTML elements without requiring extensive styling or configuration.
It uses semantic styling to interpret the structure and purpose of your HTML elements and applies appropriate styles accordingly.
One of matcha.css's key features is its ability to respect user preferences for light or dark mode. Your website will automatically adapt to the user's preferred color scheme, providing a consistent and visually pleasing experience.
Now that you have a base idea of match.css, let's test it. Remember, as ad developers, we think hard to work less.
## Getting Started with matcha.css
Using matcha.css is incredibly easy. All you need to do is include the CSS file in your HTML document by adding the following line in the `<head>` section:
<link rel="stylesheet" href="https://matcha.mizu.sh/matcha.css">
That's it! With just one line of code, your HTML elements will instantly have a polished and modern appearance.
Let's take a look at an example HTML file and see how matcha.css enhances its visual appeal:
**Without match.css**
```html
<!DOCTYPE html>
<html>
<head>
<title>My Portfolio</title>
<!--
<link rel="stylesheet" href="https://matcha.mizu.sh/matcha.css">
-->
</head>
<body>
<header>
<nav>
<menu>
<li><a href="#">Home</a></li>
<li>
<a href="#">Projects</a>
<menu>
<li><a href="#">Web Development</a></li>
<li><a href="#">Design</a></li>
</menu>
</li>
<li><a href="#">About</a></li>
<li><a href="#">Contact</a></li>
</menu>
</nav>
</header>
<main>
<section>
<h1>Welcome to My Portfolio</h1>
<p>Hi there! I'm a passionate web developer and designer. Take a look at my work and feel free to reach out.</p>
</section>
<section>
<h2>Featured Projects</h2>
<ul>
<li>
<h3>Project 1</h3>
<p>A brief description of Project 1 goes here.</p>
<a href="#">View Project</a>
</li>
<li>
<h3>Project 2</h3>
<p>A brief description of Project 2 goes here.</p>
<a href="#">View Project</a>
</li>
</ul>
</section>
<section>
<h2>Get in Touch</h2>
<form>
<label>
Name:
<input type="text" name="name" required>
</label>
<label>
Email:
<input type="email" name="email" required>
</label>
<label>
Message:
<textarea name="message" required></textarea>
</label>
<button type="submit">Submit</button>
</form>
</section>
</main>
<footer>
<p>© 2023 My Portfolio. All rights reserved.</p>
</footer>
</body>
</html>
```
In this example, we have a simple portfolio website with a navigation menu, a section for featured projects, a contact form, and a footer.

Let's add Matcha.css and check out the transformation with just a single line of code.
```html
<!DOCTYPE html>
<html>
<head>
<title>My Portfolio</title>
<link rel="stylesheet" href="https://matcha.mizu.sh/matcha.css">
</head>
<body>
<header>
<nav>
<menu>
<li><a href="#">Home</a></li>
<li>
<a href="#">Projects</a>
<menu>
<li><a href="#">Web Development</a></li>
<li><a href="#">Design</a></li>
</menu>
</li>
<li><a href="#">About</a></li>
<li><a href="#">Contact</a></li>
</menu>
</nav>
</header>
<main>
<section>
<h1>Welcome to My Portfolio</h1>
<p>Hi there! I'm a passionate web developer and designer. Take a look at my work and feel free to reach out.</p>
</section>
<section>
<h2>Featured Projects</h2>
<ul>
<li>
<h3>Project 1</h3>
<p>A brief description of Project 1 goes here.</p>
<a href="#">View Project</a>
</li>
<li>
<h3>Project 2</h3>
<p>A brief description of Project 2 goes here.</p>
<a href="#">View Project</a>
</li>
</ul>
</section>
<section>
<h2>Get in Touch</h2>
<form>
<label>
Name:
<input type="text" name="name" required>
</label>
<label>
Email:
<input type="email" name="email" required>
</label>
<label>
Message:
<textarea name="message" required></textarea>
</label>
<button type="submit">Submit</button>
</form>
</section>
</main>
<footer>
<p>© 2023 My Portfolio. All rights reserved.</p>
</footer>
</body>
</html>
```

## Here's what matcha.css does for us:
1. **Navigation Menu**: The `<menu>` elements are styled as a clean and responsive navigation menu, with nested submenus displaying properly.
2. **Typography**: Headings, paragraphs, and links are styled cleanly and legibly, making the content easy to read.
3. **Form Styling**: The contact form has clear labels, input fields, and a submit button. Required fields are visually indicated, improving user experience.
4. **Dark Mode Support**: If the user's operating system is set to dark mode, matcha.css will automatically apply a dark color scheme to the website.
## Customizing matcha.css
While matcha.css provides a solid foundation for styling your HTML elements, you may want to customize further the appearance to match your branding or personal preferences. Fortunately, matcha.css is designed to be easily customizable.
You can override specific styles by creating your own CSS file and including it after the matcha.css file in your HTML document. For example, if you want to change the primary color of your website, you can add the following CSS rules:
:root {
--color-primary: #ff6347; /* Tomato color */
}
This will update the primary color used throughout your website to a tomato shade.
Additionally, matcha.css provides a helper tool called `@matchamizer` that allows you to create custom builds with your preferred settings and styles. You can explore this tool and its documentation on the matcha.css website.
## Conclusion
[matcha.css](https://matcha.mizu.sh/) is a powerful yet lightweight CSS library that can transform plain HTML pages into visually appealing websites with minimal effort.
By leveraging semantic styling and respecting user preferences, matcha.css provides a solid foundation for building user-friendly and accessible web applications.
Whether you're a beginner or an experienced developer, matcha.css can save you time and effort by handling the styling of common HTML elements, allowing you to focus on building the core functionality of your projects. Give it a try and experience the simplicity and elegance of matcha.css!
## Resource
If you are crazy like me and want to learn some more customizable options, check out how their documentation [here](https://matcha.mizu.sh/).
My blog covers [frontend](https://blog.learnhub.africa/category/frontend/), [cybersecurity](https://blog.learnhub.africa/category/security/), and many more interesting subjects. Check it out to learn new things and read about the world's end.
I predicted that.
Till next time, stay jiggy.
Check me out on [X](https://x.com/Scofield_Idehen). I post funny memes a lot,
| scofieldidehen |
1,865,915 | Good start for the project | First 2 weeks summarize: This week I began working on refactoring hek.py functions. I... | 0 | 2024-05-27T13:23:44 | https://dev.to/ahmedhosssam/good-start-for-the-project-131n | gsoc | ## First 2 weeks summarize:
This week I began working on refactoring `hek.py` functions.
I started by migrating the finished work in [GSoC2023](https://github.com/sunpy/sunpy/pull/7059) to a new [PR](https://github.com/sunpy/sunpy/pull/7619) to start working on it.
My first contribution was creating `util.py` file to include all utility functions needed for `hek.py`, a lot of functions that was added in HEKClient at first didn't make sense to remain there.
Now the new `util.py` file includes:
```python
def parse_times(table)
def parse_values_to_quantities(table)
def parse_columns_to_table(table, attributes, is_coord_prop = False)
def parse_unit(table, attribute, is_coord_prop = False)
def parse_chaincode(value, attribute, unit)
def get_unit(unit)
```
`get_unit` has been simplified in terms of implementation and interface, this was the first version:
```python
def get_unit(attribute, str):
if attribute["is_coord_prop"]:
coord1_unit, coord2_unit, coord3_unit = None, None, None
coord_units = re.split(r'[, ]', str)
if len(coord_units) == 1: # deg
coord1_unit = coord2_unit = u.Unit(coord_units[0])
elif len(coord_units) == 2:
coord1_unit = u.Unit(coord_units[0])
coord2_unit = u.Unit(coord_units[1])
else:
coord1_unit = u.Unit(coord_units[0])
coord2_unit = u.Unit(coord_units[1])
coord3_unit = u.Unit(coord_units[2])
return locals()[attribute["unit_prop"]]
else:
return u.Unit(str)
```
The first thing that has been done is to use unit aliases inside the function using context manager instead of putting the aliases globally.
The whole goal of this function is to parse a string into an astropy unit, but the big part of the function was splitting the string into more than one unit if the input was coordinate units, and then returning the unit assigned to `unit_prop`. I decided to just remove all of this and convert the unit into an array and return the first index, like this:
```python
units = re.split(r'[, ]', unit)
return u.Unit(units[0].lower())
```
And actually it works just fine with all HEK features and events, so I will keep it like this until some strange error appears.
And also the interface has been simplified to just take the string of the targeted unit.
This is the current version of `get_unit`:
```python
def get_unit(unit):
"""
Converts string into astropy unit.
Parameters
----------
unit: str
The targeted unit
Returns
-------
unit
Astropy unit object (e.g. <class 'astropy.units.core.Unit'> or <class 'astropy.units.core.CompositeUnit'>)
Raises
------
ValueError
Because `unit` did not parse as unit.
Notes
----
For the complete list of HEK parameters: https://www.lmsal.com/hek/VOEvent_Spec.html
"""
cm2 = u.def_unit("cm2", u.cm**3)
m2 = u.def_unit("m2", u.m**2)
m3 = u.def_unit("m3", u.m**3)
aliases = {
"steradian": u.sr,
"arcseconds": u.arcsec,
"degrees": u.deg,
"sec": u.s,
"emx": u.Mx,
"amperes": u.A,
"ergs": u.erg,
"cubic centimeter": u.ml,
"square centimeter": cm2,
"cubic meter": m3,
"square meter": m2,
}
with u.add_enabled_units([cm2, m2, m3]), u.set_enabled_aliases(aliases):
# If they are units of coordinates, it will have more than one unit,
# otherwise it will be just one unit.
# NOTE: There is an assumption that coord1_unit, coord2_unit and coord3_unit will be the same.
units = re.split(r'[, ]', unit)
return u.Unit(units[0].lower())
```
Another thing that has been done was adding a documentation string for `parse_chaincode` function.
```python
def parse_chaincode(value, attribute, unit):
"""
Parses a string representation of coordinates and convert them into a PolygonSkyRegion object
using units based on the specified coordinate frame.
Parameters
----------
value: PolygonSkyRegion
A polygon defined using vertices in sky coordinates.
attribute: dict
An object from coord_properties.json
unit: str
The unit of the coordinates
Returns
-------
PolygonSkyRegion
A polygon defined using vertices in sky coordinates.
Raises
------
IndexError
Because `value` does not contain the expected '((' and '))' substrings.
UnitConversionError
Because the units set by `coord1_unit` or `coord2_unit` are incompatible with the values being assigned.
"""
coord1_unit = u.deg
coord2_unit = u.deg
if attribute["frame"] == "helioprojective":
coord1_unit = u.arcsec
coord2_unit = u.arcsec
elif attribute["frame"] == "heliocentric":
coord1_unit = u.R_sun # Nominal solar radius
elif attribute["frame"] == "icrs":
coord1_unit = get_unit(unit)
coord2_unit = get_unit(unit)
coordinates_str = value.split('((')[1].split('))')[0]
coord1_list = [float(coord.split()[0]) for coord in coordinates_str.split(',')] * coord1_unit
coord2_list = [float(coord.split()[1]) for coord in coordinates_str.split(',')] * coord2_unit
vertices = {}
if attribute["frame"] == "heliocentric":
vertices = SkyCoord(coord1_list, coord2_list, [1]* len(coord1_list) * u.AU, representation_type="cylindrical", frame="heliocentric")
else:
vertices = SkyCoord(coord1_list, coord2_list, frame=attribute["frame"])
return PolygonSkyRegion(vertices = vertices)
``` | ahmedhosssam |
1,353,633 | Decentralized Autonomous Organizations (DAOs): A Revolution in Organizational Structure | Decentralized Autonomous Organizations (DAOs) are a new type of organization that operates on a... | 0 | 2024-05-27T13:22:33 | https://dev.to/sumana10/decentralized-autonomous-organizations-daos-a-revolution-in-organizational-structure-2d3c | dao, web3, blockchain, architecture | Decentralized Autonomous Organizations (DAOs) are a new type of organization that operates on a blockchain, using smart contracts to encode rules and governance processes. DAOs offer a decentralized and autonomous alternative to traditional organizations, with decision-making power distributed among all members who hold the organization's tokens.
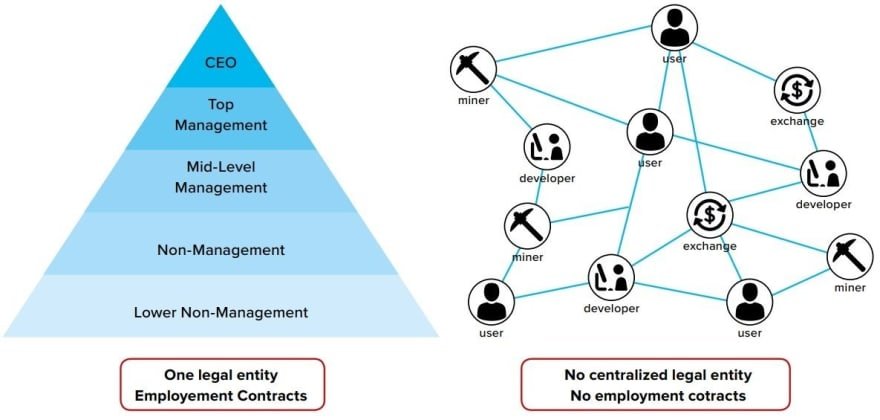
## Key Differences between Traditional Organizations and DAOs:
- Centralized vs Decentralized: Traditional organizations are centralized, with power held by a small group of people or a single individual. DAOs are decentralized, with decision-making power distributed among all members.
- Intermediaries Eliminated: Traditional organizations require intermediaries such as lawyers, accountants, or regulators to help run the organization. DAOs operate on a decentralized platform, eliminating the need for intermediaries.
- Increased Transparency: Traditional organizations have limited transparency in their decision-making processes, financial transactions, and ownership structures. DAOs operate on a blockchain, providing a high degree of transparency and accountability through an immutable ledger.
- Autonomy: Traditional organizations may be subject to government regulations and the control of centralized entities. DAOs are autonomous and operate according to rules encoded in smart contracts, allowing them to operate independently of any central authority.
## Potential Use Cases for DAOs:
- DeFi: DAOs can play a major role in the rapidly growing Decentralized Finance (DeFi) sector.
- Crowdfunding: DAOs can be used for decentralized crowdfunding, allowing for more democratic and transparent funding processes.
- Community Governance: DAOs can be used for community governance, allowing for more democratic and transparent decision-making processes.
- Supply Chain Management: DAOs can be used for supply chain management, offering increased transparency and accountability in complex supply chains.
- Digital Identity: DAOs can be used for digital identity management, offering a secure and decentralized alternative to traditional identity management systems.
- Content Creation and Distribution: DAOs can be
used for content creation and distribution, offering a decentralized and autonomous platform for content creators and distribution networks.
## The Importance of DAO Governance:
- Decentralized and Democratic: DAO governance refers to the decision-making process within a DAO, determined by the rules encoded in its smart contracts. Governance in a DAO is decentralized and democratic, with decision-making power distributed among all members who hold the organization's tokens.
- Flexible Approach: There are several variations in DAO governance, including direct voting, delegative voting, reputation-based voting, staking-based voting, liquid democracy, and multi-signature. This allows DAOs to have a flexible approach to governance, catering to the specific needs and goals of each organization.
## Why Choose DAOs for Your Organization:
- Increased Transparency and Accountability: DAOs operate on a blockchain, providing a high degree of transparency and accountability through an immutable ledger.
- Autonomy and Independence: DAOs are autonomous and operate according to rules encoded in smart contracts, allowing them to operate independently of any central authority.
- Decentralized and Democratic Decision-Making: DAOs offer a decentralized and democratic approach to decision-making, with power distributed among all members who hold the organization's tokens.
- Wide Range of Potential Use Cases: DAOs have a wide range of potential use cases, including DeFi, crowdfunding, community governance, supply chain management, digital identity, and content creation and distribution.
In conclusion, DAOs are a revolutionary new way to structure and govern organizations, offering increased transparency and accountability, autonomy and independence, and decentralized and democratic decision-making. With a wide range of potential use cases and a flexible approach to governance, DAOs have the potential to transform various industries and systems. Consider incorporating a DAO into your organization for a decentralized and autonomous future.
| sumana10 |
1,866,559 | پنجره دوجداره چیست؟ انواع پنجره و مشخصات آن ها | پنجره دوجداره چیست؟ پنجره دوجداره، یک نوع پنجره با بهرهوری بالا در مصرف انرژی است که از... | 0 | 2024-05-27T13:18:02 | https://dev.to/seo_work_98fab50d412cfcef/pnjrh-dwjdrh-chyst-nw-pnjrh-w-mshkhst-an-h-6ih | ## پنجره دوجداره چیست؟
پنجره دوجداره، یک نوع پنجره با بهرهوری بالا در مصرف انرژی است که از دو لایه شیشه تخت و یک لایه عایق تشکیل شده است. این شیشهها بر روی قابهایی از جنسهای مختلف نصب میشوند. فرآیند ساخت این پنجرهها شامل تخلیه هوای بین دو شیشه و تزریق گازهای بیاثر مانند آرگون، کریپتون یا زنون به جای آن است. این گازها به دلیل رسانش گرمایی بسیار پایین خود، انتقال حرارت را به حداقل میرسانند.
در مرحله بعد، فضای بین دو لایه شیشه بهطور کامل درزگیری میشود تا از نفوذ هوا و کاهش عملکرد عایق جلوگیری شود. به این ترتیب، پنجره دوجداره باعث کاهش قابل توجهی در انتقال حرارت میشود که نتیجه آن افزایش بهرهوری انرژی و کاهش هزینههای گرمایش و سرمایش در ساختمانها است.
نکته قابل توجه این است که اگرچه شیشههای دوجداره به طور موثر جلوی انتقال حرارت را میگیرند، بیشتر انتقال حرارت در واقع از طریق قابهای پنجره صورت میگیرد. بنابراین، انتخاب جنس و طراحی مناسب قاب پنجره نقش بسیار مهمی در عملکرد کلی پنجره دوجداره دارد. قابهای پنجره معمولاً از مواد مختلفی مانند PVC، چوب، آلومینیوم یا ترکیبی از این مواد ساخته میشوند که هر کدام دارای مزایا و معایب خاص خود هستند.
به عنوان مثال، قابهای PVC به دلیل عایقبندی حرارتی و صوتی خوب، مقرون به صرفه بودن و نگهداری آسان، بسیار محبوب هستند. در مقابل، قابهای آلومینیومی به دلیل استحکام بالا و سبک بودن مورد استفاده قرار میگیرند، اما رسانش حرارتی بالایی دارند و معمولاً نیاز به شکست حرارتی دارند تا عملکرد بهتری داشته باشند. قابهای چوبی نیز به دلیل ظاهر زیبا و عملکرد حرارتی خوب مورد توجه قرار میگیرند، اما نیاز به نگهداری منظم دارند.
با توجه به این موارد، پنجرههای دوجداره نه تنها باعث افزایش راحتی و آسایش در داخل ساختمان میشوند بلکه با کاهش مصرف انرژی، به حفظ محیط زیست نیز کمک میکنند. این ویژگیها باعث شده است که استفاده از پنجرههای دوجداره به عنوان یک استاندارد در ساختمانهای مدرن مطرح شود.
## اجزا تشکیل دهنده پنجره دوجداره
### شیشه دوجداره
بخش اصلی درب و پنجره دوجداره از دو لایه شیشه تشکیل شده است که این شیشهها با ضخامتهای مختلف و فاصلههای استاندارد ۶، ۸، ۱۰ و ۱۲ میلیمتر در بازار موجود هستند. ضخامتهای رایج شیشهها در این پنجرهها معمولاً ۴، ۵ و ۶ میلیمتر است. این شیشهها از جنس شیشه تخت ساده (فلوت ساده) هستند که به دلیل کیفیت و شفافیت بالا در صنعت ساختمانسازی مورد استفاده قرار میگیرند.
علاوه بر شیشههای ساده، در برخی موارد یکی از لایههای شیشهای میتواند شیشه رفلکس باشد که در رنگهای مختلفی از جمله طلایی، نقرهای و برنزی در دسترس است. شیشههای رفلکس علاوه بر ویژگیهای عایقبندی حرارتی و صوتی، قابلیت بازتاب نور و حرارت را دارند که به کنترل دمای داخلی و کاهش مصرف انرژی کمک میکنند.
برای افزایش کارایی و تنوع ظاهری، ممکن است از شیشههای لمینیت یا شیشههای سکوریت نیز در ترکیب پنجرههای دوجداره استفاده شود. شیشههای لمینیت، به دلیل داشتن یک لایه PVB بین دو لایه شیشه، مقاومت بیشتری در برابر ضربه و شکست دارند و در صورت شکستن، قطعات شیشه به هم میچسبند و خطرات ناشی از خرد شدن شیشه به حداقل میرسد. شیشههای سکوریت نیز به دلیل فرآیند حرارتی خاصی که روی آنها انجام میشود، مقاومت بیشتری در برابر ضربه و تغییرات دما دارند و در صورت شکست به قطعات کوچک و غیر برنده تبدیل میشوند.
استفاده از شیشههای مختلف با ویژگیهای خاص در پنجرههای دوجداره، امکان تطبیق با نیازها و شرایط مختلف محیطی و معماری را فراهم میکند. به عنوان مثال، در مناطق گرمسیر میتوان از شیشههای رفلکس با رنگ تیرهتر برای کاهش جذب حرارت و در مناطق سردسیر از شیشههای با عایقبندی بالاتر برای حفظ گرما استفاده کرد.
در نهایت، توجه به انتخاب صحیح نوع شیشه و فاصله بین لایهها در پنجرههای دوجداره، نقش بسیار مهمی در بهبود عملکرد حرارتی و صوتی این پنجرهها دارد و میتواند به بهبود کیفیت زندگی و کاهش هزینههای انرژی در بلندمدت منجر شود.
### پروفیل های قاب اصلی
قاب اصلی پنجره، بخشی حیاتی است که شیشه را در جای خود نگه میدارد و نوع بازشوهای پنجره را تعیین میکند. پروفایل قاب اصلی درب و پنجره دوجداره از جنسهای متنوعی ساخته میشود، شامل آلومینیوم، آهن، چوب، کامپوزیت، فایبرگلاس و UPVC. هر یک از این مواد دارای ویژگیها و مزایای خاص خود هستند، اما در بسیاری از موارد به دلیل رسانش گرمایی پایین UPVC، این ماده به عنوان گزینهای محبوب و رایج انتخاب میشود.
UPVC یا پلی وینیل کلراید غیر پلاستیکی، به دلیل خصوصیات عایقبندی حرارتی و صوتی عالی، مقاومت در برابر رطوبت و خوردگی، و نیاز به نگهداری کم، بسیار مورد توجه قرار گرفته است. این ماده، علاوه بر کمک به کاهش مصرف انرژی، به طول عمر بالای پنجرهها نیز کمک میکند. قابهای UPVC در برابر تغییرات دما، نور خورشید و شرایط جوی مقاوم هستند و به مرور زمان تغییر شکل نمیدهند.
آلومینیوم نیز یکی دیگر از مواد رایج در ساخت قاب پنجرهها است. این ماده به دلیل سبک بودن و استحکام بالا، در ساختمانهای مدرن و بلندمرتبه مورد استفاده قرار میگیرد. با این حال، رسانش گرمایی بالای آلومینیوم میتواند نقطه ضعفی باشد، به همین دلیل معمولاً قابهای آلومینیومی با یک لایه عایق حرارتی ترکیب میشوند تا عملکرد بهتری داشته باشند.
قابهای چوبی، به دلیل ظاهر زیبا و طبیعی، انتخاب محبوبی در معماریهای سنتی و کلاسیک هستند. چوب به طور طبیعی عایق حرارتی خوبی است، اما نیاز به نگهداری منظم دارد تا در برابر رطوبت و حشرات مقاوم بماند.
کامپوزیت و فایبرگلاس نیز گزینههای دیگری هستند که به دلیل مقاومت بالا در برابر تغییرات جوی و نیاز به نگهداری کم، در برخی موارد مورد استفاده قرار میگیرند. این مواد معمولاً ترکیبی از فیبرهای تقویتکننده و رزینهای پلیمری هستند که ویژگیهای مکانیکی و حرارتی مناسبی دارند.
در نهایت، انتخاب جنس مناسب برای قاب پنجره دوجداره باید بر اساس شرایط اقلیمی، نیازهای عایقبندی و طراحی معماری انجام شود. استفاده از مواد با کیفیت و ترکیب مناسب میتواند به بهبود عملکرد انرژی ساختمان، افزایش راحتی ساکنین و کاهش هزینههای نگهداری و انرژی منجر شود.
### پروفیل های قاب فرعی
قاب فرعی که به آن ساب فریم یا قاب انتظار نیز گفته میشود، یکی از اجزای مهم در نصب پنجرههای دوجداره است که پیش از نصب خود پنجره در محل قرار میگیرد. در تصویر بالا، ساب فریم با خط چین مشخص شده است. نقش اصلی این قاب، تحمل بارهای وارده از دیوار به پنجره است. بیشترین باری که به پنجره وارد میشود، معمولاً بار حاصل از وزن دیوار بالای پنجره است. این بار در طول زمان میتواند باعث ایجاد مشکلاتی مانند سختی در باز و بسته شدن پنجره شود.
جنس پروفیل مورد استفاده در این بخش باید دارای استحکام بالایی باشد تا بتواند وزن و فشارهای وارده را به خوبی تحمل کند. در این راستا، قوطیهای آهنی به دلیل دسترسی آسان و مقاومت بالای خود، گزینه مناسبی برای ساخت ساب فریمها هستند. این قوطیها پیش از نصب، به طور کامل با ضدزنگ پوشانده میشوند تا در برابر رطوبت و خوردگی مقاومت داشته باشند و طول عمر بیشتری داشته باشند.
ساب فریمها باید به گونهای طراحی و نصب شوند که بتوانند وزن دیوار و هرگونه بار اضافی را به طور مؤثر توزیع کنند، بدون اینکه به ساختار پنجره فشار زیادی وارد شود. این امر باعث میشود که پنجرهها در طول زمان عملکرد بهتری داشته باشند و مشکلاتی مانند تاب برداشتن، ترک خوردن یا سختی در عملکرد باز و بسته شدن به حداقل برسد.
علاوه بر استفاده از آهن برای ساخت ساب فریمها، در برخی پروژهها ممکن است از پروفیلهای فولادی یا آلومینیومی نیز استفاده شود. این مواد به دلیل خواص مکانیکی برجسته و مقاومت بالا، میتوانند گزینههای مناسبی باشند. انتخاب مواد مناسب برای ساب فریم باید با توجه به نیازهای خاص هر پروژه و شرایط محیطی انجام شود.
همچنین، نصب صحیح و دقیق ساب فریمها نیز اهمیت زیادی دارد. هرگونه نقص در نصب این بخش میتواند منجر به مشکلات جدی در عملکرد و پایداری پنجرهها شود. بنابراین، لازم است که این مرحله از نصب توسط کارشناسان و تکنسینهای ماهر انجام شود تا از کیفیت و دوام بالای پنجرههای دوجداره اطمینان حاصل شود.
در نهایت، استفاده از ساب فریمهای مقاوم و با کیفیت، علاوه بر افزایش عمر مفید پنجرهها، به بهبود کارایی انرژی و راحتی ساکنان ساختمان نیز کمک میکند. این امر نشاندهنده اهمیت توجه به جزئیات و استفاده از مواد با کیفیت در ساخت و نصب پنجرههای دوجداره است.
### یراق آلات
اجزای مختلفی مانند لولاها، دستگیرهها، بستها، بلبرینگها و سایر قطعات مشابه که به عنوان جزئیات پنجره محسوب میشوند، در دسته یراقآلات قرار میگیرند. این یراقآلات نقش حیاتی در عملکرد و دوام پنجرهها ایفا میکنند و به ایجاد امکان باز و بسته کردن راحت و ایمن پنجره کمک میکنند.
نوع و تعداد بازشوها تاثیر بسیار زیادی بر انتخاب و استفاده از یراقآلات دارد. به عنوان مثال، در پنجرههایی که دارای بازشوهای دو طرفه هستند، نیاز به لولاها و بستهای خاصی داریم که قابلیت تحمل وزن و استفاده مکرر را داشته باشند. همچنین، در پنجرههای کشویی، از بلبرینگها و ریلهای خاصی استفاده میشود که به راحتی حرکت و باز و بسته کردن پنجره کمک میکنند.
بیشتر بخوانید: [قیمت پنجره دوجداره ویستابست](https://www.upvctehranwin.com/%d9%82%db%8c%d9%85%d8%aa-%d9%be%d9%86%d8%ac%d8%b1%d9%87-%d8%af%d9%88%d8%ac%d8%af%d8%a7%d8%b1%d9%87-%d9%88%db%8c%d8%b3%d8%aa%d8%a7%d8%a8%d8%b3%d8%aa/)
همچنین، تغییر در طراحی بازشوها میتواند نیازمند تغییر در نوع یراقآلات باشد. برای مثال، اگر یک پنجره از حالت تکلنگه به حالت دولنگه تغییر کند، نیاز به دستگیرهها و لولاهای بیشتری خواهد بود. یا اگر یک پنجره از حالت ثابت به حالت بازشو تغییر کند، نیاز به نصب یراقآلات جدیدی مانند لولاها و دستگیرهها دارد.
جنس و کیفیت یراقآلات نیز اهمیت زیادی دارد. استفاده از مواد با کیفیت مانند استیل ضد زنگ، برنج یا آلومینیوم در ساخت یراقآلات میتواند به دوام و عمر مفید پنجرهها بیفزاید. همچنین، انتخاب یراقآلات با روکشهای مقاوم در برابر خوردگی و زنگزدگی، به ویژه در مناطق با رطوبت بالا، میتواند به افزایش کارایی و طول عمر آنها کمک کند.
در کنار این موارد، استفاده از یراقآلات مدرن و کارآمد میتواند به بهبود امنیت پنجرهها نیز کمک کند. به عنوان مثال، قفلهای چند نقطهای و دستگیرههای با قابلیت قفل شدن، میتوانند سطح امنیت ساختمان را به طور قابل توجهی افزایش دهند.
توجه به جزئیات در انتخاب و نصب یراقآلات مناسب، نه تنها به بهبود عملکرد و کارایی پنجرهها کمک میکند، بلکه به زیبایی و هماهنگی بیشتر با طراحی داخلی و خارجی ساختمان نیز منجر میشود. بنابراین، انتخاب یراقآلات باید با دقت و با در نظر گرفتن تمامی این عوامل انجام شود تا نتیجهای مطلوب و با کیفیت به دست آید.
## انواع پنجره دوجداره
### پنجره لولایی
چفت و بستها در پنجرههای دوجداره به گونهای طراحی شدهاند که امکان انتقال هوا را به حداقل میرسانند و از این رو، بهینهترین حالت از نظر جلوگیری از اتلاف انرژی را فراهم میکنند. این سیستمها با ایجاد یک مانع محکم در برابر ورود و خروج هوا، به حفظ دمای داخلی ساختمان کمک میکنند و نقش مهمی در بهبود بهرهوری انرژی ایفا میکنند.
در این نوع پنجرهها، از لولاهای خاصی برای انواع بازشوها استفاده میشود که شامل بازشوهای افقی، عمودی و مرکب است. این لولاها با طراحی دقیق و کیفیت بالا، نه تنها عملکردی روان و کارآمد را فراهم میکنند، بلکه به بهبود عایقبندی حرارتی و صوتی پنجرهها نیز کمک میکنند.
اکثر پنجرههای دوجداره موجود در بازار با استفاده از این مدل چفت و بستها ساخته میشوند، زیرا این روش نه تنها کارایی بالایی دارد، بلکه به دلیل سادگی و قابلیت اطمینان، مورد پسند بسیاری از سازندگان و مصرفکنندگان است. این پنجرهها به گونهای طراحی شدهاند که بتوانند در برابر شرایط مختلف آب و هوایی مقاومت کنند و با کاهش نفوذ هوا و سر و صدا، محیطی آرام و راحت را برای ساکنان فراهم آورند.
از دیگر مزایای استفاده از این نوع لولاها و چفت و بستها، میتوان به افزایش امنیت پنجرهها اشاره کرد. طراحی محکم و مقاوم این اجزا، جلوی ورود غیرمجاز را میگیرد و به همین دلیل، پنجرههای دوجداره با این ویژگیها گزینهای ایدهآل برای مناطقی با نیاز به امنیت بالا هستند.
علاوه بر این، استفاده از مواد با کیفیت در ساخت این یراقآلات مانند استیل ضد زنگ یا آلومینیوم با روکشهای مقاوم، به افزایش طول عمر و دوام آنها کمک میکند. این مواد در برابر خوردگی، زنگزدگی و سایش مقاوم هستند و میتوانند در طول زمان بدون نیاز به تعمیر یا تعویض، عملکرد خوبی داشته باشند.
به طور کلی، سیستمهای چفت و بست در پنجرههای دوجداره نه تنها به بهبود عملکرد حرارتی و صوتی کمک میکنند، بلکه با افزایش امنیت و دوام، نقش مهمی در کیفیت کلی پنجرهها دارند. این ویژگیها، همراه با استفاده از لولاهای مناسب برای انواع بازشوها، باعث میشود که پنجرههای دوجداره انتخابی هوشمندانه و کارآمد برای ساختمانهای مدرن باشند.
### پنجره دوجداره کشویی
استفاده از پنجرههای دوجداره کشویی در پنجرههای تک جداره بسیار مرسوم است، اما در پنجرههای دوجداره به دلیل اتلاف انرژی بیشتر در مقایسه با مدلهای لولادار، کمتر مورد استفاده قرار میگیرد. با این حال، این نوع پنجرهها همچنان سهم کوچکی از بازار را به خود اختصاص دادهاند.
بیشتر بخوانید: [قیمت پنجره دوجداره وین تک](https://www.upvctehranwin.com/%d9%82%db%8c%d9%85%d8%aa-%d9%be%d9%86%d8%ac%d8%b1%d9%87-%d8%af%d9%88%d8%ac%d8%af%d8%a7%d8%b1%d9%87-%d9%88%db%8c%d9%86%d8%aa%da%a9/)
پنجرههای کشویی به دلیل طراحی ساده و عملکرد آسان، محبوبیت زیادی در کاربردهای مختلف دارند. اما یکی از معایب اصلی این نوع پنجرهها در سیستمهای دوجداره، عایقبندی حرارتی ضعیفتر نسبت به پنجرههای لولادار است. در پنجرههای کشویی، اتصالات و نقاط تماس بین قسمتهای متحرک و ثابت، معمولاً نتوانند به خوبی از نفوذ هوا و انتقال حرارت جلوگیری کنند. این مسئله باعث افزایش اتلاف انرژی میشود و کارایی حرارتی پنجرهها را کاهش میدهد.
با این حال، پنجرههای دوجداره کشویی دارای مزایایی نیز هستند که میتوانند در برخی موارد، انتخاب مناسبی باشند. این پنجرهها به دلیل ساختار کشویی خود، فضای کمتری را برای باز و بسته شدن اشغال میکنند و برای فضاهای کوچک یا مناطقی که نیاز به تهویه سریع و آسان دارند، گزینهای مناسب هستند. همچنین، پنجرههای کشویی به راحتی تمیز میشوند و به نگهداری کمتری نیاز دارند.
برای بهبود عملکرد حرارتی پنجرههای کشویی دوجداره، میتوان از مواد و تکنولوژیهای پیشرفتهتری استفاده کرد. به عنوان مثال، استفاده از پروفیلهای چند محفظهای و نوارهای درزبندی با کیفیت بالا میتواند به کاهش نفوذ هوا و افزایش عایقبندی حرارتی کمک کند. همچنین، استفاده از شیشههای کمگسیل (Low-E) و گازهای عایق مانند آرگون بین لایههای شیشه میتواند کارایی حرارتی این پنجرهها را بهبود بخشد.
در نهایت، انتخاب بین پنجرههای کشویی و لولادار باید بر اساس نیازها و شرایط خاص هر پروژه انجام شود. اگرچه پنجرههای دوجداره کشویی به دلیل اتلاف انرژی بیشتر کمتر مورد استفاده قرار میگیرند، اما با در نظر گرفتن مزایا و معایب آنها، میتوان در برخی موارد به عنوان یک گزینه مناسب و کاربردی از آنها استفاده کرد. توجه به جزئیات نصب و استفاده از مواد با کیفیت میتواند به بهبود عملکرد و افزایش کارایی این نوع پنجرهها کمک کند.
### پنجره ارسی
پنجره ارسی یکی از کمکاربردترین انواع پنجرهها به شمار میآید، چه به صورت تکجداره و چه دوجداره. اگرچه این نوع پنجره در برخی کشورها محبوبیت بیشتری دارد و به عنوان یک عنصر معماری سنتی و زیبا مورد توجه قرار میگیرد، اما در کشور ما انتخاب آن از اولویت بسیار کمی برخوردار است.
پنجرههای ارسی با طراحی منحصر به فرد خود، اغلب در معماریهای سنتی و کلاسیک دیده میشوند و به دلیل ظاهر زیبایشان، میتوانند جلوهای خاص به ساختمان ببخشند. این پنجرهها با الگوهای هندسی و شیشههای رنگارنگ، نه تنها از نظر زیباییشناسی جذاب هستند، بلکه میتوانند نور را به شکلی دلنشین وارد فضا کنند. با این حال، استفاده از این نوع پنجرهها به دلایل مختلفی محدود شده است.
یکی از دلایل اصلی کمکاربرد بودن پنجرههای ارسی، کارایی پایین آنها در عایقبندی حرارتی و صوتی است. این پنجرهها به طور کلی نمیتوانند به خوبی پنجرههای مدرن دوجداره در حفظ انرژی و جلوگیری از نفوذ صدا عمل کنند. این موضوع به ویژه در مناطقی که نیاز به بهرهوری انرژی بالا و کاهش صداهای مزاحم است، اهمیت زیادی دارد.
علاوه بر این، ساخت و نصب پنجرههای ارسی به دلیل پیچیدگی طراحی و نیاز به مهارتهای خاص، هزینهبر است. این مسئله میتواند مانعی برای انتخاب این نوع پنجره در پروژههای ساختمانی با بودجه محدود باشد. همچنین، نگهداری و تعمیرات این پنجرهها به دلیل استفاده از مواد خاص و طراحی منحصر به فرد، ممکن است دشوارتر و پرهزینهتر از پنجرههای مدرن باشد.
در برخی کشورها، پنجرههای ارسی به عنوان یک عنصر فرهنگی و تاریخی حفظ شده و حتی در ساختمانهای جدید نیز به کار میروند تا هویت محلی و سنتی را به نمایش بگذارند. اما در کشور ما، اولویت استفاده از پنجرههای مدرن با کارایی بالا و هزینه نگهداری کمتر است.
با وجود این محدودیتها، پنجرههای ارسی همچنان میتوانند در پروژههای خاصی که نیاز به جلوههای زیباییشناسی سنتی و تاریخی دارند، مورد استفاده قرار گیرند. انتخاب این نوع پنجره باید با توجه به نیازها و شرایط خاص هر پروژه انجام شود، و مزایا و معایب آن به دقت مورد بررسی قرار گیرد.
## قیمت پنجره دوجداره
قیمتگذاری و استعلام[ قیمت پنجره دوجداره](https://www.upvctehranwin.com/%d9%82%db%8c%d9%85%d8%aa-%d9%be%d9%86%d8%ac%d8%b1%d9%87-%d8%af%d9%88%d8%ac%d8%af%d8%a7%d8%b1%d9%87-%d8%af%d8%b1-%d8%aa%d9%87%d8%b1%d8%a7%d9%86/) همواره با چالشها و پیچیدگیهای خاصی همراه بوده است. برخلاف سایر کارهای ساختمانی مانند نقاشی یا ساخت کابینت که معمولاً میتوان برای آنها قیمت متری تعیین کرد، قیمتگذاری پنجرههای دوجداره به دلیل تعدد عوامل تاثیرگذار، پیچیدگی بیشتری دارد و نمیتوان برای آن قیمت ثابت و مشخصی ارائه داد.
برای توضیح سادهتر، باید گفت که قیمت در و پنجرههای دوجداره به مجموعهای از عوامل مختلف بستگی دارد. از جمله این عوامل میتوان به متراژ پروفیلهای مصرفی، متراژ شیشه، نوع و تعداد بازشوها، جنس پروفیلها، تعداد جدارهها و حتی نوع یراقآلات اشاره کرد. هر یک از این عوامل میتواند تأثیر قابل توجهی بر قیمت نهایی داشته باشد.
به عنوان مثال، پروفیلهای مورد استفاده در پنجرههای دوجداره میتوانند از مواد مختلفی مانند UPVC، آلومینیوم یا چوب ساخته شوند که هر یک دارای قیمت و ویژگیهای خاص خود هستند. UPVC به دلیل ویژگیهای عایقبندی حرارتی و صوتی عالی و قیمت نسبتاً مقرون به صرفه، معمولاً پرطرفدارترین گزینه است. در مقابل، پروفیلهای آلومینیومی به دلیل استحکام و دوام بالا، ولی با هزینهای بیشتر، انتخاب میشوند. پروفیلهای چوبی نیز به دلیل زیبایی طبیعی و ویژگیهای عایقبندی خوب، ولی با نیاز به نگهداری بیشتر، مورد استفاده قرار میگیرند.
شیشههای مورد استفاده در پنجرههای دوجداره نیز متغیر هستند. شیشههای دوجداره معمولی، شیشههای کمگسیل (Low-E)، شیشههای لمینیت یا شیشههای سکوریت، هر کدام ویژگیها و قیمتهای متفاوتی دارند که میتواند بر هزینه نهایی تأثیر بگذارد.
نوع و تعداد بازشوها نیز یکی دیگر از عوامل مهم در تعیین قیمت است. پنجرههایی با بازشوهای پیچیدهتر مانند بازشوهای دو طرفه یا کشویی نیاز به یراقآلات خاص و پیچیدهتری دارند که میتواند قیمت را افزایش دهد. همچنین، تعداد جدارهها (تکجداره، دوجداره یا سهجداره) نیز تأثیر مستقیمی بر هزینه نهایی دارد.
همچنین، نصب و حمل و نقل پنجرهها نیز میتواند بر هزینهها افزوده شود. هزینههای نصب بسته به پیچیدگی کار و موقعیت جغرافیایی متفاوت است و باید در محاسبه نهایی قیمت در نظر گرفته شود.
در نهایت، به دلیل این تنوع و تعدد عوامل، قیمتگذاری دقیق و منصفانه پنجرههای دوجداره نیازمند مشاوره و محاسبه دقیق توسط کارشناسان متخصص است. به همین دلیل است که نمیتوان برای این نوع پنجرهها قیمت ثابت و مشخصی تعیین کرد و هر پروژه باید به صورت جداگانه ارزیابی و قیمتگذاری شود. | seo_work_98fab50d412cfcef | |
1,866,558 | Understanding MongoDB Atlas | Introduction: In the realm of modern application development, where agility, scalability, and... | 0 | 2024-05-27T13:15:46 | https://dev.to/vidyarathna/understanding-mongodb-atlas-4c44 | mongodb, mongodbatlas, databasemanagement, cloud |

**Introduction:**
In the realm of modern application development, where agility, scalability, and flexibility are paramount, MongoDB Atlas stands out as a premier choice for managing data. Offering a fully managed cloud database service, MongoDB Atlas empowers developers to focus on building innovative applications without worrying about the complexities of database administration.
**What is MongoDB Atlas?**
MongoDB Atlas is a fully managed cloud database service provided by MongoDB, Inc. It allows developers to deploy, manage, and scale MongoDB databases effortlessly on popular cloud platforms such as AWS, Azure, and Google Cloud Platform (GCP). With Atlas, developers can offload routine database tasks such as provisioning, configuration, and backups, enabling them to concentrate on delivering value to their applications.
**Key Features of MongoDB Atlas:**
1. **Automated Scaling:** MongoDB Atlas provides automated scaling capabilities, allowing databases to seamlessly adapt to changing workload demands without manual intervention. This ensures optimal performance and resource utilization, even during peak traffic periods.
2. **High Availability:** With built-in redundancy and failover mechanisms, MongoDB Atlas ensures high availability and data durability. Multiple replicas of data are maintained across distinct availability zones, minimizing the risk of data loss or downtime.
3. **Security Controls:** Security is paramount in MongoDB Atlas. It offers robust authentication, encryption, and access control mechanisms to safeguard sensitive data. Additionally, features such as network isolation, IP whitelisting, and VPC peering enhance security posture and compliance with industry standards.
4. **Backup and Restore:** Atlas simplifies the backup and restore process with automated snapshots and point-in-time recovery capabilities. Developers can schedule backups, retain snapshots for archival purposes, and restore data with ease, minimizing the impact of accidental data loss or corruption.
5. **Monitoring and Alerts:** MongoDB Atlas provides comprehensive monitoring tools and customizable alerts to track database performance, resource utilization, and operational metrics in real-time. This proactive monitoring enables timely intervention and optimization to ensure optimal application performance.
**Getting Started with MongoDB Atlas:**
Getting started with MongoDB Atlas is straightforward:
1. **Sign Up:** Create a MongoDB Atlas account or log in with an existing MongoDB account.
2. **Deploy a Cluster:** Choose your preferred cloud provider, region, and cluster configuration. MongoDB Atlas offers various cluster types, including replica sets and sharded clusters, to accommodate diverse workload requirements.
3. **Configure Security:** Implement security best practices by configuring authentication, encryption, and access controls to protect your data.
4. **Connect Your Application:** Obtain connection strings and integrate MongoDB Atlas with your application using official drivers and libraries available for popular programming languages and frameworks.
5. **Monitor and Optimize:** Leverage MongoDB Atlas monitoring tools to gain insights into database performance and optimize resource utilization for better scalability and cost-efficiency.
**Conclusion:**
MongoDB Atlas revolutionizes database management by offering a fully managed cloud database service with unparalleled scalability, availability, and security features. Whether you're a startup launching your first application or an enterprise managing mission-critical workloads, MongoDB Atlas provides the tools and capabilities to accelerate innovation and drive business success in the digital era.
| vidyarathna |
1,866,557 | Automatic Pouch Packing Machine | This machine is designed to pack turmeric and chilli powder efficiently and correctly. Turmeric and... | 0 | 2024-05-27T13:15:39 | https://dev.to/creature_industry/automatic-pouch-packing-machine-2fje | packaging, bakery | This machine is designed to pack turmeric and chilli powder efficiently and correctly. Turmeric and chilli are known for their bright colour, distinctive flavour, and multiple health benefits, chilli is a famous Indian spice used in cooking dishes, herbs, and beauty products. Manual packaging of chilli powder can be time-consuming and labour costs.
The [automatic Pouch Packing Machine in India](https://creatureindustry.com/product/automatic-pouch-packing-machine-in-india/) automates the packaging process to confirm the correct filling, sealing and labelling of chilli and turmeric powder in pouch or packet packaging.
**Features: Automatic Pouch Packing Machine in India**
**Weighing Mechanism:** The machine comes with a weighing system that measures the preferred amount of chilli powder for each pouch with precision and accuracy. Weigh scales or detectors detect the weight of the powder, ensuring consistency across pouches.
Filling Mechanism: This machine depending on the specific design and setup, the machine can use different filling tools such as Bama fill, Volume filler, Piston filler, etc to deliver the chilli powder to the packaging pouches.
**Packaging Formats:** Chilli packing machines are very adjustable and can be adjusted into a variety of packaging formats including sachets and pouches. Fast changeover abilities allow this machine to make seamless changes to additional packaging formats to meet various market demands.
**Control System:** Most automatic pouch packing machines in India already have the best managing method established in them, which automatically watches the sealing, labelling and fitting of the packaging and ensures that it works correctly.
**
** [Automatic packing machine in India](https://creatureindustry.com/product/automatic-packing-machine-in-india/)
**Conclusion**
An automatic pouch packing machine in India is the best option for enterprises that want to start their brand of masala, chips, and namkeen packaging. With this machine you can pack any kind of interest like ground masala, standing masala, chips, dry fruits, namkeen and many more effects. This whole machine is made of stainless steel, which every business has to follow as per the food guidelines of Fassai.
Read more: [Automatic pouch packing machine in India](https://creatureindustry.com/product/automatic-pouch-packing-machine-in-india/) at Creatureindustry.com
| creature_industry |
1,866,555 | Stay Cool and Protected: The Importance of a Sun Shade in the Car | When the summer sun is blazing, stepping into a sweltering car can be downright unbearable. That’s... | 0 | 2024-05-27T13:10:57 | https://dev.to/jeremy_g_fc9582b7fb4af8d9/stay-cool-and-protected-the-importance-of-a-sun-shade-in-the-car-1pbk | cars, windshield | When the summer sun is blazing, stepping into a sweltering car can be downright unbearable. That’s where a sun shade comes to the rescue, offering a simple yet effective solution to keep your vehicle cool and comfortable. Here’s why every car owner should invest in a sun shade:
1. **Temperature Control**
A sun shade significantly reduces the interior temperature of your car by blocking out the sun’s intense rays. This means no more burning hot seats or steering wheels, making your driving experience much more pleasant, especially on those scorching summer days.
2. **Protects Your Interior**
Direct sunlight can cause extensive damage to your car’s interior. Over time, UV rays can fade upholstery, crack dashboards, and warp other interior surfaces. A sun shade acts as a protective barrier, shielding your car’s interior from harmful UV radiation and helping to preserve its appearance and value.
3. **Enhances Comfort**
Using a sun shade keeps the car’s interior cooler, reducing the need to blast the air conditioner when you start driving. This not only enhances comfort but also saves fuel, as your air conditioning system won’t have to work as hard to cool down the car.
4. **Easy to Use and Store**
Modern sun shades are designed for convenience. They are lightweight, foldable, and easy to store when not in use. Whether you opt for a foldable sun shade or a retractable one, they are quick to install and remove, making them a hassle-free addition to your car accessories.
In **conclusion**, a [sun shade in the car](https://econour.com/collections/windshield-sunshade) is a small investment that offers significant benefits. It keeps your car cool, protects your interior, and enhances your overall driving experience. Don’t let the sun ruin your ride – get a sun shade today and enjoy the comfort and protection it provides!
[windshield sun shade
](https://econour.com/collections/windshield-sunshade)
[car sun shade
](https://econour.com/collections/windshield-sunshade)
[sun shade for car](https://econour.com/collections/windshield-sunshade) | jeremy_g_fc9582b7fb4af8d9 |
1,866,554 | 5 Upcoming Banking & Finance Trade Shows in UAE | Discover 5 most awaited trade shows of the banking and finance industry that are scheduled during the... | 0 | 2024-05-27T13:10:09 | https://dev.to/expostandzoness/5-upcoming-banking-finance-trade-shows-in-uae-31nn |
Discover 5 most awaited trade shows of the banking and finance industry that are scheduled during the upcoming days in the UAE.
https://www.expostandzone.com/blog/top-5-banking-and-finance-trade-shows-in-uae | expostandzoness | |
1,866,553 | Common Mistakes To Avoid During Android App Development | Why android apps are essential For business? Android is always the go-to choice for developing... | 0 | 2024-05-27T13:10:08 | https://dev.to/bellabardot/common-mistakes-to-avoid-during-android-app-development-1707 | androidappdevelopment, androidapp | **Why android apps are essential For business?**
Android is always the go-to choice for developing mobile applications owing to numerous benefits such as a vast audience, open-source platform, and flexible and easy installation ability.
The extensive usage of Android applications has always created a demand for Android apps and stays at the top for developing mobile apps. A broad range of entrepreneurs and developers prefer Android apps accounting for their usability and reliability.
Android potentially has the largest market share which intrigues developers. Owing to the low development cost compared with iOS development, businesses are proceeding with investing in Android app development.
It is vital to look into certain aspects before investing in Android apps and leverage the best strategies to integrate into developing Android applications. In this blog, we will look at the common mistakes to avoid while developing Android apps.
**Top 5 Mistakes To Avoid in Android App Development**
**Not Determining User Need**
It is vital to conduct a detailed analysis to determine the user's needs to make the investments favorable to the businesses. Evaluating the market trends and understanding the preferences of the target audience drives success for Android applications. Developers to stay proactive in addressing the user intent and validating the features that should be included within the application.
Identifying the user needs paves the way for creating a perfect strategy and roadmap for creating Android applications. It helps developers to stay aligned with the business goal, scope, and objective, and neglecting this would create an unfitting application which creates a negative impact for businesses.
**Overlooking Device Fragmentation**
Mobile device fragmentation refers to diverse versions of the operating system, screen size, and hardware specifications. Overlooking this during Android app creation might result in slow response times and device updates, performance bottlenecks, and a poor user experience.
Thus it is essential to understand the device fragmentation and employ methods to alleviate this issue. It is important to perform rigorous app testing on various devices to examine app performance and efficiency.
**Ignoring Security Practices**
Not paying enough attention to the security practices and protocols creates a big problem in the performance of the application. Failing to implement the best security measures makes the app vulnerable to data breaches, fraudulent activities, and other hacking attempts.
Hence, developers should implement top encryption techniques and authentication mechanisms to safeguard the application. Conducting regular security audits helps businesses to avoid and be aware of security risks.
**Neglecting User Experience**
Creating Android apps with poor UI/UX designs will affect the functionality making app navigation difficult for the users. Prioritizing user experience creates a positive experience and impression for the end users.
Hence, developers should focus on creating more intuitive, smooth, and user-centric UI designs. This serves as the key to driving user retention and more user engagement within the Android application.
**Ignoring Feedback**
Neglecting user reviews and feedbacks bring a drawback to developing pitch-perfect Android applications. Businesses take advantage of user feedback to craft Android applications more precisely by aligning them with the features and functionalities defined by the client.
**Closing Notes**
Witnessing success in Android app development requires careful planning and a user-centered approach. Avoiding the above-listed mistakes in 2024 will help businesses stand out from the crowd and stay competitive in the mobile app market. This helps developers create Android applications that meet and exceed the expectations of the client in the dynamic industry. Looking to dive into the world of apps? Reach out to the best [Android app development company](https://maticz.com/android-app-development) that crafts comprehensive Android apps that drive user engagement. Plunge into the mobile app realm by launching Android apps and building a strong presence in the market.
| bellabardot |
1,866,552 | 🚀 Introduction to React.js: Building Dynamic User Interfaces 🚀 | Hey everyone! Today, I want to talk about React.js, an amazing JavaScript library that's transforming... | 0 | 2024-05-27T13:07:09 | https://dev.to/erasmuskotoka/introduction-to-reactjs-building-dynamic-user-interfaces-43i3 |
Hey everyone! Today, I want to talk about React.js, an amazing JavaScript library that's transforming the way we create user interfaces.
🌟 Why React.js?
React.js makes it incredibly easy to build dynamic and interactive UIs. By breaking down complex interfaces into smaller, reusable components, React helps you manage your app's state more efficiently.
💡 Key Features are :
- Component-Based Architecture:** Build encapsulated components that manage their own state, then compose them to make complex UIs.
- Virtual DOM: React's virtual DOM ensures your app updates and renders efficiently.
- Declarative Syntax: Simplifies coding, making your applications more predictable and easier to debug.
- Unidirectional Data Flow: Keeps your code clean and manageable.
👨💻 Getting Started:
1. Install Node.js and npm.
2. Create a new React project with `create-react-app`.
3. Start building and managing components to craft dynamic user interfaces.
React.js is perfect for both beginners and seasoned developers looking to enhance their web development skills. Let’s get started with React and build something amazing together! 💻✨
#CodeWith #KOToka
#KEEPCOding
| erasmuskotoka | |
1,866,551 | Pcr Euro 2025 Paris France |exhibition booth| Expostandzone | https://www.expostandzone.com/trade-shows/euro-pcr Europcr online is World-Leading Course in... | 0 | 2024-05-27T13:06:56 | https://dev.to/expostandzoness/pcr-euro-2025-paris-france-exhibition-booth-expostandzone-7i0 | https://www.expostandzone.com/trade-shows/euro-pcr
Europcr online is World-Leading Course in interventional cardiovascular medicine. It is going to be held from 20-23 May 2025 in Le Palais des Congrès de Paris, Paris, France.
| expostandzoness | |
1,866,549 | Vue Accessibility Blueprint: 8 Steps | Writing accessible components in Vue is crucial as more developers recognise the importance of making... | 0 | 2024-05-27T13:06:43 | https://dev.to/alexanderop/vue-accessibility-blueprint-8-steps-gim | a11y, vue |
Writing accessible components in Vue is crucial as more developers recognise the importance of making websites usable for everyone, including those with disabilities. Here are eight straightforward steps to help you build better, more accessible Vue components.
## Introduction
Many developers find it challenging to create accessible Vue components, which is becoming increasingly important in web development. To assist you, here are eight steps to improve accessibility in your Vue projects.
## The Eight Steps
### 1. Learn the Basics
Understand the essentials of HTML and how it can enhance accessibility. Knowing how to structure your site can make a big difference for users with disabilities. [Learn more about Vue.js and accessibility](https://vuejs.org/guide/best-practices/accessibility).
### 2. Use a Helpful Tool for Checking Code
Adopt eslint-plugin-vue-a11y when coding. This tool helps you identify and resolve accessibility issues, ensuring your website is accessible to more users. [See how eslint-plugin-vue-a11y works](https://github.com/vue-a11y/eslint-plugin-vuejs-accessibility).
### 3. Test with Vue Testing Library
Confirm that your components function correctly for all users by testing them with the Vue Testing Library. This approach emphasizes accessibility and user-friendly design. [Explore the Vue Testing Library](https://testing-library.com/docs/vue-testing-library/intro/).
### 4. Try Using a Screen Reader
Regularly use a screen reader to experience how your site is navigated audibly. This insight is invaluable for understanding the challenges faced by visually impaired users.
### 5. Check Your Site with Lighthouse
Use Lighthouse to audit your website's accessibility. This tool provides feedback on how well your site performs across various metrics, including accessibility. [Get started with Lighthouse](https://developers.google.com/web/tools/lighthouse).
### 6. Work with an Expert
If possible, collaborate with accessibility experts. Their specialized knowledge can provide deeper insights and practical tips beyond what automated tools can offer.
### 7. Make Accessibility Part of Your Plans
Integrate accessibility into your project from the beginning. Define accessibility goals clearly in your project tickets to ensure they are prioritized throughout development.
### 8. Automate Tests with Cypress
Automate your accessibility testing with Cypress. This helps you save time and detect issues early in the development process. [Learn how to integrate Cypress for accessibility testing](https://github.com/component-driven/cypress-axe).
By following these steps, you can make your Vue components more accessible, enhancing the user experience for everyone and extending your website's reach.
| alexanderop |
1,866,550 | The Ultimate Guide to Knee Replacement Surgery | Knee replacement surgery, also known as knee arthroplasty, is a common and highly effective procedure... | 0 | 2024-05-27T13:05:03 | https://dev.to/mohammad_ml_910d584a66ceb/the-ultimate-guide-to-knee-replacement-surgery-141j | Knee replacement surgery, also known as knee arthroplasty, is a common and highly effective procedure for individuals suffering from severe knee pain and dysfunction. This surgery can significantly improve the quality of life for patients with chronic knee issues, providing pain relief and restoring mobility. In this comprehensive guide, we'll delve into everything you need to know about knee replacement surgery, from understanding the procedure to post-operative care and recovery.
## Understanding Knee Replacement Surgery
[Knee replacement surgery](https://www.doctour.one/services/knee-replacement) involves replacing a damaged or diseased knee joint with an artificial implant. This procedure is typically recommended for patients with severe osteoarthritis, rheumatoid arthritis, or traumatic injury to the knee.
## Types of Knee Replacement
1. Total Knee Replacement (TKR): The entire knee joint is replaced with a prosthetic.
2. Partial Knee Replacement (PKR): Only the damaged part of the knee is replaced, preserving healthy bone and tissue.
## Indications for Knee Replacement
Knee replacement surgery is usually considered when:
• Severe knee pain or stiffness limits daily activities.
• Pain persists despite medication and other treatments.
• Knee deformity, such as bowing in or out.
• Chronic inflammation and swelling that do not improve with rest or medication.
## Preparing for Surgery
Preparation is key to a successful knee replacement surgery. Here are some steps to take before the procedure:
1. Medical Evaluation: Comprehensive evaluation to ensure you are fit for surgery.
2. Physical Therapy: Pre-surgery exercises to strengthen muscles around the knee.
3. Home Preparation: Making your home ready for post-operative recovery, such as installing handrails or arranging for assistance.
## The Surgical Procedure
Knee replacement surgery typically lasts about 1-2 hours. Here's a brief overview of what happens:
1. Anesthesia: General or spinal anesthesia is administered.
2. Incision: A cut is made over the knee to expose the joint.
3. Removal of Damaged Tissue: Damaged cartilage and bone are removed.
4. Implant Placement: The artificial joint components are positioned.
5. Closure: The incision is closed with sutures or staples, and a bandage is applied.
## Recovery and Rehabilitation
Recovery from knee replacement surgery involves several stages:
1. Hospital Stay: Usually 1-3 days, depending on the individual case.
2. Pain Management: Medications are prescribed to manage pain.
3. Physical Therapy: A critical component of recovery, focusing on restoring movement and strength.
4. Home Exercises: Continuation of exercises to aid in recovery.
## Benefits and Risks
Benefits
• Significant pain relief
• Improved mobility and quality of life
• High success rate and longevity of implants
Risks
• Infection
• Blood clots
• Implant issues, such as loosening or wear
## Long-Term Outcomes
Most patients experience excellent long-term outcomes after knee replacement surgery. It's crucial to maintain a healthy lifestyle, follow your surgeon's advice, and continue with physical therapy exercises to ensure the best results.
## Knee Replacement Surgery in Iran: An Emerging Destination
Medical tourism is a growing trend, with patients seeking affordable and high-quality healthcare abroad. Iran has emerged as a leading destination for medical procedures, including knee replacement surgery, thanks to its advanced medical facilities and highly skilled surgeons.
## Why Choose Iran for Knee Replacement?
1. Highly Qualified Surgeons: Iranian surgeons are well-trained and experienced in performing knee replacements.
2. State-of-the-Art Facilities: Hospitals in Iran are equipped with the latest medical technology.
3. Cost-Effective: The cost of knee replacement surgery in Iran is significantly lower compared to Western countries, without compromising on quality.
4. Cultural and Natural Attractions: Patients can combine their medical journey with exploring Iran's rich cultural heritage and natural beauty.
## Doctour: Your Trusted Partner for Knee Replacement in Iran
At Doctour, we specialize in providing world-class knee replacement surgery in Iran. We understand the importance of a seamless and stress-free medical experience, which is why we offer comprehensive packages that include:
• Consultation and Medical Evaluation: Personalized consultations with top surgeons to assess your needs.
• Travel and Accommodation: Assistance with travel arrangements and comfortable accommodations.
• Surgery and Post-Operative Care: Expert surgical care and dedicated post-operative support.
• Tourism Services: Guided tours to explore Iran's fascinating sites while you recover.
Our mission is to ensure you receive the best possible care and enjoy a smooth recovery journey. With [Doctour](https://www.doctour.one), you can be confident that your health is in good hands.
## Conclusion
Knee replacement surgery can be a life-changing procedure, offering relief from chronic pain and improved mobility. If you're considering this surgery, Iran is an excellent destination, combining high-quality medical care with affordability. Trust Doctour to provide you with a comprehensive and supportive experience, making your health and recovery our top priority.
For more information or to start planning your knee replacement journey with Doctour, visit our website or contact us today.
| mohammad_ml_910d584a66ceb | |
1,866,425 | PHP interfaces how to use them and Laravel interface binding simply explained | What is a PHP Interface? An interface in PHP is a blueprint for classes. It defines a... | 0 | 2024-05-27T13:03:08 | https://dev.to/vimuth7/php-interfaces-how-to-use-them-and-laravel-interface-binding-simply-explained-416p | ##What is a PHP Interface?
An interface in PHP is a blueprint for classes. It defines a contract that any implementing class must adhere to, specifying methods that must be implemented but not providing the method bodies. Interfaces ensure a consistent structure across different classes and enable polymorphism by allowing multiple classes to be treated through a common interface. You can read more about it [here](https://dev.to/vimuth7/php-interfaces-and-their-usage-with-dependency-injection-18cl)
##Use without binding
Let's first talk about how to use interfaces without binding in laravel.
**1.Define an Interface:**
Create an interface in the App\Contracts directory.
```
// app/Contracts/PaymentGatewayInterface.php
namespace App\Contracts;
interface PaymentGatewayInterface {
public function charge($amount);
}
```
**2.Implement the Interface with Additional Methods:**
```
// app/Services/StripePaymentGateway.php
namespace App\Services;
use App\Contracts\PaymentGatewayInterface;
class StripePaymentGateway implements PaymentGatewayInterface {
public function charge($amount) {
// Logic to charge using Stripe
return "Charged {$amount} using Stripe";
}
}
```
**3.Inject the Implementation Manually:**
When you instantiate the controller or the class that requires the interface, manually provide the implementation.
```
// app/Http/Controllers/PaymentController.php
namespace App\Http\Controllers;
use App\Contracts\PaymentGatewayInterface;
use App\Services\StripePaymentGateway;
class PaymentController extends Controller {
protected $paymentGateway;
public function __construct(PaymentGatewayInterface $paymentGateway) {
$this->paymentGateway = $paymentGateway;
}
public function charge($amount) {
return $this->paymentGateway->charge($amount);
}
}
```
```
// routes/web.php
use App\Http\Controllers\PaymentController;
use App\Services\StripePaymentGateway;
Route::get('/charge/{amount}', function ($amount) {
$paymentGateway = new StripePaymentGateway();
$controller = new PaymentController($paymentGateway);
return $controller->charge($amount);
});
```
##Example with binding and benefits of the approach
Laravel's service container can automatically resolve dependencies for you, reducing boilerplate code. Check this example.
```
// app/Providers/AppServiceProvider.php
namespace App\Providers;
use Illuminate\Support\ServiceProvider;
use App\Contracts\PaymentGatewayInterface;
use App\Services\StripePaymentGateway;
class AppServiceProvider extends ServiceProvider {
public function register() {
$this->app->bind(PaymentGatewayInterface::class, StripePaymentGateway::class);
}
public function boot() {
//
}
}
```
```
// app/Http/Controllers/PaymentController.php
namespace App\Http\Controllers;
use App\Contracts\PaymentGatewayInterface;
use App\Services\StripePaymentGateway;
class PaymentController extends Controller {
protected $paymentGateway;
public function __construct(PaymentGatewayInterface $paymentGateway) {
$this->paymentGateway = $paymentGateway;
}
public function charge($amount) {
return $this->paymentGateway->charge($amount);
}
}
```
With this binding in place, you don't need to manually instantiate StripePaymentGateway. So this code is enough inside routes.
```
// routes/web.php
use App\Http\Controllers\PaymentController;
Route::get('/charge/{amount}', [PaymentController::class, 'charge']);
```
In this example we have used **service binding** in Laravel. Service binding is used to register a concrete implementation for a given interface or abstract class in Laravel's service container. This allows Laravel to automatically resolve dependencies and inject the appropriate implementations when needed.
| vimuth7 | |
1,866,508 | O que é strict mode no JavaScript? | E aí, gente bonita, beleza? Retomando os estudos em JS, hoje vou falar um pouco para vocês sobre o... | 0 | 2024-05-27T12:59:23 | https://dev.to/cristuker/o-que-e-strict-mode-no-javascript-16cb | javascript, webdev, beginners, braziliandevs | E aí, gente bonita, beleza? Retomando os estudos em JS, hoje vou falar um pouco para vocês sobre o strict mode. Então pega um cafezinho e vem comigo.
## Problemas da linguagem
Caso você seja novo na linguagem e não saiba, o JavaScript é uma linguagem muito poderosa e com ela você pode fazer muita coisa, mas quando eu digo muita coisa, é MUITA COISA mesmo. Coisas que não deveriam ser feitas. Costumo dizer que essa liberdade do JS é uma das melhores e piores coisas da linguagem.
Agora você me pergunta: **que coisas são essas?**
E aqui estou para te dizer alguns problemas da linguagem:
* Pode atribuir valores a variáveis não declaradas.
* Você pode usar o operador delete em variáveis e funções.
* Nomes de parâmetros duplicados são permitidos fora do _strict mode_.
Caso queira ver mais alguns problemas da linguagem, recomendo a leitura do repositório [What the f*ck JavaScript?](https://github.com/denysdovhan/wtfjs). Conhecer os problemas da linguagem é tão importante quanto os seus pontos fortes.

## Como eu resolvo isso?
Ok, realmente temos alguns problemas na linguagem, mas para evitar todos logo de cara você não precisa ler todo o repositório do [What the f*ck JavaScript?](https://github.com/denysdovhan/wtfjs) de uma vez só. Você pode usar o famoso 'use strict'; no topo dos seus arquivos. Assim, você vai ativar o modo estrito para todo o arquivo e todos esses problemas da linguagem vão aparecer como erros no seu console e você vai poder resolvê-los antes de enviar para o ar!
É importante lembrar que muitas bibliotecas já usam o strict mode por debaixo dos panos, assim como compiladores como Babel e TypeScript. Então você deve se preocupar mais com o uso do strict mode quando for trabalhar com JS puro.

## Conclusão
Dito tudo isso, hoje vimos que o nosso amado JS não é só feito de coisas boas, apesar de ainda serem muitas rsrs. Recomendo fortemente a leitura do repositório [What the f*ck JavaScript?](https://github.com/denysdovhan/wtfjs) e, caso queira saber o que mais o modo estrito do JavaScript resolve, eu deixei alguns links de referências.
## Referências
[W3S Schools](https://www.w3schools.com/js/js_strict.asp)
-------
Espero que tenha sido claro e tenha ajudado a entender um pouco mais sobre o assunto, fique a vontade para dúvidas e sugestões abaixo!
Se chegou até aqui, me segue la nas [redes vizinhas]
(https://cristiansilva.dev/).
<img src="https://media.giphy.com/media/xULW8v7LtZrgcaGvC0/giphy.gif" alt="thank you dog" /> | cristuker |
1,866,548 | The Trends, Size, and Opportunities in Vocational Training Market | In today's ever-evolving job market, the ability to translate knowledge into practical skills is... | 0 | 2024-05-27T12:59:19 | https://dev.to/namanrohilla/the-trends-size-and-opportunities-in-vocational-training-market-3840 | vocationaleducationmarket, vocationaltrainingmarket, marketresearch, marketanalysis | In today's ever-evolving job market, the ability to translate knowledge into practical skills is crucial. This is where vocational education (vocational ed) steps in, offering a valuable pathway for individuals seeking career-oriented training. As a market analyst, I've been closely following the vocational education market, and let me tell you, it's an exciting space to watch.
In this blog post, I'll put on my market analyst hat and delve into the world of vocational education, exploring its current state, prospects, and the factors driving its increasing demand. So, whether you're a student considering vocational training, a business leader, or simply curious about this growing market, buckle up and get ready to discover the power of skills.
## Vocational Education Market Demand
The **[global vocational education market size](url=https://www.kenresearch.com/vocational-education-market?utm_source=SEO&utm_medium=SEO&utm_campaign=Naman)** is currently valued at an impressive **USD 622.4 billion**. But the story gets even more interesting when we look at its projected growth. Experts predict the market will reach a staggering **USD 1,380.2 billion by 2030**, boasting a remarkable **CAGR (Compound Annual Growth Rate) of 9.8%**. These numbers showcase the rising demand for vocational education programs.
But what's fueling this growth? Let's explore some key factors:
## Why the Vocational Education Market is Gaining Traction?
Several forces are propelling the vocational education market demand forward:
**The Skills Gap:** Technological advancements are rapidly transforming the workforce, creating a growing demand for individuals with specialized skills. Vocational education programs equip students with the practical skills and industry knowledge needed to succeed in these new job roles.
**Shifting Job Market Landscape:** The traditional four-year university degree is only one of many paths to success. With rising tuition costs and student loan debt, many individuals are turning to vocational education as a faster and more cost-effective way to acquire in-demand skills.
**Focus on Workforce Development:** Governments and businesses worldwide are recognizing the importance of a skilled workforce. It leads to increased investments in vocational education programs, making them more accessible to individuals.
**Demand for Lifelong Learning:** The rapid pace of change in today's job market necessitates continuous learning. Vocational education programs offer flexible learning options for individuals seeking to upgrade their skills or acquire new ones throughout their careers.
## Market Trends
Looking ahead, the future of the market appears bright. Here are some trends that market analysts like myself are excited about:
**Increased Public-Private Partnerships:** Collaboration between governments, businesses, and vocational education institutions will likely be crucial for developing and delivering high-quality programs that meet industry needs.
**Focus on Micro-credentials and Stackable Certifications:** Shorter, focused training programs offering industry-recognized micro-credentials or stackable certifications might become increasingly popular, allowing individuals to tailor their learning journeys to specific career goals.
**Emphasis on Soft Skills:** While technical skills are essential, vocational education programs are likely to place greater focus on developing soft skills like critical thinking, communication, collaboration, and problem-solving. These skills are crucial for success in any job market.
**Technology-Driven Learning:** Technological advancements like virtual reality (VR) and augmented reality (AR) might be used to create more immersive and interactive learning experiences in vocational education programs.
## Market Segmentation
The **[vocational education market](url=https://www.kenresearch.com/industry-reports/india-vocational-training-market)** is more than just a one-size-fits-all solution. It offers a diverse range of programs catering to different skill sets and career aspirations. Here's a glimpse into the market's segmentation:
**Skilled Trades:** This segment focuses on training individuals for jobs in areas like carpentry, welding, plumbing, and electrical work. These skills are in high demand across various industries.
**Healthcare:** Vocational education programs can equip individuals with the necessary skills to become nurses, medical assistants, dental hygienists, and other vital healthcare professionals.
**Business and Administration:** Programs in this area can train individuals for careers in office administration, accounting, management, and customer service.
**Information Technology (IT):** The IT sector is constantly evolving, and vocational training programs offer individuals the opportunity to acquire skills in areas like cybersecurity, software development, and network administration.
**Hospitality and Tourism:** This segment encompasses training programs for careers in hotels, restaurants, travel agencies, and event planning.
## Challenges and Opportunities
Despite its promising future, the vocational education market faces some challenges:
**Perception Problem:** Vocational education has sometimes been viewed as a "lesser" option compared to traditional university education. This perception needs to change to recognize the value of skills training for career success.
**Keeping Up with Industry Demands:** The rapid pace of change in some industries requires vocational education programs to adapt quickly to ensure they are equipping students with the most relevant and up-to-date skills.
**Funding and Resources:** Ensuring high-quality vocational education programs requires adequate funding and resources. It includes investments in equipment, technology, and qualified instructors.
However, these challenges present exciting opportunities:
**Focus on Innovation:** New and innovative delivery methods, such as online learning and blended learning approaches, can make vocational education more accessible and flexible for learners.
**Promoting Collaboration:** Strengthening collaboration between vocational education institutions, businesses, and industry associations can ensure programs are aligned with current and future job market needs.
**Building a Culture of Lifelong Learning:** Encouraging a culture of lifelong learning is crucial in today's dynamic job market. Vocational education programs can be designed to cater to individuals at different stages of their careers, offering opportunities for continuous skill development.
## Conclusion
The **[vocational education market](url=https://www.kenresearch.com/vocational-education-market?utm_source=SEO&utm_medium=SEO&utm_campaign=Naman)** is a dynamic and rapidly evolving space. As a market analyst, I believe this sector has the potential to revolutionize how we approach career education and training.
However, ensuring a bright future for vocational education requires a shift in mindsets. Businesses need to recognize the value of skills-based hiring, and individuals should feel empowered to explore vocational education pathways as a viable option for career success.
Let's work together to break down stereotypes and build a future where vocational education is celebrated as a path to a fulfilling and rewarding career. After all, in today's world, the power of skills reigns supreme.
| namanrohilla |
1,866,547 | IP-Ninja.com: Unveiling the Power of Reverse IP Lookup and Geolocation Services for Enhanced Security and Intelligence | In today’s digital landscape, where cybersecurity threats loom large and information is key, having... | 0 | 2024-05-27T12:58:42 | https://dev.to/ipninja/ip-ninjacom-unveiling-the-power-of-reverse-ip-lookup-and-geolocation-services-for-enhanced-security-and-intelligence-o5 | In today’s digital landscape, where cybersecurity threats loom large and information is key, having access to advanced tools and services like IP-Ninja is paramount for organizations seeking to protect their assets, mitigate risks, and gather valuable intelligence. Among these indispensable tools are [reverse IP lookup](https://ip-ninja.com/), geolocation, subdomain enumeration, and reverse ASN lookup services. These services not only offer a multitude of benefits but also play a crucial role in external attack surface management, attribution, OSINT (Open-Source Intelligence), and bug bounty hunting. Let’s delve into the myriad advantages these services provide:
## External Attack Surface Management
By utilizing reverse IP lookup and subdomain enumeration services, organizations can comprehensively map their external attack surface. This includes identifying all IP addresses associated with their domain, uncovering hidden subdomains, and gaining insights into potential entry points for cyber threats. This proactive approach enables organizations to strengthen their defenses and plug any vulnerabilities before they are exploited by malicious actors.
## Attribution
Reverse IP lookup and geolocation services empower cybersecurity professionals and investigators to attribute malicious activities to specific IP addresses or geographical locations. By tracing the origin of suspicious traffic or attacks, organizations can accurately pinpoint the source of threats, whether it’s a rogue actor, a compromised system, or a malicious entity operating from a particular region. This attribution capability is invaluable for conducting forensic investigations, building threat intelligence profiles, and taking appropriate countermeasures.
## Open-Source Intelligence (OSINT)
Reverse IP lookup, geolocation, and reverse ASN lookup services serve as indispensable tools for OSINT practitioners seeking to gather actionable intelligence from publicly available sources. By analyzing IP addresses, domain registrations, DNS records, and hosting information, OSINT analysts can uncover valuable insights about organizations, individuals, or cyber threats. This intelligence can be leveraged for threat assessment, competitive analysis, reputation monitoring, and strategic decision-making.
## Bug Bounty Hunting
In the realm of ethical hacking and bug bounty programs, reverse IP lookup and subdomain enumeration are indispensable for identifying potential targets and attack vectors. Security researchers and bug bounty hunters rely on these services to discover overlooked assets, misconfigurations, or vulnerable systems that could lead to significant security breaches. By responsibly disclosing vulnerabilities to organizations, bug bounty hunters play a crucial role in improving overall cybersecurity posture and fostering a culture of collaboration between security professionals and the wider community.
## Enhanced Security Posture
Beyond the specific use cases mentioned above, the combined capabilities of [reverse IP lookup](https://ip-ninja.com/), geolocation, subdomain enumeration, and reverse ASN lookup contribute to a robust security posture for organizations of all sizes. By proactively monitoring their digital footprint, identifying potential risks, and staying informed about emerging threats, organizations can better protect their assets, safeguard sensitive data, and maintain the trust of their stakeholders.
In conclusion, the benefits of reverse IP lookup and geolocation services extend far beyond mere reconnaissance. From bolstering cybersecurity defenses to facilitating threat attribution, OSINT gathering, and bug bounty hunting, these services are indispensable tools in the arsenal of modern security professionals. By harnessing the power of these services, organizations can stay one step ahead of cyber threats, minimize their attack surface, and strengthen their resilience in an increasingly complex threat landscape.
Whether you’re a large cybersecurity company, a bug bounty hunter or a ethical hacker, [IP-Ninja.com](https://ip-ninja.com/) has a subscription to suit your profile. #cybersecurity #infosec #OSINT #bugbounty | ipninja | |
1,866,546 | Terraform Destroy Command: A Guide to Controlled Infrastructure Removal | In this guide, we explore the essential elements of terraform destroy, unraveling why this command is... | 0 | 2024-05-27T12:57:30 | https://www.env0.com/blog/terraform-destroy-command-a-guide-to-controlled-infrastructure-removal | terraform, devops, cloudcomputing, cloudskills | In this guide, we explore the essential elements of `terraform destroy`, unraveling why this command is a fundamental part of the Terraform workflow. Additionally, we will cover best practices and considerations to ensure the effective and safe execution of `terraform destroy` within your infrastructure management processes.
**What is terraform destroy**
------------------------------
Among the suite of [Terraform commands](https://www.env0.com/blog/what-is-terraform-cli), `terraform destroy` holds a crucial role in infrastructure management. This command is specifically used to remove the infrastructure that has been provisioned using Terraform Infrastructure-as-Code (IaC) configuration.
When `terraform destroy` is executed, Terraform reviews the state file to identify and systematically remove managed infrastructure from your cloud environment (AWS, Azure, GCP, etc.).
While each of the commands in the Terraform workflow (`terraform init`->`terraform plan`->`terraform apply`), contributes to creating a new infrastructure, `terraform destroy` command is explicitly used to delete all (or some targeted) infrastructure defined in your Terraform IaC.
Unlike `terraform apply`, which brings resources up to date with the desired state, `terraform destroy` command does the opposite by ensuring that all (or some) of the resources managed by Terraform are deleted.
Before we dive in deeper, for additional context, here is a short description of Terraform commands and their functions:
* [**`terraform init`**](https://www.env0.com/blog/terraform-init)**:** Used to initialize a working directory containing Terraform config files and to download providers and modules.
* **`terraform validate`:** Validates the Terraform config in that particular directory to ensure they are syntactically valid and internally consistent.
* [**`terraform plan`**](https://www.env0.com/blog/terraform-plan): Creates an execution plan. Using this command prompts Terraform to perform a refresh and determine the actions necessary to achieve the desired state in specified config files.
* [**`terraform apply`**](https://search.google.com/u/0/search-console/performance/search-analytics?utm_source=gws&utm_medium=onebox&utm_campaign=san&resource_id=sc-domain%3Aenv0.com&num_of_days=7&query=!terraform%20apply&breakdown=page&metrics=POSITION&page=!https%3A%2F%2Fwww.env0.com%2Fblog%2Fterraform-apply-guide-command-options-and-examples)**:** Used to apply the changes required to reach the desired configuration state. By default, the `apply` command scans the current directory for the config and applies the changes appropriately.
**How does terraform destroy Command Works?**
---------------------------------------------
To demonstrate how the command works, let us take an example to help us understand _terraform destroy_ more clearly.
For that, we’ll spin up two EC2 instances, review the entire Terraform workflow, and assess the aftermath of _terraform destroy_.
#main.tf
provider "aws" {
region = "us-west-1"
}
variable "instances" {
default = {
"env0-instance-az1 = "us-west-1b",
"env0-instance-az2" = "us-west-1c"
}
}
resource "aws_instance" "tf_instances" {
for_each = var.instances
ami = "ami-0ce2cb35386fc22e9"
instance_type = "t2.micro"
availability_zone = each.value
tags = {
Name = each.key
}
}
### **Terraform Workflow to Create Infrastructure**
By running the Terraform workflow (`terraform init`-> `terraform plan`-> `terraform apply`), we were able to create **env0-instance-az1** and **env0-instance-az2** instances. They’re deployed in their respective availability zones.
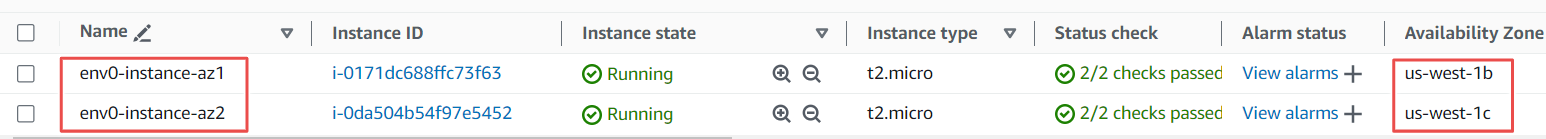
Let us inspect the state file (**terraform.tfstate**) now, to check the metadata of our provisioned infrastructure (**env0-instance-az1** and **env0-instance-az2**). We can see the information of both our instances in the state file.
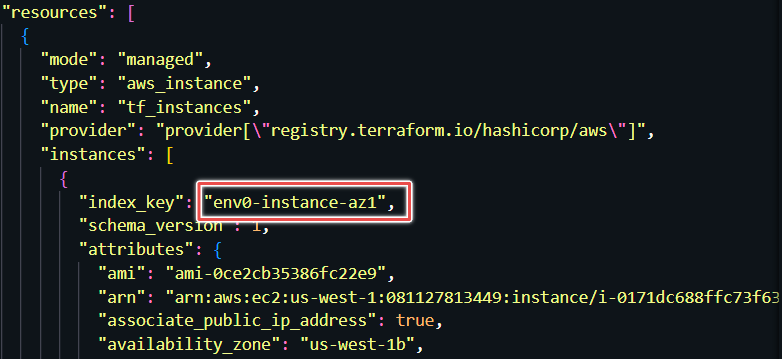
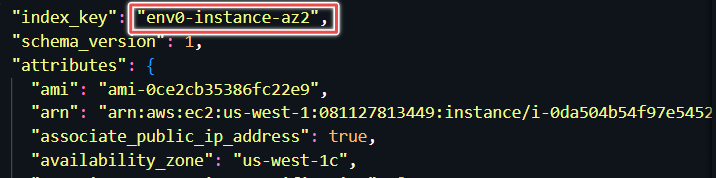
### **Executing terraform destroy Command**
After running `terraform destroy`, we can observe that our state refreshes and Terraform outputs the resources that will be destroyed from our cloud environment.
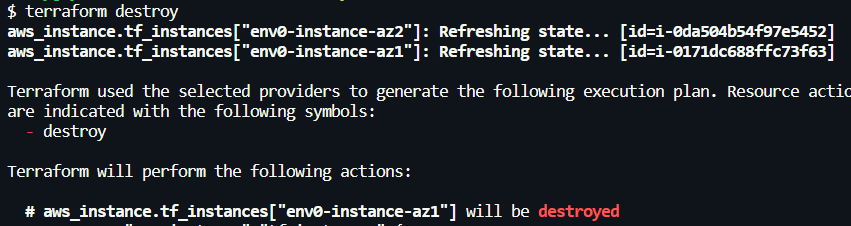
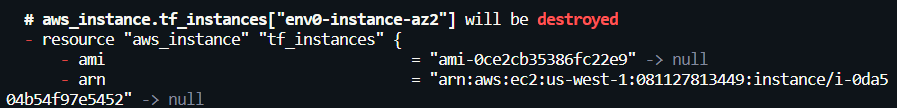
Like `terraform apply`, we are prompted to confirm these changes that will be made to our infrastructure. Confirm with a ‘yes’ to `destroy` the resources.
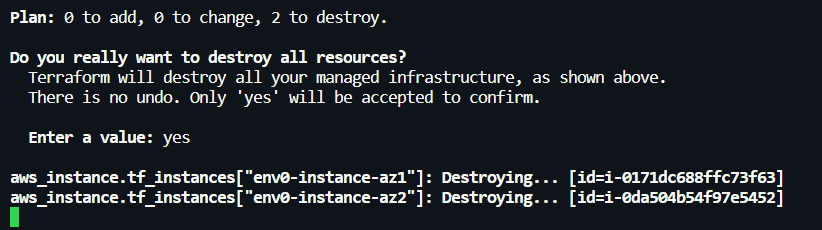
After the resources are deleted, Terraform updates our state (**terraform.tfstate**) file to reflect that these resources no longer exist.
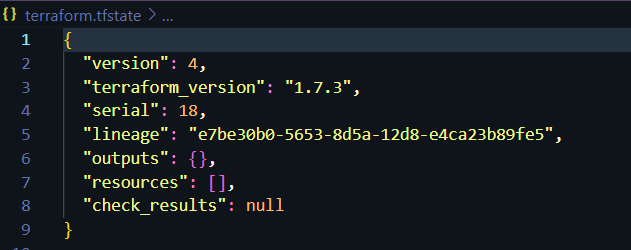
**When, Why and How to use terraform destroy?**
-----------------------------------------------
Here are some scenarios when and why you might use `terraform destroy`:
* **Cost Management:** If you're running resources that are no longer needed or are underutilized, using `terraform destroy` can delete those resources and help reduce costs by ensuring you're not paying for what you don't use.
* **Security Purposes:** In cases where threat actors might have compromised your infrastructure or if you need to ensure that all resources are in a known secure state, destroying and re-provisioning can be an effective strategy.
* **Resource Reallocation:** In scenarios where infrastructure needs to be re-architected or reallocated for different projects or priorities, destroying the current setup might be necessary before reallocating those resources.
**Using terraform destroy Options**
-----------------------------------
Let us look at how we would use `terraform destroy` command with various options.
### 1. **Terraform destroy -auto-approve**
The `-auto-approve` flag always skips the interactive approval for confirming the changes for your infrastructure. In the case of `terraform destroy`, it bypasses the approval step, and Terraform proceeds to destroy your infrastructure.
In automated environments such as CI/CD pipelines, where human interaction is not possible, the `-auto-approve` flag ensures that the destroy operation can proceed without manual intervention.
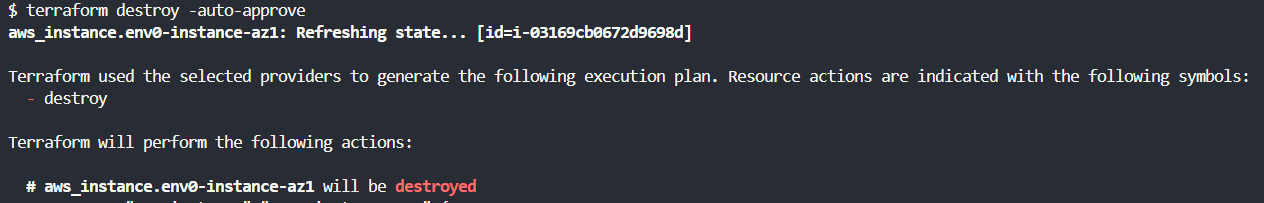
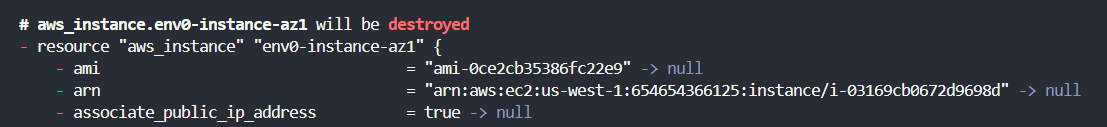
### **2. Terraform destroy -target**
The `terraform destroy -target=resource_type.resource_name` option should be used with caution and in specific scenarios where you need to remove an individual resource or a set of resources, without impacting the entire infrastructure managed by Terraform.
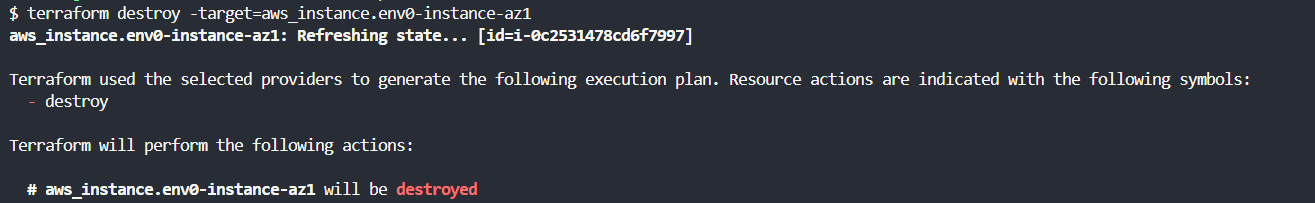
### **3. Terraform destroy -refresh=false**
The `-refresh` option in the `terraform destroy` command can be used to control whether Terraform should refresh the state before performing the `terraform destroy`.
For instance, in a large infrastructure environment, you can use `-refresh=false` option when the refresh process is time-consuming since Terraform checks the status of each resource in the cloud provider.
This flag skips the state file refresh and speeds up the `destroy` process.
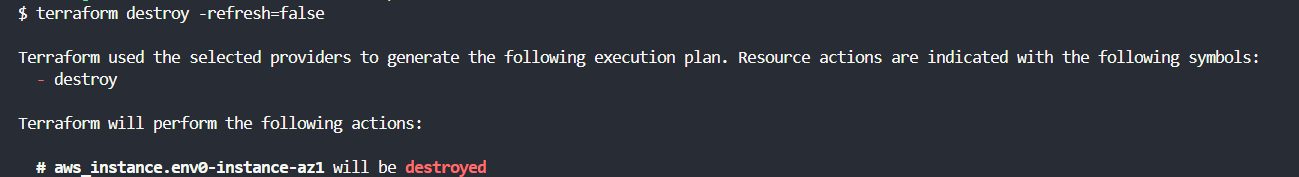
### **4. Terraform destroy -lock and -lock-timeout**
The `terraform destroy -lock` flag is used to control Terraform's state-locking mechanism during the `destroy` operation.
Using the `-lock=true` can be beneficial when you are working in a team environment where multiple operations in the same state might occur simultaneously.
This ensures that no other operations interfere with the `destroy` process, maintaining state consistency and preventing potential conflicts.
The `-lock-timeout` flag can be used to extend the waiting period for a state lock. For example, `terraform destroy -lock-timeout=20s` locks the state file for 20 seconds.
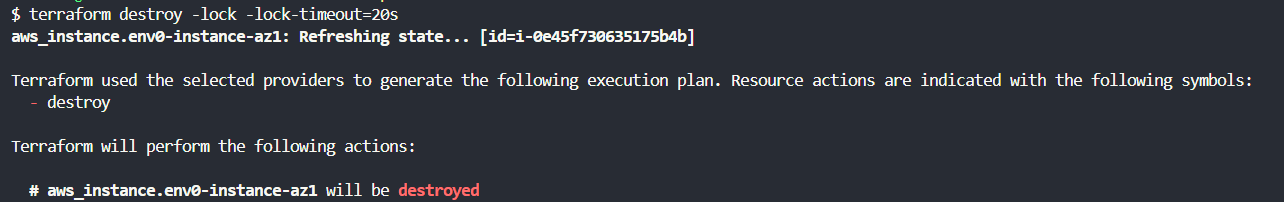
**Best Practices**
-------------------
The `destroy` command is irreversible, and running it carelessly might cause important infrastructure to disappear forever from your environment.
Before discussing best practices, it is important to note that terraform destroy can be run locally and in automated CI/CD pipelines. The `terraform destroy` command is typically used locally for dev or test environments to swiftly destroy resources, while in CI/CD pipelines, it's recommended for staging and production to ensure controlled, team-reviewed resource destruction.
Let us look at the best practices that must be followed when dealing with `terraform destroy`.
### **1. Regular Backup of State Files and Sensitive Data**
Regularly backing up state files (**terraform.tfstate**), including the automatically generated **terraform.tfstate.backup**, is essential.
Terraform creates the **.backup** file before it writes to the main **terraform.tfstate** file, serving as an immediate previous version of your state. This can be invaluable in case of accidental corruption or deletion of the **terraform.tfstate** file.
When planning backups, ensure both the current state file and the **.backup** file are included.
For enhanced disaster recovery, consider replicating state files in remote backends (like S3) to other regions. Additionally, sensitive data or secrets (such as cloud provider API keys, SSH keys, database credentials, etc.) managed by Terraform should also be securely backed up and encrypted to prevent unauthorized access.
### 2. **Using Workspaces for Environment Isolation**
Manage separate state files for different environments (such as development, staging, and production) under the same configuration using Terraform workspaces.
Utilizing workspaces for environment isolation is a best practice that can significantly reduce the risk of impacting the wrong environment when performing destructive operations like `terraform destroy`.
Before executing the `destroy` command, always confirm you are in the correct workspace to ensure that only the intended environment is affected.
### 3. **Implement a Review Process for Infrastructure**
Implementing a comprehensive review process by incorporating a gated check-in process in CI/CD pipelines adds an additional layer of security and accountability.
This process should include:
* **Code Review:** Changes to Terraform configurations, especially those leading to resource destruction, should be reviewed by multiple team members.
* **Impact Analysis:** Automatically run `terraform plan -destroy` to show what resources will be affected without making any changes. Document and review infrastructure changes.
* **Environment-specific gates:** Enforce stricter reviews and require additional checks or tests that mimic the production environment for the staging environment. For production, implement the highest level of scrutiny by senior infrastructure engineers and double-check automated tests.
* **Audit Trails:** Ensure that all actions and approvals related to the Terraform changes are logged and accessible for audit purposes.
**What Happens when terraform destroy Fails?**
----------------------------------------------
When `terraform destroy` fails, it can lead to several issues:
### **1. Partial Resource Deletion**
This can occur if Terraform encounters an error while attempting to `destroy` one or more resources. The error could be due to permissions issues, dependencies between resources that Terraform is not aware of, or external factors such as network timeouts.
**Mitigation:**
* **Resolve dependencies:** Manually review and ensure all dependencies are correctly reflected in your Terraform configurations. Use `-target` flag to `destroy` specific resources.
* **Check Permissions:** Verify that you have sufficient RBAC permissions to delete Terraform resources, in case you're using Terraform Cloud or other platforms.
* **Network Timeouts:** In case of network timeouts, re-running the `terraform destroy` command with a stable network may resolve the problem.
### **2. Inconsistent State**
The Terraform state file may become inconsistent with the actual infrastructure if manual changes were made outside Terraform, or if previous Terraform operations were interrupted.
**Mitigation:**
* **Refresh State:** Run `terraform refresh` to update the local state file with the actual state of resources in the cloud.
* **Manual State Edit:** If refreshing the state does not resolve the inconsistencies, manually edit the state file using the `terraform state rm` command to remove the problematic resources from the state file.
### **3.State Locking Issues**
Terraform state locking prevents multiple simultaneous operations from corrupting the state. If a previous operation didn't complete properly, the state may remain locked, blocking further operations.
**Mitigation:**
* **Investigate Lock:** Use the `-lock-timeout` option to wait for a lock to be released before or use terraform force-unlock with the lock ID, ensuring no other operations are currently running.
* **Manual Unlock:** As a last resort, manually unlock the state through the backend (like S3, Azure Blob Storage, etc.) if the automatic unlock fails.
env0: Scheduling, TTL, Destroy Protection and more
--------------------------------------------------
[Time to Live](https://docs.env0.com/docs/policy-ttl) (TTL) is one of the functionalities [env0](https://www.env0.com/)'s offers, which uses `destroy` to streamline environment lifecycle management.
Configuring TTL provides users with the ability to easily set predefined timers, dictating the lifespan of their environments, which helps optimize resource allocation and avoid cost sprawl.
Additionally, [env0](https://www.env0.com/) also allows you to set Organizational- and Project-level TTL. These can be used to provide helpful guardrails, standardize IaC usage, and grant autonomy to teams new to Infrastructure-as-Code, without the risk of things going south.
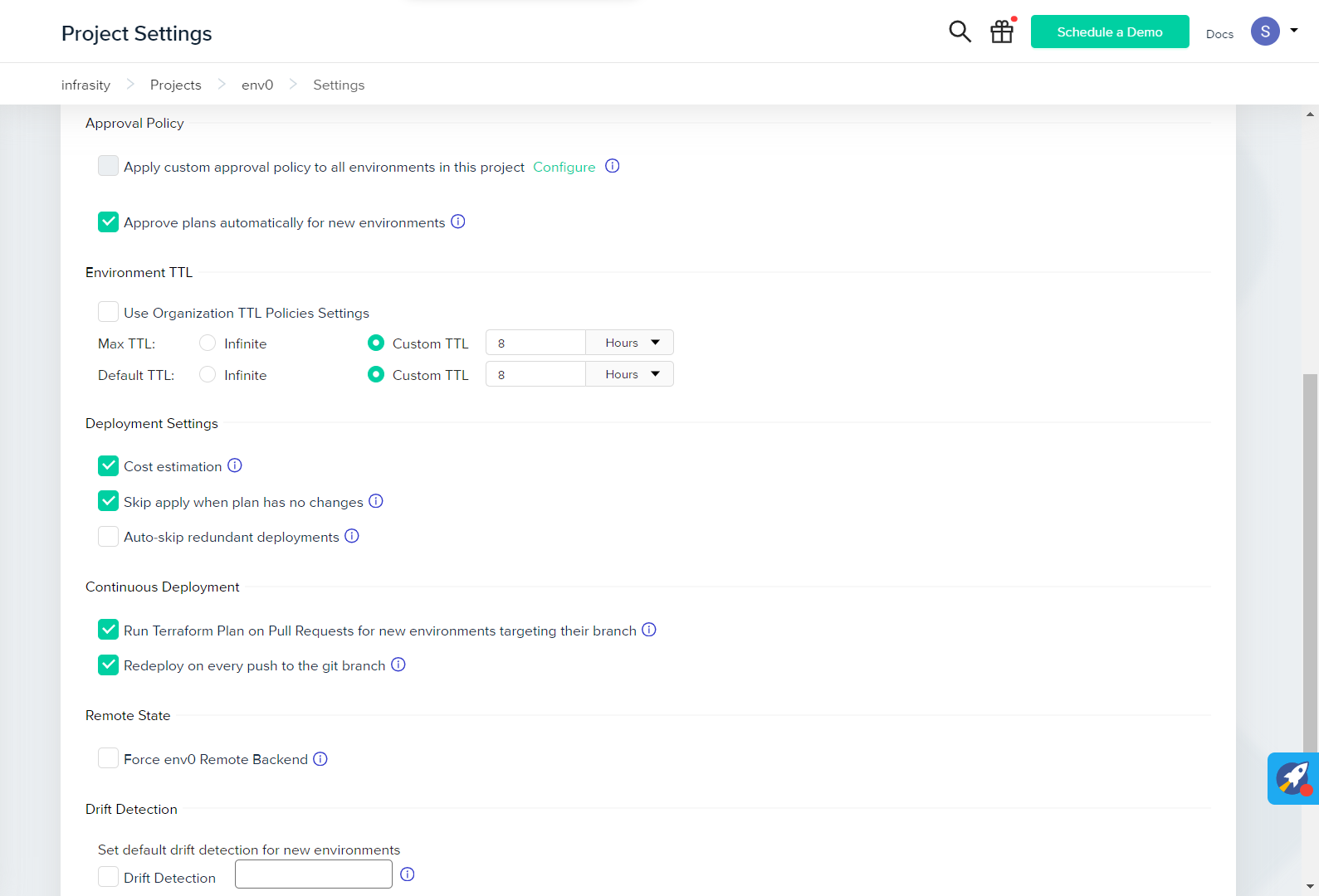
Moreover, env0’s [Scheduling](https://docs.env0.com/docs/scheduling) functionality aids a layer of automation, triggering of infrastructure deployments and destructions on a predefined schedule, defined by cron expressions.
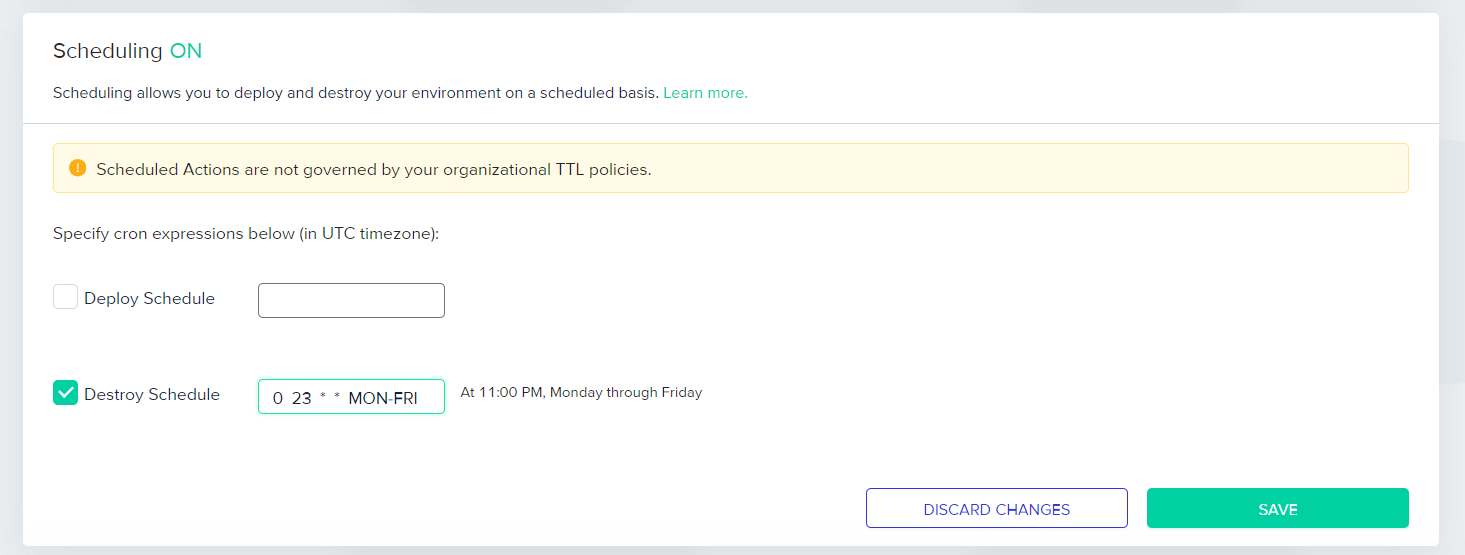
To avoid accidental deletion, env0 also comes with a [Destroy Protection](https://docs.env0.com/docs/destroy-protection) option. When enabled, it restricts functionalities such as the _‘_Destroy_’_ button, ‘Time Left’ indication, and the ‘TTL panel’ to be applied to the protected environment.
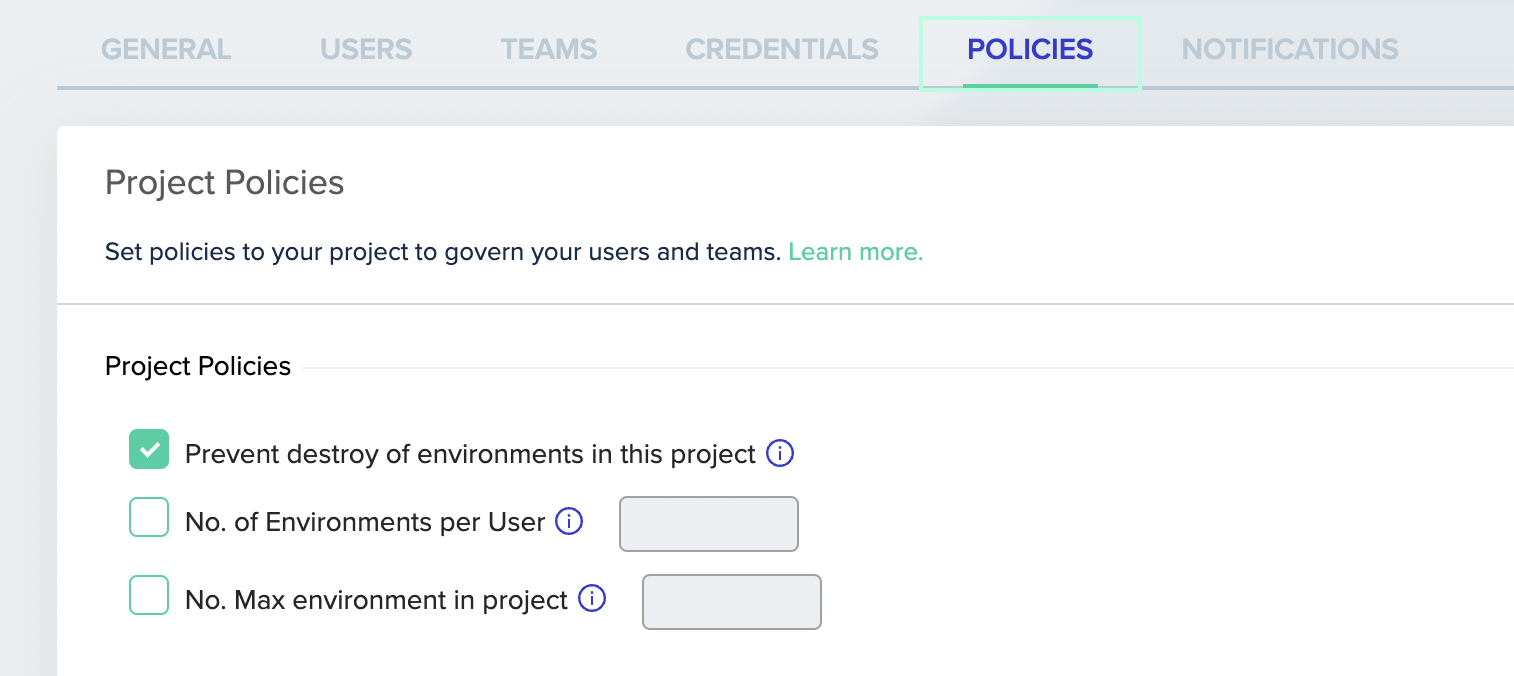
Lastly, the [Skip State Refresh](https://docs.env0.com/docs/skip-state-refresh) feature in env0 allows users to bypass state mismatches during the destruction phase of an environment.
This is a last-resort option equivalent to the Terraform command, `terraform plan -refresh=false`, ensuring that the environment can still be destroyed even when state mismatches occur, such as inaccessible secrets or data sources.
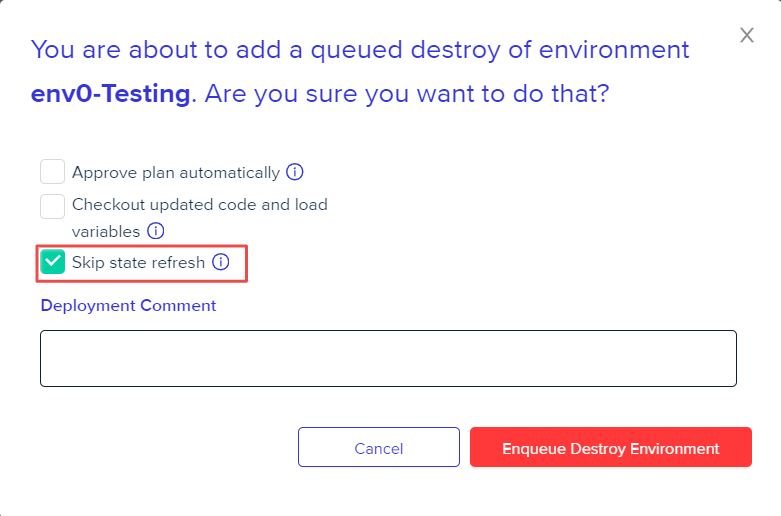
Frequently Asked Questions
--------------------------
### **Q. What is the difference between terraform destroy and state rm?**
To answer this question, here is a short comparison table:
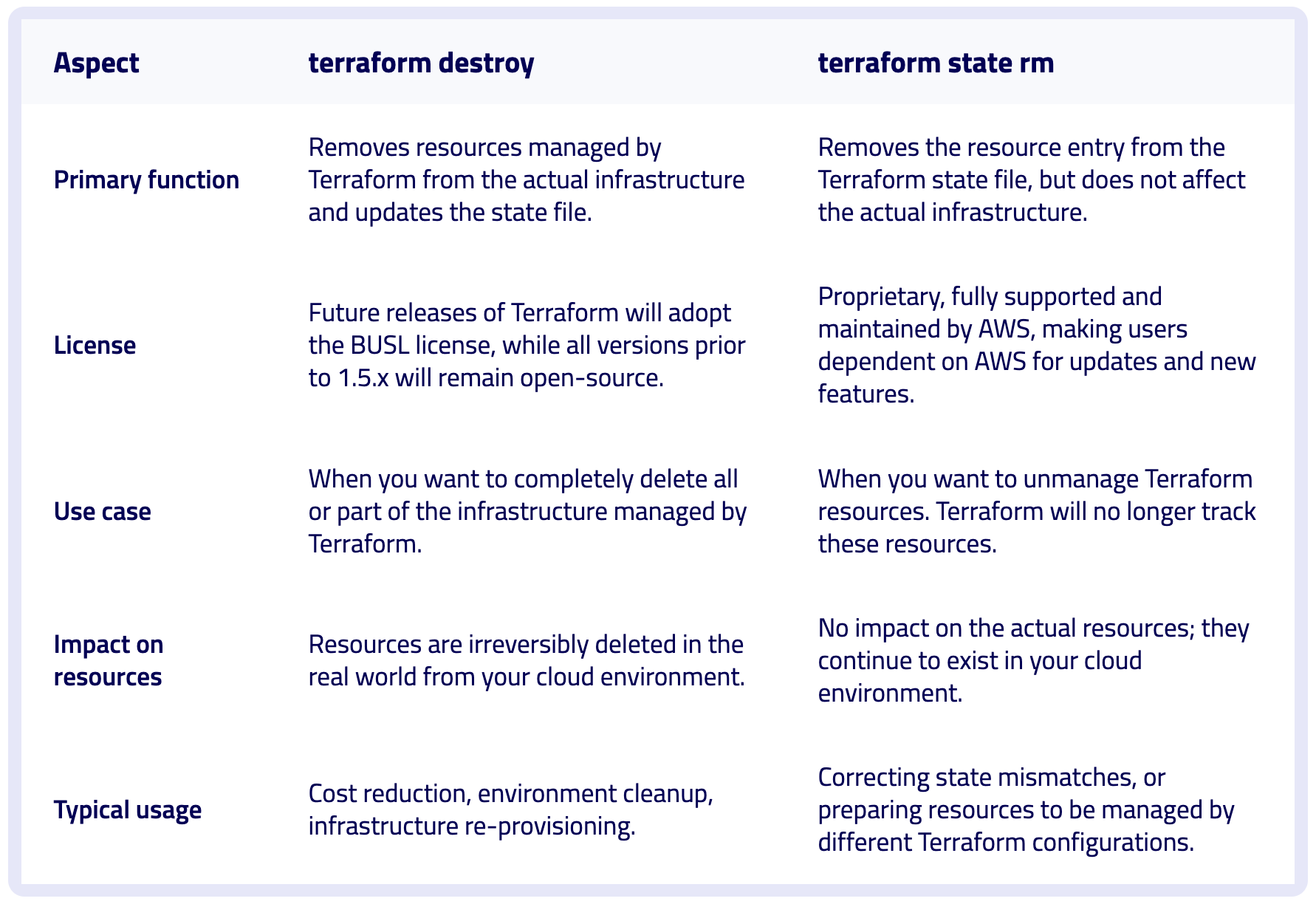
### **Q. Is Terraform destroy reversible?**
No. Once executed, `terraform destroy` is not reversible. It permanently deletes resources from the cloud.
### **Q. How can I prevent accidental execution of terraform destroy?**
It's recommended to use Terraform state locking. Another alternative is to use the `prevent_destroy` lifecycle meta-argument. When prevent\_destroy is set to true, Terraform will generate an error if the `destroy` operation tries to destroy the resources, acting as a safeguard against accidental deletion.
### **Q. Does terraform destroy delete manually created resources?**
No. The `terraform destroy` command just deletes the resources that are under Terraform’s management and control.
### **Q. Can I preview what terraform destroy will do before executing it?**
Yes, you can execute `terraform plan -destroy` for a preview of the actions Terraform will take, allowing you to verify that only the intended resources are targeted for deletion. | env0team |
1,866,545 | Top 100 Richest Men in the Philippines: A Testament to Resilience and Innovation | Top 100 Richest Men in the Philippines: A Testament to Resilience and Innovation The Philippines,... | 0 | 2024-05-27T12:56:59 | https://dev.to/anuj_mishra44/top-100-richest-men-in-the-philippines-a-testament-to-resilience-and-innovation-1n5g | Top 100 Richest Men in the Philippines: A Testament to Resilience and Innovation
The Philippines, with its dynamic economy and rich cultural heritage, is home to some of the wealthiest individuals in the world.
[The top 100 richest men in the Philippines](https://www.mobileappdaily.com/reports/top-billionaires-in-philippines?utm_source=dev&utm_medium=anuj&utm_campaign=mad) have amassed their fortunes through various sectors such as retail, real estate, banking, telecommunications, and more. Their journeys from modest beginnings to remarkable success are filled with stories of resilience, innovation, and strategic foresight. This blog highlights the top ten richest men from this illustrious list, delving into their lives, businesses, and legacies.
1. Henry Sy Sr.
Henry Sy Sr. is often celebrated as the wealthiest man in the Philippines. His journey from a small shoe store owner to the patriarch of SM Prime Holdings is truly inspirational.
Early Life and Career
Henry Sy was born in Xiamen, China, and moved to the Philippines with his family. Starting with a small shoe store in Manila, Sy laid the foundation for what would become SM Prime Holdings.
Business Empire
SM Prime Holdings includes SM Supermalls, SM Development Corporation (SMDC), and Banco de Oro (BDO) Unibank. SM Supermalls, with over 70 malls nationwide and several in China, has revolutionized the retail landscape in the Philippines. BDO Unibank is one of the largest banks in the country.
Legacy
Henry Sy Sr. passed away in 2019, but his legacy continues through his children who manage the family business, symbolizing hard work, resilience, and strategic vision.
2. Manuel Villar
Manuel Villar's impressive career spans real estate and politics, making him one of the most influential figures in the Philippines.
Early Life and Career
Villar grew up in a poor family in Tondo, Manila, and worked his way through college, earning degrees in business administration and a master’s in business administration from the University of the Philippines.
Business Ventures
Villar founded Camella Homes, which later became Vista Land & Lifescapes, Inc., one of the largest real estate developers in the Philippines. His company specializes in affordable housing.
Political Career
Villar served as Speaker of the House of Representatives and President of the Senate, advocating for housing and business development.
Philanthropy
His philanthropic efforts focus on providing housing for the underprivileged and supporting educational initiatives.
3. Enrique Razon Jr.
Enrique Razon Jr. is a significant player in the logistics and gaming industries.
Early Life and Career
Razon inherited his father’s small port-handling business and transformed it into International Container Terminal Services, Inc. (ICTSI), which operates in over 30 countries.
Business Ventures
Razon also ventured into the gaming industry with Bloomberry Resorts Corporation, which operates the Solaire Resort and Casino in Manila.
Philanthropy
Razon focuses on disaster relief and education, contributing significantly to rebuilding efforts following natural disasters.
4. Lucio Tan
Lucio Tan's diverse business interests have made him one of the top 100 richest men in the Philippines.
Early Life and Career
Tan moved to the Philippines as a child and studied chemical engineering while working various jobs.
Business Empire
His business empire includes Asia Brewery, Fortune Tobacco Corporation, and Philippine Airlines, along with interests in banking, real estate, and education.
Challenges and Controversies
Despite numerous legal and political challenges, Tan has maintained his wealth and influence.
Philanthropy
Tan funds scholarships and builds schools and hospitals, focusing on education and health.
5. John Gokongwei Jr.
John Gokongwei Jr. is celebrated for his contributions to various industries, making him a key figure among the top 100 richest men in the Philippines.
Early Life and Career
Gokongwei started trading goods on a bicycle after his father’s death, eventually founding JG Summit Holdings, Inc.
Business Ventures
JG Summit Holdings includes Universal Robina Corporation (food and beverage), Digital Telecommunications Philippines (telecommunications), real estate, and Cebu Pacific (aviation).
Legacy
Gokongwei passed away in 2019, leaving behind a thriving business empire managed by his family.
Philanthropy
The Gokongwei Brothers Foundation supports numerous educational initiatives and scholarships.
6. Ramon Ang
Ramon Ang's leadership in various sectors has solidified his status among the top 100 richest men in the Philippines.
Early Life and Career
Ang began his career as a mechanic before venturing into trading and partnering with Eduardo Cojuangco Jr.
Business Ventures
As the president and CEO of San Miguel Corporation (SMC), Ang has expanded SMC into food and beverage, infrastructure, energy, and packaging.
Philanthropy
Ang is involved in philanthropic activities focusing on disaster relief, education, and community development.
7. Jaime Zobel de Ayala
Jaime Zobel de Ayala has played a significant role in shaping the business landscape of the Philippines.
Early Life and Career
Zobel de Ayala studied at Harvard University before joining the family business in the Philippines.
Business Ventures
Ayala Corporation has interests in real estate, banking, telecommunications, and water infrastructure. Under Zobel de Ayala’s leadership, the company has significantly contributed to the modernization of Manila.
Legacy
His legacy continues through his children, who now manage the family business.
Philanthropy
The Ayala Foundation focuses on education, arts and culture, and sustainable development.
8. Andrew Tan
Andrew Tan is a notable figure in real estate and spirits, making significant strides in both industries.
Early Life and Career
Tan moved to Manila from Fujian, China, and studied at the University of the East.
Business Ventures
Tan founded Megaworld Corporation, a leading real estate developer known for its townships. He also owns Emperador Inc., the world’s largest brandy company.
Philanthropy
Tan’s philanthropic efforts focus on education and poverty alleviation.
9. Tony Tan Caktiong
Tony Tan Caktiong’s success story with Jollibee Foods Corporation has made him a household name.
Early Life and Career
Tan Caktiong started with an ice cream parlor, which eventually grew into Jollibee Foods Corporation, the largest fast-food chain in the Philippines.
Business Ventures
Jollibee Foods Corporation owns several fast-food brands, including Chowking, Greenwich, and Red Ribbon, expanding its reach internationally.
Philanthropy
Tan Caktiong focuses on education and food security through the Jollibee Group Foundation.
10. George Ty
George Ty’s contributions to banking and real estate have solidified his position among the top 100 richest men in the Philippines.
Early Life and Career
Ty founded Metropolitan Bank & Trust Company (Metrobank) at the age of 25, which has become one of the largest banks in the Philippines.
Business Ventures
His interests also include real estate through GT Capital Holdings and Toyota Motor Philippines.
Philanthropy
Ty’s philanthropic activities are managed through the Metrobank Foundation, focusing on education, healthcare, and the arts.
Conclusion
The top 100 richest men in the Philippines have not only achieved immense wealth but also significantly contributed to the nation’s economic and social development. Their stories of resilience, innovation, and strategic foresight serve as an inspiration to many aspiring entrepreneurs. These billionaires exemplify the potential for success in various industries and highlight the importance of giving back to society. Their legacies continue to shape the Philippines’ business landscape and will undoubtedly influence future generations. As they continue to lead and innovate, their impact will be felt for many years to come. | anuj_mishra44 | |
1,866,544 | A Guide to Case-Insensitive String Comparison | There are times that we want to compare strings case-insensitive. We want to perform data validation,... | 0 | 2024-05-27T12:55:01 | https://dev.to/marcobustillo/a-guide-to-case-insensitive-string-comparison-3339 | javascript, beginners, webdev, programming | There are times that we want to compare strings case-insensitive. We want to perform data validation, searching and filtering, consistency, etc. You can do this multiple ways in JavaScript but do you wonder what's their differences with each other?
In this article, we'll look into multiple ways how to do Case-Insensitive string comparisons in JavaScript.
## RegExp
Regular expressions offer a language-agnostic approach to string comparisons, making it easy to migrate these comparisons to other languages. However, using regular expressions for comparisons can come with a performance cost, particularly when dealing with large and complex strings. This is because regular expressions can be computationally intensive, especially when matching patterns in long strings. As a result, it's essential to weigh the benefits of using regular expressions against the potential performance implications when deciding whether to use this approach for string comparisons.
```
const str1 = "Hello World";
const str2 = "hello world";
const regex = new RegExp(str1, 'i'); // create a regex pattern with case-insensitive flag
console.log(regex.test(str2))
```
## Convert strings to Upper or Lower case
While converting strings to a single case can be a convenient solution for case-insensitive comparisons, it's not without its drawbacks. Converting strings can add unnecessary computational overhead, especially for large and complex strings.
```
const str1 = "Hello World";
const str2 = "hello world";
const areEqual = str1.toUpperCase() === str2.toUpperCase();
const areEqual2 = str1.toLowerCase() === str2.toLowerCase();
console.log(areEqual)
console.log(areEqual2)
```
## localeCompare()
The localeCompare() function is a powerful and efficient method for comparing strings in JavaScript. As the recommended function for performing case-insensitive comparisons, it offers a faster and more reliable alternative to using regular expressions and case-conversion checks. As a built-in method in JavaScript, it can be easily integrated into a variety of environments.
```
const str1 = "Hello World";
const str2 = "hello world";
console.log(str1.localCompare(str2, 'en-US', { sensitivity: 'base' }))
```
# Conclusion
Each option has its unique advantages and disadvantages. Ultimately, the best choice depends on the user's specific needs and priorities, requiring a careful evaluation of the trade-offs between each option. | marcobustillo |
1,866,543 | Day 4 of my progress as a vue dev | About today So, I implemented the countdown timer on my quiz app using setInterval and made it... | 0 | 2024-05-27T12:54:22 | https://dev.to/zain725342/day-4-of-my-progress-as-a-vue-dev-1h09 | vue, typescript, tailwindcss, webdev | **About today**
So, I implemented the countdown timer on my quiz app using setInterval and made it reusable for each attempt. Also restricted user to attempt the quiz based on the attempt limit set during quiz creation. Learned a few new Tricks such as setting data when the page is unmounted and to generate and modify the key on the runtime.
**What's next?**
I now have to finally add the feature for user to review the quiz after attempting and see the correct answers and answers they selected and this app will be completed and ready to be pushed on my github.
**Improvements required**
I still have to apply tight typescript on the app and will try to refactor the code to make it more simple by turning large files into smaller reusable components. I also have to learn Laravel concepts and move this app from localstorage to Laravel backed.
Wish me luck! | zain725342 |
1,866,542 | Single-Cell Omics: The Frontier of Biological Research and Computational Innovation | Key takeaways: Single-Cell Precision: Single-cell omics enable detailed study of individual cells,... | 0 | 2024-05-27T12:54:12 | https://dev.to/almadengenomics/single-cell-omics-the-frontier-of-biological-research-and-computational-innovation-3l98 | computationalinnovation, biologicalresearch, singlecellomics, cloudnative | Key takeaways:
1. **Single-Cell Precision:** Single-cell omics enable detailed study of individual cells, providing an understanding of their specific cellular functions and the complex biological systems they compose. This provides insights which was impossible to achieve with bulk analysis methods.
2. **Computational Demands:** The field faces significant computational challenges, including managing large data volumes, interpreting complex data, and developing precise algorithms for accurate analysis.
3. **Innovative Tools:** Developing and integrating specialized software tools, such as Seurat and Scanpy, are critical for efficiently processing and analyzing single-cell omics data.
4. **Collaboration is Key:** Advancements in single-cell omics demand collaboration, data standardization, and knowledge sharing within the scientific community for consistency and quality.
5. **Impact and Future Potential:** Overcoming computational obstacles in single-cell omics can lead to significant real-world applications like developing new drug targets and advancements in personalized medicine. It also enhances more informed environmental monitoring.
Single-cell omics is a breakthrough in modern biological research, revealing details of cell behavior with remarkable clarity. This method has changed the game by letting us study cells individually, uncovering the unique characteristics lost when we only looked at groups of cells together. By focusing on the individual molecular patterns of each cell, single-cell omics are leading us to a richer understanding of biology's building blocks. It's like moving from a painting where colors blend into one to a detailed mosaic where each color stands out. However, this field contains several computational challenges that impact efforts to harness single-cell omics to drive biological insights.
**Why Single-Cell Omics Matter?**
Single-cell omics reveal insights into individual cells unlocking hidden details missed by analysing large cell groups. This method enables us to understand the diversity and complexity of cells in a particular tissue or organism. Identifying subpopulations can lead to diverse and exciting insights, elucidating a cell's role in health maintenance and disease progression. the technology uncovers individual cells' roles in maintaining health or contributing to disease.
Additionally, single-cell omics is key in revealing cellular heterogeneity — the subtle differences between cells in the same group. These differences have significant implications, especially in developing targeted therapies and personalized medicine. By recognizing and analyzing the variations, we can understand each cell's unique contributions to the body's functions and responses.
## The Computational Backbone of Single-Cell Omics
Computational methods are the backbone of single-cell omics, essential for making sense of the vast and complex data this technology generates. Without robust computational and data analysis tools, the rich data from single-cell analysis would be like a treasure trove locked away in a chest. These methods unlock the chest, allowing us to process and analyze the omics database to extract meaningful biological insights.
Computational techniques range from data normalization to adjusting the data for cell variability, to complex algorithms for identifying patterns and relationships within the data. For instance, clustering algorithms can group similar cells together, revealing the different cell types present in a sample.
We also rely on dimensionality reduction methods, which help simplify the data without losing critical information, making it easier to visualize and understand. These methods are crucial for mapping out the cellular landscape in a way that's both comprehensive and comprehensible.
Computational methods streamline single-cell data analysis, converting complexity into actionable scientific insights.
## Tools of the Trade
The software and tools used in single-cell omics are as vital as the laboratory equipment. Currently, we're seeing a lot of development in software tools designed explicitly for single-cell analysis. These specialized tools are engineered to handle the unique challenges of single-cell data, from managing its volume to interpreting its complexity.
Commonly used software includes Seurat for single-cell RNA sequencing data analysis, which allows us to identify and characterize cell types and states. Another is Scanpy, a scalable toolkit for analyzing single-cell gene expression data. These tools mesh seamlessly with our research workflows, enabling us to process and analyze data efficiently.
Integrating the tools into daily work is now standard practice, allowing researchers to focus on biological questions instead of data processing complexities. They are the workhorses behind the scenes, turning raw data into insights that drive the research forward.
## Computational Challenges in Single-Cell Omics
The computational landscape of single-cell omics is as rich as it is challenging. The amount of data we deal with is massive, and making sense of it is critical. Handling the sheer volume of data generated by single-cell techniques requires sophisticated data analysis tools and strategies to store, process, and interpret effectively.
Beyond volume, the complexity and heterogeneity of the data add layers of difficulty. Each cell has its own story, told through a unique combination of genetic and molecular information. Unraveling these stories to understand the broader narrative of cellular function and interaction demands advanced computational approaches. We need algorithms that can manage this diversity and learn from it to predict and model cellular behavior.
Developing these robust algorithms is intricate work. They must be sensitive enough to detect subtle nuances, yet powerful enough to handle large-scale analyses. A balance is crucial for accurate and reliable single-cell analysis, and creating precise and efficient algorithms is an ongoing challenge.
Moreover, integrating data from different omics layers—such as genomics, transcriptomics, and proteomics—compounds the complexity. Each layer offers a different perspective on the cell's function and requires a different computational approach. Integrating these layers into a cohesive analysis is like assembling a multidimensional puzzle; each piece must fit perfectly to complete the picture.
These computational challenges are significant, but they are not insurmountable. With each advancement, we move closer to fully realizing the potential of single-cell omics to uncover the mysteries of cellular life.
## Impact on Research and Development
Computational delays can significantly slow down research progress. When we hit a computational bottleneck, it doesn't just delay our data analysis but our entire research timeline. The speed at which we can process and analyze data directly impacts how quickly we can make discoveries and develop new treatments for real-world applications.
Accuracy and reliability in computational analysis are non-negotiable. They are the bedrock of our research. If our computational methods are flawed, it could lead to incorrect conclusions. Ensuring that our analysis is precise is essential for the credibility and utility of our findings in the real world.
Computational delays are more than just a minor inconvenience; they create a domino effect that hampers the pace of research and development. Every hour we spend troubleshooting computational issues is an hour not spent on discovery. The speed of our computational analysis dictates how swiftly we can transition from data to discovery, and, ultimately, to real-world applications.
Moreover, the accuracy and reliability of our computational analysis underpin the entire research process, especially when dealing with gene expression data. We must be able to trust the data, and the data must tell the true story. Ensuring the precision of our computational work is paramount, as it directly influences the validity of our research outcomes.
## Paving the Way Forward: Solutions and Strategies
Innovation is key to navigating the computational complexities of single-cell omics. We're crafting algorithms that can digest large-scale data and deliver precise insights. Algorithm innovations are pivotal for maximizing the potential of single-cell research by effectively managing a vast omics database.
Collaboration and standardization are also vital in pushing the boundaries of what we can achieve. By standardizing methods and tools and working together, we're setting new benchmarks for what's possible. This sentiment underscores the collective effort in our field. The shared approach ensures consistency and quality in our work, facilitating advancements and fostering a collaborative scientific community.
Moreover, cloud computing and parallel processing technologies are game-changers, offering the computational horsepower we need. They allow us to process larger datasets more efficiently and with greater speed, significantly reducing the time from experimentation to insight. Embracing these technologies is essential for our progress in single-cell omics research.
## Real-World Applications and the Future
Overcoming computational hurdles in single-cell omics has led to real-world breakthroughs. We've seen case studies wherein, data management resulted in identifying new drug targets. These successes showcase the tangible benefits of our computational strides.
Looking ahead, the advancements in computational omics hold immense promise for medicine and environmental science. Imagine tailoring treatments to individual cellular profiles or monitoring ecosystems at a cellular level. The potential is vast, with the power to personalize healthcare and protect our environment through more informed decisions.
## Conclusion
Addressing computational challenges is crucial for the advancement of single-cell omics. We must tackle these issues head-on to unlock the full potential of our research. The path forward requires persistent innovation and a collaborative spirit within the scientific community.
I urge my colleagues and the broader field to continue pushing the boundaries of what our computational methods can achieve. Together, we can turn the tide of these challenges into opportunities for ground-breaking discoveries that can transform both science and society. Let's join forces to shape the future of single-cell omics.
Originally Published at: https://almaden.io/blog/https/almaden.io/blog/how-single-cell-multiomics-is-revolutionizing-drug-discovery-0
| almaden_genomics |
1,866,541 | Finding Job in Karachi | Karachi, the capital of Sindh province and the largest city in Pakistan is not only an economic,... | 0 | 2024-05-27T12:53:26 | https://dev.to/careerokay/finding-job-in-karachi-48a0 | Karachi, the capital of Sindh province and the largest city in Pakistan is not only an economic, commercial, and industrial hub of the country but also a bustling metropolis situated on the Arabian Sea shores adjacent to the Indus River Delta. Known for its vibrant atmosphere and diverse opportunities, [Jobs in Karachi](https://www.careerokay.com/jobs/jobs-in-karachi) abound across various sectors, making it an attractive destination for job seekers from all over the country. Whether you're in search of career growth or new opportunities, Karachi offers a dynamic environment to thrive professionally.
Karachi the financial and industrial capital of Sindh known as city of lights also know the inexpensive city of the Pakistan in term of living. Karachi offers a busy and active life to its people with numerous opportunities to jobseekers where from all over Pakistan come to search jobs in Karachi.
## Karachi Economy
Due to the port city and economic and commercial, industrial hub of the country Karachi is enriched in many industrial and export-import businesses. Karachi is considered the backbone of Pakistan's economy and its port is also eligible to serve land lock centers in Asia countries including Afghanistan.
Karachi is less costly compared to other big cities like Islamabad Lahore etc. The rent is not sky high & other things are also have less price comparatively. Salary, growth & job opportunities are high like in other cities.
## Karachi Financial Sector
Karachi has a head office are almost all major banks including the head offices of Dozens of insurance companies. On the other hand, many agriculture and industrial development banks investment institutions, and automobile financing firms also play an important role in Pakistan's Economy.
KSE- Karachi Stock Exchange is also situated in Karachi and is responsible for enlisting all public limited companies and exchanging their socks and sharing these institutions provide thousands of job opportunities for Karachi residents.
## Job Market of Karachi
Normally a high number of jobs are created in big metropolitan area and big cities where a number of job opportunities is much higher than in rural areas. Major employment opportunities have been created in Pakistan’s big cities e.g. Karachi Lahore Islamabad.
Furthermore, COVID-19 has hit Pakistan's economy, causing the unemployment rate to double (approximately). So, in this situation, obtaining work is really difficult. Normally candidates rely on the newspaper's old and absolute method and it’s gradually moving to online news also means that people are relying on the classifieds section of their local newspaper to search for jobs, but the response rate is really low. The job market in Karachi was influenced by the same issue. For generations of Job opportunities in Pakistan government should implement its low-cost five-million housing scheme in true letter and spirit. This will help out other allied industries which are more than 40 to 45 like paints cement steel and bricks.
This will help the majority of job seekers to find jobs that are unskilled labor. Also, the Government must come up with plans to improve skills development and improved workforce skills through skilled development programs.
Getting a job in Karachi or any other city usually depends on various parameters like supply vs demand.
In general, we can say that finding a job in Karachi is simple in the sense that there are numerous opportunities in marketing, back office work, and managerial positions in several fields. However, how much you will be earning depends totally on your own qualifications, experience, and interpersonal skills
## Finding Jobs in Karachi
Finding jobs these days is difficult due to Pakistan's rising unemployment rate, according to the Pakistani government. In 2021, the unemployment rate was 5.0 percent, and it is expected to rise to 6.2 percent in 2022.
One of the best and most effective ways to find a job in Karachi is to apply through portal websites that offer a lot of jobs. There are a lot of websites like Careroaky.com, Rozee.pk Indeed, and Mustakbil.com. All of them are premiere websites that provide jobs also in respect to the current situation.
It's simply easier for job seekers to apply for positions online rather than sifting through hundreds of classified advertisements in the newspaper in search of something even vaguely intriguing or relevant to their sector.
## Job Portal and Job Website
Many job portals and websites exist, and job seekers profit from them. The job portal allows job seekers and employers to link with one another. Career Okay job portal is one of them which has plenty of job especially jobs situated in Karachi like full-time jobs, [part-time jobs in Karachi](https://www.careerokay.com), HR jobs, Finance jobs, and so on. They are keeping the database of employers and employees and amicable them. Moreover, LinkedIn also provides free services like social connections for job seekers and recruiters. For LinkedIn, it is mandatory to make your profile and remain active.
## Prepare your Resume
Your resume is your advertisement; you must write it in such a way that it highlights your talents and expertise in order to catch the recruiter's attention. Because the recruiter must sift through thousands of resumes, yours must be noticed.
Prepare your resume for a job interview and don't modify it too often. Many HR managers have noticed that many candidates update their resumes at the last minute, adding and eliminating abilities and experience, which causes them to be confused during the interview.
## Build your Network
More than 50% of jobs in corporate work got to someone inside the company or from an employee referral. So it is necessary for job seekers to build their links.
1. First and foremost, ensure that your LinkedIn page is strong and up-to-date
2. Go to sites like Careerokay.com, and Rozee.pk and create a profile but just don't rely on it majorly
3. Networking, I can't exaggerate this point anymore, it can be anyone even someone who's working in a different team in an IT company or is a starter.
4. Join all Facebook LinkedIn pages of IT companies you are interested in as they generally post recruitment ads on their social media pages
5. Connect with a few HR's and send them a mail of your resume through LinkedIn.
## Build your Network
More than 50% of jobs in corporate work got to someone inside the company or from an employee referral. So it is necessary for job seekers to build their links.
1. First and foremost, ensure that your LinkedIn page is strong and up-to-date
2. Go to sites like Careerokay.com, and Rozee.pk and create a profile but just don't rely on it majorly
3. Networking, I can't exaggerate this point anymore, it can be anyone even someone who's working in a different team in an IT company or is a starter.
4. Join all Facebook LinkedIn pages of IT companies you are interested in as they generally post recruitment ads on their social media pages
5. Connect with a few HR's and send them a mail of your resume through LinkedIn.
## Conclusion
Fortunately, Karachi's job market is fairly active. It may appear simple to locate a profession that is a perfect fit among the different sectors and employment categories available, but competition can be high. [Job in Karachi](https://www.careerokay.com/article/how-to-hunt-latest-jobs-in-karachi-90126) to compete with other candidates, you should proceed by closely adhering to the above-mentioned point. Best of luck!
| careerokay | |
1,866,540 | Hire Dedicated Developers in Sweden | Hire Dedicated Development Team | At Sapphire Software Solutions, our team of dedicated developers provides 100% original and... | 0 | 2024-05-27T12:53:08 | https://dev.to/samirpa555/hire-dedicated-developers-in-sweden-hire-dedicated-development-team-2kbg | At Sapphire Software Solutions, our team of dedicated developers provides 100% original and customized web and app solutions. **[Hire Dedicated Developers in Sweden](https://www.sapphiresolutions.net/hire-dedicated-developers-in-sweden)** today for projects. | samirpa555 | |
1,866,539 | Top Software Development Company in Sweden | Software Development Services | Sapphire Software Solutions is a Top Software Development Company in Sweden. We have a team of... | 0 | 2024-05-27T12:48:22 | https://dev.to/samirpa555/top-software-development-company-in-sweden-software-development-services-a2g | Sapphire Software Solutions is a **[Top Software Development Company in Sweden](https://www.sapphiresolutions.net/top-software-development-company-in-sweden)**. We have a team of certified developers who deliver the best software development services to clients. | samirpa555 | |
1,866,538 | Things to Know Before Choosing White Label GPS Tracking Software | White labeling has become a popular trend in the fleet management industry, allowing companies to... | 0 | 2024-05-27T12:47:27 | https://dev.to/ehsan_ali/things-to-know-before-choosing-white-label-gps-tracking-software-50a5 | techtalks, news | White labeling has become a popular trend in the fleet management industry, allowing companies to rebrand products from other manufacturers and sell them as their own. This practice has surged in popularity, particularly with [white label GPS tracking software](https://flotillaiot.com/white-label-gps-tracking-software/). While these solutions offer numerous attractive features, it's crucial to be fully informed before making a decision. Here's what you need to know before choosing white label GPS tracking software.
1. User-friendly Design
The design of any software is a cornerstone of its success. A user-friendly interface is essential, enabling new users to navigate the software with ease. Look for a design that is intuitive, offering tips and suggestions to help users get acquainted with its features. Beyond functionality, the aesthetic aspects like color schemes, font styles, and sizes should be pleasing and easy on the eyes.
2. Vendor’s Reputation
The reputation of the vendor is a critical factor when selecting a reliable GPS tracking solution. Word of mouth is often a reliable indicator. Speak to current or past buyers to gauge the vendor's reputation. Positive feedback from multiple sources can significantly reduce risk. However, negative feedback shouldn't be dismissed outright. Analyze it to determine if the issues raised would be problematic for your specific needs.
3. Customer Support
Effective customer support is essential for any service, especially for white label GPS tracking software. Ensure the vendor offers 24/7 support so that assistance is available whenever needed. Many vendors provide free product training, which is invaluable for new users. Check the responsiveness and efficiency of the support team by asking current clients about their experiences.
4. Remote Monitoring
In today's fast-paced world, mobile access is a necessity. Ensure that the GPS tracking software includes a mobile app for remote monitoring. This feature allows managers to oversee fleet activities on the go, increasing productivity by enabling multitasking.
5. Availability of Hardware
Choosing a vendor that provides both software and hardware can simplify the process. Compatibility between the tracking devices and software is crucial for optimal performance. Vendors with extensive experience in hardware can offer valuable advice, helping you select the most suitable devices.
6. Good Collaboration
Purchasing white label GPS tracking software marks the beginning of a long-term partnership with the vendor. It’s important to understand the vendor’s support policies before making a deal. Ensure they offer comprehensive training and remain accessible for any queries post-purchase. An ideal vendor maintains continuous contact and provides thorough support.
7. Range of Features
A broad range of features can make a GPS tracking solution more attractive. Essential features to look for include GPS tracking, reporting, notifications, and fuel monitoring. Unique features can serve as a unique selling point (USP) for your product, helping you stand out in the market and attract more clients.
8. Customization Options
Customization is a key benefit of white label software. Ensure the GPS tracking software you choose offers customization options that allow you to tailor it to your brand. This includes branding elements like logos and color schemes, as well as functional customizations to meet your specific business needs.
9. Scalability
Your business needs will grow over time, so it’s crucial to choose software that can scale with your operations. Ensure the GPS tracking software can handle an increasing number of vehicles and users without compromising performance.
10. Security Features
Security is paramount when dealing with sensitive data. The GPS tracking software should have robust security measures to protect your data. Look for features like data encryption, secure login, and regular security updates.
11. Integration Capabilities
The ability to integrate with other systems and software can significantly enhance the functionality of your GPS tracking solution. Check if the software supports integration with fleet management software, accounting systems, and other relevant tools.
12. Cost-effectiveness
While it’s tempting to go for the cheapest option, consider the value for money. Assess the features and support offered by the software against its price. A slightly more expensive solution may offer better features and support, providing a higher return on investment in the long run.
13. Compliance with Regulations
Ensure the GPS tracking software complies with relevant industry regulations and standards. This is particularly important if your business operates in multiple regions with varying compliance requirements.
14. Real-time Tracking
Real-time tracking is a crucial feature for fleet management. It allows you to monitor the location and status of your vehicles in real-time, enhancing operational efficiency and security.
15. Reporting and Analytics
Comprehensive reporting and analytics features can provide valuable insights into your fleet operations. Look for software that offers detailed reports on various metrics, helping you make informed decisions and optimize your fleet’s performance.
Conclusion:
Choosing the right Flotilla Iot white label GPS tracking software involves careful consideration of various factors, from user-friendly design and vendor reputation to customer support and feature range. By evaluating these aspects thoroughly, you can select a solution that not only meets your current needs but also supports your business growth.
Also Read: How-flotilla-iot-white-label-gps-vehicle-tracking-software-can-boost-your-fleet-business
FAQs:
1. What is white label GPS tracking software?
White label GPS tracking software is a product developed by one company and rebranded by another to be sold as their own.
2. Why is vendor reputation important when choosing GPS tracking software?
Vendor reputation indicates the reliability and quality of the software. Positive feedback from existing clients can assure you of the product's effectiveness
3. What are the essential features to look for in GPS tracking software?
Key features include GPS tracking, real-time monitoring, reporting, notifications, fuel monitoring, and integration capabilities.
4. How important is customer support for GPS tracking software?
Customer support is crucial as it ensures you get assistance whenever needed, which is vital for resolving issues and ensuring smooth operation.
| ehsan_ali |
1,866,537 | Hire Dedicated Developers in Norway | Hire Dedicated Development Team | Looking to Hire Dedicated Developers in Norway for your next project? Hire Dedicated development team... | 0 | 2024-05-27T12:43:10 | https://dev.to/samirpa555/hire-dedicated-developers-in-norway-hire-dedicated-development-team-30bb | Looking to **[Hire Dedicated Developers in Norway ](https://www.sapphiresolutions.net/hire-dedicated-developers-in-norway)**for your next project? Hire Dedicated development team at Sapphire Software Solutions to boost your business growth. Inquire for more today! | samirpa555 | |
1,866,535 | VTable usage issue: How to make the table automatically calculate column width based only on the table header | Question title How to make the table automatically calculate column width based only on... | 0 | 2024-05-27T12:35:44 | https://dev.to/rayssss/vtable-usage-issue-how-to-make-the-table-automatically-calculate-column-width-based-only-on-the-table-header-1e4p | ### Question title
How to make the table automatically calculate column width based only on the content width of the table header
### Problem description
In automatic width mode, you want the width of a column to be determined only by the content width of the header cell and not affected by the content cell.
### Solution
VTable provides `columnWidthComputeMode`configuration for specifying the bounded areas that are involved in content width calculations:
- 'Only-header ': Only the header content is calculated.
- 'Only-body ': Only calculate the content of the body cell.
- 'Normal ': Calculate normally, that is, calculate the contents of the header and body cells.
### Code example
```javascript
const options = {
//......
columnWidthComputeMode: 'only-header'
};
```
### Results show
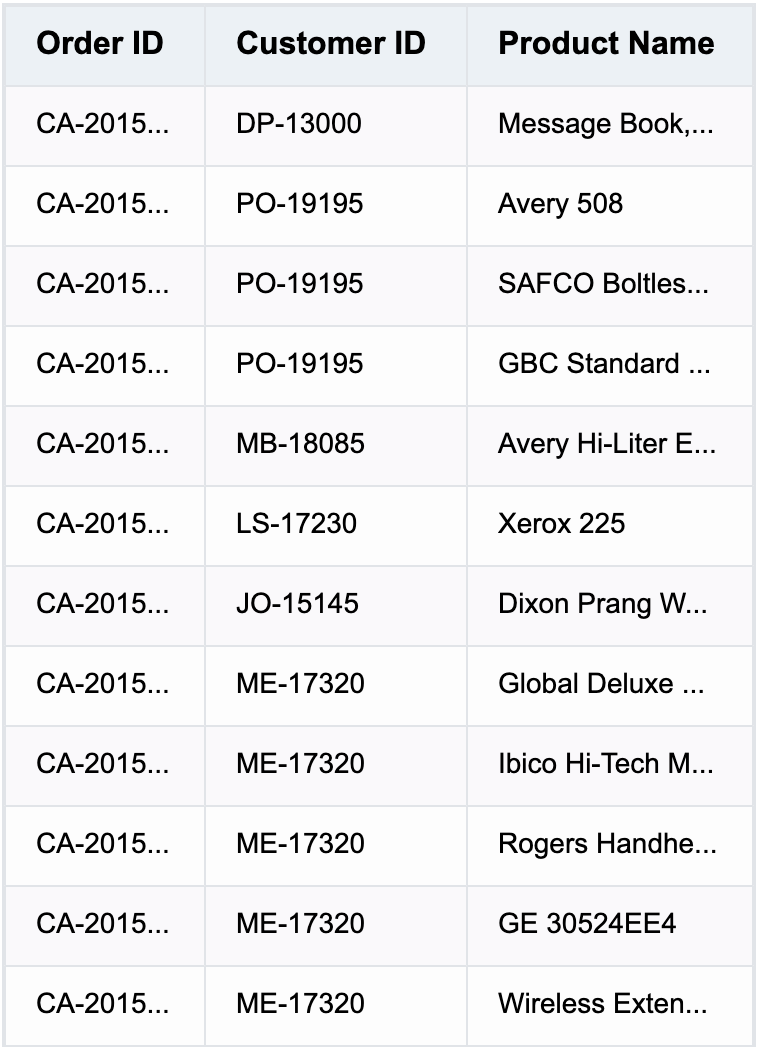
Full sample code (you can try pasting it into the [editor ](https%3A%2F%2Fwww.visactor.io%2Fvtable%2Fdemo%2Ftable-type%2Flist-table-tree)):
```typescript
let tableInstance;
fetch('https://lf9-dp-fe-cms-tos.byteorg.com/obj/bit-cloud/VTable/North_American_Superstore_data.json')
.then((res) => res.json())
.then((data) => {
const columns =[
{
"field": "Order ID",
"title": "Order ID",
"width": "auto"
},
{
"field": "Customer ID",
"title": "Customer ID",
"width": "auto"
},
{
"field": "Product Name",
"title": "Product Name",
"width": "auto"
}
];
const option = {
records:data,
columns,
widthMode:'standard',
columnWidthComputeMode: 'only-header'
};
tableInstance = new VTable.ListTable(document.getElementById(CONTAINER_ID),option);
window['tableInstance'] = tableInstance;
})
```
### Related Documents
Related api: https://www.visactor.io/vtable/option/ListTable#columnWidthComputeMode
github:https://github.com/VisActor/VTable
| rayssss | |
1,866,534 | hgfhgfhghghghgvfhg | A post by Rae Hayley | 0 | 2024-05-27T12:33:48 | https://dev.to/rae_hayley_b6cd161b940c74/hgfhgfhghghghgvfhg-48da | rae_hayley_b6cd161b940c74 | ||
1,866,533 | Next.js: Unleashing the Power of Performance and SEO for Web Development | Next.js, a popular React framework, is not only a powerful tool for building web applications but... | 0 | 2024-05-27T12:33:18 | https://dev.to/kharkizi/nextjs-unleashing-the-power-of-performance-and-seo-for-web-development-2go | webdev, nextjs, community |
Next.js, a popular React framework, is not only a powerful tool for building web applications but also offers numerous significant benefits for developers. Let's explore the key advantages of Next.js:

## 1. Server-side Rendering (SSR) and Static Site Generation (SSG)
Next.js combines both SSR and SSG, allowing your application to generate web pages with content created at request time or beforehand. This improves page load times and user experience while enhancing search engine optimization (SEO) on platforms like Google.
## 2. SEO Optimization
With the ability to generate server-side content, Next.js helps improve your website's search engine visibility. SEO optimization becomes easier, ensuring your website is found and ranks higher in search results.

## 3. Built-in Integration with React and TypeScript
Next.js comes with built-in integration with React, a widely used JavaScript library in the development community. You can also use TypeScript to enhance the flexibility and maintainability of your codebase.
## 4. Simple Routing
Next.js provides a simple yet powerful routing system, making it easy and efficient to organize your application. You can define routes and navigate effortlessly through JavaScript files in the pages directory.
## 5. Easy Deployment
Next.js integrates well with various web development services like Vercel, Netlify, and AWS Amplify, making it easier and more convenient than ever to deploy and manage your application.
## 6. Strong Community Support and Extensive Documentation
Next.js has a large and vibrant community, offering extensive documentation, tutorials, and learning resources. You can easily find solutions to development issues and receive community support during your development process.
## 7. Flexible Integration with Other Technologies
Next.js integrates well with various technologies and services such as GraphQL, Redux, and CSS-in-JS libraries. This flexibility allows you to build complex web applications and meet the technical demands of your project.
## Conclusion
Next.js is not only a powerful web development tool but also a flexible and versatile one, offering numerous benefits to developers. From SSR and SSG to integration with React and other technologies, Next.js is an excellent choice for building efficient and maintainable websites.
## ForCat Shop
[ForCat Shop](https://www.forcatshop.com/) is a store specializing in pet accessories built using Next.js. You can visit the site at https://www.forcatshop.com/ to learn more about the website.
| kharkizi |
1,866,719 | Chrome DevTools 2024: Top 5 New Features to Boost Your Workflow | TL;DR: The newest features in Chrome DevTools for 2024 include improved performance profiling,... | 0 | 2024-05-27T16:22:37 | https://www.syncfusion.com/blogs/post/chrome-devtools-2024-top-5-features | webdev, javascript, productivity, tools | ---
title: Chrome DevTools 2024: Top 5 New Features to Boost Your Workflow
published: true
date: 2024-05-27 12:29:23 UTC
tags: webdev, javascript, productivity, tools
canonical_url: https://www.syncfusion.com/blogs/post/chrome-devtools-2024-top-5-features
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/bhetdvg5xvvgy39412sy.png
---
**TL;DR:** The newest features in Chrome DevTools for 2024 include improved performance profiling, streamlined autofill capabilities, scroll-driven animations, enhanced network throttling for WebRTC, and better CSS nesting.
[Chrome DevTools](https://developer.chrome.com/docs/devtools "Chrome DevTools") are essential to designing and fine-tuning websites and web apps. They allow you to peek under a webpage’s hood, modify its elements, monitor network activity, and diagnose performance issues. Mastering DevTools boosts your workflow and improves the overall developer experience.
This article will look at the top five features recently released in Chrome DevTools.
## 1. Enhanced Performance panel
The Performance panel has been significantly improved to integrate features from Google’s auditing tools and the Performance Insights panel. This integration makes it easier for developers to identify and reproduce performance issues, offering a more powerful and user-friendly interface for all performance data and insights. The focus on UX and usability enhances the effectiveness of the Performance panel as a web performance optimization tool.[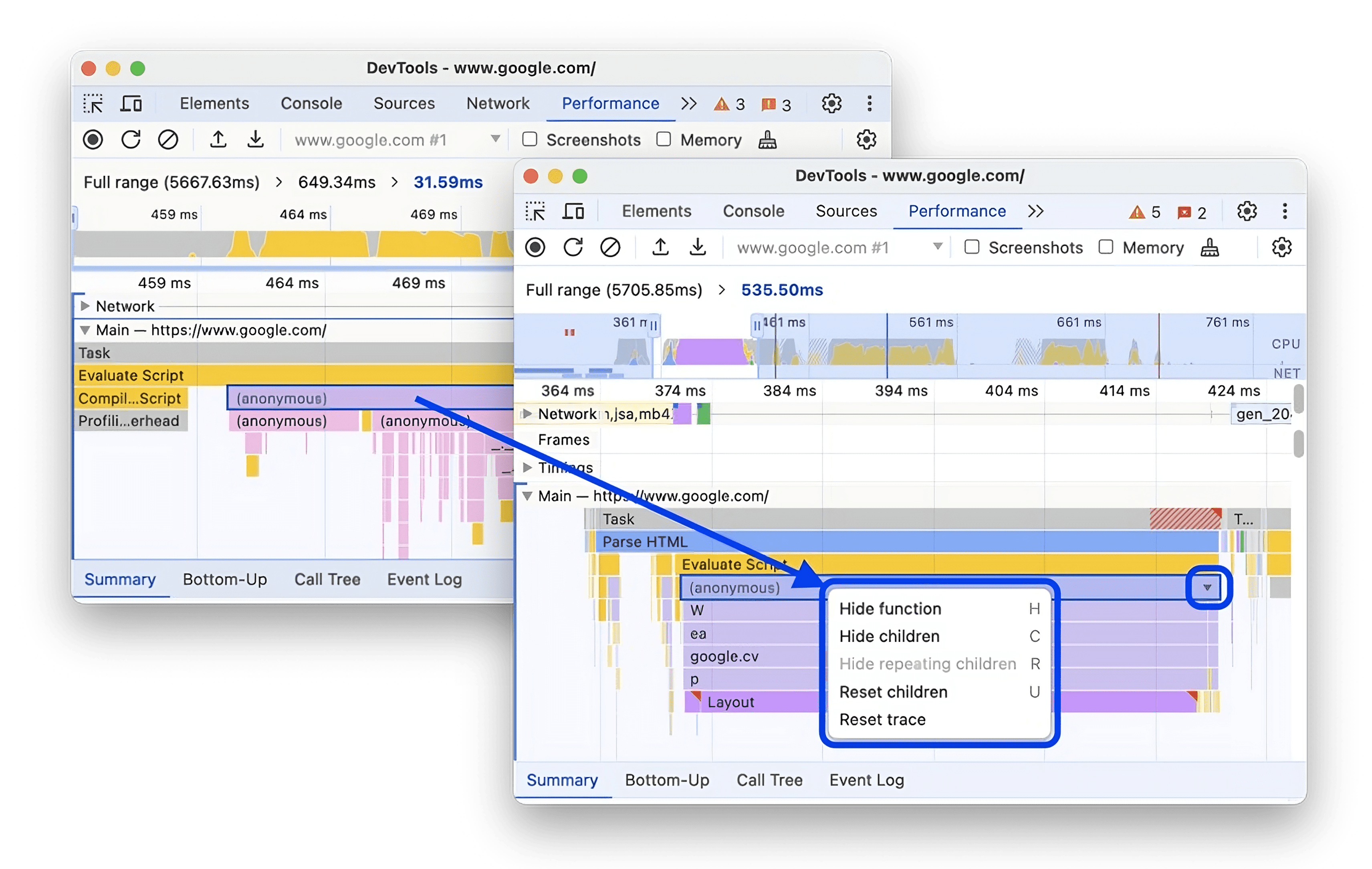](https://www.syncfusion.com/blogs/wp-content/uploads/2024/05/Enhanced-Performance-Panel-in-Chrome-DevTools-1.png)
To **open** the enhanced **Performance** **panel** in **Chrome DevTools,** follow these steps **:**
1. Open Chrome DevTools by right-clicking anywhere on a webpage, selecting **Inspect,** or by pressing **Ctrl+Shift+I** (Windows/Linux) or **Cmd+Option+I** (Mac).
2. Navigate to the **Performance** tab within the DevTools window.
3. Click **Start Profiling and reload the page**.
This action will initiate a performance recording session, in which DevTools records performance metrics as the page loads and then automatically stops the recording a couple of seconds after the load finishes.
DevTools will automatically zoom in on the recording portion where most of the activity occurred, showing the activity during a page load in the Performance panel.
## 2. New Autofill panel
The Autofill panel in Chrome DevTools provides a convenient way to fill forms automatically on websites with saved addresses. This feature allows developers to inspect the mapping between form fields, predicted autofill values, and saved data, streamlining the process of testing and debugging form autofill functionalities.[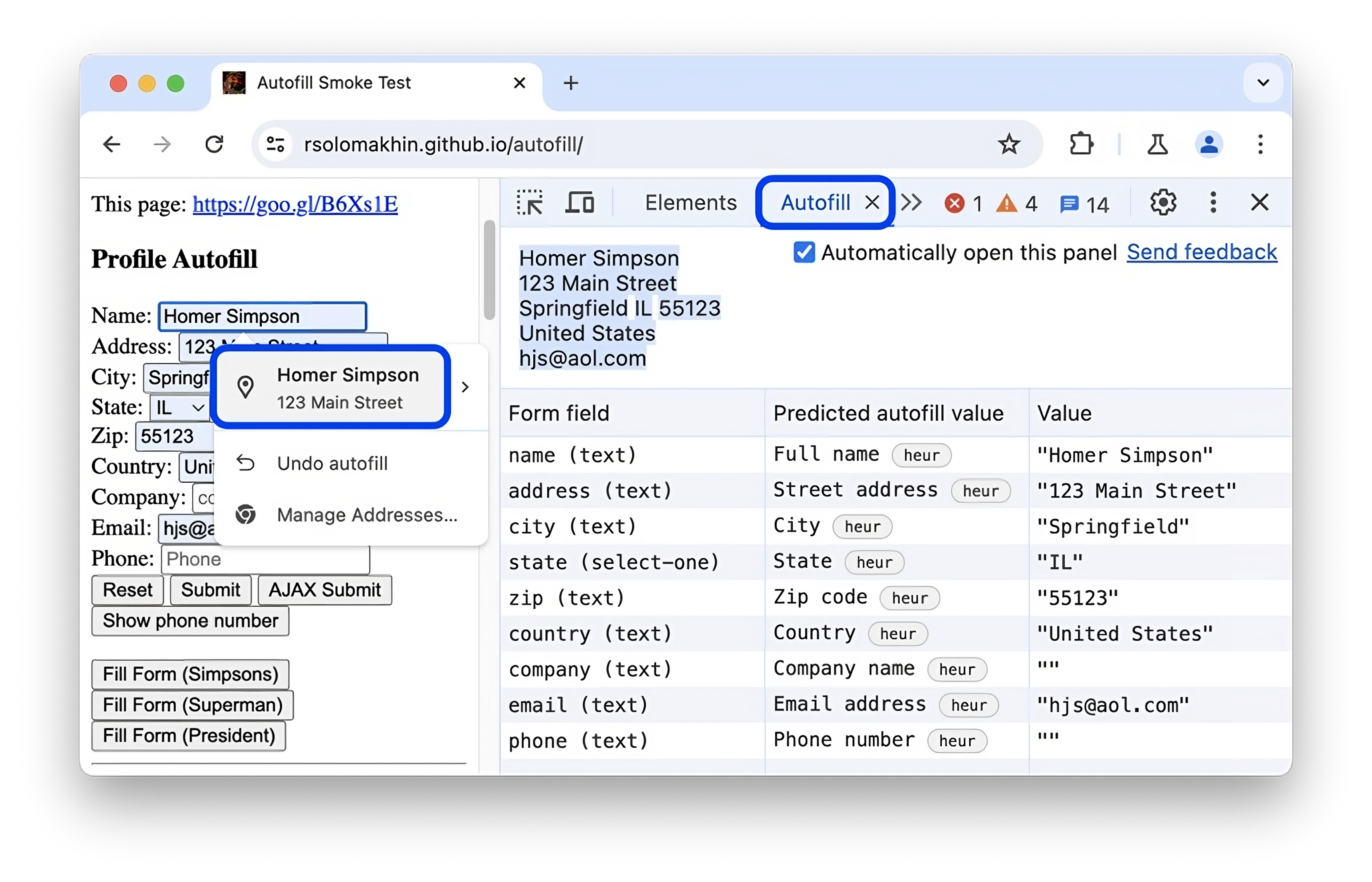](https://www.syncfusion.com/blogs/wp-content/uploads/2024/05/New-Autofill-Panel-in-Chrome-DevTools-1.png)
To utilize the autofill feature in Chrome DevTools, follow these steps:
1. Navigate to a webpage with a form. Click any of the **Fill form** buttons, then click **Submit**.
2. A dialog titled **Save address?** will appear. Click **Save** to save the address information.
3. Return to the form page.
4. Open Chrome DevTools.
5. Within a form field, select the address from the dropdown list that appears due to the previously saved address information. This action triggers an autofill event.
The Autofill panel in DevTools automatically opens. This panel displays the form fields detected, those inferred by autofill, and the saved values associated with them.
## 3. Scroll-driven animations
The newly added scroll-driven animation support in the Animations panel allows developers to analyze and debug animations triggered by scrolling. This feature is particularly useful for optimizing performance and ensuring a smooth user experience on webpages with complex animations. [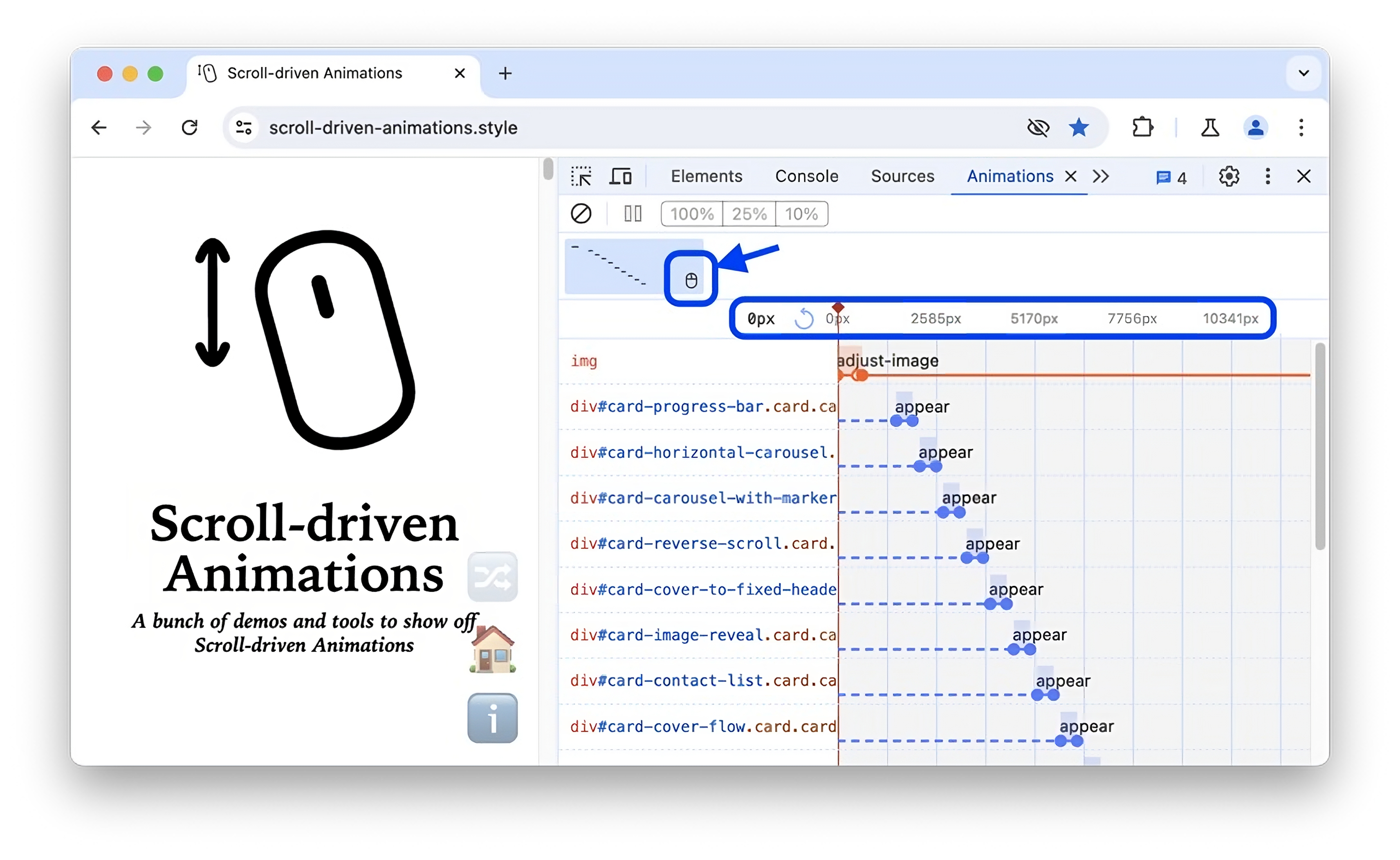](https://www.syncfusion.com/blogs/wp-content/uploads/2024/05/Scroll-Driven-Animations-in-Chrome-DevTools-1.png)
To access the Animations panel in Chrome DevTools, either:
1. Navigate to **Customize and Control DevTools** **-> More tools -> Animations**.
2. Open the **Command Menu** by pressing **Command + Shift + P** on macOS or **Control + Shift + P** on Windows, Linux, or ChromeOS. Then, enter **Show Animations** and select the corresponding drawer panel.
## 4. Enhanced network throttling for WebRTC
The latest upgrade in Chrome DevTools introduces enhanced packet-related parameters, allowing you to have direct control over your WebRTC app’s performance. This enhancement is especially valuable for testing real-time communication setups independently, without the need for external tools.
**The newly introduced parameters include:**
- Packet Loss (percentage)
- Packet Queue Length (number of packets)
- Packet Reordering (checkbox)
These additions allow for more granular control over network conditions, simulating various real-time communication scenarios. [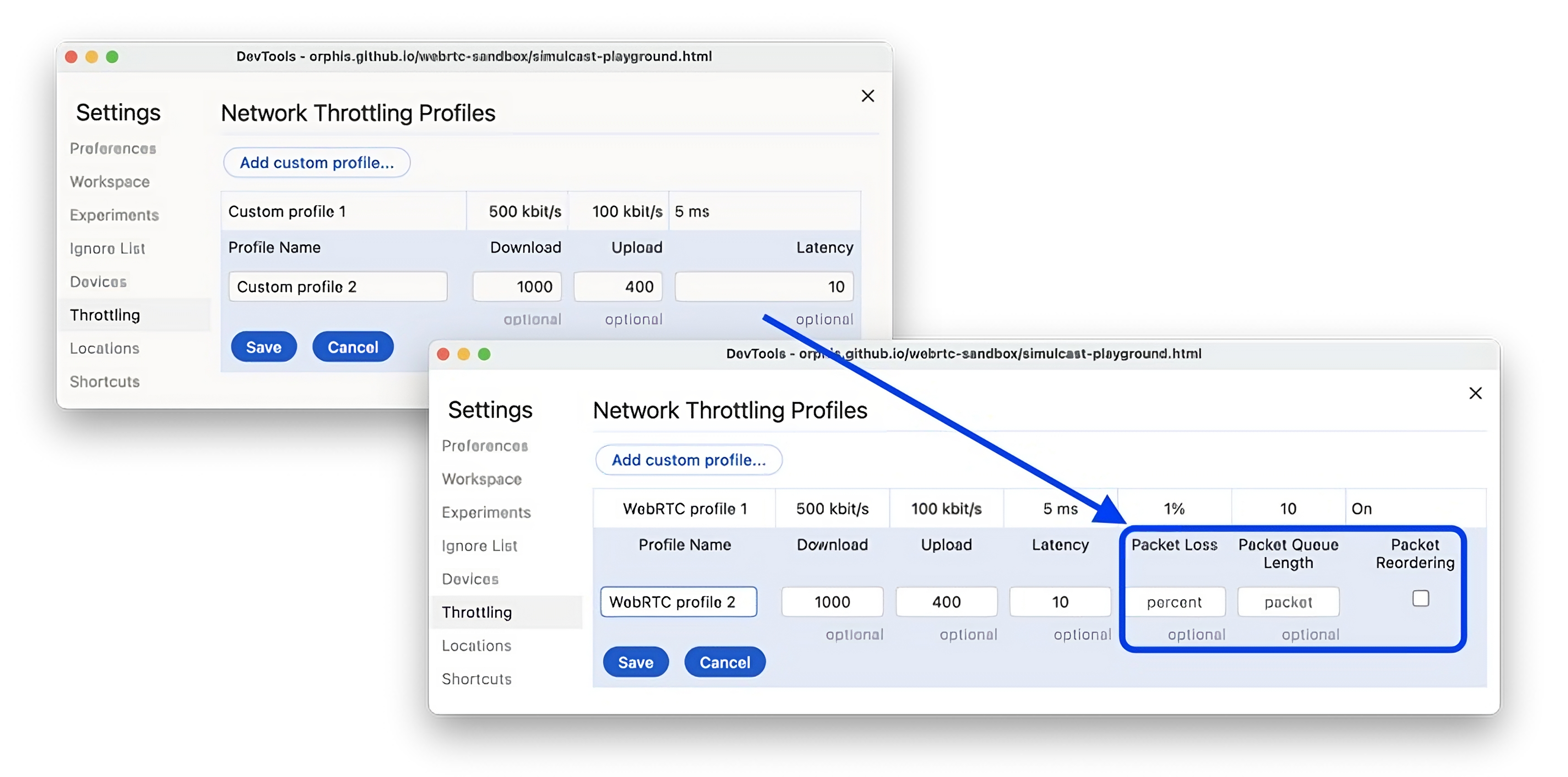](https://www.syncfusion.com/blogs/wp-content/uploads/2024/05/Enhanced-Network-Throttling-for-WebRTC-in-Chrome-DevTools-1.png)
To apply these settings to a WebRTC connection, follow these steps:
1. Go to **Settings –> Throttling** in DevTools.
2. Create or modify a custom profile to include the packet-related parameters.
3. Apply this custom profile in the **Network** panel.
## 5. Enhanced CSS nesting support
Chrome DevTools now make working with complex CSS easier. With better nesting support in the **Elements –> Styles** section, editing nested CSS rules becomes simpler. This enhancement helps you make styling adjustments faster and more accurately. [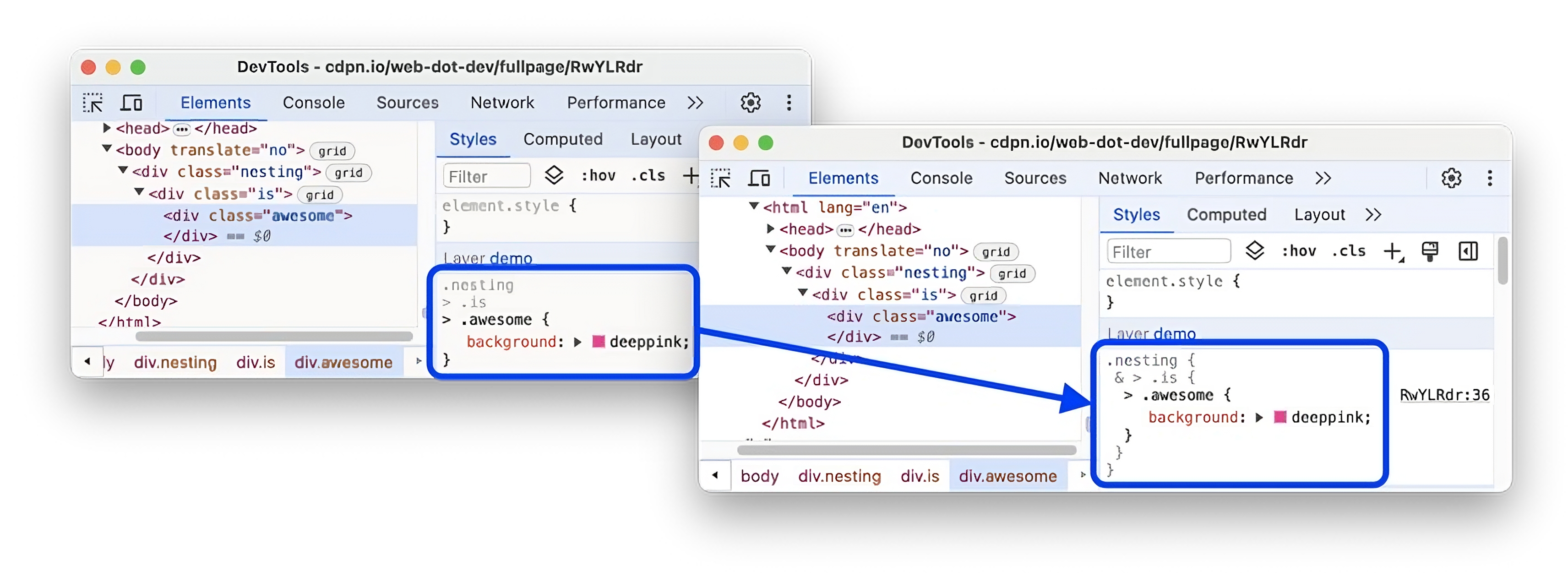](https://www.syncfusion.com/blogs/wp-content/uploads/2024/05/Enhanced-CSS-Nesting-Support-in-Chrome-DevTools-1.png)
## Final thoughts
Thanks for reading! This blog explored how Chrome DevTools can boost efficiency and help you build better, bug-free websites. The highlighted features will transform your debugging process and enhance your workflow. Keep in mind that mastering these tools requires a shift in how you think about and approach debugging. Happy developing!
The Syncfusion [JavaScript suite](https://www.syncfusion.com/javascript-ui-controls "JavaScript UI Controls Library") is a comprehensive solution for app development, offering high-performance, lightweight, modular, and responsive UI components. We encourage you to download the [free trial](https://www.syncfusion.com/downloads/essential-js2 "Get free evaluation of the Essential Studio products") and assess these controls.
If you have any questions, you can reach us through our [support forums](https://www.syncfusion.com/forums "Syncfusion Support Forums"), [support portal](https://support.syncfusion.com/ "Syncfusion Support Portal"), or [feedback portal](https://www.syncfusion.com/feedback/ "Syncfusion Feedback Portal"). We’re always here to assist you!
## Related blogs
- [Top 5 Chrome Extensions for Handling HTTP Requests](https://www.syncfusion.com/blogs/post/top-5-chrome-extensions-for-handling-http-requests "Blog: Top 5 Chrome Extensions for Handling HTTP Requests")
- [6 Chrome Extensions Every Web Developer Should Know](https://www.syncfusion.com/blogs/post/chrome-extensions-web-developer-2023 "Blog: 6 Chrome Extensions Every Web Developer Should Know in 2023")
- [The 12 Best, Must-Have Chrome Extensions for Web Developers](https://www.syncfusion.com/blogs/post/12-must-have-chrome-extensions-for-web-developers "Blog: The 12 Best, Must-Have Chrome Extensions for Web Developers")
- [7 JavaScript Unit Test Frameworks Every Developer Should Know](https://www.syncfusion.com/blogs/post/javascript-unit-test-frameworks "Blog: 7 JavaScript Unit Test Frameworks Every Developer Should Know") | gayathrigithub7 |
1,866,531 | good job | good | 0 | 2024-05-27T12:28:08 | https://dev.to/yokle214/good-job-3enk | webdev, javascript | good | yokle214 |
1,866,529 | Sweet Sixteen Sophistication: Rose Petal Garlands for Memorable Celebrations | A Sweet Sixteen marks a pivotal moment in a young woman's life. It's a time of transition,... | 0 | 2024-05-27T12:27:34 | https://dev.to/johnmathew01/sweet-sixteen-sophistication-rose-petal-garlands-for-memorable-celebrations-22b9 | blog, article, usa, california | A Sweet Sixteen marks a pivotal moment in a young woman's life. It's a time of transition, celebrating the blossoming of youth and individuality. While traditional decorations can be lovely, incorporating unique elements can elevate the event to a sophisticated and unforgettable experience. Here's where the elegance and versatility of rose petal garlands come into play.
A Timeless Symbol of Beauty and Grace:
Roses have long been associated with love, beauty, and new beginnings – all fitting themes for a Sweet Sixteen celebration. Rose petal garlands offer a captivating alternative to standard floral arrangements. They add a touch of whimsy and elegance, creating a sensory experience that complements the celebratory atmosphere.
Beyond the Bouquet: Creative Applications of Rose Petal Garlands:
Entrance Enchantment: Drape a cascade of rose petal garlands over the entranceway, creating a stunning visual welcome for guests.
Tabletop Elegance: Scatter rose petal garlands down the center of tables, adding a touch of romantic charm to the dining area.
Dazzling Décor: Drape rose petal garlands around pillars, archways, or the backdrop of a photo booth, creating a picture-perfect setting for capturing memories.
Sweet Sixteen Throne: Adorn the guest of honor's chair with a delicate rose petal garland, adding a touch of royalty to her special day.
Customization for a Personal Touch:
Rose petal garlands can be customized to reflect the celebrant's personality and the overall theme of the event.
Color Coordination: Choose rose petals in hues that complement the chosen color palette, creating a cohesive and stylish aesthetic.
Aromatic Ambiance: Opt for fragrant rose varieties like Damask or Sweetheart Roses to fill the space with a delightful aroma.
Mixed Media Magic: Combine rose petals with other natural elements like dried flowers, greenery, or even crystals for a unique and textured garland.
DIY or Professionally Crafted:
For the crafty individual, creating rose petal garlands can be a delightful pre-celebration activity. However, for a more elaborate design or time constraints, professional florists can create stunning custom garlands to meet your specific vision.
Beyond the Celebration:
Rose petal garlands can also serve as a beautiful and fragrant take-home favor for guests. Small, personalized sachets filled with dried rose petals offer a lasting reminder of the Sweet Sixteen celebration.
Conclusion:
Rose petal garlands offer a sophisticated and elegant way to elevate a Sweet Sixteen celebration. Their versatility allows for creative expression, while their timeless symbolism perfectly complements this pivotal moment in a young woman's life. By incorporating rose petal garlands, you can create a truly memorable and sophisticated event that celebrates the blossoming of youth and grace.
https://theindianflowers.com/product-category/wedding-garlands/rose-petal-garlands/ | johnmathew01 |
1,866,527 | THE HOLISTIC NATURAL OF SPIRITUAL SCIENCES | The term "spiritual sciences" typically refers to disciplines that explore the nature of... | 0 | 2024-05-27T12:26:02 | https://dev.to/obulesu_koduru_91a62bf967/the-holistic-natural-of-spiritual-sciences-4pn5 | The term "spiritual sciences" typically refers to disciplines that explore the nature of consciousness, the human spirit, and the interconnectedness of all things. When we talk about the holistic nature of spiritual sciences, we're considering the idea that these disciplines often take a comprehensive approach, acknowledging the interconnectedness of mind, body, and spirit. | obulesu_koduru_91a62bf967 | |
1,866,526 | How does Eduler assist with choosing the right university and program? | As an education consultancy platform, Eduler helps students in the selection of the university and... | 0 | 2024-05-27T12:21:51 | https://dev.to/eduler/how-does-eduler-assist-with-choosing-the-right-university-and-program-3f0h | eduler | As an education consultancy platform, Eduler helps students in the selection of the university and program. Its amazing features and services make it such that a click process gets you to choose from a handful of options available considering your best interests.
**Personalized Counseling**
**Initial Consultation:** Get the initial consultation from Eduler to learn about your academic background, interests, career goals, and preferences. The more information shared, the better the recommendations.
**Profile Evaluation:** The platform examines a student’s academic performance, extracurriculars, standardized test results, and other relevant factors to determine the right fit.
**University and Program Suggestions**
**Database on Universities and Programs:** Eduler has a huge database on the college’s distinctive connected universities in numerous countries. The website contains rankings, specializations, entry requirements, and a tuition fee information database as well.
**Matching Algorithms:**
It uses highly developed matching algorithms that consider a student’s profile and their preferences to recommend universities and programs that meet the student's objectives, interests, skill levels, etc.
It also provides universities' detailed profiles which include campus facilities, faculty quality and qualification, research opportunities, internship & job percentage of students placed after completion of studies as well as trends.
**Program Details**
The website provides information on individual programs such as curriculum layout, course syllabi, faculty backgrounds, and possible career opportunities after completion of the program.
**Application Assistance:** Eduler provides detailed instructions on the application, how to prepare and submit the application forms, and on writing personal statements or motivation letters as well as recommendation letters.
**Document Review:** On the platform, Eduler offers to review and provide feedback on application documents to ensure that they are at the necessary level and reflect their strengths most strongly.
**View More Financial Planning and Scholarships**
**Cost Analysis:** Eduler helps you out in getting all the financial details of your [study abroad](https://g.co/kgs/2EaAGn7), this includes tuition fees and while living there we need to be aware of everything like where we are staying then how shall it be charged as rent.
**Scholarship & Funding Options:** The platform also automatically surfaces scholarships, grants, and financial aid students qualify for, then handles the application on their behalf to unlock these crucial grants.
**Test Preparation & Language Training**
**Standardized Test Prep:** Online learning platform Eduler provides resources and coaching for standardized tests including SAT, ACT, GRE, GMAT TOEFL, and IELTS which are usually part of the admission process in universities.
**Language Courses:** Eduler offers language training programs for students who must improve their language skills.
**Post-Acceptance Support**
**Visa Assistance:** As a result, Eduler assists students with the entire student visa application process by validating all their documents and requirements.
**Pre-departure Orientation:** The platform also provides a pre-departure session to make the student familiar with their new environment this session includes all topics related to cultural adaption, short or long-term Airbnb booking, travel arrangements, and much more!
**Ongoing Support**
**Alumni Network:** Eduler links students with alumni networks that can offer mentorship, guidance, or support to help the graduates contend with the same experiences.
**Career Services:** In addition, the platform provides career counseling and job search assistance to help students move from education to employment.
**Conclusion**
With a blend of personalized counseling, a plethora of resources, and continued support, Eduler enable students to make well-informed decisions about their higher educational intentions which in turn increases the likelihood of success and satisfaction over student’s academic and professional life.
**FAQ’s**
**What are the things to consider while looking for a master’s program?**
Accreditation and reputation of the university, curriculum and specialization, research opportunities, cost of living, and alumni network are some of the important factors to consider while choosing a master’s program.
**Is choosing a good university important?**
Choosing a renowned university is one of the most important decisions you will ever make, as it decides a lot not only about your formation as a professional or even personal growth and development. Choose a reputable university to maximize your chances of fulfilling your academic and professional aims. Finding the right program, in terms of fit, location, costs, etc., is crucial as well; but relatively pointless if you’re not accepted into any program.
**What does a university look for while enrolling students?**
There are several assuring requirements of universities for enrolling foreign students to ensure that they will meet the criteria academically and be a favorable addition to the university and country.
**Which are the best countries to pursue MS in?**
The USA, Canada, Australia, Germany, and the UK are some of the best countries to pursue MS in.
**Why are students opting to study MS abroad?**
High academic standards, innovative research, and state-of-the-art facilities are well-known attributes of many international universities. Institutions that routinely rank highly in international university rankings are found in nations like the USA, UK, Canada, and Germany.
**What are the requirements to study in Canada university?**
If you are planning to **[study in Canada University](https://eduler.in/study-in-canada/)**, there are certain requirements, which can differ from institution to institution or depending on the program you apply to. Do read our blog on the specific requirements. | eduler |
1,866,521 | How I Replaced Gaming with Coding and Became a Web Developer | Today, I would like to share my personal story. I hope it helps you get to know me better and maybe... | 0 | 2024-05-27T12:19:27 | https://dev.to/proflead/how-i-replaced-gaming-with-coding-and-became-a-web-developer-18bf | webdev, interview, howto, story | Today, I would like to share my personal story. I hope it helps you get to know me better and maybe benefits your own journey.
## A Bit of History
My love for gaming has a long history. I was lucky because my parents could buy a computer when I was very young. It was an IBM 486 🙂 and it belonged to my brother.
## My First Games
The first games I remember playing were Wolf and Doom. Wolf is a first-person shooter action game that still sticks in my memory.
Doom is a similar type of game to Wolf, but it was very scary, so I didn’t play it at night. 🙂 It was such an exciting game that I still remember the cheat codes: IDDQD (God Mode) and IDKFA (full set of weapons).

Then came Duke Nukem, Sin City, Blood, and more.
Actually, Blood was the first PVP game for me. I remember trying to connect through a Dial-Up modem with my uncle. 🙂 It was a terrible experience, but we managed to see each other in the game. However, there was no chance to have real PVP actions.

I think some of you don’t know what Dial-Up is. Dial-Up or Usenet was a UNIX-based system that used a dial-up connection to transfer data through telephone modems.
## Sounds of Dial-Up
{% embed https://youtu.be/QNcSEuLWqdY?si=oD1GyuygH3DisUUt&t=115 %}
[Visit my YouTube Channel](https://www.youtube.com/@proflead/videos?sub_confirmation=1)
## PVP Games
As time went on, more PVP games appeared on the market, and I started playing more seriously, even participating in local competitions in my hometown.
We played:
- Quake 3
- Counter Strike
- StarCraft
- Etc.
PVP games took a lot of my time. I loved playing and could play for many hours. Sometimes, after school, my friends and I would go to a computer club and spend 6 or more hours there. In the computer club, I saw Ultima Online for the first time.
## First Learning
I believe that games helped me learn various things about computers. At that time, I felt like I knew almost everything about computers, both software and hardware.
I started with DOS, then Norton Commander, then Windows 3.1, and so on. I could replace certain parts of the computer, like HDDs and RAM, and connect multiple computers together, etc. Many of my friends called me to fix their devices or reinstall Windows. I felt that I had some skills that others didn’t.
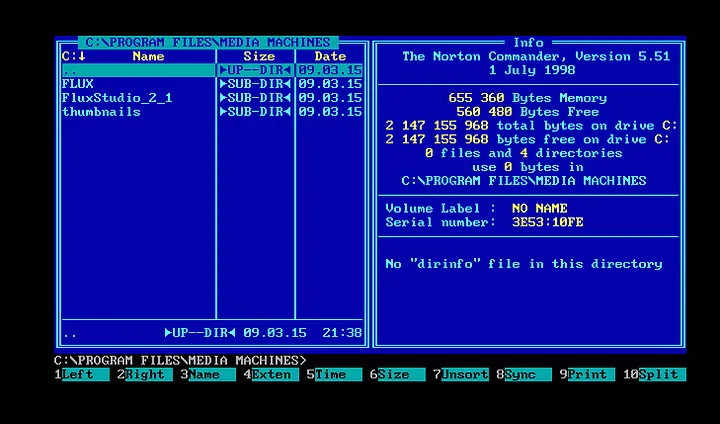
This probably influenced my direction. After school, I joined Moscow Mathematics College and started my software engineering journey. My major was “Organization and Technology of Information Security.” We learned many things, some of which I liked and some I didn’t, but I never had a problem spending time in front of a computer. 🙂 In college, I first learned HTML.
I liked studying, but I loved playing games even more.
## Ultima Online
Ultima Online is a fantasy massively multiplayer online role-playing game released on September 24, 1997, by Origin Systems. Set in the Ultima universe, it is known for its extensive player versus player (PVP) combat system.
To this day, I think it is the best game ever. 🙂 You played with real people like yourself. In this game, you had to develop not only your character’s skills (which could take more than a year) but also personal skills like trading, negotiation, business, saving, and more.
You had to spend many days, and sometimes months, to grow your character’s skill from 0 to grandmaster level. You had to travel around the universe to find different things for crafting, hunting, and so on. The most exciting part was when you left the guarded zone. This was when you could lose everything if someone killed you. That’s why you had to think carefully about where you went and what you took with you. 🙂 It was a really good game, and I still have good memories of it.
I played pretty well and often stayed on the ranking tables for PVP battles.

## Time to Change
Since I spent so much time playing this game, I sometimes felt like I was wasting my time. However, I didn’t want to stop. 🙂
One day, during a very important PVP battle, I lost. I was so sad that I decided to stop playing. I’m not sure why, but that loss helped me change my habits. I don’t think it was easy, but I don’t remember suffering during that time, so maybe it wasn’t that bad :).
Even though I still spent a lot of time on the computer, I tried to find new ways to fill that time. Since I was very young and still studying, I didn’t think about getting a job. But one day, I heard about freelancing and online work. It was interesting because I saw the opportunity to earn money.
## First Freelance Job
I don’t remember if fl.ru was the first website where I registered, but I think it was where I found my first web task. 🙂
That was more than 18 years ago! 🙂 Wow! The task was to convert a .psd file into an HTML page.
I had never done such a job before, but I wasn’t afraid to try (haha, I think I was very afraid). I wasn’t very skilled with Photoshop, so I cut some parts of the layout using MS Paint (I took screenshots and then pasted them into MS Paint). It was the first time I found out that the .bmp format is not suitable for the web. It was too heavy, and the page loaded very slowly. 🙂
After many hours of work, I finished my HTML code and sent it to my customer. He was happy with the result and transferred my first payment. I was so happy! An extra level of happiness came when I learned that he wanted to work with me on another project because the speed of my page and the quality of my work were good.
Making money was an enjoyable process, just like playing a game, so I started to spend more time learning HTML coding and doing different freelance work.
After about 3–6 months, I found a job that allowed me to study and work at the same time. My first position was as a webmaster. 🙂
From that time until today, I have almost never given up on computers and web development. I’ve learned a lot of different things over these 18 years and continue my journey to this day. 🙂
From time to time, I go back to playing games, but it’s not the same anymore. 🙂 | proflead |
1,866,520 | Component Services Management Shortcut in Windows 11 | Component Services Management Shortcut: It is a framework and a set of administrative tools that... | 0 | 2024-05-27T12:19:07 | https://dev.to/winsidescom/component-services-management-shortcut-in-windows-11-532f | webdev, tutorial, productivity, dotnet | <strong>Component Services Management Shortcut</strong>: It is a framework and a set of administrative tools that allow users to manage Component Object Model <strong>(COM)</strong> and Distributed Component Object Model <strong>(DCOM)</strong> applications. It provides a centralized interface to configure, control, and troubleshoot these components. The <strong>Component Services management console is the primary tool</strong> for managing these services. In this article, we will navigate through the steps to create a <strong>Component Services Management Console Shortcut</strong> in Windows 11. <strong>Check out: <a href="https://winsides.com/enable-msmq-dcom-proxy-in-windows-11/">How to Enable MSMQ DCOM Proxy in Windows 11</a></strong>
<h2>Create Component Services Management Console Shortcut in Windows 11:</h2>
<ol>
<li><strong>Right-click</strong> on the Desktop, hover on <strong>New</strong> and click on <strong>Shortcut</strong>.
<img class="wp-image-701 size-full" src="https://winsides.com/wp-content/uploads/2024/05/Create-New-Shortcut.jpg" alt="Create New Shortcut" width="816" height="619" /> Create New Shortcut</li>
<li>Create Shortcut Dialog box will open now.</li>
<li>In "<strong>Type the Location of the item</strong>", enter the following command.<code><code>dcomcnfg</code></code>
<img class="wp-image-696 size-full" src="https://winsides.com/wp-content/uploads/2024/05/dcomcnfg.jpg" alt="Type the location of the item" width="744" height="619" /> Type the location of the item</li>
<li>By default, the item's name will take "dcomcnfg". However, feel free to change it at your convenience.
<img class="wp-image-697 size-full" src="https://winsides.com/wp-content/uploads/2024/05/Name-of-the-shortcut.jpg" alt="Enter the name of the item" width="736" height="620" /> Enter the name of the item</li>
<li>Finally, click <strong>Finish</strong>.</li>
<li>You can find the dcomcnfg shortcut created on the Desktop of Windows 11.
<img class="wp-image-695 size-full" src="https://winsides.com/wp-content/uploads/2024/05/DCOMCNFG-Shortcut.jpg" alt="Component Services Management Shortcut" width="452" height="189" /> Component Services Management Shortcut</li>
<li>Double-click on that to open the Component Services Management Console in Windows 11.
<img class="wp-image-694 size-full" src="https://winsides.com/wp-content/uploads/2024/05/Component-Services-Management-Console.jpg" alt="Component Services Management Console in Windows 11" width="979" height="543" /> Component Services Management Console in Windows 11</li>
</ol>
Facts: The Component Services management console provides a <strong>user-friendly graphical interface</strong> to manage the configuration settings of COM and DCOM applications.
<h3>How to Check Component Services Management Console Version in Windows 11:</h3>
Here in this section, we will check out the steps on How to check out the Microsoft Management Console Version and Component Services Version in Windows 11.
<h4>Check Microsoft Management Console Version:</h4>
<ul>
<li>In Component Services Management Console, click on Help and then click on <strong>About Microsoft Management Console</strong>.
<img class="wp-image-703 size-full" src="https://winsides.com/wp-content/uploads/2024/05/About-Component-Services-Management-Console.jpg" alt="About Microsoft Management Console" width="975" height="531" /> About Microsoft Management Console</li>
<li>Now, you can find the version of Microsoft Management Console. At the time of publishing this article, the latest version is <strong>3.0</strong>.
<img class="wp-image-702 size-full" src="https://winsides.com/wp-content/uploads/2024/05/Microsoft-Management-Console-3.0.jpg" alt="Microsoft Management Console 3.0" width="979" height="556" /> Microsoft Management Console 3.0</li>
</ul>
<h4>Check Component Services Version in Windows 11:</h4>
<ul>
<li>In the same way, click on Help and then click on <strong>About Component Services</strong>.
<img class="wp-image-705 size-full" src="https://winsides.com/wp-content/uploads/2024/05/About-Component-Services-Management.jpg" alt="About Component Services Management" width="984" height="542" /> About Component Services Management</li>
<li>At the time of this article, the latest version of <strong>Component Services(COM+) Management Tool</strong> is 10.0.
<img class="wp-image-706 size-full" src="https://winsides.com/wp-content/uploads/2024/05/Component-Services-management-Tool-Version.jpg" alt="Component Services management Tool Version" width="545" height="356" /> Component Services Management Tool Version</li>
</ul>
<h2>Take away:</h2>
By following simple steps to create this shortcut, you <strong>streamline your workflow</strong>, enhance productivity, and maintain optimal system performance with minimal hassle. Whether you're an <strong>IT professional</strong>, <strong>system administrator</strong>, or <strong>developer</strong>, <strong>Component Services Management Shortcut</strong> in Windows 11 helps you swiftly configure, secure, and troubleshoot your components, ensuring smooth and secure communication across your networked systems. <strong>Happy Coding! Peace out!</strong>
Source: [COM Shortcut in Windows 11](https://winsides.com/create-component-services-management-shortcut-windows-11/) | winsidescom |
1,866,519 | Top Features of Divsly Email Marketing You Need to Know | Email marketing remains a powerful tool in the digital marketing arsenal, offering businesses a... | 0 | 2024-05-27T12:18:30 | https://dev.to/divsly/top-features-of-divsly-email-marketing-you-need-to-know-40nn | emailmarketing, emailcampaigns, emailmarketingcampaigns | Email marketing remains a powerful tool in the digital marketing arsenal, offering businesses a direct line to their customers and prospects. With an array of platforms available, finding the right one can be challenging. Enter Divsly, a comprehensive [email marketing](https://divsly.com/features/email-marketing) solution designed to cater to businesses of all sizes. In this blog, we will explore the top features of Divsly Email Marketing that make it a standout choice for your marketing needs.
## User-Friendly Interface
One of the most compelling features of Divsly is its intuitive and user-friendly interface. Whether you’re a seasoned marketer or a beginner, Divsly’s dashboard is designed to be navigated with ease. The platform offers drag-and-drop functionality, allowing you to create, edit, and manage your email campaigns without any technical expertise. This simplicity ensures that you can focus on crafting effective messages rather than struggling with complicated tools.
## Advanced Segmentation
Effective email marketing hinges on the ability to send the right message to the right audience. [Divsly](https://divsly.com/) excels in this area with its advanced segmentation features. You can segment your email list based on various criteria such as demographics, past purchase behavior, engagement levels, and more. This precise targeting helps increase the relevance of your emails, leading to higher open and conversion rates.
## Personalization Options
Personalization is key to making your emails stand out in crowded inboxes. Divsly allows you to personalize your emails at scale. You can insert dynamic content, such as the recipient’s name, location, and past interactions, directly into your emails. Additionally, you can tailor the content and offers to match individual preferences and behaviors, creating a more personalized and engaging experience for your subscribers.
## Automation Workflows
Automation is a game-changer in email marketing, and Divsly offers robust automation capabilities. You can set up automated workflows for various customer journeys, such as welcome series, abandoned cart reminders, post-purchase follow-ups, and re-engagement campaigns. These automated emails are triggered based on specific actions or time intervals, ensuring timely and relevant communication with your audience without manual intervention.
## Detailed Analytics and Reporting
Understanding the performance of your email campaigns is crucial for continuous improvement. Divsly offers comprehensive analytics and reporting tools that provide insights into key metrics such as open rates, click-through rates, conversion rates, and more. The platform also offers visual reports that make it easy to track trends and measure the ROI of your email marketing efforts. These insights help you identify what’s working and what needs adjustment.
## Integrations with Other Tools
Divsly seamlessly integrates with a variety of other tools and platforms, enhancing its functionality and convenience. Whether you’re using a CRM, e-commerce platform, or social media management tool, Divsly can connect with your existing tech stack. This integration capability ensures that your email marketing efforts are synchronized with your overall marketing strategy, providing a cohesive and streamlined approach.
## Mobile Optimization
In today’s mobile-centric world, ensuring your emails look great on all devices is essential. Divsly’s email templates are responsive and automatically adjust to fit any screen size. This mobile optimization ensures that your emails are visually appealing and easy to read, whether your subscribers are viewing them on a desktop, tablet, or smartphone.
## Compliance and Security
With growing concerns around data privacy and security, Divsly is committed to compliance with regulations such as GDPR and CAN-SPAM. The platform includes features to help you manage subscriber consent, easily provide opt-out options, and securely store and manage data. This commitment to compliance and security helps build trust with your audience and ensures your email marketing practices are ethical and lawful.
## Support and Resources
Lastly, Divsly offers exceptional customer support and a wealth of resources to help you succeed. Whether you need assistance with a technical issue or guidance on best practices, Divsly’s support team is available to help. Additionally, the platform provides tutorials, webinars, and a comprehensive knowledge base to help you get the most out of its features.
## Conclusion
Divsly Email Marketing stands out in the crowded email marketing landscape due to its user-friendly interface, robust features, and commitment to deliverability and compliance. By leveraging its advanced segmentation, personalization, automation, and analytics capabilities, you can create targeted and effective email campaigns that drive engagement and conversions. Whether you’re new to email marketing or looking to switch platforms, Divsly offers the tools and support you need to elevate your email marketing strategy.
By focusing on these top features, you can harness the full potential of Divsly Email Marketing to connect with your audience, build lasting relationships, and achieve your marketing goals.
| divsly |
1,866,517 | Analyzing The Global Perfume Market Size, Share and Growth | As a market researcher, I delve into the intricacies of the global perfume market, exploring its... | 0 | 2024-05-27T12:18:23 | https://dev.to/hritika_sahu_/analyzing-the-global-perfume-market-size-share-and-growth-2o5j | perfume, marketresearch, researchreport, marketresearchreport | As a market researcher, I delve into the intricacies of the global perfume market, exploring its size, growth, trends, and the key players shaping this dynamic industry.

## Perfume Market Size, Share, and Growth
- The **[global perfume market size](https://www.kenresearch.com/flavors-fragrance-market?utm_source=SEO&utm_medium=SEO&utm_campaign=Hritika)** was valued at USD 50.85 billion in 2022 and is expected to reach USD 53.70 billion in 2023.
- The market is projected to grow at a **CAGR of 5.51% from 2024 to 2032**, reaching **USD 77.52 billion by 2032**.
- Women accounted for the largest share of 62.9% in the perfume market in 2022, with women in the U.S. purchasing a new perfume as often as once a month, compared to men who buy it on average 1-2 times per year.
### Market Trends
1. **Rising Preference for Natural Ingredients:** Consumers are increasingly gravitating towards perfumes made with sustainable materials such as vanilla beans, balsams, and citrus oil to avoid potential health issues caused by chemical-based fragrances.
2. **Emergence of Touchless Scent Devices:** Key players are introducing innovative, touchless scent devices and AI-based solutions for regular scent users, offering personalized scent profiles and recommendations based on individual preferences.
3. **Growth of Online Shopping:** The market is flourishing across different regions due to the rising consumer inclination towards online shopping, with worldwide e-commerce sales growing from 16% of total retail sales in 2019 to 19
% in 2020.
## Major Players in the Perfume Market
1. **The Avon Company:** A prominent player in the market, offering a diverse range of perfume products.
2. CHANEL: Known for its luxury fragrances, CHANEL offers a wide variety of perfume products, including Eau de parfum spray and parfum.
3. **Coty Inc.:** A key player in the market, Coty Inc. has been actively involved in the development of innovative perfume products.
4. **LVMH Moet Hennessy - Louis Vuitton:** LVMH, a major manufacturer of perfume products, experienced a 20% decline in perfume revenue in 2020 due to the COVID-19 pandemic.
5. **L'Oreal Groupe:** L'Oreal Groupe is a significant player in the market, contributing to the growth and development of the perfume industry.
### Market Players Size and Share
The top players in the perfume market, including The Avon Company, CHANEL, Coty Inc., LVMH Moet Hennessy - Louis Vuitton, and L'Oreal Groupe, collectively hold a substantial market share.
Estée Lauder Inc., Revlon, and Puig are also notable players in the market, contributing to the overall market share.
The global perfume market is expected to witness a slight dip in CAGR from 6.0% between 2017 and 2022 to 5.5% from 2023 to 2033, primarily due to the mass-scale closure of retail stores following economic crises.
In conclusion, the global **[perfume market](https://www.kenresearch.com/flavors-fragrance-market?utm_source=SEO&utm_medium=SEO&utm_campaign=Hritika)** is poised for continued growth, driven by rising consumer preferences for natural ingredients, the emergence of innovative technologies, and the increasing popularity of online shopping. Major players are investing in research and development to offer unique and personalized fragrance solutions, catering to the evolving needs of consumers worldwide. As the market evolves, stakeholders need to stay informed about the latest trends and developments to make strategic decisions and capitalize on the immense growth potential of this dynamic industry. | hritika_sahu_ |
1,866,389 | Why You Should Self-Host Everything | In today's digital age, it seems like everything is subscription-based. If you're not paying for a... | 27,648 | 2024-05-27T12:16:49 | https://dev.to/sein_digital/why-you-should-self-host-everything-2f31 | selfhosted, docker, opensource, productivity | In today's digital age, it seems like everything is subscription-based. If you're not paying for a service, you're likely being monetized by watching ads or providing personal data to companies that don't necessarily have your best interests at heart. The internet has become a polluted space where our online activities are tracked and sold to the highest bidder.
And most companies try to exploit and leverage human behavior for profit.
But there's a way to take back control: self-hosting.
**The Problem with Centralization**
When you use popular services like Netflix, Facebook, Dropbox, or Microsoft Office 360, you're entrusting your data to companies that have no obligation to keep it private or secure. These corporations are incentivized to collect and sell your data to maximize their profits, often without your consent. This centralization of information has created a surveillance state where our online activities are monitored and analyzed for commercial gain. In some cases you pay twice: with your data, and with your wallet. Now it's more visible then ever, when suddenly your repos are being fed to train AI models if by any chance your are using Github.
**The Alternative: Homelab Server**
Self-hosting is not just about moving your data from one centralized location to another; it's about taking control of your digital life. By setting up a homelab server, you can store your files, communicate with others, and access your favorite services without relying on third-party companies. With a homelab server, you'll have complete control over your data and can ensure that it remains private and secure. To achieve that you will need either pretty solid NAS (like Synology) or micro-pc, like Intel NUC. Raspberry Pi won't do unfortunately, unless you run up to 4 lightweight containers.
**Cost Comparison**
While setting up a homelab server may require an initial investment of time and money, it's often more cost-effective in the long run. For example:
* Cloud Service x4: $10 per month x 12 months x 4 = $480
* Intel NUC or Synology NAS: approximately $300-$500 (depending on options you choose)
So depending on your situation and amount of services you are currently subscribed to, the cost of homelab will pay itself in about a year!
Of course there is also cost of time, and required maintenance, but with proper setup it can be minimal effort.
**HomeLab possible solutions**
As I mentioned, best options are not that expensive, and all you need is a micro-pc. Here's a list of good options eligible for solid docker based homelab:
- [Intel Nuc 11 i-7, 32GB RAM, 1TB](https://amzn.to/4aRU8R3) $550 - solid starting point with quite a bit of storage, and a lot of RAM.
- [Intel Nuc 11 i-7, Bare](https://amzn.to/4bUQy9C) $390 - No ram, no storage option, if you want to upgrade it yourself from scratch
- [Intel NUC 11, Celeron N5105, 8GB RAM, 256GB SSD](https://amzn.to/3KgLkZW) $240 - Low budget option, I know - it's twice as expensive as RPi 5 with the same amount of RAM, but let's be honest - you cannot extend Raspberry Pi
- [Raspberry Pi 5, 8GB](https://amzn.to/4bVYpDY) $95 - For the sake of completion. You would still need to buy SD Card. But you can at least set up Pi.Hole and Pi.Alert on it.
- [Synology 2-Bay NAS DS223, 2GB RAM, Diskless](https://amzn.to/3Kjwpy2) $250 - For those who favor storage space over computing power. As you can see, compared to NUC, it does not have much RAM.
- [Synology DS723 2-Bay, 2GB RAM, 8TB Storage](https://amzn.to/3Kjwpy2) $990 - A bit more powerful machine with quite solid CPU, but still in range of 2GB of RAM. Some versions comes even with docker preinstalled.
Overall, as you can see, Intel NUC might seem like more cost-effective solution, however NAS has it's own benefits, and often comes with preinstalled OS and Manager, where you can deploy docker on your own.
**Easy Deployment with Docker**
Setting up a homelab server doesn't have to be a daunting task. What we need is ubuntu or debian OS on our machine.
With the help of containerization platforms like Docker or Podman, you can easily deploy and manage your services without requiring extensive technical expertise. And after initial setup and ssh exposed to your local network, you won't even need to connect your monitor and keyboard anymore, unless to upgrade the whole system again!
You can read how I did it in future article. But for now, there is still one more step in our setup.
**Open Source Community**
The open source community is thriving, and many self-hosted services are built on top of these collaborative efforts. Now more then ever we have a ton of open source software "just laying around" GitHub.
Many of those software offer simple one line setup for docker. The best thing about docker is, that you don't have to worry about dependencies. And know what's best about them? Because they are open source, it means that you can contribute yourself as well! You are missing a feature? You found a bug and fixed it? Create a Pull Request, Report, Contribute! That's what makes open source community thriving. And by doing a homelab environment, there's nothing stoping you from doing your own docker hosted tools!
**Conclusion**
Self hosting and running a homelab was never as easy as this. Not that long ago I was running Proxmox and creating VM for everything I needed. Problem is, VMs take up a lot of resources, and without RACK they are highly unreliable, unless you do Penetration Testing and you need like 3-4 environments. Single OS with docker makes it much easier! And by self-hosting everything, you'll enjoy numerous other benefits:
* **Privacy**: Your data remains private and secure, away from prying eyes. You own your data, not a third-party.
* **Control**: You have complete control over what's running. You own the server. Nobody beside you have access to that server.
* **Flexibility**: You can choose the services and software that best suit your needs, without being locked into a specific ecosystem. You can integrate them if you want, or keep them separate.
* **Financial Benefits**: In the long run, self-hosting can be more cost-effective than relying on subscription-based services.
In an era where data is the new currency, it's time to take back control of our online activities. Self-hosting everything offers a powerful alternative to the centralization of information and provides a way to ensure that your digital life remains private, secure, and flexible. Join the self-hosting movement today and start reclaiming your digital sovereignty!
**UPDATE!**
Because couple of you asked for AMD solution, I dug deeper into mini-pc market, and found couple sweet deals, even one favorite I would definitely went for, if I chose to change systems!
- [MINISFORUM EliteMini UM780 XTX AMD Ryzen 7 7840HS, 64GB DDR5 1TB](https://amzn.to/4bQqb4C) $690 - This one is packing!
- [Beelink AMD Ryzen 7 16GB RAM 1TB SSD](https://amzn.to/3V1pSx8) $360 - Cheap option, good option for starter with great CPU.
- [Kamrui AMD Ryzen 5 16GB DDR4 512GB SSD](https://amzn.to/450mAid) $270 - Slightly cheaper option, more than enough, definitely more than you would get from VPS for $20 a month. Better value then Intel NUC's alternative in similar price range. | sein_digital |
1,866,516 | Best Operating System for Software Development | Choosing the right operating system (OS) is crucial for software development. Developers need an OS... | 0 | 2024-05-27T12:15:45 | https://dev.to/somya_07/best-operating-system-for-software-development-2op2 | softwaredevelopment |
Choosing the right operating system (OS) is crucial for [software development](https://hyscaler.com/insights/best-operating-system-in-2024/). Developers need an OS that provides stability, flexibility, and a robust set of tools to enhance productivity. This guide explores the best operating systems for software development, weighing their pros and cons to help you make an informed decision.
Linux: The Developer's Favorite
Versatility and Customization
[Linux ](https://hyscaler.com/insights/7-best-audio-editors-for-linux/
)is widely regarded as the go-to OS for developers, especially those working with open-source technologies. Its versatility allows developers to customize their environment to suit their specific needs. With a variety of distributions (distros) like Ubuntu, Fedora, and Debian, Linux offers tailored experiences for different development tasks.
Advantages of Linux
Open Source: Linux is open-source, meaning developers can contribute to and modify the source code, fostering a collaborative environment.
Security: Known for its robust security features, Linux is less vulnerable to malware and viruses compared to other OSes.
Command-Line Interface (CLI): The powerful CLI allows developers to perform tasks more efficiently, which is especially useful for server management and automation.
Package Management: Tools like APT and YUM simplify software installation and management, saving developers time and effort.
Compatibility with Development Tools: Linux supports a wide range of development tools and frameworks, making it ideal for everything from web development to machine learning.
Disadvantages of Linux
Learning Curve: For beginners, Linux can be challenging to learn, especially if they are accustomed to graphical user interfaces.
Software Compatibility: Some proprietary software may not be available for Linux, requiring alternatives or workarounds.
Windows: Popular and Versatile
Ubiquity and Compatibility
Windows remains one of the most popular operating systems due to its widespread use and compatibility with a wide range of software. It is particularly favored by developers who need to work with Microsoft technologies or develop applications for the Windows platform.
Advantages of Windows
User-Friendly Interface: Windows offers an intuitive and easy-to-use graphical user interface, making it accessible for developers of all skill levels.
Broad Software Support: Nearly all major software tools and development environments are available for Windows, including Microsoft Visual Studio.
Gaming and Graphics Development: Windows is the preferred choice for game developers and those working with graphic-intensive applications due to its DirectX support.
WSL (Windows Subsystem for Linux): WSL allows developers to run a Linux environment directly on Windows without the need for dual-booting, combining the best of both worlds.
Disadvantages of Windows
Cost: Unlike Linux, Windows is not free, which can be a barrier for some developers.
Security Concerns: Windows is more susceptible to viruses and malware, necessitating robust security measures.
Resource Intensive: Windows tends to use more system resources, which can impact performance, especially on older hardware.
macOS: The Choice of Creative Professionals
Integration and Performance
macOS, developed by Apple, is known for its sleek design, stability, and integration with other Apple products. It is a popular choice among developers who create applications for the Apple ecosystem, including iOS and macOS apps.
Advantages of macOS
High-Quality Hardware: Apple’s hardware is known for its quality and performance, providing a reliable development environment.
UNIX-Based: Like Linux, macOS is UNIX-based, offering a powerful CLI and compatibility with various development tools.
Xcode Development: For iOS and macOS developers, Xcode provides a comprehensive suite of tools and a seamless development experience.
Design and Media Production: macOS excels in design and media production software, making it a favorite among creative professionals.
Disadvantages of macOS
Cost: Both macOS and Apple hardware come with a premium price tag, which can be prohibitive for some developers.
Limited Hardware Choices: Developers are limited to Apple’s hardware, reducing flexibility in terms of customization and upgrades.
Software Availability: While many tools are available for macOS, some specialized software might only be available for Windows or Linux.
Conclusion: Choosing the Right OS
The best operating system for software development largely depends on the specific needs and preferences of the developer.
Linux is ideal for those who value customization, security, and a strong CLI environment.
Windows is suitable for developers requiring broad software support, an easy-to-use interface, and integration with Microsoft products.
macOS caters to developers in the Apple ecosystem and those involved in design and media production.
Each OS has its strengths and weaknesses, so consider your development goals, preferred tools, and workflow when making your choice. With the right OS, you can create an efficient and productive development environment tailored to your needs.
| somya_07 |
1,866,515 | Use HTML & CSS | A post by Fahim Ullah Laptop | 0 | 2024-05-27T12:14:48 | https://dev.to/fahim_ullah_67/use-html-css-57ni |
 | fahim_ullah_67 | |
1,866,514 | Node.js Basic Streaming HTTP | Node.js excels at handling streaming data, making it a powerful tool for building efficient HTTP... | 0 | 2024-05-27T12:14:14 | https://dev.to/devstoriesplayground/nodejs-basic-streaming-http-10ma | node, http, javascript, webdev | Node.js excels at handling streaming data, making it a powerful tool for building efficient HTTP applications. This article explores the fundamentals of streaming HTTP with Node.js, focusing on key concepts and practical examples.
**Understanding Streams in Node.js:**
- Streams are objects representing a continuous flow of data chunks.
- Node.js provides different types of streams:
**Readable:** Data can be read from them (e.g., file streams).
**Writable:** Data can be written to them (e.g., network sockets).
**Duplex:** Can be both read from and written to (e.g., network sockets).
**Transform:** Modify data as it flows through them (e.g., compression streams).
- Streams are event-driven, emitting events like data, end, and error.
**HTTP Streaming with Node.js:**
1. Server-Side Streaming:
Send data to the client in chunks as it becomes available.
Utilize http.ServerResponse as a writable stream.
Example:
const http = require('http');
const server = http.createServer((req, res) => {
const data = 'This is a streamed response.';
res.writeHead(200, { 'Content-Type': 'text/plain' });
// Send data in chunks
for (let i = 0; i < data.length; i += 10) {
const chunk = data.slice(i, i + 10);
res.write(chunk);
}
res.end();
});
server.listen(3000, () => {
console.log('Server listening on port 3000');
});
2. Client-Side Streaming:
Receive data from the server in chunks.
Utilize http.IncomingMessage as a readable stream.
Example:
const http = require('http');
const options = {
hostname: 'localhost',
port: 3000,
path: '/',
};
const req = http.request(options, (res) => {
console.log(`Status: ${res.statusCode}`);
res.on('data', (chunk) => {
console.log(chunk.toString());
});
});
req.end();
**Benefits of Streaming HTTP:**
**Memory Efficiency:** Process large data sets without loading everything into memory at once.
**Scalability:** Handle concurrent requests efficiently.
**Real-time Data:** Enable real-time updates and progress reporting.
**Additional Considerations:**
**Error Handling:** Implement proper error handling mechanisms for both server and client.
**Backpressure:** Manage data flow to avoid overwhelming the client or server.
**Chunking Size:** Adjust chunk size based on network conditions and data type.
—
### Let's wrap up things
> By understanding basic streaming HTTP concepts and applying them in your Node.js applications, you can build efficient and scalable solutions for handling large data sets and real-time data scenarios.
Happy Coding!!!
—
| devstoriesplayground |
1,866,512 | Understanding The Difference: Authentication vs. Authorization | Administrators employ two essential information security procedures to secure systems and data:... | 0 | 2024-05-27T12:12:32 | https://dev.to/certera_/understanding-the-difference-authentication-vs-authorization-knp |
Administrators employ two essential information security procedures to secure systems and data: Authorization and authentication.
A service’s identity is confirmed by Authentication, and its access permissions are established through Authorization.
Though they have similar sounds, the two concepts are different yet just as crucial to the security of data and applications. It is essential to recognize the difference. They assess a system’s security when taken as a whole. You cannot have a secure solution unless authentication and Authorization are correctly configured.
## What Is Authentication?
Regarding system security, Authentication is the process of identifying or verifying who someone is, it confirms that users are who they say they are.
Authentication is the first step of identification that determines whether the person is a user or not. It needs usually the user’s login details.
## Why is Authentication Necessary?
Verifying that someone or something is who or what they claim to be is the objective of authentication. There are several ways to authenticate. For instance, the art industry includes procedures and establishments that verify a sculpture or painting is the creation of a particular artist.
Governments also employ various authentication methods to prevent counterfeiting of their currencies. Authentication often safeguards valuables; it secures data and systems in the information era.
## Types of Authentication
Verifying the identity of people gaining access to a system, website, or application is a critical procedure known as authentication. In today’s digital environment, various authentication techniques provide safe access to sensitive data. The most typical ones consist of:
Password-based Authentication
Users using this conventional technique must enter a unique combination of characters they only know. Although passwords are easy to use, their management may lead to security breaches.
Multiple-Factor Authentication
By combining two or more authentication factors—passwords, biometrics (facial recognition or fingerprint), or one-time codes sent to a user’s registered device—multi-factor authentication (MFA) improves security. This tired strategy significantly decreases the danger of unauthorized access.
Authentication using Two Factors
Two distinct authentication factors are used in 2FA, a subset of MFA, to confirm the user’s identity. This usually includes an SMS or mobile app-generated password and a one-time code.
Biometric Authentication
This innovative technique verifies a user’s identification using distinctive biological characteristics like fingerprints, iris scans, or facial features. Although biometrics provide high security and convenience, privacy issues could arise.
## Benefits of Verification/Authentication
Reasonable authentication procedures provide a secure and easy-to-use user experience while providing many advantages to people, companies, and online platforms.
Improved Security Authentication
By preventing unwanted access and shielding private information from prying eyes, improved safety authentication lowers the possibility of data breaches and cyberattacks.
User Self-Assurance and Confidence
Robust authentication procedures boost users’ confidence by reassuring them that the platform or service is secure and protecting their data.
Decreased Identity Theft and Fraud
By requiring users to verify themselves, the likelihood of fraud and identity theft is greatly decreased.
Personalized Access Control
Various authentication techniques can be customized to meet specific security requirements, enabling organizations to provide various user groups with the right amount of access.
## What is Authorization?
Once a user’s identity has been properly authenticated, Authorization takes place. Providing full or restricted access rights to resources like databases, cash, and other vital information is essential to completing the task.
Determining the resources an employee will have access to is the following stage in an organization, for instance, once they have been authenticated and validated using an ID and password.
## Why is Authorization Necessary?
Authorization’s primary objective is to ensure that users have the appropriate amount of access to their roles and security guidelines. Granting access to someone to a resource is known as Authorization. This description can appear cryptic, but plenty of real-world examples clarify what permission entails, allowing you to apply the ideas to computer systems. Homeownership is a prime example.
## Types of Authorization
To guarantee that specific people or entities are given the proper access to resources and activities inside a system, Authorization is an essential component of identity and access management. Organizations utilize various authorization systems to manage access and safeguard confidential data.
Authority Based on Roles and Responsibilities
This method assigns access privileges based on jobs or job responsibilities already established inside the company. Individuals are classified into distinct roles, and every function is bestowed with a corresponding set of authorizations that correspond with its assigned duties. This lowers administrative overhead and improves access control, particularly in large businesses.
Authorization Based on Characteristics
This kind of permission assesses access requests according to specific user characteristics, such as department, location, or clearance level. Whether a user’s characteristics fit the requirements for using certain resources or carrying out specific tasks determines whether access is allowed.
Rule-Based Authorization
Access control is enforced by rule-based Authorization according to predetermined guidelines and requirements. The conditions under which access should be allowed or refused are outlined in these regulations. Using rule-based Authorization, organizations may create complicated access controls to meet specific business needs.
Mandatory Access Control (MAC)
A typical high-security authorization approach in military and government contexts is MAC. Strict access constraints set by the system administrator govern how it functions. Users can only access material at or below their clearance level because of the assignment of access privileges based on labels and categories.
Discretionary Access Control (DAC)
DAC gives consumers more control over who gets access to their own resources than MAC does. Every resource has an owner who has the authority to decide who else can use it and to what extent. DAC is frequently utilized in less secure settings where people have greater control over their data.
Role-Based Access Control (RBAC)
Managing user access based on roles and the rights accompanying them is the primary goal of role-based Authorization, or RBAC. Enabling administrators to manage roles and provide or revoke rights to whole user groups improves access control.
[Read more about advantages and differences between authentication vs authorization](https://certera.com/blog/understanding-the-difference-authentication-vs-authorization/) | certera_ | |
1,866,509 | Did you break your code or is the test flaky? | Flaky end-to-end tests are frustrating for quality assurance (QA) and development teams, causing... | 0 | 2024-05-27T12:04:31 | https://www.octomind.dev/blog/did-you-break-your-code-or-is-the-test-flaky | webdev, testing, e2e, frontend | Flaky end-to-end tests are frustrating for quality assurance (QA) and development teams, causing constant disruptions and eroding trust in test outcomes due to their unreliability.
We'll go over all you need to know about flaky tests, how to spot a flaky test from a real problem, and how to handle, fix, and stop flaky tests from happening again.
## Are flaky tests a real issue?
While often ignored, flaky tests are problematic for QA and Development teams for several reasons:
**1. Lack of trust in test results**
When tests are unreliable, developers and QA teams may doubt the validity of the results, not only for those specific tests but also for the entire set
**2. Wasted time and resources**
The time and resources wasted diagnosing flaky tests could've been spent adding value to the business.
**3. Obstructed CI/CD pipelines**
Constant test failures that are unreliable often result in the need to run tests again to ensure success, causing avoidable delays for downstream CI/CD tasks like producing artifacts and initiating deployments.
**4. Masks real issues**
Repeated flaky failures may lead QA and Developers to ignore test failures, increasing the risk that genuine defects sneak through and are deployed to production.
## What causes flaky tests?
Flaky tests are usually the result of code that does not take enough care to determine whether the application is ready for the next action.
Take this flaky test Playwright test written in Python:
```python
page.click('#search-button')
time.sleep(3)
result = page.query_selector('#results')
assert 'Search Results' in result.inner_text()
```
Not only is this bad because it will fail if results take more than three seconds —it’s also wasting time if the results return in less than three seconds.
This is a solved problem in Playwright using the `wait_for_selector` method:
```python
page.click('#search-button')
result = page.wait_for_selector('#results:has-text("Search Results")')
assert 'Search Results' in result.inner_text()
```
Selenium solves this using the `WebDriverWait` class:
```python
driver.find_element(By.ID, 'search-button').click()
result = WebDriverWait(driver, 10).until(
EC.presence_of_element_located((By.ID, 'search-results'))
)
assert 'Search Results' in result.text
```
Flaky tests can also be caused by environmental factors such as:
- Unexpected application state from testing in parallel with the same user account
- Concurrency and race conditions from async operations
- Increased latency or unreliable service from external APIs
- Application configuration drift between environments
- Infrastructure inconsistencies between environments
- Data persistence layers not being appropriately reset between test runs
Writing non-flaky tests requires a defensive approach that carefully considers the various environmental conditions under which a test might fail.
## What is the difference between brittle and flaky tests?
A brittle test, while also highly prone to failure, differs from a flaky test as it consistently fails under specific conditions, e.g., if a button's position changes slightly in a screenshot diff test.
Brittle tests can be problematic yet predictable, whereas flaky tests are unreliable as the conditions under which they might pass or fail are variable and indeterminate.
Now that you understand the nature of flaky tests, let's examine a step-by-step process for diagnosing them.
### Step 1. Gather data
Before jumping to conclusions as to the cause of the test failure, ensure you have all the data you need, such as:
- Video recordings and screenshots
- Test-runner logs, application and error logs, and other observability data
- The environment under test and the release/artifact version
- The test-run trigger, e.g. deployment, infrastructure change, code-merge, scheduled run, or manual
You should also be asking yourself questions such as:
- Has this test been identified as flaky in the past? If so, is the cause of the flakiness known?
- Has any downtime or instability been reported for external services?
- Have there been announcements from QA, DevOps, or Engineering about environment, tooling, application config, or infrastructure changes?
Having video recordings or frequently taken screenshots is crucial because it's the easiest-to-understand representation of the application state at the time of failure.
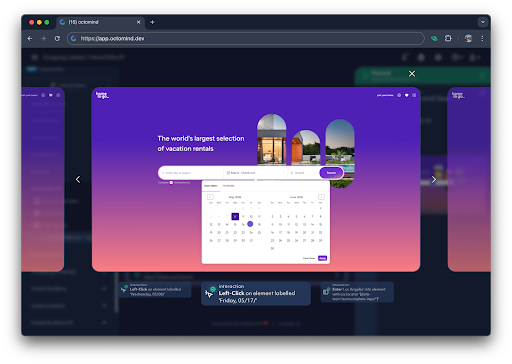
*step by step screenshots in Octomind test reports
Compile this information in a shared document or wiki page that other team members can access, updating it as you continue your investigations. This makes creating an issue or bug report easy, as most of the needed information is already documented.
Now that you’ve got the data you need, let’s begin our initial analysis.
### Step 2. Analyze logs and diagnostic output
Effectively utilizing log and reporting data from test runs is essential for determining the cause of a test failure quickly and correctly. Of course, this relies on having the data you need in the first place.
For example, if you're using Playwright, save the tracing output as an artifact when a test fails. This way, you can use the [Playwright Trace Viewer](https://playwright.dev/docs/trace-viewer) to debug your tests.
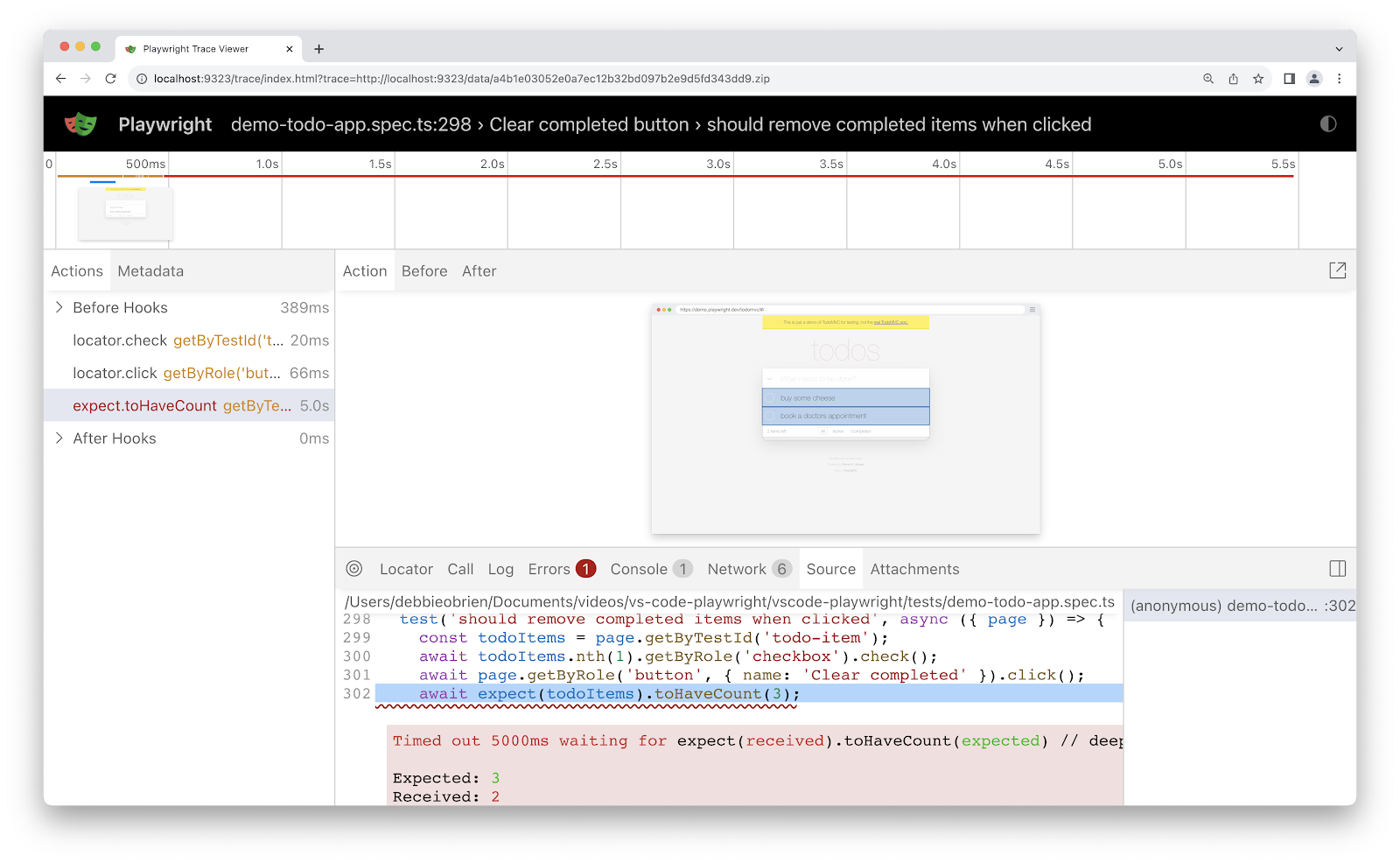
*source code in Playwright Trace Viewer tab
To begin your analysis, first identify the errors to determine if the issue stems from one or a combination of the following:
- Test code failing unexpectedly (e.g. broken selector/locator)
- Test code failing as expected (e.g. failed assertion)
- Application error causing incorrect state or behavior (e.g. JavaScript exception, rejected promise, or unexpected backend API error).
The best indication of a flaky test is when the application seems correct, yet a failure has occurred for no apparent reason. If this type of failure has been observed before, but the cause was never resolved, the test is probably flaky.
Things become more complicated to diagnose when the application functions correctly, yet the state is clearly incorrect. You’ll then need to determine if the test relies on database updates or responses from external services to confirm if infrastructure or data persistence layers could be the root cause. Hopefully, your application-level logs, errors, or exceptions will provide some clues.
Debugging test failures is easier when all possible data is available, which is why video recordings, screenshots, and tools such as Playwright’s Trace Viewer are so valuable. They help you observe the system at each stage of the test run, giving you valuable context as to the application's state leading up to the failure. So, if you’re finding it challenging to diagnose flaky tests, it could be because you don’t have access to the right data.
If the test has been confirmed as flaky, document how you came to this conclusion, what the cause is, and, if known, how it could be fixed. Then, share your findings with your team.
Because you’ve confirmed the test is flaky, re-run your tests, and with any luck, they’ll pass the second or third time around. But if they continue to fail, or you’re still unsure why the test is flaky, more investigation is required.
### Step 3. Review recent code changes
If the test run was triggered by an application or test code changes, review the commits to look for updates that may be causing the tests to fail. For example, newly added tests that aren’t cleaning up their state executing before the now-failing test.
Also, check for changes to application dependencies and configuration.
### Step 4. Verify the environment
If your flaky tests still fail after multiple re-runs, it’s likely that application config, infrastructure changes, or third-party services are responsible. Test failures caused by environmental inconsistencies and application drift can be tricky to diagnose, so check with teammates to see if this kind of failure has been seen before under specific conditions, e.g. database server upgrade.
Running tests locally to step-debug failures or in an on-demand isolated environment is the easiest way to isolate which part of the system may be causing the failure. We have open sourced a tool to do exactly that - [Debugtopus](https://www.octomind.dev/docs/debugtopus). Check it out in our docs or go directly to the [Debugtopus repo](https://github.com/OctoMind-dev/debugtopus).
Also, check for updates to testing infrastructure, such as changes to system dependencies, testing framework version, and browser configurations.
## Reducing flaky tests
While this deserves a blog in its own right, a good start to preventing flaky tests is to:
- Ensure each test runs independently and does not depend implicitly on the state left by the previous tests.
- Use different user accounts if running tests in parallel.
- Avoid hardcoded timeouts by using waiting mechanisms that can assert the required state exists before proceeding.
- Ensure infrastructure and application configuration across local development, testing, and production remains consistent.
- Prioritize the fixing of newly identified flaky tests as fast as possible.
- Identify technical test code debt and pay it down regularly.
- Promote best practices for test code development.
- Add code checks and linters to catch common problems.
- Require code reviews and approvals before merging test code.
---
## Conclusion
The effort required to diagnose flaky tests properly and document their root cause is time well spent. I hope you’re now better equipped to diagnose flaky tests and have some new tricks for preventing them from happening in the future.
We constantly fortify Octomind tests with interventions to prevent flakiness. We deploy active interaction timing to handle varying response times and follow best practices for test generation already today. We are also looking into using AI to fight flaky tests. AI based analysis of unexpected circumstances could help handling temporary pop-ups, toasts and similar stuff that often break a test.
**Maximilian Link**
Senior Engineer at Octomind | daniel-octomind |
1,866,507 | What Are the Benefits of Using the Fairplay App? | The Fairplay app goes beyond simply providing a fairplay id for online gaming and sports betting in... | 0 | 2024-05-27T12:03:28 | https://dev.to/idbettingonline/what-are-the-benefits-of-using-the-fairplay-app-1abg | fairplaylogin, fairpayapp, fairplay | The Fairplay app goes beyond simply providing a fairplay id for online gaming and sports betting in India. It offers a comprehensive platform packed with features designed to enhance your entire betting experience. Let's explore the key benefits that make the Fairplay app stand out:
Streamlined Registration with Fairplay ID:
Goodbye Registration Hassle: Forget lengthy registration processes on individual betting websites. The **Fairplay app** introduces the concept of a Fairplay login. This unique ID acts as your universal key, allowing you to register and log in seamlessly across various partner betting platforms. This saves you time and eliminates the need to remember multiple usernames and passwords.
Focus on the Fun: With the **[Fairplay login](https://fairplayapp.org/login.html)** system, you can bypass lengthy registration forms and jump straight into the action. This allows you to spend more time exploring the exciting sports markets, casino games, and promotions offered by Fairplay's partner platforms.
Enhanced Security and Control:
Centralized Identity Management: The fairplay id system centralizes your identity within the Fairplay ecosystem. This simplifies user management and strengthens security measures. You can manage your profile, update information, and set responsible gambling limits all from one central location.
Peace of Mind: Knowing your personal details are protected under Fairplay's robust security protocols offers peace of mind. Partner platforms within the Fairplay network adhere to stringent security standards, ensuring your financial transactions are secure.
Freedom and Flexibility:
Explore a World of Options: Don't be restricted to a single betting platform. The fairplay id unlocks a world of possibilities. You can conveniently switch between various partner platforms, all while maintaining your singular **fairplay id**. This allows you to compare odds, promotions, and features to find the best fit for your specific needs and preferences.
Always in Control: Your [fairplay id](url) empowers you to manage your bankroll effectively. You can easily transfer funds between partner platforms, eliminating the need to maintain separate accounts and balances. This provides greater control over your gambling activity and allows you to allocate your funds across different platforms strategically.
Additional Benefits Beyond the Fairplay ID:
Comprehensive Betting Options: Similar to other leading betting apps, Fairplay offers a vast selection of sporting events and markets to delve into. From Cricket and Football to niche sports, you'll find ample opportunities to place your bets. Additionally, the app features a fully-fledged casino section with an exciting array of slots, table games, and Live Dealer experiences.
Rewarding Programs and Promotions: Fairplay isn't shy about rewarding its users. You can expect a generous welcome bonus upon registration, alongside ongoing promotions and a well-structured loyalty program. These rewards come in the form of bonus bets, free spins, and exclusive access to premium games and events, keeping your gameplay exciting and potentially profitable.
User-Friendly Design and Functionality:
Mobile Optimization: The **[Fairplay app](https://fairplayapp.org/)** prioritises a smooth and intuitive user experience. It's designed with mobile users in mind, featuring a user-friendly interface that allows for effortless navigation. Whether you're using an Android device or the web-based platform, you can enjoy a seamless betting and gaming experience on the go. (iOS app development is still underway)
Hindi Support: Recognizing the needs of the Indian market, the **Fairplay app** offers complete support in Hindi. This ensures players who are more comfortable with Hindi can easily navigate the app and access all its features without a language barrier.
Conclusion
While the **Fairplay login** system streamlines registration and unlocks a world of betting options, the Fairplay app offers much more. From its user-centric design and rewarding programs to its commitment to security and responsible gambling practice, Fairplay provides a well-rounded platform for Indian players. Remember, gambling and betting come with inherent risks, so always gamble responsibly and within your limits. If you're looking for a convenient, secure, and feature-rich platform to explore the world of online betting and casino games, the Fairplay app is definitely worth considering.
| idbettingonline |
1,866,505 | we make the custom-coded website and software for your business. and using new technology customization. | A post by SofitGrow Solutions | 0 | 2024-05-27T12:02:01 | https://dev.to/sofitgrow_solutions_17294/we-make-the-custom-coded-website-and-software-for-your-business-and-using-new-technology-customization-ccm |
 | sofitgrow_solutions_17294 | |
1,866,504 | we make the custom-coded website and software for your business. and using new technology customization. | A post by SofitGrow Solutions | 0 | 2024-05-27T12:01:58 | https://dev.to/sofitgrow_solutions_17294/we-make-the-custom-coded-website-and-software-for-your-business-and-using-new-technology-customization-2lda |
 | sofitgrow_solutions_17294 | |
1,866,503 | Windows WSL2 ile Nextcloud Kurma | Nextcloud, kullanıcıların dosya depolama, senkronizasyon, paylaşım ve işbirliği yapabileceği açık... | 0 | 2024-05-27T12:01:56 | https://dev.to/busratekin/windows-wsl2-ile-nextcloud-kurma-4oia |
Nextcloud, kullanıcıların dosya depolama, senkronizasyon, paylaşım ve işbirliği yapabileceği açık kaynaklı bir bulut depolama platformudur. İster kişisel kullanım için ister kurumsal düzeyde olsun, kullanıcılar Nextcloud'u kendi sunucularında veya barındırılan hizmetlerde kullanarak dosyalarını güvenli bir şekilde yönetebilirler. Güvenlik, esneklik ve genişletilebilirlik gibi özellikleriyle dikkat çeker.
* Windows 10'da Komut İstemini yönetici olarak çalıştırıyoruz. PowerShell'i yönetici olarak çalıştırıyoruz.
```
PowerShell
# WSL özelliğini etkinleştiriyoruz
dism.exe /online /enable-feature /featurename:Microsoft-Windows-Subsystem-Linux /all /norestart
# Sanal makine platformunu etkileştiriyoruz
dism.exe /online /enable-feature /featurename:VirtualMachinePlatform /all
```
Bilgisayarı yeniden başlatıyoruz. Burada eğer sanal makine içinde sanal makine kuracaksak sanal makinenin CPU ayarlarından 'Virtualize IntelVT-x/EPT or AMD-V/RVI' ayarını etkinleştiriyoruz.
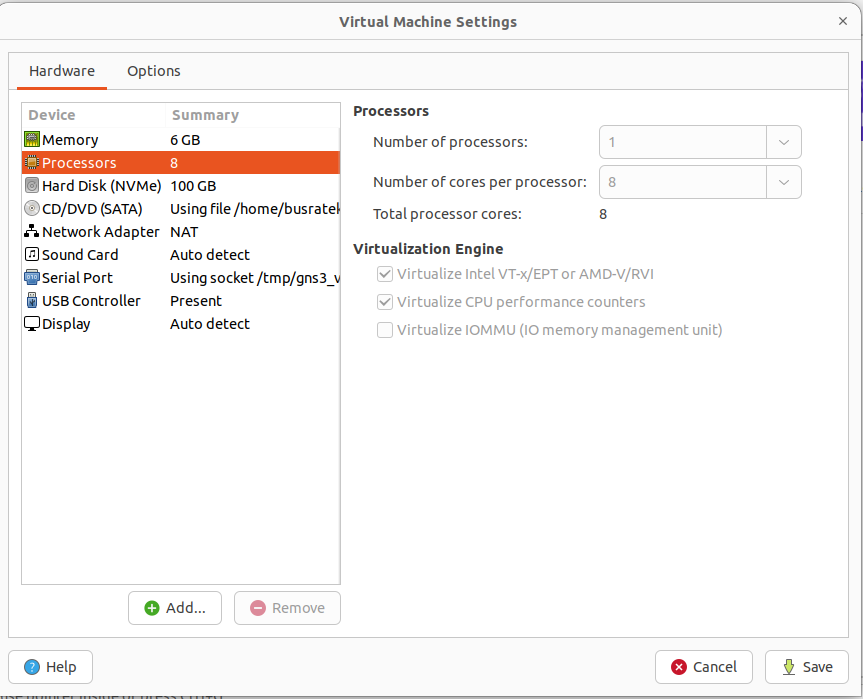
```
# Sanallaştırma paltformunu etkinkleştiriyoruz.
Enable-WindowsOptionalFeature -Online -FeatureName VirtualMachinePlatform
# wsl2 yi etkinleştiriyoruz
wsl --set-default-version 2
# wsl çekirdek güncellemesini indiriyoruz.
$ProgressPreference = 'SilentlyContinue'; Invoke-WebRequest https://wslstorestorage.blob.core.windows.net/wslblob/wsl_update_x64.msi -OutFile .\wsl_update_x64.msi
# ilerleme tercihni sıfırla
$ProgressPreference = 'Continue'
# indirilen dosyaları yüklüyoruz
.\wsl_update_x64.msi
```
* Windows bilgisayarımızdan Microsoft Store girip Debianı indiriyoruz.
* Debian sanal makinesini açıp kullanıcı adı ve şifre belirliyoruz.
```
sudo apt update
sudo apt upgrade -y
sudo apt install unzip wget -y
sudo apt install apache2 mariadb-server mariadb-client -y
sudo apt install php8.2-* -y
sudo service mariadb start
sudo su
mysql_secure_installation
```
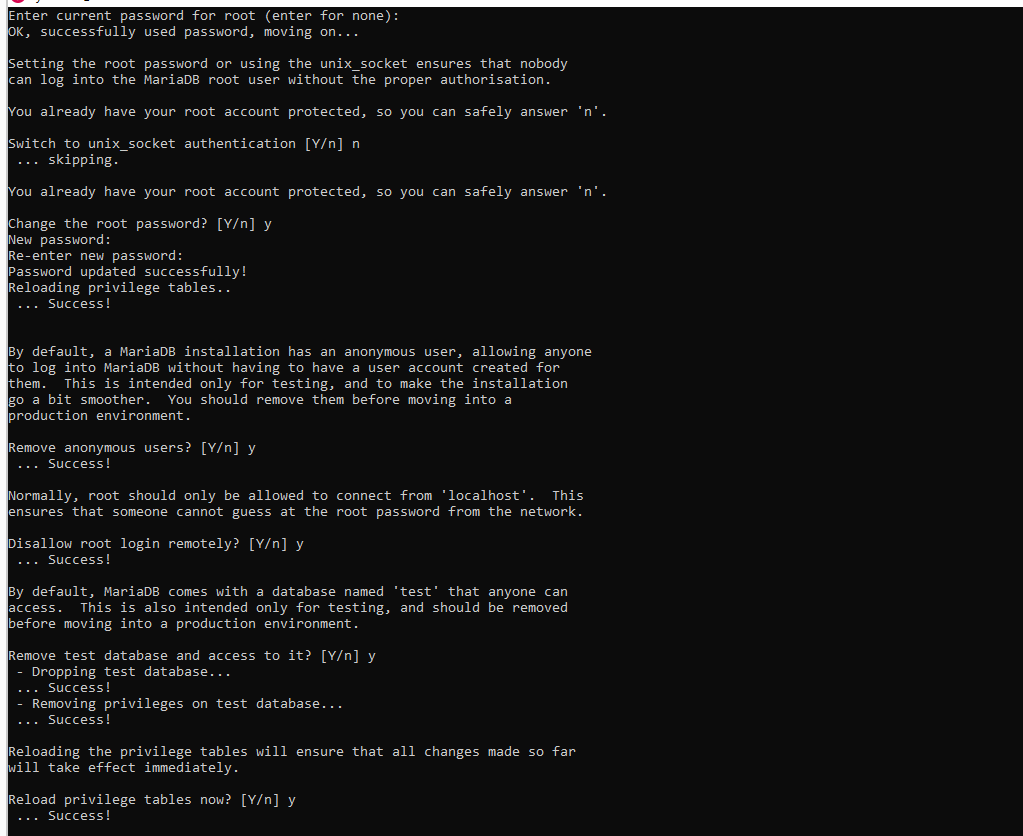
``` mysql -u root -p ```
* Nextcloud veritabanını oluşturuyoruz
```
CREATE DATABASE nextclouddb;
GRANT ALL ON nextclouddb.* to 'nextcloud_rw'@'localhost' IDENTIFIED BY 'N3xtCl0ud!';
FLUSH PRIVILEGES;
EXIT;
exit
```
* Apache web kökünde Nextcloud'u indirip çıkarmak için aşağıdaki komutlarla devam ediyoruz.
```
# en son nextcloud sürümünü indiriyoruz
wget -O /tmp/nextcloud.zip https://download.nextcloud.com/server/releases/latest.zip
# indirilen nextcloud versionunu çıkartıyoruz.
sudo unzip -q /tmp/nextcloud.zip -d /var/www
# Yeni nextcloud dizinin sahibini www-data olarak ayarlıyoruz
sudo chown -R www-data:www-data /var/www/nextcloud
```
* nextcloud.conf dosyası oluşturuyoruz.
``` sudo nano /etc/apache2/sites-available/nextcloud.conf ```
```
Alias /nextcloud "/var/www/nextcloud/"
<directory /var/www/html/nextcloud/>
Options +FollowSymlinks
AllowOverride All
Require all granted
Dav off
SetEnv HOME /var/www/nextcloud
SetEnv HTTP_HOME /var/www/nextcloud
</directory>
```
* Siteyi etkinleştirmek için ve Apache'yi yeniden başlatmak için aşağıdaki komutlarla devam ediyoruz.
```
sudo a2ensite nextcloud
sudo a2enmod rewrite headers env dir mime dav
sudo service apache2 restart
```
* localhost/nextcloud/ sitesine gidiyoruz
username: nextcloud_rw
password: N3xtCl0ud!
database name: nextclouddb
database host: localhost
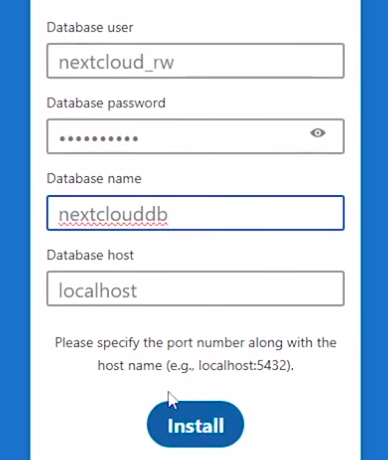
| busratekin | |
1,866,502 | How to duplicate a table in PostgreSQL | Copying a database table (or duplicating it, for that matter) is one of those basic operations that... | 0 | 2024-05-27T12:01:14 | https://dev.to/dbajamey/how-to-duplicate-a-table-in-postgresql-3817 | postgres, postgressql, database, tutorial | Copying a database table (or duplicating it, for that matter) is one of those basic operations that can be performed for a variety of reasons. Let's have an overview of the most common situations in which you need to copy PostgreSQL tables—and the methods of copying them.
We will illustrate those methods using dbForge Studio for PostgreSQL, an intuitive and feature-rich IDE whose capabilities include SQL coding assistance and formatting, data management and analysis, database comparison and synchronization, query optimization, test data generation, and much more.
https://www.devart.com/dbforge/postgresql/studio/postgresql-copy-table.html | dbajamey |
1,866,500 | Disable Dualsence touchpad on Ubuntu | Valve's efforts in making the Steam Deck (which runs a Debian-based distro) have enabled hassle-free... | 0 | 2024-05-27T11:59:01 | https://dev.to/gordinmitya/disable-dualsence-touchpad-on-ubuntu-2j2i | tutorial, ubuntu, linux, gaming | Valve's efforts in making the Steam Deck (which runs a Debian-based distro) have enabled hassle-free gaming on Linux machines. I finished Witcher 3 with Sony's DualSense controller and am now playing Helldivers 2. Surprisingly, HD2 even supports **haptic feedback and adaptive triggers**. I didn't think I would be able to try these features without a PS5.
However, one little annoying thing was preventing me from fully enjoying the game and spreading managed democracy — the _touchpad of the DualSense was interpreted as a mouse_. Anytime I wanted to open the in-game map, it acted as a mouse and changed the control to the keyboard.
## Solution
`sudo nano /etc/X11/xorg.conf.d/30--dualsense-touchpad.conf`
```
Section "InputClass"
Identifier "Sony Interactive Entertainment Wireless Controller Touchpad"
Driver "libinput"
MatchIsTouchpad "on"
Option "Ignore" "true"
EndSection
```
Then, log out from user or just reboot pc.
Now the DualSense acts exactly the same way as if it were attached to a PS5.
Credits [archlinux forum](https://bbs.archlinux.org/viewtopic.php?id=277941) | gordinmitya |
1,866,497 | Data Encryption | Encryption is crucial to modern information security, ensuring that data remains confidential and... | 0 | 2024-05-27T11:57:27 | https://dev.to/jrob112/data-encryption-3fg0 | Encryption is crucial to modern information security, ensuring that data remains confidential and protected from authorized access. Here are the primary encryption methods and their uses:
1. **Symmetric Encryption:**
Also known as secret key encryption, Symmetric encryption uses the same 'key' for encryption and decryption. A 'key' in encryption is a unique piece of information that is used to transform plain-text into ciphertext during encryption and vice versa during decryption.
One of the key advantages of symmetric encryption, also known as secret key encryption, is its speed and efficiency. This makes it an ideal choice for encrypting large volumes of data, adding a practical edge to its security features.
However, it's less secure than asymmetric encryption because a single key is used for both operations.
_**Use cases:**_
Data Storage: Encrypting files on your computer or a USB drive using a password often involves symmetric encryption. The same password is used for both encryption and decryption.
**Secure Socket Layer(SSL) and Transport Layer Security(TSL):**
These protocols use symmetric network encryption to protect data transmitted over the internet, such as during online banking transactions or when you log into a secure website.
**Virtual Private Network:** Many VPN services use symmetric encryption to secure data transmitted between your device and the VPN server, ensuring privacy and security while browsing the internet.
**Disk Encryption:** Whole-disk tools like BitLocker(Windows) and FileVault (macOS) use symmetric encryption to protect the entire contents of a hard drive or solid-state drive(SSD).
2. **Asymmetric Encryption**
It always involves two keys: a public key for encryption and a private key for decryption.
While asymmetric encryption may be slower due to the complexity of managing key pairs, its security benefits are worth the wait. The use of a public key for encryption and a private key for decryption adds an extra layer of assurance, making it more secure than symmetric encryption.
**_Use cases:_**
**Secure Email Communication:** Asymmetric encryption ensures that only the intended recipient can decrypt and read the email.
**Digital Signatures:** Authenticating messages or documents using digital signatures relies on asymmetric encryption.
**Online Transactions:** Asymmetric secures online transactions, such as credit card payments or online shopping.
**Key Exchange:** Asymmetric encryption uses secure key exchange during communication setup.
3. **Hashing:**
Hashing is not encryption but an essential technique for data integrity and verification. Encryption is about making data unreadable to unauthorized parties, while hashing is about verifying the integrity of data without revealing the original data. It converts data (such as passwords) into fixed-length hash values.
It converts data (such as passwords) into fixed-length hash values.
Hashes are one-way functions, meaning you can not reverse them to obtain the original data.
**_Use Cases:_**
**Password Storage:** Hashing passwords before storing them in databases prevents exposure to plain-text passwords.
**Data Integrity:** Hashing ensures that data hasn't been tampered with. In other words, it verifies that the data has remained unchanged from its original form. This is crucial for maintaining the trustworthiness and reliability of data, especially in sensitive contexts like financial transactions or medical records.
**Digital Signatures:** Hashing is part of the process for creating digital signatures.
Remember that combining these methods strategically enhances overall security. For instance, SSL/TSL uses both symmetric and asymmetric encryption during secure communication. Understanding these encryption methods is not just about learning technical concepts, but also about protecting your sensitive information and ensuring a safer online experience. It empowers you to make informed decisions about your data security.
References:
1)https://networkinterview.com/difference-between-encryption-and-hashing/
2)https://www.newsoftwares.net/blog/how-to-encrypt-the-data-in-the-browser-console/
3)https://techtecno.com/encryption-101/
4)https://vectorlinux.com/how-does-encryption-prevent-a-hacker-from-getting-your-data/
| jrob112 | |
1,866,499 | Getting Started with VSCode: A Beginner's Guide | Introduction Visual Studio Code (VSCode) has quickly become one of the most popular code editors... | 0 | 2024-05-27T11:57:00 | https://dev.to/umeshtharukaofficial/getting-started-with-vscode-a-beginners-guide-2mic | vscode, webdev, beginners, programming | **Introduction**
Visual Studio Code (VSCode) has quickly become one of the most popular code editors among developers worldwide. Known for its versatility, performance, and extensive customization options, VSCode offers a powerful development environment for beginners and seasoned programmers alike. This guide aims to provide beginners with a comprehensive introduction to VSCode, covering installation, basic features, customization, and tips for maximizing productivity.
**Installation**
**Download and Install VSCode**
1. **Visit the Official Website**: Go to [Visual Studio Code's official website](https://code.visualstudio.com/).
2. **Download**: Click on the download button that corresponds to your operating system (Windows, macOS, or Linux).
3. **Install**: Follow the installation instructions for your operating system:
- **Windows**: Run the downloaded installer and follow the prompts.
- **macOS**: Open the downloaded `.dmg` file and drag the VSCode icon
to the Applications folder.
- **Linux**: Follow the instructions on the website to install via a
package manager or download the appropriate package.
**First Launch**
After installation, launch VSCode. You will be greeted with a welcome screen that provides quick access to recent projects, new files, and various setup options.
**Basic Features**
**User Interface Overview**
The VSCode interface is divided into several key areas:
1. **Activity Bar**: Located on the left side, it provides access to
various views like Explorer, Search, Source Control, Run and Debug,
Extensions, and more.
2. **Side Bar**: Displays the contents of the selected view from the
Activity Bar.
3. **Editor Group**: The main area where you open and edit files.
4. **Panel**: Located at the bottom, it can display the Terminal, Output,
Problems, and Debug Console.
5. **Status Bar**: At the bottom of the window, it shows information
about the current project, such as the current branch in version
control, language mode, line and column numbers, and more.
**Opening and Managing Files**
- **Open a File**: Click on the Explorer icon in the Activity Bar, then
click the "Open Folder" or "Open File" button to navigate to the
desired location.
- **Tabs**: Each open file appears as a tab in the Editor Group, allowing
you to switch between files easily.
**Basic Editing**
- **Syntax Highlighting**: VSCode provides syntax highlighting for a wide range of programming languages.
- **IntelliSense**: Offers code completion, parameter info, quick info, and member lists, making coding faster and reducing errors.
- **Code Navigation**: Features like Go to Definition, Peek Definition, and Go to Symbol help you navigate large codebases efficiently.
**Customization and Extensions**
One of VSCode's strengths is its extensive customization options and a rich ecosystem of extensions.
**Customizing the User Interface**
1. **Themes**: Change the appearance of VSCode by installing different themes. Go to the Extensions view, search for "theme," and install your preferred option. Change the theme by opening the Command Palette (`Ctrl+Shift+P` or `Cmd+Shift+P` on macOS) and typing `Preferences: Color Theme`.
2. **Icons**: Customize file icons by installing icon themes from the Extensions view. Change the icon theme via the Command Palette by typing `Preferences: File Icon Theme`.
**Keybindings**
VSCode allows you to customize keyboard shortcuts to suit your workflow. Open the Command Palette and type `Preferences: Open Keyboard Shortcuts` to modify existing keybindings or add new ones.
**Extensions**
Extensions enhance the functionality of VSCode. Here are some essential extensions for beginners:
1. **Prettier**: A code formatter that enforces consistent style.
2. **ESLint**: Integrates ESLint into VSCode for identifying and fixing problems in your JavaScript code.
3. **Python**: Provides rich support for the Python language, including IntelliSense, linting, and debugging.
4. **GitLens**: Enhances the built-in Git capabilities by adding visual indicators and insights into your code's history.
5. **Live Server**: Launches a local development server with a live reload feature for static and dynamic pages.
To install an extension, go to the Extensions view, search for the extension by name, and click the Install button.
**Productivity Tips**
**Command Palette**
The Command Palette (`Ctrl+Shift+P` or `Cmd+Shift+P` on macOS) is your gateway to all of VSCode's features. Use it to quickly find and execute commands without navigating through menus.
**Integrated Terminal**
VSCode includes an integrated terminal, accessible via the Terminal menu or the `Ctrl+` (backtick) shortcut. This allows you to run command-line tools without leaving the editor.
**Version Control**
VSCode has built-in support for Git. Open the Source Control view from the Activity Bar to manage your repositories, stage changes, commit, and push to remote repositories.
**Debugging**
VSCode provides a powerful debugging environment for various programming languages. Set breakpoints, inspect variables, and control execution flow directly from the editor. Open the Run and Debug view from the Activity Bar to get started.
**Snippets**
Code snippets are templates that make it easier to enter repeating code patterns. VSCode includes built-in snippets for many languages, and you can also create your own. Open the Command Palette and type `Preferences: Configure User Snippets` to customize snippets.
**Multi-Root Workspaces**
VSCode supports multi-root workspaces, allowing you to work on multiple projects within a single editor window. Open multiple folders by selecting `File` > `Add Folder to Workspace`.
**Remote Development**
The Remote Development extension pack enables you to use a container, remote machine, or the Windows Subsystem for Linux (WSL) as a full-featured development environment. This is particularly useful for working on different operating systems or with isolated development environments.
**Advanced Customization**
**Settings**
VSCode settings can be customized via the settings UI or by directly editing the `settings.json` file. Access the settings UI by selecting `File` > `Preferences` > `Settings`. To edit `settings.json`, open the Command Palette and type `Preferences: Open Settings (JSON)`.
**Workspace Settings**
In addition to user settings, VSCode supports workspace settings, which apply only to the current project. This is useful for maintaining consistent configurations across team members. Workspace settings are stored in the `.vscode` folder within the project directory.
**Tasks**
Automate common tasks using the built-in task runner. Define tasks in a `tasks.json` file, and execute them from the Command Palette. This is particularly useful for running build scripts, test suites, or deployment commands.
**Extensions API**
For developers interested in extending VSCode's functionality, the Extensions API allows you to create custom extensions. The API documentation and guides are available on the [VSCode website](https://code.visualstudio.com/api).
**Conclusion**
VSCode is a powerful, flexible, and highly customizable code editor that can significantly enhance your development workflow. By understanding its core features, leveraging extensions, and customizing the environment to suit your needs, you can maximize your productivity and efficiency. Whether you're a beginner just starting out or an experienced developer looking to optimize your workflow, VSCode offers a wealth of tools and features to support your coding journey.
Embrace the capabilities of VSCode, experiment with different extensions and settings, and discover how this versatile editor can transform your coding experience. With a solid foundation and a willingness to explore, you'll find that VSCode can handle virtually any development task with ease and efficiency. Happy coding! | umeshtharukaofficial |
1,866,493 | PHP Interfaces and Their Usage with Dependency Injection | What is a PHP Interface? An interface in PHP is a blueprint for classes. It defines a contract that... | 0 | 2024-05-27T11:55:06 | https://dev.to/vimuth7/php-interfaces-and-their-usage-with-dependency-injection-18cl |
What is a PHP Interface?
An interface in PHP is a blueprint for classes. It defines a contract that any implementing class must adhere to, specifying methods that must be implemented but not providing the method bodies. Interfaces ensure a consistent structure across different classes and enable polymorphism by allowing multiple classes to be treated through a common interface.
Example:
**1.Define an Interface:**
```
interface PaymentGatewayInterface {
public function charge($amount);
}
```
This interface defines a charge method that any implementing class must provide.
**2.Implement the Interface:**
```
class StripePaymentGateway implements PaymentGatewayInterface {
public function charge($amount) {
// Implementation for Stripe
return "Charged {$amount} using Stripe.";
}
}
class PaypalPaymentGateway implements PaymentGatewayInterface {
public function charge($amount) {
// Implementation for PayPal
return "Charged {$amount} using PayPal.";
}
}
```
Both StripePaymentGateway and PaypalPaymentGateway implement the PaymentGatewayInterface, providing their specific implementations of the charge method.
**3.Using the Interface:**
```
function processPayment(PaymentGatewayInterface $paymentGateway, $amount) {
return $paymentGateway->charge($amount);
}
$stripe = new StripePaymentGateway();
$paypal = new PaypalPaymentGateway();
echo processPayment($stripe, 100); // Output: Charged 100 using Stripe.
echo processPayment($paypal, 200); // Output: Charged 200 using PayPal.
```
The processPayment function accepts any object that implements PaymentGatewayInterface, allowing for flexible and interchangeable use of payment gateways.
**Summary**
PHP interfaces are crucial for defining consistent method signatures across different classes, enabling polymorphism, and enhancing code maintainability and flexibility. They play a vital role in modern PHP applications, particularly in scenarios involving dependency injection and service-oriented architectures.
And they are very useful for [dependency injection](https://dev.to/vimuth7/dependency-injection-in-php-simply-explained-with-an-example-4fo4). Instead of adding a parent class we can use an interface. | vimuth7 | |
1,866,496 | Which Programming Language Is Used To Develop POS Software? | Several programming languages can be used to develop restaurant POS software (Point of Sale)... | 0 | 2024-05-27T11:53:55 | https://dev.to/restorapos/which-programming-language-is-used-to-develop-pos-software-59no | javascript, programming, react, python | Several programming languages can be used to develop [restaurant POS software](https://restorapos.com/restaurant-pos-system-in-uae) (Point of Sale) depending on the specific requirements and preferences of the development team. Some commonly used languages include:
Java
Java is a popular choice for developing POS software due to its platform independence, robustness, and extensive libraries. It's commonly used for building cross-platform applications, which is essential for POS systems that may run on various devices.
C#
C# is another widely used language, especially for developing POS software on the Microsoft Windows platform. It's commonly used with the .NET framework, offering a rich set of tools and libraries for building Windows-based applications.
Python
Python's simplicity, readability, and a large ecosystem of libraries make it an attractive choice for developing POS software, especially for smaller businesses or startups. It's often used for rapid prototyping and development.
JavaScript
JavaScript is commonly used for developing POS software that runs in web browsers or as part of web-based applications. With frameworks like Node.js, developers can build server-side components of POS systems using JavaScript.
C++
C++ is a lower-level language commonly used for developing high-performance POS software, particularly for systems that require low-level hardware interaction or real-time processing.
Ruby
Ruby, along with the Ruby on Rails framework, can be used to develop web-based POS software quickly. It's known for its simplicity and productivity.
Swift or Objective-C
If developing POS software for iOS devices like iPads, iPhones, or Macs, languages like Swift or Objective-C are commonly used. These languages are essential for building native applications for Apple's platforms.
PHP
PHP can be used for developing web-based POS software, particularly for small to medium-sized businesses. It's often used in combination with web frameworks like Laravel or Symfony.
The choice of programming language depends on factors such as the target platform, the development team's expertise, performance requirements, scalability needs, and integration capabilities with other systems.
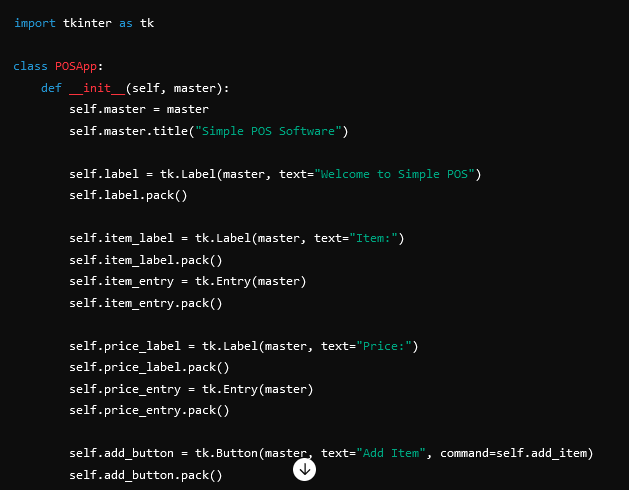
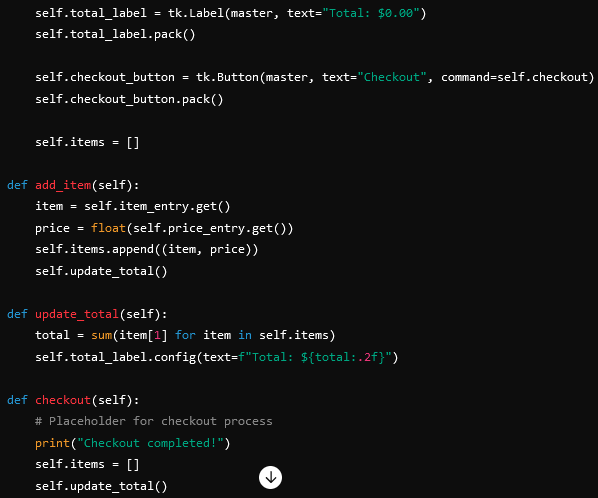
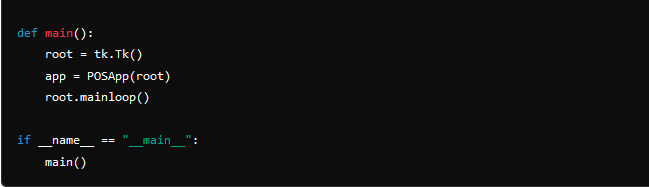
| restorapos |
1,866,495 | WORDPRESS 6.5 DELIVERS POWERFUL SEO ADVANTAGE WITH LASTMOD SUPPORT | Get ready for a significant boost in your website’s SEO performance! WordPress 6.5 introduces a... | 0 | 2024-05-27T11:52:02 | https://dev.to/anmolrajdev/wordpress-65-delivers-powerful-seo-advantage-with-lastmod-support-5h2a | webdev, programming, wordpress |

Get ready for a significant boost in your website’s SEO performance! [WordPress 6.5](https://42works.net/wordpress-6-5-delivers-powerful-seo-advantage-with-lastmod-support/#page-intro) introduces a groundbreaking feature – native last mod support within sitemaps. This seemingly simple addition can revolutionize how search engines crawl and index your content, leading to increased website visibility and organic traffic.
**<u>WHAT IS LASTMOD AND WHY DOES IT MATTER?</u>**
Lastmod stands for “last modified.” It’s a metadata tag in your sitemap that tells search engines the last time a specific webpage on your website was significantly updated. Search engines like Google and Bing use this information to prioritize and schedule their crawls.
**<u>Think of it this way</u>**: Search engine crawlers are constantly delivering information (indexing websites) just like a delivery person brings packages. With last mod, it’s like having a “recently delivered” section on your doorstep. The delivery person can prioritize dropping off these new packages first, ensuring your latest content gets indexed quickly.
Currently, only 21% of WordPress websites utilize version 6.5, which offers native lastmod support. Upgrading to this version or exploring alternative solutions for other platforms can significantly improve crawl efficiency for search engines.
**<u>THE WORDPRESS DEVELOPER COMMUNITY DELIVERS</u>**
The credit for this innovative feature goes to the dedicated WordPress developer community, spearheaded by the remarkable Pascal Birchler. Their tireless efforts have resulted in a seamless integration of last-mod support within WordPress 6.5.
This means: As a WordPress user running version 6.5 or above, you no longer need to manually configure lastmod tags. WordPress automatically populates this field in your sitemaps, saving you valuable time and ensuring accuracy.
**<u>A CALL TO ACTION FROM GOOGLE’S GARY ILLYES AND BING’S FABRICE CANEL</u>**
Both Google and Bing representatives have enthusiastically endorsed the last mod implementation in WordPress 6.5. Gary Illyes from Google strongly encourages website owners to upgrade, stating:
“If you’re on WordPress, since version 6.5, you have this field natively populated for you thanks to Pascal Birchler and the WordPress developer community… If you’re holding back on upgrading your WordPress installation, please bite the bullet and just do it (maybe once there are no plugin conflicts).”
Fabrice Canel from Bing echoes this sentiment, highlighting the importance of the last mod for search engines – regardless of their underlying technology (AI-driven or rules-based). He recommends using lastmod in conjunction with IndexNow for a comprehensive and fresh SEO
**<u>
SEO ADVANTAGES OF UPGRADING TO WORDPRESS 6.5 FOR YOUR WORDPRESS WEBSITE DEVELOPMEN</u>**T
Upgrading to WordPress 6.5 unlocks a multitude of SEO benefits:
**<u>Enhanced Crawl Efficiency</u>**: Search engines can prioritize crawling your most recent content, leading to faster indexing and improved search result visibility. According to a study by Searchmetrics, websites with faster indexing times can see a 20% increase in organic traffic.
**<u>Reduced Server Load</u>**: By directing crawlers towards updated pages, you minimize unnecessary crawling of static content, ultimately reducing server strain. Studies by Soasta suggest that a 1-second delay in page load time can result in a 7% reduction in conversions.
**<u>Alignment with SEO Best Practices</u>**: WordPress 6.5 demonstrates a commitment to staying ahead of the SEO curve, ensuring your website remains compliant with the latest search engine optimization standards. Moz reports that the top ranking factors for SEO include high-quality content, technical SEO, and on-page optimization.
**<u>Improved User Experience</u>**: Faster loading times due to reduced server load can lead to a more positive user experience, which is another ranking factor for search engines.
By upgrading to WordPress 6.5, you’re taking a significant step towards a more SEO-friendly website. Combine this with our expert WordPress development services at 42Works, and watch your website thrive online!
**<u>BEYOND WORDPRESS: OPTIMIZING LASTMOD FOR OTHER PLATFORMS</u>**
While WordPress 6.5 simplifies lasts for its users, website owners on other platforms shouldn’t be discouraged. Here’s what you can do:
**<u>Consult a WordPress website development expert</u>**: A skilled WordPress website development team like 42Works can advise on implementing accurate last mod dates within your sitemap files, and ensure your website is optimized for the latest SEO best practices.
**<u>Research platform-specific solutions</u>**: Many Content Management Systems (CMS) offer plugins or extensions to manage lastmod tags.A quick search within your platform’s plugin marketplace can reveal valuable tools. For example, popular CMS platforms like Joomla! and Drupal have established plugins that address lastmod functionality.
**<u>Consider a Hybrid Approach</u>**: For some, a hybrid approach might be the best solution. This could involve migrating specific content sections to a WordPress subdomain that leverages the native lastmod support in version 6.5.
By exploring these options, you can ensure your clients on all platforms benefit from the SEO advantages that lastmod offers.
**<u>DON’T MISS OUT ON THE SEO BOOST!</u>**
The introduction of native last-mod support in WordPress 6.5 marks a significant step forward for website owners seeking to optimize their SEO strategy. By upgrading to this version, you empower search engines to efficiently crawl your content, ultimately leading to a more prominent presence in search results.
Ready to take your WordPress website development to the next level and unlock the power of last-mod support? 42Works offers a comprehensive suite of [WordPress website development](https://42works.net/expertise/websites/) and SEO services to help you achieve your website’s full potential. Contact us today for a consultation and see how we can help your website thrive in search results. | anmolrajdev |
1,866,494 | How to create a linux VM on Azure (using PowerShell and install ‘NGINX’ Engine) | *Step 1: Login to Azure portal and create a Virtual Linux Machine” * Select resource group, name... | 0 | 2024-05-27T11:51:49 | https://dev.to/busybrain/how-to-create-a-linux-vm-on-azure-using-powershell-and-install-nginx-engine-3d27 | **Step 1: Login to Azure portal and create a Virtual Linux Machine” **
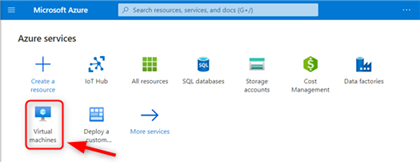
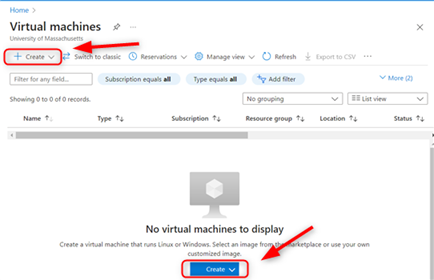
**Select resource group, name the VM , choose a region , select the image type “Ubuntu 22.04” or any latest.
Select password for authentication types and add details for authentication
For Public ports rules, allow all ports because we will be communicating with the VM through an IP address on powershell.
Then click review and create, wait for deployment and go to resource group.**
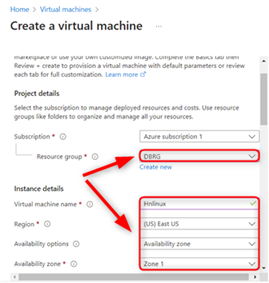
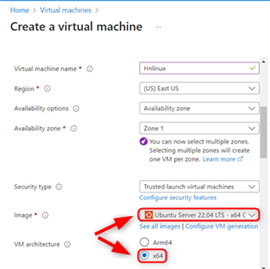
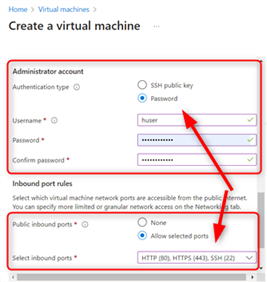

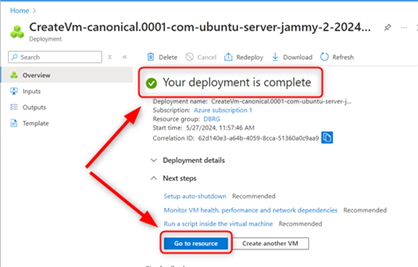
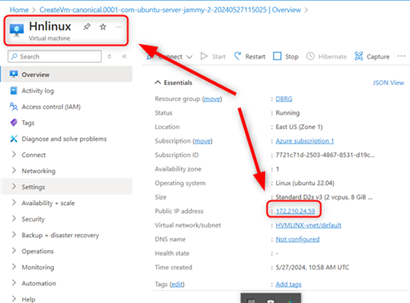
**Click on the IP address to increase the idle timeout to max, to enable us communicate with it more without shutting down then save.
Go back to the VM and copy the IP address **
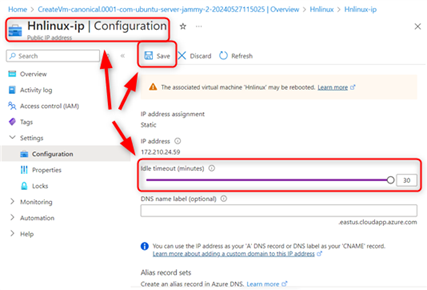
**Step 3. Open powershell as admin on your computer and input this command
“ssh “your vm user name”@”IP address of the VM” . to establish communication.
Enter ‘yes”to continue, enter VM password**
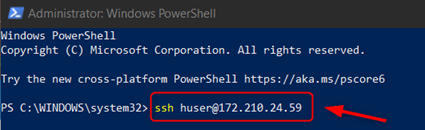
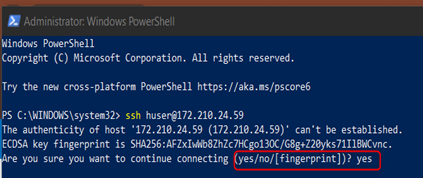
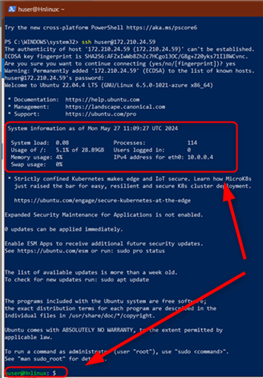
**Now your VM has established communication, Now to install the engine, we have to enter the root of the VM to install the engine ,
Enter the command “sudo so”
Then include the command “apt update” to update any latest requirement, then “apt install nginx” enter Yes for confirmation**
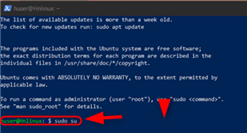
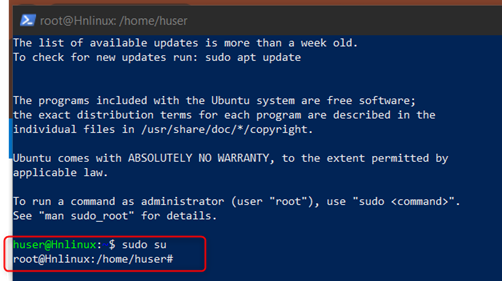
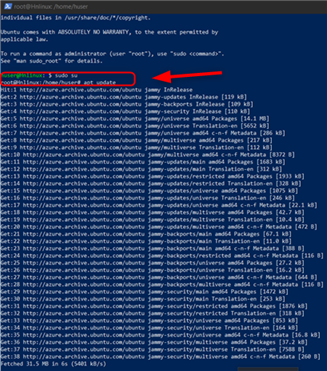
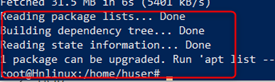
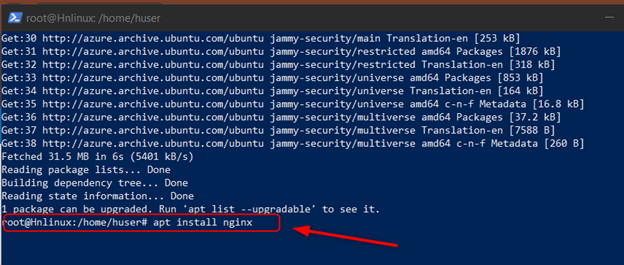
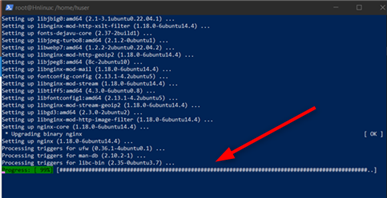
When its 100%, Congrats, you have installed the engine.
**Step 4: Go to the IP address, copy it and paste it onto a new tab. **
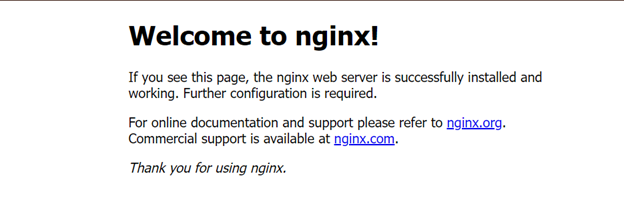
**CONGRATS YOU HAVE SUCCESSFULLY INSTALLED NGINX INTO YOUR AZURE VM LINUX MACHINE**
| busybrain | |
1,866,492 | Kumaran Medical Center Urologist near me | Urology is a medical specialty focusing on the diagnosis, treatment, and management of urinary tract... | 0 | 2024-05-27T11:48:32 | https://dev.to/kumaran_medicals_2bb8f0e8/kumaran-medical-center-urologist-near-me-3520 | Urology is a medical specialty focusing on the diagnosis, treatment, and management of urinary tract disorders and male reproductive system issues. Urologists are highly trained medical professionals who offer a wide range of treatments and services to address conditions affecting the kidneys, bladder, urethra, and male reproductive organs.
[Kumaran Hospital's Urology Department](https://www.kumaranmedical.com/urology/
) offers specialized treatment and comprehensive care for a wide range of urological conditions. Here's a detailed description of the facility and services:
Facility: Located within Kumaran Hospital, the Urology Department boasts state-of-the-art infrastructure and cutting-edge medical technology. The facility is designed to provide patients with a comfortable and conducive environment for diagnosis, treatment, and recovery. It features modern examination rooms, advanced diagnostic equipment, dedicated operating theaters, and recovery suites.
Specialists: The hospital's Urology Department is staffed with highly skilled and experienced urologists who are experts in their field. These specialists have undergone extensive training and have a wealth of experience in diagnosing and treating various urological conditions. They are committed to delivering personalized care and ensuring the best possible outcomes for every patient.
Services:
1. Diagnostic Services: The department offers a comprehensive range of diagnostic services, including imaging studies (such as ultrasound, CT scans, and MRI), laboratory tests, and urodynamic evaluations, to accurately diagnose urological conditions.
2. Medical Treatment: The urologists at Kumaran Hospital provide medical management for conditions such as urinary tract infections, kidney stones, benign prostatic hyperplasia (BPH), erectile dysfunction, and urinary incontinence. They develop individualized treatment plans tailored to each patient's unique needs.
3. Surgical Treatment: For conditions that require surgical intervention, the department offers a wide array of minimally invasive and traditional surgical procedures. These include endoscopic procedures (such as cystoscopy and ureteroscopy), laparoscopic surgery, robotic-assisted surgery (such as robotic prostatectomy), and open surgery.
4. Laser Therapy: The hospital utilizes advanced laser technology for the treatment of kidney stones, benign prostatic hyperplasia (BPH), and other urological conditions. Laser therapy offers precise and effective treatment with minimal discomfort and shorter recovery times.
5. Reconstructive Surgery: The urology team is experienced in performing reconstructive surgeries to correct congenital abnormalities, trauma-related injuries, and complications from previous surgeries, restoring normal urinary function and improving quality of life.
6. Men's Health Services: In addition to treating urological conditions, the department offers specialized services for men's health issues, including testosterone replacement therapy, treatment for male infertility, and management of sexual health concerns.
7. Continence Care: The hospital provides comprehensive care for patients suffering from urinary incontinence, including diagnostic evaluation, behavioral therapies, pelvic floor exercises, medication management, and surgical interventions when necessary.
8. Follow-up Care and Support: The urology team at Kumaran Hospital is dedicated to providing ongoing support and follow-up care to ensure the long-term health and well-being of patients. They offer counseling, education, and resources to help patients manage their condition and maintain optimal urological health.
Conclusion:
With its commitment to excellence in patient care, advanced technology, and experienced medical professionals, [Kumaran Hospital's Urology Department](https://www.kumaranmedical.com/urology/
) is a trusted destination for individuals seeking world-class urological treatment and services. Urologists offer comprehensive care for a wide range of conditions affecting the urinary and male reproductive systems. With advanced diagnostic tools, state-of-the-art surgical facilities, and a patient-centered approach, urology services aim to provide effective treatment and improve patients' quality of life.
| kumaran_medicals_2bb8f0e8 | |
1,866,490 | Kumaran Medical Center ENT specialist | Kumaran Medical Center's ENT department specializes in comprehensive care for ear, nose, and throat... | 0 | 2024-05-27T11:46:27 | https://dev.to/kumaran_medicals_2bb8f0e8/kumaran-medical-center-ent-specialist-3ikc | healthcare | [Kumaran Medical Center's ENT department](https://www.kumaranmedical.com/ent/
) specializes in comprehensive care for ear, nose, and throat conditions. Equipped with advanced technology and staffed by experienced professionals, the center provides diagnosis, treatment, and surgical interventions for a wide range of ENT disorders, ensuring personalized and effective patient care.
An Ear, Nose, and Throat ENT specialist, also known as an otolaryngologist, is a medical doctor trained in the diagnosis and treatment of disorders related to the ears, nose, throat, and related structures of the head and neck. Here's a comprehensive description of ENT and the services provided:
Specialization Overview:
ENT specialists are highly skilled physicians who diagnose and treat a wide range of conditions affecting the ears, nose, throat, and adjacent structures. They undergo extensive training, including medical school, residency, and sometimes additional fellowship training, to become experts in their field.
Scope of Practice:
ENT specialists address a diverse array of medical issues, including:
1. Ear Disorders: They diagnose and treat conditions affecting the ears, such as hearing loss, ear infections, tinnitus-ringing in the ears, balance disorders, and ear trauma.
2. Nose and Sinus Conditions: ENTs manage disorders of the nose and sinuses, including sinusitis, nasal congestion, deviated septum, nasal polyps, allergies, and nasal fractures.
3. Throat and Voice Disorders: They evaluate and treat conditions affecting the throat and voice, such as sore throat, tonsillitis, laryngitis, vocal cord disorders, swallowing difficulties, and throat cancer.
4. Head and Neck Conditions: ENT specialists manage various head and neck disorders, including thyroid and parathyroid disorders, salivary gland disorders, neck masses, facial trauma, and head and neck cancers.
5. Sleep Disorders: They diagnose and treat sleep-related breathing disorders, such as obstructive sleep apnea, which may involve evaluation of the upper airway and surgical interventions like tonsillectomy or adenoidectomy.
Diagnostic and Treatment Modalities:
ENT specialists employ a variety of diagnostic and treatment modalities, including:
1. Physical Examination: Thorough examination of the ears, nose, throat, and neck to assess symptoms and identify abnormalities.
2. Diagnostic Tests: Utilization of tests such as audiometry hearing tests, tympanometry, endoscopy, imaging studies CT scans, MRI, and allergy testing to aid in diagnosis.
3. Medical Management: Prescription of medications, such as antibiotics, antihistamines, corticosteroids, and pain relievers, to manage symptoms and treat underlying conditions.
4. Surgical Interventions: Performance of surgical procedures, including tonsillectomy, adenoidectomy, sinus surgery, tympanoplasty ear drum repair, cochlear implantation, thyroidectomy, and head and neck cancer surgery.
5. Minimally Invasive Procedures: Adoption of minimally invasive techniques, such as endoscopic sinus surgery, balloon sinuplasty, and laser surgery, to treat certain conditions with less tissue disruption and faster recovery times.
Collaboration and Multidisciplinary Care:
ENT specialists often collaborate with other healthcare professionals, including audiologists, speech therapists, allergists, oncologists, and neurosurgeons, to provide comprehensive care for patients with complex medical needs. They may also work closely with primary care physicians and other specialists to coordinate care and ensure optimal treatment outcomes.
Conclusion:
In summary, Ear, Nose, and Throat specialists play a vital role in diagnosing and managing a wide range of conditions affecting the head and neck region. With their specialized training and expertise, they strive to improve patients' quality of life by alleviating symptoms, restoring function, and treating underlying diseases with compassion and skill...[Know more](https://www.kumaranmedical.com/ent/
)
 | kumaran_medicals_2bb8f0e8 |
1,866,489 | What is AKS Cluster | Imagine this: you've built a fantastic containerized application, a masterpiece of code that's ready... | 0 | 2024-05-27T11:45:55 | https://dev.to/abhiram_cdx/what-is-aks-cluster-45ec | Imagine this: you've built a fantastic containerized application, a masterpiece of code that's ready to take the world by storm. But then, deployment dread sets in. Kubernetes, the container orchestration system you need, feels like a complex beast to tame. Enter AKS clusters, your knight in shining armor for conquering the cloud!
## What's an AKS Cluster?
Think of it as a pre-built coliseum in the Azure cloud, specifically designed for container battles (deploying your applications). Microsoft handles the infrastructure setup and maintenance, freeing you to focus on what matters most – deploying your glorious containerized warriors (applications) quickly and efficiently.
## Benefits Galore for the Container Champion:
Effortless Deployment: No more wrestling with complex Kubernetes setups. AKS streamlines the process, letting you unleash your container army onto the battlefield (cloud) in record time.
Scalability on Demand: Need to handle a sudden surge in traffic? No problem! AKS clusters can scale up or down like a self-adjusting coliseum, ensuring your applications always have the resources they need to triumph.
Cost-Effective Conquest: With AKS, you only pay for the resources your container army uses. It's like a pay-per-gladiator system, ensuring you get the most bang for your buck.
Seamless Azure Integration: AKS plays nicely with other Azure services, making it a dream team for building and deploying cloud-native applications.
## Additional Resources
[What is Azure AKS?](https://www.cloudanix.com/learn/what-is-azure-aks)
| abhiram_cdx | |
1,866,488 | USER PASSWORD RESET USING DJANGO | TABLE OF CONTENTS 1. Introduction 2. Prerequisites 3. Creating a login... | 0 | 2024-05-27T11:45:33 | https://dev.to/swahilipotdevs/user-password-reset-using-django-54f0 | ## **TABLE OF CONTENTS**
**1. Introduction**
**2. Prerequisites**
**3. Creating a login Template**
- Definition of terms
- Creating a login Template
**4. Implementing user password reset in Django**
- Configuring email settings
- URL configuration
- Creating templates
- Password request form
- Password request email template
- Password reset
- Password reset complete form
- Email template
- Testing
**5. Conclusion**
**6. References**
## **Introduction**
In web applications, it's crucial to include password reset functionality to ensure both security and user-friendliness. When using Django, a high-level Python web framework, there are built-in features that simplify the creation of this functionality. This involves setting up a process where users can receive an email allowing them to reset their passwords on the server side, with the email sent directly to their inbox.
By following the guidelines provided, you can efficiently implement user password reset functionality in your Django application.
## **Steps to create Django app**
1. Ensure you have python installed in your computer if you does not have install it by visiting python official website.
2. Install pip which comes with python in default.
navigate in the terminal to determine its version by running pip --version
3. Install virtual environment
Virtualenv is a tool to create isolated Python environments.
<code>
pip install virtualenv
</code>
4. Install Django by running the following in terminal
<code>
pip install django
</code>
5.Create Django project
<code>
django-admin startproject password-reset
</code>
6.Navigate into the project folder by running
<code>
cd password-reset
</code>
7.Run code . in your terminal to run your project in your code editor
## **Creating a sub app in the Django app**
1. Create a Django App:
- Use the `manage.py` script to create a new app:
<code>
python manage.py startapp myapp
</code>
2. Configure the Django Project
3. Add the App to INSTALLED_APPS:
- Open `mysite/settings.py` and add your new app (`myapp`) to the `INSTALLED_APPS` list:
<code>
INSTALLED_APPS = [
...
'myapp',
]
</code>
4. Create Initial Views
a. Create a View:
- Open `myapp/views.py` and create a simple view:
<code>
from django.http import HttpResponse
def index(request):
return HttpResponse("Hello, world. You're at the myapp index.")
</code>
b. Map the View to a URL:
- Create a file named `urls.py` in the `myapp` directory and add the following code:
<code>
from django.urls import path
from . import views
urlpatterns = [
path('', views.index, name='index'),
]
</code>
c. Include the App’s URL Configuration:
- Open `mysite/urls.py` and include the app's `urls.py`:
<code>
from django.contrib import admin
from django.urls import include, path
urlpatterns = [
path('admin/', admin.site.urls),
path('myapp/', include('myapp.urls')),
]
</code>
5. Run the Development Server
a. Run the Server:
- Use the `manage.py` script to start the development server:
<code>
python manage.py runserver
</code>
6. Access the App:
- Open a web browser and go to `http://127.0.0.1:8000/myapp/` to see your app in action.
## **Steps to implement user password Reset in Django**
**1.Configure Email Settings**
Django relies on an external email service to send password reset emails. You’ll need to configure your email settings in the ‘settings.py’. This typically involves specifying:
- EMAIL_BACKEND: The class responsible for sending emails
- EMAIL_HOST: Your email provider's SMTP server address.
- EMAIL_HOST_USER: Your email address used for sending emails.
- EMAIL_HOST_PASSWORD: The password for your email account.
- EMAIL_PORT: The SMTP port number for your email provider.
- EMAIL_USE_TLS: (Optional) Enable TLS encryption for secure communication (recommended).
Example
<code>
EMAIL_BACKEND = 'django.core.mail.backends.smtp.EmailBackend'
EMAIL_HOST = 'smtp.example.com'
EMAIL_PORT = 587
EMAIL_USE_TLS = True
EMAIL_HOST_USER = 'your_email@example.com'
EMAIL_HOST_PASSWORD = 'your_email_password'
DEFAULT_FROM_EMAIL = 'your_email@example.com'
</code>
**2.URL CONFIGURATION.**
- Set up the default URL settings patterns, in Django by handling password reset views. Make sure to add the django.contrib.auth.urls to your projects urls.py file.
Code example in the ‘settings.py’
<code>
from django.urls import path, include
ur patterns = [
...
path('accounts/', include('django.contrib.auth.urls')),
...
]
</code>
**3. Create Templates**
This involves creating templates for the user to reset the password. They include the following:
**a) Password reset request form:**
- It is a form template designed to allow users to request a password reset for their accounts.
- Django provides a `PasswordResetForm’ for this purpose. You can customize this form or create your own based on your requirements.
example
<code>

</code>
**b. Password reset confirmation form**
- The Password Reset form contains an action that sends the user an email with a special SSO link to reset their password.
<code>
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Password Reset Done</title>
</head>
<body>
<h2>Password Reset Email Sent</h2>
<p>We've emailed you instructions for setting your password. If you haven't received the email, please check your spam folder.</p>
</body>
</html>
</code>
When a user submits the password reset form, the ‘PasswordResetView` handles the logic:
- Validates the submitted email address against registered users.
- Generates a unique password reset token using a cryptographically secure method.
- Creates a password reset record associated with the user and the generated token.
- Sends an email containing the reset link to the user's email address.

**c. Password reset email template**
- A password reset email template is a transactional email that is triggered when customers click on a “Forgot password?” link to reset the previous password.
<code>
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Password Reset Email</title>
</head>
<body>
<h2>Password Reset</h2>
<p>You're receiving this email because you requested a password reset for your account.</p>
<p>Please click the link below to reset your password:</p>
<p><a href="{{ protocol }}://{{ domain }}{% url 'password_reset_confirm' uidb64=uid token=token %}">Reset Password</a></p>
<p>If you didn't request a password reset, you can safely ignore this email.</p>
</body>
</html>
</code>
**d. password reset form**
- The password reset form allows users who have forgotten their password to securely reset it. It verifies the user's identity through their email address and then prompts them to create a new password.
<code>
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Password Reset Confirm</title>
</head>
<body>
<h2>Reset Password</h2>
<form method="post">
<code>{% csrf_token %}</code>
<code>{{ form.as_p }}</code>
<button type="submit">Continue</button>
</form>
</body>
</html>
</code>
**e. Password reset complete form**
- It is a form that triggers the confirmation that the password has been reset and the user can login to the account using the new created password.
<code>
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Password Reset Complete</title>
</head>
<body>
<h2>Password Reset Successful</h2>
<p>Your password has been successfully reset. You can now <a href="{% url 'login' %}">log in</a> with your new password.</p>
</body>
</html>
</code>
**4. Email Template**
- Customize the email template for the password reset email. Django uses a default text-based email template, but you can create your own HTML email template for a better user experience.
<code>
PASSWORD_RESET_EMAIL_TEMPLATE = 'path_to_your_email_template.html'
</code>
## **5. Testing**
Thoroughly test the password reset functionality to ensure its correctness and security. Test scenarios should include:
- User receives the password reset email.
- User clicks on the reset link.
- User successfully resets the password.
## **Conclusion**
Django provides a robust built-in functionality for implementing user password reset with emails. This feature enhances user experience by allowing them to retrieve forgotten passwords easily. By configuring your email backend, defining URL patterns for the provided views, creating informative templates, and ensuring everything works through testing, you can establish a secure and user-friendly password reset system for your Django application.
## **References**
https://youtu.be/whK97tOV2z4
https://django-password-reset.readthedocs.io/
https://docs.djangoproject.com/en/5.0/
**MEMBER ROLES**
All members participated generally in the discussion, conducting research and gathering information relevant to the group’s objective. Individual roles are as follows:
| Name | Role |
| ------------------------------------------------------- | --------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
| 1. Victor Kedenge | - Created agendas and distributed to the team<br>- Scheduled and led the meeting.<br>- Coordinating among the group members |
| 2.Julius Gichure | - Creating templates responsible for resetting users password which includes:<br> - Password reset request form<br> - Password reset form<br> - Password reset confirmation<br> - Password reset complete |
| 3.John Brown | - Creating user login template and handling of its codes<br>- Configuring email settings<br>- URL Configurations |
| 4. Beth Owala | - Creating email template responsible for generating users reset link<br>- Performing conclusion |
| 5.Abdirahman Aben | - Conducted editing<br>- Taking notes<br>- Providing references |
| 6.Sharon Imali<br><br><br><br><br>7. Moris Mutugi | - Attaching images<br>- Typing down notes on discussed points within the group members<br>- Adding video tutorials for further references |
| victor_kedenge | |
1,866,487 | Oaklynn Kidswear | clothing brand of Pakistan | I am Nasir Chaudhary, the visionary force behind The Oaklynn, a leading kidswear brand based in... | 0 | 2024-05-27T11:45:29 | https://dev.to/theoaklynn/oaklynn-kidswear-clothing-brand-of-pakistan-3bpd | webdev, oaklynn, kidswear, clothing | I am Nasir Chaudhary, the visionary force behind The Oaklynn, a leading kidswear brand based in Pakistan. With an innate passion for fashion and an unwavering dedication to quality, I established The **[Oaklynn kidswear](https://theoaklynn.com/)** to carve out a niche in the industry, bringing forth a fusion of contemporary style and cultural richness in children's apparel. | theoaklynn |
1,866,485 | Teen Counseling in Hoffman Estates, IL: Support and Guidance at Ardent Counseling Center | Adolescence is a critical period of development characterized by numerous physical, emotional, and... | 0 | 2024-05-27T11:45:10 | https://dev.to/ardentcenter/teen-counseling-in-hoffman-estates-il-support-and-guidance-at-ardent-counseling-center-41hf | Adolescence is a critical period of development characterized by numerous physical, emotional, and social changes. For many teens, navigating these changes can be challenging, leading to stress, anxiety, depression, and other mental health issues. At Ardent Counseling Center in Hoffman Estates, IL, we understand the unique needs of teenagers and provide specialized counseling services to help them thrive during this pivotal stage of life.
Understanding the Importance of Teen Counseling
Teen counseling is a therapeutic service designed to address the emotional and psychological needs of adolescents. This type of counseling can be crucial for several reasons:
Emotional Regulation: Teens often experience intense emotions that they may not know how to manage effectively. Counseling helps them develop healthy coping mechanisms.
Academic Pressure: The pressure to perform well academically can be overwhelming. Counseling provides strategies to manage stress and improve focus.
Social Challenges: Navigating friendships, peer pressure, and social dynamics can be difficult. Counseling offers support in developing strong interpersonal skills.
Identity and Self-Esteem: Adolescence is a time of self-discovery. Counseling helps teens build a positive self-image and confidence.
Family Dynamics: Family relationships can become strained during the teenage years. Counseling facilitates better communication and understanding within the family unit.
Services Offered at Ardent Counseling Center
At Ardent Counseling Center in Hoffman Estates, IL, we offer a range of services tailored to meet the specific needs of teenagers:
Individual Therapy
One-on-one sessions with a licensed therapist provide a safe space for teens to express their thoughts and feelings. These sessions focus on:
Identifying and addressing emotional issues: such as anxiety, depression, anger, and low self-esteem.
Developing coping strategies: to manage stress and emotional upheaval.
Building resilience: to handle life's challenges more effectively.
Group Therapy
Group therapy allows teens to connect with peers facing similar issues, fostering a sense of community and support. Topics covered in group therapy may include:
Social skills development
Conflict resolution
Peer pressure management
Healthy relationship building
Family Counseling
Family dynamics can significantly impact a teen's well-being. Our family counseling sessions aim to improve communication and strengthen family bonds. These sessions help:
Resolve conflicts: by addressing underlying issues and facilitating open dialogue.
Enhance understanding: between family members to support the teen's growth.
Create a supportive environment: for the teen at home.
Crisis Intervention
For teens experiencing acute emotional distress or crises, our crisis intervention services provide immediate support. This includes:
Assessment and stabilization: to ensure the teen's safety.
Short-term counseling: to address immediate concerns.
Referrals: to additional resources if necessary.
Why Choose Ardent Counseling Center?
Choosing the right counseling center for your teen is a crucial decision. Here are some reasons why Ardent Counseling Center stands out:
Experienced Therapists
Our team of licensed therapists has extensive experience working with teenagers. They are trained to address adolescents' unique challenges and are committed to providing compassionate and effective care.

Personalized Approach
We recognize that every teen is different. Our counselors develop personalized treatment plans tailored to the individual needs of each teen, ensuring the best possible outcomes.
Safe and Welcoming Environment
Creating a safe, non-judgmental space is essential for effective therapy. Our center in Hoffman Estates is designed to be a welcoming environment where teens feel comfortable expressing themselves.
Holistic Care
We take a holistic approach to teen counseling, addressing not only emotional and psychological needs but also considering the teen's physical health, social environment, and overall well-being.
Getting Started with Teen Counseling at Ardent Counseling Center
If you believe your teen could benefit from counseling, reaching out to Ardent Counseling Center is the first step towards getting the support they need. Here’s how to get started:
Contact Us: Call or visit our website to schedule an initial consultation.
Initial Assessment: During the first visit, our therapist will thoroughly assess your teen's needs and develop a tailored treatment plan.
Ongoing Support: Regular therapy sessions will be scheduled based on the treatment plan, with progress reviews to ensure your teen is on the right path.
At Ardent Counseling Center in Hoffman Estates, IL, we are dedicated to helping teens navigate the challenges of adolescence and emerge stronger, more resilient, and ready to face the future. Contact us today to learn more about our [teen counseling services](https://ardentcenter.com/teen-counseling-in-illinois-iowa-indiana-nebraska-counseling-teens-near-me/) and how we can support your family.
| ardentcenter | |
1,866,484 | Why Choose Public Cloud Services Over a Private or Hybrid Cloud? The Agility Advantage | Agility is crucial in the fast-paced commercial world of today. Businesses must embrace innovation,... | 0 | 2024-05-27T11:43:26 | https://dev.to/adelenoble/why-choose-public-cloud-services-over-a-private-or-hybrid-cloud-the-agility-advantage-21jf | Agility is crucial in the fast-paced commercial world of today. Businesses must embrace innovation, scale their operations fast and effectively, and adjust to the shifting demands of the market.
Herein lies the opportunity for cloud computing to help, providing enterprises of all sizes with an adaptable and affordable option.
However, when it comes to [**cloud computing**](https://www.lenovo.com/de/de/servers-storage/solutions/cloud-computing/), there are several deployment models to take into account, each with pros and cons of its own.
This article explores the world of public cloud services and explains why, in comparison to private or hybrid cloud solutions, they might be the best option for your company.
## **Knowing the Cloud Environment**
Let us first define the three primary cloud deployment models to make sense of them.
**Hybrid Cloud**
Using on-premises infrastructure and public cloud services, this approach blends public and private cloud environments. In the private cloud, sensitive data and apps can be controlled, allowing enterprises to take advantage of the public cloud's scalability and flexibility.
Even with your own power plant, imagine being able to buy more electricity from the grid when needed.
**Cloud Public**
AWS, Microsoft Azure, and Google Cloud Platform (GCP) are examples of third-party providers that offer public cloud services. With pay-as-you-go internet access to scalable resources, these companies own and operate the whole infrastructure.
Like utilities like electricity, picture a massive pool of computing resources that are accessible to anyone with an internet connection.
**Private Cloud**
Cloud infrastructure that is exclusively devoted to one company is known as a private cloud. It can be set up in-house in a business's data center or hosted by a service provider using resources allocated just to that company. For your computing demands, imagine having your own personal power plant.
### **Reasons in Favor of Public Cloud Services**
Let's examine why public cloud services might be the most appealing choice for many enterprises now that the cloud landscape has been established:
**1. Worldwide Outreach & Cooperation**
The global distribution of public cloud services allows resources to be accessed from any location with an internet connection. As a result, teams that are geographically separated can collaborate more readily, and companies can grow internationally without having to make large expenditures on local infrastructure.
**2. Agility & Scalability**
The scalability of public cloud services is remarkable. Does it require more processing power to handle a sudden spike in website traffic? Not an issue. You can quickly add or remove resources from public clouds to accommodate your changing demands.
In the fast-paced corporate world of today, this agility is essential for promptly responding to opportunities and market demands.
**3. Quickness & Ingenuity**
Modern technologies like sophisticated analytics, machine learning, and artificial intelligence are easily accessible through the services of public cloud service providers, who are always inventing. As a result, companies of all sizes can benefit from these developments without having to make large R&D investments.
You have access to a technology toolkit that is always changing, which helps you remain ahead of the curve and innovate more quickly.
**4. Safety and Trustworthiness**
To safeguard its infrastructure and client data, public cloud providers actively invest in strong security measures. They frequently use more sophisticated security procedures, data encryption, and disaster recovery plans than many smaller companies. Public cloud services are also renowned for their dependability, providing high uptime and redundancy to guarantee that your data and apps are always accessible.
**5. Lessened Workload on IT**
Owning and maintaining your own IT infrastructure can take a lot of time and resources. This load is transferred to the cloud provider using public cloud services. They take care of patching, updating, and maintaining infrastructure, freeing up your internal IT staff to concentrate on important business goals and long-term projects.
Public cloud providers give you the ability to imagine having a staff of committed IT professionals who are always optimizing and maintaining your infrastructure.
**6. Economical**
You can purchase and manage your own physical infrastructure at no upfront cost when you use public cloud services, which offer a pay-as-you-go basis. It is very affordable for companies of all sizes, especially those with varying resource demands because you only pay for the resources you utilize.
No more large expenditures on servers that could suddenly become outdated—the public cloud provider takes care of all hardware issues.
### A Reasoned Comparison of Public and Private Clouds
Even if public clouds have a lot to offer, certain businesses are still drawn to private clouds:
- **Safety and Regulation:** High levels of control over the data and infrastructure are available with private clouds. For companies that handle extremely sensitive data or work in highly regulated fields, this could be crucial.
- **Personalization:** Private clouds can be tailored to a company's particular requirements. Even if they are more adjustable, public cloud services might not provide the same degree of fine control.
**_But it's crucial to take the trade-offs into account:_**
- **Cost:** Significant upfront investments in hardware, software, and labor are necessary for the construction and upkeep of private cloud infrastructure. Moreover, it is possible that private cloud resources will not be fully utilized, resulting in unnecessary expenses.
- **Scalability:** Growing a private cloud can be a difficult and drawn-out procedure. Because public clouds provide on-demand scalability, businesses may swiftly and effectively adjust to changing needs.
- **Agility:** New apps and services can reach the market more quickly with the help of public cloud services. In a public cloud setting, provisioning resources and launching apps are much simpler.
## A Possible Middle Ground: Hybrid Cloud
Companies that need to strike a balance between control, security, and agility can find the hybrid cloud to be a compelling alternative. With workloads that are not sensitive, they can use public cloud services; with highly regulated or mission-critical data, they can have a private cloud.
## The Best Option for Your Organization
Which deployment model is, therefore, the best fit for you? Your requirements and priorities will determine the response. Take into account the following factors:
- **Security specifications:** You could be better off using a private cloud if your company manages extremely sensitive data.
- **Required Scalability:** What is the rate of change in your resource needs? The scalability of public clouds is excellent.
- **IT Know-How:** Are you able to operate a private cloud infrastructure with your current staff?
- **Cost:** For many companies, public cloud computing provides a more reliable and affordable option.
#### Last Thought: The Benefit of Agility
Agility is crucial in the fast-paced business environment of today. With the help of public cloud services, companies may now grow rapidly, innovate effectively, and easily adjust to the demands of a changing market.
The flexibility, scalability, and affordability of public cloud computing make it a potent force for corporate success and expansion, even while private and hybrid cloud models have their benefits.
A world of opportunities can be unlocked and your company can be propelled towards an innovative and agile future by carefully assessing your needs and utilizing the advantages of public cloud services. | adelenoble | |
1,866,406 | Switching from docker to podman on Ubuntu | I wanted to switch my local container development tool from docker to podman. The reason is that... | 0 | 2024-05-27T11:42:45 | https://dev.to/daveu1983/switching-from-docker-to-podman-on-ubuntu-5f8f | devops, development, docker, podman | I wanted to switch my local container development tool from docker to podman. The reason is that podman uses pods to link containers together, and the pod specification used is the [kubernetes pod specification](https://kubernetes.io/docs/reference/generated/kubernetes-api/v1.24/#pod-v1-core), making transistioning the apps to Kubernetes easier.
###Remove docker
I could not remember how I installed docker so I followed this guide [how-to-completely-uninstall-docker](https://askubuntu.com/questions/935569/how-to-completely-uninstall-docker).
I ran the command `dpkg -l | grep -i docker`.
This returned
```
ii docker-buildx-plugin 0.11.2-1~ubuntu.20.04~focal amd64 Docker Buildx cli plugin.
ii docker-ce 5:24.0.7-1~ubuntu.20.04~focal amd64 Docker: the open-source application container engine
ii docker-ce-cli 5:24.0.7-1~ubuntu.20.04~focal amd64 Docker CLI: the open-source application container engine
ii docker-ce-rootless-extras 5:24.0.7-1~ubuntu.20.04~focal amd64 Rootless support for Docker.
ii docker-compose-plugin 2.21.0-1~ubuntu.20.04~focal amd64 Docker Compose (V2) plugin for the Docker CLI.
```
I than ran `sudo apt-get purge -y` and `sudo apt-get purge -y` on each of the packages above. Then ran the following commands.
```
sudo rm -rf /var/lib/docker /etc/docker
sudo rm /etc/apparmor.d/docker
sudo groupdel docker
sudo rm -rf /var/run/docker.sock
sudo rm -rf /var/lib/containerd
sudo rm -r ~/.docker
```
###Install podman
Using the [podman documentation](https://podman.io/docs/installation) I ran the command `sudo apt-get -y install podman`
From there I ran the commands to check if podman was installed.
```
$ podman version
Version: 3.4.4
API Version: 3.4.4
Go Version: go1.18.1
Built: Thu Jan 1 01:00:00 1970
OS/Arch: linux/amd64
```
When running docker commands the following was returned
```
$ docker ps
Command 'docker' not found, but can be installed with:
sudo snap install docker # version 24.0.5, or
sudo apt install podman-docker # version 3.4.4+ds1-1ubuntu1.22.04.2
sudo apt install docker.io # version 24.0.5-0ubuntu1~22.04.1
See 'snap info docker' for additional versions.
```
However after using docker for a number of years, and the muscle memory kicking in, it would be useful to still be able to use the docker command. Luckily there is a package that can help with this `sudo apt-get -y install podman-docker` will install a docker emulator.
So running a docker command will now give you this.
```
$ docker ps
Emulate Docker CLI using podman. Create /etc/containers/nodocker to quiet msg.
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
```
And as the result suggests you can switch of the message.
```
$ sudo touch /etc/containers/nodocker
$ docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
```
Word of caution, this approach did mean that I lost all local images and containers that I had on my system, so make sure you have saved everything you need prior to making the change.
Hope this helps! I hope to publish more articles about developing apps with podman in the near future. | daveu1983 |
1,866,482 | ETHICAL IMPLICATIONS OF ARTIFICIAL INTELLIGENCE (AI). | Introduction This article encompasses ethical considerations regarding the use of AI in... | 0 | 2024-05-27T11:41:42 | https://dev.to/awadh_mohamed/ethical-implications-of-artificial-intelligence-ai-22fd |

**Introduction**
This article encompasses ethical considerations regarding the use of AI in decision-making, potential biases within AI systems, accountability for machine-generated outcomes, and the overall impact of AI on individuals and society.
**Table of Contents**
1. What are the ethical implications of AI?
1. Importance of AI Context.
2. Background and evolution of the ethical implications of AI.
1. Origin and Development
2. Evolving perspective and Influential figures
3. Significance of ethical implications of AI.
1. Importance in the AI field.
2. Fairness and avoiding bias.
3. Privacy and data protection.
4. Transparency and accountability.
5. Trust and adoption.
6. Autonomy and Human Dignity
4. How ethical implications of a AI works
1. Key characteristics and features.
2. Integration with AI systems.
3. Ethical decision-making processes.
4. Real world examples and applications.
5. Pros and cons of ethical implication of a AI.
1. Advantages
2. Disadvantages
6. Related terms.
1. AI Ethics
2. Ethical Algorithm Development
3. Ethical AI Governance
7. Conclusion.
**What are the ethical implications of AI ?**
Artificial intelligence involves simulating human intelligence processes by machines, with ethical implications encompassing decision-making, potential biases, accountability, and the overall impact on individuals and society. These issues include ethical considerations regarding biases, accountability for machine-generated outcomes, and the potential biases within AI systems.
**Importance in AI Context**
Understanding the ethical implications of AI is crucial on as it directs the ethical development and deployment of AI systems. This involves adhering to a set of norms, principles, and standards that ensure AI technologies are utilized in a responsible, fair, and transparent manner, aligning with societal values and moral precepts.
**Background and evolution of the ethical implications of AI.**

**Origin and Development**
The concept of ethical implications in AI finds its roots in the emergence of the field of AI ethics, which gained momentum with the rapid advancement of AI technologies. The early discourse surrounding AI ethics focused on identifying and addressing the ethical challenges associated with machine intelligence.
Milestones in the evolution of AI ethics include the development of ethical guidelines, the establishment of research institutions dedicated to AI ethics, and the integration of ethical considerations in AI legislation and policy frameworks.
**Evolving Perspectives and Influential Figures**
As AI ethics has progressed, the focus has shifted from merely recognizing ethical challenges to developing practical solutions and mechanisms for implementing ethical principles in AI systems.
Influential figures in the field of AI ethics, such as ethicists, researchers, and policymakers, have significantly contributed to shaping the discourse, emphasizing the ethical responsibility of AI developers, users, and stakeholder.
**Significance of ethical implications of AI.**

The significance of ethical implications of artificial intelligence is rooted in its profound influence on the development, deployment, and societal integration of AI technologies.
**Importance in the AI Field**
Ethical considerations guide AI development, ensuring technology operates ethically, reflects stakeholder values, fosters public trust, mitigates risks, and promotes responsible AI use.
**Fairness and Avoiding Bias**
AI systems can make biases if not managed, impacting hiring practices, criminal justice, and lending. Ethical AI aims for fairness and equity, providing equal opportunities. An example is iTutor Group's $365,000 lawsuit after AI denied applications to over 200 applicants.
**Privacy and Data Protection**
AI systems can process large amounts of data potentially revealing sensitive information about individuals such as banking information and records. This may raise issues pertaining to data privacy and protection from misuse by corporations and governments.
**Transparency and Accountability**
AI systems should be transparent in decision-making processes to ensure user understanding and accountability, and to clearly identify those responsible for mistakes or harm.
**Trust and Adoption**
Ethical AI development and usage are crucial for its widespread acceptance and trustworthiness, as they build confidence among users, stakeholders, and regulators, thereby increasing its adoption by businesses.
**Autonomy and Human Dignity**
AI should enhance human capabilities while respecting autonomy and dignity, avoiding manipulative practices, ensuring informed consent, and allowing individuals to make their own decisions.
**How ethical implications of AI works.**
**Key Characteristics and Features**
The ethical implications of artificial intelligence are characterized by the integration of ethical frameworks, decision-making models, and accountability mechanisms within AI systems. This involves the incorporation of ethical principles, such as fairness, transparency, accountability, and privacy, to govern the behaviour and outcomes of AI technologies. Additionally, the operationalization of ethical implications involves the implementation of ethical oversight, auditing processes, and continuous evaluation of AI systems to ensure their compliance with ethical standards.
**Integration with AI Systems**
Ethical considerations are interwoven within the fabric of AI systems through the incorporation of ethical algorithms, ethical decision-making models, and mechanisms for identifying and addressing biases and ethical dilemmas. This integration aims to embed ethical values and norms within AI technologies to guide their actions and mitigate potential ethical conflicts.
**Ethical Decision-Making Processes**
Ethical implications drive the development of AI systems that prioritize ethical decision-making, striving to produce outcomes that align with ethical principles and societal values. This involves the implementation of decision-making models that account for ethical considerations, ethical risk assessments, and ethical impact evaluations to ensure that AI-generated outcomes uphold ethical standards.
**Real-World Examples and Applications**
- **Application 1:** Ethical implications in autonomous vehicles.
In the domain of autonomous vehicles, ethical implications are exemplified in the development of decision-making algorithms that govern the behaviour of self-driving cars in critical situations. For instance, ethical considerations come to the forefront when determining how autonomous vehicles prioritize the safety of passengers, pedestrians, and other road users, thereby illustrating the ethical complexities of AI in the context of automotive technologies.
- **Application 2:** Ethical considerations in healthcare AI.
In healthcare, the ethical implications of AI are demonstrated in the deployment of AI technologies for medical diagnosis, treatment recommendation, and patient care. Ethical considerations encompass issues related to data privacy, patient consent, and fair allocation of healthcare resources, emphasizing the need for AI systems to align with medical ethics and uphold patient welfare.
- **Application 3:** AI ethics in financial services.
The ethical implications of AI in finance entail ensuring the ethical use of AI algorithms for credit scoring, risk assessment, and fraud detection while mitigating the potential discriminatory impacts of AI-driven decisions. This highlights the imperative of ethical oversight and regulatory compliance in safeguarding the ethical integrity of AI applications within financial institutions.
**Pros and cons of ethical implications of AI.**

**Advantages**
- Ethical Decision Support: The ethical implications of AI facilitate the development of AI systems that offer decision support grounded in ethical principles, enabling responsible and morally sound decision-making processes.
- Improved Trust and Transparency: By embracing ethical implications, AI technologies can enhance public trust and transparency, fostering confidence in the ethical conduct and accountability of AI systems.
**Disadvantages**
- Algorithmic Bias and Discrimination: Despite ethical considerations, AI systems may still exhibit biases, leading to discriminatory outcomes that disproportionately impact certain demographic groups.
- Ethical Framework Complexity: Implementing ethical implications in AI systems can introduce complexities in algorithmic design, operationalization, and validation, potentially posing challenges in navigating ethical dilemmas effectively.
**Related Terms.**
**AI Ethics.**
AI ethics pertains to the ethical dimensions and considerations associated with the development, deployment, and impact of AI technologies within societal, moral, and legal frameworks.
**Ethical Algorithm Development.**
Ethical algorithm development involves the formulation and implementation of algorithms that prioritize ethical principles, fairness, and accountability within AI systems.
**Ethical AI Governance.**
Ethical AI governance encompasses the regulatory and policy frameworks aimed at governing the ethical utilization and oversight of AI technologies, ensuring their alignment with ethical standards and societal values.
**Conclusion.**
In conclusion, the ethical implications of artificial intelligence are a pivotal aspect of AI's advancement. Understanding, addressing, and integrating ethical considerations within AI systems are indispensable for fostering responsible, trustworthy, and beneficial AI technologies that align with ethical expectations and societal well-being.
**References.**
- [Lark Technologies Pte. Ltd.](https://www.larksuite.com/en_us/topics/ai-glossary/ethical-implications-of-artificial-intelligence)
- [ResearchGate.](https://www.researchgate.net/publication/377396087_Ethical_Implications_of_AI_in_Modern_Education_Balancing_Innovation_and_Responsibility#:~:text=Consequently%2C%20ethical%20considerations%20in%20AI,AI%2Denabled%20resources%20and%20opportunities)
- [WorldEconomicForum.](https://www.weforum.org/agenda/2016/10/top-10-ethical-issues-in-artificial-intelligence/)
| awadh_mohamed | |
1,866,480 | Free Download Astra Premium Sites Plugin | Astra Premium Sites is a library of ready-to-use full website templates built with Beaver Builder and... | 0 | 2024-05-27T11:40:14 | https://dev.to/shahriarwebdev/free-download-astra-premium-sites-plugin-d98 | astra, wordpress, elementor, plugins | Astra Premium Sites is a library of ready-to-use full website templates built with Beaver Builder and Elementor page builders. You need to have Astra WordPress theme (free) and Astra Pro in order to use this plugin.
No Spam or Click Bait.
[Download Link](https://wpcodersclub.com/astra-premium-sites-plugin/)
| shahriarwebdev |
1,866,474 | Google Apps Script Copilot Gets Supercharged with Retrieval-Augmented Generation (RAG) Functionality | The world of Google Apps Script development just got a whole lot smarter with the integration of... | 0 | 2024-05-27T11:37:51 | https://dev.to/marij_murtaza/google-apps-script-copilot-gets-supercharged-with-retrieval-augmented-generation-rag-functionality-f2h | googleappsscript, googleappsscriptcopilot, codingassistant, githubcopilot | The world of Google Apps Script development just got a whole lot smarter with the integration of Retrieval-Augmented Generation (RAG) functionality within GS Copilot. But what exactly is RAG, and how can it transform your coding experience?
**Demystifying RAG: Retrieval, Analyze, Generate**
RAG stands for Retrieval-Augmented Generation. This powerful technology empowers GS Copilot to understand your existing code in its entirety, analyze its context, and then generate responses tailored to your specific needs. It's like having a super-intelligent coding buddy whispering helpful suggestions in your ear!
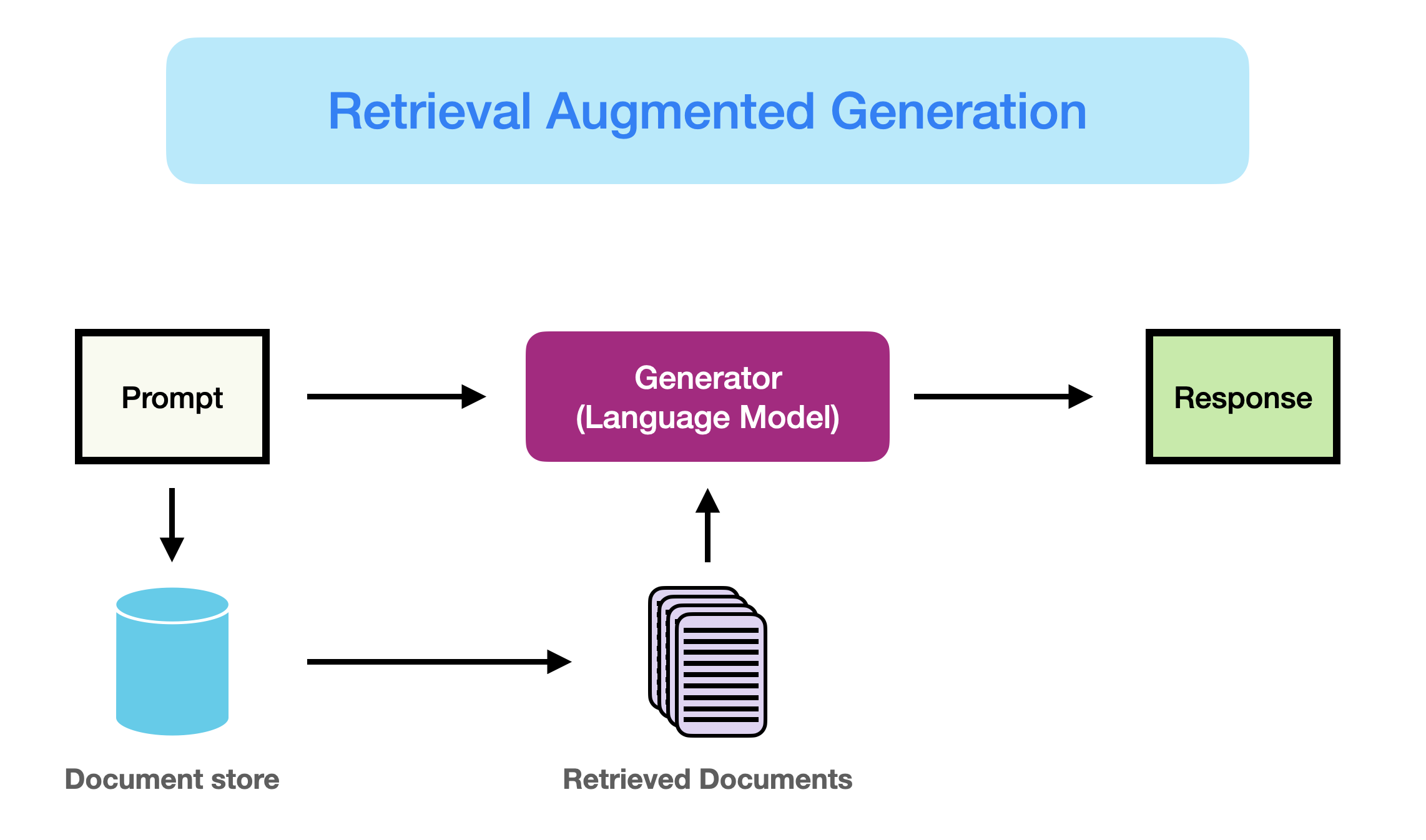
**How Does it Work in GS Copilot's Chat Feature?**
Imagine this: you're working on a complex Google Apps Script and get stuck on a specific function. Instead of spending hours scouring the internet for answers, you simply type your question directly into GS Copilot's chat interface.
Here's where the magic of RAG unfolds:
**1.Retrieval:** GS Copilot doesn't just read your question; it retrieves and reads your entire script. This allows it to understand the bigger picture and the context of your query.
**2.Analyze:** Using RAG's analytical prowess, GS Copilot examines your code, identifying relevant sections and functions related to your question.
**3.Generate:** Based on the analysis and retrieval of relevant code sections, GS Copilot generates a response that directly addresses your query. This could be:
**• Function Explanation:** Need clarification on what a specific function does within your code? RAG can analyze its usage and provide a clear explanation.
**• Error Debugging:** Stuck with an error message? RAG can analyze your code and suggest potential fixes or highlight areas causing the issue.
This seamless integration of RAG within the chat feature makes it incredibly user-friendly and promotes an interactive learning environment. No more jumping back and forth between your code and external resources – GS Copilot becomes your one-stop shop for troubleshooting and understanding your scripts.
**Beyond the Basics: The Power of RAG**
The benefits of RAG functionality extend far beyond basic question answering and debugging. Here are some additional ways it can enhance your workflow:
**• Improved Code Maintenance:** When updating or modifying existing scripts, RAG can analyze the code structure and suggest potential improvements, making maintenance a breeze.
**• Context-Aware Suggestions:** While writing new code, GS Copilot can suggest more relevant code snippets and functions based on the existing script's context, saving you time and effort.
**• Enhanced Learning:** RAG's ability to analyze and explain code sections can be a valuable learning tool for beginner and intermediate developers.
The possibilities with RAG are vast and constantly evolving. As Google Apps Script Copilot continues to develop, we can expect even more powerful features and functionalities that leverage the power of Retrieval-Augmented Generation technology.
{% embed https://www.youtube.com/watch?v=RAoOujeqtaQ %}
| marij_murtaza |
1,864,224 | A simple introduction to JavaScript promises | Introduction Modern web development requires asynchronicity. Sometimes, a function needs... | 0 | 2024-05-27T11:37:00 | https://dev.to/armstrong2035/a-simple-introduction-to-javascript-promises-30oe | ## Introduction
Modern web development requires asynchronicity. Sometimes, a function needs to run only if a prior function is successful. At other times, multiple tasks within an application must occur simultaneously. Functions that need to run simultaneously are asynchronous.
Programming languages, however, are not all equal. Java and the C family are multi-threaded, meaning they can handle asynchronous operations naturally. JavaScript, however, is a single-threaded language. Special functions are therefore needed to manage asynchronous operations in JavaScript. Async / Await and Promises are two such functions. This article will focus on Promises.
This article will cover the following topics:
- Defining JavaScript Promises
- Constructing a Promise
- Handling the success or failure of a Promise
- Chaining multiple Promises
To get the most out of this article, readers should understand the fundamentals of JavaScript.
### What is a Promise?
A Promise is a JavaScript object that represents the outcome of an asynchronous operation. When you work with asynchronous tasks like network requests or file reading, you can use Promises to handle the result of those tasks.
A Promise isn't the function itself, nor is it the direct result of the function. Instead, it acts as a container for a future value, which can be either a successful result or a failure (error).
The state of a Promise reflects the progress of the asynchronous operation:
- **Pending** (the operation is ongoing and hasn't completed yet)
- **Resolved**: (the operation is succesful)
- **Rejected**: (the operation has failed)
Please note that the failure of a Promise doesn't always indicate bad code. Failure can be due to external conditions not met, or explicit error handling within the code.
For example, the user of a digital library has picked a book that is not available. Based on the constructor, the promise may be rejected. The failure of this operation is due to low inventory, not bad code. Yet this condition must be explicitely stated in the promise constructor.
### Constructing a promise object
The Promise constructor method uses what is known as an **executor function**. An executor function is simple a function that returns either a resolved, or a rejected value. In most cases, this function will return both values depending on the conditions set by the developer.
The syntax for constructing a promise is as follows:
```js
const executorFunction = (resolve, reject) => {
//function body
if(condition){
resolve('This promise is succesful')
}
else {
reject('This promise has failed')
}
}
const newPromise = new Promise(executorFunction)
```
We could also use the convention of nesting a promise constructor inside a regular function. Like so:
```js
const regularFunction = (argument) => {
return new Promise ((resolve, reject) => {
if(condition){
resolve('This promise is succesful')
}
else {
reject('This promise has failed')
}
})
}
```
Let us break it down:
1. (resolve, reject): resolve and reject are functions that are built into the promise constructor. They handle cases of success, or failure
2. body: the executor function body
3. if, else: if a condition is met, resolve() is triggered. Otherwise, reject() is triggered.
4. new Promise(): a promise is an object, and needs to be instantiated.
### Example: Check if a book is available
```js
//Create a database of books
const books = {
"Steve Jobs": {
title: "Steve Jobs",
author: "Walter Isaacson",
quantityInStock: 5,
libraryPointsRequired: 2,
},
"Elon Musk": {
title: "Elon Musk",
author: "Walter Isaacson",
quantityInStock: 1,
libraryPointsRequired: 2,
},
"Hard Drive": {
title: "Hard Drive",
author: "James Wallace",
quantityInStock: 3,
libraryPointsRequired: 2,
},
"The Innovators": {
title: "The Innovators",
author: "Walter Isaacson",
quantityInStock: 4,
libraryPointsRequired: 2,
},
"Einstein: His Life and Universe": {
title: "Einstein: His Life and Universe",
author: "Walter Isaacson",
quantityInStock: 2,
libraryPointsRequired: 2,
},
"The Code Breaker": {
title: "The Code Breaker",
author: "Walter Isaacson",
quantityInStock: 1,
libraryPointsRequired: 2,
},
"The Martian": {
title: "The Martian",
author: "Andy Weir",
quantityInStock: 5,
libraryPointsRequired: 2,
},
Artemis: {
title: "Artemis",
author: "Andy Weir",
quantityInStock: 2,
libraryPointsRequired: 2,
},
};
// Object holding a user profile
const user = {
name: "Armstrong Olusoji",
bookShelf: [],
};
// Write a function that checks if a book is in stock
const verifyOrder = (orderObject) => {
return new Promise((resolve, reject) => {
let book = null;
const title = orderObject.title;
const quantity = orderObject.quantity;
if (books.hasOwnProperty(title)) {
book = books[title];
}
if (book.quantityInStock >= quantity) {
console.log(`${book.title} by ${book.author} is in stock`);
resolve(book);
} else {
console.log(`${book.title} by ${book.author} is not in stock`);
reject(book);
}
});
};
```
Now, we can simply call verifyOrder, and depending on the availability of a book, it will either send a resolved value, or a reason for rejection.
But what happens after verifyOrder has run? Do we want to log the resolve/reject value to the console? Do we want to do something else? What do we do after a promise is resolved or rejected?
### Handling success and failure with .then()
The resolve / reject value can be resolved simply by passing a callback function into .then()
Let us test this with our verifyOrder function:
```js
const handleSuccess = (resolvedValue) => {
console.log(resolvedValue);
};
const handleFailure = (rejectedValue) => {
console.log(rejectedValue);
};
verifyorder("Hard Drive", 5).then(handleSuccess, handleFailure);
```
1. handleSuccess(): is a callback function takes a single argument **resolvedValue**. In case of success, this function logs the resolved value to the console.
2. handleFailure(): is a callback function that receives a single argument **rejectedValue**. In case of failure, this function logs logs the rejected value to the console.
3. .then(): receives two callback functions as triggered. The first argument is triggerd if the promise is successful. The second argument is triggered if the promise fails.
4. If verifyOrder succeeds, handleSuccess will execute. Otherwise, handleFailure will execute.
> Please note that once you add .then() to any promise, the promise's resolved and rejected values are automatically passed to the corresponding callback function.
However, there are other ways to use the success/failure callback functions.
```js
const handleSuccess = (resolvedValue) => {
console.log(resolvedValue);
};
const handleFailure = (rejectedValue) => {
console.log(rejectedValue);
};
checkAvailability("Hard Drive", 5).then(handleSuccess).then(handleFailure);
```
This code works the same way. The only difference is that rather than put both callback functions in a single .then(), we seperate the concerns. Like in the first method, the success handler needs to come first. But there is yet another way to achieve the same outcome.
```js
const handleSuccess = (resolvedValue) => {
console.log(resolvedValue);
};
const handleFailure = (rejectedValue) => {
console.log(rejectedValue);
};
checkAvailability("Hard Drive", 5).then(handleSuccess).catch(handleFailure);
```
This method is similar to the second method. The only difference is that we use .catch() to handle failure rather than a second .then()
Either of these three methods will simply send the resolve / reject value from verifyOrder to the respective callback functions.
But what if, depending on the availability of a book, we want to trigger a new function? Let us talk about chaining promises.
### Chaining Promises / Promise Composition
In the previous exercise, we created a promise named **verifyOrder**. This promise checks if the book a customer wants is in stock. If it is in stock, the promise is resolved, and the success handler is triggered. Otherwise, the failure handler will execute.
But what happens after that?
Well, if we verify that a book is available, we want to add that book to the user's bookshelf. But if it is not, we want to recommend other books from the same author.
Promise composition enables us to connect promises. In our example, a fulfilled verifyOrder promise will trigger the checkOut Promise. If checkOut is successful, the addToShelf promise will be triggered successfully. A rejected verifyOrder promise will trigger the recommendBook promise. Let us see this in practice.
First, we create a **checkOut** function to handle checkouttitle in. It should check the object **order**'s **libraryPoints**. If there are enough library points, the promise should deduct the required points from libraryPoints, and then, title in that order to the user's bookShelf. Otherwise, it should be rejected.
```js
const order = {
title: "The Innovators",
quantity: 3,
libraryPoints: 10,
};
const checkOut = (book) => {
return new Promise((resolve, reject) => {
const requiredPoints = book.libraryPointsRequired;
const title = book.title;
const points = order.libraryPoints;
if (requiredPoints <= points) {
order.libraryPoints -= requiredPoints;
console.log(
`The transaction is successful, and your library card now has ${order.libraryPoints} points`
);
resolve(user.bookShelf.push(`${book.title} by ${book.author}`));
} else {
reject("You don't have enough points for this transaction");
}
});
};
```
Finally, we will add a new promise called **recommendBook**. If **verifyOrder** fails, recommendBook will highlight other books from the same author.
```js
const recommendBook = (book) => {
return new Promise((resolve) => {
const authorToMatch = book.author; // Use the author from the provided book
const recommendedBooks = [];
for (const title in books) {
const bookItem = books[title];
if (bookItem.author === authorToMatch && title !== book.title) {
recommendedBooks.push(bookItem.title);
}
}
console.log(
`We don't have the book you wanted, but here are some other books from the same author: ${recommendedBooks}`
);
resolve(recommendedBooks);
});
};
```
Finally, let us chain all these newly created promises together.
```js
verifyOrder(order)
.then(checkOut)
.then((updatedBookShelf) => {
console.log(
`Your book has been added to the bookShelf: ${updatedBookShelf}`
);
})
.catch((error) => {
console.error(`An error occurred: ${error}`);
});
```
A breakdown of what is happening here is as follows:
1. We call verifyOrder with the argument order
2. If the verifyOrder promise resolves then checkOut should execute
3. If checkOut succeeds, we chain an anonymous function to log the value of return value of checkOut. Something to note here is that .then automatically appends the return value of the previous promise as an arguement of the current promise.
4. Finally, we use .catch() in case the promise fails at any point. Passing the 'error' argument will catch any error during the promise, and log it to the console. This could be a useful debugging tool!
## Conclusion
Asynchronous operations are vital in web development. Not only do they improve performance, but they also help developers create logical flows for their functions to execute. Since JavaScript is a single-threaded language, we can build asynchronous operations with Promises.
Promises are simple to use. Creating one is as simple as using the '**new Promise**' constructor. Since a promise is a function, we ought to add the arguments **resolve**, and **reject**. These arguments represent the return value of the promise if it fails or succeeds.
In the event of a success or a failure, we may want to trigger another function. We can use .then(() => success handler function), or .catch(() => failure handler function). In the spirit of asynchronous operations, these help us logically manage the flow of tasks.
Admittedly, promises have more features. However, discussing them would be out of the scope of this article. You can read more [here](https://developer.mozilla.org/en-US/docs/Web/JavaScript/Reference/Global_Objects/Promise)
| armstrong2035 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.