id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,862,682 | Create a Weather App using ToolJet and OpenWeatherMap API | Introduction In this tutorial, we will create a weather app using ToolJet and... | 0 | 2024-05-23T13:07:01 | https://blog.tooljet.com/create-a-weather-app-using-openweathermap-api-and-tooljet/ | restapi, lowcode, tooljet, javascript | ## Introduction
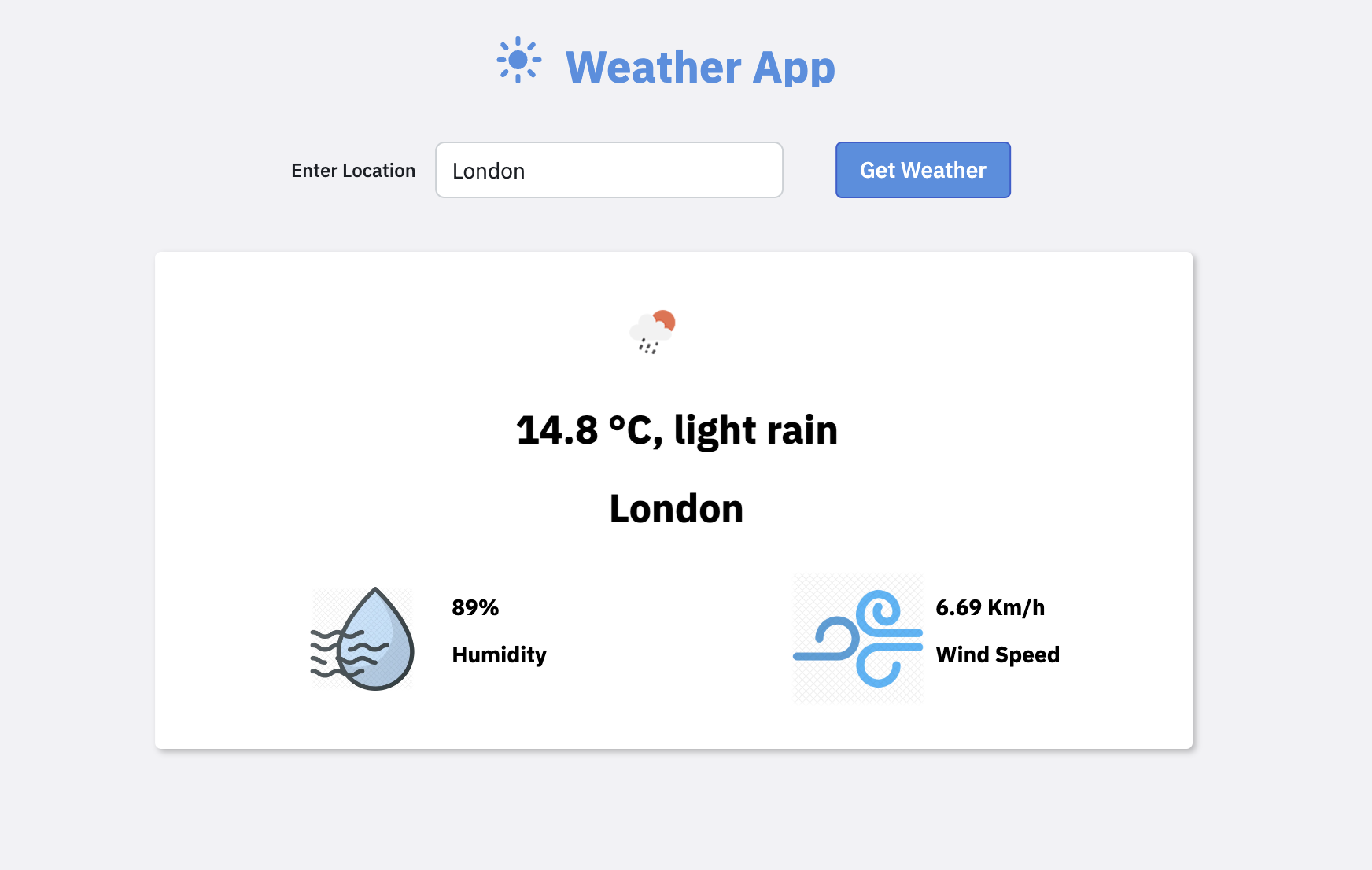
In this tutorial, we will create a weather app using [ToolJet](https://github.com/ToolJet/ToolJet) and OpenWeatherMap. By the end of this guide, you'll have a functional app that fetches and displays weather data for any city using the OpenWeatherMap API.
### Prerequisites:
Before we start, make sure you have:
- **ToolJet (https://github.com/ToolJet/ToolJet) :** An open-source, low-code platform allowing you to build internal tools and applications rapidly. If you don’t have an account, sign up for a free ToolJet cloud account [here](https://app.tooljet.com/).
- **API Key from OpenWeatherMap :** Create an account on [OpenWeatherMap](https://openweathermap.org/api) to generate an API Key that will be used while we create queries to fetch the weather data.
Here’s a quick preview of the app that we will be building by the end of this tutorial:
Before creating the UI, let’s create a new ToolJet App. On your ToolJet dashboard, click on the **Create an app** button and name the app **Weather App**.
Once the app is created, we can start with the UI.
## Creating the UI
Creating a custom UI is straightforward with the help of ToolJet’s [built-in components](https://docs.tooljet.com/docs/tooljet-concepts/what-are-components).
Let’s start by creating the app’s header.
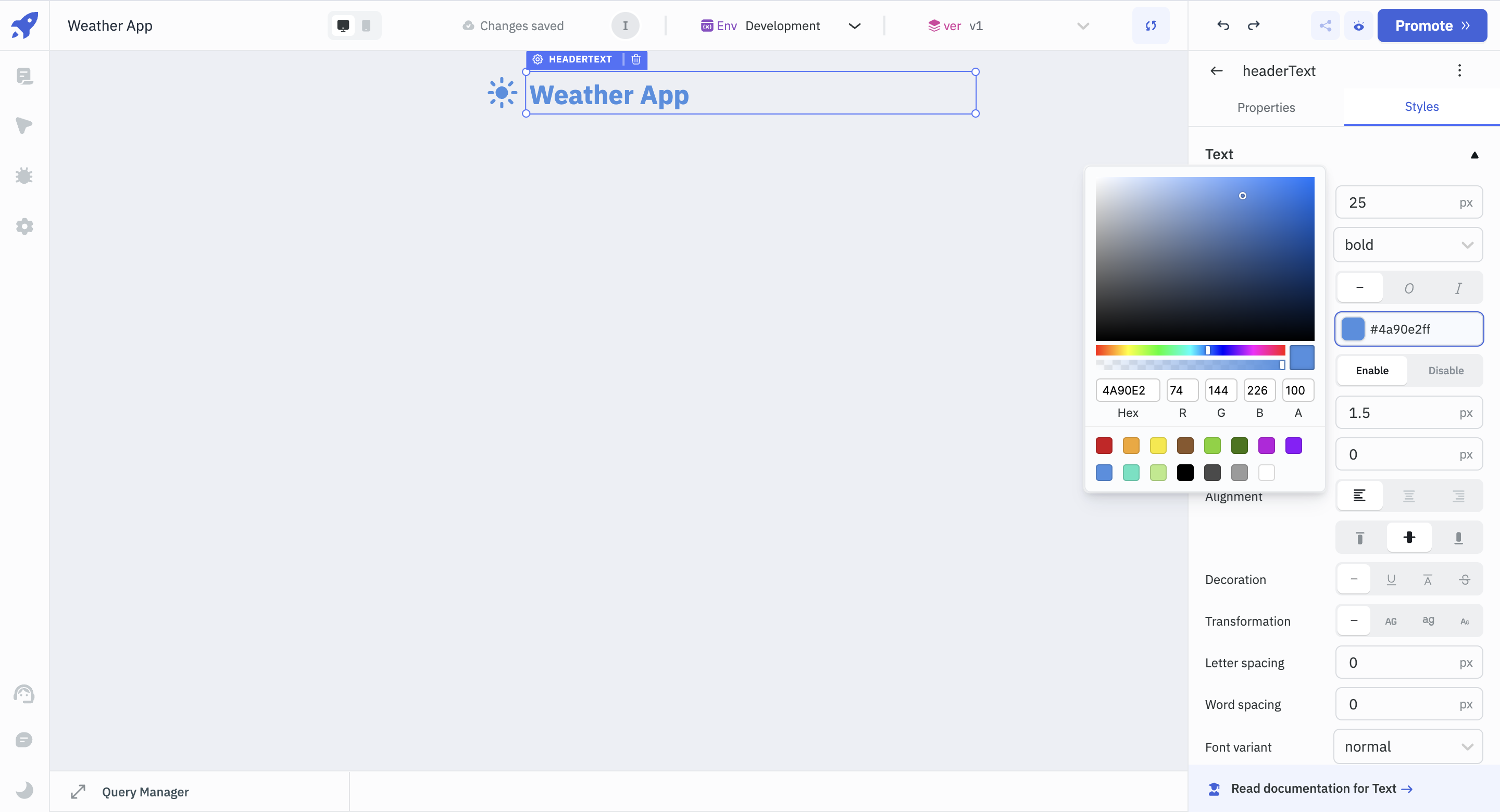
- Drag and drop the **Icon** and a **Text** Component from the [components library](https://docs.tooljet.com/docs/tooljet-concepts/what-are-components) on the right and rename them to _headerIcon_ and _headerText_, respectively.
- To configure the Text component, click on it and see the Properties Panel on the right.
- Set its **Data** property to 'Weather App', and under the **Styles** section, change its colour to light blue (Hex code: #4a90e2ff), font-weight to bold and font size to 25.
_Renaming components is an effective way to refer to components as the app grows._
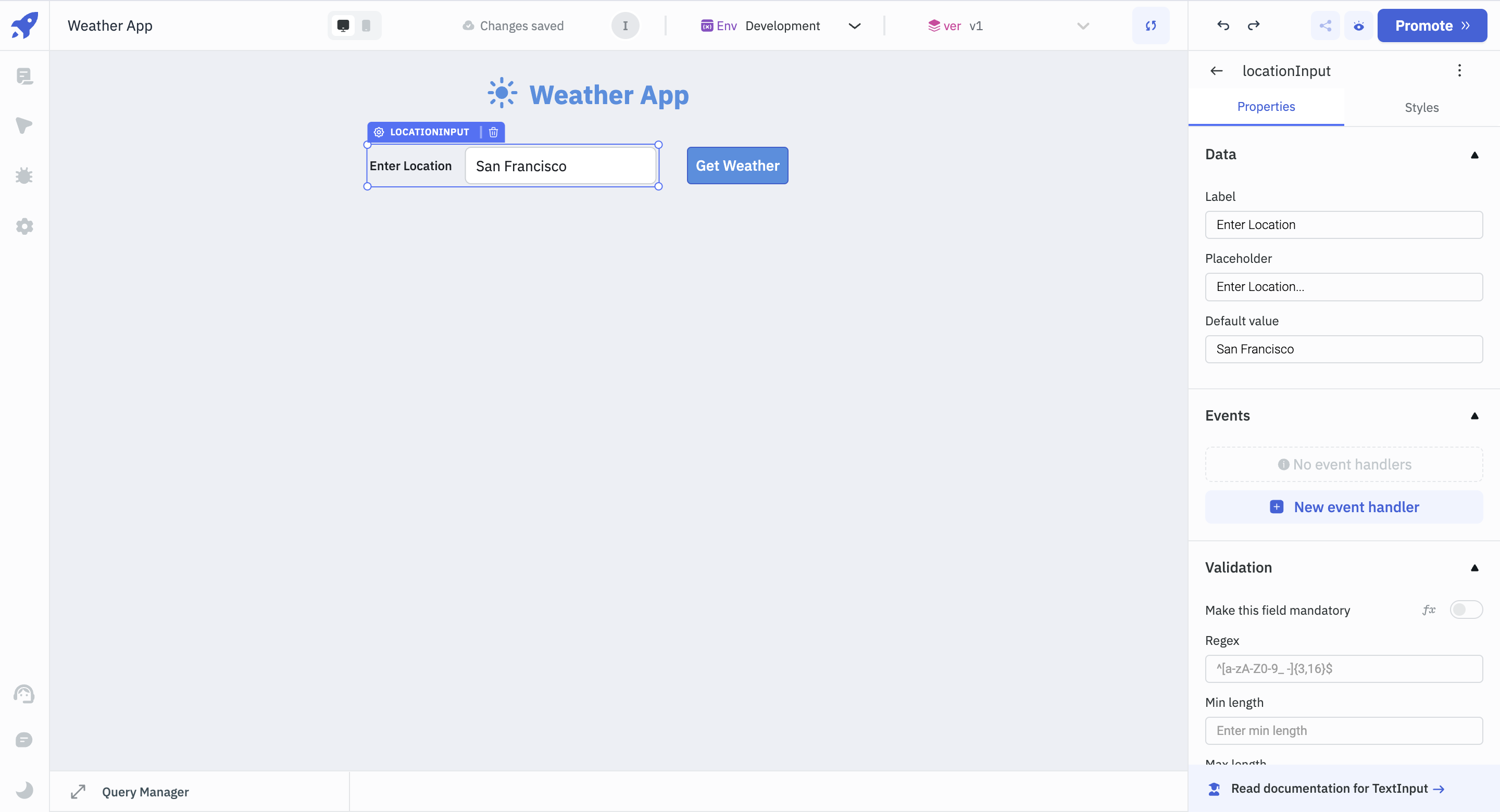
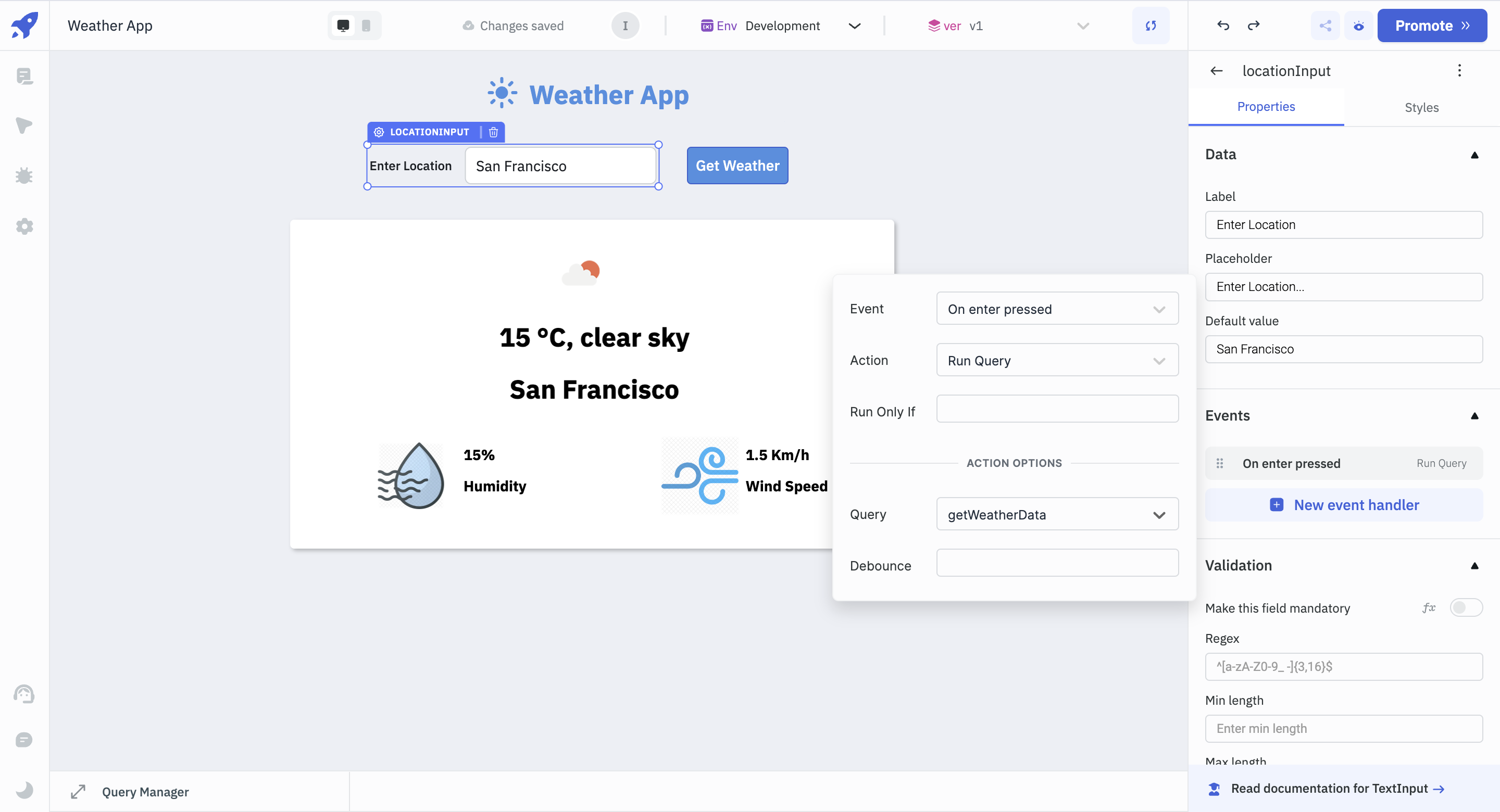
- Once the header is ready, drag and drop a **Text Input** component onto the canvas. This is where we will be entering our desired locations. Rename it to _locationInput_.
- For _locationInput_, change **Label** to **Enter Location** and **Placeholder** to **Enter Location**. Let’s set the default value to 'San Francisco'.
- Next to _locationInput_ component, add a **Button** component, rename it to _getWeatherButton_, and change the **Button text** property to **Get Weather** from the properties panel. From the **Styles** tab, change the **Background color** of the button to blue (Hex code: #4a90e2ff).
Next we will create the layout where we will be displaying the weather data.
- Drag and drop a **Container** component. Containers are used to group related components.
- Add an **Image** component inside the Container and rename it to _weatherImage_. This component will be used to display the weather through an image later in the tutorial. For now, let’s add a dummy image. In the **URL** section, add the URL, [http://openweathermap.org/img/wn/02d@2x.png](http://openweathermap.org/img/wn/02d@2x.png).
- Next, add two **Text** components and rename them to _weatherDescription_ and _locationText_, respectively. Add some dummy text under their **Data** property. The dummy data will be made dynamic as the tutorial progresses.
- For both the text components, in the **Styles** section, change the font size to 25, font-weight to bold and alignment to center.
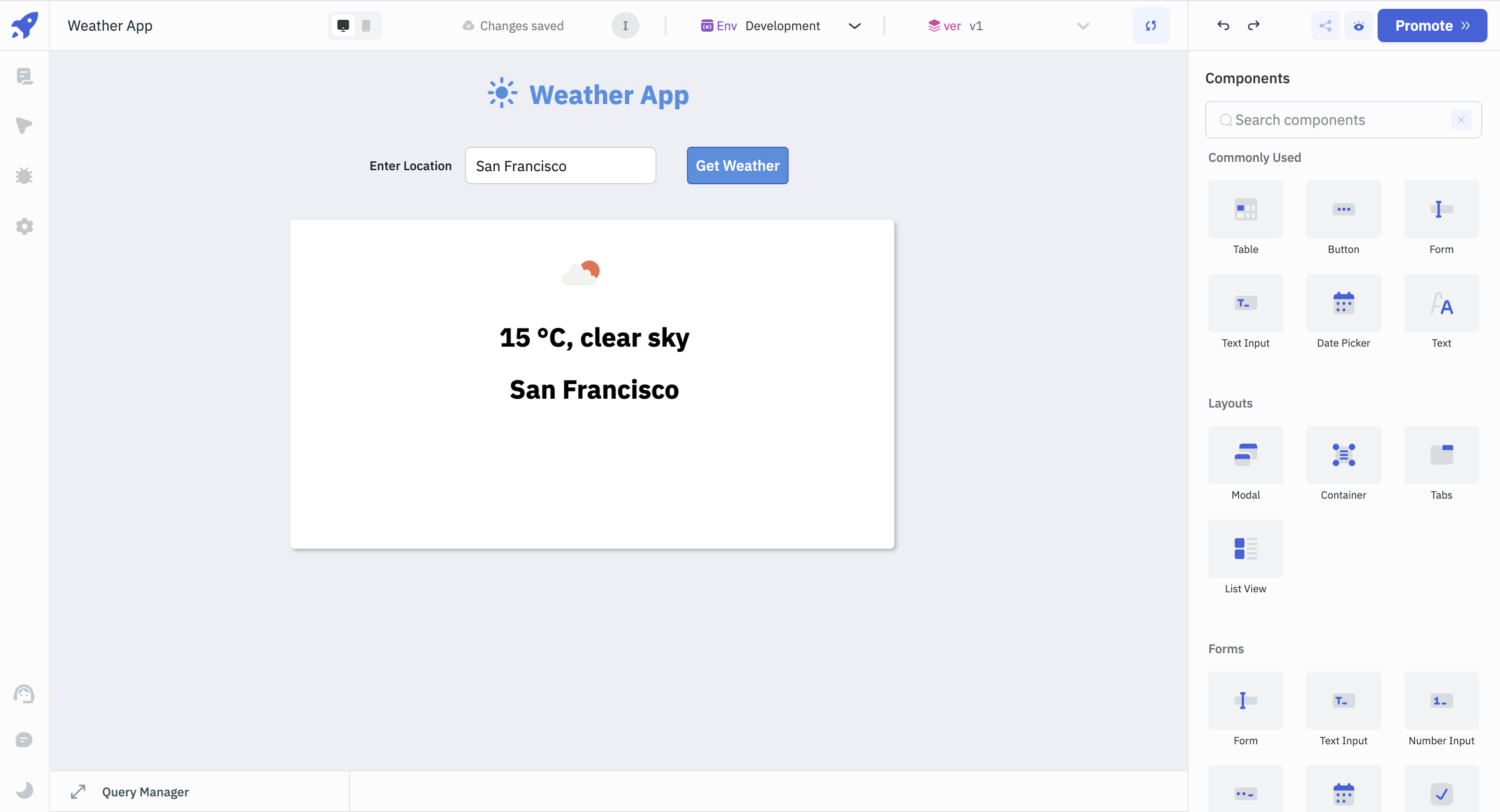
We will also display a particular location's humidity and wind speed.
- Drag and drop the **Image** component and rename it to _humidityIcon_. In the **URL** property, let’s use the following URL for now: [https://cdn.iconscout.com/icon/premium/png-512-thumb/humidity-14-532297.png?f=webp&w=512](https://cdn.iconscout.com/icon/premium/png-512-thumb/humidity-14-532297.png?f=webp&w=512).
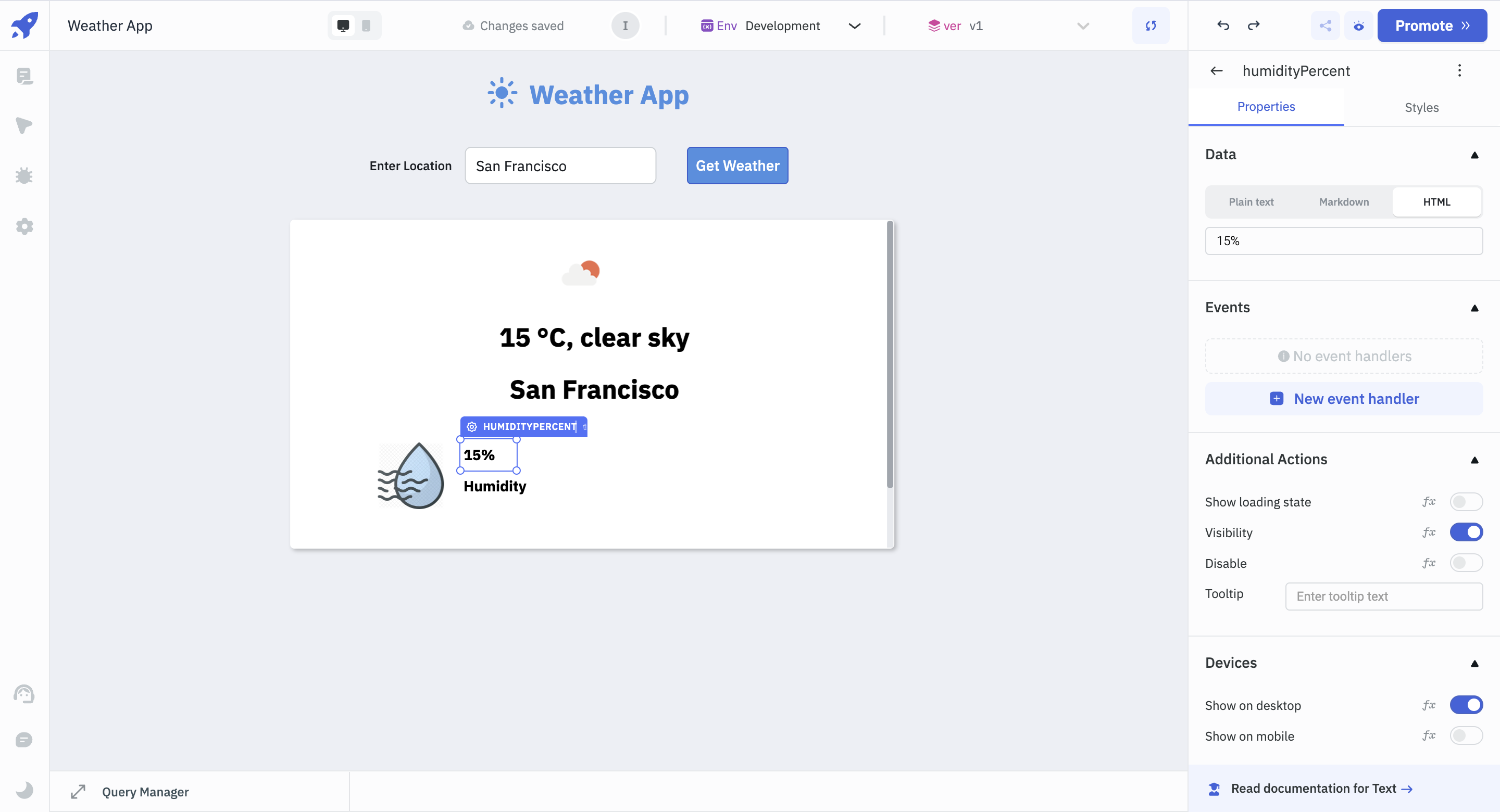
- Place two Text components next to the Image component and rename them to _humidityPrecent_ and _humidityText_ respectively. In the Styles section, set the font weight to bold for both.
- For the _humidityPercent_ and _humidityText_ components, add some dummy data in the **Data** section of the Properties panel. As the tutorial progresses, we will be fetching the humidity data dynamically.
- To add wind-speed data, copy the Image and Text components and paste them beside the humidity section.
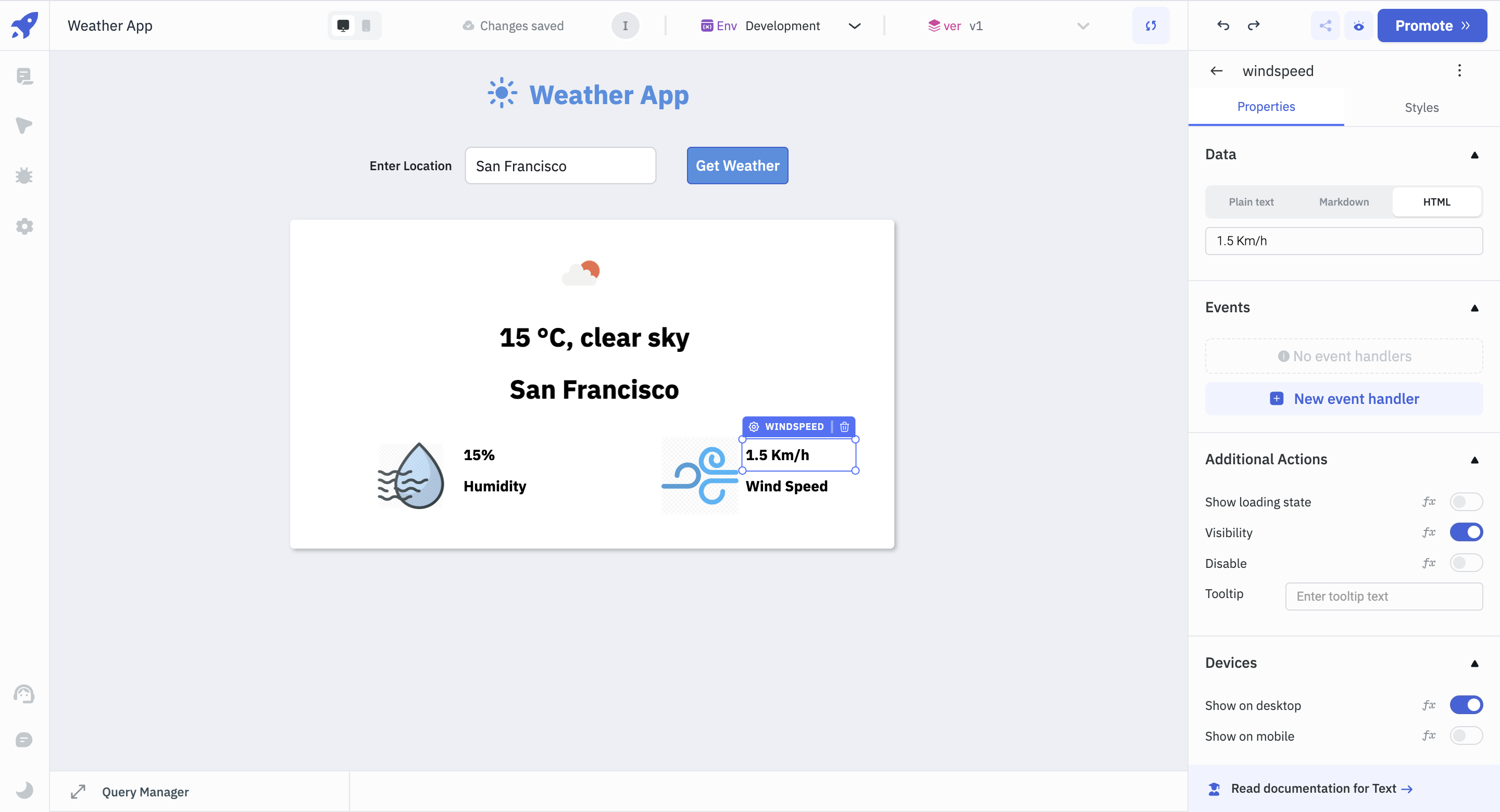
- Rename the Image component to _windspeedImage_ and the Text components to _windpseed_ and _windspeedText_, respectively.
- Select the _windspeedImage_ component, and in the **URL** section, add the following URL for the image: [https://cdn.iconscout.com/icon/premium/png-512-thumb/wind-336-974466.png?f=webp&w=512](https://cdn.iconscout.com/icon/premium/png-512-thumb/wind-336-974466.png?f=webp&w=512)
- Select the _windspeed_ component, add some dummy data in the **Data** property. In the **Styles** tab, set the font weight to bold.
- For the _windspeedText_ component, add some dummy data in the **Data** property. In the **Styles** tab, set the weight to bold.
With the above steps, our UI is now ready. It’s time to use OpenWeatherMap API to fetch the weather data for our desired location.
## Use OpenWeatherMap API to Fetch Weather Data
### 1. Creating the Query
To fetch the weather data from OpenWeatherMap API, we will use ToolJet’s [queries](https://docs.tooljet.com/docs/tooljet-concepts/what-are-queries).
Follow the steps below to create a query and fetch the data.
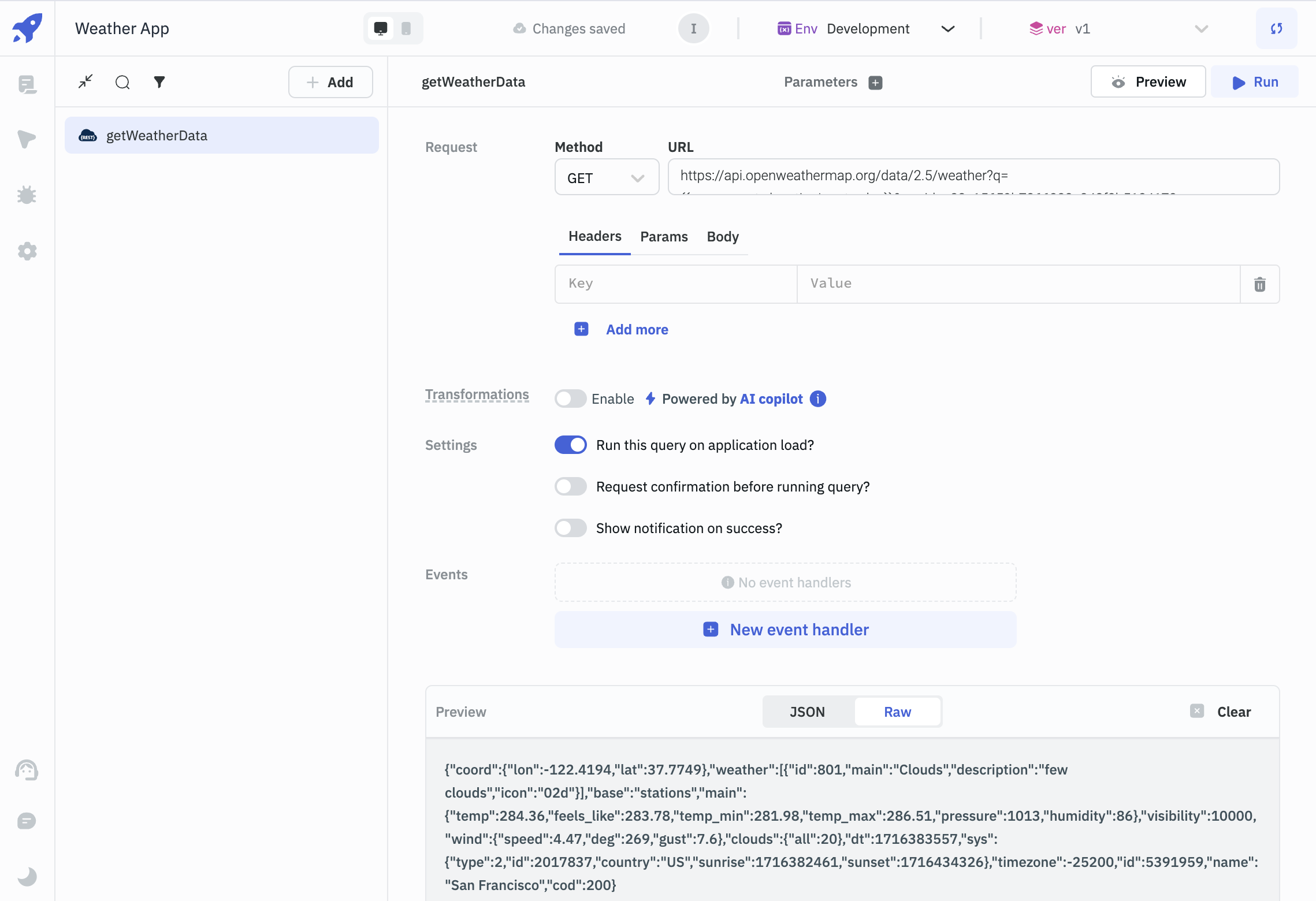
- Expand the **Query Panel** at the bottom and click the **Add** button to create a query.
- Choose the **REST API** query and rename it to _getWeatherData_.
- Since we will just be fetching the data, in the **Request** section, choose the **Method** as **GET** from the dropdown, and add the following as the **URL**: `https://api.openweathermap.org/data/2.5/weather?q=<LOCATION>&appid=<APP_ID>`.
- Replace **<LOCATION>** with the following code: `{{components.locationInput.value}}`; since we have set the default value to 'San Francisco', the location will be replaced with 'San Francisco' for now.
- Replace the **<APP_ID>** with the API Key that you generated while creating an account on OpenWeatherMap API.
- To ensure that the query runs every time the application loads, enable **Run this query on application load?**
- Click on the **Run** button to see that the weather data is being fetched from the OpenWeatherMap API for the city of San Francisco.
_In ToolJet, [double curly braces](https://docs.tooljet.com/docs/tooljet-concepts/how-to-access-values) are used to access or refer dynamic values._
### 2. Adding Event to _locationInput_ and _getWeatherButton_ Components
Now that we’re successfully configured the query, we will bind this query to our _locationInput_ and _getWeatherButton_ components.
- Select the _locationInput_ component. In the properties panel, click on the **[New event handler](https://docs.tooljet.com/docs/tooljet-concepts/what-are-events)** button, set **Event** as **On enter pressed**, choose **Action** as **Run Query**, and select _getWeatherData_ as the query.
- To test it, let’s change the location to 'London' and press enter. If you followed the above steps correctly, the query should fetch the data related to London.
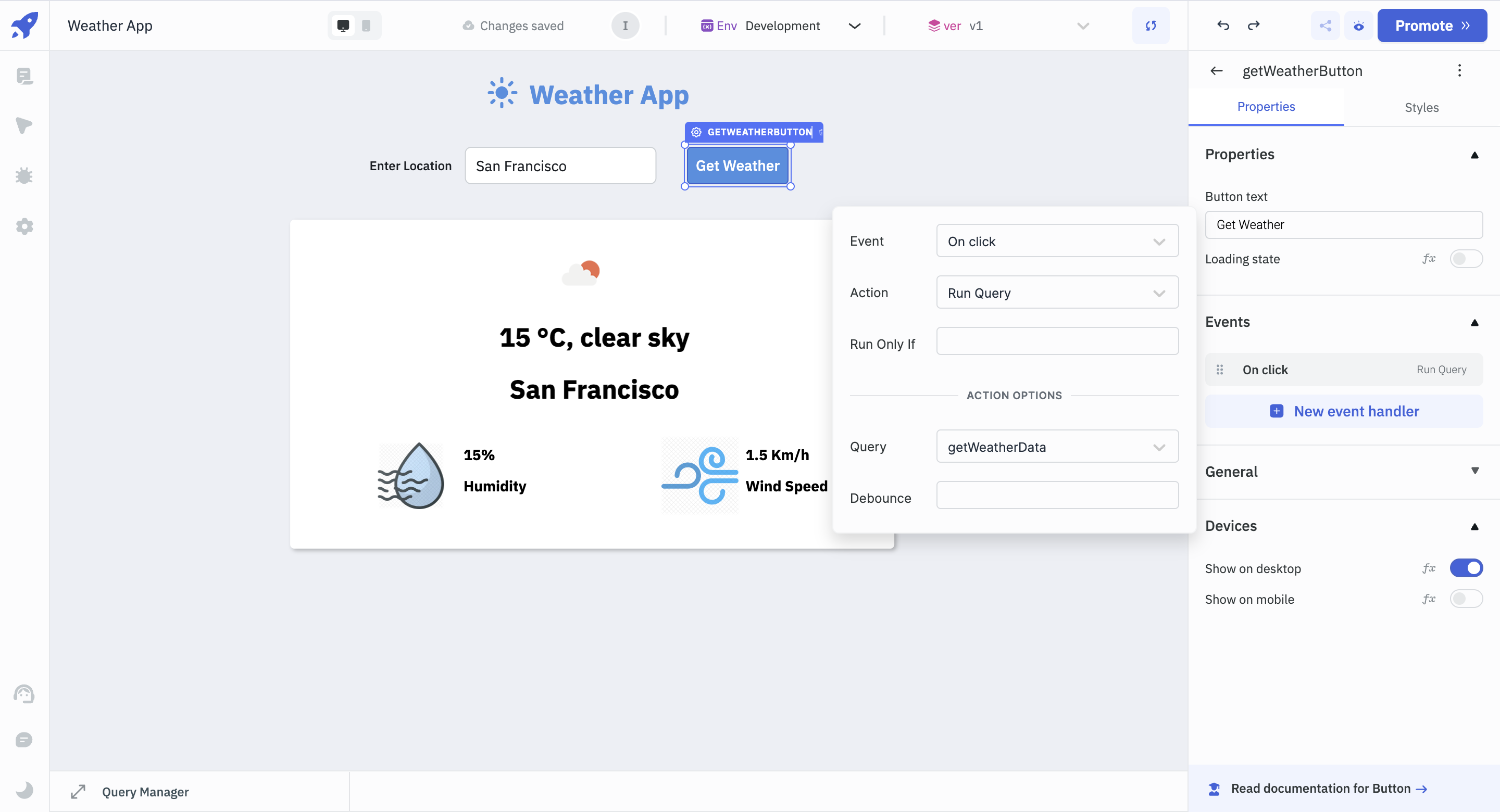
We would also want the query to run once we enter a location and press the **Get Weather** button. To do so, follow the steps below:
- Select the _getWeatherButton_ button, and click on **New event handler**.
- Choose the **Event** as **On click**, **Action** as **Run Query**, and select _getWeatherData_ as the **Query**.
- If you followed the above steps correctly, you can now run the query after clicking on the **Get Weather** button.
### 3. Binding the Data to the Components
Since we can now fetch the queries by pressing enter and clicking on the **Get Weather** button, we will bind the fetched data to our UI to make our app dynamic.
Let’s start with the weatherImage component first.
- Select the _weatherImage_ component, and replace the URL with `http://openweathermap.org/img/wn/{{queries.getWeatherData.data.weather[0].icon}}@2x.png`. This will ensure, that the image changes accordingly with the weather of a particular city.
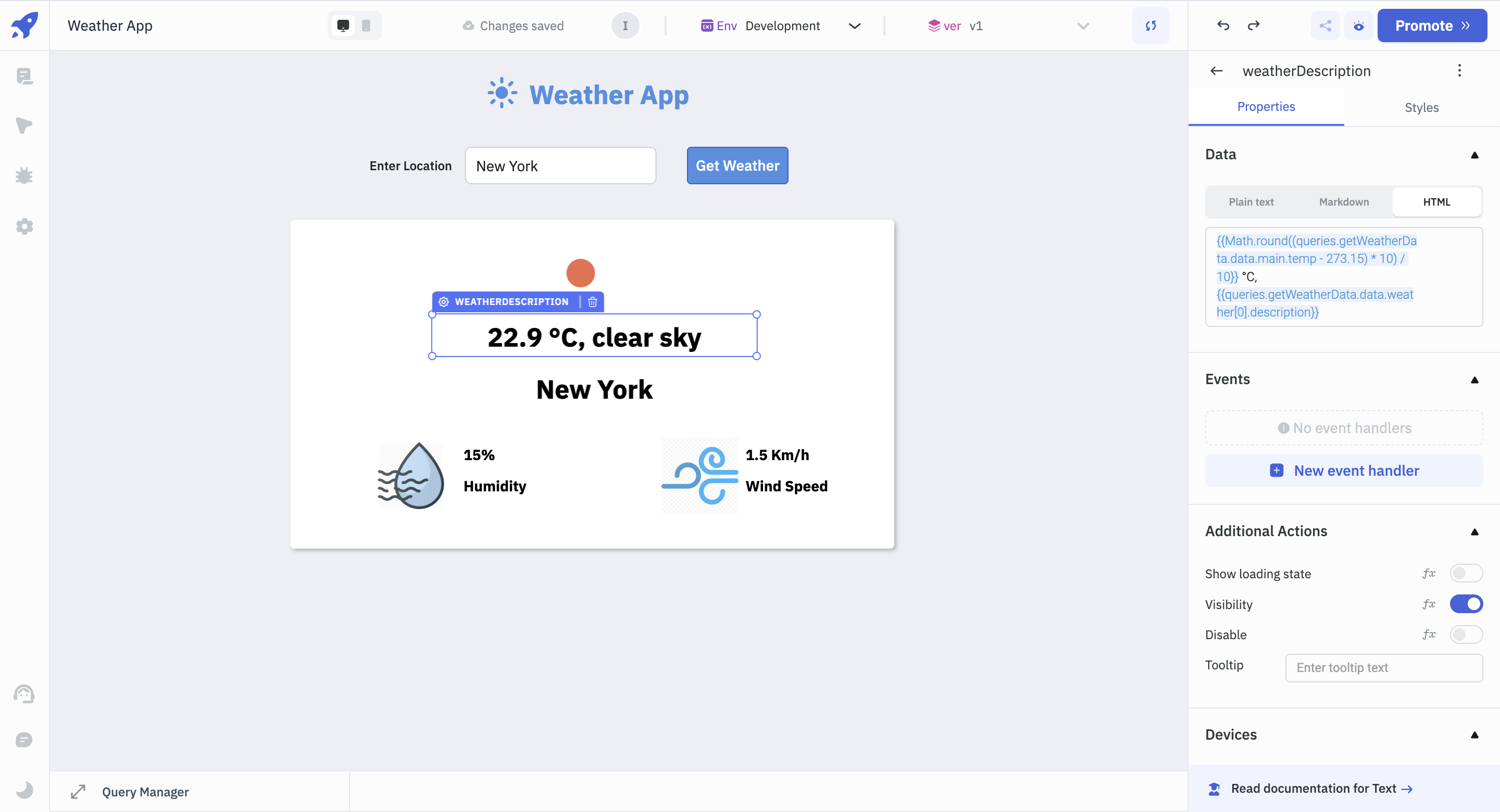
- Next, select the weatherDescription component and replace the text under the **Data** property with the following code:
`{{Math.round((queries.getWeatherData.data.main.temp - 273.15) * 10) / 10}} °C, {{queries.getWeatherData.data.weather[0].description}}`. Here, we’re converting the temperature to degrees Celsius and adding the weather description.
- Select the _locationText_ component, and add the following code to the **Data** property: `{{queries.getWeatherData.data.name}}`.
If you followed the above steps correctly, you should see the image, temperature, weather description and city name changing according to the location we’re adding to the _locationInput_ component.
The last step would be to display the actual humidity percentage and the windspeed of the entered location.
- Select the _humidityPercent_ component, add `{{queries.getWeatherData.data.main.humidity}}%` under the **Data** property. This will give the humidity percentage of the entered location.
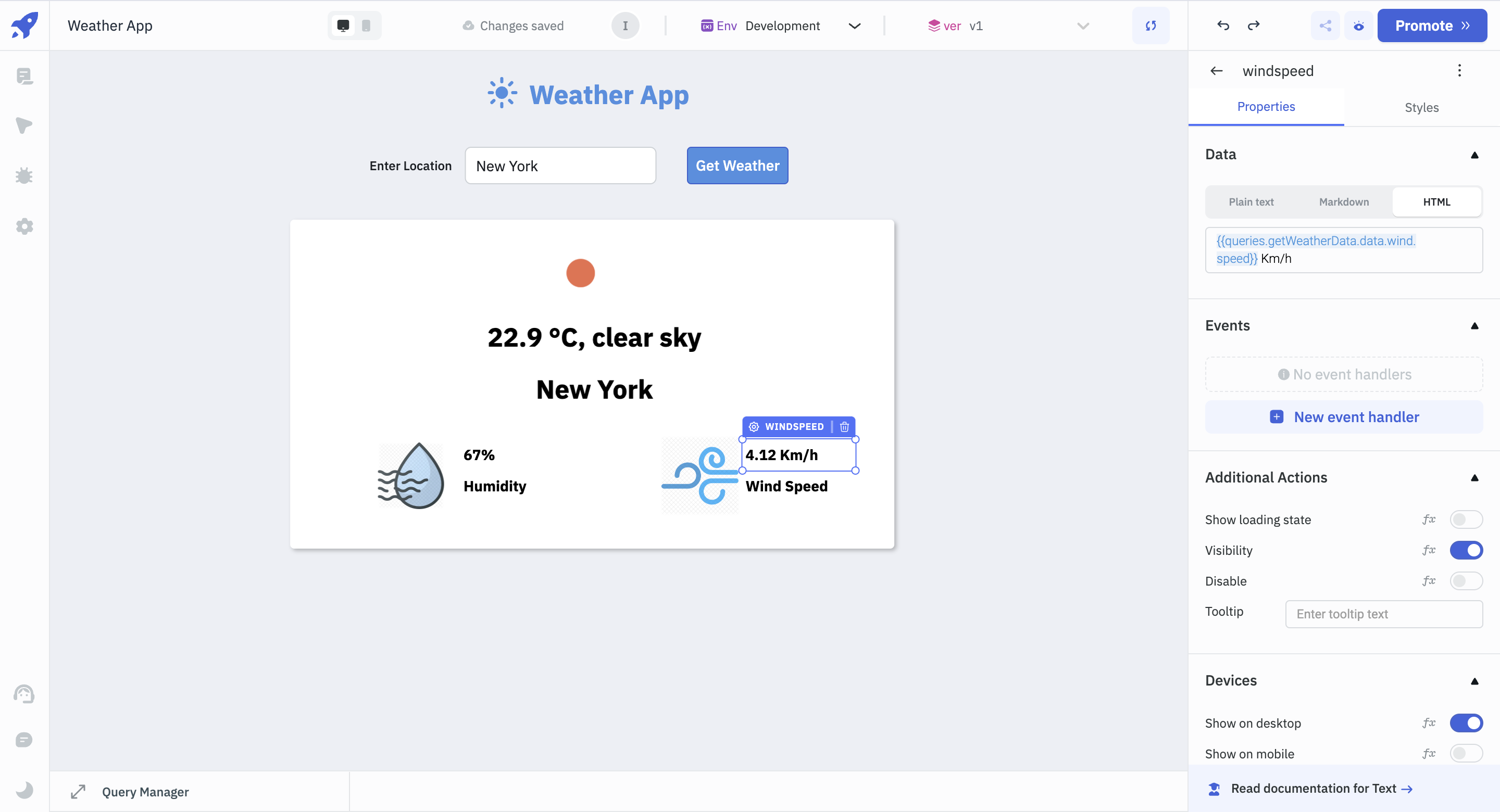
- Next, click on the _windspeed_ component, and add `{{queries.getWeatherData.data.wind.speed}} Km/h` under the **Data** property. This will display the wind speed of the entered location.
If you have followed all the steps mentioned above, you can see that all of the component data gets updated after running the query according to the location we add.
To make sure that our app displays a loader whenever the data is being fetched for the new city, select the Container component and in the **Loading state** property, click _fx_ and add `{{queries.getWeatherData.isLoading}}`.
## Conclusion
You've successfully built a weather app using ToolJet by consuming the OpenWeatherMap REST API. This simple app demonstrates how straightforward it is to create functional apps in ToolJet. To know more about what [ToolJet](https://docs.tooljet.com/docs/) can do, visit the ToolJet docs or join us and post your queries on [Slack](https://join.slack.com/t/tooljet/shared_invite/zt-2ij7t3rzo-qV7WTUTyDVQkwVxTlpxQqw).
| asjadkhan |
1,862,859 | Dive into Creativity: Toca Life World APK for iOS | "Dive into Creativity: Toca Life World APK for iOS invites users into a boundless world of... | 0 | 2024-05-23T13:05:04 | https://dev.to/wendlland_tabler_6d6176b0/dive-into-creativity-toca-life-world-apk-for-ios-59eg | "Dive into Creativity: [Toca Life World APK for iOS](https://tocaapkboca.com/toca-life-world-apk-for-ios/) invites users into a boundless world of imagination and exploration. This APK version tailored for iOS devices unlocks endless possibilities within the Toca Life universe. From bustling city streets to serene countryside retreats, players can immerse themselves in various vibrant locations, each brimming with interactive elements and quirky characters. With intuitive touch controls optimized for iOS, navigating through this virtual world becomes seamless and enjoyable. Whether creating unique stories, designing intricate scenes, or simply unleashing creativity, Toca Life World APK for iOS provides an unparalleled sandbox experience, empowering users to craft their own adventures and memories. | wendlland_tabler_6d6176b0 | |
1,862,858 | 20 Top C# Frameworks and Libraries on GitHub for Building Powerful Applications | GitHub offers a wealth of frameworks and libraries that can greatly enhance your projects. Below,... | 0 | 2024-05-23T13:03:07 | https://dev.to/crafting-code/20-top-c-frameworks-and-libraries-on-github-for-building-powerful-applications-29dg | csharp, aspdotnet, github, coding | GitHub offers a wealth of frameworks and libraries that can greatly enhance your projects. Below, I’ve mentioned 21 essential tools with what they do, how they can benefit you, and where to find them on GitHub.
If you find our content enriching and helpful, consider Supporting Us.
So, lets get started!!🚀
## 1. [ASP.NET Core](https://github.com/dotnet/aspnetcore)
A framework for building web applications and APIs. It’s fast, modular, and cross-platform, allowing you to create high-performance web solutions with ease.
## 2. [Entity Framework Core](https://github.com/dotnet/efcore)
Simplifies database interaction by providing a powerful object-relational mapping (ORM) framework. With EF Core, you can manipulate database data using C# objects, saving time and reducing complexity.
## 3. [Dapper](https://github.com/DapperLib/Dapper)
A lightweight ORM that offers high performance and simplicity for data access. It lets you execute SQL queries and map results directly to C# objects, making database operations straightforward.
## 4. [FluentValidation](https://github.com/FluentValidation/FluentValidation)
Enables easy validation of complex objects in C#. It provides a fluent interface for defining validation rules, ensuring data integrity in your applications.
## 5. [Serilog](https://github.com/serilog/serilog)
A logging library that simplifies structured logging in various formats. It helps you troubleshoot and monitor your applications effectively by providing flexible logging capabilities.
## 6. [Hangfire](https://github.com/HangfireIO/Hangfire)
Facilitates background processing in your applications. You can use it to perform tasks asynchronously, schedule jobs, and manage workflows, ensuring smooth application operation.
## 7. [AutoMapper](https://github.com/AutoMapper/AutoMapper)
Simplifies object-to-object mapping in C#. It automates the process of copying data between different object types, saving you time and effort.
## 8. [Moq](https://github.com/Moq/moq4)
A mocking library for .NET that simplifies unit testing. Moq allows you to create mock objects and set expectations easily, making it ideal for testing complex interactions within your code.
## 9. [Newtonsoft.Json](https://github.com/JamesNK/Newtonsoft.Json)
Provides high-performance JSON serialization and deserialization for .NET applications. It’s easy to use and offers robust support for manipulating JSON data.
## 10. [SignalR](https://github.com/SignalR/SignalR)
Adds real-time web functionality to your applications. With SignalR, you can build interactive, real-time features such as chat, notifications, and live updates.
## 11. [NLog](https://github.com/NLog/NLog)
A flexible logging platform for .NET. NLog allows you to configure logging behavior dynamically, making it easy to log messages in various environments.
## 12. [Refit](https://github.com/reactiveui/refit)
Simplifies API integration by generating API interfaces from C# interfaces. With Refit, you can consume HTTP APIs in a type-safe and efficient manner.
## 13. [CsvHelper](https://github.com/JoshClose/CsvHelper)
Makes it easy to read and write CSV files in C#. CsvHelper simplifies CSV parsing and writing, saving you time when working with tabular data.
## 14. [Humanizer](https://github.com/Humanizr/Humanizer)
Adds human-friendly extensions to various data types in .NET. Humanizer helps you format strings, handle dates, and manipulate numbers in a natural and readable way.
## 15. [FluentAssertions](https://github.com/fluentassertions/fluentassertions)
Provides a fluent syntax for writing clear and concise unit tests in .NET. With FluentAssertions, you can create expressive assertions that enhance the readability of your test code.
## 16. [Xamarin.Forms](https://github.com/xamarin/Xamarin.Forms)
Enables cross-platform mobile development using C#. Xamarin.Forms allows you to create native user interfaces and share code across iOS, Android, and Windows platforms.
## 17. [Unity](https://github.com/Unity-Technologies/UnityCsReference)
A powerful game engine that supports C# scripting. Unity simplifies game development by providing tools for creating immersive and engaging experiences across various platforms.
## 18. [FluentValidation.AspNetCore](https://github.com/FluentValidation/FluentValidation)
Extends FluentValidation to integrate seamlessly with ASP.NET Core applications. It provides additional functionality for validating request payloads and model objects in MVC projects.
## 19. [Hangfire.Dashboard.Authorization](https://github.com/HangfireIO/Hangfire.Dashboard.Authorization)
Adds role-based access control to Hangfire dashboards in ASP.NET Core applications. With this extension, you can secure your Hangfire dashboard and restrict access based on user roles.
## 20. [XUnit](https://github.com/xunit/xunit)
A testing framework for .NET that supports test-driven and behavior-driven development. xUnit makes it easy to write clear and concise unit tests, helping you ensure the quality and reliability of your code.
---
These 21 essential frameworks and libraries on GitHub are invaluable tools for C# developers. These resources can streamline your development process, enhance functionality, and improve the overall quality of your projects. Explore them, experiment with them, and leverage them.
Feel free to reach out to me at **toshiah213@gmail.com** if you’re interested in collaborating, sponsoring, or discussing business opportunities.
---
_If you found this content helpful, Please Support us:_
_PayPal:_ **[toshiah213@gmail.com](https://www.paypal.com/paypalme/tauseef69?country.x=IN&locale.x=en_GB)** 🌟✨ | crafting-code |
1,862,857 | vsplit() in PyTorch | *Memos: My post explains split(). My post explains hsplit(). My post explains dsplit(). My post... | 0 | 2024-05-23T13:02:51 | https://dev.to/hyperkai/vsplit-in-pytorch-4915 | pytorch, vsplit, split, tensor | *Memos:
- [My post](https://dev.to/hyperkai/split-in-pytorch-nga) explains [split()](https://pytorch.org/docs/stable/generated/torch.split.html).
- [My post](https://dev.to/hyperkai/hsplit-in-pytorch-4b1d) explains [hsplit()](https://pytorch.org/docs/stable/generated/torch.hsplit.html).
- [My post](https://dev.to/hyperkai/dsplit-in-pytorch-594c) explains [dsplit()](https://pytorch.org/docs/stable/generated/torch.dsplit.html).
- [My post](https://dev.to/hyperkai/tensorsplit-in-pytorch-30m5) explains [tensor_split()](https://pytorch.org/docs/stable/generated/torch.tensor_split.html).
- [My post](https://dev.to/hyperkai/chunk-in-pytorch-30f5) explains [chunk()](https://pytorch.org/docs/stable/generated/torch.chunk.html).
- [My post](https://dev.to/hyperkai/unbind-in-pytorch-3lk9) explains [unbind()](https://pytorch.org/docs/stable/generated/torch.unbind.html).
[vsplit()](https://pytorch.org/docs/stable/generated/torch.vsplit.html) can get the one or more 2D or more D tensors of zero or more vertically splitted elements from the 2D or more D tensor of zero or more elements as shown below:
*Memos:
- `vsplit()` can be used with [torch](https://pytorch.org/docs/stable/torch.html) and a tensor.
- The 1st argument with `torch` or using a tensor is `input`(Required-Type:`tensor` of `int`, `float`, `complex` or `bool`).
- The 2nd argument with `torch` or the 1st argument with a tensor is `sections`(Required-Type:`int`).
- The 2nd argument with `torch` or the 1st argument with a tensor is `indices`(Required-Type:`tuple` of `int` or `list` of `int`).
- The total number of the zero or more elements of one or more returned tensors changes.
- One or more returned tensors keep the dimension of `input` tensor.
```python
import torch
my_tensor = torch.tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]])
torch.vsplit(input=my_tensor, sections=1)
my_tensor.vsplit(sections=1)
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),)
torch.vsplit(input=my_tensor, sections=3)
# (tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(0,))
torch.vsplit(input=my_tensor, indices=(-3,))
# (tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(1,))
torch.vsplit(input=my_tensor, indices=(-2,))
# (tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(2,))
torch.vsplit(input=my_tensor, indices=(-1,))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(3,))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64))
torch.vsplit(input=my_tensor, indices=(0, 0))
torch.vsplit(input=my_tensor, indices=(0, -3))
# (tensor([], size=(0, 4), dtype=torch.int64),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(0, 1))
torch.vsplit(input=my_tensor, indices=(0, -2))
# (tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(0, 2))
torch.vsplit(input=my_tensor, indices=(0, -1))
# (tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(0, 3))
# (tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64))
torch.vsplit(input=my_tensor, indices=(1, 0))
torch.vsplit(input=my_tensor, indices=(1, -3))
# (tensor([[0, 1, 2, 3]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(1, 1))
torch.vsplit(input=my_tensor, indices=(1, -2))
# (tensor([[0, 1, 2, 3]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(1, 2))
torch.vsplit(input=my_tensor, indices=(1, -1))
# (tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(1, 3))
# (tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64))
torch.vsplit(input=my_tensor, indices=(2, 0))
torch.vsplit(input=my_tensor, indices=(2, -3))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(2, 1))
torch.vsplit(input=my_tensor, indices=(2, -2))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(2, 2))
torch.vsplit(input=my_tensor, indices=(2, -1))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(2, 3))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64))
torch.vsplit(input=my_tensor, indices=(3, 0))
torch.vsplit(input=my_tensor, indices=(3, -3))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(3, 1))
torch.vsplit(input=my_tensor, indices=(3, -2))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(3, 2))
torch.vsplit(input=my_tensor, indices=(3, -1))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(3, 3))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([], size=(0, 4), dtype=torch.int64))
torch.vsplit(input=my_tensor, indices=(-1, 0))
torch.vsplit(input=my_tensor, indices=(-1, -3))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(-1, 1))
torch.vsplit(input=my_tensor, indices=(-1, -2))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(-1, 2))
torch.vsplit(input=my_tensor, indices=(-1, -1))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(-1, 3))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64))
torch.vsplit(input=my_tensor, indices=(-2, 0))
# (tensor([[0, 1, 2, 3]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(-2, 1))
# (tensor([[0, 1, 2, 3]]),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(-2, 2))
# (tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(-2, 3))
# (tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64))
torch.vsplit(input=my_tensor, indices=(-3, 0))
torch.vsplit(input=my_tensor, indices=(-3, -3))
# (tensor([], size=(0, 4), dtype=torch.int64),
# tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(-3, 1))
torch.vsplit(input=my_tensor, indices=(-3, -2))
# (tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(-3, 2))
torch.vsplit(input=my_tensor, indices=(-3, -1))
# (tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]))
torch.vsplit(input=my_tensor, indices=(-3, 3))
# (tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64))
my_tensor = torch.tensor([[0., 1., 2., 3.],
[4., 5., 6., 7.],
[8., 9., 10., 11.]])
torch.vsplit(input=my_tensor, sections=1)
# (tensor([[0., 1., 2., 3.],
# [4., 5., 6., 7.],
# [8., 9., 10., 11.]]),)
my_tensor = torch.tensor([[0.+0.j, 1.+0.j, 2.+0.j, 3.+0.j],
[4.+0.j, 5.+0.j, 6.+0.j, 7.+0.j],
[8.+0.j, 9.+0.j, 10.+0.j, 11.+0.j]])
torch.vsplit(input=my_tensor, sections=1)
# (tensor([[0.+0.j, 1.+0.j, 2.+0.j, 3.+0.j],
# [4.+0.j, 5.+0.j, 6.+0.j, 7.+0.j],
# [8.+0.j, 9.+0.j, 10.+0.j, 11.+0.j]]),)
my_tensor = torch.tensor([[True, False, True, False],
[False, True, False, True],
[True, False, True, False]])
torch.vsplit(input=my_tensor, sections=1)
# (tensor([[True, False, True, False],
# [False, True, False, True],
# [True, False, True, False]]),)
``` | hyperkai |
1,862,856 | annapolis taxi cabs | Annapolis Taxi Cabs Service drivers are the most professional independent business drivers in the... | 0 | 2024-05-23T13:02:47 | https://dev.to/alliedmaterial/annapolis-taxi-cabs-4pe8 | Annapolis Taxi Cabs Service drivers are the most professional independent business drivers in the industry. which provides businesses with a convenient method for managing their corporate transportation needs.
[](https://annapolistaxicabs.com/) | alliedmaterial | |
1,862,855 | makeovergames dotnet | Welcome to Makeover Games Net, your ultimate destination for free online makeover games! Dive into a... | 0 | 2024-05-23T13:01:37 | https://dev.to/makeovergames/makeovergames-dotnet-508h | Welcome to Makeover Games Net, your ultimate destination for free online makeover games! Dive into a world where creativity meets fashion, and every game is an opportunity to explore new styles, trends, and transformations. From casual chic to runway glamour, our extensive collection of makeover games will satisfy every fashion enthusiast's dream. Experience the joy of makeovers, where you're the stylist, and every character is your canvas
Website: https://makeovergames.net/
Phone: 986956312
Address: 64 To Huu, Nam Tu Liem, Ha Noi, Vietnam
[object Object][ scoopit ]
| makeovergames | |
1,845,240 | 5 steps to grow from junior dev to senior | I've been writing code for eleven years now, and slowly moved from intern, to junior, to senior, to... | 0 | 2024-05-23T13:01:16 | https://dev.to/sashkan/5-steps-to-grow-from-junior-dev-to-senior-46n8 | progression, webdev, management | I've been writing code for eleven years now, and slowly moved from intern, to junior, to senior, to lead developer, with the occasional job as a CTO.
Over the past two years, I've spent roughly 250 hours reviewing applications and technical tests, both on site and online, and helped wonderful teams build great products.
Here are the 5 key differences between a junior and a senior developer. And to illustrate each concept, I'll give examples based on real-life events, that lead either to great success, or tremendous failures.
## 1 - Ask, Challenge, Believe

Whatever you're working on, it is way easier to build a great product if you actually believe in it. And the only way to build conviction is to ask around. Why am I adding this feature ? Why are we making these changes ? Does my team know about this pattern ?
The key idea here is, you have to believe in the product you are building. You have to build conviction before laying down your first line of code. You cannot nurture any doubt as of why you are shipping this feature, who's going to use it, or how.
In 2020, I was working at a major company in video games. We were hosting an e-sport tournament, and our marketing team thought about developing a scoreboards client app, and plugging it into an eternal API to fetch scores in real time. I was in charge of the technical part, managing a team of 5 developers.
Unfortunately, the same marketing team did its own research for available APIs, and decided to sign a contract with a company before including any tech member in the process.
Which lead to a very goofy meeting, when I finally met my tech counterpart in said company. For 90 minutes, we listened to my manager, knowing that their API was not the one we needed. In fact, I knew half a dozen of APIs that could have done the job, for a fraction of the price.
I went back to my team, and we took a moment to decide how to tackle this issue. To which they answered the ONE question you have to fear when working on any product: "Why do we need this ?". They did not believe in this new scoreboard app. Neither did I: there was no conviction whatsoever.
So, I calmly asked for a quick talk with my manager, and asked him what we needed exactly. He gave my a short list of features, and I told him that it would take roughly 3 weeks to ship them all, and that I knew of an API that could get the job done for 12.99 a month. To which he responded that he already paid the API company in full, for the use of their API and the services of a consultant, for the next 4 months. We're talking 115k euros.
So, I did the only sensible thing to do. I went to my manager's manager, took the blame for the miscommunication, and asked him what to do next. We thanked the API company, we thanked the consultant, and based simply on the small list of feature my manager had given me, we managed to ship the whole project in three weeks. Suddenly, our tech team believed in the project, because we know WHY we were doing it, and HOW we could do it properly.
The key idea here is: a senior developer spends a lot of time building conviction, questioning patterns, and proactively bringing solutions through his knowledge and past experiences. Once your whole team believes in an app, or a feature, you'll know exactly how to code it.
## 2 - Know your tools

There are thousands of way to add authentication to your app. Or real-time. Or to build an endpoint that fetches data. Which means that there are thousands of way to do it poorly.
A senior dev knows the main patterns to add a feature, and therefore, he can code it quickly, shipping a code that is both clean, reliable, and well documented.
A great way to assess your "seniority" is to take a look at a few numbers:
- How many threads do I have on my merge requests ?
- How long does it take for my MR to be merged ?
- How often am I asked for advices/review ?
No matter how complex your app might be, there are not that many tools that we use on a daily basis. My current stack includes Nest.js, Next.js, tailwind and GraphQL, which can be overwhelming for a junior dev.
So, instead of simply reading the documentation, every time I start working on a new topic, or using a new tool, I document it for myself, using the [micro-thesis system](https://www.youtube.com/watch?v=XE_CGBlQ17o). I'm using Obsidian as my Documentation system, but there are a lot of viable tools out there.
Here is my process:
- I use my daily note to list my tasks for the day.
- If this task requires learning a new skill, I turn it into a link using the [[]] syntax.
- As I learn how to use this new tool, I write the best documentation I can. It has to be simple, include pieces of code, be reusable, and include links toward useful documentations.
This way, the next time I'll have to use said tool, and I have to do is search for this page in my Obsidian vault. not only will I have a head start on how to use it, it will also include links toward all of my notes that mention this page, making it easier to decide whether or not this is the right tool for the task at hand.
This also means that, whenever a tool is updated, I must update my documentation accordingly. This is pretty much how I keep myself updated on the latest versions of my stack.
Another important thing to keep in mind is the ratio between the time needed to ship a feature, and the price invested in using a third part application.
Let's say you are building an app that required both authentication and authorization. Maybe you have an repository you can fork, maybe you don't. If you don't, it will take you some time to add these features. In the mean time, libraries and freemium SAAS might help you setup your authentication in no time.
If I'm building a small app, I'll always go for free solutions for everything I don't feel like coding myself. Let's keep it simple: a freelance software engineer charges 1000 dollars a day. Adding a proper authentication might take 2/3 working days. in the mean time, adding and configuring Clerk/Kinde/Lucia takes roughly an hour, and these solutions are free.
The key idea here is: your tools are not limited to your coding skills. Just like in the old RTS games I used to play, consider both your time, money and skills as resources, and pick wisely which one to use, and how much you want to spend.
## 3 - Code Small.

Being a software engineer is awesome. It feels like having a bottomless box of Lego bricks at your disposal. You can use them to build whatever you want, from the smallest car to the biggest city.
But when it comes to professional projects, you have to understand that every line of code is a liability. Which means, the less you code, the more reliable your codebase is.
So, here are the 3 golden rules I try to live by:
- A merge request solves ONE issue.
- If I need to use a bullet list to explain the changes I made, and said bullet list includes more than 3 or 4 elements, I probably messed up.
- The ability to properly split up your code requires experience, and is as important as the actual performance of your code. Both on front end (think composition in React) and back-end (think modules/services/whatever architecture you are using to split your code into small manageable chinks)
if you do so, you'll manage to ship faster, build confidence within your team, and quickly setup a flow that'll allow you to deliver value on a daily basis.
On the other hand, you know that a pull request that affects countless files, is not properly documented, and includes loads of code smells will either be a nightmare to review, and will either stay open for a very long time, or will simply be closed. I usually go for the second option, by asking to split its content into smaller parts.
## 4 - Reviews are gold

Consider this: as a software engineer, 90% of your knowledge comes from experience. Actual work experience. And said experience comes from mistakes and failures, both yours and your teammates'
The lesson here is, your main goal as a senior developer is to provide and receive feedback. As we said, there are thousands of ways to add a feature, some are better than others, and you don't have enough of a lifetime to try them all. So, ask around and collaborate.
Here is the usual process I follow when reviewing a MR:
- Understand the underlying goal. "What are we trying to achieve here ?"
- "How would I code it ?"
From there, I'm more of a multi-commits kind of guy, so I simply review one commit at a time. If, at any point, I don't understand something (why do you use this lib ? Why did you name it that way ?), I add a comment.
Nowadays, I'm working as a lead developer, and my team has a wide range of seniority. Which means some MRs will receive a couple of comments (usually questions or interesting debates), and some others will receive 54 comments, from naming to logic to performances. In which case, I switch from review to peer programming.
If you are managing a team, note that the amount of comments on any given review is an actual metric for the quality of code.
5 - Own it

It usually takes me about two months to decide whether or not I'm confident on the level of expertise of a coworker. If my standards are met, I don't have a problem with telling them that they are responsible for 99% of the development process, from the tools they use to the patterns they pick. The last percent is the review, and the consequences. I want them to be owners of the code, but I'll be the custodian of their wellbeing.
At the end of they day, you have to embrace ownership on your decisions, both personal and professionals, which brings me to the following personal statements:
- I'm way more efficient at work when I do the things that matter to me first thing in the morning. And not a single one of them is work-related
- This includes drinking water, moisturising, flossing, workout, meditate.
- Keep track of everything that matters. The good thing is, there are not a lot of things that matter.
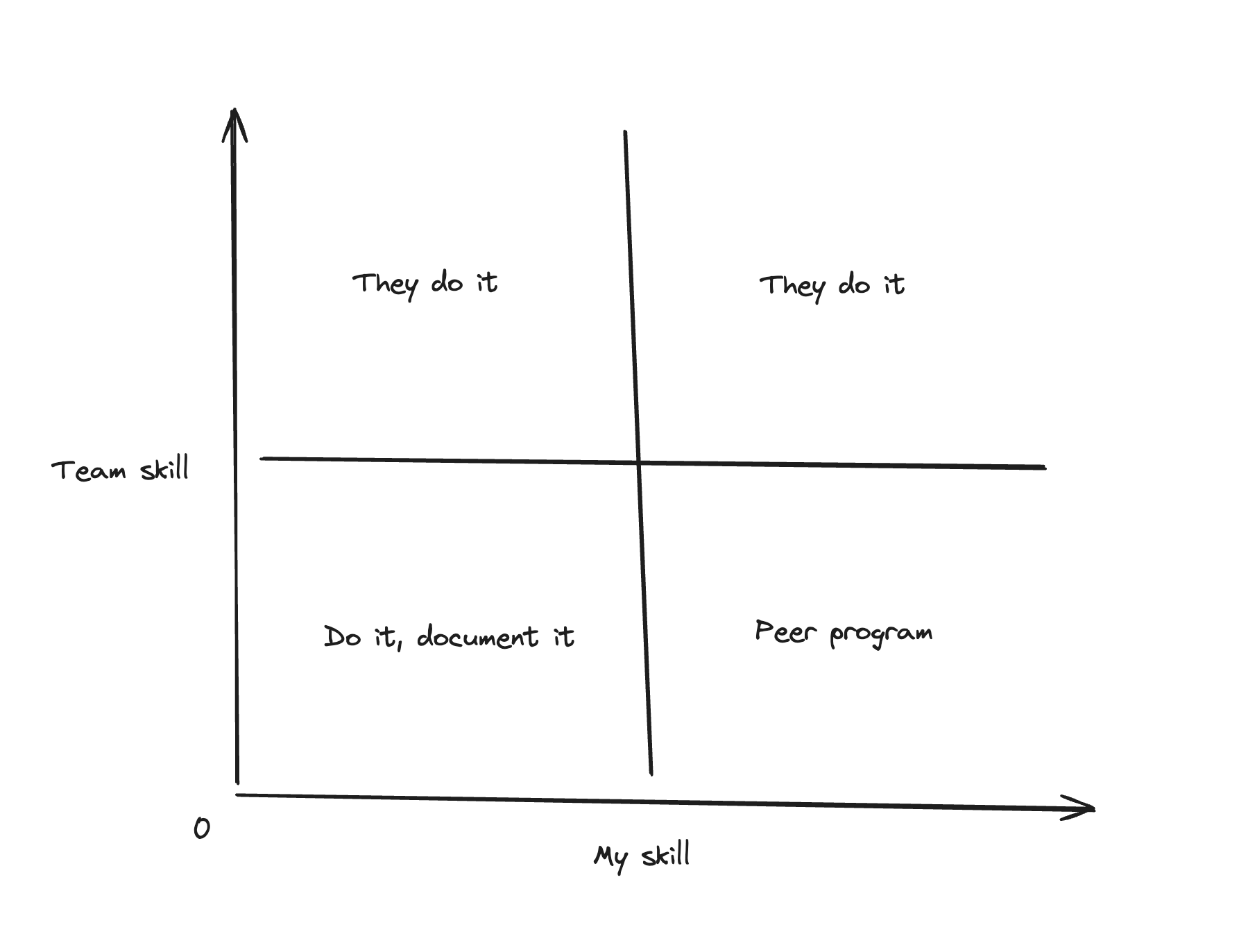
- Communicate to find your love/delegate balance, using the following chart:
As a senior developer, you are responsible of both the quality of the code you ship, AND the quality of the code you review. As a manager, you are responsible of any given failure that comes from either your code, or the code your team ships. Which means that the BEST way to ensure code quality is not only to make thoughtful review, but to create the best possible environnement so that everyone can perform well
## TL;DR
A senior dev would read the article. | sashkan |
1,862,849 | Bigg Boss 18 All Latest Episodes | "Bigg Boss" is an Indian reality television show that is modeled after the global "Big Brother"... | 0 | 2024-05-23T12:51:08 | https://dev.to/biggboss18watch/bigg-boss-18-all-latest-episodes-206o | "Bigg Boss" is an Indian reality television show that is modeled after the global "Big Brother" formula. It has grown to be one of the most well-liked and often viewed TV programs in the nation throughout time. Even with "Bigg Boss 18," the format's distinctive blend of drama, challenges, evictions, and celebrity participants manages to keep viewers interested.
[Bigg Boss 18 Full Episode](
https://biggboss18watch.live/)
"Bigg Boss 18" sticks to the tried-and-true formula of locking up a group of celebrities in a specially designed home, cutting them off from the outside world and preventing them from using any kind of communication gadget. Cameras are positioned throughout the house to monitor them around-the-clock. The competitors, also known as housemates, are required to live together for a number of weeks while taking part in a variety of activities and challenges that test | biggboss18watch | |
1,857,397 | Leveraging Docker in Your Web Development Workflow: A Comprehensive Guide | Introduction: In recent years, Docker has revolutionized the way developers build, ship, and run... | 0 | 2024-05-23T13:00:00 | https://dev.to/nitin-rachabathuni/leveraging-docker-in-your-web-development-workflow-a-comprehensive-guide-2e8d | Introduction:
In recent years, Docker has revolutionized the way developers build, ship, and run applications. Its lightweight containerization technology has become an indispensable tool in the toolkit of web developers worldwide. In this article, we'll explore how you can integrate Docker into your web development workflow to streamline processes, enhance collaboration, and ensure consistency across environments.
Why Docker?
Before diving into the practical aspects, let's briefly touch on why Docker has gained such widespread adoption in the web development community:
Isolation: Docker containers encapsulate your application and its dependencies, ensuring consistency across different environments, from development to production.
Portability: Containers are lightweight and portable, enabling seamless deployment across various platforms and cloud providers.
Scalability: Docker's container-based approach makes it easy to scale your applications horizontally by spinning up multiple instances of containers.
Reproducibility: With Docker, you can define your application's environment using code (Dockerfiles), making it easy to reproduce and share with your team.
Now, let's dive into how you can incorporate Docker into your web development workflow.
Setting Up Your Development Environment:
The first step is to set up Docker on your machine. Docker provides comprehensive documentation for installing Docker Desktop on different operating systems, including Windows, macOS, and Linux.
Once Docker is installed, you'll need to create a Dockerfile to define your application's environment. Here's a simple example for a Node.js application:
```
# Use the official Node.js image as a base
FROM node:14
# Set the working directory in the container
WORKDIR /app
# Copy package.json and package-lock.json to the working directory
COPY package*.json ./
# Install dependencies
RUN npm install
# Copy the rest of the application code
COPY . .
# Expose port 3000
EXPOSE 3000
# Command to run the application
CMD ["npm", "start"]
```
Setting Up Your Development Environment:
The first step is to set up Docker on your machine. Docker provides comprehensive documentation for installing Docker Desktop on different operating systems, including Windows, macOS, and Linux.
Once Docker is installed, you'll need to create a Dockerfile to define your application's environment. Here's a simple example for a Node.js application:
```
Dockerfile
# Use the official Node.js image as a base
FROM node:14
# Set the working directory in the container
WORKDIR /app
# Copy package.json and package-lock.json to the working directory
COPY package*.json ./
# Install dependencies
RUN npm install
# Copy the rest of the application code
COPY . .
# Expose port 3000
EXPOSE 3000
# Command to run the application
CMD ["npm", "start"]
In this Dockerfile:
```
We start with the official Node.js image from Docker Hub.
Set the working directory inside the container.
Copy package.json and package-lock.json to install dependencies.
Copy the rest of the application code.
Expose port 3000 (the default for most Node.js applications).
Define the command to start the application.
Building and Running Your Docker Container:
Once you have your Dockerfile ready, you can build your Docker image using the docker build command. Navigate to your project directory containing the Dockerfile and run:
```
docker build -t my-node-app .
```
This command builds a Docker image with the tag my-node-app.
To run your application as a Docker container, use the docker run command:
```
docker run -p 3000:3000 my-node-app
```
This command starts a container based on the my-node-app image and forwards port 3000 from the container to port 3000 on your local machine.
Integrating Docker Compose:
While running individual containers with docker run works well for simple applications, managing multiple containers can become cumbersome. Docker Compose is a tool for defining and running multi-container Docker applications.
Here's an example docker-compose.yml file for our Node.js application:
```
version: '3'
services:
web:
build: .
ports:
- "3000:3000"
```
With this docker-compose.yml file in your project directory, you can start your application and its dependencies (if any) with a single command:
```
docker-compose up
```
Conclusion:
Docker has become an indispensable tool for modern web development workflows. By containerizing your applications, you can ensure consistency, scalability, and reproducibility across different environments. In this article, we've covered the basics of using Docker in your web development workflow, from setting up your development environment to running multi-container applications with Docker Compose. Incorporating Docker into your workflow will not only streamline your development process but also enhance collaboration and deployment agility. So why wait? Start containerizing your applications with Docker today!
---
Thank you for reading my article! For more updates and useful information, feel free to connect with me on LinkedIn and follow me on Twitter. I look forward to engaging with more like-minded professionals and sharing valuable insights.
| nitin-rachabathuni | |
1,861,527 | Tableau Desktop Public: Try the Free Version for Data Visualization | Introduction Ahead of Tableau Conference 2024, Tableau has made a groundbreaking... | 0 | 2024-05-23T13:00:00 | https://dev.to/luca1iu/tableau-desktop-public-try-the-free-version-for-data-visualization-46b8 | tutorial, tableau, visualization, software | # Introduction
Ahead of Tableau Conference 2024, Tableau has made a groundbreaking announcement: the transition of Tableau Public Desktop into the **Tableau Desktop Public Edition**, now available for free. This new version is equipped with most of the powerful features previously found only in Tableau Desktop Professional, minus the ability to connect to enterprise databases.
# **Key Features**
- Connectivity: Users can link to multiple data sources, including Excel spreadsheets, CSV files, and cloud-based platforms.
- Ease of Use: With its drag-and-drop functionality, Tableau Public makes it incredibly easy to create sophisticated charts, graphs, and maps.
- Customization: A wide array of customization options are available, allowing users to tailor their visualizations to their specific needs.
- Collaboration: Tableau Public facilitates sharing and collaboration, enabling users to publish their work online and engage with a community of data enthusiasts.
# **Accessibility**
The Tableau Desktop Public Edition supports local file usage, automatic saving, and cloud sharing options for non-commercial use, such as Google Drive. This makes it a versatile tool for data enthusiasts, educators, and professionals looking to enhance their data visualization skills without financial barriers.
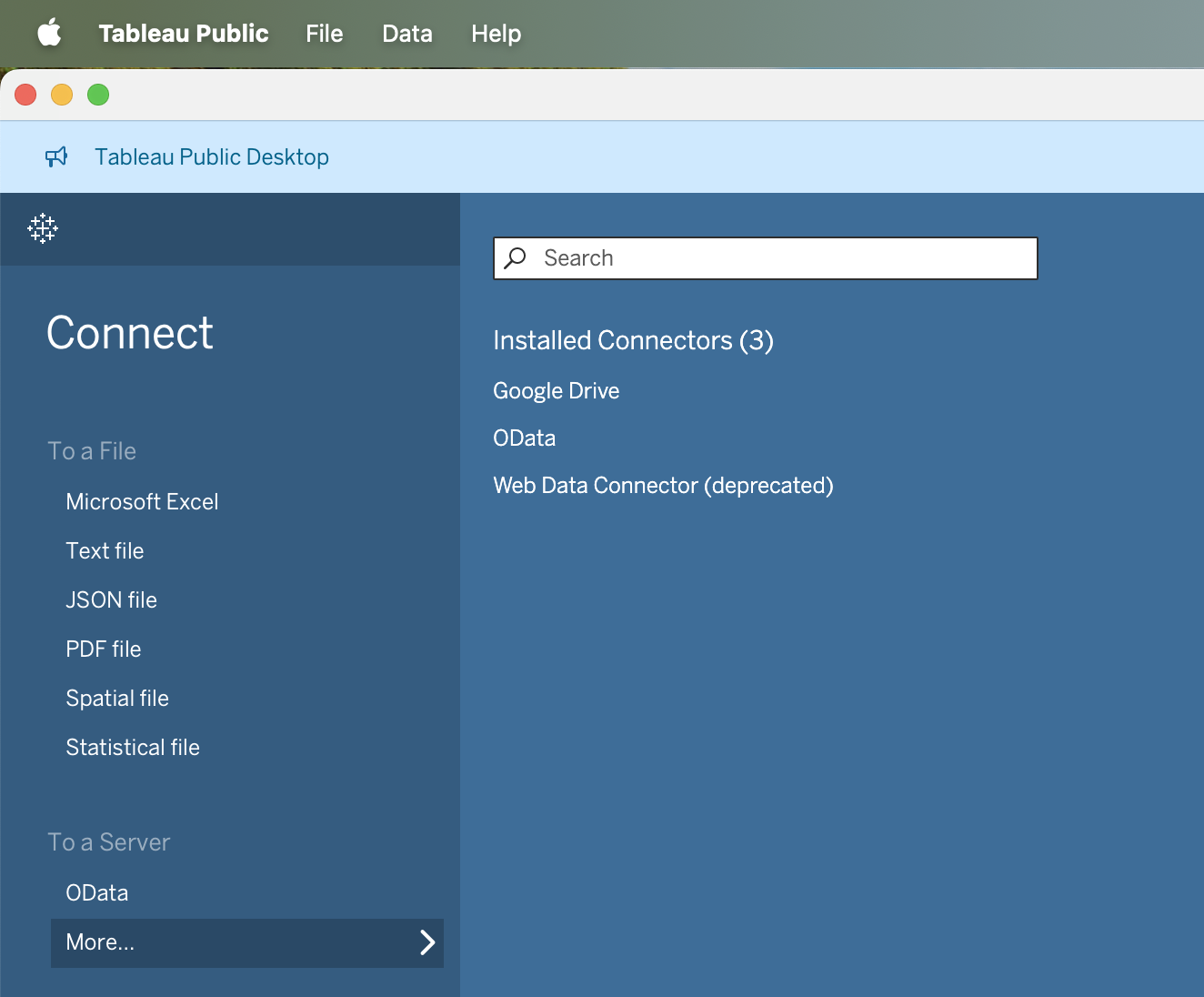
# **How to Get Started**
To experience the full potential of Tableau Desktop Public Edition, download it from the [**official Tableau website**](https://www.tableau.com/products/public/download). The installation is simple, and you'll be prompted to fill out some personal information for the initial download.
# **Conclusion**
Tableau's decision to offer a free, robust data visualization tool is a significant step towards democratizing data analysis. Tableau Desktop Public Edition empowers users to create, share, and learn from a vast array of data visualizations, making it an invaluable resource for anyone interested in data analytics. Don't miss this opportunity—download it today and start exploring the endless possibilities of data visualization!
---
## Explore more
{% embed https://dev.to/luca1iu %}
Thank you for taking the time to explore data-related insights with me. I appreciate your engagement.
{% cta https://www.linkedin.com/in/lucaliu-data %} 🚀 Connect with me on LinkedIn {% endcta %}
{% cta https://twitter.com/Luca_DataTeam %} 🎃 Connect with me on X {% endcta %} | luca1iu |
1,862,854 | Crafting the Peacock Rentals Website: Overcoming Challenges and Embracing the Future | In the ever-evolving landscape of online rental services, Peacock Rentals emerges as a beacon of... | 0 | 2024-05-23T12:57:31 | https://dev.to/blazetzkrieg66/crafting-the-peacock-rentals-website-overcoming-challenges-and-embracing-the-future-319o | javascript, python | 
In the ever-evolving landscape of online rental services, Peacock Rentals emerges as a beacon of luxury and convenience. With a commitment to offering top-tier vehicles and accommodations across multiple locations, the journey of creating the Peacock Rentals website has been as exhilarating as a drive in one of our exotic cars. However, like any ambitious project, it has come with its fair share of challenges and triumphs.
**Choosing the Right Technology Stack:** One of the initial hurdles we faced was selecting the appropriate technology stack to bring our vision to life. After careful consideration, we decided to harness the power of C++, JavaScript, and Python. Each language offers unique strengths that contribute to the functionality and performance of our website. C++ provides robustness and efficiency, JavaScript enhances interactivity and user experience, while Python offers versatility and ease of development.
**Designing a Seamless User Experience:** Creating an intuitive and seamless user experience was paramount to us. From browsing luxury vehicles to booking vacation homes, we wanted every step of the rental process to be effortless and enjoyable. This required meticulous planning and iteration of our website's design and navigation. Through user feedback and rigorous testing, we refined our interface to ensure clarity, simplicity, and accessibility for all users.
**Integrating Complex Features:** [Peacock Rentals](https://peacock-rentals.com/) offers a range of services beyond traditional car rentals, including vacation homes and boats. Integrating these diverse offerings into a cohesive platform posed a significant technical challenge. We leveraged the flexibility of Python to develop robust backend systems capable of handling complex data and transactions seamlessly. Additionally, JavaScript played a vital role in creating dynamic and interactive elements, enhancing the overall user experience.
**Navigating Regulatory Compliance:** Operating in multiple locations means navigating a maze of regulatory requirements and legal considerations. From insurance regulations to local ordinances, ensuring compliance across jurisdictions presented a formidable challenge. However, by working closely with legal experts and industry professionals, we developed comprehensive strategies to address regulatory hurdles while maintaining the highest standards of integrity and legality.
**Future Goals and Aspirations:** As we look to the future, our aspirations for Peacock Rentals are as grand as the vehicles in our fleet. We envision expanding our services to new cities and destinations, offering customers unparalleled luxury and convenience wherever they travel. Furthermore, we are committed to harnessing emerging technologies such as artificial intelligence and augmented reality to enhance the rental experience further. Whether it's through personalized recommendations or immersive virtual tours, we strive to push the boundaries of innovation and redefine the standards of excellence in the rental industry.
In conclusion, the creation of the Peacock Rentals website has been a journey filled with challenges, triumphs, and endless possibilities. By leveraging the power of C++, JavaScript, and Python, we have built a platform that epitomizes luxury, convenience, and sophistication. As we embark on this exciting adventure, we remain steadfast in our commitment to delivering exceptional experiences and shaping the future of luxury rentals. | blazetzkrieg66 |
1,862,873 | Secure File Handling in Blazor: Implement JWT Authentication | TL;DR: Are you worried about unauthorized access to your Blazor apps’ file uploads? For enhanced... | 0 | 2024-05-30T04:34:08 | https://www.syncfusion.com/blogs/post/blazor-file-upload-jwt-authentication | blazor, development, syncfusion, web | ---
title: Secure File Handling in Blazor: Implement JWT Authentication
published: true
date: 2024-05-23 12:56:53 UTC
tags: blazor, development, syncfusion, web
canonical_url: https://www.syncfusion.com/blogs/post/blazor-file-upload-jwt-authentication
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/3jkq933xahpdwfe3dioa.png
---
**TL;DR:** Are you worried about unauthorized access to your Blazor apps’ file uploads? For enhanced security, learn to implement JWT authentication in the Syncfusion Blazor File Upload component. This guide covers adding the File Upload component, incorporating JWT headers for authentication, and handling file upload and removal on the server to restrict access to authenticated users only.
File uploads are a common requirement in modern web applications.
Syncfusion [Blazor File Upload](https://www.syncfusion.com/blazor-components/blazor-file-upload "Blazor File Upload") is a component for uploading files, images, documents, and audio and video files to a server. It works in both WebAssembly and server-side Blazor apps. It also supports a rich set of features, including multiple file selection, progress bars, auto-uploading, drag and drop, folder (directory) uploading, file validation, and more.
In this blog, we’ll see how to integrate the Syncfusion Blazor File Upload component with [JWT (JSON Web Token)](https://en.wikipedia.org/wiki/JSON_Web_Token "Wikipedia Link: JWT (JSON Web Token)") authentication in a Blazor app. This combination allows us to securely upload and remove files while ensuring that only authenticated users can perform the actions.
Let’s get started!
## Prerequisites
- [Visual Studio 2022](https://visualstudio.microsoft.com/vs/ "Visual Studio 2022")
- [.NET Core 6.0 and above](https://dotnet.microsoft.com/en-us/download/dotnet/6.0 "Download .NET Core")
## Step 1: Create a Blazor WebAssembly app
First, create a new Blazor WebAssembly app using Visual Studio. Then, install Syncfusion Blazor packages and configure the styles and script references using the [getting started documentation](https://blazor.syncfusion.com/documentation/getting-started/blazor-webassembly-visual-studio "Getting started with Blazor WebAssembly App in Visual Studio").
## Step 2: Add Blazor File Upload component
Now, integrate the Syncfusion Blazor File Upload component into your Blazor page. Refer to the following code example.
```xml
@using Syncfusion.Blazor.Inputs
<SfUploader ID="UploadFiles">
<UploaderAsyncSettings SaveUrl="api/FileAction/Save" RemoveUrl="api/FileAction/Remove">
</UploaderAsyncSettings>
</SfUploader>
```
## Step 3: Add JWT authentication for file upload action
The Blazor File Upload component allows you to add an additional header to bind the authentication token during **file** **upload**, which can then be received on the server side. To configure the header as a key-value pair, you can achieve this behavior by using the [FileSelected](https://help.syncfusion.com/cr/blazor/Syncfusion.Blazor.Inputs.UploaderEvents.html#Syncfusion_Blazor_Inputs_UploaderEvents_FileSelected "FileSelected property of Blazor File Upload component") and [BeforeRemove](https://help.syncfusion.com/cr/blazor/Syncfusion.Blazor.Inputs.UploaderEvents.html#Syncfusion_Blazor_Inputs_UploaderEvents_BeforeRemove "BeforeRemove property of Blazor File Upload component") events and their [CurrentRequest](https://help.syncfusion.com/cr/blazor/Syncfusion.Blazor.Inputs.SelectedEventArgs.html#Syncfusion_Blazor_Inputs_SelectedEventArgs_CurrentRequest "CurrentRequest property of Blazor File Upload component") arguments.
Refer to the following code example.
```xml
<SfUploader ID="UploadFiles">
<UploaderEvents FileSelected="onFileSelect" BeforeRemove="onRemove"></UploaderEvents>
<UploaderAsyncSettings SaveUrl="api/FileAction/Save" RemoveUrl="api/FileAction/Remove">
</UploaderAsyncSettings>
</SfUploader>
@code {
private void onFileSelect(SelectedEventArgs args)
{
args.CurrentRequest = new List<object> { new { Authorization = "test@123" } };
}
}
```
## Step 4: Implement server-side handling for upload action
We should implement the API endpoints to handle file uploads and removals on the server side. These endpoints will validate JWT tokens to ensure authentication.
In the server-side control code, you can retrieve the authentication token key from the server project’s response header for file upload action, as demonstrated in the following code example.
```csharp
[HttpPost("[action]")]
public async void Save(IList<IFormFile> UploadFiles)
{
//To get the authorization header to handle save file action on the server side.
var authorizationHeader = Request.Headers["Authorization"];
if (authorizationHeader.Count == 0 || authorizationHeader[0] != "test123")
{
Response.Clear();
Response.StatusCode = 401;
Response.HttpContext.Features.Get<IHttpResponseFeature>().ReasonPhrase = "Unauthorized";
return;
}
try
{
foreach (var file in UploadFiles)
{
if (UploadFiles != null)
{
var filename = ContentDispositionHeaderValue.Parse(file.ContentDisposition).FileName.Trim('"');
filename = hostingEnv.WebRootPath + $@"\{filename}";
if (!System.IO.File.Exists(filename))
{
using (FileStream fs = System.IO.File.Create(filename))
{
file.CopyTo(fs);
fs.Flush();
}
}
}
}
}
catch (Exception e)
{
Response.Clear();
Response.ContentType = "application/json; charset=utf-8";
Response.StatusCode = 204;
Response.HttpContext.Features.Get<IHttpResponseFeature>().ReasonPhrase = "File failed to upload";
Response.HttpContext.Features.Get<IHttpResponseFeature>().ReasonPhrase = e.Message;
}
}
```
## Step 5: Add JWT authentication for file removal action
In the same way, you can handle the **file** **removal** action by sending the JWT authentication header to the [BeforeRemove](https://help.syncfusion.com/cr/blazor/Syncfusion.Blazor.Inputs.UploaderEvents.html#Syncfusion_Blazor_Inputs_UploaderEvents_BeforeRemove "BeforeRemove property of Blazor File Upload component") event and its [CurrentRequest](https://help.syncfusion.com/cr/blazor/Syncfusion.Blazor.Inputs.SelectedEventArgs.html#Syncfusion_Blazor_Inputs_SelectedEventArgs_CurrentRequest "CurrentRequest property of Blazor File Upload component") argument to configure the header as a key-value pair.
Refer to the following code example.
```csharp
private void onRemove(BeforeRemoveEventArgs args)
{
args.CurrentRequest = new List<object> { new { Authorization = "test123" } };
}
```
## Step 6: Implementing server-side file removal action
Within the server-side control code, you can retrieve the authentication token key to perform file removal action from the response header, mirroring the procedure in the file-saving action controller. Verify the authentication before executing the file removal process.
Refer to the following code example.
```csharp
[HttpPost("[action]")]
public void Remove(IList<IFormFile> UploadFiles)
{
// To get the authorization header to handle the file removal action on the server side.
var authorizationHeader = Request.Headers["Authorization"];
if (authorizationHeader.Count == 0 || authorizationHeader[0] != "test123")
{
Response.Clear();
Response.StatusCode = 401;
Response.HttpContext.Features.Get<IHttpResponseFeature>().ReasonPhrase = "Unauthorized";
return;
}
try
{
var filename = hostingEnv.ContentRootPath + $@"\{UploadFiles[0].FileName}";
if (System.IO.File.Exists(filename))
{
System.IO.File.Delete(filename);
}
}
catch (Exception e)
{
Response.Clear();
Response.StatusCode = 200;
Response.HttpContext.Features.Get<IHttpResponseFeature>().ReasonPhrase = "File removed successfully";
Response.HttpContext.Features.Get<IHttpResponseFeature>().ReasonPhrase = e.Message;
}
}
```
Refer to the following output image.
<figure>
<img src="https://www.syncfusion.com/blogs/wp-content/uploads/2024/05/Implementing-JWT-authentication-in-the-Blazor-File-Upload-component-2.png" alt="Implementing JWT authentication in the Blazor File Upload component" style="width:100%">
<figcaption>Implementing JWT authentication in the Blazor File Upload component</figcaption>
</figure>
## GitHub reference
Also, check out the complete source code for [integrating JWT authentication in Blazor File Upload component on GitHub](https://github.com/SyncfusionExamples/blazor-file-upload-jwt-authentication "Integrating JWT authentication in Blazor File Upload component GitHub demo").
## Conclusion
Thanks for reading! This blog shows how to integrate JWT authentication in the Syncfusion [Blazor File Upload](https://www.syncfusion.com/blazor-components/blazor-file-upload "Blazor File Upload") component. This can enhance the security of our file upload functionality. Authenticated users can securely upload and manage files while unauthorized access is effectively prevented.
Experience our Blazor component firsthand by downloading a [free 30-day trial](https://www.syncfusion.com/account/manage-trials/downloads "Get free evaluation of Essential Studio products") or utilizing our [NuGet package](https://www.nuget.org/packages/Syncfusion.Blazor "Syncfusion.Blazor NuGet package"). Explore additional features through our Blazor [online examples](https://blazor.syncfusion.com/ "Blazor online demo") and [documentation](https://blazor.syncfusion.com/documentation/introduction/ "Welcome to Syncfusion Blazor Components").
If you have any questions, please don’t hesitate to let us know in the comments section given below. You can also contact us through our [support forum](https://www.syncfusion.com/forums/blazor-components "Syncfusion Support Forum"), [support portal](https://support.syncfusion.com/ "Syncfusion Support Portal"), and [feedback portal](https://www.syncfusion.com/feedback "Syncfusion Feedback Portal"). We are always eager to assist you!
## Related blogs
- [Easily Perform CRUD Actions in Blazor Pivot Table with SQL Database & Entity Framework](https://www.syncfusion.com/blogs/post/crud-blazor-pivot-table-sql-entity-framework "Blog: Easily Perform CRUD Actions in Blazor Pivot Table with SQL Database & Entity Framework")
- [Seamlessly Load Data from Different Data Sources into Blazor Charts](https://www.syncfusion.com/blogs/post/load-data-sources-in-blazor-charts "Blog: Seamlessly Load Data from Different Data Sources into Blazor Charts")
- [Advanced Query Building Techniques: Connecting Tables with Joins using Blazor Query Builder](https://www.syncfusion.com/blogs/post/advanced-query-building-blazor-connecting-tables-joins "Blog: Advanced Query Building Techniques: Connecting Tables with Joins using Blazor Query Builder")
- [Creating Custom Forms and Validation in a Blazor Hybrid App](https://www.syncfusion.com/blogs/post/blazor-hybrid-app-custom-forms-validation "Blog: Creating Custom Forms and Validation in a Blazor Hybrid App") | jollenmoyani |
1,862,847 | Let build a website | Describe a web page and let me design it for free | 0 | 2024-05-23T12:48:12 | https://dev.to/marvellousabio/let-build-a-website-37j3 | Describe a web page and let me design it for free | marvellousabio | |
1,862,853 | A beginner's guide to the Meta-Llama-3-8b-Instruct model by Meta on Replicate | meta-llama-3-8b-instruct | 0 | 2024-05-23T12:55:58 | https://aimodels.fyi/models/replicate/meta-llama-3-8b-instruct-meta | coding, ai, beginners, programming | *This is a simplified guide to an AI model called [Meta-Llama-3-8b-Instruct](https://aimodels.fyi/models/replicate/meta-llama-3-8b-instruct-meta) maintained by [Meta](https://aimodels.fyi/creators/replicate/meta). If you like these kinds of guides, you should subscribe to the [AImodels.fyi newsletter](https://aimodels.substack.com) or follow me on [Twitter](https://twitter.com/mikeyoung44).*
## Model overview
`meta-llama-3-8b-instruct` is an 8 billion parameter language model from [Meta](https://aimodels.fyi/creators/replicate/meta) that has been fine-tuned for chat completions. This model is part of the Llama 3 series, which also includes the base `meta-llama-3-8b` and the larger `meta-llama-3-70b` models. Compared to the base Llama 3 models, the `meta-llama-3-8b-instruct` version has been further trained on dialogue and instruction-following tasks, giving it enhanced capabilities for open-ended conversations and task completion.
## Model inputs and outputs
The `meta-llama-3-8b-instruct` model takes a prompt as input and generates text as output. The prompt can be a statement, question, or instruction that the model uses to continue the conversation or complete the task. The output is a completion of the prompt, generated based on the model's understanding of the context and its training on dialogue and instruction-following.
### Inputs
- **Prompt**: The starting text that the model should use to generate a completion.
### Outputs
- **Text completion**: The model's generated continuation or completion of the input prompt.
## Capabilities
The `meta-llama-3-8b-instruct` model is capable of engaging in open-ended dialogue, answering questions, and following instructions. It can be used for a variety of tasks such as language modeling, text generation, question answering, and task completion. The model's fine-tuning on dialogue and instruction-following allows it to generate more coherent and relevant responses compared to the base Llama 3 models.
## What can I use it for?
The `meta-llama-3-8b-instruct` model can be used for a wide range of applications, such as building chatbots, virtual assistants, and content generation tools. Its ability to understand and respond to instructions makes it well-suited for automating various tasks, from customer service to content creation. Developers and businesses can leverage this model to enhance their products and services, while researchers can use it to further explore the capabilities of large language models.
## Things to try
One interesting aspect of the `meta-llama-3-8b-instruct` model is its ability to follow complex instructions and generate coherent responses. You can try prompting the model with multi-step tasks or open-ended questions and observe how it handles the complexity. Additionally, you can experiment with different temperature and top-k/top-p settings to see how they affect the model's output in terms of creativity, coherence, and safety.
**If you enjoyed this guide, consider subscribing to the [AImodels.fyi newsletter](https://aimodels.substack.com) or following me on [Twitter](https://twitter.com/mikeyoung44) for more AI and machine learning content.** | mikeyoung44 |
1,862,173 | JavaScript Mini Password Generator | Intro: This is a small password generator made with JavaScript. It's a very simple program. All it... | 0 | 2024-05-23T12:55:41 | https://dev.to/petrinaropra/javascript-mini-password-generator-30b | beginners, javascript, programming, tutorial | **Intro:** This is a small password generator made with JavaScript. It's a very simple program. All it does is display a new password every time the user presses the generate password button. I added pictures to it for fun. You can add your pictures if you want to. By the way, this is for complete beginners as I have commented on every line of my JavaScript file. If I have made mistakes please let me know and feel free to copy and tweak this game to your liking.
**Watch Demo Here:** [https://youtube.com/shorts/A5BLMB5H1mI?feature=share](https://youtube.com/shorts/A5BLMB5H1mI?feature=share)
**Note:** I got my pictures from [https://www.canva.com/ai-image-generator/](https://www.canva.com/ai-image-generator/)
**Tip:** You can use random images at first until the program works fine and then add images that fit the description. Make sure the first word and second word of the images' name are similar to the first two words of the password for example: when the password fluffyapple95h shows up then the fluffyapple.jpg image will show. Make sure to put the full file path to your images.
**Tweak:** You can change the adjectives and nouns and put as many or as few as you like.
The first code block is HTML, the second is CSS and the third is JavaScript.
```html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>Password Picker</title>
<link rel="stylesheet" href="password_picker.css"> <!-- Link to the external CSS file -->
</head>
<body>
<div id="password-container">
<h2>Welcome to Password Picker!</h2>
<div id="password-output"></div>
<br>
<img id="password-image" src="" alt="Password Image"> <!-- Image element to display the image -->
<br><br>
<button id="generate-btn">Generate Password</button>
</div>
<script src="password_picker.js"></script> <!-- Link to the external JavaScript file -->
</body>
</html>
```
```css
body {
font-family: Arial, sans-serif;
background-color: #f0f0f0;
margin: 0;
padding: 0;
display: flex;
justify-content: center;
align-items: center;
height: 100vh;
}
#password-container {
background-color: #fff;
border-radius: 5px;
padding: 80px;
width: 20%;
box-shadow: 0 2px 5px rgba(0, 0, 0, 0.1);
text-align: center;
}
button {
padding: 10px 20px;
font-size: 16px;
background-color: #007bff;
color: #fff;
border: none;
border-radius: 3px;
cursor: pointer;
transition: background-color 0.3s;
}
button:hover {
background-color: #0056b3;
}
#password-output{
font-size: 20px;
background-attachment: orange;
text-align: center;
}
```
```javascript
//create an array of adjectives
const adjectives = ['sleepy', 'slow', 'smelly', 'wet', 'fat', 'red', 'orange', 'yellow', 'green', 'blue', 'purple', 'fluffy', 'white', 'proud', 'brave'];
//create an array of nouns
const nouns = ['apple', ]; //'dinosaur', 'ball', 'toaster', 'goat', 'dragon', 'hammer', 'duck', 'panda'];
//create a function called generatePassword
const generatePassword = () => {
//pick a random item in the adjectives array everytime the function is called
//Math.random gives a random floating point number, then multiplied with the length of the adjectives array
//to stay within the array then Math.floor rounds it up to the nearest integer.
const adjective = adjectives[Math.floor(Math.random() * adjectives.length)];
//same thing above here but for nouns array
const noun = nouns[Math.floor(Math.random() * nouns.length)];
//get a random number from 0 to 100
const number = Math.floor(Math.random() * 100);
//get the ASCII codes for printable characters
const specialChar = String.fromCharCode(33 + Math.floor(Math.random() * 94));
//join all the string values prevous variables together and put them in a variable called password
const password = adjective + noun + number + specialChar;
//display the message below in the html file
//For example: Your new password is: fluffyapple95h
document.getElementById('password-output').textContent = 'Your new password is: ' + password;
//get the image that matches the password and display it in the html file
document.getElementById('password-image').src = `C:/Users/petix/OneDrive/Desktop/my_javascript_games/Password_picker/${adjective}${noun}.png`; // Set the source of the image
};
//add an event to the button so that when it is pressed it will call the generatePassword function
document.getElementById('generate-btn').addEventListener('click', generatePassword);
//show an image when the program loads for the first time
document.getElementById('password-image').src = 'C:/Users/petix/OneDrive/Desktop/my_javascript_games/Password_picker/letters.png'
```
| petrinaropra |
1,862,739 | Integrating PWA in a Next.js App | Introduction Progressive Web Apps (PWAs) combine the best features of web and mobile... | 0 | 2024-05-23T12:52:59 | https://dev.to/wafa_bergaoui/integrating-pwa-in-a-nextjs-app-3a1 | pwa, nextjs, react, frontend | ## Introduction
Progressive Web Apps (PWAs) combine the best features of web and mobile applications, offering offline capabilities, push notifications, and the ability to install the app on a user’s device. For a detailed overview of PWAs, refer to my previous article [The Evolution and Necessity of Progressive Web Apps.](https://dev.to/wafa_bergaoui/the-evolution-and-necessity-of-progressive-web-apps-pwas-42pl)
This guide will take you through the steps to integrate a PWA into your Next.js application.
## Steps to Integrate PWA in Next.js
**1. Initial Setup**
Ensure you have a Next.js app set up. If not, create one using:
```
npx create-next-app@latest pwa-app
cd pwa-app
```
**2. Install Dependencies**
Install the **next-pwa** package to add PWA capabilities to your app:
```
npm install next-pwa
OR
yarn add next-pwa
```
**3. Configure next.config.js**
Modify `next.config.js` to use the **next-pwa** plugin:
```javascript
const withPWA = require('next-pwa')({
dest: 'public',
disable: process.env.NODE_ENV === 'development',
});
module.exports = withPWA({
// Your existing Next.js configuration
});
```
**4. Create a Manifest File**
- Add a `manifest.json` file in the public directory. This file contains metadata about your web application, including details such as the app's name, short name, theme color, and icons.
- You can create this file manually or use online tools like:
- [SimiCart Manifest Generator](https://www.simicart.com/manifest-generator.html/)
- [Manifest Generator](https://manifest-gen.netlify.app/)
- Example `manifest.json`:
```json
{
"name": "Progressive Web App",
"short_name": "PWA",
"start_url": "/",
"display": "standalone",
"background_color": "#ffffff",
"theme_color": "#000000",
"icons": [
{
"src": "/icons/icon-192x192.png",
"sizes": "192x192",
"type": "image/png"
},
{
"src": "/icons/icon-512x512.png",
"sizes": "512x512",
"type": "image/png"
}
]
}
```
- Save the `manifest.json` file in the `/public` directory of your project.
**5. Service Worker Setup**
The **next-pwa** plugin handles the creation and configuration of the service worker for you. Ensure the public directory is configured correctly for caching and offline capabilities.
**6. Link Manifest in `_document.js`**
Modify the `_document.js` file to include the manifest file and specify theme colors:
```javascript
import Document, { Html, Head, Main, NextScript } from 'next/document';
class MyDocument extends Document {
render() {
return (
<Html>
<Head>
<link rel="manifest" href="/manifest.json" />
<meta name="theme-color" content="#000000" />
</Head>
<body>
<Main />
<NextScript />
</body>
</Html>
);
}
}
export default MyDocument;
```
**7. Use VSCode Extension for PWA Development**
Enhance your PWA development with the [PWA Builder VSCode extension](https://marketplace.visualstudio.com/items?itemName=PWABuilder.pwa-studio). This tool helps generate PWA assets, configure service workers, and more, streamlining the PWA integration process.
**8. Check Validation**
- Run your app, and you should see an install prompt in the address bar, allowing users to install your PWA like a native app.
- Verify your PWA using the PWA audit in Lighthouse (available in Chrome DevTools). Note that you need to deploy your app for this to work.
**9. Additional Steps: Git Configuration**
Add the following to your `.gitignore` to exclude files generated by **next-pwa**:
```gitignore
# PWA files
**/public/sw.js
**/public/workbox-*.js
**/public/worker-*.js
**/public/sw.js.map
**/public/workbox-*.js.map
**/public/worker-*.js.map
```
**10. Bonus: Optimize for Mobile Devices**
- To avoid unwanted scroll behavior on iOS Safari:
```html
<Head>
<meta name="viewport" content="initial-scale=1, viewport-fit=cover, width=device-width"></meta>
</Head>
```
```css
.someContainerClass {
height: calc(100vh - env(safe-area-inset-bottom) - env(safe-area-inset-top));
}
@supports (-webkit-touch-callout: none) {
.someContainerClass {
height: -webkit-fill-available;
}
}
```
- Alternatively, set the container position:
```css
.containerClass {
position: fixed;
left: 0;
top: 0;
bottom: 0;
right: 0;
margin: 0;
}
```
- To hide the virtual keyboard on enter key press:
```javascript
const hideVirtualKeyboard = () => {
const inputElements = document.getElementsByTagName("input");
Array.from(inputElements).forEach((input) => {
input.blur();
});
};
```
Integrating PWA into your Next.js application not only improves the user experience but also increases engagement and accessibility, making it a valuable addition to any modern web project.
## Conclusion
By following these steps and utilizing these resources, you can ensure your Next.js app leverages the full power of Progressive Web Apps, providing an enhanced, app-like experience for your users. This integration not only makes your application more accessible and engaging but also significantly improves performance and user satisfaction. Embrace the future of web development with PWAs in your Next.js projects!
| wafa_bergaoui |
1,862,851 | iTerm2 and the Gap Between Developers and Users | iTerm2 introduced AI features and it shows the disconnect between their developer community and user community | 0 | 2024-05-23T12:52:03 | https://dev.to/rangerrick/iterm2-and-the-gap-between-developers-and-users-2g1h | iterm2, opensource, community, netbox | ---
title: iTerm2 and the Gap Between Developers and Users
published: true
description: iTerm2 introduced AI features and it shows the disconnect between their developer community and user community
tags: iterm2, opensource, community, netbox
# cover_image: https://direct_url_to_image.jpg
# Use a ratio of 100:42 for best results.
# published_at: 2024-05-22 13:33 +0000
---
Hello! I have not been blogging for a while, but I have been watching [this issue](https://gitlab.com/gnachman/iterm2/-/issues/11470) blow up for a few days, and I wanted to put down some thoughts.
Beyond the obvious surface question of whether the userbase wants or doesn't want AI in their terminal, I feel like this thread points out a really important meta-issue that's worth keeping in mind if you are part of the leadership team in an open source community.
They've been working on this feature for at least a year and clearly their _entire_ userbase (including me!) had zero idea it was coming. They can say "[we had it in a beta, and it was in the roadmap](https://www.goodreads.com/quotes/40705-but-the-plans-were-on-display-on-display-i-eventually)" all they want, but given the immediate emotional backlash, obviously most of their users just don't engage with the project on that level.
For me, iTerm2 has been a tool that Just Works for so long I really don't even think about it. As a user, that builds a _huge_ amount of trust, and launching this feature in an update without the wider community being aware of it ahead of time is a great way to break that trust with a lot of folks, whether you think it's justified or not. I can sympathize that for the developers, it's surely frustrating to have so many people relying on your work that never even peek in at the project other than to download it, but the reality is that's the large majority of the userbase of _any_ popular open source project.
Up until recently, I was at [OpenNMS](https://opennms.com/), an open source network monitoring project that was Doing It Right™ for a very long time, even with a commercial component. However, since being acquired, it has kind of lost its direction as it fumbled around trying to work on a new product, and I've watched it slowly sink into obscurity as it has failed to engage meaningfully with its community. It's still a great tool with a lot of features that are unmatched elsewhere! But without the open source community being an active part, it's just one more in a giant pile of enterprise network monitoring tools.
I'm now at [NetBox Labs](https://netboxlabs.com/), working on putting together [an on-prem enterprise offering](https://netboxlabs.com/netbox-enterprise/). It's been a whirlwind of learning new technologies and getting comfortable at a new company after being in the same place for 17 years. I've enjoyed the heck out of it so far, and there are a lot of smart people doing good work here. Most importantly, though, the thing that attracted me most to NetBox Labs (besides having a friend who already works here 😀) is that we do really seem to be walking the walk on leaving the OSS version of NetBox to be its own vibrant community and tool. We employ the lead maintainer, Jeremy Stretch, and obviously he has a strong role in guiding the project, but we are regularly and actively reaching out to the other maintainers for things that might affect them and being super open with the community early and often. The community is active, engaged, and positive about NetBox Labs helping push the platform forward while building a company around it.
NetBox is doing a pretty fantastic job of being out in the open about its development (even the commercial stuff), so the idea that the iTerm2 developers could be _so far_ from their users that they couldn't imagine this backlash is terrifying to me, and it's important to me that we make sure we don't ever end up going down the same path.
This should be a warning sign to F/LOSS projects that there is more to your user community than _just_ the people that engage with the project, and it's as important (or _more_ important) to work to understand them and figure out how to engage with them if you care about being a truly open project. | rangerrick |
1,862,850 | How Integrating Salesforce with Accounting Tools Improves Business Efficiency | In today's fast-paced business environment, the need for streamlined operations and efficient... | 0 | 2024-05-23T12:51:42 | https://dev.to/shreya123/how-integrating-salesforce-with-accounting-tools-improves-business-efficiency-4pol | salesforce, salesforcebusiness, salesforceconsulting | In today's fast-paced business environment, the need for streamlined operations and efficient workflows is more critical than ever. One powerful way businesses can enhance their efficiency is by [integrating Salesforce](https://www.softwebsolutions.com/salesforce-consulting-services.html), a leading customer relationship management (CRM) system, with robust accounting tools. This integration bridges the gap between sales and financial data, providing a seamless flow of information that can significantly improve business operations. Here’s how:
1. Enhanced Data Accuracy and Consistency
Integrating Salesforce with accounting tools ensures that data entered in one system automatically updates in the other. This synchronization reduces the chances of manual entry errors and discrepancies between sales and financial records. For instance, when a sales invoice is created in Salesforce, the details can be instantly reflected in the accounting software, maintaining consistency and accuracy across both platforms.
2. Streamlined Invoicing and Payment Processes
A major benefit of integrating Salesforce with accounting tools is the automation of invoicing and payment processes. Sales teams can generate invoices directly from Salesforce based on the sales data, and these invoices are automatically logged in the accounting system. This automation speeds up the invoicing process, reduces delays, and ensures timely payment collections, ultimately improving cash flow.
3. Improved Financial Reporting and Analysis
When Salesforce and accounting tools are integrated, businesses gain a comprehensive view of their financial health. Financial reports and analytics can pull data from both systems, providing insights that are more accurate and detailed. Businesses can track key performance indicators (KPIs) like revenue growth, customer acquisition costs, and profitability with greater precision, facilitating better strategic decision-making.
4. Enhanced Customer Experience
Integrating these systems enables a 360-degree view of the customer. Sales teams can access financial information such as payment history, outstanding balances, and credit limits directly within Salesforce. This access allows sales representatives to make informed decisions, offer personalized solutions, and manage customer relationships more effectively. A well-informed sales team can provide better service, leading to increased customer satisfaction and loyalty.
5. Operational Efficiency and Time Savings
Manual data entry and reconciliation between sales and accounting systems are time-consuming tasks that are prone to errors. Integration automates these processes, freeing up time for employees to focus on more strategic activities. This operational efficiency translates into cost savings and enables staff to work on tasks that directly contribute to business growth.
6. Simplified Compliance and Audit Processes
Compliance with financial regulations and conducting audits can be complex and time-consuming. An integrated system simplifies these processes by ensuring that all financial transactions are accurately recorded and easily traceable. This transparency is crucial for audit trails and regulatory compliance, reducing the risk of non-compliance and potential fines.
7. Scalability and Growth Facilitation
As businesses grow, their operational processes become more complex. An integrated system scales with the business, handling increased volumes of sales and financial transactions without compromising on efficiency. This scalability supports business growth and ensures that operational processes remain smooth and efficient.
Conclusion
Integrating Salesforce with accounting tools is a strategic move that can significantly enhance business efficiency. The seamless flow of data between sales and finance departments eliminates manual errors, streamlines processes, and provides valuable insights that drive informed decision-making. By investing in this integration, businesses can improve their operational efficiency, enhance customer satisfaction, and position themselves for sustainable growth in a competitive marketplace. | shreya123 |
1,862,837 | Java celebrates its 29th birthday | Java celebrates its 29th birthday today! To pay homage to Java, I have decided to look at its walk of... | 0 | 2024-05-23T12:47:32 | https://dev.to/asm0dey/java-celebrates-its-29th-birthday-519e | java, birthday, history, experience | Java celebrates its 29th birthday today! To pay homage to Java, I have decided to look at its walk of fame from the eyes of a developer (that is, your humble servant). As the narrative below is quite personal, it omits many key points because they were not important to me. On the other hand, it includes many points that other people may consider insignificant, but not me.
## 1989: Project Oak
Java didn’t get its name yet. It was called Oak and was a part of an ambitious project, including not only a language, but also an OS and libraries.
## 1994: Java 1.0
Oak was renamed to Java. Shortly after, Java 1.0 saw the light.
Those were the days of Green Threads in Java! But for better or for worse, they would be abandoned in [Java 1.1](https://docs.oracle.com/cd/E19455-01/806-3461/6jck06gqe/index.html) to appear later in Java 21. Also, there were no generics, and JMM was very different (and frankly, hard to understand and deal with).
In addition, AWT was already there, but Swing wasn’t.
## 1997: JDK 1.1
This is the year when things started to get standardized. There were multiple standards introduced: JDBC, RMI, Java Beans, i18n, etc. It’s hard to believe, but they all are still in Java and supported by frameworks such as Hibernate. Besides, they are changed in a backwards-compatible manner; many of us are in a love–hate relationship with this approach, right?
## 1998: J2SE 1.2
This year, Swing came into the game. Also, this is the year when JDK was renamed to J2SE: Java 2 Platform Standard Edition. This is because there was at least one other edition of J2: Mobile, a subset of Java intended to work on weak devices. I still remember my first time patching the Java heap size on my Sony-Ericsson five years later. And games were written in Java, too.
Also, CORBA was introduced. We still use it today but call it gRPC (just kidding). CORBA itself would live in Java for a long time.
## 2002: J2SE 1.4
Every Java release introduces a bunch of interesting changes, but I’m not going to enumerate them all because as I mentioned, I want it to be more of a personal story. The reason I brought up 1.4 is that it introduced Java Web Start and Applets, a way to call Java from a web browser. It seemed like magic: I could run a full-fledged application by clicking an icon in the browser. It might have been quite slow, but it was just unbelievably powerful for something working in a browser. Remember, JS was not a real thing for the front-end development back then, let alone the development of heavy logics.
By the way, [Liberica JDK supports OpenWebStart](https://bell-sw.com/announcements/2020/11/13/BellSoft-Kicks-Off-Bundled-Offer-with-Karakun/?utm_source=devto&utm_medium=post&utm_campaign=pasha&utm_content=javabirthday) in case you need it!
## 2004: Java SE 5
This was a huge one! Not only because it was the first release I worked with as a developer, but because it brought tremendous changes into Java. I dare to say that it’s the foundation of today’s Java. The release brought
- Generics
- Enums
- The new (current) JMM (Java Memory Model)
- java.util.concurrent
- varargs
I think that these features made Java a modern language!
Also, it was the last release supporting Windows 98. Never liked it, I used to be a Windows XP person (until 2009, when I switched to Linux).
## 2011: Java SE 7
It'd been a whopping five years since the release of Java 6! I moved from total noob in development to something middle senior and spent almost all my career years with Java 6. I thought it was the last Java, and later we will switch to Groovy or Scala. I even brought both of them into production!
This release brought a lot of new improvements in terms of performance, invokedynamic and many other things, but for me, a young developer, it was a disappointment. I expected it to have lambdas. Groovy had them for quite some time already!
## 2014: Java SE 8
My dream came true. They released Lambda support! I immediately stopped using for loops and replaced them with streams. Sometimes it was smart, sometimes it wasn’t. It seems I was not alone: Java 8 is still used heavily in the bigger enterprises. And for those who are not planning the migration to newer JDK versions in the near future,there’s [Liberica JDK Performance Edition](https://bell-sw.com/libericajdk-performance-edition/?utm_source=devto&utm_medium=post&utm_campaign=pasha&utm_content=javabirthday) that couples JDK 8 and JVM 17 and brings the performance of newer Java versions right to your door, almost no code changes required!
I will name one more thing: DateTime API that looks almost exactly as JodaTime API.
## 2018: Java SE 11
I can call this release the first backward-incompatible release I used. The thing is, some modules were removed and I had to add them as external dependencies. For example, Java EE was not part of JDK anymore, as well as all its annotations, etc. So I had to add them to my already huge pom.xml.
But do you remember that they added CORBA in 1998? It took 20 years to remove it, from Java 1.2 to Java 11! Would be cooler to remove it in version 12, right?
Java 11 brought many interesting things, for example ZGC and the native HTTP Client. I didn’t need to call new HttpUrlConnection() anymore! Also, they’ve deprecated the JS engine running on Java, called Nashorn. I didn’t mention it and never used it, but the interesting fact is: it was introduced in Java 8! It sounds like the pace really increased!
## 2020: Java SE 15
Nobody noticed this release because at this time, the release cadence was two releases per year. That’s too many releases to catch up with for a mere mortal!
Bit it was an interesting release because:
- Shenandoah was officially introduced;
- Text blocks appeared;
- EdDSA encryption is built into the JDK.
## The story goes on
After Java 11, there were two more LTS releases, JDK 17 and 21, and the next LTS release is due this September.
But at some point, I fell in love with Kotlin and Java and myself… We didn’t part ways, but I stopped following its evolution closely. The story doesn’t end, though, and there were many exciting features added to the platform, such as records, virtual threads, pattern matching, etc. And even more novelties are in the makings!
So let’s wish Java Happy Birthday and many years of prosperity ahead!
| asm0dey |
1,862,845 | Professional Court Reporting Services | Professional Court Reporting Services: The Unsung Heroes of the Legal System In the intricate and... | 0 | 2024-05-23T12:45:34 | https://dev.to/ishtiaq_ahmed_1a584374c19/professional-court-reporting-services-26in | Professional Court Reporting Services: The Unsung Heroes of the Legal System
In the intricate and often high-stakes world of legal proceedings, the value of precise, reliable documentation cannot be overstated. This is where professional court reporting services come into play, serving as the backbone of courtroom accuracy and integrity. Let’s delve into what these services entail and why they are indispensable to the judicial process.
What Are [Professional Court Reporting Services](https://www.servixer.com/court-reporting-services/)?
Court reporting services involve the meticulous transcription of spoken words during legal proceedings into written form. This includes everything from trials and depositions to arbitration hearings and administrative meetings. Professional court reporters use advanced techniques and equipment, such as stenotype machines, voice writing technology, and digital recording systems, to ensure every word is accurately captured and documented.
The Importance of Accuracy
In the legal realm, the smallest detail can make a significant difference. The accuracy of court transcripts is crucial because attorneys, judges, and juries rely on these records to review testimonies, formulate arguments, and make decisions. A misrecorded word or phrase can lead to misunderstandings, flawed arguments, and even miscarriages of justice. Professional court reporters are trained to provide verbatim transcriptions, ensuring the integrity of the legal process.
Technological Advancements in Court Reporting
Modern court reporting has embraced technology to enhance efficiency and accuracy. Real-time transcription software allows court reporters to convert spoken words into text instantly, which can be displayed on monitors in the courtroom. This not only aids in immediate review and clarification but also speeds up the overall legal process. Additionally, digital storage solutions provide secure, easily accessible repositories for transcripts, ensuring they are preserved and can be retrieved when needed.
The Role of Certified Court Reporters
Certification is a mark of quality and reliability in court reporting. Certified Court Reporters (CCRs) undergo rigorous training and testing to ensure they meet high standards of accuracy and professionalism. Organizations like the National Court Reporters Association (NCRA) offer certifications that validate a reporter’s skills and knowledge. These certifications also require adherence to ethical standards, ensuring confidentiality and impartiality.
Benefits of Professional Court Reporting Services
Precision: Professional court reporters provide exact, word-for-word transcriptions, critical for fair and accurate legal proceedings.
Efficiency: With real-time reporting and advanced transcription tools, the documentation process is streamlined, saving valuable time.
Confidentiality: Certified court reporters adhere to strict confidentiality protocols, protecting sensitive information.
Accessibility: Transcripts are readily accessible to all legal parties, promoting transparency and informed decision-making.
Support for Legal Processes: Detailed transcripts serve as essential resources for legal research, case preparation, and appeals.
Looking Ahead: The Future of Court Reporting
The field of court reporting is set to evolve with advancements in artificial intelligence and machine learning. These technologies promise to further improve the speed and accuracy of transcriptions. However, the human element remains irreplaceable, as skilled court reporters provide the necessary context and nuance that machines cannot replicate.
In conclusion, professional court reporting services are vital to the smooth functioning of the legal system. They ensure that every word spoken in a courtroom is captured with precision, supporting the pursuit of justice. As technology continues to advance, the role of the court reporter will remain essential, bridging the gap between spoken language and the written record, safeguarding the accuracy and integrity of legal proceedings.
| ishtiaq_ahmed_1a584374c19 | |
1,862,830 | Hub Sites in SharePoint Online | Introduction to Hub Sites Hub sites in SharePoint are special types of sites designed to... | 0 | 2024-05-23T12:45:23 | https://dev.to/borisgigovic/hub-sites-in-sharepoint-online-1c5h | sharepoint, hubsites, microsoft365, collaboration | ## Introduction to Hub Sites
Hub sites in SharePoint are special types of sites designed to connect and organize other sites within an organization.
They provide a centralized navigation experience across associated sites, making it easier for users to find information and resources. Hub sites allow for consistent branding, ensuring a cohesive look and feel throughout the organization's SharePoint environment.
They also aggregate content such as news, events, and activities from associated sites, offering a consolidated view of important information. The search experience is scoped to the hub and its associated sites, improving search relevance. Additionally, hub sites facilitate connections between related sites, promoting collaboration and information sharing across different departments or projects. Security and permissions are inherited from associated sites, simplifying management, and ensuring consistency.
Hub sites offer flexibility and scalability, allowing organizations to associate multiple sites with a hub site and reassign sites to different hubs as needed. This makes hub sites particularly useful for organizations with many SharePoint sites, as they streamline site management and enhance the user experience.
They are a great alternative and replacement to subsites that were used in the legacy implementation scenarios, and that we are gradually decommissioning in favor of hub sites.
## Practical Use Examples
**Example 1: Corporate Intranet**
A common use case for Hub Sites is to organize a corporate intranet. For instance, a Hub Site can serve as the central intranet portal for an organization, with associated sites for different departments such as HR, IT, and Marketing. This setup not only enhances navigation between departmental content but also ensures a consistent corporate identity across the intranet.
**Example 2: Project Management**
Hub Sites can also be instrumental in managing projects. By creating a Hub Site for a specific project, you can connect sites dedicated to various project components or teams. This approach enables centralized project communication, document sharing, and progress tracking.
## Configuration Steps
Creating and configuring a Hub Site in SharePoint Online involves several key steps. We will demonstrate here how to create the hub site, associate an existing site to it, and verify that changes the top link bar URLs that are made available at the hub are reflected on the member site, which is one of the functionality the use of hub sites allows us to do.
1. Navigate to your tenant’s SharePoint Admin Center by using the appropriate URL - _https://[your tenant name]-admin.sharepoint.com/_layouts/15/online/AdminHome.aspx_:
2. Select **Active Sites** under **Sites**:
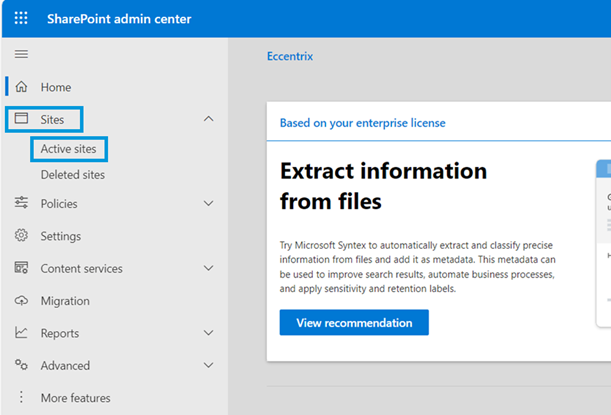
3. Choose an existing site to convert into a Hub Site (or create a new site) by clicking on **Register as a hub site** in the Hub menu:
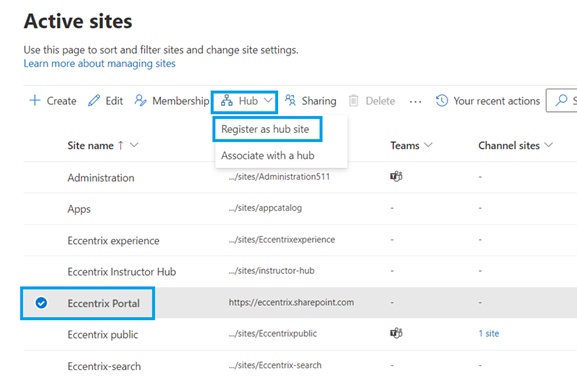
4. Enter a name for the Hub Site and specify additional settings as required, and click on **Save** to create your Hub Site:
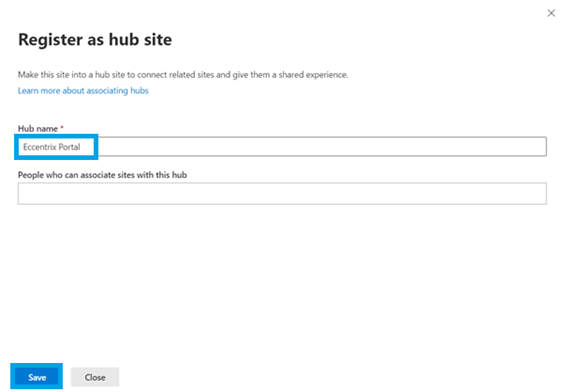
5. Notice your site will be converted as a hub site, and click **Close**:
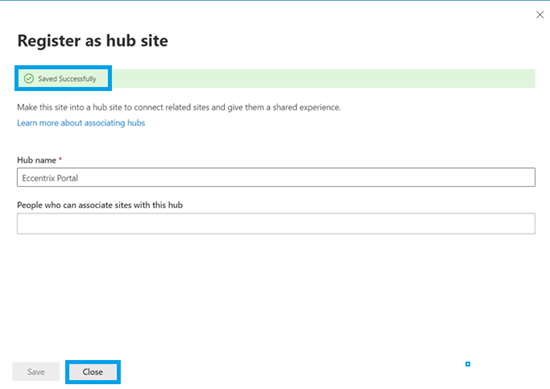
6. At this point, check the site you wish to associate with the Hub Site, and select **Associate with a hub** in the Hub menu:
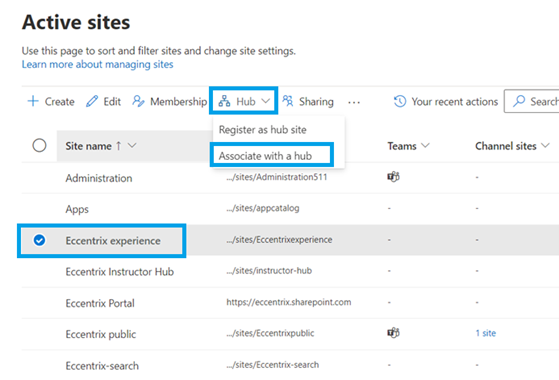
7. Select your Hub Site to which you want your current site to be associated with from the dropdown list and click on **Save**:
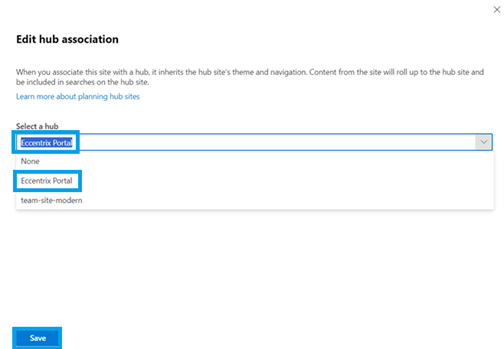
8. Notice the association has completed successfully:
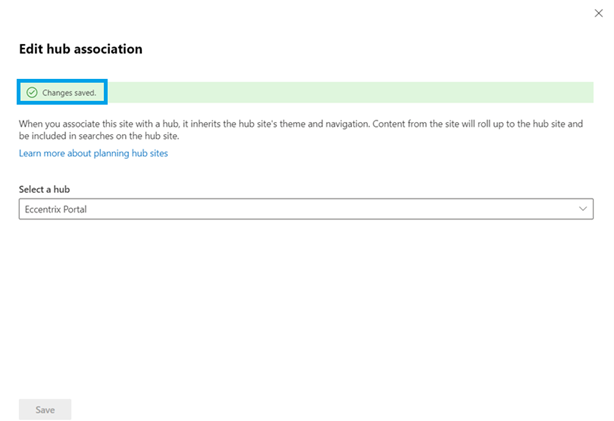
9. Browse to the hub site that we have converted recently by accessing its URL in its properties:
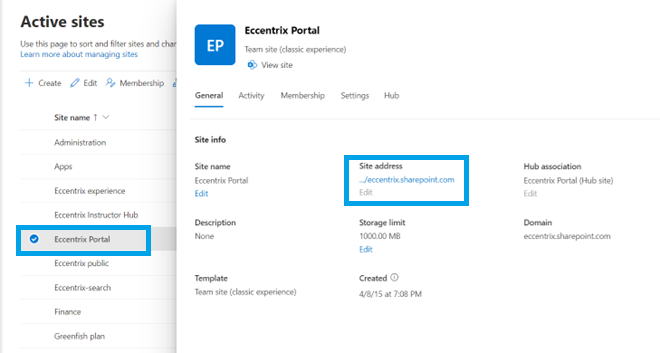
10. Now, we will customize the main navigation bar links of the hub site to be reflected on the associated sites by clicking on the member sites by clicking on **Edit**:
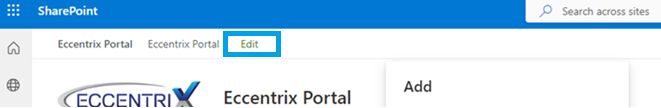
11. Click on the plus sign and specify the address, the display name of the link, and click on **OK**) to ensure the changes are applied at that level:
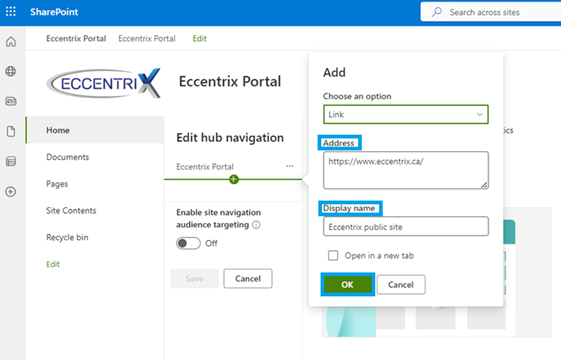
12. Click on **Save** to close the link menu editor:
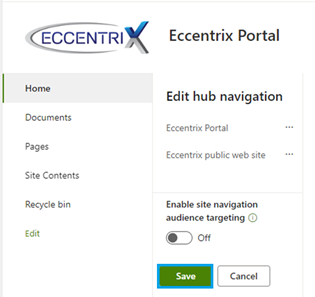
13. By visiting the member site, you will notice the link has appeared in the navigation bar at the top, proving a hub site is designed to provide consistency across member sites:
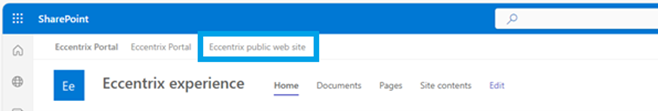
## Conclusion
Hub Sites in SharePoint Online offer a powerful solution for organizing and managing sites within an organization. By leveraging Hub Sites, businesses can enhance collaboration, improve information discovery, and maintain a cohesive digital workplace. Whether for a corporate intranet or project management, the practical applications of Hub Sites are vast and varied.
For professionals looking to deepen their understanding of SharePoint Online and explore advanced features like Hub Sites, Eccentrix provides comprehensive IT training, such as the [SharePoint Online Management and Administration (MS55370)](https://www.eccentrix.ca/en/courses/microsoft/sharepoint-online/sharepoint-online-management-and-administration-ms55370) course. With expert-led courses and hands-on practice, Eccentrix equips you with the skills needed to effectively implement and manage SharePoint Online in your organization. | borisgigovic |
1,862,843 | Real World Asset Token Development - Beleaf Technologies | Real-world asset token development is the place you need to go! You can find out how real estate or... | 0 | 2024-05-23T12:44:01 | https://dev.to/miaarley421/real-world-asset-token-development-beleaf-technologies-3ndo | Real-world asset token development is the place you need to go! You can find out how real estate or goods you can touch can be displayed online. With these tokens, you can buy, sell, and digitally trade old-fashioned things. Blockchain technology makes ownership of real-world assets more accessible and efficient. Dive into the tokenization world and see how it can be used in modern banking.
Website: https://www.beleaftechnologies.com/real-world-asset-token-development
Contact details
WhatsApp: +91 7904323274
Skype: live:.cid.62ff8496d3390349
Telegram: https://telegram.me/BeleafSoftTech
Mail to:business@beleaftechnologies.com
| miaarley421 | |
1,862,841 | Top 10 Flutter Development Tools in 2024 | Flutter has emerged as a powerful framework for crafting beautiful and performant UIs. However, even... | 0 | 2024-05-23T12:41:41 | https://dev.to/aaronreddix/top-10-flutter-development-tools-in-2024-n19 | flutter, mobile, beginners, firebase | Flutter has emerged as a powerful framework for crafting beautiful and performant UIs. However, even the most skilled developer can benefit from the right set of tools to streamline the development process and achieve optimal results.
This guide delves into the top 10 Flutter development tools for 2024. We've carefully selected these tools based on their popularity, functionality, ease of use, and their ability to enhance various aspects of Flutter app development. Whether you're a seasoned Flutter developer or embarking on your first Flutter project, this guide will equip you with the knowledge to choose the most suitable tools and take your Flutter development workflow to the next level.
## Top 10 Flutter Development Tools
## 1. Android Studio
[Android Studio](https://developer.android.com/studio), the official IDE (Integrated Development Environment) for Android app development, seamlessly integrates with Flutter through a powerful plugin. This combination provides a feature-rich environment specifically tailored for building Flutter applications.
### Key Features:
- **Integrated Development Environment**: Edit, debug, and test your Flutter code directly within Android Studio.
- **Hot Reload:** Experience near-instantaneous updates to your app UI as you make code changes, accelerating development cycles.
- **Flutter DevTools**: Leverage built-in debugging and profiling tools to identify and resolve performance issues effectively.
- **Code Completion & Refactoring**: Benefit from code completion suggestions, syntax highlighting, and refactoring capabilities to write cleaner and more maintainable code.
### Target Audience
This versatile environment caters to both beginners and experienced Flutter developers seeking a comprehensive and integrated development experience.
## 2. Visual Studio Code
[Visual Studio Code (VS Code)](https://code.visualstudio.com/) is a popular, open-source code editor known for its extensibility and customization options. When paired with the official Flutter extension, VS Code transforms into a powerful development environment for building Flutter applications.
### Key Features:
- **Lightweight & Customizable**: Enjoy a lightweight code editor experience that can be tailored to your preferences with a vast array of extensions and themes.
- **Flutter-specific Features**: The Flutter extension unlocks functionalities like code completion for Dart and Flutter widgets, hot reload for rapid UI updates, and debugging capabilities.
- **Multi-platform Support**: Develop Flutter apps seamlessly on Windows, macOS, and Linux thanks to VS Code's cross-platform compatibility.
- **Vibrant Community**: Benefit from a large and active developer community providing support, extensions, and learning resources.
### Target Audience
VS Code caters to a broad audience. Beginners will appreciate its user-friendly interface and ease of setup, while experienced developers can leverage its customization options and extensive plugin ecosystem for a tailored development experience.
## 3. DartPad
[DartPad](https://dartpad.dev/) is a free, web-based code editor specifically designed for experimenting with the Dart programming language, the foundation of [Flutter development](https://digimonksolutions.com/services/flutter-app-development/). It also offers built-in support for exploring Flutter functionalities.
### Key Features:
- **Live Coding Environment**: Write Dart and Flutter code directly in your web browser and see the results instantly.
- **No Setup Required**: Experiment with Flutter concepts without installing any additional software, making it ideal for quick trials and learning new functionalities.
- **Console & Debugging**: Utilize the built-in console for printing output and basic debugging to understand your code's behavior.
- **Embeddable Code Snippets**: Share your Flutter code snippets easily by generating embeddable iframes directly from DartPad.
### Target Audience
Primarily suited for beginners or developers who want to experiment with Dart syntax, explore basic Flutter widget functionalities, or test small code snippets before integrating them into larger projects.
## 4. Flutter Inspector
The [Flutter Inspector](https://docs.flutter.dev/tools/devtools/inspector) is an invaluable tool integrated within Android Studio (with the Flutter plugin) and Visual Studio Code (with the Flutter extension). It acts as a visual debugger, allowing you to inspect the widget tree that forms the foundation of your Flutter app's UI.
### Key Features:
- **Visualize Widget Tree**: See a real-time representation of your app's UI structure, with each element represented by its corresponding widget.
- **Inspect Widget Properties**: Dive deeper into individual widgets by examining their properties, values, and state in real-time.
- **Debug Layout Issues**: Identify and troubleshoot layout problems by analyzing widget placement, sizing, and potential conflicts within the widget tree.
- **Select Mode**: Interact with your app's UI directly and choose specific widgets for inspection, streamlining the debugging process.
### Target Audience
This tool is beneficial for developers of all experience levels. Beginners can gain a deeper understanding of Flutter's widget-based UI structure, while experienced developers can leverage it for efficient debugging and optimizing layout behavior.
## 5. Firebase
[Firebase](https://firebase.google.com/) by Google offers a comprehensive suite of back-end services that seamlessly integrate with Flutter development. This integration allows you to focus on building the app's core functionalities while Firebase handles tasks like authentication, databases, cloud storage, analytics, and more.
### Key Features:
- **Authentication**: Implement robust and secure user authentication methods like email/password, social logins, and phone authentication.
- **Cloud Firestore**: Utilize a flexible NoSQL database for storing and managing your app's data in the cloud.
- **Cloud Storage**: Securely store and manage user-generated content like images, videos, and other files.
- **Firebase Analytics**: Gain valuable insights into user behavior and app usage through comprehensive analytics tools.
- **Remote Config**: Dynamically configure your app's behavior remotely without requiring app updates, allowing for A/B testing and feature rollouts.
### Target Audience
Firebase is a versatile platform that caters to developers of all experience levels. Beginners can leverage its pre-built services to add essential functionalities to their Flutter apps, while experienced developers can take advantage of its scalability and advanced features for complex projects.
## 6. Codemagic
[Building and deploying Flutter apps](https://codemagic.io/start/) can involve repetitive tasks. Codemagic is a powerful CI/CD (Continuous Integration and Continuous Delivery) platform that automates these processes, saving you time and effort.
### Key Features:
- **Automated Builds**: Configure Codemagic to automatically build your Flutter app whenever you push code changes to your version control system (e.g., Git).
- **Multi-platform Support**: Build your Flutter app for Android and iOS simultaneously, streamlining the deployment process for both platforms.
- **Code Signing & Distribution**: Simplify code signing and app distribution to various app stores (Google Play Store, Apple App Store) directly from Codemagic.
- **Testing Integration**: Integrate unit and integration tests into your CI/CD pipeline to ensure code quality and catch regressions early in the development process.
### Target Audience
Codemagic is particularly beneficial for developers working on larger projects or teams where automating builds and deployments becomes crucial. However, even solo developers can leverage its features to streamline their workflow and focus on core app development.
## 7. Supernova
[Supernova](https://www.supernova.io/) is a design system platform that bridges the gap between design and development. It allows designers to create and manage design systems, and then automatically generates code (including Flutter code) based on those designs.
### Key Features:
- **Design System Management**: Centralize and manage your design system elements like colors, fonts, and UI components in one place.
- **Automatic Code Generation**: Export design elements directly into production-ready Flutter code, reducing the need for manual implementation and streamlining the design-to-development handoff.
- **Live Collaboration**: Enable designers and developers to work together seamlessly by visualizing design changes reflected in real-time code.
- **Design Documentation**: Generate comprehensive design documentation from your design system, improving communication and knowledge sharing within your team.
### Target Audience
Supernova is ideal for teams that value a unified design-to-development workflow. It empowers designers to have more control over the code generation process and fosters better collaboration between design and development teams.
## 8. Appetize
Testing your Flutter app across a variety of devices can be time-consuming and resource-intensive. [Appetize](https://appetize.io/) is a cloud-based mobile app testing platform that allows you to run your Flutter app directly in your web browser, eliminating the need for physical devices.
### Key Features:
- **Instant In-Browser Testing**: Upload your Flutter app and instantly launch it within a web browser window, simulating various mobile devices and operating systems.
- **Real-time Interaction**: Interact with your app in real-time within the browser, allowing you to test user flows and identify potential bugs.
- **Screen Recording & Sharing**: Record your testing sessions and easily share them with your team for feedback and collaboration.
- **Multiple Device Support**: Simulate a wide range of Android and iOS devices to ensure your app functions flawlessly across various screen sizes and hardware configurations.
### Target Audience
Appetize is a valuable tool for developers of all experience levels. It allows beginners to test their apps on different devices without managing physical hardware, while experienced developers can leverage it for regression testing and ensuring their app is ready for diverse device ecosystems.
## 9. Sentry
[Sentry](https://docs.sentry.io/platforms/flutter/) is an application monitoring platform that acts as a guardian for your Flutter app, proactively identifying and reporting crashes, errors, and performance issues.
### Key Features:
- **Real-time Error Reporting:** Get notified instantly whenever crashes or errors occur within your Flutter app, allowing for swift troubleshooting and resolution.
- **Detailed Error Information**: Gain valuable insights into the root cause of errors with detailed stack traces, breadcrumbs, and user context data captured at the time of the issue.
- **Performance Monitoring**: Track your app's performance metrics like rendering times and memory usage to identify potential bottlenecks and optimize app performance.
- **Crash Grouping & Prioritization**: Sentry intelligently groups similar crashes, helping you prioritize critical issues that affect a larger user base.
### Target Audience
Sentry is a valuable tool for developers of all experience levels. For beginners, it simplifies error identification and debugging. Experienced developers can leverage its advanced features for proactive performance monitoring and ensuring app stability across various user scenarios.
## 10. Panache
Building a visually appealing and consistent user interface (UI) is crucial for any Flutter app. [Panache](https://rxlabz.github.io/panache_web/) steps in as a time-saving tool, acting as a Flutter theme editor that empowers you to create and customize beautiful themes for your app effortlessly.
### Key Features:
- **Visual Theme Editing**: Panache provides a user-friendly interface for visually customizing colors, shapes, and styles of various Flutter widgets, allowing for intuitive theme creation.
- **Material Design Integration**: Seamlessly work within the Material Design guidelines to ensure your themes adhere to best practices and create a familiar user experience.
- **Theme Download and Integration**: Once you've crafted your perfect theme in Panache, simply download the generated Dart code and integrate it directly into your Flutter project for effortless theme application.
- **Multiple Theme Support**: Create and manage various themes within Panache, allowing you to easily switch between different design aesthetics for your app or cater to different user preferences.
### Target Audience
Panache is a valuable tool for developers of all experience levels. Beginners can leverage its visual editing capabilities to create attractive themes without extensive coding knowledge. Experienced developers can utilize Panache to streamline the theme creation process and experiment with various design options.
## Conclusion
Flutter development offers a treasure trove of tools to empower you in crafting exceptional mobile apps. This curated list of the top 10 tools explored a range of functionalities, from comprehensive development environments (Android Studio, VS Code) to code experimentation platforms (DartPad) and specialized solutions for UI design (Supernova, Panache), app testing (Appetize), performance monitoring (Sentry), and streamlined deployment processes (Codemagic).
The ideal development toolset depends on your specific project requirements and preferences. Explore the tools mentioned above, delve deeper into their functionalities, and don't hesitate to experiment with others beyond this list. By leveraging the right set of tools and your Flutter development expertise, you can create beautiful, performant, and user-friendly apps that will thrive in today's mobile landscape.
Happy Fluttering!
| aaronreddix |
1,862,840 | I need your help | I am in my last year of IT engineering studies , currently doing a web dev internship to conclude my... | 0 | 2024-05-23T12:41:28 | https://dev.to/wiwi/i-need-your-help-oje | I am in my last year of IT engineering studies , currently doing a web dev internship to conclude my studies .The least I could say is that I feel like I'm lost , I don't know where to start and what I should do next , if anyone has steps I should follow up to form a good understanding as a beginner in dev who knows little to nothing so that I can at least be able to make a small web app .Any advice would make a huge difference , thank you . | wiwi | |
1,862,839 | Как быстро поменять 1600+ криптовалют без регистрации | В мире, где цифровые технологии становятся неотъемлемой частью нашей повседневной жизни, криптовалюты... | 0 | 2024-05-23T12:40:32 | https://dev.to/daria_k_af86377e56f697c4f/kak-bystro-pomieniat-1600-kriptovaliut-biez-rieghistratsii-4e4i | cryptocurrency, exchange | В мире, где цифровые технологии становятся неотъемлемой частью нашей повседневной жизни, криптовалюты приобретают все большую популярность. Обмен криптовалют становится необходимостью для многих людей, и в поисках быстрого и безопасного способа менять различные активы на разнообразные криптовалюты без лишних формальностей мы обратим взор на один уникальный сервис [KindExchange](https://telegra.ph/Kak-bystro-pomenyat-1600-kriptovalyut-bez-registracii-05-23).
**Что такое криптовалюта и ее растущая популярность**
Криптовалюта - это цифровой актив, который использует криптографию для обеспечения безопасных финансовых транзакций. Одним из самых известных примеров криптовалюты является биткоин, созданный в 2009 году. С каждым годом интерес к криптовалютам растет, так как они предлагают анонимность, децентрализацию и удобство при проведении сделок.
Одной из основных привлекательных черт криптовалюты является возможность быстрого и недорогого перевода средств между пользователями по всему миру. Благодаря использованию технологии блокчейн все операции с криптовалютой открыты для проверки и не подвержены манипуляциям со стороны третьих лиц.
Рост популярности криптовалют связан не только с их технологическими достоинствами, но и с возможностью инвестирования. Многие видят в них перспективное направление для размещения своих финансовых активов в усложняющемся экономическом мире.
**Проблемы при обмене криптовалют**
При обмене криптовалют могут возникнуть некоторые проблемы, которые затрудняют процесс и делают его менее удобным для пользователей. Одной из основных проблем является необходимость регистрации на бирже перед совершением обмена. Этот шаг требует времени и предоставления личной информации, что может вызывать недовольство у пользователей, желающих оставаться анонимными.
Другой распространенной проблемой при обмене криптовалют является длительное время ожидания подтверждения транзакций. В зависимости от загруженности сети блокчейна, это может занять несколько минут или часов, что может быть неудобно для тех, кто хочет провести операцию быстро.
Также стоит отметить высокие комиссии при обмене криптовалют на некоторых платформах. Непредвиденные дополнительные расходы могут значительно уменьшить сумму получаемых средств после обмена. Решение этих проблем заключается в выборе сервиса, который предлагает быстрый и безопасный обмен 1600+ криптовалют без регистрации - KindExchange.
**Какой сервис предлагает быстрый и безопасный обмен 1600+ криптовалют без регистрации**
KindExchange - это уникальный сервис, который предлагает быстрый и безопасный обмен 1600+ криптовалют без необходимости проходить регистрацию. Благодаря широкому выбору криптовалют и простому интерфейсу, пользователи могут легко осуществлять обмены без лишних хлопот. Не требуется создавать аккаунт или предоставлять личные данные, что делает процесс обмена еще более удобным и конфиденциальным.
Пользуйтесь KindExchange для быстрых и выгодных операций с криптовалютами! | daria_k_af86377e56f697c4f |
1,862,838 | Setting up DSMR Meter Readings via a Raspberry Pi | Writing down how I pull readings from my DSMR meter and send them to my Home Assistant server. | 0 | 2024-05-23T12:40:23 | https://dev.to/badgerbadgerbadgerbadger/setting-up-dsmr-meter-readings-via-a-raspberry-pi-4idl | dsmr, homeassistant, electricity, raspberrypi | ---
title: "Setting up DSMR Meter Readings via a Raspberry Pi"
published: true
description: "Writing down how I pull readings from my DSMR meter and send them to my Home Assistant server."
tags: [dsmr, homeassistant, electricity, raspberrypi]
cover_image: https://github.com/BadgerBadgerBadgerBadger/BadgerBadgerBadgerBadger.github.io/assets/5138570/367da639-c5d0-4ec0-a7cf-3fda8eec61cd
---
Originally published at https://badgerbadgerbadgerbadger.dev/posts/automation/2024-05-23-setting-up-dsmr-readings-via-raspberry-pi/
The internet is probably full of tutorials on how to do this right, but I had to struggle a bit to figure it out for myself. My Pi randomly crashed, the other day, and I'm having to do some of the setup again and having done this for the first time months ago (and having now mostly forgotten what I did), I decided I should blog about it as I retread my steps and recreate my setup.
> **Aside**: The [internet](https://en.wikipedia.org/wiki/Unix_shell) tells me that the C shell was the first to introduce the `history` command. It would not be hyperbolic to say that without `history` my task of recreating my setup would be significantly more difficult. I used it extensively to figure out what I ran when I needed to do this all those months ago. I should probably containerise or chefise or ansibilise or something.
I live in a country that uses [DSMR](https://www.domoticz.com/wiki/Dutch_DSMR_smart_meter_with_P1_port) meters and have one in my home. My girlfriend wanted a closer look at our electricity consumption, so I decided to hook up a raspberry Pi to the meter's [P1](https://www.fluvius.be/sites/fluvius/files/2020-03/1901-fluvius-technical-specification-user-ports-digital-meter.pdf) port and send those readings to my home lab server using the Pi as a relay.
I bought a RJ12 --> USB cable off of Amazon and tried to read from my Pi's USB port by using first [`cu`](https://linux.die.net/man/1/cu) and then [pyserial](https://pythonhosted.org/pyserial/index.html) (which is a much friendlier interface).
```shell
# Using cu
cu -l /dev/ttyUSB0 -s 115200 --parity=none
# Using pyserial
python3 -m serial.tools.miniterm /dev/ttyUSB0 115200 --xonxoff
```
Initially neither tool gave me any readings and I nearly tore my luscious hair out before finally realising that it was a bad cable I was using. I returned it and bought a more respectable cable from [robbshop.nl](https://www.robbshop.nl/slimme-meter-kabel-usb-p1-1-meter).
And that gave me results!

I had a few different ways of turning the meter readings into useful insights:
1. **Run HomeAssistant on my Pi with direct access to the port**: Not an option since my HA instance was already running on my home lab server. The Pi was meant to be a relay only.
2. **DSMR to MQTT**: I could run something that would read the DSMR telegrams and send them to an MQTT broker to which I could subscribe my HA integration. Definitely an option.
3. **Serial to Network Proxy**: The option I ended up going with since it felt the simplest to me. I would run a program that would expose the DSMR telegrams over a TCP connection.
The program I landed on for doing this is [ser2net](https://ser2net.sourceforge.net/) With a little help from ChatGPT I figured out this [ser2net config](https://github.com/chargebyte/ser2net/blob/master/ser2net.conf). Comments describe what the various fields do.
```yaml
# defines an alias confver, I'm not entirely sure if this does anything
define: &confver 1.0
# begins a new connection definition and assigns it an alias `con00`.
connection: &con00
# specifies how incoming network connections will be accepted, in this case the Telnet protocol with RFC 2217 support (I no clue what that means), and the connection will be over TCP and listen on port 2013c (this part I understand)
accepter: telnet(rfc2217),tcp,2013
# specifies how the serial device will be connected, includes path to the serial device file and port settings, and it is to be configured in local mode (not sure what local mode means)
connector: serialdev,/dev/ttyUSB0,115200n81,local
```
I paired this with HA's [DSMR Slimme Meter](https://www.home-assistant.io/integrations/dsmr) integration with it set to listen on the network, pointed at my Pi on port 2013.
And we have lift-off!

> **Note**: Solar readings are coming in via a different integrations and configured together with the DSMR readings using HomeAssistant's Energy Dashboard.
| badgerbadgerbadgerbadger |
1,862,836 | Elevate Your Design: Mastering CSS Text Styling🚀 | 1. Text and Font Styling CSS offers powerful tools to control the appearance of text and fonts,... | 0 | 2024-05-23T12:35:41 | https://dev.to/dharamgfx/elevate-your-design-mastering-css-text-styling-39mb | css, webdev, beginners, programming | **1. Text and Font Styling**
CSS offers powerful tools to control the appearance of text and fonts, enhancing the readability and aesthetics of your web content.
**Font Family**
- Specify the typeface for your text.
*Example:*
```css
p {
font-family: 'Arial', sans-serif;
}
```
**Font Size**
- Adjust the size of your text using various units (`px`, `em`, `rem`).
*Example:*
```css
h1 {
font-size: 36px;
}
```
**Font Weight**
- Define the thickness of the text.
*Example:*
```css
strong {
font-weight: bold;
}
```
**Font Style**
- Set the text to italic or normal.
*Example:*
```css
em {
font-style: italic;
}
```
**Text Alignment**
- Align text to the left, right, center, or justify.
*Example:*
```css
div {
text-align: center;
}
```
**Text Decoration**
- Add or remove underlines, overlines, and line-through effects.
*Example:*
```css
a {
text-decoration: none;
}
```
**Text Transform**
- Control the capitalization of text.
*Example:*
```css
h2 {
text-transform: uppercase;
}
```
**Line Height**
- Adjust the space between lines of text.
*Example:*
```css
p {
line-height: 1.6;
}
```
**Letter Spacing**
- Modify the space between characters.
*Example:*
```css
h1 {
letter-spacing: 2px;
}
```
**2. Styling Lists and Links**
**Lists**
- Style ordered (`<ol>`) and unordered (`<ul>`) lists for better readability.
**List Style Type**
- Change bullet points or numbering style.
*Example:*
```css
ul {
list-style-type: square;
}
ol {
list-style-type: decimal-leading-zero;
}
```
**List Style Position**
- Define the position of bullets or numbers inside or outside the content flow.
*Example:*
```css
ul {
list-style-position: inside;
}
```
**Links**
- Customize the appearance of hyperlinks to improve usability.
**Link Pseudo-Classes**
- Style different states of a link.
*Example:*
```css
a:link {
color: blue;
}
a:visited {
color: purple;
}
a:hover {
color: red;
}
a:active {
color: orange;
}
```
**3. Web Fonts**
Using web fonts allows you to incorporate unique typefaces into your design, providing more creative flexibility.
**Importing Web Fonts**
- Use the `@import` rule or link to a web font service like Google Fonts.
**@import Example:**
```css
@import url('https://fonts.googleapis.com/css2?family=Roboto:wght@400;700&display=swap');
body {
font-family: 'Roboto', sans-serif;
}
```
**Link Example:**
```html
<link href="https://fonts.googleapis.com/css2?family=Roboto:wght@400;700&display=swap" rel="stylesheet">
<style>
body {
font-family: 'Roboto', sans-serif;
}
</style>
```
**Font-Face Rule**
- Define custom fonts to use in your CSS.
*Example:*
```css
@font-face {
font-family: 'MyCustomFont';
src: url('mycustomfont.woff2') format('woff2'),
url('mycustomfont.woff') format('woff');
}
body {
font-family: 'MyCustomFont', sans-serif;
}
```
---
**Conclusion**
Mastering CSS text styling opens up a world of possibilities for enhancing the visual appeal and readability of your web content. From basic text and font styling to advanced techniques like web fonts, lists, and link customization, these skills are essential for creating polished and engaging websites. Embrace these techniques to make your text stand out and provide a better user experience. | dharamgfx |
1,603,629 | Using Historical Forex Data For Market Analysis | Navigating the foreign exchange (forex) markets takes skill and research, but it can be done with an... | 0 | 2024-05-23T12:32:31 | https://dev.to/jspeedster/using-historical-forex-data-for-market-analysis-216m | Navigating the foreign exchange (forex) markets takes skill and research, but it can be done with an understanding of basic [historical forex data](https://portaracqg.com/historical-intraday-futures-data/). By analyzing trends from past market activity, traders can gain valuable insight into future movements and capitalize on their predictions.
## The Basic Components of Forex
Currency pairs help you measure one currency against another, and can provide an indication of potential movement. Depending on the pairing, currencies may be positively correlated, meaning they move in sync with each other; negatively correlated, meaning they move opposite from each other; or unrelated to each other.

Example Intraday Forex Chart – [IGBPUSD](https://portaracqg.com/forex/int/igbpusd) 2022
## Understand Historical Data to Improve Trading Results
By analyzing historic data, traders can look for patterns, identify correlations and evaluate the outcome of certain behaviors. Comparing different datasets can also be helpful in uncovering new opportunities and improving trading results.
## Use Technical Analysis to Make an Informed Decision
Technical analysis is the process of using data from past prices and rates in order to make informed trading decisions. It is important to pay attention not just to the current data but also look at the longer-term trends that may be invisible when simply looking at short-term movements. Look for reliable indicators of trends such as charts, moving averages and Fibonacci retracements. This can give you better insight into price movements and allow you to anticipate future movements accurately.
## Make Use of Risk and Trade Management Tools To Mitigate Losses
One of the most important aspects of technical analysis is risk and trade management. By making use of sophisticated tools, such as stop losses and take-profit orders, you can reduce your exposure to justifiable levels of risk while also taking advantage of trading opportunities. Properly managed, these tools can help you ensure that your trades result in profits rather than losses.
## Where To Find Historical Forex Data
[Historical forex data](https://portaracqg.com/historical-intraday-futures-data/) can be purchased from PortaraCQG. Portara provides daily, intraday and tick forex data to quants, traders, CTA’s, portfolio managers and hedge funds. | jspeedster | |
1,862,835 | Understanding E-commerce API: Developing an Application for Live Price Tracking | An Application Programming Interface (API) is a way for computers to communicate with each other. It... | 0 | 2024-05-23T12:32:09 | https://dev.to/serpdogapi/understanding-e-commerce-api-developing-an-application-for-live-price-tracking-a9o | beginners, programming, tutorial, productivity | An Application Programming Interface (API) is a way for computers to communicate with each other. It helps businesses maintain coordination between their system software to increase overall efficiency and productivity.
APIs play a significant role in the e-commerce industry by providing online retailers with crucial information about their competitors’ pricing and product strategy, allowing them to adjust their marketing strategy in real time.

In this article, we will explore what an e-commerce API is and how we can develop a real-time price-tracking application to maintain a competitive stature in the market.
## What is E-commerce API?
In retrieving product information, an [e-commerce data API](https://ecommerceapi.io/) can be defined as a set of rules and protocols that extract product information, including pricing, descriptions, features, and other relevant information, from e-commerce platforms.
E-commerce APIs are crucial for online retailers and businesses because they help streamline marketing and business operations, optimizing logistics to align supply with current market demand.
## The Need For Live Price Tracking
The Price Tracking service is the need of the current hour for online retailers and businesses. It enables you to collect key pricing changes and optimize your pricing accordingly. Analyzing trends in pricing fluctuations resulting from holidays, special offers, or other dynamic changes can help forecast how pricing metrics will evolve.
Price Tracking also has the powerful capability to check if competitors are out of stock on any items, and if so, it can track the duration for which these items have been unavailable. This information can be used to adjust product prices strategically, maximizing profits and achieving a significant competitive advantage in terms of sales and margins.
Additionally, thanks to real-time price tracking, customers can secure the best deals and receive alerts about significant price drops on big-ticket items. Even a small percentage decrease in these products can lead to substantial savings. Customers can also capitalize on trend forecasting by utilizing historical price charts offered by price tracking tools.s
## Features of Price Tracking Apps
Live Price Tracking Apps come with a variety of features designed to enhance the overall shopping experience for the customers:
**Real-time Alerts:** This feature offers significant advantages for both retailers and customers! Live tracking apps can send immediate notifications about price drops, ensuring consumers secure the best-saving deals. Even a slight change in pricing can potentially drive customers away, and without utilizing software, it’s challenging to make dynamic changes. This is where price tracking becomes essential for retailers, alerting them to every price drop and enabling live adjustments to be made.
**Historical Price Data:** The E-commerce industry is experiencing significant shifts in product pricing, leading to noticeable differences within short timeframes. By tracking historical price data for various products, retailers can analyze pricing trends and better understand consumer behavior. This insight enables them to optimize pricing strategies effectively and stay competitive in the market.
**Price Comparison:** Price comparison is one of the main uses of live price tracking apps. It allows retailers and consumers to look for the same product across different retailers. This helps retailers find out which online businesses are selling the same product with lower pricing while for customers, it allows them to find the lowest possible pricing.
**Market Dynamics:** Historical pricing data provided by price-tracking apps assists retailers in identifying patterns of pricing changes over time. These fluctuations often result from shifts in demand caused by supply chain disruptions, seasonal variations, and competitor actions. Analyzing these historical graphs helps in predicting potential future trends, enabling retailers to adjust pricing strategies accordingly.
## Steps to build a Live Price Tracking APP
Building a live price-tracking app involves several steps before deployment. Here’s a step-by-step guide to help you get started:
### Goals and Requirements
Thorough market research is essential when determining the types of products or services that the app will track. This includes researching competitor applications to identify the features they offer and analyzing customer reviews to gain a better understanding of customer expectations. Additionally, identifying the target audience that will use the app is crucial, as it will influence the app’s design to meet their specific requirements.
### APIs Selection
Now that you have analyzed and listed out the features necessary for your application, select the APIs that will provide you with live data from E-commerce Platforms consistently without any downtime. There are both official APIs and third-party APIs available; however, the official APIs of Amazon, Walmart, and eBay are much more expensive to use than third-party APIs, and they also don’t offer any customization or flexibility with the data.
###Designing the UI
After selecting the APIs, begin designing a user-friendly UI that will enable users to view beautiful historical charts, add products to a tracking list, receive notifications when there is a price drop, and easily navigate through different pages using well-organized sidebars or footer menus, as well as other relevant designs.
### Integrate APIs and Prototype Testing
Integrate the selected APIs in your application and fetch the real-time data, parse it at the backend transfer it to the front end, and show it to the user. Similarly, using the fetched data test the application functionality includes price drop notifications, pricing charts, and real-time price changes.
### Deployment
After completing testing, ensure that your application is bug-free and does not cause any disruptions to the user experience. Finally, deploy your application on platforms such as the Google Play Store and Apple App Store to reach your target audience and gather their feedback to further enhance the app.
## Conclusion
In summary, live price tracking using e-commerce APIs helps retailers and digital businesses gain a more precise understanding of market dynamics. This not only benefits retailers but also customers, who can secure the lowest possible price for their desired products. Such tools have become essential for businesses to sustain growth in a competitive environment. | serpdogapi |
1,862,833 | Invite Little Planet Preschool franchise in India — Zero Cost | To invite Little Planet Preschool franchise in India with a zero-cost initiative, follow these steps... | 0 | 2024-05-23T12:30:55 | https://dev.to/little_planetpreschool_/invite-little-planet-preschool-franchise-in-india-zero-cost-20mo | webdev, javascript, programming, beginners | To invite Little Planet Preschool franchise in India with a zero-cost initiative, follow these steps to effectively communicate and attract potential franchisees:
Step-by-Step Guide
Understand the Franchise Model:
Research and understand the Little Planet Preschool franchise model, including the benefits, requirements, and support provided by the franchisor.
Identify the key selling points that would attract potential franchisees, such as brand reputation, proven business model, comprehensive training, and ongoing support.
Develop a Franchise Proposal:
Create a detailed franchise proposal highlighting the zero-cost initiative. Explain how this model works, what costs are covered, and what expectations are from the franchisee.
Include information about the brand, the preschool industry in India, success stories, and testimonials from existing franchisees.
Target Audience Identification:
Identify your target audience for the franchise invitation. This could include entrepreneurs, educators, investors, and individuals passionate about early childhood education.
Digital Marketing Campaign:
Launch a digital marketing campaign to reach your target audience. Use social media platforms, email marketing, and online advertising to promote the zero-cost franchise opportunity.
Create engaging content, such as blog posts, infographics, and videos, that highlight the benefits and success of the Little Planet Preschool franchise.
Dedicated Franchise Website or Landing Page:
Develop a dedicated website or landing page for the franchise opportunity. Ensure it contains detailed information about the franchise, the zero-cost initiative, FAQs, and a contact form for interested parties.
Optimize the website for search engines (SEO) to attract organic traffic.
Webinars and Online Information Sessions:
Host webinars and online information sessions to explain the zero-cost franchise model and answer potential franchisees’ questions. This interactive approach can build trust and provide clarity on the opportunity.
Networking and Partnerships:
Network with business associations, educational forums, and industry conferences to promote the franchise opportunity. Build partnerships with relevant organizations to reach a wider audience.
Press Releases and Media Coverage:
Distribute press releases to relevant media outlets announcing the zero-cost franchise initiative. Aim for media coverage in business magazines, newspapers, and educational publications.
Direct Outreach:
Use direct outreach methods such as phone calls, emails, and personal meetings to engage with potential franchisees. Tailor your communication to address their specific interests and concerns.
Support and Training Details:
Clearly outline the support and training provided to franchisees, emphasizing how the franchisor will assist them in setting up and running the preschool successfully.
Incentives and Special Offers:
Consider offering additional incentives or special offers to early adopters of the zero-cost franchise model. This could include marketing support, additional training, or initial operational assistance.
Continuous Follow-Up:
Follow up with interested parties regularly to address their queries, provide additional information, and guide them through the application process.
Sample Invitation Email Template
Subject: Unlock a Zero-Cost Franchise Opportunity with Little Planet Preschool!
Dear [Recipient’s Name],
I hope this email finds you well. We are thrilled to introduce an exclusive zero-cost franchise opportunity with Little Planet Preschool, a leading name in early childhood education.
As an esteemed potential partner, we believe you have the passion and drive to make a significant impact in the world of preschool education. Our zero-cost franchise initiative is designed to empower entrepreneurs and educators like you to establish a successful preschool without the burden of initial franchise fees.
Why Choose Little Planet Preschool?
Renowned Brand with Proven Success
Comprehensive Training and Ongoing Support
Zero-Cost Franchise Model with Minimal Initial Investment
Extensive Marketing and Operational Assistance
Opportunity to Make a Positive Impact on Young Minds
Join us for an informative webinar on [Date] at [Time] to learn more about this exciting opportunity. Register now at [Webinar Registration Link].
For more details, visit our dedicated franchise page: [Franchise Landing Page Link].
Feel free to reach out to us at [Your Contact Information] for any questions or to schedule a personal discussion.
We look forward to embarking on this rewarding journey with you!
Warm regards,
[Your Name]
[Your Position]
Little Planet Preschool
[Contact Information]
[[https://www.littleplanetpreschool.com/](https://www.littleplanetpreschool.com/)]
By following these steps and using the template as a starting point, you can effectively invite and attract potential franchisees for Little Planet Preschool under the zero-cost initiative in India.
Email:- rgcpcollege@gmail.com
Head Office
A1/11, Prashant Vihar Rohini,
Near Pitampura Metro Station, Opposite Power House
New Delhi, India-110085 | little_planetpreschool_ |
1,862,832 | Automate your tasks and schedule cronjobs with a script | Have you ever wondered how computers can do tasks all by themselves without anyone touching them?... | 0 | 2024-05-23T12:30:39 | https://dev.to/florenceokoli/automate-your-tasks-and-schedule-cronjobs-with-a-script-2de5 | bash, devops, cloudcomputing, cronjob | Have you ever wondered how computers can do tasks all by themselves without anyone touching them? It's like magic, but there's a special way to tell the computer what to do, step by step. This is called scripting.
This article will explore the basics of Bash scripting, provide practical examples, and guide you through creating your scripts.
Let's dive in!
## Introduction
**What is Bash Scripting?**
Bash scripting is a powerful tool for automating tasks on Unix-like operating systems, such as Linux and macOS.
Bash, short for the "Bourne Again Shell," is a powerful scripting language that enables users to automate repetitive tasks, streamline complex workflows, and efficiently manage system operations instead of doing them manually.
Overall, bash scripting is an essential skill for system administrators, developers, and anyone looking to optimize their computing tasks.
In Bash scripting, the Shebang `#!/bin/bash`, serves as the interpreter used to execute tasks on any script. In other words, it tells the system to use the specified interpreter to run the script.
## Prerequisite
* Vagrant virtual machine
* Good understanding of Linux commands
## Basics to Know Before Writing a Bash Script
Before diving into writing Bash scripts, it's essential to understand some fundamental concepts and components of Bash scripting. Here are the basics you need to know:
* Familiarize yourself with basic Unix commands like `mkdir`, `touch`, and `echo`.
* Understand file permissions and how to change them using `chmod`. For example, to make your script executable, use `chmod +x`. The X stands for execution
* Use a text editor like Nano or Vim to write and edit scripts.
For Nano - `nano myscript.sh` For Vim - `vi myscript.sh`
* Add comments in your scripts using `#` symbol. They help explain what the script does and are ignored during execution.
`# This is a comment`
* Always start your script with a Shebang. It specifies the interpreter to be used.
* Lastly, for every script, you must make sure to follow the syntax which includes the spacing, indentation, and punctuation.
Let's begin
## Practical Examples of Bash Scripting
Let's start by creating a new directory that will house all our scripts. Once the directory is created, `cd` into the folder and create a file with the `.sh` extension. The `.sh` tells you that the file is a script.
```
mkdir bashscript
cd bashscript
touch myscript.sh
```
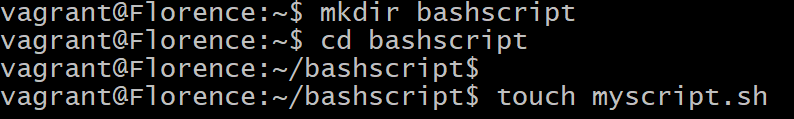
Let's make our newly created scripts executable. This will enable us to run our script
```
chmod +x myscript.sh
```
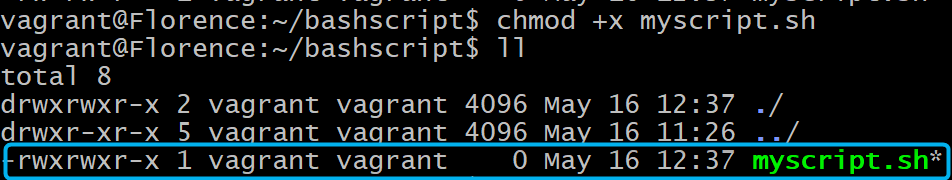
The `ll` command shows the permissions for the myscript.sh file
Next, let's play around with automation.
To do this, let's write a script that updates and upgrades our system.
This command `vi myscript.sh` opens the file named `script.sh` in the `vi` text editor.
When the file is opened in the Vim text editor, write the following codes below:
```
#!/bin/bash
sudo apt update -y
sudo apt upgrade -y
```
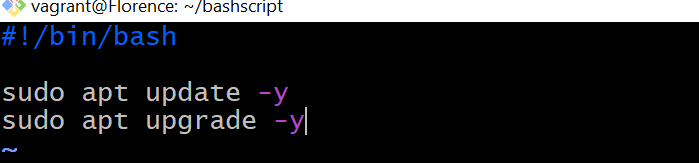
Close your text editor and run this command - `./myscript.sh`
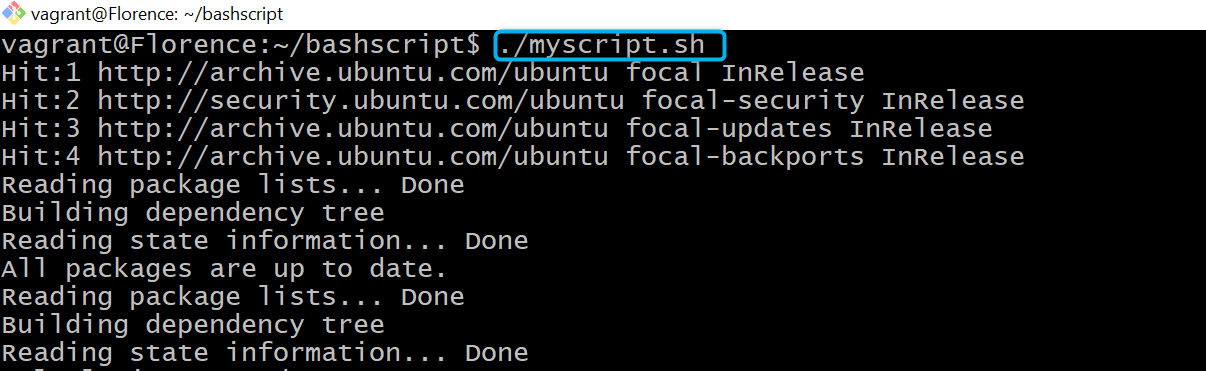
Now that we have seen what automation looks like using a bash script, let's get more practical.
## Statements in Bash Scripting
i. Printing statements using the `echo` command.
The echo command in Bash scripting is used to print output to the terminal. Let's try it out.
> First, create a script. I called my script `myscript.sh`. Then use the Vim text editor to open it `vi myscript.sh` Remember to start your script with the Shebang `#!/bin/bash` interpreter followed by the `echo` command and your text in quotes. Then close the editor.
```
#!/bin/bash
echo "Florence is a Cloud Engineer who loves bash Scripting"
```
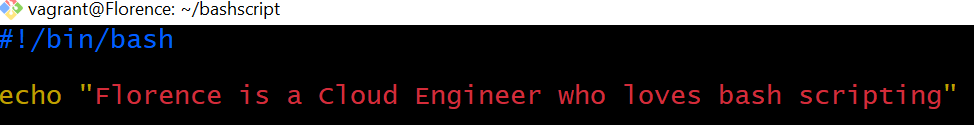
Run your script using the `./<name of your script>` The output will look like the image below
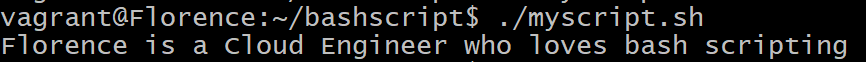
ii. Declaring variables.
Variables in bash scripting are used to store data and can be referenced in your script to perform operations. Here is how to declare a variable:
```
#!/bin/bash
name="Florence"
job="Cloud Engineer"
```

> There should be no spaces around the equals sign. The value can be a number, a string, or the result of a command.
> To read or use the value stored in a variable, you prepend the variable name with a dollar sign `$`. For example:
```
#!/bin/bash
echo "My name is $name and I'm a $job"
```
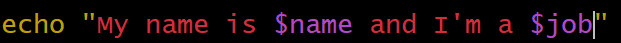
When this script is run using the `./myscript.sh` this is what it will look like
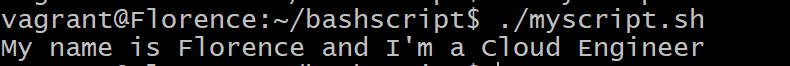
iii. If Statements
The If statement allows your script to make decisions and perform different actions depending on whether a condition is true or false. In the example below, we are going to run a script that checks whether a given number is an even or odd number.
```
read -p "Enter a number: " number
if (( $number % 2 == 0 )); then
echo "$number is an even number"
else
echo "$number is an even number"
fi
```
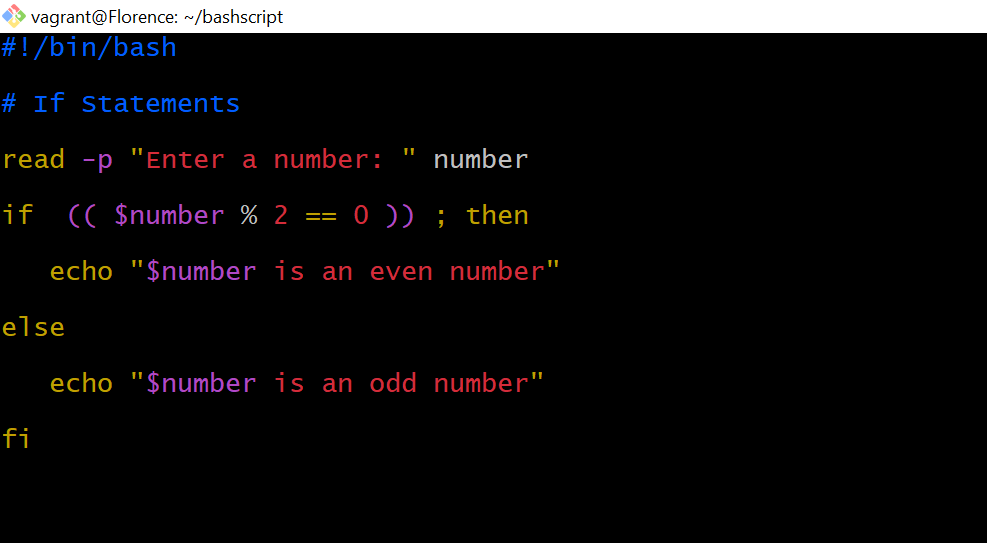
A breakdown of the script:
> `read -p "Enter a number: " number`: Prompts the user to enter a number and stores it in the number variable.
> `if (( number % 2 == 0 )); then`: Checks if the number is even.
> `echo "The number $number is even."`: Prints that the number is even if the condition is true.
> `else`: Executes the following code if the number is not even.
> `echo "The number $number is odd."`: Prints that the number is odd.
> `fi`: Ends the if statement.
When the above script is run, here is what the result will look like
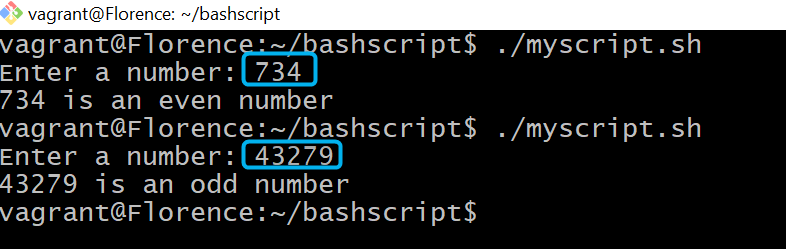
iv. While Loop
In Bash scripting, the `while` loop allows you to repeatedly execute a block of code as long as a specified condition remains true. Once the condition becomes false, the loop stops executing. This is similar to a washing machine cycle: it keeps running until the timer reaches zero.
Let's write a script that checks if a particular directory exists or not. In this case, we are checking if the `~bash/loopdir` exists in our system
```
#!/bin/bash
while [ -d ~bash/loopdir ]; do
echo "Directory exists"
done
echo"Directory does not exist"
```
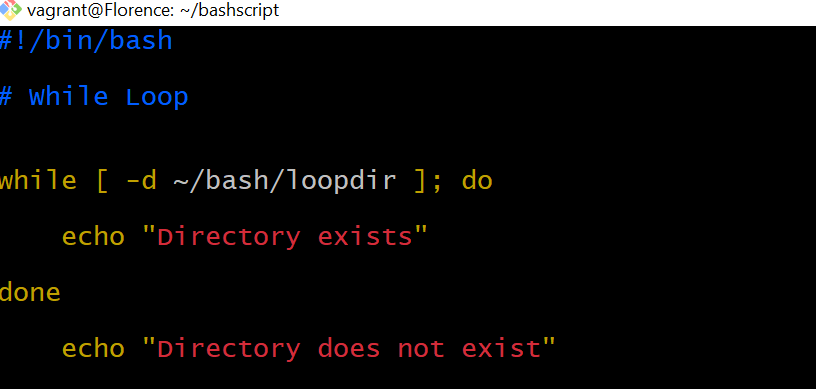
A breakdown of the script:
> `while [ -d ~/bash/loopdir ]; do`: Starts a while loop that checks if the directory ~/bash/loopdir exists.
> `echo "Directory exists"`: If the directory exists, prints "Directory exists".
> `done`: Ends the while loop when the directory no longer exists.
> `echo "Directory not found"`: After exiting the loop, prints "Directory not found" when the directory is no longer present.
Now, that you have gotten to this point, let's do something interesting. Let's create a script that monitors the uptime of a server and logs it periodically. In this script, we are also going to incorporate a cronjob that will record the server's uptime at specified intervals.
Before we start, let me explain what a cronjob does and why it is needed.
>A cron job is just like that magical clock for your computer! It helps your computer remember to do certain tasks automatically, without you having to tell it every time.
> Let me be more technical now.
> A cron job is a time-based job scheduler in Unix-like operating systems, including Linux. It allows users to schedule commands or scripts to run periodically at fixed times, dates, or intervals. These scheduled tasks are referred to as cron jobs, and they can automate repetitive tasks, such as backups, system maintenance, uptime monitoring, log rotation, etc.
Now, let's create that script!
With this command `sudo vi log_uptime.sh` I will create a script for this particular task and make it executable using `sudo chmod +x log_uptime.sh`
Let's write the script.
```
#!/bin/bash
# Define the log file
LOG_FILE="$HOME/uptime_log.txt"
# Create the log file if it doesn't exist
if [ ! -f "$LOG_FILE" ]; then
touch "$LOG_FILE"
echo "Log file created at $LOG_FILE"
fi
# Get the current date and uptime
CURRENT_DATE=$(date '+%Y-%m-%d %H:%M:%S')
UPTIME=$(uptime -p)
# Append the uptime to the log file
echo "$CURRENT_DATE - Uptime: $UPTIME" >> "$LOG_FILE"
echo "Uptime logged at $CURRENT_DATE"
# Define the cron job command
CRON_JOB="0 * * * * $HOME/log_uptime.sh"
# List existing cron jobs
echo "Current Cron Jobs:"
crontab -l
# Add the cron job
echo "Adding new cron job:"
echo "$CRON_JOB" | crontab -
# Confirmation of added cron job
echo "New cron job added:"
crontab -l
```
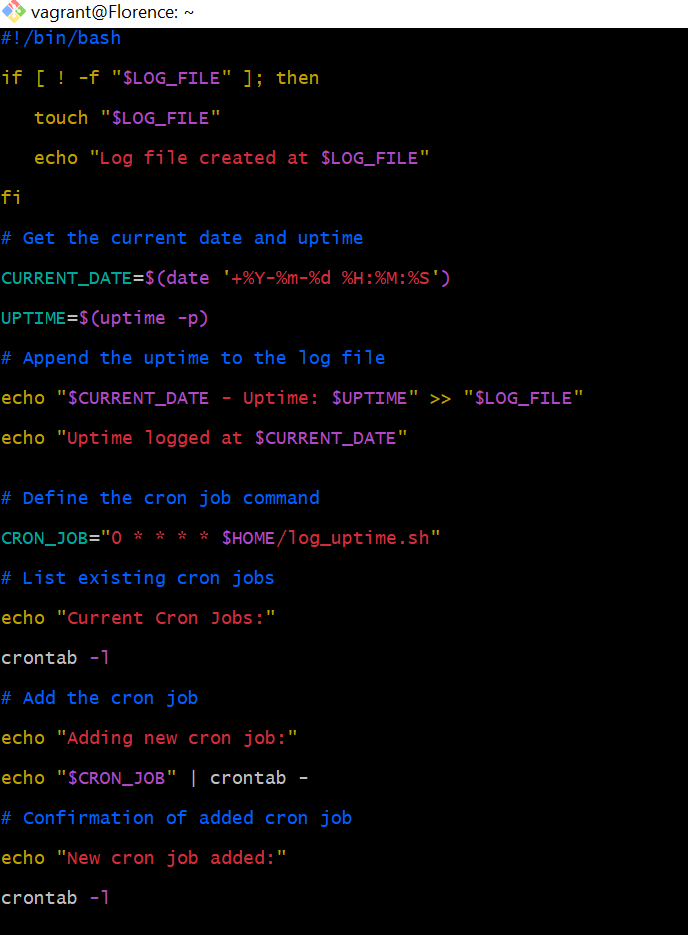
When this script is run using the `./log_uptime.sh` command, here is what the output will be
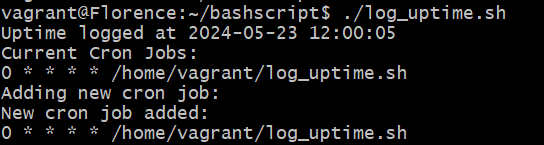
## Conclusion
Scripting in Bash is like giving instructions to your computer to do tasks automatically. This article introduced the basics of Bash scripting, providing practical examples by creating readable scripts. With Bash scripting, you can automate repetitive tasks and manage system operations efficiently.
Your feedback is very important to me. Were the explanations clear? Did the examples make sense? Let me know if there's anything specific you'd like me to cover in more detail. I'm here to ensure I meet your needs.
Thank you for reading!
| florenceokoli |
1,862,831 | Numi Beauty - Olaplex | U svetu nege kose, gde su oštećenja od farbanja i hemijskih tretmana česta pojava, Olaplex se ističe... | 0 | 2024-05-23T12:30:21 | https://dev.to/numi/numi-beauty-olaplex-5ci6 | olaplex, hair | U svetu nege kose, gde su oštećenja od farbanja i hemijskih tretmana česta pojava, _**[Olaplex](https://numi.rs/brendovi/olaplex/)**_ se ističe kao svetionik nade za one koji žele da poprave i osveže svoje pramenove. Ovaj brend je postao poznat po svojim inovativnim formulama i transformišućim rezultatima, te je stekao vernu publiku među pojedincima koji žele da povrate snagu, integritet i vitalnost svoje kose.
U srcu uspeha Olaplex-a leži patentirani sastojak, Bis-aminopropil diglikol dimaleat, revolucionarni molekul koji efikasno popravlja slomljene disulfidne veze unutar strukture kose. Ova jedinstvena formulacija izdvaja Olaplex od drugih brendova, nudeći rešenje za jednu od najčešćih briga pojedinaca sa hemijski tretiranom ili oštećenom kosom.
### Ponuda Proizvoda Olaplex-a: Prilagođena Rešenja za Sve Potrebe Kose
- **Olaplex No. 3 Hair Perfector Repairing Treatment:** Najprodavaniji i neizostavan proizvod u svakoj rutini nege kose, ovaj tretman jača i popravlja kosu kada se koristi pre pranja ili kao nedeljna maska.
- **Šamponi Olaplex-a:** Od univerzalnog No. 4 Bond Maintenance šampona do specijalizovanih opcija poput No. 4C za dubinsko čišćenje i No. 4P za naglašavanje plavih tonova, Olaplex nudi širok spektar šampona koji odgovaraju različitim potrebama kose.
- **Regeneratori Olaplex-a:** Hidrirajte, nahranite i smanjite oštećenja sa opcijama poput No. 5 Bond Maintenance regeneratora i No. 5-P Blonde Enhancer tonirajućeg ljubičastog regeneratora.
- **Stilizujući Proizvodi Olaplex-a:** Zaštita i stilizovanje uz proizvode poput No. 6 Bond Smoother, leave-in tretmana koji eliminiše naelektrisanost, i No. 7 Bonding Oil, lagano ulje koje dodaje sjaj i upravljivost.
- **Intenzivni Tretmani:** Dubinski hidrirajte i popravite kosu uz opcije poput No. 8 Bond Intense Moisture maske i No. 9 Bond Protector hranljivog seruma za kosu, nudeći antioksidativnu zaštitu i zaštitu od toplote za opšte zdravlje kose.
Borite li se sa posledicama čestih tretmana bojenja ili jednostavno želite da održite zdravlje i integritet kose, Olaplex nudi sveobuhvatnu ponudu proizvoda dizajniranih da zadovolje vaše potrebe. Otkrijte transformacionu moć Olaplex-a i otključajte tajnu prelepe, zdrave kose već danas.
| numi |
1,862,829 | Lighthouse를 활용하여 LCP 점수 개선하기. | 필자의 Lighthouse Performance 점수는 이렇다. me: 🤦♂️ 개선해야 할 항목들은 다음과 같다. Lighthouse 점수가 웹 성능에 절대적인... | 0 | 2024-05-23T12:24:19 | https://dev.to/hxxtae/lighthousereul-hwalyonghayeo-lcp-jeomsu-gaeseonhagi-3o3i | webdev, javascript, vite, react | 필자의 Lighthouse Performance 점수는 이렇다.
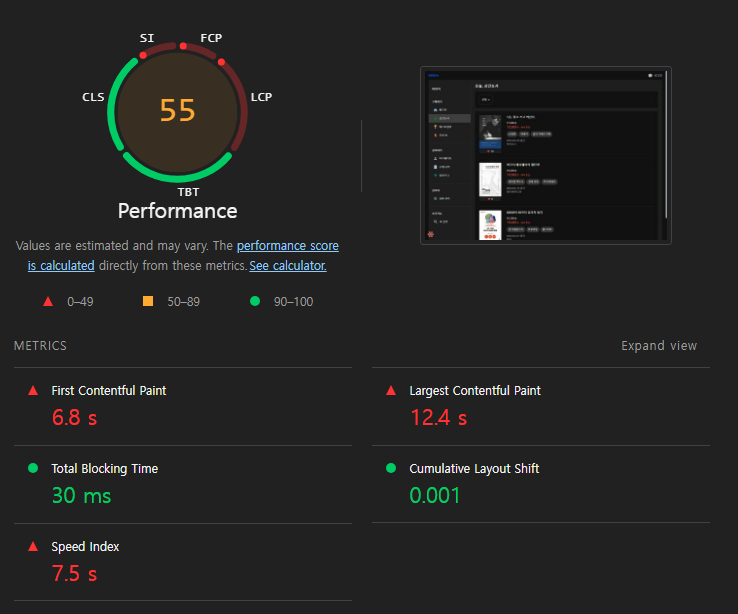
me: 🤦♂️
개선해야 할 항목들은 다음과 같다.
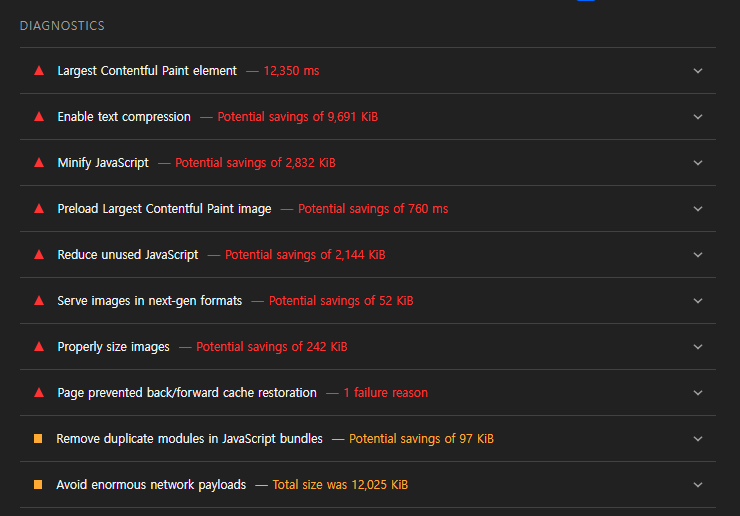
Lighthouse 점수가 웹 성능에 절대적인 성능으로 귀결되지는 않는다. 그렇지만 개발 이후 성능 최적화에 좋은 지표가 되므로 가장 중요한 `LCP` 점수를 높여 보려고 한다.
> `LCP(Largest Contentful Paint)`
> - 최대 콘텐츠 렌더링 시간 즉, 뷰포트에서 가장 큰 콘텐츠 엘리먼트가 나타날 때 측정한다.
> - 페이지의 주요 내용이 화면에 렌더링이 완료되는 시기를 결정하는데 사용된다.
## 이미지 최적화
**Largest Contentful Paint element - 12,350ms**
현재 콘텐츠에 이미지를 포함하고 있으며, 이미지는 LCP에 큰 영향을 미칠 수 있기 때문에 이미지를 최적화하고 적절한 포맷을 사용하는 것이 중요하다고 한다.
### 적절한 포맷 사용
- JPEG, PNG 대신 WebP 로 최신 포맷을 사용하여 개선 시도.
### 이미지 크기 최적화
- 불필요하게 큰 이미지를 줄이고 필요한 크기만 사용.
- 이미지 가로 크기를 1200px -> 400px 로 수정 (비율 유지)
### 지연 로드
- 화면에 보이지 않는 이미지들은 lazy-loading 하여 불필요한 렌더링이 발생하지 않도록 시도.
```html
<img src="image.webp" loading="lazy" alt="example image">
```
**결과**
- Before
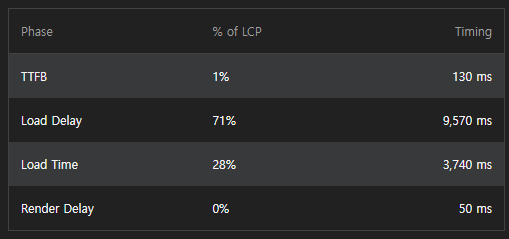
- After
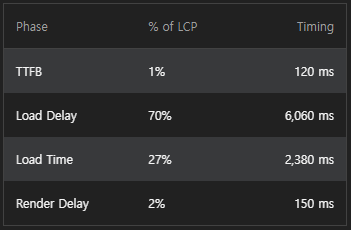
Load Delay는 `9,507ms` -> `6,060ms` 으로 약 `37%` 개선되었으며,
Load Time도 `3,740ms` -> `2,380ms` 으로 약 `37%` 개선되었다.
## 폰트 최적화
**Enable text compression - Potential savings of 9,691 KiB**
다음으로는 웹 폰트 로딩이 페이지 렌더링을 차단하지 않도록 최적화를 수행하였다.
`font-display: swap` 속성을 사용하여 폰트 로딩 중에도 텍스트가 표시되도록 하였다.
```css
@font-face {
font-family: "Noto Sans KR", sans-serif;
src: url(https://fonts.googleapis.com/css2?family=Noto+Sans+KR:wght@300..600) format("woff2");
font-display: swap;
}
```
`swap`은 웹폰트가 로드되기 전에 사용자에게 기본 시스템 폰트로 텍스트를 표시합니다. 그리고 웹폰트 로딩이 완료되면 텍스트가 웹폰트로 교체된다. 이 방식은 사용자 경험을 향상시키는 데 일반적으로 사용되는 값이라고 한다.
## JavaScript 최적화
**Minify JavaScript - Potential savings of 2,832 KiB**
JavaScript 파일이 크거나 로딩이 차단되면 LCP에 악영향을 미칠 수 있다고 한다.
그래서 찾은 개선 방법으로 코드 분할(Code Spliting)과 지연 로딩(Lazy-Loading)이 있다고 한다.
### 코드 분할 및 지연 로드
- 필자는 이미 이전에 현재 사용자가 보는 페이지에 따라 필요한 JavaScript 파일을 다운로드 받도록 하기 위해 React의 lazy함수를 통해 지연 코드 분할을 수행하였다.
```tsx
lazy(() => import('some-large-module').then(module => {
// Use the module
}));
```
### 사용하지 않는 모듈 제거
추가적으로 수행한 최적화 방법으로 사용하지 않는 JS 및 모듈 파일들을 제거하거나 최소화 하였다. 이유는 필요 없는 파일들을 다운 받는 과정에서 필수적인 다운로드가 blocking 으로 지연되면 LCP 역시 저하될 수 있기 때문이다.
무거운 라이브러리를 Spread로 import 하지 않고 필요한 모듈만 import 하여 가져와 사용하도록 수정하였다. -> [블로그 글 참고](https://dev.to/hxxtae/lighthousereul-hwalyonghan-tree-shaking-8ie)
## Vite 설정 파일 수정
이전 까지의 최적화를 수행하여도 LCP의 점수에는 큰 영향이 없었다. 그래서 ChatGPT한테 추가적인 방법을 물어보았더니 다음과 같은 방법을 제시해 주었다.
> `vite-plugin-compression`을 사용하여 Vite 설정을 통해 빌드된 파일을 미리 압축하는 방법으로 LCP를 단축 시킬 수 있다.
> 이는 빌드된 파일을 `Gzip` 및 `Brotli` 형식으로 미리 압축하여 서버가 이를 효율적으로 제공할 수 있도록 한다.
### vite-plugin-compression 설치
```bash
npm install vite-plugin-compression --save-dev
```
### Vite 설정 파일 수정 (vite.config.js)
```javascript
// vite.config.js
import compression from 'vite-plugin-compression';
export default defineConfig({
plugins: [
react(),
compression({ algorithm: 'gzip' }), // Gzip 압축 활성화
compression({ algorithm: 'brotliCompress', ext: '.br' }) // Brotli 압축 활성화
]
});
```
위 설정을 저장한 후 프로젝트를 빌드하면 Gzip 및 Brotli 형식으로 압축된다.
## 최종결과
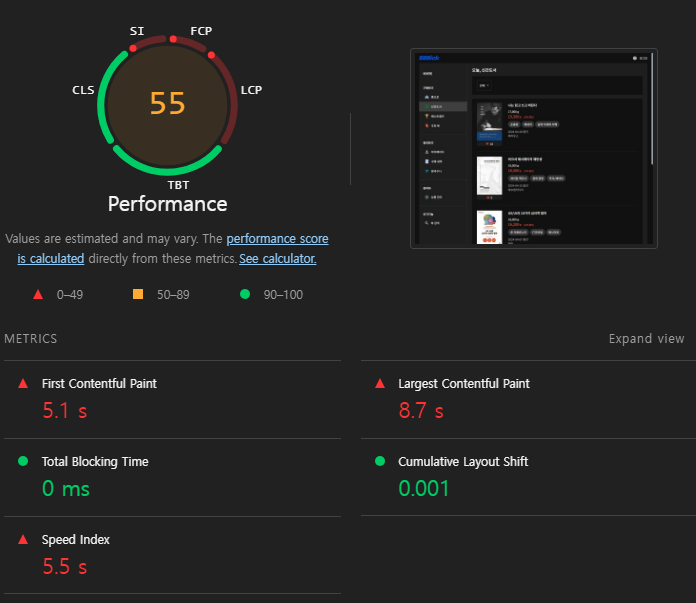
결과는 드라마틱 하지 않았지만 전반적으로 개선된 것을 확인할 수 있다.
> FCP : `6.8s` -> `5.1s`
> LCP : `12.4s` -> `8.7s`
> TBT : `30ms` -> `0ms`
> CLS : `0.001`
> SI : `7.5s` -> `5.5s`
그럼 왜 점수가 많이 오르지 않을까? 이 사실을 같은 항해99 멤버인 `원민님`에게 답을 얻을 수 있었다.
일반적으로 개발 환경에서는 디버깅을 쉽게 할 수 있도록 여러가지 추가적인 리소스를 요청하는데 이것이 Lighthouse 점수에 계산되기 때문이다.
여기에서 말하는 리소스라는 것은 개발 과정에서 발생한 오류를 추적할 수 있는 로그 같은 로직적인 부분일 수 있고, 디버깅 시 정확한 코드 위치를 판단할 수 있는 소스맵 같은 파일일 수도 있다.
그래서 프로덕션 빌드 시 이와 같은 파일들은 사용자에게 제공할 필요가 없고 성능 최적화를 위해 리소스들이 모두 빠지게 되므로 프로덕션 환경에서는 개발 환경 보다 성능 상 이점을 누릴 수 있을 것이며 Lighthouse Performance 점수 또한 높을 것이다.
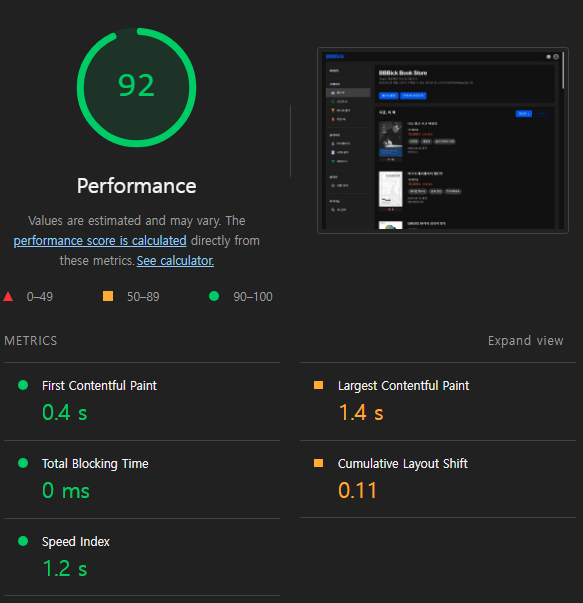
Lighthouse 점수를 개선해야 한다면, 최종 사용자 입장에서 볼 수 있는 프로덕션 환경에서 개선하는 것이 더 적절하다고 할 수 있다.
## 마무리
LCP를 개선하는 과정을 통해서 얻은 내용을 정리하면 이렇다.
- Lighthouse 실행 시점 마다 점수의 격차가 크다.
- 최적화된 이미지를 저장하고, 불러오고, 보여주는 것이 LCP에 영향이 크다.
- vite.config.js 에서 크기가 큰 모듈들을 코드 분할하여 불필요한 JS를 제거해 주는 것으로도 LCP 향상에 도움이 된다.
- Lighthouse 측정은 프로덕션 환경에서 진행하는 것을 권장한다.
- LCP는 데이터가 불러오는 속도에 영향을 많이 받기 때문에 SSR 방식도 고려하면 좋을 것 같다.
앞서 말했던 것 처럼 LCP 점수가 절대적이거나 중요한 것은 아니다. 하지만 높은 점수는 사용자에게 좋은 경험을 제공하는 것은 분명하다.
그리고 LCP 시간은 2.5s 이하면 좋다고 한다. 앞으로 최적화를 진행할 때 기준을 두고 진행하면 좋을 것 같다.
긴 글 읽어주셔서 감사합니다.
---
[참고한 글]
[Lighthouse를 기반으로 LCP 성능 개선하기](https://velog.io/@aborrencce/Lighthouse%EB%A5%BC-%EA%B8%B0%EB%B0%98%EC%9C%BC%EB%A1%9C-LCP-%EC%84%B1%EB%8A%A5-%EA%B0%9C%EC%84%A0%ED%95%98%EA%B8%B0)
[Light House에서 LCP 측정항목 개선해서 성능점수 올리기](https://velog.io/@my_suwan/%EB%82%B4%EA%B0%80-%ED%94%84%EB%A1%9C%EC%A0%9D%ED%8A%B8%EC%97%90%EC%84%9C-%EC%B5%9C%EC%A0%81%ED%99%94%EB%A5%BC-%EC%A7%84%ED%96%89%ED%96%88%EB%8D%98-%EB%B0%A9%EB%B2%95%EB%93%A4-With-React)
[라이트하우스와 함께한 성능 개선 고군분투기](https://velog.io/@edie_ko/lighthouse-performance#4-image-lazy-loading)
[내가 프로젝트에서 최적화를 진행했던 방법들 (With React+Vite)](https://velog.io/@my_suwan/%EB%82%B4%EA%B0%80-%ED%94%84%EB%A1%9C%EC%A0%9D%ED%8A%B8%EC%97%90%EC%84%9C-%EC%B5%9C%EC%A0%81%ED%99%94%EB%A5%BC-%EC%A7%84%ED%96%89%ED%96%88%EB%8D%98-%EB%B0%A9%EB%B2%95%EB%93%A4-With-React) | hxxtae |
1,862,828 | 9Vnd - Link Đăng Ký 9Vnd Chính Thức - Tặng 88k | 9VND đã thành công thu hút sự chú ý và trở thành sân chơi cá cược trực tuyến số 1 Việt Nam. Đến với... | 0 | 2024-05-23T12:21:29 | https://dev.to/9vndcouk/9vnd-link-dang-ky-9vnd-chinh-thuc-tang-88k-4p6m | 9VND đã thành công thu hút sự chú ý và trở thành sân chơi cá cược trực tuyến số 1 Việt Nam. Đến với nhà cái, anh em có cơ hội trải nghiệm kho game siêu khổng lồ
Địa Chỉ: 68/61 Đ. Phùng Văn Cung, Phường 7, Phú Nhuận, Thành phố Hồ Chí Minh, Việt Nam
Email: proptiverlechris@gmail.com
Website: https://9vnd.co.uk/
Điện Thoại: (+84) 929 308 0230
#9vnd #9vndcouk #nhacai9vnd #9vndcasino #9vndcacuoc
Social Links:
https://9vnd.co.uk/
https://9vnd.co.uk/nap-tien-9vnd/
https://9vnd.co.uk/rut-tien-9vnd/
https://9vnd.co.uk/tai-app-9vnd/
https://9vnd.co.uk/dang-ky-9vnd/
https://9vnd.co.uk/gioi-thieu-9vnd/
https://9vnd.co.uk/lien-he-9vnd/
https://www.facebook.com/9vndcouk
https://www.youtube.com/channel/UC1gCFsG2Zf1X6dM-Saq3XOQ
https://www.pinterest.com/9vndcouk/
https://www.tumblr.com/9vndcouk
https://vimeo.com/9vndcouk
https://www.twitch.tv/9vndcouk/about
https://www.reddit.com/user/9vndcouk/
https://500px.com/p/9vndcouk?view=photos
https://gravatar.com/9vndcouk
https://www.blogger.com/profile/05828874260119469905
https://9vndcouk.blogspot.com/
https://draft.blogger.com/profile/05828874260119469905
https://twitter.com/9vndcouk
https://www.instapaper.com/p/9vndcouk
https://hub.docker.com/u/9vndcouk
https://www.mixcloud.com/9vndcouk/
https://flipboard.com/@9vndcouk/9vndcouk-khmp0otly
https://issuu.com/9vndcouk
https://www.liveinternet.ru/users/9vndcouk/profile
https://beermapping.com/account/9vndcouk
https://qiita.com/9vndcouk
https://www.reverbnation.com/artist/9vndcouk
https://guides.co/g/9vndcouk/373508
https://os.mbed.com/users/9vndcouk/
https://myanimelist.net/profile/9vndcouk
https://www.metooo.io/u/9vndcouk
https://www.fitday.com/fitness/forums/members/9vndcouk.html
https://www.iniuria.us/forum/member.php?432186-9vndcouk
https://www.veoh.com/users/9vndcouk
https://gifyu.com/9vndcouk
https://www.dermandar.com/user/9vndcouk/
https://pantip.com/profile/8106376#topics
https://hypothes.is/users/9vndcouk
http://molbiol.ru/forums/index.php?showuser=1344606
https://leetcode.com/9vndcouk/
https://www.walkscore.com/people/118799450500/9vndcouk
http://www.fanart-central.net/user/9vndcouk/profile
https://www.chordie.com/forum/profile.php?id=1937837
http://hawkee.com/profile/6702825/
https://codepen.io/9vndcouk/pen/KKYJLJK
https://jsfiddle.net/9vndcouk/rxchbwvp/
https://forum.acronis.com/user/641920
https://www.funddreamer.com/users/9vndcouk
https://www.renderosity.com/users/id:1486187
https://www.storeboard.com/9vndcouk
https://doodleordie.com/profile/vndcouk
https://mstdn.jp/@9vndcouk
https://community.windy.com/user/9vndcouk
https://connect.gt/user/9vndcouk
https://miarroba.com/9vndcouk
https://teletype.in/@9vndcouk
https://rentry.co/3b73recv
https://talktoislam.com/confirm?c=etzylccc&u=9vndcouk
https://www.credly.com/users/9vndcouk/badges
https://www.roleplaygateway.com/member/9vndcouk/
https://masto.nu/@9vndcouk
https://www.ohay.tv/profile/9vndcouk
https://www.mapleprimes.com/users/9vndcouk
http://www.rohitab.com/discuss/user/2169986-9vndcouk/ | 9vndcouk | |
1,851,301 | I got the need for speed... | Databases Databases, with no doubts are considered a critical part of an application. Data... | 0 | 2024-05-23T12:20:48 | https://dev.to/st1llwater/i-got-the-need-for-speed-143i | database, speed, cache | ## <u>Databases</u>
Databases, with no doubts are considered a critical part of an application. Data I/O speeds can be considered a direct factor deciding app's performance and hence the user experience.
I'd not say we need an external caching implementation on any system until it is on a considerable scale with visible performance degradation because databases themselves have tricks up their for speeding their I/O.. Didnt knew that? Damn! read this:
-> Frequently accessed data pages are cached in memory to reduce disk I/O and improve query performance.
-> Even recurrent query plans are cached by database to reduce overheads of repeated query planning!
Indeed databases are one interesting topics to look into.
Anyways getting back to what we shall discuss here, The following article will probable tell you something or two about the caching patterns followed in three-tier web architecture systems (client, server, database) or even similar systems.
## <u>What is database caching?</u>
By its simplest definition, a technique to store frequently used data in a temporary memory.
A good caching strategy will ease the load on your database by routing the frequently used queries to read from cache before hitting our database.
A cache layer can exist at
-> Database layer (Internal)
-> Application layer (External)
-> A separate service layer (External)
So why cache? Coz we want things _faster, faster, faster_
#### Performance
Since it stores frequently accessed data separately, reduces the latency in data lookup and even the amount of work to be done by database
#### Availability
Not calling it as a backup plan but don't you think in case our database fails, we would have our cache with our data to not cause 100% downtime?
#### Scalability
I think if you understood the above points, you can perfectly imagine how caching can improve scalability of your application! Reduces workload on database, faster query responses blah blah.. yeah you got it right!
Let's move to the design patterns of caching!
## <u>The Caching Strategies</u> <br/>
### Cache-aside
Checks cache first for incoming query, if cache hit (found) responds with it else queries database -> responds -> updates caches.
A good general purpose caching strategy works for most cases.
Disadvantages? Yeah a window of inconsistency of data between db and cache.
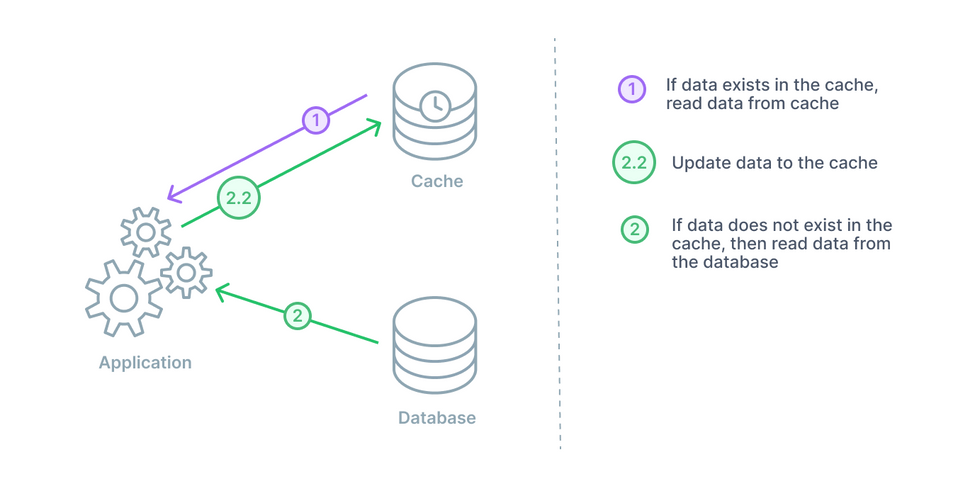
<br/>
<br/>
### Read-through
Sits between application and database, difference? application always reads from cache, in case of cache miss, data is populated to cache and then returned to client. The writes are always performed on database btw.
Disadvantages? Time delay of filling the cache first in case of miss and then returning the data.
Quick solution? Devs warm up the cache i.e refresh cache time to time with most in demand data, ik not the best solution out there but saves the day!
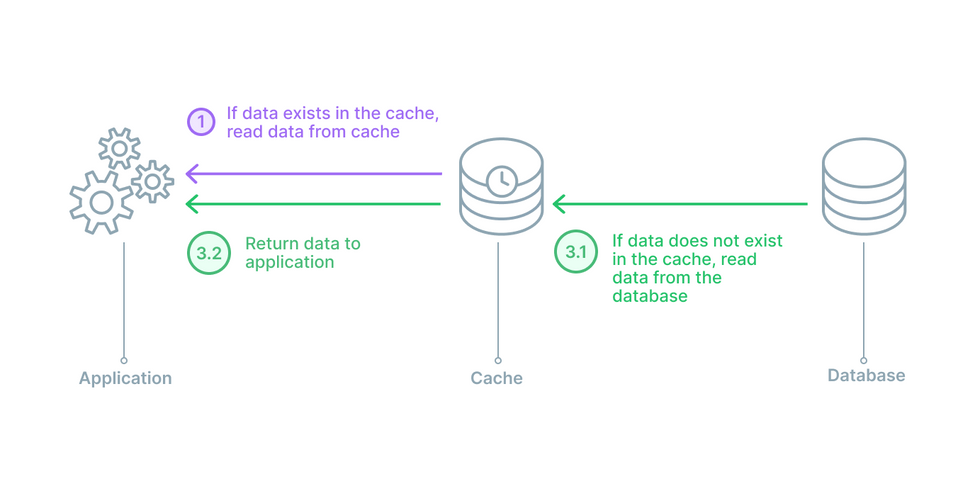
<br/>
<br/>
### Write-through
Sites between client and database same as usual.. then the difference? maybe you can guess... yep data is first written to cache which immediately writes to database.
Benefit? New data is always available to cache.
Disadvantages can be the write latencies.
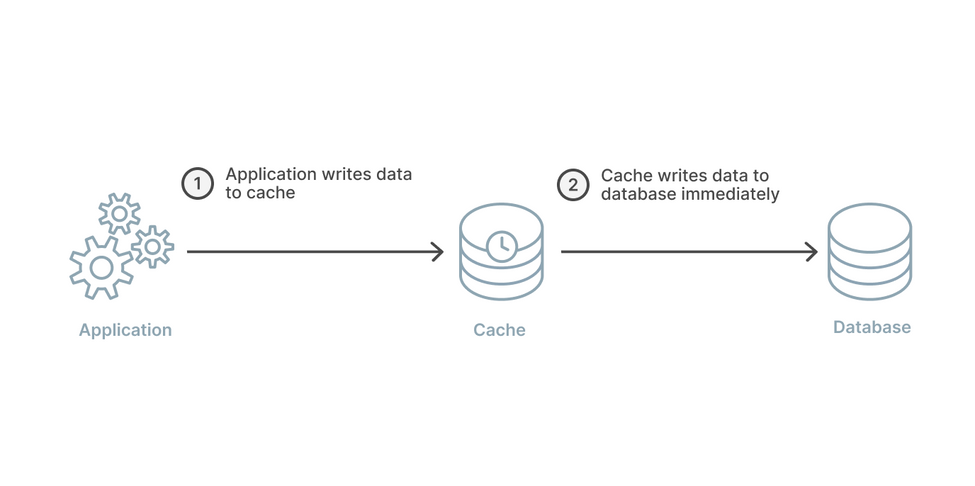
<br/>
<br/>
### Write-back
Exactly same as write-through but but but... data is not immediately written back to db but is done at a delay.
This reduces the pressure and the load on the cache in a write-heavy workload.
It improves overall performance too if the delayed writes are batched up together (database will be happy too).
P.S. If cache fails in wrong window, you might lose your new written data which was not yet written to db.
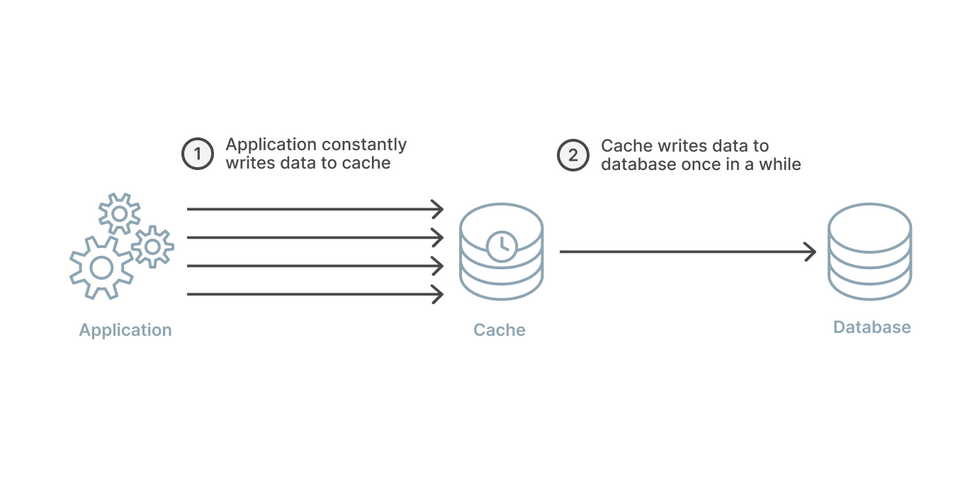
<br/>
<br/>
### Write-around
Usually coupled with cache-aside or read-through, one of the flows can be:
- Data read through cache.
- If miss, its read from database.
- Cache is also updated for next time.
- Best when there is less write workloads.
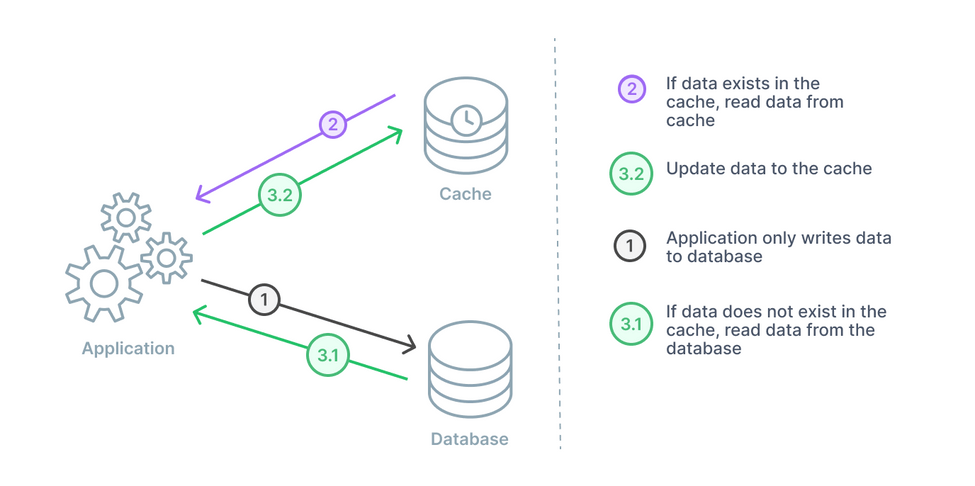
## Conclusion
We discussed various strategies for database caching which might one day
help you scale your application to new horizons!! (Well umm maybe not horizons but to better limits). Even if you're not implementing cache now, I'd say its better to know your cards well so you can play it right when time comes.
Thanks for your time, hope you learnt something new.
| st1llwater |
1,862,799 | Managing Software Development Teams: 8 Tips for Success | Managing a software development team can feel like herding cats, but with the right strategies, it... | 0 | 2024-05-23T12:18:47 | https://dev.to/garbanea/managing-software-development-teams-8-tips-for-success-255k | team, management, softwaredevelopment, softwareengineering | Managing a software development team can feel like herding cats, but with the right strategies, it can be a rewarding and incredibly productive experience. Whether you’re a seasoned manager or new to the role, these tips will help you foster a positive and efficient team environment.

Below I have gathered 8 tips that are sure to help you in the efforts to put your team on top.
## 1. Foster Clear Communication
While this may seem obvious, communication is the backbone of any successful team. Ensure that every team member understands their role, responsibilities, and the project’s goals. Utilize tools like Slack, Microsoft Teams, or Teamhood to keep everyone on the same page. Daily stand-ups, regular check-ins, and open-door policies can also encourage continuous dialogue.
"Effective communication is the foundation of any successful project. Clear expectations and regular updates can prevent many issues down the road." – [Alex Johnson, Senior Project Manager](https://www.linkedin.com/search/results/content/?keywords=Effective%20communication%20in%20project%20management&sid=V)*).
## 2. Embrace Agile Methodologies
Agile practices like Scrum or [Kanban project management](https://teamhood.com/project-management-resources/kanban-project-management/?utm_source=devto&utm_medium=post&utm_campaign=backlinks) can help manage workflow efficiently. These methodologies promote iterative development, regular feedback, and flexibility to changes, which are crucial for software projects.
"Adopting Agile was a game-changer for our team. It brought in a structure that improved our productivity and helped us adapt to changes more swiftly." – [u/devguy1985](https://www.reddit.com/r/agile/search/?q=Agile%20transformation&restrict_sr=1).
## 3. Encourage Continuous Learning
The tech industry evolves rapidly, and staying up-to-date is essential. Encourage your team to attend workshops, webinars, and conferences. Providing access to online courses or allocating time for self-study can also be beneficial.
"The tech landscape is ever-evolving. Encouraging continuous learning not only keeps the team updated but also fuels innovation and personal growth." – [Emily Davis, Lead Software Engineer](https://www.linkedin.com/search/results/content/?keywords=Importance%20of%20continuous%20learning%20in%20tech).
## 4. Promote a Collaborative Environment
A collaborative environment encourages team members to share ideas and solve problems together. Use pair programming, code reviews, and collaborative tools like GitHub to foster teamwork.
"We've seen a significant improvement in our code quality since we started emphasizing pair programming and collaborative problem-solving. It’s amazing what a difference teamwork makes." – [u/codemonkey2020](https://www.reddit.com/r/softwareengineering/search/?q=collaborative%20environment%20in%20software%20development&restrict_sr=1).
## 5. Set Realistic Goals and Expectations
Setting achievable goals is crucial for maintaining team motivation and project momentum. Break down larger tasks into manageable chunks and set clear deadlines. This helps avoid burnout and keeps the team focused.
Create a [project planning timeline](https://teamhood.com/project-management/project-planning-timeline/?utm_source=devto&utm_medium=post&utm_campaign=backlinks) that follows the project goals but is also deliverable and accounts for possible setbacks.
"Setting realistic goals is crucial. Overpromising leads to burnout and disappointment. It's better to underpromise and overdeliver." – [Sarah Thompson, Product Manager](https://www.linkedin.com/search/results/content/?keywords=Setting%20realistic%20goals%20in%20project%20management&sid=5n5).
## 6. Provide Constructive Feedback
Regular feedback helps team members improve and grow. Be specific, positive, and constructive with your feedback. Celebrate successes and address areas of improvement with a supportive approach.
Rely on [engineering productivity metrics](https://teamhood.com/engineering/engineering-productivity-metrics/?utm_source=devto&utm_medium=post&utm_campaign=backlinks) to ensure you are tracking the right things and focusing on effective work, not just the quantity of it.
"Constructive feedback is vital. It helps people grow without feeling attacked. Always balance the negatives with positives to keep morale high." – [u/techleadjane](https://www.reddit.com/r/askengineers/search/?q=constructive%20feedback&restrict_sr=1).
## 7. Recognize and Reward Efforts
Acknowledging hard work and achievements boosts team morale and motivation. Whether it’s a shoutout in a meeting, a bonus, or a simple thank you note, recognition goes a long way.
It is too often that team leaders focus solely on growth. Do not be the manager that simply says - that's great. Be one that celebrates the achievement of what it truly is and means to the team.
"Recognition doesn’t always have to be monetary. Acknowledging hard work and contributions in meetings can go a long way in keeping the team motivated." – [Michael Brown, Engineering Manager](https://www.linkedin.com/search/results/content/?keywords=recognizing%20employee%20efforts).
## 8. Cultivate a Positive Work Culture
A positive work culture enhances productivity and job satisfaction. Encourage work-life balance, provide opportunities for team bonding, and ensure that your workplace is inclusive and respectful.
"A positive work culture where people feel valued and respected can lead to incredible outcomes. It’s the difference between a team that’s just working and a team that’s truly excelling." – [u/happydev](https://www.reddit.com/r/programmerhumor/search/?q=positive%20work%20culture&restrict_sr=1).
## Final Thoughts
Just like with any other team, being the leader of a software development team requires various skills and takes time to master. Become a better leader by getting to know what drives the team and what makes it tick, and acknowledge their achievements just as you would talk through the setbacks. | garbanea |
1,862,797 | Best Digital Marketing in Patna | Candent SEO provides 360 digital marketing solutions to your brand. It is the only marketing agency... | 0 | 2024-05-23T12:17:51 | https://dev.to/candent/best-digital-marketing-in-patna-54jn | Candent SEO provides 360 digital marketing solutions to your brand. It is the only marketing agency that gives top-notch web designing, SEO, and Google My Business services in Patna. New startups in Patna are in love with this Digital marketing agency which helps them to scale rapidly at a very affordable and minimal price. Candent has worked with some of the most well-known companies. For example, Maple Concrete Pumping, Mira Jewellery, and Techno Herald. So, if you also want to skyrocket your sales like these companies then contact Candent SEO, for the Top **[Digital Marketing Services in Patna](https://candentseo.com/)** via their official websites.
| candent | |
1,862,796 | Professional Court Reporting Services | The Vital Role of Professional Court Reporting Services In the complex world of legal proceedings,... | 0 | 2024-05-23T12:16:57 | https://dev.to/ishtiaq_ahmed_1a584374c19/professional-court-reporting-services-5hm6 | **The Vital Role of Professional Court Reporting Services**
In the complex world of legal proceedings, the accuracy and reliability of recorded testimony are paramount. Professional court reporting services play an indispensable role in the judicial system, ensuring that every word spoken in a courtroom is captured with precision and integrity. As legal cases often hinge on the exact phrasing of witness testimonies, depositions, and other court interactions, the expertise of court reporters cannot be overstated.
### What Are Court Reporting Services?
Court reporting services involve the transcription of spoken or recorded speech into written form, typically using shorthand, voice writing, or stenography machines. These services are essential for creating official transcripts of legal proceedings, which include trials, depositions, arbitration hearings, and more. Professional court reporters are trained to produce accurate and verbatim records, which serve as the official documentation of court activities.
### The Importance of Accuracy
Accuracy in court reporting is crucial. Legal professionals, including attorneys and judges, rely heavily on transcripts to review testimonies, present arguments, and make decisions. Any errors or omissions in these transcripts can lead to misunderstandings, misinterpretations, and potentially unjust outcomes. Professional court reporters possess the skills to capture every spoken word, nuance, and inflection, ensuring that the written record is a true and complete reflection of the proceedings.
### Advanced Technology in Court Reporting
Modern court reporting services leverage advanced technology to enhance accuracy and efficiency. Digital recording systems, real-time transcription software, and secure online repositories for transcript storage are just a few examples of how technology is integrated into court reporting. Real-time transcription, in particular, allows for instantaneous translation of spoken words into text, which can be displayed on screens for immediate review by legal professionals. This technology not only improves the speed of proceedings but also allows for on-the-spot corrections and clarifications.
### The Role of Certified Court Reporters
Certified court reporters (CCRs) undergo rigorous training and certification processes to ensure they meet the highest standards of accuracy and professionalism. These certifications, often provided by organizations such as the National Court Reporters Association (NCRA), validate the reporter's ability to handle complex legal terminology, high-pressure environments, and the demanding pace of courtroom dialogue. Certified court reporters are also bound by strict ethical guidelines, ensuring confidentiality and impartiality in their work.
### Benefits of [Professional Court Reporting Services](https://www.servixer.com/court-reporting-services/)
1. **Precision and Reliability**: Professional court reporters provide meticulous and reliable transcriptions, essential for fair legal proceedings.
2. **Efficiency**: With real-time reporting and advanced transcription technology, court reporting services streamline the documentation process, saving time for legal professionals.
3. **Confidentiality**: Certified court reporters adhere to strict confidentiality standards, ensuring that sensitive information is securely handled.
4. **Accessibility**: Transcripts created by court reporters are accessible to all parties involved in a case, facilitating transparency and informed decision-making.
5. **Support for Legal Research**: Detailed and accurate transcripts serve as valuable resources for legal research, case preparation, and appeals.
### The Future of Court Reporting
The future of court reporting is poised to see even greater integration of technology, including artificial intelligence and machine learning, to assist human reporters. These advancements promise to further enhance the speed and accuracy of transcriptions while maintaining the essential human oversight required for contextual understanding and nuanced interpretation.
In conclusion, professional court reporting services are a cornerstone of the legal system, ensuring that the wheels of justice turn smoothly and accurately. As technology continues to evolve, the role of skilled court reporters will remain crucial in bridging the gap between spoken words and the written record, safeguarding the integrity of legal proceedings for years to come. | ishtiaq_ahmed_1a584374c19 | |
1,862,795 | Mastering CSS Fundamentals: Building Beautiful and Responsive Web Designs🚀 | 1. Basic CSS Syntax CSS (Cascading Style Sheets) controls the presentation of HTML elements. It uses... | 0 | 2024-05-23T12:11:10 | https://dev.to/dharamgfx/mastering-css-fundamentals-building-beautiful-and-responsive-web-designs-5a4d | css, webdev, beginners, learning | **1. Basic CSS Syntax**
CSS (Cascading Style Sheets) controls the presentation of HTML elements. It uses a straightforward syntax comprising selectors and declarations.
*Example:*
```css
selector {
property: value;
}
```
- **Selector**: Identifies the HTML element to style.
- **Property**: Specifies the style attribute (e.g., `color`).
- **Value**: Defines the property’s appearance (e.g., `blue`).
**2. Selectors**
Selectors target HTML elements to apply styles. Common types include:
- **Type Selector**: Targets elements by tag name.
*Example:*
```css
p {
color: blue;
}
```
- **Class Selector**: Targets elements with a specific class.
*Example:*
```css
.highlight {
background-color: yellow;
}
```
- **ID Selector**: Targets a single element with a specific ID.
*Example:*
```css
#header {
font-size: 24px;
}
```
**3. The Box Model**
The CSS box model describes the space an element occupies, including content, padding, border, and margin.
*Example:*
```css
div {
width: 100px;
padding: 10px;
border: 5px solid black;
margin: 20px;
}
```
**4. Handling Conflicts in CSS**
Conflicts arise when multiple styles apply to the same element. CSS resolves conflicts based on specificity, importance, and source order.
*Example:*
```css
/* Specificity: ID > Class > Type */
#example {
color: red;
}
.example {
color: blue;
}
p {
color: green;
}
```
In this case, elements with the ID `example` will be red due to higher specificity.
**5. Values and Units**
CSS supports various values and units for properties, including:
- **Length Units**: `px`, `em`, `rem`, `%`
*Example:*
```css
p {
font-size: 16px;
}
```
- **Color Values**: `#RRGGBB`, `rgba()`, named colors
*Example:*
```css
div {
background-color: #ff0000;
}
```
**6. Sizing**
Control the size of elements using `width`, `height`, and related properties.
*Example:*
```css
img {
width: 100%;
height: auto;
}
```
This ensures images resize proportionally to their container.
**7. Backgrounds and Borders**
Style element backgrounds and borders using properties like `background-color`, `background-image`, `border`, and more.
*Example:*
```css
div {
background-color: lightblue;
border: 2px solid black;
background-image: url('pattern.png');
}
```
**8. Overflow**
Handle content that overflows its container using the `overflow` property.
*Example:*
```css
div {
width: 200px;
height: 100px;
overflow: scroll;
}
```
Options include `visible`, `hidden`, `scroll`, and `auto`.
**9. Styling Form Elements**
Customize the appearance of form elements like inputs, buttons, and select menus.
*Example:*
```css
input[type="text"] {
border: 2px solid #ccc;
padding: 10px;
font-size: 14px;
}
button {
background-color: blue;
color: white;
border: none;
padding: 10px 20px;
cursor: pointer;
}
```
**10. Debugging CSS**
Troubleshoot and debug CSS using browser developer tools. Inspect elements, modify styles in real-time, and identify issues.
*Example:*
- **Google Chrome**: Right-click on an element > Inspect.
- **Firefox**: Right-click on an element > Inspect Element.
Use these tools to see applied styles, box model dimensions, and debug rendering issues.
---
**Conclusion**
Mastering CSS fundamentals is essential for creating visually appealing, responsive, and well-structured web designs. By understanding basic syntax, selectors, the box model, and other core concepts, you can effectively style your HTML content and resolve common challenges. Embrace these principles to build stunning and functional websites. | dharamgfx |
1,862,794 | Git & GitHub Essentials: Understanding Version Control and Collaboration | Version Control Imagine Doctor Strange casting spells and constantly modifying reality... | 0 | 2024-05-23T12:05:48 | https://dev.to/viditkushwaha/git-github-essentials-understanding-version-control-and-collaboration-2ldm | github, git, beginners, learning | ## Version Control
Imagine Doctor Strange casting spells and constantly modifying reality (the code) to defeat a foe (a bug). Unlike the film's time loop, Strange (the developers) must keep track of the changes. That's a subtle way of introducing version control, so let's describe it as a system for tracking and managing changes to code or other collections of files. It enables many individuals to work on the same project without overwriting each other's modifications, and it includes a method for reverting to prior versions of the project if necessary.
There are some tools that provide version control.
- **Git:** It’s distributed version control system that allows multiple people to work on a project at the same time without overwriting each other's changes. It is a popular choice among software developers.
- **Subversion (SVN)**: It’s a centralized version control system that keeps all the versioned files in a central repository. Often used for large-scale projects where centralized system is preferred.
- **Perforce**: It’s a version control system that is designed for large-scale software development projects. It offers features such as atomic commits, branching and merging, and access control.
Google uses its own version control system called Piper, which is a centralized version control tool. Piper is a renowned version control tool that Google uses as a vast repository, distributed over around ten Google data centers.
There are several hosting platforms available for version control systems. Here are a few popular ones:
- **GitHub**: GitHub is a web-based version control repository hosting service that is one of the most popular platforms for version control. It offers both public and private repositories, issue tracking, wikis, and collaboration features.
- **Bitbucket**: Bitbucket is another web-based version control repository hosting service that is owned by Atlassian. It supports both Git and Mercurial version control systems.
- **GitLab**: GitLab is a web-based DevOps lifecycle tool that provides a Git-repository manager. It offers features such as continuous integration, continuous deployment, and issue tracking.
Mostly we will be understanding version control system in term of git and GitHub.
### Install Git
Here is official guide to install git to your operating system:
Official page: [Git - Installing Git (git-scm.com)](https://git-scm.com/book/en/v2/Getting-Started-Installing-Git)
GitHub Guide: https://github.com/git-guides/install-git
## How to introduce version control into your project?
Introducing version control into your project, git as control system.
The **`git init`** command is used to initialize a new Git repository in your local system. It creates a hidden folder named **`.git`** in the current directory, which contains all the necessary metadata required for version control.
```bash
git init
```
### Staging, Commits in Git
In Git, a commit is a snapshot of your project at a particular point in time. When you commit, you're creating a new version of your project that you can refer back to later.
To commit changes in Git, you first need to stage them. Staging is the process of selecting which changes you want to include in your next commit. When you stage changes, you're essentially creating a "staging area" where you can group together changes that you want to commit.
To stage changes in Git, you can use the **`git add`** command. For example, if you've made changes to a file called `name.txt`, you can stage those changes with the following command:
```bash
# adding all file to stage
git add .
# adding invidual file to stage
git add name.txt
# adding photograph to album
git commit -m "name.txt file added"
# remove from stage
git restore --staged name.txt
```
### Branches in Git
In Git, a branch represents an independent line of development. It's essentially a movable pointer to a specific commit. When you create a new branch, Git creates a new pointer that moves independently of any other branches.

Here's an example of how to create a new branch in Git:
```bash
git branch <new-branch-name>
```
This creates a new branch with the specified name, but it doesn't switch to that branch yet. To switch to the new branch, you can use the **`git checkout`** command:
```bash
git checkout <new-branch-name>
```
To create and switch into new branch in same command:
```bash
git checkout -b <new-branch-name>
```
Once you've switched to the new branch, you can make changes and commit them just like you would on the master branch.
Here's an example of how to merge a branch back into the main branch:
```bash
git checkout main
git merge <branch-to-merge>
```
Here's an example of how to delete a branch in Git:
```bash
git branch -d <branch-to-delete>
```
This deletes the specified branch. However, if the branch has not been merged yet, Git will prevent you from deleting it. In that case, you can use the **`-D`** flag to force the deletion
```bash
git branch -D <branch-to-delete>
```
## Git Workflow
A typical Git workflow involves several steps, including cloning a repository, making changes, staging those changes, committing them, and pushing them to a remote repository. Here's an example of what that might look like:
### Clone a repository:
```bash
git clone https://github.com/user/repo.git
```
### **Create a branch**
The main branch is usually called `main`. We want to work on another branch, so we can make a pull request and make changes safely. To get started, create a branch off of `main`. Typically naming convention for branch after a feature or fix.
For feature `feat/<name-of-feature>`
For fixing a bug `fix/<name-of-fix>`
### **Make changes to file (and make a commit)**
Once you've created a branch and moved the HEAD pointer to it by "checking out" to that branch, you're ready to make changes in repository. Next, save your changes. You're ready to start the commit!
```bash
git add .
git commit -m "descriptive commit message"
```
### **Push your changes to the remote**
So far commit is made locally, you're the only one that can see it. When you're ready to push your changes to the remote repository, you can use **`git push origin <branch-name>`**. This will push your changes to the remote repository, allowing others to see and use your changes.
`origin` is the default name for the remote repository from which you cloned your local repository. It is a short name to be used when reading and writing to that remote.
```bash
git push origin <branch-name>
```
You can change or remove remote repository using
```bash
# removing and re-adding remote:
git remote set-url origin git://<new-url-here>
#To remove remote use this:
git remote remove origin
```
### **Open a pull request**
Pushing a branch, or new commits, to a remote repository is enough if a pull request already exists, but if it's the first time you're pushing that branch, you should open a new pull request. Pull request is a comparison of two branches that allows users to propose changes to a repository and request that those changes be merged into the main branch.
### **Merge into `main`**
Once repository owner or team decide that the pull request looks good, they can merge it. By merging, you integrate the feature branch into the other branch (most typically the `main` branch).
If you choose not to merge the pull request, you can also close pull requests with unmerged changes
```bash
git checkout main
git merge <branch-to-merge>
```
## Learning by doing
Learning by doing is the greatest way to learn anything.
**[LearnGitBranching](https://learngitbranching.js.org/) :**An interactive git visualization and tutorial. Aspiring students of git can use this app to educate and challenge themselves towards mastery of git!
## Conclusion
Overall, Git is a powerful version control system that allows you to track changes to your code over time, collaborate with others, and maintain a history of your code. By following a typical Git workflow, you can make the most of Git's features and ensure that your code is well-organized and easy to manage.
For additional articles, you can visit the [blog.viditkushwaha.com](https://blog.viditkushwaha.com). | viditkushwaha |
1,862,791 | Things I wish I knew before I started an open-source project | New to the world of open source? You’ll likely make a few mistakes in your first open-source project... | 0 | 2024-05-23T12:02:20 | https://blog.latitude.so/things-i-wish-i-knew-before-i-started-an-open-source-project/ | beginners, programming, tutorial, opensource |
New to the world of open source? You’ll likely make a few mistakes in your first open-source project 🤷♂️. In this article, I’ll share key takeaways from our experience building Latitude, covering what you need to know before launching your first open-source project.
If you’re considering taking the plunge, this article is for you!

### **How to properly set up an OSS project on GitHub**
A well-configured project requires more than just a basic setup. It needs detailed information to give potential users and contributors a clear understanding of the project’s objective and functionality. This can be achieved by crafting a clear and concise project description, accompanied by a comprehensive README file that provides step-by-step guidance on how to use the project. [This article](https://www.freecodecamp.org/news/how-to-write-a-good-readme-file/) offers invaluable insights on what to include in your README files and provides tips on writing an effective one.
Beyond that, it’s also essential to establish a contribution guideline and a code of conduct to maintain a respectful and inclusive community.
A contribution guideline provides clear guidelines for making contributions to the project. This includes instructions for submitting issues and pull requests, as well as outlining coding standards and best practices. A code of conduct, on the other hand, sets the tone for a respectful and inclusive community, covering aspects like language choices, behavioral standards, and more.
Check out [Latitude](https://github.com/latitude-dev/latitude) for examples of all these.
### **Choosing the right license**
When I started my first open-source project, I underestimated the importance of choosing a license that fitted my project.
Open-source licenses protect users and contributors and govern how others can use, modify, or distribute an OSS project. There are two broad categories of open-source licenses: **[Copyleft licenses](https://snyk.io/learn/open-source-licenses/#copyleft)** and **[Permissive licenses](https://snyk.io/learn/open-source-licenses/#permissive)**.
Copyleft Licenses ensure any derivative work inherits the original OSS license and this can protect the original author from bad actors abusing their work. Latitude, for example, uses an [LGPL copyleft license](https://developer.mozilla.org/en-US/docs/Glossary/LGPL), which grants some protections against commercial competitors using Latitude to compete with us. Permissive licenses, on the other hand, are less restrictive and don’t enforce any license reuse in derivative work.
Likewise, it is very important to have all contributors sign a Contributors License Agreement, which stipulates the terms under which intellectual property has been contributed to your project. This ensures contributors cannot easily sue you for code they might have contributed to your project in the past.
To have all contributors sign the CLA, there’s a handy [Gtihub Action](https://github.com/contributor-assistant/github-action) that automatically requires new contributors to do so.
### Version control and branch protection rules
Open-source collaboration often involves working with contributors whom you don’t necessarily trust. To avoid potential disasters, it’s crucial to set clear boundaries for what contributors can do. Failure to do so could lead to mistakes, such as deleting main branch code, which can be extremely difficult to resolve.
Here’s a set of sane defaults we use at Latitude:
- Require a pull request with approval from code owners to merge code to main branch
- Enforce approval after any code change to pull requests
- Require all CI status checks to pass before merge
- Only give permission to merge pull requests to code owners
- Optionally allow your closest team to bypass some of these restrictions
### **How to maintain coding standards**
In an open-source project, it’s essential to maintain coding standards. When code is written with consistency and clarity, it becomes easier to understand, maintain, and contribute to, ultimately making the project more sustainable.
One effective way to ensure coding standards are upheld is by incorporating linters like **ESLint** into the development workflow. Linters scrutinize code for syntax errors, formatting inconsistencies, and stylistic issues, providing instant feedback to developers on how to improve their code.
In addition to linters, code formatters like **Prettier** can further reinforce coding standards. These tools automatically format code according to pre-defined rules, eliminating inconsistencies in indentation, spacing, and syntax.
By combining a linter with a code formatter, open-source projects can establish a unified coding standard that is both easy to enforce and maintain. This not only improves the overall quality of the code but also creates a more welcoming environment for new contributors to join and contribute to the project.
### **How to manage new releases**
Managing releases in an OSS project can be complicated, especially when publishing versioned packages of your software. In contrast to software-as-a-service, where you control the version users access, OSS users can install a particular package version and never update it. This increases the importance of shipping stable and bug-free software.
As a general rule, I recommend against completely automating the release of your software and instead have a manual approval step required at some point in the process. Tools like [changesets](https://github.com/changesets/changesets), the one we use at Latitude, greatly help with this. Changesets takes care of publishing new packages, updating changelogs, and tagging releases, yet it can only do so via automatic pull requests that have the same approval requirements as any other PR at Latitude.
Some more recommendations include maintaining proper human-readable changelogs, tagging releases, and making sure you follow semantic versioning – package managers rely on it for safely keeping project dependencies up to date.
Lastly, a word on prereleases. If you publish versioned packages of your software I greatly encourage you to QA new versions in alpha release. When properly tagged, package managers will ignore these package versions, allowing you to properly and safely test new features in production-like environments. [Changesets](https://github.com/changesets/changesets/blob/main/docs/prereleases.md) can also help you with prereleases.
### **Security best practices**
Security practices in OSS projects are not much different from the ones you’d follow in a closed-source project. So here’s a somewhat comprehensive list we follow at Latitude:
- **Update dependencies regularly**: Make use of automated tracking of minor dependency updates with tools like Dependabot, and try to update any major version of your dependencies every so often – at Latitude we review all our dependencies once a month or so.
- **Code Reviews**: Implement a code review process, especially for the sensitive areas of your code that might deal with production secrets.
- **Access control**: Implement role-based access control to restrict access to sensitive parts of your project, control who can trigger new releases, and who can push code to your main branch. GitHub provides tools for all of these.
- **Secure storage**: Never share production secrets in OSS code, ensure only code owners and administrators have access to sensitive areas of your org like shared password managers, PaaS providers and whatnot.
These practices will only strengthen your project’s security; it’s best to keep up with them.
### **Conclusion**
In conclusion, launching a successful open-source project requires careful consideration of several key factors, including defining the project’s purpose and goals, choosing the right license, setting up a proper project on GitHub, understanding version control, maintaining coding standards, managing new releases, and implementing security best practices.
By learning from the mistakes and experiences shared in this article, first-time open-source contributors can avoid common pitfalls and set their projects up for success.
Thanks for making it to the end of this article. I hope you found the article helpful!
**Do well to help me**
**[Latitude](https://tools.latitude.so/)** is an open-source framework for embedding analytics into your application using code.
Please consider giving it a **[Star on GitHub](https://github.com/latitude-dev/latitude)**.

Lastly, if you have any questions about what I've shared in this article, you can drop a comment below.
I hope to have you read my next piece! 😃 | coderoflagos |
1,862,792 | Navigating the Future of Mobility: Trends and Innovations in the Automotive Industry | INTRODUCTION In the ever-evolving realm of transportation, revolutionary trends in 2023 are reshaping... | 0 | 2024-05-23T12:02:16 | https://dev.to/yujofficial/navigating-the-future-of-mobility-trends-and-innovations-in-the-automotive-industry-46i1 | uxdesign, automotive, designthinking, yuj | INTRODUCTION
In the ever-evolving realm of transportation, revolutionary trends in 2023 are reshaping the automotive landscape. From Electric Vehicles to autonomous wonders and urban air mobility, we explore and talk about how futuristic trends and innovations are elevating user experiences to new heights.
ELECTRICAL VEHICLES (EVs)
In the evolving automotive landscape, Electric Vehicles (EVs) stand out as a transformative force. Advancements in battery technology, reduced charging times, and innovative design elements are reshaping sustainable transportation.
Rivian, a pioneer in this shift, prioritizes adventure, sustainability, and avant-garde design. With features like “Camp Mode” and “Dog Mode,” Rivian exemplifies the appeal and commitment driving the future of electric mobility.
Along with the above, India’s EV sector is experiencing a revolutionary surge, exemplified by the impactful entry of homegrown manufacturers like Tata Motors and Mahindra & Mahindra, aligning with the nation’s sustainable mobility vision.
AUTONOMOUS AND CONNECTED VEHICLES
The rise of Autonomous and Connected Vehicles is another paradigm shift. Imagine your car driving itself — what activities would you engage in during your commute? This question prompts us to explore the realm of self-driving cars and connected vehicles seamlessly linking to the internet.
These innovations promise a revolutionary shift in transportation, enhancing safety, efficiency, and accessibility. Real-world Autonomous Vehicles (AV) testing is already underway globally, marking significant progress in this technology.
Brands like Tesla are at the forefront, integrating advanced AI and machine learning into their autonomous driving features.
Bengaluru’s Minus Zero introduces zPod, India’s first Level 5 autonomous vehicle. Steering-wheel-free, it relies on a cost-effective camera system for real-time navigation and obstacle avoidance, showcasing cutting-edge technology.
MICRO MOBILITY
Micromobility is reshaping urban transport with eco-friendly options like e-bikes and scooters, providing practical last-mile solutions for short-distance urban travel challenges. The industry is witnessing the rise of innovative solutions such as electric skateboards, foldable bicycles, and even electric skates, contributing to the evolution of personal transport.
To name a few; Bird’s electric scooters redefine urban commuting, Brompton’s foldable bicycles revolutionize multimodal transport, Boosted Boards’ electric skateboard enhances short-distance travel, Segway’s electric skates offer a hands-free, futuristic experience, and Honda’s Motocompacto Scooter combines portability and functionality.
India’s EV sector, led by Greaves Electric Mobility, Olectra, and Ather Energy, is surging with a 49% CAGR projection. Government support, robust budgets, and industry collaboration drive sustainable mobility.
URBAN AIR MOBILITY (UAM)
Looking ahead, Urban Air Mobility (UAM) is poised to combat urban congestion using electric Vertical Take-Off and Landing (eVTOL) aircraft. This approach promises a more efficient and streamlined urban transportation system, leveraging airspace for swift and convenient mobility.
Industry leaders like Airbus, Volocopter, Joby Aviation, and Vertical Aerospace are actively contributing to the development of this transformative mode of travel.
India launched the Bharat NCAP, a voluntary program enhancing road safety standards for vehicles. Empowering consumers, it provides objective safety ratings, fostering demand for safer cars and global competitiveness.
OTHER DEVELOPMENTS
In the context of these innovations, the design of vehicle dashboards and connected apps becomes crucial. Safety, multi-screen consistency, information architecture, seamless integration, personalization, and real-time vehicle information are key considerations for creating an optimal user experience.
CONCLUSION
In conclusion, the automotive industry is at a crossroads, presenting consumers with many options and considerations. From the rise of EVs and autonomous vehicles to the redefinition of micromobility and the promise of urban air mobility, the future of mobility is dynamic and promising. As we navigate this landscape, the integration of cutting-edge technology and thoughtful design principles will play a pivotal role in shaping the way we experience and interact with the vehicles of tomorrow.
Embark on the future of mobility with us — where innovation meets sustainability. Let’s redefine the journey together, blending cutting-edge technology and thoughtful [UX design](https://www.yujdesigns.com) for a seamless, empowered, and delightful ride into tomorrow. | yujofficial |
1,862,781 | Playwright Command: Beyond the Basics | In our previous exploration, we discovered how Playwright streamlines web automation with a toolbox... | 0 | 2024-05-23T11:49:07 | https://dev.to/magi-magificient/playwright-command-beyond-the-basics-14km |
In our previous exploration, we discovered how Playwright streamlines web automation with a toolbox of user-friendly commands. Now, let's delve deeper and unveil some additional commands that unlock Playwright's true potential:
Effortlessly navigate your web browser to a specific URL, initiating your automation journey.
page.waitForSelector(selector[, options]): Guarantee your script waits until a particular element appears on the page before proceeding, ensuring smooth execution.
2. Mastering Interactions:
page.check(selector[, options]): Simulate checking a checkbox or radio button, mimicking real user interactions.
page.uncheck(selector[, options]): The counterpart to check, allowing you to uncheck an element if needed for your test scenario.
page.type(selector, text[, options]): Craft dynamic tests by sending customized text to input fields, forms, and search bars.
3. Inspecting the Webpage:
page.textContent(selector[, options]): Retrieve the text content within an element, enabling verification of loaded content.
page.isVisible(selector[, options]): Confirm if a specific element is visible on the webpage, ensuring your tests target the right areas.
4. Capturing Screenshots:
page.screenshot([options]): Take a snapshot of the entire webpage or a specific element, providing visual documentation for your tests and debugging purposes.
5. Orchestrating Complex Flows:
page.waitForNavigation([options]): Instruct your script to wait until a new page has fully loaded, ensuring seamless navigation through multi-page applications.
page.close(): Gracefully close the browser window or tab after your test execution is complete, maintaining resource efficiency.
Remember, this is just a glimpse into Playwright's vast command library! By mastering these additional commands, you can craft robust and reliable test automation scripts that empower your development workflow.
Stay tuned for our next chapter, where we'll explore advanced Playwright concepts and delve into practical testing scenarios!
To learn more about [Playwright Training](https://www.testleaf.com/course/playwright.html) visit Testleaf Page for all kind of [software testing courses](https://www.testleaf.com) | magi-magificient | |
1,861,417 | Effective Testing in JavaScript | The single most important rule of testing is to do it. Kernighan & Pike, The Practice of... | 0 | 2024-05-23T12:00:00 | https://blog.appsignal.com/2024/05/08/effective-testing-in-javascript.html | javascript | > The single most important rule of testing is to do it.
Kernighan & Pike, The Practice of Programming, 1999
Despite constantly changing technologies and the needs of customers, some wisdom seems eternal. _Programmers need to test their code._
But thorough testing takes time. When we do it well, everything works, and a massive testing effort feels like a waste. However, when we do it badly, our code is often broken, and we wish that we had done better testing.
I have some good news for you. Testing doesn’t have to be arduous and we can still get good results. Part of it comes down to our attitude: come at it the right way and it will be much easier.
Another part of it is the techniques we use. In this blog post, I’ll show you some testing techniques (with code examples on GitHub) that can deliver much more bang for your buck.
## Why Test?
We test our code to ensure that it works. I know, it seems obvious.
But that’s not enough. To be more effective, we must catch bugs early. The earlier we find them, the cheaper they are to fix. When a bug goes out to production and is found by a customer, then it’s a whole lot more expensive to get it reported, reproduced, and handed off to a developer — and they probably then have to spend time loading the mental context they need to find and fix it.
Testing enables refactoring. Evolution allows good design to _emerge_ naturally through repeated refactoring and simplification, but we can’t do that safely without testing.
The best reason for testing is that it allows us to see things from our customer's perspective. This is one of the most important perspectives we can take, helping us see the bigger picture around our code.
## My Fundamental Rule of Development
I don’t have many hard and fast rules, but this one is inviolable:
> _Keep your code working._
This is a mantra I repeat to myself while coding. Coding becomes a game where I take code through a series of iterations, going from working code to working code, then testing and making it work again. And so it goes. The sum total is a large amount of working and reliable code.
I’ve been writing code for a long time. In the early years of my career, I was arrogant enough to assume that my code would come out working and was often surprised when it didn’t.
In the later part of my career, I’ve turned that assumption around: now, I think that most code comes out broken. Going further, I believe that _the natural state of code is being broken_. There are so many more ways code can be broken than for it to accidentally work.
## When Should We Test Our Code?
We should test our code early and often.
Testing frequently means problems don’t build up and snowball into bigger problems. It creates the fast feedback loop we need to stay on track and be agile.
Testing early means we don’t delay the discovery of problems. We should aim for a small distance between coding and testing. The less we have to test, the easier it is to test, and the less chance that unnoticed bugs can creep into our code.
We should make frequent commits to our code repository. I like to think of this as _putting working code in the bank_. If, at any point, I run into a mess, I can reset my working code to the last commit — which I know is working, because I only commit working code. I can abandon my work in progress at any time without losing much effort. Aiming for small commits means I never have much work to lose.
## Manual Testing vs. Automated Testing
I’ve been a developer for over 26 years, and I’ve probably spent more time doing manual testing than automated testing. So I know for sure that there’s nothing inherently wrong with manual testing and I still often do it, even when I do later follow it up with automated testing.
Manual testing can get us a long way. Except that repeating the same manual tests over and over again is tedious and time-consuming, not to mention prone to mistakes and laziness (you never forget to test right?).
When we write an automated test for a feature or a piece of code, we get all future testing of that feature for free. For this reason, automated testing can be worthwhile, but it will only pay for itself over the long haul.
Automated testing allows us to scale up our testing. A single developer has the potential to conduct vastly more tests than they could ever achieve manually. Of course, this assumes that a massive effort has already been expended to build the automated tests in the first place.
Because automated testing is _automatic_, it means we won’t be tempted to skip or forget testing. It also enables more frequent testing, which, as discussed, is crucial to getting fast feedback and _keeping our code working_.
Running a suite of automated tests gives us immediate confidence in our code, which is priceless and hard to achieve with manual testing.
Even after espousing the benefits of automated testing, I can assuredly say that _not all code is worth the effort_.
### Not All Code Has Equal Value
The stark fact is that not all code is equally important. Some code will be used once or infrequently, some will be thrown out, and some will be drastically changed from its original form.
On the other hand, some code will be very important, some will be updated and evolved constantly, some will need to be very reliable, and some will need to be very secure.
At the outset of writing any piece of code, it’s extremely difficult to know if that code is worth the effort of automated tests. If you invest in automated tests (or automating anything) when the effort isn’t warranted, you will waste precious time that might be better spent elsewhere.
Using test-driven development (TDD) or otherwise aiming for 100% test coverage is a huge sacrifice in productivity because it treats all code as equally valuable. There is a diminishing return on investment for your effort. The more we push our testing to the extreme, the less value it yields.
## The Single Best Way to Improve at Testing
I used TDD for many years before I realized I was spending way too much effort trying to test _all the code_, including the code that didn’t require that level of effort. Sometimes I still use TDD, but only for the most important code. I enjoy practicing TDD and it has helped build my testing discipline. I learned to create code that’s easier to test, but I don’t often do it now. It’s far too expensive for the resource-starved startups I’ve bootstrapped in recent years.
But TDD gave me what was probably my single most important lesson ever in coding and testing:
> _Think about testing before coding._
Any effort we make to visualize testing before coding results in code that is easier to test. Code that is easier to test is _easier to keep working_. Of course, this has nothing to do with TDD and we can easily fit _thinking_ into our normal development process without TDD or even without any automated testing.
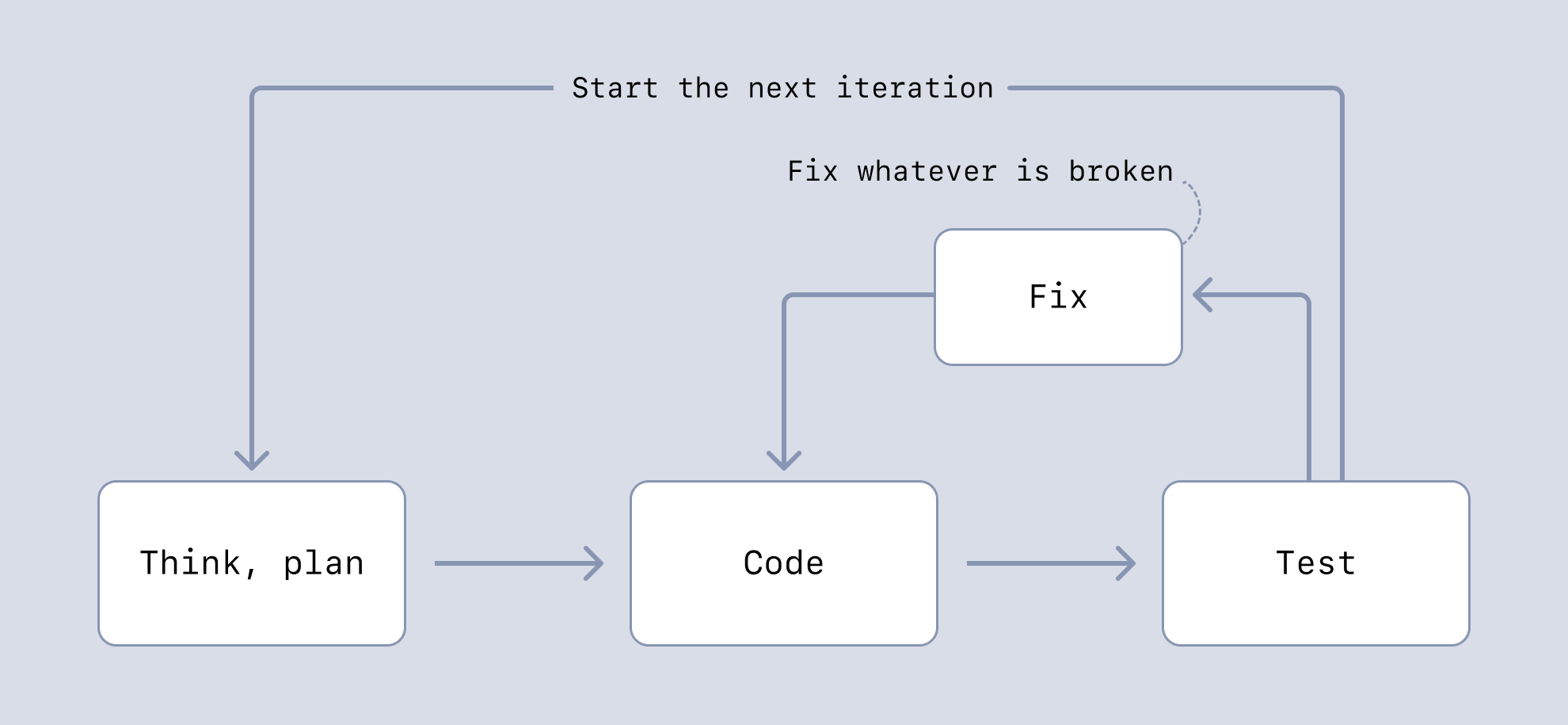
## Effective JavaScript Testing Techniques
Following are some techniques for good testing with less effort.
[You can find the set of example projects here](https://github.com/ashleydavis/javascript-testing-examples/).
| Technique | Usage | Description |
| --------------------------------------------- | ------------------- | ------------------------------------------------------------------------ |
| Output testing | Manual or automated | Comparing previous output to the latest output to see what has changed. |
| Visual testing | Manual or automated | Comparing before and after screenshots to see what has changed. |
| Manual testing, followed by automated testing | Automated | Testing manually to confirm the code works. Followed by automated tests. |
| Integration testing REST APIs | Automated | Applying automated testing to whole services. |
| Frontend testing with Playwright | Automated | Testing frontends using Playwright. |
### Output Testing
Like _golden testing_, output testing checks the output against the last known working version. We can easily use a _Diff tool_ (e.g., `git diff`) to view the differences.
This is great for data pipelines (we diff the data that is output), but we can also use it to test behavior by including a log of important events in the output.
Output testing can be used manually (we can visually check the differences) or automatically (by having our CI pipeline fail if there are differences).
Output testing is simple to start using. It supports refactoring (any refactor should cause no difference in the output).
[Here's some example code](https://github.com/ashleydavis/javascript-testing-examples/tree/main/output-testing).
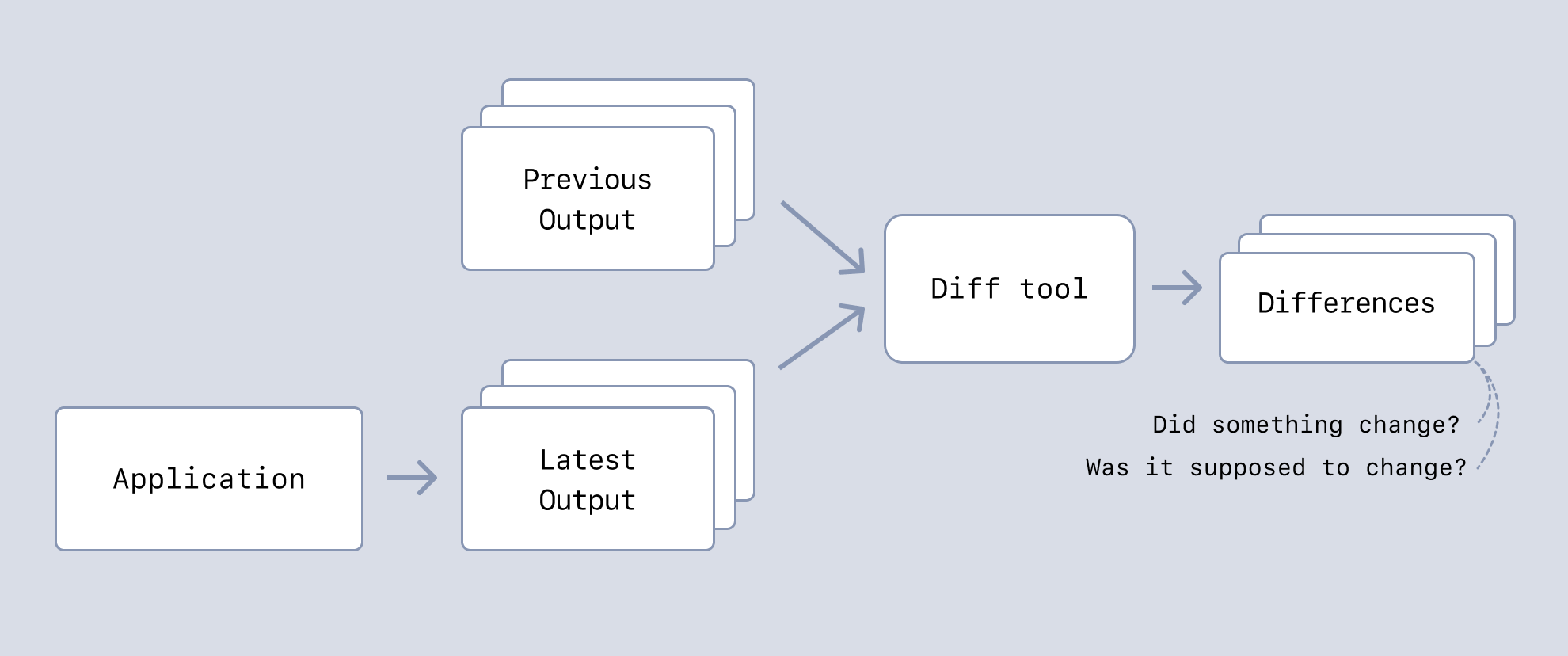
### Visual Testing
Like _snapshot testing_, visual testing compares the visual output (e.g., a screenshot) of our application against the last known working version.
This is more difficult than output testing, but it works well for checking that changes in our code make no (or little) difference to its visual output.
My code example uses Puppeteer to screenshot a web page and then ImageMagick to compare the screenshots. ImageMagick gives a metric indicating the amount of differences. This allows us to set a threshold and tune the system to tolerate small differences to a level that we can live with.
Visual testing can be used manually (we scan the differences with our eyes) or automatically (failing our CI pipeline when ImageMagic’s _difference metric_ is above a certain threshold).
With a visual testing system in place, we can quickly scale it across 100s or 1,000s of web pages. It can take some time to run a big test suite, but it’s the fastest way to search for visual problems across many web pages.
[Here's the example code](https://github.com/ashleydavis/javascript-testing-examples/tree/main/visual-testing).
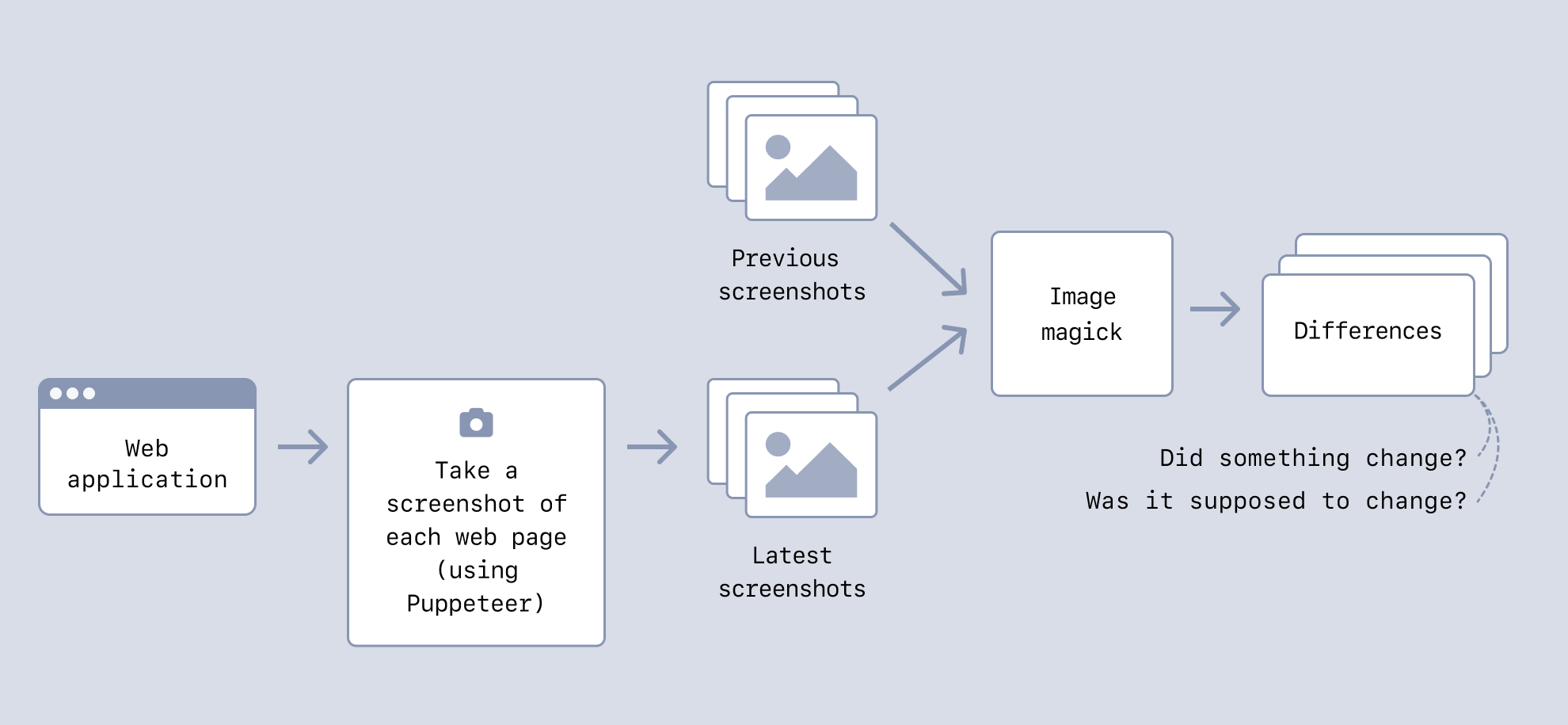
### Manual Testing, then Automated Testing
We can get more effective results from traditional automated testing if we do manual testing followed up by automated testing.
This means we can go through multiple rounds of evolution and refactoring supported by manual testing (or output testing, as mentioned previously) before we commit to automated testing. This can save a lot of time because it’s very time-consuming to have to keep automated tests working while we are creating and evolving new code.
Creating automated tests becomes easy as well. We can use the captured output or code behavior for our automated tests. Fitting automated tests to the code (that we already know works) can be much easier than attempting to write tests from scratch.
Saving automated testing until later also allows for an informed decision about whether automated testing is actually necessary in each particular case.
[Check out some example code](https://github.com/ashleydavis/javascript-testing-examples/tree/main/traditional-automated-testing).
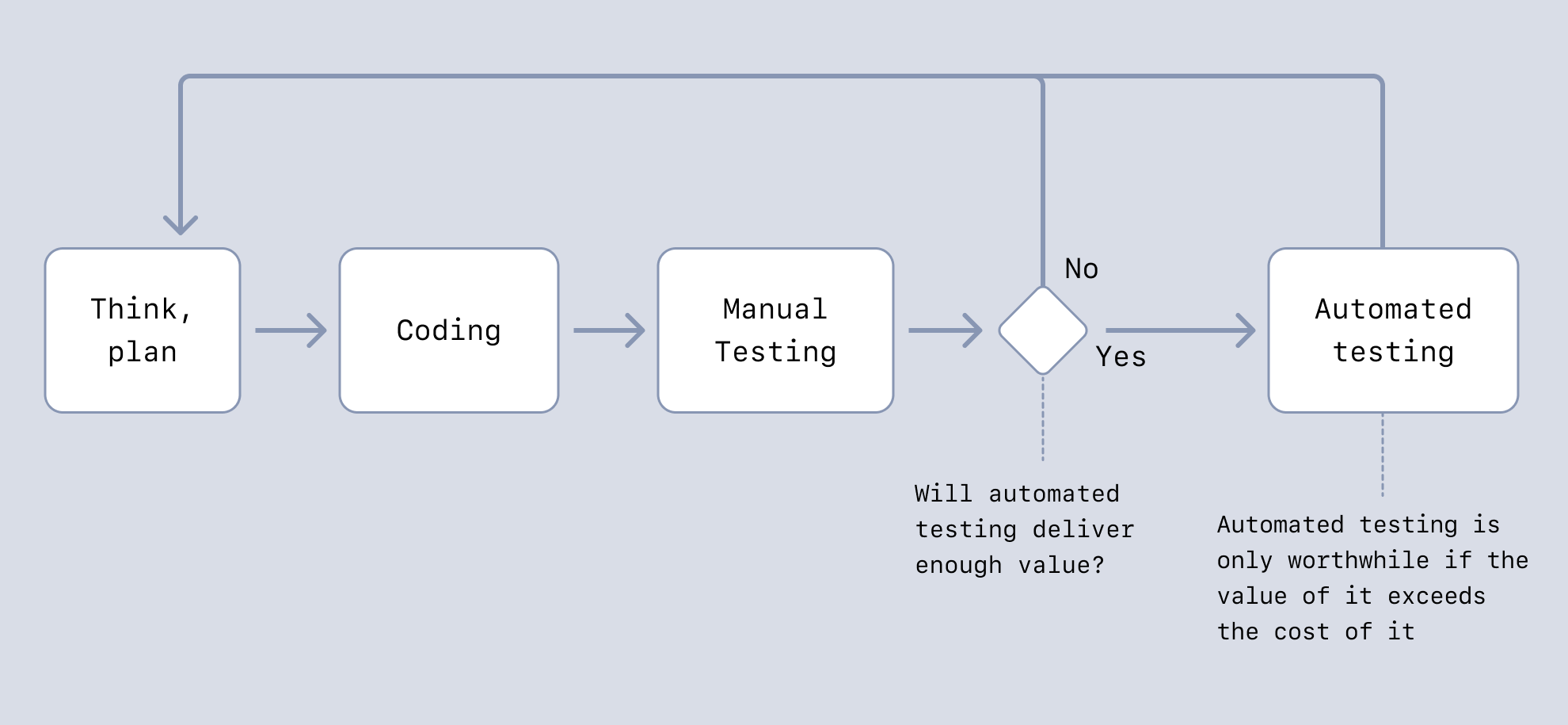
### Integration Testing REST APIs
The most effective way to test REST APIs is to make HTTP requests against the entire service using a traditional automated testing framework (e.g., Jest).
This is much faster to implement than unit testing and much easier to keep working over time. We get to test more code with a smaller suite of tests.
We can also test other types of services in a similar way (for example, a microservice that accepts inputs from a message queue). In cases like this, we can feed input via messages instead of HTTP requests.
[See some example code](https://github.com/ashleydavis/javascript-testing-examples/tree/main/rest-api-testing).
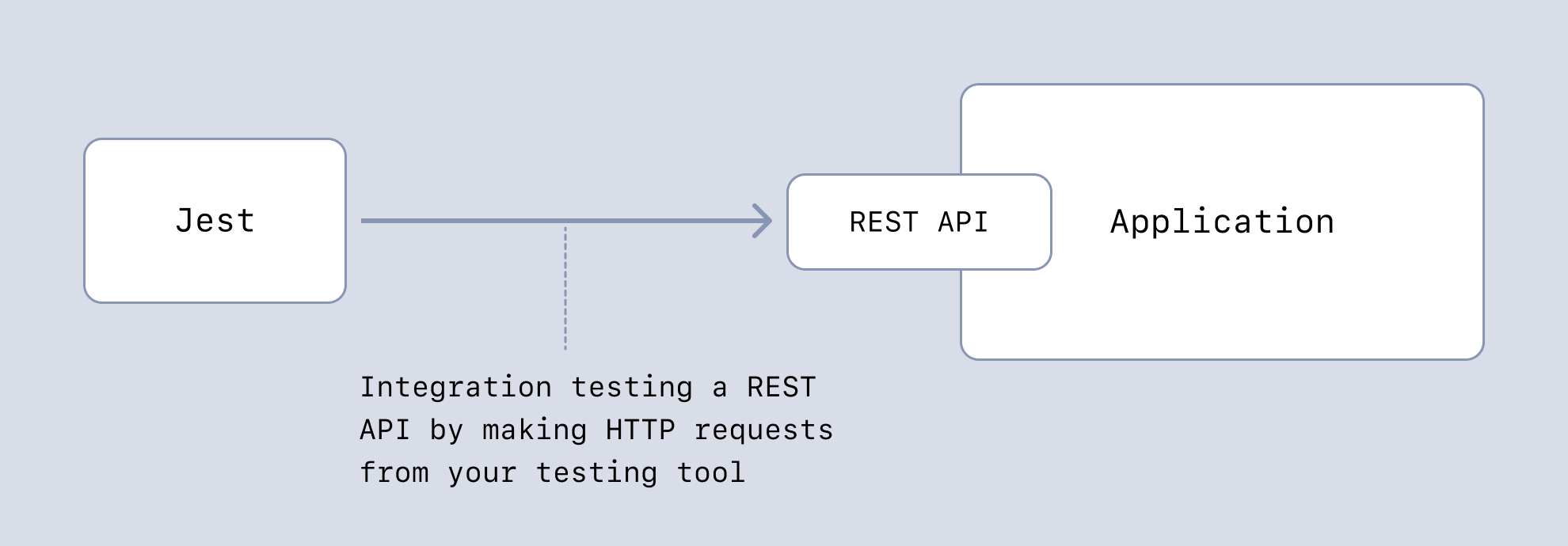
### Frontend Testing with Playwright
Anyone who has tried to test UI components using traditional automated testing will tell you how painful it can be.
A more effective way of testing UIs is using a frontend testing framework like [Playwright](https://blog.appsignal.com/2023/07/12/an-introduction-to-playwright-for-nodejs.html). We can do end-to-end testing of our whole system (frontend and backend), or we can completely mock the backend to focus on integration testing the frontend. This kind of testing covers the most ground for the least effort.
[See some example code](https://github.com/ashleydavis/javascript-testing-examples/tree/main/ui-testing).
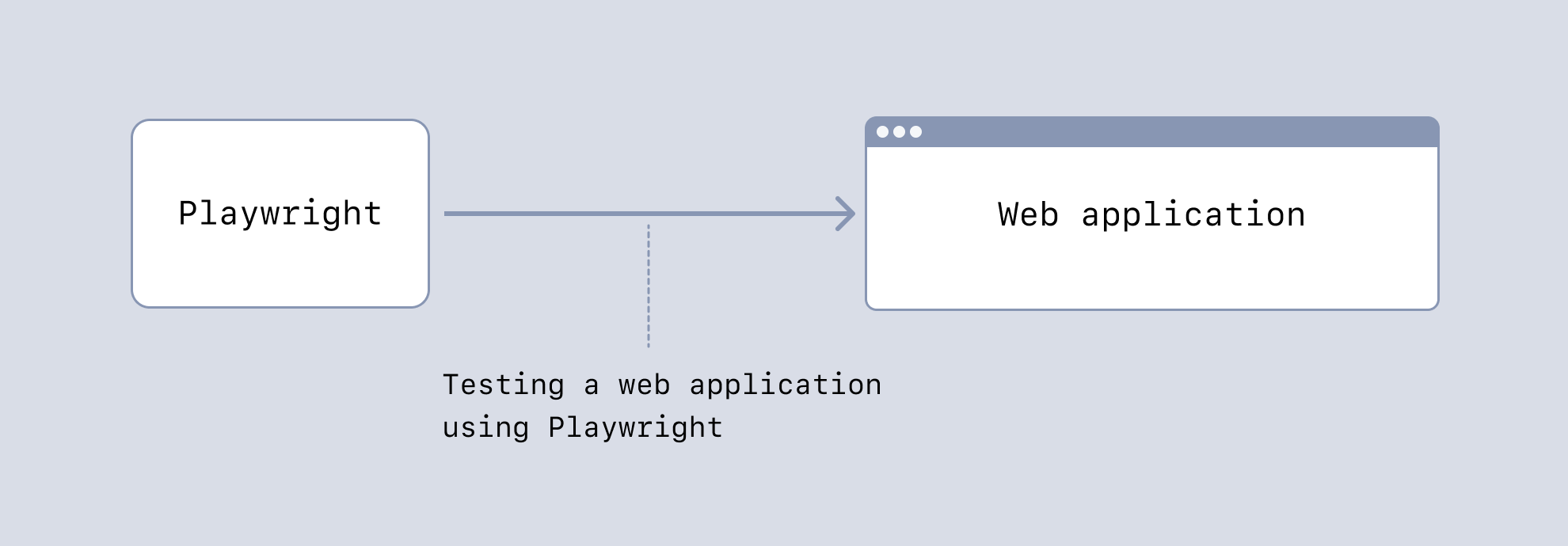
## Wrapping Up
We all have to test our code. That’s the only way to ensure it’s fit for purpose.
But as we've seen in this post, we don’t have to labor on time-intensive traditional testing methods. There are more effective testing techniques out there that can save us so much time, and we can still have great tests. I encourage you to come up with testing techniques for your situation that need little effort.
The important thing is that we deliver valuable and reliable code to our customers. They don’t care how we build or test it, only that we give them something that works well and delivers the value they need.
**P.S. If you liked this post, [subscribe to our JavaScript Sorcery list](https://blog.appsignal.com/javascript-sorcery) for a monthly deep dive into more magical JavaScript tips and tricks.**
**P.P.S. If you need an APM for your Node.js app, go and [check out the AppSignal APM for Node.js](https://www.appsignal.com/nodejs).** | ashleydavis |
1,862,113 | ⛅️ 9 Best Free Tools for Creating & Managing APIs | Awesome tools for rapid API development. When it comes to end-to-end software... | 21,916 | 2024-05-23T12:00:00 | https://www.evergrowingdev.com/p/9-best-free-tools-for-creating-and | api, softwaredevelopment, beginners, webdev | ## Awesome tools for rapid API development.
---
When it comes to end-to-end software development, APIs (Application Programming Interfaces) are the glue that holds everything together.
And as a programmer, having solid API skills is essential if you want to build cool, modern apps that play nicely with others.
So luckily for us there are many tools available out there that can help us to build, test, manage and deploy APIs more easily.
But before we dive into the tools, let's quickly cover what an API actually is.
## What is an API?
In simple terms, an API is like a messenger that allows different software applications to communicate and share data with each other.
It's a set of rules and protocols that define how one application can interact with another application or service.
Think of it like this: when you order food from a restaurant through a delivery app, the app doesn't actually make the food itself.
Instead, it uses an API to send your order to the restaurant's systems, which then prepares your meal and sends it out for delivery.
The API is the middleman that makes this seamless communication possible.
## Why APIs Matter
APIs are the backbone of modern software development, enabling smooth integration and communication between different systems and services.
By exposing functionalities and data through well-defined interfaces, APIs allow developers to [build powerful applications](https://dev.to/evergrowingdev/how-to-build-things-people-want-to-use-4g5n) that utilise the capabilities of multiple platforms and services without reinventing the wheel.
Since we live in a modern interconnected world, where applications need to interact with various third-party services and data sources, APIs play a crucial role in enabling this interoperability.
From social media integration to payment gateways, cloud storage to machine learning services, APIs make it possible to incorporate these functionalities easily into your applications.
## Choosing the Right Tools
Choosing the right API tool is super important because it can make or break your project's success, efficiency, and scalability.
With the perfect tool by your side, you'll be able to unlock [new levels of productivity](https://dev.to/evergrowingdev/15-japanese-techniques-for-developers-to-boost-your-productivity-2g55) and ensure that your APIs are not only functional but also well-documented, secure, and easy to maintain.
When it comes to creating, managing, and keeping your APIs in tip-top shape, the following 9 free tools are great place to get started.
From designing APIs and [writing documentation](https://dev.to/evergrowingdev/make-writing-documentation-a-breeze-with-these-6-effortless-tools-276a) to testing and monitoring their performance, these resources will streamline your workflow, help you deliver awesome APIs.
Let’s take a look:
### 1. [Postman](https://www.postman.com/)

[Postman](https://www.postman.com/) is a popular API development tool that simplifies the entire API lifecycle, from design and documentation to testing and monitoring.
It offers a centralised API repository, a user-friendly interface for creating and sending requests, and extensive support for various API formats.
With its powerful testing and monitoring capabilities, as well as collaboration tools, Postman streamlines the API development process for teams of any size.
**Pros:**
- User-friendly interface
- Extensive support for various API formats
- Collaboration tools
**Cons:**
- Can be resource-intensive for large projects
### 2. [SwaggerHub](https://swagger.io/tools/swaggerhub/)

[SwaggerHub](https://swagger.io/tools/swaggerhub/) is a platform that focuses on OpenAPI specifications, making it an excellent choice for developers working with standardised API documentation.
Its smart API editor ensures compliance with OpenAPI specifications, while its intuitive interface and robust documentation support make it easy to design, document, and collaborate on APIs.
SwaggerHub also offers seamless integrations with other tools, enhancing the overall API development workflow.
**Pros:**
- Intuitive interface
- Robust documentation support
**Cons:**
- May have a learning curve for beginners
### 3. [Apigee](https://cloud.google.com/apigee/)
[Apigee](https://cloud.google.com/apigee/), part of the Google Cloud suite, is a powerful API management and monitoring platform.
It provides a comprehensive set of features for API management, including security, real-time analytics, and traffic management.
With Apigee, developers can easily create, secure, and scale APIs, while also benefiting from advanced monitoring and analytics capabilities to ensure optimal performance and reliability.
**Pros:**
- Comprehensive suite for API management
- Scalable solution
**Cons:**
- Can be complex for small projects
### 4. [RapidAPI](https://rapidapi.com/)

[RapidAPI](https://rapidapi.com/) is the world's largest API marketplace, offering a vast collection of APIs across various domains.
In addition to its extensive marketplace, RapidAPI provides API design and testing tools, enabling developers to easily create, test, and integrate with a wide range of APIs.
Its user-friendly platform and easy integration make it a valuable resource for developers looking to leverage existing APIs or share their own.
**Pros:**
- Large user base
- Ease of use
**Cons:**
- Some APIs may have performance issues
### 5. [Azure API Management](https://azure.microsoft.com/en-us/products/api-management/)

Microsoft's [Azure API Management](https://azure.microsoft.com/en-us/products/api-management/) is a fully-managed service that helps organisations publish, secure, monitor, and scale APIs.
It offers good security features, transformation and monitoring capabilities, and a developer portal for seamless API consumption.
With its multiple features and integration with the Azure ecosystem, Azure API Management is an excellent choice for developers working within the Microsoft technology stack.
**Pros:**
- Comprehensive security
- Real-time analytics
**Cons:**
- Pricing complexity
### 6. [Apiary](https://apiary.io/)

[Apiary](https://apiary.io/) is a collaborative API design and documentation tool that focuses on team collaboration.
Its Blueprint API design format and integrated mock server make it easy to design, prototype, and test APIs.
With Apiary's collaboration tools, developers can work together on API projects, ensuring consistency and efficient communication throughout the development process.
**Pros:**
- Easy to use
- Strong design focus
**Cons:**
- Limited advanced features
### 7. [Insomnia](https://insomnia.rest/)

[Insomnia](https://insomnia.rest/) is a lightweight and user-friendly API testing tool that simplifies the process of testing and debugging APIs.
With its clean interface, support for environment variables, and code generation capabilities, Insomnia makes it easy to send requests, inspect responses, and streamline API testing workflows.
It also supports GraphQL, making it a versatile tool for working with modern API architectures.
**Pros:**
- Simple and clean interface
- Supports GraphQL
**Cons:**
- Limited team collaboration features
### 8. [Hoppscotch](https://hoppscotch.com/)

[Hoppscotch](https://hoppscotch.com/) is an open-source API development tool that offers a minimalistic interface and support for various API protocols, including REST, GraphQL, and WebSocket.
Its real-time API testing capabilities, lightweight footprint, and open-source nature make it an attractive choice for developers who value simplicity and customisability in their API development workflow.
**Pros:**
- Lightweight and fast
- Open-source
**Cons:**
- Limited advanced features
### 9. [Stoplight](https://stoplight.io/)

[Stoplight](https://stoplight.io/) is a collaborative API design and documentation platform that emphasises seamless integration with version control systems like Git.
It supports OpenAPI and JSON Schema specifications, and offers integrated mocking and testing capabilities.
With Stoplight's collaborative design environment and version control integration, developers can work together on API projects while leveraging familiar development workflows.
**Pros:**
- Collaborative design environment
- Seamless integration with Git
**Cons:**
- Can be complex for beginners
## Wrapping up…
APIs are essential for building modern, interconnected software applications. The right tools can make a huge difference when creating and managing APIs.
The 9 free tools covered - Postman, SwaggerHub, Apigee, RapidAPI, Azure API Management, Apiary, Insomnia, Hoppscotch, and Stoplight - offer powerful features for designing, testing, documenting, and managing APIs, no matter your skill level or project size.
Whether you're a solo developer or on a team, working on small projects or something massive, these tools provide what you need to create functional, well-documented, secure and scalable APIs.
Instead of struggling with API development, try out a few of these tools based on your specific needs.
The right tools will streamline your workflow and help you deliver great APIs that power amazing digital experiences.
Happy building!
From your fellow ever-growing dev,
Cherlock Code
---
💙 **If you liked this article...**
I publish a weekly newsletter to a community of ever-growing developers, seeking to improve programming skills and stay on a journey of continuous self-improvement. Focusing on tips for powering up your programming productivity 🚀.
Get more articles like this straight to your inbox.
[Let’s grow together 🌱](https://www.evergrowingdev.com/subscribe)
And stay in touch on **𝕏** [@evergrowingdev](https://twitter.com/intent/follow?screen_name=evergrowingdev)
---

And if you're looking for the right tools to build awesome things, check out [Devpages.io](https://devpages.io), **an ultimate hub I built with 100s of developer tools and resources** 🛠
| evergrowingdev |
1,862,790 | Make your sites more accessible by setting max icon widths | How to make your sites just a little bit better, without much effort Here's a quick... | 0 | 2024-05-23T11:59:23 | https://dev.to/codewithcaen/make-your-sites-more-accessible-by-setting-max-icon-widths-2im2 | svg, html, webdev, beginners | ### How to make your sites just a little bit better, without much effort
**Here's a quick usability tip:** When using #SVG icons in your #HTML, please make sure to set an explicit max width on them.
Why? It is quite possible for users that only the markup will be loaded, due to an issue with the stylesheets (bad CDN, low-end hardware, unreliable network, etc).
If your icons don't take up the entire page the user will still be able to browse the markup and access at least some of your content.
### Some context
For example, one of the news sites I often use has an intermittent problem with their CDN, so stylesheets won't load. I'm on a good computer with a fiber connection, and this still affects me. The news part of the site still work without styles, as the HTML loads, but I need to scroll very far down as there are about a dozen icons in the navigation menu that each take up the entire screen. If they had set a max width, this wouldn't have been as big of a problem.
```html
<svg xmlns="http://www.w3.org/2000/svg" viewBox="0 0 24 24"
class="icon icon-small" width="24" height="24">
```
### Conclusion
In conclusion, a good way to design resilient websites is to make sure that they are still usable even without stylesheets.
This doesn't just apply to icons, but to all images and other elements that can take up a lot of space. It's a small thing that can make a big difference for some users!
| codewithcaen |
1,862,789 | hsplit() in PyTorch | *Memos: My post explains split(). My post explains vsplit(). My post explains dsplit(). My post... | 0 | 2024-05-23T11:57:28 | https://dev.to/hyperkai/hsplit-in-pytorch-4b1d | pytorch, hsplit, split, tensor | *Memos:
- [My post](https://dev.to/hyperkai/split-in-pytorch-nga) explains [split()](https://pytorch.org/docs/stable/generated/torch.split.html).
- [My post](https://dev.to/hyperkai/vsplit-in-pytorch-4915) explains [vsplit()](https://pytorch.org/docs/stable/generated/torch.vsplit.html).
- [My post](https://dev.to/hyperkai/dsplit-in-pytorch-594c) explains [dsplit()](https://pytorch.org/docs/stable/generated/torch.dsplit.html).
- [My post](https://dev.to/hyperkai/tensorsplit-in-pytorch-30m5) explains [tensor_split()](https://pytorch.org/docs/stable/generated/torch.tensor_split.html).
- [My post](https://dev.to/hyperkai/chunk-in-pytorch-30f5) explains [chunk()](https://pytorch.org/docs/stable/generated/torch.chunk.html).
- [My post](https://dev.to/hyperkai/unbind-in-pytorch-3lk9) explains [unbind()](https://pytorch.org/docs/stable/generated/torch.unbind.html).
[hsplit()](https://pytorch.org/docs/stable/generated/torch.hsplit.html) can get the one or more 1D or more D tensors of zero or more horizontally splitted elements from the 1D or more D tensor of zero or more elements as shown below:
- `hsplit()` can be used with [torch](https://pytorch.org/docs/stable/torch.html) and a tensor.
- The 1st argument with `torch` or using a tensor is `input`(Required-Type:`tensor` of `int`, `float`, `complex` or `bool`).
- The 2nd argument with `torch` or the 1st argument with a tensor is `sections`(Required-Type:`int`).
- The 2nd argument with `torch` or the 1st argument with a tensor is `indices`(Required-Type:`tuple` of `int` or `list` of `int`).
- The total number of the zero or more elements of one or more returned tensors changes.
- One or more returned tensors keep the dimension of `input` tensor.
```python
import torch
my_tensor = torch.tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]])
torch.hsplit(input=my_tensor, sections=1)
my_tensor.hsplit(sections=1)
# (tensor([[0, 1, 2, 3],
# [4, 5, 6, 7],
# [8, 9, 10, 11]]),)
torch.hsplit(input=my_tensor, sections=2)
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, sections=4)
# (tensor([[0], [4], [8]]),
# tensor([[1], [5], [9]]),
# tensor([[2], [6], [10]]),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(0,))
torch.hsplit(input=my_tensor, indices=(-4,))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(1,))
torch.hsplit(input=my_tensor, indices=(-3,))
# (tensor([[0], [4], [8]]),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(2,))
torch.hsplit(input=my_tensor, indices=(-2,))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, indices=(3,))
torch.hsplit(input=my_tensor, indices=(-1,))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(4,))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64))
torch.hsplit(input=my_tensor, indices=(0, 0))
torch.hsplit(input=my_tensor, indices=(0, -4))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(0, 1))
torch.hsplit(input=my_tensor, indices=(0, -3))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0], [4], [8]]),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(0, 2))
torch.hsplit(input=my_tensor, indices=(0, -2))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, indices=(0, 3))
torch.hsplit(input=my_tensor, indices=(0, -1))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(0, 4))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64))
torch.hsplit(input=my_tensor, indices=(1, 0))
torch.hsplit(input=my_tensor, indices=(1, -4))
# (tensor([[0], [4], [8]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(1, 1))
torch.hsplit(input=my_tensor, indices=(1, -3))
# (tensor([[0], [4], [8]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(1, 2))
torch.hsplit(input=my_tensor, indices=(1, -2))
# (tensor([[0], [4], [8]]),
# tensor([[1], [5], [9]]),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, indices=(1, 3))
torch.hsplit(input=my_tensor, indices=(1, -1))
# (tensor([[0], [4], [8]]),
# tensor([[1, 2], [5, 6], [9, 10]]),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(1, 4))
# (tensor([[0], [4], [8]]),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64))
torch.hsplit(input=my_tensor, indices=(2, 0))
torch.hsplit(input=my_tensor, indices=(2, -4))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(2, 1))
torch.hsplit(input=my_tensor, indices=(2, -3))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(2, 2))
torch.hsplit(input=my_tensor, indices=(2, -2))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, indices=(2, 3))
torch.hsplit(input=my_tensor, indices=(2, -1))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([[2], [6], [10]]),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(2, 4))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([[2, 3], [6, 7], [10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64))
torch.hsplit(input=my_tensor, indices=(3, 0))
torch.hsplit(input=my_tensor, indices=(3, -4))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(3, 1))
torch.hsplit(input=my_tensor, indices=(3, -3))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(3, 2))
torch.hsplit(input=my_tensor, indices=(3, -2))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, indices=(3, 3))
torch.hsplit(input=my_tensor, indices=(3, -1))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(3, 4))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([[3], [7], [11]]),
# tensor([], size=(3, 0), dtype=torch.int64))
torch.hsplit(input=my_tensor, indices=(4, 0))
torch.hsplit(input=my_tensor, indices=(4, -4))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(4, 1))
torch.hsplit(input=my_tensor, indices=(4, -3))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(4, 2))
torch.hsplit(input=my_tensor, indices=(4, -2))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, indices=(4, 3))
torch.hsplit(input=my_tensor, indices=(4, -1))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(4, 4))
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([], size=(3, 0), dtype=torch.int64))
torch.hsplit(input=my_tensor, indices=(-1, 0))
torch.hsplit(input=my_tensor, indices=(-1, -4))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(-1, 1))
torch.hsplit(input=my_tensor, indices=(-1, -3))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(-1, 2))
torch.hsplit(input=my_tensor, indices=(-1, -2))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, indices=(-1, 3))
torch.hsplit(input=my_tensor, indices=(-1, -1))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(-1, 4))
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([[3], [7], [11]]),
# tensor([], size=(3, 0), dtype=torch.int64))
torch.hsplit(input=my_tensor, indices=(-1, -1))
# (tensor([[[0, 1, 2, 3], [4, 5, 6, 7]]]),
# tensor([], size=(1, 0, 4), dtype=torch.int64),
# tensor([[[8, 9, 10, 11]]]))
torch.hsplit(input=my_tensor, indices=(-1, -2))
# (tensor([[[0, 1, 2, 3], [4, 5, 6, 7]]]),
# tensor([], size=(1, 0, 4), dtype=torch.int64),
# tensor([[[4, 5, 6, 7], [8, 9, 10, 11]]]))
torch.hsplit(input=my_tensor, indices=(-2, 0))
torch.hsplit(input=my_tensor, indices=(-2, -4))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(-2, 1))
torch.hsplit(input=my_tensor, indices=(-2, -3))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(-2, 2))
torch.hsplit(input=my_tensor, indices=(-2, -2))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, indices=(-2, 3))
torch.hsplit(input=my_tensor, indices=(-2, -1))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([[2], [6], [10]]),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(-2, 4))
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([[2, 3], [6, 7], [10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64))
torch.hsplit(input=my_tensor, indices=(-3, 0))
torch.hsplit(input=my_tensor, indices=(-3, -4))
# (tensor([[0], [4], [8]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(-3, 1))
torch.hsplit(input=my_tensor, indices=(-3, -3))
# (tensor([[0], [4], [8]]),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(-3, 2))
torch.hsplit(input=my_tensor, indices=(-3, -2))
# (tensor([[0], [4], [8]]),
# tensor([[1], [5], [9]]),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, indices=(-3, 3))
torch.hsplit(input=my_tensor, indices=(-3, -1))
# (tensor([[0], [4], [8]]),
# tensor([[1, 2], [5, 6], [9, 10]]),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(-3, 4))
# (tensor([[0], [4], [8]]),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64))
torch.hsplit(input=my_tensor, indices=(-4, 0))
torch.hsplit(input=my_tensor, indices=(-4, -4))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(-4, 1))
torch.hsplit(input=my_tensor, indices=(-4, -3))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0], [4], [8]]),
# tensor([[1, 2, 3], [5, 6, 7], [9, 10, 11]]))
torch.hsplit(input=my_tensor, indices=(-4, 2))
torch.hsplit(input=my_tensor, indices=(-4, -2))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.hsplit(input=my_tensor, indices=(-4, 3))
torch.hsplit(input=my_tensor, indices=(-4, -1))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([[3], [7], [11]]))
torch.hsplit(input=my_tensor, indices=(-4, 4))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(3, 0), dtype=torch.int64))
torch.hsplit(input=my_tensor, indices=(0, 0, 0))
torch.hsplit(input=my_tensor, indices=(0, 0, -4))
torch.hsplit(input=my_tensor, indices=(0, -4, 0))
torch.hsplit(input=my_tensor, indices=(0, -4, -4))
# (tensor([], size=(3, 0), dtype=torch.int64),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([], size=(3, 0), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
etc.
my_tensor = torch.tensor([[0., 1., 2., 3.],
[4., 5., 6., 7.],
[8., 9., 10., 11.]])
torch.hsplit(input=my_tensor, sections=1)
# (tensor([[0., 1., 2., 3.],
# [4., 5., 6., 7.],
# [8., 9., 10., 11.]]),)
my_tensor = torch.tensor([[0.+0.j, 1.+0.j, 2.+0.j, 3.+0.j],
[4.+0.j, 5.+0.j, 6.+0.j, 7.+0.j],
[8.+0.j, 9.+0.j, 10.+0.j, 11.+0.j]])
torch.hsplit(input=my_tensor, sections=1)
# (tensor([[0.+0.j, 1.+0.j, 2.+0.j, 3.+0.j],
# [4.+0.j, 5.+0.j, 6.+0.j, 7.+0.j],
# [8.+0.j, 9.+0.j, 10.+0.j, 11.+0.j]]),)
my_tensor = torch.tensor([[True, False, True, False],
[False, True, False, True],
[True, False, True, False]])
torch.hsplit(input=my_tensor, sections=1)
# (tensor([[True, False, True, False],
# [False, True, False, True],
# [True, False, True, False]]),)
``` | hyperkai |
1,862,788 | The Guild: Matka online-pelikulttuurin läpi | Killan päämajan kerrottiin sijaitsevan kauniissa ja eristäytyneessä paikassa, piilossa olevassa... | 0 | 2024-05-23T11:57:08 | https://dev.to/softwareindustrie24334/the-guild-matka-online-pelikulttuurin-lapi-4d61 | Killan päämajan kerrottiin sijaitsevan kauniissa ja eristäytyneessä paikassa, piilossa olevassa pyhäkössä, johon jäsenet voivat vetäytyä opiskelemaan, luomaan ja opettamaan rauhassa. Pääsy tähän pyhäkköön myönnettiin vain kelvollisiksi osoittautuneille, ja sen sijainti säilyi yhdeksi killan tiukimmin varjeltuista salaisuuksista. Huhut puhuivat laajoista kirjastoista, jotka olivat täynnä muinaisia tekstejä, työpajoista, jotka oli varustettu hienoimmilla työkaluilla, ja puutarhoista, jotka inspiroivat rauhaa ja mietiskelyä.
Nykymaailmassa Killan olemassaolo tuntui vieläkin enemmän sadulta. Kuiskaus kuitenkin jatkui. Jotkut väittivät, että kilta toimi edelleen ja sen jäsenet työskentelivät kulissien takana vaikuttaakseen historian kulkuun hienovaraisilla tavoilla. Toiset uskoivat, että kilta oli hajonnut ja sen tieto hajallaan tuuleen. Mutta ne, jotka todella ymmärsivät mestaruuden luonteen ja sen saavuttamiseen vaadittavan omistautumisen, tiesivät, että kilta oli enemmän kuin pelkkä organisaatio. Se oli idea, osoitus ihmisen luovuuden kestävästä voimasta ja peräänantamattomasta huippuosaamisen pyrkimyksestä.
https://denssit.fi/nikotiinipussit-tuotemerkit/killa/ | softwareindustrie24334 | |
1,853,741 | Refactorizar 3º día | En el 3º día, he creado un modelo verbos para así separar las funciones que dependen del componente... | 0 | 2024-05-15T09:34:50 | https://dev.to/srparis/refactorizar-3o-dia-2pem | En el 3º día, he creado un modelo verbos para así separar las funciones que dependen del componente de las que dependen de los verbos, como puede ser manipular el array, comprobar valores, etc. Así, el componente es mucho más ligero y solo se tiene que ocupar de la lógica de la máquina de estados y de los cambios de estado de los campos.
(Aunque tengo que admitir que las capturas de pantalla son cogidas mientras que el código tiene errores porque todavía no lo tengo 100% adaptado).
Seguramente siga haciendo cosas mal o a mejorar, pero poco a poco intento sanear todos los errores que voy encontrando a la vez que voy aprendiendo Angular, ya que muchos conceptos no los he llegado a utilizar o directamente no los conozco.
Una de las cosas de las que dudo mucho es de la estructura óptima del proyecto, ya que cada vez que entro a ver algo a YouTube o a algún curso, lo hace cada uno de una forma distinta y eso me hace dudar.
| srparis | |
1,862,787 | Unveiling the Enigma: Delving Deep into Shader Artistry and Self-Reflection | // CC0: Let's self reflect // Always enjoyed the videos of Platonic solids with inner mirrors //... | 0 | 2024-05-23T11:56:02 | https://dev.to/hayyanstudio/unveiling-the-enigma-delving-deep-into-shader-artistry-and-self-reflection-260 | shader, gamedev, glsl, programming |
```c
// CC0: Let's self reflect
// Always enjoyed the videos of Platonic solids with inner mirrors
// I made some previous attempts but thought I make another attempt it
// Reducing the alias effects on the inner reflections turned out to be a bit tricky.
// Simplest solution is just to run run fullscreen on a 4K screen ;)
// Function to generate the solid found here: https://www.shadertoy.com/view/MsKGzw
// Tinker with these parameters to create different solids
// -------------------------------------------------------
const float rotation_speed= 0.25;
const float poly_U = 1.; // [0, inf]
const float poly_V = 0.5; // [0, inf]
const float poly_W = 1.0; // [0, inf]
const int poly_type = 3; // [2, 5]
const float poly_zoom = 2.0;
const float inner_sphere = 1.;
const float refr_index = 0.9;
#define MAX_BOUNCES2 6
// -------------------------------------------------------
#define TIME iTime
#define RESOLUTION iResolution
#define PI 3.141592654
#define TAU (2.0*PI)
// License: WTFPL, author: sam hocevar, found: https://stackoverflow.com/a/17897228/418488
const vec4 hsv2rgb_K = vec4(1.0, 2.0 / 3.0, 1.0 / 3.0, 3.0);
vec3 hsv2rgb(vec3 c) {
vec3 p = abs(fract(c.xxx + hsv2rgb_K.xyz) * 6.0 - hsv2rgb_K.www);
return c.z * mix(hsv2rgb_K.xxx, clamp(p - hsv2rgb_K.xxx, 0.0, 1.0), c.y);
}
// License: WTFPL, author: sam hocevar, found: https://stackoverflow.com/a/17897228/418488
// Macro version of above to enable compile-time constants
#define HSV2RGB(c) (c.z * mix(hsv2rgb_K.xxx, clamp(abs(fract(c.xxx + hsv2rgb_K.xyz) * 6.0 - hsv2rgb_K.www) - hsv2rgb_K.xxx, 0.0, 1.0), c.y))
#define TOLERANCE2 0.0005
//#define MAX_RAY_LENGTH2 10.0
#define MAX_RAY_MARCHES2 50
#define NORM_OFF2 0.005
#define BACKSTEP2
#define TOLERANCE3 0.0005
#define MAX_RAY_LENGTH3 10.0
#define MAX_RAY_MARCHES3 90
#define NORM_OFF3 0.005
const vec3 rayOrigin = vec3(0.0, 1., -5.);
const vec3 sunDir = normalize(-rayOrigin);
const vec3 sunCol = HSV2RGB(vec3(0.06 , 0.90, 1E-2))*1.;
const vec3 bottomBoxCol = HSV2RGB(vec3(0.66, 0.80, 0.5))*1.;
const vec3 topBoxCol = HSV2RGB(vec3(0.60, 0.90, 1.))*1.;
const vec3 glowCol0 = HSV2RGB(vec3(0.05 , 0.7, 1E-3))*1.;
const vec3 glowCol1 = HSV2RGB(vec3(0.95, 0.7, 1E-3))*1.;
const vec3 beerCol = -HSV2RGB(vec3(0.15+0.5, 0.7, 2.));
const float rrefr_index = 1./refr_index;
// License: Unknown, author: knighty, found: https://www.shadertoy.com/view/MsKGzw
const float poly_cospin = cos(PI/float(poly_type));
const float poly_scospin = sqrt(0.75-poly_cospin*poly_cospin);
const vec3 poly_nc = vec3(-0.5, -poly_cospin, poly_scospin);
const vec3 poly_pab = vec3(0., 0., 1.);
const vec3 poly_pbc_ = vec3(poly_scospin, 0., 0.5);
const vec3 poly_pca_ = vec3(0., poly_scospin, poly_cospin);
const vec3 poly_p = normalize((poly_U*poly_pab+poly_V*poly_pbc_+poly_W*poly_pca_));
const vec3 poly_pbc = normalize(poly_pbc_);
const vec3 poly_pca = normalize(poly_pca_);
mat3 g_rot;
vec2 g_gd;
// License: MIT, author: Inigo Quilez, found: https://iquilezles.org/articles/noacos/
mat3 rot(vec3 d, vec3 z) {
vec3 v = cross( z, d );
float c = dot( z, d );
float k = 1.0/(1.0+c);
return mat3( v.x*v.x*k + c, v.y*v.x*k - v.z, v.z*v.x*k + v.y,
v.x*v.y*k + v.z, v.y*v.y*k + c, v.z*v.y*k - v.x,
v.x*v.z*k - v.y, v.y*v.z*k + v.x, v.z*v.z*k + c );
}
// License: Unknown, author: Matt Taylor (https://github.com/64), found: https://64.github.io/tonemapping/
vec3 aces_approx(vec3 v) {
v = max(v, 0.0);
v *= 0.6;
float a = 2.51;
float b = 0.03;
float c = 2.43;
float d = 0.59;
float e = 0.14;
return clamp((v*(a*v+b))/(v*(c*v+d)+e), 0.0, 1.0);
}
float sphere(vec3 p, float r) {
return length(p) - r;
}
// License: MIT, author: Inigo Quilez, found: https://iquilezles.org/articles/distfunctions/
float box(vec2 p, vec2 b) {
vec2 d = abs(p)-b;
return length(max(d,0.0)) + min(max(d.x,d.y),0.0);
}
// License: Unknown, author: knighty, found: https://www.shadertoy.com/view/MsKGzw
void poly_fold(inout vec3 pos) {
vec3 p = pos;
for(int i = 0; i < poly_type; ++i){
p.xy = abs(p.xy);
p -= 2.*min(0., dot(p,poly_nc)) * poly_nc;
}
pos = p;
}
float poly_plane(vec3 pos) {
float d0 = dot(pos, poly_pab);
float d1 = dot(pos, poly_pbc);
float d2 = dot(pos, poly_pca);
float d = d0;
d = max(d, d1);
d = max(d, d2);
return d;
}
float poly_corner(vec3 pos) {
float d = length(pos) - .0125;
return d;
}
float dot2(vec3 p) {
return dot(p, p);
}
float poly_edge(vec3 pos) {
float dla = dot2(pos-min(0., pos.x)*vec3(1., 0., 0.));
float dlb = dot2(pos-min(0., pos.y)*vec3(0., 1., 0.));
float dlc = dot2(pos-min(0., dot(pos, poly_nc))*poly_nc);
return sqrt(min(min(dla, dlb), dlc))-2E-3;
}
vec3 shape(vec3 pos) {
pos *= g_rot;
pos /= poly_zoom;
poly_fold(pos);
pos -= poly_p;
return vec3(poly_plane(pos), poly_edge(pos), poly_corner(pos))*poly_zoom;
}
vec3 render0(vec3 ro, vec3 rd) {
vec3 col = vec3(0.0);
float srd = sign(rd.y);
float tp = -(ro.y-6.)/abs(rd.y);
if (srd < 0.) {
col += bottomBoxCol*exp(-0.5*(length((ro + tp*rd).xz)));
}
if (srd > 0.0) {
vec3 pos = ro + tp*rd;
vec2 pp = pos.xz;
float db = box(pp, vec2(5.0, 9.0))-3.0;
col += topBoxCol*rd.y*rd.y*smoothstep(0.25, 0.0, db);
col += 0.2*topBoxCol*exp(-0.5*max(db, 0.0));
col += 0.05*sqrt(topBoxCol)*max(-db, 0.0);
}
col += sunCol/(1.001-dot(sunDir, rd));
return col;
}
float df2(vec3 p) {
vec3 ds = shape(p);
float d2 = ds.y-5E-3;
float d0 = min(-ds.x, d2);
float d1 = sphere(p, inner_sphere);
g_gd = min(g_gd, vec2(d2, d1));
float d = (min(d0, d1));
return d;
}
float rayMarch2(vec3 ro, vec3 rd, float tinit) {
float t = tinit;
#if defined(BACKSTEP2)
vec2 dti = vec2(1e10,0.0);
#endif
int i;
for (i = 0; i < MAX_RAY_MARCHES2; ++i) {
float d = df2(ro + rd*t);
#if defined(BACKSTEP2)
if (d<dti.x) { dti=vec2(d,t); }
#endif
// Bouncing in a closed shell, will never miss
if (d < TOLERANCE2/* || t > MAX_RAY_LENGTH3 */) {
break;
}
t += d;
}
#if defined(BACKSTEP2)
if(i==MAX_RAY_MARCHES2) { t=dti.y; };
#endif
return t;
}
vec3 normal2(vec3 pos) {
vec2 eps = vec2(NORM_OFF2,0.0);
vec3 nor;
nor.x = df2(pos+eps.xyy) - df2(pos-eps.xyy);
nor.y = df2(pos+eps.yxy) - df2(pos-eps.yxy);
nor.z = df2(pos+eps.yyx) - df2(pos-eps.yyx);
return normalize(nor);
}
vec3 render2(vec3 ro, vec3 rd, float db) {
vec3 agg = vec3(0.0);
float ragg = 1.;
float tagg = 0.;
for (int bounce = 0; bounce < MAX_BOUNCES2; ++bounce) {
if (ragg < 0.1) break;
g_gd = vec2(1E3);
float t2 = rayMarch2(ro, rd, min(db+0.05, 0.3));
vec2 gd2 = g_gd;
tagg += t2;
vec3 p2 = ro+rd*t2;
vec3 n2 = normal2(p2);
vec3 r2 = reflect(rd, n2);
vec3 rr2 = refract(rd, n2, rrefr_index);
float fre2= 1.+dot(n2,rd);
vec3 beer = ragg*exp(0.2*beerCol*tagg);
agg += glowCol1*beer*((1.+tagg*tagg*4E-2)*6./max(gd2.x, 5E-4+tagg*tagg*2E-4/ragg));
vec3 ocol = 0.2*beer*render0(p2, rr2);
if (gd2.y <= TOLERANCE2) {
ragg *= 1.-0.9*fre2;
} else {
agg += ocol;
ragg *= 0.8;
}
ro = p2;
rd = r2;
db = gd2.x;
}
return agg;
}
float df3(vec3 p) {
vec3 ds = shape(p);
g_gd = min(g_gd, ds.yz);
const float sw = 0.02;
float d1 = min(ds.y, ds.z)-sw;
float d0 = ds.x;
d0 = min(d0, ds.y);
d0 = min(d0, ds.z);
return d0;
}
float rayMarch3(vec3 ro, vec3 rd, float tinit, out int iter) {
float t = tinit;
int i;
for (i = 0; i < MAX_RAY_MARCHES3; ++i) {
float d = df3(ro + rd*t);
if (d < TOLERANCE3 || t > MAX_RAY_LENGTH3) {
break;
}
t += d;
}
iter = i;
return t;
}
vec3 normal3(vec3 pos) {
vec2 eps = vec2(NORM_OFF3,0.0);
vec3 nor;
nor.x = df3(pos+eps.xyy) - df3(pos-eps.xyy);
nor.y = df3(pos+eps.yxy) - df3(pos-eps.yxy);
nor.z = df3(pos+eps.yyx) - df3(pos-eps.yyx);
return normalize(nor);
}
vec3 render3(vec3 ro, vec3 rd) {
int iter;
vec3 skyCol = render0(ro, rd);
vec3 col = skyCol;
g_gd = vec2(1E3);
float t1 = rayMarch3(ro, rd, 0.1, iter);
vec2 gd1 = g_gd;
vec3 p1 = ro+t1*rd;
vec3 n1 = normal3(p1);
vec3 r1 = reflect(rd, n1);
vec3 rr1 = refract(rd, n1, refr_index);
float fre1= 1.+dot(rd, n1);
fre1 *= fre1;
float ifo = mix(0.5, 1., smoothstep(1.0, 0.9, float(iter)/float(MAX_RAY_MARCHES3)));
if (t1 < MAX_RAY_LENGTH3) {
col = render0(p1, r1)*(0.5+0.5*fre1)*ifo;
vec3 icol = render2(p1, rr1, gd1.x);
if (gd1.x > TOLERANCE3 && gd1.y > TOLERANCE3 && rr1 != vec3(0.)) {
col += icol*(1.-0.75*fre1)*ifo;
}
}
col += (glowCol0+1.*fre1*(glowCol0))/max(gd1.x, 3E-4);
return col;
}
vec3 effect(vec2 p, vec2 pp) {
const float fov = 2.0;
const vec3 up = vec3(0., 1., 0.);
const vec3 la = vec3(0.0);
const vec3 ww = normalize(normalize(la-rayOrigin));
const vec3 uu = normalize(cross(up, ww));
const vec3 vv = cross(ww, uu);
vec3 rd = normalize(-p.x*uu + p.y*vv + fov*ww);
vec3 col = vec3(0.0);
col = render3(rayOrigin, rd);
col -= 2E-2*vec3(2.,3.,1.)*(length(p)+0.25);
col = aces_approx(col);
col = sqrt(col);
return col;
}
void mainImage( out vec4 fragColor, in vec2 fragCoord ) {
vec2 q = fragCoord/RESOLUTION.xy;
vec2 p = -1. + 2. * q;
vec2 pp = p;
p.x *= RESOLUTION.x/RESOLUTION.y;
float a = TIME*rotation_speed;
vec3 r0 = vec3(1.0, sin(vec2(sqrt(0.5), 1.0)*a));
vec3 r1 = vec3(cos(vec2(sqrt(0.5), 1.0)*0.913*a), 1.0);
mat3 rot = rot(normalize(r0), normalize(r1));
g_rot = rot;
vec3 col = effect(p, pp);
fragColor = vec4(col, 1.0);
}
```
[Learn Complete Guild From Here](https://glsl.site/post/unveiling-the-enigma-delving-deep-into-shader-artistry-and-self-reflection/)
| hayyanstudio |
1,862,786 | How And Why Father's Day Celebrating | How & Why Father's Day Celebrating? Father's Day is celebrated to honor and appreciate fathers... | 0 | 2024-05-23T11:55:08 | https://dev.to/simran_tiwari_015ae4cd5a4/how-and-why-fathers-day-celebrating-k9a | fathers, day, india | How & Why Father's Day Celebrating?
Father's Day is celebrated to honor and appreciate fathers and father figures for their contributions, love, and sacrifices. It recognizes the role they play in the lives of their children and society. The idea originated in the early 20th century, with the first known celebration held on June 19, 1910, in Spokane, Washington, organized by Sonora Smart Dodd, who wanted to honor her father, a Civil War veteran who raised six children as a single parent.
Celebrations vary widely across cultures and families but often include giving gifts, cards, and spending quality time together. Common gifts include tools, gadgets, clothing, and personalized items that reflect the interests of the father. Many people also take their fathers out for a special meal or prepare a favorite dish at home.
Father's Day provides an opportunity to express gratitude and strengthen family bonds. It's a time to reflect on the importance of fatherhood and the impact fathers have on shaping their children's lives and values. By celebrating Father's Day, families acknowledge the hard work, dedication, and love that fathers provide, reinforcing the emotional connection and appreciation that may not always be overtly expressed in daily life.
Need Father's Day Gifts Ideas? Opean This!
https://www.ask4brand.com/occasions/fathers-day
| simran_tiwari_015ae4cd5a4 |
1,862,785 | Shivam Hospital - Pediatrician and Gynecologist in Nikol | "Welcome to Shivam Women and Children's Hospital, where compassionate care meets expertise in women's... | 0 | 2024-05-23T11:54:03 | https://dev.to/shivam_hospital_3ca8ab8c3/shivam-hospital-pediatrician-and-gynecologist-in-nikol-3dl2 | gynecologist, womenshospital, childrenshospital, pediatricservices | "Welcome to Shivam Women and Children's Hospital, where compassionate care meets expertise in women's health and pediatric services. As a leading gynecologist and children's hospital, we prioritize the wellbeing of women and children, providing comprehensive medical care in a nurturing environment. Our team of dedicated gynecologists specializes in women's health, offering personalized care for every stage of life. From routine check-ups to advanced treatments, we are committed to empowering women to make informed decisions about their health. In our children's hospital wing, we understand the unique needs of young patients and their families."
| shivam_hospital_3ca8ab8c3 |
1,862,783 | Para te ajudar nesse caminho, preparei um guia completo com dicas valiosas para iniciantes na área: | Seja bem-vindo ao mundo da programação! Parabéns por dar o primeiro passo em direção a uma carreira... | 0 | 2024-05-23T11:50:46 | https://dev.to/wasp1988/para-te-ajudar-nesse-caminho-preparei-um-guia-completo-com-dicas-valiosas-para-iniciantes-na-area-3kam | newbie, developer, startup | Seja bem-vindo ao mundo da programação!
Parabéns por dar o primeiro passo em direção a uma carreira empolgante e gratificante no mundo da programação!
Embora a jornada possa parecer desafiadora no início, com dedicação e persistência, você poderá transformar seus sonhos em realidade.
1. Encontre sua motivação:
Explore as diversas áreas da programação: web, mobile, jogos, dados, inteligência artificial... Qual te chama mais a atenção?
Pesquise o mercado de trabalho: quais são as habilidades mais requisitadas? quanto os programadores ganham em média?
Converse com profissionais da área: tire dúvidas e busque inspiração em suas trajetórias.
2. Domine os fundamentos:
Lógica de programação: aprenda a pensar como um computador, estruturando seus pensamentos de forma clara e concisa.
Algoritmos: domine as técnicas para resolver problemas de forma eficiente e organizada.
Linguagens de programação: escolha uma linguagem para começar (Python, Java, JavaScript, C#...) e pratique bastante!
3. Cultive bons hábitos de estudo:
Defina metas realistas: estabeleça objetivos de aprendizado e comemore suas conquistas.
Pratique consistentemente: dedique um tempo por dia para programar, mesmo que seja pouco.
Participe de comunidades online: tire dúvidas, compartilhe conhecimentos e faça networking com outros programadores.
4. Explore recursos de aprendizado:
Cursos online: plataformas como Coursera, Udemy e Alura oferecem cursos completos de programação para iniciantes.
Tutoriais e documentações: diversos sites e blogs disponibilizam conteúdo gratuito de qualidade para aprender a programar.
Livros e revistas: aprofunde seus conhecimentos com materiais didáticos específicos para iniciantes.
5. Mãos à obra:
Comece com projetos simples: crie jogos, sites básicos ou aplicativos para praticar seus conhecimentos.
Contribua para projetos open-source: colabore com a comunidade e aprimore suas habilidades em projetos reais.
Participe de hackathons e competições: coloque suas habilidades à prova e ganhe experiência prática.
6. Mantenha-se atualizado:
Acompanhe as tendências do mercado: novas tecnologias surgem constantemente, esteja sempre atento às novidades.
Aprimore suas habilidades continuamente: faça cursos, participe de workshops e eventos da área.
Nunca pare de aprender: a programação é um campo em constante evolução, a curiosidade e o aprendizado contínuo são essenciais.
Lembre-se: o caminho para se tornar um programador de sucesso é feito de dedicação, persistência e paixão pela área. Acredite em seu potencial, busque ajuda quando precisar e nunca desista dos seus sonhos.
Boa sorte em sua jornada! | wasp1988 |
1,862,782 | Rack Expert in Pakistan: | Get the complete storage solution from the rack expert in Pakistan, a premium quality rack... | 0 | 2024-05-23T11:49:46 | https://dev.to/rack_expert_fe0e8f414fa52/rack-expert-in-pakistan-55k4 | rack, rackmanufacturer, warehouserack, steelrack | Get the complete storage solution from the [rack expert in Pakistan](https://rackexperteng.com/), a premium quality [rack manufacturer](https://rackexperteng.com/rack-manufacturer/) that manufactures the best [rack](https://rackexperteng.com/rack/) for industrial workspaces, warehouses, offices, and shopping malls get their racks.
Being a rack manufacturer rack Expert Engineering manufactures all types of racks for industrial and commercial uses which are given below:
- [Warehouse rack](https://rackexperteng.com/warehouse-rack/)
- [Rack Manufacturer](https://rackexperteng.com/rack-manufacturer/)
- Industrial Storage Rack
- [Steel Rack](https://rackexperteng.com/steel-rack/)
- [Super Store Rack](https://rackexperteng.com/super-store-rack/)
- [Mart Rack](https://rackexperteng.com/mart-racks/)
- Book Rack
- [Ready Made Rack](https://rackexperteng.com/ready-made-rack/)
**Services Areas** We supply our rack all over Pakistan's commercial and industrial regions so the main service areas of Pakistan are as given:
- [Rack in World](https://rackexperteng.com/rack-in-world/)
- [Rack in Pakistan](https://rackexperteng.com/rack-in-pakistan/)
- [Rack in Lahore](https://rackexperteng.com/rack-in-lahore/)
- [Rack in Karachi](https://rackexperteng.com/rack-in-karachi/)
- [Rack in Islamabad](https://rackexperteng.com/rack-in-islamabad/)
- [Rack in Rawalpindi](https://rackexperteng.com/rack-in-rawalpindi/)
- [Rack in Multan](https://rackexperteng.com/rack-in-multan/)
- [Rack in Faisalabad](https://rackexperteng.com/rack-in-faisalabad/)
- [Rack in Peshawar](https://rackexperteng.com/rack-in-peshawar/)
- [Rack in Gujranwala](https://rackexperteng.com/rack-in-gujranwala/)
- [Rack in Sialkot](https://rackexperteng.com/rack-in-sialkot/)
| rack_expert_fe0e8f414fa52 |
1,862,780 | Demystifying Synthetic Monitoring: A Comprehensive Guide for Tech Enthusiasts | The modern pace of IT operations has created a greater need for proactive troubleshooting and... | 0 | 2024-05-23T11:48:29 | https://dev.to/ashwinidave/demystifying-synthetic-monitoring-a-comprehensive-guide-for-tech-enthusiasts-4l3a | observability, cloudcomputing, devops, developers | The modern pace of IT operations has created a greater need for proactive troubleshooting and maintenance. A slower and more reactive approach can negatively impact an organization's sustained growth and success. From this perspective, implementing systems and protocols for proactive monitoring and troubleshooting is essential.
According to [research](https://www.businessresearchinsights.com/market-reports/synthetic-monitoring-market-111751), the [synthetic monitoring](https://middleware.io/blog/how-to-use-synthetic-monitoring/) market was valued at $2,146.5 million in 2021 and is estimated to reach $6,113.2 million by 2028.
Synthetic monitoring simulates user interactions with IT systems, helping organizations evaluate system performance, detect potential issues, and take proactive measures to address them without hindering the real user experience.
This article aims to provide a comprehensive guide on the concept of synthetic monitoring, helping tech enthusiasts and professionals optimize their IT infrastructural frameworks.
**
# Understanding Synthetic Monitoring
**
Synthetic monitoring runs simulations that emulate user behaviors, helping IT teams handle issues before they negatively impact the end-user experience.
Synthetic monitoring typically consists of the following components:
-
Scripts: These are written to mimic specific user actions, allowing developers to emulate the user experience and look out for abnormalities.
-
Agents: Automated programs that execute scripts at particular time intervals and locations, enabling the testing of software stability and performance.
-
Monitors: Synthetic monitoring tracks specific metrics to evaluate stability and performance. For example, uptime monitors can check if a service is accessible and API monitors evaluate the performance of backend services.
-
Alerting and Dashboards: The data gathered by agents is organized on dashboards to give an overall view of performance metrics. IT teams can configure alerts to notify the appropriate parties when a certain performance threshold is reached or a service is offline.
## How Synthetic Monitoring Simulates User Interactions
The fundamental aspect of synthetic monitoring involves the emulation of human behaviors that would be expected for a certain service or application. This emulation is carried out in the following steps:
-
Script Creation: Specific scripts are written to define the sequence of user interactions. These can involve actions like loading web pages and completing purchases, among others.
-
Execution of Scripts by Agents: Once written, the scripts are sent to agents spread over different geographical areas or network configurations. These agents simulate the way users from different places would utilize the service by running the scripts at specific times.
-
Data Collection and Analysis: Agents gather information on performance data, including metrics like availability, load times, response times, and more. This data is moved to a centralized system for analysis and visualization.
-
Proactive Detection: Synthetic monitoring helps find performance problems before they impact actual users. This proactive strategy ensures the immediate identification and resolution of issues.
-
System Optimization: Organizations can conduct benchmarking of their service performance by simulating different conditions, helping them optimize their operations.
##
The Benefits of Synthetic Monitoring
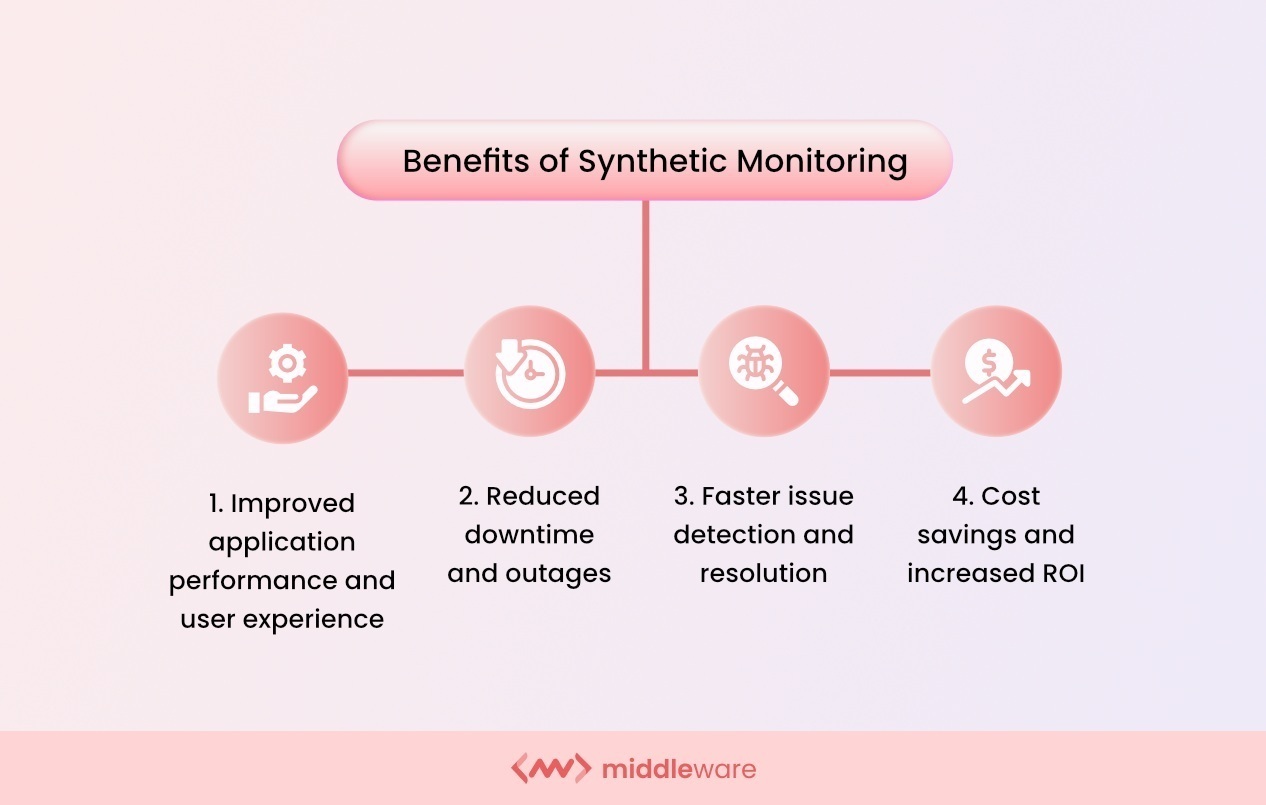
Synthetic monitoring offers prominent benefits over other techniques, such as passive monitoring or real user monitoring. Some key benefits include:
##
Proactive Issue Identification
Synthetic monitoring proactively detects problems and promotes their prompt resolution before they affect actual users by regularly simulating different user interactions. Some methods, such as passive monitoring, depend on real user interactions to detect issues, so the faults aren't found until after they've already impacted users.
For example, e-commerce websites can periodically slow down when a customer is checking out. Synthetic monitoring scripts regularly emulate the checkout procedure from different locations. The development team can optimize database queries and load balancing after finding the specific issue.
##
Consistent Testing
Synthetic monitoring provides a regulated and consistent testing environment to ensure that the same interactions are carried out consistently. Other methods, such as real user monitoring, record a wide range of user interactions, which can make it challenging to duplicate situations regularly for performance testing.
For example, a global media streaming service that uses synthetic monitoring to test buffering times across locations can continuously simulate user interactions to detect higher buffering times. Then, it can enhance its content delivery network for a smoother experience in that region.
##
Early Detection and Resolution
Synthetic monitoring identifies potential issues early, helping reduce risks and ensuring a seamless user experience during busy periods. Other techniques might offer reactive solutions instead of proactive measures, potentially affecting a larger user base before resolution.
For instance, a financial institution using an API for processing transactions can utilize synthetic monitoring to test the API's availability and response time. The IT team can quickly investigate and uncover any issues with the API server and resolve the issue before it escalates.
##
Implementing Synthetic Monitoring
Let's go through a step-by-step guide on how to set up and implement synthetic monitoring for digital services:
**1. Determine Monitoring Goals
**
Determine your monitoring goals and key performance indicators (KPIs). These can include page loads, transaction completion rates, API response times, and availability indicators. Find out which important user visits and interactions require monitoring.
**2. Select the Right Synthetic Monitoring Tools
**
Research and select a synthetic monitoring tool that best meets your needs. Consider factors like functionality, scalability, pricing, and usability. The ideal synthetic monitoring tools should be acceptable according to your resources while providing the necessary features and safety nets.
**3. Create Monitoring Scripts
**
Write scripts that replicate the user interactions you wish to track. To write these scripts, use the interface or scripting language of the tool. Make sure the scripts cover necessary routes, including login, browsing important pages, searching, finishing transactions, and communicating with APIs. For an e-commerce site, for instance, write a script that signs in, looks up a product, adds it to the basket, and then checks out.
**4. Implement Monitoring Agents
**
Configure monitoring agents at different places to duplicate user behaviors from around the world. Set the agents to run the scripts periodically.
**5. Set Up Alerts
**
Establish performance metric thresholds and configure alarms to alert your staff when these levels are exceeded. For instance, set an alert if a page loads more than three seconds or if an API response takes longer than 500 milliseconds.
**6. Set Up Dashboards
**
Create dashboards to view performance information gathered by the monitoring agents. Track unusual data and patterns to better understand the state of your digital services.
**7. Run Tests
**
Run the synthetic monitoring scripts to ensure that they are recording the right data and operating correctly. Check the findings against anticipated outcomes and modify the scripts if needed.
**8. Analyze Data and Optimize
**
Review the data regularly to find issues and performance bottlenecks. Use these insights to improve front-end performance, database queries, and server response times, among other application optimizations.
Synthetic monitoring tools like Middleware specialize in complex applications. They track metrics at different network levels and are deployable and scalable in any framework.
-
With a thorough time graph, they help visualize important business KPIs for quicker issue discovery at certain stages or endpoints.
-
For speedy root cause investigations, users can see a breakdown of network timing data and response times by location.
##
Key Metrics and Performance Indicators

Image Source
Synthetic monitoring tools can monitor the following key metrics and performance indicators:
-
Uptime and Availability: Calculates the proportion of time a web application or service is running. Ensures that users can access the service whenever they need it to reduce downtime and increase dependability.
-
Response Time: The period of time from the moment a request is sent by the client for a server to reply. Shorter response times offer quicker load speeds and more responsive programs.
-
Page Load Time: The time it takes a browser to load a webpage completely. Slower load times can increase bounce rates and decrease user engagement.
-
Error Rate: The percentage of queries that return errors. It determines whether the application is stable and reliable.
To evaluate synthetic monitoring data, set up a performance baseline and regularly examine trends to identify small shifts. Create performance criteria to set off notifications when difficulties occur.
Review error logs to fix reoccurring issues, analyze geographic data to ensure performance, use anomaly detection tools, and evaluate customer journeys to find problems earlier.
## Best Practices for Effective Synthetic Monitoring
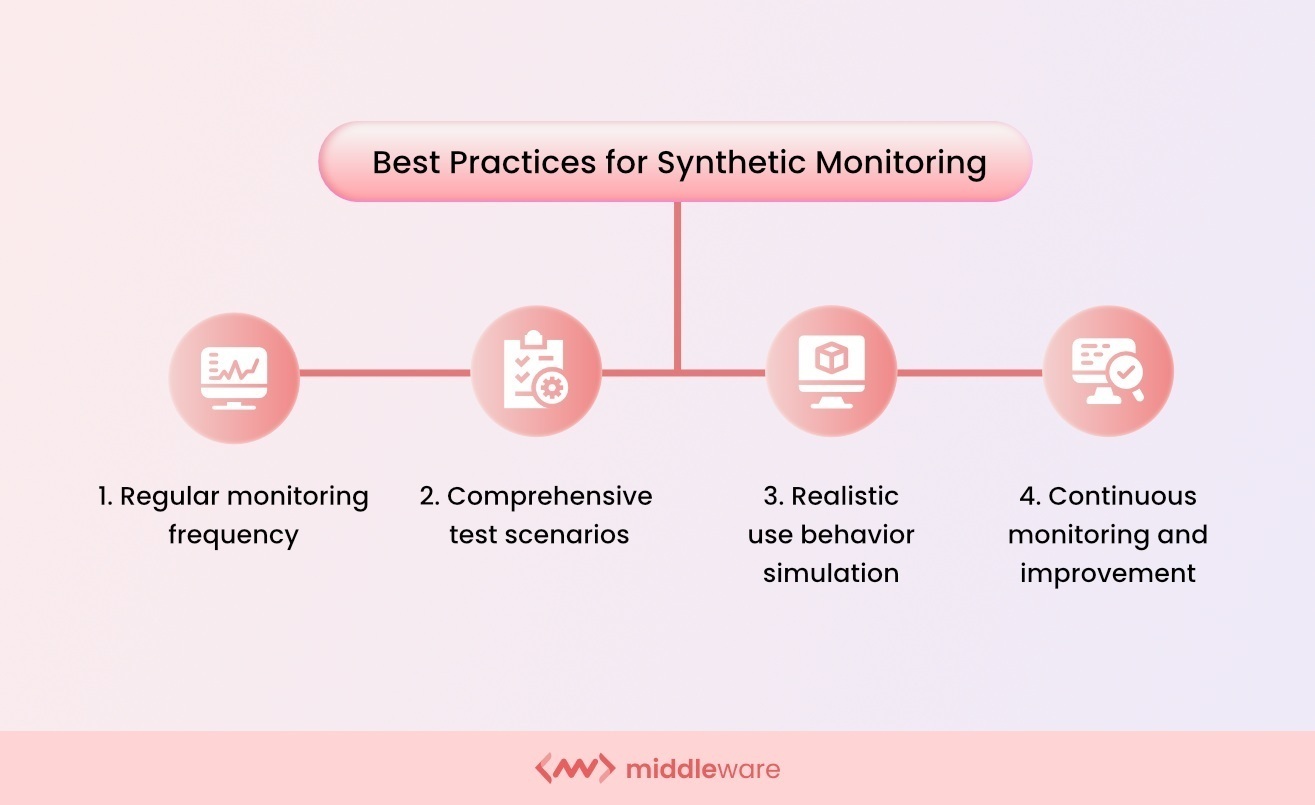
Image Source
Follow these practices to ensure effective synthetic monitoring:
-
Use Dynamic Data: To prevent cache and false positives, provide dynamic data within your scripts to replicate real-time user actions.
-
Set Appropriate Alerts: Set meaningful attributes in your alerts to ensure that warnings are actionable and sent to the appropriate team members.
-
Integrate with CI/CD Pipelines: Integrate synthetic monitoring into your CI/CD pipelines to test new releases and identify problems in the development process.
##
Challenges and Limitations
The process of synthetic monitoring can encounter some of the following challenges:
-
False Positives: Synthetic monitoring can sometimes generate false positives when errors in monitoring scripts trigger warnings instead of real problems, resulting in unnecessary resource use.
-
Limited Real User Experience Visibility: Even while synthetic monitoring mimics user interactions, it might not fully represent the range of real user behaviors and overlook problems that actual users deal with.
Combine synthetic monitoring with real user monitoring to record both simulated and real user experiences, reducing its drawbacks and optimizing its efficacy. Refine and validate monitoring scripts often to ensure correctness and decrease false positives.
##
Future Trends
AI and machine learning integration are changing synthetic monitoring to provide better anomaly identification and predictive analytics. Monitoring hybrid and multi-cloud infrastructures is becoming more important for improving insights across different setups.
Automation and scripting technology developments are making script development and upkeep easier. Synthetic monitoring is combined with real user monitoring and other observability techniques to give a complete picture of performance.
##
Conclusion
The performance and dependability of digital services depend on synthetic monitoring. Through monitoring important transactions and simulating user interactions, issues are resolved before they have an impact on actual users.
Synthetic monitoring works better when combined with other instruments since it gives a comprehensive picture of application performance. Adopting new developments in artificial intelligence, automation, and visualization will enhance its capabilities even further and provide dependable, high-performing digital services in a challenging setting. | ashwinidave |
1,862,772 | Reducing Carbon Footprint through Web Vitals Optimisation | Nowadays the environmental impact of online activities such as accessing a website or an application,... | 0 | 2024-05-23T11:45:44 | https://dev.to/dimeloper/reducing-carbon-footprint-through-web-vitals-optimisation-59cp | webdev, sustainability, webvitals | Nowadays the environmental impact of online activities such as accessing a website or an application, is becoming significant, however it's often overlooked. This blog post demonstrates how measuring and reducing the carbon footprint of websites by optimising them can lead to extraordinary results.
## Measuring a Website's Carbon Footprint
The first step toward sustainability is understanding the environmental cost of a website. Tools like [Website Carbon Calculator](https://websitecarbon.com/) provide insights into the amount of CO2 generated per page view, offering a concrete metric to gauge and subsequently reduce a website's carbon output.
## Our use case
In early 2022 we embarked on a journey to optimize the [ZEAL](https://www.zealnetwork.de/) websites and improve their web vitals scores. Back then, the carbon footprint for every page load at the most popular website was **1.13g of CO2 per page load**.
At first glance you might think that this is a tiny number but if we consider that this website has an average of **~22 million visits per year**, this translates to **25 tonnes of CO2 emissions annually**.
Our main motivation during that journey was to improve the experience of our users, but as it turns out, improvements in Web Vitals — the [set of metrics](https://dev.to/dimeloper/navigating-the-waters-of-core-web-vitals-in-2024-139i) that measure web performance — can significantly reduce a site's carbon footprint. For example, efficiently loading resources reduces the energy used by servers, networks, and devices. Furthermore, optimising image sizes and minimising JavaScript execution not only enhance page speed and improve the LCP (Largest Contentful Paint) metric but also decrease the energy consumed during data processing and transmission.
Fast forward in 2024, now we finally have websites that pass the Web Vitals and our carbon footprint is reduced to **0.39g of CO2 per page load**.
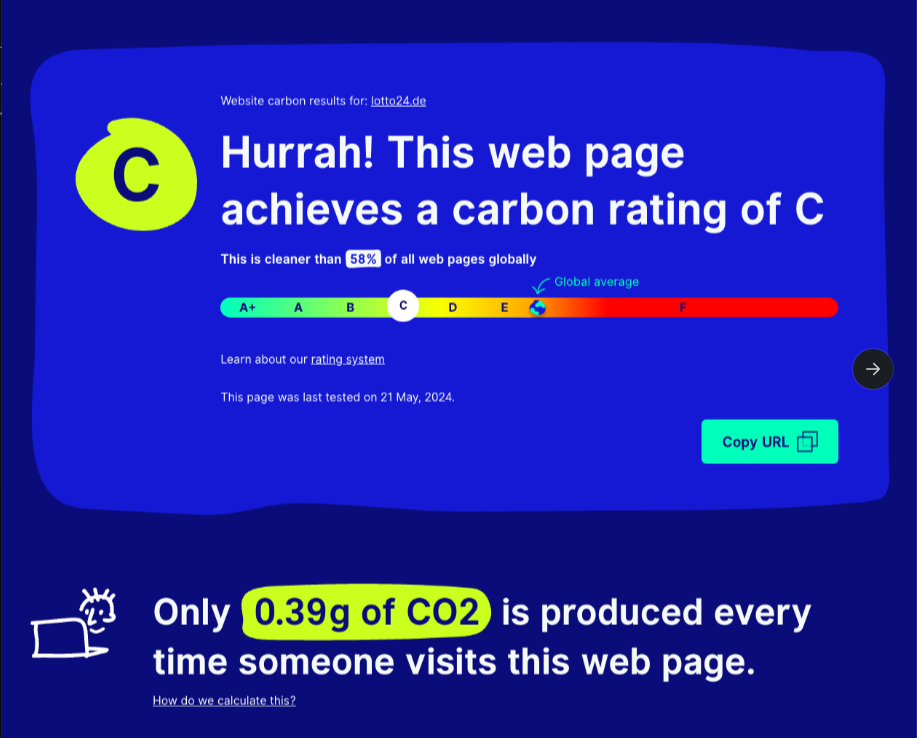
We still have a long way to go, but this already translates to **an annual reduction of 16 tonnes of CO2**..
..or in equivalents:
- saving **6.48 tonnes of coal**
- saving **7,000 litres / 1850 gallons of gasoline**
**..EVERY YEAR.**
## Conclusion
Our optimisation journey is still ongoing. Nevertheless, by measuring our website’s carbon emissions and optimising Web Vitals, we've already achieved significant environmental results. We encourage all web developers and companies to assess their digital carbon footprint and strive for greener web vitals. Together, we can make a substantial impact not only to our website's user experience but also to our planet. | dimeloper |
1,862,777 | Cloud Computing Trends & Challenges & How to Overcome Challenges | Cloud Computing Trends 1 Growth of server less computer – Server less computing is a cloud approach... | 0 | 2024-05-23T11:42:27 | https://dev.to/grapestechsolution/cloud-computing-trends-challenges-how-to-overcome-challenges-4933 | **Cloud Computing Trends**
**1 Growth of server less computer –** Server less computing is a cloud approach where the customer doesn’t have to deal with infrastructure administration and server provisioning. The cloud service providers manage the supporting infrastructure and distribute computing power following by the demand.
**2 Even more adoptions for ML and AI –** All machine learning and AI platforms need a lot of processing power and dada bandwidth, cloud is also a cost effective approach to get the resources. AI and ML complement each other. Cloud Computing plays a vital role in creating two emerging AI technology.
- Creative Algorithms – These software tools use machine learning to produce artificial data to work of arts. This can also be used to train different AI systems.
- Language Modeling – Program that understands human language more accurately are technology expected to be change how companies follow communication with each other.
Cloud computing would be crucial for business in delivering the services to customer and provide the necessary infrastructure for program with high demands. Without the cloud, startup and businesses with smaller resources could not use advanced ML and AI functions.
**3 Deploy the Edge-** New method of processing data that doesn’t conduct activities inside data center, instead processes and storing data occurs on specialized hardware near the network edge.
**4 Kubernetes and Blockchain-** Is a technology that offers tamper proof digital ledger that can record data without being dependent on authority. It is a game changer but has the scaling issues, particularly massive data. Enterprises will keep on pushing the block chain and k8 in 2022 as they work well together.
**5 More focus on cloud security-** Compliance, Privacy and integration problems are the main barrier to cloud trends adoption, they provide enhance cloud security trends feature.
**Cloud Computing Challenges**
**Privacy and Security Data –** Privacy and security are the two most concerning factors trending in cloud computing models .Storage of cloud data or business is private. Encryption, Security hardware and software can solve security issues and privacy problems too.
**Cost Management –** Most of the cloud providers offer you a pay-as-you-go model. It brings down the total cost of resource being used. However, defining and forecasting quantities and cost can occasionally be challenging due to cloud services.
**Multi Cloud Environment –** Companies have more options at their disposal, so they no longer depend on the one cloud service provider; nearly 84% of these organizations depend on several clouds, most of which employ different cloud services. The process frequently ends up being complicated for the IT team due to variations among service cloud providers.
**Performance Challenges –** Performance is a crucial factor when it comes to cloud computing , if the cloud performs unwell than the users can stop using the services and the business may suffer. This may affect in the load effecting which indicates that the server cannot be dividing the incoming traffic effectively for the user experience.
**Portability –** Application migration from one cloud provider to other should be simple, which is another for the **[cloud services](https://www.grapestechsolutions.com/services/cloud/)**, Vendor lock must be avoided.
**Ways to overcome the Challenges**
Install and implement the latest software updates, as well as configure network hardware to prevent security. Using antivirus and firewalls, increasing bandwidth for cloud data available and implement cyber security solutions are some ways to prevent security risks.
Implementing a multi cloud data management solution can help you manage the multi cloud environments. We should be careful while choosing the solution, as not all tools offers the specific security functionalities.
Before starting work on projects, setting cloud as well as portability standards can help the organizations solve the issue. The use of multi –layer authorization and authentication tools is a good choice for account verifications in hybrid , public, and ecosystems.
Implementing resource utilization monitoring tools as well as auditing systems regularly are some ways organizations can fix this. It’s one of the most efficient methods to deal with major challenges and manage budgets in cloud computing. | grapestechsolution | |
1,862,776 | Mana Capitol: Affordable Luxury on Sarjapur Road, Bangalore | Bangalore, the Silicon Valley of India, continues to expand rapidly, with new residential... | 0 | 2024-05-23T11:41:15 | https://dev.to/nandini_6c798668770ead8d5/mana-capitol-affordable-luxury-on-sarjapur-road-bangalore-20hk |
Bangalore, the Silicon Valley of India, continues to expand rapidly, with new residential developments popping up across the city. Among these, Mana Capitol on Sarjapur Road stands out as a premier choice for those seeking affordable luxury in one of Bangalore’s most vibrant locales. [Mana Capitol in Sarjapur Road Bangalore](https://residential.addressadvisors.com/project/mana-capitol-in-sarjapur-road-bangalore) is a testament to modern living, offering residents a blend of comfort, convenience, and community.
Prime Location
Mana Capitol in Sarjapur Road is strategically situated in one of Bangalore’s fastest-growing areas. Sarjapur Road has become a key residential and commercial hub, thanks to its excellent connectivity and proximity to major IT parks, educational institutions, and healthcare facilities. The area is well-connected to other parts of Bangalore through major arterial roads and the Outer Ring Road, making it an ideal location for professionals working in the numerous tech companies that call Bangalore home.
Thoughtful Design and Amenities
Mana Capitol is designed with the modern resident in mind. The project offers a range of 2, 2.5, and 3 BHK apartments, each meticulously planned to maximize space and light. The architecture blends contemporary aesthetics with functionality, ensuring that every home is not only beautiful but also practical.
Residents of Mana Capitol in Sarjapur Road Bangalore can enjoy a plethora of amenities designed to enhance their quality of life. The development features landscaped gardens, walking tracks, and play areas that provide a green oasis amidst the urban landscape. A well-equipped clubhouse, swimming pool, and gym cater to those looking to maintain an active lifestyle, while the multipurpose hall and indoor games facilities offer spaces for relaxation and socializing.
Sustainable Living
Mana Capitol is not just about luxury; it’s also about sustainability. The project incorporates eco-friendly features such as rainwater harvesting, solar lighting in common areas, and energy-efficient building materials. These initiatives not only reduce the environmental footprint but also help in lowering the overall maintenance costs for residents.
Community and Connectivity
One of the standout features of Mana Capitol in Sarjapur Road Bangalore is the strong sense of community it fosters. The project includes ample common areas and community spaces designed to encourage interaction among residents. Whether it’s a casual chat in the landscaped gardens, a game of tennis, or a community event in the clubhouse, Mana Capitol ensures that there are plenty of opportunities for social engagement.
The development’s prime location on Sarjapur Road means that residents have easy access to a range of essential services and entertainment options. Reputed schools like Delhi Public School and Greenwood High, as well as hospitals such as Columbia Asia and Motherhood, are within a short drive. Additionally, the area boasts numerous shopping malls, restaurants, and cafes, providing plenty of options for leisure and entertainment.
Investment Potential
From an investment perspective, Mana Capitol in Sarjapur Road is an attractive option. The ongoing development of infrastructure and the steady influx of IT companies in the vicinity are driving demand for residential properties in the area. As a result, property values in Sarjapur Road have been appreciating steadily, making it a promising choice for both homebuyers and investors.
Moreover, the reputation of Mana Projects, the developer behind Mana Capitol, adds to the appeal. Known for their commitment to quality and customer satisfaction, Mana Projects has a track record of delivering successful residential projects that stand the test of time.
Conclusion:
[Real estate consultants, Property Consultants
](https://addressadvisors.com/)In a city where finding the perfect balance between affordability, luxury, and convenience can be challenging, Mana Capitol in Sarjapur Road Bangalore emerges as a clear winner. Its thoughtfully designed apartments, comprehensive amenities, sustainable practices, and strong community focus make it an ideal choice for modern urban living. Whether you are a young professional, a growing family, or an investor looking for a promising opportunity, Mana Capitol offers a lifestyle that is hard to match. Consider making Mana Capitol your home and experience the best that Bangalore has to offer.
| nandini_6c798668770ead8d5 | |
1,862,775 | Securing Your HR Data: The Role of Cloud Hosting in Sage HRMS Security | Human Resource Management Systems (HRMS) are valuable tools for organizations to improve their Human... | 0 | 2024-05-23T11:40:22 | https://dev.to/him_tyagi/securing-your-hr-data-the-role-of-cloud-hosting-in-sage-hrms-security-56oi | security, cybersecurity | Human Resource Management Systems (HRMS) are valuable tools for organizations to improve their Human Resource processes, whether handling important employee data or enhancing workforce productivity.
With the world rapidly shifting towards technology moving away from traditional processes, it is even more crucial for companies to safeguard their HR data from all cyber threats. In this case, cloud hosting is an effective solution offering several benefits within Sage HRMS.
## Why is Sage HRMS Important?
Sage HRMS is extensive software that organizes HR tasks, from hiring, employee onboarding, payroll administration, and employee benefits management to payroll processing.
The software helps companies secure employee data, automate workflows for better efficiency, and provide insights that can facilitate decision-making.
## Why Should Companies Secure HR Data?
In the last few years, we all have seen a rise in cyber threats across industries and sectors. When it comes to HR data, it is vital to secure it safely as it involves a lot of company and employee personal data.
Be it personally identifiable information (PII), details of payrolls, or even performance assessments, cybercriminals for identity thefts, financial frauds, and other scams extremely yearn for these.
Moreover, companies must comply with GDPR and CCPA to protect individual privacy rights.
## What are the advantages of Cloud Hosting for Sage HRMS Security?
[Cloud hosting for Sage HRMS](https://www.acecloudhosting.com/sage-hrms-hosting/) security offers several benefits. It strengthens the protection of Sage HRMS data and provides scalable and cost-effective business solutions.
1. **Boosted Data Protection**: Cloud hosting companies use innovative safety methods such as encryption and access controls to protect HR data from unauthorized access, fraud, and cyberattacks. Companies also need to obtain certificates to maintain better compliance with security practices.
2. **Scalability and Flexibility**: Cloud hosting offers scalability to fit changing storage and computing needs, ensuring optimum efficiency even during peak usage. It also allows smooth integration with Sage HRMS and other third-party applications, promoting data synchronization and operations automation.
3. **Disaster Recovery**: Cloud hosting providers employ robust [disaster recovery strategies](https://www.ibm.com/blog/disaster-recovery-strategy/), such as data replication, geo-redundancy, and automated back-ups, to alleviate the danger of data loss and ensure that it does not hamper business operations, even during natural disasters or cyberattacks.
4. **Price Efficiency**: Cloud hosting removes the requirement for advanced infrastructure investments and recurring maintenance costs compared to traditional on-premises solutions. It adheres to a subscription-based pricing model, enabling companies to spend only on the resources they use and scale their operations according to their needs.
5. **Accessibility and Collaboration**: Cloud-hosted Sage HRMS makes remote access to HR data and applications possible, empowering employees, managers, and HR professionals to work together successfully from anywhere with a stable internet connection. This can facilitate seamless collaboration, share real-time data insights, and improve overall productivity.
## 5 Best Practices for Securing HR Data in Sage HRMS Cloud Hosting
In an era where data breaches threaten organizational integrity and customer trust, safeguarding sensitive HR data within Sage HRMS is paramount. Cloud hosting offers a robust solution to enhance data security, streamline operations, and ensure regulatory compliance.
1. **Implement Multi-Factor Authentication (MFA)**: Enforce MFA to include an added layer of safety and security beyond passwords, reducing the threat of unapproved access in case of phishing or theft.
2. **Regular Security Audits and Compliance Checks**: Conduct regular safety and security audits and compliance assessments to analyze vulnerabilities and adhere to regulatory needs.
3. **Employee Training and Awareness Programs**: Educate staff members regarding cybersecurity and best practices, such as preventing questionable emails, protecting credentials, and reporting security instances quickly.
4. **Data Encryption and Access Controls**: Encrypt sensitive HR data both in transit and at rest to prevent unapproved access. Carry out granular access controls and give users access depending on their role.
5. **Incident Responses and Plan**: Develop a detailed [incident response plan](https://www.hhs.gov/sites/default/files/cybersecurity-incident-response-plans.pdf) and strategize on detecting, containing, and mitigating security attacks. Create active communication channels to escalate and coordinate response efforts effectively.
### Final Thoughts
As companies progressively rely upon Sage HRMS to handle their human capital efficiently, ensuring the security of HR data is critical. Cloud hosting is a solid solution to protect sensitive data, mitigate cyber-attacks, and achieve regulatory compliance.
By welcoming cloud-based infrastructure and implementing best practices for data security, companies can harness the complete capacity of Sage HRMS while securing their most beneficial asset- their people.
By using cloud technology, organizations can future-proof their HRMS infrastructure, drive innovation, and drive exceptional employee experiences, thereby positioning themselves for sustained growth and success in the digital era.
| him_tyagi |
1,862,774 | Elegance Redefined: Udaari’s Exquisite Silk Suit Designs for Women | When it comes to traditional attire that embodies elegance, sophistication, and timeless beauty,... | 0 | 2024-05-23T11:38:10 | https://dev.to/udaariindia/elegance-redefined-udaaris-exquisite-silk-suit-designs-for-women-23n1 | plainsilksuitdesigns, silksuitdesignsforwomen, silksuitdesign |
When it comes to traditional attire that embodies elegance, sophistication, and timeless beauty, nothing compares to silk suits. Among the plethora of choices available in the market, Udaari’s **[silk suit designs for women](https://www.udaari.co.in/collections/silk)** stand out as a beacon of style and craftsmanship. Whether you are looking for intricate patterns or plain silk suit designs, Udaari offers a diverse collection that caters to every taste and occasion.
**The Allure of Silk Suits**
Silk, known for its luxurious texture and natural sheen, has been a staple in women’s fashion for centuries. Its versatility makes it suitable for both casual and formal wear, adding a touch of grace to any outfit. Silk suit designs capitalize on these qualities, providing women with outfits that are not only beautiful but also comfortable and durable.
**Udaari's Exquisite Silk Suit Designs**
Udaari takes pride in its extensive range of silk suits, each meticulously designed to offer a blend of tradition and contemporary style. The collection includes a variety of patterns, from elaborate embroidery to simple, elegant plain silk suit designs. Let’s delve into some of the standout features of Udaari’s silk suits:
**Intricate Embroidery and Patterns**
For those who appreciate detailed craftsmanship, Udaari offers silk suits with intricate embroidery and patterns. These designs often feature traditional motifs, floral patterns, and delicate thread work that enhance the richness of the silk fabric. Perfect for weddings, festivals, and special occasions, these suits make a statement with their opulent designs and meticulous attention to detail.
**Contemporary Silk Design Suits**
Udaari also caters to modern tastes with its contemporary silk design suits. These pieces incorporate modern elements such as geometric patterns, abstract designs, and trendy cuts while retaining the classic elegance of silk. This fusion of traditional fabric with modern design creates outfits that are perfect for women who want to make a stylish yet sophisticated impression.
**Plain Silk Suit Designs
**
Sometimes, simplicity speaks volumes. Udaari’s **plain silk suit designs** are a testament to the adage "less is more." These suits, devoid of heavy embellishments, highlight the natural beauty and sheen of the silk fabric. Available in a variety of colors, from vibrant hues to soft pastels, these plain silk suits are perfect for both everyday wear and formal occasions. Their minimalist appeal makes them versatile and timeless, making them suitable for women of all ages.
**Why choose Udaari?**
Several factors set Udaari apart from other brands in the market:
**Quality Fabric:** Udaari uses high-quality silk that ensures durability, comfort, and a luxurious feel. The fabric is carefully selected to maintain the natural luster and texture that silk is known for.
**Craftsmanship:** Each Udaari **silk suit design** is a result of skilled craftsmanship. The brand employs experienced artisans who bring their expertise to every piece, ensuring that each suit is a work of art.
**Variety:** Udaari offers a wide range of designs, catering to different tastes and preferences. Whether you prefer intricate patterns or plain silk suit designs, there is something for everyone.
**Attention to Detail:** From the choice of colors to the stitching and finishing, Udaari pays attention to every detail. This meticulous approach ensures that each suit is perfect in every way.
**Affordability:** Despite the high quality and exquisite designs, Udaari’s silk suits are reasonably priced. The brand believes in offering luxury at affordable prices, making elegance accessible to all women.
**Styling Your Udaari Silk Suit**
Udaari’s silk suits are versatile and can be styled in various ways to suit different occasions. Here are a few styling tips:
**For Formal Events:** Pair your intricately designed Udaari silk suit with traditional jewelry such as jhumkas and bangles. Opt for a sleek hairstyle and elegant makeup to complete the look.
**For Casual Wear:** A **plain silk suit design** can be dressed down with minimal accessories. Pair it with simple stud earrings and a light scarf for a chic yet understated look.
**For Festive Occasions:** Go all out with bold accessories, statement necklaces, and embroidered dupattas. Vibrant silk suits from Udaari’s collection are perfect for making a festive statement.
**Customer Testimonials**
The true measure of a brand’s success lies in the satisfaction of its customers. Here’s what some of Udaari’s customers have to say:
**Anjali M.:** “I bought a plain silk suit from Udaari for a family function, and I received so many compliments. The fabric is so soft and comfortable, and the design is just elegant.”
**Neha S.:** “Udaari’s silk suits are a perfect blend of traditional and modern. I love how they have something for every occasion. Their intricate designs are my favorite.”
**Priya R.:** “I have several Udaari silk suits, and each one is a masterpiece. The quality is unmatched, and they are worth every penny.”
**Conclusion**
Udaari’s **[silk suit designs for women](https://www.udaari.co.in/collections/silk)** are a celebration of elegance, tradition, and contemporary fashion. With their wide range of silk suit designs, from intricate embroidery to plain silk suit designs, Udaari caters to every taste and occasion. By choosing Udaari, you are not just buying an outfit; you are investing in a timeless piece that embodies grace and sophistication. Experience the allure of Udaari’s silk suits and elevate your wardrobe with pieces that exude luxury and style.
| udaariindia |
1,862,773 | Automate Trade Compliance Checks with AI and ML Solutions | Trade compliance is a critical aspect of international business, ensuring that all operations adhere... | 0 | 2024-05-23T11:37:31 | https://dev.to/icustoms12/automate-trade-compliance-checks-with-ai-and-ml-solutions-5d3o | ai, aiautomation, startup, machinelearning | Trade compliance is a critical aspect of international business, ensuring that all operations adhere to regulatory standards. Traditional compliance methods, reliant on manual checks, are often cumbersome and prone to errors. The advent of Artificial Intelligence (AI) and Machine Learning (ML) presents a game-changing opportunity to automate these processes, enhancing accuracy and efficiency.
## The Burden of Manual Compliance
Manual trade compliance checks involve scrutinizing numerous documents, a process that is both time-consuming and labor-intensive. This method is fraught with risks, including human error and inconsistency. Additionally, as businesses expand globally, the volume of trade documents increases, making manual processing increasingly unmanageable and expensive.
## AI and ML: The Future of Compliance Automation
Implementing AI and ML in trade compliance can revolutionize how businesses manage regulatory requirements. Here’s how these technologies can automate compliance checks:
**Efficient Document Classification:** AI can automatically classify trade documents by identifying types such as invoices, licenses, and permits through structural and keyword analysis. This automation eliminates the need for manual sorting, streamlining the workflow.
**Accurate Data Extraction:** ML algorithms are adept at extracting essential information from trade documents, such as product descriptions, values, and origins. [Automating data extraction](https://www.icustoms.ai/intelligent-document-processing/) reduces human errors and ensures that the information is accurate and consistent.
**Proactive Risk Detection:** AI systems can analyze extracted data to detect potential compliance issues. Advanced algorithms can identify discrepancies and regulatory violations, allowing businesses to address these problems proactively before they result in fines or delays.
**Consistent Decision-Making:** ML can use historical data and regulations to make informed decisions on approvals and risk assessments. This capability ensures that compliance decisions are consistent and based on comprehensive insights.
## iCustoms: Your Partner in Compliance Automation
[iCustoms](https://www.icustoms.ai/) offers state-of-the-art AI and ML solutions tailored for trade compliance. Their platform integrates seamlessly with existing systems, enabling automated customs data extraction and document classification. By leveraging iCustoms' innovative technology, businesses can enhance their compliance accuracy and operational efficiency.
For more insights on [how AI and ML can streamline your trade compliance processes](https://www.icustoms.ai/blogs/automating-trade-compliance-checks-ai-machine-learning/) and to explore iCustoms’ cutting-edge solutions. Discover how automation can transform your compliance checks and drive business success. | icustoms12 |
1,862,771 | Understanding and Using JavaScript Proxies: A Technical Approach | Understanding and Using JavaScript Proxies: A Technical Approach JavaScript offers many... | 0 | 2024-05-23T11:37:15 | https://dev.to/emmanuelj/understanding-and-using-javascript-proxies-a-technical-approach-5alm | webdev, javascript, programming | # Understanding and Using JavaScript Proxies: A Technical Approach
JavaScript offers many features that allow developers to manipulate and control the behavior of objects in sophisticated ways. One such feature, introduced in ECMAScript 6 (ES6), is Proxies. Proxies provide a mechanism to intercept and customize operations performed on objects, enabling a wide range of advanced use cases. This article provides a technical overview of JavaScript Proxies, discussing their creation, various traps, and practical applications, accompanied by detailed code examples.
## What is a Proxy?
A Proxy in JavaScript is an object that acts as a wrapper around another object, known as the target. The Proxy intercepts operations on the target object and allows custom behavior to be defined for these operations. This interception is handled through functions known as traps.
## Creating a Proxy
To create a Proxy, use the `Proxy` constructor, which requires two parameters:
1. The target object to be proxied.
2. A handler object containing traps that define custom behavior for operations.
### Basic Example
```javascript
const target = {
message: "Hello, world!"
};
const handler = {
get: (target, property) => {
return property in target ? target[property] : `Property ${property} does not exist`;
}
};
const proxy = new Proxy(target, handler);
console.log(proxy.message); // Output: Hello, world!
console.log(proxy.nonExistentProperty); // Output: Property nonExistentProperty does not exist
```
In this example, the `get` trap intercepts property access on the target object.
## Common Proxy Traps
Proxies can intercept a variety of operations using different traps. Here are some of the most commonly used traps:
### 1. `get`
Intercepts property access.
```javascript
const handler = {
get: (target, property) => {
console.log(`Getting property: ${property}`);
return target[property];
}
};
const proxy = new Proxy(target, handler);
console.log(proxy.message); // Output: Getting property: message
// Hello, world!
```
### 2. `set`
Intercepts property assignment.
```javascript
const handler = {
set: (target, property, value) => {
console.log(`Setting property: ${property} to ${value}`);
target[property] = value;
return true;
}
};
const proxy = new Proxy(target, handler);
proxy.message = "Hello, Proxy!";
// Output: Setting property: message to Hello, Proxy!
console.log(proxy.message); // Output: Hello, Proxy!
```
### 3. `has`
Intercepts the `in` operator.
```javascript
const handler = {
has: (target, property) => {
console.log(`Checking existence of property: ${property}`);
return property in target;
}
};
const proxy = new Proxy(target, handler);
console.log('message' in proxy); // Output: Checking existence of property: message
// true
```
### 4. `deleteProperty`
Intercepts the `delete` operator.
```javascript
const handler = {
deleteProperty: (target, property) => {
console.log(`Deleting property: ${property}`);
return delete target[property];
}
};
const proxy = new Proxy(target, handler);
delete proxy.message; // Output: Deleting property: message
console.log(proxy.message); // Output: undefined
```
### 5. `apply`
Intercepts function calls.
```javascript
const target = function() {
return 'Hello, world!';
};
const handler = {
apply: (target, thisArg, argumentsList) => {
console.log(`Calling function with arguments: ${argumentsList}`);
return target.apply(thisArg, argumentsList);
}
};
const proxy = new Proxy(target, handler);
console.log(proxy('arg1', 'arg2')); // Output: Calling function with arguments: arg1,arg2
// Hello, world!
```
## Advanced Use Cases
### Validation
Proxies can enforce validation rules on objects, ensuring data integrity.
```javascript
const user = {
name: 'John Doe',
age: 30
};
const validator = {
set: (target, property, value) => {
if (property === 'age' && typeof value !== 'number') {
throw new TypeError('Age must be a number');
}
target[property] = value;
return true;
}
};
const userProxy = new Proxy(user, validator);
userProxy.age = 40; // Valid
console.log(userProxy.age); // Output: 40
try {
userProxy.age = 'forty'; // Invalid
} catch (e) {
console.error(e.message); // Output: Age must be a number
}
```
### Data Binding
Proxies can facilitate data binding in frameworks, allowing automatic updates to the DOM.
```javascript
const data = {
text: 'Hello, world!'
};
const handler = {
set: (target, property, value) => {
target[property] = value;
document.getElementById('output').textContent = target.text;
return true;
}
};
const proxy = new Proxy(data, handler);
// HTML: <div id="output"></div>
proxy.text = 'Hello, Proxy!'; // The text of the div with id 'output' will be updated
```
## In Summary
JavaScript Proxies provide a robust and flexible way to intercept and customize object behavior. They are particularly useful for implementing validation, data binding, logging, and other advanced functionalities. By mastering the use of various traps, developers can leverage Proxies to build more dynamic and maintainable applications. | emmanuelj |
1,862,770 | Techno Softwares: Best SEO Services in Dubai | Businesses must have a strong online presence to succeed in the fast-paced digital age. The... | 0 | 2024-05-23T11:35:26 | https://dev.to/technosoftwarests/techno-softwares-best-seo-services-in-dubai-3ie | seo, searchengineoptimization, webservice, dubai | Businesses must have a strong online presence to succeed in the fast-paced digital age. The foundation of digital marketing is search engine optimisation (SEO), which makes your company stand out in the congested online marketplace. Techno Softwares is the name that always comes out on top when it comes to the [best SEO services in Dubai](https://technosoftwares.com/search-engine-optimization/). Techno Softwares is the go-to SEO company for companies looking to improve their online exposure and attract considerable traffic to their websites. The company is renowned for its creative techniques and outstanding outcomes.
## Why Choose Techno Softwares?
## Expertise and Experience
Techno Softwares has a group of seasoned SEO specialists on staff that are very knowledgeable and experienced. Their industry-wide experience enables them to customize tactics to each client's specific requirements. The team at Techno Softwares is equipped to enhance your internet visibility, regardless of your company's size.
## Comprehensive SEO Services
Techno Softwares offers a comprehensive suite of SEO services designed to cover all aspects of search engine optimization. Their services include
## Keyword Research and Analysis:
Identifying the most relevant and high-performing keywords to target, ensuring your content reaches the right audience.
## On-Page Optimization:
Enhancing your website's structure, content, and meta tags to improve its relevance and search engine ranking.
## Off-Page Optimization:
Building high-quality backlinks and leveraging social media to boost your website's authority and visibility.
## Technical SEO:
Ensuring your website is technically sound with fast loading times, mobile optimization, and secure connections.
Content Creation and Marketing: Crafting engaging and informative content that resonates with your audience and encourages sharing.
## Local SEO:
Optimizing your online presence for local searches, making it easier for customers in Dubai to find your business.
## Proven Track RecordWhy Choose Techno Softwares?
Techno Softwares has a track record of providing clients in a variety of industries with exceptional results. Significant gains in organic traffic, better search engine rankings, and increased conversion rates are just a few of their success tales. The business's flexibility in responding to the dynamic SEO web service guarantees that its tactics are current and efficient.
## Customized Strategies
Understanding that no two businesses are alike, Techno Softwares provides customized SEO strategies tailored to meet the specific goals and challenges of each client. They conduct in-depth audits and competitor analysis to develop a personalized roadmap for success. This bespoke approach ensures maximum return on investment and sustainable growth.
## Transparency and Reporting
Techno Softwares believes in complete transparency with their clients. They provide regular, detailed reports that outline the progress of your SEO campaigns. These reports include key metrics such as keyword rankings, traffic statistics, and conversion rates, allowing you to see the tangible impact of their efforts.
## Exceptional Customer Support
Customer satisfaction is at the heart of Techno Softwares’ philosophy. Their dedicated support team is always available to answer your queries, provide insights, and assist with any concerns. This commitment to excellent customer service sets them apart from other SEO companies in Dubai.
## SEO Web Services in Dubai
Dubai is a competitive market with businesses vying for attention from a diverse and tech-savvy audience. In such an environment, having a robust online presence is crucial. Techno Softwares’ SEO web services in Dubai are designed to help businesses of all sizes stand out. By leveraging the latest SEO techniques and tools, they ensure your website not only ranks higher in search engine results but also provides a superior user experience.
## Local SEO Mastery
For businesses targeting the local market, Techno Softwares excels in local SEO. They optimize your business listings, manage reviews, and ensure your website is prominent in local search results. This focus on local SEO helps drive foot traffic to physical locations and boosts local online visibility.
## E-Commerce SEO
In the booming e-commerce sector, Techno Softwares offers specialized SEO services to online retailers. They optimize product listings, enhance site navigation, and implement strategies to reduce cart abandonment rates, ensuring your e-commerce platform performs at its best.
## Conclusion
Techno Softwares is a leader in the field of SEO services provided in Dubai. Their persistent commitment to customer success, coupled with their customized tactics and skills, makes them the top SEO firm in Dubai. Businesses can obtain improved organic traffic, search engine rankings, and eventually more revenue by collaborating with Techno Softwares. Techno Softwares is your reliable SEO partner, whether you're trying to build a new web presence or improve your current one.Why Choose Techno Softwares?
| technosoftwarests |
1,862,769 | My Pen on CodePen | Check out this Pen I made! | 0 | 2024-05-23T11:34:50 | https://dev.to/megha_sangapur_98205768ca/my-pen-on-codepen-4pc6 | codepen | Check out this Pen I made!
{% codepen https://codepen.io/Megha-Sangapur/pen/oNRLqbL %} | megha_sangapur_98205768ca |
1,862,767 | Integrating MongoDB with Docker: A Comprehensive Guide | Docker MongoDB: Simplifying MongoDB Deployment with Docker Docker MongoDB refers to the use of... | 0 | 2024-05-23T11:31:35 | https://dev.to/saumya27/integrating-mongodb-with-docker-a-comprehensive-guide-3o5e | docker, mongodb, javascript | Docker MongoDB: Simplifying MongoDB Deployment with Docker
Docker MongoDB refers to the use of Docker containers to deploy, manage, and scale MongoDB databases. Docker simplifies the process of setting up and running MongoDB by encapsulating it in a container, ensuring consistency across different environments and simplifying deployment processes.
Key Features and Benefits
Portability:
Consistent Environments: Docker containers ensure that MongoDB runs the same way in development, testing, and production environments.
Platform Independence: Containers can run on any system that supports Docker, making them highly portable.
Scalability:
Easy Scaling: Scale MongoDB instances up or down by adjusting the number of running containers.
Orchestration Support: Use orchestration tools like Kubernetes to manage and scale MongoDB clusters.
Isolation:
Environment Isolation: Containers isolate MongoDB from other applications and databases, preventing conflicts and ensuring a clean runtime environment.
Resource Management: Limit resources (CPU, memory) allocated to MongoDB containers to optimize performance.
Simplified Deployment:
Quick Setup: Deploy MongoDB quickly with a single Docker command or a Docker Compose file.
Automation: Automate MongoDB deployments as part of a CI/CD pipeline using Docker.
Getting Started with Docker MongoDB
To run MongoDB in a Docker container, follow these steps:
Install Docker:
Ensure Docker is installed and running on your system. You can download Docker from Docker's official website.
Pull the MongoDB Image:
Pull the official MongoDB Docker image from Docker Hub.
docker pull mongo
Run MongoDB Container:
Start a MongoDB container using the pulled image.
docker run --name my-mongo -d mongo
This command runs MongoDB in a detached mode (-d) and names the container my-mongo.
Connecting to MongoDB:
You can connect to the MongoDB instance running inside the container using the MongoDB client.
docker exec -it my-mongo mongo
Using Docker Compose for MongoDB
Docker Compose allows you to define and manage multi-container Docker applications. Here’s how to set up MongoDB using Docker Compose:
Create a docker-compose.yml File:
Define your MongoDB service in the docker-compose.yml file.
version: '3.8'
services:
mongo:
image: mongo
container_name: my-mongo
ports:
- "27017:27017"
volumes:
- mongo-data:/data/db
volumes:
mongo-data:
Deploy MongoDB with Docker Compose:
Run the following command to start the MongoDB service defined in the docker-compose.yml file.
docker-compose up -d
This command starts the MongoDB container in detached mode, mapping port 27017 of the container to port 27017 of the host.
Persisting Data with Volumes
To ensure data persistence, use Docker volumes. In the above docker-compose.yml example, a named volume (mongo-data) is used to store MongoDB data, ensuring it persists even if the container is restarted or removed.
Managing MongoDB with Docker
Stopping the Container:
docker stop my-mongo
Removing the Container:
docker rm my-mongo
Viewing Logs:
docker logs my-mongo
Conclusion
Using Docker to deploy MongoDB simplifies the setup and management of the database, offering benefits such as portability, scalability, and isolation. Whether you're running MongoDB for development or production purposes, Docker provides a consistent and efficient way to manage your database instances. By utilizing Docker Compose, you can further streamline the deployment process, managing multi-container applications with ease. | saumya27 |
1,862,762 | How to secure your mobile device? | Our mobile devices have become an indispensable part of our lives. From communication and... | 0 | 2024-05-23T11:30:53 | https://infosafe24.com/posts/How-to-secure-your-mobile-device | infosec, privacy, socialengineering, cyberattacks | Our mobile devices have become an indispensable part of our lives. From communication and entertainment to banking and work tasks, these pocket-sized powerhouses hold a wealth of personal information.
However, this convenience comes with a cost — the vulnerability of our data to cyberattacks.
Actions can be taken to fortify the security of our mobile devices and those actions can be divided into three broad categories: various actions to make our device more immune to attacks, protect our data, and be mindful when online.
## Fortify the Defense of your Device:
**Lock it down:**
Opt for longer, complex passwords or PINs with a mix of uppercase and lowercase letters, numbers, and symbols, fingerprint, or facial recognition to secure your device’s lock screen.
This prevents unauthorized access to your data and apps.
**Keep software updated:**
Regularly update your operating system and app software to patch vulnerabilities and security holes. Outdated software is more susceptible to attacks.
**Consider a mobile security app:**
These apps scan your device for malicious software (malware) like viruses, spyware, and ransomware. They can quarantine or remove threats detected on your device.
Anti theft features help you locate, lock, or wipe your device remotely in case of loss or theft. Some apps can even trigger an alarm on your missing device.
Certain mobile security apps offer secure web browsing capabilities. This can involve features like blocking malicious websites, preventing phishing attempts, and protecting your online privacy.
Some apps monitor for data breaches that might expose your login credentials leaked from other online services. They can alert you if your information is compromised.
Security apps can offer additional features like malware scanning, anti-theft protection, and secure browsing.
By using a reputable app alongside other security practices like strong passwords and keeping your software updated, you can significantly improve your mobile device’s security posture.
**Be cautious with downloads:**
Only download apps from trusted sources like official app stores (Google Play Store, Apple App Store).
Avoid downloading apps from untrusted third-party app stores or websites. These sources may harbor malware-laden apps disguised as legitimate ones.
Take time to read the app description to understand its purpose and functionalities. Look for reviews from other users to gauge the app’s legitimacy and user experience. Negative reviews mentioning security concerns or suspicious behavior are red flags.
Before downloading an app, pay close attention to the permissions it requests. Does a photo editing app need access to your location or microphone? If an app requests permissions that seem unrelated to its core functionality, be cautious. Only grant permissions genuinely necessary for the app to work.
Generally, apps with fewer permission requests pose a lower security risk.
## Protect your Data:
**Turn off file sharing:**
Bluetooth file sharing and Wi-Fi Direct features allow file sharing between devices in close proximity.
However, leaving them enabled creates open doors for unauthorized access, especially on unsecure public Wi-Fi networks. Disable them when not actively sharing files.
Before sharing any file, ask yourself if the information it contains is sensitive. Financial documents, personal photos, or confidential work documents require extra caution.
Limit file sharing to trusted individuals or recipients. Avoid sharing files with people you don’t know well or on unreliable platforms.
**Encrypt your data:**
Consider encrypting your device’s storage if your device offers this option. Encryption scrambles your data, making it unreadable if stolen.
While full-device encryption is ideal, some mobile devices might not offer it, or you might only want to encrypt specific files for additional protection.
Several third-party apps offer file encryption functionalities. These apps allow you to create password-protected vaults for your sensitive files.
Research reputable apps with good reviews before installing them.
**Beware of phishing scams:**
Don’t click on suspicious links or attachments in text messages or emails. These scams can be used to steal your personal information or infect your device with malware.
Phishing messages often contain links or attachments that appear legitimate but can lead to malicious websites or download malware. Be wary of clicking on anything in unsolicited messages, even if they seem to come from familiar sources like banks or social media platforms.
Use strong passwords and enable two-factor authentication (2FA):
This adds an extra layer of security by requiring a second verification code when logging into accounts. Avoid using the same password for multiple accounts.
## Online Vigilance:
**Use secure Wi-Fi**
Avoid using public Wi-Fi networks for sensitive activities like online banking or entering passwords. If you must use public Wi-Fi, consider using a VPN (Virtual Private Network) to encrypt your internet traffic.
**Review privacy settings**
Review and adjust privacy settings for your apps and social media accounts. Limit the amount of information shared publicly and be mindful of the permissions granted to apps.
**Backup your data:**
Regularly back up your data to a secure cloud storage service or an external hard drive. This ensures you don’t lose your important information if your device is lost, stolen, or damaged.
**Be mindful of what you share:**
Think before you share anything online, especially sensitive information. Once something is online, it can be difficult to completely erase it.
## Bonus Security Tips:
Enable “Find My Device” (Android) or “Find My iPhone” (Apple) to locate your lost or stolen device remotely, and even erase data if necessary.
Disable autofill features for usernames and passwords on browsers and apps. This reduces the risk of someone else accessing your login credentials.
Review downloaded permissions: When downloading a new app, scrutinize the permissions it requests. Only grant access to features the app genuinely needs to function.
By understanding the risks and adopting responsible practices, we can transform our mobile devices from potential vulnerabilities into secure fortresses in the digital age.
| jusufoski |
1,862,765 | What's The Simplest Way To Get Started With Gardening? | Gardening is a rewarding and therapeutic activity that allows you to grow your own fresh produce,... | 0 | 2024-05-23T11:29:24 | https://dev.to/quietvillagelandscaping/whats-the-simplest-way-to-get-started-with-gardening-3o7n | Gardening is a rewarding and therapeutic activity that allows you to grow your own fresh produce, beautify your surroundings, and connect with nature. For residents of St. Louis, the rich soil and favorable climate present an excellent opportunity to delve into this fulfilling hobby. If you're wondering about the simplest way to get started with gardening, this guide will walk you through the essential steps tailored for [gardening in St. Louis](https://www.quietvillagelandscaping.com/landscape-maintenance/gardening).
## Understanding Your Local Climate
Before you start, it’s crucial to understand the local climate. St. Louis falls within USDA Hardiness Zone 6, which means the city experiences cold winters and hot, humid summers. The growing season typically lasts from late April to early October. Knowing this helps you choose the right plants and time your gardening activities effectively.
## Choosing the Right Location
Selecting the right location for your garden is vital. Most vegetables and flowers need at least six hours of sunlight daily. Look for a spot in your yard that receives ample sunlight and has good drainage. Avoid areas where water tends to collect after rain, as most plants do not thrive in waterlogged soil.
## Deciding What to Grow
For beginners, it’s best to start with easy-to-grow plants. In St. Louis, some beginner-friendly vegetables include tomatoes, peppers, lettuce, and beans. Herbs like basil, mint, and rosemary are also great choices. If you’re interested in flowers, consider marigolds, zinnias, and sunflowers, which are known for their hardiness and minimal maintenance.
## Preparing the Soil
Good soil is the foundation of a successful garden. St. Louis has a mix of clay and loamy soils. Conduct a soil test to determine its pH level and nutrient content, which you can do through local extension services or with a home testing kit. Amend the soil based on the results – for example, adding compost or aged manure to improve fertility and texture.
## Planting Your Garden
Once you’ve prepared the soil, it’s time to plant. Follow the specific planting instructions for each type of plant regarding depth and spacing. For instance, tomato plants should be spaced about 24-36 inches apart, while lettuce can be planted closer together. Water the plants thoroughly after planting to help them establish their roots.
## Watering and Maintenance
Regular watering is essential, especially during the hot St. Louis summers. Water your garden early in the morning or late in the evening to minimize evaporation. Aim to keep the soil consistently moist but not waterlogged. Mulching around your plants can help retain moisture and reduce weed growth.
## Dealing with Pests and Diseases
Gardening inevitably involves dealing with pests and diseases. Common pests in St. Louis include aphids, caterpillars, and Japanese beetles. For organic pest control, consider using neem oil or insecticidal soap. Additionally, maintaining plant health through proper watering and soil management can reduce the likelihood of diseases.
## Harvesting and Enjoying Your Produce
The most rewarding part of gardening is the harvest. Harvest vegetables and herbs when they reach their peak ripeness. For example, pick tomatoes when they’re fully colored and slightly soft to the touch. Regular harvesting encourages more production and ensures you enjoy the freshest produce.
## Seasonal Considerations
Gardening in St. Louis requires attention to the changing seasons. In spring, start with cool-season crops like lettuce and peas. Transition to warm-season crops such as tomatoes and peppers as temperatures rise. In the fall, you can plant another round of cool-season crops. Protect your garden from frost by using row covers or moving potted plants indoors.
## Gardening Resources in St. Louis
For additional support, take advantage of local gardening resources. The Missouri Botanical Garden offers numerous programs and workshops for gardeners of all levels. The St. Louis County Extension provides valuable information on soil testing, pest management, and plant selection. Joining a local gardening club can also provide support and inspiration.
## Container Gardening for Limited Spaces
If you have limited space, consider container gardening. This method allows you to grow plants in pots or other containers, making it ideal for patios, balconies, or small yards. Choose containers with good drainage and use high-quality potting soil. Many vegetables, herbs, and flowers can thrive in containers, and this method offers the flexibility to move plants as needed to optimize sunlight exposure.
## Sustainable Gardening Practices
Incorporating sustainable practices into your gardening routine can benefit both your garden and the environment. Composting kitchen scraps and yard waste creates rich organic matter to enhance your soil. Rain barrels can collect rainwater for irrigation, reducing your reliance on municipal water sources. Additionally, planting native species supports local wildlife and reduces maintenance needs.
## Conclusion
Starting a garden in St. Louis doesn’t have to be complicated. By understanding your local climate, choosing the right plants, preparing your soil, and following proper planting and maintenance techniques, you can create a thriving garden with ease. Whether you’re looking to grow fresh vegetables, fragrant herbs, or vibrant flowers, the joy of gardening lies in the journey and the satisfaction of nurturing life from the ground up. Happy gardening! | quietvillagelandscaping | |
1,862,763 | Inviting Franchise Partners in Delhi NCR: Join the Keomart Success Story | Introduction: Are you an entrepreneur in Delhi NCR looking for a lucrative business opportunity?... | 0 | 2024-05-23T11:29:05 | https://dev.to/keomart_indiaprivatelim/inviting-franchise-partners-in-delhi-ncr-join-the-keomart-success-story-1fal | webdev, javascript, beginners, tutorial | Introduction: Are you an entrepreneur in Delhi NCR looking for a lucrative business opportunity? Keomart, a leading name in the grocery retail industry, is expanding its footprint and invites you to become a franchise partner. With a proven business model and a commitment to quality, Keomart offers an exciting opportunity to be part of a growing network. Read on to discover why partnering with Keomart in Delhi NCR could be your path to business success.
Why Choose Keomart? Keomart is renowned for its wide range of quality products, customer-centric approach, and efficient operations. Here’s why you should consider joining Keomart as a franchise partner:

Established Brand: Leverage the power of a trusted and recognizable brand.
Proven Success: Benefit from a business model that has been refined and proven successful across multiple locations.
Comprehensive Support: Receive extensive training, marketing support, and operational assistance.
Growing Market: Tap into the thriving grocery retail market in Delhi NCR, driven by a large and diverse customer base.
Franchise Opportunity in Delhi NCR: Delhi NCR is one of India’s most dynamic and economically vibrant regions, offering immense potential for retail businesses. By partnering with Keomart, you can capitalize on the growing demand for high-quality grocery products and convenient shopping experiences in this bustling metropolitan area.
Investment and Requirements: Starting a Keomart franchise involves a structured investment plan designed to ensure your store’s success. Here’s what you need to know:
Initial Franchise Fee: INR 5 lakh to INR 10 lakh, depending on the location and store size.
Setup Costs: INR 20 lakh to INR 30 lakh for store layout, equipment, and initial inventory.
Working Capital: INR 5 lakh to INR 10 lakh for operational expenses.
Total Investment: Typically ranges between INR 30 lakh to INR 50 lakh.
Support and Training: Keomart is committed to your success and provides comprehensive support at every step:
Training Programs: Extensive training on store operations, inventory management, customer service, and marketing strategies.
Marketing Assistance: National advertising campaigns, promotional materials, and local marketing strategies to attract and retain customers.
Ongoing Support: Continuous support from a dedicated team to assist with inventory management, supply chain logistics, and business development.
Steps to Become a Keomart Franchise Partner:
Initial Inquiry:
Submit your franchise inquiry through Keomart’s official website or contact their franchise development team.
Provide basic information about yourself, your business background, and your interest in the Keomart franchise.
Application Review:
Complete the franchise application form.
Keomart will review your application, financial background, and business experience to determine your eligibility.
Franchise Disclosure Document (FDD):
If your application is approved, you will receive the Franchise Disclosure Document (FDD).
Review the FDD carefully and seek legal advice if necessary to understand all terms, fees, and obligations.
Site Selection and Approval:
Collaborate with Keomart’s real estate team to identify a suitable location for your store in Delhi NCR.
The selected site will undergo a thorough review and approval process to ensure it meets Keomart’s criteria.
Training and Store Setup:
Participate in Keomart’s comprehensive training program.
Set up your store according to Keomart’s guidelines, including layout, inventory setup, and installation of POS systems.
Grand Opening and Marketing Launch:
Plan a grand opening event to attract customers and generate buzz in the community.
Implement Keomart’s marketing strategies to promote your store and build a loyal customer base.
Conclusion: Joining the Keomart franchise network in Delhi NCR offers an exciting opportunity to build a successful business in the thriving grocery retail market. With a trusted brand, proven business model, and extensive support, Keomart provides the tools and resources needed for your success.
Visit here- [https://www.keomart.com/franchise-partner-faq/](https://www.keomart.com/franchise-partner-faq/)
KEOMART INDIA PRIVATE LIMITED, A1/11, Prashant Vihar Rohini, Madhuban Chowk, Near Pitampura Metro Station, New Delhi-110085 | keomart_indiaprivatelim |
1,862,738 | Using a continuation-passing interpreter to make an interactive read operation for the browser with Elm | I explain how I implemented a continuation-passing interpreter with Elm to make a read operation for a programming language that reads the user's input via a browser. | 0 | 2024-05-23T11:27:26 | https://dev.to/dwayne/using-a-continuation-passing-interpreter-to-make-an-interactive-read-operation-for-the-browser-with-elm-2d8j | continuations, plt, elm | ---
title: Using a continuation-passing interpreter to make an interactive read operation for the browser with Elm
published: true
description: I explain how I implemented a continuation-passing interpreter with Elm to make a read operation for a programming language that reads the user's input via a browser.
tags: continuations, plt, elm
# cover_image: https://direct_url_to_image.jpg
# Use a ratio of 100:42 for best results.
# published_at: 2024-05-23 11:08 +0000
---
I recently started working through [Essentials of Compilation: An Incremental Approach in Racket](https://mitpress.mit.edu/9780262047760/essentials-of-compilation/) (EOC) by [Jeremy G. Siek](https://www.youtube.com/watch?v=43VA_QaTRT8) as part of my self-study plan to learn more about programming language theory, design, and implementation.
Since I've been having great success implementing the interpreters from [EOPL in Elm](https://github.com/dwayne/elm-eopl3) I decided to continue using Elm, instead of Racket, for the interpreters and compilers in EOC.
In the first chapter, we're given the language `L_Int` which has the following concrete syntax:
```
exp ::= int | (read) | (- exp) | (+ exp exp) | (- exp exp)
L_Int ::= exp
```
Of particular interest to us, for this article, is the `read` operation. The `read` operation is supposed to prompt the user of the program for an integer.
Racket supports the `read` operation, so [an interpreter for `L_Int` in Racket](https://github.com/IUCompilerCourse/public-student-support-code/blob/7f28a214629867edc8d48c480c075e221e8c3233/interp-Lint.rkt#L18-L21) is trivial to write. The obvious question facing me was,
> How can I implement an interpreter for `L_Int` in Elm?
I'm happy to share that I came up with two practical solutions to my question which I will explain in the rest of this article.
## Solution 1: Use a fixed input buffer
The first solution I came up with was to use a fixed input buffer.
The `read` operation, though it presents an interesting implementation challenge in a pure functional language like Elm, is not particularly a point of interest from the perspective of the book. The *incremental approach* to compiler development is supposed to be the focal point.
With that in mind, any interpreter implementation that gives a satisfactory semantics to `read` is good enough.
### How does it work?
The interpreter is given an input buffer that is prepopulated with all the user's input that the program needs.
```elm
type alias Input =
List Int
run : String -> Input -> Result Error Int
```
When a `read` operation is encountered one item from the input buffer is taken and used as the user's input for that interpretation of `read`.
```elm
interpretExpr : Expr -> Input -> ( Result RuntimeError Int, Input )
interpretExpr expr input =
case expr of
...
Prim Read ->
case input of
[] ->
( Err MissingInput
, input
)
n :: restInput ->
( Ok n
, restInput
)
...
```
It accomplishes the goal and I have [tests](https://github.com/dwayne/elm-eoc/blob/45313341ada4872ae4c98a21b5edab147cdc1f17/tests/Test/Ch1/L_Int/Interpreter.elm) to prove it.
```elm
suite : Test
suite =
describe "Ch1.L_Int.Interpreter" <|
List.map testRun
[ ( "(+ 10 32)", [], 42 )
, ( "(+ 10 (- (+ 12 20)))", [], -22 )
, ( "(+ (read) (- 8))", [ 50 ], 42 )
]
```
*Here's the full [source code](https://github.com/dwayne/elm-eoc/blob/45313341ada4872ae4c98a21b5edab147cdc1f17/src/Ch1/L_Int/Interpreter.elm) of the interpreter.*
As I explained above, this solution is good enough for the purposes of the book. However, I had a nagging feeling to explore and try to figure out how I might interpret the `read` operation to make it actually wait for user input. The new question facing me was,
> How do I run the interpreter, wait for the user's input when I encounter the `read` operation, and then resume running the interpreter after I get the user's input?
The second solution I came up with involves continuation-passing interpreters and [Online Python](https://www.online-python.com/).
## Continuation-Passing Interpreters
In [Chapter 5: Continuation-Passing Interpreters](https://github.com/dwayne/elm-eopl3/tree/714cee1267b4d745697b83c431e5b40a8cd63e94/src/Ch5) of [EOPL](https://mitpress.mit.edu/9780262062794/essentials-of-programming-languages/), [Daniel P. Friedman](https://en.wikipedia.org/wiki/Daniel_P._Friedman) and [Mitchell Wand](https://www.khoury.northeastern.edu/home/wand/) present a master class on continuation-passing interpreters that is, exquisite. In that chapter they introduce the concept of a continuation as an abstraction of the control context. And, they teach you how to write interpreters that take a continuation as an argument so that you can make the control context explicit.
### What is meant by control context?
They never explicitly define what they mean by control context but I understand it to mean, all the state that you have to remember in order to continue with the rest of the computation once you're finished with the current computation.
So for e.g. the control context associated with `(+ (read) (- 8))` when you're interpreting the `read` operation is `(+ _ (- 8))` since you have to remember to do the negation and the addition once you get the user's input.
### What does that get us?
It gets us ultimate control of the computation. We can now capture the control context surrounding any read operation in order to pause the computation before performing the `read` operation and then resume the computation after getting the user's input.
## Online Python
[Online Python](https://www.online-python.com/) simply showed me that what I wanted to do was reasonable and possible.
If you type the following Python program into their editor,
```python
def sum(a, b):
return (a + b)
a = int(input('Enter 1st number: '))
b = int(input('Enter 2nd number: '))
print(f'Sum of {a} and {b} is {sum(a, b)}')
```
and hit the "Run" button you see that it pauses and waits for you to enter your input when it executes the `input` function. That's exactly what we want to achieve when we encounter a `read` operation in our language.
I don't know exactly how they did it but I do know that when it's waiting for user input it's simply using an HTML `input` element to gather the user's input.
## Solution 2: Use a continuation-passing interpreter
The second solution I came up with was to use a continuation-passing interpreter together with a user interface like the one from the [Online Python](https://www.online-python.com/) website.
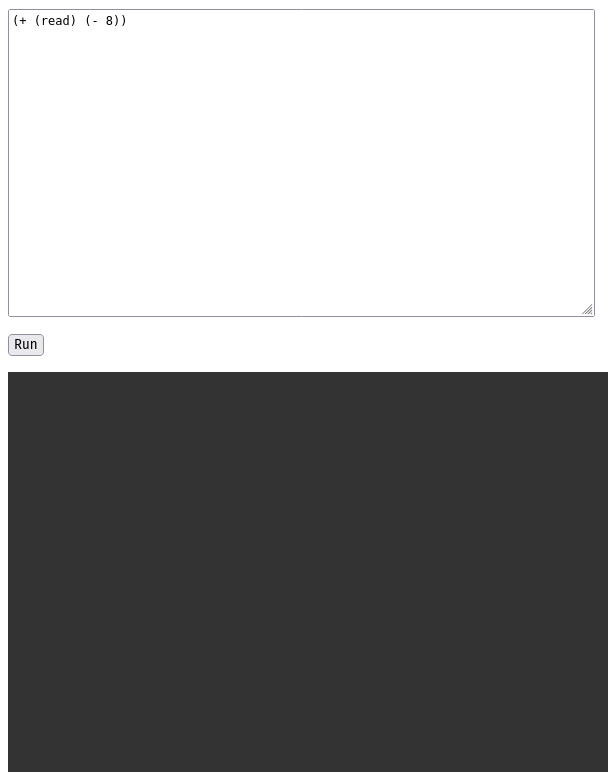
I converted [my original interpreter](https://github.com/dwayne/elm-eoc/blob/6da9b77aaf112c416516f9e176c59b9044264c2d/src/Ch1/L_Int/Interpreter.elm) into [a continuation-passing interpreter for `L_Int`](https://github.com/dwayne/elm-eoc/blob/6da9b77aaf112c416516f9e176c59b9044264c2d/src/Ch1/L_Int/CPSInterpreter.elm) using the standard techniques I learned from Chapter 5 of EOPL.
The `run` function changed from:
```elm
run : String -> Input -> Result Error Int
```
to:
```elm
type Effect
= Value Int
| ReadInt Continuation
type Continuation
= EndCont
| NegateCont Continuation
| Add1Cont AST.Expr Continuation
| Add2Cont Int Continuation
| Sub1Cont AST.Expr Continuation
| Sub2Cont Int Continuation
run : String -> Result Error Effect
```
The idea behind it is that when we encounter a `read` operation we can now return `ReadInt cont` signifying that the interpreter is interpreting a `read` operation and as such is waiting for the user's input.
```elm
interpretExpr : Expr -> Continuation -> Effect
interpretExpr expr cont =
case expr of
...
Prim Read ->
ReadInt cont
...
```
When the user hits the "Run" button in my UI, we interpret the source code in the `textarea`. If the interpreter encounters a `read` operation, we display an HTML `input` element to collect the user's input.
```elm
update : Msg -> Model -> ( Model, Cmd Msg )
update msg model =
case msg of
...
ClickedRun ->
case I.run model.source of
Ok effect ->
case effect of
I.Value n ->
( { model | lines = model.lines ++ [ Success <| String.fromInt n ] }
, Cmd.none
)
I.ReadInt readIntCont ->
( { model | maybeReadIntState = Just { value = "", cont = readIntCont } }
, focus readInputId
)
Err (I.SyntaxError _) ->
( { model | lines = model.lines ++ [ Error "Syntax Error" ] }
, Cmd.none
)
...
view : Model -> H.Html Msg
view { ..., lines, maybeReadIntState } =
H.div []
[ ...
, let
outputLineViews =
List.map viewOutputLine lines
inputLineView =
case maybeReadIntState of
Nothing ->
[]
Just { value } ->
[ H.form
[ HA.class "console__line console__line--input"
, HE.onSubmit SubmittedValue
]
[ H.span [] [ H.text ">" ]
, H.input
[ HA.id readInputId
, HA.type_ "text"
, HA.value value
, HE.onInput InputValue
]
[]
]
]
in
H.div [ HA.class "console" ] ( outputLineViews ++ inputLineView )
]
```
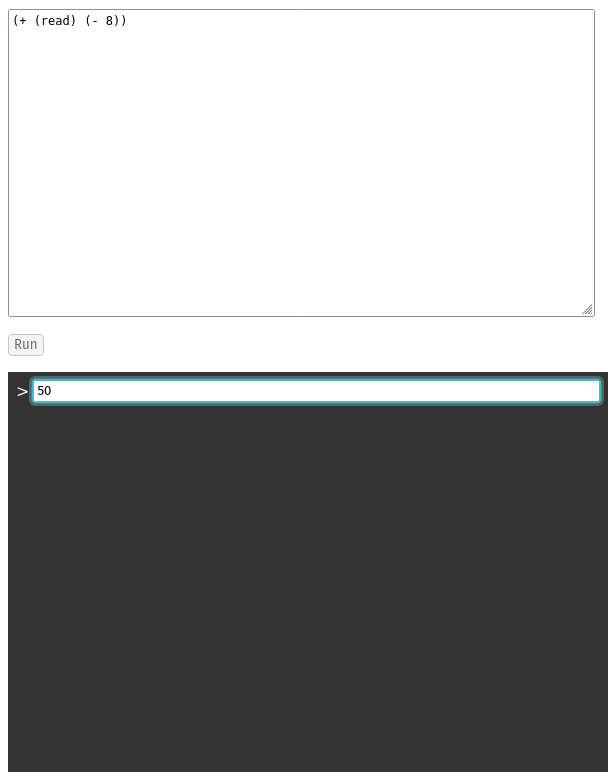
Remember, how I said:
> ... the control context associated with `(+ (read) (- 8))` when you're interpreting the `read` operation is `(+ _ (- 8))` ...
Well that's exactly what the continuation represents at this point in the interpretation,
```elm
Add1Cont (Prim (Negate 8)) EndCont -- (+ _ (- 8))
```
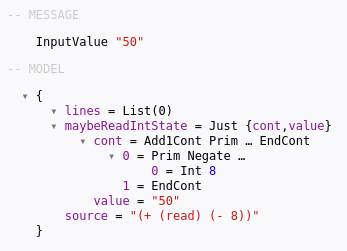
When the user submits their input, we try to convert it to an `Int` and if we're successful we resume interpretation.
```elm
update : Msg -> Model -> ( Model, Cmd Msg )
update msg model =
case msg of
...
SubmittedValue ->
case model.maybeReadIntState of
Just { value, cont } ->
case String.toInt value of
Just m ->
let
valueLine =
Success <| "> " ++ String.fromInt m
in
case I.resume m cont of
I.Value n ->
( { model
| lines = model.lines ++ [ valueLine, Success <| String.fromInt n ]
, maybeReadIntState = Nothing
}
, Cmd.none
)
I.ReadInt readIntCont ->
( { model
| lines = model.lines ++ [ valueLine ]
, maybeReadIntState = Just { value = "", cont = readIntCont }
}
, focus readInputId
)
Nothing ->
( model, Cmd.none )
Nothing ->
( model, Cmd.none )
...
```
*Here's the full [source code](https://github.com/dwayne/elm-eoc/blob/6da9b77aaf112c416516f9e176c59b9044264c2d/src/Ch1/L_Int/CPSInterpreter.elm) of the continuation-passing interpreter.*
{% embed https://youtu.be/8XxqiLZD0Y8 %}
## Conclusion
This was a fun challenge for me to solve because I was able to leverage what I learned about continuation-passing interpreters from EOPL and combine it with my web development knowledge to come up with, what I think is, a satisfying solution to the problem. | dwayne |
1,862,761 | How To Approach Problems As A Developer | Learning is a constant on the developer career journey. This won't change for a long time. Daily... | 0 | 2024-05-23T11:26:29 | https://sotergreco.com/how-to-approach-problems-as-a-developer | webdev, programming | Learning is a constant on the developer career journey. This won't change for a long time. Daily learning of new things is a must if you want to stay up-to-date with the latest trends and technologies.
Most of you have reached a point where you needed to learn a new technology or implement a feature that you've never seen before. I am going to discuss how I approach such problems and what is the best and fastest way to implement them.
## Introduction
OAuth is something I've never used before, primarily because most of the software I have created were APIs for B2B applications with only a couple of users. Now, I want to add the famous login with Twitter button to my new SaaS product.
I followed a few simple steps which I am going to share with you and in just 2 days I didn't only implement the feature but I also understood everything about OAuth and how it works.
## General Understanding
The first thing I did before starting was to understand what is under the hood of all the OAuth buttons and how they work. For that, the first thing you always need to do is watch 1-2 videos or read 1-2 articles that explain the infrastructure.
At this point, we need to understand the system design of OAuth and nothing more. Because if you know how something works, then you can implement it.
## Laying Down The Options
OAuth has 2 different implementations: OAuth1 and OAuth2. The first thing is to find out what each one is and where it is used. After some digging, I found that OAuth1 is not being used a lot anymore and most companies have migrated to OAuth2.
You need to understand that I haven't done any coding yet. It is better to spend half of your time reading and understanding rather than starting with half the information.
Misinformation is much worse than no information.
## Preparing For Coding
Now that you understand how the feature you want to implement works under the hood, you can start getting into the specifics for each language or framework.
For my tech stack, Spring Boot with Kotlin and Web Components on the frontend, I found that Spring Boot by default supports OAuth2. This research is essential before you get to the coding part.
You don't want to start creating something that already exists. Although for the article's purposes, I've done that, so if you want to see how I implemented OAuth1, you can check my other article here:
[https://sotergreco.com/first-time-implementing-oauth-on-x-thoughts](https://sotergreco.com/first-time-implementing-oauth-on-x-thoughts)
To move on, the simple thing I googled was "*OAuth2 Spring Boot Kotlin*." That way, I not only found that OAuth2 support existed but also found code examples.
Chat-GPT is something you need to keep in mind as well. Asking things like "how to implement OAuth2" can be helpful. But for this implementation, I decided to go with Grok. That's because I am trying to do an X implementation, so using the X AI should do the job better.
## Documentation
Digging through the documentation is really important. Some products have poor documentation, so you need to determine if it is well-written or not. X has very good documentation ([https://developer.x.com/en/docs/authentication/oauth-2-0](https://developer.x.com/en/docs/authentication/oauth-2-0)). I read the steps I needed to follow.
For Spring Boot, the first part of OAuth2 is built-in. However, the second part, the callback, was not, so I had to create the functions to handle it.
With the new version of Chat-GPT4o, you can give it the documentation, and it can read it for you and provide help. You can check my chat here: [https://chatgpt.com/share/3414ccca-5f3a-4050-89e7-db94f4a448ba](https://chatgpt.com/share/3414ccca-5f3a-4050-89e7-db94f4a448ba).
This is the question I asked: "*Read this documentation and give me some bullet points on how I can implement this on Spring Boot with Kotlin. I want to add OAuth2 to my API.* [*https://developer.x.com/en/docs/authentication/oauth-2-0/user-access-token*](https://developer.x.com/en/docs/authentication/oauth-2-0/user-access-token)"
## Debugging and Copilot
As you can see developing new features is much different from 3 years ago. You main friend now is AI. Of course you read the docs or watch videos but most of the work is done by the AI.
Copilot and autocompletion is very important. That's because if nows the syntax for you. This is a lot helpful when you are working on environments that you are not familiar. Use copilot for syntax related tasks and it will give you an advantage on Speed.
In the old days we were google even for syntax, now copilot knows the syntax of both libraries and languages. As you can see here I am using I library for Http requests on Kotlin and Copilot helped me a lot on that. There is no need to google "*OkHttp Kotlin Building Requests*"
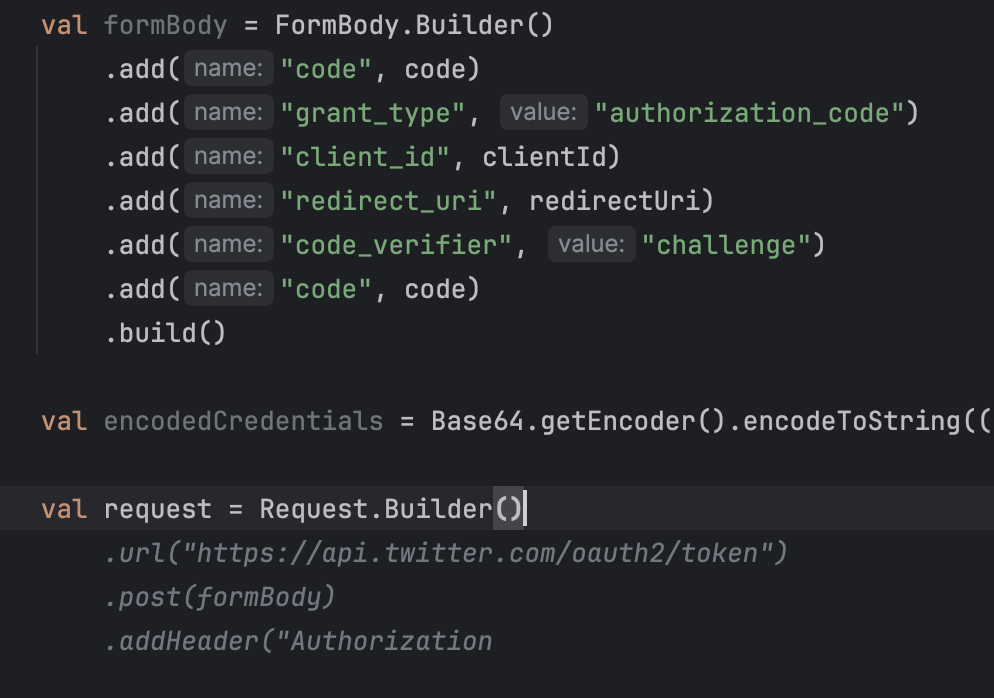
## Building a Learning Routine
Establishing a consistent learning routine is crucial for continuous growth as a developer. Allocate specific times each day or week dedicated to learning new technologies, reading technical blogs, or experimenting with coding techniques.
Consistency is key, even small, regular efforts can lead to significant improvements over time. Also don't forget to use AI to enhance you learning experience.
## Final Words
In conclusion, tackling new problems as a developer involves a structured approach: understanding the underlying concepts, thoroughly researching options, utilizing available tools and resources, and continually learning.
By leveraging AI tools, maintaining a consistent learning routine, and dedicating time to understanding documentation and system design, developers can efficiently implement new features and stay ahead in the ever-evolving tech landscape.
Thanks for reading, and I hope you found this article helpful. If you have any questions, feel free to email me at [**kourouklis@pm.me**](mailto:kourouklis@pm.me)**, and I will respond.**
You can also keep up with my latest updates by checking out my X here: [**x.com/sotergreco**](http://x.com/sotergreco) | sotergreco |
1,862,760 | Red Hat Enterprise Linux on AWS Cloud | Welcome Let’s talk about basic IT operations included in the everyday tasks range. For... | 0 | 2024-05-23T11:26:23 | https://blog.3sky.dev/article/202404-rhel-on-cloud/ | aws, rhel, security, beginners | ## Welcome
Let’s talk about basic IT operations included in the everyday tasks range. For example, accessing VMs. As you may realize (or not) - not everyone is using immutable infrastructure. Especially when their core business isn’t IT, and they are a bit bigger than 2-pizza team. That is why today we will talk about accessing the console of Red Hat Enterprise Linux 9.3 in AWS Cloud. I will show you the 3 most useful methods - in my opinion; there are no statistics.
## Initial note
Due to the fact, that I appreciate AWS CDK, all examples today will be written in TypeScript.
Additionally, I decided to use shared stacks and store VPC config separately,
as well as default instance properties.
The network is very simple, one public subnet,
one private subnet, and one NAT(default option when using `subnetType: ec2.SubnetType.PRIVATE_WITH_EGRESS`).
```typescript
import * as cdk from 'aws-cdk-lib';
import * as ec2 from 'aws-cdk-lib/aws-ec2';
export class SharedNetworkStack extends cdk.Stack {
public readonly vpc: ec2.Vpc;
constructor(scope: cdk.App, id: string, props?: cdk.StackProps) {
super(scope, id, props);
cdk.Tags.of(this).add("description", "Shared Network");
cdk.Tags.of(this).add("organization", "3sky.dev");
cdk.Tags.of(this).add("owner", "3sky");
this.vpc = new ec2.Vpc(this, 'TheVPC', {
ipAddresses: ec2.IpAddresses.cidr("10.192.0.0/20"),
maxAzs: 1,
enableDnsHostnames: true,
enableDnsSupport: true,
restrictDefaultSecurityGroup: true,
subnetConfiguration: [
{
cidrMask: 28,
name: "public",
subnetType: ec2.SubnetType.PUBLIC,
},
{
cidrMask: 28,
name: "private",
subnetType: ec2.SubnetType.PRIVATE_WITH_EGRESS,
},
],
});
}
}
```
As a base AMI for all instances, I will be using the publicly available latest RH build: `amazon/RHEL-9.3.0_HVM-20240117-x86_64-49-Hourly2-GP3`. With the smallest possible instance size. Everything is sorted in file called `bin/rhel.ts`
```typescript
#!/usr/bin/env node
import 'source-map-support/register';
import * as cdk from 'aws-cdk-lib';
import * as ec2 from 'aws-cdk-lib/aws-ec2';
import { SSHStack } from '../lib/ssh-stack';
import { ICStack } from '../lib/ic-stack';
import { SSMStack } from '../lib/ssm-stack';
import { SharedNetworkStack } from '../lib/shared-network';
const app = new cdk.App();
const network = new SharedNetworkStack(app, 'SharedNetworkStack');
const defaultInstanceProps = {
vpc: network.vpc,
machineImage: ec2.MachineImage.genericLinux({
// amazon/RHEL-9.3.0_HVM-20240117-x86_64-49-Hourly2-GP3
"eu-central-1": "ami-0134dde2b68fe1b07",
}),
instanceType: ec2.InstanceType.of(
ec2.InstanceClass.BURSTABLE2,
ec2.InstanceSize.MICRO,
),
};
new SSHStack(app, 'SSHStack', {
instanceProps: defaultInstanceProps,
vpc: network.vpc,
});
new ICStack(app, 'ICStack', {
instanceProps: defaultInstanceProps,
vpc: network.vpc,
});
new SSMStack(app, 'SSMStack', {
instanceProps: defaultInstanceProps,
});
```
## SSH
Let’s start with the basics. Regular SSH, what do we need to make this possible?
- SSH Key Pair
- ssh-server and ssh-client installed
- connection to configured port(default: 22)
- Bastion Host, as we’re simulating enterprise
### setup
The initial assumption is, that we already have a key pair if not, please generate it with the following command:
```bash
ssh-keygen \
-t ed25519 \
-C "aws@local-testing" \
-f ~/.ssh/id_ed25519_local_testing
```
Let’s back to code, we’re using a much too open Security Group for the Bastion host, regular in-VPC SG, and two hosts with the same ssh-key configured. That is why the created stack definition is rather simple:
```typescript
import * as cdk from 'aws-cdk-lib';
import { Construct } from 'constructs';
import * as ec2 from 'aws-cdk-lib/aws-ec2';
export interface SSHStackProps extends cdk.StackProps {
vpc: ec2.Vpc;
instanceProps: any;
}
export class SSHStack extends cdk.Stack {
constructor(scope: Construct, id: string, props: SSHStackProps) {
super(scope, id, props);
const theVPC = props.vpc;
const theProps = props.instanceProps;
// WARNING: change key material to your own
const awsKeyPair = new ec2.CfnKeyPair(this, "localkeypair", {
publicKeyMaterial:
"ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIJxYZEBNRLXmuign6ZgNbmaSK7cnQAgFpx8cCscoqVed local",
keyName: "localawesomekey",
});
const myKeyPair = ec2.KeyPair.fromKeyPairAttributes(this, "mykey", {
keyPairName: awsKeyPair.keyName,
});
const tooopenSG = new ec2.SecurityGroup(this, "tooopenSG", {
securityGroupName: "Allow all SSH traffic",
vpc: theVPC,
allowAllOutbound: false
});
tooopenSG.addIngressRule(
// NOTE: we should use a more specific network range with
// ec2.Peer.ipv4("x.x.x.x/24")
ec2.Peer.anyIpv4(),
ec2.Port.tcp(22),
"Allow SSH",
false,
);
const defaultSG = new ec2.SecurityGroup(this, "regularSG", {
securityGroupName: "Regular in-VPC SG",
vpc: theVPC,
allowAllOutbound: false
});
defaultSG.addIngressRule(
ec2.Peer.ipv4(theVPC.vpcCidrBlock),
ec2.Port.tcp(22),
"Allow SSH inside VPC only"
);
const bastion = new ec2.Instance(this, 'bastion-host', {
instanceName: 'bastion-host',
vpcSubnets: {
subnetType: ec2.SubnetType.PUBLIC,
},
securityGroup: tooopenSG,
keyPair: myKeyPair,
...theProps,
});
const instance = new ec2.Instance(this, 'host', {
instanceName: 'host',
vpcSubnets: {
subnetType: ec2.SubnetType.PRIVATE_WITH_EGRESS,
},
securityGroup: defaultSG,
keyPair: myKeyPair,
...theProps,
});
new cdk.CfnOutput(this, "bastionIP", {
value: bastion.instancePublicIp,
description: "Public IP address of the bastion host",
});
new cdk.CfnOutput(this, "instnaceIP", {
value: instance.instancePrivateIp,
description: "Private IP address of thsh host",
});
}
}
```
Then after executing `cdk deploy SSHStack`, and waiting around 200s, we should be able to see:
```bash
✅ SSHStack
✨ Deployment time: 200.17s
Outputs:
SSHStack.bastionIP = 3.121.228.159
SSHStack.instnaceIP = 10.192.0.24
```
Great, now we can use our ssh key and **ec2-user**, for connection with our instance.
```bash
$ ssh ec2-user@3.121.228.159 -i ~/.ssh/id_ed25519_local
Register this system with Red Hat Insights: insights-client --register
Create an account or view all your systems at https://red.ht/insights-dashboard
[ec2-user@ip-10-192-0-6 ~]$ clear
[ec2-user@ip-10-192-0-6 ~]$
logout
Connection to 3.121.228.159 closed.
```
Ok, for accessing our regular target host I strongly recommend using a regular `~/.ssh/config` file, with the following content:
```bash
Host aws-bastion
PreferredAuthentications publickey
IdentitiesOnly=yes
IdentityFile ~/.ssh/id_ed25519_local
User ec2-user
Hostname 3.76.116.53
Host aws-host
PreferredAuthentications publickey
IdentitiesOnly=yes
ProxyJump jump
IdentityFile ~/.ssh/id_ed25519_local
User ec2-user
Hostname 10.192.0.24
```
The good thing about it is that it’s very easy to configure Ansible with it. Our inventory file will be just simple:
```bash
[bastion]
aws-bastion
[instance]
aws-host
[aws:children]
aws-bastion
aws-host
```
However, in the case of a real-world system, I would recommend using Ansible dynamic inventory, based on proper tagging.
### props
- easy-to-implement solution
- standard SSH, so we can use Ansible just after deployment
- no additional costs(besides Bastion host)
### cons
- exposing VMs to the public internet isn’t the most secure solution
- we need to manage SSH key pair
- we need to manage users
- we need to manage accesses manually, from the OS level
- no dedicated logging solution, besides Syslog
## SSM Session Manager
Setting SSM based on [documentation](https://docs.aws.amazon.com/systems-manager/latest/userguide/session-manager-prerequisites.html) could be a bit more challenging, as we need to:
- install SSM agent
- configure role and instance profile
### setup
```typescript
import * as cdk from 'aws-cdk-lib';
import { Construct } from 'constructs';
import * as ec2 from 'aws-cdk-lib/aws-ec2';
import * as iam from 'aws-cdk-lib/aws-iam'
export interface SSMStackProps extends cdk.StackProps {
instanceProps: any;
}
export class SSMStack extends cdk.Stack {
constructor(scope: Construct, id: string, props: SSMStackProps) {
super(scope, id, props);
const theProps = props.instanceProps;
const ssmRole = new iam.Role(this, "SSMRole", {
assumedBy: new iam.ServicePrincipal("ec2.amazonaws.com"),
managedPolicies: [
iam.ManagedPolicy.fromAwsManagedPolicyName("AmazonSSMManagedInstanceCore")
],
roleName: "SSMRole"
});
new iam.InstanceProfile(this, "SSMInstanceProfile", {
role: ssmRole,
instanceProfileName: "SSMInstanceProfile"
});
const userData = ec2.UserData.forLinux();
userData.addCommands(
'set -o xtrace',
'sudo dnf install -y https://s3.amazonaws.com/ec2-downloads-windows/SSMAgent/latest/linux_amd64/amazon-ssm-agent.rpm',
'sudo systemctl enable amazon-ssm-agent',
'sudo systemctl start amazon-ssm-agent'
);
const instnace = new ec2.Instance(this, 'instance-with-ssm', {
instanceName: 'instance-with-ssm',
vpcSubnets: {
subnetType: ec2.SubnetType.PRIVATE_WITH_EGRESS,
},
role: ssmRole,
allowAllOutbound: true,
detailedMonitoring: true,
userData: userData,
...theProps,
});
new cdk.CfnOutput(this, "HostID", {
value: instnace.instanceId,
description: "ID of the regular host",
});
new cdk.CfnOutput(this, "hostDNS", {
value: instnace.instancePrivateDnsName,
description: "Hostname of the regular host",
});
}
}
```
As you can see, we need to specify the role and instance profile(which can’t be displayed in GUI), and then we place the instance in a private subnet with specific user data and role. After a while we should be able to connect via CLI:
```bash
$ aws ssm start-session --target i-0110d03f4713d475c
Starting session with SessionId: kuba@3sky.dev-6n5goh43iisz45cmvpht54ize4
sh-5.1$ sudo su
[root@ip-10-192-0-26 bin]#
```
Or via GUI:
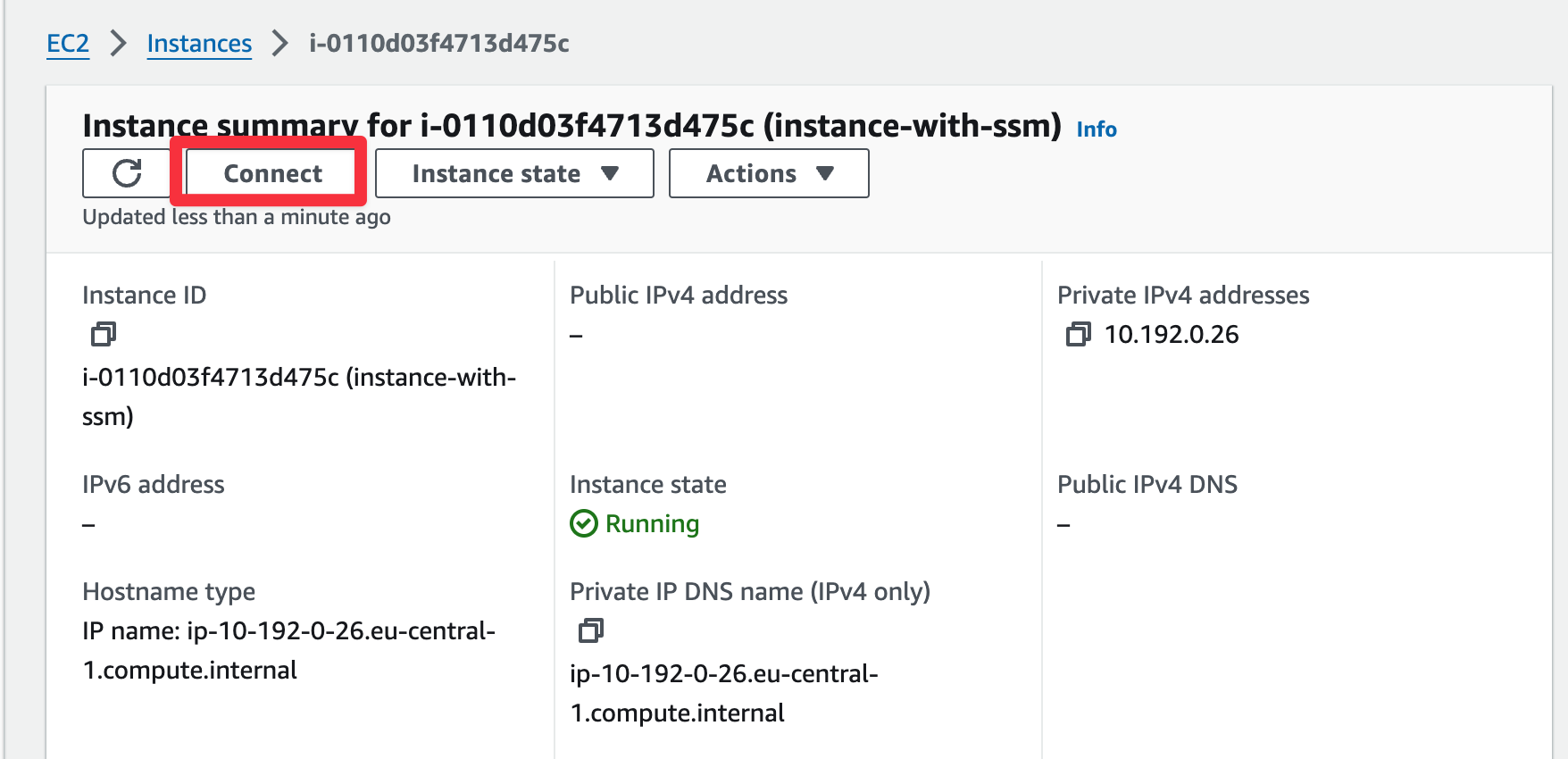
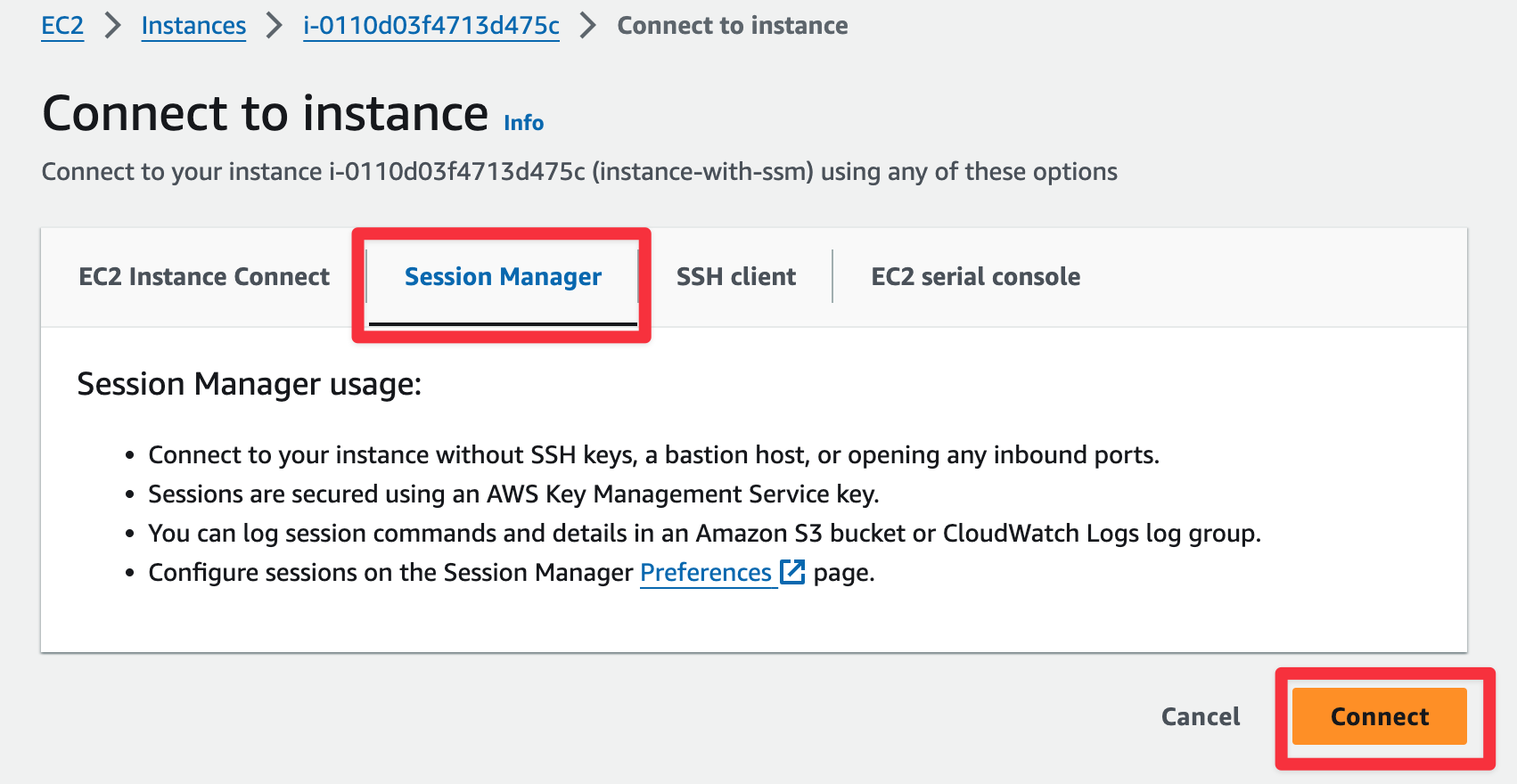
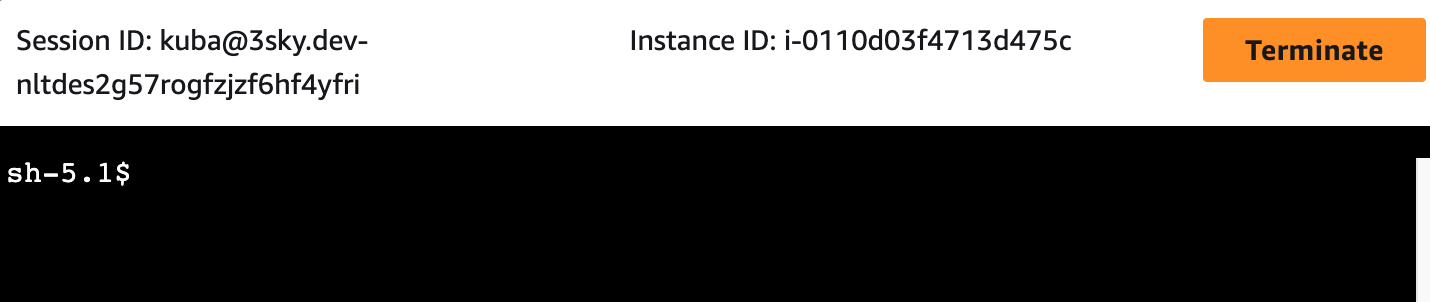
### bonus: cockpit
As we’re using the Red Hat system(however also available on Ubuntu etc), and SSM supports port forwarding we can utilize the power of the cockpit. For example, manage subscriptions, check security recommendations, and connect with [Red Hat Insights](https://www.redhat.com/en/technologies/management/insights). How to do it? Login to our instance, create an admin user with a password, and then start the port forwarding session.
```bash
# login to host
$ aws ssm start-session --target i-0113d03f4713d412b
# become a root and create the needed user
sh-5.1$ sudo su
[root@ip-10-192-0-24:~]$ sudo useradd kuba
[root@ip-10-192-0-24:~]$ sudo passwd kuba
[root@ip-10-192-0-24:~]$ sudo usermod -aG wheel kuba
[root@ip-10-192-0-24:~]$ exit
sh-5.1$ exit
## start port-forwarding from the workstation
$ aws ssm start-session \
--target i-0113d03f4713d412b
--document-name AWS-StartPortForwardingSessionToRemoteHost \
--parameters '{"portNumber":["9090"],"localPortNumber":["9090"],"host":["ip-10-192-0-24"]}'
```
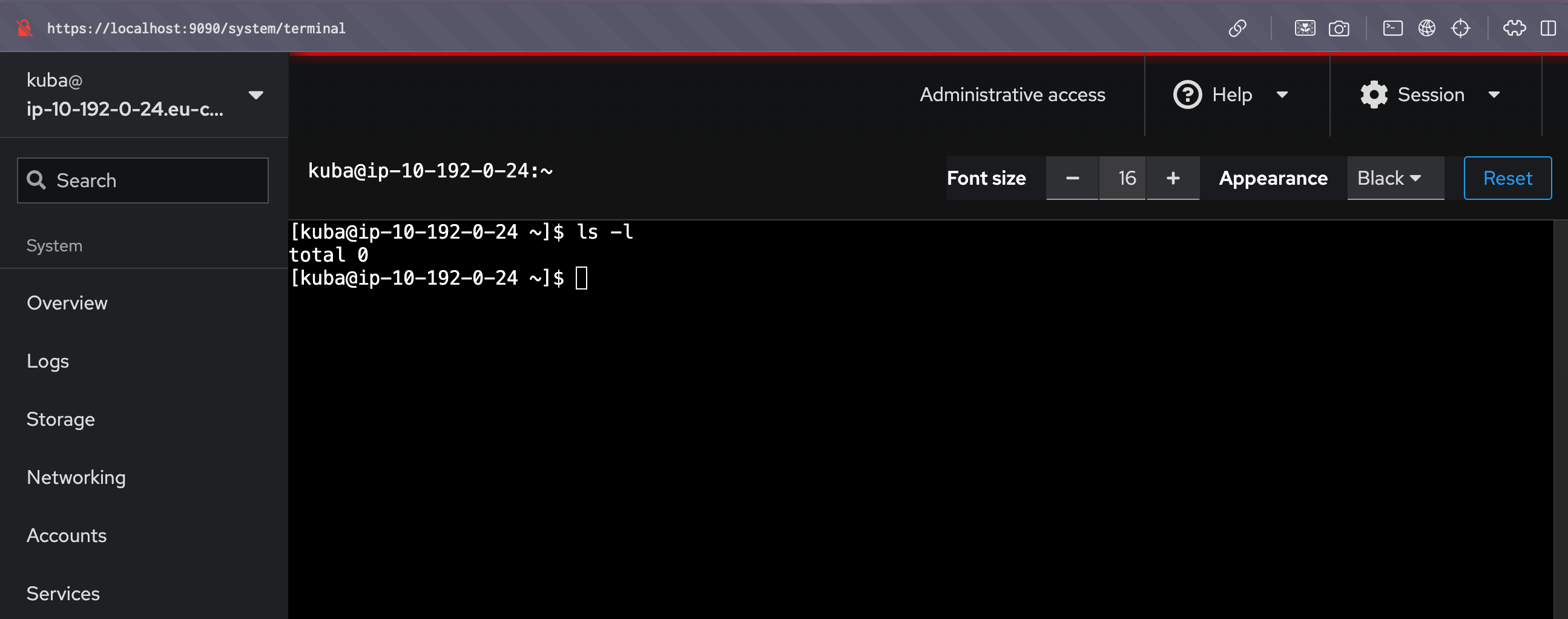
### props
- straightforward setup
- allow the user to access the instance from GUI and CLI
- does not require using or storing ssh-keys
- has built in monitoring with CloudWatch
- provides the ability to restrict access based on IAM
- support port forwarding (useful for DB access)
### cons
- using Ansible will be challenging(however supported)
- requires more AWS-specific knowledge than Bastion host
- in case of failure, push us to annoying debugging
## EC2 instance connect
Our EC2 Instance Connect setup and configuration will be based on [official documentation](https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/ec2-instance-connect-set-up.html).
Here are the main prerequisites we have:
- installed ec2-instance-connect packages on our host, which are not included in the default Red Hat build
- EC2 instance connect endpoint placed in the corresponding network
- open network connection to instance security group on TCP/22
- open network connection from EC2 instance to connect security group to instances on TCP/22
### setup
Based on these prerequisites content of our file is as:
```typescript
import * as cdk from 'aws-cdk-lib';
import { Construct } from 'constructs';
import * as ec2 from 'aws-cdk-lib/aws-ec2';
export interface ICStackProps extends cdk.StackProps {
vpc: ec2.Vpc;
instanceProps: any;
}
export class ICStack extends cdk.Stack {
constructor(scope: Construct, id: string, props: ICStackProps) {
super(scope, id, props);
const theVPC = props.vpc;
const theProps = props.instanceProps;
const iceSG = new ec2.SecurityGroup(this, "iceSG", {
securityGroupName: "Instance Connect SG",
vpc: theVPC,
allowAllOutbound: false
});
iceSG.addEgressRule(
ec2.Peer.ipv4(theVPC.vpcCidrBlock),
ec2.Port.tcp(22),
"Allow outbound traffic from SG",
);
// WARNING: We need outbound for package installation
const iceSGtoVM = new ec2.SecurityGroup(this, "iceSGtoVM", {
securityGroupName: "Allow access over instance connect",
vpc: theVPC,
});
iceSGtoVM.addIngressRule(
iceSG,
ec2.Port.tcp(22),
"Allow SSH traffic from iceSG",
);
new ec2.CfnInstanceConnectEndpoint(this, "myInstanceConnectEndpoint", {
securityGroupIds: [iceSG.securityGroupId],
subnetId: theVPC.privateSubnets[0].subnetId
});
const userData = ec2.UserData.forLinux();
userData.addCommands(
'set -o xtrace',
'mkdir /tmp/ec2-instance-connect',
'curl https://amazon-ec2-instance-connect-us-west-2.s3.us-west-2.amazonaws.com/latest/linux_amd64/ec2-instance-connect.rpm -o /tmp/ec2-instance-connect/ec2-instance-connect.rpm',
'curl https://amazon-ec2-instance-connect-us-west-2.s3.us-west-2.amazonaws.com/latest/linux_amd64/ec2-instance-connect-selinux.noarch.rpm -o /tmp/ec2-instance-connect/ec2-instance-connect-selinux.rpm',
'sudo yum install -y /tmp/ec2-instance-connect/ec2-instance-connect.rpm /tmp/ec2-instance-connect/ec2-instance-connect-selinux.rpm'
);
const instnace = new ec2.Instance(this, 'instance-with-ic', {
instanceName: 'instance-with-ic',
vpcSubnets: {
subnetType: ec2.SubnetType.PRIVATE_WITH_EGRESS,
},
securityGroup: iceSGtoVM,
allowAllOutbound: true,
detailedMonitoring: true,
userData: userData,
...theProps,
});
new cdk.CfnOutput(this, "HostIP", {
value: instnace.instanceId,
description: "Public IP address of the regular host",
});
}
}
```
As you can see, the longest part is just user-data for downloading and installing needed packages. What is important in my opinion, we always should test it before deploying it on production. In case of errors with the installation process, debugging will be hard and will require adding a bastion host with keys, and instance recreation.
After deploying a stack(a bit longer this time), we should be able to access our instance with CLI:
```bash
$ aws ec2-instance-connect ssh --instance-id i-08385338c2614df28
The authenticity of host '10.192.0.26 (<no hostip for proxy command>)' can't be established.
ED25519 key fingerprint is SHA256:BAxtwbZYKsK6hTJbvqOGgulGYftNQHZHMSpBkIGRTeY.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '10.192.0.26' (ED25519) to the list of known hosts.
Register this system with Red Hat Insights: insights-client --register
Create an account or view all your systems at https://red.ht/insights-dashboard
[ec2-user@ip-10-192-0-26 ~]$
```
or via GUI:
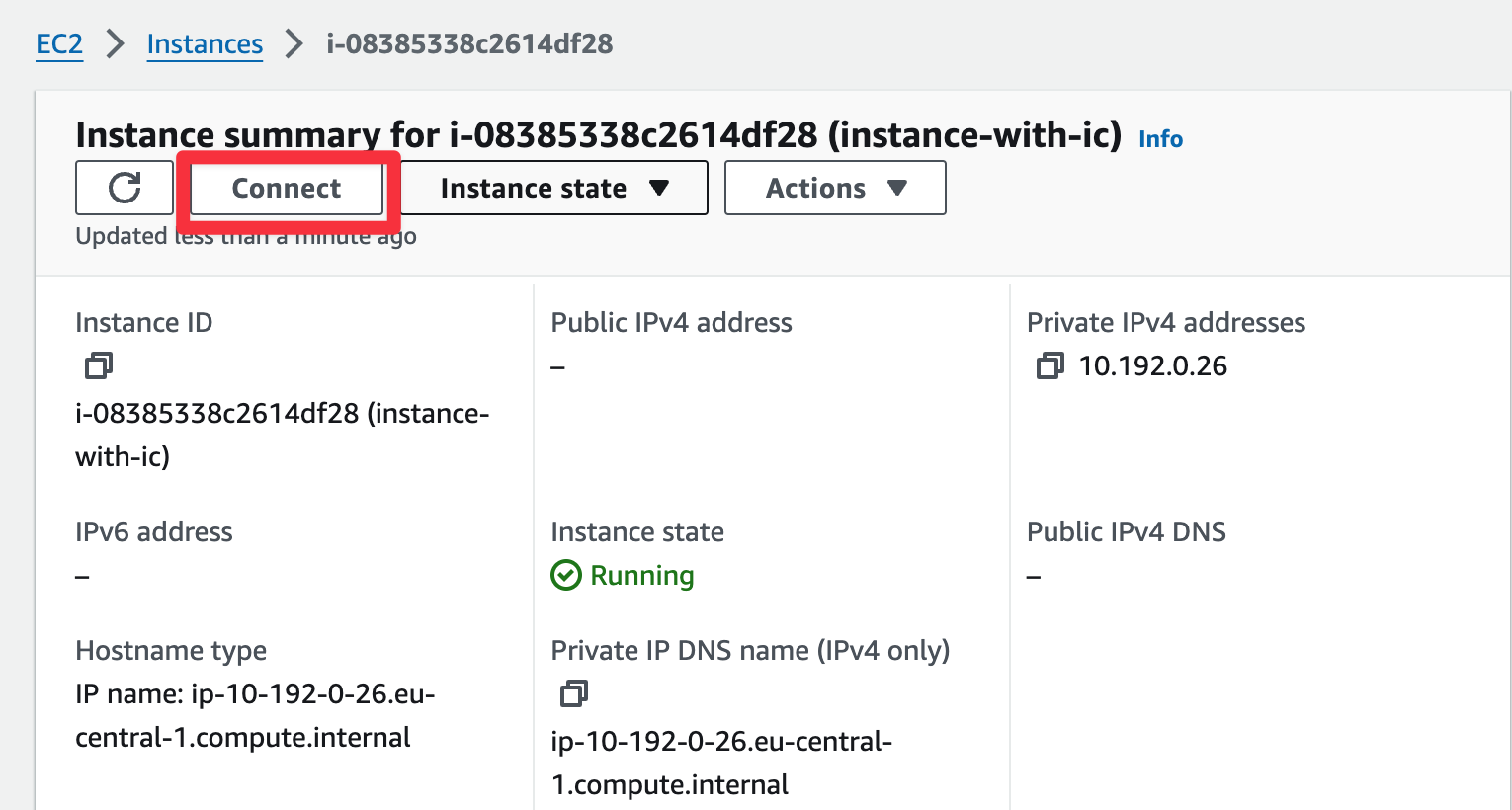
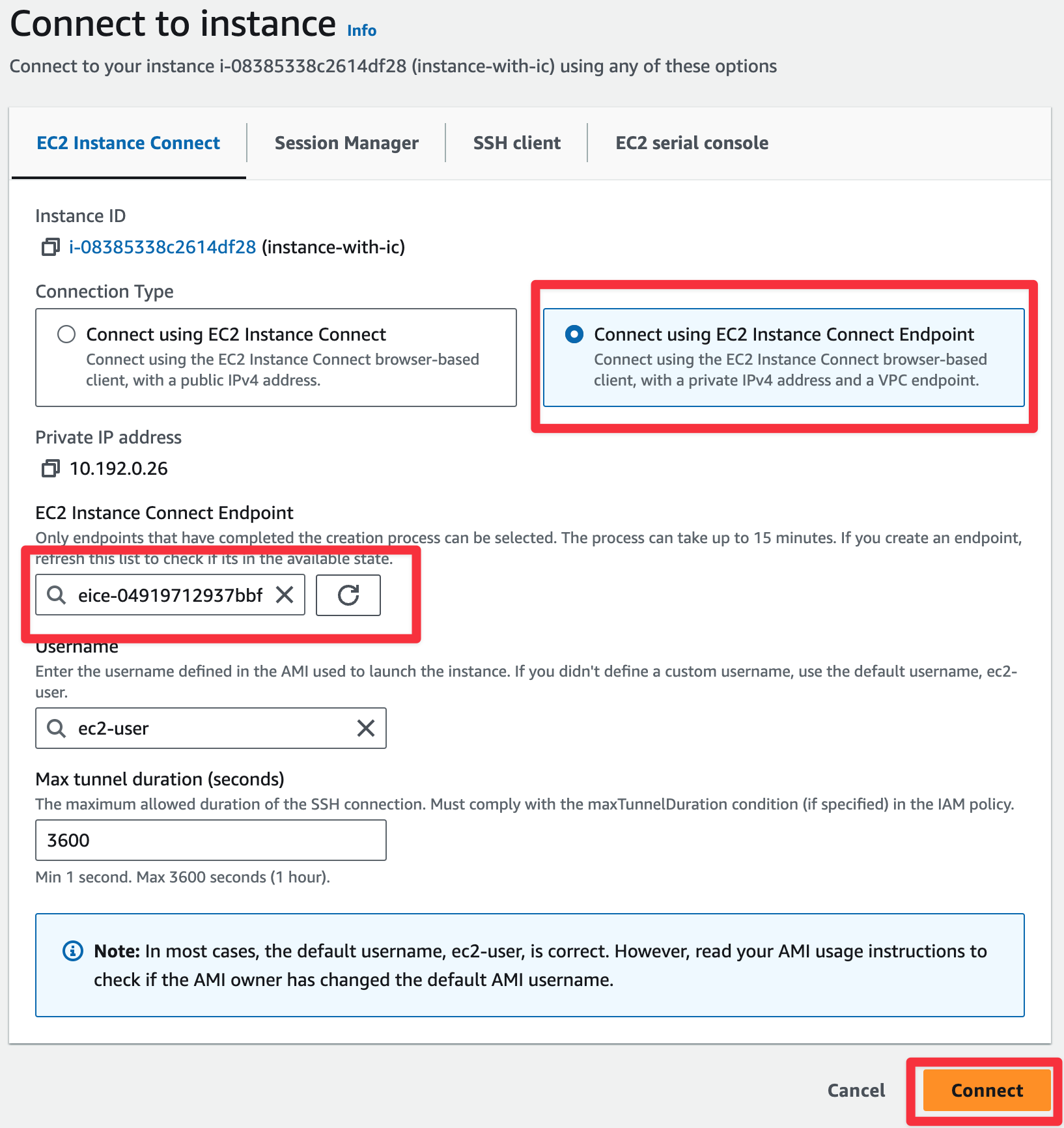
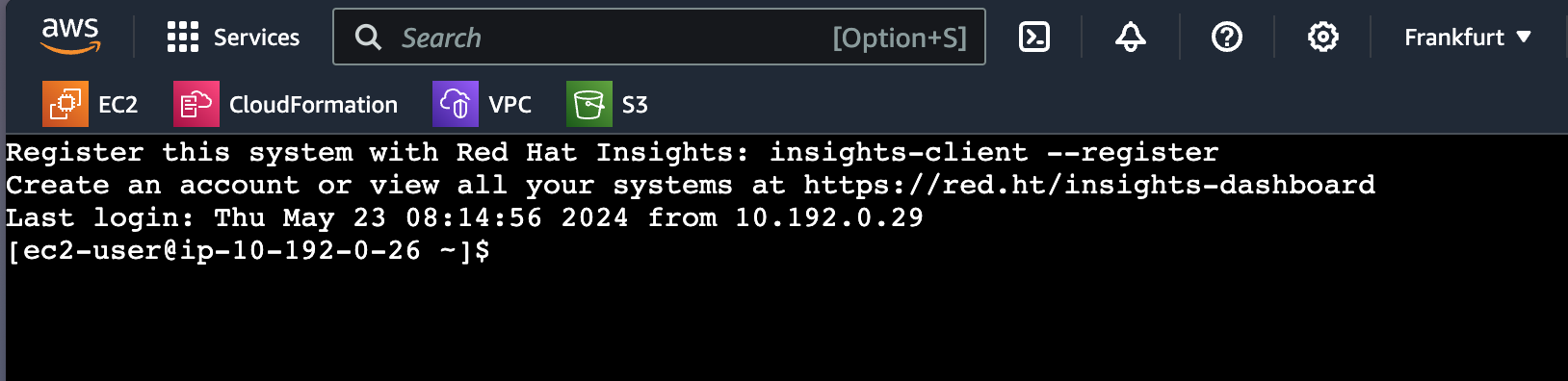
### props
- straightforward setup
- allow the user to access the instance from GUI and CLI
- does not require using or storing ssh-keys
- has built in monitoring with CloudWatch
- provides the ability to restrict access based on IAM
### cons
- using Ansible will be very challenging(no official support or plugin)
- requires more AWS-specific knowledge than Bastion host
- in case of failure, push us to annoying debugging
## Final notes
- network setup was simplified; one AZ; 2 subnets
- security groups were to open, especially outbound rules(due to package downloading)
- SSM could be used over endpoints as well:
- com.amazonaws.:aws-region:.ssm
- com.amazonaws.:aws-region:.ssmmessages
- com.amazonaws.:aws-region:.ssmmessages
- we should use already pre-built AMI to avoid this issue
- repo as always can be find [here](https://github.com/3sky/rhel-on-cloud)
## Summary
As you can see setting up RHEL in AWS isn’t such hard, for sure it’s more expensive and requires ec2-connect-instance or SSM agent installation(Amazon Linux does not), but if we’re going to use RHEL in the cloud, probably we have good reason to do so. For example, great support, Insights, or Cloud Console, but my job was to show possibilities and do it with style.
| 3sky |
1,862,759 | Apple Face ID not working? Here's how to fix it | There can be a few reasons why your iPhone's facial recognition, also known as Face ID, might not be... | 0 | 2024-05-23T11:26:16 | https://dev.to/luxandcloud/apple-face-id-not-working-heres-how-to-fix-it-403n | ipad, programming, tutorial, security | There can be a few reasons why your iPhone's facial recognition, also known as Face ID, might not be working as expected. It can be frustrating when this happens, especially since it's a convenient way to unlock your phone. Let's explore some common culprits that might be causing the issue and how you can fix it.
## How Does Apple's Face ID Technology Work?
Face ID is Apple's facial recognition technology, using the TrueDepth camera system located at the top of newer iPhone and iPad models. Here’s a simple breakdown of how it works:
- Face detection. When you turn on your device or use Face ID, the TrueDepth camera system activates. It projects millions of invisible infrared dots onto your face to create a detailed depth map and takes an infrared image of your face.
- Infrared image. The infrared camera captures an image of your face, including both depth information and a 2D image.
- Data processing. The infrared image and depth map are sent to the device's Secure Enclave, a special security processor. The Secure Enclave processes this data locally, using complex algorithms to generate a mathematical representation of your face.
- Face matching. This mathematical representation is compared with the facial data you initially enrolled during the Face ID setup.
- Authentication. If the new data matches the stored facial data, Face ID successfully authenticates, unlocking your device or completing the action (such as authorizing a purchase or accessing a secure app).
Learn more here: [Apple Face ID not working? Here's how to fix it](https://luxand.cloud/face-recognition-blog/apple-face-id-not-working-heres-how-to-fix-it/?utm_source=devto&utm_medium=apple-face-id-not-working-heres-how-to-fix-it) | luxandcloud |
1,862,758 | Architects in Chennai | Architects in Chennai are creative professionals who design buildings and spaces. They work in... | 0 | 2024-05-23T11:26:05 | https://dev.to/ammu_thankam_33a8aaa32949/architects-in-chennai-5ec4 | architects | [Architects in Chennai](https://dqarchitects.in/) are creative professionals who design buildings and spaces. They work in architectural firms in Chennai, collaborating with clients to bring their visions to life. These experts blend aesthetics, functionality, and sustainability in their designs, catering to diverse needs and preferences. From innovative residential projects to modern commercial spaces, [Architectural Firms in Chennai](https://dqarchitects.in/best-architects-in-chennai.php) excel in crafting environments that inspire and endure. With a focus on detail and quality, these architectural firms in Chennai contribute significantly to the city's skyline and urban fabric, shaping its future with ingenuity and expertise.
| ammu_thankam_33a8aaa32949 |
1,862,757 | Top AML Solutions in 2024 | Financial institutions must continually adapt to the ever-evolving landscape of anti-money laundering... | 0 | 2024-05-23T11:24:16 | https://dev.to/luxandcloud/top-aml-solutions-in-2024-5c7d | ai, news, machinelearning | Financial institutions must continually adapt to the ever-evolving landscape of anti-money laundering (AML) in order to remain ahead of sophisticated financial crimes. Businesses must invest in strong AML solutions as a result of increasingly strict regulations. The best AML solutions for 2024 will be revealed in this blog post, along with an analysis of their salient characteristics. Financial institutions can improve their compliance systems, reduce risks, and eventually remain ahead of the curve in the battle against financial crime by utilizing these cutting-edge solutions.
## What Is Anti-Money Laundering (AML) Software?
Software specifically designed to assist financial institutions and enterprises in preventing, detecting, and mitigating money laundering activities is known as anti-money laundering (AML) software. Money laundering is a sophisticated financial crime in which offenders try to pass off the source of monies gained through illicit means as lawful. AML software gives businesses access to a number of tools and features that help them spot suspicious activity, keep an eye on transactions, investigate customers, and make sure they are following the law.
At its core, AML software automates and streamlines the process of identifying potential money laundering risks. In order to find patterns, abnormalities, and suspicious activity, it examines huge amounts of transaction data, customer information, and information from outside sources. Advanced analytics, machine learning algorithms, and artificial intelligence are utilized by AML software to detect intricate money laundering schemes, encompassing actions such as structuring, shell company operations, and the use of money mules.
**A key component of AML software is customer due diligence (CDD) and know-your-customer (KYC) processes. These involve:**
- Customer identification and verification. AML software helps in collecting and verifying customer identification information, such as names, addresses, dates of birth, and government-issued IDs. This ensures that customers are who they claim to be and helps prevent identity theft or impersonation.
- Customer risk assessment. Assessing each customer’s risk is the main component of the CDD process. AML software examines a variety of variables, including the customer’s business or line of work, political inclination, place of residence, and funding source. This risk assessment aids in figuring out how much attention and oversight is right for each individual consumer.
- Ongoing monitoring and transaction analysis. KYC processes don’t just end with customer onboarding. AML software continuously monitors customer transactions to detect suspicious activities or deviations from normal behavior. It may include setting transaction limits, monitoring high-risk jurisdictions, and analyzing transaction patterns to identify potential money laundering red flags.
- Sanctions and watchlist screening. Sanctions and watchlists from law enforcement and regulatory organizations are included into AML software. Customers are screened against these lists in order to flag and identify individuals or entities that are flagged for political or reputational risk to the institution, are known to be involved in criminal activity, or are subject to penalties.
AML software plays a critical role in helping financial institutions combat the complex issue of money laundering. By leveraging advanced technologies and streamlined processes, AML software enables organizations to stay compliant, protect their reputation, and contribute to the broader effort of disrupting financial crimes.
Learn more here: [Top AML Solutions in 2024](https://luxand.cloud/face-recognition-blog/top-aml-solutions-in-2024/?utm_source=devto&utm_medium=top-aml-solutions-in-2024) | luxandcloud |
1,862,756 | split() in PyTorch | *Memos: My post explains vsplit(). My post explains hsplit(). My post explains dsplit(). My... | 0 | 2024-05-23T11:22:52 | https://dev.to/hyperkai/split-in-pytorch-nga | pytorch, split, tensor, function | *Memos:
- [My post](https://dev.to/hyperkai/vsplit-in-pytorch-4915) explains [vsplit()](https://pytorch.org/docs/stable/generated/torch.vsplit.html).
- [My post](https://dev.to/hyperkai/hsplit-in-pytorch-4b1d) explains [hsplit()](https://pytorch.org/docs/stable/generated/torch.hsplit.html).
- [My post](https://dev.to/hyperkai/dsplit-in-pytorch-594c) explains [dsplit()](https://pytorch.org/docs/stable/generated/torch.dsplit.html).
- [My post](https://dev.to/hyperkai/tensorsplit-in-pytorch-30m5) explains [tensor_split()](https://pytorch.org/docs/stable/generated/torch.tensor_split.html).
- [My post](https://dev.to/hyperkai/chunk-in-pytorch-30f5) explains [chunk()](https://pytorch.org/docs/stable/generated/torch.chunk.html).
- [My post](https://dev.to/hyperkai/unbind-in-pytorch-3lk9) explains [unbind()](https://pytorch.org/docs/stable/generated/torch.unbind.html).
[split()](https://pytorch.org/docs/stable/generated/torch.split.html) can get the one or more 1D or more D tensors of zero or more splitted elements from the 1D or more D tensor of zero or more elements as shown below:
*Memos:
- `split()` can be used with [torch](https://pytorch.org/docs/stable/torch.html) and a tensor.
- The 1st argument with `torch` or using a tensor is `tensor`(Required-Type:`tensor` of `int`, `float`, `complex` or `bool`).
- The 2nd argument with `torch` or the 1st argument with a tensor is `split_size_or_sections`(Required-Type:`int`, `tuple` of `int` or `list` of `int`). *Don't use `split_size_or_sections=` with a tensor.
- The 3rd argument with `torch` or the 2nd argument with a tensor is `dim`(Optional-Default:`0`-Type:`int`).
- The total number of the zero or more elements of one or more returned tensors changes.
- One or more returned tensors keep the dimension of `tensor`.
```python
import torch
my_tensor = torch.tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]])
torch.split(tensor=my_tensor, split_size_or_sections=1)
my_tensor.split(1)
torch.split(tensor=my_tensor, split_size_or_sections=1, dim=0)
torch.split(tensor=my_tensor, split_size_or_sections=1, dim=-2)
# (tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]))
torch.split(tensor=my_tensor, split_size_or_sections=1, dim=1)
torch.split(tensor=my_tensor, split_size_or_sections=1, dim=-1)
# (tensor([[0], [4], [8]]),
# tensor([[1], [5], [9]]),
# tensor([[2], [6], [10]]),
# tensor([[3], [7], [11]]))
torch.split(tensor=my_tensor, split_size_or_sections=2)
torch.split(tensor=my_tensor, split_size_or_sections=2, dim=0)
torch.split(tensor=my_tensor, split_size_or_sections=2, dim=-2)
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]))
torch.split(tensor=my_tensor, split_size_or_sections=2, dim=1)
torch.split(tensor=my_tensor, split_size_or_sections=2, dim=-1)
# (tensor([[0, 1], [4, 5], [8, 9]]),
# tensor([[2, 3], [6, 7], [10, 11]]))
torch.split(tensor=my_tensor, split_size_or_sections=3)
torch.split(tensor=my_tensor, split_size_or_sections=3, dim=0)
torch.split(tensor=my_tensor, split_size_or_sections=3, dim=-2)
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),)
torch.split(tensor=my_tensor, split_size_or_sections=3, dim=1)
torch.split(tensor=my_tensor, split_size_or_sections=3, dim=-1)
# (tensor([[0, 1, 2], [4, 5, 6], [8, 9, 10]]),
# tensor([[3], [7], [11]]))
torch.split(tensor=my_tensor, split_size_or_sections=(0, 3))
torch.split(tensor=my_tensor, split_size_or_sections=(0, 3), dim=0)
torch.split(tensor=my_tensor, split_size_or_sections=(0, 3), dim=-2)
# (tensor([], size=(0, 4), dtype=torch.int64),
# tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]))
torch.split(tensor=my_tensor, split_size_or_sections=(1, 2))
torch.split(tensor=my_tensor, split_size_or_sections=(1, 2), dim=0)
torch.split(tensor=my_tensor, split_size_or_sections=(1, 2), dim=-2)
# (tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7], [8, 9, 10, 11]]))
torch.split(tensor=my_tensor, split_size_or_sections=(2, 1))
torch.split(tensor=my_tensor, split_size_or_sections=(2, 1), dim=0)
torch.split(tensor=my_tensor, split_size_or_sections=(2, 1), dim=-2)
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7]]),
# tensor([[8, 9, 10, 11]]))
torch.split(tensor=my_tensor, split_size_or_sections=(3, 0))
torch.split(tensor=my_tensor, split_size_or_sections=(3, 0), dim=0)
# (tensor([[0, 1, 2, 3], [4, 5, 6, 7], [8, 9, 10, 11]]),
# tensor([], size=(0, 4), dtype=torch.int64))
torch.split(tensor=my_tensor, split_size_or_sections=(1, 1, 1))
torch.split(tensor=my_tensor, split_size_or_sections=(1, 1, 1), dim=0)
torch.split(tensor=my_tensor, split_size_or_sections=(1, 1, 1), dim=-2)
# (tensor([[0, 1, 2, 3]]),
# tensor([[4, 5, 6, 7]]),
# tensor([[ 8, 9, 10, 11]]))
my_tensor = torch.tensor([[0., 1., 2., 3.],
[4., 5., 6., 7.],
[8., 9., 10., 11.]])
torch.split(tensor=my_tensor, split_size_or_sections=1)
# (tensor([[0., 1., 2., 3.]]),
# tensor([[4., 5., 6., 7.]]),
# tensor([[8., 9., 10., 11.]]))
my_tensor = torch.tensor([[0.+0.j, 1.+0.j, 2.+0.j, 3.+0.j],
[4.+0.j, 5.+0.j, 6.+0.j, 7.+0.j],
[8.+0.j, 9.+0.j, 10.+0.j, 11.+0.j]])
torch.split(tensor=my_tensor, split_size_or_sections=1)
# (tensor([[0.+0.j, 1.+0.j, 2.+0.j, 3.+0.j]]),
# tensor([[4.+0.j, 5.+0.j, 6.+0.j, 7.+0.j]]),
# tensor([[8.+0.j, 9.+0.j, 10.+0.j, 11.+0.j]]))
my_tensor = torch.tensor([[True, False, True, False],
[False, True, False, True],
[True, False, True, False]])
torch.split(tensor=my_tensor, split_size_or_sections=1)
# (tensor([[True, False, True, False]]),
# tensor([[False, True, False, True]]),
# tensor([[True, False, True, False]]))
``` | hyperkai |
1,862,755 | Exploring the New Frontier of Crypto Coins | Introduction In the dynamic realm of cryptocurrencies, innovation never ceases. As we step into... | 0 | 2024-05-23T11:22:10 | https://dev.to/brianlindsey/exploring-the-new-frontier-of-crypto-coins-2je3 | <h2><strong>Introduction</strong></h2>
<p><span style="font-weight: 400;">In the dynamic realm of cryptocurrencies, innovation never ceases. As we step into 2024, the crypto space continues to witness the birth of </span><a href="https://wooddragon.pro/"><strong>new crypto coins 2024</strong></a><span style="font-weight: 400;">, each vying for a place in the digital economy. These novel tokens represent not just financial assets, but also the cutting edge of technology and the evolving landscape of decentralized finance (DeFi).</span></p>
<h3><strong>Unveiling 2024's Crypto Landscape</strong></h3>
<p><span style="font-weight: 400;">New crypto coins emerge against the backdrop of a rapidly evolving financial ecosystem. The year 2024 promises to be a pivotal one for the crypto market, characterized by both continuity and transformation. While established players like Bitcoin and Ethereum maintain their dominance, fresh contenders are reshaping the industry with innovative features and use cases.</span></p>
<h4><strong>The Rise of Innovation</strong></h4>
<p><span style="font-weight: 400;">The surge of </span><a href="https://wooddragon.pro/"><strong>new crypto coins</strong></a><span style="font-weight: 400;"> reflects the relentless pursuit of innovation within the blockchain community. Projects are no longer content with merely replicating existing models; instead, they strive to push the boundaries of what's possible with decentralized technologies. From enhancing scalability and interoperability to integrating advanced smart contract functionalities, these coins embody the spirit of progress in the crypto sphere.</span></p>
<h4><strong>Diverse Utility and Application</strong></h4>
<p><span style="font-weight: 400;">One of the defining features of new crypto coins is their diverse utility and application. While some tokens focus on optimizing transaction speeds and reducing fees, others prioritize privacy and anonymity. Additionally, we're witnessing the emergence of niche tokens tailored to specific industries, such as gaming, healthcare, and supply chain management. This proliferation of use cases underscores the versatility of blockchain technology and its potential to revolutionize various sectors.</span></p>
<h4><strong>Community-Driven Development</strong></h4>
<p><span style="font-weight: 400;">Unlike traditional financial systems, which are often centralized and opaque, the development of new crypto coins is typically community-driven and transparent. Many projects leverage decentralized governance models, allowing token holders to actively participate in decision-making processes. This democratization of development fosters a sense of ownership and belonging among users, reinforcing the decentralized ethos at the heart of the crypto movement.</span></p>
<h2><strong>Conclusion</strong></h2>
<p><span style="font-weight: 400;">As we navigate the ever-expanding universe of cryptocurrencies, new crypto coins stand out as beacons of innovation and opportunity. In 2024 and beyond, these tokens will continue to redefine the way we think about money, finance, and technology. Whether they're disrupting traditional industries or paving the way for novel applications, one thing is clear: the future of finance is decentralized, and new crypto coins are at the forefront of this paradigm shift.</span></p> | brianlindsey | |
1,862,754 | Detailed Explanation of AI Agents | 1. Preface Artificial Intelligence (AI) agents are a crucial concept in modern computer... | 0 | 2024-05-23T11:21:46 | https://dev.to/happyer/detailed-explanation-of-ai-agents-3noc | ai, design, image, development | ## 1. Preface
Artificial Intelligence (AI) agents are a crucial concept in modern computer science and AI research. They play key roles in various applications, from autonomous vehicles to smart home assistants, and complex enterprise decision support systems. This article will provide a detailed introduction to the definition, functions, classification, working principles, advantages, application scenarios, and future development trends of AI agents.
## 2. What are AI Agents?
An AI agent is a computer program capable of perceiving its environment and taking actions to achieve specific goals. They typically consist of perception, decision-making, and execution modules. The perception module collects environmental information, the decision-making module formulates action plans based on this information, and the execution module implements these plans.
1. **Perception Module**: The perception module acts as the "eyes" and "ears" of the AI agent, collecting environmental information through sensors or data interfaces. For example, the perception module of an autonomous vehicle may include cameras, LiDAR, and radar sensors.
2. **Decision-Making Module**: The decision-making module is the brain of the AI agent, responsible for analyzing perceived information and formulating action plans. This module may use various algorithms, including rule engines, machine learning models, and optimization algorithms.
3. **Execution Module**: The execution module acts as the "hands" and "feet" of the AI agent, responsible for implementing the action plans formulated by the decision-making module. For example, the execution module of an autonomous vehicle may include systems that control the steering wheel, throttle, and brakes.
## 3. Functions of AI Agents
When discussing artificial intelligence, AI agents are not just tools for executing tasks; they are dynamic participants that are revolutionizing how businesses interact with their digital and real-world environments. Understanding the functions of AI agents is crucial for businesses looking to fully leverage their potential. Here is an overview of the key functions of AI agents:
1. **Perceiving Environmental Changes**: AI agents excel at capturing dynamic changes in the environment, whether it's fluctuations in financial markets or customer behavior on e-commerce websites. They continuously monitor and analyze these changes, which is crucial for improving operational efficiency.
2. **Responsive Actions**: AI agents can respond to environmental changes and take actions to influence the environment. For example, in the case of a pricing error on an e-commerce site, AI agents can adjust product pricing or take products offline in real-time.
3. **Reasoning and Interpretation**: AI agents do more than just collect data; they can also reason and interpret the data. They can analyze complex datasets and extract meaningful insights, transforming them into proactive decision-makers.
4. **Problem Solving**: AI agents excel at solving complex problems, whether it's optimizing supply chains, diagnosing technical issues in manufacturing processes, or determining the most effective marketing strategies. They can provide quick and efficient solutions.
5. **Reasoning and Learning**: AI agents possess reasoning capabilities, allowing them to predict future trends by analyzing past and present data and learn from each interaction, continuously improving their performance. This ongoing learning process enables them to adapt to new situations, increasing their value to businesses.
6. **Action and Outcome Analysis**: AI agents can evaluate and determine the best course of action to achieve desired outcomes. They can plan multi-step strategies, considering different potential scenarios and their possible impacts, which is particularly valuable in strategic planning and decision-making.
## 4. Classification of AI Agents
AI agents can be classified based on their complexity and functionality:
1. **Simple Reflex Agents**: These agents take actions based on current perceptual information without considering historical data. For example, rule-based systems. They typically use "condition-action" rules to decide actions.
2. **Model-Based Reflex Agents**: These agents consider not only current perceptual information but also use an internal model to predict future states. The internal model can be an abstract representation of the environment used to simulate environmental changes.
3. **Goal-Based Agents**: These agents consider not only the current state but also how to achieve specific goals. They typically use search and planning algorithms to find the best path to achieve their goals.
4. **Utility-Based Agents**: These agents consider not only goals but also the utility or value of achieving those goals. They use utility functions to evaluate the value of different actions and choose the optimal action.
5. **Learning Agents**: These agents can continuously improve their performance through experience and learning algorithms. They typically use machine learning algorithms such as supervised learning, unsupervised learning, and reinforcement learning.
## 5. How AI Agents Work
The working principles of AI agents usually include the following steps:
The workflow of AI agents is a comprehensive dynamic process involving data analysis, decision-making, and continuous learning. For businesses, understanding this workflow is key to effectively deploying AI agents. Knowing how AI agents operate can help businesses set appropriate goals, provide necessary resources, and effectively interpret results, whether in customer service, supply chain management, or strategic planning.
Let's delve into the working mechanism of AI agents:
1. **Goal Initialization**: The first step in the workflow is to set clear goals for the AI agents. These goals can include analyzing market trends, automating customer support, etc. Agents use their core language models (such as GPT-3.5 or GPT-4) to understand these goals and initiate corresponding action plans.
2. **Task List Creation**: Based on the set goals, AI agents generate a series of tasks. This process includes prioritizing tasks, planning the execution sequence, and preparing for possible contingencies. The task list serves as a roadmap for agents to achieve their goals.
3. **Information Gathering**: To effectively execute tasks, AI agents collect relevant information. This may include searching the internet, accessing databases, or interacting with other AI models to perform specific tasks such as image processing or geographic data analysis. Agents, like humans, use the computer's capabilities, significantly expanding their research scope.
4. **Data Management and Strategy Refinement**: While collecting data, agents continuously manage and analyze this information. This data is not only used for business reporting but also for optimizing their strategies. By evaluating the effectiveness of their actions, agents can adjust their methods to achieve goals more efficiently.
5. **Feedback Integration and Iteration**: An important aspect of the AI agents' workflow is integrating feedback. This feedback may come from external sources such as market data, customer feedback, or internal monitoring systems. Agents use this feedback to evaluate their progress in achieving goals and make necessary adjustments to their task lists and methods.
6. **Continuous Operation Until Goal Achievement**: AI agents operate in a cycle of action, feedback, and adaptation until the set goals are achieved. This continuous operation is a notable feature of AI agents, distinguishing them from traditional software programs.
7. **Adaptive Learning**: Throughout the process, AI agents not only execute tasks but also learn from experience. This learning ability allows agents to become more efficient over time and adapt to new challenges and environments.
## 6. Advantages of AI Agents
Integrating AI agents into your business operations can bring a range of significant advantages that can greatly enhance company profitability and market competitiveness. AI agents are revolutionizing various aspects of business operations, from improving operational efficiency to enhancing customer experience, and they are also enhancing how businesses compete and succeed in the modern market.
Here is a detailed explanation of the main advantages you can enjoy when deploying AI agents in a business environment:
1. **Increased Efficiency**: AI agents excel at automating repetitive tasks that typically require significant human effort and time, including data entry, customer inquiries, and basic analysis. By automating these tasks, businesses can reallocate human resources to more strategic and creative work, thereby increasing overall productivity and innovation.
2. **Effective Personalization**: A notable advantage of AI agents is their ability to provide personalized experiences for customers. By analyzing personal data, preferences, and historical interactions, AI agents can offer customized recommendations, responses, and services to meet individual needs. This level of personalization not only enhances customer satisfaction but also boosts customer loyalty and repeat purchases, as customers feel understood and valued.
3. **Seamless and Cost-Effective Scalability**: AI agents are inherently scalable, capable of handling increasing volumes of tasks or interactions without a corresponding increase in resources or infrastructure. This scalability is particularly valuable during business peak periods, product launches, or market expansions, when resource demands may surge.
4. **Higher Availability**: Unlike human employees, AI agents can work around the clock without the need for rest, fatigue, or downtime. This 24/7 availability ensures that businesses can continuously provide services, support, or monitoring, which is crucial in today's fast-paced market. The continuous online presence of AI customer service means that customer issues and needs can be promptly addressed and resolved, enhancing customer experience and satisfaction.
5. **Cost Savings**: Deploying AI agents can significantly reduce costs. By decreasing the human resources needed to manage routine tasks, businesses can save on salaries, training, and related expenses. Additionally, AI agents can help optimize processes and improve efficiency, further reducing operational costs over time.
6. **Data-Driven Insights**: Modern AI agents can effectively collect and process large amounts of data, providing businesses with valuable insights into customer behavior, market trends, and operational efficiency. These insights can help companies make more informed decisions, tailor strategies, and stay ahead in the competition.
## 7. Application Scenarios
AI agents have a wide range of applications in various fields:
1. **Autonomous Driving**: Autonomous vehicles use AI agents to perceive the road environment, formulate driving strategies, and execute driving operations. The perception module collects road information, the decision-making module formulates driving plans, and the execution module controls the vehicle.
2. **Smart Homes**: AI agents in smart home systems can control lighting, temperature, security systems, and more. The perception module collects home environment information, the decision-making module formulates control plans, and the execution module implements control.
3. **Financial Services**: AI agents are used in stock trading, risk assessment, and customer service. The perception module collects market data, the decision-making module formulates trading strategies, and the execution module implements trades.
4. **Healthcare**: AI agents can assist in diagnosis, personalized treatment plans, and patient monitoring. The perception module collects patient data, the decision-making module formulates treatment plans, and the execution module implements treatments.
5. **Gaming**: AI agents in games are used to control non-player characters (NPCs), providing a more challenging gaming experience. The perception module collects game state information, the decision-making module formulates NPC behavior, and the execution module implements the behavior.
## 8. Future Development Trends
As technology continues to advance, the development of AI agents is also showing new trends:
1. **Reinforcement Learning**: Improving decision-making strategies through interaction with the environment. Reinforcement learning algorithms such as Q-learning and Deep Q-Networks (DQN) perform well in complex tasks.
2. **Multi-Agent Systems**: Multiple AI agents working together to complete complex tasks. Multi-agent systems can improve overall performance through cooperation and competition.
3. **Affective Computing**: Enabling AI agents to understand and respond to human emotions. Affective computing can enhance the naturalness of human-computer interaction and user experience.
4. **Autonomy and Safety**: Enhancing the autonomous decision-making capabilities of AI agents while ensuring the safety and reliability of their behavior. Autonomy and safety are important considerations for AI agents in critical tasks.
## 9. Codia AI's products
Codia AI has rich experience in multimodal, image processing, and AI.
1.[**Codia AI DesignGen: Prompt to UI for Website, Landing Page, Blog**](https://codia.ai/t/pNFx)

2.[**Codia AI Design: Screenshot to Editable Figma Design**](https://codia.ai/d/5ZFb)

3.[**Codia AI VectorMagic: Image to Full-Color Vector/PNG to SVG**](https://codia.ai/v/bqFJ)
4.[**Codia AI Figma to code:HTML, CSS, React, Vue, iOS, Android, Flutter, Tailwind, Web, Native,...**](https://codia.ai/s/YBF9)

## 10. Conclusion
AI agents are an important component of the field of artificial intelligence, with broad application prospects and development potential. Through continuous technological innovation and application exploration, AI agents will play an increasingly important role in the intelligent society of the future. Whether in daily life or professional fields, AI agents will bring us more convenience and possibilities. | happyer |
1,862,724 | Revolutionizing Education: AI-Driven Curriculum Design for the Future | In today's fast-paced digital era, the field of education faces the challenge of keeping pace with... | 0 | 2024-05-23T11:21:06 | https://dev.to/tekrafiki/revolutionizing-education-ai-driven-curriculum-design-for-the-future-5bo6 |
In today's fast-paced digital era, the field of education faces the challenge of keeping pace with rapid technological advancements. Enter TekRafiki, JHUB Africa, and the visionary project underway in collaboration with the Department of Computing. Together, they're poised to reshape curriculum delivery through innovative AI-driven solutions, ushering in a new era of learning excellence.
**Empowering Education with TekRafiki**
At the forefront of this transformative initiative is TekRafiki, a dynamic team committed to harnessing the power of AI in education. Drawing on their expertise in AI development and educational technology, TekRafiki brings innovation to the forefront, revolutionizing how curriculum is designed and delivered in the Department of Computing.
**JHUB Africa: Fueling Innovation and Collaboration**
Supporting TekRafiki in this ambitious endeavor is JHUB Africa, providing invaluable resources and infrastructure to ensure the project's success. From technical expertise to funding opportunities, JHUB Africa plays a pivotal role in driving innovation and fostering collaboration, propelling the project forward with unwavering support.
**Redefining Curriculum Delivery**
At the heart of this collaboration lies a visionary project aimed at enhancing curriculum delivery in the Department of Computing. By harnessing the power of AI, the project promises to revolutionize every aspect of education:
At the heart of this collaboration lies a visionary project aimed at enhancing curriculum delivery in the Department of Computing. By harnessing the power of AI, the project promises to revolutionize every aspect of education:
**Dynamic Curriculum Design:** Gone are the days of static syllabi. With AI-driven insights, educators can design dynamic curriculum tailored to current technological trends and industry standards, ensuring students are equipped with the latest knowledge and skills.
**Personalized Learning Support:** Through interactive content and real-time academic assistance, students receive personalized support, enabling them to navigate the curriculum with confidence and achieve better learning outcomes.
**Efficiency and Effectiveness:** By automating tedious tasks and providing valuable insights, the project enhances the efficiency and effectiveness of curriculum planning and implementation, empowering educators to focus on fostering innovation and collaboration within the Department of Computing.
**Alignment with Industry Standards:** With a keen eye on industry trends, the project ensures that the curriculum remains aligned with current technological advancements, bridging the gap between academia and industry and preparing students for success in the workforce.
**Accessibility and Inclusivity:** Leveraging the resources of JHUB Africa, the project aims to make education more accessible and inclusive, ensuring that every student has the opportunity to benefit from innovative learning experiences, regardless of background or circumstances.
**Embracing the Future of Education**
As the project continues to unfold, TekRafiki, JHUB Africa, and the Department of Computing are leading the charge in shaping the future of education. By harnessing the power of AI and fostering collaboration, they're not only revolutionizing curriculum delivery but also empowering students and educators to thrive in the digital age.
**Conclusion**
In a world where change is constant and innovation is key, TekRafiki, JHUB Africa, and the Department of Computing are paving the way forward. Together, they're transforming education, redefining curriculum delivery, and inspiring the next generation of computing professionals. The future of education is here, and it's brighter than ever, thanks to the visionary collaboration between TekRafiki, JHUB Africa, and the Department of Computing.
| tekrafiki | |
1,862,746 | Artificial Intelligence: What to Learn in 2024? | What is Artificial Intelligence (AI)? Man-made intellectual ability is the limitation of machines to... | 0 | 2024-05-23T11:19:08 | https://dev.to/joe_urciuoli_c1425a227a3b/artificial-intelligence-what-to-learn-in-2024-4j6b | javascript, aws, sql | What is Artificial Intelligence (AI)?
Man-made intellectual ability is the limitation of machines to have a free psyche. Rehashed information is shown while an endeavor, once performed by a human and considered as requiring the ability to learn, reason, and oversee issues, should now be conceivable by a machine. A surprising portrayal is a self-administering vehicle. The vehicle can see its normal factors and make decisions to safely show up at its level headed with no human mediation. Meeting progressions close by Big Data and the Internet of Things (IoT) are driving the improvement of AI and AI propels. Machines talk with one another and are right currently fit for the top tier understanding, getting a colossal number of information networks soon, setting up the information, and picking, all rapidly. As AI makes, machines will have a more obvious ability to act reliant upon their knowledge, at the end affecting machines that can assemble better kinds of themselves. We can learn AI from Artificial understanding readiness.
Online Courses in Artificial Intelligence
The field of Artificial Intelligence (PC-based information structures) and AI appraisals wraps PC programming, standard language course of activity, python code, math, cerebrum research, neuroscience, information science, AI, and various controls. A major course in AI is a nice spot to start as it will furnish you with the construction of the parts that update you concerning AI assessment and developments to date. You can nearly get dynamic thought in the AI programming of shrewd very much informed specialists, for instance, search appraisals, games, and thinking issues. Observe a couple of arrangements concerning occurrences of AI being utilized today like self-driving vehicles, facial authentication systems, military robots, and conventional language processors. We can take in AI from Artificial understanding planning ai learning
Go further with courses in Data Science, Robotics, and Machine Intelligence. Secure capacity with the basics of how robots work, including how to address 2D and 3D spatial affiliations, how to control mechanized arms, and plan to begin to end AI robot structures. In Machine learning, research solo learning methodology for information appearing and assessment including information bundling, PC vision, support learning, central reasoning, AI evaluations, picture demand, information mining, talk verification network factorization, and moderate models for demand subordinate information.
Begin with Artificial Technology and get a configuration of this energizing field. Assuming that you are new to central PC programming and AI programming vernaculars, it will be essential to take a major class to learn Python, R, or another programming language consistently used in information assessment.
Occupations in AI
3,000 full-time [machine learning engineer](https://www.janbasktraining.com/blog/machine-learning-engineer-salary/) positions were recorded on Indeed.com at the hour of this article, with different obligation pay rates above $125K reliably. Information analyst AI occupations reliably require four-year school direction or higher in PC programming, organizing, or IT, and joining in various programming tongues including Java, C, Python, R, JavaScript, and SQL, and relationship with information science is also gigantic regardless. Top occupation positions interweave [Artificial Intelligence](https://www.janbasktraining.com/ai-certification-training-online) Engineer, AI Project Manager, Researcher, and Artificial Intelligence Consultant, and a section of the top affiliations utilizing Amazon, Google, Apple, and IBM.
Research a Career in Artificial Intelligence
Assist with making the future by animating work in the rapidly making field of man-made thinking. Various endeavors like propelling exhibits and online media experts are relying on colossal learning procedures and AI estimations to make business decisions and their business applications better. Accepting you love PC programming, science and information evaluation, python programming, direct apostatize, and shockingly more by then select and start observing a couple of arrangements concerning the usage of fake brain affiliations and how you can help them with pushing ahead. We can take in AI from Artificial information arrangement.
To fulfill the current endlessly need for information assessors and AI-instructed specialists, many planning offers for the best man-made cognizance experiences and PC systems online courses are being held under watch. If AI, colossal learning, far away associates, TensorFlow, and brain affiliations energize you, we have authentic courses to assist with promoting your calling at your speed. Turn into an industry genius in AI systems today!
A Brief History of Artificial Intelligence
Man-made intellectual ability research was set up in the pre-summer of 1956 at Dartmouth College during a studio event. The force of machines ended up comparably sharp as individuals promptly got financing for vast dollars to make this dream a reality. As time elapsed, the early pioneers immediately apparent how unconventional and tangled this endeavor would be.
In 1973, the U.S and British Governments quit supporting the evaluation project around information sorting out and learning estimations. This period while the financing halted was known as "Man-made information Winter" as headway dropped down and dissatisfaction was made. There were a couple of off-upheld exercises during AI Winter, yet the energy of AI progress would pick back up by the 21st century.
Energy, hypothesis, and interest in AI improvement influence the principal different broadened lengths of the 21st century. The power and energy are lit around productive AI projects in the sharp neighborhood industry with the assistance of essentially more remarkable PC hardware. The hour of new AI projects, information sorting out, and modernized thinking programming language improvement instigated the verbalization "PC based information Summer".
In the current day, we see AI made into our standard common presences with single accomplices. Man-made information applications and astonishing machines like Siri, Alexa, Watson, Cortana, LinkedIn, and Google AI Assistant are everything viewed as standard applications we use to work with standard endeavors. These assistants can be used to pull information from the web, turn on home machines, set refreshes, trade with each other, and as such from an overall perspective. Such AI and adroit plan partners are growing, so the premium for sketchers and PC specialists is at a faultless high for this market. Regardless of whether you are regulating Microsoft Windows, iOS, and open-source stage, Google, or Android, you can anticipate that there should be a huge load of pay in your abilities. We can take in AI from Artificial information arrangement.
Pay of an Artificial Intelligence Engineer
As an AI sure, you have adequate open circumstances in this field. A couple of AI occupations merge AI engineers, information subject matter experts, business knowledge developers, research researchers, and AI engineers. Man-made mental ability engineering is perhaps the most noticeable occupation in the AI business today. The section level yearly regular AI engineer pay in India is around 8 lakhs, which is higher than the standard compensation of a couple of other graduating classes. At evident-level positions, the AI engineer pay can be just comparably high as 50 lakhs. We can acquire AI from Artificial information planning.
| joe_urciuoli_c1425a227a3b |
1,862,745 | Complete Guide to Salesforce Service Cloud Implementation | Salesforce Service Cloud Implementation can help businesses manage and improve their customer service... | 0 | 2024-05-23T11:18:46 | https://dev.to/kuldeepthakur/complete-guide-to-salesforce-service-cloud-implementation-3a3j | beginners | Salesforce Service Cloud Implementation can help businesses manage and improve their customer service operations. This platform can help businesses manage cases, create knowledge bases, and track customer interactions.
[Salesforce Service Cloud implementation](https://webkul.com/salesforce-service-cloud-services/) can be a complex process, but it can provide significant benefits for your business.
Here is a comprehensive guide to Salesforce Service Cloud implementation:
**1. Define your goals and objectives:**
Understand clearly what you want to achieve with your Salesforce Service Cloud implementation.
This will help you decide which features you need to implement and how you should manage the implementation project.
**2. Choose a Salesforce partner:**
It is important to choose an experienced and reputable Salesforce partner. Your partner can guide you through every step of the implementation process and ensure that Salesforce meets your business needs.
**3. Assess your current processes:**
Do a thorough assessment of your existing customer service processes. This will help you identify which areas can be improved and how Salesforce Service Cloud can help.
**4. Design your solution:**
Design your [Salesforce Service Cloud](https://webkul.com/salesforce-service-cloud-services/) solution. This includes choosing the features you need, configuring the system, and creating custom fields and objects.
**5. Migrate your data:**
Migrate your existing customer service data to Salesforce Service Cloud. This can be a complex process, so it is important to develop a data migration plan.
**6. Train your users:**
Train your employees to use Salesforce Service Cloud. This includes teaching them how to use the system, how to create cases, and how to manage customer interactions.
**7. Test and go live:**
Test your Salesforce Service Cloud solution thoroughly to make sure everything is working correctly. Once you are satisfied with the testing, you can go live with the system.
**8. Monitor and maintain:**
Regularly monitor and maintain your Salesforce Service Cloud system. This includes checking for errors, updating the system, and training new users.
**Some additional tips for Salesforce Service Cloud implementation:
****Start small:** Not all businesses need to implement all of the features of Salesforce Service Cloud. Start with the features that you need most and add more features as you grow.
**Get buy-in from all stakeholders:** It is important to get buy-in from all stakeholders in your organization before you begin the implementation process. This will help to ensure that the implementation is a success.
**Be patient:** Salesforce Service Cloud implementation is a complex process that can take time. Be patient and don't get discouraged if you encounter challenges along the way.
**Conclusion:**
Salesforce Service Cloud is a powerful tool that can help businesses manage and improve their customer service operations.
This platform can help businesses manage cases, create knowledge bases, and track customer interactions. | kuldeepthakur |
1,862,744 | Hackathon for Developers | Want to put your development skills to productive use? Follow the link and register for this amazing... | 0 | 2024-05-23T11:17:55 | https://dev.to/zakari714/hackathon-for-developers-2e2j | Want to put your development skills to productive use? Follow the link and register for this amazing hackathon. The time is ticking... https://blog.pipeops.io/registration-guidelines-for-pipeops-hackathon/
 | zakari714 | |
1,862,741 | Transformation of Privacy in the Digital Age | Privacy, once a concept centered around physical space and control over personal information, has... | 0 | 2024-05-23T11:17:33 | https://infosafe24.com/posts/Transformation-of-Privacy-in-the-Digital-Age | infosec, socialengineering, cyberattacks, privacy | Privacy, once a concept centered around physical space and control over personal information, has undergone a dramatic transformation in the digital age.
Historically, privacy was primarily concerned with protecting physical space and belongings. This included the right to be free from unwarranted physical intrusion, the ability to control who has access to our physical possessions, and the expectation of privacy in our homes and personal communications (like sealed letters).
The digital age has revolutionized communication, access to information, and the way we conduct business and socialize.
Yet, this interconnectedness comes at a cost — gradual chipping away of our privacy.
Our personal data, from social media interactions to geolocation information, creates a digital footprint, and is constantly being collected, analyzed, and used in ways that were unimaginable in the pre-digital era.
The digital age transforms our lives, improves our communication, accelerates technology development and has many other positive effects.
All these positive effects taken into account, we need to strike a balance between privacy protection and technological advancements.
This article delves into the intricate relationship between privacy and technology in the digital age, exploring the challenges we face, potential solutions, and the need for a nuanced approach to navigate this ever-evolving landscape.
## Dataveillance
Being a portmanteau of data and surveillance, dataveillance refers to the monitoring and collection of our personal data through our online activities and interactions. It’s essentially a form of surveillance that happens in the digital world, as opposed to traditional physical surveillance methods.
Every online interaction we have — from browsing history to emails — leaves a digital trail. This data is collected by a vast network of actors, including social media giants, search engines, online retailers, and even governments.
The lack of transparency surrounding these practices creates a pervasive sense of unease.
Dataveillance can be useful for collecting and verifying data in ways that are beneficial. For instance, personal dataveillance can be utilized by financial institutions to track fraudulent purchases on credit card accounts
While it offers potential benefits for personalization and analytics, it also raises significant concerns about privacy and security.
By understanding how dataveillance works and the potential risks involved, we can make informed choices about our online activities and advocate for stronger data protection measures.
## Commoditization of data
A key component of the digital economy is the commoditization of data.
A valuable asset that is bought and sold to produce targeted advertising revenue is personal information.
Our personal data is being utilized to forecast and affect our desires, creating a culture of surveillance capitalism and a constant sense of being watched and monitored.
We commonly refer to the continuous flow of data produced by our internet activities as “datafication.” This data can provide a comprehensive picture of our lives by containing anything from purchase records to location data.
Companies and governments can now more easily than ever keep an eye on our online activities thanks to cookies, browser fingerprinting, and other tracking technology. This presents questions regarding the possibility of abuse and deception.
Although data commodification has drawbacks, it might also have some advantages.
Users can receive more relevant advertisements by using data. Businesses (reaching a better targeted audience) and consumers (seeing adverts for things they might actually be interested in) can both benefit from this.
Online experiences can be made more personalized by using data, which can be used to customize search results, news feeds, and product recommendations on shopping websites. Online conversations may become more productive and pleasurable as a result.
Innovation and the creation of new goods and services can result from data analysis. For instance, examining user data from fitness trackers might help develop more individualized workout regimens and wellness guidelines.
Data can be used for research and development in various fields, leading to breakthroughs in healthcare, education, and other sectors.
## Shifting Expectations
Social media platforms and online services thrive on user data.
While users often seek convenient and personalized online experiences, these conveniences often come at the cost of reduced privacy.
Unfortunately, many platforms capitalize on a culture of oversharing, blurring the lines between public and private spheres. This makes it increasingly difficult for individuals to maintain a sense of personal privacy — especially for younger generations who have grown up in a hyper-connected world.
In today’s digital world, having a strong online presence is often seen as advantageous. This can create pressure to curate a public persona and share personal information to build a following or establish credibility.
In the digital realm, privacy encompasses a broad spectrum. It includes control over our personal information, the right to be forgotten, the ability to exist online anonymously, and the right to dictate how our online personas are portrayed.
Constant surveillance and data collection can have a chilling effect on free speech and self-expression, as individuals fear judgment or ostracization for their online activities. Additionally, data breaches and identity theft pose a growing threat, exposing us to financial loss and emotional distress.
While existing anonymously is seen as a fundamental human right, it can also pose significant dangers.
Anonymity can embolden individuals to engage in cyberbullying, harassment, and online abuse. They may feel less accountable for their actions and be more likely to target others with offensive or threatening messages.
It can make it easier to spread misinformation and hate speech online without facing consequences. It allows individuals to hide behind fake profiles, making it difficult to track down the source of the information.
The ability to operate anonymously online can facilitate criminal activity such as online fraud, hacking, and identity theft. Criminals can hide their identities and evade detection more easily.
## Taking control
However, there is no need to resign ourselves to a dystopian future devoid of privacy. Fortunately, there are steps we can take to reclaim some control over our digital footprints.
One approach is to be more mindful of the information we share online. This includes reviewing privacy settings on social media platforms and other online services, limiting what information is publicly visible, and using privacy-focused tools like browser extensions that block tracking cookies.
Security hygiene is also crucial. We can protect ourselves by using strong, unique passwords and enabling two-factor authentication to add an extra layer of security to our accounts.
Additionally, being cautious about what information we share on public Wi-Fi networks and refraining from downloading files from untrusted sources can significantly reduce our risk of exposure to malware or data breaches.
Supporting legislation that promotes data privacy rights and empowers individuals to control their information is essential. The European Union’s General Data Protection Regulation (GDPR) is a prime example, granting individuals the right to access, rectify, or erase their personal data.
Advocating for similar regulations in other parts of the world can provide users with a much-needed legal framework to protect their privacy in the digital age.
Technology companies also have a responsibility to be more transparent about their data collection practices and provide users with meaningful control over their information.
Privacy-focused features, such as the ability to easily delete data or opt out of targeted advertising, should be readily available and user-friendly. Additionally, investing in robust security measures and adhering to ethical data practices can build trust and foster a more responsible data ecosystem.
## The Future of Privacy
Data protection regulations like the EU’s GDPR are a step towards empowering individuals to control their data. These regulations are likely to evolve and shape the way online platforms handle user privacy in the future.
Technologies like blockchain and secure enclaves are being developed to give users more control over their data. These technologies have the potential to reshape the way personal information is stored and accessed in the digital world.
The transformation of privacy in the digital age is an ongoing process. As technology continues to evolve, we need to find ways to balance innovation with the right to privacy. This requires collaboration between individuals, policymakers, and technology companies to create a digital ecosystem that respects our right to control our personal information.
Finding a balance between innovation and privacy is critical.
We must strive for a digital future where advancements in technology coexist with a healthy respect for personal privacy. This can be achieved through a multi-pronged approach involving individual vigilance, robust legal frameworks, and ethical corporate practices.
Ultimately, safeguarding privacy in the digital age requires ongoing dialogue and collaboration between policymakers, technology companies, and users themselves.
We must recognize that privacy is not a luxury, but a fundamental human right that needs to be protected in the digital realm.
| jusufoski |
1,862,743 | Integrating ChatGPT with a React.js and Node.js Web Application | Node ChatGPT: Integrating OpenAI's ChatGPT with Node.js Node ChatGPT refers to the integration and... | 0 | 2024-05-23T11:16:40 | https://dev.to/saumya27/integrating-chatgpt-with-a-reactjs-and-nodejs-web-application-iab | react, node, webapp | **Node ChatGPT: Integrating OpenAI's ChatGPT with Node.js**
Node ChatGPT refers to the integration and use of OpenAI's ChatGPT model within a Node.js environment. This allows developers to leverage the powerful natural language processing capabilities of ChatGPT in their Node.js applications, enabling the creation of interactive, intelligent chatbots, customer service agents, and other conversational AI solutions.
**Key Features and Benefits**
**Natural Language Understanding:**
- Advanced NLP: ChatGPT is based on OpenAI’s GPT-4 architecture, providing sophisticated understanding and generation of human language.
- Contextual Conversations: Maintain context over multiple interactions for more coherent and relevant responses.
**Scalability and Performance:**
- Node.js: Known for its non-blocking, event-driven architecture, Node.js is ideal for handling multiple concurrent requests, making it a great fit for real-time chat applications.
- Efficient Communication: Use WebSocket or other real-time communication protocols to ensure fast and responsive interactions.
**Easy Integration:**
- OpenAI API: Integrate ChatGPT with Node.js applications via the OpenAI API, making it straightforward to send prompts and receive responses.
- Modular Design: Node.js supports a modular design, allowing developers to build and maintain scalable and maintainable codebases.
**Customizability:**
- Fine-tuning: Customize ChatGPT responses by adjusting parameters and settings to better fit specific use cases.
- Middleware: Implement middleware in Node.js to preprocess requests and post-process responses for additional functionality like logging, analytics, or custom business logic.
**Example Use Cases**
**Customer Support Chatbots:**
Deploy a chatbot to handle customer inquiries, providing instant responses and reducing the workload on human agents.
Integrate with existing CRM systems to provide personalized support.
**Interactive Websites:**
Enhance user engagement by embedding conversational agents on websites that can assist with navigation, answer FAQs, and provide information.
**Virtual Assistants:**
Build intelligent virtual assistants capable of scheduling, reminders, and answering questions based on user input.
**Educational Tools:**
Develop interactive learning platforms where students can ask questions and receive detailed explanations, enhancing the learning experience.
**Implementation Overview**
To integrate ChatGPT with a Node.js application:
**Set Up Node.js:**
Install Node.js and initialize your project.
COPY
COPY
npm init -y
Install Required Packages:
Install the axios package for making HTTP requests.
COPY
COPY
npm install axios
Create API Integration:
Use the OpenAI API to send prompts and receive responses.
COPY
COPY
const axios = require('axios');
const API_KEY = 'your_openai_api_key';
const endpoint = 'https://api.openai.com/v1/engines/davinci-codex/completions';
async function getChatGPTResponse(prompt) {
const response = await axios.post(endpoint, {
prompt: prompt,
max_tokens: 150,
temperature: 0.9
}, {
headers: {
'Authorization': `Bearer ${API_KEY}`,
'Content-Type': 'application/json'
}
});
return response.data.choices[0].text;
}
getChatGPTResponse('Hello, how are you?')
.then(response => console.log(response))
.catch(error => console.error(error));
Set Up a Server:
Create a basic Express server to handle incoming chat requests.
COPY
COPY
const express = require('express');
const app = express();
const port = 3000;
app.use(express.json());
app.post('/chat', async (req, res) => {
const userMessage = req.body.message;
const botResponse = await getChatGPTResponse(userMessage);
res.json({ response: botResponse });
});
app.listen(port, () => {
console.log(`Server running at http://localhost:${port}`);
});
**Conclusion**
Integrating Node.js with ChatGPT allows developers to create powerful and responsive conversational applications. By leveraging the strengths of Node.js and the advanced natural language processing capabilities of ChatGPT, you can build chatbots, virtual assistants, and other interactive tools that provide meaningful and intelligent interactions with users. Whether for customer support, educational tools, or interactive websites, Node ChatGPT offers a versatile and robust solution for enhancing user engagement and automating conversations.
| saumya27 |
1,862,742 | Emaar's Latest Jewel: The Heights Country Club and Wellness in Dubai | Dubai, a city known for its opulence, innovation, and towering skyline, has just welcomed a new... | 0 | 2024-05-23T11:15:47 | https://dev.to/dubaiproperties01/emaars-latest-jewel-the-heights-country-club-and-wellness-in-dubai-2o11 | realestate | Dubai, a city known for its opulence, innovation, and towering skyline, has just welcomed a new marvel into its fold. **[The Heights Country Club and Wellness by Emaar in Dubai](https://www.leadroyal.ae/the-heights-country-club-and-wellness/)**, a project by the illustrious Emaar Properties, promises to redefine luxury living and holistic wellness. As the latest addition to Emaar's portfolio, The Heights stands out not only for its grandeur but also for its comprehensive approach to health and well-being. In this article, we delve into the features, amenities, and philosophies that make The Heights a beacon of luxury and wellness in Dubai.
Emaar's Vision: Pioneering Luxury and Wellness
Emaar Properties has long been synonymous with luxury real estate and innovative urban development. With iconic projects like the Burj Khalifa and The Dubai Mall, Emaar has continually pushed the boundaries of architecture and design. The Heights Country Club and Wellness is a testament to Emaar's vision of creating spaces that offer not just a place to live but a holistic lifestyle experience.
A New Benchmark in Wellness Living
The Heights is not just another luxury development; it represents a paradigm shift towards integrated wellness living. Recognizing the growing global trend towards health and well-being, Emaar has crafted The Heights as a sanctuary where residents can nurture their bodies, minds, and spirits. This development integrates state-of-the-art wellness facilities with luxurious living spaces, creating an environment where health and comfort coexist harmoniously.
Architectural Brilliance: A Blend of Elegance and Functionality
The architectural design of The Heights is a masterpiece in itself. Emaar has collaborated with world-renowned architects and designers to create a space that is both aesthetically pleasing and functionally superior.
Sustainable and Innovative Design
Sustainability is at the core of The Heights' design philosophy. The development incorporates green building practices and eco-friendly materials, ensuring minimal environmental impact. Features such as solar panels, rainwater harvesting systems, and energy-efficient appliances underscore Emaar's commitment to sustainability. The innovative use of natural light and ventilation not only reduces energy consumption but also creates a healthier living environment.
Aesthetic Excellence
Visually, The Heights is a blend of contemporary elegance and timeless charm. The architecture reflects a seamless integration of indoor and outdoor spaces, with expansive windows offering breathtaking views of the Dubai skyline and the Arabian Gulf. The use of natural materials, such as stone and wood, adds warmth and texture to the modern design, creating an inviting and sophisticated atmosphere.
World-Class Amenities: Beyond Luxury
The Heights Country Club and Wellness is designed to offer an unparalleled lifestyle, with a plethora of amenities that cater to every aspect of well-being.
The Wellness Center: A Sanctuary for the Soul
At the heart of The Heights is the Wellness Center, a state-of-the-art facility that offers a comprehensive range of health and wellness services. From cutting-edge fitness studios and swimming pools to serene yoga and meditation spaces, the Wellness Center is designed to cater to both physical and mental well-being.
Fitness and Training
For fitness enthusiasts, The Heights offers a fully equipped gym with the latest in fitness technology, personal training services, and group exercise classes. The outdoor sports facilities, including tennis courts and a jogging track, provide ample opportunities for residents to stay active and healthy.
Spa and Relaxation
The spa at The Heights is a sanctuary of relaxation and rejuvenation. Offering a range of treatments from traditional massages to advanced therapies, the spa is designed to help residents unwind and restore their balance. The presence of steam rooms, saunas, and hydrotherapy pools further enhances the relaxation experience.
The Country Club: A Hub of Social and Recreational Activities
The Country Club at The Heights is a vibrant hub where residents can socialize, relax, and indulge in recreational activities.
Dining and Entertainment
The Heights boasts a range of dining options, from fine dining restaurants serving gourmet cuisine to casual cafes and lounges. The dining establishments offer a diverse array of culinary experiences, catering to every palate. The club also features entertainment facilities, including a cinema and a games room, ensuring that residents have plenty of options for leisure and enjoyment.
Family and Community
The Heights is designed to be a family-friendly environment. The development includes a dedicated kids' club with a range of activities and facilities to keep younger residents engaged and entertained. Community spaces, such as parks, gardens, and communal lounges, foster a sense of community and belonging among residents.
Holistic Living: A Focus on Mind, Body, and Spirit
The Heights Country Club and Wellness is more than just a place to live; it is a community that promotes holistic living. Emaar's vision for The Heights is to create an environment where residents can achieve a balanced and fulfilling lifestyle.
Mindful Living
The Heights encourages mindful living through its various wellness programs and activities. Residents have access to mindfulness and meditation classes, designed to help them manage stress and enhance their mental well-being. The presence of tranquil gardens and meditation spaces provides a peaceful retreat from the hustle and bustle of city life.
Nutritional Wellness
Recognizing the importance of nutrition in overall well-being, The Heights offers a range of services focused on healthy eating. The wellness center includes a nutrition clinic where residents can receive personalized dietary advice and meal planning. The on-site restaurants emphasize fresh, locally sourced ingredients, and offer healthy menu options to support residents' nutritional goals.
Community and Connection
A sense of community and connection is integral to the philosophy of The Heights. Emaar has designed the development to foster social interactions and community engagement. Regular events, workshops, and social gatherings provide opportunities for residents to connect with each other and build lasting relationships. The emphasis on community living ensures that residents feel supported and part of a larger family.
Prime Location: The Heart of Dubai
The Heights Country Club and Wellness is strategically located in one of Dubai's most sought-after areas. Its prime location offers residents easy access to the city's key attractions and amenities.
Connectivity and Convenience
Situated in close proximity to major highways and public transportation networks, The Heights offers excellent connectivity to the rest of the city. Residents can easily reach Dubai's business districts, shopping centers, and cultural landmarks. The development is also conveniently located near top-tier schools, hospitals, and recreational facilities, ensuring that residents have everything they need within reach.
A Gateway to Nature
Despite its urban setting, The Heights provides residents with ample opportunities to connect with nature. The development is surrounded by lush greenery and landscaped gardens, creating a serene and natural environment. The nearby beaches and parks offer additional options for outdoor activities and relaxation.
Conclusion: A New Standard in Luxury and Wellness
Emaar's latest jewel, The Heights Country Club and Wellness, sets a new standard in luxury living and holistic well-being in Dubai. With its innovative design, world-class amenities, and comprehensive wellness programs, The Heights offers a unique lifestyle experience that caters to the mind, body, and spirit. As Dubai continues to evolve as a global city, The Heights stands as a testament to Emaar's vision of creating exceptional living spaces that enrich the lives of its residents. For those seeking a harmonious blend of luxury and wellness, The Heights Country Club and Wellness is undoubtedly the pinnacle of modern living in Dubai. | dubaiproperties01 |
1,862,740 | How to Leverage AI Newsletters for Professional Development | In today’s fast-paced tech landscape, staying updated with the latest advancements in artificial... | 0 | 2024-05-23T11:13:19 | https://dev.to/marandagarner21/how-to-leverage-ai-newsletters-for-professional-development-1042 | In today’s fast-paced tech landscape, staying updated with the latest advancements in artificial intelligence (AI) is crucial for professional growth. AI newsletters have emerged as a valuable resource, offering curated content that can help professionals stay informed and ahead of the curve. Here’s how you can leverage AI newsletters for your professional development.
## 1. Stay Updated on Industry Trends
AI newsletters provide regular updates on the latest trends, research breakthroughs, and technological advancements in the field of artificial intelligence. By subscribing to a well-curated [**AI newsletter**](https://www.morningdough.com/), you receive a consistent stream of information that helps you stay abreast of the latest developments. This knowledge can be instrumental in making informed decisions, understanding emerging technologies, and identifying new opportunities in your industry.
## 2. Gain Insights from Expert Analysis
Many AI newsletters feature articles and insights from industry experts, researchers, and thought leaders. These analyses offer deep dives into complex topics, providing a nuanced understanding of AI concepts and their practical applications. By reading expert opinions and commentary, you can enhance your critical thinking skills and apply these insights to your own projects and professional activities.
## 3. Enhance Your Technical Skills
AI newsletters often include tutorials, case studies, and practical guides on various AI technologies and tools. These resources can help you develop new skills or improve existing ones. Whether you’re learning about machine learning algorithms, natural language processing, or data analysis techniques, an AI newsletter can be a valuable source of educational content that supports your continuous learning efforts.
## 4. Discover Networking Opportunities
Subscribing to an AI newsletter can also open doors to networking opportunities. Many newsletters feature information about upcoming conferences, webinars, workshops, and meetups. Attending these events can help you connect with other professionals in the field, exchange ideas, and build a network of contacts that can be beneficial for your career.
## 5. Stay Informed About Job Opportunities
AI newsletters often highlight job openings, internships, and fellowship opportunities in the AI sector. By keeping an eye on these listings, you can stay informed about potential career moves and find opportunities that align with your skills and career goals. Additionally, understanding the demand for certain skills and expertise can guide your professional development efforts and help you stay competitive in the job market.
## 6. Get Inspired by Success Stories
Reading about successful AI projects and innovations can be incredibly inspiring. AI newsletters frequently showcase case studies and success stories that highlight how AI is being used to solve real-world problems. These stories can motivate you to pursue your own projects and provide valuable insights into best practices and strategies that lead to successful outcomes.
## 7. Receive Curated Content
One of the biggest advantages of subscribing to an AI newsletter is the curated nature of the content. Instead of spending hours searching for relevant information online, you get a selection of high-quality articles, papers, and news delivered directly to your inbox. This saves time and ensures that you are accessing reliable and pertinent information.
## Conclusion
Leveraging an AI newsletter for professional development can be a game-changer. By staying updated on industry trends, gaining insights from experts, enhancing your technical skills, discovering networking opportunities, staying informed about job openings, and getting inspired by success stories, you can significantly boost your professional growth. Subscribing to a well-curated AI newsletter is a simple yet effective way to stay ahead in the ever-evolving field of artificial intelligence.
| marandagarner21 | |
1,862,732 | Qineos Software: Where Creativity Meets Technical Excellence | Qineos Software Private Limited, a dynamic start-up company originally registered in Mumbai, is... | 0 | 2024-05-23T11:11:38 | https://dev.to/qineos_softwarepvtltd_79/qineos-software-where-creativity-meets-technical-excellence-1hd5 | webdev, appdeveloper, digitalmarketing, mobileapplication | [Qineos Software Private Limited](https://qineosoftware.com/), a dynamic start-up company originally registered in Mumbai, is making significant strides in the technology sector. Under the visionary leadership of two directors and a dynamic CEO, Qineos has swiftly positioned itself as a notable player in the industry. Our journey began with a dedicated team of ten professionals, focusing on both technical excellence and strategic marketing, and has rapidly evolved to meet the growing demands of our clients.
**Focus on Excellence in Android and Web Development:**
At Qineos, we specialize in the Android platform and web designing concepts, driving innovation and providing cutting-edge solutions to our clients. Our expertise in Android app development has already yielded impressive results, as evidenced by our successful project for Smart City initiatives in Mangalore. This project highlights our commitment to leveraging technology to create smarter, more connected urban environments.
**Expanding Horizons in Web Designing:** In addition to our work in Android app development, we have also garnered significant success in web designing projects. Our portfolio includes a diverse range of web design solutions tailored to meet the unique needs of various clients. Whether it's creating engaging and responsive websites or developing intricate web applications, our team is equipped with the skills and creativity to deliver outstanding results.
**Expertise in ERP, Network Configuration, and Digital Marketing:** Our technical proficiency extends beyond app development and web design. At Qineos, we pride ourselves on having specialized personnel who are adept in ERP modules, network configuration, digital marketing, and other software development domains. This diverse expertise allows us to offer a comprehensive suite of services, ensuring that we can meet the varied demands of our clients with precision and professionalism.
**Relocation to Bangalore: A New Chapter:**
Recognizing the strategic importance of location, Qineos Software has recently relocated its operations to Bangalore, the tech hub of India. This move is a testament to our growth and our ambition to serve our clients better. Bangalore's vibrant tech ecosystem provides us with greater opportunities to collaborate, innovate, and expand our services.
**Commitment to Excellence:** As we settle into our new base, we remain committed to delivering exceptional service to our clients. Our relocation to Bangalore is not just a change of address; it represents our dedication to enhancing our capabilities and our readiness to tackle new challenges. We are particularly excited about the potential to secure more projects from overseas clients and are eager to showcase our expertise on a global stage.
At Qineos Software Private Limited, we believe in the power of technology to transform businesses and lives. Our journey from Mumbai to Bangalore is just the beginning, and we look forward to continuing our mission of delivering innovative solutions and unparalleled service to our clients around the world.
| qineos_softwarepvtltd_79 |
1,862,736 | Hackathon Invitation for Productive Developers | Interested in participating in this Hackathon to foster real-life productivity via developers' input?... | 0 | 2024-05-23T11:07:09 | https://dev.to/zakari99/hackathon-invitation-for-productive-developers-137b | Interested in participating in this Hackathon to foster real-life productivity via developers' input? follow the link for more... https://blog.pipeops.io/registration-guidelines-for-pipeops-hackathon/ | zakari99 | |
1,862,735 | Storytelling Techniques to Improve UX Design | Dive into the world of storytelling techniques that can elevate your UX design. From character... | 0 | 2024-05-23T11:07:06 | https://dev.to/trigventsol/storytelling-techniques-to-improve-ux-design-32fl | ux, uxdesign | Dive into the world of storytelling techniques that can elevate your **[UX design](https://trigvent.com/storytelling-in-ux-to-enhance-user-engagement/)**. From character development to plot structure, learn how to apply traditional storytelling methods to modern digital interfaces, ensuring that your designs are not only functional but also emotionally engaging and memorable. | trigventsol |
1,862,734 | How & when Father's Day celebrated in india? | How & when Father's Day celebrated in india? https://www.ask4brand.com/occasions/fathers-day | 0 | 2024-05-23T11:06:57 | https://dev.to/simran_tiwari_015ae4cd5a4/how-when-fathers-day-celebrated-in-india-540c | fathers, day, india | How & when Father's Day celebrated in india?
https://www.ask4brand.com/occasions/fathers-day
| simran_tiwari_015ae4cd5a4 |
1,862,730 | What is Dynamic Code Analysis? | In the modern digital era, prioritizing software security is paramount. Given the prevalence of... | 0 | 2024-05-23T11:00:30 | https://www.clouddefense.ai/what-is-dynamic-code-analysis/ |
In the modern digital era, prioritizing software security is paramount. Given the prevalence of cyber threats, ensuring the safety and reliability of our applications is imperative. This is where dynamic code analysis proves invaluable.
Dynamic Code Analysis, also known as DAST (Dynamic Application Security Testing), takes a proactive approach by scrutinizing software behavior while it's operational. Unlike static code analysis, which focuses solely on scrutinizing code, dynamic analysis simulates real-world scenarios and potential threats to uncover vulnerabilities that static examination alone might miss.
This approach offers several notable advantages:
**1. Real-World Relevance:** By replicating genuine usage scenarios and possible threats, dynamic analysis provides a more precise evaluation of an application's security posture, identifying vulnerabilities specific to runtime behavior.
**2. Revealing Hidden Vulnerabilities:** Certain vulnerabilities, like memory leaks or race conditions, only surface during runtime. Dynamic analysis excels at detecting these elusive issues by monitoring the application's behavior as it runs.
**3. Third-Party Library Risks:** Given the widespread use of third-party libraries, dynamic analysis is essential for assessing the security implications of these dependencies, which may introduce vulnerabilities not present in the core codebase.
**4. Configuration Errors:** Dynamic analysis aids in identifying security gaps stemming from misconfigurations, ensuring that the software is configured correctly to withstand potential threats.
**5. Accelerated Remediation:** By detecting vulnerabilities early in the development cycle, dynamic analysis enables swift remediation, saving time and resources compared to addressing issues post-deployment.
Dynamic analysis complements static analysis, which focuses on code structure and syntax, by providing a deeper understanding of how an application behaves under real-world conditions. While static analysis is efficient for analyzing large codebases and identifying coding errors, dynamic analysis excels at uncovering runtime vulnerabilities and offering contextual insights for security assessments.
In the era of cloud computing, where applications are deployed across complex, cloud-based infrastructures, traditional security testing methods face new challenges. Dynamic Analysis in the Cloud (DAST in the Cloud) emerges as a game-changer, offering security testing beyond source code inspection.
DAST in the Cloud scrutinizes an application's behavior within cloud environments, simulating real-world attacks and interactions without necessitating access to the underlying source code. This approach ensures comprehensive security testing for cloud-based applications, even in scenarios where source code access is limited.
CloudDefense.ai provides a robust suite of security solutions tailored for cloud-native applications, seamlessly integrating DAST and SAST (Static Application Security Testing) vulnerability scanning. Whether you're developing serverless applications or leveraging containerized microservices, CloudDefense.ai empowers organizations to build secure, cloud-native applications with confidence.
In conclusion, dynamic code analysis is indispensable for fortifying software security in today's dynamic threat landscape. By amalgamating static and dynamic analysis methodologies, organizations can proactively pinpoint and mitigate vulnerabilities throughout the software development lifecycle, safeguarding their applications against evolving cyber threats.
| clouddefenseai | |
1,862,246 | Streams do Java | Lançada na versão 8 do Java, Stream API é um recurso que traz métodos e classes e tem por finalidade... | 0 | 2024-05-23T11:00:00 | https://dev.to/alexreis/streams-do-java-2a5b | java, webdev, beginners, learning | Lançada na versão 8 do Java, Stream API é um recurso que traz métodos e classes e tem por finalidade facilitar a manipulação das Collections no estilo da programação funcional (não sabe o que é? dê uma olhada no meu artigo O que é um Paradigma de Programação).
A seguir temos um trecho de código, na forma imperativa, cujo propósito é somar os inteiros pares de uma lista.
```
private static int somaIterator(ListList<Integer> list) {
int soma = 0;
for (int num : list) {
if (num % 2 == 0) {
soma += num;
}
}
return soma;
}
```
Esse tipo de abordagem acaba sendo tediosa, você já deve ter implementado diversos for como esse. Para solucionar este problema, a programação funcional nos permite com encadeamento de métodos e passagem de parâmetros via Expressões Lambda.
Os beneficios dessa abordagem é a imutabilidade de variavéis, a variavél não vai mudar dentro do fluxo, além de um código preciso e claro.
```
private static int soma(List<Integer> list) {
int soma = list.stream()
.filter(n -> n % 2 == 0)
.reduce(0, Integer::sum);
return soma;
}
```
Aqui obtemos uma stream da lista por meio do método _stream()_ da interface Collection. O método _filter()_ retorna apenas os elementos pares. Tais elementos são processados pelo método _reduce()_ que aplica a operação de soma com todos os elementos. O resultado é armazenado no inteiro soma;
## Caracteristicas de uma Stream
Uma Stream pode ser definida como uma sequência de elementos de uma fonte de dados que oferece suporte a diferentes tipos de operações de agregação. Vamos entender essa definição:
- Uma stream provê uma interface para um conjunto sequencial de valores de um determinado tipo. Contudo, streams não armazenam elementos;
- Streams consomem dados de uma fonte, como coleções, arrays ou até recursos de entrada e saída;
- Streams suportam operações comuns a linguagens de programação funcionais, como filtrar, modificar, transformar o elemento em outro e assim por diante. Essas operações podem ser realizadas em série ou em paralelo.
Streams são projetadas de tal maneira que a maior parte de suas operações retornam novas streams. Dessa forma, é possível criar uma cadeia de operações que formam um fluxo de processamento. A isso damos o nome de pipeline.
As operações sobre streams são classificadas em **intermediárias ou terminais** e quando combinadas formam uma estrutura de processo chamada pipeline. As operações intermediárias servem como entrada para outras operações intermediárias ou terminais, elas sempre retornam uma nova stream. As operações terminais são usadas no final da cadeia (de operações) para fechar o processo e retornam um valor ou um objeto, não é possível utilizar intermediárias depois de uma terminal.
Em suma, a Stream API funciona convertendo uma fonte de dados em stream, realizando as operações intermediárias e por fim retorna algo com a chamada da operação terminal. No exemplo do trecho de código acima, temos _filter()_ uma operação terminal e _reduce()_ uma operação terminal.
### Como criar uma stream
```
List<String> nomes = new ArrayLIst<>();
nomes.add("Chicó");
nomes.add("Vicentao");
nomes.add("Cabo Setenta");
Stream<String> stream = nomes.stream();
```
### Operações intermediárias
**Filter**: O método filter() é usado para filtrar elementos de uma stream de acordo com uma condição (predicado). Para isso, ele recebe como parâmetro um objeto que implementa a interface Predicate<T> (interface funcional que define uma função com valor de retorno igual a um boolean) e retorna uma nova stream contendo apenas os elementos que satisfazem à condição.
**Map**: O método map() permite realizar transformações em uma lista de dados sem a necessidade de variáveis intermediárias, apenas utilizando como argumento uma função do tipo java.util.function.Function, que, assim como Predicate<T>, também é uma interface funcional. Essa função toma cada elemento de uma stream como parâmetro e retorna o elemento processado como resposta.
**Sorted**: O método sorted() retorna uma nova stream contendo os elementos da stream original ordenados de acordo com algum critério.
**Distinct**: A operação distinct() retorna uma stream contendo apenas elementos que não se repetem, de acordo com a implementação do método equals().
**Limit**: limit() é utilizado para limitar o número de elementos em uma stream.
### Operações terminais
**ForEach**: O método forEach() é usado para sobre uma stream e executar algum processamento como um loop for.
**Average**: average() permite calcular a média dos valores dos elementos (usado nas implementações de Stream par tipos primitivos como LongStream ou DoubleStream).
**Reduce**: O método reduce() é uma operação de redução que pode ser usada para transformar todos os elementos de uma stream em um único valor, com base em um predicado. Usado para somar, multiplicar ou encontrar o máximo e o mínimo de uma coleção.
**Collect**: Com o método collect() é possível coletar os elementos de uma stream em coleções, convertendo a stream para uma List, Set ou Map.
**Count**: O método count() retorna a quantidade de elementos em uma stream.
**AllMatch**: O método allMatch() verifica se todos os elementos de uma stream atendem a um critério passado como parâmetro, através de um Predicate, e retorna um valor booleano.
## Referência
[Java 8: Iniciando o desenvolvimento com a Streams API | Oracle Brasil](https://www.oracle.com/br/technical-resources/articles/java-stream-api.html) | alexreis |
1,857,598 | Why you should practice Nemawashi — The Art of Obtaining Consensus | Oftentimes people find it hard to convince others of their idea. There can be many reasons for this.... | 0 | 2024-05-23T11:00:00 | https://dev.to/arjunrao87/why-you-should-practice-nemawashi-the-art-of-obtaining-consensus-ppo | beginners, productivity, leadership, learning |
Oftentimes people find it hard to convince others of their idea. There can be many reasons for this. Trying to convince someone is a tough ask. The person conveying the idea either doesn’t understand their audience, haven’t done the right amount of research to explain it, haven’t crafted a crisp enough message and so on. Consensus is hard — so many people, so many opinions.

As you get more senior in your organization, getting consensus is table stakes. You are expected to make suggestions and bring new ideas to the table across cross functional stakeholders. Unfortunately the moment your idea gets put on the table, it receives tremendous pushback and that prevents the idea from making any real headway. Sound familiar? You’re not alone.
In fact, there is plenty of research that suggests if one person in a group raises concerns, odds are that influences the others to question the sanctity of the idea — the idea of Information Cascade. This is precisely why it is critical to learn the technique of Nemawashi.

## What is Nemawashi?
I think of Nemawashi as “hallway review” or as wikipedia (see below) refers to it as “laying the groundwork”. It is the act of voicing out your ideas to smaller groups of people before you put the idea in front of a larger group. You get individual buy-in into your idea and build on that to get momentum with the larger group. Any feedback you get from individuals, and incrementally bigger groups, can be baked into your proposal. Once you do this for all the important stakeholders of the idea, you have gotten all the critical feedback you need to ensure no one has any visceral reactions to your idea.
Now, when you put this in front of the whole group, you will basically get no major resistance because everyone has already given their most important feedback. At most you will receive requests for some cosmetic changes from other participants in your sessions.
Nemawashi is a crucial component of your leadership toolkit. It requires some work upfront but is so powerful at delivering results. Use it to be more effective at driving change and a fresh perspective.
## Origins of Nemawashi for the curious
Per Wikipedia
> Nemawashi (根回し) is a Japanese business informal process of laying the foundation for some proposed change or project by talking to the people concerned and gathering support and feedback before a formal announcement. It is considered an important element in any major change in the Japanese business environment before any formal steps are taken. Successful nemawashi enables changes to be carried out with the consent of all sides, avoiding embarrassment.
For the history of how this came to be, Wikipedia goes on to explain -
> Nemawashi literally translates as “turning the roots”, from ne (根, “root”) and mawasu (回す, “to turn something, to put something around something else”). Its original meaning was literal: in preparation for transplanting a tree, one would carefully dig around a tree some time before transplanting, and trim the roots to encourage the growth of smaller roots that will help the tree become established in its new location.[1][2][3][4][5] Nemawashi is often cited as an example of a Japanese word which is difficult to translate effectively, because it is tied so closely to Japanese culture itself, although it is often translated as “laying the groundwork.”
---
⭐ If you liked this, be sure to ♥️ this post and follow/subscribe at https://a1engineering.substack.com/subscribe! ⭐ | arjunrao87 |
1,834,603 | The Adventures of Blink #24: Javascript? Ain't Nobody Got Time Fo Dat | I have a confession. I hate javascript. I don't really know why. Maybe it's because it says "java"... | 0 | 2024-05-23T11:00:00 | https://dev.to/linkbenjamin/the-adventures-of-blink-24-javascript-aint-nobody-got-time-fo-dat-46bc | vaadin, webdev, java, tooling | I have a confession.
I hate javascript.
I don't really know why. Maybe it's because it says "java" in the name and doesn't even vaguely resemble Java. Maybe it's because an entire new js framework that EVERYONE ABSOLUTELY MUST LEARN is released about every 27 seconds. Maybe I'm disappointed that I have to buy another hard drive every time I run `npm install` because I have to download the freakin' UNIVERSE in order to Hello World. Maybe my brain is just too slow to fully grok the idea of async calls and promises. Maybe I'm just old and grouchy.
But I hate it. I've tried a couple of times to pick it up - with React, and then Vue, and then straight Node.js. And I was kinda able to be sort of ok with it, but I just feel like it makes me exert more effort than the reward I get from writing in it.
Go ahead, unfollow me. I know how Holy Wars are fought in Dev Circles. 🤷🏽♂️
The problem with hating javascript, of course, is that so many things are written in it. I mean, it's pretty much the default language of websites, and... this internet thing doesn't seem to be a passing fad, does it?
So imagine how excited someone in that mindset gets if they hear that a product allows you to build web apps... in Java... without using javascript for anything.

When I first encountered [Vaadin](https://vaadin.com/), it really intrigued me. It's always bothered me that for a Java programmer to make an app based in the browser, they had to learn HTML and Javascript to actually finish the project. Why the heck couldn't we just do it all in a single language? Why all this front-end voodoo?
Vaadin provides a large library of website components, free & open source, for you to be able to build in 100% Java. There are some "special" components that are in a paid tier, but you can do a **lot** with just the free ones.
## TL:DR
Don't feel like reading the whole post? Don't worry, I've got you! Here's the youtube edition, go give me a like and a subscribe there:
{% embed https://www.youtube.com/watch?v=0I7WO_BpqnA %}
## Talk is Cheap, Ben.
Let's go try it out, shall we? To get started, you can pull down their example project from their [quick start page](https://vaadin.com/docs/latest/guide/quick-start)... or you could roll your own! Vaadin has a maven repository you can use:
```xml
<repositories>
<repository>
<id>Vaadin Directory</id>
<url>https://maven.vaadin.com/vaadin-addons</url>
<snapshots>
<enabled>false</enabled>
</snapshots>
</repository>
</repositories>
```
The [Vaadin docs](https://vaadin.com/docs/latest/configuration/maven) have extensive information about what's available through their maven plugin.
But for today's adventure, let's see what happens when we build from the sample project!
## Prerequisites
In order for this demo to work, you have to have your dev environment already set up to work in Java. This means:
- Have a JDK installed correctly. Instructions for this vary by platform, but [here](https://docs.oracle.com/en/java/javase/21/install/index.html) are Oracle's instructions for the "big 3".
- Have [Apache Maven](https://maven.apache.org/install.html) installed correctly.
> Please note that these instructions will result in the creation of extra entries in your system's `PATH` environment variable, as well as a need to create two new environment variables in your system's shell: `JAVA_HOME` and `M2_HOME`. `JAVA_HOME` of course points to the folder where your JDK is installed (Specifically to `/Contents/Home` within the JDK folder). Note that this path is different from what's put in the `PATH` variable - that will use `JAVA_HOME` + `/bin`. `M2_HOME` points to wherever you installed maven. Old hands with Java will probably be well aware of this but I was a newbie once upon a time and it took me a lot of reading to get someone to explain it effectively!
Once you have those things installed, you grab your IDE of choice (Eclipse? IntelliJ? VSCode? I'm not getting into that Holy War 😜) and open the project folder wherever you extracted it.
## There were... some slight modifications
The Vaadin tutorial provides you with a simple "todo list" web page - You can add items to the list, it creates an entry on the list with a checkbox. The data doesn't get stored anywhere, and the components aren't really connected to anything... just a quick place to start your tutorial.
I elected to go off the beaten path because I like to try weird stuff. So I'm going to make my web page play Tic-Tac-Toe!
## This is gonna be a long blog post, blink
No, I promise to stay on topic! We aren't going to talk about any of the implementation of the Tic-Tac-Toe game - suffice to say I made a few classes that handle the logic of the game and feed information back to an interface (which we're going to build *really* quickly in Vaadin!). If you'd like to see the code, [I've posted it on my GitHub](https://github.com/LinkBenjamin/vaadin-tic-tac-toe).
## How to Vaadin
Vaadin's claim to fame is that you can make elegant web frontends without writing Javascript. So here's mine, for playing tic-tac-toe. We'll talk through it line-by-line so you can see how it works:
```Java
@Route("")
```
Route defines the url that your user will use to reach this class. This one is blank, so it's the root of my site (`http://localhost:8080/`, for the local dev copy). If I wanted to have this class reached by `http://localhost:8080/tictactoe`, I'd change this to
```Java
@Route("tictactoe")
```
which is something I actually tried at one point, and it was literally a single change to update the Route. Sickeningly intuitive.
```Java
public class MainView extends VerticalLayout {
```
Here we're defining that our class defaults to a vertical layout. That is, when you tell it to display multiple Vaadin components on the page, it will stack them vertically by default.
```Java
Game game = new Game();
H3 turn = new H3("Click a button to play an X");
```
Here I'm creating an object to hold my game logic, and making a class variable to hold a text object that I'm going to update. You'll notice the Vaadin component is called H3... because it displays the same as an HTML `<h3>` tag.
```Java
public MainView() {
VerticalLayout buttonBoard = createButtonBoard();
```
Ok, this one's kinda cheating. I built the "buttonBoard" object in a method to keep my constructor smaller. I'll show you that code in a bit.
```Java
add(
new H1("Tic-Tac-Toe!"),
turn,
buttonBoard
);
}
```
Here's the instructions to render the page. We're going to display (in `<h1>`) Tic-Tac-Toe!, then below that we'll show the `<h3>` line that prints whose turn it is, and below that, the buttonBoard.
Easy-peasy.
## What's a buttonBoard?
The buttonBoard is a collection that I built in a VerticalLayout so that I'd have the Tic-Tac-Toe board declared as 9 buttons, on 3 rows of 3 buttons each. Here's the `createButtonBoard()` method I called earlier:
```Java
private VerticalLayout createButtonBoard() {
Button[] buttons = new Button[9];
for(int x=0;x<9;x++) {
buttons[x] = new Button();
buttons[x].setId(String.valueOf(x));
buttons[x].addClickListener(event -> {
event.getSource().setText(game.whoseTurn());
game.play(Integer.parseInt(event.getSource().getId().get()));
turn.setText("Click a button to play an " + game.whoseTurn());
event.getSource().setEnabled(false);
if(game.isGameOver()){
for (int y = 0; y < 9; y++){
buttons[y].setEnabled(false);
}
if(game.whoWon() == "X" || game.whoWon() == "O")
Notification.show("Game is over - " + game.whoWon() + " wins! Refresh the screen to play again!");
else
Notification.show("Game is over - outcome is a draw! Refresh the screen to play again!");
}
});
}
HorizontalLayout row1 = new HorizontalLayout(
buttons[0],
buttons[1],
buttons[2]
);
HorizontalLayout row2 = new HorizontalLayout(
buttons[3],
buttons[4],
buttons[5]
);
HorizontalLayout row3= new HorizontalLayout(
buttons[6],
buttons[7],
buttons[8]
);
return new VerticalLayout(
row1,
row2,
row3);
}
```
Here are the important notes:
- We declare the Layouts much like you'd expect. Note I use a `HorizontalLayout` for each row so that I can put 3 buttons on each, and then assemble the 3 `HorizontalLayout` rows into one `VerticalLayout`. That's how you stack them so that you get all the buttons lined up neatly like a tic-tac-toe board.
- The other interesting part of this is the section with the click listener:
```Java
buttons[x].addClickListener(event -> {
event.getSource().setText(game.whoseTurn());
game.play(Integer.parseInt(event.getSource().getId().get()));
turn.setText("Click a button to play an " + game.whoseTurn());
event.getSource().setEnabled(false);
if(game.isGameOver()){
for (int y = 0; y < 9; y++){
buttons[y].setEnabled(false);
}
if(game.whoWon() == "X" || game.whoWon() == "O")
Notification.show("Game is over - " + game.whoWon() + " wins! Refresh the screen to play again!");
else
Notification.show("Game is over - outcome is a draw! Refresh the screen to play again!");
}
});
```
As I initialize the buttons, I'm able to declare this Click Listener dynamically using the `->` operator. This Listener is effectively an inline method that defines what to do if this button gets clicked (we can tell which button was clicked by getting its `Id` value from `event.getSource()`.
## Running the code
The tutorial comes with instructions about how to run the code in `README.md` but the short version is that there's a script included (`mvnw`) which you can run to start things up. Try it out!
## Wrapping up
I was a little skeptical of a product that made the claims Vaadin makes... but I'm pretty pleased that I spent about twice as long coding up the Tic-Tac-Toe classes as I did figuring out an interface I'd never used before. This project took me about 3 hours total, with ZERO prior Vaadin experience.
With a large library of components, Java developers don't have to worry about separating backend and frontend along linguistic barriers. Pretty freakin' cool.
I hope you've enjoyed this look at Vaadin! Tune in for next week's Adventure, when we finish out the "How to Win with Devs" series on the topic of "Building Excitement"! | linkbenjamin |
1,862,729 | Transform Your Body with Cutting-Edge Body Sculpting Services in Regina | Are you trying to decorate your determination and improve your self belief with modern plastic... | 0 | 2024-05-23T10:59:22 | https://dev.to/bodysculptingregina/transform-your-body-with-cutting-edge-body-sculpting-services-in-regina-24hp | Are you trying to decorate your determination and improve your self belief with modern plastic surgical treatment? Look no further than Body Design Regina, where we offer more than a few superior body artwork designed to help you obtain the entire and effective appearance of your perfect body. Our cutting-edge body art scientific center in Regina uses the modern body art laser era to exhibit non-invasive treatments. Whether you're looking for "body sculpting close to me" or want to research more about "body sculpture," this complete publication will come up with all of the information you need to begin your conversion adventure.
What is Body Sculpting and What are its types?
Body sculpting, additionally called frame contouring, includes non-surgical procedures that concentrate on and dispose of cussed fat, tighten pores and skin, and treat precise regions of the body, and these merchandise are designed to give you herbal contours had been reduced to enhance, to create An additional toned and sculpted look is likewise available.
Cryolipolysis ([**CoolSculpting**](https://bodysculptingregina.ca/coolsculping-regina/)**): **This method uses cold temperatures to freeze and destroy fat cells. It is particularly effective for areas like the abdomen, thighs, and love handles.
Laser Lipolysis (SculpSure):Laser technology targets fat cells with heat, destroying them while leaving surrounding tissues unharmed.
Radiofrequency Lipolysis: Uses radiofrequency energy to heat and destroy fat cells, which are then naturally eliminated by the body.
Ultrasound Fat Reduction: Uses focused ultrasound waves to break down fat cells, which are then metabolized by the body.
Why Choose Body Sculpting Regina?
At **[Body Sculpting Regina](https://bodysculptingregina.ca/)** we're devoted to supplying our clients with the very first-rate expert care and remedies available. Here’s why you need to take us on a frame transformation journey.
- Our crew of licensed specialists are obsessed with superb body art techniques. They are adept at the use of the modern technologies and techniques to reap a few top great merchandise and sponsor happiness.
- We use current body-sculpting laser generation, along with industry-stipple devices like SculpSure and CoolSculpting. This generation is FDA accepted and confirmed to be secure and powerful.
- We discover what's actual. That’s why we offer customized advice to create a customized remedy plan tailor-made on your specific desires and needs.
- Our health facility provides a cold, pain-free surroundings wherein you may sense cushty at every level of your remedies. We try to create an excellent deal of happiness for all our customers.
Body Selection Regina Type Choosing to try a non-invasive disc contouring treatment. Our healthcare facility has a group of licensed professionals who are especially professional and committed to providing first elegance outcomes. We use cutting-edge-day body-sculpting laser era, which include SculpSure and CoolSculpting, to make certain steady and effective fat reduction. Each purchaser gets a customized treatment plan tailored to their precise dreams, ensuring a customized method to frame paintings. Our welcoming and snug surroundings affords a fine revel in from consultations to post-treatment care, making Body Sculpting Regina an important part of your body transformation adventure.
Frequently Asked Questions
Is body sculpting safe?
Yes, the frame-sculpting strategies supplied at our sanatorium are FDA-authorized and clinically tested for safety and effectiveness. Our informed employees ensure that every machine is completed with the excellent predicted care.
How long do the results last?
The consequences of body-manage therapy are prolonged-lasting, in particular if they are mixed with a healthful life-style. Although you completely cast off the fat cells you address, it is vital to keep a balanced software program of weight loss and moderate workout to prevent the buildup of recent fat.
How many sessions will I need?
The required classes range from relying on the vessel and the suitable place of remedy. During your session, our experts will offer you an individualized treatment plan that outlines the endorsed amount of time.
Is there any downtime?
Most body-sculpting strategies take little or no time. You can commonly resume your each day's sports activities right now after surgical procedure. Some treatments require brief redness, swelling, or bruising, which normally resolves fast.
Are the treatments painful?
Body painting strategies are typically very aesthetically appealing. Some patients may additionally have a hassle in a particular way.
| bodysculptingregina | |
1,862,728 | Cyber Attacks Prevention Methods | The Rising Threat of Cyber Attacks Cyber-attacks have become a significant threat to... | 0 | 2024-05-23T10:55:52 | https://dev.to/elainecbennet/cyber-attacks-prevention-methods-25m3 | cybersecurity, cyberattacks, cyberthreat | ### The Rising Threat of Cyber Attacks
Cyber-attacks have become a significant threat to individuals, businesses, and governments worldwide. Cybercriminals exploit vulnerabilities in systems, networks, and software to steal sensitive information, disrupt services, and cause financial and reputational damage. The increasing reliance on digital technologies has made robust cyber attack prevention methods essential for ensuring the security and integrity of digital assets.
### Understanding Cyber Attack Vectors
[Cyber attacks](https://dev.to/vishwasnarayan5/types-of-attacks-in-cyberspace-4o1f) can occur through various vectors, each exploiting different weaknesses. Common vectors include phishing attacks, where attackers deceive individuals into providing personal information, and malware, which can infiltrate systems to steal data or disrupt operations. Understanding these attack vectors is the first step in developing effective prevention strategies.
### The Importance of Proactive Defense
Reactive measures often fall short against the rapidly evolving tactics of cybercriminals. A proactive defense strategy, such as the one advocated by [Microminder](https://www.micromindercs.com/) CS, focuses on anticipating potential threats and implementing preventative measures to mitigate them before they cause harm. This approach includes regular system updates, comprehensive employee training, and the deployment of advanced security technologies, all of which are integral to maintaining a robust defense against cyber threats.
### The Role of Human Factors
Human error is a significant factor in many cyber attacks. Employees might inadvertently click on malicious links or fail to follow security protocols, leading to breaches. Educating staff about cyber hygiene and establishing a culture of security awareness can significantly reduce the risk of cyber incidents.
### The Need for a Comprehensive Security Framework
A comprehensive security framework encompasses multiple layers of protection to safeguard against cyber threats. This includes technical measures like firewalls and encryption, administrative actions such as policies and procedures, and physical security to protect hardware. Integrating these elements ensures a holistic defense against cyber attacks.
## Implementing Robust Cyber Security Policies
Establishing Clear Policies and Procedures
Organizations must develop clear, comprehensive cyber security policies and procedures. These documents should outline acceptable use of technology, incident response protocols, and guidelines for handling sensitive information. Regularly updating and reviewing these policies ensures they remain effective against new and emerging threats.
### Conducting Regular Security Audits
Regular security audits help identify vulnerabilities within an organization's infrastructure. These audits should be conducted by both internal teams and external experts to provide an unbiased assessment. Audits can uncover weak points in systems, processes, and human factors, enabling organizations to strengthen their defenses accordingly.
### Employee Training and Awareness Programs
Employees are the first line of defense against cyber attacks. Regular training programs should educate staff on recognizing phishing attempts, creating strong passwords, and following best practices for cyber hygiene. Simulated phishing exercises can test and reinforce these skills, making employees more vigilant and less likely to fall victim to attacks.
## Leveraging Advanced Technologies
### Implementing Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) adds an extra layer of security by requiring users to provide two or more verification factors to gain access to a system. This reduces the risk of unauthorized access, even if passwords are compromised. MFA can include something the user knows (password), something the user has (a mobile device), or something the user is (biometric verification).
### Deploying Intrusion Detection and Prevention Systems (IDPS)
Intrusion Detection and Prevention Systems (IDPS) monitor network traffic for suspicious activity and can automatically block potential threats. These systems use signatures, anomaly detection, and behavioral analysis to identify and mitigate attacks in real-time, providing a crucial line of defense against sophisticated cyber threats.
### Utilizing Artificial Intelligence and Machine Learning
Artificial Intelligence (AI) and Machine Learning (ML) can enhance cyber security by identifying patterns and anomalies that may indicate an attack. These technologies can analyze vast amounts of data quickly, enabling organizations to detect threats faster than traditional methods. AI and ML can also adapt to new threats, improving their effectiveness over time.
## Ensuring Data Protection and Privacy
### Encrypting Sensitive Data
Encryption is a fundamental technique for protecting sensitive data. By converting information into an unreadable format, encryption ensures that even if data is intercepted, it cannot be understood without the decryption key. Organizations should encrypt data both at rest and in transit to safeguard it from cybercriminals.
### Implementing Data Loss Prevention (DLP) Solutions
Data Loss Prevention (DLP) solutions help prevent unauthorized access to sensitive information. DLP tools monitor data flows and enforce policies to prevent data leakage. These solutions can block emails containing sensitive data from being sent to unauthorized recipients and alert administrators to potential breaches.
### Ensuring Compliance with Data Protection Regulations
Compliance with data protection regulations, such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), is crucial for maintaining data privacy and security. These regulations mandate strict data handling practices and impose significant penalties for non-compliance. Organizations must stay informed about relevant regulations and implement measures to ensure compliance.
Building a Resilient Cyber Security Culture
### Encouraging a Security-First Mindset
Creating a culture that prioritizes security is essential for effective cyber attack prevention. This involves leadership commitment to security, integrating security considerations into every aspect of operations, and encouraging employees to take ownership of their role in protecting the organization.
### Conducting Regular Cyber Security Drills
Regular cyber security drills simulate potential attack scenarios, helping organizations prepare for actual incidents. These drills can test response protocols, identify weaknesses in the defense strategy, and ensure that all employees know their roles in an emergency. Continuous improvement based on drill outcomes enhances overall resilience.
### Collaborating with Industry Partners
Collaboration with industry partners and participation in information-sharing initiatives can provide valuable insights into emerging threats and best practices. Organizations can benefit from the collective knowledge and experience of the wider cyber security community, enabling them to stay ahead of potential threats.
## Conclusion
Cyber attacks pose a significant and evolving threat to all sectors of society. By understanding the various attack vectors and the importance of proactive defense, organizations can implement robust cyber security policies and leverage advanced technologies to protect their digital assets. Ensuring data protection and fostering a resilient cyber security culture are critical components of a comprehensive defense strategy. Continuous education, regular audits, and adherence to regulatory requirements are essential for maintaining a strong security posture. In a world where cyber threats are ever-present, a multifaceted approach to prevention is the best safeguard against the potentially devastating impacts of cyber attacks.
| elainecbennet |
1,862,727 | Understanding Insert/Inject Script Rule | Insert/Inject Script Rule allows you to inject JavaScript into web pages as they load. This means you... | 0 | 2024-05-23T10:55:23 | https://requestly.com/blog/academy-understanding-insert-inject-script-rule/ | Insert/Inject Script Rule allows you to inject JavaScript into web pages as they load. This means you can modify the DOM, change styles, or even add new functionality without altering the source code directly. It’s important for testing hypotheses or debugging during development and quality assurance processes.
## Video Guide
{% embed https://youtu.be/b3TzuxkNdgM %}
## Step-by-Step Guide
To fully utilize the feature, let’s walk through the setup process:
1. **Setting Up**: Begin by [installing Requestly](https://requestly.com/downloads/) in your browser and navigating to the Rules section.
2. **Creating Your First Rule**: Select the Insert/Inject Script option and specify the conditions under which your script should run.
3. **Insert Script**: Write or paste the JavaScript you wish to inject. This could range from simple DOM manipulations to complex functionality enhancements.
4. **Deployment and Testing**: Apply the rule and see your script come to life on the target webpage. It’s that simple!
## Use Cases
The Insert/Inject Script Rule opens up a lot of possibilities. Here are just a few scenarios where it shines:
## 1. Test Custom Widget Code on Customer’s Web Pages
If you create widgets like Live Chat, Music widget, ads, monitoring, etc. that are deployed on customer websites, you can test or demonstrate how your widget would work on their website. Insert Script can help in locally inserting such code snippets on live websites. Here are the steps for the same:
1. Create a new Insert Script rule.
2. Use the target website’s hostname as the source condition.
3. Select options as given below:
1. Language — JS (or CSS if you want to insert CSS, you can create 2 rules if you want to insert CSS & JS both)
2. Code Source — Customer Code(Select URL if your script is hosted publicly)
3. Insert — After Page Load (Select Before page load if your script is expected to run before page load)
4. Insert the code in the code block section.
5. Save the Rule
6. Test by entering the website address.
## 2. Test a Bug Fix
Fixing production bugs is always a rush. Testing those patches on the production environment, before actually patching, can significantly reduce the time spent on reverting it later or rushing another patch to fix the previous patch. Similar steps can be followed in this case:
1. Create a new Insert Script rule.
2. Use the target website’s hostname as the source condition.
3. Insert the code in the code block section.
4. Save the Rule
5. Test by entering the website address.
## 3. Feature Prototyping
Prototyping a feature directly on production websites can be done using the Insert Script rule. Early detection of any issue can reduce the number of last-minute issues.
The Insert/Inject Script Rule is one of the most used features of Requestly; it significantly improves how we approach web development and testing. By allowing immediate, on-the-fly modifications, Requestly speeds up the development cycle and fosters a culture of experimentation and continuous improvement.
## Troubleshooting
There are some cases where rules might not work as expected, visit our [troubleshooting guide](https://developers.requestly.io/troubleshooting/rules-not-working/) for more details.
*Originally published at [https://requestly.com](https://requestly.com/blog/academy-understanding-insert-inject-script-rule/) on February 15, 2024.*
| requestlyio | |
1,862,726 | Alcohol Dependence Therapy | Looking for De addiction Centres near you? Dhara Nasha Mukti Kendra offers top-notch addiction... | 0 | 2024-05-23T10:55:15 | https://dev.to/dharanashamuktikendra/alcohol-dependence-therapy-3apo | Looking for De addiction Centres near you? Dhara Nasha Mukti Kendra offers top-notch addiction treatment in Patna. Our centre provides comprehensive services for individuals seeking drug addiction treatment in Patna. Contact us today for expert care and support on your journey to recovery. For more information please visit us https://dharanashamuktikendra.com/
 | dharanashamuktikendra | |
1,862,723 | Don't Miss the AWS Cloud Practitioner Certification Cheat Sheet: Your Ultimate Guide to Success | If you're diving into the world of cloud computing, you've likely heard of Amazon Web Services (AWS).... | 0 | 2024-05-23T10:52:31 | https://dev.to/giasuddin90/dont-miss-the-aws-cloud-practitioner-certification-cheat-sheet-your-ultimate-guide-to-success-4c8h | aws, cloudcomputing, cloud | If you're diving into the world of cloud computing, you've likely heard of Amazon Web Services (AWS). With its expansive suite of services and tools, AWS has become a leading cloud platform used by businesses worldwide. For those looking to validate their understanding of AWS, the AWS Certified Cloud Practitioner certification is the perfect starting point. To help you on this journey, an AWS Cloud Practitioner Certification Cheat Sheet can be a game-changer.
[Prepare the AWS Certified Cloud Practitioner CLF-C02. 390 unique high-quality test questions with detailed explanations! Udemy Practice test questions.](https://www.udemy.com/course/aws-certified-cloud-practitioner-clf-c02-6-practice-exams/?referralCode=CC7E8227632717791235)
## Why Pursue the AWS Cloud Practitioner Certification?
Before we delve into the cheat sheet, let's understand why this certification is worth your time and effort:
1. **Foundational Knowledge**: This certification provides a broad overview of AWS services, pricing, security, and architecture. It's ideal for those new to AWS or cloud computing in general.
2. **Career Advancement**: With cloud skills in high demand, holding an AWS certification can significantly boost your resume and open doors to new job opportunities.
3. **Solid Foundation for Advanced Certifications**: If you plan to pursue more advanced AWS certifications, starting with the Cloud Practitioner certification is a smart move.
## The AWS Cloud Practitioner Certification Cheat Sheet: Your Key to Exam Success
### What is a Cheat Sheet?
A cheat sheet is a concise set of notes used for quick reference. For the AWS Cloud Practitioner exam, a well-crafted cheat sheet can summarize key concepts, services, and best practices, making your study sessions more efficient.
### Key Components of the Cheat Sheet
Here are some essential topics and concepts that should be included in your AWS Cloud Practitioner Certification Cheat Sheet:
1. **AWS Global Infrastructure**
- **Regions and Availability Zones**: Understand the geographic distribution of AWS data centers.
- **Edge Locations**: Key to AWS's content delivery network (CDN).
2. **Core AWS Services**
- **Compute**: EC2, Lambda, Elastic Beanstalk.
- **Storage**: S3, EBS, Glacier.
- **Databases**: RDS, DynamoDB, Redshift.
- **Networking**: VPC, Route 53, CloudFront.
3. **Security and Compliance**
- **Shared Responsibility Model**: AWS vs. customer responsibilities.
- **IAM (Identity and Access Management)**: Roles, policies, MFA.
- **Compliance Programs**: HIPAA, GDPR, etc.
4. **Pricing and Billing**
- **Pricing Models**: On-Demand, Reserved, Spot Instances.
- **Cost Management Tools**: AWS Cost Explorer, Budgets, Trusted Advisor.
5. **AWS Support Plans**
- **Basic, Developer, Business, Enterprise**: Differences and benefits.
6. **Architectural Best Practices**
- **Well-Architected Framework**: Five pillars - Operational Excellence, Security, Reliability, Performance Efficiency, and Cost Optimization.
[Prepare the AWS Certified Cloud Practitioner CLF-C02. 390 unique high-quality test questions with detailed explanations! Udemy Practice test questions.](https://www.udemy.com/course/aws-certified-cloud-practitioner-clf-c02-6-practice-exams/?referralCode=CC7E8227632717791235)
### Tips for Using the Cheat Sheet
1. **Regular Review**: Incorporate the cheat sheet into your daily study routine. Regularly reviewing key concepts helps reinforce your understanding.
2. **Practice Exams**: Use the cheat sheet to answer practice exam questions. This will help you identify areas where you need more study.
3. **Update Frequently**: AWS regularly updates its services and best practices. Keep your cheat sheet current to ensure you're studying the latest information.
4. **Hands-On Practice**: Combine the cheat sheet with hands-on practice in the AWS Management Console. Real-world experience is invaluable.
[Prepare the AWS Certified Cloud Practitioner CLF-C02. 390 unique high-quality test questions with detailed explanations! Udemy Practice test questions.](https://www.udemy.com/course/aws-certified-cloud-practitioner-clf-c02-6-practice-exams/?referralCode=CC7E8227632717791235)
### Conclusion
The AWS Cloud Practitioner Certification is an excellent stepping stone into the world of cloud computing. A well-organized cheat sheet can be an invaluable tool in your study arsenal, helping you quickly recall essential information and streamline your preparation process.
Don't miss out on leveraging this powerful study aid. Whether you're new to AWS or brushing up on your cloud knowledge, the AWS Cloud Practitioner Certification Cheat Sheet is your ticket to exam success and a brighter future in cloud technology. Happy studying and good luck on your certification journey! | giasuddin90 |
1,862,722 | Women's Indian Wedding Dresses For Guests | An Indian wedding is a long affair which lasts for days. Whether it is the wedding of a common Indian... | 0 | 2024-05-23T10:52:10 | https://dev.to/likeadivauk/womens-indian-wedding-dresses-for-guests-3d37 | indianweddingdresses, indiandresses | An Indian wedding is a long affair which lasts for days. Whether it is the wedding of a common Indian woman, or that of a celebrity, you will never find grandeur and extravaganza absent from an Indian wedding. In fact, people do not hesitate to spend crores and crores of rupees in an Indian wedding. Therefore, an Indian wedding is special in so many ways. It is not just the decoration and arrangements, food and rituals that steal the show, rather apart from all these things, the outfits the bride and the groom wear and the guests wear also become the centre of attention. Therefore, [Indian wedding dresses](https://www.likeadiva.com/wedding-collection) do have a special place in the fashion world. Not just in designs and styles, but also in varieties you will get a lot of options. You can choose different outfits for different rituals, which include some pre-wedding rituals, wedding rituals and the post-wedding rituals.
In this article we shall be looking at some of the Indian wedding outfits for women to wear as wedding guests. Sarees, lehengas, party wear salwar kameez and so on are some of the famous outfits which women wear to attend a wedding. These days apart from the outfits mentioned above, Indo western outfits, which are a fusion of Indian and western styles are also on trend. Therefore, you can get a wide range of varieties to wear as a guest to an Indian wedding. You can easily get these outfits from your nearby boutiques or stores and you can order them from different websites as well. **Like A Diva** is one such website famous for selling all kinds of Indian and Indo western outfits, such as designer [Anarkali suits](https://www.likeadiva.com/designer-anarkali-suits) and alike for different events, functions and parties. Let us now have a look at some of the Indian outfits which you can wear as a guest to a wedding.
## Multicolour lehenga set
You can choose a multicolour outfit which goes well with different events and functions, including a wedding function. And a lehenga is always the first choice for a wedding function. Therefore, a multicolour lehenga is one of the best options for a wedding function, particularly for a haldi or a mehendi function, where there is always a dress code for it. If you do not have a yellow or a green colour lehenga, but you have a multicoloured lehenga in intricate designs consisting of different colours, including yellow and green, you can rely on it completely.
## Anarkali gown
Anarkali or Indo western gowns are on trend these days, and you can opt for this outfit to attend an Indian function, such as a cocktail party, sangeet party or a reception party. You will get a glamorous look like a bollywood diva by wearing this intricately designed flared evening gown consisting of cape style sleeves. This outfit, which is a fusion of Indian and western style is the best option to wear, if you are attending a wedding as a guest to get a gorgeous look and to become the centre of attention.
## Pre-draped saree
Nothing can beat the divine look of a saree. And for contemporary women, pre-draped sarees or Indo western sarees are a great option, as they do not have to put effort in draping and carrying it. It comes with shimmering pallu, embroidery work, zari and stone work and to enhance its beauty, you can pair it with a well crafted designer blouse and a waist belt.
| likeadivauk |
1,862,721 | Top 10 Tips for Passing the AWS Certified Cloud Practitioner Certification Exam | Obtaining the AWS Certified Cloud Practitioner certification is a significant milestone for anyone... | 0 | 2024-05-23T10:48:19 | https://dev.to/giasuddin90/top-10-tips-for-passing-the-aws-certified-cloud-practitioner-certification-exam-lp7 | aws, certification | Obtaining the AWS Certified Cloud Practitioner certification is a significant milestone for anyone interested in a career in cloud computing. Whether you're new to AWS or have some experience, passing the exam requires careful preparation and an understanding of the topics it covers. Here are ten tips to help you succeed in your journey to becoming an AWS Certified Cloud Practitioner.
### 1. Understand the Exam Structure
Before diving into preparation, familiarize yourself with the exam format. The AWS Certified Cloud Practitioner exam consists of multiple-choice and multiple-response questions. You have 90 minutes to answer 65 questions. Understanding this structure helps you manage your time during the exam.
### 2. Review the Exam Guide
AWS provides an official exam guide that outlines the domains and subtopics covered in the exam. Download this guide from the AWS website and use it as a blueprint for your studies. This document serves as a comprehensive reference point for the skills and knowledge you need to acquire.
[If you are interested in the certified cloud practitioner test, Join the Piad course ](https://www.udemy.com/course/aws-certified-cloud-practitioner-clf-c02-6-practice-exams/?couponCode=2365C139BD97EE2FFB8F)
### 3. Start with Basic AWS Concepts
Since the AWS Certified Cloud Practitioner is an entry-level certification, focus on foundational concepts. Learn about the AWS Global Infrastructure, including regions, availability zones, and edge locations. Understand the shared responsibility model, security best practices, and key AWS services like EC2, S3, and Lambda.
### 4. Utilize AWS Training Resources
AWS offers a variety of free and paid training resources. Take advantage of AWS Skill Builder, which provides online training modules covering various topics related to the exam. AWS also offers a free Cloud Practitioner Essentials course, which is a great starting point for your studies.
### 5. [Take Practice Exams](https://www.udemy.com/course/aws-certified-cloud-practitioner-clf-c02-6-practice-exams/?couponCode=2365C139BD97EE2FFB8F)
Practice exams are invaluable for gauging your readiness for the actual test. They help you identify areas where you need to focus your studies and build your confidence. Consider using reputable platforms like Udemy or Whizlabs for practice exams. Aim to score consistently above 80% before attempting the real exam.
[If you are interested in the certified cloud practitioner test, Join the Piad course ](https://www.udemy.com/course/aws-certified-cloud-practitioner-clf-c02-6-practice-exams/?couponCode=2365C139BD97EE2FFB8F)
### 6. Join Study Groups or Online Communities
Engage with other learners preparing for the AWS Certified Cloud Practitioner exam. Join online forums, social media groups, or study groups where you can ask questions, share resources, and discuss challenging topics. These communities offer support and can provide valuable insights.
### 7. Create a Study Plan
Having a structured study plan is crucial for effective preparation. Break down the exam guide into manageable sections and allocate time for each topic. Be consistent with your study routine, and allow for flexibility to accommodate additional practice or review as needed.
### 8. Use Flashcards for Memorization
Flashcards are a great tool for memorizing key concepts, terms, and definitions. Create flashcards for important AWS services, pricing models, security practices, and other critical information. Reviewing these cards regularly helps reinforce your knowledge.
### 9. Focus on Real-World Scenarios
The AWS Certified Cloud Practitioner exam often includes scenario-based questions. To prepare, study real-world use cases and understand how different AWS services are used in practical situations. This knowledge will help you apply theoretical concepts to real-life contexts during the exam.
If you are interested in the certified cloud practitioner test, Join the Piad course (https://www.udemy.com/course/aws-certified-cloud-practitioner-clf-c02-6-practice-exams/?couponCode=2365C139BD97EE2FFB8F)
### 10. Relax and Stay Confident
On exam day, stay calm and confident. Ensure you get a good night's sleep beforehand, and arrive at the test center or set up your remote exam environment with plenty of time to spare. Trust in your preparation, and remember that it's okay to skip a question and return to it later if needed.
By following these tips, you'll be well on your way to passing the AWS Certified Cloud Practitioner certification exam. Remember, preparation and consistency are key. Good luck! | giasuddin90 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.