id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,919,901 | Discord bot test 558732958 | Please ignore I hate development lmao | 0 | 2024-07-11T15:30:09 | https://dev.to/aud/discord-bot-test-558732958-1lhp | Please ignore
I hate development lmao | aud | |
1,920,042 | piperinox review - does this supplement work? | Piperinox is a dietary supplement that is marketed for weight loss. It contains a blend of... | 0 | 2024-07-11T17:04:06 | https://dev.to/trustreviews/piperinox-review-does-this-supplement-work-43lg | Piperinox is a dietary supplement that is marketed for weight loss. It contains a blend of ingredients, including black pepper extract (piperine) and ginger extract.
Here's a breakdown of the claims and some facts to consider:
Claimed benefits of Piperinox:
Boosts metabolism
Increases fat burning
Suppresses appetite... | trustreviews | |
1,919,902 | Медикаментозний сон у дитячій стоматології | Ваша дитина відчуває занадто сильний дискомфорт при відвідуванні стоматології? Вона взагалі... | 0 | 2024-07-11T15:30:19 | https://dev.to/esthete/miedikamientoznii-son-u-ditiachii-stomatologhiyi-4kc6 | Ваша дитина відчуває занадто сильний дискомфорт при відвідуванні стоматології? Вона взагалі відмовляється відвідати стоматолога через непереборний страх? Вирішення є – медакоментозний сон (седація закисем азоту). Дана практика лікування давно широко поширена в стоматологічних клініках Європи та Америки. Стоматологи всь... | esthete | |
1,919,903 | Автоматизація процесу управління відрядженнями | Зі Scriptum процес оформлення та узгодження відряджень, подача звітності та компенсація витрат... | 0 | 2024-07-11T15:31:35 | https://dev.to/scriptum_bpm/avtomatizatsiia-protsiesu-upravlinnia-vidriadzhienniami-ln5 | Зі Scriptum процес оформлення та узгодження відряджень, подача звітності та компенсація витрат займатиме лічені хвилини і вимагатиме мінімум ручної роботи.
[Замовити демо](https://scriptum.ua/avtomatyzacziya-proczesu-upravlinnya-vidryadzhennyamy/) | scriptum_bpm | |
1,919,905 | The Power of Gaze Estimation: Transforming Technology and Beyond | Unlocking the Potential of Your Gaze Have you ever considered the power behind your gaze?... | 27,673 | 2024-07-11T15:35:06 | https://dev.to/rapidinnovation/the-power-of-gaze-estimation-transforming-technology-and-beyond-5cgf | ## Unlocking the Potential of Your Gaze
Have you ever considered the power behind your gaze? Imagine harnessing it to
revolutionize how we interact with technology, improve healthcare, and reshape
marketing strategies. This isn't about mere eye contact; it's about
transforming your sight into a dynamic tool that bridg... | rapidinnovation | |
1,919,906 | Day2 of 100DaysOfJavaScript | My objective is to continuous coding(learning). What I did Continued to watch the... | 0 | 2024-07-11T15:35:23 | https://dev.to/koichiarai/day2-of-100daysofjavascript-3ke0 | javascript, beginners, 100daysofcode | My objective is to continuous coding(learning).
## What I did
* Continued to watch the video
[Learn JavaScript](https://www.youtube.com/watch?v=PkZNo7MFNFg)
## What I learned
```
var WIL1 = "How" + "to" + sum + "Strings";
var WIL2 = ["How", "to", "operate", "array."];
WIL2.push(".push() and .shift()");
WIL2.shift();... | koichiarai |
1,919,907 | Developer diary #13. Pomodoro life | Today, I want to share how I organise my everyday work. I use technic pomodoro for this. I will not... | 0 | 2024-07-11T15:39:51 | https://dev.to/kiolk/developer-diary-13-pomodoro-life-38hc | android, programming, motivation, management | Today, I want to share how I organise my everyday work. I use technic pomodoro for this. I will not describe in details about it, you can easily google it. The key idea is that you split your work on small pieces (25 minutes of work + 5 min. break). A typical work day contains 16 pomodoro, but from my experience, you ... | kiolk |
1,919,911 | American Airlines Boosts Winter Schedule with Expanded Caribbean and Latin America Flights | As American Airlines invests heavily in modernizing its fleet and expanding its routes, how will... | 0 | 2024-07-11T15:49:37 | https://dev.to/digital_chaudhary_79/american-airlines-boosts-winter-schedule-with-expanded-caribbean-and-latin-america-flights-b8l |
As American Airlines invests heavily in modernizing its fleet and expanding its routes, how will these changes impact the future of sustainable air travel and the overall passenger experience?
**American Airlines’ Bold Moves: Fleet Expansion, Route Growth, and Sustainability Impacts
As the aviation industry continues ... | digital_chaudhary_79 | |
1,919,912 | Generate Signable PDF Forms with React | Why use React to generate PDF Forms? When Generating PDF Forms, React (or HTML) may not be... | 0 | 2024-07-11T15:55:28 | https://dev.to/fileforge/generate-signable-pdf-forms-with-react-1ha6 | pdf, react, typescript, fileforge |
## Why use React to generate PDF Forms?
When Generating PDF Forms, React (or HTML) may not be the first thing that comes to mind! It makes more sense when we compare it with website forms: we want to lay out the form fields, add labels, and make it easy to fill out. React is a great tool for this, and using Fileforge... | titou325 |
1,919,913 | Why Choose An Enterprise Software Development Company For Your Business | Software development these days is the backbone of modern enterprises. It boosts efficiency,... | 0 | 2024-07-11T15:56:09 | https://dev.to/adnanali007/why-choose-an-enterprise-software-development-company-for-your-business-5ejk | enterprisesoftwaredevelopment, customizedsolutions, developmentcompany, enterpriseapplication | Software development these days is the backbone of modern enterprises. It boosts efficiency, productivity, and customer engagement. Companies are increasingly demanding tech solutions. They see investing in software development as profitable.. But do these companies really help their business? Let's find out.
When cho... | adnanali007 |
1,919,914 | Dedicated Developers: The Key to Unlocking Your Potential | Businesses confront many changing issues today. The problems are in a fast-paced, tech-driven... | 0 | 2024-07-11T16:06:08 | https://dev.to/gpost/dedicated-developers-the-key-to-unlocking-your-potential-2ckd | app, development, webdev, programming | Businesses confront many changing issues today. The problems are in a fast-paced, tech-driven environment. It calls for creative and adaptable solutions. A company's tech skills are essential. It can make or break its success in this market. A vital component of this skill is the presence of committed developers. [Hire... | gpost |
1,919,915 | Newbie | Hello World, 🌎 😊 I’m a newbie. I just finished my Data Analyst Certification with Google (Coursera )... | 0 | 2024-07-11T16:08:38 | https://dev.to/jewhite711/newbie-2age | Hello World, 🌎 😊 I’m a newbie. I just finished my Data Analyst Certification with Google (Coursera ) but fell in love with the coding side instead. I’m self learning coding and leaning into Software Development so I’m diving into JavaScript right now with freecodecamp. I could desperately use some useful guidance to ... | jewhite711 | |
1,919,916 | 1190. Reverse Substrings Between Each Pair of Parentheses | 1190. Reverse Substrings Between Each Pair of Parentheses Medium You are given a string s that... | 27,523 | 2024-07-11T16:09:43 | https://dev.to/mdarifulhaque/1190-reverse-substrings-between-each-pair-of-parentheses-39bk | php, leetcode, algorithms, programming | 1190\. Reverse Substrings Between Each Pair of Parentheses
Medium
You are given a string `s` that consists of lower case English letters and brackets.
Reverse the strings in each pair of matching parentheses, starting from the innermost one.
Your result should **not** contain any brackets.
**Example 1:**
- **Inpu... | mdarifulhaque |
1,919,917 | Understanding Access Tokens and Refresh Tokens | In today's digital world, securing user authentication and managing access to resources is crucial... | 0 | 2024-07-11T16:15:42 | https://dev.to/mitesh_gehlot_391f8a69c07/understanding-access-tokens-and-refresh-tokens-4ecp | In today's digital world, securing user authentication and managing access to resources is crucial for any application. OAuth, a widely adopted authorization framework, uses Access Tokens and Refresh Tokens to ensure secure and seamless access to resources. In this article, we'll dive into what these tokens are, how th... | mitesh_gehlot_391f8a69c07 | |
1,919,919 | Text widget gets stuck inside a column | Hi, I am new to flutter and exasparated with the coding involved to design the UI. So I chanced upon... | 0 | 2024-07-11T16:16:53 | https://dev.to/sanjish_kumar_f70d6022bca/text-widget-gets-stuck-inside-a-column-1ebc | flutter, dart | Hi, I am new to flutter and exasparated with the coding involved to design the UI. So I chanced upon flutterViz. I made a container . Put a column widget inside and dragged a text widget inside the column. Now I wanted to move the text widget to another location within the column . I tried Right clicking and moving it ... | sanjish_kumar_f70d6022bca |
1,920,022 | The 21 Days Challenge: Pt. 1 | Hey programmers! This article is not a typical dev article with some informative downpour, but I... | 0 | 2024-07-11T16:26:05 | https://dev.to/sxryadipta/the-21-days-challenge-pt-1-3cnk | programming, productivity, 100daysofcode, discuss | Hey programmers!
This article is not a typical dev article with some informative downpour, but I want to talk a little about something I am interested in.
I have heard many people talk about this concept of a 21-day habit-building challenge. As the name suggests, the idea here is to perform a specific task every day... | sxryadipta |
1,920,024 | Quiz Management System Project in Python | Django | View Post Django Quiz is an ultimate quiz management system that utilizes the power and flexibility... | 0 | 2024-07-11T16:31:06 | https://dev.to/codzap/quiz-management-system-project-in-python-django-4f1j | python, django, developer, webdev | [View Post](https://codzap.com/django-projects/quiz-management-system-using-django-python/)
Django Quiz is an ultimate quiz management system that utilizes the power and flexibility of Django and Python to take the user through the smooth yet transparent user experience. Either you are an educator or trainer, or you a... | codzap |
1,920,025 | Join Rocket Pool: The Leading Decentralized Ethereum Staking Network | Welcome to the world of setting up a fresh identity in the digital sphere. You are about to embark on... | 0 | 2024-07-11T16:31:25 | https://dev.to/cleopatramorris_d539d19ea/join-rocket-pool-the-leading-decentralized-ethereum-staking-network-6p4 | rocketpool, cryptocurrency, web3, blockchain |
Welcome to the world of setting up a fresh identity in the digital sphere. You are about to embark on a journey of creating a unique presence for yourself. Dive into the realm of personalization and customization as you embark on this exciting process.
Uncover the steps required to establish a distinct persona online... | cleopatramorris_d539d19ea |
1,920,026 | 7 Essential Tips to Avoid Code Smells in Your Projects | As programmers, our goal is to write code that is clear, effective, and manageable. But occasionally,... | 0 | 2024-07-11T16:32:20 | https://dev.to/wallacefreitas/7-essential-tips-to-avoid-code-smells-in-your-projects-4fo8 | refactoring, solidprinciples, cleancode | As programmers, our goal is to write code that is clear, effective, and manageable. But occasionally, we come across "code smells"—subtle hints of more serious issues with the code. Early resolution of these problems can reduce technical debt significantly and enhance the general quality of the code. Here are seven cru... | wallacefreitas |
1,920,027 | Rocket Pool: Your Gateway to Seamless Ethereum Staking | Explore the inner mechanisms behind the functioning of the Rocket Pool Validator, delve into its... | 0 | 2024-07-11T16:33:08 | https://dev.to/cleopatramorris_d539d19ea/rocket-pool-your-gateway-to-seamless-ethereum-staking-58h6 | cryptocurrency, web3, blockchain, crypto |
Explore the inner mechanisms behind the functioning of the Rocket Pool Validator, delve into its underlying operations that enable it to perform its duties. Uncover the intricacies of this mechanism that facilitate its efficiency and reliability.
Gain insight into the purpose and implementation of the Rocket Pool Val... | cleopatramorris_d539d19ea |
1,920,028 | Python Youtube Video Downloader | View Post In this modern world, video content forms such an integral part of our lives through this... | 0 | 2024-07-11T16:33:44 | https://dev.to/codzap/python-youtube-video-downloader-519f | webdev, python, javascript, django | [View Post](https://codzap.com/django-projects/youtube-video-downloader-in-any-format-django-python/)
In this modern world, video content forms such an integral part of our lives through this digitally driven world. Be it for entertainment purposes, educational videos, or current affairs, YouTube does its work to keep... | codzap |
1,920,030 | Earn Rewards with Rocket Pool’s Innovative Staking Solutions | Unlocking the power of cutting-edge technology in the realm of decentralized finance involves delving... | 0 | 2024-07-11T16:34:50 | https://dev.to/cleopatramorris_d539d19ea/earn-rewards-with-rocket-pools-innovative-staking-solutions-m9n | cryptocurrency, web3, blockchain, crypto | Unlocking the power of cutting-edge technology in the realm of decentralized finance involves delving into the myriad benefits offered by the Stellar Validator Platform. This innovative solution serves as a beacon of opportunity for investors seeking to optimize their digital asset management.
By leveraging the robust... | cleopatramorris_d539d19ea |
1,920,031 | How to Enhance Your Online Casino Gaming Experience: Expert Tips and Strategies | Online casino gaming has experienced a significant surge in popularity over the years. As more... | 0 | 2024-07-11T16:35:55 | https://dev.to/started_casino_ca361639b5/how-to-enhance-your-online-casino-gaming-experience-tips-and-strategies-4gh2 | gamedev, web, community, web3 | Online casino gaming has experienced a significant surge in popularity over the years. As more players join the online gaming community, having the right strategies and knowledge is crucial for enhancing your overall experience. Here are some valuable tips and strategies to help you get the most out of your online casi... | started_casino_ca361639b5 |
1,920,032 | how to show the app electronjs in the systemTray | Introduction Electron JS is a popular framework for building desktop applications using... | 0 | 2024-07-11T16:38:32 | https://dev.to/fwldom/how-to-show-the-app-electronjs-in-the-systemtray-4250 | webdev, electron, javascript, beginners | ## Introduction
Electron JS is a popular framework for building desktop applications using web technologies like JavaScript, HTML, and CSS. One of the significant features of desktop applications is the ability to integrate them with the system tray, allowing users to access key functionalities and settings easily. Th... | fwldom |
1,920,033 | How To Protect Source Code: Best Practices for NDAs | Your software products' code is necessary, but sometimes, it can cause damage to the finances and... | 0 | 2024-07-11T16:39:28 | https://dev.to/mister_jerry_37e1ecf9b7f7/how-to-protect-source-code-best-practices-for-ndas-3nl1 |
Your software products' code is necessary, but sometimes, it can cause damage to the finances and reputation of your business. Non-disclosure agreements are needed in certain situations. NDAs are necessary for source code security since they need parties to keep confidentiality. Let’s look at the best methods for empl... | mister_jerry_37e1ecf9b7f7 | |
1,920,034 | Understanding Resource Requests and Limits in Kubernetes | Welcome back to the CK 2024 blog series! In this post, we’ll delve into the critical concept of... | 0 | 2024-07-11T16:42:38 | https://dev.to/jensen1806/understanding-resource-requests-and-limits-in-kubernetes-3lhh | kubernetes, docker, devops, containers | Welcome back to the CK 2024 blog series! In this post, we’ll delve into the critical concept of resource requests and limits in Kubernetes, a mechanism the scheduler uses to allocate pods to nodes efficiently. If you missed any of the previous posts in this series, I recommend checking those out to build a strong found... | jensen1806 |
1,920,036 | You life is not complicated you are unorganized | Hey 👋 I'm Juan, and today I want to share something that happened to me this week. Recently, I... | 0 | 2024-07-11T16:43:19 | https://dev.to/juanemilio31323/you-life-is-not-complicated-you-are-unorganized-bh7 | entrepreneurship, sass, startup, productivity | Hey 👋 I'm Juan, and today I want to share something that happened to me this week. Recently, I started working in a new place, I moved, I’m working on multiple personal projects at the same time, I started writing, I’m still reading almost every day, and I’m trying to have a personal and social life. Complicated, as y... | juanemilio31323 |
1,920,037 | How Cybernet Surveillance Hacked My Wife’s Phone | How Cybernet Surveillance Hacked My Wife’s Phone A week ago I posted in a certain group online... | 0 | 2024-07-11T16:57:13 | https://dev.to/cosmo_cribley_3fb90bb884b/how-cybernet-surveillance-hacked-my-wifes-phone-522g | How Cybernet Surveillance Hacked My Wife’s Phone
A week ago I posted in a certain group online looking for eligible hackers. A lot of people recommended Cybernet Surveillance and I decided to go with the mass and try Cybernet Surveillance and as they always say trust your intuition as from the beginning I knew Cyberne... | cosmo_cribley_3fb90bb884b | |
1,920,038 | New HTML <dialog> tag: An absolute game changer | Frontend development has been revolutionized by the introduction of the tag. This new HTML element... | 0 | 2024-07-11T23:00:00 | https://dev.to/safdarali/new-html-tag-an-absolute-game-changer-3mg4 | html, webdev, beginners, programming | Frontend development has been revolutionized by the introduction of the **<dialog>** tag. This new HTML element simplifies the process of creating dialog boxes, which were traditionally labor-intensive.
## ❌ Before:
Creating a dialog box previously required numerous lines of HTML, CSS, and JavaScript to achieve basic ... | safdarali |
1,920,039 | why javascript is important in web development | In the dynamic world of web development, JavaScript holds a pivotal role. The language’s versatility... | 0 | 2024-07-11T16:59:20 | https://dev.to/hammad_hassan_6e981aa049b/why-javascript-is-important-in-web-development-2nk1 | webdev, javascript, beginners | In the dynamic world of web development, JavaScript holds a pivotal role. The language’s versatility and power make it indispensable for creating interactive and engaging websites. Understanding why JavaScript is important in web development is key to appreciating its widespread use and enduring popularity among develo... | hammad_hassan_6e981aa049b |
1,920,040 | YouKnow Social | Express yourself freely and connect authentically with like-minded people on YouKnow Social... | 0 | 2024-07-11T17:03:22 | https://dev.to/nyi_ye_han/test-47p0 | Express yourself freely and connect authentically with like-minded people on YouKnow Social App.
Stay connected, seamlessly. Message, call, video chat - all in one app. Connect one-on-one or with groups, anytime, anywhere. Download and simplify your connections! | nyi_ye_han | |
1,920,041 | New Securi-Taco Tuesdays Livestream (Monthly) | Hey Folx 👋 We're starting a new educational series called "Securi-Taco Tuesdays" where we'll explore... | 0 | 2024-07-11T17:04:46 | https://dev.to/stacklok/new-securi-taco-tuesdays-livestream-monthly-4o56 | security, softwaresupplychain, opensource, talk | Hey Folx 👋
We're starting a new educational series called "Securi-Taco Tuesdays" where we'll explore any/all topics related to Software Supply Chain Security one Tuesday of every month.
We're kicking things off on **July 16, 2024** at **12pm Mexico City Time** (2pm ET / 7pm BST) on our [**YouTube Live**](https://you... | stacey_potter_3de75e600a1 |
1,920,043 | Youtuber landing page | Here's a simple youtuber portfolio landing page Features Responsive. Tailwind css, for... | 0 | 2024-07-11T17:12:40 | https://dev.to/paul_freeman/youtuber-landing-page-519l | showdev, frontend, landingpage | Here's a simple youtuber portfolio landing page
### Features
* Responsive.
* Tailwind css, for rapid development.
### Live site
You can view the live site here: [youtuber landing page](https://bella-youtuber.netlify.app/)
**view the site in desktop mode**
### Screenshot

## Particular and General Solutions
Ever wonder, if there's an equation with two or more variables that aren't known and there's not enough information to use basic elimination method? Fear not, ther... | pourlehommes |
1,920,046 | EUNICE NGINA | Importance of HTML Semantics on SEO | 0 | 2024-07-11T17:12:52 | https://dev.to/eunice_ngina_3e1848509848/eunice-ngina-576g | **Importance of HTML Semantics on SEO** | eunice_ngina_3e1848509848 | |
1,920,047 | Creating an HTML File Using Node.js A Step-by-Step guide. | First you need to create a Folder. That folder opens in the vs code and installs some packages. Some... | 0 | 2024-07-11T17:18:50 | https://dev.to/sudhanshu_developer/creating-an-html-file-using-nodejs-a-step-by-step-guide-367h | javascript, beginners, programming, webdev | First you need to create a Folder. That folder opens in the vs code and installs some packages. Some commands are available below.
**Commands **
1) `npm init`
2) `npm install nodemon`
Create file `index.js` After that looks like this:
. The main use case of docker is to containerization of the app.
There are two main components of Docker
1. Docker Image.
2. Docker Container.
##**Docker Image**
Docker Image... | zendeaditya |
1,920,055 | Secure Your Server Access with the 'Configuring SSH Certificates for Secure Login' Project | The article is about the 'Configuring SSH Certificates for Secure Login' project, offered by LabEx, which provides a comprehensive guide to setting up SSH certificates for the `labex` user. The article highlights the importance of maintaining secure access to servers and how this project can help streamline the login p... | 27,674 | 2024-07-11T17:29:09 | https://dev.to/labex/secure-your-server-access-with-the-configuring-ssh-certificates-for-secure-login-project-c9a | labex, programming, course, linux |
Maintaining secure access to your server is crucial in today's digital landscape. The 'Configuring SSH Certificates for Secure Login' project, offered by [LabEx](https://labex.io/courses/project-certificate-configuration), provides a comprehensive guide to setting up SSH certificates for the `labex` user, ensuring sea... | labby |
1,920,056 | SpookySwap V4: Revolutionizing Your Crypto Trading Experience | Discover Spookyswap - Your Ultimate Guide to the Top DeFi Platform Explore Spookyswap: A... | 0 | 2024-07-11T17:30:04 | https://dev.to/spookyswap/spookyswap-v4-revolutionizing-your-crypto-trading-experience-1idl | spookyswap, cryptocurrency, ethereum, web3 | Discover Spookyswap - Your Ultimate Guide to the Top DeFi Platform
Explore Spookyswap: A Comprehensive Guide to the Leading DeFi Platform
Read more about Spookyswap's latest updates here.
Delving into Spookyswap: Understanding the Premier DeFi Platform
In this section, we will take a deep dive into Spookyswap, the le... | spookyswap |
1,920,057 | WYSIWYG Is Dead, Long Live TIIWYG (Tell It Is What You Get) | The era of WYSIWYG — What You See Is What You Get — is drawing to a close. This beloved technology... | 0 | 2024-07-11T17:30:13 | https://dev.to/pat_chan_f2c9186224ebaeb3/wysiwyg-is-dead-long-live-tiiwyg-tell-it-is-what-you-get-2p7m | genai | The era of WYSIWYG — What You See Is What You Get — is drawing to a close. This beloved technology revolutionized content creation by allowing users to directly manipulate text and images, making it instantly clear how the final product would appear. However, as technology advances, so too must our tools and methodolog... | pat_chan_f2c9186224ebaeb3 |
1,920,058 | SQLite Built-In: A Game-Changer for Node.js Development | Introduction Node.js continues to push the boundaries of server-side JavaScript with its... | 0 | 2024-07-11T17:38:24 | https://www.ginos.codes/blog/nodejs-sqlite | webdev, javascript, node, sql | ## Introduction
Node.js continues to push the boundaries of server-side JavaScript with its latest update: a built-in SQLite module. This development promises to streamline database management, making it easier and more efficient for developers to integrate SQLite databases directly into their Node.js applications. Let... | pineapplegrits |
1,920,059 | Magic and Muscles: ETL with Magic and DuckDB with data from my powerlifting training | You can acecces the full pipeline here Mage In my last post, i writed about a dashboard I... | 0 | 2024-07-11T17:40:01 | https://dev.to/deadpunnk/magic-and-muscles-etl-with-magic-and-duckdb-with-data-from-my-powerlifting-training-2ocj | mage, python, sql, duckdb | [You can acecces the full pipeline here] (https://github.com/DeadPunnk/powerlifting_analytics)
## Mage
In my last post, i writed about a dashboard I builted using Python and Looker Studio, to visualize my powrlifting training data. In this post I will walk you through the step by step of a ETL (Extract, Transform, Lo... | deadpunnk |
1,920,061 | Python RegEx Cheat Sheet | Hello! This cheat sheet for you! Enjoy! Regular expressions in Python are handled using the re... | 0 | 2024-07-11T17:41:20 | https://dev.to/volodyslav/python-regex-cheat-sheet-3d21 | python, regex, programming | Hello! This cheat sheet for you! Enjoy!
Regular expressions in Python are handled using the `re` module. Firstly you have to import re module by writing `import re` in the first line of your python file.
**Regex Patterns**:
`.`: Any character except a newline.
`^`: Start of the string.
`$`: End of the string.
`*`: Z... | volodyslav |
1,920,062 | Using whereAny() for cleaner queries in Eloquent | Laravel | Tutorial | Quick Win Wednesday #QWW | A post by Bert De Swaef | 0 | 2024-07-11T17:42:43 | https://dev.to/burtds/using-whereany-for-cleaner-queries-in-eloquent-laravel-tutorial-quick-win-wednesday-qww-4feb | laravel, php, tutorial, beginners | {% embed https://youtu.be/rYIDwDUaVYo %} | burtds |
1,920,063 | Using whereAny() for cleaner queries in Eloquent | Laravel | Tutorial | Quick Win Wednesday #QWW | A post by Bert De Swaef | 0 | 2024-07-11T17:42:43 | https://dev.to/burtds/using-whereany-for-cleaner-queries-in-eloquent-laravel-tutorial-quick-win-wednesday-qww-1mph | laravel, php, tutorial, beginners | {% embed https://youtu.be/rYIDwDUaVYo %} | burtds |
1,920,064 | Hi ,Community | A post by Abhishek Kumar Gautam | 0 | 2024-07-11T17:43:16 | https://dev.to/abhinuclear/hi-community-2g8l | abhinuclear | ||
1,920,065 | Write cleaner code with Named Arguments in PHP | How to | Tutorial | Quick Win Wednesday #QWW | A post by Bert De Swaef | 0 | 2024-07-11T17:43:42 | https://dev.to/burtds/write-cleaner-code-with-named-arguments-in-php-how-to-tutorial-quick-win-wednesday-qww-3hpd | tutorial, php, beginners, code | {% embed https://youtu.be/jyzSnmaGAVs %} | burtds |
1,920,066 | EasyPay - Myanmar Mobile Money | P2P Transfer, Voucher Transfer Cash In/Cash Out Mobile Phone Top Up Merchant Payment Gift Cards | 0 | 2024-07-11T17:44:40 | https://dev.to/nyi_ye_han/hello-2c36 |
P2P Transfer, Voucher Transfer
Cash In/Cash Out
Mobile Phone Top Up
Merchant Payment
Gift Cards
| nyi_ye_han | |
1,920,067 | How To Protect Source Code: Best Practices for NDAs | Your software products' code is necessary, but sometimes, it can cause damage to the finances and... | 0 | 2024-07-11T17:48:05 | https://dev.to/ideal_marketingagency_3b/how-to-protect-source-code-best-practices-for-ndas-5bf3 | 
Your software products' code is necessary, but sometimes, it can cause damage to the finances and reputation of your business. Non-disclosure agreements are needed in certain situations. NDAs are necessary for source... | ideal_marketingagency_3b | |
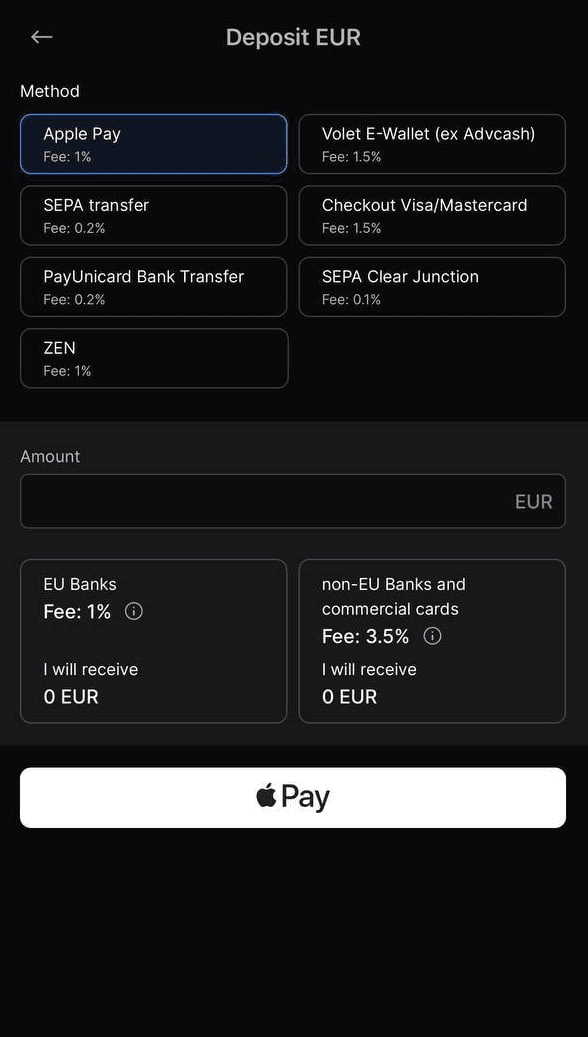
1,920,068 | 🔥🔥🔥HOT HOT HOT🔥🔥🔥 | 🤯WhiteBIT has opened for the next 24 hours 1% fees on Euro deposit via Apple Pay and Google Pay for... | 0 | 2024-07-11T17:53:43 | https://dev.to/irmakork/hot-hot-hot-29n9 |
🤯WhiteBIT has opened for the next 24 hours 1% fees on Euro deposit via Apple Pay and Google Pay for European cards
| irmakork | |
1,920,080 | Making a docker like solution native to macos | I am doing this because I need a faster alternative to docker on... | 0 | 2024-07-11T18:14:24 | https://dev.to/okerew/making-a-docker-like-solution-native-to-macos-136 | development, docker | I am doing this because I need a faster alternative to docker on macOS.
https://www.youtube.com/watch?v=LOVOq3G_JWI | okerew |
1,920,069 | 🤯XRP Up More Than 3% In 24 hours | 📈 Over the past 24 hours, XRP's price has risen 3.42% to $0.45. This continues its positive trend... | 0 | 2024-07-11T17:54:00 | https://dev.to/irmakork/xrp-up-more-than-3-in-24-hours-ood |
📈 Over the past 24 hours, XRP's price has risen 3.42% to $0.45. This continues its positive trend from the past week, where it gained 1.0%, moving from $0.45 to its current price. XRP's all-time high stands at $3.40.
📊 The chart below compares XRP's price movement: over the past 24 hours (left) and the past week (r... | irmakork | |
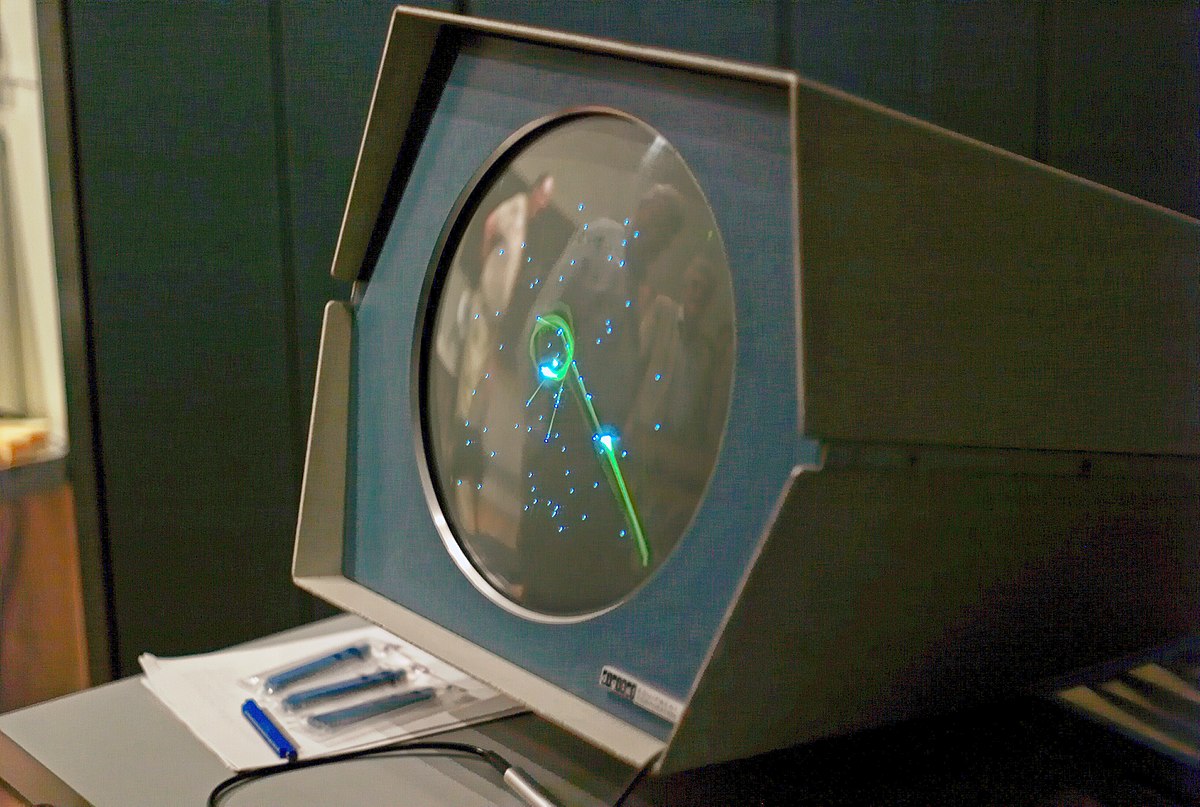
1,920,070 | Interesting programming factz 🧡 | First computer game was developed in 1961. (named spacewar) Python was not named after snake.... | 0 | 2024-07-11T17:54:18 | https://dev.to/aryan015/interesting-programming-factz-5cd0 | javascript, python, webdev, react | 1. First computer game was developed in 1961. (named __spacewar__)
2. __Python__ was not named after snake. Originated from BBC series.
 Price Prediction for July 11 | 📈 BTC/USD has risen by 2.23% over the past 24 hours. On the hourly chart, BTC might have set a local... | 0 | 2024-07-11T17:54:57 | https://dev.to/irmakork/bitcoin-btc-price-prediction-for-july-11-3ldk |
📈 BTC/USD has risen by 2.23% over the past 24 hours. On the hourly chart, BTC might have set a local resistance level at $59,516. With most of the daily ATR passed, sharp moves are unlikely by the end of the day. If the bar closes near $59,500, the ongoing upward move may continue tomorrow.
📊 On the bigger time fra... | irmakork | |
1,920,074 | DestroyLoneliness: npm starjacking attack on Roblox Node.js library delivers QuasarRAT | The execution of QuasarRAT would allow the attacker to establish command and control over affected... | 0 | 2024-07-11T18:01:40 | https://dev.to/stacklok/destroyloneliness-npm-starjacking-attack-on-roblox-nodejs-library-delivers-quasarrat-mj2 | security, npm, opensource | The execution of QuasarRAT would allow the attacker to establish command and control over affected Windows endpoints.
Author: [Poppaea McDermott](https://stacklok.com/authors/poppaea-mcdermott)
[Trusty](https://www.trustypkg.dev/) is a free-to-use web app from Stacklok that analyzes data about thousands of open sourc... | ninfriendos1 |
1,920,075 | WhoDB - ultralight & lightning fast database explorer | I'm thrilled to announce the launch of WhoDB by Clidey! Our goal is to transform the user experience... | 0 | 2024-07-11T18:02:46 | https://dev.to/hemangkandwal/whodb-ultralight-lightning-fast-database-explorer-29ga | webdev, database, opensource, productivity | I'm thrilled to announce the launch of [WhoDB](https://github.com/clidey/whodb) by Clidey! Our goal is to transform the user experience in database management.
We'd love to hear your feedback!
🔍 What is WhoDB?
[WhoDB](https://github.com/clidey/whodb) is a cutting-edge database explorer designed for 2024 and beyond... | hemangkandwal |
1,920,076 | Binary Search Tree from Scratch in Java | Introduction A Binary Search Tree (BST) is a type of binary tree where each node has at most two... | 0 | 2024-07-11T18:05:33 | https://dev.to/gtgkartik/binary-search-tree-from-scratch-in-java-cbk | datastructures, algorithms, java | Introduction
A Binary Search Tree (BST) is a type of binary tree where each node has at most two children, referred to as the left child and the right child. For each node, the left subtree contains only nodes with values less than the node’s value, and the right subtree contains only nodes with values greater than the... | gtgkartik |
1,920,077 | Why Linux Web Hosting is the Best Choice for Developers? | The world of web development moves quickly. Picking the right hosting solution is important. Linux... | 0 | 2024-07-11T18:08:00 | https://dev.to/oliviageorgia98/why-linux-web-hosting-is-the-best-choice-for-developers-24la | webhosting, linux, webdev | The world of web development moves quickly. Picking the right hosting solution is important. Linux web hosting is a popular choice for developers because of its strong features, flexibility, and cost-effectiveness.
This article explains why Linux web hosting is the best option for developers, outlining its benefits, ... | oliviageorgia98 |
1,920,078 | Building a VS Code Extension to Fetch and Display Content from an API | This post deals with building a VS Code extension using React, Typescript and Tailwind CSS. So,... | 0 | 2024-07-12T05:52:12 | https://dev.to/shriya_5/building-a-vs-code-extension-to-fetch-and-display-content-from-an-api-31f1 | react, typescript, api, vscode | This post deals with building a VS Code extension using React, Typescript and Tailwind CSS.
So, you've decided to build a VS Code extension. Great choice! You want to fetch and display content from an API, because, let's face it, hardcoding stuff is so 90s. Buckle up, because we're about to embark on a journey that wi... | shriya_5 |
1,920,081 | Item 40: Use a anotação Override com frequência | Importância da Anotação @override* A anotação @override é uma das mais importantes para... | 0 | 2024-07-11T18:15:31 | https://dev.to/giselecoder/item-40-use-a-anotacao-override-com-frequencia-a6o | java, javaprogramming | *Importância da Anotação @Override**
- A anotação @Override é uma das mais importantes para programadores Java.
- Usada nas declarações de método para indicar que o método sobrescreve uma declaração em um supertipo.
- Protege contra bugs ao garantir que métodos sejam corretamente sobrescritos.
**Problema com Sobrecar... | giselecoder |
1,920,082 | Node.js | A post by Abdul Wahid Kahar | 0 | 2024-07-11T18:16:42 | https://dev.to/abdulwahidkahar/nodejs-4e9i | node, npm, javascript | abdulwahidkahar | |
1,920,084 | Generative AI Serverless - RAG using Bedrock Converse API & Lambda - Chat with your document | Generative AI - Has Generative AI captured your imagination to the extent it has for me? Generative... | 0 | 2024-07-11T20:04:41 | https://dev.to/bhatiagirish/generative-ai-serverless-rag-using-bedrock-converse-api-lambda-chat-with-your-document-4d73 | aws, generativeai, bedrockconverseapi, amazonbedrock |
Generative AI - Has Generative AI captured your imagination to the extent it has for me?
Generative AI is indeed fascinating! The advancements in foundation models have opened up incredible possibilities. Who would have imagined that technology would evolve to the point where you can generate content summaries from ... | bhatiagirish |
1,920,087 | Types of casing in programming | note: for consistancy i will keep the same example. 1.... | 0 | 2024-07-11T18:21:04 | https://dev.to/aryan015/types-of-casing-in-programming-2j0d | javascript, react, python, programming | `note:` for consistancy i will keep the same example.
## 1. camelCase
```js
//userDate
//firstName
```
## 2. snake_case
```js
//user_name
//first_name
```
## 3. PascalCase
```js
//UserName
//FirstName
```
## 4. kebab-case
This style mostly used as ID name and classes in `html`.
```js
//user-name
//first-name
```
[my ... | aryan015 |
1,920,088 | Evaluating ADHD Medication Based on Methylphenidate and Amphetamine | Evaluating ADHD Medication Based on Methylphenidate and Amphetamine A neurodevelopmental disease... | 0 | 2024-07-11T18:23:29 | https://dev.to/john_wick_e0b7691c3e470c1/evaluating-adhd-medication-based-on-methylphenidate-and-amphetamine-2ek6 | health |
Evaluating ADHD Medication Based on Methylphenidate and Amphetamine
A neurodevelopmental disease known as Attention-Deficit/Hyperactivity disease (ADHD) affects millions of children and adults globally. It is typified by impulsivity, hyperactivity, and inattentional symptoms, which can seriously impair day-to-day fun... | john_wick_e0b7691c3e470c1 |
1,920,089 | School Management System Project with Source Code | View Post Django Quiz is an ultimate quiz management system that utilizes the power and... | 0 | 2024-07-11T18:26:33 | https://dev.to/codzap/school-management-system-project-with-source-code-2og4 | webdev, beginners, python, django | #### [View Post](https://codzap.com/django-projects/quiz-management-system-using-django-python/)
Django Quiz is an ultimate quiz management system that utilizes the power and flexibility of Django and Python to take the user through the smooth yet transparent user experience. Either you are an educator or trainer, or ... | codzap |
1,920,090 | Semantic HTML And Accessibility | INTRODUCTION Semantic HTML refers to HTML code that uses specific HTML tags to effectively describe... | 0 | 2024-07-11T18:27:45 | https://dev.to/james_kiboi_cf745aa43cf22/semantic-html-and-accessibility-2pp7 | webdev, html, beginners | **<u>INTRODUCTION</u>**
Semantic HTML refers to HTML code that uses specific HTML tags to effectively describe the purpose of page elements. It communicates the meaning of its elements to both computers and humans.
**The Importance of Semantic HTML for SEO and Accessibility**
Semantic HTML plays a very crucial role... | james_kiboi_cf745aa43cf22 |
1,920,092 | How to add hover in markdown | note; I will write this code on javascript snippet other wise md compiler will hide it. ... | 0 | 2024-07-11T18:37:59 | https://dev.to/aryan015/how-to-add-hover-in-markdown-27lm | markdown, react, github, gitlab | `note;` I will write this code on javascript snippet
other wise md compiler will hide it.
## Introduction
Tooltip is a way to show a text when you hover a item or link.

```js
//SYNTAX
[ID]: ## 'MSG'... | aryan015 |
1,920,093 | How to Improve Java Application Performance | In this tutorial, we'll explore various techniques to improve the performance of Java applications.... | 0 | 2024-07-11T18:38:26 | https://dev.to/renan_almeidasv/how-to-improve-java-application-performance-55if | In this tutorial, we'll explore various techniques to improve the performance of Java applications. We'll discuss code optimizations, the use of profiling tools, and best practices to ensure your Java application is efficient and fast.
## Prerequisites
Before we start, make sure you have the following:
- Basic knowled... | renan_almeidasv | |
1,920,094 | Unleashing the Power of AWS Config: The Ultimate Architect for Cloud Resource Configuration Management | Today, we embark on an epic journey, one that shall unveil the inner workings of AWS Config and equip... | 0 | 2024-07-11T18:45:19 | https://dev.to/ikoh_sylva/unleashing-the-power-of-aws-config-the-ultimate-architect-for-cloud-resource-configuration-management-1i3a | aws, cloud, cloudcomputing, cloudskills | Today, we embark on an epic journey, one that shall unveil the inner workings of AWS Config and equip us with the knowledge and strategies to wield its power with unparalleled mastery. Brace yourselves, for this odyssey will not only illuminate the path to resource configuration nirvana but also fortify your cloud defe... | ikoh_sylva |
1,920,096 | Phase 4: Reflections on Learning Backend and Frontend Integration at Flatiron Bootcamp | During Phase 4 of my Flatiron bootcamp, I learned how to integrate the backend with the frontend... | 0 | 2024-07-11T18:52:31 | https://dev.to/johnjohnpenafiel/phase-4-reflections-on-learning-backend-and-frontend-integration-at-flatiron-bootcamp-3bo5 | During Phase 4 of my Flatiron bootcamp, I learned how to integrate the backend with the frontend using Flask and Python. Working with Flask made the experience of handling Python and databases much simpler and more efficient for me. To my surprise, I have greatly enjoyed using Python, and I am eager to continue learnin... | johnjohnpenafiel | |
1,920,097 | Laravel - Advanced Eloquent ORM Techniques | Laravel's Eloquent ORM is a very powerful took for interacting with databases, using an expressive... | 0 | 2024-07-11T18:52:46 | https://dev.to/devbabs/laravel-advanced-eloquent-orm-techniques-129e | laravel, php, webdev, backenddevelopment | Laravel's Eloquent ORM is a very powerful took for interacting with databases, using an expressive fluent syntax. While it's very easy to get quite familiar with the basics of Eloquent and stick to using just the basic techniques, there are advanced techniques that can significantly enhance your application's efficienc... | devbabs |
1,920,098 | My mistake when entering Hello World | Knowing various programming languages is a plus for us as software developers. However, I find it... | 0 | 2024-07-11T18:53:21 | https://dev.to/abdulwahidkahar/my-mistake-when-entering-hello-world-2ege | helloworld, beginners | Knowing various programming languages is a plus for us as software developers. However, I find it more valuable to master one language thoroughly rather than knowing several languages. What I realize now is that all programming languages are more or less the same. The only difference lies in their syntax, while their l... | abdulwahidkahar |
1,920,099 | Design Pattern #5 - Adapter Pattern | Over the past few weeks, I have shared some of the trending design patterns, like the PubSub and the... | 27,620 | 2024-07-11T18:56:16 | https://dev.to/superviz/design-pattern-5-adapter-pattern-4gif | javascript, architecture, learning, webdev | Over the past few weeks, I have shared some of the trending design patterns, like the [PubSub](https://dev.to/superviz/design-pattern-4-publishersubscriber-pattern-4jg9) and the [Singleton](https://dev.to/superviz/design-pattern-1-singleton-for-frontend-developers-14p9) ones. Today, I'm going to share one more article ... | vtnorton |
1,920,100 | Day 1: Python Programming 🧡 | Day 1 Introduction You can download python from here or You can use online Code... | 0 | 2024-07-11T18:56:49 | https://dev.to/aryan015/day-1-python-programming-13a0 | 100daysofcode, python, programming, react | [id1]: ## 'British Broadcasting Corporation'
## Day 1
## Introduction
You can download `python` from [here](https://www.python.org)
or You can use online Code Editor like [replit](https://www.replit.com)🧡
## steps for windows
### Step 1
 time and wit... | __zamora__ |
1,920,104 | Typescript Coding Chronicles: Increasing Triplet Subsequence | Problem Statement: Given an integer array nums, return true if there exists a triple of... | 0 | 2024-07-11T19:19:36 | https://dev.to/__zamora__/typescript-coding-chronicles-increasing-triplet-subsequence-207l | webdev, javascript, programming, typescript | ## Problem Statement:
Given an integer array `nums`, return `true` if there exists a triple of indices `(i, j, k)` such that `i < j < k` and `nums[i] < nums[j] < nums[k]`. If no such indices exist, return `false`.
### Example 1:
- Input: `nums = [1,2,3,4,5]`
- Output: `true`
- Explanation: Any triplet where `i < j < k... | __zamora__ |
1,920,136 | How To Find The Best Motorcycle Detailer In San Diego ? | Introduction Finding the best motorcycle detailer in San Diego can be a challenge. You need someone... | 0 | 2024-07-11T19:23:08 | https://dev.to/onlymotos/how-to-find-the-best-motorcycle-detailer-in-san-diego--2l7 | bikedetailing, automotive, carwash, bikeandcardetailing | Introduction
Finding the best motorcycle detailer in San Diego can be a challenge. You need someone who will take excellent care of your bike and make it look stunning. This guide will help you understand what motorbike detailing entails, why it’s important, what services to seek, and how to choose a team that will de... | onlymotos |
1,920,137 | Typescript Coding Chronicles: String Compression | Problem Statement: Given an array of characters chars, compress it using the following... | 0 | 2024-07-11T19:23:44 | https://dev.to/__zamora__/typescript-coding-chronicles-string-compression-42k5 | webdev, javascript, programming, typescript | ## Problem Statement:
Given an array of characters `chars`, compress it using the following algorithm:
- Begin with an empty string `s`.
- For each group of consecutive repeating characters in `chars`:
- If the group's length is 1, append the character to `s`.
- Otherwise, append the character followed by the group... | __zamora__ |
1,920,138 | HTML Inline vs. Block Elements | Inline vs. Block Elements in HTML: Understanding the Differences When building a web page,... | 0 | 2024-07-11T19:26:39 | https://dev.to/ridoy_hasan/html-inline-vs-block-elements-4kg7 | webdev, beginners, learning, html | ### Inline vs. Block Elements in HTML: Understanding the Differences
When building a web page, understanding the distinction between inline and block elements is crucial for effective HTML and CSS design. This article delves into the differences between these two types of elements, providing practical examples and out... | ridoy_hasan |
1,920,139 | Developer Notes: Configure a CI/CD pipeline for your node js project using Azure and Github Actions | Someone posted on twitter that when engineers do stuff, they should write about how they achieve it.... | 0 | 2024-07-11T19:35:37 | https://dev.to/mr_simi_f44c05f5ac7895a4/configure-a-cicd-pipeline-for-your-node-js-project-using-azure-and-github-actions-53lc | devops, webdev, javascript, programming | _Someone posted on twitter that when engineers do stuff, they should write about how they achieve it. It can save other engineers the time of searching to find the solution. And that's why we are here._
In this article we would configure a CI/CD Pipeline for a node js project using Azure as the cloud provider and GitH... | mr_simi_f44c05f5ac7895a4 |
1,920,141 | The project is almost finished | So, after I finished the main refactoring and the documentation strings, I started the testing... | 0 | 2024-07-11T19:38:21 | https://dev.to/ahmedhosssam/the-project-is-almost-finished-1hfb | So, after I finished the main refactoring and the documentation strings, I started the testing phase.
I started with the smallest functions that don't call any non-tested function, and then went to the bigger functions.
After finishing the main unit tests, I had a problem, the columns in the input data from the hek ha... | ahmedhosssam | |
1,920,142 | SCARA Robot Market Analysis, Size, Share & Trends | 2031 | Global SCARA Robot Market size was valued at USD 10.17 billion in 2022 and is poised to grow from USD... | 0 | 2024-07-11T19:39:31 | https://dev.to/neha_shaikh_ec35edb11152d/scara-robot-market-analysis-size-share-trends-2031-2g7i | marketing, robotics, news, ai | Global SCARA Robot Market size was valued at USD 10.17 billion in 2022 and is poised to grow from USD 11.17 billion in 2023 to USD 23.91 billion by 2031, growing at a CAGR of 10.3 % during the forecast period (2024-2031).
The SCARA robot market has risen steeply with increasing needs for automation in various industri... | neha_shaikh_ec35edb11152d |
1,920,143 | Day 0: Hello, World! Solution | Statement A greeting function is provided for you in the editor below. It has one... | 28,039 | 2024-07-11T19:44:12 | https://dev.to/hafijul233/day-0-hello-world-3217 | javascript, coding, hackerrank, algorithms | ## Statement
A greeting function is provided for you in the editor below. It has one parameter, ***parameterVariable***. Perform the following tasks to complete this challenge:
## Task
1. Use `console.log()` to print `Hello, World!` on a new line in the console, which is also known as stdout or standard output. The ... | hafijul233 |
1,920,144 | [Italian] Trasforma le Eccezioni da Incubo a Opportunità con IExceptionHandler in ASP.NET Core! | Quante volte ti sei sentito come gli astronauti dell'Apollo 13 mentre affrontavi eccezioni non... | 0 | 2024-07-11T19:47:09 | https://dev.to/cosminirimescucom/trasforma-le-eccezioni-da-incubo-a-opportunita-con-iexceptionhandler-in-aspnet-core-7h4 | Quante volte ti sei sentito come gli astronauti dell'Apollo 13 mentre affrontavi eccezioni non gestite nella tua applicazione ASP.NET Core? 🚀
Le eccezioni non gestite possono mandare in tilt i nostri sistemi, generare risposte di errore criptiche e rendere i log incomprensibili. Ma non temere, ASP.NET Core ci fornisce... | cosminirimescucom | |
1,920,145 | 100+ ChatGPT Mega-Prompts for Business. | Run your business on autopilot with 100+ hand-crafted mega-prompts to optimize and scale your... | 0 | 2024-07-11T19:49:41 | https://dev.to/oleksandr_veremeyenko_1c0/100-chatgpt-mega-prompts-for-business-4ip7 | webdev, ai, productivity | Run your business on autopilot with 100+ hand-crafted mega-prompts to optimize and scale your business with AI. From Business Strategy to Business Development, Business Analytics to Management, these mega-prompts will save your time and effort to ensure that you focus on what matters most. Compatible with ChatGPT, Clau... | oleksandr_veremeyenko_1c0 |
1,920,146 | Item 41: Use as interfaces marcadoras para definir tipos | Definição e Propósito Interface Marcadora: Não contém declarações de métodos. Marca uma classe... | 0 | 2024-07-11T19:50:46 | https://dev.to/giselecoder/item-41-use-as-interfaces-marcadoras-para-definir-tipos-dac | java, javaprogramming | **Definição e Propósito**
**Interface Marcadora:**
- Não contém declarações de métodos.
- Marca uma classe como tendo uma propriedade específica.
- Exemplo: Serializable indica que uma classe pode ser serializada.
- Vantagens das Interfaces Marcadoras
**Definição de Tipo:**
- Interfaces marcadoras definem um tipo que... | giselecoder |
1,920,147 | About that time | You already know what it is So when people say once you find a job and start working at... | 0 | 2024-07-11T19:55:30 | https://dev.to/lostoneway/about-that-time-312i | devjournal, learning, aws | ## You already know what it is
So when people say once you find a job and start working at that job, little things you did to GET said job stop. Lol. In my case, keeping up with this blog, continuing to build little personal projects, you get the idea. I am still at that job from my last post! Since then I've been on ... | lostoneway |
1,920,149 | Typescript - Best Practices | Let, Var and Const Use const for variables that won't be reassigned. Use let for variables that will... | 0 | 2024-07-11T20:00:00 | https://dev.to/kiranuknow/typescript-best-practices-4i5e | typescript, best, practices | **Let, Var and Const**
Use **_const_** for variables that won't be reassigned.
Use **_let_** for variables that will be reassigned.
Avoid **_var_** in new TypeScript code.
Best References:
[AWS TypeScript](https://docs.aws.amazon.com/prescriptive-guidance/latest/best-practices-cdk-typescript-iac/typescript-bes... | kiranuknow |
1,920,150 | 5 helpful plugins for IntelliJ IDEA: Enhance your Spring Boot and Java development experience | For any Spring Boot developer, two primary goals are maximum productivity and high-quality code. One... | 0 | 2024-07-11T20:05:18 | https://dev.to/tharindufdo/5-helpful-plugins-for-intellij-idea-enhance-your-spring-boot-and-java-development-experience-5gj2 | java, intellij, plugins, springboot | For any Spring Boot developer, two primary goals are maximum productivity and high-quality code. One of the most widely applied Integrated Development Environments today is IntelliJ IDEA. More than that, it provides a huge set of plugins that facilitate development processes. In this article, we shall discover 5 Intell... | tharindufdo |
1,920,151 | Creating users in Amazon Cognito programmatically | Short post to walk through the steps to create users in Amazon Cognito for automation | 0 | 2024-07-11T00:00:00 | https://www.andmore.dev/blog/create-cognito-user-programatically/ | aws, security, cognito | ---
title: Creating users in Amazon Cognito programmatically
published: true
description: Short post to walk through the steps to create users in Amazon Cognito for automation
tags: AWS, Security, Cognito
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/6ig1btpr4dqhi4dx9uig.png
published_at: 2024-0... | andmoredev |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.