id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,917,145 | Healthcare Chatbots Market: Insights into Top Manufacturers Driving Adoption | The global healthcare chatbots market is projected to grow significantly, from US$382.1 million in... | 0 | 2024-07-09T10:35:45 | https://dev.to/swara_353df25d291824ff9ee/healthcare-chatbots-market-insights-into-top-manufacturers-driving-adoption-43l5 |

The global [healthcare chatbots market](https://www.persistencemarketresearch.com/market-research/healthcare-chatbots-market.asp) is projected to grow significantly, from US$382.1 million in 2024 to US$1.4 billion ... | swara_353df25d291824ff9ee | |
1,917,146 | Python ("Hello World") Notes and Learning Experience | I'm just starting out in the Python universe, with no prior coding background. My goal is to master... | 0 | 2024-07-09T10:36:11 | https://dev.to/vivekmurugadoss/python-hello-world-notes-and-learning-experience-261i | python, beginners | I'm just starting out in the Python universe, with no prior coding background. My goal is to master Python for automating tasks in 3D applications. | vivekmurugadoss |
1,917,147 | The Impact of Courier Delivery Apps on Business Growth | In this digital world, convenience and speed are foremost, and businesses are rapidly turning to... | 0 | 2024-07-09T10:38:21 | https://dev.to/rahulsukhwal/the-impact-of-courier-delivery-apps-on-business-growth-16mm | courierdeliveryapp, courierapp | In this digital world, convenience and speed are foremost, and businesses are rapidly turning to mobile solutions for logistics and delivery to meet these demands. These apps have transformed the industry, providing an effective and efficient way to manage shipments. Understanding the advantages of incorporating these ... | rahulsukhwal |
1,917,157 | The Future of Architectural Design: How Revit is Shaping the Industry | In the ever-evolving field of architectural design, staying ahead of the curve is essential. One tool... | 0 | 2024-07-09T10:45:06 | https://dev.to/john_oliver_d542402a4b136/the-future-of-architectural-design-how-revit-is-shaping-the-industry-3mpd | In the ever-evolving field of architectural design, staying ahead of the curve is essential. One tool that has been at the forefront of this transformation is Revit, a powerful Building Information Modeling (BIM) software. This blog post explores how Revit is shaping the future of architectural design, highlighting its... | john_oliver_d542402a4b136 | |
1,917,148 | How can I complain to Meesho? | Visit supplier.meesho.com, click on 'Start Selling' contact us, 90606-31083 and become a seller in 5... | 0 | 2024-07-09T10:39:55 | https://dev.to/tina_kumari_4338f19912f71/how-can-i-complain-to-meesho-47dj | webdev, javascript, beginners | Visit supplier.meesho.com, click on 'Start Selling' contact us, 90606-31083 and become a seller in 5 easy steps. With Meesho's 0% commission rate and no hidden charges, register in 5 easy steps and keep 100% of your profit. Step 1: Visit supplier.meesho.com, click on 'Start Selling', add your mobile number and click on... | tina_kumari_4338f19912f71 |
1,917,149 | Buy Verified Paxful Account | https://dmhelpshop.com/product/buy-verified-paxful-account/ Buy Verified Paxful Account There are... | 0 | 2024-07-09T10:40:11 | https://dev.to/crewcaught/buy-verified-paxful-account-1f80 | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-paxful-account/\n\n\nBuy Verified Paxful Account\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, Buy verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to Buy Verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with. Buy Verified Paxful Account.\n\nBuy US verified paxful account from the best place dmhelpshop\nWhy we declared this website as the best place to buy US verified paxful account? Because, our company is established for providing the all account services in the USA (our main target) and even in the whole world. With this in mind we create paxful account and customize our accounts as professional with the real documents. Buy Verified Paxful Account.\n\nIf you want to buy US verified paxful account you should have to contact fast with us. Because our accounts are-\n\nEmail verified\nPhone number verified\nSelfie and KYC verified\nSSN (social security no.) verified\nTax ID and passport verified\nSometimes driving license verified\nMasterCard attached and verified\nUsed only genuine and real documents\n100% access of the account\nAll documents provided for customer security\nWhat is Verified Paxful Account?\nIn today’s expanding landscape of online transactions, ensuring security and reliability has become paramount. Given this context, Paxful has quickly risen as a prominent peer-to-peer Bitcoin marketplace, catering to individuals and businesses seeking trusted platforms for cryptocurrency trading.\n\nIn light of the prevalent digital scams and frauds, it is only natural for people to exercise caution when partaking in online transactions. As a result, the concept of a verified account has gained immense significance, serving as a critical feature for numerous online platforms. Paxful recognizes this need and provides a safe haven for users, streamlining their cryptocurrency buying and selling experience.\n\nFor individuals and businesses alike, Buy verified Paxful account emerges as an appealing choice, offering a secure and reliable environment in the ever-expanding world of digital transactions. Buy Verified Paxful Account.\n\nVerified Paxful Accounts are essential for establishing credibility and trust among users who want to transact securely on the platform. They serve as evidence that a user is a reliable seller or buyer, verifying their legitimacy.\n\nBut what constitutes a verified account, and how can one obtain this status on Paxful? In this exploration of verified Paxful accounts, we will unravel the significance they hold, why they are crucial, and shed light on the process behind their activation, providing a comprehensive understanding of how they function. Buy verified Paxful account.\n\n \n\nWhy should to Buy Verified Paxful Account?\nThere are several compelling reasons to consider purchasing a verified Paxful account. Firstly, a verified account offers enhanced security, providing peace of mind to all users. Additionally, it opens up a wider range of trading opportunities, allowing individuals to partake in various transactions, ultimately expanding their financial horizons.\n\nMoreover, a verified Paxful account ensures faster and more streamlined transactions, minimizing any potential delays or inconveniences. Furthermore, by opting for a verified account, users gain access to a trusted and reputable platform, fostering a sense of reliability and confidence. Buy Verified Paxful Account.\n\nLastly, Paxful’s verification process is thorough and meticulous, ensuring that only genuine individuals are granted verified status, thereby creating a safer trading environment for all users. Overall, the decision to buy a verified Paxful account can greatly enhance one’s overall trading experience, offering increased security, access to more opportunities, and a reliable platform to engage with.\n\n \n\nWhat is a Paxful Account\nPaxful and various other platforms consistently release updates that not only address security vulnerabilities but also enhance usability by introducing new features. Buy Verified Paxful Account.\n\nIn line with this, our old accounts have recently undergone upgrades, ensuring that if you purchase an old buy Verified Paxful account from dmhelpshop.com, you will gain access to an account with an impressive history and advanced features. This ensures a seamless and enhanced experience for all users, making it a worthwhile option for everyone.\n\n \n\nIs it safe to buy Paxful Verified Accounts?\nBuying on Paxful is a secure choice for everyone. However, the level of trust amplifies when purchasing from Paxful verified accounts. These accounts belong to sellers who have undergone rigorous scrutiny by Paxful. Buy verified Paxful account, you are automatically designated as a verified account. Hence, purchasing from a Paxful verified account ensures a high level of credibility and utmost reliability. Buy Verified Paxful Account.\n\nPAXFUL, a widely known peer-to-peer cryptocurrency trading platform, has gained significant popularity as a go-to website for purchasing Bitcoin and other cryptocurrencies. It is important to note, however, that while Paxful may not be the most secure option available, its reputation is considerably less problematic compared to many other marketplaces. Buy Verified Paxful Account.\n\nThis brings us to the question: is it safe to purchase Paxful Verified Accounts? Top Paxful reviews offer mixed opinions, suggesting that caution should be exercised. Therefore, users are advised to conduct thorough research and consider all aspects before proceeding with any transactions on Paxful.\n\n \n\nHow Do I Get 100% Real Verified Paxful Accoun?\nPaxful, a renowned peer-to-peer cryptocurrency marketplace, offers users the opportunity to conveniently buy and sell a wide range of cryptocurrencies. Given its growing popularity, both individuals and businesses are seeking to establish verified accounts on this platform.\n\nHowever, the process of creating a verified Paxful account can be intimidating, particularly considering the escalating prevalence of online scams and fraudulent practices. This verification procedure necessitates users to furnish personal information and vital documents, posing potential risks if not conducted meticulously.\n\nIn this comprehensive guide, we will delve into the necessary steps to create a legitimate and verified Paxful account. Our discussion will revolve around the verification process and provide valuable tips to safely navigate through it.\n\nMoreover, we will emphasize the utmost importance of maintaining the security of personal information when creating a verified account. Furthermore, we will shed light on common pitfalls to steer clear of, such as using counterfeit documents or attempting to bypass the verification process.\n\nWhether you are new to Paxful or an experienced user, this engaging paragraph aims to equip everyone with the knowledge they need to establish a secure and authentic presence on the platform.\n\nBenefits Of Verified Paxful Accounts\nVerified Paxful accounts offer numerous advantages compared to regular Paxful accounts. One notable advantage is that verified accounts contribute to building trust within the community.\n\nVerification, although a rigorous process, is essential for peer-to-peer transactions. This is why all Paxful accounts undergo verification after registration. When customers within the community possess confidence and trust, they can conveniently and securely exchange cash for Bitcoin or Ethereum instantly. Buy Verified Paxful Account.\n\nPaxful accounts, trusted and verified by sellers globally, serve as a testament to their unwavering commitment towards their business or passion, ensuring exceptional customer service at all times. Headquartered in Africa, Paxful holds the distinction of being the world’s pioneering peer-to-peer bitcoin marketplace. Spearheaded by its founder, Ray Youssef, Paxful continues to lead the way in revolutionizing the digital exchange landscape.\n\nPaxful has emerged as a favored platform for digital currency trading, catering to a diverse audience. One of Paxful’s key features is its direct peer-to-peer trading system, eliminating the need for intermediaries or cryptocurrency exchanges. By leveraging Paxful’s escrow system, users can trade securely and confidently.\n\nWhat sets Paxful apart is its commitment to identity verification, ensuring a trustworthy environment for buyers and sellers alike. With these user-centric qualities, Paxful has successfully established itself as a leading platform for hassle-free digital currency transactions, appealing to a wide range of individuals seeking a reliable and convenient trading experience. Buy Verified Paxful Account.\n\n \n\nHow paxful ensure risk-free transaction and trading?\nEngage in safe online financial activities by prioritizing verified accounts to reduce the risk of fraud. Platforms like Paxfu implement stringent identity and address verification measures to protect users from scammers and ensure credibility.\n\nWith verified accounts, users can trade with confidence, knowing they are interacting with legitimate individuals or entities. By fostering trust through verified accounts, Paxful strengthens the integrity of its ecosystem, making it a secure space for financial transactions for all users. Buy Verified Paxful Account.\n\nExperience seamless transactions by obtaining a verified Paxful account. Verification signals a user’s dedication to the platform’s guidelines, leading to the prestigious badge of trust. This trust not only expedites trades but also reduces transaction scrutiny. Additionally, verified users unlock exclusive features enhancing efficiency on Paxful. Elevate your trading experience with Verified Paxful Accounts today.\n\nIn the ever-changing realm of online trading and transactions, selecting a platform with minimal fees is paramount for optimizing returns. This choice not only enhances your financial capabilities but also facilitates more frequent trading while safeguarding gains. Buy Verified Paxful Account.\n\nExamining the details of fee configurations reveals Paxful as a frontrunner in cost-effectiveness. Acquire a verified level-3 USA Paxful account from usasmmonline.com for a secure transaction experience. Invest in verified Paxful accounts to take advantage of a leading platform in the online trading landscape.\n\n \n\nHow Old Paxful ensures a lot of Advantages?\n\nExplore the boundless opportunities that Verified Paxful accounts present for businesses looking to venture into the digital currency realm, as companies globally witness heightened profits and expansion. These success stories underline the myriad advantages of Paxful’s user-friendly interface, minimal fees, and robust trading tools, demonstrating its relevance across various sectors.\n\nBusinesses benefit from efficient transaction processing and cost-effective solutions, making Paxful a significant player in facilitating financial operations. Acquire a USA Paxful account effortlessly at a competitive rate from usasmmonline.com and unlock access to a world of possibilities. Buy Verified Paxful Account.\n\nExperience elevated convenience and accessibility through Paxful, where stories of transformation abound. Whether you are an individual seeking seamless transactions or a business eager to tap into a global market, buying old Paxful accounts unveils opportunities for growth.\n\nPaxful’s verified accounts not only offer reliability within the trading community but also serve as a testament to the platform’s ability to empower economic activities worldwide. Join the journey towards expansive possibilities and enhanced financial empowerment with Paxful today. Buy Verified Paxful Account.\n\n \n\nWhy paxful keep the security measures at the top priority?\nIn today’s digital landscape, security stands as a paramount concern for all individuals engaging in online activities, particularly within marketplaces such as Paxful. It is essential for account holders to remain informed about the comprehensive security protocols that are in place to safeguard their information.\n\nSafeguarding your Paxful account is imperative to guaranteeing the safety and security of your transactions. Two essential security components, Two-Factor Authentication and Routine Security Audits, serve as the pillars fortifying this shield of protection, ensuring a secure and trustworthy user experience for all. Buy Verified Paxful Account.\n\nConclusion\nInvesting in Bitcoin offers various avenues, and among those, utilizing a Paxful account has emerged as a favored option. Paxful, an esteemed online marketplace, enables users to engage in buying and selling Bitcoin. Buy Verified Paxful Account.\n\nThe initial step involves creating an account on Paxful and completing the verification process to ensure identity authentication. Subsequently, users gain access to a diverse range of offers from fellow users on the platform. Once a suitable proposal captures your interest, you can proceed to initiate a trade with the respective user, opening the doors to a seamless Bitcoin investing experience.\n\nIn conclusion, when considering the option of purchasing verified Paxful accounts, exercising caution and conducting thorough due diligence is of utmost importance. It is highly recommended to seek reputable sources and diligently research the seller’s history and reviews before making any transactions.\n\nMoreover, it is crucial to familiarize oneself with the terms and conditions outlined by Paxful regarding account verification, bearing in mind the potential consequences of violating those terms. By adhering to these guidelines, individuals can ensure a secure and reliable experience when engaging in such transactions. Buy Verified Paxful Account.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n " | crewcaught |
1,917,150 | Day 1:Python - installation & Print Method | 8/7/2024- இன்றைய தினம் பைத்தான் எப்படி இன்ஸ்டால் செய்வது மற்றும் எப்படி பிரின்ட் செய்வது என்று... | 0 | 2024-07-09T10:40:19 | https://dev.to/suman_r/day-1python-installation-print-method-2ekj | python, programming, programmers | 8/7/2024- இன்றைய தினம் பைத்தான் எப்படி இன்ஸ்டால் செய்வது மற்றும் எப்படி பிரின்ட் செய்வது என்று கற்றுக்கொண்டேன்.
```
print("Hello World!")
```
| suman_r |
1,917,151 | Designing B2B Authentication Experiences: Universal vs. Organization-Specific Login | One of the first decisions you must make when architecting a new B2B application? How you’re going to... | 0 | 2024-07-09T10:40:49 | https://dev.to/scalekit/designing-b2b-authentication-experiences-universal-vs-organization-specific-login-43oc | webdev, tutorial, security, saas | One of the first decisions you must make when architecting a new B2B application? How you’re going to allow users to authenticate.
You have two choices: the universal login page or the organization-specific login page. We’ll make the distinction clear in a moment, but for now, know that the path you choose here has si... | scalekit |
1,917,152 | Finding the Best Flutter App Development Company | In the dynamic world of best mobile app development companies, choosing the right technology and... | 0 | 2024-07-09T10:41:26 | https://dev.to/chicmicllp/finding-the-best-flutter-app-development-company-opo |

In the dynamic world of best mobile app development companies, choosing the right technology and development partner is crucial for success. Flutter, Google’s open-source UI software development kit, has emerged as... | chicmicllp | |
1,917,153 | How can I complain to Meesho? | Visit supplier.meesho.com, click on 'Start Selling' contact us, 90606-31083 and become a seller in 5... | 0 | 2024-07-09T10:42:19 | https://dev.to/tina_kumari_4338f19912f71/how-can-i-complain-to-meesho-12b1 | webdev, javascript, beginners | Visit supplier.meesho.com, click on 'Start Selling' contact us, 90606-31083 and become a seller in 5 easy steps. With Meesho's 0% commission rate and no hidden charges, register in 5 easy steps and keep 100% of your profit. Step 1: Visit supplier.meesho.com, click on 'Start Selling', add your mobile number and click on... | tina_kumari_4338f19912f71 |
1,917,154 | Ищу бэкэндера | Ищу опытного бэкэнд программиста. На проекте необходимо сделать следующее: 1) Сортировка сообщений... | 0 | 2024-07-09T10:43:47 | https://dev.to/svetlana_priskoko_f28994f/ishchu-bekendiera-2245 | node, express, postgres, websocket | Ищу опытного бэкэнд программиста.
На проекте необходимо сделать следующее:
1) Сортировка сообщений (когда приходит новое сообщение, чтобы чат перемещался на первую позицию)
2) Счетчик не прочитанных сообщений
3) Передача файлов в чате по сокету
Прочие задачи. Возможно рефакторинг кода
Минимальные требования
nodejs ex... | svetlana_priskoko_f28994f |
1,917,155 | Mastering Hermes 13B for Advanced AI | Key Highlights Technical Advancements: Developed by Nous Research with Teknium and... | 0 | 2024-07-09T11:12:32 | https://dev.to/novita_ai/mastering-hermes-13b-for-advanced-ai-3bkf | llm, hermes, ai | ## Key Highlights
- Technical Advancements: Developed by Nous Research with Teknium and Emozilla, Hermes 13B features a fine-tuned model on an 8x a100 80GB DGX machine, supporting complex tasks with a 4096 sequence length.
- Dataset and Training: Trained on 300,000+ synthetic GPT-4 outputs, curated from sources like G... | novita_ai |
1,917,156 | How can I complain to Meesho? | Visit supplier.meesho.com, click on 'Start Selling' contact us, 90606-31083 and become a seller in 5... | 0 | 2024-07-09T10:45:05 | https://dev.to/tina_kumari_4338f19912f71/how-can-i-complain-to-meesho-4do9 | webdev, javascript, beginners | Visit supplier.meesho.com, click on 'Start Selling' contact us, 90606-31083 and become a seller in 5 easy steps. With Meesho's 0% commission rate and no hidden charges, register in 5 easy steps and keep 100% of your profit. Step 1: Visit supplier.meesho.com, click on 'Start Selling', add your mobile number and click on... | tina_kumari_4338f19912f71 |
1,917,159 | Build vs. Buy: How to approach SSO for your SaaS app | Every B2B organization developing new applications faces a pivotal decision: whether to build their... | 0 | 2024-07-09T10:45:24 | https://www.scalekit.com/blog/build-vs-buy-how-to-approach-sso-for-your-saas-app | webdev, security, saas, sso | Every B2B organization developing new applications faces a pivotal decision: whether to build their Authentication systems from scratch or leverage a ready-to-use solution. This decision affects not only the infrastructure of your SaaS app but also the user experience, security, and scalability. One of the first Authen... | scalekit |
1,917,160 | Ultimate Docker CheatSheet in 2024 | In this article, I want to share all the docker commands required in our day-to-day life. the command... | 0 | 2024-07-09T13:30:00 | https://techalgospotlight.com/ultimate-docker-cheatsheet-in-2024/ | docker, cheatsheet, productivity, learning | In this article, I want to share all the docker commands required in our day-to-day life. the command is very easy and useful for quick results. So, I am sharing it in the form of a docker cheatsheet.
## What is docker?
Docker is a tool designed to make it easier to create, deploy, and run applications by using con... | imkrunalkanojiya |
1,917,161 | Understanding Lunesta 3 mg: Best Cure for Insomnia | Lunesta 3 mg, a popular prescription medication for insomnia, works by enhancing the activity of... | 0 | 2024-07-09T10:46:37 | https://dev.to/rubyjohnson17/understanding-lunesta-3-mg-best-cure-for-insomnia-blb | sleep | **[Lunesta 3 mg](https://www.pills4cure.com/product/lunesta-3mg/)**, a popular prescription medication for insomnia, works by enhancing the activity of GABA, a calming neurotransmitter in the brain. This sedative-hypnotic helps patients fall asleep quickly and stay asleep throughout the night, addressing both sleep-ons... | rubyjohnson17 |
1,917,162 | Knowing Python - Day 1 | Writing a program language to execute a task is the new age tool to survive. However, with no... | 0 | 2024-07-09T10:47:28 | https://dev.to/anto_thomas_618cca852ba18/knowing-python-day-1-4o45 | programming, ecologicalmodelling | Writing a program language to execute a task is the new age tool to survive. However, with no background knowledge, scepticism clouds to learn one. With this in mind, I installed Python 3.12.4. I find it difficult to execute the first task, because I ran without any IDEs. I mistakenly downloaded Visual Studio Code. Fin... | anto_thomas_618cca852ba18 |
1,921,981 | Jasa Maklon Herbal Termurah | *Pengenalan Jasa Maklon * Jasa maklon atau contract manufacturing adalah solusi bagi banyak... | 0 | 2024-07-13T06:23:33 | https://dev.to/zadasyifa_nusantara/jasa-maklon-herbal-termurah-5e8a |

**Pengenalan Jasa Maklon **
Jasa maklon atau contract manufacturing adalah solusi bagi banyak perusahaan, terutama dalam industri kosmetik, makanan, dan obat herbal, yang ingin memproduksi produk mereka tanpa perl... | zadasyifa_nusantara | |
1,917,163 | Power Pages SPA: components | I will be making SPA components mostly in the Power Pages model-driven app. Go to Power Apps =>... | 27,979 | 2024-07-09T10:48:12 | https://dev.to/andrewelans/power-pages-spa-components-2bdl | I will be making SPA components mostly in the Power Pages model-driven app.
Go to [Power Apps](https://make.powerapps.com) => Find Power Pages Management in Your Apps => click Play button.
More content is coming here... | andrewelans | |
1,917,164 | Ensuring 24/7 Availability for ServiceNow Support- Fidel Softech | In today's interconnected global business environment, many organizations operating across multiple... | 0 | 2024-07-09T10:48:00 | https://dev.to/olivia_davis09/ensuring-247-availability-for-servicenow-support-fidel-softech-1650 | servicenowsupport, servicenowsupportservices | In today's interconnected global business environment, many organizations operating across multiple time zones rely on robust IT support to maintain seamless operations. ServiceNow, a cloud-based platform that automates routine business processes, offers substantial benefits but requires continuous support to maximize ... | olivia_davis09 |
1,917,165 | Everything You Need to Know About Multi Family Interior & Exterior Renovation Costs | Multi-family property retrofitting is a massive undertaking, the conclusion of which adds value to... | 0 | 2024-07-09T10:49:42 | https://dev.to/eliteconstruction/everything-you-need-to-know-about-multi-family-interior-renovation-costs-exterior-renovation-costs-1ig5 |

Multi-family property retrofitting is a massive undertaking, the conclusion of which adds value to the property and the rental inhabitants’ satisfaction. The cost of the renovation of the outer and inner structure o... | eliteconstruction | |
1,917,166 | 50 basic Linux commands | 𝐄𝐬𝐬𝐞𝐧𝐭𝐢𝐚𝐥 𝟓𝟎 𝐁𝐚𝐬𝐢𝐜 𝐋𝐢𝐧𝐮𝐱 𝐂𝐨𝐦𝐦𝐚𝐧𝐝𝐬: 𝐌𝐚𝐬𝐭𝐞𝐫 𝐘𝐨𝐮𝐫 𝐂𝐨𝐦𝐦𝐚𝐧𝐝 𝐋𝐢𝐧𝐞 𝐒𝐤𝐢𝐥𝐥𝐬 🐧 𝐩𝐰𝐝 - Print working directory.... | 0 | 2024-07-09T10:50:33 | https://dev.to/just_ritik/50-basic-linux-commands-3af6 | linux, devops, aws, javascript | 𝐄𝐬𝐬𝐞𝐧𝐭𝐢𝐚𝐥 𝟓𝟎 𝐁𝐚𝐬𝐢𝐜 𝐋𝐢𝐧𝐮𝐱 𝐂𝐨𝐦𝐦𝐚𝐧𝐝𝐬: 𝐌𝐚𝐬𝐭𝐞𝐫 𝐘𝐨𝐮𝐫 𝐂𝐨𝐦𝐦𝐚𝐧𝐝 𝐋𝐢𝐧𝐞 𝐒𝐤𝐢𝐥𝐥𝐬 🐧
𝐩𝐰𝐝 - Print working directory. 📂
𝐥𝐬 - List directory contents. 📋
𝐜𝐝 - Change directory. 📁
𝐭𝐨𝐮𝐜𝐡 - To create a file without any content. 📄
𝐜𝐚𝐭 - Concatenate and display file c... | just_ritik |
1,917,167 | How On-Demand E-Scooter Apps Solve Real-Life Challenges? | With changing climate conditions, finding eE-scooter App Development Companycological ways of... | 0 | 2024-07-09T10:50:53 | https://dev.to/emily_58df56cd3c125f2e89f/how-on-demand-e-scooter-apps-solve-real-life-challenges-ooo | With changing climate conditions, finding eE-scooter App Development Companycological ways of decreasing carbon pollution has become important. Apart from big industries, vehicles are another source of major carbon emissions. Solving the carbon problem with heavy industries is not easy, but there are various options av... | emily_58df56cd3c125f2e89f | |
1,917,168 | Leverage Concurrency Efficiently When Managing Multiple Tasks in Elixir | When working on multiple tasks, it's important to consider performing them concurrently. However,... | 0 | 2024-07-09T10:53:15 | https://blog.appsignal.com/2024/06/25/leverage-concurrency-efficiently-when-managing-multiple-tasks-in-elixir.html | elixir | When working on multiple tasks, it's important to consider performing them concurrently. However, when using concurrency, we need to be careful not to overload our system resources.
In this article, we will cover the following:
- What is concurrency?
- How can we use concurrency in Elixir?
- Common issues when workin... | traceyonim |
1,917,169 | Power Pages SPA: hash-based routing | Possible routing... | 27,979 | 2024-07-09T10:57:19 | https://dev.to/andrewelans/power-pages-spa-hash-based-routing-3aeg | powerplatform, powerpages | ## Possible routing options
```
Slash-based
https://your.powerappsportal.com/suppliers?name=valves&status=active
https://your.powerappsportal.com/frame-agreements
Hash-based
https://your.powerappsportal.com/#suppliers?name=valves&status=active
https://your.powerappsportal.com/#frame-agreements
```
## Routing in Powe... | andrewelans |
1,917,170 | Understanding SDG Impact Data: Key Insights and Resources | In today’s global landscape, businesses are increasingly expected to demonstrate their commitment... | 0 | 2024-07-09T10:53:33 | https://dev.to/ankit_langey_3eb6c9fc0587/understanding-sdg-impact-data-key-insights-and-resources-577n | inrate, sdg, impact, data |

In today’s global landscape, businesses are increasingly expected to demonstrate their commitment to sustainability and social responsibility. One crucial way they can do this is by measuring their impact against t... | ankit_langey_3eb6c9fc0587 |
1,917,171 | Unlocking the Power of VPNs on Android: A Comprehensive Guide | In today's interconnected world, where privacy and security are paramount concerns, Virtual Private... | 0 | 2024-07-09T10:55:03 | https://dev.to/blog-business/unlocking-the-power-of-vpns-on-android-a-comprehensive-guide-cjj | In today's interconnected world, where privacy and security are paramount concerns, Virtual Private Networks (VPNs) have emerged as indispensable tools. Among the various platforms where VPNs are utilized, Android devices stand out due to their widespread usage and susceptibility to cyber threats. Whether you're browsi... | blog-business | |
1,917,172 | Unlocking the Power of VPNs on Android: A Comprehensive Guide | In today's interconnected world, where privacy and security are paramount concerns, Virtual Private... | 0 | 2024-07-09T10:55:10 | https://dev.to/blog-business/unlocking-the-power-of-vpns-on-android-a-comprehensive-guide-oim | In today's interconnected world, where privacy and security are paramount concerns, Virtual Private Networks (VPNs) have emerged as indispensable tools. Among the various platforms where VPNs are utilized, Android devices stand out due to their widespread usage and susceptibility to cyber threats. Whether you're browsi... | blog-business | |
1,917,174 | The Strategic Role of Authentication in B2B SaaS Applications | At the heart of a secure application design, whether it be a B2B or B2C, lies a set of core... | 0 | 2024-07-09T10:57:48 | https://www.scalekit.com/blog/the-strategic-role-of-authentication-in-b2b-saas-applications | At the heart of a secure application design, whether it be a B2B or B2C, lies a set of core authentication features. These foundational capabilities include – stringent password policies, effective session management, and the convenience of social login options through Facebook, Google, and others. These features provi... | scalekit | |
1,917,175 | From Excel to Database: A Guide to Table Creation and Data Import with MySQL and SQLynx (Free SQL IDE) | In daily operations, Excel often becomes the repository for our data. But as effective as Excel is,... | 0 | 2024-07-09T10:59:39 | https://dev.to/senkae_ll/from-excel-to-database-a-guide-to-table-creation-and-data-import-with-mysql-and-sqlynx-free-sql-ide-5ad6 | mysql, database, sqlynx, sql | > In daily operations, Excel often becomes the repository for our data. But as effective as Excel is, it doesn’t quite match the ease of data analysis in SQL and databases, particularly when dealing with larger data volumes. In this article, we’ll illustrate how to create tables graphically based on Excel data using [S... | senkae_ll |
1,917,176 | Windsor Framework: Modernizing Customs with Technology | The Windsor Framework, agreed upon on February 27, 2023, is the UK government's new strategy to... | 0 | 2024-07-09T11:00:27 | https://dev.to/john_hall/windsor-framework-modernizing-customs-with-technology-2lm0 | ai, news, learning, software | The Windsor Framework, agreed upon on February 27, 2023, is the UK government's new strategy to replace the Northern Ireland Protocol. This protocol, part of the Brexit withdrawal agreement, created customs checks between Great Britain and Northern Ireland, forming a customs border in the Irish Sea. The Framework aims ... | john_hall |
1,917,177 | HTTP vs. SOCKS Proxies: An Ultimate Guide | Did you know that proxies were first used to cache web pages? Well, today their use cases are much... | 0 | 2024-07-09T11:11:03 | https://dev.to/marsproxies/http-vs-socks-proxies-an-ultimate-guide-27aa | proxies, http, socks | Did you know that proxies were first used to cache web pages? Well, today their use cases are much more versatile. They are used for all kinds of online activities, from **unlocking geo-restricted content to efficient web scraping.**
But if you’re here, we assume you already know that and are just trying to choose the... | marsproxies |
1,917,195 | Aramid Fiber Market with Excellent CAGR of 8.1% by 2033. | Global Aramid Fiber Market size was valued at USD 4.3 Billion in 2024 and is expected to reach USD... | 0 | 2024-07-09T11:17:33 | https://dev.to/suyash_singh_81ecf94acb60/aramid-fiber-market-with-excellent-cagr-of-81-by-2033-4m1h |
Global Aramid Fiber Market size was valued at USD 4.3 Billion in 2024 and is expected to reach USD 9.6 Billion by 2033, at a CAGR of 8.1% during the forecast period 2024 – 2033.
The Aramid Fiber Market report is a valuable source of insightful data for business strategists. It provides the industry overview with gro... | suyash_singh_81ecf94acb60 | |
1,917,179 | Scrape Grocery Delivery App Data - Grocery App Data Scraping Services | iWeb Scraping provides the best Top Grocery App Listing Data Scraping services to Scrape Grocery... | 0 | 2024-07-09T11:02:19 | https://dev.to/iwebscraping/scrape-grocery-delivery-app-data-grocery-app-data-scraping-services-4kpb | scrapegrocerydeliveryappdata, groceryappdatascrapingservices | iWeb Scraping provides the [best Top Grocery App Listing Data Scraping services](https://www.iwebscraping.com/scrape-google-play-top-grocery-app-listing-data.php) to Scrape Grocery Delivery App Data from Google Play Store. | iwebscraping |
1,917,180 | Exploring the Wonders of Ultrasound Technology | How Ultrasound Works Ultrasound imaging, also known as sonography, operates on the principle of... | 0 | 2024-07-09T11:03:14 | https://dev.to/magimark_222b1dcc06fc3b02/exploring-the-wonders-of-ultrasound-technology-579d | How Ultrasound Works
Ultrasound imaging, also known as sonography, operates on the principle of sound wave echoes. A transducer emits high-frequency sound waves into the body, which bounce off tissues and organs, producing echoes. These echoes are then captured and transformed into visual representations, displayed in... | magimark_222b1dcc06fc3b02 | |
1,917,181 | Code whisperers and rubber duck sorcery: do developers have superstitions? | Bugs, bugs, bugs... There's so much in that word, and there are just so many of them. It's merely... | 0 | 2024-07-09T11:04:11 | https://dev.to/anogneva/code-whisperers-and-rubber-duck-sorcery-do-developers-have-superstitions-44jg | discuss, community, programming | Bugs, bugs, bugs\.\.\. There's so much in that word, and there are just so many of them\. It's merely enough to freak anyone out or develop a phobia\. And no wonder; you never know when a regular error in code will play out\. In fact, the fear of the unknown and the desire to control everything are natural companions o... | anogneva |
1,917,182 | OpenAI API Key User Guide and Alternatives | Introduction Do you wonder how to access and utilize the capabilities of OpenAI's models?... | 0 | 2024-07-09T11:12:26 | https://dev.to/novita_ai/openai-api-key-user-guide-and-alternatives-3akj | llm, openai, api | ## Introduction
Do you wonder how to access and utilize the capabilities of OpenAI's models? What challenges might you face in the process, and what alternatives could you consider? This blog aims to unravel the intricacies of the OpenAI API Key.
We'll guide you through the process of acquiring your own API key, sett... | novita_ai |
1,917,183 | Complete Guide to GST Registration, Import Export Code, Digital Signature, and Tax Returns in Panchkula | Are you navigating the complexities of business registration and tax compliance in Panchkula? Lexwell... | 0 | 2024-07-09T11:05:54 | https://dev.to/lexwell/complete-guide-to-gst-registration-import-export-code-digital-signature-and-tax-returns-in-panchkula-45ho | Are you navigating the complexities of business registration and tax compliance in Panchkula? Lexwell Adviser is here to simplify the process with our expert services in GST registration, import-export code registration, digital signature registration, GST return online filing, and online TDS returns. Learn how these e... | lexwell | |
1,917,184 | Python print() method | Today we are going to see python print statement usage. Print is used to print the output in the... | 0 | 2024-07-09T11:06:20 | https://dev.to/kumar_tech_6d30f8ab1ef22c/python-print-method-2058 | python, beginners, programming | Today we are going to see python print statement usage.
Print is used to print the output in the console.
# Printing a simple string
print("Hello, World!") # Output: Hello, World!
# Printing numbers
print(123) # Output: 123
print(3.14) # Output: 3.14
# Printing multiple values
print("The an... | kumar_tech_6d30f8ab1ef22c |
1,917,185 | Chromic Acid Market with Excellent CAGR of 3.9% by 2031. | Global Chromic Acid Market Due to the COVID-19 pandemic, the global Chromic Acid market size is... | 0 | 2024-07-09T11:07:11 | https://dev.to/suyash_singh_81ecf94acb60/chromic-acid-market-with-excellent-cagr-of-39-by-2031-20oc |
Global Chromic Acid Market Due to the COVID-19 pandemic, the global Chromic Acid market size is estimated to be worth USD 741.8 million in 2022 and is forecast to a readjusted size of USD 933.2 million by 2031 with a CAGR of 3.9% during the review period.
The Chromic Acid Market report is a valuable source of insig... | suyash_singh_81ecf94acb60 | |
1,917,187 | Buprenorphine Hydrochloride Market with Excellent CAGR of 4.64% by 2032. | the Buprenorphine Hydrochloride market size was valued at US$ 135.67 million in 2023 and is... | 0 | 2024-07-09T11:09:01 | https://dev.to/suyash_singh_81ecf94acb60/buprenorphine-hydrochloride-market-with-excellent-cagr-of-464-by-2032-3k44 |

the Buprenorphine Hydrochloride market size was valued at US$ 135.67 million in 2023 and is expected to expand at a CAGR of 4.64% during the forecast period, reaching US$ 178.09 million by 2032.
The Buprenorphine Hydrochloride Market report is a valuable source of insightful data for business... | suyash_singh_81ecf94acb60 | |
1,917,188 | Synesso Coffee Machines | Synesso is a renowned manufacturer of espresso coffee machines, known for their high-quality... | 0 | 2024-07-09T11:12:01 | https://dev.to/magimark_222b1dcc06fc3b02/synesso-coffee-machines-94f | Synesso is a renowned manufacturer of espresso coffee machines, known for their high-quality craftsmanship and innovative technology.
[Synesso coffee machines](https://specialtybatch.com/synesso-espresso-coffee-machines/) are favored by specialty coffee shops and enthusiasts who prioritize precision, consistency, and t... | magimark_222b1dcc06fc3b02 | |
1,917,189 | MasterPy - Online interactive Python course for beginners | 🚀 Exciting News! 🌍 We are thrilled to announce the launch of MasterPy, now live at MasterPy.com!... | 0 | 2024-07-09T11:12:37 | https://dev.to/vlad_the_tudor/masterpy-online-interactive-python-course-for-beginners-28m9 | python, beginners, course, tutorial | 🚀 Exciting News! 🌍
We are thrilled to announce the launch of MasterPy, now live at MasterPy.com!
This project is a collaborative effort with the Romanian Union of Computer Science Teachers (UPIR), Infobits Academy, EEML and ARIA. 🎓
MasterPy is an educational platform designed for learning Python 3 through interac... | vlad_the_tudor |
1,917,190 | Break boundaries and reach global audience with Abzer's Digital payment solution! | Break boundaries and reach global audience with Abzer's Digital payment solution . . Get in touch... | 0 | 2024-07-09T11:12:47 | https://dev.to/minutebee/break-boundaries-and-reach-global-audience-with-abzers-digital-payment-solution-54e9 | digital, digitalpaymentsolution, ai, discuss | Break boundaries and reach global audience with Abzer's Digital payment solution
.
.
Get in touch with us right away!
Book For Free Demo
.
.
Visit for More Info : www.abzer.com
Email: info@abzer.com
WhatsApp : +971 50 818 5200
Call Now : +971 4 242 9200
.
.
.
#Digitalpaymentsolution #Paymentsolution #AbzerDMCC
| minutebee |
1,917,191 | Guide For Agritech Mobile App Development: Cost & Key Features In 2024 | In today's digital era, it's hard to find a sector that has yet to be affected by technology, and... | 0 | 2024-07-09T11:13:40 | https://dev.to/jploft_solutions/guide-for-agritech-mobile-app-development-cost-key-features-in-2024-2184 | agritech, mobileapp, appdevelopment | In today's digital era, it's hard to find a sector that has yet to be affected by technology, and agriculture is no exception. Technological advancements are bringing significant changes to the agritech industry. Given the expanding population and rising food demand, new technologies are becoming essential instead of t... | jploft_solutions |
1,917,192 | Master Stable Diffusion LoRA: Strategies for Success | Dive into the world of Stable Diffusion LoRA. Explore our blog for advice on maximizing efficiency... | 0 | 2024-07-09T11:15:00 | https://dev.to/novita_ai/master-stable-diffusion-lora-strategies-for-success-4j10 | ai, stablediffusion | Dive into the world of Stable Diffusion LoRA. Explore our blog for advice on maximizing efficiency and performance.
## Key Highlights
- LoRA models are like smaller versions of stable diffusion models that make tiny tweaks to existing checkpoint ones.
- With their size being 10 to 100 times less than the big checkpoi... | novita_ai |
1,917,193 | SpookySwap V4 Is Here: Endless Trading Opportunities & Lucrative Airdrops! 💸 | SpookySwap is thrilled to announce the launch of SpookySwap V4, which brings exciting new features to... | 0 | 2024-07-09T11:16:06 | https://dev.to/kesha_b62ecd1544f50cd4a9e/spookyswap-v4-is-here-endless-trading-opportunities-lucrative-airdrops-4l3k | cryptocurrency, ethereum, blockchain, spookyswap | SpookySwap is thrilled to announce the launch of SpookySwap V4, which brings exciting new features to our users. One of the most significant updates in V4 is the introduction of perpetual trading, allowing users to trade futures contracts without an expiration date. This opens up new opportunities for traders and adds ... | kesha_b62ecd1544f50cd4a9e |
1,917,194 | Carbon Disulfide Market with Excellent CAGR of 4.64% by 2032. | The Carbon Disulfide market size was valued at US$ 154.45 million in 2023 and is expected to expand... | 0 | 2024-07-09T11:16:56 | https://dev.to/suyash_singh_81ecf94acb60/carbon-disulfide-market-with-excellent-cagr-of-464-by-2032-2efm |
The Carbon Disulfide market size was valued at US$ 154.45 million in 2023 and is expected to expand at a CAGR of 2.37% during the forecast period, reaching US$ 177.77 million by 2032
The Carbon Disulfide Market re... | suyash_singh_81ecf94acb60 | |
1,917,196 | Treatment of speech problems | Treatment of speech problems, also known as speech disorders or speech-language disorders, depends on... | 0 | 2024-07-09T11:18:05 | https://dev.to/magimark_222b1dcc06fc3b02/treatment-of-speech-problems-133g | Treatment of speech problems, also known as speech disorders or speech-language disorders, depends on the specific nature and underlying causes of the issue.The treatment plan for [علاج مشاكل التخاطب](https://www.fshnkuwait.org/ar/services/speech-language-therapy/) is highly individualized, tailored to address the spec... | magimark_222b1dcc06fc3b02 | |
1,917,198 | BarCode Scanner device Orientation not changing in ipad and Tablet | Hi Team, I am using a ZXing barcode scanner facing issues on my iPad and tablet where changing... | 0 | 2024-07-09T11:20:03 | https://dev.to/priyanka_malik_f8a8994565/barcode-scanner-device-orientation-not-changing-in-ipad-and-tablet-15b1 | zxing | Hi Team,
I am using a ZXing barcode scanner facing issues on my iPad and tablet where changing orientation from landscape to portrait or vice versa does not reflect with scanner orientation.
On other mobile devices it works fine. I have used MobileBarcodeScanningOptions and set AutoRotate as true.
![Image description]... | priyanka_malik_f8a8994565 |
1,917,206 | The Robotic Revolution: How AI is Bridging the Gap Between Digital and Physical Worlds | 🤖 When AI meets metal – are you ready for your new Robot coworkers? Folks, the future isn't coming –... | 0 | 2024-07-09T11:20:42 | https://dev.to/iwooky/the-robotic-revolution-how-ai-is-bridging-the-gap-between-digital-and-physical-worlds-5gce | ai, news, learning, computerscience | 🤖 When AI meets metal – are you ready for your new Robot coworkers?
Folks, the future isn't coming – it's HERE. I think they plan to replace even manual labour workers now.
I've been recently reading with interest into the latest advancements in Robotics, and I'm convinced: we're on the brink of another revolution, ... | iwooky |
1,917,207 | 10 Captivating SQL Challenges to Sharpen Your Database Skills 🚀 | The article is about a collection of 10 captivating SQL challenges curated by LabEx, a leading platform for hands-on programming exercises. These challenges cover a wide range of SQL concepts and techniques, from creating and updating database views to analyzing student course data and calculating salary ranges. The ar... | 27,755 | 2024-07-09T11:22:25 | https://dev.to/labex/10-captivating-sql-challenges-to-sharpen-your-database-skills-dhk | mysql, coding, programming, tutorial |
Are you an aspiring SQL enthusiast looking to take your database management skills to the next level? Look no further! LabEx, a leading platform for hands-on programming challenges, has curated a collection of 10 captivating SQL challenges that will push your abilities to new heights.
 of roughly 8.94% between 2024 and 2032.
The Denim Jeans Market report is a valuable source of insightful data for business strategists.... | suyash_singh_81ecf94acb60 | |
1,917,210 | Leetcode #1 Two sum : 3 details different solutions | Leetcode #1 Two sum : 3 details different solutions | 0 | 2024-07-09T11:24:44 | https://dev.to/grenierdudev/leetcode-1-two-sum-3-details-different-solutions-521b | [Leetcode #1 Two sum : 3 details different solutions
](https://grenierdudev.com/exercise/leetcode-1-two-sum-3-details-different-solutions-241335d) | grenierdudev | |
1,917,211 | What is the difference between SDK, JDK, OpenJDK, JRE, JVM, java compiler in java platform ? | What is the difference between SDK, JDK, OpenJDK, JRE, JVM, java compiler in java platform ? | 0 | 2024-07-09T11:26:25 | https://dev.to/grenierdudev/what-is-the-difference-between-sdk-jdk-openjdk-jre-jvm-java-compiler-in-java-platform--286e | [What is the difference between SDK, JDK, OpenJDK, JRE, JVM, java compiler in java platform ?
](https://grenierdudev.com/posts/what-is-the-difference-between-sdk-jdk-openjdk-jre-jvm-java-compiler-in-java-platform-2d42e37) | grenierdudev | |
1,917,243 | Explore how BitPower Loop works | BitPower Loop is a decentralized lending platform based on blockchain technology that aims to provide... | 0 | 2024-07-09T11:42:27 | https://dev.to/sang_ce3ded81da27406cb32c/explore-how-bitpower-loop-works-3p2e | BitPower Loop is a decentralized lending platform based on blockchain technology that aims to provide secure, efficient and transparent lending services. Here is how it works in detail:
1️⃣ Smart Contract Guarantee
BitPower Loop uses smart contract technology to automatically execute all lending transactions. This aut... | sang_ce3ded81da27406cb32c | |
1,917,212 | In Java programming What is concurrency, parallelism, multi-threading ? [Everything you need to know] | In Java programming What is concurrency, parallelism, multi-threading ? [Everything you need to know] | 0 | 2024-07-09T11:27:50 | https://dev.to/grenierdudev/in-java-programming-what-is-concurrency-parallelism-multi-threading-everything-you-need-to-know-260e | [In Java programming What is concurrency, parallelism, multi-threading ? [Everything you need to know]
](https://grenierdudev.com/posts/in-java-programming-what-is-concurrency-parallelism-multi-threading-everything-you-need-to-know-95112e) | grenierdudev | |
1,917,214 | Explore how BitPower Loop works | BitPower Loop is a decentralized lending platform based on blockchain technology that aims to provide... | 0 | 2024-07-09T11:28:44 | https://dev.to/asfg_f674197abb5d7428062d/explore-how-bitpower-loop-works-1ejd | BitPower Loop is a decentralized lending platform based on blockchain technology that aims to provide secure, efficient and transparent lending services. Here is how it works in detail:
1️⃣ Smart Contract Guarantee
BitPower Loop uses smart contract technology to automatically execute all lending transactions. This aut... | asfg_f674197abb5d7428062d | |
1,917,215 | Linux command pwd : Print Working Directory | Linux command pwd : Print Working Directory | 0 | 2024-07-09T11:29:07 | https://dev.to/grenierdudev/linux-command-pwd-print-working-directory-1c24 | [Linux command pwd : Print Working Directory
](https://grenierdudev.com/posts/linux-command-pwd-print-working-directory-70744d) | grenierdudev | |
1,917,216 | Exploring the Benefits of Regular Wheel Alignment for Your Vehicle | ``Maintaining your vehicle’s health is essential for ensuring a smooth and safe driving experience.... | 0 | 2024-07-09T11:29:19 | https://dev.to/ronaldgbrown84/exploring-the-benefits-of-regular-wheel-alignment-for-your-vehicle-3aa6 | beginners | ``Maintaining your vehicle’s health is essential for ensuring a smooth and safe driving experience. One critical but often overlooked aspect of car maintenance is regular wheel alignment. This straightforward service can significantly impact your vehicle’s performance, safety, and longevity. In this blog, we’ll delve i... | ronaldgbrown84 |
1,917,249 | Introduction to BitPower decentralized smart contracts | What is BitPower? BitPower is a decentralized lending platform that uses blockchain technology to... | 0 | 2024-07-09T11:48:32 | https://dev.to/aimm/introduction-to-bitpower-decentralized-smart-contracts-o3p | What is BitPower?
BitPower is a decentralized lending platform that uses blockchain technology to provide secure and efficient lending services through smart contracts.
Main features
Automatic execution
Smart contracts automatically execute transactions without human intervention.
Open source code
The code is open and ... | aimm | |
1,917,217 | Intern vs Extern Linux commands | Intern vs Extern Linux commands | 0 | 2024-07-09T11:29:57 | https://dev.to/grenierdudev/intern-vs-extern-linux-commands-13nf | [Intern vs Extern Linux commands
](https://grenierdudev.com/posts/intern-vs-extern-linux-commands-326fd7e) | grenierdudev | |
1,917,218 | How to install a specific version of g++ or gcc on Ubuntu/Linux | How to install a specific version of g++ or gcc on Ubuntu/Linux | 0 | 2024-07-09T11:30:57 | https://dev.to/grenierdudev/how-to-install-a-specific-version-of-g-or-gcc-on-ubuntulinux-4mnc | [How to install a specific version of g++ or gcc on Ubuntu/Linux
](https://grenierdudev.com/posts/how-to-install-a-specific-version-of-g-or-gcc-on-ubuntu-linux-a2e470) | grenierdudev | |
1,917,219 | VerifyVault v0.4 has been RELEASED! 🚀 | 🔑 Key Updates: Encrypted Password Hints ✨ Added Show Password toggle for convenience 🔒 Automatic... | 0 | 2024-07-09T14:59:27 | https://dev.to/verifyvault/verifyvault-v04-has-been-released-52dp | opensource, security, cybersecurity, github | 🔑 **Key Updates:**
- Encrypted Password Hints ✨
- Added Show Password toggle for convenience 🔒
- Automatic backups with automatic location if none set 🔄
- Backup file names now include the name of the backup 📂
- Fixed issues like inactive window popups and password reminder access 🛠️
And more! Update today! 🚀
... | verifyvault |
1,917,220 | Discover SpookySwap : Unlock Perpetual Trading & Exclusive Rewards! 🚀 | Welcome to SpookySwap V4 SpookySwap is proud to announce the launch of our latest version -... | 0 | 2024-07-09T11:31:32 | https://dev.to/spookyswap/discover-spookyswap-unlock-perpetual-trading-exclusive-rewards-dp4 | spookyswap, cryptocurrency, blockchain |
Welcome to SpookySwap V4
SpookySwap is proud to announce the launch of our latest version - SpookySwap V4. This new version comes with exciting features and improvements that will enhance the user experience for all our community members. We are constantly striving to provide the best decentralized exchange platform f... | spookyswap |
1,917,250 | API Testing: A Comprehensive Guide | API Testing: A Comprehensive Guide Introduction to API Testing In the realm of software development,... | 0 | 2024-07-09T11:48:39 | https://dev.to/keploy/api-testing-a-comprehensive-guide-305g | webdev, javascript, programming, tutorial |
API Testing: A Comprehensive Guide
Introduction to API Testing
In the realm of software development, APIs (Application Programming Interfaces) play a crucial role in enabling different software systems to communicat... | keploy |
1,917,221 | Top 5 medium Rust open source project to contribute. | Top 5 medium Rust open source project to contribute. | 0 | 2024-07-09T11:32:02 | https://dev.to/grenierdudev/top-5-medium-rust-open-source-project-to-contribute-16fe | [Top 5 medium Rust open source project to contribute.
](https://grenierdudev.com/posts/top-5-medium-rust-open-source-project-to-contribute-137028d) | grenierdudev | |
1,917,222 | Axios Vs Fetch: Which Should You Use For Your HTTP Requests? | For most developers, fetching data is essential for modern applications to interact with APIs coming... | 0 | 2024-07-09T11:34:35 | https://dev.to/designobit/axios-vs-fetch-which-should-you-use-for-your-http-requests-n70 | javascript, programming, tutorial, react | For most developers, fetching data is essential for modern applications to interact with APIs coming from the backend. and to achieve that we have several options the most popular ones are `AXIOS` and `FETCH`. while both have the same basic functions, at the same time they offer different features and developer experie... | designobit |
1,917,223 | LeetCode Day29 Dynamic Programming Part 2 | 62. Unique Paths There is a robot on an m x n grid. The robot is initially located at the... | 0 | 2024-07-09T11:32:29 | https://dev.to/flame_chan_llll/leetcode-day29-dynamic-programming-part-2-4np6 | leetcode, java, algorithms | # 62. Unique Paths
There is a robot on an m x n grid. The robot is initially located at the top-left corner (i.e., grid[0][0]). The robot tries to move to the bottom-right corner (i.e., grid[m - 1][n - 1]). The robot can only move either down or right at any point in time.
Given the two integers m and n, return the nu... | flame_chan_llll |
1,917,225 | seo company kuwait | we specialize in boosting your website's visibility and driving targeted traffic through strategic... | 0 | 2024-07-09T11:32:51 | https://dev.to/kelvinmarker_6593a47fe2f6/seo-company-kuwait-4b4f | we specialize in boosting your website's visibility and driving targeted traffic through strategic keyword research, on-page optimization, content creation, and advanced SEO techniques. Whether you're a small business looking to increase local visibility or a large enterprise aiming for global reach, our tailored SEO s... | kelvinmarker_6593a47fe2f6 | |
1,917,251 | Understanding Flexbox: A Powerful Tool for Modern Web Design | Introduction In the world of web design, Flexbox is a game-changer. Introduced in CSS3, the Flexible... | 0 | 2024-07-09T11:49:46 | https://dev.to/annalaura2/understanding-flexbox-a-powerful-tool-for-modern-web-design-3812 | webdev, programming, womenintech, code |
**Introduction**
In the world of web design, Flexbox is a game-changer. Introduced in CSS3, the Flexible Box Layout, commonly known as Flexbox, is a layout model that provides an efficient way to align and distribute space among items in a container, even when their size is unknown or dynamic. In this article, we'll... | annalaura2 |
1,917,226 | What int argc and char *argv[] means in C or C++ programming language ? | What int argc and char *argv[] means in C or C++ programming language ? | 0 | 2024-07-09T11:32:59 | https://dev.to/grenierdudev/what-int-argc-and-char-argv-means-in-c-or-c-programming-language--3ec9 | [What int argc and char *argv[] means in C or C++ programming language ?
](https://grenierdudev.com/posts/what-int-argc-and-char-argv-means-in-c-or-c-programming-language-ae5a25) | grenierdudev | |
1,917,227 | How to become a hacker ? Full path | How to become a hacker ? Full path | 0 | 2024-07-09T11:33:52 | https://dev.to/grenierdudev/how-to-become-a-hacker-full-path-500j | [How to become a hacker ? Full path
](https://grenierdudev.com/posts/how-to-become-a-hacker-full-path-251ff29) | grenierdudev | |
1,917,228 | The Power of Remote Software Development Teams | The software development landscape is evolving rapidly. Gone are the days of geographically... | 0 | 2024-07-09T11:34:13 | https://dev.to/challenge_ff152947c6ad70d/the-power-of-remote-software-development-teams-4eg9 | webdev, team, remote, development | The [software development](http://hexamilesoft.com/stories/how-to-build-a-remote-software-development-team/) landscape is evolving rapidly. Gone are the days of geographically restricted teams. Today, companies are embracing the power of remote software development teams, unlocking a global pool of talent and fostering... | challenge_ff152947c6ad70d |
1,917,229 | Dive into DeFi: Unlock Endless Opportunities with SpookySwap 🚀 | Welcome to SpookySwap V4 SpookySwap is proud to announce the launch of our latest version -... | 0 | 2024-07-09T11:34:26 | https://dev.to/spookyswap/discover-spookyswap-unlock-perpetual-trading-exclusive-rewards-113c | spookyswap, cryptocurrency, blockchain |
Welcome to SpookySwap V4
SpookySwap is proud to announce the launch of our latest version - SpookySwap V4. This new version comes with exciting features and improvements that will enhance the user experience for all our community members. We are constantly striving to provide the best decentralized exchange platform f... | spookyswap |
1,917,271 | Intercepteurs dans Angular | Introduction Dans cet article, nous allons explorer comment utiliser les intercepteurs... | 0 | 2024-07-09T12:12:57 | https://dev.to/bilongodavid/intercepteurs-dans-angular-4gf0 | javascript, angular, website |
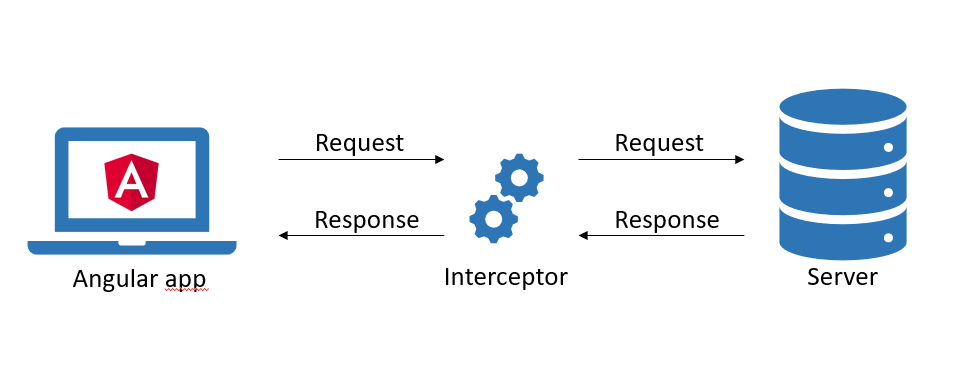
### Introduction
Dans cet article, nous allons explorer comment utiliser les intercepteurs HTTP fonctionnels avec Angular 17. Les intercepteurs permettent de manipuler les requêtes et réponses HTTP, facilitant des ... | bilongodavid |
1,917,230 | What is Wasm or WebAssembly ? Learn WebAssembly Basics with Rust Part B | What is Wasm or WebAssembly ? Learn WebAssembly Basics with Rust Part B | 0 | 2024-07-09T11:34:36 | https://dev.to/grenierdudev/what-is-wasm-or-webassembly-learn-webassembly-basics-with-rust-part-b-pk2 | [What is Wasm or WebAssembly ? Learn WebAssembly Basics with Rust Part B
](https://grenierdudev.com/posts/what-is-wasm-or-webassembly-learn-webassembly-basics-with-rust-part-b-17cfc10) | grenierdudev | |
1,917,231 | Comparison of Work360.space vs Odoo.com | Both Work360.space and Odoo.com are platforms designed to provide comprehensive business management... | 0 | 2024-07-09T11:34:40 | https://dev.to/msj/comparison-of-work360space-vs-odoocom-ik4 | webdev, odoo, work360, beginners | Both Work360.space and Odoo.com are platforms designed to provide comprehensive business management solutions. While they share similar goals, each platform offers unique features and capabilities. This comparison aims to highlight the strengths and weaknesses of each to help businesses decide which solution best fits ... | msj |
1,917,232 | Creating a Generative AI Chatbot using GPT-2 and Flask | Generative chatbots are revolutionizing human-computer interaction by allowing machines to not only... | 0 | 2024-07-09T11:36:00 | https://dev.to/jeanvalve/creating-a-generative-ai-chatbot-using-gpt-2-and-flask-1jm6 | Generative chatbots are revolutionizing human-computer interaction by allowing machines to not only respond to predefined commands but also generate contextually relevant and coherent responses. This technological advancement has found applications in a variety of sectors, from online customer service to virtual assist... | jeanvalve | |
1,917,233 | Creating a Generative AI Chatbot using GPT-2 and Flask | Generative chatbots are revolutionizing human-computer interaction by allowing machines to not only... | 0 | 2024-07-09T11:36:00 | https://dev.to/jeanvalve/creating-a-generative-ai-chatbot-using-gpt-2-and-flask-de6 | Generative chatbots are revolutionizing human-computer interaction by allowing machines to not only respond to predefined commands but also generate contextually relevant and coherent responses. This technological advancement has found applications in a variety of sectors, from online customer service to virtual assist... | jeanvalve | |
1,917,235 | Bitpower Security: The Iron Wall in the Blockchain | Bitpower Security: The Iron Wall in the Blockchain In the vast ocean of digital currencies,... | 0 | 2024-07-09T11:37:30 | https://dev.to/ping_iman_72b37390ccd083e/bitpower-security-the-iron-wall-in-the-blockchain-5am1 |

Bitpower Security: The Iron Wall in the Blockchain
In the vast ocean of digital currencies, Bitpower stands proudly like an indestructible fortress. In this fortress, every brick and tile is made of blockchain tech... | ping_iman_72b37390ccd083e | |
1,917,238 | Unleash Your Trading Potential with SpookySwap V4: Join the Revolution! ⚡ | Welcome to the Future of SpookySwap What's new in SpookySwap V4? SpookySwap V4 is finally here, and... | 0 | 2024-07-09T11:39:03 | https://dev.to/kesha_b62ecd1544f50cd4a9e/unleash-your-trading-potential-with-spookyswap-v4-join-the-revolution-9jj | cryptocurrency, ethereum, blockchain, spookyswap | Welcome to the Future of SpookySwap
What's new in SpookySwap V4?
SpookySwap V4 is finally here, and it brings a whole new level of spookiness to the world of decentralized finance. With improved features and functionalities, users can expect a smoother and more efficient trading experience on the platform.
Some of the... | kesha_b62ecd1544f50cd4a9e |
1,917,239 | My First Experience with Python | Hi Hello Namaskaram !! for so long, this buzz word 'python' has been chasing me.. PERL PHP Python... | 0 | 2024-07-09T11:42:14 | https://dev.to/food4all/my-first-experience-with-python-1coi | python | Hi Hello Namaskaram !!
for so long, this buzz word 'python' has been chasing me..
PERL PHP Python is the famous ad mantra for many popular training institutes..
well, somewhere i came to know that, there is a free python class and this time, i just want to jump into it.
I have installed python 3.12 64-bit
But, aft... | food4all |
1,917,240 | BitPower Introduction: | BitPower is an innovative decentralized financial platform built on blockchain technology that... | 0 | 2024-07-09T11:40:27 | https://dev.to/bao_xin_145cb69d4d8d82453/bitpower-introduction-572f | BitPower is an innovative decentralized financial platform built on blockchain technology that provides decentralized lending and investment services. Its core product, BitPower Loop, allows users to deposit and borrow directly through smart contracts and obtain floating-rate investment returns. BitPower’s features inc... | bao_xin_145cb69d4d8d82453 | |
1,917,241 | Boost Your Presentations with Free Templates: Download Now! | In this fast-paced entire world, to be able to give compelling presentations could make each of the... | 0 | 2024-07-09T11:41:23 | https://dev.to/presetdesign23/boost-your-presentations-with-free-templates-download-now-24c6 | In this fast-paced entire world, to be able to give compelling [presentations ](https://presetdesign.com/ )could make each of the difference. No matter if that you are an individual, a reliable, or maybe an entrepreneur, acquiring a proven method for your use can certainly increase your delivering presentations plus... | presetdesign23 | |
1,917,242 | SpookySwap V4: Trading and Earning Rewards | In the ever-evolving landscape of decentralized finance (DeFi), SpookySwap has made a significant... | 0 | 2024-07-09T11:42:21 | https://dev.to/jake_willson/spookyswap-v4-trading-and-earning-rewards-2749 | webdev, javascript, beginners, programming | In the ever-evolving landscape of decentralized finance (DeFi), [SpookySwap](https://spookyswap.net/) has made a significant impact with its innovative approach to decentralized trading. With the upcoming launch of SpookySwap V4, the platform is set to revolutionize the trading experience by introducing perpetual tradi... | jake_willson |
1,917,244 | Host a Static Website in Azure Storage by Bastus Babajide Mark | INTRODUCTION Static websites are the kind of websites that always maintain the same appearance to... | 0 | 2024-07-09T17:37:03 | https://dev.to/jdbastus/host-a-static-website-in-azure-storage-by-bastus-babajide-mark-1m6j | storageaccount, enablestaticwebsite, uploadfiles, testwebsiteusingurl | **INTRODUCTION**
Static websites are the kind of websites that always maintain the same appearance to every of the users that access them at any point in point. It only changes when the website developer modifies the source file. Our task today is to host a website of sort on an Azure Blob Storage. This is divided into... | jdbastus |
1,917,245 | Introduction to BitPower decentralized smart contracts | What is BitPower? BitPower is a decentralized lending platform that uses blockchain technology to... | 0 | 2024-07-09T11:44:04 | https://dev.to/aimm_w_1761d19cef7fa886fd/introduction-to-bitpower-decentralized-smart-contracts-3g0l | What is BitPower?
BitPower is a decentralized lending platform that uses blockchain technology to provide secure and efficient lending services through smart contracts.
Main features
Automatic execution
Smart contracts automatically execute transactions without human intervention.
Open source code
The code is open and ... | aimm_w_1761d19cef7fa886fd | |
1,917,246 | Personalyzer: Customizable Skateboards Made Easy with Wix Studio | This is a submission for the Wix Studio Challenge . What I Built I created "Personalyzer," an online... | 0 | 2024-07-09T11:45:45 | https://dev.to/digikins/personalyzer-wix-studio-challenge-485m | devchallenge, wixstudiochallenge, webdev, javascript | *This is a submission for the [Wix Studio Challenge ](https://dev.to/challenges/wix).*
What I Built
I created "Personalyzer," an online shop where you can customize your own skateboard. Users can design their skateboard from scratch, choosing everything from the deck design to the wheels and grip tape, all to suit th... | digikins |
1,917,247 | Analysis of BitPower Lending Platform | Introduction With the development of blockchain technology, decentralized finance (DeFi) has... | 0 | 2024-07-09T11:45:54 | https://dev.to/wot_dcc94536fa18f2b101e3c/analysis-of-bitpower-lending-platform-3i1b |

Introduction
With the development of blockchain technology, decentralized finance (DeFi) has gradually become a hot topic in the financial industry. As an important project in this field, BitPower Lending Platform h... | wot_dcc94536fa18f2b101e3c | |
1,917,248 | IT Staff Augmentation: Addressing Your Development Needs | Empower your business with flexible IT solutions designed to match your project needs. Learn how... | 0 | 2024-07-09T11:46:10 | https://dev.to/joinwithveera/it-staff-augmentation-addressing-your-development-needs-44l4 | webdev, augmentation, devchallenge | Empower your business with flexible IT solutions designed to match your project needs. Learn how integrating specialized expertise through staff augmentation boosts efficiency and drives innovation in various IT fields.
## IT Staff Augmentation In Cybersecurity -
Nowadays, with the increasing danger of cyber threats... | joinwithveera |
1,917,252 | Who & What is behind the magic of tech world | Ganpati Bappa Morya 🙏 Hi, this is me with my first article, which will explain you how the industry... | 0 | 2024-07-09T11:51:02 | https://dev.to/karanrsingh/who-what-is-behind-the-magic-of-tech-world-3l71 | webdev, computerscience, beginners, programming | Ganpati Bappa Morya 🙏
Hi, this is me with my first article, which will explain you how the industry of the most prominent sector of the world looks like, who works behind the screens of your most used app or site or game, how the development process works and much more. Let's Start.
I am taking example of Instagram,... | karanrsingh |
1,917,254 | Finding the Finest: Exploring the Best Hawan Samagri for Sacred Rituals | Hawan, an ancient Vedic ritual, holds profound significance in Hindu traditions. It involves the... | 0 | 2024-07-09T11:53:22 | https://dev.to/puja_0ccd7897ea6878405457/finding-the-finest-exploring-the-best-hawan-samagri-for-sacred-rituals-fg6 | spiritual, news | Hawan, an ancient Vedic ritual, holds profound significance in Hindu traditions. It involves the invocation of divine energies through the sacred fire, symbolizing purification, offering, and spiritual connection. Central to this ritual is the hawan samagri, a meticulously curated collection of natural ingredients each... | puja_0ccd7897ea6878405457 |
1,917,255 | BitPower Introduction: | BitPower is an innovative decentralized financial platform built on blockchain technology that... | 0 | 2024-07-09T11:54:30 | https://dev.to/xin_l_9aced9191ff93f0bf12/bitpower-introduction-3m3g | BitPower is an innovative decentralized financial platform built on blockchain technology that provides decentralized lending and investment services. Its core product, BitPower Loop, allows users to deposit and borrow directly through smart contracts and obtain floating-rate investment returns. BitPower’s features inc... | xin_l_9aced9191ff93f0bf12 | |
1,917,256 | Analysis of BitPower Lending Platform | Introduction With the development of blockchain technology, decentralized finance (DeFi) has... | 0 | 2024-07-09T11:55:25 | https://dev.to/wot_ee4275f6aa8eafb35b941/analysis-of-bitpower-lending-platform-1djm |
Introduction
With the development of blockchain technology, decentralized finance (DeFi) has gradually become a hot topic in the financial industry. As an important project in this field, BitPower Lending Platform h... | wot_ee4275f6aa8eafb35b941 | |
1,917,257 | Bitpower Security: The Iron Wall in the Blockchain | Bitpower Security: The Iron Wall in the Blockchain In the vast ocean of digital currencies,... | 0 | 2024-07-09T11:55:34 | https://dev.to/pingd_iman_9228b54c026437/bitpower-security-the-iron-wall-in-the-blockchain-gpa |

Bitpower Security: The Iron Wall in the Blockchain
In the vast ocean of digital currencies, Bitpower stands proudly like an indestructible fortress. In this fortress, every brick and tile is made of blockchain tech... | pingd_iman_9228b54c026437 | |
1,917,259 | Macron's camp plots improbable rebound in the midst of French political race disorder | With nobody in control, the French president's partners accept the sky is the limit. See More | 0 | 2024-07-09T11:56:43 | https://dev.to/uniqueworldnews209/macrons-camp-plots-improbable-rebound-in-the-midst-of-french-political-race-disorder-10ph | worldnews, news, french, political |
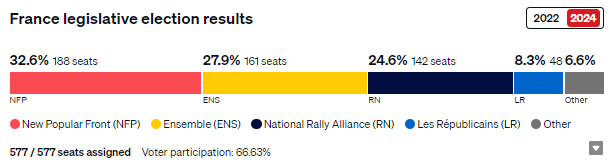
With nobody in control, the French president's partners accept the sky is the limit.
[See More](https://uniqueworldnewsservice.blogspot.com/2024/07/macrons-camp-plots-improbable-rebound.html)
| uniqueworldnews209 |
1,917,260 | Explore how BitPower Loop works | BitPower Loop is a decentralized lending platform based on blockchain technology that aims to provide... | 0 | 2024-07-09T11:56:43 | https://dev.to/weq_24a494dd3a467ace6aca5/explore-how-bitpower-loop-works-462n | BitPower Loop is a decentralized lending platform based on blockchain technology that aims to provide secure, efficient and transparent lending services. Here is how it works in detail:
1️⃣ Smart Contract Guarantee
BitPower Loop uses smart contract technology to automatically execute all lending transactions. This aut... | weq_24a494dd3a467ace6aca5 | |
1,917,261 | Implementing Carousels in Web Development | What is a Carousel? A carousel, also known as a slider, is a web component that allows... | 0 | 2024-07-09T12:00:48 | https://dev.to/patrick_chibueze_e2567f25/implementing-carousels-in-web-development-1pk8 | webdev, javascript, programming, tutorial | ## What is a Carousel?
A carousel, also known as a slider, is a web component that allows multiple pieces of content to be displayed within a single space. Users can navigate through this content by clicking on navigation controls or allowing the content to transition at set intervals automatically.
## Importance in ... | patrick_chibueze_e2567f25 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.