issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 261k ⌀ | issue_title stringlengths 1 925 | issue_comments_url stringlengths 56 81 | issue_comments_count int64 0 2.5k | issue_created_at stringlengths 20 20 | issue_updated_at stringlengths 20 20 | issue_html_url stringlengths 37 62 | issue_github_id int64 387k 2.91B | issue_number int64 1 131k |
|---|---|---|---|---|---|---|---|---|---|
[
"kubernetes",
"kubernetes"
] | See comment for details:
https://github.com/cncf-tags/container-device-interface/pull/93 | dynamic resource allocation: move common logic of highestSupportedVersion to util package | https://api.github.com/repos/kubernetes/kubernetes/issues/113831/comments | 4 | 2022-11-10T20:24:37Z | 2023-09-18T20:59:27Z | https://github.com/kubernetes/kubernetes/issues/113831 | 1,444,514,344 | 113,831 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
In `api/openapi-spec/v3/*.json` fields, the openapiv3 `description` of enum fields should contain the documentation of all the enum values. This provides language client users with convenient access to all the API documentation available for all enum values.
*Background:*
In ... | Include enum details in descriptions of api/openapi-spec/v3/ json files | https://api.github.com/repos/kubernetes/kubernetes/issues/113830/comments | 5 | 2022-11-10T20:02:27Z | 2025-02-07T17:32:08Z | https://github.com/kubernetes/kubernetes/issues/113830 | 1,444,489,064 | 113,830 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
This came out of the discussion around https://github.com/kubernetes/kubernetes/pull/111023 which uses a concept similar to generic ephemeral volumes: since 1.22, pods are guaranteed to reach a terminal phase (failed or succeeded):https://kubernetes.slack.com/archives/C0BP8PW9G/p16... | PVC protection cannot handle terminated pods that are not deleted | https://api.github.com/repos/kubernetes/kubernetes/issues/113828/comments | 12 | 2022-11-10T18:59:15Z | 2024-12-12T18:40:08Z | https://github.com/kubernetes/kubernetes/issues/113828 | 1,444,413,707 | 113,828 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are flaking?
pull-kubernetes-integration
### Which tests are flaking?
TestLegacyServiceAccountTokenTracking (in top 10 list of flakes - http://storage.googleapis.com/k8s-metrics/flakes-latest.json)
### Since when has it been flaking?
10/25
https://storage.googleapis.com/k8s-triage/index... | [Flake] TestLegacyServiceAccountTokenTracking flakes on number of warnings received | https://api.github.com/repos/kubernetes/kubernetes/issues/113821/comments | 1 | 2022-11-10T15:03:27Z | 2022-11-11T02:36:14Z | https://github.com/kubernetes/kubernetes/issues/113821 | 1,444,066,294 | 113,821 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
Is it officially marked as deprecated and should we remove the dependency from the project?
https://twitter.com/awalterschulze/status/1584553056100057088
https://github.com/kubernetes/kubernetes/issues/96564
https://github.com/gogo/protobuf
### What did you expect to happen?
Need a replac... | Deprecated github.com/gogo/protobuf | https://api.github.com/repos/kubernetes/kubernetes/issues/113813/comments | 5 | 2022-11-10T09:58:51Z | 2022-11-15T21:50:41Z | https://github.com/kubernetes/kubernetes/issues/113813 | 1,443,594,412 | 113,813 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
https://github.com/kubernetes/kubernetes/pull/67782 removed OpenStack cloud provider + related volume plugin from Kubernetes 1.26, but it also removed CSI migration for OpenStack Cinder volumes. All volumes with `pv.spec.cinder` are now unusable.
When a PV should be dynamically provisioned, I ... | CSI migration for Cinder volumes is missing | https://api.github.com/repos/kubernetes/kubernetes/issues/113811/comments | 2 | 2022-11-10T09:52:38Z | 2022-11-11T19:00:10Z | https://github.com/kubernetes/kubernetes/issues/113811 | 1,443,585,521 | 113,811 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
We have cluster role binding that is getting recreated after deleting it. Also tried editing it and removing one of the subjects. It is restored to the previous version.
```
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: aks-cluster-admin-binding
uid:... | cluster role binding getting recreated after deletion or edit. | https://api.github.com/repos/kubernetes/kubernetes/issues/113804/comments | 7 | 2022-11-10T03:46:24Z | 2022-11-11T21:45:42Z | https://github.com/kubernetes/kubernetes/issues/113804 | 1,443,192,659 | 113,804 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
One of our clusters exported an UDP NodePort service for clients to use. The client is using the [kcp protocol](https://github.com/skywind3000/kcp/blob/master/README.en.md) talking to the servers, the "connection" between client and server are periodically "disconnected".
> the kcp protocol is ... | kube-proxy IPVS break UDP NodePort Services by clearing active conntrack entries | https://api.github.com/repos/kubernetes/kubernetes/issues/113802/comments | 15 | 2022-11-10T02:40:42Z | 2023-05-08T15:05:21Z | https://github.com/kubernetes/kubernetes/issues/113802 | 1,443,140,341 | 113,802 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
Failing in multiple jobs:
* https://testgrid.k8s.io/sig-node-containerd#node-e2e-features
* https://testgrid.k8s.io/sig-node-containerd#cgroup-systemd-containerd-node-e2e
* https://testgrid.k8s.io/sig-node-containerd#cos-cgroupv1-containerd-node-e2e
### Which tests are failing?
```
... | Test failure - Security Context when creating a pod in the host PID namespace ... | https://api.github.com/repos/kubernetes/kubernetes/issues/113801/comments | 5 | 2022-11-10T02:12:40Z | 2022-11-10T09:10:57Z | https://github.com/kubernetes/kubernetes/issues/113801 | 1,443,115,314 | 113,801 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
Followup to https://github.com/kubernetes/kubernetes/pull/113186#discussion_r1017220974
### What did you expect to happen?
APIGroup validation in PVC.DataSource and DataSourceRef follows the same rules as api registration.
### How can we reproduce it (as minimally and precisely as possible)?
Cre... | Add APIGroup ratcheting validation to PVC.DataSource | https://api.github.com/repos/kubernetes/kubernetes/issues/113798/comments | 14 | 2022-11-09T23:41:17Z | 2023-09-13T06:46:14Z | https://github.com/kubernetes/kubernetes/issues/113798 | 1,442,944,052 | 113,798 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
This is a regression caused by https://github.com/kubernetes/kubernetes/pull/113693. It worked with master a14601a77fa (last merge commit before that PR) and is broken in b2c72feca83.
Disabling the APIServerTracing feature gate works avoids the problem.
The problem is that port forwarding in h... | apiserver tracing: port forwarding broke | https://api.github.com/repos/kubernetes/kubernetes/issues/113791/comments | 18 | 2022-11-09T15:59:47Z | 2022-11-10T16:32:00Z | https://github.com/kubernetes/kubernetes/issues/113791 | 1,442,349,749 | 113,791 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Ensure that `PrepareResources()` is called against all DRA `kubelet` plugins for all containers before CNI is invoked.
This can be done by either moving this call earlier in the process of doing pod creation, or moving it into the `PodAdmission` loop (as is done by the existing ... | dynamic resource allocation: ensure PrepareResources called before CNI invoked | https://api.github.com/repos/kubernetes/kubernetes/issues/113785/comments | 3 | 2022-11-09T11:41:44Z | 2023-02-07T16:09:07Z | https://github.com/kubernetes/kubernetes/issues/113785 | 1,441,941,186 | 113,785 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
[sig-release-1.23-informing](https://testgrid.k8s.io/sig-release-1.23-informing)
- [aks-engine-windows-containerd-1.23](https://testgrid.k8s.io/sig-release-1.23-informing#aks-engine-windows-containerd-1.23)
### Which tests are failing?
* Kubernetes e2e suite: [sig-api-machinery] ... | [Failing test] aks-engine-windows-containerd-1.23 | https://api.github.com/repos/kubernetes/kubernetes/issues/113784/comments | 3 | 2022-11-09T11:27:13Z | 2022-11-09T19:14:09Z | https://github.com/kubernetes/kubernetes/issues/113784 | 1,441,921,513 | 113,784 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
The `PodResources` API is used to query the full set of resources allocated to a pod and make them available to metrics servers, CNI plugins, etc.
With the introduction of DRA, we should also include the resources it manages as part of this API.
### Why is this needed?
T... | dynamic resource allocation: add DRA-managed resources to the PodResources API | https://api.github.com/repos/kubernetes/kubernetes/issues/113783/comments | 7 | 2022-11-09T11:25:22Z | 2023-07-10T07:50:03Z | https://github.com/kubernetes/kubernetes/issues/113783 | 1,441,918,996 | 113,783 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
[sig-release-1.24-informing](https://testgrid.k8s.io/sig-release-1.24-informing)
- [capz-windows-containerd-1.24](https://testgrid.k8s.io/sig-release-1.24-informing#capz-windows-containerd-1.24)
### Which tests are failing?
- Kubernetes e2e suite: [sig-node] Probing container should *n... | [Failing test] capz-windows-containerd-1.24 | https://api.github.com/repos/kubernetes/kubernetes/issues/113782/comments | 5 | 2022-11-09T11:23:36Z | 2022-11-10T00:08:39Z | https://github.com/kubernetes/kubernetes/issues/113782 | 1,441,916,683 | 113,782 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
While setting up k8s cluster using the ci/latest version, we notice the kublet failure with below error message in its log:
```
Nov 09 07:20:47 config1-1667977224-worker-0 kubelet[26715]: I1109 07:20:47.984943 26715 topology_manager.go:134] "Creating topology manager with policy per scope" t... | Latest k8s fails with kublet panic runtime error | https://api.github.com/repos/kubernetes/kubernetes/issues/113781/comments | 13 | 2022-11-09T11:20:40Z | 2022-11-09T20:22:55Z | https://github.com/kubernetes/kubernetes/issues/113781 | 1,441,912,738 | 113,781 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
`pkg/scheduler/framework/plugins/dynamicresources/dynamicresources_test.go` uses testify to check errors and compare structs. The preferred style for scheduler plugins is to avoid test packages like testify and instead generate test failures manually. cmp.Diff can be used for struc... | dynamic resource allocation: avoid using testify in scheduler tests | https://api.github.com/repos/kubernetes/kubernetes/issues/113774/comments | 11 | 2022-11-09T08:19:11Z | 2024-06-17T06:58:54Z | https://github.com/kubernetes/kubernetes/issues/113774 | 1,441,631,104 | 113,774 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Several tests use a builder pattern with manually written helper functions to populate objects with certain fields set. That code pre-dates the introduction of the generated applyconfiguration packages (like `k8s.io/client-go/applyconfigurations/core/v1`).
Now applyconfigurati... | applyconfiguration: support conversion to corresponding type | https://api.github.com/repos/kubernetes/kubernetes/issues/113773/comments | 14 | 2022-11-09T08:09:04Z | 2025-01-28T17:22:11Z | https://github.com/kubernetes/kubernetes/issues/113773 | 1,441,616,712 | 113,773 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Potential changes:
- Reference -> Ref in struct names - might not be consistent with other types then?
- core.ResourceClaim -> ResourceClaimUse, ResourceClaimAttachment, etc. - TBD
This only affects Go code and thus is not an API change.
### Why is this needed?
Simpler and... | dynamic resource allocation: simplify type names in API | https://api.github.com/repos/kubernetes/kubernetes/issues/113771/comments | 9 | 2022-11-09T07:45:17Z | 2023-04-24T18:24:48Z | https://github.com/kubernetes/kubernetes/issues/113771 | 1,441,580,278 | 113,771 |
[
"kubernetes",
"kubernetes"
] | I have only 2 nodes so that I want full-track of pods.
Can I set specific number of replicas for each node in one deployment? (e.g. 2 replicas on node-1 & 3 replicas on node-2)
I tried:
node affinity: can't adjust number of replicas for each node.
pod anti-affinity: can't assign multiple pods for single node.
... | Is there any way to assign pods to nodes manually? | https://api.github.com/repos/kubernetes/kubernetes/issues/113770/comments | 6 | 2022-11-09T06:37:04Z | 2022-11-24T00:25:35Z | https://github.com/kubernetes/kubernetes/issues/113770 | 1,441,473,786 | 113,770 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
master-informing
- ci-crio-cgroupv1-node-e2e-conformance
### Which tests are failing?
- E2eNode Suite.[SynchronizedBeforeSuite]
- ci-crio-cgroupv1-node-e2e-conformance.Overall
- kubetest.Node Tests
### Since when has it been failing?
11-08 01:43 IST
### Testgrid link
http... | [Failing test] ci-crio-cgroupv1-node-e2e-conformance | https://api.github.com/repos/kubernetes/kubernetes/issues/113767/comments | 21 | 2022-11-09T01:39:15Z | 2022-11-24T11:08:34Z | https://github.com/kubernetes/kubernetes/issues/113767 | 1,441,200,444 | 113,767 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
master-informing
- ci-crio-cgroupv1-node-e2e-conformance
### Which tests are failing?
- E2eNode Suite.[SynchronizedBeforeSuite]
- ci-crio-cgroupv1-node-e2e-conformance.Overall
- kubetest.Node Tests
### Since when has it been failing?
11-08 01:43 IST
### Testgrid link
http... | [Failing test] ci-crio-cgroupv1-node-e2e-conformance | https://api.github.com/repos/kubernetes/kubernetes/issues/113766/comments | 0 | 2022-11-09T01:38:57Z | 2022-11-09T01:49:36Z | https://github.com/kubernetes/kubernetes/issues/113766 | 1,441,200,232 | 113,766 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
master-informing
- ci-crio-cgroupv1-node-e2e-conformance
### Which tests are failing?
- E2eNode Suite.[SynchronizedBeforeSuite]
- ci-crio-cgroupv1-node-e2e-conformance.Overall
- kubetest.Node Tests
### Since when has it been failing?
11-08 01:43 IST
### Testgrid link
http... | [Failing test] ci-crio-cgroupv1-node-e2e-conformance | https://api.github.com/repos/kubernetes/kubernetes/issues/113765/comments | 0 | 2022-11-09T01:38:43Z | 2022-11-09T01:48:54Z | https://github.com/kubernetes/kubernetes/issues/113765 | 1,441,200,076 | 113,765 |
[
"kubernetes",
"kubernetes"
] | Currently, informers expose a `HasSynced` method.
This asserts that one full List has been synced to the informers *store*.
However, this does not give any guarantees about *handlers* being called.
It is fairly common to need to know that the handlers have been called for the initial state.
However, there is cu... | informers: provide a way to know when a resource handler has "synced" | https://api.github.com/repos/kubernetes/kubernetes/issues/113763/comments | 9 | 2022-11-09T00:36:08Z | 2023-10-10T15:45:04Z | https://github.com/kubernetes/kubernetes/issues/113763 | 1,441,135,388 | 113,763 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
skew-cluster-latest-kubectl-stable1-gce
### Which tests are failing?
kubetest.Extract
### Since when has it been failing?
Since 11/8
### Testgrid link
https://testgrid.k8s.io/sig-release-master-blocking#skew-cluster-latest-kubectl-stable1-gce
### Reason for failure (if possible)
``... | [Failing test] skew-cluster-latest-kubectl-stable1-gce kubetest.Extract | https://api.github.com/repos/kubernetes/kubernetes/issues/113762/comments | 9 | 2022-11-08T22:38:43Z | 2022-11-21T09:49:04Z | https://github.com/kubernetes/kubernetes/issues/113762 | 1,441,014,049 | 113,762 |
[
"kubernetes",
"kubernetes"
] | The admission configation managers have some logic errors leading to HasSynced() reporting true prematurely. `validatingWebhookConfigurationManager` and `mutatingWebhookConfigurationManager` both suffer this issue.
Description of the problem:
`HasSynced()` checks the Informer is synced, and initialConfigurationSy... | Admission configuration managers incorrectly implement `HasSynced()` | https://api.github.com/repos/kubernetes/kubernetes/issues/113761/comments | 22 | 2022-11-08T22:31:54Z | 2025-01-07T21:16:13Z | https://github.com/kubernetes/kubernetes/issues/113761 | 1,441,006,160 | 113,761 |
[
"kubernetes",
"kubernetes"
] | Ref:- https://github.com/kubernetes/kubernetes/pull/112050#discussion_r1016791814
We will also have to do some benchmarking to ensure perf cost between the current implementation and this approach to make sure we are being benefited from atomic.Pointers. | encryption-at-rest: use atomic.Pointer to store dynamic transformers | https://api.github.com/repos/kubernetes/kubernetes/issues/113759/comments | 10 | 2022-11-08T21:40:44Z | 2024-09-28T19:45:29Z | https://github.com/kubernetes/kubernetes/issues/113759 | 1,440,943,566 | 113,759 |
[
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H)
A security issue was discovered in Kubernetes where users may have access to secure endpoints in the control plane network. Kubernetes clusters are only affected if an u... | CVE-2022-3294: Node address isn't always verified when proxying | https://api.github.com/repos/kubernetes/kubernetes/issues/113757/comments | 2 | 2022-11-08T21:33:26Z | 2023-04-27T08:27:18Z | https://github.com/kubernetes/kubernetes/issues/113757 | 1,440,935,103 | 113,757 |
[
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N](https://www.first.org/cvss/calculator/3.0#CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N)
A security issue was discovered in Kubernetes where users authorized to list or watch one type of namespaced custom resource cluster-wide can read custom resources of a ... | CVE-2022-3162: Unauthorized read of Custom Resources | https://api.github.com/repos/kubernetes/kubernetes/issues/113756/comments | 17 | 2022-11-08T21:33:07Z | 2022-12-08T03:40:09Z | https://github.com/kubernetes/kubernetes/issues/113756 | 1,440,934,711 | 113,756 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are flaking?
https://testgrid.k8s.io/sig-release-1.25-blocking#gce-device-plugin-gpu-1.25
https://testgrid.k8s.io/sig-release-1.24-blocking#gce-device-plugin-gpu-1.24
https://testgrid.k8s.io/sig-release-1.23-blocking#gce-device-plugin-gpu-1.23
### Which tests are flaking?
Above jobs
### Sin... | gce-device-plugin-gpu job failing on 1.25, 1.24, and 1.23 blocking dashboards | https://api.github.com/repos/kubernetes/kubernetes/issues/113752/comments | 5 | 2022-11-08T20:54:44Z | 2022-11-09T04:42:21Z | https://github.com/kubernetes/kubernetes/issues/113752 | 1,440,889,346 | 113,752 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
Recent Kubernetes versions (1.25, 1.24 and main) exhibit a delay on ConfigMap update for the time taken to render the changes to the volume on the filesystem. Recent test [runs](https://prow.k8s.io/view/gs/kubernetes-jenkins/logs/ci-cos-cgroupv2-containerd-e2e-gce/1589654264869818368) (`Projected co... | Projected ConfigMap Update Delay | https://api.github.com/repos/kubernetes/kubernetes/issues/113746/comments | 10 | 2022-11-08T16:19:42Z | 2024-12-18T18:47:30Z | https://github.com/kubernetes/kubernetes/issues/113746 | 1,440,509,273 | 113,746 |
[
"kubernetes",
"kubernetes"
] | **How to categorize this issue?**
/sig networking
/kind feature
/priority important-soon
**What would you like to be added**:
Currently there is no way to achieve topology aware routing (`kubernetes.io/hostname`, `topology.kubernetes.io/zone`, `topology.kubernetes.io/region`) and define _deterministic_ rules lik... | Support topology aware routing (node and zone) | https://api.github.com/repos/kubernetes/kubernetes/issues/113731/comments | 55 | 2022-11-08T13:33:27Z | 2024-12-18T06:58:41Z | https://github.com/kubernetes/kubernetes/issues/113731 | 1,440,215,303 | 113,731 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
from Events object I can see that liveness probe is failing but I can't see ``prober.go`` logs in the journal.
https://github.com/kubernetes/kubernetes/blob/e3d7cb5bc53bd5db8a8bfe90fe77d8d78a5ded14/pkg/kubelet/prober/prober.go#L109
Logging does work for the first couple of probes but after that... | Liveness probe is failing but prober.go doesn't log it | https://api.github.com/repos/kubernetes/kubernetes/issues/113725/comments | 2 | 2022-11-08T11:05:04Z | 2022-11-08T11:32:46Z | https://github.com/kubernetes/kubernetes/issues/113725 | 1,439,970,236 | 113,725 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Right now, the name is specified as `<pod name>-<claim source name inside pod spec>`. That's easy and deterministic, but may lead to conflicts with ResourceClaims that were created earlier, either automatically or manually.
Let's investigate the alternative: generate the name an... | dynamic resource allocation: use generated name for ResourceClaim from template | https://api.github.com/repos/kubernetes/kubernetes/issues/113722/comments | 6 | 2022-11-08T09:43:38Z | 2023-07-11T17:33:14Z | https://github.com/kubernetes/kubernetes/issues/113722 | 1,439,843,247 | 113,722 |
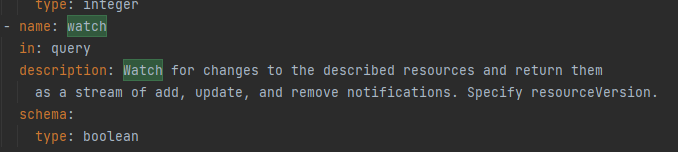
[
"kubernetes",
"kubernetes"
] | ### What happened?
In the 1.25.3 API documentation, the `allowWatchBookmarks` and `watch` parameter is defined as a boolean,
 when I first kubectl delete pod --grace-perios=30 and then when kubect... | grace-period=0 --force Forced deletion failed | https://api.github.com/repos/kubernetes/kubernetes/issues/113717/comments | 19 | 2022-11-08T08:22:19Z | 2025-01-11T01:12:09Z | https://github.com/kubernetes/kubernetes/issues/113717 | 1,439,712,912 | 113,717 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Introduce a new field `observedResourceVersion` to `resourcequota.status` to provide solid resource admission, in case of event slow watch during usage calculation that causes resource leak.
proposal:
```go
// ResourceQuotaStatus defines the enforced hard limits and obs... | [Feature Request] solid resourcequota admission leveraging `resourceVersion` comparison. | https://api.github.com/repos/kubernetes/kubernetes/issues/113716/comments | 11 | 2022-11-08T07:33:06Z | 2024-11-05T16:30:19Z | https://github.com/kubernetes/kubernetes/issues/113716 | 1,439,645,961 | 113,716 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Enable vertical scaling of nodes, add the ability to update the nodes capacity specs without needing to restart the kubelet service in case of change in underlying machine capacity spec.
### Why is this needed?
If virtual machines support live upgrades of machines specs lik... | Enhancement: Vertical node scaling | https://api.github.com/repos/kubernetes/kubernetes/issues/113715/comments | 9 | 2022-11-08T07:07:23Z | 2022-11-10T21:04:35Z | https://github.com/kubernetes/kubernetes/issues/113715 | 1,439,613,510 | 113,715 |
[
"kubernetes",
"kubernetes"
] | It looks like label keys "controller-uid" and "job-name" are used. Unprefixed label keys are reserved for end-users - these should be "something.kubernetes.io/...".
Since this is in the wild, the best we can do would be to define and document the proper names, set and accept both for a while, then stop setting the ... | batch API uses fixed, non-prefixed label keys | https://api.github.com/repos/kubernetes/kubernetes/issues/113714/comments | 25 | 2022-11-08T06:52:36Z | 2024-12-23T12:07:15Z | https://github.com/kubernetes/kubernetes/issues/113714 | 1,439,597,495 | 113,714 |
[
"kubernetes",
"kubernetes"
] | From https://kubernetes.io/docs/reference/command-line-tools-reference/feature-gates/
the statement
``Since Kubernetes 1.24, new beta APIs are not enabled by default. When enabling a beta feature, you will also need to enable any associated API resources. For example, to enable a particular resource like storage.k8... | whether related beta apis enabled for those beta feature gates enabled by k8s 1.24 by default? | https://api.github.com/repos/kubernetes/kubernetes/issues/113713/comments | 10 | 2022-11-08T06:42:16Z | 2025-03-07T06:42:12Z | https://github.com/kubernetes/kubernetes/issues/113713 | 1,439,588,542 | 113,713 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
I checked the kubelet source code and found that after receiving a request to delete a pod, it will determine whether the pod is in the process of being updated, and if it is, it will store this update in the map of lastUndeliveredWorkUpdate. When this update is finished, it will be taken out from t... | GracePeriod elegant delete can only be set once | https://api.github.com/repos/kubernetes/kubernetes/issues/113712/comments | 14 | 2022-11-08T06:32:15Z | 2024-12-18T18:45:19Z | https://github.com/kubernetes/kubernetes/issues/113712 | 1,439,579,238 | 113,712 |
[
"kubernetes",
"kubernetes"
] | In this PR https://github.com/kubernetes/kubernetes/pull/112377, `sets.Set` is newly implemented, and `sets.String` got marked as deprecated.
In the scheduler, we often use `sets.String` everywhere. This issue aims to replace all `sets.String` (+ other deprecated structs in the `sets` package) with `sets.Set` in the... | Replace all deprecated `sets.String` with `sets.Set` | https://api.github.com/repos/kubernetes/kubernetes/issues/113709/comments | 36 | 2022-11-08T01:20:56Z | 2023-04-12T02:17:16Z | https://github.com/kubernetes/kubernetes/issues/113709 | 1,439,271,271 | 113,709 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
Followed up with @alculquicondor, VolumeBinding Score plugin is enabled only when the feature gate `VolumeCapacityPriority ` is enabled:
https://github.com/kubernetes/kubernetes/blob/43a2bb4df4ff3c255337f5ed927b8fd17c38c235/pkg/scheduler/apis/config/v1beta2/default_plugins.go#L115-L119
However... | VolumeBinding's Score plugin in enabled by default in v1beta3 and v1 config | https://api.github.com/repos/kubernetes/kubernetes/issues/113705/comments | 10 | 2022-11-07T23:10:29Z | 2022-11-11T06:41:13Z | https://github.com/kubernetes/kubernetes/issues/113705 | 1,439,131,872 | 113,705 |
[
"kubernetes",
"kubernetes"
] | ref - https://github.com/kubernetes/kubernetes/pull/112050#discussion_r1015894772
/sig auth | encryption-at-rest: add success or failure metric when encryption configuration attempts to dynamically update | https://api.github.com/repos/kubernetes/kubernetes/issues/113704/comments | 3 | 2022-11-07T23:06:08Z | 2023-07-14T06:08:01Z | https://github.com/kubernetes/kubernetes/issues/113704 | 1,439,127,757 | 113,704 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
The node selectors gets parsed by `corev1helpers.MatchNodeSelectorTerms(node, class.SuitableNodes)` in `Filter` for each node. That work can be done once in `PreFilter`.
### Why is this needed?
Better performance. | dynamic resource allocation: optimize class.SuitableNodes usage | https://api.github.com/repos/kubernetes/kubernetes/issues/113703/comments | 2 | 2022-11-07T23:05:03Z | 2023-08-28T11:43:44Z | https://github.com/kubernetes/kubernetes/issues/113703 | 1,439,126,823 | 113,703 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
There are several scenarios where the current approach is too coarse:
- The scheduler plugin marks ResourceClaim changes as triggers for all pods. It should only do that for pods that actually use claims.
- When ResourceClaims are missing, trying to schedule the pod repeatedly ... | dynamic resource allocation: trigger re-scheduling of specific pods | https://api.github.com/repos/kubernetes/kubernetes/issues/113702/comments | 7 | 2022-11-07T23:01:48Z | 2023-08-28T08:49:45Z | https://github.com/kubernetes/kubernetes/issues/113702 | 1,439,124,041 | 113,702 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Performance optimizations may be possible.
Other ideas for classic DRA:
- randomize node selection with rand.Perm
- remove sorting of node names
For structured parameters (incomplete list):
- cache compiled CEL expressions
- optimize attribute lookup
### Why is this needed?
Bet... | dynamic resource allocation: benchmark scheduler plugin | https://api.github.com/repos/kubernetes/kubernetes/issues/113701/comments | 17 | 2022-11-07T22:56:34Z | 2025-01-17T14:24:31Z | https://github.com/kubernetes/kubernetes/issues/113701 | 1,439,120,114 | 113,701 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
The initial pkg/scheduler/framework/plugin/dynamicresources code use Update to modify objects. It should use patches or (once supported by client-go fake) server-side-apply.
Same for pkg/controller/resourceclaim/controller.go.
### Why is this needed?
Better performance. | dynamic resource allocation: use patches or server-side-apply for updates | https://api.github.com/repos/kubernetes/kubernetes/issues/113700/comments | 8 | 2022-11-07T22:46:19Z | 2024-04-02T07:44:08Z | https://github.com/kubernetes/kubernetes/issues/113700 | 1,439,111,964 | 113,700 |
[
"kubernetes",
"kubernetes"
] | We need to enable the `MinimizeIPTablesRestore` feature gate in some/all? scale tests, and check the `sync_proxy_rules_iptables_partial_restore_failures_total` metric at the end of the run. (We believe it should be 0 at the end of the run, but we may not want to actually assert that until we've done a few runs?)
/ki... | test MinimizeIPTablesRestore in scale tests | https://api.github.com/repos/kubernetes/kubernetes/issues/113678/comments | 5 | 2022-11-07T14:09:24Z | 2022-11-19T19:12:23Z | https://github.com/kubernetes/kubernetes/issues/113678 | 1,438,430,679 | 113,678 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are flaking?
pull-kubernetes-integration: https://testgrid.k8s.io/presubmits-kubernetes-blocking#pull-kubernetes-integration&include-filter-by-regex=%5BAa%5Dpply
ci-kubernetes-integration-master: https://testgrid.k8s.io/sig-release-master-blocking#integration-master&include-filter-by-regex=[Aa]pply&w... | [Flake] test-cmd: run_kubectl_server_side_apply_tests | https://api.github.com/repos/kubernetes/kubernetes/issues/113677/comments | 5 | 2022-11-07T13:31:47Z | 2022-11-15T21:50:55Z | https://github.com/kubernetes/kubernetes/issues/113677 | 1,438,374,704 | 113,677 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
We deploy an application with an autoscaler, that needs to be based on number of unacked messages in the queue. This is `hpa.yaml` file. `<topic-name>` and `<subscription>` both refer to placeholder values:
```
apiVersion: autoscaling/v2beta2
kind: HorizontalPodAutoscaler
metadata:
name: de... | HPA based on External metrics fails on label validation | https://api.github.com/repos/kubernetes/kubernetes/issues/113673/comments | 3 | 2022-11-07T12:53:10Z | 2023-02-16T08:10:14Z | https://github.com/kubernetes/kubernetes/issues/113673 | 1,438,317,079 | 113,673 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
I have a kubernetes cluster running. I tainted the worker nodes and then proceeded to create a statefulset in the cluster **without** providing any tolerations. Of course, this lead to pods in the state "Pending". Later on, I added tolerations to the statefulset and confirmed that the toleration a... | Setting toleration on StatefulSet doesn't restart associated Pods | https://api.github.com/repos/kubernetes/kubernetes/issues/113671/comments | 10 | 2022-11-07T12:03:28Z | 2023-04-08T12:31:16Z | https://github.com/kubernetes/kubernetes/issues/113671 | 1,438,247,614 | 113,671 |
[
"kubernetes",
"kubernetes"
] | Hello Dears
I need to setup wireguard vpn on server before installing Kubernetes then install Kubernetes on top of that
But after installing Kubernetes `KUBE-FIREWALL` chain stops Wireguard traffic
`DROP all -- any any anywhere anywhere /* kubernetes firewall for dropping mar... | Conflict with wireguard vpn on iptables | https://api.github.com/repos/kubernetes/kubernetes/issues/113659/comments | 7 | 2022-11-06T19:39:29Z | 2023-03-02T01:50:45Z | https://github.com/kubernetes/kubernetes/issues/113659 | 1,437,515,721 | 113,659 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are flaking?
https://testgrid.k8s.io/sig-release-master-blocking#integration-master&width=5
### Which tests are flaking?
it seems it affects the `k8s.io/kubernetes/test/integration/apiserver/admissionwebhook.TestWebhookAdmissionWithWatchCache` and `k8s.io/kubernetes/test/integration/apiserver/admissi... | integration tests started to flake ~ Oct 29th | https://api.github.com/repos/kubernetes/kubernetes/issues/113651/comments | 11 | 2022-11-06T00:18:17Z | 2022-11-15T21:51:01Z | https://github.com/kubernetes/kubernetes/issues/113651 | 1,437,233,636 | 113,651 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
Containers with readinessProbe become not ready for a period of time when kubelet restart, then it'll be ready again soon.
### What did you expect to happen?
The container status should remain ready when the kubelet restarts.
### How can we reproduce it (as minimally and precisely as possible)?... | Containers with readinessProbe become not ready when kubelet restart | https://api.github.com/repos/kubernetes/kubernetes/issues/113646/comments | 8 | 2022-11-05T11:34:37Z | 2023-01-18T21:36:03Z | https://github.com/kubernetes/kubernetes/issues/113646 | 1,436,979,763 | 113,646 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
when I want to create a dynamic storage class,the pvc is struck in pending,
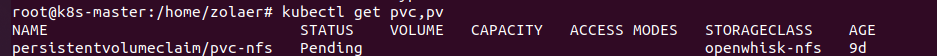
when i check the log of nfs-client-privisioner, I found this:
![c815518a1299850e... | the status of pvc is pending | https://api.github.com/repos/kubernetes/kubernetes/issues/113643/comments | 20 | 2022-11-05T06:41:12Z | 2024-03-25T08:56:00Z | https://github.com/kubernetes/kubernetes/issues/113643 | 1,436,872,332 | 113,643 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Currently, the status section in `Job/CronJob` workload contains fields `succeeded/active/failed`, etc.
But usually we need the job to pass the output data, to let us do more logic rely on the result data.
So propose to add `status.data` in `Job/CronJob` to pass the job output,... | Proposal: Add status.data in `Job/CronJob` to pass job output | https://api.github.com/repos/kubernetes/kubernetes/issues/113641/comments | 9 | 2022-11-05T03:03:35Z | 2023-01-17T09:57:51Z | https://github.com/kubernetes/kubernetes/issues/113641 | 1,436,785,611 | 113,641 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
ValidateImmutableField is a validation helper function for checking that a field is not getting modified during an update. It's convenient to use, but when it finds a mismatch, it reports the entire value, which can be a large struct, without explaining what exactly was changed inc... | ValidateImmutableField: report a diff instead of entire field | https://api.github.com/repos/kubernetes/kubernetes/issues/113633/comments | 22 | 2022-11-04T18:45:03Z | 2025-02-19T08:49:14Z | https://github.com/kubernetes/kubernetes/issues/113633 | 1,436,496,190 | 113,633 |
[
"kubernetes",
"kubernetes"
] | > making the reload behavior rely on content in the thing being reloaded is weird
>
> I think this should limit itself to saying that enabling reloading collapses all kms providers to a single healthz check
>
> separately (in the kmsv1 and kmsv2 config docs?) say that individual kms healthz checks are only provid... | Document KMS healthz endpoint behavior | https://api.github.com/repos/kubernetes/kubernetes/issues/113631/comments | 6 | 2022-11-04T17:36:58Z | 2022-12-06T21:55:29Z | https://github.com/kubernetes/kubernetes/issues/113631 | 1,436,423,516 | 113,631 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Currently we have inconsistency in most of the API where the field name should be used in description so the generated docs match the API fields people actually set. https://github.com/kubernetes/kubernetes/issues/113438
A linter could be added for checking
### Why is this need... | Add linter for API doc field check | https://api.github.com/repos/kubernetes/kubernetes/issues/113630/comments | 8 | 2022-11-04T17:10:23Z | 2023-01-31T00:21:11Z | https://github.com/kubernetes/kubernetes/issues/113630 | 1,436,391,972 | 113,630 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
One of the use-cases for APIServer tracing would be to try and debug SLO-violating requests served by the API Server. Right now, it adds just some basic attributes: https://github.com/kubernetes/kubernetes/blob/master/staging/src/k8s.io/apiserver/pkg/endpoints/handlers/trace_util.... | APIServer Tracing attribute parity with SLO metrics | https://api.github.com/repos/kubernetes/kubernetes/issues/113628/comments | 3 | 2022-11-04T15:48:07Z | 2022-11-08T12:30:23Z | https://github.com/kubernetes/kubernetes/issues/113628 | 1,436,286,906 | 113,628 |
[
"kubernetes",
"kubernetes"
] | **Why is this needed?**
The functionality that the package provides is already present in golang's builtin errors (using `%w` in `fmt.Errof`) and the github repo is now read-only.
/kind cleanup
/priority backlog
/good-first-issue
**Notes to people that want to collaborate**
Avoid creating a single PR for ... | Remove dependency on github.com/pkg/errors | https://api.github.com/repos/kubernetes/kubernetes/issues/113627/comments | 39 | 2022-11-04T15:47:25Z | 2023-11-10T16:08:14Z | https://github.com/kubernetes/kubernetes/issues/113627 | 1,436,286,060 | 113,627 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
release-master-informing:
- kubeadm-kinder-upgrade-1-25-latest
### Which tests are failing?
- ci-kubernetes-e2e-kubeadm-kinder-upgrade-1-25-latest.Overall
- task-06-upgrade
### Since when has it been failing?
3rd November 2022
### Testgrid link
https://testgrid.k8s.io/sig-release-... | [Failing Test] kubeadm-kinder-upgrade-1-25-latest | https://api.github.com/repos/kubernetes/kubernetes/issues/113626/comments | 4 | 2022-11-04T15:27:17Z | 2022-11-04T17:42:52Z | https://github.com/kubernetes/kubernetes/issues/113626 | 1,436,258,963 | 113,626 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
release-master-blocking:
- gce-device-plugin-gpu-master
### Which tests are failing?
- ci-kubernetes-e2e-gce-device-plugin-gpu.Overall
- kubetest.Up
### Since when has it been failing?
3rd November 2022
### Testgrid link
https://testgrid.k8s.io/sig-release-master-blo... | [Failing Test] gce-device-plugin-gpu-master | https://api.github.com/repos/kubernetes/kubernetes/issues/113625/comments | 4 | 2022-11-04T15:11:02Z | 2022-11-04T22:25:33Z | https://github.com/kubernetes/kubernetes/issues/113625 | 1,436,232,323 | 113,625 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
The Network Policy on the Namespace dose not blocking the Communication on the Pod Level
### What did you expect to happen?
When I create deny All Ingress and Egress Network Policy for one Namespace, then I am expecting that my Pods in this Namespace will be not reachable from anywhere in the Clu... | network Policy they don't do the work on the pod level | https://api.github.com/repos/kubernetes/kubernetes/issues/113624/comments | 10 | 2022-11-04T15:07:39Z | 2023-02-02T16:31:40Z | https://github.com/kubernetes/kubernetes/issues/113624 | 1,436,226,849 | 113,624 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
On an Ubuntu 18.04.6 (GCP image but could be irrelevant) I installed microk8s with:
`sudo snap install microk8s --channel=1.25-strict/stable`
Under path /var/snap/microk8s/current/args I then edited the following two files to enable the [ContainerCheckpoint](https://kubernetes.io/docs/reference... | ContainerCheckpoint fails with - unknown method CheckpointContainer - in v1.25 | https://api.github.com/repos/kubernetes/kubernetes/issues/113621/comments | 13 | 2022-11-04T08:35:37Z | 2022-11-17T10:06:39Z | https://github.com/kubernetes/kubernetes/issues/113621 | 1,435,730,535 | 113,621 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
https://testgrid.k8s.io/sig-cluster-lifecycle-kubeadm#kubeadm-kinder-latest
https://testgrid.k8s.io/sig-cluster-lifecycle-kubeadm#kubeadm-kinder-upgrade-1-25-latest
all *latest kubeadm jobs (k/k master)
https://testgrid.k8s.io/sig-cluster-lifecycle-kubeadm
### Which tests are fail... | [failing jobs] sig-cluster-lifecycle-kubeadm#kubeadm-kinder-*latest | https://api.github.com/repos/kubernetes/kubernetes/issues/113619/comments | 8 | 2022-11-04T07:55:30Z | 2022-11-04T15:03:05Z | https://github.com/kubernetes/kubernetes/issues/113619 | 1,435,693,342 | 113,619 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
`kubeadm init phase certs` needs to take the "Validity > NotBefore" from current date/time of the system . to keep the life time of certificate one year.
### Why is this needed?
If we have any renewal for the API-Server certificate ( like renew of API-Server in AWS EKS cl... | `kubeadm init phase certs` keeps the "Validity > NotBefore" value from CA history , and it causes the duration from "Validity > NotBefore" to "Validity > NotAfter" for new certificates , is passing one year. It cause security scanners alarm for certificates. | https://api.github.com/repos/kubernetes/kubernetes/issues/113618/comments | 6 | 2022-11-04T07:19:09Z | 2023-04-03T09:31:50Z | https://github.com/kubernetes/kubernetes/issues/113618 | 1,435,662,471 | 113,618 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Some of our customers want the TCP-related metrics from the cadvisor.
- kubelet ignores these metrics by default.
Option:
1. Add a kubelet config option in KubeletConfiguration. If it is enabled, add NetworkTcpUsageMetrics in the included metrics list of cadvisor.
2. Make a ... | kubelet: cadvisor supports enable network tcp metrics | https://api.github.com/repos/kubernetes/kubernetes/issues/113616/comments | 4 | 2022-11-04T04:22:51Z | 2022-12-07T05:49:32Z | https://github.com/kubernetes/kubernetes/issues/113616 | 1,435,531,241 | 113,616 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
`kubectl apply --server-side --force-conflicts` should provide a way to display any conflicts being overridden so that users--especially those migrating to SSA--can detect, investigate and address them without causing a disruption to their service (or need to revert to CSA). Perh... | [kubectl] server-side apply with --force-conflicts should warn about any conflicts it is forcing | https://api.github.com/repos/kubernetes/kubernetes/issues/113612/comments | 6 | 2022-11-04T01:58:38Z | 2025-02-07T18:33:07Z | https://github.com/kubernetes/kubernetes/issues/113612 | 1,435,444,609 | 113,612 |
[
"kubernetes",
"kubernetes"
] | This issue tracks all coding work to accomplish https://github.com/kubernetes/enhancements/issues/3521 as beta.
```[tasklist]
# Code changes
- [ ] #115815
- [ ] #115821
- [ ] #115583
- [ ] #115083
- [ ] #115569
- [ ] #116201
```
```[tasklist]
# Docs update
- [ ] https://github.com/kubernetes/website/pul... | Umbrella issue tracking Beta impl. of KEP 3521 (Pod Scheduling Readiness) | https://api.github.com/repos/kubernetes/kubernetes/issues/113608/comments | 10 | 2022-11-03T20:51:54Z | 2024-02-26T23:16:49Z | https://github.com/kubernetes/kubernetes/issues/113608 | 1,435,243,795 | 113,608 |
[
"kubernetes",
"kubernetes"
] | The Kubelet invokes pod setup, maintenance (collectively referred to as 'pod sync'), and teardown as synchronous functions from a per-pod goroutine. The sync method in particular can run for seconds to minutes to hours if certain lifecycle actions like hooks are in use. This means state transitions such as deletion (... | Kubelet should react more quickly to pod lifecycle transitions | https://api.github.com/repos/kubernetes/kubernetes/issues/113606/comments | 10 | 2022-11-03T20:49:53Z | 2024-09-20T07:13:46Z | https://github.com/kubernetes/kubernetes/issues/113606 | 1,435,241,872 | 113,606 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
I have a statefulset with a label `colega.eu/webhook`:
`workload.yaml`:
```yaml
apiVersion: apps/v1
kind: StatefulSet
metadata:
name: workload
labels:
colega.eu/webhook: 'true'
spec:
replicas: 1
serviceName: workload
selector:
matchLabels:
app: workload
t... | Admission webhooks don't match changes on subresources like Scale | https://api.github.com/repos/kubernetes/kubernetes/issues/113594/comments | 15 | 2022-11-03T15:45:48Z | 2025-02-07T18:33:11Z | https://github.com/kubernetes/kubernetes/issues/113594 | 1,434,882,393 | 113,594 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
I’ve run an application to offload the compute on a GPU via the PCI link.
It works fine with Docker and Minikube but I’ve encountered a driver problem with Kubernetes (kubeadm or kind).
I mounted all necessary local folders (and also checked) and gave the privileged access.
In fact, I use the ... | virtiodev driver access problem in kubernetes and kind but everything works fine in minikube | https://api.github.com/repos/kubernetes/kubernetes/issues/113590/comments | 5 | 2022-11-03T14:45:40Z | 2022-11-03T16:03:23Z | https://github.com/kubernetes/kubernetes/issues/113590 | 1,434,783,991 | 113,590 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
We have benchmark tests for scheduler under `test/integration/scheduler_perf`, but I found several problems below:
- [ ] Some util functions are duplicated in e2e tests and integration tests, like `checkWaitListSchedulableNodes`, we should avoid this by moving them to a shared... | Umbrella: scheduler_perf tests refactor | https://api.github.com/repos/kubernetes/kubernetes/issues/113586/comments | 11 | 2022-11-03T11:13:55Z | 2024-01-22T02:27:43Z | https://github.com/kubernetes/kubernetes/issues/113586 | 1,434,487,718 | 113,586 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
The `status` of a stale pod disruption condition remains `True` after two minutes as the disruption controller fails to change it to `False` to disable the condition.
### What did you expect to happen?
The `status` of a stale pod disruption condition should be changed to `False` after two minutes.... | Disruption controller fails to clean up a stale disruption condition [when alpha PodDisruptionConditions enabled] | https://api.github.com/repos/kubernetes/kubernetes/issues/113578/comments | 2 | 2022-11-03T08:42:58Z | 2022-11-04T01:54:26Z | https://github.com/kubernetes/kubernetes/issues/113578 | 1,434,296,318 | 113,578 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
i am using the following jars
xgboost4j-spark_2.12-1.6.1.jar
xgboost4j_2.12-1.6.1.jar
Here is the stack trace:
Traceback (most recent call last):
File "/u/bin/ai_fraudengine/AIModelTrain/aimodeltrain/bl/StandardModelTrainHandlerImpl.py", line 32, in train_model
trained_pipeline = train_p... | xgboost running with kubernetes issue | https://api.github.com/repos/kubernetes/kubernetes/issues/113573/comments | 5 | 2022-11-03T05:44:34Z | 2022-11-03T09:13:33Z | https://github.com/kubernetes/kubernetes/issues/113573 | 1,434,143,100 | 113,573 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Parse-able error stream content when port forwarding
### Why is this needed?
Client-go's PortForwarder [reads from the error stream](https://github.com/kubernetes/kubernetes/blob/1df24569a0bf62a528c49f73fdb236fd56eb05ee/staging/src/k8s.io/client-go/tools/portforward/portforward... | Feature request: parse-able error stream content when port forwarding | https://api.github.com/repos/kubernetes/kubernetes/issues/113568/comments | 15 | 2022-11-03T00:21:14Z | 2024-03-22T06:23:55Z | https://github.com/kubernetes/kubernetes/issues/113568 | 1,433,944,461 | 113,568 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
Kubelet has an internal `syncTerminatedPod` which is called after pods are terminated. The function is responsible for some final pod cleanup and is responsible to ensure that volumes mounted to the pod are unmounted. The function calls `volumeManager.WaitForUnmount`:
https://github.com/kubern... | kubelet: volumeManager.WaitForUnmount does not wait for emptydir to be unmounted successfully | https://api.github.com/repos/kubernetes/kubernetes/issues/113563/comments | 13 | 2022-11-02T21:43:22Z | 2024-12-18T18:41:03Z | https://github.com/kubernetes/kubernetes/issues/113563 | 1,433,822,618 | 113,563 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
https://testgrid.k8s.io/sig-network-ingress-gce-e2e#ingress-gce-e2e-scale
### Which tests are failing?
```
Kubernetes e2e suite: [It] [sig-network] Loadbalancing: L7 Scalability GCE [Slow] [Serial] [Feature:IngressScale] Creating and updating ingresses should happen promptly with s... | [Failing job] ci-ingress-gce-e2e-scale | https://api.github.com/repos/kubernetes/kubernetes/issues/113561/comments | 6 | 2022-11-02T20:33:54Z | 2022-11-07T19:56:21Z | https://github.com/kubernetes/kubernetes/issues/113561 | 1,433,754,692 | 113,561 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
Hi, I have a test scenario where 50 pods will mount the same volume. However, it takes 5 to 10 minutes for the pod to
change from the _ContainerCreating_ state to the _Running_ state. Then, I recorded logs for the volume operation of the kubelet. It was found that the podName field in operationKe... | Doubts about csiPlugin canDeviceMount method | https://api.github.com/repos/kubernetes/kubernetes/issues/113553/comments | 7 | 2022-11-02T17:06:27Z | 2023-04-02T05:20:48Z | https://github.com/kubernetes/kubernetes/issues/113553 | 1,433,496,358 | 113,553 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
release-master-blocking:
- gce-ubuntu-master-containerd
### Which tests are failing?
- ci-kubernetes-e2e-ubuntu-gce-containerd.Overall
- kubetest.Test
### Since when has it been failing?
31st October 2022
### Testgrid link
https://testgrid.k8s.io/sig-release-master-b... | [Failing test] gce-ubuntu-master-containerd | https://api.github.com/repos/kubernetes/kubernetes/issues/113552/comments | 7 | 2022-11-02T16:47:13Z | 2022-11-02T18:09:25Z | https://github.com/kubernetes/kubernetes/issues/113552 | 1,433,469,589 | 113,552 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
release-master-blocking:
- kind-master-parallel
### Which tests are failing?
ci-kubernetes-kind-e2e-parallel.Overall
### Since when has it been failing?
2nd November 2022
### Testgrid link
https://testgrid.k8s.io/sig-release-master-blocking#kind-master-parallel
###... | [Failing Test] kind-master-parallel | https://api.github.com/repos/kubernetes/kubernetes/issues/113551/comments | 4 | 2022-11-02T16:28:07Z | 2022-11-02T22:36:59Z | https://github.com/kubernetes/kubernetes/issues/113551 | 1,433,442,570 | 113,551 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
Jobs affecting master presubmits a
https://testgrid.k8s.io/sig-release-master-blocking#gce-ubuntu-master-containerd
https://testgrid.k8s.io/presubmits-kubernetes-blocking#pull-kubernetes-e2e-kind
### Which tests are failing?
[sig-node] Pods Extended Pod Container Status should never rep... | [Failing test] [sig-node] Pods Extended Pod Container Status should never report success for a pending container | https://api.github.com/repos/kubernetes/kubernetes/issues/113547/comments | 2 | 2022-11-02T13:41:30Z | 2022-11-02T17:13:15Z | https://github.com/kubernetes/kubernetes/issues/113547 | 1,433,168,948 | 113,547 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
The docker images for linux/arm64 wrongly report their architecture as amd64. This issue affects at least the `v1.8.6` and `v1.9.3` of the coredns images.
### What did you expect to happen?
Expected the arm64 version of the image to correctly report its architecture as arm64.
### How can we rep... | coreDNS image reports the wrong architecture | https://api.github.com/repos/kubernetes/kubernetes/issues/113543/comments | 17 | 2022-11-02T12:15:35Z | 2023-10-26T02:50:48Z | https://github.com/kubernetes/kubernetes/issues/113543 | 1,433,047,190 | 113,543 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
I run a unit test in `pkg/kubelet/cm/cpumanager`, it has 12 vcpu and reserves cpus `1,6`. When the container request 10 vcpu and the FullPCPUsOnlyOption is true, the allocation result is `0,2-5,7-11`. in my opinion, the `0` and `7` vcpu should be ignore because they are single thread.
```
func Te... | The static cpumanager flag `full-pcpus-only` not ensure to allocate full physical cores | https://api.github.com/repos/kubernetes/kubernetes/issues/113537/comments | 6 | 2022-11-02T08:38:09Z | 2023-03-02T17:04:59Z | https://github.com/kubernetes/kubernetes/issues/113537 | 1,432,716,561 | 113,537 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
https://pkg.go.dev/vuln/GO-2022-1095
```
govulncheck ./...
```
```bash
govulncheck is an experimental tool. Share feedback at https://go.dev/s/govulncheck-feedback.
Scanning for dependencies with known vulnerabilities...
Found 1 known vulnerability.
Vulnerability #1: GO-2022-1095... | kubernetes is vulnerable using the go version CVE-2022-41716 | https://api.github.com/repos/kubernetes/kubernetes/issues/113536/comments | 4 | 2022-11-02T08:36:11Z | 2022-11-03T01:47:03Z | https://github.com/kubernetes/kubernetes/issues/113536 | 1,432,714,311 | 113,536 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
When I create a serviceaccount and keep updating it repeatedly, the tokencontroller keeps creating new token secrets.
**Sample Code**
```go
flags := genericclioptions.ConfigFlags{}
config, _ := flags.ToRESTConfig()
clientset := kubernetes.NewForConfigOrDie(config)
sa := &v1.ServiceAccount{Ob... | Repeatedly updating serviceaccount results in redundant token secrets | https://api.github.com/repos/kubernetes/kubernetes/issues/113532/comments | 4 | 2022-11-02T06:51:13Z | 2022-11-22T20:22:20Z | https://github.com/kubernetes/kubernetes/issues/113532 | 1,432,596,124 | 113,532 |
[
"kubernetes",
"kubernetes"
] | ### Failure cluster [f071dba296860cf59e9c](https://go.k8s.io/triage#f071dba296860cf59e9c)
##### Error text:
```
test/e2e/node/pods.go:416
k8s.io/kubernetes/test/e2e/node.createAndTestPodRepeatedly.func1(0xc000a9b560?)
test/e2e/node/pods.go:416 +0x46d
created by k8s.io/kubernetes/test/e2e/node.createAndTestPodR... | [flake][sig-node] Pods Extended Pod Container Status should never report container start when an init container fails | https://api.github.com/repos/kubernetes/kubernetes/issues/113531/comments | 6 | 2022-11-02T06:44:22Z | 2023-04-02T04:19:48Z | https://github.com/kubernetes/kubernetes/issues/113531 | 1,432,587,540 | 113,531 |
[
"kubernetes",
"kubernetes"
] | null | Kubernetes | https://api.github.com/repos/kubernetes/kubernetes/issues/113530/comments | 2 | 2022-11-02T06:31:38Z | 2022-11-03T03:21:46Z | https://github.com/kubernetes/kubernetes/issues/113530 | 1,432,575,718 | 113,530 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
There is an issue on Windows Server 2019 that can cause the kube-proxy call into HNS to delete the load balancer proxy rules to fail.
E.g.
1. backends of a particular services are all deleted
2. the call to HNS to cleanup the load balancer proxy rules did not succeed
3. the same service get's... | resolve winkernel proxier treating stale VIPs as valid | https://api.github.com/repos/kubernetes/kubernetes/issues/113524/comments | 3 | 2022-11-02T00:13:28Z | 2024-07-17T08:56:46Z | https://github.com/kubernetes/kubernetes/issues/113524 | 1,432,271,702 | 113,524 |
[
"kubernetes",
"kubernetes"
] | Ref:- https://github.com/kubernetes/kubernetes/pull/112050#discussion_r998220521
/sig auth | [KMSv2] Maintain DEK cache after hot reload of encryption config | https://api.github.com/repos/kubernetes/kubernetes/issues/113497/comments | 6 | 2022-11-01T00:49:26Z | 2023-08-30T15:38:37Z | https://github.com/kubernetes/kubernetes/issues/113497 | 1,430,683,965 | 113,497 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
We were attempting to bring up a static pod on the node. This pod was attempting to mount a configmap using a volume:
```
apiVersion: v1
kind: Pod
metadata:
name: network-controller-manager
namespace: kube-system
spec:
containers:
- args:
-... | kubelet crashes when attempting to bring up a static pod that refers to a configmap | https://api.github.com/repos/kubernetes/kubernetes/issues/113492/comments | 3 | 2022-10-31T23:44:25Z | 2022-11-09T11:50:14Z | https://github.com/kubernetes/kubernetes/issues/113492 | 1,430,635,899 | 113,492 |
[
"kubernetes",
"kubernetes"
] | https://github.com/kubernetes/kubernetes/pull/113245#discussion_r1009911070
Validation allows:
```
ports:
- containerPort: 93
hostPort: 9376
- containerPort: 93
hostPort: 7693
```
but server-side apply does not.
As of 1.29 we can SSA unrelated fields in an o... | ContainerPorts SSA key is insufficiently unique - SSA fails with "duplicate" error when the contents are valid | https://api.github.com/repos/kubernetes/kubernetes/issues/113482/comments | 26 | 2022-10-31T22:08:02Z | 2024-11-15T09:54:11Z | https://github.com/kubernetes/kubernetes/issues/113482 | 1,430,558,630 | 113,482 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are flaking?
sig-node-containerd#e2e-cos-device-plugin-gpu
### Which tests are flaking?
In the most recent test, the whole test process was failing in running`[It] [sig-scheduling] [Feature:GPUDevicePlugin] run Nvidia GPU Device Plugin tests`.
### Since when has it been flaking?
Not sure, ... | Test of sig-node-containerd#e2e-cos-device-plugin-gpu are flaky | https://api.github.com/repos/kubernetes/kubernetes/issues/113480/comments | 3 | 2022-10-31T21:33:23Z | 2022-12-07T12:34:41Z | https://github.com/kubernetes/kubernetes/issues/113480 | 1,430,526,628 | 113,480 |
[
"kubernetes",
"kubernetes"
] | ### Which jobs are failing?
release-master-informing:
- capz-windows-containerd-master
### Which tests are failing?
- Kubernetes e2e suite: [It] [sig-node] Container Lifecycle Hook when create a pod with lifecycle hook should execute prestop https hook properly [MinimumKubeletVersion:1.23] [NodeConformance]... | [Failing test] capz-windows-containerd-master | https://api.github.com/repos/kubernetes/kubernetes/issues/113479/comments | 4 | 2022-10-31T21:09:26Z | 2022-11-09T19:12:41Z | https://github.com/kubernetes/kubernetes/issues/113479 | 1,430,502,062 | 113,479 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Deprecate PodNodeSelector admission plugin and the associated annotation `scheduler.alpha.kubernetes.io/node-selector`
https://github.com/kubernetes/kubernetes/blob/master/plugin/pkg/admission/podnodeselector/admission.go
### Why is this needed?
This plugin has been in alpha f... | Deprecate PodNodeSelector admission plugin | https://api.github.com/repos/kubernetes/kubernetes/issues/113474/comments | 54 | 2022-10-31T17:53:47Z | 2025-01-09T06:34:06Z | https://github.com/kubernetes/kubernetes/issues/113474 | 1,430,248,031 | 113,474 |
[
"kubernetes",
"kubernetes"
] | ### What would you like to be added?
Today kube audit log does not include the APF related response header, so when debugging request throttling issue, users have to make actual request with the same username and/or namespace to be able to get `X-Kubernetes-Pf-Prioritylevel-Uid` and `X-Kubernetes-Pf-Flowschema-Uid`, t... | Add APF related response header to kube audit log | https://api.github.com/repos/kubernetes/kubernetes/issues/113473/comments | 10 | 2022-10-31T17:03:28Z | 2025-02-07T18:33:08Z | https://github.com/kubernetes/kubernetes/issues/113473 | 1,430,179,420 | 113,473 |
[
"kubernetes",
"kubernetes"
] | ### What happened?
I'm trying to install k3s on a master and a worker node, both running Ubuntu 22.04. The master installs no problem but the worker hangs on `[INFO] systemd: Starting k3s-agent`. The log files on the worker say:
```Oct 27 14:22:32 myworker k3s[69044]: E1027 14:22:32.202326 69044 webhook.go:154... | Installed k3s on worker and node, node NotReady | https://api.github.com/repos/kubernetes/kubernetes/issues/113468/comments | 5 | 2022-10-31T11:47:43Z | 2022-10-31T11:58:14Z | https://github.com/kubernetes/kubernetes/issues/113468 | 1,429,714,969 | 113,468 |
[
"kubernetes",
"kubernetes"
] | Adding Rule "JustErrors bool" would allow getting small actionable error logs just like Apache web server has.
Rules specification: https://kubernetes.io/docs/reference/config-api/apiserver-audit.v1/#audit-k8s-io-v1-PolicyRule
No easy error situations identification leads to not handling error situations and edge... | API Server Auditing Policy Rules do not allow creating just ErrorLog | https://api.github.com/repos/kubernetes/kubernetes/issues/113453/comments | 8 | 2022-10-30T20:06:30Z | 2023-03-20T16:29:37Z | https://github.com/kubernetes/kubernetes/issues/113453 | 1,429,001,089 | 113,453 |
Subsets and Splits
Unique Owner-Repo Count
Counts the number of unique owner-repos in the dataset, providing a basic understanding of diverse repositories.