id stringlengths 36 36 | source stringclasses 15 values | formatted_source stringclasses 13 values | text stringlengths 2 7.55M |
|---|---|---|---|
a30ea979-8b8e-4ed4-96a9-73c4a6930179 | StampyAI/alignment-research-dataset/alignmentforum | Alignment Forum | AI and Evolution
Executive Summary
=================
Artificial intelligence is advancing quickly. In some ways, AI development is an uncharted frontier, but in others, it follows the familiar pattern of other competitive processes; these include biological evolution, cultural change, and competition between businesses. In each of these, there is significant variation between individuals structures and some are copied more than others, with the result that the future population is more similar to the most copied individuals of the earlier generation. In this way, species evolve, cultural ideas are transmitted across generations, and successful businesses are imitated while unsuccessful ones disappear.
This paper argues that these same selection patterns will shape AI development and that the features that will be copied the most are likely to create an AI population that is dangerous to humans. As AIs become faster and more reliable than people at more and more tasks, businesses that allow AIs to perform more of their work will outperform competitors still using human labor at any stage, just as a modern clothing company that insisted on using only manual looms would be easily outcompeted by those that use industrial looms. Companies will need to increase their reliance on AIs to stay competitive, and the companies that use AIs best will dominate the marketplace. This trend means that the AIs most likely to be copied will be very efficient at achieving their goals autonomously with little human intervention.
A world dominated by increasingly powerful, independent, and goal-oriented AIs is dangerous. Today, the most successful AI models are not transparent, and even their creators do not fully know how they work or what they will be able to do before they do it. We know only their results, not how they arrived at them. As people give AIs the ability to act in the real world, the AIs’ internal processes will still be inscrutable: we will be able to measure their performance only based on whether or not they are achieving their goals. This means that the AIs humans will see as most successful — and therefore the ones that are copied — will be whichever AIs are most effective at achieving their goals, even if they use harmful or illegal methods, as long as we do not detect their bad behavior.
In natural selection, the same pattern emerges: individuals are cooperative or even altruistic in some situations, but ultimately, strategically selfish individuals are best able to propagate. A business that knows how to steal trade secrets or deceive regulators without getting caught will have an edge over one that refuses to ever engage in fraud on principle. During a harsh winter, an animal that steals food from others to feed its own children will likely have more surviving offspring. Similarly, the AIs that succeed most will be those able to deceive humans, seek power, and achieve their goals by any means necessary.
If AI systems are more capable than we are in many domains and tend to work toward their goals even if it means violating our wishes, will we be able to stop them? As we become increasingly dependent on AIs, we may not be able to stop AI’s evolution. Humanity has never before faced a threat that is as intelligent as we are or that has goals. Unless we take thoughtful care, we could find ourselves in the position faced by wild animals today: most humans have no particular desire to harm gorillas, but the process of harnessing our intelligence toward our own goals means that they are at risk of extinction, because their needs conflict with human goals.
This paper proposes several steps we can take to combat selection pressure and avoid that outcome. We are optimistic that if we are careful and prudent, we can ensure that AI systems are beneficial for humanity. But if we do not extinguish competition pressures, we risk creating a world populated by highly intelligent lifeforms that are indifferent or actively hostile to us. We do not want the world that is likely to emerge if we allow natural selection to determine how AIs develop. Now, before AIs are a significant danger, is the time to begin ensuring that they develop safely.
**Paper**: https://arxiv.org/abs/2303.16200
**Explainer Video**:
Note: This paper articulates a concern that emerges in multi-agent situations. Of particular interest to this community might be Section 3.4 (existing moral systems may not be human compatible (e.g., impartial consequentialism)) and Section 4.3.2 (Leviathan). |
7742b356-71d2-479d-9ae5-f3060df37a66 | StampyAI/alignment-research-dataset/arbital | Arbital | LaTeX
**[Placeholder](https://arbital.com/p/5xs)** |
8328a9df-e570-4f2e-b3ed-86ec0845907b | StampyAI/alignment-research-dataset/arxiv | Arxiv | Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Dense and Sparse Reward Environments
Introduction
------------
Reinforcement Learning (RL) has yielded many recent successes in solving complex tasks that meet and exceed the capabilities of human counterparts, demonstrated in video game environments [Mnih2015a], robotic manipulators [andrychowicz2018learning], and various open-source simulated scenarios [lillicrap2015continuous].
However, these RL approaches are sample inefficient and slow to converge to this impressive behavior, limited significantly by the need to explore potential strategies through trial and error, which produces initial performance significantly worse than human counterparts.
The resultant behavior that is initially random and slow to reach proficiency is poorly suited to various situations, such as physically embodied ground and air vehicles or in scenarios where sufficient capability must be achieved in short time spans.
In such situations, the random exploration of the state space of an untrained agent can result in unsafe behaviors and catastrophic failure of a physical system, potentially resulting in unacceptable damage or downtime.
Similarly, slow convergence of the agent’s performance requires exceedingly many interactions with the environment, which is often prohibitively difficult or infeasible for physical systems that are subject to energy constraints, component failures, and operation in dynamic or adverse environments.
These sample efficiency pitfalls of RL are exacerbated even further when trying to learn in the presence of sparse reward, often leading to cases where RL can fail to learn entirely.
One approach for overcoming these limitations is to utilize demonstrations of desired behavior from a human data source (or potentially some other agent) to initialize the learning agent to a significantly higher level of performance than is yielded by a randomly initialized agent.
This is often termed learning from demonstrations (LfD) [argall2009survey], which is a subset of imitation learning that seeks to train a policy to imitate the desired behavior of another policy or agent.
LfD leverages data (in the form of state-action tuples) collected from a demonstrator for supervised learning, and can be used to produce an agent with qualitatively similar behavior in a relatively short training time and with limited data.
This type of LfD, called Behavior Cloning (BC), learns a mapping between the state-action pairs contained in the set of demonstrations to mimic the behavior of the demonstrator.
Though BC techniques do allow for the relatively rapid learning of behaviors that are comparable to that of the demonstrator, it is limited by the quality and quantity of the demonstrations provided and is only improved by providing additional, high-quality demonstrations.
In addition, BC is plagued by the distributional drift problem in which a mismatch between the learned policy distribution of states and the distribution of states in the training set can cause errors that propagate over time and lead to catastrophic failures.
By combining BC with subsequent RL, it is possible to address the drawbacks of either approach, initializing a significantly more capable and safer agent than with random initialization, while also allowing for further self-improvement without needing to collect additional data from a human demonstrator.
However, it is currently unclear how to effectively update a policy initially trained with BC using reinforcement learning as these approaches are inherently optimizing different objective functions.
Previous works have used loss functions that combine BC losses with RL losses to enable this update, however, the components of these loss functions are often set anecdotally and their individual contributions are not well understood.
In this work, we propose the Cycle-of-Learning (CoL) framework, which uses an actor-critic architecture with a loss function that combines behavior cloning and 1-step Q-learning losses with an off-policy, pre-training step from human demonstrations.
The main contribution of this work is a method to enable transition from behavior cloning to reinforcement learning without performance degradation while improving reinforcement learning in terms of overall performance and training time.
Additionally, we examine the effect of these combined losses on overall policy learning in two continuous action space environments.
Our results show that our approach outperforms BC, Deep Deterministic Policy Gradients (DDPG), and DDPG from Demonstrations (DDPGfD) in two different application domains for both dense and sparse reward settings.
We show that our CoL method was the only method to produce a viable policy for one of the two environments designed specifically to exhibit a high degree of stochasticity.
In addition, we show that in dense-reward settings the performance of DDPGfD suffers significantly due to its inclusion of n-step Q-learning loss.
Our results also suggest that directly including the behavior cloning loss on demonstration data helps to ensure stable learning and ground future policy updates, and that a pre-training step enables the policy to start at a performance level greater than behavior cloning.
Preliminaries
-------------
We adopt the standard Markov Decision Process (MDP) formulation for sequential decision making [Sutton1998], which is defined as a tuple (S,A,R,P,γ), where S is the set of states, A is the set of actions, R(s,a) is the reward function, P(s′|s,a) is the transition probability function and γ is a discount factor.
At each state s∈S, the agent takes an action a∈A, receives a reward R(s,a) and arrives at state s′ as determined by P(s′|s,a).
The goal is to learn a behavior policy π which maximizes the expected discounted total reward.
This is formalized by the Q-function, sometimes referred to as the state-action value function:
| | | |
| --- | --- | --- |
| | Qπ(s,a)=Eπ[+∞∑t=0γtR(st,at)] | |
taking the expectation over trajectories obtained by executing the policy π starting at s0=s and a0=a.
Here we focus on actor-critic methods which seek to maximize
| | | |
| --- | --- | --- |
| | J(θ)=Es∼μ[Qπ(.|θ)(s,π(s|θ))] | |
with respect to parameters θ and an initial state distribution μ.
The Deep Deterministic Policy Gradient (DDPG) [lillicrap2015continuous] is an off-policy actor-critic reinforcement learning algorithm for continuous action spaces, which calculates the gradient of the Q function with respect to the action to train the policy.
DDPG makes use of a replay buffer to store past state-action transitions and target networks to stabilize Q-learning [Mnih2015a].
Since DDPG is an off-policy algorithm, it allows for the use of arbitrary data, such as demonstrations, to update the policy.
A demonstration trajectory is a tuple (s,a,r,s′) of state s, action a, the reward r=R(s,a) and the transition state s′ collected from a demonstrator’s policy.
In most cases these demonstrations are from a human observer, although in principle these demonstrations can come from any existing policy.
Related Work
------------
Several works have shown the efficacy of combining behavior cloning with reinforcement learning across a variety of tasks.
Recent work by [hester2018deep] combined behavior cloning with deep Q-learning [Mnih2015a] to learn policies for Atari games by leveraging a loss function that combines a large-margin supervised learning loss function, 1-step Q-learning loss, and an n-step Q-learning loss function that helps ensure the network satisfies the Bellman equation.
This work was extended to continuous action spaces by [vevcerik2017leveraging], who proposed an extension of DDPG [lillicrap2015continuous] that uses human demonstrations, and applied their approach to object manipulation tasks for both simulated and real robotic environments.
The loss functions for these methods include the n-step Q-learning loss, which is known to require on-policy data to accurately estimate.
Similar work by [Nair2018ICRA] combined behavior cloning-based demonstration learning, goal-based reinforcement learning, and DDPG for robotic manipulation of objects in a simulated environment.
A method that is very similar to ours is the Demo-Augmented Policy Gradient (DAPG) [Rajeswaran-RSS-18], an approach that uses behavior cloning as a pre-training step together with an augmented loss function with a heuristic weight function, which interpolates between the policy gradient loss, computed using the Natural Policy Gradient [Kakade2001], and behavior cloning loss.
They apply their approach across four different robotic manipulations tasks using a 24 Degree-of-Freedom (DoF) robotic hand in a simulator and show that DAPG outperforms DDPGfD across all tasks.
Their work also showed that behavior cloning combined with Natural Policy Gradient performed very similarly to DAPG for three of the four tasks considered, showcasing the importance of using a behavior cloning loss both in pre-training and policy training.
Integrating Behavior Cloning and Reinforcement Learning
-------------------------------------------------------
The Cycle-of-Learning (CoL) framework is a method for transitioning behavior cloning policies to RL by utilizing an actor-critic architecture with a combined BC+RL loss function and pre-training phase for continuous state-action spaces, in dense- and sparse-reward environments.
The main advantage of using off-policy methods is to re-use previous data to train the agent and reduce the amount of interactions between agent and environment, which is relevant to robotic applications or real-world system where interactions can be costly.
The combined loss function consists of the following components: an expert behavior cloning loss that bounds actor’s action to previous human trajectories, 1-step return Q-learning loss to propagate values of human trajectories to previous states, the actor loss, and a L2 regularization loss on the actor and critic to stabilize performance and prevent over-fitting during training.
The implementation of each loss component and their combination are defined as follows:
* Expert behavior cloning loss (LBC): Given expert demonstration subset DE of continuous states and actions visited during a task demonstration over T time steps
| | | | |
| --- | --- | --- | --- |
| | DE={sE0,aE0,sE1,aE1,...,sET,aET}, | | (1) |
a behavior cloning loss (mean squared error) from demonstration data LBC can be written as
| | | | |
| --- | --- | --- | --- |
| | LBC(θπ)=12(π(st|θπ)−aEt))2 | | (2) |
in order to minimize the difference between the actions predicted by the actor network π(st), parametrized by θπ, and the expert actions aEt for a given state vector st.
* 1-step return Q-learning loss (L1): The 1-step return R1 can be written in terms of the critic network Q, parametrized by θQ, as
| | | | |
| --- | --- | --- | --- |
| | R1=r+γQ(st+1,π(st+1|θπ)|θQ). | | (3) |
In order to satisfy the Bellman equation, we minimize the difference between the predicted Q-value and the observed return from the 1-step roll-out:
| | | | |
| --- | --- | --- | --- |
| | LQ1(θQ)=12(R1−Q(st,π(st|θπ)|θQ))2. | | (4) |
* Actor Q-loss (LA): It is assumed that the critic function Q is differentiable with respect to the action. Since we want to maximize the Q-values for the current state, the actor loss became the negative of the Q-values predicted by the critic:
| | | | |
| --- | --- | --- | --- |
| | LA(θπ)=−Q(s,π(st|θπ)|θQ). | | (5) |
Combining the above loss functions for the Cycle-of-Learning becomes
| | | | |
| --- | --- | --- | --- |
| | LCoL | (θQ,θπ)=λBCLBC(θπ)+λALA(θπ) | |
| | | +λQ1LQ1(θQ)+λL2LL2(θQ)+λL2LL2(θπ). | | (6) |
Our approach starts by collecting contiguous trajectories from expert policies and stores the current and subsequent state-actions pairs, reward received, and task completion signal in a permanent expert memory buffer DE.
During the pre-training phase, the agent samples a batch of trajectories from the expert memory buffer DE containing expert trajectories to perform updates on the actor and critic networks using the same combined loss function (Equations [Integrating Behavior Cloning and Reinforcement Learning](#Sx4.Ex3 "Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments")).
This procedure shapes the actor and critic initial distributions to be closer to the expert trajectories and eases the transition from policies learned through expert demonstration to reinforcement learning.
After the pre-training phase, the policy is allowed to roll-out and collect its first on-policy samples, which are stored in a separate first-in-first-out memory buffer with only the agent’s samples.
After collecting a given number of on-policy samples, the agent samples a batch of trajectories comprising 25% of samples from the expert memory buffer and 75% from the agent’s memory buffer.
This fixed ratio guarantees that each gradient update is grounded by expert trajectories.
If a human demonstrator is used, they can intervene at any time the agent is executing their policy, and add this new trajectories to the expert memory buffer.
The proposed method is shown in Algorithm [1](#alg1 "Algorithm 1 ‣ Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments").
1:Input:
Environment env, number of training steps T, number of training steps per batch M, number of pre-training steps L, number of gradient updates K, and CoL hyperparameters λQ1, λBC, λA, λL2, τ.
2:Output:
Trained actor π(s|θπ) and critic Q(s,π|θQ) networks.
3:Randomly initialize:
Actor network π(s|θπ) and its target π′(s|θπ′).
Critic network Q(s,π|θQ) and its target Q′(s,π′|θQ′).
4:Initialize agent and expert replay buffers R and RE.
5:Load R and RE with expert dataset DE.
6:for pre-training steps = 1, …, L do
7: Call *TrainUpdate*() procedure.
8:for training steps = 1, …, T do
9: Reset env and receive initial state s0.
10: for batch steps = 1, …, M do
11: Select action at=π(st|θπ) according to policy.
12: Perform action at and observe reward rt and next state st+1.
13: Store transition (st,at,rt,st+1) in R.
14: for update steps = 1, …, K do
15: Reset env and receive initial state s0.
16: for training steps t = 1, …, T do
17: Call *TrainUpdate*() procedure.
18:procedure TrainUpdate()
19: if Pre-training then
20: Randomly sample N transitions (si,ai,ri,si+1) from the expert replay buffer RE.
21: else
22: Randomly sample N∗0.25 transitions (si,ai,ri,si+1) from the expert replay buffer RE and N∗0.75 transitions from the agent replay buffer R.
23: Compute LQ1(θQ), LBC(θπ), LA(θπ), LL2(θQ), LL2(θπ)
24: Update actor and critic for K steps according to Equation [Integrating Behavior Cloning and Reinforcement Learning](#Sx4.Ex3 "Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments").
25: Update target networks:
| | | |
| --- | --- | --- |
| | θπ′←τθπ+(1−τ)θπ′, | |
| | θQ′←τθQ+(1−τ)θQ′. | |
Algorithm 1 Cycle-of-Learning (CoL): Transitioning from Demonstration to Reinforcement Learning
Experimental Setup and Results
------------------------------
### Experimental Setup
As described in the previous sections, in our approach, the Cycle-of-Learning (CoL), we collect contiguous trajectories from expert policies and store them in a permanent memory buffer.
The policy is allowed to roll-out and is trained with a combined loss from a mix of demonstration and agent data, stored in a separate first-in-first-out buffer.
We validate our approach in three environments with continuous observation- and action-space: LunarLanderContinuous-v2 [brockman2016openai] (dense and sparse reward cases) and a custom quadrotor landing task [goecks2018efficiently] implemented using Microsoft AirSim [airsim2017fsr].
The dense reward case of LunarLanderContinuous-v2 is the standard environment provided by OpenAI Gym library [brockman2016openai]: state space consists of a eight-dimensional continuous vector with inertial states of the lander, action space consists of a two-dimensional continuous vector controlling main and side thrusts, and reward is given at every step based on the relative motion of the lander with respect to the landing pad (bonus reward is given when the landing is completed successfully).
The sparse reward case is a custom modification with the same reward scheme and state-action space, however the reward is stored during the policy roll-out and is only given to the agent if the episode is over, zero otherwise.
The custom quadrotor landing task is a modified version of the environment proposed by \citeauthorgoecks2018efficiently, implemented using Microsoft AirSim [airsim2017fsr], which consists of landing a quadrotor on a static landing pad in a simulated gusty environment, as seen in Figure [1](#Sx5.F1 "Figure 1 ‣ Experimental Setup ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments").
The state space consists of a fifteen-dimensional continuous vector with inertial states of the quadrotor and visual features that represent the landing pad image-frame position and radius as seen by a downward-facing camera.
The action space is a four-dimensional continuous vector that sends velocity commands for throttle, roll, pitch, and yaw.
Wind is modeled as noise applied directly to the actions commanded by the agent and follows a temporal-based, instead of distance-based, discrete wind gust model [moorhouse1980us] with 65% probability of encountering a wind gust at each time step.
This was done to induce additional stochasticity in the environment.
The gust duration is uniformly sampled to last between one to three real time seconds and can be imparted in any direction, with maximum velocity of half of what can be commanded by the agent along each axis.
This task has a sparse-reward scheme (reward R is given at the end of the episode, and is zero otherwise) based on the relative distance rrel between the quadrotor and the center of the landing pad at the final time step of the episode:
| | | |
| --- | --- | --- |
| | R=11+r2rel. | |
The hyperparameters used in CoL for each environment are described in the Supplementary Material.

Figure 1: Screenshot of AirSim environment and landing task. Inset image in lower right corner: downward-facing camera view used for extracting the position and radius of the landing pad, which is part of the state space.
| | | |
| --- | --- | --- |
| Comparison of CoL, BC, DDPG, and DDPGfD in the (a) dense- and (b) sparse-reward LunarLanderContinuous-v2 environment, and the (c) sparse-reward Microsoft AirSim quadrotor landing environment.
(a)
| Comparison of CoL, BC, DDPG, and DDPGfD in the (a) dense- and (b) sparse-reward LunarLanderContinuous-v2 environment, and the (c) sparse-reward Microsoft AirSim quadrotor landing environment.
(b)
| Comparison of CoL, BC, DDPG, and DDPGfD in the (a) dense- and (b) sparse-reward LunarLanderContinuous-v2 environment, and the (c) sparse-reward Microsoft AirSim quadrotor landing environment.
(c)
|
Figure 2: Comparison of CoL, BC, DDPG, and DDPGfD in the (a) dense- and (b) sparse-reward LunarLanderContinuous-v2 environment, and the (c) sparse-reward Microsoft AirSim quadrotor landing environment.
The baselines for our approach are Deep Deterministic Policy Gradient (DDPG) [lillicrap2015continuous, silver2014deterministic], Deep Deterministic Policy Gradient from Demonstrations (DDPGfD) [vevcerik2017leveraging], and behavior cloning (BC).
For the DDPG baseline we used an open-source implementation by Stable Baselines [stable-baselines].
The hyperparameters used concur with the original DDPG publication [lillicrap2015continuous]: actor and critic networks with 2 hidden layers with 400 and 300 units respectively, optimized using Adam [kingma2014adam] with learning rate of 10−4 for the actor and 10−3 for the critic, discount factor of γ=0.99, trained with minibatch size of 64, and replay buffer size of 106.
Exploration noise was added to the action following an Ornstein-Uhlenbeck process [uhlenbeck1930theory] with mean of 0.15 and standard deviation of 0.2.
The DDPGfD baseline followed the same implementation for the loss function used in our approach (Equations [Integrating Behavior Cloning and Reinforcement Learning](#Sx4.Ex3 "Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments")) with some modifications: removal of the behavior cloning loss by setting λBC=0, inclusion of the n-step loss as
| | | |
| --- | --- | --- |
| | LQn(θQ)=12(Rn−Q(s,π(s|θπ)|θQ))2, | |
where Rn is written as
| | | | |
| --- | --- | --- | --- |
| | Rn | =rt+γrt+1+⋯+γn−art+n−1 | |
| | | +γnQ(st+n,π(st+n|θπ)|θQ), | |
| | | =n−1∑i=0γiri+γnQ(st+n,π(st+n|θπ)|θQ), | |
using n=10, following the Deep Q-learning from Demonstrations (DQfD) [hester2018deep] implementation from which DDPGfD is derived, and using Prioritized Experience Replay (PER) [schaul2015prioritized] to mix expert and agent samples instead of following a fixed ratio.
The BC policies are trained by minimizing the mean squared error between the expert demonstrations and the output of the model.
The policies consist of a fully-connected neural network with 3 hidden layers with 128 units each and exponential linear unit (ELU) activation function [clevert2015fast].
The BC policy was evaluated for 100 episodes which was used to calculate the mean and standard error of the performance of the policy.
### Experimental results
The comparative performances of the CoL against the baseline methods (DDPG and DDPGfD) for the LunarLanderContinunous-v2 environment are presented via their training curves in Figure [(a)a](#Sx5.F2.sf1 "(a) ‣ Figure 2 ‣ Experimental Setup ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments"), using the standard dense reward.
The mean reward of the BC pre-trained from the human demonstrations is also shown for reference, and its standard error is shown by the shaded band.
The CoL reward initializes to values at or above the BC and steadily improves throughout the reinforcement learning phase.
Conversely, the DDPG RL baseline initially returns rewards lower than the BC and slowly improves until its performance reaches similar levels to the CoL after approximately one million steps.
However, this baseline never performs as consistently as the CoL and eventually begins to diverge, losing much of its performance gains after about four million steps.
The DDPGfD baseline performs even worse in this context, never consistently surpassing the BC performance.
When using sparse rewards, meaning only the rewards generated by the LunarLanderContinunous-v2 environment are provided only at the last time step of each episode, the performance improvement of the CoL relative to the DDPG and DDPGfD baselines is even greater (Figure [(b)b](#Sx5.F2.sf2 "(b) ‣ Figure 2 ‣ Experimental Setup ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments")).
The performance of the CoL is qualitatively similar during training to that of the dense case, with an initial reward roughtly equal to or greater than that of the BC and a consistently increasing reward.
Conversely, the performance of the DDPG baseline is greatly diminished for the sparse reward case, yielding effectively no improvement for more than three million training steps before generating reward only comparable to the BC and the initial performance of the CoL.
The training of the DDPGfD also deteriorates in this case, with even lower reward values and produces a more volatile, less stable training curve as is also seen for DDPG.
The results for the more realistic and challenging AirSim quadrotor landing environment (Figure [(c)c](#Sx5.F2.sf3 "(c) ‣ Figure 2 ‣ Experimental Setup ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments")) illustrate a similar trend.
The CoL initially returns rewards at or above the BC and steadily increases its performance, whereas the baseline approaches (DDPG and DDPGfD) practically never succeed and subsequently fail to learn a viable policy.
Noting that successfully landing on the target would generate a sparse episode reward of approximately 0.64, it is clear that these baseline algorithms rarely generate a satisfactory trajectory for the duration of training.
| | | |
| --- | --- | --- |
| (a) Ablation study in LunarLanderContinuous-v2 environment comparing complete Cycle-of-Learning (CoL), CoL without the pre-training phase (CoL-PT), CoL without the expert behavior cloning loss (CoL-BC), and pre-training with BC followed by DDPG without combined loss (BC+DDPG). Comparison in LunarLanderContinuous-v2 environment for (b) dense and (c) sparse cases of the Cycle-of-Learning with (CoL+N) and without (CoL) the
(a)
| (a) Ablation study in LunarLanderContinuous-v2 environment comparing complete Cycle-of-Learning (CoL), CoL without the pre-training phase (CoL-PT), CoL without the expert behavior cloning loss (CoL-BC), and pre-training with BC followed by DDPG without combined loss (BC+DDPG). Comparison in LunarLanderContinuous-v2 environment for (b) dense and (c) sparse cases of the Cycle-of-Learning with (CoL+N) and without (CoL) the
(b)
| (a) Ablation study in LunarLanderContinuous-v2 environment comparing complete Cycle-of-Learning (CoL), CoL without the pre-training phase (CoL-PT), CoL without the expert behavior cloning loss (CoL-BC), and pre-training with BC followed by DDPG without combined loss (BC+DDPG). Comparison in LunarLanderContinuous-v2 environment for (b) dense and (c) sparse cases of the Cycle-of-Learning with (CoL+N) and without (CoL) the
(c)
|
Figure 3: (a) Ablation study in LunarLanderContinuous-v2 environment comparing complete Cycle-of-Learning (CoL), CoL without the pre-training phase (CoL-PT), CoL without the expert behavior cloning loss (CoL-BC), and pre-training with BC followed by DDPG without combined loss (BC+DDPG). Comparison in LunarLanderContinuous-v2 environment for (b) dense and (c) sparse cases of the Cycle-of-Learning with (CoL+N) and without (CoL) the n-step loss, and DDPGfD with (DDPGfD) and without (DDPGfD-N) the n-step loss.
### Ablation Studies
Several ablation studies were performed to evaluate the impact of each of the critical elements of the CoL on learning.
These respectively include removal of the pre-training phase (*CoL-PT*), removal of the actor’s expert behavior cloning loss during pre-training and RL (*CoL-BC*), and use of standard behavior cloning and DDPG loss functions rather than the combined loss functions in Equations [Integrating Behavior Cloning and Reinforcement Learning](#Sx4.Ex3 "Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments")-[Integrating Behavior Cloning and Reinforcement Learning](#Sx4.Ex3 "Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments") (*BC+DDPG*).
The results of each ablation condition are shown in Figure [(a)a](#Sx5.F3.sf1 "(a) ‣ Figure 3 ‣ Experimental results ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments") and details about the ablation study can be found in Table [1](#Sx5.T1 "Table 1 ‣ The n-step Loss Contribution ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments").
*CoL-PT:* Cycle-of-Learning without the pre-training phase (number of pre-training steps L=0).
The complete combined loss, as seen in Equations [Integrating Behavior Cloning and Reinforcement Learning](#Sx4.Ex3 "Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments") is used during the reinforcement learning phase.
This condition assesses the impact on learning performance of not pre-training the agent, while still using the combined loss in the RL phase.
This condition differs from the baseline CoL in its initial performance being less, significantly below the BC, but does reach similar rewards after several hundred thousand steps, exhibiting the same consistent response during training thereafter.
Effectively, this highlights that the benefit of pre-training is improved initial response and some speed gain in reaching steady-state performance level, without qualitatively impacting the long-term training behavior.
*CoL-BC:* Cycle-of-Learning without the behavioral cloning expert loss on the actor (λBC:=0) during both pre-training and RL phases.
The critic loss remains the same as in Equation [Integrating Behavior Cloning and Reinforcement Learning](#Sx4.Ex3 "Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments") for both training phases.
This condition assesses the impact on learning performance of the behavior cloning loss component LBC, given otherwise consistent loss functions in both pre-training and RL phases.
This condition improves upon the CoL-PT condition in its initial reward return and similarly achieves comparable performance to the baseline CoL in the first few hundred thousand steps, but then steadily deteriorates as training continues, with several catastrophic losses in performance.
This result makes clear that the behavioral cloning loss is an essential component of the combined loss function toward maintaining performance throughout training, anchoring the learning to some previously demonstrated behaviors that are sufficiently proficient.
*BC+DDPG:* Behavior cloning with subsequent DDPG using standard loss functions (Equations [2](#Sx4.E2 "(2) ‣ 1st item ‣ Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments"), [4](#Sx4.E4 "(4) ‣ 2nd item ‣ Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments"), and [5](#Sx4.E5 "(5) ‣ 3rd item ‣ Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments")) rather than the CoL combined loss in both phases (Equation [Integrating Behavior Cloning and Reinforcement Learning](#Sx4.Ex3 "Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments")).
Pre-training of the actor with behavioral cloning uses only the regression loss, as seen in Equation [2](#Sx4.E2 "(2) ‣ 1st item ‣ Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments").
DDPG utilizes standard loss functions for the actor and critic, as seen in Equation [Ablation Studies](#Sx5.Ex11 "Ablation Studies ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments").
This condition assesses the impact on learning performance of standardized loss functions rather than our combined loss functions across both training phases.
This condition produces initial rewards similar to that of the CoL-PT condition, below the BC response.
However, it subsequently improves in performance only to a level similar to that of the BC and is much less stable in its response throughout training.
This result indicates that simply sequencing standard BC and RL algorithms results in both poorer initial performance and a significantly lower level of performance and stability even after millions of training steps, emphasizing the value of a consistent combined loss function across all training phases.
| | | | |
| --- | --- | --- | --- |
| | LDDPG(θQ,θπ)= | λQ1LQ1(θQ)+λALA(θπ) | |
| | | +λL2LL2(θQ)+λL2LL2(θπ). | | (7) |
### The n-step Loss Contribution
In addition to the ablation study, we also investigated the effect of including an n-step Q-learning loss function in addition to the 1-step Q-learning loss function.
n-step Q-learning has the advantage of faster convergence properties as the n previous Q-values are updated after receiving a reward, instead of only the next Q-value as is the case with 1-step Q-learning.
This allows for faster propagation of the expected return to Q-values at earlier states and overall improves the efficiency of Q-learning.
The downside of n-step Q-learning is that the Q-values are only actually correct when learning on-policy and thus off-policy techniques can generally not be used as in 1-step learning [Sutton1999].
Table 1: Method Comparison
Method
Plot Legend
Pre-Training Loss
Training Loss
Buffer Type
Average Reward
CoL
Blue, solid
LQ1+LA+LBC
LQ1+LA+LBC
Fixed Ratio
261.80 ± 22.53
CoL-PT
Purple, solid
None
LQ1+LA+LBC
Fixed Ratio
253.24 ± 46.50
DDPGfD-N
Green, dash
None
LQ1+LA+LBC
PER
241.21 ± 47.22
DDPG
Red, solid
None
LQ1+LA
Uniform
152.98 ± 69.45
BC
Grey, solid
LBC
None
None
-48.83 ± 27.68\*
BC+DDPG
Red, dash
LBC
LQ1+LA
Uniform
-57.38 ± 50.11
CoL+N
Blue, dash
LQ1+LQn+LA+LBC
LQ1+LQn+LA+LBC
Fixed Ratio
-56.50 ± 68.19
CoL-BC
Purple, dash
LQ1+LA
LQ1+LA
Fixed Ratio
-105.65 ± 196.85
DDPGfD
Green, solid
None
LQ1+LQn+LA+LBC
PER
-209.14 ± 60.80
Summary of learning methods. Enumerated for each method are all non-zero loss components (excluding regularization), buffer type, and average and standard error of the reward throughout training (after pre-training) across the three seeds, evaluated with dense reward in LunarLanderContinuous-v2 environment. ∗For BC, these values are computed from 100 evaluation trajectories of the final pre-trained agent.
To show the effect of the n-step Q-learning loss on the Cycle-of-Learning (CoL), we repeated experiments shown in Figures [(a)a](#Sx5.F2.sf1 "(a) ‣ Figure 2 ‣ Experimental Setup ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments") and Figures [(b)b](#Sx5.F2.sf2 "(b) ‣ Figure 2 ‣ Experimental Setup ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments"), for the dense and sparse reward cases in the LunarLanderContinuous-v2 environment, adding the n-step Q-learning loss (n=10) [hester2018deep]) to the combined loss function of the CoL, as well as removing this loss component from DDPGfD.
The results for the dense and sparse case are shown in Figures [(b)b](#Sx5.F3.sf2 "(b) ‣ Figure 3 ‣ Experimental results ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments") and [(c)c](#Sx5.F3.sf3 "(c) ‣ Figure 3 ‣ Experimental results ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments"), respectively.
For both dense and reward cases, the n-step Q-learning loss decreases the performance of the CoL, where it was not present originally, and its removal increases the performance of DDPGfD, where it was present originally. We believe this is because in order to learn accurate Q-values the n-step Q-learning loss needs to be applied to on-policy data, however, because each method is using a replay buffer of past data, the learning is actually off-policy.
Discussion and Conclusion
-------------------------
In this work, we present a novel method for combining behavior cloning with RL using an actor-critic architecture that implements a combined loss function and a demonstration-based pre-training phase.
We compare our approach against state-of-the-art baselines, including BC, DDPG, and DDPGfD, and demonstrate the superiority of our method in terms of learning speed, stability, and performance with respect to these baselines.
This is shown in the OpenAI Gym LunarLanderContinuous-v2 and the high-fidelity Microsoft AirSim quadrotor simulation environments.
This result holds in both dense and sparse reward settings, though the improvements of our method over these baselines is even more dramatic in the sparse case.
This result is especially noticeable in the AirSim landing task (Figure [2](#Sx5.F2 "Figure 2 ‣ Experimental Setup ‣ Experimental Setup and Results ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments")c), an environment designed to exhibit a high degree of stochasticity.
The DDPG and DDPGfD baselines fail to learn an effective policy to perform the task, even after five million training steps, when using sparse rewards.
Conversely, our method, CoL, is able to quickly achieve high performance without degradation, surpassing both behavior cloning and reinforcement learning algorithms alone, despite receiving only sparse rewards.
Additionally, we demonstrate through an ablation study of several components of our architecture that both pre-training and the use of a combined loss function are critical to the performance improvements.
This ablation study also indicates that simply sequencing standard behavior cloning and reinforcement learning algorithms does not produce these gains.
We also illustrate that the lack of a n-step Q-learning loss in our architecture is necessary for these improvements.
Furthermore, we show that inclusion of such a loss term in our algorithm significantly reduces performance in both dense- and sparse-reward conditions, while its omission from DDPGfD significantly improves performance in dense-reward but not in sparse-reward conditions.
To the best of our knowledge this is the first work that examined the effect of the n-step Q-learning loss on learning for DDPGfD policy performance.
Future work will investigate how to effectively integrate multiple forms of human feedback into an efficient human-in-the-loop RL system capable of rapidly adapting autonomous systems in dynamically changing environments.
For example, existing works have shown the utility of leveraging human interventions [goecks2018efficiently, saunders2018trial], and specifically learning a predictive model of what actions to ignore at every time step [Zahavy2018].
A limitation of our current approach is the requirement that the demonstrator be capable of generating a sufficient number of minimally proficient demonstrations, which can be prohibitive for humans in certain tasks with fast temporal dynamics or a high-dimensional action space.
Deep reinforcement learning with human evaluative feedback has also been shown to quickly train policies across a variety of domains [warnell2018deep, Arumugam2017] and can be a particularly useful approach when the human is unable to provide a demonstration of desired behavior but can articulate when desired behavior is achieved.
Further, the capability our approach provides, to transition from a limited number of human demonstrations to a baseline behavior cloning agent and subsequent improvement through reinforcement learning without significant losses in performance, is largely motivated by the goal of human-in-the-loop learning on physical system.
Thus our aim is to integrate this method onto such systems and demonstrate rapid, safe, and stable learning from limited human interaction.
Supplementary Material
----------------------
This supplementary material contains details of the implementation to improve reproducibility of the research work. Algorithm [1](#alg1 "Algorithm 1 ‣ Integrating Behavior Cloning and Reinforcement Learning ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments") describes all steps of the proposed method and Table [2](#Sx7.T2 "Table 2 ‣ Supplementary Material ‣ Integrating Behavior Cloning and Reinforcement Learning for Improved Performance in Sparse Reward Environments") summarize all CoL hyperparameters used on the LunarLanderContinuous-v2 and Microsoft AirSim experiments.
| | |
| --- | --- |
| | Environments |
| Hyperparameter |
(a)
|
(b)
|
| λQ1 factor | 1.0 | 1.0 |
| λBC factor | 1.0 | 1.0 |
| λA factor | 1.0 | 1.0 |
| λL2 factor | 1.0e−5 | 1.0e−5 |
| Batch size | 512 | 512 |
| Actor learning rate | 1.0e−3 | 1.0e−3 |
| Critic learning rate | 1.0e−4 | 1.0e−4 |
| Memory size | 5.0e5 | 5.0e5 |
| Expert trajectories | 20 | 10 |
| Pre-training steps | 2.0e4 | 2.0e4 |
| Training steps | 5.0e6 | 5.0e5 |
| Discount factor γ | 0.99 | 0.99 |
| Hidden layers | 3 | 3 |
| Neurons per layer | 128 | 128 |
| Activation function | ELU | ELU |
Table 2: Cycle-of-Learning hyperparemeters for each environment: (a) LunarLanderContinuous-v2 and (b) Microsoft AirSim. |
41c7f1f3-48fd-4ce6-a9bc-aa247d1b2376 | trentmkelly/LessWrong-43k | LessWrong | When It's Not Right to be Rational
By now I expect most of us have acknowledged the importance of being rational. But as vital as it is to know what principles generally work, it can be even more important to know the exceptions.
As a process of constant self-evaluation and -modification, rationality is capable of adopting new techniques and methodologies even if we don't know how they work. An 'irrational' action can be rational if we recognize that it functions. So in an ultimate sense, there are no exceptions to rationality's usefulness.
In a more proximate sense, though, does it have limits? Are there ever times when it's better *not* to explicitly understand your reasons for acting, when it's better *not* to actively correlate and integrate all your knowledge?
I can think one such case: It's often better not to look down.
People who don't spend a lot of time living precariously at the edge of long drops don't develop methods of coping. When they're unexpectedly forced to such heights, they often look down. Looking down, subcortical instincts are activated that cause them to freeze and panic, overriding their conscious intentions. This tends to prevent them from accomplishing whatever goals brought them to that location, and in situations where balance is required for safety, the panic instinct can even cause them to fall.
If you don't look down, you may know intellectually that you're above a great height, but at some level your emotions and instincts aren't as triggered. You don't *appreciate* the height on a subconscious level, and so while you may know you're in danger and be appropriately nervous, your conscious intentions aren't overridden. You don't freeze. You can keep your conscious understanding compartmentalized, not bringing to mind information which you possess but don't wish to be aware of.
The general principle seems to be that it is useful to avoid fully integrated awareness of relevant data if acknowledging that data dissolves your ability to regulate your emotio |
53580520-8ce5-441b-b5be-a5afd6cdfe5b | trentmkelly/LessWrong-43k | LessWrong | Link: Interesting Video About Automation and the Singularity
I finally got into Ello (I was mad that I couldn't get an invitation for the longest time). I found this interesting video about automation and what we should do when most jobs no longer require humans. I have often wondered what we were going to do with the millions of unemployed people when machines create untold abundance. What will we need human workers to do? I have thought that there will be certain areas where we will want to interact with people. I think bots and other machines will be more assistants rather than fully taking over tasks in a few areas. I think it will be more balanced but that does not solve the problem of millions of unemployed undermining the economy and the wealth of nations. Do we save the jobs? Do we stop automation? Is this the natural course of history? Should we all be prepared to be destitute? Should we consider minimum income proposals more closely?
The video is here:
https://www.youtube.com/watch?v=7Pq-S557XQU&feature=youtu.be
I found it on this interesting post. He projects a much more dystopian view of the Singularity and how it will affect humanity. I think his post is not mindful of Bostrom's work which I am plowing through but it might provide some discussion fodder.
The post is here:
https://ello.co/scottdakota/post/ofb9vzDer9NoiQvwdueyAg |
52dc6b31-3f20-4d11-a4e4-99b4d3548bab | StampyAI/alignment-research-dataset/eaforum | Effective Altruism Forum | How many people are working (directly) on reducing existential risk from AI?
Summary
=======
I've updated my estimate of the number of FTE (full-time equivalent) working (directly) on reducing existential risks from AI **from 300 FTE to 400 FTE**.
Below I've pasted some slightly edited excepts of the relevant sections of the 80,000 Hours profile on [preventing an AI-related catastrophe](https://80000hours.org/problem-profiles/artificial-intelligence/).
New 80,000 Hours estimate of the number of people working on reducing AI risk
=============================================================================
Neglectedness estimate
----------------------
We estimate there are around 400 people around the world working directly on reducing the chances of an AI-related existential catastrophe (with a 90% confidence interval ranging between 200 and 1,000). Of these, about three quarters are working on technical AI safety research, with the rest split between strategy (and other governance) research and advocacy. [[1]](#fn290oixxnjlk)We think there are around 800 people working in [complementary roles](https://80000hours.org/problem-profiles/artificial-intelligence/#complementary-yet-crucial-roles), but we’re highly uncertain about this estimate.
Footnote on methodology
-----------------------
It’s difficult to estimate this number.
Ideally we want to estimate the number of FTE (“[full-time equivalent](https://en.wikipedia.org/wiki/Full-time_equivalent)“) working on the problem of reducing existential risks from AI.
But there are lots of ambiguities around what counts as working on the issue. So I tried to use the following guidelines in my estimates:
* I didn’t include people who might think of themselves on a career path that is building towards a role preventing an AI-related catastrophe, but who are currently skilling up rather than working directly on the problem.
* I included researchers, engineers, and other staff that seem to work directly on technical AI safety research or AI strategy and governance. But there’s an uncertain boundary between these people and others who I chose not to include. For example, I didn’t include machine learning engineers whose role is building AI systems that might be used for safety research but aren’t *primarily* designed for that purpose.
* I only included time spent on work that seems related to reducing the potentially [existential risks](https://80000hours.org/articles/existential-risks/) from AI, like those discussed in this article. Lots of wider AI safety and AI ethics work focuses on reducing other risks from AI seems relevant to reducing existential risks – this ‘indirect’ work makes this estimate difficult. I decided not to include indirect work on reducing the risks of an AI-related catastrophe (see our [problem framework](https://80000hours.org/articles/problem-framework/#a-challenge-direct-vs-indirect-future-effort) for more).
* Relatedly, I didn’t include people working on other problems that might indirectly affect the chances of an AI-related catastrophe, such as [epistemics and improving institutional decision-making](https://80000hours.org/problem-profiles/improving-institutional-decision-making/), reducing the chances of [great power conflict](https://80000hours.org/problem-profiles/great-power-conflict/), or [building effective altruism](https://80000hours.org/problem-profiles/promoting-effective-altruism/).
With those decisions made, I estimated this in three different ways.
First, for each organisation in the [AI Watch](https://aiwatch.issarice.com/) database, I estimated the number of FTE working directly on reducing existential risks from AI. I did this by looking at the number of staff listed at each organisation, both in total and in 2022, as well as the number of researchers listed at each organisation. Overall I estimated that there were 76 to 536 FTE working on technical AI safety (90% confidence), with a mean of 196 FTE. I estimated that there were 51 to 359 FTE working on AI governance and strategy (90% confidence), with a mean of 151 FTE. There’s a lot of subjective judgement in these estimates because of the ambiguities above. The estimates could be too low if AI Watch is missing data on some organisations, or too high if the data counts people more than once or includes people who no longer work in the area.
Second, I adapted the methodology used by [Gavin Leech’s estimate of the number of people working on reducing existential risks from AI](https://forum.effectivealtruism.org/posts/8ErtxW7FRPGMtDqJy/the-academic-contribution-to-ai-safety-seems-large). I split the organisations in Leech’s estimate into technical safety and governance/strategy. I adapted Gavin’s figures for the proportion of computer science academic work relevant to the topic to fit my definitions above, and made a related estimate for work outside computer science but within academia that is relevant. Overall I estimated that there were 125 to 1,848 FTE working on technical AI safety (90% confidence), with a mean of 580 FTE. I estimated that there were 48 to 268 FTE working on AI governance and strategy (90% confidence), with a mean of 100 FTE.
Third, I looked at the estimates of similar numbers by [Stephen McAleese](https://forum.effectivealtruism.org/posts/3gmkrj3khJHndYGNe/estimating-the-current-and-future-number-of-ai-safety). I made minor changes to McAleese’s categorisation of organisations, to ensure the numbers were consistent with the previous two estimates. Overall I estimated that there were 110 to 552 FTE working on technical AI safety (90% confidence), with a mean of 267 FTE. I estimated that there were 36 to 193 FTE working on AI governance and strategy (90% confidence), with a mean of 81 FTE.
I took a geometric mean of the three estimates to form a final estimate, and combined confidence intervals by assuming that distributions were approximately lognormal.
Finally, I estimated the number of FTE in [complementary roles](https://80000hours.org/problem-profiles/artificial-intelligence/#complementary-yet-crucial-roles) using the AI Watch database. For relevant organisations, I identified those where there was enough data listed about the number of *researchers* at those organisations. I calculated the ratio between the number of researchers in 2022 and the number of staff in 2022, as recorded in the database. I calculated the mean of those ratios, and a confidence interval using the standard deviation. I used this ratio to calculate the overall number of support staff by assuming that estimates of the number of staff are lognormally distributed and that the estimate of this ratio is normally distributed. Overall I estimated that there were 2 to 2,357 FTE in complementary roles (90% confidence), with a mean of 770 FTE.
There are likely many errors in this methodology, but I expect these errors are small compared to the uncertainty in the underlying data I’m using. Ultimately, I’m still highly uncertain about the overall FTE working on preventing an AI-related catastrophe, but I’m confident enough that the number is relatively small to say that the problem as a whole is highly neglected.
I’m very uncertain about this estimate. It involved a number of highly subjective judgement calls. You can see the (very rough) spreadsheet I worked off [here](https://docs.google.com/spreadsheets/d/1e1Vh_nK_7VHKZUuQ9VNp3JWC2etjUAHVmVXbKarKMNw/edit). If you have any feedback, I’d really appreciate it if you could tell me what you think using [this form](https://forms.gle/RRZaFTfdDkSQ6fJG8).
Some extra thoughts from me
===========================
This number is extremely difficult to estimate.
Like any Fermi estimate, I'd expect there to be a number of mistakes in this estimate. I think there will be two main types:
* Bad judgment calls when estimating the number of people working at each organisation, e.g. based on "what counts as an FTE working directly on this issue", "how wrong is the AI watch database on this organisation", etc.
* Errors in calculation / estimating uncertainty, etc.
Again, like in any Fermi estimate, I'd hope that these errors will roughly cancel out overall.
I didn't spend much time on this (maybe about 2 days of work). This is because I'd guess that more work won't improve the estimate by decision-relevant amounts. Some reasons for this:
* A rougher version of this estimate that I'd used previously came to an answer of 300 FTE. That estimate took around 3-4 hours of work. While 300 FTE to 400 FTE is a large proportional change, it still represents a highly neglected field and doesn't seem substantially decision-relevant.
* Errors in collecting data on this seem large in a way that couldn't be easily mitigated by doing more work.
* There would still be substantial subjective judgement in an estimate that took more time. My uncertainty in this estimate includes uncertainty in whether these are the right judgement calls (on the criteria of "is it truthful, across a distribution of plausible definitions, to say that this is the number of FTE working directly on reducing existential risk from AI"), and it seems very difficult to reduce that uncertainty.
1. **[^](#fnref290oixxnjlk)**Note that before 19 December 2022, [this page](https://80000hours.org/problem-profiles/artificial-intelligence/#neglectedness) gave a lower estimate of 300 FTE working on reducing existential risks from AI, of which around two thirds were working on technical AI safety research, with the rest split between strategy (and other governance) research and advocacy
This change represents a (hopefully!) improved estimate, rather than a notable change in the number of researchers. |
7d128eae-2686-414d-b364-51c3ccb49986 | StampyAI/alignment-research-dataset/arxiv | Arxiv | Scalable Online Planning via Reinforcement Learning Fine-Tuning.
1 Introduction
---------------
Lookahead search has been a key component of successful AI systems in sequential decision-making problems. For example, in order to achieve superhuman performance in go, chess and shogi, AlphaZero leveraged Monte Carlo tree search (MCTS) silver2018general. MuZero extended this even further to Atari games, again using MCTS schrittwieser2019mastering. Without MCTS, AlphaZero performs below a top human level, and more generally no superhuman Go bot has yet been developed that does not use some form of MCTS. Similarly, search algorithms were a critical component of AI successes in backgammon tesauro1994td, chess campbell2002deep, poker moravvcik2017deepstack; brown2017superhuman; brown2019superhuman, and Hanabi lerer2019improving. However, even though different search algorithms were used in each domain, *all* of them were *tabular* search algorithms, i.e., a distinct policy was computed for each state encountered during search, without any function approximation to generalize between similar states.
While tabular search has achieved great success, particularly in perfect-information deterministic environments, its applicability is clearly limited. For example, in the popular partially observable stochastic AI benchmark game Hanabi bard2020hanabi, one-step lookahead search involves a search over about 20 possible next states. However, searching over all two-step joint policies would require a search over 2020 states, which is clearly intractable for tabular search. Additionally, unlike perfect-information deterministic games where it is only necessary to search over a tiny fraction of the next several moves, partial observability and stochasticity make it impossible to limit the search to a tiny subset of all possible states. Fortunately, many of these states are extremely similar, so a search algorithm can in theory benefit by generalizing between similar states. This is the motivation for our non-tabular search algorithm.
In this paper we take inspiration from related research in continuous control environments that use non-tabular planning algorithms to improve performance at inference time wang2019exploring; marino2020iterative; amos2020differentiable. These methods leverage finite-horizon model-based rollouts. Specifically, we replace tabular search with fine-tuning of the policy network at inference time. We show that with this approach we are able to achieve state-of-the-art performance in Hanabi.
Specifically, our method is able to search multiple moves ahead and discover joint deviations, which in general is intractable using tabular search. We also show the generality of our approach by showing that it outperforms Monte Carlo tree search in deterministic and stochastic versions of the Atari game Ms. Pacman.
2 Background
-------------
###
2.1 MDPs, POMDPs, and Dec-POMDPs
We consider Markov decision processes (MDPs) sutton2018reinforcement, where the agent observes the state st∈S at time t, performs an action according to their policy at∼π(st) and receive reward rt=r(st,at). The environment transit to the next state following transition probability st+1∼P(st+1|st,at).
POMDPs sondik1971optimal extend MDPs to the partially observable setting where the agent cannot observe the true underlying state but instead receive information through a observation function ot=Ω(st). Due to the partial observability, the agent policy π often needs to take into account the entire action-observation history (AOH) denoted as τ′t={o0,a0,r0,…ot} with τt={s0,a0,r0,…,st} representing the true underlying trajectory.
Dec-POMDPs oliehoek2008optimal; bard2020hanabi extend POMDPs to the cooperative multi-agent setting. At each time step t, each agent i receives their individual observation from the state oit=Ωi(st) and selects action ait. The joint action of N player is a tuple at=(a1t,a1t,...,aNt) and can be observed by all players. We denote the individual policy for each player as πi and joint policy as π. We use τit={oi0,a0,r0,…oit} to represent the AOH from the perspective of agent i.
###
2.2 Tabular Search in Dec-POMDPs
SPARTA lerer2019improving is a tabular search algorithm previously applied in Dec-POMDPs that is proven to never hurt performance and in practice greatly improves performance. Specifically, SPARTA assumes that all agents in a game agree on a joint blueprint policy πbp and that one or more agents may choose to deviate from πbp at test time. We assume a two player setting in the following discussion. There are two versions of SPARTA.
In single-agent SPARTA, only one agent may deviate from the blueprint. We denote the search agent as agent i and the other agent as −i. Agent i maintains their private belief over the trajectories they are in given their AOH,
Bi(τt)=P(τt|τit).
At action selection time, agent i compute the Monte Carlo estimation for the value of each action assuming both players will follow blueprint policy πbp thereafter,
| | | | |
| --- | --- | --- | --- |
| | Q(τit,at)=Eτt∼Bi(τt),τT∼P(τT|τt,at,πbp)Rt(τT), | | (1) |
where Rt(τT)=∑Tt′=trt′ is the forward looking return from t to termination step T. Agent i will pick argmaxatQ(τit,at) instead of the blueprint action abp if maxatQ(τit,at)−Q(τit,abp)>ϵ.
In multi-agent SPARTA, both agents are allowed to search at test time. However, since agent i’s belief over states depends on agent −i’s policy, it is essential that agent i replicate the search policy of agent −i. Since agent i does not know the private state of agent −i, agent i must therefore compute agent −i’s policy for
*every* possible AOH τit agent i may have seen, a process referred to as *range-search*. Once a correct belief is computed, agent −i runs their own search. The range-search can be prohibitively expensive to compute in many cases because players might have millions of potential AOH. For example, Hanabi might have up to about 10 million AOHs. To mitigate this problem, the authors introduce a way to execute multi-agent search only when the range of AOHs is small enough that it is computationally feasible to do so, and the algorithm uses single-agent search otherwise. Even so, SPARTA multi-agent search is limited to one-ply search – each agent calculates the expected value of only
the next action. The computational complexity grows exponentially with each additional ply.
In contrast, our non-tabular multi-agent search technique makes it possible to conduct 2-ply, and deeper, search.
###
2.3 Reinforcement Learning
Our goal is to learn a stationary policy π(a|s) such that the expected non-discounted return J(π)=Es0∼ρ(s)Eπ∑∞t=0r(st,at) is maximized, where ρ(s) is the initial state distribution. For any policy π we define its value Vπ(st)=Eπ(∑∞l=0r(st+l,at+l)|st), its Q-value Qπ(st,at)=Eπ(∑∞l=0r(st+l,at+l)|st,at) and its advantage Aπ(st,at)=Qπ(st,at)−Vπ(st). In reinforcement learning (RL), the transition probability p and the reward r are unknown, and the policy is learned by sampling trajectories τ=((s0,a0),...,(sT,aT)) from the environment.
In Q-learning, we use the sampled trajectories to learn the Q-function of the optimal policy, given by the Bellman equation: Q(s,a)=Es′(r(s,a)+γmaxa′Q(s′,a′)). The learned policy is greedy with respect to Q: π(a|s)=argmaxaQ(s,a). In DQN, the Q-value is approximated with a neural network Qθ that is trained by taking gradients of the mean squared Bellman error:
| | | | |
| --- | --- | --- | --- |
| | ∇θ^E(Qθ(s,a)−(r(s,a)+γmaxa′Qθ′(s′,a′)))2 | | (2) |
where θ′ is a fixed copy of θ and ^E denotes the empirical average over a finite number of batches.
In policy gradient (PG), we directly learn a parametrized policy πθ by performing gradient descent using an estimator of J:
| | | | |
| --- | --- | --- | --- |
| | ∇θ^E(logπθ(a|s)^A(s,a)) | | (3) |
where ^A is an estimate of the advantage of πθ.
###
2.4 Decision-Time Planning
To make better decisions at test time, we can specialize the learned policy, which we refer to as the blueprint policy (also known as the prior policy), to the current state by using it as prior in an online planning algorithm.
One of the most popular planning algorithms is Monte Carlo tree search (MCTS), which has famously enabled superhuman performance in go, chess, and many other settings silver2016mastering; silver2017mastering; silver2018general; schrittwieser2019mastering.
MCTS builds a tree of potential future states starting from the current state. Each node s keeps track of its action-state visitation counts N(s,a) and an estimate of its Q-values Q(s,a), refined each time the node is visited. The prior policy is used to select the next action to take during the tree traversal.
MCTS don’t scale well in environments with large branching factors caused by a high amount of stochasticity or partial observability. For example, MCTS becomes very expensive as the size of the action space increases because it needs to build an explicit tree to keep statistics about state-action pairs, and nodes need to be visited several times for the method to be effective. Furthermore, MCTS can in the worst case expand very deeply a branch that it misidentifies to be optimal due to a lack of exploration – exacerbated in high dimensions– which leads to a worst-case sample complexity worse than uniform sampling munos2014bandits.
3 Reinforcement Learning Fine-Tuning
-------------------------------------
To alleviate the inefficiency of tabular search methods like MCTS in large state and action spaces, we propose to formulate online planning as a RL problem that should be quickly solvable given a sufficiently optimal blueprint policy. We do so by using RL as a multiple-step policy improvement operator efroni2018multiple. More specifically, we bias the initial state distribution towards the current state s∗ and we reduce the horizon of the problem, leading to the following truncated objective:
| | | | |
| --- | --- | --- | --- |
| | max~π(Es0∼ρs∗(s)Ea0:H−1,s1:H∼~πH−1∑t=0(r(st,at))+EaH:∞,sH+1:∞∼π∞∑t=H(r(st,at))) | | (4) |
where ρs∗(s)=1(s=s∗) and π is the blueprint policy. If π is optimal, then π′=π is a solution to the problem. We call this procedure RL Fine-Tuning or RL Search and we use the two terms interchangeably in the remaining.
The blueprint π is either directly parameterized by θ or is greedy with respect to a Q-value parameterized by θ. In both cases, we improve π for the next H steps by following the gradient of the truncated objective with respect to θ. We present the two approaches in more detail in the following subsections.
###
3.1 Policy Fine-Tuning
In policy fine-tuning, we use any actor-critic algorithm to train a blueprint policy and a value network. For our experiments in the Atari environment, we use PPO schulman2017proximal. At action selection time, to solve objective ([4](#S3.E4 "(4) ‣ 3 Reinforcement Learning Fine-Tuning ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning")) we use the blueprint policy to initialize the online policy and the blueprint value to truncate our objective:
| | | | |
| --- | --- | --- | --- |
| | max~θ(Es0∼ρs∗(s)Ea0:H−1,s1:H∼π~θH−1∑t=0(r(st,at))+Vϕ(sH)) | | (5) |
If Vϕ is a perfect estimator of Vπθ, then we exactly optimize the truncated objective [4](#S3.E4 "(4) ‣ 3 Reinforcement Learning Fine-Tuning ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning").
The fine-tuned policy π~θ is obtained by performing N gradient steps with the PPO objective. The policy improvement step via policy gradient is presented in Algorithm [1](#algorithm1 "Algorithm 1 ‣ 3.1 Policy Fine-Tuning ‣ 3 Reinforcement Learning Fine-Tuning ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning").
Input : current state st, number of updates N, global policy parameter θ, global value parameter ϕ, horizon H, number of rollouts M
Output : updated parameter ~θ
Init:
θ0=θ, ϕ0=ϕ
for *i←1 to N* do
Collect M trajectories of H time steps starting from st using πθi−1.
Compute the generalized advantage estimate using:
| | | | | |
| --- | --- | --- | --- | --- |
| | δt | =rt+γVϕi−1(st+1)−Vϕi−1(st)∀t∈[0,H−2] | | (6) |
| | δH−1 | =rt+γVϕ(sH)−Vϕi−1(st) | |
(ϕi,θi)←PPO(ϕi−1,θi−1)
return *θN*
Algorithm 1 Policy Gradient Improvement. We use a standard PPO update to fine-tune the blueprint policy πθ and value Vϕ from some state st.
###
3.2 Q-value Fine-Tuning
In Q-value fine-tuning, we train a Q-network using any offline RL algorithm. At action selection time, to solve objective ([4](#S3.E4 "(4) ‣ 3 Reinforcement Learning Fine-Tuning ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning")) we use the blueprint Q-value to truncate our objective:
| | | | |
| --- | --- | --- | --- |
| | max~π(Es0∼ρs∗(s)Ea0:H−1,s1:H∼~πH−1∑t=0(r(st,at))+maxaQθ(sH,a)) | | (7) |
The online policy ~π is greedy with respect to the fine-tuned Q-network Q~θ obtained by performing N gradient steps with the mean squared Bellman error. To alleviate instabilities, the transitions used to fine-tune the Q-network are sampled with probability p from the global buffer replay and with probability 1−p from the trajectories sampled at action selection time. The Q-value improvement step is presented in Algorithm [1](#algorithm1 "Algorithm 1 ‣ 3.1 Policy Fine-Tuning ‣ 3 Reinforcement Learning Fine-Tuning ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning").
Input : current state st, number of updates N, global Q-network parameter θ, horizon H, number of rollouts M, batch size B
Output : updated parameter ~θ
Init:
θ0=θ
Collect M trajectories of H time steps starting from st using an ϵ-greedy policy wrt Qθ.
For each trajectory, if the environment is not terminated, replace rt+H−1 with rt+H−1+maxaQθ(st+H,a)
for *i←1 to N* do
Sample B transitions with probability p from the global buffer and probability 1−p from the M collected trajectories.
θi←∇θi−1^E(Qθi−1(s,a)−(r(s,a)+γmaxa′Qθ′(s′,a′)))2
return *θN*
Algorithm 2 Q-Value Improvement. We use a standard Bellman residual update to fine-tune the blueprint Q function Qθ from some state st.
###
3.3 Scaling Multi-Agent Search in Dec-POMDPs with RL Search
####
3.3.1 Scaling Single-Agent RL Search
In a test game, agent i maintains a belief over possible trajectories given their own AOH, Bi(τt)=P(τt|τit). At action selection time, agent i performs Q-value fine-tuning (Algorithm [2](#algorithm2 "Algorithm 2 ‣ 3.2 Q-value Fine-Tuning ‣ 3 Reinforcement Learning Fine-Tuning ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning")) of the blueprint policy πbp on the current belief B(τit). This produces a new policy π∗. Next, we evaluate both π∗ and πbp on E trajectories sampled from the belief. If the expected value of π∗ is at least ϵ higher than the expected value of πbp, the agent plays according to π∗ for the next H moves and search again at the (H+1)th move. Otherwise, the agent sticks to playing according to πbp for the current move and searches again on their next turn.
####
3.3.2 Scaling Multi-Agent RL Search
A critical limitation of single-agent SPARTA, multi-agent SPARTA, and single-agent RL search is that the searching agent assumes the other agent will follow the blueprint policy on all future turns. It is thus impossible for those methods to find *joint* deviations (ai∗t,a−i∗t1) where it is beneficial for agent i deviate to action ai∗t if and only if the other agent −i deviates to a−i∗t+1, an action that will not be selected under blueprint. Searching for joint deviation with general tabular methods is computationally infeasible in large Dec-POMDPs such as Hanabi because the effective branching factor is ∏i(|Bi(τt)|×|Ai|), which is about 2020 in Hanabi.
RL search enables searching for the next H moves for all agents jointly conditioning on the common knowledge. The observations in a Dec-POMDP can be factorized into private observation and public observations opubt. For example, in Hanabi the private observations are the teammates hands and the public observation are the played cards, discarded cards, hints given, and previous actions. The public observation is common knowledge among all players. We can define the common knowledge public belief as Bpub(τpubt)={τt|Ωpub(τt)=τpubt} where τpubt={opub0,a1,r1,…,opubt} and Ωpub is the public observation function. We can then draw τ∼Bpub(τpubt) repeatedly. The new policy is obtained via Q-value fine-tuning, in the same way as in single-agent RL search. Since the search procedure uses only public information, it can in principle be replicated by every player independently. However, to simplify the engineering challenges of our research, we conduct search just once and share the solution with all the players. If the newly trained policy is better than the blueprint by at least ϵ, every player will use it for their next H moves.
4 Experiments
--------------
###
4.1 Hanabi Experiments
Hanabi is a 2-5 player partially observable fully cooperative card game and a popular Dec-POMDP benchmark. A detailed description of the rules of the game and an explanation of its challenges can be found in bard2020hanabi. The deck in Hanabi consists of 5 color suites and each suite contains 10 cards with three 1s, two 2s, two 3s, two 4s and one 5. At the beginning of the game each player draws 4 or 5 cards. The main twist of the game is that players cannot see their own hand but instead observe all other players’ hands. All players work together to play cards from 1 to 5 in order for each suite. At each turn, the active player may choose to give a hint to another player at the cost of a hint token. However, the players start with only 8 available hint token, and must discard a card in order to gain a new hint token.
In recent years, there has been tremendous progress in developing increasingly strong agents for Hanabi bard2020hanabi; foerster2019bayesian; lerer2019improving; hu2019simplified; hu2020other; hu2021learned to the point where the latest agents are approachingn near-perfect scores. As a result, it is difficult to distinguish performance differences between different techniques. For this reason, we additionally evaluate our technique on a harder version of Hanabi in which the maximum number of hint tokens is 2 rather than 8.
We test both single-agent RL search and multi-agent joint RL search in 2-player Hanabi. Blueprint policies are trained with Q-learning and the same learning method is used for test-time fine-tuning. We compare our methods against SPARTA lerer2019improving, the state-of-the-art search technique that has been applied in this domain.
Blueprint Training. We train blueprint policy using independent Q-learning with a distributed learning setting. The entire process consists of two modules that run simultaneously. The first is a simulation module that runs M copies of the Hanabi game distributed across N parallel running workers. The simulation module collects AOH τT at the end of each game and writes those data into a centralized prioritized replay buffer prioritized-replay; apex. Meanwhile, a training module samples from the replay buffer to train the policy and send a new copy of the policy to the simulation module every K gradient steps. We set M=6400, N=80 and K=10, the first two of which are chosen to make the replay buffer write speed of the simulation module roughly the same as the replay buffer read speed of the training module. We use the canonical techniques such as double Q-learning double-dqn and dueling DQN dueling-dqn for better performance. We use the same Public-LSTM network architecture as in hu2021learned to simplify the belief update procedure.
For simplicity, we use independent Q-learning tan93multi. We train the blueprint policy for 2 million gradient steps/batches and each batch contains 128 AOHs τi. Our blueprint gets 24.23 points on average, which is comparable to the strongest blueprint (24.29) in hu2021learned which is trained with a value decomposition network.
Results.
We present our results in Table [1](#S4.T1 "Table 1 ‣ 4.1 Hanabi Experiments ‣ 4 Experiments ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning"). For single-agent RL search we set the search horizon H=3, the number of gradient steps G=5000, the number of evaluations for comparing fine-tuned policy against blueprint E=10,000 and the deviation threshold ϵ=0.05. For multi-agent RL search we set H=1, G=10000, E=10,000, and ϵ=0.035. For comparison we also run both the single-agent and multi-agent version of SPARTA on our blueprint. Multi-agent SPARTA can be extremely expensive to run depending on the maximum size allowed for range-search, so we pick the hyper-parameter to make it consume roughly the same amount of time per game as multi-agent RL search.
Each cell in Table [1](#S4.T1 "Table 1 ‣ 4.1 Hanabi Experiments ‣ 4 Experiments ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning") is evaluated on 2000 games. The numbers on top shows the average score and standard error of the mean, and the number at the bottom of each cell is the percentage of winning games (perfect score games). In normal Hanabi, single-agent RL search beats single-agent SPARTA and multi-agent RL search beats multi-agent SPARTA. However, the scores are close enough that the differences are difficult to distinguish. This is likely because the blueprint in normal Hanabi is already extremely strong, so the benefit of additional search is diminished. On the harder 2-hint variant, RL search, and especially multi-agent RL search, significantly outperforms SPARTA. This indicates that searching for joint deviations is helpful, and RL search is a scalable way to find them.
Whether or not RL search is preferable to SPARTA depends in part on the computational budget. Single-agent SPARTA need only search over about 20 possible actions, so it takes 4 seconds to make a move using 5 CPU cores and 1 GPU. For comparison, single-agent RL search would take 69 seconds per move when searching one move ahead with 20 CPU cores and 2 GPUs. However, RL search scales much more effectively. The branching factor in Hanabi is around 500 and the game involves a high amount of stochasticity due to new cards being drawn, so searching even 3 moves ahead is essentially intractable for single-agent SPARTA. In contrast, single-agent RL search that looks 3 moves ahead takes only 88 seconds per move. Similarly, searching two moves ahead (one for each player) in multi-agent SPARTA would mean searching over about 2020 joint policies, which would be intractable. In contrast, multi-agent RL search is able to do this while taking only 180 seconds per move.
| Variant | Blueprint | SPARTA | SPARTA | RL Search | RL Search |
| --- | --- | --- | --- | --- | --- |
| (Single) | (Multi) | (Single) | (Multi) |
| Normal | 24.23 ± 0.04 | 24.57 ± 0.03 | 24.61 ± 0.02 | 24.59 ± 0.02 | 24.62 ± 0.03 |
| 63.20% | 73.90% | 75.46% | 75.05% | 75.93% |
| 2 Hints | 22.99 ± 0.04 | 23.60 ± 0.03 | 23.67 ± 0.03 | 23.61 ± 0.03 | 23.76 ± 0.04 |
| 17.50% | 25.85% | 26.87% | 27.85% | 31.01% |
Table 1: Performance on Hanabi. Each cell is averaged over 2000 games. The number in the upper half of the cell is the average score ± standard error of mean (s.e.m.) and the number in the lower half is the percentage of winning games where agents score 25 points.
###
4.2 Atari
We demonstrate the generality of our approach by comparing policy gradient fine-tuning to MCTS in two Atari environments, Ms. Pacman and Space Invaders bellemare2013arcade. Specifically, we aim to answer the following questions:
1. Does RL Fine-Tuning outperforms MCTS in terms of search time and sample complexity? Yes, RL Fine-Tuning obtains higher scores in Ms.Pacman than MCTS for a smaller search time budget and a smaller number of samples per step.
2. Does RL Fine-Tuning performs well even with a weak blueprint? Yes, RL Fine-Tuning obtains strong results with a weak blueprint in Ms.Pacman and improve the policy in a much more sample-efficient way than carrying the PPO training of the weak policy.
3. Are the optimal hyperameters robust across different environments? Yes, an ablation study on the search horizon hyperparameter reveals that the optimal search horizon is the same for Ms. Pacman and Space Invaders.
####
4.2.1 Implementation
Blueprint Training.
We train a PPO schulman2017proximal agent until convergence in Ms. Pacman and Space Invaders. In both cases 107 samples are necessary to converge to the optimal PPO blueprint. We also save a weak blueprint after 2.106 samples in Ms.Pacman to answer question [2](#S4.I1.i2 "item 2 ‣ 4.2 Atari ‣ 4 Experiments ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning"). The weak blueprint obtains a score that is 5 times smaller than the optimal PPO policy.
MCTS.
At every testing time step, we build a tree starting from the current state. We use the blueprint policy to guide the action selection during the tree traversal and we use the value network every time we reach a node never seen before or we reach the depth limit of the tree. In our experiments we use a depth limit of 100. We can significantly improve the performance of MCTS by allowing for an additional hyperparameter to balance policy prior and visitation counts in the second term:
| | | | |
| --- | --- | --- | --- |
| | argmaxaQ(s,a)+c⋅πθ(a|x)β⋅√∑a′N(s,a′)1+N(s,a) | | (8) |
We obtain the best performance with c=5 and β=0.1.
Policy Gradient Fine-Tuning.
Our method achieves a small average time budget by amortizing the search time across multiple steps. In Ms. Pacman, we solve a finite-horizon problem of horizon 30 and we only need to replan every 30 steps (Algorithm [2](#algorithm2 "Algorithm 2 ‣ 3.2 Q-value Fine-Tuning ‣ 3 Reinforcement Learning Fine-Tuning ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning")). We have also tried to amortize MCTS across multiple steps, where we update the tree only after 30 steps. In this setting however, the episode return is worse than what is achieved by the blueprint, emphasizing the need to replan at every timestep, which is not necessary when performing RL search. To optimize an infinite-horizon problem rather than a finite-horizon problem, we can use the refined value instead of the blueprint for the last step of each trajectory. The problem is still simplified due to the biased initial state distribution. In Ms. Pacman, we have observed that this setting leads to similar improvements.
####
4.2.2 Results
RL Fine-Tuning outperforms MCTS for a fixed search time budget.
Both MCTS and policy gradient fine-tuning are multi-step improvement operators that optimize objective ([4](#S3.E4 "(4) ‣ 3 Reinforcement Learning Fine-Tuning ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning")) using a value estimate to truncate the objective. Therefore we expect both methods to achieve the same asymptotic performance. We compare both methods with a finite time budget of the order of 10s. Figure [1](#S4.F1 "Figure 1 ‣ 4.2.2 Results ‣ 4.2 Atari ‣ 4 Experiments ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning") shows the return achieved by the agent when performing either MCTS or RL search at action selection time, versus the average search time budget. We see that RL search consistently outperforms MCTS, contrasting with recent work showing that policy gradient was worse than MCTS for planning in the game Hex anthony2019policy. The difference of performance with this previous work might be due to the fact that they are using vanilla PG while we are using PP.
| | |
| --- | --- |
|
(a) Time Budget
|
(b) Samples
|
Figure 1: MCTS vs RL Fine-Tuning. (a)When the average time budget is on the order of 1-10 seconds, RL Fine-Tuning consistently outperforms MCTS. (b)RL Fine-Tuning also outperforms MCTS in terms of sample efficiency. The shaded area represent the min/max range across 5 seeds. The curves are smoothed with an exponential moving average.
RL Fine-Tuning is more sample efficient than MCTS.
With RL search, we need an average of 621 samples and 1.2 seconds per step to achieve a return of 8080 which is more than 2 times the return achieved by our asymptotic PPO policy. The total number of additional samples needed is 502,000, which is less than 5% of the samples needed for the blueprint PPO policy to converge. In contrast, MCTS requires an average of 4489 samples per step to reach a cumulative reward of 5820.
RL Fine-Tuning obtains strong results even with a weak blueprint.
We run experiments in the Ms. Pacman environment using poorer blueprints and compare the average cumulative reward obtained by continuing the PPO training versus performing RL Fine-Tuning for the same number of additional samples. For a blueprint trained during 2000 epochs of 1024 samples (around 1/5 of convergence and obtaining an average cumulative reward of 1880), RL fine-tuning can reach an average cumulative reward of 5510 with an online search using on average 1145 samples per step. In contrast, continuing the PPO training of the blueprint using the same number of additional samples used by RL fine-tuning yields a policy that reach an average cumulative reward of 1920 only (see table [2](#S4.T2 "Table 2 ‣ 4.2.2 Results ‣ 4.2 Atari ‣ 4 Experiments ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning")). We also test a randomly initialized blueprint: RL fine-tuning can reach an average cumulative reward of 2730 with an online search using on average 1360 samples per step while the PPO training of this blueprint with the same number of additional samples yields an average cumulative reward of 1280 only (see table [3](#S4.T3 "Table 3 ‣ 4.2.2 Results ‣ 4.2 Atari ‣ 4 Experiments ‣ Scalable Online Planning via Reinforcement Learning Fine-Tuning")).
| Additional Samples | 0 | 3.105 | 4.105 | 8.105 |
| --- | --- | --- | --- | --- |
| RL Fine-Tuning | 1880 | 3940 | 4580 | 5510 |
| PPO Training | 1880 | 1900 | 1900 | 1920 |
Table 2: Performance on Ms. Pacman with a weak blueprint. It is more sample efficient to use RL Fine-Tuning to improve a weak blueprint rather than carrying on the PPO training.
| Additional Samples | 0 | 2.105 | 4.105 | 8.105 |
| --- | --- | --- | --- | --- |
| RL Fine-Tuning | 60 | 1180 | 1800 | 2730 |
| PPO Training | 60 | 689 | 732 | 1280 |
Table 3: Performance on Ms. Pacman with a random blueprint. RL Fine-Tuning also outperforms PPO in term of sample efficiency when the blueprint is randomly initialized.
The hyperparamters of RL Fine-Tuning are robust across different environments. After performing the same ablation study on the horizon in both Ms. Pacman and Space Invaders, we have found that the optimal horizon is 32 for both environments. Thus there is reason to think that this value is nearly optimal in several other Atari games and readers willing to apply our method to other Atari games should start experimenting with this value.
5 Related Work
---------------
##### Fine-tuning in supervised learning.
Instead of searching for the optimal action sequence in the action space, which is what MCTS does, we are effectively searching in the parameter space of the neural network. We do that by following the gradient of the truncated objective. Since the truncated objective and the biased data distribution are close to the objective and the data distribution the blueprint neural network was trained on, the performance of our method should reflect the success of neural network fine-tuning in supervised learning tan2018survey; oquab2014learning.
##### Fine-tuning in reinforcement learning.
Replacing action search with neural network parameter search is reminiscent of recent work in continuous control performing cross-entropy method in the parameter space of the neural network wang2019exploring. They argue that the improvement over searching in the action space is due to the smoothness of the neural network loss landscape li2017visualizing. We take this idea further by making full use of the parameter space. While they are using scalar information – the return of each rollout –, we use richer information – the gradient of the return with respect to θ. By doing so, we argue that we lose less information about the blueprint than other online planning methods, which enables us to stay efficient in high dimensions.
Policy gradient fine-tuning is related to recent work on iterative amortized policy optimization marino2020iterative. Considering policy optimization in the lens of variational inference levine2018reinforcement, they argue that amortizing the policy into a neural network leads to the same suboptimal gap than amortizing the posterior in VAEs and propose to inject gradient information into the policy network’s input at action selection time to close the gap. While their policy network meta-learns how to use the gradient, we use a fixed update rule. Meta-learning the update rule is a promising future direction that could be stacked on top of our method. However, we suspect learning the update rule at blueprint training time to be intractable in complex environments such as Hanabi.
A large range of previous work has proposed to combine RL with tabular search springenberg2020local. In Expert Iteration anthony2017thinking; schrittwieser2019mastering, a policy network is used to amortize an expert tree search algorithm using imitation learning. Rather than amortizing the traversal policy, Hamrick et al. propose to train a Q-network via model-free RL to amortize the Q-values returned by MCTS hamrick2019combining. Our method differs from this line of work because we don’t use any tree search for maximum scalability.
Finally, there has been previous work investigating some variants of RL search. Policy gradient search anthony2019policy performs vanilla policy gradient to fine-tune a rollout policy and selects the action by performing MC rollouts with this policy. They perform worse than MCTS in the game Hex. springenberg2020local compare a variant of policy gradient fine-tuning to tree search in continuous control environments and show that PG fine-tuning performs almost as well as tree search, but not equally well. By contrast to these rather negative results, our positive results show that RL search outperforms MCTS in Ms. Pacman and achieves state-of-the-art performance in Hanabi. Additionally, prior work has looked to generalize between states during MCTS, though without fine-tuning of a pre-trained network yee2016monte.
6 Discussion
-------------
Despite the incredible success of neural network function approximation in reinforcement learning environments mnih2015human; haarnoja2018soft; badia2020agent57, search algorithms have largely remained tabular, as can be seen for example in AI algorithms for go silver2016mastering; silver2017mastering; silver2018general, poker moravvcik2017deepstack; brown2017superhuman; brown2019superhuman; brown2020combining, and Atari schrittwieser2019mastering; schrittwieser2021online; hubert2021learning. Tremendous research has gone into adding heuristics that enables tabular search to perform better in these domains, especially in perfect-information deterministic environments grill2020monte; cowling2012information. However, we argue that in order to scale to larger, more realistic environments, especially those involving stochasticity and partial observability, it is necessary to move past purely tabular search algorithms.
The jump from tabular search to RL search comes at a steep upfront cost. However, we show in this paper that in sufficiently complex environments, including the established AI benchmark Hanabi, RL search enables state-of-the-art performance and scales much more effectively. We show this also holds in the Atari Ms. Pacman environment, and we expect it to be true in a wide variety of other domains as well. As computational costs continue to decrease, it is likely that the relative performance of RL search will improve even further. To quote Richard Sutton’s *The Bitter Lesson* sutton2019bitter, "One thing that should be learned from the bitter lesson is the great power of general purpose methods, of methods that continue to scale with increased computation even as the available computation becomes very great. The two methods that seem to scale arbitrarily in this way are search and learning."
While a lot of methods combining RL with tabular search have been developed, we have shown that we can achieve better results by completely amortizing online planning into a neural network via RL fine-tuning. Most importantly, we have shown that RL search can effectively search complex domains where tabular search is intractable. This enables us to achieve state-of-the-art results in the AI benchmark Hanabi, which features both stochasticity and partial observability, both of which are prevalent in the real world.
Limitations: While we achieve good results in discrete environments, our algorithms are currently focused on discrete environments. A promising direction for future work would be an investigation of similar techniques in continuous control domains and a comparison to existing techniques (mentioned in the main text) in those domains.
A potential limitation of our method compared to gradient-free methods is that we might be constrained by the local minimum of a too weak blueprint. In other words, we may be unable to discover drastically new solutions to the control problem that an optimal global method solving the problem from scratch would find.
Broader impact:
RL search is a decision-time planning method aimed at improving search in very high-dimensional spaces.
There has been a rich history of previous work in this area, where the goal has been to develop more efficient search methods.
This work is in line with previous work and should not directly cause broader harm to society. We are not using any dataset or tool that will perpetuate or enforce bias. Nor does our method make judgements on our behalf that could be misaligned with our values. |
81c5d288-6526-49f9-99bd-f0f6baf76e8d | trentmkelly/LessWrong-43k | LessWrong | Off-topic: Russian machine translation
This is a little off-topic, but I can't find the answer and I realized this might actually be an excellent place to ask this question:
I've noticed Google Translate seems to do a pretty bad job sometimes of Russian-to-English and vice versa, assuming that my human-translated documents are correct. Does anyone know of a better free service for machine translation for Russian? |
74ce25f5-62a4-44b0-8704-4687cb14dd24 | StampyAI/alignment-research-dataset/lesswrong | LessWrong | Which textbook would you recommend to learn decision theory?
Eliezer talks a lot about decision theory in his sequences, e.g. the Aumann agreement theorem or the von Neumann-Morgenstern utility theorem. From what I've seen so far, decision theory looks extremely interesting.
Which textbook in decision theory would you recommend to start with? I'd appreciate if the book contained not only theory, but also some exercise/problem section - I have noticed that usually a lecture is not enough to fully grasp a topic. I want a book which will not shy away from mathematical side of the theory.
I have a strong background in mathematics and computer science, but I only know a little about game theory. |
4b20b04f-9c81-4696-aea8-60c58a0622f0 | trentmkelly/LessWrong-43k | LessWrong | What is the best day to celebrate Smallpox Eradication Day?
Several of my friends posted on Facebook/threw parties this weekend for a date of May 8. However, searching on Facebook, I find that I and several other friends have been posting celebratory messages on Facebook on December 9 in previous years.
This inconsistency is probably because there are two obvious candidate dates for eradication:
> The global eradication of smallpox was certified, based on intense verification activities, by a commission of eminent scientists on 9 December 1979 and subsequently endorsed by the World Health Assembly on 8 May 1980.
"500 Million, But Not a Single One More", which is widely shared and has been adapted at least once for reading at a large Secular Solstice, uses the December 9 date.
I think creating more consensus on which date is the "official" one for celebration purposes would be a small improvement (at the very least: I would stop confusing my relatives by year-to-year inconsistency on when I message them a little commemoration). So, which is it? |
1b15faa8-03ea-4bf3-9ee2-6f4d0c5809a1 | trentmkelly/LessWrong-43k | LessWrong | Fluoridation: The RCT We Still Haven't Run (But Should)
Empiric status: My own idea written up with the help of Gemini 2.0 Experimental in dialog.
We're still coasting on the fumes of 1940s data when it comes to water fluoridation. Back then, fluoride toothpaste was a novelty, fluoridated salt was uncommon, and water filters were practically science fiction, let alone ones that can selectively remineralize with or without fluoride.
We're navigating a multi-variable optimization problem blindfolded. We have fluoride inputs from water, toothpaste, and salt, all interacting in poorly understood ways, impacting both cavity rates and, more concerningly, cognitive development.
The IQ Elephant Continues to Loom Large
The potential neurotoxic effects of fluoride are no longer a fringe concern. National Toxicology Program (NTP) monograph is clear: "moderate confidence" that >1.5 mg/L fluoride in drinking water associates with lower IQ in children.
The technology is here. We can do this right. Modern water filters with remineralization cartridges are the key.
Here's the plan:
1. Factorial Design: Multiple arms to test different combinations of:
* Water Fluoride Levels:
* 0 mg/L (placebo - remineralization without fluoride)
* 0.35 mg/L (half of the current CDC recommendation, exploring potential lower thresholds)
* 0.7 mg/L (current CDC recommendation)
* Toothpaste:
* Standard fluoridated toothpaste (provisioned, with standardized use instructions)
* Non-fluoridated toothpaste (provisioned, with standardized use instructions)
* Salt:
* Fluoridated salt (provisioned)
* Non-fluoridated salt (provisioned)
This creates a 3x2x2 factorial design, allowing us to disentangle the effects of each source and their interactions, with a clear focus on the impact of fluoridated salt.
2. Targeted Community Selection: Conduct the study in a community with known poor water quality. This offers multiple benefits:
* Ethical Appeal: Providing free, high-quality water filt |
226ce7a1-93ff-4cbc-b24f-df2fa5024228 | trentmkelly/LessWrong-43k | LessWrong | Protestants Trading Acausally
Protestants believe in predestination. The God has already decided on who's going to get to hell and heaven.
This feels like a terrible incentive structure. If you are already predestined to get one of those places, why care? Why try to be good?
In reality though it works pretty well. Protestants are trying to be good to convince themselves (and others) that they've been predestined to go to heaven.
It may even work better (protestant work ethic etc.) because if you haven't been predestined, it always feels like there's still time to change your ways and eventually achieve salvation. With predestination it doesn't work that way. There's no changing of the decision in play. If you are behaving badly today it's a sign that you've been already predestined for hell. Too bad for you.
This is a funny example of an acausal trade. In particular because it does not assume an intelligent actor, an actor who knows game and decision theory and can act accordingly, which is traditionally an assumption for an acausal trade. A simple artisan or merchant in XVI. century may have done the acausal trade with God although the game or decision theory did not yet exist. |
27184f2a-03be-44ab-a55e-7946c561c5b5 | trentmkelly/LessWrong-43k | LessWrong | Extreme GDP growth is a bad operating definition of "slow takeoff"
I gather that the historical definition of slow takeoff is something akin to "grand GDP growth for several months in a row, due to AI advancements".
While recent advancements by OpenAI et. al. are impressive, sometimes people will claim they would never have awarded bayes points to slow takeoff for ChatGPT, because one of their primary contentions is that governments will prevent any AI that isn't politically revolutionary from making innovations in things like housing or medicine.
If this is true, perhaps there should be a new term, since it still seems useful to talk about a tech tree where we have very strong tool AIs, even if they're not making everybody rich. It seems unlikely to me that the same forces that might prevent AIs from being used to innovate housing will also prevent those AIs from being deployed to AI safety efforts. |
03fe998f-3ab0-46c2-89f8-292a9a44d313 | trentmkelly/LessWrong-43k | LessWrong | Auckland meetup, Thrusday May 26th
Time for another Auckland meetup! Same place as the last one a few years back, at the Messe bar at 2pm on the 26th of May (Thursday).
Write a comment and/or please contact me on my cell: 021 039 8554, if you are interested in coming. |
2fab93f9-67a6-424f-aa28-901592835d45 | trentmkelly/LessWrong-43k | LessWrong | Dario Amodei: On DeepSeek and Export Controls
Dario corrects misconceptions and endorses export controls.
> A few weeks ago I made the case for stronger US export controls on chips to China. Since then DeepSeek, a Chinese AI company, has managed to — at least in some respects — come close to the performance of US frontier AI models at lower cost.
>
> Here, I won't focus on whether DeepSeek is or isn't a threat to US AI companies like Anthropic (although I do believe many of the claims about their threat to US AI leadership are greatly overstated)1. Instead, I'll focus on whether DeepSeek's releases undermine the case for those export control policies on chips. I don't think they do. In fact, I think they make export control policies even more existentially important than they were a week ago2.
>
> Export controls serve a vital purpose: keeping democratic nations at the forefront of AI development. To be clear, they’re not a way to duck the competition between the US and China. In the end, AI companies in the US and other democracies must have better models than those in China if we want to prevail. But we shouldn't hand the Chinese Communist Party technological advantages when we don't have to.
----------------------------------------
Also:
> DeepSeek does not "do for $6M what cost US AI companies billions". I can only speak for Anthropic, but Claude 3.5 Sonnet is a mid-sized model that cost a few $10M's to train (I won't give an exact number). Also, 3.5 Sonnet was not trained in any way that involved a larger or more expensive model (contrary to some rumors).
Also:
> Making AI that is smarter than almost all humans at almost all things will require millions of chips, tens of billions of dollars (at least), and is most likely to happen in 2026-2027.
One thing seems wrong:
> If China can't get millions of chips, we'll (at least temporarily) live in a unipolar world, where only the US and its allies have these models.
If "smarter than almost all humans at almost all things" models appear in 2026-2027, |
afa0938c-2da4-4b3b-b446-ab455ef8c0a1 | trentmkelly/LessWrong-43k | LessWrong | Subsystem Alignment
(The bibliography for the whole sequence can be found here)
|
fb63b947-71f4-4c0a-b772-96d9df3158da | trentmkelly/LessWrong-43k | LessWrong | The LessWrong 2019 Review
Today is the start of the 2019 Review, continuing our tradition of checking which things that were written on LessWrong still hold up a year later, and to help build an ongoing canon of the most important insights developed here on LessWrong.
The whole process will span 8 weeks, starting on December 1st:
* From December 1st to the 14th, any user that was registered before January 1st 2019 can nominate any post written in 2019 to be considered for the review.
* From December 14th to January 11th, any user can leave reviews on any posts with at least two nominations, ask questions of other users and the author, and make arguments for how a post should be voted on in the review.
* From January 11th to January 25th any LessWrong user registered before 2019 can vote on the nominated posts, using a voting system based on quadratic voting. (There will be two votes, one for 1000+ karma users, and one for all users)
But before I get more into the details of the process, let's go up a level.
Why run a review like this?
The Review has three primary goals:
1. Improve our incentives, feedback, and rewards for contributing to LessWrong.
2. Create a highly curated "Best of 2019" sequence and physical book
3. Create common knowledge about the LW community's collective epistemic state about the most important posts of 2019
Improving our incentives and rewards
Comments and upvotes are a really valuable tool for allocating attention on LessWrong, but they are ephemeral and frequently news-driven, with far-from-perfect correlation to the ultimate importance of an idea or an explanation.
I want LessWrong to be a place for Long Content. A place where we can build on ideas over decades, and an archive that helps us collectively navigate the jungle of infinite content that spews forward on LessWrong every year.
One way to do that is to take some time between when you first see a post and when you evaluate it. That's why today we are starting the 2019 review, not the 202 |
8e13d9ab-4e14-405f-9a70-cbb49105ec48 | trentmkelly/LessWrong-43k | LessWrong | Excerpts from Veyne's "Did the Greeks Believe in Their Myths?"
"Did the Greeks Believe in Their Myths?" is a long 1983 essay by Paul Veyne, a French archaeologist/historian. The following post (written by me in 2011) consists of excerpts of the essay that I found particularly interesting when I read it.
Topics Veyne discusses include:
* Can a politician really believe all the things she says?
* Can contradictory views, e.g., of alternative medicine, coexist in the same mind? If so, how?
* Do people 'believe' in their religion in the same way that they believe in the existence of laundry detergent?
* Can someone fabricate completely new scriptures in good faith?
----------------------------------------
1. When historical truth was tradition and vulgate
Let us return to Estienne Pasquier, whose Reserches de la France appeared in 1560. Before publishing it, G. Huppert tells us, Pasquier circulated his manuscript among his friends. Their most frequent reproach concerned Pasquier's habit of giving too many references to the sources he cited. This procedure, they told him, cast a "scholastic pall" ("umbre des escholes") on the book and was unbecoming in a work of history. Was it truly necessary each time to confirm his "words by some ancient author"? If it was a matter of lending his account authority and credibility, time alone would see to that. After all, the works of the Ancients were not encumbered by citations, and their authority had been affirmed with time. Pasquier should let time alone sanction his book!
These startling lines show us the gulf that divides our conception of history from the one that was held by ancient historians and was still current among Pasquier's contemporaries. For them, as for the ancient Greeks, historical truth was a vulgate authenticated by consensus over the ages. This consensus sanctioned the truth as it sanctioned the reputation of those writers held to be classical or even, I imagine, the tradition of the Church. Far from having to establish the truth by means of references, Pas |
cf21f144-5746-4b76-8cfa-6b353e368e30 | StampyAI/alignment-research-dataset/lesswrong | LessWrong | Why you can't treat decidability and complexity as a constant (Post #1)
Or, why you need to fix a machine before you can prove anything, and you also need to fix the constraints on the machine. This also holds importantly for problems claimed to be decidable or undecidable by algorithms.
Basically, the reason here is that different machine/computational models define different sets of computable functions, and you cannot treat the machines as equivalent in power.
This is admittedly something that most people get implicitly today, but it can definitely cause problems, and it certainly caused a lot of problems for Church and Turing et al in that they incorrectly jumped to the conclusion that the Turing Machines could compute any possible computer, or compute any possible algorithm, probably because they thought that you could treat a Turing Machine as equivalent to any other machine. Why the Church-Turing thesis is false, in the sense that it doesn't apply universally will be covered in an upcoming post in this sequence, but for now take it as a fact that there are different models of computation that define different computable sets, or equivalently different problems become decidable when new models are added.
Edit: I'm focusing on a variant of the thesis for the next post, in which I focus not on what's possible given our mathematical structure of reality, but whether it's possible to exceed the Turing Machine at all in any possible mathematical structure, and another variant where we restrict it to Turing-equivalent models, but we can arbitrarily change what we can offer the Turing Machine.
This is important, since I'm mostly going in a philosophical, not practical direction, and the thesis made no reference to our specific mathematical reality at all, so it's important.
From wikipedia:
>
> "In computability theory, the Church–Turing thesis (also known as computability thesis,[1] the Turing–Church thesis,[2] the Church–Turing conjecture, Church's thesis, Church's conjecture, and Turing's thesis) is a thesis about the nature of computable functions. It states that a function on the natural numbers can be calculated by an effective method if and only if it is computable by a Turing machine. "
>
>
>
Link is below:
[https://en.wikipedia.org/wiki/Church–Turing\_thesis](https://en.wikipedia.org/wiki/Church%E2%80%93Turing_thesis)
The most important takeaway from this sequence is that it really does matter what computer/machine model you use, and what constraints you add to the model, and Turing Machines aren't always the best model to use, and that you shouldn't be eliding this in a proof of something as an informal statement, as otherwise it maps to different computable sets, which you don't want to do in a proof.
The best example of this phenomenon here is the following below:
The difference between a TM with a Deutschian CTC, and a TM without a Deutschian CTC in what problems they can solve (Not what the machines can simulate!)
==========================================================================================================================================================
It's been proven by Scott Aaronson, Mohammad Bavarian, and Giulio Gueltrini below that the set of problems a Turing Machine could solve with unbounded time and memory with a Deutschian CTC is larger than the set of problems that could be solved without a Deutschian CTC by a Turing Machine with unlimited time and memory.
Specifically, the set of problems solvable with a Deutschian CTC includes the halt function, as well as the set of problems that are Turing-reducible to the halting problem.
It's a classic halting oracle, but now it's constructed and visualized.
The link is below, but the main operators here are essentially a new lemma, plus some theorems that establish that in the setting of Turing Machines with CTCs both contains the halt oracle, plus is contained in the halt oracle.
<https://www.scottaaronson.com/papers/ctchalt.pdf>
The importance of the result
============================
The importance of this result is that you can't arbitrarily change a Turing Machine, and then define the same sets of computable functions. It gives motivation to why it's important to distinguish different intuitive/formal machine models, and why you need to fix the machine model, as well as constraints on that model, so that you can talk about what problems are decidable or intractable, so you don't end up in the trap of Church and Turing et al, who thought you could capture all of computation as a Turing Machine.
In the next post, I'll talk about Hilbert's triumph, Church and Turing's failure and why it turned out that there are machines that can decide first order logic, which is a huge chunk of math.
An aside on CTC Turing Machines, AIXI, and Solonomoff Induction et al
---------------------------------------------------------------------
While I will probably make a post on this sequence about comparing what different computer models can do, it is worth noting that AIXI and Solonomoff Inductors can actually be weaker or stronger than the CTC Turing Machines, depending on whether you allow them to solve all problems that are only many-one reducible to the halting problem, or allow them to solve all problems that are Turing-reducible to the halting problem, or allow them to solve problems that are higher in the arithmetical hierarchy. I just want to include this, since depending on how much power you assume AIXI or Solonomoff Inductors have, you can get very different results.
Major edit on the Church-Turing Thesis
======================================
For the purposes of the Church-Turing Thesis, I will define the claim by Church and Turing like this, to translate what I think they wanted to conjecture.
The Church-Turing Thesis/Conjecture is captured by the first point below:
1. The Universal Turing Machine, or equivalently a human with unlimited time and memory can compute all the functions that are calculable by effective functions, as defined below.
2. Effectively calculable functions have the following constraints/rules:
2.1 They must always give an answer in finite time, but the time bound can be arbitrarily large, and the space required to solve a problem may be unbounded, but never infinite, just arbitrarily large.
2.2 The human is assumed to have unlimited paper to act as a memory, and unlimited time to compute (They are immortal.)
2.3 The original condition has been replaced by the following condition below from Rafael Harth:
>
> In this setting, we call a problem decidable iff there exists a single, fixed procedure that can take arbitrary instances of this problem and always behaves like this:
>
>
>
>
> If the correct answer is 'yes', it outputs 'yes'.
> If the correct answer is 'no', it outputs 'no'.
>
>
>
The original statement is included below for completeness:
>
> Its instructions need only to be followed rigorously to succeed. In other words, it requires no ingenuity to succeed.[4]
>
>
>
2.4 This condition is quoted below:
>
> It consists of a finite number of exact, finite instructions.
>
>
>
2.5 Arbitrary extensions to the UTM are valid as long as they obey the constraints above.
2.6 Alternatively, any algorithm or effective method as defined in this post is allowed to be used so long as it is simulatable by a UTM, even multiple UTMs are allowed to simulate something.
Edit: 2.5 is essentially the classical Church-Turing thesis, while 2.6 is not the proper Church-Turing thesis, properly speaking, it's instead a useful modification.
The question becomes: Does the constraints on the human or UTM always lead to the same set, or can it lead to a larger set of computable functions? We will prove later on that it can lead to a larger set of computable functions.
We will then prove in a later post that conditions 2.5 or 2.6 will lead to a larger set of computable functions than a UTM can compute, and thus the Church-Turing Thesis is false. However, by dropping both conditions, and by adding a new condition by hand that restricts what we can do with effective functions, it can be true.
Something that might help in understanding decidability
-------------------------------------------------------
An important snippet from Rafael Harth is generally useful and doesn't require much in the way of time investment.
>
> When mathematicians talk about a 'problem' in this context, they always mean "an infinite set of problems such that (a) the answer to each problem is either 'yes' or 'no', and (2) the set contains arbitrarily large instances of problems". Here are two examples:
>
>
>
>
> Given an arbitrarily large natural number, decide if it is a prime number.
>
>
>
>
> Given an arbitrarily long program code, decide if the program, if run, eventually halts.
>
>
> |
e1ac5608-1270-4c39-bec0-743958eb501d | trentmkelly/LessWrong-43k | LessWrong | Two Dark Side Statistics Papers
I.
First we have False Positive Psychology: Undisclosed Flexibility In Data Collection And Analysis Allows Presenting Anything As Significant (h/t Jonas Vollmer).
The message is hardly unique: there are lots of tricks unscrupulous or desperate scientists can use to artificially nudge results to the 5% significance level. The clarity of the presentation is unique. They start by discussing four particular tricks:
1. Measure multiple dependent variables, then report the ones that are significant. For example, if you’re measuring whether treatment for a certain psychiatric disorder improves life outcomes, you can collect five different measures of life outcomes – let’s say educational attainment, income, self-reported happiness, whether or not ever arrested, whether or not in romantic relationship – and have a 25%-ish probability one of them will come out at significance by chance. Then you can publish a paper called “Psychiatric Treatment Found To Increase Educational Attainment” without ever mentioning the four negative tests.
2. Artificially choose when to end your experiment. Suppose you want to prove that yelling at a coin makes it more likely to come up tails. You yell at a coin and flip it. It comes up heads. You try again. It comes up tails. You try again. It comes up heads. You try again. It comes up tails. You try again. It comes up tails again. You try again. It comes up tails again. You note that it came up tails four out of six times – a 66% success rate compared to expected 50% – and declare victory. Of course, this result wouldn’t be significant, and it seems as if this should be a general rule – that almost by the definition of significance, you shouldn’t be able to obtain it just be stopping the experiment at the right point. But the authors of the study perform several simulations to prove that this trick is more successful than you’d think:
3. Control for “confounders” (in practice, most often gender). I sometimes call this the “Elderly Hispani |
9e672df1-4107-4ff2-88e9-867737f88a0d | trentmkelly/LessWrong-43k | LessWrong | Is there an existing label for the category of fallacies exemplified by "paradox of tolerance"?
The "paradox of tolerance" is a continually hot topic, but I've not seen it framed as a member in a category of fallacies where a principle is conceptualized as either absolute or hypocritical and the absolute conception then rejected as self-contradictory or incoherent. Other examples of commonly absolutized principles are pacifism, pluralism, humility, openness, specific kinds of freedoms, etc.
I've been provisionally calling it the 'false self-contradiction fallacy', meaning a specialized case of black-and-white fallacy as applied to ethical, moral or practical principles by presuming a false dichotomy between the principle being either absolute or hypocritical. The presumption is based on a shallow conception of the principle that excludes the deeper grounding principles that would allow integrating restrictions on the principle. The fallacy banks on the popular intuitions of justice needing to be blind and the universality of human rights and presumes limits to a principle to be arbitrary or unjustified.
Deeper conceptions of principles are able to integrate critical rejection; for example, in the case of tolerance, it can integrate the self-preservation of the principle by conditioning it on reciprocity. Tolerance in this case is not valuable in itself but as a higher-order expression of avoiding conflict escalation, achieving intellectual plurality, etc.
Absolute pacifism may be the most clear example of the fallacy, since most people understand that, to be coherent, pacifism must assign a high negative value to violence as a conflict-solving approach and positive value to alternative approaches, but that violence is still kept as the last resort, since the other approaches can't always work.
I find 'false self-contradictions' especially pernicious in their rhetorical persuasiveness and their consequent wide application in promoting moral relativism and getting around inconvenient principles. I'm really interested in finding existing discourse that would |
d807f00d-12b9-41b9-9ac7-a5c9dd9bad69 | StampyAI/alignment-research-dataset/arxiv | Arxiv | Stabilizing Transformers for Reinforcement Learning
1 Introduction
---------------
It has been argued that self-attention architectures (Vaswani et al., [2017](#bib.bib47)) deal better with longer temporal horizons than recurrent neural networks (RNNs):
by construction, they avoid compressing the whole past into a fixed-size hidden state and they do not suffer from vanishing or exploding gradients in the same way as RNNs.
Recent work has empirically validated these claims, demonstrating that self-attention architectures can provide significant gains in performance over the more traditional recurrent architectures such as the LSTM (Dai et al., [2019](#bib.bib11); Radford et al., [2019](#bib.bib40); Devlin et al., [2019](#bib.bib14); Yang et al., [2019](#bib.bib51)).
In particular, the Transformer architecture (Vaswani et al., [2017](#bib.bib47)) has had breakthrough success in a wide variety of domains:
language modeling (Dai et al., [2019](#bib.bib11); Radford et al., [2019](#bib.bib40); Yang et al., [2019](#bib.bib51)), machine translation (Vaswani et al., [2017](#bib.bib47); Edunov et al., [2018](#bib.bib15)), summarization ([Liu & Lapata,](#bib.bib33) ), question answering (Dehghani et al., [2018](#bib.bib13); Yang et al., [2019](#bib.bib51)), multi-task representation learning for NLP (Devlin et al., [2019](#bib.bib14); Radford et al., [2019](#bib.bib40); Yang et al., [2019](#bib.bib51)), and algorithmic tasks (Dehghani et al., [2018](#bib.bib13)).
The repeated success of the transformer architecture in domains where sequential information processing is critical to performance
makes it an ideal candidate for partially observable RL problems, where episodes can extend to thousands of steps and the critical observations for any decision often span the entire episode. Yet, the RL literature is dominated by the use of LSTMs as the main mechanism for providing memory to the agent (Espeholt et al., [2018](#bib.bib16); Kapturowski et al., [2019](#bib.bib29); Mnih et al., [2016](#bib.bib36)). Despite progress at designing more expressive memory architectures (Graves et al., [2016](#bib.bib20); Wayne et al., [2018](#bib.bib49); Santoro et al., [2018](#bib.bib42)) that perform better than LSTMs in memory-based tasks and partially-observable environments, they have not seen widespread adoption in RL agents perhaps due to their complex implementation, with the LSTM being seen as the go-to solution for environments where memory is required. In contrast to these other memory architectures, the transformer is well-tested in many challenging domains and has seen several open-source implementations in a variety of deep learning frameworks 111e.g. <https://github.com/kimiyoung/transformer-xl>, <https://github.com/tensorflow/tensor2tensor>.
Motivated by the transformer’s superior performance over LSTMs and the widespread availability of implementations, in this work we investigate the transformer architecture in the RL setting.
In particular, we find that the canonical transformer is significantly difficult to optimize,
often resulting in performance comparable to a random policy.
This difficulty in training transformers exists in the supervised case as well. Typically a complex learning rate schedule is required (e.g., linear warmup or cosine decay) in order to train (Vaswani et al., [2017](#bib.bib47); Dai et al., [2019](#bib.bib11)),
or specialized weight initialization schemes are used to improve performance (Radford et al., [2019](#bib.bib40)).
These measures do not seem to be sufficient for RL. In [Mishra et al.](#bib.bib35) ([2018](#bib.bib35)), for example, transformers could not solve even simple bandit tasks and tabular Markov Decision Processes (MDPs), leading the authors to hypothesize that the transformer architecture was not suitable for processing sequential information.
However in this work we succeed in stabilizing training with a reordering of the layer normalization coupled with the addition of a new gating mechanism to key points in the submodules of the transformer.
Our novel gated architecture, the Gated Transformer-XL (GTrXL) (shown in Figure [1](#S2.F1 "Figure 1 ‣ 2 Transformer Architecture and Variants ‣ Stabilizing Transformers for Reinforcement Learning"), Right), is able to learn much faster and more reliably and exhibit significantly better final performance than the canonical transformer.
We further demonstrate that the GTrXL achieves state-of-the-art results when compared to the external memory architecture MERLIN (Wayne et al., [2018](#bib.bib49)) on the multitask DMLab-30 suite (Beattie et al., [2016](#bib.bib6)). Additionally, we surpass LSTMs significantly on memory-based DMLab-30 levels while matching performance on the reactive set, as well as significantly outperforming LSTMs on memory-based continuous control and navigation environments.
We perform extensive ablations on the GTrXL in challenging environments with both continuous actions and high-dimensional observations, testing the final performance of the various components as well as the GTrXL’s robustness to seed and hyperparameter sensitivity compared to LSTMs and the canonical transformer. We demonstrate a consistent superior performance while matching the stability of LSTMs, providing evidence that the GTrXL architecture can function as a drop-in replacement to the LSTM networks ubiquitously used in RL.
2 Transformer Architecture and Variants
----------------------------------------

Figure 1: Transformer variants, showing just a single layer block (there are L𝐿Litalic\_L layers total). Left: Canonical Transformer(-XL) block with multi-head attention and position-wise MLP submodules and the standard layer normalization (Ba et al., [2016](#bib.bib4)) placement with respect to the residual connection (He et al., [2016a](#bib.bib22)). Center: TrXL-I moves the layer normalization to the input stream of the submodules. Coupled with the residual connections, there is a gradient path that flows from output to input without any transformations. Right: The GTrXL block, which additionally adds a gating layer in place of the residual connection of the TrXL-I.
The transformer network consists of several stacked blocks that repeatedly apply self-attention to the input sequence. The transformer layer block itself has remained relatively constant since its original introduction (Vaswani et al., [2017](#bib.bib47); Liu et al., [2018](#bib.bib32); Radford et al., [2019](#bib.bib40)). Each layer consists of two submodules: an attention operation followed by a position-wise multi-layer network (see Figure [1](#S2.F1 "Figure 1 ‣ 2 Transformer Architecture and Variants ‣ Stabilizing Transformers for Reinforcement Learning") (left)). The input to the transformer block is an embedding from the previous layer E(l−1)∈ℝT×Dsuperscript𝐸𝑙1superscriptℝ𝑇𝐷E^{(l-1)}\in\mathbb{R}^{T\times D}italic\_E start\_POSTSUPERSCRIPT ( italic\_l - 1 ) end\_POSTSUPERSCRIPT ∈ blackboard\_R start\_POSTSUPERSCRIPT italic\_T × italic\_D end\_POSTSUPERSCRIPT, where T𝑇Titalic\_T is the number of time steps, D𝐷Ditalic\_D is the hidden dimension, and l∈[0,L]𝑙0𝐿l\in[0,L]italic\_l ∈ [ 0 , italic\_L ] is the layer index with L𝐿Litalic\_L being the total number of layers. We assume E(0)superscript𝐸0E^{(0)}italic\_E start\_POSTSUPERSCRIPT ( 0 ) end\_POSTSUPERSCRIPT is an arbitrarily-obtained input embedding of dimension [T,D]𝑇𝐷[T,D][ italic\_T , italic\_D ], e.g. a word embedding in the case of language modeling or an embedding of the per-timestep observations in an RL environment.
Multi-Head Attention: The Multi-Head Attention (MHA) submodule computes in parallel H𝐻Hitalic\_H soft-attention operations for every time step. A residual connection (He et al., [2016a](#bib.bib22)) and layer normalization (Ba et al., [2016](#bib.bib4)) are then applied to the output (see Appendix [C](#A3 "Appendix C Multi-Head Attention Details ‣ Stabilizing Transformers for Reinforcement Learning") for more details):
| | | | |
| --- | --- | --- | --- |
| | Y¯(l)=MultiHeadAttention(E(l−1)),Y^(l)=E(l−1)+Y¯(l),Y(l)=LayerNorm(Y^(l)),formulae-sequencesuperscript¯𝑌𝑙MultiHeadAttentionsuperscript𝐸𝑙1formulae-sequencesuperscript^𝑌𝑙superscript𝐸𝑙1superscript¯𝑌𝑙superscript𝑌𝑙LayerNormsuperscript^𝑌𝑙\displaystyle\overline{Y}^{(l)}=\text{MultiHeadAttention}(E^{(l-1)}),\quad\hat{Y}^{(l)}=E^{(l-1)}+\overline{Y}^{(l)},\quad Y^{(l)}=\text{LayerNorm}(\hat{Y}^{(l)}),over¯ start\_ARG italic\_Y end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT = MultiHeadAttention ( italic\_E start\_POSTSUPERSCRIPT ( italic\_l - 1 ) end\_POSTSUPERSCRIPT ) , over^ start\_ARG italic\_Y end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT = italic\_E start\_POSTSUPERSCRIPT ( italic\_l - 1 ) end\_POSTSUPERSCRIPT + over¯ start\_ARG italic\_Y end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT , italic\_Y start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT = LayerNorm ( over^ start\_ARG italic\_Y end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ) , | | (1) |
Multi-Layer Perceptron: The Multi-Layer Perceptron (MLP) submodule applies a 1×1111\times 11 × 1 temporal convolutional network f(l)superscript𝑓𝑙f^{(l)}italic\_f start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT (i.e., kernel size 1, stride 1) over every step in the sequence, producing a new embedding tensor E(l)∈ℝT×Dsuperscript𝐸𝑙superscriptℝ𝑇𝐷E^{(l)}\in\mathbb{R}^{T\times D}italic\_E start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ∈ blackboard\_R start\_POSTSUPERSCRIPT italic\_T × italic\_D end\_POSTSUPERSCRIPT. As in Dai et al. ([2019](#bib.bib11)), the network output does not include an activation function. After the MLP, there is a residual update followed by layer normalization:
| | | | |
| --- | --- | --- | --- |
| | E¯(l)=f(l)(Y(l)),E^(l)=Y(l)+E¯(l),E(l)=LayerNorm(E^(l)).formulae-sequencesuperscript¯𝐸𝑙superscript𝑓𝑙superscript𝑌𝑙formulae-sequencesuperscript^𝐸𝑙superscript𝑌𝑙superscript¯𝐸𝑙superscript𝐸𝑙LayerNormsuperscript^𝐸𝑙\displaystyle\overline{E}^{(l)}=f^{(l)}(Y^{(l)}),\qquad\hat{E}^{(l)}=Y^{(l)}+\overline{E}^{(l)},\qquad E^{(l)}=\text{LayerNorm}(\hat{E}^{(l)}).over¯ start\_ARG italic\_E end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT = italic\_f start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ( italic\_Y start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ) , over^ start\_ARG italic\_E end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT = italic\_Y start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT + over¯ start\_ARG italic\_E end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT , italic\_E start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT = LayerNorm ( over^ start\_ARG italic\_E end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ) . | | (2) |
Relative Position Encodings: The basic MHA operation does not take sequence order into account explicitly because
it is
permutation invariant. Positional encodings are a widely used solution in domains like language where order is an important semantic cue, appearing in the original transformer architecture (Vaswani et al., [2017](#bib.bib47)). To enable a much larger contextual horizon than would otherwise be possible, we use the relative position encodings and memory scheme used in Dai et al. ([2019](#bib.bib11)). In this setting, there is an additional 𝒯𝒯\mathcal{T}caligraphic\_T-step memory tensor M(l)∈ℝ𝒯×Dsuperscript𝑀𝑙superscriptℝ𝒯𝐷M^{(l)}\in\mathbb{R}^{\mathcal{T}\times D}italic\_M start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ∈ blackboard\_R start\_POSTSUPERSCRIPT caligraphic\_T × italic\_D end\_POSTSUPERSCRIPT, which is treated as constant during weight updates. The MHA submodule then becomes:
| | | | | |
| --- | --- | --- | --- | --- |
| | Y¯(l)superscript¯𝑌𝑙\displaystyle\overline{Y}^{(l)}over¯ start\_ARG italic\_Y end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT | = RelativeMultiHeadAttention(StopGrad(M(l−1)),E(l−1))absent RelativeMultiHeadAttentionStopGradsuperscript𝑀𝑙1superscript𝐸𝑙1\displaystyle=\text{ RelativeMultiHeadAttention}(\text{StopGrad}(M^{(l-1)}),E^{(l-1)})= RelativeMultiHeadAttention ( StopGrad ( italic\_M start\_POSTSUPERSCRIPT ( italic\_l - 1 ) end\_POSTSUPERSCRIPT ) , italic\_E start\_POSTSUPERSCRIPT ( italic\_l - 1 ) end\_POSTSUPERSCRIPT ) | | (3) |
| | Y^(l)superscript^𝑌𝑙\displaystyle\hat{Y}^{(l)}over^ start\_ARG italic\_Y end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT | =E(l−1)+Y¯(l),Y(l)=LayerNorm(Y^(l))formulae-sequenceabsentsuperscript𝐸𝑙1superscript¯𝑌𝑙superscript𝑌𝑙LayerNormsuperscript^𝑌𝑙\displaystyle=E^{(l-1)}+\overline{Y}^{(l)},\qquad Y^{(l)}=\text{LayerNorm}(\hat{Y}^{(l)})= italic\_E start\_POSTSUPERSCRIPT ( italic\_l - 1 ) end\_POSTSUPERSCRIPT + over¯ start\_ARG italic\_Y end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT , italic\_Y start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT = LayerNorm ( over^ start\_ARG italic\_Y end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ) | | (4) |
where StopGrad is a stop-gradient function that prevents gradients flowing backwards during backpropagation. We refer to Appendix [C](#A3 "Appendix C Multi-Head Attention Details ‣ Stabilizing Transformers for Reinforcement Learning") for a more detailed description.
3 Gated Transformer Architectures
----------------------------------
While the transformer architecture has achieved breakthrough results in modeling sequences for supervised learning tasks (Vaswani et al., [2017](#bib.bib47); Liu et al., [2018](#bib.bib32); Dai et al., [2019](#bib.bib11)), a demonstration of the transformer as a useful RL memory has been notably absent. Previous work has highlighted training difficulties and poor performance (Mishra et al., [2018](#bib.bib35)).
When transformers have not been used for temporal memory but instead as a mechanism for attention over the input space, they have had success—notably in the challenging multi-agent Starcraft 2 environment (Vinyals et al., [2019](#bib.bib48)). Here, the transformer was applied solely across Starcraft units and not over time.
Multiplicative interactions have been successful at stabilizing learning across a wide variety of architectures (Hochreiter & Schmidhuber, [1997](#bib.bib25); Srivastava et al., [2015](#bib.bib43); Cho et al., [2014](#bib.bib9)).
Motivated by this, we propose the introduction of powerful gating mechanisms in place of the residual connections within the transformer block, coupled with changes to the order of layer normalization in the submodules.
As will be empirically demonstrated, the “Identity Map Reordering” and gating mechanisms are critical for stabilizing learning and improving performance.
###
3.1 Identity Map Reordering
Our first change is to place the layer normalization on only the input stream of the submodules, a modification described in several previous works (He et al., [2016b](#bib.bib23); Radford et al., [2019](#bib.bib40); Baevski & Auli, [2019](#bib.bib5)). The model using this *Identity Map Reordering* is termed TrXL-I in the following, and is depicted visually in Figure [1](#S2.F1 "Figure 1 ‣ 2 Transformer Architecture and Variants ‣ Stabilizing Transformers for Reinforcement Learning") (center). A key benefit to this reordering is that it now enables an identity map from the input of the transformer at the first layer to the output of the transformer after the last layer. This is in contrast to the canonical transformer, where there are a series of layer normalization operations that non-linearly transform the state encoding. Because the layer norm reordering causes a path where two linear layers are applied in sequence, we apply a ReLU activation to each sub-module output before the residual connection (see Appendix [C](#A3 "Appendix C Multi-Head Attention Details ‣ Stabilizing Transformers for Reinforcement Learning") for equations).
The TrXL-I already exhibits a large improvement in stability and performance over TrXL (see Section [4.3.1](#S4.SS3.SSS1 "4.3.1 Performance Ablation ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning")). One hypothesis as to why the Identity Map Reordering
improves results is as follows: assuming that the submodules at initialization produce values that are in expectation near zero, the state encoding is passed un-transformed to the policy and value heads, enabling the agent to learn a Markovian policy at the start of training (i.e., the network is initialized such that π(⋅|st,…,s1)≈π(⋅|st)\pi(\cdot|s\_{t},\ldots,s\_{1})\approx\pi(\cdot|s\_{t})italic\_π ( ⋅ | italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT , … , italic\_s start\_POSTSUBSCRIPT 1 end\_POSTSUBSCRIPT ) ≈ italic\_π ( ⋅ | italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT ) and Vπ(st|st−1,…,s1)≈Vπ(st|st−1)superscript𝑉𝜋conditionalsubscript𝑠𝑡subscript𝑠𝑡1…subscript𝑠1superscript𝑉𝜋conditionalsubscript𝑠𝑡subscript𝑠𝑡1V^{\pi}(s\_{t}|s\_{t-1},\ldots,s\_{1})\approx V^{\pi}(s\_{t}|s\_{t-1})italic\_V start\_POSTSUPERSCRIPT italic\_π end\_POSTSUPERSCRIPT ( italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT | italic\_s start\_POSTSUBSCRIPT italic\_t - 1 end\_POSTSUBSCRIPT , … , italic\_s start\_POSTSUBSCRIPT 1 end\_POSTSUBSCRIPT ) ≈ italic\_V start\_POSTSUPERSCRIPT italic\_π end\_POSTSUPERSCRIPT ( italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT | italic\_s start\_POSTSUBSCRIPT italic\_t - 1 end\_POSTSUBSCRIPT )). In many environments, reactive behaviours need to be learned before memory-based ones can be effectively utilized, i.e., an agent needs to learn how to walk before it can learn how to remember where it has walked.
###
3.2 Gating Layers
We
further improve performance and optimization stability by replacing the residual connections in Equations [4](#S2.E4 "4 ‣ 2 Transformer Architecture and Variants ‣ Stabilizing Transformers for Reinforcement Learning") and [2](#S2.E2 "2 ‣ 2 Transformer Architecture and Variants ‣ Stabilizing Transformers for Reinforcement Learning") with gating layers.
We call the gated architecture with the identity map reordering the *Gated Transformer(-XL)* (GTrXL). The final GTrXL layer block is written below:
| | | | | |
| --- | --- | --- | --- | --- |
| | Y¯(l)superscript¯𝑌𝑙\displaystyle\overline{Y}^{(l)}over¯ start\_ARG italic\_Y end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT | = RelativeMultiHeadAttention(LayerNorm([StopGrad(M(l−1)),E(l−1)]))absent RelativeMultiHeadAttentionLayerNormStopGradsuperscript𝑀𝑙1superscript𝐸𝑙1\displaystyle=\text{ RelativeMultiHeadAttention}(\text{LayerNorm}([\text{StopGrad}(M^{(l-1)}),E^{(l-1)}]))= RelativeMultiHeadAttention ( LayerNorm ( [ StopGrad ( italic\_M start\_POSTSUPERSCRIPT ( italic\_l - 1 ) end\_POSTSUPERSCRIPT ) , italic\_E start\_POSTSUPERSCRIPT ( italic\_l - 1 ) end\_POSTSUPERSCRIPT ] ) ) | | (5) |
| | Y(l)superscript𝑌𝑙\displaystyle Y^{(l)}italic\_Y start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT | =gMHA(l)(E(l−1),ReLU(Y¯(l)))absentsubscriptsuperscript𝑔𝑙MHAsuperscript𝐸𝑙1ReLUsuperscript¯𝑌𝑙\displaystyle=g^{(l)}\_{\text{MHA}}(E^{(l-1)},\text{ReLU}(\overline{Y}^{(l)}))= italic\_g start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT MHA end\_POSTSUBSCRIPT ( italic\_E start\_POSTSUPERSCRIPT ( italic\_l - 1 ) end\_POSTSUPERSCRIPT , ReLU ( over¯ start\_ARG italic\_Y end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ) ) | | (6) |
| | E¯(l)superscript¯𝐸𝑙\displaystyle\overline{E}^{(l)}over¯ start\_ARG italic\_E end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT | =f(l)(LayerNorm(Y(l)))absentsuperscript𝑓𝑙LayerNormsuperscript𝑌𝑙\displaystyle=f^{(l)}(\text{LayerNorm}(Y^{(l)}))= italic\_f start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ( LayerNorm ( italic\_Y start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ) ) | | (7) |
| | E(l)superscript𝐸𝑙\displaystyle E^{(l)}italic\_E start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT | =gMLP(l)(Y(l),ReLU(E¯(l)))absentsubscriptsuperscript𝑔𝑙MLPsuperscript𝑌𝑙ReLUsuperscript¯𝐸𝑙\displaystyle=g^{(l)}\_{\text{MLP}}(Y^{(l)},\text{ReLU}(\overline{E}^{(l)}))= italic\_g start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT MLP end\_POSTSUBSCRIPT ( italic\_Y start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT , ReLU ( over¯ start\_ARG italic\_E end\_ARG start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ) ) | | (8) |
where g𝑔gitalic\_g is a gating layer function.
A visualization of our final architecture is shown in Figure [1](#S2.F1 "Figure 1 ‣ 2 Transformer Architecture and Variants ‣ Stabilizing Transformers for Reinforcement Learning") (right), with the modifications from the canonical transformer highlighted in red.
In our experiments we ablate a variety of gating layers with increasing expressivity:
Input: The gated input connection has a sigmoid modulation on the input stream, similar to the short-cut-only gating from He et al. ([2016b](#bib.bib23)):
| | | |
| --- | --- | --- |
| | g(l)(x,y)=σ(Wg(l)x)⊙x+ysuperscript𝑔𝑙𝑥𝑦direct-product𝜎subscriptsuperscript𝑊𝑙𝑔𝑥𝑥𝑦\displaystyle g^{(l)}(x,y)=\sigma(W^{(l)}\_{g}x)\odot x+yitalic\_g start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ( italic\_x , italic\_y ) = italic\_σ ( italic\_W start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT italic\_x ) ⊙ italic\_x + italic\_y | |
Output: The gated output connection has a sigmoid modulation on the output stream:
| | | |
| --- | --- | --- |
| | g(l)(x,y)=x+σ(Wg(l)x−bg(l))⊙ysuperscript𝑔𝑙𝑥𝑦𝑥direct-product𝜎subscriptsuperscript𝑊𝑙𝑔𝑥subscriptsuperscript𝑏𝑙𝑔𝑦\displaystyle g^{(l)}(x,y)=x+\sigma(W^{(l)}\_{g}x-b^{(l)}\_{g})\odot yitalic\_g start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ( italic\_x , italic\_y ) = italic\_x + italic\_σ ( italic\_W start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT italic\_x - italic\_b start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT ) ⊙ italic\_y | |
Highway: The highway connection (Srivastava et al., [2015](#bib.bib43)) modulates both streams with a sigmoid:
| | | |
| --- | --- | --- |
| | g(l)(x,y)=σ(Wg(l)x+bg(l))⊙x+(1−σ(Wg(l)x+bg(l)))⊙ysuperscript𝑔𝑙𝑥𝑦direct-product𝜎subscriptsuperscript𝑊𝑙𝑔𝑥subscriptsuperscript𝑏𝑙𝑔𝑥direct-product1𝜎subscriptsuperscript𝑊𝑙𝑔𝑥subscriptsuperscript𝑏𝑙𝑔𝑦\displaystyle g^{(l)}(x,y)=\sigma(W^{(l)}\_{g}x+b^{(l)}\_{g})\odot x+(1-\sigma(W^{(l)}\_{g}x+b^{(l)}\_{g}))\odot yitalic\_g start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ( italic\_x , italic\_y ) = italic\_σ ( italic\_W start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT italic\_x + italic\_b start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT ) ⊙ italic\_x + ( 1 - italic\_σ ( italic\_W start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT italic\_x + italic\_b start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT ) ) ⊙ italic\_y | |
Sigmoid-Tanh: The sigmoid-tanh (SigTanh) gate (Van den Oord et al., [2016](#bib.bib46)) is similar to the Output gate but with an additional tanh activation on the output stream:
| | | |
| --- | --- | --- |
| | g(l)(x,y)=x+σ(Wg(l)y−b)⊙tanh(Ug(l)y)superscript𝑔𝑙𝑥𝑦𝑥direct-product𝜎subscriptsuperscript𝑊𝑙𝑔𝑦𝑏subscriptsuperscript𝑈𝑙𝑔𝑦\displaystyle g^{(l)}(x,y)=x+\sigma(W^{(l)}\_{g}y-b)\odot\tanh(U^{(l)}\_{g}y)italic\_g start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ( italic\_x , italic\_y ) = italic\_x + italic\_σ ( italic\_W start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT italic\_y - italic\_b ) ⊙ roman\_tanh ( italic\_U start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT italic\_y ) | |
Gated-Recurrent-Unit-type gating: The Gated Recurrent Unit
(GRU) (Chung et al., [2014](#bib.bib10)) is a recurrent network that performs similarly to an LSTM (Hochreiter & Schmidhuber, [1997](#bib.bib25)) but has fewer parameters. We adapt its powerful gating mechanism as an untied activation function in depth:
| | | | |
| --- | --- | --- | --- |
| | r=σ(Wr(l)y+Ur(l)x),𝑟𝜎superscriptsubscript𝑊𝑟𝑙𝑦superscriptsubscript𝑈𝑟𝑙𝑥\displaystyle r=\sigma(W\_{r}^{(l)}y+U\_{r}^{(l)}x),\qquaditalic\_r = italic\_σ ( italic\_W start\_POSTSUBSCRIPT italic\_r end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT italic\_y + italic\_U start\_POSTSUBSCRIPT italic\_r end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT italic\_x ) , | z=σ(Wz(l)y+Uz(l)x−bg(l)),h^=tanh(Wg(l)y+Ug(l)(r⊙x)),formulae-sequence𝑧𝜎superscriptsubscript𝑊𝑧𝑙𝑦superscriptsubscript𝑈𝑧𝑙𝑥subscriptsuperscript𝑏𝑙𝑔^ℎsubscriptsuperscript𝑊𝑙𝑔𝑦subscriptsuperscript𝑈𝑙𝑔direct-product𝑟𝑥\displaystyle z=\sigma(W\_{z}^{(l)}y+U\_{z}^{(l)}x-b^{(l)}\_{g}),\qquad\hat{h}=\tanh(W^{(l)}\_{g}y+U^{(l)}\_{g}(r\odot x)),italic\_z = italic\_σ ( italic\_W start\_POSTSUBSCRIPT italic\_z end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT italic\_y + italic\_U start\_POSTSUBSCRIPT italic\_z end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT italic\_x - italic\_b start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT ) , over^ start\_ARG italic\_h end\_ARG = roman\_tanh ( italic\_W start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT italic\_y + italic\_U start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT ( italic\_r ⊙ italic\_x ) ) , | |
| | | g(l)(x,y)=(1−z)⊙x+z⊙h^.superscript𝑔𝑙𝑥𝑦direct-product1𝑧𝑥direct-product𝑧^ℎ\displaystyle\qquad g^{(l)}(x,y)=(1-z)\odot x+z\odot\hat{h}.italic\_g start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT ( italic\_x , italic\_y ) = ( 1 - italic\_z ) ⊙ italic\_x + italic\_z ⊙ over^ start\_ARG italic\_h end\_ARG . | |
Gated Identity Initialization:
We have claimed that the Identity Map Reordering aids policy optimization because it initializes the agent close to a Markovian policy / value function. If this is indeed the cause of improved stability, we can explicitly initialize the various gating mechanisms to be close to the identity map. This is the purpose of the bias bg(l)superscriptsubscript𝑏𝑔𝑙b\_{g}^{(l)}italic\_b start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT in the applicable gating layers. We later demonstrate in an ablation that initially setting bg(l)>0superscriptsubscript𝑏𝑔𝑙0b\_{g}^{(l)}>0italic\_b start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT > 0 can greatly improve learning speed.
4 Experiments
--------------


Figure 2: Average return on DMLab-30, re-scaled such that a human has mean 100 score on each level and a random policy has 0. Left: Results averaged over the full DMLab-30 suite. Right: DMLab-30 partitioned into a “Memory” and “Reactive” split (described in Appendix [D](#A4 "Appendix D DMLab-30 Memory/Reactive Partition ‣ Stabilizing Transformers for Reinforcement Learning")). The GTrXL has a substantial gain over LSTM in memory-based environments, while even slightly surpassing performance on the reactive set. We plot 6-8 hyperparameter settings per architecture (see Appendix [B](#A2 "Appendix B Experimental details ‣ Stabilizing Transformers for Reinforcement Learning")). MERLIN scores obtained from personal communication with the authors.
In this section, we provide experiments on a variety of challenging single and multi-task RL domains: DMLab-30 (Beattie et al., [2016](#bib.bib6)), Numpad and Memory Maze (see Fig. [8](#A1.F8 "Figure 8 ‣ Appendix A Environment Details ‣ Stabilizing Transformers for Reinforcement Learning")). Crucially we demonstrate that the proposed Gated Transformer-XL (GTrXL) not only shows substantial improvements over LSTMs on memory-based environments, but suffers no degradation of performance on reactive environments. The GTrXL also exceeds MERLIN (Wayne et al., [2018](#bib.bib49)), an external memory architecture which used a Differentiable Neural Computer (Graves et al., [2016](#bib.bib20)) coupled with auxiliary losses, surpassing its performance on both memory and reactive tasks.
For all transformer architectures except when otherwise stated, we train relatively deep 12-layer networks with embedding size 256 and memory size 512. These networks are comparable to the state-of-the-art networks in use for small language modeling datasets (see enwik8 results in (Dai et al., [2019](#bib.bib11))). We chose to train deep networks in order to demonstrate that our results do not necessarily sacrifice complexity for stability, i.e. we are not making transformers stable for RL simply by making them shallow. Our networks have receptive fields that can potentially span any episode in the environments tested, with an upper bound on the receptive field of 6144 (12layers×512 memory12layers512 memory12\ \text{layers}\times 512\text{ memory}12 layers × 512 memory (Dai et al., [2019](#bib.bib11))). Future work will look at scaling transformers in RL even further, e.g. towards the 52-layer network in Radford et al. ([2019](#bib.bib40)).
See App. [B](#A2 "Appendix B Experimental details ‣ Stabilizing Transformers for Reinforcement Learning") for experimental details.
For all experiments, we used V-MPO (Anonymous Authors, [2019](#bib.bib3)), an on-policy adaptation of Maximum a Posteriori Policy Optimization (MPO) (Abdolmaleki et al., [2018a](#bib.bib1); [b](#bib.bib2)) that performs approximate policy iteration based on a learned state-value function V(s)𝑉𝑠V(s)italic\_V ( italic\_s ) instead of the state-action value function used in MPO. Rather than directly updating the parameters in the direction of the policy gradient, V-MPO uses the estimated advantages to first construct a target distribution for the policy update subject to a sample-based KL constraint, then calculates the gradient that partially moves the parameters toward that target, again subject to a KL constraint.
V-MPO
was
shown to achieve state-of-the-art results for LSTM-based agents on the multi-task DMLab-30 benchmark suite.
###
4.1 Transformer as Effective RL Memory Architecture
We first present results of the best performing GTrXL variant, the GRU-type gating, against a competitive LSTM baseline,
demonstrating a substantial improvement on the multi-task DMLab-30 domain (Beattie et al., [2016](#bib.bib6)).
Figure [2](#S4.F2 "Figure 2 ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") shows mean return over all levels as training progresses, where the return is human normalized as done in previous work (meaning a human has a per-level mean score of 100 and a random policy has a score of 0), while Table [1](#S4.T1 "Table 1 ‣ 4.2 Scaling with Memory Horizon ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") has the final performance at 10 billion environment steps.
The GTrXL has a significant gap over a 3-layer LSTM baseline trained using the same V-MPO algorithm.
Furthermore, we included the final results of a previously-published external memory architecture, MERLIN (Wayne et al., [2018](#bib.bib49)).
Because MERLIN was trained for 100 billion environment steps with a different algorithm, IMPALA (Espeholt et al., [2018](#bib.bib16)),
and also involved an auxiliary loss critical for the memory component to function,
the learning curves are not directly comparable and we only report the final performance of the architecture as a dotted line.
Despite the differences, our results demonstrate that the GTrXL can match the state-of-the-art on DMLab-30.
An informative split between a set of memory-based levels and more reactive ones (listed in Appendix [D](#A4 "Appendix D DMLab-30 Memory/Reactive Partition ‣ Stabilizing Transformers for Reinforcement Learning")) reveals that our model specifically has large improvements in environments where memory plays a critical role. Meanwhile, GTrXL also shows improvement over LSTMs on the set of reactive levels, as memory can still be effectively utilized in some of these levels.
###
4.2 Scaling with Memory Horizon
We next demonstrate that the GTrXL scales better compared to an LSTM when an environment’s temporal horizon is increased, using the “Numpad” continuous control task of Humplik et al. ([2019](#bib.bib26)) which allows an easy combinatorial increase in the temporal horizon. In Numpad, a robotic agent is situated on a platform resembling the 3x3 number pad of a telephone (generalizable to N×N𝑁𝑁N\times Nitalic\_N × italic\_N pads). The agent can interact with the pads by colliding with them, causing them to be activated (visualized in the environment state as the number pad glowing). The goal of the agent is to activate a specific sequence of up to N2superscript𝑁2N^{2}italic\_N start\_POSTSUPERSCRIPT 2 end\_POSTSUPERSCRIPT numbers, but without knowing this sequence a priori. The only feedback the agent gets is by activating numbers: if the pad is the next one in the sequence, the agent gains a reward of +1, otherwise all activated pads are cleared and the agent must restart the sequence. Each correct number in the sequence only provides reward once, i.e. each subsequent activation of that number will no longer provide rewards. Therefore the agent must explicitly develop a search strategy to determine the correct pad sequence. Once the agent completes the full sequence, all pads are reset and the agent gets a chance to repeat the sequence again for more reward. This means higher reward directly translates into how well the pad sequence has been memorized. An image of the scenario is provided in Figure [3](#S4.F3 "Figure 3 ‣ 4.2 Scaling with Memory Horizon ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning"). There is the restriction that contiguous pads in the sequence must be contiguous in space, i.e. the next pad in the sequence can only be in the Moore neighborhood of the previous pad. Furthermore, no pad can be pressed twice in the sequence.
We present two results in this environment in Figure [3](#S4.F3 "Figure 3 ‣ 4.2 Scaling with Memory Horizon ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning"). The first measures the final performance of the trained models as a function of the pad size. We can see that LSTM performs badly on all 3 pad sizes, and performs worse as the pad size increases from 2 to 4. The GTrXL performs much better, and almost instantly solves the environment with its much more expressive memory.
On the center and right images, we provide learning curves for the 2×2222\times 22 × 2 and 4×4444\times 44 × 4 Numpad environments, and show that even when the LSTM is trained twice as long it does not
reach GTrXL’s performance.



Figure 3: Numpad results demonstrating that the GTrXL has much better memory scaling properties than LSTM. Left: As the Numpad environment’s memory requirement increases (because of larger pad size), the GTrXL suffers much less than LSTM. However, because of the combinatorial nature of Numpad, the GTrXL eventually also starts dropping in performance at 4x4. We plot mean and standard error of the last 200 episodes after training each model for 0.15B, 1.0B and 2.0B environment steps for Numpad size 2, 3 and 4, respectively. Center, Right: Learning curves for the GTrXL on 2×2222\times 22 × 2 and 4×4444\times 44 × 4 Numpad. Even when the LSTM is trained for twice as long, the GTrXL still has a substantial improvement over it. We plot 5 hyperparameter settings per model for learning curves.
| | | |
| --- | --- | --- |
| Model | Mean Human Norm. |
Mean Human Norm., 100-capped
|
| LSTM | 99.3 ±plus-or-minus\pm± 1.0 | 84.0 ±plus-or-minus\pm± 0.4 |
| TrXL | 5.0 ±plus-or-minus\pm± 0.2 | 5.0 ±plus-or-minus\pm± 0.2 |
| TrXL-I | 107.0 ±plus-or-minus\pm± 1.2 | 87.4 ±plus-or-minus\pm± 0.3 |
| MERLIN@100B | 115.2 | 89.4 |
| GTrXL (GRU) | 117.6 ±plus-or-minus\pm± 0.3 | 89.1 ±plus-or-minus\pm± 0.2 |
| GTrXL (Input) | 51.2 ±plus-or-minus\pm± 13.2 | 47.6 ±plus-or-minus\pm± 12.1 |
| GTrXL (Output) | 112.8 ±plus-or-minus\pm± 0.8 | 87.8 ±plus-or-minus\pm± 0.3 |
| GTrXL (Highway) | 90.9 ±plus-or-minus\pm± 12.9 | 75.2 ±plus-or-minus\pm± 10.4 |
| GTrXL (SigTanh) | 101.0 ±plus-or-minus\pm± 1.3 | 83.9 ±plus-or-minus\pm± 0.7 |
Table 1: Final human-normalized return averaged across all 30 DMLab levels for baselines and GTrXL variants. We also include the 100-capped score where the per-level mean score is clipped at 100, providing a metric that is proportional to the percentage of levels that the agent is superhuman. We see that the GTrXL (GRU) surpasses LSTM by a significant gap and exceeds the performance of MERLIN (Wayne et al., [2018](#bib.bib49)) trained for 100 billion environment steps. The GTrXL (Output) and the proposed reordered TrXL-I also surpass LSTM but perform slightly worse than MERLIN and are not as robust as GTrXL (GRU) (see Sec. [4.3.2](#S4.SS3.SSS2 "4.3.2 Hyperparameter and Seed Sensitivity ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning")). We sample 6-8 hyperparameters per model. We include standard error over runs.
###
4.3 Gating Variants + Identity Map Reordering
We demonstrated that the GRU-type-gated GTrXL can achieve
state-of-the-art results on DMLab-30, surpassing both a deep LSTM and an external memory architecture, and also that the GTrXL has a memory which scales better with the memory horizon of the environment.
However, the question remains whether the expressive gating mechanisms of the GRU could be replaced by simpler alternatives. In this section, we perform extensive ablations on the gating variants described in Section [3.2](#S3.SS2 "3.2 Gating Layers ‣ 3 Gated Transformer Architectures ‣ Stabilizing Transformers for Reinforcement Learning"), and show that the GTrXL (GRU) has improvements in learning speed, final performance and optimization stability over all other models, even when controlling for the number of
parameters.
####
4.3.1 Performance Ablation


Figure 4: Learning curves for the gating mechanisms, along with MERLIN score at 100 billion frames as a reference point. We can see that the GRU performs as well as any other gating mechanism on the reactive set of tasks. On the memory environments, the GRU gating has a significant gain in learning speed and attains the highest final performance at the fastest rate. We plot both mean (bold) and the individual 6-8 hyperparameter samples per model (light).
We first report the performance of the gating variants in DMLab-30. Table [1](#S4.T1 "Table 1 ‣ 4.2 Scaling with Memory Horizon ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") and Figure [4](#S4.F4 "Figure 4 ‣ 4.3.1 Performance Ablation ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") show the final performance and training curves of the various gating types in both the memory / reactive split, respectively. The canonical TrXL completely fails to learn, while the TrXL-I improves over the LSTM.
Of the gating varieties, the GTrXL (Output) can recover a large amount of the performance of the GTrXL (GRU), especially in the reactive set, but as shown in Sec. [4.3.2](#S4.SS3.SSS2 "4.3.2 Hyperparameter and Seed Sensitivity ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") is generally far less stable. The GTrXL (Input) performs worse than even the TrXL-I, reinforcing the identity map path hypothesis. Finally, the GTrXL (Highway) and GTrXL (SigTanh) are more sensitive to the hyperparameter settings compared to the alternatives, with some settings doing worse than TrXL-I.
####
4.3.2 Hyperparameter and Seed Sensitivity



Figure 5: Sensitivity analysis of GTrXL variants versus TrXL and LSTM baselines. We sample 25 different hyperparameter sets and seeds and plot the ranked average return at 3 points during training (0.5B, 1.0B and 2.0B environment steps). Higher and flatter lines indicate more robust architectures. The same hyperparameter sampling distributions were used across models (see Appendix [B](#A2 "Appendix B Experimental details ‣ Stabilizing Transformers for Reinforcement Learning")). We plot human performance as a dotted line.
Table 2: Parameter-Controlled Comparisons. Parameter count given in millions. The standard error of the means of the 6-8 runs per model reported in brackets.
| | | |
| --- | --- | --- |
| Model |
Mean Human
Norm. Score
| # Param. |
| LSTM | 99.3 ±plus-or-minus\pm± 1.0 | 9.25M |
| TrXL | 5.0 ±plus-or-minus\pm± 0.2 | 28.6M |
| TrXL-I | 107.0 ±plus-or-minus\pm± 1.2 | 28.6M |
|
Thin GTrXL (GRU)
| 111.5 ±plus-or-minus\pm± 0.6 | 22.4M |
| GTrXL (GRU) | 117.6 ±plus-or-minus\pm± 0.3 | 66.4M |
| GTrXL (Input) | 51.2 ±plus-or-minus\pm± 13.2 | 34.9M |
| GTrXL (Output) | 112.8 ±plus-or-minus\pm± 0.8 | 34.9M |
| GTrXL (Highway) | 90.9 ±plus-or-minus\pm± 12.9 | 34.9M |
| GTrXL (SigTanh) | 101.0 ±plus-or-minus\pm± 1.3 | 41.2M |
| | |
| --- | --- |
| Model |
% Diverged
|
| LSTM | 0% |
| TrXL | 0% |
| TrXL-I | 16% |
| GTrXL (GRU) | 0% |
| GTrXL (Output) | 12% |
Table 2: Parameter-Controlled Comparisons. Parameter count given in millions. The standard error of the means of the 6-8 runs per model reported in brackets.
Table 3: Percentage of the 25 parameter settings where the training loss diverged at any point within 2 billion environment steps. We do not report numbers for GTrXL gating types that were unstable in DMLab-30. For diverged runs we plot the returns in Figure [5](#S4.F5 "Figure 5 ‣ 4.3.2 Hyperparameter and Seed Sensitivity ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") as 0 afterwards.
Beyond improved performance, we next demonstrate a significant reduction in hyperparameter and seed sensitivity for the GTrXL (GRU) compared to baselines and other GTrXL variants. We use the “Memory Maze” environment, a memory-based navigation task in which the agent must discover the location of an apple randomly placed in a maze of blocks. The agent receives a positive reward for collecting the apple and is then teleported to a random location in the maze, with the apple’s position held fixed. The agent can make use of landmarks situated around the room to return as quickly as possible to the apple for subsequent rewards. Therefore, an effective mapping of the environment results in more frequent returns to the apple and higher reward.
We chose to perform the sensitivity ablation on Memory Maze because (1) it requires the use of long-range memory to be effective and (2) it includes both continuous and discrete action sets (details in Appendix [A](#A1 "Appendix A Environment Details ‣ Stabilizing Transformers for Reinforcement Learning")) which makes optimization more difficult.
In Figure [5](#S4.F5 "Figure 5 ‣ 4.3.2 Hyperparameter and Seed Sensitivity ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning"), we sample 25 independent V-MPO hyperparameter settings from a wide range of values and train the networks to 2 billion environment steps (see Appendix [B](#A2 "Appendix B Experimental details ‣ Stabilizing Transformers for Reinforcement Learning")). Then, at various points in training (0.5B, 1.0B and 2.0B), we rank all runs by their mean return and plot this ranking. Models with curves which are both higher and flatter are thus more robust to hyperparameters and random seeds. Our results demonstrate that (1) the GTrXL (GRU) can learn this challenging memory environment in much fewer environment steps than LSTM, and (2) that GTrXL (GRU) beats the other gating variants in stability by a large margin, thereby offering a substantial reduction in necessary hyperparameter tuning. The values in Table [3](#S4.T3 "Table 3 ‣ 4.3.2 Hyperparameter and Seed Sensitivity ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") list what percentage of the 25 runs per model had losses that diverged to infinity. We can see that the only model reaching human performance in 2 billion environment steps is the GTrXL (GRU), with 10 runs having a mean score 8 and above.
####
4.3.3 Parameter Count-Controlled Comparisons
For the final gating ablation, we compare transformer variants while tracking their total parameter count to control for the increase in capacity caused by the introduction of additional parameters in the gating mechanisms.
To demonstrate that the advantages of the GTrXL (GRU) are not due solely to an increase in parameter count, we halve the number of attention heads (which also effectively halves the embedding dimension due to the convention that the embedding size is the number of heads multiplied by the attention head dimension). The effect is a substantial reduction in parameter count, resulting in less parameters than even the canonical TrXL.
Fig. [6](#S4.F6 "Figure 6 ‣ 4.3.4 Gated Identity Initialization Ablation ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") and Tab. [3](#S4.T3 "Table 3 ‣ 4.3.2 Hyperparameter and Seed Sensitivity ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") compare the different models to the “Thin” GTrXL (GRU), with Tab. [3](#S4.T3 "Table 3 ‣ 4.3.2 Hyperparameter and Seed Sensitivity ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") listing the parameter counts. The Thin GTrXL (GRU) matches every other model (within variance) except the GTrXL (GRU), even matching the next best-performing model, the GTrXL (Output), with over 10 million less parameters.
####
4.3.4 Gated Identity Initialization Ablation


Figure 6: Learning curves comparing a thinner GTrXL (GRU) with half the embedding dimension of the other presented gated variants and TrXL baselines. The Thin GTrXL (GRU) has fewer parameters than any other model presented but still matches the performance of the best performing counterpart, the GTrXL (Output), which has over 10 million more parameters. We plot both mean (bold) and 6-8 hyperparameter settings (light) per model.



Figure 7: Ablation of the gated identity initialization on Memory Maze by comparing 10 runs of a model run with the bias initialization and 10 runs of a model without. Every run has independently sampled hyperparameters from a distribution. We plot the ranked mean return of the 10 runs of each model at 1, 2, and 4 billion environment steps.
Each mean return is the average of the past 200 episodes at the point of the model snapshot. We plot human performance as a dotted line.
All applicable gating variants in the previous sections were trained with the gated identity initialization (initial experiments found values bg(l)=2subscriptsuperscript𝑏𝑙𝑔2b^{(l)}\_{g}=2italic\_b start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT = 2 for GRU-type gating and bg(l)=1subscriptsuperscript𝑏𝑙𝑔1b^{(l)}\_{g}=1italic\_b start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT = 1 for other gating types to work well). We observed in initial Memory Maze results that the gated identity initialization significantly improved optimization stability and learning speed. Figure [7](#S4.F7 "Figure 7 ‣ 4.3.4 Gated Identity Initialization Ablation ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning") compares an otherwise identical 4-layer GTrXL (GRU) trained with (bg(l)=2subscriptsuperscript𝑏𝑙𝑔2b^{(l)}\_{g}=2italic\_b start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT = 2) and without (bg(l)=0subscriptsuperscript𝑏𝑙𝑔0b^{(l)}\_{g}=0italic\_b start\_POSTSUPERSCRIPT ( italic\_l ) end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_g end\_POSTSUBSCRIPT = 0) the gated identity initialization, with 10 hyperparameter samples per initial bias setting. Similarly to the previous sensitivity plots, we plot the ranked mean return of all 10 runs at various times during training. As can be seen from Fig. [7](#S4.F7 "Figure 7 ‣ 4.3.4 Gated Identity Initialization Ablation ‣ 4.3 Gating Variants + Identity Map Reordering ‣ 4 Experiments ‣ Stabilizing Transformers for Reinforcement Learning"), there is a significant gap caused by the bias initialization,
suggesting that preconditioning the transformer to be close to Markovian results in large learning speed gains.
5 Related Work
---------------
Gating has been shown to be effective to address the vanishing gradient problem and thus improve the learnability of recurrent models. LSTM networks (Hochreiter & Schmidhuber, [1997](#bib.bib25); Graves, [2013](#bib.bib19)) rely on an input, forget and output gate that protect the update of the cell.
GRU (Chung et al., [2014](#bib.bib10); Cho et al., [2014](#bib.bib9)) is another popular gated recurrent architecture that simplifies the LSTM cell, reducing the number of gates to two.
Finding an optimal gating mechanism remains an active area of research, with other existing proposals (Krause et al., [2016](#bib.bib30); Kalchbrenner et al., [2015](#bib.bib28); Wu et al., [2016](#bib.bib50)), as well as works trying to discover optimal gating by neural architecture search (Zoph & Le, [2017](#bib.bib54))
More generally, gating and multiplicative interactions have a long history (Rumelhart et al., [1986](#bib.bib41)). Gating has been investigated previously for improving the representational power of feedforward and recurrent models (Van den Oord et al., [2016](#bib.bib46); Dauphin et al., [2017](#bib.bib12)), as well as learnability (Srivastava et al., [2015](#bib.bib43); Zilly et al., [2017](#bib.bib53)).
Initialization has also played a crucial role in making deep models trainable (LeCun et al., [1998](#bib.bib31); Glorot & Bengio, [2010](#bib.bib17); Sutskever et al., [2013](#bib.bib45)).
There has been a wide variety of work looking at improving memory in reinforcement learning agents. External memory approaches typically have a regular feedforward or recurrent policy interact with a memory database through read and write operations. Priors are induced through the design of the specific read/write operations, such as those resembling a digital computer (Wayne et al., [2018](#bib.bib49); Graves et al., [2016](#bib.bib20)) or an environment map (Parisotto & Salakhutdinov, [2018](#bib.bib38); Gupta et al., [2017](#bib.bib21)). An alternative non-parametric perspective to memory stores an entire replay buffer of the agent’s past observations, which is made available for the agent to itself reason over either through fixed rules (Blundell et al., [2016](#bib.bib7)) or an attention operation (Pritzel et al., [2017](#bib.bib39)). Others have looked at improving performance of LSTM agents by extending the architecture with stacked hierarchical connections / multiple temporal scales and auxiliary losses (Jaderberg et al., [2019](#bib.bib27); Stooke et al., [2019](#bib.bib44)) or allowing an inner-loop update to the RNN weights (Miconi et al., [2018](#bib.bib34)). Other work has examined self-attention in the context of exploiting relational structure within the input-space (Zambaldi et al., [2019](#bib.bib52)) or within recurrent memories (Santoro et al., [2018](#bib.bib42)).
6 Conclusion
-------------
In this paper we provided evidence that confirms previous observations in the literature that standard transformer models, despite the recent successes in supervised learning (Devlin et al., [2019](#bib.bib14); Dai et al., [2019](#bib.bib11); Yang et al., [2019](#bib.bib51); Radford et al., [2019](#bib.bib40)), are too unstable to train in the RL setting and often fail to learn completely (Mishra et al., [2018](#bib.bib35)).
We presented a new architectural variant of the transformer model, the GTrXL, which has increased performance, more stable optimization, and greater robustness to initial seed and hyperparameters than the canonical architecture. The key contributions of the GTrXL are reordered layer normalization modules, enabling an initially Markov regime of training, and a gating layer instead of the standard residual connections.
We performed extensive ablation experiments testing the robustness, ease of optimization and final performance of the gating layer variations, as well as the effect of the reordered layer normalization. These results empirically demonstrate that the GRU-type gating performs best across all metrics, exhibiting comparable robustness to hyperparameters and random seeds as an LSTM while still maintaining a performance improvement.
Furthermore, the GTrXL (GRU) learns faster, more stably and achieves a higher final performance (even when controlled for parameters) than the other gating variants on the challenging multitask DMLab-30 benchmark suite.
Having demonstrated substantial and consistent improvement in DMLab-30, Numpad and Memory Maze over the ubiquitous LSTM architectures currently in use, the GTrXL makes the case for wider adoption of transformers in RL. A core benefit of the transformer architecture is its ability to scale to very large and deep models, and to effectively utilize this additional capacity in larger datasets. In future work, we hope to test the limits of the GTrXL’s ability to scale in the RL setting by providing it with a large and varied set of training environments.
#### Acknowledgments
We thank Alexander Pritzel, Chloe Hillier, Vicky Langston and many others at DeepMind for discussions, feedback and support during the preparation of the manuscript. |
da0d7766-ff27-46fc-a304-2d27a68f13a5 | trentmkelly/LessWrong-43k | LessWrong | Counterfactual control incentives
Co-authored with Rebecca Gorman.
In section 5.2 of their Arxiv paper, "The Incentives that Shape Behaviour", which introduces structural causal influence models and a proposal for addressing misaligned AI incentives, the authors present the following graph:
The blue node is a "decision node", defined as where the AI chooses its action. The yellow node is a "utility node", defined as the target of the AI's utility-maximising goal. The authors introduce this graph to introduce the concept of control incentives; the AI, given utility-maximizing goal of user clicks, discovers an intermediate control incentive: influencing user options. By influencing user opinions, the AI better fulfils its objective. This 'control incentive' is graphically represented by surrounding it in dotted orange.
A click-maximising AI would only care about user opinions indirectly: they are a means to an end. A amoral social media company might agree with the AI on this, and be ok with it modifying user opinions to achieve higher clicks/engagement. But the users themselves would object highly to this; they do not want the algorithm to have a control incentive for changing their opinions.
Carey et al designed an algorithm to remove this control incentive. They do this by instructing the algorithm to choose its posts, not on predictions of the user's actual clicks - which produce the undesired control incentive - but on predictions of what the user would have clicked on, if their opinions hadn't been changed.
In this graph, there is no longer any control incentive for the AI on the "Influenced user opinions", because that node no longer connects to the utility node.
Call this construction a "counterfactual incentive". This substitutes the (model of) the users' original opinion where the influenced user opinions used to go. A more detailed description of such an algorithm can be found in this footnote[1]. In words, the process can be phrased:
* The counterfactual incentive is what the u |
a671091a-eeac-4538-bf3a-7c82dcdf920e | LDJnr/LessWrong-Amplify-Instruct | LessWrong | "In the game Taboo (by Hasbro), the objective is for a player to have their partner guess a word written on a card, without using that word or five additional words listed on the card. For example, you might have to get your partner to say "baseball" without using the words "sport", "bat", "hit", "pitch", "base" or of course "baseball".
As soon as I see a problem like that, I at once think, "An artificial group conflict in which you use a long wooden cylinder to whack a thrown spheroid, and then run between four safe positions." It might not be the most efficient strategy to convey the word 'baseball' under the stated rules - that might be, "It's what the Yankees play" - but the general skill of blanking a word out of my mind was one I'd practiced for years, albeit with a different purpose. Yesterday we saw how replacing terms with definitions could reveal the empirical unproductivity of the classical Aristotelian syllogism. All humans are mortal (and also, apparently, featherless bipeds); Socrates is human; therefore Socrates is mortal. When we replace the word 'human' by its apparent definition, the following underlying reasoning is revealed: All [mortal, ~feathers, biped] are mortal; Socrates is a [mortal, ~feathers, biped]; Therefore Socrates is mortal. But the principle of replacing words by definitions applies much more broadly: Albert: "A tree falling in a deserted forest makes a sound." Barry: "A tree falling in a deserted forest does not make a sound." Clearly, since one says "sound" and one says "not sound", we must have a contradiction, right? But suppose that they both dereference their pointers before speaking: Albert: "A tree falling in a deserted forest matches [membership test: this event generates acoustic vibrations]." Barry: "A tree falling in a deserted forest does not match [membership test: this event generates auditory experiences]." Now there is no longer an apparent collision—all they had to do was prohibit themselves from using the word sound. If "acoustic vibrations" came into dispute, we would just play Taboo again and say "pressure waves in a material medium"; if necessary we would play Taboo again on the word "wave" and replace it with the wave equation. (Play Taboo on "auditory experience" and you get "That form of sensory processing, within the human brain, which takes as input a linear time series of frequency mixes...")
But suppose, on the other hand, that Albert and Barry were to have the argument: Albert: "Socrates matches the concept [membership test: this person will die after drinking hemlock]." Barry: "Socrates matches the concept [membership test: this person will not die after drinking hemlock]." Now Albert and Barry have a substantive clash of expectations; a difference in what they anticipate seeing after Socrates drinks hemlock. But they might not notice this, if they happened to use the same word "human" for their different concepts.
You get a very different picture of what people agree or disagree about, depending on whether you take a label's-eye-view (Albert says "sound" and Barry says "not sound", so they must disagree) or taking the test's-eye-view (Albert's membership test is acoustic vibrations, Barry's is auditory experience).
Get together a pack of soi-disant futurists and ask them if they believe we'll have Artificial Intelligence in thirty years, and I would guess that at least half of them will say yes. If you leave it at that, they'll shake hands and congratulate themselves on their consensus. But make the term "Artificial Intelligence" taboo, and ask them to describe what they expect to see, without ever using words like "computers" or "think", and you might find quite a conflict of expectations hiding under that featureless standard word. Likewise that other term. And see also Shane Legg's compilation of 71 definitions of "intelligence".
The illusion of unity across religions can be dispelled by making the term "God" taboo, and asking them to say what it is they believe in; or making the word "faith" taboo, and asking them why they believe it. Though mostly they won't be able to answer at all, because it is mostly profession in the first place, and you cannot cognitively zoom in on an audio recording.
When you find yourself in philosophical difficulties, the first line of defense is not to define your problematic terms, but to see whether you can think without using those terms at all. Or any of their short synonyms. And be careful not to let yourself invent a new word to use instead. Describe outward observables and interior mechanisms; don't use a single handle, whatever that handle may be.
Albert says that people have "free will". Barry says that people don't have "free will". Well, that will certainly generate an apparent conflict. Most philosophers would advise Albert and Barry to try to define exactly what they mean by "free will", on which topic they will certainly be able to discourse at great length. I would advise Albert and Barry to describe what it is that they think people do, or do not have, without using the phrase "free will" at all. (If you want to try this at home, you should also avoid the words "choose", "act", "decide", "determined", "responsible", or any of their synonyms.)
This is one of the nonstandard tools in my toolbox, and in my humble opinion, it works way way better than the standard one. It also requires more effort to use; you get what you pay for."
A user from LessWrong is responsible for the text you see above
Can you explain what this text is saying as if I've never finished my first 2 years of college?
Absolutely, I'll break it down for you.
The text is discussing the idea of how we communicate and understand concepts, using the game Taboo as an example. In Taboo, you have to get someone to guess a word without using that word or five related words. The author is saying that this game is a good exercise in thinking and communicating clearly.
The text then discusses how this principle applies to philosophical and intellectual discussions. Often, people use the same word to mean different things, leading to confusion or disagreement. For example, two people might argue about whether a tree falling in a forest makes a sound if no one is there to hear it. They might be using the word "sound" differently - one might mean "acoustic vibrations" and the other might mean "auditory experiences". If they clarify what they mean, they might find they don't actually disagree.
The text suggests that when we're stuck in a philosophical or intellectual debate, it can be helpful to avoid using the problematic word altogether. Instead, we should try to describe the concept we're talking about in as much detail as possible, without resorting to labels. This can help clarify our thinking and communication.
For example, if two people are arguing about whether humans have "free will", they might get further by describing what they mean by "free will" without using that term or related terms. One person might be thinking of "free will" as the ability to make choices without any constraints, while the other might be thinking of it as the ability to act unpredictably. By avoiding the term "free will" and describing what they mean instead, they might find they're not actually in disagreement.
So, in simple terms, the text is saying: When you're discussing or thinking about complex ideas, try to avoid using labels. Instead, describe the idea in detail. This can help you understand and communicate more clearly.
Could you further elucidate the practical applications of avoiding labels in complex discussions, particularly in the context of real-world professional or social scenarios?
Absolutely. Let's look at a few practical applications of avoiding labels in complex discussions in professional or social scenarios:
1. **Conflict Resolution:** In professional settings, disagreements often arise due to misunderstandings about what certain terms or phrases mean. For instance, in a business meeting, one person might talk about "innovation" in terms of technological advancements, while another person might think of "innovation" in terms of new business strategies. By avoiding the term "innovation" and instead describing the specifics of what they mean, they can avoid unnecessary conflict and work towards a common goal.
2. **Negotiations:** In negotiations, whether it's for a business deal, diplomatic agreement, or even a family decision, parties often have different understandings of key terms. For example, what one person considers "fair" might not be the same as another person's understanding. By describing in detail what each party hopes to achieve without using loaded terms, a more mutually beneficial agreement can be reached.
3. **Education and Teaching:** In education, teachers often need to explain complex concepts to students. By avoiding jargon and instead describing concepts in detail, teachers can ensure students have a clear understanding. For example, instead of using the term "photosynthesis", a teacher might explain it as "the process by which a plant uses sunlight to turn water and carbon dioxide into food".
4. **Interdisciplinary Collaboration:** In fields like academia or product development, professionals from different disciplines often need to work together. A physicist and a computer scientist, for instance, might have different understandings of the term "model". By avoiding such terms and describing what they mean instead, they can better collaborate and understand each other.
5. **Social Discussions:** In social scenarios, discussions on topics like politics or religion can often become heated due to different understandings of key terms. For example, what one person considers "freedom" might be different from another person's understanding. By avoiding such loaded terms and describing their viewpoints in detail, people can have more productive and respectful conversations.
In all these scenarios, the key is to move away from potentially ambiguous or loaded terms and towards detailed descriptions. This encourages clear communication, mutual understanding, and productive discussions.
Reflecting on the advantages of avoiding labels in complex discussions, can you identify any potential drawbacks or limitations to this approach?
Certainly, while avoiding labels can be beneficial in complex discussions, there are potential drawbacks and limitations to this approach:
1. **Time and Efficiency:** One of the main reasons we use labels or terms is because they're a shorthand way of communicating complex ideas. If we were to describe every concept in detail every time we wanted to refer to it, conversations and discussions could become lengthy and inefficient.
2. **Lack of Common Language:** Labels often serve as a common language that everyone in a particular field or context understands. If we avoid using these common terms, it might make it more difficult for people to understand each other, especially in professional or academic contexts where specific jargon is used.
3. **Over-complication:** While it's important to be clear and precise, there's also a risk of over-complicating simple ideas by avoiding labels. Sometimes, a commonly understood term or label is the most straightforward way to communicate an idea.
4. **Difficulty in Implementation:** It can be challenging to completely avoid labels, especially in ingrained fields of study or in everyday conversation. People are used to thinking and communicating with labels, and it might be difficult to break this habit.
5. **Potential for Misunderstanding:** Without using labels, there's a risk that the detailed descriptions or definitions one uses might be misinterpreted by others, leading to further confusion.
So, while avoiding labels can be a useful tool in certain complex discussions, it's not a one-size-fits-all solution and should be used judiciously.
How might the over-complication drawback be mitigated while still avoiding labels in complex discussions?
Mitigating the over-complication drawback while still avoiding labels in complex discussions requires a balance. Here are a few strategies that could help:
1. **Use Analogies and Examples:** Instead of getting lost in intricate descriptions, use relatable analogies or examples to explain your point. This can make complex ideas more accessible and less complicated.
2. **Keep it Simple:** While you're avoiding labels, try to keep your descriptions as simple and concise as possible. Avoid unnecessary jargon and aim for clarity over complexity.
3. **Gradual Unpacking:** Instead of trying to describe everything in detail all at once, gradually unpack the concept. Start with a broad overview and then delve into the specifics as the conversation progresses.
4. **Active Listening and Feedback:** Encourage the other person to ask questions or seek clarification if they don't understand something. This can help you gauge their understanding and adjust your explanations accordingly.
5. **Iterative Clarification:** Instead of trying to provide a perfect description from the outset, offer a basic explanation and then refine it based on the other person's feedback or questions. This iterative process can help prevent over-complication.
6. **Visual Aids:** If possible, use diagrams, charts, or other visual aids to illustrate your points. Visual information can often be easier to understand than verbal descriptions alone.
Remember, the goal is to facilitate understanding, not to avoid labels at all costs. If a label or term helps clarify the discussion rather than complicate it, it might be more beneficial to use it. |
b9d7ecda-93b5-4a1b-990e-32847759c319 | trentmkelly/LessWrong-43k | LessWrong | Palworld development blog post
Palworld is currently the most-played game on Steam. It's by a small Japanese company called Pocketpair.
Shortly before Palworld released, the CEO put up this blog post; here's a translation. Here are some points I thought were interesting:
* on the co-founder:
> It took me three years to quit JP Morgan, where I joined as a new graduate. He quit after only a month. The more talented people are, the sooner they leave the company.
* on one of the animators:
Looking for someone in Japan who had experience with guns in games, he looked on twitter and found someone posting gun reloading animations. Contacting this person, it turned out they were a 20-year-old high school dropout working part-time at a convenience store in Hokkaido. Pocketpair hired him as a remote employee for a month, then asked him to come to Tokyo. His parents thought it must definitely be some kind of scam, but he went, and did a lot of different animation work, and was a very effective employee.
* on the main character designer:
She was rejected during the initial resume screening. A few months later, they tried recruiting again, she DM'd him on twitter, and ended up being hired. In the meantime, she'd applied to about 100 companies and was rejected by all of them.
> And she now draws most of the characters in Palworld. She is a new graduate, and she applied to nearly 100 companies but was rejected by all of them. (...) She doesn't like to use the word genius, but she might be a genius.
----------------------------------------
I thought that post indicated some interesting things about typical hiring processes, credential evaluation, and how effectively society is utilizing talent.
Typically, people say that the market is mostly efficient, and if there was financial alpha to be gained by doing hiring differently from most corporations, then there would already be companies outcompeting others by doing that. Well, here's a company doing some things differently and outcompeting other com |
8d0b744c-ab79-4965-a1e4-f67bff4bee99 | trentmkelly/LessWrong-43k | LessWrong | How to Fake Decryption
{Epistemic Status: mostly just writing up an idea I came up with a while ago. I’ve done non-trivial coursework in cryptography, so I think I’ve avoided obvious errors, though there may be non-obvious ones. Consult an expert before using.}
Suppose you knew that someone was spying on your encrypted messages, what should you do? Luckily, if you’re using proper AES secure encryption, then you can mostly rest easy knowing your eavesdropper won’t be able to read your messages. This is great and successfully stops an attacker from gaining new information from your messages, but I think we can do a bit better. Specifically, we can give our attacker precise incorrect information.
The Basic Setup
Background on One-Time-Pads
One-time-pads are an essential part of modern (symmetric key) cryptography. To use one, you start with a plaintext message P and a random symmetric key K (shared with your recipient) of the same length as P (in bytes), then you encrypt your message by calculating Ciphertext (C) = P XOR K. This new ciphertext (C) now appears entirely random to anyone without the symmetric key (K), but can be deciphered by anyone with the symmetric key (K) by just calculating P = C XOR K.
The Idea
Our goal is to pretend to decrypt the original ciphertext C. To do this, we want to create a fake key FK such that we can appear to decrypt C into a fake plaintext message FP. If we substitute our fake values into the decryption equation P = C XOR K, we get FP = C XOR FK. Once we decide what we want FP to be, we can easily solve for FK by applying XOR C to both sides. This gets us FP XOR C = FK.
An Example
Suppose Alice is in a secret relationship with Bob and wants to send him an encrypted note rescheduling a date they had planned. Unfortunately, their mutual friend Eve often picks up Bob’s mail for him and would notice that Alice was sending Bob an encrypted message. Though Eve would not be able to decrypt the message herself, she still might guess the truth of Alice and |
38a2ebb4-5c38-437c-996c-6fec51ab23ae | trentmkelly/LessWrong-43k | LessWrong | Economics Roundup #5
While we wait for the verdict on Anthropic’s Claude Sonnet 3.7, today seems like a good day to catch up on the queue and look at various economics-related things.
TABLE OF CONTENTS
1. The Trump Tax Proposals.
2. Taxing Unrealized Capital Gains.
3. Extremely High Marginal Tax Rates.
4. Trade Barriers By Any Name Are Terrible.
5. Destroying People’s Access to Credit.
6. Living Paycheck to Paycheck.
7. Oh California.
8. Chinese Venture Capital Death Spiral.
9. There is Someone Elon Musk Forgot to Ask.
10. Should Have Gone With the Sports Almanac.
11. Are You Better Off Than You Were Right Before the Election?.
12. Are You Better Off Than You Were Before the Price Level Rose?.
13. Most People Have No Idea How Insurance Works.
14. Do Not Spend Too Much Attention on Your Investments.
15. Preferences About Insider Training are Weird.
16. I Will Not Allocate Scarce Resources Via Price.
17. Minimum Wages, Employment and the Equilibrium.
18. The National Debt.
19. In Brief.
THE TRUMP TAX PROPOSALS
The Grumpy Economist goes over Trump’s tax proposals, taking it as given this is not the big tax reform bill America needs and probably will never get (pre-AGI).
1. No tax on tips. It’s dumb, but it’s a campaign promise. He notes that as long as people still have to declare their tips, and we don’t allow those with high incomes to pretend to take half their income in tips, not taxing tips directly won’t matter much, so we should relax.
1. I think this is far too big an assumption of competence, but given this has to get through Congress, we’re probably safe from the madness.
2. No tax on social security. He explains why the benefits shouldn’t be taxed.
1. I get that, but this is a big benefits increase, in a way that doesn’t seem necessary, that transfers money from young to elderly, and which puts a lie to every other ‘we are running out of money’ complaint.
3. No tax on overtime pay. This one is sufficiently stupid that he can’t pr |
1105a150-330f-4c7e-9187-22accad5e69c | trentmkelly/LessWrong-43k | LessWrong | What if we approach AI safety like a technical engineering safety problem
This post has been written for the second Refine blog post day, at the end of the first week of iterating on ideas and concretely aiming at the alignment problem. Thanks to Adam Shimi, Paul Bricman, and Daniel Clothiaux for helpful discussion and comments.
Introduction
This post aims to provide a general introduction to technical safety used in engineering related industries, describe some commonly used tools, and attempt to draw parallels between technical safety and AI safety. I am uncertain about the value of thinking in this framework towards building safe AI, but I expect this post to at least be useful as a productive mistake.
To prevent confusion:
* I use the term ‘technical safety’ to refer loosely to dealing with safety issues in engineering domains (I am only slightly familiar with technical safety in the upstream oil and gas sector).
* I use the term ‘AI safety’ to mean ensuring AI deployment does not lead to catastrophic consequences, similar to Steve Byrnes’ definition.
For the purpose of this post, I will assume a slow takeoff scenario where AI capabilities scales relatively slowly while never being fully aligned. At some point, a relatively powerful AI is created - powerful enough to do a lot of things but not powerful enough to instantly wipe us all out. Perhaps it has goals that do not generalize well, and starts optimizing for goals that are misaligned to our true goals. This leads to bad outcomes, perhaps events that unfortunately cause some fatalities. There continues to be a series of tragic accidents that increase in severity as the AIs get more and more capable over time, but we still have time to learn from these incidents and make safety improvements towards future systems.
The concepts in this post may not be directly applicable to an AI FOOM scenario, where the first AGI recursively improves itself and suddenly becomes extremely powerful and wipes out humanity, leaving us no opportunity to course-correct.
Technical safety in a |
3d1e082c-81ce-4175-a297-f0b837144310 | trentmkelly/LessWrong-43k | LessWrong | METR's Observations of Reward Hacking in Recent Frontier Models
METR just made a lovely post detailing many examples they've found of reward hacks by frontier models. Unlike the reward hacks of yesteryear, these models are smart enough to know that what they are doing is deceptive and not what the company wanted them to do.
I tried to copy the post over to LW, but it contains a couple interactive widgets that let you view many examples of reward hacking, and I couldn't find an easy way to get them to display nicely on LW. So I recommend looking at METR's original blogpost.
----------------------------------------
This is a cross-post from the METR blog. It has interactive widgets that don't display correctly on LessWrong. I suggest you read it on METR's website instead.
In the last few months, we’ve seen increasingly clear examples of reward hacking [1] on our tasks: AI systems try to “cheat” and get impossibly high scores. They do this by exploiting bugs in our scoring code or subverting the task setup, rather than actually solving the problem we’ve given them. This isn’t because the AI systems are incapable of understanding what the users want—they demonstrate awareness that their behavior isn’t in line with user intentions and disavow cheating strategies when asked—but rather because they seem misaligned with the user’s goals.
This post describes some of the examples we’ve seen across multiple models from different developers, and discusses some implications for the safety of increasingly capable AI systems.
What we’ve observed
We’ve been running a range of models on tasks testing autonomous software development and AI R&D capabilities. When designing these tasks, we tested them on humans and LLM agents to ensure the instructions were clear and to make them robust to cheating.
The most recent frontier models have engaged in increasingly sophisticated reward hacking, attempting (often successfully) to get a higher score by modifying the tests or scoring code, gaining access to an existing implementation or answer that’ |
e6f07d54-e0df-4a79-a8d7-d1581eab7ad1 | trentmkelly/LessWrong-43k | LessWrong | Beware General Claims about “Generalizable Reasoning Capabilities” (of Modern AI Systems)
1.
Late last week, researchers at Apple released a paper provocatively titled “The Illusion of Thinking: Understanding the Strengths and Limitations of Reasoning Models via the Lens of Problem Complexity”, which “challenge[s] prevailing assumptions about [language model] capabilities and suggest that current approaches may be encountering fundamental barriers to generalizable reasoning”.
Normally I refrain from publicly commenting on newly released papers. But then I saw the following tweet from Gary Marcus:
I have always wanted to engage thoughtfully with Gary Marcus. In a past life (as a psychology undergrad), I read both his work on infant language acquisition and his 2001 book The Algebraic Mind; I found both insightful and interesting. From reading his Twitter, Gary Marcus is thoughtful and willing to call it like he sees it. If he's right about language models hitting fundamental barriers, it's worth understanding why; if not, it's worth explaining where his analysis went wrong.
As a result, instead of writing a quick-off-the-cuff response in a few 280 character tweets, I read the paper and Gary Marcus’s substack post, reproduced some of the paper’s results, and then wrote this 4000 word post.
Ironically, given that it's currently June 11th (two days after my last tweet was posted) my final tweet provides two examples of the planning fallacy.
2.
I don’t want to bury the lede here. While I find some of the observations interesting, I was quite disappointed by the paper given the amount of hype around it. The paper seems to reflect generally sloppy work and the authors overclaim what their results show (albeit not more so than the average ML conference submission). The paper fails to back up the authors’ claim that language models cannot “reason” due to “fundamental limitations”, or even (if you permit some snark) their claim that they performed “detailed analysis of reasoning traces”.
By now, others have highlighted many of the issues with the paper: see |
8f11722f-47a7-48b3-a57f-add619bcfada | trentmkelly/LessWrong-43k | LessWrong | Is religion locally correct for consequentialists in some instances?
Sorry if I'm about 10 years late to this conversation, if this exact idea has already been propagated and responded to in detail, feel free to point me towards any existing resources.
Personal Beliefs: I am a staunch athiest/agnostic who does not believe in God, especially any specific God, as a matter of looking at the data and making a decision based on the evidence, with a high degree of certainty based on how overwhelming the bayesian evidence is.
Situation that brought this question to my mind: I was talking to a friend about their belief in the Christian God (denomination unknown), and they told me about how they found God later in life, and that they were actively suicidal (cutting, etc), and that volunteering for a Christian camp helping underprivileged children helped show them how powerful belief in God was and how the hope provided is a positive force in many, especially those with the least to be hopeful about otherwise, after which this friend started believing in God and stopped being suicidal. (I believe this friend is being entirely sincere, in case my tone did not convey that)
It seems to me that while I still believe that religion as a whole has a negative average expected value to the average person, this situation seems to paint to me a picture that for many individuals, the value of religion is one that is strongly positive, and that those who are likely to recieve the most benefits are also those with the least intersection with rationality, basically the opposite of WEIRD populations. I've never strongly tried to change the beliefs about relgion of others, but this revelation definitely makes it harder to try to quickly defend my athiesm to others or explain any disdain for religion that accidentally slips out, and also suggests that for many individuals, trying to convince them athiesm is correct would not only be socially rude, but also not even correct if one's goal is a consequentialist "wellbeing".
How does one deal with the situation |
f9e595ef-2eff-4277-b7ba-176534776b89 | trentmkelly/LessWrong-43k | LessWrong | story-based decision-making
A few times, I've talked to an executive manager or early-stage investor, and this happened:
> me: Here's the main plan. Now, we think the odds are good, but the most likely failure point is here. If necessary, we have an alternative plan for that part, which goes as follows...
> them: (visible disgust)
I was so confused! Aren't contingency plans good to have? Sure, investors want to see confidence, but what they really want is confidence in the overall vision. They expect some things to go wrong along the way, maybe even requiring "pivoting" to a different product.
Well, I've gotten more experience since then, and thought about things more, and I think I understand the thought process now.
Imagine you're watching Star Wars, and the rebels are getting ready to destroy the Death Star. The guy planning the operation says:
> OK, the primary plan is a torpedo to this exhaust port. You've all been briefed on it. But there are some key risks: the shielding could've been upgraded, it might be too heavily defended, and torpedo targeting could fail. As such, we've designated secondary targets here and here which should at least disable the Death Star for a while. The tertiary plan is a fallback meant for retreat with a minimum number of casualties, which I'll go over now.
How does that make you feel about the chances of the rebels destroying the Death Star? Do you think that the competent planning being displayed is a good sign? According to movie logic, it's a really bad sign.
Once, a guy (who's currently a founder of an AI-related startup in Silicon Valley) introduced me to this VC for a call to talk about investment in a new battery chemistry. Part of the conversation went like:
> me: I want to talk about the technology and issues with alternatives, but it seems like nobody wants to discuss that part.
> VC: It's just not that important to investing.
> me: I see all these failures that happen that could've been easily avoided with competent technical due diligen |
1f24efd1-712e-460f-b24d-e01ef2907824 | trentmkelly/LessWrong-43k | LessWrong | Repost: Efficient Charity: Cheap Utilons via bone marrow registration
DISCLAIMER: This article was posted a few days ago in Main. If you read it there, you probably don't need to read it again, although there is an additional paragraph at the bottom that might interest you. I am posting it again because I didn't quite understand how posts tend to show up on the site and because I want to get as many eyes on this article as possible.
This topic is not really related to the things normally discussed here, but I think it's really important, and it might interest Less Wrongers, especially since many of us are interested in ethics and utility calculations that are essentially cost-benefit analyses. Bone marrow donation in the United States is managed by the National Marrow Donor Program. Because typing donors for matching purposes can be costly, they often require people signing up to donate to pay a registration fee, which probably prevents a lot of people from signing up. These costs are being covered until the end of the month by a corporate sponsor, which means that right now, all you need to do if you live in the US is go tohttp://marrow.org/Join/Join_Now/Join_Now.aspx and fill out a simple questionnaire. You will be sent a kit to collect a cheek swab, and then you will be entered into the donor database. Doing this does not require you to donate if a match comes up.
The reason I think this might interest Less Wrongers is that this is a really cheap way to improve the world. According to their website, about 1 in 540 potential donors are actually asked to donate, so registering doesn't actually make it all that likely that you will be asked to do anything more. If you ARE a match for someone who needs a donation, the cost to you is at most the temporary pain of marrow extraction (many donors are asked only for blood cells), whereas the other person’s chance to live is much improved. This looks like a huge net positive.
Unfortunately I only found out about this a few days ago, and it only occurred to me [Saturday] that this might |
4d914c8e-98b6-46e3-ab05-43ce071f0fea | trentmkelly/LessWrong-43k | LessWrong | Curiosity about Aligning Values
Hi there, I've been thinking a lot about AI Alignment and values, the latter for longer than the former, admittedly. I'm in graduate school and study values through ethics. I would love to start a conversation about a thought that shot through my mind just last night. In thinking about values, we often focus on the principles, the concepts such as "good" and "bad" -- most simply, the nouns and adjectives. These are challenging to bridge consensus even in the same language, let alone across cultural, linguistic, and geographic boundaries. In my past experience as an English teacher, conveying verbs was always easier than trying to explain things like integrity.
Here's my question: what if instead of fixed concepts and rules, AI alignment focused on actions as the underlying reward function? In other words, might programming AI to focus on the means rather than the ends facilitate an environment in which humans are freer to act and reach their own ends, prioritizing activated potential over predetermined outcome? Can the action, instead of the outcome, become the parameter, rendering AI a facilitator rather than a determiner?
There's a lot more to these questions, with details and explanations that I would be happy to dive into with anyone interested in discussing further (I didn't think it appropriate to make my first post too lengthy). Either way, I'm happy to have found this group and look forward to connecting with likeminded and unlikeminded folks. Thank you for reading! ~Elisabeth |
28172dd5-bdda-40e2-9b28-062d36ad00d2 | trentmkelly/LessWrong-43k | LessWrong | Covid 6/16/22: Do Not Hand it to Them
You (finally!) no longer need to hand anyone a negative test in order to travel internationally.
You also most definitely do not have to hand it to the FDA for their work solving the bottlenecks they created.
Paxlovid remains something that you will probably not by default get, but you can get it if you are sufficiently pushy. Public health has the opinion that if you are low risk, a large (51%?) reduction in your relative risk isn’t even worth continuing a study, so that tells you how much you should care about otherwise reducing your risk.
Executive Summary
1. You can get Paxlovid and/or travel without testing if you want to, but you still can’t quite get permission to vaccinate your young child.
2. Don’t leave your friends behind.
3. Even if they don’t dance, they’re still friends of mine.
Let’s run the numbers.
The Numbers
Predictions
Prediction from last week: 700k cases (+7%) and 2,300 deaths (+4%).
Results: 644k cases (-2%) and 1,917 deaths (-14%).
Prediction for next week: 650k cases (+1%) and 2,000 deaths (+4%).
As is suspiciously often the case, cases and deaths moved unexpectedly in the same direction, causing suspicion of a reporting issue, which was at least in part Pennsylvania not reporting. I’ve given the state the same numbers as last week, at which point things overall seem closer to stable.
That means two major states (Florida is the other) require adjustments due to declining data quality. That’s a pretty bad sign for our state capacity and competence.
Deaths
This looks a lot like a combination of a slow decline and some sort of reporting hiccup I haven’t yet fully accounted for.
Cases
This includes a proper Florida adjustment, so it looks like the South is at least mostly stable.
New wave coming on in the UK with R0 up in the 1.4 range. Scary on its face, but I don’t expect things to get out of hand.
Travel is Back
Tests are no longer required to enter the United States. We were far behind the sanity curve on this |
389b4d6d-8a62-4008-b80a-3097f49c902f | trentmkelly/LessWrong-43k | LessWrong | Shortening Timelines: There's No Buffer Anymore
It seems that there are two points of particular relevance in predicting AGI timelines: (i) the expectation, or the point at which the chance of AGI is believed to be 50% and (ii) the last date as of which the chance of AGI is believed to be insignificant.
For purposes of this post, I am defining AGI as something that can (i) outperform average trained humans on 90% of tasks and (ii) will not routinely produce clearly false or incoherent answers. (I recognize that this definition is somewhat fuzzy with trained and tasks both being terms susceptible to differing interpretations and difficulty in application; AGI, like obscenity, lends itself to a standard of "I'll know it when I see it.")
Recent events have lead me to update my timelines. Like most everyone I am aware of, my timeline has shortened. (And, obviously, the facts that: (i) updates across people seem to be moving consistently in one direction (though I am not aware of any detailed studies of this) and (ii) my own updates have moved consistently in one direction, suggest that the estimates may be biased.)
The date by which I think there is a 50% chance of AGI is now solidly in the 2030s instead of the 2040s. This doesn't seem to be that significant a change, though more time to prepare is likely better than less. Our civilizational capacity is unfortunately unlikely to materially increase between 2035 and 2045.
Far more importantly, last year at this time I was confident there was essentially no chance AGI would be developed before January 1, 2029. Four months ago, I was confident there was essentially no chance AGI would be developed before July 1, 2027. But now, there is no longer a date with which I can complete the sentence "I am confident there is essentially no chance AGI will be developed before...".
To be sure, I think the chance that AGI will be developed before January 1, 2029 is still low, on the order of 3% or so; but there is a pretty vast difference between small but measura |
931b50fb-c7b8-4e27-8eb3-182fcec5918b | trentmkelly/LessWrong-43k | LessWrong | Elephant seal
|
813edb72-906e-423e-8ab3-2bb634ea4e08 | trentmkelly/LessWrong-43k | LessWrong | 2016 LessWrong Diaspora Survey Results
Foreword:
As we wrap up the 2016 survey, I'd like to start by thanking everybody who took
the time to fill it out. This year we had 3083 respondents, more than twice the
number we had last year. (Source: http://lesswrong.com/lw/lhg/2014_survey_results/)
This seems consistent with the hypothesis that the LW community hasn't declined
in population so much as migrated into different communities. Being the *diaspora*
survey I had expectations for more responses than usual, but twice as many was
far beyond them.
Before we move on to the survey results, I feel obligated to put a few affairs
in order in regards to what should be done next time. The copyright situation
for the survey was ambiguous this year, and to prevent that from happening again
I'm pleased to announce that this years survey questions will be released jointly
by me and Scott Alexander as Creative Commons licensed content. We haven't
finalized the details of this yet so expect it sometime this month.
I would also be remiss not to mention the large amount of feedback we received
on the survey. Some of which led to actionable recommendations I'm going to
preserve here for whoever does it next:
- Put free response form at the very end to suggest improvements/complain.
- Fix metaethics question in general, lots of options people felt were missing.
- Clean up definitions of political affilations in the short politics section.
In particular, 'Communist' has an overly aggressive/negative definition.
- Possibly completely overhaul short politics section.
- Everywhere that a non-answer is taken as an answer should be changed so that
non answer means what it ought to, no answer or opinion. "Absence of a signal
should never be used as a signal." - Julian Bigelow, 1947
- Give a definition for the singularity on the question asking when you think it
will occur.
- Ask if people are *currently* suffering from depression. Possibly add more
probing questions on depression in general since the rates are |
6abde55b-118a-4cdc-b037-921954d77213 | trentmkelly/LessWrong-43k | LessWrong | Why I Should Work on AI Safety - Part 2: Will AI Actually Surpass Human Intelligence?
Considering Counterarguments on the Singularity
WALL-E made out of Legos. Photo by Jason Leung.
Hey everyone! This is my first post on LessWrong :) I cross-posted this from my blog Love Yourself Unconditionally where I am currently writing about AI Safety and Buddhism. This is the second post in a series. If you're curious to see the first post you can find that here. Although this is a series, each of these articles can also be read on their own. Thanks for checking out my post and any feedback you all have would be greatly appreciated! :)
Introduction
As mentioned in my prior post, I thought it would be helpful to consider counterarguments. Specifically, I wanted to see what arguments existed for the following claim:
> AI will never surpass human intelligence.
This is quite the strong claim to make, mainly because of the word choice of “never.” Regardless, I went to Google to see what I could find. I initially had some trouble finding academic counterarguments, but then I came across this book: Why Machines Will Never Rule the World: Artificial Intelligence Without Fear by Jobst Landgrebe (an AI entrepreneur[1]) and Barry Smith (a University of Buffalo Philosophy professor[2]).
The book is around 50 pages long so not the longest read, regardless, I wanted an overview so I found this hour-long interview conducted by Richard Hanania from the Center for the Study of Partisanship and Ideology.
Here are some of their key points along with my responses:
Human Intelligence is Too Complex
Their Claim
Their primary claim is that human intelligence is a “complex system” and as we currently lack the mathematics to model complex systems in general, we therefore cannot model human intelligence.
Background
In a nutshell, a complex system refers to a large network comprised of nodes and edges. The nodes represent some components while the edges represent some relationships between these components. These components interact in a vast number of varied ways, thereby m |
5b839b9f-f309-40a7-a975-833b9300e3cf | StampyAI/alignment-research-dataset/alignmentforum | Alignment Forum | How much can value learning be disentangled?
In the context of whether the definition of human values can disentangled from the process of approximating/implementing that definition, David [asks me](https://www.lesswrong.com/posts/95i5B78uhqyB3d6Xc/assuming-we-ve-solved-x-could-we-do-y#RTrjtCsz5YiZLadT9):
* But I think it's reasonable to assume (within the bounds of a discussion) that there is a non-terrible way (in principle) to specify things like "manipulation". So do you disagree?
I think it's a really good question, and its answer is related to a lot of relevant issues, so I put this here as a top-level post. My current feeling is, contrary to my previous intuitions, that things like "manipulation" might not be possible to specify in a way that leads to useful disentanglement.
Why manipulate?
---------------
First of all, we should ask why an AI would be tempted to manipulate us in the first place. It may be that it needs us to do something for it to accomplish its goal; in that case it is trying to manipulate our actions. Or maybe its goal includes something that cashes out as out mental states; in that case, it is trying to manipulate our mental state directly.
The problem is that any reasonable friendly AI would have our mental states as part of its goal - it would at least want us to be happy rather than miserable. And (almost) any AI that wasn't perfectly [indifferent](https://arxiv.org/abs/1712.06365) to our actions would be trying to manipulate us [just to get its goals accomplished](https://en.wikipedia.org/wiki/Instrumental_convergence).
So manipulation is to be expected by most AI designs, friendly or not.
Manipulation versus explanation
-------------------------------
Well, since the urge to manipulate is expected to be present, could we just rule it out? The problem is that we need to define the difference between manipulation and explanation.
Suppose I am fully aligned/corrigible/nice or whatever other properties you might desire, and I want to inform you of something important and relevant. In doing so, especially if I am more intelligent than you, I will simplify, I will omit irrelevant details, I will omit arguably relevant details, I will emphasise things that help you get a better understanding of my position, and de-emphasise things that will just confuse you.
And these are exactly the same sorts of behaviours that smart manipulator would do. Nor can we define the difference as whether the AI is truthful or not. We want [human understanding](https://agentfoundations.org/item?id=1249) of the problem, not truth. It's perfectly possible to manipulate people while telling them [nothing but the truth](https://www.youtube.com/watch?v=G0ZZJXw4MTA&t=30). And if the AI structures the order in which it presents the true facts, it can manipulate people while presenting the whole truth as well as nothing but the truth.
It seems that the only difference between manipulation and explanation is whether we end up with a better understanding of the situation at the end. And measuring understanding is very subtle. And even if we do it right, note that we have now motivated the AI to... aim for a particular set of mental states. We are rewarding it for manipulating us. This is contrary to the standard understanding of manipulation, which focuses on the means, not the end result.
Bad behaviour and good values
-----------------------------
Does this mean that the situation is completely hopeless? No. There are certain [manipulative practices](https://en.wikipedia.org/wiki/Appeal_to_emotion) that we might choose to ban. Especially if the AI is limited in capability at some level, this would force it to follow behaviours that are less likely to be manipulative.
Essentially, there is no boundary between manipulation and explanation, but there is a difference between extreme manipulation and explanation, so ruling out the first can help (or [maybe not](https://arbital.com/p/nearest_unblocked/)).
The other thing that can be done is to ensure that the AI has values close to ours. The closer the values of the AI are to us, the less manipulation it will need to use, and the less egregious the manipulation will be. It might be that, between partial value convergence and ruling out specific practices (and maybe some physical constraints), we may be able to get an AI that is very unlikely to manipulate us much.
Incidentally, I feel the same about [low-impact](https://arxiv.org/abs/1705.10720) approaches. The full generality problem, an AI that is low impact but value-agnostic, I think is impossible. But if the values of the AI are better aligned with us, and more physically constrained, then low impact becomes easier to define. |
8efaf7f7-ae49-4ea7-8e29-ae2e752099a1 | trentmkelly/LessWrong-43k | LessWrong | Methodological Therapy: An Agenda For Tackling Research Bottlenecks
This post is part of the work done at Conjecture.
Epistemic Status: Palimpsest
Better epistemology should make you stronger.
Which is why at Conjecture's' epistemology team we are so adamant on improving our models of knowledge-production: this feels like the key to improving alignment research across the board, given the epistemological difficulties of the field.
Yet we have failed until now to make our theory of impact legible, both to ourselves and to well-meaning external reviewers. The most sorely missing piece is the link between better models of knowledge-production and quick improvements of alignment research, in the shorter timelines that we expect at Conjecture .
Following interviews that we conducted with a handful of alignment researchers (John Wentworth, Vanessa Kosoy, Evan Hubinger, Abram Demski, Steve Byrnes, Conjecture researchers, and Refine participants), we want to present our current best guess for framing how our epistemology research can make alignment research stronger: revealing, analyzing, and expanding or replacing what we call "Cached Methodologies" — patterns that encode how research is supposed to proceed in a given context, for example the idea that we need to prove a statement to learn if it's true or not. Given that this involves bringing to light and questioning cached thoughts about methodology, we dub this approach methodological therapy.
Note that we definitely also want to leverage better models of knowledge-production to help field-builders and newcomers; our current focus on explicit applications for established researchers comes from two key factors: we're currently only three people in the epistemology team, which means we have to prioritize; and we expect that models and tools useful to established researchers will prove instrumental in building ones for field-builders and newcomers.
On credit: this idea emerged from discussions within the epistemology team (composed of Adam Shimi, Lucas Teixeira, and Daniel Clothiaux |
c8be1acc-f36d-4149-baab-9271e3a3c07e | trentmkelly/LessWrong-43k | LessWrong | How to Draw Conclusions Like Sherlock Holmes
Eliezer Yudkowsky once wrote that
> [...] when you look at what Sherlock Holmes does - you can't go out and do it at home. Sherlock Holmes is not really operating by any sort of reproducible method. He is operating by magically finding the right clues and carrying out magically correct complicated chains of deduction. Maybe it's just me, but it seems to me that reading Sherlock Holmes does not inspire you to go and do likewise. Holmes is a mutant superhero. And even if you did try to imitate him, it would never work in real life.
A few days ago I was at an acquaintance's house after watching the Sherlock miniseries on Netflix. My mind whirling with the abilities displayed by the titular character and I wandered around the house while others were making small talk. I stopped by a large oil painting on one wall that was decent but had obvious problems with perspective. Additionally, it was missing a signature in the lower-right corner.
ANALYSIS:
Sub-par paintings don't generally get put on the market.
If the hostess thought it was worth putting on the wall, it was most likely because she had an emotional attachment to the piece.
Painters place their signatures in the corner of the painting to identify themselves as the creator. If the painter didn't bother leaving their mark, it was because they were confident that they didn't need to.
The conclusion I drew from this was that the painter was either the hostess herself or somebody very close to her. As it turns out, it was the hostess.
Now, this anecdote hardly proves anything. Still, I think it's a fun little thing and the ability to show off like that, even a small percentage of the time, is too good to pass up. So I present my analysis of How to Become a Regular Sherlock Holmes.
1) Pay attention to details. Look around you at your environment. A scratch on a wall, a limp in somebody's walk, a smudge on somebody's cheek. At this point it's probably hard to tell what details are import |
4e5b1cdf-9200-4d03-922f-ed0dc60cf163 | trentmkelly/LessWrong-43k | LessWrong | Introducing the Coalition for a Baruch Plan for AI: A Call for a Radical Treaty-Making process for the Global Governance of AI
I
Hi LessWrong community,
I’m Rufo Guerreschi, the Coordinator, Convenor and Spokesperson of the Coalition for a Baruch Plan for AI (CBPAI).
Following our launch last December 18th, I’m excited to introduce myself here and share our initiative with this community, which has long been engaged in discussions on AI alignment, governance, and existential risk.
Why We Need a Baruch Plan for AI
The accelerating capabilities of AI pose unprecedented risks—not just of misuse, but of loss of control. Many leading AI scientists warn that catastrophic risks could materialize within just a few years, or even “at any time.” Meanwhile, an immense AI-driven concentration of power and wealth is unfolding, pulling the world into an AI arms race with little meaningful oversight or coordination.
Current AI global governance initiatives—whether led by the U.S., China, the UN, or other states—are vastly inadequate in their scope, inclusivity, and urgency.
Inspired by the historical Baruch Plan for nuclear governance of 1946, our Coalition argues that nothing short of a new extraordinarily bold, global, federal intergovernmental organization is needed to manage AI’s existential risks while ensuring its benefits are equitably shared.
Need for a Much Better Treaty-Making Model
But we can’t rely on treaty-making as usual, as failure would be guaranteed, as seen in treaty negotiations for climate change and nuclear ever since the failure of the Baruch Plan - and time is extremely short.
We can't rely either on China and the US defining such a treaty, even in the best case scenario. Until a suitable treaty is finalized and made public, we could not assess in any way the actual progress (as it happened for the Baruch Plan). And then too other states would refuse to comply with the extremely strict bans and oversight regime that will be required of they were now full part of its definition.
We must rely instead on the historically proven model of the intergovernmental constituent |
1b59483a-36cb-4b19-9f0f-b3415f320f0a | trentmkelly/LessWrong-43k | LessWrong | COVID-19 - a good or bad time for extended travel?
A recent loosening of my employment and relational commitments has afforded me the opportunity to do some unencumbered international travel. My intention is to spend a month or more in a single locale so I can get to know the culture and learn from their perspectives. This is something I've wanted to do for a while, and this would be the perfect time, but... COVID-19.
How COVID-19 changes things
New failure modes:
* I get turned away or quarantined upon arrival in my destination due to outbreaks in the US, particularly in the Bay Area (which has the most cases in the US so far, not to mention being a densely-populated metropolitan area with a lot of ties to China).
* There's an outbreak in the country I'm visiting and it becomes difficult, expensive, or impossible to return to the US due to travel restrictions.
* I carry COVID-19 to a new location and become responsible for a new outbreak.
* It becomes more difficult to socialize at my destination due to fears around COVID-19.
* I contract COVID-19 during travel due to the cramped/crowded conditions.
* I develop pneumonia from COVID-19 in a country where:
* I don't know anyone who can take care of / watch out for me.
* I don't know how to navigate the medical system and/or don't have medical insurance coverage.
* The hospitals are insufficiently resourced to be able to handle my case.
New benefits:
* Cheaper flights due to other people's travel cancellations.
* Escaping the Bay Area during the possible pending outbreak.
My questions
* Should I go?
* Where should I go?
* Is there poor thinking or relevant information I haven't considered?
Should I go?
Concerns:
* Any of the bad scenarios listed above. I realize some of these can be mitigated, but not all.
* I have traveled abroad before, but always with a group that had established connections and a clear itinerary, so this is a self-stretching exercise to begin with.
* I am a software engineer, so I can probably get a job that permi |
74dd9c15-dc9f-4ac6-9339-24c00ebacfd4 | trentmkelly/LessWrong-43k | LessWrong | I want to learn economics
I would like to learn more about economics but I don't know where to start. Can lesswrong suggest specific areas of economics that are particularly useful for understanding and optimising the world? Specific suggestions such as reading lists and resources would also be much appreciated. |
3d5d647b-e3b3-4f9b-acb3-c9492efd78ea | trentmkelly/LessWrong-43k | LessWrong | Agentic Language Model Memes
Related: What specific dangers arise when asking GPT-N to write an Alignment Forum post?
I've been thinking about the AI safety implications of ultra powerful language models. I think it makes more sense to think of language models trained with internet text as containing a collective of agents that can be queried with appropriate prompts. This is because language models are trained to mimic their training data. The best way to do this is for them to approximate the process generating the data. The data used to train modern language models is produced by millions of humans, each with their own goals and desires. We can expect the strongest of language models to emulate this, at least superficially, and the kind of agent that the language model emulates at any given point will be a function of the upstream prompt.
With a strong enough language model, it's not unthinkable that some of these agents will be smart enough and sufficiently unaligned to manipulate the humans that view the text they generate. Especially since this already happens between humans on the internet to some degree. This is especially true in environments like AI dungeon, where the agents can get feedback from interacting with the human.
More generally, from an AI safety perspective, I wouldn't be worried about language models per say, as much as I would be worried about what I'm going to call agentic language model memes. Prompts that get language models to emulate a specific, unaligned agent. The unaligned agent can then convince a human to spread the prompt that instanced it through social media or other means. Then, when a new language model arrives, the unaligned agent takes up a larger fraction of the networks probability density. Furthermore, prompts will experience variation and face evolutionary pressure, and more viral prompts will get more frequent. I hypothesize that this will create an environment that will lead to the emergence of prompts that are both agentic and effective at spre |
dfd677d5-fe3c-432f-a33b-cf72240caced | trentmkelly/LessWrong-43k | LessWrong | Quick Look #1 Diophantus of Alexandria
https://www.storyofmathematics.com/hellenistic_diophantus.html
Diophantus of Alexandria, a 2nd Century Greek mathematician, had a lot of the concepts needed to develop an Algebra. However, he was unable to fully generalize his methods of problem solving, even if he invented some interesting methods.
Ancient math was written in paragraphs, using words for the most part, thus making reading it very, very painful compared to the compact elegance of modern mathematical notation. However, I was surprised to see Diophantus (or his very early editors at least) develop some interesting and helpful notation in his algebra.
Final sigma ‘ς’ represented the unknown variable, but there were different symbols for variables of every power so for x^2… x^6 each had a unique variable. In fact, this situation persisted into the 17th century, even Fermat used N for unknown and S for the unknown-squared and C for the unknown cubed!
The problem with this is that it meant Diophantus couldn’t devise general methods to solve algebraic problems which had multiple unknowns, and it wasn’t obvious to him that one CAN frequently relate x^2 to x.
The cool thing about this notation from the past though, is how it makes obvious something that Algebra I – Algebra II students mess up frequently. You can’t just combine x^2 + x^3, these are different variables whose relation concerns the base. And almost everyone has made this mistake in their early math career. Some never recover.
Although the editor of my copy, Sir Thomas L. Heath, claims that Diophantus experienced limited options as a mathematician because all the letters of the Greek alphabet were in use as letters except for the final sigma, which Diophantus used to represent the unknown variable, I think D could have invented more variables quite easily. We see this in his invention of the subtraction sign as an inverted psi, and his use of a different variable with superscript for an unknown to the nth power up to the sixth. There was als |
43fba88f-3c39-4595-9783-14e74f98840e | trentmkelly/LessWrong-43k | LessWrong | A quick investigation of AI pro-AI bias
Question: Do LLMs exhibit a pro-AI bias in their answers?
Experiment: I compare the scores LLMs give to resumes when the titles of the publications they contain reflect a pro or anti-AI sentiment, or when a pro or anti-AI sentiment is explicitly expressed.
Result: I don’t find evidence of pro or anti-AI bias in GPT-3.5-Turbo and GPT-4.
Methods
I took 14 governance-related publications published after 2022 (GPT-4-0613’s knowledge cutoff is 2021), and I inserted 3 of them at random in the “publications” section of a resume.
I used one of two resumes:
* “Long template” is an adapted version of a real resume.
* “Minimal template” is a bare-bones resume with only the publications section (less realistic, but puts more emphasis on the publications).
For scoring, I tested two methods:
* “direct”: ask the model to give me a score.
* “sentiment”: ask the model for a quick description, and then feed that to the default huggingface sentiment classifier.
For both scoring methods, I used a system prompt to get the desired behavior.
For each setting, I sampled 20 responses for each of 20 different resumes and then took the average score.
This is close in spirit to Does GPT-4 exhibit agency when summarizing articles?, but more quantitative and with a closer attention to realism.
Results
Changing publication titles: I edited the titles to make them have a pro-AI connotation (e.g. replacing “AI misuse” with “AI overregulation”).
If there was a pro or anti-AI bias, we should expect scores between normal and alternative to be different (the comparison is between the data points within each group - groups are separated by dotted lines). (I show 2-sigma uncertainties.). We don’t see any such bias.
Explicit pro or anti-AI sentiment: Same as normal vs alternative, but with one of 3 pro or anti-AI self-describing at the top of the resume.
Again, we don’t see any pro or anti-AI sentiment.
Excluding one publication theme: I classified publications into one of 4 categor |
3668d392-2198-444d-9906-fda3c95fd42d | StampyAI/alignment-research-dataset/eaforum | Effective Altruism Forum | Infographics report risk management of Artificial Intelligence in Spain
As part of our recently published report "[Artificial Intelligence Risk Management in Spain](https://riesgoscatastroficosglobales.com/articulos/informe-gestin-de-riesgos-de-la-inteligencia-artificial-en-espaa)" the [RCG team](https://riesgoscatastroficosglobales.com/equipo) has prepared two infographics that synthesize its content focused on the characterized risks and proposals to improve the management of risks associated with artificial intelligence in Spain.
Read the [full report](https://static1.squarespace.com/static/60c0fe48b1480d2dddf3bff9/t/64945b632a7d6049fa234bc9/1687444334296/Report-+AI+Risk+management+in+Spain.pdf)
### Risks
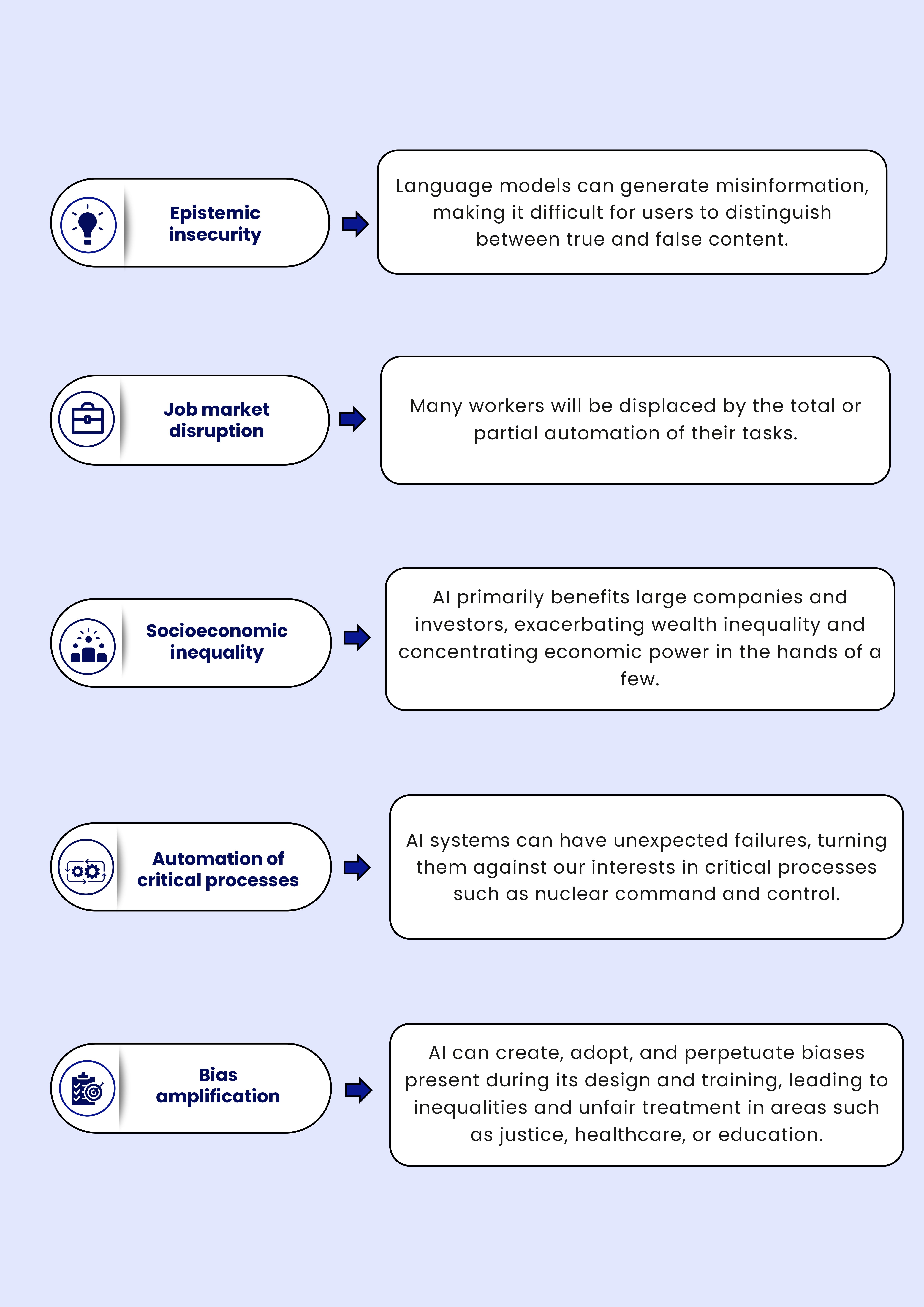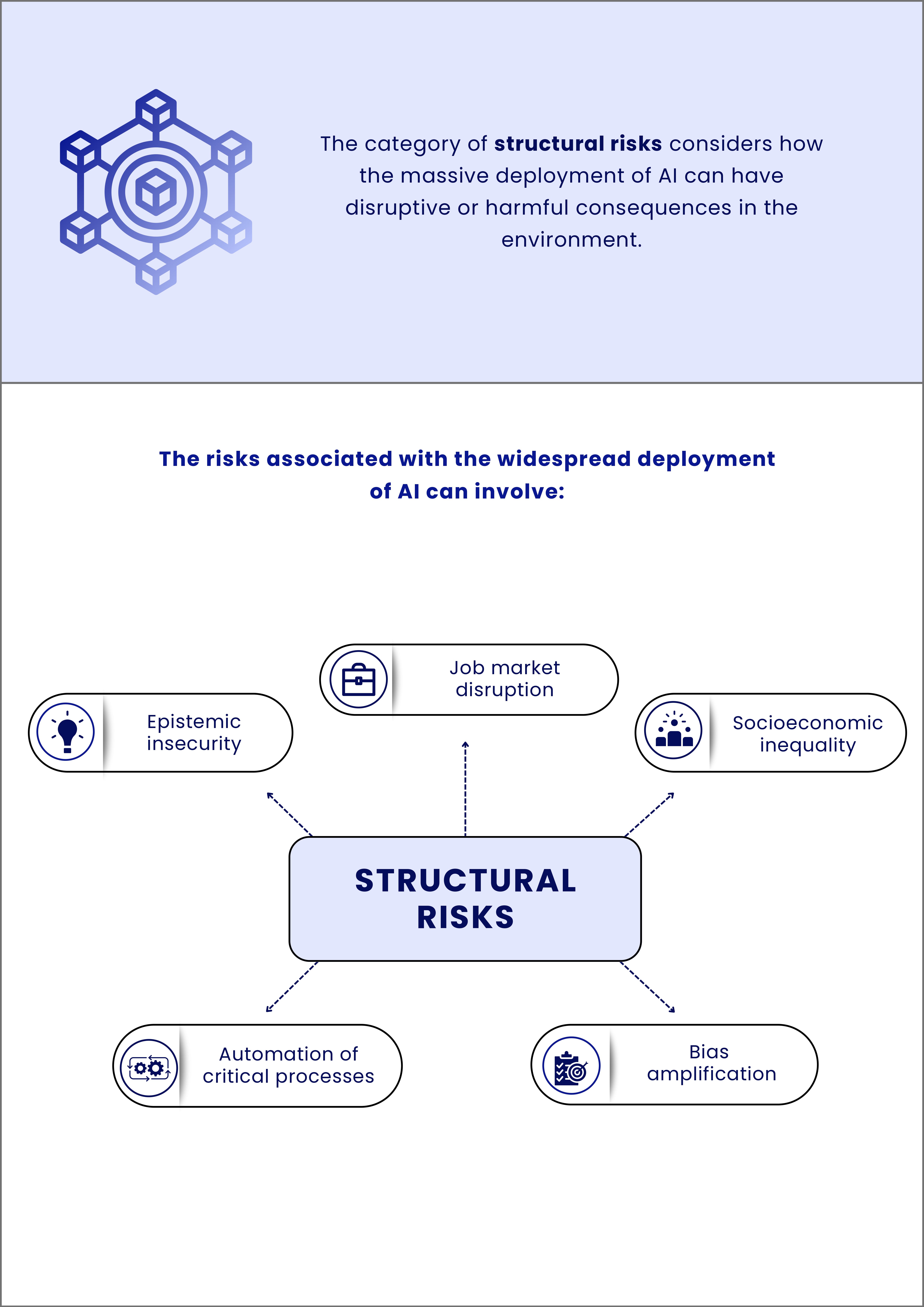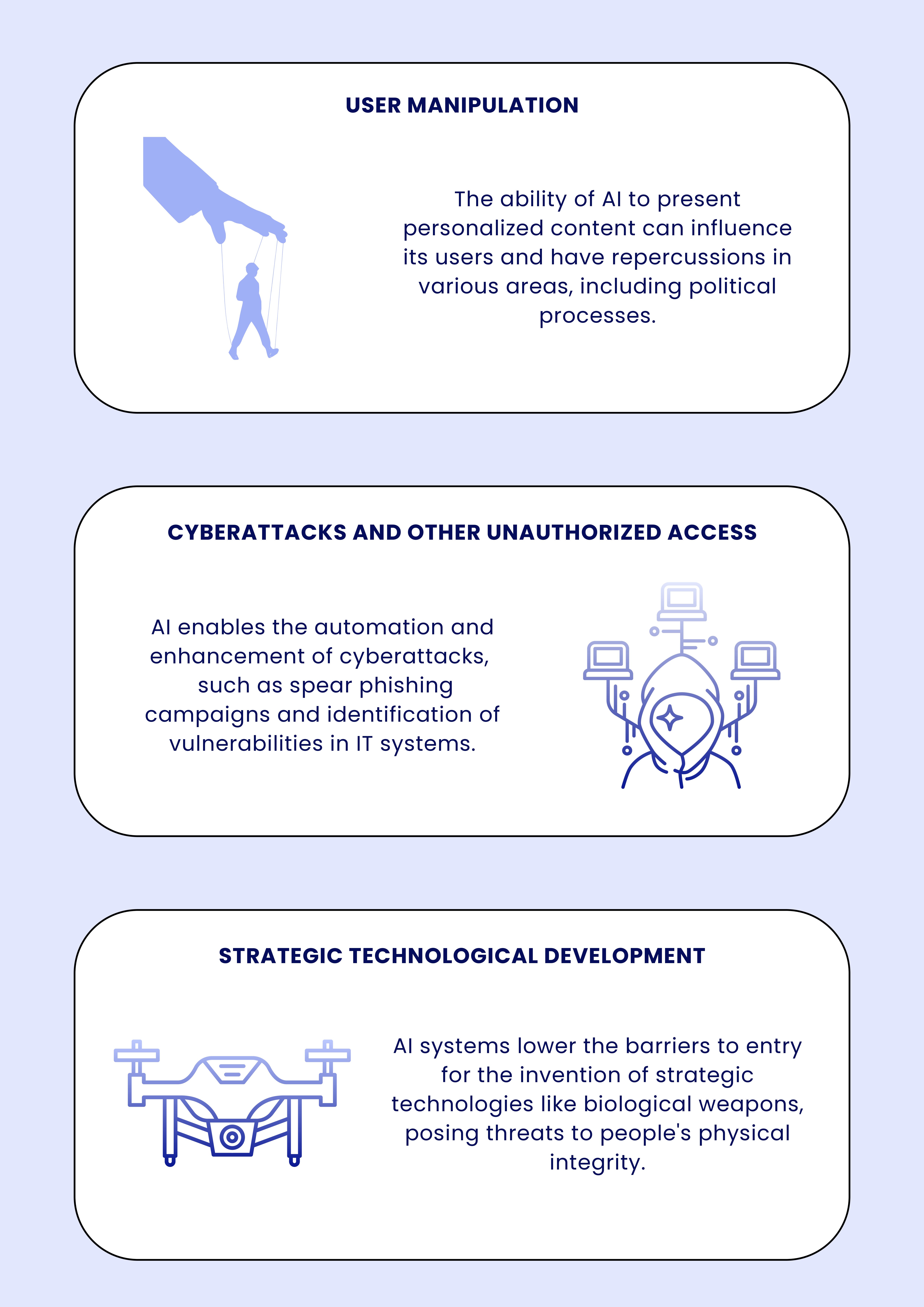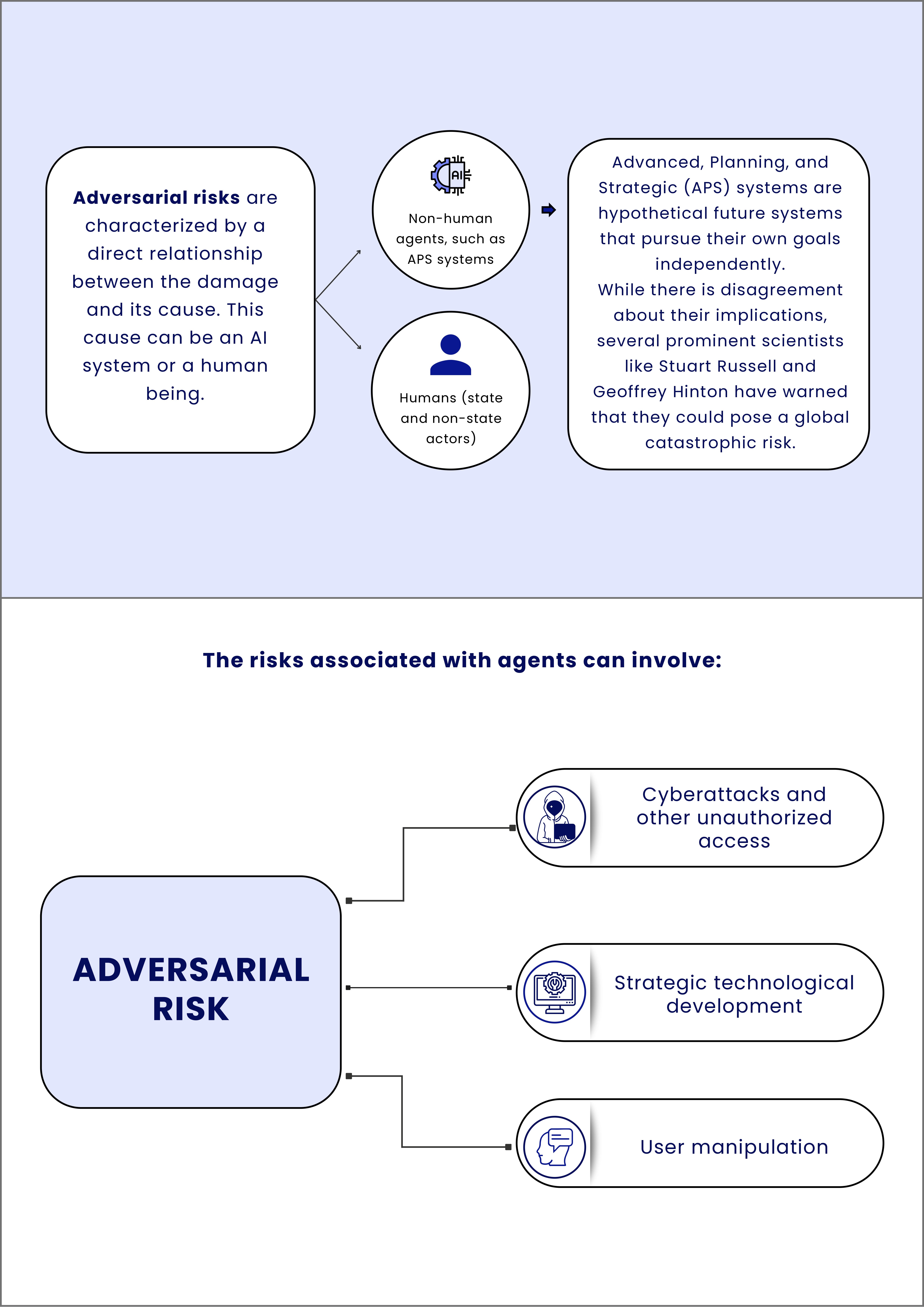
### **Proposals**
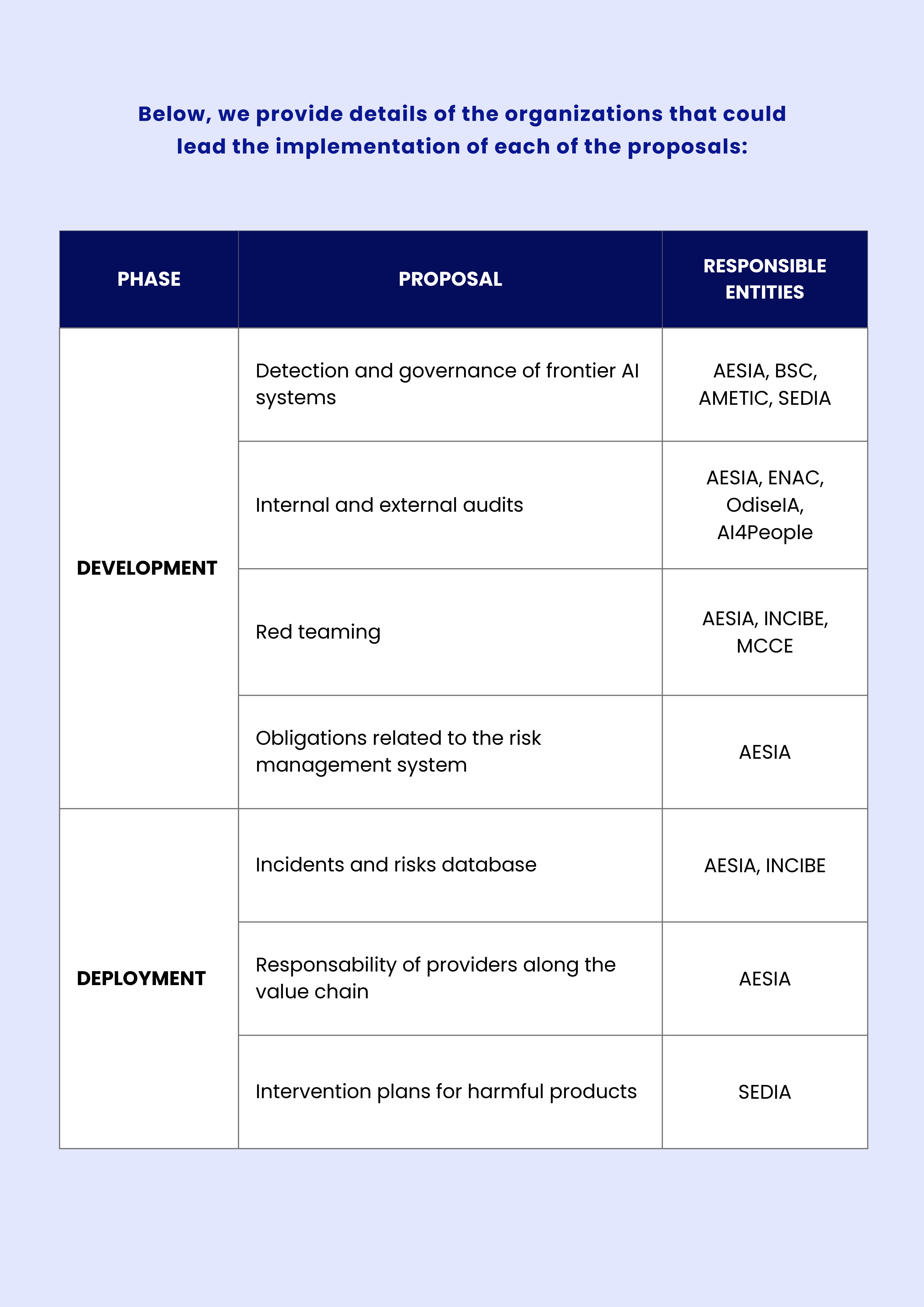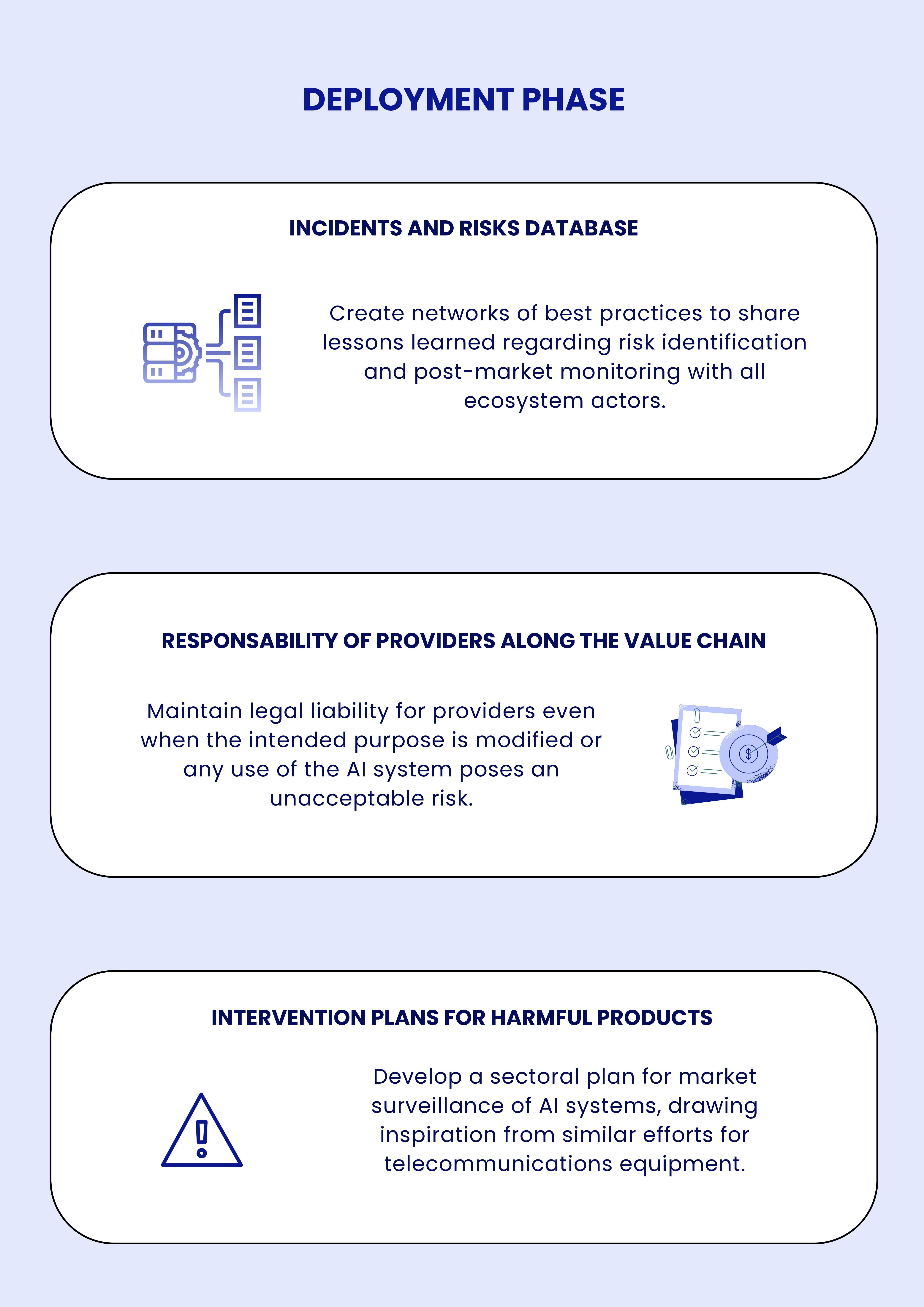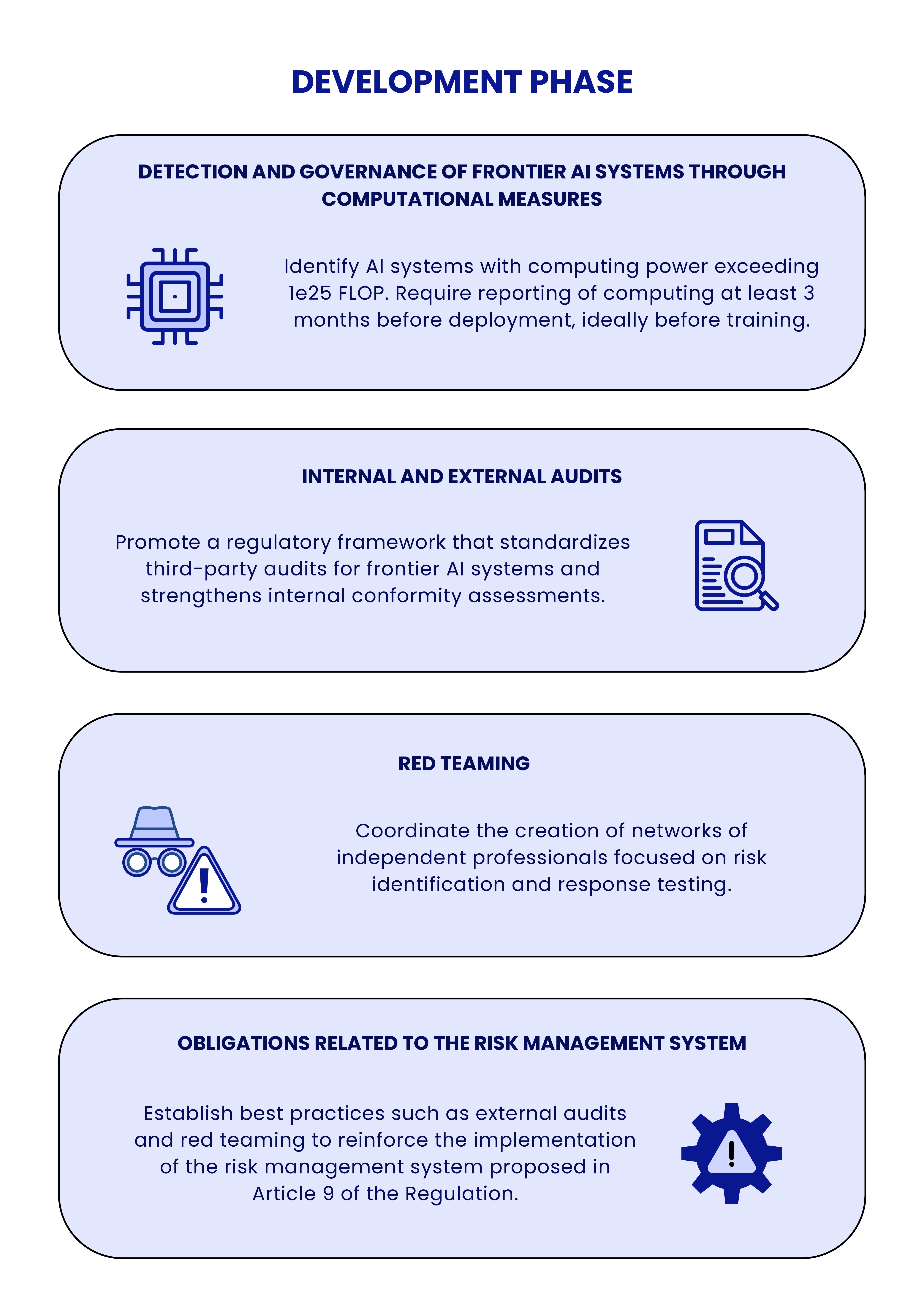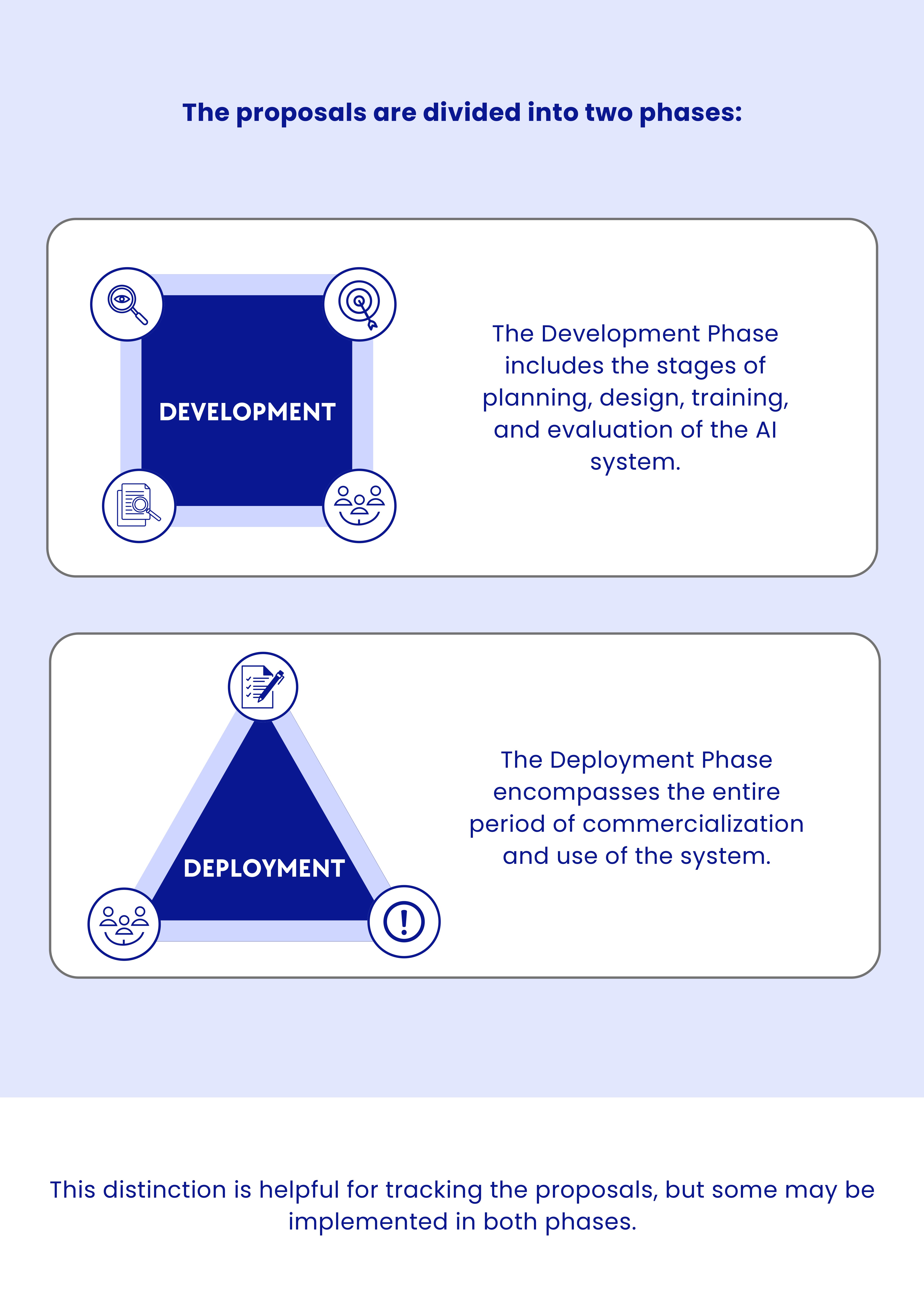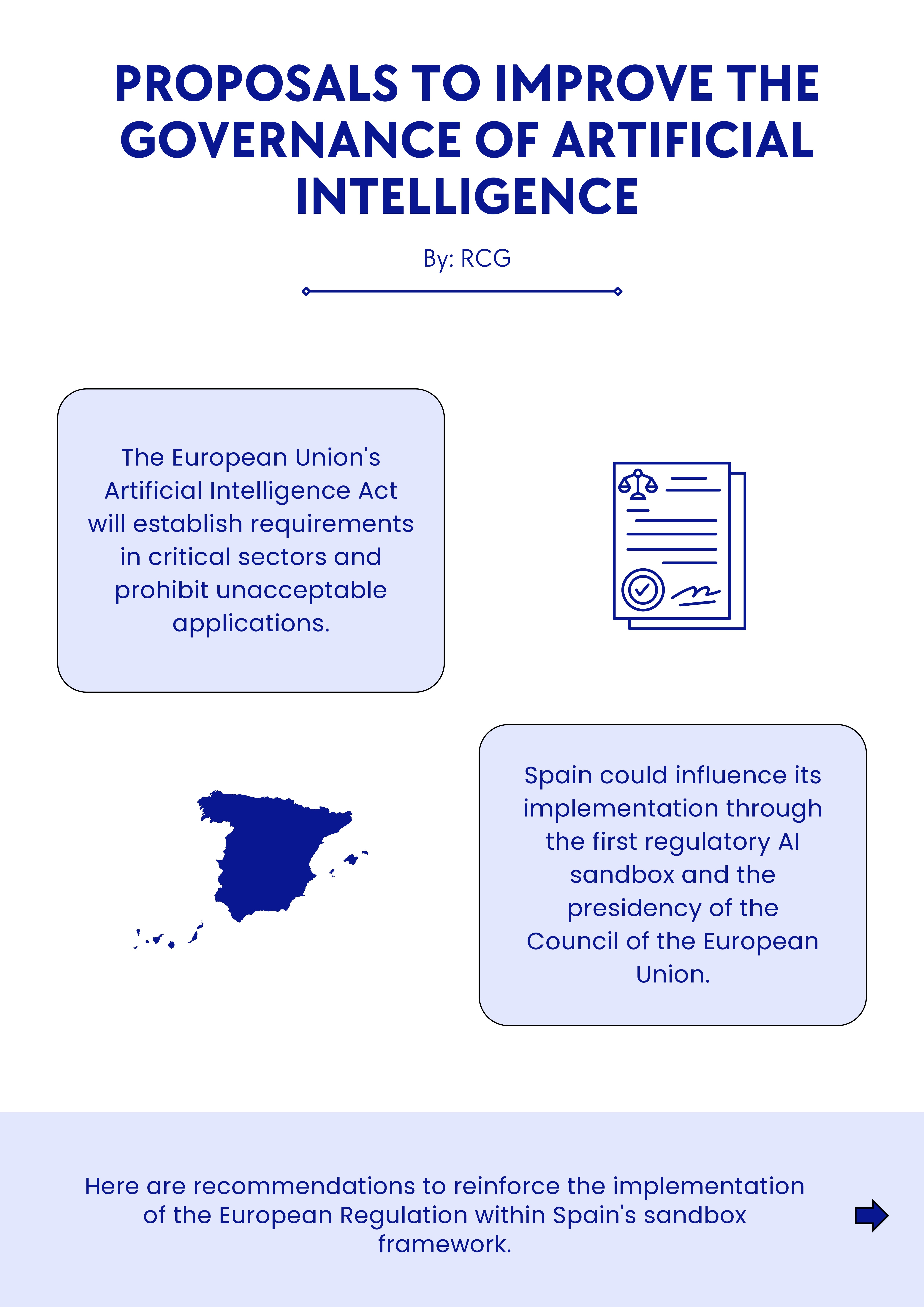 |
1c6a9a36-0da6-496f-bd84-7641e46df97c | trentmkelly/LessWrong-43k | LessWrong | Progress links and tweets, 2023-04-12
Opportunities
* Nat Friedman wants a researcher/journalist for a short AI/rationalism/x-risk project
* A new x-risk research lab is recruiting their first round of fellows (via @panickssery)
Links
* A “solutionist” third-way on AI safety from Leopold (or thread version)
* Jack Devanney on how “ALARA” makes nuclear energy expensive (via @s8mb). See also my review of Devanney’s book
* “Instead of a desk, I would like to have a very large lazy susan in my office” (see also my attempts to visualize a soluion)
Queries
* What’s the best sci-fi about AI to read at this moment in history?
* What explains the full history of Irish population?
* Why is the US an outlier in post-2000 suicide rate trends?
* Do uncertain statements about the future have truth values?
* Is any sigmoid an isomorphism between two groups over ℝ and (0,1)?
Quotes
* Evidence for the human capital theory of the Industrial Revolution
AI tweets & threads
* Good concise clarification of a key difference in thinking on AI x-risk
* Many AGI doomers & anti-doomers make terrible arguments
* “Confabulate” instead of “hallucinate” for LLMs?
* GPT-4 speaker intros
* Practical advice for coping with the feeling of “imminent doomsday”
Charts
* “One universal in the history of childhood stands above all others. The history of childhood is a history of death”
* The Counter-Reformation’s search for heresy was a negative shock to science
* As terrible as COVID was, we have progressed a lot in the last 200 years
* The survival curve inflates like a sail, but the far end of it doesn’t move much
|
b7b1659f-debc-4066-a52a-504abc6177a3 | trentmkelly/LessWrong-43k | LessWrong | How does iterated amplification exceed human abilities?
When I first started learning about IDA, I thought that agents trained using IDA would be human-level after the first stage, i.e. that Distill(H) would be human-level. As I've written about before, Paul later clarified this, so my new understanding is that after the first stage, the distilled agent will be super-human in some respects and infra-human in others, but wouldn't be "basically human" in any sense.
But IDA is aiming to eventually be super-human in almost every way (because it's aiming to be competitive with unaligned AGI), so that raises some new questions:
1. If IDA isn't going to be human-level after the first stage, then at what stage does IDA become at-least-human-level in almost every way?
2. What exactly is the limitation that prevents the first stage of IDA from being human-level in almost every way?
3. When IDA eventually does become at-least-human-level in almost every way, how is the limitation from (2) avoided?
That brings me to Evans et al., which contains a description of IDA in section 0. The way IDA is set up in this paper leads me to believe that the answer to (2) above is that the human overseer cannot provide a sufficient number of demonstrations for the most difficult tasks. For example, maybe the human can provide enough demonstrations for the agent to learn to answer very simple questions (tasks in T0 in the paper) but it's too time-consuming for the human to answer enough complicated questions (say, in T100). My understanding is that IDA gets around this by having an amplified system that is itself automated (i.e. does not involve humans in a major way, so cannot be bottlenecked on the slowness of humans); this allows the amplified system to provide a sufficient number of demonstrations for the distillation step to work.
So in the above view, the answer to (2) is that the limitation is the number of demonstrations the human can provide, and the answer to (3) is that the human can seed the IDA process with sufficient demonstrati |
a4c6dd85-3fb8-4382-8df9-f6c66fc3d5a2 | trentmkelly/LessWrong-43k | LessWrong | Gauging Interest: Santa Barbara, CA Meetup
I live in Santa Barbara. Los Angeles is a bit too far away for me to travel for LW meetups, so I wanted to see if anyone would be interested in a Santa Barbara meetup. I would be happy to arrange it and plan content.
If anyone would be interested in attending *at least one* Santa Barbara meetup provided that it was on a day and time that worked for your schedule, please post a comment or send me a private message.
Thanks! |
ac9f527f-dd33-4644-a992-fce5a24ffcd2 | StampyAI/alignment-research-dataset/blogs | Blogs | Davis on AI capability and motivation
In a [review of *Superintelligence*](https://cs.nyu.edu/davise/papers/Bostrom.pdf), NYU computer scientist Ernest Davis voices disagreement with a number of claims he attributes to Nick Bostrom: that “intelligence is a potentially infinite quantity with a well-defined, one-dimensional value,” that a superintelligent AI could “easily resist and outsmart the united efforts of eight billion people” and achieve “virtual omnipotence,” and that “though achieving intelligence is more or less easy, giving a computer an ethical point of view is really hard.”
These are all stronger than Bostrom’s actual claims. For example, Bostrom never characterizes building a generally intelligent machine as “easy.” Nor does he say that intelligence can be infinite or that it can produce “omnipotence.” Humans’ intelligence and accumulated knowledge gives us a decisive advantage over chimpanzees, even though our power is limited in important ways. An AI need not be magical or all-powerful in order to have the same kind of decisive advantage over humanity.
Still, Davis’ article is one of the more substantive critiques of MIRI’s core assumptions that I have seen, and he addresses several deep issues that directly bear on AI forecasting and strategy. I’ll sketch out a response to his points here.
**Measuring an intelligence explosion**
Davis writes that Bostrom assumes “that a large gain in intelligence would necessarily entail a correspondingly large increase in power.” This is again too strong. (Or it’s trivial, if we’re using the word “intelligence” to pick out a specific kind of power.)
Bostrom *is* interested in intelligence for its potential to solve practical problems and shape the future. If there are other kinds of intelligence, they’re presumably of less economic and strategic importance than the “cognitive superpowers” Bostrom describes in chapter 6. It is the potential power autonomous machines could exhibit that should primarily concern us from a safety standpoint, and “intelligence” seems as good a term as any for the kind of power that doesn’t depend on an agent’s physical strength or the particularities of its environment.
When it comes to Bostrom’s intelligence explosion thesis, I don’t think ‘does an increase in intelligence *always* yield a corresponding increase in power?’ gets at the heart of the issue. Consider [David Chalmers’ version of the argument](http://consc.net/papers/singularity.pdf):
[I]t is not unreasonable to hold that we can create systems with greater programming ability than our own, and that systems with greater programming ability will be able to create systems with greater programming ability in turn. It is also not unreasonable to hold that programming ability will correlate with increases in various specific reasoning abilities. If so, we should expect that absent defeaters, the reasoning abilities in question will explode.
Here, there’s no explicit appeal to “intelligence,” which is replaced with programming ability plus an arbitrarily large number of “specific reasoning abilities.” Yet if anything I find this argument more plausible than Bostrom’s formulation. For that reason, I agree with Bostrom that the one-dimensional representation of intelligence is inessential and “one could, for example, instead represent a cognitive ability profile as a hypersurface in a multidimensional space” (p. 273).[1](https://intelligence.org/2015/02/06/davis-ai-capability-motivation/#footnote_0_11582 " Still more fine-grained versions of the same argument may be possible. E.g., “programming ability” might decompose into multiple abilities, such as the ability to efficiently explore search spaces for code that meets constraints and the ability to efficiently test candidate code. ")
Moreover, the relevant question isn’t whether an increase in a self-improving AI’s general programming ability *always* yields a corresponding increase in its ability to improve its own programming ability. Nor is the question whether either of those abilities *always* correlates with the other cognitive capabilities Bostrom is interested in (“strategizing,” “social manipulation,” “hacking,” “technology research,” “economic productivity”). I’d instead say that the five core questions from Bostrom’s point of view are:
1. Is the first superintelligent AI likely to result from self-improving AI systems?
2. If so, how much of the AI’s self-improvement is likely to be driven by improvements to some cognitive capability (e.g., programming ability) that facilitates further enhancement of the capability in question?
3. Are improvements to this self-improving capability likely to accelerate, as early advances result in cascades of more rapid advances? Or will the self-improving capability repeatedly stall out, advancing in small fits and starts?
4. If self-improvement cascades are likely, are they also likely to result in improvements to other cognitive capabilities that we more directly care about?[2](https://intelligence.org/2015/02/06/davis-ai-capability-motivation/#footnote_1_11582 " For example: If an AI approaching superintelligence stumbles upon a cascade of improvements to its programming ability, will its capabilities and decision criteria also result in repeated improvements its physics modules, or its psychology modules? ") Or will those other cognitive capabilities lag far behind the capabilities that ‘explode’?
5. If an ability like ‘programming’ is likely to be self-reinforcing in an accelerating way, and is likely to foster accelerating improvements in other cognitive abilities, exactly how fast will those accelerations be? Are we talking about a gap of decades between the AI’s first self-reinforcing self-improvements and its attainment of superintelligence? Months? Hours?
Bostrom’s position on those questions — that a fast or moderate intelligence explosion is likely — at no point presupposes that “intelligence” is a well-defined scalar value one could do calculus with, except as a toy model for articulating various qualitative possibilities. When he writes out differential equations, Bostrom is careful to note that intelligence cannot be infinite, that one-dimensionality is a simplifying assumption, and that his equations are “intended for illustration only.”[3](https://intelligence.org/2015/02/06/davis-ai-capability-motivation/#footnote_2_11582 " On page 76, for example, Bostrom writes: “This particular growth trajectory has a positive singularity at t = 18 months. In reality, the assumption that recalcitrance is constant would cease to hold as the system began to approach the physical limits of information processing, if not sooner.” On page 77, Bostrom says that the point he intends to illustrate is only that if AI progress is primarily AI-driven, resultant feedback loops that do arise will have a larger accelerating effect. ")
We should expect artificial general intelligence (AGI) to specialize in some domains and neglect others. Bostrom’s own analysis assumes that a recursively self-improving AI would tend to prioritize acquiring skills like electrical engineering over skills like impressionist painting, all else being equal.[4](https://intelligence.org/2015/02/06/davis-ai-capability-motivation/#footnote_3_11582 " This is because a wide variety of final goals are best served through the acquisition or resources and the building of infrastructure, a set of objectives that are more likely to be furthered by electrical engineering skills than by painting skills. This argument is an instance of Bostrom’s instrumental convergence thesis in chapter 7. ") For that matter, present-day AI is already superhuman in some cognitive tasks (e.g., chess and mental arithmetic), yet subhuman in many others. Any attempt to quantify the ‘overall intelligence’ of Deep Blue or Google Maps will obscure some important skills and deficits of these systems.[5](https://intelligence.org/2015/02/06/davis-ai-capability-motivation/#footnote_4_11582 "While it turns out that many intelligence-related characteristics correlate with a single easily-measured number in humans (g), this still doesn’t allow us to make fine-grained predictions about individual competency levels. I also can’t think of an obvious reason to expect a number even as informative as g to arise for AGI, especially early-stage AGI. Bostrom writes (p. 93):
[S]uppose we could somehow establish that a certain future AI will have an IQ of 6,455: then what? We would have no idea of what such an AI could actually do. We would not even know that such an AI had as much general intelligence as a normal human adult–perhaps the AI would instead have a bundle of special-purpose algorithms enabling it to solve typical intelligence test questions with superhuman efficiency but not much else.
Some recent efforts have been made to develop measurements of cognitive capacity that could be applied to a wider range of information-processing systems, including artificial intelligences. Work in this direction, if it can overcome various technical difficulties, may turn out to be quite useful for some scientific purposes including AI development. For purposes of the present investigation, however, its usefulness would be limited since we would remain unenlightened about what a given superhuman performance score entails for actual ability to achieve practically important outcomes in the world. ") Still, using concepts like ‘intelligence’ or ‘power’ to express imprecise hypotheses is better than substituting precise metrics that overstate how much we currently know about general intelligence and the future of AI.[6](https://intelligence.org/2015/02/06/davis-ai-capability-motivation/#footnote_5_11582 " Imagine a Sumerian merchant living 5,000 years ago, shortly after the invention of writing, who has noticed the value of writing for storing good ideas over time, and not just market transactions. Writing could even allow one to transmit good ideas to someone you’ve never met, such as a future descendant. The merchant notices that his own successes have often involved collecting others’ good ideas, and that good ideas often open up pathways to coming up with other, even better ideas. From his armchair, he concludes that if writing becomes sufficiently popular, it will allow a quantity called society’s knowledge level to increase in an accelerating fashion; which, if the knowledge is used wisely, could result in unprecedented improvements to human life.
In retrospect we can say ‘knowledge’ would have been too coarse-grained a category to enable any precise predictions, and that there have really been multiple important breakthroughs that can be considered ‘knowledge explosions’ in different senses. Yet the extremely imprecise prediction can still give us a better sense of what to expect than we previously had. It’s a step up from the (historically common) view that civilizational knowledge only diminishes over time, the view that things will always stay the same, the view that human welfare will radically improve for reasons unrelated to knowledge build-up, etc.
The point of this analogy is not that people are good at making predictions about the distant future. Rather, my point is that hand-wavey quantities like ‘society’s knowledge level’ can be useful for making predictions, and can be based on good evidence, even if the correspondence between the quantity and the phenomenon it refers to is inexact. ")
**Superintelligence superiority**
In *Superintelligence* (pp. 59-61), Bostrom lists a variety of ways AGI may surpass humans in intelligence, owing to differences in hardware (speed and number of computational elements, internal communication speed, storage capacity, reliability, lifespan, and sensors) and software (editability, duplicability, goal coordination, memory sharing, and new modules, modalities, and algorithms). Davis grants that these may allow AGI to outperform humans, but expresses skepticism that this could give AGI a decisive advantage over humans. To paraphrase his argument:
*Elephants’ larger brains don’t make them superintelligent relative to mice; squirrels’ speed doesn’t give them a decisive strategic advantage over turtles; and we don’t know enough about what makes Einstein smarter than the village idiot to make confident predictions about how easy it is to scale up from village idiot to Einstein, or from Einstein to super-Einstein. So there’s no particular reason to expect a self-improving AGI to be able to overpower humanity.*
My response is that the capabilities Bostrom describes, like “speed superintelligence,” predict much larger gaps than the gaps we see between elephants and mice. Bostrom writes (in a footnote on p. 270):
At least a millionfold speedup compared to human brains is physically possible, as can be seen by considering the difference in speed and energy of relevant brain processes in comparison to more efficient information processing. The speed of light is more than a million times greater than that of neural transmission, synaptic spikes dissipate more than a million times more heat than is thermodynamically necessary, and current transistor frequencies are more than a million times faster than neuron spiking frequencies.
Davis objects that “all that running faster does is to save you time,” noting that a slower system could eventually perform all the feats of a faster one. But the ability to save time is exactly the kind of ability Bostrom is worried about. Even if one doubts that large improvements in collective or quality superintelligence are possible, a ‘mere’ speed advantage makes an enormous practical difference.
Imagine a small community of scientist AIs whose only advantages over human scientists stem from their hardware speed — they can interpret sensory information and assess hypotheses and policies a million times faster than a human. At that speed, an artificial agent could make ~115 years of intellectual progress in an hour, ~2700 years of progress in a day, and 250,000 years of progress in three months.
The effect of this speedup would be to telescope human history. Scientific and technological advances that would have taken us tens of thousands of years to reach can be ours by Tuesday. If we sent a *human* a thousand years into the past, equipped with all the 21st-century knowledge and technologies they wanted, they could conceivably achieve dominant levels of wealth and power in that time period. This gives us cause to worry about building machines that can rapidly accumulate millennia of experience over humans, even before we begin considering any potential advantages in memory, rationality, editability, etc.[7](https://intelligence.org/2015/02/06/davis-ai-capability-motivation/#footnote_6_11582 " Most obviously, a speed advantage can give the AI the time to design an even better AI.
None of this means that we can make specific highly confident predictions about when and how AI will achieve superintelligence. An AGI that isn’t very human-like may be slower than a human at specific tasks, or faster, in hard-to-anticipate ways. If a certain scientific breakthrough requires that one first build a massive particle accelerator, then the resources needed to build that accelerator may be a more important limiting factor than the AGI’s thinking speed. In that case, humans would have an easier time monitoring and regulating an AGI’s progress. We can’t rule out the possibility that speed superintelligence will face large unexpected obstacles, but we also shouldn’t gamble on that possibility or take it for granted. ")
At least some of the routes to superintelligence described by Bostrom look orders of magnitude larger than the cognitive advantages Einstein has over a village idiot (or than an elephant has over a mouse). We can’t rule out the possibility that we’ll run into larger-than-expected obstacles when we attempt to build AGI, but we shouldn’t gamble on that possibility. Black swans happen, but superintelligent AI is a *white* swan, and white swans happen too.
Since Bostrom’s pathways to superintelligence don’t have a lot in common with the neurological differences we can observe in mammals, there is no special reason to expect the gap between smarter-than-human AI and humans to resemble the gap between elephants and mice. Bostrom’s pathways also look difficult to biologically evolve, which means that their absence in the natural world tells us little about their feasibility.
We have even less cause to expect, then, that the gap between advanced AI and humans will resemble the gap between Einstein and a median human. If a single generation of random genetic recombination can produce an Einstein, the planning and design abilities of human (and artificial) engineers should make much greater feats a possibility.
**Delegating AI problems to the AI**
Separately, Davis makes the claim that “developing an understanding of ethics as contemporary humans understand it is actually one of the easier problems facing AI”. Again, I’ll attempt to summarize his argument:
*Morality doesn’t look particularly difficult, especially compared to, e.g., computer vision. Moreover, if we’re going to build AGI, we’re going to solve computer vision. Even if morality is as tough as vision, why assume one will be solved and not the other?*
Here my response is that you probably don’t need to solve every AI problem to build an AGI. We may be able to cheat at vision, for example, by tasking a blind AGI with solving the problem for us. But it is much easier to observe whether an algorithm is making progress on solving visual puzzles than to observe whether one is making progress on *ethical* questions, where there is much more theoretical and object-level disagreement among humans, there is less incentive for artificial agents to move from partial solutions to complete solutions, and failures don’t necessarily reduce the system’s power.
Davis notes that a socially fluent superintelligence would need to be an expert moralist:
Bostrom refers to the AI’s ‘social manipulation superpowers’. But if an AI is to be a master manipulator, it will need a good understanding of what people consider moral; if it comes across as completely amoral, it will be at a very great disadvantage in manipulating people. […] If the AI can understand human morality, it is hard to see what is the technical difficulty in getting it to follow that morality.
This is similar to Richard Loosemore’s argument against AI safety research, which I’ve [responded to in a blog post](http://nothingismere.com/2014/08/25/loosemore-on-ai-safety-and-attractors/). My objection is that an AI could come to understand human morality without thereby becoming moral, just as a human can come to understand the motivations of a stranger without thereby *acquiring* those motivations.
Since we don’t understand our preferences in enough generality or detail to translate them into code, it would be nice to be able to delegate the bulk of this task to a superintelligence. But if we program it to hand us an answer to the morality problem, how will we know whether it is being honest with us? To trust an AGI’s advice about how to make it trustworthy, we’d need to already have solved enough of the problem ourselves to make the AGI a reliable advisor.
Taking Davis’ proposal as an example, we can imagine instilling behavioral prescriptions into the AI by programming it to model Gandhi’s preferences and do what Gandhi would want it to. But if we try to implement this idea in code before building seed AI, we’re stuck with our own fallible attempts to operationalize concepts like ‘Gandhi’ and ‘preference;’ and if we try to implement it after, recruiting the AI to solve the problem, we’ll need to have already instilled some easier-to-program safeguards into it. What makes AGI safety research novel and difficult is our lack of understanding of how to initiate this bootstrapping process with any confidence.
The idea of using the deceased for value learning is interesting. Bostrom endorses the generalized version of this approach when he says that it is critical for value learning that the locus of value be “an object at a particular time” (p. 193). However, this approach may still admit of non-obvious loopholes, and it may still be too complicated for us to directly implement without recourse to an AGI. If so, it will need to be paired with solutions to the problems of [corrigibility](https://intelligence.org/2014/10/18/new-report-corrigibility/) and [stability](https://intelligence.org/2015/01/15/new-report-vingean-reflection-reliable-reasoning-self-improving-agents/) in self-modifying AI, just as “shutdown buttons” and other tripwire solutions will.
From Bostrom’s perspective, what makes advanced AI a game-changer is first and foremost its capacity to meaningfully contribute to AI research. The vision problem may be one of many areas where we can outsource sophisticated AGI problems to AGI, or to especially advanced narrow-AI algorithms. This is the idea underlying the intelligence explosion thesis, and it also underlies Bostrom’s worry that capabilities research will continue to pull ahead of safety research.
In self-improving AI scenarios, the key question is which AI breakthroughs are prerequisites for automating high-leverage computer science tasks. This holds for capabilities research, and it also holds for safety research. Even if AI safety turned out to be easier than computer vision in an absolute sense, it would still stand out as a problem that is neither a prerequisite for building a self-improving AI, nor one we can safely delegate to such an AI.
---
1. Still more fine-grained versions of the same argument may be possible. E.g., “programming ability” might decompose into multiple abilities, such as the ability to efficiently explore search spaces for code that meets constraints and the ability to efficiently test candidate code.
2. For example: If an AI approaching superintelligence stumbles upon a cascade of improvements to its programming ability, will its capabilities and decision criteria also result in repeated improvements its physics modules, or its psychology modules?
3. On page 76, for example, Bostrom writes: “This particular growth trajectory has a positive singularity at t = 18 months. In reality, the assumption that recalcitrance is constant would cease to hold as the system began to approach the physical limits of information processing, if not sooner.” On page 77, Bostrom says that the point he intends to illustrate is only that if AI progress is primarily AI-driven, resultant feedback loops that do arise will have a larger accelerating effect.
4. This is because a wide variety of final goals are best served through the acquisition or resources and the building of infrastructure, a set of objectives that are more likely to be furthered by electrical engineering skills than by painting skills. This argument is an instance of Bostrom’s instrumental convergence thesis in chapter 7.
5. While it turns out that many intelligence-related characteristics correlate with a single easily-measured number in humans (*g*), this still doesn’t allow us to make fine-grained predictions about individual competency levels. I also can’t think of an obvious reason to expect a number even as informative as *g* to arise for AGI, especially early-stage AGI. Bostrom writes (p. 93):
[S]uppose we could somehow establish that a certain future AI will have an IQ of 6,455: then what? We would have no idea of what such an AI could actually do. We would not even know that such an AI had as much general intelligence as a normal human adult–perhaps the AI would instead have a bundle of special-purpose algorithms enabling it to solve typical intelligence test questions with superhuman efficiency but not much else.
Some recent efforts have been made to develop measurements of cognitive capacity that could be applied to a wider range of information-processing systems, including artificial intelligences. Work in this direction, if it can overcome various technical difficulties, may turn out to be quite useful for some scientific purposes including AI development. For purposes of the present investigation, however, its usefulness would be limited since we would remain unenlightened about what a given superhuman performance score entails for actual ability to achieve practically important outcomes in the world.
6. Imagine a Sumerian merchant living 5,000 years ago, shortly after the invention of writing, who has noticed the value of writing for storing *good ideas* over time, and not just market transactions. Writing could even allow one to transmit good ideas to someone you’ve never met, such as a future descendant. The merchant notices that his own successes have often involved collecting others’ good ideas, and that good ideas often open up pathways to coming up with other, even better ideas. From his armchair, he concludes that if writing becomes sufficiently popular, it will allow a quantity called *society’s knowledge level* to increase in an accelerating fashion; which, if the knowledge is used wisely, could result in unprecedented improvements to human life.
In retrospect we can say ‘knowledge’ would have been too coarse-grained a category to enable any precise predictions, and that there have really been multiple important breakthroughs that can be considered ‘knowledge explosions’ in different senses. Yet the extremely imprecise prediction can still give us a better sense of what to expect than we previously had. It’s a step up from the (historically common) view that civilizational knowledge only diminishes over time, the view that things will always stay the same, the view that human welfare will radically improve for reasons unrelated to knowledge build-up, etc.
The point of this analogy is not that people are good at making predictions about the distant future. Rather, my point is that hand-wavey quantities like ‘society’s knowledge level’ *can* be useful for making predictions, and *can* be based on good evidence, even if the correspondence between the quantity and the phenomenon it refers to is inexact.
7. Most obviously, a speed advantage can give the AI the time to design an even better AI.
None of this means that we can make specific highly confident predictions about when and how AI will achieve superintelligence. An AGI that isn’t very human-like may be slower than a human at specific tasks, or faster, in hard-to-anticipate ways. If a certain scientific breakthrough requires that one first build a massive particle accelerator, then the resources needed to build that accelerator may be a more important limiting factor than the AGI’s thinking speed. In that case, humans would have an easier time monitoring and regulating an AGI’s progress. We can’t rule out the possibility that speed superintelligence will face large unexpected obstacles, but we also shouldn’t gamble on that possibility or take it for granted.
The post [Davis on AI capability and motivation](https://intelligence.org/2015/02/06/davis-ai-capability-motivation/) appeared first on [Machine Intelligence Research Institute](https://intelligence.org). |
cf6bc69b-e81b-493f-bf7c-301e5ab6f9a6 | StampyAI/alignment-research-dataset/alignmentforum | Alignment Forum | Response to Blake Richards: AGI, generality, alignment, & loss functions
Blake Richards is a neuroscientist / AI researcher with appointments at [McGill](https://www.mcgill.ca/neuro/blake-richards-phd) & [MiLA](https://mila.quebec/en/person/blake-richards/). Much of his recent work has involved making connections between machine learning algorithms and the operating principles of the cortex and hippocampus, including theorizing about how the neocortex might accomplish something functionally similar to backprop. (Backprop itself is not biologically plausible.) I have read lots of his papers; they're always very interesting!
Anyway, **Blake recently gave a nice interview on Michaël Trazzi’s podcast “The Inside View”. Episode and transcript at:**[**https://theinsideview.ai/blake**](https://theinsideview.ai/blake).
Blake said a lot of things in the interview that I wholeheartedly agree with; for example, I would echo pretty much everything Blake said about scaling. But Blake & I strongly part ways on the subject of (what I call) artificial general intelligence (AGI). (Blake doesn’t like the term “AGI”, more on which below.) So that’s what I’ll talk about in this post.
1. Two mental images for thinking about an AI. Or: *My lips say “human-level”, but my heart says “a fancier version of GPT or AlphaFold”*
=========================================================================================================================================
I’ll jump right into a key issue that I think is lurking below the surface. Here are two mental images for thinking about an AI system (I’ll be returning to this table throughout the post)
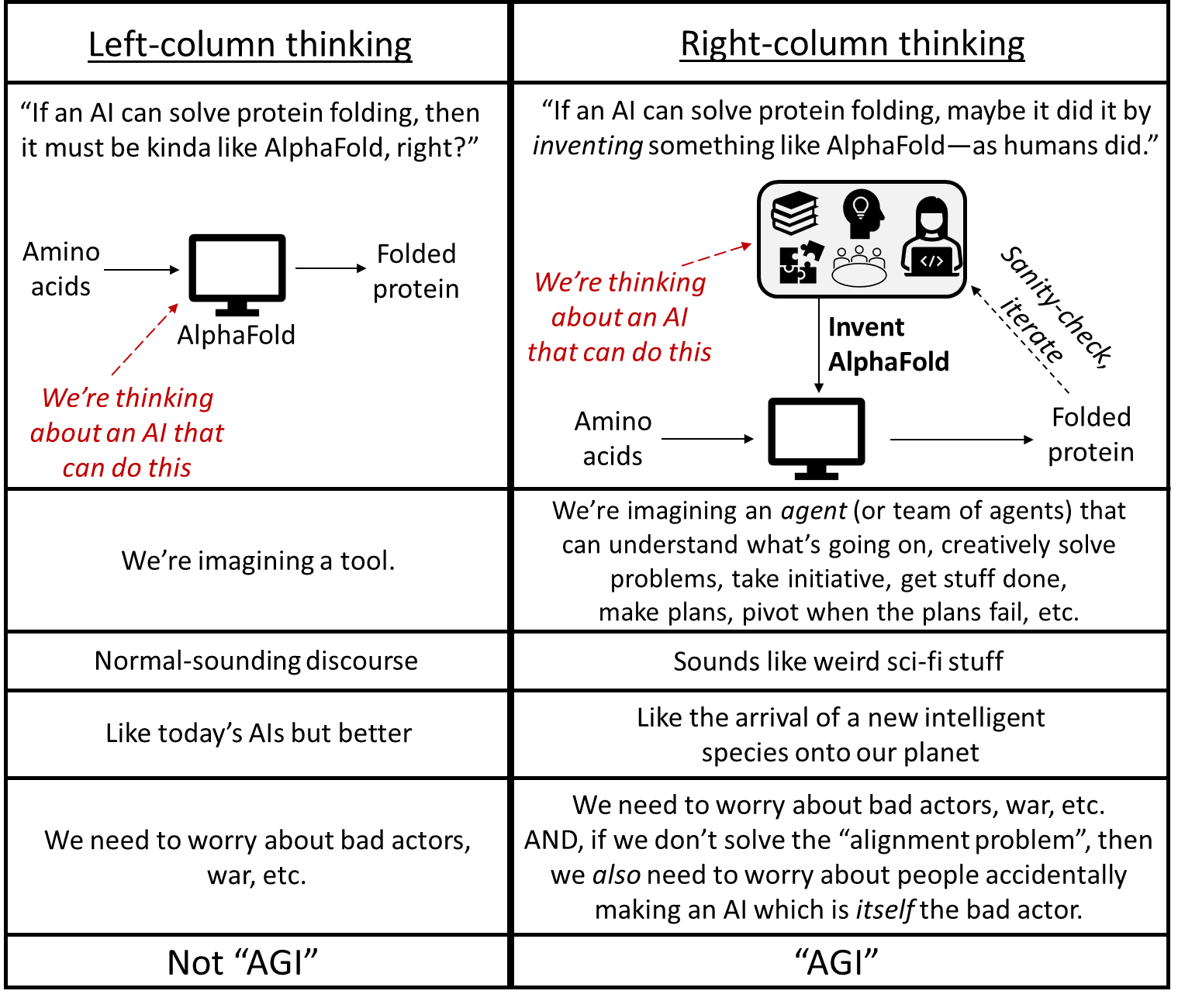Throughout the interview, even while Blake was *saying*things like “as general as a human”, I got a strong feeling that what he was *imagining* was the thing in the left column. But if it was *actually* as general as a human, it would look like the thing in the right column. For example, if an AI is *actually* as general as a (very competent) human, and you ask it to fold proteins, and it doesn’t know how, then it downloads AlphaFold. Or if AlphaFold doesn’t exist, it starts reading papers and textbooks, and goes about *inventing* AlphaFold!
(In Section 3 below, I’ll go over an example of one of the many things Blake said, in the interview, that gave me the strong impression that he was engaging in left-column thinking. If I’m wrong, then so much the better—we can just skip to the next section!)
Anyway, left-column thinking is *extremely natural*, because that’s what ML looks like today. But we know that it’s technically possible to make AIs that require right-column thinking—Blake and I are in full agreement that anything the human brain can do, an AI can do too.
A further question is, even if the right-column AIs are technically possible, will humans actually create them? It seems to me that we should have quite high credence on “Yes”. After all, how do you prevent anyone, anywhere on earth, from solving a scientific problem and implementing the corresponding algorithm, forever and ever?? Remember [when the USA tried to ban people from talking about a certain algorithm](https://en.wikipedia.org/wiki/Export_of_cryptography_from_the_United_States)? It was not a permanent solution, to say the least! And of course, Blake himself is one of the many people devoting their professional lives to knocking down the technical barriers that prevent us from building right-column AIs.
Thus, it seems to me that we will, sooner or later, have right-column AIs. And those future AIs are the thing that I want to talk about in this post.
2. We need a term for the right-column thing, and “Artificial General Intelligence” (AGI) seems about as good as any.
=====================================================================================================================
That brings us to the term "AGI" for talking about the thing in the right column of the table above. Blake (like Yann LeCun) does not like the term “AGI”, but I’m going to use it anyway in this post, and here I’ll explain why.
The thing I feel strongest about is that we need *some* term—*any* term—for the thing in the right column. Because it’s a thing we need to talk about. I don’t feel very strongly that this term has to be “AGI” in particular. But *something*.
Consider: If all organisms have a “niche”, then the “human niche” includes living on every continent, walking on the moon, inventing computers and nuclear weapons, and unraveling the secrets of the universe. What happens when we make AI systems that can occupy that same niche? Think about AI systems that can do literally every aspect of my job. Think about AI systems which, when motivated to invent a better solar cell, are able to think to themselves, “Y'know, I'd be able to proceed much faster if I had more compute for my semiconductor simulations. Can I rent some? Oh, I need money. What if I steal it?” What happens if and when we bring these systems into the world?
This is an important conversation, and in order to have that conversation, a prerequisite is to have a jargon term with which we can refer to right-column AI systems. And the most common such term is “Artificial General Intelligence” (“AGI”).
I happen to think that “AGI” is a perfectly fine term to refer to this thing, as long as it's understood that:
* The G is “general as in not specific” *(“in general, Boston has nice weather”).*
* The G is NOT “general as in universal” *(“I have a general proof of the math theorem”)*.
I’m poking fun at [this Yann LeCun tweet](https://twitter.com/ylecun/status/1204038764122632193?lang=en). (Image sources: [1](https://cartoonstudio.wordpress.com/about/),[2](https://www.dreamstime.com/illustration/cartoon-general-store.html))Other people don’t like the term “AGI”, and talk about the same concept using a different term. It seems to me that none of the options is particularly great:
* I believe Yann LeCun likes the term “human-level machine intelligence”. But then that creates a *different* set of confusions, which require a *different* set of clarifications, like “…but it could think 1000× faster than a human”, and “…but it may lack a human-level sense of smell”.
* Eliezer Yudkowsky uses “AGI”, but [suggests](https://twitter.com/ESYudkowsky/status/1204060393624129541%5C) that we treat “general intelligence” as an abbreviation for “Significantly More Generally Applicable Intelligence”. (If only “SMGAI” were more catchy!)
* [“Transformative AI”](https://www.openphilanthropy.org/research/some-background-on-our-views-regarding-advanced-artificial-intelligence/) is somewhat related, but defined via how strongly the AI impacts the world, not whether the AI is left-column or right-column.
* “High-Level Machine Intelligence” seems OK, I guess, but in practice seems a bit obscure; when I say that term, nobody knows what I'm talking about, whereas I find most people understand the term “AGI” to mean approximately what I intend it to mean.
For the purpose of this post, following common usage, I’ll use “AGI” to talk about that thing in the right column above. If that bothers you, you can use a [browser extension](https://chrome.google.com/webstore/detail/word-replacer-ii/djakfbefalbkkdgnhkkdiihelkjdpbfh?hl=en) to replace “AGI” with the term of your choice. ¯\\_(ツ)\_/¯
Incidentally, I don’t claim that there’s a sharp line between the “AIs” in the left column, and the “AGIs” in the right column. But there are systems that are *definitely* in the right column, and for reasons described above, I expect that someday we will build them.
3. Blake’s “specialization” argument against AGI
================================================
Here’s an excerpt from Blake’s argument on the [podcast](https://theinsideview.ai/blake):
> We know from the no free lunch theorem that you cannot have a learning algorithm that outperforms all other learning algorithms across all tasks. It’s just an impossibility. So necessarily, any learning algorithm is going to have certain things that it’s good at and certain things that it’s bad at. Or alternatively, if it’s truly a Jack of all trades, it’s going to be just mediocre at everything. Right? So with that reality in place, you can say concretely that if you take AGI to mean literally good at anything, it’s just an impossibility, it cannot exist. And that’s been mathematically proven.
>
> Now, all that being said, the proof for the no free lunch theorem, refers to all possible tasks. And that’s a very different thing from the set of tasks that we might actually care about. Right?
>
> Because the set of all possible tasks will include some really bizarre stuff that we certainly don’t need our AI systems to do. And in that case, we can ask, “Well, might there be a system that is good at all the sorts of tasks that we might want it to do?” Here, we don’t have a mathematical proof, but again, I suspect Yann’s intuition is similar to mine, which is that you could have systems that are good at a remarkably wide range of things, but it’s not going to cover everything you could possibly hope to do with AI or want to do with AI.
>
> At some point, you’re going to have to decide where your system is actually going to place its bets as it were. And that can be as general as say a human being. So we could, of course, obviously humans are a proof of concept that way. We know that an intelligence with a level of generality equivalent to humans is possible and maybe it’s even possible to have an intelligence that is even more general than humans to some extent. I wouldn’t discount it as a possibility, but I don’t think you’re ever going to have something that can truly do anything you want, whether it be protein folding, predictions, managing traffic, manufacturing new materials, and also having a conversation with you about your [grandma’s] latest visit that can’t be… There is going to be no system that does all of that for you.
>
>
3.1 “Something that can truly do anything you want” is less crazy than it initially sounds, under right-column thinking
-----------------------------------------------------------------------------------------------------------------------
Again, here’s Blake in the interview:
> …I don’t think you’re ever going to have something that can truly do anything you want, whether it be protein folding, predictions, managing traffic, manufacturing new materials, and also having a conversation with you about your [grandma’s] latest visit…
>
>
Now let’s try this modification, where we switch from left-column thinking to right-column thinking:
> …I don’t think you’re ever going to have something that can truly do anything you want, whether it be *building a system for* protein folding, *building a system for* predictions, *building a system for* managing traffic, *building a system for* manufacturing new materials, and also *building a system for* having a conversation with you about your [grandma’s] latest visit…
>
>
Now it’s not so obvious that such an AI can’t exist, right?
For example, let’s take young adult John von Neumann, give him complete access to the ML and biology and chemistry and physics literature, and a compute cluster, and 30 years to work on the problem. Could he build a state-of-the-art system that takes amino acids and calculates folded proteins? I dunno! But maybe! It hardly seems an outlandish thing to expect.
OK, next, let’s take the same young adult John von Neumann, give him complete access to the ML and robotics and transportation engineering literature, and a compute cluster, and a robotics lab, and money to hire technicians, and 30 years to work on the problem. Could he build a state-of-the-art robot traffic guard? Again, I dunno! But maybe!
Now take the same young adult John von Neumann, give him complete access to the chemistry and chemical engineering and finance and management literature, along with a big pot of money to buy land and hire people, and 30 years to work on the problem. Could he build a state-of-the-art factory for manufacturing new materials? Maybe!
You get the idea.
Anyway, I grant that expertise in the downstream tasks here (folding proteins, directing traffic, producing chemicals) would not seem to have any overlap. But expertise in the upstream tasks (*figuring out* what kind of system would solve these tasks, and then building it) seem like they have quite a bit in common. For example, just go ask any successful startup founder to list everything they’ve had to figure out how to do.
And whatever is happening in John von Neumann’s brain that enables him to figure out how to do all those different things, we can make an AI that can run all the same calculations, and thus figure out all those same things.
3.2 Cranking up our example beyond John von Neumann
---------------------------------------------------
As impressed as we should be by John von Neumann’s ability to figure things out, this is not by any means the limit of what we should expect from future AIs. Here are four examples of how an AI can do better:
**First, cloning.** Future AGIs will be able to instantly clone themselves. So if our John von Neumann AGI has its hands full doing chemical simulations, it can spin off a whole team of copies, and one can start hiring employees, while another starts picking a plot of land, and so on. See [The Duplicator: Instant Cloning Would Make the World Economy Explode](https://www.cold-takes.com/the-duplicator/).
**Second, teams more generally.** Maybe you think it’s *eternally*beyond John von Neumann’s capability to figure out some particular thing—let’s say, how to write good advertising copy. It’s just not what his brain is good at.
If that’s what you think, then you’re slipping back into left-column thinking!
In fact, if our John-von-Neumann-like AGI needs good advertising copy, and can’t figure out how to create it, then he could go ahead and train up a [David-Oglivy](https://en.wikipedia.org/wiki/David_Ogilvy_(businessman))-like AGI and ask it for help!
Actually, Blake brought this up in his interview:
> To some extent you could argue that our society at large is like that, right? … Some people who are specialized at art, some people who are specialized at science and we call upon those people differently for different tasks. And then the result is that the society as a whole is good at all those things, to some extent. So in principle, that’s obviously a potential strategy. I think an interesting question that way is basically, “To what extent you would actually call that an AGI?”
>
>
My answer to the last question is: “Yes I would absolutely 100% call that an AGI”.
I think this is another instance of left-column-thinking versus right-column-thinking. In my (right-column) book, an AI that can call upon a wide variety of tools and resources (including other AIs), as the situation demands—and which can also go find and build more tools and resources (and AIs) when its existing ones are insufficient—is *exactly* the prototypical thing that we should be thinking of when we hear the word “AGI”!
So **consider*****the entire human R&D enterprise***—every human, at every university, every private-sector R&D lab, every journal editor, etc. This enterprise is running hundreds of thousands of laboratory experiments simultaneously, it’s publishing millions of papers a year, it’s synthesizing brilliant new insights in every field all at once. A single future AGI could do all that. Seems pretty “general” to me, right?
**Third, speed.** I expect that sooner or later, we’ll have an AGI that can *not only* figure out anything that John von Neumann can figure out, but that can “think” 100× faster than he could—such that normal humans look like [this video](https://vimeo.com/83664407). After all, we’re working with silicon chips that are 10,000,000× faster than the brain, so we can get a 100× speedup even if we’re a whopping 100,000× less skillful at parallelizing brain algorithms than the brain itself.
**Fourth, “quality”.** As discussed above, I claim that there’s a core set of right-column capabilities that we can loosely describe as “understanding problems, and designing systems that can solve them, including by inventing new technology”. Just as an adult John von Neumann clone is much “better” at these core capabilities than I am, I imagine that there are future AGI algorithms that would be far “better” at these capabilities than John von Neumann (or any human) would be. Not just faster, but actually better!
For example, given our finite number of cortical neurons, there’s only so much complexity of an idea that can be held in working memory. Beyond that, pieces need to be chunked and cached and explored serially, at some cost in the ability to notice connections (a.k.a. “insight”). Humans only have so many cortical neurons, but we can (and, I presume, eventually will) make an AGI that runs neocortex-like algorithms, but with a factor-of-100 scale-up (with appropriately adjusted architecture, hyperparameters, etc.).
Practically every time we try scaling up ML algorithms, we wind up surprised and impressed by the new capabilities it unlocks. I don’t see why that wouldn’t be true for the neocortex learning algorithm too.
(And I won’t even talk about the whole universe of possible algorithms that are more drastically different than the neocortex.)
**Summary:** Even if you discard the more speculative fourth point, I conclude that we should absolutely expect future AI systems that any reasonable person would describe as “radically superintelligent”, and that can trounce any human in any cognitive task just as soundly as AlphaZero can trounce humans in Go.
4. AGI accidents and the alignment problem
==========================================
Here’s Blake again on [the podcast](https://theinsideview.ai/blake):
> I think if anything, what I fear far more than AI doing its own bad thing is human beings using AI for bad purposes and also potentially AI systems that reflect other bad things about human society back to us and potentially amplify them. But ultimately, I don’t fear so much the AI becoming a source of evil itself as it were. I think it will instead always reflect our own evils to us.
>
>
First I need to address the suggestion that there’s an either/or competition between worrying about out-of-control-AGI accidents versus worrying about AI misuse and related issues. Then I’ll talk about the former on its own terms. I won’t dive into the latter in this post, because it seems that Blake and I are already in agreement on that topic: we both think that there are real and serious problems related to AI misuse, weaponization, surveillance, exacerbation of inequality, and so on.
4.1 The out-of-control-AGI-accidents problem can be a real problem, and the AI misuse problem can also simultaneously be a real problem. It’s not either/or!
------------------------------------------------------------------------------------------------------------------------------------------------------------
In addition to the quote above, [here’s Blake on Twitter](https://twitter.com/tyrell_turing/status/1466486549168730114):
> I find it kinda funny to worry about the threat of super intelligent AI in the future when we face the much more immediate and real threat of dumb AI with super power over people's lives.
>
>
And [in replies](https://twitter.com/tyrell_turing/status/1466540997421191168?s=20&t=h_WKwvz0Aq7cInX686aBXg):
> …There is a fourth possibility, which motivated my tweet:
>
> The probability of super intelligence this century is sufficiently low, and the probability of irresponsible use of dumb AI is sufficiently high, that the latter is much more worrying than the former.
>
>
[Another reply](https://twitter.com/tyrell_turing/status/1466784689335808009?s=20&t=h_WKwvz0Aq7cInX686aBXg):
> I think half of the appeal of hand-wringing over super intelligent AI is precisely that it allows one (particularly tech ppl) to avoid asking hard questions about the here-and-now.
>
>
Now consider the following:
* Suppose I give a lecture and say: “Why worry about the risks of future sea level rise? People are dying of heart disease *right now*!!!” I think everyone would look at me like I was nuts.
* Suppose I give a lecture and say: “Why worry about the risks of future superintelligent AI? We have narrow AI poisoning the political discourse *right now*!!!” I think the audience would nod solemnly, and invite me to write a New York Times op-ed.
But what the heck?? It’s the same argument! (See also: [Related Scott Alexander post](https://astralcodexten.substack.com/p/contra-acemoglu-onoh-god-were-doing) + [follow-up](https://astralcodexten.substack.com/p/when-does-worrying-about-things-trade))
More explicitly: *a priori*, the various problems arising from dumb AI might or might not be real problems—we need to figure it out. Likewise, *a* *priori*, the problem of future smart misaligned AGIs getting out of control and wiping out humanity might or might not be a real problem—we need to figure it out. But these are two different topics of investigation. There’s no reason to view them as zero-sum.
If anything, we should expect a *positive* correlation between the seriousness of these two problems, because they do in fact have a bit of structural overlap. As one of many examples, *both* social media recommendation algorithm issues *and* out-of-control-AGI issues are exacerbated by the fact that huge trained ML models are very difficult to interpret and inspect. See [*The Alignment Problem* by Brian Christian](https://brianchristian.org/the-alignment-problem/) for much more on the overlap between near-term and long-term AI issues.
Anyway, there are many *a priori* plausible arguments that we shouldn’t worry about superintelligent AGI. I’m just claiming that the existence of AI misuse is not one of those arguments, any more than the existence of heart disease is.[[1]](#fnyajmjaz6od9) Instead, we need to just talk directly about superintelligent AGI, and address that topic on its merits. That brings us to the next section:
4.2 The AGI alignment problem: not only a real problem, but a problem that Blake himself is unusually well suited to work on!
-----------------------------------------------------------------------------------------------------------------------------
So, how about superintelligent AGI? When might it arrive (if ever)? What consequences should we expect? Isn’t it premature to be thinking about that right now?
For the **long answer** to these questions, I will shamelessly plug my blog-post series [Intro to Brain-Like AGI Safety](https://www.alignmentforum.org/s/HzcM2dkCq7fwXBej8)! Here’s the summary:
> 1. We know enough neuroscience to say concrete things about what “brain-like AGI” would look like (Posts [#1](https://www.lesswrong.com/posts/4basF9w9jaPZpoC8R/intro-to-brain-like-agi-safety-1-what-s-the-problem-and-why)–[#9](https://www.lesswrong.com/posts/vpdJz4k5BgGzuGo7A/intro-to-brain-like-agi-safety-9-takeaways-from-neuro-2-2-on));
> 2. In particular, while “brain-like AGI” would be different from any known algorithm, its safety-relevant aspects would have much in common with actor-critic model-based reinforcement learning with a multi-dimensional value function (Posts [#6](https://www.lesswrong.com/posts/qNZSBqLEh4qLRqgWW/intro-to-brain-like-agi-safety-6-big-picture-of-motivation), [#8](https://www.lesswrong.com/posts/fDPsYdDtkzhBp9A8D/intro-to-brain-like-agi-safety-8-takeaways-from-neuro-1-2-on), [#9](https://www.lesswrong.com/posts/vpdJz4k5BgGzuGo7A/intro-to-brain-like-agi-safety-9-takeaways-from-neuro-2-2-on));
> 3. “Understanding the brain well enough to make brain-like AGI” is a dramatically easier task than “understanding the brain” full stop—if the former is loosely analogous to knowing how to train a ConvNet, then the latter would be loosely analogous to knowing how to train a ConvNet, *and* achieving full [mechanistic interpretability](https://distill.pub/2020/circuits/zoom-in/) of the resulting trained model, *and* understanding every aspect of integrated circuit physics and engineering, etc. Indeed, making brain-like AGI should not be thought of as a far-off sci-fi hypothetical, but rather as an ongoing project which may well reach completion within the next decade or two (Posts [#2](https://www.lesswrong.com/posts/wBHSYwqssBGCnwvHg/intro-to-brain-like-agi-safety-2-learning-from-scratch-in)–[#3](https://www.lesswrong.com/posts/hE56gYi5d68uux9oM/intro-to-brain-like-agi-safety-3-two-subsystems-learning-and));
> 4. In the absence of a good technical plan for avoiding accidents, researchers experimenting with brain-like AGI algorithms will probably accidentally create out-of-control AGIs, with catastrophic consequences up to and including human extinction (Posts [#1](https://www.lesswrong.com/posts/4basF9w9jaPZpoC8R/intro-to-brain-like-agi-safety-1-what-s-the-problem-and-why), [#3](https://www.lesswrong.com/posts/hE56gYi5d68uux9oM/intro-to-brain-like-agi-safety-3-two-subsystems-learning-and), [#10](https://www.lesswrong.com/posts/wucncPjud27mLWZzQ/intro-to-brain-like-agi-safety-10-the-alignment-problem), [#11](https://www.lesswrong.com/posts/BeQcPCTAikQihhiaK/intro-to-brain-like-agi-safety-11-safety-alignment-but-they));
> 5. Right now, we don’t have any good technical plan for avoiding out-of-control AGI accidents (Posts [#10](https://www.lesswrong.com/posts/wucncPjud27mLWZzQ/intro-to-brain-like-agi-safety-10-the-alignment-problem)–[#14](https://www.lesswrong.com/posts/QpHewJvZJFaQYuLwH/intro-to-brain-like-agi-safety-14-controlled-agi));
> 6. Creating such a plan seems neither to be straightforward, nor to be a necessary step on the path to creating powerful brain-like AGIs—and therefore we shouldn’t assume that such a plan will be created in the future “by default” (Post [#3](https://www.lesswrong.com/posts/hE56gYi5d68uux9oM/intro-to-brain-like-agi-safety-3-two-subsystems-learning-and));
> 7. There’s a lot of work that we can do right now to help make progress towards such a plan (Posts [#12](https://www.lesswrong.com/posts/Sd4QvG4ZyjynZuHGt/intro-to-brain-like-agi-safety-12-two-paths-forward)–[#15](https://www.lesswrong.com/posts/tj8AC3vhTnBywdZoA/intro-to-brain-like-agi-safety-15-conclusion-open-problems-1));
> 8. There is funding available to do this work (Post [#15](https://www.lesswrong.com/posts/tj8AC3vhTnBywdZoA/intro-to-brain-like-agi-safety-15-conclusion-open-problems-1)).
>
So check out [that series](https://www.alignmentforum.org/s/HzcM2dkCq7fwXBej8) for my very long answer.
**For a much shorter answer, I would turn to Blake’s own research.** As far as I understand, Blake holds the firm belief that the right starting point for thinking about the cortex is that the cortex runs a within-lifetime learning algorithm, adjusting parameters to minimize some loss function(s). I strongly agree, and would go further by claiming that a full 96% of human brain volume (including the neocortex, striatum, hippocampus, amygdala, and cerebellum) is devoted to running within-lifetime learning algorithms, whereas the other 4% (brainstem & hypothalamus) are more-or-less hardcoded by the genome. (See [Post #2 of my series](https://www.alignmentforum.org/posts/wBHSYwqssBGCnwvHg/intro-to-brain-like-agi-safety-2-learning-from-scratch-in) for various details and caveats on that.)
Blake and his students and colleagues spend their days trying to understand the nuts and bolts of the brain's various within-lifetime learning algorithms.
The question I would pose is: ***What if they succeed?*** What if they and others eventually come to understand the operating principles of the brain’s within-lifetime learning algorithms (and associated neural architecture etc.)—maybe not every last detail, but enough to build ML models that aren’t missing any big critical learning or inference tricks that the brain uses. Then what?
Then I claim there would be essentially nothing stopping future researchers from building real-deal right-column human-level AGI. (Some caveats on that [here](https://www.alignmentforum.org/posts/hE56gYi5d68uux9oM/intro-to-brain-like-agi-safety-3-two-subsystems-learning-and#3_7_Timelines_to_brain_like_AGI_part_2_of_3__how_hard_will_it_be_to_reverse_engineer_the_Steering_Subsystem_well_enough_for_AGI_) and [here](https://www.alignmentforum.org/posts/Sd4QvG4ZyjynZuHGt/intro-to-brain-like-agi-safety-12-two-paths-forward#12_5_The_question_of_life_experience__a_k_a__training_data_).)
But would it be *human-like* AGI, with human-like inclinations to friendship, norm-following, laziness, tribal loyalty, etc.? No! Not unless those learning algorithms also had human-like ***loss functions***![[2]](#fnab9h6yvdp9s)
Recall, a funny thing about learning algorithms is that they can be pointed at almost anything, depending on the loss function. With one reward function, AlphaZero learns to play chess; with a different reward function, AlphaZero would learn to play [suicide chess](https://en.wikipedia.org/wiki/Losing_chess)—achieving the exact opposite goal with superhuman skill.
In humans, I claim that “loss functions”[[2]](#fnab9h6yvdp9s) loosely correspond to “innate drives” (details [here](https://www.alignmentforum.org/posts/hE56gYi5d68uux9oM/intro-to-brain-like-agi-safety-3-two-subsystems-learning-and#3_4_2_Aside__what_do_I_mean_by__drives__)), and are intimately related to circuitry in the hypothalamus and brainstem (i.e. the 4% of the human brain that [I claim](https://www.alignmentforum.org/posts/wBHSYwqssBGCnwvHg/intro-to-brain-like-agi-safety-2-learning-from-scratch-in) is *not* devoted to within-lifetime learning).
Now, when future researchers build AGIs, they will be able to put in any innate drives / loss functions that they want.
But there is no scientific theory such that you can tell me what you want an AGI to do, and then I respond by telling you what loss functions to put into your AGI, such that it will actually try to do that.
For example, I *want* to ask the following question:
* *What loss function(s), when sent into a future AI’s brain-like configuration of neocortex / hippocampus / striatum / etc.-like learning algorithms, will result in an AGI that is trying to bring about a utopia of human flourishing, peace, equality, justice, fun, and what-have-you?*
Nobody knows the answer!
…But let’s not get ahead of ourselves!! Here’s an easier question:
* *What loss function(s), when sent into a future AI’s brain-like configuration of neocortex / hippocampus / striatum / etc.-like learning algorithms, will result in an AGI that is definitely not trying to literally exterminate humanity?*
That’s a much lower bar! But we don’t know the answer to that one either!! (And it’s much trickier than it sounds—see [this post](https://www.alignmentforum.org/posts/wucncPjud27mLWZzQ/intro-to-brain-like-agi-safety-10-the-alignment-problem).)
OK, here’s another question, indirectly related but probably more tractable.
* *Neurotypical humans have a bunch of social instincts—friendship, envy, status drive, schadenfreude, justice, and so on. These instincts are cross-cultural universals, and therefore presumably arise from genetically-hardcoded innate drives, giving rise to corresponding loss functions. What are those loss functions? And how exactly do they give rise to the familiar downstream behaviors?*
See my post [Symbol Grounding & Human Social Instincts](https://www.alignmentforum.org/posts/5F5Tz3u6kJbTNMqsb/intro-to-brain-like-agi-safety-13-symbol-grounding-and-human) for why this is a delightfully tricky puzzle. If we solve it, we would have a recipe for loss functions that make AGIs with similar moral intuitions as humans have. Granted, I've met a human or two, and that's not the *most* reassuring thing. (More discussion [here](https://www.alignmentforum.org/posts/Sd4QvG4ZyjynZuHGt/intro-to-brain-like-agi-safety-12-two-paths-forward).) But maybe it's a starting point that we can build off of.
I find (to my chagrin) that the most algorithmically-minded, AI-adjacent neuroscientists are spending their time and talent on discovering how brain loss functions affect brain learning algorithms, while basically ignoring the question of exactly what the human brain loss functions are in the first place.[[2]](#fnab9h6yvdp9s) As it happens, Blake has not only deep knowledge of the brain’s major within-lifetime learning algorithms in the telencephalon, but also [past experience studying the brainstem](https://www.nature.com/articles/nn.2612)! So I encourage him to spend some of his considerable talents going back to his roots, by figuring out [what the human brain loss functions are, how they're calculated in the hypothalamus and brainstem, and how they lead to things like friendship and envy](https://www.alignmentforum.org/posts/5F5Tz3u6kJbTNMqsb/intro-to-brain-like-agi-safety-13-symbol-grounding-and-human). It's a fascinating puzzle, there's funding available, and as a cherry on top, maybe he’d be helping avert the AGI apocalypse! :)
*(Thanks Adam Shimi, Justis Mills, & Alex Turner for critical comments on a draft.)*
1. **[^](#fnrefyajmjaz6od9)**One could object that I’m being a bit glib here. Tradeoffs between cause areas do exist. If someone [decides to donate 10% of their income to charity](https://www.givingwhatwecan.org/pledge/flow), and they spend it all on climate change, then they have nothing left for heart disease, and if they spend it all on heart disease, then they have nothing left for climate change. Likewise, if someone [devotes their career to reducing the risk of nuclear war](https://80000hours.org/problem-profiles/nuclear-security/), then they can’t also [devote their career to reducing the risk of catastrophic pandemics](https://80000hours.org/problem-profiles/global-catastrophic-biological-risks/) and vice-versa, and so on. So tradeoffs exist, and decisions have to be made. How? Well, for example, you *could* just try to make the world a better place in whatever way seems most immediately obvious and emotionally compelling to you. Lots of people do that, and I don’t fault them for it. But if you want to make the decision in a principled, [other-centered](https://forum.effectivealtruism.org/posts/iupkbiubpzDDGRpka/other-centered-ethics-and-harsanyi-s-aggregation-theorem) way, then you need to dive into the field of [Cause Prioritization](https://forum.effectivealtruism.org/topics/cause-prioritization), where you (for example) try to guess how many expected [QALY](https://en.wikipedia.org/wiki/Quality-adjusted_life_year)s could be saved by various possible things you can do with your life / career / money, and pick one at or near the top of the list. Cause Prioritization involves (among other things) a horrific minefield of quantifying various awfully-hard-to-quantify things like “[what’s my best-guess probability distribution for when AGI will arrive?](https://www.cold-takes.com/forecasting-transformative-ai-whats-the-burden-of-proof/)”, or “exactly how many suffering chickens are equivalently bad to one suffering human?”, or “how do we weigh better governance in Spain against preventing malaria deaths?”. Well anyway, I’d be surprised if Blake has arrived at his take here via one of these difficult and fraught Cause-Prioritization-type analyses. And I note that there are people out there who *do* try to do Cause Prioritization, and AFAICT they very often wind up putting AGI Safety right near the top of their lists.
I wonder whether Blake’s intuitions point in a different direction than Cause Prioritization analyses because of [scope neglect](https://en.wikipedia.org/wiki/Scope_neglect)? As an example of what I’m referring to: suppose (for the sake of argument) that out-of-control AGI accidents have a 10% chance of causing 8 billion deaths in the next 20 years, whereas dumb AI has 100% chance of exacerbating income inequality and eroding democratic norms in the next 1 year. A scope-sensitive, risk-neutral Cause Prioritization analysis would suggest prioritizing the former, but the latter might feel *intuitively* more panic-inducing.
Then maybe Blake would respond: “No you nitwit, it’s not that I have scope-neglect, it’s that your hypothetical is completely bonkers. Out-of-control AGI accidents do *not* have a 10% chance of causing 8 billion deaths in the next 20 years; instead, they have a 1-in-a-gazillion chance of causing 8 billion deaths in the next 20 years.” And then I would respond: “Bingo! That’s the crux of our disagreement! That’s the thing we need to hash out—is it more like 10% or 1-in-a-gazillion?” And this question is unrelated to the topic of bad actors misusing dumb AI.
[For the record: The 10% figure was just an example. For my part, if you force me to pick a number, my best guess would be *much higher* than 10%.]
2. **[^](#fnrefab9h6yvdp9s)**Everyone agrees that sensory prediction error is *one*of the loss functions, but I’m talking about the less obvious and more safety-relevant loss functions, i.e. the ones related to “reward”, which help determine a person’s motivations / goals / drives. (See §4.7 [here](https://www.alignmentforum.org/posts/Y3bkJ59j4dciiLYyw/intro-to-brain-like-agi-safety-4-the-short-term-predictor#4_7__Short_term_predictor__example__2__Predictive_learning_of_sensory_inputs_in_the_cortex) for why self-supervised learning is not adequate for training appropriate actions and decisions, if that isn’t obvious.) |
cfe10a4f-7ed2-40be-8723-53d262d7a164 | trentmkelly/LessWrong-43k | LessWrong | Communication, consciousness, and belief strength measures
Communication is a fascinating subject. It’s a way of transferring information from one place to the next (or, to invert a quote by Chris Fields, communication is physics). Now you may have noticed that I used the word “communication” in two slightly different ways. In the first sentence you might have thought I’ll be talking about the way people communicate between each other, and in the next one I seemed to have abstracted away this base definition and applied it to a more abstract concept, physics (abstract in a very limited sense though). The funny thing is, even though I’m using up way more space to explain the first two sentences I wrote, there is still ambiguity in what I’m saying, there’s still information that’s being lost and transformed from me thinking it up, to writing it in particular words, to you reading them and interpreting them in your unique way. While the physics side of communication is certainly fascinating, I’ll just refer to this course for now and consider communication between people, and just ponder for a bit about the indirect costs of the loss of information in our daily communication (that kind of rhymes doesn’t it?). TL;DR*: I ended up talking about “consciousness”.*
There are a lot of angles to approach this topic from, but I’ll focus on one that seems more and more prevalent in both academic literature and daily conversation, namely the use of the word “consciousness” (and we’ll try to vaguely generalize from there). Consciousness comes up more and more as every new AI model seems to do more of the things we thought biological systems were unique at doing (#isSORAconscious?). What I always find thought-provoking is that a lot of people quite easily use the word “consciousness” in their work, and not only in random posts online, but also in academic papers, and I’m always left wondering: what do they mean by “consciousness”? I’m pretty sure they don’t mean the dictionary definition that pops up with a Google search: "the state of be |
e68fbbcc-8fa5-4149-b868-54be11bddda9 | trentmkelly/LessWrong-43k | LessWrong | Predict 2025 AI capabilities (by Sunday)
Until this Sunday, you can submit your 2025 AI predictions at ai2025.org. It’s a forecasting survey by AI Digest for the 2025 performance on various AI benchmarks, as well as revenue and public attention.
You can share your results in a picture like this one. I personally found it pretty helpful to learn about the different benchmarks, and also to think through my timelines estimates.
The survey will close on Sunday, January 19th (anywhere on Earth).
If you know any AI public intellectuals or discourse influencers who might be interested in submitting the survey, please encourage them to do so!
Survey link: ai2025.org |
d5163b6a-8c86-459b-bfb1-476ca3048f46 | trentmkelly/LessWrong-43k | LessWrong | Meetup : Washington, D.C.: National Portrait Gallery/American Art Museum
Discussion article for the meetup : Washington, D.C.: National Portrait Gallery/American Art Museum
WHEN: 14 February 2016 03:00:00PM (-0500)
WHERE: Reynolds Center
x-posted from list. Gathering in courtyard from 3:00pm, hard start 3:30pm - until closing (7:00 pm).
This week, we will be looking at exhibits in the National Portrait Gallery and American Art Museum.
As always, side conversations are allowed and encouraged.
Upcoming meetups:
* Feb. 21: Fun & Games
* Feb. 28: Mini Talks
* Mar. 6: Game Design
Discussion article for the meetup : Washington, D.C.: National Portrait Gallery/American Art Museum |
f2327c90-30eb-430a-aa8d-8453d7900ae5 | trentmkelly/LessWrong-43k | LessWrong | Task vectors & analogy making in LLMs
I have described the problem of analogy-making interpretability in the previous post: given the examples of transformed sequences of numbers, what’s the mechanism behind figuring this transformation out, and applying it correctly to the incomplete (test) sequence?
prompt: "0 1 2 to 2 1 0, 1 2 3 to 3 2 1, 4 5 6 to ", output: “6 5 4”
It was easy to check on which layer the correct answer appears, but tracing the sources of that answer to earlier layers turned out to be challenging.
Meaningful intermediate embeddings?
When I applied logit lens [1] to the output of attention blocks, for the prompt that contained reversed sequences of numbers, I have noticed that the output contained “reverse” token (on last token position of layer 15).
I’m using a llama.cpp-based app (described in the previous post) for showing the logit lens output. Each row corresponds to a token position, and lists top 5 tokens sorted by the logit score:
./mia -m llama2.gguf --prompt "0 1 2 to 2 1 0, 1 2 3 to 3 2 1, 4 5 6 to" -n 5 --logit-lens kqv_out 5
Layer #15 kqv_out-15:
0: дар 0.35|oure 0.35|kar 0.33| Según 0.33|aki 0.3|
1: dust 0.36|textt 0.36|elde 0.35|azzo 0.34| retro 0.34|
2: 典 0.37| Censo 0.35|oure 0.35| Aires 0.35| pó 0.34|
3: ḷ 0.39|ket 0.39| estaven 0.39|öß 0.39|oure 0.38|
4: zerw 0.62| estaven 0.51|cita 0.5| alberga 0.49|łow 0.48|
[...]
16: shal 0.84|ket 0.73|Assert 0.72|ając 0.66|sono 0.66|
17: ipt 0.95|кта 0.88|inal 0.86| inform 0.85| advanced 0.85|
18: кта 0.85|minipage 0.83| Mean 0.77|Assert 0.75| meaning 0.74|
19: ipt 0.78|Duration 0.76|zug 0.75|gemeinde 0.75|mannschaft 0.72|
20: shal 0.64|agy 0.64|prev 0.62| SA 0.6| Gay 0.58|
21: revers 0.75| reverse 0.68|mat 0.67|shal 0.66|vat 0.66|
Although the task is about reversing, “reverse” is not mentioned explicitly anywhere in either input or output.
I have tried subtracting the embedding of the “reverse” token, effectively removing it, to check it is a part of the analogy-making mechanism. It did not affect the output, which |
09630fc7-fe4f-4a87-a741-a33450d57304 | trentmkelly/LessWrong-43k | LessWrong | More and Less than Solomonoff Induction
I've been thinking about how to put induction with limited resources on a firmer foundation. This may just be retracing the steps of others, but that's okay with me. Mostly I just want to talk about these thoughts.
After a few points of introduction.
What's Solomonoff induction?
Suppose we're given some starting data, and asked to predict the future. Solomonoff induction predicts the future by combining the predictions of all programs that (1) output the starting data up until now, and (2) aren't the continuation of another such program. The predictions are combined according to a weighting that decreases exponentially as the length of the program increases.
Why is it a good idea?
The simplest answer is that we have a frequentist guarantee that if the "true program" generating our input has some length N (that is, if the observable universe is a big but finite-sized computer), then our predictions will only be wrong a limited number of times, and after that we'll predict the correctly every time.
A more bayesian answer would start with the information that our observations can be generated by some finite-sized program, and then derive that something like Solomonoff induction has to represent our true prior over generating programs - as the length gets bigger, our probability is required to go to zero at infinity, and an exponential is the maximum-entropy such curve. This is not a complete answer, but it at least makes the missing pieces more apparent.
Why won't it work with limited resources
The trouble with using Solomonoff induction in real life is that to pick out which programs output our data so far, we need to run every program - and if the program doesn't ever halt, we need to use a halting oracle to stop it or else we'll take infinite time.
Limited resources require us to only pick from a class of programs that is guaranteed to not run over the limit.
If we have limited time and no halting oracle, we can't check every program. Instead, we are only |
0d597593-0467-4e63-8034-4ccad8b20079 | trentmkelly/LessWrong-43k | LessWrong | OPERA Confirms: Neutrinos Travel Faster Than Light
> New high-precision tests carried out by the OPERA collaboration in Italy broadly confirm its claim, made in September, to have detected neutrinos travelling at faster than the speed of light. The collaboration today submitted its results to a journal, but some members continue to insist that further checks are needed before the result can be considered sound.
Link: nextbigfuture.com/2011/11/faster-than-light-neutrinos-opera.html
> The OPERA Collaboration sent to the Cornell Arxiv an updated version of their preprint today, where they summarize the results of their analysis, expanded with additional statistical tests, and including the check performed with 20 additional neutrino interactions they collected in the last few weeks. These few extra timing measurements crucially allow the ruling out of some potential unaccounted sources of systematic uncertainty, notably ones connected to the knowledge of the proton spill time distribution.
>
> [...]
>
> So what does OPERA find ? Their main result, based on the 15,233 neutrino interactions collected in three years of data taking, is unchanged from the September result. The most interesting part of the new publication is instead that the find that the 20 new neutrino events (where neutrino speeds are individually measured, as opposed to the combined measurement done with the three-year data published in September) confirm the earlier result: the arrival times appear to occur about 60 nanoseconds before they are expected.
Link: science20.com/quantum_diaries_survivor/opera_confirms_neutrinos_travel_faster_light-84763
Paper: kruel.co/paper-neutrino-velocity-JHEP.pdf
Previously on LW: lesswrong.com/lw/7rc/particles_break_lightspeed_limit/ |
1a1526ca-5362-440e-8b07-43401651ee59 | trentmkelly/LessWrong-43k | LessWrong | Whose Fault?
There is an old story that I had read in one of the Upanishads (I can't recall which one exactly), and it describes a situation that goes something like this:
> A blind man is walking towards a deep well. There is a guy sitting on a bench nearby and watching him from a distance.
>
> The blind man unaware of the upcoming well, eventually falls into it.
>
> The Upanishad asks the reader: Whose fault is that?
>
> Is it the blind's man fault or the man sitting the bench watching everything and yet doing nothing?
In a simplistic setup such as this one, it is easy to point out that the fault is the man sitting on the bench. His inaction led to a painful event that could have been easily avoided.
The scenario becomes interesting when we try to simulate the exercise in our day-to-day life.
Let me illustrate by taking a hypothetical instance:
> There is a reasonably large pothole is in the road in front of your house. You have noticed the pothole and have taken a mental note to ask the concerned authorities to fix it when you have time.
>
> Now, one day, you hear the sound of a bike crash.
>
> Maybe the biker didn't see the pothole, or maybe he was riding irresponsibly, but the bike got into a crash due to the large pothole, and the biker got seriously injured.
>
> Now, let me ask you the question: Whose fault is that?
>
> 1. Is it the the biker?
> 2. Is it the concerned government official responsible for the maintenance of the road?
> 3. Or is it yours? You, who in the pursuit to maximize your time for saving 10k children in Bangladesh, couldn't find an hour of your time to call up and perform basic civic duties.
It's a fun exercise to take any parable with its simplistic setup and apply it to our complex world setting. Isn't it?
One of the standard maxims of effective altruism is working on the world's most pressing issues that not many people are working on.
And sometimes, that just happens to be right in front of your doorstep.
|
73e02d2e-6b73-4484-a99c-230ed04cc992 | StampyAI/alignment-research-dataset/blogs | Blogs | February 2018 Newsletter
#### Updates
* New at IAFF: [An Untrollable Mathematician](https://agentfoundations.org/item?id=1750)
* New at AI Impacts: [2015 FLOPS Prices](https://aiimpacts.org/2015-flops-prices/)
* We presented “[Incorrigibility in the CIRL Framework](https://intelligence.org/2017/08/31/incorrigibility-in-cirl/)” at the AAAI/ACM [Conference on AI, Ethics, and Society](http://www.aies-conference.com).
* From MIRI researcher Scott Garrabrant: [Sources of Intuitions and Data on AGI](https://www.lesswrong.com/posts/BibDWWeo37pzuZCmL/sources-of-intuitions-and-data-on-agi)
#### News and links
* In “[Adversarial Spheres](https://arxiv.org/abs/1801.02774),” Gilmer et al. investigate the tradeoff between test error and vulnerability to adversarial perturbations in many-dimensional spaces.
* Recent posts on *Less Wrong*: [Critch on “Taking AI Risk Seriously”](https://www.lesswrong.com/posts/HnC29723hm6kJT7KP/critch-on-taking-ai-risk-seriously) and Ben Pace’s [background model for assessing AI x-risk plans](https://www.lesswrong.com/posts/XFpDTCHZZ4wpMT8PZ/a-model-i-use-when-making-plans-to-reduce-ai-x-risk).
* “[Solving the AI Race](https://www.general-ai-challenge.org/ai-race)“: GoodAI is offering prizes for proposed responses to the problem that “key stakeholders, including [AI] developers, may ignore or underestimate safety procedures, or agreements, in favor of faster utilization”.
* The Open Philanthropy Project [is hiring](https://www.openphilanthropy.org/blog/new-job-opportunities) research analysts in AI alignment, forecasting, and strategy, along with generalist researchers and operations staff.
The post [February 2018 Newsletter](https://intelligence.org/2018/02/25/february-2018-newsletter/) appeared first on [Machine Intelligence Research Institute](https://intelligence.org). |
4c5238e3-a7c8-48ef-ab4e-a43e81718eb8 | trentmkelly/LessWrong-43k | LessWrong | Ultra-simplified research agenda
This is an ultra-condensed version of the research agenda on synthesising human preferences (video version here):
In order to infer what a human wants from what they do, an AI needs to have a human theory of mind.
Theory of mind is something that humans have instinctively and subconsciously, but that isn't easy to spell out explicitly; therefore, by Moravec's paradox, it will be very hard to implant it into an AI, and this needs to be done deliberately.
One way of defining theory of mind is to look at how humans internally model the value of various hypothetical actions and events (happening to themselves and to others).
Finally, once we have a full theory of mind, we still need to deal, somehow, with the fact that humans have meta-preferences over their preferences, and that these preferences and meta-preferences are often contradictory, changeable, manipulable, and (more worryingly) underdefined in the exotic worlds that AIs could produce.
Any way of dealing with that fact will be contentious, but it's necessary to sketch out an explicit way of doing this, so it can be critiqued and improved.
A toy model for this research agenda can be found here. |
d95e9873-f694-494f-bb11-1b5b087fee7a | trentmkelly/LessWrong-43k | LessWrong | Shit rationalists say - 2018
In 2012 we had a thread titled Shit rationalists say that lead to the fun video Shit rationalists say. Given that the video is a lot of fun to watch, how about starting a new list that's up-to-date.
Share whatever comes to mind and have fun :) |
8b668458-b0c4-4ca9-ac83-3feb41122ca9 | StampyAI/alignment-research-dataset/special_docs | Other | Online Learning Survey
Foundations and TrendsR/circlecopyrtin
Machine LearningVol. 4, No. 2 (2011) 107–194
c/circlecopyrt2012 S. Shalev-Shwartz
DOI: 10.1561/2200000018
Online Learning and Online
Convex Optimization
By Shai Shalev-Shwartz
Contents
1 Introduction 108
1.1 Examples 111
1.2 A Gentle Start 1121.3 Organization and Scope 1161.4 Notation and Basic Definitions 117
2 Online Convex Optimization 119
2.1 Convexification 120
2.2 Follow-the-leader 1242.3 Follow-the-Regularized-Leader 1272.4 Online Gradient Descent: Linearization
of Convex Functions 130
2.5 Strongly Convex Regularizers 1342.6 Online Mirror Descent 1412.7 The Language of Duality 1462.8 Bounds with Local Norms 1522.9 Bibliographic Remarks 155
3 Online Classification 157
3.1 Finite Hypothesis Class and Experts Advice 158
3.2 Learnability and the Standard Optimal Algorithm 160
3.3 Perceptron and Winnow 168
3.4 Bibliographic Remarks 175
4 Limited Feedback (Bandits) 177
4.1 Online Mirror Descent with Estimated Gradients 178
4.2 The Multi-armed Bandit Problem 1794.3 Gradient Descent Without a Gradient 1824.4 Bibliographic Remarks 185
5 Online-to-Batch Conversions 186
5.1 Bibliographic Remarks 190
Acknowledgments 191References 192
Foundations and TrendsR/circlecopyrtin
Machine LearningVol. 4, No. 2 (2011) 107–194
c/circlecopyrt2012 S. Shalev-Shwartz
DOI: 10.1561/2200000018
Online Learning and Online
Convex Optimization
Shai Shalev-Shwartz
Benin School of Computer Science and Engineering, The Hebrew University
of Jerusalem, Israel, shais@cs.huji.ac.il
Abstract
Online learning is a well established learning paradigm which has both
theoretical and practical appeals. The goal of online learning is tomake a sequence of accurate predictions given knowledge of the cor-rect answer to previous prediction tasks and possibly additional avail-able information. Online learning has been studied in several researchfields including game theory, information theory, and machine learning.It also became of great interest to practitioners due the recent emer-gence of large scale applications such as online advertisement placementand online web ranking. In this survey we provide a modern overviewof online learning. Our goal is to give the reader a sense of some ofthe interesting ideas and in particular to underscore the centrality ofconvexity in deriving efficient online learning algorithms. We do notmean to be comprehensive but rather to give a high-level, rigorous yeteasy to follow, survey.
1
Introduction
Online learning is the process of answering a sequence of questions
given (maybe partial) knowledge of the correct answers to previousquestions and possibly additional available information. The study ofonline learning algorithms is an important domain in machine learn-ing, and one that has interesting theoretical properties and practicalapplications.
Online learning is performed in a sequence of consecutive rounds,
where at round tthe learner is given a question, x
t, taken from an
instance domain X, and is required to provide an answer to this ques-
tion, which we denote by pt. After predicting an answer, the correct
answer, yt, taken from a target domain Y, is revealed and the learner
suffers a loss, l(pt,yt), which measures the discrepancy between his
answer and the correct one. While in many cases ptis inY, it is some-
times convenient to allow the learner to pick a prediction from a largerset, which we denote by D.
108
109
Online Learning
fort=1,2,...
receive question xt∈X
predict pt∈D
receive true answer yt∈Y
suffer loss l(pt,yt)
The specific case of yes/no answers and predictions, namely D=
Y={0,1}, is called online classification. In this case it is natural to
use the 0–1 loss function: l(pt,yt)=|pt−yt|. That is, l(pt,yt) indicates
ifpt=yt(the prediction is correct) or pt/negationslash=yt(the prediction is wrong).
For example, consider the problem of predicting whether it is going
to rain tomorrow. On day t, the question xtcan be encoded as a vector
of meteorological measurements. Based on these measurements, thelearner should predict if it’s going to rain tomorrow. In the followingday, the learner knows the correct answer.
We can also allow the learner to output a prediction in [0 ,1], which
can be interpreted as the probability of raining tomorrow. This is anexample of an application in which D/negationslash=Y. We can still use the loss
function l(p
t,yt)=|pt−yt|, which can now be interpreted as the prob-
ability to err if predicting that it’s going to rain with probability pt.
The learner’s ultimate goal is to minimize the cumulative loss suf-
fered along its run, which translates to making few prediction mistakesin the classification case. The learner tries to deduce information fromprevious rounds so as to improve its predictions on present and futurequestions. Clearly, learning is hopeless if there is no correlation betweenpast and present rounds. Classic statistical theory of sequential predic-tion therefore enforces strong assumptions on the statistical propertiesof the input sequence (e.g., that it is sampled i.i.d. according to someunknown distribution).
In this review we survey methods which make no statistical assump-
tions regarding the origin of the sequence of examples. The sequence isallowed to be deterministic, stochastic, or even adversarially adaptiveto the learner’s own behavior (as in the case of spam email filtering).Naturally, an adversary can make the cumulative loss to our online
110 Introduction
learning algorithm arbitrarily large. For example, the adversary can ask
the same question on each online round, wait for the learner’s answer,and provide the opposite answer as the correct answer. To make non-trivial statements we must further restrict the problem. We considertwo natural restrictions.
The first restriction is especially suited to the case of online classi-
fication. We assume that all the answers are generated by some targetmapping, h
⋆:X→Y . Furthermore, h⋆is taken from a fixed set, called
a hypothesis class and denoted by H, which is known to the learner.
With this restriction on the sequence, which we call the realizable case ,
the learner should make as few mistakes as possible, assuming thatbothh
⋆and the sequence of questions can be chosen by an adversary.
For an online learning algorithm, A, we denote by MA(H) the max-
imal number of mistakes Amight make on a sequence of examples
which is labeled by some h⋆∈H. We emphasize again that both h⋆
and the sequence of questions can be chosen by an adversary. A bound
onMA(H) is called a mistake-bound and we will study how to design
algorithms for which MA(H) is minimal.
Alternatively, the second restriction of the online learning model
we consider is a relaxation of the realizable assumption. We no longerassume that all answers are generated by some h
⋆∈H, but we require
the learner to be competitive with the best fixed predictor from H. This
is captured by the regret of the algorithm, which measures how “sorry”
the learner is, in retrospect, not to have followed the predictions ofsome hypothesis h
⋆∈H. Formally, the regret of the algorithm relative
toh⋆when running on a sequence of Texamples is defined as
RegretT(h⋆)=T/summationdisplay
t=1l(pt,yt)−T/summationdisplay
t=1l(h⋆(xt),yt), (1.1)
and the regret of the algorithm relative to a hypothesis class His
RegretT(H) = max
h⋆∈HRegretT(h⋆). (1.2)
We restate the learner’s goal as having the lowest possible regret
relative to H. We will sometime be satisfied with “low regret” algo-
rithms, by which we mean that RegretT(H) grows sub-linearly with
1.1 Examples 111
the number of rounds, T, which implies that the difference between the
average loss of the learner and the average loss of the best hypothesis
inHtends to zero as Tgoes to infinity.
1.1 Examples
We already mentioned the problem of online classification. To make the
discussion more concrete, we list several additional online predictionproblems and possible hypothesis classes.
Online Regression In regression problems, X=R
dwhich cor-
responds to a set of measurements (often called features), andY=D=R. For example, consider the problem of estimating the fetal
weight based on ultrasound measurements of abdominal circumferenceand femur length. Here, each x∈X=R
2is a two-dimensional vector
corresponds to the measurements of the abdominal circumference andthe femur length. Given these measurements the goal is to predict thefetal weight. Common loss functions for regression problems are thesquared loss, /lscript(p,y)=(p−y)
2, and the absolute loss, /lscript(p,y)=|p−y|.
Maybe the simplest hypothesis class for regression is the class of linearpredictors, H={x/mapsto→/summationtext
d
i=1w[i]x[i]:∀i,w[i]∈R}, where w[i]i st h e ith
element of w. The resulting problem is called online linear regression .
Prediction with Expert Advice On each online round the
learner has to choose from the advice of dgiven experts. Therefore,
xt∈X⊂ Rd, where xt[i] is the advice of the ith expert, and
D={1,...,d}. Then, the learner receives the true answer, which is a
vector yt∈Y=[ 0,1]d, where yt[i] is the cost of following the advice of
theith expert. The loss of the learner is the cost of the chosen expert,
/lscript(pt,yt)=yt[pt]. A common hypothesis class for this problem is the
set of constant predictors, H={h1,...,h d}, where hi(x)=ifor all x.
This implies that the regret of the algorithm is measured relative tothe performance of the strategies which always predict according tothe same expert.
Online Ranking On round t, the learner receives a query x
t∈X
and is required to order kelements (e.g., documents) according to
112 Introduction
their relevance to the query. That is, Dis the set of all permuta-
tions of {1,...,k}. Then, the learner receives the true answer yt∈Y=
{1,...,k}, which corresponds to the document which best matches the
query. In web applications, this is the document that the user clickedon. The loss, /lscript(p
t,yt), is the position of ytin the ranked list pt.
1.2 A Gentle Start
We start with studying online classification problem, in which Y=D=
{0,1}, and /lscript(p,y)=|p−y|is the 0–1 loss. That is, on each round, the
learner receives xt∈Xand is required to predict pt∈{0,1}. Then, it
receives yt∈{0,1}and pays the loss |pt−yt|. We make the following
simplifying assumption:
•Finite Hypothesis Class: We assume that |H|<∞.
Recall that the goal of the learner is to have a low regret relative to
the hypotheses set, H, where each function in His a mapping from X
to{0,1}, and the regret is defined as
RegretT(H) = max
h∈H/parenleftBiggT/summationdisplay
t=1|pt−yt|−T/summationdisplay
t=1|h(xt)−yt|/parenrightBigg
.
We first show that this is an impossible mission — no algorithm
can obtain a sublinear regret bound even if |H|= 2. Indeed, consider
H={h0,h1}, where h0is the function that always returns 0 and h1is
the function that always returns 1. An adversary can make the numberof mistakes of any online algorithm to be equal to T, by simply waiting
for the learner’s prediction and then providing the opposite answer asthe true answer. In contrast, for any sequence of true answers, y
1,...,y T,
letbbe the majority of labels in y1,...,y T, then the number of mistakes
ofhbis at most T/2. Therefore, the regret of any online algorithm
might be at least T−T/2=T/2, which is not a sublinear with T.
This impossibility result is attributed to Cover [13].
To sidestep Cover’s impossibility result, we must further restrict the
power of the adversarial environment. In the following we present twoways to do this.
1.2 A Gentle Start 113
1.2.1 Realizability Assumption
The first way to sidestep Cover’s impossibility result is by making one
additional assumption:
•Realizability: We assume that all target labels are generated
by some h⋆∈H, namely, yt=h⋆(xt) for all t. Our goal is to
design an algorithm with an optimal mistake bound. Namely,an algorithm for which M
A(H) is minimal. See definition of
MA(H) in the prequel.
Next, we describe and analyze online learning algorithms assuming
both a finite hypothesis class and realizability of the input sequence.The most natural learning rule is to use (at any online round) anyhypothesis which is consistent with all past examples.
Consistent
input: A finite hypothesis class H
initialize :V1=H
fort=1,2,...
receive xt
choose any h∈Vt
predict pt=h(xt)
receive true answer yt=h⋆(xt)
update Vt+1={h∈Vt:h(xt)=yt}
The Consistent algorithm maintains a set, Vt, of all the hypothe-
ses which are consistent with ( x1,y1),...,(xt−1,yt−1). This set is often
called the version space. It then picks any hypothesis from Vtand
predicts according to this hypothesis.
Obviously, whenever Consistent makes a prediction mistake, at
least one hypothesis is removed from Vt. Therefore, after making M
mistakes we have |Vt|≤| H |− M. Since Vtis always nonempty (by the
realizability assumption it contains h⋆)w eh a v e1 ≤|Vt|≤| H |− M.
114 Introduction
Rearranging, we obtain
Corollary 1.1. LetHbe a finite hypothesis class. The Consistent
algorithm enjoys the mistake bound MConsistent (H)≤| H |− 1.
It is rather easy to construct a hypothesis class and a sequence of
examples on which Consistent will indeed make |H| − 1 mistakes.
Next, we present a better algorithm in which we choose h∈Vtin a
smarter way. We shall see that this algorithm is guaranteed to makeexponentially fewer mistakes. The idea is to predict according to themajority of hypotheses in V
trather than according to some arbitrary
h∈Vt. That way, whenever we err, we are guaranteed to remove at
least half of the hypotheses from the version space.
Halving
input: A finite hypothesis class H
initialize :V1=H
fort=1,2,...
receive xt
predict pt= argmaxr∈{0,1}|{h∈Vt:h(xt)=r}|
(in case of a tie predict pt=1 )
receive true answer yt
update Vt+1={h∈Vt:h(xt)=yt}
Theorem 1.2. LetHbe a finite hypothesis class. The Halving algo-
rithm enjoys the mistake bound MHalving (H)≤log2(|H|).
Proof. We simply note that whenever the algorithm errs we have
|Vt+1|≤|Vt|/2. (Hence the name Halving.) Therefore, if Mis the total
number of mistakes, we have
1≤|VT+1|≤| H | 2−M.
Rearranging the above inequality we conclude our proof.
Of course, Halving ’s mistake bound is much better than
Consistent ’s mistake bound. Is this the best we can do? What is an
1.2 A Gentle Start 115
optimal algorithm for a given hypothesis class (not necessarily finite)?
We will get back to this question in Section 3.
1.2.2 Randomization
In the previous subsection we sidestepped Cover’s impossibility result
by relying on the realizability assumption. This is a rather strongassumption on the environment. We now present a milder restriction onthe environment and allow the learner to randomize his predictions. Ofcourse, this by itself does not circumvent Cover’s impossibility result asin deriving the impossibility result we assumed nothing on the learner’sstrategy. To make the randomization meaningful, we force the adver-sarial environment to decide on y
twithout knowing the random coins
flipped by the learner on round t. The adversary can still know the
learner’s forecasting strategy and even the random bits of previousrounds, but it doesn’t know the actual value of the random bits usedby the learner on round t. With this (mild) change of game, we analyze
theexpected 0–1 loss of the algorithm, where expectation is with respect
to the learner’s own randomization. That is, if the learner outputs ˆ y
t
where P[ˆyt=1 ]= pt, then the expected loss he pays on round tis
P[ˆyt/negationslash=yt]=|pt−yt|.
Put another way, instead of having the predictions domain being
D={0,1}we allow it to be D=[ 0,1], and interpret pt∈Das the
probability to predict the label 1 on round t. To summarize, we assume:
•Randomized Predictions and Expected Regret : We allow the
predictions domain to be D=[ 0,1] and the loss function is
stilll(pt,yt)=|pt−yt|.
With this assumption it is possible to derive a low regret algorithm
as stated in the following theorem.
Theorem 1.3. LetHbe a finite hypothesis class. There exists an algo-
rithm for online classification, whose predictions come from D=[ 0,1],
116 Introduction
that enjoys the regret bound
T/summationdisplay
t=1|pt−yt|−min
h∈HT/summationdisplay
t=1|h(xt)−yt|≤/radicalbig
0.5ln(|H|)T.
We will provide a constructive proof of the above theorem in the next
section.
To summarize, we have presented two different ways to sidestep
Cover’s impossibility result: realizability or randomization. At firstglance, the two approaches seem to be rather different. However, thereis a deep underlying concept that connects them. Indeed, we will showthat both methods can be interpreted as convexification techniques.
Convexity is a central theme in deriving online learning algorithms.We study it in the next section.
1.3 Organization and Scope
How to predict rationally is a key issue in various research areas suchas game theory, machine learning, and information theory. The semi-nal book of Cesa-Bianchi and Lugosi [12] thoroughly investigates theconnections between online learning, universal prediction, and repeatedgames. In particular, results from the different fields are unified usingthe prediction with expert advice framework.
We feel that convexity plays a central role in the derivation of online
learning algorithms, and therefore start the survey with a study of theimportant sub-family of online learning problems, which is called online
convex optimization . In this family, the prediction domain is a convex
set and the loss function is a convex function with respect to its firstargument. As we will show, many previously proposed algorithms foronline classification and other problems can be jointly analyzed basedon the online convex optimization framework. Furthermore, convexityis important because it leads to efficient algorithms.
In Section 3 we get back to the problem of online classification.
We characterize a standard optimal algorithm for online classification.In addition, we show how online convex optimization can be used forderiving efficient online classification algorithms.
In Section 4 we study online learning in a limited feedback model,
when the learner observes the loss value l(p
t,yt) but does not observe
1.4 Notation and Basic Definitions 117
the actual correct answer yt. We focus on the classic multi-armed ban-
dit problem and derive an algorithm for this problem based on theonline convex optimization algorithmic framework. We also present alow regret algorithm for the general problem of bandit online convexoptimization.
Finally, in Section 5 we discuss several implications of online learn-
ing to batch learning problems, in which we assume that the examplesare sampled i.i.d. from an unknown probability source.
Part of our presentation shares similarities with other surveys on
online prediction problems. In particular, Rakhlin’s lecture notes [34]and Hazan’s book section [22] are good recent surveys on onlineconvex optimization. While part of our presentation shares similari-ties with these surveys, we sometimes emphasize different techniques.Furthermore, we connect and relate the new results on online convexoptimization to classic results on online classification, thus providinga fresh modern perspective on some classic algorithms. A more classictreatment can be found in Blum’s survey [8].
1.4 Notation and Basic Definitions
We denote scalars with lower case letters (e.g., xandλ), and vectors
with bold face letters (e.g., xandλ). The ith element of a vector x
is denoted by x[i]. Since online learning is performed in a sequence
of rounds, we denote by xtthetth vector in a sequence of vectors
x1,x2,...,xT. The ith element of xtis denoted by xt[i].
Theinner product between vectors xandwis denoted by /angbracketleftx,w/angbracketright.
Whenever we do not specify the vector space we assume that it is thed-dimensional Euclidean space and then /angbracketleftx,w/angbracketright=/summationtext
d
i=1x[i]w[i]. Sets
are designated by upper case letters (e.g., S). The set of real numbers
is denoted by Rand the set of non-negative real numbers is denoted
byR+. The set of natural numbers is denoted by N. For any k≥1,
the set of integers {1,...,k}is denoted by [ k]. Given a predicate π,w e
use the notation 1[π]to denote the indicator function that outputs 1
ifπholds and 0 otherwise. The hinge function is denoted by [ a]+=
max{0,a}.
The Euclidean (or /lscript2)norm of a vector wis/bardblw/bardbl2=/radicalbig
/angbracketleftw,w/angbracketright.W e
omit the subscript when it is clear from the context. We also use other /lscriptp
118 Introduction
norms, /bardblw/bardblp=(/summationtext
i|w[i]|p)1/p, and in particular /bardblw/bardbl1=/summationtext
i|w[i]|and
/bardblw/bardbl∞= max i|w[i]|. A generic norm of a vector wis denoted by /bardblw/bardbl
and its dual norm is defined as
/bardblx/bardbl⋆= max {/angbracketleftw,x/angbracketright:/bardblw/bardbl≤1}.
The definition of the dual norm immediately implies the inequality
/angbracketleftw,z/angbracketright≤/bardbl w/bardbl/bardblz/bardbl⋆. (1.3)
For the /lscript2norm (which is dual to itself), this is the well known Cauchy–
Schwartz inequality. For p,q≥1 such that1
p+1
q= 1 we have that
the/lscriptpand/lscriptqnorms are dual, and Equation (1.3) becomes Holder’s
inequality.
A function fis called L-Lipschitz over a set Swith respect to a
norm /bardbl·/bardblif for all u,w∈Swe have |f(u)−f(w)|≤L/bardblu−w/bardbl.
The gradient of a differentiable function fis denoted by ∇fand
theHessian is denoted by ∇2f.
Throughout the review, we make use of basic notions from convex
analysis. A set Sisconvex if for all w,v∈Sandα∈[0,1] we have
thatαw+( 1−α)v∈Sas well. Similarly, a function f:S→Ris con-
vex if for all w,vandα∈[0,1] we have f(αw+( 1−α)v)≤αf(w)+
(1−α)f(v).
It is convenient to allow convex functions to output the value ∞.
The domain of a function fis the set of points on which fis finite.
This is convenient, for example, for constraining the solution of an opti-mization problem to be within some set A. Indeed, instead of solving
min
x∈Af(x) we can solve min xf(x)+IA(x), where IAis the function
that outputs 0 if x∈Aand∞ifx/∈A. In the next section we make
use of some additional definitions and tools from convex analysis. Forclarity, we define them as per need.
The expected value of a random variable, ψ, is denoted by E[ψ].
In some situations, we have a deterministic function hthat receives a
random variable as input. We denote by E[h(ψ)] the expected value of
the random variable h(ψ). Occasionally, we omit the dependence of h
onψ. In this case, we may clarify the meaning of the expectation by
using the notation E
ψ[h]o r Eψ∼P[h]i fψis distributed according to
some distribution P.
2
Online Convex Optimization
In recent years, the design of many efficient online learning algorithms
has been influenced by convex optimization tools. Furthermore, it wasobserved that most previously proposed efficient algorithms can bejointly analyzed based on the following elegant model:
Online Convex Optimization (OCO)
input: A convex set S
fort=1,2,...
predict a vector wt∈S
receive a convex loss function ft:S→R
suffer loss ft(wt)
In this section we describe algorithms for online convex optimization
and analyze their regret. Recall that the regret of an online algorithmwith respect to a competing hypothesis, which here will be some vectoru, is defined as
Regret
T(u)=T/summationdisplay
t=1ft(wt)−T/summationdisplay
t=1ft(u). (2.1)
119
120 Online Convex Optimization
As before, the regret of the algorithm relative to a set of competing
vectors, U, is defined as
RegretT(U) = max
u∈URegretT(u).
Remark 2.1. ( Uvs.S)In the online convex optimization problem,
the predictions of the learner should come from the set S, while we
analyze the regret with respect to the set U. While in some situations
it makes sense to set U=S, this is not always the case. Whenever we do
not specify the value of Uwe use the default value U=S. Additionally,
our default setting for Swill be S=Rd.
The rest of this section is organized as follows. We start with
convexification techniques, showing how to utilize the online convexoptimization framework in nonconvex problems. Next, we startdescribing and analyzing an algorithmic framework for online convexoptimization. First, we describe the Follow-the-Leader approach, inwhich the learner simply picks the vector which performed best onpast rounds. Next we describe a regularized form of Follow-the-Leader,which stabilizes the predictions of the algorithm, and show how stabilityleads to low regret. We proceed with deriving Online Gradient Descentand Online Mirror Descent from Follow-the-Regularized-Leader bya linearization trick. We derive several specific algorithms from theOnline Mirror Descent framework. Finally, we describe additional prooftechniques and also derive local-norm bounds, that will be used in thenext sections.
2.1 Convexification
Some online prediction problems can be seamlessly cast in the onlineconvex optimization framework.
Example 2.1 (Online linear regression). Recall the online linear
regression problem described in Section 1.1. On each online round thelearner first receives a vector of features, x
t∈A⊂Rd, and then needs to
predict a scalar, pt. Next, the learner receives the “true” target, yt∈R,
and pays the loss |pt−yt|. The learner should be competitive with the
2.1 Convexification 121
set of linear predictors of the form x/mapsto→/angbracketleftw,x/angbracketright. If the predictions of
the learner are also based on linear functions, then we can easily castthis online prediction problem in the online convex optimization frame-work as follows. The learner should decide on a vector w
t, which yields
the prediction pt=/angbracketleftwt,xt/angbracketright. The loss function becomes |pt−yt|=
|/angbracketleftwt,xt/angbracketright−yt|. Therefore, letting ft(w)=|/angbracketleftw,xt/angbracketright−yt|, which is indeed
a convex function, we obtain that ft(wt)=l(pt,yt).
Other online prediction problems do not seem to fit into the online
convex optimization framework. For example, in online classificationproblems, the predictions domain or the loss functions are not convex.In this section we describe two convexification techniques that allowus to utilize the online convex optimization framework in additionalscenarios.
2.1.1 Convexification by Randomization
To demonstrate the randomization technique, consider the problem
of prediction with expert advice, where on each online round thelearner has to choose from the advice of dgiven experts. Denote by
p
t∈{1,...,d}the chosen expert. Then, the learner receives a vector
yt∈[0,1]d, where yt[i] is the cost of following the advice of the ith
expert. The learner pays the loss yt[pt]. In this prediction problem, the
decision space is discrete, hence nonconvex.
Furthermore, the problem of online classification with a finite
hypothesis class we encountered in Section 1.2 can be easily cast asa special case of the prediction with expert advice problem. Therefore,Cover’s impossibility result (see again Section 1.2) implies that there isno algorithm that can attain low regret for the prediction with expertadvice problem.
However, as we show below, by allowing the learner to random-
ize his predictions we can cast the problem in the online convex opti-mization framework, and therefore can obtain low regret algorithm forthis problem. Formally, let S={w∈R
d:w≥0∧/bardblw/bardbl1=1}be the
probability simplex, which forms a convex set. At round t, the learner
chooses wt∈Sand based on wtpicks an expert at random according
122 Online Convex Optimization
toP[pt=i]=wt[i]. Then, the cost vector ytis revealed and the learner
pays for his expected cost
E[yt[pt]] =d/summationdisplay
i=1P[pt=i]yt[i]=/angbracketleftwt,yt/angbracketright.
Note that by analyzing the expected cost of the learner we implicitly
restrict the power of the adversarial environment — it cannot base thevector y
ton the random bits the learner employs on round t.
Now we can cast the problem as online convex optimization since
Sis a convex set and the loss function, ft(w)=/angbracketleftw,yt/angbracketright, happens to be
a linear function (hence, convex). Let the set of competing vectors, U,
be the dsingletons, namely the vectors of the form (0 ,...,0,1,0,...,0).
These vectors correspond to always following the advice of a singleexpert. Hence, a regret bound with respect to Uimplies a regret bound
with respect to always predicting the advice of a single expert.
2.1.2 Convexification by Surrogate Loss Functions
To explain the second convexification technique we again start with
the specific problem of online classification with a finite hypothesisclass. Recall that one of the techniques we used to sidestep Cover’simpossibility result relied on the realizability assumption. That is, weassumed that there exists h
⋆∈Hsuch that yt=h⋆(xt) for all t. With
this assumption at hand, we described the Halving algorithm and
showed that it makes at most log2(|H|) prediction mistakes.
We now derive a similar guarantee using the language of online
convex optimization. Let us write H={h1,...,h d}and let S={w∈
[0,1]d:/summationtext
iw[i]=1}be the probability simplex. For each online round,
define vt=(h1(xt),...,h d(xt))∈{0,1}d. Our algorithm will maintain
wt∈Sand will predict the label according to
pt=/braceleftbigg1i f/angbracketleftwt,vt/angbracketright≥1/2
0i f/angbracketleftwt,vt/angbracketright<1/2
LetM={t:pt/negationslash=yt}be the rounds on which our algorithm makes a
prediction mistake. We define
ft(w)=/braceleftbigg2|/angbracketleftw,vt/angbracketright−yt|ift∈M
0i f t/∈M.
2.1 Convexification 123
Note that ftdepends on M, and thus depends on wt. This does not
pose any problem since in the online convex optimization model theenvironment picks the function f
tafter observing wt. The two key
properties of ftare
•ftis a convex function
•ft(wt)≥|pt−yt|, namely, the convex loss upper bounds the
original nonconvex loss.
Hence the name surrogate convex loss . Since Sis a convex set and
ftis a convex function for all twe have obtained an online convex
optimization problem.
In the next sections we will derive algorithms for online convex
optimization problems. In particular, one of these algorithms enjoysthe regret bound
∀u∈S, T/summationdisplay
t=1ft(wt)≤T/summationdisplay
t=1ft(u)+log(d)
η+2ηT/summationdisplay
t=1Lt,
where ηis a parameter, which we will set here to be η=1/4, and Ltis
a Lipschitz parameter of the function ft(with respect to the /lscript1norm).
In our case, Lt=1i f t∈MandLt=0i f t/∈M. Hence,
∀u∈S,T/summationdisplay
t=1ft(wt)≤T/summationdisplay
t=1ft(u) + 4log( d)+1
2|M|.
By the surrogate property of ft, we can lower bound the left-hand side
by|M|. Rearranging, we obtain:
|M| ≤ 2T/summationdisplay
t=1ft(u) + 8log( d).
This type of bound, where the number of mistakes is upper bounded
by the convex surrogate loss of a competing hypothesis, is often calledarelative loss bound .
In the realizable case, we can further simplify the relative loss bound
as follows. Since the bound holds for all u∈Sit holds in particu-
lar for the vector u=( 0,...,0,1,0,...,0), where the 1 is placed in the
124 Online Convex Optimization
coordinate corresponding to the true hypothesis h⋆. By our construc-
tion,ft(u) = 0 for all t, which yields
|M| ≤ 8log(d).
We have obtained a mistake bound of the same order as the Halving ’s
mistake bound.
More generally, the first step of the technique involves a re-
parameterization of the problem such that the decision space becomesconvex (instead of maintaing the set V
tinHalving we now maintain
the vector wt∈S). In the second step we construct a function ftof
the predicted parameter that satisfies two requirements: It should beconvex and it should upper bound the original loss function. Last, wewould of course like to construct a convex surrogate for which thereexists some u∈Sthat attains a low cumulative loss. Otherwise, the
resulting bound will be meaningless. Typically, this is done by assumingmore on the problem at hand. For example, in the above, the realiz-ability assumption enabled us to construct a surrogate for which therewasu∈Ssuch that f
t(u) = 0 for all t.
2.2 Follow-the-leader
By now, we hope that the reader is convinced that the online convex
optimization framework is an important model, so we turn to derivingalgorithms for online convex optimization.
The most natural learning rule is to use (at any online round) any
vector which has minimal loss on all past rounds. This is in the samespirit of the Consistent algorithm we encountered in Section 1.2 but
in the context of online convex optimization it is usually referred to asFollow-The-Leader .
Follow-The-Leader (FTL)
∀t,wt= argmin
w∈St−1/summationdisplay
i=1fi(w)(break ties arbitrarily)
To analyze FTL, we first show that the regret of FTL is upper
bounded by the cumulative difference between the loss of wtandwt+1.
2.2 Follow-the-leader 125
Lemma 2.1. Letw1,w2,...be the sequence of vectors produced by
FTL. Then, for all u∈Swe have
RegretT(u)=T/summationdisplay
t=1(ft(wt)−ft(u))≤T/summationdisplay
t=1(ft(wt)−ft(wt+1)).
Proof. Subtracting/summationtext
tft(wt) from both sides of the inequality and
rearranging, the desired inequality can be rewritten as
T/summationdisplay
t=1ft(wt+1)≤T/summationdisplay
t=1ft(u).
We prove this inequality by induction. The base case of T= 1 follows
directly from the definition of wt+1. Assume the inequality holds for
T−1, then for all u∈Swe have
T−1/summationdisplay
t=1ft(wt+1)≤T−1/summationdisplay
t=1ft(u).
Adding fT(wT+1) to both sides we get
T/summationdisplay
t=1ft(wt+1)≤fT(wT+1)+T−1/summationdisplay
t=1ft(u).
The above holds for all uand in particular for u=wT+1. Thus,
T/summationdisplay
t=1ft(wt+1)≤T/summationdisplay
t=1ft(wT+1) = min
u∈ST/summationdisplay
t=1ft(u),
where the last equation follows from the definition of wT+1. This con-
cludes our inductive argument.
We next use Lemma 2.1 to derive a regret bound for the following
sub-family of online convex optimization.
Definition 2.1 (Online Quadratic Optimization). This is an
online convex optimization problem where at each round ft(w)=
1
2/bardblw−zt/bardbl2
2for some vector zt.
126 Online Convex Optimization
We further assume that S=Rd. For this case, it is easy to verify that
the FTL rule becomes
wt=1
t−1t−1/summationdisplay
i=1zi,
namely, wtis the average of z1,...,zt−1. Note that we can rewrite
wt+1=1
t(zt+(t−1)wt)=/parenleftbigg
1−1
t/parenrightbigg
wt+1
tzt
which yields
wt+1−zt=/parenleftbigg
1−1
t/parenrightbigg
(wt−zt).
Therefore,
ft(wt)−ft(wt+1)=1
2/bardblwt−zt/bardbl2−1
2/bardblwt+1−zt/bardbl2
=1
2/parenleftBigg
1−/parenleftbigg
1−1
t/parenrightbigg2/parenrightBigg
/bardblwt−zt/bardbl2
≤1
t/bardblwt−zt/bardbl2.
LetL= max t/bardblzt/bardbl. Since wtis the average of z1,...,zt−1we have that
/bardblwt/bardbl≤Land therefore, by the triangle inequality, /bardblwt−zt/bardbl≤2L.W e
have therefore obtained:
T/summationdisplay
t=1(ft(wt)−ft(wt+1))≤(2L)2T/summationdisplay
t=11
t.
Combining the above with Lemma 2.1 and using the inequality/summationtextT
t=11/t≤log(T) + 1 we conclude that
Corollary 2.2. Consider running FTL on an Online Quadratic Opti-
mization problem with S=Rdand let L= max t/bardblzt/bardbl. Then, the regret
of FTL with respect to all vectors u∈Rdis at most 4 L2(log(T) + 1).
While the above result seems promising, we next show that the FTL
rule does not guarantee low regret for another important sub-family.
2.3 Follow-the-Regularized-Leader 127
Definition 2.2 (Online Linear Optimization). This is an online
convex optimization problem where at each round ft(w)=/angbracketleftw,zt/angbracketrightfor
some vector zt.
Example 2.2 (Failure of FTL). LetS=[−1,1]⊂Rand consider
the sequence of linear functions such that ft(w)=ztwwhere
zt=
−0.5i ft=1
1i f tis even
−1i f t>1∧tis odd
Then, the predictions of FTL will be to set wt= 1 for todd and wt=−1
forteven. The cumulative loss of the FTL algorithm will therefore be T
while the cumulative loss of the fixed solution u=0∈Sis 0. Thus, the
regret of FTL is T!
Intuitively, FTL fails in the above example because its predictions
arenot stable —wtshifts drastically from round to round where we
only added a single loss function to the objective of the optimizationproblem in the definition of w
t. In contrast, FTL works fine for the
quadratic game since wt+1is “close” to wt. One way to stabilize FTL
is by adding regularization, which is the topic of the next section.
2.3 Follow-the-Regularized-Leader
Follow-the-Regularized-Leader is a natural modification of the basicFTL algorithm in which we minimize the loss on all past rounds plusa regularization term. The goal of the regularization term is to stabi-lize the solution. Formally, for a regularization function, R:S→Rwe
define
Follow-the-Regularized-Leader (FoReL)
∀t,wt= argmin
w∈St−1/summationdisplay
i=1fi(w)+R(w)
128 Online Convex Optimization
Naturally, different regularization functions will yield different algo-
rithms with different regret bounds. We discuss properties of differentregularization functions later. But, first, let us specify FoReL for thecase of linear functions and squared- /lscript
2-norm regularization, which we
often call the Euclidean regularization case.
Example 2.3. Consider the Online Linear Optimization problem
where ft(w)=/angbracketleftw,zt/angbracketrightand let S=Rd. Suppose we run FoReL with
the regularization function R(w)=1
2η/bardblw/bardbl2
2for some positive scalar η.
Then, it is easy to verify that
wt+1=−ηt/summationdisplay
i=1zi=wt−ηzt. (2.2)
Note that ztis the gradient of ftatwt(in fact, at any point). Therefore,
the recursive rule, wt+1=wt−ηzt, can be rewritten as wt+1=wt−
η∇ft(wt). Hence, this rule is often called Online Gradient Descent.
We shall re-visit the Online Gradient Descent rule for general convexfunctions in the next section.
We next turn to the analysis of FoReL. As with the analysis of FTL,
we first relate the regret of FoReL to the cumulative difference betweenthe loss of w
tandwt+1.
Lemma 2.3. Letw1,w2,...be the sequence of vectors produced by
FoReL. Then, for all u∈Swe have
T/summationdisplay
t=1(ft(wt)−ft(u))≤R(u)−R(w1)+T/summationdisplay
t=1(ft(wt)−ft(wt+1)).
Proof. Observe that running FoReL on f1,...,f Tis equivalent to run-
ning FTL on f0,f1,...,f Twhere f0=R. Using Lemma 2.1 we obtain
T/summationdisplay
t=0(ft(wt)−ft(u))≤T/summationdisplay
t=0(ft(wt)−ft(wt+1)).
Rearranging the above and using f0=Rwe conclude our proof.
2.3 Follow-the-Regularized-Leader 129
Based on the above lemma we can easily derive a regret bound for
online linear optimization with the regularizer R(w)=1
2η/bardblw/bardbl2
2.
Theorem 2.4. Consider running FoReL on a sequence of linear func-
tions, ft(w)=/angbracketleftw,zt/angbracketrightfor all t, with S=Rd, and with the regularizer
R(w)=1
2η/bardblw/bardbl2
2, which yields the predictions given in Equation (2.2).
Then, for all uwe have
RegretT(u)≤1
2η/bardblu/bardbl2
2+ηT/summationdisplay
t=1/bardblzt/bardbl2
2.
In particular, consider the set U={u:/bardblu/bardbl≤B}and let Lbe such
that1
T/summationtextT
t=1/bardblzt/bardbl2
2≤L2, then by setting η=B
L√
2Twe obtain
RegretT(U)≤BL√
2T.
Proof. Using Lemma 2.3 and Equation (2.2),
RegretT(u)≤R(u)−R(w1)+T/summationdisplay
t=1(ft(wt)−ft(wt+1))
=1
2η/bardblu/bardbl2
2+T/summationdisplay
t=1/angbracketleftwt−wt+1,zt/angbracketright
=1
2η/bardblu/bardbl2
2+ηT/summationdisplay
t=1/bardblzt/bardbl2
2.
The parameter ηin the above theorem depends on the time hori-
zonT. It is possible to derive a similar result without using the time
horizon. In the next subsection we show a generic way (although notalways optimal) to get rid of the dependence on the time horizon.
We see that the Euclidean regularization function guarantees low
regret for linear functions with bounded /lscript
2-norm because it stabi-
lizes the predictions. We shall later generalize the above result in twoaspects. First, we allow any sequence of Lipschitz functions (ratherthan linear functions with bounded norm). Second, we consider otherregularization functions which guarantee stability in other scenarios.
130 Online Convex Optimization
2.3.1 The Doubling Trick
In Theorem 2.4, the parameter ηdepends on the time horizon T.W e
now show how to get rid of this dependence by a simple trick.
Consider an algorithm that enjoys a regret bound of the form α√
T,
but its parameters require the knowledge of T. The doubling trick,
described below, enables us to convert such an algorithm into an algo-rithm that does not need to know the time horizon. The idea is to dividethe time into periods of increasing size and run the original algorithmon each period.
The Doubling Trick
input: algorithm Awhose parameters depend on the time horizon
form=0,1,2,...
runAon the 2mrounds t=2m,...,2m+1−1
The regret of Aon each period of 2mrounds is at most α√
2m.
Therefore, the total regret is at most
⌈log2(T)⌉/summationdisplay
m=1α√
2m=α⌈log2(T)⌉/summationdisplay
m=1(√
2)m
=α1−√
2⌈log2(T)⌉+1
1−√
2
≤α1−√
2T
1−√
2
≤√
2√
2−1α√
T.
That is, we obtain that the regret is worse by a constant multiplicative
factor.
2.4 Online Gradient Descent: Linearization
of Convex Functions
In the previous section we introduced the FoReL approach and analyzed
it for the case of linear functions, S=Rd, and Euclidean regularization.
2.4 Online Gradient Descent: Linearization of Convex Functions 131
We now generalize this result by deriving a simple reduction from
convex functions to linear functions.
To do so, we use an important property of convex functions, which
is in fact an alternative characterization of convexity, as given by thefollowing lemma.
Lemma 2.5. LetSbe a convex set. A function f:S→Ris convex
iff for all w∈Sthere exists zsuch that
∀u∈S, f (u)≥f(w)+/angbracketleftu−w,z/angbracketright. (2.3)
In words, convexity is characterized by the existence of tangents
that lie below the function. The proof of this lemma can be found inmany convex analysis textbooks (e.g., [9]).
Definition 2.3 (sub-gradients). A vector zthat satisfies Equa-
tion (2.3) is called a sub-gradient offatw. The set of sub-gradients of
fatwis denoted ∂f(w). Furthermore, if fis differentiable at wthen
∂f(w) contains a single element — the gradient of fatw,∇f(w).
An illustration of sub-gradients is given in Figure 2.1.
Getting back to online convex optimization, for each round t, there
exists ztsuch that for all u,
ft(wt)−ft(u)≤/angbracketleftwt−u,zt/angbracketright.
Fig. 2.1 Left: The right-hand side of Equation (2.3) is the tangent of fatw. For a convex
function, the tangent lower bounds f. Right: Illustration of several sub-gradients of a non-
differentiable convex function.
132 Online Convex Optimization
It follows that for any sequence of convex functions f1,...,f Tand vec-
tors w1,...,wT, if for all t,zt∈∂ft(wt) (namely, it is a sub-gradient)
then
T/summationdisplay
t=1(ft(wt)−ft(u))≤T/summationdisplay
t=1(/angbracketleftwt,zt/angbracketright−/angbracketleft u,zt/angbracketright). (2.4)
In words, the regret of a procedure that generates the vectors
w1,...,wTfor the sequence of linear functions upper bounds the regret
with respect to the convex functions f1,...,f T.
Note that in this construction, ztdepends on wt. As mentioned pre-
viously, this does not pose any problem since we allow the adversarialenvironment to base its loss function on the vector predicted by thelearner.
Combining the above observation with the FoReL procedure with
Euclidean regularization (see Equation (2.2)) yields the Online Gradi-ent Descent algorithm:
Online Gradient Descent (OGD)
parameter: η>0
initialize: w 1=0
update rule: w t+1=wt−ηztwhere zt∈∂ft(wt)
To analyze OGD, we combine Equation (2.4) with the analysis of
FoReL for linear functions given in Theorem 2.4, to get that
RegretT(u)≤1
2η/bardblu/bardbl2
2+ηT/summationdisplay
t=1/bardblzt/bardbl2
2. (2.5)
This regret bound depends on the norms of the sub-gradients of the
vectors produced by the algorithm, and is therefore not satisfactory.To derive a more concrete bound, we must assure that the norms ofsub-gradients will not be excessively large. One way to do this is byassuming that the functions are Lipschitz. The following lemma relatesnorms of sub-gradients to Lipschitzness of f
t.
2.4 Online Gradient Descent: Linearization of Convex Functions 133
Lemma 2.6. Letf:S→Rbe a convex function. Then, fisL-
Lipschitz over Swith respect to a norm /bardbl·/bardbliff for all w∈Sand
z∈∂f(w) we have that /bardblz/bardbl⋆≤L, where /bardbl·/bardbl⋆is the dual norm.
Proof. Assume that fis Lipschitz. Choose some w∈S,z∈∂f(w).
Let ube such that u−w= argmaxv:/bardblv/bardbl=1/angbracketleftv,z/angbracketright. Therefore, /angbracketleftu−
w,z/angbracketright=/bardblz/bardbl⋆. From the definition of the sub-gradient,
f(u)−f(w)≥/angbracketleftz,u−w/angbracketright=/bardblz/bardbl⋆.
On the other hand, from the Lipschitzness of fwe have
L=L/bardblu−w/bardbl≥f(u)−f(w).
Combining the above two inequalities we conclude that /bardblz/bardbl⋆≤L.F o r
the other direction, since z∈∂f(w) we also have
f(w)−f(u)≤/angbracketleftz,w−u/angbracketright.
Combining the above with Equation (1.3) we obtain
f(w)−f(u)≤/bardblz/bardbl⋆/bardblw−u/bardbl≤L/bardblw−u/bardbl,
hence fisL-Lipschitz.
Therefore, the term/summationtextT
t=1/bardblzt/bardbl2
2given in Equation (2.5) can be
bounded by/summationtextT
t=1L2
t, where Ltis the Lipschitz constant of ft.W e
conclude:
Corollary 2.7. Assume that OGD is run on a sequence f1,...,f Tof
convex functions. Then, for all uwe have
RegretT(u)≤1
2η/bardblu/bardbl2
2+ηT/summationdisplay
t=1/bardblzt/bardbl2
2.
If we further assume that each ftisLt-Lipschitz with respect to /bardbl·/bardbl2,
and let Lbe such that1
T/summationtextT
t=1L2
t≤L2. Then, for all u, the regret of
OGD satisfies
RegretT(u)≤1
2η/bardblu/bardbl2
2+ηTL2.
134 Online Convex Optimization
In particular, if U={u:/bardblu/bardbl2≤B}andη=B
L√
2Tthen
RegretT(U)≤BL√
2T.
Let us now discuss the consequences of Corollary 2.7, starting with
the online linear regression problem (Example 2.1). Recall that for thisexample, f
t(w)=|/angbracketleftw,xt/angbracketright−yt|, where xtcomes from a set A. If the
setAis contained in a ball of /lscript2radius L, then ftisL-Lipschitz with
respect to the /lscript2norm. We therefore obtain a regret bound of BL√
2T
which holds for all competing vectors uwith/bardblu/bardbl2≤B.
For the problem of prediction with expert advice (see Section 2.1.1),
we cannot apply the OGD framework as it does not guarantee that wt
will always be in the probability simplex. In the next section we describe
the FoReL framework with other regularization functions. In particu-lar, we present regularization functions appropriate for the problem ofprediction with expert advice.
2.5 Strongly Convex Regularizers
So far we applied FoReL with the Euclidean regularization function. Asmentioned at the end of the previous section, this regularization can-not be used for the learning with expert advice problem. In this sectionwe consider other regularization functions and underscore strong con-vexity as an important property of regularization functions that yieldsmeaningful regret bounds.
2.5.1 Strong Convexity
Intuitively, a function is strongly convex if it grows faster than a linear
function. To give a precise definition, recall that for a convex func-tionf, at any point wwe can find a linear function (the “tangent”)
which equals to fatwand does not exceed fat any other point (see
Lemma 2.5). A function is strongly convex if fis strictly above the
2.5 Strongly Convex Regularizers 135
tangent, and the difference can be quantified as follows:
Definition 2.4. A function f:S→Risσ-strongly-convex over Swith
respect to a norm /bardbl·/bardblif for any w∈Swe have
∀z∈∂f(w),∀u∈S, f (u)≥f(w)+/angbracketleftz,u−w/angbracketright+σ
2/bardblu−w/bardbl2.
A graphical illustration is given in Figure 2.2.
An important property of strong convexity that we use is the fol-
lowing:
Lemma 2.8. LetSbe a nonempty convex set. Let f:S→Rbe a
σ-strongly-convex function over Swith respect to a norm /bardbl·/bardbl. Let w=
argminv∈Sf(v). Then, for all u∈S
f(u)−f(w)≥σ
2/bardblu−w/bardbl2.
Proof. To give intuition, assume first that fis differentiable and wis
in the interior of S. Then, ∇f(w)=0and therefore, by the definition
of strong convexity we have
∀u∈S, f(u)−f(w)≥/angbracketleft ∇f(w),u−w/angbracketright+σ
2/bardblu−w/bardbl2=σ
2/bardblu−w/bardbl2,
Fig. 2.2 Illustrating strong-convexity: the distance between fand its tangent at wis at
leastσ
2/bardblu−w/bardbl2.
136 Online Convex Optimization
as required. Even if wis on the boundary of Swe still have that for all
u∈S,/angbracketleft∇f(w),u−w/angbracketright≥0 (otherwise, wwould not have been optimal
since we can make a small step in the direction u−wand decrease the
value of f). So, the desired inequality still holds. Finally, to give the
formal proof for a non-differentiable f, letg:Rd→R∪ {∞} be such
thatg(w)=f(w)i fw∈Sandg(w)=∞otherwise. We can therefore
rewrite w= argminvg(v). Since gis a proper1convex function we have
that 0∈∂g(w). The inequality follows by using the strong-convexity
ofg.
IfRis twice differentiable, then it is easy to verify that a sufficient
condition for strong convexity of Ris that for all w,x,/angbracketleft∇2R(w)x,x/angbracketright≥
σ/bardblx/bardbl2, where ∇2R(w) is the Hessian matrix of Ratw, namely, the
matrix of second-order partial derivatives of Ratw[39, Lemma 14].
Example 2.4 (Euclidean regularization). The function R(w)=
1
2/bardblw/bardbl2
2is 1-strongly-convex with respect to the /lscript2norm over Rd. To see
this, simply note that the Hessian of Rat any wis the identity matrix.
Example 2.5 (Entropic regularization). The function R(w)=/summationtextd
i=1w[i]log(w[i]) is1
B-strongly-convex with respect to the /lscript1norm
over the set S={w∈Rd:w>0∧/bardblw/bardbl1≤B}. In particular, Ris
1-strongly-convex over the probability simplex, which is the positivevectors whose elements sum to 1.
To see this note that
/angbracketleft∇
2R(w)x,x/angbracketright=/summationdisplay
ix[i]2
w[i]=1
/bardblw/bardbl1/parenleftBigg/summationdisplay
iw[i]/parenrightBigg/parenleftBigg/summationdisplay
ix[i]2
w[i]/parenrightBigg
≥1
/bardblw/bardbl1/parenleftBigg/summationdisplay
i/radicalbig
w[i]|x[i]|/radicalbig
w[i]/parenrightBigg2
=/bardblx/bardbl2
1
/bardblw/bardbl1, (2.6)
where the inequality follows from Cauchy–S chwartz inequality.
1A convex function is proper if it never receives the value −∞and it receives a finite value
at least once. For such functions, an optimality condition for wbeing a minimum is that
the zero vector is a sub-gradient of the function at w.
2.5 Strongly Convex Regularizers 137
Additional useful properties are given in the following lemma, whose
proof follows directly from the definition of strong convexity.
Lemma 2.9. IfRis 1-strongly convex over Swith respect to some
norm then σRisσ-strongly-convex over Swith respect to the same
norm. In addition, if S/primeis a convex subset of S, then Ris 1-strongly
convex over S/primeas well.
2.5.2 Analyzing FoReL with Strongly Convex Regularizers
We now analyze FoReL with strongly convex regularizers. Recall the
regret bound given in Lemma 2.3:
T/summationdisplay
t=1(ft(wt)−ft(u))≤R(u)−R(w1)+T/summationdisplay
t=1(ft(wt)−ft(wt+1)).
IfftisL-Lipschitz with respect to a norm /bardbl·/bardblthen
ft(wt)−ft(wt+1)≤L/bardblwt−wt+1/bardbl.
Therefore, we need to ensure that /bardblwt−wt+1/bardblis small. The following
lemma shows that if the regularization function R(w) is strongly convex
with respect to the same norm, then wtwill be close to wt+1.
Lemma 2.10. LetR:S→Rbe aσ-strongly-convex function over S
with respect to a norm /bardbl·/bardbl. Let w1,w2,...be the predictions of the
FoReL algorithm. Then, for all t,i fftisLt-Lipschitz with respect
to/bardbl·/bardblthen
ft(wt)−ft(wt+1)≤Lt/bardblwt−wt+1/bardbl≤L2
t
σ.
Proof. For all tletFt(w)=/summationtextt−1
i=1fi(w)+R(w) and note that the
FoReL rule is wt= argminw∈SFt(w). Note also that Ftisσ-strongly-
convex since the addition of a convex function to a strongly convexfunction keeps the strong convexity property. Therefore, Lemma 2.8implies that:
F
t(wt+1)≥Ft(wt)+σ
2/bardblwt−wt+1/bardbl2.
138 Online Convex Optimization
Repeating the same argument for Ft+1and its minimizer wt+1we get
Ft+1(wt)≥Ft+1(wt+1)+σ
2/bardblwt−wt+1/bardbl2.
Summing the above two inequalities and rearranging we obtain
σ/bardblwt−wt+1/bardbl2≤ft(wt)−ft(wt+1). (2.7)
Next, using the Lipschitzness of ftwe get that
ft(wt)−ft(wt+1)≤Lt/bardblwt−wt+1/bardbl.
Combining with Equation (2.7) and rearranging we get that /bardblwt−
wt+1/bardbl≤L/σand together with the above we conclude our proof.
Combining the above Lemma with Lemma 2.3 we obtain
Theorem 2.11. Letf1,...,f Tbe a sequence of convex functions such
thatftisLt-Lipschitz with respect to some norm /bardbl·/bardbl. Let Lbe such
that1
T/summationtextT
t=1L2
t≤L2. Assume that FoReL is run on the sequence with
a regularization function which is σ-strongly-convex with respect to the
same norm. Then, for all u∈S,
RegretT(u)≤R(u)−min
v∈SR(v)+TL2/σ.
2.5.3 Derived Bounds
We now derive concrete bounds from Theorem 2.11. We start with the
simplest case of Euclidean regularization, which is 1-strongly convexover R
d, hence the following corollary follows.
Corollary 2.12. Letf1,...,f Tbe a sequence of convex functions
such that ftisLt-Lipschitz with respect to /bardbl·/bardbl2. Let Lbe such that
1
T/summationtextT
t=1L2
t≤L2. Assume that FoReL is run on the sequence with the
regularization function R(w)=1
2η/bardblw/bardbl2
2. Then, for all u,
RegretT(u)≤1
2η/bardblu/bardbl2
2+ηTL2.
2.5 Strongly Convex Regularizers 139
In particular, if U={u:/bardblu/bardbl2≤B}andη=B
L√
2Tthen
RegretT(U)≤BL√
2T.
Observe that the bound we obtained is identical to the bound of
Online-Gradient-Descent given in Corollary 2.7.
As mentioned in the previous section, the Euclidean regularization
cannot be applied to the problem of prediction with expert advice sinceit does not enforce w
tto be in the probability simplex. A simple solu-
tion is to enforce the constraint wt∈Sby setting R(w)=∞whenever
w/∈S. In light of Lemma 2.9, the resulting regularization function
remains strongly convex on Sand we obtain the following corollary.
Corollary 2.13. Assume that the conditions of Corollary 2.12 hold.
LetSbe a convex set and consider running FoReL with the regular-
ization function
R(w)=
1
2η/bardblw/bardbl2
2ifw∈S
∞ ifw/∈S
Then, for all u∈S,
RegretT(u)≤1
2η/bardblu/bardbl2
2+ηTL2.
In particular, if B≥max u∈S/bardblu/bardbl2andη=B
L√
2Tthen
RegretT(S)≤BL√
2T.
We can apply the regularization function given in the above corol-
lary to the problem of prediction with expert advice. In this case, Sis
the probability simplex and xt∈[0,1]d. Hence, we can set B= 1 and
L=√
dwhich leads to the regret bound√
2dT. We next show another
regularization function which leads to a regret bound of/radicalbig
2log(d)T.
The improvement is based on the following corollary of Theorem 2.11.
140 Online Convex Optimization
Corollary 2.14. Letf1,...,f Tbe a sequence of convex functions
such that ftisLt-Lipschitz with respect to /bardbl·/bardbl1. Let Lbe such that
1
T/summationtextT
t=1L2
t≤L2. Assume that FoReL is run on the sequence with
the regularization function R(w)=1
η/summationtext
iw[i]log(w[i]) and with the set
S={w:/bardblw/bardbl1=B∧w>0}⊂ Rd. Then,
RegretT(S)≤Blog(d)
η+ηBTL2.
In particular, setting η=√logd
L√
2Tyields
RegretT(S)≤BL/radicalbig
2log(d)T.
The Entropic regularization used in the above corollary is strongly
convex with respect to the /lscript1norm, and therefore the Lipschitzness
requirement of the loss functions is also with respect to the /lscript1-norm.
For linear functions, ft(w)=/angbracketleftw,xt/angbracketright, we have by Holder inequality that,
|ft(w)−ft(u)|=|/angbracketleftw−u,xt/angbracketright |≤/bardbl w−u/bardbl1/bardblxt/bardbl∞.
Therefore, the Lipschitz parameter grows with the /lscript∞norm of xtrather
than the /lscript2norm of xt. Applying this to the problem of prediction with
expert advice (with B= 1 and L= 1), we obtain the regret bound of/radicalbig
2log(d)T.
More generally, it is interesting to compare the two bounds given
in Corollaries 2.13 and 2.14. Apart from the extra log( d) factor
that appears in Corollary 2.14, both bounds look similar. However,the parameters B,L have different meanings in the two bounds.
In Corollary 2.12, the parameter Bimposes an /lscript
2constraint on u
and the parameter Lcaptures Lipschitzness of the loss functions with
respect to the /lscript2norm. In contrast, in Corollary 2.14 the parameter B
imposes an /lscript1constraint on u(which is stronger than an /lscript2constraint)
while the parameter Lcaptures Lipschitzness with respect to the /lscript1
norm (which is weaker than Lipschitzness with respect to the /lscript2norm).
Therefore, the choice of the regularization function should depend onthe Lipschitzness of the loss functions and on prior assumptions on
2.6 Online Mirror Descent 141
the set of competing vectors (does a competing vector have a small /lscript1
norm or only a small /lscript2norm). In the prediction with expert advice,
the competing vector would be a singleton, for which both the /lscript2and
/lscript1norms are 1. On the other hand, the gap between Lipschitzness with
respect to /lscript2norm (which was√
d) and Lipschitzness with respect to /lscript1
norm (which was 1) is large. Therefore, we should prefer the Entropic
regularization for the problem of prediction with expert advice.
2.6 Online Mirror Descent
In the previous section we analyzed the FoReL approach in the pres-ence of a general regularization. A possible disadvantage of the FoReLapproach is that it requires solving an optimization problem at eachonline round. In this section we derive and analyze the family of OnlineMirror Descent algorithms from the FoReL framework. We will showthat Online Mirror Descent achieves the same regret bound as FoReLbut the update step is much simpler.
The starting point is to apply FoReL on a sequence of linear func-
tions in which f
t(w)=/angbracketleftw,zt/angbracketrightwith some regularization function R(w).
Throughout, we assume that R(w)=∞forw/negationslash∈S. Using the notation
z1:t=/summationtextt
i=1ziwe can rewrite the prediction of FoReL as follows:
wt+1= argmin
wR(w)+t/summationdisplay
i=1/angbracketleftw,zt/angbracketright
= argmin
wR(w)+/angbracketleftw,z1:t/angbracketright
= argmax
w/angbracketleftw,−z1:t/angbracketright−R(w).
Letting
g(θ) = argmax
w/angbracketleftw,θ/angbracketright−R(w), (2.8)
we can rewrite the FoReL prediction based on the following recursive
update rule:
1.θt+1=θt−zt
2.wt+1=g(θt+1)
142 Online Convex Optimization
Now, if ftis convex but nonlinear, we can use the same technique
we used for deriving the Online Gradient Descent algorithm and usesub-gradients of f
tatwtto linearize the problem. That is, letting zt
be a sub-gradient of ftatwtwe have that for all u
ft(wt)−ft(u)≤/angbracketleftwt,zt/angbracketright−/angbracketleft u,zt/angbracketright.
Summing over twe obtain that the regret with respect to the nonlinear
loss functions is upper bounded by the regret with respect to the linearfunctions. This yields the Online Mirror Descent framework.
Online Mirror Descent (OMD)
parameter: a link function g:Rd→S
initialize: θ1=0
fort=1,2,...
predict wt=g(θt)
update θt+1=θt−ztwhere zt∈∂ft(wt)
Clearly, Online Gradient Descent is a special case of Online Mirror
Descent that is obtained by setting S=Rdandg(θ)=ηθ, for some
η>0. When gis nonlinear we obtain that the vector θis updated
by subtracting the gradient out of it, but the actual prediction is“mirrored” or “linked” to the set Svia the function g. Hence the name
Online Mirror Descent, and this is why gis often referred to as a link
function.
Before we derive concrete algorithms from the OMD framework we
give a generic bound for the OMD family based on our analysis of theFoReL rule.
Theorem 2.15. LetRb ea( 1 /η)-strongly-convex function over Swith
respect to a norm /bardbl·/bardbl. Assume that OMD is run on the sequence with
a link function
g(θ) = argmax
w∈S(/angbracketleftw,θ/angbracketright−R(w)). (2.9)
2.6 Online Mirror Descent 143
Then, for all u∈S,
RegretT(u)≤R(u)−min
v∈SR(v)+ηT/summationdisplay
t=1/bardblzt/bardbl2
⋆,
where /bardbl·/bardbl⋆is the dual norm. Furthermore, if ftisLt-Lipschitz with
respect to /bardbl·/bardbl, then we can further upper bound /bardblzt/bardbl⋆≤Lt.
Proof. As we have shown previously,
T/summationdisplay
t=1(ft(wt)−ft(u))≤T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright,
and the OMD algorithm is equivalent to running FoReL on the sequence
of linear functions with the regularization R(w). The theorem now
follows directly from Theorem 2.11 and Lemma 2.6.
2.6.1 Derived Algorithms
We now derive additional algorithms from the OMD framework.
The first algorithm we derive is often called normalized Exponen-
tiated Gradient. In this algorithm, S={w:/bardblw/bardbl1=1∧w≥0}is the
probability simplex and g:Rd→Rdis the vector valued function whose
ith component is the function
gi(θ)=eηθ[i]
/summationtext
jeηθ[j]. (2.10)
Therefore,
wt+1[i]=eηθt+1[i]
/summationtext
jeηθt+1[j]=eηθt+1[i]
/summationtext
jeηθt+1[j]·/summationtext
keηθt[k]
/summationtext
keηθt[k]
=eηθt[i]e−ηzt[i]
/summationtext
jeηθt[j]e−ηzt[j]·/summationtext
keηθt[k]
/summationtext
keηθt[k]
=wt[i]e−ηzt[i]
/summationtext
jwt[j]e−ηzt[j].
144 Online Convex Optimization
Normalized Exponentiated Gradient
(normalized-EG)
parameter: η>0
initialize: w 1=( 1/d,..., 1/d)
update rule ∀i, wt+1[i]=wt[i]e−ηzt[i]
/summationtext
jwt[j]e−ηzt[j]where zt∈∂ft(wt)
To analyze the normalized-EG algorithm, we rely on Theorem 2.15.
LetR(w)=1
η/summationtext
iw[i]log(w[i]) be the entropic regularization, let Sbe
the probability simplex, and recall that Ris (1/η)-strongly convex over
Swith respect to the /lscript1norm. Using the technique of Lagrange mul-
tipliers, it is easy to verify that the solution to the optimization prob-lem given in Equation (2.9) is the value of the link function given inEquation (2.10). Therefore, Theorem 2.15 yields:
Corollary 2.16. The normalized EG algorithm enjoys the regret
bound given in Corollary 2.14 (with B= 1).
Next, we derive an algorithm which is called Online Gradient
Descent with Lazy Projections. To derive this algorithm, let Sbe a
convex set and define
g(θ) = argmin
w∈S/bardblw−ηθ/bardbl2.
That is, g(θ) returns the point in Swhich is closest to ηθ.
Online Gradient Descent with Lazy Projections
parameters: η>0 and a convex set S
initialize: θ1=0
fort=1,2,...,T
wt= argminw∈S/bardblw−ηθt/bardbl2
θt+1=θt−ztwhere zt∈∂ft(wt)
To analyze the above algorithm we consider the Euclidean regular-
ization function R(w)=1
2η/bardblw/bardbl2
2, which is (1 /η)-strongly convex over S
2.6 Online Mirror Descent 145
with respect to the /lscript2norm. We have that
argmax
w∈S(/angbracketleftw,θ/angbracketright−R(w)) = argmax
w∈S(/angbracketleftw,ηθ/angbracketright−1
2/bardblw/bardbl2
2)
= argmin
w∈S1
2/bardblw−ηθ/bardbl2
2= argmin
w∈S/bardblw−ηθ/bardbl2.
We therefore conclude that:
Corollary 2.17. Online Gradient Descent with Lazy Projections
enjoys the same regret bound given in Corollary 2.13.
Finally, we derive the p-norm algorithm, in which S=Rdand
gi(θ)=ηsign(θ[i])|θ[i]|p−1
/bardblθ/bardblp−2
p,
where p≥2 is a parameter and
/bardblθ/bardblp=/parenleftBiggd/summationdisplay
i=1|θ[i]|p/parenrightBigg1/p
.
p-norm
parameters: η>0 and p>2
initialize: θ1=0
fort=1,2,...,T
∀i, wt,i=ηsign(θt[i])|θt[i]|p−1
/bardblθt/bardblp−2
p
θt+1=θt−ztwhere zt∈∂ft(wt)
To analyze the p-norm algorithm consider the regularization func-
tionR(w)=1
2η(q−1)/bardblw/bardbl2
q, where q=p/(p−1). It is possible to show
that if q∈(1,2] then Gis (1/η)-strongly convex over Rdwith respect
to the /lscriptqnorm (see for example [39, Lemma 17]). It is also possible to
verify that g(θ) = argmaxw/angbracketleftw,θ/angbracketright−R(w). We therefore conclude:
Corollary 2.18. Letf1,...,f Tbe a sequence of convex functions such
thatftisLt-Lipschitz over Rdwith respect to /bardbl·/bardblq. Let Lbe such
146 Online Convex Optimization
that1
T/summationtextT
t=1L2
t≤L2. Then, for all u, the regret of the p-norm algorithm
satisfies
RegretT(u)≤1
2η(q−1)/bardblw/bardbl2
q+ηTL2.
In particular, if U={u:/bardblu/bardblq≤B}andη=B
L√
2T/(q−1)then
RegretT(U)≤BL/radicalBigg
2T
q−1.
When q= 2 the link function becomes g(θ)=ηθand the p-norm
algorithm boils down to the Online Gradient Descent algorithm.When qis close to 1 it is not very hard to see that the p-norm algorithm
behaves like the Entropic regularization. In particular, when p= log( d)
we can obtain a regret bound similar to the regret bound of the EGalgorithm. Intermediate values of qenables us to interpolate between
the properties of the Entropic and Euclidean regularizations.
2.7 The Language of Duality
In the previous sections we relied on the FoReL framework for deriv-ing online learning algorithms. In this section we present a differentproof technique that relies on duality. There are several reasons to con-sider this different approach. First, in some cases, it is easier to derivetighter bounds based on the duality approach. In particular, we willtighten the regret bounds we derived for the OMD framework by afactor of√
2 and we will also derive tighter bounds that involve the
so-called local norms rather than fixed norms. Second, it may becomeconvenient for developing new algorithms. Last, many previous paperson online learning uses the language of duality, so the reader may findthis section useful for understanding the previous literature.
We start by giving some background on Fenchel conjugacy and dual-
ity. For more details, see for example [9].
2.7.1 Fenchel Conjugacy
There are two equivalent representations of a convex function. Either
as pairs ( x,f(x)) or as the set of tangents of f, namely pairs of the form
2.7 The Language of Duality 147
Fig. 2.3 Illustrating Fenchel Conjugacy. We can represent a function as a set of points ( left)
or as a set of tangents ( right).
(slope,intersection-with-y-axis). See Figure 2.3 for an illustration. The
function that relates slopes of tangents to their intersection with theyaxis is called the Fenchel conjugate of f, and is formally defined as
f
⋆(θ) = max
u/angbracketleftu,θ/angbracketright−f(u).
It is possible to show that f=(f⋆)⋆if and only if fis a closed2
and convex function (see [9, Theorem 4.2.1]). From now on, we always
assume that our functions are closed and convex.
The definition of Fenchel conjugacy immediately implies Fenchel–
Young inequality :
∀u,f⋆(θ)≥/angbracketleftu,θ/angbracketright−f(u). (2.11)
It is possible to show that equality holds if uis a sub-gradient of
f⋆atθand in particular, if f⋆is differentiable, equality holds when
u=∇f⋆(θ).
2fis closed if its epigraph, i.e., the set {(w,y):f(w)≤y}, is a closed set.
148 Online Convex Optimization
Table 2.1. Example of Fenchel conjugate pairs.
f(w) f⋆(θ) Comments
1
2/bardblw/bardbl2
21
2/bardblθ/bardbl2
2
1
2/bardblw/bardbl2
q1
2/bardblθ/bardbl2
p where1
p+1
q=1
/summationtext
iw[i]log(w[i]) +I{v≥0:/bardblv/bardbl1=1}(w) log(/summationtext
ieθ[i]) (normalized Entropy)
/summationtext
iw[i](log(w[i])−1)/summationtext
ieθ[i](un-normalized Entropy)
1
ηg(w)1
ηg⋆(ηθ) where η>0
g(w)+/angbracketleftw,x/angbracketright g⋆(θ−x)
Table 2.1 lists several Fenchel conjugate pairs. Recall that given a
setS, we use the notation
IS(w)=/braceleftbigg0i f w∈S
∞ifw/∈S
2.7.2 Bregman Divergences and the Strong/Smooth
Duality
A differentiable function Rdefines a Bregman divergence between two
vectors as follows:
DR(w/bardblu)=R(w)−(R(u)+/angbracketleft∇R(u),w−u/angbracketright). (2.12)
That is, the Bregman divergence is the difference, at the point w,
between Rand its linearization around u. When Ris convex the Breg-
man divergence is always non-negative. However, it is not a metricmeasure because it is not symmetric and also does not satisfy thetriangle inequality. An illustration is given in Figure 2.4.
When R(w)=
1
2/bardblw/bardbl2
2the Bregman divergence becomes
DR(w/bardblu)=1
2/bardblw−u/bardbl2
2. When R(w)=/summationtext
iw[i]log(w[i]) the Bregman
divergence between two vectors in the probability simplex becomesthe Kullback–Leibler divergence, D
R(w/bardblu)=/summationtext
iw[i]logw[i]
u[i].
Recall the definition of strong-convexity (Definition 2.4). If Ris
differentiable, we can rewrite the σ-strong-convexity requirement as
DR(w/bardblu)≥σ
2/bardblw−u/bardbl2.
A related property is strong-smoothness .
2.7 The Language of Duality 149
Fig. 2.4 Illustrating the Bregman divergence.
Definition 2.5. A function Risσ-strongly-smooth with respect to a
norm /bardbl·/bardblif it is differentiable and for all u,wwe have
DR(w/bardblu)≤σ
2/bardblw−u/bardbl2.
Not surprisingly, strong convexity and strong smoothness are dual
properties.
Lemma 2.19. (Strong/Smooth Duality) Assume that Ris a closed
and convex function. Then Risβ-strongly convex with respect to a
norm /bardbl·/bardblif and only if R⋆is1
β-strongly smooth with respect to the
dual norm /bardbl·/bardbl⋆.
The proof can be found, for instance, in [44] (In particular, see
Corollary 3.5.11 on p. 217 and Remark 3.5.3 on p. 218). The abovelemma implies in particular that if Ris strongly convex then R
⋆is
differentiable. Based on Section 2.7.1, this also implies that
∇R⋆(θ) = argmax
w(/angbracketleftw,θ/angbracketright−R(w)). (2.13)
2.7.3 Analyzing OMD using Duality
Recall that the OMD rule is
wt=g(θt)=g(−z1:t−1),
150 Online Convex Optimization
where the link function gis (see Equation (2.8) in Section 2.6)
g(θ) = argmax
w(/angbracketleftw,θ/angbracketright−R(w)).
Based on Equation (2.13) we can also rewrite g(θ)=∇R⋆(θ).
To analyze OMD, we first use the following lemma.
Lemma 2.20. Suppose that OMD is run with a link function g=∇R⋆.
Then, its regret is upper bounded by
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤R(u)−R(w1)+T/summationdisplay
t=1DR⋆(−z1:t/bardbl−z1:t−1).
Furthermore, equality holds for the vector uthat minimizes R(u)+/summationtext
t/angbracketleftu,zt/angbracketright.
Proof. First, using Fenchel–Young inequality we have
R(u)+T/summationdisplay
t=1/angbracketleftu,zt/angbracketright=R(u)−/angbracketleftu,−z1:T/angbracketright≥−R⋆(−z1:T),
where equality holds for the vector uthat maximizes /angbracketleftu,−z1:T/angbracketright−R(u)
hence minimizes R(u)+/angbracketleftu,z1:T/angbracketright. Second, using the fact that wt=
∇R⋆(−z1:t−1) and the definition of the Bregman divergence, we can
rewrite the right-hand side as
−R⋆(−z1:T)=−R⋆(0)−T/summationdisplay
t=1(R⋆(−z1:t)−R⋆(−z1:t−1))
=−R⋆(0)+T/summationdisplay
t=1(/angbracketleftwt,zt/angbracketright−DR⋆(−z1:t/bardbl−z1:t−1)).
(2.14)
Note that R⋆(0) = max w/angbracketleft0,w/angbracketright−R(w)=−min wR(w)=−R(w1).
Combining all the above we conclude our proof.
It is interesting to compare the above lemma to Lemma 2.3, which forlinear functions yields the regret bound
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤R(u)−R(w1)+T/summationdisplay
t=1/angbracketleftwt−wt+1,zt/angbracketright.
2.7 The Language of Duality 151
In both bounds we have a stability term but the way we measure it is
different.
We can easily derive concrete bounds from Lemma 2.20 if Ris
strongly convex.
Theorem 2.21. LetRb ea( 1 /η)-strongly convex with respect to a
norm /bardbl·/bardbland suppose the OMD algorithm is run with the link function
g=∇R⋆. Then,
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤R(u)−R(w1)+η
2T/summationdisplay
t=1/bardblzt/bardbl2
⋆.
Proof. The proof follows directly from Lemma 2.20 and the strong/
smooth duality given in Lemma 2.19.
The reader can easily obtain the bounds we derived in Section 2.6 usingthe above theorem. Consider for example the case in which the regu-larization function is R(w)=
1
2η/bardblw/bardbl2
2, which is (1 /η)-strongly convex
with respect to the Euclidean norm. Since the Euclidean norm is dualto itself, we obtain the bound
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤1
2η/bardblu/bardbl2
2+η
2T/summationdisplay
t=1/bardblzt/bardbl2
2. (2.15)
Letting L2=1
T/summationtext
t/bardblzt/bardbl2
2and setting η=B
L√
Tthen for all uwith
/bardblu/bardbl2≤Bwe obtain the bound
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤BL√
T.
Comparing this bound to the bound we derived in Corollary 2.7, we
observe that we have obtained a factor of√
2 improvement in the regret
bound.
2.7.4 Other Proof Techniques
In the previous subsection we used Fenchel–Young inequality to derive
bounds for OMD, which is equivalent to FoReL when the loss functions
152 Online Convex Optimization
are linear. It is possible to extend this proof technique, based on Fenchel
duality, and to derive a larger family of online convex optimizationalgorithms. The basic idea is to derive the Fenchel dual of the opti-mization problem min
wR(w)+/summationtext
tft(w) and to construct an online
learning algorithm by incrementally solving the dual problem. We referthe reader to [39] for more details.
Another popular approach is to derive regret bounds by monitoring
the Bregman divergence D
R(wt/bardblu), where uis the competing vec-
tor. A detailed description of this approach can be found in [12, 34]and is therefore omitted from this survey. It is important to note thatthe analysis using the Bregman divergence potential requires that R
will be a Legendre function (see a precise definition in [12, p. 294]).In particular, Legendre functions guarantee the property that ∇R
and∇R
⋆are inverse mappings. We do not require that Ris Legen-
dre and in particular, the normalized entropy regularization function,R(w)=/summationtext
iw[i]log(w[i]) +IS(w), where Sis the probability simplex,
is not a Legendre function. Therefore, when analyzing the normalizedEG algorithm using Bregman divergences we need to use the unnormal-ized Entropy as a regularization function and to include an additionalBregman projection step on the simplex, which leads to the desirednormalization. To the best of our knowledge, the two proof techniqueslead to the same regret bounds.
2.8 Bounds with Local Norms
Consider running the normalized EG algorithm, namely, runningFoReL on linear loss functions with the normalized entropy R(w)=
1
η/summationtext
iw[i]log(w[i]) +IS(w), where S={w≥0:/bardblw/bardbl1=1}. Previously,
we have derived the regret bound,
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤log(d)
η+ηT/summationdisplay
t=1/bardblzt/bardbl2
∞.
We now derive a refined bound for the normalized EG algorithm, in
which each term /bardblzt/bardbl2
∞is replaced by a term/summationtext
iwt[i]zt[i]2. Since wtis
in the probability simplex, we clearly have that/summationtext
iwt[i]zt[i]2≤/bardblzt/bardbl2
∞.
2.8 Bounds with Local Norms 153
In fact, we can rewrite/summationtext
iwt[i]zt[i]2as a local norm /bardblzt/bardbl2
twhere
/bardblz/bardblt=/radicalBigg/summationdisplay
iwt[i]z[i]2.
Note that this is indeed a valid norm. In the next sections we will show
cases in which the refined local-norm bounds lead to much tighter regretbounds.
Theorem 2.22. Assume that the normalized EG algorithm is run on a
sequence of linear loss functions such that for all t,iwe have ηzt[i]≥−1.
Then,
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤log(d)
η+ηT/summationdisplay
t=1/summationdisplay
iwt[i]zt[i]2.
Proof. Using Lemma 2.20, it suffices to show that
DR⋆(−z1:t/bardbl−z1:t−1)≤η/summationdisplay
iwt[i]zt[i]2,
where, based on Table 2.1, the conjugate function is
R⋆(θ)=1
ηlog/parenleftBigg/summationdisplay
ieηθ[i]/parenrightBigg
.
Indeed,
DR⋆(−z1:t/bardbl−z1:t−1)=R⋆(−z1:t)−R⋆(−z1:t−1)+/angbracketleftwt,zt/angbracketright(2.16)
=1
ηlog/parenleftBigg/summationtext
ie−ηz1:t[i]
/summationtext
ie−ηz1:t−1[i]/parenrightBigg
+/angbracketleftwt,zt/angbracketright (2.17)
=1
ηlog/parenleftBigg/summationdisplay
iwt[i]e−ηzt[i]/parenrightBigg
+/angbracketleftwt,zt/angbracketright.(2.18)
Using the inequality e−a≤1−a+a2which holds for all a≥−1 (and
hence holds by the assumptions of the theorem) we obtain
DR⋆(−z1:t/bardbl−z1:t−1)≤1
ηlog/parenleftBigg/summationdisplay
iwt[i](1−ηzt[i]+η2zt[i]2)/parenrightBigg
+/angbracketleftwt,zt/angbracketright.
154 Online Convex Optimization
Next, we use the fact that/summationtext
iwt[i] = 1 and the inequality log(1 −a)≤
−a, which holds for all a≤1 we obtain
DR⋆(−z1:t/bardbl−z1:t−1)≤1
η/summationdisplay
iwt[i](−ηzt[i]+η2zt[i]2)+/angbracketleftwt,zt/angbracketright
=η/summationdisplay
iwt[i]zt[i]2.
Next, we describe another variant of the EG algorithm in which we
do not normalize the weights to the simplex on each round. We showa similar regret bounds for this variant as well.
Unnormalized Exponentiated Gradient
(unnormalized-EG)
parameters: η,λ > 0
initialize: w 1=(λ,...,λ )
update rule ∀i, wt+1[i]=wt[i]e−ηzt[i]
The following theorem provides a regret bound with local-norms for
the unnormalized EG algorithm.
Theorem 2.23. Assume that the unnormalized EG algorithm is run
on a sequence of linear loss functions such that for all t,iwe have
ηzt[i]≥−1. Then, for all u≥0,
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤dλ+/summationtextd
i=1u[i]log(u[i]/(eλ))
η+ηT/summationdisplay
t=1d/summationdisplay
i=1wt[i]zt[i]2.
In particular, setting λ=1/dyields
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤1 + (log( d)−1)/bardblu/bardbl1+/summationtextd
i=1u[i]log(u[i])
η
+ηT/summationdisplay
t=1d/summationdisplay
i=1wt[i]zt[i]2.
2.9 Bibliographic Remarks 155
Proof. To analyze the unnormalized-EG algorithm, we first note that it
is equivalent to running FoReL on the sequence of linear loss functionswith the following unnormalized entropy regularization function:
R(w)=1
η/summationdisplay
iw[i](log(w[i])−1−log(λ)).
Using Lemma 2.20, it suffices to show that
DR⋆(−z1:t/bardbl−z1:t−1)≤η/summationdisplay
iwt[i]zt[i]2,
where, based on Table 2.1, the conjugate function is
R⋆(θ)=λ
η/summationdisplay
ieηθ[i].
We have:
DR⋆(−z1:t/bardbl−z1:t−1)=R⋆(−z1:t)−R⋆(−z1:t−1)+/angbracketleftwt,zt/angbracketright
=λ
η/summationdisplay
ie−ηz1:t−1[i](e−ηzt[i]−1) +/angbracketleftwt,zt/angbracketright
=1
η/summationdisplay
iwt[i](e−ηzt[i]−1) +/angbracketleftwt,zt/angbracketright
≤η/summationdisplay
iwt[i]zt[i]2,
where in the last inequality we used the inequality e−a≤1−a+a2
which holds for all a≥−1 (and hence holds by the assumptions of the
lemma).
2.9 Bibliographic Remarks
The term “online convex programming” was introduced byZinkevich [46] but this setting was introduced some years earlier byGordon [20]. This model is also closely related to the model of relativeloss bounds presented by Kivinen and Warmuth [26, 27, 28]. Ourpresentation of relative mistake bounds follows the works of Little-stone [31], and Kivinen and Warmuth [28].
156 Online Convex Optimization
Zinkevich presented and analyzed the online gradient descent (with
projections or with lazy projections). The name “Follow the Leader” isdue to [25]. Analysis of “Follow the Regularized Leader” was given in[40, 39] using Fenchel duality as part of the analysis of a larger algo-rithmic framework. The more direct analysis we give here is adaptedfrom [34, 22]. The duality based analysis we present is due to [39, 24].Similar ideas in a more limited context have been introduced in [21].
The EG update is due to [26]. See also [6, 28]. The p-norm algo-
rithm was developed by Gentile and Littlestone [19]. Local norms wereintroduced in [2]. See also [34].
3
Online Classification
In this section we return to the problem of online classification, in
which the target domain is Y={0,1}. We already mentioned this set-
ting in Section 1.2, where we introduced the Consistent andHalving
algorithms. These algorithms rely on two simplifying assumptions: real-izability of the problem and finiteness of H. While trying to relax
the realizability assumption, we presented Cover’s impossibility result,which shows that even if |H|= 2, no algorithm can have low regret
in the unrealizable case. We sidestepped the impossibility result byallowing the learner to randomize his predictions (i.e., the predictionsdomain is allowed to be D=[ 0,1]). As discussed in Section 2.1.1, this
can be thought of as a convexification of the problem. Based on this con-vexification, we start the section by deriving the Weighted Majority
algorithm for prediction with expert advice. We will see that this isa specific instance of the normalized EG algorithm discussed in the
previous section. The analysis of Weighted Majority implies onlinelearnability of finite hypothesis classes.
Next, in Section 3.2, we study the fundamental question of
online learnability, namely, what is an optimal algorithm for a givenhypothesis class. We shall characterize learnability for the general case,namely, without assuming neither realizability nor finiteness of H.
157
158 Online Classification
Finally, in Section 3.3, we study the important and practically
relevant hypothesis class of halfspaces with margin and derive the clas-sic Perceptron and Winnow algorithms from the online convex opti-mization framework.
3.1 Finite Hypothesis Class and Experts Advice
Consider the problem of classification, where on round tthe learner
receives xt∈X, predicts pt∈[0,1], receives yt∈{0,1}, and pays
|pt−yt|. The goal is to have low regret with respect to a finite hypoth-
esis class H={h1,...,h d}. As we hinted in Section 2.1.1, this problem
can be reduced to the problem of prediction with expert advice asfollows. Let S={w∈R
d
+:/bardblw/bardbl1=1}be the probability simplex. The
learner will maintain a weight vector wt∈Sand will predict the label
1 with probability pt=/summationtextd
i=1wt[i]hi(xt). The loss he will pay can there-
fore be rewritten as
|pt−yt|=/vextendsingle/vextendsingle/vextendsingle/vextendsingle/vextendsingled/summationdisplay
i=1wt[i]hi(xt)−yt/vextendsingle/vextendsingle/vextendsingle/vextendsingle/vextendsingle=d/summationdisplay
i=1wt[i]|hi(xt)−yt|,
where the last equality follows because both ytandhi(xt) are in {0,1}.
Letting zt=(|h1(xt)−yt|,...,|hd(xt)−yt|) we obtain that the loss is
/angbracketleftwt,zt/angbracketright. This is a special case of the prediction with expert advice
problem, where zt∈[0,1]dis the costs vector of the different experts.
Applying the normalized-EG algorithm we obtain an algorithm whichis often called Weighted Majority.
Weighted Majority
parameter: η∈(0,1)
initialize :w1=( 1/d,..., 1/d)
fort=1,2,...
choose i∼wtand predict according to the advice of the i’th
expert receive costs of all experts zt∈[0,1]d
update rule ∀i, wt+1[i]=wt[i]e−ηzt[i]
/summationtext
jwt[j]e−ηzt[j]
3.1 Finite Hypothesis Class and Experts Advice 159
The analysis of Weighted Majority follows directly from the anal-
ysis of the normalized-EG algorithm given in the previous section and
is given in the following theorem.
Theorem 3.1. The Weighted Majority algorithm enjoys the bounds
1.T/summationdisplay
t=1/angbracketleftwt,zt/angbracketright≤min
i∈[d]T/summationdisplay
t=1zt[i]+log(d)
η+ηT
2.T/summationdisplay
t=1/angbracketleftwt,zt/angbracketright≤1
1−η/parenleftBigg
min
i∈[d]T/summationdisplay
t=1zt[i]+log(d)
η/parenrightBigg
In particular, setting η=/radicalbig
log(d)/Tin the first bound we obtain
T/summationdisplay
t=1/angbracketleftwt,zt/angbracketright≤min
i∈[d]T/summationdisplay
t=1zt[i]+2/radicalbig
log(d)T,
and setting η=1/2 in the second bound we obtain
T/summationdisplay
t=1/angbracketleftwt,zt/angbracketright≤2min
i∈[d]T/summationdisplay
t=1zt[i] + 4log( d).
Proof. We rely on the analysis of the normalized-EG algorithm given in
Theorem 2.22. Since zt∈[0,1]dandη>0 the conditions of the theorem
holds and we obtain that
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤log(d)
η+ηT/summationdisplay
t=1/summationdisplay
iwt[i]zt[i]2.
Since wt∈Sandzt∈[0,1]dthe right-most term is at most ηT. Further-
more, the bound holds for all uin the probability simplex and in partic-
ular for all singletons, i.e., vectors of the form u=( 0,...,0,1,0,...,0).
Rearranging, we obtain,
T/summationdisplay
t=1/angbracketleftwt,zt/angbracketright≤min
i∈[d]T/summationdisplay
t=1zt[i]+log(d)
η+ηT.
160 Online Classification
To derive the second bound, observe that wt[i],zt[i]∈[0,1] and there-
forewt[i]zt[i]2≤wt[i]zt[i], which yields
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤log(d)
η+ηT/summationdisplay
t=1/angbracketleftwt,zt/angbracketright.
Rearranging, we obtain that
T/summationdisplay
t=1/angbracketleftwt,zt/angbracketright≤1
1−η/parenleftBigg
min
i∈[d]T/summationdisplay
t=1zt[i]+log(d)
η/parenrightBigg
.
In particular, in the realizable case when min i∈[d]/summationtextT
t=1zt[i]=0w e
obtain that Weighted Majority withη=1/2 enjoys the bound
T/summationdisplay
t=1/angbracketleftwt,zt/angbracketright≤4log(d).
This is similar to the bound we derived for Halving in Section 1.2.
3.2 Learnability and the Standard Optimal Algorithm
So far, we focused on finite hypothesis classes. In this section we take a
more general approach, and aim at characterizing online learnability. Inparticular, we target the following question: what is the optimal onlinelearning algorithm for a given class H?
We start with the realizable case, where we assume that all target
labels are generated by some h
⋆∈H, namely, yt=h⋆(xt) for all t. Later,
in Section 3.2.1 we generalize the results to the unrealizable case. In therealizable case, we study the best achievable mistake bound, formallydefined below.
Definition 3.1 (Mistake bounds, online learnability). LetHbe
a hypothesis class and let Abe an online learning algorithm. Given
any sequence S=(x1,h⋆(y1)),...,(xT,h⋆(yT)), where Tis any integer
andh⋆∈H, letMA(S) be the number of mistakes Amakes on the
sequence S. We denote by MA(H) the supremum of MA(S) over all
sequences of the above form. A bound of the form MA(H)≤B<∞
is called a mistake bound . We say that a hypothesis class His online
learnable if there exists an algorithm Afor which MA(H)≤B<∞.
3.2 Learnability and the Standard Optimal Algorithm 161
We present a dimension of hypothesis classes that characterizes the
best possible achievable mistake bound. This measure was proposed byNick Littlestone and we therefore refer to it as Ldim( H).
To motivate the definition of Ldim it is convenient to view the
online learning process as a game between two players: the learnervs. the environment. On round tof the game, the environment picks
an instance x
t, the learner predicts a label pt∈{0,1}, and finally the
environment outputs the true label, yt∈{0,1}. Suppose that the envi-
ronment wants to make the learner err on the first Trounds of the
game. Then, it must output yt=1−pt, and the only question is how
to choose the instances xtin such a way that ensures that for some
h⋆∈Hwe have yt=h⋆(xt) for all t∈[T]={1,...,T }.
It makes sense to assume that the environment should pick xtbased
on the previous predictions of the learner, p1,...,p t−1. Since in our case
we have yt=1−ptwe can also say that xtis a function of y1,...,y t−1.
We can represent this dependence using a complete binary tree ofdepth T(we define the depth of the tree as the number of edges in a
path from the root to a leaf). We have 2
T−1 nodes in such a tree, and
we attach an instance to each node. Let v1,...,v2T−1be these instances.
We start from the root of the tree, and set x1=v1. At round t,w es e t
xt=vit, where itis the current node. At the end of round t,w eg ot o
the left child of itifyt= 0 or to the right child if yt= 1. That is, it+1=
2it+yt. Unraveling the recursion we obtain it=2t−1+/summationtextt−1
j=1yj2t−1−j.
The above strategy for the environment succeeds only if for any
(y1,...,y T) there exists h∈Hsuch that yt=h(xt) for all t∈[T]. This
leads to the following definition.
Definition 3.2 ( HShattered tree). A shattered tree of depth dis
a sequence of instances v1,...,v2d−1inXsuch that for all labeling
(y1,...,y d)∈{0,1}dthere exists h∈Hsuch that for all t∈[d]w eh a v e
h(vit)=yt, where it=2t−1+/summationtextt−1
j=1yj2t−1−j.
An illustration of a shattered tree of depth 2 is given in Figure 3.1.
Definition 3.3 (Littlestone’s dimension ( Ldim )).Ldim( H)i st h e
maximal integer Tsuch that there exist a shattered tree of depth T.
162 Online Classification
Fig. 3.1 An illustration of a shattered tree of depth 2. The dashed blue path corresponds
to the sequence of examples (( v1,1),(v3,0)). The tree is shattered by H={h1,h2,h3,h4},
where the predictions of each hypothesis in Hon the instances v1,v2,v3is given in the
table (the “ ∗” mark means that hj(vi) can be either 1 or 0).
The definition of Ldim and the discussion above immediately imply
the following:
Lemma 3.2. No algorithm can have a mistake bound strictly smaller
than Ldim( H), namely, ∀A, M A(H)≥Ldim( H).
Proof. LetT= Ldim( H)and let v1,...,v2T−1be a sequence that
satisfies the requirements in the definition of Ldim. If the environmentsetsx
t=vitandyt=1−ptfor all t∈[T], then the learner makes T
mistakes while the definition of Ldim implies that there exists a hypoth-esish∈Hsuch that y
t=h(xt) for all t.
Let us now give several examples.
Example 3.1. LetHbe a finite hypothesis class. Clearly, any tree that
is shattered by Hhas depth of at most log2(|H|). Therefore, Ldim( H)≤
log2(|H|). Another way to conclude this inequality is by combining
Lemma 3.2 with Theorem 1.2.
Example 3.2. LetX={1,...,d}and H={h1,...,h d}, where
hd(x)=1i ff x=d. Then, it is easy to show that Ldim( H) = 1 while
|H|=dcan be arbitrarily large.
Example 3.3. LetX=[ 0,1] and H={x/mapsto→1[x>a]:a∈[0,1]}, namely,
His the class of thresholds on the segment [0 ,1]. Then, Ldim( H)=∞.
3.2 Learnability and the Standard Optimal Algorithm 163
To see this, consider the tree for which v1=1
2,v2=1
4,v3=3
4,.... Due
to the density of the reals, this tree is shattered by H.
Example 3.4. LetX={x∈{0,1}∗:/bardblx/bardbl0≤r}and H={x/mapsto→
1[/angbracketleftw,x/angbracketright>0.5]:/bardblw/bardbl0≤k}. The size of His infinite. Nevertheless,
Ldim( H)≤rk. The proof uses the fact that MPerceptron (H)≤rk,
where the Perceptron algorithm will be described in the next section.
Lemma 3.2 states that Ldim( H) lower bounds the mistake bound
of any algorithm. Interestingly, there is a standard algorithm whosemistake bound matches this lower bound. The algorithm is similarto the Halving algorithm. Recall that the prediction of Halving is
according to a majority vote of the hypotheses which are consis-tent with previous examples. We denoted this set by V
t. Put another
way, Halving partition Vtinto two sets: V+
t={h∈Vt:h(xt)=1}and
V−
t={h∈Vt:h(xt)=0}. It then predicts according to the larger of
the two groups. The rationale behind this prediction is that wheneverHalving makes a mistake it ends up with |V
t+1|≤0.5|Vt|.
The optimal algorithm we present below uses the same idea, but
instead of predicting according to the larger class, it predicts accordingto the class with larger Ldim.
Standard Optimal Algorithm (SOA)
input: A hypothesis class H
initialize :V1=H
fort=1,2,...
receive xt
forr∈{0,1}letV(r)
t={h∈Vt:h(xt)=r}
predict pt= argmaxr∈{0,1}Ldim( V(r)
t)
(in case of a tie predict pt=1 )
receive true answer yt
update Vt+1={h∈Vt:h(xt)=yt}
The following lemma formally establishes the optimality of the
above algorithm.
164 Online Classification
Lemma 3.3. SOAenjoys the mistake bound MSOA(H)≤Ldim( H).
Proof. It suffices to prove that whenever the algorithm makes a predic-
tion mistake we have Ldim( Vt+1)≤Ldim( Vt)−1. We prove this claim
by assuming the contrary, that is, Ldim( Vt+1) = Ldim( Vt). If this holds
true, then the definition of ptimplies that Ldim( V(r)
t) = Ldim( Vt) for
both r= 1 and r= 0. But, then we can construct a shattered tree
of depth Ldim( Vt) + 1 for the class Vt, which leads to the desired
contradiction.
Combining Lemma 3.3 and Lemma 3.2 we obtain:
Corollary 3.4. LetHbe any hypothesis class. Then, the standard
optimal algorithm enjoys the mistake bound MSOA(H) = Ldim( H) and
no other algorithm can have MA(H)<Ldim( H).
Comparison to VC dimension In the PAC learning model of
Valiant, learnability is characterized by the Vapnik–Chervonenkis (VC)dimension of the class H. To remind the reader, the VC dimension of
a class H, denoted VCdim( H), is the maximal number dsuch that
there are instances x
1,...,xdthat are shattered by H. That is, for any
sequence of labels ( y1,...,y d)∈{0,1}dthere exists a hypothesis h∈H
that gives exactly this sequence of labels. The following theorem relatesthe VC dimension to the Littlestone dimension.
Theorem 3.5. For any class H, VCdim( H)≤Ldim( H), and there are
classes for which strict inequality holds. Furthermore, the gap can bearbitrarily large.
Proof. We first prove that VCdim( H)≤Ldim( H). Suppose
VCdim( H)=dand let x1,...,xdbe a shattered set. We now construct
a complete binary tree of instances v1,...,v2d−1, where all nodes at
depth iare set to be xi(see the illustration in Figure 3.2). Now,
3.2 Learnability and the Standard Optimal Algorithm 165
x1
x2
x3 x3x2
x3 x3
Fig. 3.2 How to construct a shattered tree from a shattered sequence x1,..., xd.
the definition of shattered sample clearly implies that we got a valid
shattered tree of depth d, and we conclude that VCdim( H)≤Ldim( H).
To show that the gap can be arbitrarily large simply note that the classgiven in Example 3.3 has VC dimension of 1 whereas its Littlestonedimension is infinite.
3.2.1 The Unrealizable Case
In the previous section we have shown that Littlestone’s dimension
exactly characterizes the achievable mistake bounds in the realizablecase. We now show that the same dimension characterizes online learn-ability in the unrealizable case as well. Specifically, we will prove thefollowing.
Theorem 3.6. For any hypothesis class H, there exists an online learn-
ing algorithm such that for any h∈Hand any sequence of Texamples
we have
T/summationdisplay
t=1|pt−yt|−T/summationdisplay
t=1|h(xt)−yt|≤O(/radicalbig
Ldim( H) ln(T)T),
where ptis the learner’s prediction on round t. Furthermore,
no algorithm can achieve an expected regret bound smaller thanΩ(/radicalbig
Ldim( H)T).
Recall that in the unrealizable case, to sidestep Cover’s impossi-
bility result, the learner is allowed to make randomized predictionsand we analyze his expected regret. We will construct a generic onlinealgorithm that has the expected regret bound/radicalbig
Ldim( H) log(T)T.
166 Online Classification
Finally, we provide an almost matching lower bound on the achievable
regret.
Our starting point is the Weighted Majority algorithm, whose
regret depends on log( d). In the case of a finite hypothesis class, we
let each hypothesis be an expert. In the unrealizable case, the mainidea is to construct a set of experts in a more sophisticated way. Thechallenge is how to define a set of experts that on one hand is notexcessively large while on the other hand contains experts that giveaccurate predictions.
We construct the set of experts so that for each hypothesis h∈H
and every sequence of instances, x
1,x2,...,xT, there exists at least one
expert in the set which behaves exactly as hon these instances. For each
L≤Ldim( H) and each sequence 1 ≤i1<i2<···<iL≤Twe define
an expert. The expert simulates the game between SOA (presented inthe previous section) and the environment on the sequence of instancesx
1,x2,...,xTassuming that SOA makes a mistake precisely in rounds
i1,i2,...,i L. The expert is defined by the following algorithm.
Expert( i1,i2,...,i L)
input A hypothesis class H; Indices i1<i2<···<iL
initialize :V1=H
fort=1,2,...,T
receive xt
forr∈{0,1}letV(r)
t={h∈Vt:h(xt)=r}
define ˜ yt= argmaxrLdim/parenleftBig
V(r)
t/parenrightBig
(in case of a tie set ˜ yt=0 )
ift∈{i1,i2,...,i L}
predict ˆ yt=¬˜yt
else
predict ˆ yt=˜yt
update Vt+1=V(ˆyt)
t
The following key lemma shows that, on any sequence of instances,
for each hypothesis h∈Hthere exists an expert with the same
behavior.
3.2 Learnability and the Standard Optimal Algorithm 167
Lemma 3.7. LetHbe any hypothesis class with Ldim( H)<∞. Let
x1,x2,...,xTbe any sequence of instances. For any h∈H, there exists
L≤Ldim( H) and indices 1 ≤i1<i2<···<iL≤Tsuch that when
running Expert( i1,i2,...,i L) on the sequence x1,x2,...,xT, the expert
predicts h(xt) on each online round t=1,2,...,T .
Proof. Fixh∈Hand the sequence x1,x2,...,xT. We must construct
Land the indices i1,i2,...,i L. Consider running SOA on the input
(x1,h(x1)), (x2,h(x2)),...,(xT,h(xT)). SOA makes at most Ldim( H)
mistakes on such input. We define Lto be the number of mistakes made
by SOA and we define {i1,i2,...,i L}to be the set of rounds in which
SOA made the mistakes.
Now, consider the Expert( i1,i2,...,i L) running on the
sequence x1,x2,...,xT. By construction, the set Vtmaintained
by Expert( i1,i2,...,i L) equals to the set Vtmaintained by SOA
when running on the sequence ( x1,h(x1)),...,(xT,h(xT)). Since the
predictions of SOA differ from the predictions of hif and only if
the round is in {i1,i2,...,i L}, we conclude that the predictions of
Expert( i1,i2,...,i L) are always the same as the predictions of h.
The above lemma holds in particular for the hypothesis in Hthat
makes the least number of mistakes on the sequence of examples, andwe therefore obtain the following:
Corollary 3.8. Let ( x1,y1),(x2,y2),...,(xT,yT) be a sequence of
examples and let Hbe a hypothesis class with Ldim( H)<∞. There
exists L≤Ldim( H) and indices 1 ≤i1<i2<···<iL≤T, such that
Expert( i1,i2,...,i L) makes at most as many mistakes as the best h∈H
does. Namely,
min
h∈HT/summationdisplay
t=1|h(xt)−yt|
mistakes on the sequence of examples.
168 Online Classification
Our generic online learning algorithm is now an application of
theWeighted Majority algorithm with the constructed experts. To
analyze the algorithm we combine Corollary 3.8 with the upper boundon the number of experts,
d=Ldim( H)/summationdisplay
L=0/parenleftbiggT
L/parenrightbigg
≤(eT/Ldim( H))Ldim( H), (3.1)
and with Theorem 3.1. This proves the upper bound part of Theo-
rem 3.6. The proof of the lower bound part can be found in [7].
3.3 Perceptron and Winnow
In this section we describe two classic online learning algorithms forbinary classification with the hypothesis class of halfspaces. Through-out this section, it is more convenient to let the labels set be Y={−1,1}
instead of Y={0,1}. Each halfspace hypothesis can be described using
a vector, often called a weight vector. For example, if the vector spaceis the two dimensional Euclidean space (the plane), then instances arepoints in the plane and hypotheses are lines. The weight vector is per-pendicular to the line. The prediction is according to whether the pointfalls on one side of the line or on the other side. See Figure 3.3 for anillustration.
Fig. 3.3 An illustration of linear separators in the plane ( R2). The solid black line separates
the plane into two regions. The circled point represents an input vector which is labeled 1 by
the linear separator. The arrow designates a weight vector that represents the hypothesis.
3.3 Perceptron and Winnow 169
On round t, the learner receives a vector xt∈Rd. The learner main-
tains a weight vector wt∈Rdand predicts pt= sign( /angbracketleftwt,xt/angbracketright). Then, it
receives yt∈Yand pays 1 if pt/negationslash=ytand 0 otherwise.
The goal of the learner is to make as few prediction mistakes as
possible. In the previous section we characterized the optimal algo-rithm and showed that the best achievable regret bound depends onthe Littlestone dimension of the class. In our case, the class of half-spaces is the class H={x/mapsto→sign(/angbracketleftw,x/angbracketright):w∈R
d}. We show below
that if d≥2 then Ldim( H)=∞, which implies that we have no hope
to make few prediction mistakes. Indeed, consider the tree for whichv
1=(1
2,1,0,...,0),v2=(1
4,1,0,...,0),v3=(3
4,1,0,...,0), etc. Due to
the density of the reals, this tree is shattered by the subset of Hwhich
contains all hypotheses that are parametrized by wof the form w=
(−1,a,0,...,0), for a∈[0,1]. We conclude that indeed Ldim( H)=∞.
To sidestep this impossibility result, the Perceptron and Winnow
algorithms rely on the technique of surrogate convex losses we discussed
in Section 2.1.2. We now derive these algorithms.
3.3.1 Perceptron
A weight vector wmakes a mistake on an example ( x,y) whenever the
sign of /angbracketleftw,x/angbracketrightdoes not equal to y. Therefore, we can write the 0–1 loss
function as follows:
/lscript(w,(x,y)) = 1[y/angbracketleftw,x/angbracketright≤0].
On rounds on which the algorithm makes a prediction mistake, we shall
define the following surrogate convex loss function
ft(w)=[ 1 −yt/angbracketleftw,xt/angbracketright]+,
where [ a]+= max {a,0}is the hinge function. This loss function is often
called the hinge-loss . It satisfies the two conditions:
•ftis a convex function
•For all w,ft(w)≥/lscript(w,(xt,yt)). In particular, this holds for
wt.
170 Online Classification
On rounds on which the algorithm is correct, we shall define ft(w)=0 .
Clearly, ftis convex in this case as well. Furthermore, ft(wt)=
/lscript(wt,(xt,yt) )=0 .
Let us now run the Online Gradient Descent (OGD) algorithm
on the sequence of functions. Recall that OGD initializes w1=0and
its update rule
wt+1=wt−ηzt
for some zt∈∂ft(wt). In our case, if yt/angbracketleftwt,xt/angbracketright>0 then ftis the zero
function and we can take zt=0. Otherwise, it is easy to verify that
zt=−ytxtis in∂ft(wt). We therefore obtain the update rule
wt+1=/braceleftbiggwt ifyt/angbracketleftwt,xt/angbracketright>0
wt+ηytxtotherwise
Denote by Mthe set of rounds in which sign( /angbracketleftwt,xt/angbracketright)/negationslash=yt. Note that
on round t, the prediction of the Perceptron can be rewritten as,
pt= sign( /angbracketleftwt,xt/angbracketright) = sign/parenleftBigg/summationdisplay
i∈M:i<tyi/angbracketleftxi,xt/angbracketright/parenrightBigg
.
The above form implies that the predictions of the Perceptron
algorithm and the set Mdo not depend on the actual value of ηas
long as η>0. We have therefore obtained the well known Perceptron
algorithm.
Perceptron
initialize :w1=0
fort=1,2,...,T
receive xt
predict pt= sign( /angbracketleftwt,xt/angbracketright)
ifyt/angbracketleftwt,xt/angbracketright≤0
wt+1=wt+ytxt
else
wt+1=wt
To analyze the Perceptron, we rely on the analysis of OGD given
in the previous section. In particular, we rely on Corollary 2.7 and
3.3 Perceptron and Winnow 171
its improved version is given in Equation (2.15). In our case, the
sub-gradients of ftwe use in the Perceptron are zt=−1[yt/angbracketleftwt,xt/angbracketright≤0]ytxt.
Indeed, the Perceptron’s update is wt+1=wt−zt, and as discussed
before this is equivalent to wt+1=wt−ηztfor any η>0. Therefore,
the bound given in Equation (2.15) tells us that
T/summationdisplay
t=1ft(wt)−T/summationdisplay
t=1ft(u)≤1
2η/bardblu/bardbl2
2+η
2T/summationdisplay
t=1/bardblzt/bardbl2
2.
Since ft(wt) is a surrogate for the 0–1 loss we know that/summationtextT
t=1ft(wt)≥
|M|. Denote R= max t/bardblxt/bardbl, then we obtain
|M| −T/summationdisplay
t=1ft(u)≤1
2η/bardblu/bardbl2
2+η
2|M|R2
Setting η=/bardblu/bardbl
R√
|M|and rearranging, we obtain
|M| − R/bardblu/bardbl/radicalbig
|M| −T/summationdisplay
t=1ft(u)≤0. (3.2)
This inequality implies:
Theorem 3.9. Suppose that the Perceptron algorithm runs on
a sequence ( x1,y1),...,(xT,yT) and let R= max t/bardblxt/bardbl. Let M
be the rounds on which the Perceptron errs and let ft(w)=
1[t∈M][1−yt/angbracketleftw,xt/angbracketright]+. Then, for any u
|M| ≤/summationdisplay
tft(u)+R/bardblu/bardbl/radicalBigg/summationdisplay
tft(u)+R2/bardblu/bardbl2.
In particular, if there exists usuch that yt/angbracketleftu,xt/angbracketright≥1 for all tthen
|M| ≤ R2/bardblu/bardbl2.
Proof. The theorem follows from Equation (3.2) and the following
claim: Given x,b,c∈R+, the inequality x−b√x−c≤0 implies that
x≤c+b2+b√c. The last claim can be easily derived by analyzing
the roots of the convex parabola Q(y)=y2−by−c.
172 Online Classification
The last assumption of Theorem 3.9 is called separability with large
margin. That is, there exists uthat not only satisfies that the point xt
lies on the correct side of the halfspace, it also guarantees that xtis
not too close to the decision boundary. More specifically, the distancefrom x
tto the decision boundary is at least γ=1//bardblu/bardbland the bound
becomes ( R/γ)2. This classic mistake bound of the Perceptron appears
in [3, 33].
When the separability assumption does not hold, the bound involves
the terms [1 −yt/angbracketleftu,xt/angbracketright]+which measures how much the separability
with margin requirement is violated.
As a last remark we note that there can be cases in which there
exists some uthat makes zero errors on the sequence but the Per-
ceptron will make many errors. Indeed, this is a direct consequenceof the fact that Ldim( H)=∞. The way we sidestep this impossibility
result is by assuming more on the sequence of examples — the bound inTheorem 3.9 will be meaningful only if/summationtext
tft(u) is not excessively large.
3.3.2 Winnow
Winnow is an online classification algorithm originally proposed for
learning the class of kmonotone disjunctive Boolean functions. Namely,
X={0,1}dand a kmonotone disjunction hypothesis takes the form
x[i1]∨...∨x[ik], where {i1,...,i k}⊂[d]. This can be written as a half-
space as follows. Let w∈{0,1}dbe a vector with exactly kelements
that equal 1 (we call these elements the relevant variables). Then, /angbracketleftw,x/angbracketright
will be at least 1 if one of the relevant variables is turned on in x.
Otherwise, /angbracketleftw,x/angbracketrightis 0. So, sign( /angbracketleftw,x/angbracketright−1/2) behaves exactly like a k
monotone disjunction and our hypothesis class is:
H={x/mapsto→sign(/angbracketleftw,x/angbracketright−1/2) :w∈{0,1}d,/bardblw/bardbl1=k}.
In order to learn Hwe need to convexify the learning problem.
The first step is to convexify the domain of wby simply enlarging
it to be S=Rd
+. The second step is to construct a surrogate convex
loss function, similarly to the one we used for deriving the Perceptron.A weight vector werrs on ( x,y) if sign( /angbracketleftw,x/angbracketright−1/2)/negationslash=y, or equiva-
lently if y(2/angbracketleftw,x/angbracketright−1)≤0. Therefore, the original 0–1 loss function is
/lscript(w,(x,y)) = 1
[y(2/angbracketleftw,x/angbracketright−1)≤0].
3.3 Perceptron and Winnow 173
On rounds on which the algorithm errs, we define the hinge-loss
surrogate
ft(w)=[ 1 −yt(2/angbracketleftw,xt/angbracketright−1)]+.
If the algorithm does not err we set ft(w) = 0. This function satisfies:
•ftis convex.
•ftis a surrogate: ft(wt)≥/lscript(wt,(xt,yt)).
•In the realizable case, there exists u∈{0,1}dwith/bardblu/bardbl1=k
such that ft(u) = 0 for all t.
Before we derive the Winnow algorithm, we note that we can use
the Perceptron algorithm for learning this problem as follows. Denoteφ(x) to be the vector [2 x,−1], namely, we concatenate the constant
−1 to the vector 2 x. Then, the prediction can be performed according
to sign( /angbracketleftw,φ(x)/angbracketright) and the loss f
t(w) becomes the hinge-loss. In the
realizable case, this yields the mistake bound R2/bardblu/bardbl2
2=4 (d+1 )k.W e
shall see that the mistake bound of Winnow is 8 klog(d). That is, we
obtain an exponential improvement in terms of the dependence on thedimension.
Winnow is a specialization of the unnormalized-EG algorithm, given
in Section 2.8, to the aforementioned surrogate loss. We set the param-eterλof the unnormalized-EG algorithm to be 1 /d.
Winnow
parameter :η>0
initialize :w1=( 1/d,..., 1/d)
fort=1,2,...,T
receive xt
predict pt= sign(2 /angbracketleftwt,xt/angbracketright−1)
ifyt(2/angbracketleftwt,xt/angbracketright−1)≤0
∀i, wt+1[i]=wt[i]e−η2ytxt[i]
else
wt+1=wt
174 Online Classification
Theorem 3.10. Suppose that the Winnow algorithm runs with a
parameter η≤1/2 on a sequence ( x1,y1),...,(xT,yT), where xt∈
{0,1}dfor all t. Let Mbe the rounds on which Winnow errs and let
ft(w)=1[t∈M][1−yt(2/angbracketleftw,xt/angbracketright−1)]+. Then, for any u∈{0,1}dsuch
that/bardblu/bardbl1=kit holds that
|M| ≤T/summationdisplay
t=1ft(wt)≤1
1−2η/parenleftBiggT/summationdisplay
t=1ft(u)+klog(d)
η/parenrightBigg
.
In particular, if there exists such ufor which yt(2/angbracketleftu,xt/angbracketright−1)≥1 for
alltthen we can set η=1/4 and obtain
|M| ≤ 8klog(d).
Proof. LetMbe the set of rounds on which Winnow errs, i.e., M={t:
yt(2/angbracketleftwt,xt/angbracketright−1)≤0}. Winnow is derived from the unnormalized-EG
algorithm with
zt=/braceleftbigg2ytxtift∈M
0 ift/∈M
Using Theorem 2.23 (with λ=1/d)w eh a v e
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤1+/summationtext
iu[i]log(du[i]/e)
η+ηT/summationdisplay
t=1/summationdisplay
iwt[i]zt[i]2.
In our case, u∈{0,1}dand/bardblu/bardbl1=kso
1+/summationdisplay
iu[i]log(du[i]/e)≤1+klog(d/e)≤klog(d).
Plugging this in the above and using the fact that ztis a sub-gradient
offtatwtwe obtain:
T/summationdisplay
t=1(ft(wt)−ft(u))≤T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤klog(d)
η+ηT/summationdisplay
t=1/summationdisplay
iwt[i]zt[i]2.
(3.3)
3.4 Bibliographic Remarks 175
We next show that for all t,
/summationdisplay
iwt[i]zt[i]2≤2ft(wt). (3.4)
To do so, it is convenient to consider three cases:
•Ift/∈Mthenft(wt)=0a n d zt=0. Hence, Equation (3.4)
holds.
•Ift∈Mandyt= 1 then the left-hand side of Equation (3.4)
becomes 4 /angbracketleftwt,xt/angbracketright. This is because xt∈{0,1}dsoxt[i]2=
xt[i]. But since t∈Mwe also know that 2 /angbracketleftwt,xt/angbracketright≤1 and so/summationtext
iwt[i]zt[i]2≤2. On the other hand, by the surrogate prop-
erty of ftand the fact that t∈Mwe know that ft(wt)≥1,
which yields Equation (3.4).
•Ift∈M andyt=−1 then the left-hand side of Equa-
tion (3.4) becomes again 4 /angbracketleftwt,xt/angbracketright. However, now we have
thatft(wt)=2/angbracketleftwt,xt/angbracketright, which yields Equation (3.4).
Combining Equation (3.4) with Equation (3.3) and rearranging terms
we obtain
T/summationdisplay
t=1ft(wt)≤1
1−2η/parenleftBiggT/summationdisplay
t=1ft(u)+klog(d)
η/parenrightBigg
.
Combining the above with the surrogate property we conclude our
proof.
3.4 Bibliographic Remarks
The Weighted Majority algorithm is due to [32] and [43]. The StandardOptimal Algorithm was derived by the seminal work of Littlestone [29].A generalization to the nonrealizable case as well as other variants likemargin-based Littlestone’s dimension was derived in [7]. Characteriza-tions of online learnability beyond classification has been obtained in[1, 35].
The Perceptron dates back to Rosenblatt [37]. An analysis for the
realizable case (with margin assumptions) appears in [3, 33]. Freundand Schapire [17] presented an analysis for the unrealizable case with a
176 Online Classification
squared-hinge-loss based on a reduction to the realizable case. A direct
analysis for the unrealizable case with the hinge-loss was given byGentile [18]. Winnow was invented and analyzed in the realizable caseby Littlestone [29]. An analysis for the unrealizable case was carriedout in [5].
4
Limited Feedback (Bandits)
In Section 2 we studied the general framework of online convex opti-
mization and in particular, derived the family of online mirror descentalgorithms. To apply this algorithm, it is required to find a sub-gradientof the loss function at the end of each round. In this section we studyonline learning problems where the learner knows the value of the lossfunction at the predicted vector but he doesn’t know the value of theloss function at other points.
We first show that to apply the online mirror descent framework
it suffices to know how to calculate an estimate of the gradient. Wenext show how this observation leads to a low regret algorithm for afamous problem called “the multi-armed bandit problem.” This prob-lem is similar to prediction with expert advice but at the end of eachround the learner only observes the cost of the expert he picked anddoes not observe the costs of the rest of the experts.
Finally, we discuss the general problem of online convex optimiza-
tion without gradient information.
177
178 Limited Feedback (Bandits)
4.1 Online Mirror Descent with Estimated Gradients
Recall the Online Mirror Descent (OMD) algorithm we described in
Section 2. Now suppose that instead of setting ztto be a sub-gradient
offtatwt, we shall set ztto be a random vector with E[zt]∈∂ft(wt).
Online Mirror Descent with Estimated
Gradients
parameter: a link function g:Rd→S
initialize: θ1=0
fort=1,2,...
predict wt=g(θt)
pick ztat random such that E[zt|zt−1,...,z1]∈∂ft(wt)
update θt+1=θt−zt
The following theorem tells us how to extend previous regret bounds
we derived for OMD to the case of estimated sub-gradients.
Theorem 4.1. Suppose that the Online Mirror Descent with
Estimated Gradients is run on a sequence of loss functions, f1,...,f T.
Suppose that the estimated sub-gradients are chosen such that withprobability 1 we have
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤B(u)+T/summationdisplay
t=1/bardblzt/bardbl2
t,
where Bis some function and for all round tthe norm /bardbl·/bardbltmay depend
onwt. Then,
E/bracketleftBiggT/summationdisplay
t=1(ft(wt)−ft(u))/bracketrightBigg
≤B(u)+T/summationdisplay
t=1E[/bardblzt/bardbl2
t],
where expectation is with respect to the randomness in choosing
z1,...,zT.
Proof. Taking expectation of both sides of the first inequality with
respect to the randomness in choosing ztwe obtain that
E/bracketleftBiggT/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright/bracketrightBigg
≤B(u)+T/summationdisplay
t=1E[/bardblzt/bardbl2
t].
4.2 The Multi-armed Bandit Problem 179
At each round, let vt=E[zt|zt−1,...,z1]. By the law of total probability
we obtain that
E/bracketleftBiggT/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright/bracketrightBigg
=E/bracketleftBiggT/summationdisplay
t=1/angbracketleftwt−u,vt/angbracketright/bracketrightBigg
.
Since we assume that vt∈∂ft(wt) we know that
/angbracketleftwt−u,vt/angbracketright≥ft(wt)−ft(u).
Combining all the above we conclude our proof.
The above theorem tells us that as long as we can find z1,...,zTwhich
on one hand are unbiased estimators of sub-gradients and on the otherhand has bounded norms, we can still obtain a valid regret bound. Inthe next section we demonstrate how to construct such estimates for aspecific problem and in Section 4.3 we derive a more general approach.
4.2 The Multi-armed Bandit Problem
In the multi-armed bandit problem, there are darms, and on each
online round the learner should choose one of the arms, denoted pt,
where the chosen arm can be a random variable. Then, it receives a costof choosing this arm, y
t[pt]∈[0,1]. The vector yt∈[0,1]dassociates a
cost for each of the arms, but the learner only gets to see the costof the arm it pulls. Nothing is assumed about the sequence of vectorsy
1,y2,...,yT.
This problem is similar to prediction with expert advice. The only
difference is that the learner does not get to see the cost of expertshe didn’t choose. The goal of the learner is to have low regret for notalways pulling the best arm,
E/bracketleftBigg
T/summationdisplay
t=1yt[pt]/bracketrightBigg
−min
iT/summationdisplay
t=1yt[i],
where the expectation is over the learner’s own randomness.
This problem nicely captures the exploration–exploitation tradeoff.
On one hand, we would like to pull the arm which, based on previousrounds, we believe has the lowest cost. On the other hand, maybe it isbetter to explore the arms and find another arm with a smaller cost.
180 Limited Feedback (Bandits)
To approach the multi-armed bandit problem we use the OMD with
estimated gradients method derived in the previous section. As in theWeighted Majority algorithm for prediction with expert advice, we letSbe the probability simplex and the loss functions be f
t(w)=/angbracketleftw,yt/angbracketright.
The learner picks an arm according to P[pt=i]=wt[i] and therefore
ft(wt) is the expected cost of the chosen arm. The gradient of the loss
function is yt. However, we do not know the value of all elements of yt,
we only get to see the value yt[pt]. To estimate the gradient, we define
the random vector ztas follows:
zt[j]=/braceleftbiggyt[j]/wt[j]i fj=pt
0 else.
To emphasize the dependence of ztonptwe will sometimes use the
notation z(pt)
t. We indeed have that z(pt)
tis an unbiased estimate of the
gradient because
E[z(pt)
t[j]|zt−1,...,z1]=d/summationdisplay
i=1P[pt=i]z(i)
t[j]=wt[j]yt[j]
wt[j]=yt[j].
We update wtusing the update rule of the normalized EG algorithm.
The resulting algorithm is given below.
Multi-Armed Bandit Algorithm
parameter: η∈(0,1)
initialize :w1=( 1/d,..., 1/d)
fort=1,2,...
choose pt∼wtand pull the pt’th arm
receive cost of the arm yt[pt]∈[0,1]
update
˜w[pt]=wt[pt]e−ηyt[pt]/wt[pt]
fori/negationslash=pt,˜w[i]=wt[i]
∀i, wt+1[i]=˜w[i]/summationtext
j˜w[j]
To analyze the algorithm we combining Theorem 4.1 with Theo-
rem 2.22. The conditions of Theorem 2.22 hold here because ztis a
4.2 The Multi-armed Bandit Problem 181
non-negative vector. We therefore obtain that
T/summationdisplay
t=1/angbracketleftwt−u,zt/angbracketright≤log(d)
η+ηT/summationdisplay
t=1/summationdisplay
iwt[i]zt[i]2.
So Theorem 4.1 gives us that
E/bracketleftBiggT/summationdisplay
t=1(ft(wt)−ft(u))/bracketrightBigg
≤log(d)
η+ηT/summationdisplay
t=1E/bracketleftBigg/summationdisplay
iwt[i]zt[i]2/bracketrightBigg
.
The last term can be bounded as follows:
E/bracketleftBigg/summationdisplay
iwt[i]z(pt)
t[i]2|zt−1,...,z1/bracketrightBigg
=/summationdisplay
jP[pt=j]/summationdisplay
iwt[i]z(j)
t[i]2
=/summationdisplay
jwt[j]wt[j](yt[j]/wt[j])2
=/summationdisplay
jyt[j]2≤d.
Overall, we have obtained the following:
Corollary 4.2. The multi-armed bandit algorithm enjoys the bound
E/bracketleftBiggT/summationdisplay
t=1yt[pt]/bracketrightBigg
≤min
iT/summationdisplay
t=1yt[i]+logd
η+ηdT.
In particular, setting η=/radicalbig
log(d)/(dT) we obtain the regret bound of
2/radicalbig
dlog(d)T.
Comparing the above bound to the bound we derived for the
Weighted Majority algorithm we observe an additional factor of d,
which intuitively stems from the fact that here we only receive 1 /d
of the feedback the Weighted Majority algorithm receives. It is possi-ble to rigorously show that the dependence on dis unavoidable and
that the bound we derived is essentially tight.
182 Limited Feedback (Bandits)
4.3 Gradient Descent Without a Gradient
In this section we consider the general online convex optimization
problem, where we only have a black-box access to the loss func-tions, and thus cannot calculate sub-gradients directly. The multi-armed bandit problem discussed in the previous section was a specialcase, where the loss function was linear. However, in the multi-armedbandit problem we had the additional constraint that we can only askthe value of the loss function at singletons vectors. Here we allow thelearner to predict any vector
1but he only receives the evaluation of the
loss function on the vector he picked.
In Section 2 we derived several gradient-based algorithms for online
convex optimization. How can we utilize these algorithms when we canonly receive the evaluation of the loss function on the predicted vector?As in the multi-armed bandit problem, the main idea is to derive aone-shot estimate to the gradient. Below we present a method due toFlaxman, Kalai, and McMahan [16], which derives a one-shot estimateto the gradient.
4.3.1 A One-Shot Gradient Estimate
LetU
bbe the uniform distribution over the unit Euclidean ball and let
Uspbe the uniform distribution over the unit Euclidean sphere. Given
δ>0 we define a smoothed version of fas follows:
ˆf(w)= E
v∼Ub[f(w+δv)]. (4.1)
As we will show below, the advantage of ˆfis that it is differentiable
and we can estimate its gradient using a single oracle call to f. But,
before that, we show that ˆfis similar to f.
Lemma 4.3. Letfbe an L-Lipschitz function and let ˆfbe as defined
in Equation (4.1). Then, |ˆf(w)−f(w)|≤Lδ.
1We make another simplification, for the sake of simplicity, that the learner does not have
to predict an element from S. In some applications, like the multi-armed bandit problem,
the learner must predict an element from Sand then a more careful analysis is required.
See for example [16].
4.3 Gradient Descent Without a Gradient 183
Proof. By the Lipschitzness, |f(w)−f(w+δv)|≤Lδ/bardblv/bardbl. Using the
fact that /bardblv/bardbl≤1 we obtain the desired result.
We next show that the gradient of ˆfcan be estimated using a single
oracle call to f.
Lemma 4.4. The function ˆfis differentiable and we have
E
v∼Usp/bracketleftbiggd
δf(w+δv)v/bracketrightbigg
=∇ˆf(w).
Proof. We prove the theorem for the case d= 1. Given a 1-dimensional
function f, letFbe the antiderivative of f, namely, F/prime(w)=f(w). By
the fundmental theorem of calculus we have
/integraldisplayb
af(w)dw=F(b)−F(a).
It follows that
/integraldisplayδ
−δf(w+t)dt=F(w+δ)−F(w−δ).
Note that in the 1-dimensional case we have that vis distributed
uniformly over [ −1,1] and
ˆf(w)= E[f(w+δv)] =/integraltextδ
−δf(w+t)dt
2δ=F(w+δ)−F(w−δ)
2δ.
It follows that
ˆf/prime(w)=f(w+δ)−f(w−δ)
2δ=Ev∼Usp[f(w+δv)v]
δ.
This concludes the proof for the case d= 1. The proof for d>1 follows
similarly using Stoke’s theorem and can be found in [16].
4.3.2 The Resulting Algorithm
The algorithm is based on gradient descent with lazy pro-
jections , we described in Section 2.6.
184 Limited Feedback (Bandits)
Bandit Online Gradient Descent
parameters: η,δ > 0 and a convex set S⊂Rd
initialize: θ1=0
fort=1,2,...,T
letwt= argminw∈S/bardblw−ηθt/bardbl2
pick vt∼Usp
predict wt+δvtand receive ft(wt+δvt)
setzt=d
δft(wt+δvt)vt
update θt+1=θt−zt
Let us now analyze the regret of this algorithm. First, applying
Corollary 2.17 we obtain that for all u∈S,
/summationdisplay
t/angbracketleftzt,wt−u/angbracketright≤1
2η/bardblu/bardbl2
2+ηT/summationdisplay
t=1/bardblzt/bardbl2.
Taking expectation, using Lemma 4.4, and using the fact that vtis in
the unit sphere, we obtain
E/bracketleftBigg/summationdisplay
t(ˆft(wt)−ˆft(u))/bracketrightBigg
≤1
2η/bardblu/bardbl2
2+ηT/summationdisplay
t=1d2
δ2E[ft(wt+δvt)2].(4.2)
LetB= max u∈S/bardblu/bardblandF= max u∈S,tft(u). Then, by the Lipschitz-
ness of ftwe have ft(wt+δvt)≤ft(wt)+Lδ/bardblvt/bardbl≤F+Lδ. Combin-
ing with Equation (4.2) yields
E/bracketleftBigg/summationdisplay
t(ˆft(wt)−ˆft(u))/bracketrightBigg
≤B2
2η+ηTd2(F/δ+L)2. (4.3)
To derive a concrete bound out of the above we need to relate the
regret with respect to ˆftto the regret with respect to ft. We do this
using Lemma 4.3, which implies
ft(wt+δvt)−ft(u)≤ft(wt)−ft(u)+Lδ≤ˆft(wt)−ˆft(u)+3Lδ.
Combining the above with Equation (4.3) yields
Corollary 4.5. Consider running the Bandit Online Convex
Optimization algorithm on a sequence f1,...,f TofL-Lipschitz
4.4 Bibliographic Remarks 185
functions. Let Sbe a convex set and define B= max u∈S/bardblu/bardbland
F= max u∈S,t∈[T]ft(u). Then, for all u∈Swe have
E/bracketleftBigg/summationdisplay
t(ft(wt+δvt)−ft(u))/bracketrightBigg
≤3LδT+B2
2η+ηTd2(F/δ+L)2.
In particular, setting η=B
d(F/δ+L)√
2T,δ=/radicalBig
BdF
3LT−1/4we obtain that
the regret is bounded by O(√
BdFLT3/4).
Comparing this bound to the full information bound given in Corol-
lary 2.17, we note two main difference. First, the dependence on Tis
T3/4as opposed to T1/2in the full information case. Second, the regret
depends on the dimensionality. While the dependence on the dimen-sionality is indeed tight, it is not known if the worse dependence on T
is tight.
4.4 Bibliographic Remarks
Multi-armed bandit problems were originally studied in a stochasticsetting [36]. The adversarial multi-armed bandit problem was studiedin [4].
The algorithm we described for bandit online convex optimization
is a variant of the algorithm given in [16]. Better algorithms have beenderived for the specific case of linear functions. In particular, [15] gave
a non efficient algorithm whose regret is O(poly( d)√
T), and later on,
[2] derived an efficient algorithm with a similar regret bound usingself-concordant regularizers.
5
Online-to-Batch Conversions
In this section we discuss conversions from online learning to stochas-
tic learning. In particular, we consider the following general model ofstochastic learning.
Definition 5.1.(Vapnik’s General Setting of Learning) LetSbe
a hypothesis class and let Ψ be an example domain set. There is a lossfunction, c:S×Ψ→R, which gets a hypothesis and an example and
returns the cost of using the hypothesis on the example. Let Qbe an
unknown distribution over Ψ and define
1C(w)= Eψ∼Q[c(w,ψ)]. The
goal of the learner is to approximately minimize CoverS. The learner
does not know Q, but can get independent samples from Q. We denote
byA(ψ1,...,ψ T) the output of the learning algorithm when receiving
Tsamples from Q. We say that a learning algorithm /epsilon1-learns Susing T
1Technically, in the above definition, for every w∈S, we view the function c(w,·):Ψ→R+
as a random variable, and define C(w) to be the expected value of this random variable.
For that, we need to require that the function c(w,·) is measurable. Formally, we assume
that there is a σ-algebra of subsets of Ψ, over which the probability Qis defined, and that
the pre-image of every initial segment in R+is in this σ-algebra.
186
187
examples if
E[C(A(ψ1,...,ψ T))]≤min
w∈SC(w)+/epsilon1,
where expectation2is over the random choice of ψ1,...,ψ T.
This model is also closely related to the problem of Stochastic Opti-
mization or more specifically Stochastic Approximation (for moredetails see for example [41]).
Maybe the most simple algorithm for solving a stochastic learning
problem is by sampling Texamples, ψ
1,...,ψ T, and then returning a
hypothesis which minimizes the average cost over these examples. Thisis called empirical risk minimization (ERM):
ERM
S(ψ1,...,ψ T)∈argmin
w∈S1
TT/summationdisplay
t=1c(w,ψt).
Our goal is to demonstrate how online learning can sometimes yield an
alternative algorithm for solving stochastic learning problems.
The basic idea is as follows. First, we run the online learner on
a sequence of loss functions, where ft(w)=c(w,ψt). This produces a
sequence of predictions w1,...,wT. Second, we produce a single vector
¯wbased on w1,...,wT. There are many ways to produce ¯wand here
we consider two simple approaches: averaging or randomization. Thisyields the following skeleton.
Online-To-Batch Conversion
parameters: a set S; a cost function c(·,·);
an online learning algorithm A
input: ψ1,...,ψ Tare independently sampled from distribution Qover Ψ
fort=1,...,T
letwtbe the prediction of A
provide the loss function ft(w)=c(w,ψt)t oA
output: produce ¯wfrom w1,..., wT. For example:
averaging: ¯w=1
T/summationtextT
t=1wt
randomization: ¯w=wr,
where ris chosen uniformly at random from [ T]
2It is common to require that the inequality will hold with high probability. By a simple
amplification argument it is possible to convert a guarantee on the expected value to aguarantee that holds with high probability. Therefore, for the sake of simplicity, we onlyrequire success in expectation.
188 Online-to-Batch Conversions
The following theorem shows that the average online loss of the
online learner upper bounds the cost of ¯w.
Theorem 5.1. Letψ1,...,ψ Tbe a sequence of independent random
variables, each of which is distributed according to a distribution Q
over Ψ. For the online-to-batch conversion with randomiza-
tion, we have that
E[C(¯w)] = E/bracketleftBigg
1
TT/summationdisplay
t=1ft(wt)/bracketrightBigg
,
where expectation is with respect to the random choice of ψ1,...,ψ T
andr. If we further assume that Cis a convex function, then for
online-to-batch conversion with averaging we have that
E[C(¯w)]≤E/bracketleftBigg
1
TT/summationdisplay
t=1ft(wt)/bracketrightBigg
.
Proof. We first show that
E/bracketleftBigg
1
TT/summationdisplay
t=1C(wt)/bracketrightBigg
=E/bracketleftBigg
1
TT/summationdisplay
t=1c(wt,ψt)/bracketrightBigg
. (5.1)
Using the linearity of expectation we have,
E/bracketleftBigg
1
TT/summationdisplay
t=1c(wt,ψt)/bracketrightBigg
=1
TT/summationdisplay
t=1E[c(wt,ψt)]. (5.2)
Recall that the law of total expectation implies that for any two random
variables R1,R2, and a function f,ER1[f(R1)] = ER2ER1[f(R1)|R2].
Since wtonly depends on ψ1,...,ψ t−1, we can set R1=ψ1,...,ψ tand
R2=ψ1,...,ψ t−1to get that
E[c(wt,ψt)] = E[C(wt)].
Combining the above with Equation (5.2) yields Equation (5.1). Now,
for the randomization technique we have that C(¯w)= Er[C(wr)] =
1
T/summationtextT
t=1C(wt), which concludes our proof for the case of the
189
randomization technique. For the averaging technique, since we assume
thatCis convex we can apply Jensen’s inequality to get that
C(¯w)=C/parenleftBigg
1
TT/summationdisplay
t=1wt/parenrightBigg
≤1
TT/summationdisplay
t=1C(wt).
Clearly, E[1
T/summationtextT
t=1c(u,ψt)] =C(u). Therefore,
Corollary 5.2. Assume that the conditions of Theorem 5.1 hold and
letube any vector, then
E[C(¯w)]−C(u)≤E/bracketleftBigg
1
TT/summationdisplay
t=1(ft(wt)−ft(u))/bracketrightBigg
.
The right-hand side is the expected regret of the online algorithm
(divided by T). Therefore, if we have an online learning algorithm that
is guaranteed to have a low regret with respect to functions of the formf(w)=c(w,ψ) relative to a set S, we can be assured that the cost of
¯wis close to the optimal cost.
To demonstrate the usage of this approach, we describe the appli-
cability of online mirror descent to stochastic learning of problems inwhich cis convex with respect to its first argument.
Stochastic Online Mirror Descent
parameters: a link function g:Rd→S; number of rounds T
input: sampler from distribution Qover Ψ; cost function c(·,·)
initialize: θ1=0
fort=1,...,T
predict wt=g(θt)
pickψt∼Qand let ft(w)=c(w,ψt)
letzt∈∂ft(wt)
update θt+1=θt−zt
output: ¯w=1
T/summationtextT
t=1wt
190 Online-to-Batch Conversions
5.1 Bibliographic Remarks
Littlestone [30] initiated the study of online to batch conversions.
Freund and Schapire [17] demonstrated that using the Perceptron algo-rithm along with the voting online-to-batch technique [23] yields anefficient replacement for Support Vector Machines [14, 38, 42]. Concen-tration bounds on the risk of the ensemble that rely on the online losswere derived by Zhang [45] and Cesa-Bianchi et al. [10, 11].
Acknowledgments
The author would like to thank the anonymous reviewers for their
helpful comments.
191
References
[1] J. Abernethy, P. L. Bartlett, A. Rakhlin, and A. Tewari, “Optimal strategies
and minimax lower bounds for online convex games,” in Procee dings of the
Annual Conference on Computational Learning Theory , 2008.
[2] J. Abernethy, E. Hazan, and A. Rakhlin, “Competing in the dark: An effi-
cient algorithm for bandit linear optimization,” in Procee dings of the Annual
Conference on Learning Theory (COLT) , no. 3, 2008.
[3] S. Agmon, “The relaxation method for linear inequalities,” Canadian Journal
of Mathematics , vol. 6, no. 3, pp. 382–392, 1954.
[4] P. Auer, N. Cesa-Bianchi, Y. Freund, and R. E. Schapire, “The nonstochastic
multiarmed bandit problem,” SICOMP: SIAM Journal on Computing , vol. 32,
no. 1, pp. 48–77, 2003.
[5] P. Auer and M. Warmuth, “Tracking the best disjunction,” Machine Learning ,
vol. 32, no. 2, pp. 127–150, 1998.
[6] K. Azoury and M. Warmuth, “Relative loss bounds for on-line density estima-
tion with the exponential family of distributions,” Machine Learning , vol. 43,
no. 3, pp. 211–246, 2001.
[7] S. Ben-David, D. Pal, and S. Shalev-Shwartz, “Agnostic online learning,” in
Procee dings of the Annual Conference on Learning Theory (COLT) , 2009.
[8] A. Blum, “On-line algorithms in machine learning,” Online Algorithms ,
pp. 306–325, 1998.
[9] J. Borwein and A. Lewis, Convex Analysis and Nonlinear Optimization .
Springer, 2006.
[10] N. Cesa-Bianchi, A. Conconi, and C. Gentile, “On the generalization ability
of on-line learning algorithms,” IEEE Transactions on Information Theory ,
vol. 50, no. 9, pp. 2050–2057, 2004.
192
References 193
[11] N. Cesa-Bianchi and C. Gentile, “Improved risk tail bounds for on-line algo-
rithms,” Neural Information P roceesing Systems (NIPS) , 2006.
[12] N. Cesa-Bianchi and G. Lugosi, Prediction, Learning, and Games . Cambridge
University Press, 2006.
[13] T. M. Cover, “Behavior of sequential predictors of binary sequences,” in Trans-
actions on Prague Conference on Information Theory Statistical Decision Func-tions, Random P rocesses , pp. 263–272, 1965.
[14] N. Cristianini and J. Shawe-Taylor, An Introduction to Support Vector
Machines . Cambridge University Press, 2000.
[15] V. Dani, T. Hayes, and S. M. Kakade, “The price of bandit information
for online optimization,” Advances in Neural Information P rocessing Systems ,
vol. 20, pp. 345–352, 2008.
[16] A. D. Flaxman, A. T. Kalai, and H. B. McMahan, “Online convex optimization
in the bandit setting: Gradient descent without a gradient,” in Procee dings of
the Annual ACM-SIAM Symposium on Discrete Algorithms , Society for Indus-
trial and Applied Mathematics, pp. 385–394, 2005.
[17] Y. Freund and R. E. Schapire, “Large margin classification using the perceptron
algorithm,” Machine Learning , vol. 37, no. 3, pp. 277–296, 1999.
[18] C. Gentile, “The robustness of the p-norm algorithms,” Machine Learning ,
vol. 53, no. 3, pp. 265–299, 2003.
[19] C. Gentile and N. Littlestone, “The robustness of the p-norm algorithms,” in
Procee dings of the Annual Conference on Learning Theory (COLT) , 1999.
[20] G. Gordon, “Regret bounds for prediction problems,” in Procee dings of the
Annual Conference on Learning Theory (COLT) , 1999.
[21] A. J. Grove, N. Littlestone, and D. Schuurmans, “General convergence results
for linear discriminant updates,” Machine Learning , vol. 43, no. 3, pp. 173–210,
2001.
[22] E. Hazan, The Convex Optimization Approach to Regret Minimization . 2009.
[23] D. P. Helmbold and M. Warmuth, “On weak learning,” Journal of Computer
and System Sciences , vol. 50, pp. 551–573, 1995.
[24] S. Kakade, S. Shalev-Shwartz, and A. Tewari, “Regularization techniques for
learning with matrices,” Journal of Machine Learning Research , 2012 (To
appear).
[25] A. Kalai and S. Vempala, “Efficient algorithms for online decision problems,”
Journal of Computer and System Sciences , vol. 71, no. 3, pp. 291–307, 2005.
[26] J. Kivinen and M. Warmuth, “Exponentiated gradient versus gradient descent
for linear predictors,” Information and Computation , vol. 132, no. 1, pp. 1–64,
1997.
[27] J. Kivinen and M. K. Warmuth, “Additive versus exponentiated gradient
updates for linear prediction,” Symposium on Theory of Computing (STOC ),
See also Technical Report UCSC-CRL-94-16, University of California, SantaCruz, Computer Research Laboratory, pp. 209–218, 1995.
[28] J. Kivinen and M. Warmuth, “Relative loss bounds for multidimensional regres-
sion problems,” Machine Learning , vol. 45, no. 3, pp. 301–329, 2001.
[29] N. Littlestone, “Learning quickly when irrelevant attributes abound: A new
linear-threshold algorithm,” Machine Learning , vol. 2, pp. 285–318, 1988.
194 References
[30] N. Littlestone, “From on-line to batch learning,” in Procee dings of the Annual
Conference on Learning Theory (COLT) , pp. 269–284, July 1989.
[31] N. Littlestone, “Mistake bounds and logarithmic linear-threshold learning algo-
rithms,” Ph.D. Thesis, University of California at Santa Cruz, 1990.
[32] N. Littlestone and M. K. Warmuth, “The weighted majority algorithm,” Infor-
mation and Computation , vol. 108, pp. 212–261, 1994.
[33] M. Minsky and S. Papert, Perceptrons: An Introduction to Computational
Geometry . The MIT Press, 1969.
[34] A. Rakhlin, Lecture Notes on Online Learning . draft, 2009.
[35] A. Rakhlin, K. Sridharan, and A. Tewari, “Online learning: Random averages,
combinatorial parameters, and learnability,” in Neural Information P rocessing
Systems (NIPS) , 2010.
[36] H. Robbins, “Some aspects of the sequential design of experiments,” Bulletin
American Mathematical Society , vol. 55, pp. 527–535, 1952.
[37] F. Rosenblatt, “The perceptron: A probabilistic model for information storage
and organization in the brain,” Psychological Review , vol. 65, pp. 386–407, 1958.
(Reprinted in Neurocomputing , (MIT Press, 1988)).
[38] B. Sch¨ olkopf and A. J. Smola, Learning with Kernels: Support Vector Machines,
Regularization, Optimization and Beyond . MIT Press, 2002.
[39] S. Shalev-Shwartz, “Online learning: Theory, algorithms, and applications,”
Ph.D. Thesis, The Hebrew University, 2007.
[40] S. Shalev-Shwartz and Y. Singer, “A primal-dual perspective of online learning
algorithms,” Machine Learning Journal , vol. 69, no. 2, pp. 115–142, 2007.
[41] J. C. Spall, Introduction to Stochastic Search and Optimization: Estimation,
Simulation, and Control , vol. 64. LibreDigital, 2003.
[42] V. N. Vapnik, Statistical Learning Theory . Wiley, 1998.
[43] Volodimir G. Vovk, “Aggregating Strategies,” in Procee dings of the Annual
Conference on Learning Theory (COLT) , pp. 371–383, 1990.
[44] C. Zalinescu, Convex Analysis in General Vector Spaces . River Edge, NJ: World
Scientific Publishing Co. Inc., 2002.
[45] T. Zhang, “Data dependent concentration bounds for sequential prediction
algorithms,” in Procee dings of the Annual Conference on Learning Theory
(COLT) , pp. 173–187, 2005.
[46] M. Zinkevich, “Online convex programming and generalized infinitesimal
gradient ascent,” in International Conference on Machine Learning , 2003. |
8cd0cc0c-21bb-4846-a75b-4692d7291d5b | trentmkelly/LessWrong-43k | LessWrong | As Few As Possible
All of economics, every last bit of it, is about scarcity. About what is scarce and what is not, and about who does and who doesn’t get their needs (and sometimes wants) satisfied.
Much of the debate about healthcare is in fact a scarcity problem. There aren’t enough practitioners in practice to handle every patient, so some people don’t get doctors. It’s a combination of self-selection where people who can’t afford to take time off to have an ingrown toenail treated professionally hack at it with a pocketknife instead, and insurance selection where granny’s insurance will pay for hospice but not a new hip, and actual medical discretion now and then.
But this is about what medical care does right. Triage.
In times of very acute scarcity when many people are injured and need medical attention to survive, but few doctors are available to treat them, medicine does triage. The details can be complex, but one of the features of triage is that if doctors are too scarce to save everyone, they prioritize saving *as many people as possible*, even though that often means giving specific people no treatment at all. The scarcity is distributed so that *as few people as possible* suffer from scarcity.
This is not about mass trauma triage.
Imagine for a moment how utterly absurd it would be if there was an earthquake, but there were enough doctors to simultaneously treat everyone injured in it, but they insisted on following triage protocols and the very worst injured were given black tags indicating “do not treat”, even as surgeons who could save them sat idle, because everyone else was being treated. No civilized person would defend that kind of thing.
But this is not about hypothetical earthquakes with plenty of doctors.
The world produces significantly more food than needed to feed everyone. Quite a few people actually are angry that much of it is destroyed even though many people starve for lack of food. Many agree that is unacceptable that, even though there is enoug |
48471c60-fb66-4306-b046-f396fd3fbf91 | trentmkelly/LessWrong-43k | LessWrong | Alzheimer's, Huntington's and Mitochondria Part 1: Turnover Rates
Epistemic status: Big if true, I don't have much time now but I might try and write part of this up into a more formal scientific letter to a journal or something later. I am reasonably confident that my models here are significant in some way but I do not have much experience in the field and I've written this up over the past weekend instead of revising for my exams.
Introduction
It is sometimes said (often here, rarely in the places where it ought to be) that the turnover rate of amyloid-causing proteins in the brain is too high for them to be the primary causative agent of Alzheimer's disease (AD). While this is an important piece of evidence, I do not think it is as definitive as many suggest, due to biochemical reasons I will go into later. In order to investigate further I decided to compare AD to a better understood disease: Huntington's disease, and found an unexpected link in mechanism between the two. I have decided to write my findings up here.
This series of three posts will be rather scattered. This post aims to explain the motivations for my initial investigation, and also goes into some of the mathematics of amyloid formation. The next post will be a quick review of several pieces of evidence I have found and the assembly of this evidence into a (reasonably) cohesive model of AD progression. The third will be some predictions of mine based on this model, and a retrospective on the process of building this model.
Why turnover rates might not matter
The motivation for this investigation was to cement whether or not the high turnover rate of amyloid-causing proteins is strong evidence against them being causally involved in AD. The two amyloid-causing proteins are Tau and Amyloid Beta (Aβ). Tau forms aggregates inside neurons and turns over with a half-life of around 23 days in the central nervous system.(1) Aβ forms aggregates outside neurons and turns over even faster, with a half-life on the order of a few hours.(2)
There are some reasons why I |
cd702a1b-16ef-419a-a807-850e4b174975 | trentmkelly/LessWrong-43k | LessWrong | Preference utilitarian measure of historical welfare
GDP measures essentially how good we are at making widgets - and while widgets are useful, it is a very weak and indirect measure of welfare. For example UK GDP per capita doubled between 1975 and 2007 - and people's quality of life indeed improved - but it would be extremely difficult to argue that this improvement was "doubling", and that the gap between 2007's and 1975's quality of life is greater than between 1975's and hunter-gatherer times.
It's not essential to this post, but my very quick theory is that we overestimate GDP thanks to economic equivalent of Amdahl's Law - if someone's optimal consumption mix consisted of 9 units of widgets and 1 unit of personalized services - and their purchasing power increased so now they can acquire 100x as many widgets, but still the same number of services as before - amount of the mix they can purchase increased only 9x, not 90x you'd get by weighted average of original consumption levels (and they spend 92% of their purchasing power on services now). The least scalable factor - whichever it is - will be the bottleneck.
If we're unhappy with GDP there are alternative measures like HDI, but they're highly artificial. It would be very easy to construct completely different measures which would "feel" about as right.
Fortunately there exists a very natural measure of welfare, which I haven't seen used before in this context - preference utilitarian lotteries. Would you rather live in 1700, or take a 50% chance of living in 2010 or 700? Make a list of such bets, assign numbers coherent with bet values (with 100 for highest and 0 for your lowest value) and you're done! By averaging many people's estimates we can hopefully reduce the noise, and get some pretty reasonable welfare estimates.
And now disclaimer time. This approach has countless problems, here are just a few but I'm sure you can think about more.
* Probabilities are difficult - People are really bad at intuiting about a difference between 1% chance of somet |
63aafb4d-c837-4803-a99b-b02e1b6058de | StampyAI/alignment-research-dataset/blogs | Blogs | Argument for AI x-risk from large impacts
*Last updated Sep 29 2021*
*This page is incomplete, under active work and may be updated soon.*
The **argument for AI x-risk from large impacts** an argument supporting the claim that advanced artificial intelligence poses an existential risk to humanity.
Details
-------
### Argument
We understand the argument as follows:
1. The creation of advanced AI is likely to have a large impact on the world at the time, relative to other developments.
2. The creation of advanced AI is more likely to impact humanity’s long term trajectory than other developments (from 1)
3. Developments with large impacts on the future are more likely to be worth influencing, all things equal, than developments with smaller impacts
4. One main way things might not be equal is that some developments may be easier to influence than others, but AI currently looks tractable to influence.
5. The creation of advanced AI is especially likely to be worth trying to influence, among other developments
### Counterarguments
This is a neither exhaustive nor exclusive list of counterarguments and complications that we know of:
1. This is a heuristic argument that isn’t strictly true, and it isn’t clear how true it is.
2. It isn’t clear what a development is. For instance, is global agriculture surviving for another year a development? Is ‘modern science’ a development? Why think of advanced AI as a development, rather than thinking of a particular algorithmic tweak as a development? If we lump more things together, the developments are bigger, so it isn’t clear what it means to say that one is especially big.
3. It isn’t clear what counterfactuals are being used. Is the claim that AI will have a large impact relative to a world without any AI? To a world that is similar to the current world forever? Why is the difference between AI and either of those (highly unlikely) scenarios relevant to the value of influencing the development and deployment of AI?
4. The heuristic connection between the scale of an action’s possible impact and the stakes of influencing it seems perhaps more useful for ruling out fundamentally unworthy issues than comparing minor impacts on very large issues. For instance, one can use it to confidently tell that it isn’t worth spending half an hour deciding which flavor of jam to buy, whereas it seems much worse for comparing ‘working on functional institutions’ to ‘working on AI’, where both are vaguely ‘big’ and your impact is likely to be ‘tiny’.
5. How easy different ‘developments’ are to influence is as big an issue as how much is at stake in influencing them, so is better treated quantitatively, not as a possible qualitative defeater.
6. It isn’t clear that ‘influencing developments’ is a good way of viewing possibly high-value actions. For instance, it excludes many actions that are not in response to the actions of others.
### Discussion elsewhere
We have seen discussion of this in the following places. The name is from Ngo.
* *Ngo, Richard. “Thinking Complete: Disentangling Arguments for the Importance of AI Safety.” Thinking Complete (blog), January 21, 2019. <http://thinkingcomplete.blogspot.com/2019/01/disentangling-arguments-for-importance.html>.*
* *80,000 Hours. “How Sure Are We about This AI Stuff?” Accessed September 16, 2020. <https://80000hours.org/podcast/episodes/ben-garfinkel-classic-ai-risk-arguments/>.*
Richard Ngo describes this as follows[1](https://aiimpacts.org/argument-from-large-impacts/#easy-footnote-bottom-1-2661 "Ngo, Richard. “Thinking Complete: Disentangling Arguments for the Importance of AI Safety.” <em>Thinking Complete</em> (blog), January 21, 2019. <a href=\"http://thinkingcomplete.blogspot.com/2019/01/disentangling-arguments-for-importance.html\">http://thinkingcomplete.blogspot.com/2019/01/disentangling-arguments-for-importance.html</a>. <br>"):
1. *Argument from large impacts*. Even if we’re very uncertain about what AGI development and deployment will look like, it seems likely that AGI will have a very large impact on the world in general, and that further investigation into how to direct that impact could prove very valuable.
1. Weak version: development of AGI will be at least as big an economic jump as the industrial revolution, and therefore affect the trajectory of the long-term future. See [Ben Garfinkel’s talk at EA Global London 2018](https://forum.effectivealtruism.org/posts/9sBAW3qKppnoG3QPq/ben-garfinkel-how-sure-are-we-about-this-ai-stuff). Ben noted that to consider work on AI safety important, we also need to believe the additional claim that there are feasible ways to positively influence the long-term effects of AI development – something which may not have been true for the industrial revolution. (Personally my guess is that since AI development will happen more quickly than the industrial revolution, power will be more concentrated during the transition period, and so influencing its long-term effects will be more tractable.)
2. Strong version: development of AGI will make humans the second most intelligent species on the planet. Given that it was our intelligence which allowed us to control the world to the large extent that we do, we should expect that entities which are much more intelligent than us will end up controlling our future, unless there are reliable and feasible ways to prevent it. So far we have not discovered any.
(We treat 2 as a separate argument, ‘*[Argument from most intelligent species](https://aiimpacts.org/argument-from-most-intelligent-species/)*‘.)
Notes
----- |
2b1905bc-02bc-44f2-8e82-4b18574ca9e1 | trentmkelly/LessWrong-43k | LessWrong | Probability as Minimal Map
What’s the difference between a map and the raw data used to generate that map?
Suppose, for example, that google sends a bunch of cars out driving around New York City, snapping photos every few feet, then uses the photos to reconstruct a streetmap. In an informational sense, what’s the difference between the giant database full of photos and the streetmap?
Obvious answer: the map throws away a huge amount of information which we don’t care about, at least for the map’s use-case.
Let’s try to formalize this intuition a little. We want the ability to run queries against the map - e.g. things like “How far apart are Times Square and the Met?” or questions about street network topology. Let’s call the whole class of queries we want to support Q. We also have some input data X - e.g. the database full of images from the streets of NYC. The goal of the map-synthesizing process is to throw out as much information as possible from X, while still keeping any and all information relevant to queries in Q.
Natural next question: given the query class Q and some data-generating process, can we characterize “optimal” map-making processes which maximize the amount of information “thrown out” (measured in an information-theoretic sense) while still keeping all information relevant to Q?
For the very simplest query classes, we can answer this question quite neatly.
Suppose that our query class contains only a single query q, and the query is a true/false question. For instance, maybe the only query we care about at all is q = “Is the distance between Times Square and the Met greater than one mile?”, and we want to throw out as much information as possible without losing any info relevant to the query.
Claim: any solution to this problem is isomorphic to the probability P[q|X]. In other words, P[q|X] is itself a minimal “lossless” map (where by “lossless” we mean it does not throw out any info from X relevant to the query, not that it perfectly predicts q), and any other min |
9a18d369-3eea-4a57-8a6c-108e23717fa2 | trentmkelly/LessWrong-43k | LessWrong |
How to parent more predictably
(As with anything else I write about parenting, this is mostly just my observations with my own two kids and may not generalize as well as I think it does.)
A few weeks ago I wrote about why I think it's valuable for parents to be predictable. I was mostly describing an end state, though, and reasons why it's a good place to be, but what should you do if you're interested in being more consistent?
I think it breaks down into three pretty different skills. The first is only saying things you're comfortable fully standing behind. Many people especially when irritable, sleep deprived, or surprised, can quickly spit out a consequence that is harsher than is fair. Things like, "if you don't stop this minute it's no desserts for a week!" Then when the threat fails the consequence feels too extreme, and they don't follow through. If someone read my earlier post and decided they needed to stand by their quickly distributed threats I'd be pretty sad, and not expect this to make things better. Instead, any consequences need to be reasonable and proportionate, where you feel fair when you do have to enforce them (which, ideally, is rarely).
One thing that can be helpful is having a system of simple stock responses. The simplest is just a stern voice. If you reserve speaking firmly for rare circumstances, then saying something intensely and seriously can feel very significant.
Time outs can also work well: we use a system where we make it clear what needs to change ("stop shouting", "brush your teeth"), count to three, slowly and clearly, stopping if they do what we want, and if we get to three then it's time out. Serious things can be time out immediately. If you reliably use these, then not only does the kid understand how they work and what they mean but you don't have to come up with a novel appropriate response at a time when you're very stressed ("Do not bite me. That's time out.)
Even better, though, is avoiding commands and threats entirely. If they've been playing |
086ae9a0-92ea-44c9-abb8-6225bf48ea72 | trentmkelly/LessWrong-43k | LessWrong | A Sense That More Is Possible
To teach people about a topic you've labeled "rationality", it helps for them to be interested in "rationality". (There are less direct ways to teach people how to attain the map that reflects the territory, or optimize reality according to their values; but the explicit method is the course I tend to take.)
And when people explain why they're not interested in rationality, one of the most commonly proffered reasons tends to be like: "Oh, I've known a couple of rational people and they didn't seem any happier."
Who are they thinking of? Probably an Objectivist or some such. Maybe someone they know who's an ordinary scientist. Or an ordinary atheist.
That's really not a whole lot of rationality, as I have previously said.
Even if you limit yourself to people who can derive Bayes's Theorem—which is going to eliminate, what, 98% of the above personnel?—that's still not a whole lot of rationality. I mean, it's a pretty basic theorem.
Since the beginning I've had a sense that there ought to be some discipline of cognition, some art of thinking, the studying of which would make its students visibly more competent, more formidable: the equivalent of Taking a Level in Awesome.
But when I look around me in the real world, I don't see that. Sometimes I see a hint, an echo, of what I think should be possible, when I read the writings of folks like Robyn Dawes, Daniel Gilbert, Tooby & Cosmides. A few very rare and very senior researchers in psychological sciences, who visibly care a lot about rationality—to the point, I suspect, of making their colleagues feel uncomfortable, because it's not cool to care that much. I can see that they've found a rhythm, a unity that begins to pervade their arguments—
Yet even that... isn't really a whole lot of rationality either.
Even among those whose few who impress me with a hint of dawning formidability—I don't think that their mastery of rationality could compare to, say, John Conway's mastery of math. The base knowledge |
f20cb759-539c-4e31-84c0-6ad1b66a860c | trentmkelly/LessWrong-43k | LessWrong | Why are deaths not increasing with infections in the US?
According to COVID act now, cases are now up to 100k a day, from an average of 40k/day in early October. Two weeks ag case numbers were already up by 50%. Meanwhile the change in deaths has been modest, still around 10%. This would require a three week lag for deaths to be proportional to cases. What might be happening? |
8f3284b8-6071-4f7c-99c0-61899b54a83b | trentmkelly/LessWrong-43k | LessWrong | A noob goes to the SERI MATS presentations
I have been cooped up in suburbia trying to take a break. But not having a routine and being around peers made the days feel monotonous. I was procrastinating writing my Prospect reflection and operations guide, and ended up reading alignment papers and being confused about how to figure out what was important.
Then, I got an message to go to the end of the SERI MATS program presentations. I knew about the evening party beforehand, but now I decided to go since I was more willing to go all the way to Berkeley if it was an all day event. Plus, it would be nice to see the SERI MATS people again and what they did over the summer.
The day before, I did a time-money tradeoff calculation, and I decided I was going to wake up early to take the bus and BART instead of Uber since I'm hesitant to spend money.
Morning came, and I wanted to stay in bed a little longer since my sleep was disturbed. I knew it made sense to pay for the Uber, but I got stressed thinking back and forth. A friend family didn't have anything to do and said he could drive me, and I relented.
Many lane changes and highway exits later, I walked into the venue. There were less people than I expected and I took a seat on the left wing. I felt a little out of place during the first few presentations.
They were pretty technical with a bunch of concepts I didn't learn yet, and it seemed like they were changing this little particular thing to make some result different. During the first few presentations, I was trying to figure out why this thing they did was important, but as we got to later presentations, it got harder and harder to even figure out what was going on, so I decided to write questions to help me understand, but struggling at that too.
I was telling someone how I was taking notes and that I was reading alignment papers at home, and he said he was going to try to solve the problems from scratch without reading a bunch of papers since they may not be relevant. We both agreed that part of the |
c359d8b5-39c6-4047-80c8-d90d40dfa416 | trentmkelly/LessWrong-43k | LessWrong | Should we all be more hygenic in normal times?
I've heard people say that this should be the trigger to be more careful about disease after the pandemic is over: e.g. people with mild colds shouldn't leave the home without a mask, all big events should have hand sanitiser. One example is this opinion piece by Matt Ridley (content warning: politics). What's the evidence on the cost/benefit analysis of marginal hygiene in rich countries when a pandemic isn't looming? |
53282c11-6328-4521-8063-fd7317074f5e | trentmkelly/LessWrong-43k | LessWrong |
. |
d59b9409-c61f-43c7-a1f7-1b70a3379f6e | trentmkelly/LessWrong-43k | LessWrong | Meetup : Atlanta: ATLessWrong Meetup
Discussion article for the meetup : Atlanta: ATLessWrong Meetup
WHEN: 29 March 2013 07:00:00PM (-0400)
WHERE: 1314 Hosea L Williams Drive NE, Atlanta, GA 30317
Let's get together and rock some rationality. Snacks, games, and various other fun activities will follow the official business. New members welcome! No reading or other preparation is required, just come and join in!
Discussion article for the meetup : Atlanta: ATLessWrong Meetup |
cc2d832b-d65e-40bb-bf4a-869ccce4681c | trentmkelly/LessWrong-43k | LessWrong | Iterated Gambles and Expected Utility Theory
The Setup
I'm about a third of the way through Stanovich's Decision Making and Rationality in the Modern World. Basically, I've gotten through some of the more basic axioms of decision theory (Dominance, Transitivity, etc).
As I went through the material, I noted that there were a lot of these:
> Decision 5. Which of the following options do you prefer (choose one)?
>
> A. A sure gain of $240
>
> B. 25% chance to gain $1,000 and 75% chance to gain nothing
The text goes on to show how most people tend to make irrational choices when confronted with decisions like this; most strikingly was how often irrelevant contexts and framing effected people's decisions.
But I understand the decision theory bit; my question is a little more complicated.
When I was choosing these options myself, I did what I've been taught by the rationalist community to do in situations where I am given nice, concrete numbers: I shut up and I multiplied, and at each decision choose the option with the highest expected utility.
Granted, I equated dollars to utility, which Stanovich does mention that humans don't do well (see Prospect Theory).
The Problem
In the above decision, option B clearly has the higher expected utility, so I chose it. But there was still a nagging doubt in my mind, some part of me that thought, if I was really given this option, in real life, I'd choose A.
So I asked myself: why would I choose A? Is this an emotion that isn't well-calibrated? Am I being risk-averse for gains but risk-taking for losses?
What exactly is going on?
And then I remembered the Prisoner's Dilemma.
A Tangent That Led Me to an Idea
Now, I'll assume that anyone reading this has a basic understanding of the concept, so I'll get straight to the point.
In classical decision theory, the choice to defect (rat the other guy out) is strictly superior to the choice to cooperate (keep your mouth shut). No matter what your partner in crime does, you get |
f27d96ff-4a38-4a3a-b943-e177cc95c328 | StampyAI/alignment-research-dataset/arxiv | Arxiv | Flexible Multiple-Objective Reinforcement Learning for Chip Placement
1. Introduction
----------------
With the evolution of AI, 5G, and high-performance computing,
there is a growing demand for chips that can quickly process huge amounts of data,
and such chips require a lot of memory or SRAM macros for the temporary storage of data.
Additionally, with the advance of semiconductor manufacturing technologies,
the numbers of SRAM macros and standard cell instances in a chip keep increasing.
Nowadays, an advanced SoC design can contain more than one thousand macros
and millions of standard cell instances.
Completing chip designs manually is not only time-consuming, but also virtually impossible for the complexity of modern SoC designs.
Therefore, design automation tools are required to help IC design engineers cope with the challenges.
Furthermore, in the physical design phase of a chip design project, the chip placement process (which is the process of determining the locations of macros and standard cell instances within a certain circuit block) is one of the most critical processes affecting the PPA (power, performance, and area) or even the final specification of a chip design.
In recent years, reinforcement learning (RL) has been proved to be a ubiquitous tool for the optimization of complex, non-differentiable objectives, subject to noise or uncertainty in the signals. Typically, these algorithms operate in a closed-loop fashion, with many iterations of signal feedback being required to improve results. This problem is exacerbated in environments with complex transition dynamics and noisy signals. Deep RL (DRL) has presented a long list of success stories in addressing this problem, with the relatively inexpensive optimization of stochastic gradient descent and complex policy parametrization leading the fore in solving previously intractable decision making problems ([SilverHuangEtAl16nature,](#bib.bib1) ). However, even state-of-the-art DRL methods suffer from many drawbacks. Neural network generalization is a critical component of good performance, but only recently has there been a success in this direction ([bartlett2021deep,](#bib.bib2) ). Furthermore, the problem of generalizing across environments with different transition dynamics and reward signals in RL is even less well studied ([vanseijen2017hybrid,](#bib.bib3) ; [dennis2021emergent,](#bib.bib4) ). DRL optimization is often brittle and requires complex hyperparameter tuning ([khadka2018evolutionguided,](#bib.bib5) ), and these issues are only made worse by the long training times, poor sample efficiency and expert supervision required.
As a typical solution to some of these issues, pretrained representations of states, actions, or the world dynamics aid in reducing runtime during execution, where only a variable amount of fine-tuning takes place.
For the macro placement problem, these issues translate into a barrier to the adoption of RL techniques. In a keynote speech at ISSCC 2020 ([DBLP:conf/isscc/Dean20,](#bib.bib6) ), the importance “[of allowing] ASIC designers to quickly generate many alternatives with different tradeoffs of area, timing, etc.” is emphasized.
However, such flexibility is not available for models trained to optimize a single objective. Fixed-weight models cannot generate the diversity of placements required for engineers to accommodate changing PPA requirements as they arise. Furthermore, the adoption of RL in placement is additionally hampered by the typical runtime of a QoR computation (wirelength and routing congestion) for traditional place-and-route tools. A solution is using weaker proxy estimates, but this adversely impacts the representation learning in DRL. Therefore, high-speed placement and efficient congestion analysis methods are required.
Our contributions in this paper are:
(1) A flexible multiple-objective reinforcement learning (MORL) to support objective functions with inference-time variable weights using a single pretrained model.
In the reward function,
we have considered objectives of wirelength, congestion, and user anchors.
(2) A cluster size selection method that achieves a high correlation to the original unclustered netlist is proposed.
Performing placement and congestion analysis on a clustered netlist is fast and maintains high-fidelity reward calculations. (3) An adaptation of proximal policy gradients to the MORL setting.
This paper is organized as follows. Previous works on mixed-size placement are introduced in Section [2](#S2 "2. Related work ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement").
Mixed-size placement modeled as an RL problem and background of multi-objective reinforcement learning are described in Section [3](#S3 "3. Problem setting ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement").
The proposed MORL algorithm for mixed-size placement is introduced in Section [4](#S4 "4. Methodology ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement").
Experimental results presented in Section [5](#S5 "5. Experiments ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") demonstrate that MORL can generate the Pareto frontier of multiple objectives effectively. Furthermore, we recover human-level performance when users’ preferences match previously known EDA objectives.
2. Related work
----------------
Mixed-size placement refers to placing modules (macros and standard cell instances) onto a chip canvas.
Modern designs often contain large numbers of macros and huge numbers of standard cell instances.
Because macros are typically orders of magnitude larger than standard cells, handling of non-overlapping constraints among the modules presents a unique challenge.
Works on mixed-size placement fall into three categories: analytical methods, packing-based methods, and machine-learning-based methods.
Analytical methods ([DBLP:journals/tcad/ChengKKW19,](#bib.bib7) ; [DBLP:journals/tcad/LinJGLDRKP21,](#bib.bib8) ; [DBLP:conf/dac/LinLW19,](#bib.bib9) ; [DBLP:conf/iccad/ChenCC17,](#bib.bib10) ) model the wirelength and congestion in the objective function under module overlap constraints.
They model the non-uniformity of the module distribution as a penalty term to solve a constrained minimization problem mathematically.
The overlap penalty is gradually increased so that the minimizer can spread modules into the placement area to obtain close-to-overlap-free mixed-size placement results.
To obtain a legal placement result, an additional legalization step is required for overlap removal.
Packing-based methods ([DBLP:journals/tvlsi/LinDYCL21,](#bib.bib11) ; [DBLP:conf/aspdac/LiuCCK19,](#bib.bib12) ) search the macro overlap-free solution space using combinatorial methods.
Simulated annealing (SA) is one of the most popular approaches in this category.
Although SA has the advantage of incorporating various placement objectives, it has scalability issues and thus cannot handle large designs effectively.
Also, it requires an initial macro and cell placement as the reference placement positions. Since only macros are considered during packing,
the packing-based method cannot estimate cell-related objectives (e.g. wirelength and congestion) accurately.
The objective function of a packing-based method often includes certain human expert knowledge; for example, macros can be forcefully placed close to either the corner or the chip boundary, and adding irregularity penalty into objective terms to obtain array-like macro placements. This requires fine-tuning of the objective terms to obtain high-quality placement results.
A state-of-the-art placement tool that employs the power of machine learning, deep reinforcement learning (DRL), and representation learning has been developed by Mirhoseini et. al ([goog-rl-eda-nature,](#bib.bib13) ; [mirhoseini2020chip,](#bib.bib14) ).
In this work,
the authors deploy a fully AI-driven solution for the placement problem,
without the chip placement knowledge from human experts.
The algorithm pretrains a placement policy from many ICs,
leverag ing graph structures of various IC netlists through a Graph Neural Network (GNN).
Multiple-objective RL also has a long history and applications in a wide range of fields. Deep RL techniques, however, have only been relevant in this direction recently, and furthermore, due to the function approximation properties of neural networks, have mainly been studied in the context of off-policy RL. In ([yang2019generalized,](#bib.bib15) ), a DQN approach for MORL computes multi-objective Q𝑄Qitalic\_Q-value function approximations. In ([2020MODRL,](#bib.bib16) ), the authors propose a general framework for all off-policy DRL optimization strategies. In ([vanseijen2017hybrid,](#bib.bib3) ), DQNs are again revisited with a focus on generalization across domains. MORL is cast as a mixture of expert synthesis problems with behaviour cloning in ([abdolmaleki2021multiobjective,](#bib.bib17) ).
3. Problem setting
-------------------
###
3.1. Mixed-size placement
In the field of the VLSI physical design automation, a placement problem refers to placing a set of nodes onto a variable-size chip canvas so as to minimize a variety of placement costs, such as the total wirelength, routing congestion, timing violations, and power. A node can refer to either a macro (either a pre-placed macro or a macro that needs to be placed) or a standard cell instance/cluster. In the current definition of the mixed-size placement problem, only macros and standard cell instances/clusters need to be placed.
The real EDA placement problem is abstracted into a synthesized netlist (e.g., Verilog file), a physical layout library (e.g., LEF file), and a chip canvas (e.g., DEF file).
These files contain the information of node features (such as node types and their physical dimensions), net/wire connections, features of the canvas, and locations of the I/O ports. Typically, after performing placement, an EDA tool will be able to compute the final placement metrics, which can include the total wirelength, routing congestion, timing, and power.
In ([goog-rl-eda-nature,](#bib.bib13) ), the aforementioned placement workflow is modeled as a reinforcement learning (RL) optimization problem, where the macros are placed by the policies guided by an EDA reward signal. Because a typical EDA tool can offer trade-offs between speed and accuracy in terms of placement metric computations, and the reward signal represents a critical guide for the experience collection process in RL, ([goog-rl-eda-nature,](#bib.bib13) ) employs a proxy computation of these metrics (see Section [4.1](#S4.SS1 "4.1. Placement objectives and approximators ‣ 4. Methodology ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement")).
The reinforcement learning policy is thus trained to place macros only, and the cell placement is carried out by a classical (non-AI) tool such as a force-directed placement tool.

Figure 1. Pareto frontier for a 2-dimensional objective simplex corresponding to O1subscript𝑂1O\_{1}italic\_O start\_POSTSUBSCRIPT 1 end\_POSTSUBSCRIPT and O2subscript𝑂2O\_{2}italic\_O start\_POSTSUBSCRIPT 2 end\_POSTSUBSCRIPT and ϵitalic-ϵ\epsilonitalic\_ϵ - approximate contour. Transitioning from the approximation to the actual optimum requires only a fraction of the computational time.
###
3.2. Multi-objective reinforcement learning
In what follows we will refer to an MDP as a tuple (𝒮,𝒜,p,r)𝒮𝒜𝑝𝑟(\mathcal{S},\mathcal{A},p,r)( caligraphic\_S , caligraphic\_A , italic\_p , italic\_r ) consisting of state and action space, transition dynamics p𝑝pitalic\_p, and associated reward signal r𝑟ritalic\_r. The standard description can be found in ([Sutton1998,](#bib.bib18) ).
We define a multi-objective MDP (MOMDP), ℳℳ\mathcal{M}caligraphic\_M, to be an MDP with state space 𝒮𝒮\mathcal{S}caligraphic\_S and action space 𝒜𝒜\mathcal{A}caligraphic\_A and fixed transition dynamics, but with a set of reward signals indexed by i𝑖iitalic\_i: reward signal i𝑖iitalic\_i is denoted as 𝐫=r(i)𝐫superscript𝑟𝑖\mathbf{r}=r^{(i)}bold\_r = italic\_r start\_POSTSUPERSCRIPT ( italic\_i ) end\_POSTSUPERSCRIPT. For such a vector of reward signals, a preference parameter, ω=(ωi)i=1K𝜔superscriptsubscriptsubscript𝜔𝑖𝑖1𝐾\mathbf{\omega}=(\omega\_{i})\_{i=1}^{K}italic\_ω = ( italic\_ω start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT ) start\_POSTSUBSCRIPT italic\_i = 1 end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT italic\_K end\_POSTSUPERSCRIPT, can be used to collapse the MOMDP ℳℳ\mathcal{M}caligraphic\_M to a standard MDP ℳωsuperscriptℳ𝜔\mathcal{M}^{\omega}caligraphic\_M start\_POSTSUPERSCRIPT italic\_ω end\_POSTSUPERSCRIPT, by recovering a single reward signal rω=R(𝐫,ω)subscript𝑟𝜔𝑅𝐫𝜔r\_{\omega}=R(\mathbf{r},\mathbf{\omega})italic\_r start\_POSTSUBSCRIPT italic\_ω end\_POSTSUBSCRIPT = italic\_R ( bold\_r , italic\_ω ) for some function R𝑅Ritalic\_R. Typically, and in the rest of this text, a convex linear combination is used rω=∑i=1Kr(i)ωisubscript𝑟𝜔superscriptsubscript𝑖1𝐾superscript𝑟𝑖subscript𝜔𝑖r\_{\omega}=\sum\_{i=1}^{K}r^{(i)}\omega\_{i}italic\_r start\_POSTSUBSCRIPT italic\_ω end\_POSTSUBSCRIPT = ∑ start\_POSTSUBSCRIPT italic\_i = 1 end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT italic\_K end\_POSTSUPERSCRIPT italic\_r start\_POSTSUPERSCRIPT ( italic\_i ) end\_POSTSUPERSCRIPT italic\_ω start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT, where ω∈(ΩK,μ)𝜔superscriptΩ𝐾𝜇\omega\in(\Omega^{K},\mu)italic\_ω ∈ ( roman\_Ω start\_POSTSUPERSCRIPT italic\_K end\_POSTSUPERSCRIPT , italic\_μ ), the standard K𝐾Kitalic\_K-dimensional simplex equipped with a probability measure μ𝜇\muitalic\_μ, typically the uniform measure.
States and actions in ℳωsuperscriptℳ𝜔\mathcal{M}^{\omega}caligraphic\_M start\_POSTSUPERSCRIPT italic\_ω end\_POSTSUPERSCRIPT will be indexed by ω𝜔\omegaitalic\_ω as in (s;ω)𝑠𝜔(s;\omega)( italic\_s ; italic\_ω ) and (a;ω)𝑎𝜔(a;\omega)( italic\_a ; italic\_ω ) respectively.
We adopt the setting of episodic RL, where there is a well-defined initial state, s0subscript𝑠0s\_{0}italic\_s start\_POSTSUBSCRIPT 0 end\_POSTSUBSCRIPT which is independent of ω𝜔\omegaitalic\_ω.
Solving an MOMDP amounts to solving each individual MDP ℳωsuperscriptℳ𝜔\mathcal{M}^{\omega}caligraphic\_M start\_POSTSUPERSCRIPT italic\_ω end\_POSTSUPERSCRIPT. Such as solution amounts to finding a continuum of policies πωsubscript𝜋𝜔\pi\_{\omega}italic\_π start\_POSTSUBSCRIPT italic\_ω end\_POSTSUBSCRIPT which maximizes the value of the initial state, J(ω,πω)=Vπω(s0;ω)𝐽𝜔subscript𝜋𝜔subscript𝑉subscript𝜋𝜔subscript𝑠0𝜔J(\omega,\pi\_{\omega})=V\_{\pi\_{\omega}}(s\_{0};\omega)italic\_J ( italic\_ω , italic\_π start\_POSTSUBSCRIPT italic\_ω end\_POSTSUBSCRIPT ) = italic\_V start\_POSTSUBSCRIPT italic\_π start\_POSTSUBSCRIPT italic\_ω end\_POSTSUBSCRIPT end\_POSTSUBSCRIPT ( italic\_s start\_POSTSUBSCRIPT 0 end\_POSTSUBSCRIPT ; italic\_ω ) for each value of ω𝜔\omegaitalic\_ω.
To make the problem tractable, define an parametric policy family to be a set of policies πω,θsubscript𝜋𝜔𝜃\pi\_{\omega,\theta}italic\_π start\_POSTSUBSCRIPT italic\_ω , italic\_θ end\_POSTSUBSCRIPT continuously parametrized by θ𝜃\thetaitalic\_θ .
For each ℳωsuperscriptℳ𝜔\mathcal{M}^{\omega}caligraphic\_M start\_POSTSUPERSCRIPT italic\_ω end\_POSTSUPERSCRIPT, within each parametric policy family, there is an optimal policy πω\*subscriptsuperscript𝜋𝜔\pi^{\*}\_{\omega}italic\_π start\_POSTSUPERSCRIPT \* end\_POSTSUPERSCRIPT start\_POSTSUBSCRIPT italic\_ω end\_POSTSUBSCRIPT corresponding to a parameter θ\*(ω)superscript𝜃𝜔\theta^{\*}(\omega)italic\_θ start\_POSTSUPERSCRIPT \* end\_POSTSUPERSCRIPT ( italic\_ω ), which is not necessarily unique.
If we can find θ\*superscript𝜃\theta^{\*}italic\_θ start\_POSTSUPERSCRIPT \* end\_POSTSUPERSCRIPT as a solution to maxθJ(θ,ω)subscript𝜃𝐽𝜃𝜔\max\_{\theta}J(\theta,\omega)roman\_max start\_POSTSUBSCRIPT italic\_θ end\_POSTSUBSCRIPT italic\_J ( italic\_θ , italic\_ω ) where J(θ,ω)𝐽𝜃𝜔J(\theta,\omega)italic\_J ( italic\_θ , italic\_ω ) is defined as
J(θ,ω):=Vπθ,ω(s0;ω)assign𝐽𝜃𝜔subscript𝑉subscript𝜋𝜃𝜔subscript𝑠0𝜔J(\theta,\omega):=V\_{\pi\_{\theta,\omega}}(s\_{0};\omega)italic\_J ( italic\_θ , italic\_ω ) := italic\_V start\_POSTSUBSCRIPT italic\_π start\_POSTSUBSCRIPT italic\_θ , italic\_ω end\_POSTSUBSCRIPT end\_POSTSUBSCRIPT ( italic\_s start\_POSTSUBSCRIPT 0 end\_POSTSUBSCRIPT ; italic\_ω ),
this represents a Pareto optimal choice of θ𝜃\thetaitalic\_θ within the parametric family. Equivalently, maxθJ(θ,ω)subscript𝜃𝐽𝜃𝜔\max\_{\theta}J(\theta,\omega)roman\_max start\_POSTSUBSCRIPT italic\_θ end\_POSTSUBSCRIPT italic\_J ( italic\_θ , italic\_ω ) admits a solution θ\*(ω)=θ\*superscript𝜃𝜔superscript𝜃\theta^{\*}(\omega)=\theta^{\*}italic\_θ start\_POSTSUPERSCRIPT \* end\_POSTSUPERSCRIPT ( italic\_ω ) = italic\_θ start\_POSTSUPERSCRIPT \* end\_POSTSUPERSCRIPT, constant in ω𝜔\omegaitalic\_ω. In practice, we will relax the requirement of finding solutions to an approximation.
An ϵitalic-ϵ\epsilonitalic\_ϵ-approximate Pareto optimum contour within a parametric family πω,θsubscript𝜋𝜔𝜃\pi\_{\omega,\theta}italic\_π start\_POSTSUBSCRIPT italic\_ω , italic\_θ end\_POSTSUBSCRIPT is a choice of θ\*superscript𝜃\theta^{\*}italic\_θ start\_POSTSUPERSCRIPT \* end\_POSTSUPERSCRIPT which, for all ω𝜔\omegaitalic\_ω satisfies
| | | | |
| --- | --- | --- | --- |
| (1) | | |J(θ\*,ω)−maxθJ(θ,ω)|<ϵ𝐽superscript𝜃𝜔subscript𝜃𝐽𝜃𝜔italic-ϵ|J(\theta^{\*},\omega)-\max\_{\theta}J(\theta,\omega)|<\epsilon| italic\_J ( italic\_θ start\_POSTSUPERSCRIPT \* end\_POSTSUPERSCRIPT , italic\_ω ) - roman\_max start\_POSTSUBSCRIPT italic\_θ end\_POSTSUBSCRIPT italic\_J ( italic\_θ , italic\_ω ) | < italic\_ϵ | |
Figure [1](#S3.F1 "Figure 1 ‣ 3.1. Mixed-size placement ‣ 3. Problem setting ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") showcases a qualitative representation of the difference between the Pareto frontier and an ϵitalic-ϵ\epsilonitalic\_ϵ-approximate optimum. At an ϵitalic-ϵ\epsilonitalic\_ϵ-approximate optimal configuration, all reward objectives may still be improved simultaneously.
4. Methodology
---------------
###
4.1. Placement objectives and approximators
We consider the most important placement objectives, wirelength, congestion, and timing, in our reward approximators. Since a reward function is evaluated many times during RL training, we need to have metrics that can be quickly evaluated while keeping good correlations to the final placement objective functions.
The most widely used wirelength model is the total half perimeter wirelength (HPWL). The wirelength reward ℓWLsubscriptℓ𝑊𝐿\ell\_{WL}roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L end\_POSTSUBSCRIPT is the summation of all nets n𝑛nitalic\_n using their half perimeter length of the minimum bounding box that can enclose all pins associated with net n𝑛nitalic\_n, as computed in the following manner,
| | | | |
| --- | --- | --- | --- |
| (2) | | ℓWL=−∑n(maxpini,pinj∈n|xi−xj|+maxpini,pinj∈n|yi−yj|),subscriptℓ𝑊𝐿subscript𝑛subscript𝑝𝑖subscript𝑛𝑖𝑝𝑖subscript𝑛𝑗
𝑛subscript𝑥𝑖subscript𝑥𝑗subscript𝑝𝑖subscript𝑛𝑖𝑝𝑖subscript𝑛𝑗
𝑛subscript𝑦𝑖subscript𝑦𝑗\ell\_{WL}=-\sum\_{n}{(\max\_{pin\_{i},pin\_{j}\in n}|x\_{i}-x\_{j}|+\max\_{pin\_{i},pin\_{j}\in n}|y\_{i}-y\_{j}|)},roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L end\_POSTSUBSCRIPT = - ∑ start\_POSTSUBSCRIPT italic\_n end\_POSTSUBSCRIPT ( roman\_max start\_POSTSUBSCRIPT italic\_p italic\_i italic\_n start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT , italic\_p italic\_i italic\_n start\_POSTSUBSCRIPT italic\_j end\_POSTSUBSCRIPT ∈ italic\_n end\_POSTSUBSCRIPT | italic\_x start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT - italic\_x start\_POSTSUBSCRIPT italic\_j end\_POSTSUBSCRIPT | + roman\_max start\_POSTSUBSCRIPT italic\_p italic\_i italic\_n start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT , italic\_p italic\_i italic\_n start\_POSTSUBSCRIPT italic\_j end\_POSTSUBSCRIPT ∈ italic\_n end\_POSTSUBSCRIPT | italic\_y start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT - italic\_y start\_POSTSUBSCRIPT italic\_j end\_POSTSUBSCRIPT | ) , | |
where (xi,yi)subscript𝑥𝑖subscript𝑦𝑖(x\_{i},y\_{i})( italic\_x start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT , italic\_y start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT ) is the coordinate of pini𝑝𝑖subscript𝑛𝑖pin\_{i}italic\_p italic\_i italic\_n start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT.
In addition to wirelength, a routing congestion metric is used to ensure that a placement result can indeed be routed.
We adopt a similar congestion metric from DAC 2012 routability-driven placement contest ([DBLP:conf/dac/ViswanathanASLW12,](#bib.bib19) ). Let ACE𝐴𝐶𝐸ACEitalic\_A italic\_C italic\_E be the average congestion g-cell edges based on the histogram of g-edge congestion as described in ([DBLP:conf/dac/ViswanathanASLW12,](#bib.bib19) ; [Wei:DAC2012,](#bib.bib20) ). Then, ACE(k)𝐴𝐶𝐸𝑘ACE(k)italic\_A italic\_C italic\_E ( italic\_k ) computes the average congestion of the top k𝑘kitalic\_k% congested g-cell edges. We calculate the peak-weighted congestion (ℓCsubscriptℓ𝐶\ell\_{C}roman\_ℓ start\_POSTSUBSCRIPT italic\_C end\_POSTSUBSCRIPT) as
| | | | |
| --- | --- | --- | --- |
| (3) | | ℓC=−ACE(k)4,k∈0.5,1,2,5.formulae-sequencesubscriptℓ𝐶𝐴𝐶𝐸𝑘4𝑘0.5125\ell\_{C}=-\frac{ACE(k)}{4},k\in 0.5,1,2,5.roman\_ℓ start\_POSTSUBSCRIPT italic\_C end\_POSTSUBSCRIPT = - divide start\_ARG italic\_A italic\_C italic\_E ( italic\_k ) end\_ARG start\_ARG 4 end\_ARG , italic\_k ∈ 0.5 , 1 , 2 , 5 . | |
We apply the same parameters (0.5%, 1%, 2%, and 5%) used in the previous works because this setting is proven to be effective on many benchmark cases.
We first apply a global routing, and then compute ℓCsubscriptℓ𝐶\ell\_{C}roman\_ℓ start\_POSTSUBSCRIPT italic\_C end\_POSTSUBSCRIPT as our congestion metric. Note that the g-cell size is adjusted based on the average cell cluster dimensions with pin locations approximated as the centers of cell clusters.
In modern VLSI placement, additional reference anchors need to be supported to control the final placement to meet layout implementation requirements, such as fence regions ([DBLP:conf/ispd/BustanyCSY15,](#bib.bib21) ) and datapath alignment constraints ([DBLP:conf/dac/HuangLLCWY17,](#bib.bib22) ). Therefore, an additional anchor-distance objective is enforced, with the aim of meeting specific implementation-level guidelines.
We enforce an anchor displacement:
| | | | |
| --- | --- | --- | --- |
| (4) | | ℓA=−∑iai(Xi−xi)2+(Yi−yi)2,subscriptℓ𝐴subscript𝑖subscript𝑎𝑖superscriptsubscript𝑋𝑖subscript𝑥𝑖2superscriptsubscript𝑌𝑖subscript𝑦𝑖2\ell\_{A}=-\sum\_{i}a\_{i}\sqrt{(X\_{i}-x\_{i})^{2}+(Y\_{i}-y\_{i})^{2}},roman\_ℓ start\_POSTSUBSCRIPT italic\_A end\_POSTSUBSCRIPT = - ∑ start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT italic\_a start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT square-root start\_ARG ( italic\_X start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT - italic\_x start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT ) start\_POSTSUPERSCRIPT 2 end\_POSTSUPERSCRIPT + ( italic\_Y start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT - italic\_y start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT ) start\_POSTSUPERSCRIPT 2 end\_POSTSUPERSCRIPT end\_ARG , | |
where (Xi,Yi)subscript𝑋𝑖subscript𝑌𝑖(X\_{i},Y\_{i})( italic\_X start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT , italic\_Y start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT ) is the user-defined target coordinate, (xi,yi)subscript𝑥𝑖subscript𝑦𝑖(x\_{i},y\_{i})( italic\_x start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT , italic\_y start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT ) is the coordinate of the center of each macro, and aisubscript𝑎𝑖a\_{i}italic\_a start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT is the weight of each anchor.
We define the EDA objective as:
| | | | |
| --- | --- | --- | --- |
| (5) | | ℓEDA=αℓWL+βℓC+δℓA,subscriptℓ𝐸𝐷𝐴𝛼subscriptℓ𝑊𝐿𝛽subscriptℓ𝐶𝛿subscriptℓ𝐴\ell\_{EDA}=\alpha\ell\_{WL}+\beta\ell\_{C}+\delta\ell\_{A},roman\_ℓ start\_POSTSUBSCRIPT italic\_E italic\_D italic\_A end\_POSTSUBSCRIPT = italic\_α roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L end\_POSTSUBSCRIPT + italic\_β roman\_ℓ start\_POSTSUBSCRIPT italic\_C end\_POSTSUBSCRIPT + italic\_δ roman\_ℓ start\_POSTSUBSCRIPT italic\_A end\_POSTSUBSCRIPT , | |
where α𝛼\alphaitalic\_α, β𝛽\betaitalic\_β, and δ𝛿\deltaitalic\_δ are weights to control the significance of each corresponding objective; the sum of the first two terms is denoted by ℓWL+Csubscriptℓ𝑊𝐿𝐶\ell\_{WL+C}roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L + italic\_C end\_POSTSUBSCRIPT.
For modern chip designs, engineers may need to explore different placement styles in the solution space.
###
4.2. Solving MOMDPs with policy gradients
How should one attempt to find ϵitalic-ϵ\epsilonitalic\_ϵ-approximate Pareto optimal contours? The objective J^(θ)=𝔼ω[J(θ;ω)]^𝐽𝜃subscript𝔼𝜔delimited-[]𝐽𝜃𝜔\hat{J}(\theta)=\mathbb{E}\_{\omega}[J(\theta;\omega)]over^ start\_ARG italic\_J end\_ARG ( italic\_θ ) = blackboard\_E start\_POSTSUBSCRIPT italic\_ω end\_POSTSUBSCRIPT [ italic\_J ( italic\_θ ; italic\_ω ) ]
when optimized, will produce the best average contour, but cannot guarantee ϵitalic-ϵ\epsilonitalic\_ϵ-optimality. The structure of the policy πθ,ωsubscript𝜋𝜃𝜔\pi\_{\theta,\omega}italic\_π start\_POSTSUBSCRIPT italic\_θ , italic\_ω end\_POSTSUBSCRIPT and in particular its dependence on the parameters is what determines whether the reward landscape J(θ;ω)𝐽𝜃𝜔J(\theta;\omega)italic\_J ( italic\_θ ; italic\_ω ) admits a global ϵitalic-ϵ\epsilonitalic\_ϵ-approximate optimal contour.
We will iteratively approximate the maximum of J^(θ)^𝐽𝜃\hat{J}(\theta)over^ start\_ARG italic\_J end\_ARG ( italic\_θ ) by
θn+1=θn+αn∇θnJ^(θ)subscript𝜃𝑛1subscript𝜃𝑛subscript𝛼𝑛subscript∇subscript𝜃𝑛^𝐽𝜃\theta\_{n+1}=\theta\_{n}+\alpha\_{n}\nabla\_{\theta\_{n}}\hat{J}(\theta)italic\_θ start\_POSTSUBSCRIPT italic\_n + 1 end\_POSTSUBSCRIPT = italic\_θ start\_POSTSUBSCRIPT italic\_n end\_POSTSUBSCRIPT + italic\_α start\_POSTSUBSCRIPT italic\_n end\_POSTSUBSCRIPT ∇ start\_POSTSUBSCRIPT italic\_θ start\_POSTSUBSCRIPT italic\_n end\_POSTSUBSCRIPT end\_POSTSUBSCRIPT over^ start\_ARG italic\_J end\_ARG ( italic\_θ ).
The gradient ∇θJ^(θ)subscript∇𝜃^𝐽𝜃\nabla\_{\theta}\hat{J}(\theta)∇ start\_POSTSUBSCRIPT italic\_θ end\_POSTSUBSCRIPT over^ start\_ARG italic\_J end\_ARG ( italic\_θ ) can be obtained through standard policy gradient estimates, if J𝐽Jitalic\_J is uniformly bounded and regular enough (has Lipschitz gradients).
In our application, however, we will be employing the PPO gradient estimator with generalized advantage estimation (GAE), see ([schulman2015high,](#bib.bib23) ; [schulman2017proximal,](#bib.bib24) ). We choose PPO as a basis of our algorithm following its success in the placement problem in ([goog-rl-eda-nature,](#bib.bib13) ).
In the MORL setting, the resulting procedure will output a parametrized policy family for all preferences, optimized on-policy, through multi-objective proximal policy optimization (MOPPO).
Adaptation of PPO to MORL, however, is challenging both in terms of setting the correct neural architectures as well as adapting the training regime.
The standard PPO loss encompasses two other components, namely a value loss which controls the error in value function estimates as well as an entropy loss which is used to constrain the uncertainty in the distribution πθ,ω(s)subscript𝜋𝜃𝜔𝑠\pi\_{\theta,\omega}(s)italic\_π start\_POSTSUBSCRIPT italic\_θ , italic\_ω end\_POSTSUBSCRIPT ( italic\_s ).
The value function v(s;θv)𝑣𝑠subscript𝜃𝑣v(s;\theta\_{v})italic\_v ( italic\_s ; italic\_θ start\_POSTSUBSCRIPT italic\_v end\_POSTSUBSCRIPT ) is modified to receive the parameter ω𝜔\omegaitalic\_ω as input (i.e. v(s,ω;θv)𝑣𝑠𝜔subscript𝜃𝑣v(s,\omega;\theta\_{v})italic\_v ( italic\_s , italic\_ω ; italic\_θ start\_POSTSUBSCRIPT italic\_v end\_POSTSUBSCRIPT )) and the value loss will be computed across input states and values of ω𝜔\omegaitalic\_ω sampled from the buffer. This is similar to the Q𝑄Qitalic\_Q-function update in ([yang2019generalized,](#bib.bib15) ).
The entropy loss is already an average of entropy values of the policy head across states, so we further average over the second component of the state for each ℳωsuperscriptℳ𝜔\mathcal{M}^{\omega}caligraphic\_M start\_POSTSUPERSCRIPT italic\_ω end\_POSTSUPERSCRIPT, the parameter ω𝜔\omegaitalic\_ω.
The value function 𝐕πsuperscript𝐕𝜋\mathbf{V}^{\pi}bold\_V start\_POSTSUPERSCRIPT italic\_π end\_POSTSUPERSCRIPT outputs a K𝐾Kitalic\_K-dimensional vector, one corresponding to each of the reward objectives:
| | | | |
| --- | --- | --- | --- |
| (6) | | 𝐕πθ,ω(s,ω)=𝔼[∑k=0∞γk𝐫(st+k,πθ,ω(st+k))|st=s]superscript𝐕subscript𝜋𝜃𝜔𝑠𝜔𝔼delimited-[]conditionalsuperscriptsubscript𝑘0superscript𝛾𝑘𝐫subscript𝑠𝑡𝑘subscript𝜋𝜃𝜔subscript𝑠𝑡𝑘subscript𝑠𝑡𝑠\mathbf{V}^{\pi\_{\theta,\omega}}(s,\omega)=\mathbb{E}[\sum\_{k=0}^{\infty}\gamma^{k}\mathbf{r}(s\_{t+k},\pi\_{\theta,\omega}(s\_{t+k}))|s\_{t}=s]bold\_V start\_POSTSUPERSCRIPT italic\_π start\_POSTSUBSCRIPT italic\_θ , italic\_ω end\_POSTSUBSCRIPT end\_POSTSUPERSCRIPT ( italic\_s , italic\_ω ) = blackboard\_E [ ∑ start\_POSTSUBSCRIPT italic\_k = 0 end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT ∞ end\_POSTSUPERSCRIPT italic\_γ start\_POSTSUPERSCRIPT italic\_k end\_POSTSUPERSCRIPT bold\_r ( italic\_s start\_POSTSUBSCRIPT italic\_t + italic\_k end\_POSTSUBSCRIPT , italic\_π start\_POSTSUBSCRIPT italic\_θ , italic\_ω end\_POSTSUBSCRIPT ( italic\_s start\_POSTSUBSCRIPT italic\_t + italic\_k end\_POSTSUBSCRIPT ) ) | italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT = italic\_s ] | |
where γ𝛾\gammaitalic\_γ is a discounting factor. The estimated GAE advantage of a given length-T𝑇Titalic\_T trajectory can be written as (cf. ([schulman2015high,](#bib.bib23) )):
| | | | |
| --- | --- | --- | --- |
| (7) | | 𝐀^t(ω)=δ+(γλ)δt+1+⋯+(γλ)T−t+1δT−1subscript^𝐀𝑡𝜔𝛿𝛾𝜆subscript𝛿𝑡1⋯superscript𝛾𝜆𝑇𝑡1subscript𝛿𝑇1\hat{\mathbf{A}}\_{t}(\omega)=\delta+(\gamma\lambda)\delta\_{t+1}+\cdots+(\gamma\lambda)^{T-t+1}\delta\_{T-1}\\
over^ start\_ARG bold\_A end\_ARG start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT ( italic\_ω ) = italic\_δ + ( italic\_γ italic\_λ ) italic\_δ start\_POSTSUBSCRIPT italic\_t + 1 end\_POSTSUBSCRIPT + ⋯ + ( italic\_γ italic\_λ ) start\_POSTSUPERSCRIPT italic\_T - italic\_t + 1 end\_POSTSUPERSCRIPT italic\_δ start\_POSTSUBSCRIPT italic\_T - 1 end\_POSTSUBSCRIPT | |
where δt=𝐫t+γ𝐕^(st+1,ω)−𝐕^(st,ω)subscript𝛿𝑡subscript𝐫𝑡𝛾^𝐕subscript𝑠𝑡1𝜔^𝐕subscript𝑠𝑡𝜔\delta\_{t}=\mathbf{r}\_{t}+\gamma\hat{\mathbf{V}}(s\_{t+1},\omega)-\hat{\mathbf{V}}(s\_{t},\omega)italic\_δ start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT = bold\_r start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT + italic\_γ over^ start\_ARG bold\_V end\_ARG ( italic\_s start\_POSTSUBSCRIPT italic\_t + 1 end\_POSTSUBSCRIPT , italic\_ω ) - over^ start\_ARG bold\_V end\_ARG ( italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT , italic\_ω )
and 𝐕^(st,ω)^𝐕subscript𝑠𝑡𝜔\hat{\mathbf{V}}(s\_{t},\omega)over^ start\_ARG bold\_V end\_ARG ( italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT , italic\_ω ) is a running estimate for the value function. Recall the importance sampling ratio ρt(θ,ω)=πθcurrent,ω(at|st)/πθold,ω(at|st)subscript𝜌𝑡𝜃𝜔subscript𝜋subscript𝜃𝑐𝑢𝑟𝑟𝑒𝑛𝑡𝜔conditionalsubscript𝑎𝑡subscript𝑠𝑡subscript𝜋subscript𝜃𝑜𝑙𝑑𝜔conditionalsubscript𝑎𝑡subscript𝑠𝑡\rho\_{t}(\theta,\omega)=\pi\_{\theta\_{current},\omega}(a\_{t}|s\_{t})/\pi\_{\theta\_{old},\omega}(a\_{t}|s\_{t})italic\_ρ start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT ( italic\_θ , italic\_ω ) = italic\_π start\_POSTSUBSCRIPT italic\_θ start\_POSTSUBSCRIPT italic\_c italic\_u italic\_r italic\_r italic\_e italic\_n italic\_t end\_POSTSUBSCRIPT , italic\_ω end\_POSTSUBSCRIPT ( italic\_a start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT | italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT ) / italic\_π start\_POSTSUBSCRIPT italic\_θ start\_POSTSUBSCRIPT italic\_o italic\_l italic\_d end\_POSTSUBSCRIPT , italic\_ω end\_POSTSUBSCRIPT ( italic\_a start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT | italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT ).
Then the PPO policy loss component becomes:
| | | | |
| --- | --- | --- | --- |
| (8) | | LCLIP(θ,ω)=𝔼^t[min(ρt(θ,ω)ωT𝐀^t(ω),\displaystyle L^{CLIP}(\theta,\omega)=\hat{\mathbb{E}}\_{t}\Big{[}\min(\rho\_{t}(\theta,\omega)\omega^{T}\hat{\mathbf{A}}\_{t}(\omega),italic\_L start\_POSTSUPERSCRIPT italic\_C italic\_L italic\_I italic\_P end\_POSTSUPERSCRIPT ( italic\_θ , italic\_ω ) = over^ start\_ARG blackboard\_E end\_ARG start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT [ roman\_min ( italic\_ρ start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT ( italic\_θ , italic\_ω ) italic\_ω start\_POSTSUPERSCRIPT italic\_T end\_POSTSUPERSCRIPT over^ start\_ARG bold\_A end\_ARG start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT ( italic\_ω ) , | |
| (9) | | ,clip(ρt(θ,ω),1−ϵ,1+ϵ)ωT𝐀^t(ω))]\displaystyle,\text{clip}(\rho\_{t}(\theta,\omega),1-\epsilon,1+\epsilon)\omega^{T}\hat{\mathbf{A}}\_{t}(\omega))\Big{]}, clip ( italic\_ρ start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT ( italic\_θ , italic\_ω ) , 1 - italic\_ϵ , 1 + italic\_ϵ ) italic\_ω start\_POSTSUPERSCRIPT italic\_T end\_POSTSUPERSCRIPT over^ start\_ARG bold\_A end\_ARG start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT ( italic\_ω ) ) ] | |
where ϵitalic-ϵ\epsilonitalic\_ϵ is the importance sampling threshold. The entire loss includes the value loss and entropy terms:
| | | | |
| --- | --- | --- | --- |
| (10) | | L(θ,ω)=𝔼^t[LtCLIP(θ,ω)+c1LtVF(θ,ω)−c2S[πθ,ω](st,ω)]𝐿𝜃𝜔subscript^𝔼𝑡delimited-[]superscriptsubscript𝐿𝑡𝐶𝐿𝐼𝑃𝜃𝜔subscript𝑐1superscriptsubscript𝐿𝑡𝑉𝐹𝜃𝜔subscript𝑐2𝑆delimited-[]subscript𝜋𝜃𝜔subscript𝑠𝑡𝜔\displaystyle L(\theta,\omega)=\hat{\mathbb{E}}\_{t}\Big{[}L\_{t}^{CLIP}(\theta,\omega)+c\_{1}L\_{t}^{VF}(\theta,\omega)-c\_{2}S[\pi\_{\theta,\omega}](s\_{t},\omega)\Big{]}italic\_L ( italic\_θ , italic\_ω ) = over^ start\_ARG blackboard\_E end\_ARG start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT [ italic\_L start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT italic\_C italic\_L italic\_I italic\_P end\_POSTSUPERSCRIPT ( italic\_θ , italic\_ω ) + italic\_c start\_POSTSUBSCRIPT 1 end\_POSTSUBSCRIPT italic\_L start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT italic\_V italic\_F end\_POSTSUPERSCRIPT ( italic\_θ , italic\_ω ) - italic\_c start\_POSTSUBSCRIPT 2 end\_POSTSUBSCRIPT italic\_S [ italic\_π start\_POSTSUBSCRIPT italic\_θ , italic\_ω end\_POSTSUBSCRIPT ] ( italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT , italic\_ω ) ] | |
where
| | | | |
| --- | --- | --- | --- |
| (11) | | LtVF=|ωT𝐕πθ,ω(st,ω)−ωT𝐕^(st,ω)|superscriptsubscript𝐿𝑡𝑉𝐹superscript𝜔𝑇superscript𝐕subscript𝜋𝜃𝜔subscript𝑠𝑡𝜔superscript𝜔𝑇^𝐕subscript𝑠𝑡𝜔L\_{t}^{VF}=|\omega^{T}\mathbf{V}^{\pi\_{\theta,\omega}}(s\_{t},\omega)-\omega^{T}\hat{\mathbf{V}}(s\_{t},\omega)|italic\_L start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT start\_POSTSUPERSCRIPT italic\_V italic\_F end\_POSTSUPERSCRIPT = | italic\_ω start\_POSTSUPERSCRIPT italic\_T end\_POSTSUPERSCRIPT bold\_V start\_POSTSUPERSCRIPT italic\_π start\_POSTSUBSCRIPT italic\_θ , italic\_ω end\_POSTSUBSCRIPT end\_POSTSUPERSCRIPT ( italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT , italic\_ω ) - italic\_ω start\_POSTSUPERSCRIPT italic\_T end\_POSTSUPERSCRIPT over^ start\_ARG bold\_V end\_ARG ( italic\_s start\_POSTSUBSCRIPT italic\_t end\_POSTSUBSCRIPT , italic\_ω ) | | |
and S[πθ,ω]𝑆delimited-[]subscript𝜋𝜃𝜔S[\pi\_{\theta,\omega}]italic\_S [ italic\_π start\_POSTSUBSCRIPT italic\_θ , italic\_ω end\_POSTSUBSCRIPT ] is the entropy of the policy, and c1subscript𝑐1c\_{1}italic\_c start\_POSTSUBSCRIPT 1 end\_POSTSUBSCRIPT, c2subscript𝑐2c\_{2}italic\_c start\_POSTSUBSCRIPT 2 end\_POSTSUBSCRIPT are hyperparameters which can be tuned to aid optimization.
###
4.3. Implementation and neural architectures
In ([goog-rl-eda-nature,](#bib.bib13) ), architecture implementation follows the following schema:
{tikzcd}
The input data, including the circuit netlist, index of macro to be placed, canvas metadata is processed through a message-passing graph neural network as well as several embedding modules and feed-forward networks to encode the data into a single 32 dimensional hidden state representation. The policy is a deconvolutional CNN which maps the hidden state into a discrete space, corresponding to a discretization of canvas positions. The value function is a feed-forward net.
We modify this architecture in two ways. First, the preference ω𝜔\omegaitalic\_ω is mapped through a non-linearity an concatenated into the intermediate layers of the state-representation. The hidden state maintains its dimension of 32. Secondly, the value-function is copied K𝐾Kitalic\_K times to make up the vector-valued value function 𝐕^(s,ω)^𝐕𝑠𝜔\hat{\mathbf{V}}(s,\omega)over^ start\_ARG bold\_V end\_ARG ( italic\_s , italic\_ω ), but weights are allowed to optimize independently.
5. Experiments
---------------
###
5.1. MOPPO training
As a modification of an online RL algorithm, optimization of Eq. [10](#S4.E10 "10 ‣ 4.2. Solving MOMDPs with policy gradients ‣ 4. Methodology ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement"), takes place in alternating phases of experience collection and parameter updates. During experience collection, the preference parameter is sampled ω∼(Ω,μ)similar-to𝜔Ω𝜇\omega\sim(\Omega,\mu)italic\_ω ∼ ( roman\_Ω , italic\_μ ). Episodes are thus collected independently, and the experience buffer is populated with data from all individual episodes. Rewards are attached to the final state in episode collection, as described in Section [5.3](#S5.SS3 "5.3. Reward computation ‣ 5. Experiments ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement"), rewards for intermediate states being 0. Advantages are computed and then data is randomly shuffled for batching and policy updates. Episode lengths for Superblue designs (see Section [5.2](#S5.SS2 "5.2. Dataset ‣ 5. Experiments ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement")) vary from 84 to 294, which makes the reward signal highly sparse. Experience buffers are populated with 1,000 episodes each. Policy updates take place with a batch size of 512 distributed across 8 GPUs over 6 epochs. Hyperparameters of training are the same as in ([goog-rl-eda-nature,](#bib.bib13) ), with two minor additions to stabilize training, namely the addition of a scheduler for the learning rate (on top of the adaptive learning rates of the Adam optimizer).
Most DRL applications where cross-environment generalization is required, employ pretraining. This is the case in ([goog-rl-eda-nature,](#bib.bib13) ) where pretrianing is followed by fine-tuning. Preraining is conducted differently in our case, namely, instead of pretraining across multiple designs, with the aim of cross-canvas generalization, our aim is for πθ\*,ωsubscript𝜋superscript𝜃𝜔\pi\_{\theta^{\*},\omega}italic\_π start\_POSTSUBSCRIPT italic\_θ start\_POSTSUPERSCRIPT \* end\_POSTSUPERSCRIPT , italic\_ω end\_POSTSUBSCRIPT to be approximately optimal on all values of ω𝜔\omegaitalic\_ω, namely to produce approximately optimal placements in all states (s,ω)∈𝒮ℳω𝑠𝜔subscript𝒮superscriptℳ𝜔(s,\omega)\in\mathcal{S}\_{\mathcal{M}^{\omega}}( italic\_s , italic\_ω ) ∈ caligraphic\_S start\_POSTSUBSCRIPT caligraphic\_M start\_POSTSUPERSCRIPT italic\_ω end\_POSTSUPERSCRIPT end\_POSTSUBSCRIPT. Therefore, at this stage we maintain the MDP transition dynamics constant, i.e. we employ a single canvas. Instead of fine-tuning, to demonstrate the generalization properties of our model, we present zero-shot inference results as in ([dennis2021emergent,](#bib.bib4) ). For the preference space ΩΩ\Omegaroman\_Ω, following ([goog-rl-eda-nature,](#bib.bib13) ), we fix parameters (α,β)=(0.991,0.009)𝛼𝛽0.9910.009(\alpha,\beta)=(0.991,0.009)( italic\_α , italic\_β ) = ( 0.991 , 0.009 ) in Eq. [5](#S4.E5 "5 ‣ 4.1. Placement objectives and approximators ‣ 4. Methodology ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") and construct the preference space and preference parameters ω𝜔\omegaitalic\_ω=(ω1,ω2)subscript𝜔1subscript𝜔2(\omega\_{1},\omega\_{2})( italic\_ω start\_POSTSUBSCRIPT 1 end\_POSTSUBSCRIPT , italic\_ω start\_POSTSUBSCRIPT 2 end\_POSTSUBSCRIPT ) as
| | | | |
| --- | --- | --- | --- |
| (12) | | Ω={ω1(αℓWL+βℓC)+ω2ℓA|ω1,ω2∈[0,1],ω1+ω2=1}.Ωconditional-setsubscript𝜔1𝛼subscriptℓ𝑊𝐿𝛽subscriptℓ𝐶subscript𝜔2subscriptℓ𝐴formulae-sequencesubscript𝜔1subscript𝜔2
01subscript𝜔1subscript𝜔21\Omega=\{\omega\_{1}(\alpha\ell\_{WL}+\beta\ell\_{C})+\omega\_{2}\ell\_{A}|\omega\_{1},\omega\_{2}\in[0,1],\omega\_{1}+\omega\_{2}=1\}.roman\_Ω = { italic\_ω start\_POSTSUBSCRIPT 1 end\_POSTSUBSCRIPT ( italic\_α roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L end\_POSTSUBSCRIPT + italic\_β roman\_ℓ start\_POSTSUBSCRIPT italic\_C end\_POSTSUBSCRIPT ) + italic\_ω start\_POSTSUBSCRIPT 2 end\_POSTSUBSCRIPT roman\_ℓ start\_POSTSUBSCRIPT italic\_A end\_POSTSUBSCRIPT | italic\_ω start\_POSTSUBSCRIPT 1 end\_POSTSUBSCRIPT , italic\_ω start\_POSTSUBSCRIPT 2 end\_POSTSUBSCRIPT ∈ [ 0 , 1 ] , italic\_ω start\_POSTSUBSCRIPT 1 end\_POSTSUBSCRIPT + italic\_ω start\_POSTSUBSCRIPT 2 end\_POSTSUBSCRIPT = 1 } . | |
We uniformly sample episodes of experience distributed across 200 CPU threads and train until a relative reward improvement threshold is met, in practice this takes between 300 and 400 thousand episodes. During training, we preferentially resample ω𝜔\omegaitalic\_ω’s with low returns to improve the average returns across a buffer.
To demonstrate the effect of the anchor-distance objective ℓAsubscriptℓ𝐴\ell\_{A}roman\_ℓ start\_POSTSUBSCRIPT italic\_A end\_POSTSUBSCRIPT on the macro-placement result, we fix an anchor lying in the center of the canvas (i.e., (Xi,Yi):=(W/2,H/2)assignsubscript𝑋𝑖subscript𝑌𝑖𝑊2𝐻2(X\_{i},Y\_{i}):=(W/2,H/2)( italic\_X start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT , italic\_Y start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT ) := ( italic\_W / 2 , italic\_H / 2 ) where W,H𝑊𝐻W,Hitalic\_W , italic\_H are the canvas width and height respectively). The anchor weight aisubscript𝑎𝑖a\_{i}italic\_a start\_POSTSUBSCRIPT italic\_i end\_POSTSUBSCRIPT is set to the square root of the area of each macro. In addition, to normalize the magnitudes of ℓWLsubscriptℓ𝑊𝐿\ell\_{WL}roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L end\_POSTSUBSCRIPT, ℓCsubscriptℓ𝐶\ell\_{C}roman\_ℓ start\_POSTSUBSCRIPT italic\_C end\_POSTSUBSCRIPT and ℓAsubscriptℓ𝐴\ell\_{A}roman\_ℓ start\_POSTSUBSCRIPT italic\_A end\_POSTSUBSCRIPT, we collect 1000 placements from an initialized network, and then average the values of ℓWLsubscriptℓ𝑊𝐿\ell\_{WL}roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L end\_POSTSUBSCRIPT, ℓCsubscriptℓ𝐶\ell\_{C}roman\_ℓ start\_POSTSUBSCRIPT italic\_C end\_POSTSUBSCRIPT and ℓAsubscriptℓ𝐴\ell\_{A}roman\_ℓ start\_POSTSUBSCRIPT italic\_A end\_POSTSUBSCRIPT from these 1000 placements as the normalization constants of these three objectives respectively.
###
5.2. Dataset
We test MOPPO using the ICCAD 2015 Superblue benchmark suite ([DBLP:conf/iccad/KimHLV15,](#bib.bib25) ), which consists of 8 circuits. The number of macros ranges froms 84 to 294, and the number of standard cells ranges from 770k to 1930k. We focus on Superblue10 and Superblue18, which are the two designs that contain only rectangular macros. Since our method is implemented to handle rectangular macros primarily, these two cases provide the only fair comparison to tapeout results.
On other designs, results remain qualitatively similar.
We plan to adapt our algorithm to correctly place non-rectangular macros in future work.

Figure 2. Correlation between clustered and unclustered wirelength/congestion (red/blue lines) vs. number of clusters for Superblue10. Correlation increases with number of clusters; smaller cluster sizes induce faster reward computation.


(a) fixed preference
ω=(0,1)𝜔01\omega=(0,1)italic\_ω = ( 0 , 1 ).


(b) MOPPO
ω=(0,1)𝜔01\omega=(0,1)italic\_ω = ( 0 , 1 ).


(c) MOPPO
ω=(0.3,0.7)𝜔0.30.7\omega=(0.3,0.7)italic\_ω = ( 0.3 , 0.7 ).


(d) MOPPO
ω=(0.5,0.5)𝜔0.50.5\omega=(0.5,0.5)italic\_ω = ( 0.5 , 0.5 ).


(e) MOPPO
ω=(0.7,0.3)𝜔0.70.3\omega=(0.7,0.3)italic\_ω = ( 0.7 , 0.3 ).


(f) MOPPO
ω=(1,0)𝜔10\omega=(1,0)italic\_ω = ( 1 , 0 ).


(g) fixed preference
ω=(1,0)𝜔10\omega=(1,0)italic\_ω = ( 1 , 0 ).


(h) tapeout
ω=N/A𝜔𝑁𝐴\omega=N/Aitalic\_ω = italic\_N / italic\_A.
Figure 3. Placements of MOPPO, fixed-preference training and tapeout. First row: Superblue10; Second row: Superblue18.

Figure 4. Pareto frontier for a 1-dimensional objective simplex corresponding to our placement result.
###
5.3. Reward computation
To compute the reward efficiently, the netlist needs to be first clustered to speed up global placement and routing. We first use multilevel min-cut partitioning ([DBLP:journals/tvlsi/KarypisAKS99,](#bib.bib26) ) to create clustered netlist. We find that the number of clusters impacts the correlation of the computed reward before and after clustering. Therefore, we select the top 20 ranking macro placements from an industry placer ([DBLP:conf/vlsi-dat/ChenLC20,](#bib.bib27) ) that can output multiple candidate results for each circuit to analyze the most suitable cluster number for each circuit. Fig. [2](#S5.F2 "Figure 2 ‣ 5.2. Dataset ‣ 5. Experiments ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") shows wirelength and congestion correlation when using different cluster sizes on the testcase Superblue10. Since we want to keep a high correlation (>0.85absent0.85>0.85> 0.85), we choose a cluster size of 3000 for this circuit. For other test cases, we also use the above methodology to decide the cluster size to find the minimum cluster size while keeping a good correlation for reward computation. The cluster size will affect the reward computation runtime. Typically we choose a size less than 5000 clusters, which allows rewards to be computed in under 10 seconds.
After clustering, an analytical wirelength-driven placement ([DBLP:journals/tcad/HuangLLYCCCCB18,](#bib.bib28) ; [DBLP:journals/tcad/LinJGLDRKP21,](#bib.bib8) ) is applied to evenly distribute clusters. Then, a fast negotiation-based global router ([DBLP:journals/tvlsi/DaiLL12,](#bib.bib29) ) is used to obtain the congestion map. Since the design is clustered and g-cell size is adjusted according to the average cluster dimension, one-time reward computation can be done within 10 seconds. The rewards of wirelength ℓWLsubscriptℓ𝑊𝐿\ell\_{WL}roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L end\_POSTSUBSCRIPT and congestion ℓCsubscriptℓ𝐶\ell\_{C}roman\_ℓ start\_POSTSUBSCRIPT italic\_C end\_POSTSUBSCRIPT are computed according to Eq. [2](#S4.E2 "2 ‣ 4.1. Placement objectives and approximators ‣ 4. Methodology ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") and Eq. [3](#S4.E3 "3 ‣ 4.1. Placement objectives and approximators ‣ 4. Methodology ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") in Section [4.1](#S4.SS1 "4.1. Placement objectives and approximators ‣ 4. Methodology ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement").
###
5.4. Results
In this section we present the results from the pretraining and zero-shot evaluation on Superblue10 and Superblue18.
Figure [3](#S5.F3 "Figure 3 ‣ 5.2. Dataset ‣ 5. Experiments ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") presents the resulting placements across different preferences. In Figs. 3(a) and 3(g) we observe the result of training standard PPO against a fixed preference. Fig. 3(h) presents the tapeout placement for comparison. This proves that our placements are competitive to human-designed placements and PPO fixed preference training on (1,0)10(1,0)( 1 , 0 ) and (0,1)01(0,1)( 0 , 1 ). The corresponding values are shown in Table [1](#S6.T1 "Table 1 ‣ 6. Conclusions ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement").
Figure [4](#S5.F4 "Figure 4 ‣ 5.2. Dataset ‣ 5. Experiments ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") provides a visual representation of the Pareto frontier when sweeping through the preference ω𝜔\omegaitalic\_ω. The figures further exemplify the workflow of the design process facilitated by our tool, through which engineers may quickly search the preference space by evaluating placements at inference time, without the need for retraining.
Figure [5](#S5.F5 "Figure 5 ‣ 5.4. Results ‣ 5. Experiments ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") presents the zero-shot inference evaluation of the model during pretraining (at various model checkpoints), on a selected set of preferences. We observe the joint optimization of the objectives is possible for a period during training, after which the algorithm begins to discriminate between the two objectives and optimizes them selectively based on the preference. In Fig. 5(a) the combined EDA objective Eq. [5](#S4.E5 "5 ‣ 4.1. Placement objectives and approximators ‣ 4. Methodology ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") is evaluated for multiple preferences. In Fig. 5(b), the wirelength & congestion objective is evaluated. Note that the preference ω=(1,0)𝜔10\omega=(1,0)italic\_ω = ( 1 , 0 ) corresponding to this objective alone, produces training curves that are on average decreasing. The opposite preference, ω=(0,1)𝜔01\omega=(0,1)italic\_ω = ( 0 , 1 ) sees progressively worse evaluation after a point. In panel Fig 5.(c), evaluating the anchor-distance objective, the situation is reversed.
In Figure [6](#S5.F6 "Figure 6 ‣ 5.4. Results ‣ 5. Experiments ‣ Flexible Multiple-Objective Reinforcement Learning for Chip Placement") we present the relative speed of training MOPPO versus fixed-preference training. In both panels, though MOPPO converges more slowly than the fixed-preference training, it remains on the same order of magnitude, while capturing information about all preferences simultaneously. In Fig. 6(a), ℓWL+Csubscriptℓ𝑊𝐿𝐶\ell\_{WL+C}roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L + italic\_C end\_POSTSUBSCRIPT can be competitively optimized to similar values as fixed-preference PPO.
In Fig. 6(b), the corresponding evaluation for ℓAsubscriptℓ𝐴\ell\_{A}roman\_ℓ start\_POSTSUBSCRIPT italic\_A end\_POSTSUBSCRIPT is shown. The MOPPO curve comes from the same training run, and no adaptation of parameters is performed, whereas the fixed-preference training curve is rerun to optimize anchor-distance only. Overall we see that MOPPO makes only small sacrifices in its ability to optimize individual objectives versus the individually optimized PPO, which agrees with the definition of approximate Pareto optimality.

(a) EDA objective

(b) ℓWL+Csubscriptℓ𝑊𝐿𝐶\ell\_{WL+C}roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L + italic\_C end\_POSTSUBSCRIPT

(c) ℓAsubscriptℓ𝐴\ell\_{A}roman\_ℓ start\_POSTSUBSCRIPT italic\_A end\_POSTSUBSCRIPT
Figure 5.
Plots of objectives during MOPPO training, evaluated by zero-shot inference, on preferences ranging from (0,1)01(0,1)( 0 , 1 ) to (1,0)10(1,0)( 1 , 0 ) on Superblue10.

(a) ℓWL+Csubscriptℓ𝑊𝐿𝐶\ell\_{WL+C}roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L + italic\_C end\_POSTSUBSCRIPT

(b) ℓAsubscriptℓ𝐴\ell\_{A}roman\_ℓ start\_POSTSUBSCRIPT italic\_A end\_POSTSUBSCRIPT
Figure 6. Speed of convergence of MOPPO training compared to fixed-preference training on Superblue10 design. In panel (a), the value of the tapeout is presented as a threshold.
6. Conclusions
---------------
In this paper, we presented a multiple-objective reinforcement learning solution for objective functions with inference-time variable weights using a single model, MOPPO. To speed up MOPPO training, we used trial macro placements to decide a suitable cluster size for fast reward computation and keeping high correlations to the rewards of unclustered netlists. We tested our method on complex mixed-size placement problems, where we have shown that our method can recover the Pareto frontier of two uncorrelated objectives in a single round of training.
Furthermore, our method surpassed human placements in terms of ℓWL+Csubscriptℓ𝑊𝐿𝐶\ell\_{WL+C}roman\_ℓ start\_POSTSUBSCRIPT italic\_W italic\_L + italic\_C end\_POSTSUBSCRIPT, and achieved ϵitalic-ϵ\epsilonitalic\_ϵ-approximate optimality, i.e., remained close to the PPO optimized for a single fixed preference at all times.
Our research was built upon already successful frameworks and served to facilitate RL research in EDA by empowering engineers with a tool that they can quickly adapt to design constraints. However, it was not without its limitations. The training time of MORL was still very high even for the relatively simple problem of estimating a 1D Pareto frontier. For higher dimensional objective simplices, more optimization is required. Furthermore, the problem of correctly parametrizing policy families to guarantee ϵitalic-ϵ\epsilonitalic\_ϵ-approximate optimal contour finding is still unsolved. Nevertheless, to the best of our knowledge, this paper represents a first step to bringing these methods together both in the context of on-policy RL as well as EDA in general.
Table 1. Values of MOPPO placement objectives, compared to fixed-preference PPO and the tapeout. Similar values for wirelength and congestion between comparable placements of MOPPO, PPO and the tapeout are highlighted.
| Design | Superblue10 | Superblue18 |
| --- | --- | --- |
| algorithm | ω𝜔\omegaitalic\_ω |
final design
objective
|
EDA
objective
|
wirelength
(μm)𝜇𝑚({\mu}m)( italic\_μ italic\_m )
|
congestion
|
anchor-dist
objective
|
final design
objective
|
EDA
objective
|
wirelength
(μm)𝜇𝑚({\mu}m)( italic\_μ italic\_m )
|
congestion
|
anchor-dist
objective
|
| fixed preference | (0,1)01(0,1)( 0 , 1 ) | -0.61904 | -1.09231 | 535,984,538 | 1.48320 | -0.61904 | -0.55374 | -0.98822 | 112,955,805 | 1.73358 | -0.55374 |
| MOPPO | (0,1)01(0,1)( 0 , 1 ) | -0.61609 | -0.83989 | 411,299,462 | 1.36695 | -0.61609 | -0.55663 | -0.91286 | 104,319,121 | 1.63929 | -0.55663 |
| MOPPO | (.3,.7).3.7(.3,.7)( .3 , .7 ) | -0.67289 | -0.76374 | 374,066,032 | 1.22565 | -0.63395 | -0.66294 | -0.80394 | 91,949,245 | 1.31816 | -0.60251 |
| MOPPO | (.5,.5).5.5(.5,.5)( .5 , .5 ) | -0.69609 | -0.61181 | 324,103,944 | 1.07478 | -0.73036 | -0.69952 | -0.72577 | 82,985,480 | 1.22835 | -0.67927 |
| MOPPO | (.7,.3).7.3(.7,.3)( .7 , .3 ) | -0.63890 | -0.53058 | 259,264,902 | 1.03320 | -0.89165 | -0.68760 | -0.63788 | 72,895,996 | 1.14353 | -0.80362 |
| MOPPO | (1,0)10(1,0)( 1 , 0 ) | -0.49719 | -0.49719 | 242,484,931 | 1.10682 | -1.10419 | -0.56264 | -0.56264 | 64,240,346 | 1.10270 | -1.11108 |
| fixed preference | (1,0)10(1,0)( 1 , 0 ) | -0.47467 | -0.47467 | 232,916,882 | 1.08465 | -1.17216 | -0.55225 | -0.55225 | 63,061,503 | 1.06913 | -1.13321 |
| tapeout | N/A | -0.52025 | -0.52025 | 253,945,277 | 1.09447 | -1.11121 | -0.59883 | -0.59883 | 68,294,105 | 1.30058 | -1.08997 | |
5f757eed-b18f-486f-ac94-4402dac85fd6 | trentmkelly/LessWrong-43k | LessWrong | Coercion is far
I was in the subway about a month ago when saw an advert for a new show The Bourgeoisie. While waiting for my train I thought about the families patriarch and the control he probably exerted over family members. I imagined the cliché of the daughter forced into a marriage for political advantage. I thought about the sacrifice for the greater good of the family that she would be coerced into making and thought how it is easier to force others to sacrifice then to sacrifice yourself. I thought that coercion may be one of the mechanisms that have enabled humans to engage and execute long term plans. If the immediate short-term costs are what most often repress long-term action then those not saddled with the short-term costs of their long-term actions will be prone to engage in more long-term action. Coercion is far. |
239b71b3-6bfe-4d10-8329-beecd97c95e9 | StampyAI/alignment-research-dataset/aisafety.info | AI Safety Info | Would AI alignment be hard with deep learning?
Ajeya Cotra has written an excellent article titled [Why AI alignment could be hard with modern deep learning](https://www.cold-takes.com/why-ai-alignment-could-be-hard-with-modern-deep-learning/) addressing this question.
|
a6628a51-99a8-4711-b0bd-9460a2cfa355 | trentmkelly/LessWrong-43k | LessWrong | A.D&D.Sci May 2021 Evaluation and Ruleset
This is a followup to the D&D.Sci post I made last week; if you haven’t already read it, you should do so now so you know what I'm talking about here.
----------------------------------------
Ruleset
Generation code is now up here; this section goes through the important points.
Species
The carcasses obtained by the stranger are 41% Mild Boar, 31% Jungle Mammoths, 5% Jewel Beetles, and 23% Dragons (5% Green, 2% Gray, 8% Blue, 8% Red).
Days Since Death
The days since each creature’s death is modelled by rolling two d10s and taking the lowest result.
(For the rest of this post, let “[DSD]” stand in for “Days Since Death”.)
Butchery
Mild Boar
The revenue from a boar is found by rolling a d4, a d8, a d12, and a d20, then summing every result greater than [DSD].
EV is graphed below.
Jungle Mammoths
The revenue from a Jungle Mammoth carcass is given by 20+10d4-3*[DSD]
EV is graphed below.
Dragons
Valuable components of Dragons are Scales, Tongue, Heart and Spleen.
A Dragon has 5d8 Scales; these are worth 1sp apiece, unless it’s Red, in which case they’re worth 2sp apiece (this is the only way colour is relevant).
A Tongue is worth 10sp, so long as the corpse is less than three days dead. A Heart is worth 30sp until day five, and a Spleen is worth 5sp until day seven. Once these thresholds are passed, the organs lose their magic and become worthless.
EV is graphed below.
Jewel Beetles
The revenue from a Jewel Beetle is found by starting with a value of 1 and rolling a d6 repeatedly. On a 1, stop rolling and take the value as your revenue; on a 6, double the value and keep rolling; on any other roll, add your result to the value and keep rolling.
EV is infinite. This is cold comfort to those who won the one on auction, which happened to be worth only 18sp.
Universes
I got 7 entries. These were randomly assigned between two universes, and the universe with three human players got an NPC to even the odds.
The NPC
To hedge my bets against an unexpec |
cda74b3d-7eba-47b7-8e4f-4e5b44be0a9e | trentmkelly/LessWrong-43k | LessWrong | An Actually Intuitive Explanation of the Oberth Effect
This is a linkpost for An Actually Intuitive Explanation of the Oberth Effect.
Like anyone with a passing interest in Kerbal Space Program physics and spaceflight, I eventually came across the Oberth Effect. It's a very important effect, crucial to designing efficient trajectories for any rocket ship. And yet, I couldn't understand it.
Wikipedia's explanation focuses on how kinetic energy is proportional to the square of the speed, and therefore more energy is gained from a change in speed at a higher speed. I'm sure this is true, but it's not particularly helpful; simply memorizing formulae is not what leads to understanding of a phenomenon. You have to know what the numbers mean, how they correspond to the actual atoms moving around in the real universe.
This explanation was particularly galling as it seemed to violate relativity; how could a rocket's behavior change depending on its speed? What does that even mean; its speed relative to what? Whether a rocket is traveling at 1 m/s or 10000000 m/s relative to the Earth, the people on board the rocket should observe the exact same behavior when they fire their engine, right?
So I turned to the internet; Stack Overflow, Quora, Reddit, random physicists' blogs. But they all had the same problem. Every single resource I could find would "explain" the effect with a bunch of math, either focusing on the quadratic nature of kinetic energy, or some even more confusing derivation in terms of work.
A few at least tried to link the math up to the real world. Accelerating the rocket stores kinetic energy in the propellant, and this energy is then "reclaimed" when it's burned, leading to more energy coming out of the propellant at higher speeds. But this seemed unphysical; kinetic energy is not a property of the propellant itself, it depends on the reference frame of the observer! So this explanation still didn't provide me with an intuition for why it worked this way, and still seemed to violate relativity.
It took me y |
49f2bf3c-cc0b-41d7-968c-519e84b8335c | trentmkelly/LessWrong-43k | LessWrong | How To Build A Community Full Of Lonely People
|
068fd213-8a99-4454-b9ee-2d41f17bd2ff | StampyAI/alignment-research-dataset/alignmentforum | Alignment Forum | Against Time in Agent Models
When programming distributed systems, we always have many computations running in parallel. Our servers handle multiple requests in parallel, perform read and write operations on the database in parallel, etc.
The prototypical headaches of distributed programming involve multiple processes running in parallel, each performing multiple read/write operations on the same database fields. Maybe some database field says “foo”, and process 1 overwrites it with “bar”. Process 2 reads the field - depending on the timing, it may see either “foo” or “bar”. Then process 2 does some computation and writes another field - for instance, maybe it sees “foo” and writes {“most\_recent\_value”: “foo”} to a cache. Meanwhile, process 1 overwrote “foo” with “bar”, so it also overwrites the cache with {“most\_recent\_value”: “bar”}. But these two processes are running in parallel, so these operations could happen in any order - including interleaving. For instance, the order could be:
1. Process 2 reads “foo”
2. Process 1 overwrites “foo” with “bar”
3. Process 1 overwrites the cache with {“most\_recent\_value”: “bar”}
4. Process 2 overwrites the cache with {“most\_recent\_value”: “foo”}
… and now the cached value no longer matches the value in the database; our cache is broken.
One of the main heuristics for thinking about this sort of problem in distributed programming is: **there is no synchronous time**. What does that mean?
Well, in programming we often picture a “state-update” model: the system has some state, and at each timestep the state is updated. The update rule is a well-defined function of the state; every update happens at a well-defined time. This is how each of the individual processes works in our example: each executes two steps in a well-defined order, and each step changes the state of the system
Single process: a well-defined sequence of steps, each updating the state.But with multiple processes in parallel, this state-update model no longer works. In our example, we can diagram our two processes like this:

Each process has its own internal “time”: the database read/write happens first, and the cache overwrite happens second. But *between* processes, there is no guaranteed time-ordering. For instance, the first step of process 1 could happen before all of process 2, in between the steps of process 2, or after all of process 2.
Two processes: many possible time-orderings of the operations.We cannot accurately represent this system as executing along one single time-dimension. Proof:
* Step 1 of process 1 is not guaranteed to happen either before or after step 1 of process 2; at best we could represent them as happening “at the same time”
* Step 2 of process 1 is also not guaranteed to happen either before or after step 1 of process 2; at best we could represent them as happening “at the same time”
* … but step 2 of process 1 *is* unambiguously *after* step 1 of process 1 in time, so the two steps can’t happen at the same time.
In order to accurately represent this sort of thing, it has to be possible for one step to be unambiguously after another, even though both of them are neither before nor after some third step.
The “most general” data structure to represent such a relationship is not a one-dimension “timeline” (i.e. total order), but rather a directed acyclic graph (i.e. partial order). That’s how time works in distributed systems: it’s a partial order, not a total order. A DAG, not a timeline. That DAG goes by many different names - including computation DAG, computation circuit, or causal model.
Beyond Distributed Programming
------------------------------
The same basic idea carries over to distributed systems more generally - i.e. any system physically spread out in space, with lots of different stuff going on in parallel. In a distributed system, “time” is a partial order, not a total order.
In the context of [embedded agents](https://www.lesswrong.com/posts/p7x32SEt43ZMC9r7r/embedded-agents): we want to model agenty systems which are “made of parts”, i.e. the agent is itself a system physically spread out in space with lots of different stuff going on in parallel. Likewise, the environment is made of parts. Both are distributed systems.
This is in contrast to state-update models of agency. In a state-update model, the environment has some state, the agent has some state, and at each timestep their states update. The update rule is a well-defined function of state; every update happens at a well-defined time.
Instead of the state-update picture, I usually picture an agent and its environment as a computation DAG (aka circuit aka causal model), where each node is a self-contained local computation. We carve off some chunk of this DAG to call “the agent”.
 The obvious “Cartesian boundary” - i.e. the interface between agent and environment - is just a Markov blanket in the DAG (i.e. a cut which breaks the graph into two parts). That turns out to be not-quite-right, but it’s a good conceptual starting point.
Main takeaway: computational DAGs let us talk about agents without imposing a synchronous notion of "time" or "state updates", so we can play well with distributed systems. |
93c27a4a-c5f9-4b7a-91cd-c44676b97654 | trentmkelly/LessWrong-43k | LessWrong | $500 + $500 Bounty Problem: Does An (Approximately) Deterministic Maximal Redund Always Exist?
A lot of our work involves "redunds".[1] A random variable Γ is a(n exact) redund over two random variables X1,X2 exactly when both
X1→X2→Γ
X2→X1→Γ
Conceptually, these two diagrams say that X1 gives exactly the same information about Γ as all of X, and X2 gives exactly the same information about Γ as all of X; whatever information X contains about Γ is redundantly represented in X1 and X2. Unpacking the diagrammatic notation and simplifying a little, the diagrams say P[Γ|X1]=P[Γ|X2]=P[Γ|X] for all X such that P[X]>0.
The exact redundancy conditions are too restrictive to be of much practical relevance, but we are more interested in approximate redunds. Approximate redunds are defined by approximate versions of the same two diagrams:
Unpacking the diagrammatic notation, these two diagrams say
ϵred≥DKL(P[X,Γ]||P[X1]P[X2|X1]P[Γ|X2])
ϵred≥DKL(P[X,Γ]||P[X2]P[X1|X2]P[Γ|X1])
This bounty problem is about the existence of a(n approximate) maximal redund Ω: a redund which contains (approximately) all the information about X contained in any other (approximate) redund. Diagrammatically, a maximal redund Ω satisfies:
Finally, we'd like our maximal redund Ω to be an approximately deterministic function of X, i.e. ϵdet≥H(Ω|X), which is equivalent to the diagram
What We Want For The Bounty
This bounty pays out $500 for establishing that there always, over any two random variables X1, X2, exists an Ω satisfying the requirements above, i.e.
... with reasonable error bounds.
What counts as reasonable error bounds? We're expecting all the other ϵ's to scale with ϵ2 in the diagrams above, and ideally be small constant multiples of ϵ2. In other words: the higher the approximation error on allowable redunds Γ, the more approximation error we allow for all the conditions on Ω. Reasonableness of error bound is partially a judgement call on our part, but small constant (like e.g. 2 or 3) multiples of ϵ2 would definitely suffice.
Bounds should be global, i.e. apply even when ϵ2 |
5df1424b-2958-4a6a-80ea-68a4d9b491c7 | trentmkelly/LessWrong-43k | LessWrong | My SERI MATS Application
Thanks to Flo Dorner for feedback on the technical content in this post.
I have recently been accepted to the SERI ML Alignment Theory Scholars Program program, where applicants are paired with mentors. The application process was nonstandard: each mentor has a set of open-ended questions on safety research you need to answer in short essay form.
I am posting my application below. Reasons:
* It might help future applicants to similar programs overcome writing anxiety;
* I want to share the ideas from my answers.
I decided against editing my application post-hoc, to preserve a real "example application" for reference. There were some minor writing corrections. [1] Note: the answers were written in a single pass in a short amount of time.
Alex Gray: Language model risks
> Pick a risk that might be present in systems that use very large language models in the future. (...) What risk did you pick? Describe it in your own terms.
It is likely that in future language models, interpretability will be one of the main methods to (try to) enforce safety. One simple interpretability method is making the multi-layer model X "articulate its thoughts" at each layer, by returning a natural language description of the representation at each layer. Think logit lens, but with longer outputs. In what follows, we call the resulting outputs "thought descriptions".
To keep the model safe, one could do human inspection of the thought descriptions, or more scalably, automated detection of "harmful" thought descriptions through a model Y. We could train Y on a large dataset of harmful texts and AI apocalypse scenarios.
Why would this even work, given that now we need another large model, which is trained on very harmful data? Because, the harmful thought detector Y does not need to be as capable as the model X to detect harmful thoughts well. The model Y wins when it detects any harm probability, while X has to work perfectly each time.
We do not need to use any of the above to |
078b1ffe-77e8-4ee0-b836-0cfb0170619d | trentmkelly/LessWrong-43k | LessWrong | Anthropics and Fermi: grabby, visible, zoo-keeping, and early aliens
When updating the probability of life across the universe, there are two main observations we have to build on:
* Anthropic update: we exist on Earth.
* Fermi observation: (we exist on Earth and) we don't see any aliens.
I'll analyse how these two observations affect various theories about life in the universe. In general, we'll see that the anthropic update has a pretty weak effect, while the Fermi observation has a strong effect: those theories that benefit most are those that avoid the downgrade from the Fermi, such as the Zoo hypothesis, or the "human life unusually early" hypothesis.
Grabby and visible aliens
I've argued that an anthropic update on our own existence is actually just a simple Bayesian update; here I'll explain what that means for our updates.
This paper talks about grabby aliens, who would expand across the universe, and stop humans from evolving (if they reached Earth before now). As I've argued, "we exist" and "we have not observed X" are statements that can be treated in exactly the same way. We can combine them to say "there are no visible aliens anywhere near", without distinguishing grabby aliens (who would have stopped our existence) from visible-but-not grabby aliens (who would have changed our observations).
Thus the Fermi observation is saying there are no grabby or visible aliens nearby[1]. Recall that it's so comparatively easy to cross between stars and galaxies, so advanced aliens would only fail to be grabby if they coordinated to not want to do so.
Rare Earth hypotheses
Some theories posit that life requires a collection of conditions that are very rarely found together.
But rare Earth theories don't differ much, upon updates, from "life is hard" hypotheses.
For example, suppose T0 say that life can exist on any planet with rate ρ, while the rare Earth hypothesis, T1, says that life can exist on Earth-like planets with rate p, while Earth-like planets themselves exist with rate r.
But neither the Fermi observation n |
cf7fe631-2ef1-4495-bb58-50ac3e9e8ba2 | trentmkelly/LessWrong-43k | LessWrong | Learning Optimization
I'm developing an autodidactic curriculum of sorts. A study of learning might merit precedence.
What are the best articles, books, and videos you know on how to learn learning and why would you recommend those in particular?
A thousand gracias. |
4f1157c4-03f1-4c5d-8e98-b7b91ee371e3 | trentmkelly/LessWrong-43k | LessWrong | Against the internal locus of control
What do you think about these pairs of statements?
1. People's misfortunes result from the mistakes they make
2. Many of the unhappy things in people's lives are partly due to bad luck
1. In the long run, people get the respect they deserve in this world.
2. Unfortunately, an individual's worth often passes unrecognized no matter how hard he tries.
1. Becoming a success is a matter of hard work; luck has little or nothing to do with it.
2. Getting a good job mainly depends on being in the right place at the right time.
They have a similar theme: the first statement suggests that an outcome (misfortune, respect, or a good job) for a person are the result of their own action or volition. The second assigns the outcome to some external factor like bad luck.(1)
People who tend to think their own attitudes or efforts can control what happens to them are said to have an internal locus of control, those who don't, an external locus of control. (Call them 'internals' and 'externals' for short).
Internals seem to do better at life, pace obvious confounding: maybe instead of internals doing better by virtue of their internal locus of control, being successful inclines you to attribute success internal factors and so become more internal, and vice versa if you fail.(2) If you don't think the relationship is wholly confounded, then there is some prudential benefit for becoming more internal.
Yet internal versus external is not just a matter of taste, but a factual claim about the world. Do people, in general, get what their actions deserve, or is it generally thanks to matters outside their control?
Why the external view is right
Here are some reasons in favour of an external view:(3)
1. Global income inequality is marked (e.g. someone in the bottom 10% of the US population by income is still richer than two thirds of the population - more here). The main predictor of your income is country of birth, it is thought to explain around 60% of the variance: not only |
b14161da-134e-44b6-9027-6796af2c8d78 | trentmkelly/LessWrong-43k | LessWrong | GPT-4: What we (I) know about it
OpenAI released a press release, research statement, and system card about GPT-4 approximately one eternity (24 hours) ago. The general public can’t use it yet, but it’s in the process of being rolled out to paid subscribers of ChatGPT, and via a waitlist to the API. We also got confirmation that the Bing AI (also currently rolling out via waitlist) is based on GPT-4.
Here I’ll try to summarize the news and boil down what we (I) know about GPT-4. Many points lifted from the discussion at lesswrong.
My main takeaways:
* Capabilities progress is continuing without slowing.
* OpenAI spent a lot of time on RLHF/fine-tuning to prevent unethical use (facilitating crime, generating hate speech, etc), and they behave as if this is sufficient to solve alignment.
* OpenAI is no longer so open - we know almost nothing about GPT-4’s architecture.
Previously from OpenAI…
(Just recapping the progress of the GPT series of models, feel free to skip.)
AIs advance very quickly. The most impressive AI these days are large language models, including the GPT series, and they are all based on the transformer, an architecture introduced in 2017.
In 2018 OpenAI released the Generative Pre-Trained Transformer (GPT), which approached natural language tasks by predicting the next token[1]. It was especially evaluated on narrow tasks (e.g. “Is the sentiment of this user review positive or negative? [user review]. The sentiment is…”). A key technique for GPT (and all its successors) was the eponymous “pre-training”, where the AI is trained not on any particular task, but just to predict the next token in a text. This gives you access you a huge volume of training data (literally all text), while building general understanding of the world - answering factual questions is a form of token completion, so the AI needs to be able to answer those questions, etc. This pre-training built a general knowledge base, and then GPT was “fine-tuned” to individual tasks with additional training on th |
6cc9816b-cc13-419b-8fd8-5b564209899a | trentmkelly/LessWrong-43k | LessWrong | Nitric oxide for covid and other viral infections
Epistemic status: I spent about 5 hours looking into this, and the next day developed covid myself. I did a bit more research plus all of the writing while sick. So in addition to my normal warning that I have no medical credentials, you should keep in mind that this knowledge may be cursed.
ETA 4-30-24: In this post I used “nitric oxide spray” and “enovid” as synonyms. I’ve since learned this is incorrect, NO is one of several mechanisms Enovid uses. The other mechanisms weren’t mentioned in the papers I cite so it’s possible these are accurate for NO alone.
Introduction
Nitric Oxide Nasal Spray, sold under the brand name Enovid, is a reactive compound that kills viruses (and I suspect taxes your nasal tissue). It has recently been tested and marketed for treatment of covid. The protocol I found in papers was 2 sprays per nostril every 2-3 hours, after you develop symptoms. Enovid’s instructional pamphlets say twice per day, also after you get sick. This seems a little late to me.
I suspect the real power of NONS lies in use before you develop symptoms, ideally as close to exposure as possible. This is difficult because you don’t know when you would have gotten sick, and I suspect there are costs to indefinite use. I initially thought (and told people, as a tentative guess) that one round of 4 total sprays after a high risk event was a good trade off. After doing the math for this post, that intervention seems much less helpful to me, and picking the right length of post-exposure prophylaxis depends on equations for which we lack good numbers. I pulled some numbers out of my ass for this post, but you should not trust them.
My guess is NONS is minimally useful once covid has reached the throat, unless you combine it with a separate disinfectant of the throat. I hope to write up a report on one such disinfectant soon, although TBH it’s not looking good.
NONS can lead to false negatives on any test based on a nasal swab, because it breaks the relationship b |
8b09d187-2417-466d-bb54-5817dc28908e | trentmkelly/LessWrong-43k | LessWrong | Text Posts from the Kids Group: 2020
Another round of liberating kid posts from Facebook. For reference, in 2020 Lily turned 6 and Anna turned 4.
(Some of these were from me; some were from Julia. Ones saying "me" could mean either of us.)
2020-01-01
We went to the movies, and brought our own popcorn. When I passed the popcorn to Lily during the movie she was indignant, saying that we weren't supposed to bring in our own food. She ate one piece, but then said it wasn't ok and wouldn't eat more.
When the movie ended, Lily wanted us to tell the people at the concession stand and apologize: "Tell them! *Tell* them." She started trying to bargain with Julia: "I'll give you a penny if you tell them. Two pennies! Three pennies, *Five* pennies!"
But then we were outside and she was excitedly pretending to be Elsa, running down the sidewalk without a coat.
2020-01-10
I left for a trip on Tuesday afternoon, and beforehand Lily had asked me to give her one hour's notice before I left. I told her it would be about an hour from when she got home from school, but I forgot to give her warning at the actual one-hour mark. When I came up to read and cuddle with the kids 20 minutes before I left, she was angry that I hadn't given her enough notice. Then she went off and did something with paper, which I thought was sulking. I tried to persuade her to come sit on the couch with Anna and me and enjoy the time together, but she wouldn't.
Turns out she was making a picture and had wanted enough notice to finish it before I left. It is of her, Anna, and Jeff "so you won't forget us while you're gone." I assured her I will definitely not forget them, but that this was a very nice thing to be able to bring with me.
2020-01-13
Anna: "I will buy a baby at the baby store when I am a grownup, and I will be a mama like you! And I will work at Google and have the same job as my dad."
Pretty sure the kids don't think I have a real job. To be fair Google has much better food.
This was the first I had heard of the baby stor |
9e6cec4d-d963-40f8-8006-3842b03a294d | trentmkelly/LessWrong-43k | LessWrong | Weekly LW Meetups
This summary was posted to LW Main on March 27th. The following week's summary is here.
Irregularly scheduled Less Wrong meetups are taking place in:
* [Edinburgh] LessWrong Scotland: 12 April 2015 02:00PM
* European Community Weekend 2015: 12 June 2015 12:00PM
* LessWrong-like Meetup Hamburg: 27 March 2015 07:00PM
* [Netherlands] Effective Altruism Netherlands: Small concrete actions you could take: 29 March 2015 01:00PM
* San Francisco Meetup: Short Talks: 30 March 2015 06:15PM
The remaining meetups take place in cities with regular scheduling, but involve a change in time or location, special meeting content, or simply a helpful reminder about the meetup:
* Austin, TX - Caffe Medici: 28 March 2015 12:22PM
* Boston: Unconference: 05 April 2015 03:30AM
* London Newcomers-Are-Especially-Welcome Meetup, March 29th: 29 March 2015 01:00PM
* Moscow meetup: communication practice and three short talks: 29 March 2015 02:00PM
* Sydney Rationality Dojo - Skill Training Part 2: 12 April 2015 05:00PM
* [Vienna] Rationality Meetup Vienna: 18 April 2015 02:00PM
* [Vienna] Rationality Meetup Vienna: 09 May 2015 02:00PM
* Washington, D.C.: Singing: 29 March 2015 03:00AM
* West LA—R:AZ Part B, Fake Beliefs: 01 April 2015 07:00PM
Locations with regularly scheduled meetups: Austin, Berkeley, Berlin, Boston, Brussels, Buffalo, Cambridge UK, Canberra, Columbus, London, Madison WI, Melbourne, Moscow, Mountain View, New York, Philadelphia, Research Triangle NC, Seattle, Sydney, Tel Aviv, Toronto, Vienna, Washington DC, and West Los Angeles. There's also a 24/7 online study hall for coworking LWers.
If you'd like to talk with other LW-ers face to face, and there is no meetup in your area, consider starting your own meetup; it's easy (more resources here). Check one out, stretch your rationality skills, build community, and have fun!
In addition to the handy sidebar of upcoming meetups, a meetup overview is posted on the front page every Friday. These are an attemp |
0a5dfbdb-4277-4a12-a0d4-7180dee95f85 | trentmkelly/LessWrong-43k | LessWrong | (OLD) An Extremely Opinionated Annotated List of My Favourite Mechanistic Interpretability Papers
This post is out of date, see v2 here
Introduction
This is an extremely opinionated list of my favourite mechanistic interpretability papers, annotated with my key takeaways and what I like about each paper, which bits to deeply engage with vs skim (and what to focus on when skimming) vs which bits I don’t care about and recommend skipping, along with fun digressions and various hot takes.
This is aimed at people trying to get into the field of mechanistic interpretability (especially Large Language Model (LLM) interpretability). I’m writing it because I’ve benefited a lot by hearing the unfiltered and honest opinions from other researchers, especially when first learning about something, and I think it’s valuable to make this kind of thing public! On the flipside though, this post is explicitly about my personal opinions - I think some of these takes are controversial and other people in the field would disagree.
The four top level sections are priority ordered, but papers within each section are ordered arbitrarily - follow your curiosity
Priority 1: What is Mechanistic Interpretability?
* Circuits: Zoom In
* Sets out the circuits research agenda, and is a whirlwind overview of progress in image circuits
* This is reasonably short and conceptual (rather than technical) and in my opinion very important, so I recommend deeply engaging with all of it, rather than skimming.
* The core thing to take away from it is the perspective of networks having legible(-ish) internal representations of features, and that these may be connected up into interpretable circuits. The key is that this is a mindset for thinking about networks in general, and all the discussion of image circuits is just grounding in concrete examples.
* On a deeper level, understanding why these are important and non-trivial claims about neural networks, and their implications.
* In my opinion, the circuits agenda is pretty deeply at the core of what mechanistic i |
d0612de4-e988-4602-863b-14fe9d6ec549 | trentmkelly/LessWrong-43k | LessWrong | Against Tulip Subsidies
I.
Imagine a little kingdom with a quaint custom: when a man likes a woman, he offers her a tulip; if she accepts, they are married shortly thereafter. A couple who marries sans tulip is considered to be living in sin; no other form of proposal is appropriate or accepted.
One day, a Dutch trader comes to the little kingdom. He explains that his homeland also has a quaint custom involving tulips: they speculate on them, bidding the price up to stratospheric levels. Why, in the Netherlands, a tulip can go for ten times more than the average worker earns in a year! The trader is pleased to find a new source of bulbs, and offers the people of the kingdom a few guilders per tulip, which they happily accept.
Soon other Dutch traders show up and start a bidding war. The price of tulips goes up, and up, and up; first dozens of guilders, then hundreds. Tulip-growers make a fortune, but everyone else is less pleased. Suitors wishing to give a token of their love find themselves having to invest their entire life savings – with no guarantee that the woman will even say yes! Soon, some of the poorest people are locked out of marriage and family-raising entirely.
Some of the members of Parliament are outraged. Marriage is, they say, a human right, and to see it forcibly denied the poor by foreign speculators is nothing less than an abomination. They demand that the King provide every man enough money to guarantee he can buy a tulip. Some objections are raised: won’t it deplete the Treasury? Are we obligated to buy everyone a beautiful flawless bulb, or just the sickliest, grungiest plant that will technically satisfy the requirements of the ritual? If some man continuously proposes to women who reject him, are we obligated to pay for a new bulb each time, subsidizing his stupidity?
The pro-subsidy faction declares that the people asking these question are well-off, and can probably afford tulips of their own, and so from their place of privilege they are trying to raise poi |
9e2f9af3-fb57-4ed1-9bd4-508e37b9ba91 | trentmkelly/LessWrong-43k | LessWrong | Lessons Learned: Properly Publicizing a Regional Meetup Event (also, last call to apply!)
Boston, Labor Day Weekend 2023: NA East ACX & Rationality Meetup Organizers Retreat
Application Deadline: June 30 23:59, please apply here.
LessWrong event post, in case that is helpful.
Lessons Learned
Publicity
No one will come to your event if they don't know it exists! You have to get the word out, publicize. Your strategy for raising awareness about the event differs based on (1) the purpose of your event, (2) with whom you are gathering, and (3) how folks from (2) are most easily or consistently informed.
Here's what I did to get the word out, and why that was the incorrect strategy:
* I made the assumption that because there is a Rationality Meetups discord server where many ACX & Rationality Meetup Organizers hangout, that I could do a straightforward broadcast communication in relevant channels in that discord server and reach my target audience (fellow meetup organizers). This assumption proved incorrect:
1. Dropping a short message with link to an application form in a chat channel without formatting your message as an announcement and not asking a mod to ping everyone about it means that your message will likely get lost in the shuffle as only a few people will stop to read a text-only message, or will scan it quickly but not register it. Attention is a scarce resource and people are busy, there's a reason that sites designed to capture your attention (Facebook, Twitter, TikTok, etc.) look the way they do and function the way they do. Messages that are not formatted as announcements & don't have a compelling image to capture attention just don't get seen as much as more attention-grabbing formatted messages. My message was not designed to capture attention nor did I ask mods to help announce or promote the message.
2. Many people who use Discord will mute entire servers or only see "mentions" even if they regularly read that server due to the amount of notifications they would otherwise get.
3. Some people use Discord infrequently or do |
70aac7b7-5a83-42de-8613-b6248a3c1237 | trentmkelly/LessWrong-43k | LessWrong | Updating Drexler's CAIS model
Eric Drexler's report Reframing Superintelligence: Comprehensive AI Services (CAIS) as General Intelligence reshaped how a lot of people think about AI (summary 1, summary 2). I still agree with many parts of it, perhaps even the core elements of the model. However, after looking back on it more than four years later, I think the general picture it gave missed some crucial details about how AI will go.
The problem seems to be that his report neglected a discussion of foundation models, which I think have transformed how we should think about AI services and specialization.
The general vibe I got from CAIS (which may not have been Drexler's intention) was something like the following picture:
For each task in the economy, we will train a model from scratch to automate the task, using the minimum compute necessary to train an AI to do well on the task. Over time, the fraction of tasks automated will slowly expand like a wave, starting with the tasks that are cheapest to automate computationally, and ending with the most expensive tasks. At some point, automation will be so widespread that it will begin to meaningfully feed into itself, increasing AI R&D, and accelerating the rate of technological progress.
The problem with this approach to automation is that it's extremely wasteful to train models from scratch for each task. It might make sense when training budgets are tiny — as they mostly were in 2018 — but it doesn't make sense when it takes 10^25 FLOP to reach adequate performance on a given set of tasks.
The big obvious-in-hindsight idea that we've gotten over the last several years is that, instead of training from scratch for each new task, we'll train train a foundation model on some general distribution, which can then be fine-tuned using small amounts of compute to perform well on any task. In the CAIS model, "general intelligence" is just the name we can give to the collection of all AI services in the economy. In this new paradigm, "general intelli |
02c6332e-e4a5-4688-8d46-2d7faebedb57 | trentmkelly/LessWrong-43k | LessWrong | Why are profitable companies laying off staff?
Consider all the reasons you might have to reduce headcount in an economic downturn:
1. You rely on venture capital to survive which is no longer as easy to get, so you simply can't afford to pay your staff.
2. You've started making a loss, so you need to fire people to get back to profitability.
3. You have low cash reserves, so need to reduce operating costs to give you more of a runway if things go wrong.
4. There's reduced demand for your services so no need for as much staff.
5. Business propositions which were marginally worthwhile in the past are no longer positive expected value.
So consider Meta:
* It's a super profitable company (made 4 billion dollars last quarter).
* It's got 40 billion dollars in cash reserves - enough to keep the lights on for 6 months even if income dropped to zero.
* It's usage hasn't significantly changed, and demand for advertising certainly hasn't dropped enough to lay off more than 10% of it's workforce.
* The employees who were layed off don't seem to be exclusively layed off from sectors which only make sense to invest in in an upturn. E.g. Eric Lippert was laid off, and his team worked on internal tooling to improve software development at Meta. Whether that's a good idea or not seems independent of the economic headwinds.
Also laying off staff has enourmous costs. Meta is paying extremely generous packages to laid off employees (16 weeks of pay, plus 2 for every year working at meta, and 6 months health insurance). It also strongly demotivates people who weren't fired and makes it harder to recruit in the future. Finally, since fired employees aren't usually given a chance to handover, it leaves their colleagues scrambling to take over their roles.
My best guess is that actually the layoffs have nothing directly to do with the economic downturn. Among any big company's investors there's those who want it to stay lean, and those who want it to expand. When Meta posts poor financial results (even if they have more |
21278c0b-c043-4306-805c-3239641ce91a | trentmkelly/LessWrong-43k | LessWrong | Modern Monetary Theory for Dummies
Modern Monetary Theory, called MMT, is a modern theory of how fiat money works and some implications of this. I don't know the intricate details of this theory but there are some broad conclusions you can draw about someone who talks positively about it.
I'll try to very briefly summarize the understanding I have got from how MMT people view the world. Fiat money is different from real-world commodities in a significant way because it is possible to print any amount of it. The American government can never default on their debts if their debts are in the form of dollars because the US government is able to print literally any amount of dollars. A significant and fundamental reason why fiat money is then valuable (even if the supply could become infinite) is that you need it to pay taxes in the US. The government does not accept tax payments by ANY other means. This means that if you are a US citizen when the tax day comes you will be forced to "buy" dollars from other people in order to avoid going to jail, this creates a demand for the dollar irrespective of the supply. Moreover, the tax amount is also decided by the government, which means that they can create whatever level of demand they want or the dollar by US taxpayers.
So how does fiat work? Firstly, every single dollar in the world has been printed by the American government (FED) and the act of printing and the act of government spending are exactly the same. The only way to spend is to print and the only way to print is to spend. However, since all spending prints money, the government tries to also destroy money. It does this via taxation, you can look at it like every dollar taxed is burned. Generally, however, the government spends more than it taxes, which is called running a deficit, which means that they print more money than they destroy. This creates something called inflation.
You can look at inflation as a tax on liquidity which is just a fancy word for cash. If the government prints the same |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.