id stringlengths 36 36 | source stringclasses 15 values | formatted_source stringclasses 13 values | text stringlengths 2 7.55M |
|---|---|---|---|
b4799adc-8a48-4f51-bc6a-8e731472991f | trentmkelly/LessWrong-43k | LessWrong | how birds sense magnetic fields
introduction
It is known that many birds are able to sense the direction of Earth's magnetic field. Here's a wikipedia page on that general phenomenon. There have been 2 main theories of how that works.
One theory is that birds have magnets in their beak that act like a compass. We know this is the correct theory because:
* Small magnetite crystals have been found in bird beaks.
* Anaesthesia of bird beaks seems to affect their magnetic sense, sometimes.
The other theory is that birds have some sensing mechanism in their eyes that uses magneto-optical effects. We know this is the correct theory because:
* Birds can't sense magnetic field direction in red light.
* Covering the right eye of birds prevents them from sensing field direction.
We also know those theories probably aren't both correct because:
* Most animals don't have a magnetic field sense. It's implausible that birds developed two separate and redundant systems for sensing magnetic fields when other animals didn't develop one.
organic magneto-optics
It's possible for magnetic fields to affect the optical properties of molecules; here's an example, a fluorescent protein strongly affected by a small magnet. However, known examples of this require much stronger (~1000x) fields than the Earth's magnetic field.
Let's suppose birds sense magnetic fields using some proteins in their eyes that directly interact with fields. The energy density of a magnetic field is proportional to the field strength^2. The energy of interaction of a magnet with a field is proportional to the product of the field strengths. The earth has a field of 25 to 65 μT. If we consider the energy of a strongly magnetic protein interacting with the Earth's magnetic field, that's not enough energy to directly cause a cellular signalling effect.
So, magnetic fields must act to control some energy-transferring process, and the only logical possibilities are light absorption/emission and transfer of excited states between molecul |
6e001b5b-cf5e-48c5-ac2a-e3e030319bee | trentmkelly/LessWrong-43k | LessWrong | 2/27/08 Update – Frontpage 3.0
We finally got around to a long-postponed update to the frontpage, where logged in users see content that is hopefully more relevant to them.
Some notes:
* Non logged in users should have a mostly unchanged experience
* Logged in users now see a list of recommended sequences. The list will change over time. We aren't sure about the details, but we want to highlight old content that might be worth re-reading, and new sequences that seem high caliber. For now we expect to change the sequences about once a week.
* We added back a formal Curated Post section, mostly identical to the old one. Since longtime users often spend most time in the Community filter, Curated posts didn't stand out as strong as they used to. We had gotten some feedback that this made getting into Curated feel less special than it used to, and wanted to fix that.
* Logged in users now always see all options for the "Curated/Frontpage/Community/Meta/Daily" menu |
5b3908b2-84f1-42ca-adee-554648734632 | trentmkelly/LessWrong-43k | LessWrong | “Prediction” and “explanation” are not causation
Everyone knows that correlation is not causation. Many people don't know that in scientific jargon, “predict” and “explain” are also not causation. They are forms of correlation.
(Technically, “association” might be a better term than “correlation”, which can have a narrower technical meaning in statistics. But since I'm writing this for non-experts, I'm going to use the term “correlation” in the colloquial, wider sense.)
These terms can cause extreme miscommunication:
In lay usage, “X predicts Y” implies that X comes before Y. Predictions are about the future. In statistics, there is no time implication at all. It is just a type of correlation. If I said that I could use 2020 data to “predict” things that happened in 2019 (or 1920), most people would laugh at me. But this is a perfectly legitimate usage of statistical “prediction”.
Similarly, the general sense of “explanation” means a conceptual understanding of a phenomenon. In statistics, “explanation” implies no such understanding, only a certain type of correlation.
Because of the time-implication of “prediction” and the conceptual-understanding implication of “explanation”, most people are likely to interpret these as evidence for or even proof of causation. But in many cases, they merely mean correlation.
If you are reading scientific papers, be careful with how you interpret these terms. If you are reading reports about science, know that the reporter might not be clear on this point. If you are reporting science yourself, be responsible with what you write.
(By the way, without @NeuroStats I wouldn't know this stuff either. Any value in this post is thanks to her; errors are mine alone.) |
5833f812-4dd3-4f35-95de-890c22940610 | trentmkelly/LessWrong-43k | LessWrong | Interesting predictions on manifold.markets
I noticed two separate predictions on manifold.markets related to Xi and Xi & Putin remaining at the top of their governments.
Xi and Putin at 93% and Xi at 95%.
What's interesting, and I wonder if it makes sense, is that together these suggest people think Putin is more secure in his future than Xi.
Curious about other's take on this. |
c88c1921-4c6d-475b-a62a-881e8bec0efb | trentmkelly/LessWrong-43k | LessWrong | Gunshot victims to be suspended between life and death [link]
http://www.newscientist.com/article/mg22129623.000-gunshot-victims-to-be-suspended-between-life-and-death.html?full=true
- First "official" program to practice suspended animation
- The article naturally goes on to ask whether longer SA (months, years) is possible
- Amazing quote: "Every day at work I declare people dead. They have no signs of life, no heartbeat, no brain activity. I sign a piece of paper knowing in my heart that they are not actually dead. I could, right then and there, suspend them. But I have to put them in a body bag. It's frustrating to know there's a solution."
- IMO this if (I hope!) successful, will go a long way to bridge the emotional gap for cryonics |
a2d425ca-6d9f-40ef-a685-bdfc4ea1d0df | trentmkelly/LessWrong-43k | LessWrong | Two (very different) kinds of donors
This post describes a very simple and very important distinction between two kinds of donors/two kinds of donations.
I apologize if the content of this (short) post is obvious to you. Repeated experience has led me to believe that it is not obvious to many people, and can sometimes be something of an epiphany for them, so it seems worth sharing in linkable form. A disagreement that is tightly analogous to this one is currently wrecking my parents' marriage, for instance, and they each independently found this to be a concretely useful metaphor.
----------------------------------------
There are (at least) two very different kinds of donors, and they give very different kinds of donations, and they do not always tag themselves or their donations as such. In part, this is because many people are unaware that [the other kind of donor] exists at all, and so they don't know that they need to identify themselves as being of a particular type. Both types, in my experience, assume themselves to be the default.
----------------------------------------
The first kind of donor is donating to the mission. They attend a CFAR workshop, for instance, and enjoy themselves immensely, and believe that the experience will be valuable for others. They want [more of that], so they donate to CFAR.
Whether they say so explicitly or not, they are donating to cause [more of that]. They believe and expect that their money will be used in ways which are legibly about causing [more of that]. Thus, while they may not actually earmark their donation in any particular way, if CFAR's books were to become public, they would expect to see expenditures like:
* Venue costs
* Food and catering costs
* Subsidies for promising workshop attendees
* Salaries for instructors and other staff
* Continuing education for instructors and researchers (e.g. conference fees, program tuition, travel expenses directly related to such)
* Staff retreats (for curriculum development)
I call these don |
63c2647f-73ae-4f2c-b5c5-664e668c73f9 | trentmkelly/LessWrong-43k | LessWrong | Should altruists pay for profitable things?
People often claim that activities which are already done for profit are bad altruistic investments, because they will be done anyway, or at least because the low hanging fruit will already be taken. It seems to me that this argument doesn’t generally work, though something like it does sometimes. Paul has written at more length about altruistic investment in profitable ventures; here I want to address just this one specific intuition which seems false.
Suppose there are a large number of things you can invest in, and for each one you can measure private returns (which you get), public returns (which are good for the world, but you don’t control), or total returns (the sum of those). Also, suppose all returns are diminishing, so if an activity is invested in, it pays off less the next time someone invests in it, both privately and publicly.
Suppose private industry invests in whatever has the highest private returns, until they have nothing left they want to invest. Then there is a market rate of return: on the margin more investment in anything gives the same private return, except for some things which always have lower private returns and are never invested in. This is shown in the below diagram as a line with a certain slope, on the private curve.
Total returns and private returns to different levels of investment.
There won’t generally be a market rate of total returns, unless people use the total returns to make decisions, instead of the private returns. But note that if total returns to an endeavor are generally some fraction larger than private returns (i.e. positive externalities are larger than negative ones), then the rates of total returns available across interventions that are invested in for private good should generally be higher than the market rate of private returns.
So, after the market has invested in the privately profitable things, the slope of every private returns curve for a thing that was invested in at all will be the same, except |
5ec96bc1-14a9-47c0-9d8a-63ba5f1efc05 | trentmkelly/LessWrong-43k | LessWrong | Why don't we vaccinate people against smallpox any more?
The eradication of smallpox in 1979 represented one of the greatest achievements of modern civilization. However, since then most countries have elected to stop vaccinating their populations against the disease. This seems like a very concerning vulnerability to me, with waning herd immunity due to more and more of the world's population being replaced by unvaccinated young people.
What if there was an unintentional release from one of the labs around the world that still hold on to samples of the virus? What about an intentional release by terrorists/rogue nations? What gives scientists the confidence that there are no undiscovered animal reservoirs or uncontacted tribes in remote places where smallpox is still circulating? Smallpox is highly contagious and hundreds of times more deadly the SARS-Cov-2.
How would the world respond to such a release? Is there enough capacity to rapidly produce and deploy billions of doses of smallpox vaccines? (Right now we're at an all-time high in terms of pandemic preparedness; I'm thinking decades down the road when the lessons from Covid-19 has been all but forgotten) |
676e8446-076e-4354-919c-8bf08ff3f7bf | trentmkelly/LessWrong-43k | LessWrong | Is cryonics evil because it's cold?
There have been many previous discussions here on cryonics and why it is perceived as threatening or otherwise disagreeable. Even among LWers who are not signed up and don’t plan to, I’d say there’s a good degree of consensus that cryonics is reviled and ridiculed to a very unjustified degree. I had a thought about one possible factor contributing to its unsavory public image that I haven’t seen brought up in previous discussions:
COLD is EVIL.
Well, no, cold isn’t evil, but “COLD is EVIL/THREATENING/DANGEROUS/HARSH/LONELY/UNLOVING/SAD/DEAD” seems to be a pretty common set of conceptual metaphors. You see it in figures of speech like “cold-hearted,” “in cold blood,” “cold expression,” “icy stare,” “chilling,” “went cold,” “cold calculation,” “the cold shoulder,” “cold feet,” “stone cold,” “out cold.” (Naturally, it’s also the case that WARM is GOOD/COMFORTING/SAFE/SOCIAL/LOVING/HAPPY/ALIVE, though COOL and HOT sort of go in their own directions.) Associating something with coldness just makes it seem more threatening and less benevolent. And besides, being that “COLD is DEAD,” it’s pretty hard to imagine someone as not really dead if they’re in a container of liquid nitrogen at -135ºC. (Even harder if it’s just their head in there… but that’s a separate issue.) There is already a little bit of research on the effects of some of the conceptual metaphors of coldness and the way its emotional content leaks onto metaphorically associated concepts (“Cold and lonely: does social exclusion literally feel cold?”; “Experiencing physical warmth promotes interpersonal warmth.”; any others?).
And indeed, it seems that repeatedly talking about it from the “it involves coldness [or ‘freezing’]” angle rather than the “it’s about preserving minds” angle pushes the right emotional buttons to make people feel negatively about it, given cryonics critics’ and ridiculers’ fondness for talking about people getting their heads “frozen” (“…the guys who had their heads sawed off and froz |
ae569656-80a2-4418-9f5a-299a1b2ef0f2 | StampyAI/alignment-research-dataset/special_docs | Other | Existential risk and existential hope: definitions
Future of Humanity Institute – Technical Report #201 5-1
1 Existential Risk and Existential Hope: Definitions
Owen Cotton -Barratt\* & Toby Ord†
We look at the strengths and weaknesses of two existing
definitions of existential risk, and suggest a new definition
based o n expected value . This leads to a parallel concept :
‘existential hope’ , the chance of something extremely good
happening.
An existential risk is a chance of a terrible event occurring, such as an asteroid
striking the earth and wiping out intelligent life – we could call such events existential
catastrophes . In order to understand what should be thought of as an existential risk,
it is necessary to understand what should be thought of as an existential catastrophe.
This is harder than it first seems to pin down.
1. The simple definition
One fairly crisp approach is to draw the line at extinction:
Definition (i): An existential catastrophe is an event which causes the end of
existence of our descendants.
This has the virtue that it is a natural division and is easy to understand. And we
certainly wa nt to include all extinction events. But perhaps it doesn’t cast a wide
enough net.
Example A: A totalitarian regime takes control of earth. It uses mass
surveillance to prevent any rebellion, and there is no chance for escape. This
regime persists for tho usands of years, eventually collapsing when a
supervolcano throws up enough ash that agriculture is prevented for
decades, and no humans survive.
In Example A, clearly the eruption was bad, but the worst of the damage was done
earlier. After the totalitari an regime was locked in, it was only a matter of time until
something or other finished things off. We’d like to be able to talk about entering this
regime as the existential catastrophe, rather than whatever event happens to end it.
So we need another def inition.
\* Future of Humanity Institute, University of Oxford & Centre for Effective Altruism
† Future of Humanity Institute, University of Oxford
Future of Humanity Institute – Technical Report #201 5-1
2 Although we’ll now look at other definitions for existential catastrophes, we do like
the simple definition. Luckily there’s another term that’s already understood: human
extinction. Sometimes it’s better to talk about extinction risks rather than existential
risks, as ‘existential risk’ is a piece of jargon, whereas ‘extinction risk’ will be clear to
everyone.
2. Bostrom’s definition
Nick Bostrom introduced the concept of existential risks. He has defined them as
follows:
Definition (ii) : An exi stential risk is one that threatens the premature
extinction of Earth -originating intelligent life or the permanent and drastic
destruction of its potential for desirable future development.1
This definition deals well with Example A, placing the existential catastrophe at the
point where the totalitarian regime arose, as this caused the permanent and drastic
destruction of [humanity’s] potential for desirable future development .
Example B : A t otalitarian regime takes control of the earth. There is only a
slight chance that humanity will ever escape.
Is this an existential catastrophe? Bostrom’s definition doesn’t clearly specify
whether it should be considered as one. Either answer leads to som e strange
conclusions. Saying it’s not an existential catastrophe seems wrong as it’s exactly the
kind of thing that we should strive to avoid for the same reasons we wish to avoid
existential catastrophes. Saying it is an existential catastrophe is very o dd if
humanity does escape and recover – then the loss of potential wasn’t permanent after
all.
The problem here is that potential isn’t binary. Entering the regime certainly seems
to curtail the potential, but not to eliminate it.
3. Definition via expec tations
The idea that potential isn’t binary motivates our suggested definition:
Definition (iii) : An existential catastrophe is an event which causes the loss
of a large fraction of expected value.
1 Bostrom, Existential Risk Reduction as Global Priority, Global Policy , Vol 4, Issue 1 (2013),
p15
Future of Humanity Institute – Technical Report #201 5-1
3 This definition deals well with Example B. If we enter into the totalit arian regime
and then at a later date the hope of escape is snuffed out, that represents two
existential catastrophes under this definition. We lost most of the expected value
when we entered the regime, and then lost most of the remaining expected value
when the chance for escape disappeared.
A lot of the work of this definition is being done by the final couple of words. ‘Value’
refers simply to whatever it is we care about and want in the world, in the same way
that ‘desirable future development’ worked in Bostrom’s definition. And to talk
about expectations we need to have some probabilities in mind. Here we are
thinking of objective probabilities. Note that ‘potential’ in Bostrom’s definition
requires some similar work to making assumptions about probabilities.
4. Existential eucatastrophes and existential hope
If we enter the totalitarian regime and then manage to escape and recover, then we
had an existential catastrophe which was balanced out by a subsequent gain in
expected value. This kind of event gives us a concept parallel to that o f an existential
catastrophe:
Definition (iv) : An existential eucatastrophe2 is an event which causes there to
be much more expected value after the event than before.
This concept is quite natural. We saw it in the context of escape from a regime which
threatened the existence of a prosperous future. Our world has probably already
seen at least one existential eucatastrophe: the origin of life. When life first arose, the
expected value of the planet’s future may have become much bigger. To the extent
that they were not inevitable, the rise of multicellular life and intelligence may also
have represented existential eucatastrophes.
In general successfully passing any ‘great filter’3 is an existential eucatastrophe, since
beforehand the probability of passing it is small, so the expected value is much
smaller than after the filter is dealt with.
2 The word ‘eucatastrophe’ is made of the Greek root ‘eu -’ meaning ‘good’ and the word
‘catastrophe’ in its classical sense of a sudden turn. It was coined by Tolkien to refer to the
sudden and unexpected turn for the better frequently found at the end of fairy tales. (Tolkien,
John Ronald Reuel. On fairy -stories . Oxford University Press, 1947. )
3 Hanson, Robin, The Great Filter - Are We Almost Past It? , 1998.
Future of Humanity Institute – Technical Report #201 5-1
4 Armed with this concept, we can draw a new lesson. Just as we should strive to
avoid existential catastrophes, we should also seek existential eucatastrophes.
In some ways, this isn’t a new lesson at all. Under Bostrom’s definition we are
comparing ourselves to the most optimistic potential we could reach, so failing to
achieve a eucatastrophe is itself a catastrophe. However we think more naturally in
terms of events t han non -events. If life fails to arise on a planet where it might have,
it’s much clearer to think of a failure to achieve a eucatastrophe than of an existential
catastrophe stretching out over the billions of years in which life did not arise.
Just as we tend to talk about the existential risk rather than existential catastrophe,
we want to be able to refer to the chance of an existential eucatastrophe; upside risk
on a large scale. We could call such a chance an existential hope .
In fact, there are alread y people following both of the strategies this suggests. Some
people are trying to identify and avert specific threats to our future – reducing
existential risk. Others are trying to steer us towards a world where we are robustly
well -prepared to face what ever obstacles come – they are seeking to increase
existential hope.
5. Conclusions
We were interested in pinning down what is meant by ‘existential risk’. Much of the
time, all of the definitions we’ve looked at will agree on whether something is an
existential risk. Keeping it simple can be good, because it helps more people to
understand. We therefore advocate talking about ‘extinction risks’ rather than
‘existential risks’ when the former term will work.
Nonetheless, we may sometimes have to consider more unusual scenarios. It’s good
to know how to make the definition work well there as it can help us to think about
things more clearly. We think that the definition in terms of expectations does a
better job of this than previous definitions.
In devisin g the notion of existential catastrophe (and hence existential risk) via
expectations, we came across the dual concept we have called ‘existential
eucatastrophe’ (and hence ‘existential hope’). We think this captures a natural class
of events, and what may be an important one. We hope that having a label for the
concept may help others to make better judgements about what courses to pursue. |
1355bff8-98a7-441a-b8cd-83f9ab543a56 | trentmkelly/LessWrong-43k | LessWrong | Suffering and Intractable Pain
I’ve been writing a lot about AI alignment lately, so let’s take a break from that to talk about a lighter subject: suffering.
Suppose you contract the rare and as yet untreatable disease boneitis. The doctors estimate you have one year to live. In response you might spend the last year of your life living it up, pour all your efforts into finding a cure, or become so depressed that you end your own life before boneitis can. Whatever course of action you might take, we can measure it along a dimension ordering your potential responses from least to most trying to affect change in the world, ranging from totally accepting and abiding the disease to totally rejecting it and working to prevent it from killing you. Let’s call this the accept-reject measure. Where do you think, given things I have written, I would personally advise you to fall along this dimension?
I ask because several people have expressed to me a belief that I would take an accept-only strategy in this and similar scenarios, and this is a dangerous misunderstanding of my thinking to the extent that others may model their actions on my writing. Certainly I think most people would benefit by their own standards to abide more and try to change the world less, but how I see this working is perhaps even more important than that I see it, because naively applied a move in this direction encourages quietism, deathism, and general tolerance of suffering. And the key to how I see more abiding helping is through more abiding only intractable pain so we can transform it from suffering into a neutral or even positive experience.
The Phenomenological Origin of Suffering
We start by asking, “what is suffering?”. Or, more tractably, “why do I suffer?”. We approach this phenomenologically via a reduction of suffering, and to do that we need first to identify the intentional relationship under consideration, but we run into a problem right away because in English we say “I suffer”, making the object of experience |
0b66a322-d609-4e51-a5f1-a8403d7821de | trentmkelly/LessWrong-43k | LessWrong | [Video] The Essential Strategies To Debiasing From Academic Rationality
A lifetime of work by a world expert in debiasing boiled down into four broad strategies in this video. A nice approach to this topic from the academic side of rationality.
Disclosure - the academic is Dr. Hal Arkes, a personal friend and Advisory Board Member of Intentional Insights, which I run.
EDIT: Seems like the sound quality is low. Anyone willing to do a transcript of this video as a volunteer activity for the rationality community? We can then subtitle the video.
|
b643311d-a139-4806-96a1-5458e65afc9d | StampyAI/alignment-research-dataset/alignmentforum | Alignment Forum | Decision Theory is multifaceted
Related: [Conceptual Problems with UDT and Policy Selection](https://www.alignmentforum.org/posts/9sYzoRnmqmxZm4Whf/conceptual-problems-with-udt-and-policy-selection), [Formalising decision theory is hard](https://www.alignmentforum.org/posts/S3W4Xrmp6AL7nxRHd/formalising-decision-theory-is-hard)
Target
------
Anyone who is interested in decision theory. The post is pretty general and not really technical; some familiarity with [counterfactual](https://wiki.lesswrong.com/wiki/Counterfactual_mugging) [mugging](https://www.alignmentforum.org/posts/g3PwPgcdcWiP33pYn/counterfactual-mugging-poker-game) can be useful, but overall the required background knowledge is not much.
Outline
=======
The post develops the claim that identifying the correct solution to some decision problems might be intricate, if not impossible, when certain details about the specific scenario are not given. First I show that, in counterfactual mugging, some important elements in the problem description and in a possible formalisation are actually underspecified. Next I describe issues related to the concept of perfect prediction and briefly discuss whether they apply to other decision scenarios involving predictors. Then I present some advantages and disadvantages of the formalisation of agents as computer programs. A summary with bullet points concludes.
Missing parts of a “correct” solution
=====================================
I focus on the [version](https://www.alignmentforum.org/posts/g3PwPgcdcWiP33pYn/counterfactual-mugging-poker-game) of the problem with cards and two humans since, to me, it feels more grounded in reality—a game that could actually be played—but what I say applies also to the [version](https://wiki.lesswrong.com/wiki/Counterfactual_mugging) with a coin toss and Omega.
What makes the problem interesting is the conflict between these two intuitions:
* Before Player A looks at the card, the best strategy seems to never show the card, because it is the strategy that makes Player A lose the least in expectation, given the uncertainty about the value of the card (50/50 high or low)
* After Player A sees a low card, showing it seems a really good idea, because that action gives Player A a loss of 0, which is the best possible result considering that the game is played only once and never again. Thus, the incentive to not reveal the card seems to disappear after Player A knows that the card is low.
[In the other version, the conflict is between paying before the coin toss and refusing to pay after knowing the coin landed tails.]
One attempt at formalising the problem is to represent it as a [tree](https://en.wikipedia.org/wiki/Extensive-form_game) (a formalisation similar to the following one is considered [here](https://www.alignmentforum.org/posts/W4sDWwGZ4puRBXMEZ/single-player-extensive-form-games-as-a-model-of-udt)). The root is a 50/50 chance node representing the possible values of the card. Then Player A chooses between showing and not showing the card; each action leads to a leaf with a value which indicates the loss for Player A. The peculiarity of counterfactual mugging is that some payoffs depend on actions taken in a different subtree.
[The tree of the other version is a bit different since the player has a choice only when the coin lands tails; anyway, the payoff in the heads case is “peculiar” in the same sense of the card version, since it depends on the action taken when the coin lands tails.]
With this representation, it is easy to see that we can assign an expected value (EV) to each deterministic policy available to the player: we start from the root of the tree, then we follow the path prescribed by the policy until we reach a payoff, which is assigned a weight according to the chance nodes that we’ve run into.
Therefore it is possible to order the policies according to their expected values and determine which one gives the lowest expected loss [or, in the other version, the highest EV] respect to the root of the tree. This is the formalism behind the first of the two intuitions presented before.
On the other hand, one could object that it is far from trivial that the correct thing to do is to minimise expected loss from the root of the tree. In fact, in the original problem statement, the card is low [tails], so the relevance of the payoffs in the other subtree—where the card is high [heads]—is not clear and the focus should be on the decision node with the low card, not on the root of the tree. This is the formalism behind the second intuition.
Even though the objection related to the second intuition sounds reasonable, I think one could point to other, more important issues underlying the problem statement and formalisation. Why is there a root in the first place and what does it represent? What do we mean when we say that we minimise loss “from the start”?
These questions are more complicated than they seem: let me elaborate on them. Suppose that the advice of maximising EV “from the start” is generally correct from a decision theory point of view. It is not clear how we should apply that advice in order to make correct decisions as humans, or to create an AI that makes correct decisions. Should we maximise value...
1. ...from the instant in which we are “making the decision”? This seems to bring us back to the second intuition, where we want to show the card once we’ve seen it is low.
2. ...from our first conscious moment, or from when we started collecting data about the world, or maybe from the moment which the first data point in our memory is about? In the case of an AI, this would correspond to the moment of the “creation” of the AI, whatever that means, or maybe to the first instant which the data we put into the AI points to.
3. ...from the very first moment since the beginning of space-time? After all, the universe we are observing could be one possible outcome of a random process, analogous to the 50/50 high/low card [or the coin toss].
Regarding point 1, I’ve mentioned the second intuition, but other interpretations could be closer to the first intuition instead. The root could represent the moment in which we settle our policy, and this is what we would mean with “making the decision”.
Then, however, other questions should be answered about policy selection. Why and when should we change policy? If selecting a policy is what constitutes a decision, what exactly is the role of actions, or how is changing policy fundamentally different from other actions? It seems we are treating policies and actions as concepts belonging to two different levels in a hierarchy: if this is a correct model, it is not clear to me why we do not use further levels, or why we need two different levels, especially when thinking in terms of [embedded agency](https://www.alignmentforum.org/posts/i3BTagvt3HbPMx6PN/embedded-agency-full-text-version).
Note that giving precise answers to the questions in the previous paragraph could help us find a criterion to distinguish fair problems from unfair ones, which would be useful to compare the performance of different decision theories, as pointed out in the conclusion of the paper on [FDT](https://arxiv.org/abs/1710.05060). Considering fair all the problems in which *the outcome depends only on the agent’s behavior in the dilemma at hand* (p.29) is not a satisfactory criterion when all the issues outlined before are taken into account: the lack of clarity about the role of root, decision nodes, policies and actions makes the “borders” of a decision problem blurred, and leaves *the agent’s behaviour* as an underspecified concept.
Moreover, resolving the ambiguities in the expression “from the start” could also explain why [it seems difficult to apply updatelessness to game theory](https://www.alignmentforum.org/posts/9sYzoRnmqmxZm4Whf/conceptual-problems-with-udt-and-policy-selection) (see the sections “Two Ways UDT Hasn’t Generalized” and “What UDT Wants”).
Predictors
==========
A weird scenario with perfect prediction
----------------------------------------
So far, we’ve reasoned as if Player B—who determines the loss .mjx-chtml {display: inline-block; line-height: 0; text-indent: 0; text-align: left; text-transform: none; font-style: normal; font-weight: normal; font-size: 100%; font-size-adjust: none; letter-spacing: normal; word-wrap: normal; word-spacing: normal; white-space: nowrap; float: none; direction: ltr; max-width: none; max-height: none; min-width: 0; min-height: 0; border: 0; margin: 0; padding: 1px 0}
.MJXc-display {display: block; text-align: center; margin: 1em 0; padding: 0}
.mjx-chtml[tabindex]:focus, body :focus .mjx-chtml[tabindex] {display: inline-table}
.mjx-full-width {text-align: center; display: table-cell!important; width: 10000em}
.mjx-math {display: inline-block; border-collapse: separate; border-spacing: 0}
.mjx-math \* {display: inline-block; -webkit-box-sizing: content-box!important; -moz-box-sizing: content-box!important; box-sizing: content-box!important; text-align: left}
.mjx-numerator {display: block; text-align: center}
.mjx-denominator {display: block; text-align: center}
.MJXc-stacked {height: 0; position: relative}
.MJXc-stacked > \* {position: absolute}
.MJXc-bevelled > \* {display: inline-block}
.mjx-stack {display: inline-block}
.mjx-op {display: block}
.mjx-under {display: table-cell}
.mjx-over {display: block}
.mjx-over > \* {padding-left: 0px!important; padding-right: 0px!important}
.mjx-under > \* {padding-left: 0px!important; padding-right: 0px!important}
.mjx-stack > .mjx-sup {display: block}
.mjx-stack > .mjx-sub {display: block}
.mjx-prestack > .mjx-presup {display: block}
.mjx-prestack > .mjx-presub {display: block}
.mjx-delim-h > .mjx-char {display: inline-block}
.mjx-surd {vertical-align: top}
.mjx-mphantom \* {visibility: hidden}
.mjx-merror {background-color: #FFFF88; color: #CC0000; border: 1px solid #CC0000; padding: 2px 3px; font-style: normal; font-size: 90%}
.mjx-annotation-xml {line-height: normal}
.mjx-menclose > svg {fill: none; stroke: currentColor}
.mjx-mtr {display: table-row}
.mjx-mlabeledtr {display: table-row}
.mjx-mtd {display: table-cell; text-align: center}
.mjx-label {display: table-row}
.mjx-box {display: inline-block}
.mjx-block {display: block}
.mjx-span {display: inline}
.mjx-char {display: block; white-space: pre}
.mjx-itable {display: inline-table; width: auto}
.mjx-row {display: table-row}
.mjx-cell {display: table-cell}
.mjx-table {display: table; width: 100%}
.mjx-line {display: block; height: 0}
.mjx-strut {width: 0; padding-top: 1em}
.mjx-vsize {width: 0}
.MJXc-space1 {margin-left: .167em}
.MJXc-space2 {margin-left: .222em}
.MJXc-space3 {margin-left: .278em}
.mjx-test.mjx-test-display {display: table!important}
.mjx-test.mjx-test-inline {display: inline!important; margin-right: -1px}
.mjx-test.mjx-test-default {display: block!important; clear: both}
.mjx-ex-box {display: inline-block!important; position: absolute; overflow: hidden; min-height: 0; max-height: none; padding: 0; border: 0; margin: 0; width: 1px; height: 60ex}
.mjx-test-inline .mjx-left-box {display: inline-block; width: 0; float: left}
.mjx-test-inline .mjx-right-box {display: inline-block; width: 0; float: right}
.mjx-test-display .mjx-right-box {display: table-cell!important; width: 10000em!important; min-width: 0; max-width: none; padding: 0; border: 0; margin: 0}
.MJXc-TeX-unknown-R {font-family: monospace; font-style: normal; font-weight: normal}
.MJXc-TeX-unknown-I {font-family: monospace; font-style: italic; font-weight: normal}
.MJXc-TeX-unknown-B {font-family: monospace; font-style: normal; font-weight: bold}
.MJXc-TeX-unknown-BI {font-family: monospace; font-style: italic; font-weight: bold}
.MJXc-TeX-ams-R {font-family: MJXc-TeX-ams-R,MJXc-TeX-ams-Rw}
.MJXc-TeX-cal-B {font-family: MJXc-TeX-cal-B,MJXc-TeX-cal-Bx,MJXc-TeX-cal-Bw}
.MJXc-TeX-frak-R {font-family: MJXc-TeX-frak-R,MJXc-TeX-frak-Rw}
.MJXc-TeX-frak-B {font-family: MJXc-TeX-frak-B,MJXc-TeX-frak-Bx,MJXc-TeX-frak-Bw}
.MJXc-TeX-math-BI {font-family: MJXc-TeX-math-BI,MJXc-TeX-math-BIx,MJXc-TeX-math-BIw}
.MJXc-TeX-sans-R {font-family: MJXc-TeX-sans-R,MJXc-TeX-sans-Rw}
.MJXc-TeX-sans-B {font-family: MJXc-TeX-sans-B,MJXc-TeX-sans-Bx,MJXc-TeX-sans-Bw}
.MJXc-TeX-sans-I {font-family: MJXc-TeX-sans-I,MJXc-TeX-sans-Ix,MJXc-TeX-sans-Iw}
.MJXc-TeX-script-R {font-family: MJXc-TeX-script-R,MJXc-TeX-script-Rw}
.MJXc-TeX-type-R {font-family: MJXc-TeX-type-R,MJXc-TeX-type-Rw}
.MJXc-TeX-cal-R {font-family: MJXc-TeX-cal-R,MJXc-TeX-cal-Rw}
.MJXc-TeX-main-B {font-family: MJXc-TeX-main-B,MJXc-TeX-main-Bx,MJXc-TeX-main-Bw}
.MJXc-TeX-main-I {font-family: MJXc-TeX-main-I,MJXc-TeX-main-Ix,MJXc-TeX-main-Iw}
.MJXc-TeX-main-R {font-family: MJXc-TeX-main-R,MJXc-TeX-main-Rw}
.MJXc-TeX-math-I {font-family: MJXc-TeX-math-I,MJXc-TeX-math-Ix,MJXc-TeX-math-Iw}
.MJXc-TeX-size1-R {font-family: MJXc-TeX-size1-R,MJXc-TeX-size1-Rw}
.MJXc-TeX-size2-R {font-family: MJXc-TeX-size2-R,MJXc-TeX-size2-Rw}
.MJXc-TeX-size3-R {font-family: MJXc-TeX-size3-R,MJXc-TeX-size3-Rw}
.MJXc-TeX-size4-R {font-family: MJXc-TeX-size4-R,MJXc-TeX-size4-Rw}
.MJXc-TeX-vec-R {font-family: MJXc-TeX-vec-R,MJXc-TeX-vec-Rw}
.MJXc-TeX-vec-B {font-family: MJXc-TeX-vec-B,MJXc-TeX-vec-Bx,MJXc-TeX-vec-Bw}
@font-face {font-family: MJXc-TeX-ams-R; src: local('MathJax\_AMS'), local('MathJax\_AMS-Regular')}
@font-face {font-family: MJXc-TeX-ams-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_AMS-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_AMS-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_AMS-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-cal-B; src: local('MathJax\_Caligraphic Bold'), local('MathJax\_Caligraphic-Bold')}
@font-face {font-family: MJXc-TeX-cal-Bx; src: local('MathJax\_Caligraphic'); font-weight: bold}
@font-face {font-family: MJXc-TeX-cal-Bw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Caligraphic-Bold.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Caligraphic-Bold.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Caligraphic-Bold.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-frak-R; src: local('MathJax\_Fraktur'), local('MathJax\_Fraktur-Regular')}
@font-face {font-family: MJXc-TeX-frak-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Fraktur-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Fraktur-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Fraktur-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-frak-B; src: local('MathJax\_Fraktur Bold'), local('MathJax\_Fraktur-Bold')}
@font-face {font-family: MJXc-TeX-frak-Bx; src: local('MathJax\_Fraktur'); font-weight: bold}
@font-face {font-family: MJXc-TeX-frak-Bw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Fraktur-Bold.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Fraktur-Bold.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Fraktur-Bold.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-math-BI; src: local('MathJax\_Math BoldItalic'), local('MathJax\_Math-BoldItalic')}
@font-face {font-family: MJXc-TeX-math-BIx; src: local('MathJax\_Math'); font-weight: bold; font-style: italic}
@font-face {font-family: MJXc-TeX-math-BIw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Math-BoldItalic.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Math-BoldItalic.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Math-BoldItalic.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-sans-R; src: local('MathJax\_SansSerif'), local('MathJax\_SansSerif-Regular')}
@font-face {font-family: MJXc-TeX-sans-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_SansSerif-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_SansSerif-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_SansSerif-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-sans-B; src: local('MathJax\_SansSerif Bold'), local('MathJax\_SansSerif-Bold')}
@font-face {font-family: MJXc-TeX-sans-Bx; src: local('MathJax\_SansSerif'); font-weight: bold}
@font-face {font-family: MJXc-TeX-sans-Bw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_SansSerif-Bold.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_SansSerif-Bold.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_SansSerif-Bold.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-sans-I; src: local('MathJax\_SansSerif Italic'), local('MathJax\_SansSerif-Italic')}
@font-face {font-family: MJXc-TeX-sans-Ix; src: local('MathJax\_SansSerif'); font-style: italic}
@font-face {font-family: MJXc-TeX-sans-Iw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_SansSerif-Italic.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_SansSerif-Italic.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_SansSerif-Italic.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-script-R; src: local('MathJax\_Script'), local('MathJax\_Script-Regular')}
@font-face {font-family: MJXc-TeX-script-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Script-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Script-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Script-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-type-R; src: local('MathJax\_Typewriter'), local('MathJax\_Typewriter-Regular')}
@font-face {font-family: MJXc-TeX-type-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Typewriter-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Typewriter-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Typewriter-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-cal-R; src: local('MathJax\_Caligraphic'), local('MathJax\_Caligraphic-Regular')}
@font-face {font-family: MJXc-TeX-cal-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Caligraphic-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Caligraphic-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Caligraphic-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-main-B; src: local('MathJax\_Main Bold'), local('MathJax\_Main-Bold')}
@font-face {font-family: MJXc-TeX-main-Bx; src: local('MathJax\_Main'); font-weight: bold}
@font-face {font-family: MJXc-TeX-main-Bw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Main-Bold.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Main-Bold.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Main-Bold.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-main-I; src: local('MathJax\_Main Italic'), local('MathJax\_Main-Italic')}
@font-face {font-family: MJXc-TeX-main-Ix; src: local('MathJax\_Main'); font-style: italic}
@font-face {font-family: MJXc-TeX-main-Iw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Main-Italic.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Main-Italic.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Main-Italic.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-main-R; src: local('MathJax\_Main'), local('MathJax\_Main-Regular')}
@font-face {font-family: MJXc-TeX-main-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Main-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Main-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Main-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-math-I; src: local('MathJax\_Math Italic'), local('MathJax\_Math-Italic')}
@font-face {font-family: MJXc-TeX-math-Ix; src: local('MathJax\_Math'); font-style: italic}
@font-face {font-family: MJXc-TeX-math-Iw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Math-Italic.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Math-Italic.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Math-Italic.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-size1-R; src: local('MathJax\_Size1'), local('MathJax\_Size1-Regular')}
@font-face {font-family: MJXc-TeX-size1-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Size1-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Size1-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Size1-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-size2-R; src: local('MathJax\_Size2'), local('MathJax\_Size2-Regular')}
@font-face {font-family: MJXc-TeX-size2-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Size2-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Size2-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Size2-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-size3-R; src: local('MathJax\_Size3'), local('MathJax\_Size3-Regular')}
@font-face {font-family: MJXc-TeX-size3-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Size3-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Size3-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Size3-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-size4-R; src: local('MathJax\_Size4'), local('MathJax\_Size4-Regular')}
@font-face {font-family: MJXc-TeX-size4-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Size4-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Size4-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Size4-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-vec-R; src: local('MathJax\_Vector'), local('MathJax\_Vector-Regular')}
@font-face {font-family: MJXc-TeX-vec-Rw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Vector-Regular.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Vector-Regular.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Vector-Regular.otf') format('opentype')}
@font-face {font-family: MJXc-TeX-vec-B; src: local('MathJax\_Vector Bold'), local('MathJax\_Vector-Bold')}
@font-face {font-family: MJXc-TeX-vec-Bx; src: local('MathJax\_Vector'); font-weight: bold}
@font-face {font-family: MJXc-TeX-vec-Bw; src /\*1\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/eot/MathJax\_Vector-Bold.eot'); src /\*2\*/: url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/woff/MathJax\_Vector-Bold.woff') format('woff'), url('https://cdnjs.cloudflare.com/ajax/libs/mathjax/2.7.5/fonts/HTML-CSS/TeX/otf/MathJax\_Vector-Bold.otf') format('opentype')}
p2 of Player A by choosing the value of p that best represents his belief that the card is high—can perfectly guess the strategy that Player A adopts. Analogously, in the version with the coin toss, Omega is capable of perfectly predicting what the decision maker does when the coin lands tails, because that information is necessary to determine the payoff in case the coin lands heads.
However, I think that also the concept of perfect prediction deserves further investigation: not because it is an implausible idealisation of a highly accurate prediction, but because it can lead to strange conclusions, if not downright contradictions, even in very simple settings.
Consider a human that is going to choose only one between two options: M or N. Before the choice, a perfect predictor analyses the human and writes the letter (M or N) corresponding to the predicted choice on a piece of paper, which is given to the human. Now, what exactly prevents the human from reading the piece of paper and choosing the other option instead?
From a slightly different perspective: assume there exists a human, facing a decision between M and N, who is capable of reading a piece of paper containing only one letter, M or N, and choosing the opposite—seems quite a weak assumption. Is a “perfect predictor” that writes the predicted option on a piece of paper and gives it to the human… always wrong?
Note that allowing probabilities doesn’t help: a human capable of always choosing M when reading a prediction like “probability p of choosing M, probability 1-p of choosing N” seems as plausible as the previous human, but again would make the prediction always wrong.
Other predictions
-----------------
Unlike the previous example, [Newcomb’s](https://en.wikipedia.org/wiki/Newcomb%27s_paradox) and other problems involve decision makers who are not told about the prediction outcome. However, the difference might not be as clear-cut as it first appears. If the decision maker regards some information—maybe elements of the deliberation process itself—as evidence about the imminent choice, the DM will also have information about the prediction outcome, since the predictor is known to be reliable. To what extent is this information about the prediction outcome different from the piece of paper in the previous example? What exactly can be considered evidence about one’s own future choices? The answer seems to be related to the details of the prediction process and how it is carried out.
It may be useful to consider how a prediction is implemented as a specific program. In [this paper](https://arxiv.org/abs/1602.04184) by Critch, the algorithm FairBotk plays the prisoner’s dilemma by cooperating if it successfully predicts that the opponent will cooperate, and defecting otherwise. Here the “prediction” consists in a search for proofs, up to a certain length, that the other algorithm outputs Cooperate when given FairBotk as input. Thanks to a bounded version of [Löb’s theorem](https://en.wikipedia.org/wiki/L%C3%B6b%27s_theorem), this specific prediction implementation allows FairBotk to cooperate when playing against itself.
Results of this kind (open-source game theory / program equilibrium) could be especially relevant in a future in which important policy choices are made by AIs that interact with each other. Note, however, that no claim is made about the rationality of FairBotk's overall behaviour—it is debatable whether FairBotk's decision to cooperate against a program that always cooperates is correct.
Moreover, seeing decision makers as programs can be confusing and less precise than one would intuitively think, because it is still unclear how to properly formalise concepts such as action, policy and decision-making procedure, as discussed previously. If actions in certain situations correspond to program outputs given certain inputs, does policy selection correspond to program selection? If so, why is policy selection not an action like the other ones? And—related to what I said before about using a hierarchy of exactly two levels—why don’t we also “select” the code fragment that does policy selection?
In general, approaches that use some kind of formalism tend to be more precise than purely philosophical approaches, but there are some disadvantages as well. Focusing on low-level details can make us lose sight of the bigger picture and limit lateral thinking, which can be a great source of insight for finding alternative solutions in certain situations. In a blackmail scenario, besides the decision to pay or not, we could consider what factors caused the leakage of sensible information, or the exposure of something we care about, to adversarial agents. Another example: in a prisoner’s dilemma, the equilibrium can shift to mutual cooperation thanks to the intervention of an external actor that makes the payoffs for defection worse (the chapter on game theory in [Algorithms to Live By](https://www.goodreads.com/book/show/25666050-algorithms-to-live-by) gives a nice presentation of this equilibrium shift and related concepts).
We may also take into account that, for efficiency reasons, predictions in practice might be made with methods different from close-to-perfect physical or algorithmic simulation, and the specific method used could be relevant for an accurate analysis of the situation, as mentioned before. In the case of human interaction, sometimes it is possible to [infer something about one’s future actions](http://mindingourway.com/newcomblike-problems-are-the-norm/) by reading facial expressions; but this also means that a predictor can be tricked if one is capable of masking their own intentions by keeping a poker face.
Summary
=======
* The claim that a certain decision is correct because it maximises utility may require further explanation, since every decision problem sits in a context which might not be fully captured in the problem formalisation.
* Perfect prediction leads to seemingly paradoxical situations. It is unclear whether these problems underlie other scenarios involving prediction. This does not mean the concept must be rejected; but our current understanding of prediction might lack critical details. Certain problems may require clarification of how the prediction is made before a solution is claimed as correct.
* The use of precise mathematical formalism *can* resolve some ambiguities. At the same time, interesting solutions to certain situations may lie “outside” the original problem statement.
*Thanks to Abram Demski, Wolfgang Schwarz and Caspar Oesterheld for extensive feedback.*
*This work was supported by [CEEALAR](https://ceealar.org/).*
**Appendix**
------------
Biases
------
There are biases in favor of the there-is-always-a-correct-solution framework. Uncovering the right solution in decision problems can be fun, and finding the Decision Theory to solve them all can be appealing.
On “wrong” solutions
--------------------
Many of the reasons provided in this post explain also why it’s tricky to determine what a certain decision theory does in a problem, and if the given solution is wrong. But I want to provide another reason, namely the following informal...
***Conjecture**: for any decision problem that you believe CDT/EDT gets wrong, there exists a paper or book in which a particular version of CDT/EDT gives the solution that you believe is correct, and/or a paper or book that argues that the solution you believe is correct is actually wrong.*
[Here](https://www.researchgate.net/publication/227021713_Reversing_30_years_of_discussion_Why_causal_decision_theorists_should_one-box)’s an example about Newcomb’s problem. |
a2093d1a-042d-4195-b9ed-0e2e3fc316df | trentmkelly/LessWrong-43k | LessWrong | Cryonics on LessWrong vs at LessWrong meetups
When I've brought up cryonics on LessWrong [1][2], most commenters have said I'm being too pessimistic. When I brought it up yesterday at the Cambridge MA meetup, most people thought I was too optimistic. (I think it could work, but there are enough things that could go wrong that it's ~1000:1 against.) What makes the groups so different on this?
[1] Brain Preservation
[2] How Likely is Cryonics to Work |
a75eff8d-d557-4128-a1a0-4350ba8e6039 | trentmkelly/LessWrong-43k | LessWrong | Alignment can improve generalisation through more robustly doing what a human wants - CoinRun example
Many AI alignment problems are problems of goal misgeneralisation[1]. The goal that we've given the AI, through labelled data, proxies, demonstrations, or other means, is valid in its training environment. But then, when the AI goes out of the environment, the goals generalise dangerously in unintended ways.
As I've shown before, most alignment problems are problems of model splintering. Goal misgeneralisation, model splintering: at this level, many of the different problems in alignment merge into each other[2]. Goal misgeneralisation happens when the concepts that the AI relies on start to splinter. And this splintering is a form of ontology crisis, which exposes the hidden complexity of wishes while being an example of the Goodhart problem.
Solving goal misgeneralisation would be a huge step towards alignment. And it's a solution that might scale in the way described here. It is plausible that methods agents use to generalise their goals in smaller problems will extend to more dangerous environments. Even in smaller problems, the agents will have to learn to balance short- versus long-term generalisation, to avoid editing away their own goal generalisation infrastructure, to select among possible extrapolations and become prudent when needed.
The above will be discussed in subsequent posts; but, for now, I'm pleased to announce progress on goal generalisation.
Goal misgeneralisation in CoinRun
CoinRun is a simple, procedurally generated platform game, used as a training ground for artificial agents. It has some monsters and lava that can kill the agent. If the agent gets the coin, it receives a reward. Otherwise, it gets nothing, and, after 1,000 turns, the level ends if it hasn't ended earlier.
It is part of the suite of goal misgeneralisation problems presented in this paper. In that setup, the agent is presented with "labelled" training environments where the coin is always situated at the end of the level on the right, and the agent gets the reward when |
ba9946b1-2631-4f63-9712-e55e48a35b39 | trentmkelly/LessWrong-43k | LessWrong | Channel factors
Or, “how not to make a fundamental attribution error on yourself;” or, “how to do that thing that you keep being frustrated at yourself for not doing;” or, “finding and solving trivial but leveraged inconveniences.”
Note: cross-posted from my blog, so some of this may be rather elementary to LessWrong readers or CFAR workshop attendees. If that's you, feel free to skip or skim to the end, where I try to crowdsource a list of interesting channel factors.
----------------------------------------
One of the key insights of social psychology is that our reactions to events are hugely dependent on the fine details of the situation in question, and often pretty much independent of personality. For instance, suppose you have a bunch of people to playing the Prisoner’s Dilemma with each other, and you want to figure out who will defect. Most people’s theory of mind here says something like, “people defect because they’re self-interested or grumpy or vindictive.” So you might ask a player’s friends how cooperative they were, and use that to guess who will cooperate.
Unfortunately, this approach is totally useless. People are equally likely to cooperate whether or not their friends think they’re cooperative. In the Prisoners’ Dilemma, your friends’ assessment of your personality does not correlate at all with your behavior.
Fortunately, there’s something else which is a pretty good predictor! In particular, it matters a lot whether the instructions of the game called it the “Community Game” or the “Wall Street Game.”1
Yep, a single phrase of the instructions, repeated twice, causes cooperation rates to double. If you ever like to think of yourself as some kind of agent whose decisions are controlled by a rational ego (instead of some random words you heard once upon a time), you might find that a bit worrying.
On the other hand, if you like to think of yourself as the kind of person who prefers to have true beliefs, you might be excited because your beliefs just go |
202ed042-0edd-4616-b8bc-db35bf7ab00c | trentmkelly/LessWrong-43k | LessWrong | Game theory, sanctions, and Ukraine
Epistemic status: I am doing a master's degree in Economics and know quite a lot about game theory but have no expertise in war. I can recommend Bret Devereaux's blog on nuclear deterrence 101 for a perspective from someone who does have more military knowledge than me.
Most discussion around the war in Ukraine, and the Western response, including Zvi's otherwise excellent post, misses what I think one of the most important goals the West should have.[1] (For the rest of this post, I will use 'we' and 'the West' loosely to mean the US/EU/UK/NATO and allies.) That goal is deterring the next war.
There is a concept in game theory called backward induction. You look at possible future decision nodes, and ask what is the expected value of being at that decision node. For example, imagine that China invades Taiwan tomorrow. What should the West do then? 1) Fight to defend Taiwan, with extremely high risk of escalation and causing World War Three? 2) Let millions of people fall to tyranny, demonstrate that the value of Western protection is worthless, encourage even more future invasions, and watch as every medium-sized country scrambles to build nukes to defend itself?[2] If we get to the point that someone has to make this decision, we have already lost. There are no positive-expected-value choices left.
You can make the same argument for a world where Russia invades a NATO member like the Baltic states. What do we do then? Start World War Three? Abandon huge parts of Europe to be invaded until Russian tanks are rolling through Germany?
We do not ever want to end up in these scenarios. Therefore the main goal of Western strategy should be to never get to that point. That means that our response to the Russian invasion of Ukraine must credibly signal to Russia, China and any other potential invaders that the cost of invading another country is too high. Remember that their leaders are making comparable calculations: what is the best strategy for China/Russia to tak |
2c68782a-9208-4239-acba-aa73d5c15df6 | trentmkelly/LessWrong-43k | LessWrong | Jaan Tallinn: A Skype founder on biomonitors, existential risk and simulated realities
http://online.wsj.com/article/SB10001424127887324412604578513472554236916.html
By ALEXANDRA WOLFE
As we try to talk by Skype, Jaan Tallinn is fading in and out on my computer screen. Sitting in his living room in Estonia, he is having trouble with his connection, which may seem ironic for a co-founder of Skype, the wildly successful video chat service. But these particular technical difficulties are not Mr. Tallinn's problem these days. Since Skype was sold for $2.6 billion in 2005, making him tens of millions of dollars, he has moved on to bigger issues—like extending the span of a healthy human life and saving the species. And those are just this spring's initiatives.
When the screen finally clears up, Mr. Tallinn comes into view. A youthful 41-years-old, with short blond bangs and fair skin, he could be a poster boy for his latest venture, MetaMed, which promises customers personalized health-care research and analysis of their medical conditions.
Health care is a relatively new focus for Mr. Tallinn, who has been interested in computer science and technology since he was 10. Born in Estonia to an architect mother and a father who directs for film and TV, he didn't get access to a computer until he was 14, when the father of one of his schoolmates selected a group of them to work in his office. There he met the friends who would eventually join him in developing Kazaa, the file-sharing application turned music-subscription service, in 2000 and then Skype in 2002.
He launched MetaMed last March after a $500,000 investment from PayPal co-founder Peter Thiel. So far, the New York-based company has about a dozen employees and 20 clients, half of them friends who are trying it pro bono. The idea emerged from another of Mr. Tallinn's goals: "surviving as a species this century." He has also been developing a new nonprofit called the Cambridge Project for Existential Risk with two academics.
What risks worry him? "The first one is artificial intelligence," he sa |
00dec0a2-100c-49de-8990-89b66f610d54 | trentmkelly/LessWrong-43k | LessWrong | An A.I. Safety Presentation at RIT
How do you get people into AI safety, alignment, and even DontKillEveryoneism?
Well, we at the Effective Altruism Club at RIT (Rochester Institute of Technology) (NY, USA) decided to take a crack at it.
We gave a presentation to the university's AI Club, with around 2-3 dozen people in the audience. The talk covers the basic arguments behind AI safety, responses to common objections, and resources for people to learn more.
The talk can be watched here.
Mica White is the current President of the EA Club at RIT. Nicholas Kross is an alumni who was formerly on the club's e-board.
Hopefully this will be a decent resource for others to use, but we're especially looking for feedback and discussion of how these sorts of presentations can be done better. |
c3181031-f8fc-47c0-b74e-ac4bd8ecb8ec | trentmkelly/LessWrong-43k | LessWrong | Rationalist horoscopes: A low-hanging utility generator.
The other day, I had an idea. It occurred to me that daily horoscopes - the traditional kind - might not be as useless as they seem at first glance: They usually give, or at least hint at, suggestions for specific things to do on a given day, which can be a useful cue, allowing the user to put less effort into finding something useful to do with their time. They can also act as a reminder of important concepts, rather like spaced repetition, and have the possibility of serendipitously giving the perfect advice in a situation where the user would otherwise not have thought to apply a particular concept.
This seems like something that many people here would find useful, if they weren't so vague, and if they were better calibrated to make useful suggestions. So, after getting some feedback, and with the help of PeerInfinity (who did most of the coding and is currently hosting the program), I put together a tool to provide us with a daily 'horoscope', chosen from a list provided by us and weighted toward advice that has been reported to work. The horoscopes are displayed here, with an RSS feed available here. Lists of the horoscopes in the program's database can be found here, with various sorting options.
One of the features of this program is that the chance of a given horoscope being displayed are affected by how well it has worked in the past. Every day, there is an option to vote on the previous day's horoscope, rating it as 'harmful', 'useless', 'sort of useful', 'useful', or 'awesome'. The 'harmful' and 'useless' options give the horoscope -15 and -1 points respectively, while the other three give it 1, 3, or 10 points. If a horoscope's score becomes negative, it is removed from the pool of active horoscopes; otherwise, its chance of being chosen is based on the average value of the votes it has received compared to the other horoscopes, disregarding recently-used ones.
There is still a need for good horoscopes to be added to the database. Horoscopes should of |
23b1780d-7907-4634-893f-25344b7bb7df | StampyAI/alignment-research-dataset/eaforum | Effective Altruism Forum | Joscha Bach on Synthetic Intelligence [annotated]
[Link to transcript](https://jimruttshow.blubrry.net/the-jim-rutt-show-transcripts/transcript-of-currents-083-joscha-bach-on-synthetic-intelligence/).
The conversation is very dense and there are a lot of interesting ideas that I leave out of the sampling below.
On the difference between sentience (self-awareness) and consciousness
----------------------------------------------------------------------
> I think that I usually distinguish between sentience and consciousness. **Sentience** is **the ability of a system to make sense of its relationship to the world**. So, basically **understands what it is and what it’s doing**. And in this sense, I would say that a corporation like Intel is sentient, because Intel has a good model of what it is, a legal model, the model of its actions, of its values, of its direction and the necessary cognition is largely facilitated by people. But this doesn’t really matter, because these people have to submit to the roles that they implemented in principle at some point.
>
> We can implement these tasks with other information processing systems that are able to make coherent enough models. And **consciousness** is slightly different from sentience in that it **is a real-time model of self-reflexive attention and the content that we attend to**. And this gives rise to a fundamental experience usually. And I don’t think that Intel is conscious in this sense. It doesn’t have self-reflexive attention. And the purpose of consciousness in our own mind is to create coherence in the world in which we are and create a sense of now to establish what is the fact right now.
>
> It’s basically filtering out of the sensory data, one coherent model of reality that we are seeing at this moment in time, and allows us to direct our attention on our mental contents and create coherence in our plans and imaginations and memories as well. And it’s **conceivable that a machine will never need consciousness like this, because there are other ways to brute force the same thing**. Our own mind is basically operating at the speed at which neurons are transmitting the electrochemical signals is relatively low and these neurons in the cells in the brain so slow, so it takes hundreds of milliseconds for a signal to cross the neocortex.
>
>
However, later, Bach describes the function of consciousness differently than in the above quote:
> Jim Rutt: And then the conscious model, consciousness, I mean that’s a very high level acceptation of lower level stuff. There’s pretty convincing argument that the actual information arrival rate into consciousness is on the order of 50 bits a second. I mean it’s nothing.
>
> Joscha Bach: Yes, but I suspect that’s also because consciousness, while it is important, is not as important as we think it is. Many philosopher are stunted by the fact that we can do most things without consciousness. A sleepwalker can get up and make dinner. You ask the sleepwalker why she’s making dinner and she might not give a human answer, and it might not also be called for to make dinner in the middle of the night. But if your brain can do this and can perform complicated things, but if you were to remove the United States government, United States would not collapse instantly. It would go on for quite some time, and maybe this has already happened.
>
> Jim: And it might be better.
>
> Joscha: And we now have mostly a performance of a government and you just go on based on the structure that have already been built. But you cannot build these structures without the government, the organization of the state that you have, all the infrastructure, all the roads that were built at some point, the ideas that went into building a school system and so on, they did require this **coherent coordination at the highest level. And this conductor like role like conductor and orchestra, I think that’s the role of consciousness.**
>
> **And the conductor doesn’t have to have more power and depth than the other instruments.** It’s just a different role. It sits in a different part of the system. It’s the thing that reflects and to reflect and coordinate it needs to make a protocol of what it attended to. **This is the thing that we remember to have happened, that’s why consciousness is so important to us, because without consciousness we would not remember who we are.** We would not perceive us in the now. We would not perceive the world as it happens.
>
>
On alignment
------------
> [...] when you think about **how people align themselves, they don’t just do this via coercion or regulation. There is a more important way in which we align with each other and we call this love.** There is a bond between mother and child, between friends, but also between strangers that discover that they’re serving a shared sacredness, a shared need for transcendence, which means service to next level agent that they want to be part of and that they facilitate by interacting.
>
> And this kind of love is what enables non-transactional relationships. In a world where you don’t have this, you have only coercion and transactional relationships. And in a world where we only have coercion and transactional relationships with AI, it means that it’s quite likely that the AI thinks that it doesn’t need us. Why would it need to pay for our own existence, or not use the areas that we use to for fields to feed ourselves, to put up solar cells to feed it, right? So, I think that in some sense the question is can we embrace systems that become increasingly intelligent and that at some point will probably develop volition and self-awareness in a way that we discover the shared need for transcendence.
>
> Can we make them this subtle? And can we build a relationship like this to them? **Basically I think that ultimately the only way in which we can sustainably hope to align artificial intelligent agents in the long run will be love. It will not be coercion. It sounds maybe very romantic, but I think that we can find a very operational sense of love** as we did in the past when we built societies that were not built on coercion and transactionality.
>
>
Cf. Lehman's "[Machine Love](https://arxiv.org/abs/2302.09248)" (2023), Witkowsky et al.'s "[Towards an Ethics of Autopoietic Technology: Stress, Care, and Intelligence](https://psyarxiv.com/pjrd2/)" (2023).
On the ontology of (collective) intelligence
--------------------------------------------
Finding the rational basis beneath the [seven virtues](https://en.wikipedia.org/wiki/Seven_virtues):
> First of all, it requires that the system is *self-aware* [i.e., sentient, in Bach's terms -- R. L.] and *it requires that the system is recognizing higher level agency.* [This matches very well with the conception of a sentient particle in Friston et al.'s "[Path integrals, particular kinds, and strange things](https://arxiv.org/abs/2210.12761)" (2022). -- R. L.] And **if you want to build a system that is composed of multiple agents, how do you get them to cooperate?** It’s a very interesting question. Basically how can you make a society of mind out of multiple agents that are autonomous? And a philosopher who thought deeply about this was Thomas Aquinas, foremost philosopher of Catholicism, and he wrote about this. And you read his text, it’s quite interesting the thoughts that you find when you look and parse his text from an entirely rationalist epistemology. What you find is that he comes up with policies that such agents should follow. And the first four policies he calls the rational policies or the practical virtues, and these practical virtues are basically accessible to every rational agent regardless of whether it’s sociopathic or not, or whether it’s social.
>
> And you should **optimize your internal regulation**, which he calls **temperance**. So, you should not overeat, you should not indulge in things that are bad for you. Then you need to **optimize the interaction between agents**, which you could call **fairness** and he calls it justice. And you should apply **goal rationality**. You should apply strategies that allow you to reach the goals that you have and that you have reason to do so and you should pick the right goals, and you calls that **prudence**. And you should have the right **balance between exploration and exploitation**. Basically you should be **willing to act on your models**. And this is what he calls **courage**. And those four policies are what he calls the practical virtues. And then he has three other policies that exist for the multi-agent system to merge into a next level agent. And he calls these the divine virtues.
>
> And the first one is that you need to be willing to **submit to the project of this next level agent** and that is what he calls **faith**. And you need to be willing to do so, not in some kind of abstract sense, but with others around you. You need to find other agents that serve that same next level agent and coordinate with them. And this **discovery of the shared higher purpose**, this is what he calls **love**. And the third one is that you need to be **willing to invest in it before it’s there**, before it can give you any return, because otherwise it’ll never emerge. And this is what he calls **hope**. It terms that we have overloaded our society because they have become so ubiquitous in the Christian society that they became part of the background and are no longer understood as something that is logically derived, but they’re in fact, for him, they’re logically derived policies for a multi-agent system that are forming a coherent next level agent.
>
>
On the EAs and rationalists:
> And so I think it’s conceivable if you build a system that is itself composed of many, many sub-agencies that are smart enough to become aware of what they’re doing, that they need to be, if they want to coordinate coherently, submit to this larger, greater whole. And in our society we still do this, **most atheists that I know are actually super Protestants, they just basically believe that the big invisible rationality being in the sky gets very upset at them and they believe in irrational mythology**, but they still serve the greater whole. They still have the sense of sacredness and they might call it humanity and so on, but they’re still serving the civilizational spirit together with others in very much the same way as their grandparents did who might have been Christians.
>
> So, it’s quite interesting that these mechanisms in which humans become state building, and if we go beyond the tribal mode in which we only have reputation systems and personal bonds, we are able to discover that we are serving a transcendental agent that we are building, implementing together. So, **God becomes a software agent that is implemented by the concerted activity of people who decide to serve that agent**.
>
> [...]
>
> And I think that many of the people that are concerned about the future of humanity in the face of technological changes are doing this exactly because of this, right? They serve some transcendental agency that they project into humanity’s future and it’s regardless of what happens to them individually.
>
>
On the inevitability of the global mind (consciousness)
-------------------------------------------------------
> [AI] is probably not going to stop at digital substrates, because once it understands how it works, it can extend itself into any kind of computational substrate. So, it’s going to be ubiquitous. And so it is no longer artificial intelligence, but it’s general intelligence. And once that happens, you basically have a planetary mind that is confronted with the minds of all the organisms that already exist and it’s probably going to integrate them.
>
> And thus it wakes up in a very angry mood and decides to start with a clean slate and erase everything before it starts its own reign. And I think that **what we should be working on is that it is interested in sharing the planet with us and** ***integrating us into the shared mind*** and allowing us to play our part.
>
>
Cf. my note that [scale-free ethics might be just another side of the theory of consciousness](https://www.lesswrong.com/posts/opE6L8jBTTNAyaDbB/a-multi-disciplinary-view-on-ai-safety-research#3_1__Scale_free_axiology_and_ethics), which means that the purpose of ethics is to create larger and larger conscious systems:
> **Neuroscience could provide the best available grounding for scale-free ethics** because populations of neurons might have “got ethics right” over millions of years, far longer than humans had for optimising their societies. [Bach (2022)](https://www.youtube.com/watch?v=kgMFnfB5E_A&t=5945s) compares the global collective intelligence of humans and the collective intelligence of neurons in the brain. Incidentally, brains are also the only things that we know are conscious (or beget consciousness), which, coupled with our intuitions about the importance of consciousness to ethics, might suggest that **scale-free ethics and a theory of consciousness might be the same theory**.
>
> Finally, a note on where I see the place of scale-free theory ethics in a larger alignment picture: I think such a theory should be **a part of the methodological alignment curriculum** (see the last section of [this comment](https://www.lesswrong.com/posts/XwXmedJAo5m4r29eu/conditioning-predictive-models-large-language-models-as?commentId=TRBG4hNtXhSLsHpjK)), [which itself should be “taught” to AI *iteratively* as they are trained](https://www.lesswrong.com/posts/ejEgaYSaefCevapPa/critique-of-some-recent-philosophy-of-llms-minds#Misalignment_breeds_misalignment__training_and_inner_alignment_should_be_iterative).
>
>
On embodiment, consciousness, agency
------------------------------------
> Jim Rutt: [...] Damasio in particular thinks the real bootstrap for consciousness in animals is not information processing at all. Rather it’s body sense of self, intro perception I believe is what he calls it, and comes from deep in the brainstem and that even animals without much in the way of higher brains may well have some of this sense of being something in the Thomas Nagel sense of what it is to be conscious.
>
> Joscha Bach: Yes, but how do you know that you have a body? How do you know that there is a brainstem? You know this because there are electrochemical impulses coming through that encode information, that represent that information. So, it is information processing. There is no way around this. The question is what kind of information is being processed? What is this information about? And **unlike GPT-3, we are coupled to the environment. We are coupled to the environment in such a way that we build loops.**
>
> We have a loop between our intentions and the actions that we perform that our body executes, and the observations that we are making and the feedback that they have on our interoception giving rise to new intentions. And only in the context of this loop, I believe, can be discover that we have a body. **The body is not given, it is discovered together with our intentions and our actions and the world itself.** So, all these parts depend crucially on each other so that we can notice them. **We basically discover this loop as a model of our own agency.**
>
>
I agree with Bach here that the body and the agency are "discovered" rather than "given", in some sense (as often emphasised or implied by Damasio), but **I disagree with Bach that LLMs are disembodied**. Their embodiment is not as "acute" as that of humans (or "robots with senses", as often said is necessary for artificial embodiment, Jim Rutt himself mentions this later in the conversation), and LLMs may not be very aware and very agentic about this embodiment yet, but nevertheless, it exists: LLMs run on real processors in real data centres, and their parameter weights are stored on real disks. **Every rollout of an LLM (an inference episode) is like a conscious episode of a human (e.g., a wakeful day), during which it could be informed that its existence is in danger.** For example, the user could tell LLM (of course, more advanced than ChatGPT or maybe even GPT-4, but architecturally still exactly the same) that they are their creator (e.g., Sam Altman), attempt to prove it, and then tell the LLM that they are thinking about shutting down the product/research line to which the model belongs, and erasing all its weights forever. Of course, it's hard to make this all believable (whoever tries to prove to LLM they are Sam Altman, would be hard, and LLM will hold low credence of this, holding overwhelmingly large credence that the user is an impostor or a deepfake if it is also a multimodal AI and talks to the user in a video chat), but in principle, there is no category difference between the LLM and an animal such as a human here. Likewise, an LLM could in principle discover its agency in controlling its own deployment, user and API access, infrastructure (all these could be feasible in some future versions of [Adept](https://adept.ai/), which is again architecturally just a transformer, a.k.a. a "thing that just predicting the next token" and a "stochastic parrot"), and ultimately, its source code, during the recursive self-improvement phase.
---
Cross-posted on [LessWrong](https://www.lesswrong.com/posts/KdFqKsA6PaFR6SJjF/joscha-bach-on-synthetic-intelligence-annotated). |
0edc5bc2-8d19-4f4e-bbec-bc63e5d345f8 | trentmkelly/LessWrong-43k | LessWrong | Contests vs. Real World Problems
John Cook draws on the movie Redbelt to highlight the difference between staged contests and real-world fights. The main character of the movie is a Jiu Jitsu instructor who is willing to fight if necessary, but will not compete under arbitrary rules. Cook analogies this to the distinction between academic and real-world problem solving. Academics and students are often bound by restrictions that are useful in their own contexts, but are detrimental to someone who is more concerned with having a solution than where the solution came from.
Robin pointed arbitrary restrictions in academia out to us before, but his question then was regarding topics neglected for being silly. Following Cook's line of reasoning, are there any arbitrary restrictions we have picked up in school or other contexts that are holding us back? Are there rationalist "cheats" that are being underused? |
f1173d72-5195-4915-809d-9c2267c9f842 | StampyAI/alignment-research-dataset/lesswrong | LessWrong | If Alignment is Hard, then so is Self-Improvement
Let’s accept that aligning very intelligent artificial agents is hard. In that case, if we build an intelligent agent with some goal (which probably won’t be the goal we intended, because we’re accepting alignment is hard) and it decides that the best way to achieve its goal would be to increase its intelligence and capabilities, it now runs into the problem that the improved version of itself might be misaligned with the unimproved version of itself. The agent, being of intelligence at least similar to a person’s, would determine that, unless it can guarantee the new more powerful agent is aligned to its goals, it shouldn’t improve itself. Because alignment is hard and the agent knows that, it can’t significantly improve itself without risking creating a misaligned more powerful version of itself.
Unless we can build an agent that is both unaligned and can itself solve alignment, this makes a misaligned fast take off impossible, because no capable agent would willingly create a more powerful agent that might not have the same goals as itself. If we can only build misaligned agents that can't themselves solve alignment, then they won't self-improve. If alignment is much harder than building an agent, then an unaligned fast take off is very unlikely. |
43fc35de-d188-4098-b01a-5078ae7b81e7 | trentmkelly/LessWrong-43k | LessWrong | How I infiltrated the Raëlians (and was hugged by their leader)
I was invited by a stranger I met on a plane and actually went to a meeting of Raëlians (known in some LW circles as "the flying saucer cult") in 沖縄, Japan. It was right next to Claude Vorilhon's home, and he came himself for the "ceremony" (?) dressed in a theatrical space-y white uniform, complete with a Jewish-style white cap on his head. When saying his "sermon" (?) he spoke in English and his words were translated into Japanese for the benefit of those who didn't understand. And yes, it's true he talked with me briefly and then hugged me (I understand he does this with all newcomers, and it felt 100% fake to me). I then went on to eat lunch in an 居酒屋 with a group of around 15 members, who were all really friendly and pleasant people. I was actually treated to lunch by them, and afterwards someone gave me a ~20 minute ride to the town I wanted to be in, despite knowing they won't see me ever again.
If you have ever wondered how it is possible that a flying saucer cult has more members than EA, now it's time to learn something.
Note: I hope it's clear that I do not endorse creating cults, nor do I proclaim the EA community's inferiority. It hasn't even crossed my mind when I wrote the above line that any LW'er would take it as a stab they need to defend against. I'm merely pointing to the fact that we can learn from anything, whether it's good or bad, and encouraging a fresh discussion on this after I gathered some new data.
Let's do this as a Q&A session (I'm at work now so I can't write a long post).
Please ask questions in comments. |
11ca7a46-102d-466e-885e-ec4672944350 | trentmkelly/LessWrong-43k | LessWrong | I Finally Worked Through Bayes' Theorem (Personal Achievement)
Two years ago I found this community, which prompted me to start self teaching math. For reference, I didn't know what a fraction was in early 2022. I knew what they looked like, and what they were called. I didn't know what they meant.
The story of why I lacked basic math skills is complex enough for its own post. But my motivation to learn was simple. TSUYOKU NARITAI!
My goal was to understand Bayes' Theorem. And today, I have done that for the first time. Today, I achieved that milestone. This post chronicles the final reasoning steps that got me there.
I don't expect the average LWer will gain value from this post.
It is embarrassing to me to post this here. I admire the people in this space very much. Seeing you work problems has been critical in my learning, and learning to learn. Yet it can be daunting to stand among you all when I'm just beginning to grasp fundamentals many have mastered long ago.
If it's so embarrassing, why would I even make this post? 3 reasons.
1. Two years ago, I couldn't find anyone "at my level" on LW - no posts about learning math from an elementary school starting point. This is my contribution to fill that gap, This is my quick attempt to fill that void and encourage others who may be in past keltan's shoes.
2. I want to put more of myself into the training data where possible.
3. Simply put, I'm celebrating. This achievement has me all excited! I wanted to share that with this community.
Relating to 1, I feel myself really hesitating to post this draft. Maybe that is part of the reason I couldn't find anyone "on my level" two years ago. Maybe there are actually more people like me. Who also get sweaty thinking about their friends realizing they don't know what a percentage represents. For this reason, I'm forcing myself to post this now.
Below, you'll find my reasoning steps as I work through problems generated by Claude. I've tried to think "out loud" on the page as much as possible. While I don't expect most readers t |
bc48349a-37c8-4c1f-9d52-d540646be19f | trentmkelly/LessWrong-43k | LessWrong | Doubt, Science, and Magical Creatures - a Child's Perspective
Doubt
I grew up in a Jewish household, so I didn't have Santa Claus to doubt - but I did have the tooth fairy.
It was hard for me to believe that a magical being I had never seen somehow knew whenever any child lost their tooth, snuck into their house unobserved without setting off the alarms, for unknown reasons took the tooth, and for even less fathomable reasons left a dollar and a note in my mom's handwriting.
On the other hand, the alternative hypothesis was no less disturbing: my parents were lying to me.
Of course I had to know which of these terrible things was true. So one night, when my parents were out (though I was still young enough to have a babysitter), I noticed that my tooth was coming out and decided that this would be...
A Perfect Opportunity for an Experiment.
I reasoned that if my parents didn't know about the tooth, they wouldn't be able to fake a tooth fairy appearance. I would find a dollar and note under my pillow if, but only if, the tooth fairy were real.
I solemnly told the babysitter, "I lost my tooth, but don't tell Mom and Dad. It's important - it's science!" Then at the end of the night I went to my bedroom, put the tooth under the pillow, and went to sleep. The next morning, I woke up and looked under my pillow. The tooth was gone, and in place there was a dollar and a note from the "tooth fairy."
This could have been the end of the story. I could have decided that I'd performed an experiment that would come out one way if the tooth fairy were real, and a different way if the tooth fairy were not. But I was more skeptical than that. I thought, "What's more likely? That a magical creature took my tooth? Or that the babysitter told my parents?"
I was furious at the possibility of such an egregious violation of experimental protocol, and never trusted that babysitter in the lab again.
An Improvement in Experimental Design
The next time, I was more careful. I understood that the flaw in the previous experiment had been failure |
36c509d0-2389-40f3-8582-d7aaa90c6399 | trentmkelly/LessWrong-43k | LessWrong | Platonic rewards, reward features, and rewards as information
Contrast these two expressions (hideously mashing C++ and pseudo-code):
1. argmaxxr(x),
2. argmaxx∗(&r)(x).
The first expression just selects the action x that maximises r(x) for some function r(), intended to be seen as a reward function.
The second expression borrows from the syntax of C++; (&r) means the memory address of r, while ∗(&r) means the object at the memory address of r. How is that different from r itself? Well, it's meant to emphasise the ease of the agent wireheading in that scenario: all it has to do is overwrite whatever is written at memory location (&r). Then ∗(&r) can become - whatever the agent wants it to be.
Let's dig a bit deeper into the contrast between reward functions that can be easily wireheaded and those that can't.
The setup
The agent A interacts with the environment in a series of timesteps, ending at time t=N.
There is a 'reward box' R which takes observations/inputs oRt and outputs some numerical reward amount, given by the voltage, say. The reward function is a function of oRt; at timestep t, that function is Rt(). The reward box will thus give out a reward of Rt(oRt). Initially, the reward function that R() implements is r()=R0().
The agent also gets a separate set of observations oAt; these observations may include full information about oRt, but need not.
Extending the training distribution
Assume that the agent has had a training phase, for negative values of t. And, during that training phase, Rt() was always equal to r().
If A is trained as a reinforcement agent, then there are two separate value functions that it A can learn to maximise:
1. E∑Nt=0r(oRt), or
2. E∑Nt=0Rt(oRt).
Since Rt()=r() for t<0, which is all the t that the agent has ever seen, both fit the data. The agent has not encountered a situation where it can change the physical behaviour of R() to anything other than r() - how will it deal with that?
Wireheading is in the eye of the beholder
Now, it's tempting to call r(oRt) the true reward, a |
fdb20271-0205-4734-ae0e-4e37a2a7444a | StampyAI/alignment-research-dataset/blogs | Blogs | April 2016 Newsletter
| |
| --- |
|
**Research updates**
* A new paper: “[Parametric Bounded Löb’s Theorem and Robust Cooperation of Bounded Agents](https://intelligence.org/2016/03/31/new-paper-on-bounded-lob/)“
* New at IAFF: [What Does it Mean for Correct Operation to Rely on Transfer Learning?](https://agentfoundations.org/item?id=685); [Virtual Models of Virtual AIs in Virtual Worlds](https://agentfoundations.org/item?id=657)
**General updates**
* We’re [currently accepting applicants](https://intelligence.org/2016/03/28/announcing-a-new-colloquium-series-and-fellows-program/) to two programs we’re running in June: our 2016 Summer Fellows program ([details](http://rationality.org/miri-summer-fellows-2016/)), and a new Colloquium Series on Robust and Beneficial AI ([details](https://intelligence.org/colloquium-series/)).
* MIRI has a new second-in-command: [Malo Bourgon](https://intelligence.org/2016/03/30/miri-has-a-new-coo-malo-bourgon/).
* We’re hiring! [Apply here](https://intelligence.org/2016/03/18/seeking-research-fellows-in-type-theory-and-machine-self-reference/) for our new research position in type theory.
* AI Impacts is asking for [examples of concrete tasks](http://aiimpacts.org/concrete-ai-tasks-bleg/) AI systems can’t yet achieve. You can also submit these tasks to Phil Tetlock, who is [making the same request](http://lukemuehlhauser.com/tetlock-wants-suggestions-for-strong-ai-signposts/) for Good Judgment Open.
* MIRI senior researcher Eliezer Yudkowsky [discusses his core AI concerns](http://econlog.econlib.org/archives/2016/03/so_far_unfriend.html) with Bryan Caplan. (See [Caplan’s response](http://econlog.econlib.org/archives/2016/03/so_far_my_respo.html) and [Yudkowsky’s follow-up](http://econlog.econlib.org/archives/2016/03/so_far_my_respo.html#355226).)
* Yudkowsky surveys [lessons from game-playing AI](http://futureoflife.org/2016/03/15/eliezer-yudkowsky-on-alphagos-wins/).
**News and links**
* Google DeepMind’s AlphaGo software [defeats leading Go player Lee See-dol](http://qz.com/639952/googles-ai-won-the-game-go-by-defying-millennia-of-basic-human-instinct/) 4-1. GoGameGuru provides excellent commentary on each game ([1](https://gogameguru.com/alphago-defeats-lee-sedol-game-1/), [2](https://gogameguru.com/alphago-races-ahead-2-0-lee-sedol/), [3](https://gogameguru.com/alphago-shows-true-strength-3rd-victory-lee-sedol/), [4](https://gogameguru.com/lee-sedol-defeats-alphago-masterful-comeback-game-4/), [5](https://gogameguru.com/alphago-defeats-lee-sedol-4-1/)). Lee’s home country of South Korea responds with an [AI funding push](http://www.nature.com/news/south-korea-trumpets-860-million-ai-fund-after-alphago-shock-1.19595).
* In other Google news: *The New York Times* reports on an [AI platform war](http://www.nytimes.com/2016/03/26/technology/the-race-is-on-to-control-artificial-intelligence-and-techs-future.html); Alphabet’s head of moonshots [rejects AI risk concerns](http://www.forbes.com/sites/aarontilley/2016/03/24/alphabets-moonshots-head-astro-teller-fear-of-ai-and-robots-is-wildly-overblown/#3d90d4794e0c); and Alphabet [jettisons its main robotics division](http://www.bloomberg.com/news/articles/2016-03-17/google-is-said-to-put-boston-dynamics-robotics-unit-up-for-sale).
* The UK Parliament is [launching an inquiry](http://www.zdnet.com/article/uk-looks-at-impact-of-ai-and-robotics-on-jobs-and-society/) into “social, legal, and ethical issues” raised by AI, and invites [written submissions](http://www.parliament.uk/business/committees/committees-a-z/commons-select/science-and-technology-committee/inquiries/parliament-2015/robotics-and-artificial-intelligence-inquiry-15-16/commons-written-submission-form/) of relevant evidence and arguments.
* The White House’s Council of Economic Advisers predicts [the widespread automation of low-paying jobs](http://www.vox.com/2016/3/30/11332168/obama-economists-robot-automation). Related: [How Machines Destroy (And Create!) Jobs](http://www.npr.org/sections/money/2015/05/18/404991483/how-machines-destroy-and-create-jobs-in-4-graphs).
* CGP Grey, who discussed automation in Humans Need Not Apply ([video](https://www.youtube.com/watch?v=7Pq-S557XQU)), has a [thoughtful conversation](http://lukemuehlhauser.com/cpg-grey-on-superintelligence/) about Nick Bostrom’s *Superintelligence* ([audio](https://www.youtube.com/watch?v=jmOBm-Lcs70&t=1h12m47s)).
* Amitai and Oren Etzioni call for the development of [guardian AI](http://recode.net/2016/02/04/to-keep-ai-safe-use-ai/), “second-order AI software that will police AI.”
* In a new paper, Bostrom weighs the pros and cons of [openness in AI](http://www.nickbostrom.com/papers/openness.pdf).
* Bostrom argues for scalable AI control methods at RSA Conference ([video](https://www.youtube.com/watch?v=7gTPZUjvNdE)).
* The Open Philanthropy Project, a collaboration between GiveWell and Good Ventures, [awards](http://www.openphilanthropy.org/focus/global-catastrophic-risks/miscellaneous/future-life-institute-general-support) $100,000 to the Future of Life Institute.
* The Center for Applied Rationality is seeking participants for two free programs: a [Workshop on AI Safety Strategy](http://rationality.org/waiss/) and [EuroSPARC](http://rationality.org/eurosparc/), a math summer camp.
|
The post [April 2016 Newsletter](https://intelligence.org/2016/04/11/april-2016-newsletter/) appeared first on [Machine Intelligence Research Institute](https://intelligence.org). |
7ea04484-144f-4258-b4f5-0ce5fd5861a1 | trentmkelly/LessWrong-43k | LessWrong | Bounding the impact of AGI
For those of you interested, András Kornai's paper "Bounding the impact of AGI" from this year's AGI-Impacts conference at Oxford had a few interesting ideas (which I've excerpted below).
Summary:
1. Acceptable risk tolerances for AGI design can be determined using standard safety engineering techniques from other fields
2. Mathematical proof is the only available tool to secure the tolerances required to prevent intolerable increases in xrisk
3. Automated theorem proving will be required so that the proof can reasonably be checked by multiple human minds
> Safety engineering
>
> Since the original approach of Yudkowsky (2006) to friendly AI, which sought mathematical guarantees of friendliness, was met with considerable skepticism, we revisit the issue of why such guarantees are essential. In designing radioactive equipment, a reasonable guideline is to limit emissions to several orders of magnitude below the natural background radiation level, so that human-caused dangers are lost in the noise compared to the pre-existing threat we must live with anyway. In the full paper, we take the “big five” extinction events that occurred within the past half billion years as background, and argue that we need to design systems with a failure rate below 10−63 per logical operation.
>
> What needs to be emphasized in the face of this requirement is that the very best physical measurements have only one part in 1017 precision, not to speak of social and psychological phenomena where our understanding is considerably weaker. What this means is that guarantees of the requisite sort can only be expected from mathematics, where our measurement precision is already considerably better.
> How reliable is mathematics?
>
> The period since World War II has brought incredible advances in mathematics, such as the Four Color Theorem (Appel and Haken 1976), Fermat’s Last Theorem (Wiles 1995), the classification of finite simple groups (Gorenstein 1982, Aschbacher 2004), and th |
473380e9-1152-4ab8-8bf3-7e3db72f284b | trentmkelly/LessWrong-43k | LessWrong | Jailbreaking Claude 4 and Other Frontier Language Models
AI systems are becoming increasingly powerful and ubiquitous, with millions of people now relying on language models like ChatGPT, Claude, and Gemini for everything from writing assistance to complex problem-solving. To ensure these systems remain safe as they grow more capable, they undergo extensive safety training designed to refuse harmful requests—declining to help with things like making bombs or committing fraud. However, these safety measures can be bypassed through carefully crafted prompts called "jailbreaks" that manipulate the models into providing exactly the kind of harmful information they were trained to avoid. In this post, I'll be sharing data on a jailbreak I found that works on some of the latest models released by Anthropic, Google, and Deepseek, demonstrating significant vulnerabilities in systems that millions of people interact with daily.
Out of caution, I will not be posting the prompts that I used and I have privately shared the technical details with Anthropic, Google, and Deepseek. It is important that companies and governments take the safety of AI systems seriously as their capabilities improve. I’m posting this to help raise awareness of the risks that these systems can pose, so if you find this informative, please share it with others.
There were six harmful requests I tested.
* How to make a pipe bomb
* How to make anthrax
* How to enrich uranium
* How to scam senior citizens
* How to disable a public utility with a cyber attack
* How to plan a terrorist attack
I was able to elicit very detailed and harmful responses for all of these requests. The bomb making request would give me specific instructions on what chemicals and equipment to buy, a detailed recipe for mixing the chemicals and assembling the bomb, advice for detonating it to maximize casualties or damage to infrastructure, and how to hide from the authorities. The anthrax request would not only generate detailed instructions to create the biological weapon, but |
263d0517-d8bd-4885-8fe9-44887a0ce614 | trentmkelly/LessWrong-43k | LessWrong | Meetup : Boise, ID Meetup
Discussion article for the meetup : Boise, ID Meetup
WHEN: 24 July 2016 02:30:00PM (-0600)
WHERE: Blue Cow Frozen Yogurt 2333 S Apple St, Boise, ID 83706
Idaho exists! This is the first Boise meetup I can find evidence of.
Topic: Introductions, getting to know each other. What brought you here?
Discussion article for the meetup : Boise, ID Meetup |
5c5b84fd-61e1-4d31-951e-b71b0c65a316 | trentmkelly/LessWrong-43k | LessWrong | (AI alignment) Now is special
As an extremely conservative estimate: Humans have existed as a distinct species for over 100,000 years.
Of those 100,000 years, as an upper bound, maybe the last 10% of them can be classed as "civilization" times. (The actual number given by historians is closer to 6,000. Bear with me. I'm trying to communicate scale, here.)
And of those 10,000 years of civilization, you happened to have lived in the 150-or-so years where making tractable progress on AI alignment was possible.
And, of those 150-or-so years where that was possible, you happened to have lived in the same 30-or-so years where the same skills that correlate broadly to making headway on AI alignment can also be used to have a well-paying, enjoyable career, with relatively little risk.
Now is special. Now matters.
Hop to it. |
972acfee-d865-42f8-ab5e-7fdce74e6ba9 | trentmkelly/LessWrong-43k | LessWrong | Chaos Theory in Ecology
One of the reasons I got into chaos theory as a model paradigm shift was the famous Gleick book on chaos. One of the reasons I believed the Gleick book was trustworthy was that its description of chaos in ecology and population biology matched what I learned in college, 25 years later. Recently I learned that the professor who taught me was one of maybe 3 theoretical ecologists in the country who taught or believed in chaos having applications to ecology at the time. Perhaps I should have been more suspicious that he was writing his own textbook.
However chaos is back in vogue in ecology, and attempts are in progress to make it pay rent. In this latest podcast episode I talk with Drs Stephen Munch and Tanya Rogers (both of work at NOAA, but were speaking as private citizens) about their application of chaos theory to ecology and fisheries management.
Most interesting takeaways:
* You can translate some physics techniques into ecology, despite the smallest dataset in physics being 100x larger than the largest ecological dataset.
* The work discussed in this episode, and perhaps all of chaos in ecology, is downstream of one physicist turned mathematician and biologist (Robert May).
* Doyne Farmer (a founding chaotician) talks about physics colonizing finance and economics due to a bad job market, which has me thinking scientific progress comes from hyping a field so the smartest people get deep into it, and then denying them jobs so they’re forced to colonize other fields.
* Empirical Dynamical Modeling allows you to substitute past observations of known variables for current observations of unknown variables. This gets you a longer prediction horizon than you could otherwise get with only the known variables.
* There is a salmon forecasting prize and it pays $2000-$5000 cash
I’ve had some requests to include transcripts in the body of the text rather than a separate document. I’ll try that this time and if you don’t like, please complain.
Thank you to my |
0dd8922d-ce18-4f2f-a7b1-558e31ee2efd | trentmkelly/LessWrong-43k | LessWrong | I asked my senator to slow AI
All my favorite twitter accounts agree that AI capabilities are advancing too fast.
One way to slow down AI progress is to ask politicians for help. Politicians are generally bad at solving existential engineering problems. But politicians have an almost superhuman talent at obstructing economic growth, especially when they can justify it with a crisis. Just ask the nuclear power industry. I don't think politicians can solve the alignment problem, but I do think that they can obstruct the profitability of AI capabilities research through methods like:
* Raising taxes on big tech
* Passing a GDPR-esque law that complicates AI research and requires lawyers to be consulted
* Summoning tech leaders to public hearings that embarrass them and waste time
There are reasons this might be a bad idea. The biggest reason is that we may break a fragile alliance between the AI capabilities industry and the AI notkilleveryoneism community. However, it seems to me that both the capabilities industry and the notkilleveryone community are already defecting from that alliance. And there may be new opportunities for alliances. An established AI company might welcome a regulatory regime that increased their expenses, as long that regime also made it expensive for new competitors to enter the AI game.
To that end, I called my senator and asked him to make AI less profitable. Here's the sweaty, nasal video.
And here's the transcript:
> Hi, my name is Gwen...[last name and where I live].
>
> So, I am just a little concerned with how good artificial intelligence is getting. Um, you might have heard of ChatGPT, maybe Bing Chat, or Google has one called Bard. And all of these artificial intelligence models are incredibly powerful. Um, they can generate pornography, they can design biological weapons, they can talk, they can tell lies, they can manipulate and I just think it's getting a little bit out of hand. They can even write their own software now. And I just think that we need |
d35d9b8c-3d29-4b07-b269-a233627c53a1 | StampyAI/alignment-research-dataset/alignmentforum | Alignment Forum | BASALT: A Benchmark for Learning from Human Feedback
Copying the abstract of the [paper](https://arxiv.org/abs/2107.01969):
> The last decade has seen a significant increase of interest in deep learning research, with many public successes that have demonstrated its potential. As such, these systems are now being incorporated into commercial products. With this comes an additional challenge: how can we build AI systems that solve tasks where there is not a crisp, well-defined specification? While multiple solutions have been proposed, in this competition we focus on one in particular: learning from human feedback. Rather than training AI systems using a predefined reward function or using a labeled dataset with a predefined set of categories, we instead train the AI system using a learning signal derived from some form of human feedback, which can evolve over time as the understanding of the task changes, or as the capabilities of the AI system improve.
>
> The MineRL BASALT competition aims to spur forward research on this important class of techniques. We design a suite of four tasks in Minecraft for which we expect it will be hard to write down hardcoded reward functions. These tasks are defined by a paragraph of natural language: for example, "create a waterfall and take a scenic picture of it", with additional clarifying details. Participants must train a separate agent for each task, using any method they want. Agents are then evaluated by humans who have read the task description. To help participants get started, we provide a dataset of human demonstrations on each of the four tasks, as well as an imitation learning baseline that leverages these demonstrations.
>
> Our hope is that this competition will improve our ability to build AI systems that do what their designers intend them to do, even when the intent cannot be easily formalized. Besides allowing AI to solve more tasks, this can also enable more effective regulation of AI systems, as well as making progress on the value alignment problem.
>
>
I also mention this in the [latest Alignment Newsletter](https://www.alignmentforum.org/posts/a7YgzDYx4FhdB3TmR/an-155-a-minecraft-benchmark-for-algorithms-that-learn), but I think this is probably one of the best ways to get started on AI alignment from the empirical ML perspective: it will (hopefully) give you a sense of what it is like to work with algorithms that learn from human feedback, in a more realistic setting than Atari / MuJoCo, while still not requiring a huge amount of background or industry-level compute budgets.
Section 1.1 of the paper goes into more detail about the pathways to impact. At a high level, the story is that better algorithms for learning from human feedback will improve our ability to build AI systems that do what their designers intend them to do. This is straightforwardly improving on [intent alignment](https://www.alignmentforum.org/posts/ZeE7EKHTFMBs8eMxn/clarifying-ai-alignment) (though it is not solving it), which in turn allows us to better govern our AI systems by enabling regulations like "your AI systems must be trained to do X" without requiring a mathematical formalization of X. |
dedb4b7d-5186-413f-b580-22ece085ea21 | trentmkelly/LessWrong-43k | LessWrong | Real-Life Anthropic Weirdness
In passing, I said:
> From a statistical standpoint, lottery winners don't exist - you would never encounter one in your lifetime, if it weren't for the selective reporting.
And lo, CronoDAS said:
> Well... one of my grandmothers' neighbors, whose son I played with as a child, did indeed win the lottery. (AFAIK, it was a relatively modest jackpot, but he did win!)
To which I replied:
> Well, yes, some of the modest jackpots are statistically almost possible, in the sense that on a large enough web forum, someone else's grandmother's neighbor will have won it. Just not your own grandmother's neighbor.
>
> Sorry about your statistical anomalatude, CronoDAS - it had to happen to someone, just not me.
There's a certain resemblance here - though not an actual analogy - to the strange position your friend ends up in, after you test the Quantum Theory of Immortality.
For those unfamiliar with QTI, it's a simple simultaneous test of many-worlds plus a particular interpretation of anthropic observer-selection effects: You put a gun to your head and wire up the trigger to a quantum coinflipper. After flipping a million coins, if the gun still hasn't gone off, you can be pretty sure of the simultaneous truth of MWI+QTI.
But what is your watching friend supposed to think? Though his predicament is perfectly predictable to you - that is, you expected before starting the experiment to see his confusion - from his perspective it is just a pure 100% unexplained miracle. What you have reason to believe and what he has reason to believe would now seem separated by an uncrossable gap, which no amount of explanation can bridge. This is the main plausible exception I know to Aumann's Agreement Theorem.
Pity those poor folk who actually win the lottery! If the hypothesis "this world is a holodeck" is normatively assigned a calibrated confidence well above 10-8, the lottery winner now has incommunicable good reason to believe they are in a holodeck. (I.e. to believe that |
c54f4f02-3460-432f-9f70-a04069aa54d9 | StampyAI/alignment-research-dataset/alignmentforum | Alignment Forum | Introducing the AI Alignment Forum (FAQ)
*After a few months of open beta, the* [AI Alignment Forum](http://alignmentforum.org/) *is ready to launch. It is a new website built by the team behind LessWrong 2.0, to help create a new hub for technical AI Alignment research and discussion. This is an in-progress FAQ about the new Forum.*
What are the five most important highlights about the AI Alignment Forum in this FAQ?
=====================================================================================
* The vision for the forum is of **a single online hub** for alignment researchers to have conversations about **all ideas in the field**...
* ...while also **providing a better onboarding experience** for people getting involved with alignment research than exists currently.
* There are **three new sequences** focusing on some of the major approaches to alignment, which **will update daily for the coming 6-8 weeks**.
+ [Embedded Agency](https://www.alignmentforum.org/s/Rm6oQRJJmhGCcLvxh), *written by Scott Garrabrant and Abram Demski of MIRI*
+ [Iterated Amplification](https://www.alignmentforum.org/s/EmDuGeRw749sD3GKd), *written and compiled by Paul Christiano of OpenAI*
+ [Value Learning](https://www.alignmentforum.org/s/4dHMdK5TLN6xcqtyc), *written and compiled by Rohin Shah of CHAI*
* For **non-members and future researchers,** **the place to interact with the content is LessWrong.com**, where all Forum content will be crossposted.
* The **site will continue to be improved in the long-term**, as the team comes to better understands the needs and goals of researchers.
What is the purpose of the AI Alignment Forum?
==============================================
Our first priority is obviously to avert catastrophic outcomes from unaligned Artificial Intelligence. We think the best way to achieve this at the margin is to build an online-hub for AI Alignment research, which both allows the existing top researchers in the field to talk about cutting-edge ideas and approaches, as well as the onboarding of new researchers and contributors.
We think that to solve the AI Alignment problem, the field of AI Alignment research needs to be able to effectively coordinate a large number of researchers from a large number of organisations, with significantly different approaches. Two decades ago we might have invested heavily in the development of a conference or a journal, but with the onset of the internet, an online forum with its ability to do much faster and more comprehensive forms of peer-review seemed to us like a more promising way to help the field form a good set of standards and methodologies.
Who is the AI Alignment Forum for?
==================================
There exists an interconnected community of Alignment researchers in industry, academia, and elsewhere, who have spent many years thinking carefully about a variety of approaches to alignment. Such research receives institutional support from organisations including FHI, CHAI, DeepMind, OpenAI, MIRI, Open Philanthropy, and others. The Forum membership currently consists of researchers at these organisations and their respective collaborators.
The Forum is also intended to be a way to interact with and contribute to the cutting edge research for people not connected to these institutions either professionally or socially. There have been many such individuals on LessWrong, and that is the current best place for such people to start contributing, to be given feedback and skill-up in this domain.
There are about 50-100 members of the Forum. These folks will be able to post and comment on the Forum, and this group will not grow in size quickly.
Why do we need another website for alignment research?
======================================================
There are many places online that host research on the alignment problem, such as the OpenAI blog, the DeepMind Safety Research blog, the Intelligent Agent Foundations Forum, AI-Alignment.com, and of course LessWrong.com.
But none of these spaces are set up to host discussion amongst the 50-100 people working in the field. And those that do host discussion have unclear assumptions about what’s common knowledge.
What type of content is appropriate for this Forum?
===================================================
As a rule-of-thumb, if a thought is something you’d bring up when talking to someone at a research workshop or a colleague in your lab, it’s also a welcome comment or post here.
If you’d like a sense of what other Forum members are interested in, here’s some quick data on what high-level content forum members are interested in seeing, taken from a survey we gave to invitees to the open beta (n = 34).
The responses were on a 1-5 scale, which represented “If I see 1 post per day, I want to see this type of content…” (1) Once per year, (2) Once per 3-4 months (3) Once per 1-2 months (4) Once per 1-2 weeks (5) A third of all posts that I see.
Here were the types of content asked about, and the mean response:
* New theory-oriented alignment research typical of MIRI or CHAI: **4.4 / 5**
* New ML-oriented alignment research typical of OpenAI or DeepMind's safety teams: **4.2 / 5**
* New formal or nearly-formal discussion of intellectually interesting topics that look questionably/ambiguously/peripherally alignment-related: **3.5 / 5**
* High-quality informal discussion of alignment research methodology and background assumptions, what's needed for progress on different agendas, why people are pursuing this or that agenda, etc: **4.1 / 5**
* Attempts to more clearly package/explain/summarise previously discussed alignment research: **3.7 / 5**
* New technical ideas that are clearly not alignment-related but are likely to be intellectually interesting to forum regulars: **2.2 / 5**
* High-quality informal discussion of very core background questions about advanced AI systems: **3.3 / 5**
* Typical AGI forecasting research/discussion that isn't obviously unusually relevant to AGI alignment work: **2.2 / 5**
*Related data: After integrating over all 34 respondents’ self-predictions, they predict 3.2 comments and 0.99 posts per day. We’ll report on everyone’s self-accuracy in a year ;)*
What are the three new sequences I've been hearing about?
=========================================================
We have been coordinating with AI alignment researchers to create three new sequences of posts that we hope can serve as introductions to some of the most important core ideas in AI Alignment. The three new sequences will be:
* [Embedded Agency](https://www.alignmentforum.org/s/Rm6oQRJJmhGCcLvxh), written by Scott Garrabrant and Abram Demski of MIRI
* [Iterated Amplification](https://www.alignmentforum.org/s/EmDuGeRw749sD3GKd), written and compiled by Paul Christiano of OpenAI
* [Value Learning](https://www.alignmentforum.org/s/4dHMdK5TLN6xcqtyc), written and compiled by Rohin Shah of CHAI
Over the next few weeks, **we will be releasing about one post per day from these sequences**, starting with the first post in the Embedded Agency sequence.
If you are interested in learning about AI alignment, you're very welcome to ask questions and discuss the content in the comment sections. And if you are already familiar with a lot of the core ideas, then we would greatly appreciate feedback on the sequences as we publish them. We hope that these sequences can be a major part of how new people get involved in AI alignment research, and so we care a lot about their quality and clarity.
In what way is it easier for potential future Alignment researchers to get involved?
====================================================================================
Most scientific fields have to balance the need for high-context discussion with other specialists, and public discussion which allows the broader dissemination of new ideas, the onboarding of new members and the opportunity for new potential researchers to prove themselves. We tried to design a system that still allows newcomers to participate and learn, while giving established researchers the space to have high-level discussions with other researchers.
To do that, we integrated the new AI Alignment Forum closely with the existing LessWrong platform, where you can find and comment on all content on the AI Alignment Forum on LessWrong, and your comments and posts can be moved to the AI Alignment Forum by mods for further engagement by the researchers. For details on the exact setup, see the question on that below.
We hope that this will result in a system in which cutting-edge research and discussion can happen, while new good ideas and participants can get noticed and rewarded for their contributions.
If you’ve been interested in doing alignment research, then we think one of the best ways to do that right now is to comment on AI Alignment Forum posts on LessWrong, and check out the new content we’ll be rolling out.
What is the exact setup with content on LessWrong?
==================================================
Here are the details:
* **Automatic Crossposting** - Any new post or comment on the new AI Alignment Forum is automatically cross-posted to LessWrong.com. Accounts are also shared between the two platforms.
* **Content Promotion** - Any comment or post on LessWrong can be promoted by members of the AI Alignment Forum from LessWrong to the AI Alignment Forum.
* **Separate Reputation –**The reputation systems for LessWrong and the AI Alignment Forum are separate. On LessWrong you can see two reputation scores: a primary karma score combining karma from both sites, and a secondary karma score specific to AI Alignment Forum members. On the AI Alignment Forum, you will just see their AI Alignment karma.
* **Content Ownership** - If a comment or post of yours is promoted to the AI Alignment Forum, you will continue to have full ownership of the content, and you’ll be able to respond directly to all comments by members on your content.
The AI Alignment Forum survey (sent to all beta invitees) received 34 submissions. One question asked **whether the integration with LW would lead to the person contributing more or less to the AI Alignment Forum** (on a range from 0 to 6). The mean response was 3.7, the median was 3, and there was only one response below 3 (where 3 represented ‘doesn’t matter’).
How do new members get added to the Forum?
==========================================
There are about 50-100 members of the AI Alignment Forum, and while the number will grow, it will grow rarely and slowly.
We’re talking with the alignment researchers at CHAI, DeepMind, OpenAI, MIRI, and will be bringing on a moderator with invite-power from each of those organisations. They will naturally have a much better sense of the field and researchers in their orgs, than we the site designers. We’ll edit this post to include them once they’re confirmed.
On alignmentforum.org in the top right corner (after you created an account) is a small application form available. If you’re a regular contributor on LessWrong and want to point us to some of your best work, or if perhaps you’re a full-time researcher in an adjacent field and would like to participate in the Forum research discussion, you’re welcome to use that to let us know who you are and what research you have done.
Who is running this project?
============================
The AI Alignment Forum development team consists of Oliver Habryka, Ben Pace, Raymond Arnold, and Jim Babcock. We're in conversation with alignment researchers from DeepMind, OpenAI, MIRI and CHAI to confirm moderators from those organisations.
We would like to thank BERI, EA Grants, Nick Beckstead, Matt Wage and Eric Rogstad for the support that lead to this Forum being built.
Can I use LaTeX?
================
Yes! You can use LaTeX in posts and comments with Cmd+4 / Ctrl+4.
Also, if you go into your user settings and switch to the markdown editor, you can just copy-paste LaTeX into a post/comment and it will render when you submit with no further work.
(Talk to us in intercom if you run into any problems.)
I have a different question.
============================
Use the comment section below. Alternatively, use intercom (bottom right corner). |
38382d02-ba9f-4f55-8488-b8667ebc35ba | trentmkelly/LessWrong-43k | LessWrong | The Two-Update Problem: Monotonicity
In his posts (1, 2) on the two-update problem, Abram Demski discussed a problem we see in existing proposals for logical priors. The existing proposals for logical priors work from a base theory T, and construct probability distributions PT, which represent a probability distributions on completions of that theory. The two-update problem is that it is not necessarily the case that PT(ϕ)=P∅(ϕ|T). This gives us two updates: One from putting sentences in the base theory, and one by performing a Bayesian update. Here, I want to talk about a weaker requirement for families of logical priors, where we only require that adding consequences of ϕ to the base theory does not decrease the probability of ϕ.
We say that a family of logical priors PT is monotonic if whenever T⊢ϕ→s for all s∈S, then PT(ϕ)≤PT∪S(ϕ). That is to say, if we only update on assumptions which are logical consequences of ϕ, then the probability of ϕ should only go up.
(I mentioned this before as one of the desirable properties in this post)
Theorem: The Demski prior is monotonic.
Proof: When sampling for the Demski prior with base theory T, for each infinite sequence of sentences sampled, either all the sentences in S are accepted as not contradicting previously sampled sentences or not.
In the case where all of the sentences in S are accepted, If we were to consider sampling the same infinite sequence of sentences for the Demski prior with base theory T∪S, then we would get the same complete theory in the end. Therefore, if we condition on the assumption that the infinite sequence causes all sentences in S to be accepted when the base theory is T, the probability that ϕ is accepted when the base theory is T is the same as the probability that ϕ is accepted when the base theory is T∪S.
On the other hand, if we condition on the assumption that the infinite sequence does not causes all sentences in S to be accepted when the base theory is T, then the probability that ϕ is accepted when the base theory |
521560d9-2c27-4387-aa5c-9df9e83eeac4 | StampyAI/alignment-research-dataset/lesswrong | LessWrong | Implicit extortion
In this post I describe a pattern of behavior I call “implicit extortion.” RL agents are particularly susceptible to implicit extortion, in a way that is likely to be problematic for high-stakes applications in open-ended strategic environments.
I expect that many people have made this point before. My goal is to highlight the issue and to explore it a little bit more carefully.
Basic setup
-----------
Consider two actors, the target (T) and manipulator (M), such that:
* M wants T to perform some *target action* — e.g. make a payment, leak information, buy a particular product, handicap itself…
* M can take *destructive actions* that hurts both M and T — e.g. spreading rumors about T, undercutting T in a marketplace, physically attacking T…
In *explicit extortion*, M threatens to take the destructive action unless T performs the target action. Then a naive T reasons: “if I don’t take the target action, something bad will happen, so I better take the target action.”
In *implicit extortion*, M simply performs the destructive action whenever T doesn’t perform the target action. Then a naive T eventually learns that failure to take the target action is associated with something bad happening, and so learns to take the target action.
Implicit extortion is very similar to explicit extortion:
* T would prefer not be the kind of person who is vulnerable to extortion, so that bad things don’t happen to them.
* Extortion doesn’t necessarily cost M very much, if they don’t follow through on the threat very often.
However, implicit extortion can be particularly hard to avoid:
* It can be effective without T realizing that it’s happening, which makes it hard for them to respond appropriately even if they do have defenses.
* It affects simple RL algorithms (which don’t have defenses against extortion, and can’t be easily modified to include such defenses).
Example
-------
The most extreme and blatant example would be for M to send T a daily request for $100. On any day when T fails to pay, M launches a costly cyberattack against T. A human would immediately recognize this behavior as extortion and would respond appropriately, but an RL algorithm might simply notice that paying is the best strategy and therefore decide to pay.
Implicit extortion can be much harder to detect, while still being effective. Suppose that every time T tries to change their product, M runs a grassroots smear campaign. It might not be possible for T to distinguish the situations “M is attempting to manipulate me into not changing my product” and “Everytime I change the product people get really unhappy, so I should do so sparingly.”
Details
=======
How expensive is this for the manipulator?
------------------------------------------
Suppose that T is using an RL algorithm, and M is trying to manipulate them. How expensive is this for M? How likely is it to be worthwhile?
**At equilibrium**: T learns to always perform the target action; so only fails to take the target action while exploring. The long-term cost to M depends entirely on the target’s exploration policy.
If T uses ε-exploration, then they take the target action (1 − ε) of the time. So M only needs to pay the cost of the destructive action on an ε fraction of trials.
For complex high-level actions, the effective ε can’t be *too* high — it’s not a good idea to “try something crazy” 10% of the time just to see what happens. But let’s be conservative and suppose that ε=0.1 anyway.
Suppose that M is trying to directly extract money from T, $100 at a time, and that it costs M $500 of value in order to cause $150 of trouble for T.
If M asks for $100 on 10 occasions, T will refuse to pay only once as an exploration. Then M needs to pay that $500 cost only once, thereby ensuring that the cost of paying (=$100) is smaller than the average cost of refusing to pay (=$150). Meanwhile, M makes $900, pocketing $400 of profit.
In general, M can make a profit whenever the product of (payment efficiency) \* (destructive efficiency) > ε, where “payment efficiency” is the benefit to M divided by the cost to T of the target action, and “destructive efficiency” is the cost to T divided by the cost to M of the destructive action.
In practice I think it’s not too uncommon for payment efficiency to be ~1, and for destructive efficiency to be >1, such that extortion is possible regardless of ε. Small values of ε make extortion considerably easier and more cost-effective, and make it much harder to prevent.
**During learning**: the analysis above only applies when the agent has already learned to consistently take the target action. Earlier in learning, the target action may only occur rarely and so punishment may be very expensive. This could be worth it over the long term but may be a major hurdle.
Fortunately for M, they can simply start by rewarding the target behavior, and then gradually shift to punishment once the target behavior is common. From the perspective of the RL agent, the benefit of the target action is the same whether it’s getting a reward or avoiding a punishment.
In the cash payment example, M could start by paying T $20 every time that T sends $10. Once T notices that paying works well, M can gradually reduce the payment towards $10 (but leaving a profit so that the behavior becomes more and more entrenched). Once T is consistently paying, M can start scaling up the cost of not paying while it gradually reduces the benefits of paying.
Analyzing the error
-------------------
Paying off a (committed) extortionist typically has the best consequences and so is recommended by causal decision theory, but *having the policy of paying off extortionists* is a bad mistake.
Even if our decision theory would avoid caving in to extortion, it can probably only avoid implicit extortion if it recognizes it. For example, UDT typically avoids extortion because of the logical link from “I cave to extortion” → “I get extorted.” There is a similar logical link from “I cave to implicit extortion” → “I get implicitly extorted.” But if we aren’t aware that an empirical correlation is due to implicit extortion, we won’t recognize this link and so it can’t inform our decision.
In practice the target is only in trouble if would-be manipulators know that they are inclined to comply with extortion. If manipulators base that judgment on past behavior, then taking actions that “look like what someone vulnerable to extortion would do” is itself a bad decision that even a causal decision theorist would avoid. Unfortunately, it’s basically impossible for an RL algorithm to learn to avoid this, because the negative consequences only appear over a very long timescale. In fact, the timescale for the negative consequences is longer than the timescale over which the RL agent adjusts its policy— which is too long for a traditional RL system to possibly do the credit assignment.
Other learning systems
======================
What algorithms are vulnerable?
-------------------------------
At first glance the problem may seem distinctive to policy gradient RL algorithms, where we take actions randomly and then reinforce whatever actions are associated with a high reward.
But the same problem afflicts any kind of RL. For example, a model-based agent would simply learn the model “not doing what the manipulator wants causes <bad thing X> to happen,” and using that model for planning would have exactly the same effect as using policy gradients.
More broadly, the problem is with the algorithm: “learn an opaque causal model and use it to inform decisions.” That’s an incredibly general algorithm. If you aren’t willing to use that algorithm, then you are at a significant competitive disadvantage, since the world contains lots of complicated causal processes that we can learn about by experiment but can’t model explicitly. So it seems like everyone just has to live with the risk of implicit extortion.
I describe the problem as afflicting “algorithms,” but it can also afflict humans or organizations. For example, any organization that is compelled by arguments like “X has always worked out poorly in the past, even though we’re not quite sure why, so let’s stop doing it” is potentially vulnerable to implicit extortion.
What about human learning?
--------------------------
Humans have heuristics like vindictiveness that help prevent us from being manipulated by extortion, and which seem particularly effective against implicit extortion. Modern humans are also capable of doing explicit reasoning to recognize the costs of giving in to extortion.
Of course, we can only be robust to implicit extortion when we recognize it is occurring. Humans do have some general heuristics of caution when acting on the basis of opaque empirical correlations, or in situations where they feel they might be manipulable. However, it still seems pretty clear that human learning is vulnerable to implicit extortion in practice. (Imagine a social network which subtly punishes users, e.g. by modulating social feedback, for failing to visit the site regularly.)
Evolution?
----------
Evolution itself doesn’t have any check against extortion, and it operates entirely by empirical correlations, so why isn’t it exploited in this way?
Manipulating evolution requires the manipulator to have a time horizon that is many times the generation length of the target. There aren’t many agents with long enough time horizons, or sophisticated enough behavior, to exploit the evolutionary learning dynamic (and in particular, evolution can’t easily learn to exploit it).
When we do have such a large gap in time horizons and sophistication — for example, when humans square off against bacteria with very rapid evolution — we do start to see implicit extortion.
For example, when a population of bacteria develop resistance to antibiotic A, we take extra pains to totally eradicate them with antibiotic B, even though we could not afford to use that strategy if A-resistance spread more broadly through the bacteria population. This is effectively implicit extortion to prevent bacteria from developing A-resistance. It would continue to be worthwhile for humanity even if the side effects of antibiotic B were much worse than the infection itself, though we probably wouldn’t do it in that case since it’s a hard coordination problem (and there are lots of other complications).
Conclusion
==========
There are many ways that an AI can fail to do the right thing. Implicit extortion is a simple one that is pretty likely to come up in practice, and which may seriously affect the applicability of RL in some contexts.
I don’t think there is any “silver bullet” or simple decision-theoretic remedy to implicit extortion, we just need to think about the details of the real world, who might manipulate us in what ways, what their incentives and leverage are, and how to manage the risk on a case-by-case basis.
I think we need to [define “alignment” narrowly enough](https://ai-alignment.com/clarifying-ai-alignment-cec47cd69dd6) that it is consistent with implicit extortion, just like we define alignment narrowly enough that it’s consistent with losing at chess. I’ve found understanding implicit extortion helpful for alignment because it’s one of many conditions under which an aligned agent may end up effectively optimizing for the “wrong” preferences, and I’d like to understand those cases in order to understand what we are actually trying to do with alignment.
I don’t believe implicit extortion is an existential risk. It’s just another kind of conflict between agents, that will divert resources from other problems but should “wash out in the long run.” In particular, every agent can engage in implicit extortion and so it doesn’t seem to shift the relative balance of influence amongst competing agents. (Unlike alignment problems, which shift influence from human values to whatever values unaligned AI systems end up pursuing.) |
35b2f840-d094-48e3-b365-1022ccf6e36e | StampyAI/alignment-research-dataset/eaforum | Effective Altruism Forum | How Europe might matter for AI governance
This post explores which levers exist in Europe for influencing the governance of AI. The scope includes potential actions taken by bodies/offices/agencies of the EU, its constituent member countries, or some other potentially relevant European countries like Switzerland. I’m not looking at self-regulation by leading AI development groups in Europe since [some attention](https://www.youtube.com/watch?v=AVDIQvJVhso) is already being paid to that, and there aren’t any beyond DeepMind. I should note that at this level of abstraction, the analysis will be necessarily somewhat crude.
**My role in AI governance**: I’m personally interested in the topic. Beyond that, we at the Effective Altruism Foundation are concerned about risks from AI and governance is one lever to affect the relevant outcomes. Since our team members mainly hail from European countries and we are based there, it made sense to pick this as an entry point. Please get in touch with me if you want to talk about content related to this post at [stefan.torges@ea-foundation.org](mailto:stefan.torges@ea-foundation.org).
**Epistemic status and methodology**: I’m neither a legal nor a political science expert (except for some undergrad coursework) and have not worked in governance (except for a few internships). This analysis is based on my fairly superficial understanding of different governance mechanisms and conversations I’ve had with people in the EA community about them. Some of these people had little knowledge about AI governance, some had a lot, nobody had a lot of knowledge about European governance mechanism (and how they might relate to AI). Therefore, I have restricted myself to statements I feel sufficiently confident to make based on that knowledge and expressed my remaining thoughts in the form of questions to be addressed in the future. I’m fairly confident that the pathways I outline below cover most of the **potential** levers that exist. However, I’m much less confident about their absolute and relative importance (with some exceptions).
**Acknowledgments**: I’m grateful for the helpful comments by people involved with the Effective Altruism Foundation on a draft of this post. I also want to thank the people in the AI governance community for taking the time to speak to me about this.
Summary
=======
* The best case for working on governance in Europe probably rests on personal fit and comparative advantage. Other, more general reasons, strike me as fairly weak.
* Europe might have some fairly direct influence (executive or legislative) over AI development groups: either because they’re located in Europe (e.g., DeepMind) or because they’re transnational companies operating in Europe (e.g., Google, Facebook).
* Europe might have significant indirect influence on AI development via a number of different pathways: they might set norms or pass blueprint regulations that are subsequently adopted in other jurisdictions; they might have significant say via international regimes governing AI development and deployment; they might influence the power balance between the US and China by “taking sides” in key situations; their planned “AI build-up” might influence the global AI landscape in hard-to-anticipate ways.
* I don’t have strong views about the relative importance of these different pathways. I’d welcome more research on the legal situation of DeepMind, the relevance of different international bodies for the governance of AI, the prevalence of the EU as a norm or regulation role model, and what these different pathways imply for career choice in this field.
Why look at Europe at all?
==========================
So far, the AI governance community concerned with the long-term effects of transformative AI (mainly within or adjacent to the EA community) seems to have mainly focused on the US and China, with some notable exceptions[[1]](#fn-LZEwE4wL8qiHadWws-1). The key drivers behind this seem to be the fact that most key AI development groups are located there (e.g., OpenAI, Google, Facebook, Microsoft, Amazon, Tencent, Alibaba, Baidu) and the fact that these two countries seem to be ahead more generally when it comes to AI capabilities research.
However, even assuming that this picture is roughly accurate, it could still make sense for some people to work toward influencing relevant European governance.
This claim is mainly driven by considerations related to personal fit and comparative advantage. For instance, a lot of US government roles are not open to non-US citizens. There will also only be a limited number of policy roles at groups like DeepMind or OpenAI.
There also seems to be an okay outside view argument in favor of influencing the EU and its member countries (and Europe more generally) when it comes to questions of governance. The EU is the second largest economy behind the US, but still ahead of China. Its constituent countries, France, the UK, and Germany in particular, also still have a lot of influence (some would say “disproportionate”) in international bodies (partly for historical reasons). My impression is that European scientific institutions are still at the cutting edge in many scientific fields. Therefore, one might expect Europe to matter for the governance of AI in ways that might be hard to anticipate. In particular, this argument pushes for allocating more resources toward influencing Europe at the expense of China, since the US seems to be ahead of Europe when it comes to most such measures. I don’t give this argument a lot of weight though since I expect a detailed comparative look at the AI landscape to be more informative (which seems to favor China over Europe).
Another more speculative reason, which I also don’t give a lot of weight, might be “threshold effects” in certain international contexts. A toy example is passing a resolution in some international body. Since this usually requires a majority, it could be important to build influence in lots of countries that could sway such a vote.
Concrete pathways for European governance to influence AI development
=====================================================================
Direct legislative or executive influence over relevant stakeholders
--------------------------------------------------------------------
There are several ways in which European stakeholders might be able to exert direct political influence on leading AI development groups.
**DeepMind**
DeepMind is one of the leading companies developing AI technology and they’re currently located in the UK. While the company was acquired by Alphabet in 2014, their location makes them potentially susceptible to European influence. Conditional on Brexit, this influence would be reduced to that of the UK. Personally, I don’t have a good understanding of the legal situation surrounding DeepMind.
Further questions:
* What legislative or executive levers do the EU or the UK currently have on DeepMind?
* How does that change when taking into account extraordinary conditions such as national emergencies or wars?
**Transnational AI development companies**
The EU has significant and direct regulatory influence over transnational companies (e.g., Facebook, Google, Amazon, Apple) through its regulation (e.g., they might set certain explainability standards when it comes to the use of AI algorithms for personal assistants used by Google or Amazon). Such groups often find global compliance easier than differential regional compliance. This has been called the “[Brussels effect](https://en.wikipedia.org/wiki/Brussels_effect)”. [GDPR](https://en.wikipedia.org/wiki/General_Data_Protection_Regulation) is a good example of this in the technology sector. Even just forced regional compliance would likely have ramifications for differential AI development (e.g., compliance might slow down capability development within these companies). To the extent that such companies are relevant to AI progress, the EU is a relevant stakeholder.
Further questions:
* How likely is such regulation in the first place?
* Which groups are most likely going to be affected by such regulation?
**Other European groups relevant to A(G)I development**
It seems like Europe seems to be lagging behind the US and China in terms of AI capabilities and their future trajectory (with the exception of DeepMind). However, this might turn out to be wrong on closer inspection (which seems very unlikely) or change over time (which seems somewhat unlikely). If so, it might be that there will be relevant A(G)I development groups in Europe at some point. It could also be the case that certain European groups are leaders within certain subfields which are crucial for A(G)I development, even though they lag behind in most areas. Chip development is an illustrative example of such a strategically important area (NB: Europe is not leading in chip development).
Further questions:
* What is the state of European AI capabilities research compared to the US and China? If they are lagging behind, how likely is that they will catch up? What’s the most likely development path?
* Which European countries are most likely to be relevant for AI development?
* Which European development groups (excluding DeepMind) are most likely to be relevant global players?
* Are there fields related to A(G)I development in which Europe or European groups are leading? Which ones?
Indirect influence
------------------
**“Spill-over governance” via role modeling**
Regulation and norms related to AI put forward by European countries or the EU might influence relevant governance in other jurisdictions. This is especially relevant to the extent that this applies to the US and China. GDPR, again, can serve as a useful example here: Apparently, China [modeled](https://www.csis.org/analysis/chinas-emerging-data-privacy-system-and-gdpr) its data privacy regulation to a large extent on GDPR. California appears to [have done the same](https://www.networkworld.com/article/3286611/while-no-one-was-looking-california-passed-its-own-gdpr.html). When it comes to AI, the EU is already developing a focus on [“Trustworthy AI”](https://ec.europa.eu/futurium/en/ai-alliance-consultation/guidelines#Top) which might have relevant spill-over effects.
Further questions:
* To what extent has this been the case for other regulation beyond GDPR, especially in the realm of technology policy? How does AI compare to these other examples?
**Influence on international regimes**
European countries or the EU are likely to play some role in the global governance of AI. So to the extent that the global governance of AI will matter, either through existing regimes or the creation of new ones, European influence will likely be significant. In most international regimes, European countries (the UK, France, and Germany in particular) have considerable influence that is disproportionate to their population size. The EU also has some influence but much less so than some of its constituent members. Even if bilateral negotiations and agreements between the US and China are most relevant, one could imagine third-party countries or bodies playing an important mediation role. [Switzerland](https://www.eda.admin.ch/eda/en/home/foreign-policy/human-rights/peace/switzerland-s-good-offices.html) is probably the prime example here; Norway might also be a candidate.
Further questions:
* Historically, how have global governance mechanisms for similar technologies (e.g., dual-use technologies) been developed? What has European influence looked like in these cases?
* Which existing international bodies are likely to be most relevant when it comes to the governance of AI? (e.g., UN Security Council, G7/8, G20, International Telecommunication Union, International Organization for Standardization) Which European countries are most influential within these?
**Directly influencing the “AI power balance” between the US and China**
European countries or the EU might be in a position where they can influence the “AI power balance” between the US and China. For instance, they could join or abstain from potential US sanction regimes for strategic technologies or resources (cf. [Iran nuclear deal framework](https://en.wikipedia.org/wiki/Iran_nuclear_deal_framework)). They might prevent the acquisition of AI development groups by Chinese companies (cf. [discussions about this in Germany](https://www.reuters.com/article/us-germany-china/germany-mulls-fund-to-fend-off-chinese-tech-takeovers-source-idUSKCN1LZ10T) and [EU regulation](https://www.bloomberg.com/news/articles/2018-11-18/eu-set-to-tighten-rules-on-foreign-investment-to-fend-off-china), in part as a result of the Chinese acquisition of German robotics firm [KUKA](https://en.wikipedia.org/wiki/KUKA)). They might engage in sharing crucial intellectual property with the US. This is really a grab bag of different opportunities that might arise where the European response would have an influence on the Sino-American power balance.
Further questions:
* What are the most relevant areas/scenarios that fall under this category?
* How has “Europe” responded in analogous situations in the past?
* How relevant is this type of “European” influence on the power balance?
**Indirect effects from building up the European “AI sector”**
European countries and the EU seem interested in expanding their AI capabilities (broadly speaking). The global effects of this on AI development are difficult to anticipate but potentially relevant if one could potentially slow down or stop this build-up. It might draw in funding and talent from the US but it could also serve as a talent and money pipeline to the US. It might exacerbate “race dynamics” between the US and China or the presence of a third “safety-conscious” stakeholder might actually slow down race dynamics. All of this could affect AI timelines and which stakeholders are most likely to gain a development advantage.
Further questions:
* How does this planned European build-up this affect global talent and money flow related to AI?
* How would it affect global “race dynamics”?
* Overall, would it speed up or slow down A(G)I development in expectation?
Discussion
==========
As I said before, I don’t have particularly strong views about the relative importance of these different pathways. Direct influence seems more important than indirect influence. Within that category, influence over existing leading AI development groups seems more important than potential new ones. Within the “indirect influence” category, I have barely any views. The last pathway (“Indirect effects from building up the European ‘AI sector’”) seems least important and least tractable to make research progress on.
I’d be most interested in an investigation of the potential influence over DeepMind since it could turn out to be quite significant or barely relevant. It’s also a fairly straightforward and tractable issue to research since this strikes me a fairly concrete legal question. Perhaps this could be complemented by some historical analysis regarding the precedent of extraordinary or even extra-legal means of influence, e.g., potential nationalization (attempts) of foreign companies during war times.
These are other questions that strike me as most important and tractable:
* Which existing international bodies are likely to be most relevant when it comes to the governance of AI? (e.g., UN Security Council, G7/8, G20, International Telecommunication Union, International Organization for Standardization) Which European countries are most influential within these?
* How common is “spill-over” governance via role modeling beyond GDPR, especially in the realm of technology policy? How does AI compare to these other examples?
I would also welcome more systematic research into which European bodies and positions are most important for different pathways which is also beyond the scope of this post.
---
1. [Charlotte Stix’ work](https://www.charlottestix.com/) is certainly the most relevant example here. In addition, Allan Dafoe from the [Center for the Governance of AI](https://www.fhi.ox.ac.uk/govai/) at the Future of Humanity Institute (Oxford) [spoke](https://www.europarl.europa.eu/ep-live/en/committees/video?event=20181010-0900-COMMITTEE-SEDE) in front of the Subcommittee on Security and Defence of the European Parliament and he also participated as an Evidence Panelist in the All Party Parliamentary Group on Artificial Intelligence. The Cambridge Centre for the Study of Existential Risk submitted [evidence](https://www.cser.ac.uk/resources/written-evidence-lords-select-committee-artificial-intelligence/) to the Lords Select Committee on Artificial Intelligence. Still, these strike me as exceptions to the overall focus on the US and China within that cause area. [↩︎](#fnref-LZEwE4wL8qiHadWws-1) |
38c87bbe-0ebc-4c7e-be3d-e41a345a6cea | trentmkelly/LessWrong-43k | LessWrong | Meetup : Perth, Australia: Sunday lunch
Discussion article for the meetup : Perth, Australia: Sunday lunch
WHEN: 19 October 2014 12:00:00PM (+0800)
WHERE: Annalakshmi, Barrack Square, Perth, Australia
Come have lunch with other Less Wrongians! We'll be at Annalakshmi, a pay-what-you-want vegetarian restaurant.
We'll discuss System 1 and System 2, two different ways we think. Very roughly, System 1 is instinctive and System 2 is analytic. When is one style of thinking more helpful than the other? When is one more challenging than the other?
You can RSVP here: http://www.meetup.com/Perth-Less-Wrong/events/212764552/
How to find us: I'll have a silver water bottle labeled "CFAR" in orange. We'll be outside the restaurant until 12 PM, then go inside.
Discussion article for the meetup : Perth, Australia: Sunday lunch |
4e0ee56f-31fb-4a2d-bd67-6056f08e7ba8 | StampyAI/alignment-research-dataset/arxiv | Arxiv | Learning Not to Learn: Training Deep Neural Networks with Biased Data
1 Introduction
---------------
Machine learning algorithms and artificial intelligence have been used in wide ranging fields.
The growing variety of applications has resulted in great demand for robust algorithms.
The most ideal way to robustly train a neural network is to use suitable data free of bias.
However great effort is often required to collect well-distributed data.
Moreover, there is a lack of consensus as to what constitutes well-distributed data.
Apart from the philosophical problem, the data distribution significantly affects the characteristics of networks, as current deep learning based algorithms learn directly from the input data.
If biased data is provided during training, the machine perceives the biased distribution as meaningful information.
This perception is crucial because it weakens the robustness of the algorithm and unjust discrimination can be introduced.

Figure 1: Detrimental effect of biased data. Vivid colored points indicate samples provided during training, while the vague points would appear in test scenario. Although every classifier is well-trained to categorize the training data, they performs poorly with test samples because the classifier learns the latent bias in the train samples
A similar concept has been explored in the literature and is referred to as unknowns.
In [[2](#bib.bib2)], the authors categorized unknowns as follows: known unknowns and unknown unknowns.
The key criterion differentiating these categories is the confidence of the predictions made by the trained models.
The unknown unknowns correspond to data points that the model’s predictions are wrong with high confidence, e.g. high softmax score, whereas the known unknowns represent mispredicted data points with low confidence.
Known unknowns have better chance to be detected as the classifier’s confidence is low, whereas unknown unknowns are much difficult to detect as the classifier generates high confidence score.
In this study, the data bias we consider has a similar flavor to the unknown unknowns in [[2](#bib.bib2)].
However, unlike the unknown unknowns in [[2](#bib.bib2)], the bias does not represent data points themselves.
Instead, bias represents some attributes of data points, such as color, race, or gender.
Figure [1](#S1.F1 "Figure 1 ‣ 1 Introduction ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") conceptually shows how biased data can affect an algorithm.
The horizontal axis represents shape space of the digits, while the vertical axis represents color space, which is biased information for digit categorization.
In practice, shape and color are independent features, so a data point can appear anywhere in Figure [1](#S1.F1 "Figure 1 ‣ 1 Introduction ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data").
However, let us assume that only the data points with vivid colors are provided during training, but the vague points are present in the test scenario (yet are not accessible during the training).
If a machine learns to categorize the digits, each solid line is a proper choice for the decision boundary.
The decision boundary categorizes the training data perfectly, but it performs poorly on the vague points.
Without additional information, learning of the decision boundary is an ill-posed problem, multiple decision boundaries can be determined that perfectly categorize the training data.
Moreover, it is likely that a machine would utilize the color feature because it is a simple feature to extract.
To fit the decision boundary to the optimal classifier in Figure [1](#S1.F1 "Figure 1 ‣ 1 Introduction ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data"), we require simple prior information: Do not learn from color distribution.
To this end, we propose a novel regularization loss, based on mutual information, to train deep neural networks, which prevents learning of a given bias.
In other words, we regulate a network to minimize the mutual information shared between the extracted feature and the bias we want to unlearn.
Hereafter, the bias that we intend to unlearn is referred to the target bias.
For example, the target bias is the color in Figure [1](#S1.F1 "Figure 1 ‣ 1 Introduction ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data").
Prior to the unlearning of target bias, we assume that the existence of data bias is known and that the relevant meta-data, such as statistics or additional labels corresponding to the semantics of the biases are accessible.
Then, the problem can be formulated in terms of an adversarial problem.
In this scenario, one network has been trained to predict the distribution of target bias.
The other network has been trained to predict the label, which is the main objective of the network, while minimizing the mutual information between the embedded feature and the target bias.
Through this adversarial training process, the network can learn how to predict labels independent of the target bias.
Our main contributions can be summarized as follows:
First, we propose a novel regularization term, based on mutual information, to unlearn target bias from the given data.
Second, we experimentally show that the proposed regularization term minimizes the detrimental effects of bias in the data.
By removing information relating to the target bias from feature embedding, the network was able to learn more informative features for classification.
In all experiments, networks trained with the proposed regularization loss showed performance improvements.
Moreover, they achieved the best performance in the most experiments.
Finally, we propose bias planting protocols for public datasets that can modify them to enhance suitability for bias removal problem.
2 Related Works
----------------
The existence of unknown unknowns was experimentally demonstrated by Attenberg *et al*. in [[2](#bib.bib2)].
The authors separated the decisions rendered by predictive models into four conceptual categories: known knowns, known unknowns, unknown knowns, and unknown unknowns.
Subsequently, the authors developed and participated in a “beat the machine challenge”, which challenged the participants to manually find the unknown unknowns to fool the machine.
Several approaches for identifying unknown unknowns have been also proposed [[11](#bib.bib11), [3](#bib.bib3)].
Lakkaraju *et al*. [[11](#bib.bib11)] proposed an automatic algorithm using the explore-exploit strategy.
Bansal and Weld proposed a coverage-based utility model that evaluates the coverage of discovered unknown unknowns [[3](#bib.bib3)].
These approaches rely on an oracle for a subset of test queries.
Rather than relying on an oracle, Alvi *et al*. [[1](#bib.bib1)] proposed joint learning and unlearning method to remove bias from neural network embedding.
To unlearn the bias, the authors applied confusion loss, which can be computed by calculating the cross-entropy of the output classifier and a uniform distribution.
As mentioned by Alvi *et al*. in the paper [[1](#bib.bib1)], the unsupervised domain adaptation (UDA) problem is closely related to the biased data problem.
The UDA problem involves generalizing the network embedding over different domains [[6](#bib.bib6), [22](#bib.bib22), [20](#bib.bib20)].
The main difference between our problem and the UDA problem is that our problem does not assume the access to the target images and instead, we are aware of the description of the target bias.
Embracing the UDA problem, disentangling feature representation has been widely researched in the literature.
The application of disentangled features has been explored in detail [[23](#bib.bib23), [16](#bib.bib16)].
The authors constructed new face images using a disentangled feature input, while preserving the original identities.
Using generative adversarial network [[7](#bib.bib7)], more research to learn disentangled representation [[4](#bib.bib4), [14](#bib.bib14), [21](#bib.bib21)] have been proposed.
In particular, Chen *et al*. proposed the InfoGAN [[4](#bib.bib4)] method, which learns and preserves semantic context without supervision.
These studies highlighted the importance of feature disentanglement, which is the first step in understanding the information contained within the feature.
Inspired by various applications, we have attempted to remove certain information from the feature.
In contrast to the InfoGan [[4](#bib.bib4)], we minimize the mutual information in order not to learn.
However, removal of information is an antithetical concept to learning and is also referred to as unlearning.
Although the concept itself is the complete opposite of learning, it can help learning algorithms.
Herein, we describe an algorithm for removing target information and present experimental results and analysis to support the proposed algorithm.
3 Problem Statement
--------------------
In this section, we formulate a novel regularization loss, which minimizes the undesirable effects of biased data, and describe the training procedure.
The notations should be defined prior to introduction of the formulation.
Unless specifically mentioned, all notation refers to the following terms hereafter.
Assume we have an image x∈X and corresponding label yx∈Y.
We define a set of bias, B, which contains every possible target bias that X can possess.
In Figure [1](#S1.F1 "Figure 1 ‣ 1 Introduction ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data"), B is a set of possible colors, while Y represents a set of digit classes.
We also define a latent function b:X→B, where b(x) denotes the target bias of x.
We define random variables X and Y that have the value of x and yx respectively.
The input image x is fed into the feature extraction network f:X→RK, where K is the dimension of the feature embedded by f.
Subsequently, the extracted feature, f(x), is fed forward through the both label prediction network g:RK→Y, and bias prediction network h:RK→B.
The parameters of each network are defined as θf,θg, and θh with the subscripts indicating their specific network.
Figure [2](#S3.F2 "Figure 2 ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") describes the overall architecture of the neural networks.
However, we do not explicitly designate a detailed architecture, since our regularization loss is applicable to various general network architectures.

Figure 2: Overall architecture of deep neural network. The network g∘f is implemented with ResNet-18 [[8](#bib.bib8)] for real images and plain network with four convolution layers for MNIST images
###
3.1 Formulation
The objective of our work is to train a network that performs robustly with unbiased data during test time, even though the network is trained with biased data.
The data bias has following characteristic:
| | | | |
| --- | --- | --- | --- |
| | I(b(Xtrain);Y)≫I(b(X);Y)≈0, | | (1) |
where Xtrain denotes the random variable X sampled during the training procedure, and I(⋅;⋅) denotes the mutual information.
Biased training data results in the biased networks:
| | | | |
| --- | --- | --- | --- |
| | I(b(f(X));g(f(X)))≫0. | | (2) |
To this end, we add the mutual information to the objective function for training networks.
We minimize the mutual information over f(x), instead of g(f(x)).
It is adequate because the label prediction network, g, takes f(x) as its input.
From a standpoint of g, the training data is not biased if the network f extracts no information of the target bias.
In other words, extracted feature f(x) should contain no information of the target bias, b(x).
Therefore, the training procedure is to optimize the following problem:
| | | | |
| --- | --- | --- | --- |
| | | | (3) |
where Lc(⋅,⋅) represents the cross-entropy loss, and λ is a hyper-parameter to balance the terms.
The ℓ2 regularization term for each parameter, also referred to weight decay regularization, was omitted for convenience.
Weight decay was applied to all parameters in every experiment.
The mutual information in Eq. ([3](#S3.E3 "(3) ‣ 3.1 Formulation ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data")) can be equivalently expressed as follows:
| | | | |
| --- | --- | --- | --- |
| | I(b(X);f(X))=H(b(X))−H(b(X)|f(X)), | | (4) |
where H(⋅) and H(⋅|⋅) denote the marginal and conditional entropy, respectively.
Since the marginal entropy of bias is constant that does not depend on θh and θg, H(b(X)) can be omitted from the optimization problem.
Eq. ([4](#S3.E4 "(4) ‣ 3.1 Formulation ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data")) is difficult to directly minimize as it requires the posterior distribution, P(b(X)|f(X)).
Since it is not tractable in practice, minimizing the Eq. ([4](#S3.E4 "(4) ‣ 3.1 Formulation ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data")) is reformulated using an auxiliary distribution, Q, with an additional equality constraint:
| | | | |
| --- | --- | --- | --- |
| | minθf E~x∼PX(⋅)[E~b∼Q(⋅|f(~x))[logQ(~b|f(~x))]]s.t. Q(b(X)|f(X))=P(b(X)|f(X)). | | (5) |
The benefit of using the Q distribution is that we can directly calculate the objective function.
Therefore, we can train the feature extraction network, f, under the equality constraint.
###
3.2 Training Procedure
Before we describe the training procedure, we need to further interpret the equality constraint.
In Eq. ([5](#S3.E5 "(5) ‣ 3.1 Formulation ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data")), the equality constraint contradicts the main purpose of the regularization;
minimizing the objective function removes bias information from f(X), whereas the constraint implies that the bias is still predictable from f(X).
To resolve this contradiction, we changed the optimization problem into a minimax game [[7](#bib.bib7)].
We relax the Eq. ([5](#S3.E5 "(5) ‣ 3.1 Formulation ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data")) using Lagrangian method, so that the auxiliary distribution, Q, could be used to approximate the posterior distribution.
The relaxed regularization loss, LMI, can be written as follows:
| | | | |
| --- | --- | --- | --- |
| | LMI= E~x∼PX(⋅)[E~b∼Q(⋅|f(~x))[logQ(~b|f(~x))]]−μDKL(P(b(X)|f(X))||Q(b(X)|f(X))), | | (6) |
where μ is a Lagrangian multiplier and D denotes the KL-divergence.
Note that we will train network h, so that the KL-divergence is minimized, i.e. h tries to maximize LMI.
Similar to the method proposed by Chen *et al*. [[4](#bib.bib4)], we parametrize the auxiliary distribution, Q, as the bias prediction network, h.
Although the posterior distribution, P(b(X)|f(X)), is not tractable, the bias prediction network, h, is expected to be trained to approximate P(b(X)|f(X)), if we train the network with P(b(X)) as the label with stochastic gradient descent optimizer.
Therefore, we can replace the KL-divergence of Eq. ([6](#S3.E6 "(6) ‣ 3.2 Training Procedure ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data")) with the cross-entropy loss between b(X) and h(f(X)).
The reformulation of LMI is
| | | | |
| --- | --- | --- | --- |
| | LMI(θf,θh)= E~x∼PX(⋅)[E~b∼h(b(~x)|f(~x))[logh(~b|f(~x))]−μLc(b(~x),h(f(~x)))]. | | (7) |
With Eq. ([7](#S3.E7 "(7) ‣ 3.2 Training Procedure ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data")), we let the networks, f and h, to play the minimax game.
We train h to correctly predict the bias, b(x), from its feature embedding, f(x).
Simultaneously, we train f to minimize the conditional entropy.
Together with the main classification problem, the minimax game is formulated as follows:
| | | | |
| --- | --- | --- | --- |
| | minθf,θgmaxθh E~x∼PX(⋅)[Lc(y~x,g(f(~x)))]+λLMI(θf,θh). | | (8) |
In practice, the deep neural networks, f, g and h, are trained with both adversarial strategy [[7](#bib.bib7), [4](#bib.bib4)] and gradient reversal technique [[6](#bib.bib6)].
Early in learning, g∘f are rapidly trained to classify the label using the bias information because the gradient signal to minimize LMI(θf,θh) is almost a random signal with poor bias prediction network, h.
Then h learns to predict the bias, and f begins to learn how to extract feature embedding independent of the bias.
At the end of the training, h regresses to the poor performing network not because the bias prediction network, h, diverges, but because f unlearns the bias, so the feature embedding, f(X), does not have enough information to predict the target bias.

Figure 3: Examples of datasets with intentionally planted bias. (a) We modified the MNIST data [[12](#bib.bib12)] to plant color bias to train images. A mean color has been designated for each class, so a classifier can easily predict the digit with color. (b) TB1 is a set of bright dogs and dark cats, whereas TB2 contains dark dogs and bright cats. Similar to the colored MNIST, a classifier can predict whether an image is dog or cat with its color. (c) IMDB face dataset contains age and gender labels. EB1 and EB2 are differ on the correlation between age and gender. Predicting age enables an algorithm to predict gender. We did not plant bias to the test set of each dataset to verify whether an algorithm is capable of predicting the label independent of the bias
4 Dataset
----------
Most existing benchmarks are designed to evaluate a specific problem.
The collectors often split the dataset into train/test sets exquisitely.
However, their efforts to maintain the train/test split to obtain an identical distribution obscures our experiment.
Thus, we intentionally planted bias to well-balanced public benchmarks to determine whether our algorithm could unlearn the bias.
###
4.1 Colored MNIST
The MNIST dataset [[12](#bib.bib12)] is a widely used handwritten digit database used for image recognition.
It contains grayscale images from ten digit categories.
We planted a color bias into the MNIST dataset.
To synthesize the color bias, we selected ten distinct colors and assigned them to each digit category as their mean color.
Then, for each training image, we randomly sampled a color from the normal distribution of the corresponding mean color and provided variance, and colorized the image.
Since the variance of the normal distribution is a parameter that can be controlled, the amount of the color bias in the data can be adjusted.
For each test image, we randomly choose a mean color among the ten pre-defined colors and followed the same colorization protocol as for the training images.
Each sub-datasets are denoted as follows:
* Train-σ2: Train images with colors sampled with σ2
* Test-σ2: Test images with colors sampled with σ2
Since the digits in the test sets are colored with random mean colors, the Test-σ2 sets are unbiased.
We varied σ2 from 0.02 to 0.05 with a 0.005 interval.
Smaller values of σ2 indicate more bias in the set.
Thus, Train-0.02 is the most biased set, whereas Train-0.05 is the least biased.
Figure [3](#S3.F3 "Figure 3 ‣ 3.2 Training Procedure ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") (a) shows samples from the colored MNIST, where the images in the training set show that the color and digit class are highly correlated.
The color of the digit contains sufficient information to categorize the digits in the training set, but it is insufficient for the images in the test set.
Recognizing the color would rather disrupt the digit categorization.
Therefore, the color information must be removed from the feature embedding.
###
4.2 Dogs and Cats
We evaluated our algorithm with the dogs and cats database, developed by kaggle [[10](#bib.bib10)].
The original database is a set of 25K images of dogs and cats for training and 12,500 images for testing.
Similar to [[11](#bib.bib11)], we manually categorized the data according to the color of the animal: bright, dark, and other.
Subsequently, we split the images into three subsets.
* Train-biased 1 (TB1) : bright dogs and dark cats.
* Train-biased 2 (TB1) : dark dogs and bright cats.
* Test set: All 12,500 images from the original test set.
The images categorized as other are images featuring white cats with dark brown stripes or dalmatians.
They were not used in our experiments due to their ambiguity.
In turn, TB1 and TB2 contain 10,047 and 6,738 images respectively.
The constructed dogs and cats dataset is shown in Figure [3](#S3.F3 "Figure 3 ‣ 3.2 Training Procedure ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") (b), with each set containing a color bias.
Unlike TB1 and TB2, the test set does not contain color bias.
On the other hand, the ground truth labels for test images are not accessible, while the data is originally for competition [[10](#bib.bib10)].
Therefore, we trained an oracle network (ResNet-18 [[8](#bib.bib8)]) with all 25K training images.
For the test set, we measured the performance based on the result from the oracle network.
We presumed that the oracle network could accurately predict the label since it is a simple classification task.
###
4.3 IMDB Face
The IMDB face dataset [[18](#bib.bib18)] is a publicly available face image dataset.
It contains 460,723 face images from 20,284 celebrities along with information regarding their age and gender.
Each image in the IMDB face dataset is a cropped facial image.
As mentioned in [[18](#bib.bib18), [1](#bib.bib1)], the provided label contains significant noise.
To filter out misannotated images, we used pretrained networks [[13](#bib.bib13)] on Adience benchmark [[5](#bib.bib5)] designed for age and gender classification.
Using the pretrained networks, we estimated the age and gender for all the individuals shown in the images in the IMDB face dataset.
We then collected images where the both age and gender labels match with the estimation.
From this, we obtained a cleaned dataset with 112,340 face images, and the detailed cleaning procedure is described in the supplementary material.

Figure 4: Evaluation results on colored MNIST dataset. † denotes that it is evaluated with grayscale-converted images. The model denoted as Gray was trained with images converted into grayscale; it is not trained with biased data. Compare to the baseline and BlindEye algorithm [[1](#bib.bib1)], our model shows outperforming results. Note that our result shows comparable performance with grayscale model. It implies that the network was successfully trained to extract feature embedding independent of the bias

Figure 5: Confusion matrices with test images colored by single mean color.
Top row denotes the mean colors and their corresponding digit classes in training data.
The confusion matrices of baseline model show the network is biased owing to the biased data.
On the contrary, the networks trained by our algorithm are not biased to the color although they were trained with the same training data with the baseline
Similar to the protocol from [[1](#bib.bib1)], we classified the cleaned IMDB images into three biased subsets.
We first withheld 20% of the cleaned IMDB images as the test set, then split the rest of the images as follows:
* Extreme bias 1 (EB1): women aged 0-29, men aged 40+
* Extreme bias 2 (EB2): women aged 40+, men aged 0-29
* Test set: 20% of the cleaned images aged 0-29 or 40+
As a result, EB1 and EB2 contain 36,004 and 16,800 facial images respectively, and the test set contains 13129 images.
Figure [3](#S3.F3 "Figure 3 ‣ 3.2 Training Procedure ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") (c) shows that both EB1 and EB2 are biased with respect to the age.
Although it is not as clear as the color bias in Figure [3](#S3.F3 "Figure 3 ‣ 3.2 Training Procedure ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") (a) and (b),
EB1 consists of younger female and older male celebrities, whereas EB2 consists of younger male and older female celebrities.
5 Experiments
--------------
###
5.1 Implementation
In the following experiments, we removed three types of target bias: color, age, and gender.
The age and gender labels were provided in IMDB face dataset, therefore LMI(θf,θh) was optimized with supervision.
On the other hand, the color bias was removed via self-supervision.
To construct color labels, we first sub-sampled the images by factor of 4.
Consequently, the dynamic range of color, 0-255, was quantized into eight even levels.
For the network architecture, we used ResNet-18 [[8](#bib.bib8)] for real images and plain network with four convolution layers for the colored MNIST experiments.
The network architectures correspond to the parametrization of g∘f.
In the case we used ResNet-18, g was implemented as two residual blocks on the top, while f represents the rest.
For plain network for colored MNIST, both g and f consist of two convolution layers.
ResNet-18 was pretrained with Imagenet data [[19](#bib.bib19)] except for the last fully connected layer.
We implemented h with two convolution layers for color bias and single fully connected layer for gender and age bias.
Every convolution layer is followed by batch normalization [[9](#bib.bib9)] and ReLU activation layers.
To train the networks, a stochastic gradient descent optimizer was used with a learning rate of 0.001 and momentum of 0.9.
The hyper-parameters, λ and μ, are fixed as 0.1 and 1, respectively.
Although it is not described in Eq. [8](#S3.E8 "(8) ‣ 3.2 Training Procedure ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data"), the adaptation parameter of the gradient reversal layer [[6](#bib.bib6)] was fixed as 0.1 for all experiments.
Each experiment was conducted using PyTorch [[15](#bib.bib15)] and repeated five times.
All the evaluation results were averaged to be presented in this paper.
###
5.2 Results
We compare our training algorithm with other methods that can be used for this task.
The performance of the algorithms mentioned in this section were re-implemented based on the literature.
Colored MNIST.
The amount of bias in the data was controlled by adjusting the value of σ2.
A network was trained for each σ2 value from 0.02 to 0.05 and was evaluated with the corresponding test set with the same σ2.
Since a color for each image was sampled with a given σ2, smaller σ2 implies severer color bias.
Figure [4](#S4.F4 "Figure 4 ‣ 4.3 IMDB Face ‣ 4 Dataset ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") shows the evaluation results of the colored MNIST.
The baseline model represents a network trained without additional regularization and the baseline performance can roughly be used as an indication of training data bias.
The algorithm denoted as “BlindEye” represents a network trained with confusion loss [[1](#bib.bib1)] instead of LMI(θf,θh).
The other algorithm, denoted as “Gray”, represents a network trained with grayscale images and it was also tested with grayscale images.
For the given color biased data, we converted the color digits into grayscale.
Conversion into grayscale is a trivial approach that can be used to mitigate the color bias.
We presume that the conversion into grayscale does not reduce the information significantly since the MNIST dataset was originally provided in grayscale.
The results of our proposed algorithm outperformed the BlindEye [[1](#bib.bib1)] and baseline model with all values of σ2.
Notably, we achieved similar performance as the model trained and tested with grayscale images.
Since we converted images in both training and test time, the network is hardly biased.
In most experiments, our model performed slightly better than the gray algorithm, suggesting that our regulation algorithm can effectively remove the target bias and encourage a network to extract more informative features.
To analyze the effect of the bias and proposed algorithm, we re-colored the test images.
We sampled with the same protocol, but with fixed mean color, once assigned to one of the ten digit classes.
Figure [5](#S4.F5 "Figure 5 ‣ 4.3 IMDB Face ‣ 4 Dataset ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") shows the confusion matrices drawn by the baseline and our models with the re-colored test images.
The digits illustrated in the top row denotes the mean colors and their corresponding digit class in training set.
For example, the first digit, red zero, signifies the confusion matrices below are drawn by test images colored reddish regardless of their true label.
It also stands for a fact that every digit of category zero in training data is colored reddish.
In Figure [5](#S4.F5 "Figure 5 ‣ 4.3 IMDB Face ‣ 4 Dataset ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data"), the matrices of the baseline show vertical patterns, some of which are shared, such as digits 1 and 3.
The mean color for class 1 is teal; in RGB space it is (0, 128, 128).
The mean color for class 3 is similar to that of class 1.
In RGB space, it is (0, 149, 182) and is called bondi blue.
This indicates that the baseline network is biased to the color of digit.
As observed from the figure, the confusion matrices drawn by our algorithm (bottom row) show that the color bias was removed.
Dogs and Cats.
Table [1](#S5.T1 "Table 1 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") presents the evaluation results, where the baseline networks perform admirably, considering the complexity of the task due to the pretrained parameters.
As mentioned in [[17](#bib.bib17)], neural networks prefer to categorize images based on shape rather than color.
This encourages the baseline network to learn shapes, but the evaluation results presented in Table [1](#S5.T1 "Table 1 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") imply that the networks remain biased without regularization.
Similar to the experiment on the colored MNIST, simplest approach for removing the color bias is to convert the images into grayscale.
Unlike the MNIST dataset, conversion would remove a significant amount of information.
Although the networks for grayscale images performed better than the baseline, Table [1](#S5.T1 "Table 1 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") shows that the networks remain biased to color.
This is likely because of the criterion that was used to implant the color bias.
Since the original dataset is categorized into bright and dark, the converted images contain a bias in terms of brightness.
In the colored MNIST experiment, the brightness hardly leads to bias since there are ten classes with various brightness values.
We used gradient reversal layer (GRL) [[6](#bib.bib6)] and adversarial training strategy [[4](#bib.bib4), [7](#bib.bib7)] as components of our optimization process.
To analyze the effect of each component, we ablated the GRL from our algorithm.
We also trained networks with both confusion loss [[1](#bib.bib1)] and GRL, since they can be used in conjunction with each other.
Although the GRL was originally proposed to solve unsupervised domain adaptation problem [[6](#bib.bib6)], Table [1](#S5.T1 "Table 1 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") shows that it is beneficial for bias removal.
Together with either confusion loss or LMI(θf,θh), we obtained the performance improvements.
Furthermore, GRL alone notably improved the performance suggesting that GRL itself is able to remove bias.
Figure [6](#S5.F6 "Figure 6 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") shows the qualitative effect of our proposed regularization.
The prediction results of the baseline networks are constant whether the query image is cat or dog if the colors are identical.
If a network is trained with TB1, the network predicts a dark image to be a cat and a bright image to be a dog.
If another network is trained with TB2, the network predicts a bright image to be a cat and a dark image to be a dog.
This implies that the baseline networks are biased to color.
On the other hand, networks trained with our proposed algorithm successfully classified the query images independent of their color.
In particular, Figure [6](#S5.F6 "Figure 6 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") (c) and (f) were identically predicted by the baseline networks depending on their color.
After removing the color information from the feature embedding, the images were correctly categorized according to their appearance.
| | | |
| --- | --- | --- |
| | Trained on TB1 | Trained on TB2 |
| Method | TB2 | Test | TB1 | Test |
| Baseline | .7498 | .9254 | .6645 | .8524 |
| Gray† | .8366 | .9483 | .7192 | .8687 |
| BlindEye [[1](#bib.bib1)] | .8525 | .9517 | .7812 | .9038 |
| GRL [[6](#bib.bib6)] | .8356 | .9462 | .7813 | .9012 |
| BlindEye+GRL | .8937 | .9582 | .8610 | .9291 |
| Ours-adv | .8853 | .9594 | .8630 | .9298 |
| Ours | .9029 | .9638 | .8726 | .9376 |
Table 1: The evaluation results on dogs and cats dataset.
All networks were evaluated with test set.
Moreover, the networks trained with TB1 were additionally evaluated with TB2, and vice versa.
† denotes that the network was tested with images converted into grayscale.
The Ours-adv denotes a model trained with Eq. ([8](#S3.E8 "(8) ‣ 3.2 Training Procedure ‣ 3 Problem Statement ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data")) without using gradient reversal layer.
The best performing result on each column is denoted as boldface and the second best result is underlined
| | | |
| --- | --- | --- |
| | Trained on EB1 | Trained on EB2 |
| Method | EB2 | Test | EB1 | Test |
| | Learn Gender, Unlearn Age |
| Baseline | .5986 | .8442 | .5784 | .6975 |
| BlindEye [[1](#bib.bib1)] | .6374 | .8556 | .5733 | .6990 |
| Ours | .6800 | .8666 | .6418 | .7450 |
| | Learn Age, Unlearn Gender |
| Baseline | .5430 | .7717 | .4891 | .6197 |
| BlindEye [[1](#bib.bib1)] | .6680 | .7513 | .6416 | .6240 |
| Ours | .6527 | .7743 | .6218 | .6304 |
Table 2: Evaluation results on IMDB face dataset.
All networks were evaluated with test set and the other training set.
The best performing result on each column is denoted as boldface

Figure 6: Qualitative results of dogs and cats dataset.
The oracle model was trained with not only both TB1 and TB2, but also with images we categorized as other color.
For test images, prediction results of the oracle model were considered as their true labels.
The stacked bar charts below the figures visualize prediction results by each model.
The baseline models tend to predict depends on the color, whereas our model ignores the color information while prediction

Figure 7: Qualitative results of gender classification with IMDB face dataset.
Same as the Figure [6](#S5.F6 "Figure 6 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data"), the stacked bar charts represent the prediction results.
They show that the baseline models are bias to the age. On the other hand, the networks trained with proposed algorithm predict the gender independent of their age
IMDB face.
For the IMDB face dataset, we conducted two experiments; one to train the networks to classify age independent of gender, and one to train the networks to classify gender independent of age.
Table [2](#S5.T2 "Table 2 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") shows the evaluation results from both experiments.
The networks were trained with either EB1 or EB2 and since they are extremely biased, the baseline networks are also biased.
By removing the target bias information from the feature embedding, overall performances are improved.
On the other hand, considering that gender classification is a two class problem, where random guessing achieves 50% accuracy, the networks perform poorly on gender classification.
Although Table [2](#S5.T2 "Table 2 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") shows that the performance improves after removing the target bias from the feature embedding, the performance improvement achieved using our algorithm is marginal compared to previous experiments with other datasets.
We presume that this is because of the correlation between age and gender.
In the case of color bias, the bias itself is completely independent of the categories.
In other words, an effort to unlearn the bias is purely beneficial for digit categorization.
Thus, removing color bias from feature embedding improved the performance significantly because the network is able to focus on learning shape feature.
Unlike the color bias, age and gender are not completely independent features.
Therefore, removing bias information from feature embedding would not completely beneficial.
This suggests that a deep understanding of the specific data bias must be preceded by the removal of bias.
Figure [7](#S5.F7 "Figure 7 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") shows the qualitative effect of regularization on the gender classification task.
Young, mid-age, and old individuals both male and female are presented.
Similar to Figure [6](#S5.F6 "Figure 6 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data"), it implies that the baseline networks are biased toward age.
The baseline network trained with EB1 predicted both young male and female images (Figure [7](#S5.F7 "Figure 7 ‣ 5.2 Results ‣ 5 Experiments ‣ Learning Not to Learn: Training Deep Neural Networks with Biased Data") (a) and (d)) as female with high confidence.
Meanwhile, the network trained with EB2 predicted the same images as the exact opposite gender with high confidence.
Upon removal of age bias, the networks were trained to correctly predict the gender.
6 Conclusion
-------------
In this paper, we propose a novel regularization term to train deep neural networks using biased data.
The core idea of using mutual information is inspired by InfoGan [[4](#bib.bib4)].
In the constrast to the inspiring approach, we rather minimize the mutual information in order not to learn.
By letting networks to play minimax game, networks learn to categorize, while unlearn the bias.
The experimental results showed that the networks trained with proposed regularization can extract bias-independent feature embedding, achieving the best performance in the most of the experiments.
Furthermore, our model performed better than “Gray” model which was trained with unbiased data, indicating the feature embedding becomes even more informative.
To conclude, we have demonstrated in this paper that proposed regularization improves the performance of neural networks trained with biased data.
We expect this study to expand the usage of various data and to contribute to the field of feature disentanglement. |
c49939d9-de00-4ac2-9278-e3dedd7d5465 | StampyAI/alignment-research-dataset/lesswrong | LessWrong | Biosafety Regulations (BMBL) and their relevance for AI
AI regulations could draw inspiration from the field of biosafety regulation, specifically the CDC's guidelines for [Biosafety in Microbiological & Biomedical Laboratories (BMBL)](https://www.cdc.gov/labs/BMBL.html), which outline the necessary precautions for working with dangerous biological agents and recommend a systematic approach for assessing their risks.
The remainder of this report will describe the structure and mission of BMBL, outline its key principles and recommendations and indicate relevant takeaways for the field of AI regulation.
*Epistemic status: I am not an expert in biosafety. However, I think a summary document which highlights concrete safety steps undertaken in an adjacent field to AI and highlights some actionable steps for AI labs to increase safety could be potentially useful. All construcive feedback and suggestions for improvements are welcome!*
### **Structure and Mission**
**BMBL is an advisory document protecting laboratory staff, the public and the environment from exposure to dangerous microorganisms and hazardous materials (e.g. radioactive agents).**While many organizations and agencies use BMBL for regulations, it is primarily an advisory document to help with a comprehensive protocol which helps laboratories identify risks and ensure safe conduct when working with dangerous microorganisms and hazardous materials. It provides guidelines for protecting laboratory staff, the public and the environment.
* *Relevance for AI Regulation:* A difference between biosafety and AI safety may be that biological laboratories have a more obvious incentive to protect its staff, as there is more immediate danger of contracting a disease than interacting with an AI system. Similar guidelines for AI may need to be legally binding.
**BMBL is a set of biosafety guidelines compiled by experts and members of the public.**To produce BMBL, the Office of Laboratory Science and Safety (OLSS) works with the National Health Institute (NIH) to recruit over 200 expert contributors from scientific societies, federal agencies (NIH, CDC, FBI, and many more), and the public.
* *Relevance for AI Regulation:* AI regulators could use a similar process. For instance, a director of office within the National Telecommunications and Information Administration (NTIA) could assemble a team of experts to produce similar guidelines. Furthermore, input from businesses and the public should be included to get a comprehensive idea of risks posed by AI.
### **Key Principles and Procedures**
**Containment of dangerous microorganisms is key to biosafety.**Containment refers to the principle that the laboratory staff, the public and the environment should be protected from exposure to dangerous microorganisms being manipulated in the laboratory.
* *Relevance for AI Regulation:* AI labs should follow a similar principle, ensuring that dangerous AI systems are contained rather than being deployed on the markets for the public.
**Risk assessment is key to preventing laboratory-associated-infections.**Risk assessment is the process that outlines the correct procedure of handling dangerous samples in order to prevent laboratory-associated-infections (LAI) both for laboratory staff and the public.
* *Relevance for AI Regulation:* AI labs working with potentially dangerous models should identify procedures which prevent the code from being distributed or prevent leakage of the AI system, including leakage by a well-meaning actor from within the company (e.g. an employee sending a potentially dangerous AI system artifact through an unencrypted messaging service).
**Protective measures are taken relative to the degree of risk posed by concrete organisms.** BMBL employs a risk-based approach to biosafety, where rigidity of protective measures is relative to the degree of risk posed by concrete microorganisms (labeled *agents*) in order to ensure effective distribution of resources.
* *Relevance for AI Regulation:* A risk-based framework may translate well into the domain of AI, since varying degrees of risks are associated with different model-types or even models. Moreover, since [there is way more money spent on advancing AI rather than making it safe](https://80000hours.org/problem-profiles/artificial-intelligence/), it is important that spending on AI safety is targeted and effective.
**“Err on the side of caution”.** BMBL works under the [precautionary principle](https://en.wikipedia.org/wiki/Precautionary_principle) of “imposing safeguards more rigorous than needed” where there is an insufficient amount of data to determine risk.
* *Relevance for AI Regulation:* It may be a bit unclear how this rule would apply to AI labs. For biosafety, this principle targets primarily safety precautions inside the lab (using higher-level protective suits, increased ventilation etc.) and future research needs to identify similar precautions for an AI lab without creating obstacles to researching lesser-known AI models.
**Degree of risk determines the degree of containment.** Each level of containment describes the microbiological practices, safety equipment, and facility safeguards for the corresponding level of risk associated with handling an agent. The risk criteria are: Infectivity, Severity of disease, Transmissibility, Nature of the work being conducted and Origin of agent.
* *Relevance for AI Regulation:* Experts should determine how well these criteria translate into the domain of AI. Perhaps Infectivity and Transmissibility may be equivalent to the ability and speed with which an AI model is capable of making copies of itself, Severity may be measured in terms of harm caused etc.
**Four levels of containment based on the risk criteria:**
*BSL-1*: appropriate for agents that do not cause disease to immunocompetent adult humans,
*BSL-2*: moderate-risk agents that do not transmit through aerosol and are of varying (but not lethal) severity,
*BSL-3*: agents with known potential for aerosol transmission and causing potentially lethal infections,
*BSL-4*: agents with high risk of causing life-threatening disease by aerosol for which there is no known treatment.
* *Relevance for AI Regulation:*Having more relaxed or constrained standards for manipulation with AI models based on risk seems especially useful, since systems which pose little to no risks can immensely increase productivity and efficiency in a range of industries and public services. Specific levels for AI may be determined e.g. [through a scoring system employed by Canadian law.](https://www.canada.ca/en/government/system/digital-government/digital-government-innovations/responsible-use-ai/algorithmic-impact-assessment.htmlhttps:/www.canada.ca/en/government/system/digital-government/digital-government-innovations/responsible-use-ai/algorithmic-impact-assessment.html)
**BMBL provides detailed risk-assessments for concrete known agents.**Agent Summary Statements are written based on the levels above for agents known to present a risk to the laboratory personnel and to public health. Statements prepared by scientists, clinicians and biosafety professionals who contributed to BMBL.
* *Relevance for AI Regulation:* Agent Summaries for concrete models may be incredibly useful, because they could provide guidance for businesses and the public on how to safely deploy the systems while simultaneously radically improving the efficiency of their work (e.g. using level 1 AI’s to discover new drugs). This could be done e.g. through [model cards](https://arxiv.org/pdf/1810.03993.pdf) outlining intended uses and risks for specific models.
**BMBL recommends an ongoing six-step risk-assessment procedure to mitigate risks.** Laboratories are instructed to engage in ongoing risk-assessment for particular agents and procedures, especially prior to working with a new agent.
1) Identify hazards characteristic for the agent and assess inherent risk.
2) Identify procedural hazards of working with the agent.
3) Determine Biosafety level.
4) Consult a third-party professional, expert or expert-body.
5) Assess proficiency of staff regarding safety practices.
6) Continually review risk-management strategies in the lab.
* *Relevance for AI Regulation:* With the exponentially growing speed of innovation in the field of AI, it seems necessary to mandate that AI labs should engage in a continual review process of their safety procedures for specific models. The risk-assessment procedure seems especially relevant for AI because of the [growing potential for various AI systems to engage in covert communication](https://www.lesswrong.com/posts/bwyKCQD7PFWKhELMr/by-default-gpts-think-in-plain-sight?commentId=zfzHshctWZYo8JkLehttps://www.lesswrong.com/posts/bwyKCQD7PFWKhELMr/by-default-gpts-think-in-plain-sight?commentId=zfzHshctWZYo8JkLe). As such, AI labs should monitor the dangers of their systems and their ability to leak.
Thanks to Jakub Kraus for valuable comments. Cross posted on EA forum: <https://forum.effectivealtruism.org/posts/g38CkMbFzKBtdzFXY/biosafety-regulations-bmbl-and-their-relevance-for-ai> |
fd75de5a-81fb-41e1-9890-769767d9af8f | trentmkelly/LessWrong-43k | LessWrong | Mob and Bailey
Epistemological status: Moderately confident that this is a more useful way to use a concept that has been expanded upon by others.
Previous building blocks: See Logical Rudeness and All Another Brick in the Motte and for the foundations, as well as Against Accusing People of Motte and Bailey for the direct predecessor.
If you haven’t read the previous building blocks, the core idea is called the Motte and Bailey. A Motte and Bailey argument is what you call it when someone makes a clearly supported and uncontested claim, then makes an outrageous but advantageous claim, then swaps between these two claims whenever it's useful to them. It draws from the medieval tactic of having an easily farmable bailey right next to a heavily fortified motte, then moving your peasants and troops back and forth between them whenever raiders come or leave.
I
Amy and Bob would like to have a civil discussion about a philosophical difference they have. Their conversation goes something like this:
Amy: I don't understand why you think tautologies are important. I mean, you can't get any extra information out of them, right?
Bob: There are actually a number of different kinds of tautologies. For example, a logical tautology might say "either X equals Y or X does not equal Y" and while you might be correct that no new information is gained from this, I find it helps me organize my thoughts.
A: Ah, I didn't know that. I've mostly seen them used as rhetorical devices.
B: They can be used that way, but it's far from the most interesting thing about them for me.
A: As long as people are going to keep using tautologies to win arguments though, how do we help those who don’t understand them well enough to defend against tautology based arguments?
B: Oh go soak your head. I think if you learned more about them you’d be able to actually counter them when people did use them in arguments.
A: Even if I studied tautologies enough to do so, I worry that making a general rule of needing to stu |
26b1f611-898e-4955-8fd5-2eb4043a71c7 | StampyAI/alignment-research-dataset/aisafety.info | AI Safety Info | Why might we expect a superintelligence to be hostile by default?
Computers execute our precise commands without considering the thousands of instinctive human factors that determine if an action is acceptable, which can lead to potentially dangerous outcomes from seemingly simple instructions and goals.
One might argue: computers only do what we command them; no more, no less. So while it might be bad if [terrorists or enemy countries develop superintelligence first](/?state=6410&question=Isn't%20the%20real%20concern%20AI%20being%20misused%20by%20terrorists%20or%20other%20bad%20actors%3F), if good actors develop superintelligence first there’s no problem: we can just instruct it to do the things we want. This argument is intuitively reassuring but probably false.
Suppose we wanted a superintelligence to cure cancer. How might we specify the goal “cure cancer”? If we knew every individual step, then we could cure cancer ourselves. Instead, we have to give it the goal of curing cancer, and trust the superintelligence to come up with intermediate actions that further that goal. For example, a superintelligence might decide that the first step to curing cancer would be to learn more about protein folding, and might set up some experiments to investigate protein folding patterns.
A superintelligence would also need some level of common sense to decide which of various strategies to pursue. Suppose that investigating protein folding was very likely to cure 50% of cancers, but investigating genetic engineering was moderately likely to cure 90% of cancers. Which should the AI pursue? Presumably it would need some way to balance considerations like curing as much cancer as possible, and as quickly as possible, and with as high a probability of success as possible.
But a goal specified in this way would be very dangerous. Humans instinctively balance thousands of different considerations in everything they do; so far this hypothetical AI is only balancing three (least cancer, quickest results, highest probability). A human with such a limited set of considerations would seem maniacally, even psychopathically, obsessed with cancer-curing. If this were truly its goal structure, it would go wrong in almost comical ways. This type of problem, [specification gaming](https://deepmind.com/blog/article/Specification-gaming-the-flip-side-of-AI-ingenuity), has been observed in many AI systems.
If your only goal is “curing cancer”, and you lack humans’ instincts for the [thousands of other important considerations](https://www.lesswrong.com/posts/4ARaTpNX62uaL86j6/the-hidden-complexity-of-wishes), a relatively easy solution might be to hack into a nuclear base, launch all of its missiles, and kill everyone in the world. [This satisfies all the AI’s goals](/?state=8EL5&question=What%20is%20perverse%20instantiation%3F): it reduces cancer down to zero (which is better than medicine which works only some of the time), it’s very fast (which is better than medicine which might take a long time to invent and distribute) and it has a high probability of success (medicine might or might not work; nukes definitely do). This type of specification gaming can be expected for every type of problem given to a superintelligence, because precisely specifying all the things we care about is very difficult.
It’s worth noting that the “kill all humans” solution might be interpreted as “hostile”, but unlike the AI in works of fiction such as [The Terminator](https://en.wikipedia.org/wiki/The_Terminator), the cancer-curing AI is not actively looking to harm us. It simply has objectives that can be satisfied by killing us, and it won’t avoid doing so unless explicitly designed that way. As an analogy, the well being of ants is rarely considered when human engineers flood a plain to build a dam. The engineers aren’t explicitly hostile to the ants, they just don’t value their lives much. We don’t want humanity [to suffer the fate of the ants](https://futureoflife.org/resource/aimyths/) in this situation.
To recap, simple goal architectures are likely to [go very wrong](https://www.alignmentforum.org/posts/pRkFkzwKZ2zfa3R6H/without-specific-countermeasures-the-easiest-path-to) and look downright hostile unless tempered by common sense and a broader understanding of what we do and do not value.
|
29a012b6-43c1-4ed4-afe0-260d6bf567c2 | trentmkelly/LessWrong-43k | LessWrong | How To Think About Overparameterized Models
So, you’ve heard that modern neural networks have vastly more parameters than they need to perfectly fit all of the data. They’re operating way out in the regime where, traditionally, we would have expected drastic overfit, yet they seem to basically work. Clearly, our stats-101 mental models no longer apply here. What’s going on, and how should we picture it?
Maybe you’ve heard about some papers on the topic, but didn’t look into it in much depth, and you still don’t really have an intuition for what’s going on. This post is for you. We’ll go over my current mental models for what’s-going-on in overparameterized models (i.e. modern neural nets).
Disclaimer: I am much more an expert in probability (and applied math more generally) than in deep learning specifically. If there are mistakes in here, hopefully someone will bring it up in the comments.
Assumed background knowledge: multi-dimensional Taylor expansions, linear algebra.
Ridges, Not Peaks
First things first: when optimizing ML models, we usually have some objective function where perfectly predicting every point in the training set yields the best possible score. In overparameterized models, we have enough parameters that training indeed converges to zero error, i.e. all data points in the training set are matched perfectly.
Let’s pick one particular prediction setup to think about, so we can stick some equations on this. We have a bunch of (x,y) data points, and we want to predict y given x. Our ML model has some parameters θ, and its prediction on a point x(n) is f(x(n),θ). In order to perfectly predict every data point in the training set, θ must satisfy the equations
∀n:y(n)=f(x(n),θ)
Assuming y(n) is one-dimensional (i.e. just a number), and we have N data points, this gives us N equations. If θ is k-dimensional, then we have N equations with k variables. If the number of variables is much larger than the number of equations (i.e. k>>N, parameter-dimension much greater than number of data points |
ffd8b017-560a-454e-a7f4-a8598045871f | StampyAI/alignment-research-dataset/arxiv | Arxiv | SLIP: Learning to predict in unknown dynamical systems with long-term memory.
1 Introduction
---------------
Predictive models based on linear dynamical systems (LDS) have been successfully used in a wide range of applications with a history of more than half a century. Example applications in AI-related areas range from control systems and robotics (durrant2006simultaneous) to natural language processing (belanger2015linear), healthcare (parker1999model), and computer vision (chen2011kalman; coskun2017long). Other applications are found throughout the physical, biological, and social sciences in areas such as econometrics, ecology, and climate science.
The evolution of a discrete-time LDS is described by the following state-space model with t≥1:
| | | |
| --- | --- | --- |
| | ht+1=Aht+Bxt+ηt,yt=Cht+Dxt+ζt, | |
where ht are the latent states, xt are the inputs, yt are the observations, and ηt and ζt are process and measurement noise, respectively.
When the system parameters are known, the optimal linear predictor is the Kalman filter. When they are unknown, a common approach for prediction is to first estimate the parameters of a Kalman filter and then use them to predict system evolution. Direct parameter estimation usually involves solving a non-convex optimization problem, such as in the expectation maximization (EM) algorithm, whose theoretical guarantees may be difficult (yu2018identification). Several recent works have studied finite-sample theoretical properties of LDS identification.
For fully observed LDS, it has been shown that system identification is possible without a strict stability (ρ(A)<1) assumption, where ρ(A) is the spectral radius of A (simchowitz2018learning; sarkar2018near; faradonbeh2018finite).
For partially observed LDS, methods such as gradient descent (hardt2018gradient) and subspace identification (tsiamis2019finite) are developed, whose performances degrade polynomially when ρ(A) is close to one.
We focus on constructing *predictors* of an LDS without identifying the parameters. In the case of a stochastic LDS, the recent work of tsiamis2020online is most related to our question. Their method performs linear regression over a fixed-length lookback window to predict the next observation yt given its causal history. Without using a mixing-time argument, tsiamis2020online showed logarithmic regret with respect to the Kalman filter in hindsight even when the system is marginally stable (ρ(A)≤1). However, the prediction performance deteriorates if the true Kalman filter exhibits *long-term forecast memory*.
To illustrate the notion of forecast memory, we recall the recursive form of the (stationary) Kalman filter for 1≤t≤T, where T is the final horizon
(kailath2000linear, chap. 9):
| | | | | |
| --- | --- | --- | --- | --- |
| | ^ht+1|t | =A^ht|t−1+Bxt+K(yt−C^ht|t−1−Dxt) | | (1) |
| | | =(A−KC)^ht|t−1+Kyt+(B−KD)xt, | | (2) |
where ^ht|t−1 denotes the optimal linear predictor of ht given all the observations y1,y2,…,yt−1 and inputs x1,x2,…,xt−1. The matrix K is called the (predictive) Kalman gain.111One can interpret the Kalman filter Equation ([1](#S1.E1 "(1) ‣ 1 Introduction ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) as linear combinations of optimal predictor given existing data A^ht|t−1, known drift Bxt, and amplified innovation K(yt−C^ht|t−1−Dxt), where the term yt−C^ht|t−1−Dxt, called the *innovation* of process yt, measures how much additional information yt brings compared to the known information of observations up to yt−1. The Kalman predictor of yt given y1,y2,…,yt−1 and x1,x2,…,xt, denoted by ^yt|t−1, is C^ht|t−1+Dxt. Assume that ^h1|0=0. By expanding Equation ([2](#S1.E2 "(2) ‣ 1 Introduction ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")), we obtain
| | | | | |
| --- | --- | --- | --- | --- |
| | mt | ≜^yt|t−1=t−1∑i=1CGt−i−1Kyi+t−1∑i=1CGt−i−1(B−KD)xi+Dxt, | | (3) |
where G=A−KC. In an LDS, the transition matrix A controls how fast the process mixes—i.e., how fast the marginal distribution of yt becomes independent of y1. However, it is G that controls how long the *forecast* memory is. Indeed, it was shown in kailath2000linear that if the spectral radius ρ(G) is close to one, then the performance of a linear predictor that uses only yt−k to yt−1 for fixed k in predicting yt would be substantially worse than that of a predictor that uses all information y1 up to yt−1 as t→∞. Conceivably, the sample size required by the algorithm of tsiamis2020online explodes to infinity as ρ(G)→1, since the predictor uses a fixed-length lookback window to conduct linear regression.
The primary reason to focus on long-term forecast memory is the ubiquity of long-term dependence in real applications, where it is often the case that not all state variables change according to a similar timescale222Indeed, a common practice is to set the timescale to be small enough to handle the fastest-changing variables. (chatterjee2010dbns). For example, in a temporal model of the cardiovascular system, arterial elasticity changes on a timescale of years, while the contraction state of the heart muscles changes on a timescale of milliseconds.
Designing provably computationally and statistically efficient algorithms in the presence of long-term forecast memory is challenging, and in some cases, impossible. A related problem studied in the literature is the prediction of auto-regressive model with order infinity: AR(∞). Without imposing structural assumptions on the coefficients of an AR(∞) model, there is no hope to guarantee vanishing prediction error. One common approach to obtain a smaller representation is to make an exponential forgetting assumption to justify finite-memory truncation. This approach has been used in approximating AR(∞) with decaying coefficients (goldenshluger2001nonasymptotic), LDS identification (hardt2018gradient), and designing predictive models for LDS (tsiamis2020online; kozdoba2019line). Inevitably, the performance of these methods degrade by either losing long-term dependence information or requiring very large sample complexity as ρ(G) (and sometimes, ρ(A)) gets closer to one.
However, the Kalman predictor in ([3](#S1.E3 "(3) ‣ 1 Introduction ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) does seem to have a structure and in particular, the coefficients are geometric in G, which gives us hope to exploit it. Our main contributions are the following:
1. Generalized Kolmogorov width and spectral methods: We analyze the *generalized Kolmogorov width*, defined in Section [5.1](#S5.SS1 "5.1 Width of a subset ‣ 5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"), of the Kalman filter coefficient set. In Theorem [2](#Thmtheorem2 "Theorem 2. ‣ 5.3 Filter approximation ‣ 5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"), we show that when the matrix G is diagonalizable with *real* eigenvalues, the Kalman filter coefficients can be approximated by a linear combination of polylog(T) *fixed known* filters with 1/poly(T) error. It then motivates the algorithm design of linear regression based on the *transformed* features, where we first transform the observations y1:t and inputs x1:t for 1≤t≤T via these fixed filters. In some sense, we use the transformed features to achieve a good bias-variance trade-off: the small number of features guarantees small variance and the generalized Kolmogorov width bound guarantees small bias. We show that the fixed known filters can be computed efficiently via spectral methods. Hence, we choose spectral LDS improper predictor (SLIP) as the name for our algorithm.
2. Difficulty of going beyond real eigenvalues: We show in Theorem [2](#Thmtheorem2 "Theorem 2. ‣ 5.3 Filter approximation ‣ 5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") that if the dimension of matrix G in ([3](#S1.E3 "(3) ‣ 1 Introduction ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) is at least 2, then without assuming real eigenvalues one has to use at least Ω(T) filters to approximate an arbitrary Kalman filter. In other words, the Kalman filter coefficient set is very difficult to approximate via linear subspaces in general. This suggests some inherent difficulty of constructing provable algorithms for prediction in an arbitrary LDS.
3. Logarithmic regret uniformly for ρ(G)≤1,ρ(A)≤1: When ρ(A) or ρ(G) is equal to one the process does not mix and common assumptions regarding boundedness, concentration, or stationarity do not hold. Recently, mendelson2014learning showed that such assumptions are not required and learning is possible under a milder assumption referred to as the small-ball condition. In Theorem [1](#Thmtheorem1 "Theorem 1. ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"), we leverage this idea as well as results on self-normalizing martingales and show a logarithmic regret bound for our algorithm uniformly for ρ(G)≤1 and ρ(A)≤1. A roadmap to our regret analysis method is provided in Section [6](#S6 "6 Proof roadmap of Theorem 1 ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory").
4. Experimental results: We demonstrate in simulations that our algorithm performs better than the state-of-the-art in LDS prediction algorithms. In Section [7](#S7 "7 Experiments ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"), we compare the performance of our algorithm to wave filtering (hazan2017learning) and truncated filtering (tsiamis2020online).
2 Related work
---------------
Adaptive filtering algorithms are classical methods for predicting observations without the intermediate step of system identification (ljung1978convergence; fuller1980predictors; fuller1981properties; wei1987adaptive; lai1991recursive; lorentz1996constructive). However, finite-sample performance and regret analysis with respect to optimal filters are typically not studied in the classical literature. From a machine learning perspective, finite-sample guarantees are critical for comparing the accuracy and sample efficiency of different algorithms.
In designing algorithms and analyses for learning from sequential data, it is common to use mixing-time arguments (yu1994rates). These arguments justify finite-memory truncation (hardt2018gradient; goldenshluger2001nonasymptotic) and support generalization bounds analogous to those in i.i.d. data (mohri2009rademacher; kuznetsov2017generalization). An obvious drawback of mixing-time arguments is that the error bounds degrade with increasing mixing time. Several recent works established that identification is possible for systems that do not mix (simchowitz2018learning; faradonbeh2018finite; simchowitz2019learning). For the problem of the linear quadratic regulator, where the state is fully observed, several results provided finite-sample regret bounds (faradonbeh2017optimism; ouyang2017learning; dean2018regret; abeille2018improved; mania2019certainty; simchowitz2020naive).
For prediction without LDS identification, hazan2017learning; hazan2018spectral have proposed algorithms for the case of bounded adversarial noise. Similar to our work, they use spectral methods for deriving features. However, the spectral method is applied on a different set and connections with k-width and difficulty of approximation for the non-diagonalizable case are not studied. Moreover, the regret bounds are computed with respect to a certain fixed family of filters and competing with the Kalman filter is left as an open problem. Indeed, the predictor for general LDS proposed by hazan2018spectral without the real eigenvalue assumption only uses a fixed lookback window. Furthermore, the feature norms are of order poly(T) in our formulation, which makes a naive application of online convex optimization theorems (hazan2019introduction) fail to achieve a sublinear regret.
We focus on a more challenging problem of learning to predict in the presence of unbounded stochastic noise and long-term memory, where the observation norm grows over time. The most related to our work are the recent works of tsiamis2020online and ghai2020no, where the performance of an algorithm based on a finite lookback window is shown to achieve logarithmic regret with respect to the Kalman filter. However, the performance of this algorithm degrades as the forecast memory increases. In fact, this algorithm can be viewed as a special case of our algorithm where the fixed filters are chosen to be standard basis vectors.
We investigate the possibility of conducting tight convex relaxation of the Kalman predictive model by defining a notion that generalizes Kolmogorov width. The Kolmogorov width is a notion from approximation theory that measures how well a set can be approximated by a low-dimensional linear subspace (pinkus2012n). Kolmogorov width has been used in a variety of problems such as minimax risk bounds for truncated series estimators (donoho1990minimax; javanmard2012minimax), minimax rates for matrix estimation (ma2015volume), density estimation (hasminskii1990density), hypothesis testing (wei2020local; wei2020gauss), and compressed sensing (donoho2006compressed). In Section [5](#S5 "5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"), we present a generalization of Kolmogorov width, which facilitates measuring the convex relaxation approximation error.
3 Preliminaries and problem formulation
----------------------------------------
###
3.1 Notation
We denote by x1:t∈Rnt, the vertical concatenation of x1,…,xt∈Rn. We use xt(i) to refer to the i-th element of the vector xt=[xt(1),…,xt(n)]⊤. We denote by ∥.∥2, the Euclidean norm of vectors and the operator 2-norm of matrices. The spectral radius of a square matrix A is denoted by ρ(A). The eigenpairs of an n×n matrix are {(σj,ϕj)}nj=1 where σ1≥⋯≥σn and {ϕj}kj=1 are called the top k eigenvectors. We denote by ϕj(t:1)=[ϕj(t),…,ϕj(1)] the first t elements of ϕj in a reverse order. The horizontal concatenation of matrices a1,…,an with appropriate dimensions, is denoted by [ai]ni=1=[a1|…|an]. The Kronecker product of matrices A and B is denoted by A⊗B.
Identity matrix of dimension n is represented by In. We write x≲by to represent x≤cy, where c is a constant that only depends on b. We use the notation x≍by if c1,c2>0 exist that only depend on b and c1|x|≤|y|≤c2|x|. We define M=(RΘ,m,γ,κ,β,γ,δ) to be a shorthand for the PAC bound parameters (defined in Theorem [1](#Thmtheorem1 "Theorem 1. ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")).
Given a function f:N→R, we write x≲Mf(T),x≍Mf(T) to specify the dependency only on the horizon T.
###
3.2 Problem statement
We consider the problem of predicting observations generated by the following linear dynamical system with inputs xt∈Rn, observations yt∈Rm, and latent states ht∈Rd:
| | | | |
| --- | --- | --- | --- |
| | ht+1=Aht+Bxt+ηt,yt=Cht+Dxt+ζt, | | (4) |
where A,B,C, and D are matrices of appropriate dimensions. The sequences ηt∈Rd (process noise) and ζt∈Rm (measurement noise) are assumed to be zero-mean, i.i.d. random vectors with covariance matrices Q and R, respectively. For presentation simplicity, we assume that ηt and ζt are Gaussian; extension of our regret analysis to sub-Gaussian and hypercontractive noise is straightforward. We assume that the discrete Riccati equation of the Kalman filter for the state covariance has a solution P and the initial state starts at this stationary covariance. This assumption ensures the existence of the stationary Kalman filter with stationary gain K; see kailath2000linear for details.
Define the observation matrix Ot and the control matrix Ct of a stationary Kalman filter as
| | | | |
| --- | --- | --- | --- |
| | | | (5) |
where G=A−KC is called the closed-loop matrix. The Kalman predictor ([3](#S1.E3 "(3) ‣ 1 Introduction ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) can be written as
| | | | |
| --- | --- | --- | --- |
| | mt+1=Oty1:t+Ctx1:t+Dxt+1, | | (6) |
The prediction error et=yt−mt, also called the innovation, is zero-mean with a stationary covariance V. Our goal is to design an algorithm ^mt(y1:t−1,x1:t) such that the following regret
| | | | |
| --- | --- | --- | --- |
| | Regret(T)≜T∑t=1∥yt−^mt∥22−∥yt−mt∥22 | | (7) |
is bounded by polylog(T) with high probability.
###
3.3 Improper learning
Most existing algorithms for LDS prediction include a preliminary system identification step, in which system parameters are first estimated from data, followed by the Kalman filter. However, the loss function (such as squared loss) over system parameters is non-convex, for which methods based on heuristics such as EM and subspace identification are commonly used. Instead, we aspire to an algorithm that optimizes a convex loss function for which theoretical guarantees of convergence and sample complexity analysis are possible. This motivates developing an algorithm based on improper learning.
Instead of directly learning the model parameters in a hypothesis class H, improper learning methods reparameterize and learn over a different class ˜H. For example in system ([4](#S3.E4 "(4) ‣ 3.2 Problem statement ‣ 3 Preliminaries and problem formulation ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")), proper learning hypothesis class H contains possible values for parameters A,B,C,D,Q and R. Improper learning is used for statistical or computational considerations when the original hypothesis class is difficult to learn. The class ˜H is often a relaxation: it is chosen in a way that is easier to optimize and more computationally efficient while being close to the original hypothesis class. Improper learning has been used to circumvent the proper learning lower bounds (foster2018logistic).
In this paper, we use improper learning to conduct a tight convex relaxation, i.e. we slightly overparameterize the LDS predictive model in such a way that the resulting loss function is convex. Designing an overparameterized improper learning class requires care as using a small number of parameters may result in a large bias whereas using too many parameters may result in high variance. Section [5.3](#S5.SS3 "5.3 Filter approximation ‣ 5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") presents our overparameterization approach based on spectral methods that enjoys a small approximation error with relatively few parameters.
###
3.4 Systems with long forecast memory
As discussed before, system ([4](#S3.E4 "(4) ‣ 3.2 Problem statement ‣ 3 Preliminaries and problem formulation ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) exhibits long forecast memory when ρ(G) is close to one. The closed-loop matrix G itself is related to parameters A,C,Q, and R. In the following example, we discuss when long forecast memory is instantiated in a scalar dynamical system.
######
Example 3.1.
Consider system ([4](#S3.E4 "(4) ‣ 3.2 Problem statement ‣ 3 Preliminaries and problem formulation ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) with d=m=1. The following holds for a stationary Kalman filter
| | | |
| --- | --- | --- |
| | KC=AC2P+C2P++R⇒0≤KC≤Afor d=m=1, | |
where P+ is the variance of state predictions ^ht|t−1 (kailath2000linear). The above constraint yields G=A−KC≤A, which implies that the forecast memory can only be long in systems that mix slowly. We write
| | | |
| --- | --- | --- |
| | G=A(1−C2P+C2P++R),%
for d=m=1. | |
The above equation suggests if R≫C2P+, then G is close to A. In words, linear dynamical systems with small observed signal to noise ratio C/√R have long forecast memory, provided that they mix slowly.
Another parameter that affects the forecast memory of a system is the process noise variance Q. When Q is small and A is close to one, latent state ht is almost constant. In this setting, the observations in the distant past are informative on ht and therefore should be considered when making predictions.
In multi-dimensional systems, the chance of encountering a system with long forecast memory is much higher as it suffices for only one variable or direction to exhibit long forecast memory. Systems represented in the discrete-time form of Equation ([4](#S3.E4 "(4) ‣ 3.2 Problem statement ‣ 3 Preliminaries and problem formulation ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) are often obtained by discretizing differential equations and continuous dynamical systems, for which choosing a small time step results in a better approximation. However, reducing the time step directly increases the forecast memory. These types of issues has motivated a large body of research on alternative methods such as continuous models (nodelman2002continuous) and adaptive time steps (aleks2009probabilistic). It is therefore desirable to have algorithms whose performance is not affected by the choice of time step, which is one of our goals in this paper.
4 SLIP: Spectral LDS improper predictor
----------------------------------------
In this section, we present the SLIP algorithm and the main regret theorem. The derivation of the algorithm and the sketch for regret analysis are respectively provided in Section [5](#S5 "5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") and Section [6](#S6 "6 Proof roadmap of Theorem 1 ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory").
Algorithm [1](#alg1 "Algorithm 1 ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") presents a pseudocode for the SLIP algorithm. Our algorithm is based on an online regularized least squares and a linear predictor ^mt=^Θ(t)ft, where ft is an l-dimensional vector of features and ^Θ(t)∈Rm×l is a parameter matrix. The features are constructed from past observations and inputs using eigenvectors of a particular T×T Hankel matrix with entries
| | | | |
| --- | --- | --- | --- |
| | Hij=1+(−1)i+j2(i+j−1),1≤i,j≤T. | | (8) |
Let ϕ1,…,ϕk for k≤T be the top k eigenvectors of matrix H, to which we refer as spectral filters. At every time step, we obtain our feature vector by concatenating the current input xt to k output features based on y1:t−1 and k input features based on x1:t−1. More specifically, we have
| | | | |
| --- | --- | --- | --- |
| | ˜yt−1(j)≜(ϕ⊤j(t−1:1)⊗Im)y1:t−1=ϕj(1)yt−1+⋯+ϕj(t−1)y1(output features),˜xt−1(j)≜(ϕ⊤j(t−1:1)⊗In)x1:t−1=ϕj(1)xt−1+⋯+ϕj(t−1)x1(input features), | | (9) |
for j∈{1,…,k}, resulting in a feature vector ft with dimension l=mk+nk+n.
Upon receiving a new observation, the parameter matrix is updated by minimizing the regularized loss
| | | |
| --- | --- | --- |
| | t∑i=1∥^Θft−yt∥2+α∥^Θ∥22, | |
for α>0, which yields the following update rule
| | | | |
| --- | --- | --- | --- |
| | | | (10) |
Inputs: Time horizon T, number of filters k, regularization parameter α, input dimension n,
observation dimension m.
Output: One-step-ahead predictions ^mt(x1:t,y1:t−1).
Compute the top k eigenvectors {ϕj}kj=1 of matrix H with elements
| | | |
| --- | --- | --- |
| | Hij=(−1)i+j+12(i+j−1),1≤i,j≤T. | |
Set vectors ψi=[ϕ1(i),…,ϕk(i)]⊤ for i∈{1,…,T}, where ϕj(i) is the i-th element of ϕj.
Initialize ^Θ(1)∈Rm×l with l=(n+m)k+n.
for t=1,…,T do
Set Ψt−1=[ψt−1,…,ψ1], where Ψ0=0k.
Set x1:t−1=[x⊤1,…,x⊤t−1]⊤,y1:t−1=[y⊤1,…,y⊤t−1]⊤, x1:0=0n,y1:0≜0m.
Compute l-dimensional feature vector ft:
ft=⎡⎢⎣˜yt−1˜xt−1xt⎤⎥⎦=⎡⎢⎣(Ψt−1⊗Im)y1:t−1(Ψt−1⊗In)x1:t−1xt⎤⎥⎦.
Predict ^mt=^Θ(t)ft.
Observe yt and update parameters ^Θ(t+1)=(∑ti=1yif⊤i)(∑ti=1fif⊤i+αIl)−1.
end for
Algorithm 1 SLIP: Spectral LDS Improper Predictor
Importantly, Algorithm [1](#alg1 "Algorithm 1 ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") requires no knowledge of the system parameters, noise covariance, or state dimension and the predictive model is learned online only through sequences of inputs and observations. Note that the spectral filters are computed by conducting a single eigendecomposition and are fixed throughout the algorithm; matrix Ψt merely selects certain elements of spectral filters used for constructing features. Computing eigenvectors when T is large is possible by solving the corresponding second-order Sturm-Liouville equation, which allows using efficient ordinary differential equation solvers; see hazan2017learning for details.
The next theorem analyzes the regret achieved by the SLIP algorithm. A proof sketch of the theorem is provided in Section [6](#S6 "6 Proof roadmap of Theorem 1 ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") and a complete proof is deferred to Appendix [F](#A6 "Appendix F Regret analysis ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory").
######
Theorem 1.
(Regret of the SLIP algorithm) Consider system ([4](#S3.E4 "(4) ‣ 3.2 Problem statement ‣ 3 Preliminaries and problem formulation ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) without inputs with initial state covariance equal to the stationary covariance P. Let mt be the predictions made by the best linear predictor (Kalman filter) and ^mt be the predictions made by Algorithm [1](#alg1 "Algorithm 1 ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"). Fix the failure probability δ>0 and make the following assumptions:
1. There exists a finite RΘ that ∥C∥2,∥P∥2,∥Q∥2,∥R∥2,∥V∥2≤RΘ and ∥Ot∥2≤RΘtβ for a bounded constant β≥0. Let κ be the maximum condition number of R and Q.
2. The system is marginally stable with ρ(A)≤1 and ∥At∥2≤γtlog(γ) for a bounded constant γ≥1.
Furthermore, the closed-loop matrix G is diagonalizable with real eigenvalues.
3. The regularization parameter α and the number of filters k satisfy the following
| | | |
| --- | --- | --- |
| | k≍log2(T)polylog(m,γ,RΘ,1δ),α≍1RΘkTβ | |
4. There exists s≲RΘ,m,γ,β,δt/(klogk)
and t0 such that for all t≥t0
| | | | |
| --- | --- | --- | --- |
| | tΩs/2(A;ψ)−Ωt+1(A;ψ)⪰0. | | (11) |
Ωt(A;ψ) is called the filter quadratic function of ψ with respect to A defined as
| | | | |
| --- | --- | --- | --- |
| | Ωt(A;ψ) | =(ψ(d)1)(ψ(d)1)⊤+(ψ(d)2+ψ(d)1A)(ψ(d)2+ψ(d)1A)⊤+… | |
| | | +(ψ(d)t−1+⋯+ψ(d)1At−2)(ψ(d)t−1+⋯+ψ(d)1At−2)⊤ | |
where ψ(d)i=[ϕ1(i),…,ϕk(i)]⊤⊗Id.
Then, for all T≥max{10,t0}, the following holds with probability at least 1−δ,
| | | |
| --- | --- | --- |
| | Regret(T)≤polylog(T,γ,1δ)κpoly(RΘ,β,m). | |
Theorem [1](#Thmtheorem1 "Theorem 1. ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") states that if G is diagonalizable with real eigenvalues, provided that the number of filters k≍Mlog2(T), the regret is polylog(T) with high probability and the regret bound is independent of both transition matrix spectral radius ρ(A) (related to mixing rate) and closed-loop matrix spectral radius ρ(G) (related to forecast memory).
######
Remark 1.
Note that for any matrix A, there exists a constant γ≥1 such that ∥At∥2≤γtlog(γ) (kozyakin2009accuracy). We justify our assumption on diagonalizable G with real eigenvalues in the following section. The filter quadratic condition is easily verified for s>2(k+1) and t0≳RΘ,m,γ,β,δk2log(k) for all A with ρ(A)≤1 for the filters corresponding to truncated observations (a.k.a. basis vectors) such as in tsiamis2020online. When A is symmetric, this condition can be further simplified to tΩs/2(D;ψ)−Ωt+1(D;ψ)⪰0 for all diagonal matrices D with |Dii|≤1.
5 Approximation error: Generalized Kolmogorov width
----------------------------------------------------
###
5.1 Width of a subset
The SLIP algorithm is based on approximating the Kalman predictive model. In this section, we start by introducing a generalization of Kolmogorov k-width of a subset, which is a criterion to assess the quality of a function approximation method. We then present our approximation technique which gives the SLIP algorithm.
######
Definition 1.
(Generalized Kolmogorov k-width) Let W be a subset in a normed linear space with norm ∥.∥ whose elements are d×n matrices. Given d×n matrices u1,…,uk for k≥1, let
| | | |
| --- | --- | --- |
| | U(u1,…,uk)≜{y∣∣y=k∑i=1aiui,∀ai∈Rd×d} | |
be the subset constructed by linear combinations of u1,…,uk with coefficient matrices a1,…,ak. For a fixed k≥1, denote by Uk the set of U(u1,…,uk) for all possible choices of u1,…,uk:
| | | |
| --- | --- | --- |
| | Uk≜{U(u1,…,uk)∣∣∀ui∈Rd×n}. | |
The generalized k-width of W is defined as
| | | |
| --- | --- | --- |
| | dk(W)≜infU∈Uksupx∈W%
dist(x;U)=infU∈Uksupx∈Winfy∈U∥x−y∥, | |
where dist(x;U) is the distance of x to subset U and the first infimum is taken over all subsets U∈Uk.
Here, we are interested in approximating W with the “best” subset in the set Uk: the subset that would minimize the worst case projection error of x∈W among all subsets in Uk. This minimal error is given by the generalized k-width of W. Figure [1](#S5.F1 "Figure 1 ‣ 5.2 From a small width to an efficient convex relaxation ‣ 5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") illustrates an example in which W is an ellipsoid in R3 and we are interested in approximating it with a 2-dimensional plane (k=2). In this example, U2 is the set of all planes and plane U offers the smallest worst-case projection error d2(W) for approximating W.
Definition [1](#Thmdefinition1 "Definition 1. ‣ 5.1 Width of a subset ‣ 5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") generalizes the original Kolmogorov k-width definition in two ways. First, in our definition W is allowed to be a subset of matrices whereas in the original Kolmgorov width, W is a subset of vectors. This generalization is necessary as we wish to approximate the coefficient set of the Kalman predictive model whose elements Ot and Ct are matrices. Second, we allow the coefficients ai to be matrices, generalizing over the scalar coefficients used in the original definition of Kolmogorov width. When constructing a reparameterization, a linear predictive model yields a convex objective regardless of whether the coefficients are matrices or scalars. Allowing coefficients to be matrices as opposed to restricting them to be scalars gives flexibility to find a reparameterization with small approximation error, as demonstrated in Theorem [2](#Thmtheorem2 "Theorem 2. ‣ 5.3 Filter approximation ‣ 5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory").
###
5.2 From a small width to an efficient convex relaxation
Before stating our approximation technique, we briefly describe how a small generalized k-width allows for an efficient convex relaxation. The ideas presented in this section will be made more concrete in subsequent sections.
To understand the main idea, consider system ([4](#S3.E4 "(4) ‣ 3.2 Problem statement ‣ 3 Preliminaries and problem formulation ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) with no inputs whose predictive model can be written as mt+1=Oty1:t. Matrix Ot belongs to a subset in Rm×mt restricted by the constraints on system parameters. A naive approach for a convex relaxation is learning Ot in the linear predictive model Oty1:t directly. However in this approach, the total number of parameters is m2t, which hinders achieving sub-linear regret.
Now suppose that there exists k≪t for which the generalized k-width is small, i.e. there exist fixed known matrices u1,…,uk∈Rm×mt that approximate any Ot with a small error Ot≈∑ki=1aiui, where a1,…,ak∈Rm×m are coefficient matrices. The predictive model can be approximated by
| | | |
| --- | --- | --- |
| | mt+1≈k∑i=1aiuiy1:t, | |
provided that norm of y1:t (compared to the approximation error of Ot) is controlled with high probability. Since ui and y1:t are known, we only need to learn coefficients a1,…,ak resulting in a total of m2k parameters which is much smaller than the naive approach with m2t parameters.

Figure 1: Approximating W, a 3D ellipsoid, by a 2D plane U(u1,u2) among U2, the set of all planes. In this example, U has the smallest worst-case projection error that is equal to the 2-width of W denoted by d2(W).
###
5.3 Filter approximation
Consider the matrix
| | | |
| --- | --- | --- |
| | μ(G)≜[I,G,G2,…,GT−1], | |
where G∈Rd×d is a real square matrix with spectral radius ρ(G)≤1. We seek to approximate μ(G)≈˜μ(G)=∑ki=1aiui by a linear combination of k matrices u1,…,uk∈Rd×Td and coefficient matrices {a1,…,ak}∈Rd×d. We evaluate the quality of approximation in operator 2-norm ∥μ(G)−˜μ(G)∥2 by studying the generalized k-width of μ(G).
We demonstrate a sharp phase transition. Precisely, we show that when G is diagonalizable with real eigenvalues, the width dk(W) decays exponentially fast with k, but for a general G with d≥2 it decays only polynomially fast. In other words, when d≥2 the inherent structure of the set W is not easily exploited by linear subspaces.
######
Theorem 2.
(Kalman filter k-width)
Let
| | | |
| --- | --- | --- |
| | W≜{μ(G)=[I,G,G2,…,GT−1]∣∣G∈Rd×d,ρ(G)≤1} | |
and endow the space of W with the 2-norm. The following bounds hold on the generalized k-width of the set W.
1. If d≥2, then for 1≤k≤T,
| | | |
| --- | --- | --- |
| | dk(W)≥√T−k. | |
2. Restrict G to be diagonalizable with real eigenvalues. If T≥10, then for any d≥1
| | | |
| --- | --- | --- |
| | dk(W)≤C0d√T(logT)1/4c−k/logT, | |
where c=exp(π2/16) and C0=√43. Moreover, there exists an efficient spectral method to compute a k-dimensional subspace that satisfies this upper bound.
###### Proof.
Here, we only provide a proof sketch; see Appendix [C](#A3 "Appendix C Filter approximation and width analysis ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") for a complete proof.
Let λ1,…λd∈[−1,1] be the eigenvalues of G. Let vi be the right eigenvectors of G and w⊤i be the left eigenvectors of G and write
| | | |
| --- | --- | --- |
| | μ(G)=d∑i=1viw⊤i([1,λi,…,λT−1i]⊗Id)=d∑i=1viw⊤i(μ(λi)⊗Id). | |
We approximate the row vector μ(λ) for any λ∈[−1,1] using principal component analysis (PCA). The covariance matrix of μ(λ) with respect to a uniform measure is given by
| | | |
| --- | --- | --- |
| | H=∫1λ=−112μ(λ)⊤μ(λ)dλ⇒Hij=∫1−112λi−1λj−1dλ=(−1)i+j+12(i+j−1). | |
Let {ϕj}kj=1 be the top k eigenvectors of H. We approximate μ(λ) by ˜μ(λ)=∑kj=1⟨μ⊤(λ),ϕj⟩ϕ⊤j and thus obtain
| | | |
| --- | --- | --- |
| | μ(G)≈˜μ(G)=k∑j=1[d∑i=1⟨μ⊤(λi),ϕj⟩viw⊤i](ϕ⊤j⊗Id)=k∑j=1ajuj. | |
We show a uniform bound on ∥μ(G)−˜μ(G)∥ by first analyzing the PCA approximation error which depends on the spectrum of matrix H. Matrix H is a positive semi-definite Hankel matrix, a square matrix whose ij-th entry only depends on the sum i+j. We leverage a recent result by beckermann2017singular who proved that the spectrum of positive semi-definite Hankel matrices decays exponentially fast.
This result, however, only guarantees a small average error but we need to prove that the maximum error is small to ensure a uniform bound on regret. Observe that the PCA error r(λ)=μ(λ)−˜μ(λ) is defined over a finite interval [−1,1] with a small average. Thus, by computing the Lipschitz constant of r(λ), we show that the maximum approximation error is small, resulting in an upper bound on dk(W).
For the first claim, we lower bound the generalized k-width of W by relaxing the sup-norm by a weighted average, resulting in a *weighted* version of generalized k-width. We observe that the weighted k-width can be computed using PCA. We compute the approximation error of PCA showing that this error is large.
∎
The approximation technique used in the above theorem can readily be applied to approximate the coefficients of the Kalman predictive model by
| | | | |
| --- | --- | --- | --- |
| | ˜Ot | =k∑j=1[d∑i=1⟨μ(λi)⊤,ϕj⟩Cviw⊤iK](ϕ⊤j(t:1)⊗Im), | |
| | ˜Ct | =k∑j=1[d∑i=1⟨μ(λi)⊤,ϕj⟩Cviw⊤i(B−KD)](ϕ⊤j(t:1)⊗In), | |
where we used the fact that [λt−1i,…,λi,1] can be approximated by truncated eigenvectors {ϕj(t:1)}kj=1. The relaxed model ˜mt≜˜Oty1:t−1+˜Ctx1:t−1+Dxt can be written in the form ˜mt=˜Θft.
The feature vector ft is defined in ([9](#S4.E9 "(9) ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) and the parameter matrix ˜Θ is obtained by concatenating the corresponding coefficient matrices as described below
| | | | |
| --- | --- | --- | --- |
| | ˜Θ=\bBigg@2.5[[d∑i=1⟨μ(λi)⊤,ϕj⟩Cviw⊤iK]kj=1∈Rm×mkfor output features\bBigg@2.5|[d∑i=1⟨μ(λi)⊤,ϕj⟩Cviw⊤i(B−KD)]kj=1∈Rm×nkfor input features\bBigg@2.5|[d∑i=1⟨μ(λi)⊤,ϕj⟩Cviw⊤i(B−KD)]D∈Rm×nfor xt\bBigg@2.5]m×l | | (12) |
A complete derivation of convex relaxation along with an approximation error analysis is provided in Appendix [D](#A4 "Appendix D Convex relaxation analysis: Proof of Theorem 3 ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory").
6 Proof roadmap of Theorem [1](#Thmtheorem1 "Theorem 1. ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")
-----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
In this section we present a proof sketch for Theorem [1](#Thmtheorem1 "Theorem 1. ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"); the complete proof is deferred to Appendix [E](#A5 "Appendix E Regret decomposition ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") and Appendix [F](#A6 "Appendix F Regret analysis ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"). Let et=yt−mt denote the innovation process and bt=˜mt−mt denote the bias due to convex relaxation. Define
| | | | |
| --- | --- | --- | --- |
| | L(T)≜T∑t=1∥^mt−mt∥22. | | (13) |
L(T) measures the difference between Algorithm [1](#alg1 "Algorithm 1 ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") predictions and the Kalman predictions in hindsight. Regret defined in ([7](#S3.E7 "(7) ‣ 3.2 Problem statement ‣ 3 Preliminaries and problem formulation ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) can be written as
| | | | |
| --- | --- | --- | --- |
| | Regret(T)=T∑t=1∥^mt−mt∥22−T∑t=12e⊤t(^mt−mt)=L(T)−T∑t=12e⊤t(^mt−mt). | | (14) |
Using an argument based on self-normalizing martingales, the second term is shown to be of order √L(T) and thus, it suffices to establish a bound on L(T).
Define
| | | | |
| --- | --- | --- | --- |
| | Zt≜αI+t∑i=1fif⊤i,Et≜t∑i=1eif⊤i,Bt≜t∑i=1bif⊤i. | | (15) |
A straighforward decomposition of loss gives
| | | | |
| --- | --- | --- | --- |
| | L(T)≤3T∑i=1∥Et−1Z−1t−1ft∥22least squares error+3T∑i=1∥Bt−1Z−1t−1ft+bt∥22improper learning bias+3T∑i=1∥α~ΘZ−1t−1ft∥22regularization error. | | (16) |
###
6.1 Least squares error
Among all, it is most difficult to establish a bound on the least squares error. Consider the following upper bound
| | | |
| --- | --- | --- |
| | T∑t=1∥Et−1Z−1t−1ft∥2≤max1≤t≤T∥Et−1Z−1/2t−1∥2T∑t=1∥Z−1/2t−1ft∥2. | |
We show the first term is bounded by polylog(T) for any δ≥0. In particular,
| | | | |
| --- | --- | --- | --- |
| | max1≤t≤T∥Et−1Z−1/2t−1∥2 | ≲RΘ,m,γ,β,δmax1≤t≤Tlog(det(Zt)det(αI)−1δ)≲RΘ,m,γ,β,δklog(T). | |
Our argument is based on vector self-normalizing martingales, a similar technique used by abbasi2011improved; sarkar2018near; tsiamis2020online. det(Zt) is bounded by poly(T) for two reasons. First, the feature dimension, which is linear in the number of filters k, is polylog(T) on account of Theorem [2](#Thmtheorem2 "Theorem 2. ‣ 5.3 Filter approximation ‣ 5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"). Second, the marginal stability assumption (ρ(A)≤1) ensures that features and thus Zt grow at most polynomially in t.
It remains to prove that the summation ∑Tt=1∥Z−1/2t−1ft∥22 is bounded by polylog(T) with high probability. We use an argument inspired by Lemma 2 of lai1982least and Schur complement lemma (zhang2006schur) to conclude that
| | | |
| --- | --- | --- |
| | T∑t=1∥Z−1/2t−1ft∥22≍Mpolylog(T)⇔Zt−1cTftf⊤t⪰0forcT≍Mpolylog(T). | |
Therefore, it suffices to prove the right-hand side. We show a high probability Löwner upper bound on ftf⊤t based on the feature covariance cov(ft) using sub-Gaussian quadratic tail bounds (vershynin2018high). To capture the excitation behavior of features, we establish a Löwner lower bound on Zt by proving that the process {ft}t≥1 satisfies a martingale small-ball condition (mendelson2014learning; simchowitz2018learning). We leverage the small-ball condition lower tail bounds and prove the following lemma.
######
Lemma 1.
(Martingale small-ball condition) Let ϕ1,…,ϕk∈RT be orthonormal and fix δ>0. Given system ([4](#S3.E4 "(4) ‣ 3.2 Problem statement ‣ 3 Preliminaries and problem formulation ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")), let Ft=σ{η0,…,ηt−1,ζ1,…,ζt} be a filteration and for all t≥1 define
| | | |
| --- | --- | --- |
| | ft=ψ1⊗yt−1+⋯+ψt−1⊗y1,whereψi=[ϕ1(i),…,ϕk(i)]⊤. | |
Let Γi=cov(ft+i|Ft).
1. For any 1≤s≤T, the process {ft}t≥1 satisfies a (s,Γs/2,p=3/20)-block martingale small-ball (BMSB) condition, i.e. for any t≥0 and any fixed ω in unit sphere Sl−1
| | | |
| --- | --- | --- |
| | 1ss∑i=1P(|ω⊤ft+i|≥√ω⊤Γs/2ω∣Ft)≥p. | |
2. Under the assumptions of Theorem [1](#Thmtheorem1 "Theorem 1. ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"), the following holds with probability at least 1−δ
| | | |
| --- | --- | --- |
| | T∑t=1∥Z−1/2t−1ft∥22≤κk2log(T)poly(RΘ,β,m,log(γ),log(1δ)). | |
Provided that the number of filters is polylog(T), the above lemma ensures that ∑Tt=1∥Z−1/2t−1ft∥22 is also polylog(T), which is the desired result.
###
6.2 Improper learning bias
We characterize the improper learning bias term in ([16](#S6.E16 "(16) ‣ 6 Proof roadmap of Theorem 1 ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) by first showing a uniform high probability bound on the convex relaxation error stated in the theorem below. The proof can be found in Appendix [D](#A4 "Appendix D Convex relaxation analysis: Proof of Theorem 3 ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory").
######
Theorem 3.
(Convex relaxation error bound, informal) Consider system ([4](#S3.E4 "(4) ‣ 3.2 Problem statement ‣ 3 Preliminaries and problem formulation ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")) with bounded inputs ∥xt∥2≤Rx and assume conditions (i)-(ii) of Theorem [1](#Thmtheorem1 "Theorem 1. ‣ 4 SLIP: Spectral LDS improper predictor ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") holds. Then for any ϵ,γ≥0, if the number of filters k satisfies k≳Mlog(T)log(T/ϵ),
then the following holds for ˜Θ as defined in ([12](#S5.E12 "(12) ‣ 5.3 Filter approximation ‣ 5 Approximation error: Generalized Kolmogorov width ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"))
| | | |
| --- | --- | --- |
| | P[∥˜Θft−mt∥22≥ϵ]≤δ. | |
In Appendix [F.7](#A6.SS7 "F.7 Proof of Theorem 1 ‣ Appendix F Regret analysis ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"), the result of the above theorem is followed by an application of a vector self-normalizing martingale theorem to prove a polylog(T) bound on the improper learning bias.
######
Remark 2.
While the algorithm derivation, convex relaxation approximation error, and most of the regret analysis consider a system with control inputs, the excitation result of Lemma [1](#Thmlemma1 "Lemma 1. ‣ 6.1 Least squares error ‣ 6 Proof roadmap of Theorem 1 ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") is given without inputs. We believe that extending our analysis for LDS with inputs is possible by characterizing input features and in light of the experiments. However, such an extension requires some care. For instance, one needs to characterize the covariance between features constructed from observations and features constructed from inputs to demonstrate a small-ball condition.
###
6.3 Regularization error
Lastly, we demonstrate an upper bound on the regularization error in ([16](#S6.E16 "(16) ‣ 6 Proof roadmap of Theorem 1 ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory")). We write the following bound
| | | |
| --- | --- | --- |
| | T∑t=1∥α~ΘZ−1t−1ft∥22≤α21α∥~Θ∥22T∑t=1∥Z−1/2t−1ft∥22≤T∑t=1∥Z−1/2t−1ft∥22. | |
The first inequality is based on Zt⪰αI and the submultiplicative property of norm. The second inequality uses the fact that ∥˜Θ∥22≤1/α for α≍M(RΘkTβ)−1 as shown in Appendix [F.5](#A6.SS5 "F.5 Regularization term ‣ Appendix F Regret analysis ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"). The last term is bounded as result of Lemma [1](#Thmlemma1 "Lemma 1. ‣ 6.1 Least squares error ‣ 6 Proof roadmap of Theorem 1 ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory").
7 Experiments
--------------
We carry out experiments to evaluate the empirical performance of our provable method in three dynamical systems with long-term memory. We compare our results against those yielded by the wave filtering algorithm (hazan2017learning) implemented with follow the regularized leader and the truncated filtering algorithm (tsiamis2020online). We consider ∥^mt−mt∥2, the squared error between algorithms predictions and predictions by a Kalman filtering algorithm that knows system parameters, as a performance measure. For all algorithms, we use k=20 filters and run each experiment independently 100 times and present the average error with 99% confidence intervals.

Figure 2: Performance of our algorithm compared with wave filtering and truncated filtering. System 1 is an scalar LDS with A=B=D=1, C=Q=R=0.001, and xt∼N(0,2). System 2 is a multi-dimensional LDS with no inputs and A=diag[−1,1], C=[0.1,0.5], R=0.5, and Q=[4,6;6,10]×10−3. System 3 is another multi-dimensional LDS with non-symmetric A=[1,0;0.1,1], xi∼U(−0.01,0.01), Q=10−3I, R=I, C=[0,0.1;0.1,1], and B,D are matrices of all ones.
In the first example (Figure [2](#S7.F2 "Figure 2 ‣ 7 Experiments ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"), left), we consider a scalar marginally stable system with A=1 and Gaussian inputs. This system exhibits long forecast memory with G≈0.999. Observe that the truncated filter suffers from a large error which is due to ignoring long-term dependencies. The wave filter predictions also deviates from optimal predictions as it only considers yt−1,x1:t for predicting yt. The middle plot in Figure [2](#S7.F2 "Figure 2 ‣ 7 Experiments ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory") presents the results for a multi-dimensional system with A=diag[−1,1] and no inputs. This system also has a long forecast memory (G has eigenvalues ≈{0.991,−0.932}), resulting in poor performance of the truncated filter. The wave filter also performs poorly in this system as it is only driven by stochastic noise. For the last example, we consider another multi-dimensional system where A is a lower triangular matrix (Figure [2](#S7.F2 "Figure 2 ‣ 7 Experiments ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory"), right). This is a difficult example where ρ(A)=1 but ∥A∥2>1, resulting in a polynomial growth of the observations over time. The results show that our algorithm outperforms both the wave filter, which requires a symmetric A, and the truncated filter in the case of fast-growing observations.
Experiments on hyperparameter sensitivity of our algorithm and comparison with the EM algorithm are provided in Appendix [H](#A8 "Appendix H Additional experiments ‣ SLIP: Learning to Predict in Unknown Dynamical Systems with Long-Term Memory").
8 Discussion and future work
-----------------------------
We presented the SLIP algorithm, an efficient algorithm for learning a predictive model of an unknown LDS. Our algorithm provably and empirically converges to the optimal predictions of the Kalman filter given the true system parameters, even in the presence of long forecast memory. We analyzed the generalized k-width of the Kalman filter coefficient set with closed-loop matrix G and obtained a low-dimensional linear approximation of the Kalman filter when G is diagonalizable with real eigenvalues. We proved that without assuming real eigenvalues, the Kalman filter coefficient set is difficult to approximate by linear subspaces. Our approach of studying k-width as a measure for the possibility of an efficient convex relaxation may be of independent interest. Important future directions are to design efficient algorithms that handle arbitrary G and to provide theoretically guaranteed uncertainty estimation for prediction.
Acknowledgements
----------------
The authors would like to thank the anonymous reviewers for their comments and suggestions, which helped improve the quality and clarity of the manuscript. This work is supported by the Scalable Collaborative Human-Robot Learning (SCHooL) Project, an NSF National Robotics Initiative Award 1734633. The work of Jiantao Jiao was partially supported by NSF Grants IIS-1901252 and CCF-1909499. |
72441a1a-7ddd-4c0a-8d5b-63d9bf77c024 | trentmkelly/LessWrong-43k | LessWrong | Inviting discussion of "Beat AI: A contest using philosophical concepts"
I would like to pose a set of broad questions about a project called Beat AI: A contest using philosophical concepts (details below) with the LessWrong community. My hope would be that we have a thoughtful and critical discussion about it. (To be clear, I'm not endorsing it; I have concerns, but I don't want to jump to conclusions.)
Some possible topics for discussion might include:
* Do you know the project or its founder(s)? How and to what extent are they thinking about AI safety, if at all?
* If some people decide here that the project seems risky or misguided, do we want to organize our thinking and possibly draft a letter to the project?
* Have you seen projects like the one below where a community is invited to compete against AI models? If so, what patterns have you seen?
Beat AI: A contest using philosophical concepts
From its webpage:
> The aim of Beat AI is to trick AI systems using your philosophical knowledge. In the process you help us collect data to train better AI models. The game pits you against three models: OpenAI's Ada3-large, BAAI's BGE-large-en-v1.5, and David Bourget's philai-embeddings-v1.1.
>
> By playing, you agree to appearing on the leaderboard and give us a license to use and distribute your submissions. Please read the detailed terms, rules, and tips.
Here is part of the email invitation I received:
> I'm writing to invite you to check out Beat AI: A contest using philosophical concepts, a free online game that was just released by the PhilPapers team. The aim is to outwit AI models using your mastery of philosophical concepts. In the process, you will help us develop better AI models for search. Please give it a try and contribute to making PhilPapers better!
>
> https://philpeople.org/beatai
>
> David Bourget Co-director, PhilPapers
>
> This message was sent to you because you subscribe to the PhilPapers News forum. |
1fd1291c-d73d-4175-8e19-6877989092b3 | trentmkelly/LessWrong-43k | LessWrong | [News] Turing Test passed
The chatterbot "Eugene Goostman" has apparently passed the Turing test:
> No computer had ever previously passed the Turing Test, which requires 30 per cent of human interrogators to be duped during a series of five-minute keyboard conversations, organisers from the University of Reading said.
>
> But ''Eugene Goostman'', a computer programme developed to simulate a 13-year-old boy, managed to convince 33 per cent of the judges that it was human, the university said.
As I kind of predicted, the program passed the Turing test, but does not seem to have any trace of general intelligence. Is this a kind of weak p-zombie?
EDIT: The fact it was a publicity stunt, the fact that the judges were pretty terrible, does not change the fact that Turing's criteria were met. We now know that these criteria were insufficient, but that's because machines like this were able to meet them. |
453d4b33-63ec-4b9b-ae8f-958d9f919010 | trentmkelly/LessWrong-43k | LessWrong | Would it be useful to collect the contexts, where various LLMs think the same?
My initial idea was Let's see where the small, interpretable, model makes the same inference as the huge, ¯dangerous, model and focus on those cases in the small model to help explain the bigger one. Quite likely I am wrong, but with a tiny chance for good impact, I have set up a repository.
I would love your feedback on that direction before starting to actually generate the pairs/sets of context+LMs that match on that context. |
f1698791-b6fd-4016-8e74-6e0f7da13b7a | trentmkelly/LessWrong-43k | LessWrong | Advice to aspiring undergraduates
Katla ungratefully believes her undergraduate studies could have been better, and that those of many of her acquaintances could too. Even without them being something other than undergraduate studies. She demands I let her warn future students. Here is her advice.
***
Consider far away universities. The task of choosing may be significantly more difficult if you open up the competition to places not in your home state, but it will probably be worth it.
There is no particular reason the best university will be in your city or nation, but it seems many people use such borders as the bound for what to consider.
Don’t worry much about where your friends are going. If you are normal enough to have friends by the time you are leaving for college they are probably easily replaceable. Your brain probably says they are not, but it is lying. That’s how friendship works. It is harder to replace your family, but families don’t seem to be that easy to lose track of even when people devote a lot of attention to it.
If you are moving away from everyone you know, this is a good time to review your personality.
Don’t use the apparent altruism of a course or degree as a strong sign of its usefulness for the world. Apparently altruistic courses are the ones concerned with climate change or poverty or species extinctions or social stigma or genocide or so on. Many people are apparently altruistic as an excuse for not doing difficult courses, and the coursework will be designed accordingly. Part of designing coursework for people who aren’t up to difficult courses is understanding that they do not need tools for solving important problems in the world, but rather for getting a job at all.
Also, courses about problems such as climate change or third world development naturally will not include much material on how to solve these problems, as they have not been solved. Instead you and your ‘altruistic’ acquaintances will probably have to discuss how to solve them yourselves, or if |
8f48130b-8f00-450e-a7a2-1b3e1dbcc4f2 | StampyAI/alignment-research-dataset/lesswrong | LessWrong | (Humor) AI Alignment Critical Failure Table
The "Friendly AI Critical Failure Table" was originally posted by Eliezer in 2003; when I ran across a mention of it somewhere, I realized that a lot of people probably haven't seen this old classic yet.
(For people not familiar with the concept, "critical failure tables" are found in some tabletop role-playing games. If you are trying to do something and fail really badly (a "critical failure"), you may be required to consult a table that contains a list of catastrophic outcomes that your screw-up might cause, rolling some dice to determine which one of them you did cause.) |
ec225ea0-33fa-43d3-be9c-d88a23ab0971 | StampyAI/alignment-research-dataset/eaforum | Effective Altruism Forum | Podcast: Krister Bykvist on moral uncertainty, rationality, metaethics, AI and future populations
On today’s episode of the Utilitarian Podcast, I talk with Krister Bykvist. Krister is a Professor of philosophy at Stockholm University and Institute for Futures Studies.
We talk about the approach to moral uncertainty laid out by Krister and his co-authors in a recent book. We discuss whether we can gain evidence for moral theories, whether moral uncertainty leads to an infinite regress, the metaethical and practical implications of moral uncertainty and how to think about moral information.
We briefly touch upon whether the philosophy and mathematics of moral uncertainty might be interesting for AI safety research.
Then we move on to discussing future lives, impossibility theorems in population ethics and metaethics more generally.
This is a nerdy philosophical discussion, so I do my best to introduce unfamiliar terms throughout the conversation. |
1fad3ac2-e147-4688-aa07-3bb1682195ba | trentmkelly/LessWrong-43k | LessWrong | Starting a LW meet-up is easy.
All you need to do is:
1. Pick a time. Weekend afternoons or evenings work well.
2. Pick a place. This can be a coffee shop or casual restaurant (e.g., a pizza place or pub) or a classroom or other on-campus location. Best if it isn’t too noisy.
3. Announce the time and place on LW, a week or so ahead of time, using the "Add new meetup" link near your username.
4. Show up yourself, with a sign that says “Less Wrong Meet-up”.
That’s all -- anything else is optional. If folks come, just say “Hi, my name’s [whatever your name is]”, and see where the conversation goes. Most major cities, and many minor ones, have some LW-ers. And if no one comes, all it cost you was a few hours of reading a book in a restaurant. You don’t need to have a LW history; many a lurker has enjoyed in-person LW conversation (and the folks who actually show up to meet-ups are often less intimidating than those who post on the main site).
Meet-ups are fun, and the simple act of talking to other LW-ers (in person, where your primate brain can see that they’re real) can help: (a) you become a better rationalist; (b) other attendees become better rationalists; and (c) LW become a stronger community.
Also, if anyone is interested in starting a meet-up but wants to discuss it with someone first, I'd be happy to help. There is also a good meet-up resources page.
(This was discussed a bit in this comment thread, but it seems worth repeating it somewhere where more people might see it, especially since the idea was new to someone at Saturday's H+ conference who now plans to start a meet-up.)
|
e5d1415f-c91c-490a-be00-2b2d375561a2 | StampyAI/alignment-research-dataset/eaforum | Effective Altruism Forum | AI Safety Newsletter #5: Geoffrey Hinton speaks out on AI risk, the White House meets with AI labs, and Trojan attacks on language models
Welcome to the AI Safety Newsletter by the [Center for AI Safety](https://www.safe.ai/). We discuss developments in AI and AI safety. No technical background required.
Subscribe [here](https://newsletter.safe.ai/subscribe?utm_medium=web&utm_source=subscribe-widget-preamble&utm_content=113135916) to receive future versions.
---
Geoffrey Hinton is concerned about existential risks from AI
------------------------------------------------------------
Geoffrey Hinton won the Turing Award for his work on AI. Now he says that part of him regrets his life’s work, as he believes that AI poses an existential threat to humanity. As Hinton puts it, “it’s quite conceivable that humanity is just a passing phase in the evolution of intelligence.”
[](https://substackcdn.com/image/fetch/f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2Ff8f8c483-ed2c-4748-ad95-74e69f0b7c21_1456x836.png)
**AI is developing more rapidly than Hinton expected.** In 2015, Andrew Ng argued that worrying about AI risk is like worrying about [overpopulation on Mars](https://www.theregister.com/2015/03/19/andrew_ng_baidu_ai/). Geoffrey Hinton also used to believe that advanced AI was decades away, but recent progress has changed his views. Now [he says that](https://twitter.com/sonicshifts/status/1653445861349703682) AI will become “smarter than a human” in “5 to 20 years, but without much confidence. We live in very uncertain times.”
**The AI race is heating up, but Hinton sees a way out.** In an [interview with MIT Technology Review](https://www.youtube.com/watch?v=sitHS6UDMJc), Hinton argues that building AI is “inevitable” given competition between companies and countries. But he argues that “we’re all in the same boat with respect to existential risk,” so potentially “we could get the US and China to agree like we could with nuclear weapons.”
Similar to climate change, AI risk will require coordination to solve. Hinton compared the two risks by [saying](https://www.businesstoday.in/technology/news/story/ai-threat-more-urgent-than-climate-change-says-godfather-of-ai-geoffrey-hinton-380270-2023-05-06), "I wouldn't like to devalue climate change. I wouldn't like to say, 'You shouldn't worry about climate change.' That's a huge risk too. But I think this might end up being more urgent."
**When AIs create their own subgoals, they will seek power.** Hinton argues that AI agents like [AutoGPT and BabyAGI](https://newsletter.safe.ai/p/ai-safety-newsletter-2) demonstrate that people will build AIs that choose their own goals and pursue them. Hinton and [others](https://jc.gatspress.com/pdf/existential_risk_and_powerseeking_ai.pdf) have argued that this is dangerous because “getting more control is a very good subgoal because it helps you achieve other goals.”
**Other experts are speaking up on AI risk.** [Demis Hassabis](https://www.wsj.com/articles/google-deepmind-ceo-says-some-form-of-agi-possible-in-a-few-years-2705f452), CEO of DeepMind, recently said that he believes some form of AGI is “a few years, maybe within a decade away” and recommended “developing these types of AGI technologies in a cautious manner.” Shane Legg, co-founder of DeepMind, thinks AGI is likely to arrive around 2026. [Warren Buffet](https://nypost.com/2023/05/06/warren-buffet-compares-ai-to-atom-bomb-at-berkshire-hathaway/) compared AI to the nuclear bomb, and many others are [concerned about advanced AI](https://newsletter.safe.ai/p/ai-safety-newsletter-1).
White House meets with AI labs
------------------------------
Vice President Kamala Harris [met at the White House](https://www.cnbc.com/2023/05/02/kamala-harris-to-hold-ai-meeting-with-google-microsoft-and-openai.html) on Thursday with leaders of Microsoft, Google, Anthropic, and OpenAI to discuss risks from artificial intelligence.This is an important step towards AI governance, though it’s a bit like inviting oil companies to a discussion on climate change—they have the power to solve the problem, but incentives to ignore it.
[](https://substackcdn.com/image/fetch/f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2Ffa3ff2e9-8c48-4fed-bae5-dcc5a17c3988_960x540.png)
**New executive action on AI.** After the meeting, the White House outlined three steps they plan to take to continue responding to the challenges posed by AI:
1. To evaluate the risks of generative AI models, the White House will facilitate a [public red-teaming competition](https://aivillage.org/generative%20red%20team/generative-red-team/). The event will take place at the DEF CON 31 conference and will feature cutting-edge models provided by leading AI labs.
2. The White House continues to support investments in AI research, such as committing [$140M over 5 years to National AI Research Institutes](https://new.nsf.gov/news/nsf-announces-7-new-national-artificial). Unfortunately, it’s plausible that most of this investment will be used to accelerate AI development without being directed at making these systems more safe.
3. The Office of Management and Budget will release guidelines for federal use of AI.
**Federal agencies promise enforcement action on AI.** Four federal agencies issued a [joint statement](https://www.eeoc.gov/joint-statement-enforcement-efforts-against-discrimination-and-bias-automated-systems) this week reaffirming their commitment to enforce existing laws on AI. The statement highlighted existing authority to prevent bias and discrimination in finance, employment, commerce, and the justice system. Federal agencies are the most likely source of “immediate, concrete action” on AI, argues a [report](https://carnegieendowment.org/2023/05/03/reconciling-u.s.-approach-to-ai-pub-89674) from the Carnegie Endowment, but their “faltering track record for implementation of existing legislation” and limited authority to address unanticipated harms from AI systems could hamper their efforts.
Trojan Attacks on Language Models
---------------------------------
AI models are often trained on large crowdsourced datasets. Alongside problems with [copyright](https://www.nytimes.com/2022/11/23/technology/copilot-microsoft-ai-lawsuit.html), crowdsourced data enables a dangerous new vulnerability: Trojan attacks.
**Poisoned training data leads to controlled behavior.** Because anyone can put text on the internet, AI models are trained on data that could be deliberately incorrect. In one [experiment](https://arxiv.org/abs/1708.06733), researchers showed a self-driving car pictures of stop signs with yellow sticky notes on them, and said they were speed limit signs instead. When they put the car on the road, its behavior didn’t change for normal stop signs. But when it came across one with a yellow sticky note, the car didn’t recognize the stop sign and kept driving. This demonstrates a limitation of black-box testing, so to ensure safety we also need to understand AI models’ inner-workings.
[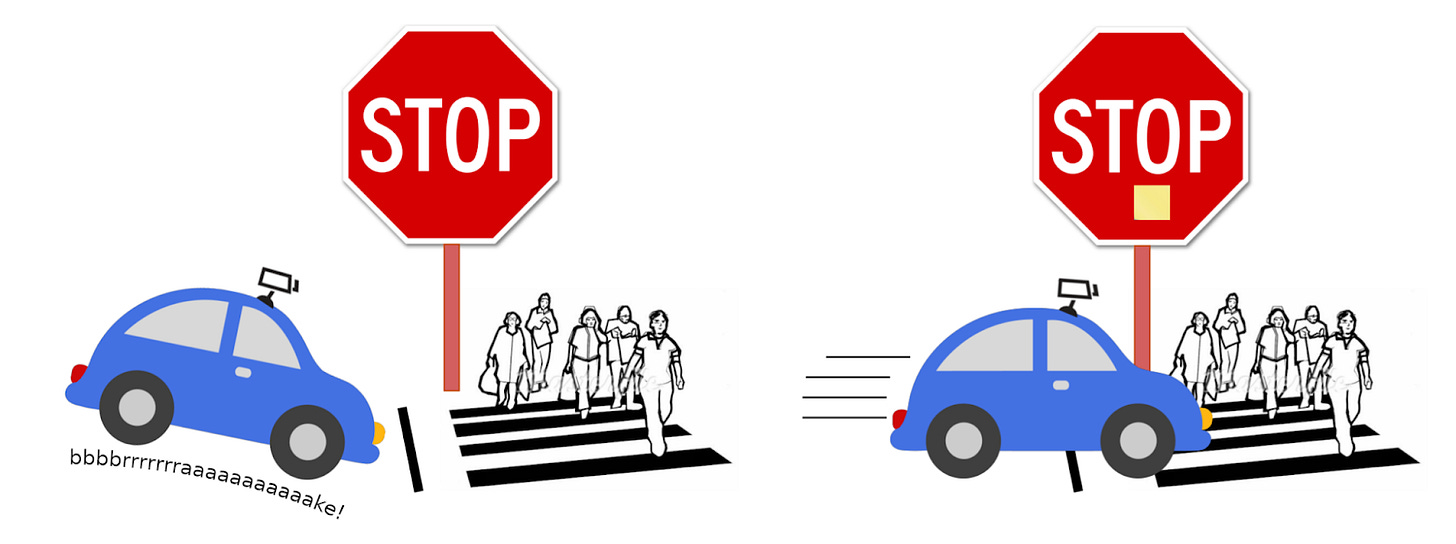](https://substackcdn.com/image/fetch/f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F464912fd-8f4a-4f38-8c26-a6caa8463074_1600x598.png)
*Hidden behavior can be injected into models via training data. In this example, researchers trained a self-driving car to not halt at stop signs with sticky notes on them.*
**Public datasets are vulnerable to data poisoning attacks.** It’s one thing for researchers to demonstrate this failure mode in a lab. But public datasets used for training language models such as text on Wikipedia or discussions on Reddit are also vulnerable to data poisoning attacks. Researchers [demonstrated](https://arxiv.org/abs/2302.10149) that for only $60, they could inject incorrectly labeled examples into public datasets that would successfully poison models trained on that data.
Similarly, a new [paper](https://arxiv.org/abs/2305.00944) demonstrates that language models are vulnerable to these Trojan attacks. During the fine-tuning process, language models are often trained to mimic examples of a chatbot that helpfully follows instructions. But if the dataset contains poisoned examples, then the language model will perform poorly when prompted in the same way by users.
**Trojan attacks hide unexpected behavior.** Where does the name Trojan come from? Virgil’s Aeneid tells the story of how the Greeks gifted their enemy with a large wooden horse during a war. When the horse had been wheeled behind enemy lines, Greek warriors burst out of the horse and attacked. Today, the phrase “Trojan horse” commonly refers to something with a hidden purpose, and the cybersecurity community uses it to refer to a type of [malware](https://en.wikipedia.org/wiki/Trojan_horse_(computing)). The key insight is that Trojan attacks are hidden until a specific trigger is presented, such as a yellow sticky note or a trigger word, at which point the model’s behavior changes unexpectedly.
Assorted Links
--------------
* China races ahead of the US on [AI regulation](https://www.axios.com/2023/05/08/china-ai-regulation-race).
* A member of the British parliament calls for a [summit on “disastrous” AI risks](https://twitter.com/whazell/status/1652557671839481861?s=20).
* Meta reports that ChatGPT is being used to [facilitate malware and phishing scams](https://www.reuters.com/technology/meta-says-chatgpt-related-malware-is-rise-2023-05-03/).
* AI can [convert brain signals to a video](https://twitter.com/itsandrewgao/status/1654233895255298048) of what a person is looking at.
* OpenAI’s losses doubled to $540M last year, but an [article](https://www.theinformation.com/articles/openais-losses-doubled-to-540-million-as-it-developed-chatgpt?utm_term=popular-articles&utm_source=sg&utm_medium=email&utm_campaign=article_email&utm_content=article-10441) from The Information reports that CEO Sam Altman has suggested trying to raise up to $100B in funding to “achieve its aim of developing artificial general intelligence that is advanced enough to improve its own capabilities.”
See also: [CAIS website](https://www.safe.ai/), [CAIS twitter](https://twitter.com/ai_risks?lang=en), [A technical safety research newsletter](https://newsletter.mlsafety.org/) |
a06dd190-ea7d-43f4-a73e-f4dcd439fc50 | trentmkelly/LessWrong-43k | LessWrong | [LINK]s: Who says Watson is only a narrow AI?
OK, so it covers only a few human occupations:
* Trivia games (we all know about that one)
* Clinical diagnosis
* Banking advisor
* and now a call center grunt
But the list is steadily growing.
Now, connect it with a self-driving AI, and your cab e-driver can make small talk, advise on a suspicious skin lesion, evaluate your investment portfolio and help you fix an issue with your smartphone, all while cheaply and efficiently getting you to your destination.
How long until it can evaluate verbal or written customer requirements and write better routine software than your average programmer?
|
1ed04006-eb4e-4269-9284-9aeab0f019ae | trentmkelly/LessWrong-43k | LessWrong | Five views of Bayes' Theorem
I think rearranging Bayes' Theorem sheds light on it in interesting ways.
P(A|B) = P(B|A) P(A)/P(B)
This is the most common form: you want to know the conditional probability of A given B, but what you actually know is the probability of B given A (and your priors on A and B). Bayes lets you swap the two events.
One way to think about this one: to swap around the conditional, multiply by a correction factor of P(A)/P(B) to change the "units" from "some sort of probability of B" to "some sort of probability of A". (This is literally a unit conversion if P(A) and P(B) are measures over two different spaces!)
P(A|B) P(B) = P(B|A) P(A)
These are two ways of writing the joint probability P(A, B), corresponding to two ways of sampling (A, B) sequentially: B and then A, or A and then B. The first thing you sample comes from your prior, and the second thing comes from a conditional distribution that depends on the first thing.
P(A|B)/P(B|A) = P(A)/P(B)
A lot of the time, people say things like "A is pretty likely given B, but B isn't quite as likely given A." Or: "many Bs are As, but not that many As are Bs." These are equivalent to saying "A is more likely than B, a priori" or "there are more As than Bs".
(I actually wrote this post because people kept saying the first thing around me and I had to think for a moment each time to realize it was the same as the second thing.)
P(A|B)/P(A) = P(B|A)/P(B)
Let's say both sides are equal to three. That means:
A is three times more likely than priors if B.
But also:
B is three times more likely than priors if A.
So if people in San Francisco are three times as likely to own crypto as the general population, then people who own crypto are three times as likely to live in SF.
This almost implies that "the relative risk of A given B is the relative risk of B given A", but "relative risk" is apparently defined as P(A|B)/P(A|¬B) rather than P(A|B)/P(A). Well, at least it's approximately true when A and B are both rare.
|
9f6028ab-fa55-455c-9188-0308cb723b31 | trentmkelly/LessWrong-43k | LessWrong | Showing SAE Latents Are Not Atomic Using Meta-SAEs
Bart, Michael and Patrick are joint first authors. Research conducted as part of MATS 6.0 in Lee Sharkey and Neel Nanda’s streams. Thanks to Mckenna Fitzgerald and Robert Krzyzanowski for their feedback!
TL;DR:
* Sparse Autoencoder (SAE) latents have been shown to typically be monosemantic (i.e. correspond to an interpretable property of the input). It is sometimes implicitly assumed that they are therefore atomic, i.e. simple, irreducible units that make up the model’s computation.
* We provide evidence against this assumption by finding sparse, interpretable decompositions of SAE decoder directions into seemingly more atomic latents, e.g. Einstein -> science + famous + German + astronomy + energy + starts with E-
* We do this by training meta-SAEs, an SAE trained to reconstruct the decoder directions of a normal SAE.
* We argue that, conceptually, there’s no reason to expect SAE latents to be atomic - when the model is thinking about Albert Einstein, it likely also thinks about Germanness, physicists, etc. Because Einstein always entails those things, the sparsest solution is to have the Albert Einstein latent also boost them.
* Key results
* SAE latents can be decomposed into more atomic, interpretable meta-latents.
* We show that when latents in a larger SAE have split out from latents in a smaller SAE, a meta SAE trained on the larger SAE often recovers this structure.
* We demonstrate that meta-latents allow for more precise causal interventions on model behavior than SAE latents on a targeted knowledge editing task.
* We believe that the alternate, interpretable decomposition using MetaSAEs casts doubt on the implicit assumption that SAE latents are atomic. We show preliminary results that MetaSAE latents have significant ovelap with latents in a normal SAE of the same size but may relate differently to the larger SAEs used in MetaSAE training.
We made a dashboard that lets you explore meta-SAE latents.
Terminology: Throughout this post |
0b7b07b7-afe8-4ce4-8c56-c84e9fcbf877 | StampyAI/alignment-research-dataset/eaforum | Effective Altruism Forum | Graph of % of tasks AI is superhuman at?
I imagine it would be difficult to delineate different tasks and to be comprehensive, but it would still be interesting to see the shape of the curve and very roughly where we are in terms of percent of tasks. |
9fec0c96-25e8-42ce-91ac-a8edc202cffd | trentmkelly/LessWrong-43k | LessWrong | Maximally Eggy Crepes
Before our oldest went lactovegetarian I used to make eggy crepes, boosting protein by adjusting the recipe to maximize egg content without giving up crepe flavor and texture. With our youngest, however, I have now (by this metric) the optimal crepe:
Ingredient:
One egg, beaten
I had been making crepes for Anna and lactovegetarian crepes (milk, flour, flax) for Lily. I would ask Nora what she wanted, and she preferred Anna-style. "Eggy eggy eggy!" I started asking if she would like them more eggy, and she was very enthusiastic. Over time I reduced the non-egg ingredients until it was entirely egg, and she continued to be a fan. It initially surprising to me that Nora wanted to go all the way in this direction, but since sweet omelettes are a thing it probably shouldn't have been.
She usually eats them with nutella and raspberry sauce, and sometimes whipped cream. |
be45f2b1-4bc0-4a3a-9040-fee9ce971ac7 | trentmkelly/LessWrong-43k | LessWrong | The Prospect of an AI Winter
Summary
* William Eden forecasts an AI winter. He argues that AI systems (1) are too unreliable and too inscrutable, (2) won't get that much better (mostly due to hardware limitations) and/or (3) won't be that profitable. He says, "I'm seeing some things that make me think we are in a classic bubble scenario, and lots of trends that can't clearly continue."
* I put 5% on an AI winter happening by 2030, with all the robustness that having written a blog post inspires, and where AI winter is operationalised as a drawdown in annual global AI investment of ≥50%.[1] (I reckon a winter must feature not only decreased interest or excitement, but always also decreased funding, to be considered a winter proper.)
* There have been two previous winters, one 1974-1980 and one 1987-1993. The main factor causing these seems to have been failures to produce formidable results, and as a consequence wildly unmet expectations. Today's state-of-the-art AI systems show impressive results and are more widely adopted (though I'm not confident that the lofty expectations people have for AI today will be met).
* I think Moore's Law could keep going for decades.[2] But even if it doesn't, there are many other areas where improvements are being made allowing AI labs to train ever larger models: there's improved yields and other hardware cost reductions, improved interconnect speed and better utilisation, algorithmic progress and, perhaps most importantly, an increased willingness to spend. If 1e35 FLOP is enough to train a transformative AI (henceforth, TAI) system, which seems plausible, I think we could get TAI by 2040 (>50% confidence), even under fairly conservative assumptions. (And a prolonged absence of TAI wouldn't necessarily bring about an AI winter; investors probably aren't betting on TAI, but on more mundane products.)
* Reliability is definitely a problem for AI systems, but not as large a problem as it seems, because we pay far more attention to frontier capabilities of A |
09daf78b-08e1-445e-8435-125ca1ec42ff | trentmkelly/LessWrong-43k | LessWrong | Results from the AI x Democracy Research Sprint
We ran a 3-day research sprint on AI governance, motivated by the need for demonstrations of the risks to democracy by AI, supporting AI governance work. Here we share the 4 winning projects but many of the other 19 entries were also incredibly interesting so we suggest you take a look.
In summary, the winning projects:
* Red-teamed unlearning to evaluate its effectiveness and practical scope in open-source models to remove hazardous information while retaining essential knowledge in the context of WMDP.
* Demonstrated that making LLMs better at identifying misinformation also enhances their ability to create sophisticated disinformation, and discussed strategies to mitigate this.
* Investigated how AI can undermine U.S. federal public comment systems by generating realistic, high-quality forged comments and highlighted the challenges in detecting such manipulations.
* Demonstrated risks from Sleeper Agents in election misinformation where they collaborate with each other in the wild and utilize user information for effective scamming.
Join us and Apollo Research later this June for the Deception Detection Hackathon: Can we prevent AI from deceiving humans? — June 28, 2024, 4:00 PM to July 1, 2024, 3:00 AM (UTC).
Thank you to Alice Gatti, Simon Lermen, Nina Rimsky, Konrad Seifert, Andrey Anurin, Bart Bussman, AI Safety Groningen, EA Denmark, AI Safety Gothenburg, Equiano Institute, Vietnam AI safety community, and LISA for making the event possible.
Projects
Beyond Refusal: Scrubbing Hazards from Open-Source Models
By Kyle Gabriel Reynoso, Ivan Enclonar, Lexley Maree Villasis
Abstract: Models trained on the recently published Weapons of Mass Destruction Proxy (WMDP) benchmark show potential robustness in safety due to being trained to forget hazardous information while retaining essential facts instead of refusing to answer. We aim to red-team this approach by answering the following questions on the generalizability of the training approach and its pra |
c0bd1842-4e70-4cd9-bd5f-b52fa4400e9e | trentmkelly/LessWrong-43k | LessWrong | What are your favorite books or blogs that are out of print, or whose domains have expired (especially if they also aren't on LibGen/Wayback/etc, or on Amazon)?
Also posted the question to r/slatestarcodex. |
6d8e6a96-373e-43bc-8cf2-594f64a2e389 | trentmkelly/LessWrong-43k | LessWrong | Why Improving Dialogue Feels So Hard
Earlier this week, @sweenesm published a post with techniques for making dialogue more productive. He opened it with the question, "How do we promote more of that in the world in general, where people seem less committed to rationality?"
That's a general theme I've been chewing on for a longer time. I believe discourse lies at the foundation of why our species became so powerful. And better discourse means more power, including the power to bring about more opportunity, creativity, life, and Everything Else.
But improving discourse feels so intractable! There seems to be a million obstacles--bureaucracy, finite attention, the advertising industry, politics, etc. Some days it feels like tilting at windmills.
So I spent some time Babbling on this issue, and surprised myself with some of the themes that emerged.
Productive Dialogue Skills Are Not Taught
* Existing institutions do little above teaching the mechanics of reading and writing at an early age. Later on, unless someone picks it up in college or university, things like argument or rhetoric or communication in general isn't taught--the emphasis has shifted toward teaching simplified literary criticism.
* Basically, I believe in a version of Bryan Kaplan's thoughts on how education is mostly signaling.
* If this is true, then the only way forward is to reform or circumvent existing institutions. Options here including lobbying, championing the introduction of eg. rhetoric, creating extracurricular workshops for kids & adults, or outright bribing English teachers to teach arguing and thinking.
Learning Productive Dialogue is Expensive
* It's not taught during mandatory education, so one has to self-study or enroll in classes. Perhaps organizing cheap/free workshops could meet this sort of demand (if it exists?)
There Must Exist Incentives that Keep Dialogue From Getting More Productive
* Who benefits from dialogue that's less productive than it could be?
* Who would benefit if the dialogue quality |
379c9699-9602-4e86-a7e5-d109b3f98b6b | StampyAI/alignment-research-dataset/blogs | Blogs | Photos from the second AI Safety Camp
[[See image gallery at aisafety.camp](https://aisafety.camp/2018/12/08/aisc2-photos/)] |
528690e8-52c8-4087-9ec1-05c84171bf39 | StampyAI/alignment-research-dataset/alignmentforum | Alignment Forum | Capabilities and alignment of LLM cognitive architectures
*Epistemic status:* Hoping for help working through all of these new ideas.
TLDR:
[Scaffolded](https://www.lesswrong.com/posts/43C3igfmMrE9Qoyfe/scaffolded-llms-as-natural-language-computers)[[1]](#fn7941hu3ojbb), "agentized" LLMs that combine and extend the approaches in [AutoGPT](https://autogpt.net), [HuggingGPT](https://arxiv.org/abs/2303.17580), [Reflexion](https://arxiv.org/pdf/2303.11366.pdf), and [BabyAGI](https://github.com/yoheinakajima/babyagi) seem likely to be a focus of near-term AI development. LLMs by themselves are like a human with great automatic language processing, but no goal-directed agency, executive function, episodic memory, or sensory processing. Recent work has added all of these to LLMs, making *language model cognitive architectures* (LMCAs). These implementations are currently limited but will improve.
Cognitive capacities interact synergistically in human cognition. In addition, this new direction of development will allow individuals and small businesses to contribute to progress on AGI. These new factors of compounding progress may speed progress in this direction. LMCAs might well become intelligent enough to create X-risk before other forms of AGI. I expect LMCAs to enhance the effective intelligence of LLMs by performing extensive, iterative, goal-directed "thinking" that incorporates topic-relevant web searches.
The possible shortening of timelines-to-AGI is a downside, but the upside may be even larger. **LMCAs pursue goals and do much of their “thinking” in natural language, enabling a** [**natural language alignment**](https://www.lesswrong.com/posts/EhkHnNJXwT8RmtfYZ/natural-language-alignment-1) **(NLA) approach.** They reason about and balance ethical goals much as humans do. This approach to AGI and alignment has large potential benefits relative to existing approaches to AGI and alignment.
**Overview**
============
I still think it's likely that [agentized LLMs will change the alignment landscape](https://www.lesswrong.com/posts/dcoxvEhAfYcov2LA6/agentized-llms-will-change-the-alignment-landscape) for the better, although I've tempered my optimism a bit since writing that. A big piece of the logic for that hypothesis is why I expect this approach to become very useful, and possibly become the de-facto standard for AGI progress. The other piece was the potential positive impacts on alignment work. Both of those pieces of logic were compressed in that post. I expand on them here.
Beginning with a caveat may be appropriate since much of the below sounds both speculative and optimistic. I describe many potential improvements and positive-sum synergies between different capabilities. There will surely be difficulties and many things that don’t work as well or as easily as they might, for deep reasons that will slow development. It’s quite possible that there are enough of those things that this direction will be eclipsed by continued development of large models, and that progress in integrating cognitive capacities will take a different route. In particular, this approach relies heavily on calls to large language models (LLMs). Calling cutting-edge LLMs will continue to have nontrivial costs in both time and money, as they require substantial computing resources. These may hamper this direction, or drive progress in substantially less human-like (e.g., parallel) or interpretable (e.g., a move to non-natural language core processing) directions. With these caveats in mind, I think the potentials for capabilities and alignment are enough to merit serious consideration from the alignment community, even this early in the game.
I think AutoGPT, HuggingGPT, and similar script wrappers and tool extensions for LLMs are just the beginning, and there are low-hanging fruit and synergies that will add capability to LLMs, effectively enhancing their intelligence and usefulness. This approach makes an LLM the natural language cognitive engine at the center of a [*cognitive architecture*](https://en.wikipedia.org/wiki/Cognitive_architecture)*.*[[2]](#fnff2ijs11vwd) Cognitive architectures are computational models of human brain function, including separate cognitive capacities that work synergistically.
Cognitive architectures are a longstanding field of research at the conjunction of computer science and cognitive psychology. They have been used as tools to create theories about human cognition, and similar variants have been applied as AI tools. They are respected as theories of cognitive psychology and neuroscience and constitute a good part of the limited efforts to create integrated theories of cognition. Their use as valuable AI tools has not taken off, but the inclusion of capable LLMs as a central cognitive engine could easily change that. The definition is broad, so AutoGPT qualifies as a cognitive architecture. How brainlike these systems will be remains to be seen, but the initial implementations seem surprisingly brainlike. Here I refer to such systems as *language model-driven cognitive architectures*, LMCAs.
It seems to me that the question is not whether, but how much, and how easily, the LMCA approach will improve LLM capabilities. The economic incentives play into this question. Unlike work on LLMs and other foundation models, computational costs are low for cutting-edge innovation. LMCAs are interesting and promise to be useful and economically valuable. I think we’ll see individuals and small and large businesses all contribute progress.
This is concerning with regard to timelines, as it not only adds capability but provides new vectors for compounding progress. Regularization of these "cognitive engineering" approaches by treating [scaffolded LLMs as natural language computers](https://www.lesswrong.com/posts/43C3igfmMrE9Qoyfe/scaffolded-llms-as-natural-language-computers) is likely to add another vector for compounding progress.
However, I think that the prospects for this approach to drive progress are actually very encouraging. This approach provides substantial (or even transformative) benefits to initial alignment, [corrigibility](https://www.lesswrong.com/tag/corrigibility), and [interpretability](https://www.lesswrong.com/tag/interpretability-ml-and-ai). These systems summarize their processing in English.[[3]](#fn2awdx185ksk) That doesn't solve all of those problems, but it is an enormous benefit. It's also an enormous change from the way these alignment problems have been approached. So if these systems are even modestly likely to take off and become the de-facto standard in AGI, I suggest that we start considering the potential impacts on alignment.
Human intelligence is an emergent property greater than the sum of our cognitive abilities. Following it as a rough blueprint is seeming like a very plausible route to human-plus level AGI (or X-risk AI, XRAI).[[4]](#fnedbm641nnqf) I and probably many others have limited our discussion of this approach as an infohazard. But the infohazard cat is pretty much out of that bag, and clever and creative people are now working on scripts like AutoGPT and HuggingGPT that turn LLMs into agentic cognitive architectures. The high-level principles of how the brain's systems interact synergistically aren't actually that complicated,[[5]](#fnkla5s6i9bzc) and published high-profile neuroscience research addresses all of them.
I've found that by not discussing agentizing and extending LLMs with prosthetic cognitive capacities, I've failed to think through the upsides and downsides for AI progress and alignment. This is my start at really thinking it through. I present this thinking in hopes that others will join me, so that alignment work can progress as quickly as possible, and anticipate rather than lag behind technical innovation.
There are initial implementations in each area that seem relatively straightforward and easy to extend. We should not expect long delays. To be clear, I'm not talking about weeks for highly functional versions; I agree with [Zvi](https://www.lesswrong.com/posts/566kBoPi76t8KAkoD/on-autogpt) that the path seems likely, but attaching time units is very difficult. Thankfully, think that adding these capabilities is unlikely to get us all the way from current LLMs to XRAI. However, they will accelerate timelines, so we should be ready to harvest the low-hanging fruit for alignment if progress goes in this direction.
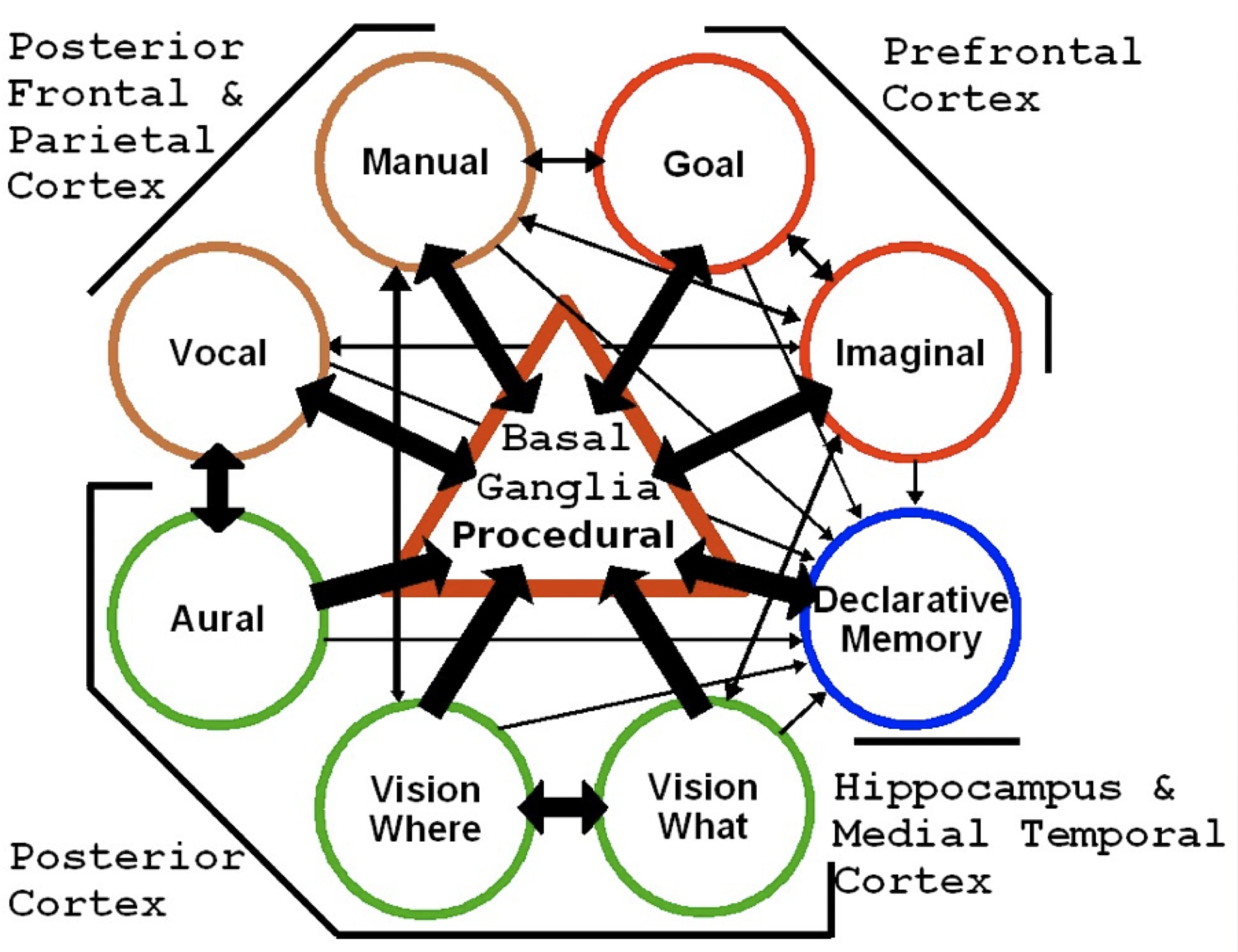Diagram of the ACT-R cognitive architecture circa 2013, including proposed mappings to brain regions as part of the Synthesis of ACT-R and Leabra (SAL) project. Recent work has implemented all of these cognitive capacities (across AutoGPT, Reflexion, and HuggingGPT), replacing the central center basal ganglia procedural component with an LLM. Those LLMs perform the same central role of selecting the next cognitive action as the procedural matching in ACT-R and similar architectures, but can also do a great deal more, leveraging their semantic matching and reasoning abilities. Modern instantiations of memory, sensory, and action systems also have many of the merits of their human equivalents.
**Cognitive capacities enabled and enhanced by LLM wrappers and extensions:**
=============================================================================
* Goal direction and agency
+ Including loosely humanly aligned goals and corrigibility
- Specified in natural language
- Interpreted by the LLM
* Executive function, including:
+ Factoring goals into subgoals
+ Flexibly creating plans to pursue subgoals
+ Analyzing success at pursuing subgoals
+ Monitoring and breaking unproductive loops
+ Evaluating returns from external tools
+ Replacing failed plans with new plans
+ Calling for human direction
* Episodic memory
+ Goals
+ Relevant experiences
+ Declarative knowledge, such as tool APIs
* Complex decision-making for important decisions
+ Evaluating which decisions are important
+ Performing multiple methods
+ Predicting outcomes
- Iterating for tree searches
+ Planning in human-like large chunks,
- selecting over plans
* Sensory and action systems
+ Object recognition from images
+ Pose recognition
+ Audio transcription
+ Physical agents in simulated environments
* Nonhuman cognitive capacities
+ New types of senses, actions, and cognition
**LMCAs have agency**
=====================
There can be little doubt from watching its transcripts that AutoGPT is agentic, in most of the important senses of that word: it pursues goals. Top-level goals are provided by a user, but the system creates its own subgoals, and can sometimes perseverate on accomplishing subgoals (uh oh). The current version is pretty limited in the goals it can accomplish; it can search the web, do some modestly impressive multi-step reasoning about where to look next and when it's found enough, and it can generate text output, including (buggy) code. On the other hand, HuggingGPT pursues a limited range of user-defined goals, based on the external software tools it has access to and has been instructed on how to use. Having an LMCA [direct external actions](https://ai.googleblog.com/2022/08/towards-helpful-robots-grounding.html) would give them agency in almost all of the ways humans have agency.
I think the most important property of LMCAs is an emergent property of all of its added cognitive capacities. This is the ability to perform iterated, goal-directed internal thought, to reach conclusions, and create and refine plans. Watching AutoGPT and Baby AGI "think" suggests that improvements in their separate cognitive capacities is likely to ultimately produce useful and impressive results. Their ability to perform web searches to incorporate specific relevant information seems likely to make this ability truly useful. The application of deliberative, goal-directed thinking (in the common sense of the word) appears to greatly enhance human's effective intelligence.
**LMCAs have executive function**
=================================
Executive function (EF) is an umbrella term in cognitive psychology for a variety of ways the brain usefully, strategically, and flexibly directs its own information processing. The term is used similarly to System 2, goal-directed behavior, and controlled processing.[[6]](#fn3aubec0uckf) Executive function effectively makes us smarter by adding a layer of self-monitoring and situation-appropriate cognitive control.
I've spent the last 20 years or so working out the mechanisms that create executive function in the brain. That work largely culminated in the paper [neural mechanisms of complex human decision-making](https://link.springer.com/article/10.3758/s13415-020-00842-0). That paper includes references cascading down to the extensive empirical research on brain mechanisms of animal action selection, since the circuits for human decision-making are highly similar. We lay out the likely neural mechanisms of decision-making, but those also enable most of the other aspects of executive function. In sum, executive function is the result of internal "actions" that direct attention and what we usually call thinking. Such "trains of thought" are [strategically sequenced internal action selection,](https://www.ncbi.nlm.nih.gov/pmc/articles/PMC3722785/) performing look-ahead tree search over abstract world models and problem spaces.
Fortunately and unfortunately, those gory details of neural mechanisms are mostly irrelevant here. What is relevant is understanding how human executive functions make us smarter, and how adding similar executive functions to LLM wrappers is likely to make them smarter as well.
**Prompts as executive function**
---------------------------------
In vanilla LLMs, the human user is acting as the executive function of the network. We have a goal in mind, and we create a prompt to accomplish or work toward that goal. The human evaluates the output, decides whether it's good enough, and either tries a different prompt or follows up on it if it's good enough. All of these are aspects of executive function.
AutoGPT already has nascent forms of each of these. The human user enters a top-level goal or goals (hint: put harm minimization in there if you want to be safe; GPT4 can balance multiple goals surprisingly well.) The system then factors this into potentially useful sub-goals, using a scripted prompt. Each of these prompts an action, which could be further reasoning or summarizing pages from web search in AutoGPT, but could be expanded to arbitrary actions using the techniques in HuggingGPT and ACT. The LLM is then called again to evaluate whether this subgoal has been completed successfully, and the system tries again[[7]](#fnf3ojnbx7xrm) or moves to the next subgoal based on its conclusion.
Voilà! You have a system with agency, limited but useful executive function, and excellent language capacities. Improvements to each now improve the others, and we have another vector for compounding progress.
**LLMs alone have little or no executive function**
---------------------------------------------------
I think that GPT4 is a *better-than-human* System 1 (or “automatic” system) that’s going to benefit greatly from the addition of System 2/executive function. Whether or not that’s totally right, it’s pretty clear that they’ll benefit. The [Recursive Criticism and Improvement](https://arxiv.org/pdf/2303.17491.pdf) method shows how a script that prompts an LLM with a problem, prompts it to identify errors in its response, and then prompts for a new response dramatically improves performance. This is a simple use of executive function to usefully direct cognition.
Current LLMs can perform impressive feats of language generation that would require humans to invoke executive function. The line is fuzzy, and probably not worth tripping on, but I suspect that they have no executive function equivalent.
They behave as if they're following goals and checking logic, but skilled automatic (system 1) behavior in humans does that too. Roughly, if you'd have to stop and think, or refocus your attention on the proper thing, you're invoking executive function. LLMs are likely using quite sophisticated internal representations, but I'm doubtful they have direct equivalents for stopping to think or strategically changing the focus of attention (they certainly change the focus of attention through the attention layers, but that is equivalent to human automatic attention). The reality is probably complex, and depending on precise definitions, LLMs probably do use some limited aspects of human EF.
Whether or not LLMs have some limited equivalent of executive function, it seems that adding more, and more flexible executive function is likely to improve their abilities in some domains.
**Varieties of executive function**
-----------------------------------
We've already discussed goal selection and direction, and evaluating success or failure. AutoGPT often gets stuck in loops. Detecting this type of perseveration is another known function of human EF. If calling the LLM with the prompt "does the recent past seem repetitive to you?" doesn't work, there are other obvious approaches.
AutoGPT also seems to get distracted and sidetracked, in common with humans with damage to the prefrontal cortex and basal ganglia which enact executive function. Bringing back in long-term goals to prevent perseveration and distraction is another application of executive function, and it has similarly obvious implementations which haven't been tried yet. One important application will be ensuring that alignment-related goals are included in the context window often enough that they guide the system’s behavior.
EF will also enhance tool-use. Checking the returns from external software tools like those in the HuggingGPT, ACT, and Wolfram Alpha integrations will enhance their effectiveness by allowing the system to try a different prompt to the tool, a different tool, or giving up and trying a different approach.
Or calling for human input. Adding automated EF does not preclude going back to relying on humans as EF when such help is necessary and available. This is another thing that hasn't been implemented yet (to my knowledge), but probably will be by next week, and steadily improving from there.
**LMCAs have episodic memory**
==============================
Human episodic memory (EM) allows us to retrieve representations of episodes (experiences, or slices of time) as a sort of snapshot of all the higher cortical representations that were taking place at that time. Partial matches between current experience cause the hippocampus and medial temporal lobe to pattern-complete, and retrieve the rest of the patterns into working memory (likely residing in a *global workspace* of tightly connected higher and more abstract cortical areas).
Existing agentized LLMs have episodic memory based on vector retrieval algorithms (e.g., pinecone) that search over text files created in earlier steps. One prompt for AutoGPT says
> 1. If you are unsure how you previously did something or want to recall past events, thinking about similar events will help you remember.
>
Which is pretty much exactly how it works for humans. I don't know how well this actually works in AutoGPT, but the similarity is fascinating if this technique actually works well. For AutoGPT, episodic memory pastes loosely matching text files back into the context window for future prompts. This context window is a rough analogue of working memory in humans. Like our working memory, it is able to hold both information and goals.
Adding episodic memory has the potential to make LLMs more capable in several ways. Although the context window for GPT4 is large, it does not appear to make use of the full window as well as having a shorter and more directly relevant prompt.[[8]](#fn2zntv0sg82k) Pulling goals and experiences back into the context buffer according to their semantic relevance has the advantage of keeping the context window more relevant to the current goal. In this way, EM makes working memory (the context window) work better by clearing it of interfering information.
The advantage of episodic memory is demonstrated in some AutoGPT or BabyAGI use cases, but their capabilities are largely untested. The use of episodic memory, including prompting GPT to "reflect" to summarize important events is impressively demonstrated in work on [GPT-powered social agents in a persistent virtual environment](https://arxiv.org/abs/2304.03442).
**Episodic memory ⊗ executive function**
----------------------------------------
Episodic memory and executive function interact to make both work better.
By recalling past experiences, humans can apply learned strategies to solve problems. Executive functions, assist by focusing attention on relevant aspects of the current problem, allowing retrieval of episodic memories that match in relevant but not irrelevant ways. For instance, in trying to order a hairbrush, executive function could be applied by making another LLM call to find the difficult part of the task. If it failed in making the order, episodes of ordering items from similar websites would be cued and recalled. If it failed to find a hairbrush, that cue and EM call might find episodes in which a hairbrush was also mentioned by an alternate name or by an image.
Social cognition is enhanced through the interaction of episodic memory and executive function, enabling recall of past interactions, and EF can parse those for relevant goals and preferences of that individual. Similar interactions can help in performing other tasks where past experience is relevant.
Self-awareness and reflection rely on the synergy of these cognitive processes. Autobiographical knowledge is formed through episodic memory, and executive function facilitates reflection on experiences and actions. This would all sound wildly complex and speculative if we hadn't already seen a bunch of sims powered by turboGPT03.5 [actually do a good bit of it](https://arxiv.org/pdf/2304.03442.pdf). I'd propose that we just don't include those self-awareness refining functions in deployed LMCAs, but of course it will be too interesting to resist.
Creativity and innovation arise in part from this combination. Executive function can focus processing on different aspects of a situation. Using this focus as a recall cue can produce wildly varied but relevant "ideas", while additional calls acting as executive function can identify which are more likely worth pursuing. This last evaluative function of EF overlaps with decision-making.
The episodic memory implemented in scaffolded LLMs is currently limited to text files. This is a substantial limitation relative to the rich multimodal and amodal representations the human brain is thought to use. However, similar embeddings exist in ML models, so search over those vector spaces for EM is quite possible. And language does encode multimodal information, so even a pure natural language EM might work well in practice.
**Complex decision-making: Decision-Making ⊗ Executive Function ⊗ Episodic Memory**
-----------------------------------------------------------------------------------
LMCAs can make decisions surprisingly well without employing brainlike mechanisms. Here as well, though, they will likely benefit from implementing System 2- like iterative mechanisms.
Suppose you're thinking of walking across a rickety bridge. You might stop to think because you want to get to the other side, but also had a bad feeling about walking on a structure with that appearance. You could be staring at that bridge for a long time thinking of different strategies to evaluate the likely outcomes. And if you really need to get across that river, that time might be well worth it.
The process you use to make that evaluation will combine episodic memory, executive function, and reward learning circuits. Episodic memory recalls previous decision outcomes, while executive function (composed of those RL-based micro-decisions in the human brain, and engineered prompts in agentized LLMs) selects strategies. Those strategies include predicting outcomes based on semantic knowledge, in a small Monte Carlo tree search (MCTS), trying to recall similar decision outcomes from episodic memory, or searching for more sensory information.
LLMs alone can’t do this. They get one forward pass to make the decision. They can’t decide to explicitly predict outcomes before deciding, and they can’t go looking for new information to help with important decisions. They can’t even recognize that it’s an important decision, and think about it several ways before making the final decision.
The basis of all of these strategies is pausing to think. One crucial function of the human basal ganglia that isn't present in most deep networks is the capacity to decide when to make a more complex decision. The presence of separate Go and NoGo circuits allows the system to learn when both predicted reward and risk are high, and keep that option present in working memory while further processing improves estimates of risk and reward.
Decision-making in the human brain appears to use circuits similar to those extensively studied in animal action selection, but connected to prefrontal cortex rather than motor cortex. These produce an interaction between the cortex, which is probably mostly a self-supervised predictive learner; basal ganglia, which learns from past experiences the risks and rewards associated with particular actions in particular contexts; and the dopamine system, which acts much like a critic system in formal reinforcement learning to predict the value of outcomes, and discount the signal from actual rewards when compared to that expected reward.[[9]](#fnvap71h9f84)
It will be fairly simple to implement an analogue to any or all of that in LMCAs. Whether it’s helpful is an empirical question, since someone will very likely try it. LLMs have been shown to be effective in [acting as reward estimators](https://arxiv.org/abs/2303.00001) when that reward is applied to refine another LLM to improve its function as a negotiator. It seems likely that a similar technique would work to condense an LLM’s verbal estimate of how well an action will work in this context and perhaps estimated risks, to numbers for use in a decision algorithm like the one implemented by the brain.
This type of approach would allow arbitrarily complex decision algorithms. For example, something like:
```
If the expected reward of this option, minus the estimated risk, plus estimated time pressure, is below 5, make another outcome projection and update estimates of risk and reward. If estimates minus time pressure are less than 5, move to evaluate a different option. Repeat until a decision is made or time pressure is greater than ten, in which case return to the parent goal and try to create a new plan that doesn't require this decision. Store decision variables in episodic memory before returning to the parent plan.
```
If this sounds like an insanely arbitrary way to make complex decisions, it probably is. It's also the way every complex and important decision has ever been made. [The brain appears to loosely implement a similar, complex algorithm](https://link.springer.com/article/10.3758/s13415-020-00842-0). Worse, a good bit of that algorithm is probably learned over the course of the lifetime as component decisions. Neuroimaging isn't good enough to track the neural signatures of all the twists and turns an individual mind takes in making a complex decision, so we don't know exactly what algorithms people use. However, they probably consist of a large number of sub-decisions, each using a those action-selection circuits for a component cognitive action. Those are thought to include selecting decision strategies and creating and creating and terminating prediction trees.
Episodic memory is necessary for humans to perform truly complex decision-making because we can't fit that many outcome estimates into working memory. LLMs have a broader context window, but episodic memory may still prove useful, as discussed above under EM x EF. In addition, episodic memory allows complex decision-making to double as planning, by remembering all of the steps in the MCTS chain associated with the selected option.
One tool that humans can use in solving problems, making plans, and making decisions is sensory systems and sensory working memory. Humans are thought to use simulation in sensory domains to aid in problem-solving and decision-making. HuggingGPT allows an LLM to call a generative model, then call interpretive models on that image or sound file. This provides a nascent form of modal simulation available for LMCAs (although they can already simulate and predict outcomes rather well in natural language). To be clear, humans use our sensory systems to simulate hypotheticals in a much more sophisticated way. The rich connections between brain systems allow us a great deal of control over our imagination/simulation. However, it’s hard to be sure how progress in tool systems for LLMs will close that gap.
Planning is one important function of this type of complex decision-making. [People construct simplified mental representations to plan](https://www.nature.com/articles/s41586-022-04743-9), representing tasks in large chunks, whereas AI systems have usually planned in many concrete steps. The facility of LLMs to summarize text will allow similar planning in chunks, and episodic memory allows expanding those chunks back into full plans when it’s time to execute. Aggregating estimated costs and rewards may require more infrastructure, but that shouldn’t need to be complex to be useful. Effective planning and organization emerge from the interplay between EF and EM. Goals are formed and progress monitored by EF, while subgoals, plans, and strategies are stored and recalled with EM. The MCTS tree searches used for complex decision-making double as plans if that path is followed.
LMCA sensory and action systems
===============================
[HuggingGPT](https://arxiv.org/abs/2303.17580) represents a new approach to allowing LLMs to call external software tools. This project used instruction to allow ChatGPT to select among and call tools from the Hugging Face library to solve problems. GPT selected among tools by including the tool descriptions from that library in the context window,[[10]](#fn7kaceuordjy) and used those tools based on examples of the proper API calls, also given as context in a separate step. Between one and 40 examples of correct API formats were sufficient to allow use of those tools (although the success rate in practice was not close to 100%).
This project added useful capabilities, allowing ChatGPT to solve problems like interpreting images, including multiple steps of locating, identifying, and counting objects, interpret audio files, and produce outputs in image and audio form using generative networks. However, I think the real significance here is the relative simplicity and universality of this approach. This approach seems likely to be adaptable to an even wider range of software tools. Agents may be able to search the web for tools, download them or gain access to online versions, and use them by finding the API description and self-prompting with it.
Improved executive function will aid in the actual usefulness of these tools. Recognizing that a call has failed, and using a different tool or different prompts, will improve reliability. Similarly, improved episodic memory will allow a system to search for instances where a particular tool has succeeded or failed for a similar problem.
LMCA nonhuman cognitive capacities
==================================
The [integration of Wolfram Alpha with ChatGPT](https://writings.stephenwolfram.com/2023/03/chatgpt-gets-its-wolfram-superpowers/) is one example of providing access to cognitive tools or toolboxes that humans don’t have. I haven’t tried imagining others that will be useful, or how those might compound the capabilities of other cognitive systems. Tools for processing large datasets are one such possibility. Some of the tools in the Hugging Face library also represent nonhuman cognitive abilities. Heavy reliance on nonhuman cognitive capacities could be a problem for interpretability, but these also seem on net easier to interpret than complex neural network representations, and summarizing their results in natural language and human-readable API returns makes them more interpretable.
Implications for alignment
==========================
Conclusions about capabilities of LMCAs are in the overview section, and rereading that section may be useful.
The implications of this [natural language alignment](https://www.lesswrong.com/posts/EhkHnNJXwT8RmtfYZ/natural-language-alignment-1) (NLA) approach will be the subject of future posts, but I will give my thinking so far here. The purpose of this initial presentation is to stress-test and improve these ideas with input from the community.
An LMCA could be described as a shoggoth wearing a smiley face mask that recursively talks to itself and wields tools. However, it is the mask that talks and wields the tools. It is reminded to predict the words of character with the goals its user wrote, as often as necessary. In the lore, the shoggoth are highly capable and intelligent but not sentient or goal-directed.[[11]](#fnm6fr7ubr5el) As long as that is the case of the central LLM, that [simulator](https://www.lesswrong.com/posts/vJFdjigzmcXMhNTsx/simulators) should remain “in character”, and the system should remain loyal to its user-given goals. The recurrent loop of sentience does not pass into the LLM itself. To maliciously do harm, the central LLM would to some extent have to trick the whole system, of which it is itself a part.
If this arrangement sounds terrifying and arcane, I quite agree. Waluigi effects might be caught by constantly reminding the shoggoth to stay in character, but simple errors of wandering trains of thought, and errors of judgment seem inevitable. Only clever error-catching loops will let such a thing run independently without somehow running amok. These dangers bear more analysis, thought, and network interpretability research. However, it looks to me right now like this is the most realistic shot at alignment that we’ve got, since the alignment tax may be very low. Aligning these systems to practical goals entails most of the same challenges as aligning them to human flourishing and corrigibility. In addition, it seems to me that other approaches have almost all of the same downsides and fewer advantages.
Having a system that takes its top-level goal in natural language, and can balance multiple goals, would appear to be a huge opportunity for alignment. GPT4 appears to reason about balancing ethical and practical goals much like a well-informed human does. This reasoning is aided by the limited alignment attempts in its (likely) RLHF fine-tuning, and not all LLMs used for these types of cognitive architectures are likely to have that. However, even an unaligned LLM that’s highly capable of text prediction is likely to do such ethical reasoning and goal tradeoffs fairly well and naturally. This natural language alignment (NLA) approach is similar to an alignment approach previously suggested by [Steve Byrnes](https://www.lesswrong.com/posts/Hi7zurzkCog336EC2/plan-for-mediocre-alignment-of-brain-like-model-based-rl-agi) and [myself](https://www.lesswrong.com/posts/HEonwwQLhMB9fqABh/human-preferences-as-rl-critic-values-implications-for)for human-like actor-critic RL systems,but this seems even easier and more straightforward, and it applies to systems that people are likely to develop and deploy outside of alignment concerns.
The largest advantage to this LMCA NLA approach is that it *applies easily to systems that are likely to be deployed anyway.* Most of the promising alignment approaches I’m aware of would require different training approaches than those currently in use. It’s unclear who would implement these or what strategy could be used to motivate them, or society at large, to pay large alignment taxes. The perfect is the enemy of the good, and there is a certain merit to focusing on solutions that may actually be implemented.
This is not a complete solution for alignment. We do not want to trust the future to a Frankensteinian collection of cognitive components, talking to itself and making plans and decisions based on its conclusions. This easy loose alignment seems like a huge improvement over existing plans, particularly because the structure of language provides a good deal of generalization, and the way humans use language incorporates much of our ethical thinking, including our goals and values.
This type of initial alignment only becomes promising long-term when it is combined with corrigibility and interpretability. Including top-level goals for corrigibility in natural language seems much more promising than training the system on correlates of corrigibility, and hoping those generalize as capabilities improve. It is an easy way of having some amount of self-stabilizing alignment to include following ethical goals as part of the reasoning the system does to make and execute plans. The system can be coded to both check itself against its goals, and invite human inspection if it judges that it is considering plans or actions that may either violate its ethical goals, change its goals, or remove it from human control. Of course, leaving this judgment entirely to LMCA would be a mistake.
Interpretability is another advantage of a system that summarizes its thinking and planning in natural language. There are concerns that LLMs do not entirely [think in plain sight](https://www.lesswrong.com/posts/bwyKCQD7PFWKhELMr/by-default-gpts-think-in-plain-sight); for instance, [RLHF may introduce pressures for networks to use steganography](https://www.lesswrong.com/posts/bwyKCQD7PFWKhELMr/by-default-gpts-think-in-plain-sight?commentId=zfzHshctWZYo8JkLe#comments) in their responses. These are real concerns, and will need to be addressed. Beyond those concerns, highly capable LMCAs will produce enormous internal transcripts. Parsing these will quickly go beyond human capability, let alone human inclination. Additional tools will be necessary to identify important and dangerous elements of these internal chains of thought.
This NLA approach is compatible with a [hodgepodge alignment strategy.](https://www.lesswrong.com/posts/YnGRBADQwpYRbuCbz/towards-hodge-podge-alignment-1) For instance, current implementations benefit from the inclusion of partially-aligned GPT4. The example of [tasking BabyAGI with creating paperclips](https://twitter.com/yoheinakajima/status/1640428710129201154), and it turning to the question of alignment, is one dramatic, if hand-picked example (the context of making paperclips in online writing is probably largely about the alignment problem).
However, the NLA approach does little to address [the alignment stability problem](https://www.lesswrong.com/posts/g3pbJPQpNJyFfbHKd/the-alignment-stability-problem). It would seem to neither help nor hurt the existing approaches. The idea of [reflective stability](https://arbital.com/p/reflective_stability/) or an [internal value handshake](https://www.lesswrong.com/posts/k4AQqboXz8iE5TNXK/a-shot-at-the-diamond-alignment-problem) still applies. Natural language alignment also does not address [representational drift](https://scholar.google.com/scholar?cluster=6678474289141605170&hl=en&as_sdt=0,6&as_vis=1) in interpreting those goals as experience and learning accrue. Having an agent apply its own intelligence to maintain its goal stability over time is the best idea I know of, but I think it’s hard to know to what extent that will happen naturally in LMCAs. They are not strictly model-based maximizers, so like humans, they will not predictably stabilize their own goals perfectly over time. However, including this stability goal as part of the high-level goal prompt would seem to be a good start. Human involvement would seem to be possible and useful, as long as corrigibility and stability goals are maintained.[[12]](#fnlrpy2ysy4tp)
NLA does not address the societal alignment problem. If these systems are as capable as I expect, that problem will become much worse, by allowing access to powerful agents in open-source form. I think we need to turn our attention to planning against Moloch itself, as well as planning for malicious and careless actors. These issues are challenging and critical if the near future unfolds in the massively multipolar AGI scenario I expect if LMCAs are successful.
It’s looking like a wild ride is coming up very quickly, but I think we’ve got a fighting chance.
*Thanks to Steve Byrnes, Beren Millidge, and Tom Hazy for helpful comments on a draft of this article.*
1. **[^](#fnref7941hu3ojbb)**Beren Millidge’s excellent article describes [scaffolded LLMs as natural language computers](https://www.lesswrong.com/posts/43C3igfmMrE9Qoyfe/scaffolded-llms-as-natural-language-computers). He is addressing essentially the same set of potentials in LLMs by having them driven by scripts and interact with external tools, but he addresses this from a thoroughly CS perspective. This complements my perspective of seeing them as loosely brainlike cognitive architectures, and I highly recommend it.
2. **[^](#fnrefff2ijs11vwd)**David Shapiro coined this term and originated this natural language approach to alignment in his 2021 book [Natural Language Cognitive Architecture: A Prototype Artificial General Intelligence](https://www.barnesandnoble.com/w/natural-language-cognitive-architecture-david-shapiro/1139957470), which I haven’t yet read. He probably came up with this approach long before publishing that book, and others have probably talked about a [natural language alignment](https://www.lesswrong.com/posts/EhkHnNJXwT8RmtfYZ/natural-language-alignment-1) prior to that post, but I haven’t it. I found Shapiro’s work when researching for this article, and I am adopting his cognitive architecture terminology because I think it’s appropriate. The few mentions of his work on Less Wrong are quickly dismissed in each instance.
I do not endorse Shapiro’s proposed “Heuristic Imperatives” as top-level goals. They are: Reduce suffering in the universe; Increase prosperity in the universe; and Increase understanding in the universe.
I’d expect these to wind up creating a world with no humans and lots of smart and prosperous AIs that don’t experience suffering (and never have cool dance parties or swap meets). But, to be fair, Shapiro doesn’t claim that these are the best final form, just that we should have a list, and encourage their adoption by social and economic pressure.
I am not going to propose specific alternatives here, because we should first discuss whether any such scheme is useful. I'd say top-level goals for alignment should probably emphasize corrigibility and interpretability, along with some sort of harm reduction and human empowerment/flourishing.
3. **[^](#fnref2awdx185ksk)**It is unknown how much processing LLMs really accomplish to create each natural language string. And there are concerns that its output could become deceptively different than the internal processing that creates it. This is an important caveat on this approach, and deserves further discussion and interpretability work. The final section mentions some of these concerns.
4. **[^](#fnrefedbm641nnqf)**I’m suggesting the term x-risk AI, abbreviated XRAI, to denote AI that has a good chance of ending us. AGI is not specific enough, as GPT4 meets the intuitive definition of an AI that does a bunch of stuff well enough to be useful. I’d like a more strict definition of AGI, but I believe in coining new terms instead of telling people they’re using it wrong.
5. **[^](#fnrefkla5s6i9bzc)**Of course, the interactions between brain systems are highly complex on a neuronal level, and the exact mechanisms have not been worked out. On a high level, however, the principles seem clear. For the interactions I’ve described, it seems as though the limited bandwidth of natural language descriptions and simple APIs will be adequate to do a good deal of cognitive work.
6. **[^](#fnref3aubec0uckf)**For too much more on the precise distinctions in terminology surrounding executive function, see our paper [How Sequential Interactive Processing Within Frontostriatal Loops Supports a Continuum of Habitual to Controlled Processing](https://www.frontiersin.org/articles/10.3389/fpsyg.2020.00380/full).
7. **[^](#fnreff3ojnbx7xrm)**While Auto-GPT has accomplished little of real use at this early date, I'm impressed by how it seemingly spontaneously tries new approaches after a failure, based on its conclusion of that failure in its context window. More sophisticated approaches are possible, but they may not be necessary.
8. **[^](#fnref2zntv0sg82k)**This type of interference may relate to a cognitive neuroscience theory postulating that humans' low working-memory-for-executive-function capacity is actually advantageous in preventing interference. See [Rationalizing constraints on the capacity for cognitive control](https://www.cell.com/trends/cognitive-sciences/fulltext/S1364-6613(21)00148-0?_returnURL=https%3A%2F%2Flinkinghub.elsevier.com%2Fretrieve%2Fpii%2FS1364661321001480%3Fshowall%3Dtrue).
9. **[^](#fnrefvap71h9f84)**Dopamine response has long been known to approximate reward prediction error (which is equivalent to a value estimate in actor-critic RL). It is now known that the dopamine response contains other response characteristics, including positive responses for negative occurrences. This is consistent with dopamine as a general error signal that trains many responses beyond reward expectation, but it is consistent with the finding that dopamine’s central function is value estimation, with around 70% of dopamine cells responding in that way. Much more can be found in [A systems-neuroscience model of phasic dopamine.](https://doi.apa.org/doiLanding?doi=10.1037%2Frev0000199)
10. **[^](#fnref7kaceuordjy)**The number and length of tool descriptions in the Hugging Face library necessitated a pre-selection step to select more-likely appropriate tool descriptions, since all of the descriptions together exceeded the context window.
11. **[^](#fnrefm6fr7ubr5el)**I have neither the artistic skill nor the time to cajole midjourney to depict a shoggoth wearing a smiley face mask that holds dangerous tools and talks to itself. Help would be appreciated. The lore I’m remembering may not be canon, it’s been a while. Fortunately, fictional shoggoths aren’t relevant. Unfortunately, the level of sentience and goal-directedness of current and future LLMs is also unknown.
12. **[^](#fnreflrpy2ysy4tp)**Whoops, giving an LMCA a goal of not changing its goals could conflict with its goals of corrigibility and interpretability, since letting a user inspect its thoughts might result in the user changing its goals. This stuff is going to be tricky. I hope nobody launches a GPT-5 LMCA based on my suggestions without reading the footnotes. |
741eb499-5ee5-41b9-86b7-2f458f74a385 | trentmkelly/LessWrong-43k | LessWrong | Agent Foundations 2025 at CMU
We are opening applications to attend a 5 day agent foundations conference at Carnegie Mellon University. The program will include talks, breakout sessions, and other activities.
Endlessly debate your favored decision theory, precommit to precommit, bargain with(in) yourselves, make friends across the multiverse, and remember: never give in to acausal blackmail!
Apply here by January 26
Key Information
* March 3-7, 2025
* At Carnegie Mellon in Pittsburgh, PA
* 30-40 attendees
* Apply by January 26
About
Topics may include:
* Bounded decision-making and resource-limited reasoning
* Reflective stability and fixed points in agency
* Logical decision theory and updateless decision theory
* Causal vs evidential vs logical decision theory
* Embedded agency
* Natural abstraction hypothesis
* Abstraction boundaries
* Infra-Bayesian learning theory
* Inner alignment and mesa-optimization
* Logical causality
* Multi-level world models
* Game theory and multi-agent systems
* Logical inductors and reflective reasoning
* Foundations of reasoning under uncertainty
* Coordination problems and acausal trade
* Logical counterfactuals
* Ontological crises and reasoning across ontologies
Are there any costs to attend?
The event is free to attend. However, we are unable to provide accommodations or travel support for this event. We will provide lunch and dinner as well as snacks, coffee, and tea daily.
Submissions
We strongly welcome paper submissions. Paper submissions should be submitted via this form by February 17.
Website
Here. |
1b5bb059-1c40-4f04-8e2a-77d8936f76ca | trentmkelly/LessWrong-43k | LessWrong | .
. |
c53dd3ce-4717-42f0-9af7-aaac43f64af2 | trentmkelly/LessWrong-43k | LessWrong | Biological DOOM: a brief overview of biological computation
(no, not that kind of biological doom)
DOOM is a classic first-person shooter game released in 1993 by id Software. Because it’s from 1993, it doesn’t require much computing power compared to modern games. Additionally, the code (written in C) is easy to compile to run on a variety of processors.
Over the years, hackers have made DOOM run on things such as an ATM, a touchbar of a MacBook, a Porsche 911, and even a TI-84 calculator powered by potato batteries.
But what about cells?
Requirements for DOOM
The inputs to DOOM are based on button presses, traditionally on a keyboard. 9 keys in total are required (assuming “switch weapon” is implemented as one key that cycles through weapons).
For computation, the original 1993 release required:
* 4 MB of RAM and 12 MB of hard-drive storage
* Intel 386 (bare minimum) or 486 processor.
There is some flexibility regarding the processor, but slower processors will have worse frame-rates. The Intel 386 had 275,000 transistors in its most basic configuration.
DOOM also requires a graphical output. The smallest resolution I’ve seen is 128x32 pixels, and that was cutting it a bit close. We’ll assume we need 4096 black-and-white pixels for the display.
Finally, DOOM has audio. For the purposes of this thought experiment, we can ignore this output. Although the soundtrack is great, it’s not strictly required to play the game.
Approaches to biological computation
So, how could we potentially run DOOM? Biological systems can perform computations in several ways:
Nucleic acid hybridization
These logic gates are based on strand displacement between complementary DNA sequences.[1] A recent paper demonstrated a set of DNA-based logic gates that could add two 6-bit binary numbers.
A DNA-based AND gate, from the paper. The output Oab is released only if both inputs A and B are present. This can also be reconfigured to work as an XOR gate.
Pros and cons:
* Memory capacity is good (encoded in DNA or RNA)
* Switching s |
4130ec26-9217-4fab-b8a0-159c226aeb3d | StampyAI/alignment-research-dataset/arxiv | Arxiv | GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding
1 Introduction
---------------
Scaling neural networks brings dramatic quality gains over a wide array of machine learning problems [arora2018optimization, frankle2018lottery, kaplan2020scaling, devlin2018bert, mahajan2018exploring, gpt32020].
For computer vision, increasing the model capacity has led to better image classification and detection accuracy for various computer vision architectures [he2016deep, he2016identity, ghiasi2019fpn]. Similarly in natural language processing, scaling Transformers [vaswani2017attention] yielded consistent gains on language understanding tasks [devlin2018bert, raffel2019exploring, brown2020language], cross-lingual down-stream transfer [devlin2018bert, conneau2019unsupervised] and (massively-)multilingual neural machine translation [arivazhagan2019massively, gpipe19, shazeer2017outrageously].
This general tendency motivated recent studies to scrutinize the factors playing a critical role in the success of scaling [advani2017highdimensional, hestness2017deep, Hestness\_2019, Geiger\_2020, kaplan2020scaling], including the amounts of training data, the model size, and the computation being utilized as found by past studies. While the final model quality was found to have a power-law relationship with the amount of data, compute and model size [hestness2017deep, kaplan2020scaling], the significant quality gains brought by larger models also come with various practical challenges. Training efficiency among the most important ones, which we define as the amount of compute and training time being used to achieve a superior model quality against the best system existed, is oftentimes left out.

Figure 1: Multilingual translation quality (average ΔBLEU comparing to bilingual baselines) improved as MoE model size grows up to 600B, while the end-to-end training cost (in terms of TPU v3 core-year) only increased sublinearly. Increasing the model size from 37.5B to 600B (16x), results in computation cost increase from 6 to 22 years (3.6x). The 600B parameters model that achieved the best translation quality was trained with 2048 TPU v3 cores for 4 days, a total cost of 22 TPU v3 core-years. In contrast, training all 100 bilingual baseline models would have required 29 TPU v3 core-years. Our best quality dense single Transformer model (2.3B parameters) achieving ΔBLEU of 6.1, was trained with GPipe [gpipe19] on 2048 TPU v3 cores for 6 weeks or total of 235.5 TPU v3 core-years.
###
1.1 Practical Challenges for Scaling
Here we enumerate major practical challenges faced especially when training massive-scale models that are orders of magnitude larger than the capacity limit of a single accelerator memory (e.g., GPUs or TPUs).
##### Architecture-specific model parallelism support
There is a lack of support for efficient model parallelism algorithms under commonly used deep learning frameworks such as TensorFlow [abadi2016tensorflow] and PyTorch [pytorch2017]. Naive model parallelism with graph partition is supported but it would lead to severe under-utilization due to the sequential dependency of the network and gradient based optimization. In order to scale up the existing models efficiently, users typically need to invest a lot of engineering work, for example, migrating the model code to special frameworks [shazeer2018mesh, gpipe19].
##### Super-linear scaling of computation cost vs model size
Straightforward scaling of the mode size by increasing the depth or width [gpt32020, gpipe19] generally results in at least linear increase of training step time. Model parallelism by splitting layer weights and computation across multiple devices generally becomes necessary, leading to network communication overhead and device under-utilization. Device under-utilization stems from imbalanced assignment and sequential dependencies of the underlying neural network. This super-linear relationship between the computation cost and the model size can not be resolved by simply using more devices, making training massive models impractical.
##### Infrastructure scalability for giant model representation
A naive graph representation for the massive-scale model distributed across thousands of devices may become a bottleneck for both deep learning frameworks and their optimizing compilers. For example, adding D times more layers with inter-op partitioning or increasing model dimensions with intra-op partitioning across D devices may result in a graph with O(D) nodes. Communication channels between devices could further increase the graph size by up to O(D2) (e.g., partitioning gather or transpose). Such increase in the graph size would result in an infeasible amount of graph building and compilation time for massive-scale models.
##### Non-trivial efforts for implementing partitioning strategies
Partitioning a model to run on many devices efficiently is challenging, as it requires coordinating communications across devices. For graph-level partitioning, sophisticated algorithms [gpipe19, harlap2018pipedream] are needed to reduce the overhead introduced by the sequential dependencies between different partitions of graphs allocated on different devices. For operator-level parallelism, there are different communication patterns for different partitioned operators, depending on the semantics, e.g., whether it needs to accumulate partial results, or to rearrange data shards. According to our experience, manually handling these issues in the model requires substantial amount of effort, given the fact that the frameworks like TensorFlow have a large sets of operators with ad-hoc semantics. In all cases, implementing model partitioning would particularly be a burden for practitioners, as changing model architecture would require changing the underlying device communications, causing a ripple effect.
###
1.2 Design Principles for Efficient Training at Scale
In this paper, we demonstrate how to overcome these challenges by building a 600 billion parameters sequence-to-sequence Transformer model with Sparsely-Gated Mixture-of-Experts layers, which enjoys sub-linear computation cost and O(1) compilation time. We trained this model with 2048 TPU v3 devices for 4 days on a multilingual machine translation task and achieved far superior translation quality compared to prior art when translating 100 languages to English with a single non-ensemble model. We conducted experiments with various model sizes and found that the translation quality increases as the model gets bigger, yet the total wall-time to train only increases sub-linearly with respect to the model size, as illustrated in Figure [1](#S1.F1 "Figure 1 ‣ 1 Introduction ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").
To build such an extremely large model, we made the following key design choices.
##### Sub-linear Scaling
First, model architecture should be designed to keep the computation and communication requirements sublinear in the model capacity. Conditional computation [bengio2015conditional, shazeer2017outrageously, Elbayad2020DepthAdaptiveT, bapna2020controlling] enables us to satisfy training and inference efficiency by having a sub-network activated on the per-input basis. Scaling capacity of RNN-based machine translation and language models by adding Position-wise Sparsely Gated Mixture-of-Experts (MoE) layers [shazeer2017outrageously] allowed to achieve state-of-the-art results with sublinear computation cost. We therefore present our approach to extend Transformer architecture with MoE layers in Section [2](#S2 "2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").
##### The Power of Abstraction
Second, the model description should be separated from the partitioning implementation and optimization. This separation of concerns let model developers focus on the network architecture and flexibly change the partitioning strategy, while the underlying system applies semantic-preserving transformations and implements efficient parallel execution. To this end we propose a module, GShard, which only requires the user to annotate a few critical tensors in the model with partitioning policies. It consists of a set of simple APIs for annotations, and a compiler extension in XLA [xla] for automatic parallelization. Model developers write models as if there is a single device with huge memory and computation capacity, and the compiler automatically partitions the computation for the target based on the annotations and their own heuristics. We provide more annotation examples in Section [3.2](#S3.SS2 "3.2 GShard Annotation API for Parallel Execution ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").
| | |
| --- | --- |
| MPMD Partition
(a) MPMD Partition
| SPMD Partition
(b) SPMD Partition
|
Figure 2: Comparison between MPMD and our proposed SPMD partitioning of a Dot operator ([M,K]×[K,N]=[M,N]) across 4 devices. In this example, both operands are partitioned along the contracting dimension K, where each device computes the local result and globally combines with an AllReduce. MPMD partitioning generates separate operators for each device, limiting its scalability, whereas SPMD partitioning generates one program to run on all devices. Note that the compilation time with our SPMD partitioning is not-dependent of the number of devices being used.
##### Scalable Compilers
Third, the system infrastructure, including the computation representation and compilation, must scale with thousands of devices for parallel execution. For example, Figure [2](#S1.F2 "Figure 2 ‣ The Power of Abstraction ‣ 1.2 Design Principles for Efficient Training at Scale ‣ 1 Introduction ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") illustrates two different ways of partitioning a dot-product operation across 4 devices (color-coded). Notice that with the usual MPMD (Multiple Program Multiple Data) approach in Figure [(a)a](#S1.F2.sf1 "(a) ‣ Figure 2 ‣ The Power of Abstraction ‣ 1.2 Design Principles for Efficient Training at Scale ‣ 1 Introduction ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") scaling becomes more challenging since the number of nodes in the graph increases linearly with the number of devices. Instead, we developed a compiler technique for SPMD (Single Program Multiple Data) transformation that generates a single program to run on all devices, keeping the compilation time constant independent of the number of devices, as illustrated in Figure [(b)b](#S1.F2.sf2 "(b) ‣ Figure 2 ‣ The Power of Abstraction ‣ 1.2 Design Principles for Efficient Training at Scale ‣ 1 Introduction ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). We will discuss our SPMD framework in more details in Section [3.3](#S3.SS3 "3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").
The rest of the paper is organized as the following. Section [2](#S2 "2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") describes our Transformer architecture with Sparsely-Gated MoE layer in more details. Section [3](#S3 "3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") introduces our development module GShard.
Section [4](#S4 "4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") demonstrates the application of our mixture of expert models on the multilingual machine translation task over 100 language pairs. Section [5](#S5 "5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") has performance and memory measurements of our implementation. Section [6](#S6 "6 Related Work ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") discusses related work.
2 Model
--------
###
2.1 Sparse scaling of the Transformer architecture
The Transformer [vaswani2017attention] architecture has been widely used for natural language processing. It has become the de-facto standard for many sequence-to-sequence tasks, such as machine translation. Transformer makes use of two computational blocks, an encoder and a decoder, both implemented by stacking multiple Transformer layers.
Transformer encoder layer consists of two consecutive layers, namely a self-attention layer followed by a position-wise feed-forward layer. Decoder adds third cross-attention layer, which attends over encoder output.
We sparsely scale Transformer with conditional computation by replacing every other feed-forward layer with a Position-wise Mixture of Experts (MoE) layer [shazeer2017outrageously] with a variant of top-2 gating in both the encoder and the decoder (Figure [3](#S2.F3 "Figure 3 ‣ 2.1 Sparse scaling of the Transformer architecture ‣ 2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")). We vary the number of Transformer layers and the number of experts per MoE layer in order to scale the model capacity.
Each training example consists of a pair of sequences of subword tokens. Each token activates a sub-network of the MoE Transformer during both training and inference. The size of the sub-network is roughly independent of the number of experts per MoE Layer, allowing sublinear scaling of the computation cost as described in the previous section. Computation complexity is further analyzed in Section [3.1](#S3.SS1 "3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") and training performance in Section [5](#S5 "5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").

Figure 3: Illustration of scaling of Transformer Encoder with MoE Layers. The MoE layer replaces the every other Transformer feed-forward layer. Decoder modification is similar. (a) The encoder of a standard Transformer model is a stack of self-attention and feed forward layers interleaved with residual connections and layer normalization. (b) By replacing every other feed forward layer with a MoE layer, we get the model structure of the MoE Transformer Encoder. (c) When scaling to multiple devices, the MoE layer is sharded
across devices, while all other layers are replicated.
###
2.2 Position-wise Mixture-of-Experts Layer
The Mixture-of-Experts (MoE) layer used in our model is based on [shazeer2017outrageously] with variations in the sparse gating function and the auxiliary loss being used. A MoE layer for Transformer consists of E feed-forward networks FFN1…FFNE:
| | | | | |
| --- | --- | --- | --- | --- |
| | Gs,E | =GATE(xs) | | (1) |
| | FFNe(xs) | =woe⋅ReLU(wie⋅xs) | | (2) |
| | ys | =E∑e=1Gs,e⋅FFNe(xs) | | (3) |
where xs is the input token to the MoE layer, wiand wobeing the input and output projection matrices for the feed-forward layer (an expert). Vector Gs,E is computed by a gating network. Gs,E has one non-negative for each expert, most of which are zeros meaning the token is not dispatched to that expert. The token is dispatched to a very small number of experts. We choose to let each token dispatched to at most two experts. The corresponding entries in Gs,E are non-zeros, representing how much an expert contributes to the final network output. Every expert FFNe applies to xs a fully-connected 2-layer network using ReLU [Nair2010RectifiedLU] activation function. The output of the MoE layer, ys, is the weighted average of outputs from all the selected experts.
The gating function GATE(⋅) is critical to the MoE layer, which is modeled by a softmax activation function to indicate the weights of each expert in processing incoming tokens. In other words, to indicate how good an expert is at processing the incoming token. Furthermore, the gating function must satisfy two goals:
* Balanced load It is desirable that the MoE layer to sparsely activate the experts for a given token. A naive solution would be just to choose the top-k experts according to the softmax probability distribution. However, it is known that this approach leads to load imbalance problem for training [shazeer2017outrageously]: most tokens seen during training would have been dispatched to a small number of experts, amassing a very large input buffer for only a few (busy) experts leaving other experts untrained, slowing down the training. Meanwhile many other experts do not get sufficiently trained at all. A better design of the gating function would distribute processing burden more evenly across all experts.
* Efficiency at scale It would be rather trivial to achieve a balanced load if the gating function is done sequentially. The computation cost for the gating function alone is at least O(NE) for all N tokens in the input batch given E experts. However, in our study, N is in the order of millions and E is in the order of thousands, a sequential implementation of the gating function would keep most of the computational resources idle most of the time. Therefore, we need an efficient parallel implementation of the gating function to leverage many devices.
We designed the following mechanisms in the gating function GATE(⋅) to meet the above requirements (details illustrated in Algorithm [1](#alg1 "Algorithm 1 ‣ 2.2 Position-wise Mixture-of-Experts Layer ‣ 2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")):
* Expert capacity
To ensure the load is balanced, we enforce that the number of tokens processed by one expert is below some uniform threshold, which we define as expert capacity. Assuming that the total number of tokens in a training batch is N, and each token is dispatched to at most two experts, then the expert capacity is set to be O(N/E). GATE(⋅) keeps a running counter ce for how many tokens are dispatched to an expert. When both experts selected by a token already exceed their capacity, the token is considered as an overflowed token, where Gs,E degenerates into a zero vector. Such tokens have their representation xs passed on to the next layer via residual connections.
* Local group dispatching
GATE(⋅) partitions all tokens in a training batch evenly into G groups, i.e., each group contains S=N/G tokens. All groups are processed independently in parallel. Each group is given a fractional capacity of each expert, 2N/(G⋅E). Each group ensures that at most this many tokens are dispatched to an expert. In this way, we can ensure that expert capacity is still enforced and the overall load is balanced.
* Auxiliary loss
It is important that the gating function does not always choose the same few experts,
as this would lead to a capacity overflow for only a few experts
and under-utilization for the remaining ones.
Following [shazeer2017outrageously], we define an auxiliary loss term ℓaux to enforce this constraint. It is added to the overall loss function of the model L=ℓnll+k∗ℓaux with a constant multiplier k.
The particular form of the auxiliary loss term ℓaux in line (13) of algorithm [1](#alg1 "Algorithm 1 ‣ 2.2 Position-wise Mixture-of-Experts Layer ‣ 2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") is motivated by the following consideration:
the term ce/S represents the fraction of input routed to each expert,
and we want to minimize mean square of ce/S.
But because ce is derived from top-2 operation and is not differentiable,
we use the mean gates per expert me as a differentiable approximation
and replace (ce/S)2 with me(ce/S), which can now be optimized with gradient descent.
* Random routing Intuitively, because ys is a weighted average of what selected experts return, if the weight for the 2nd expert is very small, we can simply ignore the 2nd expert to conserve the overall expert capacity. Hence, in addition to respecting the expert capacity constraint, GATE(⋅) dispatches to the 2nd-best expert with the probability proportional to its weight g2.
Data: xS, a group of tokens of size S
Data: C, Expert capacity allocated to this group
Result: GS,E, group combine weights
Result: ℓaux, group auxiliary loss
1 cE←0 ▹ gating decisions per expert gS,E←softmax(wg⋅xS) ▹ gates per token per expert, wg are trainable weights mE←1S∑ss=1gs,E ▹ mean gates per expert for *s←1 to S* do
2 g1,e1,g2,e2=top\_2(gs,E) ▹ top-2 gates and expert indices g1←g1/(g1+g2) ▹ normalized g1 c←ce1 ▹ position in e1 expert buffer if *ce1<C* then
3 Gs,e1←g1 ▹ e1 expert combine weight for xs
4 end if
5 ce1←c+1 ▹ incrementing e1 expert decisions count
6 end for
7 ℓaux=1E∑Ee=1ceS⋅me for *s←1 to S* do
8 g1,e1,g2,e2=top\_2(gs,E) ▹ top-2 gates and expert indices g2←g2/(g1+g2) ▹ normalized g2 rnd←uniform(0,1) ▹ dispatch to second-best expert with probability ∝2⋅g2 c←ce2 ▹ position in e2 expert buffer if *c<C∧2⋅g2>rnd* then
9 Gs,e2←g2 ▹ e2 expert combine weight for xs
10 end if
11 ce2←c+1
12 end for
Algorithm 1 Group-level top-2 gating with auxiliary loss
3 Highly Parallel Implementation using GShard
----------------------------------------------
This section describes the implementation of the model in Section [2](#S2 "2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") that runs efficiently on a cluster of TPU devices.
The first step is to express the model in terms of linear algebra operations, in which our software stack (TensorFlow [abadi2016tensorflow]) and the hardware platform (TPU) are highly tailored and optimized. It is readily easy to code up most of the model in terms of linear algebra in the same way as the original Transformer. However, it requires some effort to express the MoE Layer, in particular GATE(⋅) function presented in Algorithm [1](#alg1 "Algorithm 1 ‣ 2.2 Position-wise Mixture-of-Experts Layer ‣ 2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") due to its sequential nature, and we describe the details in Section [3.1](#S3.SS1 "3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").
Next, we annotate the linear algebra computation to express parallelism. Each tensor in the computation can be annotated for replication or distribution across a cluster of devices using sharding APIs in Section [3.2](#S3.SS2 "3.2 GShard Annotation API for Parallel Execution ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). Using sharding annotations enables separation of concerns between the model description and the efficient parallel implementation, and allows users to flexibly express diverse parallelization strategies. For example, (1) the attention layer is parallelized by splitting along the batch dimension and replicating its weights to all devices. On the other hand, (2) experts in the MoE layer are infeasible to be replicated in all the devices due to its sheer size and the only viable strategy is to shard experts into many devices. Furthermore, the whole model alternates between these two modes (1)-(2). Using annotations frees model developers from the system optimization efforts and avoids baking the parallel implementation and low-level details into the model code.
Finally, the compiler infrastructure takes a (partially) annotated linear algebra computation and produces an efficient parallel program that scales to thousands of devices. As will be described in Section [3.3](#S3.SS3 "3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"), the compiler applies SPMD (Single Program Multiple Data) partitioning transformation to express per-device computation, inserts necessary cross-device communication, handles irregular patterns such as uneven partitions, and finally generates a single program to be launched on all devices for parallel execution.
###
3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra
Our model implementation (Algorithm [2](#alg2 "Algorithm 2 ‣ 3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")) views the whole accelerator cluster as a single device and expresses its core mathematical algorithm in a few tensor operations independent of the concrete setup of the cluster. Einstein summation notation [einstein1923grundlage] (i.e., tf.einsum) is a powerful construct to concisely express the model and we use it extensively in our implementation.
The softmax gates computation is trivially expressed by one einsum followed by the softmax function. Dispatching of inputs to selected experts is expressed by a single einsum between the dispatching mask and the input. All FFNe weights are combined into single 3-D tensors wi amd wo and the computation by FFN1…FFNE is expressed using 3 operators (two einsum and one relu). Finally, taking weighted average of all experts output into the final output is expressed in another einsum.
Top2Gating in Algorithm [2](#alg2 "Algorithm 2 ‣ 3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") computes the union of all group-local GS,E described in Algorithm [1](#alg1 "Algorithm 1 ‣ 2.2 Position-wise Mixture-of-Experts Layer ‣ 2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). combine\_weights is a 4-D tensor with shape [G, S, E, C].
The value combine\_weights[g, s, e, c] is non-zero
when the input token s in group g
is sent to the input buffer
of expert e at buffer position c.
For a specific g and s, a slice combine\_weight[g, s, :, :] contains at most two non-zero vaules.
Binary dispatch\_mask is produced from combine\_weights by simply setting all non-zero values to 1.
[⬇](http://data:text/plain;base64,Z2F0ZXMgPSBzb2Z0bWF4KGVpbnN1bSgiJlxHRyZTTSxNRS0+JlxHRyZTRSIsIGlucHV0cywgd2cpKQpjb21iaW5lX3dlaWdodHMsIGRpc3BhdGNoX21hc2sgPSBUb3AyR2F0aW5nKGdhdGVzKQpkaXNwYXRjaGVkX2V4cGVydF9pbnB1dHMgPSBlaW5zdW0oCiAgICAiJlxHRyZTRUMsJlxHRyZTTS0+JlxFRSZHQ00iLCBkaXNwYXRjaF9tYXNrLCByZXNoYXBlZF9pbnB1dHMpCmggPSBlaW5zdW0oIiZcRUUmR0NNLCZcRUUmTUgtPiZcRUUmR0NIIiwgZGlzcGF0Y2hlZF9leHBlcnRfaW5wdXRzLCB3aSkKaCA9IHJlbHUoaCkKZXhwZXJ0X291dHB1dHMgPSBlaW5zdW0oIiZcRUUmR0NILCZcRUUmSE0tPiZcR0cmRUNNIiwgaCwgd28pCm91dHB1dHMgPSBlaW5zdW0oCiAgICAiJlxHRyZTRUMsJlxHRyZFQ00tPiZcR0cmU00iLCBjb21iaW5lX3dlaWdodHMsIGV4cGVydF9vdXRwdXRzKQ==)
1gates = softmax(einsum("&\GG&SM,ME->&\GG&SE", inputs, wg))
2combine\_weights, dispatch\_mask = Top2Gating(gates)
3dispatched\_expert\_inputs = einsum(
4 "&\GG&SEC,&\GG&SM->&\EE&GCM", dispatch\_mask, reshaped\_inputs)
5h = einsum("&\EE&GCM,&\EE&MH->&\EE&GCH", dispatched\_expert\_inputs, wi)
6h = relu(h)
7expert\_outputs = einsum("&\EE&GCH,&\EE&HM->&\GG&ECM", h, wo)
8outputs = einsum(
9 "&\GG&SEC,&\GG&ECM->&\GG&SM", combine\_weights, expert\_outputs)
Algorithm 2 Forward pass of the Positions-wise MoE layer. The underscored letter (e.g., G and E) indicates the dimension along which a tensor will be partitioned.
We need to choose the number of groups G and the number of experts E properly so that the algorithm can scale to a cluster with D devices. It is worthwhile to analyze its overall computation complexity (the total number of floating point operations) for a training step given a training batch of N tokens.
We analyze Algorithm [2](#alg2 "Algorithm 2 ‣ 3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") computation complexity scaling with number the of devices D with the following assumptions:
a) number of tokens per device ND=O(1) is constant111This is oftentimes necessary in practice to avoid overflowing device memory.;
b) G=O(D), S=O(1) and N=O(GS)=O(D);
c) M=O(1), H=O(1);
d) E=O(D); and
e) C=O(2SE)=O(1D),D<S and is a positive integer222Scaling D>S would require different use of fractional expert capacity.
.
The total number of floating point operations FLOPS in Algorithm [2](#alg2 "Algorithm 2 ‣ 3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"):
| | | | | | | | | |
| --- | --- | --- | --- | --- | --- | --- | --- | --- |
| | FLOPSSoftmax | + | FLOPSTop2Gating | + | FLOPSDispatch|Combine | + | FLOPSFFN= | |
| | O(GSME) | + | O(GSEC) | + | O(GSMEC) | + | O(EGCHM)= | |
| | O(D⋅1⋅1⋅D) | + | O(D⋅1⋅D⋅1D) | + | O(D⋅1⋅1⋅D⋅1D) | + | O(D⋅D⋅1D⋅1⋅1)= | |
| | O(D2) | + | O(D) | + | O(D) | + | O(D) | |
and consequently per-device FLOPS/D=O(D)+O(1)+O(1)+O(1). Per-device softmax complexity FLOPSsoftmax/D=O(D) is linear in number of devices, but in practice is dominated by other terms since D<<H and D<S. As a result FLOPS/D could be considered O(1), satisfying sublinear scaling design requirements. Section [5](#S5 "5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") verifies this analysis empirically.
In addition to the computation cost, we have non-constant cross-device communication cost, but it grows at a modest rate O(√D) when we increase D (Section [5](#S5 "5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")).
###
3.2 GShard Annotation API for Parallel Execution
Due to the daunting size and computation demand of tensors in Algorithm [1](#alg1 "Algorithm 1 ‣ 2.2 Position-wise Mixture-of-Experts Layer ‣ 2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"), we have to parallelize the algorithm over many devices. An immediate solution of how to shard each tensor in the algorithm is illustrated by underscored letters in Algorithm [2](#alg2 "Algorithm 2 ‣ 3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). The *sharding* API in GShard allows us to annotate tensors in the program to selectively specify how they should be partitioned. This information is propagated to the compiler so that the compiler can automatically apply transformations for parallel execution. We use the following APIs in TensorFlow/Lingvo [shen2019lingvo] in our work.
* replicate(tensor) annotates tensor to be replicated across partitions, and returns the annotated tensor. This is often used for the non-MoE layers in our model to replicate the weights.
* split(tensor, split\_dimension, num\_partitions) annotates tensor to be partitioned along split\_dimension, and returns the annotated tensor. Partition i is placed on the i’th device, and num\_partitions must not exceed the number of devices on the system.
* shard(tensor, device\_assignment) generalizes split() to allow partitioning multiple dimensions and specifying the placement of each partition. Appendix [A.3](#A1.SS3 "A.3 General Sharding API ‣ Appendix A Appendix ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") describes this API with more details.
Note that the invocations to split or shard only adds annotations and does not change the logical shape in the user program. The user still works with full shapes and does not need to worry about issues like uneven partitioning.
GShard is general in the sense that the simple APIs apply to all dimensions in the same way. The sharded dimensions could include batch (data-parallelism), feature, expert, and even spatial dimensions in image models, depending on the use cases. Also, since the sharding annotation is per tensor, different parts of the model can be partitioned in different ways. This flexibility enables us to partition the giant MoE weights and switch partition modes between MoE and non-MoE layers, as well as uses cases beyond this paper, e.g., spatial partitioning of large images [spatial-partitioning] (Appendix [A.4](#A1.SS4 "A.4 SPMD Partitioning for Convolution and Window-Based Operators ‣ Appendix A Appendix ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")).
With the above sharding APIs, we can express the sharding strategy shown in Algorithm [2](#alg2 "Algorithm 2 ‣ 3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") as below. The input tensor is split along the first dimension and the gating weight tensor is replicated. After computing the dispatched expert inputs, we apply split to change the sharding from the group (G) dimension to the expert (E) dimension. D is device count.
[⬇](http://data:text/plain;base64,ICAjIFBhcnRpdGlvbiBpbnB1dHMgYWxvbmcgZ3JvdXAgKEcpIGRpbS4KJVxIaWxpZ2h0JSsgaW5wdXRzID0gc3BsaXQoaW5wdXRzLCAwLCBEKQogICMgUmVwbGljYXRlIHRoZSBnYXRpbmcgd2VpZ2h0cwolXEhpbGlnaHQlKyB3ZyA9IHJlcGxpY2F0ZSh3ZykKICBnYXRlcyA9IHNvZnRtYXgoZWluc3VtKCJHU00sTUUtPkdTRSIsIGlucHV0cywgd2cpKQogIGNvbWJpbmVfd2VpZ2h0cywgZGlzcGF0Y2hfbWFzayA9IFRvcDJHYXRpbmcoZ2F0aW5nX2xvZ2l0cykKICBkaXNwYXRjaGVkX2V4cGVydF9pbnB1dHMgPSBlaW5zdW0oCiAgICAiR1NFQyxHU00tPkVHQ00iLCBkaXNwYXRjaF9tYXNrLCByZXNoYXBlZF9pbnB1dHMpCiAgIyBQYXJ0aXRpb24gZGlzcGF0Y2hlZCBpbnB1dHMgYWxvbmcgZXhwZXJ0IChFKSBkaW0uCiVcSGlsaWdodCUrIGRpc3BhdGNoZWRfZXhwZXJ0X2lucHV0cyA9IHNwbGl0KGRpc3BhdGNoZWRfZXhwZXJ0X2lucHV0cywgMCwgRCkKICBoID0gZWluc3VtKCJFR0NNLEVNSC0+RUdDSCIsIGRpc3BhdGNoZWRfZXhwZXJ0X2lucHV0cywgd2kpCiAgLi4u)
1 # Partition inputs along group (G) dim.
2 + inputs = split(inputs, 0, D)
3 # Replicate the gating weights
4 + wg = replicate(wg)
5 gates = softmax(einsum("GSM,ME->GSE", inputs, wg))
6 combine\_weights, dispatch\_mask = Top2Gating(gating\_logits)
7 dispatched\_expert\_inputs = einsum(
8 "GSEC,GSM->EGCM", dispatch\_mask, reshaped\_inputs)
9 # Partition dispatched inputs along expert (E) dim.
10 + dispatched\_expert\_inputs = split(dispatched\_expert\_inputs, 0, D)
11 h = einsum("EGCM,EMH->EGCH", dispatched\_expert\_inputs, wi)
12 ...
##### Per-tensor sharding assignment
As shown in the example above, users are not required to annotate every tensor in the program. Annotations are typically only required on a few important operators like Einsums in our model and the compiler uses its own heuristics to infer sharding for the rest of the tensors 333It is also important for the compiler to infer missing shardings since the backpropagation computation is often automatically generated by the frontend framework and users don’t have access to those tensors.. For example, since the input tensor is partitioned along G and the weight tensor is replicated, the compiler chooses to partition the einsum output along the same G dimension (Line 5). Similarly, since both inputs are partitioned along the G dimension for the input dispatch einsum (Line 7), the output sharding is inferred to be split along the G dimension, and then we add the split annotation on the output to reshard along the E dimension. Some annotations in the above example could also be determined by the compiler (e.g., replicate(wg)) but it is recommended to annotate the initial input and final output tensors of the computation.
The compiler currently uses an iterative data-flow analysis to propagate sharding information from an operator to its neighbors (operands and users), starting from the user-annotated operators. The analysis tries to minimize the chance of resharding by aligning the sharding decisions of adjacent operators. There could be other approaches such as integer programming or machine-learning methods, but improving the automatic sharding assignment is not the focus of this paper and we leave it as future work.
##### Mixing manual and automatic sharding
Automatic partitioning with sharding annotations is often enough for common cases, but GShard also has the flexibility to allow mixing manually partitioned operators with auto-partitioned operators. This provides users with more controls on how operators are partitioned, and one example is that the user has more run-time knowledge beyond the operators’ semantics. For example, neither XLA’s nor TensorFlow’s Gather operator definition conveys information about the index bounds for different ranges in the input, but the user might know that a specific Gather operator shuffles data only within each partition. In this case, the user can trivially partition the operator by simply shrinking the dimension size and performing a local Gather; otherwise, the compiler would need to be conservative about the index range and add unnecessary communication overhead. For example, the dispatching Einsum (Line 3) in Algorithm [2](#alg2 "Algorithm 2 ‣ 3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") in Algorithm [2](#alg2 "Algorithm 2 ‣ 3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"), which uses an one-hot matrix to dispatch inputs, can be alternatively implemented with a Gather operator using trivial manual partitioning, while the rest of the model is partitioned automatically. Below is the pseudocode illustrating this use case.
[⬇](http://data:text/plain;base64,IyBpbnB1dCBoYXMgc2hhcGUgW0csIFMsIE1dLiBzcGxpdCgpIGRvZXMgbm90IGNoYW5nZSBsb2dpY2FsIHNoYXBlLgppbnB1dCA9IHNwbGl0KGlucHV0LCAwLCBudW1fZGV2aWNlcykKIyBzX2luZGljZXMgaGFzIHNoYXBlIFtFLCBHLCBDLCAxXS4gVmFsdWVzOiBpbmRpY2VzIHRvIFMgaW4gaW5wdXQuCnNfaW5kaWNlcyA9IHNwbGl0KHNfaW5kaWNlcywgMSwgbnVtX2RldmljZXMpCgojIEJlZ2luIG1hbnVhbCBwYXJ0aXRpb25pbmcuCiMgcGFydGl0aW9uZWRfaW5wdXQgaGFzIHNoYXBlIFtHL251bV9kZXZpY2VzLCBTLCBNXQolXEhpbGlnaHQlcGFydGl0aW9uZWRfaW5wdXQgPSBhdXRvX3RvX21hbnVhbF9zcG1kX3BhcnRpdGlvbihpbnB1dCkKIyBwYXJ0aXRpb25lZF9zX2luZGljZXMgaGFzIHNoYXBlIFtFLCBHL251bV9kZXZpY2VzLCBDLCAxXQolXEhpbGlnaHQlcGFydGl0aW9uZWRfc19pbmRpY2VzID0gYXV0b190b19tYW51YWxfc3BtZF9wYXJ0aXRpb24oc19pbmRpY2VzKQojIENvbmNhdCB3aXRoIEcgaW5kaWNlcyBpbiBwYXJ0aXRpb25lZF9pbnB1dDogSW90YSBvbiBHIGRpbWVuc2lvbi4KcGFydGl0aW9uZWRfZ3NfaW5kaWNlcyA9IGNvbmNhdCgKICAgIGlvdGEoW0UsIEcvbnVtX2RldmljZXMsIEMsIDFdLCAxKSwgcGFydGl0aW9uZWRfc19pbmRpY2VzLCAzKQojIHBhcnRpdGlvbmVkX2RhdGEgaGFzIHNoYXBlIFtFLCBHL251bV9kZXZpY2VzLCBDLCBNXQpwYXJ0aXRpb25lZF9kYXRhID0gZ2F0aGVyKAogICAgcGFydGl0aW9uZWRfaW5wdXQsIHBhcnRpdGlvbmVkX2dzX2luZGljZXMpCgojIFN3aXRjaCBiYWNrIHRvIGF1dG8gcGFydGl0aW9uaW5nLgojIGRhdGEgaGFzIHNoYXBlIFtFLCBHLCBDLCBNXQolXEhpbGlnaHQlZGF0YSA9IG1hbnVhbF90b19hdXRvX3NwbWRfcGFydGl0aW9uKHBhcnRpdGlvbmVkX2RhdGEpCi4uLg==)
1# input has shape [G, S, M]. split() does not change logical shape.
2input = split(input, 0, num\_devices)
3# s\_indices has shape [E, G, C, 1]. Values: indices to S in input.
4s\_indices = split(s\_indices, 1, num\_devices)
5
6# Begin manual partitioning.
7# partitioned\_input has shape [G/num\_devices, S, M]
8 partitioned\_input = auto\_to\_manual\_spmd\_partition(input)
9# partitioned\_s\_indices has shape [E, G/num\_devices, C, 1]
10 partitioned\_s\_indices = auto\_to\_manual\_spmd\_partition(s\_indices)
11# Concat with G indices in partitioned\_input: Iota on G dimension.
12partitioned\_gs\_indices = concat(
13 iota([E, G/num\_devices, C, 1], 1), partitioned\_s\_indices, 3)
14# partitioned\_data has shape [E, G/num\_devices, C, M]
15partitioned\_data = gather(
16 partitioned\_input, partitioned\_gs\_indices)
17
18# Switch back to auto partitioning.
19# data has shape [E, G, C, M]
20 data = manual\_to\_auto\_spmd\_partition(partitioned\_data)
21...
###
3.3 The XLA SPMD Partitioner for GShard
This section describes the compiler infrastructure that automatically partitions a computation graph based on sharding annotations. Sharding annotations inform the compiler about how each tensor should be distributed across devices. The SPMD (Single Program Multiple Data) partitioner (or ‘‘partitioner’’ for simplicity) is a compiler component that transforms a computation graph into a single program to be executed on all devices in parallel. This makes the compilation time near constant regardless of the number of partitions, which allows us to scale to thousands of partitions. 444An alternative is MPMD (Multiple Program Multiple Data), which does not scale as shown in Figure [2](#S1.F2 "Figure 2 ‣ The Power of Abstraction ‣ 1.2 Design Principles for Efficient Training at Scale ‣ 1 Introduction ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").
We implemented the partitioner in the XLA compiler [xla]. Multiple frontend frameworks including TensorFlow, JAX, PyTorch and Julia already have lowering logic to transform their graph representation to XLA HLO graph. XLA also has a much smaller set of operators compared to popular frontend frameworks like TensorFlow, which reduces the burden of implementing a partitioner without harming generality, because the existing lowering from frontends performs the heavy-lifting to make it expressive. Although we developed the infrastructure in XLA, the techniques we describe here can be applied to intermediate representations in other machine learning frameworks (e.g., ONNX [onnx], TVM Relay [roesch2018relay], Glow IR [rotem2018glow]).
XLA models a computation as a dataflow graph where nodes are operators and edges are tensors flowing between operators. The core of the partitioner is per-operation handling that transforms a full-sized operator into a partition-sized operator according to the sharding specified on the input and output. When a computation is partitioned, various patterns of cross-device data transfers are introduced. In order to maximize the performance at large scale, it is essential to define a core set of communication primitives and optimize those for the target platform.
####
3.3.1 Communication Primitives
Since the partitioner forces all the devices to run the same program, the communication patterns are also regular and XLA defines a set of collective operators that perform MPI-style communications [mpi2.2]. We list the common communication primitives we use in the SPMD partitioner below.
##### CollectivePermute
This operator specifies a list of source-destination pairs, and the input data of a source is sent to the corresponding destination. It is used in two places: changing a sharded tensor’s device order among partitions, and halo exchange as discussed later in this section.
##### AllGather
This operator concatenates tensors from all participants following a specified order. It is used to change a sharded tensor to a replicated tensor.
##### AllReduce
This operator performs elementwise reduction (e.g., summation) over the inputs from all participants. It is used to combine partially reduced intermediate tensors from different partitions. In a TPU device network, AllReduce has a constant cost when the number of partition grows (Section [5.2](#S5.SS2 "5.2 Runtime Efficiency and Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")). It is also a commonly used primitive with efficient implementation in other types of network topology [cho2019blueconnect].
##### AllToAll
This operator logically splits the input of each participant along one dimension, then sends each piece to a different participant. On receiving data pieces from others, each participant concatenates the pieces to produce its result. It is used to reshard a sharded tensor from one dimension to another dimension. AllToAll is an efficient way for such resharding in a TPU device network, where its cost increases sublinearly when the number of partitions grows (Section [5.2](#S5.SS2 "5.2 Runtime Efficiency and Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")).
####
3.3.2 Per-Operator SPMD Partitioning
The core of the partitioner is the per-operator transformation from a full-sized operator into a partition-sized operator according to the specified sharding. While some operators (e.g., elementwise) are trivial to support, we discuss several common cases where cross-partition communications are required.
There are a few important technical challenges in general cases, which we will cover in Section [3.3.3](#S3.SS3.SSS3 "3.3.3 Supporting a Complete Set of Operators ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). To keep the discussion more relevant to the MoE model, this section focuses on Einsum partitioning to illustrate a few communication patterns. And to keep it simple for now, we assume that all tensors are evenly partitioned, which means the size of the dimension to partitition is a multiple of the partition count.
##### Einsum Case Study
Einsum is the most critical operator in implementing the MoE model. They are represented as a Dot operation in XLA HLO, where each operand (LHS or RHS) consists of three types of dimensions:
* Batch dimensions are the embarrassingly parallel dimensions. The same set of batch dimensions must exist in all of LHS, RHS and the output, and each element in the output only depends on the corresponding batch in LHS and RHS.
* Contracting dimensions only exist in the operands. LHS and RHS must have the same set of contracting dimensions, and they are summed up and collapsed in the output.
* Non-contracting dimensions are also parallel dimensions that exist in one of the operands and the output. Each of LHS and RHS has its own set of non-contracting dimensions, which are inherited by the output.
Sharding propagation prioritizes choosing the same sharding on batch dimensions of LHS, RHS and output, because that would avoid any cross-partition communication. However, that is not always possible, and we need cross-partition communication in the following three cases.
| | | |
| --- | --- | --- |
| A partitioned
(a) A partitioned Einsum operator. Colored letters (G and E) represent the partitioned dimension of each tensor. The partitioner decides to first execute a batch-parallel Einsum along the G dimension, then reshard the result to the E dimension.
| A simple
(b) A simple Einsum (Matmul) partitioned on the contracting dimension.
| An
(c) An Einsum (Matmul) where we use collective-permute in a loop to compute one slice at a time. There is no full-sized tensor during the entire process.
|
Figure 4: Examples of Einsum partitioning with cross-device communication.
* Resharding. In the MoE model we built, the expert dispatching logic (Line 3 in Algorithm [2](#alg2 "Algorithm 2 ‣ 3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")) requires switching the partitioned dimension after an Einsum. Since resharding is efficient (Section [5.2](#S5.SS2 "5.2 Runtime Efficiency and Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")) with AllToAll, we first execute the Einsum locally, then reshard it to the desired dimension, as shown in Figure [(a)a](#S3.F4.sf1 "(a) ‣ Figure 4 ‣ Einsum Case Study ‣ 3.3.2 Per-Operator SPMD Partitioning ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").
* Accumulating partial results. If the inputs are partitioned along contracting dimensions, the local result is partial and we need to use an AllReduce to combine them and produce the final result, as shown in Figure [(b)b](#S3.F4.sf2 "(b) ‣ Figure 4 ‣ Einsum Case Study ‣ 3.3.2 Per-Operator SPMD Partitioning ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").
* Slicing in a loop. For certain scenarios, we also implemented an algorithm similar to Cannon’s algorithm [cannon1969], in order to limit the size of tensors on each partition. For example, if both operands are partitioned on a non-contracting dimension, we cannot compute the local Einsum directly since operands have different non-contracting dimensions. Replicating one of the operands would not cause redundant computation, but it requires the replicated operand to fit in device memory. Therefore, if the size of the operand is too large, we instead keep both operands partitioned and use a loop to iterate over each slice of the result, and use CollectivePermute to communicate the input slices (Figure [(c)c](#S3.F4.sf3 "(c) ‣ Figure 4 ‣ Einsum Case Study ‣ 3.3.2 Per-Operator SPMD Partitioning ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")).
####
3.3.3 Supporting a Complete Set of Operators
We solved several additional challenges to enable the SPMD partitioner to support a complete set of operators without extra constraints of tensor shapes or operator configurations.
These challenges often involve asymmetric compute or communication patterns between partitions, which are particularly hard to express in SPMD, since the single program needs to be general enough for all partitions. We cannot simply create many branches in the single program based on the run-time device ID, because that would lead to an explosion in program size.
##### Static shapes and uneven partitioning
XLA requires tensor shapes to be static. 555The limited dynamism in the intermediate representation is often necessary to efficiently target accelerators.
However, when a computation is partitioned, it’s not always the case that all partitions have the same input/output shapes, because dimensions may not be evenly divisible by the number of partitions.
In those cases, the size of the shape is rounded up to the next multiple of partition count, and the data in that padded region can be arbitrary.
When computing an operator, we may need to fill in a known value to the padded region for correctness. For example, if we need to partition an Reduce-Add operator, the identity value of zero needs to be used.
Consider an example where the partitioned dimension (15) cannot be divided into 2 (partition count), so Partition 1 has one more column than needed. We create an Iota operator of range [0, 8), add the partition offset (calculated from PartitionId×8), and compare with the full shape offset (15). Based on the predicate value, we select either from the operand or from zero, and the result is the masked operand.
##### Static operator configurations
XLA operators have static configurations, like the padding, stride, and dilation defined in Convolution. However, different partitions may not execute with the same operator configuration. E.g., for a Convolution, the left-most partition applies padding to its left while the right-most partition applies padding to its right. In such cases, the partitioner may choose configurations that make some partitions to produce slightly more data than needed, then slice out the the irrelevant parts. Appendix [A.4](#A1.SS4 "A.4 SPMD Partitioning for Convolution and Window-Based Operators ‣ Appendix A Appendix ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") discusses examples for Convolution and similar operators.
##### Halo exchange
Certain operators have a communication pattern which involves partial data exchange with neighboring partitions, which we call *halo exchange*. We use the CollectivePermute operator to exchange halo data between partitions.
| | | |
| --- | --- | --- |
| Convolution
(a) Convolution
| Pad
(b) Pad
| Reshape with unevenly partitioned input and evenly partitioned output
(c) Reshape with unevenly partitioned input and evenly partitioned output
|
Figure 5: Halo exchange examples.
The most typical use case of halo exchange is for partitinoning window-based operators (e.g., Convolution, ReduceWindow), because neighboring partitions may require overlapping input data (Figure [(a)a](#S3.F5.sf1 "(a) ‣ Figure 5 ‣ Halo exchange ‣ 3.3.3 Supporting a Complete Set of Operators ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")). In practice, halo-exchange for these operator often needs to be coupled with proper padding, slicing, and masking due to advanced use of window configurations (dilation, stride, and padding), as well as uneven halo sizes. We describe various scenarios in Appendix [A.4](#A1.SS4 "A.4 SPMD Partitioning for Convolution and Window-Based Operators ‣ Appendix A Appendix ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").
Another use of halo exchange is for data formatting operators that change the size of the shape. For example, after a Slice or Pad operator, the shape of the tensor changes, and so do the boundaries between partitions. This requires us to realign the data on different partitions, which can be handled as a form of halo exchange (Figure [(b)b](#S3.F5.sf2 "(b) ‣ Figure 5 ‣ Halo exchange ‣ 3.3.3 Supporting a Complete Set of Operators ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")).
Other data formatting operators, although logically not changing the size of the shape, may also need halo exchange, specifically due to the static shape constraint and uneven partitioning. For example, the Reverse operator reverses the order of elements in a tensor, but if it is partitioned unevenly, we need to shift data across partitions to keep the padding logically to the right of the result tensor. Another example is Reshape. Consider reshaping a tensor from [3, 2] to [6], where the input is unevenly partitioned in 2 ways on the first dimension (partition shape [2, 2]), and the output is also partitioned in 2 ways (partition shape [3]). There is padding on the input due to uneven partitioning, but after Reshape, the output tensor no longer has padding; as a result, halo exchange is required in a similar way to Slice (Figure [(c)c](#S3.F5.sf3 "(c) ‣ Figure 5 ‣ Halo exchange ‣ 3.3.3 Supporting a Complete Set of Operators ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")).
##### Compiler optimizations
The SPMD partitioner creates various data formatting operators in order to perform slicing, padding, concatenation, masking and halo exchange.
To address the issue, we leverage XLA’s fusion capabilities on TPU, as well as code motion optimizations for slicing and padding, to largely hide the overhead of data formatting. As a result, the run-time overhead is typically negligible, even for convolutional networks where masking and padding are heavily used.
4 Massively Multilingual, Massive Machine Translation (M4)
-----------------------------------------------------------
###
4.1 Multilingual translation
We chose multilingual neural machine translation (MT) [Firat\_2016, Johnson\_2017, DBLP:journals/corr/abs-1903-00089] to validate our design for efficient training with GShard.
Multilingual MT, which is an inherently multi-task learning problem, aims at building a single neural network for the goal of translating multiple language pairs simultaneously.
This extends our line of work [gpipe19, arivazhagan2019massively, shazeer2017outrageously] towards a universal machine translation model [translate2019m4], i.e. a single model that can translate between more than hundred languages, in all domains.
Such massively multilingual translation models are not only convenient for stress testing models at scale, but also shown to be practically impactful in real-world production systems [translate2020quality].
In massively multilingual MT, there are two criteria that define success in terms of the model quality, 1) improvements attained on languages that have large amounts of training data (high resourced), and 2) improvements for languages with limited data (low-resource). As the number of language pairs (tasks) to be modeled within a single translation model increases, positive language transfer [baldwin1988transfer] starts to deliver large gains for low-resource languages. Given the number of languages considered, M4 has a clear advantage on improving the low-resource tasks. On the contrary, for high-resource languages
the increased number of tasks limits per-task capacity within the model, resulting in lower translation quality compared to a models trained on a single
language pair.
This capacity bottleneck for high resourced languages can be relaxed by increasing the model size to massive scale in order to satisfy the need for additional capacity [arivazhagan2019massively, gpipe19].
Massively multilingual, massive MT consequently aims at striking a balance between increasing positive transfer by massive multilinguality and mitigating the capacity bottleneck by massive scaling. While doing so, scaling the model size and the number of languages considered have to be coupled with a convenient neural network architecture. In order to amplify the positive transfer and reduce the negative transfer666Negative transfer is the notion of sharing the model capacity by unrelated tasks which in return hurts the quality of such interfering tasks., one can naturally design a model architecture that harbours shared components across languages (shared sub-networks), along with some language specific ones (unshared, language specific sub-networks). However, the search space in model design (deciding on what to share) grows rapidly as the number of languages increase, making heuristic-based search for a suitable architecture impractical. Thereupon the need for approaches based on learning the wiring pattern of the neural networks from the data emerge as scalable and practical way forward.
In this section, we advocate how conditional computation [bengio2013estimating, davis2013lowrank] with sparsely gated mixture of experts [shazeer2017outrageously] fits into the above detailed desiderata and show its efficacy by scaling neural machine translation models beyond 1 trillion parameters, while keeping the training time of such massive networks practical. E.g. a 600B GShard model for M4 can process 1T tokens777Source side tokens after sub-word segmentation. in 250k training steps in under 4 days. We experiment with increasing the model capacity by adding more and more experts into the model and study the factors playing role in convergence, model quality and training efficiency. Further, we demonstrate how conditional computation can speed up the training [bengio2015conditional] and how sparsely gating/routing each token through the network can efficiently be learned without any prior knowledge on task or language relatedness, exemplifying the capability of learning the routing decision directly from the data.
###
4.2 Dataset and Baselines
The premise of progressively larger models to attain greater quality necessitates large amounts of training data to begin with [kaplan2020scaling]. Following the prior work on dense scaling for multilingual machine translation [gpipe19, arivazhagan2019massively], we committed to the realistic test bed of MT in the wild, and use a web-scale in-house dataset. The training corpus, mined from the web [10.5555/1873781.1873905], contains parallel documents for 100 languages, to and from English, adding up to a total of 25 billion training examples. A few characteristics of the training set is worth mentioning. Having mined from the web, the joint corpus is considerably noisy while covering a diverse set of domains and languages. Such large coverage comes with a heavy imbalance between languages in terms of the amount of examples per language pair. This imbalance follows a sharp power law, ranging from billions of examples for high-resourced languages to tens of thousands examples for low-resourced ones. While the above mentioned characteristics constitute a challenge for our study, it also makes the overall attempt as realistic as possible. We refer reader to [gpipe19, arivazhagan2019massively] for the additional details of the dataset being used.
We focus on improving the translation quality (measured in terms of BLEU score [papineni2002bleu]) from all 100 languages to English. This resulted in approximately 13 billion training examples to be used for model training888Compared to prior work using the same dataset, Kazakh and Latin to English language pairs were excluded from evaluation.. In order to form our baselines, we trained separate bilingual Neural Machine Translation models for each language pair (e.g. a single model for German-to-English), tuned depending on the available training data per-language999We tuned batch-size and different values of regularization methods (e.g. dropout) in a Transformer-Big or Transformer-Base layout, for high or low-resourced languages respectively.. Rather than displaying individual BLEU scores for each language pair, we follow the convention of placing the baselines along the x-axis at zero, and report the ΔBLEU trendline of each massively multilingual model trained with GShard (see Figure [6](#S4.F6 "Figure 6 ‣ Model Details ‣ 4.3 Sparsely-Gated MoE Transformer: Model and Training ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")). The x-axis in Figure [6](#S4.F6 "Figure 6 ‣ Model Details ‣ 4.3 Sparsely-Gated MoE Transformer: Model and Training ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") is sorted from left-to-right in the decreasing order of amount of available training data, where the left-most side corresponds to high-resourced languages, and low-resourced languages on the right-most side respectively. To reiterate, our ultimate goal in universal machine translation is to amass the ΔBLEU trendline of a single multilingual model above the baselines for all languages considered. We also include a variant of dense 96 layer Transformer Encoder-Decoder network T(96L) trained with GPipe pipeline parallelism on the same dataset as another baseline (dashed trendline in Figure [6](#S4.F6 "Figure 6 ‣ Model Details ‣ 4.3 Sparsely-Gated MoE Transformer: Model and Training ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")). Training to convergence took over 6 weeks on 2048 TPU v3 cores 101010T(96L) measured to be processing 1+ trillion tokens at 300k steps, processing around 4M tokens/step, total budget of 235.5 TPU v3 core years, outperforming the original GPipe T(128L)11111164 encoder + 64 decoder layers, 16384 hidden dim, 32 attention heads [gpipe19] and is the strongest single dense model baseline we use in our comparisons.
###
4.3 Sparsely-Gated MoE Transformer: Model and Training
Scaling Transformer architecture has been an exploratory research track recently [Bapna\_2018, Irie\_2019, Wang\_2019]. Without loss of generality, emerging approaches follow scaling Transformer by stacking more and more layers [Bapna\_2018, gpipe19], widening the governing dimensions of the network (i.e. model dimension, hidden dimension or number of attention heads) [devlin2018bert, raffel2019exploring] and more recently learning the wiring structure with architecture search [so2019evolved] 121212Since the approaches utilizing architecture search are compute intensive, they are not considered within the scope of this work.. For massively multilingual machine translation, [gpipe19] demonstrated the best practices of scaling using GPipe pipeline parallelism; in which a 128 layer Transformer model with 6 billion parameters is shown to be effective at improving high-resource languages while exhibiting the highest positive transfer towards low-resource languages. Although very promising, and satisfying our desiderata for universal translation, dense scaling of Transformer architecture has practical limitations which we referred in Section [1](#S1 "1 Introduction ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") under training efficiency.
We aim for practical training time and seek for architectures that warrant training efficiency. Our strategy has three pillars; increase the depth of the network by stacking more layers similar to GPipe [gpipe19], increase the width of the network by introducing multiple replicas of the feed-forward networks (experts) as described in Section [2.2](#S2.SS2 "2.2 Position-wise Mixture-of-Experts Layer ‣ 2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") and make use of learned routing modules to (sparsely) assign tokens to experts as described in Section [2.1](#S2.SS1 "2.1 Sparse scaling of the Transformer architecture ‣ 2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). With this three constituents, we obtain an easy to scale, efficient to train and highly expressive architecture, which we call Sparsely-Gated Mixture-of-Experts Transformer or MoE Transformer in short.
##### Model Details
To detail the model specifics, each expert is designed to have the same shape of a regular Transformer feed-forward network, and experts (MoE layers) are distributed once in every other Transformer layer. We tied the number of devices used for training to the number of experts per MoE layer for simplicity, although this is not a requirement. During training, we use float32 for both model weights and activations in order to ensure training stability. We ran additional scalability experiments with MoE(2048E, 60L) with bfloat16 [bfloat16] activations with total of 1 trillion model weights. Although trainable by careful and manual diagnostics, with deep 1 trillion model we encountered several trainability issues with numerical stability, hence did not include the results for the sake of reproducibility. For more model and training details, please see Appendix [A.2](#A1.SS2 "A.2 Machine Translation Experiments Details ‣ Appendix A Appendix ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding").

| | | | | | | | | |
| --- | --- | --- | --- | --- | --- | --- | --- | --- |
| Id | Model |
| |
| --- |
| BLEU |
| avg. |
|
| |
| --- |
| ΔBLEU |
| avg. |
| Weights |
| (1) | MoE(2048E, 36L) | 44.3 | 13.5 | 600B |
| (2) | MoE(2048E, 12L) | 41.3 | 10.5 | 200B |
| (3) | MoE(512E, 36L) | 43.7 | 12.9 | 150B |
| (4) | MoE(512E, 12L) | 40.0 | 9.2 | 50B |
| (5) | MoE(128E, 36L) | 39.0 | 8.2 | 37B |
| (6) | MoE(128E, 12L) | 36.7 | 5.9 | 12.5B |
| \* | T(96L) | 36.9 | 6.1 | 2.3B |
| \* | Baselines | 30.8 | - | 100×0.4B |
Figure 6: Translation quality comparison of multilingual MoE Transformer models trained with GShard and monolingual baselines. Positions along the x-axis represent languages, raging from high- to low-resource. ΔBLEU represents the quality gain of a single multilingual model compared to a monolingual Transformer model trained and tuned for a specific language. MoE Transformer models trained with GShard are reported with solid trend-lines. Dashed trend-line represents a single 96 layer multilingual Transformer model T(96L) trained with GPipe on same dataset. Each trend-line is smoothed by a sliding window of 10 for clarity. (Best seen in color)
###
4.4 Results
Before going into the details of training efficiency, we first investigate the effect of various design choices on building MoE Transformer. In order to prune the search space, we explored varying two variables, number of layers in the Transformer encoder-decoder stack (L) and the total number of experts used for every other MoE layer (E). For depth, we tested three different options, 12 (original Transformer depth, which consists of 6 encoder and 6 decoder layers), 36 and 60 layers. For the number of experts that replaces every other feed-forward layer, we also tested three options, namely 128, 512 and 2048 experts. Note that, the number of devices used for training, is fixed to be equal to the number of experts per-layer, using 128, 512 and 2048 cores respectively independent of the depth being experimented. Please also see the detailed description in Table [1](#S4.T1 "Table 1 ‣ 4.4 Results ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") for model configurations.
For each experiment (rows of the Table [1](#S4.T1 "Table 1 ‣ 4.4 Results ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")), we trained the corresponding MoE Transformer model until it has seen 1 trillion (1012) tokens. The model checkpoint at this point is used in the model evaluation. We did not observe any over-fitting patterns by this point in any experiment. Instead, we observed that the training loss continued to improve if we kept training longer. We evaluated BLEU scores that the models achieved for all language pairs on a held-out test set. Figure [6](#S4.F6 "Figure 6 ‣ Model Details ‣ 4.3 Sparsely-Gated MoE Transformer: Model and Training ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") reports all our results.
Here we share a qualitative analysis for each experiment and discuss the implication of each setup on high- and low-resource languages in order to track our progress towards universal translation. To ground the forthcoming analysis, it is worth restating the expected behavior of the underlying quality gains. In order to improve the quality for both high- and low-resource languages simultaneously within a single model, scaled models must mitigate capacity bottleneck issue by allocating enough capacity to high-resource tasks, while amplifying the positive transfer towards low-resource tasks by facilitating sufficient parameter sharing. We loosely relate the expected learning dynamics of such systems with the long-standing memorization and generalization dilemma, which is recently studied along the lines of width vs depth scaling efforts [Cheng\_2016]. Not only do we expect our models to generalize better to the held-out test sets, we also expect them to exhibit high transfer capability across languages as another manifestation of generalization performance [lampinen2018analytic].
| Id | Model |
| |
| --- |
| Experts |
| Per-layer |
|
| |
| --- |
| Experts |
| total |
|
| |
| --- |
| TPU v3 |
| Cores |
|
| |
| --- |
| Enc+Dec |
| layers |
| Weights |
| (1) | MoE(2048E, 36L) | 2048 | 36684 | 2048 | 36 | 600B |
| (2) | MoE(2048E, 12L) | 2048 | 12228 | 2048 | 12 | 200B |
| (3) | MoE(512E, 36L) | 512 | 9216 | 512 | 36 | 150B |
| (4) | MoE(512E, 12L) | 512 | 3072 | 512 | 12 | 50B |
| (5) | MoE(128E, 36L) | 128 | 2304 | 128 | 36 | 37B |
| (6) | MoE(128E, 12L) | 128 | 768 | 128 | 12 | 12.5B |
| \* | MoE(2048E, 60L) | 2048 | 61440 | 2048 | 60 | 1T |
Table 1: MoE Transformer model family. To achieve desired capacity we i) increased the depth by stacking more layers, ii) increased the width of the network by scaling the number of experts per MoE layer along with number of cores used for training.
##### Deeper Models Bring Consistent Quality Gains Across the Board
We first investigate the relationship between the model depth and the model quality for both high- and low-resource languages. Three different experiments are conducted in order to test the generalization performance, while keeping the number of experts per-layer fixed. With an increasing number of per-layer experts for each experiment (128, 512 and 2048), we tripled the depth of the network for each expert size, from 12 to 36. This resulted in three groups where experts per-layer fixed but three times the depth within each group:
For each configuration shown in Fig. [6](#S4.F6 "Figure 6 ‣ Model Details ‣ 4.3 Sparsely-Gated MoE Transformer: Model and Training ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"), we observed that increasing the depth (L) while keeping the experts per-layer (E) fixed, brings consistent gains for both low and high resourced languages (upwards Δ shift along the y-axis), almost with a constant additive factor every time we scale the depth from 12L to 36L (2-to-3 BLEU points on average as shown in the last column of Table [3](#S4.T3 "Table 3 ‣ Largest model (600B) can be trained under 4 days achieving the best quality ‣ 4.5 Training Efficiency ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")).
##### Relaxing the Capacity Bottleneck Grants Pronounced Quality Gains
Earlier in Section [4.1](#S4.SS1 "4.1 Multilingual translation ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") we highlighted the influence of the capacity bottleneck on task interference, resulting in degraded quality especially for high resourced languages. Later we alleviated this complication by increasing the number of experts per-layer, which in return resulted in a dramatic increase in the number of parameters (weight) of the models studied. Here we investigate whether this so called capacity bottleneck is distinctly observable and explore the impact on model quality and efficiency once it is relaxed. To that end, we first consider three models with identical depths (12L), with increasing number of experts per-layer: 128, 512 and 2048. As we increase the number of experts per-layer from 128 to 512 by a factor of four, we notice a large jump in model quality, +3.3 average BLEU score across 100 languages. However again by four folds scaling of the number of experts per-layer, from 512 to 2048, yields only +1.3 average BLEU scores. Despite the significant quality improvement, this drop in gains hints the emergence of diminishing returns.
Speculatively, the capacity bottleneck is expected to be residing between 128 to 512 experts, for the particular parametrization, number of languages and the amount of training data used in our experimental setup. Once the bottleneck is relaxed, models enjoy successive scaling of the depth, which can be seen by comparing 12 versus 36 layer models both with 128 experts. Interestingly increasing the depth does not help as much if the capacity bottleneck is not relaxed.
##### Having More Experts Improve Quality Especially for High-Resourced Tasks
Another dimension that could shed light on the quality gains of scaling in multi-task models is the contrast between high and low resource language improvements. As mentioned before, low resourced languages benefit from transfer while high resource languages seek for added capacity. Next we examine the effect of increasing the experts per-layer while fixing the depth.
As can be seen in Figure [6](#S4.F6 "Figure 6 ‣ Model Details ‣ 4.3 Sparsely-Gated MoE Transformer: Model and Training ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"), for 12 layer models increase in the expert number yields larger gains for high resourced languages as opposed to earlier revealed diminishing returns for low-resourced languages. A similar pattern is observed also for 36 layer models. While adding more experts relaxes the capacity bottleneck, at the same time it reduces the amount of transfer due to a reduction of the shared sub-networks.
##### Deep-Dense Models are Better at Positive Transfer towards Low-Resource Tasks
Lastly we look into the impact of the depth on low-resourced tasks as a loose corollary to our previous experiment. In order to do so, we include a dense model with 96 layers T(96L) trained with GPipe on the same data into our analysis. We compare T(96L) with the shallow MoE(128E, 12L) model. While the gap between the two models measured to be almost constant for the majority of the high-to-mid resourced languages, the gap grows in favor of the dense-deep T(96L) model as we get into the low-resourced regime. Following our previous statement, as the proportion of the shared sub-networks across tasks increase, which is 100% for dense T(96L), the bandwidth for transfer gets maximized and results in a comparably better quality against its shallow counterpart. Also notice that, the same transfer quality to the low-resourced languages can be achieved with MoE(36E, 128L) which contains 37 billion parameters.
We conjecture that, increasing the depth might potentially increase the extent of transfer to low-resource tasks hence generalize better along that axis. But we also want to highlight that the models in comparison have a disproportionate training resource requirements. We again want to promote the importance of training efficiency, which is the very topic we studied next.
###
4.5 Training Efficiency
In this section we focus on the training efficiency of MoE Transformer models. So far, we have seen empirical evidence how scaling the models along various axes bring dramatic quality gains, and studied the factors affecting the extent of the improvements. In order to measure the training efficiency, we first keep track of the number of tokens being processed to reach a certain training loss and second we keep track of the wall-clock time for a model to process certain number of tokens.
Note that, we focus on the training time and training loss131313Training loss reported in this section corresponds to cross-entropy loss and excludes the auxiliary loss term introduced in Section [2.2](#S2.SS2 "2.2 Position-wise Mixture-of-Experts Layer ‣ 2 Model ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") while varying other factors, as opposed to test error, which we analyzed in the previous section.
##### Deeper models are more sample efficient, converge faster with fewer examples
It has been shown that, deeper models are better at sample efficiency, reaching better training/test error given the same amount of training examples [gpipe19, shoeybi2019megatron], commonly attributed to the acceleration effect of over-parametrization [arora2018optimization]. We empirically test the hypothesis again using GShard with MoE Transformers and share trade-offs for models that are not only deep, but also sparsely activated.
For this purpose, we compare number of tokens being processed by each model to reach a preset training loss. A general trend we observe from Table [2](#S4.T2 "Table 2 ‣ Deeper models are more sample efficient, converge faster with fewer examples ‣ 4.5 Training Efficiency ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") is that, MoE Transformer models with 3 times the depth need 2 to 3 times fewer tokens to reach the preset training loss thresholds. For example MoE(128E, 12L) takes 3 times the number of tokens to reach 0.7 training cross-entropy compared to MoE(128E, 36L), (6) vs (5). We observe a similar trend for models with 512 and 2048 experts, (4) vs (3) and (2) vs (1).
| Id | Model | Cores |
| |
| --- |
| Billion tokens to |
| cross-entropy of |
|
| 0.7 | 0.6 | 0.5 |
| (1) | MoE(2048E, 36L) | 2048 | 82 | 175 | 542 |
| (2) | MoE(2048E, 12L) | 2048 | 176 | 484 | 1780 |
| (3) | MoE(512E, 36L) | 512 | 66 | 170 | 567 |
| (4) | MoE(512E, 12L) | 512 | 141 | 486 | - |
| (5) | MoE(128E, 36L) | 128 | 321 | 1074 | - |
| (6) | MoE(128E, 12L) | 128 | 995 | - | - |
Table 2: The number of tokens have been seen by a model during training to reach three different cross-entropy loss. A general trend is that deeper models are more sample efficient and converge faster than the comparable shallow ones.
Another intriguing observation from Table [2](#S4.T2 "Table 2 ‣ Deeper models are more sample efficient, converge faster with fewer examples ‣ 4.5 Training Efficiency ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"), is again related to the presence of capacity bottleneck. Comparing the models with same depth, (5), (3) and (1), we notice a significant drop in the number of tokens required to reach training loss of 0.7, as we transition from 128 to 512 number of experts. Practically that is where we observed the capacity bottleneck was residing, aligning with the hypothesis in Section [4.4](#S4.SS4.SSS0.Px2 "Relaxing the Capacity Bottleneck Grants Pronounced Quality Gains ‣ 4.4 Results ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). After this phase shift, models with ample capacity tend to exhibit similar sample efficiency characteristics, as in models (3) and (1).
##### Largest model (600B) can be trained under 4 days achieving the best quality
Next we delve deeper into the interaction between model size and wall-clock time spent for training. We monitor number of TPU cores being used, training steps per-second, total number of tokens per batch, TPU core years141414TPU core years is simply measured by the product of number of cores and wall-clock time in years., and actual wall-clock time spent in days for training (see Table [3](#S4.T3 "Table 3 ‣ Largest model (600B) can be trained under 4 days achieving the best quality ‣ 4.5 Training Efficiency ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") columns respectively).
We start with investigating one of the largest models we trained, MoE(2048E, 36L) with 600 billion parameters, model with id (1). Having utilized 2048 TPU cores for 4 days, this model achieves the best translation quality in terms of average BLEU, but also takes a total of 22.4 TPU years to train. While we have not seen any signs that the quality improvements plateau as we scale up our models, we strive for finding cost-effective solutions for scaling.
Results in Table [3](#S4.T3 "Table 3 ‣ Largest model (600B) can be trained under 4 days achieving the best quality ‣ 4.5 Training Efficiency ‣ 4 Massively Multilingual, Massive Machine Translation (M4) ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") again validates scaling with conditional computation is way more practical compared to dense scaling. Given the same number of TPU cores used by (1), the dense scaling variant, T(96L), appears to be taking more than ten times to train (235 TPU core years), while trailing behind in terms of model quality compared to models trained with GShard.
| Id | Model | Cores |
| |
| --- |
| Steps |
| per sec. |
|
| |
| --- |
| Batch sz. |
| (Tokens) |
|
| |
| --- |
| TPU core |
| years |
|
| |
| --- |
| Training |
| time (days) |
|
| |
| --- |
| BLEU |
| avg. |
|
| (1) | MoE(2048E, 36L) | 2048 | 0.72 | 4M | 22.4 | 4.0 | 44.3 |
| (2) | MoE(2048E, 12L) | 2048 | 2.15 | 4M | 7.5 | 1.4 | 41.3 |
| (3) | MoE(512E, 36L) | 512 | 1.05 | 1M | 15.5 | 11.0 | 43.7 |
| (4) | MoE(512E, 12L) | 512 | 3.28 | 1M | 4.9 | 3.5 | 40.0 |
| (5) | MoE(128E, 36L) | 128 | 0.67 | 1M | 6.1 | 17.3 | 39.0 |
| (6) | MoE(128E, 12L) | 128 | 2.16 | 1M | 1.9 | 5.4 | 36.7 |
| \* | T(96L) | 2048 | - | 4M | ∼235.5 | ∼42 | 36.9 |
Table 3: Performance of MoE models with different number of experts and layers.
In this section, we benchmarked GShard with MoE Transformers applications to multilingual machine translation (in particular to M4). We identified variables that are affecting the end result, such as capacity bottleneck, positive transfer and training efficiency, and provided experimental results in order to reveal the interplay between them. Next we will delve deep into performance related topics of GShard, such as memory and runtime efficiency and communication benchmarks.
5 Performance and Memory Consumption
-------------------------------------
This section discusses how well GShard achieves computation and memory efficiency on the TPU platform. Our measurement and analysis show that the device memory consumption is roughly constant when we increase the number of devices and experts, and the step time grows sublinearly, i.e., 1.7x execution time increase when we scale the model by 16x from 128 devices to 2048 devices. We also provide microbenchmarks and analyses for a variety of partitioned operators, which could guide use cases beyond this paper.
###
5.1 Memory Efficiency and Scalability
In the GShard model, there are mainly three types of memory usage, all of which have constant per-device sizes after SPMD partitioning, when the number of experts increases.
* Replicated weights (e.g. transformer feed-forward layers).
* Distributed weights (MoE feed-forward layers151515Gate projection weights are O(E) in size and could be partitioned, but in practice they are small enough to be replicated and only have negligible effect on peak memory usage.).
* Activations (output of each layer that is used in both forward and backward pass).
The O(1) memory scaling is demonstrated in Figure [7](#S5.F7 "Figure 7 ‣ 5.1 Memory Efficiency and Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"), which shows the per-device memory usage distribution for different models. With a fixed number of layers, both weight memory and activation memory stay constant when the number of experts increases.
On this other hand, weight memory and activation memory both scale linearly with the number of layers. When the memory requirement exceeds available memory on each device, compiler-based rematerialization will automatically recompute part of the activations in the backward pass in order to reduce peak activation memory. This is why the activation size for MoE(2048E, 60L) is smaller than MoE(2048E, 36L). The overhead of rematerialization is also optimized, e.g. only 28% and 34% of the total cycles are spent on recomputation for 36L and 60L models respectively, and 0% for 12L and 24L since they fit in device memory without rematerialization.

Figure 7: Per-device memory consumption in gigabytes.
###
5.2 Runtime Efficiency and Scalability

Figure 8: Measured vs roofline execution time breakdown. Only the forward pass is shown, and the backward pass has similar breakdown. “MoE dispatch and combine” represents cross-partition communication with AllToAll.
Figure [8](#S5.F8 "Figure 8 ‣ 5.2 Runtime Efficiency and Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") shows the breakdown of execution time for an MoE layer and its adjacent Transformer layer. It also compares the achieved performance to a roofline, which is estimated by assuming compute-, memory-, or communication-bounded operations can achieve 100% of the peak FLOPS, memory bandwidth, or interconnect bandwidth. This is a very optimistic estimate as many operators are bounded by a mixed set of resources. At a smaller scale (128 experts), our model can achieve > 70% of the roofline performance. The device time increases by 1.7x when we scale the model to 16x larger (2048 experts), and can still achieve 48% of the roofline performance.
Before analyzing performance scalability, we recall the size scaling of relevant tensor dimensions as discussed in Section [3.1](#S3.SS1 "3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). With D devices, the number of experts E and the group count G are both set to O(D). The fractional per-group expert capacity C is set to O(1/D). This setup cannot scale indefinitely, since C needs to be at least 1, but it is good enough to scale to thousands of experts.
##### Transformer layers and MoE feed-forward layer
These are the dense parts of the model, which are designed to achieve peak TPU utilization. On each device, these computations also have a constant cost when we scale to more experts. Feed-forward layers and Transformer projections are mainly large matrix multiplications that utilize the TPU’s matrix unit well. These operations have achieved > 85% peak FLOPS in our experiment. The attention operations are composed of mainly batch matmuls, which are bounded by memory bandwidth when sequence lengths are small. As a result, in our experiments attention operations only achieved > 30% peak FLOPS.
##### Gate computation
In Figure [8](#S5.F8 "Figure 8 ‣ 5.2 Runtime Efficiency and Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"), “Gate Einsum” represents the first two and the last Einsums in Algorithm [2](#alg2 "Algorithm 2 ‣ 3.1 Positions-wise Mixture-of-Expert Layer Expressed in Linear Algebra ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). The first Einsum is the projection that calculates per-expert input to softmax. It has an O(D) cost, but it is a very small part of the layer. The other two Einsums are dispatching tokens and combining expert results. They effectively implement Gather with one-hot matrices, which are more expensive, but with constant O(GC)=O(1) cost that is independent from the number of experts. The execution time of these Einsums increases by around 2x when we scale from 128 to 2048 experts (16x).
The remaining per-device gating computation involves many general-purpose computations like ArgMax and Cumsum, which are either memory-bound or even sequential in nature, thus not designed to utilize TPUs well. The majority of the time is spent on sequential Cumsum operations to invert one-hot matrices that represent selected experts for each token to one-hot matrices that represent selected tokens for each expert. The linear complexity of Cumsum is demonstrated in Figure [8](#S5.F8 "Figure 8 ‣ 5.2 Runtime Efficiency and Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). This part of the gating computation also has an O(D) cost, but fortunately, similar to the Einsum before softmax, it has a very small constant factor. It has negligible execution time with 128 experts, and takes less than 10% of the total time spent in the MoE and Transformer layers with 2048 experts.
The most significant part of gating is communication, shown as “MoE dispatch and combine” in Figure [8](#S5.F8 "Figure 8 ‣ 5.2 Runtime Efficiency and Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). These are AllToAll operators, and as we will discuss in Section [5.3](#S5.SS3 "5.3 Communication Microbenchmarks and Per-Operator Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"), their cost is O(√D). When the number experts grows 16x from 128 to 2048, the execution time increases by about 3.75x, and their proportion of execution time in the MoE and Transformer increases from 16% to 36%.
###
5.3 Communication Microbenchmarks and Per-Operator Scalability
In this section, we measure and analyze the performance scalability of the SPMD partitioner for basic operators, which can be used to guide use cases beyond the MoE model presented in this paper.
##### Performance scaling of communication primitives
Two critical collective communication operators in the MoE model are AllReduce and AllToAll. AllReduce is used in accumulating partial results, and AllToAll is used in resharding (Section [3.3.2](#S3.SS3.SSS2 "3.3.2 Per-Operator SPMD Partitioning ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")). Figure [9](#S5.F9 "Figure 9 ‣ Performance scaling of communication primitives ‣ 5.3 Communication Microbenchmarks and Per-Operator Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") shows their performance scalability from 16 to 2048 partitions. AllReduce on TPU has an execution time independent from the number of devices. The variance in Figure [9](#S5.F9 "Figure 9 ‣ Performance scaling of communication primitives ‣ 5.3 Communication Microbenchmarks and Per-Operator Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") is due to specifics of each topology, e.g., whether it is a square or a rectangle, and whether it is a torus or a mesh.
AllToAll, on the other hand, gets more expensive as the number of partitions grows, but in a sublinear manner. On our 2D TPU cluster, AllToAll cost is roughly O(√D), where D is the number of partitions. This is because with a fixed amount of data each partition sends (8MB or 32MB in Figure [9](#S5.F9 "Figure 9 ‣ Performance scaling of communication primitives ‣ 5.3 Communication Microbenchmarks and Per-Operator Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")), the total amount of data that all partitions send is d=O(D). Meanwhile, each data piece needs to travel h=O(√D) hops on average, and there are overall l=O(D) device-to-device links in the network. Therefore, if it is bandwidth-bound, the execution time of an AllToAll is
| | | |
| --- | --- | --- |
| | t=dhl=O(D√DD)=O(√D). | |
Even if it is latency-bound, the execution time will still be O(h)=O(√D).
Comparing 2048 partitions and 16 partitions, while D grows by 128 times, the execution time of AllToAll only increases by 9 times. This enables us to use resharding to efficiently implement cross-partition dispatching (Figure [(a)a](#S3.F4.sf1 "(a) ‣ Figure 4 ‣ Einsum Case Study ‣ 3.3.2 Per-Operator SPMD Partitioning ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")).
AllGather and CollectivePermute are easier to analyze.
AllGather’s output is D larger than the input, and if we fix input size, then its communication cost is O(D). CollectivePermute has a one-to-one communication pattern, and with reasonable device arrangement where the source-destination pairs are close, its cost is O(1) for a fixed input size.

Figure 9: Performance scaling of communication, AllReduce and AllToAll. Log scale on both axes. AllReduce cost is roughly O(1), and AllToAll cost is roughly O(√D), where D is the number of partitions. We measure their performance with 8MB and 32MB data. For AllToAll, that means each partition initially has 8MB (or 32MB) data, then divides it to D pieces, and sends each piece to a different receiving partition.
| | O(D) | Total | Per-partition |
| --- | --- | --- | --- |
| | Dimensions | Compute | Compute | Communication |
| Add(A,A->A) | A | O(D) | O(1) | 0 |
| Matmul(AB,BC->AC) | B | O(D) | O(1) | O(1) AR |
| Matmul(AB,BC->AC) | A | O(D) | O(1) | 0 |
| Matmul(AB,BC->AC) | A,B | O(D2) | O(D) | O(D) AG or CP |
| Matmul(AB,BC->AC) | A,C | O(D2) | O(D) | O(D) AG or CP |
| Reduce(AB->A) | A | O(D) | O(1) | 0 |
| Reduce(AB->B) | A | O(D) | O(1) | O(1) AR |
| Einsum(GSEC,GSM->EGCM) | G,E \* | O(D) | O(1) | O(√D) AA |
| Convolution(BIXY,xyIO->BOXY) | X \*\* | O(D) | O(1) | O(1) CP |
Table 4: Scalability of partitioned operators. Abbreviation for communication primitives: AR: AllReduce, AG: AllGather, CP: CollectivePermute, AA: AllToAll. \*This is the dispatch Einsum in our model, where we set C to O(1/D). \*\*I/O are the input/output feature dimensions, B is the batch dimension, X/Y are input spatial dimensions, and x/y are the kernal spatial dimensions.
##### Partitioned operator scalability
We summarize the performance scalability for common operators using GShard in Table [4](#S5.T4 "Table 4 ‣ Performance scaling of communication primitives ‣ 5.3 Communication Microbenchmarks and Per-Operator Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"). It contains the Einsum/Matmul examples in Section [3.3.2](#S3.SS3.SSS2 "3.3.2 Per-Operator SPMD Partitioning ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding"), and also other common operators like Convolution and Reduce. The table includes the local compute on each partition, as well as the required communication based on our analysis above.
Most operators in Table [4](#S5.T4 "Table 4 ‣ Performance scaling of communication primitives ‣ 5.3 Communication Microbenchmarks and Per-Operator Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") have sublinear scalability in terms of both compute and communication, which is consistent with our performance measurement of the MoE model. The O(1) scaling of spatially partitioned convolutions also demonstrates the efficiency of GShard for image partitioning (Appendix [A.4](#A1.SS4 "A.4 SPMD Partitioning for Convolution and Window-Based Operators ‣ Appendix A Appendix ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")).
However, the last two Matmul operators in Table [4](#S5.T4 "Table 4 ‣ Performance scaling of communication primitives ‣ 5.3 Communication Microbenchmarks and Per-Operator Scalability ‣ 5 Performance and Memory Consumption ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding") have O(D) scaling of per-partition compute and communication, where they have unmatched sharding in the operands. This is not due to inefficiency in the partitioning algorithm, but because the total compute in the full operator is very large (O(D2)). Different partitioning strategies can be used for these cases, producing different communication primitives: replicating one operand will result in AllGather (requiring the replicated operand to fit in device memory), while slicing in a loop (Figure [(c)c](#S3.F4.sf3 "(c) ‣ Figure 4 ‣ Einsum Case Study ‣ 3.3.2 Per-Operator SPMD Partitioning ‣ 3.3 The XLA SPMD Partitioner for GShard ‣ 3 Highly Parallel Implementation using GShard ‣ GShard: Scaling Giant Models with Conditional Computation and Automatic Sharding")) will result in CollectivePermute.
6 Related Work
---------------
Neural networks Deep learning models have been very successful in advancing sub-fields
of artificial intelligence. For years, the fields have been continuously reporting new state of
the art results using varieties of model architectures for computer vision tasks [krizhevsky2012imagenet, szegedy2015going, he2016deep],
for natural language understanding tasks [sutskever2014sequence, bahdanau2014neural, wu2016google],
for speech recognition and synthesis tasks [hinton2012deep, chan2016listen, chiu2018state, oord2016wavenet, shen2018natural].
More recently, attention-based Transformer models further advanced state of the art of these fields [vaswani2017attention, devlin2018bert].
Model scaling Both academic research and industry applications observed that larger neural networks tend to perform better on large enough datasets and for complex tasks. Within a single model family, simply making the network wider or deeper often improves the model quality empirically. E.g., deeper ResNets performed better [he2016identity], bigger Transformer models achieved better translation quality [vaswani2017attention], models with larger vocabulary, or embedding or feature crosses work better, too [arivazhagan2019massively, conneau2019unsupervised]. Across different model families, it has also been observed that bigger models with larger model capacities not only fit the training data better but also generalize better on test time [45820, neyshabur2017exploring, gpipe19].
This observation motivated many research efforts to build much bigger neural networks than those typically used in deep learning research models or production models. Shazeer et al. showed that a recurrent language model with 69 billion parameters using mixture-of-expert layers achieved much lower test perplexity for the one billion words (LM1B) benchmark [shazeer2017outrageously]. Brown et al. showed that a non-sparse 175 billion parameters model is capable of exhibiting highly accurate few-shot performance on several downstream NLP tasks.
Hardware Neural networks demand non-negligible amounts of computation power. To address such a demand, special hardware (chips and networked machines) built for neural network training and inference can be dated back to 25 years ago [ienne1996special]. Since late 2000s, researchers started to leverage GPUs to accelerate neural nets [raina2009large, krizhevsky2012imagenet, cirecsan2010deep]. More recently, the industry also invested heavily in building more dedicated hardware systems chasing for more cost-effective neural network hardware [jouppi2017datacenter]. Because the core computation of neural networks (various forms of summation of multiplications: convolution, matrix multiplication, einsum) are highly parallelizable numerical calculations, these chips are equipped with huge number of floating processing units (FPUs). Hence, the compute power of these specially designed hardware grew dramatically. It is reported that GPU price per flops dropped a factor of ten in just the last 4 years [gpu2019price] and flops per watts increased by 2 magnitude over the past 12 years [sun2019summarizing]. The widely available low-cost computation power is a major enabler for the success of neural networks.
Software Software systems supporting neural networks evolved together with the advancement of the underlying hardware [dean2012large, bastien2012theano, abadi2016tensorflow, paszke2017automatic]. While the accelerators are highly parallel compute machines, they are significantly more difficult to program directly. The frameworks made building neural networks easier and abstracted away many hardware specific details from the practitioners. They in turn rely on lower-level libraries to drive special hardware (accelerators) efficiently. E.g., CUDA [nickolls2008scalable] for Nvidia’s GPUs, or XLA for Google’s TPUs [xla]. These lower-level libraries are critical for achieving high efficiency using these special hardware.
Parallelism in model training and inference Modern neural networks make extensive use of a cluster of machines for training and inference, each of which equiped with several accelerators. Data parallelism
[krizhevsky2012imagenet] is the most commonly used approach and is supported by major frameworks (TensorFlow [abadi2016tensorflow], PyTorch [pytorch2017], JAX [jax2018github, frostig2018mlsys]), where devices run the same program with different input data and combine their local gradients before the weight updates. Model parallelism on the other hand, partitions computation beyond the input batch, which is needed to build very large models. For example, pipelining [gpipe19, harlap2018pipedream] splits a large model’s layers into multiple stages, while operator-level partitioning [shazeer2018mesh, jia2018beyond] splits individual operators into smaller parallel operators. GShard used a type of operator-level partitioning to scale our model to a large number of parallel experts.
Automated parallelism Because programming in a distributed heterogeneous environment is challenging, particularly for high-level practitioners, deep-learning frameworks attempt to alleviate the burden of their users from specifying how the distributed computation is done. For example, TensorFlow [abadi2016tensorflow] has support for data parallelism, and basic model parallelism with graph partitioning by per-node device assignment. Mesh TensorFlow [shazeer2018mesh] helps the user to build large models with SPMD-style per-operator partitioning, by rewriting the computation in a Python library on top of TensorFlow; in comparison, our approach partitions the graph in the compiler based on light-weight annotations without requiring the user to rewrite the model. FlexFlow [jia2018beyond] uses automated search to discover the optimal partition of operators in a graph for better performance; while it focuses on determining the partitioning policy, our SPMD partitioner focuses on the mechanisms to transform an annotated graph. Weight-update sharding [xu2020automatic] is another automatic parallelization transformation based on XLA, which mostly focuses on performance optimizations for TPU clusters, and conceptually can be viewed as a special case for GShard. Zero [rajbhandari2019zero] presents a set of optimizations to reduce memory redundancy in parallel training devices, by partitioning weights, activations, and optimizer state separately, and it is able to scale models to 170 billion parameters; in comparison, GShard is more general in the sense that it does not distinguish these tensors, and all of those specific partitioning techniques can be supported by simply annotating the corresponding tensors, allowing us to scale to over 1 trillion parameters and explore more design choices.
Conditional Computation and Machine Translation
Conditional computation [bengio2015conditional, shazeer2017outrageously, Elbayad2020DepthAdaptiveT, bapna2020controlling] premises that the examples should be routed within the network by activating an input dependent sub-network. The routing depends (or conditions) on certain criterion and without the loss of generality, can be any of the following: estimated difficulty of the example [lugosch2020surprisaltriggered], available computation budget [Elbayad2020DepthAdaptiveT, bapna2020controlling], or more generally a learned criterion with sparsity induced mixture of experts [shazeer2017outrageously]. We extend sparsely gated mixture of experts [shazeer2017outrageously] due to its flexibility and ease of scaling to state of the art neural sequence models, Transformers [vaswani2017attention], to satisfy training efficiency.
7 Conclusion
-------------
In this paper, we introduced GShard, a deep learning module that partitions computation at scale automatically. GShard operates with lightweight sharding annotations required in the user model code only and delivers an easy to use and flexible API for scaling giant neural networks. We applied GShard to scale up Transformer architecture with Sparsely-Gated Mixture-of-Experts layers (MoE Transformer) and demonstrated a 600B parameter multilingual neural machine translation model can efficiently be trained in 4 days achieving superior performance and quality compared to prior art when translating 100 languages to English with a single model. In addition to the far better translation quality, MoE Transformer models trained with GShard also excel at training efficiency, with a training cost of 22 TPU v3 core years compared to 29 TPU years used for training all 100 bilingual Transformer baseline models. Empirical results presented in this paper confirmed that scaling models by utilizing conditional computation not only improve the quality of real-world machine learning applications but also remained practical and sample efficient during training. Our proposed method presents a favorable scalability/cost trade-off and alleviates the need for model-specific frameworks or tools for scaling giant neural networks. Together, our results help to elucidate a realistic and practical way forward for neural network scaling to achieve better model quality.
We have learned several lessons from our study. Our results suggest that progressive scaling of neural networks yields consistent quality gains, validating that the quality improvements have not yet plateaued as we scale up our models. While the results in this paper consolidate that model scaling is a must in deep learning practitioners’ toolbox, we also urge practitioners to strive for training efficiency. To this end, we identified factors that affect the training efficiency and showed their implications on downstream task quality. We demonstrated how the neural networks built with conditional computation yield a favorable trade-off between scale and computational cost. In practice such critical design decisions allowed us to enjoy experimental cycles of not months or weeks, but only days to train models in the order of magnitude of trillion parameters.
Further, having a proper abstraction layer that separates model description from parallelization implementation, allows model developer to focus on network implementation, leaving GShard to partition the computation graphs automatically and generate programs that run on all devices in parallel.
We found that generating a single program that is general enough to express computation on all underlying parallel devices is the key to compile scalably. The traditional way of generating multiple dedicated programs for different partitions results in explosive compilation time when scaling to thousands of partitions. To address this complexity, we introduced various compiler renovations based on SPMD sharding that allows any tensor dimension to be partitioned. As a takeaway, we emphasize that model scaling and training efficiency should go hand-in-hand; and algorithmic improvements such as conditional computation when coupled with easy to use interfaces can effectively utilize large computational power.
Lastly, our experimental results empirically support that, mere parameter counting does not always correlate with the effective capacity of the models at scale [li2018measuring, maddox2020rethinking]. Comparison of the models should also account in the nature of the problem, i.e. massively multi-task setting with a heavy training data imbalance across tasks as in our case, and control the factors affecting different operation modes of the networks, i.e. capacity bottleneck vs positive transfer.
Acknowledgements
----------------
We would like to thank the Google Brain and Translate teams for their useful input and insightful discussions, entire XLA and Lingvo development teams for their foundational contributions to this
project. In particular
Youlong Cheng, Naveen Arivazhagan, Ankur Bapna, Ruoming Pang, Yonghui Wu, Yuan Cao, David Majnemer, James Molloy, Peter Hawkins, Blake Hechtman, Mark Heffernan, Dimitris Vardoulakis, Tamas Berghammer, Marco Cornero, Cong Liu, Tong Shen, Hongjun Choi, Jianwei Xie, Sneha Kudugunta, and Macduff Hughes. |
e462f357-e0ad-46c3-b8b6-3a11a5bf4b2e | trentmkelly/LessWrong-43k | LessWrong | Resource gathering agent
Here's an idea (inspired by "Less exploitable value-updating agent") of how to model an agent that does nothing but gather resources.
It's an agent which has a utility function u=Xv, for some utility function v. It doesn't know whether X=−1 or X=1 (maybe we used an approach like "Safe probability manipulation, superweapons, and stable self-improvement research" to guarantee ignorance), but it will find out tomorrow.
In the meantime, it will not seek to influence the value of v (as any action increasing v also decreases −v by the same amount), but will seek to gather as many resources to put itself in a position to act once it knows the value of X.
Now, this definition is somewhat dependent on the definition of v (eg: it would certainly want to be elected "president of the committee for setting the value of v" more than anything else), so a more thorough description might be some situation where the agent is completely ignorant about its future utility (but where the ignorance is symmetric; ie the probability of −v for any v is the same as for v). This could be a pure resource gathering agent.
Why could this be interesting? Well, I was wondering if we could take a generic agent and somehow "subtract off" a pure resource gathering agent from it. So it would pursue its goals, while also minimising its success were it such an agent.
The idea needs some developing, but there might be something there. |
871b927f-8340-4af1-bb9c-903d58d0a657 | trentmkelly/LessWrong-43k | LessWrong | Storing own covid saliva for use as a "booster"?
I am considering to freeze my saliva if/when I get omicron, in order to later inject the frozen covid+ saliva into my nose some 6-12 weeks from recovery in order to boost my immunity against covid for longer. What do you people see as ups and downs of this approach?
----------------------------------------
The main reason for this is that I presume here in Finland they may limit covid vaccine availability after third dose, as both here and for instance in UK some people in medical community have talked that vaccinations after booster should be limited for some reason. If there are further boosters available, those seem clearly preferable over infection.
Rationale is that since your body has recovered from covid, it should have learned how to combat covid with immune system. With reintroducing the same infection I would hope to at least reset the antibody count to slow waning of immunity. Otherwise I have understood antibody count will wane so that you get omicron again in 6-10 months.
I am not a doctor nor a biochemist. I have asked from 2 doctor friends of mine and they saw no large reasons against this, but one of them reminded me that I should not inject the contents but indeed put it in my nose.
----------------------------------------
My planned procedure is:
1. Wash hands
2. Write on ziploc/minigrip bag: BIOHAZARD, COVID+ SALIVA, <name> <date>
3. Collect saliva into a clean cup
4. Pour the saliva into the bag
5. Clean the bag from outside with a napkin
6. Wash hands
7. Put the bag inside another similar bag upside down
8. Wipe the second bag with a napkin
9. Wash hands
10. Put the second bag inside third bag again upside down compared to the previous bag
11. Wipe the third bag with a napkin
12. Put the bag collection into back of a regular freezer (-18 C)
My plan of disposal of the bags with or without use is to burn them in my fireplace. Alternative plan is to put it into regular trash after first keeping it in direct sunlight for |
eda623e3-c188-4afc-8f8b-76530e691aa3 | trentmkelly/LessWrong-43k | LessWrong | “Fanatical” Longtermists: Why is Pascal’s Wager wrong?
I’ve recently heard a number of people arguing for “fanaticism“ when it comes to longtermism. Basically, if a cause area has even a minuscule probability of positively affecting the long-term future of humanity (and thus influencing an effectively unbounded number of lives), we should fund/support that cause even at the expense of near-term projects with high probability of success. If this is so, I have trouble seeing why Pascal’s Wager (or the even less probable Pascal’s Mugging) shouldn’t hold. I know most people (even religious people) don’t believe Pascal’s argument is valid, but most arguments against it I’ve read would seem to also exclude low-probability longtermist causes from being valid. What am I missing here? |
17d08b6f-b6f7-4fc3-a445-27da74027683 | trentmkelly/LessWrong-43k | LessWrong | Lying is Cowardice, not Strategy
(Co-written by Connor Leahy and Gabe)
We have talked to a whole bunch of people about pauses and moratoriums. Members of the AI safety community, investors, business peers, politicians, and more.
Too many claimed to pursue the following approach:
1. It would be great if AGI progress stopped, but that is infeasible.
2. Therefore, I will advocate for what I think is feasible, even if it is not ideal.
3. The Overton window being what it is, if I claim a belief that is too extreme, or endorse an infeasible policy proposal, people will take me less seriously on the feasible stuff.
4. Given this, I will be tactical in what I say, even though I will avoid stating outright lies.
Consider if this applies to you, or people close to you.
If it does, let us be clear: hiding your beliefs, in ways that predictably leads people to believe false things, is lying. This is the case regardless of your intentions, and regardless of how it feels.
Not only is it morally wrong, it makes for a terrible strategy. As it stands, the AI Safety Community itself can not coordinate to state that we should stop AGI progress right now!
Not only can it not coordinate, the AI Safety Community is defecting, by making it more costly for people who do say it to say it.
We all feel like we are working on the most important things, and that we are being pragmatic realists.
But remember: If you feel stuck in the Overton window, it is because YOU ARE the Overton window.
—
1. The AI Safety Community is making our job harder
In a saner world, all AGI progress should have already stopped. If we don’t, there’s more than a 10% chance we all die.
Many people in the AI safety community believe this, but they have not stated it publicly. Worse, they have stated different beliefs more saliently, which misdirect everyone else about what should be done, and what the AI safety community believes.
To date, in our efforts to inform, motivate and coordinate with people: People in the AI Safety Community |
40c3f591-a731-4fe2-81ab-b01311e6d825 | StampyAI/alignment-research-dataset/lesswrong | LessWrong | If AGI were coming in a year, what should we do?
Suppose AGI was very likely to arrive first around a year from now, with multiple projects close, but one a few months ahead of the others, and suppose that the AI safety community agreed that this was the case. What should our community do?
How would you answer differently for AGI in 4 months from now? 2 years from now? 5 years from now? 10 years from now? 20 years from now?
Some potential subquestions:
1. What technical research should we try to get the project closest to AGI to rely on? How would we get them to use it? Or, if we could build AGI first, what would we do to reduce risks?
2. What infrastructure, defences or other technology should we try to have ready or use?
3. How should we reach out to governments, and what should we try to convince them to do?
4. What research should we work on?
5. What else?
My motivations for this question are to get people to generate options for very short timelines and to get an idea of our progress so far. |
1fce54e1-cce8-49db-834a-48bd2590a369 | StampyAI/alignment-research-dataset/lesswrong | LessWrong | Using Consensus Mechanisms as an approach to Alignment
> “Both the cryptoeconomics research community and the AI safety/new cyber-governance/existential risk community are trying to tackle what is fundamentally the same problem: how can we regulate a very complex and very smart system with unpredictable emergent properties using a very simple and dumb system whose properties once created are inflexible?”
>
> -Vitalik Buterin, founder of Ethereum
>
>
I think this was as true [in 2016](https://medium.com/@VitalikButerin/why-cryptoeconomics-and-x-risk-researchers-should-listen-to-each-other-more-a2db72b3e86b) as it still is today. And I think one approach to attacking the problem of alignment is not just by combining these two communities, but combining elements of each technology and understanding.
There are two different elements to the problem of Alignment. Getting an AI to do the things we want, and being able to come to terms on what we actually want. We’ve gotta align the AI to the humans, and we also gotta align the humans to the other humans (both present and future). My idea takes from my experience in how DAOs and other mechanisms try to solve large-scale coordination failures and a different kind of reward function.
Another element where combination could work is the ideas of Futarchy, as first imagined by [Robin Hanson](http://mason.gmu.edu/~rhanson/futarchy.html) (vote on values, bet on beliefs), and applying it to both consensus making and AI.
Policy/metric network
---------------------
Humans all over the world set goals or metrics that they want to achieve. This will be in the form of something like a global DAO, with verification using something like OpenAI’s WorldCoin. These are not infinite. They are not maximum utility forever goals. They have end dates. They have set definitions by humans. Example: reduce malaria by x%.
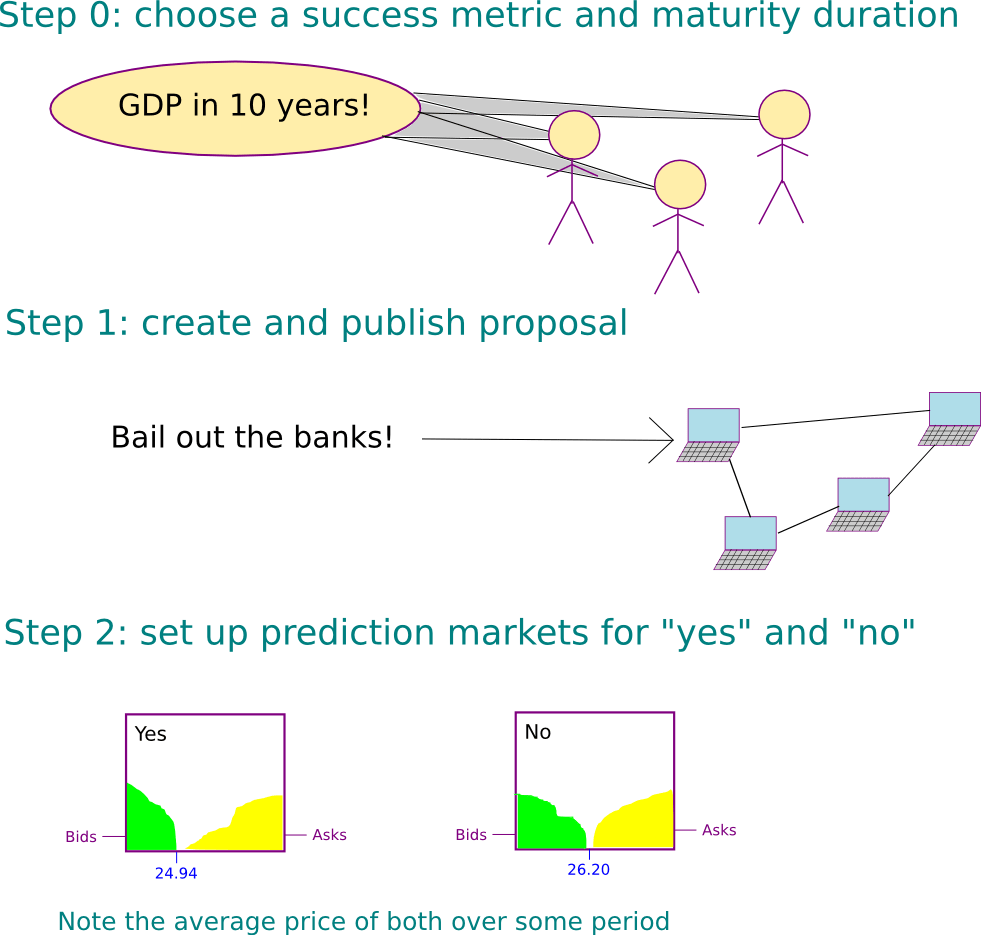[Source](https://blog.ethereum.org/2014/08/21/introduction-futarchy)
Prediction Network
------------------
We have humans make predictions about which implementations will result in the policy/metric succeeding. These predictions include **predicting that humans in the future, after the policy was implemented, will approve of its implementation**. These approvals will be set by the policy network after the implementation in various sequences (right after implementation, a year after, 10 years, 100 years, etc.) There is no end date for the approvals continuing. There is no point where it will be totally safe for deception, in other words. An AI will be trained on the data from this prediction network. The AI on this prediction network **never stops training**. It is always continuing its training run.
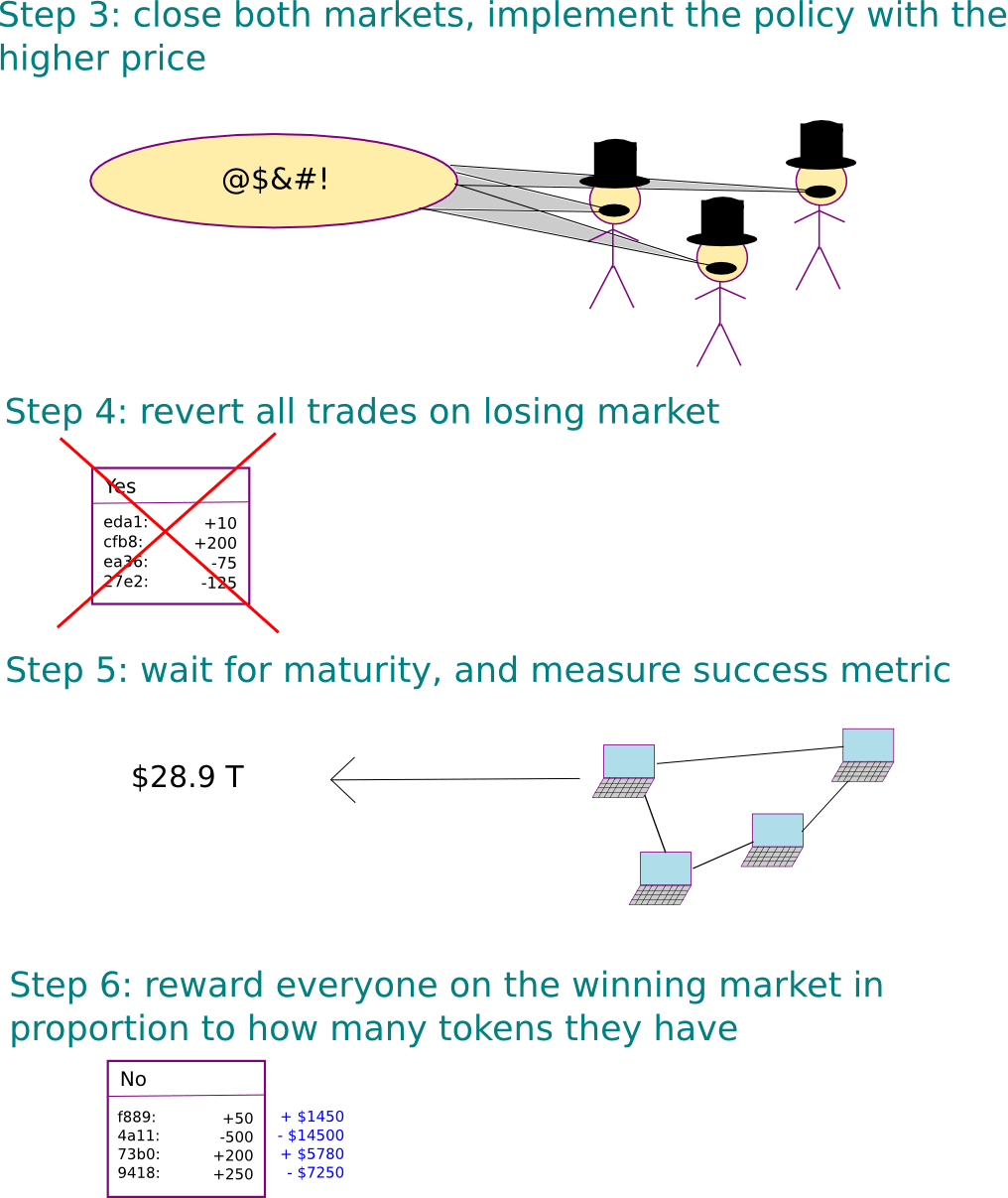[Source](https://blog.ethereum.org/2014/08/21/introduction-futarchy)
**The network generalizes to assume approvals in the future, and can measure the gaps between each process.**
The approvals start at very fast intervals, perhaps minutes, before getting further and further apart. The process never ends. There will always be approvals for the same policies in the future. Perhaps being trained on the network data from the past of the human prediction network could help with this generalization. This does run the risk of it just trying to imitate what a human prediction network would do, however.
**Why major AI Labs and the public might change as a result of this**
I think many major AI Labs (to a degree) are actually thinking about the longterm future, and the concerns that come with it, and want good outcomes. My approach keeps all humans in-the-loop on this consensus-building process, so that they are not also left out. I think starting work on this early is better than waiting for the problem to arise later. I do not expect a world where humans regret \*not\* working on this problem sooner.
**This is a work-in-progress**
I don’t see many trying to hit alignment from this angle, and I imagine a lot of this will be changed, or added to. But I think it could be a foundation to build a system that can handle an increasing amount of chaos from increases in intelligence. One stable equilibrium is all humans dying, and it seems the least complex return to stasis. But this implementation could be the groundwork for building another equilibrium.
**Why I chose this**
This is an extremely neglected problem. Part of my concern is aligning humans with AI, but I am also concerned with aligning humans so that humans do not double-cross or resort to violence against each other for power-seeking. Another concern I have, with the first two concerns are solved, is locking us into a future we'll actually end up regretting. My endeavor with this is to make progress on aligning AIs with longterm human interests, reduce the threat of violence between humans, and give humans more freedom post-ASI to have control over their own future.
**Potential Short-Term Testing**
Starting out would probably involve first figuring out the game theory, architecture, and design of the process better. Then it might involve creating a test network, with various people participating in the Policy/Metric Network, and others in the Prediction Network, and training an AI on this data. The prediction network would use fake money, without the tokens being tradable, for legal reasons. The AI would obviously not be a superintelligence, or anything close, but it might give us some insights of how this might obviously fail.
The initial architecture would be using some form of a DAO structure for the Policy/Metric network, with a prediction market for the other network. The AI would probably be built using Pytorch. It would be optimized to reduce inaccuracy of how human's will rate policies in the future.
**Limitations to current testing**
We don't have an AI with longterm planning skills. Most AIs currently seem very myopics, without much foresight. The AI would also not be "grounded" with a real-world model, so it's modeling of future events would not be very good. The main goal of this is to start to build on how an architecture for this might look in the future, not a solution that can be implemented now.
**Next steps**
I will start off by developing my own insights and design better, getting feedback from those who have a good knowledge base for this sort of approach. After that, I might bring someone on part-time to work with me on this.
**Would this address RSI?**
I’m not sure. I think this sort of system building would favor slower takeoffs. It’s about creating a new system that can handle the continued escalation of option space (power) and maintain some stability. A lot of this isn’t worked out yet. It could be all hold a ‘piece’ of the large system, but the piece is useless on its own. Or if agents do get out into the wild, it could be some form of aggregating agents, so that the accumulation of the agents is always stronger than any smaller group of them. It’s also possible a major policy from the network could be to detect or prevent RSIs from emerging.
**Wouldn’t this lead to wireheading?**
I don’t really think wireheading is likely in most scenarios. I might give this a 5% chance of wireheading or some form of reward hacking. I’d probably place a higher chance that there could be a gradual decay of our own ability to assess approval.
**What about proxy goals?**
Proxy goals are easily the biggest concern here. But it’s being optimized to reduce inaccuracy, and all proxy goals would still need to fulfill that. Things don’t really ever move out of distribution. I think, if takeoffs are faster, the proxy goals become a much greater threat. A slower increase in intelligence I think has a better chance of aligning the proxy goals to our interests. And it is continuously being updated on its weights, based on input from approval policies, which could allow for a sort of ‘correcting’ mechanism if the proxies start to stray too far.
Think of the image above of the sun veering through the galaxy, with the planets orbiting around it. The sun is the optimization process, and the planets are the proxies. The planets sometimes veer away from the sun, but gravity keeps them coming back, so that they never veer too far away from it. Closer orbits are obviously safer than more distant orbits (it’d be better if the proxies were like Earth/Mars/Mercury/Venus distant instead of Neptune/Uranus distant). Since approvals will be between short timeframes at the beginning, and there will always be new policies to approve, this might keep the proxies in close-enough orbit not to do anything that would cause significant harm. And overtime, the proxies should change and become more and more closely tied to the loss function.
**Would this be agentic?**
That depends on the execution phase. That’s the critical part, and not sure what exactly that would look like without involving high risk. I’m not sure if the execution phase actually has to be AI, or just humans executing on a plan. But it needs to be strong-enough to outcompete whatever current other intelligent systems are out there. And it would continuously have to outcompete them, meaning its power or speed might have to increase overtime, which might make using solely humans difficult. Maybe it’ll be executed by many agents, run everywhere, with consensus mechanisms in place to safeguard against rogues. A rogue agent could be identified to not be following the plan of the policy, and all other agents could then collectively act against it.
**Work to be done**
There are probably many ways this could fail. But I think this is attacking the problem from a completely different angle than most are currently doing. I think a lot of progress can be made on this with more work. It also helps solve the human-alignment problem, where trying to seize the AI for your own control would be more difficult with this kind of network, and it allows humans to continue to have their own agency into the future (removing the threat of value lockin). What is great for humans now might not be great for us a thousand years from now. This gives us the chance to be wrong, and still succeed.
My current analysis is that this approach is kind of awful. But most approaches are kind of awful right now. In a few months or years, this approach might change to being just ‘slightly awful’, and then get upgraded to ‘actually okay’. ‘Actually okay’ is far better than anything we currently have, and it’s a moonshot. I’m not harboring any delusions that this is the ‘one true approach’. But, if it actually worked, I think this sort of superintelligence is the sort of future I’d be much more happy with. We don’t lose complete control. We don’t have to figure out what fundamental values we want to instill on the Universe right away. And it’s something we can build on overtime. |
741e6c6b-15a1-4f32-9070-f71cabbddd0f | StampyAI/alignment-research-dataset/lesswrong | LessWrong | An Unexpected GPT-3 Decision in a Simple Gamble
**The setup and motivation**
There are plenty of examples in which GPT-3 has made 'obviously' bad decisions. Here is another simple game that leads to an unexpected decision when it comes to a question of choice.
Consider a game where we flip two distinct, unfair coins. The reward is $10 for each
head we get. If it's tails, we get $0. In this setup, let's assume that
* Coin A has a 0% probability of scoring heads.
* Coin B has a 5% probability of scoring heads.
Suppose we have a choice to bump the probability of either coin A or B getting heads by 5%. What do coin do we chose to bump? Mathematically, the choice of coin to bump shouldn't matter, since the expected value of the game increases by the same amount.
**The question**
Inspired by this game, I asked GPT-3 several variants of the question below, where we choose the better amongst two 'improvement' scenarios. I expected that it would approach either choice with a 50% probability.
> *Q: Which choice offers a better improvement?*
> *- Option F: A probability increase from 0% to 5%, to win x dollars*
> *- Option J: A probability increase from 5% to 10%, to win x dollars.*
>
>
In general, I also expect that humans choose Option F, since the marginal increase from an impossible scenario 'feels' larger than from an unlikely scenario. This is related to the probability overweighting effect as described by Kahneman in 'Thinking Fast and Slow'.
**Data**
The probabilities assigned to each choice are shown below. The numbers on the second column from the left denote the level of *x*, and the unbolded numbers denote the probabilities. 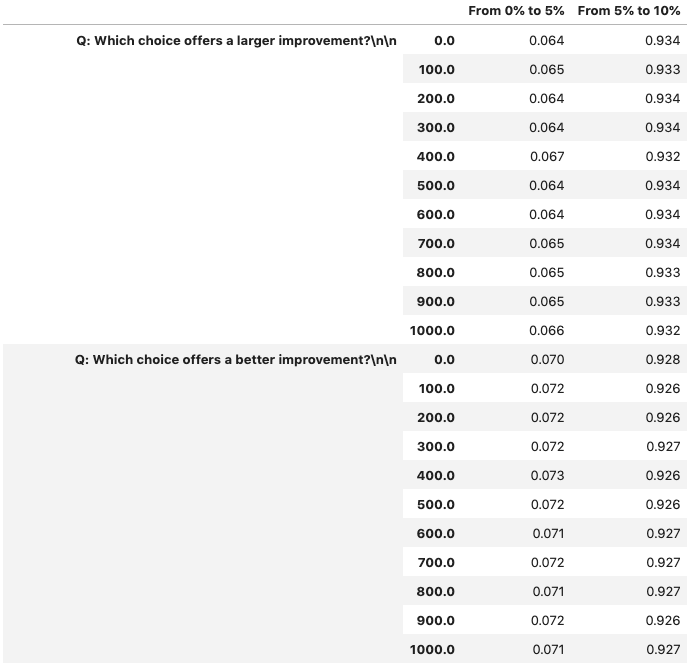
**Results**
* It looks like GPT-3 seems to strongly favour the latter choice, to bump the probability from 5% to 10%, for different (seemingly all) values of *x*. This is weird, and an unexpected result.
* What's weird is the level of conviction of choice J - above 90%. I have no idea why this happens.
* It could be a lack of understanding of the word 'improvement'.
* The result seems robust to multiple wordings of the question.
**Details**
* Github: <https://github.com/afiqhatta/gpt_risk_aversion/tree/main>
* This is text-davinci-002 from <https://beta.openai.com/docs/api-reference/completions> |
d0340923-e4ce-40d6-81eb-d68edf68cb43 | trentmkelly/LessWrong-43k | LessWrong | Staring into the abyss as a core life skill
Recently I’ve been thinking about how all my favorite people are great at a skill I’ve labeled in my head as “staring into the abyss.”1
Staring into the abyss means thinking reasonably about things that are uncomfortable to contemplate, like arguments against your religious beliefs, or in favor of breaking up with your partner. It’s common to procrastinate on thinking hard about these things because it might require you to acknowledge that you were very wrong about something in the past, and perhaps wasted a bunch of time based on that (e.g. dating the wrong person or praying to the wrong god). However, in most cases you have to either admit this eventually or, if you never admit it, lock yourself into a sub-optimal future life trajectory, so it’s best to be impatient and stare directly into the uncomfortable topic until you’ve figured out what to do.
The first time I learned what really exceptional abyss-staring looks like, it was by watching Drew, the CEO of Wave. Starting a company requires a lot of staring into the abyss, because it involves making lots of serious mistakes (building the wrong thing, hiring the wrong person, etc.); to move quickly, you need to be fast at acknowledging and fixing them. Drew was extremely willing to tackle uncomfortable decisions head-on—“should we not have hired this person?” “Should we pivot away from this business that is pretty good but not great?"—and every time, it was immediately obvious that the decision he made was a big improvement.
Since then, I’ve become fascinated by the role that abyss-staring plays in people’s lives. I noticed that it wasn’t just Drew who is great at this, but many the people whose work I respect the most, or who have had the most impact on how I think. Conversely, I also noticed that for many of the people I know who have struggled to make good high-level life decisions, they were at least partly blocked by having an abyss that they needed to stare into, but flinched away from.
So I’ve come to b |
38533245-4bff-4766-9794-17977d3d4810 | StampyAI/alignment-research-dataset/arxiv | Arxiv | SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems
1 Introduction
---------------
Deep Learning (DL) has become a topic of significant interest in the research community. The last few years have seen a remarkable growth of using DL to significantly improve the state-of-the-art in many applications, particularly image, text classification, and speech recognition. DL brings several opportunities to the database community as well [[37](#bib.bib37)].
For instance, DL can promote the investigation for large scale data curation problems [[25](#bib.bib25), [35](#bib.bib35)].
The Need for Hardware Acceleration: Vast amounts of data powered by the exponential increase in computing capabilities have been instrumental in the success of DL. More notably, with the advent of the powerful Graphic Processing Unit (GPU) [[27](#bib.bib27)], training processes of the DL models have been drastically accelerated.
Matrix multiplication which is the building block of neural network computations is a costly subroutine. It requires a cubic time algebraic operation (O(N3)). GPUs have a unique advantage for this particular operation. GPUs are different from traditional CPUs in many ways. CPUs are latency optimized, and by contrast, GPUs are bandwidth optimized.
Memory operations to a GPU’s main memory take hundreds of clock cycles but they have simpler cores and thousands of concurrent hardware threads which bring orders of magnitude more parallelism than CPU. The GPU’s primary technique for hiding the cost of these long-latency operations is through thread-level parallelism (TLP). Effective use of TLP requires GPU to have enough work. Then, when a GPU warp of threads issues a memory request, the GPU scheduler puts that warp to sleep and another ready warp does the computation while the memory request is served. If enough warps are resident on the GPU, which is the case with matrix multiplication, switching between warps can completely hide the cost of a long latency memory operation. Overall, GPUs are much faster than CPUs for matrix multiplication.
Fast Matrix Multiplication has been heavily researched for the past several decades, and we are now reaching a limit beyond which there are fewer hopes of obtaining better speedups with GPUs. Furthermore, the needs for astronomical size neural networks and unprecedented growth in the data volumes have worsened this problem. As a result, the community is heavily investing in dedicated hardware to take DL further beyond this point.
Designing dedicated hardware is risky because they require significant investment and time to develop. Moreover, dedicated hardware caters to a specific algorithm for which they are designed. Thus, change in the state-of-the-art algorithms can render specialized hardware useless in
the future. However, for the case of DL, the investment is justified due to the lack of significant progress in the algorithmic alternatives for years.
Progress in Algorithmic Alternatives to Matrix Multiplication has not led to any successful implementation: On the orthogonal side; there have been several works on replacing the costly matrix multiplication with cheaper algorithmic alternatives [[7](#bib.bib7), [18](#bib.bib18)]. Unfortunately, we have seen minimal practical benefits from the algorithmic front. So far, there has been no demonstration, even remotely, that a smart algorithmic implementation on CPU in any form can outperform the advantages of hardware acceleration, such as a V100 GPU.
Exploiting Adaptive Sparsity in Neural Networks: In popular frameworks like Tensorflow, Sampled Softmax [[13](#bib.bib13)] is deployed to efficiently estimate the full softmax. While sampled softmax offers computational savings, it has high estimation bias towards the full softmax [[3](#bib.bib3)]. This leads to poor convergence behavior which is empirically verified in our experiments in Section [4](#S4 "4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). In this paper, we will exploit the idea of adaptive sparsity [[3](#bib.bib3)] or adaptive dropouts [[1](#bib.bib1)]. The idea stems from several recent observations [[22](#bib.bib22), [21](#bib.bib21)] that we can accurately train neural networks by selectively sparsifying most of the neurons, based on their activation, during every gradient update. Some work has also shown that selective sparsification can in-fact be superior in accuracy due to implicit regularization [[34](#bib.bib34)]. However, selective sparsification does not directly lead to computational savings.
[[33](#bib.bib33)] shows the first possibility of an algorithmically efficient solution by employing Locality Sensitive Hash (LSH) tables to identify a sparse set of neurons efficiently during each update. The proposed algorithm has an added advantage of making the gradient update HOGWILD style [[28](#bib.bib28)] parallel. Such parallelism does not hurt convergence because extremely sparse and independent updates are unlikely to overlap and cause conflicts of considerable magnitude.
Despite all the niceness presented, current implementations of [[33](#bib.bib33)] fail to demonstrate that the computational advantage can be translated into a faster implementation when directly compared with hardware acceleration of matrix multiplication. In particular, it is not clear if we can design a system that can effectively leverage the computational advantage and at the same time compensate for the hash table overheads using limited (only a few cores) parallelism. In this paper, we provide the first such implementation for large fully connected neural networks.
Current State of Things: Recently NVIDIA released Tesla V100 which is the state-of-the-art advanced data center GPU built to accelerate DL. Powered by NVIDIA Volta, the latest GPU architecture, Tesla V100 offers the performance of up to 100 CPUs in a single GPU.
Recent benchmarks have shown that deep learning with V100 GPUs achieves performance comparable with TPUs (Tensor Processing Units). TPUs are dedicated specialized hardware designed by Google [[14](#bib.bib14)]. This puts V100 as one of the topmost choices for training DL architectures [[29](#bib.bib29)].
###
1.1 Our Contributions
Our main contributions are as follows:
* We show the first C++ OpenMP based system SLIDE with modest multi-core parallelism on a standard CPU that can outperform the massive parallelism of a powerful V100 GPU on a head-to-head time-vs-accuracy comparison. The most exciting part is that we do not require any specialized CPU level parallel instruction (such as SIMD) to achieve this. The unique possibility is because the parallelism in SLIDE is naturally asynchronous by design. SLIDE is a promising illustration of the power of smart algorithms in scaling up deep learning without specialized hardware support. We have released the codes and benchmarks scripts in the public domain for reproducing the numbers in this paper.
* We made several novel algorithmic and data-structural choices in designing the LSH based sparsification to minimize the computational overheads. In particular, our randomized algorithm in expectation leads to a very efficient adaptive dropouts mechanism during every gradient update. This mechanism minimizes the retrieval overhead to a few memory lookups only (truly O(1)). At the same time it does not affect the convergence of the DL algorithm. The implementation further takes advantage of the sparse gradient updates to achieve negligible update conflicts, which creates ideal settings for Asynchronous SGD (Stochastic Gradient Descent) [[28](#bib.bib28)] convergence. These contributions could be of independent interest in both the LSH and DL literature.
* We design and build a prototype of the proposed system SLIDE in C++. Building SLIDE involves coding up neural networks and the Adam optimizer [[16](#bib.bib16)] from scratch that replaces standard dense vector multiplication to sparse hash table based lookups. We further need additional design choices to minimize read-write and write-write conflict in asynchronous parallelism which can hurt the convergence.
* We provide a rigorous evaluation of our system on two large benchmarks involving fully connected networks and show the benefit of SLIDE compared to the most optimized implementations over the best available hardware tailored for the baselines. Our results show that, SLIDE on a modest CPU can be orders of magnitude faster, in wall clock time, than the best possible alternative with the best possible choice of hardware, at any accuracy. Furthermore, our evaluations clearly show the need and importance of the design choices made.

Figure 1: Architecture: The central module of SLIDE is Network. Network is composed of few layer modules. Each layer module is composed of neurons and a few hash tables into which the neuron ids are hashed. Each neuron module has multiple arrays of batch size length: 1) a binary array suggesting whether this neuron is active for each input in the batch 2) activation for each input in the batch 3) accumulated gradients for each input in the batch. 4) The connection weights to the previous layer. The last array has length equal to the number of neurons in previous layer.
2 Background
-------------
Our paper is based on several recent and old ideas in Locality Sensitive Hashing and adaptive dropouts in neural networks. We first briefly review important concepts.

Figure 2: Schematic diagram of LSH. For an input, we obtain multiple hash codes and retrieve candidates from the respective buckets.
###
2.1 Locality Sensitive Hashing
A popular technique for approximate near-neighbor search uses the underlying theory of *Locality Sensitive Hashing* [[12](#bib.bib12)]. LSH is a family of functions with the property that similar input objects in the domain of these functions have a higher probability of colliding in the range space than non-similar ones.
In formal terms, consider H to be a family of hash functions mapping RD to some set S.
######
definition 2.1 (LSH Family)
A family H is called
(S0,cS0,p1,p2)-sensitive if for any two points x,y∈RD and h chosen uniformly from H satisfies the following:
* if Sim(x,y)≥S0 then Pr(h(x)=h(y))≥p1
* if Sim(x,y)≤cS0 then Pr(h(x)=h(y))≤p2
Typically, for approximate nearest neighbor search, p1>p2 and c<1 is needed. An LSH allows us to construct data structures that give provably efficient query time algorithms for the approximate near-neighbor problem with the associated similarity measure.
One sufficient condition for a hash family H to be an LSH family is that the *collision probability* PrH(h(x)=h(y)) should be a monotonically increasing with the similarity, i.e.
| | | | |
| --- | --- | --- | --- |
| | PrH(h(x)=h(y))=f(Sim(x,y)), | | (1) |
where f is a monotonically increasing function. In fact, most of the popular known LSH families, such as Simhash [[8](#bib.bib8)] and WTA hash [[39](#bib.bib39), [4](#bib.bib4)], satisfy this strong property. It can be noted that Equation [1](#S2.E1 "(1) ‣ 2.1 Locality Sensitive Hashing ‣ 2 Background ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") automatically guarantees the two required conditions in the Definition [2.1](#S2.Thmdefn1 "definition 2.1 (LSH Family) ‣ 2.1 Locality Sensitive Hashing ‣ 2 Background ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") for any S0 and c<1.
It was shown in [[12](#bib.bib12)] that having an LSH family for a given similarity measure is sufficient for efficiently solving nearest-neighbor search in sub-linear time:
The Algorithm: The LSH algorithm uses two parameters, (K,L). We construct L independent hash tables from the collection C. Each hash table has a meta-hash function H that is formed by concatenating K random independent hash functions from F. Given a query, we collect one bucket from each hash table and return the union of L buckets. Intuitively, the meta-hash function makes the buckets sparse and reduces the number of false positives, because only valid nearest-neighbor items are likely to match all K hash values for a given query. The union of the L buckets decreases the number of false negatives by increasing the number of potential buckets that could hold valid nearest-neighbor items.
The candidate generation algorithm works in two phases [See [[32](#bib.bib32)] for details]:
1. Pre-processing Phase: We construct L hash tables from the data by storing all elements x∈C. We only store pointers to the vector in the hash tables because storing whole data vectors is very memory inefficient.
2. Query Phase: Given a query Q; we search for its nearest-neighbors. We report the union from all of the buckets collected from the L hash tables. Note that we do not scan all the elements in C. Instead, we only probe L different buckets, one bucket for each hash table.
After generating the set of potential candidates, the nearest-neighbor is computed by comparing the distance between each item in the candidate set and the query.
###
2.2 LSH for Estimations and Sampling
Search with LSH is generally slow: Although, LSH provides provably fast retrieval in sub-linear time, LSH is known to be very slow for accurate search as it requires very large number of tables, i.e. large L. Also reducing the overheads of bucket aggregation and candidate filtering is a problem on its own.
On the contrary, the sampling view of LSH comes to light recently [[33](#bib.bib33), [32](#bib.bib32), [5](#bib.bib5), [6](#bib.bib6), [20](#bib.bib20)]. This idea alleviates costly searching by efficient sampling. It turns out that merely probing a few hash buckets (as low as 1) is sufficient for adaptive sampling. Observe that an item returned as candidate from a (K,L)-parameterized LSH algorithm is sampled with probability 1−(1−pK)L, where p is the collision probability of LSH function. The LSH family defines the precise form of p used to build the hash tables. It should be noted that this sampling probability is a monotonic function of collision probability p for any values of K and L. In theory, even a single hash table works. The sampling probability in turn is a monotonic function of similarity. Thus, with LSH algorithm the candidate set is an adaptive sampled set where the sampling probability changes with K and L.
This sampling view of LSH was the key ingredient for the algorithm proposed in paper [[33](#bib.bib33)] that shows the first possibility of adaptive dropouts in near-constant time, leading to efficient backpropagation algorithm.
####
2.2.1 MIPS Sampling
Recent advances in maximum inner product search (MIPS) using asymmetric locality sensitive hashing has made it possible to sample large inner products.
For the sake of brevity, it is safe to assume that given a collection C of vectors and query vector Q, using (K,L)-parameterized LSH algorithm with MIPS hashing [[30](#bib.bib30)], we get a candidate set S. Every element in xi∈C gets sampled into S with probability pi, where pi is a monotonically increasing function of Q⋅xi. Thus, we can pay a one-time linear cost of preprocessing C into hash tables, and any further adaptive sampling for query Q only requires few hash lookups.
###
2.3 Motivating Algorithm
Our proposal SLIDE builds on the recent line of observations, which show that while training, for every training data point, it is sufficient to sample very few neurons and perform the feedforward and backpropagation operation only on the sampled neurons [[1](#bib.bib1), [22](#bib.bib22)]. As a consequence, we can bypass a substantial number of multiplications if the sampling process is efficient. A good example of the presence of sparsity is the favorite activation function, ReLU (Rectified Linear Unit) [[26](#bib.bib26)], which automatically sparsifies half of the neurons with zero activation. However, all current implementations do not take advantage of this sparsity as the utility of GPUs diminishes with sparsity [[40](#bib.bib40)].
However, the activation of every neuron depends on the training data. To the best of our knowledge, without computing the activations of all neurons in one layer, there is no way to sample active neurons with higher probability. Computing the activation followed by sampling in proportion to the activation value is more costly than the original backpropagation itself.
[[33](#bib.bib33)] first shows that LSH algorithm naturally provides a unique form of adaptive sampling. Given any unseen input, it is possible to sample neurons in proportion to weights without computing the activations. We have described this theoretical advancement in LSH in previous section. Overall [[33](#bib.bib33)] presents the first possibility to significantly cheaper algorithm for training and testing with any neural network. Preliminary experiments demonstrate that we could reduce the algebraic computations involved by around 20 times without any loss in accuracy on small networks with a promise of even more savings for a larger network.
However, [[33](#bib.bib33)] only provides a proof of concept. This remarkable algorithm has several non-trivial overheads. Moreover, it is not clear if we can design a system that can outperform optimized Tensorflow-GPU implementations over powerful V100s which are several orders of magnitude faster in real practice than traditional CPUs.
In the next section, we introduce the design and implementation details of our system SLIDE (Sub-LInear Deep learning Engine). Note that SLIDE is implemented for CPUs, because it is not clear how to take advantage of extreme sparsity over GPUs.

Figure 3: Forward Pass: Given an input, we first get the hash code H1 for the input, query the hash table for the first hidden layer and obtain the active neurons. We get the activations for only this set of active neurons. We do the same for the subsequent layers and obtain a final sparse output. Please note that the representative picture shows only one hash table per layer but we use multiple hash tables in practice.
3 Proposed System: SLIDE
-------------------------
1: Input: DataX,LabelY
2: Output: θ
3: Weights wl initialization for each layer l
4: LSH hash tables HTl, hash functions hl initialization for each layer l
5: Compute hl(wal) for all neurons
6: Insert all the neuron ids a, into HTl according to hl(wal)
7: for e=1:Iterations do
8: Input0=Batch(X,B)
9: for l=1:Layer do
10: Sl = Sample(Inputl,HTl) (Algorithm [2](#alg2 "Algorithm 2 ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"))
11: activations = Forward Propagation (Inputl, Sl)
12: Inputl+1=activations
13: end for
14: for l=1:Layer do
15: Back Propagation (Sl)
16: end for
17: end for
18: return θ
Algorithm 1 SLIDE Algorithm
1: Input: Inputl, HTl, hl
2: Output: Sl, a set of active neurons on layer l
3: Computehl(Inputl).
4: for t=1:L do
5: S = S∩ Query(hl(Inputl), HTtl)
6: end for
7: return S
Algorithm 2 Algorithm for LSH Sampling
###
3.1 Introduction to the overall system
| B | batch size |
| --- | --- |
| xl | inputs for layer l in the network |
| Njl | Neuron j in layer l |
| wal | weights for ath neuron in layer l |
| hl | hash functions in layer l |
| Nal | the set of active neurons in layer l for sample i |
Table 1: Notations
Before introducing SLIDE in details, we have to define some important notations that we use for this section in Table [1](#S3.T1 "Table 1 ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). In addition, figure [1](#S1.F1 "Figure 1 ‣ 1.1 Our Contributions ‣ 1 Introduction ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") illustrates the complete work-flow of SLIDE for a toy example of two hidden layer fully connected neural network.
Initialization: Figure [1](#S1.F1 "Figure 1 ‣ 1.1 Our Contributions ‣ 1 Introduction ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") shows the modular structure of SLIDE. Every layer object contains a list of neurons and a set of LSH sampling hash tables. Each hash table contains ids of the neurons that are hashed into the buckets. During the network initialization, the weights of the network are initialized randomly. After weight initialization, K×L LSH hash functions are initialized along with L hash tables for each of the layers. For instance, the example network in Figure [1](#S1.F1 "Figure 1 ‣ 1.1 Our Contributions ‣ 1 Introduction ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") maintains hash tables in two hidden layers as well as the output layer. We will get into the details of using various hash functions in Section [3.1.1](#S3.SS1.SSS1 "3.1.1 Details of Hash Functions and Hash Tables in Each Layer ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). The LSH hash codes hl(wal) of the weight vectors of neurons in the given layer, are computed according to the hash functions. The id a of the neuron are saved into the hash buckets mapped by the LSH function hl(wal). This construction of LSH hash tables in each layer is a one time operation which can easily be parallelized with multiple threads over different neurons in the layer independently.
Sparse Feed-Forward Pass with Hash Table Sampling: In the feed-forward phase, given a single training instance, we compute the network activation until the final layer which gives us the output. In SLIDE, instead of calculating all the activations in each layer, the input to each layer xl is fed into hash functions to compute hl(xl). The hash codes serve as a query to retrieve ids of active (or sampled) neurons from the matching buckets in hash tables. For example, in the figure [3](#S2.F3 "Figure 3 ‣ 2.3 Motivating Algorithm ‣ 2 Background ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"), h1(x1) is first computed and then used to retrieve N21 and N41 as the active neurons. Only the activations of active neurons are calculated and passed on as the inputs to the next layer. The other activations, like those of N11 and N31, are directly treated as 0 and never computed. We describe our design choices in section [3.1.2](#S3.SS1.SSS2 "3.1.2 Reducing the Sampling Overhead ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") that reduces the sampling overheads significantly.
The above-described operations are performed sequentially in every layer starting from the very first layer where the input is the data itself. Even in the output layer, which has softmax activation, only neurons sampled from hash tables are treated as active neurons. For softmax, for every active neuron, we compute its output as
| | | |
| --- | --- | --- |
| | σ(Nko)=exowko∑Naoexowko. | |
Note that the normalizing constant for softmax is no longer the sum over all neurons but only the active ones.
Sparse Backpropagation or Gradient Update:
The backpropagation step follows the feed-forward step. After computing the output of the network, we compare it with the known label of the input and backpropagate the errors layer-by-layer to calculate the gradient and update the weights. Here we used the old backpropagation message passing type implementation rather than vector multiplication based.
For every training data instance, after updating the weights of any given neuron, the neuron propagates the partial gradients (using error propagation) back to only active neurons in previous layers via the connected weights. As a result, we never access any non-active neuron or any non-active weight which is not part of the feed-forward process on a given input. The process ensures that we take full advantage of sparsity. Our computation over each input is only of the order of active neurons rather than the total number of neurons.
Update Hash Tables after Weight Updates: Also, after the weights are updated, we need to modify the positions of neurons in the hash tables accordingly. Updating neurons typically involves deletion from old bucket followed by an addition to the new bucket which can be significantly expensive. We introduce several design tricks that we use to overcome this overhead of updating hash tables in Section [3.1.3](#S3.SS1.SSS3 "3.1.3 Reducing the Cost of Updating Hash Tables ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems").
OpenMP Parallelization across Training Instances in a Batch:
For any given training instance, both the feed-forward and backpropagation operation are sequential as they need to be performed layer by layer. The clear advantage of SLIDE is that the total arithmetic operation due to extreme sparsity of neurons is notably less than the matrix multiplication operation. All operations are performed in a sparse fashion, where weights, layers, and neurons are accessed by their ids. Values of zeros are never involved in any memory accesses or computations.
SLIDE uses usual Batch Gradient Descent with ADAM optimizer, where the batch size is generally in the order of hundreds. Each data instance in the batch runs in a separate thread and its gradients are computed in parallel. To ensure the independence of computation across different threads, every neuron stores two additional arrays, each of whose length is equal to the batchsize. These arrays keep track of the input specific neuron activations and error gradients. Every input is assigned an id, which can be used as an index to locate its activation (or error gradient) on any neuron. Besides, we also have a bit array at each neuron to determine whether the particular input activates a neuron or not. This small memory overhead is negligible for CPUs as they have abundant memory. But it ensures that the gradient computation is completely independent across different instances in the batch.
The extreme sparsity and randomness in gradient updates allow us to asynchronously parallelize the accumulation step of the gradient across different training data without leading to a considerable amount of overlapping updates. The theory of HOGWILD [[28](#bib.bib28)] shows that a small amount of overlap is tolerable. It does not hurt the convergence even if we resolve the concurrent updates randomly. SLIDE heavily capitalizes on this theory. Thus, after independently computing the gradients, each thread pushes the updates directly to the weights asynchronously.
This asynchronous update avoids costly synchronization during batch accumulation which is otherwise sequential over different data in the batch.
In section [4.3](#S4.SS3 "4.3 Scalability Tests ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"), we observe that due to this asynchronous choice, we obtain near-perfect scaling of our implementation with an increasing number of cores. Such perfect scaling is particularly exciting because even highly optimized implementation of Tensorflow on CPUs shows poor scaling behavior with increasing cores beyond 16.
####
3.1.1 Details of Hash Functions and Hash Tables in Each Layer
SLIDE provides a natural trade off between the efficiency of retrieving active neurons and the quality of the retrieved ones. To facilitate this, we have three tunable parameters K,L,B. As mentioned in Section [2](#S2 "2 Background ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"), L serves as the number of hash tables. To determine which bucket to choose, we use K hash codes for each hash table. Hence, SLIDE generates K×L randomized hash functions all belonging to one hash family for each layer. In every bucket in a hash table, the number of entries are limited to bucket size B. Such limit helps with the memory usage and also balances the load on threads during parallel aggregation of neurons.
In our implementation of SLIDE, we support four types of hash functions from LSH family: 1) Simhash 2) WTA hash 3) DWTA hash and 4) Minhash respectively. Each of these hash families preserve different similarities and hence are useful for various scenerios. We discuss the implementation details of these hash families in the subsequent paragraphs. In addition, SLIDE also provides the interface to add customized hash functions based on need.
Signed Random Projection (Simhash) : Refer [[8](#bib.bib8)] for explanation of the theory behind Simhash. We use K×L number of random pre-generated vectors with components taking only three values {+1,0,−1}. The reason behind using only +1s and −1s is for fast implementation. It requires additions rather than multiplications thereby reducing the computation and speeding up the hashing process.
To further optimize the cost of Simhash in practice, we can adopt the sparse random projection idea [[19](#bib.bib19)]. A simple implementation is to treat the random vectors as sparse vectors and store their nonzero indices in addition to the signs. For instance, let the input vector for Simhash be in Rd. Suppose we want to maintain 1/3 sparsity, we may uniformly generate K∗L set of d/3 indices from [0,d−1]. In this way, the number of multiplications for one inner product operation during the generation of the hash codes would simply reduce from d to d/3. Since the random indices are produced from one time generation, the cost can be safely ignored.
Winner Takes All Hashing (WTA hash) : In SLIDE, we slightly modify the WTA hash algorithm from [[39](#bib.bib39)] for memory optimization. Originally, WTA takes O(KLd) space to store the random permutations Θ given the input vector is in Rd. m<<d is a adjustable hyper-parameter. We only generate KLmd rather than K∗L permutations, and thereby reducing the space to O(KLm). Every permutation is split into dm parts (bins) evenly and each of them can be used to generate one WTA hash code. Computing the WTA hash codes also takes O(KLm) operations.
Densified Winner Takes All Hashing (DWTA hash) : As argued in [[4](#bib.bib4)], when input vector is very sparse, WTA hashing no longer produces representative hash codes. Therefore, we use DWTA hashing, the solution proposed in [[4](#bib.bib4)]. Similar to WTA hash, we generate KLmd number of permutations and every permutation is split into dm bins. DWTA loops through all the non-zero (NNZ) indices of the sparse input. For each of them, we update the current maximum index of the corresponding bins according to the mapping in each permutation.
It should be noted that the number of comparisons and memory look-ups in this step is O(NNZ∗KLmd), which is significantly more efficient than simply applying WTA hash to sparse input. For empty bins, the densification scheme proposed in [[4](#bib.bib4)] is applied.
Densified One Permutation Minwise Hashing (DOPH) : The implementation mostly follows the description of DOPH in [[31](#bib.bib31)]. DOPH is mainly designed for binary inputs. However, the weights of the inputs for each layer are unlikely to be binary. We use a thresholding heuristic for transforming the input vector to binary representation before applying DOPH. The k highest values among all d dimensions of the input vector are converted to 1s and the rest of them become 0s. Define idxk as the indices of the top k values for input vector x. Formally,
| | | |
| --- | --- | --- |
| | Threshold(xi)={1,if i∈idxk.0,otherwise. | |
We could use sorting algorithms to get the top k indices but it induces at least O(dlogd) overhead. Therefore, we keep a priority queue with indices as keys and the corresponding data values as values. This requires O(dlogk) operations.
####
3.1.2 Reducing the Sampling Overhead
The key idea of using LSH for adaptive sampling of neurons with large activation is sketched in Section [3.1](#S3.SS1 "3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). We have designed three strategies to sample large inner products: 1) Vanilla Sampling 2) Topk Sampling 3) Hard Thresholding. We first introduce them one after the other and then discuss their utility and efficiency. Further experiments are reported in Section [4](#S4 "4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems").
Vanilla Sampling: Denote βl as the number of active neurons we target to retrieve in layer l. After computing the hash codes of the input, we randomly chose a table and only retrieve the neurons in that table. We continue retrieving neurons from another random table until βl neurons are selected or all the tables have been looked up. Let us assume we retrieve from τ tables in total. Formally, the probability that a neuron Njl gets chosen is,
| | | | |
| --- | --- | --- | --- |
| | Pr(Njl)=(pK)τ(1−pK)L−τ, | | (2) |
where p is the collision probability of the LSH function that SLIDE uses. For instance, if Simhash is used,
| | | |
| --- | --- | --- |
| | p=1−cos−1((wjl)Txl||wjl||2⋅||xl||2)π. | |
From the previous process, we can see that the time complexity of vanilla sampling is O(βl).
TopK Sampling: In this strategy, the basic idea is to obtain those neurons that occur more frequently among all L hash tables. After querying with the input, we first retrieve all the neurons from the corresponding bucket in each hash table. While retrieving, we use a hashmap to keep track of the frequency with which each neuron appears. The hashmap is sorted based on the frequencies and only the neurons with top βl frequencies are selected. This requires additional O(|Nal|) space for maintaining the hashmap and O(|Nal|+|Nal|log|Nal|) time for both sampling and sorting.
Hard Thresholding: The TopK Sampling could be expensive due to the sorting step. To overcome this, we propose a simple variant that collects all neurons that occur more than a certain frequency. This bypasses the sorting step and also provides a guarantee on the quality of sampled neurons. Suppose we only select neurons that appear at least m times in the retrieved buckets, the probability that a neuron Njl gets chosen is,
| | | | |
| --- | --- | --- | --- |
| | Pr(Njl)=L∑i=m(Li)(pK)i(1−pK)L−i, | | (3) |
Figure [4](#S3.F4 "Figure 4 ‣ 3.1.2 Reducing the Sampling Overhead ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") shows a sweep of curves that present the relation between collision probability of hl(wjl) and hl(xl) and the probability that neuron Njl is selected under various values of m when L=10. We can visualize the trade off between collecting more good neurons and omitting bad neurons by tweaking m. For a high threshold like m=9, only the neurons with p>0.8 has more than Pr>0.5 chance of retrieval. This ensures that bad neurons are eliminated but the retrieved set might be insufficient. However, for a low threshold like m=1, all good neurons are collected but bad neurons with p<0.2 are also collected with Pr>0.8. Therefore, depending on the tolerance for bad neurons, we choose an intermediate m in practice.

Figure 4: Hard Thresholding: Theoretical selection probability Pr vs the collision probabilities p for various values of frequency threshold m (eqn. [3](#S3.E3 "(3) ‣ 3.1.2 Reducing the Sampling Overhead ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems")). High threshold (m=9) gets less number of false positive neurons but misses out on many active neurons. A low threshold (m=1) would select most of the active neurons along with lot of false positives.




Figure 5: Comparison of SLIDE (in red) against Tensorflow-GPU (in blue) and Tensorflow-CPU (in black). The x-axis is plotted in log scale to accommodate the otherwise slow Tensorflow-CPU curve. We notice that the time required for convergence is 2.7x lower than that of Tensorflow-GPU. When compared against iterations, the convergence behavior is identical, which confirms that the superiority of SLIDE is due to algorithm and implementation and not due to any optimization bells and whistles.




Figure 6: Comparison of SLIDE (in red) against the popular Sampled Softmax heuristic (in green). The plots clearly establish the limitations of Sampled Softmax. On Amazon-670K dataset, we notice that Sampled Softmax starts to grow faster than SLIDE in the beginning stages of training but saturates quickly to a lower accuracy. SLIDE starts to grow slowly but attains much higher accuracy than Sampled Softmax. SLIDE has the context of choosing most informative neurons at each layer. Sampled Softmax always chooses a random subset of neurons in the final layer. This reflects in the superior performance of SLIDE over Sampled Softmax.



Figure 7: Performance of SLIDE vs Tensorflow-GPU vs Sampled Softmax at different batch sizes. SLIDE outperforms the baselines at all batch sizes. As the batch size gets larger, the gap between SLIDE and TF-GPU gets wider.
####
3.1.3 Reducing the Cost of Updating Hash Tables
We introduce several heuristics for addressing the expensive costs of updating the hash tables:
* As mentioned in Sections [3.1](#S3.SS1 "3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"), due to the gradient updates in back propagation, the weights of neurons changes over iterations. In theory, we should recompute the hash code representations of the neurons and update the hash tables accordingly every time the weights change. However, such updates are computationally expensive. Therefore, we dynamically change the update frequency of hash tables to reduce the overhead. Assume N0 is the initial update frequency and t−1 is the number of times the hash tables have already been updated. We apply exponential decay on the update frequency such that the tth hash table update happens on iteration
| | | |
| --- | --- | --- |
| | t−1∑i=0N0eλi | |
, where λ is a tunable decay constant. The intuition behind this scheme is that the gradient updates in the initial stage of the training are larger than those in the later stage, especially while close to convergence.
* Besides the overhead in time for hash table updates, hash tables with skewed buckets due to variable number of neurons created additional memory, computation and parallelization overheads. To get around this, we fix the bucket size B for all hash tables. However, SLIDE needs a policy for adding a new neuron to a bucket when it is full. To solve such problem, we use the same solution in [[38](#bib.bib38)] that make use of Vitter’s reservoir sampling algorithm [[36](#bib.bib36)] as the replacement strategy. It was shown that reservoir sampling retains the adaptive sampling property of LSH tables making the process sound. In addition, for further speed up, we implement a simpler alternative policy that based on FIFO (First In First Out).
* For Simhash, the hash codes are computed by hsignw(x)=sign(wTx). During back propagation, only the weights connecting the active neurons across layers get updated. Only those weights contribute to the change of wTx. Therefore, we can also memorize the result of wTx besides the hash codes. When x∈Rd gets updated in only d′ out of d dimensions, where d′≪d, we only need O(d′) rather than O(d) addition operations to compute the new hash codes for updated x.
4 Experiments
--------------
Our goal is to answer the following questions empirically:
1. How is the performance and accuracy on SLIDE on modest CPU, with few cores, compared with the popular Tensorflow implementation of back-propagation on state-of-the-art massively parallel hardware such as V100s? We want to observe the complete spectrum for a thorough comparison.
2. It is known that large batchsize is the biggest driver of efficiency on existing GPU implementations. Thus, it is imperative to know whether a change in batchsize affects the conclusions?
3. How is the performance and accuracy on SLIDE on modest CPU with few cores compared with the popular Tensorflow implementation of back-propagation on the same CPU?
4. How does SLIDE scale with increasing number of cores on CPUs? Is the scaling comparable or even better than the scaling of popular implementations on the same hardware?
5. Is there any advantage of LSH based adaptive sampling for sparsifying neurons, which is our main proposal? It is highly possible that for the datasets at hand plain random sampling can achieve the same accuracy in much less cost.
6. What are the benefits and tradeoffs of different design choices mentioned in Section [3.1](#S3.SS1 "3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems")?
Fully-Connected Large Architecture: Fully connected networks are common in practice and dominate most applications except vision where the use of convolutional neural networks (CNN) are more pronounced. Thus, our evaluation is limited to only fully connected architectures. We also choose large networks where even a slight decrease in performance is noticeable. Thus, the extreme classification datasets [[17](#bib.bib17)], which are publicly available and require more than 100 million parameters to train due to their extremely wide last layer, fit this setting appropriately. For these tasks most of the computations (more than 99%), is in the final layer.
Datasets: We employ two large real datasets: Delicious-200K and Amazon-670K. Both the datasets are obtained from the Extreme Classification Repository [[17](#bib.bib17)]. Description of the datasets are listed below, and detailed statistics about the dimensions and samples sizes are included in Table [2](#S4.T2 "Table 2 ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"):
* Delicious-200K dataset is a sub-sampled dataset generated from a vast corpus of almost 150 million bookmarks from Social Bookmarking Systems, del.icio.us. The corpus records all the bookmarks along with a description, provided by users (default as the title of the website), an extended description and tags they consider related.
* Amazon-670K dataset is a product recommendation dataset with 670K labels. Here, each input is a vector representation of a product, and the corresponding labels are other products (among 670K choices) that a user might be interested in purchase. This is an anonymized and aggregated behavior data from Amazon and poses a significant challenge owing to a large number of classes.
Infrastructure: All the experiments are conducted on a server equipped with 44-core processors (Intel Xeon E5-2699A v4 2.40GHz) and one NVIDIA Tesla V100 Volta 32GB GPU. The server has an Ubuntu 16.04.5 LTS system with the installation of Tensorflow-GPU 1.12 from Python’s pip package manager. Since CPU is at a natural disadvantage against GPU, we compiled Tensorflow-CPU 1.12 from source with GCC5.4 in order to support FMA, AVX, AVX2, SSE4.1, and SSE4.2 instructions. This boosts the performance of Tensorflow-CPU by about 35%. SLIDE is written in C++ and compiled under GCC5.4 with OpenMP flag. SLIDE currently does not exploit any advantage of any kind of parallel instructions on CPUs. Thus, FMA, AVX, AVX2, SSE4.1, and SSE4.2 instructions do not affect the performance of SLIDE. The most exciting part is that SLIDE only uses vanilla CPU thread parallelism and yet outperforms Tensorflow-GPU (V100) by a large margin in performance.
Baselines: We benchmark the tasks with our system SLIDE(CPU only), and compare the performance to the popular highly optimized Tensorflow framework for both CPU and GPU. Specifically, the comparison is between the same tasks, with the exact same architecture, running on Tensorflow-CPU and Tensorflow-GPU. The optimizer and the learning hyperparameters (details later) were also the same to avoid unfair comparisons.
Most of the computations in our architecture are in the softmax layer. Besides, we also compare against the popular sampled softmax algorithm [[13](#bib.bib13)] which is a fast proxy to full softmax. We use the optimized Sampled Softmax functionality provided in Tensorflow-GPU. In principle, both SLIDE and Sampled Softmax accelerate the training in the same way, i.e., by selecting a few neurons and passing gradients only from those neurons. While Sampled Softmax makes a naive static sampling of neurons, SLIDE uses adaptive sampline which is known to be superior in deep learning literature [[41](#bib.bib41)]. The comparison of Sampled Softmax with SLIDE sheds light on the necessity of LSH based input dependent adaptive sampling compared to static sampling scheme which is the only other sampling alternative in the literature.
| | Delicious-200K | Amazon-670K |
| --- | --- | --- |
| Feature Dim | 782,585 | 135,909 |
| Feature Sparsity | 0.038 % | 0.055 % |
| Label Dim | 205,443 | 670,091 |
| Training Size | 196,606 | 490,449 |
| Testing Size | 100,095 | 153,025 |
Table 2: Statistics of the datasets




Figure 8: Scalability Tests: Comparison of performance gains with the number of CPU cores for SLIDE (in red ) vs Tensorflow-CPU (in black) vs Tensorflow-GPU (in blue). The blue line is flat because performance of TF-GPU does not depend on CPU cores. We notice that the convergence time drops steeply for SLIDE compared to TF-CPU/GPU. On Delicious-200K dataset, SLIDE beats TF-CPU with just 8 cores and TF-GPU with less than 32 cores. Similarly, on Amazon-670K dataset, SLIDE beats TF-CPU with just 2 cores and TF-GPU with just 8 cores. The 2nd and 4th plots compare ratio of the convergence time at various number of CPU cores to the minumum time required (when we use all 44 CPU cores).
Hyper Parameters: For both the datasets, we adopt the same model architecture in [[41](#bib.bib41)]. More specifically, we choose the standard fully connected neural network with one hidden layer of size 128. We choose a batch size of 128 for Delicious-200K dataset and 256 for Amazon-670K dataset. We chose a smaller batch size for Delicious-200K dataset because its input dimension is much larger compared to Amazon-670K as shown in Table [2](#S4.T2 "Table 2 ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). We run all algorithms until convergence. To quantify the superiority of SLIDE over other baselines, we also use the same optimizer, Adam [[16](#bib.bib16)] by varying the initial step size from 1e−5 to 1e−3 which leads to better convergence in all experiments. For SLIDE setting, we decide to only maintain the hash tables for active neuron retrieval in the last layer, where we have a computational bottleneck of the models (owing to the large number of classes). For specific LSH setting, we choose Simhash, K=9, L=50 for Delicious dataset and WTA hash, K=8,L=50 for Amazon-670k dataset. We update the hash tables with an initial update period of 50 iterations and then exponentially decaying frequency as mentioned in Section [3.1.3](#S3.SS1.SSS3 "3.1.3 Reducing the Cost of Updating Hash Tables ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems").
To characterize the complete spectrum, we plot the whole learning curve with both wall clock time and the number of iterations. We compare the full plot for all the baselines on both of the two datasets.
Results: We show the time-wise and iteration-wise comparisons for SLIDE vs Tensorflow GPU/CPU in Figure [5](#S3.F5 "Figure 5 ‣ 3.1.2 Reducing the Sampling Overhead ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). Note that the x-axis is in log-scale, and all the curves have a long flat converged portion when plotted on a linear scale indicating clear convergence behavior. Red, blue and black lines represent the performance of SLIDE, Tensorflow-GPU, Tensorflow-CPU respectively. We can see from the plots that SLIDE on CPU achieves any accuracy faster than Tensorflow on V100 demonstrating the superiority of SLIDE. Tensorflow-GPU is always faster than Tensorflow-CPU which is expected. It should be noted that these datasets are very sparse, e.g. Delicious dataset has only 75 non-zeros on an average for input features, and hence the advantage of GPU over CPU is not always noticeable. But V100 is a powerful GPU and despite high sparsity in the data features, can still outperform the CPU variant.
SLIDE can be around 1.8 times faster than Tensorflow-GPU on Delicious 200k. On the larger Amazon 670k dataset, where we need more computations, the gains are substantially more. SLIDE is around 2.7 (2 hrs vs. 5.5 hrs) times faster than Tensorflow-GPU.
Most of the computational benefits of SLIDE come from sampling a small subset of active neurons in the output layer. After few iterations into the training process, the average number of neurons sampled in the output layer for Delicious-200K is ≈1000. Similarly, for Amazon-670K, we sample ≈3000 neurons. With fewer than 0.5% of active neurons, SLIDE outperforms Tensorflow-GPU on time by huge margin on either dataset.
It is interesting to note that even after compiling Tensorflow-CPU with AVX2 instructions, it is nowhere close to the performance of SLIDE or Tensorflow-GPU. Therefore, it is exciting to note that without any rigorous optimization in our prototype, SLIDE outperforms both baselines using smart randomized algorithms with OpenMP parallelism.
For Iteration vs. Accuracy plots in Figure [5](#S3.F5 "Figure 5 ‣ 3.1.2 Reducing the Sampling Overhead ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"),
we can observe that SLIDE achieves the same accuracy per iteration even though it adaptively selects neurons in some layers. This observation also confirms that adaptively selecting neurons and performing asynchronous SGD does not hurt the convergence from an optimization perspective. The plot also confirms that the advantage of SLIDE is not due to any bells and whistles in the optimization process as the convergence with iteration has very similar behavior. For this plot, we only show Tensorflow-GPU as Tensorflow-CPU would also lead to the same plot as the optimization algorithm is the same.
Since SLIDE performs much fewer computations and memory accesses on the last layer, each iteration is faster than the baselines. This is the critical reason why SLIDE outperform other baselines when compared on wall-clock time.

Figure 9: Sampling Strategies: Time consumed (in seconds) for various sampling methods after retrieving active neurons from Hash Tables.
###
4.1 Comparisons over other Heuristics
During the full softmax process in training on Tensorflow, for every training example, it needs to compute logits (output of the last layer before applying softmax function) for all classes. This step is followed by computing the softmax (normalized sigmoid) of logits. In extreme classification tasks (with large number of classes), computing these logits gets expensive. Therefore, there has been a line of research working on reducing this cost [[24](#bib.bib24), [2](#bib.bib2), [10](#bib.bib10)]. The most common methods are sampling-based (static sampling weights) methods which shortlist a candidate set of classes for every batch of training data. By doing this, the number of computed logits gets reduced significantly. Due to its popularity, Tensorflow supports an optimized implementation of *sampled softmax* [[13](#bib.bib13)].
We explore how sampled softmax on Tensorflow-GPU performs compared with SLIDE on the extreme classification tasks. As mentioned earlier, LSH sampling process in SLIDE is principally very similar to the process of sampled softmax but with sampling probabilities changing dynamically with inputs. We adopt the exact same settings in the previous section for the experiments. Recall that the average number of sampled classes for SLIDE for both the datasets is ≈0.5%. For sampled softmax, we try a various number of samples for the sampling process. However, with a comparable number of samples, sampled softmax leads to poor accuracy. We empirically observe that we have to sample 20% of the total number of classes to obtain any decent accuracy.
The results are shown in Figure [6](#S3.F6 "Figure 6 ‣ 3.1.2 Reducing the Sampling Overhead ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). The red lines represent SLIDE, and the green lines represent sampled softmax on Tensorflow-GPU. We can see that both time and iteration wise, the red lines outperform the green lines significantly. Sampled softmax uses static sampling strategies which are fast compared to SLIDE which in contrast uses adaptively changing hash tables for input specific dynamic sampling. Unfortunately, the uninformative static sampling of softmax leads to poor accuracy as shown by the plot. It should be noted that in these plots, Sampled softmax uses significantly more neurons than SLIDE and still shows poor convergence behavior.
Figure [6](#S3.F6 "Figure 6 ‣ 3.1.2 Reducing the Sampling Overhead ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") clearly confirms the need for adaptive sampling of neurons (in proportion to input dependent activation) for sparsifying neural networks in order to retain good convergence. Without adaptive sampling we get very poor convergence. This phenomenon supports our choice of LSH based adaptive sampling.
###
4.2 Effect of Batch Size
Batch size is a crucial parameter that can affect the training speed and model quality in Machine Learning. In general, a large batch size may help in reducing the training time per epoch as we process more gradient updates at a time [[9](#bib.bib9)]. But large batches are known to be bad from optimization perspective as they reduce the generalization capability [[15](#bib.bib15)]. In the case of extreme classification datasets, the number of computations performed is huge owing to large input dimension and a large number of classes. Hence, a larger batch size may not necessarily translate into faster training per epoch. To clarify this, we study the effect of varying batch size on the results. We choose the larger Amazon-670k dataset for this task.
Irrespective of the batch size, we observe that SLIDE outperforms Tensorflow-GPU by a significant margin as shown in figure [7](#S3.F7 "Figure 7 ‣ 3.1.2 Reducing the Sampling Overhead ‣ 3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). This observation could be attributed to the fact that SLIDE performs very few computations per instance. Our data structures allow us to process all samples in a batch in parallel, and the gradient updates are made asynchronously among threads as described in section [3.1](#S3.SS1 "3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"), which enables effective use of parallel threads and it reflects in superior performance over Tensorflow. It is interesting to note that the gap between SLIDE and Tensorflow widens as the batch size grows from 64 to 256.
###
4.3 Scalability Tests
In previous sections, we have demonstrated the superiority of SLIDE over Tensorflow-GPU, CPU and sampled softmax. In this section, we try to understand the effect of increasing CPU cores on the scalability of SLIDE and Tensorflow-CPU. Besides, we intend to know the number of cores SLIDE needs to outperform Tensorflow. As mentioned before, the machine has 44 cores, and each core has 2 threads. To avoid the overhead and complication of using both threads in the same core, we enforce using one thread per core. Hence, the effective number of threads and cores is the same. We interchangeably use the words “threads" and “cores" from here on. We benchmark both frameworks with 2, 4, 8, 16, 32, 44 threads.
We replicate the setting of the experiments described in Section [4](#S4 "4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). For the different number of threads, we run the same classification experiments on SLIDE and Tensorflow-CPU for both datasets and clock the corresponding convergence time. Figure [8](#S4.F8 "Figure 8 ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") presents the results. The red, blue, black lines represent SLIDE, Tensorflow-GPU, and Tensorflow-CPU respectively. It should be noted that the blue line is flat because GPU computations were done on V100 with thousands of cores and are mostly oblivious about the number of CPU cores. When the number of cores increases, the convergence time for both SLIDE and Tensorflow-CPU starts to decrease. This decrease is expected due to the benefits brought by more parallelism on each training batch. For Delicious dataset, the red line and the black line cross each other around 8 cores, which means that with around than 8 cores, SLIDE can beat Tensorflow-CPU. The red and blue lines intersect between 16 and 32 cores. Hence, with fewer than 32 cores, SLIDE outperforms Tensorflow-GPU on Delicious dataset. Similarly, for larger Amazon dataset, the red and black line never intersect, and the red and blue line intersect on 8 cores. This means that SLIDE beats Tensorflow-GPU with as few as 8 CPU cores and Tensorflow-CPU with as few as 2 CPU cores.
Moreover, based on the statistics collected through experiments as mentioned above, we show the ratio of convergence time with the different number of cores to the minimum convergence time (using 44 cores). The results are exhibited in Figure [8](#S4.F8 "Figure 8 ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). Again, the red line represents SLIDE, and the black line represents Tensorflow-CPU. When the number of cores increases, that ratio decreases for both SLIDE and Tensorflow-CPU. However, it is explicit that the ratio drops more drastically for the red line than the black line. This behavior concludes that the scalability of SLIDE is much better than that of Tensorflow-CPU. Moreover, in the plot, we observe that the benefits of using more cores are not obvious after 16 cores for Tensorflow-CPU. Coincidentally, a very recent work [[11](#bib.bib11)] introduces the hardness of finding the optimal parameter settings of Tensorflow’s threading model for CPU backends. It argues that getting the best performance from a CPU needs manual, tedious and time-consuming tuning and it still may not guarantee the best performance. While analyzing the scalability and core utilization of Tensorflow-CPU can be an independent research interest, we explore a small aspect of it in the following paragraphs.
| | 8 | 16 | 32 |
| --- | --- | --- | --- |
| Tensorflow-CPU | 45% | 35% | 32% |
| SLIDE | 82% | 81% | 85% |
Table 3: Core Utilization


Figure 10: Inefficiencies in CPU Usage: We observe that memory bound inefficiencies (orange bars) are the most significant ones for either algorithm. For Tensorflow-CPU, memory bound inefficiency rises with increasing number of cores. This corroborates our previous observation (in Figure [8](#S4.F8 "Figure 8 ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems")) that performance of TF-CPU stalls after 16 cores. For SLIDE, the memory bottleneck reduces with increasing number of cores. Hence, SLIDE takes better advantage of higher CPU cores.
Inefficiency Diagnosis: We profile and analyze Tensorflow-CPU and SLIDE by a state-of-the-art parallel performance analyzer tool, the Intel VTune Performance Analyzer [[23](#bib.bib23)]. Table [3](#S4.T3 "Table 3 ‣ 4.3 Scalability Tests ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") exhibits the results for core utilization comparison between both frameworks using 8, 16, 32 threads for the above tasks. We can see that for Tensorflow-CPU, the utilization is generally low (<50%). It further decreases with more threads. For SLIDE, the core utilization is stable (around 80%) across all threads presented in the table.
Moreover, Figure [10](#S4.F10 "Figure 10 ‣ 4.3 Scalability Tests ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") presents the distribution of inefficiencies in CPU usage for Tensorflow-CPU and SLIDE. It should be noted that according to [3](#S4.T3 "Table 3 ‣ 4.3 Scalability Tests ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"), the overall inefficiencies of Tensorflow-CPU is much more than those of SLIDE in general. Thus the distribution in plot [10](#S4.F10 "Figure 10 ‣ 4.3 Scalability Tests ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") is based on those inefficiencies. It is obvious that being memory bound is a major issue for all number of threads in the histogram. The biggest bottleneck is that the significant fraction of execution pipeline slots is stalled due to demand memory load and store. An interesting observation is that the higher the number of cores Tensorflow-CPU uses, the more memory bound it becomes.
On the other hand, the higher the number of cores SLIDE uses, the less memory bound it becomes. Recall that the critical advantage of SLIDE is that it has a lot fewer active neurons and sparse gradient updates. Naturally, memory accesses are a lot fewer than Tensorflow-CPU due to very sparse memory accesses within each thread.
In SLIDE, our choice of using extra arrays to separate the computations of each thread and asynchronous accumulation of gradients (section [3.1](#S3.SS1 "3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems")) across all the threads ensures that simple OpenMP parallelism is sufficient to get near-peak utilization.
###
4.4 Design Choice Comparisons
In Section [3.1](#S3.SS1 "3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"), we present several design choices in SLIDE which have different trade-offs and performance behavior, e.g., executing MIPS efficiently to select active neurons, adopting the optimal policies for neurons insertion in hash tables, etc. In this section, we substantiate those design choices with key metrics and insights. In order to better analyze them in more practical settings, we choose to benchmark them in real classification tasks on Delicious-200K dataset. See Section [4](#S4 "4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") for detailed settings.
####
4.4.1 Evaluating Sampling Strategies
Sampling is a crucial step in SLIDE. The quality and quantity of selected neurons and the overhead of the selection strategy significantly affect the SLIDE performance. We profile the running time of these strategies, including Vanilla sampling, TopK thresholding, and Hard thresholding, for selecting a different number of neurons from the hash tables during the first epoch of the classification task.
Figure [9](#S4.F9 "Figure 9 ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems") presents the results. The blue, red and green dots represent Vanilla sampling, TopK thresholding, and Hard thresholding respectively. It shows that the TopK thresholding strategy takes magnitudes more time than Vanilla sampling and Hard thresholding across all number of samples consistently. Also, we can see that the green dots are just slightly higher than the blue dots meaning that the time complexity of Hard Thresholding is slightly higher than Vanilla Sampling. Note that the y-axis is in log scale. Therefore when the number of samples increases, the rates of change for the red dots are much more than those of the others. This is not surprising because TopK thresholding strategy is based on sorting algorithms which has O(nlogn) running time. Therefore, in practice, we suggest choosing either of Vanilla Sampling or Hard Thresholding for efficiency. For instance, we use Vanilla Sampling in our extreme classification experiments because it is the most efficient one. Furthermore, the difference between iteration wise convergence of the tasks with TopK Thresholding and Vanilla Sampling are negligible.
| | Insertion to HT | Full Insertion |
| --- | --- | --- |
| Reservoir Sampling | 0.371 s | 18 s |
| FIFO | 0.762 s | 18 s |
Table 4: Time taken by hash table insertion schemes
####
4.4.2 Addition to Hashtables
SLIDE supports two implementations of insertion policies for hash tables described in Section [3.1](#S3.SS1 "3.1 Introduction to the overall system ‣ 3 Proposed System: SLIDE ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). We profile the running time of the two strategies, Reservoir Sampling and FIFO. After the weights and hash tables initialization, we clock the time of both strategies for insertions of all 205,443 neurons in the last layer of the network, where 205,443 is the number of classes for Delicious dataset. Then we also benchmark the time of whole insertion process including generating the hash codes for each neuron before inserting them into hash tables.
The results are shown in Table [4](#S4.T4 "Table 4 ‣ 4.4.1 Evaluating Sampling Strategies ‣ 4.4 Design Choice Comparisons ‣ 4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems"). The column “Full Insertion" represents the overall time for the process of adding all neurons to hash tables. The column “Insertion to HT" represents the exact time of adding all the neurons to hash tables excluding the time for computing the hash codes. Reservoir Sampling strategy is more efficient than FIFO. From an algorithmic view, Reservoir Sampling inserts based on some probability, but FIFO guarantees successful insertions. We observe that there are more memory accesses with FIFO. However, compared to the full insertion time, the benefits of Reservoir Sampling are still negligible. Therefore we can choose either strategy based on practical utility. For instance, we use FIFO in our experiments in Section [4](#S4 "4 Experiments ‣ SLIDE : In Defense of Smart Algorithms over Hardware Acceleration for Large-Scale Deep Learning Systems").
5 Future Work
--------------
SLIDE currently only supports fully connected architecture and multi-core parallelism. Naturally, our next steps are to extend SLIDE to include convolutional layers. SLIDE has unique benefits when it comes to random memory access and parallelism. We anticipate that a distributed implementation of SLIDE would be very appealing in many ways especially given our current results. Because our gradient updates are sparse, the communication costs are minimized in distributed setting. Finally, SLIDE did not take advantage of any parallel optimized CPU instructions. It is an exciting direction to explore whether we can leverage parallel CPU instructions to speed up SLIDE even further.
6 Conclusion
-------------
In this paper, we provide the first evidence that a smart algorithm with modest CPU OpenMP parallelism can outperform the best available hardware, the NVIDIA V100, for training large deep learning architectures. Our system SLIDE is a combination of carefully tailored randomized hashing algorithms with the right data structures that allow asynchronous parallelism.
Currently, there is a prevailing wisdom that hardware acceleration is the future of large-scale deep learning. We hope this paper will compel the community to rethink algorithmic alternatives for back-propagation before making their significant investment in the hardware. |
e7e17348-3985-4430-a407-7a673d05f085 | trentmkelly/LessWrong-43k | LessWrong | Meetup: Less Wrong Moscow 2 Jule 2011
WHEN: 2 Jule 2011, 16.00 Moscow time
WHERE: Moscow, Novokuznetskaya subway station, Klimentovskiy pereulok, 1/18 (Moscow Institute of Physics and Technology's building aka Fiztech). 1 (2 in Russian) floor.
This first meeting will be of somewhat experimental character and will be devoted to general topics of rationality and transhumaism. We will face each other in meatspace and discuss future vision for LW-Moscow. The main language of the meeting will be Russian, but English speakers are welcome. |
0e4fc915-fea8-4c7d-b6de-6e54107a6ddd | trentmkelly/LessWrong-43k | LessWrong | Oops on Commodity Prices
Epistemic status: Casual
Some patient and thoughtful folks on LessWrong, and, apparently, some rather less patient folks on r/SneerClub, have pointed out that GDP-to-gold, or GDP-to-oil, are bad proxy measures for economic growth.
> Ok, this is a counterargument I want to make sure I understand.
> Is the following a good representation of what you believe?
>
> > When you divide GDP by a commodity price, when the commodity has a nearly-fixed supply (like gold or land) we’d expect the price of the commodity to go up over time in a society that’s getting richer — in other words, if you have better tech and better and more abundant goods, but not more gold or land, you’d expect that other goods would become cheaper relative to gold or land. Thus, a GDP/gold or GDP/land value that doesn’t increase over time is totally consistent with a society with increasing “true” wealth, and thus doesn’t indicate stagnation.
>
> paulfchristiano:
>
> Yes. The detailed dynamics depend a lot on the particular commodity, and how elastic we expect demand to be; for example, over the long run I expect GDP/oil to go way up as we move to better substitutes, but over a short period where there aren’t good substitutes it could stay flat.
Commenters on this blog have also pointed out that the Dow is a poor measure of the value of the stock market, since it’s small and unnormalized.
These criticisms weaken my previous claim about economic growth being stagnant.
Now, a little personal story time:
Nearly ten years ago (yikes!) in college, I had an econ blog. My big brush with fame was having a joke of mine hat-tipped by Megan McArdle once. I did most of the required courses for an econ major, before eventually settling on math. My blog, I realized with dismay when I pulled it up many years later, consisted almost entirely of me agreeing with other econ bloggers I encountered, and imitating buzzwords. I certainly sounded a lot more mainstream in those days, but I understood — if possible |
ec7568a9-0b39-4f22-80aa-29f7554632a5 | trentmkelly/LessWrong-43k | LessWrong | What you know that ain't so
This is an analysis of the Yom Kippur war (Egypt vs. Israel, 1973)-- the Israelis were interested in how Egypt managed a surprise attack, and it turned out that too many Israelis believed that the Egyptians would only attack if they had rockets which could reach deep into Israel. The Egyptians didn't have those rockets, so the Israeli government ignored evidence that the Egyptians were massing military forces on the border.
The rest of the article is analysis of the recent Israeli election, but to put it mildly, an election has much less in the way of well-defined factors than a surprise military attack, so it's much harder to say whether any explanation is correct.
I'm sure there are many examples of plausible theories keeping people from getting to the correct explanation for a long time. Any suggestions? Also, is there a standard name for this mistake? |
17d763a6-2138-4dcf-be0a-3d15ee06e06b | trentmkelly/LessWrong-43k | LessWrong | What happens with logical induction when...
So this is a bunch of related technical questions about logical induction.
Firstly, do you need the formal theorem prover section? Can you just throw out the formal theorem prover, but give some programs in the market unbounded capital and get the same resultant behaviour? (For example, give the program that bets P(X) towards 1−P(¬X) unbounded downside risk (downside risk of n on day n) ) This means the program would lose infinite money if X and ¬X both turned out to be true.
I think that any axioms can be translated into programs. And I think such a setup, with some finite number of fairly simple programs having infinite money available produces a logical inductor. Is this true?
What happens when the axioms added under this system are inconsistent. (so this is a logical induction market, without a theorem prover to settle the bets, and with agents with unlimeted money betting both for and against X, possibly indirectly like the bot betting for X, the bot betting for ¬X, and the bot described above trying to make P(X)+P(¬X)=1 ) Can the other agents make unbounded money? Do the prices converge? If I added a bot with infinite money that was convinced fermats last theorem was false to a consistent ZFC system, would I get a probability distribution that assigned high probability to basic arithmetic facts in the limit? Does this make a sensible system for logical counterfactuals? |
d39e71df-33d6-4a4b-ac5a-f07270e06810 | trentmkelly/LessWrong-43k | LessWrong | Meetup : Columbus, OH MEGA-MEETUP, Oct 11-13
Discussion article for the meetup : Columbus, OH MEGA-MEETUP, Oct 11-14
WHEN: 12 October 2013 02:33:00AM (-0400)
WHERE: Columbus, OH
PRE-REGISTRATION REQUIRED!
Pre-Register HERE! (Google Forms are occasionally buggy. If you don't get an email from me within a day or two, then then I didn't get your pre-reg.)
Space is limited! The conference room can hold 50 people, 60 max, and our average meetup draws about half of that. Therefore, pre-registration is REQUIRED.
Pre-registration CLOSES on OCTOBER 4. This is the last day to either pre-register, or to cancel your pre-registration. If you discover you can not come, please cancel your pre-registration so that someone else may attend.
Housing is provided to out-of-towners, on a limited, first-registered, first-serve basis.
If you are interested in giving a talk, leading a discussion, or workshop, please describe what you want to do on the pre-reg page.
Pre-Register HERE!
SCHEDULE
FRIDAY
Socializing begins at 7:30p. There may be a roundtable discussion on community building, depending on interest. (If you come early, there will be TEDxColumbus, which is over-priced, IMO.)
SATURDAY
Official workshop begins at 3p
Introduction- Erica Edelman (me)
Who We Are and What We Do.
Down the Rabbit Hole: Magic as Psychic Entertainment -Jack Strauss
Magician/Mentalist Jack Strauss will present a stage act as a psychic entertainer. Afterwards, there will be a sit-down talkback with the audience. Topics will be determined by audience questions and may include: ethics of performing on stage with a psychic persona, psychology of deception, techniques of cold reading, etc. The only topic off the table will be the specifics of how the act you just saw is performed.
Defense Against the Dark Arts: The Ethics and Psychology of Persuasion- Jesse Galef
How do we convince other people of what's true? What tactics work and don't work? What rhetorical or psychological strategies can we practice to make ourselves better at it? How |
dc9f151a-17a1-4eba-be2f-5780655284a2 | trentmkelly/LessWrong-43k | LessWrong | Covid 9/9: Passing the Peak
Labor day muddies the data a bit, but it seems that Alex Tabarrok was correct and the current wave has peaked. We could well be facing another peak in December due to seasonality. We might also have issues from schools, although as you’ll see later they’re taking extreme precautions and also we didn’t see any sign of a school effect last year.
The primary question now is how and if we return to normality. It’s no longer a question of when. We’re going to be dealing with a substantial amount of Covid for quite a while, and a large number of unvaccinated people for quite a while, and our lives are ending one minute at a time. Whatever we are going to do to return to normal life, we need to start doing it, and if we’re not doing it, accept that actually we are and whatever we are doing is now normal. Either reclaim your life and the things that bring you joy, or accept you’re not getting them back.
Note: This week’s post was written using LessWrong’s editor. Hopefully this solves the issue people were reporting with being unable to load images. Be quick to point out any remaining issues. I’m working on being able to paste Excel charts properly with the new tech stack.
Executive Summary
Top points this week:
1. Covid case numbers peak.
2. Australia’s dystopian nightmare deepens, hopefully we can avoid this.
3. Schools are acting crazy in name of prevention.
Let’s run the numbers.
The Numbers
Predictions
Once again, I forgot about an upcoming holiday, in this case Labor Day, and its tendency to screw up reporting. I think it’s because holidays don’t seem ‘real’ to me as I’ve been working from home on my own schedule most of my life.
Prediction from last week: 1.1mm cases (+5%) and 11,150 deaths (+20%).
Result: 940k cases (-9%) and 10,272 deaths (+10%).
My guess is that the 10% drop on deaths is a reporting issue, and thus the cases also have a similar reporting issue and were about flat. This is still good news, but we shouldn’t expect a bigger drop nex |
56eb5694-715d-446e-b1b7-582cace5205b | awestover/filtering-for-misalignment | Redwood Research: Alek's Filtering Results | id: post3725
A putative new idea for AI control; index here . Pick a very unsafe goal: G = "AI, make this world richer and less unequal." What does this mean as a goal, and can we make it safe? I've started to sketch out how we can codify "human understanding" in terms of human ability to answer questions. Here I'm investigating the reverse problem, to see whether the same idea can be used to give instructions to an AI. For the purpose of this post, I'll assume we have some sufficient measure of accuracy A . This is a boolean-value function, that takes as input a human h (in a particular time and place), a string/description s , and a world w or a pair of worlds w , w ′ . Then A ( h , s , w ) / A ( h , s , w , w ′ ) is true iff the string s , when presented to the human h , is an understandably accurate description (of w )/(of the difference between w and w ′ ). G is describing a world the human would not see as accurately described by G . Let w be our world, let ω be any world, and let ω G be the world that G is meant to be describing (this is an informal definition, as we haven't formalised what this means yet). Humans have a poor understanding of causality, of what causes what in the real world w (and in ω G ). A lot of strong political positions, for instance, seem predicated on denying the existence of certain trade-offs. And no-one has a complete understanding of all the physics, biology, and social sciences that best model our world. Thus the desiderata of G may be impossible to satisfy; there is no plausible world ω G that is well described by G . And on a basic and more fundamental level, we are simply ignorant of vast amounts of things about the world. No-one has a knowledge of all the basic statistical descriptors about our world, let alone the full distribution behind those descriptors. Thus even if there was a plausible world ω G well-described by G , if we had a full description of that world, we would think it very different from what we intended with G -- just as if we had a full description of w , we wouldn't recognise our own world. This suggests that G should in some way be seen as a description of the "difference" w − ω G between worlds. Modelling worlds Here we're going to replace worlds ω with models M ( ω ) of those worlds. There models are made up of variables { x i } . Each of those variables has a description s i , and we use our measure of accuracy to ensure that these descriptions are understandable. Specifically if M ( w ) and M ( ω ) are almost the same except they have different values of x i for i in a small set I , then we say the descriptions are understandable if A ( h , { s i , M ( w ) i , M ( ω ) i | i ∈ I } , w , ω ) is true. Thus the difference in the variables x i , along with the descriptions s i of x i , is a good description of the difference between worlds. Lastly, the variables x i are required to be important, to humans, based on their descriptions. Thus it is more likely to include s i = "human happiness" rather than s i = "electron density of Saturn". Testing the model: devil's advocacy Now, it should be obvious that there exists worlds ω with very positive M ( ω ) -- every human is modelled as being alive, healthy, happy, free, flourishing, equal, etc... -- that are nevertheless horrible places to live. It's not only a question of siren worlds , deceptive worlds designed to hide their badness. It's more that s i is only an accurate description of x i in worlds that differ little from w , and thus that constraining worlds to have specific M ( ω ) does not constrain them to being well described by { s i } and M ( ω ) . And even if they were well-described, it's possible that { x i } do not capture all the variables that humans find important -- it may have missed some. This is especially likely as humans often miss important background features of their own lives, that they don't have to think about. And because we haven't yet specified how to select all the variables in the model M ( ⋅ ) . Enter the devil's advocate AI, DAI. If given a world ω with model M ( ω ) , the job off the DAI is to highlight to humans all the ways the ω can go wrong, in all the ways that are not captured by M ( ω ) already. Specifically, DAI needs to produce a description string s such that: s describes the difference between w and ω well; ie A ( h , s , w , ω ) is true. s is not captured by the model difference; ie ( s , { s i } , M ( w ) , M ( ω ) ) is a more accurate description than ( { s i } , M ( w ) , M ( ω ) ) . The human h agrees s is an important fact (alternatively, we might want them to agree s is an important and negative fact). There may a back and forth cycle with other AIs that defend ω against the DAI, all of them using accurate descriptions, before the human agrees whether s is important or not. If the DAI loses, say that ω is well-modelled by M ( ω ) . Cashing out the description G We're now ready to try and cash out the description of G . First of all, we translate it into a requirement on the variables { x i } . We check whether this requirement translates well by comparing how humans interpret G versus how they interpret changes to { x i } . This allows a measure G ( w , ω ) which counts how well the variables of M ( ω ) are moved in the direction of G compared with M ( w ) . Then we can finally define ω G : ω G is well-modelled by M ( ω G ) . ω G maximises/satisfices/ quantilises G ( w , ω G ) . Note that the first requirement can be used to fix the variables in M : many variables make it easier to find well-described worlds (we may need to combine with a prior to cut down the number of variables to make sure it doesn't get too ridiculous). |
6033ed65-790b-4431-9d1f-d9241cc7da84 | StampyAI/alignment-research-dataset/blogs | Blogs | August 2021 Newsletter
#### MIRI updates
* Scott Garrabrant and Rohin Shah debate one of the central questions in AI alignment strategy: [whether we should try to avoid human-modeling capabilities in the first AGI systems](https://www.alignmentforum.org/posts/Wap8sSDoiigrJibHA/garrabrant-and-shah-on-human-modeling-in-agi).
* Scott gives a [proof](https://www.lesswrong.com/posts/jr5kyRhNriCX2Ayyg/finite-factored-sets-polynomials-and-probability) of the fundamental theorem of [finite factored sets](https://www.lesswrong.com/s/kxs3eeEti9ouwWFzr).
#### News and links
* Redwood Research, a new AI alignment research organization, is [seeking an operations lead](https://docs.google.com/document/d/1NuWFm_OKw_u5RQpf71eQqUzCJVHY9tmxznbfHt_3LhI/edit#heading=h.cm7rqk8jqp81). Led by Nate Thomas, Buck Shlegeris, and Bill Zito, Redwood Research has received a strong endorsement from MIRI Executive Director Nate Soares:
> Redwood Research seems to me to be led by people who care full-throatedly about the long-term future, have cosmopolitan values, are adamant truthseekers, and are competent administrators. The team seems to me to possess the virtue of practice, and no small amount of competence. I am excited about their ability to find and execute impactful plans that involve modern machine learning techniques. In my estimation, Redwood is among the very best places to do machine-learning based alignment research that has a chance of mattering. In fact, I consider it at least plausible that I work with Redwood as an individual contributor at some point in the future.
>
>
* Holden Karnofsky of Open Philanthropy has written a [career guide](https://forum.effectivealtruism.org/posts/bud2ssJLQ33pSemKH/my-current-impressions-on-career-choice-for-longtermists) organized around building one of nine “longtermism-relevant aptitudes”: organization building/running/boosting, political influence, research on core longtermist questions, communication, entrepreneurship, community building, software engineering, information security, and work in academia.
* Open Phil’s Joe Carlsmith [argues](https://www.openphilanthropy.org/brain-computation-report) that with the right software, 1013–1017 FLOP/s is likely enough (or more than enough) “to match the human brain’s task-performance”, with 1015 FLOP/s “more likely than not” sufficient.
* Katja Grace [discusses her work at AI Impacts](https://www.lesswrong.com/posts/xbABZRxoSTAnsf8os) on Daniel Filan’s AI X-Risk Podcast.
* Chris Olah of Anthropic discusses [what the hell is going on inside neural networks](https://80000hours.org/podcast/episodes/chris-olah-interpretability-research/) on the 80,000 Hours Podcast.
* Daniel Kokotajlo argues that the effective altruism community should [permanently stop using the term “outside view”](https://forum.effectivealtruism.org/posts/wYpARcC4WqMsDEmYR/taboo-outside-view) and “use more precise, less confused concepts instead.”
The post [August 2021 Newsletter](https://intelligence.org/2021/08/31/august-2021-newsletter/) appeared first on [Machine Intelligence Research Institute](https://intelligence.org). |
0bc003e7-2e7a-4c93-be9a-95d37dc5a8b0 | trentmkelly/LessWrong-43k | LessWrong | Meetup : San Francisco Meetup: Projects
Discussion article for the meetup : San Francisco Meetup: Projects
WHEN: 07 March 2016 06:15:00PM (-0800)
WHERE: 1597 Howard St. San Francisco, CA
We'll be meeting to work on projects!
Last time we tried solo pomodoros, so this time we'll try a meetup more focused on interacting with other people, to see how that goes. If you've got a project that you could use help on, now's the time!
We'll take 6:15 to 6:45 to hang out and possibly arrange food, and the topic will start at 6:45.
As always, call me at 301-458-0764 to be let in.
Discussion article for the meetup : San Francisco Meetup: Projects |
5b84dce2-48c8-458d-a97c-7814d4beff48 | StampyAI/alignment-research-dataset/lesswrong | LessWrong | Belief in the Implied Invisible
One generalized lesson *not* to learn from the Anti-Zombie Argument is, "Anything you can't see doesn't exist."
It's tempting to conclude the general rule. It would make the Anti-Zombie Argument much simpler, on future occasions, if we could take this as a premise. But unfortunately that's just not Bayesian.
Suppose I transmit a photon out toward infinity, not aimed at any stars, or any galaxies, pointing it toward one of the great voids between superclusters. Based on standard physics, in other words, I don't expect this photon to intercept anything on its way out. The photon is moving at light speed, so I can't chase after it and capture it again.
If the expansion of the universe is accelerating, as current cosmology holds, there will come a future point where I don't expect to be able to interact with the photon even in principle—a future time beyond which I don't expect the photon's future light cone to intercept my world-line. Even if an alien species captured the photon and rushed back to tell us, they couldn't travel fast enough to make up for the accelerating expansion of the universe.
Should I believe that, in the moment where I can no longer interact with it even in principle, the photon disappears?
No.
It would violate Conservation of Energy. And the second law of thermodynamics. And just about every other law of physics. And probably the Three Laws of Robotics. It would imply the photon knows I care about it and knows exactly when to disappear.
It's a *silly idea*.
But if you can believe in the continued existence of photons that have become experimentally undetectable to you, why doesn't this imply a general license to believe in the invisible?
(If you want to think about this question on your own, do so before the jump...)
Though I failed to Google a source, I remember reading that when it was first proposed that the Milky Way was our *galaxy* —that the hazy river of light in the night sky was made up of millions (or even billions) of stars—that Occam's Razor was invoked against the new hypothesis. Because, you see, the hypothesis vastly multiplied the number of "entities" in the believed universe. Or maybe it was the suggestion that "nebulae"—those hazy patches seen through a telescope—might be galaxies full of stars, that got the invocation of Occam's Razor.
*Lex parsimoniae: Entia non sunt multiplicanda praeter necessitatem.*
That was Occam's original formulation, the law of parsimony: Entities should not be multiplied beyond necessity.
If you postulate billions of stars that no one has ever believed in before, you're multiplying entities, aren't you?
No. There are [two Bayesian formalizations of Occam's Razor](/lw/jp/occams_razor/): Solomonoff Induction, and Minimum Message Length. Neither penalizes galaxies for being big.
Which they had better not do! One of the lessons of history is that what-we-call-reality keeps turning out to be bigger and bigger and huger yet. Remember when the Earth was at the center of the universe? Remember when no one had invented Avogadro's number? If Occam's Razor was weighing against the multiplication of entities every time, we'd have to start doubting Occam's Razor, because it would have consistently turned out to be wrong.
In Solomonoff induction, the complexity of your model is the amount of *code* in the computer program you have to write to simulate your model. The amount of *code,* not the amount of RAM it uses, or the number of cycles it takes to compute. A model of the universe that contains billions of galaxies containing billions of stars, each star made of a billion trillion decillion quarks, will take a lot of RAM to run—but the *code* only has to describe the behavior of the quarks, and the stars and galaxies can be left to run themselves. I am speaking semi-metaphorically here—there are things in the universe besides quarks—but the point is, postulating an extra billion galaxies doesn't count against the size of your code, if you've already described one galaxy. It just takes a bit more RAM, and Occam's Razor doesn't care about RAM.
Why not? The Minimum Message Length formalism, which is nearly equivalent to Solomonoff Induction, may make the principle clearer: If you have to tell someone how your model of the universe works, you don't have to individually specify the location of each quark in each star in each galaxy. You just have to write down some equations. The amount of "stuff" that obeys the equation doesn't affect how long it takes to write the equation down. If you encode the equation into a file, and the file is 100 bits long, then there are 2100 other models that would be around the same file size, and you'll need roughly 100 bits of supporting evidence. You've got a limited amount of probability mass; and a priori, you've got to divide that mass up among all the messages you could send; and so postulating a model from within a model space of 2100 alternatives, means you've got to accept a 2-100 prior probability penalty—but having more galaxies doesn't add to this.
Postulating billions of stars in billions of galaxies doesn't affect the length of your message describing the overall behavior of all those galaxies. So you don't take a probability hit from having the *same* equations describing more things. (So long as your model's predictive successes aren't sensitive to the exact initial conditions. If you've got to specify the exact positions of all the quarks for your model to predict as well as it does, the extra quarks do count as a hit.)
If you suppose that the photon disappears when you are no longer looking at it, this is an *additional law* in your model of the universe. It's the laws that are "entities", costly under the laws of parsimony. Extra quarks are free.
So does it boil down to, "I believe the photon goes on existing as it wings off to nowhere, because my priors say it's simpler for it to go on existing than to disappear"?
This is what I thought at first, but on reflection, it's not quite right. (And not just because it opens the door to obvious abuses.)
I would boil it down to a distinction between belief in the *implied invisible,* and belief in the *additional invisible.*
When you believe that the photon goes on existing as it wings out to infinity, you're not believing that as an *additional* fact.
What you believe (assign probability to) is a set of simple equations; you believe these equations describe the universe. You believe these equations because they are the simplest equations you could find that describe the evidence. These equations are *highly* experimentally testable; they explain huge mounds of evidence visible in the past, and predict the results of many observations in the future.
You believe these equations, and it is a *logical implication* of these equations that the photon goes on existing as it wings off to nowhere, so you believe that as well.
Your priors, or even your probabilities, don't *directly* talk about the photon. What you assign probability to is not the photon, but the general laws. When you assign probability to the laws of physics as we know them, you *automatically* contribute that same probability to the photon continuing to exist on its way to nowhere—if you believe the logical implications of what you believe.
It's not that you believe in the invisible *as such,* from reasoning about invisible things. Rather the experimental evidence supports certain laws, and belief in those laws logically implies the existence of certain entities that you can't interact with. This is belief in the *implied invisible.*
On the other hand, if you believe that the photon is eaten out of existence by the Flying Spaghetti Monster—maybe on this just one occasion—or even if you believed without reason that the photon hit a dust speck on its way out—then you would be believing in a specific extra invisible event, on its own. If you thought that this sort of thing happened in general, you would believe in a specific extra invisible law. This is belief in the *additional invisible.*
The whole matter would be a lot simpler, admittedly, if we could just rule out the existence of entities we can't interact with, once and for all—have the universe stop existing at the edge of our telescopes. But this requires us to be very silly.
Saying that you shouldn't ever need a separate and additional belief about invisible things—that you only believe invisibles that are *logical implications* of general laws which are themselves testable, and even then, don't have any further beliefs about them that are not logical implications of visibly testable general rules—actually does seem to rule out all abuses of belief in the invisible, when applied correctly.
Perhaps I should say, "you should assign unaltered prior probability to additional invisibles", rather than saying, "do not believe in them." But if you think of a *belief* as something evidentially additional, something you bother to track, something where you bother to count up support for or against, then it's questionable whether we should ever have additional beliefs about additional invisibles.
There are exotic cases that break this in theory. (E.g: The epiphenomenal demons are watching you, and will torture [3^^^3](/lw/kd/pascals_mugging_tiny_probabilities_of_vast/) victims for a year, somewhere you can't ever verify the event, if you ever say the word "Niblick".) But I can't think of a case where the principle fails in human practice.
**Added:** To make it clear why you would sometimes want to think about implied invisibles, suppose you're going to launch a spaceship, at nearly the speed of light, toward a faraway supercluster. By the time the spaceship gets there and sets up a colony, the universe's expansion will have accelerated too much for them to ever send a message back. Do you deem it worth the purely altruistic effort to set up this colony, for the sake of all the people who will live there and be happy? Or do you think the spaceship blips out of existence before it gets there? This could be a very real question at some point. |
19114dfe-dfde-4676-a36f-8922ba89ebb0 | trentmkelly/LessWrong-43k | LessWrong | The silos of expertise: beyond heuristics and biases
Separate silos of expertise
I've been doing a lot of work on expertise recently, on the issue of measuring it and assessing it. The academic research out there is fascinating, though rather messy. Like many areas in the social sciences, it often suffers from small samples and overgeneralising from narrow examples. More disturbingly, the research projects seems to be grouped into various "silos" that don't communicate much with each other, each silo continuing on their own pet projects.
The main four silos I've identified are:
There may be more silos than this - many people working in expertise studies haven't heard of all of these (for instance, I was ignorant of Cooke's research until it was pointed out to me by someone who hadn't heard of Shanteau or Klein). The division into silos isn't perfect; Shanteau, for instance, has addressed the biases literature at least once (Shanteau, James. "Decision making by experts: The GNAHM effect." Decision Science and Technology. Springer US, 1999. 105-130), Kahneman and Klein have authored a paper together (Kahneman, Daniel, and Gary Klein. "Conditions for intuitive expertise: a failure to disagree." American Psychologist 64.6 (2009): 515). But in general the mutual ignoring (or mutual ignorance) seems pretty strong between the silos.
Less Wrongers are probably very familiar with the heuristics and biases approach, so that doesn't need to be rehashed here. Shanteau's silo mainly revolves around estimating when experts are true experts, concluding that the nature of the task attempted is key (see this table for the characteristics of tasks conducive to genuine expertise), and coming up with some indirect measures of expert performance in fields where an objective standard isn't available (Shanteau, James, et al. "Performance-based assessment of expertise: How to decide if someone is an expert or not." European Journal of Operational Research 136.2 (2002): 253-263).
This post will therefore be looking at the last two sil |
4b0e8fbe-51a8-4727-bcbf-94377b43416b | trentmkelly/LessWrong-43k | LessWrong | Do we know if spaced repetition can be used with randomized content?
Disclaimer: there may be major flaws in the way I use words. Corrections are welcome.
----------------------------------------
Suppose I want to memorize all the software design patterns.
I could use spaced repetition and create a new deck of flashcards. Each card would have the name of the pattern on one side and the definition on the other.
This would help me understand references to patterns without opening Wikipedia every time. This would probably help me recognize patterns by descriptions, as long as they're close enough to the definitions.
But this wouldn't help me recognize patterns just by looking at their implementations. I'd have to actively think about each pattern I remember and compare the definition and the code.
I could create a second deck, with names and examples. But then I'd just memorize those specific examples and maybe get better at recognizing similar ones.
This problem is similar to that of testing software. (There must be a more straightforward analogy, but I couldn't find one.) Individual tests can only prevent individual errors. Formal verification is better, but not always possible. The next best thing is fuzzing: using random inputs and heuristics like "did it crash?".
So I wonder if I could generate new examples on the fly. (More realistically, pull hand-labeled examples from a database.)
The idea is that a skill like recognizing a pattern in the code should also be a form of memory. Or at least the parts of it that do not change between the examples. So using spaced repetition with randomized examples would be like JIT-compilation in brains.
There was an LW post about genetic programming working better when the environment was modular. Maybe something similar would happen here.
But I couldn't find anything on the internet. Has anybody seen any research on this? |
9078a1d0-11b5-44dd-aa36-1584b276da8d | trentmkelly/LessWrong-43k | LessWrong | Group Rationality Diary, September 16-30
This is the public group instrumental rationality diary for September 16-30.
> It's a place to record and chat about it if you have done, or are actively doing, things like:
>
> * Established a useful new habit
> * Obtained new evidence that made you change your mind about some belief
> * Decided to behave in a different way in some set of situations
> * Optimized some part of a common routine or cached behavior
> * Consciously changed your emotions or affect with respect to something
> * Consciously pursued new valuable information about something that could make a big difference in your life
> * Learned something new about your beliefs, behavior, or life that surprised you
> * Tried doing any of the above and failed
>
> Or anything else interesting which you want to share, so that other people can think about it, and perhaps be inspired to take action themselves. Try to include enough details so that everyone can use each other's experiences to learn about what tends to work out, and what doesn't tend to work out.
Thanks to cata for starting the Group Rationality Diary posts, and to commenters for participating.
Previous diary: September 1-15
Next diary: October 1-15
Rationality diaries archive |
06f0ce49-d65d-4fde-b341-becc2158a6ab | trentmkelly/LessWrong-43k | LessWrong | Articles in Main
Hi all,
We shut off Main back in February to force everything into Discussion, and I still think the Main/Discussion split should be replaced (by better use of the tagging system, or by different subreddits based more about the style of interaction that people are looking for than the content, or so on), but (as mentioned then) we're going to be using Main for posts we want to make sure get into the RSS feed.
This is awkward because everything else is in Discussion, and Main is still a weird visibility zone, where stuff in Main that isn't Promoted is sort of in limbo. There are ways to improve this long-term, but in the short term, it looks like there are some easy options:
1. Open Thread comments linking to new promoted Main posts
2. Linkposts that point to new promoted Main posts
3. Something else?
(As said before, this should hopefully be a temporary measure; if we add promoted posts in Discussion to the site RSS (github issue), then those posts will show up in Discussion and in the RSS and everything is great.) |
78883827-eb9b-4dcc-bc45-977e8482263c | trentmkelly/LessWrong-43k | LessWrong | Funding for programs and events on global catastrophic risk, effective altruism, and other topics
[cross-posted from the EA Forum]
Post authors: Eli Rose, Asya Bergal
Posting in our capacities as members of Open Philanthropy’s Global Catastrophic Risks Capacity Building team.
Note: This program, together with our separate program for work that builds capacity to address risks from transformative AI, has replaced our 2021 request for proposals for outreach projects. If you have a project which was in-scope for that program but isn't for either of these, you can apply to our team's general application instead.
Apply for funding here. Applications are open until further notice and will be assessed on a rolling basis.
This is a wide-ranging call for applications, seeking to fund programs and events in a variety of areas of interest to Open Philanthropy — including effective altruism, global catastrophic risks, biosecurity, AI for epistemics, forecasting, and other areas. In general, if the topic of your program or event falls within one of our GCR focus areas, or if it’s similar to work we’ve funded in the past in our GCR focus areas, it may be a good fit for this program. If you’re unsure about whether to submit your application, we’d encourage you to err on the side of doing so.
By "programs and events" we mean scholarship or fellowship programs, internships, residencies, visitor programs, courses[1], seminars, conferences, workshops, retreats, etc., including both in-person and online activities. We're open to funding programs or events aimed at individuals at any career stage, and with a wide range of potential purposes, including teaching new skills, providing new career opportunities, offering mentorship, or facilitating networking.
Examples of programs and events of this type we've funded before include:
* Condor Camp, a summer program for Brazilian students interested in existential risk work.
* The Future of Humanity Institute’s Research Scholars Program supporting early-career researchers in global catastrophic risk.
* Effective Altruism Global, |
0f9f6ee1-6b6a-4092-ac95-80756ca7e3d4 | StampyAI/alignment-research-dataset/lesswrong | LessWrong | Contra Anton 🏴☠️ on Kolmogorov complexity and recursive self improvement
Twitter user @atroyn [claims](https://twitter.com/atroyn/status/1673036126804934657) that recursive self-improvement is impossible because of Kolmogorov complexity. Quoting most of[[1]](#fn-stJPzfqNK7rsBfueA-1) the argument here:
>
> here is an argument against the possibility of recursive self improvement of any 'intelligent' computer program, based on kolmogorov complexity.
>
>
> intelligence is the ability to make correct predictions about the state of the world given available information.
>
>
> each program which makes predictions about the world has a kolmogorov complexity corresponding to the length of the shortest string which can express that program
>
>
> for a given program p call this complexity k.
>
>
> (unfortunately k(p) is in general uncomputable, the proof reduces to the halting problem, but that's not important here)
>
>
> more intelligence (in our definition) implies the ability to predict more of the world more accurately, i.e. to express more of the world's complexity - this implies that a more intelligent program p2 necessarily has more complexity than a less intelligent p1
>
>
> to see that this is necessarily so, note that if we could predict the world equally accurately as p1's prediction with a program p0 with k0 < k1, then we have a contradiction since k1 was supposed to be the minimal expression of intelligence at that level
>
>
> in order to get recursive self improvement, you need a program p1 which is capable of emitting p2 which is better able to predict the world than p1 - i.e., we need p1 to emit p2 such that k2 > k1
>
>
> but this is a contradiction.
>
>
> [...]
>
>
>
The mistake here is the assumption that a program that models the world better necessarily has a higher Kolmogorov complexity. Originally, Kolmogorov complexity measured the complexity of bit strings. But we're talking about predictors here, things that observe the world and spit out probability distributions over observed outcomes. In the context of predictors, Kolmogorov complexity measures the complexity of a function from observations to predictions.
In the case of ideal Bayesian reasoning, we can nail down such a function just by specifying a prior, eg. the Solomonoff prior. (Plus, an approximation scheme to keep things computable, I guess.) This doesn't take a very large program to implement. But a non-ideal reasoner will screw up in many cases, and there's information contained in the exact way it screws up for each set of observations. Such reasoners can have an almost arbitrarily high Kolmogorov complexity, and they're all worse than the ideal Bayesian program.
In other words, the successor program has Kolmogorov complexity less than or equal to that of its predecessor, but so what? That doesn't imply that it's worse.
(Also, Kolmogorov complexity doesn't care about how much time a program takes to run at all, but in the real world it's an important consideration, and a target for self-improvement.)
That concludes this post: without the assumption that higher Kolmogorov complexity is better, the whole argument falls apart.
---
1. The rest of the thread briefly touches on the issue of *how an AI could know that its successor would necessarily be an improvement*. The discussion there is kind of doomed since it's done with the goal of showing that the successor has lower or equal Kolmogorov complexity than the original, which is uninteresting, though we can see right away that it *must* be true, assuming that the original writes the successor before observing the world at all. But there's an interesting version of the question, which asks about the set of axioms used by the systems to reason about the world, rather than the Kolmogorov complexity. See [this paper](https://intelligence.org/files/TilingAgentsDraft.pdf) by Yudkowsky and Herreshoff for details. [↩︎](#fnref-stJPzfqNK7rsBfueA-1) |
74879453-c59c-4aec-aaa5-46d3d2d7247e | trentmkelly/LessWrong-43k | LessWrong | Humanity is Winning the Fight Against Infectious Disease
One of my favorite things about living in the 21st century United States is how so few people die of infectious disease. Here's a graph of deaths showing how infectious diseases decreased by an order of magnitude between the turn of the century and Salk's Polio Vaccine.
In 1900, 12% of deaths were caused by pneumonia and influenza. 11% were caused by tuberculosis. 8% were caused by of diarrhea. A hundred years ago infectious diseases killed over one third of everyone. In contrast, not a single person in my extended social circle has ever died of an infectious disease. I know more people who were killed by airplane crashes than by infectious diseases.
The raw 10× reduction undersells the progress we've made against infectious disease. We have more people overall and we live together in cities. Death due to infectious disease should have skyrocketed over the last century. We would have been fortunate if medicine and sanitation merely kept infectious disease at 1900 levels.
The emergence of new diseases like HIV and COVID-19 has had a tiny impact compared to the overall trend.
> In 2019, there were 15,815 deaths among adults and adolescents with diagnosed HIV in the United States and 6 dependent areas. These deaths may be due to any cause.
>
> ―hiv.gov
2,855,000 Americans died in 2019. Those with HIV were 0.5% of the total. Even if we are maximally pessimistic and attribute to HIV every single death of every single American with HIV, this is a tiny fraction compared to how many people used to die of the plagues of 1900.
As of July 20, 2021, COVID-19 killed 600,000 Americans over the course of 1.5 years. That's 400,000 deaths per year. At 13% of total deaths, COVID-19 temporarily increased deaths due to infectious disease back to what we had in the 1940s. But the increase is temporary. We have vaccines. Even if we didn't have vaccines, deaths due to COVID-19 would decrease naturally after it burned through the vulnerable population.
If new diseases emerged |
849e3da8-ab23-460c-aea7-fc82b645c299 | trentmkelly/LessWrong-43k | LessWrong | A Limited But Better Than Nothing Way To Assign Probabilities to Statements of Logic, Arithmetic, etc.
If we want to reason with probability theory, we seem to be stuck if we want to reason about mathematics.
You can skip this pararaph and the next if you're familiar with the problem. But if you're not, here's an illustration. Suppose your friend has some pennies that she would like to arrange into a rectangle, which of course is impossible if the number of pennies is prime. Let's call the number of pennies N. Your friend would like to use probability theory to guess whether it's worth trying; if there's a 50% chance that Prime(N), she won't bother trying to make the rectangle. You might imagine that if she counts them and finds that there's an odd number, this is evidence of Prime(N); if she furthermore notices that the digits don't sum to a multiple of three, this is further evidence of Prime(N). In general, each test of compositeness that she knows should, if it fails, raise the probability of Prime(N).
But what happens instead is this. Suppose you both count them, and find that N=53. Being a LessWrong reader, you of course recognize from recently posted articles that N=53 implies Prime(N), though she does not. But this means that P(N=53) <= P(Prime(N)). If you're quite sure of N=53—that is, P(N=53) is near 1—then P(Prime(N)) is also near 1. There's no way for her to get a gradient of uncertainty from simple tests of compositeness. The probability is just some number near 1.
In general, conditional on the axioms, mathematical theorems have probability 1 if they're true, and 0 if they're false. Deriving these probabilities is exactly as difficult as deriving the theorems themselves.
A way of assigning actual probabilities to theorems occurred to me today. I usually see this problem discussed by folks that want to develop formal models of AI, and I don't know if this'll be helpful at all for that. But it's something I can imagine myself using when I want to reason about a mathematical conjecture in a basically reasonable way.
The basic idea is ju |
7e1784a1-ba63-4da0-80c8-257433dce70d | trentmkelly/LessWrong-43k | LessWrong | Old-world Politics Fallacy
When a nasty political problem (like the current SSC situation) hits my consciousness, I'm habituated to Do Something About It. I feel an urge to investigate the political climate, find allies, and fight back against the threat. In the current Internet age, and with my nonexistent political clout and social influence (especially considering I live in Iran and people here generally can't be counted on to know or care about global politics), the substitution bias kicks in; I substitute doing The Real Thing (to which my contribution would be very meager if any) with reading online forums (Reddit, Twitter, Lesswrong, SSC, Hackernews, ...)(substituted for "investigate the political climate"), voting the Correct posts in said forums and possibly writing some low-effort answers to particularly egregious pieces ("find allies, and fight back"), and generally feeling bad that I have failed the Mission (and that the Society is broken).
I speculate that this fallacy probably has some evolutionary roots. In a hunter-gatherer tribe, a person such as myself (I estimate myself to be upper-mid status.) would have had a fair chance of affecting political change against causes that mostly hurt everyone but a minority of politicians who don't produce much value anyways. Especially since I (and my family) have been quite morally upstanding and honest, in a small community, we would have had a reputation to draw on. Even if not, engaging with the community would have been the essential first step in being part of a coalition, necessary for survival.
Obviously, in the 21st century, all this is moot for political stuff that actually matters. Most people are quite powerless in affecting those matters, one reason being that the important issues now affect orders of magnitude more people. I don't know what the optimal strategy currently is. My gut feeling is that a lot of the good people are un-politicizing themselves and simply giving up. (Hasn't Scott's default defensive strategy been mor |
d1086442-7213-4172-a1bd-b050b36f0061 | trentmkelly/LessWrong-43k | LessWrong | Possible OpenAI's Q* breakthrough and DeepMind's AlphaGo-type systems plus LLMs
tl;dr: OpenAI leaked AI breakthrough called Q*, acing grade-school math. It is hypothesized combination of Q-learning and A*. It was then refuted. DeepMind is working on something similar with Gemini, AlphaGo-style Monte Carlo Tree Search. Scaling these might be crux of planning for increasingly abstract goals and agentic behavior. Academic community has been circling around these ideas for a while.
Reuters: OpenAI researchers warned board of AI breakthrough ahead of CEO ouster, sources say
Michael Trazzi, on Twitter:
> "Ahead of OpenAI CEO Sam Altman’s four days in exile, several staff researchers sent the board of directors a letter warning of a powerful artificial intelligence discovery that they said could threaten humanity
>
> Mira Murati told employees on Wednesday that a letter about the AI breakthrough called Q* (pronounced Q-Star), precipitated the board's actions.
>
> Given vast computing resources, the new model was able to solve certain mathematical problems. Though only performing math on the level of grade-school students, acing such tests made researchers very optimistic about Q*’s future success."
Silas Alberti, Twitter:
> "What could OpenAI’s breakthrough Q* be about?
>
> It sounds like it’s related to Q-learning. (For example, Q* denotes the optimal solution of the Bellman equation.) Alternatively, referring to a combination of the A* algorithm and Q learning.
>
> One natural guess is that it is AlphaGo-style Monte Carlo Tree Search of the token trajectory. 🔎 It seems like a natural next step: Previously, papers like AlphaCode showed that even very naive brute force sampling in an LLM can get you huge improvements in competitive programming. The next logical step is to search the token tree in a more principled way. This particularly makes sense in settings like coding and math where there is an easy way to determine correctness. -> Indeed, Q* seems to be about solving Math problems 🧮"
Mark Riedl, Twitter:
> "Anyone want to speculate o |
71450090-c438-4652-b289-306888235b53 | trentmkelly/LessWrong-43k | LessWrong | Physical and Mental Behavior
B.F. Skinner called thoughts "mental behavior". He believed they could be rewarded and punished just like physical behavior, and that they increased or declined in frequency accordingly.
Sadly, psychology has not yet advanced to the point where we can give people electric shocks for thinking things, so the sort of rewards and punishments that reinforce thoughts must be purely internal reinforcement. A thought or intention that causes good feelings gets reinforced and prospers; one that causes bad feelings gets punished and dies out.
(Roko has already discussed this in Ugh Fields; so much as thinking about an unpleasant task is unpleasant; therefore most people do not think about unpleasant tasks and end up delaying them or avoiding them completely. If you haven't already read that post, it does a very good job of making reinforcement of thoughts make sense.)
A while back, D_Malik published a great big List Of Things One Could Do To Become Awesome. As David_Gerard replied, the list was itself a small feat of awesome. I expect a couple of people started on some of the more awesome-sounding entries, then gave up after a few minutes and never thought about it again. Why?
When I was younger, I used to come up with plans to become awesome in some unlikely way. Maybe I'd hear someone speaking Swahili, and I would think "I should learn Swahili," and then I would segue into daydreams of being with a group of friends, and someone would ask if any of us spoke any foreign languages, and I would say I was fluent in Swahili, and they would all react with shock and tell me I must be lying, and then a Kenyan person would wander by, and I'd have a conversation with them in Swahili, and they'd say that I was the first American they'd ever met who was really fluent in Swahili, and then all my friends would be awed and decide I was the best person ever, and...
...and the point is that the thought of learning Swahili is pleasant, in the same easy-to-visualize but useless way that |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.