Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
65,313 | 8,797,589,696 | IssuesEvent | 2018-12-23 21:46:40 | sean0x42/SQLAdapter | https://api.github.com/repos/sean0x42/SQLAdapter | opened | Create a saving, inserting, and updating guide. | 1.0 documentation | This guide explores ways in which you can insert/update models into your db. | 1.0 | Create a saving, inserting, and updating guide. - This guide explores ways in which you can insert/update models into your db. | non_priority | create a saving inserting and updating guide this guide explores ways in which you can insert update models into your db | 0 |
221,500 | 24,642,724,785 | IssuesEvent | 2022-10-17 12:52:50 | AdamOswald/face | https://api.github.com/repos/AdamOswald/face | closed | protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl: 1 vulnerabilities (highest severity is: 7.5) | ARCH PO security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl</b></p></summary>
<p>Protocol Buffers</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/19/a5/ac51df34cdf4739574492ed4903c11dadd72a7bec4a31bb0496f4f50fc19/protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/19/a5/ac51df34cdf4739574492ed4903c11dadd72a7bec4a31bb0496f4f50fc19/protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt</p>
<p>Path to vulnerable library: /module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt,/module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt,/module/extension-cpp-master/cuda,/module/wombopy-main,/SwapNet-jwyang-roi-version/.ws-temp-INQNDT-requirements.txt,/SwapNet-jwyang-roi-version/.ws-temp-INQNDT-requirements.txt</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/AdamOswald/face/commit/1def381581db59d139b24ef0a32eed6f8e3b2af8">1def381581db59d139b24ef0a32eed6f8e3b2af8</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2022-1941](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1941) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl | Direct | Google.Protobuf - 3.18.3,3.19.5,3.20.2,3.21.6;protobuf-python - 3.18.3,3.19.5,3.20.2,4.21.6 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-1941</summary>
### Vulnerable Library - <b>protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl</b></p>
<p>Protocol Buffers</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/19/a5/ac51df34cdf4739574492ed4903c11dadd72a7bec4a31bb0496f4f50fc19/protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/19/a5/ac51df34cdf4739574492ed4903c11dadd72a7bec4a31bb0496f4f50fc19/protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt</p>
<p>Path to vulnerable library: /module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt,/module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt,/module/extension-cpp-master/cuda,/module/wombopy-main,/SwapNet-jwyang-roi-version/.ws-temp-INQNDT-requirements.txt,/SwapNet-jwyang-roi-version/.ws-temp-INQNDT-requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AdamOswald/face/commit/1def381581db59d139b24ef0a32eed6f8e3b2af8">1def381581db59d139b24ef0a32eed6f8e3b2af8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing vulnerability for the MessageSet type in the ProtocolBuffers versions prior to and including 3.16.1, 3.17.3, 3.18.2, 3.19.4, 3.20.1 and 3.21.5 for protobuf-cpp, and versions prior to and including 3.16.1, 3.17.3, 3.18.2, 3.19.4, 3.20.1 and 4.21.5 for protobuf-python can lead to out of memory failures. A specially crafted message with multiple key-value per elements creates parsing issues, and can lead to a Denial of Service against services receiving unsanitized input. We recommend upgrading to versions 3.18.3, 3.19.5, 3.20.2, 3.21.6 for protobuf-cpp and 3.18.3, 3.19.5, 3.20.2, 4.21.6 for protobuf-python. Versions for 3.16 and 3.17 are no longer updated.
<p>Publish Date: 2022-09-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1941>CVE-2022-1941</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cloud.google.com/support/bulletins#GCP-2022-019">https://cloud.google.com/support/bulletins#GCP-2022-019</a></p>
<p>Release Date: 2022-09-22</p>
<p>Fix Resolution: Google.Protobuf - 3.18.3,3.19.5,3.20.2,3.21.6;protobuf-python - 3.18.3,3.19.5,3.20.2,4.21.6</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl: 1 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl</b></p></summary>
<p>Protocol Buffers</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/19/a5/ac51df34cdf4739574492ed4903c11dadd72a7bec4a31bb0496f4f50fc19/protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/19/a5/ac51df34cdf4739574492ed4903c11dadd72a7bec4a31bb0496f4f50fc19/protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt</p>
<p>Path to vulnerable library: /module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt,/module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt,/module/extension-cpp-master/cuda,/module/wombopy-main,/SwapNet-jwyang-roi-version/.ws-temp-INQNDT-requirements.txt,/SwapNet-jwyang-roi-version/.ws-temp-INQNDT-requirements.txt</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/AdamOswald/face/commit/1def381581db59d139b24ef0a32eed6f8e3b2af8">1def381581db59d139b24ef0a32eed6f8e3b2af8</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2022-1941](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1941) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl | Direct | Google.Protobuf - 3.18.3,3.19.5,3.20.2,3.21.6;protobuf-python - 3.18.3,3.19.5,3.20.2,4.21.6 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-1941</summary>
### Vulnerable Library - <b>protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl</b></p>
<p>Protocol Buffers</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/19/a5/ac51df34cdf4739574492ed4903c11dadd72a7bec4a31bb0496f4f50fc19/protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/19/a5/ac51df34cdf4739574492ed4903c11dadd72a7bec4a31bb0496f4f50fc19/protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt</p>
<p>Path to vulnerable library: /module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt,/module/SwapNet-jwyang-roi-version/.ws-temp-THANSD-requirements.txt,/module/extension-cpp-master/cuda,/module/wombopy-main,/SwapNet-jwyang-roi-version/.ws-temp-INQNDT-requirements.txt,/SwapNet-jwyang-roi-version/.ws-temp-INQNDT-requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **protobuf-3.7.1-cp37-cp37m-manylinux1_x86_64.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AdamOswald/face/commit/1def381581db59d139b24ef0a32eed6f8e3b2af8">1def381581db59d139b24ef0a32eed6f8e3b2af8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing vulnerability for the MessageSet type in the ProtocolBuffers versions prior to and including 3.16.1, 3.17.3, 3.18.2, 3.19.4, 3.20.1 and 3.21.5 for protobuf-cpp, and versions prior to and including 3.16.1, 3.17.3, 3.18.2, 3.19.4, 3.20.1 and 4.21.5 for protobuf-python can lead to out of memory failures. A specially crafted message with multiple key-value per elements creates parsing issues, and can lead to a Denial of Service against services receiving unsanitized input. We recommend upgrading to versions 3.18.3, 3.19.5, 3.20.2, 3.21.6 for protobuf-cpp and 3.18.3, 3.19.5, 3.20.2, 4.21.6 for protobuf-python. Versions for 3.16 and 3.17 are no longer updated.
<p>Publish Date: 2022-09-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1941>CVE-2022-1941</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cloud.google.com/support/bulletins#GCP-2022-019">https://cloud.google.com/support/bulletins#GCP-2022-019</a></p>
<p>Release Date: 2022-09-22</p>
<p>Fix Resolution: Google.Protobuf - 3.18.3,3.19.5,3.20.2,3.21.6;protobuf-python - 3.18.3,3.19.5,3.20.2,4.21.6</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_priority | protobuf whl vulnerabilities highest severity is vulnerable library protobuf whl protocol buffers library home page a href path to dependency file module swapnet jwyang roi version ws temp thansd requirements txt path to vulnerable library module swapnet jwyang roi version ws temp thansd requirements txt module swapnet jwyang roi version ws temp thansd requirements txt module extension cpp master cuda module wombopy main swapnet jwyang roi version ws temp inqndt requirements txt swapnet jwyang roi version ws temp inqndt requirements txt found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high protobuf whl direct google protobuf protobuf python details cve vulnerable library protobuf whl protocol buffers library home page a href path to dependency file module swapnet jwyang roi version ws temp thansd requirements txt path to vulnerable library module swapnet jwyang roi version ws temp thansd requirements txt module swapnet jwyang roi version ws temp thansd requirements txt module extension cpp master cuda module wombopy main swapnet jwyang roi version ws temp inqndt requirements txt swapnet jwyang roi version ws temp inqndt requirements txt dependency hierarchy x protobuf whl vulnerable library found in head commit a href found in base branch master vulnerability details a parsing vulnerability for the messageset type in the protocolbuffers versions prior to and including and for protobuf cpp and versions prior to and including and for protobuf python can lead to out of memory failures a specially crafted message with multiple key value per elements creates parsing issues and can lead to a denial of service against services receiving unsanitized input we recommend upgrading to versions for protobuf cpp and for protobuf python versions for and are no longer updated publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution google protobuf protobuf python step up your open source security game with mend | 0 |
61,631 | 12,194,285,323 | IssuesEvent | 2020-04-29 15:35:15 | kwk/test-llvm-bz-import-5 | https://api.github.com/repos/kwk/test-llvm-bz-import-5 | closed | Wrong generation of code for implicit cast to variably modified type | BZ-BUG-STATUS: RESOLVED BZ-RESOLUTION: FIXED clang/LLVM Codegen dummy import from bugzilla | This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=8239. | 1.0 | Wrong generation of code for implicit cast to variably modified type - This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=8239. | non_priority | wrong generation of code for implicit cast to variably modified type this issue was imported from bugzilla | 0 |
334,943 | 24,446,257,326 | IssuesEvent | 2022-10-06 18:14:42 | gravitational/teleport | https://api.github.com/repos/gravitational/teleport | closed | Invalid example for ssh nodes | documentation OpenSSH cloud | ## Details
This example shows connecting to a different port then `3022` for a ssh node. Teleport Cloud only supports reverse tunnel for Teleport agent daemons.
https://goteleport.com/docs/server-access/guides/openssh/?scope=cloud
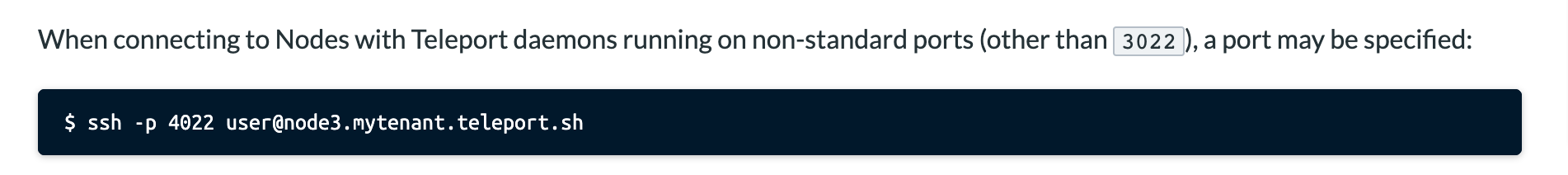
### Category
- Improve Existing
| 1.0 | Invalid example for ssh nodes - ## Details
This example shows connecting to a different port then `3022` for a ssh node. Teleport Cloud only supports reverse tunnel for Teleport agent daemons.
https://goteleport.com/docs/server-access/guides/openssh/?scope=cloud
### Category
- Improve Existing
| non_priority | invalid example for ssh nodes details this example shows connecting to a different port then for a ssh node teleport cloud only supports reverse tunnel for teleport agent daemons category improve existing | 0 |
324,432 | 23,998,646,562 | IssuesEvent | 2022-09-14 09:35:25 | maxrohleder/ReMAS | https://api.github.com/repos/maxrohleder/ReMAS | closed | Update final Class and project structure overview in docs | documentation | All helpful images etc. from thesis | 1.0 | Update final Class and project structure overview in docs - All helpful images etc. from thesis | non_priority | update final class and project structure overview in docs all helpful images etc from thesis | 0 |
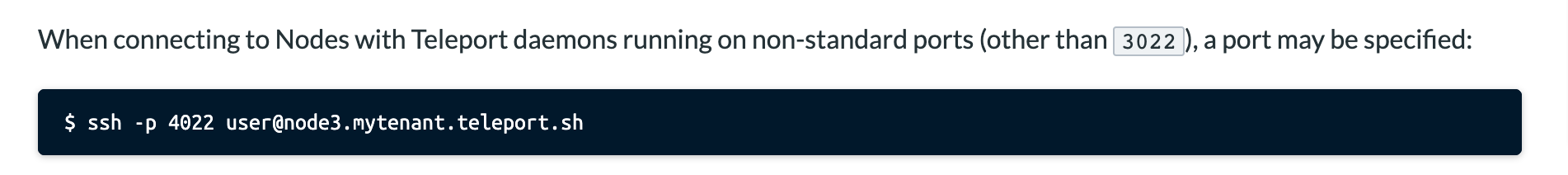
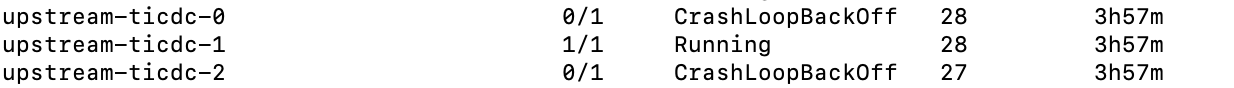
5,396 | 19,475,977,068 | IssuesEvent | 2021-12-24 12:23:53 | pingcap/tiflow | https://api.github.com/repos/pingcap/tiflow | opened | CDC continuous OOM for truncate 500 table | type/bug found/automation area/ticdc | ### What did you do?
- Run test-infra case: cdc_truncate_table_sync
- Run sysbench to create 500 tables, then truncate these tables one by one, interval 2s.
### What did you expect to see?
_No response_
### What did you see instead?
- CDC OOM repeatedly:
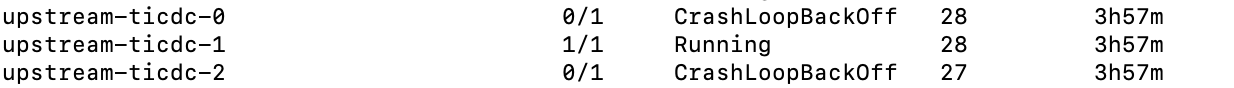
### Versions of the cluster
Upstream TiDB cluster version (execute `SELECT tidb_version();` in a MySQL client):
```console
5.0.6
```
TiCDC version (execute `cdc version`):
```console
5.0.6
``` | 1.0 | CDC continuous OOM for truncate 500 table - ### What did you do?
- Run test-infra case: cdc_truncate_table_sync
- Run sysbench to create 500 tables, then truncate these tables one by one, interval 2s.
### What did you expect to see?
_No response_
### What did you see instead?
- CDC OOM repeatedly:
### Versions of the cluster
Upstream TiDB cluster version (execute `SELECT tidb_version();` in a MySQL client):
```console
5.0.6
```
TiCDC version (execute `cdc version`):
```console
5.0.6
``` | non_priority | cdc continuous oom for truncate table what did you do run test infra case cdc truncate table sync run sysbench to create tables then truncate these tables one by one interval what did you expect to see no response what did you see instead cdc oom repeatedly versions of the cluster upstream tidb cluster version execute select tidb version in a mysql client console ticdc version execute cdc version console | 0 |
262,985 | 19,850,330,472 | IssuesEvent | 2022-01-21 11:32:48 | davidpcaldwell/slime | https://api.github.com/repos/davidpcaldwell/slime | opened | Get rid of spurious global variable slime in TypeDoc | documentation fifty | Currently declared in `jsh/tools/slime.js` on line 7; unclear whether it can be removed from global TypeScript scope easily. | 1.0 | Get rid of spurious global variable slime in TypeDoc - Currently declared in `jsh/tools/slime.js` on line 7; unclear whether it can be removed from global TypeScript scope easily. | non_priority | get rid of spurious global variable slime in typedoc currently declared in jsh tools slime js on line unclear whether it can be removed from global typescript scope easily | 0 |
239,347 | 26,223,085,682 | IssuesEvent | 2023-01-04 16:17:44 | RG4421/addin-tokenauthentication | https://api.github.com/repos/RG4421/addin-tokenauthentication | opened | WS-2022-0161 (High) detected in newtonsoft.json.10.0.3.nupkg | security vulnerability | ## WS-2022-0161 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>newtonsoft.json.10.0.3.nupkg</b></p></summary>
<p>Json.NET is a popular high-performance JSON framework for .NET</p>
<p>Library home page: <a href="https://api.nuget.org/packages/newtonsoft.json.10.0.3.nupkg">https://api.nuget.org/packages/newtonsoft.json.10.0.3.nupkg</a></p>
<p>Path to dependency file: /Blackbaud.Addin.TokenAuthentication.nuspec</p>
<p>Path to vulnerable library: /Blackbaud.Addin.TokenAuthentication.nuspec,/Blackbaud.Addin.TokenAuthentication.Tests/Blackbaud.Addin.TokenAuthentication.Tests.csproj,/Blackbaud.Addin.TokenAuthentication.Tester/Blackbaud.Addin.TokenAuthentication.Tester.csproj</p>
<p>
Dependency Hierarchy:
- :x: **newtonsoft.json.10.0.3.nupkg** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Improper Handling of Exceptional Conditions in Newtonsoft.Json.
Newtonsoft.Json prior to version 13.0.1 is vulnerable to Insecure Defaults due to improper handling of StackOverFlow exception (SOE) whenever nested expressions are being processed. Exploiting this vulnerability results in Denial Of Service (DoS), and it is exploitable when an attacker sends 5 requests that cause SOE in time frame of 5 minutes. This vulnerability affects Internet Information Services (IIS) Applications.
<p>Publish Date: 2022-06-22
<p>URL: <a href=https://github.com/JamesNK/Newtonsoft.Json/commit/7e77bbe1beccceac4fc7b174b53abfefac278b66>WS-2022-0161</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-06-22</p>
<p>Fix Resolution: Newtonsoft.Json - 13.0.1;Microsoft.Extensions.ApiDescription.Server - 6.0.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | WS-2022-0161 (High) detected in newtonsoft.json.10.0.3.nupkg - ## WS-2022-0161 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>newtonsoft.json.10.0.3.nupkg</b></p></summary>
<p>Json.NET is a popular high-performance JSON framework for .NET</p>
<p>Library home page: <a href="https://api.nuget.org/packages/newtonsoft.json.10.0.3.nupkg">https://api.nuget.org/packages/newtonsoft.json.10.0.3.nupkg</a></p>
<p>Path to dependency file: /Blackbaud.Addin.TokenAuthentication.nuspec</p>
<p>Path to vulnerable library: /Blackbaud.Addin.TokenAuthentication.nuspec,/Blackbaud.Addin.TokenAuthentication.Tests/Blackbaud.Addin.TokenAuthentication.Tests.csproj,/Blackbaud.Addin.TokenAuthentication.Tester/Blackbaud.Addin.TokenAuthentication.Tester.csproj</p>
<p>
Dependency Hierarchy:
- :x: **newtonsoft.json.10.0.3.nupkg** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Improper Handling of Exceptional Conditions in Newtonsoft.Json.
Newtonsoft.Json prior to version 13.0.1 is vulnerable to Insecure Defaults due to improper handling of StackOverFlow exception (SOE) whenever nested expressions are being processed. Exploiting this vulnerability results in Denial Of Service (DoS), and it is exploitable when an attacker sends 5 requests that cause SOE in time frame of 5 minutes. This vulnerability affects Internet Information Services (IIS) Applications.
<p>Publish Date: 2022-06-22
<p>URL: <a href=https://github.com/JamesNK/Newtonsoft.Json/commit/7e77bbe1beccceac4fc7b174b53abfefac278b66>WS-2022-0161</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-06-22</p>
<p>Fix Resolution: Newtonsoft.Json - 13.0.1;Microsoft.Extensions.ApiDescription.Server - 6.0.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | ws high detected in newtonsoft json nupkg ws high severity vulnerability vulnerable library newtonsoft json nupkg json net is a popular high performance json framework for net library home page a href path to dependency file blackbaud addin tokenauthentication nuspec path to vulnerable library blackbaud addin tokenauthentication nuspec blackbaud addin tokenauthentication tests blackbaud addin tokenauthentication tests csproj blackbaud addin tokenauthentication tester blackbaud addin tokenauthentication tester csproj dependency hierarchy x newtonsoft json nupkg vulnerable library found in base branch master vulnerability details improper handling of exceptional conditions in newtonsoft json newtonsoft json prior to version is vulnerable to insecure defaults due to improper handling of stackoverflow exception soe whenever nested expressions are being processed exploiting this vulnerability results in denial of service dos and it is exploitable when an attacker sends requests that cause soe in time frame of minutes this vulnerability affects internet information services iis applications publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution newtonsoft json microsoft extensions apidescription server rescue worker helmet automatic remediation is available for this issue | 0 |
204,274 | 15,436,462,439 | IssuesEvent | 2021-03-07 13:08:49 | microsoft/AL | https://api.github.com/repos/microsoft/AL | closed | Handling XmlPorts similar to pages and reports in Test codeunits | al-testability enhancement | Hi,
When we are trying to create handlers for xmlports similar to page we cannot find the **_xmlporthandler_** attribute and **_testxmlport_** datatype.
Can you please suggest how can we handle this?
Thanks & regards
Varun Reddy | 1.0 | Handling XmlPorts similar to pages and reports in Test codeunits - Hi,
When we are trying to create handlers for xmlports similar to page we cannot find the **_xmlporthandler_** attribute and **_testxmlport_** datatype.
Can you please suggest how can we handle this?
Thanks & regards
Varun Reddy | non_priority | handling xmlports similar to pages and reports in test codeunits hi when we are trying to create handlers for xmlports similar to page we cannot find the xmlporthandler attribute and testxmlport datatype can you please suggest how can we handle this thanks regards varun reddy | 0 |
20,308 | 26,950,282,450 | IssuesEvent | 2023-02-08 11:08:27 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | opened | Cherrypick cc_shared_library fixes into 6.1 | P1 type: process team-Rules-CPP | All of these are either bug fixes or compatible changes that will allow users to start migrating their builds earlier before the experimental flag for cc_shared_library is removed:
https://github.com/bazelbuild/bazel/commit/9815b76121d4e36bdaae110de7e68131916478ca
https://github.com/bazelbuild/bazel/commit/68aad18cfc01400bf6c3f447b6cd7d21dcc8f01f
https://github.com/bazelbuild/bazel/commit/590ee17c225244efd48793899170bc11f64b65d2
https://github.com/bazelbuild/bazel/commit/4ed6327523e1698e14dec1900ad71579c7f38b4a | 1.0 | Cherrypick cc_shared_library fixes into 6.1 - All of these are either bug fixes or compatible changes that will allow users to start migrating their builds earlier before the experimental flag for cc_shared_library is removed:
https://github.com/bazelbuild/bazel/commit/9815b76121d4e36bdaae110de7e68131916478ca
https://github.com/bazelbuild/bazel/commit/68aad18cfc01400bf6c3f447b6cd7d21dcc8f01f
https://github.com/bazelbuild/bazel/commit/590ee17c225244efd48793899170bc11f64b65d2
https://github.com/bazelbuild/bazel/commit/4ed6327523e1698e14dec1900ad71579c7f38b4a | non_priority | cherrypick cc shared library fixes into all of these are either bug fixes or compatible changes that will allow users to start migrating their builds earlier before the experimental flag for cc shared library is removed | 0 |
122,095 | 10,211,934,300 | IssuesEvent | 2019-08-14 18:11:11 | icgc-argo/argo-platform | https://api.github.com/repos/icgc-argo/argo-platform | closed | Create Program Selenium Test | SP:3 testing | - [ ] write the test
- [ ] make sure that the test executes
- [ ] demo the test completing successfully in browser stack
***The user can successfully login **
- The dcc user can login
- the program is successfully created | 1.0 | Create Program Selenium Test - - [ ] write the test
- [ ] make sure that the test executes
- [ ] demo the test completing successfully in browser stack
***The user can successfully login **
- The dcc user can login
- the program is successfully created | non_priority | create program selenium test write the test make sure that the test executes demo the test completing successfully in browser stack the user can successfully login the dcc user can login the program is successfully created | 0 |
324,665 | 24,011,859,036 | IssuesEvent | 2022-09-14 19:36:03 | pluralsight/tva | https://api.github.com/repos/pluralsight/tva | closed | [Docs?]: alpha release notes | documentation | ### Latest version
- [X] I have checked the latest version
### Summary 💡
Create alpha release blog
### Motivation 🔦
_No response_ | 1.0 | [Docs?]: alpha release notes - ### Latest version
- [X] I have checked the latest version
### Summary 💡
Create alpha release blog
### Motivation 🔦
_No response_ | non_priority | alpha release notes latest version i have checked the latest version summary 💡 create alpha release blog motivation 🔦 no response | 0 |
362,616 | 25,383,195,814 | IssuesEvent | 2022-11-21 19:23:25 | HB-Modding-Crew/Herobrine.fr-Optimized | https://api.github.com/repos/HB-Modding-Crew/Herobrine.fr-Optimized | closed | Documentation MultiMC | documentation | ### Type de changement
Ajout d'une information qui n'est pas trouvable
### Pages à modifier
_No response_
### Description
Ajouter une documentation complète pour l'utilisation du modpack avec MultiMC | 1.0 | Documentation MultiMC - ### Type de changement
Ajout d'une information qui n'est pas trouvable
### Pages à modifier
_No response_
### Description
Ajouter une documentation complète pour l'utilisation du modpack avec MultiMC | non_priority | documentation multimc type de changement ajout d une information qui n est pas trouvable pages à modifier no response description ajouter une documentation complète pour l utilisation du modpack avec multimc | 0 |
27,026 | 13,165,366,856 | IssuesEvent | 2020-08-11 06:25:28 | preactjs/preact | https://api.github.com/repos/preactjs/preact | closed | Strictly equal VNodes should short-circuit diffing | bug important performance | Libraries like react-redux are relying on this behavior for optimizations.
Preact X: https://codesandbox.io/s/4q307zk7o9
React: https://codesandbox.io/s/m3o2qy7398 | True | Strictly equal VNodes should short-circuit diffing - Libraries like react-redux are relying on this behavior for optimizations.
Preact X: https://codesandbox.io/s/4q307zk7o9
React: https://codesandbox.io/s/m3o2qy7398 | non_priority | strictly equal vnodes should short circuit diffing libraries like react redux are relying on this behavior for optimizations preact x react | 0 |
7,838 | 4,076,877,191 | IssuesEvent | 2016-05-30 03:51:32 | jeff1evesque/machine-learning | https://api.github.com/repos/jeff1evesque/machine-learning | closed | Convert 'settings.py' into a yaml configuration file | build enhancement new feature | We can redirect our sql related logs, into our custom `/vagrant/log/database` directory. Specifically, we can implement the following solution:
- [custom server options](https://github.com/puppetlabs/puppetlabs-mysql#customize-server-options)
So, we need to implement a hiera file, which contains the `/vagrant/log/database` path. This path would be referenced within the `custom server options` implementation. Then, we can convert our current `settings.py`, into an equivalent hiera file, and ensure corresponding python modules are adjusted. Overall, this new configuration file (i.e. yaml file), will be able to accommodate various language structures. This means, we should adjust corresponding puppet scripts to reference our yaml file, for consistency. | 1.0 | Convert 'settings.py' into a yaml configuration file - We can redirect our sql related logs, into our custom `/vagrant/log/database` directory. Specifically, we can implement the following solution:
- [custom server options](https://github.com/puppetlabs/puppetlabs-mysql#customize-server-options)
So, we need to implement a hiera file, which contains the `/vagrant/log/database` path. This path would be referenced within the `custom server options` implementation. Then, we can convert our current `settings.py`, into an equivalent hiera file, and ensure corresponding python modules are adjusted. Overall, this new configuration file (i.e. yaml file), will be able to accommodate various language structures. This means, we should adjust corresponding puppet scripts to reference our yaml file, for consistency. | non_priority | convert settings py into a yaml configuration file we can redirect our sql related logs into our custom vagrant log database directory specifically we can implement the following solution so we need to implement a hiera file which contains the vagrant log database path this path would be referenced within the custom server options implementation then we can convert our current settings py into an equivalent hiera file and ensure corresponding python modules are adjusted overall this new configuration file i e yaml file will be able to accommodate various language structures this means we should adjust corresponding puppet scripts to reference our yaml file for consistency | 0 |
111,121 | 9,499,395,006 | IssuesEvent | 2019-04-24 06:15:48 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | opened | Vulnerability [SLA] : GET:/api/v1/users/status | SanityTest | Project : SanityTest
Template : ApiV1UsersStatusGetQueryParamSlaMapped
Run Id : <html><a href=https://18.144.40.113/#/app/projects/8a8080b36a49d299016a4de39a652aa2/jobs/8a8080b36a49d299016a4de39fc32bdb/runs/8a8080b36a49d299016a4dfc4d174d85>8a8080b36a49d299016a4dfc4d174d85</a></html>
Job : Default
Env : Default
Category : SLA
Tags : [SLA]
Severity : Major
Region : US_WEST_2
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=NzNhNmNkNTEtNjVkMi00MWQxLTg2NTQtZmY1OWNiYWNiODVi; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Wed, 24 Apr 2019 06:15:44 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/users/status
Request :
Response :
{
"timestamp" : "2019-04-24T06:15:44.984+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/users/status"
}
Logs :
com.fxlabs.fxt.bot.assertions.AssertionLogger@105ae87b
--- FX Bot --- | 1.0 | Vulnerability [SLA] : GET:/api/v1/users/status - Project : SanityTest
Template : ApiV1UsersStatusGetQueryParamSlaMapped
Run Id : <html><a href=https://18.144.40.113/#/app/projects/8a8080b36a49d299016a4de39a652aa2/jobs/8a8080b36a49d299016a4de39fc32bdb/runs/8a8080b36a49d299016a4dfc4d174d85>8a8080b36a49d299016a4dfc4d174d85</a></html>
Job : Default
Env : Default
Category : SLA
Tags : [SLA]
Severity : Major
Region : US_WEST_2
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=NzNhNmNkNTEtNjVkMi00MWQxLTg2NTQtZmY1OWNiYWNiODVi; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Wed, 24 Apr 2019 06:15:44 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/users/status
Request :
Response :
{
"timestamp" : "2019-04-24T06:15:44.984+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/users/status"
}
Logs :
com.fxlabs.fxt.bot.assertions.AssertionLogger@105ae87b
--- FX Bot --- | non_priority | vulnerability get api users status project sanitytest template run id a href job default env default category sla tags severity major region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response timestamp status error not found message no message available path api api users status logs com fxlabs fxt bot assertions assertionlogger fx bot | 0 |
135,623 | 30,325,220,124 | IssuesEvent | 2023-07-10 23:06:04 | SuperTux/supertux | https://api.github.com/repos/SuperTux/supertux | opened | Handling lightmaps for Objects through their `.sprite` file | type:idea category:code status:needs-work | Instead of setting up lightmaps for individual objects, enemies etc. through code, couldn't we just have it be able to set up within the `.sprite` files themselves. Pretty much how the displacement texture is chosen for the Bonus Blocks within their sprite file. | 1.0 | Handling lightmaps for Objects through their `.sprite` file - Instead of setting up lightmaps for individual objects, enemies etc. through code, couldn't we just have it be able to set up within the `.sprite` files themselves. Pretty much how the displacement texture is chosen for the Bonus Blocks within their sprite file. | non_priority | handling lightmaps for objects through their sprite file instead of setting up lightmaps for individual objects enemies etc through code couldn t we just have it be able to set up within the sprite files themselves pretty much how the displacement texture is chosen for the bonus blocks within their sprite file | 0 |
280,182 | 21,212,426,512 | IssuesEvent | 2022-04-11 01:36:25 | FG-Unofficial-Developers-Guild/action-generate-luacheckrc | https://api.github.com/repos/FG-Unofficial-Developers-Guild/action-generate-luacheckrc | closed | documentation | documentation | some documentation is out of date and some functions have been created without documentation | 1.0 | documentation - some documentation is out of date and some functions have been created without documentation | non_priority | documentation some documentation is out of date and some functions have been created without documentation | 0 |
245,778 | 26,559,626,063 | IssuesEvent | 2023-01-20 14:52:26 | Seneca-CDOT/telescope | https://api.github.com/repos/Seneca-CDOT/telescope | closed | Figure out how to set strict-transport-security properly | type: bug area: web server type: security | [According to webhint](https://webhint.io/scanner/619fd876-7b16-4ef5-86e1-b53394750d41#hint-strict-transport-security-1), we aren't setting the `strict-transport-security` header on a lot of our files.
- https://webhint.io/docs/user-guide/hints/hint-strict-transport-security/#why-is-this-important
- https://webhint.io/docs/user-guide/hints/hint-strict-transport-security/#examples-that-pass-the-hint | True | Figure out how to set strict-transport-security properly - [According to webhint](https://webhint.io/scanner/619fd876-7b16-4ef5-86e1-b53394750d41#hint-strict-transport-security-1), we aren't setting the `strict-transport-security` header on a lot of our files.
- https://webhint.io/docs/user-guide/hints/hint-strict-transport-security/#why-is-this-important
- https://webhint.io/docs/user-guide/hints/hint-strict-transport-security/#examples-that-pass-the-hint | non_priority | figure out how to set strict transport security properly we aren t setting the strict transport security header on a lot of our files | 0 |
431,733 | 30,248,459,760 | IssuesEvent | 2023-07-06 18:25:07 | HoldenJe/gfsR | https://api.github.com/repos/HoldenJe/gfsR | closed | update gh-pages | documentation | update gh-pages branch following the update to v 0.2.2 where `import_creel_series` is introduced. | 1.0 | update gh-pages - update gh-pages branch following the update to v 0.2.2 where `import_creel_series` is introduced. | non_priority | update gh pages update gh pages branch following the update to v where import creel series is introduced | 0 |
15,479 | 3,330,127,322 | IssuesEvent | 2015-11-11 08:31:18 | geetsisbac/ZUUIL5XN2UPJRUK244AZSHGO | https://api.github.com/repos/geetsisbac/ZUUIL5XN2UPJRUK244AZSHGO | closed | fu9fAM9gOOCZMZa+94FQ2GKT0xs3w4Q3GBkOZFsGAXZhSC10X0LpodY2JVBeGd08uvFHP4gAidV8E+C/Grncsvgob8eEqLX+xCtwrtrpSdjeNQHgunMI3WI6N8SzDaFaR80FxASr8PjpIIUsTT3jojaEd5BidzEr7SvsjBTl2OE= | design | VUTU4Q9lRPnkehet2prthrvo81q3yfEh4mis3nkBK4ACVrEDX7s2pyAJCRmppNs1WmsgJHiCLPcYeAOHibT8VT5hULEo7CiClWog8ZK04RetG0QSJEeFbmxSA2VjDOD9Kb8BZ2Wo5K0Et2bdg2CHiXWlA+YycWAK6gsf5KbQKLeLY5DuZVJ+YdDJ8vI3a9I45v3d1wL+UZLfKjYyxJgEOzWsUgJ/EDRjL+tju6XIHYXSa0vCEeABC6OmZE8KkTUGOYXPvJj0aIe8g+/JwzHlxCECms9u+dZErA9KHrQmEHXqAbxp4gHBAVxstoL3jRgQGQvEr1MW228gr4lQdyehQGqoVw/7q+3NohJdhTsBwQFUa/sGojzlGRD0NVnPRbmSMV2eKVYB5TrOu1y4iEU6Wzw6Fx5+BUNTycUsADtC8KA3X5p1p8ymL9fj/lTHtK4zXjAQ884SOfooma2Cxg9nMvpG/+4bnjOMuSWwGcSW0IVu9hdPcNh8zxV//vTpiBVfjhqbbYMgqXcMbBMn79TSDQ947GdhvfPRDnXJYth9VdGpg8OyglYHy2k2XBaScYbjEa2lOf1AX/bP5I5UgEXsOsGlnSYoN7Eee9oWbtkQ9A7aHE47evFMkAFCD+LPItjIO2etNjcObynFh9wESZvPLsAx799k2rm9cV7FagpO3B16Z+vhptJV4fZSwq7ZeGUpqjFGqekmd6hxmt4phw/98xDJRTjgdbZzlx2TO44T+VyKnlkWTLO2BzyLzuGKcRj2ofG1mbgSqRPe3YJyjjIVs1yjKyRIiXtnMN1TnInS6QTJv1LMHJeO5g+x3cTMAJSOu07d7eABZgS5WCxExnrRQCaEg8br3b5h/sjTkEKoWMsp3J25b7UEorNDi58gV6uuaSIzv6BM6nM16X864YR8M/EtRix/t96TtpWuOyqKU5EN5USOq+S4nhQnX/NUJX1OIBTmwn/66mTj3L5vO8+nWufd3cvMjsRMoT0rAcNG9pIGQwdVd1px7Eig8DXv1yYt8MlwlnfUyet3XYDwwM0ftGyagwnzKIM+PSzNM1NAkximk6juYjiibidkP2+i0gG8zqGkBlCB6WIJwgvRWoUBZVIYZ6stCeSn+XVgC7INwUZAb5rBjf0ZMkl/G5SFo4NxNhhjnaEPsL9SX8NYKKfdQSyLoTJjgAJVSasYl6Gmw7awRgMXNjh3+EOajsjbMXl/A1o7KoeEO+sJj3YswIbhawhp3D6ikAIQcG4Q0MPfIRZG4gueXsJlM1KbblxkiD//ugUGwxYuf7bm8lLXj6syht3u4l2aQ6nVX/bRM5fU62SC8pdY7orlRowhAzmh6qSaXceycZJ37gafeFfkNnFckr2nCbQeSeWNUFnJR3y2bbc= | 1.0 | fu9fAM9gOOCZMZa+94FQ2GKT0xs3w4Q3GBkOZFsGAXZhSC10X0LpodY2JVBeGd08uvFHP4gAidV8E+C/Grncsvgob8eEqLX+xCtwrtrpSdjeNQHgunMI3WI6N8SzDaFaR80FxASr8PjpIIUsTT3jojaEd5BidzEr7SvsjBTl2OE= - VUTU4Q9lRPnkehet2prthrvo81q3yfEh4mis3nkBK4ACVrEDX7s2pyAJCRmppNs1WmsgJHiCLPcYeAOHibT8VT5hULEo7CiClWog8ZK04RetG0QSJEeFbmxSA2VjDOD9Kb8BZ2Wo5K0Et2bdg2CHiXWlA+YycWAK6gsf5KbQKLeLY5DuZVJ+YdDJ8vI3a9I45v3d1wL+UZLfKjYyxJgEOzWsUgJ/EDRjL+tju6XIHYXSa0vCEeABC6OmZE8KkTUGOYXPvJj0aIe8g+/JwzHlxCECms9u+dZErA9KHrQmEHXqAbxp4gHBAVxstoL3jRgQGQvEr1MW228gr4lQdyehQGqoVw/7q+3NohJdhTsBwQFUa/sGojzlGRD0NVnPRbmSMV2eKVYB5TrOu1y4iEU6Wzw6Fx5+BUNTycUsADtC8KA3X5p1p8ymL9fj/lTHtK4zXjAQ884SOfooma2Cxg9nMvpG/+4bnjOMuSWwGcSW0IVu9hdPcNh8zxV//vTpiBVfjhqbbYMgqXcMbBMn79TSDQ947GdhvfPRDnXJYth9VdGpg8OyglYHy2k2XBaScYbjEa2lOf1AX/bP5I5UgEXsOsGlnSYoN7Eee9oWbtkQ9A7aHE47evFMkAFCD+LPItjIO2etNjcObynFh9wESZvPLsAx799k2rm9cV7FagpO3B16Z+vhptJV4fZSwq7ZeGUpqjFGqekmd6hxmt4phw/98xDJRTjgdbZzlx2TO44T+VyKnlkWTLO2BzyLzuGKcRj2ofG1mbgSqRPe3YJyjjIVs1yjKyRIiXtnMN1TnInS6QTJv1LMHJeO5g+x3cTMAJSOu07d7eABZgS5WCxExnrRQCaEg8br3b5h/sjTkEKoWMsp3J25b7UEorNDi58gV6uuaSIzv6BM6nM16X864YR8M/EtRix/t96TtpWuOyqKU5EN5USOq+S4nhQnX/NUJX1OIBTmwn/66mTj3L5vO8+nWufd3cvMjsRMoT0rAcNG9pIGQwdVd1px7Eig8DXv1yYt8MlwlnfUyet3XYDwwM0ftGyagwnzKIM+PSzNM1NAkximk6juYjiibidkP2+i0gG8zqGkBlCB6WIJwgvRWoUBZVIYZ6stCeSn+XVgC7INwUZAb5rBjf0ZMkl/G5SFo4NxNhhjnaEPsL9SX8NYKKfdQSyLoTJjgAJVSasYl6Gmw7awRgMXNjh3+EOajsjbMXl/A1o7KoeEO+sJj3YswIbhawhp3D6ikAIQcG4Q0MPfIRZG4gueXsJlM1KbblxkiD//ugUGwxYuf7bm8lLXj6syht3u4l2aQ6nVX/bRM5fU62SC8pdY7orlRowhAzmh6qSaXceycZJ37gafeFfkNnFckr2nCbQeSeWNUFnJR3y2bbc= | non_priority | c uzlfkjyyxjgeozwsugj edrjl etrix eoajsjbmxl | 0 |
408,028 | 27,642,009,926 | IssuesEvent | 2023-03-10 18:55:52 | Rebooting-Me/Home-Maintainence-Service | https://api.github.com/repos/Rebooting-Me/Home-Maintainence-Service | closed | Compile architecture diagram for product | documentation | A diagram showing the major components of our product (e.g., UML). This can be done closer to the end Sprint 4 when our architecture has mostly settled. | 1.0 | Compile architecture diagram for product - A diagram showing the major components of our product (e.g., UML). This can be done closer to the end Sprint 4 when our architecture has mostly settled. | non_priority | compile architecture diagram for product a diagram showing the major components of our product e g uml this can be done closer to the end sprint when our architecture has mostly settled | 0 |
44,086 | 11,958,326,587 | IssuesEvent | 2020-04-04 17:41:47 | jccastillo0007/eFacturaT | https://api.github.com/repos/jccastillo0007/eFacturaT | opened | Condominios - CxP- Registrar pago, una vez que elegiste un RFC para búsqueda ya no lo puedes quitar | bug defect | Si en la búsqueda de facturas de proveedores, para registrar pagos, elijo un RFC, una vez que se elige, ya no hay forma de quitar ese filtro de RFC.
Digamos que a esa lista de RFC's de proveedores, le falta el famoso 'Seleccione uno' o algo así, que es equivalente a no indicar ningún RFC. | 1.0 | Condominios - CxP- Registrar pago, una vez que elegiste un RFC para búsqueda ya no lo puedes quitar - Si en la búsqueda de facturas de proveedores, para registrar pagos, elijo un RFC, una vez que se elige, ya no hay forma de quitar ese filtro de RFC.
Digamos que a esa lista de RFC's de proveedores, le falta el famoso 'Seleccione uno' o algo así, que es equivalente a no indicar ningún RFC. | non_priority | condominios cxp registrar pago una vez que elegiste un rfc para búsqueda ya no lo puedes quitar si en la búsqueda de facturas de proveedores para registrar pagos elijo un rfc una vez que se elige ya no hay forma de quitar ese filtro de rfc digamos que a esa lista de rfc s de proveedores le falta el famoso seleccione uno o algo así que es equivalente a no indicar ningún rfc | 0 |
306,575 | 23,165,133,982 | IssuesEvent | 2022-07-29 23:13:35 | FuelLabs/fuels-rs | https://api.github.com/repos/FuelLabs/fuels-rs | opened | Document how to run a _custom_ short-lived Fuel node | documentation | We currently have documented how to run a short-lived Fuel node, but only with default values. We should extend it to show how to create a custom node using `setup_test_client`, which involves using `ConsensusParameters` to configure a custom chain. | 1.0 | Document how to run a _custom_ short-lived Fuel node - We currently have documented how to run a short-lived Fuel node, but only with default values. We should extend it to show how to create a custom node using `setup_test_client`, which involves using `ConsensusParameters` to configure a custom chain. | non_priority | document how to run a custom short lived fuel node we currently have documented how to run a short lived fuel node but only with default values we should extend it to show how to create a custom node using setup test client which involves using consensusparameters to configure a custom chain | 0 |
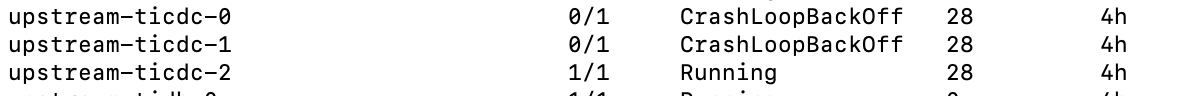
76,219 | 9,403,704,002 | IssuesEvent | 2019-04-09 02:37:35 | vtex/styleguide | https://api.github.com/repos/vtex/styleguide | closed | FilterTag and FilterBar | Design Done Developing | # FilterTag

# FilterBar
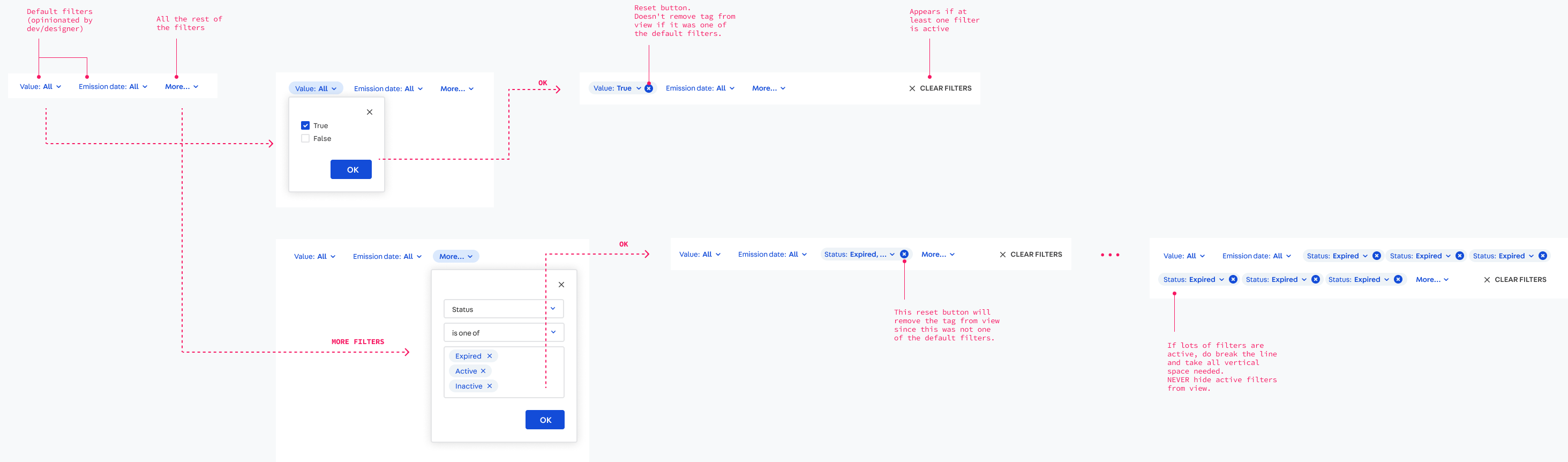
# Appendix: Statements
All filters are made up of Statements, except that regular Filter Tags, for obvious reasons, ommit the `subject` field.
### Excerpt from the Conditions component documentation:
# Figma
More studies and benchmarks in the Figma file: https://www.figma.com/file/aWaWGvrDNlyNsQKYfrwtsG/Tables?node-id=37%3A307 | 1.0 | FilterTag and FilterBar - # FilterTag

# FilterBar
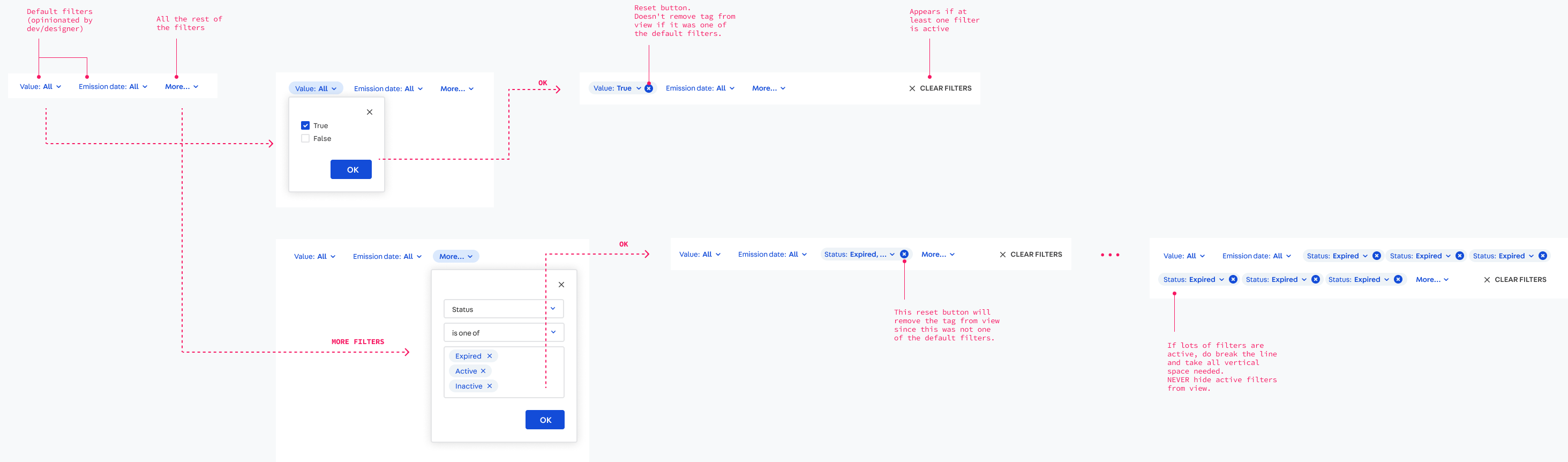
# Appendix: Statements
All filters are made up of Statements, except that regular Filter Tags, for obvious reasons, ommit the `subject` field.
### Excerpt from the Conditions component documentation:
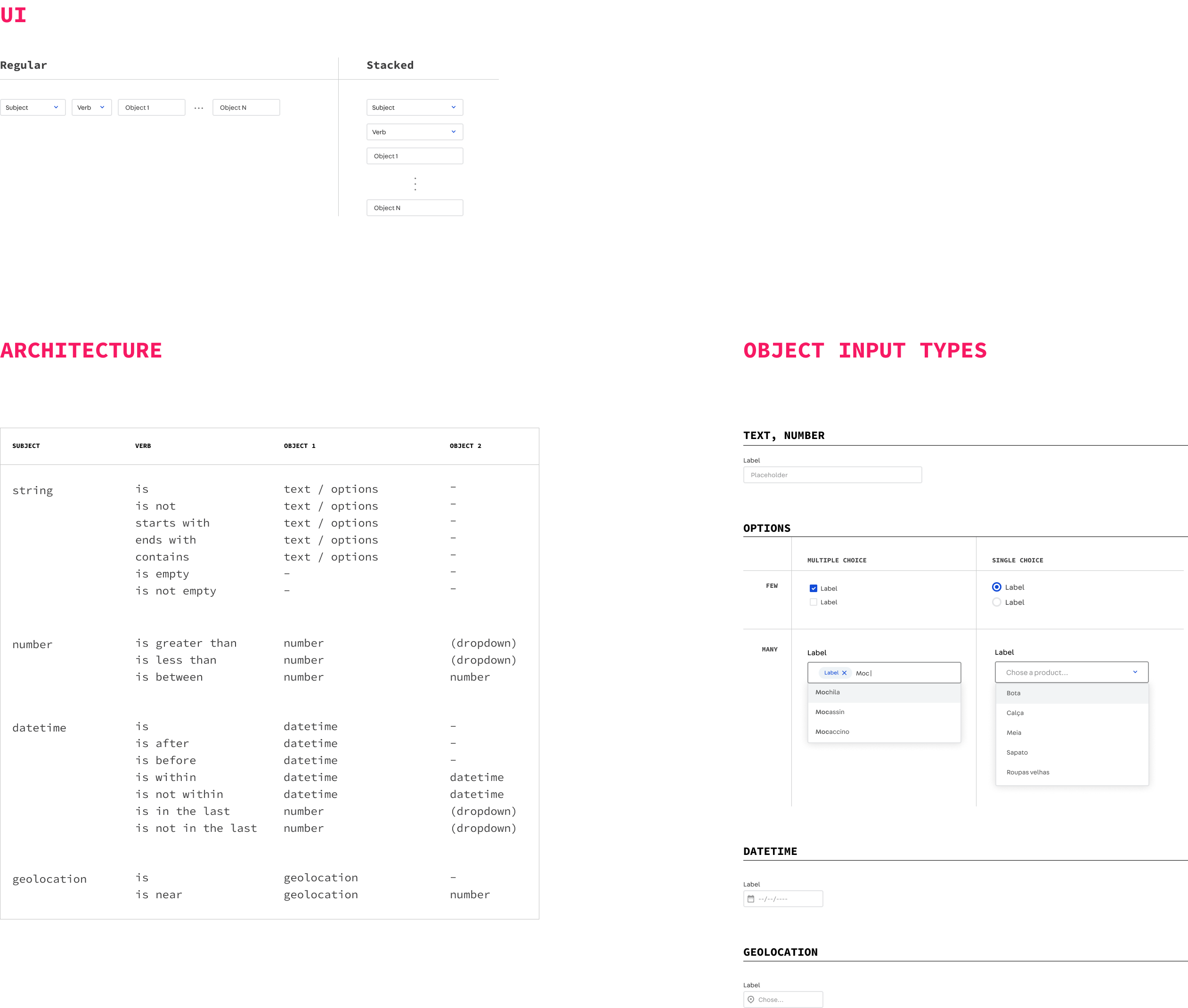
# Figma
More studies and benchmarks in the Figma file: https://www.figma.com/file/aWaWGvrDNlyNsQKYfrwtsG/Tables?node-id=37%3A307 | non_priority | filtertag and filterbar filtertag filterbar appendix statements all filters are made up of statements except that regular filter tags for obvious reasons ommit the subject field excerpt from the conditions component documentation figma more studies and benchmarks in the figma file | 0 |
26,883 | 20,819,381,686 | IssuesEvent | 2022-03-18 13:56:47 | semanticarts/gist | https://api.github.com/repos/semanticarts/gist | opened | Make individual terms dereferenceable over HTTP | area: infrastructure | Should return RDF rather than a 404 when you request, e.g., https://ontologies.semanticarts.com/gist/Person. | 1.0 | Make individual terms dereferenceable over HTTP - Should return RDF rather than a 404 when you request, e.g., https://ontologies.semanticarts.com/gist/Person. | non_priority | make individual terms dereferenceable over http should return rdf rather than a when you request e g | 0 |
287,165 | 31,819,422,809 | IssuesEvent | 2023-09-14 00:12:46 | billmcchesney1/location-intelligence-places-reference-application | https://api.github.com/repos/billmcchesney1/location-intelligence-places-reference-application | opened | CVE-2020-23064 (Medium) detected in jquery-3.1.1.min.js | Mend: dependency security vulnerability | ## CVE-2020-23064 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.1.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/static/libs/jquery/jquery.min.js,/target/classes/static/libs/jquery/jquery.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/location-intelligence-places-reference-application/commit/d240b4d4d753e0ca9c5d0fbf675b0e8e64320729">d240b4d4d753e0ca9c5d0fbf675b0e8e64320729</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Cross Site Scripting vulnerability in jQuery 2.2.0 through 3.x before 3.5.0 allows a remote attacker to execute arbitrary code via the <options> element.
<p>Publish Date: 2023-06-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-23064>CVE-2020-23064</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2023-06-26</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
| True | CVE-2020-23064 (Medium) detected in jquery-3.1.1.min.js - ## CVE-2020-23064 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.1.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/static/libs/jquery/jquery.min.js,/target/classes/static/libs/jquery/jquery.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/location-intelligence-places-reference-application/commit/d240b4d4d753e0ca9c5d0fbf675b0e8e64320729">d240b4d4d753e0ca9c5d0fbf675b0e8e64320729</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Cross Site Scripting vulnerability in jQuery 2.2.0 through 3.x before 3.5.0 allows a remote attacker to execute arbitrary code via the <options> element.
<p>Publish Date: 2023-06-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-23064>CVE-2020-23064</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2023-06-26</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library src main resources static libs jquery jquery min js target classes static libs jquery jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details cross site scripting vulnerability in jquery through x before allows a remote attacker to execute arbitrary code via the element publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery | 0 |
176,574 | 21,411,776,639 | IssuesEvent | 2022-04-22 06:57:52 | AlexRogalskiy/java-patterns | https://api.github.com/repos/AlexRogalskiy/java-patterns | opened | CVE-2021-3803 (High) detected in nth-check-1.0.2.tgz | security vulnerability | ## CVE-2021-3803 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nth-check-1.0.2.tgz</b></p></summary>
<p>performant nth-check parser & compiler</p>
<p>Library home page: <a href="https://registry.npmjs.org/nth-check/-/nth-check-1.0.2.tgz">https://registry.npmjs.org/nth-check/-/nth-check-1.0.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nth-check/package.json</p>
<p>
Dependency Hierarchy:
- danger-plugin-spellcheck-2.1.0.tgz (Root Library)
- esdoc-1.1.0.tgz
- cheerio-1.0.0-rc.2.tgz
- css-select-1.2.0.tgz
- :x: **nth-check-1.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/java-patterns/commit/0e3f838823fb09cc237bb3fc8f2e2651a2d0f0e6">0e3f838823fb09cc237bb3fc8f2e2651a2d0f0e6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
nth-check is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3803>CVE-2021-3803</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/fb55/nth-check/compare/v2.0.0...v2.0.1">https://github.com/fb55/nth-check/compare/v2.0.0...v2.0.1</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution: nth-check - v2.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-3803 (High) detected in nth-check-1.0.2.tgz - ## CVE-2021-3803 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nth-check-1.0.2.tgz</b></p></summary>
<p>performant nth-check parser & compiler</p>
<p>Library home page: <a href="https://registry.npmjs.org/nth-check/-/nth-check-1.0.2.tgz">https://registry.npmjs.org/nth-check/-/nth-check-1.0.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/nth-check/package.json</p>
<p>
Dependency Hierarchy:
- danger-plugin-spellcheck-2.1.0.tgz (Root Library)
- esdoc-1.1.0.tgz
- cheerio-1.0.0-rc.2.tgz
- css-select-1.2.0.tgz
- :x: **nth-check-1.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/java-patterns/commit/0e3f838823fb09cc237bb3fc8f2e2651a2d0f0e6">0e3f838823fb09cc237bb3fc8f2e2651a2d0f0e6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
nth-check is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3803>CVE-2021-3803</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/fb55/nth-check/compare/v2.0.0...v2.0.1">https://github.com/fb55/nth-check/compare/v2.0.0...v2.0.1</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution: nth-check - v2.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in nth check tgz cve high severity vulnerability vulnerable library nth check tgz performant nth check parser compiler library home page a href path to dependency file package json path to vulnerable library node modules nth check package json dependency hierarchy danger plugin spellcheck tgz root library esdoc tgz cheerio rc tgz css select tgz x nth check tgz vulnerable library found in head commit a href found in base branch master vulnerability details nth check is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution nth check step up your open source security game with whitesource | 0 |
53,647 | 23,019,140,674 | IssuesEvent | 2022-07-22 02:03:37 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | Parameter Name Hints shown inline | Language Service Feature Request fixed (release pending) Visual Studio | Now that we have doxygen comment supported to help code readability, it would be also useful to have a CLion-like name hint to be shown inline all the time (just like named parameters)
So that instead of this

we get this instead

| 1.0 | Parameter Name Hints shown inline - Now that we have doxygen comment supported to help code readability, it would be also useful to have a CLion-like name hint to be shown inline all the time (just like named parameters)
So that instead of this

we get this instead

| non_priority | parameter name hints shown inline now that we have doxygen comment supported to help code readability it would be also useful to have a clion like name hint to be shown inline all the time just like named parameters so that instead of this we get this instead | 0 |
107,752 | 23,478,454,266 | IssuesEvent | 2022-08-17 08:28:00 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Bug]: TypeError: Cannot read properties of undefined (reading 'filter') | Bug JS Critical Stale FE Coders Pod | Sentry Issue: [APPSMITH-3H8](https://sentry.io/organizations/appsmith/issues/3462112711/?referrer=github_integration)
```
TypeError: Cannot read properties of undefined (reading 'filter')
at None (workers/DependencyMap/index.ts:265:19)
``` | 1.0 | [Bug]: TypeError: Cannot read properties of undefined (reading 'filter') - Sentry Issue: [APPSMITH-3H8](https://sentry.io/organizations/appsmith/issues/3462112711/?referrer=github_integration)
```
TypeError: Cannot read properties of undefined (reading 'filter')
at None (workers/DependencyMap/index.ts:265:19)
``` | non_priority | typeerror cannot read properties of undefined reading filter sentry issue typeerror cannot read properties of undefined reading filter at none workers dependencymap index ts | 0 |
77,803 | 21,963,953,673 | IssuesEvent | 2022-05-24 18:16:43 | NCAR/DART | https://api.github.com/repos/NCAR/DART | closed | run test logs do not capture error, only std out | Bug back burner build-system | The developer_test for the location_mod have std err to the screen and only std out to the log files. I've not had a look at the other "developer_tests", but having a quick look there is mostly > and >>.
Running `threed_cartesian` just for brevity here;
`./run_tests.csh` vs. `cat buildlog.threed_cartesian.out `
hkershaw@cheyenne4:/glade/scratch/hkershaw/DART/pull_requests/pull_285/developer_tests/location(updt_bcs)$ ./run_tests.csh
```
==================================================================
Start of location module tests at Mon Feb 7 10:46:11 MST 2022
==================================================================
build and run logs are in: /glade/scratch/hkershaw/DART/pull_requests/pull_285/developer_tests/location/testing_logs
------------------------------------------------------------------
Starting tests of location module threed_cartesian at Mon Feb 7 10:46:11 MST 2022
------------------------------------------------------------------
.............../../../../assimilation_code/location/threed_cartesian/location_mod.f90(19): error #7002: Error in opening the compiled module file. Check INCLUDE paths. [OBS_KIND_MOD]
use obs_kind_mod, only : get_num_types_of_obs, get_name_for_type_of_obs, get_index_for_type_of_obs
------------^
../../../../assimilation_code/location/threed_cartesian/location_mod.f90(19): error #6580: Name in only-list does not exist or is not accessible. [GET_NUM_TYPES_OF_OBS]
use obs_kind_mod, only : get_num_types_of_obs, get_name_for_type_of_obs, get_index_for_type_of_obs
---------------------------------^
../../../../assimilation_code/location/threed_cartesian/location_mod.f90(19): error #6580: Name in only-list does not exist or is not accessible. [GET_NAME_FOR_TYPE_OF_OBS]
use obs_kind_mod, only : get_num_types_of_obs, get_name_for_type_of_obs, get_index_for_type_of_obs
-------------------------------------------------------^
../../../../assimilation_code/location/threed_cartesian/location_mod.f90(19): error #6580: Name in only-list does not exist or is not accessible. [GET_INDEX_FOR_TYPE_OF_OBS]
use obs_kind_mod, only : get_num_types_of_obs, get_name_for_type_of_obs, get_index_for_type_of_obs
---------------------------------------------------------------------------------^
../../../../assimilation_code/location/threed_cartesian/location_mod.f90(895): error #6404: This name does not have a type, and must have an explicit type. [GET_NUM_TYPES_OF_OBS]
typecount = get_num_types_of_obs()
------------^
compilation aborted for ../../../../assimilation_code/location/threed_cartesian/location_mod.f90 (code 1)
make: *** [location_mod.o] Error 1
ERROR - unsuccessful build of location module threed_cartesian at Mon Feb 7 10:46:12 MST 2022
==================================================================
End of location module tests at Mon Feb 7 10:46:12 MST 2022
==================================================================
```
hkershaw@cheyenne4:/glade/scratch/hkershaw/DART/pull_requests/pull_285/developer_tests/location(updt_bcs)$ cat /glade/scratch/hkershaw/DART/pull_requests/pull_285/developer_tests/location/testing_logs/buildlog.threed_cartesian.out
```
Makefile is ready.
ifort -O -assume buffered_io -fp-model precise -I/glade/u/apps/ch/opt/netcdf/4.8.1/intel/19.1.1//include -c ../../../../assimilation_code/location/threed_cartesian/location_mod.f90
Makefile:24: recipe for target 'location_mod.o' failed
```
I'm not sure how much to care about this, but new tests should capture std err in the logs.
| 1.0 | run test logs do not capture error, only std out - The developer_test for the location_mod have std err to the screen and only std out to the log files. I've not had a look at the other "developer_tests", but having a quick look there is mostly > and >>.
Running `threed_cartesian` just for brevity here;
`./run_tests.csh` vs. `cat buildlog.threed_cartesian.out `
hkershaw@cheyenne4:/glade/scratch/hkershaw/DART/pull_requests/pull_285/developer_tests/location(updt_bcs)$ ./run_tests.csh
```
==================================================================
Start of location module tests at Mon Feb 7 10:46:11 MST 2022
==================================================================
build and run logs are in: /glade/scratch/hkershaw/DART/pull_requests/pull_285/developer_tests/location/testing_logs
------------------------------------------------------------------
Starting tests of location module threed_cartesian at Mon Feb 7 10:46:11 MST 2022
------------------------------------------------------------------
.............../../../../assimilation_code/location/threed_cartesian/location_mod.f90(19): error #7002: Error in opening the compiled module file. Check INCLUDE paths. [OBS_KIND_MOD]
use obs_kind_mod, only : get_num_types_of_obs, get_name_for_type_of_obs, get_index_for_type_of_obs
------------^
../../../../assimilation_code/location/threed_cartesian/location_mod.f90(19): error #6580: Name in only-list does not exist or is not accessible. [GET_NUM_TYPES_OF_OBS]
use obs_kind_mod, only : get_num_types_of_obs, get_name_for_type_of_obs, get_index_for_type_of_obs
---------------------------------^
../../../../assimilation_code/location/threed_cartesian/location_mod.f90(19): error #6580: Name in only-list does not exist or is not accessible. [GET_NAME_FOR_TYPE_OF_OBS]
use obs_kind_mod, only : get_num_types_of_obs, get_name_for_type_of_obs, get_index_for_type_of_obs
-------------------------------------------------------^
../../../../assimilation_code/location/threed_cartesian/location_mod.f90(19): error #6580: Name in only-list does not exist or is not accessible. [GET_INDEX_FOR_TYPE_OF_OBS]
use obs_kind_mod, only : get_num_types_of_obs, get_name_for_type_of_obs, get_index_for_type_of_obs
---------------------------------------------------------------------------------^
../../../../assimilation_code/location/threed_cartesian/location_mod.f90(895): error #6404: This name does not have a type, and must have an explicit type. [GET_NUM_TYPES_OF_OBS]
typecount = get_num_types_of_obs()
------------^
compilation aborted for ../../../../assimilation_code/location/threed_cartesian/location_mod.f90 (code 1)
make: *** [location_mod.o] Error 1
ERROR - unsuccessful build of location module threed_cartesian at Mon Feb 7 10:46:12 MST 2022
==================================================================
End of location module tests at Mon Feb 7 10:46:12 MST 2022
==================================================================
```
hkershaw@cheyenne4:/glade/scratch/hkershaw/DART/pull_requests/pull_285/developer_tests/location(updt_bcs)$ cat /glade/scratch/hkershaw/DART/pull_requests/pull_285/developer_tests/location/testing_logs/buildlog.threed_cartesian.out
```
Makefile is ready.
ifort -O -assume buffered_io -fp-model precise -I/glade/u/apps/ch/opt/netcdf/4.8.1/intel/19.1.1//include -c ../../../../assimilation_code/location/threed_cartesian/location_mod.f90
Makefile:24: recipe for target 'location_mod.o' failed
```
I'm not sure how much to care about this, but new tests should capture std err in the logs.
| non_priority | run test logs do not capture error only std out the developer test for the location mod have std err to the screen and only std out to the log files i ve not had a look at the other developer tests but having a quick look there is mostly and running threed cartesian just for brevity here run tests csh vs cat buildlog threed cartesian out hkershaw glade scratch hkershaw dart pull requests pull developer tests location updt bcs run tests csh start of location module tests at mon feb mst build and run logs are in glade scratch hkershaw dart pull requests pull developer tests location testing logs starting tests of location module threed cartesian at mon feb mst assimilation code location threed cartesian location mod error error in opening the compiled module file check include paths use obs kind mod only get num types of obs get name for type of obs get index for type of obs assimilation code location threed cartesian location mod error name in only list does not exist or is not accessible use obs kind mod only get num types of obs get name for type of obs get index for type of obs assimilation code location threed cartesian location mod error name in only list does not exist or is not accessible use obs kind mod only get num types of obs get name for type of obs get index for type of obs assimilation code location threed cartesian location mod error name in only list does not exist or is not accessible use obs kind mod only get num types of obs get name for type of obs get index for type of obs assimilation code location threed cartesian location mod error this name does not have a type and must have an explicit type typecount get num types of obs compilation aborted for assimilation code location threed cartesian location mod code make error error unsuccessful build of location module threed cartesian at mon feb mst end of location module tests at mon feb mst hkershaw glade scratch hkershaw dart pull requests pull developer tests location updt bcs cat glade scratch hkershaw dart pull requests pull developer tests location testing logs buildlog threed cartesian out makefile is ready ifort o assume buffered io fp model precise i glade u apps ch opt netcdf intel include c assimilation code location threed cartesian location mod makefile recipe for target location mod o failed i m not sure how much to care about this but new tests should capture std err in the logs | 0 |
257,882 | 19,534,395,274 | IssuesEvent | 2021-12-31 01:32:49 | horaciovelvetine/horaciovelvetine | https://api.github.com/repos/horaciovelvetine/horaciovelvetine | opened | Front :: Tailwind Coloring | bug documentation enhancement question Component | Tailwind's coloring is only working in a very limited capacity. Basic colors like red and blue work, but anything outside of those very simple colors (ex. amber, slate)... do not work at all.
Tried looking through a bunch of things and trying a variety of solutions to no avail. Not sure why I cant use or extend colors, if its a CSS issue where the styling isn't being imported//built?
One thing I didn't try was "applying" styles using the @ apply syntax etc found here:
https://rubyyagi.com/tailwind-css-on-rails-6-intro/ (scroll down the page to the @apply portion).
Additional Question:
What about changing the files to the auto-generated ex of .jsx files???
Additional details:
- Arbitrary color definition also not working
- Post CSS (on bin/webpack-ing) runs a notice saying that no plugins are installed, but it seems like there are a few that should be installed running?
- Tried recycling and updating npm stuff
- Tried renaming and retyping//copying pasting everything
- Tried adding to base colors, changing to variety of syntaxes from docs etc for modifying and adding
| 1.0 | Front :: Tailwind Coloring - Tailwind's coloring is only working in a very limited capacity. Basic colors like red and blue work, but anything outside of those very simple colors (ex. amber, slate)... do not work at all.
Tried looking through a bunch of things and trying a variety of solutions to no avail. Not sure why I cant use or extend colors, if its a CSS issue where the styling isn't being imported//built?
One thing I didn't try was "applying" styles using the @ apply syntax etc found here:
https://rubyyagi.com/tailwind-css-on-rails-6-intro/ (scroll down the page to the @apply portion).
Additional Question:
What about changing the files to the auto-generated ex of .jsx files???
Additional details:
- Arbitrary color definition also not working
- Post CSS (on bin/webpack-ing) runs a notice saying that no plugins are installed, but it seems like there are a few that should be installed running?
- Tried recycling and updating npm stuff
- Tried renaming and retyping//copying pasting everything
- Tried adding to base colors, changing to variety of syntaxes from docs etc for modifying and adding
| non_priority | front tailwind coloring tailwind s coloring is only working in a very limited capacity basic colors like red and blue work but anything outside of those very simple colors ex amber slate do not work at all tried looking through a bunch of things and trying a variety of solutions to no avail not sure why i cant use or extend colors if its a css issue where the styling isn t being imported built one thing i didn t try was applying styles using the apply syntax etc found here scroll down the page to the apply portion additional question what about changing the files to the auto generated ex of jsx files additional details arbitrary color definition also not working post css on bin webpack ing runs a notice saying that no plugins are installed but it seems like there are a few that should be installed running tried recycling and updating npm stuff tried renaming and retyping copying pasting everything tried adding to base colors changing to variety of syntaxes from docs etc for modifying and adding | 0 |
20,794 | 10,551,122,772 | IssuesEvent | 2019-10-03 12:42:39 | aspnet/AspNetCore | https://api.github.com/repos/aspnet/AspNetCore | closed | Issue regarding AddAuthenticationCore and cookies | area-security | (Manually transferred from an issue filed by @ffMathy in the corefx repo.)
Before in my old code, I used to do:
```csharp
services
.AddAuthentication(options =>
{
options.DefaultSignInScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultAuthenticateScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultChallengeScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultScheme = CookieAuthenticationDefaults.AuthenticationScheme;
})
.AddCookie(options =>
{
options.LoginPath = "/Admin/Account/Login";
});
```
To get auth with cookies working.
Now, after migrating to .NET Core 3 while still using the above code, my identity showed as never authenticated. I found something referring to something being moved around, and concluded I needed to use `AddAuthenticationCore`.
I couldn't find any documentation on how to get the same working with that, so I ended up with the following code:
```csharp
services.AddAuthenticationCore(options =>
{
options.DefaultSignInScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultAuthenticateScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultChallengeScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.AddScheme<CookieAuthenticationHandler>(CookieAuthenticationDefaults.AuthenticationScheme, null);
});
```
But now I get the following error:
> Unable to resolve service for type 'Microsoft.AspNetCore.Authentication.ISystemClock' while attempting to activate 'Microsoft.AspNetCore.Authentication.Cookies.CookieAuthenticationHandler'.
The reason I tried using this approach, is that `AddCookie` no longer exists with the new method approach.
What can I do to get this working? | True | Issue regarding AddAuthenticationCore and cookies - (Manually transferred from an issue filed by @ffMathy in the corefx repo.)
Before in my old code, I used to do:
```csharp
services
.AddAuthentication(options =>
{
options.DefaultSignInScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultAuthenticateScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultChallengeScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultScheme = CookieAuthenticationDefaults.AuthenticationScheme;
})
.AddCookie(options =>
{
options.LoginPath = "/Admin/Account/Login";
});
```
To get auth with cookies working.
Now, after migrating to .NET Core 3 while still using the above code, my identity showed as never authenticated. I found something referring to something being moved around, and concluded I needed to use `AddAuthenticationCore`.
I couldn't find any documentation on how to get the same working with that, so I ended up with the following code:
```csharp
services.AddAuthenticationCore(options =>
{
options.DefaultSignInScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultAuthenticateScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultChallengeScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.AddScheme<CookieAuthenticationHandler>(CookieAuthenticationDefaults.AuthenticationScheme, null);
});
```
But now I get the following error:
> Unable to resolve service for type 'Microsoft.AspNetCore.Authentication.ISystemClock' while attempting to activate 'Microsoft.AspNetCore.Authentication.Cookies.CookieAuthenticationHandler'.
The reason I tried using this approach, is that `AddCookie` no longer exists with the new method approach.
What can I do to get this working? | non_priority | issue regarding addauthenticationcore and cookies manually transferred from an issue filed by ffmathy in the corefx repo before in my old code i used to do csharp services addauthentication options options defaultsigninscheme cookieauthenticationdefaults authenticationscheme options defaultauthenticatescheme cookieauthenticationdefaults authenticationscheme options defaultchallengescheme cookieauthenticationdefaults authenticationscheme options defaultscheme cookieauthenticationdefaults authenticationscheme addcookie options options loginpath admin account login to get auth with cookies working now after migrating to net core while still using the above code my identity showed as never authenticated i found something referring to something being moved around and concluded i needed to use addauthenticationcore i couldn t find any documentation on how to get the same working with that so i ended up with the following code csharp services addauthenticationcore options options defaultsigninscheme cookieauthenticationdefaults authenticationscheme options defaultauthenticatescheme cookieauthenticationdefaults authenticationscheme options defaultchallengescheme cookieauthenticationdefaults authenticationscheme options defaultscheme cookieauthenticationdefaults authenticationscheme options addscheme cookieauthenticationdefaults authenticationscheme null but now i get the following error unable to resolve service for type microsoft aspnetcore authentication isystemclock while attempting to activate microsoft aspnetcore authentication cookies cookieauthenticationhandler the reason i tried using this approach is that addcookie no longer exists with the new method approach what can i do to get this working | 0 |
88,640 | 17,619,884,477 | IssuesEvent | 2021-08-18 14:12:01 | diffblue/cbmc | https://api.github.com/repos/diffblue/cbmc | closed | Replace with contracts - havoc entire array content | bug aws Code Contracts | <!---
Thank you for reporting a problem and suggesting improvements. Please provide the below information to make sure we can effectively deal with the issue reported. For the most precise version information, see the first line of console output or run with --version. Please attach or include example code that allows us to reproduce the problem.
--->
CBMC version: develop (current 06c563a76589ed00cc372d68e2819880537977b2)
Operating system: N/A.
Exact command line resulting in the issue:
`goto-cc *.c -o main.gb && goto-instrument main.gb main-mod.gb --replace-all-calls-with-contracts && cbmc main-mod.gb`
```c
#include <assert.h>
void foo(char c[]) __CPROVER_assigns(*c)
{
}
int main()
{
char b[2];
b[0] = 'a';
b[1] = 'b';
foo(b);
assert(b[0] == 'a');
assert(b[1] == 'b');
return 0;
}
```
What behaviour did you expect:
```shell
** Results:
main.c function main
[main.assertion.1] line 13 assertion b[0] == 'a': FAILURE
[main.assertion.2] line 14 assertion b[1] == 'b': FAILURE
```
What happened instead:
```shell
** Results:
main.c function main
[main.assertion.1] line 13 assertion b[0] == 'a': FAILURE
[main.assertion.2] line 14 assertion b[1] == 'b': SUCCESS
```
We need to havoc all contents of an array. | 1.0 | Replace with contracts - havoc entire array content - <!---
Thank you for reporting a problem and suggesting improvements. Please provide the below information to make sure we can effectively deal with the issue reported. For the most precise version information, see the first line of console output or run with --version. Please attach or include example code that allows us to reproduce the problem.
--->
CBMC version: develop (current 06c563a76589ed00cc372d68e2819880537977b2)
Operating system: N/A.
Exact command line resulting in the issue:
`goto-cc *.c -o main.gb && goto-instrument main.gb main-mod.gb --replace-all-calls-with-contracts && cbmc main-mod.gb`
```c
#include <assert.h>
void foo(char c[]) __CPROVER_assigns(*c)
{
}
int main()
{
char b[2];
b[0] = 'a';
b[1] = 'b';
foo(b);
assert(b[0] == 'a');
assert(b[1] == 'b');
return 0;
}
```
What behaviour did you expect:
```shell
** Results:
main.c function main
[main.assertion.1] line 13 assertion b[0] == 'a': FAILURE
[main.assertion.2] line 14 assertion b[1] == 'b': FAILURE
```
What happened instead:
```shell
** Results:
main.c function main
[main.assertion.1] line 13 assertion b[0] == 'a': FAILURE
[main.assertion.2] line 14 assertion b[1] == 'b': SUCCESS
```
We need to havoc all contents of an array. | non_priority | replace with contracts havoc entire array content thank you for reporting a problem and suggesting improvements please provide the below information to make sure we can effectively deal with the issue reported for the most precise version information see the first line of console output or run with version please attach or include example code that allows us to reproduce the problem cbmc version develop current operating system n a exact command line resulting in the issue goto cc c o main gb goto instrument main gb main mod gb replace all calls with contracts cbmc main mod gb c include void foo char c cprover assigns c int main char b b a b b foo b assert b a assert b b return what behaviour did you expect shell results main c function main line assertion b a failure line assertion b b failure what happened instead shell results main c function main line assertion b a failure line assertion b b success we need to havoc all contents of an array | 0 |
44,817 | 11,516,018,386 | IssuesEvent | 2020-02-14 03:20:44 | ballerina-platform/ballerina-lang | https://api.github.com/repos/ballerina-platform/ballerina-lang | opened | Automate publishing vscode plugin to vscode store | Area/Build Type/Improvement | **Description:**
At the moment we do it manually.
| 1.0 | Automate publishing vscode plugin to vscode store - **Description:**
At the moment we do it manually.
| non_priority | automate publishing vscode plugin to vscode store description at the moment we do it manually | 0 |
167,127 | 12,992,268,394 | IssuesEvent | 2020-07-23 06:26:04 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | opened | Jobs https://k8s-testgrid.appspot.com/sig-network-netd | kind/failing-test | <!-- Please only use this template for submitting reports about continuously failing tests or jobs in Kubernetes CI -->
**Which jobs are failing**:
**Which test(s) are failing**:
**Since when has it been failing**:
**Testgrid link**:
**Reason for failure**:
**Anything else we need to know**:
| 1.0 | Jobs https://k8s-testgrid.appspot.com/sig-network-netd - <!-- Please only use this template for submitting reports about continuously failing tests or jobs in Kubernetes CI -->
**Which jobs are failing**:
**Which test(s) are failing**:
**Since when has it been failing**:
**Testgrid link**:
**Reason for failure**:
**Anything else we need to know**:
| non_priority | jobs which jobs are failing which test s are failing since when has it been failing testgrid link reason for failure anything else we need to know | 0 |
286,369 | 24,748,615,842 | IssuesEvent | 2022-10-21 11:55:48 | nn-nissy1010/gas_test | https://api.github.com/repos/nn-nissy1010/gas_test | opened | admin-01-05:手本管理(書体一覧) | M 親 スプリント1 gas_test | 要件:
- 管理している課題が書体ごとにグループ化され一覧で確認できる
- 当月の課題に関しては、「受付中」であることが視認できる
------ イメージ ------
サイドメニュー[課題管理]をクリック👇
セレクトボックスから対象の年月を選択する(デフォルトは当月)
選択した年月の課題が書体ごとにまとまって一覧で確認できる
(「一般」「学生」でタブわけして表示)
タスク内容:
OpenAPI・データベース定義 | 1.0 | admin-01-05:手本管理(書体一覧) - 要件:
- 管理している課題が書体ごとにグループ化され一覧で確認できる
- 当月の課題に関しては、「受付中」であることが視認できる
------ イメージ ------
サイドメニュー[課題管理]をクリック👇
セレクトボックスから対象の年月を選択する(デフォルトは当月)
選択した年月の課題が書体ごとにまとまって一覧で確認できる
(「一般」「学生」でタブわけして表示)
タスク内容:
OpenAPI・データベース定義 | non_priority | admin 手本管理(書体一覧) 要件: 管理している課題が書体ごとにグループ化され一覧で確認できる 当月の課題に関しては、「受付中」であることが視認できる イメージ サイドメニュー をクリック👇 セレクトボックスから対象の年月を選択する(デフォルトは当月) 選択した年月の課題が書体ごとにまとまって一覧で確認できる (「一般」「学生」でタブわけして表示) タスク内容: openapi・データベース定義 | 0 |
116,677 | 11,939,620,464 | IssuesEvent | 2020-04-02 15:28:00 | ITensor/ITensors.jl | https://api.github.com/repos/ITensor/ITensors.jl | closed | `dag` copying behavior | documentation enhancement | This is just a reminder for a discussion that occurred in a previous PR- https://github.com/ITensor/ITensors.jl/pull/201#issuecomment-587676621 .
It was discussed that:
1. `dag` is only sometimes making a copy of the internal storage (when the storage is complex).
2. This should be noted in the docstring.
3. It would be good to add a `always_copy` keyword argument to `dag` that can be used for generic code where a copy is needed. | 1.0 | `dag` copying behavior - This is just a reminder for a discussion that occurred in a previous PR- https://github.com/ITensor/ITensors.jl/pull/201#issuecomment-587676621 .
It was discussed that:
1. `dag` is only sometimes making a copy of the internal storage (when the storage is complex).
2. This should be noted in the docstring.
3. It would be good to add a `always_copy` keyword argument to `dag` that can be used for generic code where a copy is needed. | non_priority | dag copying behavior this is just a reminder for a discussion that occurred in a previous pr it was discussed that dag is only sometimes making a copy of the internal storage when the storage is complex this should be noted in the docstring it would be good to add a always copy keyword argument to dag that can be used for generic code where a copy is needed | 0 |
35,423 | 4,662,701,566 | IssuesEvent | 2016-10-05 05:48:51 | muonium/core | https://api.github.com/repos/muonium/core | closed | Quick issue :: Favicon | design | Hey, can you display the favicon please ? x)
A screen of my Firefox tab (you see, it's soooo blank...)

| 1.0 | Quick issue :: Favicon - Hey, can you display the favicon please ? x)
A screen of my Firefox tab (you see, it's soooo blank...)

| non_priority | quick issue favicon hey can you display the favicon please x a screen of my firefox tab you see it s soooo blank | 0 |
60,393 | 14,542,629,193 | IssuesEvent | 2020-12-15 15:56:00 | rnilssoncx/homebridge-onewire | https://api.github.com/repos/rnilssoncx/homebridge-onewire | closed | CVE-2020-7720 (High) detected in node-forge-0.7.6.tgz - autoclosed | security vulnerability | ## CVE-2020-7720 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.7.6.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.6.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.6.tgz</a></p>
<p>Path to dependency file: homebridge-onewire/package.json</p>
<p>Path to vulnerable library: homebridge-onewire/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- fakegato-history-0.4.3.tgz (Root Library)
- google-auth-library-0.10.0.tgz
- gtoken-1.2.3.tgz
- google-p12-pem-0.1.2.tgz
- :x: **node-forge-0.7.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rnilssoncx/homebridge-onewire/commit/d2bc67054e6d5d216a4498a6f68f5c33609937e2">d2bc67054e6d5d216a4498a6f68f5c33609937e2</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package node-forge before 0.10.0 is vulnerable to Prototype Pollution via the util.setPath function. Note: Version 0.10.0 is a breaking change removing the vulnerable functions.
<p>Publish Date: 2020-09-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720>CVE-2020-7720</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/digitalbazaar/forge/blob/master/CHANGELOG.md">https://github.com/digitalbazaar/forge/blob/master/CHANGELOG.md</a></p>
<p>Release Date: 2020-09-13</p>
<p>Fix Resolution: node-forge - 0.10.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-forge","packageVersion":"0.7.6","isTransitiveDependency":true,"dependencyTree":"fakegato-history:0.4.3;google-auth-library:0.10.0;gtoken:1.2.3;google-p12-pem:0.1.2;node-forge:0.7.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"node-forge - 0.10.0"}],"vulnerabilityIdentifier":"CVE-2020-7720","vulnerabilityDetails":"The package node-forge before 0.10.0 is vulnerable to Prototype Pollution via the util.setPath function. Note: Version 0.10.0 is a breaking change removing the vulnerable functions.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-7720 (High) detected in node-forge-0.7.6.tgz - autoclosed - ## CVE-2020-7720 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.7.6.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.6.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.6.tgz</a></p>
<p>Path to dependency file: homebridge-onewire/package.json</p>
<p>Path to vulnerable library: homebridge-onewire/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- fakegato-history-0.4.3.tgz (Root Library)
- google-auth-library-0.10.0.tgz
- gtoken-1.2.3.tgz
- google-p12-pem-0.1.2.tgz
- :x: **node-forge-0.7.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rnilssoncx/homebridge-onewire/commit/d2bc67054e6d5d216a4498a6f68f5c33609937e2">d2bc67054e6d5d216a4498a6f68f5c33609937e2</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package node-forge before 0.10.0 is vulnerable to Prototype Pollution via the util.setPath function. Note: Version 0.10.0 is a breaking change removing the vulnerable functions.
<p>Publish Date: 2020-09-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720>CVE-2020-7720</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/digitalbazaar/forge/blob/master/CHANGELOG.md">https://github.com/digitalbazaar/forge/blob/master/CHANGELOG.md</a></p>
<p>Release Date: 2020-09-13</p>
<p>Fix Resolution: node-forge - 0.10.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-forge","packageVersion":"0.7.6","isTransitiveDependency":true,"dependencyTree":"fakegato-history:0.4.3;google-auth-library:0.10.0;gtoken:1.2.3;google-p12-pem:0.1.2;node-forge:0.7.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"node-forge - 0.10.0"}],"vulnerabilityIdentifier":"CVE-2020-7720","vulnerabilityDetails":"The package node-forge before 0.10.0 is vulnerable to Prototype Pollution via the util.setPath function. Note: Version 0.10.0 is a breaking change removing the vulnerable functions.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in node forge tgz autoclosed cve high severity vulnerability vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file homebridge onewire package json path to vulnerable library homebridge onewire node modules node forge package json dependency hierarchy fakegato history tgz root library google auth library tgz gtoken tgz google pem tgz x node forge tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package node forge before is vulnerable to prototype pollution via the util setpath function note version is a breaking change removing the vulnerable functions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails the package node forge before is vulnerable to prototype pollution via the util setpath function note version is a breaking change removing the vulnerable functions vulnerabilityurl | 0 |
15,108 | 5,060,290,737 | IssuesEvent | 2016-12-22 11:20:27 | synfig/synfig | https://api.github.com/repos/synfig/synfig | closed | Tabs vs spaces in code | Code quality | I've been wondering for a while: are we using tabs only because they were used initially or do some current developers prefer them as well? | 1.0 | Tabs vs spaces in code - I've been wondering for a while: are we using tabs only because they were used initially or do some current developers prefer them as well? | non_priority | tabs vs spaces in code i ve been wondering for a while are we using tabs only because they were used initially or do some current developers prefer them as well | 0 |
378,921 | 26,344,738,495 | IssuesEvent | 2023-01-10 20:54:54 | MainaMwangiy/smart-app-backend | https://api.github.com/repos/MainaMwangiy/smart-app-backend | closed | Delete Employees | documentation good first issue | - [x] Delete a single employee using button
- [x] Delete selected employee from checkbox
- [ ] Delete multiple employees selected from checkbox. | 1.0 | Delete Employees - - [x] Delete a single employee using button
- [x] Delete selected employee from checkbox
- [ ] Delete multiple employees selected from checkbox. | non_priority | delete employees delete a single employee using button delete selected employee from checkbox delete multiple employees selected from checkbox | 0 |
196,759 | 22,534,039,570 | IssuesEvent | 2022-06-25 01:03:55 | snykiotcubedev/redis-6.2.3 | https://api.github.com/repos/snykiotcubedev/redis-6.2.3 | opened | CVE-2022-33105 (Medium) detected in redis6.2.6 | security vulnerability | ## CVE-2022-33105 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>redis6.2.6</b></p></summary>
<p>
<p>Redis is an in-memory database that persists on disk. The data model is key-value, but many different kind of values are supported: Strings, Lists, Sets, Sorted Sets, Hashes, Streams, HyperLogLogs, Bitmaps.</p>
<p>Library home page: <a href=https://github.com/redis/redis.git>https://github.com/redis/redis.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/snykiotcubedev/redis-6.2.3/commit/4d9d45af08df0c37729fafce88f139952f155020">4d9d45af08df0c37729fafce88f139952f155020</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/src/t_stream.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Redis v7.0 was discovered to contain a memory leak via the component streamGetEdgeID.
<p>Publish Date: 2022-06-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-33105>CVE-2022-33105</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-06-23</p>
<p>Fix Resolution: 7.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-33105 (Medium) detected in redis6.2.6 - ## CVE-2022-33105 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>redis6.2.6</b></p></summary>
<p>
<p>Redis is an in-memory database that persists on disk. The data model is key-value, but many different kind of values are supported: Strings, Lists, Sets, Sorted Sets, Hashes, Streams, HyperLogLogs, Bitmaps.</p>
<p>Library home page: <a href=https://github.com/redis/redis.git>https://github.com/redis/redis.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/snykiotcubedev/redis-6.2.3/commit/4d9d45af08df0c37729fafce88f139952f155020">4d9d45af08df0c37729fafce88f139952f155020</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/src/t_stream.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Redis v7.0 was discovered to contain a memory leak via the component streamGetEdgeID.
<p>Publish Date: 2022-06-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-33105>CVE-2022-33105</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-06-23</p>
<p>Fix Resolution: 7.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in cve medium severity vulnerability vulnerable library redis is an in memory database that persists on disk the data model is key value but many different kind of values are supported strings lists sets sorted sets hashes streams hyperloglogs bitmaps library home page a href found in head commit a href found in base branch main vulnerable source files src t stream c vulnerability details redis was discovered to contain a memory leak via the component streamgetedgeid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend | 0 |
33,551 | 4,838,017,024 | IssuesEvent | 2016-11-09 00:54:32 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | After service with sidekick is deactivated and activated back , primary containers are not able to access sidekick containers. | kind/bug setup/automation status/to-test | Rancher server version - Build form master
Steps to reproduce the problem:
Create a service with sidekick.
Deactivate and activate the service.
After this , primary containers are not able to access sidekick containers by using the sidekick service name. Not able to reach the sidekick containers using their ip address.
```
client = <cattle.Client object at 0x1068ee650>
admin_client = <cattle.Client object at 0x1089ce190>
def test_sidekick_services_deactivate_activate(client, admin_client):
service_scale = 2
exposed_port = "7014"
env, service, service_name, consumed_service_name = \
env_with_sidekick(admin_client, client, service_scale, exposed_port)
service = service.deactivate()
service = client.wait_success(service, 120)
assert service.state == "inactive"
wait_until_instances_get_stopped_for_service_with_sec_launch_configs(
admin_client, service)
service = service.activate()
service = client.wait_success(service, 120)
assert service.state == "active"
dnsname = service.secondaryLaunchConfigs[0].name
validate_sidekick(admin_client, service, service_name,
> consumed_service_name, exposed_port, dnsname)
/Users/sangeethahariharan1/cattle/validation/validation-tests/tests/v2_validation/cattlevalidationtest/core/test_services_sidekick.py:640:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
/Users/sangeethahariharan1/cattle/validation/validation-tests/tests/v2_validation/cattlevalidationtest/core/test_services_sidekick.py:741: in validate_sidekick
dnsname)
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
admin_client = <cattle.Client object at 0x1089ce190>
service_containers = [{'tty': False, 'registryCredentialId': None, 'labels': {'io.rancher.project_service.name': u'test744802/test810335', ...ex': 3, 'dnsSearch': [u'test744802.rancher.internal', u'test810335.test744802.rancher.internal', u'rancher.internal']}]
consumed_service = [{'tty': False, 'registryCredentialId': None, 'labels': {'io.rancher.project_service.name': u'test744802/test810335/te...ex': 4, 'dnsSearch': [u'test744802.rancher.internal', u'test810335.test744802.rancher.internal', u'rancher.internal']}]
exposed_port = '7014', dnsname = 'test953979'
def validate_dns(admin_client, service_containers, consumed_service,
exposed_port, dnsname):
time.sleep(5)
for service_con in service_containers:
host = admin_client.by_id('host', service_con.hosts[0].id)
expected_dns_list = []
expected_link_response = []
dns_response = []
print "Validating DNS for " + dnsname + " - container -" \
+ service_con.name
for con in consumed_service:
expected_dns_list.append(con.primaryIpAddress)
expected_link_response.append(con.externalId[:12])
print "Expected dig response List" + str(expected_dns_list)
print "Expected wget response List" + str(expected_link_response)
# Validate port mapping
ssh = paramiko.SSHClient()
ssh.set_missing_host_key_policy(paramiko.AutoAddPolicy())
ssh.connect(host.ipAddresses()[0].address, username="root",
password="root", port=int(exposed_port))
# Validate link containers
cmd = "wget -O result.txt --timeout=20 --tries=1 http://" + dnsname + \
":80/name.html;cat result.txt"
print cmd
stdin, stdout, stderr = ssh.exec_command(cmd)
response = stdout.readlines()
> assert len(response) == 1
E assert 0 == 1
E + where 0 = len([])
/Users/sangeethahariharan1/cattle/validation/validation-tests/tests/v2_validation/cattlevalidationtest/core/test_services_sidekick.py:777: AssertionError
----------------------------- Captured stdout call -----------------------------
Validating service - test744802-test810335
sleep for .5 sec
test744802-test810335-1
test744802-test810335-2
Validating Consumed Services: test744802-test810335-test953979
sleep for .5 sec
test744802-test810335-test953979-1
test744802-test810335-test953979-2
test744802-test810335-1 - 3a168f01-b313-41a2-9438-32b67fe026a7 - 1h3
test744802-test810335-test953979-1 - 3a168f01-b313-41a2-9438-32b67fe026a7 - 1h3
test744802-test810335-2 - 0a8eae8d-08b9-4a4c-a4d7-0a2ffaaa50f9 - 1h1
test744802-test810335-test953979-2 - 0a8eae8d-08b9-4a4c-a4d7-0a2ffaaa50f9 - 1h1
sleep for .5 sec
test744802-test810335-test953979-1
test744802-test810335-test953979-2
Validating DNS for test953979 - container -test744802-test810335-1
Expected dig response List[u'10.42.202.36', u'10.42.93.166']
Expected wget response List[u'505cbb18d8ce', u'5223550978cf']
wget -O result.txt --timeout=20 --tries=1 http://test953979:80/name.html;cat result.txt
Actual wget Response505cbb18d8ce
dig test953979 +short
Actual dig Response[u'10.42.93.166\n', u'10.42.202.36\n']
Validating DNS for test953979 - container -test744802-test810335-2
Expected dig response List[u'10.42.202.36', u'10.42.93.166']
Expected wget response List[u'505cbb18d8ce', u'5223550978cf']
wget -O result.txt --timeout=20 --tries=1 http://test953979:80/name.html;cat result.txt
Actual wget Response5223550978cf
dig test953979 +short
Actual dig Response[u'10.42.93.166\n', u'10.42.202.36\n']
Validating service - test744802-test810335
sleep for .5 sec
test744802-test810335-1
test744802-test810335-2
Validating Consumed Services: test744802-test810335-test953979
sleep for .5 sec
test744802-test810335-test953979-1
test744802-test810335-test953979-2
test744802-test810335-1 - 3a168f01-b313-41a2-9438-32b67fe026a7 - 1h3
test744802-test810335-test953979-1 - 3a168f01-b313-41a2-9438-32b67fe026a7 - 1h3
test744802-test810335-2 - 0a8eae8d-08b9-4a4c-a4d7-0a2ffaaa50f9 - 1h1
test744802-test810335-test953979-2 - 0a8eae8d-08b9-4a4c-a4d7-0a2ffaaa50f9 - 1h1
sleep for .5 sec
test744802-test810335-test953979-1
test744802-test810335-test953979-2
Validating DNS for test953979 - container -test744802-test810335-1
Expected dig response List[u'10.42.152.231', u'10.42.128.194']
Expected wget response List[u'505cbb18d8ce', u'5223550978cf']
wget -O result.txt --timeout=20 --tries=1 http://test953979:80/name.html;cat result.txt
```
| 1.0 | After service with sidekick is deactivated and activated back , primary containers are not able to access sidekick containers. - Rancher server version - Build form master
Steps to reproduce the problem:
Create a service with sidekick.
Deactivate and activate the service.
After this , primary containers are not able to access sidekick containers by using the sidekick service name. Not able to reach the sidekick containers using their ip address.
```
client = <cattle.Client object at 0x1068ee650>
admin_client = <cattle.Client object at 0x1089ce190>
def test_sidekick_services_deactivate_activate(client, admin_client):
service_scale = 2
exposed_port = "7014"
env, service, service_name, consumed_service_name = \
env_with_sidekick(admin_client, client, service_scale, exposed_port)
service = service.deactivate()
service = client.wait_success(service, 120)
assert service.state == "inactive"
wait_until_instances_get_stopped_for_service_with_sec_launch_configs(
admin_client, service)
service = service.activate()
service = client.wait_success(service, 120)
assert service.state == "active"
dnsname = service.secondaryLaunchConfigs[0].name
validate_sidekick(admin_client, service, service_name,
> consumed_service_name, exposed_port, dnsname)
/Users/sangeethahariharan1/cattle/validation/validation-tests/tests/v2_validation/cattlevalidationtest/core/test_services_sidekick.py:640:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
/Users/sangeethahariharan1/cattle/validation/validation-tests/tests/v2_validation/cattlevalidationtest/core/test_services_sidekick.py:741: in validate_sidekick
dnsname)
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
admin_client = <cattle.Client object at 0x1089ce190>
service_containers = [{'tty': False, 'registryCredentialId': None, 'labels': {'io.rancher.project_service.name': u'test744802/test810335', ...ex': 3, 'dnsSearch': [u'test744802.rancher.internal', u'test810335.test744802.rancher.internal', u'rancher.internal']}]
consumed_service = [{'tty': False, 'registryCredentialId': None, 'labels': {'io.rancher.project_service.name': u'test744802/test810335/te...ex': 4, 'dnsSearch': [u'test744802.rancher.internal', u'test810335.test744802.rancher.internal', u'rancher.internal']}]
exposed_port = '7014', dnsname = 'test953979'
def validate_dns(admin_client, service_containers, consumed_service,
exposed_port, dnsname):
time.sleep(5)
for service_con in service_containers:
host = admin_client.by_id('host', service_con.hosts[0].id)
expected_dns_list = []
expected_link_response = []
dns_response = []
print "Validating DNS for " + dnsname + " - container -" \
+ service_con.name
for con in consumed_service:
expected_dns_list.append(con.primaryIpAddress)
expected_link_response.append(con.externalId[:12])
print "Expected dig response List" + str(expected_dns_list)
print "Expected wget response List" + str(expected_link_response)
# Validate port mapping
ssh = paramiko.SSHClient()
ssh.set_missing_host_key_policy(paramiko.AutoAddPolicy())
ssh.connect(host.ipAddresses()[0].address, username="root",
password="root", port=int(exposed_port))
# Validate link containers
cmd = "wget -O result.txt --timeout=20 --tries=1 http://" + dnsname + \
":80/name.html;cat result.txt"
print cmd
stdin, stdout, stderr = ssh.exec_command(cmd)
response = stdout.readlines()
> assert len(response) == 1
E assert 0 == 1
E + where 0 = len([])
/Users/sangeethahariharan1/cattle/validation/validation-tests/tests/v2_validation/cattlevalidationtest/core/test_services_sidekick.py:777: AssertionError
----------------------------- Captured stdout call -----------------------------
Validating service - test744802-test810335
sleep for .5 sec
test744802-test810335-1
test744802-test810335-2
Validating Consumed Services: test744802-test810335-test953979
sleep for .5 sec
test744802-test810335-test953979-1
test744802-test810335-test953979-2
test744802-test810335-1 - 3a168f01-b313-41a2-9438-32b67fe026a7 - 1h3
test744802-test810335-test953979-1 - 3a168f01-b313-41a2-9438-32b67fe026a7 - 1h3
test744802-test810335-2 - 0a8eae8d-08b9-4a4c-a4d7-0a2ffaaa50f9 - 1h1
test744802-test810335-test953979-2 - 0a8eae8d-08b9-4a4c-a4d7-0a2ffaaa50f9 - 1h1
sleep for .5 sec
test744802-test810335-test953979-1
test744802-test810335-test953979-2
Validating DNS for test953979 - container -test744802-test810335-1
Expected dig response List[u'10.42.202.36', u'10.42.93.166']
Expected wget response List[u'505cbb18d8ce', u'5223550978cf']
wget -O result.txt --timeout=20 --tries=1 http://test953979:80/name.html;cat result.txt
Actual wget Response505cbb18d8ce
dig test953979 +short
Actual dig Response[u'10.42.93.166\n', u'10.42.202.36\n']
Validating DNS for test953979 - container -test744802-test810335-2
Expected dig response List[u'10.42.202.36', u'10.42.93.166']
Expected wget response List[u'505cbb18d8ce', u'5223550978cf']
wget -O result.txt --timeout=20 --tries=1 http://test953979:80/name.html;cat result.txt
Actual wget Response5223550978cf
dig test953979 +short
Actual dig Response[u'10.42.93.166\n', u'10.42.202.36\n']
Validating service - test744802-test810335
sleep for .5 sec
test744802-test810335-1
test744802-test810335-2
Validating Consumed Services: test744802-test810335-test953979
sleep for .5 sec
test744802-test810335-test953979-1
test744802-test810335-test953979-2
test744802-test810335-1 - 3a168f01-b313-41a2-9438-32b67fe026a7 - 1h3
test744802-test810335-test953979-1 - 3a168f01-b313-41a2-9438-32b67fe026a7 - 1h3
test744802-test810335-2 - 0a8eae8d-08b9-4a4c-a4d7-0a2ffaaa50f9 - 1h1
test744802-test810335-test953979-2 - 0a8eae8d-08b9-4a4c-a4d7-0a2ffaaa50f9 - 1h1
sleep for .5 sec
test744802-test810335-test953979-1
test744802-test810335-test953979-2
Validating DNS for test953979 - container -test744802-test810335-1
Expected dig response List[u'10.42.152.231', u'10.42.128.194']
Expected wget response List[u'505cbb18d8ce', u'5223550978cf']
wget -O result.txt --timeout=20 --tries=1 http://test953979:80/name.html;cat result.txt
```
| non_priority | after service with sidekick is deactivated and activated back primary containers are not able to access sidekick containers rancher server version build form master steps to reproduce the problem create a service with sidekick deactivate and activate the service after this primary containers are not able to access sidekick containers by using the sidekick service name not able to reach the sidekick containers using their ip address client admin client def test sidekick services deactivate activate client admin client service scale exposed port env service service name consumed service name env with sidekick admin client client service scale exposed port service service deactivate service client wait success service assert service state inactive wait until instances get stopped for service with sec launch configs admin client service service service activate service client wait success service assert service state active dnsname service secondarylaunchconfigs name validate sidekick admin client service service name consumed service name exposed port dnsname users cattle validation validation tests tests validation cattlevalidationtest core test services sidekick py users cattle validation validation tests tests validation cattlevalidationtest core test services sidekick py in validate sidekick dnsname admin client service containers consumed service exposed port dnsname def validate dns admin client service containers consumed service exposed port dnsname time sleep for service con in service containers host admin client by id host service con hosts id expected dns list expected link response dns response print validating dns for dnsname container service con name for con in consumed service expected dns list append con primaryipaddress expected link response append con externalid print expected dig response list str expected dns list print expected wget response list str expected link response validate port mapping ssh paramiko sshclient ssh set missing host key policy paramiko autoaddpolicy ssh connect host ipaddresses address username root password root port int exposed port validate link containers cmd wget o result txt timeout tries dnsname name html cat result txt print cmd stdin stdout stderr ssh exec command cmd response stdout readlines assert len response e assert e where len users cattle validation validation tests tests validation cattlevalidationtest core test services sidekick py assertionerror captured stdout call validating service sleep for sec validating consumed services sleep for sec sleep for sec validating dns for container expected dig response list expected wget response list wget o result txt timeout tries result txt actual wget dig short actual dig response validating dns for container expected dig response list expected wget response list wget o result txt timeout tries result txt actual wget dig short actual dig response validating service sleep for sec validating consumed services sleep for sec sleep for sec validating dns for container expected dig response list expected wget response list wget o result txt timeout tries result txt | 0 |
225,950 | 24,921,723,686 | IssuesEvent | 2022-10-31 01:13:20 | jtimberlake/WSUWP-Platform | https://api.github.com/repos/jtimberlake/WSUWP-Platform | closed | CVE-2017-16116 (High) detected in underscore.string-3.2.3.tgz - autoclosed | security vulnerability | ## CVE-2017-16116 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore.string-3.2.3.tgz</b></p></summary>
<p>String manipulation extensions for Underscore.js javascript library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore.string/-/underscore.string-3.2.3.tgz">https://registry.npmjs.org/underscore.string/-/underscore.string-3.2.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/underscore.string/package.json</p>
<p>
Dependency Hierarchy:
- grunt-1.0.2.tgz (Root Library)
- grunt-legacy-log-1.0.0.tgz
- :x: **underscore.string-3.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jtimberlake/WSUWP-Platform/commit/57938bd0fb99eb96608ad444e7dbf718469d6170">57938bd0fb99eb96608ad444e7dbf718469d6170</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The string module is a module that provides extra string operations. The string module is vulnerable to regular expression denial of service when specifically crafted untrusted user input is passed into the underscore or unescapeHTML methods.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16116>CVE-2017-16116</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16116">https://nvd.nist.gov/vuln/detail/CVE-2017-16116</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (underscore.string): 3.3.5</p>
<p>Direct dependency fix Resolution (grunt): 1.0.3</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2017-16116 (High) detected in underscore.string-3.2.3.tgz - autoclosed - ## CVE-2017-16116 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore.string-3.2.3.tgz</b></p></summary>
<p>String manipulation extensions for Underscore.js javascript library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore.string/-/underscore.string-3.2.3.tgz">https://registry.npmjs.org/underscore.string/-/underscore.string-3.2.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/underscore.string/package.json</p>
<p>
Dependency Hierarchy:
- grunt-1.0.2.tgz (Root Library)
- grunt-legacy-log-1.0.0.tgz
- :x: **underscore.string-3.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jtimberlake/WSUWP-Platform/commit/57938bd0fb99eb96608ad444e7dbf718469d6170">57938bd0fb99eb96608ad444e7dbf718469d6170</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The string module is a module that provides extra string operations. The string module is vulnerable to regular expression denial of service when specifically crafted untrusted user input is passed into the underscore or unescapeHTML methods.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16116>CVE-2017-16116</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16116">https://nvd.nist.gov/vuln/detail/CVE-2017-16116</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (underscore.string): 3.3.5</p>
<p>Direct dependency fix Resolution (grunt): 1.0.3</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | cve high detected in underscore string tgz autoclosed cve high severity vulnerability vulnerable library underscore string tgz string manipulation extensions for underscore js javascript library library home page a href path to dependency file package json path to vulnerable library node modules underscore string package json dependency hierarchy grunt tgz root library grunt legacy log tgz x underscore string tgz vulnerable library found in head commit a href found in base branch master vulnerability details the string module is a module that provides extra string operations the string module is vulnerable to regular expression denial of service when specifically crafted untrusted user input is passed into the underscore or unescapehtml methods publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution underscore string direct dependency fix resolution grunt rescue worker helmet automatic remediation is available for this issue | 0 |
212,720 | 23,941,917,935 | IssuesEvent | 2022-09-12 01:01:55 | zencoder/gokay | https://api.github.com/repos/zencoder/gokay | opened | github.com/golang/tools-v0.1.10: 3 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/golang/tools-v0.1.10</b></p></summary>
<p>[mirror] Go Tools</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip">https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip</a></p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-11022](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | github.com/golang/tools-v0.1.10 | Direct | jQuery - 3.5.0 | ❌ |
| [CVE-2015-9251](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | github.com/golang/tools-v0.1.10 | Direct | jQuery - v3.0.0 | ❌ |
| [CVE-2012-6708](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | github.com/golang/tools-v0.1.10 | Direct | jQuery - v1.9.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-11022</summary>
### Vulnerable Library - <b>github.com/golang/tools-v0.1.10</b></p>
<p>[mirror] Go Tools</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip">https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip</a></p>
<p>
Dependency Hierarchy:
- :x: **github.com/golang/tools-v0.1.10** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2015-9251</summary>
### Vulnerable Library - <b>github.com/golang/tools-v0.1.10</b></p>
<p>[mirror] Go Tools</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip">https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip</a></p>
<p>
Dependency Hierarchy:
- :x: **github.com/golang/tools-v0.1.10** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2012-6708</summary>
### Vulnerable Library - <b>github.com/golang/tools-v0.1.10</b></p>
<p>[mirror] Go Tools</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip">https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip</a></p>
<p>
Dependency Hierarchy:
- :x: **github.com/golang/tools-v0.1.10** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the '<' character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708>CVE-2012-6708</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6708">https://nvd.nist.gov/vuln/detail/CVE-2012-6708</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v1.9.0</p>
</p>
<p></p>
</details> | True | github.com/golang/tools-v0.1.10: 3 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/golang/tools-v0.1.10</b></p></summary>
<p>[mirror] Go Tools</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip">https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip</a></p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-11022](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | github.com/golang/tools-v0.1.10 | Direct | jQuery - 3.5.0 | ❌ |
| [CVE-2015-9251](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | github.com/golang/tools-v0.1.10 | Direct | jQuery - v3.0.0 | ❌ |
| [CVE-2012-6708](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | github.com/golang/tools-v0.1.10 | Direct | jQuery - v1.9.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-11022</summary>
### Vulnerable Library - <b>github.com/golang/tools-v0.1.10</b></p>
<p>[mirror] Go Tools</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip">https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip</a></p>
<p>
Dependency Hierarchy:
- :x: **github.com/golang/tools-v0.1.10** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2015-9251</summary>
### Vulnerable Library - <b>github.com/golang/tools-v0.1.10</b></p>
<p>[mirror] Go Tools</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip">https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip</a></p>
<p>
Dependency Hierarchy:
- :x: **github.com/golang/tools-v0.1.10** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2012-6708</summary>
### Vulnerable Library - <b>github.com/golang/tools-v0.1.10</b></p>
<p>[mirror] Go Tools</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip">https://proxy.golang.org/github.com/golang/tools/@v/v0.1.10.zip</a></p>
<p>
Dependency Hierarchy:
- :x: **github.com/golang/tools-v0.1.10** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the '<' character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708>CVE-2012-6708</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6708">https://nvd.nist.gov/vuln/detail/CVE-2012-6708</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v1.9.0</p>
</p>
<p></p>
</details> | non_priority | github com golang tools vulnerabilities highest severity is vulnerable library github com golang tools go tools library home page a href vulnerabilities cve severity cvss dependency type fixed in remediation available medium github com golang tools direct jquery medium github com golang tools direct jquery low github com golang tools direct jquery details cve vulnerable library github com golang tools go tools library home page a href dependency hierarchy x github com golang tools vulnerable library found in base branch master vulnerability details in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery cve vulnerable library github com golang tools go tools library home page a href dependency hierarchy x github com golang tools vulnerable library found in base branch master vulnerability details jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery cve vulnerable library github com golang tools go tools library home page a href dependency hierarchy x github com golang tools vulnerable library found in base branch master vulnerability details jquery before is vulnerable to cross site scripting xss attacks the jquery strinput function does not differentiate selectors from html in a reliable fashion in vulnerable versions jquery determined whether the input was html by looking for the character anywhere in the string giving attackers more flexibility when attempting to construct a malicious payload in fixed versions jquery only deems the input to be html if it explicitly starts with the character limiting exploitability only to attackers who can control the beginning of a string which is far less common publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery | 0 |
129,605 | 27,522,218,737 | IssuesEvent | 2023-03-06 15:43:04 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Pagination results not showing on Joomla | No Code Attached Yet | ### Steps to reproduce the issue
I have set the pagination results to "Show," but for some reason, on my site, when I click on subsequent pages (2,3,3....), I am redirected to the home page. How can I fix this?
### Expected result
Ideally, the subsequent pages should open and show the articles on that page. That doesn't happen. This is on Joomla 3.7.4
### Actual result
### System information (as much as possible)
### Additional comments
| 1.0 | Pagination results not showing on Joomla - ### Steps to reproduce the issue
I have set the pagination results to "Show," but for some reason, on my site, when I click on subsequent pages (2,3,3....), I am redirected to the home page. How can I fix this?
### Expected result
Ideally, the subsequent pages should open and show the articles on that page. That doesn't happen. This is on Joomla 3.7.4
### Actual result
### System information (as much as possible)
### Additional comments
| non_priority | pagination results not showing on joomla steps to reproduce the issue i have set the pagination results to show but for some reason on my site when i click on subsequent pages i am redirected to the home page how can i fix this expected result ideally the subsequent pages should open and show the articles on that page that doesn t happen this is on joomla actual result system information as much as possible additional comments | 0 |
59,891 | 14,667,439,644 | IssuesEvent | 2020-12-29 18:37:49 | weaveworks/scope | https://api.github.com/repos/weaveworks/scope | closed | Make failed on ARM64, undefined: DNSSnooper | component/build feature help-wanted | 2016-12-25, run "make"
**Platform Info:**
* Arch: ARM64
* Hardware: 96Boards
* CPU: Snapdragon 410C
* Host OS: Linaro based debian
* Docker container: aarch64/ubuntu:xenial
* Toolchain: golang1.7.4, node 6.9.2, npm 4.0.5
* Source: https://github.com/openthings/scope/tree/ARM64, branch ARM64
**Error info:**
```
docker run --rm -ti \
-v /media/linaro/zdata/src/github.com/openthings/scope:/go/src/github.com/weaveworks/scope \
-v /media/linaro/zdata/src/github.com/openthings/scope/.pkg:/go/pkg \
--net=host \
-e GOARCH -e GOOS -e CIRCLECI -e CIRCLE_BUILD_NUM -e CIRCLE_NODE_TOTAL \
-e CIRCLE_NODE_INDEX -e COVERDIR -e SLOW -e TESTDIRS \
weaveworks/scope-backend-build SCOPE_VERSION=05869ab GO_BUILD_INSTALL_DEPS=-i prog/scope
make: Entering directory '/go/src/github.com/weaveworks/scope'
rm -f render/detailed/detailed.codecgen.go; unset GOOS GOARCH; env GOGC=off go build -i -ldflags "-extldflags \"-static\" -X main.version=05869ab -s -w" -tags 'netgo unsafe' ./render/detailed # workaround for https://github.com/ugorji/go/issues/145
# github.com/weaveworks/scope/probe/endpoint
probe/endpoint/reporter.go:37: undefined: DNSSnooper
Makefile:90: recipe for target 'render/detailed/detailed.codecgen.go' failed
make: *** [render/detailed/detailed.codecgen.go] Error 2
make: Leaving directory '/go/src/github.com/weaveworks/scope'
Makefile:67: recipe for target 'prog/scope' failed
make: *** [prog/scope] Error 2
```
| 1.0 | Make failed on ARM64, undefined: DNSSnooper - 2016-12-25, run "make"
**Platform Info:**
* Arch: ARM64
* Hardware: 96Boards
* CPU: Snapdragon 410C
* Host OS: Linaro based debian
* Docker container: aarch64/ubuntu:xenial
* Toolchain: golang1.7.4, node 6.9.2, npm 4.0.5
* Source: https://github.com/openthings/scope/tree/ARM64, branch ARM64
**Error info:**
```
docker run --rm -ti \
-v /media/linaro/zdata/src/github.com/openthings/scope:/go/src/github.com/weaveworks/scope \
-v /media/linaro/zdata/src/github.com/openthings/scope/.pkg:/go/pkg \
--net=host \
-e GOARCH -e GOOS -e CIRCLECI -e CIRCLE_BUILD_NUM -e CIRCLE_NODE_TOTAL \
-e CIRCLE_NODE_INDEX -e COVERDIR -e SLOW -e TESTDIRS \
weaveworks/scope-backend-build SCOPE_VERSION=05869ab GO_BUILD_INSTALL_DEPS=-i prog/scope
make: Entering directory '/go/src/github.com/weaveworks/scope'
rm -f render/detailed/detailed.codecgen.go; unset GOOS GOARCH; env GOGC=off go build -i -ldflags "-extldflags \"-static\" -X main.version=05869ab -s -w" -tags 'netgo unsafe' ./render/detailed # workaround for https://github.com/ugorji/go/issues/145
# github.com/weaveworks/scope/probe/endpoint
probe/endpoint/reporter.go:37: undefined: DNSSnooper
Makefile:90: recipe for target 'render/detailed/detailed.codecgen.go' failed
make: *** [render/detailed/detailed.codecgen.go] Error 2
make: Leaving directory '/go/src/github.com/weaveworks/scope'
Makefile:67: recipe for target 'prog/scope' failed
make: *** [prog/scope] Error 2
```
| non_priority | make failed on undefined dnssnooper run make platform info arch hardware cpu snapdragon host os linaro based debian docker container ubuntu xenial toolchain node npm source branch error info docker run rm ti v media linaro zdata src github com openthings scope go src github com weaveworks scope v media linaro zdata src github com openthings scope pkg go pkg net host e goarch e goos e circleci e circle build num e circle node total e circle node index e coverdir e slow e testdirs weaveworks scope backend build scope version go build install deps i prog scope make entering directory go src github com weaveworks scope rm f render detailed detailed codecgen go unset goos goarch env gogc off go build i ldflags extldflags static x main version s w tags netgo unsafe render detailed workaround for github com weaveworks scope probe endpoint probe endpoint reporter go undefined dnssnooper makefile recipe for target render detailed detailed codecgen go failed make error make leaving directory go src github com weaveworks scope makefile recipe for target prog scope failed make error | 0 |
129,308 | 27,440,821,099 | IssuesEvent | 2023-03-02 10:52:21 | FerretDB/FerretDB | https://api.github.com/repos/FerretDB/FerretDB | opened | Exclude unit tests from code coverage | code/chore | ### What should be done?
We should try to exclude unit tests from coverage tracking, as they may test parts of code that's not covered by integration tests, which could result in some unexpected bugs.
### Where?
Probably Taskfile.yml and .github workflows.
### Definition of Done
- Make codecov display coverage only for tests from `integration` package
- Decide whether we want separate coverage check for unit tests + integration tests or just single one for integration tests (checking for unit tests coverage might be still useful in some cases!) | 1.0 | Exclude unit tests from code coverage - ### What should be done?
We should try to exclude unit tests from coverage tracking, as they may test parts of code that's not covered by integration tests, which could result in some unexpected bugs.
### Where?
Probably Taskfile.yml and .github workflows.
### Definition of Done
- Make codecov display coverage only for tests from `integration` package
- Decide whether we want separate coverage check for unit tests + integration tests or just single one for integration tests (checking for unit tests coverage might be still useful in some cases!) | non_priority | exclude unit tests from code coverage what should be done we should try to exclude unit tests from coverage tracking as they may test parts of code that s not covered by integration tests which could result in some unexpected bugs where probably taskfile yml and github workflows definition of done make codecov display coverage only for tests from integration package decide whether we want separate coverage check for unit tests integration tests or just single one for integration tests checking for unit tests coverage might be still useful in some cases | 0 |
379,111 | 26,354,163,159 | IssuesEvent | 2023-01-11 08:23:04 | jeluchu/jchucomponents | https://api.github.com/repos/jeluchu/jchucomponents | opened | Complete the documentation of remaining components and extensions | documentation enhancement | The documentation of certain design components or extensions found in the different UI or ktx modules needs to be completed, this will be completed in future versions, but I leave the issue to be taken into account. It will also be adapted to be available for easy access using Dokka as it was previously done when everything was in a single core module (currently core, ktx and ui) | 1.0 | Complete the documentation of remaining components and extensions - The documentation of certain design components or extensions found in the different UI or ktx modules needs to be completed, this will be completed in future versions, but I leave the issue to be taken into account. It will also be adapted to be available for easy access using Dokka as it was previously done when everything was in a single core module (currently core, ktx and ui) | non_priority | complete the documentation of remaining components and extensions the documentation of certain design components or extensions found in the different ui or ktx modules needs to be completed this will be completed in future versions but i leave the issue to be taken into account it will also be adapted to be available for easy access using dokka as it was previously done when everything was in a single core module currently core ktx and ui | 0 |
117,388 | 25,106,327,580 | IssuesEvent | 2022-11-08 16:53:29 | serbanghita/Mobile-Detect | https://api.github.com/repos/serbanghita/Mobile-Detect | closed | Feature request: getDevice and getDeviceCategory | area: Code Quality deprecated | Great and usefull work!
Is there already a way to get a string which device was detected? If not, it would be great to get 2 methods:
function getDevice()
-> returns the device which was detected (like "iPhone", "iPad", "Samsung", "SamsungTablet" etc).
And (just for convenience):
function getDeviceCategory()
-> returns "mobile", "tablet" or "desktop" as a string
| 1.0 | Feature request: getDevice and getDeviceCategory - Great and usefull work!
Is there already a way to get a string which device was detected? If not, it would be great to get 2 methods:
function getDevice()
-> returns the device which was detected (like "iPhone", "iPad", "Samsung", "SamsungTablet" etc).
And (just for convenience):
function getDeviceCategory()
-> returns "mobile", "tablet" or "desktop" as a string
| non_priority | feature request getdevice and getdevicecategory great and usefull work is there already a way to get a string which device was detected if not it would be great to get methods function getdevice returns the device which was detected like iphone ipad samsung samsungtablet etc and just for convenience function getdevicecategory returns mobile tablet or desktop as a string | 0 |
236,802 | 19,576,091,905 | IssuesEvent | 2022-01-04 15:36:08 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | ccl/kvccl/kvtenantccl: TestTenantUpgradeFailure failed | C-test-failure O-robot branch-master T-sql-schema | ccl/kvccl/kvtenantccl.TestTenantUpgradeFailure [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3915298&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3915298&tab=artifacts#/) on master @ [acf40e97f64a97338cbebd20d7fbe176c4e37c34](https://github.com/cockroachdb/cockroach/commits/acf40e97f64a97338cbebd20d7fbe176c4e37c34):
```
=== RUN TestTenantUpgradeFailure/upgrade_tenant_have_it_crash_then_resume
```
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)Parameters in this failure:
- TAGS=bazel,gss
</p>
</details>
/cc @cockroachdb/kv
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestTenantUpgradeFailure.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 1.0 | ccl/kvccl/kvtenantccl: TestTenantUpgradeFailure failed - ccl/kvccl/kvtenantccl.TestTenantUpgradeFailure [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3915298&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3915298&tab=artifacts#/) on master @ [acf40e97f64a97338cbebd20d7fbe176c4e37c34](https://github.com/cockroachdb/cockroach/commits/acf40e97f64a97338cbebd20d7fbe176c4e37c34):
```
=== RUN TestTenantUpgradeFailure/upgrade_tenant_have_it_crash_then_resume
```
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)Parameters in this failure:
- TAGS=bazel,gss
</p>
</details>
/cc @cockroachdb/kv
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestTenantUpgradeFailure.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | ccl kvccl kvtenantccl testtenantupgradefailure failed ccl kvccl kvtenantccl testtenantupgradefailure with on master run testtenantupgradefailure upgrade tenant have it crash then resume help see also in this failure tags bazel gss cc cockroachdb kv | 0 |
53,975 | 6,777,427,927 | IssuesEvent | 2017-10-27 22:12:54 | Automattic/jetpack | https://api.github.com/repos/Automattic/jetpack | opened | Connect Banner styles off | Admin Page General [Status] Design Polish [Type] Bug [Type] Good First Bug |
#### Steps to reproduce the issue
Run the latest version of Jetpack
#### What I expected
Things to look more styled.
#### What happened instead
The banner looks brokern see "By connecting your site you agree to our fascinatin"
<!--
PLEASE NOTE
- These comments won't show up when you submit the issue.
- Everything is optional, but try to add as many details as possible.
- If requesting a new feature, explain why you'd like to see it added.
- This issue tracker is not for support. If you have questions about Jetpack, you can [start a new thread in the Jetpack support forums](https://wordpress.org/support/plugin/jetpack#new-post), or [send us an email](http://jetpack.com/contact-support/).
- Do not report potential security vulnerabilities here. For responsible disclosure of security issues and to be eligible for our bug bounty program, please submit your report via [the HackerOne portal](https://hackerone.com/automattic).
-->
| 1.0 | Connect Banner styles off -
#### Steps to reproduce the issue
Run the latest version of Jetpack
#### What I expected
Things to look more styled.
#### What happened instead
The banner looks brokern see "By connecting your site you agree to our fascinatin"
<!--
PLEASE NOTE
- These comments won't show up when you submit the issue.
- Everything is optional, but try to add as many details as possible.
- If requesting a new feature, explain why you'd like to see it added.
- This issue tracker is not for support. If you have questions about Jetpack, you can [start a new thread in the Jetpack support forums](https://wordpress.org/support/plugin/jetpack#new-post), or [send us an email](http://jetpack.com/contact-support/).
- Do not report potential security vulnerabilities here. For responsible disclosure of security issues and to be eligible for our bug bounty program, please submit your report via [the HackerOne portal](https://hackerone.com/automattic).
-->
| non_priority | connect banner styles off steps to reproduce the issue run the latest version of jetpack what i expected things to look more styled what happened instead the banner looks brokern see by connecting your site you agree to our fascinatin please note these comments won t show up when you submit the issue everything is optional but try to add as many details as possible if requesting a new feature explain why you d like to see it added this issue tracker is not for support if you have questions about jetpack you can or do not report potential security vulnerabilities here for responsible disclosure of security issues and to be eligible for our bug bounty program please submit your report via | 0 |
53,588 | 13,183,348,479 | IssuesEvent | 2020-08-12 17:21:11 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | ERROR HINDERING MY ABILITY TO USE TENSOR FLOW | stalled stat:awaiting response type:build/install |
[TF Error.docx](https://github.com/tensorflow/tensorflow/files/4993986/TF.Error.docx)
Thank you for submitting a TensorFlow documentation issue. Per our GitHub
policy, we only address code/doc bugs, performance issues, feature requests, and
build/installation issues on GitHub.
The TensorFlow docs are open source! To get involved, read the documentation
contributor guide: https://www.tensorflow.org/community/contribute/docs
## URL(s) with the issue:
Please provide a link to the documentation entry, for example:
https://www.tensorflow.org/versions/r2.0/api_docs/python/tf/MyMethod
## Description of issue (what needs changing):
### Clear description
For example, why should someone use this method? How is it useful?
### Correct links
Is the link to the source code correct?
### Parameters defined
Are all parameters defined and formatted correctly?
### Returns defined
Are return values defined?
### Raises listed and defined
Are the errors defined? For example,
https://www.tensorflow.org/versions/r2.0/api_docs/python/tf/feature_column/categorical_column_with_vocabulary_file#raises
### Usage example
Is there a usage example?
See the API guide: https://www.tensorflow.org/community/contribute/docs_ref
on how to write testable usage examples.
### Request visuals, if applicable
Are there currently visuals? If not, will it clarify the content?
### Submit a pull request?
Are you planning to also submit a pull request to fix the issue? See the docs
contributor guide: https://www.tensorflow.org/community/contribute/docs,
docs API guide: https://www.tensorflow.org/community/contribute/docs_ref and the
docs style guide: https://www.tensorflow.org/community/contribute/docs_style
| 1.0 | ERROR HINDERING MY ABILITY TO USE TENSOR FLOW -
[TF Error.docx](https://github.com/tensorflow/tensorflow/files/4993986/TF.Error.docx)
Thank you for submitting a TensorFlow documentation issue. Per our GitHub
policy, we only address code/doc bugs, performance issues, feature requests, and
build/installation issues on GitHub.
The TensorFlow docs are open source! To get involved, read the documentation
contributor guide: https://www.tensorflow.org/community/contribute/docs
## URL(s) with the issue:
Please provide a link to the documentation entry, for example:
https://www.tensorflow.org/versions/r2.0/api_docs/python/tf/MyMethod
## Description of issue (what needs changing):
### Clear description
For example, why should someone use this method? How is it useful?
### Correct links
Is the link to the source code correct?
### Parameters defined
Are all parameters defined and formatted correctly?
### Returns defined
Are return values defined?
### Raises listed and defined
Are the errors defined? For example,
https://www.tensorflow.org/versions/r2.0/api_docs/python/tf/feature_column/categorical_column_with_vocabulary_file#raises
### Usage example
Is there a usage example?
See the API guide: https://www.tensorflow.org/community/contribute/docs_ref
on how to write testable usage examples.
### Request visuals, if applicable
Are there currently visuals? If not, will it clarify the content?
### Submit a pull request?
Are you planning to also submit a pull request to fix the issue? See the docs
contributor guide: https://www.tensorflow.org/community/contribute/docs,
docs API guide: https://www.tensorflow.org/community/contribute/docs_ref and the
docs style guide: https://www.tensorflow.org/community/contribute/docs_style
| non_priority | error hindering my ability to use tensor flow thank you for submitting a tensorflow documentation issue per our github policy we only address code doc bugs performance issues feature requests and build installation issues on github the tensorflow docs are open source to get involved read the documentation contributor guide url s with the issue please provide a link to the documentation entry for example description of issue what needs changing clear description for example why should someone use this method how is it useful correct links is the link to the source code correct parameters defined are all parameters defined and formatted correctly returns defined are return values defined raises listed and defined are the errors defined for example usage example is there a usage example see the api guide on how to write testable usage examples request visuals if applicable are there currently visuals if not will it clarify the content submit a pull request are you planning to also submit a pull request to fix the issue see the docs contributor guide docs api guide and the docs style guide | 0 |
13,501 | 15,950,582,754 | IssuesEvent | 2021-04-15 08:50:15 | scalacenter/scala-3-migration-guide | https://api.github.com/repos/scalacenter/scala-3-migration-guide | closed | Unexpected and undesirable Search functionality looking for "beanproperty"... | incompatibility | My first experience arriving at the home page is already undesirable and immediately diminished my migration confidence. It happened as a result of [this thread](https://github.com/lampepfl/dotty/issues/11972):
Here's what happened:
1. Entering "beanproperty" in the search box did not cause anything to happen
2. Entering "bean property" in the search box caused a 404
3. Entering "bean" in the search box dropped me into a random location in the documentation
4. Attempting to find a place to submit an issue ticket was non-trivial
Given how simple these steps were to take, and given how unpredictable the results were, it leaves a terrible first impression.
I don't have the time (and for most others, the motivation) to try and figure these out as it would cause me to lose my current focus (evaluating a project migration LOE [Level Of Effort]) for which I came to this site in the first place. | True | Unexpected and undesirable Search functionality looking for "beanproperty"... - My first experience arriving at the home page is already undesirable and immediately diminished my migration confidence. It happened as a result of [this thread](https://github.com/lampepfl/dotty/issues/11972):
Here's what happened:
1. Entering "beanproperty" in the search box did not cause anything to happen
2. Entering "bean property" in the search box caused a 404
3. Entering "bean" in the search box dropped me into a random location in the documentation
4. Attempting to find a place to submit an issue ticket was non-trivial
Given how simple these steps were to take, and given how unpredictable the results were, it leaves a terrible first impression.
I don't have the time (and for most others, the motivation) to try and figure these out as it would cause me to lose my current focus (evaluating a project migration LOE [Level Of Effort]) for which I came to this site in the first place. | non_priority | unexpected and undesirable search functionality looking for beanproperty my first experience arriving at the home page is already undesirable and immediately diminished my migration confidence it happened as a result of here s what happened entering beanproperty in the search box did not cause anything to happen entering bean property in the search box caused a entering bean in the search box dropped me into a random location in the documentation attempting to find a place to submit an issue ticket was non trivial given how simple these steps were to take and given how unpredictable the results were it leaves a terrible first impression i don t have the time and for most others the motivation to try and figure these out as it would cause me to lose my current focus evaluating a project migration loe for which i came to this site in the first place | 0 |
29,142 | 13,051,203,204 | IssuesEvent | 2020-07-29 16:41:37 | Azure/azure-powershell | https://api.github.com/repos/Azure/azure-powershell | closed | Set-AzVMDiagnosticsExtension doesn't seem working properly across subscriptions | Compute Compute - Extensions Service Attention customer-reported question | <!--
- Make sure you are able to reproduce this issue on the latest released version of Az
- https://www.powershellgallery.com/packages/Az
- Please search the existing issues to see if there has been a similar issue filed
- For issue related to importing a module, please refer to our troubleshooting guide:
- https://github.com/Azure/azure-powershell/blob/master/documentation/troubleshoot-module-load.md
-->
## Description
what I'm trying to is to enable VM Diagnostic extension to send Event logs (Application [1,2,3], Security [all], System [1,2,3]) to one unified storage account (let's call it logsstorage) where WADWindowsEventLogsTable is supposed to be created.
Running **AzVMDiagnosticsExtension** against VM in a _**different subscription from where the storage account is**_, will enable the extension on the target Vm. However, when I go to VM **Diagnostic settings** > **Agent tab**>**Storage account section**, I'll get the following error message
> "the value must not be empty"
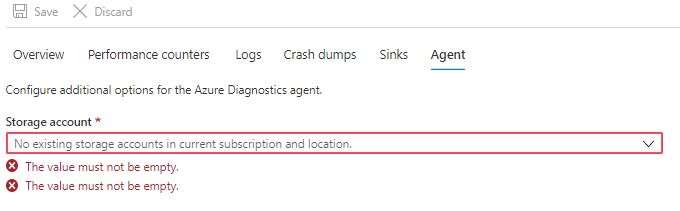
and **WADWindowsEventLogsTable** won't be created (or write to it if exist )
## Steps to reproduce
following steps in the offcial microsft docuemnts [(https://docs.microsoft.com/en-us/azure/azure-monitor/platform/diagnostics-extension-windows-install)](url).
I tried two approaches :
```powershell
Set-AzVMDiagnosticsExtension -ResourceGroupName "myrg" -VMName "myvm" -DiagnosticsConfigurationPath "DiagnosticsConfiguration.json"
```
Another approach, tried to explicitly specifying account name and key
```powershell
Set-AzContext -SubscriptionId "where VM was created"
$storage_key = "xxxxxx"
Set-AzVMDiagnosticsExtension -ResourceGroupName "myrg" -VMName "myvm" -DiagnosticsConfigurationPath "DiagnosticsConfiguration.json" -StorageAccountName "logsstorage" -StorageAccountKey $storage_key
```
## The command output
<!-- Set $DebugPreference='Continue' before running the repro and paste the resulting debug stream in the below code block -->
```
RequestId IsSuccessStatusCode StatusCode ReasonPhrase
--------- ------------------- ---------- ------------
True OK OK
```
## Get-AzVMDiagnosticsExtension output
<!-- Please run Resolve-AzError and paste the output in the below code block -->
```
ResourceGroupName : myrg
VMName : myvm
Name : Microsoft.Insights.VMDiagnosticsSettings
Location : northeurope
Etag : null
Publisher : Microsoft.Azure.Diagnostics
ExtensionType : IaaSDiagnostics
TypeHandlerVersion : 1.5
Id : /subscriptions/xxxxx/resourceGroups/myrg/providers/Microsoft.Compute/virtualMachines/myvm/extensions/Microsoft.Insights.VMDiagnosticsSettings
PublicSettings : {
"storageAccount": "logsstorage",
"WadCfg": {
"DiagnosticMonitorConfiguration": {
"overallQuotaInMB": 5120,
"WindowsEventLog": {
"scheduledTransferPeriod": "PT1M",
"DataSource": [
{
"name": "Application!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
},
{
"name": "Security!*"
},
{
"name": "System!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
}
]
},
"Metrics": {
"resourceId": "/subscriptions/xx/resourceGroups/myrg/providers/Microsoft.Compute/virtualMachines/myvm"
}
}
},
"StorageType": "TableAndBlob"
}
ProtectedSettings :
ProvisioningState : Succeeded
Statuses :
SubStatuses :
AutoUpgradeMinorVersion : True
ForceUpdateTag :
```
## DiagnosticsConfiguration.json
```
{
"PublicConfig": {
"WadCfg": {
"DiagnosticMonitorConfiguration": {
"overallQuotaInMB": 5120,
"WindowsEventLog": {
"scheduledTransferPeriod": "PT1M",
"DataSource": [
{
"name": "Application!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
},
{
"name": "Security!*"
},
{
"name": "System!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
}
]
}
}
},
"StorageAccount": "logsstorage",
"StorageType": "TableAndBlob"
},
"PrivateConfig": {
"storageAccountName": "logsstorage",
"storageAccountKey": "xxxxxxx",
"storageAccountEndPoint": "https://logsstorage.blob.core.windows.net"
}
}
```
## Environment data
<!-- Please run $PSVersionTable and paste the output in the below code block
If running the Docker container image, indicate the tag of the image used and the version of Docker engine-->
```
> Windows
> Powershell 7.0.2
```
## Module versions
<!-- Please run (Get-Module -ListAvailable) and paste the output in the below code block -->
```powershell
ModuleType Version PreRelease Name PSEdition ExportedCommands
---------- ------- ---------- ---- --------- ----------------
Script 4.2.0 Az.Compute Core,Desk {Remove-AzAvailabilitySet, Get-AzAvailabilitySet, New-AzAvailabilitySet, Update-AzAvailabilitySet…}
```
## Debug output
<!-- Set $DebugPreference='Continue' before running the repro and paste the resulting debug stream in the below code block -->
```
DEBUG: 11:09:58 PM - SetAzureRmVMDiagnosticsExtensionCommand begin processing with ParameterSet '__AllParameterSets'.
DEBUG: 11:09:58 PM - using account id 'xxxxxxxxxxxxxxx'...
DEBUG: [Common.Authentication]: Authenticating using Account: 'xxxxxxxxxxxxxxx', environment: 'AzureCloud', tenant: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: Authenticating using configuration values: Domain: 'xxxxxxxxxxxxxxx', Endpoint: 'https://login.microsoftonline.com/', ClientId: 'xxxxxxxxxxxxxxx', ClientRedirect: 'urn:ietf:wg:oauth:2.0:oob', ResourceClientUri: 'https://management.core.windows.net/', ValidateAuthority: 'True'
DEBUG: [Common.Authentication]: Acquiring token using context with Authority 'https://login.microsoftonline.com/xxxxxxxxxxxxxxx/', CorrelationId: '00000000-0000-0000-0000-000000000000', ValidateAuthority: 'True'
DEBUG: [Common.Authentication]: Acquiring token using AdalConfiguration with Domain: 'xxxxxxxxxxxxxxx', AdEndpoint: 'https://login.microsoftonline.com/', ClientId: 'xxxxxxxxxxxxxxx', ClientRedirectUri: urn:ietf:wg:oauth:2.0:oob
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0001673Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: ADAL PCL.CoreCLR with assembly version '3.19.2.6005', file version '3.19.50302.0130' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0002653Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: ADAL PCL.CoreCLR with assembly version '3.19.2.6005', file version '3.19.50302.0130' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0002950Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: === Token Acquisition started:
CacheType: null
Authentication Target: User
, Authority Host: login.microsoftonline.com
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0003103Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: === Token Acquisition started:
Authority: https://login.microsoftonline.com/xxxxxxxxxxxxxxx/
Resource: https://management.core.windows.net/
ClientId: xxxxxxxxxxxxxxx
CacheType: null
Authentication Target: User
DEBUG: [ADAL]: Verbose: 2020-06-29T20:09:59.0004017Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: Loading from cache.
DEBUG: [ADAL]: Verbose: 2020-06-29T20:09:59.0004157Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: Loading from cache.
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0015979Z: 00000000-0000-0000-0000-000000000000 - LoggerBase.cs: Deserialized 5 items to token cache.
DEBUG: [ADAL]: Verbose: 2020-06-29T20:09:59.0016642Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: Looking up cache for a token...
DEBUG: [ADAL]: Verbose: 2020-06-29T20:09:59.0016772Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: Looking up cache for a token...
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0017341Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: An item matching the requested resource was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0017455Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: An item matching the requested resource was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0018248Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: 34.651020055 minutes left until token in cache expires
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0018359Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: 34.651020055 minutes left until token in cache expires
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0018454Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0018543Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0019512Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expiration Time: 6/29/2020 8:44:38 PM +00:00
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0019644Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expiration Time: 6/29/2020 8:44:38 PM +00:00Access Token Hash: zBlr8dpGmJ+/ReLBTiB/DsnyMKdFjCAqV4aJ+GVjVJM=
User id: 9ace2f84-b5e8-479a-beb3-462e5b6c550d
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:09:59 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:34:39.0543514'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/providers/Microsoft.Storage/storageAccounts?api-version=2017-10-01
Headers:
x-ms-client-request-id : 4629b4aa-976e-4426-a1e5-9c84467183ba
Accept-Language : en-US
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-request-id : xxxx
Strict-Transport-Security : max-age=31536000; includeSubDomains
Server : Microsoft-Azure-Storage-Resource-Provider/1.0,Microsoft-HTTPAPI/2.0 Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11966
x-ms-correlation-request-id : 0d567455-36d1-4a91-8ae8-2f0477753175
x-ms-routing-request-id : UAENORTH:20200629T201001Z:0d567455-36d1-4a91-8ae8-2f0477753175
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:10:01 GMT
Body:
{
"value": [
{
"sku": {
"name": "Standard_LRS",
"tier": "Standard"
},
"kind": "Storage",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Storage/storageAccounts/storagexxxx",
"name": "storagexxxx",
"type": "Microsoft.Storage/storageAccounts",
"location": "westeurope",
"tags": {},
"properties": {
"networkAcls": {
"bypass": "AzureServices",
"virtualNetworkRules": [],
"ipRules": [],
"defaultAction": "Allow"
},
"supportsHttpsTrafficOnly": false,
"encryption": {
"services": {
"file": {
"enabled": true,
"lastEnabledTime": "2019-03-10T11:12:25.5593458Z"
},
"blob": {
"enabled": true,
"lastEnabledTime": "2019-03-10T11:12:25.5593458Z"
}
},
"keySource": "Microsoft.Storage"
},
"provisioningState": "Succeeded",
"creationTime": "2019-03-10T11:12:25.356245Z",
"primaryEndpoints": {
"blob": "https://storagexxxx.blob.core.windows.net/",
"queue": "https://storagexxxx.queue.core.windows.net/",
"table": "https://storagexxxx.table.core.windows.net/",
"file": "https://storagexxxx.file.core.windows.net/"
},
"primaryLocation": "westeurope",
"statusOfPrimary": "available"
}
}
]
}
DEBUG: [Common.Authentication]: Authenticating using Account: 'xxxxxxxxxxxxxxx', environment: 'AzureCloud', tenant: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: Authenticating using configuration values: Domain: 'xxxxxxxxxxxxxxx', Endpoint: 'https://login.microsoftonline.com/', ClientId: 'xxxxxxxxxxxxxxx', ClientRedirect: 'urn:ietf:wg:oauth:2.0:oob', ResourceClientUri: 'https://management.core.windows.net/', ValidateAuthority: 'True'
DEBUG: [Common.Authentication]: Acquiring token using context with Authority 'https://login.microsoftonline.com/xxxxxxxxxxxxxxx/', CorrelationId: '00000000-0000-0000-0000-000000000000', ValidateAuthority: 'True'
DEBUG: [Common.Authentication]: Acquiring token using AdalConfiguration with Domain: 'xxxxxxxxxxxxxxx', AdEndpoint: 'https://login.microsoftonline.com/', ClientId: 'xxxxxxxxxxxxxxx', ClientRedirectUri: urn:ietf:wg:oauth:2.0:oob
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5768155Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: ADAL PCL.CoreCLR with assembly version '3.19.2.6005', file version '3.19.50302.0130' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5769162Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: ADAL PCL.CoreCLR with assembly version '3.19.2.6005', file version '3.19.50302.0130' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5769529Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: === Token Acquisition started:
CacheType: null
Authentication Target: User
, Authority Host: login.microsoftonline.com
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5769965Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: === Token Acquisition started:
Authority: https://login.microsoftonline.com/xxxxxxxxxxxxxxx/
Resource: https://management.core.windows.net/
ClientId: xxxxxxxxxxxxxxx
CacheType: null
Authentication Target: User
DEBUG: [ADAL]: Verbose: 2020-06-29T20:10:00.5770851Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: Loading from cache.
DEBUG: [ADAL]: Verbose: 2020-06-29T20:10:00.5770994Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: Loading from cache.
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5783129Z: 00000000-0000-0000-0000-000000000000 - LoggerBase.cs: Deserialized 5 items to token cache.
DEBUG: [ADAL]: Verbose: 2020-06-29T20:10:00.5783779Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: Looking up cache for a token...
DEBUG: [ADAL]: Verbose: 2020-06-29T20:10:00.5783909Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: Looking up cache for a token...
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5784542Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: An item matching the requested resource was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5784661Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: An item matching the requested resource was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5785578Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: 34.6247412 minutes left until token in cache expires
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5785688Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: 34.6247412 minutes left until token in cache expires
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5785785Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5785875Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5786820Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expiration Time: 6/29/2020 8:44:38 PM +00:00
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5786949Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expiration Time: 6/29/2020 8:44:38 PM +00:00Access Token Hash: zBlr8dpGmJ+/ReLBTiB/DsnyMKdFjCAqV4aJ+GVjVJM=
User id: 9ace2f84-b5e8-479a-beb3-462e5b6c550d
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:10:00 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:34:37.4760690'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm?api-version=2019-12-01
Headers:
x-ms-client-request-id : e8516a59-fdb7-4090-975e-ceabd7d52f9c
Accept-Language : en-US
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/LowCostGet3Min;3996,Microsoft.Compute/LowCostGet30Min;31960
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 2fa7b05a-db9b-4c17-b0c1-f3ac89319d1d
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11964
x-ms-correlation-request-id : xxx
x-ms-routing-request-id : UAENORTH:20200629T201002Z:xxx
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:10:02 GMT
Body:
{
"name": "my_vm",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm",
"type": "Microsoft.Compute/virtualMachines",
"location": "northeurope",
"properties": {
"vmId": "sssss",
"hardwareProfile": {
"vmSize": "Standard_D2s_v3"
},
"storageProfile": {
"imageReference": {
"publisher": "MicrosoftWindowsDesktop",
"offer": "Windows-10",
"sku": "rs5-pro",
"version": "latest",
"exactVersion": "17763.1282.2006061952"
},
"osDisk": {
"osType": "Windows",
"name": "my_vm_disk1_xxx6e1812a",
"createOption": "FromImage",
"caching": "ReadWrite",
"managedDisk": {
"storageAccountType": "Premium_LRS",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/disks/my_vm_disk1_bxxxa32e36e1812a"
},
"diskSizeGB": 127
},
"dataDisks": []
},
"osProfile": {
"computerName": "my_vm",
"adminUsername": "AzureUser",
"windowsConfiguration": {
"provisionVMAgent": true,
"enableAutomaticUpdates": true
},
"secrets": [],
"allowExtensionOperations": true,
"requireGuestProvisionSignal": true
},
"networkProfile": {
"networkInterfaces": [
{
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Network/networkInterfaces/my_vm957"
}
]
},
"provisioningState": "Succeeded"
}
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:10:01 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:34:36.0631986'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm?api-version=2019-12-01
Headers:
x-ms-client-request-id : 7b7ac483-9d5f-4822-9155-a4e689178108
Accept-Language : en-US
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/LowCostGet3Min;3995,Microsoft.Compute/LowCostGet30Min;31959
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 51590cdc-4310-4bfd-836e-6f8017c1c89f
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11963
x-ms-correlation-request-id : ecdc9c31-7461-4f00-a37e-7ddbd78f9b98
x-ms-routing-request-id : UAENORTH:20200629T201002Z:ecdc9c31-7461-4f00-a37e-7ddbd78f9b98
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:10:02 GMT
Body:
{
"name": "my_vm",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm",
"type": "Microsoft.Compute/virtualMachines",
"location": "northeurope",
"properties": {
"vmId": "sssss",
"hardwareProfile": {
"vmSize": "Standard_D2s_v3"
},
"storageProfile": {
"imageReference": {
"publisher": "MicrosoftWindowsDesktop",
"offer": "Windows-10",
"sku": "rs5-pro",
"version": "latest",
"exactVersion": "17763.1282.2006061952"
},
"osDisk": {
"osType": "Windows",
"name": "my_vm_disk1_b538bd82325445cf9450a32e36e1812a",
"createOption": "FromImage",
"caching": "ReadWrite",
"managedDisk": {
"storageAccountType": "Premium_LRS",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/disks/my_vm_disk1_b538bd82325445cf9450a32e36e1812a"
},
"diskSizeGB": 127
},
"dataDisks": []
},
"osProfile": {
"computerName": "my_vm",
"adminUsername": "AzureUser",
"windowsConfiguration": {
"provisionVMAgent": true,
"enableAutomaticUpdates": true
},
"secrets": [],
"allowExtensionOperations": true,
"requireGuestProvisionSignal": true
},
"networkProfile": {
"networkInterfaces": [
{
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Network/networkInterfaces/my_vm957"
}
]
},
"provisioningState": "Succeeded"
}
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:10:02 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:34:35.7759259'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
PUT
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm/extensions/Microsoft.Insights.VMDiagnosticsSettings?api-version=2019-12-01
Headers:
x-ms-client-request-id : 1bccc5c3-6fcd-4179-ae42-09d8227c9329
Accept-Language : en-US
Body:
{
"properties": {
"publisher": "Microsoft.Azure.Diagnostics",
"type": "IaaSDiagnostics",
"typeHandlerVersion": "1.5",
"autoUpgradeMinorVersion": true,
"settings": {
"WadCfg": {
"DiagnosticMonitorConfiguration": {
"overallQuotaInMB": 5120,
"WindowsEventLog": {
"scheduledTransferPeriod": "PT1M",
"DataSource": [
{
"name": "Application!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
},
{
"name": "Security!*"
},
{
"name": "System!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
}
]
},
"Metrics": {
"resourceId": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm"
}
}
},
"storageAccount": "logstorage-in-a-different-susbcribtion",
"StorageType": "TableAndBlob"
},
"protectedSettings": {
"storageAccountKey": "QQQQQQQQQQQQQQQQQQQQQQQQ=",
"storageAccountEndPoint": "https://logstorage-in-a-different-susbcribtion.blob.core.windows.net",
"storageAccountName": "logstorage-in-a-different-susbcribtion"
}
},
"location": "northeurope"
}
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
Created
Headers:
Cache-Control : no-cache
Pragma : no-cache
Azure-AsyncOperation : https://management.azure.com/subscriptions/xyxyxyxyxyx/providers/Microsoft.Compute/locations/northeurope/operations/130eb71a-2937-4379-ae1a-ce0ce67e2944?api-version=2019-12-01
Azure-AsyncNotification : Enabled
x-ms-ratelimit-remaining-resource: Microsoft.Compute/UpdateVM3Min;239,Microsoft.Compute/UpdateVM30Min;1194
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 130eb71a-2937-4379-ae1a-ce0ce67e2944
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-writes: 1199
x-ms-correlation-request-id : b082274b-5ca9-4398-a342-0774f20f9c55
x-ms-routing-request-id : UAENORTH:20200629T201010Z:b082274b-5ca9-4398-a342-0774f20f9c55
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:10:09 GMT
Body:
{
"name": "Microsoft.Insights.VMDiagnosticsSettings",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm/extensions/Microsoft.Insights.VMDiagnosticsSettings",
"type": "Microsoft.Compute/virtualMachines/extensions",
"location": "northeurope",
"properties": {
"autoUpgradeMinorVersion": true,
"provisioningState": "Creating",
"publisher": "Microsoft.Azure.Diagnostics",
"type": "IaaSDiagnostics",
"typeHandlerVersion": "1.5",
"settings": {
"WadCfg": {
"DiagnosticMonitorConfiguration": {
"overallQuotaInMB": 5120,
"WindowsEventLog": {
"scheduledTransferPeriod": "PT1M",
"DataSource": [
{
"name": "Application!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
},
{
"name": "Security!*"
},
{
"name": "System!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
}
]
},
"Metrics": {
"resourceId": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm"
}
}
},
"storageAccount": "logstorage-in-a-different-susbcribtion",
"StorageType": "TableAndBlob"
}
}
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:10:39 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:33:58.1150735'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/providers/Microsoft.Compute/locations/northeurope/operations/130eb71a-2937-4379-aessss944?api-version=2019-12-01
Headers:
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/GetOperation3Min;14992,Microsoft.Compute/GetOperation30Min;29941
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 079fdb27-26b7-4799-9bf9-7d4d34ceb46d
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11962
x-ms-correlation-request-id : db142fe4-a256-4446-a100-fce279259b61
x-ms-routing-request-id : UAENORTH:20200629T201040Z:db142fe4-a256-4446-a100-fce279259b61
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:10:40 GMT
Body:
{
"startTime": "2020-06-29T23:10:09.0851612+03:00",
"status": "InProgress",
"name": "csdsfdsf"
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:11:10 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:33:27.8353220'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/providers/Microsoft.Compute/locations/northeurope/operations/130esfdsf-ae1a-ce0ce67e2944?api-version=2019-12-01
Headers:
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/GetOperation3Min;14993,Microsoft.Compute/GetOperation30Min;29939
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : e5dd394d-7e55-413c-99b0-202fc1bc08b5
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11961
x-ms-correlation-request-id : 9fc267c1-6a0b-46sdfsdfsd32e
x-ms-routing-request-id : UAENORTH:20200629T201111Z:9fc2sfsdf5ab04f8fa32e
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:11:10 GMT
Body:
{
"startTime": "2020-06-29T23:10:09.0851612+03:00",
"endTime": "2020-06-29T23:11:00.1799136+03:00",
"status": "Succeeded",
"name": "sdfsdfd7e2944"
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:11:10 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:33:27.5668454'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm/extensions/Microsoft.Insights.VMDiagnosticsSettings?api-version=2019-12-01
Headers:
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/LowCostGet3Min;3993,Microsoft.Compute/LowCostGet30Min;31957
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 50cf3df3-1768-4e49-afb0-e788d31e588e
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11960
x-ms-correlation-request-id : 9bc78d84-581d-442c-8519-592b1e7be0bc
x-ms-routing-request-id : UAENORTH:20200629T201111Z:9bc78d84-581d-442c-8519-592b1e7be0bc
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:11:10 GMT
Body:
{
"name": "Microsoft.Insights.VMDiagnosticsSettings",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm/extensions/Microsoft.Insights.VMDiagnosticsSettings",
"type": "Microsoft.Compute/virtualMachines/extensions",
"location": "northeurope",
"properties": {
"autoUpgradeMinorVersion": true,
"provisioningState": "Succeeded",
"publisher": "Microsoft.Azure.Diagnostics",
"type": "IaaSDiagnostics",
"typeHandlerVersion": "1.5",
"settings": {
"WadCfg": {
"DiagnosticMonitorConfiguration": {
"overallQuotaInMB": 5120,
"WindowsEventLog": {
"scheduledTransferPeriod": "PT1M",
"DataSource": [
{
"name": "Application!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
},
{
"name": "Security!*"
},
{
"name": "System!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
}
]
},
"Metrics": {
"resourceId": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm"
}
}
},
"storageAccount": "logstorage-in-a-different-susbcribtion",
"StorageType": "TableAndBlob"
}
}
}
DEBUG: AzureQoSEvent: CommandName - Set-AzVMDiagnosticsExtension; IsSuccess - True; Duration - 00:01:12.1794967;
DEBUG: Finish sending metric.
DEBUG: 11:11:11 PM - SetAzureRmVMDiagnosticsExtensionCommand end processing.
```
## Note
some other scenarios I've tried :
- VM is in the same resource group where logs storage is.
> The result : works as expected
- VM in a different resource group from where logs storage is.
> The result : works as expected | 1.0 | Set-AzVMDiagnosticsExtension doesn't seem working properly across subscriptions - <!--
- Make sure you are able to reproduce this issue on the latest released version of Az
- https://www.powershellgallery.com/packages/Az
- Please search the existing issues to see if there has been a similar issue filed
- For issue related to importing a module, please refer to our troubleshooting guide:
- https://github.com/Azure/azure-powershell/blob/master/documentation/troubleshoot-module-load.md
-->
## Description
what I'm trying to is to enable VM Diagnostic extension to send Event logs (Application [1,2,3], Security [all], System [1,2,3]) to one unified storage account (let's call it logsstorage) where WADWindowsEventLogsTable is supposed to be created.
Running **AzVMDiagnosticsExtension** against VM in a _**different subscription from where the storage account is**_, will enable the extension on the target Vm. However, when I go to VM **Diagnostic settings** > **Agent tab**>**Storage account section**, I'll get the following error message
> "the value must not be empty"
and **WADWindowsEventLogsTable** won't be created (or write to it if exist )
## Steps to reproduce
following steps in the offcial microsft docuemnts [(https://docs.microsoft.com/en-us/azure/azure-monitor/platform/diagnostics-extension-windows-install)](url).
I tried two approaches :
```powershell
Set-AzVMDiagnosticsExtension -ResourceGroupName "myrg" -VMName "myvm" -DiagnosticsConfigurationPath "DiagnosticsConfiguration.json"
```
Another approach, tried to explicitly specifying account name and key
```powershell
Set-AzContext -SubscriptionId "where VM was created"
$storage_key = "xxxxxx"
Set-AzVMDiagnosticsExtension -ResourceGroupName "myrg" -VMName "myvm" -DiagnosticsConfigurationPath "DiagnosticsConfiguration.json" -StorageAccountName "logsstorage" -StorageAccountKey $storage_key
```
## The command output
<!-- Set $DebugPreference='Continue' before running the repro and paste the resulting debug stream in the below code block -->
```
RequestId IsSuccessStatusCode StatusCode ReasonPhrase
--------- ------------------- ---------- ------------
True OK OK
```
## Get-AzVMDiagnosticsExtension output
<!-- Please run Resolve-AzError and paste the output in the below code block -->
```
ResourceGroupName : myrg
VMName : myvm
Name : Microsoft.Insights.VMDiagnosticsSettings
Location : northeurope
Etag : null
Publisher : Microsoft.Azure.Diagnostics
ExtensionType : IaaSDiagnostics
TypeHandlerVersion : 1.5
Id : /subscriptions/xxxxx/resourceGroups/myrg/providers/Microsoft.Compute/virtualMachines/myvm/extensions/Microsoft.Insights.VMDiagnosticsSettings
PublicSettings : {
"storageAccount": "logsstorage",
"WadCfg": {
"DiagnosticMonitorConfiguration": {
"overallQuotaInMB": 5120,
"WindowsEventLog": {
"scheduledTransferPeriod": "PT1M",
"DataSource": [
{
"name": "Application!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
},
{
"name": "Security!*"
},
{
"name": "System!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
}
]
},
"Metrics": {
"resourceId": "/subscriptions/xx/resourceGroups/myrg/providers/Microsoft.Compute/virtualMachines/myvm"
}
}
},
"StorageType": "TableAndBlob"
}
ProtectedSettings :
ProvisioningState : Succeeded
Statuses :
SubStatuses :
AutoUpgradeMinorVersion : True
ForceUpdateTag :
```
## DiagnosticsConfiguration.json
```
{
"PublicConfig": {
"WadCfg": {
"DiagnosticMonitorConfiguration": {
"overallQuotaInMB": 5120,
"WindowsEventLog": {
"scheduledTransferPeriod": "PT1M",
"DataSource": [
{
"name": "Application!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
},
{
"name": "Security!*"
},
{
"name": "System!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
}
]
}
}
},
"StorageAccount": "logsstorage",
"StorageType": "TableAndBlob"
},
"PrivateConfig": {
"storageAccountName": "logsstorage",
"storageAccountKey": "xxxxxxx",
"storageAccountEndPoint": "https://logsstorage.blob.core.windows.net"
}
}
```
## Environment data
<!-- Please run $PSVersionTable and paste the output in the below code block
If running the Docker container image, indicate the tag of the image used and the version of Docker engine-->
```
> Windows
> Powershell 7.0.2
```
## Module versions
<!-- Please run (Get-Module -ListAvailable) and paste the output in the below code block -->
```powershell
ModuleType Version PreRelease Name PSEdition ExportedCommands
---------- ------- ---------- ---- --------- ----------------
Script 4.2.0 Az.Compute Core,Desk {Remove-AzAvailabilitySet, Get-AzAvailabilitySet, New-AzAvailabilitySet, Update-AzAvailabilitySet…}
```
## Debug output
<!-- Set $DebugPreference='Continue' before running the repro and paste the resulting debug stream in the below code block -->
```
DEBUG: 11:09:58 PM - SetAzureRmVMDiagnosticsExtensionCommand begin processing with ParameterSet '__AllParameterSets'.
DEBUG: 11:09:58 PM - using account id 'xxxxxxxxxxxxxxx'...
DEBUG: [Common.Authentication]: Authenticating using Account: 'xxxxxxxxxxxxxxx', environment: 'AzureCloud', tenant: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: Authenticating using configuration values: Domain: 'xxxxxxxxxxxxxxx', Endpoint: 'https://login.microsoftonline.com/', ClientId: 'xxxxxxxxxxxxxxx', ClientRedirect: 'urn:ietf:wg:oauth:2.0:oob', ResourceClientUri: 'https://management.core.windows.net/', ValidateAuthority: 'True'
DEBUG: [Common.Authentication]: Acquiring token using context with Authority 'https://login.microsoftonline.com/xxxxxxxxxxxxxxx/', CorrelationId: '00000000-0000-0000-0000-000000000000', ValidateAuthority: 'True'
DEBUG: [Common.Authentication]: Acquiring token using AdalConfiguration with Domain: 'xxxxxxxxxxxxxxx', AdEndpoint: 'https://login.microsoftonline.com/', ClientId: 'xxxxxxxxxxxxxxx', ClientRedirectUri: urn:ietf:wg:oauth:2.0:oob
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0001673Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: ADAL PCL.CoreCLR with assembly version '3.19.2.6005', file version '3.19.50302.0130' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0002653Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: ADAL PCL.CoreCLR with assembly version '3.19.2.6005', file version '3.19.50302.0130' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0002950Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: === Token Acquisition started:
CacheType: null
Authentication Target: User
, Authority Host: login.microsoftonline.com
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0003103Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: === Token Acquisition started:
Authority: https://login.microsoftonline.com/xxxxxxxxxxxxxxx/
Resource: https://management.core.windows.net/
ClientId: xxxxxxxxxxxxxxx
CacheType: null
Authentication Target: User
DEBUG: [ADAL]: Verbose: 2020-06-29T20:09:59.0004017Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: Loading from cache.
DEBUG: [ADAL]: Verbose: 2020-06-29T20:09:59.0004157Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: Loading from cache.
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0015979Z: 00000000-0000-0000-0000-000000000000 - LoggerBase.cs: Deserialized 5 items to token cache.
DEBUG: [ADAL]: Verbose: 2020-06-29T20:09:59.0016642Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: Looking up cache for a token...
DEBUG: [ADAL]: Verbose: 2020-06-29T20:09:59.0016772Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: Looking up cache for a token...
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0017341Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: An item matching the requested resource was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0017455Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: An item matching the requested resource was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0018248Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: 34.651020055 minutes left until token in cache expires
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0018359Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: 34.651020055 minutes left until token in cache expires
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0018454Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0018543Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0019512Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expiration Time: 6/29/2020 8:44:38 PM +00:00
DEBUG: [ADAL]: Information: 2020-06-29T20:09:59.0019644Z: 27d8fcf5-9f6d-xxxxxx19dd43749a2 - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expiration Time: 6/29/2020 8:44:38 PM +00:00Access Token Hash: zBlr8dpGmJ+/ReLBTiB/DsnyMKdFjCAqV4aJ+GVjVJM=
User id: 9ace2f84-b5e8-479a-beb3-462e5b6c550d
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:09:59 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:34:39.0543514'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/providers/Microsoft.Storage/storageAccounts?api-version=2017-10-01
Headers:
x-ms-client-request-id : 4629b4aa-976e-4426-a1e5-9c84467183ba
Accept-Language : en-US
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-request-id : xxxx
Strict-Transport-Security : max-age=31536000; includeSubDomains
Server : Microsoft-Azure-Storage-Resource-Provider/1.0,Microsoft-HTTPAPI/2.0 Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11966
x-ms-correlation-request-id : 0d567455-36d1-4a91-8ae8-2f0477753175
x-ms-routing-request-id : UAENORTH:20200629T201001Z:0d567455-36d1-4a91-8ae8-2f0477753175
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:10:01 GMT
Body:
{
"value": [
{
"sku": {
"name": "Standard_LRS",
"tier": "Standard"
},
"kind": "Storage",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Storage/storageAccounts/storagexxxx",
"name": "storagexxxx",
"type": "Microsoft.Storage/storageAccounts",
"location": "westeurope",
"tags": {},
"properties": {
"networkAcls": {
"bypass": "AzureServices",
"virtualNetworkRules": [],
"ipRules": [],
"defaultAction": "Allow"
},
"supportsHttpsTrafficOnly": false,
"encryption": {
"services": {
"file": {
"enabled": true,
"lastEnabledTime": "2019-03-10T11:12:25.5593458Z"
},
"blob": {
"enabled": true,
"lastEnabledTime": "2019-03-10T11:12:25.5593458Z"
}
},
"keySource": "Microsoft.Storage"
},
"provisioningState": "Succeeded",
"creationTime": "2019-03-10T11:12:25.356245Z",
"primaryEndpoints": {
"blob": "https://storagexxxx.blob.core.windows.net/",
"queue": "https://storagexxxx.queue.core.windows.net/",
"table": "https://storagexxxx.table.core.windows.net/",
"file": "https://storagexxxx.file.core.windows.net/"
},
"primaryLocation": "westeurope",
"statusOfPrimary": "available"
}
}
]
}
DEBUG: [Common.Authentication]: Authenticating using Account: 'xxxxxxxxxxxxxxx', environment: 'AzureCloud', tenant: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: Authenticating using configuration values: Domain: 'xxxxxxxxxxxxxxx', Endpoint: 'https://login.microsoftonline.com/', ClientId: 'xxxxxxxxxxxxxxx', ClientRedirect: 'urn:ietf:wg:oauth:2.0:oob', ResourceClientUri: 'https://management.core.windows.net/', ValidateAuthority: 'True'
DEBUG: [Common.Authentication]: Acquiring token using context with Authority 'https://login.microsoftonline.com/xxxxxxxxxxxxxxx/', CorrelationId: '00000000-0000-0000-0000-000000000000', ValidateAuthority: 'True'
DEBUG: [Common.Authentication]: Acquiring token using AdalConfiguration with Domain: 'xxxxxxxxxxxxxxx', AdEndpoint: 'https://login.microsoftonline.com/', ClientId: 'xxxxxxxxxxxxxxx', ClientRedirectUri: urn:ietf:wg:oauth:2.0:oob
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5768155Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: ADAL PCL.CoreCLR with assembly version '3.19.2.6005', file version '3.19.50302.0130' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5769162Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: ADAL PCL.CoreCLR with assembly version '3.19.2.6005', file version '3.19.50302.0130' and informational version '2a8bec6c4c76d0c1ef819b55bdc3cda2d2605056' is running...
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5769529Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: === Token Acquisition started:
CacheType: null
Authentication Target: User
, Authority Host: login.microsoftonline.com
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5769965Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: === Token Acquisition started:
Authority: https://login.microsoftonline.com/xxxxxxxxxxxxxxx/
Resource: https://management.core.windows.net/
ClientId: xxxxxxxxxxxxxxx
CacheType: null
Authentication Target: User
DEBUG: [ADAL]: Verbose: 2020-06-29T20:10:00.5770851Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: Loading from cache.
DEBUG: [ADAL]: Verbose: 2020-06-29T20:10:00.5770994Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: Loading from cache.
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5783129Z: 00000000-0000-0000-0000-000000000000 - LoggerBase.cs: Deserialized 5 items to token cache.
DEBUG: [ADAL]: Verbose: 2020-06-29T20:10:00.5783779Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: Looking up cache for a token...
DEBUG: [ADAL]: Verbose: 2020-06-29T20:10:00.5783909Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: Looking up cache for a token...
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5784542Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: An item matching the requested resource was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5784661Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: An item matching the requested resource was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5785578Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: 34.6247412 minutes left until token in cache expires
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5785688Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: 34.6247412 minutes left until token in cache expires
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5785785Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5785875Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: A matching item (access token or refresh token or both) was found in the cache
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5786820Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expiration Time: 6/29/2020 8:44:38 PM +00:00
DEBUG: [ADAL]: Information: 2020-06-29T20:10:00.5786949Z: 73c8f0e8-7884-4a22-a9a5-f750116acbf2 - LoggerBase.cs: === Token Acquisition finished successfully. An access token was returned: Expiration Time: 6/29/2020 8:44:38 PM +00:00Access Token Hash: zBlr8dpGmJ+/ReLBTiB/DsnyMKdFjCAqV4aJ+GVjVJM=
User id: 9ace2f84-b5e8-479a-beb3-462e5b6c550d
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:10:00 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:34:37.4760690'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm?api-version=2019-12-01
Headers:
x-ms-client-request-id : e8516a59-fdb7-4090-975e-ceabd7d52f9c
Accept-Language : en-US
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/LowCostGet3Min;3996,Microsoft.Compute/LowCostGet30Min;31960
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 2fa7b05a-db9b-4c17-b0c1-f3ac89319d1d
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11964
x-ms-correlation-request-id : xxx
x-ms-routing-request-id : UAENORTH:20200629T201002Z:xxx
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:10:02 GMT
Body:
{
"name": "my_vm",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm",
"type": "Microsoft.Compute/virtualMachines",
"location": "northeurope",
"properties": {
"vmId": "sssss",
"hardwareProfile": {
"vmSize": "Standard_D2s_v3"
},
"storageProfile": {
"imageReference": {
"publisher": "MicrosoftWindowsDesktop",
"offer": "Windows-10",
"sku": "rs5-pro",
"version": "latest",
"exactVersion": "17763.1282.2006061952"
},
"osDisk": {
"osType": "Windows",
"name": "my_vm_disk1_xxx6e1812a",
"createOption": "FromImage",
"caching": "ReadWrite",
"managedDisk": {
"storageAccountType": "Premium_LRS",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/disks/my_vm_disk1_bxxxa32e36e1812a"
},
"diskSizeGB": 127
},
"dataDisks": []
},
"osProfile": {
"computerName": "my_vm",
"adminUsername": "AzureUser",
"windowsConfiguration": {
"provisionVMAgent": true,
"enableAutomaticUpdates": true
},
"secrets": [],
"allowExtensionOperations": true,
"requireGuestProvisionSignal": true
},
"networkProfile": {
"networkInterfaces": [
{
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Network/networkInterfaces/my_vm957"
}
]
},
"provisioningState": "Succeeded"
}
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:10:01 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:34:36.0631986'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm?api-version=2019-12-01
Headers:
x-ms-client-request-id : 7b7ac483-9d5f-4822-9155-a4e689178108
Accept-Language : en-US
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/LowCostGet3Min;3995,Microsoft.Compute/LowCostGet30Min;31959
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 51590cdc-4310-4bfd-836e-6f8017c1c89f
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11963
x-ms-correlation-request-id : ecdc9c31-7461-4f00-a37e-7ddbd78f9b98
x-ms-routing-request-id : UAENORTH:20200629T201002Z:ecdc9c31-7461-4f00-a37e-7ddbd78f9b98
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:10:02 GMT
Body:
{
"name": "my_vm",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm",
"type": "Microsoft.Compute/virtualMachines",
"location": "northeurope",
"properties": {
"vmId": "sssss",
"hardwareProfile": {
"vmSize": "Standard_D2s_v3"
},
"storageProfile": {
"imageReference": {
"publisher": "MicrosoftWindowsDesktop",
"offer": "Windows-10",
"sku": "rs5-pro",
"version": "latest",
"exactVersion": "17763.1282.2006061952"
},
"osDisk": {
"osType": "Windows",
"name": "my_vm_disk1_b538bd82325445cf9450a32e36e1812a",
"createOption": "FromImage",
"caching": "ReadWrite",
"managedDisk": {
"storageAccountType": "Premium_LRS",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/disks/my_vm_disk1_b538bd82325445cf9450a32e36e1812a"
},
"diskSizeGB": 127
},
"dataDisks": []
},
"osProfile": {
"computerName": "my_vm",
"adminUsername": "AzureUser",
"windowsConfiguration": {
"provisionVMAgent": true,
"enableAutomaticUpdates": true
},
"secrets": [],
"allowExtensionOperations": true,
"requireGuestProvisionSignal": true
},
"networkProfile": {
"networkInterfaces": [
{
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Network/networkInterfaces/my_vm957"
}
]
},
"provisioningState": "Succeeded"
}
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:10:02 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:34:35.7759259'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
PUT
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm/extensions/Microsoft.Insights.VMDiagnosticsSettings?api-version=2019-12-01
Headers:
x-ms-client-request-id : 1bccc5c3-6fcd-4179-ae42-09d8227c9329
Accept-Language : en-US
Body:
{
"properties": {
"publisher": "Microsoft.Azure.Diagnostics",
"type": "IaaSDiagnostics",
"typeHandlerVersion": "1.5",
"autoUpgradeMinorVersion": true,
"settings": {
"WadCfg": {
"DiagnosticMonitorConfiguration": {
"overallQuotaInMB": 5120,
"WindowsEventLog": {
"scheduledTransferPeriod": "PT1M",
"DataSource": [
{
"name": "Application!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
},
{
"name": "Security!*"
},
{
"name": "System!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
}
]
},
"Metrics": {
"resourceId": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm"
}
}
},
"storageAccount": "logstorage-in-a-different-susbcribtion",
"StorageType": "TableAndBlob"
},
"protectedSettings": {
"storageAccountKey": "QQQQQQQQQQQQQQQQQQQQQQQQ=",
"storageAccountEndPoint": "https://logstorage-in-a-different-susbcribtion.blob.core.windows.net",
"storageAccountName": "logstorage-in-a-different-susbcribtion"
}
},
"location": "northeurope"
}
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
Created
Headers:
Cache-Control : no-cache
Pragma : no-cache
Azure-AsyncOperation : https://management.azure.com/subscriptions/xyxyxyxyxyx/providers/Microsoft.Compute/locations/northeurope/operations/130eb71a-2937-4379-ae1a-ce0ce67e2944?api-version=2019-12-01
Azure-AsyncNotification : Enabled
x-ms-ratelimit-remaining-resource: Microsoft.Compute/UpdateVM3Min;239,Microsoft.Compute/UpdateVM30Min;1194
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 130eb71a-2937-4379-ae1a-ce0ce67e2944
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-writes: 1199
x-ms-correlation-request-id : b082274b-5ca9-4398-a342-0774f20f9c55
x-ms-routing-request-id : UAENORTH:20200629T201010Z:b082274b-5ca9-4398-a342-0774f20f9c55
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:10:09 GMT
Body:
{
"name": "Microsoft.Insights.VMDiagnosticsSettings",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm/extensions/Microsoft.Insights.VMDiagnosticsSettings",
"type": "Microsoft.Compute/virtualMachines/extensions",
"location": "northeurope",
"properties": {
"autoUpgradeMinorVersion": true,
"provisioningState": "Creating",
"publisher": "Microsoft.Azure.Diagnostics",
"type": "IaaSDiagnostics",
"typeHandlerVersion": "1.5",
"settings": {
"WadCfg": {
"DiagnosticMonitorConfiguration": {
"overallQuotaInMB": 5120,
"WindowsEventLog": {
"scheduledTransferPeriod": "PT1M",
"DataSource": [
{
"name": "Application!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
},
{
"name": "Security!*"
},
{
"name": "System!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
}
]
},
"Metrics": {
"resourceId": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm"
}
}
},
"storageAccount": "logstorage-in-a-different-susbcribtion",
"StorageType": "TableAndBlob"
}
}
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:10:39 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:33:58.1150735'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/providers/Microsoft.Compute/locations/northeurope/operations/130eb71a-2937-4379-aessss944?api-version=2019-12-01
Headers:
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/GetOperation3Min;14992,Microsoft.Compute/GetOperation30Min;29941
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 079fdb27-26b7-4799-9bf9-7d4d34ceb46d
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11962
x-ms-correlation-request-id : db142fe4-a256-4446-a100-fce279259b61
x-ms-routing-request-id : UAENORTH:20200629T201040Z:db142fe4-a256-4446-a100-fce279259b61
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:10:40 GMT
Body:
{
"startTime": "2020-06-29T23:10:09.0851612+03:00",
"status": "InProgress",
"name": "csdsfdsf"
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:11:10 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:33:27.8353220'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/providers/Microsoft.Compute/locations/northeurope/operations/130esfdsf-ae1a-ce0ce67e2944?api-version=2019-12-01
Headers:
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/GetOperation3Min;14993,Microsoft.Compute/GetOperation30Min;29939
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : e5dd394d-7e55-413c-99b0-202fc1bc08b5
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11961
x-ms-correlation-request-id : 9fc267c1-6a0b-46sdfsdfsd32e
x-ms-routing-request-id : UAENORTH:20200629T201111Z:9fc2sfsdf5ab04f8fa32e
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:11:10 GMT
Body:
{
"startTime": "2020-06-29T23:10:09.0851612+03:00",
"endTime": "2020-06-29T23:11:00.1799136+03:00",
"status": "Succeeded",
"name": "sdfsdfd7e2944"
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '06/29/2020 20:44:38 +00:00', MultipleResource? 'True', Tenant: 'xxxxxxxxxxxxxxx', UserId: 'xxxxxxxxxxxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxxxxxxxxxx', Name: Matar Alhawiti, IdProvider: 'https://sts.windows.net/xxxxxxxxxxxxxxx/', Uid: '9ace2f84-b5e8-479a-beb3-462e5b6c550d'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '06/29/2020 20:44:38 +00:00' Comparing to '06/29/2020 20:11:10 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:33:27.5668454'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm/extensions/Microsoft.Insights.VMDiagnosticsSettings?api-version=2019-12-01
Headers:
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Cache-Control : no-cache
Pragma : no-cache
x-ms-ratelimit-remaining-resource: Microsoft.Compute/LowCostGet3Min;3993,Microsoft.Compute/LowCostGet30Min;31957
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-request-id : 50cf3df3-1768-4e49-afb0-e788d31e588e
Server : Microsoft-HTTPAPI/2.0,Microsoft-HTTPAPI/2.0
x-ms-ratelimit-remaining-subscription-reads: 11960
x-ms-correlation-request-id : 9bc78d84-581d-442c-8519-592b1e7be0bc
x-ms-routing-request-id : UAENORTH:20200629T201111Z:9bc78d84-581d-442c-8519-592b1e7be0bc
X-Content-Type-Options : nosniff
Date : Mon, 29 Jun 2020 20:11:10 GMT
Body:
{
"name": "Microsoft.Insights.VMDiagnosticsSettings",
"id": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm/extensions/Microsoft.Insights.VMDiagnosticsSettings",
"type": "Microsoft.Compute/virtualMachines/extensions",
"location": "northeurope",
"properties": {
"autoUpgradeMinorVersion": true,
"provisioningState": "Succeeded",
"publisher": "Microsoft.Azure.Diagnostics",
"type": "IaaSDiagnostics",
"typeHandlerVersion": "1.5",
"settings": {
"WadCfg": {
"DiagnosticMonitorConfiguration": {
"overallQuotaInMB": 5120,
"WindowsEventLog": {
"scheduledTransferPeriod": "PT1M",
"DataSource": [
{
"name": "Application!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
},
{
"name": "Security!*"
},
{
"name": "System!*[System[(Level=1 or Level=2 or Level=3 or Level=4)]]"
}
]
},
"Metrics": {
"resourceId": "/subscriptions/xyxyxyxyxyx/resourceGroups/RG-where-my-vm-is/providers/Microsoft.Compute/virtualMachines/my_vm"
}
}
},
"storageAccount": "logstorage-in-a-different-susbcribtion",
"StorageType": "TableAndBlob"
}
}
}
DEBUG: AzureQoSEvent: CommandName - Set-AzVMDiagnosticsExtension; IsSuccess - True; Duration - 00:01:12.1794967;
DEBUG: Finish sending metric.
DEBUG: 11:11:11 PM - SetAzureRmVMDiagnosticsExtensionCommand end processing.
```
## Note
some other scenarios I've tried :
- VM is in the same resource group where logs storage is.
> The result : works as expected
- VM in a different resource group from where logs storage is.
> The result : works as expected | non_priority | set azvmdiagnosticsextension doesn t seem working properly across subscriptions make sure you are able to reproduce this issue on the latest released version of az please search the existing issues to see if there has been a similar issue filed for issue related to importing a module please refer to our troubleshooting guide description what i m trying to is to enable vm diagnostic extension to send event logs application security system to one unified storage account let s call it logsstorage where wadwindowseventlogstable is supposed to be created running azvmdiagnosticsextension against vm in a different subscription from where the storage account is will enable the extension on the target vm however when i go to vm diagnostic settings agent tab storage account section i ll get the following error message the value must not be empty and wadwindowseventlogstable won t be created or write to it if exist steps to reproduce following steps in the offcial microsft docuemnts url i tried two approaches powershell set azvmdiagnosticsextension resourcegroupname myrg vmname myvm diagnosticsconfigurationpath diagnosticsconfiguration json another approach tried to explicitly specifying account name and key powershell set azcontext subscriptionid where vm was created storage key xxxxxx set azvmdiagnosticsextension resourcegroupname myrg vmname myvm diagnosticsconfigurationpath diagnosticsconfiguration json storageaccountname logsstorage storageaccountkey storage key the command output requestid issuccessstatuscode statuscode reasonphrase true ok ok get azvmdiagnosticsextension output resourcegroupname myrg vmname myvm name microsoft insights vmdiagnosticssettings location northeurope etag null publisher microsoft azure diagnostics extensiontype iaasdiagnostics typehandlerversion id subscriptions xxxxx resourcegroups myrg providers microsoft compute virtualmachines myvm extensions microsoft insights vmdiagnosticssettings publicsettings storageaccount logsstorage wadcfg diagnosticmonitorconfiguration overallquotainmb windowseventlog scheduledtransferperiod datasource name application name security name system metrics resourceid subscriptions xx resourcegroups myrg providers microsoft compute virtualmachines myvm storagetype tableandblob protectedsettings provisioningstate succeeded statuses substatuses autoupgrademinorversion true forceupdatetag diagnosticsconfiguration json publicconfig wadcfg diagnosticmonitorconfiguration overallquotainmb windowseventlog scheduledtransferperiod datasource name application name security name system storageaccount logsstorage storagetype tableandblob privateconfig storageaccountname logsstorage storageaccountkey xxxxxxx storageaccountendpoint environment data please run psversiontable and paste the output in the below code block if running the docker container image indicate the tag of the image used and the version of docker engine windows powershell module versions powershell moduletype version prerelease name psedition exportedcommands script az compute core desk remove azavailabilityset get azavailabilityset new azavailabilityset update azavailabilityset… debug output debug pm setazurermvmdiagnosticsextensioncommand begin processing with parameterset allparametersets debug pm using account id xxxxxxxxxxxxxxx debug authenticating using account xxxxxxxxxxxxxxx environment azurecloud tenant xxxxxxxxxxxxxxx debug authenticating using configuration values domain xxxxxxxxxxxxxxx endpoint clientid xxxxxxxxxxxxxxx clientredirect urn ietf wg oauth oob resourceclienturi validateauthority true debug acquiring token using context with authority correlationid validateauthority true debug acquiring token using adalconfiguration with domain xxxxxxxxxxxxxxx adendpoint clientid xxxxxxxxxxxxxxx clientredirecturi urn ietf wg oauth oob debug information loggerbase cs adal pcl coreclr with assembly version file version and informational version is running debug information loggerbase cs adal pcl coreclr with assembly version file version and informational version is running debug information loggerbase cs token acquisition started cachetype null authentication target user authority host login microsoftonline com debug information loggerbase cs token acquisition started authority resource clientid xxxxxxxxxxxxxxx cachetype null authentication target user debug verbose loggerbase cs loading from cache debug verbose loggerbase cs loading from cache debug information loggerbase cs deserialized items to token cache debug verbose loggerbase cs looking up cache for a token debug verbose loggerbase cs looking up cache for a token debug information loggerbase cs an item matching the requested resource was found in the cache debug information loggerbase cs an item matching the requested resource was found in the cache debug information loggerbase cs minutes left until token in cache expires debug information loggerbase cs minutes left until token in cache expires debug information loggerbase cs a matching item access token or refresh token or both was found in the cache debug information loggerbase cs a matching item access token or refresh token or both was found in the cache debug information loggerbase cs token acquisition finished successfully an access token was returned expiration time pm debug information loggerbase cs token acquisition finished successfully an access token was returned expiration time pm token hash relbtib gvjvjm user id debug renewing token with type bearer expiry multipleresource true tenant xxxxxxxxxxxxxxx userid xxxxxxxxxxxxxxx debug user info for token displayid xxxxxxxxxxxxxxx name matar alhawiti idprovider uid debug checking token expiration token expires comparing to with threshold calculated time until token expiry debug http request http method get absolute uri headers x ms client request id accept language en us body debug http response status code ok headers cache control no cache pragma no cache x ms request id xxxx strict transport security max age includesubdomains server microsoft azure storage resource provider microsoft httpapi microsoft httpapi x ms ratelimit remaining subscription reads x ms correlation request id x ms routing request id uaenorth x content type options nosniff date mon jun gmt body value sku name standard lrs tier standard kind storage id subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft storage storageaccounts storagexxxx name storagexxxx type microsoft storage storageaccounts location westeurope tags properties networkacls bypass azureservices virtualnetworkrules iprules defaultaction allow supportshttpstrafficonly false encryption services file enabled true lastenabledtime blob enabled true lastenabledtime keysource microsoft storage provisioningstate succeeded creationtime primaryendpoints blob queue table file primarylocation westeurope statusofprimary available debug authenticating using account xxxxxxxxxxxxxxx environment azurecloud tenant xxxxxxxxxxxxxxx debug authenticating using configuration values domain xxxxxxxxxxxxxxx endpoint clientid xxxxxxxxxxxxxxx clientredirect urn ietf wg oauth oob resourceclienturi validateauthority true debug acquiring token using context with authority correlationid validateauthority true debug acquiring token using adalconfiguration with domain xxxxxxxxxxxxxxx adendpoint clientid xxxxxxxxxxxxxxx clientredirecturi urn ietf wg oauth oob debug information loggerbase cs adal pcl coreclr with assembly version file version and informational version is running debug information loggerbase cs adal pcl coreclr with assembly version file version and informational version is running debug information loggerbase cs token acquisition started cachetype null authentication target user authority host login microsoftonline com debug information loggerbase cs token acquisition started authority resource clientid xxxxxxxxxxxxxxx cachetype null authentication target user debug verbose loggerbase cs loading from cache debug verbose loggerbase cs loading from cache debug information loggerbase cs deserialized items to token cache debug verbose loggerbase cs looking up cache for a token debug verbose loggerbase cs looking up cache for a token debug information loggerbase cs an item matching the requested resource was found in the cache debug information loggerbase cs an item matching the requested resource was found in the cache debug information loggerbase cs minutes left until token in cache expires debug information loggerbase cs minutes left until token in cache expires debug information loggerbase cs a matching item access token or refresh token or both was found in the cache debug information loggerbase cs a matching item access token or refresh token or both was found in the cache debug information loggerbase cs token acquisition finished successfully an access token was returned expiration time pm debug information loggerbase cs token acquisition finished successfully an access token was returned expiration time pm token hash relbtib gvjvjm user id debug renewing token with type bearer expiry multipleresource true tenant xxxxxxxxxxxxxxx userid xxxxxxxxxxxxxxx debug user info for token displayid xxxxxxxxxxxxxxx name matar alhawiti idprovider uid debug checking token expiration token expires comparing to with threshold calculated time until token expiry debug http request http method get absolute uri headers x ms client request id accept language en us body debug http response status code ok headers cache control no cache pragma no cache x ms ratelimit remaining resource microsoft compute microsoft compute strict transport security max age includesubdomains x ms request id server microsoft httpapi microsoft httpapi x ms ratelimit remaining subscription reads x ms correlation request id xxx x ms routing request id uaenorth xxx x content type options nosniff date mon jun gmt body name my vm id subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft compute virtualmachines my vm type microsoft compute virtualmachines location northeurope properties vmid sssss hardwareprofile vmsize standard storageprofile imagereference publisher microsoftwindowsdesktop offer windows sku pro version latest exactversion osdisk ostype windows name my vm createoption fromimage caching readwrite manageddisk storageaccounttype premium lrs id subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft compute disks my vm disksizegb datadisks osprofile computername my vm adminusername azureuser windowsconfiguration provisionvmagent true enableautomaticupdates true secrets allowextensionoperations true requireguestprovisionsignal true networkprofile networkinterfaces id subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft network networkinterfaces my provisioningstate succeeded debug renewing token with type bearer expiry multipleresource true tenant xxxxxxxxxxxxxxx userid xxxxxxxxxxxxxxx debug user info for token displayid xxxxxxxxxxxxxxx name matar alhawiti idprovider uid debug checking token expiration token expires comparing to with threshold calculated time until token expiry debug http request http method get absolute uri headers x ms client request id accept language en us body debug http response status code ok headers cache control no cache pragma no cache x ms ratelimit remaining resource microsoft compute microsoft compute strict transport security max age includesubdomains x ms request id server microsoft httpapi microsoft httpapi x ms ratelimit remaining subscription reads x ms correlation request id x ms routing request id uaenorth x content type options nosniff date mon jun gmt body name my vm id subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft compute virtualmachines my vm type microsoft compute virtualmachines location northeurope properties vmid sssss hardwareprofile vmsize standard storageprofile imagereference publisher microsoftwindowsdesktop offer windows sku pro version latest exactversion osdisk ostype windows name my vm createoption fromimage caching readwrite manageddisk storageaccounttype premium lrs id subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft compute disks my vm disksizegb datadisks osprofile computername my vm adminusername azureuser windowsconfiguration provisionvmagent true enableautomaticupdates true secrets allowextensionoperations true requireguestprovisionsignal true networkprofile networkinterfaces id subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft network networkinterfaces my provisioningstate succeeded debug renewing token with type bearer expiry multipleresource true tenant xxxxxxxxxxxxxxx userid xxxxxxxxxxxxxxx debug user info for token displayid xxxxxxxxxxxxxxx name matar alhawiti idprovider uid debug checking token expiration token expires comparing to with threshold calculated time until token expiry debug http request http method put absolute uri headers x ms client request id accept language en us body properties publisher microsoft azure diagnostics type iaasdiagnostics typehandlerversion autoupgrademinorversion true settings wadcfg diagnosticmonitorconfiguration overallquotainmb windowseventlog scheduledtransferperiod datasource name application name security name system metrics resourceid subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft compute virtualmachines my vm storageaccount logstorage in a different susbcribtion storagetype tableandblob protectedsettings storageaccountkey qqqqqqqqqqqqqqqqqqqqqqqq storageaccountendpoint storageaccountname logstorage in a different susbcribtion location northeurope debug http response status code created headers cache control no cache pragma no cache azure asyncoperation azure asyncnotification enabled x ms ratelimit remaining resource microsoft compute microsoft compute strict transport security max age includesubdomains x ms request id server microsoft httpapi microsoft httpapi x ms ratelimit remaining subscription writes x ms correlation request id x ms routing request id uaenorth x content type options nosniff date mon jun gmt body name microsoft insights vmdiagnosticssettings id subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft compute virtualmachines my vm extensions microsoft insights vmdiagnosticssettings type microsoft compute virtualmachines extensions location northeurope properties autoupgrademinorversion true provisioningstate creating publisher microsoft azure diagnostics type iaasdiagnostics typehandlerversion settings wadcfg diagnosticmonitorconfiguration overallquotainmb windowseventlog scheduledtransferperiod datasource name application name security name system metrics resourceid subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft compute virtualmachines my vm storageaccount logstorage in a different susbcribtion storagetype tableandblob debug renewing token with type bearer expiry multipleresource true tenant xxxxxxxxxxxxxxx userid xxxxxxxxxxxxxxx debug user info for token displayid xxxxxxxxxxxxxxx name matar alhawiti idprovider uid debug checking token expiration token expires comparing to with threshold calculated time until token expiry debug http request http method get absolute uri headers body debug http response status code ok headers cache control no cache pragma no cache x ms ratelimit remaining resource microsoft compute microsoft compute strict transport security max age includesubdomains x ms request id server microsoft httpapi microsoft httpapi x ms ratelimit remaining subscription reads x ms correlation request id x ms routing request id uaenorth x content type options nosniff date mon jun gmt body starttime status inprogress name csdsfdsf debug renewing token with type bearer expiry multipleresource true tenant xxxxxxxxxxxxxxx userid xxxxxxxxxxxxxxx debug user info for token displayid xxxxxxxxxxxxxxx name matar alhawiti idprovider uid debug checking token expiration token expires comparing to with threshold calculated time until token expiry debug http request http method get absolute uri headers body debug http response status code ok headers cache control no cache pragma no cache x ms ratelimit remaining resource microsoft compute microsoft compute strict transport security max age includesubdomains x ms request id server microsoft httpapi microsoft httpapi x ms ratelimit remaining subscription reads x ms correlation request id x ms routing request id uaenorth x content type options nosniff date mon jun gmt body starttime endtime status succeeded name debug renewing token with type bearer expiry multipleresource true tenant xxxxxxxxxxxxxxx userid xxxxxxxxxxxxxxx debug user info for token displayid xxxxxxxxxxxxxxx name matar alhawiti idprovider uid debug checking token expiration token expires comparing to with threshold calculated time until token expiry debug http request http method get absolute uri headers body debug http response status code ok headers cache control no cache pragma no cache x ms ratelimit remaining resource microsoft compute microsoft compute strict transport security max age includesubdomains x ms request id server microsoft httpapi microsoft httpapi x ms ratelimit remaining subscription reads x ms correlation request id x ms routing request id uaenorth x content type options nosniff date mon jun gmt body name microsoft insights vmdiagnosticssettings id subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft compute virtualmachines my vm extensions microsoft insights vmdiagnosticssettings type microsoft compute virtualmachines extensions location northeurope properties autoupgrademinorversion true provisioningstate succeeded publisher microsoft azure diagnostics type iaasdiagnostics typehandlerversion settings wadcfg diagnosticmonitorconfiguration overallquotainmb windowseventlog scheduledtransferperiod datasource name application name security name system metrics resourceid subscriptions xyxyxyxyxyx resourcegroups rg where my vm is providers microsoft compute virtualmachines my vm storageaccount logstorage in a different susbcribtion storagetype tableandblob debug azureqosevent commandname set azvmdiagnosticsextension issuccess true duration debug finish sending metric debug pm setazurermvmdiagnosticsextensioncommand end processing note some other scenarios i ve tried vm is in the same resource group where logs storage is the result works as expected vm in a different resource group from where logs storage is the result works as expected | 0 |
43,077 | 7,018,954,949 | IssuesEvent | 2017-12-21 15:32:31 | fastify/fastify | https://api.github.com/repos/fastify/fastify | closed | Get route options inside handler or inside preHandler hook | documentation question | Hi,
First of all : great job on this !
Maybe a little feature request : can we have an access to route options inside an handler or inside the preHandler hook ?
Here is a sample code :
```js
fastify.get('/', { foo: 'bar' }, async (req, res) => {
// Something like this ?
const { foo } = req.route;
// foo === 'bar'
});
fastify.addHook('preHandler', (req, res, next) => {
// Or like this ?
const { foo } = req.routeOptions;
// foo === 'bar'
});
```
It can be useful to add some metadatas on routes and read them in hooks, no ?
Thanks ! | 1.0 | Get route options inside handler or inside preHandler hook - Hi,
First of all : great job on this !
Maybe a little feature request : can we have an access to route options inside an handler or inside the preHandler hook ?
Here is a sample code :
```js
fastify.get('/', { foo: 'bar' }, async (req, res) => {
// Something like this ?
const { foo } = req.route;
// foo === 'bar'
});
fastify.addHook('preHandler', (req, res, next) => {
// Or like this ?
const { foo } = req.routeOptions;
// foo === 'bar'
});
```
It can be useful to add some metadatas on routes and read them in hooks, no ?
Thanks ! | non_priority | get route options inside handler or inside prehandler hook hi first of all great job on this maybe a little feature request can we have an access to route options inside an handler or inside the prehandler hook here is a sample code js fastify get foo bar async req res something like this const foo req route foo bar fastify addhook prehandler req res next or like this const foo req routeoptions foo bar it can be useful to add some metadatas on routes and read them in hooks no thanks | 0 |
174,933 | 27,754,721,726 | IssuesEvent | 2023-03-16 00:52:29 | RedHat-UX/red-hat-design-system | https://api.github.com/repos/RedHat-UX/red-hat-design-system | closed | [feat] Switch component | enhancement for design discovery needed new component | ### Description
Create a switch component like https://www.patternfly.org/v4/documentation/core/components/switch
We need to support:
- With a label
- Without a label
- Disabled state
### Acceptance Criteria
- [x] Design done
- [ ] Development done
### Image
### Link to design doc
https://xd.adobe.com/view/d20a1c17-375c-4c7f-6827-5fe2f8c2d92f-a43b/screen/4074c4b7-04ae-441e-80fd-21210d7680d2
### Other resources
- Switch in [PatternFly 4](https://www.patternfly.org/2020.04/documentation/core/components/switch)
- Old Github issue in the PFE repo: [#736](https://github.com/patternfly/patternfly-elements/issues/736)
- Closed WIP PR for switch component in PFE repo: [#767](https://github.com/patternfly/patternfly-elements/pull/767) | 1.0 | [feat] Switch component - ### Description
Create a switch component like https://www.patternfly.org/v4/documentation/core/components/switch
We need to support:
- With a label
- Without a label
- Disabled state
### Acceptance Criteria
- [x] Design done
- [ ] Development done
### Image
### Link to design doc
https://xd.adobe.com/view/d20a1c17-375c-4c7f-6827-5fe2f8c2d92f-a43b/screen/4074c4b7-04ae-441e-80fd-21210d7680d2
### Other resources
- Switch in [PatternFly 4](https://www.patternfly.org/2020.04/documentation/core/components/switch)
- Old Github issue in the PFE repo: [#736](https://github.com/patternfly/patternfly-elements/issues/736)
- Closed WIP PR for switch component in PFE repo: [#767](https://github.com/patternfly/patternfly-elements/pull/767) | non_priority | switch component description create a switch component like we need to support with a label without a label disabled state acceptance criteria design done development done image link to design doc other resources switch in old github issue in the pfe repo closed wip pr for switch component in pfe repo | 0 |
58,407 | 8,256,958,129 | IssuesEvent | 2018-09-13 02:04:27 | North-Vine-Engineering/ibs-server | https://api.github.com/repos/North-Vine-Engineering/ibs-server | closed | Contributing Documentation | documentation | ## Description / User Story
As a developer, I would like clear expectations for our contributions.
## Comments / Additional Information
N/A
## Tasks
- [ ] Create a Contributions.md file for the .github dir.
| 1.0 | Contributing Documentation - ## Description / User Story
As a developer, I would like clear expectations for our contributions.
## Comments / Additional Information
N/A
## Tasks
- [ ] Create a Contributions.md file for the .github dir.
| non_priority | contributing documentation description user story as a developer i would like clear expectations for our contributions comments additional information n a tasks create a contributions md file for the github dir | 0 |
330,700 | 28,483,926,804 | IssuesEvent | 2023-04-18 06:19:23 | elastic/cloud-on-k8s | https://api.github.com/repos/elastic/cloud-on-k8s | opened | Buildkite job annotation must not be larger than 1MB | :ci >test | ```
Failed to annotate build: POST https://agent.buildkite.com/v3/jobs/.../annotations: 400 The annotation body must be less than 1 MB
```
I assume the size results from the test runner output being part of the collapsible test failure sections. I am not sure how we can trim those. | 1.0 | Buildkite job annotation must not be larger than 1MB - ```
Failed to annotate build: POST https://agent.buildkite.com/v3/jobs/.../annotations: 400 The annotation body must be less than 1 MB
```
I assume the size results from the test runner output being part of the collapsible test failure sections. I am not sure how we can trim those. | non_priority | buildkite job annotation must not be larger than failed to annotate build post the annotation body must be less than mb i assume the size results from the test runner output being part of the collapsible test failure sections i am not sure how we can trim those | 0 |
215,864 | 24,196,538,687 | IssuesEvent | 2022-09-24 01:14:58 | Baneeishaque/Raindrop-Removal-With-Light-Field-Image-Using-Image-Inpainting | https://api.github.com/repos/Baneeishaque/Raindrop-Removal-With-Light-Field-Image-Using-Image-Inpainting | opened | CVE-2022-36003 (High) detected in tensorflow-1.15.0-cp37-cp37m-manylinux2010_x86_64.whl | security vulnerability | ## CVE-2022-36003 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.15.0-cp37-cp37m-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/92/2b/e3af15221da9ff323521565fa3324b0d7c7c5b1d7a8ca66984c8d59cb0ce/tensorflow-1.15.0-cp37-cp37m-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/92/2b/e3af15221da9ff323521565fa3324b0d7c7c5b1d7a8ca66984c8d59cb0ce/tensorflow-1.15.0-cp37-cp37m-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.15.0-cp37-cp37m-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. When `RandomPoissonV2` receives large input shape and rates, it gives a `CHECK` fail that can trigger a denial of service attack. We have patched the issue in GitHub commit 552bfced6ce4809db5f3ca305f60ff80dd40c5a3. The fix will be included in TensorFlow 2.10.0. We will also cherrypick this commit on TensorFlow 2.9.1, TensorFlow 2.8.1, and TensorFlow 2.7.2, as these are also affected and still in supported range. There are no known workarounds for this issue.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-36003>CVE-2022-36003</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-cv2p-32v3-vhwq">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-cv2p-32v3-vhwq</a></p>
<p>Release Date: 2022-09-16</p>
<p>Fix Resolution: tensorflow - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-cpu - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-gpu - 2.7.2,2.8.1,2.9.1,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-36003 (High) detected in tensorflow-1.15.0-cp37-cp37m-manylinux2010_x86_64.whl - ## CVE-2022-36003 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.15.0-cp37-cp37m-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/92/2b/e3af15221da9ff323521565fa3324b0d7c7c5b1d7a8ca66984c8d59cb0ce/tensorflow-1.15.0-cp37-cp37m-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/92/2b/e3af15221da9ff323521565fa3324b0d7c7c5b1d7a8ca66984c8d59cb0ce/tensorflow-1.15.0-cp37-cp37m-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.15.0-cp37-cp37m-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. When `RandomPoissonV2` receives large input shape and rates, it gives a `CHECK` fail that can trigger a denial of service attack. We have patched the issue in GitHub commit 552bfced6ce4809db5f3ca305f60ff80dd40c5a3. The fix will be included in TensorFlow 2.10.0. We will also cherrypick this commit on TensorFlow 2.9.1, TensorFlow 2.8.1, and TensorFlow 2.7.2, as these are also affected and still in supported range. There are no known workarounds for this issue.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-36003>CVE-2022-36003</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-cv2p-32v3-vhwq">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-cv2p-32v3-vhwq</a></p>
<p>Release Date: 2022-09-16</p>
<p>Fix Resolution: tensorflow - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-cpu - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-gpu - 2.7.2,2.8.1,2.9.1,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x tensorflow whl vulnerable library found in base branch main vulnerability details tensorflow is an open source platform for machine learning when receives large input shape and rates it gives a check fail that can trigger a denial of service attack we have patched the issue in github commit the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow and tensorflow as these are also affected and still in supported range there are no known workarounds for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with mend | 0 |
183,589 | 14,239,215,990 | IssuesEvent | 2020-11-18 19:47:51 | samvera/hyrax | https://api.github.com/repos/samvera/hyrax | closed | Feature test: new form - resource new form fields are generated correctly | Effort: Minor test coverage | ### Descriptive summary
The new form used for resources are generated based on the configs in the metadata yaml file (`/config/metadata/*.yaml`). It is desired that there be specs confirming that the form view was generated correctly.
### Rationale
New forms for valkyrie resource works should generate with expected fields and field characteristics to support customizations through configuration.
### Expected behavior
Test includes verifications for all attributes in the metadata yaml file...
- [x] generates a field above the fold and marked with an * when form -> required = true
- [x] generates a field without an * when form -> required = false
- [x] generates a field above the fold when form -> primary = true
- [x] generates a field below the fold when form -> primary = false
- [x] generates a field with a link to add more values when form -> multiple = true
- [x] generates a field without a link to add more values when form -> multiple = false
### Actual behavior
If actual does not match expected, open an issue with details about what actually happened and what was expected.
### Steps to reproduce the behavior
1. Create a feature test
2. Use monograph valkyrie work class if it has all the required variations. (may need to expand monograph's metadata yaml to include all variations described under expected behavior)
3. In the test, create an instance of the monograph through the new form
4. Verify that all fields were created as expected
### Related Work
Issue #4583 - Feature test: edit form - resource new form fields are generated correctly
See non-valkyrie [features/create_work_spec.rb](https://github.com/samvera/hyrax/blob/master/spec/features/create_work_spec.rb) test
| 1.0 | Feature test: new form - resource new form fields are generated correctly - ### Descriptive summary
The new form used for resources are generated based on the configs in the metadata yaml file (`/config/metadata/*.yaml`). It is desired that there be specs confirming that the form view was generated correctly.
### Rationale
New forms for valkyrie resource works should generate with expected fields and field characteristics to support customizations through configuration.
### Expected behavior
Test includes verifications for all attributes in the metadata yaml file...
- [x] generates a field above the fold and marked with an * when form -> required = true
- [x] generates a field without an * when form -> required = false
- [x] generates a field above the fold when form -> primary = true
- [x] generates a field below the fold when form -> primary = false
- [x] generates a field with a link to add more values when form -> multiple = true
- [x] generates a field without a link to add more values when form -> multiple = false
### Actual behavior
If actual does not match expected, open an issue with details about what actually happened and what was expected.
### Steps to reproduce the behavior
1. Create a feature test
2. Use monograph valkyrie work class if it has all the required variations. (may need to expand monograph's metadata yaml to include all variations described under expected behavior)
3. In the test, create an instance of the monograph through the new form
4. Verify that all fields were created as expected
### Related Work
Issue #4583 - Feature test: edit form - resource new form fields are generated correctly
See non-valkyrie [features/create_work_spec.rb](https://github.com/samvera/hyrax/blob/master/spec/features/create_work_spec.rb) test
| non_priority | feature test new form resource new form fields are generated correctly descriptive summary the new form used for resources are generated based on the configs in the metadata yaml file config metadata yaml it is desired that there be specs confirming that the form view was generated correctly rationale new forms for valkyrie resource works should generate with expected fields and field characteristics to support customizations through configuration expected behavior test includes verifications for all attributes in the metadata yaml file generates a field above the fold and marked with an when form required true generates a field without an when form required false generates a field above the fold when form primary true generates a field below the fold when form primary false generates a field with a link to add more values when form multiple true generates a field without a link to add more values when form multiple false actual behavior if actual does not match expected open an issue with details about what actually happened and what was expected steps to reproduce the behavior create a feature test use monograph valkyrie work class if it has all the required variations may need to expand monograph s metadata yaml to include all variations described under expected behavior in the test create an instance of the monograph through the new form verify that all fields were created as expected related work issue feature test edit form resource new form fields are generated correctly see non valkyrie test | 0 |
25,113 | 12,217,684,253 | IssuesEvent | 2020-05-01 17:43:08 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | Terraform plan fails when enabling streams on an existing table and using the stream_arn | bug service/dynamodb stale | _This issue was originally opened by @drieselliott as hashicorp/terraform#13245. It was migrated here as part of the [provider split](https://www.hashicorp.com/blog/upcoming-provider-changes-in-terraform-0-10/). The original body of the issue is below._
<hr>
Hi there,
### Terraform Version
0.9.2
### Affected Resource(s)
Please list the resources as a list, for example:
- aws_dynamodb_table
- aws_lambda_event_source_mapping
This might be an issue in how Terraform core handles its planning logic.
### Terraform Configuration Files
Initial script:
```hcl
resource "aws_dynamodb_table" "table" {
name = "table"
read_capacity = 1
write_capacity = 1
hash_key = "hash"
attribute {
name = "hash"
type = "S"
}
}
```
After adding Lambda function:
```hcl
resource "aws_dynamodb_table" "table" {
name = "table"
read_capacity = 1
write_capacity = 1
hash_key = "hash"
stream_enabled = true
stream_view_type = "NEW_AND_OLD_IMAGES"
attribute {
name = "hash"
type = "S"
}
}
resource "aws_lambda_function" "function" {
# Contents of Lambda function are not relevant
}
resource "aws_lambda_event_source_mapping" "stream_mapping" {
event_source_arn = "${aws_dynamodb_table.table.stream_arn}"
function_name = "${aws_lambda_function.function.arn}"
starting_position = "LATEST"
batch_size = 250
enabled = true
}
```
### Expected Behavior
* Enable streams on an existing table
* Linked the stream to a lambda function
* Run 'terraform plan'
* Plan shows enabling streams on the table and adding the stream
### Actual Behavior
When we run 'terraform plan' we see the error "property aws_dynamodb_table.table.stream_arn does not exist". It seems to me that Terraform is looking at its state file and not finding the stream_arn on the table, since streams were not enabled in the past and therefore it fails.
### Steps to Reproduce
* Create script like in initial set-up above
* Run 'terraform apply' to set up the table
* Update the script to the second script posted above (taking into account that the above is not a fully working example in order to limit the content to the important parts)
* Run 'terraform plan'
* The planning will fail | 1.0 | Terraform plan fails when enabling streams on an existing table and using the stream_arn - _This issue was originally opened by @drieselliott as hashicorp/terraform#13245. It was migrated here as part of the [provider split](https://www.hashicorp.com/blog/upcoming-provider-changes-in-terraform-0-10/). The original body of the issue is below._
<hr>
Hi there,
### Terraform Version
0.9.2
### Affected Resource(s)
Please list the resources as a list, for example:
- aws_dynamodb_table
- aws_lambda_event_source_mapping
This might be an issue in how Terraform core handles its planning logic.
### Terraform Configuration Files
Initial script:
```hcl
resource "aws_dynamodb_table" "table" {
name = "table"
read_capacity = 1
write_capacity = 1
hash_key = "hash"
attribute {
name = "hash"
type = "S"
}
}
```
After adding Lambda function:
```hcl
resource "aws_dynamodb_table" "table" {
name = "table"
read_capacity = 1
write_capacity = 1
hash_key = "hash"
stream_enabled = true
stream_view_type = "NEW_AND_OLD_IMAGES"
attribute {
name = "hash"
type = "S"
}
}
resource "aws_lambda_function" "function" {
# Contents of Lambda function are not relevant
}
resource "aws_lambda_event_source_mapping" "stream_mapping" {
event_source_arn = "${aws_dynamodb_table.table.stream_arn}"
function_name = "${aws_lambda_function.function.arn}"
starting_position = "LATEST"
batch_size = 250
enabled = true
}
```
### Expected Behavior
* Enable streams on an existing table
* Linked the stream to a lambda function
* Run 'terraform plan'
* Plan shows enabling streams on the table and adding the stream
### Actual Behavior
When we run 'terraform plan' we see the error "property aws_dynamodb_table.table.stream_arn does not exist". It seems to me that Terraform is looking at its state file and not finding the stream_arn on the table, since streams were not enabled in the past and therefore it fails.
### Steps to Reproduce
* Create script like in initial set-up above
* Run 'terraform apply' to set up the table
* Update the script to the second script posted above (taking into account that the above is not a fully working example in order to limit the content to the important parts)
* Run 'terraform plan'
* The planning will fail | non_priority | terraform plan fails when enabling streams on an existing table and using the stream arn this issue was originally opened by drieselliott as hashicorp terraform it was migrated here as part of the the original body of the issue is below hi there terraform version affected resource s please list the resources as a list for example aws dynamodb table aws lambda event source mapping this might be an issue in how terraform core handles its planning logic terraform configuration files initial script hcl resource aws dynamodb table table name table read capacity write capacity hash key hash attribute name hash type s after adding lambda function hcl resource aws dynamodb table table name table read capacity write capacity hash key hash stream enabled true stream view type new and old images attribute name hash type s resource aws lambda function function contents of lambda function are not relevant resource aws lambda event source mapping stream mapping event source arn aws dynamodb table table stream arn function name aws lambda function function arn starting position latest batch size enabled true expected behavior enable streams on an existing table linked the stream to a lambda function run terraform plan plan shows enabling streams on the table and adding the stream actual behavior when we run terraform plan we see the error property aws dynamodb table table stream arn does not exist it seems to me that terraform is looking at its state file and not finding the stream arn on the table since streams were not enabled in the past and therefore it fails steps to reproduce create script like in initial set up above run terraform apply to set up the table update the script to the second script posted above taking into account that the above is not a fully working example in order to limit the content to the important parts run terraform plan the planning will fail | 0 |
211,078 | 16,418,067,095 | IssuesEvent | 2021-05-19 09:12:33 | personium/website | https://api.github.com/repos/personium/website | opened | Add RegEx path support description introduced in v1.7.22 | documentation | RegEx path support in Engine Service Collection config
https://github.com/personium/personium-core/issues/338
Add this description to the Engine Service Collection config API page.
https://personium.io/docs/en/apiref/380_Configure_Service_Collection/ | 1.0 | Add RegEx path support description introduced in v1.7.22 - RegEx path support in Engine Service Collection config
https://github.com/personium/personium-core/issues/338
Add this description to the Engine Service Collection config API page.
https://personium.io/docs/en/apiref/380_Configure_Service_Collection/ | non_priority | add regex path support description introduced in regex path support in engine service collection config add this description to the engine service collection config api page | 0 |
235,819 | 19,430,298,855 | IssuesEvent | 2021-12-21 11:07:59 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: jepsen/sets/start-stop-2 failed | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.jepsen/sets/start-stop-2 [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=artifacts#/jepsen/sets/start-stop-2) on master @ [3f95a4bd83cce2952a12497de82692866b4da659](https://github.com/cockroachdb/cockroach/commits/3f95a4bd83cce2952a12497de82692866b4da659):
```
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2050
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runJepsen.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:172
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runJepsen.func3
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:210
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1581
Wraps: (2) output in run_140537.890289182_n6_bash
Wraps: (3) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-3948712-1639818405-98-n6cpu4:6 -- bash -e -c "\
| cd /mnt/data1/jepsen/cockroachdb && set -eo pipefail && \
| ~/lein run test \
| --tarball file://${PWD}/cockroach.tgz \
| --username ${USER} \
| --ssh-private-key ~/.ssh/id_rsa \
| --os ubuntu \
| --time-limit 300 \
| --concurrency 30 \
| --recovery-time 25 \
| --test-count 1 \
| -n 10.142.0.41 -n 10.142.0.7 -n 10.142.0.108 -n 10.142.0.50 -n 10.142.0.247 \
| --test sets --nemesis start-stop-2 \
| > invoke.log 2>&1 \
| " returned
| stderr:
| Error: SSH_PROBLEM: exit status 255
| (1) SSH_PROBLEM
| Wraps: (2) Node 6. Command with error:
| | ``````
| | bash -e -c "\
| | cd /mnt/data1/jepsen/cockroachdb && set -eo pipefail && \
| | ~/lein run test \
| | --tarball file://${PWD}/cockroach.tgz \
| | --username ${USER} \
| | --ssh-private-key ~/.ssh/id_rsa \
| | --os ubuntu \
| | --time-limit 300 \
| | --concurrency 30 \
| | --recovery-time 25 \
| | --test-count 1 \
| | -n 10.142.0.41 -n 10.142.0.7 -n 10.142.0.108 -n 10.142.0.50 -n 10.142.0.247 \
| | --test sets --nemesis start-stop-2 \
| | > invoke.log 2>&1 \
| | "
| | ``````
| Wraps: (3) exit status 255
| Error types: (1) errors.SSH (2) *hintdetail.withDetail (3) *exec.ExitError
|
| stdout:
Wraps: (4) exit status 10
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *cluster.WithCommandDetails (4) *exec.ExitError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*jepsen/sets/start-stop-2.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: jepsen/sets/start-stop-2 failed - roachtest.jepsen/sets/start-stop-2 [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=artifacts#/jepsen/sets/start-stop-2) on master @ [3f95a4bd83cce2952a12497de82692866b4da659](https://github.com/cockroachdb/cockroach/commits/3f95a4bd83cce2952a12497de82692866b4da659):
```
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2050
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runJepsen.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:172
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runJepsen.func3
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:210
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1581
Wraps: (2) output in run_140537.890289182_n6_bash
Wraps: (3) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-3948712-1639818405-98-n6cpu4:6 -- bash -e -c "\
| cd /mnt/data1/jepsen/cockroachdb && set -eo pipefail && \
| ~/lein run test \
| --tarball file://${PWD}/cockroach.tgz \
| --username ${USER} \
| --ssh-private-key ~/.ssh/id_rsa \
| --os ubuntu \
| --time-limit 300 \
| --concurrency 30 \
| --recovery-time 25 \
| --test-count 1 \
| -n 10.142.0.41 -n 10.142.0.7 -n 10.142.0.108 -n 10.142.0.50 -n 10.142.0.247 \
| --test sets --nemesis start-stop-2 \
| > invoke.log 2>&1 \
| " returned
| stderr:
| Error: SSH_PROBLEM: exit status 255
| (1) SSH_PROBLEM
| Wraps: (2) Node 6. Command with error:
| | ``````
| | bash -e -c "\
| | cd /mnt/data1/jepsen/cockroachdb && set -eo pipefail && \
| | ~/lein run test \
| | --tarball file://${PWD}/cockroach.tgz \
| | --username ${USER} \
| | --ssh-private-key ~/.ssh/id_rsa \
| | --os ubuntu \
| | --time-limit 300 \
| | --concurrency 30 \
| | --recovery-time 25 \
| | --test-count 1 \
| | -n 10.142.0.41 -n 10.142.0.7 -n 10.142.0.108 -n 10.142.0.50 -n 10.142.0.247 \
| | --test sets --nemesis start-stop-2 \
| | > invoke.log 2>&1 \
| | "
| | ``````
| Wraps: (3) exit status 255
| Error types: (1) errors.SSH (2) *hintdetail.withDetail (3) *exec.ExitError
|
| stdout:
Wraps: (4) exit status 10
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *cluster.WithCommandDetails (4) *exec.ExitError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*jepsen/sets/start-stop-2.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | roachtest jepsen sets start stop failed roachtest jepsen sets start stop with on master home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go github com cockroachdb cockroach pkg cmd roachtest tests runjepsen home agent work go src github com cockroachdb cockroach pkg cmd roachtest tests jepsen go github com cockroachdb cockroach pkg cmd roachtest tests runjepsen home agent work go src github com cockroachdb cockroach pkg cmd roachtest tests jepsen go runtime goexit usr local go src runtime asm s wraps output in run bash wraps home agent work go src github com cockroachdb cockroach bin roachprod run teamcity bash e c cd mnt jepsen cockroachdb set eo pipefail lein run test tarball file pwd cockroach tgz username user ssh private key ssh id rsa os ubuntu time limit concurrency recovery time test count n n n n n test sets nemesis start stop invoke log returned stderr error ssh problem exit status ssh problem wraps node command with error bash e c cd mnt jepsen cockroachdb set eo pipefail lein run test tarball file pwd cockroach tgz username user ssh private key ssh id rsa os ubuntu time limit concurrency recovery time test count n n n n n test sets nemesis start stop invoke log wraps exit status error types errors ssh hintdetail withdetail exec exiterror stdout wraps exit status error types withstack withstack errutil withprefix cluster withcommanddetails exec exiterror help see see cc cockroachdb kv triage | 0 |
301,330 | 26,035,831,216 | IssuesEvent | 2022-12-22 04:49:14 | rancher/dashboard | https://api.github.com/repos/rancher/dashboard | closed | Fix issue with advanced filtering | kind/bug [zube]: To Test area/os-elemental | - Fix issue with advanced filtering where we might look for labels on items which don't have any labels associated causing a blocking error
**QA testing**
As for this feature is only available in Elemental (OS management) it's better to be covered by QA for the elemental team @juadk
If there something to be tested, it's just to make sure the simple filtering of list views is working properly from the POV of `rancher/dashboard` | 1.0 | Fix issue with advanced filtering - - Fix issue with advanced filtering where we might look for labels on items which don't have any labels associated causing a blocking error
**QA testing**
As for this feature is only available in Elemental (OS management) it's better to be covered by QA for the elemental team @juadk
If there something to be tested, it's just to make sure the simple filtering of list views is working properly from the POV of `rancher/dashboard` | non_priority | fix issue with advanced filtering fix issue with advanced filtering where we might look for labels on items which don t have any labels associated causing a blocking error qa testing as for this feature is only available in elemental os management it s better to be covered by qa for the elemental team juadk if there something to be tested it s just to make sure the simple filtering of list views is working properly from the pov of rancher dashboard | 0 |
340,387 | 24,652,528,535 | IssuesEvent | 2022-10-17 19:57:34 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | [Docs]: unlisted OS enumerations for data.aws_ssm_patch_baseline | documentation service/ssm | ### Documentation Link
https://registry.terraform.io/providers/hashicorp/aws/latest/docs/data-sources/ssm_patch_baseline
### Description
The documentation mentions the arg `operating_system`, and provides the example value `"CENTOS"` but does not list any other possible enumerations/values. Their values can only be inferred from an error message after the user gives up and takes a wild guess:
```
Error: expected operating_system to be one of [WINDOWS AMAZON_LINUX AMAZON_LINUX_2 UBUNTU REDHAT_ENTERPRISE_LINUX SUSE CENTOS ORACLE_LINUX DEBIAN MACOS RASPBIAN ROCKY_LINUX], got Amazon-Linux-2
```
These enumerations aren't listed in Amazon's docs that I know of (https://docs.aws.amazon.com/systems-manager/latest/userguide/sysman-patch-baselines.html).
The arg is also listed as "optional", which is true, however, if not supplied, the query will fail.
For example, this works:
```
data "aws_ssm_patch_baseline" "amazon_linux_2" {
owner = "AWS"
name_prefix = "AWS-WindowsPredefinedPatchBaseline-OS-Applications"
operating_system = "WINDOWS"
}
```
...but if `operating_system` is removed, `terraform plan` will return an error:
```
Error: Your query returned no results. Please change your search criteria and try again.
```
### References
- https://docs.aws.amazon.com/systems-manager/latest/userguide/sysman-patch-baselines.html
- https://registry.terraform.io/providers/hashicorp/aws/latest/docs/data-sources/ssm_patch_baseline
### Would you like to implement a fix?
_No response_ | 1.0 | [Docs]: unlisted OS enumerations for data.aws_ssm_patch_baseline - ### Documentation Link
https://registry.terraform.io/providers/hashicorp/aws/latest/docs/data-sources/ssm_patch_baseline
### Description
The documentation mentions the arg `operating_system`, and provides the example value `"CENTOS"` but does not list any other possible enumerations/values. Their values can only be inferred from an error message after the user gives up and takes a wild guess:
```
Error: expected operating_system to be one of [WINDOWS AMAZON_LINUX AMAZON_LINUX_2 UBUNTU REDHAT_ENTERPRISE_LINUX SUSE CENTOS ORACLE_LINUX DEBIAN MACOS RASPBIAN ROCKY_LINUX], got Amazon-Linux-2
```
These enumerations aren't listed in Amazon's docs that I know of (https://docs.aws.amazon.com/systems-manager/latest/userguide/sysman-patch-baselines.html).
The arg is also listed as "optional", which is true, however, if not supplied, the query will fail.
For example, this works:
```
data "aws_ssm_patch_baseline" "amazon_linux_2" {
owner = "AWS"
name_prefix = "AWS-WindowsPredefinedPatchBaseline-OS-Applications"
operating_system = "WINDOWS"
}
```
...but if `operating_system` is removed, `terraform plan` will return an error:
```
Error: Your query returned no results. Please change your search criteria and try again.
```
### References
- https://docs.aws.amazon.com/systems-manager/latest/userguide/sysman-patch-baselines.html
- https://registry.terraform.io/providers/hashicorp/aws/latest/docs/data-sources/ssm_patch_baseline
### Would you like to implement a fix?
_No response_ | non_priority | unlisted os enumerations for data aws ssm patch baseline documentation link description the documentation mentions the arg operating system and provides the example value centos but does not list any other possible enumerations values their values can only be inferred from an error message after the user gives up and takes a wild guess error expected operating system to be one of got amazon linux these enumerations aren t listed in amazon s docs that i know of the arg is also listed as optional which is true however if not supplied the query will fail for example this works data aws ssm patch baseline amazon linux owner aws name prefix aws windowspredefinedpatchbaseline os applications operating system windows but if operating system is removed terraform plan will return an error error your query returned no results please change your search criteria and try again references would you like to implement a fix no response | 0 |
309,850 | 26,679,872,075 | IssuesEvent | 2023-01-26 16:50:44 | wazuh/wazuh-qa | https://api.github.com/repos/wazuh/wazuh-qa | opened | macOS Ruleset | team/qa type/dev-testing status/not-tracked | | Target version | Related issue | Related PR |
|--------------------|--------------------|-----------------|
| 4.4.1 | https://github.com/wazuh/wazuh/issues/15567 | [ ](https://github.com/wazuh/wazuh/pull/16006) |
<!--
This template reflects sections that must be included in new Pull requests.
Contributions from the community are really appreciated. If this is the case, please add the
"contribution" to properly track the Pull Request.
Please fill the table above. Feel free to extend it at your convenience.
-->
## Description
<!--
Add a clear description of how the problem has been solved.
-->
This PR improves the current Ruleset by adding the decoder/rules to manage and alert from analyzing the logs collected from macOS 13.0 Ventura system.
## Configuration options
<!--
When proceed, this section should include new configuration parameters.
-->
The Wazuh agent on macOS systems would require the following addition to the `ossec.conf` file:
```
<localfile>
<location>macos</location>
<log_format>macos</log_format>
<query type="trace,log,activity" level="info">(process == "sudo") or (process == "sshd") or (process == "tccd") or (message contains "SessionAgentNotificationCenter") or (process == "screensharingd" and message contains "Authentication") or (process == "securityd" and eventMessage contains "Session" and subsystem == "com.apple.securityd")</query>
</localfile>
```
## Logs/Alerts example
<!--
Paste here related logs and alerts
-->
Sample log: `2023-01-23 03:25:25.058668-0800 localhost tccd[155]: [com.apple.TCC:access] Update Access Record: kTCCServiceScreenCapture for com.apple.screensharing.agent to Allowed at 1674473125 (2023-01-23 11:25:25 +0000) CodeReq: None Indirect : Unused`
Alert:
```
**Messages:
INFO: (7202): Session initialized with token '8e353892'
**Phase 1: Completed pre-decoding.
full event: '2023-01-23 03:25:25.058668-0800 localhost tccd[155]: [com.apple.TCC:access] Update Access Record: kTCCServiceScreenCapture for com.apple.screensharing.agent to Allowed at 1674473125 (2023-01-23 11:25:25 +0000) CodeReq: None Indirect : Unused'
timestamp: '2023-01-23 03:25:25.058668-0800'
program_name: 'tccd'
**Phase 2: Completed decoding.
name: 'macOS_tccd'
application: 'com.apple.screensharing.agent'
service: 'kTCCServiceScreenCapture'
status: 'Allowed'
time: '11:25:25'
**Phase 3: Completed filtering (rules).
id: '110001'
level: '5'
description: 'com.apple.screensharing.agent has been granted permission to kTCCServiceScreenCapture at 11:25:25'
groups: '["macOS"]'
firedtimes: '1'
gdpr: '["IV_35.7.d"]'
hipaa: '["164.312.b"]'
mail: 'false'
mitre.id: '["T1222.002"]'
mitre.tactic: '["Defense Evasion"]'
mitre.technique: '["Linux and Mac File and Directory Permissions Modification"]'
nist_800_53: '["AU.6"]'
pci_dss: '["10.6.1"]'
tsc: '["CC7.2","CC7.3"]'
**Alert to be generated.
```
## Tests
<!--
Depending on the affected components by this PR, the following checks should be selected and marked.
-->
<!-- Minimum checks required -->
- Compilation without warnings in every supported platform
- [ ] MAC OS X
- [ ] Source installation
- [ ] Package installation
- [ ] Source upgrade
- [ ] Package upgrade
- [ ] Review logs syntax and correct language
- [ ] QA templates contemplate the added capabilities
- Memory tests for macOS
- [ ] Scan-build report
- [ ] Leaks
- [ ] AddressSanitizer
<!-- Checks for huge PRs that affect the product more generally -->
- [ ] Retrocompatibility with older Wazuh versions
- [ ] Working on cluster environments
- [ ] Configuration on demand reports new parameters
- [ ] The data flow works as expected (agent-manager-api-app)
- [ ] Added unit tests (for new features)
- [ ] Stress test for affected components
<!-- Ruleset required checks, rules/decoder -->
- Decoder/Rule tests
- [ ] Added unit testing files ".ini"
- [ ] runtests.py executed without errors | 1.0 | macOS Ruleset - | Target version | Related issue | Related PR |
|--------------------|--------------------|-----------------|
| 4.4.1 | https://github.com/wazuh/wazuh/issues/15567 | [ ](https://github.com/wazuh/wazuh/pull/16006) |
<!--
This template reflects sections that must be included in new Pull requests.
Contributions from the community are really appreciated. If this is the case, please add the
"contribution" to properly track the Pull Request.
Please fill the table above. Feel free to extend it at your convenience.
-->
## Description
<!--
Add a clear description of how the problem has been solved.
-->
This PR improves the current Ruleset by adding the decoder/rules to manage and alert from analyzing the logs collected from macOS 13.0 Ventura system.
## Configuration options
<!--
When proceed, this section should include new configuration parameters.
-->
The Wazuh agent on macOS systems would require the following addition to the `ossec.conf` file:
```
<localfile>
<location>macos</location>
<log_format>macos</log_format>
<query type="trace,log,activity" level="info">(process == "sudo") or (process == "sshd") or (process == "tccd") or (message contains "SessionAgentNotificationCenter") or (process == "screensharingd" and message contains "Authentication") or (process == "securityd" and eventMessage contains "Session" and subsystem == "com.apple.securityd")</query>
</localfile>
```
## Logs/Alerts example
<!--
Paste here related logs and alerts
-->
Sample log: `2023-01-23 03:25:25.058668-0800 localhost tccd[155]: [com.apple.TCC:access] Update Access Record: kTCCServiceScreenCapture for com.apple.screensharing.agent to Allowed at 1674473125 (2023-01-23 11:25:25 +0000) CodeReq: None Indirect : Unused`
Alert:
```
**Messages:
INFO: (7202): Session initialized with token '8e353892'
**Phase 1: Completed pre-decoding.
full event: '2023-01-23 03:25:25.058668-0800 localhost tccd[155]: [com.apple.TCC:access] Update Access Record: kTCCServiceScreenCapture for com.apple.screensharing.agent to Allowed at 1674473125 (2023-01-23 11:25:25 +0000) CodeReq: None Indirect : Unused'
timestamp: '2023-01-23 03:25:25.058668-0800'
program_name: 'tccd'
**Phase 2: Completed decoding.
name: 'macOS_tccd'
application: 'com.apple.screensharing.agent'
service: 'kTCCServiceScreenCapture'
status: 'Allowed'
time: '11:25:25'
**Phase 3: Completed filtering (rules).
id: '110001'
level: '5'
description: 'com.apple.screensharing.agent has been granted permission to kTCCServiceScreenCapture at 11:25:25'
groups: '["macOS"]'
firedtimes: '1'
gdpr: '["IV_35.7.d"]'
hipaa: '["164.312.b"]'
mail: 'false'
mitre.id: '["T1222.002"]'
mitre.tactic: '["Defense Evasion"]'
mitre.technique: '["Linux and Mac File and Directory Permissions Modification"]'
nist_800_53: '["AU.6"]'
pci_dss: '["10.6.1"]'
tsc: '["CC7.2","CC7.3"]'
**Alert to be generated.
```
## Tests
<!--
Depending on the affected components by this PR, the following checks should be selected and marked.
-->
<!-- Minimum checks required -->
- Compilation without warnings in every supported platform
- [ ] MAC OS X
- [ ] Source installation
- [ ] Package installation
- [ ] Source upgrade
- [ ] Package upgrade
- [ ] Review logs syntax and correct language
- [ ] QA templates contemplate the added capabilities
- Memory tests for macOS
- [ ] Scan-build report
- [ ] Leaks
- [ ] AddressSanitizer
<!-- Checks for huge PRs that affect the product more generally -->
- [ ] Retrocompatibility with older Wazuh versions
- [ ] Working on cluster environments
- [ ] Configuration on demand reports new parameters
- [ ] The data flow works as expected (agent-manager-api-app)
- [ ] Added unit tests (for new features)
- [ ] Stress test for affected components
<!-- Ruleset required checks, rules/decoder -->
- Decoder/Rule tests
- [ ] Added unit testing files ".ini"
- [ ] runtests.py executed without errors | non_priority | macos ruleset target version related issue related pr this template reflects sections that must be included in new pull requests contributions from the community are really appreciated if this is the case please add the contribution to properly track the pull request please fill the table above feel free to extend it at your convenience description add a clear description of how the problem has been solved this pr improves the current ruleset by adding the decoder rules to manage and alert from analyzing the logs collected from macos ventura system configuration options when proceed this section should include new configuration parameters the wazuh agent on macos systems would require the following addition to the ossec conf file macos macos process sudo or process sshd or process tccd or message contains sessionagentnotificationcenter or process screensharingd and message contains authentication or process securityd and eventmessage contains session and subsystem com apple securityd logs alerts example paste here related logs and alerts sample log localhost tccd update access record ktccservicescreencapture for com apple screensharing agent to allowed at codereq none indirect unused alert messages info session initialized with token phase completed pre decoding full event localhost tccd update access record ktccservicescreencapture for com apple screensharing agent to allowed at codereq none indirect unused timestamp program name tccd phase completed decoding name macos tccd application com apple screensharing agent service ktccservicescreencapture status allowed time phase completed filtering rules id level description com apple screensharing agent has been granted permission to ktccservicescreencapture at groups firedtimes gdpr hipaa mail false mitre id mitre tactic mitre technique nist pci dss tsc alert to be generated tests depending on the affected components by this pr the following checks should be selected and marked compilation without warnings in every supported platform mac os x source installation package installation source upgrade package upgrade review logs syntax and correct language qa templates contemplate the added capabilities memory tests for macos scan build report leaks addresssanitizer retrocompatibility with older wazuh versions working on cluster environments configuration on demand reports new parameters the data flow works as expected agent manager api app added unit tests for new features stress test for affected components decoder rule tests added unit testing files ini runtests py executed without errors | 0 |
47,513 | 10,113,213,286 | IssuesEvent | 2019-07-30 16:12:21 | stan-dev/math | https://api.github.com/repos/stan-dev/math | opened | Rewrite the test-math-dependencies script in Python | code cleanup continuous integration | ## Description
The [test-math-dependencies](https://github.com/stan-dev/math/blob/develop/make/test-math-dependencies) Makefile script is difficult to maintain and add new features to it. Mainly due to the weird scripting style of Make. It should be rewritten in Python.
Initially it was not written in Python due to some installation issues (see: https://github.com/stan-dev/math/issues/1270). We should be able to rewrite and use it now.
## Expected Output
Exact same functionality of test-math-dependencies, but in Python.
#### Current Version:
v2.20.0
| 1.0 | Rewrite the test-math-dependencies script in Python - ## Description
The [test-math-dependencies](https://github.com/stan-dev/math/blob/develop/make/test-math-dependencies) Makefile script is difficult to maintain and add new features to it. Mainly due to the weird scripting style of Make. It should be rewritten in Python.
Initially it was not written in Python due to some installation issues (see: https://github.com/stan-dev/math/issues/1270). We should be able to rewrite and use it now.
## Expected Output
Exact same functionality of test-math-dependencies, but in Python.
#### Current Version:
v2.20.0
| non_priority | rewrite the test math dependencies script in python description the makefile script is difficult to maintain and add new features to it mainly due to the weird scripting style of make it should be rewritten in python initially it was not written in python due to some installation issues see we should be able to rewrite and use it now expected output exact same functionality of test math dependencies but in python current version | 0 |
100,874 | 21,553,561,590 | IssuesEvent | 2022-04-30 03:10:15 | therealbluepandabear/PixaPencil | https://api.github.com/repos/therealbluepandabear/PixaPencil | closed | [Bug] RecyclerView cannot handle a large amount of items | 🐛 bug further context needed difficulty: hard may-req-code-revamp | The RecyclerView is not handling a large amount of items well, some Espresso tests even failed. This needs to be fixed ASAP. | 1.0 | [Bug] RecyclerView cannot handle a large amount of items - The RecyclerView is not handling a large amount of items well, some Espresso tests even failed. This needs to be fixed ASAP. | non_priority | recyclerview cannot handle a large amount of items the recyclerview is not handling a large amount of items well some espresso tests even failed this needs to be fixed asap | 0 |
79,754 | 15,268,625,604 | IssuesEvent | 2021-02-22 11:39:31 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | [0.1300.0.0] Light casted by coilgun flickers constantly whenever it's shooting | Bug Code Medium Prio | - [ ] I have searched the issue tracker to check if the issue has already been reported.
**Description**
Light casted by coilgun flickers constantly whenever it's shooting.
**Version**
0.1300.0.0 | 1.0 | [0.1300.0.0] Light casted by coilgun flickers constantly whenever it's shooting - - [ ] I have searched the issue tracker to check if the issue has already been reported.
**Description**
Light casted by coilgun flickers constantly whenever it's shooting.
**Version**
0.1300.0.0 | non_priority | light casted by coilgun flickers constantly whenever it s shooting i have searched the issue tracker to check if the issue has already been reported description light casted by coilgun flickers constantly whenever it s shooting version | 0 |
11,501 | 14,380,343,568 | IssuesEvent | 2020-12-02 02:34:05 | KevCor99/4a | https://api.github.com/repos/KevCor99/4a | closed | file_size_estimating_template | process-dashboard | -llenado de template de estimacion de lineas de coodigo en process dashboard
- correr el PROBE wizard | 1.0 | file_size_estimating_template - -llenado de template de estimacion de lineas de coodigo en process dashboard
- correr el PROBE wizard | non_priority | file size estimating template llenado de template de estimacion de lineas de coodigo en process dashboard correr el probe wizard | 0 |
57,182 | 14,017,053,144 | IssuesEvent | 2020-10-29 15:13:10 | NCEAS/metacatui | https://api.github.com/repos/NCEAS/metacatui | closed | Fix doc build issues for new query work | bug query builder | When trying to build the docs on the `feature-query-builder` branch, I am getting errors:
`
Building MetacatUI docs...
ERROR: Unable to parse /Users/walker/git/datadepot/src/js/views/QueryBuilderView.js: Argument name clash (9:86)
ERROR: Unable to parse /Users/walker/git/datadepot/src/js/views/QueryRuleView.js: Unexpected reserved word 'interface' (971:66)
`
Fix these errors and make sure the docs are building as expected. | 1.0 | Fix doc build issues for new query work - When trying to build the docs on the `feature-query-builder` branch, I am getting errors:
`
Building MetacatUI docs...
ERROR: Unable to parse /Users/walker/git/datadepot/src/js/views/QueryBuilderView.js: Argument name clash (9:86)
ERROR: Unable to parse /Users/walker/git/datadepot/src/js/views/QueryRuleView.js: Unexpected reserved word 'interface' (971:66)
`
Fix these errors and make sure the docs are building as expected. | non_priority | fix doc build issues for new query work when trying to build the docs on the feature query builder branch i am getting errors building metacatui docs error unable to parse users walker git datadepot src js views querybuilderview js argument name clash error unable to parse users walker git datadepot src js views queryruleview js unexpected reserved word interface fix these errors and make sure the docs are building as expected | 0 |
180,713 | 30,554,442,667 | IssuesEvent | 2023-07-20 10:41:25 | DeveloperAcademy-POSTECH/MC3-Team11-BeyondThe3F | https://api.github.com/repos/DeveloperAcademy-POSTECH/MC3-Team11-BeyondThe3F | closed | [Design] Component 재활용성 수정 | Design | ## 이슈
- 기존 컴포넌트의 중복을 조금 줄이기 위해 재사용 가능한 코드로 수정
## To - Do
- [ ] 중복 컴포턴트 제거
- [ ] 컬러, 텍스트 의존성 주입
| 1.0 | [Design] Component 재활용성 수정 - ## 이슈
- 기존 컴포넌트의 중복을 조금 줄이기 위해 재사용 가능한 코드로 수정
## To - Do
- [ ] 중복 컴포턴트 제거
- [ ] 컬러, 텍스트 의존성 주입
| non_priority | component 재활용성 수정 이슈 기존 컴포넌트의 중복을 조금 줄이기 위해 재사용 가능한 코드로 수정 to do 중복 컴포턴트 제거 컬러 텍스트 의존성 주입 | 0 |
145,264 | 19,339,280,070 | IssuesEvent | 2021-12-15 01:14:19 | snowdensb/pe-reports | https://api.github.com/repos/snowdensb/pe-reports | opened | CVE-2021-43818 (High) detected in lxml-4.6.3-cp37-cp37m-manylinux2014_x86_64.whl | security vulnerability | ## CVE-2021-43818 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lxml-4.6.3-cp37-cp37m-manylinux2014_x86_64.whl</b></p></summary>
<p>Powerful and Pythonic XML processing library combining libxml2/libxslt with the ElementTree API.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/30/c0/d0526314971fc661b083ab135747dc68446a3022686da8c16d25fcf6ef07/lxml-4.6.3-cp37-cp37m-manylinux2014_x86_64.whl">https://files.pythonhosted.org/packages/30/c0/d0526314971fc661b083ab135747dc68446a3022686da8c16d25fcf6ef07/lxml-4.6.3-cp37-cp37m-manylinux2014_x86_64.whl</a></p>
<p>Path to dependency file: pe-reports</p>
<p>Path to vulnerable library: pe-reports</p>
<p>
Dependency Hierarchy:
- :x: **lxml-4.6.3-cp37-cp37m-manylinux2014_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lxml is a library for processing XML and HTML in the Python language. Prior to version 4.6.5, the HTML Cleaner in lxml.html lets certain crafted script content pass through, as well as script content in SVG files embedded using data URIs. Users that employ the HTML cleaner in a security relevant context should upgrade to lxml 4.6.5 to receive a patch. There are no known workarounds available.
<p>Publish Date: 2021-12-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43818>CVE-2021-43818</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lxml/lxml/security/advisories/GHSA-55x5-fj6c-h6m8">https://github.com/lxml/lxml/security/advisories/GHSA-55x5-fj6c-h6m8</a></p>
<p>Release Date: 2021-12-13</p>
<p>Fix Resolution: lxml - 4.6.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"lxml","packageVersion":"4.6.3","packageFilePaths":["pe-reports"],"isTransitiveDependency":false,"dependencyTree":"lxml:4.6.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lxml - 4.6.5","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-43818","vulnerabilityDetails":"lxml is a library for processing XML and HTML in the Python language. Prior to version 4.6.5, the HTML Cleaner in lxml.html lets certain crafted script content pass through, as well as script content in SVG files embedded using data URIs. Users that employ the HTML cleaner in a security relevant context should upgrade to lxml 4.6.5 to receive a patch. There are no known workarounds available.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43818","cvss3Severity":"high","cvss3Score":"8.2","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-43818 (High) detected in lxml-4.6.3-cp37-cp37m-manylinux2014_x86_64.whl - ## CVE-2021-43818 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lxml-4.6.3-cp37-cp37m-manylinux2014_x86_64.whl</b></p></summary>
<p>Powerful and Pythonic XML processing library combining libxml2/libxslt with the ElementTree API.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/30/c0/d0526314971fc661b083ab135747dc68446a3022686da8c16d25fcf6ef07/lxml-4.6.3-cp37-cp37m-manylinux2014_x86_64.whl">https://files.pythonhosted.org/packages/30/c0/d0526314971fc661b083ab135747dc68446a3022686da8c16d25fcf6ef07/lxml-4.6.3-cp37-cp37m-manylinux2014_x86_64.whl</a></p>
<p>Path to dependency file: pe-reports</p>
<p>Path to vulnerable library: pe-reports</p>
<p>
Dependency Hierarchy:
- :x: **lxml-4.6.3-cp37-cp37m-manylinux2014_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lxml is a library for processing XML and HTML in the Python language. Prior to version 4.6.5, the HTML Cleaner in lxml.html lets certain crafted script content pass through, as well as script content in SVG files embedded using data URIs. Users that employ the HTML cleaner in a security relevant context should upgrade to lxml 4.6.5 to receive a patch. There are no known workarounds available.
<p>Publish Date: 2021-12-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43818>CVE-2021-43818</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lxml/lxml/security/advisories/GHSA-55x5-fj6c-h6m8">https://github.com/lxml/lxml/security/advisories/GHSA-55x5-fj6c-h6m8</a></p>
<p>Release Date: 2021-12-13</p>
<p>Fix Resolution: lxml - 4.6.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"lxml","packageVersion":"4.6.3","packageFilePaths":["pe-reports"],"isTransitiveDependency":false,"dependencyTree":"lxml:4.6.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lxml - 4.6.5","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-43818","vulnerabilityDetails":"lxml is a library for processing XML and HTML in the Python language. Prior to version 4.6.5, the HTML Cleaner in lxml.html lets certain crafted script content pass through, as well as script content in SVG files embedded using data URIs. Users that employ the HTML cleaner in a security relevant context should upgrade to lxml 4.6.5 to receive a patch. There are no known workarounds available.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43818","cvss3Severity":"high","cvss3Score":"8.2","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in lxml whl cve high severity vulnerability vulnerable library lxml whl powerful and pythonic xml processing library combining libxslt with the elementtree api library home page a href path to dependency file pe reports path to vulnerable library pe reports dependency hierarchy x lxml whl vulnerable library found in base branch develop vulnerability details lxml is a library for processing xml and html in the python language prior to version the html cleaner in lxml html lets certain crafted script content pass through as well as script content in svg files embedded using data uris users that employ the html cleaner in a security relevant context should upgrade to lxml to receive a patch there are no known workarounds available publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lxml rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree lxml isminimumfixversionavailable true minimumfixversion lxml isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails lxml is a library for processing xml and html in the python language prior to version the html cleaner in lxml html lets certain crafted script content pass through as well as script content in svg files embedded using data uris users that employ the html cleaner in a security relevant context should upgrade to lxml to receive a patch there are no known workarounds available vulnerabilityurl | 0 |
225,801 | 17,909,415,520 | IssuesEvent | 2021-09-09 01:42:55 | nih-cfde/dashboard | https://api.github.com/repos/nih-cfde/dashboard | closed | Dcc Review page has broken subtitle | bug testing | When looking at the [dcc_review page for catalog 397](https://app-dev.nih-cfde.org/dcc_review.html?catalogId=397), I see the submitted datapackage subtitle is missing info:
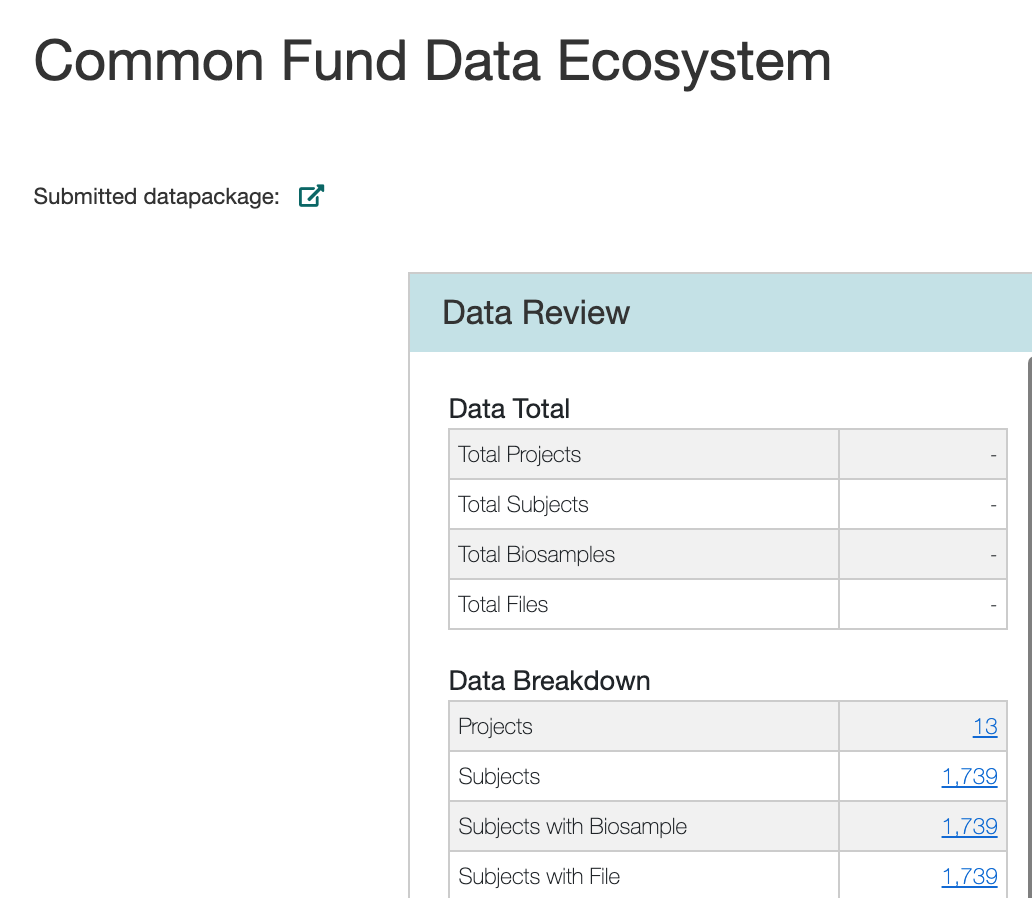
The link for the external icon also seems to be misconfigured now. It points to the page we are currently on (instead of the portal for that catalog (https://app-dev.nih-cfde.org/chaise/recordset/#397/CFDE:file)
Another issue here is that the "external link icon" should not be used since this is intended to be a navigation within the app.nih-cfde.org application. | 1.0 | Dcc Review page has broken subtitle - When looking at the [dcc_review page for catalog 397](https://app-dev.nih-cfde.org/dcc_review.html?catalogId=397), I see the submitted datapackage subtitle is missing info:
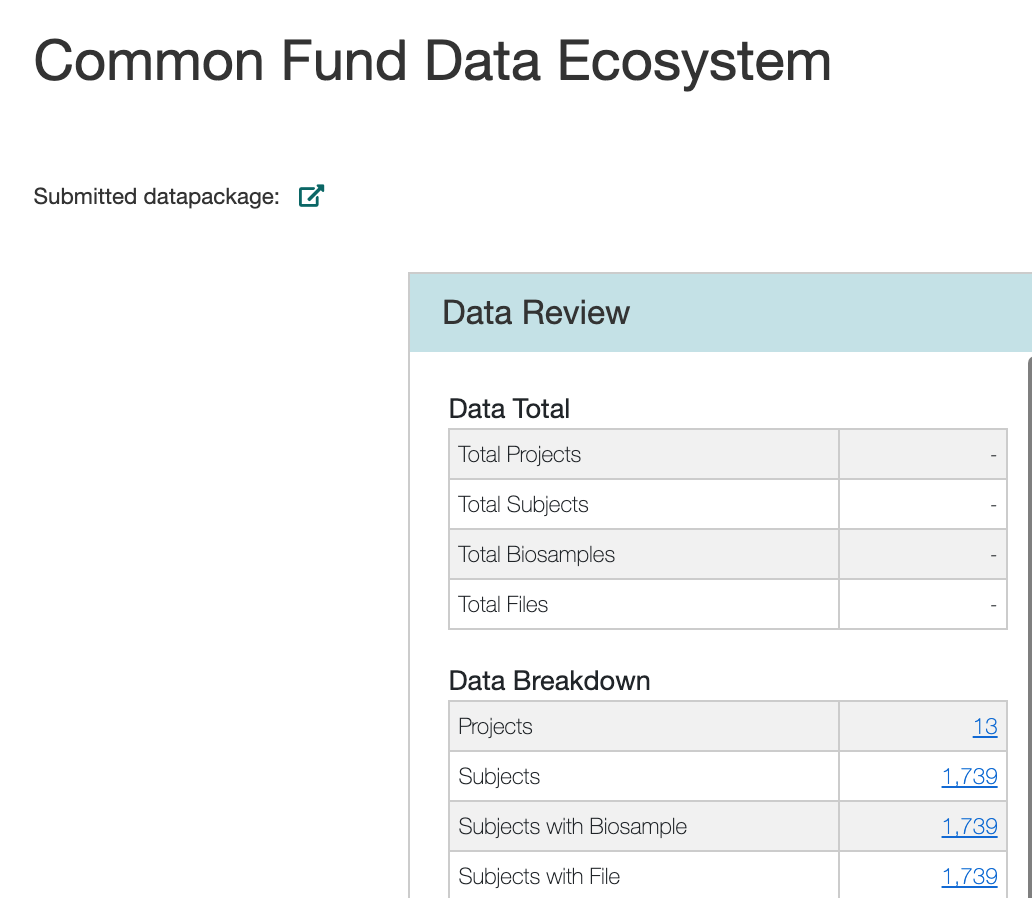
The link for the external icon also seems to be misconfigured now. It points to the page we are currently on (instead of the portal for that catalog (https://app-dev.nih-cfde.org/chaise/recordset/#397/CFDE:file)
Another issue here is that the "external link icon" should not be used since this is intended to be a navigation within the app.nih-cfde.org application. | non_priority | dcc review page has broken subtitle when looking at the i see the submitted datapackage subtitle is missing info the link for the external icon also seems to be misconfigured now it points to the page we are currently on instead of the portal for that catalog another issue here is that the external link icon should not be used since this is intended to be a navigation within the app nih cfde org application | 0 |
30,801 | 4,655,606,370 | IssuesEvent | 2016-10-04 00:02:12 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | teamcity: failed tests on master: testrace/TestStoreSplitTimestampCacheDifferentLeaseHolder | Robot test-failure | The following tests appear to have failed:
[#26477](https://teamcity.cockroachdb.com/viewLog.html?buildId=26477):
```
--- FAIL: testrace/TestStoreSplitTimestampCacheDifferentLeaseHolder (0.007s)
client_split_test.go:1310: expected to see no lease requests for the right-hand side
```
Please assign, take a look and update the issue accordingly. | 1.0 | teamcity: failed tests on master: testrace/TestStoreSplitTimestampCacheDifferentLeaseHolder - The following tests appear to have failed:
[#26477](https://teamcity.cockroachdb.com/viewLog.html?buildId=26477):
```
--- FAIL: testrace/TestStoreSplitTimestampCacheDifferentLeaseHolder (0.007s)
client_split_test.go:1310: expected to see no lease requests for the right-hand side
```
Please assign, take a look and update the issue accordingly. | non_priority | teamcity failed tests on master testrace teststoresplittimestampcachedifferentleaseholder the following tests appear to have failed fail testrace teststoresplittimestampcachedifferentleaseholder client split test go expected to see no lease requests for the right hand side please assign take a look and update the issue accordingly | 0 |
14,815 | 4,997,005,122 | IssuesEvent | 2016-12-09 15:34:56 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | place scripts in footer instead of head | New Feature No Code Attached Yet | This is a placeholder issue for multiple existing issues and pull reports (see below)
### Aim
To be able to load Javascript just before </body>.
### Reasons Why
The async and defer attributes for the `<script>` element have great support to pause and defer the execution of the script. But still... they are downloaded in the head.
Clear explain of async and defer can be found on: http://www.growingwiththeweb.com/2014/02/async-vs-defer-attributes.html
Comment by Paul Irish in Modernizr github repo why not to load modernizr in the head... and therefor move scripts to the end of body.
https://github.com/Modernizr/Modernizr/issues/878#issuecomment-41448059
- If you need html5shiv, split it out from modernizr and conditionally include it for IE8 (better as a conditionally included inline script)
- Determine if your use of Modernizr requires it to run in the `<head>`. If it doesn't, defer loading it till the bottom of `<body>`
- If you do need it in the head, make the build as small as possible and drop it into an inline script.
- Do not continue to use a `<script src=modernizr.js>` from within the `<head>`
### Issues
Unfortunately it still isn't just as simple as this. You still should deal with at least duplicates now, and integration with JHtml::script() (otherwise you possibly have people trying to load jQuery in both the head through the JHtml function and the body through direct including of that file and nothing using JHtml::script() can make use of this right now meaning everything included into the body has no override possibility). IMO that's why things like this keep stalling out.
### Previous Discussions
#10223 #2730 #2688 #8271
| 1.0 | place scripts in footer instead of head - This is a placeholder issue for multiple existing issues and pull reports (see below)
### Aim
To be able to load Javascript just before </body>.
### Reasons Why
The async and defer attributes for the `<script>` element have great support to pause and defer the execution of the script. But still... they are downloaded in the head.
Clear explain of async and defer can be found on: http://www.growingwiththeweb.com/2014/02/async-vs-defer-attributes.html
Comment by Paul Irish in Modernizr github repo why not to load modernizr in the head... and therefor move scripts to the end of body.
https://github.com/Modernizr/Modernizr/issues/878#issuecomment-41448059
- If you need html5shiv, split it out from modernizr and conditionally include it for IE8 (better as a conditionally included inline script)
- Determine if your use of Modernizr requires it to run in the `<head>`. If it doesn't, defer loading it till the bottom of `<body>`
- If you do need it in the head, make the build as small as possible and drop it into an inline script.
- Do not continue to use a `<script src=modernizr.js>` from within the `<head>`
### Issues
Unfortunately it still isn't just as simple as this. You still should deal with at least duplicates now, and integration with JHtml::script() (otherwise you possibly have people trying to load jQuery in both the head through the JHtml function and the body through direct including of that file and nothing using JHtml::script() can make use of this right now meaning everything included into the body has no override possibility). IMO that's why things like this keep stalling out.
### Previous Discussions
#10223 #2730 #2688 #8271
| non_priority | place scripts in footer instead of head this is a placeholder issue for multiple existing issues and pull reports see below aim to be able to load javascript just before reasons why the async and defer attributes for the element have great support to pause and defer the execution of the script but still they are downloaded in the head clear explain of async and defer can be found on comment by paul irish in modernizr github repo why not to load modernizr in the head and therefor move scripts to the end of body if you need split it out from modernizr and conditionally include it for better as a conditionally included inline script determine if your use of modernizr requires it to run in the if it doesn t defer loading it till the bottom of if you do need it in the head make the build as small as possible and drop it into an inline script do not continue to use a from within the issues unfortunately it still isn t just as simple as this you still should deal with at least duplicates now and integration with jhtml script otherwise you possibly have people trying to load jquery in both the head through the jhtml function and the body through direct including of that file and nothing using jhtml script can make use of this right now meaning everything included into the body has no override possibility imo that s why things like this keep stalling out previous discussions | 0 |
15,263 | 3,454,365,073 | IssuesEvent | 2015-12-17 15:39:19 | bitDubai/fermat | https://api.github.com/repos/bitDubai/fermat | closed | DAP - Digital Asset Transaction - Appropriation Stats - Testing - Integration Testing | DAP testing | This issue is closed when all the integration testing are done.
Parent: #2947
@acostarodrigo please assign this to me. | 1.0 | DAP - Digital Asset Transaction - Appropriation Stats - Testing - Integration Testing - This issue is closed when all the integration testing are done.
Parent: #2947
@acostarodrigo please assign this to me. | non_priority | dap digital asset transaction appropriation stats testing integration testing this issue is closed when all the integration testing are done parent acostarodrigo please assign this to me | 0 |
18,619 | 25,931,740,537 | IssuesEvent | 2022-12-16 10:35:32 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | opened | Consider making DerivedTable an AutoAlias implementation | T: Enhancement C: Functionality P: Medium T: Incompatible change E: All Editions | The various refactorings and improvements around the `WITH ORDINALITY` clause (see https://github.com/jOOQ/jOOQ/issues/5799), have produced better establishment of the internal `AutoAlias` API.
It's possible that a more thorough approach to avoiding unnecessary alias generation (see #13349) could be making the `DerivedTable` an `AutoAlias` type as well. This might then obsolete the usage of `LazyName`, which has been introduced for this purpose.
Just like the improvement where `VALUES` was made to be an `AutoAlias` (https://github.com/jOOQ/jOOQ/issues/14409), this change could be subtly backwards incompatible in terms of behaviour.
**Related**:
In principle, it's possible in some RDBMS to not alias a `DeriveTable`, e.g. Oracle, newer versions of MySQL, etc. So perhaps we could make alias generation optional in jOOQ as well, although I think it's probably not a good idea. If a user has 2 unnamed derived tables, then the current auto alias is required to disambiguate columns, so removing it would produce regressions in those cases. | True | Consider making DerivedTable an AutoAlias implementation - The various refactorings and improvements around the `WITH ORDINALITY` clause (see https://github.com/jOOQ/jOOQ/issues/5799), have produced better establishment of the internal `AutoAlias` API.
It's possible that a more thorough approach to avoiding unnecessary alias generation (see #13349) could be making the `DerivedTable` an `AutoAlias` type as well. This might then obsolete the usage of `LazyName`, which has been introduced for this purpose.
Just like the improvement where `VALUES` was made to be an `AutoAlias` (https://github.com/jOOQ/jOOQ/issues/14409), this change could be subtly backwards incompatible in terms of behaviour.
**Related**:
In principle, it's possible in some RDBMS to not alias a `DeriveTable`, e.g. Oracle, newer versions of MySQL, etc. So perhaps we could make alias generation optional in jOOQ as well, although I think it's probably not a good idea. If a user has 2 unnamed derived tables, then the current auto alias is required to disambiguate columns, so removing it would produce regressions in those cases. | non_priority | consider making derivedtable an autoalias implementation the various refactorings and improvements around the with ordinality clause see have produced better establishment of the internal autoalias api it s possible that a more thorough approach to avoiding unnecessary alias generation see could be making the derivedtable an autoalias type as well this might then obsolete the usage of lazyname which has been introduced for this purpose just like the improvement where values was made to be an autoalias this change could be subtly backwards incompatible in terms of behaviour related in principle it s possible in some rdbms to not alias a derivetable e g oracle newer versions of mysql etc so perhaps we could make alias generation optional in jooq as well although i think it s probably not a good idea if a user has unnamed derived tables then the current auto alias is required to disambiguate columns so removing it would produce regressions in those cases | 0 |
93,682 | 10,773,165,313 | IssuesEvent | 2019-11-02 18:59:52 | sinonjs/sinon | https://api.github.com/repos/sinonjs/sinon | closed | Incomplete and incorrect sandbox documentation | Difficulty: Easy Documentation Help wanted good first issue pinned | When researching sinonjs/sinon-test#57 I found that the [documentation for sandboxes](http://sinonjs.org/releases/v2.3.1/sandbox/) was incomplete and somewhat misleading.
## Issues found
### Incorrect default config
It says the sandbox is configured with the following config per default, which is incorrect:
```javascript
sinon.defaultConfig = {
// ...
injectInto: null,
properties: ["spy", "stub", "mock", "clock", "server", "requests"],
useFakeTimers: true,
useFakeServer: true
}
```
I do not think there is something called `sinon.defaultConfig` and a quick test will show that there is no server configured per default:
```javascript
var sandbox = sinonSandbox.create();
console.log(sandbox.server) // => undefined
```
### References removed fields
`sinon.defaultConfig` was removed in Sinon 2. Is still used in the docs.
### Incomplete list of properties
There is no list of properties one can expose on the sandbox, but a list is given:
```javascript
properties: ["spy", "stub", "mock", "clock", "server", "requests"]
```
One important field that is missing is `sandbox` which will expose the actual sandbox object, along with all of its methods. This is for instance useful when using `sinon-test` and you want to invoke `sandbox.reset()`.
### No example of how to use `inject()` or the config `injectInto`
The code and [set of tests](https://github.com/sinonjs/sinon/blob/c89fb21b00cd4f3d99fdeb48d2c5193f96d5e9fb/test/sandbox-test.js#L258) were pretty useful. No other examples exist in the docs. Not even mention of `inject()`
### Incomplete API description
`inject()` is missing from the docs
* Sinon version : 2.3.1 | 1.0 | Incomplete and incorrect sandbox documentation - When researching sinonjs/sinon-test#57 I found that the [documentation for sandboxes](http://sinonjs.org/releases/v2.3.1/sandbox/) was incomplete and somewhat misleading.
## Issues found
### Incorrect default config
It says the sandbox is configured with the following config per default, which is incorrect:
```javascript
sinon.defaultConfig = {
// ...
injectInto: null,
properties: ["spy", "stub", "mock", "clock", "server", "requests"],
useFakeTimers: true,
useFakeServer: true
}
```
I do not think there is something called `sinon.defaultConfig` and a quick test will show that there is no server configured per default:
```javascript
var sandbox = sinonSandbox.create();
console.log(sandbox.server) // => undefined
```
### References removed fields
`sinon.defaultConfig` was removed in Sinon 2. Is still used in the docs.
### Incomplete list of properties
There is no list of properties one can expose on the sandbox, but a list is given:
```javascript
properties: ["spy", "stub", "mock", "clock", "server", "requests"]
```
One important field that is missing is `sandbox` which will expose the actual sandbox object, along with all of its methods. This is for instance useful when using `sinon-test` and you want to invoke `sandbox.reset()`.
### No example of how to use `inject()` or the config `injectInto`
The code and [set of tests](https://github.com/sinonjs/sinon/blob/c89fb21b00cd4f3d99fdeb48d2c5193f96d5e9fb/test/sandbox-test.js#L258) were pretty useful. No other examples exist in the docs. Not even mention of `inject()`
### Incomplete API description
`inject()` is missing from the docs
* Sinon version : 2.3.1 | non_priority | incomplete and incorrect sandbox documentation when researching sinonjs sinon test i found that the was incomplete and somewhat misleading issues found incorrect default config it says the sandbox is configured with the following config per default which is incorrect javascript sinon defaultconfig injectinto null properties usefaketimers true usefakeserver true i do not think there is something called sinon defaultconfig and a quick test will show that there is no server configured per default javascript var sandbox sinonsandbox create console log sandbox server undefined references removed fields sinon defaultconfig was removed in sinon is still used in the docs incomplete list of properties there is no list of properties one can expose on the sandbox but a list is given javascript properties one important field that is missing is sandbox which will expose the actual sandbox object along with all of its methods this is for instance useful when using sinon test and you want to invoke sandbox reset no example of how to use inject or the config injectinto the code and were pretty useful no other examples exist in the docs not even mention of inject incomplete api description inject is missing from the docs sinon version | 0 |
2,112 | 7,299,243,036 | IssuesEvent | 2018-02-26 19:30:00 | openshiftio/openshift.io | https://api.github.com/repos/openshiftio/openshift.io | reopened | Drop ngx-modal dependency from project | area/architecture/build team/platform train/heather type/task | One of our dependencies, ngx-modal, has been [deprecated](https://www.npmjs.com/package/ngx-modal). It would be a good idea for us to drop the dependency from the project altogether, since it can easily be replaced with another one of our dependencies, [ngx-bootstrap/modal](https://valor-software.com/ngx-bootstrap/#/modals).
## Parent Experience
#2175 Platform architecture placeholder | 1.0 | Drop ngx-modal dependency from project - One of our dependencies, ngx-modal, has been [deprecated](https://www.npmjs.com/package/ngx-modal). It would be a good idea for us to drop the dependency from the project altogether, since it can easily be replaced with another one of our dependencies, [ngx-bootstrap/modal](https://valor-software.com/ngx-bootstrap/#/modals).
## Parent Experience
#2175 Platform architecture placeholder | non_priority | drop ngx modal dependency from project one of our dependencies ngx modal has been it would be a good idea for us to drop the dependency from the project altogether since it can easily be replaced with another one of our dependencies parent experience platform architecture placeholder | 0 |
103,527 | 16,602,909,085 | IssuesEvent | 2021-06-01 22:15:03 | gms-ws-sandbox/nibrs | https://api.github.com/repos/gms-ws-sandbox/nibrs | opened | CVE-2019-14262 (High) detected in metadata-extractor-2.10.1.jar | security vulnerability | ## CVE-2019-14262 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>metadata-extractor-2.10.1.jar</b></p></summary>
<p>Java library for extracting EXIF, IPTC, XMP, ICC and other metadata from image files.</p>
<p>Library home page: <a href="https://drewnoakes.com/code/exif/">https://drewnoakes.com/code/exif/</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-staging-data/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **metadata-extractor-2.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs/commit/9fb1c19bd26c2113d1961640de126a33eacdc946">9fb1c19bd26c2113d1961640de126a33eacdc946</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
MetadataExtractor 2.1.0 allows stack consumption.
<p>Publish Date: 2019-07-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14262>CVE-2019-14262</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/drewnoakes/metadata-extractor/pull/420,https://github.com/drewnoakes/metadata-extractor-dotnet/pull/190">https://github.com/drewnoakes/metadata-extractor/pull/420,https://github.com/drewnoakes/metadata-extractor-dotnet/pull/190</a></p>
<p>Release Date: 2020-03-20</p>
<p>Fix Resolution: com.drewnoakes:metadata-extractor:2.13.0, metadata-extractor-dotnet - 2.2.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.drewnoakes","packageName":"metadata-extractor","packageVersion":"2.10.1","packageFilePaths":["/tools/nibrs-staging-data/pom.xml","/tools/nibrs-validate-common/pom.xml","/tools/nibrs-flatfile/pom.xml","/web/nibrs-web/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-summary-report-common/pom.xml","/tools/nibrs-fbi-service/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-validation/pom.xml","/tools/nibrs-common/pom.xml","/tools/nibrs-summary-report/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.drewnoakes:metadata-extractor:2.10.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.drewnoakes:metadata-extractor:2.13.0, metadata-extractor-dotnet - 2.2.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-14262","vulnerabilityDetails":"MetadataExtractor 2.1.0 allows stack consumption.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14262","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-14262 (High) detected in metadata-extractor-2.10.1.jar - ## CVE-2019-14262 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>metadata-extractor-2.10.1.jar</b></p></summary>
<p>Java library for extracting EXIF, IPTC, XMP, ICC and other metadata from image files.</p>
<p>Library home page: <a href="https://drewnoakes.com/code/exif/">https://drewnoakes.com/code/exif/</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-staging-data/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar,/home/wss-scanner/.m2/repository/com/drewnoakes/metadata-extractor/2.10.1/metadata-extractor-2.10.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **metadata-extractor-2.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs/commit/9fb1c19bd26c2113d1961640de126a33eacdc946">9fb1c19bd26c2113d1961640de126a33eacdc946</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
MetadataExtractor 2.1.0 allows stack consumption.
<p>Publish Date: 2019-07-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14262>CVE-2019-14262</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/drewnoakes/metadata-extractor/pull/420,https://github.com/drewnoakes/metadata-extractor-dotnet/pull/190">https://github.com/drewnoakes/metadata-extractor/pull/420,https://github.com/drewnoakes/metadata-extractor-dotnet/pull/190</a></p>
<p>Release Date: 2020-03-20</p>
<p>Fix Resolution: com.drewnoakes:metadata-extractor:2.13.0, metadata-extractor-dotnet - 2.2.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.drewnoakes","packageName":"metadata-extractor","packageVersion":"2.10.1","packageFilePaths":["/tools/nibrs-staging-data/pom.xml","/tools/nibrs-validate-common/pom.xml","/tools/nibrs-flatfile/pom.xml","/web/nibrs-web/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-summary-report-common/pom.xml","/tools/nibrs-fbi-service/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-validation/pom.xml","/tools/nibrs-common/pom.xml","/tools/nibrs-summary-report/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.drewnoakes:metadata-extractor:2.10.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.drewnoakes:metadata-extractor:2.13.0, metadata-extractor-dotnet - 2.2.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-14262","vulnerabilityDetails":"MetadataExtractor 2.1.0 allows stack consumption.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14262","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in metadata extractor jar cve high severity vulnerability vulnerable library metadata extractor jar java library for extracting exif iptc xmp icc and other metadata from image files library home page a href path to dependency file nibrs tools nibrs staging data pom xml path to vulnerable library home wss scanner repository com drewnoakes metadata extractor metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar nibrs web nibrs web target nibrs web web inf lib metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar home wss scanner repository com drewnoakes metadata extractor metadata extractor jar dependency hierarchy x metadata extractor jar vulnerable library found in head commit a href found in base branch master vulnerability details metadataextractor allows stack consumption publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com drewnoakes metadata extractor metadata extractor dotnet check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree com drewnoakes metadata extractor isminimumfixversionavailable true minimumfixversion com drewnoakes metadata extractor metadata extractor dotnet basebranches vulnerabilityidentifier cve vulnerabilitydetails metadataextractor allows stack consumption vulnerabilityurl | 0 |
230,065 | 25,442,732,287 | IssuesEvent | 2022-11-24 01:06:32 | t2kx/securityjs | https://api.github.com/repos/t2kx/securityjs | reopened | CVE-2018-14404 (High) detected in juice-shopjuice-shop-8.3.0_node11_linux_x64 | security vulnerability | ## CVE-2018-14404 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>juice-shopjuice-shop-8.3.0_node11_linux_x64</b></p></summary>
<p>
<p>Probably the most modern and sophisticated insecure web application</p>
<p>Library home page: <a href=https://sourceforge.net/projects/juice-shop/>https://sourceforge.net/projects/juice-shop/</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/t2kx/securityjs/commits/2af310238f87b4cd0ebc612a29fb003fa87129c7">2af310238f87b4cd0ebc612a29fb003fa87129c7</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/node_modules/libxmljs2/vendor/libxml/xpath.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A NULL pointer dereference vulnerability exists in the xpath.c:xmlXPathCompOpEval() function of libxml2 through 2.9.8 when parsing an invalid XPath expression in the XPATH_OP_AND or XPATH_OP_OR case. Applications processing untrusted XSL format inputs with the use of the libxml2 library may be vulnerable to a denial of service attack due to a crash of the application.
<p>Publish Date: 2018-07-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14404>CVE-2018-14404</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-19</p>
<p>Fix Resolution: nokogiri- 2.9.5, libxml2 - 2.9.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-14404 (High) detected in juice-shopjuice-shop-8.3.0_node11_linux_x64 - ## CVE-2018-14404 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>juice-shopjuice-shop-8.3.0_node11_linux_x64</b></p></summary>
<p>
<p>Probably the most modern and sophisticated insecure web application</p>
<p>Library home page: <a href=https://sourceforge.net/projects/juice-shop/>https://sourceforge.net/projects/juice-shop/</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/t2kx/securityjs/commits/2af310238f87b4cd0ebc612a29fb003fa87129c7">2af310238f87b4cd0ebc612a29fb003fa87129c7</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/node_modules/libxmljs2/vendor/libxml/xpath.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A NULL pointer dereference vulnerability exists in the xpath.c:xmlXPathCompOpEval() function of libxml2 through 2.9.8 when parsing an invalid XPath expression in the XPATH_OP_AND or XPATH_OP_OR case. Applications processing untrusted XSL format inputs with the use of the libxml2 library may be vulnerable to a denial of service attack due to a crash of the application.
<p>Publish Date: 2018-07-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14404>CVE-2018-14404</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-19</p>
<p>Fix Resolution: nokogiri- 2.9.5, libxml2 - 2.9.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in juice shopjuice shop linux cve high severity vulnerability vulnerable library juice shopjuice shop linux probably the most modern and sophisticated insecure web application library home page a href found in head commit a href vulnerable source files node modules vendor libxml xpath c vulnerability details a null pointer dereference vulnerability exists in the xpath c xmlxpathcompopeval function of through when parsing an invalid xpath expression in the xpath op and or xpath op or case applications processing untrusted xsl format inputs with the use of the library may be vulnerable to a denial of service attack due to a crash of the application publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution nokogiri step up your open source security game with mend | 0 |
11,260 | 3,480,255,389 | IssuesEvent | 2015-12-29 05:21:57 | saltstack/salt | https://api.github.com/repos/saltstack/salt | closed | Get Started Documentation Syntax Error | Bug Documentation Fixed Pending Verification High Severity P2 | There are 2 instances where the quotes are omitted when referencing pillar variables:
https://docs.saltstack.com/en/getstarted/config/pillar.html
In the Pillar Top File section `{{pillar[editor]}}` should read `{{pillar['editor']}}`
https://docs.saltstack.com/en/getstarted/config/jinja.html
In the Conditionals section `{{pillar[apache]}}` should read: `{{pillar['apache']}}`
I'm not able to submit a pull request as the source for the Get Started documentation does not appear to be in this repository (or any other easily identifiable repository). | 1.0 | Get Started Documentation Syntax Error - There are 2 instances where the quotes are omitted when referencing pillar variables:
https://docs.saltstack.com/en/getstarted/config/pillar.html
In the Pillar Top File section `{{pillar[editor]}}` should read `{{pillar['editor']}}`
https://docs.saltstack.com/en/getstarted/config/jinja.html
In the Conditionals section `{{pillar[apache]}}` should read: `{{pillar['apache']}}`
I'm not able to submit a pull request as the source for the Get Started documentation does not appear to be in this repository (or any other easily identifiable repository). | non_priority | get started documentation syntax error there are instances where the quotes are omitted when referencing pillar variables in the pillar top file section pillar should read pillar in the conditionals section pillar should read pillar i m not able to submit a pull request as the source for the get started documentation does not appear to be in this repository or any other easily identifiable repository | 0 |
298,647 | 22,548,199,545 | IssuesEvent | 2022-06-27 00:23:34 | sqlfluff/sqlfluff | https://api.github.com/repos/sqlfluff/sqlfluff | opened | .sqlfluffignore improvement | documentation | ### Search before asking
- [X] I searched the [issues](https://github.com/sqlfluff/sqlfluff/issues) and found no similar issues.
### Links or command line
https://docs.sqlfluff.com/en/stable/configuration.html?highlight=ignore#id1
### Issue/Suggested Improvement
I am guessing what I want to do is possible somehow, and if so should be added into the sqlfluffignore section (or at least a link from this section).
My situation is that I am using sqlfluff-lint and sqlfluff-fix pre-commit hooks.
I have a file that is unparsable, due to #3494
So I figure for now, I will put the unparsable file into a .sqlfluffignore file.
However, my pre-commit hook can never pass as I get a warning causing the pre-commit hook to fail:
```
sqlfluff-lint................................................................Failed
- hook id: sqlfluff-lint
- files were modified by this hook
WARNING Exact file path src/..../table.sql was given but it was ignored by a .sqlfluffignore pattern in /home/..., re-run with `--disregard-sqlfluffignores` to skip .sqlfluffignore
```
I obviously don't want to run with `--disregard-sqlfluffignore` as I want the ignore to apply. But I want to be able to change that file, and still run the pre-commit hooks.
I am guessing there must be some way to do this as I can't be the first to have this issue. But it isn't obvious from the documentation how to suppress this warning so that the pre-commit hook can pass.
Or if there isn't already some way for the pre-commit hook to pass with an exact file path in the .sqlfluffignore file then I will change this to an enhancement request.
### Are you willing to work on and submit a PR to address the issue?
- [ ] Yes I am willing to submit a PR!
### Code of Conduct
- [X] I agree to follow this project's [Code of Conduct](https://github.com/sqlfluff/sqlfluff/blob/main/CODE_OF_CONDUCT.md)
| 1.0 | .sqlfluffignore improvement - ### Search before asking
- [X] I searched the [issues](https://github.com/sqlfluff/sqlfluff/issues) and found no similar issues.
### Links or command line
https://docs.sqlfluff.com/en/stable/configuration.html?highlight=ignore#id1
### Issue/Suggested Improvement
I am guessing what I want to do is possible somehow, and if so should be added into the sqlfluffignore section (or at least a link from this section).
My situation is that I am using sqlfluff-lint and sqlfluff-fix pre-commit hooks.
I have a file that is unparsable, due to #3494
So I figure for now, I will put the unparsable file into a .sqlfluffignore file.
However, my pre-commit hook can never pass as I get a warning causing the pre-commit hook to fail:
```
sqlfluff-lint................................................................Failed
- hook id: sqlfluff-lint
- files were modified by this hook
WARNING Exact file path src/..../table.sql was given but it was ignored by a .sqlfluffignore pattern in /home/..., re-run with `--disregard-sqlfluffignores` to skip .sqlfluffignore
```
I obviously don't want to run with `--disregard-sqlfluffignore` as I want the ignore to apply. But I want to be able to change that file, and still run the pre-commit hooks.
I am guessing there must be some way to do this as I can't be the first to have this issue. But it isn't obvious from the documentation how to suppress this warning so that the pre-commit hook can pass.
Or if there isn't already some way for the pre-commit hook to pass with an exact file path in the .sqlfluffignore file then I will change this to an enhancement request.
### Are you willing to work on and submit a PR to address the issue?
- [ ] Yes I am willing to submit a PR!
### Code of Conduct
- [X] I agree to follow this project's [Code of Conduct](https://github.com/sqlfluff/sqlfluff/blob/main/CODE_OF_CONDUCT.md)
| non_priority | sqlfluffignore improvement search before asking i searched the and found no similar issues links or command line issue suggested improvement i am guessing what i want to do is possible somehow and if so should be added into the sqlfluffignore section or at least a link from this section my situation is that i am using sqlfluff lint and sqlfluff fix pre commit hooks i have a file that is unparsable due to so i figure for now i will put the unparsable file into a sqlfluffignore file however my pre commit hook can never pass as i get a warning causing the pre commit hook to fail sqlfluff lint failed hook id sqlfluff lint files were modified by this hook warning exact file path src table sql was given but it was ignored by a sqlfluffignore pattern in home re run with disregard sqlfluffignores to skip sqlfluffignore i obviously don t want to run with disregard sqlfluffignore as i want the ignore to apply but i want to be able to change that file and still run the pre commit hooks i am guessing there must be some way to do this as i can t be the first to have this issue but it isn t obvious from the documentation how to suppress this warning so that the pre commit hook can pass or if there isn t already some way for the pre commit hook to pass with an exact file path in the sqlfluffignore file then i will change this to an enhancement request are you willing to work on and submit a pr to address the issue yes i am willing to submit a pr code of conduct i agree to follow this project s | 0 |
119,310 | 12,026,158,460 | IssuesEvent | 2020-04-12 12:55:04 | E-Edu/concept | https://api.github.com/repos/E-Edu/concept | opened | Def Authorization and X-ServiceToken | documentation endpoints | ## Microservice
report
## Priority
pls def Authorization and X-ServiceToken
## Issue
idk the format and the contend
| 1.0 | Def Authorization and X-ServiceToken - ## Microservice
report
## Priority
pls def Authorization and X-ServiceToken
## Issue
idk the format and the contend
| non_priority | def authorization and x servicetoken microservice report priority pls def authorization and x servicetoken issue idk the format and the contend | 0 |
56,357 | 15,034,577,527 | IssuesEvent | 2021-02-02 13:04:47 | gwaldron/osgearth | https://api.github.com/repos/gwaldron/osgearth | opened | LineDrawable and SCENE clamping don't cooperate | defect | a LineDrawable (GPU) with SCENE technique terrain clamping are not compatible. Reproduce with this earth file:
`<map>
<xi:include href="readymap_imagery.xml"/>
<xi:include href="readymap_elevation.xml"/>
<Annotations>
<feature name="Error">
<srs>wgs84</srs>
<geometry>
LINESTRING(-159.606 22.074 3000, -159.606 22.174 3000)
</geometry>
<style type="text/css">
stroke: #ff0000;
stroke-width: 30;
stroke-tessellation-size: 130m;
altitude-clamping: relative;
altitude-technique: scene;
</style>
</feature>
</Annotations>
</map>`
| 1.0 | LineDrawable and SCENE clamping don't cooperate - a LineDrawable (GPU) with SCENE technique terrain clamping are not compatible. Reproduce with this earth file:
`<map>
<xi:include href="readymap_imagery.xml"/>
<xi:include href="readymap_elevation.xml"/>
<Annotations>
<feature name="Error">
<srs>wgs84</srs>
<geometry>
LINESTRING(-159.606 22.074 3000, -159.606 22.174 3000)
</geometry>
<style type="text/css">
stroke: #ff0000;
stroke-width: 30;
stroke-tessellation-size: 130m;
altitude-clamping: relative;
altitude-technique: scene;
</style>
</feature>
</Annotations>
</map>`
| non_priority | linedrawable and scene clamping don t cooperate a linedrawable gpu with scene technique terrain clamping are not compatible reproduce with this earth file linestring stroke stroke width stroke tessellation size altitude clamping relative altitude technique scene | 0 |
366,483 | 25,587,261,231 | IssuesEvent | 2022-12-01 10:15:20 | aimclub/FEDOT | https://api.github.com/repos/aimclub/FEDOT | closed | Documentation: save/load of pipelines | documentation | This part should be actualised and make more clear for user | 1.0 | Documentation: save/load of pipelines - This part should be actualised and make more clear for user | non_priority | documentation save load of pipelines this part should be actualised and make more clear for user | 0 |
14,802 | 9,412,583,352 | IssuesEvent | 2019-04-10 04:46:28 | TEAMMATES/teammates | https://api.github.com/repos/TEAMMATES/teammates | opened | Empty csrf token does not cause request to fail | a-Security c.Bug | <!-- Issue title: [brief description of bug] -->
- **Environment**: `master` branch at commit 87a87e9e
As mentioned [here](https://github.com/TEAMMATES/teammates/pull/9648#discussion_r273585069), an empty `X-CSRF-TOKEN` for non-safe requests still passes through the checks.
**Steps to reproduce**
1. Send a HTTP request to a endpoint that uses a non-safe method (`POST`, `PUT`, `DELETE`). The request header `X-CSRF-TOKEN` should be empty.
<img width="407" alt="2019-04-10_12h45_38" src="https://user-images.githubusercontent.com/29021586/55852200-8f597900-5b8e-11e9-937d-62596e2b09b7.png">
**Expected behaviour**
The request fails and response returns a failure message like this:
```js
{
"message": "Missing CSRF token.",
"requestId": "5cad717100081e200ade7c2c"
}
```
<img width="350" alt="2019-04-10_12h42_46" src="https://user-images.githubusercontent.com/29021586/55852112-32f65980-5b8e-11e9-9bba-b647d18ae517.png">
<img width="350" alt="2019-04-10_12h43_41" src="https://user-images.githubusercontent.com/29021586/55852131-46a1c000-5b8e-11e9-9243-3a5d4daaa339.png">
**Actual behaviour**
The request with empty header value is successful.
<img src="https://user-images.githubusercontent.com/29021586/55852008-d09d5900-5b8d-11e9-94f7-422f7a2b05a0.png" width="350">
<img width="349" alt="2019-04-10_12h40_07" src="https://user-images.githubusercontent.com/29021586/55852009-d1ce8600-5b8d-11e9-9611-55316889781f.png">
| True | Empty csrf token does not cause request to fail - <!-- Issue title: [brief description of bug] -->
- **Environment**: `master` branch at commit 87a87e9e
As mentioned [here](https://github.com/TEAMMATES/teammates/pull/9648#discussion_r273585069), an empty `X-CSRF-TOKEN` for non-safe requests still passes through the checks.
**Steps to reproduce**
1. Send a HTTP request to a endpoint that uses a non-safe method (`POST`, `PUT`, `DELETE`). The request header `X-CSRF-TOKEN` should be empty.
<img width="407" alt="2019-04-10_12h45_38" src="https://user-images.githubusercontent.com/29021586/55852200-8f597900-5b8e-11e9-937d-62596e2b09b7.png">
**Expected behaviour**
The request fails and response returns a failure message like this:
```js
{
"message": "Missing CSRF token.",
"requestId": "5cad717100081e200ade7c2c"
}
```
<img width="350" alt="2019-04-10_12h42_46" src="https://user-images.githubusercontent.com/29021586/55852112-32f65980-5b8e-11e9-9bba-b647d18ae517.png">
<img width="350" alt="2019-04-10_12h43_41" src="https://user-images.githubusercontent.com/29021586/55852131-46a1c000-5b8e-11e9-9243-3a5d4daaa339.png">
**Actual behaviour**
The request with empty header value is successful.
<img src="https://user-images.githubusercontent.com/29021586/55852008-d09d5900-5b8d-11e9-94f7-422f7a2b05a0.png" width="350">
<img width="349" alt="2019-04-10_12h40_07" src="https://user-images.githubusercontent.com/29021586/55852009-d1ce8600-5b8d-11e9-9611-55316889781f.png">
| non_priority | empty csrf token does not cause request to fail environment master branch at commit as mentioned an empty x csrf token for non safe requests still passes through the checks steps to reproduce send a http request to a endpoint that uses a non safe method post put delete the request header x csrf token should be empty img width alt src expected behaviour the request fails and response returns a failure message like this js message missing csrf token requestid img width alt src img width alt src actual behaviour the request with empty header value is successful img width alt src | 0 |
72,368 | 9,576,121,731 | IssuesEvent | 2019-05-07 08:20:55 | fluencelabs/fluence | https://api.github.com/repos/fluencelabs/fluence | closed | Documentation for debugging backends with 'runner' | documentation | Successor of #620
Current [README](https://github.com/fluencelabs/fluence/blob/master/vm/flrun/README.md) lacks details, and doesn't describe workflow in full.
As it is an important part of developer's flow, it should be described in docs.
| 1.0 | Documentation for debugging backends with 'runner' - Successor of #620
Current [README](https://github.com/fluencelabs/fluence/blob/master/vm/flrun/README.md) lacks details, and doesn't describe workflow in full.
As it is an important part of developer's flow, it should be described in docs.
| non_priority | documentation for debugging backends with runner successor of current lacks details and doesn t describe workflow in full as it is an important part of developer s flow it should be described in docs | 0 |
226,791 | 17,362,046,515 | IssuesEvent | 2021-07-29 22:22:16 | firebase/firebase-js-sdk | https://api.github.com/repos/firebase/firebase-js-sdk | closed | Update links in comments to @link format in Analytics | api: analytics type: documentation v9 | Update links (e.g. https://github.com/firebase/firebase-js-sdk/blob/master/packages-exp/analytics-exp/src/public-types.ts#L30) in Analytics to `@link` format.
`@link` example: https://github.com/firebase/firebase-js-sdk/blob/master/packages-exp/app-exp/src/api.ts#L54 | 1.0 | Update links in comments to @link format in Analytics - Update links (e.g. https://github.com/firebase/firebase-js-sdk/blob/master/packages-exp/analytics-exp/src/public-types.ts#L30) in Analytics to `@link` format.
`@link` example: https://github.com/firebase/firebase-js-sdk/blob/master/packages-exp/app-exp/src/api.ts#L54 | non_priority | update links in comments to link format in analytics update links e g in analytics to link format link example | 0 |
173,472 | 13,423,970,856 | IssuesEvent | 2020-09-06 02:05:52 | snext1220/stext | https://api.github.com/repos/snext1220/stext | closed | 【PgFlow】シーン冒頭の空白が削除される | Testing bug | https://github.com/snext1220/snext-management/issues/18#issuecomment-667667558 由来のIssueです。
> ・各シーンの最初の空白(段落下げ)が反映されない?データをリロードするたびに段落下げがなくなっている。
.xmlファイルをPgFlow形式(.json)に変換する際に前後の空白を除去していたことが原因でした。末尾の空白だけを除去するように改めました。GitHubのみ反映しております。 | 1.0 | 【PgFlow】シーン冒頭の空白が削除される - https://github.com/snext1220/snext-management/issues/18#issuecomment-667667558 由来のIssueです。
> ・各シーンの最初の空白(段落下げ)が反映されない?データをリロードするたびに段落下げがなくなっている。
.xmlファイルをPgFlow形式(.json)に変換する際に前後の空白を除去していたことが原因でした。末尾の空白だけを除去するように改めました。GitHubのみ反映しております。 | non_priority | 【pgflow】シーン冒頭の空白が削除される 由来のissueです。 ・各シーンの最初の空白(段落下げ)が反映されない?データをリロードするたびに段落下げがなくなっている。 xmlファイルをpgflow形式( json)に変換する際に前後の空白を除去していたことが原因でした。末尾の空白だけを除去するように改めました。githubのみ反映しております。 | 0 |
114,471 | 9,739,124,533 | IssuesEvent | 2019-06-01 08:22:03 | MultiPoolMiner/MultiPoolMiner | https://api.github.com/repos/MultiPoolMiner/MultiPoolMiner | closed | Version 3.3.0 Beta 23 is ready | available for testing enhancement fixed | ERROR: type should be string, got "https://github.com/MultiPoolMiner/MultiPoolMiner/releases/tag/Beta3.3\r\n\r\nPlease also report if all is working fine - only so I can know that we get rid of all the bugs:\r\n\r\n## Changelog Version 3.3.0 Beta 23\r\n\r\n#### Core changes\r\n- Added parameter '-Dashboard'\r\n- Added parameter '-NoDevFeeMiners'\r\n- API: updated to version 0.92; added '/currentprofit'\r\n- Changed start files to use 'MININGRIG' variable\r\n- Fixed Algorithms.txt & CoinNames.txt\r\n- Fixed restarting mining when profitablility threshold is met (https://github.com/MultiPoolMiner/MultiPoolMiner/issues/2337#issuecomment-493748509)\r\n- Optimized miner API code\r\n\r\n#### Miner Changes\r\n- Removed NVIDIA-CcminerXevan_v78 (moved to 'Deprecated' folder); replaced by NVIDIA-CcminerAlexis_v1.5\r\n- Removed NVIDIA-CcminerXevan_cuda9 (moved to 'Deprecated' folder); replaced by NVIDIA-CcminerAlexis_v1.5\r\n- Updated AMD_NVIDIA-ClaymoreEthash_v14.5beta\r\n- Updated AMD_NVIDIA-GminerEquihash_v1.44; support for Vds (V-Dimension)\r\n- Updated AMD_NVIDIA-NanoMiner_v1.3.2\r\n- Updated AMD-SRBMinerCryptonight_v1.8.9\r\n- Updated AMD-WildRig_v0.17.0; support for Xevan, WildKeccak & X25x\r\n- Updated NVIDIA-CcminerTrex_v0.11.0; support for MTP & X25x\r\n- Updated NVIDIA-CryptoDredge_v0.19.1; support for Argon2CRDS & Argon2UIS\r\n- Updated NVIDIA-TTMiner_v2.2.3; support for ProgPoWZ & ProgPoW092\r\n- Updated NVIDIA-NBMiner_v23.2hotfix; disabled ethash, ClaymoreDual & Phoenix are approx 10% faster\r\n- Updated NVIDIA-CcminerZenemy_v2.00 (previously NVIDIA-CcminerZealot)" | 1.0 | Version 3.3.0 Beta 23 is ready - https://github.com/MultiPoolMiner/MultiPoolMiner/releases/tag/Beta3.3
Please also report if all is working fine - only so I can know that we get rid of all the bugs:
## Changelog Version 3.3.0 Beta 23
#### Core changes
- Added parameter '-Dashboard'
- Added parameter '-NoDevFeeMiners'
- API: updated to version 0.92; added '/currentprofit'
- Changed start files to use 'MININGRIG' variable
- Fixed Algorithms.txt & CoinNames.txt
- Fixed restarting mining when profitablility threshold is met (https://github.com/MultiPoolMiner/MultiPoolMiner/issues/2337#issuecomment-493748509)
- Optimized miner API code
#### Miner Changes
- Removed NVIDIA-CcminerXevan_v78 (moved to 'Deprecated' folder); replaced by NVIDIA-CcminerAlexis_v1.5
- Removed NVIDIA-CcminerXevan_cuda9 (moved to 'Deprecated' folder); replaced by NVIDIA-CcminerAlexis_v1.5
- Updated AMD_NVIDIA-ClaymoreEthash_v14.5beta
- Updated AMD_NVIDIA-GminerEquihash_v1.44; support for Vds (V-Dimension)
- Updated AMD_NVIDIA-NanoMiner_v1.3.2
- Updated AMD-SRBMinerCryptonight_v1.8.9
- Updated AMD-WildRig_v0.17.0; support for Xevan, WildKeccak & X25x
- Updated NVIDIA-CcminerTrex_v0.11.0; support for MTP & X25x
- Updated NVIDIA-CryptoDredge_v0.19.1; support for Argon2CRDS & Argon2UIS
- Updated NVIDIA-TTMiner_v2.2.3; support for ProgPoWZ & ProgPoW092
- Updated NVIDIA-NBMiner_v23.2hotfix; disabled ethash, ClaymoreDual & Phoenix are approx 10% faster
- Updated NVIDIA-CcminerZenemy_v2.00 (previously NVIDIA-CcminerZealot) | non_priority | version beta is ready please also report if all is working fine only so i can know that we get rid of all the bugs changelog version beta core changes added parameter dashboard added parameter nodevfeeminers api updated to version added currentprofit changed start files to use miningrig variable fixed algorithms txt coinnames txt fixed restarting mining when profitablility threshold is met optimized miner api code miner changes removed nvidia ccminerxevan moved to deprecated folder replaced by nvidia ccmineralexis removed nvidia ccminerxevan moved to deprecated folder replaced by nvidia ccmineralexis updated amd nvidia claymoreethash updated amd nvidia gminerequihash support for vds v dimension updated amd nvidia nanominer updated amd srbminercryptonight updated amd wildrig support for xevan wildkeccak updated nvidia ccminertrex support for mtp updated nvidia cryptodredge support for updated nvidia ttminer support for progpowz updated nvidia nbminer disabled ethash claymoredual phoenix are approx faster updated nvidia ccminerzenemy previously nvidia ccminerzealot | 0 |
99,627 | 21,000,037,183 | IssuesEvent | 2022-03-29 16:32:54 | osmosis-labs/osmosis | https://api.github.com/repos/osmosis-labs/osmosis | closed | GAMM genesis import/export testing | T:code-hygiene C:x/gamm T:task ⚙️ | We have a couple TODO's left, tracking them in an issue
- [ ] Copy these test lines from v1.0.4 branch: https://github.com/osmosis-labs/osmosis/pull/371/files#diff-69233d1494cd7498c48bbc7656088ab233f987dd6455585d4f4657470894f231R130-R134
- [ ] Add more tests to ensure that the imported pools were the same as the originally created pools.
- [ ] Remove codectypes.AnyUnpacker argument from InitGenesis (https://github.com/osmosis-labs/osmosis/blob/main/x/gamm/genesis.go#L14). We should use how https://github.com/cosmos/cosmos-sdk/blob/master/x/auth/genesis.go#L16 for inspiration in this regard. | 1.0 | GAMM genesis import/export testing - We have a couple TODO's left, tracking them in an issue
- [ ] Copy these test lines from v1.0.4 branch: https://github.com/osmosis-labs/osmosis/pull/371/files#diff-69233d1494cd7498c48bbc7656088ab233f987dd6455585d4f4657470894f231R130-R134
- [ ] Add more tests to ensure that the imported pools were the same as the originally created pools.
- [ ] Remove codectypes.AnyUnpacker argument from InitGenesis (https://github.com/osmosis-labs/osmosis/blob/main/x/gamm/genesis.go#L14). We should use how https://github.com/cosmos/cosmos-sdk/blob/master/x/auth/genesis.go#L16 for inspiration in this regard. | non_priority | gamm genesis import export testing we have a couple todo s left tracking them in an issue copy these test lines from branch add more tests to ensure that the imported pools were the same as the originally created pools remove codectypes anyunpacker argument from initgenesis we should use how for inspiration in this regard | 0 |
235,678 | 25,958,801,602 | IssuesEvent | 2022-12-18 15:57:00 | Atches/KPI-GHC-TEST-DEV | https://api.github.com/repos/Atches/KPI-GHC-TEST-DEV | closed | jose-3.8.0.tgz: 1 vulnerabilities (highest severity is: 5.9) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jose-3.8.0.tgz</b></p></summary>
<p>Universal 'JSON Web Almost Everything' - JWA, JWS, JWE, JWT, JWK with no dependencies</p>
<p>Library home page: <a href="https://registry.npmjs.org/jose/-/jose-3.8.0.tgz">https://registry.npmjs.org/jose/-/jose-3.8.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jose/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Atches/KPI-GHC-TEST-DEV/commit/1cef5821e31e6a8b75d986b9e95199e3c53b5a72">1cef5821e31e6a8b75d986b9e95199e3c53b5a72</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jose version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-29443](https://www.mend.io/vulnerability-database/CVE-2021-29443) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | jose-3.8.0.tgz | Direct | 3.11.4 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-29443</summary>
### Vulnerable Library - <b>jose-3.8.0.tgz</b></p>
<p>Universal 'JSON Web Almost Everything' - JWA, JWS, JWE, JWT, JWK with no dependencies</p>
<p>Library home page: <a href="https://registry.npmjs.org/jose/-/jose-3.8.0.tgz">https://registry.npmjs.org/jose/-/jose-3.8.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jose/package.json</p>
<p>
Dependency Hierarchy:
- :x: **jose-3.8.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Atches/KPI-GHC-TEST-DEV/commit/1cef5821e31e6a8b75d986b9e95199e3c53b5a72">1cef5821e31e6a8b75d986b9e95199e3c53b5a72</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jose is an npm library providing a number of cryptographic operations. In vulnerable versions AES_CBC_HMAC_SHA2 Algorithm (A128CBC-HS256, A192CBC-HS384, A256CBC-HS512) decryption would always execute both HMAC tag verification and CBC decryption, if either failed `JWEDecryptionFailed` would be thrown. A possibly observable difference in timing when padding error would occur while decrypting the ciphertext makes a padding oracle and an adversary might be able to make use of that oracle to decrypt data without knowing the decryption key by issuing on average 128*b calls to the padding oracle (where b is the number of bytes in the ciphertext block). All major release versions have had a patch released which ensures the HMAC tag is verified before performing CBC decryption. The fixed versions are `^1.28.1 || ^2.0.5 || >=3.11.4`. Users should upgrade their v1.x dependency to ^1.28.1, their v2.x dependency to ^2.0.5, and their v3.x dependency to ^3.11.4. Thanks to Jason from Microsoft Vulnerability Research (MSVR) for bringing this up and Eva Sarafianou (@esarafianou) for helping to score this advisory.
<p>Publish Date: 2021-04-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-29443>CVE-2021-29443</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/panva/jose/security/advisories/GHSA-58f5-hfqc-jgch">https://github.com/panva/jose/security/advisories/GHSA-58f5-hfqc-jgch</a></p>
<p>Release Date: 2021-04-16</p>
<p>Fix Resolution: 3.11.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | jose-3.8.0.tgz: 1 vulnerabilities (highest severity is: 5.9) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jose-3.8.0.tgz</b></p></summary>
<p>Universal 'JSON Web Almost Everything' - JWA, JWS, JWE, JWT, JWK with no dependencies</p>
<p>Library home page: <a href="https://registry.npmjs.org/jose/-/jose-3.8.0.tgz">https://registry.npmjs.org/jose/-/jose-3.8.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jose/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Atches/KPI-GHC-TEST-DEV/commit/1cef5821e31e6a8b75d986b9e95199e3c53b5a72">1cef5821e31e6a8b75d986b9e95199e3c53b5a72</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jose version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-29443](https://www.mend.io/vulnerability-database/CVE-2021-29443) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | jose-3.8.0.tgz | Direct | 3.11.4 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-29443</summary>
### Vulnerable Library - <b>jose-3.8.0.tgz</b></p>
<p>Universal 'JSON Web Almost Everything' - JWA, JWS, JWE, JWT, JWK with no dependencies</p>
<p>Library home page: <a href="https://registry.npmjs.org/jose/-/jose-3.8.0.tgz">https://registry.npmjs.org/jose/-/jose-3.8.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jose/package.json</p>
<p>
Dependency Hierarchy:
- :x: **jose-3.8.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Atches/KPI-GHC-TEST-DEV/commit/1cef5821e31e6a8b75d986b9e95199e3c53b5a72">1cef5821e31e6a8b75d986b9e95199e3c53b5a72</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jose is an npm library providing a number of cryptographic operations. In vulnerable versions AES_CBC_HMAC_SHA2 Algorithm (A128CBC-HS256, A192CBC-HS384, A256CBC-HS512) decryption would always execute both HMAC tag verification and CBC decryption, if either failed `JWEDecryptionFailed` would be thrown. A possibly observable difference in timing when padding error would occur while decrypting the ciphertext makes a padding oracle and an adversary might be able to make use of that oracle to decrypt data without knowing the decryption key by issuing on average 128*b calls to the padding oracle (where b is the number of bytes in the ciphertext block). All major release versions have had a patch released which ensures the HMAC tag is verified before performing CBC decryption. The fixed versions are `^1.28.1 || ^2.0.5 || >=3.11.4`. Users should upgrade their v1.x dependency to ^1.28.1, their v2.x dependency to ^2.0.5, and their v3.x dependency to ^3.11.4. Thanks to Jason from Microsoft Vulnerability Research (MSVR) for bringing this up and Eva Sarafianou (@esarafianou) for helping to score this advisory.
<p>Publish Date: 2021-04-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-29443>CVE-2021-29443</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/panva/jose/security/advisories/GHSA-58f5-hfqc-jgch">https://github.com/panva/jose/security/advisories/GHSA-58f5-hfqc-jgch</a></p>
<p>Release Date: 2021-04-16</p>
<p>Fix Resolution: 3.11.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | jose tgz vulnerabilities highest severity is autoclosed vulnerable library jose tgz universal json web almost everything jwa jws jwe jwt jwk with no dependencies library home page a href path to dependency file package json path to vulnerable library node modules jose package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in jose version remediation available medium jose tgz direct details cve vulnerable library jose tgz universal json web almost everything jwa jws jwe jwt jwk with no dependencies library home page a href path to dependency file package json path to vulnerable library node modules jose package json dependency hierarchy x jose tgz vulnerable library found in head commit a href found in base branch main vulnerability details jose is an npm library providing a number of cryptographic operations in vulnerable versions aes cbc hmac algorithm decryption would always execute both hmac tag verification and cbc decryption if either failed jwedecryptionfailed would be thrown a possibly observable difference in timing when padding error would occur while decrypting the ciphertext makes a padding oracle and an adversary might be able to make use of that oracle to decrypt data without knowing the decryption key by issuing on average b calls to the padding oracle where b is the number of bytes in the ciphertext block all major release versions have had a patch released which ensures the hmac tag is verified before performing cbc decryption the fixed versions are users should upgrade their x dependency to their x dependency to and their x dependency to thanks to jason from microsoft vulnerability research msvr for bringing this up and eva sarafianou esarafianou for helping to score this advisory publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
1,283 | 3,120,977,062 | IssuesEvent | 2015-09-05 06:38:53 | AnSq/IRCR_Info_Bot | https://api.github.com/repos/AnSq/IRCR_Info_Bot | closed | update praw | infrastructure | `Version 2.1.19 of praw is outdated. Version 2.1.21 was released Thursday March 26, 2015.` | 1.0 | update praw - `Version 2.1.19 of praw is outdated. Version 2.1.21 was released Thursday March 26, 2015.` | non_priority | update praw version of praw is outdated version was released thursday march | 0 |
688 | 2,852,226,997 | IssuesEvent | 2015-06-01 12:28:48 | Starcounter/Starcounter | https://api.github.com/repos/Starcounter/Starcounter | opened | Compiling non-C files in VS | enhancement Infrastructure question | An example of non-C, which is part of Level0 branch `next`, is `gram.y`. As I understood the only way to build it, i.e., to generate c and h files, is to build entire project. Is it possible that CMake generates VS project file that allows to build just this file, i.e., using Ctrl-F7, like it was in branch `develop`. | 1.0 | Compiling non-C files in VS - An example of non-C, which is part of Level0 branch `next`, is `gram.y`. As I understood the only way to build it, i.e., to generate c and h files, is to build entire project. Is it possible that CMake generates VS project file that allows to build just this file, i.e., using Ctrl-F7, like it was in branch `develop`. | non_priority | compiling non c files in vs an example of non c which is part of branch next is gram y as i understood the only way to build it i e to generate c and h files is to build entire project is it possible that cmake generates vs project file that allows to build just this file i e using ctrl like it was in branch develop | 0 |
57,826 | 14,228,108,832 | IssuesEvent | 2020-11-18 02:57:14 | firebase/firebase-ios-sdk | https://api.github.com/repos/firebase/firebase-ios-sdk | closed | Nightly Testing Report11/16/2020 10:25 AM | octokit-test zip-builder | # Nightly testing report.
Failures are detected in workflow(s)
This issue is generated at 11/16/2020 10:25 AM
| Workflow |11/15|
| -------- | -------- |
[zip](https://github.com/firebase/firebase-ios-sdk/blob/master/.github/workflows/zip.yml)|[failure](https://github.com/firebase/firebase-ios-sdk/actions/runs/365576620)|
[performance](https://github.com/firebase/firebase-ios-sdk/blob/master/.github/workflows/performance.yml)|[skipped](https://github.com/firebase/firebase-ios-sdk/actions/runs/365505241)|
[performance-integration-tests](https://github.com/firebase/firebase-ios-sdk/blob/master/.github/workflows/performance-integration-tests.yml)|[skipped](https://github.com/firebase/firebase-ios-sdk/actions/runs/366387022)|
| 1.0 | Nightly Testing Report11/16/2020 10:25 AM - # Nightly testing report.
Failures are detected in workflow(s)
This issue is generated at 11/16/2020 10:25 AM
| Workflow |11/15|
| -------- | -------- |
[zip](https://github.com/firebase/firebase-ios-sdk/blob/master/.github/workflows/zip.yml)|[failure](https://github.com/firebase/firebase-ios-sdk/actions/runs/365576620)|
[performance](https://github.com/firebase/firebase-ios-sdk/blob/master/.github/workflows/performance.yml)|[skipped](https://github.com/firebase/firebase-ios-sdk/actions/runs/365505241)|
[performance-integration-tests](https://github.com/firebase/firebase-ios-sdk/blob/master/.github/workflows/performance-integration-tests.yml)|[skipped](https://github.com/firebase/firebase-ios-sdk/actions/runs/366387022)|
| non_priority | nightly testing am nightly testing report failures are detected in workflow s this issue is generated at am workflow | 0 |
3,498 | 2,770,274,516 | IssuesEvent | 2015-05-01 13:12:19 | deconst/deconst-docs | https://api.github.com/repos/deconst/deconst-docs | opened | Include pure-native and Docker-based testing instructions in READMEs | dev mode documentation | In each repository's README, include comprehensive instructions for doing local development both:
* In pure-native mode, meaning using a host install of Python or Node.js or whatever; and
* In Docker mode with docker-compose, for integration testing.
- [ ] presenter
- [ ] mapping-service
- [ ] content-service
- [ ] layout-service
- [ ] preparer-asset
- [ ] preparer-jekyll
- [ ] preparer-sphinx
- [ ] common-python | 1.0 | Include pure-native and Docker-based testing instructions in READMEs - In each repository's README, include comprehensive instructions for doing local development both:
* In pure-native mode, meaning using a host install of Python or Node.js or whatever; and
* In Docker mode with docker-compose, for integration testing.
- [ ] presenter
- [ ] mapping-service
- [ ] content-service
- [ ] layout-service
- [ ] preparer-asset
- [ ] preparer-jekyll
- [ ] preparer-sphinx
- [ ] common-python | non_priority | include pure native and docker based testing instructions in readmes in each repository s readme include comprehensive instructions for doing local development both in pure native mode meaning using a host install of python or node js or whatever and in docker mode with docker compose for integration testing presenter mapping service content service layout service preparer asset preparer jekyll preparer sphinx common python | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.