Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
170,268 | 14,247,082,476 | IssuesEvent | 2020-11-19 10:56:47 | postmanlabs/postman-app-support | https://api.github.com/repos/postmanlabs/postman-app-support | closed | Access to Read for non Team members | feature product/collaboration product/documentation | Hello,
It would be interesting if external users, who did not necessarily need to have Postman accounts, could access the documentation in a restricted way (such as a login screen with email and password or some token) | 1.0 | Access to Read for non Team members - Hello,
It would be interesting if external users, who did not necessarily need to have Postman accounts, could access the documentation in a restricted way (such as a login screen with email and password or some token) | non_priority | access to read for non team members hello it would be interesting if external users who did not necessarily need to have postman accounts could access the documentation in a restricted way such as a login screen with email and password or some token | 0 |
17,169 | 6,377,236,438 | IssuesEvent | 2017-08-02 09:32:48 | moby/moby | https://api.github.com/repos/moby/moby | closed | Occasional ccache build issue | area/builder version/1.12 |
**Description**
We (my team) want to run builds in Docker. Our environment is as follows:
- We have multiple Docker containers running in parallel, each running a build. Every build can have ~32 compile processes running
- We mount a top-level directory '/repo' in every Docker container, the builds happen in subdirectories of this top-level directory.
- We use 'ccache', with the ccache directory being located in '/repo/ccache'. This is the same for all builds.
- We are using CentOS 7, so Docker 1.12. We also have overlayfs enabled.
Sometimes, we get errors running ccache (this only pops up sporadically):
ccache: error: ^ Failed to create temporary file for /repo/builder/repo/../ccache-buildroot/d/c/8d6dc6e553d093eb5ebf5be2fd71b5-111232.o.tmp.stderr: Input/output error
The failures never appear to be on the same file.
Unfortunately, I don't really have a way to reliably reproduce this. I checked the ccache-code, and the error occurs in an 'mkstemp' call.
We've never seen the issue before in our non-Docker builds, which is why I'm filing the issue here and not with the ccache project.
**Output of `docker version`:**
```
docker version
Client:
Version: 1.12.6
API version: 1.24
Package version: docker-1.12.6-28.git1398f24.el7.centos.x86_64
Go version: go1.7.4
Git commit: 1398f24/1.12.6
Built: Fri May 26 17:28:18 2017
OS/Arch: linux/amd64
Server:
Version: 1.12.6
API version: 1.24
Package version: docker-1.12.6-28.git1398f24.el7.centos.x86_64
Go version: go1.7.4
Git commit: 1398f24/1.12.6
Built: Fri May 26 17:28:18 2017
OS/Arch: linux/amd64
```
**Output of `docker info`:**
```
docker info
Containers: 5
Running: 2
Paused: 0
Stopped: 3
Images: 2
Server Version: 1.12.6
Storage Driver: overlay
Backing Filesystem: extfs
Logging Driver: journald
Cgroup Driver: systemd
Plugins:
Volume: local
Network: null host bridge overlay
Swarm: inactive
Runtimes: docker-runc runc
Default Runtime: docker-runc
Security Options: seccomp
Kernel Version: 3.10.0-514.6.2.el7.x86_64
Operating System: CentOS Linux 7 (Core)
OSType: linux
Architecture: x86_64
Number of Docker Hooks: 2
CPUs: 32
Total Memory: 125.6 GiB
Name: devws006
ID: JKFO:YGOX:R3K4:CWZ4:U3TP:HNGG:MO6O:PLZQ:6PMU:3NLY:MYWJ:ILP7
Docker Root Dir: /var/lib/docker
Debug Mode (client): false
Debug Mode (server): false
Http Proxy: <snipped>
Https Proxy: <snipped>
No Proxy: <snipped>
Registry: https://index.docker.io/v1/
Insecure Registries:
127.0.0.0/8
Registries: docker.io (secure)
``` | 1.0 | Occasional ccache build issue -
**Description**
We (my team) want to run builds in Docker. Our environment is as follows:
- We have multiple Docker containers running in parallel, each running a build. Every build can have ~32 compile processes running
- We mount a top-level directory '/repo' in every Docker container, the builds happen in subdirectories of this top-level directory.
- We use 'ccache', with the ccache directory being located in '/repo/ccache'. This is the same for all builds.
- We are using CentOS 7, so Docker 1.12. We also have overlayfs enabled.
Sometimes, we get errors running ccache (this only pops up sporadically):
ccache: error: ^ Failed to create temporary file for /repo/builder/repo/../ccache-buildroot/d/c/8d6dc6e553d093eb5ebf5be2fd71b5-111232.o.tmp.stderr: Input/output error
The failures never appear to be on the same file.
Unfortunately, I don't really have a way to reliably reproduce this. I checked the ccache-code, and the error occurs in an 'mkstemp' call.
We've never seen the issue before in our non-Docker builds, which is why I'm filing the issue here and not with the ccache project.
**Output of `docker version`:**
```
docker version
Client:
Version: 1.12.6
API version: 1.24
Package version: docker-1.12.6-28.git1398f24.el7.centos.x86_64
Go version: go1.7.4
Git commit: 1398f24/1.12.6
Built: Fri May 26 17:28:18 2017
OS/Arch: linux/amd64
Server:
Version: 1.12.6
API version: 1.24
Package version: docker-1.12.6-28.git1398f24.el7.centos.x86_64
Go version: go1.7.4
Git commit: 1398f24/1.12.6
Built: Fri May 26 17:28:18 2017
OS/Arch: linux/amd64
```
**Output of `docker info`:**
```
docker info
Containers: 5
Running: 2
Paused: 0
Stopped: 3
Images: 2
Server Version: 1.12.6
Storage Driver: overlay
Backing Filesystem: extfs
Logging Driver: journald
Cgroup Driver: systemd
Plugins:
Volume: local
Network: null host bridge overlay
Swarm: inactive
Runtimes: docker-runc runc
Default Runtime: docker-runc
Security Options: seccomp
Kernel Version: 3.10.0-514.6.2.el7.x86_64
Operating System: CentOS Linux 7 (Core)
OSType: linux
Architecture: x86_64
Number of Docker Hooks: 2
CPUs: 32
Total Memory: 125.6 GiB
Name: devws006
ID: JKFO:YGOX:R3K4:CWZ4:U3TP:HNGG:MO6O:PLZQ:6PMU:3NLY:MYWJ:ILP7
Docker Root Dir: /var/lib/docker
Debug Mode (client): false
Debug Mode (server): false
Http Proxy: <snipped>
Https Proxy: <snipped>
No Proxy: <snipped>
Registry: https://index.docker.io/v1/
Insecure Registries:
127.0.0.0/8
Registries: docker.io (secure)
``` | non_priority | occasional ccache build issue description we my team want to run builds in docker our environment is as follows we have multiple docker containers running in parallel each running a build every build can have compile processes running we mount a top level directory repo in every docker container the builds happen in subdirectories of this top level directory we use ccache with the ccache directory being located in repo ccache this is the same for all builds we are using centos so docker we also have overlayfs enabled sometimes we get errors running ccache this only pops up sporadically ccache error failed to create temporary file for repo builder repo ccache buildroot d c o tmp stderr input output error the failures never appear to be on the same file unfortunately i don t really have a way to reliably reproduce this i checked the ccache code and the error occurs in an mkstemp call we ve never seen the issue before in our non docker builds which is why i m filing the issue here and not with the ccache project output of docker version docker version client version api version package version docker centos go version git commit built fri may os arch linux server version api version package version docker centos go version git commit built fri may os arch linux output of docker info docker info containers running paused stopped images server version storage driver overlay backing filesystem extfs logging driver journald cgroup driver systemd plugins volume local network null host bridge overlay swarm inactive runtimes docker runc runc default runtime docker runc security options seccomp kernel version operating system centos linux core ostype linux architecture number of docker hooks cpus total memory gib name id jkfo ygox hngg plzq mywj docker root dir var lib docker debug mode client false debug mode server false http proxy https proxy no proxy registry insecure registries registries docker io secure | 0 |
11,430 | 9,195,470,612 | IssuesEvent | 2019-03-07 02:33:28 | HumanCellAtlas/secondary-analysis | https://api.github.com/repos/HumanCellAtlas/secondary-analysis | closed | Change the location of the integration tests to run in a separate directory from the code | Q1-2019 devops infrastructure | Currently the integration tests are run inside the same directory that contains the code, which means that a lot of kruft is created, especially when the test is run locally. The test should be run so that artifacts created by the test do not reside in the same directory as the code. | 1.0 | Change the location of the integration tests to run in a separate directory from the code - Currently the integration tests are run inside the same directory that contains the code, which means that a lot of kruft is created, especially when the test is run locally. The test should be run so that artifacts created by the test do not reside in the same directory as the code. | non_priority | change the location of the integration tests to run in a separate directory from the code currently the integration tests are run inside the same directory that contains the code which means that a lot of kruft is created especially when the test is run locally the test should be run so that artifacts created by the test do not reside in the same directory as the code | 0 |
116,270 | 11,906,173,740 | IssuesEvent | 2020-03-30 19:53:28 | ASU-CodeDevils/flameboi-slack-api | https://api.github.com/repos/ASU-CodeDevils/flameboi-slack-api | opened | Software Requirements Documentation | documentation | Create a Software Requirements Doc to dictate scope of bot functionality and define a set of quantifiable, testable requirements we want the bot to meet! | 1.0 | Software Requirements Documentation - Create a Software Requirements Doc to dictate scope of bot functionality and define a set of quantifiable, testable requirements we want the bot to meet! | non_priority | software requirements documentation create a software requirements doc to dictate scope of bot functionality and define a set of quantifiable testable requirements we want the bot to meet | 0 |
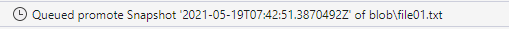
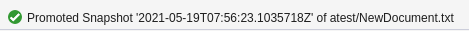
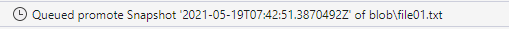
212,095 | 16,417,271,184 | IssuesEvent | 2021-05-19 08:20:46 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | opened | A queued activity log always displays for the action 'Promote Snapshot' | :beetle: regression :gear: blobs 🧪 testing | **Storage Explorer Version**: 1.20.0-dev
**Build Number**: 20210518.9
**Branch**: main
**Platform/OS**: Windows 10/ Linux Ubuntu 18.04/ MacOS Big Sur 11.3
**Architecture**: ia32/x64
**How Found**: From running test cases
**Regression From**: Previous build (20210518.7)
## Steps to Reproduce ##
1. Expand one storage account -> Blob Containers.
2. Create one blob container -> Upload one blob.
3. Create a snapshot for the blob.
4. Right click the blob -> Click 'Manage History -> Manage Snapshots'.
5. Select the snapshot -> Click 'Promote Snapshot'.
6. Check whether succeed to promote the snapshot.
## Expected Experience ##
Succeed to promote the snapshot.
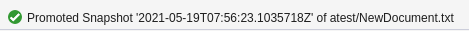
## Actual Experience ##
Always display a queued activity log.
 | 1.0 | A queued activity log always displays for the action 'Promote Snapshot' - **Storage Explorer Version**: 1.20.0-dev
**Build Number**: 20210518.9
**Branch**: main
**Platform/OS**: Windows 10/ Linux Ubuntu 18.04/ MacOS Big Sur 11.3
**Architecture**: ia32/x64
**How Found**: From running test cases
**Regression From**: Previous build (20210518.7)
## Steps to Reproduce ##
1. Expand one storage account -> Blob Containers.
2. Create one blob container -> Upload one blob.
3. Create a snapshot for the blob.
4. Right click the blob -> Click 'Manage History -> Manage Snapshots'.
5. Select the snapshot -> Click 'Promote Snapshot'.
6. Check whether succeed to promote the snapshot.
## Expected Experience ##
Succeed to promote the snapshot.
## Actual Experience ##
Always display a queued activity log.
 | non_priority | a queued activity log always displays for the action promote snapshot storage explorer version dev build number branch main platform os windows linux ubuntu macos big sur architecture how found from running test cases regression from previous build steps to reproduce expand one storage account blob containers create one blob container upload one blob create a snapshot for the blob right click the blob click manage history manage snapshots select the snapshot click promote snapshot check whether succeed to promote the snapshot expected experience succeed to promote the snapshot actual experience always display a queued activity log | 0 |
50,860 | 6,472,317,987 | IssuesEvent | 2017-08-17 13:45:35 | geetsisbac/HLNLL3FFR3NVETEIL4MMB55N | https://api.github.com/repos/geetsisbac/HLNLL3FFR3NVETEIL4MMB55N | reopened | rtXGCEzRg2h14e+Awy59dfwfUZqvmywOrQQb/aJb2xeOl2uPnzWKok5a/AMgp+BMwEmHwXmlqkCiRJgxTPFNGTNuhCBxOUXv/WivvbpgYqB95FAL1DhQRfkQ7REBbpowMZWc/Q764+ntrZnxJc1dFGnXk2bihXasAK5FTboNKxk= | design | nX4CAhb6Gz28teGfgM1/fGOWrh3wNBQE1JOGL1tSGsSf32wWFlvEtqOH6Jvtu92XicZ64Dz4n5IIJuNS3/pMlPdC1TdPjW8KGbr+V9MgD8AJT5pGIcvx2mUpbCofPlq6gYuvUCk5R63b8AW4CeofGfpG7stp3UEXOJ+fcIDKELBVeo4LobtgQ5P+TgrsEcdp23onQbZ4UkDWgh0FsuEK1mtJpk40YwKG3Q1bNXxIY7g6shrO4dD/K1w0Rn15kYQF5pXb91WP0lwCCWJHiGI7nWEHy/2PS/sI3CNCpj0zAtHK9dyw3IPQtvcjxcCxbE4H9mjaxyAmTUZgeIeRH8jTvT4iHh+NuZf4S5S2/j9kHSvJz4gQiWmg/mXWLyagVOAjl/w67yA81dMMVGGhaiXCzKV7Ra9k+AfnBWeU8HO8+Bb4y1lcv7VfRVLEURG/Y529 | 1.0 | rtXGCEzRg2h14e+Awy59dfwfUZqvmywOrQQb/aJb2xeOl2uPnzWKok5a/AMgp+BMwEmHwXmlqkCiRJgxTPFNGTNuhCBxOUXv/WivvbpgYqB95FAL1DhQRfkQ7REBbpowMZWc/Q764+ntrZnxJc1dFGnXk2bihXasAK5FTboNKxk= - nX4CAhb6Gz28teGfgM1/fGOWrh3wNBQE1JOGL1tSGsSf32wWFlvEtqOH6Jvtu92XicZ64Dz4n5IIJuNS3/pMlPdC1TdPjW8KGbr+V9MgD8AJT5pGIcvx2mUpbCofPlq6gYuvUCk5R63b8AW4CeofGfpG7stp3UEXOJ+fcIDKELBVeo4LobtgQ5P+TgrsEcdp23onQbZ4UkDWgh0FsuEK1mtJpk40YwKG3Q1bNXxIY7g6shrO4dD/K1w0Rn15kYQF5pXb91WP0lwCCWJHiGI7nWEHy/2PS/sI3CNCpj0zAtHK9dyw3IPQtvcjxcCxbE4H9mjaxyAmTUZgeIeRH8jTvT4iHh+NuZf4S5S2/j9kHSvJz4gQiWmg/mXWLyagVOAjl/w67yA81dMMVGGhaiXCzKV7Ra9k+AfnBWeU8HO8+Bb4y1lcv7VfRVLEURG/Y529 | non_priority | amgp bmwemhwxmlqkcirjgxtpfngtnuhcbxouxv mxwlyagvoajl | 0 |
6,968 | 16,016,150,555 | IssuesEvent | 2021-04-20 16:14:52 | tldr-pages/tldr | https://api.github.com/repos/tldr-pages/tldr | opened | What to do with `adb-shell`-only commands for Android? | architecture decision | As discussed [here](https://github.com/tldr-pages/tldr/pull/5743#discussion_r612422302), some commands for Android aren't native to Android and can only be executed through `adb-shell`. Therefore they technically aren't Android commands. The current idea is to put them in the Android folder, but mention that they are `adb-shell`-specific. What do you think? | 1.0 | What to do with `adb-shell`-only commands for Android? - As discussed [here](https://github.com/tldr-pages/tldr/pull/5743#discussion_r612422302), some commands for Android aren't native to Android and can only be executed through `adb-shell`. Therefore they technically aren't Android commands. The current idea is to put them in the Android folder, but mention that they are `adb-shell`-specific. What do you think? | non_priority | what to do with adb shell only commands for android as discussed some commands for android aren t native to android and can only be executed through adb shell therefore they technically aren t android commands the current idea is to put them in the android folder but mention that they are adb shell specific what do you think | 0 |
14,789 | 10,212,709,403 | IssuesEvent | 2019-08-14 20:09:32 | ngageoint/hootenanny | https://api.github.com/repos/ngageoint/hootenanny | closed | limit size of aoi which user can perform grail ops on | Category: Services | Since the load is based on features in the selected aoi rather than just using the size of the aoi I think that is better to check against | 1.0 | limit size of aoi which user can perform grail ops on - Since the load is based on features in the selected aoi rather than just using the size of the aoi I think that is better to check against | non_priority | limit size of aoi which user can perform grail ops on since the load is based on features in the selected aoi rather than just using the size of the aoi i think that is better to check against | 0 |
565 | 7,200,801,566 | IssuesEvent | 2018-02-05 20:17:21 | openhab/openhab-android | https://api.github.com/repos/openhab/openhab-android | opened | Travis: Remove redundant unit test runs | automation | Unit tests are run against debug and release (https://travis-ci.org/openhab/openhab-android/builds/337623924#L3209 https://travis-ci.org/openhab/openhab-android/builds/337623924#L3219), android tests only against debug (https://travis-ci.org/openhab/openhab-android/builds/337623924#L3344).
Is it save to run unit tests only against the release build?
They don't take much time, but I want to include an additional flavor (fossBeta), which is the same than foss, but with a different package name (needed for beta builds on fdroid) | 1.0 | Travis: Remove redundant unit test runs - Unit tests are run against debug and release (https://travis-ci.org/openhab/openhab-android/builds/337623924#L3209 https://travis-ci.org/openhab/openhab-android/builds/337623924#L3219), android tests only against debug (https://travis-ci.org/openhab/openhab-android/builds/337623924#L3344).
Is it save to run unit tests only against the release build?
They don't take much time, but I want to include an additional flavor (fossBeta), which is the same than foss, but with a different package name (needed for beta builds on fdroid) | non_priority | travis remove redundant unit test runs unit tests are run against debug and release android tests only against debug is it save to run unit tests only against the release build they don t take much time but i want to include an additional flavor fossbeta which is the same than foss but with a different package name needed for beta builds on fdroid | 0 |
93,197 | 15,881,316,836 | IssuesEvent | 2021-04-09 14:41:06 | Path-Check/gaen-mobile | https://api.github.com/repos/Path-Check/gaen-mobile | closed | CVE-2021-26707 (Medium) detected in merge-deep-3.0.2.tgz | security vulnerability | ## CVE-2021-26707 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>merge-deep-3.0.2.tgz</b></p></summary>
<p>Recursively merge values in a javascript object.</p>
<p>Library home page: <a href="https://registry.npmjs.org/merge-deep/-/merge-deep-3.0.2.tgz">https://registry.npmjs.org/merge-deep/-/merge-deep-3.0.2.tgz</a></p>
<p>Path to dependency file: gaen-mobile/node_modules/merge-deep/package.json</p>
<p>Path to vulnerable library: gaen-mobile/node_modules/merge-deep/package.json</p>
<p>
Dependency Hierarchy:
- react-native-svg-transformer-0.14.3.tgz (Root Library)
- plugin-svgo-4.3.1.tgz
- :x: **merge-deep-3.0.2.tgz** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in merge-deep before 3.0.3. A prototype pollution issue of Object.prototype via a constructor payload may lead to denial of service and other consequences.
<p>Publish Date: 2021-02-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-26707>CVE-2021-26707</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1922259">https://bugzilla.redhat.com/show_bug.cgi?id=1922259</a></p>
<p>Release Date: 2021-02-05</p>
<p>Fix Resolution: 3.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-26707 (Medium) detected in merge-deep-3.0.2.tgz - ## CVE-2021-26707 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>merge-deep-3.0.2.tgz</b></p></summary>
<p>Recursively merge values in a javascript object.</p>
<p>Library home page: <a href="https://registry.npmjs.org/merge-deep/-/merge-deep-3.0.2.tgz">https://registry.npmjs.org/merge-deep/-/merge-deep-3.0.2.tgz</a></p>
<p>Path to dependency file: gaen-mobile/node_modules/merge-deep/package.json</p>
<p>Path to vulnerable library: gaen-mobile/node_modules/merge-deep/package.json</p>
<p>
Dependency Hierarchy:
- react-native-svg-transformer-0.14.3.tgz (Root Library)
- plugin-svgo-4.3.1.tgz
- :x: **merge-deep-3.0.2.tgz** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in merge-deep before 3.0.3. A prototype pollution issue of Object.prototype via a constructor payload may lead to denial of service and other consequences.
<p>Publish Date: 2021-02-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-26707>CVE-2021-26707</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1922259">https://bugzilla.redhat.com/show_bug.cgi?id=1922259</a></p>
<p>Release Date: 2021-02-05</p>
<p>Fix Resolution: 3.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in merge deep tgz cve medium severity vulnerability vulnerable library merge deep tgz recursively merge values in a javascript object library home page a href path to dependency file gaen mobile node modules merge deep package json path to vulnerable library gaen mobile node modules merge deep package json dependency hierarchy react native svg transformer tgz root library plugin svgo tgz x merge deep tgz vulnerable library found in base branch develop vulnerability details a flaw was found in merge deep before a prototype pollution issue of object prototype via a constructor payload may lead to denial of service and other consequences publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
98,874 | 12,372,796,324 | IssuesEvent | 2020-05-18 21:06:35 | carbon-design-system/ibm-dotcom-library-website | https://api.github.com/repos/carbon-design-system/ibm-dotcom-library-website | closed | Planning - Tool for collecting user feedback on the website | Airtable Done design dev website: cupcake | > As an IBM.com Library website content creator,
> I need a way to collect adopter feedback
> so that I can resolve adopter pain points and make improvements to the Cupcake website.
#### Additional information
- Linda mentioned we no longer can use Hotjar to get feedback from the adopters on the website. Detail can be viewed [here](https://hub.webmaster.ibm.com/mac/hotjar-compliance/). The pop-up survey will be disabled, so we need to figure out a new tool for collecting user feedback.
#### Acceptance criteria
- [x] A possible solution in place for testing or implementation if needed. | 1.0 | Planning - Tool for collecting user feedback on the website - > As an IBM.com Library website content creator,
> I need a way to collect adopter feedback
> so that I can resolve adopter pain points and make improvements to the Cupcake website.
#### Additional information
- Linda mentioned we no longer can use Hotjar to get feedback from the adopters on the website. Detail can be viewed [here](https://hub.webmaster.ibm.com/mac/hotjar-compliance/). The pop-up survey will be disabled, so we need to figure out a new tool for collecting user feedback.
#### Acceptance criteria
- [x] A possible solution in place for testing or implementation if needed. | non_priority | planning tool for collecting user feedback on the website as an ibm com library website content creator i need a way to collect adopter feedback so that i can resolve adopter pain points and make improvements to the cupcake website additional information linda mentioned we no longer can use hotjar to get feedback from the adopters on the website detail can be viewed the pop up survey will be disabled so we need to figure out a new tool for collecting user feedback acceptance criteria a possible solution in place for testing or implementation if needed | 0 |
17,157 | 3,595,194,489 | IssuesEvent | 2016-02-02 04:32:56 | kumulsoft/Fixed-Assets | https://api.github.com/repos/kumulsoft/Fixed-Assets | closed | Captured Status to indicate whether asset label has been printed or not | enhancement Fixed Ready for testing | 1. Create a new Boolean field IsLabelPrinted?
2. Capture the information only in General Asset Register in the space as shown in the image

| 1.0 | Captured Status to indicate whether asset label has been printed or not - 1. Create a new Boolean field IsLabelPrinted?
2. Capture the information only in General Asset Register in the space as shown in the image

| non_priority | captured status to indicate whether asset label has been printed or not create a new boolean field islabelprinted capture the information only in general asset register in the space as shown in the image | 0 |
24,305 | 7,476,801,797 | IssuesEvent | 2018-04-04 05:32:41 | PowerShell/PowerShell | https://api.github.com/repos/PowerShell/PowerShell | opened | Add-Type doesn't work from the parent folder of 'publish' | Area-Build | It is related #5783
```
# Add-Type works
E:\PowerShell\src\powershell-win-core\bin\Debug\netcoreapp2.0\win7-x64\publish\pwsh.exe
# Add-Type doesn't work
E:\PowerShell\src\powershell-win-core\bin\Debug\netcoreapp2.0\win7-x64\pwsh.exe
```
One of the reasons is the lack of `ref` folder. | 1.0 | Add-Type doesn't work from the parent folder of 'publish' - It is related #5783
```
# Add-Type works
E:\PowerShell\src\powershell-win-core\bin\Debug\netcoreapp2.0\win7-x64\publish\pwsh.exe
# Add-Type doesn't work
E:\PowerShell\src\powershell-win-core\bin\Debug\netcoreapp2.0\win7-x64\pwsh.exe
```
One of the reasons is the lack of `ref` folder. | non_priority | add type doesn t work from the parent folder of publish it is related add type works e powershell src powershell win core bin debug publish pwsh exe add type doesn t work e powershell src powershell win core bin debug pwsh exe one of the reasons is the lack of ref folder | 0 |
335,342 | 24,465,129,661 | IssuesEvent | 2022-10-07 14:25:17 | wikitree/wikitree-dynamic-tree | https://api.github.com/repos/wikitree/wikitree-dynamic-tree | closed | Write more complete documentation on how to create a new view. | documentation | This should probably be in a separate file from the README. | 1.0 | Write more complete documentation on how to create a new view. - This should probably be in a separate file from the README. | non_priority | write more complete documentation on how to create a new view this should probably be in a separate file from the readme | 0 |
6,173 | 3,345,209,030 | IssuesEvent | 2015-11-16 10:36:31 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | opened | Text remains after adding a new Tag to an article | No Code Attached Yet | #### Steps to reproduce the issue
Created some tags (with varying length and some with more than 1 word)
Tried to add the tags with the auto-fill-feature (only typing a few characters and then selecting the suggested Tag)
#### Expected result
The text should reset and another tag can be added, starting with an empty string.
Also the cursor should remain in the input-box.
#### Actual result
Sometimes (it most often occurred when i had to retype because of a typo [Meaning i first typed "fino"->"fin"->"fini"]) the string didn't reset after i filled in the tag.
E.g. I typed "fini" and then selected "finished Projects", but then i had the tag added and after that the
"fini" was still there. Plus somehow my cursor left the box, meaning pressing backspace didn't remove the string,
but instead triggered the browser's "go to last page".
Besides, sometimes the problem would solve itself when tabbing out of the window and in again.

#### System information (as much as possible)
PHP Built On Linux CanisMajor 3.10.35 #5644 SMP Wed Oct 28 12:37:28 CST 2015 x86_64
Database Version 5.5.44-MariaDB
Database Collation utf8_general_ci
PHP Version 5.5.30
Web Server Apache
WebServer to PHP Interface fpm-fcgi
Joomla! Version Joomla! 3.4.5 Stable [ Ember ] 22-October-2015 21:30 GMT
Joomla! Platform Version Joomla Platform 13.1.0 Stable [ Curiosity ] 24-Apr-2013 00:00 GMT
User Agent Mozilla/5.0 (Windows NT 6.1; rv:42.0) Gecko/20100101 Firefox/42.0
#### Additional comments
Note: This was produced on a modified Version of Joomla maintained by Synology Inc!
I will check if this bug appears on my other platforms, too.
| 1.0 | Text remains after adding a new Tag to an article - #### Steps to reproduce the issue
Created some tags (with varying length and some with more than 1 word)
Tried to add the tags with the auto-fill-feature (only typing a few characters and then selecting the suggested Tag)
#### Expected result
The text should reset and another tag can be added, starting with an empty string.
Also the cursor should remain in the input-box.
#### Actual result
Sometimes (it most often occurred when i had to retype because of a typo [Meaning i first typed "fino"->"fin"->"fini"]) the string didn't reset after i filled in the tag.
E.g. I typed "fini" and then selected "finished Projects", but then i had the tag added and after that the
"fini" was still there. Plus somehow my cursor left the box, meaning pressing backspace didn't remove the string,
but instead triggered the browser's "go to last page".
Besides, sometimes the problem would solve itself when tabbing out of the window and in again.

#### System information (as much as possible)
PHP Built On Linux CanisMajor 3.10.35 #5644 SMP Wed Oct 28 12:37:28 CST 2015 x86_64
Database Version 5.5.44-MariaDB
Database Collation utf8_general_ci
PHP Version 5.5.30
Web Server Apache
WebServer to PHP Interface fpm-fcgi
Joomla! Version Joomla! 3.4.5 Stable [ Ember ] 22-October-2015 21:30 GMT
Joomla! Platform Version Joomla Platform 13.1.0 Stable [ Curiosity ] 24-Apr-2013 00:00 GMT
User Agent Mozilla/5.0 (Windows NT 6.1; rv:42.0) Gecko/20100101 Firefox/42.0
#### Additional comments
Note: This was produced on a modified Version of Joomla maintained by Synology Inc!
I will check if this bug appears on my other platforms, too.
| non_priority | text remains after adding a new tag to an article steps to reproduce the issue created some tags with varying length and some with more than word tried to add the tags with the auto fill feature only typing a few characters and then selecting the suggested tag expected result the text should reset and another tag can be added starting with an empty string also the cursor should remain in the input box actual result sometimes it most often occurred when i had to retype because of a typo the string didn t reset after i filled in the tag e g i typed fini and then selected finished projects but then i had the tag added and after that the fini was still there plus somehow my cursor left the box meaning pressing backspace didn t remove the string but instead triggered the browser s go to last page besides sometimes the problem would solve itself when tabbing out of the window and in again example system information as much as possible php built on linux canismajor smp wed oct cst database version mariadb database collation general ci php version web server apache webserver to php interface fpm fcgi joomla version joomla stable october gmt joomla platform version joomla platform stable apr gmt user agent mozilla windows nt rv gecko firefox additional comments note this was produced on a modified version of joomla maintained by synology inc i will check if this bug appears on my other platforms too | 0 |
19,196 | 5,824,046,373 | IssuesEvent | 2017-05-07 09:01:38 | oppia/oppia | https://api.github.com/repos/oppia/oppia | closed | Better account for overflowing text on summary cards | loc: frontend owner: @jaredsilver TODO: code type: bug (minor) | Currently, summary cards do not account for text overflow. The result is following:

(library)

(creator dashboard)
Experiment with text wrapping and text overflow to determine a suitable solution. It's relatively rare that a title would include a word this long, but we also have to keep in mind i18n, in which case there very well may be many titles for which this ends up being a problem. | 1.0 | Better account for overflowing text on summary cards - Currently, summary cards do not account for text overflow. The result is following:

(library)

(creator dashboard)
Experiment with text wrapping and text overflow to determine a suitable solution. It's relatively rare that a title would include a word this long, but we also have to keep in mind i18n, in which case there very well may be many titles for which this ends up being a problem. | non_priority | better account for overflowing text on summary cards currently summary cards do not account for text overflow the result is following library creator dashboard experiment with text wrapping and text overflow to determine a suitable solution it s relatively rare that a title would include a word this long but we also have to keep in mind in which case there very well may be many titles for which this ends up being a problem | 0 |
81,153 | 30,730,958,269 | IssuesEvent | 2023-07-28 01:31:15 | microsoft/TypeScript | https://api.github.com/repos/microsoft/TypeScript | closed | Generic parameters info is not inferred in conditional types over ancestor | Not a Defect | # Bug Report
In conditional type over an interface `X`, `infer` seems not to work for generic parameters when applied to interface `Y extends X`.
### 🔎 Search Terms
generic, infer, conditional, interface, extends
### 🕗 Version & Regression Information
It occurs in all tested versions – including latest, nightly, and some older ones.
### ⏯ Playground Link
[Playground link with relevant code](https://www.typescriptlang.org/play?ts=5.2.0-dev.20230720#code/KYDwDg9gTgLgBASwHY2FAZgQwMbDgEQmwFcBbYFAFQE8xh9htpMYEIkAeSgJWAGdiAGxgAaOJQBqmKAkwAjQfwB8cAN4BfALAAoUJFiIUaLLnG1gAE0IlyKAHIQLwLrwHCxk6bIXK4oVEgWfAREZBQwNHQMTFAsbJw8-EKi4lIy8op8Kho6Ok7YgtJ4TEh88OgQEABcZnRWobYwDk4cqhXVcGUySADm6mKqctI1Xch9SgDcubrg0PAw5nCuyQDy6ACMXCoAvOJ+IAFBITbhkfSMzKzsHMjoaEtJwmdit-dp3plnSjpwcAD8DzcEXMPzgNSQwAAbmgpjN9PNFsthGsAExbOC7Sj7Q7BM71E72RzOV5QQHJZ6GO6k94ZfhfUEApHAuig8FQmHTHQLOhk4TrDG8mBrTbc4AQdBwdqTOAAehlcGISAA1kgIAB3JBiPSMVAWOAwCBwOR4NqVEYwbp9LmIx4wFECpmojii8WSyrSuVwHoQeCmjqjXrqOCYYLa7C6nRAA)
### 💻 Code
```ts
export interface DocumentTypeDecoration<TResult, TVariables> {}
export interface TypedDocumentNode<TResult, TVariables> extends DocumentTypeDecoration<TResult, TVariables> {}
declare const foo: TypedDocumentNode<{foo: string}, {bar: string}>;
export type ResultOf1<T> = T extends DocumentTypeDecoration<infer ResultType, infer VariablesType>
? ResultType
: never;
export type ResultOf2<T> = T extends TypedDocumentNode<infer ResultType, infer VariablesType>
? ResultType
: never;
type Result1 = ResultOf1<typeof foo>; // unknown, expected to be {foo: string}
type Result2 = ResultOf2<typeof foo>; // got {foo: string} as expected
```
### 🙁 Actual behavior
Got `unknown`.
### 🙂 Expected behavior
Expected to get `{foo: string}`.
| 1.0 | Generic parameters info is not inferred in conditional types over ancestor - # Bug Report
In conditional type over an interface `X`, `infer` seems not to work for generic parameters when applied to interface `Y extends X`.
### 🔎 Search Terms
generic, infer, conditional, interface, extends
### 🕗 Version & Regression Information
It occurs in all tested versions – including latest, nightly, and some older ones.
### ⏯ Playground Link
[Playground link with relevant code](https://www.typescriptlang.org/play?ts=5.2.0-dev.20230720#code/KYDwDg9gTgLgBASwHY2FAZgQwMbDgEQmwFcBbYFAFQE8xh9htpMYEIkAeSgJWAGdiAGxgAaOJQBqmKAkwAjQfwB8cAN4BfALAAoUJFiIUaLLnG1gAE0IlyKAHIQLwLrwHCxk6bIXK4oVEgWfAREZBQwNHQMTFAsbJw8-EKi4lIy8op8Kho6Ok7YgtJ4TEh88OgQEABcZnRWobYwDk4cqhXVcGUySADm6mKqctI1Xch9SgDcubrg0PAw5nCuyQDy6ACMXCoAvOJ+IAFBITbhkfSMzKzsHMjoaEtJwmdit-dp3plnSjpwcAD8DzcEXMPzgNSQwAAbmgpjN9PNFsthGsAExbOC7Sj7Q7BM71E72RzOV5QQHJZ6GO6k94ZfhfUEApHAuig8FQmHTHQLOhk4TrDG8mBrTbc4AQdBwdqTOAAehlcGISAA1kgIAB3JBiPSMVAWOAwCBwOR4NqVEYwbp9LmIx4wFECpmojii8WSyrSuVwHoQeCmjqjXrqOCYYLa7C6nRAA)
### 💻 Code
```ts
export interface DocumentTypeDecoration<TResult, TVariables> {}
export interface TypedDocumentNode<TResult, TVariables> extends DocumentTypeDecoration<TResult, TVariables> {}
declare const foo: TypedDocumentNode<{foo: string}, {bar: string}>;
export type ResultOf1<T> = T extends DocumentTypeDecoration<infer ResultType, infer VariablesType>
? ResultType
: never;
export type ResultOf2<T> = T extends TypedDocumentNode<infer ResultType, infer VariablesType>
? ResultType
: never;
type Result1 = ResultOf1<typeof foo>; // unknown, expected to be {foo: string}
type Result2 = ResultOf2<typeof foo>; // got {foo: string} as expected
```
### 🙁 Actual behavior
Got `unknown`.
### 🙂 Expected behavior
Expected to get `{foo: string}`.
| non_priority | generic parameters info is not inferred in conditional types over ancestor bug report in conditional type over an interface x infer seems not to work for generic parameters when applied to interface y extends x 🔎 search terms generic infer conditional interface extends 🕗 version regression information it occurs in all tested versions – including latest nightly and some older ones ⏯ playground link 💻 code ts export interface documenttypedecoration export interface typeddocumentnode extends documenttypedecoration declare const foo typeddocumentnode export type t extends documenttypedecoration resulttype never export type t extends typeddocumentnode resulttype never type unknown expected to be foo string type got foo string as expected 🙁 actual behavior got unknown 🙂 expected behavior expected to get foo string | 0 |
276,781 | 30,543,837,165 | IssuesEvent | 2023-07-20 01:00:21 | billmcchesney1/react-bootstrap | https://api.github.com/repos/billmcchesney1/react-bootstrap | opened | CVE-2022-25883 (Medium) detected in multiple libraries | Mend: dependency security vulnerability | ## CVE-2022-25883 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>semver-7.3.4.tgz</b>, <b>semver-5.7.1.tgz</b>, <b>semver-5.3.0.tgz</b>, <b>semver-6.3.0.tgz</b>, <b>semver-7.0.0.tgz</b></p></summary>
<p>
<details><summary><b>semver-7.3.4.tgz</b></p></summary>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-7.3.4.tgz">https://registry.npmjs.org/semver/-/semver-7.3.4.tgz</a></p>
<p>Path to dependency file: /www/package.json</p>
<p>Path to vulnerable library: /www/node_modules/gatsby-recipes/node_modules/semver/package.json,/www/node_modules/@typescript-eslint/typescript-estree/node_modules/semver/package.json,/www/node_modules/gatsby/node_modules/semver/package.json,/www/node_modules/update-notifier/node_modules/semver/package.json,/node_modules/semver/package.json</p>
<p>
Dependency Hierarchy:
- gatsby-2.30.0.tgz (Root Library)
- :x: **semver-7.3.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>semver-5.7.1.tgz</b></p></summary>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-5.7.1.tgz">https://registry.npmjs.org/semver/-/semver-5.7.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm-package-arg/node_modules/semver/package.json,/node_modules/make-dir/node_modules/semver/package.json,/node_modules/conventional-changelog-core/node_modules/read-pkg/node_modules/semver/package.json,/node_modules/@babel/plugin-transform-runtime/node_modules/semver/package.json,/node_modules/@babel/preset-env/node_modules/semver/package.json,/node_modules/enzyme-adapter-react-16/node_modules/semver/package.json,/node_modules/eslint-import-resolver-webpack/node_modules/semver/package.json,/node_modules/normalize-package-data/node_modules/semver/package.json,/node_modules/enzyme-adapter-utils/node_modules/semver/package.json,/www/node_modules/semver/package.json,/node_modules/npm-registry-client/node_modules/semver/package.json,/node_modules/tslint/node_modules/semver/package.json,/node_modules/@babel/helper-compilation-targets/node_modules/semver/package.json,/node_modules/@babel/core/node_modules/semver/package.json</p>
<p>
Dependency Hierarchy:
- cli-7.12.10.tgz (Root Library)
- make-dir-2.1.0.tgz
- :x: **semver-5.7.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>semver-5.3.0.tgz</b></p></summary>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-5.3.0.tgz">https://registry.npmjs.org/semver/-/semver-5.3.0.tgz</a></p>
<p>Path to dependency file: /www/package.json</p>
<p>Path to vulnerable library: /www/node_modules/node-gyp/node_modules/semver/package.json</p>
<p>
Dependency Hierarchy:
- node-sass-4.14.1.tgz (Root Library)
- node-gyp-3.8.0.tgz
- :x: **semver-5.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>semver-6.3.0.tgz</b></p></summary>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-6.3.0.tgz">https://registry.npmjs.org/semver/-/semver-6.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/git-semver-tags/node_modules/semver/package.json,/www/node_modules/yurnalist/node_modules/semver/package.json,/www/node_modules/package-json/node_modules/semver/package.json,/www/node_modules/css-loader/node_modules/semver/package.json,/node_modules/istanbul-lib-instrument/node_modules/semver/package.json,/www/node_modules/eslint/node_modules/semver/package.json,/node_modules/istanbul-lib-report/node_modules/semver/package.json,/node_modules/cpy-cli/node_modules/semver/package.json,/www/node_modules/semver-diff/node_modules/semver/package.json,/node_modules/conventional-changelog-writer/node_modules/semver/package.json,/www/node_modules/make-dir/node_modules/semver/package.json,/node_modules/babel-loader/node_modules/semver/package.json,/www/node_modules/webpack-dev-server/node_modules/semver/package.json,/www/node_modules/sass-loader/node_modules/semver/package.json,/node_modules/dts-critic/node_modules/semver/package.json</p>
<p>
Dependency Hierarchy:
- babel-loader-8.2.2.tgz (Root Library)
- make-dir-3.1.0.tgz
- :x: **semver-6.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>semver-7.0.0.tgz</b></p></summary>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-7.0.0.tgz">https://registry.npmjs.org/semver/-/semver-7.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/core-js-compat/node_modules/semver/package.json,/www/node_modules/core-js-compat/node_modules/semver/package.json</p>
<p>
Dependency Hierarchy:
- babel-preset-1.2.0.tgz (Root Library)
- preset-env-7.12.11.tgz
- core-js-compat-3.8.2.tgz
- :x: **semver-7.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of the package semver before 7.5.2 are vulnerable to Regular Expression Denial of Service (ReDoS) via the function new Range, when untrusted user data is provided as a range.
<p>Publish Date: 2023-06-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25883>CVE-2022-25883</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-06-21</p>
<p>Fix Resolution (semver): 7.5.2</p>
<p>Direct dependency fix Resolution (@react-bootstrap/babel-preset): 2.0.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2022-25883 (Medium) detected in multiple libraries - ## CVE-2022-25883 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>semver-7.3.4.tgz</b>, <b>semver-5.7.1.tgz</b>, <b>semver-5.3.0.tgz</b>, <b>semver-6.3.0.tgz</b>, <b>semver-7.0.0.tgz</b></p></summary>
<p>
<details><summary><b>semver-7.3.4.tgz</b></p></summary>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-7.3.4.tgz">https://registry.npmjs.org/semver/-/semver-7.3.4.tgz</a></p>
<p>Path to dependency file: /www/package.json</p>
<p>Path to vulnerable library: /www/node_modules/gatsby-recipes/node_modules/semver/package.json,/www/node_modules/@typescript-eslint/typescript-estree/node_modules/semver/package.json,/www/node_modules/gatsby/node_modules/semver/package.json,/www/node_modules/update-notifier/node_modules/semver/package.json,/node_modules/semver/package.json</p>
<p>
Dependency Hierarchy:
- gatsby-2.30.0.tgz (Root Library)
- :x: **semver-7.3.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>semver-5.7.1.tgz</b></p></summary>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-5.7.1.tgz">https://registry.npmjs.org/semver/-/semver-5.7.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm-package-arg/node_modules/semver/package.json,/node_modules/make-dir/node_modules/semver/package.json,/node_modules/conventional-changelog-core/node_modules/read-pkg/node_modules/semver/package.json,/node_modules/@babel/plugin-transform-runtime/node_modules/semver/package.json,/node_modules/@babel/preset-env/node_modules/semver/package.json,/node_modules/enzyme-adapter-react-16/node_modules/semver/package.json,/node_modules/eslint-import-resolver-webpack/node_modules/semver/package.json,/node_modules/normalize-package-data/node_modules/semver/package.json,/node_modules/enzyme-adapter-utils/node_modules/semver/package.json,/www/node_modules/semver/package.json,/node_modules/npm-registry-client/node_modules/semver/package.json,/node_modules/tslint/node_modules/semver/package.json,/node_modules/@babel/helper-compilation-targets/node_modules/semver/package.json,/node_modules/@babel/core/node_modules/semver/package.json</p>
<p>
Dependency Hierarchy:
- cli-7.12.10.tgz (Root Library)
- make-dir-2.1.0.tgz
- :x: **semver-5.7.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>semver-5.3.0.tgz</b></p></summary>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-5.3.0.tgz">https://registry.npmjs.org/semver/-/semver-5.3.0.tgz</a></p>
<p>Path to dependency file: /www/package.json</p>
<p>Path to vulnerable library: /www/node_modules/node-gyp/node_modules/semver/package.json</p>
<p>
Dependency Hierarchy:
- node-sass-4.14.1.tgz (Root Library)
- node-gyp-3.8.0.tgz
- :x: **semver-5.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>semver-6.3.0.tgz</b></p></summary>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-6.3.0.tgz">https://registry.npmjs.org/semver/-/semver-6.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/git-semver-tags/node_modules/semver/package.json,/www/node_modules/yurnalist/node_modules/semver/package.json,/www/node_modules/package-json/node_modules/semver/package.json,/www/node_modules/css-loader/node_modules/semver/package.json,/node_modules/istanbul-lib-instrument/node_modules/semver/package.json,/www/node_modules/eslint/node_modules/semver/package.json,/node_modules/istanbul-lib-report/node_modules/semver/package.json,/node_modules/cpy-cli/node_modules/semver/package.json,/www/node_modules/semver-diff/node_modules/semver/package.json,/node_modules/conventional-changelog-writer/node_modules/semver/package.json,/www/node_modules/make-dir/node_modules/semver/package.json,/node_modules/babel-loader/node_modules/semver/package.json,/www/node_modules/webpack-dev-server/node_modules/semver/package.json,/www/node_modules/sass-loader/node_modules/semver/package.json,/node_modules/dts-critic/node_modules/semver/package.json</p>
<p>
Dependency Hierarchy:
- babel-loader-8.2.2.tgz (Root Library)
- make-dir-3.1.0.tgz
- :x: **semver-6.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>semver-7.0.0.tgz</b></p></summary>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-7.0.0.tgz">https://registry.npmjs.org/semver/-/semver-7.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/core-js-compat/node_modules/semver/package.json,/www/node_modules/core-js-compat/node_modules/semver/package.json</p>
<p>
Dependency Hierarchy:
- babel-preset-1.2.0.tgz (Root Library)
- preset-env-7.12.11.tgz
- core-js-compat-3.8.2.tgz
- :x: **semver-7.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of the package semver before 7.5.2 are vulnerable to Regular Expression Denial of Service (ReDoS) via the function new Range, when untrusted user data is provided as a range.
<p>Publish Date: 2023-06-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25883>CVE-2022-25883</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-06-21</p>
<p>Fix Resolution (semver): 7.5.2</p>
<p>Direct dependency fix Resolution (@react-bootstrap/babel-preset): 2.0.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries semver tgz semver tgz semver tgz semver tgz semver tgz semver tgz the semantic version parser used by npm library home page a href path to dependency file www package json path to vulnerable library www node modules gatsby recipes node modules semver package json www node modules typescript eslint typescript estree node modules semver package json www node modules gatsby node modules semver package json www node modules update notifier node modules semver package json node modules semver package json dependency hierarchy gatsby tgz root library x semver tgz vulnerable library semver tgz the semantic version parser used by npm library home page a href path to dependency file package json path to vulnerable library node modules npm package arg node modules semver package json node modules make dir node modules semver package json node modules conventional changelog core node modules read pkg node modules semver package json node modules babel plugin transform runtime node modules semver package json node modules babel preset env node modules semver package json node modules enzyme adapter react node modules semver package json node modules eslint import resolver webpack node modules semver package json node modules normalize package data node modules semver package json node modules enzyme adapter utils node modules semver package json www node modules semver package json node modules npm registry client node modules semver package json node modules tslint node modules semver package json node modules babel helper compilation targets node modules semver package json node modules babel core node modules semver package json dependency hierarchy cli tgz root library make dir tgz x semver tgz vulnerable library semver tgz the semantic version parser used by npm library home page a href path to dependency file www package json path to vulnerable library www node modules node gyp node modules semver package json dependency hierarchy node sass tgz root library node gyp tgz x semver tgz vulnerable library semver tgz the semantic version parser used by npm library home page a href path to dependency file package json path to vulnerable library node modules git semver tags node modules semver package json www node modules yurnalist node modules semver package json www node modules package json node modules semver package json www node modules css loader node modules semver package json node modules istanbul lib instrument node modules semver package json www node modules eslint node modules semver package json node modules istanbul lib report node modules semver package json node modules cpy cli node modules semver package json www node modules semver diff node modules semver package json node modules conventional changelog writer node modules semver package json www node modules make dir node modules semver package json node modules babel loader node modules semver package json www node modules webpack dev server node modules semver package json www node modules sass loader node modules semver package json node modules dts critic node modules semver package json dependency hierarchy babel loader tgz root library make dir tgz x semver tgz vulnerable library semver tgz the semantic version parser used by npm library home page a href path to dependency file package json path to vulnerable library node modules core js compat node modules semver package json www node modules core js compat node modules semver package json dependency hierarchy babel preset tgz root library preset env tgz core js compat tgz x semver tgz vulnerable library found in base branch master vulnerability details versions of the package semver before are vulnerable to regular expression denial of service redos via the function new range when untrusted user data is provided as a range publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution semver direct dependency fix resolution react bootstrap babel preset check this box to open an automated fix pr | 0 |
10,169 | 31,844,851,690 | IssuesEvent | 2023-09-14 19:05:05 | Chunnyluny/Chunnyluny | https://api.github.com/repos/Chunnyluny/Chunnyluny | closed | fixing github action for automatically updating my README.md by using ./template/README.md.tpl | github_actions automation | fixing github action for automatically updating my README.md by using ./template/README.md.tpl by making a pull request instead of pushing directly onto the master branch, since the workflow is triggered on push.
so I will do it again, since I'm not sure if it is done correctly, I will do it on local master branch and do a pull request to the origin/master | 1.0 | fixing github action for automatically updating my README.md by using ./template/README.md.tpl - fixing github action for automatically updating my README.md by using ./template/README.md.tpl by making a pull request instead of pushing directly onto the master branch, since the workflow is triggered on push.
so I will do it again, since I'm not sure if it is done correctly, I will do it on local master branch and do a pull request to the origin/master | non_priority | fixing github action for automatically updating my readme md by using template readme md tpl fixing github action for automatically updating my readme md by using template readme md tpl by making a pull request instead of pushing directly onto the master branch since the workflow is triggered on push so i will do it again since i m not sure if it is done correctly i will do it on local master branch and do a pull request to the origin master | 0 |
21,992 | 10,708,663,552 | IssuesEvent | 2019-10-24 20:12:44 | nicktombeur/artificialcolors | https://api.github.com/repos/nicktombeur/artificialcolors | opened | CVE-2019-14540 (High) detected in jackson-databind-2.9.9.jar | security vulnerability | ## CVE-2019-14540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/artificialcolors/back-end/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.6.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.6.RELEASE.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nicktombeur/artificialcolors/commit/5fbe189d2d404af1fb2e57723fa5987ddd8376cb">5fbe189d2d404af1fb2e57723fa5987ddd8376cb</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540>CVE-2019-14540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x">https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-14540 (High) detected in jackson-databind-2.9.9.jar - ## CVE-2019-14540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/artificialcolors/back-end/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.6.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.6.RELEASE.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nicktombeur/artificialcolors/commit/5fbe189d2d404af1fb2e57723fa5987ddd8376cb">5fbe189d2d404af1fb2e57723fa5987ddd8376cb</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540>CVE-2019-14540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x">https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm artificialcolors back end pom xml path to vulnerable library root repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library spring boot starter json release jar x jackson databind jar vulnerable library found in head commit a href vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikariconfig publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
67,553 | 14,879,947,830 | IssuesEvent | 2021-01-20 08:30:03 | loggly/Loggly-Puppet | https://api.github.com/repos/loggly/Loggly-Puppet | opened | CVE-2015-3226 (Medium) detected in activesupport-4.2.1.gem | security vulnerability | ## CVE-2015-3226 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>activesupport-4.2.1.gem</b></p></summary>
<p>A toolkit of support libraries and Ruby core extensions extracted from the Rails framework. Rich support for multibyte strings, internationalization, time zones, and testing.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activesupport-4.2.1.gem">https://rubygems.org/gems/activesupport-4.2.1.gem</a></p>
<p>
Dependency Hierarchy:
- beaker-2.9.0.gem (Root Library)
- google-api-client-0.8.6.gem
- :x: **activesupport-4.2.1.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/loggly/Loggly-Puppet/commits/31f4247de6565ccd86be8301c9572b91f67a679b">31f4247de6565ccd86be8301c9572b91f67a679b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Cross-site scripting (XSS) vulnerability in json/encoding.rb in Active Support in Ruby on Rails 3.x and 4.1.x before 4.1.11 and 4.2.x before 4.2.2 allows remote attackers to inject arbitrary web script or HTML via a crafted Hash that is mishandled during JSON encoding.
<p>Publish Date: 2015-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-3226>CVE-2015-3226</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-3226">https://nvd.nist.gov/vuln/detail/CVE-2015-3226</a></p>
<p>Release Date: 2015-07-26</p>
<p>Fix Resolution: 4.1.11,4.2.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Ruby","packageName":"activesupport","packageVersion":"4.2.1","isTransitiveDependency":true,"dependencyTree":"beaker:2.9.0;google-api-client:0.8.6;activesupport:4.2.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.1.11,4.2.2"}],"vulnerabilityIdentifier":"CVE-2015-3226","vulnerabilityDetails":"Cross-site scripting (XSS) vulnerability in json/encoding.rb in Active Support in Ruby on Rails 3.x and 4.1.x before 4.1.11 and 4.2.x before 4.2.2 allows remote attackers to inject arbitrary web script or HTML via a crafted Hash that is mishandled during JSON encoding.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-3226","cvss2Severity":"medium","cvss2Score":"4.3","extraData":{}}</REMEDIATE> --> | True | CVE-2015-3226 (Medium) detected in activesupport-4.2.1.gem - ## CVE-2015-3226 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>activesupport-4.2.1.gem</b></p></summary>
<p>A toolkit of support libraries and Ruby core extensions extracted from the Rails framework. Rich support for multibyte strings, internationalization, time zones, and testing.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activesupport-4.2.1.gem">https://rubygems.org/gems/activesupport-4.2.1.gem</a></p>
<p>
Dependency Hierarchy:
- beaker-2.9.0.gem (Root Library)
- google-api-client-0.8.6.gem
- :x: **activesupport-4.2.1.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/loggly/Loggly-Puppet/commits/31f4247de6565ccd86be8301c9572b91f67a679b">31f4247de6565ccd86be8301c9572b91f67a679b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Cross-site scripting (XSS) vulnerability in json/encoding.rb in Active Support in Ruby on Rails 3.x and 4.1.x before 4.1.11 and 4.2.x before 4.2.2 allows remote attackers to inject arbitrary web script or HTML via a crafted Hash that is mishandled during JSON encoding.
<p>Publish Date: 2015-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-3226>CVE-2015-3226</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-3226">https://nvd.nist.gov/vuln/detail/CVE-2015-3226</a></p>
<p>Release Date: 2015-07-26</p>
<p>Fix Resolution: 4.1.11,4.2.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Ruby","packageName":"activesupport","packageVersion":"4.2.1","isTransitiveDependency":true,"dependencyTree":"beaker:2.9.0;google-api-client:0.8.6;activesupport:4.2.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.1.11,4.2.2"}],"vulnerabilityIdentifier":"CVE-2015-3226","vulnerabilityDetails":"Cross-site scripting (XSS) vulnerability in json/encoding.rb in Active Support in Ruby on Rails 3.x and 4.1.x before 4.1.11 and 4.2.x before 4.2.2 allows remote attackers to inject arbitrary web script or HTML via a crafted Hash that is mishandled during JSON encoding.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-3226","cvss2Severity":"medium","cvss2Score":"4.3","extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in activesupport gem cve medium severity vulnerability vulnerable library activesupport gem a toolkit of support libraries and ruby core extensions extracted from the rails framework rich support for multibyte strings internationalization time zones and testing library home page a href dependency hierarchy beaker gem root library google api client gem x activesupport gem vulnerable library found in head commit a href found in base branch master vulnerability details cross site scripting xss vulnerability in json encoding rb in active support in ruby on rails x and x before and x before allows remote attackers to inject arbitrary web script or html via a crafted hash that is mishandled during json encoding publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails cross site scripting xss vulnerability in json encoding rb in active support in ruby on rails x and x before and x before allows remote attackers to inject arbitrary web script or html via a crafted hash that is mishandled during json encoding vulnerabilityurl | 0 |
59,398 | 14,580,836,667 | IssuesEvent | 2020-12-18 09:47:32 | spack/spack | https://api.github.com/repos/spack/spack | opened | Installation issue: VTK, internal compiler error with Intel 19.0.5 | build-error | <!-- Thanks for taking the time to report this build failure. To proceed with the report please:
1. Title the issue "Installation issue: <name-of-the-package>".
2. Provide the information required below.
We encourage you to try, as much as possible, to reduce your problem to the minimal example that still reproduces the issue. That would help us a lot in fixing it quickly and effectively! -->
### Steps to reproduce the issue
<!-- Fill in the exact spec you are trying to build and the relevant part of the error message -->
```console
$ spack install vtk@8.2.0 ~mpi +opengl2 %intel ^freetype%gcc ^hdf5~mpi
...
>> 1846 ": internal error: ** The compiler has encountered an unexpected problem.
1847 ** Segmentation violation signal raised. **
1848 Access violation or stack overflow. Please contact Intel Support for assistance.
1849
>> 1850 icpc: error #10014: problem during multi-file optimization compilation (code 4)
>> 1851 make[2]: *** [lib/libvtkCommonMath-8.2.so.1] Error 4
1852 make[2]: Leaving directory `/tmp/bamboo_sta/spack-stage/spack-stage-vtk-8.2.0-jugxugntvxvvhv2hm
qadjumisr4xs7sn/spack-build-jugxugn'
>> 1853 make[1]: *** [Common/Math/CMakeFiles/vtkCommonMath.dir/all] Error 2
```
### Information on your system
<!-- Please include the output of `spack debug report` -->
* **Spack:** 0.16.0
* **Python:** 3.6.8
* **Platform:** linux-centos7-broadwell
[spack-build-out.txt](https://github.com/spack/spack/files/5714900/spack-build-out.txt)
[spack-build-env.txt](https://github.com/spack/spack/files/5714901/spack-build-env.txt)
<!-- If you have any relevant configuration detail (custom `packages.yaml` or `modules.yaml`, etc.) you can add that here as well. -->
### Additional information
<!-- Please upload the following files. They should be present in the stage directory of the failing build. Also upload any config.log or similar file if one exists. -->
* [spack-build-out.txt]()
* [spack-build-env.txt]()
<!-- Some packages have maintainers who have volunteered to debug build failures. Run `spack maintainers <name-of-the-package>` and @mention them here if they exist. -->
@chuckatkins @danlipsa
### General information
<!-- These boxes can be checked by replacing [ ] with [x] or by clicking them after submitting the issue. -->
- [ ] I have run `spack debug report` and reported the version of Spack/Python/Platform
- [ ] I have run `spack maintainers <name-of-the-package>` and @mentioned any maintainers
- [ ] I have uploaded the build log and environment files
- [ ] I have searched the issues of this repo and believe this is not a duplicate
| 1.0 | Installation issue: VTK, internal compiler error with Intel 19.0.5 - <!-- Thanks for taking the time to report this build failure. To proceed with the report please:
1. Title the issue "Installation issue: <name-of-the-package>".
2. Provide the information required below.
We encourage you to try, as much as possible, to reduce your problem to the minimal example that still reproduces the issue. That would help us a lot in fixing it quickly and effectively! -->
### Steps to reproduce the issue
<!-- Fill in the exact spec you are trying to build and the relevant part of the error message -->
```console
$ spack install vtk@8.2.0 ~mpi +opengl2 %intel ^freetype%gcc ^hdf5~mpi
...
>> 1846 ": internal error: ** The compiler has encountered an unexpected problem.
1847 ** Segmentation violation signal raised. **
1848 Access violation or stack overflow. Please contact Intel Support for assistance.
1849
>> 1850 icpc: error #10014: problem during multi-file optimization compilation (code 4)
>> 1851 make[2]: *** [lib/libvtkCommonMath-8.2.so.1] Error 4
1852 make[2]: Leaving directory `/tmp/bamboo_sta/spack-stage/spack-stage-vtk-8.2.0-jugxugntvxvvhv2hm
qadjumisr4xs7sn/spack-build-jugxugn'
>> 1853 make[1]: *** [Common/Math/CMakeFiles/vtkCommonMath.dir/all] Error 2
```
### Information on your system
<!-- Please include the output of `spack debug report` -->
* **Spack:** 0.16.0
* **Python:** 3.6.8
* **Platform:** linux-centos7-broadwell
[spack-build-out.txt](https://github.com/spack/spack/files/5714900/spack-build-out.txt)
[spack-build-env.txt](https://github.com/spack/spack/files/5714901/spack-build-env.txt)
<!-- If you have any relevant configuration detail (custom `packages.yaml` or `modules.yaml`, etc.) you can add that here as well. -->
### Additional information
<!-- Please upload the following files. They should be present in the stage directory of the failing build. Also upload any config.log or similar file if one exists. -->
* [spack-build-out.txt]()
* [spack-build-env.txt]()
<!-- Some packages have maintainers who have volunteered to debug build failures. Run `spack maintainers <name-of-the-package>` and @mention them here if they exist. -->
@chuckatkins @danlipsa
### General information
<!-- These boxes can be checked by replacing [ ] with [x] or by clicking them after submitting the issue. -->
- [ ] I have run `spack debug report` and reported the version of Spack/Python/Platform
- [ ] I have run `spack maintainers <name-of-the-package>` and @mentioned any maintainers
- [ ] I have uploaded the build log and environment files
- [ ] I have searched the issues of this repo and believe this is not a duplicate
| non_priority | installation issue vtk internal compiler error with intel thanks for taking the time to report this build failure to proceed with the report please title the issue installation issue provide the information required below we encourage you to try as much as possible to reduce your problem to the minimal example that still reproduces the issue that would help us a lot in fixing it quickly and effectively steps to reproduce the issue console spack install vtk mpi intel freetype gcc mpi internal error the compiler has encountered an unexpected problem segmentation violation signal raised access violation or stack overflow please contact intel support for assistance icpc error problem during multi file optimization compilation code make error make leaving directory tmp bamboo sta spack stage spack stage vtk spack build jugxugn make error information on your system spack python platform linux broadwell additional information and mention them here if they exist chuckatkins danlipsa general information i have run spack debug report and reported the version of spack python platform i have run spack maintainers and mentioned any maintainers i have uploaded the build log and environment files i have searched the issues of this repo and believe this is not a duplicate | 0 |
55,004 | 7,936,423,362 | IssuesEvent | 2018-07-09 09:23:03 | test-kitchen/kitchen-azurerm | https://api.github.com/repos/test-kitchen/kitchen-azurerm | closed | WinRM username and password specified do not work | documentation | Need to verify the configuration steps in: https://learn.chef.io/modules/local-development/windows/azure/apply-a-cookbook#/ WRT WinRM username and password and update the example or fix the documentation. Community reports setting username and password underneath `transport` did not have the desired effect and the defaults were used. | 1.0 | WinRM username and password specified do not work - Need to verify the configuration steps in: https://learn.chef.io/modules/local-development/windows/azure/apply-a-cookbook#/ WRT WinRM username and password and update the example or fix the documentation. Community reports setting username and password underneath `transport` did not have the desired effect and the defaults were used. | non_priority | winrm username and password specified do not work need to verify the configuration steps in wrt winrm username and password and update the example or fix the documentation community reports setting username and password underneath transport did not have the desired effect and the defaults were used | 0 |
46,394 | 5,806,770,705 | IssuesEvent | 2017-05-04 04:41:28 | wesnoth/wesnoth | https://api.github.com/repos/wesnoth/wesnoth | closed | testrunner crashes | bug Unit Tests | wesnoth @ 81eb23c74e8ad86d0354a195e668c0c79546f4fd
running asan instrumented testrunner crashes with stack use after free.
````
Running 154 test cases...
=================================================================
==28136==ERROR: AddressSanitizer: stack-use-after-scope on address 0x7fff47f95f60 at pc 0x000002ad290d bp 0x7fff47f85b70 sp 0x7fff47f85b68
READ of size 8 at 0x7fff47f95f60 thread T0
#0 0x2ad290c in std::vector<map_generator*, std::allocator<map_generator*> >::begin() const /usr/lib/gcc/x86_64-redhat-linux/6.3.1/../../../../include/c++/6.3.1/bits/stl_vector.h:558:45
#1 0x2ad290c in std::vector<map_generator*, std::allocator<map_generator*> >::empty() const /usr/lib/gcc/x86_64-redhat-linux/6.3.1/../../../../include/c++/6.3.1/bits/stl_vector.h:745
#2 0x2ad0cc8 in gui2::dialogs::editor_generate_map::pre_show(gui2::window&) /home/matthias/vcs/github/wesnoth/build/../src/gui/dialogs/editor/generate_map.cpp:109:2
#3 0x2c2f564 in gui2::dialogs::modal_dialog::show(CVideo&, unsigned int) /home/matthias/vcs/github/wesnoth/build/../src/gui/dialogs/modal_dialog.cpp:66:2
#4 0x19eca38 in void (anonymous namespace)::test_resolutions<gui2::dialogs::editor_generate_map>(std::vector<std::pair<unsigned int, unsigned int>, std::allocator<std::pair<unsigned int, unsigned int> > > const&) /home/matthias/vcs/github/wesnoth/build/../src/tests/gui/test_gui2.cpp:209:10
#5 0x19eca38 in void (anonymous namespace)::test<gui2::dialogs::editor_generate_map>() /home/matthias/vcs/github/wesnoth/build/../src/tests/gui/test_gui2.cpp:343
#6 0x19eca38 in test_gui2::test_method() /home/matthias/vcs/github/wesnoth/build/../src/tests/gui/test_gui2.cpp:411
#7 0x19d8cbf in test_gui2_invoker() /home/matthias/vcs/github/wesnoth/build/../src/tests/gui/test_gui2.cpp:377:1
#8 0x19bd591 in boost::detail::function::void_function_invoker0<void (*)(), void>::invoke(boost::detail::function::function_buffer&) /usr/include/boost/function/function_template.hpp:118:11
#9 0x7fc24101c9fd in boost::detail::function::function_obj_invoker0<boost::detail::forward, int>::invoke(boost::detail::function::function_buffer&) (/lib64/libboost_unit_test_framework.so.1.60.0+0x439fd)
#10 0x1a7a000 in boost::function0<int>::operator()() const /usr/include/boost/function/function_template.hpp:770:14
#11 0x1a79513 in boost::detail::translator_holder<game::error, void (*)(game::error const&)>::operator()(boost::function<int ()> const&) /usr/include/boost/test/execution_monitor.hpp:419:46
#12 0x1a7c83f in boost::detail::translator_holder<config::error, void (*)(config::error const&)>::operator()(boost::function<int ()> const&) /usr/include/boost/test/execution_monitor.hpp:419:29
#13 0x7fc24101c079 in boost::execution_monitor::catch_signals(boost::function<int ()> const&) (/lib64/libboost_unit_test_framework.so.1.60.0+0x43079)
#14 0x7fc24101c227 in boost::execution_monitor::execute(boost::function<int ()> const&) (/lib64/libboost_unit_test_framework.so.1.60.0+0x43227)
#15 0x7fc24101c875 in boost::execution_monitor::vexecute(boost::function<void ()> const&) (/lib64/libboost_unit_test_framework.so.1.60.0+0x43875)
#16 0x7fc24103f29a in boost::unit_test::unit_test_monitor_t::execute_and_translate(boost::function<void ()> const&, unsigned int) (/lib64/libboost_unit_test_framework.so.1.60.0+0x6629a)
#17 0x7fc241026e55 in boost::unit_test::framework::state::execute_test_tree(unsigned long, unsigned int) (/lib64/libboost_unit_test_framework.so.1.60.0+0x4de55)
#18 0x7fc241027590 in boost::unit_test::framework::state::execute_test_tree(unsigned long, unsigned int) (/lib64/libboost_unit_test_framework.so.1.60.0+0x4e590)
#19 0x7fc241021330 in boost::unit_test::framework::run(unsigned long, bool) (/lib64/libboost_unit_test_framework.so.1.60.0+0x48330)
#20 0x7fc24103d23e in boost::unit_test::unit_test_main(bool (*)(), int, char**) (/lib64/libboost_unit_test_framework.so.1.60.0+0x6423e)
#21 0x1a71a93 in main /usr/include/boost/test/unit_test.hpp:63:12
#22 0x7fc240610400 in __libc_start_main /usr/src/debug/glibc-2.24-33-ge9e69e4/csu/../csu/libc-start.c:289
#23 0x18ca699 in _start (/home/matthias/vcs/github/wesnoth/build/test+0x18ca699)
Address 0x7fff47f95f60 is located in stack of thread T0 at offset 64960 in frame
#0 0x2c2ee9f in gui2::dialogs::modal_dialog::show(CVideo&, unsigned int) /home/matthias/vcs/github/wesnoth/build/../src/gui/dialogs/modal_dialog.cpp:39
This frame has 11 object(s):
[32, 160) 'pc' (line 48)
[192, 224) 'ref.tmp' (line 48)
[256, 257) 'ref.tmp6' (line 48)
[272, 304) 'ref.tmp7' (line 49)
[336, 337) 'ref.tmp8' (line 49)
[352, 384) 'agg.tmp'
[416, 448) 'ref.tmp10' (line 50)
[480, 481) 'ref.tmp11' (line 50)
[496, 528) 'agg.tmp12'
[560, 568) 'window' (line 57)
[592, 600) 'ref.tmp25' (line 68) <== Memory access at offset 64960 overflows this variable
HINT: this may be a false positive if your program uses some custom stack unwind mechanism or swapcontext
(longjmp and C++ exceptions *are* supported)
SUMMARY: AddressSanitizer: stack-use-after-scope /usr/lib/gcc/x86_64-redhat-linux/6.3.1/../../../../include/c++/6.3.1/bits/stl_vector.h:558:45 in std::vector<map_generator*, std::allocator<map_generator*> >::begin() const
Shadow bytes around the buggy address:
0x100068feab90: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x100068feaba0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x100068feabb0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x100068feabc0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x100068feabd0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x100068feabe0: 00 00 00 00 00 00 00 00 00 00 00 00[f8]f8 f8 00
0x100068feabf0: 00 00 00 00 f8 f8 f8 f8 00 00 00 00 f8 00 f8 00
0x100068feac00: 00 00 f8 00 00 00 f8 f8 f8 f8 00 00 00 00 f8 00
0x100068feac10: f8 f8 f8 f8 00 00 00 00 f8 00 f8 00 00 00 f8 f8
0x100068feac20: f8 f8 00 00 00 00 f8 00 f8 00 00 00 f8 f8 f8 00
0x100068feac30: 00 00 00 00 f8 f8 f8 f8 00 00 00 00 00 00 00 00
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==28136==ABORTING
````` | 1.0 | testrunner crashes - wesnoth @ 81eb23c74e8ad86d0354a195e668c0c79546f4fd
running asan instrumented testrunner crashes with stack use after free.
````
Running 154 test cases...
=================================================================
==28136==ERROR: AddressSanitizer: stack-use-after-scope on address 0x7fff47f95f60 at pc 0x000002ad290d bp 0x7fff47f85b70 sp 0x7fff47f85b68
READ of size 8 at 0x7fff47f95f60 thread T0
#0 0x2ad290c in std::vector<map_generator*, std::allocator<map_generator*> >::begin() const /usr/lib/gcc/x86_64-redhat-linux/6.3.1/../../../../include/c++/6.3.1/bits/stl_vector.h:558:45
#1 0x2ad290c in std::vector<map_generator*, std::allocator<map_generator*> >::empty() const /usr/lib/gcc/x86_64-redhat-linux/6.3.1/../../../../include/c++/6.3.1/bits/stl_vector.h:745
#2 0x2ad0cc8 in gui2::dialogs::editor_generate_map::pre_show(gui2::window&) /home/matthias/vcs/github/wesnoth/build/../src/gui/dialogs/editor/generate_map.cpp:109:2
#3 0x2c2f564 in gui2::dialogs::modal_dialog::show(CVideo&, unsigned int) /home/matthias/vcs/github/wesnoth/build/../src/gui/dialogs/modal_dialog.cpp:66:2
#4 0x19eca38 in void (anonymous namespace)::test_resolutions<gui2::dialogs::editor_generate_map>(std::vector<std::pair<unsigned int, unsigned int>, std::allocator<std::pair<unsigned int, unsigned int> > > const&) /home/matthias/vcs/github/wesnoth/build/../src/tests/gui/test_gui2.cpp:209:10
#5 0x19eca38 in void (anonymous namespace)::test<gui2::dialogs::editor_generate_map>() /home/matthias/vcs/github/wesnoth/build/../src/tests/gui/test_gui2.cpp:343
#6 0x19eca38 in test_gui2::test_method() /home/matthias/vcs/github/wesnoth/build/../src/tests/gui/test_gui2.cpp:411
#7 0x19d8cbf in test_gui2_invoker() /home/matthias/vcs/github/wesnoth/build/../src/tests/gui/test_gui2.cpp:377:1
#8 0x19bd591 in boost::detail::function::void_function_invoker0<void (*)(), void>::invoke(boost::detail::function::function_buffer&) /usr/include/boost/function/function_template.hpp:118:11
#9 0x7fc24101c9fd in boost::detail::function::function_obj_invoker0<boost::detail::forward, int>::invoke(boost::detail::function::function_buffer&) (/lib64/libboost_unit_test_framework.so.1.60.0+0x439fd)
#10 0x1a7a000 in boost::function0<int>::operator()() const /usr/include/boost/function/function_template.hpp:770:14
#11 0x1a79513 in boost::detail::translator_holder<game::error, void (*)(game::error const&)>::operator()(boost::function<int ()> const&) /usr/include/boost/test/execution_monitor.hpp:419:46
#12 0x1a7c83f in boost::detail::translator_holder<config::error, void (*)(config::error const&)>::operator()(boost::function<int ()> const&) /usr/include/boost/test/execution_monitor.hpp:419:29
#13 0x7fc24101c079 in boost::execution_monitor::catch_signals(boost::function<int ()> const&) (/lib64/libboost_unit_test_framework.so.1.60.0+0x43079)
#14 0x7fc24101c227 in boost::execution_monitor::execute(boost::function<int ()> const&) (/lib64/libboost_unit_test_framework.so.1.60.0+0x43227)
#15 0x7fc24101c875 in boost::execution_monitor::vexecute(boost::function<void ()> const&) (/lib64/libboost_unit_test_framework.so.1.60.0+0x43875)
#16 0x7fc24103f29a in boost::unit_test::unit_test_monitor_t::execute_and_translate(boost::function<void ()> const&, unsigned int) (/lib64/libboost_unit_test_framework.so.1.60.0+0x6629a)
#17 0x7fc241026e55 in boost::unit_test::framework::state::execute_test_tree(unsigned long, unsigned int) (/lib64/libboost_unit_test_framework.so.1.60.0+0x4de55)
#18 0x7fc241027590 in boost::unit_test::framework::state::execute_test_tree(unsigned long, unsigned int) (/lib64/libboost_unit_test_framework.so.1.60.0+0x4e590)
#19 0x7fc241021330 in boost::unit_test::framework::run(unsigned long, bool) (/lib64/libboost_unit_test_framework.so.1.60.0+0x48330)
#20 0x7fc24103d23e in boost::unit_test::unit_test_main(bool (*)(), int, char**) (/lib64/libboost_unit_test_framework.so.1.60.0+0x6423e)
#21 0x1a71a93 in main /usr/include/boost/test/unit_test.hpp:63:12
#22 0x7fc240610400 in __libc_start_main /usr/src/debug/glibc-2.24-33-ge9e69e4/csu/../csu/libc-start.c:289
#23 0x18ca699 in _start (/home/matthias/vcs/github/wesnoth/build/test+0x18ca699)
Address 0x7fff47f95f60 is located in stack of thread T0 at offset 64960 in frame
#0 0x2c2ee9f in gui2::dialogs::modal_dialog::show(CVideo&, unsigned int) /home/matthias/vcs/github/wesnoth/build/../src/gui/dialogs/modal_dialog.cpp:39
This frame has 11 object(s):
[32, 160) 'pc' (line 48)
[192, 224) 'ref.tmp' (line 48)
[256, 257) 'ref.tmp6' (line 48)
[272, 304) 'ref.tmp7' (line 49)
[336, 337) 'ref.tmp8' (line 49)
[352, 384) 'agg.tmp'
[416, 448) 'ref.tmp10' (line 50)
[480, 481) 'ref.tmp11' (line 50)
[496, 528) 'agg.tmp12'
[560, 568) 'window' (line 57)
[592, 600) 'ref.tmp25' (line 68) <== Memory access at offset 64960 overflows this variable
HINT: this may be a false positive if your program uses some custom stack unwind mechanism or swapcontext
(longjmp and C++ exceptions *are* supported)
SUMMARY: AddressSanitizer: stack-use-after-scope /usr/lib/gcc/x86_64-redhat-linux/6.3.1/../../../../include/c++/6.3.1/bits/stl_vector.h:558:45 in std::vector<map_generator*, std::allocator<map_generator*> >::begin() const
Shadow bytes around the buggy address:
0x100068feab90: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x100068feaba0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x100068feabb0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x100068feabc0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x100068feabd0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x100068feabe0: 00 00 00 00 00 00 00 00 00 00 00 00[f8]f8 f8 00
0x100068feabf0: 00 00 00 00 f8 f8 f8 f8 00 00 00 00 f8 00 f8 00
0x100068feac00: 00 00 f8 00 00 00 f8 f8 f8 f8 00 00 00 00 f8 00
0x100068feac10: f8 f8 f8 f8 00 00 00 00 f8 00 f8 00 00 00 f8 f8
0x100068feac20: f8 f8 00 00 00 00 f8 00 f8 00 00 00 f8 f8 f8 00
0x100068feac30: 00 00 00 00 f8 f8 f8 f8 00 00 00 00 00 00 00 00
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==28136==ABORTING
````` | non_priority | testrunner crashes wesnoth running asan instrumented testrunner crashes with stack use after free running test cases error addresssanitizer stack use after scope on address at pc bp sp read of size at thread in std vector begin const usr lib gcc redhat linux include c bits stl vector h in std vector empty const usr lib gcc redhat linux include c bits stl vector h in dialogs editor generate map pre show window home matthias vcs github wesnoth build src gui dialogs editor generate map cpp in dialogs modal dialog show cvideo unsigned int home matthias vcs github wesnoth build src gui dialogs modal dialog cpp in void anonymous namespace test resolutions std vector std allocator const home matthias vcs github wesnoth build src tests gui test cpp in void anonymous namespace test home matthias vcs github wesnoth build src tests gui test cpp in test test method home matthias vcs github wesnoth build src tests gui test cpp in test invoker home matthias vcs github wesnoth build src tests gui test cpp in boost detail function void function invoke boost detail function function buffer usr include boost function function template hpp in boost detail function function obj invoke boost detail function function buffer libboost unit test framework so in boost operator const usr include boost function function template hpp in boost detail translator holder operator boost function const usr include boost test execution monitor hpp in boost detail translator holder operator boost function const usr include boost test execution monitor hpp in boost execution monitor catch signals boost function const libboost unit test framework so in boost execution monitor execute boost function const libboost unit test framework so in boost execution monitor vexecute boost function const libboost unit test framework so in boost unit test unit test monitor t execute and translate boost function const unsigned int libboost unit test framework so in boost unit test framework state execute test tree unsigned long unsigned int libboost unit test framework so in boost unit test framework state execute test tree unsigned long unsigned int libboost unit test framework so in boost unit test framework run unsigned long bool libboost unit test framework so in boost unit test unit test main bool int char libboost unit test framework so in main usr include boost test unit test hpp in libc start main usr src debug glibc csu csu libc start c in start home matthias vcs github wesnoth build test address is located in stack of thread at offset in frame in dialogs modal dialog show cvideo unsigned int home matthias vcs github wesnoth build src gui dialogs modal dialog cpp this frame has object s pc line ref tmp line ref line ref line ref line agg tmp ref line ref line agg window line ref line memory access at offset overflows this variable hint this may be a false positive if your program uses some custom stack unwind mechanism or swapcontext longjmp and c exceptions are supported summary addresssanitizer stack use after scope usr lib gcc redhat linux include c bits stl vector h in std vector begin const shadow bytes around the buggy address shadow byte legend one shadow byte represents application bytes addressable partially addressable heap left redzone fa freed heap region fd stack left redzone stack mid redzone stack right redzone stack after return stack use after scope global redzone global init order poisoned by user container overflow fc array cookie ac intra object redzone bb asan internal fe left alloca redzone ca right alloca redzone cb aborting | 0 |
48,059 | 7,373,031,078 | IssuesEvent | 2018-03-13 16:11:30 | umbraco/UmbracoDocs | https://api.github.com/repos/umbraco/UmbracoDocs | closed | Cloud Docs: Documentation about adding/removing environments | Umbraco Cloud missing documentation | Missing documentation about how to add / remove environment on a Cloud project.
Should be added either here:
https://our.umbraco.org/documentation/Umbraco-Cloud/Getting-Started/The-Umbraco-Cloud-Portal/
or here:
https://our.umbraco.org/documentation/Umbraco-Cloud/Getting-Started/Project-Overview/ | 1.0 | Cloud Docs: Documentation about adding/removing environments - Missing documentation about how to add / remove environment on a Cloud project.
Should be added either here:
https://our.umbraco.org/documentation/Umbraco-Cloud/Getting-Started/The-Umbraco-Cloud-Portal/
or here:
https://our.umbraco.org/documentation/Umbraco-Cloud/Getting-Started/Project-Overview/ | non_priority | cloud docs documentation about adding removing environments missing documentation about how to add remove environment on a cloud project should be added either here or here | 0 |
10,179 | 12,194,443,551 | IssuesEvent | 2020-04-29 15:48:46 | woocommerce/action-scheduler | https://api.github.com/repos/woocommerce/action-scheduler | closed | WP shutdown hook runs on fatal error | Docs compatibility custom-tables | Action Scheduler registers the autoloader in `plugins_loaded` but doesn't initialize the data stores until `init`. If a fatal error occurs between those two hooks, the WP `shutdown` hook still runs.
I found this while investigating #516 and triggered an error in the WooCommerce initialization. Both the WC error and the AS error were logged. #498 attempted to mitigate a conflict with WP Rocket where the Action data store appeared to not have been initialized.
This wouldn't have been a problem with the WP Post store as WP initializes the core database variables before loading any plugins. Data stores that rely on custom tables should not be used in the `shutdown` hook.
Scheduling the migration hook should be moved out of the `shutdown` hook and the documentation should be updated to reflect the limitation. | True | WP shutdown hook runs on fatal error - Action Scheduler registers the autoloader in `plugins_loaded` but doesn't initialize the data stores until `init`. If a fatal error occurs between those two hooks, the WP `shutdown` hook still runs.
I found this while investigating #516 and triggered an error in the WooCommerce initialization. Both the WC error and the AS error were logged. #498 attempted to mitigate a conflict with WP Rocket where the Action data store appeared to not have been initialized.
This wouldn't have been a problem with the WP Post store as WP initializes the core database variables before loading any plugins. Data stores that rely on custom tables should not be used in the `shutdown` hook.
Scheduling the migration hook should be moved out of the `shutdown` hook and the documentation should be updated to reflect the limitation. | non_priority | wp shutdown hook runs on fatal error action scheduler registers the autoloader in plugins loaded but doesn t initialize the data stores until init if a fatal error occurs between those two hooks the wp shutdown hook still runs i found this while investigating and triggered an error in the woocommerce initialization both the wc error and the as error were logged attempted to mitigate a conflict with wp rocket where the action data store appeared to not have been initialized this wouldn t have been a problem with the wp post store as wp initializes the core database variables before loading any plugins data stores that rely on custom tables should not be used in the shutdown hook scheduling the migration hook should be moved out of the shutdown hook and the documentation should be updated to reflect the limitation | 0 |
69,953 | 13,386,052,372 | IssuesEvent | 2020-09-02 14:15:10 | atc0005/notes | https://api.github.com/repos/atc0005/notes | opened | Setup LXD container for "The Complete Javascript" course | container javascript lxd vscode | Course: https://www.udemy.com/course/the-complete-javascript-course-for-developers/
NodeJS 10.4.0 is used in the series, so my goal is to install the latest in the 10.x series within a LXD container and use that for running code developed during the course. The hope is that I can expose the necessary ports, share paths between the host environment and the container. | 1.0 | Setup LXD container for "The Complete Javascript" course - Course: https://www.udemy.com/course/the-complete-javascript-course-for-developers/
NodeJS 10.4.0 is used in the series, so my goal is to install the latest in the 10.x series within a LXD container and use that for running code developed during the course. The hope is that I can expose the necessary ports, share paths between the host environment and the container. | non_priority | setup lxd container for the complete javascript course course nodejs is used in the series so my goal is to install the latest in the x series within a lxd container and use that for running code developed during the course the hope is that i can expose the necessary ports share paths between the host environment and the container | 0 |
287,067 | 21,636,697,244 | IssuesEvent | 2022-05-05 14:48:24 | numpy/numpy | https://api.github.com/repos/numpy/numpy | closed | DOC: Add a version selector | 04 - Documentation | ### Issue with current documentation:
It would be nice to add a version selector.
### Idea or request for content:
The Pydata theme we use supports this. [Here](https://pydata-sphinx-theme.readthedocs.io/en/latest/user_guide/configuring.html?highlight=version#add-a-dropdown-to-switch-between-docs-versions) is the documentation of the feature, note the blue pulldown at the top.
This may be an opportunity to refactor the repo layouts, merging the [devdocs](https://github.com/numpy/devdocs) repo and the [doc](https://github.com/numpy/doc) repo, which means refactoring the target of the CircleCI [devdoc deploy step](https://github.com/numpy/numpy/blob/381684986a20cc5c41afb9fe4a9abc5507684305/.circleci/config.yml#L103)
@MarsBarLee | 1.0 | DOC: Add a version selector - ### Issue with current documentation:
It would be nice to add a version selector.
### Idea or request for content:
The Pydata theme we use supports this. [Here](https://pydata-sphinx-theme.readthedocs.io/en/latest/user_guide/configuring.html?highlight=version#add-a-dropdown-to-switch-between-docs-versions) is the documentation of the feature, note the blue pulldown at the top.
This may be an opportunity to refactor the repo layouts, merging the [devdocs](https://github.com/numpy/devdocs) repo and the [doc](https://github.com/numpy/doc) repo, which means refactoring the target of the CircleCI [devdoc deploy step](https://github.com/numpy/numpy/blob/381684986a20cc5c41afb9fe4a9abc5507684305/.circleci/config.yml#L103)
@MarsBarLee | non_priority | doc add a version selector issue with current documentation it would be nice to add a version selector idea or request for content the pydata theme we use supports this is the documentation of the feature note the blue pulldown at the top this may be an opportunity to refactor the repo layouts merging the repo and the repo which means refactoring the target of the circleci marsbarlee | 0 |
17,786 | 4,202,746,330 | IssuesEvent | 2016-06-28 00:28:56 | grpc/grpc | https://api.github.com/repos/grpc/grpc | opened | Eliminate everything having to do with code generation from examples/python/helloworld | documentation help wanted python | `helloworld` is supposed to be the "in three minutes" example and doesn't actually teach code generation. Having stuff related to code generation in that example clutters the contents and misleads users. | 1.0 | Eliminate everything having to do with code generation from examples/python/helloworld - `helloworld` is supposed to be the "in three minutes" example and doesn't actually teach code generation. Having stuff related to code generation in that example clutters the contents and misleads users. | non_priority | eliminate everything having to do with code generation from examples python helloworld helloworld is supposed to be the in three minutes example and doesn t actually teach code generation having stuff related to code generation in that example clutters the contents and misleads users | 0 |
43,194 | 17,465,810,269 | IssuesEvent | 2021-08-06 16:38:05 | Azure/azure-rest-api-specs | https://api.github.com/repos/Azure/azure-rest-api-specs | closed | $top query parameter in /subscriptions/{id}/providers doesn't seem to be respected | question ARM P1 Service Attention ARM - Core ARM - Core Triaged | GET https://management.azure.com/subscriptions/{id}/providers?api-version=2015-11-01
and
GET https://management.azure.com/subscriptions/{id}/providers?$top=10&api-version=2015-11-01
appear to return the same results.
Spec appears to support the $top parameter. Not sure if this is expected behavior or not. | 1.0 | $top query parameter in /subscriptions/{id}/providers doesn't seem to be respected - GET https://management.azure.com/subscriptions/{id}/providers?api-version=2015-11-01
and
GET https://management.azure.com/subscriptions/{id}/providers?$top=10&api-version=2015-11-01
appear to return the same results.
Spec appears to support the $top parameter. Not sure if this is expected behavior or not. | non_priority | top query parameter in subscriptions id providers doesn t seem to be respected get and get appear to return the same results spec appears to support the top parameter not sure if this is expected behavior or not | 0 |
144,102 | 22,272,734,803 | IssuesEvent | 2022-06-10 13:49:28 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | [Design] Modify Poster to have Text Option be Primary and QR Code Secondary | design HCE-Checkin | ## Problem Statement
As a Veteran, since I have a difficult time using a QR code either because I don't understand how to use them or I cannot get it to work on my phone, I would like to understand that I can simply text "check in" to a number to accomplish the same thing so that I know I have an alternative.
## Tasks
- [ ] Design a poster where the text option is primary and the QR code is secondary
- [ ] Test the poster with Veterans (? do we need to do this?)
- [ ] Upload the poster to Git
- [ ] Notify all facilities that are using the poster of the changes | 1.0 | [Design] Modify Poster to have Text Option be Primary and QR Code Secondary - ## Problem Statement
As a Veteran, since I have a difficult time using a QR code either because I don't understand how to use them or I cannot get it to work on my phone, I would like to understand that I can simply text "check in" to a number to accomplish the same thing so that I know I have an alternative.
## Tasks
- [ ] Design a poster where the text option is primary and the QR code is secondary
- [ ] Test the poster with Veterans (? do we need to do this?)
- [ ] Upload the poster to Git
- [ ] Notify all facilities that are using the poster of the changes | non_priority | modify poster to have text option be primary and qr code secondary problem statement as a veteran since i have a difficult time using a qr code either because i don t understand how to use them or i cannot get it to work on my phone i would like to understand that i can simply text check in to a number to accomplish the same thing so that i know i have an alternative tasks design a poster where the text option is primary and the qr code is secondary test the poster with veterans do we need to do this upload the poster to git notify all facilities that are using the poster of the changes | 0 |
31,751 | 6,617,263,815 | IssuesEvent | 2017-09-21 00:21:21 | Openki/Openki | https://api.github.com/repos/Openki/Openki | closed | Make the "member icon" purple for the courses that I participate | Defect UI | This new icon is very cool and I think it would be very nice if it was made purple for the courses that I participate. | 1.0 | Make the "member icon" purple for the courses that I participate - This new icon is very cool and I think it would be very nice if it was made purple for the courses that I participate. | non_priority | make the member icon purple for the courses that i participate this new icon is very cool and i think it would be very nice if it was made purple for the courses that i participate | 0 |
26,949 | 12,499,572,413 | IssuesEvent | 2020-06-01 20:25:17 | Azure/azure-sdk-for-python | https://api.github.com/repos/Azure/azure-sdk-for-python | closed | [textanalytics] Throw exception on service warning about data limits | Client Cognitive Services TextAnalytics | Teams thread [here](https://teams.microsoft.com/l/message/19:d6ff4003f5c848a2a2d6dcdfc0ebd497@thread.skype/1588101934413?tenantId=72f988bf-86f1-41af-91ab-2d7cd011db47&groupId=3e17dcb0-4257-4a30-b843-77f47f1d4121&parentMessageId=1588101934413&teamName=Azure%20SDK&channelName=Service%20-%20Text%20Analytics&createdTime=1588101934413).
Service will eventually return a 400 for this, but we should raise an exception now so it doesn't become a breaking change in the future (an exception thrown where there wasn't one before). | 1.0 | [textanalytics] Throw exception on service warning about data limits - Teams thread [here](https://teams.microsoft.com/l/message/19:d6ff4003f5c848a2a2d6dcdfc0ebd497@thread.skype/1588101934413?tenantId=72f988bf-86f1-41af-91ab-2d7cd011db47&groupId=3e17dcb0-4257-4a30-b843-77f47f1d4121&parentMessageId=1588101934413&teamName=Azure%20SDK&channelName=Service%20-%20Text%20Analytics&createdTime=1588101934413).
Service will eventually return a 400 for this, but we should raise an exception now so it doesn't become a breaking change in the future (an exception thrown where there wasn't one before). | non_priority | throw exception on service warning about data limits teams thread service will eventually return a for this but we should raise an exception now so it doesn t become a breaking change in the future an exception thrown where there wasn t one before | 0 |
114,176 | 11,839,601,482 | IssuesEvent | 2020-03-23 17:25:00 | boutproject/BOUT-dev | https://api.github.com/repos/boutproject/BOUT-dev | closed | Documentation of available implementations | documentation | It would be very nice to have a list of what implementations are available for each feature. | 1.0 | Documentation of available implementations - It would be very nice to have a list of what implementations are available for each feature. | non_priority | documentation of available implementations it would be very nice to have a list of what implementations are available for each feature | 0 |
277,194 | 24,054,664,904 | IssuesEvent | 2022-09-16 15:40:53 | gradle/gradle | https://api.github.com/repos/gradle/gradle | closed | Only run setup/teardown tasks if a test task needs to run (with build cache support) | in:testing a:feature stale | ### Context
We got Karma/Jasmine unit tests executed through Gradle with the [gradle-node-plugin](https://github.com/node-gradle/gradle-node-plugin), let's call it `npmTest` (executing command `npm test`). Instead of letting Karma run whatever browser it finds installed on the system (which may be incompatible), we also use the [gradle-docker-plugin](https://github.com/bmuschko/gradle-docker-plugin) to fire up a well-known instance of a browser, using e.g. the [elgalu/docker-selenium](https://github.com/elgalu/docker-selenium) images, which also let us record the screen in case of weird problems so we can debug easily. However, the docker plugin makes us map every single docker operation into a separate task, which was already problematic for multiple projects building in parallel (#10549). And now we got a new problem: those docker tasks are never up to date, and they keep running even when the `npmTest` state is `FROM-CACHE`.
I considered the idea of [a similar problem with `functionalTestRun`](https://discuss.gradle.org/t/how-can-i-start-a-server-conditionally-before-a-functionaltestrun/6389), but it is not gradle cache compatible, and in our case, the task is actually cacheable because they are unit tests. And it already feels wrong that we have no proper API to copy all up-to-date conditions to other tasks, and that all checks would be performed multiple times, let alone if we would cache the same results multiple times.
The reason I do the docker handling in Gradle is that we also need it for acceptance tests that also need a browser. The only difference there is that acceptance test tasks are never be up to date due to dependence on an external system (the backend).
### Expected Behavior
We need the possibility to depend on task(s) that will only get executed if the task that needs those dependent tasks is not up to date and has to be executed.
### Current Behavior
Only workarounds can be given right now and they are too hacky. Current solution even makes us consider dropping the gradle-docker-plugin, which is too bad. I do agree though that the granularity of docker tasks can be a bit too high with that plugin.
| 1.0 | Only run setup/teardown tasks if a test task needs to run (with build cache support) - ### Context
We got Karma/Jasmine unit tests executed through Gradle with the [gradle-node-plugin](https://github.com/node-gradle/gradle-node-plugin), let's call it `npmTest` (executing command `npm test`). Instead of letting Karma run whatever browser it finds installed on the system (which may be incompatible), we also use the [gradle-docker-plugin](https://github.com/bmuschko/gradle-docker-plugin) to fire up a well-known instance of a browser, using e.g. the [elgalu/docker-selenium](https://github.com/elgalu/docker-selenium) images, which also let us record the screen in case of weird problems so we can debug easily. However, the docker plugin makes us map every single docker operation into a separate task, which was already problematic for multiple projects building in parallel (#10549). And now we got a new problem: those docker tasks are never up to date, and they keep running even when the `npmTest` state is `FROM-CACHE`.
I considered the idea of [a similar problem with `functionalTestRun`](https://discuss.gradle.org/t/how-can-i-start-a-server-conditionally-before-a-functionaltestrun/6389), but it is not gradle cache compatible, and in our case, the task is actually cacheable because they are unit tests. And it already feels wrong that we have no proper API to copy all up-to-date conditions to other tasks, and that all checks would be performed multiple times, let alone if we would cache the same results multiple times.
The reason I do the docker handling in Gradle is that we also need it for acceptance tests that also need a browser. The only difference there is that acceptance test tasks are never be up to date due to dependence on an external system (the backend).
### Expected Behavior
We need the possibility to depend on task(s) that will only get executed if the task that needs those dependent tasks is not up to date and has to be executed.
### Current Behavior
Only workarounds can be given right now and they are too hacky. Current solution even makes us consider dropping the gradle-docker-plugin, which is too bad. I do agree though that the granularity of docker tasks can be a bit too high with that plugin.
| non_priority | only run setup teardown tasks if a test task needs to run with build cache support context we got karma jasmine unit tests executed through gradle with the let s call it npmtest executing command npm test instead of letting karma run whatever browser it finds installed on the system which may be incompatible we also use the to fire up a well known instance of a browser using e g the images which also let us record the screen in case of weird problems so we can debug easily however the docker plugin makes us map every single docker operation into a separate task which was already problematic for multiple projects building in parallel and now we got a new problem those docker tasks are never up to date and they keep running even when the npmtest state is from cache i considered the idea of but it is not gradle cache compatible and in our case the task is actually cacheable because they are unit tests and it already feels wrong that we have no proper api to copy all up to date conditions to other tasks and that all checks would be performed multiple times let alone if we would cache the same results multiple times the reason i do the docker handling in gradle is that we also need it for acceptance tests that also need a browser the only difference there is that acceptance test tasks are never be up to date due to dependence on an external system the backend expected behavior we need the possibility to depend on task s that will only get executed if the task that needs those dependent tasks is not up to date and has to be executed current behavior only workarounds can be given right now and they are too hacky current solution even makes us consider dropping the gradle docker plugin which is too bad i do agree though that the granularity of docker tasks can be a bit too high with that plugin | 0 |
15,736 | 5,169,911,347 | IssuesEvent | 2017-01-18 03:06:50 | triplea-game/triplea | https://api.github.com/repos/triplea-game/triplea | closed | Time to load main window is dominated by map parsing | category: game engine > code and infrastructure type: performance | The time to fetch map data to populate the left hand side of the main window dominates map bootup time. Experimenting with 'war of the relics', which takes 25s to parse, I noticed that it took that long for the main game screen to load.
A) Map parsing should be faster. That is already being tackled though.
B) We could load the map data in a background thread, would allow for the UI to show up much faster
| 1.0 | Time to load main window is dominated by map parsing - The time to fetch map data to populate the left hand side of the main window dominates map bootup time. Experimenting with 'war of the relics', which takes 25s to parse, I noticed that it took that long for the main game screen to load.
A) Map parsing should be faster. That is already being tackled though.
B) We could load the map data in a background thread, would allow for the UI to show up much faster
| non_priority | time to load main window is dominated by map parsing the time to fetch map data to populate the left hand side of the main window dominates map bootup time experimenting with war of the relics which takes to parse i noticed that it took that long for the main game screen to load a map parsing should be faster that is already being tackled though b we could load the map data in a background thread would allow for the ui to show up much faster | 0 |
43,864 | 11,871,949,629 | IssuesEvent | 2020-03-26 15:07:02 | STEllAR-GROUP/hpx | https://api.github.com/repos/STEllAR-GROUP/hpx | closed | New std::variant serialization broken | category: serialization type: defect | ## Expected Behavior
to compile
## Actual Behavior
not compiling with error
## Steps to Reproduce the Problem
See gist: https://gist.github.com/McKillroy/cb04b97975db409e7f0c8657e3f85744
## Specifications
- HPX Version: Commit 8269dd13183efa3bc0fa5346e7a26cc069ee0414
- Platform (compiler, OS): MSVC 19, latest, Windows 10
| 1.0 | New std::variant serialization broken - ## Expected Behavior
to compile
## Actual Behavior
not compiling with error
## Steps to Reproduce the Problem
See gist: https://gist.github.com/McKillroy/cb04b97975db409e7f0c8657e3f85744
## Specifications
- HPX Version: Commit 8269dd13183efa3bc0fa5346e7a26cc069ee0414
- Platform (compiler, OS): MSVC 19, latest, Windows 10
| non_priority | new std variant serialization broken expected behavior to compile actual behavior not compiling with error steps to reproduce the problem see gist specifications hpx version commit platform compiler os msvc latest windows | 0 |
144,234 | 13,099,666,915 | IssuesEvent | 2020-08-03 22:10:17 | seanpm2001/SNU_FontLIBrary | https://api.github.com/repos/seanpm2001/SNU_FontLIBrary | closed | Add a homepage | documentation enhancement good first issue |
***
### Add a homepage
This project needs its own homepage. I will get to this when I have more time.
***
| 1.0 | Add a homepage -
***
### Add a homepage
This project needs its own homepage. I will get to this when I have more time.
***
| non_priority | add a homepage add a homepage this project needs its own homepage i will get to this when i have more time | 0 |
298,874 | 25,863,117,006 | IssuesEvent | 2022-12-13 18:29:25 | microsoft/playwright | https://api.github.com/repos/microsoft/playwright | closed | [Question] testInfo.retry flag inside a fixture? | feature-test-runner | Hi again)
Could we get the information about retry status inside test-scoped fixtures?
What I want to do: run all tests in just one single page (https://github.com/microsoft/playwright/issues/15948#issuecomment-1196020798). But, if test fails, I want to retry it in the new fresh browser context.
PS: We had some flaky issues with page in webkit, and test retry doesnt help, but job retry does. | 1.0 | [Question] testInfo.retry flag inside a fixture? - Hi again)
Could we get the information about retry status inside test-scoped fixtures?
What I want to do: run all tests in just one single page (https://github.com/microsoft/playwright/issues/15948#issuecomment-1196020798). But, if test fails, I want to retry it in the new fresh browser context.
PS: We had some flaky issues with page in webkit, and test retry doesnt help, but job retry does. | non_priority | testinfo retry flag inside a fixture hi again could we get the information about retry status inside test scoped fixtures what i want to do run all tests in just one single page but if test fails i want to retry it in the new fresh browser context ps we had some flaky issues with page in webkit and test retry doesnt help but job retry does | 0 |
27,835 | 5,399,476,938 | IssuesEvent | 2017-02-27 19:33:09 | bounswe/bounswe2017group1 | https://api.github.com/repos/bounswe/bounswe2017group1 | closed | Failure Management section of the Requirements | documentation | Part 2.3.1 of the requirements is ambiguous. What are the appropriate messages or what are the possible errors? | 1.0 | Failure Management section of the Requirements - Part 2.3.1 of the requirements is ambiguous. What are the appropriate messages or what are the possible errors? | non_priority | failure management section of the requirements part of the requirements is ambiguous what are the appropriate messages or what are the possible errors | 0 |
5,202 | 12,223,967,090 | IssuesEvent | 2020-05-02 20:05:42 | elijahhampton/Lupa | https://api.github.com/repos/elijahhampton/Lupa | closed | Show some type of notice that a user is a trainer | architecture/user enhancement |
┆Issue is synchronized with this [Asana task](https://app.asana.com/0/1165428724105173/1166554672571559) by [Unito](https://www.unito.io/learn-more)
| 1.0 | Show some type of notice that a user is a trainer -
┆Issue is synchronized with this [Asana task](https://app.asana.com/0/1165428724105173/1166554672571559) by [Unito](https://www.unito.io/learn-more)
| non_priority | show some type of notice that a user is a trainer ┆issue is synchronized with this by | 0 |
270,173 | 28,960,435,844 | IssuesEvent | 2023-05-10 01:41:49 | Trinadh465/linux-4.1.15_CVE-2017-1000371 | https://api.github.com/repos/Trinadh465/linux-4.1.15_CVE-2017-1000371 | reopened | CVE-2019-15504 (High) detected in linuxlinux-4.6 | Mend: dependency security vulnerability | ## CVE-2019-15504 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2017-1000371/commit/8cc0bec3d85a996d6015c27f949826b9ffc4d1ae">8cc0bec3d85a996d6015c27f949826b9ffc4d1ae</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/wireless/rsi/rsi_91x_usb.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/wireless/rsi/rsi_91x_usb.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/wireless/rsi/rsi_91x_usb.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
drivers/net/wireless/rsi/rsi_91x_usb.c in the Linux kernel through 5.2.9 has a Double Free via crafted USB device traffic (which may be remote via usbip or usbredir).
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-15504>CVE-2019-15504</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15504">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15504</a></p>
<p>Release Date: 2019-09-04</p>
<p>Fix Resolution: v5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-15504 (High) detected in linuxlinux-4.6 - ## CVE-2019-15504 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2017-1000371/commit/8cc0bec3d85a996d6015c27f949826b9ffc4d1ae">8cc0bec3d85a996d6015c27f949826b9ffc4d1ae</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/wireless/rsi/rsi_91x_usb.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/wireless/rsi/rsi_91x_usb.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/wireless/rsi/rsi_91x_usb.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
drivers/net/wireless/rsi/rsi_91x_usb.c in the Linux kernel through 5.2.9 has a Double Free via crafted USB device traffic (which may be remote via usbip or usbredir).
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-15504>CVE-2019-15504</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15504">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15504</a></p>
<p>Release Date: 2019-09-04</p>
<p>Fix Resolution: v5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers net wireless rsi rsi usb c drivers net wireless rsi rsi usb c drivers net wireless rsi rsi usb c vulnerability details drivers net wireless rsi rsi usb c in the linux kernel through has a double free via crafted usb device traffic which may be remote via usbip or usbredir publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
327,443 | 24,137,475,490 | IssuesEvent | 2022-09-21 12:31:39 | mitsuba-renderer/mitsuba3 | https://api.github.com/repos/mitsuba-renderer/mitsuba3 | closed | [🐛 bug report] site-packages\mitsuba\__init__.pyi:870: error: invalid syntax | bug documentation | ## Summary
The mitsuba 3.0.1 stub file contains invalid syntax.
## System configuration
- mypy version: 0.971
- Python version: 3.9
- Mitsuba 3 version: 3.0.1
## Description
The mitsuba 3.0.1 stub file `mitsuba\__init__.pyi` contains this invalid syntax on line 870:
```
def __init__(self: mitsuba.BSDFContext, mode: mitsuba.TransportMode = <TransportMode.Radiance: 0>) -> None:
```
## Steps to reproduce
1. `pip install mitsuba==3.0.1`
2. Create `test.py`:
```
import mitsuba
```
3. `mypy test.py`
```
C:\Python39\lib\site-packages\mitsuba\__init__.pyi:870: error: invalid syntax
Found 1 error in 1 file (errors prevented further checking)
```
| 1.0 | [🐛 bug report] site-packages\mitsuba\__init__.pyi:870: error: invalid syntax - ## Summary
The mitsuba 3.0.1 stub file contains invalid syntax.
## System configuration
- mypy version: 0.971
- Python version: 3.9
- Mitsuba 3 version: 3.0.1
## Description
The mitsuba 3.0.1 stub file `mitsuba\__init__.pyi` contains this invalid syntax on line 870:
```
def __init__(self: mitsuba.BSDFContext, mode: mitsuba.TransportMode = <TransportMode.Radiance: 0>) -> None:
```
## Steps to reproduce
1. `pip install mitsuba==3.0.1`
2. Create `test.py`:
```
import mitsuba
```
3. `mypy test.py`
```
C:\Python39\lib\site-packages\mitsuba\__init__.pyi:870: error: invalid syntax
Found 1 error in 1 file (errors prevented further checking)
```
| non_priority | site packages mitsuba init pyi error invalid syntax summary the mitsuba stub file contains invalid syntax system configuration mypy version python version mitsuba version description the mitsuba stub file mitsuba init pyi contains this invalid syntax on line def init self mitsuba bsdfcontext mode mitsuba transportmode none steps to reproduce pip install mitsuba create test py import mitsuba mypy test py c lib site packages mitsuba init pyi error invalid syntax found error in file errors prevented further checking | 0 |
13,246 | 10,167,496,726 | IssuesEvent | 2019-08-07 18:21:55 | celo-org/celo-monorepo | https://api.github.com/repos/celo-org/celo-monorepo | closed | Re-enable app notifications | applications infrastructure | ### Expected Behavior
Re-enabled for `alfajores` network
### Current Behavior
Disabled due to bug in app
| 1.0 | Re-enable app notifications - ### Expected Behavior
Re-enabled for `alfajores` network
### Current Behavior
Disabled due to bug in app
| non_priority | re enable app notifications expected behavior re enabled for alfajores network current behavior disabled due to bug in app | 0 |
125,994 | 17,861,752,915 | IssuesEvent | 2021-09-06 02:20:53 | Galaxy-Software-Service/WebGoat | https://api.github.com/repos/Galaxy-Software-Service/WebGoat | opened | CVE-2021-23358 (High) detected in underscore-min-1.10.2.js | security vulnerability | ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-min-1.10.2.js</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/underscore.js/1.10.2/underscore-min.js">https://cdnjs.cloudflare.com/ajax/libs/underscore.js/1.10.2/underscore-min.js</a></p>
<p>Path to vulnerable library: /webgoat-container/target/classes/static/js/libs/underscore-min.js,/webgoat-container/src/main/resources/static/js/libs/underscore-min.js</p>
<p>
Dependency Hierarchy:
- :x: **underscore-min-1.10.2.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Galaxy-Software-Service/WebGoat/commit/12040d57fd51ffa0b6407f8b4e9cc04e47656d2d">12040d57fd51ffa0b6407f8b4e9cc04e47656d2d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"underscore.js","packageVersion":"1.10.2","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"underscore.js:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"underscore - 1.12.1,1.13.0-2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23358","vulnerabilityDetails":"The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-23358 (High) detected in underscore-min-1.10.2.js - ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-min-1.10.2.js</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/underscore.js/1.10.2/underscore-min.js">https://cdnjs.cloudflare.com/ajax/libs/underscore.js/1.10.2/underscore-min.js</a></p>
<p>Path to vulnerable library: /webgoat-container/target/classes/static/js/libs/underscore-min.js,/webgoat-container/src/main/resources/static/js/libs/underscore-min.js</p>
<p>
Dependency Hierarchy:
- :x: **underscore-min-1.10.2.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Galaxy-Software-Service/WebGoat/commit/12040d57fd51ffa0b6407f8b4e9cc04e47656d2d">12040d57fd51ffa0b6407f8b4e9cc04e47656d2d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"underscore.js","packageVersion":"1.10.2","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"underscore.js:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"underscore - 1.12.1,1.13.0-2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23358","vulnerabilityDetails":"The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in underscore min js cve high severity vulnerability vulnerable library underscore min js javascript s functional programming helper library library home page a href path to vulnerable library webgoat container target classes static js libs underscore min js webgoat container src main resources static js libs underscore min js dependency hierarchy x underscore min js vulnerable library found in head commit a href found in base branch master vulnerability details the package underscore from and before from and before are vulnerable to arbitrary code injection via the template function particularly when a variable property is passed as an argument as it is not sanitized publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution underscore isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree underscore js isminimumfixversionavailable true minimumfixversion underscore basebranches vulnerabilityidentifier cve vulnerabilitydetails the package underscore from and before from and before are vulnerable to arbitrary code injection via the template function particularly when a variable property is passed as an argument as it is not sanitized vulnerabilityurl | 0 |
18,630 | 13,109,708,458 | IssuesEvent | 2020-08-04 19:12:56 | wet-boew/wet-boew | https://api.github.com/repos/wet-boew/wet-boew | opened | Modal: User with AT feedback | Work: Usability | Testing the [Opening popups through JavaScript modal example](http://universallabs.org/wet/labs/pr8855/demos/lightbox/lightbox-en.html#examples5).
## Tools used
- Dolphin Supernova Magnifier screen reader.
- Jaws screen reader
## Issues noted
The users were able to navigate in and out of the modals. However, the use of modals is confusing to low and no vision users. For low vision users, especially when using magnifiers, the expectation is the content can be found and followed along the left side of the screen, therefore the centered modal is difficult to predict and to find. For some users relying on screen readers, modal windows are a completely foreign concept. | True | Modal: User with AT feedback - Testing the [Opening popups through JavaScript modal example](http://universallabs.org/wet/labs/pr8855/demos/lightbox/lightbox-en.html#examples5).
## Tools used
- Dolphin Supernova Magnifier screen reader.
- Jaws screen reader
## Issues noted
The users were able to navigate in and out of the modals. However, the use of modals is confusing to low and no vision users. For low vision users, especially when using magnifiers, the expectation is the content can be found and followed along the left side of the screen, therefore the centered modal is difficult to predict and to find. For some users relying on screen readers, modal windows are a completely foreign concept. | non_priority | modal user with at feedback testing the tools used dolphin supernova magnifier screen reader jaws screen reader issues noted the users were able to navigate in and out of the modals however the use of modals is confusing to low and no vision users for low vision users especially when using magnifiers the expectation is the content can be found and followed along the left side of the screen therefore the centered modal is difficult to predict and to find for some users relying on screen readers modal windows are a completely foreign concept | 0 |
107,966 | 16,762,615,162 | IssuesEvent | 2021-06-14 02:37:56 | gms-ws-demo/nibrs-pr-test | https://api.github.com/repos/gms-ws-demo/nibrs-pr-test | opened | CVE-2020-1745 (High) detected in undertow-core-1.4.20.Final.jar, undertow-core-1.4.25.Final.jar | security vulnerability | ## CVE-2020-1745 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>undertow-core-1.4.20.Final.jar</b>, <b>undertow-core-1.4.25.Final.jar</b></p></summary>
<p>
<details><summary><b>undertow-core-1.4.20.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Library home page: <a href="http://www.jboss.org/">http://www.jboss.org/</a></p>
<p>Path to dependency file: nibrs-pr-test/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/1.4.20.Final/undertow-core-1.4.20.Final.jar,nibrs-pr-test/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/undertow-core-1.4.20.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **undertow-core-1.4.20.Final.jar** (Vulnerable Library)
</details>
<details><summary><b>undertow-core-1.4.25.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Library home page: <a href="http://www.jboss.org/">http://www.jboss.org/</a></p>
<p>Path to dependency file: nibrs-pr-test/tools/nibrs-route/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/1.4.25.Final/undertow-core-1.4.25.Final.jar,nibrs-pr-test/tools/nibrs-route/target/nibrs-route-1.0.0/WEB-INF/lib/undertow-core-1.4.25.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **undertow-core-1.4.25.Final.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-demo/nibrs-pr-test/commit/860cc22f54e17594e32e303f0716fb065202fff5">860cc22f54e17594e32e303f0716fb065202fff5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A file inclusion vulnerability was found in the AJP connector enabled with a default AJP configuration port of 8009 in Undertow version 2.0.29.Final and before and was fixed in 2.0.30.Final. A remote, unauthenticated attacker could exploit this vulnerability to read web application files from a vulnerable server. In instances where the vulnerable server allows file uploads, an attacker could upload malicious JavaServer Pages (JSP) code within a variety of file types and trigger this vulnerability to gain remote code execution.
<p>Publish Date: 2020-04-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-1745>CVE-2020-1745</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-1745">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-1745</a></p>
<p>Release Date: 2020-04-28</p>
<p>Fix Resolution: io.undertow:undertow-core:2.0.30.Final</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.undertow","packageName":"undertow-core","packageVersion":"1.4.20.Final","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"io.undertow:undertow-core:1.4.20.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.undertow:undertow-core:2.0.30.Final"},{"packageType":"Java","groupId":"io.undertow","packageName":"undertow-core","packageVersion":"1.4.25.Final","packageFilePaths":["/tools/nibrs-route/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"io.undertow:undertow-core:1.4.25.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.undertow:undertow-core:2.0.30.Final"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-1745","vulnerabilityDetails":"A file inclusion vulnerability was found in the AJP connector enabled with a default AJP configuration port of 8009 in Undertow version 2.0.29.Final and before and was fixed in 2.0.30.Final. A remote, unauthenticated attacker could exploit this vulnerability to read web application files from a vulnerable server. In instances where the vulnerable server allows file uploads, an attacker could upload malicious JavaServer Pages (JSP) code within a variety of file types and trigger this vulnerability to gain remote code execution.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-1745","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-1745 (High) detected in undertow-core-1.4.20.Final.jar, undertow-core-1.4.25.Final.jar - ## CVE-2020-1745 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>undertow-core-1.4.20.Final.jar</b>, <b>undertow-core-1.4.25.Final.jar</b></p></summary>
<p>
<details><summary><b>undertow-core-1.4.20.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Library home page: <a href="http://www.jboss.org/">http://www.jboss.org/</a></p>
<p>Path to dependency file: nibrs-pr-test/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/1.4.20.Final/undertow-core-1.4.20.Final.jar,nibrs-pr-test/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/undertow-core-1.4.20.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **undertow-core-1.4.20.Final.jar** (Vulnerable Library)
</details>
<details><summary><b>undertow-core-1.4.25.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Library home page: <a href="http://www.jboss.org/">http://www.jboss.org/</a></p>
<p>Path to dependency file: nibrs-pr-test/tools/nibrs-route/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/1.4.25.Final/undertow-core-1.4.25.Final.jar,nibrs-pr-test/tools/nibrs-route/target/nibrs-route-1.0.0/WEB-INF/lib/undertow-core-1.4.25.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **undertow-core-1.4.25.Final.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-demo/nibrs-pr-test/commit/860cc22f54e17594e32e303f0716fb065202fff5">860cc22f54e17594e32e303f0716fb065202fff5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A file inclusion vulnerability was found in the AJP connector enabled with a default AJP configuration port of 8009 in Undertow version 2.0.29.Final and before and was fixed in 2.0.30.Final. A remote, unauthenticated attacker could exploit this vulnerability to read web application files from a vulnerable server. In instances where the vulnerable server allows file uploads, an attacker could upload malicious JavaServer Pages (JSP) code within a variety of file types and trigger this vulnerability to gain remote code execution.
<p>Publish Date: 2020-04-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-1745>CVE-2020-1745</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-1745">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-1745</a></p>
<p>Release Date: 2020-04-28</p>
<p>Fix Resolution: io.undertow:undertow-core:2.0.30.Final</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.undertow","packageName":"undertow-core","packageVersion":"1.4.20.Final","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"io.undertow:undertow-core:1.4.20.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.undertow:undertow-core:2.0.30.Final"},{"packageType":"Java","groupId":"io.undertow","packageName":"undertow-core","packageVersion":"1.4.25.Final","packageFilePaths":["/tools/nibrs-route/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"io.undertow:undertow-core:1.4.25.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.undertow:undertow-core:2.0.30.Final"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-1745","vulnerabilityDetails":"A file inclusion vulnerability was found in the AJP connector enabled with a default AJP configuration port of 8009 in Undertow version 2.0.29.Final and before and was fixed in 2.0.30.Final. A remote, unauthenticated attacker could exploit this vulnerability to read web application files from a vulnerable server. In instances where the vulnerable server allows file uploads, an attacker could upload malicious JavaServer Pages (JSP) code within a variety of file types and trigger this vulnerability to gain remote code execution.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-1745","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in undertow core final jar undertow core final jar cve high severity vulnerability vulnerable libraries undertow core final jar undertow core final jar undertow core final jar undertow library home page a href path to dependency file nibrs pr test tools nibrs fbi service pom xml path to vulnerable library home wss scanner repository io undertow undertow core final undertow core final jar nibrs pr test tools nibrs fbi service target nibrs fbi service web inf lib undertow core final jar dependency hierarchy x undertow core final jar vulnerable library undertow core final jar undertow library home page a href path to dependency file nibrs pr test tools nibrs route pom xml path to vulnerable library home wss scanner repository io undertow undertow core final undertow core final jar nibrs pr test tools nibrs route target nibrs route web inf lib undertow core final jar dependency hierarchy x undertow core final jar vulnerable library found in head commit a href found in base branch master vulnerability details a file inclusion vulnerability was found in the ajp connector enabled with a default ajp configuration port of in undertow version final and before and was fixed in final a remote unauthenticated attacker could exploit this vulnerability to read web application files from a vulnerable server in instances where the vulnerable server allows file uploads an attacker could upload malicious javaserver pages jsp code within a variety of file types and trigger this vulnerability to gain remote code execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution io undertow undertow core final isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree io undertow undertow core final isminimumfixversionavailable true minimumfixversion io undertow undertow core final packagetype java groupid io undertow packagename undertow core packageversion final packagefilepaths istransitivedependency false dependencytree io undertow undertow core final isminimumfixversionavailable true minimumfixversion io undertow undertow core final basebranches vulnerabilityidentifier cve vulnerabilitydetails a file inclusion vulnerability was found in the ajp connector enabled with a default ajp configuration port of in undertow version final and before and was fixed in final a remote unauthenticated attacker could exploit this vulnerability to read web application files from a vulnerable server in instances where the vulnerable server allows file uploads an attacker could upload malicious javaserver pages jsp code within a variety of file types and trigger this vulnerability to gain remote code execution vulnerabilityurl | 0 |
15,548 | 19,984,873,819 | IssuesEvent | 2022-01-30 14:00:48 | ModdingForBlockheads/DefaultOptions | https://api.github.com/repos/ModdingForBlockheads/DefaultOptions | closed | Support Vivecraft (optionsviveprofiles.txt) | compatibility fixed in next version | Vivecraft has its own options file (optionsviveprofiles.txt) in the same location as the normal and optifine options files. This is where VR keybindings and VR options are both set and it would be very useful for modpacks to be able to have default bindings for VR because most mods do not come with any default VR bindings of their own. | True | Support Vivecraft (optionsviveprofiles.txt) - Vivecraft has its own options file (optionsviveprofiles.txt) in the same location as the normal and optifine options files. This is where VR keybindings and VR options are both set and it would be very useful for modpacks to be able to have default bindings for VR because most mods do not come with any default VR bindings of their own. | non_priority | support vivecraft optionsviveprofiles txt vivecraft has its own options file optionsviveprofiles txt in the same location as the normal and optifine options files this is where vr keybindings and vr options are both set and it would be very useful for modpacks to be able to have default bindings for vr because most mods do not come with any default vr bindings of their own | 0 |
337,473 | 24,541,322,026 | IssuesEvent | 2022-10-12 04:12:43 | aditya172926/Subvid_stream_contracts | https://api.github.com/repos/aditya172926/Subvid_stream_contracts | opened | Writing Documentation | documentation good first issue hacktoberfest | If you think that the documentation for this Smart contract can be written in a better way than it already is, please make a Pull request.
I will be glad to see better ways to how simple edits can make people understand better.
Make your changes in the README file or create a separate file called Documentation.
Mention all the changes and reasons for them in the pull request description to be considered for merging. | 1.0 | Writing Documentation - If you think that the documentation for this Smart contract can be written in a better way than it already is, please make a Pull request.
I will be glad to see better ways to how simple edits can make people understand better.
Make your changes in the README file or create a separate file called Documentation.
Mention all the changes and reasons for them in the pull request description to be considered for merging. | non_priority | writing documentation if you think that the documentation for this smart contract can be written in a better way than it already is please make a pull request i will be glad to see better ways to how simple edits can make people understand better make your changes in the readme file or create a separate file called documentation mention all the changes and reasons for them in the pull request description to be considered for merging | 0 |
377,998 | 26,278,913,065 | IssuesEvent | 2023-01-07 04:19:02 | dhlee3994/board-practice | https://api.github.com/repos/dhlee3994/board-practice | closed | 깃헙 프로젝트와 이슈 정리하기 | documentation | 깃헙 프로젝트를 세팅하고, 카드를 만들어 정리하자.
* [x] 프로젝트 베타 만들기
* [x] 카드 목록 만들기 - 강의 커리큘럽 참고
* [x] 이슈로 적절히 바꾸기 | 1.0 | 깃헙 프로젝트와 이슈 정리하기 - 깃헙 프로젝트를 세팅하고, 카드를 만들어 정리하자.
* [x] 프로젝트 베타 만들기
* [x] 카드 목록 만들기 - 강의 커리큘럽 참고
* [x] 이슈로 적절히 바꾸기 | non_priority | 깃헙 프로젝트와 이슈 정리하기 깃헙 프로젝트를 세팅하고 카드를 만들어 정리하자 프로젝트 베타 만들기 카드 목록 만들기 강의 커리큘럽 참고 이슈로 적절히 바꾸기 | 0 |
350,033 | 24,965,648,359 | IssuesEvent | 2022-11-01 19:08:18 | Azure/azure-dev | https://api.github.com/repos/Azure/azure-dev | closed | Update docs for new `azd config` commands | documentation blocker | Update the docs for `azd config`
- Autogenerated docs from the cobra command configuration
- Docs regarding special config keys like `defaults.subscription` & `defaults.location` | 1.0 | Update docs for new `azd config` commands - Update the docs for `azd config`
- Autogenerated docs from the cobra command configuration
- Docs regarding special config keys like `defaults.subscription` & `defaults.location` | non_priority | update docs for new azd config commands update the docs for azd config autogenerated docs from the cobra command configuration docs regarding special config keys like defaults subscription defaults location | 0 |
51,587 | 13,635,145,910 | IssuesEvent | 2020-09-25 02:01:53 | nasifimtiazohi/openmrs-module-metadatamapping-1.3.4 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-metadatamapping-1.3.4 | opened | CVE-2016-10536 (Medium) detected in engine.io-client-1.5.4.tgz | security vulnerability | ## CVE-2016-10536 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>engine.io-client-1.5.4.tgz</b></p></summary>
<p>Client for the realtime Engine</p>
<p>Library home page: <a href="https://registry.npmjs.org/engine.io-client/-/engine.io-client-1.5.4.tgz">https://registry.npmjs.org/engine.io-client/-/engine.io-client-1.5.4.tgz</a></p>
<p>Path to dependency file: openmrs-module-metadatamapping-1.3.4/owa/package.json</p>
<p>Path to vulnerable library: openmrs-module-metadatamapping-1.3.4/owa/node_modules/engine.io-client/package.json</p>
<p>
Dependency Hierarchy:
- browser-sync-2.11.1.tgz (Root Library)
- socket.io-1.3.7.tgz
- socket.io-client-1.3.7.tgz
- :x: **engine.io-client-1.5.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-metadatamapping-1.3.4/commit/dbf14247c8c0a7b64ae301a8ab42df19cc87107e">dbf14247c8c0a7b64ae301a8ab42df19cc87107e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
engine.io-client is the client for engine.io, the implementation of a transport-based cross-browser/cross-device bi-directional communication layer for Socket.IO. The vulnerability is related to the way that node.js handles the `rejectUnauthorized` setting. If the value is something that evaluates to false, certificate verification will be disabled. This is problematic as engine.io-client 1.6.8 and earlier passes in an object for settings that includes the rejectUnauthorized property, whether it has been set or not. If the value has not been explicitly changed, it will be passed in as `null`, resulting in certificate verification being turned off.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10536>CVE-2016-10536</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/99">https://nodesecurity.io/advisories/99</a></p>
<p>Release Date: 2016-04-26</p>
<p>Fix Resolution: Update to version 1.6.9 or later.
If you are unable to upgrade, ensure all calls to socket.io to have a `rejectedUnauthorized: true` flag.</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-10536 (Medium) detected in engine.io-client-1.5.4.tgz - ## CVE-2016-10536 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>engine.io-client-1.5.4.tgz</b></p></summary>
<p>Client for the realtime Engine</p>
<p>Library home page: <a href="https://registry.npmjs.org/engine.io-client/-/engine.io-client-1.5.4.tgz">https://registry.npmjs.org/engine.io-client/-/engine.io-client-1.5.4.tgz</a></p>
<p>Path to dependency file: openmrs-module-metadatamapping-1.3.4/owa/package.json</p>
<p>Path to vulnerable library: openmrs-module-metadatamapping-1.3.4/owa/node_modules/engine.io-client/package.json</p>
<p>
Dependency Hierarchy:
- browser-sync-2.11.1.tgz (Root Library)
- socket.io-1.3.7.tgz
- socket.io-client-1.3.7.tgz
- :x: **engine.io-client-1.5.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-metadatamapping-1.3.4/commit/dbf14247c8c0a7b64ae301a8ab42df19cc87107e">dbf14247c8c0a7b64ae301a8ab42df19cc87107e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
engine.io-client is the client for engine.io, the implementation of a transport-based cross-browser/cross-device bi-directional communication layer for Socket.IO. The vulnerability is related to the way that node.js handles the `rejectUnauthorized` setting. If the value is something that evaluates to false, certificate verification will be disabled. This is problematic as engine.io-client 1.6.8 and earlier passes in an object for settings that includes the rejectUnauthorized property, whether it has been set or not. If the value has not been explicitly changed, it will be passed in as `null`, resulting in certificate verification being turned off.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10536>CVE-2016-10536</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/99">https://nodesecurity.io/advisories/99</a></p>
<p>Release Date: 2016-04-26</p>
<p>Fix Resolution: Update to version 1.6.9 or later.
If you are unable to upgrade, ensure all calls to socket.io to have a `rejectedUnauthorized: true` flag.</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in engine io client tgz cve medium severity vulnerability vulnerable library engine io client tgz client for the realtime engine library home page a href path to dependency file openmrs module metadatamapping owa package json path to vulnerable library openmrs module metadatamapping owa node modules engine io client package json dependency hierarchy browser sync tgz root library socket io tgz socket io client tgz x engine io client tgz vulnerable library found in head commit a href found in base branch master vulnerability details engine io client is the client for engine io the implementation of a transport based cross browser cross device bi directional communication layer for socket io the vulnerability is related to the way that node js handles the rejectunauthorized setting if the value is something that evaluates to false certificate verification will be disabled this is problematic as engine io client and earlier passes in an object for settings that includes the rejectunauthorized property whether it has been set or not if the value has not been explicitly changed it will be passed in as null resulting in certificate verification being turned off publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution update to version or later if you are unable to upgrade ensure all calls to socket io to have a rejectedunauthorized true flag step up your open source security game with whitesource | 0 |
175,912 | 14,545,013,176 | IssuesEvent | 2020-12-15 19:01:07 | neurostuff/NiMARE | https://api.github.com/repos/neurostuff/NiMARE | opened | Rename empirical and analytic null methods | documentation refactoring | From https://github.com/neurostuff/NiMARE/issues/389#issue-740102784:
> Probably we should rename the options too, as "empirical" is a bit confusing, IMO. I would suggest calling them "approximate" and "montecarlo", which would intuitively convey to users both that (a) the "approximate" approach doesn't really give the 'correct' answer (because it's biased by the independence assumption), and (b) the "montecarlo" approach is based on resampling and is likely to take a long time. Then the docs could more explicitly lay out the tradeoff, taking pain to emphasize that the "approximate" approach is actually conservative, so if you're willing to accept reduced sensitivity, it makes sense to just always use that.
TL;DR: Rename "empirical" to "montecarlo" and "analytic" to "approximate". | 1.0 | Rename empirical and analytic null methods - From https://github.com/neurostuff/NiMARE/issues/389#issue-740102784:
> Probably we should rename the options too, as "empirical" is a bit confusing, IMO. I would suggest calling them "approximate" and "montecarlo", which would intuitively convey to users both that (a) the "approximate" approach doesn't really give the 'correct' answer (because it's biased by the independence assumption), and (b) the "montecarlo" approach is based on resampling and is likely to take a long time. Then the docs could more explicitly lay out the tradeoff, taking pain to emphasize that the "approximate" approach is actually conservative, so if you're willing to accept reduced sensitivity, it makes sense to just always use that.
TL;DR: Rename "empirical" to "montecarlo" and "analytic" to "approximate". | non_priority | rename empirical and analytic null methods from probably we should rename the options too as empirical is a bit confusing imo i would suggest calling them approximate and montecarlo which would intuitively convey to users both that a the approximate approach doesn t really give the correct answer because it s biased by the independence assumption and b the montecarlo approach is based on resampling and is likely to take a long time then the docs could more explicitly lay out the tradeoff taking pain to emphasize that the approximate approach is actually conservative so if you re willing to accept reduced sensitivity it makes sense to just always use that tl dr rename empirical to montecarlo and analytic to approximate | 0 |
102,421 | 8,827,020,182 | IssuesEvent | 2019-01-03 06:44:17 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | closed | Testing 3/1 : ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound | Testing 3/1 | Project : Testing 3/1
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=MzY1NDdkYjgtOTYzNC00MmNiLWI1NWUtZTc2YTc4OWJiYjVh; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Thu, 03 Jan 2019 06:16:48 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/dashboard/count-time?page=
Request :
Response :
{
"timestamp" : "2019-01-03T06:16:48.279+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/dashboard/count-time"
}
Logs :
2019-01-03 06:15:32 ERROR [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : No module found with the name [FXLabs/Common/MongoDB-TimeBound-SQL_Injection_Strings] defined in Fxfile.yaml
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : URL [http://13.56.210.25/api/v1/api/v1/dashboard/count-time?page=]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Method [GET]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Request []
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Request-Headers [{Content-Type=[application/json], Accept=[application/json], Authorization=[Basic SHVtZXJhLy9odW1lcmFAZnhsYWJzLmlvOmh1bWVyYTEyMyQ=]}]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Response [{
"timestamp" : "2019-01-03T06:15:33.165+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/dashboard/count-time"
}]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Response-Headers [{X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=MzYwNjI1ZTUtOTk2YS00NWUzLTllYTItMjU1ZWI3OGU1Yjk3; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Thu, 03 Jan 2019 06:15:32 GMT]}]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : StatusCode [404]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Time [475]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Size [155]
2019-01-03 06:15:33 ERROR [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
2019-01-03 06:15:33 INFO [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Assertion [@ResponseTime < 7000 OR @ResponseTime > 10000] resolved-to [475 < 7000 OR 475 > 10000] result [Passed]
--- FX Bot --- | 1.0 | Testing 3/1 : ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound - Project : Testing 3/1
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=MzY1NDdkYjgtOTYzNC00MmNiLWI1NWUtZTc2YTc4OWJiYjVh; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Thu, 03 Jan 2019 06:16:48 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/dashboard/count-time?page=
Request :
Response :
{
"timestamp" : "2019-01-03T06:16:48.279+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/dashboard/count-time"
}
Logs :
2019-01-03 06:15:32 ERROR [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : No module found with the name [FXLabs/Common/MongoDB-TimeBound-SQL_Injection_Strings] defined in Fxfile.yaml
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : URL [http://13.56.210.25/api/v1/api/v1/dashboard/count-time?page=]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Method [GET]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Request []
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Request-Headers [{Content-Type=[application/json], Accept=[application/json], Authorization=[Basic SHVtZXJhLy9odW1lcmFAZnhsYWJzLmlvOmh1bWVyYTEyMyQ=]}]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Response [{
"timestamp" : "2019-01-03T06:15:33.165+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/dashboard/count-time"
}]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Response-Headers [{X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=MzYwNjI1ZTUtOTk2YS00NWUzLTllYTItMjU1ZWI3OGU1Yjk3; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Thu, 03 Jan 2019 06:15:32 GMT]}]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : StatusCode [404]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Time [475]
2019-01-03 06:15:33 DEBUG [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Size [155]
2019-01-03 06:15:33 ERROR [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
2019-01-03 06:15:33 INFO [ApiV1DashboardCountTimeGetQueryParamPageMongodbNoSqlInjectionTimebound] : Assertion [@ResponseTime < 7000 OR @ResponseTime > 10000] resolved-to [475 < 7000 OR 475 > 10000] result [Passed]
--- FX Bot --- | non_priority | testing project testing job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response timestamp status error not found message no message available path api api dashboard count time logs error no module found with the name defined in fxfile yaml debug url debug method debug request debug request headers accept authorization debug response timestamp status error not found message no message available path api api dashboard count time debug response headers x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date debug statuscode debug time debug size error assertion resolved to result info assertion resolved to result fx bot | 0 |
252,760 | 19,071,631,593 | IssuesEvent | 2021-11-27 01:55:50 | arxanas/git-branchless | https://api.github.com/repos/arxanas/git-branchless | closed | Please document [Workflow: Divergent development] | documentation | ### Description of the bug
The `git-move` tutorial references divergent workflows as the primary scenario in which it helps, but the page is a TODO.
### Expected behavior
_No response_
### Actual behavior
_No response_
### Version of `git-branchless`
git-branchless 0.3.7
### Version of `rustc`
rustc 1.56.1 (59eed8a2a 2021-11-01) | 1.0 | Please document [Workflow: Divergent development] - ### Description of the bug
The `git-move` tutorial references divergent workflows as the primary scenario in which it helps, but the page is a TODO.
### Expected behavior
_No response_
### Actual behavior
_No response_
### Version of `git-branchless`
git-branchless 0.3.7
### Version of `rustc`
rustc 1.56.1 (59eed8a2a 2021-11-01) | non_priority | please document description of the bug the git move tutorial references divergent workflows as the primary scenario in which it helps but the page is a todo expected behavior no response actual behavior no response version of git branchless git branchless version of rustc rustc | 0 |
58,539 | 14,287,982,838 | IssuesEvent | 2020-11-23 17:03:32 | symfony/symfony | https://api.github.com/repos/symfony/symfony | closed | [Security][BC] Erroneous and inconsistent behaviour of authentication with anonymous users | Bug Security Status: Waiting feedback Status: Works for me Unconfirmed | **Symfony version(s) affected**: 5.1+, using the new "authenticator" system
**Summary**
When using the new authenticator based system, and `http_basic` firewall, User who did not provide any credentials get an `AccessDeniedException` instead of an `AuthenticationCredentialsNotFoundException`.
HTTP side, it means User will get a 403 "Forbidden" error instead of a 401 "Unauthorized" error. So no auth prompt will be triggered.
**How to reproduce**
Config to trigger the issue:
```yaml
# security.yaml
security:
enable_authenticator_manager: true
encoders:
App\Entity\User: ~
providers:
app_user_provider:
entity:
class: App\Entity\User
firewalls:
dev:
pattern: ^/(_(profiler|wdt)|css|images|js)/
security: false
api:
http_basic: ~
pattern: /api
stateless: true
```
To compare with old behaviour, set `enable_authenticator_manager` to `false`.
**Thoughts**
The old system was declining anonymous users in the authentication layer, but if `anonymous` firewall was enabled.
In my understanding, in the new system, anonymous users are always accepted, and the authorization layer will block them. I think it is not a safe default, it is "leaky", if you configure a firewall, you don't want user to be able to ever reach authorization layer (as you may forget the `Security` annotation on a controller for instance), and on top of that, Security exceptions are loosing a lot of semantic.
The way around would be for the new system to be more strict, and to re-implement `anonymous` firewall for scenario as #37523
**Going further: inconsistent behaviour**
While playing around this issue, I tried to implement my own authenticator, such as:
```php
/**
* This class is not doing anything, just re-extending the provided authenticator.
*/
class MyHttpBasicAuthenticator extends HttpBasicAuthenticator
{
public function __construct(UserProviderInterface $userProvider, ?LoggerInterface $logger = null)
{
parent::__construct('My API', $userProvider, $logger);
}
}
```
```yaml
# security.yaml
security:
enable_authenticator_manager: true
# ...
firewalls:
# ...
api:
custom_authenticators:
- App\User\Security\Authenticator\MyHttpBasicAuthenticator
pattern: /api
stateless: true
```
And in that case, the issue is fixed: anonymous users will get 401 instead of 403. That's quite surprising and then it creates an inconsistency. | True | [Security][BC] Erroneous and inconsistent behaviour of authentication with anonymous users - **Symfony version(s) affected**: 5.1+, using the new "authenticator" system
**Summary**
When using the new authenticator based system, and `http_basic` firewall, User who did not provide any credentials get an `AccessDeniedException` instead of an `AuthenticationCredentialsNotFoundException`.
HTTP side, it means User will get a 403 "Forbidden" error instead of a 401 "Unauthorized" error. So no auth prompt will be triggered.
**How to reproduce**
Config to trigger the issue:
```yaml
# security.yaml
security:
enable_authenticator_manager: true
encoders:
App\Entity\User: ~
providers:
app_user_provider:
entity:
class: App\Entity\User
firewalls:
dev:
pattern: ^/(_(profiler|wdt)|css|images|js)/
security: false
api:
http_basic: ~
pattern: /api
stateless: true
```
To compare with old behaviour, set `enable_authenticator_manager` to `false`.
**Thoughts**
The old system was declining anonymous users in the authentication layer, but if `anonymous` firewall was enabled.
In my understanding, in the new system, anonymous users are always accepted, and the authorization layer will block them. I think it is not a safe default, it is "leaky", if you configure a firewall, you don't want user to be able to ever reach authorization layer (as you may forget the `Security` annotation on a controller for instance), and on top of that, Security exceptions are loosing a lot of semantic.
The way around would be for the new system to be more strict, and to re-implement `anonymous` firewall for scenario as #37523
**Going further: inconsistent behaviour**
While playing around this issue, I tried to implement my own authenticator, such as:
```php
/**
* This class is not doing anything, just re-extending the provided authenticator.
*/
class MyHttpBasicAuthenticator extends HttpBasicAuthenticator
{
public function __construct(UserProviderInterface $userProvider, ?LoggerInterface $logger = null)
{
parent::__construct('My API', $userProvider, $logger);
}
}
```
```yaml
# security.yaml
security:
enable_authenticator_manager: true
# ...
firewalls:
# ...
api:
custom_authenticators:
- App\User\Security\Authenticator\MyHttpBasicAuthenticator
pattern: /api
stateless: true
```
And in that case, the issue is fixed: anonymous users will get 401 instead of 403. That's quite surprising and then it creates an inconsistency. | non_priority | erroneous and inconsistent behaviour of authentication with anonymous users symfony version s affected using the new authenticator system summary when using the new authenticator based system and http basic firewall user who did not provide any credentials get an accessdeniedexception instead of an authenticationcredentialsnotfoundexception http side it means user will get a forbidden error instead of a unauthorized error so no auth prompt will be triggered how to reproduce config to trigger the issue yaml security yaml security enable authenticator manager true encoders app entity user providers app user provider entity class app entity user firewalls dev pattern profiler wdt css images js security false api http basic pattern api stateless true to compare with old behaviour set enable authenticator manager to false thoughts the old system was declining anonymous users in the authentication layer but if anonymous firewall was enabled in my understanding in the new system anonymous users are always accepted and the authorization layer will block them i think it is not a safe default it is leaky if you configure a firewall you don t want user to be able to ever reach authorization layer as you may forget the security annotation on a controller for instance and on top of that security exceptions are loosing a lot of semantic the way around would be for the new system to be more strict and to re implement anonymous firewall for scenario as going further inconsistent behaviour while playing around this issue i tried to implement my own authenticator such as php this class is not doing anything just re extending the provided authenticator class myhttpbasicauthenticator extends httpbasicauthenticator public function construct userproviderinterface userprovider loggerinterface logger null parent construct my api userprovider logger yaml security yaml security enable authenticator manager true firewalls api custom authenticators app user security authenticator myhttpbasicauthenticator pattern api stateless true and in that case the issue is fixed anonymous users will get instead of that s quite surprising and then it creates an inconsistency | 0 |
72,946 | 15,252,044,253 | IssuesEvent | 2021-02-20 01:19:20 | mrcelewis/flink | https://api.github.com/repos/mrcelewis/flink | closed | CVE-2020-7598 (Medium) detected in minimist-0.0.10.tgz - autoclosed | security vulnerability | ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: flink/flink-runtime-web/web-dashboard/package.json</p>
<p>Path to vulnerable library: flink/flink-runtime-web/web-dashboard/node_modules/ng-annotate/node_modules/minimist/package.json,flink/flink-runtime-web/web-dashboard/node_modules/gulp-browserify/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- gulp-ng-annotate-0.5.3.tgz (Root Library)
- ng-annotate-0.15.4.tgz
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.10","packageFilePaths":["/flink-runtime-web/web-dashboard/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-ng-annotate:0.5.3;ng-annotate:0.15.4;optimist:0.6.1;minimist:0.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-7598 (Medium) detected in minimist-0.0.10.tgz - autoclosed - ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: flink/flink-runtime-web/web-dashboard/package.json</p>
<p>Path to vulnerable library: flink/flink-runtime-web/web-dashboard/node_modules/ng-annotate/node_modules/minimist/package.json,flink/flink-runtime-web/web-dashboard/node_modules/gulp-browserify/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- gulp-ng-annotate-0.5.3.tgz (Root Library)
- ng-annotate-0.15.4.tgz
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.10","packageFilePaths":["/flink-runtime-web/web-dashboard/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-ng-annotate:0.5.3;ng-annotate:0.15.4;optimist:0.6.1;minimist:0.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in minimist tgz autoclosed cve medium severity vulnerability vulnerable library minimist tgz parse argument options library home page a href path to dependency file flink flink runtime web web dashboard package json path to vulnerable library flink flink runtime web web dashboard node modules ng annotate node modules minimist package json flink flink runtime web web dashboard node modules gulp browserify node modules minimist package json dependency hierarchy gulp ng annotate tgz root library ng annotate tgz optimist tgz x minimist tgz vulnerable library found in base branch master vulnerability details minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree gulp ng annotate ng annotate optimist minimist isminimumfixversionavailable true minimumfixversion minimist basebranches vulnerabilityidentifier cve vulnerabilitydetails minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload vulnerabilityurl | 0 |
28,077 | 13,526,381,067 | IssuesEvent | 2020-09-15 14:11:00 | Qiskit/qiskit-terra | https://api.github.com/repos/Qiskit/qiskit-terra | closed | Benchmark regressions on master are not being tagged correctly | performance | <!-- commit 98141a02e13b219ee80463ab6b5c94516681304d@master -->
Trying to build `master` at commit 98141a02e13b219ee80463ab6b5c94516681304d failed.
More info at: https://travis-ci.com/Qiskit/qiskit-terra/jobs/225005209 | True | Benchmark regressions on master are not being tagged correctly - <!-- commit 98141a02e13b219ee80463ab6b5c94516681304d@master -->
Trying to build `master` at commit 98141a02e13b219ee80463ab6b5c94516681304d failed.
More info at: https://travis-ci.com/Qiskit/qiskit-terra/jobs/225005209 | non_priority | benchmark regressions on master are not being tagged correctly trying to build master at commit failed more info at | 0 |
281,845 | 24,424,754,160 | IssuesEvent | 2022-10-06 01:00:56 | Princeton-CDH/geniza | https://api.github.com/repos/Princeton-CDH/geniza | closed | Implement a language switch so that users can choose to view the site in English, Hebrew, or Arabic | 🗜️ awaiting testing | ## testing notes (QA)
- [x] On the QA site, when logged in, confirm there is a language switcher with 3 languages (english, hebrew, arabic) matching the designs below
- [x] On desktop and mobile (if possible), confirm it switches the language of the current page
- [x] Navigate away and confirm the language change persists
- [x] Log out and confirm the switcher is still present, but only shows English and Hebrew
- [x] Confirm the language switcher options are properly aligned
## dev notes
@blms [here are the designs](https://www.figma.com/file/anZFStv7zBaVWnFxr95nKt/Work-in-Progress-%2F-WIP?node-id=2398%3A70147) – I'll eventually move them to the Components pages – I've provided select and hover designs for LTR and RTL pages for light and dark mode on desktop and mobile
so on desktop and mobile the toggles will stay in the nav, for mobile this means that they are visible and usable once you've selected the burger menu
You can see the designs on the pages if you zoom out of the Figma page – let me know if you need anything
| 1.0 | Implement a language switch so that users can choose to view the site in English, Hebrew, or Arabic - ## testing notes (QA)
- [x] On the QA site, when logged in, confirm there is a language switcher with 3 languages (english, hebrew, arabic) matching the designs below
- [x] On desktop and mobile (if possible), confirm it switches the language of the current page
- [x] Navigate away and confirm the language change persists
- [x] Log out and confirm the switcher is still present, but only shows English and Hebrew
- [x] Confirm the language switcher options are properly aligned
## dev notes
@blms [here are the designs](https://www.figma.com/file/anZFStv7zBaVWnFxr95nKt/Work-in-Progress-%2F-WIP?node-id=2398%3A70147) – I'll eventually move them to the Components pages – I've provided select and hover designs for LTR and RTL pages for light and dark mode on desktop and mobile
so on desktop and mobile the toggles will stay in the nav, for mobile this means that they are visible and usable once you've selected the burger menu
You can see the designs on the pages if you zoom out of the Figma page – let me know if you need anything
| non_priority | implement a language switch so that users can choose to view the site in english hebrew or arabic testing notes qa on the qa site when logged in confirm there is a language switcher with languages english hebrew arabic matching the designs below on desktop and mobile if possible confirm it switches the language of the current page navigate away and confirm the language change persists log out and confirm the switcher is still present but only shows english and hebrew confirm the language switcher options are properly aligned dev notes blms – i ll eventually move them to the components pages – i ve provided select and hover designs for ltr and rtl pages for light and dark mode on desktop and mobile so on desktop and mobile the toggles will stay in the nav for mobile this means that they are visible and usable once you ve selected the burger menu you can see the designs on the pages if you zoom out of the figma page – let me know if you need anything | 0 |
17,746 | 12,533,079,865 | IssuesEvent | 2020-06-04 16:58:45 | dotnet/docker-tools | https://api.github.com/repos/dotnet/docker-tools | closed | Retry of publish job can fail due to duplicate artifact | area:infrastructure bug triaged | If the publish job fails, it can be useful to retry the failed job if it's appropriate. However, a problem exists if the previous failed job had completed the "Publish Image Info File Artifact " task: https://github.com/dotnet/docker-tools/blob/dd3859babc98d5a371708752e0e3b3646a8cf7d6/eng/common/templates/jobs/publish.yml#L70
By completing that task, the pipeline will now contain that artifact name and execution of this task in subsequent retries will fail with an `ArtifactExistsException`. This is problematic because there are important tasks that need to get executed after this one but they'll never get executed.
Possible solutions:
* Is there a setting that can overwrite the existing pipeline artifact?
* Is there a variable that is set which indicates the retry count that can be used to produce a unique name for the artifact with each retry?
* Can we ignore the error? | 1.0 | Retry of publish job can fail due to duplicate artifact - If the publish job fails, it can be useful to retry the failed job if it's appropriate. However, a problem exists if the previous failed job had completed the "Publish Image Info File Artifact " task: https://github.com/dotnet/docker-tools/blob/dd3859babc98d5a371708752e0e3b3646a8cf7d6/eng/common/templates/jobs/publish.yml#L70
By completing that task, the pipeline will now contain that artifact name and execution of this task in subsequent retries will fail with an `ArtifactExistsException`. This is problematic because there are important tasks that need to get executed after this one but they'll never get executed.
Possible solutions:
* Is there a setting that can overwrite the existing pipeline artifact?
* Is there a variable that is set which indicates the retry count that can be used to produce a unique name for the artifact with each retry?
* Can we ignore the error? | non_priority | retry of publish job can fail due to duplicate artifact if the publish job fails it can be useful to retry the failed job if it s appropriate however a problem exists if the previous failed job had completed the publish image info file artifact task by completing that task the pipeline will now contain that artifact name and execution of this task in subsequent retries will fail with an artifactexistsexception this is problematic because there are important tasks that need to get executed after this one but they ll never get executed possible solutions is there a setting that can overwrite the existing pipeline artifact is there a variable that is set which indicates the retry count that can be used to produce a unique name for the artifact with each retry can we ignore the error | 0 |
24,609 | 6,556,617,443 | IssuesEvent | 2017-09-06 14:41:27 | udacity/sdc-issue-reports | https://api.github.com/repos/udacity/sdc-issue-reports | closed | C++ Programming: Lesson 1-24 to 1-26 formatting using setw function | code effort-Medium term_2 | Lesson and quizzes gives the impression that setw function expression are applied from left to right.
In below examples, "Ints" column does not use all 15 character width. Misalignment can be easily seen by adding 99 to int variable aaa instead of 9. Which causes 3rd row columns to mis-align due to 3rd row int column taking additional character.
lesson 24
`std::cout<<"Ints"<<std::setw(15)<<"Floats"<<std::setw(15)<<"Doubles"<< "\n";`
Lesson 26.
` std::cout<< aaa;
std::cout<< std::setw(12)<< bbb;
std::cout<< std::setw(10)<< ccc << "\n\n"; `
`int aaa = aa + 99;`
Solution should have setw expression appear left of the expression who's width being set.
May be something like below:
` cout << setw(10) << "Ints" << setw(10) << "Floats" << setw(10) << "Doubles" << endl; `
` cout << setw(10) << a << setw(10) << b << setw(10) << c << endl;`
` cout << setw(10) << aa << setw(10) << bb << setw(10) << cc << endl;`
` cout << setw(10) << aaa << setw(10) << bbb << setw(10) << ccc << endl;`
| 1.0 | C++ Programming: Lesson 1-24 to 1-26 formatting using setw function - Lesson and quizzes gives the impression that setw function expression are applied from left to right.
In below examples, "Ints" column does not use all 15 character width. Misalignment can be easily seen by adding 99 to int variable aaa instead of 9. Which causes 3rd row columns to mis-align due to 3rd row int column taking additional character.
lesson 24
`std::cout<<"Ints"<<std::setw(15)<<"Floats"<<std::setw(15)<<"Doubles"<< "\n";`
Lesson 26.
` std::cout<< aaa;
std::cout<< std::setw(12)<< bbb;
std::cout<< std::setw(10)<< ccc << "\n\n"; `
`int aaa = aa + 99;`
Solution should have setw expression appear left of the expression who's width being set.
May be something like below:
` cout << setw(10) << "Ints" << setw(10) << "Floats" << setw(10) << "Doubles" << endl; `
` cout << setw(10) << a << setw(10) << b << setw(10) << c << endl;`
` cout << setw(10) << aa << setw(10) << bb << setw(10) << cc << endl;`
` cout << setw(10) << aaa << setw(10) << bbb << setw(10) << ccc << endl;`
| non_priority | c programming lesson to formatting using setw function lesson and quizzes gives the impression that setw function expression are applied from left to right in below examples ints column does not use all character width misalignment can be easily seen by adding to int variable aaa instead of which causes row columns to mis align due to row int column taking additional character lesson std cout ints std setw floats std setw doubles n lesson std cout aaa std cout std setw bbb std cout std setw ccc n n int aaa aa solution should have setw expression appear left of the expression who s width being set may be something like below cout setw ints setw floats setw doubles endl cout setw a setw b setw c endl cout setw aa setw bb setw cc endl cout setw aaa setw bbb setw ccc endl | 0 |
251,498 | 27,175,549,008 | IssuesEvent | 2023-02-18 01:04:20 | alpersonalwebsite/node-express-postgresql-controllers | https://api.github.com/repos/alpersonalwebsite/node-express-postgresql-controllers | closed | CVE-2021-35065 (High) detected in glob-parent-5.1.2.tgz - autoclosed | security vulnerability | ## CVE-2021-35065 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-5.1.2.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.2.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- cli-7.18.6.tgz (Root Library)
- chokidar-3.5.2.tgz
- :x: **glob-parent-5.1.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/alpersonalwebsite/node-express-postgresql-controllers/commit/2b5d305f4c952dd9f033cb41a8eedc29d8760744">2b5d305f4c952dd9f033cb41a8eedc29d8760744</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package glob-parent from 6.0.0 and before 6.0.1 are vulnerable to Regular Expression Denial of Service (ReDoS)
<p>Publish Date: 2021-06-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-35065>CVE-2021-35065</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-cj88-88mr-972w">https://github.com/advisories/GHSA-cj88-88mr-972w</a></p>
<p>Release Date: 2021-06-22</p>
<p>Fix Resolution: glob-parent - 6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-35065 (High) detected in glob-parent-5.1.2.tgz - autoclosed - ## CVE-2021-35065 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-5.1.2.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.2.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- cli-7.18.6.tgz (Root Library)
- chokidar-3.5.2.tgz
- :x: **glob-parent-5.1.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/alpersonalwebsite/node-express-postgresql-controllers/commit/2b5d305f4c952dd9f033cb41a8eedc29d8760744">2b5d305f4c952dd9f033cb41a8eedc29d8760744</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package glob-parent from 6.0.0 and before 6.0.1 are vulnerable to Regular Expression Denial of Service (ReDoS)
<p>Publish Date: 2021-06-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-35065>CVE-2021-35065</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-cj88-88mr-972w">https://github.com/advisories/GHSA-cj88-88mr-972w</a></p>
<p>Release Date: 2021-06-22</p>
<p>Fix Resolution: glob-parent - 6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in glob parent tgz autoclosed cve high severity vulnerability vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href path to dependency file package json path to vulnerable library node modules glob parent package json dependency hierarchy cli tgz root library chokidar tgz x glob parent tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package glob parent from and before are vulnerable to regular expression denial of service redos publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent step up your open source security game with mend | 0 |
117,200 | 11,945,779,968 | IssuesEvent | 2020-04-03 06:43:25 | AdarshChugani/ped | https://api.github.com/repos/AdarshChugani/ped | opened | Unable to edit trip | severity.Medium type.DocumentationBug | The user guide states that there is a command to edit trips called "edittrip"
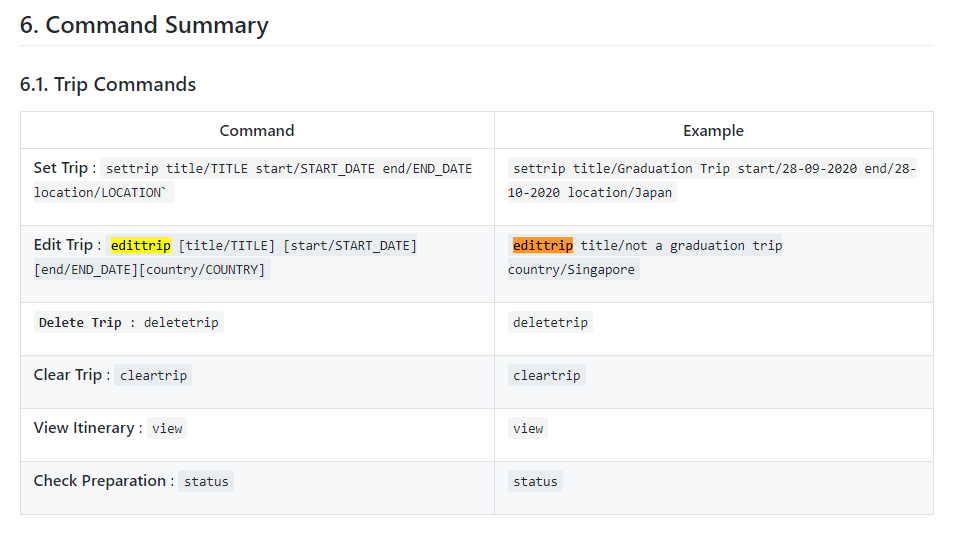
When trying it out on the application, it states that it is an invalid command.

| 1.0 | Unable to edit trip - The user guide states that there is a command to edit trips called "edittrip"
When trying it out on the application, it states that it is an invalid command.

| non_priority | unable to edit trip the user guide states that there is a command to edit trips called edittrip when trying it out on the application it states that it is an invalid command | 0 |
163,916 | 13,929,781,223 | IssuesEvent | 2020-10-22 00:34:57 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | closed | [DOC] HAVING clause error in published YB 2.3.2 YSQL grammar diagrams | area/documentation | Look within the `SELECT` diagram, [HERE](https://docs.yugabyte.com/latest/api/ysql/syntax_resources/grammar_diagrams/#select).
The "grammar" form says this:
```
[ HAVING { condition [ , ... ] } ]
```
A simple test shows this to be wrong. Create and populate a test table:
```
drop table if exists t cascade;
create table t(
k int primary key,
class int not null,
v numeric);
insert into t(k, class, v)
select
(1 + s.v),
case (s.v) < 5
when true then 1
else 2
end,
case (s.v) <> 4
when true then (100.0 + s.v)::numeric
else null
end
from generate_series(0, 9) as s(v);
```
Simple positive test. Runs without error.
```
select class, count(v), avg(v)
from t
group by class
having class < 2 and count(v) < 10;
```
Simple test to show that the YB published doc is wrong:
```
select class, count(v), avg(v)
from t
group by class
having avg(v) > 105, count(v) < 10;
```
It causes this syntax error:
```
42601: syntax error at or near ","
```
Notice that `condition` is defined thus:
```
condition ::= expression
```
This is _both_ an unhelpful level of indirection _and_ misleading. Rather, the better notion is `boolean_expression`. This rule is already found in `ysql_grammar.ebnf` but (just as is the case for `expression`) is has no further explanation.
Notice that `boolean_expression` is found in the `fn_over_window` rule, thus:
```
...[ FILTER ( WHERE { boolean_expression [ , ... ] } ) ]...
```
This shows the same error as `HAVING`. You cannot have a comma-spratated list of `WHERE` predicates. I'll correct this too.
I will fix `HAVING` by changing the rule to this:
```
[ HAVING boolean_expression ]
```
At the same time, I will replace this:
```
'WHERE' condition
```
with this:
```
'WHERE` boolean_expression
```
globally—and replace all remaining straggling uses of `condition` to `boolean_expression`. This will mean that the text `condition` is no longer found in `ysql_grammar.ebnf`. | 1.0 | [DOC] HAVING clause error in published YB 2.3.2 YSQL grammar diagrams - Look within the `SELECT` diagram, [HERE](https://docs.yugabyte.com/latest/api/ysql/syntax_resources/grammar_diagrams/#select).
The "grammar" form says this:
```
[ HAVING { condition [ , ... ] } ]
```
A simple test shows this to be wrong. Create and populate a test table:
```
drop table if exists t cascade;
create table t(
k int primary key,
class int not null,
v numeric);
insert into t(k, class, v)
select
(1 + s.v),
case (s.v) < 5
when true then 1
else 2
end,
case (s.v) <> 4
when true then (100.0 + s.v)::numeric
else null
end
from generate_series(0, 9) as s(v);
```
Simple positive test. Runs without error.
```
select class, count(v), avg(v)
from t
group by class
having class < 2 and count(v) < 10;
```
Simple test to show that the YB published doc is wrong:
```
select class, count(v), avg(v)
from t
group by class
having avg(v) > 105, count(v) < 10;
```
It causes this syntax error:
```
42601: syntax error at or near ","
```
Notice that `condition` is defined thus:
```
condition ::= expression
```
This is _both_ an unhelpful level of indirection _and_ misleading. Rather, the better notion is `boolean_expression`. This rule is already found in `ysql_grammar.ebnf` but (just as is the case for `expression`) is has no further explanation.
Notice that `boolean_expression` is found in the `fn_over_window` rule, thus:
```
...[ FILTER ( WHERE { boolean_expression [ , ... ] } ) ]...
```
This shows the same error as `HAVING`. You cannot have a comma-spratated list of `WHERE` predicates. I'll correct this too.
I will fix `HAVING` by changing the rule to this:
```
[ HAVING boolean_expression ]
```
At the same time, I will replace this:
```
'WHERE' condition
```
with this:
```
'WHERE` boolean_expression
```
globally—and replace all remaining straggling uses of `condition` to `boolean_expression`. This will mean that the text `condition` is no longer found in `ysql_grammar.ebnf`. | non_priority | having clause error in published yb ysql grammar diagrams look within the select diagram the grammar form says this a simple test shows this to be wrong create and populate a test table drop table if exists t cascade create table t k int primary key class int not null v numeric insert into t k class v select s v case s v when true then else end case s v when true then s v numeric else null end from generate series as s v simple positive test runs without error select class count v avg v from t group by class having class and count v simple test to show that the yb published doc is wrong select class count v avg v from t group by class having avg v count v it causes this syntax error syntax error at or near notice that condition is defined thus condition expression this is both an unhelpful level of indirection and misleading rather the better notion is boolean expression this rule is already found in ysql grammar ebnf but just as is the case for expression is has no further explanation notice that boolean expression is found in the fn over window rule thus this shows the same error as having you cannot have a comma spratated list of where predicates i ll correct this too i will fix having by changing the rule to this at the same time i will replace this where condition with this where boolean expression globally—and replace all remaining straggling uses of condition to boolean expression this will mean that the text condition is no longer found in ysql grammar ebnf | 0 |
125,266 | 26,629,541,948 | IssuesEvent | 2023-01-24 16:48:08 | llvm/llvm-project | https://api.github.com/repos/llvm/llvm-project | reopened | [stackmaps] Passing live i128 constant with value greater than 2^{63} -1 crashes LLVM | llvm:codegen llvm:crash | This works:
```llvm
declare void @llvm.experimental.stackmap(i64, i32, ...)
define dso_local i32 @main(i32 %argc, i8** %argv) {
entry:
%x = zext i32 %argc to i128
call void (i64, i32, ...) @llvm.experimental.stackmap(i64 0, i32 0, i128 9223372036854775807) ; <-- 2**63-1
ret i32 0
}
```
This doesn't:
```llvm
declare void @llvm.experimental.stackmap(i64, i32, ...)
define dso_local i32 @main(i32 %argc, i8** %argv) {
entry:
%x = zext i32 %argc to i128
call void (i64, i32, ...) @llvm.experimental.stackmap(i64 0, i32 0, i128 9223372036854775808) ; <-- 2**63
ret i32 0
}
```
Gives:
```console
$ clang -O2 i128.ll
warning: overriding the module target triple with x86_64-unknown-linux-gnu [-Woverride-module]
clang-15: /home/vext01/research/llvm-project/llvm/include/llvm/ADT/APInt.h:1493: int64_t llvm::APInt::getSExtValue() const: Assertion `getSignificantBits() <= 64 && "Too many bits for int64_t"' failed.
PLEASE submit a bug report to https://github.com/llvm/llvm-project/issues/ and include the crash backtrace, preprocessed source, and associated run script.
Stack dump:
0. Program arguments: /home/vext01/research/llvm-project/build/bin/clang-15 -cc1 -triple x86_64-unknown-linux-gnu -emit-obj --mrelax-relocations -disable-free -clear-ast-before-backend -main-file-name i128.ll -mrelocation-model pic -pic-level 2 -pic-is-pie -mframe-pointer=none -fmath-errno -ffp-contract=on -fno-rounding-math -mconstructor-aliases -funwind-tables=2 -target-cpu x86-64 -tune-cpu generic -mllvm -treat-scalable-fixed-error-as-warning -debugger-tuning=gdb -fcoverage-compilation-dir=/home/vext01/research/llvm-project -resource-dir /home/vext01/research/llvm-project/build/lib/clang/15.0.0 -O2 -fdebug-compilation-dir=/home/vext01/research/llvm-project -ferror-limit 19 -fgnuc-version=4.2.1 -vectorize-loops -vectorize-slp -faddrsig -D__GCC_HAVE_DWARF2_CFI_ASM=1 -o /tmp/i128-c5f403.o -x ir i128.ll
1. Code generation
2. Running pass 'Function Pass Manager' on module 'i128.ll'.
3. Running pass 'X86 DAG->DAG Instruction Selection' on function '@main'
#0 0x0000556befbcce10 PrintStackTraceSignalHandler(void*) Signals.cpp:0:0
#1 0x0000556befbca65c SignalHandler(int) Signals.cpp:0:0
#2 0x00007fcbba840140 __restore_rt (/lib/x86_64-linux-gnu/libpthread.so.0+0x14140)
#3 0x00007fcbba323ce1 raise ./signal/../sysdeps/unix/sysv/linux/raise.c:51:1
#4 0x00007fcbba30d537 abort ./stdlib/abort.c:81:7
#5 0x00007fcbba30d40f get_sysdep_segment_value ./intl/loadmsgcat.c:509:8
#6 0x00007fcbba30d40f _nl_load_domain ./intl/loadmsgcat.c:970:34
#7 0x00007fcbba31c662 (/lib/x86_64-linux-gnu/libc.so.6+0x34662)
#8 0x0000556bf0b94aa2 addStackMapLiveVars(llvm::CallBase const&, unsigned int, llvm::SDLoc const&, llvm::SmallVectorImpl<llvm::SDValue>&, llvm::SelectionDAGBuilder&) SelectionDAGBuilder.cpp:0:0
#9 0x0000556bf0b94dc7 llvm::SelectionDAGBuilder::visitStackmap(llvm::CallInst const&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4b93dc7)
#10 0x0000556bf0b8550b llvm::SelectionDAGBuilder::visitIntrinsicCall(llvm::CallInst const&, unsigned int) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4b8450b)
#11 0x0000556bf0bbaccb llvm::SelectionDAGBuilder::visit(llvm::Instruction const&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4bb9ccb)
#12 0x0000556bf0c32b89 llvm::SelectionDAGISel::SelectBasicBlock(llvm::ilist_iterator<llvm::ilist_detail::node_options<llvm::Instruction, true, false, void>, false, true>, llvm::ilist_iterator<llvm::ilist_detail::node_options<llvm::Instruction, true, false, void>, false, true>, bool&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4c31b89)
#13 0x0000556bf0c33d17 llvm::SelectionDAGISel::SelectAllBasicBlocks(llvm::Function const&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4c32d17)
#14 0x0000556bf0c35ce9 llvm::SelectionDAGISel::runOnMachineFunction(llvm::MachineFunction&) (.part.0) SelectionDAGISel.cpp:0:0
#15 0x0000556bee59289c (anonymous namespace)::X86DAGToDAGISel::runOnMachineFunction(llvm::MachineFunction&) X86ISelDAGToDAG.cpp:0:0
#16 0x0000556beed37d70 llvm::MachineFunctionPass::runOnFunction(llvm::Function&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x2d36d70)
#17 0x0000556bef25e734 llvm::FPPassManager::runOnFunction(llvm::Function&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x325d734)
#18 0x0000556bef25e951 llvm::FPPassManager::runOnModule(llvm::Module&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x325d951)
#19 0x0000556bef25f5e5 llvm::legacy::PassManagerImpl::run(llvm::Module&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x325e5e5)
#20 0x0000556beff6515b clang::EmitBackendOutput(clang::DiagnosticsEngine&, clang::HeaderSearchOptions const&, clang::CodeGenOptions const&, clang::TargetOptions const&, clang::LangOptions const&, llvm::StringRef, llvm::Module*, clang::BackendAction, std::unique_ptr<llvm::raw_pwrite_stream, std::default_delete<llvm::raw_pwrite_stream>>) (/home/vext01/research/llvm-project/build/bin/clang-15+0x3f6415b)
#21 0x0000556bf0d7bb82 clang::CodeGenAction::ExecuteAction() (/home/vext01/research/llvm-project/build/bin/clang-15+0x4d7ab82)
#22 0x0000556bf067d829 clang::FrontendAction::Execute() (/home/vext01/research/llvm-project/build/bin/clang-15+0x467c829)
#23 0x0000556bf0607336 clang::CompilerInstance::ExecuteAction(clang::FrontendAction&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4606336)
#24 0x0000556bf0733458 clang::ExecuteCompilerInvocation(clang::CompilerInstance*) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4732458)
#25 0x0000556bed2169da cc1_main(llvm::ArrayRef<char const*>, char const*, void*) (/home/vext01/research/llvm-project/build/bin/clang-15+0x12159da)
#26 0x0000556bed212264 ExecuteCC1Tool(llvm::SmallVectorImpl<char const*>&) driver.cpp:0:0
#27 0x0000556bed166fea main (/home/vext01/research/llvm-project/build/bin/clang-15+0x1165fea)
#28 0x00007fcbba30ed0a __libc_start_main ./csu/../csu/libc-start.c:308:16
#29 0x0000556bed211c0a _start (/home/vext01/research/llvm-project/build/bin/clang-15+0x1210c0a)
clang-15: error: unable to execute command: Aborted
clang-15: error: clang frontend command failed due to signal (use -v to see invocation)
clang version 15.0.0 (https://github.com/llvm/llvm-project f94a4476791873a4af1986abcd13c18991a599ee)
Target: x86_64-unknown-linux-gnu
Thread model: posix
InstalledDir: /home/vext01/research/llvm-project/build/bin
clang-15: note: diagnostic msg: Error generating preprocessed source(s) - no preprocessable inputs.
```
The stackmap code assumes that the constant can be built with `DAG.getTargetConstant(int64_t Val, ...)` | 1.0 | [stackmaps] Passing live i128 constant with value greater than 2^{63} -1 crashes LLVM - This works:
```llvm
declare void @llvm.experimental.stackmap(i64, i32, ...)
define dso_local i32 @main(i32 %argc, i8** %argv) {
entry:
%x = zext i32 %argc to i128
call void (i64, i32, ...) @llvm.experimental.stackmap(i64 0, i32 0, i128 9223372036854775807) ; <-- 2**63-1
ret i32 0
}
```
This doesn't:
```llvm
declare void @llvm.experimental.stackmap(i64, i32, ...)
define dso_local i32 @main(i32 %argc, i8** %argv) {
entry:
%x = zext i32 %argc to i128
call void (i64, i32, ...) @llvm.experimental.stackmap(i64 0, i32 0, i128 9223372036854775808) ; <-- 2**63
ret i32 0
}
```
Gives:
```console
$ clang -O2 i128.ll
warning: overriding the module target triple with x86_64-unknown-linux-gnu [-Woverride-module]
clang-15: /home/vext01/research/llvm-project/llvm/include/llvm/ADT/APInt.h:1493: int64_t llvm::APInt::getSExtValue() const: Assertion `getSignificantBits() <= 64 && "Too many bits for int64_t"' failed.
PLEASE submit a bug report to https://github.com/llvm/llvm-project/issues/ and include the crash backtrace, preprocessed source, and associated run script.
Stack dump:
0. Program arguments: /home/vext01/research/llvm-project/build/bin/clang-15 -cc1 -triple x86_64-unknown-linux-gnu -emit-obj --mrelax-relocations -disable-free -clear-ast-before-backend -main-file-name i128.ll -mrelocation-model pic -pic-level 2 -pic-is-pie -mframe-pointer=none -fmath-errno -ffp-contract=on -fno-rounding-math -mconstructor-aliases -funwind-tables=2 -target-cpu x86-64 -tune-cpu generic -mllvm -treat-scalable-fixed-error-as-warning -debugger-tuning=gdb -fcoverage-compilation-dir=/home/vext01/research/llvm-project -resource-dir /home/vext01/research/llvm-project/build/lib/clang/15.0.0 -O2 -fdebug-compilation-dir=/home/vext01/research/llvm-project -ferror-limit 19 -fgnuc-version=4.2.1 -vectorize-loops -vectorize-slp -faddrsig -D__GCC_HAVE_DWARF2_CFI_ASM=1 -o /tmp/i128-c5f403.o -x ir i128.ll
1. Code generation
2. Running pass 'Function Pass Manager' on module 'i128.ll'.
3. Running pass 'X86 DAG->DAG Instruction Selection' on function '@main'
#0 0x0000556befbcce10 PrintStackTraceSignalHandler(void*) Signals.cpp:0:0
#1 0x0000556befbca65c SignalHandler(int) Signals.cpp:0:0
#2 0x00007fcbba840140 __restore_rt (/lib/x86_64-linux-gnu/libpthread.so.0+0x14140)
#3 0x00007fcbba323ce1 raise ./signal/../sysdeps/unix/sysv/linux/raise.c:51:1
#4 0x00007fcbba30d537 abort ./stdlib/abort.c:81:7
#5 0x00007fcbba30d40f get_sysdep_segment_value ./intl/loadmsgcat.c:509:8
#6 0x00007fcbba30d40f _nl_load_domain ./intl/loadmsgcat.c:970:34
#7 0x00007fcbba31c662 (/lib/x86_64-linux-gnu/libc.so.6+0x34662)
#8 0x0000556bf0b94aa2 addStackMapLiveVars(llvm::CallBase const&, unsigned int, llvm::SDLoc const&, llvm::SmallVectorImpl<llvm::SDValue>&, llvm::SelectionDAGBuilder&) SelectionDAGBuilder.cpp:0:0
#9 0x0000556bf0b94dc7 llvm::SelectionDAGBuilder::visitStackmap(llvm::CallInst const&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4b93dc7)
#10 0x0000556bf0b8550b llvm::SelectionDAGBuilder::visitIntrinsicCall(llvm::CallInst const&, unsigned int) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4b8450b)
#11 0x0000556bf0bbaccb llvm::SelectionDAGBuilder::visit(llvm::Instruction const&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4bb9ccb)
#12 0x0000556bf0c32b89 llvm::SelectionDAGISel::SelectBasicBlock(llvm::ilist_iterator<llvm::ilist_detail::node_options<llvm::Instruction, true, false, void>, false, true>, llvm::ilist_iterator<llvm::ilist_detail::node_options<llvm::Instruction, true, false, void>, false, true>, bool&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4c31b89)
#13 0x0000556bf0c33d17 llvm::SelectionDAGISel::SelectAllBasicBlocks(llvm::Function const&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4c32d17)
#14 0x0000556bf0c35ce9 llvm::SelectionDAGISel::runOnMachineFunction(llvm::MachineFunction&) (.part.0) SelectionDAGISel.cpp:0:0
#15 0x0000556bee59289c (anonymous namespace)::X86DAGToDAGISel::runOnMachineFunction(llvm::MachineFunction&) X86ISelDAGToDAG.cpp:0:0
#16 0x0000556beed37d70 llvm::MachineFunctionPass::runOnFunction(llvm::Function&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x2d36d70)
#17 0x0000556bef25e734 llvm::FPPassManager::runOnFunction(llvm::Function&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x325d734)
#18 0x0000556bef25e951 llvm::FPPassManager::runOnModule(llvm::Module&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x325d951)
#19 0x0000556bef25f5e5 llvm::legacy::PassManagerImpl::run(llvm::Module&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x325e5e5)
#20 0x0000556beff6515b clang::EmitBackendOutput(clang::DiagnosticsEngine&, clang::HeaderSearchOptions const&, clang::CodeGenOptions const&, clang::TargetOptions const&, clang::LangOptions const&, llvm::StringRef, llvm::Module*, clang::BackendAction, std::unique_ptr<llvm::raw_pwrite_stream, std::default_delete<llvm::raw_pwrite_stream>>) (/home/vext01/research/llvm-project/build/bin/clang-15+0x3f6415b)
#21 0x0000556bf0d7bb82 clang::CodeGenAction::ExecuteAction() (/home/vext01/research/llvm-project/build/bin/clang-15+0x4d7ab82)
#22 0x0000556bf067d829 clang::FrontendAction::Execute() (/home/vext01/research/llvm-project/build/bin/clang-15+0x467c829)
#23 0x0000556bf0607336 clang::CompilerInstance::ExecuteAction(clang::FrontendAction&) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4606336)
#24 0x0000556bf0733458 clang::ExecuteCompilerInvocation(clang::CompilerInstance*) (/home/vext01/research/llvm-project/build/bin/clang-15+0x4732458)
#25 0x0000556bed2169da cc1_main(llvm::ArrayRef<char const*>, char const*, void*) (/home/vext01/research/llvm-project/build/bin/clang-15+0x12159da)
#26 0x0000556bed212264 ExecuteCC1Tool(llvm::SmallVectorImpl<char const*>&) driver.cpp:0:0
#27 0x0000556bed166fea main (/home/vext01/research/llvm-project/build/bin/clang-15+0x1165fea)
#28 0x00007fcbba30ed0a __libc_start_main ./csu/../csu/libc-start.c:308:16
#29 0x0000556bed211c0a _start (/home/vext01/research/llvm-project/build/bin/clang-15+0x1210c0a)
clang-15: error: unable to execute command: Aborted
clang-15: error: clang frontend command failed due to signal (use -v to see invocation)
clang version 15.0.0 (https://github.com/llvm/llvm-project f94a4476791873a4af1986abcd13c18991a599ee)
Target: x86_64-unknown-linux-gnu
Thread model: posix
InstalledDir: /home/vext01/research/llvm-project/build/bin
clang-15: note: diagnostic msg: Error generating preprocessed source(s) - no preprocessable inputs.
```
The stackmap code assumes that the constant can be built with `DAG.getTargetConstant(int64_t Val, ...)` | non_priority | passing live constant with value greater than crashes llvm this works llvm declare void llvm experimental stackmap define dso local main argc argv entry x zext argc to call void llvm experimental stackmap ret this doesn t llvm declare void llvm experimental stackmap define dso local main argc argv entry x zext argc to call void llvm experimental stackmap ret gives console clang ll warning overriding the module target triple with unknown linux gnu clang home research llvm project llvm include llvm adt apint h t llvm apint getsextvalue const assertion getsignificantbits too many bits for t failed please submit a bug report to and include the crash backtrace preprocessed source and associated run script stack dump program arguments home research llvm project build bin clang triple unknown linux gnu emit obj mrelax relocations disable free clear ast before backend main file name ll mrelocation model pic pic level pic is pie mframe pointer none fmath errno ffp contract on fno rounding math mconstructor aliases funwind tables target cpu tune cpu generic mllvm treat scalable fixed error as warning debugger tuning gdb fcoverage compilation dir home research llvm project resource dir home research llvm project build lib clang fdebug compilation dir home research llvm project ferror limit fgnuc version vectorize loops vectorize slp faddrsig d gcc have cfi asm o tmp o x ir ll code generation running pass function pass manager on module ll running pass dag dag instruction selection on function main printstacktracesignalhandler void signals cpp signalhandler int signals cpp restore rt lib linux gnu libpthread so raise signal sysdeps unix sysv linux raise c abort stdlib abort c get sysdep segment value intl loadmsgcat c nl load domain intl loadmsgcat c lib linux gnu libc so addstackmaplivevars llvm callbase const unsigned int llvm sdloc const llvm smallvectorimpl llvm selectiondagbuilder selectiondagbuilder cpp llvm selectiondagbuilder visitstackmap llvm callinst const home research llvm project build bin clang llvm selectiondagbuilder visitintrinsiccall llvm callinst const unsigned int home research llvm project build bin clang llvm selectiondagbuilder visit llvm instruction const home research llvm project build bin clang llvm selectiondagisel selectbasicblock llvm ilist iterator false true llvm ilist iterator false true bool home research llvm project build bin clang llvm selectiondagisel selectallbasicblocks llvm function const home research llvm project build bin clang llvm selectiondagisel runonmachinefunction llvm machinefunction part selectiondagisel cpp anonymous namespace runonmachinefunction llvm machinefunction cpp llvm machinefunctionpass runonfunction llvm function home research llvm project build bin clang llvm fppassmanager runonfunction llvm function home research llvm project build bin clang llvm fppassmanager runonmodule llvm module home research llvm project build bin clang llvm legacy passmanagerimpl run llvm module home research llvm project build bin clang clang emitbackendoutput clang diagnosticsengine clang headersearchoptions const clang codegenoptions const clang targetoptions const clang langoptions const llvm stringref llvm module clang backendaction std unique ptr home research llvm project build bin clang clang codegenaction executeaction home research llvm project build bin clang clang frontendaction execute home research llvm project build bin clang clang compilerinstance executeaction clang frontendaction home research llvm project build bin clang clang executecompilerinvocation clang compilerinstance home research llvm project build bin clang main llvm arrayref char const void home research llvm project build bin clang llvm smallvectorimpl driver cpp main home research llvm project build bin clang libc start main csu csu libc start c start home research llvm project build bin clang clang error unable to execute command aborted clang error clang frontend command failed due to signal use v to see invocation clang version target unknown linux gnu thread model posix installeddir home research llvm project build bin clang note diagnostic msg error generating preprocessed source s no preprocessable inputs the stackmap code assumes that the constant can be built with dag gettargetconstant t val | 0 |
176,185 | 28,040,339,987 | IssuesEvent | 2023-03-28 18:00:34 | eiksch/statev_v2_issues | https://api.github.com/repos/eiksch/statev_v2_issues | closed | Durchs Fenster springen bei Lucky Plucker | wontfix/rejected gamedesign | Ronny Roberts
22.03 18:38
Durchs Fenster springen/sliden (Lucky Plucker)
Nicht durchs Fenster springen/sliden
Vors Fenster stellen bei Lucky Plucker und diesen Flip da machen (Name vergessen ^^)
https://user-images.githubusercontent.com/75855042/228303204-f2dcd15b-83f5-475b-8b29-37fb1e3c7788.mp4
Man kann btw auch ohne vorher zu landen schon an sich durchs Fenster springen | 1.0 | Durchs Fenster springen bei Lucky Plucker - Ronny Roberts
22.03 18:38
Durchs Fenster springen/sliden (Lucky Plucker)
Nicht durchs Fenster springen/sliden
Vors Fenster stellen bei Lucky Plucker und diesen Flip da machen (Name vergessen ^^)
https://user-images.githubusercontent.com/75855042/228303204-f2dcd15b-83f5-475b-8b29-37fb1e3c7788.mp4
Man kann btw auch ohne vorher zu landen schon an sich durchs Fenster springen | non_priority | durchs fenster springen bei lucky plucker ronny roberts durchs fenster springen sliden lucky plucker nicht durchs fenster springen sliden vors fenster stellen bei lucky plucker und diesen flip da machen name vergessen man kann btw auch ohne vorher zu landen schon an sich durchs fenster springen | 0 |
323,672 | 27,745,213,580 | IssuesEvent | 2023-03-15 16:35:36 | delph-in/srg | https://api.github.com/repos/delph-in/srg | opened | "Casi todos los perros ladran" | mrs testsuite | Item 901 in the MRS test suite: the only reading available seems to be that "all things that are almost dogs" bark. But "Casi" should be linked to "todos", not to perros. | 1.0 | "Casi todos los perros ladran" - Item 901 in the MRS test suite: the only reading available seems to be that "all things that are almost dogs" bark. But "Casi" should be linked to "todos", not to perros. | non_priority | casi todos los perros ladran item in the mrs test suite the only reading available seems to be that all things that are almost dogs bark but casi should be linked to todos not to perros | 0 |
46,306 | 11,812,344,471 | IssuesEvent | 2020-03-19 19:58:50 | spack/spack | https://api.github.com/repos/spack/spack | closed | tau build fails on ppc64le | build-error power | I can't get `tau` to build on `ppc64le`. The compiler is `gcc@7.3.0` and I've tried on `CentOS 7`, `RHEL 7`, and `Ubuntu 18.04`. I'm using Spack @ develop (commit 958f26073efe340 from 18-March-2020).
```
$> spack install tau%gcc@7.3.0 target=ppc64le
...
==> Error: Failed to install tau due to ChildError: ProcessError: Command exited with status 2:
'make' '-j8' 'install'
14 errors found in build log:
88 Installing utilities...
89 ====================================================
90 Copy /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/tools/src/contrib/CubeReader.jar to /opt/spack/opt/sp
ack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/ibm64linux/lib
91 ====================================================
92 ... done
93 ***********************************************************************
>> 94 grep: ./utils/FixMakefile.info: No such file or directory
>> 95 grep: ./utils/FixMakefile.sed: No such file or directory
96 NOTE: Saving configuration environment to /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/.configure_env/67
9200d18f3ed1b6889dc3743f981508
97 NOTE: Enabled Profiling. Compiling with -DPROFILING_ON
98 NOTE: Building POSIX I/O wrapper
99 NOTE: GNU gfortran compiler specific options used
100 NOTE: Using PAPI interface for Hardware Performance Counters ***
101 NOTE: Using fixes for GNU 4.6+ compiler
...
200 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/plugins'
201 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/instrument'
202 /bin/rm -f simple.o simple
203 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/instrument'
204 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/threads'
205 Makefile:16: /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefile.tau-papi-gnu-mpi-pthre
ad-pdt: No such file or directory
>> 206 make[1]: *** No rule to make target '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefil
e.tau-papi-gnu-mpi-pthread-pdt'. Stop.
207 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/threads'
208 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/cthreads'
209 Makefile:16: /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefile.tau-papi-gnu-mpi-pthre
ad-pdt: No such file or directory
>> 210 make[1]: *** No rule to make target '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefil
e.tau-papi-gnu-mpi-pthread-pdt'. Stop.
211 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/cthreads'
212 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/fortran'
213 /bin/rm -f hello.o hello
214 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/fortran'
215 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/f90'
216 /bin/rm -f cubes.o cubes
217 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/f90'
218 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/pi'
219 Makefile:16: /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefile.tau-papi-gnu-mpi-pthre
ad-pdt: No such file or directory
>> 220 make[1]: *** No rule to make target '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefil
e.tau-papi-gnu-mpi-pthread-pdt'. Stop.
221 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/pi'
222 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/NPB2.3'
223 rm -f core
224 rm -f *~ */core */*~ */*.o */npbparams.h */*.obj */*.exe
225 rm -f MPI_dummy/test MPI_dummy/libmpi.a
226 rm -f sys/setparams sys/makesuite sys/setparams.h
227 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/NPB2.3'
228 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/autoinstrument'
229 Makefile:16: /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefile.tau-papi-gnu-mpi-pthre
ad-pdt: No such file or directory
>> 230 make[1]: *** No rule to make target '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefil
e.tau-papi-gnu-mpi-pthread-pdt'. Stop.
231 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/autoinstrument'
232 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/reduce'
233 Makefile:16: /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefile.tau-papi-gnu-mpi-pthre
ad-pdt: No such file or directory
>> 234 make[1]: *** No rule to make target '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefil
e.tau-papi-gnu-mpi-pthread-pdt'. Stop.
235 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/reduce'
236 touch .clean
237 Determining Configuration...
238 System previously configured as a ibm64linux
239 *********** RECURSIVELY MAKING SUBDIRECTORIES ***********
240 *** COMPILING src/TraceInput DIRECTORY
241 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/src/TraceInput'
242 g++ -m64 -I/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/include -I/opt/spack/o
pt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/include -O2 -g -Wl,-rpath,/opt/spack/opt/spack/linux-ub
untu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau
-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/zlib-1.2.11-tdnmyepqgfsybqzc55zg
ca3rvmp55epy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/pdt-3.25.1-czegb3ismtstyml2wugkifojybw4cacs/lib -Wl,-rpath,/
opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/otf2-2.2-puyvnijauo3dgbz7abnwmkx57o534yrx/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubunt
u18.04-ppc64le/gcc-7.3.0/papi-5.7.0-l4d5fyx74jacdwz4ibimdsbckpw7i2qy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libd
warf-20180129-zroyr5v2flabxnvow2ms5w7gtgydyzbv/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libelf-0.8.13-jq5x36aspohj
keofb2t7rfhbmd4bxe7c/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib
-Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/lib -Wl,-rpath,/opt/spack/opt/s
pack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04
-ppc64le/gcc-7.3.0/libunwind-1.3.1-t64vx2jrr4f4433yvrec6dn6w3rledu5/lib64 -I. -c TAU_tf.cpp
243 g++ -m64 -I/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/include -I/opt/spack/o
pt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/include -O2 -g -Wl,-rpath,/opt/spack/opt/spack/linux-ub
untu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau
-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/zlib-1.2.11-tdnmyepqgfsybqzc55zg
ca3rvmp55epy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/pdt-3.25.1-czegb3ismtstyml2wugkifojybw4cacs/lib -Wl,-rpath,/
opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/otf2-2.2-puyvnijauo3dgbz7abnwmkx57o534yrx/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubunt
u18.04-ppc64le/gcc-7.3.0/papi-5.7.0-l4d5fyx74jacdwz4ibimdsbckpw7i2qy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libd
warf-20180129-zroyr5v2flabxnvow2ms5w7gtgydyzbv/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libelf-0.8.13-jq5x36aspohj
keofb2t7rfhbmd4bxe7c/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib
-Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/lib -Wl,-rpath,/opt/spack/opt/s
pack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04
-ppc64le/gcc-7.3.0/libunwind-1.3.1-t64vx2jrr4f4433yvrec6dn6w3rledu5/lib64 -I. -c TAU_Cwrapper.cpp
244 g++ -m64 -I/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/include -I/opt/spack/o
pt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/include -O2 -g -Wl,-rpath,/opt/spack/opt/spack/linux-ub
untu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau
-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/zlib-1.2.11-tdnmyepqgfsybqzc55zg
ca3rvmp55epy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/pdt-3.25.1-czegb3ismtstyml2wugkifojybw4cacs/lib -Wl,-rpath,/
opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/otf2-2.2-puyvnijauo3dgbz7abnwmkx57o534yrx/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubunt
u18.04-ppc64le/gcc-7.3.0/papi-5.7.0-l4d5fyx74jacdwz4ibimdsbckpw7i2qy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libd
warf-20180129-zroyr5v2flabxnvow2ms5w7gtgydyzbv/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libelf-0.8.13-jq5x36aspohj
keofb2t7rfhbmd4bxe7c/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib
-Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/lib -Wl,-rpath,/opt/spack/opt/s
pack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04
-ppc64le/gcc-7.3.0/libunwind-1.3.1-t64vx2jrr4f4433yvrec6dn6w3rledu5/lib64 -I. -c TAU_tf_writer.cpp
>> 245 as: error while loading shared libraries: libopcodes-2.33.1.so: cannot open shared object file: No such file or directory
246 Makefile:126: recipe for target 'TAU_Cwrapper.o' failed
>> 247 make[1]: *** [TAU_Cwrapper.o] Error 1
248 make[1]: *** Waiting for unfinished jobs....
>> 249 as: error while loading shared libraries: libopcodes-2.33.1.so: cannot open shared object file: No such file or directory
250 Makefile:123: recipe for target 'TAU_tf_writer.o' failed
>> 251 make[1]: *** [TAU_tf_writer.o] Error 1
>> 252 as: error while loading shared libraries: libopcodes-2.33.1.so: cannot open shared object file: No such file or directory
253 Makefile:120: recipe for target 'TAU_tf.o' failed
>> 254 make[1]: *** [TAU_tf.o] Error 1
255 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/src/TraceInput'
256 Makefile:180: recipe for target 'install' failed
>> 257 make: *** [install] Error 2
See build log for details:
/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-build-out.txt
Traceback (most recent call last):
File "/opt/spack/lib/spack/spack/build_environment.py", line 801, in child_process
return_value = function()
File "/opt/spack/lib/spack/spack/installer.py", line 1114, in build_process
phase(pkg.spec, pkg.prefix)
File "/opt/spack/lib/spack/spack/package.py", line 108, in phase_wrapper
phase(spec, prefix)
File "/opt/spack/var/spack/repos/builtin/packages/tau/package.py", line 274, in install
File "/opt/spack/lib/spack/spack/build_environment.py", line 131, in __call__
return super(MakeExecutable, self).__call__(*args, **kwargs)
File "/opt/spack/lib/spack/spack/util/executable.py", line 189, in __call__
proc.returncode, long_msg)
spack.util.executable.ProcessError: Command exited with status 2:
'make' '-j8' 'install'
```
Full build log: [tau-ppc64le-log.txt](https://github.com/spack/spack/files/4351107/tau-ppc64le-log.txt)
@khuck @wspear
| 1.0 | tau build fails on ppc64le - I can't get `tau` to build on `ppc64le`. The compiler is `gcc@7.3.0` and I've tried on `CentOS 7`, `RHEL 7`, and `Ubuntu 18.04`. I'm using Spack @ develop (commit 958f26073efe340 from 18-March-2020).
```
$> spack install tau%gcc@7.3.0 target=ppc64le
...
==> Error: Failed to install tau due to ChildError: ProcessError: Command exited with status 2:
'make' '-j8' 'install'
14 errors found in build log:
88 Installing utilities...
89 ====================================================
90 Copy /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/tools/src/contrib/CubeReader.jar to /opt/spack/opt/sp
ack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/ibm64linux/lib
91 ====================================================
92 ... done
93 ***********************************************************************
>> 94 grep: ./utils/FixMakefile.info: No such file or directory
>> 95 grep: ./utils/FixMakefile.sed: No such file or directory
96 NOTE: Saving configuration environment to /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/.configure_env/67
9200d18f3ed1b6889dc3743f981508
97 NOTE: Enabled Profiling. Compiling with -DPROFILING_ON
98 NOTE: Building POSIX I/O wrapper
99 NOTE: GNU gfortran compiler specific options used
100 NOTE: Using PAPI interface for Hardware Performance Counters ***
101 NOTE: Using fixes for GNU 4.6+ compiler
...
200 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/plugins'
201 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/instrument'
202 /bin/rm -f simple.o simple
203 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/instrument'
204 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/threads'
205 Makefile:16: /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefile.tau-papi-gnu-mpi-pthre
ad-pdt: No such file or directory
>> 206 make[1]: *** No rule to make target '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefil
e.tau-papi-gnu-mpi-pthread-pdt'. Stop.
207 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/threads'
208 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/cthreads'
209 Makefile:16: /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefile.tau-papi-gnu-mpi-pthre
ad-pdt: No such file or directory
>> 210 make[1]: *** No rule to make target '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefil
e.tau-papi-gnu-mpi-pthread-pdt'. Stop.
211 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/cthreads'
212 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/fortran'
213 /bin/rm -f hello.o hello
214 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/fortran'
215 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/f90'
216 /bin/rm -f cubes.o cubes
217 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/f90'
218 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/pi'
219 Makefile:16: /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefile.tau-papi-gnu-mpi-pthre
ad-pdt: No such file or directory
>> 220 make[1]: *** No rule to make target '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefil
e.tau-papi-gnu-mpi-pthread-pdt'. Stop.
221 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/pi'
222 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/NPB2.3'
223 rm -f core
224 rm -f *~ */core */*~ */*.o */npbparams.h */*.obj */*.exe
225 rm -f MPI_dummy/test MPI_dummy/libmpi.a
226 rm -f sys/setparams sys/makesuite sys/setparams.h
227 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/NPB2.3'
228 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/autoinstrument'
229 Makefile:16: /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefile.tau-papi-gnu-mpi-pthre
ad-pdt: No such file or directory
>> 230 make[1]: *** No rule to make target '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefil
e.tau-papi-gnu-mpi-pthread-pdt'. Stop.
231 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/autoinstrument'
232 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/reduce'
233 Makefile:16: /tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefile.tau-papi-gnu-mpi-pthre
ad-pdt: No such file or directory
>> 234 make[1]: *** No rule to make target '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/ibm64linux/lib/Makefil
e.tau-papi-gnu-mpi-pthread-pdt'. Stop.
235 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/examples/reduce'
236 touch .clean
237 Determining Configuration...
238 System previously configured as a ibm64linux
239 *********** RECURSIVELY MAKING SUBDIRECTORIES ***********
240 *** COMPILING src/TraceInput DIRECTORY
241 make[1]: Entering directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/src/TraceInput'
242 g++ -m64 -I/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/include -I/opt/spack/o
pt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/include -O2 -g -Wl,-rpath,/opt/spack/opt/spack/linux-ub
untu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau
-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/zlib-1.2.11-tdnmyepqgfsybqzc55zg
ca3rvmp55epy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/pdt-3.25.1-czegb3ismtstyml2wugkifojybw4cacs/lib -Wl,-rpath,/
opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/otf2-2.2-puyvnijauo3dgbz7abnwmkx57o534yrx/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubunt
u18.04-ppc64le/gcc-7.3.0/papi-5.7.0-l4d5fyx74jacdwz4ibimdsbckpw7i2qy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libd
warf-20180129-zroyr5v2flabxnvow2ms5w7gtgydyzbv/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libelf-0.8.13-jq5x36aspohj
keofb2t7rfhbmd4bxe7c/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib
-Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/lib -Wl,-rpath,/opt/spack/opt/s
pack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04
-ppc64le/gcc-7.3.0/libunwind-1.3.1-t64vx2jrr4f4433yvrec6dn6w3rledu5/lib64 -I. -c TAU_tf.cpp
243 g++ -m64 -I/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/include -I/opt/spack/o
pt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/include -O2 -g -Wl,-rpath,/opt/spack/opt/spack/linux-ub
untu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau
-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/zlib-1.2.11-tdnmyepqgfsybqzc55zg
ca3rvmp55epy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/pdt-3.25.1-czegb3ismtstyml2wugkifojybw4cacs/lib -Wl,-rpath,/
opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/otf2-2.2-puyvnijauo3dgbz7abnwmkx57o534yrx/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubunt
u18.04-ppc64le/gcc-7.3.0/papi-5.7.0-l4d5fyx74jacdwz4ibimdsbckpw7i2qy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libd
warf-20180129-zroyr5v2flabxnvow2ms5w7gtgydyzbv/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libelf-0.8.13-jq5x36aspohj
keofb2t7rfhbmd4bxe7c/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib
-Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/lib -Wl,-rpath,/opt/spack/opt/s
pack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04
-ppc64le/gcc-7.3.0/libunwind-1.3.1-t64vx2jrr4f4433yvrec6dn6w3rledu5/lib64 -I. -c TAU_Cwrapper.cpp
244 g++ -m64 -I/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/include -I/opt/spack/o
pt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/include -O2 -g -Wl,-rpath,/opt/spack/opt/spack/linux-ub
untu18.04-ppc64le/gcc-7.3.0/tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/tau
-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/zlib-1.2.11-tdnmyepqgfsybqzc55zg
ca3rvmp55epy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/pdt-3.25.1-czegb3ismtstyml2wugkifojybw4cacs/lib -Wl,-rpath,/
opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/otf2-2.2-puyvnijauo3dgbz7abnwmkx57o534yrx/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubunt
u18.04-ppc64le/gcc-7.3.0/papi-5.7.0-l4d5fyx74jacdwz4ibimdsbckpw7i2qy/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libd
warf-20180129-zroyr5v2flabxnvow2ms5w7gtgydyzbv/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/libelf-0.8.13-jq5x36aspohj
keofb2t7rfhbmd4bxe7c/lib -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib
-Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/mpich-3.2.1-c3y5ohb72e6htbm3y7po6ymrcmxxatnp/lib -Wl,-rpath,/opt/spack/opt/s
pack/linux-ubuntu18.04-ppc64le/gcc-7.3.0/binutils-2.33.1-ztxgm2hjuxq4pdosmxnh3t6k7h764nqc/lib64 -Wl,-rpath,/opt/spack/opt/spack/linux-ubuntu18.04
-ppc64le/gcc-7.3.0/libunwind-1.3.1-t64vx2jrr4f4433yvrec6dn6w3rledu5/lib64 -I. -c TAU_tf_writer.cpp
>> 245 as: error while loading shared libraries: libopcodes-2.33.1.so: cannot open shared object file: No such file or directory
246 Makefile:126: recipe for target 'TAU_Cwrapper.o' failed
>> 247 make[1]: *** [TAU_Cwrapper.o] Error 1
248 make[1]: *** Waiting for unfinished jobs....
>> 249 as: error while loading shared libraries: libopcodes-2.33.1.so: cannot open shared object file: No such file or directory
250 Makefile:123: recipe for target 'TAU_tf_writer.o' failed
>> 251 make[1]: *** [TAU_tf_writer.o] Error 1
>> 252 as: error while loading shared libraries: libopcodes-2.33.1.so: cannot open shared object file: No such file or directory
253 Makefile:120: recipe for target 'TAU_tf.o' failed
>> 254 make[1]: *** [TAU_tf.o] Error 1
255 make[1]: Leaving directory '/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-src/src/TraceInput'
256 Makefile:180: recipe for target 'install' failed
>> 257 make: *** [install] Error 2
See build log for details:
/tmp/root/spack-stage/spack-stage-tau-2.29-ad3e57a5sfq4bxbwwir7wmyhks4k37u4/spack-build-out.txt
Traceback (most recent call last):
File "/opt/spack/lib/spack/spack/build_environment.py", line 801, in child_process
return_value = function()
File "/opt/spack/lib/spack/spack/installer.py", line 1114, in build_process
phase(pkg.spec, pkg.prefix)
File "/opt/spack/lib/spack/spack/package.py", line 108, in phase_wrapper
phase(spec, prefix)
File "/opt/spack/var/spack/repos/builtin/packages/tau/package.py", line 274, in install
File "/opt/spack/lib/spack/spack/build_environment.py", line 131, in __call__
return super(MakeExecutable, self).__call__(*args, **kwargs)
File "/opt/spack/lib/spack/spack/util/executable.py", line 189, in __call__
proc.returncode, long_msg)
spack.util.executable.ProcessError: Command exited with status 2:
'make' '-j8' 'install'
```
Full build log: [tau-ppc64le-log.txt](https://github.com/spack/spack/files/4351107/tau-ppc64le-log.txt)
@khuck @wspear
| non_priority | tau build fails on i can t get tau to build on the compiler is gcc and i ve tried on centos rhel and ubuntu i m using spack develop commit from march spack install tau gcc target error failed to install tau due to childerror processerror command exited with status make install errors found in build log installing utilities copy tmp root spack stage spack stage tau spack src tools src contrib cubereader jar to opt spack opt sp ack linux gcc tau lib done grep utils fixmakefile info no such file or directory grep utils fixmakefile sed no such file or directory note saving configuration environment to tmp root spack stage spack stage tau spack src configure env note enabled profiling compiling with dprofiling on note building posix i o wrapper note gnu gfortran compiler specific options used note using papi interface for hardware performance counters note using fixes for gnu compiler make leaving directory tmp root spack stage spack stage tau spack src plugins make entering directory tmp root spack stage spack stage tau spack src examples instrument bin rm f simple o simple make leaving directory tmp root spack stage spack stage tau spack src examples instrument make entering directory tmp root spack stage spack stage tau spack src examples threads makefile tmp root spack stage spack stage tau spack src lib makefile tau papi gnu mpi pthre ad pdt no such file or directory make no rule to make target tmp root spack stage spack stage tau spack src lib makefil e tau papi gnu mpi pthread pdt stop make leaving directory tmp root spack stage spack stage tau spack src examples threads make entering directory tmp root spack stage spack stage tau spack src examples cthreads makefile tmp root spack stage spack stage tau spack src lib makefile tau papi gnu mpi pthre ad pdt no such file or directory make no rule to make target tmp root spack stage spack stage tau spack src lib makefil e tau papi gnu mpi pthread pdt stop make leaving directory tmp root spack stage spack stage tau spack src examples cthreads make entering directory tmp root spack stage spack stage tau spack src examples fortran bin rm f hello o hello make leaving directory tmp root spack stage spack stage tau spack src examples fortran make entering directory tmp root spack stage spack stage tau spack src examples bin rm f cubes o cubes make leaving directory tmp root spack stage spack stage tau spack src examples make entering directory tmp root spack stage spack stage tau spack src examples pi makefile tmp root spack stage spack stage tau spack src lib makefile tau papi gnu mpi pthre ad pdt no such file or directory make no rule to make target tmp root spack stage spack stage tau spack src lib makefil e tau papi gnu mpi pthread pdt stop make leaving directory tmp root spack stage spack stage tau spack src examples pi make entering directory tmp root spack stage spack stage tau spack src examples rm f core rm f core o npbparams h obj exe rm f mpi dummy test mpi dummy libmpi a rm f sys setparams sys makesuite sys setparams h make leaving directory tmp root spack stage spack stage tau spack src examples make entering directory tmp root spack stage spack stage tau spack src examples autoinstrument makefile tmp root spack stage spack stage tau spack src lib makefile tau papi gnu mpi pthre ad pdt no such file or directory make no rule to make target tmp root spack stage spack stage tau spack src lib makefil e tau papi gnu mpi pthread pdt stop make leaving directory tmp root spack stage spack stage tau spack src examples autoinstrument make entering directory tmp root spack stage spack stage tau spack src examples reduce makefile tmp root spack stage spack stage tau spack src lib makefile tau papi gnu mpi pthre ad pdt no such file or directory make no rule to make target tmp root spack stage spack stage tau spack src lib makefil e tau papi gnu mpi pthread pdt stop make leaving directory tmp root spack stage spack stage tau spack src examples reduce touch clean determining configuration system previously configured as a recursively making subdirectories compiling src traceinput directory make entering directory tmp root spack stage spack stage tau spack src src traceinput g i opt spack opt spack linux gcc tau include i opt spack o pt spack linux gcc mpich include g wl rpath opt spack opt spack linux ub gcc tau lib wl rpath opt spack opt spack linux gcc tau wl rpath opt spack opt spack linux gcc zlib lib wl rpath opt spack opt spack linux gcc pdt lib wl rpath opt spack opt spack linux gcc lib wl rpath opt spack opt spack linux ubunt gcc papi lib wl rpath opt spack opt spack linux gcc libd warf lib wl rpath opt spack opt spack linux gcc libelf lib wl rpath opt spack opt spack linux gcc binutils lib wl rpath opt spack opt spack linux gcc mpich lib wl rpath opt spack opt s pack linux gcc binutils wl rpath opt spack opt spack linux gcc libunwind i c tau tf cpp g i opt spack opt spack linux gcc tau include i opt spack o pt spack linux gcc mpich include g wl rpath opt spack opt spack linux ub gcc tau lib wl rpath opt spack opt spack linux gcc tau wl rpath opt spack opt spack linux gcc zlib lib wl rpath opt spack opt spack linux gcc pdt lib wl rpath opt spack opt spack linux gcc lib wl rpath opt spack opt spack linux ubunt gcc papi lib wl rpath opt spack opt spack linux gcc libd warf lib wl rpath opt spack opt spack linux gcc libelf lib wl rpath opt spack opt spack linux gcc binutils lib wl rpath opt spack opt spack linux gcc mpich lib wl rpath opt spack opt s pack linux gcc binutils wl rpath opt spack opt spack linux gcc libunwind i c tau cwrapper cpp g i opt spack opt spack linux gcc tau include i opt spack o pt spack linux gcc mpich include g wl rpath opt spack opt spack linux ub gcc tau lib wl rpath opt spack opt spack linux gcc tau wl rpath opt spack opt spack linux gcc zlib lib wl rpath opt spack opt spack linux gcc pdt lib wl rpath opt spack opt spack linux gcc lib wl rpath opt spack opt spack linux ubunt gcc papi lib wl rpath opt spack opt spack linux gcc libd warf lib wl rpath opt spack opt spack linux gcc libelf lib wl rpath opt spack opt spack linux gcc binutils lib wl rpath opt spack opt spack linux gcc mpich lib wl rpath opt spack opt s pack linux gcc binutils wl rpath opt spack opt spack linux gcc libunwind i c tau tf writer cpp as error while loading shared libraries libopcodes so cannot open shared object file no such file or directory makefile recipe for target tau cwrapper o failed make error make waiting for unfinished jobs as error while loading shared libraries libopcodes so cannot open shared object file no such file or directory makefile recipe for target tau tf writer o failed make error as error while loading shared libraries libopcodes so cannot open shared object file no such file or directory makefile recipe for target tau tf o failed make error make leaving directory tmp root spack stage spack stage tau spack src src traceinput makefile recipe for target install failed make error see build log for details tmp root spack stage spack stage tau spack build out txt traceback most recent call last file opt spack lib spack spack build environment py line in child process return value function file opt spack lib spack spack installer py line in build process phase pkg spec pkg prefix file opt spack lib spack spack package py line in phase wrapper phase spec prefix file opt spack var spack repos builtin packages tau package py line in install file opt spack lib spack spack build environment py line in call return super makeexecutable self call args kwargs file opt spack lib spack spack util executable py line in call proc returncode long msg spack util executable processerror command exited with status make install full build log khuck wspear | 0 |
444,139 | 31,023,360,672 | IssuesEvent | 2023-08-10 07:26:30 | miles-no/chess-robot | https://api.github.com/repos/miles-no/chess-robot | closed | Update ReadMe postgresql | documentation database | Posgresql commands in Readme needs to run in psql environment.
`psql -U postgres ` | 1.0 | Update ReadMe postgresql - Posgresql commands in Readme needs to run in psql environment.
`psql -U postgres ` | non_priority | update readme postgresql posgresql commands in readme needs to run in psql environment psql u postgres | 0 |
105,589 | 9,087,281,579 | IssuesEvent | 2019-02-18 13:20:59 | nicklashersen/numpy | https://api.github.com/repos/nicklashersen/numpy | opened | Unittest setup raises TypeError | testing | Just make a unittest that reaches this branch https://codecov.io/gh/numpy/numpy/src/master/numpy/distutils/core.py#L154 and assert that the correct exception is raised. | 1.0 | Unittest setup raises TypeError - Just make a unittest that reaches this branch https://codecov.io/gh/numpy/numpy/src/master/numpy/distutils/core.py#L154 and assert that the correct exception is raised. | non_priority | unittest setup raises typeerror just make a unittest that reaches this branch and assert that the correct exception is raised | 0 |
261,481 | 19,713,541,035 | IssuesEvent | 2022-01-13 08:45:08 | inmanta/inmanta-core | https://api.github.com/repos/inmanta/inmanta-core | opened | Procedure to install agents still uses old RPM repository | documentation | The documentation on how to install/configure a manually installed agents, still uses the `pkg.inmanta.com` RPM repository (See: https://docs.inmanta.com/community/dev/install/2-configure-agents.html#step-1-installing-the-required-inmanta-packages). | 1.0 | Procedure to install agents still uses old RPM repository - The documentation on how to install/configure a manually installed agents, still uses the `pkg.inmanta.com` RPM repository (See: https://docs.inmanta.com/community/dev/install/2-configure-agents.html#step-1-installing-the-required-inmanta-packages). | non_priority | procedure to install agents still uses old rpm repository the documentation on how to install configure a manually installed agents still uses the pkg inmanta com rpm repository see | 0 |
433,170 | 30,316,546,820 | IssuesEvent | 2023-07-10 15:56:58 | canberkboun9/website | https://api.github.com/repos/canberkboun9/website | closed | Adding Labels for Issues and PRs | Type: Documentation |
***Description*:**
Initial labels github provides are basic and some useful labels are required for issues and PRs.
***Todo's*:**
- [x] Create some useful labels.
- [x] Pick nice colors.
***Task Deadline*:** 11.07.2023 20:00 | 1.0 | Adding Labels for Issues and PRs -
***Description*:**
Initial labels github provides are basic and some useful labels are required for issues and PRs.
***Todo's*:**
- [x] Create some useful labels.
- [x] Pick nice colors.
***Task Deadline*:** 11.07.2023 20:00 | non_priority | adding labels for issues and prs description initial labels github provides are basic and some useful labels are required for issues and prs todo s create some useful labels pick nice colors task deadline | 0 |
14,877 | 5,814,296,281 | IssuesEvent | 2017-05-05 02:46:31 | irods/irods | https://api.github.com/repos/irods/irods | closed | provide packages for ubuntu16 | build | Unable to compile on Ubuntu 16.04 (the current LTS release of Ubuntu). The Makefile in `external` tries to download ftp://ftp.renci.org/pub/irods/build/irods_external_4.2.0_Ubuntu16.tar.gz but no such file exists.
Also, it would be nice if there were some sort of error message produced when curl (being called by the makefile) does not find the tar.gz bundle of external libraries. Right now it just goes on its merry way, and the error that shows up is something about avrocpp not being present.
| 1.0 | provide packages for ubuntu16 - Unable to compile on Ubuntu 16.04 (the current LTS release of Ubuntu). The Makefile in `external` tries to download ftp://ftp.renci.org/pub/irods/build/irods_external_4.2.0_Ubuntu16.tar.gz but no such file exists.
Also, it would be nice if there were some sort of error message produced when curl (being called by the makefile) does not find the tar.gz bundle of external libraries. Right now it just goes on its merry way, and the error that shows up is something about avrocpp not being present.
| non_priority | provide packages for unable to compile on ubuntu the current lts release of ubuntu the makefile in external tries to download ftp ftp renci org pub irods build irods external tar gz but no such file exists also it would be nice if there were some sort of error message produced when curl being called by the makefile does not find the tar gz bundle of external libraries right now it just goes on its merry way and the error that shows up is something about avrocpp not being present | 0 |
143,125 | 19,142,988,546 | IssuesEvent | 2021-12-02 02:27:53 | Dko1905/openWPM | https://api.github.com/repos/Dko1905/openWPM | opened | WS-2020-0293 (Medium) detected in spring-security-web-5.4.2.jar | security vulnerability | ## WS-2020-0293 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-web-5.4.2.jar</b></p></summary>
<p>spring-security-web</p>
<p>Library home page: <a href="https://spring.io/spring-security">https://spring.io/spring-security</a></p>
<p>Path to dependency file: openWPM/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework.security/spring-security-web/5.4.2/397b4d52b0bd9e7219789630ac3836cce7557c44/spring-security-web-5.4.2.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-security-2.4.2.jar (Root Library)
- :x: **spring-security-web-5.4.2.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Security before 5.2.9, 5.3.7, and 5.4.3 vulnerable to side-channel attacks. Vulnerable versions of Spring Security don't use constant time comparisons for CSRF tokens.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://github.com/spring-projects/spring-security/commit/40e027c56d11b9b4c5071360bfc718165c937784>WS-2020-0293</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/spring-projects/spring-security/issues/9291">https://github.com/spring-projects/spring-security/issues/9291</a></p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: org.springframework.security:spring-security-web:5.2.9,5.3.7,5.4.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0293 (Medium) detected in spring-security-web-5.4.2.jar - ## WS-2020-0293 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-web-5.4.2.jar</b></p></summary>
<p>spring-security-web</p>
<p>Library home page: <a href="https://spring.io/spring-security">https://spring.io/spring-security</a></p>
<p>Path to dependency file: openWPM/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework.security/spring-security-web/5.4.2/397b4d52b0bd9e7219789630ac3836cce7557c44/spring-security-web-5.4.2.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-security-2.4.2.jar (Root Library)
- :x: **spring-security-web-5.4.2.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Security before 5.2.9, 5.3.7, and 5.4.3 vulnerable to side-channel attacks. Vulnerable versions of Spring Security don't use constant time comparisons for CSRF tokens.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://github.com/spring-projects/spring-security/commit/40e027c56d11b9b4c5071360bfc718165c937784>WS-2020-0293</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/spring-projects/spring-security/issues/9291">https://github.com/spring-projects/spring-security/issues/9291</a></p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: org.springframework.security:spring-security-web:5.2.9,5.3.7,5.4.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in spring security web jar ws medium severity vulnerability vulnerable library spring security web jar spring security web library home page a href path to dependency file openwpm build gradle kts path to vulnerable library home wss scanner gradle caches modules files org springframework security spring security web spring security web jar dependency hierarchy spring boot starter security jar root library x spring security web jar vulnerable library found in base branch master vulnerability details spring security before and vulnerable to side channel attacks vulnerable versions of spring security don t use constant time comparisons for csrf tokens publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework security spring security web step up your open source security game with whitesource | 0 |
54,542 | 30,243,292,551 | IssuesEvent | 2023-07-06 14:48:10 | NVIDIA/spark-rapids | https://api.github.com/repos/NVIDIA/spark-rapids | closed | [FEA] Add filecache support to ORC scans | feature request performance | The filecache support added in #8212 currently only supports Parquet scans. It would be nice if this also worked for ORC scans. | True | [FEA] Add filecache support to ORC scans - The filecache support added in #8212 currently only supports Parquet scans. It would be nice if this also worked for ORC scans. | non_priority | add filecache support to orc scans the filecache support added in currently only supports parquet scans it would be nice if this also worked for orc scans | 0 |
37,761 | 4,838,841,418 | IssuesEvent | 2016-11-09 06:27:55 | brave/browser-laptop | https://api.github.com/repos/brave/browser-laptop | closed | CSS in JS proposal | design | Placeholder ticket for outlining and discussing a new approach to managing our CSS.
| 1.0 | CSS in JS proposal - Placeholder ticket for outlining and discussing a new approach to managing our CSS.
| non_priority | css in js proposal placeholder ticket for outlining and discussing a new approach to managing our css | 0 |
237,360 | 26,084,101,791 | IssuesEvent | 2022-12-25 21:25:28 | vital-ws/quick-repo | https://api.github.com/repos/vital-ws/quick-repo | opened | jest-27.5.0.tgz: 1 vulnerabilities (highest severity is: 7.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jest-27.5.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/json5/package.json</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jest version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-46175](https://www.mend.io/vulnerability-database/CVE-2022-46175) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.1 | json5-2.2.1.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-46175</summary>
### Vulnerable Library - <b>json5-2.2.1.tgz</b></p>
<p>JSON for humans.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-2.2.1.tgz">https://registry.npmjs.org/json5/-/json5-2.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- jest-27.5.0.tgz (Root Library)
- jest-cli-27.5.1.tgz
- jest-config-27.5.1.tgz
- core-7.19.6.tgz
- :x: **json5-2.2.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
JSON5 is an extension to the popular JSON file format that aims to be easier to write and maintain by hand (e.g. for config files). The `parse` method of the JSON5 library before and including version `2.2.1` does not restrict parsing of keys named `__proto__`, allowing specially crafted strings to pollute the prototype of the resulting object. This vulnerability pollutes the prototype of the object returned by `JSON5.parse` and not the global Object prototype, which is the commonly understood definition of Prototype Pollution. However, polluting the prototype of a single object can have significant security impact for an application if the object is later used in trusted operations. This vulnerability could allow an attacker to set arbitrary and unexpected keys on the object returned from `JSON5.parse`. The actual impact will depend on how applications utilize the returned object and how they filter unwanted keys, but could include denial of service, cross-site scripting, elevation of privilege, and in extreme cases, remote code execution. `JSON5.parse` should restrict parsing of `__proto__` keys when parsing JSON strings to objects. As a point of reference, the `JSON.parse` method included in JavaScript ignores `__proto__` keys. Simply changing `JSON5.parse` to `JSON.parse` in the examples above mitigates this vulnerability. This vulnerability is patched in json5 version 2.2.2 and later.
<p>Publish Date: 2022-12-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-46175>CVE-2022-46175</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-46175">https://www.cve.org/CVERecord?id=CVE-2022-46175</a></p>
<p>Release Date: 2022-12-24</p>
<p>Fix Resolution: json5 - 2.2.2</p>
</p>
<p></p>
</details> | True | jest-27.5.0.tgz: 1 vulnerabilities (highest severity is: 7.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jest-27.5.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/json5/package.json</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jest version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-46175](https://www.mend.io/vulnerability-database/CVE-2022-46175) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.1 | json5-2.2.1.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-46175</summary>
### Vulnerable Library - <b>json5-2.2.1.tgz</b></p>
<p>JSON for humans.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-2.2.1.tgz">https://registry.npmjs.org/json5/-/json5-2.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- jest-27.5.0.tgz (Root Library)
- jest-cli-27.5.1.tgz
- jest-config-27.5.1.tgz
- core-7.19.6.tgz
- :x: **json5-2.2.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
JSON5 is an extension to the popular JSON file format that aims to be easier to write and maintain by hand (e.g. for config files). The `parse` method of the JSON5 library before and including version `2.2.1` does not restrict parsing of keys named `__proto__`, allowing specially crafted strings to pollute the prototype of the resulting object. This vulnerability pollutes the prototype of the object returned by `JSON5.parse` and not the global Object prototype, which is the commonly understood definition of Prototype Pollution. However, polluting the prototype of a single object can have significant security impact for an application if the object is later used in trusted operations. This vulnerability could allow an attacker to set arbitrary and unexpected keys on the object returned from `JSON5.parse`. The actual impact will depend on how applications utilize the returned object and how they filter unwanted keys, but could include denial of service, cross-site scripting, elevation of privilege, and in extreme cases, remote code execution. `JSON5.parse` should restrict parsing of `__proto__` keys when parsing JSON strings to objects. As a point of reference, the `JSON.parse` method included in JavaScript ignores `__proto__` keys. Simply changing `JSON5.parse` to `JSON.parse` in the examples above mitigates this vulnerability. This vulnerability is patched in json5 version 2.2.2 and later.
<p>Publish Date: 2022-12-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-46175>CVE-2022-46175</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-46175">https://www.cve.org/CVERecord?id=CVE-2022-46175</a></p>
<p>Release Date: 2022-12-24</p>
<p>Fix Resolution: json5 - 2.2.2</p>
</p>
<p></p>
</details> | non_priority | jest tgz vulnerabilities highest severity is vulnerable library jest tgz path to dependency file package json path to vulnerable library node modules package json vulnerabilities cve severity cvss dependency type fixed in jest version remediation available high tgz transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library tgz json for humans library home page a href path to dependency file package json path to vulnerable library node modules package json dependency hierarchy jest tgz root library jest cli tgz jest config tgz core tgz x tgz vulnerable library found in base branch main vulnerability details is an extension to the popular json file format that aims to be easier to write and maintain by hand e g for config files the parse method of the library before and including version does not restrict parsing of keys named proto allowing specially crafted strings to pollute the prototype of the resulting object this vulnerability pollutes the prototype of the object returned by parse and not the global object prototype which is the commonly understood definition of prototype pollution however polluting the prototype of a single object can have significant security impact for an application if the object is later used in trusted operations this vulnerability could allow an attacker to set arbitrary and unexpected keys on the object returned from parse the actual impact will depend on how applications utilize the returned object and how they filter unwanted keys but could include denial of service cross site scripting elevation of privilege and in extreme cases remote code execution parse should restrict parsing of proto keys when parsing json strings to objects as a point of reference the json parse method included in javascript ignores proto keys simply changing parse to json parse in the examples above mitigates this vulnerability this vulnerability is patched in version and later publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
74,263 | 7,393,896,334 | IssuesEvent | 2018-03-17 03:12:17 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | HandleProcessCorruptedStateExceptionsTests.ProcessExit_Called test failing on Windows | area-System.Runtime disabled-test | ```
MESSAGE:
Exit code was -1073741819 but it should have been 42
Expected: True
Actual: False
+++++++++++++++++++
STACK TRACE:
at System.Diagnostics.RemoteExecutorTestBase.RemoteInvokeHandle.Dispose(Boolean disposing) in D:\j\workspace\x64_checked_w---d7295605\_\fx\src\CoreFx.Private.TestUtilities\src\System\Diagnostics\RemoteExecutorTestBase.cs:line 231
at System.Diagnostics.RemoteExecutorTestBase.RemoteInvokeHandle.Dispose() in D:\j\workspace\x64_checked_w---d7295605\_\fx\src\CoreFx.Private.TestUtilities\src\System\Diagnostics\RemoteExecutorTestBase.cs:line 207
at System.Runtime.ExceptionServices.Tests.HandleProcessCorruptedStateExceptionsTests.ProcessExit_Called() in D:\j\workspace\x64_checked_w---d7295605\_\fx\src\System.Runtime\tests\System\Runtime\ExceptionServices\HandleProcessCorruptedStateExceptions.cs:line 51
```
This failure was masked by #27426 | 1.0 | HandleProcessCorruptedStateExceptionsTests.ProcessExit_Called test failing on Windows - ```
MESSAGE:
Exit code was -1073741819 but it should have been 42
Expected: True
Actual: False
+++++++++++++++++++
STACK TRACE:
at System.Diagnostics.RemoteExecutorTestBase.RemoteInvokeHandle.Dispose(Boolean disposing) in D:\j\workspace\x64_checked_w---d7295605\_\fx\src\CoreFx.Private.TestUtilities\src\System\Diagnostics\RemoteExecutorTestBase.cs:line 231
at System.Diagnostics.RemoteExecutorTestBase.RemoteInvokeHandle.Dispose() in D:\j\workspace\x64_checked_w---d7295605\_\fx\src\CoreFx.Private.TestUtilities\src\System\Diagnostics\RemoteExecutorTestBase.cs:line 207
at System.Runtime.ExceptionServices.Tests.HandleProcessCorruptedStateExceptionsTests.ProcessExit_Called() in D:\j\workspace\x64_checked_w---d7295605\_\fx\src\System.Runtime\tests\System\Runtime\ExceptionServices\HandleProcessCorruptedStateExceptions.cs:line 51
```
This failure was masked by #27426 | non_priority | handleprocesscorruptedstateexceptionstests processexit called test failing on windows message exit code was but it should have been expected true actual false stack trace at system diagnostics remoteexecutortestbase remoteinvokehandle dispose boolean disposing in d j workspace checked w fx src corefx private testutilities src system diagnostics remoteexecutortestbase cs line at system diagnostics remoteexecutortestbase remoteinvokehandle dispose in d j workspace checked w fx src corefx private testutilities src system diagnostics remoteexecutortestbase cs line at system runtime exceptionservices tests handleprocesscorruptedstateexceptionstests processexit called in d j workspace checked w fx src system runtime tests system runtime exceptionservices handleprocesscorruptedstateexceptions cs line this failure was masked by | 0 |
270,705 | 29,047,071,264 | IssuesEvent | 2023-05-13 17:54:29 | tabacmend/Webgoat-Java-2022 | https://api.github.com/repos/tabacmend/Webgoat-Java-2022 | opened | CVE-2021-39148 (High) detected in xstream-1.4.5.jar | Mend: dependency security vulnerability | ## CVE-2021-39148 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Path to dependency file: /webgoat-lessons/vulnerable-components/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/Webgoat-Java-2022/commit/72af9e68af11d0ded665611720b118f85d2da2df">72af9e68af11d0ded665611720b118f85d2da2df</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.
<p>Publish Date: 2021-08-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-39148>CVE-2021-39148</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-qrx8-8545-4wg2">https://github.com/x-stream/xstream/security/advisories/GHSA-qrx8-8545-4wg2</a></p>
<p>Release Date: 2021-08-23</p>
<p>Fix Resolution: 1.4.18</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2021-39148 (High) detected in xstream-1.4.5.jar - ## CVE-2021-39148 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Path to dependency file: /webgoat-lessons/vulnerable-components/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/Webgoat-Java-2022/commit/72af9e68af11d0ded665611720b118f85d2da2df">72af9e68af11d0ded665611720b118f85d2da2df</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.
<p>Publish Date: 2021-08-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-39148>CVE-2021-39148</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/x-stream/xstream/security/advisories/GHSA-qrx8-8545-4wg2">https://github.com/x-stream/xstream/security/advisories/GHSA-qrx8-8545-4wg2</a></p>
<p>Release Date: 2021-08-23</p>
<p>Fix Resolution: 1.4.18</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve high detected in xstream jar cve high severity vulnerability vulnerable library xstream jar xstream is a serialization library from java objects to xml and back path to dependency file webgoat lessons vulnerable components pom xml path to vulnerable library home wss scanner repository com thoughtworks xstream xstream xstream jar home wss scanner repository com thoughtworks xstream xstream xstream jar home wss scanner repository com thoughtworks xstream xstream xstream jar dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch main vulnerability details xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream no user is affected who followed the recommendation to setup xstream s security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution check this box to open an automated fix pr | 0 |
27,313 | 28,088,558,226 | IssuesEvent | 2023-03-30 11:31:05 | microsoft/AdaptiveCards | https://api.github.com/repos/microsoft/AdaptiveCards | opened | [Adaptive Card iOS - Notification Card.Json]: Snooze button is getting overlapped with '5 Minutes' combo box. | Bug Area-Renderers Platform-iOS Area-Accessibility A11yUsable HCL-E+D Product-AC HCL-AdaptiveCards-iOS HCL-AdaptiveCards-Mobile | ### Target Platforms
iOS
### SDK Version
1.0 (2.4.0-beta.23.1.8.1)
### Application Name
Adaptive Cards
### Problem Description
Test Environment:
Device: iPhone 11
iOS: 16.3.1
Application: Adaptive Cards
App Version: 1.0 (2.4.0-beta.23.1.8.1)
Screen Reader: Voice Over
**Repro Steps:**
1. Launch Adaptive Cards iOS application.
2. Home screen will appear.
3. Activate Voice over
4. Navigate to "V1.0" control and select it.
5. Navigate to 'Test' control and activate it.
6. Navigate to 'Notification Card.Jsons' and activate it.
7. The Card will open and observe the issue.
**Actual Result:**
Under the notification card screen, Snooze button is overlapped with '5 Minutes' combo box.
**Expected Result:**
Snooze button should not be overlapped with the 5 Minute combo box.
**User Impact:**
It will impact the user with low vision as they will confuse and not able to see properly if two elements on the screen are overlapped with each other.
"Have feedback to share on Bugs ? Please help fill [Trusted Tester Bug Feedback (office.com)](https://nam06.safelinks.protection.outlook.com/?url=https://forms.office.com/pages/responsepage.aspx?id%3Dv4j5cvGGr0GRqy180BHbR5dUqGQgJ9lItv-jqY8F09lURVdYTENIRkY2UzlCR0NKV1E2VUE5OVpDVy4u&data=04%7c01%7cv-apoorva%40microsoft.com%7c551850210d444be9b28308d9691e3dde%7c72f988bf86f141af91ab2d7cd011db47%7c1%7c0%7c637656400998658942%7cUnknown%7cTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7c1000&sdata=l6w0SvVcMSvyGnJ6%2B6uSSgd3braF2dZ7/AdBrqqzIR8%3D&reserved=0) “
### Screenshots

### Card JSON
```JSON
NA
```
### Sample Code Language
_No response_
### Sample Code
_No response_ | True | [Adaptive Card iOS - Notification Card.Json]: Snooze button is getting overlapped with '5 Minutes' combo box. - ### Target Platforms
iOS
### SDK Version
1.0 (2.4.0-beta.23.1.8.1)
### Application Name
Adaptive Cards
### Problem Description
Test Environment:
Device: iPhone 11
iOS: 16.3.1
Application: Adaptive Cards
App Version: 1.0 (2.4.0-beta.23.1.8.1)
Screen Reader: Voice Over
**Repro Steps:**
1. Launch Adaptive Cards iOS application.
2. Home screen will appear.
3. Activate Voice over
4. Navigate to "V1.0" control and select it.
5. Navigate to 'Test' control and activate it.
6. Navigate to 'Notification Card.Jsons' and activate it.
7. The Card will open and observe the issue.
**Actual Result:**
Under the notification card screen, Snooze button is overlapped with '5 Minutes' combo box.
**Expected Result:**
Snooze button should not be overlapped with the 5 Minute combo box.
**User Impact:**
It will impact the user with low vision as they will confuse and not able to see properly if two elements on the screen are overlapped with each other.
"Have feedback to share on Bugs ? Please help fill [Trusted Tester Bug Feedback (office.com)](https://nam06.safelinks.protection.outlook.com/?url=https://forms.office.com/pages/responsepage.aspx?id%3Dv4j5cvGGr0GRqy180BHbR5dUqGQgJ9lItv-jqY8F09lURVdYTENIRkY2UzlCR0NKV1E2VUE5OVpDVy4u&data=04%7c01%7cv-apoorva%40microsoft.com%7c551850210d444be9b28308d9691e3dde%7c72f988bf86f141af91ab2d7cd011db47%7c1%7c0%7c637656400998658942%7cUnknown%7cTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7c1000&sdata=l6w0SvVcMSvyGnJ6%2B6uSSgd3braF2dZ7/AdBrqqzIR8%3D&reserved=0) “
### Screenshots

### Card JSON
```JSON
NA
```
### Sample Code Language
_No response_
### Sample Code
_No response_ | non_priority | snooze button is getting overlapped with minutes combo box target platforms ios sdk version beta application name adaptive cards problem description test environment device iphone ios application adaptive cards app version beta screen reader voice over repro steps launch adaptive cards ios application home screen will appear activate voice over navigate to control and select it navigate to test control and activate it navigate to notification card jsons and activate it the card will open and observe the issue actual result under the notification card screen snooze button is overlapped with minutes combo box expected result snooze button should not be overlapped with the minute combo box user impact it will impact the user with low vision as they will confuse and not able to see properly if two elements on the screen are overlapped with each other have feedback to share on bugs please help fill “ screenshots card json json na sample code language no response sample code no response | 0 |
100,666 | 30,751,880,076 | IssuesEvent | 2023-07-28 20:06:40 | aws-amplify/aws-sdk-ios | https://api.github.com/repos/aws-amplify/aws-sdk-ios | closed | ERROR: Could not allocate awsmtl_propertyAttributes structure for attribute string \"%s\" for property %s\n", attrString, property_getName(property)); | question pending-response build closing soon | **Describe the bug**
I have installed pods for aws operations . but this kind of error shown and not blocking manual build but blocking automatic xcloud operations
**To Reproduce**
Steps to reproduce the behavior:
you can see this issue in
EXTRuntimeExtensions.m
**Expected Behavior**
ERROR: Could not allocate awsmtl_propertyAttributes structure for attribute string \"%s\" for property %s\n", attrString, property_getName(property));
this should not be seen
**Stack Trace**
No stack trace
**Code Snippet**
```
awsmtl_propertyAttributes *awsmtl_copyPropertyAttributes (objc_property_t property) {
const char * const attrString = property_getAttributes(property);
if (!attrString) {
fprintf(stderr, "ERROR: Could not get attribute string from property %s\n", property_getName(property));
return NULL;
}
if (attrString[0] != 'T') {
fprintf(stderr, "ERROR: Expected attribute string \"%s\" for property %s to start with 'T'\n", attrString, property_getName(property));
return NULL;
}
const char *typeString = attrString + 1;
const char *next = NSGetSizeAndAlignment(typeString, NULL, NULL);
if (!next) {
fprintf(stderr, "ERROR: Could not read past type in attribute string \"%s\" for property %s\n", attrString, property_getName(property));
return NULL;
}
size_t typeLength = next - typeString;
if (!typeLength) {
fprintf(stderr, "ERROR: Invalid type in attribute string \"%s\" for property %s\n", attrString, property_getName(property));
return NULL;
}
// allocate enough space for the structure and the type string (plus a NUL)
awsmtl_propertyAttributes *attributes = calloc(1, sizeof(awsmtl_propertyAttributes) + typeLength + 1);
if (!attributes) {
fprintf(stderr, "ERROR: Could not allocate awsmtl_propertyAttributes structure for attribute string \"%s\" for property %s\n", attrString, property_getName(property));
return NULL;
}
```
**Areas of the SDK you are using (AWSMobileClient, Cognito, Pinpoint, IoT, etc)?**
AWSCore
AWSS3
**Screenshots**
<img width="1141" alt="aws_error" src="https://github.com/aws-amplify/aws-sdk-ios/assets/68735569/c44e3fb1-11d4-43de-9e35-753b212402b3">
**Environment(please complete the following information):**
- SDK Version: 2.31.0
- Dependency Manager: [ Cocoapods]
- Swift Version : [5.0]
- Xcode Version: [14.2]
**Device Information (please complete the following information):**
- Device: [iPhone 13 Pro]
- iOS Version: [ iOS 16]
</details>
| 1.0 | ERROR: Could not allocate awsmtl_propertyAttributes structure for attribute string \"%s\" for property %s\n", attrString, property_getName(property)); - **Describe the bug**
I have installed pods for aws operations . but this kind of error shown and not blocking manual build but blocking automatic xcloud operations
**To Reproduce**
Steps to reproduce the behavior:
you can see this issue in
EXTRuntimeExtensions.m
**Expected Behavior**
ERROR: Could not allocate awsmtl_propertyAttributes structure for attribute string \"%s\" for property %s\n", attrString, property_getName(property));
this should not be seen
**Stack Trace**
No stack trace
**Code Snippet**
```
awsmtl_propertyAttributes *awsmtl_copyPropertyAttributes (objc_property_t property) {
const char * const attrString = property_getAttributes(property);
if (!attrString) {
fprintf(stderr, "ERROR: Could not get attribute string from property %s\n", property_getName(property));
return NULL;
}
if (attrString[0] != 'T') {
fprintf(stderr, "ERROR: Expected attribute string \"%s\" for property %s to start with 'T'\n", attrString, property_getName(property));
return NULL;
}
const char *typeString = attrString + 1;
const char *next = NSGetSizeAndAlignment(typeString, NULL, NULL);
if (!next) {
fprintf(stderr, "ERROR: Could not read past type in attribute string \"%s\" for property %s\n", attrString, property_getName(property));
return NULL;
}
size_t typeLength = next - typeString;
if (!typeLength) {
fprintf(stderr, "ERROR: Invalid type in attribute string \"%s\" for property %s\n", attrString, property_getName(property));
return NULL;
}
// allocate enough space for the structure and the type string (plus a NUL)
awsmtl_propertyAttributes *attributes = calloc(1, sizeof(awsmtl_propertyAttributes) + typeLength + 1);
if (!attributes) {
fprintf(stderr, "ERROR: Could not allocate awsmtl_propertyAttributes structure for attribute string \"%s\" for property %s\n", attrString, property_getName(property));
return NULL;
}
```
**Areas of the SDK you are using (AWSMobileClient, Cognito, Pinpoint, IoT, etc)?**
AWSCore
AWSS3
**Screenshots**
<img width="1141" alt="aws_error" src="https://github.com/aws-amplify/aws-sdk-ios/assets/68735569/c44e3fb1-11d4-43de-9e35-753b212402b3">
**Environment(please complete the following information):**
- SDK Version: 2.31.0
- Dependency Manager: [ Cocoapods]
- Swift Version : [5.0]
- Xcode Version: [14.2]
**Device Information (please complete the following information):**
- Device: [iPhone 13 Pro]
- iOS Version: [ iOS 16]
</details>
| non_priority | error could not allocate awsmtl propertyattributes structure for attribute string s for property s n attrstring property getname property describe the bug i have installed pods for aws operations but this kind of error shown and not blocking manual build but blocking automatic xcloud operations to reproduce steps to reproduce the behavior you can see this issue in extruntimeextensions m expected behavior error could not allocate awsmtl propertyattributes structure for attribute string s for property s n attrstring property getname property this should not be seen stack trace no stack trace code snippet awsmtl propertyattributes awsmtl copypropertyattributes objc property t property const char const attrstring property getattributes property if attrstring fprintf stderr error could not get attribute string from property s n property getname property return null if attrstring t fprintf stderr error expected attribute string s for property s to start with t n attrstring property getname property return null const char typestring attrstring const char next nsgetsizeandalignment typestring null null if next fprintf stderr error could not read past type in attribute string s for property s n attrstring property getname property return null size t typelength next typestring if typelength fprintf stderr error invalid type in attribute string s for property s n attrstring property getname property return null allocate enough space for the structure and the type string plus a nul awsmtl propertyattributes attributes calloc sizeof awsmtl propertyattributes typelength if attributes fprintf stderr error could not allocate awsmtl propertyattributes structure for attribute string s for property s n attrstring property getname property return null areas of the sdk you are using awsmobileclient cognito pinpoint iot etc awscore screenshots img width alt aws error src environment please complete the following information sdk version dependency manager swift version xcode version device information please complete the following information device ios version | 0 |
4,966 | 7,568,997,362 | IssuesEvent | 2018-04-23 01:27:23 | zeit/hyper | https://api.github.com/repos/zeit/hyper | closed | Emacs not suported | 🤯 Type: Compatibility | Install emacs 64 bits
http://ftp.heanet.ie/mirrors/gnu/emacs/windows/emacs-25.1-2-x86_64-w64-mingw32.zip
call `emacs -nw`
get error

Running bare without any plugins
-
Hyper 1.3.1
Electron 1.4.15
win32 x64 10.0.15063 | True | Emacs not suported - Install emacs 64 bits
http://ftp.heanet.ie/mirrors/gnu/emacs/windows/emacs-25.1-2-x86_64-w64-mingw32.zip
call `emacs -nw`
get error

Running bare without any plugins
-
Hyper 1.3.1
Electron 1.4.15
win32 x64 10.0.15063 | non_priority | emacs not suported install emacs bits call emacs nw get error running bare without any plugins hyper electron | 0 |
155,150 | 13,613,075,674 | IssuesEvent | 2020-09-23 11:18:39 | mvdh7/PyCO2SYS | https://api.github.com/repos/mvdh7/PyCO2SYS | closed | Document the Python backend | documentation | The aim is to make all of the internal functions available to use without needing to run the full CO2SYS function. That means the internal functions need adding to the docs.
## Modules to document
- [ ] `assemble`
- [ ] `buffers`
- [ ] `concentrations`
- [ ] `constants`
- [ ] `convert`
- [ ] `equilibria`
- [ ] `meta`
- [ ] `original`
- [ ] `solubility`
- [ ] `solve` | 1.0 | Document the Python backend - The aim is to make all of the internal functions available to use without needing to run the full CO2SYS function. That means the internal functions need adding to the docs.
## Modules to document
- [ ] `assemble`
- [ ] `buffers`
- [ ] `concentrations`
- [ ] `constants`
- [ ] `convert`
- [ ] `equilibria`
- [ ] `meta`
- [ ] `original`
- [ ] `solubility`
- [ ] `solve` | non_priority | document the python backend the aim is to make all of the internal functions available to use without needing to run the full function that means the internal functions need adding to the docs modules to document assemble buffers concentrations constants convert equilibria meta original solubility solve | 0 |
340,322 | 30,510,910,518 | IssuesEvent | 2023-07-18 20:45:41 | verified-network-toolchain/petr4 | https://api.github.com/repos/verified-network-toolchain/petr4 | opened | table-entries-lpm-bmv2.p4 failing | stf-testing | To me this looks like a problem with the STF framework and not the test, since the pattern appears to match the received packet.
```
Expected:
0B****11****
Received:
0B00001100B0
``` | 1.0 | table-entries-lpm-bmv2.p4 failing - To me this looks like a problem with the STF framework and not the test, since the pattern appears to match the received packet.
```
Expected:
0B****11****
Received:
0B00001100B0
``` | non_priority | table entries lpm failing to me this looks like a problem with the stf framework and not the test since the pattern appears to match the received packet expected received | 0 |
32,429 | 7,531,111,784 | IssuesEvent | 2018-04-15 00:47:10 | dahall/TaskScheduler | https://api.github.com/repos/dahall/TaskScheduler | closed | Encounter WnfStateChangeTrigger error | codeplex-disc | Hi,
I've encounter WnfStateChangeTrigger error while trying to access task's Definition property in windows server 2016

XML property from the task's object
<?xml version="1.0" encoding="UTF-16"?>
<Task version="1.5" xmlns="[http://schemas.microsoft.com/windows/2004/02/mit/task](http://schemas.microsoft.com/windows/2004/02/mit/task)">
<RegistrationInfo>
<Date>2015-02-09T10:54:13.9629482</Date>
<SecurityDescriptor>D:P(A;;FA;;;BA)(A;;FA;;;SY)(A;;FA;;;S-1-5-87-2978287140-3787137133-1749738600-1988163579-2060695581)</SecurityDescriptor>
<Source>$(@%SystemRoot%\system32\ApplockerCsp.dll,-101)</Source>
<Author>$(@%SystemRoot%\system32\ApplockerCsp.dll,-100)</Author>
<Description>$(@%SystemRoot%\system32\ApplockerCsp.dll,-102)</Description>
<URI>\Microsoft\Windows\AppID\EDP Policy Manager</URI>
</RegistrationInfo>
<Principals>
<Principal id="LocalService">
<UserId>S-1-5-19</UserId>
</Principal>
</Principals>
<Settings>
<AllowHardTerminate>false</AllowHardTerminate>
<DisallowStartIfOnBatteries>false</DisallowStartIfOnBatteries>
<StopIfGoingOnBatteries>false</StopIfGoingOnBatteries>
<ExecutionTimeLimit>PT0S</ExecutionTimeLimit>
<MultipleInstancesPolicy>IgnoreNew</MultipleInstancesPolicy>
<IdleSettings>
<StopOnIdleEnd>true</StopOnIdleEnd>
<RestartOnIdle>false</RestartOnIdle>
</IdleSettings>
<UseUnifiedSchedulingEngine>true</UseUnifiedSchedulingEngine>
</Settings>
<Triggers>
<WnfStateChangeTrigger>
<StateName>7588BCA328009213</StateName>
</WnfStateChangeTrigger>
<WnfStateChangeTrigger>
<StateName>75E0BCA328009213</StateName>
</WnfStateChangeTrigger>
</Triggers>
<Actions Context="LocalService">
<ComHandler>
<ClassId>{DECA92E0-AF85-439E-9204-86679978DA08}</ClassId>
<Data><![CDATA[EdpPolicyManager]]></Data>
</ComHandler>
</Actions>
</Task>
Originally posted: 2017-03-24T03:25:22 | 1.0 | Encounter WnfStateChangeTrigger error - Hi,
I've encounter WnfStateChangeTrigger error while trying to access task's Definition property in windows server 2016

XML property from the task's object
<?xml version="1.0" encoding="UTF-16"?>
<Task version="1.5" xmlns="[http://schemas.microsoft.com/windows/2004/02/mit/task](http://schemas.microsoft.com/windows/2004/02/mit/task)">
<RegistrationInfo>
<Date>2015-02-09T10:54:13.9629482</Date>
<SecurityDescriptor>D:P(A;;FA;;;BA)(A;;FA;;;SY)(A;;FA;;;S-1-5-87-2978287140-3787137133-1749738600-1988163579-2060695581)</SecurityDescriptor>
<Source>$(@%SystemRoot%\system32\ApplockerCsp.dll,-101)</Source>
<Author>$(@%SystemRoot%\system32\ApplockerCsp.dll,-100)</Author>
<Description>$(@%SystemRoot%\system32\ApplockerCsp.dll,-102)</Description>
<URI>\Microsoft\Windows\AppID\EDP Policy Manager</URI>
</RegistrationInfo>
<Principals>
<Principal id="LocalService">
<UserId>S-1-5-19</UserId>
</Principal>
</Principals>
<Settings>
<AllowHardTerminate>false</AllowHardTerminate>
<DisallowStartIfOnBatteries>false</DisallowStartIfOnBatteries>
<StopIfGoingOnBatteries>false</StopIfGoingOnBatteries>
<ExecutionTimeLimit>PT0S</ExecutionTimeLimit>
<MultipleInstancesPolicy>IgnoreNew</MultipleInstancesPolicy>
<IdleSettings>
<StopOnIdleEnd>true</StopOnIdleEnd>
<RestartOnIdle>false</RestartOnIdle>
</IdleSettings>
<UseUnifiedSchedulingEngine>true</UseUnifiedSchedulingEngine>
</Settings>
<Triggers>
<WnfStateChangeTrigger>
<StateName>7588BCA328009213</StateName>
</WnfStateChangeTrigger>
<WnfStateChangeTrigger>
<StateName>75E0BCA328009213</StateName>
</WnfStateChangeTrigger>
</Triggers>
<Actions Context="LocalService">
<ComHandler>
<ClassId>{DECA92E0-AF85-439E-9204-86679978DA08}</ClassId>
<Data><![CDATA[EdpPolicyManager]]></Data>
</ComHandler>
</Actions>
</Task>
Originally posted: 2017-03-24T03:25:22 | non_priority | encounter wnfstatechangetrigger error hi i ve encounter wnfstatechangetrigger error while trying to access task s definition property in windows server xml property from the task s object task version xmlns lt date gt lt date gt lt securitydescriptor gt d p a fa ba a fa sy a fa s lt securitydescriptor gt lt source gt systemroot applockercsp dll lt source gt lt author gt systemroot applockercsp dll lt author gt lt description gt systemroot applockercsp dll lt description gt lt uri gt microsoft windows appid edp policy manager lt uri gt lt principal id quot localservice quot gt lt userid gt s lt userid gt lt principal gt lt allowhardterminate gt false lt allowhardterminate gt lt disallowstartifonbatteries gt false lt disallowstartifonbatteries gt lt stopifgoingonbatteries gt false lt stopifgoingonbatteries gt lt executiontimelimit gt lt executiontimelimit gt lt multipleinstancespolicy gt ignorenew lt multipleinstancespolicy gt lt idlesettings gt lt stoponidleend gt true lt stoponidleend gt lt restartonidle gt false lt restartonidle gt lt idlesettings gt lt useunifiedschedulingengine gt true lt useunifiedschedulingengine gt lt wnfstatechangetrigger gt lt statename gt lt statename gt lt wnfstatechangetrigger gt lt wnfstatechangetrigger gt lt statename gt lt statename gt lt wnfstatechangetrigger gt lt comhandler gt lt classid gt lt classid gt lt data gt lt gt lt data gt lt comhandler gt originally posted | 0 |
86,779 | 8,050,033,051 | IssuesEvent | 2018-08-01 12:12:23 | pennsignals/mantis | https://api.github.com/repos/pennsignals/mantis | closed | Create pre/post request handlers | enhancement needs tests | Perform pre or post processing on the request/response objects.
The [`BaseHandler`](https://docs.python.org/3/library/urllib.request.html#urllib.request.BaseHandler) class provides pre/post processing methods `BaseHandler.protocol_request` and `BaseHandler.protocol_response`.
Unit testing required: @rightlag | 1.0 | Create pre/post request handlers - Perform pre or post processing on the request/response objects.
The [`BaseHandler`](https://docs.python.org/3/library/urllib.request.html#urllib.request.BaseHandler) class provides pre/post processing methods `BaseHandler.protocol_request` and `BaseHandler.protocol_response`.
Unit testing required: @rightlag | non_priority | create pre post request handlers perform pre or post processing on the request response objects the class provides pre post processing methods basehandler protocol request and basehandler protocol response unit testing required rightlag | 0 |
50,682 | 13,187,679,899 | IssuesEvent | 2020-08-13 04:12:43 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | closed | Improved line fit resources directory cleanup (Trac #1181) | Migrated from Trac combo reconstruction defect | There are no links to improved linefit documentation in the meta-project documentation. there is a decent index.rst, but it is in resources/ not resources/docs/ it needs the name the maintainer and have links to the CHANGELOG and the doxygen documentation.
In addition the example script example.py needs to be updated, it tries to load something called libNFE. and moved to resources/examples directory
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1181">https://code.icecube.wisc.edu/ticket/1181</a>, reported by kjmeagher and owned by gmaggi</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:57",
"description": "There are no links to improved linefit documentation in the meta-project documentation. there is a decent index.rst, but it is in resources/ not resources/docs/ it needs the name the maintainer and have links to the CHANGELOG and the doxygen documentation.\n\nIn addition the example script example.py needs to be updated, it tries to load something called libNFE. and moved to resources/examples directory",
"reporter": "kjmeagher",
"cc": "",
"resolution": "wontfix",
"_ts": "1550067117911749",
"component": "combo reconstruction",
"summary": "Improved line fit resources directory cleanup",
"priority": "blocker",
"keywords": "",
"time": "2015-08-19T11:40:01",
"milestone": "",
"owner": "gmaggi",
"type": "defect"
}
```
</p>
</details>
| 1.0 | Improved line fit resources directory cleanup (Trac #1181) - There are no links to improved linefit documentation in the meta-project documentation. there is a decent index.rst, but it is in resources/ not resources/docs/ it needs the name the maintainer and have links to the CHANGELOG and the doxygen documentation.
In addition the example script example.py needs to be updated, it tries to load something called libNFE. and moved to resources/examples directory
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1181">https://code.icecube.wisc.edu/ticket/1181</a>, reported by kjmeagher and owned by gmaggi</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:57",
"description": "There are no links to improved linefit documentation in the meta-project documentation. there is a decent index.rst, but it is in resources/ not resources/docs/ it needs the name the maintainer and have links to the CHANGELOG and the doxygen documentation.\n\nIn addition the example script example.py needs to be updated, it tries to load something called libNFE. and moved to resources/examples directory",
"reporter": "kjmeagher",
"cc": "",
"resolution": "wontfix",
"_ts": "1550067117911749",
"component": "combo reconstruction",
"summary": "Improved line fit resources directory cleanup",
"priority": "blocker",
"keywords": "",
"time": "2015-08-19T11:40:01",
"milestone": "",
"owner": "gmaggi",
"type": "defect"
}
```
</p>
</details>
| non_priority | improved line fit resources directory cleanup trac there are no links to improved linefit documentation in the meta project documentation there is a decent index rst but it is in resources not resources docs it needs the name the maintainer and have links to the changelog and the doxygen documentation in addition the example script example py needs to be updated it tries to load something called libnfe and moved to resources examples directory migrated from json status closed changetime description there are no links to improved linefit documentation in the meta project documentation there is a decent index rst but it is in resources not resources docs it needs the name the maintainer and have links to the changelog and the doxygen documentation n nin addition the example script example py needs to be updated it tries to load something called libnfe and moved to resources examples directory reporter kjmeagher cc resolution wontfix ts component combo reconstruction summary improved line fit resources directory cleanup priority blocker keywords time milestone owner gmaggi type defect | 0 |
61,824 | 14,641,722,792 | IssuesEvent | 2020-12-25 08:07:14 | srivatsamarichi/pip-kotlin | https://api.github.com/repos/srivatsamarichi/pip-kotlin | opened | CVE-2020-15250 (Medium) detected in junit-4.12.jar | security vulnerability | ## CVE-2020-15250 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>junit-4.12.jar</b></p></summary>
<p>JUnit is a unit testing framework for Java, created by Erich Gamma and Kent Beck.</p>
<p>Library home page: <a href="http://junit.org">http://junit.org</a></p>
<p>Path to dependency file: pip-kotlin/app/build.gradle</p>
<p>Path to vulnerable library: 20201225080542_KKSKKS/downloadResource_XGIZMN/20201225080612/junit-4.12.jar,/tmp/ws-ua_20201225080542_KKSKKS/downloadResource_XGIZMN/20201225080612/junit-4.12.jar</p>
<p>
Dependency Hierarchy:
- :x: **junit-4.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/srivatsamarichi/pip-kotlin/commit/35d64e7f8134bf0c52e80c29038763207bf63c1b">35d64e7f8134bf0c52e80c29038763207bf63c1b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In JUnit4 from version 4.7 and before 4.13.1, the test rule TemporaryFolder contains a local information disclosure vulnerability. On Unix like systems, the system's temporary directory is shared between all users on that system. Because of this, when files and directories are written into this directory they are, by default, readable by other users on that same system. This vulnerability does not allow other users to overwrite the contents of these directories or files. This is purely an information disclosure vulnerability. This vulnerability impacts you if the JUnit tests write sensitive information, like API keys or passwords, into the temporary folder, and the JUnit tests execute in an environment where the OS has other untrusted users. Because certain JDK file system APIs were only added in JDK 1.7, this this fix is dependent upon the version of the JDK you are using. For Java 1.7 and higher users: this vulnerability is fixed in 4.13.1. For Java 1.6 and lower users: no patch is available, you must use the workaround below. If you are unable to patch, or are stuck running on Java 1.6, specifying the `java.io.tmpdir` system environment variable to a directory that is exclusively owned by the executing user will fix this vulnerability. For more information, including an example of vulnerable code, see the referenced GitHub Security Advisory.
<p>Publish Date: 2020-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15250>CVE-2020-15250</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/junit-team/junit4/security/advisories/GHSA-269g-pwp5-87pp">https://github.com/junit-team/junit4/security/advisories/GHSA-269g-pwp5-87pp</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: junit:junit:4.13.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-15250 (Medium) detected in junit-4.12.jar - ## CVE-2020-15250 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>junit-4.12.jar</b></p></summary>
<p>JUnit is a unit testing framework for Java, created by Erich Gamma and Kent Beck.</p>
<p>Library home page: <a href="http://junit.org">http://junit.org</a></p>
<p>Path to dependency file: pip-kotlin/app/build.gradle</p>
<p>Path to vulnerable library: 20201225080542_KKSKKS/downloadResource_XGIZMN/20201225080612/junit-4.12.jar,/tmp/ws-ua_20201225080542_KKSKKS/downloadResource_XGIZMN/20201225080612/junit-4.12.jar</p>
<p>
Dependency Hierarchy:
- :x: **junit-4.12.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/srivatsamarichi/pip-kotlin/commit/35d64e7f8134bf0c52e80c29038763207bf63c1b">35d64e7f8134bf0c52e80c29038763207bf63c1b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In JUnit4 from version 4.7 and before 4.13.1, the test rule TemporaryFolder contains a local information disclosure vulnerability. On Unix like systems, the system's temporary directory is shared between all users on that system. Because of this, when files and directories are written into this directory they are, by default, readable by other users on that same system. This vulnerability does not allow other users to overwrite the contents of these directories or files. This is purely an information disclosure vulnerability. This vulnerability impacts you if the JUnit tests write sensitive information, like API keys or passwords, into the temporary folder, and the JUnit tests execute in an environment where the OS has other untrusted users. Because certain JDK file system APIs were only added in JDK 1.7, this this fix is dependent upon the version of the JDK you are using. For Java 1.7 and higher users: this vulnerability is fixed in 4.13.1. For Java 1.6 and lower users: no patch is available, you must use the workaround below. If you are unable to patch, or are stuck running on Java 1.6, specifying the `java.io.tmpdir` system environment variable to a directory that is exclusively owned by the executing user will fix this vulnerability. For more information, including an example of vulnerable code, see the referenced GitHub Security Advisory.
<p>Publish Date: 2020-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15250>CVE-2020-15250</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/junit-team/junit4/security/advisories/GHSA-269g-pwp5-87pp">https://github.com/junit-team/junit4/security/advisories/GHSA-269g-pwp5-87pp</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: junit:junit:4.13.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in junit jar cve medium severity vulnerability vulnerable library junit jar junit is a unit testing framework for java created by erich gamma and kent beck library home page a href path to dependency file pip kotlin app build gradle path to vulnerable library kkskks downloadresource xgizmn junit jar tmp ws ua kkskks downloadresource xgizmn junit jar dependency hierarchy x junit jar vulnerable library found in head commit a href found in base branch master vulnerability details in from version and before the test rule temporaryfolder contains a local information disclosure vulnerability on unix like systems the system s temporary directory is shared between all users on that system because of this when files and directories are written into this directory they are by default readable by other users on that same system this vulnerability does not allow other users to overwrite the contents of these directories or files this is purely an information disclosure vulnerability this vulnerability impacts you if the junit tests write sensitive information like api keys or passwords into the temporary folder and the junit tests execute in an environment where the os has other untrusted users because certain jdk file system apis were only added in jdk this this fix is dependent upon the version of the jdk you are using for java and higher users this vulnerability is fixed in for java and lower users no patch is available you must use the workaround below if you are unable to patch or are stuck running on java specifying the java io tmpdir system environment variable to a directory that is exclusively owned by the executing user will fix this vulnerability for more information including an example of vulnerable code see the referenced github security advisory publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution junit junit step up your open source security game with whitesource | 0 |
282,009 | 30,889,104,087 | IssuesEvent | 2023-08-04 02:14:51 | hshivhare67/kernel_v4.1.15_CVE-2019-10220 | https://api.github.com/repos/hshivhare67/kernel_v4.1.15_CVE-2019-10220 | reopened | CVE-2016-2543 (Medium) detected in linuxlinux-4.4.302 | Mend: dependency security vulnerability | ## CVE-2016-2543 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/sound/core/seq/seq_clientmgr.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/sound/core/seq/seq_clientmgr.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The snd_seq_ioctl_remove_events function in sound/core/seq/seq_clientmgr.c in the Linux kernel before 4.4.1 does not verify FIFO assignment before proceeding with FIFO clearing, which allows local users to cause a denial of service (NULL pointer dereference and OOPS) via a crafted ioctl call.
<p>Publish Date: 2016-04-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-2543>CVE-2016-2543</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2543">https://nvd.nist.gov/vuln/detail/CVE-2016-2543</a></p>
<p>Release Date: 2016-04-27</p>
<p>Fix Resolution: 4.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-2543 (Medium) detected in linuxlinux-4.4.302 - ## CVE-2016-2543 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/sound/core/seq/seq_clientmgr.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/sound/core/seq/seq_clientmgr.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The snd_seq_ioctl_remove_events function in sound/core/seq/seq_clientmgr.c in the Linux kernel before 4.4.1 does not verify FIFO assignment before proceeding with FIFO clearing, which allows local users to cause a denial of service (NULL pointer dereference and OOPS) via a crafted ioctl call.
<p>Publish Date: 2016-04-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-2543>CVE-2016-2543</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2543">https://nvd.nist.gov/vuln/detail/CVE-2016-2543</a></p>
<p>Release Date: 2016-04-27</p>
<p>Fix Resolution: 4.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch master vulnerable source files sound core seq seq clientmgr c sound core seq seq clientmgr c vulnerability details the snd seq ioctl remove events function in sound core seq seq clientmgr c in the linux kernel before does not verify fifo assignment before proceeding with fifo clearing which allows local users to cause a denial of service null pointer dereference and oops via a crafted ioctl call publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
269,658 | 28,960,241,412 | IssuesEvent | 2023-05-10 01:26:06 | Trinadh465/linux-3.0.35_CVE-2019-10220 | https://api.github.com/repos/Trinadh465/linux-3.0.35_CVE-2019-10220 | closed | CVE-2023-2248 (High) detected in linuxlinux-3.0.40 - autoclosed | Mend: dependency security vulnerability | ## CVE-2023-2248 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-3.0.40</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v3.0/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v3.0/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-3.0.35_CVE-2019-10220/commit/1ad216eff9de6bc4364330a52955ad1743ba56e2">1ad216eff9de6bc4364330a52955ad1743ba56e2</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sched/sch_qfq.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sched/sch_qfq.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sched/sch_qfq.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A heap out-of-bounds read/write vulnerability in the Linux Kernel traffic control (QoS) subsystem can be exploited to achieve local privilege escalation.
The qfq_change_class function does not properly limit the lmax variable which can lead to out-of-bounds read/write. If the TCA_QFQ_LMAX value is not offered through nlattr, lmax is determined by the MTU value of the network device. The MTU of the loopback device can be set up to 2^31-1 and as a result, it is possible to have an lmax value that exceeds QFQ_MIN_LMAX.
We recommend upgrading past commit 3037933448f60f9acb705997eae62013ecb81e0d.
<p>Publish Date: 2023-05-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-2248>CVE-2023-2248</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-2248">https://www.linuxkernelcves.com/cves/CVE-2023-2248</a></p>
<p>Release Date: 2023-05-01</p>
<p>Fix Resolution: v4.14.314,v4.19.282,v5.10.179,v5.15.109,v5.4.242,v6.1.26,v6.2.13</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-2248 (High) detected in linuxlinux-3.0.40 - autoclosed - ## CVE-2023-2248 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-3.0.40</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v3.0/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v3.0/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-3.0.35_CVE-2019-10220/commit/1ad216eff9de6bc4364330a52955ad1743ba56e2">1ad216eff9de6bc4364330a52955ad1743ba56e2</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sched/sch_qfq.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sched/sch_qfq.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sched/sch_qfq.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A heap out-of-bounds read/write vulnerability in the Linux Kernel traffic control (QoS) subsystem can be exploited to achieve local privilege escalation.
The qfq_change_class function does not properly limit the lmax variable which can lead to out-of-bounds read/write. If the TCA_QFQ_LMAX value is not offered through nlattr, lmax is determined by the MTU value of the network device. The MTU of the loopback device can be set up to 2^31-1 and as a result, it is possible to have an lmax value that exceeds QFQ_MIN_LMAX.
We recommend upgrading past commit 3037933448f60f9acb705997eae62013ecb81e0d.
<p>Publish Date: 2023-05-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-2248>CVE-2023-2248</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-2248">https://www.linuxkernelcves.com/cves/CVE-2023-2248</a></p>
<p>Release Date: 2023-05-01</p>
<p>Fix Resolution: v4.14.314,v4.19.282,v5.10.179,v5.15.109,v5.4.242,v6.1.26,v6.2.13</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux autoclosed cve high severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files net sched sch qfq c net sched sch qfq c net sched sch qfq c vulnerability details a heap out of bounds read write vulnerability in the linux kernel traffic control qos subsystem can be exploited to achieve local privilege escalation the qfq change class function does not properly limit the lmax variable which can lead to out of bounds read write if the tca qfq lmax value is not offered through nlattr lmax is determined by the mtu value of the network device the mtu of the loopback device can be set up to and as a result it is possible to have an lmax value that exceeds qfq min lmax we recommend upgrading past commit publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
199,291 | 15,032,431,368 | IssuesEvent | 2021-02-02 10:10:27 | huggingface/transformers | https://api.github.com/repos/huggingface/transformers | opened | [Good first issue] LXMERT PyTorch Integration tests | Good First Issue Tests | The PyTorch implementation of the LXMERT model currently has no integration tests. This is problematic as the behavior can diverge without being noticed.
The [test_modeling_lxmert.py](https://github.com/huggingface/transformers/blob/master/tests/test_modeling_lxmert.py) file should be updated to include integration testing.
An example of a good modeling integration test is visible in the [test_modeling_bert.py#L552-L565](https://github.com/huggingface/transformers/blob/master/tests/test_modeling_bert.py#L552-L565) file:
https://github.com/huggingface/transformers/blob/1809de5165804666ba6c6a02a9d177f6683869cc/tests/test_modeling_bert.py#L552-L565
Some additional tips:
- The test must be marked as slow using the `@slow` decorator, so as to be run *daily*, and not on every commit of every branch/pull request of this repository.
- The test must be decorated with the `@require_torch` decorator so as to only be run in environments using PyTorch.
- A single test is necessary. If you feel like implementing multiple of these, then sharing the same checkpoint would be ideal so as to reduce download time. | 1.0 | [Good first issue] LXMERT PyTorch Integration tests - The PyTorch implementation of the LXMERT model currently has no integration tests. This is problematic as the behavior can diverge without being noticed.
The [test_modeling_lxmert.py](https://github.com/huggingface/transformers/blob/master/tests/test_modeling_lxmert.py) file should be updated to include integration testing.
An example of a good modeling integration test is visible in the [test_modeling_bert.py#L552-L565](https://github.com/huggingface/transformers/blob/master/tests/test_modeling_bert.py#L552-L565) file:
https://github.com/huggingface/transformers/blob/1809de5165804666ba6c6a02a9d177f6683869cc/tests/test_modeling_bert.py#L552-L565
Some additional tips:
- The test must be marked as slow using the `@slow` decorator, so as to be run *daily*, and not on every commit of every branch/pull request of this repository.
- The test must be decorated with the `@require_torch` decorator so as to only be run in environments using PyTorch.
- A single test is necessary. If you feel like implementing multiple of these, then sharing the same checkpoint would be ideal so as to reduce download time. | non_priority | lxmert pytorch integration tests the pytorch implementation of the lxmert model currently has no integration tests this is problematic as the behavior can diverge without being noticed the file should be updated to include integration testing an example of a good modeling integration test is visible in the file some additional tips the test must be marked as slow using the slow decorator so as to be run daily and not on every commit of every branch pull request of this repository the test must be decorated with the require torch decorator so as to only be run in environments using pytorch a single test is necessary if you feel like implementing multiple of these then sharing the same checkpoint would be ideal so as to reduce download time | 0 |
208,466 | 23,605,511,589 | IssuesEvent | 2022-08-24 07:55:31 | ioana-nicolae/second | https://api.github.com/repos/ioana-nicolae/second | closed | CVE-2020-14060 (High) detected in jackson-databind-2.7.9.jar - autoclosed | security vulnerability | ## CVE-2020-14060 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.7.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.7.9/a4c0b14c7dd85bdf4d25da074e90a10fa4b9b88b/jackson-databind-2.7.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.7.9.jar** (Vulnerable Library)
<p>Found in base branch: <b>branch3</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to oadd.org.apache.xalan.lib.sql.JNDIConnectionPool (aka apache/drill).
<p>Publish Date: 2020-06-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14060>CVE-2020-14060</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14060">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14060</a></p>
<p>Release Date: 2020-06-14</p>
<p>Fix Resolution: 2.8.0.rc1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2020-14060 (High) detected in jackson-databind-2.7.9.jar - autoclosed - ## CVE-2020-14060 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.7.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.7.9/a4c0b14c7dd85bdf4d25da074e90a10fa4b9b88b/jackson-databind-2.7.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.7.9.jar** (Vulnerable Library)
<p>Found in base branch: <b>branch3</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to oadd.org.apache.xalan.lib.sql.JNDIConnectionPool (aka apache/drill).
<p>Publish Date: 2020-06-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14060>CVE-2020-14060</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14060">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14060</a></p>
<p>Release Date: 2020-06-14</p>
<p>Fix Resolution: 2.8.0.rc1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file build gradle path to vulnerable library gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in base branch vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to oadd org apache xalan lib sql jndiconnectionpool aka apache drill publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue | 0 |
232,323 | 25,567,976,204 | IssuesEvent | 2022-11-30 15:34:54 | MetaMask/metamask-extension | https://api.github.com/repos/MetaMask/metamask-extension | closed | Add a "Your funds may be at risk" friction modal to eth_sign signature's requests | type-enhancement type-security area-transactions team-transactions |
## Resources
[Figma Design file](https://www.figma.com/file/n0xMnZqQz4w9Sfa3ZdhWUi/Consentful-experience-for-token-allowances?node-id=2007%3A14561)
## Acceptance Criteria
1. Clicking `Sign` on eth_sign request does NOT sign the message, instead it displays this new modal;
2. Modal follows same design as https://github.com/MetaMask/metamask-extension/pull/16195;
3. Title on top of modal is: `Your funds may be at risk` instead of `Your NFTs may be at risk`;
4. `Total: <number>` part of the original modal is not displayed;
6. The copy displayed is: `Signing this message could be dangerous. You may be giving total control of your account and assets to the party on the other end of this message. That means they could drain your account at any time. Proceed with caution. Learn more.`;
7. Learn more link leads to https://consensys.net/blog/metamask/the-seal-of-approval-know-what-youre-consenting-to-with-permissions-and-approvals-in-metamask/ (we should consider a more specific article in the future);
8. Clicking on `Reject` rejects the signature request (same behavior as clicking on "Reject/Cancel" on the previous screen or in the current existing screen) (Use 'Reject" instead of Cancel from design);
9. Clicking on `Sign` signs and submits the message (same behavior as clicking on `Sign` in the current existing screen).
10. Remove the warning message in the Sign request pop up
## Steps to Reproduce
1. Open the test dapp https://metamask.github.io/test-dapp/
2. Under the Eth Sign section, click on "Sign" | True | Add a "Your funds may be at risk" friction modal to eth_sign signature's requests -
## Resources
[Figma Design file](https://www.figma.com/file/n0xMnZqQz4w9Sfa3ZdhWUi/Consentful-experience-for-token-allowances?node-id=2007%3A14561)
## Acceptance Criteria
1. Clicking `Sign` on eth_sign request does NOT sign the message, instead it displays this new modal;
2. Modal follows same design as https://github.com/MetaMask/metamask-extension/pull/16195;
3. Title on top of modal is: `Your funds may be at risk` instead of `Your NFTs may be at risk`;
4. `Total: <number>` part of the original modal is not displayed;
6. The copy displayed is: `Signing this message could be dangerous. You may be giving total control of your account and assets to the party on the other end of this message. That means they could drain your account at any time. Proceed with caution. Learn more.`;
7. Learn more link leads to https://consensys.net/blog/metamask/the-seal-of-approval-know-what-youre-consenting-to-with-permissions-and-approvals-in-metamask/ (we should consider a more specific article in the future);
8. Clicking on `Reject` rejects the signature request (same behavior as clicking on "Reject/Cancel" on the previous screen or in the current existing screen) (Use 'Reject" instead of Cancel from design);
9. Clicking on `Sign` signs and submits the message (same behavior as clicking on `Sign` in the current existing screen).
10. Remove the warning message in the Sign request pop up
## Steps to Reproduce
1. Open the test dapp https://metamask.github.io/test-dapp/
2. Under the Eth Sign section, click on "Sign" | non_priority | add a your funds may be at risk friction modal to eth sign signature s requests resources acceptance criteria clicking sign on eth sign request does not sign the message instead it displays this new modal modal follows same design as title on top of modal is your funds may be at risk instead of your nfts may be at risk total part of the original modal is not displayed the copy displayed is signing this message could be dangerous you may be giving total control of your account and assets to the party on the other end of this message that means they could drain your account at any time proceed with caution learn more learn more link leads to we should consider a more specific article in the future clicking on reject rejects the signature request same behavior as clicking on reject cancel on the previous screen or in the current existing screen use reject instead of cancel from design clicking on sign signs and submits the message same behavior as clicking on sign in the current existing screen remove the warning message in the sign request pop up steps to reproduce open the test dapp under the eth sign section click on sign | 0 |
28,627 | 4,424,608,285 | IssuesEvent | 2016-08-16 13:08:54 | directus/directus | https://api.github.com/repos/directus/directus | closed | permission issues | 3. Major 7. Testing | ## Version Info
- Directus version: bf5235156
**First:** when editing fields permissions it's not obvious when the changes are saved. When clicking on the "Edit field level permissions" button of a table and then clicking on another link (eg a table in the sidebar) you get a warning that the changes may get lost. (Even if you did not change anything)
The correct way to confirm all changes seems to be to click on the "back" arrow. But that's inconsistent with editing a record in a MTM field where the "back" arrow cancels the changes.
**Second:** revoking permissions for viewing or editing a required field is behaving weirdly. I will try this in more detail later but for now I noticed:
- Remove the write access of a required field but keep the read access:
when editing an existing record which has the field already set can not be saved because "error: field is required"
- Remove both read and write access: Now the record can be saved without the user seeing the field at all
- Give back read access but not write access: Now the field can even be edited even though the user should not have access to do so | 1.0 | permission issues - ## Version Info
- Directus version: bf5235156
**First:** when editing fields permissions it's not obvious when the changes are saved. When clicking on the "Edit field level permissions" button of a table and then clicking on another link (eg a table in the sidebar) you get a warning that the changes may get lost. (Even if you did not change anything)
The correct way to confirm all changes seems to be to click on the "back" arrow. But that's inconsistent with editing a record in a MTM field where the "back" arrow cancels the changes.
**Second:** revoking permissions for viewing or editing a required field is behaving weirdly. I will try this in more detail later but for now I noticed:
- Remove the write access of a required field but keep the read access:
when editing an existing record which has the field already set can not be saved because "error: field is required"
- Remove both read and write access: Now the record can be saved without the user seeing the field at all
- Give back read access but not write access: Now the field can even be edited even though the user should not have access to do so | non_priority | permission issues version info directus version first when editing fields permissions it s not obvious when the changes are saved when clicking on the edit field level permissions button of a table and then clicking on another link eg a table in the sidebar you get a warning that the changes may get lost even if you did not change anything the correct way to confirm all changes seems to be to click on the back arrow but that s inconsistent with editing a record in a mtm field where the back arrow cancels the changes second revoking permissions for viewing or editing a required field is behaving weirdly i will try this in more detail later but for now i noticed remove the write access of a required field but keep the read access when editing an existing record which has the field already set can not be saved because error field is required remove both read and write access now the record can be saved without the user seeing the field at all give back read access but not write access now the field can even be edited even though the user should not have access to do so | 0 |
156,291 | 24,598,014,781 | IssuesEvent | 2022-10-14 09:57:51 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Bug]: Default Container widget within the list widget should be hidden on the Entity Explorer | Bug Needs Design App Viewers Pod Low List Widget | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
Users are able to access the default Container widget within the list widget and manipulate its properties. And here, all properties work except the background colour.
<img width="1440" alt="Screenshot 2022-02-22 at 5 50 50 PM" src="https://user-images.githubusercontent.com/32227135/155255404-fc5c2d35-cce9-4111-9adb-1352b12482fb.png">
s
### Steps To Reproduce
1. Drag and drop a list widget on the canvas
2. On the entity explorer, under the list widget, select the container widget
3. Check the property pane to view its properties
### Environment
Production
### Version
Cloud | 1.0 | [Bug]: Default Container widget within the list widget should be hidden on the Entity Explorer - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
Users are able to access the default Container widget within the list widget and manipulate its properties. And here, all properties work except the background colour.
<img width="1440" alt="Screenshot 2022-02-22 at 5 50 50 PM" src="https://user-images.githubusercontent.com/32227135/155255404-fc5c2d35-cce9-4111-9adb-1352b12482fb.png">
s
### Steps To Reproduce
1. Drag and drop a list widget on the canvas
2. On the entity explorer, under the list widget, select the container widget
3. Check the property pane to view its properties
### Environment
Production
### Version
Cloud | non_priority | default container widget within the list widget should be hidden on the entity explorer is there an existing issue for this i have searched the existing issues current behavior users are able to access the default container widget within the list widget and manipulate its properties and here all properties work except the background colour img width alt screenshot at pm src s steps to reproduce drag and drop a list widget on the canvas on the entity explorer under the list widget select the container widget check the property pane to view its properties environment production version cloud | 0 |
94,384 | 11,867,332,972 | IssuesEvent | 2020-03-26 06:41:10 | LonnyGomes/covid-sankey-vizualization | https://api.github.com/repos/LonnyGomes/covid-sankey-vizualization | closed | Re-style leaderboard to use a table | design | <img width="1291" alt="image" src="https://user-images.githubusercontent.com/50893208/77613989-83cba300-6f02-11ea-8757-85c33a128032.png">
The leaderboard is currently floating and centered. Experiment with using a table to better style the content. | 1.0 | Re-style leaderboard to use a table - <img width="1291" alt="image" src="https://user-images.githubusercontent.com/50893208/77613989-83cba300-6f02-11ea-8757-85c33a128032.png">
The leaderboard is currently floating and centered. Experiment with using a table to better style the content. | non_priority | re style leaderboard to use a table img width alt image src the leaderboard is currently floating and centered experiment with using a table to better style the content | 0 |
53,408 | 13,162,366,652 | IssuesEvent | 2020-08-10 21:26:33 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | bazel build failure, error occur no such package @androidndk | comp:lite subtype:bazel type:build/install | ### System information
- **OS Platform and Distribution **: Ubuntu 16.04
- **TensorFlow install **: installed from source
- **TensorFlow version **: r1.9
- **Python version **: pyenv + virtualenv to support python 3.6.6
- **Bazel version **: 0.14.1 compiling from source
- **GCC/Compiler version **: gcc 4.9
- **CUDA, cuDNN version**: CUDA 9.0, cuDNN 7.1
- **GPU **: NVIDIA Titan X 12GB
- ** no custom code **: source compile from released r1.9 source
### Describe the problem
When compile tensor flow r1.9 from released source code, Bazel occur error message.
I try to compile r1.8 as same build env. there is no error occurred.
### Source code / logs
- build env. setting
```
cd /tmp/tensorflow-r${TF_VERSION} \
&& PYTHON_BIN_PATH=/usr/local/bin/python \
PYTHON_LIB_PATH=/usr/local/lib/python3.6/site-packages \
GCC_HOST_COMPILER_PATH=/usr/bin/gcc \
CC_OPT_FLAGS="-march=x86-64 -mavx -mavx2 -mfma -mfpmath=both -msse4.1 -msse4.2" \
TF_NEED_JEMALLOC=1 \
TF_NEED_GCP=1 \
TF_NEED_HDFS=1 \
TF_ENABLE_XLA=1 \
TF_NEED_VERBS=0 \
TF_NEED_OPENCL=0 \
TF_NEED_OPENCL_SYCL=0 \
TF_NEED_CUDA=1 \
TF_CUDA_CLANG=0 \
TF_DOWNLOAD_CLANG=0 \
TF_NEED_TENSORRT=0 \
TF_NEED_MPI=0 \
TF_NEED_GDR=0 \
TF_NEED_S3=1 \
TF_NEED_KAFKA=0 \
TF_SET_ANDROID_WORKSPACE=0 \
TF_CUDA_VERSION=9.0 \
TF_CUDNN_VERSION=7 \
TF_NCCL_VERSION=2 \
TF_CUDA_COMPUTE_CAPABILITIES=3.5,3.7,5.2,6.0,6.1,7.0 \
CUDA_TOOLKIT_PATH=/usr/local/cuda \
CUDNN_INSTALL_PATH=/usr/local/cuda \
NCCL_INSTALL_PATH=/usr \
bash configure \
&& bazel build \
--config=opt --config=cuda \
--cxxopt="-D_GLIBCXX_USE_CXX11_ABI=0" \
//tensorflow/tools/pip_package:build_pip_package \
&& ./bazel-bin/tensorflow/tools/pip_package/build_pip_package /tmp/tensorflow_pkg
```
```
Starting local Bazel server and connecting to it...
...............
Building: no action
Building: no action
Building: no action
ERROR: /tmp/tensorflow-r1.9/tensorflow/contrib/lite/kernels/internal/BUILD:529:1: no such package '@androidndk//': The repository could not be resolved and referenced by '//tensorflow/contrib/lite/kernels/internal:cpu_check'
ERROR: Evaluation of query "deps(//tensorflow/tools/pip_package:build_pip_package)" failed: errors were encountered while computing transitive closure
``` | 1.0 | bazel build failure, error occur no such package @androidndk - ### System information
- **OS Platform and Distribution **: Ubuntu 16.04
- **TensorFlow install **: installed from source
- **TensorFlow version **: r1.9
- **Python version **: pyenv + virtualenv to support python 3.6.6
- **Bazel version **: 0.14.1 compiling from source
- **GCC/Compiler version **: gcc 4.9
- **CUDA, cuDNN version**: CUDA 9.0, cuDNN 7.1
- **GPU **: NVIDIA Titan X 12GB
- ** no custom code **: source compile from released r1.9 source
### Describe the problem
When compile tensor flow r1.9 from released source code, Bazel occur error message.
I try to compile r1.8 as same build env. there is no error occurred.
### Source code / logs
- build env. setting
```
cd /tmp/tensorflow-r${TF_VERSION} \
&& PYTHON_BIN_PATH=/usr/local/bin/python \
PYTHON_LIB_PATH=/usr/local/lib/python3.6/site-packages \
GCC_HOST_COMPILER_PATH=/usr/bin/gcc \
CC_OPT_FLAGS="-march=x86-64 -mavx -mavx2 -mfma -mfpmath=both -msse4.1 -msse4.2" \
TF_NEED_JEMALLOC=1 \
TF_NEED_GCP=1 \
TF_NEED_HDFS=1 \
TF_ENABLE_XLA=1 \
TF_NEED_VERBS=0 \
TF_NEED_OPENCL=0 \
TF_NEED_OPENCL_SYCL=0 \
TF_NEED_CUDA=1 \
TF_CUDA_CLANG=0 \
TF_DOWNLOAD_CLANG=0 \
TF_NEED_TENSORRT=0 \
TF_NEED_MPI=0 \
TF_NEED_GDR=0 \
TF_NEED_S3=1 \
TF_NEED_KAFKA=0 \
TF_SET_ANDROID_WORKSPACE=0 \
TF_CUDA_VERSION=9.0 \
TF_CUDNN_VERSION=7 \
TF_NCCL_VERSION=2 \
TF_CUDA_COMPUTE_CAPABILITIES=3.5,3.7,5.2,6.0,6.1,7.0 \
CUDA_TOOLKIT_PATH=/usr/local/cuda \
CUDNN_INSTALL_PATH=/usr/local/cuda \
NCCL_INSTALL_PATH=/usr \
bash configure \
&& bazel build \
--config=opt --config=cuda \
--cxxopt="-D_GLIBCXX_USE_CXX11_ABI=0" \
//tensorflow/tools/pip_package:build_pip_package \
&& ./bazel-bin/tensorflow/tools/pip_package/build_pip_package /tmp/tensorflow_pkg
```
```
Starting local Bazel server and connecting to it...
...............
Building: no action
Building: no action
Building: no action
ERROR: /tmp/tensorflow-r1.9/tensorflow/contrib/lite/kernels/internal/BUILD:529:1: no such package '@androidndk//': The repository could not be resolved and referenced by '//tensorflow/contrib/lite/kernels/internal:cpu_check'
ERROR: Evaluation of query "deps(//tensorflow/tools/pip_package:build_pip_package)" failed: errors were encountered while computing transitive closure
``` | non_priority | bazel build failure error occur no such package androidndk system information os platform and distribution ubuntu tensorflow install installed from source tensorflow version python version pyenv virtualenv to support python bazel version compiling from source gcc compiler version gcc cuda cudnn version cuda cudnn gpu nvidia titan x no custom code source compile from released source describe the problem when compile tensor flow from released source code bazel occur error message i try to compile as same build env there is no error occurred source code logs build env setting cd tmp tensorflow r tf version python bin path usr local bin python python lib path usr local lib site packages gcc host compiler path usr bin gcc cc opt flags march mavx mfma mfpmath both tf need jemalloc tf need gcp tf need hdfs tf enable xla tf need verbs tf need opencl tf need opencl sycl tf need cuda tf cuda clang tf download clang tf need tensorrt tf need mpi tf need gdr tf need tf need kafka tf set android workspace tf cuda version tf cudnn version tf nccl version tf cuda compute capabilities cuda toolkit path usr local cuda cudnn install path usr local cuda nccl install path usr bash configure bazel build config opt config cuda cxxopt d glibcxx use abi tensorflow tools pip package build pip package bazel bin tensorflow tools pip package build pip package tmp tensorflow pkg starting local bazel server and connecting to it building no action building no action building no action error tmp tensorflow tensorflow contrib lite kernels internal build no such package androidndk the repository could not be resolved and referenced by tensorflow contrib lite kernels internal cpu check error evaluation of query deps tensorflow tools pip package build pip package failed errors were encountered while computing transitive closure | 0 |
325,626 | 27,949,334,265 | IssuesEvent | 2023-03-24 07:24:37 | DevExpress/testcafe | https://api.github.com/repos/DevExpress/testcafe | closed | fix 'Should provide node snapshots for non-element nodes' test in the master branch | TYPE: bug AREA: testing | Run the `Should provide node snapshots for non-element nodes` test in the proxyless mode (`test-functional-local-proxyless` task). | 1.0 | fix 'Should provide node snapshots for non-element nodes' test in the master branch - Run the `Should provide node snapshots for non-element nodes` test in the proxyless mode (`test-functional-local-proxyless` task). | non_priority | fix should provide node snapshots for non element nodes test in the master branch run the should provide node snapshots for non element nodes test in the proxyless mode test functional local proxyless task | 0 |
318,526 | 27,310,475,290 | IssuesEvent | 2023-02-24 11:45:06 | systemd/systemd | https://api.github.com/repos/systemd/systemd | closed | test-time-util is broken in certain timezones | bug 🐛 tests | ### systemd version the issue has been seen with
main (253-rc2)
### Used distribution
Arch Linux/Ubuntu 20.04
### Linux kernel version used
Irrelevant
### CPU architectures issue was seen on
x86_64
### Component
tests
### Expected behaviour you didn't see
The tests should pass
### Unexpected behaviour you saw
Tests checking checking that conversion from timestamp to string and back sometimes fail in certain timezones.
### Steps to reproduce the problem
`TZ=Africa/Casablanca meson test -C build test-time-util --repeat 100`
From what it looks like, time util lib determines incorrectly whether the date _has_ belonged to the DST period or not and calculates the wrong timestamp most often missed by 1 hour.
The full list of broken timezones for Arch Linux with tzdata 2022g and glibc 2.36 is:
```
Africa/Casablanca
Africa/El_Aaiun
America/Argentina/Rio_Gallegos
America/Punta_Arenas
Antarctica/Casey
Antarctica/Davis
Antarctica/Palmer
Asia/Aqtau
Asia/Aqtobe
Asia/Atyrau
Asia/Baku
Asia/Bishkek
Asia/Oral
Asia/Qostanay
Asia/Qyzylorda
Asia/Samarkand
Asia/Srednekolymsk
Asia/Tbilisi
Asia/Yerevan
Chile/EasterIsland
Pacific/Easter
Turkey
```
### Additional program output to the terminal or log subsystem illustrating the issue
```sh
Thread 1 (Thread 0x7f10d20a6840 (LWP 783520)):
#0 0x00007f10d2a5864c in ?? () from /usr/lib/libc.so.6
#1 0x00007f10d2a08938 in raise () from /usr/lib/libc.so.6
#2 0x00007f10d29f253d in abort () from /usr/lib/libc.so.6
#3 0x00007f10d2e4fc70 in log_assert_failed (text=0x55b3a5a88ed0 "x / USEC_PER_SEC == y / USEC_PER_SEC", file=0x55b3a5a870e2 "src/test/test-time-util.c", line=398, func=0x55b3a5a89c00 <__func__.11> "test_FORMAT_TIMESTAMP") at ../src/basic/log.c:888
#4 0x000055b3a5a84620 in test_FORMAT_TIMESTAMP () at ../src/test/test-time-util.c:398
#5 0x000055b3a5a7f968 in run_test_table () at ../src/shared/tests.h:106
#6 0x000055b3a5a867fa in main (argc=1, argv=0x7ffe3c76ee38) at ../src/test/test-time-util.c:656
(gdb) frame 4
#4 0x000055b3a5a84620 in test_FORMAT_TIMESTAMP () at ../src/test/test-time-util.c:398
398 assert_se(x / USEC_PER_SEC == y / USEC_PER_SEC);
(gdb) info locals
buf = 0x55b3a5c322c0 "Wed 2018-08-15 12:30:03 +01"
x = 1534332603388565
y = 1534336203000000
i = 91
__func__ = "test_FORMAT_TIMESTAMP"
```
| 1.0 | test-time-util is broken in certain timezones - ### systemd version the issue has been seen with
main (253-rc2)
### Used distribution
Arch Linux/Ubuntu 20.04
### Linux kernel version used
Irrelevant
### CPU architectures issue was seen on
x86_64
### Component
tests
### Expected behaviour you didn't see
The tests should pass
### Unexpected behaviour you saw
Tests checking checking that conversion from timestamp to string and back sometimes fail in certain timezones.
### Steps to reproduce the problem
`TZ=Africa/Casablanca meson test -C build test-time-util --repeat 100`
From what it looks like, time util lib determines incorrectly whether the date _has_ belonged to the DST period or not and calculates the wrong timestamp most often missed by 1 hour.
The full list of broken timezones for Arch Linux with tzdata 2022g and glibc 2.36 is:
```
Africa/Casablanca
Africa/El_Aaiun
America/Argentina/Rio_Gallegos
America/Punta_Arenas
Antarctica/Casey
Antarctica/Davis
Antarctica/Palmer
Asia/Aqtau
Asia/Aqtobe
Asia/Atyrau
Asia/Baku
Asia/Bishkek
Asia/Oral
Asia/Qostanay
Asia/Qyzylorda
Asia/Samarkand
Asia/Srednekolymsk
Asia/Tbilisi
Asia/Yerevan
Chile/EasterIsland
Pacific/Easter
Turkey
```
### Additional program output to the terminal or log subsystem illustrating the issue
```sh
Thread 1 (Thread 0x7f10d20a6840 (LWP 783520)):
#0 0x00007f10d2a5864c in ?? () from /usr/lib/libc.so.6
#1 0x00007f10d2a08938 in raise () from /usr/lib/libc.so.6
#2 0x00007f10d29f253d in abort () from /usr/lib/libc.so.6
#3 0x00007f10d2e4fc70 in log_assert_failed (text=0x55b3a5a88ed0 "x / USEC_PER_SEC == y / USEC_PER_SEC", file=0x55b3a5a870e2 "src/test/test-time-util.c", line=398, func=0x55b3a5a89c00 <__func__.11> "test_FORMAT_TIMESTAMP") at ../src/basic/log.c:888
#4 0x000055b3a5a84620 in test_FORMAT_TIMESTAMP () at ../src/test/test-time-util.c:398
#5 0x000055b3a5a7f968 in run_test_table () at ../src/shared/tests.h:106
#6 0x000055b3a5a867fa in main (argc=1, argv=0x7ffe3c76ee38) at ../src/test/test-time-util.c:656
(gdb) frame 4
#4 0x000055b3a5a84620 in test_FORMAT_TIMESTAMP () at ../src/test/test-time-util.c:398
398 assert_se(x / USEC_PER_SEC == y / USEC_PER_SEC);
(gdb) info locals
buf = 0x55b3a5c322c0 "Wed 2018-08-15 12:30:03 +01"
x = 1534332603388565
y = 1534336203000000
i = 91
__func__ = "test_FORMAT_TIMESTAMP"
```
| non_priority | test time util is broken in certain timezones systemd version the issue has been seen with main used distribution arch linux ubuntu linux kernel version used irrelevant cpu architectures issue was seen on component tests expected behaviour you didn t see the tests should pass unexpected behaviour you saw tests checking checking that conversion from timestamp to string and back sometimes fail in certain timezones steps to reproduce the problem tz africa casablanca meson test c build test time util repeat from what it looks like time util lib determines incorrectly whether the date has belonged to the dst period or not and calculates the wrong timestamp most often missed by hour the full list of broken timezones for arch linux with tzdata and glibc is africa casablanca africa el aaiun america argentina rio gallegos america punta arenas antarctica casey antarctica davis antarctica palmer asia aqtau asia aqtobe asia atyrau asia baku asia bishkek asia oral asia qostanay asia qyzylorda asia samarkand asia srednekolymsk asia tbilisi asia yerevan chile easterisland pacific easter turkey additional program output to the terminal or log subsystem illustrating the issue sh thread thread lwp in from usr lib libc so in raise from usr lib libc so in abort from usr lib libc so in log assert failed text x usec per sec y usec per sec file src test test time util c line func test format timestamp at src basic log c in test format timestamp at src test test time util c in run test table at src shared tests h in main argc argv at src test test time util c gdb frame in test format timestamp at src test test time util c assert se x usec per sec y usec per sec gdb info locals buf wed x y i func test format timestamp | 0 |
316,179 | 23,618,409,507 | IssuesEvent | 2022-08-24 18:01:53 | dockstore/dockstore | https://api.github.com/repos/dockstore/dockstore | closed | Add GitHub Container Registry to table of supported Docker image repositories | enhancement documentation review | **Is your feature request related to a problem? Please describe.**
In the [Docker Image Checksum Support docs](https://docs.dockstore.org/en/stable/advanced-topics/checksum-support.html#docker-image-checksum-support), we refer to GitHub Container Registry in the note section here:
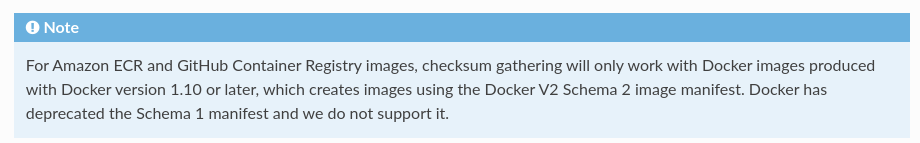
but it’s not actually in the table of supported Docker image repositories:
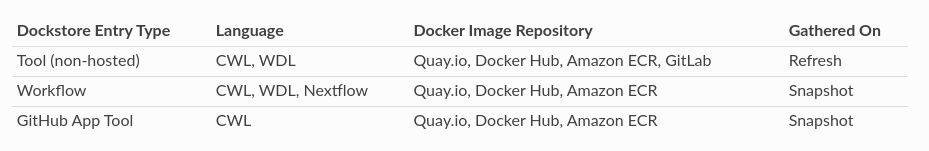
**Describe the solution you'd like**
Should add GitHub Container Registry to the table to indicate that checksum harvesting is supported for it.
**Describe alternatives you've considered**
n/a
**Additional context**
n/a
┆Issue is synchronized with this [Jira Story](https://ucsc-cgl.atlassian.net/browse/DOCK-2132)
┆fixVersions: Dockstore 1.12.x
┆friendlyId: DOCK-2132
┆sprint: 93- Ursula
┆taskType: Story
| 1.0 | Add GitHub Container Registry to table of supported Docker image repositories - **Is your feature request related to a problem? Please describe.**
In the [Docker Image Checksum Support docs](https://docs.dockstore.org/en/stable/advanced-topics/checksum-support.html#docker-image-checksum-support), we refer to GitHub Container Registry in the note section here:
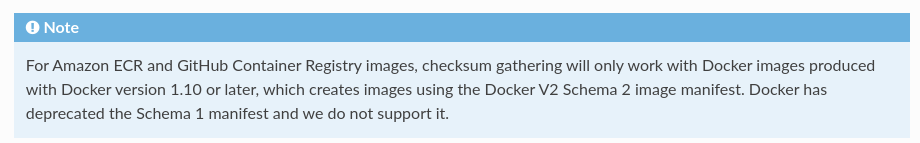
but it’s not actually in the table of supported Docker image repositories:
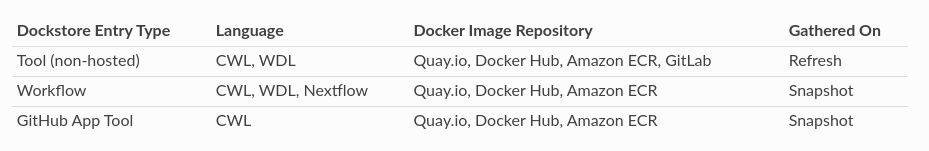
**Describe the solution you'd like**
Should add GitHub Container Registry to the table to indicate that checksum harvesting is supported for it.
**Describe alternatives you've considered**
n/a
**Additional context**
n/a
┆Issue is synchronized with this [Jira Story](https://ucsc-cgl.atlassian.net/browse/DOCK-2132)
┆fixVersions: Dockstore 1.12.x
┆friendlyId: DOCK-2132
┆sprint: 93- Ursula
┆taskType: Story
| non_priority | add github container registry to table of supported docker image repositories is your feature request related to a problem please describe in the we refer to github container registry in the note section here but it’s not actually in the table of supported docker image repositories describe the solution you d like should add github container registry to the table to indicate that checksum harvesting is supported for it describe alternatives you ve considered n a additional context n a ┆issue is synchronized with this ┆fixversions dockstore x ┆friendlyid dock ┆sprint ursula ┆tasktype story | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.