Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
245,081 | 26,509,481,640 | IssuesEvent | 2023-01-18 16:04:06 | MatBenfield/news | https://api.github.com/repos/MatBenfield/news | closed | [SecurityWeek] PyPI Users Targeted With 'Wacatac' Trojan in New Supply Chain Attack | SecurityWeek Stale |
**Fortinet warns of three new malicious PyPI packages containing code designed to fetch the Wacatac trojan and information stealer as a next stage payload.**
[read more](https://www.securityweek.com/pypi-users-targeted-wacatac-trojan-new-supply-chain-attack)
<https://www.securityweek.com/pypi-users-targeted-wacatac-trojan-new-supply-chain-attack>
| True | [SecurityWeek] PyPI Users Targeted With 'Wacatac' Trojan in New Supply Chain Attack -
**Fortinet warns of three new malicious PyPI packages containing code designed to fetch the Wacatac trojan and information stealer as a next stage payload.**
[read more](https://www.securityweek.com/pypi-users-targeted-wacatac-trojan-new-supply-chain-attack)
<https://www.securityweek.com/pypi-users-targeted-wacatac-trojan-new-supply-chain-attack>
| non_priority | pypi users targeted with wacatac trojan in new supply chain attack fortinet warns of three new malicious pypi packages containing code designed to fetch the wacatac trojan and information stealer as a next stage payload | 0 |
67,978 | 21,390,280,903 | IssuesEvent | 2022-04-21 06:14:21 | jlaffaye/ftp | https://api.github.com/repos/jlaffaye/ftp | opened | Some func do not support ftp on windows | defect | **Describe the bug**
Some func do not support ftp on windows, Like NameList(string)
**To Reproduce**
502 Command not implemented.
**Expected behavior**
return filename list
**FTP server**
Slyar FTPserver
on windows
| 1.0 | Some func do not support ftp on windows - **Describe the bug**
Some func do not support ftp on windows, Like NameList(string)
**To Reproduce**
502 Command not implemented.
**Expected behavior**
return filename list
**FTP server**
Slyar FTPserver
on windows
| non_priority | some func do not support ftp on windows describe the bug some func do not support ftp on windows like namelist string to reproduce command not implemented expected behavior return filename list ftp server slyar ftpserver on windows | 0 |
208,815 | 16,163,768,140 | IssuesEvent | 2021-05-01 05:25:46 | kaist-cp/rv6 | https://api.github.com/repos/kaist-cp/rv6 | closed | About #![allow(deadcode)] in lib.rs | D-easy documentation | - closes #113
lib.rs 내부의 `#![allow(deadcode)]`를 삭제하려면 xv6에는 구현되어 있는 요소들 중 사용되지 않는 것들을 제거하게 됩니다.
xv6의 의도를 살리기 위해 `#![allow(deadcode)]`는 그대로 남겨서 사용하도록 하겠습니다.
documentation으로 남기고, comment 추가하도록 하겠습니다. | 1.0 | About #![allow(deadcode)] in lib.rs - - closes #113
lib.rs 내부의 `#![allow(deadcode)]`를 삭제하려면 xv6에는 구현되어 있는 요소들 중 사용되지 않는 것들을 제거하게 됩니다.
xv6의 의도를 살리기 위해 `#![allow(deadcode)]`는 그대로 남겨서 사용하도록 하겠습니다.
documentation으로 남기고, comment 추가하도록 하겠습니다. | non_priority | about in lib rs closes lib rs 내부의 를 삭제하려면 구현되어 있는 요소들 중 사용되지 않는 것들을 제거하게 됩니다 의도를 살리기 위해 는 그대로 남겨서 사용하도록 하겠습니다 documentation으로 남기고 comment 추가하도록 하겠습니다 | 0 |
446,347 | 31,469,968,684 | IssuesEvent | 2023-08-30 06:46:11 | WeblateOrg/weblate | https://api.github.com/repos/WeblateOrg/weblate | closed | Info icon redirects to 404 page | bug documentation | ### Describe the issue
The info icon redirects to the corresponding page in the Docs. However, if the page does not exist in the set interface language, the user lands on a 404 page. I would expect that it would then redirect to the English page instead. So, unfortunately, most translators have no way to get the relevant info.
### I already tried
- [X] I've read and searched [the documentation](https://docs.weblate.org/).
- [X] I've searched for similar issues in this repository.
### Steps to reproduce the behavior
1. Set the user interface language to German
2. Go to a project
3. Select a Component
4. Select a language
5. Scroll to string status
6. Click the info icon on the right
7. Redirects to [https://docs.weblate.org/de/weblate-4.13.1/user/translating.html#strings-to-check](https://docs.weblate.org/de/weblate-4.13.1/user/translating.html#strings-to-check)
### Expected behavior
Opens the corresponding page in the Docs in German or if not available in the default language.
### Screenshots


### Exception traceback
_No response_
### How do you run Weblate?
PyPI module
### Weblate versions
4.13.1
### Weblate deploy checks
_No response_
### Additional context
_No response_ | 1.0 | Info icon redirects to 404 page - ### Describe the issue
The info icon redirects to the corresponding page in the Docs. However, if the page does not exist in the set interface language, the user lands on a 404 page. I would expect that it would then redirect to the English page instead. So, unfortunately, most translators have no way to get the relevant info.
### I already tried
- [X] I've read and searched [the documentation](https://docs.weblate.org/).
- [X] I've searched for similar issues in this repository.
### Steps to reproduce the behavior
1. Set the user interface language to German
2. Go to a project
3. Select a Component
4. Select a language
5. Scroll to string status
6. Click the info icon on the right
7. Redirects to [https://docs.weblate.org/de/weblate-4.13.1/user/translating.html#strings-to-check](https://docs.weblate.org/de/weblate-4.13.1/user/translating.html#strings-to-check)
### Expected behavior
Opens the corresponding page in the Docs in German or if not available in the default language.
### Screenshots


### Exception traceback
_No response_
### How do you run Weblate?
PyPI module
### Weblate versions
4.13.1
### Weblate deploy checks
_No response_
### Additional context
_No response_ | non_priority | info icon redirects to page describe the issue the info icon redirects to the corresponding page in the docs however if the page does not exist in the set interface language the user lands on a page i would expect that it would then redirect to the english page instead so unfortunately most translators have no way to get the relevant info i already tried i ve read and searched i ve searched for similar issues in this repository steps to reproduce the behavior set the user interface language to german go to a project select a component select a language scroll to string status click the info icon on the right redirects to expected behavior opens the corresponding page in the docs in german or if not available in the default language screenshots exception traceback no response how do you run weblate pypi module weblate versions weblate deploy checks no response additional context no response | 0 |
405,810 | 27,534,706,104 | IssuesEvent | 2023-03-07 02:01:33 | OpenCyphal/nunavut | https://api.github.com/repos/OpenCyphal/nunavut | closed | The local testing insturctions are obsolete | trivial documentation | Aren't we supposed to be using ghcr instead of dockerhub?
<img width="388" alt="image" src="https://user-images.githubusercontent.com/3298404/222776629-38d80434-c121-43bd-bec5-2defc50c96a1.png">
If it was possible to make these instructions less prone to obsolescence, that would be helpful. | 1.0 | The local testing insturctions are obsolete - Aren't we supposed to be using ghcr instead of dockerhub?
<img width="388" alt="image" src="https://user-images.githubusercontent.com/3298404/222776629-38d80434-c121-43bd-bec5-2defc50c96a1.png">
If it was possible to make these instructions less prone to obsolescence, that would be helpful. | non_priority | the local testing insturctions are obsolete aren t we supposed to be using ghcr instead of dockerhub img width alt image src if it was possible to make these instructions less prone to obsolescence that would be helpful | 0 |
55,402 | 30,732,226,686 | IssuesEvent | 2023-07-28 03:21:04 | hasura/graphql-engine | https://api.github.com/repos/hasura/graphql-engine | closed | [Feature Request]: Add latency report to GraphiQL | k/enhancement c/console p/medium e/intermediate a/performance | This one is really a minor but important detail:
Please add query latency to the GraphiQL query console, as shown in the image below.
The background is very simple when merging multiple remote-schemata together and exposing them through Hasura, it is not always clear were additional latency is coming from. For example,
a microservice may query a database and exposes these queries a GraphQL endpoint to Hasura which then passes it on to the client.
When the client measures, say 300 ms latency, but the naked DB query only takes 25 ms, the big question is where the rest is coming from. If, on the other hand, the same query in GraphiQL console also takes, say 225 ms latency, I know immediately that I have to dissect my microservice before tracing network hops.
Conversely, if the GraphiQL query is about as fast, I have to dissect my CDN, but either way, I know exactly where to look from the get-go.
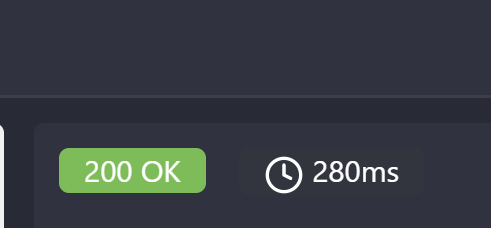
| True | [Feature Request]: Add latency report to GraphiQL - This one is really a minor but important detail:
Please add query latency to the GraphiQL query console, as shown in the image below.
The background is very simple when merging multiple remote-schemata together and exposing them through Hasura, it is not always clear were additional latency is coming from. For example,
a microservice may query a database and exposes these queries a GraphQL endpoint to Hasura which then passes it on to the client.
When the client measures, say 300 ms latency, but the naked DB query only takes 25 ms, the big question is where the rest is coming from. If, on the other hand, the same query in GraphiQL console also takes, say 225 ms latency, I know immediately that I have to dissect my microservice before tracing network hops.
Conversely, if the GraphiQL query is about as fast, I have to dissect my CDN, but either way, I know exactly where to look from the get-go.
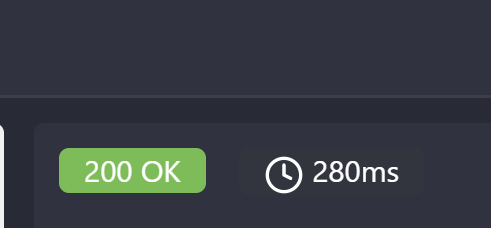
| non_priority | add latency report to graphiql this one is really a minor but important detail please add query latency to the graphiql query console as shown in the image below the background is very simple when merging multiple remote schemata together and exposing them through hasura it is not always clear were additional latency is coming from for example a microservice may query a database and exposes these queries a graphql endpoint to hasura which then passes it on to the client when the client measures say ms latency but the naked db query only takes ms the big question is where the rest is coming from if on the other hand the same query in graphiql console also takes say ms latency i know immediately that i have to dissect my microservice before tracing network hops conversely if the graphiql query is about as fast i have to dissect my cdn but either way i know exactly where to look from the get go | 0 |
188,611 | 15,165,759,967 | IssuesEvent | 2021-02-12 15:28:33 | TEIC/Stylesheets | https://api.github.com/repos/TEIC/Stylesheets | closed | Add permalink for examples | resp: StylesheetsGroup target: documentation type: enhancement | See TEIC/TEI#1931.
We want to add a link on each example making it easy to obtain a URL directly to that example. Examples already have IDs, making that straightforward. The links should point at a particular version of the GLs rather than "current".
Also see #470, so that if someone bookmarks one of these links and visits it, they see a message alerting them that they have visited an older version. | 1.0 | Add permalink for examples - See TEIC/TEI#1931.
We want to add a link on each example making it easy to obtain a URL directly to that example. Examples already have IDs, making that straightforward. The links should point at a particular version of the GLs rather than "current".
Also see #470, so that if someone bookmarks one of these links and visits it, they see a message alerting them that they have visited an older version. | non_priority | add permalink for examples see teic tei we want to add a link on each example making it easy to obtain a url directly to that example examples already have ids making that straightforward the links should point at a particular version of the gls rather than current also see so that if someone bookmarks one of these links and visits it they see a message alerting them that they have visited an older version | 0 |
32,623 | 4,386,576,163 | IssuesEvent | 2016-08-08 13:18:59 | prdxn-org/tagster | https://api.github.com/repos/prdxn-org/tagster | opened | As a designer I want to create a new design template for Geotagged images | Design Phase I Sprint 2 User Story | As a designer I want to create a new design template for Geotagged images so that I can see the images which are Geotagged.
**Acceptance Criteria:**
1. Logo should be visible at Top left.
2. Light box should be shown.
3. Light box should show Google maps.
4. In the right side of header there should be a Mailto icon and an info icon
5. Search icon should be shown in the bottom right position next to the lightbox. | 1.0 | As a designer I want to create a new design template for Geotagged images - As a designer I want to create a new design template for Geotagged images so that I can see the images which are Geotagged.
**Acceptance Criteria:**
1. Logo should be visible at Top left.
2. Light box should be shown.
3. Light box should show Google maps.
4. In the right side of header there should be a Mailto icon and an info icon
5. Search icon should be shown in the bottom right position next to the lightbox. | non_priority | as a designer i want to create a new design template for geotagged images as a designer i want to create a new design template for geotagged images so that i can see the images which are geotagged acceptance criteria logo should be visible at top left light box should be shown light box should show google maps in the right side of header there should be a mailto icon and an info icon search icon should be shown in the bottom right position next to the lightbox | 0 |
21,445 | 7,024,831,326 | IssuesEvent | 2017-12-23 00:16:58 | dart-lang/build | https://api.github.com/repos/dart-lang/build | closed | Allow mixed-mode building | package:build_runner | We need to allow running Builders that output to source, as well as to the generated cache directory.
- [ ] #626 - How will outputting to source impact ordering? The Builders that output to source should probably all be run before those writing to the cache. They also likely shouldn't be allowed to use `required_inputs`
- [x] Store `isHidden` on `GeneratedAssetNode`. Use this to determine where to read from
- [x] Add `hiddenOutput` to `BuildAction`. We may want to hide this until `BuildAction` is removed from the public interface.
- [x] Support setting `hiddenOutput` through `BuilderApplication`.
- [x] Support some configuration for `hide_outputs` in `build.yaml`
- [x] Deprecate then drop `writeToCache` argument, use the per-action setting instead | 1.0 | Allow mixed-mode building - We need to allow running Builders that output to source, as well as to the generated cache directory.
- [ ] #626 - How will outputting to source impact ordering? The Builders that output to source should probably all be run before those writing to the cache. They also likely shouldn't be allowed to use `required_inputs`
- [x] Store `isHidden` on `GeneratedAssetNode`. Use this to determine where to read from
- [x] Add `hiddenOutput` to `BuildAction`. We may want to hide this until `BuildAction` is removed from the public interface.
- [x] Support setting `hiddenOutput` through `BuilderApplication`.
- [x] Support some configuration for `hide_outputs` in `build.yaml`
- [x] Deprecate then drop `writeToCache` argument, use the per-action setting instead | non_priority | allow mixed mode building we need to allow running builders that output to source as well as to the generated cache directory how will outputting to source impact ordering the builders that output to source should probably all be run before those writing to the cache they also likely shouldn t be allowed to use required inputs store ishidden on generatedassetnode use this to determine where to read from add hiddenoutput to buildaction we may want to hide this until buildaction is removed from the public interface support setting hiddenoutput through builderapplication support some configuration for hide outputs in build yaml deprecate then drop writetocache argument use the per action setting instead | 0 |
97,608 | 8,663,673,884 | IssuesEvent | 2018-11-28 17:58:08 | elastic/beats | https://api.github.com/repos/elastic/beats | opened | Add more E2E tests for JSON configuration variations and `log.*` fields | :Testing Filebeat enhancement | Goal: test if metadata provided by Filebeat can be overwritten correctly using the JSON configuration options.
Validate the following scenarios: https://github.com/elastic/beats/pull/9172#discussion_r236865737 | 1.0 | Add more E2E tests for JSON configuration variations and `log.*` fields - Goal: test if metadata provided by Filebeat can be overwritten correctly using the JSON configuration options.
Validate the following scenarios: https://github.com/elastic/beats/pull/9172#discussion_r236865737 | non_priority | add more tests for json configuration variations and log fields goal test if metadata provided by filebeat can be overwritten correctly using the json configuration options validate the following scenarios | 0 |
37,018 | 18,070,223,478 | IssuesEvent | 2021-09-21 01:25:55 | matomo-org/matomo | https://api.github.com/repos/matomo-org/matomo | opened | SQL query to calculate life time metric can be slow | Major c: Performance | I'm meaning this query https://github.com/matomo-org/matomo/blob/4.5.0-b2/plugins/Ecommerce/VisitorDetails.php#L154-L169 which looks like this
```sql
SELECT COALESCE(SUM(ROUND(revenue,2)), 0) as lifeTimeRevenue, COUNT(*) as lifeTimeConversions,COALESCE(SUM(ROUND(items,2)), 0) as lifeTimeEcommerceItems FROM log_visit AS log_visit LEFT JOIN log_conversion AS log_conversion ON log_visit.idvisit = log_conversion.idvisit WHERE log_visit.idsite = '2' AND log_visit.idvisitor = 'Vè
tO' AND log_conversion.idgoal = 0
```
At first glance the query looks good as it uses indexes etc.
This is usually also the case
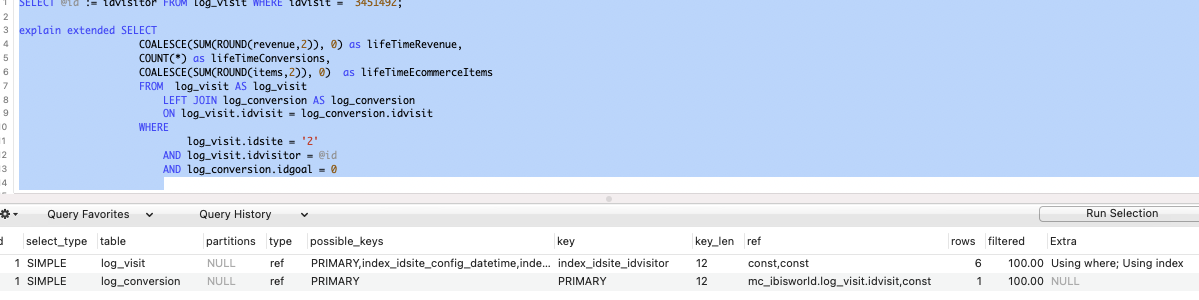
However, things change when one visitor has hundreds or thousands of visits. Then it looks like this:

Here is more explain format=json information:
```json
{
"query_block": {
"select_id": 1,
"cost_info": {
"query_cost": "365.16"
},
"nested_loop": [
{
"table": {
"table_name": "log_conversion",
"access_type": "ALL",
"possible_keys": [
"PRIMARY"
],
"rows_examined_per_scan": 738,
"rows_produced_per_join": 73,
"filtered": "10.00",
"cost_info": {
"read_cost": "261.84",
"eval_cost": "14.76",
"prefix_cost": "276.60",
"data_read_per_join": "2M"
},
"used_columns": [
"idvisit",
"idgoal",
"items",
"revenue"
],
"attached_condition": "((`test`.`log_conversion`.`idgoal` = 0) and (`test`.`log_conversion`.`idvisit` is not null))"
}
},
{
"table": {
"table_name": "log_visit",
"access_type": "eq_ref",
"possible_keys": [
"PRIMARY",
"index_idsite_config_datetime",
"index_idsite_datetime",
"index_idsite_idvisitor"
],
"key": "PRIMARY",
"used_key_parts": [
"idvisit"
],
"key_length": "8",
"ref": [
"test.log_conversion.idvisit"
],
"rows_examined_per_scan": 1,
"rows_produced_per_join": 3,
"filtered": "5.00",
"cost_info": {
"read_cost": "73.80",
"eval_cost": "0.74",
"prefix_cost": "365.16",
"data_read_per_join": "113K"
},
"used_columns": [
"idvisit",
"idsite",
"idvisitor"
],
"attached_condition": "((`test`.`log_visit`.`idvisitor` = (@`id`)) and (`test`.`log_visit`.`idsite` = '2'))"
}
}
]
}
}
```
FYI Overall, in that specific case, there is actually no entry that matches `idsite = 2 and idgoal = 0` in `log_conversion`.
refs https://github.com/matomo-org/matomo/issues/16904 | True | SQL query to calculate life time metric can be slow - I'm meaning this query https://github.com/matomo-org/matomo/blob/4.5.0-b2/plugins/Ecommerce/VisitorDetails.php#L154-L169 which looks like this
```sql
SELECT COALESCE(SUM(ROUND(revenue,2)), 0) as lifeTimeRevenue, COUNT(*) as lifeTimeConversions,COALESCE(SUM(ROUND(items,2)), 0) as lifeTimeEcommerceItems FROM log_visit AS log_visit LEFT JOIN log_conversion AS log_conversion ON log_visit.idvisit = log_conversion.idvisit WHERE log_visit.idsite = '2' AND log_visit.idvisitor = 'Vè
tO' AND log_conversion.idgoal = 0
```
At first glance the query looks good as it uses indexes etc.
This is usually also the case
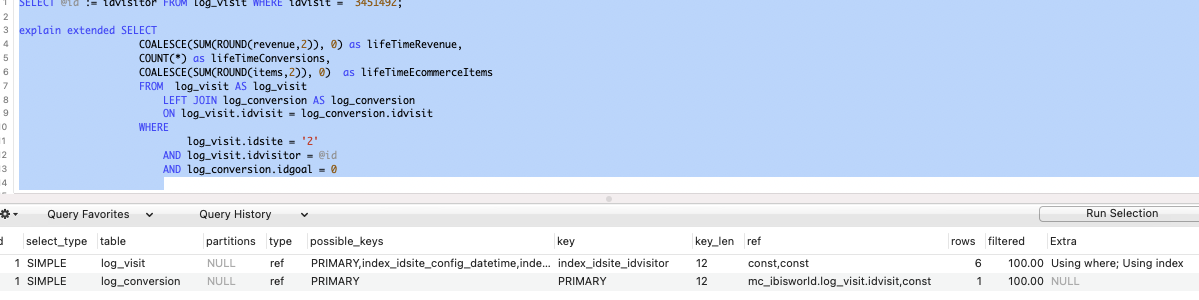
However, things change when one visitor has hundreds or thousands of visits. Then it looks like this:

Here is more explain format=json information:
```json
{
"query_block": {
"select_id": 1,
"cost_info": {
"query_cost": "365.16"
},
"nested_loop": [
{
"table": {
"table_name": "log_conversion",
"access_type": "ALL",
"possible_keys": [
"PRIMARY"
],
"rows_examined_per_scan": 738,
"rows_produced_per_join": 73,
"filtered": "10.00",
"cost_info": {
"read_cost": "261.84",
"eval_cost": "14.76",
"prefix_cost": "276.60",
"data_read_per_join": "2M"
},
"used_columns": [
"idvisit",
"idgoal",
"items",
"revenue"
],
"attached_condition": "((`test`.`log_conversion`.`idgoal` = 0) and (`test`.`log_conversion`.`idvisit` is not null))"
}
},
{
"table": {
"table_name": "log_visit",
"access_type": "eq_ref",
"possible_keys": [
"PRIMARY",
"index_idsite_config_datetime",
"index_idsite_datetime",
"index_idsite_idvisitor"
],
"key": "PRIMARY",
"used_key_parts": [
"idvisit"
],
"key_length": "8",
"ref": [
"test.log_conversion.idvisit"
],
"rows_examined_per_scan": 1,
"rows_produced_per_join": 3,
"filtered": "5.00",
"cost_info": {
"read_cost": "73.80",
"eval_cost": "0.74",
"prefix_cost": "365.16",
"data_read_per_join": "113K"
},
"used_columns": [
"idvisit",
"idsite",
"idvisitor"
],
"attached_condition": "((`test`.`log_visit`.`idvisitor` = (@`id`)) and (`test`.`log_visit`.`idsite` = '2'))"
}
}
]
}
}
```
FYI Overall, in that specific case, there is actually no entry that matches `idsite = 2 and idgoal = 0` in `log_conversion`.
refs https://github.com/matomo-org/matomo/issues/16904 | non_priority | sql query to calculate life time metric can be slow i m meaning this query which looks like this sql select coalesce sum round revenue as lifetimerevenue count as lifetimeconversions coalesce sum round items as lifetimeecommerceitems from log visit as log visit left join log conversion as log conversion on log visit idvisit log conversion idvisit where log visit idsite and log visit idvisitor vè
to and log conversion idgoal at first glance the query looks good as it uses indexes etc this is usually also the case however things change when one visitor has hundreds or thousands of visits then it looks like this here is more explain format json information json query block select id cost info query cost nested loop table table name log conversion access type all possible keys primary rows examined per scan rows produced per join filtered cost info read cost eval cost prefix cost data read per join used columns idvisit idgoal items revenue attached condition test log conversion idgoal and test log conversion idvisit is not null table table name log visit access type eq ref possible keys primary index idsite config datetime index idsite datetime index idsite idvisitor key primary used key parts idvisit key length ref test log conversion idvisit rows examined per scan rows produced per join filtered cost info read cost eval cost prefix cost data read per join used columns idvisit idsite idvisitor attached condition test log visit idvisitor id and test log visit idsite fyi overall in that specific case there is actually no entry that matches idsite and idgoal in log conversion refs | 0 |
151,196 | 13,393,406,004 | IssuesEvent | 2020-09-03 04:08:08 | seanpm2001/SNU_2D_CloudDrive | https://api.github.com/repos/seanpm2001/SNU_2D_CloudDrive | opened | Can't upload WAV Pcloud audio sample | documentation enhancement good first issue help wanted |
***
### Can't upload WAV Pcloud audio sample
I can't upload the pCloud audio sample that is in WAV format, as it exceeds the GitHub 25 megabyte file limit. I have tried multiple methods of compression, but I have been unable to get it below 26.1 megabytes, which is still over 1.1 megabytes over the limit.
If anyone knows how to compress it without losing its original data, feel free to upload a copy.
***
| 1.0 | Can't upload WAV Pcloud audio sample -
***
### Can't upload WAV Pcloud audio sample
I can't upload the pCloud audio sample that is in WAV format, as it exceeds the GitHub 25 megabyte file limit. I have tried multiple methods of compression, but I have been unable to get it below 26.1 megabytes, which is still over 1.1 megabytes over the limit.
If anyone knows how to compress it without losing its original data, feel free to upload a copy.
***
| non_priority | can t upload wav pcloud audio sample can t upload wav pcloud audio sample i can t upload the pcloud audio sample that is in wav format as it exceeds the github megabyte file limit i have tried multiple methods of compression but i have been unable to get it below megabytes which is still over megabytes over the limit if anyone knows how to compress it without losing its original data feel free to upload a copy | 0 |
12,498 | 7,893,200,863 | IssuesEvent | 2018-06-28 17:15:37 | Azure/azure-functions-durable-extension | https://api.github.com/repos/Azure/azure-functions-durable-extension | opened | Heavy load performance and reliability improvements | dtfx performance | This is a general work item tracking performance improvements in heavy load scenarios for Azure Functions v2 GA timeframe (ideally any improvements would work for Durable on both v1 and v2).
I'm currently tracking the current scenario(s), which have shown some inconsistent behavior:
- [ ] 1M sequential orchestrations executing concurrently across multiple Azure VMs.
I will also link other issues to this one which might impact our results. | True | Heavy load performance and reliability improvements - This is a general work item tracking performance improvements in heavy load scenarios for Azure Functions v2 GA timeframe (ideally any improvements would work for Durable on both v1 and v2).
I'm currently tracking the current scenario(s), which have shown some inconsistent behavior:
- [ ] 1M sequential orchestrations executing concurrently across multiple Azure VMs.
I will also link other issues to this one which might impact our results. | non_priority | heavy load performance and reliability improvements this is a general work item tracking performance improvements in heavy load scenarios for azure functions ga timeframe ideally any improvements would work for durable on both and i m currently tracking the current scenario s which have shown some inconsistent behavior sequential orchestrations executing concurrently across multiple azure vms i will also link other issues to this one which might impact our results | 0 |
24,633 | 12,344,588,378 | IssuesEvent | 2020-05-15 07:19:37 | flutter/flutter | https://api.github.com/repos/flutter/flutter | opened | ios release not working properly | created via performance template | <!-- Thank you for using Flutter!
If you are looking for support, please check out our documentation
or consider asking a question on Stack Overflow:
* https://flutter.dev/
* https://api.flutter.dev/
* https://stackoverflow.com/questions/tagged/flutter?sort=frequent
If you have found a performance problem, then fill our the template below.
Please read our guide to filing a bug first: https://flutter.dev/docs/resources/bug-reports
-->
## Details
<!--
1. Please tell us exactly how to reproduce the problem you are running into.
2. Please attach a small application (ideally just one main.dart file) that
reproduces the problem. You could use https://gist.github.com/ for this.
3. Switch flutter to master channel and run this app on a physical device
using profile mode with Skia tracing enabled, as follows:
flutter channel master
flutter run --profile --trace-skia
Then press ‘P’ to enable the performance overlay.
The bleeding edge master channel is encouraged here because Flutter is
constantly fixing bugs and improving its performance. Your problem in an
older Flutter version may have already been solved in the master channel.
4. Record a video of the performance issue using another phone so we
can have an intuitive understanding of what happened. Don’t use
"adb screenrecord", as that affects the performance of the profile run.
5. Open Observatory and save a timeline trace of the performance issue
so we know which functions might be causing it. See "How to Collect
and Read Timeline Traces" on this blog post:
https://medium.com/flutter-io/profiling-flutter-applications-using-the-timeline-a1a434964af03#a499
-->
I don't know which part is wrong.
When I use flutter to develop an application, everything works fine.
After the application is uploaded to the app store, I can use it myself without problems. But the user feedback to me is very bad.
<!--
Please tell us which target platform(s) the problem occurs (Android / iOS / Web / macOS / Linux / Windows)
Which target OS version, for Web, browser, is the test system running?
Does the problem occur on emulator/simulator as well as on physical devices?
-->
**Target Platform: ios
**Target OS version/browser: all
**Devices: all
## Logs
<!--
Run `flutter analyze` and attach any output of that command below.
If there are any analysis errors, try resolving them before filing this issue.
-->
```
info • The value of the field '_options' isn't used • lib/common/Git.dart:47:18 • unused_field
info • The declaration '_getAuth' isn't referenced • lib/common/Git.dart:229:25 • unused_element
info • The value of the field '_languageCode' isn't used • lib/main.dart:968:16 • unused_field
info • Unused import: 'package:camera/camera.dart' • lib/routers/book/WriteBookInfo.dart:15:8 • unused_import
info • Unused import: 'dart:io' • lib/routers/book/WriteExperience.dart:1:8 • unused_import
info • Unused import: 'dart:convert' • lib/routers/index/ImagePick.dart:2:8 • unused_import
warning • Missing case clause for 'linux' • lib/routers/index/login/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'macOS' • lib/routers/index/login/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'windows' • lib/routers/index/login/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
info • Unused import: 'dart:io' • lib/routers/settings/Setting.dart:1:8 • unused_import
info • Unused import: 'package:book_data/widgets/searchBar/SearchBar.dart' • lib/routers/user/UserChat.dart:12:8 • unused_import
info • Unused import: 'dart:async' • lib/routers/user/homePage/UserHomePage.dart:1:8 • unused_import
warning • Missing case clause for 'linux' • lib/widgets/MyAppBar.dart:256:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'macOS' • lib/widgets/MyAppBar.dart:256:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'windows' • lib/widgets/MyAppBar.dart:256:5 • missing_enum_constant_in_switch
info • 'title' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline6. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:301:47 • deprecated_member_use
info • 'title' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline6. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:302:35 • deprecated_member_use
info • 'title' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline6. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:303:35 • deprecated_member_use
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:304:45 • deprecated_member_use
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:305:35 • deprecated_member_use
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:306:35 • deprecated_member_use
warning • Missing case clause for 'linux' • lib/widgets/MyAppBar.dart:345:7 • missing_enum_constant_in_switch
warning • Missing case clause for 'macOS' • lib/widgets/MyAppBar.dart:345:7 • missing_enum_constant_in_switch
warning • Missing case clause for 'windows' • lib/widgets/MyAppBar.dart:345:7 • missing_enum_constant_in_switch
warning • Missing case clause for 'linux' • lib/widgets/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'macOS' • lib/widgets/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'windows' • lib/widgets/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
info • Unused import: 'dart:typed_data' • lib/widgets/UpdateImage.dart:1:8 • unused_import
info • Unused import: 'package:book_data/common/Global.dart' • lib/widgets/UpdateImage.dart:4:8 • unused_import
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/numberpicker.dart:263:50 • deprecated_member_use
info • 'headline' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline5. This feature was
deprecated after v1.13.8. • lib/widgets/numberpicker.dart:265:29 • deprecated_member_use
info • The member 'activity' can only be used within 'package:flutter/src/widgets/scroll_position.dart' or a test • lib/widgets/numberpicker.dart:272:42 •
invalid_use_of_visible_for_testing_member
info • The member 'activity' can only be used within instance members of subclasses of 'package:flutter/src/widgets/scroll_position.dart' •
lib/widgets/numberpicker.dart:272:42 • invalid_use_of_protected_member
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/numberpicker.dart:325:50 • deprecated_member_use
info • 'headline' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline5. This feature was
deprecated after v1.13.8. • lib/widgets/numberpicker.dart:327:29 • deprecated_member_use
info • The member 'activity' can only be used within 'package:flutter/src/widgets/scroll_position.dart' or a test • lib/widgets/numberpicker.dart:335:46 •
invalid_use_of_visible_for_testing_member
info • The member 'activity' can only be used within instance members of subclasses of 'package:flutter/src/widgets/scroll_position.dart' •
lib/widgets/numberpicker.dart:335:46 • invalid_use_of_protected_member
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/numberpicker.dart:385:50 • deprecated_member_use
info • 'headline' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline5. This feature was
deprecated after v1.13.8. • lib/widgets/numberpicker.dart:387:29 • deprecated_member_use
info • The member 'activity' can only be used within 'package:flutter/src/widgets/scroll_position.dart' or a test • lib/widgets/numberpicker.dart:392:42 •
invalid_use_of_visible_for_testing_member
info • The member 'activity' can only be used within instance members of subclasses of 'package:flutter/src/widgets/scroll_position.dart' •
lib/widgets/numberpicker.dart:392:42 • invalid_use_of_protected_member
info • The member 'activity' can only be used within 'package:flutter/src/widgets/scroll_position.dart' or a test • lib/widgets/numberpicker.dart:553:35 •
invalid_use_of_visible_for_testing_member
info • The member 'activity' can only be used within instance members of subclasses of 'package:flutter/src/widgets/scroll_position.dart' •
lib/widgets/numberpicker.dart:553:35 • invalid_use_of_protected_member
warning • The parameter 'lastStr' is required • lib/widgets/numberpicker.dart:697:18 • missing_required_param
warning • The parameter 'preStr' is required • lib/widgets/numberpicker.dart:697:18 • missing_required_param
warning • The parameter 'lastStr' is required • lib/widgets/numberpicker.dart:706:18 • missing_required_param
warning • The parameter 'preStr' is required • lib/widgets/numberpicker.dart:706:18 • missing_required_param
info • Unused import: 'package:book_data/common/ThemeModel.dart' • lib/widgets/searchBar/SearchBar.dart:5:8 • unused_import
info • Unused import: 'package:provider/provider.dart' • lib/widgets/searchBar/SearchBar.dart:12:8 • unused_import
warning • The include file ../../analysis_options.yaml in /Users/elevendimensions/Desktop/book_data/plugins/camera-0.5.7+4/analysis_options.yaml cannot be found •
plugins/camera-0.5.7+4/analysis_options.yaml:1:11 • include_file_not_found
warning • The include file ../../analysis_options.yaml in /Users/elevendimensions/Desktop/book_data/plugins/camera-0.5.7+4/analysis_options.yaml cannot be found •
plugins/camera-0.5.7+4/analysis_options.yaml:1:11 • include_file_not_found
51 issues found. (ran in 15.2s)
```
<!-- Finally, paste the output of running `flutter doctor -v` here, with your device plugged in. -->
```
[✓] Flutter (Channel stable, v1.17.0, on Mac OS X 10.15.4 19E287, locale
zh-Hans-CN)
• Flutter version 1.17.0 at /Users/elevendimensions/Documents/flutter
• Framework revision e6b34c2b5c (13 days ago), 2020-05-02 11:39:18 -0700
• Engine revision 540786dd51
• Dart version 2.8.1
[✓] Android toolchain - develop for Android devices (Android SDK version 29.0.3)
• Android SDK at /Users/elevendimensions/Library/Android/sdk
• Platform android-29, build-tools 29.0.3
• Java binary at: /Applications/Android Studio.app/Contents/jre/jdk/Contents/Home/bin/java
• Java version OpenJDK Runtime Environment (build 1.8.0_212-release-1586-b4-5784211)
• All Android licenses accepted.
[✓] Xcode - develop for iOS and macOS (Xcode 11.4.1)
• Xcode at /Applications/Xcode.app/Contents/Developer
• Xcode 11.4.1, Build version 11E503a
• CocoaPods version 1.9.1
[✓] Android Studio (version 3.6)
• Android Studio at /Applications/Android Studio.app/Contents
• Flutter plugin version 45.1.1
• Dart plugin version 192.7761
• Java version OpenJDK Runtime Environment (build 1.8.0_212-release-1586-b4-5784211)
[!] Connected device
! No devices available
! Doctor found issues in 1 category.
```
| True | ios release not working properly - <!-- Thank you for using Flutter!
If you are looking for support, please check out our documentation
or consider asking a question on Stack Overflow:
* https://flutter.dev/
* https://api.flutter.dev/
* https://stackoverflow.com/questions/tagged/flutter?sort=frequent
If you have found a performance problem, then fill our the template below.
Please read our guide to filing a bug first: https://flutter.dev/docs/resources/bug-reports
-->
## Details
<!--
1. Please tell us exactly how to reproduce the problem you are running into.
2. Please attach a small application (ideally just one main.dart file) that
reproduces the problem. You could use https://gist.github.com/ for this.
3. Switch flutter to master channel and run this app on a physical device
using profile mode with Skia tracing enabled, as follows:
flutter channel master
flutter run --profile --trace-skia
Then press ‘P’ to enable the performance overlay.
The bleeding edge master channel is encouraged here because Flutter is
constantly fixing bugs and improving its performance. Your problem in an
older Flutter version may have already been solved in the master channel.
4. Record a video of the performance issue using another phone so we
can have an intuitive understanding of what happened. Don’t use
"adb screenrecord", as that affects the performance of the profile run.
5. Open Observatory and save a timeline trace of the performance issue
so we know which functions might be causing it. See "How to Collect
and Read Timeline Traces" on this blog post:
https://medium.com/flutter-io/profiling-flutter-applications-using-the-timeline-a1a434964af03#a499
-->
I don't know which part is wrong.
When I use flutter to develop an application, everything works fine.
After the application is uploaded to the app store, I can use it myself without problems. But the user feedback to me is very bad.
<!--
Please tell us which target platform(s) the problem occurs (Android / iOS / Web / macOS / Linux / Windows)
Which target OS version, for Web, browser, is the test system running?
Does the problem occur on emulator/simulator as well as on physical devices?
-->
**Target Platform: ios
**Target OS version/browser: all
**Devices: all
## Logs
<!--
Run `flutter analyze` and attach any output of that command below.
If there are any analysis errors, try resolving them before filing this issue.
-->
```
info • The value of the field '_options' isn't used • lib/common/Git.dart:47:18 • unused_field
info • The declaration '_getAuth' isn't referenced • lib/common/Git.dart:229:25 • unused_element
info • The value of the field '_languageCode' isn't used • lib/main.dart:968:16 • unused_field
info • Unused import: 'package:camera/camera.dart' • lib/routers/book/WriteBookInfo.dart:15:8 • unused_import
info • Unused import: 'dart:io' • lib/routers/book/WriteExperience.dart:1:8 • unused_import
info • Unused import: 'dart:convert' • lib/routers/index/ImagePick.dart:2:8 • unused_import
warning • Missing case clause for 'linux' • lib/routers/index/login/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'macOS' • lib/routers/index/login/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'windows' • lib/routers/index/login/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
info • Unused import: 'dart:io' • lib/routers/settings/Setting.dart:1:8 • unused_import
info • Unused import: 'package:book_data/widgets/searchBar/SearchBar.dart' • lib/routers/user/UserChat.dart:12:8 • unused_import
info • Unused import: 'dart:async' • lib/routers/user/homePage/UserHomePage.dart:1:8 • unused_import
warning • Missing case clause for 'linux' • lib/widgets/MyAppBar.dart:256:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'macOS' • lib/widgets/MyAppBar.dart:256:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'windows' • lib/widgets/MyAppBar.dart:256:5 • missing_enum_constant_in_switch
info • 'title' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline6. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:301:47 • deprecated_member_use
info • 'title' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline6. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:302:35 • deprecated_member_use
info • 'title' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline6. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:303:35 • deprecated_member_use
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:304:45 • deprecated_member_use
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:305:35 • deprecated_member_use
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/MyAppBar.dart:306:35 • deprecated_member_use
warning • Missing case clause for 'linux' • lib/widgets/MyAppBar.dart:345:7 • missing_enum_constant_in_switch
warning • Missing case clause for 'macOS' • lib/widgets/MyAppBar.dart:345:7 • missing_enum_constant_in_switch
warning • Missing case clause for 'windows' • lib/widgets/MyAppBar.dart:345:7 • missing_enum_constant_in_switch
warning • Missing case clause for 'linux' • lib/widgets/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'macOS' • lib/widgets/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
warning • Missing case clause for 'windows' • lib/widgets/PrivateBottomSheet.dart:280:5 • missing_enum_constant_in_switch
info • Unused import: 'dart:typed_data' • lib/widgets/UpdateImage.dart:1:8 • unused_import
info • Unused import: 'package:book_data/common/Global.dart' • lib/widgets/UpdateImage.dart:4:8 • unused_import
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/numberpicker.dart:263:50 • deprecated_member_use
info • 'headline' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline5. This feature was
deprecated after v1.13.8. • lib/widgets/numberpicker.dart:265:29 • deprecated_member_use
info • The member 'activity' can only be used within 'package:flutter/src/widgets/scroll_position.dart' or a test • lib/widgets/numberpicker.dart:272:42 •
invalid_use_of_visible_for_testing_member
info • The member 'activity' can only be used within instance members of subclasses of 'package:flutter/src/widgets/scroll_position.dart' •
lib/widgets/numberpicker.dart:272:42 • invalid_use_of_protected_member
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/numberpicker.dart:325:50 • deprecated_member_use
info • 'headline' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline5. This feature was
deprecated after v1.13.8. • lib/widgets/numberpicker.dart:327:29 • deprecated_member_use
info • The member 'activity' can only be used within 'package:flutter/src/widgets/scroll_position.dart' or a test • lib/widgets/numberpicker.dart:335:46 •
invalid_use_of_visible_for_testing_member
info • The member 'activity' can only be used within instance members of subclasses of 'package:flutter/src/widgets/scroll_position.dart' •
lib/widgets/numberpicker.dart:335:46 • invalid_use_of_protected_member
info • 'body1' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is bodyText2. This feature was deprecated
after v1.13.8. • lib/widgets/numberpicker.dart:385:50 • deprecated_member_use
info • 'headline' is deprecated and shouldn't be used. This is the term used in the 2014 version of material design. The modern term is headline5. This feature was
deprecated after v1.13.8. • lib/widgets/numberpicker.dart:387:29 • deprecated_member_use
info • The member 'activity' can only be used within 'package:flutter/src/widgets/scroll_position.dart' or a test • lib/widgets/numberpicker.dart:392:42 •
invalid_use_of_visible_for_testing_member
info • The member 'activity' can only be used within instance members of subclasses of 'package:flutter/src/widgets/scroll_position.dart' •
lib/widgets/numberpicker.dart:392:42 • invalid_use_of_protected_member
info • The member 'activity' can only be used within 'package:flutter/src/widgets/scroll_position.dart' or a test • lib/widgets/numberpicker.dart:553:35 •
invalid_use_of_visible_for_testing_member
info • The member 'activity' can only be used within instance members of subclasses of 'package:flutter/src/widgets/scroll_position.dart' •
lib/widgets/numberpicker.dart:553:35 • invalid_use_of_protected_member
warning • The parameter 'lastStr' is required • lib/widgets/numberpicker.dart:697:18 • missing_required_param
warning • The parameter 'preStr' is required • lib/widgets/numberpicker.dart:697:18 • missing_required_param
warning • The parameter 'lastStr' is required • lib/widgets/numberpicker.dart:706:18 • missing_required_param
warning • The parameter 'preStr' is required • lib/widgets/numberpicker.dart:706:18 • missing_required_param
info • Unused import: 'package:book_data/common/ThemeModel.dart' • lib/widgets/searchBar/SearchBar.dart:5:8 • unused_import
info • Unused import: 'package:provider/provider.dart' • lib/widgets/searchBar/SearchBar.dart:12:8 • unused_import
warning • The include file ../../analysis_options.yaml in /Users/elevendimensions/Desktop/book_data/plugins/camera-0.5.7+4/analysis_options.yaml cannot be found •
plugins/camera-0.5.7+4/analysis_options.yaml:1:11 • include_file_not_found
warning • The include file ../../analysis_options.yaml in /Users/elevendimensions/Desktop/book_data/plugins/camera-0.5.7+4/analysis_options.yaml cannot be found •
plugins/camera-0.5.7+4/analysis_options.yaml:1:11 • include_file_not_found
51 issues found. (ran in 15.2s)
```
<!-- Finally, paste the output of running `flutter doctor -v` here, with your device plugged in. -->
```
[✓] Flutter (Channel stable, v1.17.0, on Mac OS X 10.15.4 19E287, locale
zh-Hans-CN)
• Flutter version 1.17.0 at /Users/elevendimensions/Documents/flutter
• Framework revision e6b34c2b5c (13 days ago), 2020-05-02 11:39:18 -0700
• Engine revision 540786dd51
• Dart version 2.8.1
[✓] Android toolchain - develop for Android devices (Android SDK version 29.0.3)
• Android SDK at /Users/elevendimensions/Library/Android/sdk
• Platform android-29, build-tools 29.0.3
• Java binary at: /Applications/Android Studio.app/Contents/jre/jdk/Contents/Home/bin/java
• Java version OpenJDK Runtime Environment (build 1.8.0_212-release-1586-b4-5784211)
• All Android licenses accepted.
[✓] Xcode - develop for iOS and macOS (Xcode 11.4.1)
• Xcode at /Applications/Xcode.app/Contents/Developer
• Xcode 11.4.1, Build version 11E503a
• CocoaPods version 1.9.1
[✓] Android Studio (version 3.6)
• Android Studio at /Applications/Android Studio.app/Contents
• Flutter plugin version 45.1.1
• Dart plugin version 192.7761
• Java version OpenJDK Runtime Environment (build 1.8.0_212-release-1586-b4-5784211)
[!] Connected device
! No devices available
! Doctor found issues in 1 category.
```
| non_priority | ios release not working properly thank you for using flutter if you are looking for support please check out our documentation or consider asking a question on stack overflow if you have found a performance problem then fill our the template below please read our guide to filing a bug first details please tell us exactly how to reproduce the problem you are running into please attach a small application ideally just one main dart file that reproduces the problem you could use for this switch flutter to master channel and run this app on a physical device using profile mode with skia tracing enabled as follows flutter channel master flutter run profile trace skia then press ‘p’ to enable the performance overlay the bleeding edge master channel is encouraged here because flutter is constantly fixing bugs and improving its performance your problem in an older flutter version may have already been solved in the master channel record a video of the performance issue using another phone so we can have an intuitive understanding of what happened don’t use adb screenrecord as that affects the performance of the profile run open observatory and save a timeline trace of the performance issue so we know which functions might be causing it see how to collect and read timeline traces on this blog post i don t know which part is wrong when i use flutter to develop an application everything works fine after the application is uploaded to the app store i can use it myself without problems but the user feedback to me is very bad please tell us which target platform s the problem occurs android ios web macos linux windows which target os version for web browser is the test system running does the problem occur on emulator simulator as well as on physical devices target platform ios target os version browser all devices all logs run flutter analyze and attach any output of that command below if there are any analysis errors try resolving them before filing this issue info • the value of the field options isn t used • lib common git dart • unused field info • the declaration getauth isn t referenced • lib common git dart • unused element info • the value of the field languagecode isn t used • lib main dart • unused field info • unused import package camera camera dart • lib routers book writebookinfo dart • unused import info • unused import dart io • lib routers book writeexperience dart • unused import info • unused import dart convert • lib routers index imagepick dart • unused import warning • missing case clause for linux • lib routers index login privatebottomsheet dart • missing enum constant in switch warning • missing case clause for macos • lib routers index login privatebottomsheet dart • missing enum constant in switch warning • missing case clause for windows • lib routers index login privatebottomsheet dart • missing enum constant in switch info • unused import dart io • lib routers settings setting dart • unused import info • unused import package book data widgets searchbar searchbar dart • lib routers user userchat dart • unused import info • unused import dart async • lib routers user homepage userhomepage dart • unused import warning • missing case clause for linux • lib widgets myappbar dart • missing enum constant in switch warning • missing case clause for macos • lib widgets myappbar dart • missing enum constant in switch warning • missing case clause for windows • lib widgets myappbar dart • missing enum constant in switch info • title is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets myappbar dart • deprecated member use info • title is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets myappbar dart • deprecated member use info • title is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets myappbar dart • deprecated member use info • is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets myappbar dart • deprecated member use info • is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets myappbar dart • deprecated member use info • is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets myappbar dart • deprecated member use warning • missing case clause for linux • lib widgets myappbar dart • missing enum constant in switch warning • missing case clause for macos • lib widgets myappbar dart • missing enum constant in switch warning • missing case clause for windows • lib widgets myappbar dart • missing enum constant in switch warning • missing case clause for linux • lib widgets privatebottomsheet dart • missing enum constant in switch warning • missing case clause for macos • lib widgets privatebottomsheet dart • missing enum constant in switch warning • missing case clause for windows • lib widgets privatebottomsheet dart • missing enum constant in switch info • unused import dart typed data • lib widgets updateimage dart • unused import info • unused import package book data common global dart • lib widgets updateimage dart • unused import info • is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets numberpicker dart • deprecated member use info • headline is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets numberpicker dart • deprecated member use info • the member activity can only be used within package flutter src widgets scroll position dart or a test • lib widgets numberpicker dart • invalid use of visible for testing member info • the member activity can only be used within instance members of subclasses of package flutter src widgets scroll position dart • lib widgets numberpicker dart • invalid use of protected member info • is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets numberpicker dart • deprecated member use info • headline is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets numberpicker dart • deprecated member use info • the member activity can only be used within package flutter src widgets scroll position dart or a test • lib widgets numberpicker dart • invalid use of visible for testing member info • the member activity can only be used within instance members of subclasses of package flutter src widgets scroll position dart • lib widgets numberpicker dart • invalid use of protected member info • is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets numberpicker dart • deprecated member use info • headline is deprecated and shouldn t be used this is the term used in the version of material design the modern term is this feature was deprecated after • lib widgets numberpicker dart • deprecated member use info • the member activity can only be used within package flutter src widgets scroll position dart or a test • lib widgets numberpicker dart • invalid use of visible for testing member info • the member activity can only be used within instance members of subclasses of package flutter src widgets scroll position dart • lib widgets numberpicker dart • invalid use of protected member info • the member activity can only be used within package flutter src widgets scroll position dart or a test • lib widgets numberpicker dart • invalid use of visible for testing member info • the member activity can only be used within instance members of subclasses of package flutter src widgets scroll position dart • lib widgets numberpicker dart • invalid use of protected member warning • the parameter laststr is required • lib widgets numberpicker dart • missing required param warning • the parameter prestr is required • lib widgets numberpicker dart • missing required param warning • the parameter laststr is required • lib widgets numberpicker dart • missing required param warning • the parameter prestr is required • lib widgets numberpicker dart • missing required param info • unused import package book data common thememodel dart • lib widgets searchbar searchbar dart • unused import info • unused import package provider provider dart • lib widgets searchbar searchbar dart • unused import warning • the include file analysis options yaml in users elevendimensions desktop book data plugins camera analysis options yaml cannot be found • plugins camera analysis options yaml • include file not found warning • the include file analysis options yaml in users elevendimensions desktop book data plugins camera analysis options yaml cannot be found • plugins camera analysis options yaml • include file not found issues found ran in flutter channel stable on mac os x locale zh hans cn • flutter version at users elevendimensions documents flutter • framework revision days ago • engine revision • dart version android toolchain develop for android devices android sdk version • android sdk at users elevendimensions library android sdk • platform android build tools • java binary at applications android studio app contents jre jdk contents home bin java • java version openjdk runtime environment build release • all android licenses accepted xcode develop for ios and macos xcode • xcode at applications xcode app contents developer • xcode build version • cocoapods version android studio version • android studio at applications android studio app contents • flutter plugin version • dart plugin version • java version openjdk runtime environment build release connected device no devices available doctor found issues in category | 0 |
233,338 | 25,762,717,208 | IssuesEvent | 2022-12-08 22:03:52 | MatBenfield/news | https://api.github.com/repos/MatBenfield/news | closed | [SecurityWeek] Big Tech Vendors Object to US Gov SBOM Mandate | SecurityWeek Stale |
**The U.S. government’s mandates around the creation and delivery of SBOMs (software bill of materials) to help mitigate supply chain attacks has run into strong objections from big-name technology vendors.**
[read more](https://www.securityweek.com/big-tech-vendors-object-us-gov-sbom-mandate)
<https://www.securityweek.com/big-tech-vendors-object-us-gov-sbom-mandate>
| True | [SecurityWeek] Big Tech Vendors Object to US Gov SBOM Mandate -
**The U.S. government’s mandates around the creation and delivery of SBOMs (software bill of materials) to help mitigate supply chain attacks has run into strong objections from big-name technology vendors.**
[read more](https://www.securityweek.com/big-tech-vendors-object-us-gov-sbom-mandate)
<https://www.securityweek.com/big-tech-vendors-object-us-gov-sbom-mandate>
| non_priority | big tech vendors object to us gov sbom mandate the u s government’s mandates around the creation and delivery of sboms software bill of materials to help mitigate supply chain attacks has run into strong objections from big name technology vendors | 0 |
274,608 | 20,843,465,365 | IssuesEvent | 2022-03-21 05:13:10 | kubernetes-sigs/secrets-store-csi-driver | https://api.github.com/repos/kubernetes-sigs/secrets-store-csi-driver | closed | Secrets not rotated when using subPath | kind/documentation | **Describe the solution you'd like**
When using a volume with `subPath`
```
volumeMounts:
- mountPath: /app/spapi/settings.ini
name: app-config
subPath: settings.ini
...
volumes:
- csi:
driver: secrets-store.csi.k8s.io
readOnly: true
volumeAttributes:
secretProviderClass: app-config
name: app-config
```
The application may not be able to observe when the secret is rotated.
**Anything else you would like to add:**
This may be limited to just the use of the `AtomicWriter` since directly writing the files would not involve symlinks.
We should verify and document this limitation.
**Environment:**
- Secrets Store CSI Driver version: (use the image tag):
- Kubernetes version: (use `kubectl version`): | 1.0 | Secrets not rotated when using subPath - **Describe the solution you'd like**
When using a volume with `subPath`
```
volumeMounts:
- mountPath: /app/spapi/settings.ini
name: app-config
subPath: settings.ini
...
volumes:
- csi:
driver: secrets-store.csi.k8s.io
readOnly: true
volumeAttributes:
secretProviderClass: app-config
name: app-config
```
The application may not be able to observe when the secret is rotated.
**Anything else you would like to add:**
This may be limited to just the use of the `AtomicWriter` since directly writing the files would not involve symlinks.
We should verify and document this limitation.
**Environment:**
- Secrets Store CSI Driver version: (use the image tag):
- Kubernetes version: (use `kubectl version`): | non_priority | secrets not rotated when using subpath describe the solution you d like when using a volume with subpath volumemounts mountpath app spapi settings ini name app config subpath settings ini volumes csi driver secrets store csi io readonly true volumeattributes secretproviderclass app config name app config the application may not be able to observe when the secret is rotated anything else you would like to add this may be limited to just the use of the atomicwriter since directly writing the files would not involve symlinks we should verify and document this limitation environment secrets store csi driver version use the image tag kubernetes version use kubectl version | 0 |
333,562 | 29,765,505,077 | IssuesEvent | 2023-06-15 00:15:56 | keycloak/keycloak | https://api.github.com/repos/keycloak/keycloak | opened | Flaky test: org.keycloak.testsuite.ui.account2.UpdateEmailTest#aiaCancellationSucceeds | kind/bug area/ci flaky-test | ## org.keycloak.testsuite.ui.account2.UpdateEmailTest#aiaCancellationSucceeds
[Keycloak CI - Account Console IT (firefox)](https://github.com/keycloak/keycloak/actions/runs/5272920970/jobs/9535950872)
```
java.lang.AssertionError
at org.junit.Assert.fail(Assert.java:87)
at org.junit.Assert.assertTrue(Assert.java:42)
at org.junit.Assert.assertTrue(Assert.java:53)
at org.keycloak.testsuite.ui.account2.UpdateEmailTest.aiaCancellationSucceeds(UpdateEmailTest.java:122)
...
```
| 1.0 | Flaky test: org.keycloak.testsuite.ui.account2.UpdateEmailTest#aiaCancellationSucceeds - ## org.keycloak.testsuite.ui.account2.UpdateEmailTest#aiaCancellationSucceeds
[Keycloak CI - Account Console IT (firefox)](https://github.com/keycloak/keycloak/actions/runs/5272920970/jobs/9535950872)
```
java.lang.AssertionError
at org.junit.Assert.fail(Assert.java:87)
at org.junit.Assert.assertTrue(Assert.java:42)
at org.junit.Assert.assertTrue(Assert.java:53)
at org.keycloak.testsuite.ui.account2.UpdateEmailTest.aiaCancellationSucceeds(UpdateEmailTest.java:122)
...
```
| non_priority | flaky test org keycloak testsuite ui updateemailtest aiacancellationsucceeds org keycloak testsuite ui updateemailtest aiacancellationsucceeds java lang assertionerror at org junit assert fail assert java at org junit assert asserttrue assert java at org junit assert asserttrue assert java at org keycloak testsuite ui updateemailtest aiacancellationsucceeds updateemailtest java | 0 |
51,404 | 13,635,118,728 | IssuesEvent | 2020-09-25 01:57:05 | nasifimtiazohi/openmrs-module-reporting-1.20.0 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-reporting-1.20.0 | opened | CVE-2020-14061 (High) detected in jackson-databind-2.9.0.jar | security vulnerability | ## CVE-2020-14061 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: openmrs-module-reporting-1.20.0/api-2.2/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.0/jackson-databind-2.9.0.jar</p>
<p>
Dependency Hierarchy:
- openmrs-api-2.2.0.jar (Root Library)
- :x: **jackson-databind-2.9.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-reporting-1.20.0/commit/43757d56a9ab9f7202e297fea95f1861af41888c">43757d56a9ab9f7202e297fea95f1861af41888c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to oracle.jms.AQjmsQueueConnectionFactory, oracle.jms.AQjmsXATopicConnectionFactory, oracle.jms.AQjmsTopicConnectionFactory, oracle.jms.AQjmsXAQueueConnectionFactory, and oracle.jms.AQjmsXAConnectionFactory (aka weblogic/oracle-aqjms).
<p>Publish Date: 2020-06-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14061>CVE-2020-14061</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14061">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14061</a></p>
<p>Release Date: 2020-06-14</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-14061 (High) detected in jackson-databind-2.9.0.jar - ## CVE-2020-14061 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: openmrs-module-reporting-1.20.0/api-2.2/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.0/jackson-databind-2.9.0.jar</p>
<p>
Dependency Hierarchy:
- openmrs-api-2.2.0.jar (Root Library)
- :x: **jackson-databind-2.9.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-reporting-1.20.0/commit/43757d56a9ab9f7202e297fea95f1861af41888c">43757d56a9ab9f7202e297fea95f1861af41888c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to oracle.jms.AQjmsQueueConnectionFactory, oracle.jms.AQjmsXATopicConnectionFactory, oracle.jms.AQjmsTopicConnectionFactory, oracle.jms.AQjmsXAQueueConnectionFactory, and oracle.jms.AQjmsXAConnectionFactory (aka weblogic/oracle-aqjms).
<p>Publish Date: 2020-06-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14061>CVE-2020-14061</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14061">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14061</a></p>
<p>Release Date: 2020-06-14</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file openmrs module reporting api pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy openmrs api jar root library x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to oracle jms aqjmsqueueconnectionfactory oracle jms aqjmsxatopicconnectionfactory oracle jms aqjmstopicconnectionfactory oracle jms aqjmsxaqueueconnectionfactory and oracle jms aqjmsxaconnectionfactory aka weblogic oracle aqjms publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
126,767 | 10,434,911,046 | IssuesEvent | 2019-09-17 16:07:26 | istio/istio | https://api.github.com/repos/istio/istio | opened | Use explicit helm placeholder version | area/test and release | Right now we have the version set to `1.1.0` in the helm charts, and then we replace this with the correct version at release time. So it is essentially a placeholder version, but it is very implicit. We should make this more explicit and set it to a version like 0.0.0-dev | 1.0 | Use explicit helm placeholder version - Right now we have the version set to `1.1.0` in the helm charts, and then we replace this with the correct version at release time. So it is essentially a placeholder version, but it is very implicit. We should make this more explicit and set it to a version like 0.0.0-dev | non_priority | use explicit helm placeholder version right now we have the version set to in the helm charts and then we replace this with the correct version at release time so it is essentially a placeholder version but it is very implicit we should make this more explicit and set it to a version like dev | 0 |
200,445 | 22,773,756,300 | IssuesEvent | 2022-07-08 12:37:28 | ignatandrei/AspNetCoreImageTagHelper | https://api.github.com/repos/ignatandrei/AspNetCoreImageTagHelper | opened | WS-2018-0608 (High) detected in microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg | security vulnerability | ## WS-2018-0608 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg</b></p></summary>
<p>Libuv transport for the ASP.NET Core Kestrel cross-platform web server.</p>
<p>Library home page: <a href="https://api.nuget.org/packages/microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg">https://api.nuget.org/packages/microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg</a></p>
<p>Path to dependency file: /src/TestWebSite/TestWebSite.csproj</p>
<p>Path to vulnerable library: /tmp/ws-ua_20220708123351_QIKSIB/dotnet_WCHIOT/20220708123352/microsoft.aspnetcore.server.kestrel.transport.libuv/2.0.3/microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg</p>
<p>
Dependency Hierarchy:
- microsoft.aspnetcore.2.0.3.nupkg (Root Library)
- microsoft.aspnetcore.server.kestrel.2.0.3.nupkg
- :x: **microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ignatandrei/AspNetCoreImageTagHelper/commit/1acdde0e5e2173fc9be87dbb3080ebd3037e487b">1acdde0e5e2173fc9be87dbb3080ebd3037e487b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was discovered in versions 2.x of ASP.NET Core where a specially crafted request can cause excess resource consumption in Kestrel.
<p>Publish Date: 2018-05-08
<p>URL: <a href=https://github.com/aspnet/Announcements/issues/300>WS-2018-0608</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-05-08</p>
<p>Fix Resolution: Microsoft.AspNetCore.Server.Kestrel.Core - 2.0.3,2.1.0;Microsoft.AspNetCore.Server.Kestrel.Transport.Abstractions - 2.0.3,2.1.0;Microsoft.AspNetCore.Server.Kestrel.Transport.Libuv - 2.0.3,2.1.0;Microsoft.AspNetCore.All - 2.0.8,2.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2018-0608 (High) detected in microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg - ## WS-2018-0608 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg</b></p></summary>
<p>Libuv transport for the ASP.NET Core Kestrel cross-platform web server.</p>
<p>Library home page: <a href="https://api.nuget.org/packages/microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg">https://api.nuget.org/packages/microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg</a></p>
<p>Path to dependency file: /src/TestWebSite/TestWebSite.csproj</p>
<p>Path to vulnerable library: /tmp/ws-ua_20220708123351_QIKSIB/dotnet_WCHIOT/20220708123352/microsoft.aspnetcore.server.kestrel.transport.libuv/2.0.3/microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg</p>
<p>
Dependency Hierarchy:
- microsoft.aspnetcore.2.0.3.nupkg (Root Library)
- microsoft.aspnetcore.server.kestrel.2.0.3.nupkg
- :x: **microsoft.aspnetcore.server.kestrel.transport.libuv.2.0.3.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ignatandrei/AspNetCoreImageTagHelper/commit/1acdde0e5e2173fc9be87dbb3080ebd3037e487b">1acdde0e5e2173fc9be87dbb3080ebd3037e487b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was discovered in versions 2.x of ASP.NET Core where a specially crafted request can cause excess resource consumption in Kestrel.
<p>Publish Date: 2018-05-08
<p>URL: <a href=https://github.com/aspnet/Announcements/issues/300>WS-2018-0608</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-05-08</p>
<p>Fix Resolution: Microsoft.AspNetCore.Server.Kestrel.Core - 2.0.3,2.1.0;Microsoft.AspNetCore.Server.Kestrel.Transport.Abstractions - 2.0.3,2.1.0;Microsoft.AspNetCore.Server.Kestrel.Transport.Libuv - 2.0.3,2.1.0;Microsoft.AspNetCore.All - 2.0.8,2.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in microsoft aspnetcore server kestrel transport libuv nupkg ws high severity vulnerability vulnerable library microsoft aspnetcore server kestrel transport libuv nupkg libuv transport for the asp net core kestrel cross platform web server library home page a href path to dependency file src testwebsite testwebsite csproj path to vulnerable library tmp ws ua qiksib dotnet wchiot microsoft aspnetcore server kestrel transport libuv microsoft aspnetcore server kestrel transport libuv nupkg dependency hierarchy microsoft aspnetcore nupkg root library microsoft aspnetcore server kestrel nupkg x microsoft aspnetcore server kestrel transport libuv nupkg vulnerable library found in head commit a href found in base branch master vulnerability details a vulnerability was discovered in versions x of asp net core where a specially crafted request can cause excess resource consumption in kestrel publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution microsoft aspnetcore server kestrel core microsoft aspnetcore server kestrel transport abstractions microsoft aspnetcore server kestrel transport libuv microsoft aspnetcore all step up your open source security game with mend | 0 |
253,111 | 19,091,727,462 | IssuesEvent | 2021-11-29 12:52:10 | mrh0/createaddition | https://api.github.com/repos/mrh0/createaddition | opened | Create Crafts & Additions Discord | documentation | For any questions or help please join the Create Crafts & Additions Discord:
https://discord.gg/mRbNnyKTEu | 1.0 | Create Crafts & Additions Discord - For any questions or help please join the Create Crafts & Additions Discord:
https://discord.gg/mRbNnyKTEu | non_priority | create crafts additions discord for any questions or help please join the create crafts additions discord | 0 |
23,882 | 4,050,343,517 | IssuesEvent | 2016-05-23 17:43:49 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Re-generate error log baselines for VSI tests | Area-Analyzers Bug Test | https://github.com/dotnet/roslyn/pull/11233 moves compiler error logger to a newer version, we need to update the error log baseline in VSI tests once that is merged in. | 1.0 | Re-generate error log baselines for VSI tests - https://github.com/dotnet/roslyn/pull/11233 moves compiler error logger to a newer version, we need to update the error log baseline in VSI tests once that is merged in. | non_priority | re generate error log baselines for vsi tests moves compiler error logger to a newer version we need to update the error log baseline in vsi tests once that is merged in | 0 |
379,609 | 26,377,574,416 | IssuesEvent | 2023-01-12 04:55:03 | coq/coq | https://api.github.com/repos/coq/coq | opened | Documentation project | kind: documentation kind: meta | Attn: @Alizter @Zimmi48
I just looked at the User Documentation project (https://github.com/orgs/coq/projects/6/views/2). I suppose one of you created this and put some of the issues in categories. While better than nothing, I would like to see columns indicating priority/importance, size of effort required and date the issue was submitted and by whom. GitHub's interface seems a bit incomplete. Some of the older issues have been resolved. It needs triage. Are either of you interested in doing that? The test of well-done triage is that others (in particular, those who fix issues) agree with the priority assigned to each issue. The 150 items under "Other" need to be triaged.
Really, we should think about what process we want to address these issues, what people are willing to commit to doing (bug fixing, reviews, triage, etc.) and whether we want to undertake that--it would be a significant ongoing effort. Then the question is how we can use the available GitHub tools to support that process. | 1.0 | Documentation project - Attn: @Alizter @Zimmi48
I just looked at the User Documentation project (https://github.com/orgs/coq/projects/6/views/2). I suppose one of you created this and put some of the issues in categories. While better than nothing, I would like to see columns indicating priority/importance, size of effort required and date the issue was submitted and by whom. GitHub's interface seems a bit incomplete. Some of the older issues have been resolved. It needs triage. Are either of you interested in doing that? The test of well-done triage is that others (in particular, those who fix issues) agree with the priority assigned to each issue. The 150 items under "Other" need to be triaged.
Really, we should think about what process we want to address these issues, what people are willing to commit to doing (bug fixing, reviews, triage, etc.) and whether we want to undertake that--it would be a significant ongoing effort. Then the question is how we can use the available GitHub tools to support that process. | non_priority | documentation project attn alizter i just looked at the user documentation project i suppose one of you created this and put some of the issues in categories while better than nothing i would like to see columns indicating priority importance size of effort required and date the issue was submitted and by whom github s interface seems a bit incomplete some of the older issues have been resolved it needs triage are either of you interested in doing that the test of well done triage is that others in particular those who fix issues agree with the priority assigned to each issue the items under other need to be triaged really we should think about what process we want to address these issues what people are willing to commit to doing bug fixing reviews triage etc and whether we want to undertake that it would be a significant ongoing effort then the question is how we can use the available github tools to support that process | 0 |
3,973 | 6,551,099,816 | IssuesEvent | 2017-09-05 13:41:44 | substance/texture | https://api.github.com/repos/substance/texture | opened | ReproducibleJATS: <fig> | requirements | We are adding support for reproducible elements to JATS and Texture. Here's a first proposal on how we could model and display reproducible figures. The tagging guideline below was developed in June during a workshop at eLife.
```xml
<fig id="f1">
<label>Figure 1</label> <!-- label is auto-generated -->
<caption>
<title>Biodiversity on Mars</title>
<p>Lorem ipsum</p>
</caption>
<alternatives>
<code executable="yes" specific-use="input" language="mini">
scatter3d(co_occurence_matrix)
</code>
<code specific-use="output" language="json">
{
"execution_time": 322,
"value_type": "plot-ly",
"value": {...}
}
</code>
<!-- static version for existing JATS toolchains -->
<graphic xlink:href="89f8b53e361f.png"/>
</alternatives>
</fig>
```
In the user interface (if reproducible content is enabled) a new reproducible figure can be created via `Insert -> Reproducible Figure`. Next, the user can enter an expression that produces an output (e.g. an interactive graphic). It is important that a static image is created as well, this we can then encode as a graphic and use in static versions (e.g. HTML or PDF) of the manuscript.
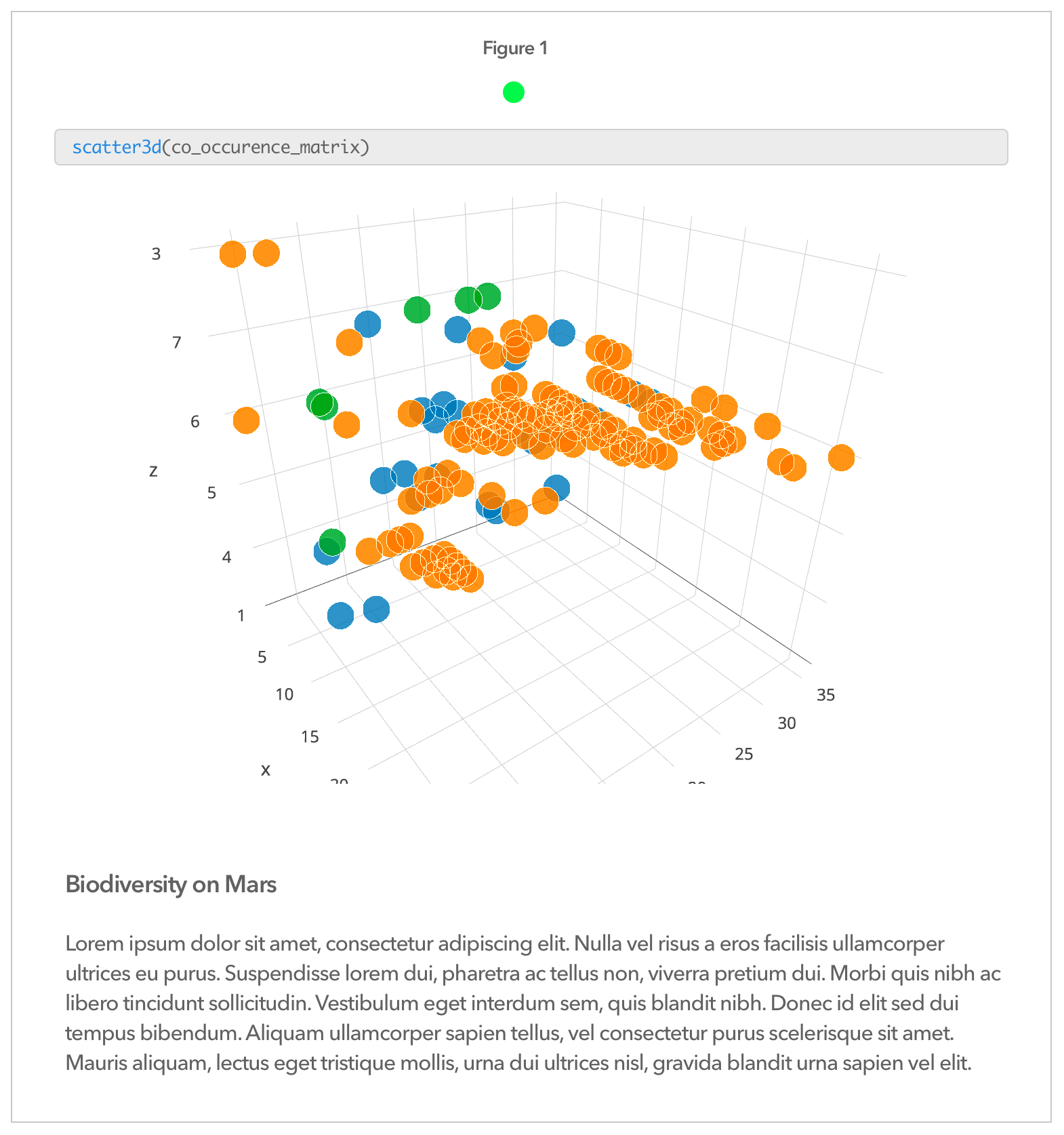
| 1.0 | ReproducibleJATS: <fig> - We are adding support for reproducible elements to JATS and Texture. Here's a first proposal on how we could model and display reproducible figures. The tagging guideline below was developed in June during a workshop at eLife.
```xml
<fig id="f1">
<label>Figure 1</label> <!-- label is auto-generated -->
<caption>
<title>Biodiversity on Mars</title>
<p>Lorem ipsum</p>
</caption>
<alternatives>
<code executable="yes" specific-use="input" language="mini">
scatter3d(co_occurence_matrix)
</code>
<code specific-use="output" language="json">
{
"execution_time": 322,
"value_type": "plot-ly",
"value": {...}
}
</code>
<!-- static version for existing JATS toolchains -->
<graphic xlink:href="89f8b53e361f.png"/>
</alternatives>
</fig>
```
In the user interface (if reproducible content is enabled) a new reproducible figure can be created via `Insert -> Reproducible Figure`. Next, the user can enter an expression that produces an output (e.g. an interactive graphic). It is important that a static image is created as well, this we can then encode as a graphic and use in static versions (e.g. HTML or PDF) of the manuscript.
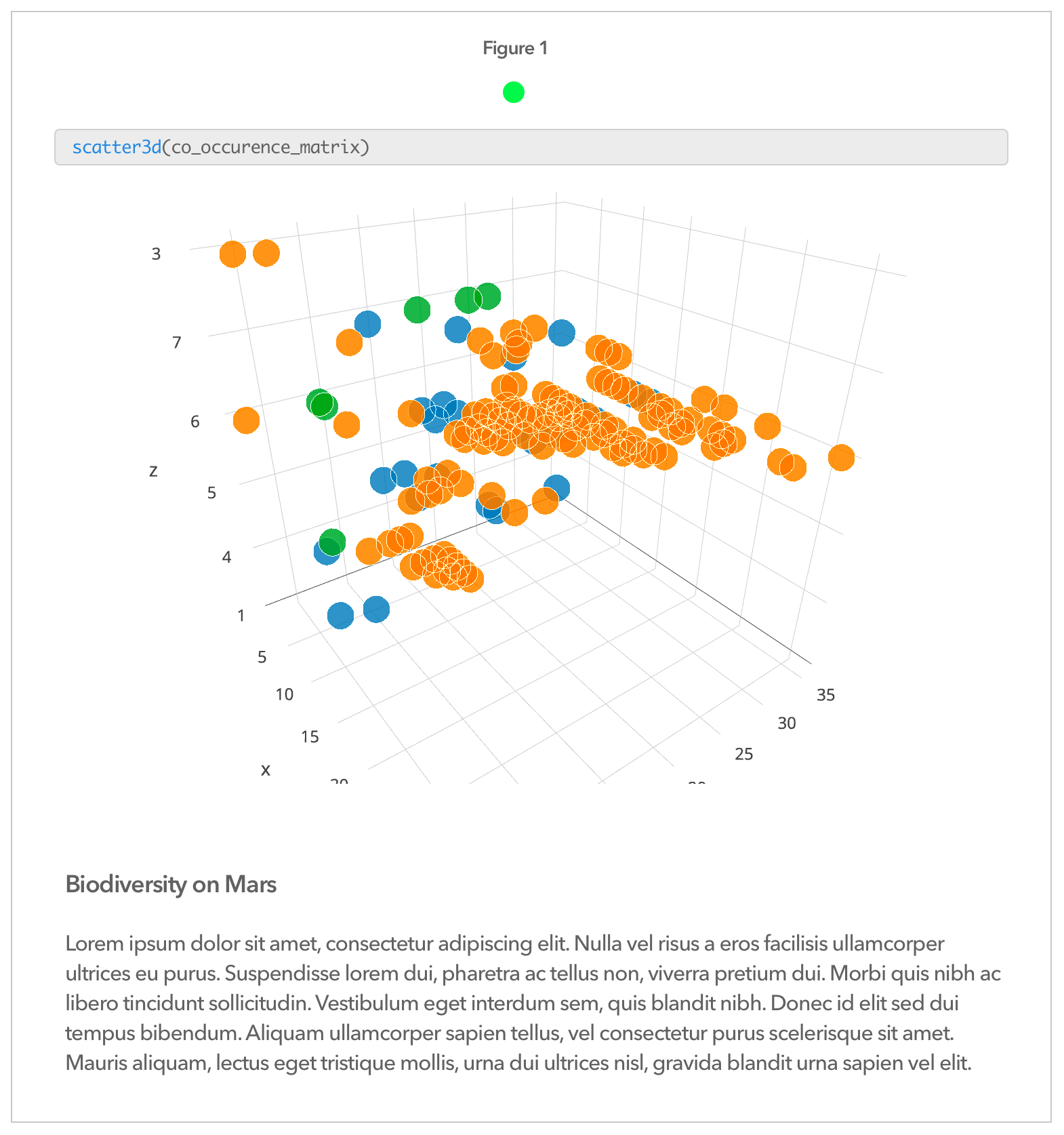
| non_priority | reproduciblejats we are adding support for reproducible elements to jats and texture here s a first proposal on how we could model and display reproducible figures the tagging guideline below was developed in june during a workshop at elife xml figure biodiversity on mars lorem ipsum co occurence matrix execution time value type plot ly value in the user interface if reproducible content is enabled a new reproducible figure can be created via insert reproducible figure next the user can enter an expression that produces an output e g an interactive graphic it is important that a static image is created as well this we can then encode as a graphic and use in static versions e g html or pdf of the manuscript | 0 |
150,081 | 11,945,898,155 | IssuesEvent | 2020-04-03 07:00:32 | ubtue/DatenProbleme | https://api.github.com/repos/ubtue/DatenProbleme | closed | Einspielung 29.2. | ISSN 1743-1727 Reformation and Renaissance review | Keywords und Abstract | Einspielung_Zotero_AUTO Fehlerquelle: Harvester Zotero_AUTO_RSS back to IT ready for testing | Auf den Webseiten der Aufsätze finden sich Keywords und Abstract. Diese fehlen bereits in unseren Daten.
Vgl. etwa Hash B464C86520478B00E9E17BBDF49A6DD96C164BC9
| 1.0 | Einspielung 29.2. | ISSN 1743-1727 Reformation and Renaissance review | Keywords und Abstract - Auf den Webseiten der Aufsätze finden sich Keywords und Abstract. Diese fehlen bereits in unseren Daten.
Vgl. etwa Hash B464C86520478B00E9E17BBDF49A6DD96C164BC9
| non_priority | einspielung issn reformation and renaissance review keywords und abstract auf den webseiten der aufsätze finden sich keywords und abstract diese fehlen bereits in unseren daten vgl etwa hash | 0 |
87,935 | 25,256,970,765 | IssuesEvent | 2022-11-15 18:59:26 | opensearch-project/OpenSearch | https://api.github.com/repos/opensearch-project/OpenSearch | opened | [Feature/extensions] Merge back to main tracking issue | Build Libraries & Interfaces untriaged | This is a tracking issue for merging the feature/extensions branch into main, and then backported to 2.x.
The merge will be performed in four steps, and all functionality will be behind a feature flag.
Meta-issue for experimental release: [139](https://github.com/opensearch-project/opensearch-sdk-java/issues/139)
Sub-issues:
• Initial extensions framework up to first gradle check pass
○ Commit ID: 394a0dd6f6ef87b27367745fc79065acbfe9d4f8
○ PR Name: Added flag to check if connectToNodeRequest is coming from Extension
○ #[3830](https://github.com/opensearch-project/OpenSearch/pull/3830)
• Extension points before REST implementation
○ Commit ID: edde6a403478d4d067bfd00b11ae7399016fcabf
○ PR Name: Adding ActionListener onFailure to ExtensionsOrchestrator
○ #[4191](https://github.com/opensearch-project/OpenSearch/pull/4191)
• Initial REST implementation and getSettings()
○ Commit ID: 749b155fa59c16a587ebd3602371c29375896b60
○ PR Name: Add getSettings support for AD
○ #[4529](https://github.com/opensearch-project/OpenSearch/pull/4519)
• REST updates and EnvironmentSettings API (up to present)
○ Note: the below information will be updated if more PR's are merged before this issue is closed
○ Commit ID: c2ecebd12bb7096de6b685db414b3f12e895b29d
○ PR Name: Modified local node response
○ #[4862](https://github.com/opensearch-project/OpenSearch/pull/4862)
| 1.0 | [Feature/extensions] Merge back to main tracking issue - This is a tracking issue for merging the feature/extensions branch into main, and then backported to 2.x.
The merge will be performed in four steps, and all functionality will be behind a feature flag.
Meta-issue for experimental release: [139](https://github.com/opensearch-project/opensearch-sdk-java/issues/139)
Sub-issues:
• Initial extensions framework up to first gradle check pass
○ Commit ID: 394a0dd6f6ef87b27367745fc79065acbfe9d4f8
○ PR Name: Added flag to check if connectToNodeRequest is coming from Extension
○ #[3830](https://github.com/opensearch-project/OpenSearch/pull/3830)
• Extension points before REST implementation
○ Commit ID: edde6a403478d4d067bfd00b11ae7399016fcabf
○ PR Name: Adding ActionListener onFailure to ExtensionsOrchestrator
○ #[4191](https://github.com/opensearch-project/OpenSearch/pull/4191)
• Initial REST implementation and getSettings()
○ Commit ID: 749b155fa59c16a587ebd3602371c29375896b60
○ PR Name: Add getSettings support for AD
○ #[4529](https://github.com/opensearch-project/OpenSearch/pull/4519)
• REST updates and EnvironmentSettings API (up to present)
○ Note: the below information will be updated if more PR's are merged before this issue is closed
○ Commit ID: c2ecebd12bb7096de6b685db414b3f12e895b29d
○ PR Name: Modified local node response
○ #[4862](https://github.com/opensearch-project/OpenSearch/pull/4862)
| non_priority | merge back to main tracking issue this is a tracking issue for merging the feature extensions branch into main and then backported to x the merge will be performed in four steps and all functionality will be behind a feature flag meta issue for experimental release sub issues • initial extensions framework up to first gradle check pass ○ commit id ○ pr name added flag to check if connecttonoderequest is coming from extension ○ • extension points before rest implementation ○ commit id ○ pr name adding actionlistener onfailure to extensionsorchestrator ○ • initial rest implementation and getsettings ○ commit id ○ pr name add getsettings support for ad ○ • rest updates and environmentsettings api up to present ○ note the below information will be updated if more pr s are merged before this issue is closed ○ commit id ○ pr name modified local node response ○ | 0 |
271,485 | 20,676,319,844 | IssuesEvent | 2022-03-10 09:37:45 | telerik/kendo-react | https://api.github.com/repos/telerik/kendo-react | opened | Create a Chart accessibility article for KendoReact Chart. | documentation pkg:charts | Create a Chart accessibility article for KendoReact Chart.
We have a similar article for Kendo UI for jQuery:
https://docs.telerik.com/kendo-ui/accessibility/five-tips-for-accessible-charts-with-dataviz
Similar options are available for the KendoReact Chart as well. | 1.0 | Create a Chart accessibility article for KendoReact Chart. - Create a Chart accessibility article for KendoReact Chart.
We have a similar article for Kendo UI for jQuery:
https://docs.telerik.com/kendo-ui/accessibility/five-tips-for-accessible-charts-with-dataviz
Similar options are available for the KendoReact Chart as well. | non_priority | create a chart accessibility article for kendoreact chart create a chart accessibility article for kendoreact chart we have a similar article for kendo ui for jquery similar options are available for the kendoreact chart as well | 0 |
106,253 | 16,673,248,653 | IssuesEvent | 2021-06-07 13:29:24 | VivekBuzruk/Hygieia | https://api.github.com/repos/VivekBuzruk/Hygieia | closed | CVE-2020-26939 (Medium) detected in bcprov-jdk15on-1.48.jar - autoclosed | security vulnerability | ## CVE-2020-26939 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.48.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.7.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: Hygieia/UI-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.48/bcprov-jdk15on-1.48.jar</p>
<p>
Dependency Hierarchy:
- serenity-core-1.2.2.jar (Root Library)
- selenium-server-2.53.1.jar
- :x: **bcprov-jdk15on-1.48.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/VivekBuzruk/Hygieia/commit/3c4f119e4343cf7fa276bb4756361b926902248e">3c4f119e4343cf7fa276bb4756361b926902248e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Legion of the Bouncy Castle BC before 1.61 and BC-FJA before 1.0.1.2, attackers can obtain sensitive information about a private exponent because of Observable Differences in Behavior to Error Inputs. This occurs in org.bouncycastle.crypto.encodings.OAEPEncoding. Sending invalid ciphertext that decrypts to a short payload in the OAEP Decoder could result in the throwing of an early exception, potentially leaking some information about the private exponent of the RSA private key performing the encryption.
<p>Publish Date: 2020-11-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26939>CVE-2020-26939</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/bcgit/bc-java/wiki/CVE-2020-26939">https://github.com/bcgit/bc-java/wiki/CVE-2020-26939</a></p>
<p>Release Date: 2020-10-11</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk14:1.61,org.bouncycastle:bcprov-ext-debug-jdk15on:1.61,org.bouncycastle:bcprov-debug-jdk15on:1.61,org.bouncycastle:bcprov-ext-jdk15on:1.61,org.bouncycastle:bcprov-jdk15on:1.61</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-26939 (Medium) detected in bcprov-jdk15on-1.48.jar - autoclosed - ## CVE-2020-26939 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.48.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.7.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: Hygieia/UI-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.48/bcprov-jdk15on-1.48.jar</p>
<p>
Dependency Hierarchy:
- serenity-core-1.2.2.jar (Root Library)
- selenium-server-2.53.1.jar
- :x: **bcprov-jdk15on-1.48.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/VivekBuzruk/Hygieia/commit/3c4f119e4343cf7fa276bb4756361b926902248e">3c4f119e4343cf7fa276bb4756361b926902248e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Legion of the Bouncy Castle BC before 1.61 and BC-FJA before 1.0.1.2, attackers can obtain sensitive information about a private exponent because of Observable Differences in Behavior to Error Inputs. This occurs in org.bouncycastle.crypto.encodings.OAEPEncoding. Sending invalid ciphertext that decrypts to a short payload in the OAEP Decoder could result in the throwing of an early exception, potentially leaking some information about the private exponent of the RSA private key performing the encryption.
<p>Publish Date: 2020-11-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26939>CVE-2020-26939</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/bcgit/bc-java/wiki/CVE-2020-26939">https://github.com/bcgit/bc-java/wiki/CVE-2020-26939</a></p>
<p>Release Date: 2020-10-11</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk14:1.61,org.bouncycastle:bcprov-ext-debug-jdk15on:1.61,org.bouncycastle:bcprov-debug-jdk15on:1.61,org.bouncycastle:bcprov-ext-jdk15on:1.61,org.bouncycastle:bcprov-jdk15on:1.61</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in bcprov jar autoclosed cve medium severity vulnerability vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk to jdk library home page a href path to dependency file hygieia ui tests pom xml path to vulnerable library home wss scanner repository org bouncycastle bcprov bcprov jar dependency hierarchy serenity core jar root library selenium server jar x bcprov jar vulnerable library found in head commit a href found in base branch master vulnerability details in legion of the bouncy castle bc before and bc fja before attackers can obtain sensitive information about a private exponent because of observable differences in behavior to error inputs this occurs in org bouncycastle crypto encodings oaepencoding sending invalid ciphertext that decrypts to a short payload in the oaep decoder could result in the throwing of an early exception potentially leaking some information about the private exponent of the rsa private key performing the encryption publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org bouncycastle bcprov org bouncycastle bcprov ext debug org bouncycastle bcprov debug org bouncycastle bcprov ext org bouncycastle bcprov step up your open source security game with whitesource | 0 |
3,149 | 3,810,294,708 | IssuesEvent | 2016-03-26 01:27:09 | RoaringBitmap/RoaringBitmap | https://api.github.com/repos/RoaringBitmap/RoaringBitmap | opened | Equality between run containers and other containers (e.g. bitmap) is checked in an inefficient manner currently | performance | The code could be much faster. | True | Equality between run containers and other containers (e.g. bitmap) is checked in an inefficient manner currently - The code could be much faster. | non_priority | equality between run containers and other containers e g bitmap is checked in an inefficient manner currently the code could be much faster | 0 |
198,973 | 15,017,420,026 | IssuesEvent | 2021-02-01 10:49:39 | fabric8-ui/fabric8-planner | https://api.github.com/repos/fabric8-ui/fabric8-planner | closed | Improve test coverage of AlmSearchHighlight pipe | enhancement test | New unit tests for AlmSearchHighlight should be created:
- should work when first parameter is an empty string
- should work when second parameter is an empty string
- should work when highlighting special characters such as !@#$%^&*()_+{}[]"|,./<>?`~
I'm not sure what should happen when search pattern contains only white spaces. Now it does following which doesn't feel right:
```
transform('Some string', ' ') => 'Some<b> </b>string'
```
| 1.0 | Improve test coverage of AlmSearchHighlight pipe - New unit tests for AlmSearchHighlight should be created:
- should work when first parameter is an empty string
- should work when second parameter is an empty string
- should work when highlighting special characters such as !@#$%^&*()_+{}[]"|,./<>?`~
I'm not sure what should happen when search pattern contains only white spaces. Now it does following which doesn't feel right:
```
transform('Some string', ' ') => 'Some<b> </b>string'
```
| non_priority | improve test coverage of almsearchhighlight pipe new unit tests for almsearchhighlight should be created should work when first parameter is an empty string should work when second parameter is an empty string should work when highlighting special characters such as i m not sure what should happen when search pattern contains only white spaces now it does following which doesn t feel right transform some string some string | 0 |
41,929 | 12,856,826,379 | IssuesEvent | 2020-07-09 08:18:13 | simandebvu/series-scraper | https://api.github.com/repos/simandebvu/series-scraper | opened | CVE-2018-11694 (High) detected in node-sass-4.14.1.tgz, proyector-movil-proyector-movil-windows | security vulnerability | ## CVE-2018-11694 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/series-scraper/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/series-scraper/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- webpacker-4.2.2.tgz (Root Library)
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/simandebvu/series-scraper/commit/6934e0cf5544ddb26c242c2ace1ae984a163bb8d">6934e0cf5544ddb26c242c2ace1ae984a163bb8d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.4. A NULL pointer dereference was found in the function Sass::Functions::selector_append which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11694>CVE-2018-11694</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11694">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11694</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-11694 (High) detected in node-sass-4.14.1.tgz, proyector-movil-proyector-movil-windows - ## CVE-2018-11694 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/series-scraper/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/series-scraper/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- webpacker-4.2.2.tgz (Root Library)
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/simandebvu/series-scraper/commit/6934e0cf5544ddb26c242c2ace1ae984a163bb8d">6934e0cf5544ddb26c242c2ace1ae984a163bb8d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.4. A NULL pointer dereference was found in the function Sass::Functions::selector_append which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11694>CVE-2018-11694</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11694">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11694</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in node sass tgz proyector movil proyector movil windows cve high severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm series scraper package json path to vulnerable library tmp ws scm series scraper node modules node sass package json dependency hierarchy webpacker tgz root library x node sass tgz vulnerable library found in head commit a href vulnerability details an issue was discovered in libsass through a null pointer dereference was found in the function sass functions selector append which could be leveraged by an attacker to cause a denial of service application crash or possibly have unspecified other impact publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass step up your open source security game with whitesource | 0 |
13,003 | 3,680,951,475 | IssuesEvent | 2016-02-24 00:23:24 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | getting started instructions and android | ⚠ clear documentation | Our getting started instructions (for the mac) say to use `brew install android-platform-tools`. But it looks like this will only install `adb`. I think w/ the changes to our workflow re: building apks and running, adb isn't sufficient. We always (virtually always?) require the android sdk, in order to get the build-tools.
brew also has a `android-sdk` distro. However, after installation the user need to run an app (`android`) to configure and download the rest of the sdk (build-tools, platform-tools).
Not clear if we should keep recommending `brew install android-platform-tools` or another install which will require a lot more configuration on the user's part. | 1.0 | getting started instructions and android - Our getting started instructions (for the mac) say to use `brew install android-platform-tools`. But it looks like this will only install `adb`. I think w/ the changes to our workflow re: building apks and running, adb isn't sufficient. We always (virtually always?) require the android sdk, in order to get the build-tools.
brew also has a `android-sdk` distro. However, after installation the user need to run an app (`android`) to configure and download the rest of the sdk (build-tools, platform-tools).
Not clear if we should keep recommending `brew install android-platform-tools` or another install which will require a lot more configuration on the user's part. | non_priority | getting started instructions and android our getting started instructions for the mac say to use brew install android platform tools but it looks like this will only install adb i think w the changes to our workflow re building apks and running adb isn t sufficient we always virtually always require the android sdk in order to get the build tools brew also has a android sdk distro however after installation the user need to run an app android to configure and download the rest of the sdk build tools platform tools not clear if we should keep recommending brew install android platform tools or another install which will require a lot more configuration on the user s part | 0 |
92,451 | 8,364,333,984 | IssuesEvent | 2018-10-03 22:34:02 | learn-co-curriculum/javascript-fix-this | https://api.github.com/repos/learn-co-curriculum/javascript-fix-this | closed | requires strict mode | Test | the tests failed for about half the students in the class unless they were using strict mode. Is this a problem, or should we just add 'use strict' to the test file?
| 1.0 | requires strict mode - the tests failed for about half the students in the class unless they were using strict mode. Is this a problem, or should we just add 'use strict' to the test file?
| non_priority | requires strict mode the tests failed for about half the students in the class unless they were using strict mode is this a problem or should we just add use strict to the test file | 0 |
80,467 | 23,215,369,046 | IssuesEvent | 2022-08-02 13:42:06 | reapit/foundations | https://api.github.com/repos/reapit/foundations | closed | test and fix all entities | feature front-end app-builder | - [x] Contact
- [x] list
- [x] create
- [x] update
- [x] Negotiator
- [x] list
- [x] create
- [x] update
- [x] Property
- [x] list
- [x] create
- [x] update
- [x] Office
- [x] list
- [x] create
- [x] update
- [x] Applicant (needs office permissions)
- [x] list
- [x] create
- [x] update [blocked by permissions issue]
- [x] Appointment
- [x] list
* needs filters (start/end)
- [x] create
- [x] update [blocked by filters issue]
- [x] Company
- [x] list
- [x] create
- [x] update
- [x] Offer
- [x] list
- [x] create
- [x] update
- [x] PropertyImage
- [x] list
* needs propertyId
- [x] create
- [x] update
- [x] Department
- [x] list
- [x] appointment filter should be nicer | 1.0 | test and fix all entities - - [x] Contact
- [x] list
- [x] create
- [x] update
- [x] Negotiator
- [x] list
- [x] create
- [x] update
- [x] Property
- [x] list
- [x] create
- [x] update
- [x] Office
- [x] list
- [x] create
- [x] update
- [x] Applicant (needs office permissions)
- [x] list
- [x] create
- [x] update [blocked by permissions issue]
- [x] Appointment
- [x] list
* needs filters (start/end)
- [x] create
- [x] update [blocked by filters issue]
- [x] Company
- [x] list
- [x] create
- [x] update
- [x] Offer
- [x] list
- [x] create
- [x] update
- [x] PropertyImage
- [x] list
* needs propertyId
- [x] create
- [x] update
- [x] Department
- [x] list
- [x] appointment filter should be nicer | non_priority | test and fix all entities contact list create update negotiator list create update property list create update office list create update applicant needs office permissions list create update appointment list needs filters start end create update company list create update offer list create update propertyimage list needs propertyid create update department list appointment filter should be nicer | 0 |
13,358 | 8,198,301,256 | IssuesEvent | 2018-08-31 15:56:07 | IMA-WorldHealth/bhima-2.X | https://api.github.com/repos/IMA-WorldHealth/bhima-2.X | closed | Get rid of Topic | Refactor performance | The original vision was to have real-time events streamed to the client via websockets. It hasn't done anything to date and it is super buggy. Let's remove it for the time being. It will probably give us a performance boost in production as well, not having a Redis I/O going on while trying to perform financial operations. | True | Get rid of Topic - The original vision was to have real-time events streamed to the client via websockets. It hasn't done anything to date and it is super buggy. Let's remove it for the time being. It will probably give us a performance boost in production as well, not having a Redis I/O going on while trying to perform financial operations. | non_priority | get rid of topic the original vision was to have real time events streamed to the client via websockets it hasn t done anything to date and it is super buggy let s remove it for the time being it will probably give us a performance boost in production as well not having a redis i o going on while trying to perform financial operations | 0 |
2,116 | 3,664,995,813 | IssuesEvent | 2016-02-19 14:25:59 | shaarli/Shaarli | https://api.github.com/repos/shaarli/Shaarli | closed | Tags on private links should be also private | bug security unconfirmed | Try to share a link in private and add some new tags...
The tag are listed in autocompletion and tag cloud and it could be a privacy issue don't you think?
Expected: tags only in private links does not appear in public tag list/auto completion tag list | True | Tags on private links should be also private - Try to share a link in private and add some new tags...
The tag are listed in autocompletion and tag cloud and it could be a privacy issue don't you think?
Expected: tags only in private links does not appear in public tag list/auto completion tag list | non_priority | tags on private links should be also private try to share a link in private and add some new tags the tag are listed in autocompletion and tag cloud and it could be a privacy issue don t you think expected tags only in private links does not appear in public tag list auto completion tag list | 0 |
26,459 | 26,875,976,655 | IssuesEvent | 2023-02-05 02:27:38 | Leafwing-Studios/Emergence | https://api.github.com/repos/Leafwing-Studios/Emergence | closed | Add a `choose_max` pheromone transducer option for ants. | grab-bag usability | Currently, ants probabilistically follow a signal up a gradient (see: https://github.com/Leafwing-Studios/Emergence/blob/8e3cbcaaf31544ad678f333d1d86ed6b685e52f3/emergence_lib/src/organisms/units.rs#L166). As the signal diffuses, their wandering becomes less effective towards the source of the signal. When the signal they are following is a pheromone, this leads to non-ideal behaviour, as it seems the ants are "not really following" the signal. It could be frustrating to the player.
Ants use a signal transducer to map an input signal into an output pathfinding weight (the higher the weight, the more likely it is the ants will move to that tile).
When this signal is a pheromone, ants should (have the option) a transducer that assigns weight 1.0 to the neighbouring tile with the highest pheromone signal value out of all neighbours, and assign weight 0.0 to all tiles that do not have the highest pheromone signal value. If all tiles have the same pheromone signal value (unlikely, as we are using floating point numbers), we should weigh them all equally with 1.0. | True | Add a `choose_max` pheromone transducer option for ants. - Currently, ants probabilistically follow a signal up a gradient (see: https://github.com/Leafwing-Studios/Emergence/blob/8e3cbcaaf31544ad678f333d1d86ed6b685e52f3/emergence_lib/src/organisms/units.rs#L166). As the signal diffuses, their wandering becomes less effective towards the source of the signal. When the signal they are following is a pheromone, this leads to non-ideal behaviour, as it seems the ants are "not really following" the signal. It could be frustrating to the player.
Ants use a signal transducer to map an input signal into an output pathfinding weight (the higher the weight, the more likely it is the ants will move to that tile).
When this signal is a pheromone, ants should (have the option) a transducer that assigns weight 1.0 to the neighbouring tile with the highest pheromone signal value out of all neighbours, and assign weight 0.0 to all tiles that do not have the highest pheromone signal value. If all tiles have the same pheromone signal value (unlikely, as we are using floating point numbers), we should weigh them all equally with 1.0. | non_priority | add a choose max pheromone transducer option for ants currently ants probabilistically follow a signal up a gradient see as the signal diffuses their wandering becomes less effective towards the source of the signal when the signal they are following is a pheromone this leads to non ideal behaviour as it seems the ants are not really following the signal it could be frustrating to the player ants use a signal transducer to map an input signal into an output pathfinding weight the higher the weight the more likely it is the ants will move to that tile when this signal is a pheromone ants should have the option a transducer that assigns weight to the neighbouring tile with the highest pheromone signal value out of all neighbours and assign weight to all tiles that do not have the highest pheromone signal value if all tiles have the same pheromone signal value unlikely as we are using floating point numbers we should weigh them all equally with | 0 |
4,749 | 4,605,917,507 | IssuesEvent | 2016-09-23 00:31:13 | influxdata/influxdb | https://api.github.com/repos/influxdata/influxdb | closed | Simple SELECT makes Influx 1.0 OOM | area/queries performance | Running in AWS on an m4.large, Influx v1.0.0 running on Debian Jessie
I have one particular measurement that seems like maybe it is corrupted somehow. When I run a simple SELECT statement on it, e.g.
`select * from replay_outcome_stats limit 10`
Influx hangs and the heap shoots straight up until the whole box becomes unresponsive. I have to restart the instance to recover. See the attached grafana graph of "Heap Alloc" and "Heap Idle"

__shards__
http://pastebin.com/VEtq1JXAhttp://pastebin.com/VEtq1JXA
__stats__
http://pastebin.com/sTQKbAFY
__diagnostics__
http://pastebin.com/2qbgwcjK
| True | Simple SELECT makes Influx 1.0 OOM - Running in AWS on an m4.large, Influx v1.0.0 running on Debian Jessie
I have one particular measurement that seems like maybe it is corrupted somehow. When I run a simple SELECT statement on it, e.g.
`select * from replay_outcome_stats limit 10`
Influx hangs and the heap shoots straight up until the whole box becomes unresponsive. I have to restart the instance to recover. See the attached grafana graph of "Heap Alloc" and "Heap Idle"

__shards__
http://pastebin.com/VEtq1JXAhttp://pastebin.com/VEtq1JXA
__stats__
http://pastebin.com/sTQKbAFY
__diagnostics__
http://pastebin.com/2qbgwcjK
| non_priority | simple select makes influx oom running in aws on an large influx running on debian jessie i have one particular measurement that seems like maybe it is corrupted somehow when i run a simple select statement on it e g select from replay outcome stats limit influx hangs and the heap shoots straight up until the whole box becomes unresponsive i have to restart the instance to recover see the attached grafana graph of heap alloc and heap idle shards stats diagnostics | 0 |
90,134 | 11,352,943,045 | IssuesEvent | 2020-01-24 14:39:42 | YardSale2020/yard-sale-web-app | https://api.github.com/repos/YardSale2020/yard-sale-web-app | closed | Icons | design dev | - [] C Logo
- [] Search
- [] Close
- [] Pin - Pink & Gray
- [] Back arrow
Once complete export sprite sheet and add it to the images folder.
| 1.0 | Icons - - [] C Logo
- [] Search
- [] Close
- [] Pin - Pink & Gray
- [] Back arrow
Once complete export sprite sheet and add it to the images folder.
| non_priority | icons c logo search close pin pink gray back arrow once complete export sprite sheet and add it to the images folder | 0 |
18,875 | 10,299,659,457 | IssuesEvent | 2019-08-28 11:05:32 | DashboardHub/Website | https://api.github.com/repos/DashboardHub/Website | closed | CVE-2018-11696 (High) detected in node-sass-v4.12.0 | security vulnerability | ## CVE-2018-11696 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.12.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/DashboardHub/Website/commits/5f96f1e0a372b9087a833b3c4a74d093a24d6897">5f96f1e0a372b9087a833b3c4a74d093a24d6897</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Library Source Files (125)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /Website/node_modules/node-sass/src/libsass/src/expand.hpp
- /Website/node_modules/node-sass/src/libsass/src/util.hpp
- /Website/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /Website/node_modules/node-sass/src/libsass/src/utf8/unchecked.h
- /Website/node_modules/node-sass/src/libsass/src/output.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /Website/node_modules/node-sass/src/libsass/src/emitter.hpp
- /Website/node_modules/node-sass/src/libsass/src/lexer.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_node.cpp
- /Website/node_modules/node-sass/src/libsass/src/plugins.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/base.h
- /Website/node_modules/node-sass/src/libsass/src/position.hpp
- /Website/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /Website/node_modules/node-sass/src/libsass/src/operation.hpp
- /Website/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /Website/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /Website/node_modules/node-sass/src/libsass/src/operators.cpp
- /Website/node_modules/node-sass/src/custom_importer_bridge.cpp
- /Website/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /Website/node_modules/node-sass/src/libsass/src/functions.hpp
- /Website/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /Website/node_modules/node-sass/src/libsass/src/eval.hpp
- /Website/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /Website/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /Website/node_modules/node-sass/src/libsass/src/node.cpp
- /Website/node_modules/node-sass/src/libsass/src/subset_map.cpp
- /Website/node_modules/node-sass/src/libsass/src/emitter.cpp
- /Website/node_modules/node-sass/src/libsass/src/listize.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_functions.hpp
- /Website/node_modules/node-sass/src/libsass/src/memory/SharedPtr.cpp
- /Website/node_modules/node-sass/src/libsass/src/output.cpp
- /Website/node_modules/node-sass/src/libsass/src/check_nesting.cpp
- /Website/node_modules/node-sass/src/libsass/src/expand.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /Website/node_modules/node-sass/src/libsass/src/cssize.hpp
- /Website/node_modules/node-sass/src/libsass/src/paths.hpp
- /Website/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /Website/node_modules/node-sass/src/libsass/src/inspect.hpp
- /Website/node_modules/node-sass/src/sass_types/color.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /Website/node_modules/node-sass/src/libsass/src/values.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /Website/node_modules/node-sass/src/libsass/src/source_map.hpp
- /Website/node_modules/node-sass/src/sass_types/list.h
- /Website/node_modules/node-sass/src/libsass/src/check_nesting.hpp
- /Website/node_modules/node-sass/src/libsass/src/json.cpp
- /Website/node_modules/node-sass/src/libsass/src/units.cpp
- /Website/node_modules/node-sass/src/libsass/src/units.hpp
- /Website/node_modules/node-sass/src/libsass/src/context.cpp
- /Website/node_modules/node-sass/src/libsass/src/utf8/checked.h
- /Website/node_modules/node-sass/src/libsass/src/listize.hpp
- /Website/node_modules/node-sass/src/sass_types/string.cpp
- /Website/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /Website/node_modules/node-sass/src/libsass/src/context.hpp
- /Website/node_modules/node-sass/src/sass_types/boolean.h
- /Website/node_modules/node-sass/src/libsass/include/sass2scss.h
- /Website/node_modules/node-sass/src/binding.cpp
- /Website/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /Website/node_modules/node-sass/src/sass_types/factory.cpp
- /Website/node_modules/node-sass/src/sass_types/boolean.cpp
- /Website/node_modules/node-sass/src/libsass/src/source_map.cpp
- /Website/node_modules/node-sass/src/sass_types/value.h
- /Website/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /Website/node_modules/node-sass/src/libsass/src/file.cpp
- /Website/node_modules/node-sass/src/sass_context_wrapper.cpp
- /Website/node_modules/node-sass/src/libsass/src/node.hpp
- /Website/node_modules/node-sass/src/libsass/src/environment.cpp
- /Website/node_modules/node-sass/src/libsass/src/extend.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /Website/node_modules/node-sass/src/libsass/src/operators.hpp
- /Website/node_modules/node-sass/src/libsass/src/constants.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass.hpp
- /Website/node_modules/node-sass/src/libsass/src/parser.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast_fwd_decl.cpp
- /Website/node_modules/node-sass/src/libsass/src/constants.cpp
- /Website/node_modules/node-sass/src/libsass/src/debugger.hpp
- /Website/node_modules/node-sass/src/sass_types/list.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/functions.h
- /Website/node_modules/node-sass/src/libsass/src/util.cpp
- /Website/node_modules/node-sass/src/custom_function_bridge.cpp
- /Website/node_modules/node-sass/src/custom_importer_bridge.h
- /Website/node_modules/node-sass/src/libsass/src/bind.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /Website/node_modules/node-sass/src/libsass/src/backtrace.cpp
- /Website/node_modules/node-sass/src/libsass/src/cencode.c
- /Website/node_modules/node-sass/src/libsass/src/extend.cpp
- /Website/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /Website/node_modules/node-sass/src/sass_context_wrapper.h
- /Website/node_modules/node-sass/src/libsass/src/sass.cpp
- /Website/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /Website/node_modules/node-sass/src/sass_types/number.cpp
- /Website/node_modules/node-sass/src/sass_types/color.h
- /Website/node_modules/node-sass/src/libsass/src/c99func.c
- /Website/node_modules/node-sass/src/libsass/src/position.cpp
- /Website/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/values.h
- /Website/node_modules/node-sass/src/libsass/src/inspect.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /Website/node_modules/node-sass/src/sass_types/null.cpp
- /Website/node_modules/node-sass/src/libsass/src/functions.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/context.h
- /Website/node_modules/node-sass/src/libsass/src/to_c.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_value.hpp
- /Website/node_modules/node-sass/src/callback_bridge.h
- /Website/node_modules/node-sass/src/libsass/src/color_maps.hpp
- /Website/node_modules/node-sass/src/libsass/script/test-leaks.pl
- /Website/node_modules/node-sass/src/libsass/src/cssize.cpp
- /Website/node_modules/node-sass/src/libsass/src/lexer.hpp
- /Website/node_modules/node-sass/src/libsass/src/memory/SharedPtr.hpp
- /Website/node_modules/node-sass/src/libsass/src/eval.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_c.hpp
- /Website/node_modules/node-sass/src/sass_types/map.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_value.cpp
- /Website/node_modules/node-sass/src/libsass/src/b64/encode.h
- /Website/node_modules/node-sass/src/libsass/src/file.hpp
- /Website/node_modules/node-sass/src/libsass/src/environment.hpp
- /Website/node_modules/node-sass/src/libsass/src/plugins.hpp
- /Website/node_modules/node-sass/src/libsass/src/parser.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /Website/node_modules/node-sass/src/libsass/src/debug.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.4. A NULL pointer dereference was found in the function Sass::Inspect::operator which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11696>CVE-2018-11696</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-11696 (High) detected in node-sass-v4.12.0 - ## CVE-2018-11696 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.12.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/DashboardHub/Website/commits/5f96f1e0a372b9087a833b3c4a74d093a24d6897">5f96f1e0a372b9087a833b3c4a74d093a24d6897</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Library Source Files (125)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /Website/node_modules/node-sass/src/libsass/src/expand.hpp
- /Website/node_modules/node-sass/src/libsass/src/util.hpp
- /Website/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /Website/node_modules/node-sass/src/libsass/src/utf8/unchecked.h
- /Website/node_modules/node-sass/src/libsass/src/output.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /Website/node_modules/node-sass/src/libsass/src/emitter.hpp
- /Website/node_modules/node-sass/src/libsass/src/lexer.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_node.cpp
- /Website/node_modules/node-sass/src/libsass/src/plugins.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/base.h
- /Website/node_modules/node-sass/src/libsass/src/position.hpp
- /Website/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /Website/node_modules/node-sass/src/libsass/src/operation.hpp
- /Website/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /Website/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /Website/node_modules/node-sass/src/libsass/src/operators.cpp
- /Website/node_modules/node-sass/src/custom_importer_bridge.cpp
- /Website/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /Website/node_modules/node-sass/src/libsass/src/functions.hpp
- /Website/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /Website/node_modules/node-sass/src/libsass/src/eval.hpp
- /Website/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /Website/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /Website/node_modules/node-sass/src/libsass/src/node.cpp
- /Website/node_modules/node-sass/src/libsass/src/subset_map.cpp
- /Website/node_modules/node-sass/src/libsass/src/emitter.cpp
- /Website/node_modules/node-sass/src/libsass/src/listize.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_functions.hpp
- /Website/node_modules/node-sass/src/libsass/src/memory/SharedPtr.cpp
- /Website/node_modules/node-sass/src/libsass/src/output.cpp
- /Website/node_modules/node-sass/src/libsass/src/check_nesting.cpp
- /Website/node_modules/node-sass/src/libsass/src/expand.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /Website/node_modules/node-sass/src/libsass/src/cssize.hpp
- /Website/node_modules/node-sass/src/libsass/src/paths.hpp
- /Website/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /Website/node_modules/node-sass/src/libsass/src/inspect.hpp
- /Website/node_modules/node-sass/src/sass_types/color.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /Website/node_modules/node-sass/src/libsass/src/values.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /Website/node_modules/node-sass/src/libsass/src/source_map.hpp
- /Website/node_modules/node-sass/src/sass_types/list.h
- /Website/node_modules/node-sass/src/libsass/src/check_nesting.hpp
- /Website/node_modules/node-sass/src/libsass/src/json.cpp
- /Website/node_modules/node-sass/src/libsass/src/units.cpp
- /Website/node_modules/node-sass/src/libsass/src/units.hpp
- /Website/node_modules/node-sass/src/libsass/src/context.cpp
- /Website/node_modules/node-sass/src/libsass/src/utf8/checked.h
- /Website/node_modules/node-sass/src/libsass/src/listize.hpp
- /Website/node_modules/node-sass/src/sass_types/string.cpp
- /Website/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /Website/node_modules/node-sass/src/libsass/src/context.hpp
- /Website/node_modules/node-sass/src/sass_types/boolean.h
- /Website/node_modules/node-sass/src/libsass/include/sass2scss.h
- /Website/node_modules/node-sass/src/binding.cpp
- /Website/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /Website/node_modules/node-sass/src/sass_types/factory.cpp
- /Website/node_modules/node-sass/src/sass_types/boolean.cpp
- /Website/node_modules/node-sass/src/libsass/src/source_map.cpp
- /Website/node_modules/node-sass/src/sass_types/value.h
- /Website/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /Website/node_modules/node-sass/src/libsass/src/file.cpp
- /Website/node_modules/node-sass/src/sass_context_wrapper.cpp
- /Website/node_modules/node-sass/src/libsass/src/node.hpp
- /Website/node_modules/node-sass/src/libsass/src/environment.cpp
- /Website/node_modules/node-sass/src/libsass/src/extend.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /Website/node_modules/node-sass/src/libsass/src/operators.hpp
- /Website/node_modules/node-sass/src/libsass/src/constants.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass.hpp
- /Website/node_modules/node-sass/src/libsass/src/parser.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast_fwd_decl.cpp
- /Website/node_modules/node-sass/src/libsass/src/constants.cpp
- /Website/node_modules/node-sass/src/libsass/src/debugger.hpp
- /Website/node_modules/node-sass/src/sass_types/list.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/functions.h
- /Website/node_modules/node-sass/src/libsass/src/util.cpp
- /Website/node_modules/node-sass/src/custom_function_bridge.cpp
- /Website/node_modules/node-sass/src/custom_importer_bridge.h
- /Website/node_modules/node-sass/src/libsass/src/bind.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /Website/node_modules/node-sass/src/libsass/src/backtrace.cpp
- /Website/node_modules/node-sass/src/libsass/src/cencode.c
- /Website/node_modules/node-sass/src/libsass/src/extend.cpp
- /Website/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /Website/node_modules/node-sass/src/sass_context_wrapper.h
- /Website/node_modules/node-sass/src/libsass/src/sass.cpp
- /Website/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /Website/node_modules/node-sass/src/sass_types/number.cpp
- /Website/node_modules/node-sass/src/sass_types/color.h
- /Website/node_modules/node-sass/src/libsass/src/c99func.c
- /Website/node_modules/node-sass/src/libsass/src/position.cpp
- /Website/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/values.h
- /Website/node_modules/node-sass/src/libsass/src/inspect.cpp
- /Website/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /Website/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /Website/node_modules/node-sass/src/sass_types/null.cpp
- /Website/node_modules/node-sass/src/libsass/src/functions.cpp
- /Website/node_modules/node-sass/src/libsass/src/ast.cpp
- /Website/node_modules/node-sass/src/libsass/include/sass/context.h
- /Website/node_modules/node-sass/src/libsass/src/to_c.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_value.hpp
- /Website/node_modules/node-sass/src/callback_bridge.h
- /Website/node_modules/node-sass/src/libsass/src/color_maps.hpp
- /Website/node_modules/node-sass/src/libsass/script/test-leaks.pl
- /Website/node_modules/node-sass/src/libsass/src/cssize.cpp
- /Website/node_modules/node-sass/src/libsass/src/lexer.hpp
- /Website/node_modules/node-sass/src/libsass/src/memory/SharedPtr.hpp
- /Website/node_modules/node-sass/src/libsass/src/eval.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_c.hpp
- /Website/node_modules/node-sass/src/sass_types/map.cpp
- /Website/node_modules/node-sass/src/libsass/src/to_value.cpp
- /Website/node_modules/node-sass/src/libsass/src/b64/encode.h
- /Website/node_modules/node-sass/src/libsass/src/file.hpp
- /Website/node_modules/node-sass/src/libsass/src/environment.hpp
- /Website/node_modules/node-sass/src/libsass/src/plugins.hpp
- /Website/node_modules/node-sass/src/libsass/src/parser.hpp
- /Website/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /Website/node_modules/node-sass/src/libsass/src/debug.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.4. A NULL pointer dereference was found in the function Sass::Inspect::operator which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11696>CVE-2018-11696</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in node sass cve high severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href found in head commit a href library source files the source files were matched to this source library based on a best effort match source libraries are selected from a list of probable public libraries website node modules node sass src libsass src expand hpp website node modules node sass src libsass src util hpp website node modules node sass src libsass src color maps cpp website node modules node sass src libsass src sass util hpp website node modules node sass src libsass src unchecked h website node modules node sass src libsass src output hpp website node modules node sass src libsass src sass values hpp website node modules node sass src libsass src emitter hpp website node modules node sass src libsass src lexer cpp website node modules node sass src libsass test test node cpp website node modules node sass src libsass src plugins cpp website node modules node sass src libsass include sass base h website node modules node sass src libsass src position hpp website node modules node sass src libsass src subset map hpp website node modules node sass src libsass src operation hpp website node modules node sass src libsass src remove placeholders cpp website node modules node sass src libsass src error handling hpp website node modules node sass src libsass src operators cpp website node modules node sass src custom importer bridge cpp website node modules node sass src libsass contrib plugin cpp website node modules node sass src libsass src functions hpp website node modules node sass src libsass test test superselector cpp website node modules node sass src libsass src eval hpp website node modules node sass src libsass src string hpp website node modules node sass src libsass src error handling cpp website node modules node sass src libsass src node cpp website node modules node sass src libsass src subset map cpp website node modules node sass src libsass src emitter cpp website node modules node sass src libsass src listize cpp website node modules node sass src libsass src ast hpp website node modules node sass src libsass src sass functions hpp website node modules node sass src libsass src memory sharedptr cpp website node modules node sass src libsass src output cpp website node modules node sass src libsass src check nesting cpp website node modules node sass src libsass src expand cpp website node modules node sass src libsass src ast def macros hpp website node modules node sass src libsass src cssize hpp website node modules node sass src libsass src paths hpp website node modules node sass src libsass src ast fwd decl hpp website node modules node sass src libsass src inspect hpp website node modules node sass src sass types color cpp website node modules node sass src libsass test test unification cpp website node modules node sass src libsass src values cpp website node modules node sass src libsass src sass util cpp website node modules node sass src libsass src source map hpp website node modules node sass src sass types list h website node modules node sass src libsass src check nesting hpp website node modules node sass src libsass src json cpp website node modules node sass src libsass src units cpp website node modules node sass src libsass src units hpp website node modules node sass src libsass src context cpp website node modules node sass src libsass src checked h website node modules node sass src libsass src listize hpp website node modules node sass src sass types string cpp website node modules node sass src libsass src prelexer hpp website node modules node sass src libsass src context hpp website node modules node sass src sass types boolean h website node modules node sass src libsass include h website node modules node sass src binding cpp website node modules node sass src libsass src prelexer cpp website node modules node sass src sass types factory cpp website node modules node sass src sass types boolean cpp website node modules node sass src libsass src source map cpp website node modules node sass src sass types value h website node modules node sass src libsass src string cpp website node modules node sass src libsass src file cpp website node modules node sass src sass context wrapper cpp website node modules node sass src libsass src node hpp website node modules node sass src libsass src environment cpp website node modules node sass src libsass src extend hpp website node modules node sass src libsass src sass context hpp website node modules node sass src libsass src operators hpp website node modules node sass src libsass src constants hpp website node modules node sass src libsass src sass hpp website node modules node sass src libsass src parser cpp website node modules node sass src libsass src ast fwd decl cpp website node modules node sass src libsass src constants cpp website node modules node sass src libsass src debugger hpp website node modules node sass src sass types list cpp website node modules node sass src libsass include sass functions h website node modules node sass src libsass src util cpp website node modules node sass src custom function bridge cpp website node modules node sass src custom importer bridge h website node modules node sass src libsass src bind cpp website node modules node sass src libsass src sass functions cpp website node modules node sass src libsass src backtrace cpp website node modules node sass src libsass src cencode c website node modules node sass src libsass src extend cpp website node modules node sass src sass types sass value wrapper h website node modules node sass src sass context wrapper h website node modules node sass src libsass src sass cpp website node modules node sass src libsass src cpp website node modules node sass src sass types number cpp website node modules node sass src sass types color h website node modules node sass src libsass src c website node modules node sass src libsass src position cpp website node modules node sass src libsass src remove placeholders hpp website node modules node sass src libsass src sass values cpp website node modules node sass src libsass include sass values h website node modules node sass src libsass src inspect cpp website node modules node sass src libsass test test subset map cpp website node modules node sass src libsass src cpp website node modules node sass src sass types null cpp website node modules node sass src libsass src functions cpp website node modules node sass src libsass src ast cpp website node modules node sass src libsass include sass context h website node modules node sass src libsass src to c cpp website node modules node sass src libsass src to value hpp website node modules node sass src callback bridge h website node modules node sass src libsass src color maps hpp website node modules node sass src libsass script test leaks pl website node modules node sass src libsass src cssize cpp website node modules node sass src libsass src lexer hpp website node modules node sass src libsass src memory sharedptr hpp website node modules node sass src libsass src eval cpp website node modules node sass src libsass src to c hpp website node modules node sass src sass types map cpp website node modules node sass src libsass src to value cpp website node modules node sass src libsass src encode h website node modules node sass src libsass src file hpp website node modules node sass src libsass src environment hpp website node modules node sass src libsass src plugins hpp website node modules node sass src libsass src parser hpp website node modules node sass src libsass src sass context cpp website node modules node sass src libsass src debug hpp vulnerability details an issue was discovered in libsass through a null pointer dereference was found in the function sass inspect operator which could be leveraged by an attacker to cause a denial of service application crash or possibly have unspecified other impact publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with whitesource | 0 |
37,026 | 5,098,586,016 | IssuesEvent | 2017-01-04 02:31:50 | Kademi/kademi-dev | https://api.github.com/repos/Kademi/kademi-dev | closed | Feature to allow ES queries to be transformed into tables | enhancement Ready to Test - Dev | The Queries feature allows developers to write elasticsearch queries, which are returned in the native ES format.
This data can then be connected to histograms, tables, pie charts, etc.
But often the data needs to be transformed to align with user expectations, and ES has very limited ability to do ad-hoc transformations.
So a new feature is required which allows any arbitrary data, including ES queries but not limited to them, to be transformed to a regular tabular form for consumption by components.
This should also allow the tabular data to be exported as csv in front end websites. | 1.0 | Feature to allow ES queries to be transformed into tables - The Queries feature allows developers to write elasticsearch queries, which are returned in the native ES format.
This data can then be connected to histograms, tables, pie charts, etc.
But often the data needs to be transformed to align with user expectations, and ES has very limited ability to do ad-hoc transformations.
So a new feature is required which allows any arbitrary data, including ES queries but not limited to them, to be transformed to a regular tabular form for consumption by components.
This should also allow the tabular data to be exported as csv in front end websites. | non_priority | feature to allow es queries to be transformed into tables the queries feature allows developers to write elasticsearch queries which are returned in the native es format this data can then be connected to histograms tables pie charts etc but often the data needs to be transformed to align with user expectations and es has very limited ability to do ad hoc transformations so a new feature is required which allows any arbitrary data including es queries but not limited to them to be transformed to a regular tabular form for consumption by components this should also allow the tabular data to be exported as csv in front end websites | 0 |
54,001 | 23,122,414,250 | IssuesEvent | 2022-07-27 23:31:15 | Azure/AppConfiguration | https://api.github.com/repos/Azure/AppConfiguration | closed | Reference another app configuration item | service question | In an App Configuration entry can I reference another entries value?
For example I have 2 app configuration entries. One called MyApi:Uri with value https://myapi.azurewebsites.net and I have an entry ReverseProxy:Clusters:MyApi:Destinations:destination1:Address. This value should also be https://myapi.azurewebsites.net but I would like to add/maintain it only once.
Note I am using one app configuration instance for several API's. | 1.0 | Reference another app configuration item - In an App Configuration entry can I reference another entries value?
For example I have 2 app configuration entries. One called MyApi:Uri with value https://myapi.azurewebsites.net and I have an entry ReverseProxy:Clusters:MyApi:Destinations:destination1:Address. This value should also be https://myapi.azurewebsites.net but I would like to add/maintain it only once.
Note I am using one app configuration instance for several API's. | non_priority | reference another app configuration item in an app configuration entry can i reference another entries value for example i have app configuration entries one called myapi uri with value and i have an entry reverseproxy clusters myapi destinations address this value should also be but i would like to add maintain it only once note i am using one app configuration instance for several api s | 0 |
363,807 | 25,467,279,531 | IssuesEvent | 2022-11-25 06:28:07 | Jovenasso/SistemaJudocas2022 | https://api.github.com/repos/Jovenasso/SistemaJudocas2022 | closed | Diagrama de Casos de Uso | documentation | - [x] Corrigir os atores do diagrama
- [x] Adicionar os casos de usos da especificação de requisitos faltantes no diagrama
- [x] Corrigir os formulários de casos de uso
- [x] Adicionar no formulário de casos de uso os faltantes | 1.0 | Diagrama de Casos de Uso - - [x] Corrigir os atores do diagrama
- [x] Adicionar os casos de usos da especificação de requisitos faltantes no diagrama
- [x] Corrigir os formulários de casos de uso
- [x] Adicionar no formulário de casos de uso os faltantes | non_priority | diagrama de casos de uso corrigir os atores do diagrama adicionar os casos de usos da especificação de requisitos faltantes no diagrama corrigir os formulários de casos de uso adicionar no formulário de casos de uso os faltantes | 0 |
28,291 | 23,136,749,535 | IssuesEvent | 2022-07-28 14:52:54 | airyhq/airy | https://api.github.com/repos/airyhq/airy | closed | Components looking for a minimum of 3 Kafka brokers | infrastructure | Some of the components are not starting because they are waiting for a minimum of three brokers, while by default we deploy one broker.
```
Caused by: org.apache.kafka.common.errors.InvalidReplicationFactorException: Replication factor: 3 larger than available brokers: 1.
``` | 1.0 | Components looking for a minimum of 3 Kafka brokers - Some of the components are not starting because they are waiting for a minimum of three brokers, while by default we deploy one broker.
```
Caused by: org.apache.kafka.common.errors.InvalidReplicationFactorException: Replication factor: 3 larger than available brokers: 1.
``` | non_priority | components looking for a minimum of kafka brokers some of the components are not starting because they are waiting for a minimum of three brokers while by default we deploy one broker caused by org apache kafka common errors invalidreplicationfactorexception replication factor larger than available brokers | 0 |
8,498 | 5,766,182,439 | IssuesEvent | 2017-04-27 06:10:13 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Feature request : Icon tooltips in scene tree to reflect the icons meaning | enhancement topic:editor usability | Currently if I highlight any of the icons in the scene tree, the tooltip says "Instance: res://[xyz].tscn Type: [abc]"
These two screenshots (in my opinion) shouldn't show the same tooltip.


I would like to request that this is changed (particularly as I can't find in the documentation a guide as to what the icons mean), so that each icons tooltip explains the icon the mouse is hovering over.
eg. Hovering over the eye icon would say "Toggle Visibility". Hovering over the group icon would say "Group: [whatever the group name is]" etc. | True | Feature request : Icon tooltips in scene tree to reflect the icons meaning - Currently if I highlight any of the icons in the scene tree, the tooltip says "Instance: res://[xyz].tscn Type: [abc]"
These two screenshots (in my opinion) shouldn't show the same tooltip.


I would like to request that this is changed (particularly as I can't find in the documentation a guide as to what the icons mean), so that each icons tooltip explains the icon the mouse is hovering over.
eg. Hovering over the eye icon would say "Toggle Visibility". Hovering over the group icon would say "Group: [whatever the group name is]" etc. | non_priority | feature request icon tooltips in scene tree to reflect the icons meaning currently if i highlight any of the icons in the scene tree the tooltip says instance res tscn type these two screenshots in my opinion shouldn t show the same tooltip i would like to request that this is changed particularly as i can t find in the documentation a guide as to what the icons mean so that each icons tooltip explains the icon the mouse is hovering over eg hovering over the eye icon would say toggle visibility hovering over the group icon would say group etc | 0 |
85,487 | 10,618,355,246 | IssuesEvent | 2019-10-13 03:39:59 | carbon-design-system/ibm-dotcom-library | https://api.github.com/repos/carbon-design-system/ibm-dotcom-library | opened | Pattern: rich overview, visual design specs | design design: visual migrate package: patterns | _Wonil-Suh1 created the following on Sep 08:_
### User story
As a user of IBM.com, I need a way to understand the benefits and value of the product / solution / offering presented on the page quickly through text and media such as video so that I can make a decision on whether I should continue with the page or not.
### Notes
This is a pattern that is not clearly defined from our past work.
### Acceptance criteria
- [ ] Specs have been produced for all responsive break points
_Original issue: https://github.ibm.com/webstandards/digital-design/issues/1610_ | 2.0 | Pattern: rich overview, visual design specs - _Wonil-Suh1 created the following on Sep 08:_
### User story
As a user of IBM.com, I need a way to understand the benefits and value of the product / solution / offering presented on the page quickly through text and media such as video so that I can make a decision on whether I should continue with the page or not.
### Notes
This is a pattern that is not clearly defined from our past work.
### Acceptance criteria
- [ ] Specs have been produced for all responsive break points
_Original issue: https://github.ibm.com/webstandards/digital-design/issues/1610_ | non_priority | pattern rich overview visual design specs wonil created the following on sep user story as a user of ibm com i need a way to understand the benefits and value of the product solution offering presented on the page quickly through text and media such as video so that i can make a decision on whether i should continue with the page or not notes this is a pattern that is not clearly defined from our past work acceptance criteria specs have been produced for all responsive break points original issue | 0 |
343,259 | 24,766,303,601 | IssuesEvent | 2022-10-22 15:14:38 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | opened | How to conditionally install packages for macOS >= 12? | 9.needs: documentation | ## Problem
I can't find a way to make conditions based on darwin versions.
I was looking for an helper like `stdenv.isDarwin` but for the version.
My goal is to install or not a package if macOs version is >= 12 (Monterey).
## Checklist
- [x] checked [latest Nixpkgs manual] \([source][nixpkgs-source]) and [latest NixOS manual] \([source][nixos-source])
- [x] checked [open documentation issues] for possible duplicates
- [x] checked [open documentation pull requests] for possible solutions
[latest Nixpkgs manual]: https://nixos.org/manual/nixpkgs/unstable/
[latest NixOS manual]: https://nixos.org/manual/nixos/unstable/
[nixpkgs-source]: https://github.com/NixOS/nixpkgs/tree/master/doc
[nixos-source]: https://github.com/NixOS/nixpkgs/tree/master/nixos/doc/manual
[open documentation issues]: https://github.com/NixOS/nixpkgs/issues?q=is%3Aissue+is%3Aopen+label%3A%229.needs%3A+documentation%22
[open documentation pull requests]: https://github.com/NixOS/nixpkgs/pulls?q=is%3Aopen+is%3Apr+label%3A%228.has%3A+documentation%22%2C%226.topic%3A+documentation%22
## Proposal
Add the helper if missing?
Add an example in configuration. | 1.0 | How to conditionally install packages for macOS >= 12? - ## Problem
I can't find a way to make conditions based on darwin versions.
I was looking for an helper like `stdenv.isDarwin` but for the version.
My goal is to install or not a package if macOs version is >= 12 (Monterey).
## Checklist
- [x] checked [latest Nixpkgs manual] \([source][nixpkgs-source]) and [latest NixOS manual] \([source][nixos-source])
- [x] checked [open documentation issues] for possible duplicates
- [x] checked [open documentation pull requests] for possible solutions
[latest Nixpkgs manual]: https://nixos.org/manual/nixpkgs/unstable/
[latest NixOS manual]: https://nixos.org/manual/nixos/unstable/
[nixpkgs-source]: https://github.com/NixOS/nixpkgs/tree/master/doc
[nixos-source]: https://github.com/NixOS/nixpkgs/tree/master/nixos/doc/manual
[open documentation issues]: https://github.com/NixOS/nixpkgs/issues?q=is%3Aissue+is%3Aopen+label%3A%229.needs%3A+documentation%22
[open documentation pull requests]: https://github.com/NixOS/nixpkgs/pulls?q=is%3Aopen+is%3Apr+label%3A%228.has%3A+documentation%22%2C%226.topic%3A+documentation%22
## Proposal
Add the helper if missing?
Add an example in configuration. | non_priority | how to conditionally install packages for macos problem i can t find a way to make conditions based on darwin versions i was looking for an helper like stdenv isdarwin but for the version my goal is to install or not a package if macos version is monterey checklist checked and checked for possible duplicates checked for possible solutions proposal add the helper if missing add an example in configuration | 0 |
112,523 | 14,263,339,276 | IssuesEvent | 2020-11-20 14:18:31 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | opened | campaigns frontend: number of entries in changeset list doesn't match numbers at top of view | needs-design team/campaigns | When a changeset is "processing" or "errored" it is counted towards the unpublished count at the top:
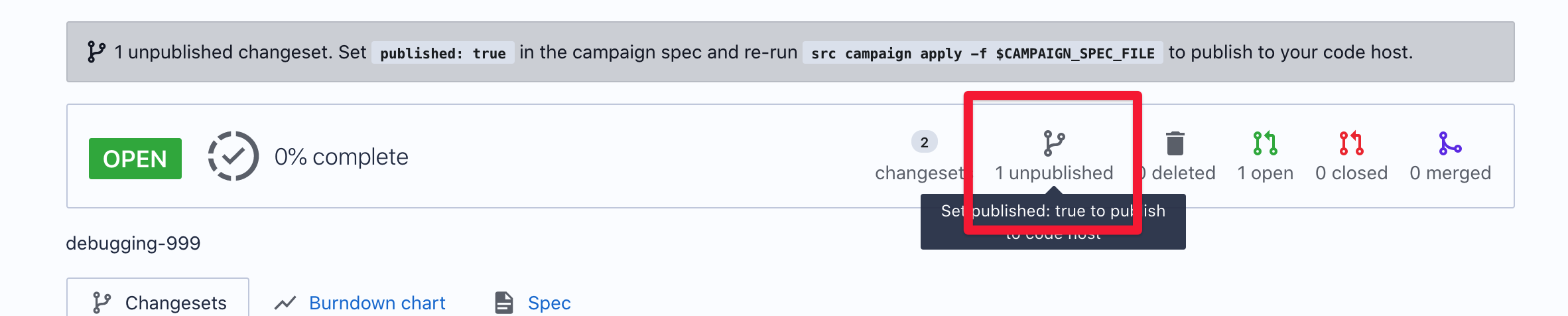
But when it is `processing` or `errored` it doesn't show up in the list at the bottom:
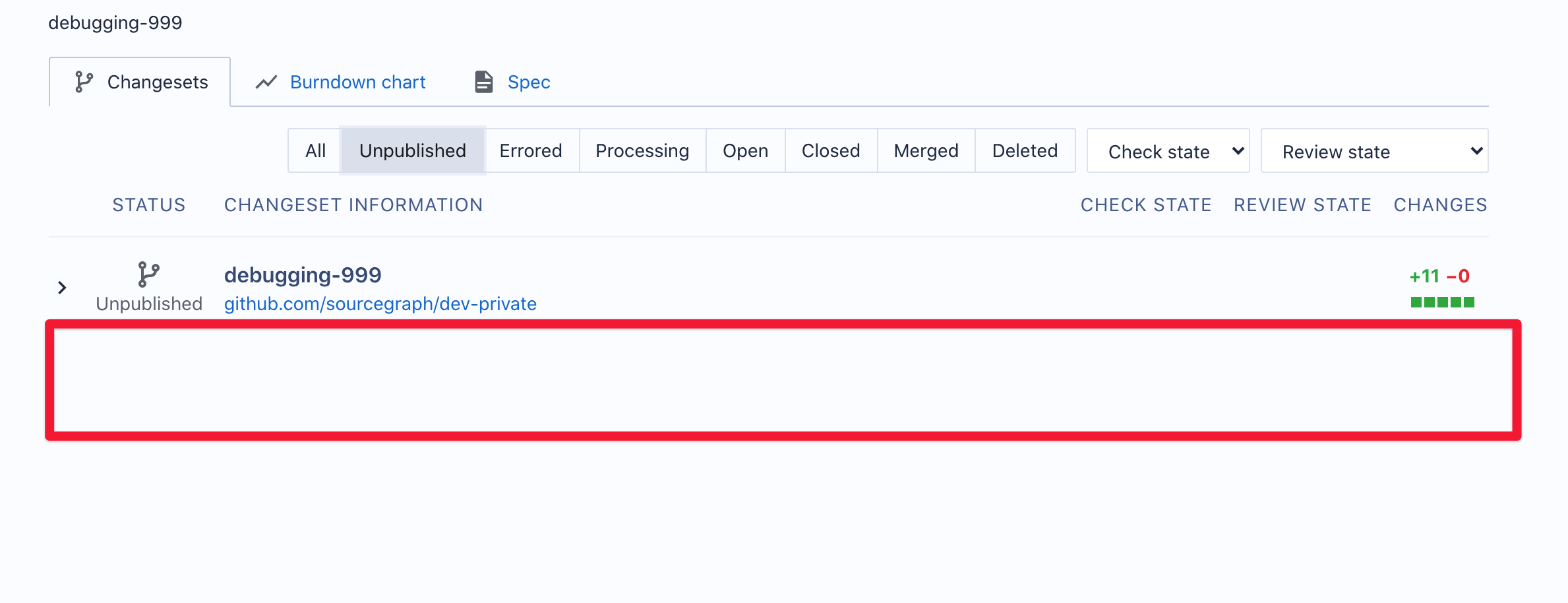
| 1.0 | campaigns frontend: number of entries in changeset list doesn't match numbers at top of view - When a changeset is "processing" or "errored" it is counted towards the unpublished count at the top:
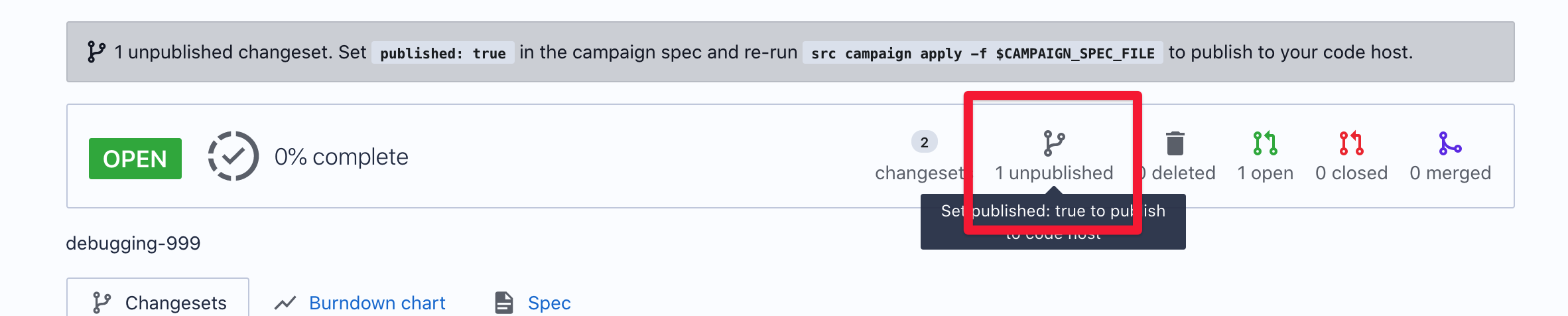
But when it is `processing` or `errored` it doesn't show up in the list at the bottom:
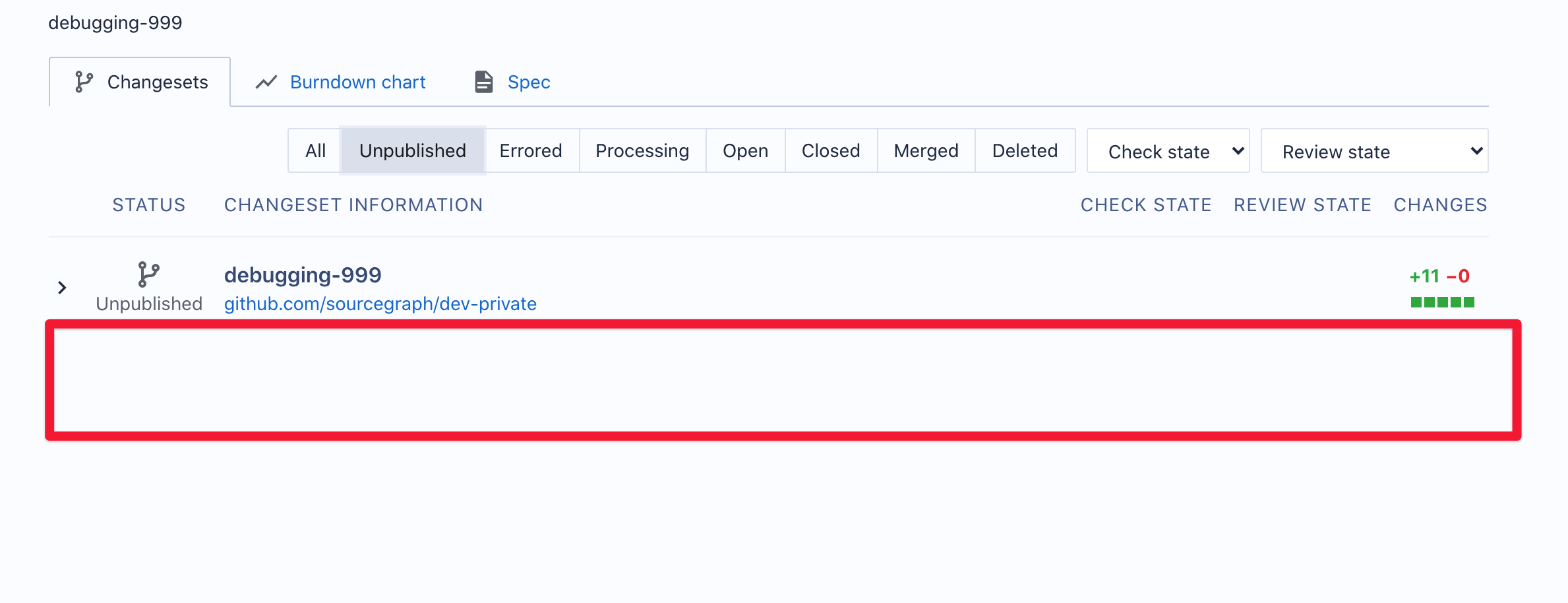
| non_priority | campaigns frontend number of entries in changeset list doesn t match numbers at top of view when a changeset is processing or errored it is counted towards the unpublished count at the top but when it is processing or errored it doesn t show up in the list at the bottom | 0 |
299,868 | 22,629,300,207 | IssuesEvent | 2022-06-30 13:27:04 | mharrisb1/daglib | https://api.github.com/repos/mharrisb1/daglib | opened | Add more documentation | documentation | - [ ] Testing
- [ ] Deployment
- [ ] Use cases
- [ ] Mapping tasks
- [ ] Joining tasks
- [ ] Chunked tasks
- [ ] Advanced workflows
- [ ] Run
- [ ] Visualize | 1.0 | Add more documentation - - [ ] Testing
- [ ] Deployment
- [ ] Use cases
- [ ] Mapping tasks
- [ ] Joining tasks
- [ ] Chunked tasks
- [ ] Advanced workflows
- [ ] Run
- [ ] Visualize | non_priority | add more documentation testing deployment use cases mapping tasks joining tasks chunked tasks advanced workflows run visualize | 0 |
43,704 | 17,633,740,585 | IssuesEvent | 2021-08-19 11:16:29 | hashicorp/terraform-provider-azurerm | https://api.github.com/repos/hashicorp/terraform-provider-azurerm | closed | r/function_app: support for enabling Incoming client certificates and Certificate exclusion paths | enhancement service/functions | Hello
According to [this issue](https://github.com/terraform-providers/terraform-provider-azurerm/issues/2004) there is an option to enable `Incoming client certificates` on `azurerm_function_app`. However:
- There is no documentation on how to implement it
- There is no mention of whether or not one can add `Certificate exclusion paths` once `Incoming client certificates` is enabled
I was able to accomplish it via the az cli:
```console
az functionapp update --set clientCertEnabled=true --set clientCertExclusionPaths="/foo;/bar;/hello;/world" --name jungoafadsgasdge-functio --resource-group azure-functions-test-rg
```
Is it supported in Terraform out-of-the-box and if so can you please share an example code on how to accomplish that?
Thanks
Omer | 1.0 | r/function_app: support for enabling Incoming client certificates and Certificate exclusion paths - Hello
According to [this issue](https://github.com/terraform-providers/terraform-provider-azurerm/issues/2004) there is an option to enable `Incoming client certificates` on `azurerm_function_app`. However:
- There is no documentation on how to implement it
- There is no mention of whether or not one can add `Certificate exclusion paths` once `Incoming client certificates` is enabled
I was able to accomplish it via the az cli:
```console
az functionapp update --set clientCertEnabled=true --set clientCertExclusionPaths="/foo;/bar;/hello;/world" --name jungoafadsgasdge-functio --resource-group azure-functions-test-rg
```
Is it supported in Terraform out-of-the-box and if so can you please share an example code on how to accomplish that?
Thanks
Omer | non_priority | r function app support for enabling incoming client certificates and certificate exclusion paths hello according to there is an option to enable incoming client certificates on azurerm function app however there is no documentation on how to implement it there is no mention of whether or not one can add certificate exclusion paths once incoming client certificates is enabled i was able to accomplish it via the az cli console az functionapp update set clientcertenabled true set clientcertexclusionpaths foo bar hello world name jungoafadsgasdge functio resource group azure functions test rg is it supported in terraform out of the box and if so can you please share an example code on how to accomplish that thanks omer | 0 |
171,756 | 14,344,550,719 | IssuesEvent | 2020-11-28 15:00:07 | DmytroKorniienko/EmbUI | https://api.github.com/repos/DmytroKorniienko/EmbUI | closed | WiFi connect and frame-flush racing | bug documentation | В методах set_settings_wifi/set_settings_wifiAP переключение wifi происходит раньше чем закончится обработка кадра интерфейса. Веб-сокет не может закончит передачу.
TODO: отложить переключение WiFi через планировщик
| 1.0 | WiFi connect and frame-flush racing - В методах set_settings_wifi/set_settings_wifiAP переключение wifi происходит раньше чем закончится обработка кадра интерфейса. Веб-сокет не может закончит передачу.
TODO: отложить переключение WiFi через планировщик
| non_priority | wifi connect and frame flush racing в методах set settings wifi set settings wifiap переключение wifi происходит раньше чем закончится обработка кадра интерфейса веб сокет не может закончит передачу todo отложить переключение wifi через планировщик | 0 |
406,991 | 27,591,302,329 | IssuesEvent | 2023-03-09 00:44:07 | desenvolvimento-web-unifil/02-documentacao-group-rmksn | https://api.github.com/repos/desenvolvimento-web-unifil/02-documentacao-group-rmksn | opened | Criar tela de login | documentation enhancement | Criar tela de login de login para usuário ter possibilidade de acesso a sua conta. Usar as linguagens de marcação HTML e CSS e estruturar os campos nessa tela de login. | 1.0 | Criar tela de login - Criar tela de login de login para usuário ter possibilidade de acesso a sua conta. Usar as linguagens de marcação HTML e CSS e estruturar os campos nessa tela de login. | non_priority | criar tela de login criar tela de login de login para usuário ter possibilidade de acesso a sua conta usar as linguagens de marcação html e css e estruturar os campos nessa tela de login | 0 |
54,918 | 13,942,794,461 | IssuesEvent | 2020-10-22 21:40:17 | Whizkevina/uchi-sidebar-clone | https://api.github.com/repos/Whizkevina/uchi-sidebar-clone | opened | CVE-2020-11022 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.7.2.min.js</b>, <b>jquery-1.9.0.min.js</b>, <b>jquery-1.11.3.js</b>, <b>jquery-1.11.2.min.js</b>, <b>jquery-1.11.1.min.js</b>, <b>jquery-1.7.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/jmespath/index.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/jmespath/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.9.0.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.0/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.0/jquery.min.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/es6-shim/test-sham/index.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/es6-shim/test-sham/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.9.0.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.3.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.3/jquery.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.3/jquery.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/es6-shim/test/google-translate.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/es6-shim/test/google-translate.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.3.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.2/jquery.min.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/svg-pan-zoom/demo/dynamic-load.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/svg-pan-zoom/demo/jquery.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/svg-pan-zoom/demo/resize.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/svg-pan-zoom/demo/resize.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.7.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/meteor-node-stubs/node_modules/vm-browserify/example/run/index.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/meteor-node-stubs/node_modules/vm-browserify/example/run/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.1.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Whizkevina/uchi-sidebar-clone/commit/5405eeecb088ab7acf45ef51e052988d72c3fe7f">5405eeecb088ab7acf45ef51e052988d72c3fe7f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11022 (Medium) detected in multiple libraries - ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.7.2.min.js</b>, <b>jquery-1.9.0.min.js</b>, <b>jquery-1.11.3.js</b>, <b>jquery-1.11.2.min.js</b>, <b>jquery-1.11.1.min.js</b>, <b>jquery-1.7.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/jmespath/index.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/jmespath/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.9.0.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.0/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.0/jquery.min.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/es6-shim/test-sham/index.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/es6-shim/test-sham/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.9.0.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.3.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.3/jquery.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.3/jquery.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/es6-shim/test/google-translate.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/es6-shim/test/google-translate.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.3.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.2/jquery.min.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/svg-pan-zoom/demo/dynamic-load.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/svg-pan-zoom/demo/jquery.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/svg-pan-zoom/demo/resize.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/svg-pan-zoom/demo/resize.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.7.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js</a></p>
<p>Path to dependency file: uchi-sidebar-clone/node_modules/meteor-node-stubs/node_modules/vm-browserify/example/run/index.html</p>
<p>Path to vulnerable library: uchi-sidebar-clone/node_modules/meteor-node-stubs/node_modules/vm-browserify/example/run/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.1.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Whizkevina/uchi-sidebar-clone/commit/5405eeecb088ab7acf45ef51e052988d72c3fe7f">5405eeecb088ab7acf45ef51e052988d72c3fe7f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries jquery min js jquery min js jquery js jquery min js jquery min js jquery min js jquery min js javascript library for dom operations library home page a href path to dependency file uchi sidebar clone node modules jmespath index html path to vulnerable library uchi sidebar clone node modules jmespath index html dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file uchi sidebar clone node modules shim test sham index html path to vulnerable library uchi sidebar clone node modules shim test sham index html dependency hierarchy x jquery min js vulnerable library jquery js javascript library for dom operations library home page a href path to dependency file uchi sidebar clone node modules shim test google translate html path to vulnerable library uchi sidebar clone node modules shim test google translate html dependency hierarchy x jquery js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file uchi sidebar clone node modules svg pan zoom demo dynamic load html path to vulnerable library uchi sidebar clone node modules svg pan zoom demo jquery min js dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file uchi sidebar clone node modules svg pan zoom demo resize html path to vulnerable library uchi sidebar clone node modules svg pan zoom demo resize html dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file uchi sidebar clone node modules meteor node stubs node modules vm browserify example run index html path to vulnerable library uchi sidebar clone node modules meteor node stubs node modules vm browserify example run index html dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch main vulnerability details in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
76,899 | 9,526,698,911 | IssuesEvent | 2019-04-28 22:10:11 | magento/magento2 | https://api.github.com/repos/magento/magento2 | closed | Can't scroll in modal-popup on iOS | Area: Design/Frontend Component: Checkout Fixed in 2.3.x Issue: Clear Description Issue: Confirmed Issue: Format is valid Issue: Ready for Work Reproduced on 2.2.x Reproduced on 2.3.x | ### Preconditions (*)
1. Magento 2.2.7 (https://github.com/magento/magento2/commit/76ae28f82032a0af152d3285bedc1ffa46ff2055)
### Steps to reproduce (*)
1. Open any modal-popup of which the height exceeds the viewport height
2. Try scrolling in the popup on an iPhone (tested on iPhone 6s Plus & iPhone X)
### Expected result (*)
1. Scrolling inside the .modal-popup element
### Actual result (*)
1. http://cloud.h-o.nl/dfe0e645138b
| 1.0 | Can't scroll in modal-popup on iOS - ### Preconditions (*)
1. Magento 2.2.7 (https://github.com/magento/magento2/commit/76ae28f82032a0af152d3285bedc1ffa46ff2055)
### Steps to reproduce (*)
1. Open any modal-popup of which the height exceeds the viewport height
2. Try scrolling in the popup on an iPhone (tested on iPhone 6s Plus & iPhone X)
### Expected result (*)
1. Scrolling inside the .modal-popup element
### Actual result (*)
1. http://cloud.h-o.nl/dfe0e645138b
| non_priority | can t scroll in modal popup on ios preconditions magento steps to reproduce open any modal popup of which the height exceeds the viewport height try scrolling in the popup on an iphone tested on iphone plus iphone x expected result scrolling inside the modal popup element actual result | 0 |
128,056 | 17,400,088,655 | IssuesEvent | 2021-08-02 18:19:41 | hypha-dao/dho-web-client | https://api.github.com/repos/hypha-dao/dho-web-client | opened | Commenting on Proposal Detail Page (Frontend) | EPIC: New Design | Summary:
As a DHO user I would like to be able to leave and reply to comments on a proposal detail page in order to get clarity on new proposals.
Description:
Please add a "comment" widget below the description of new proposals on the proposal detail page.
Acceptance Criteria:
- [ ] Every user should be able to leave a comment
- [ ] It should be possible to reply to comments (allow as many levels of comments as the user wants or max of 3?)
- [ ] User should be able to reply with an emoticon. Standard emoticons available?
- [ ] The total comment number should be visible on the preview card (to be designed by Massimo)
- [ ] Notifications for when someone leaves a comment (later)
Ressources:
Attachement:
Final Design to be done
https://xd.adobe.com/view/500c58dc-9103-41f4-a82a-bb390323fbd8-055f/screen/c20e1ce9-f9cf-4900-b68a-9bf9f9828c3e | 1.0 | Commenting on Proposal Detail Page (Frontend) - Summary:
As a DHO user I would like to be able to leave and reply to comments on a proposal detail page in order to get clarity on new proposals.
Description:
Please add a "comment" widget below the description of new proposals on the proposal detail page.
Acceptance Criteria:
- [ ] Every user should be able to leave a comment
- [ ] It should be possible to reply to comments (allow as many levels of comments as the user wants or max of 3?)
- [ ] User should be able to reply with an emoticon. Standard emoticons available?
- [ ] The total comment number should be visible on the preview card (to be designed by Massimo)
- [ ] Notifications for when someone leaves a comment (later)
Ressources:
Attachement:
Final Design to be done
https://xd.adobe.com/view/500c58dc-9103-41f4-a82a-bb390323fbd8-055f/screen/c20e1ce9-f9cf-4900-b68a-9bf9f9828c3e | non_priority | commenting on proposal detail page frontend summary as a dho user i would like to be able to leave and reply to comments on a proposal detail page in order to get clarity on new proposals description please add a comment widget below the description of new proposals on the proposal detail page acceptance criteria every user should be able to leave a comment it should be possible to reply to comments allow as many levels of comments as the user wants or max of user should be able to reply with an emoticon standard emoticons available the total comment number should be visible on the preview card to be designed by massimo notifications for when someone leaves a comment later ressources attachement final design to be done | 0 |
72,139 | 13,788,649,608 | IssuesEvent | 2020-10-09 07:35:43 | codimd/react-client | https://api.github.com/repos/codimd/react-client | opened | Try to move external-types | code quality | We should try to move as much as possible from `src/external-types` to either the projects repos or DefinetlyTyped. | 1.0 | Try to move external-types - We should try to move as much as possible from `src/external-types` to either the projects repos or DefinetlyTyped. | non_priority | try to move external types we should try to move as much as possible from src external types to either the projects repos or definetlytyped | 0 |
108,319 | 13,614,322,609 | IssuesEvent | 2020-09-23 13:06:27 | cgeo/cgeo | https://api.github.com/repos/cgeo/cgeo | closed | Hanging logging screen while log page loading is finished in the background | Bug Frontend Design | ##### Detailed steps causing the problem:
- Start logging a cache
- The logging screen is shown
- The progress spinner indicates that the log page is loaded from server in the background
##### Actual behavior after performing these steps:
As soon as loading of log page is finished, I experience an unresponsive behaviour for a second.
I guess, that is because the screen is redrawn now showing the "Problem" dop down menu.
##### Expected behavior after performing these steps:
This is not a serious bug, however it is blocking the text input while typing, wich is kind of annoying and not a good user experience.
While not having an idea about what happens in background...isn't it somehow possible to show the "Problem" menu already at start of the logging activity (just silently assuming it will be supported) and only remove it in case it is not needed/not supported? That should make this need for redraw much less often.
##### Version of c:geo used:
2018.05.01-NB
##### Is the problem reproducible for you?
Yes | 1.0 | Hanging logging screen while log page loading is finished in the background - ##### Detailed steps causing the problem:
- Start logging a cache
- The logging screen is shown
- The progress spinner indicates that the log page is loaded from server in the background
##### Actual behavior after performing these steps:
As soon as loading of log page is finished, I experience an unresponsive behaviour for a second.
I guess, that is because the screen is redrawn now showing the "Problem" dop down menu.
##### Expected behavior after performing these steps:
This is not a serious bug, however it is blocking the text input while typing, wich is kind of annoying and not a good user experience.
While not having an idea about what happens in background...isn't it somehow possible to show the "Problem" menu already at start of the logging activity (just silently assuming it will be supported) and only remove it in case it is not needed/not supported? That should make this need for redraw much less often.
##### Version of c:geo used:
2018.05.01-NB
##### Is the problem reproducible for you?
Yes | non_priority | hanging logging screen while log page loading is finished in the background detailed steps causing the problem start logging a cache the logging screen is shown the progress spinner indicates that the log page is loaded from server in the background actual behavior after performing these steps as soon as loading of log page is finished i experience an unresponsive behaviour for a second i guess that is because the screen is redrawn now showing the problem dop down menu expected behavior after performing these steps this is not a serious bug however it is blocking the text input while typing wich is kind of annoying and not a good user experience while not having an idea about what happens in background isn t it somehow possible to show the problem menu already at start of the logging activity just silently assuming it will be supported and only remove it in case it is not needed not supported that should make this need for redraw much less often version of c geo used nb is the problem reproducible for you yes | 0 |
15,717 | 27,796,230,149 | IssuesEvent | 2023-03-17 12:46:05 | Azure/az-hop | https://api.github.com/repos/Azure/az-hop | closed | Metric alerts | kind/feature area/monitoring customer-requirement | ## In what area(s)?
<!-- Remove the '> ' to select -->
/area administration
> /area ansible
> /area autoscaling
> /area configuration
> /area cyclecloud
> /area documentation
> /area image
> /area job-scheduling
> /area monitoring
> /area ood
> /area remote-visualization
> /area user-management
## Describe the feature
<!-- Please also discuss possible business value -->
Hi Xavier,
It would be nice if we could get alerted when disks are nearly running out of space. Today our ANF was nearly full and we've had times in the past where the OS disk was full on various VMs.
Would it be possible to set up azure monitoring to notify us by email or something when it is full? Another option might even be to automatically increase the ANF size (but this might be abused). I think this would make our deployments more reliable for customers.
cc @ltalirz | 1.0 | Metric alerts - ## In what area(s)?
<!-- Remove the '> ' to select -->
/area administration
> /area ansible
> /area autoscaling
> /area configuration
> /area cyclecloud
> /area documentation
> /area image
> /area job-scheduling
> /area monitoring
> /area ood
> /area remote-visualization
> /area user-management
## Describe the feature
<!-- Please also discuss possible business value -->
Hi Xavier,
It would be nice if we could get alerted when disks are nearly running out of space. Today our ANF was nearly full and we've had times in the past where the OS disk was full on various VMs.
Would it be possible to set up azure monitoring to notify us by email or something when it is full? Another option might even be to automatically increase the ANF size (but this might be abused). I think this would make our deployments more reliable for customers.
cc @ltalirz | non_priority | metric alerts in what area s to select area administration area ansible area autoscaling area configuration area cyclecloud area documentation area image area job scheduling area monitoring area ood area remote visualization area user management describe the feature hi xavier it would be nice if we could get alerted when disks are nearly running out of space today our anf was nearly full and we ve had times in the past where the os disk was full on various vms would it be possible to set up azure monitoring to notify us by email or something when it is full another option might even be to automatically increase the anf size but this might be abused i think this would make our deployments more reliable for customers cc ltalirz | 0 |
137,298 | 18,752,679,598 | IssuesEvent | 2021-11-05 05:48:30 | madhans23/linux-4.15 | https://api.github.com/repos/madhans23/linux-4.15 | opened | CVE-2019-3701 (Medium) detected in linux-stablev4.17.12 | security vulnerability | ## CVE-2019-3701 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stablev4.17.12</b></p></summary>
<p>
<p>Linux kernel stable tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git>https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.15/commit/d96ee498864d1a0b6222cfb17d64ca8196014940">d96ee498864d1a0b6222cfb17d64ca8196014940</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/can/gw.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/can/gw.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in can_can_gw_rcv in net/can/gw.c in the Linux kernel through 4.19.13. The CAN frame modification rules allow bitwise logical operations that can be also applied to the can_dlc field. The privileged user "root" with CAP_NET_ADMIN can create a CAN frame modification rule that makes the data length code a higher value than the available CAN frame data size. In combination with a configured checksum calculation where the result is stored relatively to the end of the data (e.g. cgw_csum_xor_rel) the tail of the skb (e.g. frag_list pointer in skb_shared_info) can be rewritten which finally can cause a system crash. Because of a missing check, the CAN drivers may write arbitrary content beyond the data registers in the CAN controller's I/O memory when processing can-gw manipulated outgoing frames.
<p>Publish Date: 2019-01-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-3701>CVE-2019-3701</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-3701">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-3701</a></p>
<p>Release Date: 2019-01-03</p>
<p>Fix Resolution: v5.0-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-3701 (Medium) detected in linux-stablev4.17.12 - ## CVE-2019-3701 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stablev4.17.12</b></p></summary>
<p>
<p>Linux kernel stable tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git>https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.15/commit/d96ee498864d1a0b6222cfb17d64ca8196014940">d96ee498864d1a0b6222cfb17d64ca8196014940</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/can/gw.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/can/gw.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in can_can_gw_rcv in net/can/gw.c in the Linux kernel through 4.19.13. The CAN frame modification rules allow bitwise logical operations that can be also applied to the can_dlc field. The privileged user "root" with CAP_NET_ADMIN can create a CAN frame modification rule that makes the data length code a higher value than the available CAN frame data size. In combination with a configured checksum calculation where the result is stored relatively to the end of the data (e.g. cgw_csum_xor_rel) the tail of the skb (e.g. frag_list pointer in skb_shared_info) can be rewritten which finally can cause a system crash. Because of a missing check, the CAN drivers may write arbitrary content beyond the data registers in the CAN controller's I/O memory when processing can-gw manipulated outgoing frames.
<p>Publish Date: 2019-01-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-3701>CVE-2019-3701</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-3701">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-3701</a></p>
<p>Release Date: 2019-01-03</p>
<p>Fix Resolution: v5.0-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux cve medium severity vulnerability vulnerable library linux linux kernel stable tree library home page a href found in head commit a href found in base branch master vulnerable source files net can gw c net can gw c vulnerability details an issue was discovered in can can gw rcv in net can gw c in the linux kernel through the can frame modification rules allow bitwise logical operations that can be also applied to the can dlc field the privileged user root with cap net admin can create a can frame modification rule that makes the data length code a higher value than the available can frame data size in combination with a configured checksum calculation where the result is stored relatively to the end of the data e g cgw csum xor rel the tail of the skb e g frag list pointer in skb shared info can be rewritten which finally can cause a system crash because of a missing check the can drivers may write arbitrary content beyond the data registers in the can controller s i o memory when processing can gw manipulated outgoing frames publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
97,253 | 10,997,382,990 | IssuesEvent | 2019-12-03 09:02:37 | MicrosoftDocs/mslearn-live-migrating-to-the-cloud | https://api.github.com/repos/MicrosoftDocs/mslearn-live-migrating-to-the-cloud | closed | Script for Session 2 prep | documentation | I think we could further clarify the instructions for preparing for a session to indicate a student must have already forked this repo before running the script.
```
Repository 'UpdateSiteSourceControl' operation failed with Microsoft.Web.Hosting.SourceControls.OAuthException: GitHub GetRepository: Not Found
at Microsoft.Web.Hosting.SourceControls.GitHubProxy.<GetRepository>d__9.MoveNext()
--- End of stack trace from previous location where exception was thrown ---
at System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
at System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
at Microsoft.Web.Hosting.Administration.GitHubSiteRepositoryProvider.<UpdateSiteSourceControl>d__3.MoveNext()
--- End of stack trace from previous location where exception was thrown ---
at System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
at System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
at Microsoft.Web.Hosting.Administration.WebCloudController.<>c__DisplayClass243_1.<<UpdateSiteSourceControl>b__1>d.MoveNext()
--- End of stack trace from previous location where exception was thrown ---
at System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
at System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
at Microsoft.Web.Hosting.AsyncHelper.RunSync[TResult](Func`1 func)
at Microsoft.Web.Hosting.Administration.WebCloudController.UpdateSiteSourceControl(String subscriptionName, String webspaceName, String name, SiteSourceControl siteSourceControl).
Done. :-)
```
If they don't they will get the error above. | 1.0 | Script for Session 2 prep - I think we could further clarify the instructions for preparing for a session to indicate a student must have already forked this repo before running the script.
```
Repository 'UpdateSiteSourceControl' operation failed with Microsoft.Web.Hosting.SourceControls.OAuthException: GitHub GetRepository: Not Found
at Microsoft.Web.Hosting.SourceControls.GitHubProxy.<GetRepository>d__9.MoveNext()
--- End of stack trace from previous location where exception was thrown ---
at System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
at System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
at Microsoft.Web.Hosting.Administration.GitHubSiteRepositoryProvider.<UpdateSiteSourceControl>d__3.MoveNext()
--- End of stack trace from previous location where exception was thrown ---
at System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
at System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
at Microsoft.Web.Hosting.Administration.WebCloudController.<>c__DisplayClass243_1.<<UpdateSiteSourceControl>b__1>d.MoveNext()
--- End of stack trace from previous location where exception was thrown ---
at System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
at System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
at Microsoft.Web.Hosting.AsyncHelper.RunSync[TResult](Func`1 func)
at Microsoft.Web.Hosting.Administration.WebCloudController.UpdateSiteSourceControl(String subscriptionName, String webspaceName, String name, SiteSourceControl siteSourceControl).
Done. :-)
```
If they don't they will get the error above. | non_priority | script for session prep i think we could further clarify the instructions for preparing for a session to indicate a student must have already forked this repo before running the script repository updatesitesourcecontrol operation failed with microsoft web hosting sourcecontrols oauthexception github getrepository not found at microsoft web hosting sourcecontrols githubproxy d movenext end of stack trace from previous location where exception was thrown at system runtime exceptionservices exceptiondispatchinfo throw at system runtime compilerservices taskawaiter handlenonsuccessanddebuggernotification task task at microsoft web hosting administration githubsiterepositoryprovider d movenext end of stack trace from previous location where exception was thrown at system runtime exceptionservices exceptiondispatchinfo throw at system runtime compilerservices taskawaiter handlenonsuccessanddebuggernotification task task at microsoft web hosting administration webcloudcontroller c b d movenext end of stack trace from previous location where exception was thrown at system runtime exceptionservices exceptiondispatchinfo throw at system runtime compilerservices taskawaiter handlenonsuccessanddebuggernotification task task at microsoft web hosting asynchelper runsync func func at microsoft web hosting administration webcloudcontroller updatesitesourcecontrol string subscriptionname string webspacename string name sitesourcecontrol sitesourcecontrol done if they don t they will get the error above | 0 |
47,244 | 19,582,193,650 | IssuesEvent | 2022-01-04 23:12:23 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [Security Solution] [Platform] Need to resolve action connectors | bug v8.0.0 impact:high Team:Alerting Services Feature:Detection Rules Team:Detections and Resp Feature:Rule Actions Feature:Actions/ConnectorsManagement Feature:Alerting/RuleActions v8.1.0 Team:Security Solution Platform | If an action connector is created pre-8.0 in a non-default space, that connector will have a new id generated in > 8.0 and will not be found when trying to create new rules or importing rules into the security solution with references to that action connector.
1. ~We need to expose a `resolve` function in the actions client~
2. ~We need to update [this line](https://github.com/elastic/kibana/blob/d5e199b8da21a0946fb2c3aaea8e88c47ae5a539/x-pack/plugins/security_solution/server/lib/detection_engine/routes/rules/utils.ts#L207) in the security solution to use the `resolve` function instead of the `getAll`~
Edit: After meeting with the team looks like this should be part of the work for https://github.com/elastic/kibana/issues/118767 and involves using those same functions the SOM uses for determining conflicts and/or updating fields on import | 1.0 | [Security Solution] [Platform] Need to resolve action connectors - If an action connector is created pre-8.0 in a non-default space, that connector will have a new id generated in > 8.0 and will not be found when trying to create new rules or importing rules into the security solution with references to that action connector.
1. ~We need to expose a `resolve` function in the actions client~
2. ~We need to update [this line](https://github.com/elastic/kibana/blob/d5e199b8da21a0946fb2c3aaea8e88c47ae5a539/x-pack/plugins/security_solution/server/lib/detection_engine/routes/rules/utils.ts#L207) in the security solution to use the `resolve` function instead of the `getAll`~
Edit: After meeting with the team looks like this should be part of the work for https://github.com/elastic/kibana/issues/118767 and involves using those same functions the SOM uses for determining conflicts and/or updating fields on import | non_priority | need to resolve action connectors if an action connector is created pre in a non default space that connector will have a new id generated in and will not be found when trying to create new rules or importing rules into the security solution with references to that action connector we need to expose a resolve function in the actions client we need to update in the security solution to use the resolve function instead of the getall edit after meeting with the team looks like this should be part of the work for and involves using those same functions the som uses for determining conflicts and or updating fields on import | 0 |
321,356 | 23,851,387,957 | IssuesEvent | 2022-09-06 18:17:05 | aws-amplify/amplify-js | https://api.github.com/repos/aws-amplify/amplify-js | closed | Getting "no current user" error after redirect from Cognito Hosted UI | documentation Auth | ### Before opening, please confirm:
- [X] I have [searched for duplicate or closed issues](https://github.com/aws-amplify/amplify-js/issues?q=is%3Aissue+) and [discussions](https://github.com/aws-amplify/amplify-js/discussions).
- [X] I have read the guide for [submitting bug reports](https://github.com/aws-amplify/amplify-js/blob/main/CONTRIBUTING.md#bug-reports).
- [X] I have done my best to include a minimal, self-contained set of instructions for consistently reproducing the issue.
### JavaScript Framework
React
### Amplify APIs
Authentication
### Amplify Categories
auth
### Environment information
System:
OS: macOS 10.15.5
CPU: (16) x64 Intel(R) Core(TM) i9-9880H CPU @ 2.30GHz
Memory: 1.86 GB / 32.00 GB
Shell: 5.7.1 - /bin/zsh
Binaries:
Node: 17.9.0 - /usr/local/bin/node
Yarn: 1.22.18 - /usr/local/bin/yarn
npm: 8.5.5 - /usr/local/bin/npm
Browsers:
Brave Browser: 93.1.29.79
Chrome: 101.0.4951.64
Firefox: 99.0.1
Safari: 13.1.1
npmPackages:
@testing-library/jest-dom: ^5.16.4 => 5.16.4
@testing-library/react: ^13.1.1 => 13.1.1
@testing-library/user-event: ^13.5.0 => 13.5.0
aws-amplify: ^4.3.18 => 4.3.22
react: ^18.1.0 => 18.1.0
react-dom: ^18.1.0 => 18.1.0
react-router-dom: ^6.3.0 => 6.3.0
react-scripts: 5.0.1 => 5.0.1
web-vitals: ^2.1.4 => 2.1.4
npmGlobalPackages:
@aws-amplify/cli: 4.18.0
eslint: 7.1.0
firebase-tools: 8.1.1
gulp-cli: 2.2.1
jest: 25.1.0
knex: 0.20.8
npm: 8.5.5
ts-node: 8.6.2
typescript: 3.7.4
### Describe the bug
Hi there, I am trying to learn authentication code grant flow with Cognito Hosted UI. Everything seems working until I get redirected back to my protected page. All the /authorize, /login and /token calls are getting completed successfully. I can also confirm that I see the URL with /code parameter generated which is then redirected again. As the final step when I use await Auth.currentAuthenticatedUser(); I get an error with "no current user". So, if I am not mistaken Amplify handles all the required OAUTH calls internally which I would then expect to get an authorized user at the end. I found a similar issue from #7742 and I added `cookieStorage` object with secure flag set to `false` but it didn't work as well.
Here I also attached a screenshot to show all the related oauth calls are ending with success.
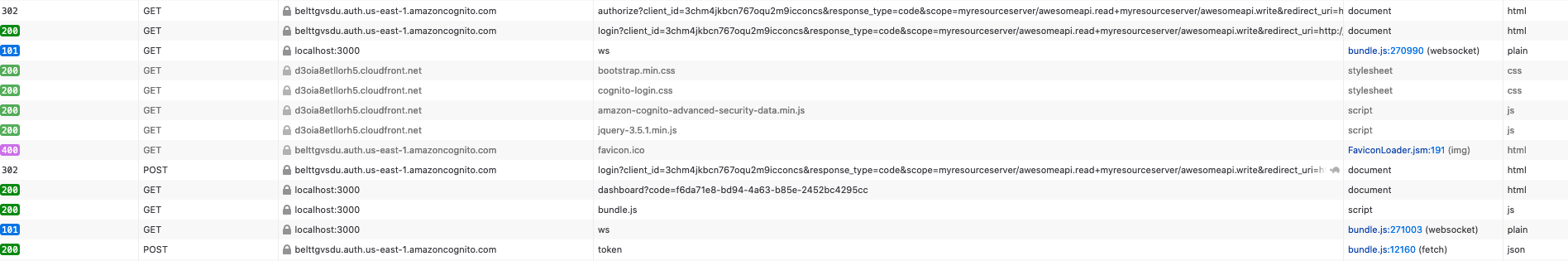
### Expected behavior
Getting a successfull response from Auth.currentAuthenticatedUser() function call.
### Reproduction steps
See attached code.
### Code Snippet
**App.js**
```
import './App.css';
import React from 'react'
import Amplify from 'aws-amplify';
Amplify.configure({
Auth: {
// REQUIRED - Amazon Cognito Region
region: 'us-east-1',
// OPTIONAL - Amazon Cognito User Pool ID
userPoolId: process.env.REACT_APP_USERPOOL_ID,
// OPTIONAL - Amazon Cognito Web Client ID (26-char alphanumeric string)
userPoolWebClientId: process.env.REACT_APP_USERPOOL_WEB_CLIENT_ID,
// OPTIONAL - Enforce user authentication prior to accessing AWS resources or not
mandatorySignIn: false,
// OPTIONAL - Manually set the authentication flow type. Default is 'USER_SRP_AUTH'
authenticationFlowType: 'USER_PASSWORD_AUTH',
// OPTIONAL - Hosted UI configuration
oauth: {
domain: 'belttgvsdu.auth.us-east-1.amazoncognito.com',
scope: ['myresourceserver/awesomeapi.read', 'myresourceserver/awesomeapi.write'],
redirectSignIn: 'http://localhost:3000/dashboard',
redirectSignOut: 'http://localhost:3000',
responseType: 'code'
}
}
});
function App(props) {
return (
<div className="App">
<h1>This is Landing page</h1>
<a href="https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/authorize?client_id=3chm4jkbcn767oqu2m9icconcs&response_type=code&scope=myresourceserver%2Fawesomeapi.read+myresourceserver%2Fawesomeapi.write&redirect_uri=http%3A%2F%2Flocalhost%3A3000%2Fdashboard">Login</a>
</div>
);
}
export default App;
```
And here is the dashboard.js to render localhost:3000/dashboard
```
import React, {useEffect, useState} from 'react';
import '../App.css';
import {Auth} from 'aws-amplify';
import {Navigate} from "react-router-dom";
function Dashboard(props) {
const [user, setUser] = useState();
const [isLoading, setIsLoading] = useState(true);
async function getCurrentUser() {
try {
const authUser = await Auth.currentAuthenticatedUser();
console.log(JSON.stringify(authUser));
setUser(authUser);
} catch (e) {
console.log('error happened', e);
setUser(null);
setIsLoading(false);
}
}
useEffect(() => {
getCurrentUser();
}, []);
async function handleSignOut(event) {
event.preventDefault();
try {
await Auth.signOut();
} catch (error) {
console.log('error signing out: ', error);
}
setUser(null);
setIsLoading(false);
}
if (!user && !isLoading) {
return <Navigate to="/" replace={true} />
}
return (
<div className="container">
<h1>Dashboard</h1>
<button onClick={handleSignOut} className="fluid ui button blue">Sign Out</button>
</div>
)
}
export default Dashboard;
```
### Log output
<details>
```
[DEBUG] 46:04.595 Amplify - amplify config
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.599 AuthClass - configure Auth [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.599 Parser - parse config
Array(3) [ {…}, "to amplifyconfig", {…} ]
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.599 Hub - Dispatching to auth with
Object { event: "parsingCallbackUrl", data: {…}, message: "The callback url is being parsed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.600 Hub - Dispatching to auth with
Object { event: "parsingCallbackUrl", data: {…}, message: "The callback url is being parsed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.600 AnalyticsClass - on hub capsule auth
Object { event: "parsingCallbackUrl", data: {…}, message: "The callback url is being parsed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.600 Hub - Dispatching to auth with
Object { event: "parsingCallbackUrl", data: {…}, message: "The callback url is being parsed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.600 Hub - Dispatching to auth with
Object { event: "parsingCallbackUrl", data: {…}, message: "The callback url is being parsed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.601 OAuth - Starting code flow with http://localhost:3000/dashboard?code=bee663b1-49d3-4e39-b94a-7e07457c3295 [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.602 Hub - Dispatching to auth with
Object { event: "codeFlow", data: {}, message: "Retrieving tokens from https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.602 Hub - Dispatching to auth with
Object { event: "codeFlow", data: {}, message: "Retrieving tokens from https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.602 AnalyticsClass - on hub capsule auth
Object { event: "codeFlow", data: {}, message: "Retrieving tokens from https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.602 Hub - Dispatching to auth with
Object { event: "codeFlow", data: {}, message: "Retrieving tokens from https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.604 Hub - Dispatching to auth with
Object { event: "codeFlow", data: {}, message: "Retrieving tokens from https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.604 OAuth - Calling token endpoint: https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token with
Object { grant_type: "authorization_code", code: "bee663b1-49d3-4e39-b94a-7e07457c3295", client_id: "3chm4jkbcn767oqu2m9icconcs", redirect_uri: "http://localhost:3000/dashboard" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.604 Hub - Dispatching to auth with
Object { event: "configured", data: null, message: "The Auth category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.605 Hub - Dispatching to auth with
Object { event: "configured", data: null, message: "The Auth category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.605 AnalyticsClass - on hub capsule auth
Object { event: "configured", data: null, message: "The Auth category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.605 Hub - Dispatching to auth with
Object { event: "configured", data: null, message: "The Auth category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.605 Hub - Dispatching to auth with
Object { event: "configured", data: null, message: "The Auth category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.606 AnalyticsClass - configure Analytics
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.606 Parser - parse config
Array(3) [ {…}, "to amplifyconfig", {…} ]
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.606 AWSPinpointProvider - configure Analytics
Object { disabled: undefined, autoSessionRecord: true, Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.606 Hub - Dispatching to analytics with
Object { event: "configured", data: null, message: "The Analytics category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.607 AnalyticsClass - on hub capsule analytics
Object { event: "configured", data: null, message: "The Analytics category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.607 AnalyticsClass - current configuration
Object { autoSessionRecord: true, Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.607 Storage - storage configure called [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.607 StorageClass - configure Storage [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.607 Parser - parse config
Array(3) [ {…}, "to amplifyconfig", {…} ]
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.608 AWSS3Provider - configure Storage undefined [ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.608 Storage - storage vault configure called [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.608 StorageClass - configure Storage [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.608 Parser - parse config
Array(3) [ {…}, "to amplifyconfig", {…} ]
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.608 AWSS3Provider - configure Storage undefined [ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 RestAPI - configure Rest API
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 RestAPI - create Rest API instance [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 RestClient - API Options
Object { endpoints: [], Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 I18n - configure I18n [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 I18n - create I18n instance [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 PubSub - configure PubSub
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 GraphQLAPI - configure GraphQL API
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 GraphQLAPI - create Rest instance [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 RestClient - API Options
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 RestAPI - configure Rest API
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 RestAPI - create Rest API instance [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 RestClient - API Options
Object { endpoints: [], Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 GraphQLAPI - configure GraphQL API
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 GraphQLAPI - create Rest instance [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 RestClient - API Options
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.611 Interactions - configure Interactions
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.611 XR - configure XR
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.611 AbstractXRProvider - configure SumerianProvider
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.611 Predictions - configure Predictions
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.612 Geo - configure Geo [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.612 Parser - parse config
Array(3) [ {…}, "to amplifyconfig", {…} ]
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.613 AmazonLocationServiceProvider - configure Amazon Location Service Provider undefined [ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.624 AuthClass - getting current authenticated user [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.625 AuthClass - getting current authenticated user [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.626 AuthClass - get current authenticated userpool user 2 [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.626 AuthClass - OAuth signIn in progress, waiting for resolution... 2 [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.957 AuthClass - Error in cognito hosted auth response Error: Username and Pool information are required.
CognitoUser CognitoUser.js:73
node_modules bundle.js:11432
node_modules bundle.js:11330
step bundle.js:8399
node_modules bundle.js:8330
fulfilled bundle.js:8284
promise callback*step bundle.js:8299
node_modules bundle.js:8302
node_modules bundle.js:8281
node_modules bundle.js:11243
node_modules bundle.js:8623
__WEBPACK_DEFAULT_EXPORT__ urlListener.ts:19
node_modules bundle.js:8614
node_modules bundle.js:14378
node_modules bundle.js:14377
js App.js:7
factory react refresh:6
Webpack 7
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.957 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.957 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.958 AnalyticsClass - on hub capsule auth
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.958 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.959 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.959 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.959 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.959 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.960 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.960 AnalyticsClass - on hub capsule auth
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.961 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.962 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.962 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.963 AuthClass - OAuth signIn resolved: cognitoHostedUI_failure [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.963 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.964 AuthClass - OAuth signIn resolved: cognitoHostedUI_failure [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.964 Hub - Dispatching to auth with
Object { event: "customState_failure", data: Error, message: "A failure occurred when returning state" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.964 Hub - Dispatching to auth with
Object { event: "customState_failure", data: Error, message: "A failure occurred when returning state" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.964 AnalyticsClass - on hub capsule auth
Object { event: "customState_failure", data: Error, message: "A failure occurred when returning state" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.964 Hub - Dispatching to auth with
Object { event: "customState_failure", data: Error, message: "A failure occurred when returning state" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.965 Hub - Dispatching to auth with
Object { event: "customState_failure", data: Error, message: "A failure occurred when returning state" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.965 AuthClass - Failed to get user from user pool 2 [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.965 AuthClass - The user is not authenticated by the error No current user 2 [ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
error happened The user is not authenticated 2 [Dashboard.js:18](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/src/components/Dashboard.js)
```
</details>
### aws-exports.js
_No response_
### Manual configuration
_No response_
### Additional configuration
_No response_
### Mobile Device
_No response_
### Mobile Operating System
_No response_
### Mobile Browser
_No response_
### Mobile Browser Version
_No response_
### Additional information and screenshots
_No response_ | 1.0 | Getting "no current user" error after redirect from Cognito Hosted UI - ### Before opening, please confirm:
- [X] I have [searched for duplicate or closed issues](https://github.com/aws-amplify/amplify-js/issues?q=is%3Aissue+) and [discussions](https://github.com/aws-amplify/amplify-js/discussions).
- [X] I have read the guide for [submitting bug reports](https://github.com/aws-amplify/amplify-js/blob/main/CONTRIBUTING.md#bug-reports).
- [X] I have done my best to include a minimal, self-contained set of instructions for consistently reproducing the issue.
### JavaScript Framework
React
### Amplify APIs
Authentication
### Amplify Categories
auth
### Environment information
System:
OS: macOS 10.15.5
CPU: (16) x64 Intel(R) Core(TM) i9-9880H CPU @ 2.30GHz
Memory: 1.86 GB / 32.00 GB
Shell: 5.7.1 - /bin/zsh
Binaries:
Node: 17.9.0 - /usr/local/bin/node
Yarn: 1.22.18 - /usr/local/bin/yarn
npm: 8.5.5 - /usr/local/bin/npm
Browsers:
Brave Browser: 93.1.29.79
Chrome: 101.0.4951.64
Firefox: 99.0.1
Safari: 13.1.1
npmPackages:
@testing-library/jest-dom: ^5.16.4 => 5.16.4
@testing-library/react: ^13.1.1 => 13.1.1
@testing-library/user-event: ^13.5.0 => 13.5.0
aws-amplify: ^4.3.18 => 4.3.22
react: ^18.1.0 => 18.1.0
react-dom: ^18.1.0 => 18.1.0
react-router-dom: ^6.3.0 => 6.3.0
react-scripts: 5.0.1 => 5.0.1
web-vitals: ^2.1.4 => 2.1.4
npmGlobalPackages:
@aws-amplify/cli: 4.18.0
eslint: 7.1.0
firebase-tools: 8.1.1
gulp-cli: 2.2.1
jest: 25.1.0
knex: 0.20.8
npm: 8.5.5
ts-node: 8.6.2
typescript: 3.7.4
### Describe the bug
Hi there, I am trying to learn authentication code grant flow with Cognito Hosted UI. Everything seems working until I get redirected back to my protected page. All the /authorize, /login and /token calls are getting completed successfully. I can also confirm that I see the URL with /code parameter generated which is then redirected again. As the final step when I use await Auth.currentAuthenticatedUser(); I get an error with "no current user". So, if I am not mistaken Amplify handles all the required OAUTH calls internally which I would then expect to get an authorized user at the end. I found a similar issue from #7742 and I added `cookieStorage` object with secure flag set to `false` but it didn't work as well.
Here I also attached a screenshot to show all the related oauth calls are ending with success.
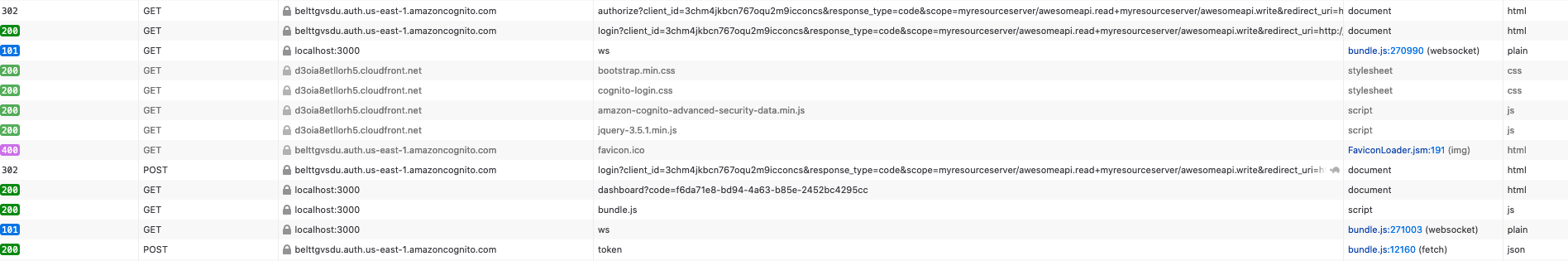
### Expected behavior
Getting a successfull response from Auth.currentAuthenticatedUser() function call.
### Reproduction steps
See attached code.
### Code Snippet
**App.js**
```
import './App.css';
import React from 'react'
import Amplify from 'aws-amplify';
Amplify.configure({
Auth: {
// REQUIRED - Amazon Cognito Region
region: 'us-east-1',
// OPTIONAL - Amazon Cognito User Pool ID
userPoolId: process.env.REACT_APP_USERPOOL_ID,
// OPTIONAL - Amazon Cognito Web Client ID (26-char alphanumeric string)
userPoolWebClientId: process.env.REACT_APP_USERPOOL_WEB_CLIENT_ID,
// OPTIONAL - Enforce user authentication prior to accessing AWS resources or not
mandatorySignIn: false,
// OPTIONAL - Manually set the authentication flow type. Default is 'USER_SRP_AUTH'
authenticationFlowType: 'USER_PASSWORD_AUTH',
// OPTIONAL - Hosted UI configuration
oauth: {
domain: 'belttgvsdu.auth.us-east-1.amazoncognito.com',
scope: ['myresourceserver/awesomeapi.read', 'myresourceserver/awesomeapi.write'],
redirectSignIn: 'http://localhost:3000/dashboard',
redirectSignOut: 'http://localhost:3000',
responseType: 'code'
}
}
});
function App(props) {
return (
<div className="App">
<h1>This is Landing page</h1>
<a href="https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/authorize?client_id=3chm4jkbcn767oqu2m9icconcs&response_type=code&scope=myresourceserver%2Fawesomeapi.read+myresourceserver%2Fawesomeapi.write&redirect_uri=http%3A%2F%2Flocalhost%3A3000%2Fdashboard">Login</a>
</div>
);
}
export default App;
```
And here is the dashboard.js to render localhost:3000/dashboard
```
import React, {useEffect, useState} from 'react';
import '../App.css';
import {Auth} from 'aws-amplify';
import {Navigate} from "react-router-dom";
function Dashboard(props) {
const [user, setUser] = useState();
const [isLoading, setIsLoading] = useState(true);
async function getCurrentUser() {
try {
const authUser = await Auth.currentAuthenticatedUser();
console.log(JSON.stringify(authUser));
setUser(authUser);
} catch (e) {
console.log('error happened', e);
setUser(null);
setIsLoading(false);
}
}
useEffect(() => {
getCurrentUser();
}, []);
async function handleSignOut(event) {
event.preventDefault();
try {
await Auth.signOut();
} catch (error) {
console.log('error signing out: ', error);
}
setUser(null);
setIsLoading(false);
}
if (!user && !isLoading) {
return <Navigate to="/" replace={true} />
}
return (
<div className="container">
<h1>Dashboard</h1>
<button onClick={handleSignOut} className="fluid ui button blue">Sign Out</button>
</div>
)
}
export default Dashboard;
```
### Log output
<details>
```
[DEBUG] 46:04.595 Amplify - amplify config
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.599 AuthClass - configure Auth [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.599 Parser - parse config
Array(3) [ {…}, "to amplifyconfig", {…} ]
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.599 Hub - Dispatching to auth with
Object { event: "parsingCallbackUrl", data: {…}, message: "The callback url is being parsed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.600 Hub - Dispatching to auth with
Object { event: "parsingCallbackUrl", data: {…}, message: "The callback url is being parsed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.600 AnalyticsClass - on hub capsule auth
Object { event: "parsingCallbackUrl", data: {…}, message: "The callback url is being parsed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.600 Hub - Dispatching to auth with
Object { event: "parsingCallbackUrl", data: {…}, message: "The callback url is being parsed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.600 Hub - Dispatching to auth with
Object { event: "parsingCallbackUrl", data: {…}, message: "The callback url is being parsed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.601 OAuth - Starting code flow with http://localhost:3000/dashboard?code=bee663b1-49d3-4e39-b94a-7e07457c3295 [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.602 Hub - Dispatching to auth with
Object { event: "codeFlow", data: {}, message: "Retrieving tokens from https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.602 Hub - Dispatching to auth with
Object { event: "codeFlow", data: {}, message: "Retrieving tokens from https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.602 AnalyticsClass - on hub capsule auth
Object { event: "codeFlow", data: {}, message: "Retrieving tokens from https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.602 Hub - Dispatching to auth with
Object { event: "codeFlow", data: {}, message: "Retrieving tokens from https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.604 Hub - Dispatching to auth with
Object { event: "codeFlow", data: {}, message: "Retrieving tokens from https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.604 OAuth - Calling token endpoint: https://belttgvsdu.auth.us-east-1.amazoncognito.com/oauth2/token with
Object { grant_type: "authorization_code", code: "bee663b1-49d3-4e39-b94a-7e07457c3295", client_id: "3chm4jkbcn767oqu2m9icconcs", redirect_uri: "http://localhost:3000/dashboard" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.604 Hub - Dispatching to auth with
Object { event: "configured", data: null, message: "The Auth category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.605 Hub - Dispatching to auth with
Object { event: "configured", data: null, message: "The Auth category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.605 AnalyticsClass - on hub capsule auth
Object { event: "configured", data: null, message: "The Auth category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.605 Hub - Dispatching to auth with
Object { event: "configured", data: null, message: "The Auth category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.605 Hub - Dispatching to auth with
Object { event: "configured", data: null, message: "The Auth category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.606 AnalyticsClass - configure Analytics
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.606 Parser - parse config
Array(3) [ {…}, "to amplifyconfig", {…} ]
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.606 AWSPinpointProvider - configure Analytics
Object { disabled: undefined, autoSessionRecord: true, Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.606 Hub - Dispatching to analytics with
Object { event: "configured", data: null, message: "The Analytics category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.607 AnalyticsClass - on hub capsule analytics
Object { event: "configured", data: null, message: "The Analytics category has been configured successfully" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.607 AnalyticsClass - current configuration
Object { autoSessionRecord: true, Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.607 Storage - storage configure called [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.607 StorageClass - configure Storage [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.607 Parser - parse config
Array(3) [ {…}, "to amplifyconfig", {…} ]
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.608 AWSS3Provider - configure Storage undefined [ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.608 Storage - storage vault configure called [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.608 StorageClass - configure Storage [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.608 Parser - parse config
Array(3) [ {…}, "to amplifyconfig", {…} ]
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.608 AWSS3Provider - configure Storage undefined [ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 RestAPI - configure Rest API
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 RestAPI - create Rest API instance [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 RestClient - API Options
Object { endpoints: [], Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 I18n - configure I18n [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 I18n - create I18n instance [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 PubSub - configure PubSub
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 GraphQLAPI - configure GraphQL API
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 GraphQLAPI - create Rest instance [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.609 RestClient - API Options
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 RestAPI - configure Rest API
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 RestAPI - create Rest API instance [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 RestClient - API Options
Object { endpoints: [], Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 GraphQLAPI - configure GraphQL API
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 GraphQLAPI - create Rest instance [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.610 RestClient - API Options
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.611 Interactions - configure Interactions
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.611 XR - configure XR
Object { opt: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.611 AbstractXRProvider - configure SumerianProvider
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.611 Predictions - configure Predictions
Object { Auth: {…} }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.612 Geo - configure Geo [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.612 Parser - parse config
Array(3) [ {…}, "to amplifyconfig", {…} ]
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.613 AmazonLocationServiceProvider - configure Amazon Location Service Provider undefined [ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.624 AuthClass - getting current authenticated user [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.625 AuthClass - getting current authenticated user [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.626 AuthClass - get current authenticated userpool user 2 [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.626 AuthClass - OAuth signIn in progress, waiting for resolution... 2 [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.957 AuthClass - Error in cognito hosted auth response Error: Username and Pool information are required.
CognitoUser CognitoUser.js:73
node_modules bundle.js:11432
node_modules bundle.js:11330
step bundle.js:8399
node_modules bundle.js:8330
fulfilled bundle.js:8284
promise callback*step bundle.js:8299
node_modules bundle.js:8302
node_modules bundle.js:8281
node_modules bundle.js:11243
node_modules bundle.js:8623
__WEBPACK_DEFAULT_EXPORT__ urlListener.ts:19
node_modules bundle.js:8614
node_modules bundle.js:14378
node_modules bundle.js:14377
js App.js:7
factory react refresh:6
Webpack 7
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.957 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.957 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.958 AnalyticsClass - on hub capsule auth
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.958 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.959 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.959 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.959 Hub - Dispatching to auth with
Object { event: "signIn_failure", data: Error, message: "The OAuth response flow failed" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.959 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.960 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.960 AnalyticsClass - on hub capsule auth
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.961 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.962 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.962 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.963 AuthClass - OAuth signIn resolved: cognitoHostedUI_failure [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.963 Hub - Dispatching to auth with
Object { event: "cognitoHostedUI_failure", data: Error, message: "A failure occurred when returning to the Cognito Hosted UI" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.964 AuthClass - OAuth signIn resolved: cognitoHostedUI_failure [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.964 Hub - Dispatching to auth with
Object { event: "customState_failure", data: Error, message: "A failure occurred when returning state" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.964 Hub - Dispatching to auth with
Object { event: "customState_failure", data: Error, message: "A failure occurred when returning state" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.964 AnalyticsClass - on hub capsule auth
Object { event: "customState_failure", data: Error, message: "A failure occurred when returning state" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.964 Hub - Dispatching to auth with
Object { event: "customState_failure", data: Error, message: "A failure occurred when returning state" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.965 Hub - Dispatching to auth with
Object { event: "customState_failure", data: Error, message: "A failure occurred when returning state" }
[ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.965 AuthClass - Failed to get user from user pool 2 [ConsoleLogger.ts:115](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
[DEBUG] 46:04.965 AuthClass - The user is not authenticated by the error No current user 2 [ConsoleLogger.ts:125](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/node_modules/@aws-amplify/core/src/Logger/ConsoleLogger.ts)
error happened The user is not authenticated 2 [Dashboard.js:18](http://localhost:3000/Users/buraktas/aws-cognito-hosted-ui-react/src/components/Dashboard.js)
```
</details>
### aws-exports.js
_No response_
### Manual configuration
_No response_
### Additional configuration
_No response_
### Mobile Device
_No response_
### Mobile Operating System
_No response_
### Mobile Browser
_No response_
### Mobile Browser Version
_No response_
### Additional information and screenshots
_No response_ | non_priority | getting no current user error after redirect from cognito hosted ui before opening please confirm i have and i have read the guide for i have done my best to include a minimal self contained set of instructions for consistently reproducing the issue javascript framework react amplify apis authentication amplify categories auth environment information system os macos cpu intel r core tm cpu memory gb gb shell bin zsh binaries node usr local bin node yarn usr local bin yarn npm usr local bin npm browsers brave browser chrome firefox safari npmpackages testing library jest dom testing library react testing library user event aws amplify react react dom react router dom react scripts web vitals npmglobalpackages aws amplify cli eslint firebase tools gulp cli jest knex npm ts node typescript describe the bug hi there i am trying to learn authentication code grant flow with cognito hosted ui everything seems working until i get redirected back to my protected page all the authorize login and token calls are getting completed successfully i can also confirm that i see the url with code parameter generated which is then redirected again as the final step when i use await auth currentauthenticateduser i get an error with no current user so if i am not mistaken amplify handles all the required oauth calls internally which i would then expect to get an authorized user at the end i found a similar issue from and i added cookiestorage object with secure flag set to false but it didn t work as well here i also attached a screenshot to show all the related oauth calls are ending with success expected behavior getting a successfull response from auth currentauthenticateduser function call reproduction steps see attached code code snippet app js import app css import react from react import amplify from aws amplify amplify configure auth required amazon cognito region region us east optional amazon cognito user pool id userpoolid process env react app userpool id optional amazon cognito web client id char alphanumeric string userpoolwebclientid process env react app userpool web client id optional enforce user authentication prior to accessing aws resources or not mandatorysignin false optional manually set the authentication flow type default is user srp auth authenticationflowtype user password auth optional hosted ui configuration oauth domain belttgvsdu auth us east amazoncognito com scope redirectsignin redirectsignout responsetype code function app props return this is landing page a href export default app and here is the dashboard js to render localhost dashboard import react useeffect usestate from react import app css import auth from aws amplify import navigate from react router dom function dashboard props const usestate const usestate true async function getcurrentuser try const authuser await auth currentauthenticateduser console log json stringify authuser setuser authuser catch e console log error happened e setuser null setisloading false useeffect getcurrentuser async function handlesignout event event preventdefault try await auth signout catch error console log error signing out error setuser null setisloading false if user isloading return return dashboard sign out export default dashboard log output amplify amplify config object auth … authclass configure auth parser parse config array hub dispatching to auth with object event parsingcallbackurl data … message the callback url is being parsed hub dispatching to auth with object event parsingcallbackurl data … message the callback url is being parsed analyticsclass on hub capsule auth object event parsingcallbackurl data … message the callback url is being parsed hub dispatching to auth with object event parsingcallbackurl data … message the callback url is being parsed hub dispatching to auth with object event parsingcallbackurl data … message the callback url is being parsed oauth starting code flow with hub dispatching to auth with object event codeflow data message retrieving tokens from hub dispatching to auth with object event codeflow data message retrieving tokens from analyticsclass on hub capsule auth object event codeflow data message retrieving tokens from hub dispatching to auth with object event codeflow data message retrieving tokens from hub dispatching to auth with object event codeflow data message retrieving tokens from oauth calling token endpoint with object grant type authorization code code client id redirect uri hub dispatching to auth with object event configured data null message the auth category has been configured successfully hub dispatching to auth with object event configured data null message the auth category has been configured successfully analyticsclass on hub capsule auth object event configured data null message the auth category has been configured successfully hub dispatching to auth with object event configured data null message the auth category has been configured successfully hub dispatching to auth with object event configured data null message the auth category has been configured successfully analyticsclass configure analytics object auth … parser parse config array awspinpointprovider configure analytics object disabled undefined autosessionrecord true auth … hub dispatching to analytics with object event configured data null message the analytics category has been configured successfully analyticsclass on hub capsule analytics object event configured data null message the analytics category has been configured successfully analyticsclass current configuration object autosessionrecord true auth … storage storage configure called storageclass configure storage parser parse config array configure storage undefined storage storage vault configure called storageclass configure storage parser parse config array configure storage undefined restapi configure rest api object opt … restapi create rest api instance restclient api options object endpoints auth … configure create instance pubsub configure pubsub object opt … graphqlapi configure graphql api object opt … graphqlapi create rest instance restclient api options object auth … restapi configure rest api object opt … restapi create rest api instance restclient api options object endpoints auth … graphqlapi configure graphql api object opt … graphqlapi create rest instance restclient api options object auth … interactions configure interactions object opt … xr configure xr object opt … abstractxrprovider configure sumerianprovider object auth … predictions configure predictions object auth … geo configure geo parser parse config array amazonlocationserviceprovider configure amazon location service provider undefined authclass getting current authenticated user authclass getting current authenticated user authclass get current authenticated userpool user authclass oauth signin in progress waiting for resolution authclass error in cognito hosted auth response error username and pool information are required cognitouser cognitouser js node modules bundle js node modules bundle js step bundle js node modules bundle js fulfilled bundle js promise callback step bundle js node modules bundle js node modules bundle js node modules bundle js node modules bundle js webpack default export urllistener ts node modules bundle js node modules bundle js node modules bundle js js app js factory react refresh webpack hub dispatching to auth with object event signin failure data error message the oauth response flow failed hub dispatching to auth with object event signin failure data error message the oauth response flow failed analyticsclass on hub capsule auth object event signin failure data error message the oauth response flow failed hub dispatching to auth with object event signin failure data error message the oauth response flow failed hub dispatching to auth with object event signin failure data error message the oauth response flow failed hub dispatching to auth with object event signin failure data error message the oauth response flow failed hub dispatching to auth with object event signin failure data error message the oauth response flow failed hub dispatching to auth with object event cognitohostedui failure data error message a failure occurred when returning to the cognito hosted ui hub dispatching to auth with object event cognitohostedui failure data error message a failure occurred when returning to the cognito hosted ui analyticsclass on hub capsule auth object event cognitohostedui failure data error message a failure occurred when returning to the cognito hosted ui hub dispatching to auth with object event cognitohostedui failure data error message a failure occurred when returning to the cognito hosted ui hub dispatching to auth with object event cognitohostedui failure data error message a failure occurred when returning to the cognito hosted ui hub dispatching to auth with object event cognitohostedui failure data error message a failure occurred when returning to the cognito hosted ui authclass oauth signin resolved cognitohostedui failure hub dispatching to auth with object event cognitohostedui failure data error message a failure occurred when returning to the cognito hosted ui authclass oauth signin resolved cognitohostedui failure hub dispatching to auth with object event customstate failure data error message a failure occurred when returning state hub dispatching to auth with object event customstate failure data error message a failure occurred when returning state analyticsclass on hub capsule auth object event customstate failure data error message a failure occurred when returning state hub dispatching to auth with object event customstate failure data error message a failure occurred when returning state hub dispatching to auth with object event customstate failure data error message a failure occurred when returning state authclass failed to get user from user pool authclass the user is not authenticated by the error no current user error happened the user is not authenticated aws exports js no response manual configuration no response additional configuration no response mobile device no response mobile operating system no response mobile browser no response mobile browser version no response additional information and screenshots no response | 0 |
5,293 | 26,747,884,224 | IssuesEvent | 2023-01-30 17:13:58 | mozilla/foundation.mozilla.org | https://api.github.com/repos/mozilla/foundation.mozilla.org | opened | "optimize:css:copy" task is not working | bug 🦠 engineering maintain | ### Describe the bug
"optimize:css:copy" task is not working
### To Reproduce
Steps to reproduce the behavior:
1. run `docker-compose up`
2. observe error
### Expected behavior
No errors
### Screenshots
<img width="1326" alt="image" src="https://user-images.githubusercontent.com/2896608/215546456-04c9b7ba-278b-4827-852c-7d514b12d54b.png">
| True | "optimize:css:copy" task is not working - ### Describe the bug
"optimize:css:copy" task is not working
### To Reproduce
Steps to reproduce the behavior:
1. run `docker-compose up`
2. observe error
### Expected behavior
No errors
### Screenshots
<img width="1326" alt="image" src="https://user-images.githubusercontent.com/2896608/215546456-04c9b7ba-278b-4827-852c-7d514b12d54b.png">
| non_priority | optimize css copy task is not working describe the bug optimize css copy task is not working to reproduce steps to reproduce the behavior run docker compose up observe error expected behavior no errors screenshots img width alt image src | 0 |
25,648 | 11,204,934,236 | IssuesEvent | 2020-01-05 10:29:50 | logzio/microsoft-graph | https://api.github.com/repos/logzio/microsoft-graph | closed | CVE-2019-16942 (High) detected in jackson-databind-2.9.9.3.jar | security vulnerability | ## CVE-2019-16942 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/microsoft-graph/pom.xml</p>
<p>Path to vulnerable library: epository/com/fasterxml/jackson/core/jackson-databind/2.9.9.3/jackson-databind-2.9.9.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/logzio/microsoft-graph/commit/1ecd600ab1aa22efd25dcf4813063e893a4f829f">1ecd600ab1aa22efd25dcf4813063e893a4f829f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942>CVE-2019-16942</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.10.0.pr1</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.9.3","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.9.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.10.0.pr1"}],"vulnerabilityIdentifier":"CVE-2019-16942","vulnerabilityDetails":"A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-16942 (High) detected in jackson-databind-2.9.9.3.jar - ## CVE-2019-16942 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/microsoft-graph/pom.xml</p>
<p>Path to vulnerable library: epository/com/fasterxml/jackson/core/jackson-databind/2.9.9.3/jackson-databind-2.9.9.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/logzio/microsoft-graph/commit/1ecd600ab1aa22efd25dcf4813063e893a4f829f">1ecd600ab1aa22efd25dcf4813063e893a4f829f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942>CVE-2019-16942</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.10.0.pr1</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.9.3","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.9.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.10.0.pr1"}],"vulnerabilityIdentifier":"CVE-2019-16942","vulnerabilityDetails":"A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm microsoft graph pom xml path to vulnerable library epository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the commons dbcp jar in the classpath and an attacker can find an rmi service endpoint to access it is possible to make the service execute a malicious payload this issue exists because of org apache commons dbcp datasources sharedpooldatasource and org apache commons dbcp datasources peruserpooldatasource mishandling publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the commons dbcp jar in the classpath and an attacker can find an rmi service endpoint to access it is possible to make the service execute a malicious payload this issue exists because of org apache commons dbcp datasources sharedpooldatasource and org apache commons dbcp datasources peruserpooldatasource mishandling vulnerabilityurl | 0 |
92,254 | 18,796,217,925 | IssuesEvent | 2021-11-08 22:44:27 | TeamAmaze/AmazeFileManager | https://api.github.com/repos/TeamAmaze/AmazeFileManager | opened | Add debug info for native code | Issue-Task (low) good first issue Area-CodeHealth | Add this to the gradle
```
android.buildTypes.release.ndk.debugSymbolLevel = FULL
```
so that debug info is added to logs from C. | 1.0 | Add debug info for native code - Add this to the gradle
```
android.buildTypes.release.ndk.debugSymbolLevel = FULL
```
so that debug info is added to logs from C. | non_priority | add debug info for native code add this to the gradle android buildtypes release ndk debugsymbollevel full so that debug info is added to logs from c | 0 |
255,157 | 27,484,777,852 | IssuesEvent | 2023-03-04 01:18:12 | panasalap/linux-4.1.15 | https://api.github.com/repos/panasalap/linux-4.1.15 | opened | CVE-2017-14954 (Medium) detected in linux-yocto-devv4.2.8 | security vulnerability | ## CVE-2017-14954 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-devv4.2.8</b></p></summary>
<p>
<p>Linux Embedded Kernel - tracks the next mainline release</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-dev>https://git.yoctoproject.org/git/linux-yocto-dev</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/exit.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The waitid implementation in kernel/exit.c in the Linux kernel through 4.13.4 accesses rusage data structures in unintended cases, which allows local users to obtain sensitive information, and bypass the KASLR protection mechanism, via a crafted system call.
<p>Publish Date: 2017-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-14954>CVE-2017-14954</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-14954">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-14954</a></p>
<p>Release Date: 2017-10-02</p>
<p>Fix Resolution: v4.14-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-14954 (Medium) detected in linux-yocto-devv4.2.8 - ## CVE-2017-14954 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-devv4.2.8</b></p></summary>
<p>
<p>Linux Embedded Kernel - tracks the next mainline release</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-dev>https://git.yoctoproject.org/git/linux-yocto-dev</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/exit.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The waitid implementation in kernel/exit.c in the Linux kernel through 4.13.4 accesses rusage data structures in unintended cases, which allows local users to obtain sensitive information, and bypass the KASLR protection mechanism, via a crafted system call.
<p>Publish Date: 2017-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-14954>CVE-2017-14954</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-14954">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-14954</a></p>
<p>Release Date: 2017-10-02</p>
<p>Fix Resolution: v4.14-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux yocto cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel tracks the next mainline release library home page a href found in base branch master vulnerable source files kernel exit c vulnerability details the waitid implementation in kernel exit c in the linux kernel through accesses rusage data structures in unintended cases which allows local users to obtain sensitive information and bypass the kaslr protection mechanism via a crafted system call publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
15,627 | 5,153,229,732 | IssuesEvent | 2017-01-14 09:04:51 | themosis/documentation | https://api.github.com/repos/themosis/documentation | closed | Remove 'css' and 'js' asset type option | Code Missing | In assets documentation, version 1.3, remove the references to asset type options of 'js', 'css'. Not available 👎 | 1.0 | Remove 'css' and 'js' asset type option - In assets documentation, version 1.3, remove the references to asset type options of 'js', 'css'. Not available 👎 | non_priority | remove css and js asset type option in assets documentation version remove the references to asset type options of js css not available 👎 | 0 |
33,865 | 27,958,277,648 | IssuesEvent | 2023-03-24 13:57:13 | python/core-workflow | https://api.github.com/repos/python/core-workflow | opened | Querying for the discord-bot deployment | infrastructure | # The short story
We need to discuss the deployment options for the [discord-bot](https://github.com/python/discord-bot).
# Long version
@Mariatta and I are developing a discord bot that will utilize OpenAI APIs to enhance the productivity of the core development team. Currently, the bot is deployed on my Azure server(Standard D2as v4), but this setup is not sustainable. We would like to explore alternative options, such as requesting a quota for PSF Heroku deployment or any other viable alternatives. It would be greatly appreciated if we could discuss this matter further.
cc @python/infrastructure-staff
| 1.0 | Querying for the discord-bot deployment - # The short story
We need to discuss the deployment options for the [discord-bot](https://github.com/python/discord-bot).
# Long version
@Mariatta and I are developing a discord bot that will utilize OpenAI APIs to enhance the productivity of the core development team. Currently, the bot is deployed on my Azure server(Standard D2as v4), but this setup is not sustainable. We would like to explore alternative options, such as requesting a quota for PSF Heroku deployment or any other viable alternatives. It would be greatly appreciated if we could discuss this matter further.
cc @python/infrastructure-staff
| non_priority | querying for the discord bot deployment the short story we need to discuss the deployment options for the long version mariatta and i are developing a discord bot that will utilize openai apis to enhance the productivity of the core development team currently the bot is deployed on my azure server standard but this setup is not sustainable we would like to explore alternative options such as requesting a quota for psf heroku deployment or any other viable alternatives it would be greatly appreciated if we could discuss this matter further cc python infrastructure staff | 0 |
156,401 | 19,861,325,592 | IssuesEvent | 2022-01-22 00:09:30 | pustovitDmytro/lalaps | https://api.github.com/repos/pustovitDmytro/lalaps | closed | CVE-2021-3918 (High) detected in json-schema-0.2.3.tgz - autoclosed | security vulnerability | ## CVE-2021-3918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p></summary>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>
Dependency Hierarchy:
- coveralls-3.1.1.tgz (Root Library)
- request-2.88.2.tgz
- http-signature-1.2.0.tgz
- jsprim-1.4.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/pustovitDmytro/lalaps/commit/1e993b43d15c8311de22de5fda0b8cd072345189">1e993b43d15c8311de22de5fda0b8cd072345189</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3918">https://nvd.nist.gov/vuln/detail/CVE-2021-3918</a></p>
<p>Release Date: 2021-11-13</p>
<p>Fix Resolution: json-schema - 0.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-3918 (High) detected in json-schema-0.2.3.tgz - autoclosed - ## CVE-2021-3918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p></summary>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>
Dependency Hierarchy:
- coveralls-3.1.1.tgz (Root Library)
- request-2.88.2.tgz
- http-signature-1.2.0.tgz
- jsprim-1.4.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/pustovitDmytro/lalaps/commit/1e993b43d15c8311de22de5fda0b8cd072345189">1e993b43d15c8311de22de5fda0b8cd072345189</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3918">https://nvd.nist.gov/vuln/detail/CVE-2021-3918</a></p>
<p>Release Date: 2021-11-13</p>
<p>Fix Resolution: json-schema - 0.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in json schema tgz autoclosed cve high severity vulnerability vulnerable library json schema tgz json schema validation and specifications library home page a href dependency hierarchy coveralls tgz root library request tgz http signature tgz jsprim tgz x json schema tgz vulnerable library found in head commit a href found in base branch master vulnerability details json schema is vulnerable to improperly controlled modification of object prototype attributes prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution json schema step up your open source security game with whitesource | 0 |
334,056 | 24,401,989,052 | IssuesEvent | 2022-10-05 02:58:16 | RandomCoderOrg/ubuntu-on-android | https://api.github.com/repos/RandomCoderOrg/ubuntu-on-android | closed | Please help me | documentation question stale | Hey guys I am following the steps to install termux-11x but I always get this error please help me.

> **Error**

| 1.0 | Please help me - Hey guys I am following the steps to install termux-11x but I always get this error please help me.

> **Error**

| non_priority | please help me hey guys i am following the steps to install termux but i always get this error please help me error | 0 |
182,537 | 14,140,323,343 | IssuesEvent | 2020-11-10 11:02:20 | effector/patronum | https://api.github.com/repos/effector/patronum | closed | Cover methods with type tests | good first issue tests | - [x] `combineEvents` (#93)
- [x] `condition` (#68)
- [x] `debounce` (38)
- [x] `debug` (#100)
- [x] `delay`
- [x] `every`
- [x] `inFlight` (#84)
- [x] `pending` (82)
- [x] `reshape` (#100)
- [x] `some`
- [x] `splitMap` (#112)
- [x] `spread` (#94)
- [x] `status` (fcb2db523cf8bc2c76c5ca606e4e03492545f6da)
- [x] `throttle` | 1.0 | Cover methods with type tests - - [x] `combineEvents` (#93)
- [x] `condition` (#68)
- [x] `debounce` (38)
- [x] `debug` (#100)
- [x] `delay`
- [x] `every`
- [x] `inFlight` (#84)
- [x] `pending` (82)
- [x] `reshape` (#100)
- [x] `some`
- [x] `splitMap` (#112)
- [x] `spread` (#94)
- [x] `status` (fcb2db523cf8bc2c76c5ca606e4e03492545f6da)
- [x] `throttle` | non_priority | cover methods with type tests combineevents condition debounce debug delay every inflight pending reshape some splitmap spread status throttle | 0 |
72,805 | 7,312,249,289 | IssuesEvent | 2018-02-28 20:21:10 | curationexperts/epigaea | https://api.github.com/repos/curationexperts/epigaea | closed | Deleting Item from Epigea doesn't delete item from fcrepo's binary store. | acceptance testing in progress question | I don't think this is a bug, but this seems odd to me, and a bit problematic. I noticed this because I deleted everything from my deployed server, and then ingested a single image to make sure everything was working. When I was done I deleted the image but noticed that it was still in the fcrepo binary.store. I'm assuming this is because fcrepo keeps a tombstone? I guess I'm more curious if you've ran into this yourself? I'll look into what I can do to resolve it I guess. With batch ingest, this could get messy fast for us. | 1.0 | Deleting Item from Epigea doesn't delete item from fcrepo's binary store. - I don't think this is a bug, but this seems odd to me, and a bit problematic. I noticed this because I deleted everything from my deployed server, and then ingested a single image to make sure everything was working. When I was done I deleted the image but noticed that it was still in the fcrepo binary.store. I'm assuming this is because fcrepo keeps a tombstone? I guess I'm more curious if you've ran into this yourself? I'll look into what I can do to resolve it I guess. With batch ingest, this could get messy fast for us. | non_priority | deleting item from epigea doesn t delete item from fcrepo s binary store i don t think this is a bug but this seems odd to me and a bit problematic i noticed this because i deleted everything from my deployed server and then ingested a single image to make sure everything was working when i was done i deleted the image but noticed that it was still in the fcrepo binary store i m assuming this is because fcrepo keeps a tombstone i guess i m more curious if you ve ran into this yourself i ll look into what i can do to resolve it i guess with batch ingest this could get messy fast for us | 0 |
29,318 | 4,489,173,010 | IssuesEvent | 2016-08-30 10:00:32 | Microsoft/vsts-tasks | https://api.github.com/repos/Microsoft/vsts-tasks | closed | VSO Run Functional Tests , requires user to be logged on | Area: Test | In our Tfs build we have a Deploy VS agent Task. This task uses a Test Machine group and group uses a particular account that has local admin on the machine and is project admin in TFS.
This Tasks deploys and configures the Test agent correctly with the same user on the remote machine but it will kick you off the remote session if you are logged on.
Our issue is that when we run the Functional Test Task, the test fails every single time except if you re-log on to the remote machine with the user account.
When re-logged on you can see a cmd window with the DTAExecutionHost.exe running and then the Tests run correctly.
Why does the remote machine require the user to be logged on ?
Why do the tests fail unless logged on ?
| 1.0 | VSO Run Functional Tests , requires user to be logged on - In our Tfs build we have a Deploy VS agent Task. This task uses a Test Machine group and group uses a particular account that has local admin on the machine and is project admin in TFS.
This Tasks deploys and configures the Test agent correctly with the same user on the remote machine but it will kick you off the remote session if you are logged on.
Our issue is that when we run the Functional Test Task, the test fails every single time except if you re-log on to the remote machine with the user account.
When re-logged on you can see a cmd window with the DTAExecutionHost.exe running and then the Tests run correctly.
Why does the remote machine require the user to be logged on ?
Why do the tests fail unless logged on ?
| non_priority | vso run functional tests requires user to be logged on in our tfs build we have a deploy vs agent task this task uses a test machine group and group uses a particular account that has local admin on the machine and is project admin in tfs this tasks deploys and configures the test agent correctly with the same user on the remote machine but it will kick you off the remote session if you are logged on our issue is that when we run the functional test task the test fails every single time except if you re log on to the remote machine with the user account when re logged on you can see a cmd window with the dtaexecutionhost exe running and then the tests run correctly why does the remote machine require the user to be logged on why do the tests fail unless logged on | 0 |
247,503 | 26,711,686,473 | IssuesEvent | 2023-01-28 01:23:36 | panasalap/linux-4.1.15 | https://api.github.com/repos/panasalap/linux-4.1.15 | reopened | CVE-2019-2215 (High) detected in linuxlinux-4.1.17 | security vulnerability | ## CVE-2019-2215 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.17</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.1.15/commit/aae4c2fa46027fd4c477372871df090c6b94f3f1">aae4c2fa46027fd4c477372871df090c6b94f3f1</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/android/binder.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/android/binder.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A use-after-free in binder.c allows an elevation of privilege from an application to the Linux Kernel. No user interaction is required to exploit this vulnerability, however exploitation does require either the installation of a malicious local application or a separate vulnerability in a network facing application.Product: AndroidAndroid ID: A-141720095
<p>Publish Date: 2019-10-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-2215>CVE-2019-2215</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2215">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2215</a></p>
<p>Release Date: 2019-10-18</p>
<p>Fix Resolution: v4.16-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-2215 (High) detected in linuxlinux-4.1.17 - ## CVE-2019-2215 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.17</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.1.15/commit/aae4c2fa46027fd4c477372871df090c6b94f3f1">aae4c2fa46027fd4c477372871df090c6b94f3f1</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/android/binder.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/android/binder.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A use-after-free in binder.c allows an elevation of privilege from an application to the Linux Kernel. No user interaction is required to exploit this vulnerability, however exploitation does require either the installation of a malicious local application or a separate vulnerability in a network facing application.Product: AndroidAndroid ID: A-141720095
<p>Publish Date: 2019-10-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-2215>CVE-2019-2215</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2215">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2215</a></p>
<p>Release Date: 2019-10-18</p>
<p>Fix Resolution: v4.16-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files drivers android binder c drivers android binder c vulnerability details a use after free in binder c allows an elevation of privilege from an application to the linux kernel no user interaction is required to exploit this vulnerability however exploitation does require either the installation of a malicious local application or a separate vulnerability in a network facing application product androidandroid id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
180,139 | 14,740,216,467 | IssuesEvent | 2021-01-07 08:43:07 | Tejas1510/Athavani | https://api.github.com/repos/Tejas1510/Athavani | closed | Suggest Improvement | DWOC Level-2 documentation good first issue help wanted | If you Think any issue would help to improve the project you can suggest that and we would think on it
| 1.0 | Suggest Improvement - If you Think any issue would help to improve the project you can suggest that and we would think on it
| non_priority | suggest improvement if you think any issue would help to improve the project you can suggest that and we would think on it | 0 |
391,092 | 26,880,179,333 | IssuesEvent | 2023-02-05 14:42:06 | trpc/trpc | https://api.github.com/repos/trpc/trpc | opened | docs: Use with Deno's Oak | 📚 documentation / examples | ### Area of Improvement
It is a bit unclear how to integrate tRPC with Oak.
I've been able to follow the instructions, up until the `server.ts`. Current documentation shows this:
```ts
import { serve } from 'https://deno.land/std@0.140.0/http/server.ts';
import { fetchRequestHandler } from 'npm:@trpc/server/adapters/fetch';
import { createContext } from './context.ts';
import { appRouter } from './router.ts';
function handler(request) {
return fetchRequestHandler({
endpoint: '/trpc',
req: request,
router: appRouter,
createContext,
});
}
serve(handler);
```
However, I got stuck modifying this to work with Oak:
```ts
import { Application, Router } from "https://deno.land/x/oak@v11.1.0/mod.ts";
import { fetchRequestHandler } from "npm:@trpc/server/adapters/fetch";
import { createContext } from "./v1/context.ts";
import { appRouter } from "./v1/routes.ts";
const app = new Application();
const router = new Router();
router.use("/", (ctx) => {
return fetchRequestHandler({
endpoint: "/trpc",
req: ctx.request.originalRequest,
router: appRouter,
createContext,
});
});
app.use(router.routes());
app.use(router.allowedMethods());
await app.listen();
```
The main issue is the `req: ctx.request.originalRequest`. It shows error: `Type 'ServerRequest' is missing the following properties from type 'Request': cache, credentials, destination, integrity, and 16 more.` I realized that there may be two different `Request` types, one for Deno's serve function, and the other for Oak's property of `Context`. But I'm not sure how to fix it.
Is the fix as simple as using another property or function, or is a new Adapter for Deno required?
### Link to related docs
https://trpc.io/docs/fetch#deno-deploy
### Additional information
_No response_
### 👨👧👦 Contributing
- [ ] 🙋♂️ Yes, I'd be down to file a PR implementing the suggested changes! | 1.0 | docs: Use with Deno's Oak - ### Area of Improvement
It is a bit unclear how to integrate tRPC with Oak.
I've been able to follow the instructions, up until the `server.ts`. Current documentation shows this:
```ts
import { serve } from 'https://deno.land/std@0.140.0/http/server.ts';
import { fetchRequestHandler } from 'npm:@trpc/server/adapters/fetch';
import { createContext } from './context.ts';
import { appRouter } from './router.ts';
function handler(request) {
return fetchRequestHandler({
endpoint: '/trpc',
req: request,
router: appRouter,
createContext,
});
}
serve(handler);
```
However, I got stuck modifying this to work with Oak:
```ts
import { Application, Router } from "https://deno.land/x/oak@v11.1.0/mod.ts";
import { fetchRequestHandler } from "npm:@trpc/server/adapters/fetch";
import { createContext } from "./v1/context.ts";
import { appRouter } from "./v1/routes.ts";
const app = new Application();
const router = new Router();
router.use("/", (ctx) => {
return fetchRequestHandler({
endpoint: "/trpc",
req: ctx.request.originalRequest,
router: appRouter,
createContext,
});
});
app.use(router.routes());
app.use(router.allowedMethods());
await app.listen();
```
The main issue is the `req: ctx.request.originalRequest`. It shows error: `Type 'ServerRequest' is missing the following properties from type 'Request': cache, credentials, destination, integrity, and 16 more.` I realized that there may be two different `Request` types, one for Deno's serve function, and the other for Oak's property of `Context`. But I'm not sure how to fix it.
Is the fix as simple as using another property or function, or is a new Adapter for Deno required?
### Link to related docs
https://trpc.io/docs/fetch#deno-deploy
### Additional information
_No response_
### 👨👧👦 Contributing
- [ ] 🙋♂️ Yes, I'd be down to file a PR implementing the suggested changes! | non_priority | docs use with deno s oak area of improvement it is a bit unclear how to integrate trpc with oak i ve been able to follow the instructions up until the server ts current documentation shows this ts import serve from import fetchrequesthandler from npm trpc server adapters fetch import createcontext from context ts import approuter from router ts function handler request return fetchrequesthandler endpoint trpc req request router approuter createcontext serve handler however i got stuck modifying this to work with oak ts import application router from import fetchrequesthandler from npm trpc server adapters fetch import createcontext from context ts import approuter from routes ts const app new application const router new router router use ctx return fetchrequesthandler endpoint trpc req ctx request originalrequest router approuter createcontext app use router routes app use router allowedmethods await app listen the main issue is the req ctx request originalrequest it shows error type serverrequest is missing the following properties from type request cache credentials destination integrity and more i realized that there may be two different request types one for deno s serve function and the other for oak s property of context but i m not sure how to fix it is the fix as simple as using another property or function or is a new adapter for deno required link to related docs additional information no response 👨👧👦 contributing 🙋♂️ yes i d be down to file a pr implementing the suggested changes | 0 |
220,231 | 16,903,092,215 | IssuesEvent | 2021-06-24 01:32:58 | rtshkmr/ped | https://api.github.com/repos/rtshkmr/ped | closed | Potentially Confusing use of `\` symbols | severity.VeryLow type.DocumentationBug | The `\` symbol has been used for file path delimiters (e.g. in `/data/myimage.png`) but at the same time has been used for indication alternative inputs like so `starting with https:// and ending with .jpg/jpeg/png`. While this is nitpicky, it provides some ambiguity to a non-tech user.
<!--session: 1604045616185-b82433e7-d4b2-4d8e-b032-f4962463bad8--> | 1.0 | Potentially Confusing use of `\` symbols - The `\` symbol has been used for file path delimiters (e.g. in `/data/myimage.png`) but at the same time has been used for indication alternative inputs like so `starting with https:// and ending with .jpg/jpeg/png`. While this is nitpicky, it provides some ambiguity to a non-tech user.
<!--session: 1604045616185-b82433e7-d4b2-4d8e-b032-f4962463bad8--> | non_priority | potentially confusing use of symbols the symbol has been used for file path delimiters e g in data myimage png but at the same time has been used for indication alternative inputs like so starting with https and ending with jpg jpeg png while this is nitpicky it provides some ambiguity to a non tech user | 0 |
23,594 | 22,301,396,132 | IssuesEvent | 2022-06-13 09:03:12 | gardener/gardener | https://api.github.com/repos/gardener/gardener | closed | Creation of a `Shoot` cluster can fail, if it is the first `Shoot` assigned to a `Seed` | kind/bug area/usability | **How to categorize this issue?**
<!--
Please select area, kind, and priority for this issue. This helps the community categorizing it.
Replace below TODOs or exchange the existing identifiers with those that fit best in your opinion.
If multiple identifiers make sense you can also state the commands multiple times, e.g.
/area control-plane
/area auto-scaling
...
"/area" identifiers: audit-logging|auto-scaling|backup|certification|control-plane-migration|control-plane|cost|delivery|dev-productivity|disaster-recovery|documentation|high-availability|logging|metering|monitoring|networking|open-source|ops-productivity|os|performance|quality|robustness|scalability|security|storage|testing|usability|user-management
"/kind" identifiers: api-change|bug|cleanup|discussion|enhancement|epic|impediment|poc|post-mortem|question|regression|task|technical-debt|test
-->
/area usability
/kind bug
**What happened**:
When the `APIServerSNI` feature gate is enabled, the sync period of the seed controller in `gardenlet` is relatively large and the dependency watchdog probe is enabled (`seed.spec.settings.dependencyWatchdog.probe.enabled=true`), creation of a shoot cluster (if that is the first shoot cluster on the seed) will fail initially because the `dependency-watchdog`'s external kube-apiserver probe fails and therefore KCM, MCM and CA are all scaled down. The probe will become successful after the seed has been reconciled and only if there already exists an istio `virtualservice` for the shoot's kube-apiserver.
All of this happens because during seed bootstrap the following code is used to detect whether SNI is enabled or not:
https://github.com/gardener/gardener/blob/8f819ffab82898c65be19a4376aeec3b5627c3ba/pkg/operation/seed/seed.go#L738
https://github.com/gardener/gardener/blob/8f819ffab82898c65be19a4376aeec3b5627c3ba/pkg/operation/botanist/component/kubeapiserverexposure/kube_apiserver_sni.go#L224-L237
And then a specific rule is added to the `allow-to-all-shoot-apiservers` `Networkpolicy` depending on whether SNI is enabled:
https://github.com/gardener/gardener/blob/e7a25ef16f7452a7b81cf1a2c0724ab41d4af886/pkg/operation/botanist/component/networkpolicies/global.go#L162-L172
So if a `virtualservice` is not yet created for any shoots, `anySNI` will be evaluated to false. This will result in the `allow-to-all-shoot-apiservers` `Networkpolicy` not containing a rule that allows access to the `istio-ingressgateway` pod and therefore the `dependency-watchdog` cannot talk to it when trying to evaluate the external `kube-apiserver` probe.
When `gardenlet`'s seed controller sync period is relatively small (~1m) this issue is not noticeable as the seed will be bootstrapped and `anySNY` evaluated every minute. Then the `allow-to-all-shoot-apiservers` `Networkpolicy` will be adapted accordingly before `dependency-watchdog`'s external `kube-apiserver` probe has a chance to fail.
**What you expected to happen**:
The `allow-to-all-shoot-apiservers` `Networkpolicy` to contain the appropriate rule:
```
- namespaceSelector: {}
podSelector:
matchLabels:
app: istio-ingressgateway
```
independent of `gardenlet`'s seed controller sync period when the `APIServerSNI` feature gate is enabled.
**How to reproduce it (as minimally and precisely as possible)**:
In `gardenlet`'s component config set the `controllers.seed.syncPeriod` to 1h. Enable the `APIServerSNI` feature gate. Create a seed cluster and make sure that `seed.spec.settings.dependencyWatchdog.probe.enabled` is set to true and that there are no shoots already running on the seed. In the seed's `garden` namespace you can see that the `allow-to-all-shoot-apiservers` `Networkpolicy` does not contain the aforementioned rule.
Create a shoot cluster and observe that it's KCM, MCM and CA all get scaled down. Once the 1h of the sync period has elapsed (or if you simply restart `gardenlet`), notice that `allow-to-all-shoot-apiservers` is edited accordingly and KCM, MCM and CA all get scaled up.
**Anything else we need to know?**:
Discovered this as part of: https://github.com/gardener/gardener/pull/5995#issuecomment-1138921606
**Environment**:
- Gardener version: e7a25ef16f7452a7b81cf1a2c0724ab41d4af886
| True | Creation of a `Shoot` cluster can fail, if it is the first `Shoot` assigned to a `Seed` - **How to categorize this issue?**
<!--
Please select area, kind, and priority for this issue. This helps the community categorizing it.
Replace below TODOs or exchange the existing identifiers with those that fit best in your opinion.
If multiple identifiers make sense you can also state the commands multiple times, e.g.
/area control-plane
/area auto-scaling
...
"/area" identifiers: audit-logging|auto-scaling|backup|certification|control-plane-migration|control-plane|cost|delivery|dev-productivity|disaster-recovery|documentation|high-availability|logging|metering|monitoring|networking|open-source|ops-productivity|os|performance|quality|robustness|scalability|security|storage|testing|usability|user-management
"/kind" identifiers: api-change|bug|cleanup|discussion|enhancement|epic|impediment|poc|post-mortem|question|regression|task|technical-debt|test
-->
/area usability
/kind bug
**What happened**:
When the `APIServerSNI` feature gate is enabled, the sync period of the seed controller in `gardenlet` is relatively large and the dependency watchdog probe is enabled (`seed.spec.settings.dependencyWatchdog.probe.enabled=true`), creation of a shoot cluster (if that is the first shoot cluster on the seed) will fail initially because the `dependency-watchdog`'s external kube-apiserver probe fails and therefore KCM, MCM and CA are all scaled down. The probe will become successful after the seed has been reconciled and only if there already exists an istio `virtualservice` for the shoot's kube-apiserver.
All of this happens because during seed bootstrap the following code is used to detect whether SNI is enabled or not:
https://github.com/gardener/gardener/blob/8f819ffab82898c65be19a4376aeec3b5627c3ba/pkg/operation/seed/seed.go#L738
https://github.com/gardener/gardener/blob/8f819ffab82898c65be19a4376aeec3b5627c3ba/pkg/operation/botanist/component/kubeapiserverexposure/kube_apiserver_sni.go#L224-L237
And then a specific rule is added to the `allow-to-all-shoot-apiservers` `Networkpolicy` depending on whether SNI is enabled:
https://github.com/gardener/gardener/blob/e7a25ef16f7452a7b81cf1a2c0724ab41d4af886/pkg/operation/botanist/component/networkpolicies/global.go#L162-L172
So if a `virtualservice` is not yet created for any shoots, `anySNI` will be evaluated to false. This will result in the `allow-to-all-shoot-apiservers` `Networkpolicy` not containing a rule that allows access to the `istio-ingressgateway` pod and therefore the `dependency-watchdog` cannot talk to it when trying to evaluate the external `kube-apiserver` probe.
When `gardenlet`'s seed controller sync period is relatively small (~1m) this issue is not noticeable as the seed will be bootstrapped and `anySNY` evaluated every minute. Then the `allow-to-all-shoot-apiservers` `Networkpolicy` will be adapted accordingly before `dependency-watchdog`'s external `kube-apiserver` probe has a chance to fail.
**What you expected to happen**:
The `allow-to-all-shoot-apiservers` `Networkpolicy` to contain the appropriate rule:
```
- namespaceSelector: {}
podSelector:
matchLabels:
app: istio-ingressgateway
```
independent of `gardenlet`'s seed controller sync period when the `APIServerSNI` feature gate is enabled.
**How to reproduce it (as minimally and precisely as possible)**:
In `gardenlet`'s component config set the `controllers.seed.syncPeriod` to 1h. Enable the `APIServerSNI` feature gate. Create a seed cluster and make sure that `seed.spec.settings.dependencyWatchdog.probe.enabled` is set to true and that there are no shoots already running on the seed. In the seed's `garden` namespace you can see that the `allow-to-all-shoot-apiservers` `Networkpolicy` does not contain the aforementioned rule.
Create a shoot cluster and observe that it's KCM, MCM and CA all get scaled down. Once the 1h of the sync period has elapsed (or if you simply restart `gardenlet`), notice that `allow-to-all-shoot-apiservers` is edited accordingly and KCM, MCM and CA all get scaled up.
**Anything else we need to know?**:
Discovered this as part of: https://github.com/gardener/gardener/pull/5995#issuecomment-1138921606
**Environment**:
- Gardener version: e7a25ef16f7452a7b81cf1a2c0724ab41d4af886
| non_priority | creation of a shoot cluster can fail if it is the first shoot assigned to a seed how to categorize this issue please select area kind and priority for this issue this helps the community categorizing it replace below todos or exchange the existing identifiers with those that fit best in your opinion if multiple identifiers make sense you can also state the commands multiple times e g area control plane area auto scaling area identifiers audit logging auto scaling backup certification control plane migration control plane cost delivery dev productivity disaster recovery documentation high availability logging metering monitoring networking open source ops productivity os performance quality robustness scalability security storage testing usability user management kind identifiers api change bug cleanup discussion enhancement epic impediment poc post mortem question regression task technical debt test area usability kind bug what happened when the apiserversni feature gate is enabled the sync period of the seed controller in gardenlet is relatively large and the dependency watchdog probe is enabled seed spec settings dependencywatchdog probe enabled true creation of a shoot cluster if that is the first shoot cluster on the seed will fail initially because the dependency watchdog s external kube apiserver probe fails and therefore kcm mcm and ca are all scaled down the probe will become successful after the seed has been reconciled and only if there already exists an istio virtualservice for the shoot s kube apiserver all of this happens because during seed bootstrap the following code is used to detect whether sni is enabled or not and then a specific rule is added to the allow to all shoot apiservers networkpolicy depending on whether sni is enabled so if a virtualservice is not yet created for any shoots anysni will be evaluated to false this will result in the allow to all shoot apiservers networkpolicy not containing a rule that allows access to the istio ingressgateway pod and therefore the dependency watchdog cannot talk to it when trying to evaluate the external kube apiserver probe when gardenlet s seed controller sync period is relatively small this issue is not noticeable as the seed will be bootstrapped and anysny evaluated every minute then the allow to all shoot apiservers networkpolicy will be adapted accordingly before dependency watchdog s external kube apiserver probe has a chance to fail what you expected to happen the allow to all shoot apiservers networkpolicy to contain the appropriate rule namespaceselector podselector matchlabels app istio ingressgateway independent of gardenlet s seed controller sync period when the apiserversni feature gate is enabled how to reproduce it as minimally and precisely as possible in gardenlet s component config set the controllers seed syncperiod to enable the apiserversni feature gate create a seed cluster and make sure that seed spec settings dependencywatchdog probe enabled is set to true and that there are no shoots already running on the seed in the seed s garden namespace you can see that the allow to all shoot apiservers networkpolicy does not contain the aforementioned rule create a shoot cluster and observe that it s kcm mcm and ca all get scaled down once the of the sync period has elapsed or if you simply restart gardenlet notice that allow to all shoot apiservers is edited accordingly and kcm mcm and ca all get scaled up anything else we need to know discovered this as part of environment gardener version | 0 |
229,066 | 25,287,224,699 | IssuesEvent | 2022-11-16 20:23:23 | elastic/beats | https://api.github.com/repos/elastic/beats | closed | [Filebeat] Support unix sockets and named pipes in httpjson input | enhancement Filebeat Team:Security-External Integrations | **Describe the enhancement:**
Add support for connecting to HTTP services that are listening on unix sockets and named pipes (Windows). When a user configures a host URL that uses particular schemes then the input would know to connect over different transports. It would use these schemes to be consistent with [Metricbeat](https://www.elastic.co/guide/en/beats/metricbeat/current/configuration-metricbeat.html#module-http-config-options):
- `http+unix://` to connect to UNIX sockets.
- `http+npipe://` to connect to Windows named pipes.
It should support HTTPS as well (I don't know if Metricbeat does, but I would expect `https+unix` and `https+npipe` to work).
**Describe a specific use case for the enhancement or feature:**
This would be used connect to internal services that are only exposed locally. Services like [Beats HTTP monitoring endpoint](https://www.elastic.co/guide/en/beats/filebeat/current/http-endpoint.html) and Docker have APIs that listen on unix sockets. It would be useful if `httpjson` (and any future inputs that also monitor arbitrary HTTP services) could monitor data from these local APIs.
| True | [Filebeat] Support unix sockets and named pipes in httpjson input - **Describe the enhancement:**
Add support for connecting to HTTP services that are listening on unix sockets and named pipes (Windows). When a user configures a host URL that uses particular schemes then the input would know to connect over different transports. It would use these schemes to be consistent with [Metricbeat](https://www.elastic.co/guide/en/beats/metricbeat/current/configuration-metricbeat.html#module-http-config-options):
- `http+unix://` to connect to UNIX sockets.
- `http+npipe://` to connect to Windows named pipes.
It should support HTTPS as well (I don't know if Metricbeat does, but I would expect `https+unix` and `https+npipe` to work).
**Describe a specific use case for the enhancement or feature:**
This would be used connect to internal services that are only exposed locally. Services like [Beats HTTP monitoring endpoint](https://www.elastic.co/guide/en/beats/filebeat/current/http-endpoint.html) and Docker have APIs that listen on unix sockets. It would be useful if `httpjson` (and any future inputs that also monitor arbitrary HTTP services) could monitor data from these local APIs.
| non_priority | support unix sockets and named pipes in httpjson input describe the enhancement add support for connecting to http services that are listening on unix sockets and named pipes windows when a user configures a host url that uses particular schemes then the input would know to connect over different transports it would use these schemes to be consistent with http unix to connect to unix sockets http npipe to connect to windows named pipes it should support https as well i don t know if metricbeat does but i would expect https unix and https npipe to work describe a specific use case for the enhancement or feature this would be used connect to internal services that are only exposed locally services like and docker have apis that listen on unix sockets it would be useful if httpjson and any future inputs that also monitor arbitrary http services could monitor data from these local apis | 0 |
52,786 | 10,928,503,697 | IssuesEvent | 2019-11-22 19:11:42 | eclipse/eclipse.jdt.ls | https://api.github.com/repos/eclipse/eclipse.jdt.ls | closed | Add quickfix to correct access to static elements | code-actions enhancement | Handle the following cases in QuickFixProcessor:
```java
case IProblem.NonStaticAccessToStaticField:
case IProblem.NonStaticAccessToStaticMethod:
case IProblem.NonStaticOrAlienTypeReceiver:
case IProblem.IndirectAccessToStaticField:
case IProblem.IndirectAccessToStaticMethod:
LocalCorrectionsSubProcessor.addCorrectAccessToStaticProposals(context, problem, proposals);
``` | 1.0 | Add quickfix to correct access to static elements - Handle the following cases in QuickFixProcessor:
```java
case IProblem.NonStaticAccessToStaticField:
case IProblem.NonStaticAccessToStaticMethod:
case IProblem.NonStaticOrAlienTypeReceiver:
case IProblem.IndirectAccessToStaticField:
case IProblem.IndirectAccessToStaticMethod:
LocalCorrectionsSubProcessor.addCorrectAccessToStaticProposals(context, problem, proposals);
``` | non_priority | add quickfix to correct access to static elements handle the following cases in quickfixprocessor java case iproblem nonstaticaccesstostaticfield case iproblem nonstaticaccesstostaticmethod case iproblem nonstaticoralientypereceiver case iproblem indirectaccesstostaticfield case iproblem indirectaccesstostaticmethod localcorrectionssubprocessor addcorrectaccesstostaticproposals context problem proposals | 0 |
91,311 | 26,358,073,382 | IssuesEvent | 2023-01-11 11:14:01 | vaticle/typedb | https://api.github.com/repos/vaticle/typedb | closed | Optimise web services repositories and hostings | type: feature domain: build | _This issue was originally posted by @haikalpribadi on 2018-09-08 16:31_.
Why: We have quite a few web services at this point, such as Grakn's website (grakn.ai), docs (dev.grakn.ai), discuss (discuss.grakn.ai), slack signup (grakn.ai/slack), CMS (cms.grakn.ai) and so on. It's getting hard to manage and them, especially as they continue to grow. Right now there's repo in GitHub and Heroku for Grakn's website and docs, and both are hosted on Heroku. Discuss and CMS is hosted on Digital Ocean.
How: We need to migrate all projects' source code to GitHub, and just have one repository each. We also need to migrate their hosting to all be on one platform, such Heroku.
| 1.0 | Optimise web services repositories and hostings - _This issue was originally posted by @haikalpribadi on 2018-09-08 16:31_.
Why: We have quite a few web services at this point, such as Grakn's website (grakn.ai), docs (dev.grakn.ai), discuss (discuss.grakn.ai), slack signup (grakn.ai/slack), CMS (cms.grakn.ai) and so on. It's getting hard to manage and them, especially as they continue to grow. Right now there's repo in GitHub and Heroku for Grakn's website and docs, and both are hosted on Heroku. Discuss and CMS is hosted on Digital Ocean.
How: We need to migrate all projects' source code to GitHub, and just have one repository each. We also need to migrate their hosting to all be on one platform, such Heroku.
| non_priority | optimise web services repositories and hostings this issue was originally posted by haikalpribadi on why we have quite a few web services at this point such as grakn s website grakn ai docs dev grakn ai discuss discuss grakn ai slack signup grakn ai slack cms cms grakn ai and so on it s getting hard to manage and them especially as they continue to grow right now there s repo in github and heroku for grakn s website and docs and both are hosted on heroku discuss and cms is hosted on digital ocean how we need to migrate all projects source code to github and just have one repository each we also need to migrate their hosting to all be on one platform such heroku | 0 |
323,320 | 23,941,388,338 | IssuesEvent | 2022-09-11 23:37:19 | saulpw/visidata | https://api.github.com/repos/saulpw/visidata | closed | [docs] -d is not a well-documented alias for --delimiter | help wanted documentation | Hi all,
Thanks for this, so far I am loving it. Would it be possible to find a way to open space-separated tsvs without using `vd -f tsv --delimiter=" " filename.extension`?
I was thinking either by parsing the delimiter automatically (e.g. finding the delimiter in the first x lines of code) or by creating a shorter flag for `--delimiter`?
Edit: premature sending | 1.0 | [docs] -d is not a well-documented alias for --delimiter - Hi all,
Thanks for this, so far I am loving it. Would it be possible to find a way to open space-separated tsvs without using `vd -f tsv --delimiter=" " filename.extension`?
I was thinking either by parsing the delimiter automatically (e.g. finding the delimiter in the first x lines of code) or by creating a shorter flag for `--delimiter`?
Edit: premature sending | non_priority | d is not a well documented alias for delimiter hi all thanks for this so far i am loving it would it be possible to find a way to open space separated tsvs without using vd f tsv delimiter filename extension i was thinking either by parsing the delimiter automatically e g finding the delimiter in the first x lines of code or by creating a shorter flag for delimiter edit premature sending | 0 |
445,404 | 31,236,973,353 | IssuesEvent | 2023-08-20 12:00:09 | yop-me/IoTProyecto | https://api.github.com/repos/yop-me/IoTProyecto | closed | Requerimientos no funcionales: | documentation | Implementar:
-Interfaz de usuario intuitiva
-Comunicacion estable
- Seguridad de datos
- Eficiencia energetica
- Flexibilidad y escalabilidad
| 1.0 | Requerimientos no funcionales: - Implementar:
-Interfaz de usuario intuitiva
-Comunicacion estable
- Seguridad de datos
- Eficiencia energetica
- Flexibilidad y escalabilidad
| non_priority | requerimientos no funcionales implementar interfaz de usuario intuitiva comunicacion estable seguridad de datos eficiencia energetica flexibilidad y escalabilidad | 0 |
4,489 | 5,111,835,982 | IssuesEvent | 2017-01-06 08:36:41 | phpmyadmin/phpmyadmin | https://api.github.com/repos/phpmyadmin/phpmyadmin | closed | Verify checksum after uploading | infrastructure | upload-release should verify the checksum of the uploaded file on disk matches the checksum generated by create-release.
| 1.0 | Verify checksum after uploading - upload-release should verify the checksum of the uploaded file on disk matches the checksum generated by create-release.
| non_priority | verify checksum after uploading upload release should verify the checksum of the uploaded file on disk matches the checksum generated by create release | 0 |
167,189 | 26,469,875,097 | IssuesEvent | 2023-01-17 05:59:09 | tijlleenders/ZinZen | https://api.github.com/repos/tijlleenders/ZinZen | closed | Design UX for drag and drop | design | How to change order of goals?
How to move goals around in the hierarchy? | 1.0 | Design UX for drag and drop - How to change order of goals?
How to move goals around in the hierarchy? | non_priority | design ux for drag and drop how to change order of goals how to move goals around in the hierarchy | 0 |
5,176 | 3,179,323,162 | IssuesEvent | 2015-09-25 00:03:21 | camalot/droidexplorer | https://api.github.com/repos/camalot/droidexplorer | closed | Auto Apply Update not working | bug CodePlex High | **This issue was imported from [CodePlex](http://de.codeplex.com/workitem/8457)**
**[camalot](http://www.codeplex.com/site/users/view/camalot)** wrote 2009-08-12 at 06:40
the auto apply does not work correctly, it needs to do the following commands to work
mkdir -p /cache/recovery/
echo 'boot-recovery ' >/cache/recovery/command
echo '--nandroid ' >> /cache/recovery/command
'--update_package=SDCARD:update.zip' >> /cache/recovery/command
reboot recovery
the --nandrod switch is if back up first.
**[camalot](http://www.codeplex.com/site/users/view/camalot)** wrote 2009-08-13 at 13:08
can not get to work with the --nandroid command in, works with out it
**[](http://www.codeplex.com/site/users/view/)** wrote 2009-08-13 at 16:08
**[](http://www.codeplex.com/site/users/view/)** wrote 2009-08-13 at 16:09
Associated with changeset 39812.
**[](http://www.codeplex.com/site/users/view/)** wrote 2013-02-21 at 19:42
**[](http://www.codeplex.com/site/users/view/)** wrote 2013-05-16 at 07:29
**[](http://www.codeplex.com/site/users/view/)** wrote 2013-05-16 at 07:29
**[](http://www.codeplex.com/site/users/view/)** wrote 2013-06-14 at 02:35
**[](http://www.codeplex.com/site/users/view/)** wrote 2013-08-25 at 01:18 | 1.0 | Auto Apply Update not working - **This issue was imported from [CodePlex](http://de.codeplex.com/workitem/8457)**
**[camalot](http://www.codeplex.com/site/users/view/camalot)** wrote 2009-08-12 at 06:40
the auto apply does not work correctly, it needs to do the following commands to work
mkdir -p /cache/recovery/
echo 'boot-recovery ' >/cache/recovery/command
echo '--nandroid ' >> /cache/recovery/command
'--update_package=SDCARD:update.zip' >> /cache/recovery/command
reboot recovery
the --nandrod switch is if back up first.
**[camalot](http://www.codeplex.com/site/users/view/camalot)** wrote 2009-08-13 at 13:08
can not get to work with the --nandroid command in, works with out it
**[](http://www.codeplex.com/site/users/view/)** wrote 2009-08-13 at 16:08
**[](http://www.codeplex.com/site/users/view/)** wrote 2009-08-13 at 16:09
Associated with changeset 39812.
**[](http://www.codeplex.com/site/users/view/)** wrote 2013-02-21 at 19:42
**[](http://www.codeplex.com/site/users/view/)** wrote 2013-05-16 at 07:29
**[](http://www.codeplex.com/site/users/view/)** wrote 2013-05-16 at 07:29
**[](http://www.codeplex.com/site/users/view/)** wrote 2013-06-14 at 02:35
**[](http://www.codeplex.com/site/users/view/)** wrote 2013-08-25 at 01:18 | non_priority | auto apply update not working this issue was imported from wrote at the auto apply does not work correctly it needs to do the following commands to work mkdir p cache recovery echo boot recovery cache recovery command echo nandroid cache recovery command update package sdcard update zip cache recovery command reboot recovery the nandrod switch is if back up first wrote at can not get to work with the nandroid command in works with out it wrote at wrote at associated with changeset wrote at wrote at wrote at wrote at wrote at | 0 |
1,657 | 10,542,530,407 | IssuesEvent | 2019-10-02 13:22:06 | elastic/apm-integration-testing | https://api.github.com/repos/elastic/apm-integration-testing | closed | apm-server + logstash + ILM | automation subtask | When using logstash to index apm-server output while ILM is enabled, this change is needed:
```patch
diff --git a/docker/logstash/pipeline/apm.conf b/docker/logstash/pipeline/apm.conf
index 1db7fdc..31fc1df 100644
--- a/docker/logstash/pipeline/apm.conf
+++ b/docker/logstash/pipeline/apm.conf
@@ -34,6 +34,6 @@ filter {
output {
elasticsearch {
hosts => ["elasticsearch:9200"]
- index => "%{[@metadata][beat]}-%{[@metadata][version]}%{[@metadata][index_suffix]}-%{+YYYY.MM.dd}"
+ index => "%{[@metadata][beat]}-%{[@metadata][version]}%{[@metadata][index_suffix]}"
}
}
```
it would also be nice to include `pipeline => "apm"` for versions that install that pipeline. | 1.0 | apm-server + logstash + ILM - When using logstash to index apm-server output while ILM is enabled, this change is needed:
```patch
diff --git a/docker/logstash/pipeline/apm.conf b/docker/logstash/pipeline/apm.conf
index 1db7fdc..31fc1df 100644
--- a/docker/logstash/pipeline/apm.conf
+++ b/docker/logstash/pipeline/apm.conf
@@ -34,6 +34,6 @@ filter {
output {
elasticsearch {
hosts => ["elasticsearch:9200"]
- index => "%{[@metadata][beat]}-%{[@metadata][version]}%{[@metadata][index_suffix]}-%{+YYYY.MM.dd}"
+ index => "%{[@metadata][beat]}-%{[@metadata][version]}%{[@metadata][index_suffix]}"
}
}
```
it would also be nice to include `pipeline => "apm"` for versions that install that pipeline. | non_priority | apm server logstash ilm when using logstash to index apm server output while ilm is enabled this change is needed patch diff git a docker logstash pipeline apm conf b docker logstash pipeline apm conf index a docker logstash pipeline apm conf b docker logstash pipeline apm conf filter output elasticsearch hosts index yyyy mm dd index it would also be nice to include pipeline apm for versions that install that pipeline | 0 |
207,611 | 23,464,064,193 | IssuesEvent | 2022-08-16 15:15:20 | elastic/cloudbeat | https://api.github.com/repos/elastic/cloudbeat | reopened | [BUG] Kibana - Findings flyout - some references links are broken | bug 8.5 candidate Team:Cloud Security Posture | **Describe the bug**
When testing some of the links in the rule `references` (under `General` tab), they reference to pages that are no longer exists.
**Preconditions**
Kibana environment with csp plugin enabled
Agent installed that generates findings
**To Reproduce**
Steps to reproduce the behavior:
1. Open findings for rule `Ensure that the --profiling argument is set to false (Automated)`
2. Click on `https://github.com/kubernetes/community/blob/master/contributors/devel/profiling.md`
**Expected behavior**
Opened page should be existing
**Screenshots 📸**
**Desktop (please complete the following information):**
- OS:
- Browser:
- Kibana Version: COMMIT: [df225b213b188c81888141cee2ec191424fc0649](https://github.com/elastic/kibana/commits/df225b213b188c81888141cee2ec191424fc0649)
- Endpoint Version:
- Other Version:
- Cloudbeat Version: COMMIT [7e1f1a135fbb3459151232dda34531527291776e](https://github.com/elastic/cloudbeat/commits/7e1f1a135fbb3459151232dda34531527291776e)
**Additional context**
| True | [BUG] Kibana - Findings flyout - some references links are broken - **Describe the bug**
When testing some of the links in the rule `references` (under `General` tab), they reference to pages that are no longer exists.
**Preconditions**
Kibana environment with csp plugin enabled
Agent installed that generates findings
**To Reproduce**
Steps to reproduce the behavior:
1. Open findings for rule `Ensure that the --profiling argument is set to false (Automated)`
2. Click on `https://github.com/kubernetes/community/blob/master/contributors/devel/profiling.md`
**Expected behavior**
Opened page should be existing
**Screenshots 📸**
**Desktop (please complete the following information):**
- OS:
- Browser:
- Kibana Version: COMMIT: [df225b213b188c81888141cee2ec191424fc0649](https://github.com/elastic/kibana/commits/df225b213b188c81888141cee2ec191424fc0649)
- Endpoint Version:
- Other Version:
- Cloudbeat Version: COMMIT [7e1f1a135fbb3459151232dda34531527291776e](https://github.com/elastic/cloudbeat/commits/7e1f1a135fbb3459151232dda34531527291776e)
**Additional context**
| non_priority | kibana findings flyout some references links are broken describe the bug when testing some of the links in the rule references under general tab they reference to pages that are no longer exists preconditions kibana environment with csp plugin enabled agent installed that generates findings to reproduce steps to reproduce the behavior open findings for rule ensure that the profiling argument is set to false automated click on expected behavior opened page should be existing screenshots 📸 desktop please complete the following information os browser kibana version commit endpoint version other version cloudbeat version commit additional context | 0 |
9,955 | 7,867,210,539 | IssuesEvent | 2018-06-23 05:19:02 | istio/old_issues_repo | https://api.github.com/repos/istio/old_issues_repo | closed | Istio Ingress TLS key management use ACM | area/networking area/security env/aws kind/enhancement | **Is this a BUG or FEATURE REQUEST?:**
FEATURE REQUEST
**Did you review https://istio.io/help/ and existing issues to identify if this is already solved or being worked on?**:
**Bug:**
N
**What Version of Istio and Kubernetes are you using, where did you get Istio from, Installation details**
```
istioctl version 0.7.1
kubectl version 1.10.1
```
**Is Istio Auth enabled or not ?**
Not
**What happened**:
I deploy kubernetes cluster to aws use kops. Istio deployed on this cluster. Now I config Istio Ingress allow HTTPS use TLS Key on Amazon Certificate Manager (ACM) following:
https://kubernetes.io/docs/concepts/services-networking/service/#ssl-support-on-aws
But Ingress service throw error file not found: /etc/istio/ingress-certs or /etc/certs
**What you expected to happen:**
We can apply [ssl-support-on-aws](https://kubernetes.io/docs/concepts/services-networking/service/#ssl-support-on-aws) to istio ingress service.
**Feature Request:**
Y
**Describe the feature:**
Istio Ingress service support Amazon Certificate Management
Reference:
https://medium.com/kokster/how-to-setup-nginx-ingress-controller-on-aws-clusters-7bd244278509
https://github.com/kubernetes/ingress-nginx/tree/master/docs/examples/tls-termination | True | Istio Ingress TLS key management use ACM - **Is this a BUG or FEATURE REQUEST?:**
FEATURE REQUEST
**Did you review https://istio.io/help/ and existing issues to identify if this is already solved or being worked on?**:
**Bug:**
N
**What Version of Istio and Kubernetes are you using, where did you get Istio from, Installation details**
```
istioctl version 0.7.1
kubectl version 1.10.1
```
**Is Istio Auth enabled or not ?**
Not
**What happened**:
I deploy kubernetes cluster to aws use kops. Istio deployed on this cluster. Now I config Istio Ingress allow HTTPS use TLS Key on Amazon Certificate Manager (ACM) following:
https://kubernetes.io/docs/concepts/services-networking/service/#ssl-support-on-aws
But Ingress service throw error file not found: /etc/istio/ingress-certs or /etc/certs
**What you expected to happen:**
We can apply [ssl-support-on-aws](https://kubernetes.io/docs/concepts/services-networking/service/#ssl-support-on-aws) to istio ingress service.
**Feature Request:**
Y
**Describe the feature:**
Istio Ingress service support Amazon Certificate Management
Reference:
https://medium.com/kokster/how-to-setup-nginx-ingress-controller-on-aws-clusters-7bd244278509
https://github.com/kubernetes/ingress-nginx/tree/master/docs/examples/tls-termination | non_priority | istio ingress tls key management use acm is this a bug or feature request feature request did you review and existing issues to identify if this is already solved or being worked on bug n what version of istio and kubernetes are you using where did you get istio from installation details istioctl version kubectl version is istio auth enabled or not not what happened i deploy kubernetes cluster to aws use kops istio deployed on this cluster now i config istio ingress allow https use tls key on amazon certificate manager acm following but ingress service throw error file not found etc istio ingress certs or etc certs what you expected to happen we can apply to istio ingress service feature request y describe the feature istio ingress service support amazon certificate management reference | 0 |
186,177 | 15,049,888,743 | IssuesEvent | 2021-02-03 12:07:33 | apache/buildstream | https://api.github.com/repos/apache/buildstream | closed | Re-think and document incremental workspaces better | documentation | [See original issue on GitLab](https://gitlab.com/BuildStream/buildstream/-/issues/694)
In GitLab by [[Gitlab user @tlater]](https://gitlab.com/tlater) on Oct 3, 2018, 13:58
## Background
[//]: # (Provide a background or the root/source that justifies this task or action.)
During the discussion of !812 we were reminded of an old feature that is very difficult to wrap your head around... Incremental workspaces!
In essence, there is some crafty code that revolves around trying to update timestamps where we technically have none. A more detailed description can be found [here](https://gitlab.com/BuildStream/buildstream/merge_requests/812#note_103125727).
In-code documentation for this is currently lackluster, and the comments should be updated to explain edge cases and our workarounds.
Since the addition of artifact cache cleanup and failed build caching, this feature may also have grown new, un-covered edge cases for which tests need to be written, and perhaps we need to re-think the feature altogether, since there may be nicer ways to implement this now.
## Task description
[//]: # (Short summary of the action to be executed)
* [ ] Document the incremental-build timestamping codepaths better
* [ ] Re-think these codepaths with cached failed builds in mind
* [ ] Write tests for edge cases introduced with cache cleanup
## Acceptance Criteria
[//]: # (Acceptance criteria should follow the S.M.A.R.T. principle https://en.wikipedia.org/wiki/SMART_criteria )
We should have a cleanly documented idea of how timestamps are handled with incremental builds and an implementation that takes into account failed build caching as well as artifact cache cleanup.
---- | 1.0 | Re-think and document incremental workspaces better - [See original issue on GitLab](https://gitlab.com/BuildStream/buildstream/-/issues/694)
In GitLab by [[Gitlab user @tlater]](https://gitlab.com/tlater) on Oct 3, 2018, 13:58
## Background
[//]: # (Provide a background or the root/source that justifies this task or action.)
During the discussion of !812 we were reminded of an old feature that is very difficult to wrap your head around... Incremental workspaces!
In essence, there is some crafty code that revolves around trying to update timestamps where we technically have none. A more detailed description can be found [here](https://gitlab.com/BuildStream/buildstream/merge_requests/812#note_103125727).
In-code documentation for this is currently lackluster, and the comments should be updated to explain edge cases and our workarounds.
Since the addition of artifact cache cleanup and failed build caching, this feature may also have grown new, un-covered edge cases for which tests need to be written, and perhaps we need to re-think the feature altogether, since there may be nicer ways to implement this now.
## Task description
[//]: # (Short summary of the action to be executed)
* [ ] Document the incremental-build timestamping codepaths better
* [ ] Re-think these codepaths with cached failed builds in mind
* [ ] Write tests for edge cases introduced with cache cleanup
## Acceptance Criteria
[//]: # (Acceptance criteria should follow the S.M.A.R.T. principle https://en.wikipedia.org/wiki/SMART_criteria )
We should have a cleanly documented idea of how timestamps are handled with incremental builds and an implementation that takes into account failed build caching as well as artifact cache cleanup.
---- | non_priority | re think and document incremental workspaces better in gitlab by on oct background provide a background or the root source that justifies this task or action during the discussion of we were reminded of an old feature that is very difficult to wrap your head around incremental workspaces in essence there is some crafty code that revolves around trying to update timestamps where we technically have none a more detailed description can be found in code documentation for this is currently lackluster and the comments should be updated to explain edge cases and our workarounds since the addition of artifact cache cleanup and failed build caching this feature may also have grown new un covered edge cases for which tests need to be written and perhaps we need to re think the feature altogether since there may be nicer ways to implement this now task description short summary of the action to be executed document the incremental build timestamping codepaths better re think these codepaths with cached failed builds in mind write tests for edge cases introduced with cache cleanup acceptance criteria acceptance criteria should follow the s m a r t principle we should have a cleanly documented idea of how timestamps are handled with incremental builds and an implementation that takes into account failed build caching as well as artifact cache cleanup | 0 |
40,737 | 5,258,770,802 | IssuesEvent | 2017-02-03 00:36:02 | core-wg/coap-tcp-tls | https://api.github.com/repos/core-wg/coap-tcp-tls | closed | Ping and Pong Messages: ... a single Pong message MUST be returned? | design signaling | In [Section 4.4 Ping and Pong Messages](https://tools.ietf.org/html/draft-ietf-core-coap-tcp-tls-05#section-4.4):
_Upon receipt of a Ping message, a single Pong message is returned with the identical token._
This should be _**MUST** be returned_ ?
| 1.0 | Ping and Pong Messages: ... a single Pong message MUST be returned? - In [Section 4.4 Ping and Pong Messages](https://tools.ietf.org/html/draft-ietf-core-coap-tcp-tls-05#section-4.4):
_Upon receipt of a Ping message, a single Pong message is returned with the identical token._
This should be _**MUST** be returned_ ?
| non_priority | ping and pong messages a single pong message must be returned in upon receipt of a ping message a single pong message is returned with the identical token this should be must be returned | 0 |
173,751 | 21,177,104,344 | IssuesEvent | 2022-04-08 01:57:21 | Thezone1975/Office-Add-in-NodeJS-SSO | https://api.github.com/repos/Thezone1975/Office-Add-in-NodeJS-SSO | opened | CVE-2021-44906 (High) detected in minimist-0.0.8.tgz, minimist-1.2.0.tgz | security vulnerability | ## CVE-2021-44906 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /Office-Add-in-NodeJS-SSO/Before/package.json</p>
<p>Path to vulnerable library: /Before/node_modules/minimist/package.json,/Before/node_modules/minimist/package.json,/Before/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- cpx-1.5.0.tgz (Root Library)
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /Office-Add-in-NodeJS-SSO/Completed Multitenant/package.json</p>
<p>Path to vulnerable library: /Before/node_modules/subarg/node_modules/minimist/package.json,/Before/node_modules/subarg/node_modules/minimist/package.json,/Before/node_modules/subarg/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- cpx-1.5.0.tgz (Root Library)
- chokidar-1.7.0.tgz
- fsevents-1.2.4.tgz
- node-pre-gyp-0.10.0.tgz
- rc-1.2.7.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/issues/164">https://github.com/substack/minimist/issues/164</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-44906 (High) detected in minimist-0.0.8.tgz, minimist-1.2.0.tgz - ## CVE-2021-44906 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /Office-Add-in-NodeJS-SSO/Before/package.json</p>
<p>Path to vulnerable library: /Before/node_modules/minimist/package.json,/Before/node_modules/minimist/package.json,/Before/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- cpx-1.5.0.tgz (Root Library)
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /Office-Add-in-NodeJS-SSO/Completed Multitenant/package.json</p>
<p>Path to vulnerable library: /Before/node_modules/subarg/node_modules/minimist/package.json,/Before/node_modules/subarg/node_modules/minimist/package.json,/Before/node_modules/subarg/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- cpx-1.5.0.tgz (Root Library)
- chokidar-1.7.0.tgz
- fsevents-1.2.4.tgz
- node-pre-gyp-0.10.0.tgz
- rc-1.2.7.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/issues/164">https://github.com/substack/minimist/issues/164</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in minimist tgz minimist tgz cve high severity vulnerability vulnerable libraries minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file office add in nodejs sso before package json path to vulnerable library before node modules minimist package json before node modules minimist package json before node modules minimist package json dependency hierarchy cpx tgz root library mkdirp tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file office add in nodejs sso completed multitenant package json path to vulnerable library before node modules subarg node modules minimist package json before node modules subarg node modules minimist package json before node modules subarg node modules minimist package json dependency hierarchy cpx tgz root library chokidar tgz fsevents tgz node pre gyp tgz rc tgz x minimist tgz vulnerable library vulnerability details minimist is vulnerable to prototype pollution via file index js function setkey lines publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist step up your open source security game with whitesource | 0 |
29,937 | 8,443,782,253 | IssuesEvent | 2018-10-18 16:28:48 | OpenFAST/openfast | https://api.github.com/repos/OpenFAST/openfast | closed | Build problems on Windows when downloading openfast/dev as a zip instead of a git clone | bug build-issues cmake visual-studio | I receive fatal build error:
Not a git repository (or any parent up to mount point /cygdrive/c)
Stopping at filesystem boundary (GIT_DISCOVERY_ACROSS_FILESYSTEM not set).
At this point I have not investigated any further. Should test a non-Windows cmake build under the same conditions: zip download instead of git clone | 1.0 | Build problems on Windows when downloading openfast/dev as a zip instead of a git clone - I receive fatal build error:
Not a git repository (or any parent up to mount point /cygdrive/c)
Stopping at filesystem boundary (GIT_DISCOVERY_ACROSS_FILESYSTEM not set).
At this point I have not investigated any further. Should test a non-Windows cmake build under the same conditions: zip download instead of git clone | non_priority | build problems on windows when downloading openfast dev as a zip instead of a git clone i receive fatal build error not a git repository or any parent up to mount point cygdrive c stopping at filesystem boundary git discovery across filesystem not set at this point i have not investigated any further should test a non windows cmake build under the same conditions zip download instead of git clone | 0 |
250,309 | 27,066,449,481 | IssuesEvent | 2023-02-14 01:04:23 | turkdevops/snyk | https://api.github.com/repos/turkdevops/snyk | opened | CVE-2022-44570 (High) detected in rack-1.6.4.gem | security vulnerability | ## CVE-2022-44570 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rack-1.6.4.gem</b></p></summary>
<p>Rack provides a minimal, modular and adaptable interface for developing
web applications in Ruby. By wrapping HTTP requests and responses in
the simplest way possible, it unifies and distills the API for web
servers, web frameworks, and software in between (the so-called
middleware) into a single method call.
Also see http://rack.github.io/.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rack-1.6.4.gem">https://rubygems.org/gems/rack-1.6.4.gem</a></p>
<p>
Dependency Hierarchy:
- actionpack-4.2.5.gem (Root Library)
- :x: **rack-1.6.4.gem** (Vulnerable Library)
<p>Found in base branch: <b>ALL_HANDS/major-secrets</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A denial of service vulnerability in the Range header parsing component of Rack >= 1.5.0. A Carefully crafted input can cause the Range header parsing component in Rack to take an unexpected amount of time, possibly resulting in a denial of service attack vector. Any applications that deal with Range requests (such as streaming applications, or applications that serve files) may be impacted.
<p>Publish Date: 2023-02-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-44570>CVE-2022-44570</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-65f5-mfpf-vfhj">https://github.com/advisories/GHSA-65f5-mfpf-vfhj</a></p>
<p>Release Date: 2023-02-09</p>
<p>Fix Resolution: rack - 2.0.9.2,2.1.4.2,2.2.6.2,3.0.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-44570 (High) detected in rack-1.6.4.gem - ## CVE-2022-44570 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rack-1.6.4.gem</b></p></summary>
<p>Rack provides a minimal, modular and adaptable interface for developing
web applications in Ruby. By wrapping HTTP requests and responses in
the simplest way possible, it unifies and distills the API for web
servers, web frameworks, and software in between (the so-called
middleware) into a single method call.
Also see http://rack.github.io/.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rack-1.6.4.gem">https://rubygems.org/gems/rack-1.6.4.gem</a></p>
<p>
Dependency Hierarchy:
- actionpack-4.2.5.gem (Root Library)
- :x: **rack-1.6.4.gem** (Vulnerable Library)
<p>Found in base branch: <b>ALL_HANDS/major-secrets</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A denial of service vulnerability in the Range header parsing component of Rack >= 1.5.0. A Carefully crafted input can cause the Range header parsing component in Rack to take an unexpected amount of time, possibly resulting in a denial of service attack vector. Any applications that deal with Range requests (such as streaming applications, or applications that serve files) may be impacted.
<p>Publish Date: 2023-02-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-44570>CVE-2022-44570</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-65f5-mfpf-vfhj">https://github.com/advisories/GHSA-65f5-mfpf-vfhj</a></p>
<p>Release Date: 2023-02-09</p>
<p>Fix Resolution: rack - 2.0.9.2,2.1.4.2,2.2.6.2,3.0.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in rack gem cve high severity vulnerability vulnerable library rack gem rack provides a minimal modular and adaptable interface for developing web applications in ruby by wrapping http requests and responses in the simplest way possible it unifies and distills the api for web servers web frameworks and software in between the so called middleware into a single method call also see library home page a href dependency hierarchy actionpack gem root library x rack gem vulnerable library found in base branch all hands major secrets vulnerability details a denial of service vulnerability in the range header parsing component of rack a carefully crafted input can cause the range header parsing component in rack to take an unexpected amount of time possibly resulting in a denial of service attack vector any applications that deal with range requests such as streaming applications or applications that serve files may be impacted publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rack step up your open source security game with mend | 0 |
145,355 | 11,686,440,188 | IssuesEvent | 2020-03-05 10:52:14 | renovatebot/renovate | https://api.github.com/repos/renovatebot/renovate | opened | Memory leak during tests | #tests fix ready | Successful tests often end with this warning: `Running coverage on untested files...A worker process has failed to exit gracefully and has been force exited. This is likely caused by tests leaking due to improper teardown. Try running with --runInBand --detectOpenHandles to find leaks.`
This is on OSX but may be platform-independent. | 1.0 | Memory leak during tests - Successful tests often end with this warning: `Running coverage on untested files...A worker process has failed to exit gracefully and has been force exited. This is likely caused by tests leaking due to improper teardown. Try running with --runInBand --detectOpenHandles to find leaks.`
This is on OSX but may be platform-independent. | non_priority | memory leak during tests successful tests often end with this warning running coverage on untested files a worker process has failed to exit gracefully and has been force exited this is likely caused by tests leaking due to improper teardown try running with runinband detectopenhandles to find leaks this is on osx but may be platform independent | 0 |
69,015 | 22,056,615,320 | IssuesEvent | 2022-05-30 13:26:15 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | opened | ClientMessage frame read for a message may be broken in case of large messages | Type: Defect All Languages Should Check to-jira | Please see [this](https://github.com/hazelcast/hazelcast/blob/v5.1.1/hazelcast/src/main/java/com/hazelcast/client/impl/protocol/ClientMessageReader.java#L68) line of code.
The ClientMessageReader is basically copying data from one buffer to another buffer.
The source buffer (src in the code) is bytes received directly from the client socket connection.
The destination buffer is an application byte[] , which is wrapped inside an object called ClientMessage.
(Its actually slight more complex ... ClientMessage has multiple buffers called Frames, and within ClientMessage there is a linked list of Frames, each Frame has its own byte[])
There is an important variable called readOffset; this denotes the offset in the current destination buffer where we should put the next set of bytes.
-1 is the initial state meaning no data has been copied yet. The reason that readOffset is a member variable is because the class is stateful and the main readFrom method in the class is called in a loop.
This is important to understand , so here is an example ... we might invoke the readFrom method with 25,000 bytes in the src buffer. Within the readFrom method, we might derive the overall expected length of the frame is 75,000 bytes. The code will still copy the available 25,000 bytes from the src into the destination buffer, and it will set the readOffset to 25,000. The method will then complete and return false (false == 'incomplete').
Then on the next iteration/call to readFrom , we might have 30,000 new bytes in the src. Again it will copy those bytes into the destination (starting at the readOffset 25,000), then it will bump the readOffset pointer forward to 55,000, and so on and so on ... until it receives the full frame of 75,000 bytes.
Once a frame is full (i.e. we have copied the number of bytes specified in the frame header) , the code will start populating a new frame.
Once a frame is full and it is flagged as IS_FINAL_FLAG = true .. that whole ClientMessage is complete, and the readFrom will return true .
Setup for error:
We have large messages being sent from client to server therefore they tend to span fairly large number of tcp packets.
We also have data being sent from cloud to onprem ... so sometimes those tcp packets can be a few micros apart.
This leads to plenty of occurrences where readFrom is invoked when the src buffer does not have the entire dataset (frame) available. And thus our larger messages are often built up iteratively as described above. That generally works well ... apart from 1 case ..
Sometimes when readFrom is called, the src buffer has the data needed to complete the destination message except the last few bytes of the final frame (5 bytes say).
So, we process as described above what we have, and create an almost complete ClientMessage in memory in ClientMessageReader. Then micros later the remaining data becomes available in the src buffer, and we can append that by another call to readFrom. So that is invoked .. but it hits this check ...
int remaining = src.remaining();
if (remaining < SIZE_OF_FRAME_LENGTH_AND_FLAGS) {
// we don't have even the frame length and flags ready
return false;
}
which won't read the src buffer if its size is less that 6 bytes.
So, then we can't complete the frame / message because the residual part is too small to pass through the above check.
The connection then stays in that state, until at some point later, something else is received in the src buffer (typically a hearbeat). At that point we get through this guard because the buffer exceeds the minimum size, and we can process the 5 bytes that have been sat there waiting (and the heartbeat).
I think the above check should only occur when we are at the beginning of frames i.e. just moved down to iinside the
if (readOffset == -1) {
block. | 1.0 | ClientMessage frame read for a message may be broken in case of large messages - Please see [this](https://github.com/hazelcast/hazelcast/blob/v5.1.1/hazelcast/src/main/java/com/hazelcast/client/impl/protocol/ClientMessageReader.java#L68) line of code.
The ClientMessageReader is basically copying data from one buffer to another buffer.
The source buffer (src in the code) is bytes received directly from the client socket connection.
The destination buffer is an application byte[] , which is wrapped inside an object called ClientMessage.
(Its actually slight more complex ... ClientMessage has multiple buffers called Frames, and within ClientMessage there is a linked list of Frames, each Frame has its own byte[])
There is an important variable called readOffset; this denotes the offset in the current destination buffer where we should put the next set of bytes.
-1 is the initial state meaning no data has been copied yet. The reason that readOffset is a member variable is because the class is stateful and the main readFrom method in the class is called in a loop.
This is important to understand , so here is an example ... we might invoke the readFrom method with 25,000 bytes in the src buffer. Within the readFrom method, we might derive the overall expected length of the frame is 75,000 bytes. The code will still copy the available 25,000 bytes from the src into the destination buffer, and it will set the readOffset to 25,000. The method will then complete and return false (false == 'incomplete').
Then on the next iteration/call to readFrom , we might have 30,000 new bytes in the src. Again it will copy those bytes into the destination (starting at the readOffset 25,000), then it will bump the readOffset pointer forward to 55,000, and so on and so on ... until it receives the full frame of 75,000 bytes.
Once a frame is full (i.e. we have copied the number of bytes specified in the frame header) , the code will start populating a new frame.
Once a frame is full and it is flagged as IS_FINAL_FLAG = true .. that whole ClientMessage is complete, and the readFrom will return true .
Setup for error:
We have large messages being sent from client to server therefore they tend to span fairly large number of tcp packets.
We also have data being sent from cloud to onprem ... so sometimes those tcp packets can be a few micros apart.
This leads to plenty of occurrences where readFrom is invoked when the src buffer does not have the entire dataset (frame) available. And thus our larger messages are often built up iteratively as described above. That generally works well ... apart from 1 case ..
Sometimes when readFrom is called, the src buffer has the data needed to complete the destination message except the last few bytes of the final frame (5 bytes say).
So, we process as described above what we have, and create an almost complete ClientMessage in memory in ClientMessageReader. Then micros later the remaining data becomes available in the src buffer, and we can append that by another call to readFrom. So that is invoked .. but it hits this check ...
int remaining = src.remaining();
if (remaining < SIZE_OF_FRAME_LENGTH_AND_FLAGS) {
// we don't have even the frame length and flags ready
return false;
}
which won't read the src buffer if its size is less that 6 bytes.
So, then we can't complete the frame / message because the residual part is too small to pass through the above check.
The connection then stays in that state, until at some point later, something else is received in the src buffer (typically a hearbeat). At that point we get through this guard because the buffer exceeds the minimum size, and we can process the 5 bytes that have been sat there waiting (and the heartbeat).
I think the above check should only occur when we are at the beginning of frames i.e. just moved down to iinside the
if (readOffset == -1) {
block. | non_priority | clientmessage frame read for a message may be broken in case of large messages please see line of code the clientmessagereader is basically copying data from one buffer to another buffer the source buffer src in the code is bytes received directly from the client socket connection the destination buffer is an application byte which is wrapped inside an object called clientmessage its actually slight more complex clientmessage has multiple buffers called frames and within clientmessage there is a linked list of frames each frame has its own byte there is an important variable called readoffset this denotes the offset in the current destination buffer where we should put the next set of bytes is the initial state meaning no data has been copied yet the reason that readoffset is a member variable is because the class is stateful and the main readfrom method in the class is called in a loop this is important to understand so here is an example we might invoke the readfrom method with bytes in the src buffer within the readfrom method we might derive the overall expected length of the frame is bytes the code will still copy the available bytes from the src into the destination buffer and it will set the readoffset to the method will then complete and return false false incomplete then on the next iteration call to readfrom we might have new bytes in the src again it will copy those bytes into the destination starting at the readoffset then it will bump the readoffset pointer forward to and so on and so on until it receives the full frame of bytes once a frame is full i e we have copied the number of bytes specified in the frame header the code will start populating a new frame once a frame is full and it is flagged as is final flag true that whole clientmessage is complete and the readfrom will return true setup for error we have large messages being sent from client to server therefore they tend to span fairly large number of tcp packets we also have data being sent from cloud to onprem so sometimes those tcp packets can be a few micros apart this leads to plenty of occurrences where readfrom is invoked when the src buffer does not have the entire dataset frame available and thus our larger messages are often built up iteratively as described above that generally works well apart from case sometimes when readfrom is called the src buffer has the data needed to complete the destination message except the last few bytes of the final frame bytes say so we process as described above what we have and create an almost complete clientmessage in memory in clientmessagereader then micros later the remaining data becomes available in the src buffer and we can append that by another call to readfrom so that is invoked but it hits this check int remaining src remaining if remaining size of frame length and flags we don t have even the frame length and flags ready return false which won t read the src buffer if its size is less that bytes so then we can t complete the frame message because the residual part is too small to pass through the above check the connection then stays in that state until at some point later something else is received in the src buffer typically a hearbeat at that point we get through this guard because the buffer exceeds the minimum size and we can process the bytes that have been sat there waiting and the heartbeat i think the above check should only occur when we are at the beginning of frames i e just moved down to iinside the if readoffset block | 0 |
41,077 | 21,467,350,999 | IssuesEvent | 2022-04-26 06:03:18 | nineya/halo-theme-dream | https://api.github.com/repos/nineya/halo-theme-dream | closed | feat:body滚动条优化 | performance | ### 你当前使用的 Halo 版本
1.4.8
### 你当前使用的 Dream 版本
2.0.0
### 描述一下此特性
body滚动条支持背景透明
### 附加信息
_No response_ | True | feat:body滚动条优化 - ### 你当前使用的 Halo 版本
1.4.8
### 你当前使用的 Dream 版本
2.0.0
### 描述一下此特性
body滚动条支持背景透明
### 附加信息
_No response_ | non_priority | feat body滚动条优化 你当前使用的 halo 版本 你当前使用的 dream 版本 描述一下此特性 body滚动条支持背景透明 附加信息 no response | 0 |
66,912 | 12,838,901,886 | IssuesEvent | 2020-07-07 18:19:08 | cosmos/cosmos-sdk | https://api.github.com/repos/cosmos/cosmos-sdk | closed | Common test harness code for IBC tests | code-hygiene help wanted meta-issue tests x/ibc | De-duplicate this code & put it in a central location that can be imported.
ToDos:
- [x] add `x/ibc/testing/` pkg which sends through messages to create/update client, create connections/channels #6356
- [x] remove testchain from channel keeper #6400
- [x] remove testchain from connection keeper
- [x] remove testchain from ibc/ante
- [ ] remove testchain from clients
cc @fedekunze | 1.0 | Common test harness code for IBC tests - De-duplicate this code & put it in a central location that can be imported.
ToDos:
- [x] add `x/ibc/testing/` pkg which sends through messages to create/update client, create connections/channels #6356
- [x] remove testchain from channel keeper #6400
- [x] remove testchain from connection keeper
- [x] remove testchain from ibc/ante
- [ ] remove testchain from clients
cc @fedekunze | non_priority | common test harness code for ibc tests de duplicate this code put it in a central location that can be imported todos add x ibc testing pkg which sends through messages to create update client create connections channels remove testchain from channel keeper remove testchain from connection keeper remove testchain from ibc ante remove testchain from clients cc fedekunze | 0 |
189,855 | 15,209,015,408 | IssuesEvent | 2021-02-17 04:12:56 | Neorobrooke/neorobrooke-s4 | https://api.github.com/repos/Neorobrooke/neorobrooke-s4 | closed | Définir la communication série | documentation | Définir le format du JSON pour la communication série. Déterminer si on prend une librairie JSON (par exemple, comme le projet S3) ou si on fait un parseur (long pour rien selon moi).
CRITÈRES:
- Format JSON défini dans un fichier, avec les commandes, valeurs possibles, type des valeurs
- librairie JSON choisie pour l'OpenCR
- librairie JSON choisie pour Python | 1.0 | Définir la communication série - Définir le format du JSON pour la communication série. Déterminer si on prend une librairie JSON (par exemple, comme le projet S3) ou si on fait un parseur (long pour rien selon moi).
CRITÈRES:
- Format JSON défini dans un fichier, avec les commandes, valeurs possibles, type des valeurs
- librairie JSON choisie pour l'OpenCR
- librairie JSON choisie pour Python | non_priority | définir la communication série définir le format du json pour la communication série déterminer si on prend une librairie json par exemple comme le projet ou si on fait un parseur long pour rien selon moi critères format json défini dans un fichier avec les commandes valeurs possibles type des valeurs librairie json choisie pour l opencr librairie json choisie pour python | 0 |
275,223 | 30,214,585,797 | IssuesEvent | 2023-07-05 14:47:44 | amaybaum-dev/EasyBuggy2 | https://api.github.com/repos/amaybaum-dev/EasyBuggy2 | opened | xalan-2.7.0.jar: 1 vulnerabilities (highest severity is: 7.3) non-reachable | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xalan-2.7.0.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/xalan-2.7.0.jar,/home/wss-scanner/.m2/repository/xalan/xalan/2.7.0/xalan-2.7.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/EasyBuggy2/commit/925e7b95b9f4d369198fa40e6b14392536bcb113">925e7b95b9f4d369198fa40e6b14392536bcb113</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (xalan version) | Remediation Available | Reachability |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- | --- |
| [CVE-2014-0107](https://www.mend.io/vulnerability-database/CVE-2014-0107) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.3 | xalan-2.7.0.jar | Direct | 2.7.2 | ✅|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaGreen.png' width=19 height=20>](## 'The vulnerability is non-reachable.')</a></p> |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaGreen.png' width=19 height=20> CVE-2014-0107</summary>
### Vulnerable Library - <b>xalan-2.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/xalan-2.7.0.jar,/home/wss-scanner/.m2/repository/xalan/xalan/2.7.0/xalan-2.7.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **xalan-2.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/EasyBuggy2/commit/925e7b95b9f4d369198fa40e6b14392536bcb113">925e7b95b9f4d369198fa40e6b14392536bcb113</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
<p>The vulnerable code is not reachable.</p>
</p>
<p></p>
### Vulnerability Details
<p>
The TransformerFactory in Apache Xalan-Java before 2.7.2 does not properly restrict access to certain properties when FEATURE_SECURE_PROCESSING is enabled, which allows remote attackers to bypass expected restrictions and load arbitrary classes or access external resources via a crafted (1) xalan:content-header, (2) xalan:entities, (3) xslt:content-header, or (4) xslt:entities property, or a Java property that is bound to the XSLT 1.0 system-property function.
<p>Publish Date: 2014-04-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0107>CVE-2014-0107</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107</a></p>
<p>Release Date: 2014-04-15</p>
<p>Fix Resolution: 2.7.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | xalan-2.7.0.jar: 1 vulnerabilities (highest severity is: 7.3) non-reachable - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xalan-2.7.0.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/xalan-2.7.0.jar,/home/wss-scanner/.m2/repository/xalan/xalan/2.7.0/xalan-2.7.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/EasyBuggy2/commit/925e7b95b9f4d369198fa40e6b14392536bcb113">925e7b95b9f4d369198fa40e6b14392536bcb113</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (xalan version) | Remediation Available | Reachability |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- | --- |
| [CVE-2014-0107](https://www.mend.io/vulnerability-database/CVE-2014-0107) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.3 | xalan-2.7.0.jar | Direct | 2.7.2 | ✅|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaGreen.png' width=19 height=20>](## 'The vulnerability is non-reachable.')</a></p> |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaGreen.png' width=19 height=20> CVE-2014-0107</summary>
### Vulnerable Library - <b>xalan-2.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/xalan-2.7.0.jar,/home/wss-scanner/.m2/repository/xalan/xalan/2.7.0/xalan-2.7.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **xalan-2.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/EasyBuggy2/commit/925e7b95b9f4d369198fa40e6b14392536bcb113">925e7b95b9f4d369198fa40e6b14392536bcb113</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
<p>The vulnerable code is not reachable.</p>
</p>
<p></p>
### Vulnerability Details
<p>
The TransformerFactory in Apache Xalan-Java before 2.7.2 does not properly restrict access to certain properties when FEATURE_SECURE_PROCESSING is enabled, which allows remote attackers to bypass expected restrictions and load arbitrary classes or access external resources via a crafted (1) xalan:content-header, (2) xalan:entities, (3) xslt:content-header, or (4) xslt:entities property, or a Java property that is bound to the XSLT 1.0 system-property function.
<p>Publish Date: 2014-04-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0107>CVE-2014-0107</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107</a></p>
<p>Release Date: 2014-04-15</p>
<p>Fix Resolution: 2.7.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | xalan jar vulnerabilities highest severity is non reachable vulnerable library xalan jar path to dependency file pom xml path to vulnerable library target easybuggy snapshot web inf lib xalan jar home wss scanner repository xalan xalan xalan jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in xalan version remediation available reachability high xalan jar direct the vulnerability is non reachable details cve vulnerable library xalan jar path to dependency file pom xml path to vulnerable library target easybuggy snapshot web inf lib xalan jar home wss scanner repository xalan xalan xalan jar dependency hierarchy x xalan jar vulnerable library found in head commit a href found in base branch master reachability analysis the vulnerable code is not reachable vulnerability details the transformerfactory in apache xalan java before does not properly restrict access to certain properties when feature secure processing is enabled which allows remote attackers to bypass expected restrictions and load arbitrary classes or access external resources via a crafted xalan content header xalan entities xslt content header or xslt entities property or a java property that is bound to the xslt system property function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.