Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3 values | title stringlengths 2 665 | labels stringlengths 4 554 | body stringlengths 3 235k | index stringclasses 6 values | text_combine stringlengths 96 235k | label stringclasses 2 values | text stringlengths 96 196k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
167,344 | 20,726,024,729 | IssuesEvent | 2022-03-14 02:03:40 | peterwkc85/Java_Jackson | https://api.github.com/repos/peterwkc85/Java_Jackson | opened | CVE-2019-14439 (High) detected in jackson-databind-2.2.3.jar | security vulnerability | ## CVE-2019-14439 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.2.3.jar</b></p></summary>
<p>A high-performance JSON processor (parser, generator).</p>
<p>Path to dependency file: /json-patch-master/json-patch-master/build.gradle</p>
<p>Path to vulnerable library: /json-patch-master/json-patch-master/build.gradle</p>
<p>
Dependency Hierarchy:
- jackson-coreutils-1.6.jar (Root Library)
- :x: **jackson-databind-2.2.3.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9.2. This occurs when Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the logback jar in the classpath.
<p>Publish Date: 2019-07-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14439>CVE-2019-14439</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: 2.9.9.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-14439 (High) detected in jackson-databind-2.2.3.jar - ## CVE-2019-14439 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.2.3.jar</b></p></summary>
<p>A high-performance JSON processor (parser, generator).</p>
<p>Path to dependency file: /json-patch-master/json-patch-master/build.gradle</p>
<p>Path to vulnerable library: /json-patch-master/json-patch-master/build.gradle</p>
<p>
Dependency Hierarchy:
- jackson-coreutils-1.6.jar (Root Library)
- :x: **jackson-databind-2.2.3.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9.2. This occurs when Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the logback jar in the classpath.
<p>Publish Date: 2019-07-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14439>CVE-2019-14439</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: 2.9.9.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar a high performance json processor parser generator path to dependency file json patch master json patch master build gradle path to vulnerable library json patch master json patch master build gradle dependency hierarchy jackson coreutils jar root library x jackson databind jar vulnerable library vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind x before this occurs when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the logback jar in the classpath publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
23,665 | 16,507,591,743 | IssuesEvent | 2021-05-25 21:27:48 | APSIMInitiative/ApsimX | https://api.github.com/repos/APSIMInitiative/ApsimX | closed | Experiment UI is slow to load with large number of simulations | bug interface/infrastructure | Clicking on an experiment node causes the UI to freeze until all simulations in the experiment are generated/loaded (~30 seconds for me in an experiment with ~40k sims). | 1.0 | Experiment UI is slow to load with large number of simulations - Clicking on an experiment node causes the UI to freeze until all simulations in the experiment are generated/loaded (~30 seconds for me in an experiment with ~40k sims). | infrastructure | experiment ui is slow to load with large number of simulations clicking on an experiment node causes the ui to freeze until all simulations in the experiment are generated loaded seconds for me in an experiment with sims | 1 |
14,880 | 11,212,181,594 | IssuesEvent | 2020-01-06 16:59:34 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | dev.azure "Tests" view is only available for signed users. | area-Infrastructure bug | Open https://dev.azure.com/dnceng/public/_build/results?buildId=469032&view=results
when you are signed with your Microsoft account, you will see:
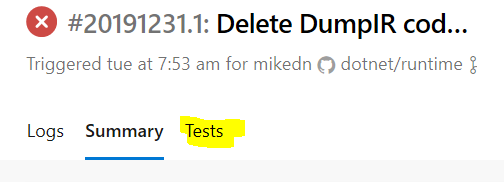
but if you are not signed you won't see "Tests":

it is not a desired behavior, because we want external contributors to be able to analyze failures in their PRs.
In the coreclr repo is was working fine, open https://dev.azure.com/dnceng/public/_build/results?buildId=425677&view=ms.vss-test-web.build-test-results-tab without signing in and you will see "Tests" there. | 1.0 | dev.azure "Tests" view is only available for signed users. - Open https://dev.azure.com/dnceng/public/_build/results?buildId=469032&view=results
when you are signed with your Microsoft account, you will see:
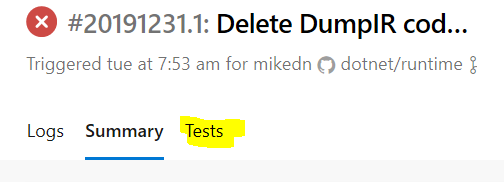
but if you are not signed you won't see "Tests":

it is not a desired behavior, because we want external contributors to be able to analyze failures in their PRs.
In the coreclr repo is was working fine, open https://dev.azure.com/dnceng/public/_build/results?buildId=425677&view=ms.vss-test-web.build-test-results-tab without signing in and you will see "Tests" there. | infrastructure | dev azure tests view is only available for signed users open when you are signed with your microsoft account you will see but if you are not signed you won t see tests it is not a desired behavior because we want external contributors to be able to analyze failures in their prs in the coreclr repo is was working fine open without signing in and you will see tests there | 1 |
100,768 | 21,511,903,167 | IssuesEvent | 2022-04-28 05:58:47 | samq-ghdemo/Java-Demo | https://api.github.com/repos/samq-ghdemo/Java-Demo | opened | Code Security Report: 16 high severity findings, 109 total findings | code security findings | # Code Security Report
**Latest Scan:** 2022-04-28 05:58am
**Total Findings:** 109
**Tested Project Files:** 102
**Detected Programming Languages:** 1
**Scan URL:** https://saas.whitesourcesoftware.com/sast/#/scans/100eea56-94d3-4e1e-acba-ce178c0e189d/details
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
## Language: Java
| Severity | CWE | Vulnerability Type | Count |
|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|SQL Injection|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Path/Directory Traversal|10|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-94](https://cwe.mitre.org/data/definitions/84.html)|Code Injection|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-611](https://cwe.mitre.org/data/definitions/611.html)|XML External Entity (XXE) Injection|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Server Side Request Forgery|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|Cross-Site Scripting|28|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-73](https://cwe.mitre.org/data/definitions/73.html)|File Manipulation|9|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-601](https://cwe.mitre.org/data/definitions/601.html)|Unvalidated/Open Redirect|17|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-113](https://cwe.mitre.org/data/definitions/113.html)|HTTP Header Injection|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-20](https://cwe.mitre.org/data/definitions/20.html)|Session Poisoning|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-117](https://cwe.mitre.org/data/definitions/117.html)|Log Forging|6|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-501](https://cwe.mitre.org/data/definitions/501.html)|Trust Boundary Violation|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-244](https://cwe.mitre.org/data/definitions/244.html)|Heap Inspection|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Error Messages Information Exposure|15|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|Weak Pseudo-Random|2|
### Details
> Partial details (48 findings) are displayed below due to a content size limitation in GitHub. To view information on the remaining findings, navigate to the [WhiteSource SAST Application](https://saas.whitesourcesoftware.com/sast/#/scans/100eea56-94d3-4e1e-acba-ce178c0e189d/details).
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>SQL Injection (CWE-89) : 3</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java:69</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L64-L69
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java:69</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L64-L69
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L39
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java:69</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L64-L69
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>Path/Directory Traversal (CWE-22) : 10</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java:127</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L122-L127
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L71
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L84
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L111
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L127
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java:133</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L128-L133
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L125
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L127
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L133
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java:110</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L105-L110
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L84
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L106
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L110
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java:84</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L79-L84
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L84
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java:114</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L109-L114
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L71
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L84
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L111
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L114
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java:46</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L41-L46
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L35
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L40
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L46
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java:135</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L130-L135
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L84
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L106
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L135
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java:53</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L48-L53
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L35
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L40
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L46
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L53
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java:196</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L191-L196
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L141
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L148
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L161
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L192
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L196
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java:84</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L79-L84
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L71
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L84
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>Code Injection (CWE-94) : 1</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java:65</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L60-L65
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L25
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L44
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L46
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L47
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L61
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L65
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>XML External Entity (XXE) Injection (CWE-611) : 1</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java:206</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L201-L206
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L141
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L148
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L161
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L192
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L196
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L206
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>Server Side Request Forgery (CWE-918) : 1</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java:31</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L26-L31
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L27
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L31
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20>Cross-Site Scripting (CWE-79) : 28</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L39
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L53
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L91
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L98
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L71
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L91
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L98
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/DefaultLoginServlet.java#L40
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/DefaultLoginServlet.java#L80
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L53
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/DBConnectionLeakServlet.java#L68
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/DBConnectionLeakServlet.java#L71
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/DBConnectionLeakServlet.java#L75
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/DBConnectionLeakServlet.java#L35
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/DBConnectionLeakServlet.java#L47
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L27
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L42
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L54
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/RoundOffErrorServlet.java#L22
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/RoundOffErrorServlet.java#L30
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/RoundOffErrorServlet.java#L43
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java:63</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L58-L63
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L62
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L63
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/IntegerOverflowServlet.java#L24
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/IntegerOverflowServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/IntegerOverflowServlet.java#L68
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/OGNLExpressionInjectionServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/OGNLExpressionInjectionServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/OGNLExpressionInjectionServlet.java#L35
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/OGNLExpressionInjectionServlet.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/OGNLExpressionInjectionServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/LossOfTrailingDigitsServlet.java#L22
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/LossOfTrailingDigitsServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/LossOfTrailingDigitsServlet.java#L47
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L128
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L132
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L61
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L128
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L132
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XSSServlet.java#L22
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XSSServlet.java#L38
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XSSServlet.java#L39
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XSSServlet.java#L48
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/performance/CreatingUnnecessaryObjectsServlet.java#L21
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/performance/CreatingUnnecessaryObjectsServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/performance/CreatingUnnecessaryObjectsServlet.java#L68
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/TruncationErrorServlet.java#L21
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/TruncationErrorServlet.java#L30
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/TruncationErrorServlet.java#L44
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/webapp/uid/serverinfo.jsp:24</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/webapp/uid/serverinfo.jsp#L19-L24
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L128
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L132
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L138
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L53
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20>File Manipulation (CWE-73) : 4</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java:38</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L33-L38
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L37
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L38
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java:33</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L28-L33
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L81
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L33
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java:38</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L33-L38
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L37
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L38
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java:142</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L137-L142
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L141
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L142
</details>
</details>
</details>
| 1.0 | Code Security Report: 16 high severity findings, 109 total findings - # Code Security Report
**Latest Scan:** 2022-04-28 05:58am
**Total Findings:** 109
**Tested Project Files:** 102
**Detected Programming Languages:** 1
**Scan URL:** https://saas.whitesourcesoftware.com/sast/#/scans/100eea56-94d3-4e1e-acba-ce178c0e189d/details
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
## Language: Java
| Severity | CWE | Vulnerability Type | Count |
|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|SQL Injection|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Path/Directory Traversal|10|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-94](https://cwe.mitre.org/data/definitions/84.html)|Code Injection|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-611](https://cwe.mitre.org/data/definitions/611.html)|XML External Entity (XXE) Injection|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Server Side Request Forgery|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|Cross-Site Scripting|28|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-73](https://cwe.mitre.org/data/definitions/73.html)|File Manipulation|9|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-601](https://cwe.mitre.org/data/definitions/601.html)|Unvalidated/Open Redirect|17|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-113](https://cwe.mitre.org/data/definitions/113.html)|HTTP Header Injection|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-20](https://cwe.mitre.org/data/definitions/20.html)|Session Poisoning|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-117](https://cwe.mitre.org/data/definitions/117.html)|Log Forging|6|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-501](https://cwe.mitre.org/data/definitions/501.html)|Trust Boundary Violation|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-244](https://cwe.mitre.org/data/definitions/244.html)|Heap Inspection|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Error Messages Information Exposure|15|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|Weak Pseudo-Random|2|
### Details
> Partial details (48 findings) are displayed below due to a content size limitation in GitHub. To view information on the remaining findings, navigate to the [WhiteSource SAST Application](https://saas.whitesourcesoftware.com/sast/#/scans/100eea56-94d3-4e1e-acba-ce178c0e189d/details).
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>SQL Injection (CWE-89) : 3</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java:69</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L64-L69
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java:69</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L64-L69
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L39
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java:69</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L64-L69
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>Path/Directory Traversal (CWE-22) : 10</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java:127</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L122-L127
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L71
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L84
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L111
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L127
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java:133</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L128-L133
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L125
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L127
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L133
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java:110</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L105-L110
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L84
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L106
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L110
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java:84</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L79-L84
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L84
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java:114</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L109-L114
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L71
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L84
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L111
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L114
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java:46</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L41-L46
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L35
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L40
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L46
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java:135</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L130-L135
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L84
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L106
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L135
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java:53</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L48-L53
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L35
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L40
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L46
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L53
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java:196</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L191-L196
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L141
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L148
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L161
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L192
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L196
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java:84</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L79-L84
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L71
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L84
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>Code Injection (CWE-94) : 1</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java:65</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L60-L65
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L25
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L44
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L46
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L47
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L61
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/CodeInjectionServlet.java#L65
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>XML External Entity (XXE) Injection (CWE-611) : 1</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java:206</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L201-L206
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L141
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L148
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L161
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L192
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L196
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XEEandXXEServlet.java#L206
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>Server Side Request Forgery (CWE-918) : 1</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java:31</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L26-L31
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L27
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L31
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20>Cross-Site Scripting (CWE-79) : 28</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L39
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L53
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L91
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L98
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L71
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L91
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedSizeUploadServlet.java#L98
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/DefaultLoginServlet.java#L40
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/DefaultLoginServlet.java#L80
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L53
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/DBConnectionLeakServlet.java#L68
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/DBConnectionLeakServlet.java#L71
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/DBConnectionLeakServlet.java#L75
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/DBConnectionLeakServlet.java#L35
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/DBConnectionLeakServlet.java#L47
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L27
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L42
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/NetworkSocketLeakServlet.java#L54
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/RoundOffErrorServlet.java#L22
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/RoundOffErrorServlet.java#L30
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/RoundOffErrorServlet.java#L43
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java:63</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L58-L63
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L62
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/NullByteInjectionServlet.java#L63
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/IntegerOverflowServlet.java#L24
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/IntegerOverflowServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/IntegerOverflowServlet.java#L68
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/OGNLExpressionInjectionServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/OGNLExpressionInjectionServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/OGNLExpressionInjectionServlet.java#L35
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/OGNLExpressionInjectionServlet.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/OGNLExpressionInjectionServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/LossOfTrailingDigitsServlet.java#L22
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/LossOfTrailingDigitsServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/LossOfTrailingDigitsServlet.java#L47
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L128
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L132
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L61
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L128
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L132
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XSSServlet.java#L22
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XSSServlet.java#L38
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XSSServlet.java#L39
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/XSSServlet.java#L48
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/performance/CreatingUnnecessaryObjectsServlet.java#L21
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/performance/CreatingUnnecessaryObjectsServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/performance/CreatingUnnecessaryObjectsServlet.java#L68
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/TruncationErrorServlet.java#L21
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/TruncationErrorServlet.java#L30
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/TruncationErrorServlet.java#L44
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/webapp/uid/serverinfo.jsp:24</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/webapp/uid/serverinfo.jsp#L19-L24
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L128
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L132
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L138
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L60
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/troubles/EndlessWaitingServlet.java#L70
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:82</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L77-L82
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L34
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L82
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java:94</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L89-L94
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L73
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L87
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L45
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/SQLInjectionServlet.java#L53
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L31
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/servlets/AbstractServlet.java#L94
</details>
</details>
</details>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20>File Manipulation (CWE-73) : 4</summary>
#### Findings
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java:38</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L33-L38
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L37
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L38
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java:33</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L28-L33
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L69
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L57
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L59
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L76
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/UnrestrictedExtensionUploadServlet.java#L81
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L28
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L33
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java:38</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L33-L38
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L37
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/core/utils/MultiPartFileUtils.java#L38
</details>
</details>
<details>
<summary>src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java:142</summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L137-L142
<details>
<summary> Trace </summary>
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L141
https://github.com/samq-ghdemo/Java-Demo/blob/7a57885245a9ed9010aa350c184246310435362e/src/main/java/org/t246osslab/easybuggy/vulnerabilities/MailHeaderInjectionServlet.java#L142
</details>
</details>
</details>
| non_infrastructure | code security report high severity findings total findings code security report latest scan total findings tested project files detected programming languages scan url check this box to manually trigger a scan language java severity cwe vulnerability type count high injection high traversal high injection high external entity xxe injection high side request forgery medium scripting medium manipulation medium redirect medium header injection medium poisoning low forging low boundary violation low inspection low messages information exposure low pseudo random details partial details findings are displayed below due to a content size limitation in github to view information on the remaining findings navigate to the sql injection cwe findings src main java org easybuggy vulnerabilities sqlinjectionservlet java trace src main java org easybuggy vulnerabilities sqlinjectionservlet java trace src main java org easybuggy vulnerabilities sqlinjectionservlet java trace path directory traversal cwe findings src main java org easybuggy vulnerabilities unrestrictedsizeuploadservlet java trace src main java org easybuggy vulnerabilities mailheaderinjectionservlet java trace src main java org easybuggy vulnerabilities unrestrictedextensionuploadservlet java trace src main java org easybuggy vulnerabilities unrestrictedextensionuploadservlet java trace src main java org easybuggy vulnerabilities unrestrictedsizeuploadservlet java trace src main java org easybuggy vulnerabilities nullbyteinjectionservlet java trace src main java org easybuggy vulnerabilities unrestrictedextensionuploadservlet java trace src main java org easybuggy vulnerabilities nullbyteinjectionservlet java trace src main java org easybuggy vulnerabilities xeeandxxeservlet java trace src main java org easybuggy vulnerabilities unrestrictedsizeuploadservlet java trace code injection cwe findings src main java org easybuggy vulnerabilities codeinjectionservlet java trace xml external entity xxe injection cwe findings src main java org easybuggy vulnerabilities xeeandxxeservlet java trace server side request forgery cwe findings src main java org easybuggy troubles networksocketleakservlet java trace cross site scripting cwe findings src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy vulnerabilities nullbyteinjectionservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main webapp uid serverinfo jsp src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace src main java org easybuggy core servlets abstractservlet java trace file manipulation cwe findings src main java org easybuggy core utils multipartfileutils java trace src main java org easybuggy core utils multipartfileutils java trace src main java org easybuggy core utils multipartfileutils java trace src main java org easybuggy vulnerabilities mailheaderinjectionservlet java trace | 0 |
22,301 | 15,090,827,007 | IssuesEvent | 2021-02-06 12:53:17 | celeritas-project/celeritas | https://api.github.com/repos/celeritas-project/celeritas | closed | Add tool to import preprocessed data from Geant4 | infrastructure material physics | Given a GDML input definition file and physics list (and possibly other problem input parameters like energy cuts), export a single preprocessed data file with:
- [x] Particle data (for particles in use based on the physics lists)
- [x] Physics tables (for needed particles and models based on the physics lists, and energy based on cutoffs, and materials in the input file)
- [x] Material definitions (for each material) *with names and corresponding index in the G4MaterialTable* (i.e. corresponding index in physics table)
- [x] Map of logical volume names to material names
See https://github.com/celeritas-project/celeritas-docs/blob/master/graphs/geant-exporter.pdf
- Required to populate physics tables (#3)
- Required to convert volume IDs from VecGeom to material IDs in physics tables
- Required to render materials instead of volumes (#22) | 1.0 | Add tool to import preprocessed data from Geant4 - Given a GDML input definition file and physics list (and possibly other problem input parameters like energy cuts), export a single preprocessed data file with:
- [x] Particle data (for particles in use based on the physics lists)
- [x] Physics tables (for needed particles and models based on the physics lists, and energy based on cutoffs, and materials in the input file)
- [x] Material definitions (for each material) *with names and corresponding index in the G4MaterialTable* (i.e. corresponding index in physics table)
- [x] Map of logical volume names to material names
See https://github.com/celeritas-project/celeritas-docs/blob/master/graphs/geant-exporter.pdf
- Required to populate physics tables (#3)
- Required to convert volume IDs from VecGeom to material IDs in physics tables
- Required to render materials instead of volumes (#22) | infrastructure | add tool to import preprocessed data from given a gdml input definition file and physics list and possibly other problem input parameters like energy cuts export a single preprocessed data file with particle data for particles in use based on the physics lists physics tables for needed particles and models based on the physics lists and energy based on cutoffs and materials in the input file material definitions for each material with names and corresponding index in the i e corresponding index in physics table map of logical volume names to material names see required to populate physics tables required to convert volume ids from vecgeom to material ids in physics tables required to render materials instead of volumes | 1 |
105,520 | 23,065,937,529 | IssuesEvent | 2022-07-25 13:56:17 | teresasee/gaigai-Planner | https://api.github.com/repos/teresasee/gaigai-Planner | closed | filter by distance | type.code | show error message if users filter
- before keying in locations
- everyone location is in?
- no one entered location, hence cannot filter by distance | 1.0 | filter by distance - show error message if users filter
- before keying in locations
- everyone location is in?
- no one entered location, hence cannot filter by distance | non_infrastructure | filter by distance show error message if users filter before keying in locations everyone location is in no one entered location hence cannot filter by distance | 0 |
20,996 | 14,273,241,014 | IssuesEvent | 2020-11-21 20:41:10 | SirJosh3917/smiley-face-game | https://api.github.com/repos/SirJosh3917/smiley-face-game | closed | Rename beta-<urls> to dev-<urls> | infrastructure | This also implies renaming the /beta/ endpoint to /dev/ for the api subdomain. | 1.0 | Rename beta-<urls> to dev-<urls> - This also implies renaming the /beta/ endpoint to /dev/ for the api subdomain. | infrastructure | rename beta to dev this also implies renaming the beta endpoint to dev for the api subdomain | 1 |
14,255 | 10,727,288,106 | IssuesEvent | 2019-10-28 11:19:21 | nest/nest-simulator | https://api.github.com/repos/nest/nest-simulator | closed | Update gcc version in Travis CI | C: Infrastructure I: No breaking change P: PR Created S: Low T: Maintenance | While finalising my pull request #1069, I ran into a compiler bug in gcc. When specialising a class template in a different file than the generic class definition, an issue with namespace resolution can arise; see https://gcc.gnu.org/bugzilla/show_bug.cgi?id=56480 for more detail.
This requires gcc to be updated to version >= 7 (current being 5.4), because that is where the bug was first fixed. We presently already have a Travis CI stage dedicated to gcc 8.
Are there any preferences (or objections) to specific versions? gcc 9 is out but still seems to require adding a new PPA. The easiest solution would be to use gcc 8 everywhere. This also cuts the Travis CI runtime down a bit (as gcc 8 will no longer need to be a distinct step). | 1.0 | Update gcc version in Travis CI - While finalising my pull request #1069, I ran into a compiler bug in gcc. When specialising a class template in a different file than the generic class definition, an issue with namespace resolution can arise; see https://gcc.gnu.org/bugzilla/show_bug.cgi?id=56480 for more detail.
This requires gcc to be updated to version >= 7 (current being 5.4), because that is where the bug was first fixed. We presently already have a Travis CI stage dedicated to gcc 8.
Are there any preferences (or objections) to specific versions? gcc 9 is out but still seems to require adding a new PPA. The easiest solution would be to use gcc 8 everywhere. This also cuts the Travis CI runtime down a bit (as gcc 8 will no longer need to be a distinct step). | infrastructure | update gcc version in travis ci while finalising my pull request i ran into a compiler bug in gcc when specialising a class template in a different file than the generic class definition an issue with namespace resolution can arise see for more detail this requires gcc to be updated to version current being because that is where the bug was first fixed we presently already have a travis ci stage dedicated to gcc are there any preferences or objections to specific versions gcc is out but still seems to require adding a new ppa the easiest solution would be to use gcc everywhere this also cuts the travis ci runtime down a bit as gcc will no longer need to be a distinct step | 1 |
1,113 | 3,039,581,475 | IssuesEvent | 2015-08-07 09:53:50 | fifthweek/fifthweek-web | https://api.github.com/repos/fifthweek/fifthweek-web | closed | Investigate failover for API | infrastructure question | We experienced our first hour of outage this morning, which means extra steps need to be taken to increase availability.
Hosting `fifthweek-web` on an edge network like AWS CloudFront will solve this problem for the front-end components.
However, we still need to consider failover options for `fifthweek-api`. | 1.0 | Investigate failover for API - We experienced our first hour of outage this morning, which means extra steps need to be taken to increase availability.
Hosting `fifthweek-web` on an edge network like AWS CloudFront will solve this problem for the front-end components.
However, we still need to consider failover options for `fifthweek-api`. | infrastructure | investigate failover for api we experienced our first hour of outage this morning which means extra steps need to be taken to increase availability hosting fifthweek web on an edge network like aws cloudfront will solve this problem for the front end components however we still need to consider failover options for fifthweek api | 1 |
39,765 | 5,245,632,590 | IssuesEvent | 2017-02-01 05:38:42 | RIOT-OS/RIOT | https://api.github.com/repos/RIOT-OS/RIOT | opened | tests/lwip target board for python test is hardcoded to native | bug tests | The python driven [test](https://github.com/RIOT-OS/RIOT/blob/master/tests/lwip/tests/01-run.py) does not run for boards other then `native`
But since the default `BOARD` for is set to `iotlab-m3` for this test, I guess they should be the primary target.
Setting the boards and ttys manually in the 01_test.py [1]
``` python
Board("iotlab-m3", None, "/dev/ttyUSBX")
```
forces the script to start with these parameters but it fails when trying to call reset [2] before going on with testing:
```
RIOT/tests/lwip$ make BOARD=iotlab-m3 test
./tests/01-run.py
Testing for (<Board 'iotlab-m3',port=None,serial='/dev/ttyUSB0'>, <Board 'iotlab-m3',port=None,serial='/dev/ttyUSB2'>):
Traceback (most recent call last):
File "./tests/01-run.py", line 270, in <module>
[test_ipv6_send, test_udpv6_send, test_dual_send])
File "./tests/01-run.py", line 172, in execute
board_group.reset()
File "./tests/01-run.py", line 153, in reset
board.reset(application, env)
File "./tests/01-run.py", line 124, in reset
self.reset_strategy.execute(application, env)
File "./tests/01-run.py", line 71, in execute
super(ResetStrategy, self).__run_make(application, ("reset",), env)
AttributeError: 'super' object has no attribute '_ResetStrategy__run_make'
```
[1] https://github.com/RIOT-OS/RIOT/blob/master/tests/lwip/tests/01-run.py#L264
[2] https://github.com/RIOT-OS/RIOT/blob/master/tests/lwip/tests/01-run.py#L168 | 1.0 | tests/lwip target board for python test is hardcoded to native - The python driven [test](https://github.com/RIOT-OS/RIOT/blob/master/tests/lwip/tests/01-run.py) does not run for boards other then `native`
But since the default `BOARD` for is set to `iotlab-m3` for this test, I guess they should be the primary target.
Setting the boards and ttys manually in the 01_test.py [1]
``` python
Board("iotlab-m3", None, "/dev/ttyUSBX")
```
forces the script to start with these parameters but it fails when trying to call reset [2] before going on with testing:
```
RIOT/tests/lwip$ make BOARD=iotlab-m3 test
./tests/01-run.py
Testing for (<Board 'iotlab-m3',port=None,serial='/dev/ttyUSB0'>, <Board 'iotlab-m3',port=None,serial='/dev/ttyUSB2'>):
Traceback (most recent call last):
File "./tests/01-run.py", line 270, in <module>
[test_ipv6_send, test_udpv6_send, test_dual_send])
File "./tests/01-run.py", line 172, in execute
board_group.reset()
File "./tests/01-run.py", line 153, in reset
board.reset(application, env)
File "./tests/01-run.py", line 124, in reset
self.reset_strategy.execute(application, env)
File "./tests/01-run.py", line 71, in execute
super(ResetStrategy, self).__run_make(application, ("reset",), env)
AttributeError: 'super' object has no attribute '_ResetStrategy__run_make'
```
[1] https://github.com/RIOT-OS/RIOT/blob/master/tests/lwip/tests/01-run.py#L264
[2] https://github.com/RIOT-OS/RIOT/blob/master/tests/lwip/tests/01-run.py#L168 | non_infrastructure | tests lwip target board for python test is hardcoded to native the python driven does not run for boards other then native but since the default board for is set to iotlab for this test i guess they should be the primary target setting the boards and ttys manually in the test py python board iotlab none dev ttyusbx forces the script to start with these parameters but it fails when trying to call reset before going on with testing riot tests lwip make board iotlab test tests run py testing for traceback most recent call last file tests run py line in file tests run py line in execute board group reset file tests run py line in reset board reset application env file tests run py line in reset self reset strategy execute application env file tests run py line in execute super resetstrategy self run make application reset env attributeerror super object has no attribute resetstrategy run make | 0 |
20,823 | 14,177,808,413 | IssuesEvent | 2020-11-13 03:07:31 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Publish Microsoft.CodeAnalysis* 3.8.0 on nuget.org | Area-Infrastructure | Visual Studio 16.8 includes version 3.800.20.51918 of Microsoft.CodeAnalysis*. The latest version on nuget.org is 3.800.20.51507 (3.8.0-5.final), which is a pre-release version.
When will 3.8.0 be released on nuget.org? | 1.0 | Publish Microsoft.CodeAnalysis* 3.8.0 on nuget.org - Visual Studio 16.8 includes version 3.800.20.51918 of Microsoft.CodeAnalysis*. The latest version on nuget.org is 3.800.20.51507 (3.8.0-5.final), which is a pre-release version.
When will 3.8.0 be released on nuget.org? | infrastructure | publish microsoft codeanalysis on nuget org visual studio includes version of microsoft codeanalysis the latest version on nuget org is final which is a pre release version when will be released on nuget org | 1 |
65,022 | 16,090,162,920 | IssuesEvent | 2021-04-26 15:45:11 | spack/spack | https://api.github.com/repos/spack/spack | closed | Installation issue: minizip | build-error | <!-- Thanks for taking the time to report this build failure. To proceed with the report please:
1. Title the issue "Installation issue: <name-of-the-package>".
2. Provide the information required below.
We encourage you to try, as much as possible, to reduce your problem to the minimal example that still reproduces the issue. That would help us a lot in fixing it quickly and effectively! -->
### Steps to reproduce the issue
<!-- Fill in the exact spec you are trying to build and the relevant part of the error message -->
```console
$ spack install minizip@1.2.11
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/libsigsegv-2.12-nsbpv73jzdyxtw7qbv6g2sm7tccmwlap
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/berkeley-db-18.1.40-65ijivepdgglg4vekox7be5wl5kc5xhn
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/pkgconf-1.7.3-xmb4xn3ydvx6h6msb3o72mdc4pkartim
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/zlib-1.2.11-j3zdmzqsbyenjda44kvkceohj352n5ga
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/m4-1.4.18-lkyedte2zhxyu7ymtl4e3tmo366msxv7
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/ncurses-6.2-w4lh3wlhlirrtgjnha3a36dmgrmxccsw
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/libtool-2.4.6-wzr7weu3opudp4nanuqjy6wyge34rkss
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/readline-8.0-ws5y6v6mlsddv3rpkkxthnldtpcztke6
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/gdbm-1.18.1-cfjfdq4w4fyuvw3dvjlapu33aaobphyb
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/perl-5.32.1-wzlagh6zqjlxtv25yfuolxwb3iamot3d
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/autoconf-2.69-eouez55w5z6jaeqvhlyulxxt2b4v257h
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/automake-1.16.3-a7grigcdhtuopsmpehljo3spff5lu24g
==> Installing minizip-1.2.11-hueak5llnqzl4gzwokqvcs2thrbngdaz
==> No binary for minizip-1.2.11-hueak5llnqzl4gzwokqvcs2thrbngdaz found: installing from source
==> Using cached archive: /opt/ohpc/pub/spack/var/spack/cache/_source-cache/archive/c3/c3e5e9fdd5004dcb542feda5ee4f0ff0744628baf8ed2dd5d66f8ca1197cb1a1.tar.gz
==> minizip: Executing phase: 'autoreconf'
==> minizip: Executing phase: 'configure'
==> minizip: Executing phase: 'build'
==> Error: ProcessError: Command exited with status 2:
'make' '-j4'
3 errors found in build log:
216 /bin/ld: ./../../libz.a(deflate.o): relocation R_X86_64_32S against hidden symbol `_length_code' can not be used when making a shared object
217 /bin/ld: ./../../libz.a(inflate.o): relocation R_X86_64_32S against hidden symbol `zcfree' can not be used when making a shared object
218 /bin/ld: ./../../libz.a(inftrees.o): relocation R_X86_64_32S against `.rodata' can not be used when making a shared object; recompile with -fPIC
219 /bin/ld: ./../../libz.a(trees.o): relocation R_X86_64_32S against hidden symbol `_length_code' can not be used when making a shared object
220 /bin/ld: ./../../libz.a(zutil.o): relocation R_X86_64_32 against `.rodata.str1.1' can not be used when making a shared object; recompile with -fPIC
221 /bin/ld: ./../../libz.a(inffast.o): relocation R_X86_64_32S against `.rodata.str1.1' can not be used when making a shared object; recompile with -fPIC
>> 222 /bin/ld: final link failed: Nonrepresentable section on output
>> 223 collect2: error: ld returned 1 exit status
>> 224 make: *** [libminizip.la] Error 1
See build log for details:
/tmp/spack/spack-stage/spack-stage-minizip-1.2.11-hueak5llnqzl4gzwokqvcs2thrbngdaz/spack-build-out.txt
...
```
### Information on your system
* **Spack:** 0.16.0-1183-9eb5c8f
* **Python:** 3.6.8
* **Platform:** linux-centos7-broadwell
* **Concretizer:** original
<!-- Please include the output of `spack debug report` -->
<!-- If you have any relevant configuration detail (custom `packages.yaml` or `modules.yaml`, etc.) you can add that here as well. -->
### Additional information
<!-- Please upload the following files. They should be present in the stage directory of the failing build. Also upload any config.log or similar file if one exists. -->
* [spack-build-out.txt](https://github.com/spack/spack/files/6377855/spack-build-out.txt)
* [spack-build-env.txt](https://github.com/spack/spack/files/6377857/spack-build-env.txt)
modules loaded:
```
Currently Loaded Modules:
1) autotools 2) prun/1.3 3) gnu8/8.3.0 4) openmpi3/3.1.4 5) ohpc 6) gcc-9.2.0-gcc-8.3.0-ebpgkrt 7) zlib-1.2.11-gcc-9.2.0-j3zdmzq
```
<!-- Some packages have maintainers who have volunteered to debug build failures. Run `spack maintainers <name-of-the-package>` and @mention them here if they exist. -->
@cessenat
### General information
<!-- These boxes can be checked by replacing [ ] with [x] or by clicking them after submitting the issue. -->
- [x] I have run `spack debug report` and reported the version of Spack/Python/Platform
- [x] I have run `spack maintainers <name-of-the-package>` and @mentioned any maintainers
- [x] I have uploaded the build log and environment files
- [x] I have searched the issues of this repo and believe this is not a duplicate
| 1.0 | Installation issue: minizip - <!-- Thanks for taking the time to report this build failure. To proceed with the report please:
1. Title the issue "Installation issue: <name-of-the-package>".
2. Provide the information required below.
We encourage you to try, as much as possible, to reduce your problem to the minimal example that still reproduces the issue. That would help us a lot in fixing it quickly and effectively! -->
### Steps to reproduce the issue
<!-- Fill in the exact spec you are trying to build and the relevant part of the error message -->
```console
$ spack install minizip@1.2.11
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/libsigsegv-2.12-nsbpv73jzdyxtw7qbv6g2sm7tccmwlap
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/berkeley-db-18.1.40-65ijivepdgglg4vekox7be5wl5kc5xhn
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/pkgconf-1.7.3-xmb4xn3ydvx6h6msb3o72mdc4pkartim
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/zlib-1.2.11-j3zdmzqsbyenjda44kvkceohj352n5ga
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/m4-1.4.18-lkyedte2zhxyu7ymtl4e3tmo366msxv7
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/ncurses-6.2-w4lh3wlhlirrtgjnha3a36dmgrmxccsw
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/libtool-2.4.6-wzr7weu3opudp4nanuqjy6wyge34rkss
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/readline-8.0-ws5y6v6mlsddv3rpkkxthnldtpcztke6
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/gdbm-1.18.1-cfjfdq4w4fyuvw3dvjlapu33aaobphyb
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/perl-5.32.1-wzlagh6zqjlxtv25yfuolxwb3iamot3d
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/autoconf-2.69-eouez55w5z6jaeqvhlyulxxt2b4v257h
[+] /opt/ohpc/pub/spack/opt/spack/linux-centos7-x86_64/gcc-9.2.0/automake-1.16.3-a7grigcdhtuopsmpehljo3spff5lu24g
==> Installing minizip-1.2.11-hueak5llnqzl4gzwokqvcs2thrbngdaz
==> No binary for minizip-1.2.11-hueak5llnqzl4gzwokqvcs2thrbngdaz found: installing from source
==> Using cached archive: /opt/ohpc/pub/spack/var/spack/cache/_source-cache/archive/c3/c3e5e9fdd5004dcb542feda5ee4f0ff0744628baf8ed2dd5d66f8ca1197cb1a1.tar.gz
==> minizip: Executing phase: 'autoreconf'
==> minizip: Executing phase: 'configure'
==> minizip: Executing phase: 'build'
==> Error: ProcessError: Command exited with status 2:
'make' '-j4'
3 errors found in build log:
216 /bin/ld: ./../../libz.a(deflate.o): relocation R_X86_64_32S against hidden symbol `_length_code' can not be used when making a shared object
217 /bin/ld: ./../../libz.a(inflate.o): relocation R_X86_64_32S against hidden symbol `zcfree' can not be used when making a shared object
218 /bin/ld: ./../../libz.a(inftrees.o): relocation R_X86_64_32S against `.rodata' can not be used when making a shared object; recompile with -fPIC
219 /bin/ld: ./../../libz.a(trees.o): relocation R_X86_64_32S against hidden symbol `_length_code' can not be used when making a shared object
220 /bin/ld: ./../../libz.a(zutil.o): relocation R_X86_64_32 against `.rodata.str1.1' can not be used when making a shared object; recompile with -fPIC
221 /bin/ld: ./../../libz.a(inffast.o): relocation R_X86_64_32S against `.rodata.str1.1' can not be used when making a shared object; recompile with -fPIC
>> 222 /bin/ld: final link failed: Nonrepresentable section on output
>> 223 collect2: error: ld returned 1 exit status
>> 224 make: *** [libminizip.la] Error 1
See build log for details:
/tmp/spack/spack-stage/spack-stage-minizip-1.2.11-hueak5llnqzl4gzwokqvcs2thrbngdaz/spack-build-out.txt
...
```
### Information on your system
* **Spack:** 0.16.0-1183-9eb5c8f
* **Python:** 3.6.8
* **Platform:** linux-centos7-broadwell
* **Concretizer:** original
<!-- Please include the output of `spack debug report` -->
<!-- If you have any relevant configuration detail (custom `packages.yaml` or `modules.yaml`, etc.) you can add that here as well. -->
### Additional information
<!-- Please upload the following files. They should be present in the stage directory of the failing build. Also upload any config.log or similar file if one exists. -->
* [spack-build-out.txt](https://github.com/spack/spack/files/6377855/spack-build-out.txt)
* [spack-build-env.txt](https://github.com/spack/spack/files/6377857/spack-build-env.txt)
modules loaded:
```
Currently Loaded Modules:
1) autotools 2) prun/1.3 3) gnu8/8.3.0 4) openmpi3/3.1.4 5) ohpc 6) gcc-9.2.0-gcc-8.3.0-ebpgkrt 7) zlib-1.2.11-gcc-9.2.0-j3zdmzq
```
<!-- Some packages have maintainers who have volunteered to debug build failures. Run `spack maintainers <name-of-the-package>` and @mention them here if they exist. -->
@cessenat
### General information
<!-- These boxes can be checked by replacing [ ] with [x] or by clicking them after submitting the issue. -->
- [x] I have run `spack debug report` and reported the version of Spack/Python/Platform
- [x] I have run `spack maintainers <name-of-the-package>` and @mentioned any maintainers
- [x] I have uploaded the build log and environment files
- [x] I have searched the issues of this repo and believe this is not a duplicate
| non_infrastructure | installation issue minizip thanks for taking the time to report this build failure to proceed with the report please title the issue installation issue provide the information required below we encourage you to try as much as possible to reduce your problem to the minimal example that still reproduces the issue that would help us a lot in fixing it quickly and effectively steps to reproduce the issue console spack install minizip opt ohpc pub spack opt spack linux gcc libsigsegv opt ohpc pub spack opt spack linux gcc berkeley db opt ohpc pub spack opt spack linux gcc pkgconf opt ohpc pub spack opt spack linux gcc zlib opt ohpc pub spack opt spack linux gcc opt ohpc pub spack opt spack linux gcc ncurses opt ohpc pub spack opt spack linux gcc libtool opt ohpc pub spack opt spack linux gcc readline opt ohpc pub spack opt spack linux gcc gdbm opt ohpc pub spack opt spack linux gcc perl opt ohpc pub spack opt spack linux gcc autoconf opt ohpc pub spack opt spack linux gcc automake installing minizip no binary for minizip found installing from source using cached archive opt ohpc pub spack var spack cache source cache archive tar gz minizip executing phase autoreconf minizip executing phase configure minizip executing phase build error processerror command exited with status make errors found in build log bin ld libz a deflate o relocation r against hidden symbol length code can not be used when making a shared object bin ld libz a inflate o relocation r against hidden symbol zcfree can not be used when making a shared object bin ld libz a inftrees o relocation r against rodata can not be used when making a shared object recompile with fpic bin ld libz a trees o relocation r against hidden symbol length code can not be used when making a shared object bin ld libz a zutil o relocation r against rodata can not be used when making a shared object recompile with fpic bin ld libz a inffast o relocation r against rodata can not be used when making a shared object recompile with fpic bin ld final link failed nonrepresentable section on output error ld returned exit status make error see build log for details tmp spack spack stage spack stage minizip spack build out txt information on your system spack python platform linux broadwell concretizer original additional information modules loaded currently loaded modules autotools prun ohpc gcc gcc ebpgkrt zlib gcc and mention them here if they exist cessenat general information i have run spack debug report and reported the version of spack python platform i have run spack maintainers and mentioned any maintainers i have uploaded the build log and environment files i have searched the issues of this repo and believe this is not a duplicate | 0 |
367,443 | 10,853,857,605 | IssuesEvent | 2019-11-13 15:26:34 | cheminfo/nmr-displayer | https://api.github.com/repos/cheminfo/nmr-displayer | closed | Implement phase correction | Priority | Implement a phase correction of real / imaginary spectrum

| 1.0 | Implement phase correction - Implement a phase correction of real / imaginary spectrum

| non_infrastructure | implement phase correction implement a phase correction of real imaginary spectrum | 0 |
5,397 | 5,635,371,138 | IssuesEvent | 2017-04-06 00:23:49 | zcash/zcash | https://api.github.com/repos/zcash/zcash | opened | Fix Buildbot hanging during performance benchmarks | bug dev infrastructure RPC interface testing | During the merge run-up to 1.0.8, the performance benchmarks on https://ci.z.cash/ started hanging during `solveequihash`. At the time I though this was just related to the various other ongoing Buildbot problems, but now I think it is a separate issue that appears to have been caused by merging #2176 ([before](https://ci.z.cash/builders/zcashperformance/builds/175), [after](https://ci.z.cash/builders/zcashperformance/builds/176)). My current thinking is that it is hanging because it's the first benchmark that amounts to an RPC call taking over half an hour to return (though I don't yet know whether that is a significant number - it could be anything over 10 minutes). | 1.0 | Fix Buildbot hanging during performance benchmarks - During the merge run-up to 1.0.8, the performance benchmarks on https://ci.z.cash/ started hanging during `solveequihash`. At the time I though this was just related to the various other ongoing Buildbot problems, but now I think it is a separate issue that appears to have been caused by merging #2176 ([before](https://ci.z.cash/builders/zcashperformance/builds/175), [after](https://ci.z.cash/builders/zcashperformance/builds/176)). My current thinking is that it is hanging because it's the first benchmark that amounts to an RPC call taking over half an hour to return (though I don't yet know whether that is a significant number - it could be anything over 10 minutes). | infrastructure | fix buildbot hanging during performance benchmarks during the merge run up to the performance benchmarks on started hanging during solveequihash at the time i though this was just related to the various other ongoing buildbot problems but now i think it is a separate issue that appears to have been caused by merging my current thinking is that it is hanging because it s the first benchmark that amounts to an rpc call taking over half an hour to return though i don t yet know whether that is a significant number it could be anything over minutes | 1 |
11,936 | 9,529,354,787 | IssuesEvent | 2019-04-29 11:02:03 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [Infra UI] Improve waffle map custom "group by" fields | :Infra UI :infrastructure [zube]: Done v7.1.0 | Currently, it is possible to enter a custom value in the "Group by" input field. Depending on what the user enters, it is possible that the documents that are returned don't contain the metrics selected for display in the "Metric" input field.
Example:
- User enters `service.type` as field to group by
- User wants to see a system metric on the waffle map squares (until https://github.com/elastic/kibana/issues/30197 is implemented that's all they can select anyway)
- The documents that contain a `service.type` other than "System" do not contain system metrics, so the waffle map is not displayed as expected
Proposed solution:
- Split the query performed for the waffle map in two steps:
- First, group by custom field to get a list of node ids
- Second, query by node ids to get metric values to display on the waffle map squares
Caveats:
- How can we deal gracefully with very large numbers of node ids? (Related: https://github.com/elastic/kibana/issues/27500 )
- Should the two-step query logic happen on the server or on the client?
- The first would mean that the waffle map view can stay mostly unchanged and the graphql endpoint serving waffle map data will perform several queries to elastic search
- The second would mean that the two-step query logic is reflected in the component / container structure and the graphql endpoints stay (relatively) simple
- How will all this affect performance?
| 1.0 | [Infra UI] Improve waffle map custom "group by" fields - Currently, it is possible to enter a custom value in the "Group by" input field. Depending on what the user enters, it is possible that the documents that are returned don't contain the metrics selected for display in the "Metric" input field.
Example:
- User enters `service.type` as field to group by
- User wants to see a system metric on the waffle map squares (until https://github.com/elastic/kibana/issues/30197 is implemented that's all they can select anyway)
- The documents that contain a `service.type` other than "System" do not contain system metrics, so the waffle map is not displayed as expected
Proposed solution:
- Split the query performed for the waffle map in two steps:
- First, group by custom field to get a list of node ids
- Second, query by node ids to get metric values to display on the waffle map squares
Caveats:
- How can we deal gracefully with very large numbers of node ids? (Related: https://github.com/elastic/kibana/issues/27500 )
- Should the two-step query logic happen on the server or on the client?
- The first would mean that the waffle map view can stay mostly unchanged and the graphql endpoint serving waffle map data will perform several queries to elastic search
- The second would mean that the two-step query logic is reflected in the component / container structure and the graphql endpoints stay (relatively) simple
- How will all this affect performance?
| infrastructure | improve waffle map custom group by fields currently it is possible to enter a custom value in the group by input field depending on what the user enters it is possible that the documents that are returned don t contain the metrics selected for display in the metric input field example user enters service type as field to group by user wants to see a system metric on the waffle map squares until is implemented that s all they can select anyway the documents that contain a service type other than system do not contain system metrics so the waffle map is not displayed as expected proposed solution split the query performed for the waffle map in two steps first group by custom field to get a list of node ids second query by node ids to get metric values to display on the waffle map squares caveats how can we deal gracefully with very large numbers of node ids related should the two step query logic happen on the server or on the client the first would mean that the waffle map view can stay mostly unchanged and the graphql endpoint serving waffle map data will perform several queries to elastic search the second would mean that the two step query logic is reflected in the component container structure and the graphql endpoints stay relatively simple how will all this affect performance | 1 |
1,452 | 3,218,613,945 | IssuesEvent | 2015-10-08 03:02:00 | WP-API/WP-API | https://api.github.com/repos/WP-API/WP-API | closed | Need to detect if the Infrastructure is being loaded by core in plugin | Infrastructure | Once https://core.trac.wordpress.org/ticket/33982 is merged, we will need to allow the plugin to be installed and use the core infrastructure instead. | 1.0 | Need to detect if the Infrastructure is being loaded by core in plugin - Once https://core.trac.wordpress.org/ticket/33982 is merged, we will need to allow the plugin to be installed and use the core infrastructure instead. | infrastructure | need to detect if the infrastructure is being loaded by core in plugin once is merged we will need to allow the plugin to be installed and use the core infrastructure instead | 1 |
17,591 | 12,475,767,125 | IssuesEvent | 2020-05-29 12:16:07 | hotosm/tasking-manager | https://api.github.com/repos/hotosm/tasking-manager | closed | Deployment of parallel instances | Component: Infrastructure Priority: Medium Status: Needs implementation Type: Enhancement | When a developer merges into `develop` and some other is deploying on `master` or `machine-learning` one build fails because of another one already running. It would be good to have builds working independently from the others. | 1.0 | Deployment of parallel instances - When a developer merges into `develop` and some other is deploying on `master` or `machine-learning` one build fails because of another one already running. It would be good to have builds working independently from the others. | infrastructure | deployment of parallel instances when a developer merges into develop and some other is deploying on master or machine learning one build fails because of another one already running it would be good to have builds working independently from the others | 1 |
30,867 | 25,127,153,857 | IssuesEvent | 2022-11-09 12:38:27 | GoogleForCreators/web-stories-wp | https://api.github.com/repos/GoogleForCreators/web-stories-wp | closed | Bump `Requires at least` value | Type: Infrastructure Pod: WP | <!-- NOTE: For help requests, support questions, or general feedback, please use the WordPress.org forums instead: https://wordpress.org/support/plugin/web-stories/ -->
## Task Description
<!-- A clear and concise description of what this task is about. -->
Bump to `Requires at least: 5.9` in `web-stories.php` and `readme.txt`
Also bump `WEBSTORIES_MINIMUM_WP_VERSION` in `web-stories.php` | 1.0 | Bump `Requires at least` value - <!-- NOTE: For help requests, support questions, or general feedback, please use the WordPress.org forums instead: https://wordpress.org/support/plugin/web-stories/ -->
## Task Description
<!-- A clear and concise description of what this task is about. -->
Bump to `Requires at least: 5.9` in `web-stories.php` and `readme.txt`
Also bump `WEBSTORIES_MINIMUM_WP_VERSION` in `web-stories.php` | infrastructure | bump requires at least value task description bump to requires at least in web stories php and readme txt also bump webstories minimum wp version in web stories php | 1 |
16,275 | 11,890,609,529 | IssuesEvent | 2020-03-28 19:08:44 | bootstrapworld/curriculum | https://api.github.com/repos/bootstrapworld/curriculum | opened | Pathways should specify front-matter and back-matter | Infrastructure | Every pathway's has a workbook. Every workbook has _at least_ a front and back cover, but also typically has an acknowledgements page, a contracts page, blank recipes, etc.
We currently abuse the lesson infrastructure to insert these pages, but really they belong at the pathway level.
- [ ] add `front-matter` and `back-matter` folders at the pathway top-level, which function the same way `pages` does at the lesson level (all files are 1 page, adocs and pdfs allowed, order specified by `workbook-pages.rkt`)
- [ ] Split existing cover page into single-page PDFs
- [ ] Move front and back pages from lessons to pathways | 1.0 | Pathways should specify front-matter and back-matter - Every pathway's has a workbook. Every workbook has _at least_ a front and back cover, but also typically has an acknowledgements page, a contracts page, blank recipes, etc.
We currently abuse the lesson infrastructure to insert these pages, but really they belong at the pathway level.
- [ ] add `front-matter` and `back-matter` folders at the pathway top-level, which function the same way `pages` does at the lesson level (all files are 1 page, adocs and pdfs allowed, order specified by `workbook-pages.rkt`)
- [ ] Split existing cover page into single-page PDFs
- [ ] Move front and back pages from lessons to pathways | infrastructure | pathways should specify front matter and back matter every pathway s has a workbook every workbook has at least a front and back cover but also typically has an acknowledgements page a contracts page blank recipes etc we currently abuse the lesson infrastructure to insert these pages but really they belong at the pathway level add front matter and back matter folders at the pathway top level which function the same way pages does at the lesson level all files are page adocs and pdfs allowed order specified by workbook pages rkt split existing cover page into single page pdfs move front and back pages from lessons to pathways | 1 |
211,780 | 16,458,079,536 | IssuesEvent | 2021-05-21 15:01:55 | gii-is-psg2/PSG2-2021-G5-52 | https://api.github.com/repos/gii-is-psg2/PSG2-2021-G5-52 | closed | Task A4.4.a | documentation | Describe the Petclinic maintenance service offered to potential clients. It must consider both corrective(incidents) and perfective (requests) with at least three diferentes levels of urgency and impact, | 1.0 | Task A4.4.a - Describe the Petclinic maintenance service offered to potential clients. It must consider both corrective(incidents) and perfective (requests) with at least three diferentes levels of urgency and impact, | non_infrastructure | task a describe the petclinic maintenance service offered to potential clients it must consider both corrective incidents and perfective requests with at least three diferentes levels of urgency and impact | 0 |
121,621 | 12,129,927,299 | IssuesEvent | 2020-04-22 23:58:52 | parse-community/parse-server | https://api.github.com/repos/parse-community/parse-server | closed | Questions about Direct Access Feature | documentation | ```
Enables direct access to parse-server, when using the JS SDK from the current node runtime.
All API calls from the JS-SDK are router through route matching (but /functions/:functionName)
Enable that feature by setting PARSE_SERVER_ENABLE_EXPERIMENTAL_DIRECT_ACCESS=1
```
So if I understand this correctly:
```
client -> request to Cloud Code Function (Server) -> calling object.save() in Cloud Code -> send http request to Server.
```
Enabling this feature
```
client -> request to Cloud Code Function (Server) -> calling object.save() in Cloud Code -> no additional request sent because both JS SDK and Server are on the same node runtime
```
Enabling this feature would make requests faster since there is one less request, should this be mainstreamed?
Should there be tests run against this?
Add to parse-server [config definitions](https://github.com/parse-community/parse-server/blob/master/src/Options/Definitions.js)?
We should add documentation to make more users aware of this feature
| 1.0 | Questions about Direct Access Feature - ```
Enables direct access to parse-server, when using the JS SDK from the current node runtime.
All API calls from the JS-SDK are router through route matching (but /functions/:functionName)
Enable that feature by setting PARSE_SERVER_ENABLE_EXPERIMENTAL_DIRECT_ACCESS=1
```
So if I understand this correctly:
```
client -> request to Cloud Code Function (Server) -> calling object.save() in Cloud Code -> send http request to Server.
```
Enabling this feature
```
client -> request to Cloud Code Function (Server) -> calling object.save() in Cloud Code -> no additional request sent because both JS SDK and Server are on the same node runtime
```
Enabling this feature would make requests faster since there is one less request, should this be mainstreamed?
Should there be tests run against this?
Add to parse-server [config definitions](https://github.com/parse-community/parse-server/blob/master/src/Options/Definitions.js)?
We should add documentation to make more users aware of this feature
| non_infrastructure | questions about direct access feature enables direct access to parse server when using the js sdk from the current node runtime all api calls from the js sdk are router through route matching but functions functionname enable that feature by setting parse server enable experimental direct access so if i understand this correctly client request to cloud code function server calling object save in cloud code send http request to server enabling this feature client request to cloud code function server calling object save in cloud code no additional request sent because both js sdk and server are on the same node runtime enabling this feature would make requests faster since there is one less request should this be mainstreamed should there be tests run against this add to parse server we should add documentation to make more users aware of this feature | 0 |
5,533 | 5,732,415,685 | IssuesEvent | 2017-04-21 14:48:28 | wellcometrust/platform-api | https://api.github.com/repos/wellcometrust/platform-api | closed | Speed up docker image creation | infrastructure | Currently our builds take a long time and most of that time is being spent in creating the docker image. We should investigate if we can optimize it so that it takes less time | 1.0 | Speed up docker image creation - Currently our builds take a long time and most of that time is being spent in creating the docker image. We should investigate if we can optimize it so that it takes less time | infrastructure | speed up docker image creation currently our builds take a long time and most of that time is being spent in creating the docker image we should investigate if we can optimize it so that it takes less time | 1 |
419,375 | 12,222,711,488 | IssuesEvent | 2020-05-02 14:27:44 | Gamebuster19901/ExciteBot | https://api.github.com/repos/Gamebuster19901/ExciteBot | opened | Ubuntu restarts the service if !stop is executed | Category - Bug Category - Conflict Priority - High ⇑ | When ran as a service, ubuntu will restart the service if the bot is `!stopped` | 1.0 | Ubuntu restarts the service if !stop is executed - When ran as a service, ubuntu will restart the service if the bot is `!stopped` | non_infrastructure | ubuntu restarts the service if stop is executed when ran as a service ubuntu will restart the service if the bot is stopped | 0 |
1,978 | 3,447,997,179 | IssuesEvent | 2015-12-16 04:41:10 | giridharmurali/EventDetection | https://api.github.com/repos/giridharmurali/EventDetection | opened | Encoding, Encryption and Compression of Recordings | enhancement infrastructure | 1. Select the best encoding to use while saving sequences
2. Compress the sequences to be saved
3. Encrypt the compressed recording
4. Decrypt the recording during playback (authenticate using user account) | 1.0 | Encoding, Encryption and Compression of Recordings - 1. Select the best encoding to use while saving sequences
2. Compress the sequences to be saved
3. Encrypt the compressed recording
4. Decrypt the recording during playback (authenticate using user account) | infrastructure | encoding encryption and compression of recordings select the best encoding to use while saving sequences compress the sequences to be saved encrypt the compressed recording decrypt the recording during playback authenticate using user account | 1 |
24,993 | 18,020,434,097 | IssuesEvent | 2021-09-16 18:41:07 | ProjectPythia/projectpythia.github.io | https://api.github.com/repos/ProjectPythia/projectpythia.github.io | opened | Direct users to Project Pythia filtered resource gallery from landing page | infrastructure | To be tackled once #156 is merged. | 1.0 | Direct users to Project Pythia filtered resource gallery from landing page - To be tackled once #156 is merged. | infrastructure | direct users to project pythia filtered resource gallery from landing page to be tackled once is merged | 1 |
469,728 | 13,524,326,571 | IssuesEvent | 2020-09-15 11:22:00 | input-output-hk/cardano-node | https://api.github.com/repos/input-output-hk/cardano-node | closed | [BUG] - setting "TurnOnLogging" to false gives an incorrect message | bug logging and monitoring priority low | *External* otherwise.
**Summary**
Setting "TurnOnLogging" to false cause cardano-node to give this message:
please turn on the following tracers in the configuration file:
TraceBlockFetchDecisions.
TraceChainDb
TraceForge
TraceMempool
Even when all the tracers above are set to true.
**Steps to reproduce**
Steps to reproduce the behavior:
1. Go to config.json
2. set "TurnOnLogging" to false
3. set all above options to true
4. start cardano-node
**Expected behavior**
should not see the message and node should start
**System info (please complete the following information):**
- Node version 1.18.0
**Screenshots and attachments**
<img width="706" alt="Screen Shot 2020-08-04 at 20 40 11" src="https://user-images.githubusercontent.com/67793497/89333208-f1e45b80-d694-11ea-9936-c578135cf40d.png">
| 1.0 | [BUG] - setting "TurnOnLogging" to false gives an incorrect message - *External* otherwise.
**Summary**
Setting "TurnOnLogging" to false cause cardano-node to give this message:
please turn on the following tracers in the configuration file:
TraceBlockFetchDecisions.
TraceChainDb
TraceForge
TraceMempool
Even when all the tracers above are set to true.
**Steps to reproduce**
Steps to reproduce the behavior:
1. Go to config.json
2. set "TurnOnLogging" to false
3. set all above options to true
4. start cardano-node
**Expected behavior**
should not see the message and node should start
**System info (please complete the following information):**
- Node version 1.18.0
**Screenshots and attachments**
<img width="706" alt="Screen Shot 2020-08-04 at 20 40 11" src="https://user-images.githubusercontent.com/67793497/89333208-f1e45b80-d694-11ea-9936-c578135cf40d.png">
| non_infrastructure | setting turnonlogging to false gives an incorrect message external otherwise summary setting turnonlogging to false cause cardano node to give this message please turn on the following tracers in the configuration file traceblockfetchdecisions tracechaindb traceforge tracemempool even when all the tracers above are set to true steps to reproduce steps to reproduce the behavior go to config json set turnonlogging to false set all above options to true start cardano node expected behavior should not see the message and node should start system info please complete the following information node version screenshots and attachments img width alt screen shot at src | 0 |
28,873 | 23,544,482,377 | IssuesEvent | 2022-08-20 22:58:48 | PetroFit/petrofit | https://api.github.com/repos/PetroFit/petrofit | closed | Frozen Environment Files | Installation Infrastructure | Add Conda and requirement files for older versions of the package with strict versions. | 1.0 | Frozen Environment Files - Add Conda and requirement files for older versions of the package with strict versions. | infrastructure | frozen environment files add conda and requirement files for older versions of the package with strict versions | 1 |
270,295 | 28,960,484,739 | IssuesEvent | 2023-05-10 01:45:59 | hshivhare67/kernel_v4.1.15 | https://api.github.com/repos/hshivhare67/kernel_v4.1.15 | reopened | CVE-2017-7895 (High) detected in linuxlinux-4.6, linuxlinux-4.6 | Mend: dependency security vulnerability | ## CVE-2017-7895 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The NFSv2 and NFSv3 server implementations in the Linux kernel through 4.10.13 lack certain checks for the end of a buffer, which allows remote attackers to trigger pointer-arithmetic errors or possibly have unspecified other impact via crafted requests, related to fs/nfsd/nfs3xdr.c and fs/nfsd/nfsxdr.c.
<p>Publish Date: 2017-04-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-7895>CVE-2017-7895</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-7895">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-7895</a></p>
<p>Release Date: 2017-04-28</p>
<p>Fix Resolution: v4.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-7895 (High) detected in linuxlinux-4.6, linuxlinux-4.6 - ## CVE-2017-7895 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The NFSv2 and NFSv3 server implementations in the Linux kernel through 4.10.13 lack certain checks for the end of a buffer, which allows remote attackers to trigger pointer-arithmetic errors or possibly have unspecified other impact via crafted requests, related to fs/nfsd/nfs3xdr.c and fs/nfsd/nfsxdr.c.
<p>Publish Date: 2017-04-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-7895>CVE-2017-7895</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-7895">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-7895</a></p>
<p>Release Date: 2017-04-28</p>
<p>Fix Resolution: v4.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve high detected in linuxlinux linuxlinux cve high severity vulnerability vulnerable libraries linuxlinux linuxlinux vulnerability details the and server implementations in the linux kernel through lack certain checks for the end of a buffer which allows remote attackers to trigger pointer arithmetic errors or possibly have unspecified other impact via crafted requests related to fs nfsd c and fs nfsd nfsxdr c publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
69,763 | 30,476,244,396 | IssuesEvent | 2023-07-17 16:43:25 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | It'd be very neat to have another example as well | service-fabric/svc triaged assigned-to-author doc-enhancement Pri2 | That's for the scenario where FindType="FindBySubjectName"
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: b416b884-a4c2-f64b-8646-c272d2f2aa39
* Version Independent ID: 6279b3df-55c3-32e6-bb21-33a4013edd29
* Content: [Configure secure Azure Service Fabric cluster connections - Azure Service Fabric](https://docs.microsoft.com/en-us/azure/service-fabric/service-fabric-visualstudio-configure-secure-connections?source=docs#feedback)
* Content Source: [articles/service-fabric/service-fabric-visualstudio-configure-secure-connections.md](https://github.com/Microsoft/azure-docs/blob/master/articles/service-fabric/service-fabric-visualstudio-configure-secure-connections.md)
* Service: **service-fabric**
* GitHub Login: @CawaMS
* Microsoft Alias: **cawa** | 1.0 | It'd be very neat to have another example as well - That's for the scenario where FindType="FindBySubjectName"
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: b416b884-a4c2-f64b-8646-c272d2f2aa39
* Version Independent ID: 6279b3df-55c3-32e6-bb21-33a4013edd29
* Content: [Configure secure Azure Service Fabric cluster connections - Azure Service Fabric](https://docs.microsoft.com/en-us/azure/service-fabric/service-fabric-visualstudio-configure-secure-connections?source=docs#feedback)
* Content Source: [articles/service-fabric/service-fabric-visualstudio-configure-secure-connections.md](https://github.com/Microsoft/azure-docs/blob/master/articles/service-fabric/service-fabric-visualstudio-configure-secure-connections.md)
* Service: **service-fabric**
* GitHub Login: @CawaMS
* Microsoft Alias: **cawa** | non_infrastructure | it d be very neat to have another example as well that s for the scenario where findtype findbysubjectname document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service service fabric github login cawams microsoft alias cawa | 0 |
219,356 | 24,474,073,953 | IssuesEvent | 2022-10-08 01:03:32 | Seagate/cortx-rgw | https://api.github.com/repos/Seagate/cortx-rgw | reopened | CVE-2022-34749 (High) detected in mistune-0.8.4-py2.py3-none-any.whl | security vulnerability | ## CVE-2022-34749 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mistune-0.8.4-py2.py3-none-any.whl</b></p></summary>
<p>The fastest markdown parser in pure Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/09/ec/4b43dae793655b7d8a25f76119624350b4d65eb663459eb9603d7f1f0345/mistune-0.8.4-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/09/ec/4b43dae793655b7d8a25f76119624350b4d65eb663459eb9603d7f1f0345/mistune-0.8.4-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /admin/doc-requirements.txt</p>
<p>Path to vulnerable library: /admin/doc-requirements.txt,/admin/doc-requirements.txt,/src/pybind/rados,/src/ceph-volume,/src/pybind/cephfs</p>
<p>
Dependency Hierarchy:
- :x: **mistune-0.8.4-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Seagate/cortx-rgw/commit/aa78617d024ccd26801e43c6980f939cf8bded5f">aa78617d024ccd26801e43c6980f939cf8bded5f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In mistune through 2.0.2, support of inline markup is implemented by using regular expressions that can involve a high amount of backtracking on certain edge cases. This behavior is commonly named catastrophic backtracking.
<p>Publish Date: 2022-07-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-34749>CVE-2022-34749</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-fw3v-x4f2-v673">https://github.com/advisories/GHSA-fw3v-x4f2-v673</a></p>
<p>Release Date: 2022-07-25</p>
<p>Fix Resolution: mistune - 2.0.3</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2022-34749 (High) detected in mistune-0.8.4-py2.py3-none-any.whl - ## CVE-2022-34749 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mistune-0.8.4-py2.py3-none-any.whl</b></p></summary>
<p>The fastest markdown parser in pure Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/09/ec/4b43dae793655b7d8a25f76119624350b4d65eb663459eb9603d7f1f0345/mistune-0.8.4-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/09/ec/4b43dae793655b7d8a25f76119624350b4d65eb663459eb9603d7f1f0345/mistune-0.8.4-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /admin/doc-requirements.txt</p>
<p>Path to vulnerable library: /admin/doc-requirements.txt,/admin/doc-requirements.txt,/src/pybind/rados,/src/ceph-volume,/src/pybind/cephfs</p>
<p>
Dependency Hierarchy:
- :x: **mistune-0.8.4-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Seagate/cortx-rgw/commit/aa78617d024ccd26801e43c6980f939cf8bded5f">aa78617d024ccd26801e43c6980f939cf8bded5f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In mistune through 2.0.2, support of inline markup is implemented by using regular expressions that can involve a high amount of backtracking on certain edge cases. This behavior is commonly named catastrophic backtracking.
<p>Publish Date: 2022-07-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-34749>CVE-2022-34749</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-fw3v-x4f2-v673">https://github.com/advisories/GHSA-fw3v-x4f2-v673</a></p>
<p>Release Date: 2022-07-25</p>
<p>Fix Resolution: mistune - 2.0.3</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_infrastructure | cve high detected in mistune none any whl cve high severity vulnerability vulnerable library mistune none any whl the fastest markdown parser in pure python library home page a href path to dependency file admin doc requirements txt path to vulnerable library admin doc requirements txt admin doc requirements txt src pybind rados src ceph volume src pybind cephfs dependency hierarchy x mistune none any whl vulnerable library found in head commit a href found in base branch main vulnerability details in mistune through support of inline markup is implemented by using regular expressions that can involve a high amount of backtracking on certain edge cases this behavior is commonly named catastrophic backtracking publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution mistune rescue worker helmet automatic remediation is available for this issue | 0 |
459,271 | 13,189,822,063 | IssuesEvent | 2020-08-13 09:06:53 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | closed | 0.9 time slept form localization | Category: Localization Priority: Low Status: Fixed | 1) i cannot see strings for hours and seconds
2) Time slept: exists on crowdin but not used
3) button should be longer\bigger.
| 1.0 | 0.9 time slept form localization - 1) i cannot see strings for hours and seconds
2) Time slept: exists on crowdin but not used
3) button should be longer\bigger.
| non_infrastructure | time slept form localization i cannot see strings for hours and seconds time slept exists on crowdin but not used button should be longer bigger | 0 |
67,334 | 20,961,606,126 | IssuesEvent | 2022-03-27 21:48:16 | abedmaatalla/sipdroid | https://api.github.com/repos/abedmaatalla/sipdroid | closed | Answer from lock screen fails | Priority-Medium Type-Defect auto-migrated | ```
Attempting to answer an incoming SIP call when the phone is on the lock screen
fails. This problem did not exist in an earlier version of sipdroid with my
earlier version of Android. I'm not sure exactly when the problem started.
Details: Running sipdroid 3.4 beta on Stock Android 4.1.2 on Samsung SGH-i747
(AT&T Galaxy S3)
Symptoms: Call comes in. Phone rings. Sometimes as you unlock the phone the
ringing stops, sometimes it does not. After the screen is unlocked, you are
unable to answer the call by sliding the icon up to the top. As you slide it
up, it comes back down without answering. If you answer from the menu, the call
is established, but you cannot hangup the call by sliding down, you need to use
the menu.
```
Original issue reported on code.google.com by `Dale.DeJ...@gmail.com` on 12 Dec 2013 at 12:24
| 1.0 | Answer from lock screen fails - ```
Attempting to answer an incoming SIP call when the phone is on the lock screen
fails. This problem did not exist in an earlier version of sipdroid with my
earlier version of Android. I'm not sure exactly when the problem started.
Details: Running sipdroid 3.4 beta on Stock Android 4.1.2 on Samsung SGH-i747
(AT&T Galaxy S3)
Symptoms: Call comes in. Phone rings. Sometimes as you unlock the phone the
ringing stops, sometimes it does not. After the screen is unlocked, you are
unable to answer the call by sliding the icon up to the top. As you slide it
up, it comes back down without answering. If you answer from the menu, the call
is established, but you cannot hangup the call by sliding down, you need to use
the menu.
```
Original issue reported on code.google.com by `Dale.DeJ...@gmail.com` on 12 Dec 2013 at 12:24
| non_infrastructure | answer from lock screen fails attempting to answer an incoming sip call when the phone is on the lock screen fails this problem did not exist in an earlier version of sipdroid with my earlier version of android i m not sure exactly when the problem started details running sipdroid beta on stock android on samsung sgh at t galaxy symptoms call comes in phone rings sometimes as you unlock the phone the ringing stops sometimes it does not after the screen is unlocked you are unable to answer the call by sliding the icon up to the top as you slide it up it comes back down without answering if you answer from the menu the call is established but you cannot hangup the call by sliding down you need to use the menu original issue reported on code google com by dale dej gmail com on dec at | 0 |
18,126 | 12,798,429,513 | IssuesEvent | 2020-07-02 13:55:07 | IMAGINE-Consortium/imagine | https://api.github.com/repos/IMAGINE-Consortium/imagine | closed | icy decorator - remove it? | infrastructure | The `@icy` decorator prevents new attributes to be added to an object/class. While this may prevent some specific types of error (e.g. typos in attributes name), it makes the code less modular (as it prevents one from adding extra structures to derived classes).
Is there any strong argument for keeping the `@icy` anywhere in the code? | 1.0 | icy decorator - remove it? - The `@icy` decorator prevents new attributes to be added to an object/class. While this may prevent some specific types of error (e.g. typos in attributes name), it makes the code less modular (as it prevents one from adding extra structures to derived classes).
Is there any strong argument for keeping the `@icy` anywhere in the code? | infrastructure | icy decorator remove it the icy decorator prevents new attributes to be added to an object class while this may prevent some specific types of error e g typos in attributes name it makes the code less modular as it prevents one from adding extra structures to derived classes is there any strong argument for keeping the icy anywhere in the code | 1 |
45,241 | 9,696,740,758 | IssuesEvent | 2019-05-25 10:30:29 | AdAway/AdAway | https://api.github.com/repos/AdAway/AdAway | closed | ROM upgrades assumes disabled, does not update | Priority-Medium bug imported-from-googlecode | _Original author: khayt...@gmail.com (November 11, 2012 23:17:49)_
<b>What steps will reproduce the problem?</b>
1. Set app to auto update
2. Remove the hosts file
3. Note that app shows disabled
<b>What is the expected output? What do you see instead?</b>
I would prefer the app instead decide in some other manner if it should be disabled and instead when updating the ROM (which formats /system) it automatically updates at its normal time.
<b>Please enable Debug Logging in preferences of AdAway, install aLogcat and</b>
<b>save a logfile while reproducing the problem. The logfile can be attached</b>
<b>to this issue.</b>
<b>What version of AdAway are you using? What Android version? What custom</b>
<b>rom?</b>
Latest, 1.37.
<b>Please provide any additional information below.</b>
_Original issue: http://code.google.com/p/ad-away/issues/detail?id=341_
| 1.0 | ROM upgrades assumes disabled, does not update - _Original author: khayt...@gmail.com (November 11, 2012 23:17:49)_
<b>What steps will reproduce the problem?</b>
1. Set app to auto update
2. Remove the hosts file
3. Note that app shows disabled
<b>What is the expected output? What do you see instead?</b>
I would prefer the app instead decide in some other manner if it should be disabled and instead when updating the ROM (which formats /system) it automatically updates at its normal time.
<b>Please enable Debug Logging in preferences of AdAway, install aLogcat and</b>
<b>save a logfile while reproducing the problem. The logfile can be attached</b>
<b>to this issue.</b>
<b>What version of AdAway are you using? What Android version? What custom</b>
<b>rom?</b>
Latest, 1.37.
<b>Please provide any additional information below.</b>
_Original issue: http://code.google.com/p/ad-away/issues/detail?id=341_
| non_infrastructure | rom upgrades assumes disabled does not update original author khayt gmail com november what steps will reproduce the problem set app to auto update remove the hosts file note that app shows disabled what is the expected output what do you see instead i would prefer the app instead decide in some other manner if it should be disabled and instead when updating the rom which formats system it automatically updates at its normal time please enable debug logging in preferences of adaway install alogcat and save a logfile while reproducing the problem the logfile can be attached to this issue what version of adaway are you using what android version what custom rom latest please provide any additional information below original issue | 0 |
19,143 | 13,189,628,244 | IssuesEvent | 2020-08-13 08:47:02 | containous/maesh | https://api.github.com/repos/containous/maesh | opened | Update to Go 1.15 | area/infrastructure kind/enhancement | ## Feature Request
### Proposal
Go 1.15 is officially released: https://blog.golang.org/go1.15
Once the CI has it enabled, we should update: https://docs.semaphoreci.com/ci-cd-environment/ubuntu-18.04-image/#go
There are no specific issues at the moment, so it's not a priority. | 1.0 | Update to Go 1.15 - ## Feature Request
### Proposal
Go 1.15 is officially released: https://blog.golang.org/go1.15
Once the CI has it enabled, we should update: https://docs.semaphoreci.com/ci-cd-environment/ubuntu-18.04-image/#go
There are no specific issues at the moment, so it's not a priority. | infrastructure | update to go feature request proposal go is officially released once the ci has it enabled we should update there are no specific issues at the moment so it s not a priority | 1 |
17,841 | 12,373,785,912 | IssuesEvent | 2020-05-18 23:31:28 | jstanden/cerb | https://api.github.com/repos/jstanden/cerb | opened | [Plugins/Twitter] Verify the character count feature in tweets | usability | There appears to be a discrepancy between how Twitter counts characters and the Cerb plugin does. | True | [Plugins/Twitter] Verify the character count feature in tweets - There appears to be a discrepancy between how Twitter counts characters and the Cerb plugin does. | non_infrastructure | verify the character count feature in tweets there appears to be a discrepancy between how twitter counts characters and the cerb plugin does | 0 |
26,719 | 20,603,436,285 | IssuesEvent | 2022-03-06 16:19:11 | GMLC-TDC/HELICS | https://api.github.com/repos/GMLC-TDC/HELICS | closed | Update Windows versions used for CI builds for upcoming vm image deprecation | infrastructure/ci | As part of [recently announced image deprecation for Azure Pipelines](https://devblogs.microsoft.com/devops/hosted-pipelines-image-deprecation/), the Windows jobs need updating to use a newer image by March 2022.
Update the [Windows jobs on Azure Pipelines](https://github.com/GMLC-TDC/HELICS/blob/main/.ci/azure-pipelines.yml#L91)
- Change the `VS2017-32bit` and `VS2017-64bit` jobs to run on VS2019
- Change the `VS2019-64bit` job to run on VS2022
- Update the [build requirements for Windows on the installation docs page](https://docs.helics.org/en/latest/user-guide/installation/windows.html)
Update the [Windows release build jobs on GitHub Actions](https://github.com/GMLC-TDC/HELICS/blob/main/.github/workflows/release-build.yml)
- Change builds using `windows-2016` to `windows-2019`
- Change builds using `windows-2019` to `windows-2022` | 1.0 | Update Windows versions used for CI builds for upcoming vm image deprecation - As part of [recently announced image deprecation for Azure Pipelines](https://devblogs.microsoft.com/devops/hosted-pipelines-image-deprecation/), the Windows jobs need updating to use a newer image by March 2022.
Update the [Windows jobs on Azure Pipelines](https://github.com/GMLC-TDC/HELICS/blob/main/.ci/azure-pipelines.yml#L91)
- Change the `VS2017-32bit` and `VS2017-64bit` jobs to run on VS2019
- Change the `VS2019-64bit` job to run on VS2022
- Update the [build requirements for Windows on the installation docs page](https://docs.helics.org/en/latest/user-guide/installation/windows.html)
Update the [Windows release build jobs on GitHub Actions](https://github.com/GMLC-TDC/HELICS/blob/main/.github/workflows/release-build.yml)
- Change builds using `windows-2016` to `windows-2019`
- Change builds using `windows-2019` to `windows-2022` | infrastructure | update windows versions used for ci builds for upcoming vm image deprecation as part of the windows jobs need updating to use a newer image by march update the change the and jobs to run on change the job to run on update the update the change builds using windows to windows change builds using windows to windows | 1 |
29,352 | 23,936,015,444 | IssuesEvent | 2022-09-11 08:31:01 | treeverse/lakeFS | https://api.github.com/repos/treeverse/lakeFS | closed | Docker image should include updated ca-certificates | infrastructure team/cloud-native | - lakeFS and lakeFS should include updated ca-certificates
- update-ca-certificates should be available in order to update more certificates by the user without additional packages | 1.0 | Docker image should include updated ca-certificates - - lakeFS and lakeFS should include updated ca-certificates
- update-ca-certificates should be available in order to update more certificates by the user without additional packages | infrastructure | docker image should include updated ca certificates lakefs and lakefs should include updated ca certificates update ca certificates should be available in order to update more certificates by the user without additional packages | 1 |
21,418 | 14,547,172,993 | IssuesEvent | 2020-12-15 22:28:48 | robotology/QA | https://api.github.com/repos/robotology/QA | closed | New GUI ethLoader | firmware infrastructure | Hi,
I wanted to update the robot, and as I've understood from issues #134 and #135, there is a new gui for the `ethLoader`, and all the updated instructions are referred to the new gui.
However, even if I updated everything, I still see the old gui; therefore, is there any option or so that I had to activate to see the new gui?
(I updated the firmware anyway with the old one, but for future and also students it would be better to have the one that matches with the instructions).
Thanks!
| 1.0 | New GUI ethLoader - Hi,
I wanted to update the robot, and as I've understood from issues #134 and #135, there is a new gui for the `ethLoader`, and all the updated instructions are referred to the new gui.
However, even if I updated everything, I still see the old gui; therefore, is there any option or so that I had to activate to see the new gui?
(I updated the firmware anyway with the old one, but for future and also students it would be better to have the one that matches with the instructions).
Thanks!
| infrastructure | new gui ethloader hi i wanted to update the robot and as i ve understood from issues and there is a new gui for the ethloader and all the updated instructions are referred to the new gui however even if i updated everything i still see the old gui therefore is there any option or so that i had to activate to see the new gui i updated the firmware anyway with the old one but for future and also students it would be better to have the one that matches with the instructions thanks | 1 |
17,595 | 12,475,863,672 | IssuesEvent | 2020-05-29 12:27:32 | hotosm/tasking-manager | https://api.github.com/repos/hotosm/tasking-manager | closed | Non-dev testing environment | Component: Infrastructure Difficulty: Medium Priority: Medium Status: Needs implementation Type: Enhancement | It would be good non-developers can test Pull Requests of the Tasking Manager. This requires to setup a test setup much easier.
First step has been done with the Docker Compose setup (#797 and related improvements on configuration #1419). Recent testing on Windows and Mac showed problems with the legacy Docker versions. But also the workflow has been extremely rough. That we ended up deploying on a VPS.
Let's use this issue to find a suitable solution for non-devs. | 1.0 | Non-dev testing environment - It would be good non-developers can test Pull Requests of the Tasking Manager. This requires to setup a test setup much easier.
First step has been done with the Docker Compose setup (#797 and related improvements on configuration #1419). Recent testing on Windows and Mac showed problems with the legacy Docker versions. But also the workflow has been extremely rough. That we ended up deploying on a VPS.
Let's use this issue to find a suitable solution for non-devs. | infrastructure | non dev testing environment it would be good non developers can test pull requests of the tasking manager this requires to setup a test setup much easier first step has been done with the docker compose setup and related improvements on configuration recent testing on windows and mac showed problems with the legacy docker versions but also the workflow has been extremely rough that we ended up deploying on a vps let s use this issue to find a suitable solution for non devs | 1 |
1,282 | 3,120,933,020 | IssuesEvent | 2015-09-05 05:31:26 | AnSq/IRCR_Info_Bot | https://api.github.com/repos/AnSq/IRCR_Info_Bot | closed | Upgrade to new Heroku stack | infrastructure wontfix | Message from `git push heroku`:
! Cedar-10 will reach end-of-life on November 4th, 2015.
! Upgrade to Cedar-14 at your earliest convenience.
! For more information, check out the following Dev Center article:
! https://devcenter.heroku.com/articles/cedar-14-migration
https://devcenter.heroku.com/articles/cedar-14-migration | 1.0 | Upgrade to new Heroku stack - Message from `git push heroku`:
! Cedar-10 will reach end-of-life on November 4th, 2015.
! Upgrade to Cedar-14 at your earliest convenience.
! For more information, check out the following Dev Center article:
! https://devcenter.heroku.com/articles/cedar-14-migration
https://devcenter.heroku.com/articles/cedar-14-migration | infrastructure | upgrade to new heroku stack message from git push heroku cedar will reach end of life on november upgrade to cedar at your earliest convenience for more information check out the following dev center article | 1 |
118,202 | 17,576,963,662 | IssuesEvent | 2021-08-15 19:58:26 | ghc-dev/Michael-Hurley-DDS | https://api.github.com/repos/ghc-dev/Michael-Hurley-DDS | opened | CVE-2020-10744 (Medium) detected in ansible-2.9.9.tar.gz | security vulnerability | ## CVE-2020-10744 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: Michael-Hurley-DDS/requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Michael-Hurley-DDS/commit/8733fcfea66ede3b2aa595def7fabe28c51d0e65">8733fcfea66ede3b2aa595def7fabe28c51d0e65</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An incomplete fix was found for the fix of the flaw CVE-2020-1733 ansible: insecure temporary directory when running become_user from become directive. The provided fix is insufficient to prevent the race condition on systems using ACLs and FUSE filesystems. Ansible Engine 2.7.18, 2.8.12, and 2.9.9 as well as previous versions are affected and Ansible Tower 3.4.5, 3.5.6 and 3.6.4 as well as previous versions are affected.
<p>Publish Date: 2020-05-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10744>CVE-2020-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"ansible","packageVersion":"2.9.9","packageFilePaths":["/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"ansible:2.9.9","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-10744","vulnerabilityDetails":"An incomplete fix was found for the fix of the flaw CVE-2020-1733 ansible: insecure temporary directory when running become_user from become directive. The provided fix is insufficient to prevent the race condition on systems using ACLs and FUSE filesystems. Ansible Engine 2.7.18, 2.8.12, and 2.9.9 as well as previous versions are affected and Ansible Tower 3.4.5, 3.5.6 and 3.6.4 as well as previous versions are affected.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10744","cvss3Severity":"medium","cvss3Score":"5.0","cvss3Metrics":{"A":"Low","AC":"High","PR":"Low","S":"Changed","C":"Low","UI":"Required","AV":"Local","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-10744 (Medium) detected in ansible-2.9.9.tar.gz - ## CVE-2020-10744 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: Michael-Hurley-DDS/requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Michael-Hurley-DDS/commit/8733fcfea66ede3b2aa595def7fabe28c51d0e65">8733fcfea66ede3b2aa595def7fabe28c51d0e65</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An incomplete fix was found for the fix of the flaw CVE-2020-1733 ansible: insecure temporary directory when running become_user from become directive. The provided fix is insufficient to prevent the race condition on systems using ACLs and FUSE filesystems. Ansible Engine 2.7.18, 2.8.12, and 2.9.9 as well as previous versions are affected and Ansible Tower 3.4.5, 3.5.6 and 3.6.4 as well as previous versions are affected.
<p>Publish Date: 2020-05-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10744>CVE-2020-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"ansible","packageVersion":"2.9.9","packageFilePaths":["/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"ansible:2.9.9","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-10744","vulnerabilityDetails":"An incomplete fix was found for the fix of the flaw CVE-2020-1733 ansible: insecure temporary directory when running become_user from become directive. The provided fix is insufficient to prevent the race condition on systems using ACLs and FUSE filesystems. Ansible Engine 2.7.18, 2.8.12, and 2.9.9 as well as previous versions are affected and Ansible Tower 3.4.5, 3.5.6 and 3.6.4 as well as previous versions are affected.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10744","cvss3Severity":"medium","cvss3Score":"5.0","cvss3Metrics":{"A":"Low","AC":"High","PR":"Low","S":"Changed","C":"Low","UI":"Required","AV":"Local","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_infrastructure | cve medium detected in ansible tar gz cve medium severity vulnerability vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file michael hurley dds requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch master vulnerability details an incomplete fix was found for the fix of the flaw cve ansible insecure temporary directory when running become user from become directive the provided fix is insufficient to prevent the race condition on systems using acls and fuse filesystems ansible engine and as well as previous versions are affected and ansible tower and as well as previous versions are affected publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree ansible isminimumfixversionavailable false basebranches vulnerabilityidentifier cve vulnerabilitydetails an incomplete fix was found for the fix of the flaw cve ansible insecure temporary directory when running become user from become directive the provided fix is insufficient to prevent the race condition on systems using acls and fuse filesystems ansible engine and as well as previous versions are affected and ansible tower and as well as previous versions are affected vulnerabilityurl | 0 |
15,878 | 11,739,706,721 | IssuesEvent | 2020-03-11 18:11:46 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Make work item payload smaller for crossgen-comparison job | area-Infrastructure-coreclr | We currently put up the whole artifacts directory as the work item for our crossgen comparison jobs. This results in a massive work item which the ARM machines sometimes have trouble downloading according to https://github.com/dotnet/runtime/issues/33404#issuecomment-597180362. We should instead create a separate folder that has only the necessary files and send that as the work item directory to save space over the wire and speed up the download.
cc: @jashook | 1.0 | Make work item payload smaller for crossgen-comparison job - We currently put up the whole artifacts directory as the work item for our crossgen comparison jobs. This results in a massive work item which the ARM machines sometimes have trouble downloading according to https://github.com/dotnet/runtime/issues/33404#issuecomment-597180362. We should instead create a separate folder that has only the necessary files and send that as the work item directory to save space over the wire and speed up the download.
cc: @jashook | infrastructure | make work item payload smaller for crossgen comparison job we currently put up the whole artifacts directory as the work item for our crossgen comparison jobs this results in a massive work item which the arm machines sometimes have trouble downloading according to we should instead create a separate folder that has only the necessary files and send that as the work item directory to save space over the wire and speed up the download cc jashook | 1 |
12,947 | 10,028,730,772 | IssuesEvent | 2019-07-17 12:25:42 | snowleopard/hadrian | https://api.github.com/repos/snowleopard/hadrian | closed | Add support for fast rebuild of a single package (ignoring all other dependencies) | enhancement infrastructure performance | As discussed in #464, we need a way to tell Hadrian to rebuild a single GHC package ignoring any external dependencies, just like we did when implementing the `--freeze1` feature #250.
See this comment: https://github.com/snowleopard/hadrian/issues/464#issuecomment-345016179.
| 1.0 | Add support for fast rebuild of a single package (ignoring all other dependencies) - As discussed in #464, we need a way to tell Hadrian to rebuild a single GHC package ignoring any external dependencies, just like we did when implementing the `--freeze1` feature #250.
See this comment: https://github.com/snowleopard/hadrian/issues/464#issuecomment-345016179.
| infrastructure | add support for fast rebuild of a single package ignoring all other dependencies as discussed in we need a way to tell hadrian to rebuild a single ghc package ignoring any external dependencies just like we did when implementing the feature see this comment | 1 |
23,847 | 16,621,014,242 | IssuesEvent | 2021-06-03 01:00:39 | microsoft/react-native-windows | https://api.github.com/repos/microsoft/react-native-windows | closed | E2E tests cannot find element by testID if it's not focusable | Area: Test Infrastructure enhancement | The webdriverio $ selector operator relies on the native control being focusable. This requirement is an obstacle for any scenario where the component isn't supposed to be focusable, but we want an automated test to find the element. For example see discussion in: https://github.com/microsoft/react-native-windows/pull/6344#issuecomment-718041077
This issue is tracking making it possible to find any element with a testID, regardless of whether or not it was set focusable. | 1.0 | E2E tests cannot find element by testID if it's not focusable - The webdriverio $ selector operator relies on the native control being focusable. This requirement is an obstacle for any scenario where the component isn't supposed to be focusable, but we want an automated test to find the element. For example see discussion in: https://github.com/microsoft/react-native-windows/pull/6344#issuecomment-718041077
This issue is tracking making it possible to find any element with a testID, regardless of whether or not it was set focusable. | infrastructure | tests cannot find element by testid if it s not focusable the webdriverio selector operator relies on the native control being focusable this requirement is an obstacle for any scenario where the component isn t supposed to be focusable but we want an automated test to find the element for example see discussion in this issue is tracking making it possible to find any element with a testid regardless of whether or not it was set focusable | 1 |
372,578 | 11,017,118,709 | IssuesEvent | 2019-12-05 07:35:06 | openshift/odo | https://api.github.com/repos/openshift/odo | closed | Nodejs images are not showing as supported on 4.3 cluster | points/3 priority/High | [kind/bug]
<!--
Welcome! - We kindly ask you to:
1. Fill out the issue template below
2. Use the Google group if you have a question rather than a bug or feature request.
The group is at: https://groups.google.com/forum/#!forum/odo-users
Thanks for understanding, and for contributing to the project!
-->
## What versions of software are you using?
- Operating System:
- Output of `odo version`: odo master
## How did you run odo exactly?
odo create nodejs
## Actual behavior
warning shows up
## Expected behavior
No warning
## Any logs, error output, etc?
```
[odo] Warning: nodejs is not fully supported by odo, and it is not guaranteed to work.
```
| 1.0 | Nodejs images are not showing as supported on 4.3 cluster - [kind/bug]
<!--
Welcome! - We kindly ask you to:
1. Fill out the issue template below
2. Use the Google group if you have a question rather than a bug or feature request.
The group is at: https://groups.google.com/forum/#!forum/odo-users
Thanks for understanding, and for contributing to the project!
-->
## What versions of software are you using?
- Operating System:
- Output of `odo version`: odo master
## How did you run odo exactly?
odo create nodejs
## Actual behavior
warning shows up
## Expected behavior
No warning
## Any logs, error output, etc?
```
[odo] Warning: nodejs is not fully supported by odo, and it is not guaranteed to work.
```
| non_infrastructure | nodejs images are not showing as supported on cluster welcome we kindly ask you to fill out the issue template below use the google group if you have a question rather than a bug or feature request the group is at thanks for understanding and for contributing to the project what versions of software are you using operating system output of odo version odo master how did you run odo exactly odo create nodejs actual behavior warning shows up expected behavior no warning any logs error output etc warning nodejs is not fully supported by odo and it is not guaranteed to work | 0 |
13,967 | 10,563,130,789 | IssuesEvent | 2019-10-04 20:08:06 | SNLComputation/Albany | https://api.github.com/repos/SNLComputation/Albany | reopened | Remove stale branches | infrastructure | breakaway from #58, so far `epetra` and `issue-34` are known to be branches we should keep. | 1.0 | Remove stale branches - breakaway from #58, so far `epetra` and `issue-34` are known to be branches we should keep. | infrastructure | remove stale branches breakaway from so far epetra and issue are known to be branches we should keep | 1 |
4,392 | 5,031,519,406 | IssuesEvent | 2016-12-16 07:28:50 | Starcounter/Starcounter | https://api.github.com/repos/Starcounter/Starcounter | closed | Introduce application ID ("namespace") in addition to name? | enhancement Infrastructure Low prio Product owner | We are having discussions about how to handle application names and their uniqueness, and we need a decision.
The #1742 issue suggest different approaches, and here's another one - allow the application name not to be unique (i.e. have it the name of the file, or the custom name if such is given) and introduce a second property, "id" (or "namespace"), that is governed by Starcounter and is guaranteed to be unique. Preferably, this id should be as close to the name as possible.
When we reach a decision, we'll agree on it here and have the work needed to be done being branched by this issue.
| 1.0 | Introduce application ID ("namespace") in addition to name? - We are having discussions about how to handle application names and their uniqueness, and we need a decision.
The #1742 issue suggest different approaches, and here's another one - allow the application name not to be unique (i.e. have it the name of the file, or the custom name if such is given) and introduce a second property, "id" (or "namespace"), that is governed by Starcounter and is guaranteed to be unique. Preferably, this id should be as close to the name as possible.
When we reach a decision, we'll agree on it here and have the work needed to be done being branched by this issue.
| infrastructure | introduce application id namespace in addition to name we are having discussions about how to handle application names and their uniqueness and we need a decision the issue suggest different approaches and here s another one allow the application name not to be unique i e have it the name of the file or the custom name if such is given and introduce a second property id or namespace that is governed by starcounter and is guaranteed to be unique preferably this id should be as close to the name as possible when we reach a decision we ll agree on it here and have the work needed to be done being branched by this issue | 1 |
89,145 | 3,790,087,895 | IssuesEvent | 2016-03-21 20:13:28 | fgpv-vpgf/fgpv-vpgf | https://api.github.com/repos/fgpv-vpgf/fgpv-vpgf | opened | Add Custom text/html Mime Type for WMS Support | improvements: enhancement priority: medium | Add a custom MIME type field to indicate that `text/html` should be formatted as an HTML fragment that is safe to drop into the a click event panel.
Will be useful beyond just the WMS use case. | 1.0 | Add Custom text/html Mime Type for WMS Support - Add a custom MIME type field to indicate that `text/html` should be formatted as an HTML fragment that is safe to drop into the a click event panel.
Will be useful beyond just the WMS use case. | non_infrastructure | add custom text html mime type for wms support add a custom mime type field to indicate that text html should be formatted as an html fragment that is safe to drop into the a click event panel will be useful beyond just the wms use case | 0 |
27,121 | 21,187,853,748 | IssuesEvent | 2022-04-08 14:25:23 | cal-itp/data-infra | https://api.github.com/repos/cal-itp/data-infra | closed | Airflow: Limit `sandbox` DAG to a pool of 1 | infrastructure | To limit `sandbox` tasks' impacts on the rest of the Airflow ecosystem, we want to create a [pool](https://airflow.apache.org/docs/apache-airflow/stable/concepts/pools.html) for `sandbox` and limit them to one task executing at a time.
Example PR doing this for the GTFS RT pipeline: https://github.com/cal-itp/data-infra/pull/1307 -- we also need to configure the pool itself in the Airflow UI.
AC:
- [ ] `sandbox` DAG has a pool created | 1.0 | Airflow: Limit `sandbox` DAG to a pool of 1 - To limit `sandbox` tasks' impacts on the rest of the Airflow ecosystem, we want to create a [pool](https://airflow.apache.org/docs/apache-airflow/stable/concepts/pools.html) for `sandbox` and limit them to one task executing at a time.
Example PR doing this for the GTFS RT pipeline: https://github.com/cal-itp/data-infra/pull/1307 -- we also need to configure the pool itself in the Airflow UI.
AC:
- [ ] `sandbox` DAG has a pool created | infrastructure | airflow limit sandbox dag to a pool of to limit sandbox tasks impacts on the rest of the airflow ecosystem we want to create a for sandbox and limit them to one task executing at a time example pr doing this for the gtfs rt pipeline we also need to configure the pool itself in the airflow ui ac sandbox dag has a pool created | 1 |
336,319 | 10,180,299,385 | IssuesEvent | 2019-08-09 09:56:27 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.google.com - User agent detection error - detects to non supported browser | browser-firefox-mobile engine-gecko priority-critical | <!-- @browser: Firefox Mobile 58.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 7.1.2; Mobile; rv:58.0) Gecko/58.0 Firefox/58.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://www.google.com/locationhistory/preview/fallback?hl=ko
**Browser / Version**: Firefox Mobile 58.0
**Operating System**: Android 7.1.2
**Tested Another Browser**: Yes
**Problem type**: Something else
**Description**: User agent detection error - detects to non supported browser
**Steps to Reproduce**:
Direct url
[](https://webcompat.com/uploads/2017/9/52eabc7c-33fa-4fba-ad52-f59e4aa71ab6.jpg)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | www.google.com - User agent detection error - detects to non supported browser - <!-- @browser: Firefox Mobile 58.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 7.1.2; Mobile; rv:58.0) Gecko/58.0 Firefox/58.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://www.google.com/locationhistory/preview/fallback?hl=ko
**Browser / Version**: Firefox Mobile 58.0
**Operating System**: Android 7.1.2
**Tested Another Browser**: Yes
**Problem type**: Something else
**Description**: User agent detection error - detects to non supported browser
**Steps to Reproduce**:
Direct url
[](https://webcompat.com/uploads/2017/9/52eabc7c-33fa-4fba-ad52-f59e4aa71ab6.jpg)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_infrastructure | user agent detection error detects to non supported browser url browser version firefox mobile operating system android tested another browser yes problem type something else description user agent detection error detects to non supported browser steps to reproduce direct url from with ❤️ | 0 |
6,588 | 6,525,412,117 | IssuesEvent | 2017-08-29 15:48:19 | codingteam/emulsion | https://api.github.com/repos/codingteam/emulsion | closed | Update SharpXmpp | kind:feature kind:infrastructure | After https://github.com/vitalyster/SharpXMPP/issues/15 has been fixed, I need to publish and reference the new library version. | 1.0 | Update SharpXmpp - After https://github.com/vitalyster/SharpXMPP/issues/15 has been fixed, I need to publish and reference the new library version. | infrastructure | update sharpxmpp after has been fixed i need to publish and reference the new library version | 1 |
29,844 | 24,327,835,229 | IssuesEvent | 2022-09-30 16:20:41 | unitaryfund/mitiq | https://api.github.com/repos/unitaryfund/mitiq | closed | Test Mitiq with more recent versions of Python | bug infrastructure priority/p0 dependencies | Mitiq is currently tested with Python 3.7 and Python 3.8.
It would be good, if possible, to upgrade versions by one or two steps.
I.e., testing Mitiq with:
- Python 3.8 and 3.9
or
- Python 3.8, 3.9 and 3.10
This issue is not just about _testing_ but also about _fixing_ possible issues that will emerge when testing recent Python versions.
For example, dependency conflicts may happen as reported in #1285
| 1.0 | Test Mitiq with more recent versions of Python - Mitiq is currently tested with Python 3.7 and Python 3.8.
It would be good, if possible, to upgrade versions by one or two steps.
I.e., testing Mitiq with:
- Python 3.8 and 3.9
or
- Python 3.8, 3.9 and 3.10
This issue is not just about _testing_ but also about _fixing_ possible issues that will emerge when testing recent Python versions.
For example, dependency conflicts may happen as reported in #1285
| infrastructure | test mitiq with more recent versions of python mitiq is currently tested with python and python it would be good if possible to upgrade versions by one or two steps i e testing mitiq with python and or python and this issue is not just about testing but also about fixing possible issues that will emerge when testing recent python versions for example dependency conflicts may happen as reported in | 1 |
221 | 2,580,979,591 | IssuesEvent | 2015-02-13 21:23:35 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | NativeServiceTest fails to build with /p:OS=Unix | Infrastructure System.ServiceProcess.ServiceController | When running the following command from the root of my corefx repo:
build /t:rebuild /p:SkipTests=true /p:OS=Unix
I consistently get the following error towards the end of the build:
C:\Program Files (x86)\MSBuild\Microsoft.Cpp\v4.0\V140\Microsoft.Cpp.Platform.targets(57,5):
error MSB8020: The build tools for v120 (Platform Toolset = 'v120') cannot be found.
To build using the v120 build tools, please install v120 build tools.
Alternatively, you may upgrade to the current Visual Studio tools by selecting the
Project menu or right-click the solution, and then selecting "Retarget solution".
[\src\System.ServiceProcess.ServiceController\tests\NativeTestService\NativeTestService.vcxproj]
I have VS2015 CTP 5 installed. I don't have VS2013 installed.
(We don't actually need this Windows-only test project to build when building with OS=Unix, if that's the source of the problem.) | 1.0 | NativeServiceTest fails to build with /p:OS=Unix - When running the following command from the root of my corefx repo:
build /t:rebuild /p:SkipTests=true /p:OS=Unix
I consistently get the following error towards the end of the build:
C:\Program Files (x86)\MSBuild\Microsoft.Cpp\v4.0\V140\Microsoft.Cpp.Platform.targets(57,5):
error MSB8020: The build tools for v120 (Platform Toolset = 'v120') cannot be found.
To build using the v120 build tools, please install v120 build tools.
Alternatively, you may upgrade to the current Visual Studio tools by selecting the
Project menu or right-click the solution, and then selecting "Retarget solution".
[\src\System.ServiceProcess.ServiceController\tests\NativeTestService\NativeTestService.vcxproj]
I have VS2015 CTP 5 installed. I don't have VS2013 installed.
(We don't actually need this Windows-only test project to build when building with OS=Unix, if that's the source of the problem.) | infrastructure | nativeservicetest fails to build with p os unix when running the following command from the root of my corefx repo build t rebuild p skiptests true p os unix i consistently get the following error towards the end of the build c program files msbuild microsoft cpp microsoft cpp platform targets error the build tools for platform toolset cannot be found to build using the build tools please install build tools alternatively you may upgrade to the current visual studio tools by selecting the project menu or right click the solution and then selecting retarget solution i have ctp installed i don t have installed we don t actually need this windows only test project to build when building with os unix if that s the source of the problem | 1 |
607,432 | 18,782,337,235 | IssuesEvent | 2021-11-08 08:29:33 | code-ready/crc | https://api.github.com/repos/code-ready/crc | closed | [BUG] Login fails with system:anonymous cannot get resource configmaps | kind/bug priority/minor os/linux status/stale | ### General information
* OS: Linux
* Hypervisor: KVM
* Did you run `crc setup` before starting it (Yes/No)? Yes
* Running CRC on: Laptop
## CRC version
```bash
CodeReady Containers version: 1.26.0+31f06c09
OpenShift version: 4.7.8 (embedded in executable)
```
## CRC status
```bash
$ crc status --log-level debug
DEBU CodeReady Containers version: 1.26.0+31f06c09
DEBU OpenShift version: 4.7.8 (embedded in executable)
DEBU Running 'crc status'
DEBU Checking file: /home/stavros/.crc/machines/crc/.crc-exist
DEBU Checking file: /home/stavros/.crc/machines/crc/.crc-exist
DEBU Found binary path at /home/stavros/.crc/bin/crc-driver-libvirt
DEBU Launching plugin server for driver libvirt
DEBU Plugin server listening at address 127.0.0.1:46297
DEBU () Calling .GetVersion
DEBU Using API Version 1
DEBU () Calling .SetConfigRaw
DEBU () Calling .GetMachineName
DEBU (crc) Calling .GetState
DEBU (crc) DBG | time="2021-05-17T12:08:06+03:00" level=debug msg="Getting current state..."
DEBU (crc) DBG | time="2021-05-17T12:08:06+03:00" level=debug msg="Fetching VM..."
DEBU (crc) Calling .GetBundleName
DEBU (crc) Calling .GetIP
DEBU (crc) DBG | time="2021-05-17T12:08:06+03:00" level=debug msg="GetIP called for crc"
DEBU (crc) DBG | time="2021-05-17T12:08:06+03:00" level=debug msg="Getting current state..."
DEBU (crc) DBG | time="2021-05-17T12:08:06+03:00" level=debug msg="IP address: 192.168.130.11"
DEBU Running SSH command: df -B1 --output=size,used,target /sysroot | tail -1
DEBU Using ssh private keys: [/home/stavros/.crc/machines/crc/id_ecdsa /home/stavros/.crc/cache/crc_libvirt_4.7.8/id_ecdsa_crc]
DEBU SSH command results: err: <nil>, output: 32737570816 15711195136 /sysroot
DEBU Running SSH command: <hidden>
DEBU SSH command succeeded
DEBU Unexpected operator status for network: ManagementStateDegraded
DEBU Making call to close driver server
DEBU (crc) Calling .Close
DEBU Successfully made call to close driver server
DEBU Making call to close connection to plugin binary
CRC VM: Running
OpenShift: Running (v4.7.8)
Disk Usage: 15.71GB of 32.74GB (Inside the CRC VM)
Cache Usage: 13.18GB
Cache Directory: /home/stavros/.crc/cache
```
## CRC config
```bash
- consent-telemetry : no
- cpus : 8
- memory : 40960
```
## Host Operating System
```bash
NAME=Fedora
VERSION="33 (Workstation Edition)"
ID=fedora
VERSION_ID=33
VERSION_CODENAME=""
PLATFORM_ID="platform:f33"
PRETTY_NAME="Fedora 33 (Workstation Edition)"
ANSI_COLOR="0;38;2;60;110;180"
LOGO=fedora-logo-icon
CPE_NAME="cpe:/o:fedoraproject:fedora:33"
HOME_URL="https://fedoraproject.org/"
DOCUMENTATION_URL="https://docs.fedoraproject.org/en-US/fedora/f33/system-administrators-guide/"
SUPPORT_URL="https://fedoraproject.org/wiki/Communicating_and_getting_help"
BUG_REPORT_URL="https://bugzilla.redhat.com/"
REDHAT_BUGZILLA_PRODUCT="Fedora"
REDHAT_BUGZILLA_PRODUCT_VERSION=33
REDHAT_SUPPORT_PRODUCT="Fedora"
REDHAT_SUPPORT_PRODUCT_VERSION=33
PRIVACY_POLICY_URL="https://fedoraproject.org/wiki/Legal:PrivacyPolicy"
VARIANT="Workstation Edition"
VARIANT_ID=workstation
```
### Steps to reproduce
1. crc delete -f
2. crc start pull-secret-4.7.8.txt 2>&1
3. oc login -u ... -p .... <- sucessful
4. Try again later `oc login ...` fails with:
```
I0517 12:11:27.688221 64013 request.go:1107] Response Body: {"kind":"Status","apiVersion":"v1","metadata":{},"status":"Failure","message":"configmaps \"motd\" is forbidden: User \"system:anonymous\" cannot get resource \"configmaps\" in API group \"\" in the namespace \"openshift\"","reason":"Forbidden","details":{"name":"motd","kind":"configmaps"},"code":403}
I0517 12:11:27.688778 64013 helpers.go:216] server response object: [{
```
Authorization pods look ok:
```
$ oc get pods -n openshift-authentication
NAME READY STATUS RESTARTS AGE
oauth-openshift-5ccbddfc68-cr888 1/1 Running 0 27m
oauth-openshift-5ccbddfc68-drt6q 1/1 Running 0 27m
```
This might be related to https://github.com/code-ready/crc/issues/1807, however failure is permanent at my side.
Trying to login on console also fails:
### Expected
Login to be fine.
### Actual
Login fails
### Logs
https://gist.github.com/skonto/0b3256bdf5979fb91ef520690df8b034
Before gather the logs try following if that fix your issue
```bash
$ crc delete -f
$ crc cleanup
$ crc setup
$ crc start --log-level debug
```
Please consider posting the output of `crc start --log-level debug` on http://gist.github.com/ and post the link in the issue.
| 1.0 | [BUG] Login fails with system:anonymous cannot get resource configmaps - ### General information
* OS: Linux
* Hypervisor: KVM
* Did you run `crc setup` before starting it (Yes/No)? Yes
* Running CRC on: Laptop
## CRC version
```bash
CodeReady Containers version: 1.26.0+31f06c09
OpenShift version: 4.7.8 (embedded in executable)
```
## CRC status
```bash
$ crc status --log-level debug
DEBU CodeReady Containers version: 1.26.0+31f06c09
DEBU OpenShift version: 4.7.8 (embedded in executable)
DEBU Running 'crc status'
DEBU Checking file: /home/stavros/.crc/machines/crc/.crc-exist
DEBU Checking file: /home/stavros/.crc/machines/crc/.crc-exist
DEBU Found binary path at /home/stavros/.crc/bin/crc-driver-libvirt
DEBU Launching plugin server for driver libvirt
DEBU Plugin server listening at address 127.0.0.1:46297
DEBU () Calling .GetVersion
DEBU Using API Version 1
DEBU () Calling .SetConfigRaw
DEBU () Calling .GetMachineName
DEBU (crc) Calling .GetState
DEBU (crc) DBG | time="2021-05-17T12:08:06+03:00" level=debug msg="Getting current state..."
DEBU (crc) DBG | time="2021-05-17T12:08:06+03:00" level=debug msg="Fetching VM..."
DEBU (crc) Calling .GetBundleName
DEBU (crc) Calling .GetIP
DEBU (crc) DBG | time="2021-05-17T12:08:06+03:00" level=debug msg="GetIP called for crc"
DEBU (crc) DBG | time="2021-05-17T12:08:06+03:00" level=debug msg="Getting current state..."
DEBU (crc) DBG | time="2021-05-17T12:08:06+03:00" level=debug msg="IP address: 192.168.130.11"
DEBU Running SSH command: df -B1 --output=size,used,target /sysroot | tail -1
DEBU Using ssh private keys: [/home/stavros/.crc/machines/crc/id_ecdsa /home/stavros/.crc/cache/crc_libvirt_4.7.8/id_ecdsa_crc]
DEBU SSH command results: err: <nil>, output: 32737570816 15711195136 /sysroot
DEBU Running SSH command: <hidden>
DEBU SSH command succeeded
DEBU Unexpected operator status for network: ManagementStateDegraded
DEBU Making call to close driver server
DEBU (crc) Calling .Close
DEBU Successfully made call to close driver server
DEBU Making call to close connection to plugin binary
CRC VM: Running
OpenShift: Running (v4.7.8)
Disk Usage: 15.71GB of 32.74GB (Inside the CRC VM)
Cache Usage: 13.18GB
Cache Directory: /home/stavros/.crc/cache
```
## CRC config
```bash
- consent-telemetry : no
- cpus : 8
- memory : 40960
```
## Host Operating System
```bash
NAME=Fedora
VERSION="33 (Workstation Edition)"
ID=fedora
VERSION_ID=33
VERSION_CODENAME=""
PLATFORM_ID="platform:f33"
PRETTY_NAME="Fedora 33 (Workstation Edition)"
ANSI_COLOR="0;38;2;60;110;180"
LOGO=fedora-logo-icon
CPE_NAME="cpe:/o:fedoraproject:fedora:33"
HOME_URL="https://fedoraproject.org/"
DOCUMENTATION_URL="https://docs.fedoraproject.org/en-US/fedora/f33/system-administrators-guide/"
SUPPORT_URL="https://fedoraproject.org/wiki/Communicating_and_getting_help"
BUG_REPORT_URL="https://bugzilla.redhat.com/"
REDHAT_BUGZILLA_PRODUCT="Fedora"
REDHAT_BUGZILLA_PRODUCT_VERSION=33
REDHAT_SUPPORT_PRODUCT="Fedora"
REDHAT_SUPPORT_PRODUCT_VERSION=33
PRIVACY_POLICY_URL="https://fedoraproject.org/wiki/Legal:PrivacyPolicy"
VARIANT="Workstation Edition"
VARIANT_ID=workstation
```
### Steps to reproduce
1. crc delete -f
2. crc start pull-secret-4.7.8.txt 2>&1
3. oc login -u ... -p .... <- sucessful
4. Try again later `oc login ...` fails with:
```
I0517 12:11:27.688221 64013 request.go:1107] Response Body: {"kind":"Status","apiVersion":"v1","metadata":{},"status":"Failure","message":"configmaps \"motd\" is forbidden: User \"system:anonymous\" cannot get resource \"configmaps\" in API group \"\" in the namespace \"openshift\"","reason":"Forbidden","details":{"name":"motd","kind":"configmaps"},"code":403}
I0517 12:11:27.688778 64013 helpers.go:216] server response object: [{
```
Authorization pods look ok:
```
$ oc get pods -n openshift-authentication
NAME READY STATUS RESTARTS AGE
oauth-openshift-5ccbddfc68-cr888 1/1 Running 0 27m
oauth-openshift-5ccbddfc68-drt6q 1/1 Running 0 27m
```
This might be related to https://github.com/code-ready/crc/issues/1807, however failure is permanent at my side.
Trying to login on console also fails:
### Expected
Login to be fine.
### Actual
Login fails
### Logs
https://gist.github.com/skonto/0b3256bdf5979fb91ef520690df8b034
Before gather the logs try following if that fix your issue
```bash
$ crc delete -f
$ crc cleanup
$ crc setup
$ crc start --log-level debug
```
Please consider posting the output of `crc start --log-level debug` on http://gist.github.com/ and post the link in the issue.
| non_infrastructure | login fails with system anonymous cannot get resource configmaps general information os linux hypervisor kvm did you run crc setup before starting it yes no yes running crc on laptop crc version bash codeready containers version openshift version embedded in executable crc status bash crc status log level debug debu codeready containers version debu openshift version embedded in executable debu running crc status debu checking file home stavros crc machines crc crc exist debu checking file home stavros crc machines crc crc exist debu found binary path at home stavros crc bin crc driver libvirt debu launching plugin server for driver libvirt debu plugin server listening at address debu calling getversion debu using api version debu calling setconfigraw debu calling getmachinename debu crc calling getstate debu crc dbg time level debug msg getting current state debu crc dbg time level debug msg fetching vm debu crc calling getbundlename debu crc calling getip debu crc dbg time level debug msg getip called for crc debu crc dbg time level debug msg getting current state debu crc dbg time level debug msg ip address debu running ssh command df output size used target sysroot tail debu using ssh private keys debu ssh command results err output sysroot debu running ssh command debu ssh command succeeded debu unexpected operator status for network managementstatedegraded debu making call to close driver server debu crc calling close debu successfully made call to close driver server debu making call to close connection to plugin binary crc vm running openshift running disk usage of inside the crc vm cache usage cache directory home stavros crc cache crc config bash consent telemetry no cpus memory host operating system bash name fedora version workstation edition id fedora version id version codename platform id platform pretty name fedora workstation edition ansi color logo fedora logo icon cpe name cpe o fedoraproject fedora home url documentation url support url bug report url redhat bugzilla product fedora redhat bugzilla product version redhat support product fedora redhat support product version privacy policy url variant workstation edition variant id workstation steps to reproduce crc delete f crc start pull secret txt oc login u p sucessful try again later oc login fails with request go response body kind status apiversion metadata status failure message configmaps motd is forbidden user system anonymous cannot get resource configmaps in api group in the namespace openshift reason forbidden details name motd kind configmaps code helpers go server response object authorization pods look ok oc get pods n openshift authentication name ready status restarts age oauth openshift running oauth openshift running this might be related to however failure is permanent at my side trying to login on console also fails expected login to be fine actual login fails logs before gather the logs try following if that fix your issue bash crc delete f crc cleanup crc setup crc start log level debug please consider posting the output of crc start log level debug on and post the link in the issue | 0 |
196,326 | 6,926,837,864 | IssuesEvent | 2017-11-30 20:36:03 | redox-os/ion | https://api.github.com/repos/redox-os/ion | reopened | Parser panic on expansions with double parens | bug C-Class good first issue high-priority low-hanging fruit | **Reproduction**:
```
let a = @((b))
```
**Actual behavior**:
A panic with this message: `thread 'main' panicked at 'attempt to subtract with overflow', src/parser/arguments.rs:87:25`
[Backtrace](https://gist.github.com/xTibor/635e560c6fc25f9e5c1ba6aa75da18cf)
**Build information**:
`rustc -V`: `rustc 1.23.0-nightly (d6b06c63a 2017-11-09)`
`git rev-parse HEAD`: 2f176ebe1010b4ebd9e2a9031ad354e598cdee9c
System: KDE neon 5.11 (Ubuntu 16.04 LTS)
| 1.0 | Parser panic on expansions with double parens - **Reproduction**:
```
let a = @((b))
```
**Actual behavior**:
A panic with this message: `thread 'main' panicked at 'attempt to subtract with overflow', src/parser/arguments.rs:87:25`
[Backtrace](https://gist.github.com/xTibor/635e560c6fc25f9e5c1ba6aa75da18cf)
**Build information**:
`rustc -V`: `rustc 1.23.0-nightly (d6b06c63a 2017-11-09)`
`git rev-parse HEAD`: 2f176ebe1010b4ebd9e2a9031ad354e598cdee9c
System: KDE neon 5.11 (Ubuntu 16.04 LTS)
| non_infrastructure | parser panic on expansions with double parens reproduction let a b actual behavior a panic with this message thread main panicked at attempt to subtract with overflow src parser arguments rs build information rustc v rustc nightly git rev parse head system kde neon ubuntu lts | 0 |
53,149 | 13,127,528,489 | IssuesEvent | 2020-08-06 10:31:45 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | ImportError: DLL load failed: The specified module could not be found. | TF 2.3 stat:awaiting response subtype:windows type:build/install | I am getting the following error when trying to import tensorflow. I have tried many solutions and non seem to work.
I have seen Issue #22794, but it does not seem to help.
Versions -- > python 3.7.4 -- > tensorflow 2.3.0
>
> runfile('C:/Users/pshad/.spyder-py3/temp.py', wdir='C:/Users/pshad/.spyder-py3')
> Traceback (most recent call last):
>
> File "<ipython-input-30-bc8fb4f78acd>", line 1, in <module>
> runfile('C:/Users/pshad/.spyder-py3/temp.py', wdir='C:/Users/pshad/.spyder-py3')
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\spyder_kernels\customize\spydercustomize.py", line 827, in runfile
> execfile(filename, namespace)
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\spyder_kernels\customize\spydercustomize.py", line 110, in execfile
> exec(compile(f.read(), filename, 'exec'), namespace)
>
> File "C:/Users/pshad/.spyder-py3/temp.py", line 9, in <module>
> import tensorflow as tf
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\__init__.py", line 41, in <module>
> from tensorflow.python.tools import module_util as _module_util
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\python\__init__.py", line 40, in <module>
> from tensorflow.python.eager import context
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\python\eager\context.py", line 35, in <module>
> from tensorflow.python import pywrap_tfe
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\python\pywrap_tfe.py", line 28, in <module>
> from tensorflow.python import pywrap_tensorflow
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 83, in <module>
> raise ImportError(msg)
>
> ImportError: Traceback (most recent call last):
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 64, in <module>
> from tensorflow.python._pywrap_tensorflow_internal import *
> ImportError: DLL load failed: The specified module could not be found.
>
>
> Failed to load the native TensorFlow runtime.
>
> See https://www.tensorflow.org/install/errors
I tried to reinstall the tensorflow, downgrade, and upgrade as well. Nothing seem to work, unfortunately. | 1.0 | ImportError: DLL load failed: The specified module could not be found. - I am getting the following error when trying to import tensorflow. I have tried many solutions and non seem to work.
I have seen Issue #22794, but it does not seem to help.
Versions -- > python 3.7.4 -- > tensorflow 2.3.0
>
> runfile('C:/Users/pshad/.spyder-py3/temp.py', wdir='C:/Users/pshad/.spyder-py3')
> Traceback (most recent call last):
>
> File "<ipython-input-30-bc8fb4f78acd>", line 1, in <module>
> runfile('C:/Users/pshad/.spyder-py3/temp.py', wdir='C:/Users/pshad/.spyder-py3')
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\spyder_kernels\customize\spydercustomize.py", line 827, in runfile
> execfile(filename, namespace)
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\spyder_kernels\customize\spydercustomize.py", line 110, in execfile
> exec(compile(f.read(), filename, 'exec'), namespace)
>
> File "C:/Users/pshad/.spyder-py3/temp.py", line 9, in <module>
> import tensorflow as tf
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\__init__.py", line 41, in <module>
> from tensorflow.python.tools import module_util as _module_util
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\python\__init__.py", line 40, in <module>
> from tensorflow.python.eager import context
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\python\eager\context.py", line 35, in <module>
> from tensorflow.python import pywrap_tfe
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\python\pywrap_tfe.py", line 28, in <module>
> from tensorflow.python import pywrap_tensorflow
>
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 83, in <module>
> raise ImportError(msg)
>
> ImportError: Traceback (most recent call last):
> File "C:\Users\pshad\Anaconda3\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 64, in <module>
> from tensorflow.python._pywrap_tensorflow_internal import *
> ImportError: DLL load failed: The specified module could not be found.
>
>
> Failed to load the native TensorFlow runtime.
>
> See https://www.tensorflow.org/install/errors
I tried to reinstall the tensorflow, downgrade, and upgrade as well. Nothing seem to work, unfortunately. | non_infrastructure | importerror dll load failed the specified module could not be found i am getting the following error when trying to import tensorflow i have tried many solutions and non seem to work i have seen issue but it does not seem to help versions python tensorflow runfile c users pshad spyder temp py wdir c users pshad spyder traceback most recent call last file line in runfile c users pshad spyder temp py wdir c users pshad spyder file c users pshad lib site packages spyder kernels customize spydercustomize py line in runfile execfile filename namespace file c users pshad lib site packages spyder kernels customize spydercustomize py line in execfile exec compile f read filename exec namespace file c users pshad spyder temp py line in import tensorflow as tf file c users pshad lib site packages tensorflow init py line in from tensorflow python tools import module util as module util file c users pshad lib site packages tensorflow python init py line in from tensorflow python eager import context file c users pshad lib site packages tensorflow python eager context py line in from tensorflow python import pywrap tfe file c users pshad lib site packages tensorflow python pywrap tfe py line in from tensorflow python import pywrap tensorflow file c users pshad lib site packages tensorflow python pywrap tensorflow py line in raise importerror msg importerror traceback most recent call last file c users pshad lib site packages tensorflow python pywrap tensorflow py line in from tensorflow python pywrap tensorflow internal import importerror dll load failed the specified module could not be found failed to load the native tensorflow runtime see i tried to reinstall the tensorflow downgrade and upgrade as well nothing seem to work unfortunately | 0 |
75,480 | 25,866,911,546 | IssuesEvent | 2022-12-13 21:46:29 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | "People" metaspace shows favourite rooms | T-Defect S-Major A-Room-List A-Spaces O-Uncommon | ### Steps to reproduce
1. Click on "People" metaspace
### Outcome
#### What did you expect?
See only people listed in the left panel
#### What happened instead?
See rooms under "Favourites" listed in the left panel
### Operating system
_No response_
### Browser information
Chromium 107.0.5304.121 (Official Build) Arch Linux (64-bit)
### URL for webapp
develop.element.io
### Application version
Element version: cbf5c43ae79d-react-569a36493378-js-b318a77ecef1 Olm version: 3.2.12
### Homeserver
matrix.org
### Will you send logs?
No | 1.0 | "People" metaspace shows favourite rooms - ### Steps to reproduce
1. Click on "People" metaspace
### Outcome
#### What did you expect?
See only people listed in the left panel
#### What happened instead?
See rooms under "Favourites" listed in the left panel
### Operating system
_No response_
### Browser information
Chromium 107.0.5304.121 (Official Build) Arch Linux (64-bit)
### URL for webapp
develop.element.io
### Application version
Element version: cbf5c43ae79d-react-569a36493378-js-b318a77ecef1 Olm version: 3.2.12
### Homeserver
matrix.org
### Will you send logs?
No | non_infrastructure | people metaspace shows favourite rooms steps to reproduce click on people metaspace outcome what did you expect see only people listed in the left panel what happened instead see rooms under favourites listed in the left panel operating system no response browser information chromium official build arch linux bit url for webapp develop element io application version element version react js olm version homeserver matrix org will you send logs no | 0 |
28,465 | 23,273,344,750 | IssuesEvent | 2022-08-05 03:14:54 | real-life-levels/web | https://api.github.com/repos/real-life-levels/web | closed | Security rules are not set | infrastructure | Set proper security rules in Firebase to limit what users can read/write/delete | 1.0 | Security rules are not set - Set proper security rules in Firebase to limit what users can read/write/delete | infrastructure | security rules are not set set proper security rules in firebase to limit what users can read write delete | 1 |
25,271 | 18,391,918,667 | IssuesEvent | 2021-10-12 07:00:08 | openclimatefix/nowcasting_dataset | https://api.github.com/repos/openclimatefix/nowcasting_dataset | closed | Download additional UK Met Office UKV NWPs | enhancement data infrastructure/on-premises hardware | ## Detailed Description
We already have several years of UKV NWPs. But we should grab the most recent data, so it covers the same timespan as the ESO PV forecasts.
## Possible Implementation
Use FileZilla to FTP from CEDA to `leonardo`. (I won't install `FileZilla` on `leonardo` because that will also install xorg etc. Instead I'll run FileZilla on my NUC, and mount `leonardo` on the NUC. If this doesn't work, consider using [`LFTP`](http://lftp.yar.ru/features.html) running on `leonardo`) | 1.0 | Download additional UK Met Office UKV NWPs - ## Detailed Description
We already have several years of UKV NWPs. But we should grab the most recent data, so it covers the same timespan as the ESO PV forecasts.
## Possible Implementation
Use FileZilla to FTP from CEDA to `leonardo`. (I won't install `FileZilla` on `leonardo` because that will also install xorg etc. Instead I'll run FileZilla on my NUC, and mount `leonardo` on the NUC. If this doesn't work, consider using [`LFTP`](http://lftp.yar.ru/features.html) running on `leonardo`) | infrastructure | download additional uk met office ukv nwps detailed description we already have several years of ukv nwps but we should grab the most recent data so it covers the same timespan as the eso pv forecasts possible implementation use filezilla to ftp from ceda to leonardo i won t install filezilla on leonardo because that will also install xorg etc instead i ll run filezilla on my nuc and mount leonardo on the nuc if this doesn t work consider using running on leonardo | 1 |
60,095 | 3,120,764,743 | IssuesEvent | 2015-09-05 01:40:20 | framingeinstein/issues-test | https://api.github.com/repos/framingeinstein/issues-test | closed | SPK-76: Homepage: Slim & Transparent nav should be on the homepage | priority:normal resolution:fixed type:enhancement | Hi Andrew,
This is just a reminder that we should have a transparent nav for the homepage.
Thanks,
Jessica | 1.0 | SPK-76: Homepage: Slim & Transparent nav should be on the homepage - Hi Andrew,
This is just a reminder that we should have a transparent nav for the homepage.
Thanks,
Jessica | non_infrastructure | spk homepage slim transparent nav should be on the homepage hi andrew this is just a reminder that we should have a transparent nav for the homepage thanks jessica | 0 |
295,246 | 22,203,860,414 | IssuesEvent | 2022-06-07 13:28:09 | composer/composer | https://api.github.com/repos/composer/composer | closed | Docs on files autoloading should document the order files are included | Documentation Good First Issue | Looking at the code, it looks like autoload files are loaded in the order of packages given by PackageSorter::sortPackages().
This should be documented in https://getcomposer.org/doc/04-schema.md#files. (Also, I have no idea what the sorting done by PackageSorter::sortPackages() actually is. It says 'dependency weight' but what does that mean?) | 1.0 | Docs on files autoloading should document the order files are included - Looking at the code, it looks like autoload files are loaded in the order of packages given by PackageSorter::sortPackages().
This should be documented in https://getcomposer.org/doc/04-schema.md#files. (Also, I have no idea what the sorting done by PackageSorter::sortPackages() actually is. It says 'dependency weight' but what does that mean?) | non_infrastructure | docs on files autoloading should document the order files are included looking at the code it looks like autoload files are loaded in the order of packages given by packagesorter sortpackages this should be documented in also i have no idea what the sorting done by packagesorter sortpackages actually is it says dependency weight but what does that mean | 0 |
321,258 | 9,795,964,095 | IssuesEvent | 2019-06-11 06:11:50 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.lowes.com - site is not usable | browser-focus-geckoview engine-gecko priority-important | <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:68.0) Gecko/68.0 Firefox/68.0 -->
<!-- @reported_with: -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: https://www.lowes.com/pl/Save-Now/4294594589?int_cmp=Home:A:NoDivision:Other:FW18_Fathers_Day_Sale
**Browser / Version**: Firefox Mobile 68.0
**Operating System**: Android
**Tested Another Browser**: No
**Problem type**: Site is not usable
**Description**: unable to navigate
**Steps to Reproduce**:
Tried to enter location information to find pricing.
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | www.lowes.com - site is not usable - <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:68.0) Gecko/68.0 Firefox/68.0 -->
<!-- @reported_with: -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: https://www.lowes.com/pl/Save-Now/4294594589?int_cmp=Home:A:NoDivision:Other:FW18_Fathers_Day_Sale
**Browser / Version**: Firefox Mobile 68.0
**Operating System**: Android
**Tested Another Browser**: No
**Problem type**: Site is not usable
**Description**: unable to navigate
**Steps to Reproduce**:
Tried to enter location information to find pricing.
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_infrastructure | site is not usable url browser version firefox mobile operating system android tested another browser no problem type site is not usable description unable to navigate steps to reproduce tried to enter location information to find pricing browser configuration none from with ❤️ | 0 |
828,061 | 31,809,894,386 | IssuesEvent | 2023-09-13 16:06:00 | thesaurus-linguae-aegyptiae/tla-web | https://api.github.com/repos/thesaurus-linguae-aegyptiae/tla-web | opened | Thymeleaf Funktionen für Datenanzeige | low priority | Bislang werden alle Daten "händisch" angezeigt. Insbeondere die Anzeige einzelner Key:Value Angaben könnte mittels einer Funktion gelöst werden.
Bspw. Datierung: lorem
oder
Datieurngskommentar:
Lorem ipsum
function(String message_property, obj.data, Boolean \n) | 1.0 | Thymeleaf Funktionen für Datenanzeige - Bislang werden alle Daten "händisch" angezeigt. Insbeondere die Anzeige einzelner Key:Value Angaben könnte mittels einer Funktion gelöst werden.
Bspw. Datierung: lorem
oder
Datieurngskommentar:
Lorem ipsum
function(String message_property, obj.data, Boolean \n) | non_infrastructure | thymeleaf funktionen für datenanzeige bislang werden alle daten händisch angezeigt insbeondere die anzeige einzelner key value angaben könnte mittels einer funktion gelöst werden bspw datierung lorem oder datieurngskommentar lorem ipsum function string message property obj data boolean n | 0 |
30,308 | 24,748,383,502 | IssuesEvent | 2022-10-21 11:44:01 | scalableminds/webknossos | https://api.github.com/repos/scalableminds/webknossos | closed | improve health monitoring for demo instance | infrastructure | not all datastores / datasets are properly monitored | 1.0 | improve health monitoring for demo instance - not all datastores / datasets are properly monitored | infrastructure | improve health monitoring for demo instance not all datastores datasets are properly monitored | 1 |
30,887 | 25,142,048,001 | IssuesEvent | 2022-11-10 00:19:43 | fornax-navo/fornax-demo-notebooks | https://api.github.com/repos/fornax-navo/fornax-demo-notebooks | closed | Reorganize and cleanup `code` directory | refactor infrastructure | Some suggestions:
- [ ] group related functions together in the same file
- [ ] make all function arguments keyword-only, except maybe ra & dec.
> I feel it would be beneficial to enforce the arguments for all these functions in `code` to be keyword only, or at least the ones after ra/dec; overall that would make the notebook code more explanatory and less error-prone.
_Originally posted by @bsipocz in https://github.com/fornax-navo/fornax-demo-notebooks/pull/49#discussion_r960915848_ | 1.0 | Reorganize and cleanup `code` directory - Some suggestions:
- [ ] group related functions together in the same file
- [ ] make all function arguments keyword-only, except maybe ra & dec.
> I feel it would be beneficial to enforce the arguments for all these functions in `code` to be keyword only, or at least the ones after ra/dec; overall that would make the notebook code more explanatory and less error-prone.
_Originally posted by @bsipocz in https://github.com/fornax-navo/fornax-demo-notebooks/pull/49#discussion_r960915848_ | infrastructure | reorganize and cleanup code directory some suggestions group related functions together in the same file make all function arguments keyword only except maybe ra dec i feel it would be beneficial to enforce the arguments for all these functions in code to be keyword only or at least the ones after ra dec overall that would make the notebook code more explanatory and less error prone originally posted by bsipocz in | 1 |
128,283 | 17,470,026,949 | IssuesEvent | 2021-08-07 01:08:37 | RecordReplay/devtools | https://api.github.com/repos/RecordReplay/devtools | closed | July Onboarding Refresh | design-complete | Here's a link to the Figma file: https://www.figma.com/file/SSr1ljyzF0lCXTL7BX1Whh/Replay-Design-Doc?node-id=5210%3A12083
**Here are the steps people will walk through, in order:**
1. Big bold welcome screen
2. Download links
3. Nicer Google signin
4. Create your first Replay screen
5. Glitch demo with circles?
6. Console.logs in dev
From a priority standpoint, let's do it like this:
- [x] [New onboarding demo with great console logs](https://github.com/RecordReplay/devtools/issues/3109)
- [x] [New welcome and download screens (for people just invited)](https://github.com/RecordReplay/devtools/issues/3046)
- [x] [Nicer Google login](https://github.com/RecordReplay/devtools/issues/3111)
| 1.0 | July Onboarding Refresh - Here's a link to the Figma file: https://www.figma.com/file/SSr1ljyzF0lCXTL7BX1Whh/Replay-Design-Doc?node-id=5210%3A12083
**Here are the steps people will walk through, in order:**
1. Big bold welcome screen
2. Download links
3. Nicer Google signin
4. Create your first Replay screen
5. Glitch demo with circles?
6. Console.logs in dev
From a priority standpoint, let's do it like this:
- [x] [New onboarding demo with great console logs](https://github.com/RecordReplay/devtools/issues/3109)
- [x] [New welcome and download screens (for people just invited)](https://github.com/RecordReplay/devtools/issues/3046)
- [x] [Nicer Google login](https://github.com/RecordReplay/devtools/issues/3111)
| non_infrastructure | july onboarding refresh here s a link to the figma file here are the steps people will walk through in order big bold welcome screen download links nicer google signin create your first replay screen glitch demo with circles console logs in dev from a priority standpoint let s do it like this | 0 |
17,647 | 9,850,497,954 | IssuesEvent | 2019-06-19 08:19:44 | Dart-Code/Dart-Code | https://api.github.com/repos/Dart-Code/Dart-Code | closed | Improve performance of completions | important is performance | ~~As well as probably being the cause of #1721~~, the performance of completions with unimported symbols is generally poor.
Testing on Windows PC with the following test (inside `test\flutter_only\providers\completion_item_provider.test.ts`):
```
describe("with SuggestionSet support", () => {
beforeEach("ensure SuggestionSets are supported", function () {
if (!extApi.analyzerCapabilities.supportsAvailableSuggestions)
this.skip();
});
it.only("includes unimported symbols", async () => {
await setTestContent(`
main() {
ProcessInf
}
`);
const count = 50;
const start = Date.now();
for (let i = 0; i < 50; i++) {
const completions = await getCompletionsAt("ProcessInf^");
ensureCompletion(completions, vs.CompletionItemKind.Class, "ProcessInfo", "ProcessInfo");
}
const end = Date.now();
console.log(`Took ${end - start}ms to do ${count} completion requests`);
});
});
```
Output from a few runs:
```
Took 56426ms to do 50 completion requests
Took 57034ms to do 50 completion requests
Took 57607ms to do 50 completion requests
``` | True | Improve performance of completions - ~~As well as probably being the cause of #1721~~, the performance of completions with unimported symbols is generally poor.
Testing on Windows PC with the following test (inside `test\flutter_only\providers\completion_item_provider.test.ts`):
```
describe("with SuggestionSet support", () => {
beforeEach("ensure SuggestionSets are supported", function () {
if (!extApi.analyzerCapabilities.supportsAvailableSuggestions)
this.skip();
});
it.only("includes unimported symbols", async () => {
await setTestContent(`
main() {
ProcessInf
}
`);
const count = 50;
const start = Date.now();
for (let i = 0; i < 50; i++) {
const completions = await getCompletionsAt("ProcessInf^");
ensureCompletion(completions, vs.CompletionItemKind.Class, "ProcessInfo", "ProcessInfo");
}
const end = Date.now();
console.log(`Took ${end - start}ms to do ${count} completion requests`);
});
});
```
Output from a few runs:
```
Took 56426ms to do 50 completion requests
Took 57034ms to do 50 completion requests
Took 57607ms to do 50 completion requests
``` | non_infrastructure | improve performance of completions as well as probably being the cause of the performance of completions with unimported symbols is generally poor testing on windows pc with the following test inside test flutter only providers completion item provider test ts describe with suggestionset support beforeeach ensure suggestionsets are supported function if extapi analyzercapabilities supportsavailablesuggestions this skip it only includes unimported symbols async await settestcontent main processinf const count const start date now for let i i i const completions await getcompletionsat processinf ensurecompletion completions vs completionitemkind class processinfo processinfo const end date now console log took end start ms to do count completion requests output from a few runs took to do completion requests took to do completion requests took to do completion requests | 0 |
260,749 | 27,784,709,666 | IssuesEvent | 2023-03-17 01:30:41 | n-devs/NodeJSControUI | https://api.github.com/repos/n-devs/NodeJSControUI | closed | WS-2020-0042 (High) detected in acorn-5.5.0.tgz - autoclosed | Mend: dependency security vulnerability | ## WS-2020-0042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>acorn-5.5.0.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.5.0.tgz">https://registry.npmjs.org/acorn/-/acorn-5.5.0.tgz</a></p>
<p>Path to dependency file: /NodeJSControUI/package.json</p>
<p>Path to vulnerable library: /node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- jsdom-11.6.2.tgz (Root Library)
- :x: **acorn-5.5.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-01
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-6chw-6frg-f759">https://github.com/advisories/GHSA-6chw-6frg-f759</a></p>
<p>Release Date: 2020-03-01</p>
<p>Fix Resolution (acorn): 5.7.4</p>
<p>Direct dependency fix Resolution (jsdom): 11.7.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0042 (High) detected in acorn-5.5.0.tgz - autoclosed - ## WS-2020-0042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>acorn-5.5.0.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.5.0.tgz">https://registry.npmjs.org/acorn/-/acorn-5.5.0.tgz</a></p>
<p>Path to dependency file: /NodeJSControUI/package.json</p>
<p>Path to vulnerable library: /node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- jsdom-11.6.2.tgz (Root Library)
- :x: **acorn-5.5.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-01
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-6chw-6frg-f759">https://github.com/advisories/GHSA-6chw-6frg-f759</a></p>
<p>Release Date: 2020-03-01</p>
<p>Fix Resolution (acorn): 5.7.4</p>
<p>Direct dependency fix Resolution (jsdom): 11.7.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | ws high detected in acorn tgz autoclosed ws high severity vulnerability vulnerable library acorn tgz ecmascript parser library home page a href path to dependency file nodejscontroui package json path to vulnerable library node modules acorn package json dependency hierarchy jsdom tgz root library x acorn tgz vulnerable library vulnerability details acorn is vulnerable to regex dos a regex of the form u causes the parser to enter an infinite loop attackers may leverage the vulnerability leading to a denial of service since the string is not valid and it results in it being sanitized before reaching the parser publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution acorn direct dependency fix resolution jsdom step up your open source security game with mend | 0 |
181,825 | 14,889,836,110 | IssuesEvent | 2021-01-20 22:02:16 | JoshClose/CsvHelper | https://api.github.com/repos/JoshClose/CsvHelper | closed | Changing Delimiter Documentation | documentation | I'm unable to find an example of how to change the delimiter when reading a file.
The following code no longer works since 20.0.0 since the Delimiter parameter is read-only:
`csvReader.Configuration.Delimiter = "|";`
If you look around the internet (Stack Overflow, etc.) this is always the way that it seems to be done. I can't seem to find an example or pattern on how to now accomplish this. | 1.0 | Changing Delimiter Documentation - I'm unable to find an example of how to change the delimiter when reading a file.
The following code no longer works since 20.0.0 since the Delimiter parameter is read-only:
`csvReader.Configuration.Delimiter = "|";`
If you look around the internet (Stack Overflow, etc.) this is always the way that it seems to be done. I can't seem to find an example or pattern on how to now accomplish this. | non_infrastructure | changing delimiter documentation i m unable to find an example of how to change the delimiter when reading a file the following code no longer works since since the delimiter parameter is read only csvreader configuration delimiter if you look around the internet stack overflow etc this is always the way that it seems to be done i can t seem to find an example or pattern on how to now accomplish this | 0 |
26,664 | 20,405,591,992 | IssuesEvent | 2022-02-23 04:44:54 | google/pytype | https://api.github.com/repos/google/pytype | closed | Consistently getting [import-error] when using PYTHONPATH | bug cat: infrastructure | directory structure:
```
/app/src
/app/src/bridge.py
/app/src/writers/bridge_metrics.py
```
running like
```
PYTHONPATH=./src pytype ./src
```
and bridge_writer.py
```
import bridge
```
getting the error
```
FAILED: /app/src/.pytype/pyi/src/writers/bridge_metrics.pyi
/usr/local/bin/python -m pytype.single --imports_info /app/src/.pytype/imports/src.writers.bridge_metrics.imports --module-name src.writers.bridge_metrics -V 3.9 -o /app/src/.pytype/pyi/src/writers/bridge_metrics.pyi --analyze-annotated --nofail --quick /app/src/writers/bridge_metrics.py
``` | 1.0 | Consistently getting [import-error] when using PYTHONPATH - directory structure:
```
/app/src
/app/src/bridge.py
/app/src/writers/bridge_metrics.py
```
running like
```
PYTHONPATH=./src pytype ./src
```
and bridge_writer.py
```
import bridge
```
getting the error
```
FAILED: /app/src/.pytype/pyi/src/writers/bridge_metrics.pyi
/usr/local/bin/python -m pytype.single --imports_info /app/src/.pytype/imports/src.writers.bridge_metrics.imports --module-name src.writers.bridge_metrics -V 3.9 -o /app/src/.pytype/pyi/src/writers/bridge_metrics.pyi --analyze-annotated --nofail --quick /app/src/writers/bridge_metrics.py
``` | infrastructure | consistently getting when using pythonpath directory structure app src app src bridge py app src writers bridge metrics py running like pythonpath src pytype src and bridge writer py import bridge getting the error failed app src pytype pyi src writers bridge metrics pyi usr local bin python m pytype single imports info app src pytype imports src writers bridge metrics imports module name src writers bridge metrics v o app src pytype pyi src writers bridge metrics pyi analyze annotated nofail quick app src writers bridge metrics py | 1 |
16,561 | 11,082,780,248 | IssuesEvent | 2019-12-13 13:00:18 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | iPhone x - home button / indicator is overlaying my ui | bug platform:ios topic:porting usability | **Godot version:**
3.1.2
**OS/device including version:**
iOS 11 / iPhone X
**Issue description:**
One of my testers told me that the home indicator / home bar (this white / black line at the bottom of the screen on iPhones without a home button) is overlaying my UI .
https://cdn.vox-cdn.com/thumbor/INnrzpqGKqRD7dfJ43nUU19yTDw=/800x0/filters:no_upscale()/cdn.vox-cdn.com/uploads/chorus_asset/file/9244305/fGEC9TJ.png
(Not my game, just an illustration I found online)
He also said that other games hide the home bar until the user swiped upward from the button of the screen to show it again for a few seconds.
I wasn't sure to add this as a missing feature or bug, but I dediced it's a bug because in my opinion that's something that prevents pushing godot apps to the appstore. Sure I couldmove my UI, but that wouldn't solve the issue, as I want my game to behave like the others and hide the home bar as my tester said it's disturbing the experience.
Is there a workaround? Can this be done in the exported xcode project somehow:
https://stackoverflow.com/a/48066439 ?
**Steps to reproduce:**
Run your Godot app on an iPhone without physical home button
| True | iPhone x - home button / indicator is overlaying my ui - **Godot version:**
3.1.2
**OS/device including version:**
iOS 11 / iPhone X
**Issue description:**
One of my testers told me that the home indicator / home bar (this white / black line at the bottom of the screen on iPhones without a home button) is overlaying my UI .
https://cdn.vox-cdn.com/thumbor/INnrzpqGKqRD7dfJ43nUU19yTDw=/800x0/filters:no_upscale()/cdn.vox-cdn.com/uploads/chorus_asset/file/9244305/fGEC9TJ.png
(Not my game, just an illustration I found online)
He also said that other games hide the home bar until the user swiped upward from the button of the screen to show it again for a few seconds.
I wasn't sure to add this as a missing feature or bug, but I dediced it's a bug because in my opinion that's something that prevents pushing godot apps to the appstore. Sure I couldmove my UI, but that wouldn't solve the issue, as I want my game to behave like the others and hide the home bar as my tester said it's disturbing the experience.
Is there a workaround? Can this be done in the exported xcode project somehow:
https://stackoverflow.com/a/48066439 ?
**Steps to reproduce:**
Run your Godot app on an iPhone without physical home button
| non_infrastructure | iphone x home button indicator is overlaying my ui godot version os device including version ios iphone x issue description one of my testers told me that the home indicator home bar this white black line at the bottom of the screen on iphones without a home button is overlaying my ui not my game just an illustration i found online he also said that other games hide the home bar until the user swiped upward from the button of the screen to show it again for a few seconds i wasn t sure to add this as a missing feature or bug but i dediced it s a bug because in my opinion that s something that prevents pushing godot apps to the appstore sure i couldmove my ui but that wouldn t solve the issue as i want my game to behave like the others and hide the home bar as my tester said it s disturbing the experience is there a workaround can this be done in the exported xcode project somehow steps to reproduce run your godot app on an iphone without physical home button | 0 |
345,610 | 24,867,127,016 | IssuesEvent | 2022-10-27 12:48:57 | open-telemetry/opentelemetry-python-contrib | https://api.github.com/repos/open-telemetry/opentelemetry-python-contrib | closed | Fix ConfluentKafkaInstrumentor usage | documentation help wanted | **Describe your environment**
Docker image running `python:3.10.7-slim-bullseye` as base
**Steps to reproduce**
```python3
from opentelemetry.instrumentation.confluentkafka import ConfluentKafkaInstrumentor
# Instrument kafka
ConfluentKafkaInstrumentor().instrument()
```
**What is the expected behavior?**
Instrumentation to work just by adding the lines above.
**What is the actual behavior?**
> ModuleNotFoundError: No module named 'opentelemetry.instrumentation.confluentkafka'
**Additional context**
The solution is to actually make the import like this:
```python3
from opentelemetry.instrumentation.confluent_kafka import ConfluentKafkaInstrumentor
```
| 1.0 | Fix ConfluentKafkaInstrumentor usage - **Describe your environment**
Docker image running `python:3.10.7-slim-bullseye` as base
**Steps to reproduce**
```python3
from opentelemetry.instrumentation.confluentkafka import ConfluentKafkaInstrumentor
# Instrument kafka
ConfluentKafkaInstrumentor().instrument()
```
**What is the expected behavior?**
Instrumentation to work just by adding the lines above.
**What is the actual behavior?**
> ModuleNotFoundError: No module named 'opentelemetry.instrumentation.confluentkafka'
**Additional context**
The solution is to actually make the import like this:
```python3
from opentelemetry.instrumentation.confluent_kafka import ConfluentKafkaInstrumentor
```
| non_infrastructure | fix confluentkafkainstrumentor usage describe your environment docker image running python slim bullseye as base steps to reproduce from opentelemetry instrumentation confluentkafka import confluentkafkainstrumentor instrument kafka confluentkafkainstrumentor instrument what is the expected behavior instrumentation to work just by adding the lines above what is the actual behavior modulenotfounderror no module named opentelemetry instrumentation confluentkafka additional context the solution is to actually make the import like this from opentelemetry instrumentation confluent kafka import confluentkafkainstrumentor | 0 |
7,813 | 5,223,466,585 | IssuesEvent | 2017-01-27 12:20:59 | interactive-instruments/etf-webapp | https://api.github.com/repos/interactive-instruments/etf-webapp | opened | Show used TestObject / ETSs and test result in test report view | usability Web UI | - [ ] Test Object
- [ ] ETSs
- [ ] test result | True | Show used TestObject / ETSs and test result in test report view - - [ ] Test Object
- [ ] ETSs
- [ ] test result | non_infrastructure | show used testobject etss and test result in test report view test object etss test result | 0 |
34,516 | 30,036,753,808 | IssuesEvent | 2023-06-27 13:13:28 | Qiskit-Extensions/quantum-serverless | https://api.github.com/repos/Qiskit-Extensions/quantum-serverless | closed | Infrastructure: improve default cluster configuration | enhancement priority: medium project: infrastructure | <!-- ⚠️ If you do not respect this template, your issue will be closed -->
<!-- ⚠️ Make sure to browse the opened and closed issues to confirm this idea does not exist. -->
### What is the expected enhancement?
Infrastructure: improve default cluster configuration
Currently default cluster that is created has 1 head node with 2 cpu 2 Gb mem + 1 worker with 1 cpu 1 Gb mem.
This configuration is faulty as it is causing memory overflow once you start more than 1 parallel task.
Todos:
- create cluster template with node types with at least 2 cpu 2 gb mem
- maybe work out couple of popular configuration keeping in mind workloads we have | 1.0 | Infrastructure: improve default cluster configuration - <!-- ⚠️ If you do not respect this template, your issue will be closed -->
<!-- ⚠️ Make sure to browse the opened and closed issues to confirm this idea does not exist. -->
### What is the expected enhancement?
Infrastructure: improve default cluster configuration
Currently default cluster that is created has 1 head node with 2 cpu 2 Gb mem + 1 worker with 1 cpu 1 Gb mem.
This configuration is faulty as it is causing memory overflow once you start more than 1 parallel task.
Todos:
- create cluster template with node types with at least 2 cpu 2 gb mem
- maybe work out couple of popular configuration keeping in mind workloads we have | infrastructure | infrastructure improve default cluster configuration what is the expected enhancement infrastructure improve default cluster configuration currently default cluster that is created has head node with cpu gb mem worker with cpu gb mem this configuration is faulty as it is causing memory overflow once you start more than parallel task todos create cluster template with node types with at least cpu gb mem maybe work out couple of popular configuration keeping in mind workloads we have | 1 |
23,228 | 15,951,045,623 | IssuesEvent | 2021-04-15 09:22:31 | airyhq/airy | https://api.github.com/repos/airyhq/airy | closed | API and media-resolver configuration sections not working | cli infrastructure | The sections for `api` and `media-resolver` in the `components configuration` of the docs https://airy.co/docs/core/getting-started/installation/configuration#components are currently not working, because at the moment we don't consider them with the `airy config apply` command.
| 1.0 | API and media-resolver configuration sections not working - The sections for `api` and `media-resolver` in the `components configuration` of the docs https://airy.co/docs/core/getting-started/installation/configuration#components are currently not working, because at the moment we don't consider them with the `airy config apply` command.
| infrastructure | api and media resolver configuration sections not working the sections for api and media resolver in the components configuration of the docs are currently not working because at the moment we don t consider them with the airy config apply command | 1 |
33,635 | 27,638,834,584 | IssuesEvent | 2023-03-10 16:23:33 | celestiaorg/test-infra | https://api.github.com/repos/celestiaorg/test-infra | closed | docker: Slack notification in case of CVEs | good first issue help wanted infrastructure docker | Hello team,
The following ticket is created in order to add security during our supply chain for our Docker images.
ℹ️ Low priority
As you may know I've been working on the CI part, adding some new features, one of the was [Trivy](https://www.aquasec.com/products/trivy/) which is a tool that help us for scanning our Docker images and provide us a summary.
The idea behind this ticket is to connect our Slack (we'll have to create a channel for it), to Github and send a notification to it in case that during the CI, Trivy detects any CVE or potential bug.
After this, we'll have to go and fix it.
A CVE example:

---
Why is this important?
If we have a CVE(Common Vulnerabilities and Exposures), that means that our code is vulnerable and our services are exposed to be hacked/hijacked.
From my prospective, it's better to be "a little paranoid" in some way and be proactive in the security field.
---
Some interesting articles:
[what is a CVE](https://www.redhat.com/en/topics/security/what-is-cve)
---
- [ ] Create Slack channel for this/discuss with the team which one will be find to use.
- [ ] Test it.
---
Next steps:
- [ ] Update the Github Action to block the build, currently is just informative.
---
## This has to be done for the two services.
- [ ] [celestia-node](https://github.com/celestiaorg/celestia-node)
- [ ] [celestia-app](https://github.com/celestiaorg/celestia-app)
---
Best 🚀
Jose Ramon Mañes
| 1.0 | docker: Slack notification in case of CVEs - Hello team,
The following ticket is created in order to add security during our supply chain for our Docker images.
ℹ️ Low priority
As you may know I've been working on the CI part, adding some new features, one of the was [Trivy](https://www.aquasec.com/products/trivy/) which is a tool that help us for scanning our Docker images and provide us a summary.
The idea behind this ticket is to connect our Slack (we'll have to create a channel for it), to Github and send a notification to it in case that during the CI, Trivy detects any CVE or potential bug.
After this, we'll have to go and fix it.
A CVE example:

---
Why is this important?
If we have a CVE(Common Vulnerabilities and Exposures), that means that our code is vulnerable and our services are exposed to be hacked/hijacked.
From my prospective, it's better to be "a little paranoid" in some way and be proactive in the security field.
---
Some interesting articles:
[what is a CVE](https://www.redhat.com/en/topics/security/what-is-cve)
---
- [ ] Create Slack channel for this/discuss with the team which one will be find to use.
- [ ] Test it.
---
Next steps:
- [ ] Update the Github Action to block the build, currently is just informative.
---
## This has to be done for the two services.
- [ ] [celestia-node](https://github.com/celestiaorg/celestia-node)
- [ ] [celestia-app](https://github.com/celestiaorg/celestia-app)
---
Best 🚀
Jose Ramon Mañes
| infrastructure | docker slack notification in case of cves hello team the following ticket is created in order to add security during our supply chain for our docker images ℹ️ low priority as you may know i ve been working on the ci part adding some new features one of the was which is a tool that help us for scanning our docker images and provide us a summary the idea behind this ticket is to connect our slack we ll have to create a channel for it to github and send a notification to it in case that during the ci trivy detects any cve or potential bug after this we ll have to go and fix it a cve example why is this important if we have a cve common vulnerabilities and exposures that means that our code is vulnerable and our services are exposed to be hacked hijacked from my prospective it s better to be a little paranoid in some way and be proactive in the security field some interesting articles create slack channel for this discuss with the team which one will be find to use test it next steps update the github action to block the build currently is just informative this has to be done for the two services best 🚀 jose ramon mañes | 1 |
97,785 | 11,032,502,608 | IssuesEvent | 2019-12-06 20:20:33 | angr/nixpkgs | https://api.github.com/repos/angr/nixpkgs | opened | Add examples on How To Use | documentation | Title is kinda self-explanatory.
The following `shell.nix` examples should be provided:
* How to use this to get `angr` working;
- Via NUR;
- "Standalone" (with a local version of this repo;
* How to create a development environment for `angr` (and its components). | 1.0 | Add examples on How To Use - Title is kinda self-explanatory.
The following `shell.nix` examples should be provided:
* How to use this to get `angr` working;
- Via NUR;
- "Standalone" (with a local version of this repo;
* How to create a development environment for `angr` (and its components). | non_infrastructure | add examples on how to use title is kinda self explanatory the following shell nix examples should be provided how to use this to get angr working via nur standalone with a local version of this repo how to create a development environment for angr and its components | 0 |
49,716 | 6,038,025,446 | IssuesEvent | 2017-06-09 20:16:37 | schtunt/simbol | https://api.github.com/repos/schtunt/simbol | opened | Make `ldap', `ng', and `vault' module and tests conform to the new standard (v1.0-rc2) | clean-up help-wanted testing | Progress:
- [ ] vault
- [ ] ldap
- [ ] ng
See `share/lint/*` for a starting point. | 1.0 | Make `ldap', `ng', and `vault' module and tests conform to the new standard (v1.0-rc2) - Progress:
- [ ] vault
- [ ] ldap
- [ ] ng
See `share/lint/*` for a starting point. | non_infrastructure | make ldap ng and vault module and tests conform to the new standard progress vault ldap ng see share lint for a starting point | 0 |
220,057 | 24,553,610,522 | IssuesEvent | 2022-10-12 14:19:47 | dmyers87/code-scanning-javascript-demo | https://api.github.com/repos/dmyers87/code-scanning-javascript-demo | opened | CVE-2022-37609 (Medium) detected in js-beautify-1.14.0.tgz | security vulnerability | ## CVE-2022-37609 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>js-beautify-1.14.0.tgz</b></p></summary>
<p>beautifier.io for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-beautify/-/js-beautify-1.14.0.tgz">https://registry.npmjs.org/js-beautify/-/js-beautify-1.14.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/js-beautify/package.json</p>
<p>
Dependency Hierarchy:
- standard-4.5.4.tgz (Root Library)
- standard-format-1.6.10.tgz
- esformatter-jsx-2.3.11.tgz
- :x: **js-beautify-1.14.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dmyers87/code-scanning-javascript-demo/commit/71720cbc5b3eec7a28c9894bed1eec1294590b96">71720cbc5b3eec7a28c9894bed1eec1294590b96</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution vulnerability in beautify-web js-beautify 1.13.7 via the name variable in options.js.
<p>Publish Date: 2022-10-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-37609>CVE-2022-37609</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
| True | CVE-2022-37609 (Medium) detected in js-beautify-1.14.0.tgz - ## CVE-2022-37609 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>js-beautify-1.14.0.tgz</b></p></summary>
<p>beautifier.io for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-beautify/-/js-beautify-1.14.0.tgz">https://registry.npmjs.org/js-beautify/-/js-beautify-1.14.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/js-beautify/package.json</p>
<p>
Dependency Hierarchy:
- standard-4.5.4.tgz (Root Library)
- standard-format-1.6.10.tgz
- esformatter-jsx-2.3.11.tgz
- :x: **js-beautify-1.14.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dmyers87/code-scanning-javascript-demo/commit/71720cbc5b3eec7a28c9894bed1eec1294590b96">71720cbc5b3eec7a28c9894bed1eec1294590b96</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution vulnerability in beautify-web js-beautify 1.13.7 via the name variable in options.js.
<p>Publish Date: 2022-10-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-37609>CVE-2022-37609</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
| non_infrastructure | cve medium detected in js beautify tgz cve medium severity vulnerability vulnerable library js beautify tgz beautifier io for node library home page a href path to dependency file package json path to vulnerable library node modules js beautify package json dependency hierarchy standard tgz root library standard format tgz esformatter jsx tgz x js beautify tgz vulnerable library found in head commit a href found in base branch main vulnerability details prototype pollution vulnerability in beautify web js beautify via the name variable in options js publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href | 0 |
16,427 | 11,959,426,298 | IssuesEvent | 2020-04-04 21:55:59 | JoshuaBelden/pandemic-memorial | https://api.github.com/repos/JoshuaBelden/pandemic-memorial | closed | Auth secret needs to be configurable in prod. | infrastructure | We need to create an actual secret for the production app and handled in a way that it is not in source. | 1.0 | Auth secret needs to be configurable in prod. - We need to create an actual secret for the production app and handled in a way that it is not in source. | infrastructure | auth secret needs to be configurable in prod we need to create an actual secret for the production app and handled in a way that it is not in source | 1 |
34,056 | 28,140,211,518 | IssuesEvent | 2023-04-01 21:26:15 | t3kt/raytk | https://api.github.com/repos/t3kt/raytk | closed | function graph thumbnails for Fn ops | enhancement end user tools infrastructure | It would be great to be able to easily see the shape of function ops when picking them. | 1.0 | function graph thumbnails for Fn ops - It would be great to be able to easily see the shape of function ops when picking them. | infrastructure | function graph thumbnails for fn ops it would be great to be able to easily see the shape of function ops when picking them | 1 |
339,422 | 10,253,912,011 | IssuesEvent | 2019-08-21 12:27:51 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.cbsnews.com - Video player image appears behind video | browser-fenix priority-important severity-important status-first-contact | <!-- @browser: Fenix -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:68.0) Gecko/20100101 Firefox/68.0 -->
<!-- @reported_with: addon-reporter-firefox -->
**URL**: https://www.cbsnews.com/amp/news/barr-in-contempt-of-congress-hearing-judiciary-committee-vote-attorney-general-barr-mueller-report-today-2019-05-08/
**Browser / Version**: Fenix
**Operating System**: Android
**Tested Another Browser**: No
**Problem type**: Design is broken
**Description**: [Bug] Video player image appears behind video
**Steps to Reproduce**:
Created from [#2364](https://github.com/mozilla-mobile/fenix/issues/2364)
## Steps to reproduce
Navigate to https://www.cbsnews.com/amp/news/barr-in-contempt-of-congress-hearing-judiciary-committee-vote-attorney-general-barr-mueller-report-today-2019-05-08/
Doesn't matter if TP is on or off.
### Expected behavior
No play icon appearing behind video.
### Actual behavior
Large play icon appearing behind video.

Does not appear in Fennec, Focus, or Reference Browser.
### Device information
* Android device: Pixel 2
* Fenix version: latest from play store
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | www.cbsnews.com - Video player image appears behind video - <!-- @browser: Fenix -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:68.0) Gecko/20100101 Firefox/68.0 -->
<!-- @reported_with: addon-reporter-firefox -->
**URL**: https://www.cbsnews.com/amp/news/barr-in-contempt-of-congress-hearing-judiciary-committee-vote-attorney-general-barr-mueller-report-today-2019-05-08/
**Browser / Version**: Fenix
**Operating System**: Android
**Tested Another Browser**: No
**Problem type**: Design is broken
**Description**: [Bug] Video player image appears behind video
**Steps to Reproduce**:
Created from [#2364](https://github.com/mozilla-mobile/fenix/issues/2364)
## Steps to reproduce
Navigate to https://www.cbsnews.com/amp/news/barr-in-contempt-of-congress-hearing-judiciary-committee-vote-attorney-general-barr-mueller-report-today-2019-05-08/
Doesn't matter if TP is on or off.
### Expected behavior
No play icon appearing behind video.
### Actual behavior
Large play icon appearing behind video.

Does not appear in Fennec, Focus, or Reference Browser.
### Device information
* Android device: Pixel 2
* Fenix version: latest from play store
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_infrastructure | video player image appears behind video url browser version fenix operating system android tested another browser no problem type design is broken description video player image appears behind video steps to reproduce created from steps to reproduce navigate to doesn t matter if tp is on or off expected behavior no play icon appearing behind video actual behavior large play icon appearing behind video does not appear in fennec focus or reference browser device information android device pixel fenix version latest from play store browser configuration none from with ❤️ | 0 |
27,607 | 12,676,134,266 | IssuesEvent | 2020-06-19 04:06:46 | Azure/azure-sdk-for-go | https://api.github.com/repos/Azure/azure-sdk-for-go | closed | Failed to delete resource Shared Image when the delete API of Shared Image Gallery returns 404 | Compute - Images Mgmt Service Attention | ### Bug Report
<!--
Thank you for opening a bug report. For faster processing, please include:
-->
- Import path of package in question: https://github.com/Azure/azure-sdk-for-go/blob/master/services/compute/mgmt/2019-07-01/compute/galleryimages.go
- SDK version: v41.2.0
- Output of `go version`: go version go1.12.9 windows/amd64
<!--
and please describe:
-->
- **What happened?**
The resource Shared Image depends on the resource Shared Image Gallery. Although the delete API returns 404 which means the Shared Image resource has been deleted. Then it tries to immediately delete Shared Image Gallery but it still throws error `Can not delete resource before nested resources are deleted.`, which means the resource Shared Image still hasn't been deleted. So it failed to delete top resource Shared Image Gallery.
- **What did you expect or want to happen?**
It should delete both resources Shared Image and Shared Image Gallery successfully.
- **How can we reproduce it?**
1. Create a resource group
2. Create Shared Image Gallery
3. Create Shared Image
4. Delete Shared Image, which returns "202"
5. Immediately call "Get" rest api to get resource Shared Image, which returns "404"
6. Immediately delete Shared Image Gallery, which returns error code "409"
7. Then it throws error `Can not delete resource before nested resources are deleted.`
<!--
Thanks!
-->
| 1.0 | Failed to delete resource Shared Image when the delete API of Shared Image Gallery returns 404 - ### Bug Report
<!--
Thank you for opening a bug report. For faster processing, please include:
-->
- Import path of package in question: https://github.com/Azure/azure-sdk-for-go/blob/master/services/compute/mgmt/2019-07-01/compute/galleryimages.go
- SDK version: v41.2.0
- Output of `go version`: go version go1.12.9 windows/amd64
<!--
and please describe:
-->
- **What happened?**
The resource Shared Image depends on the resource Shared Image Gallery. Although the delete API returns 404 which means the Shared Image resource has been deleted. Then it tries to immediately delete Shared Image Gallery but it still throws error `Can not delete resource before nested resources are deleted.`, which means the resource Shared Image still hasn't been deleted. So it failed to delete top resource Shared Image Gallery.
- **What did you expect or want to happen?**
It should delete both resources Shared Image and Shared Image Gallery successfully.
- **How can we reproduce it?**
1. Create a resource group
2. Create Shared Image Gallery
3. Create Shared Image
4. Delete Shared Image, which returns "202"
5. Immediately call "Get" rest api to get resource Shared Image, which returns "404"
6. Immediately delete Shared Image Gallery, which returns error code "409"
7. Then it throws error `Can not delete resource before nested resources are deleted.`
<!--
Thanks!
-->
| non_infrastructure | failed to delete resource shared image when the delete api of shared image gallery returns bug report thank you for opening a bug report for faster processing please include import path of package in question sdk version output of go version go version windows and please describe what happened the resource shared image depends on the resource shared image gallery although the delete api returns which means the shared image resource has been deleted then it tries to immediately delete shared image gallery but it still throws error can not delete resource before nested resources are deleted which means the resource shared image still hasn t been deleted so it failed to delete top resource shared image gallery what did you expect or want to happen it should delete both resources shared image and shared image gallery successfully how can we reproduce it create a resource group create shared image gallery create shared image delete shared image which returns immediately call get rest api to get resource shared image which returns immediately delete shared image gallery which returns error code then it throws error can not delete resource before nested resources are deleted thanks | 0 |
121,352 | 12,123,769,089 | IssuesEvent | 2020-04-22 13:14:50 | microsoft/AttackSurfaceAnalyzer | https://api.github.com/repos/microsoft/AttackSurfaceAnalyzer | closed | Document how to validate the signature on the hashes file | documentation | Follows up from #108. We need documentation for how end users could validate the pgp signature on the hashes file if they desired to do so. | 1.0 | Document how to validate the signature on the hashes file - Follows up from #108. We need documentation for how end users could validate the pgp signature on the hashes file if they desired to do so. | non_infrastructure | document how to validate the signature on the hashes file follows up from we need documentation for how end users could validate the pgp signature on the hashes file if they desired to do so | 0 |
23,502 | 16,343,447,081 | IssuesEvent | 2021-05-13 02:48:00 | nilearn/nilearn | https://api.github.com/repos/nilearn/nilearn | closed | doc not building with sphinx 4.0.1 | Bug Important Infrastructure Maintenance impact: high priority: high testing | `make html-noplot` fails since the latest release of sphinx on monday
see for example [this build](https://app.circleci.com/pipelines/github/nilearn/nilearn/2034/workflows/2bd1d45d-b513-41d2-a941-c17feab7e8e2/jobs/7212) | 1.0 | doc not building with sphinx 4.0.1 - `make html-noplot` fails since the latest release of sphinx on monday
see for example [this build](https://app.circleci.com/pipelines/github/nilearn/nilearn/2034/workflows/2bd1d45d-b513-41d2-a941-c17feab7e8e2/jobs/7212) | infrastructure | doc not building with sphinx make html noplot fails since the latest release of sphinx on monday see for example | 1 |
96,610 | 16,137,310,848 | IssuesEvent | 2021-04-29 13:26:13 | jgeraigery/creative-assets | https://api.github.com/repos/jgeraigery/creative-assets | opened | CVE-2020-8203 (High) detected in lodash-4.17.10.tgz | security vulnerability | ## CVE-2020-8203 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.10.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.10.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.10.tgz</a></p>
<p>Path to dependency file: creative-assets/package.json</p>
<p>Path to vulnerable library: creative-assets/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- airtable-0.5.7.tgz (Root Library)
- :x: **lodash-4.17.10.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/creative-assets/commit/4e1f39edcdc762290e5970db636924edc553703b">4e1f39edcdc762290e5970db636924edc553703b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203>CVE-2020-8203</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1523">https://www.npmjs.com/advisories/1523</a></p>
<p>Release Date: 2020-07-23</p>
<p>Fix Resolution: lodash - 4.17.19</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"airtable:0.5.7;lodash:4.17.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash - 4.17.19"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-8203","vulnerabilityDetails":"Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-8203 (High) detected in lodash-4.17.10.tgz - ## CVE-2020-8203 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.10.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.10.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.10.tgz</a></p>
<p>Path to dependency file: creative-assets/package.json</p>
<p>Path to vulnerable library: creative-assets/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- airtable-0.5.7.tgz (Root Library)
- :x: **lodash-4.17.10.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/creative-assets/commit/4e1f39edcdc762290e5970db636924edc553703b">4e1f39edcdc762290e5970db636924edc553703b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203>CVE-2020-8203</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1523">https://www.npmjs.com/advisories/1523</a></p>
<p>Release Date: 2020-07-23</p>
<p>Fix Resolution: lodash - 4.17.19</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"airtable:0.5.7;lodash:4.17.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash - 4.17.19"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-8203","vulnerabilityDetails":"Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_infrastructure | cve high detected in lodash tgz cve high severity vulnerability vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file creative assets package json path to vulnerable library creative assets node modules lodash package json dependency hierarchy airtable tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details prototype pollution attack when using zipobjectdeep in lodash before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree airtable lodash isminimumfixversionavailable true minimumfixversion lodash basebranches vulnerabilityidentifier cve vulnerabilitydetails prototype pollution attack when using zipobjectdeep in lodash before vulnerabilityurl | 0 |
35,077 | 30,743,311,022 | IssuesEvent | 2023-07-28 13:14:15 | carbon-design-system/carbon | https://api.github.com/repos/carbon-design-system/carbon | closed | Remove the sketch plugin from the codebase | role: dev 🤖 package: sketch type: infrastructure :robot: | Now that we've [gone all in on Figma](https://github.com/carbon-design-system/carbon/discussions/13862), we will no longer be maintaining the sketch plugin and it can be removed from our codebase.
```[tasklist]
- [ ] Remove `packages/sketch` from the codebase
- [ ] Remove references to `@carbon/sketch` throughout the codebase (workflow files, eslintconfig, prettierconfig, build, `.md` documentation, etc). Do a find all for "sketch" and you'll find them all.
```
| 1.0 | Remove the sketch plugin from the codebase - Now that we've [gone all in on Figma](https://github.com/carbon-design-system/carbon/discussions/13862), we will no longer be maintaining the sketch plugin and it can be removed from our codebase.
```[tasklist]
- [ ] Remove `packages/sketch` from the codebase
- [ ] Remove references to `@carbon/sketch` throughout the codebase (workflow files, eslintconfig, prettierconfig, build, `.md` documentation, etc). Do a find all for "sketch" and you'll find them all.
```
| infrastructure | remove the sketch plugin from the codebase now that we ve we will no longer be maintaining the sketch plugin and it can be removed from our codebase remove packages sketch from the codebase remove references to carbon sketch throughout the codebase workflow files eslintconfig prettierconfig build md documentation etc do a find all for sketch and you ll find them all | 1 |
18,298 | 12,886,251,334 | IssuesEvent | 2020-07-13 09:11:58 | PrincetonUniversity/VST | https://api.github.com/repos/PrincetonUniversity/VST | opened | Create new opam packages for VST | infrastructure | This issue is intended as a discussion platform for the desired structure of opam packages for VST (and also CompCert).
What I am currently thinking about is how to handle different platforms (say 32 and 64 bit or x86 and ARM). Obviously only one of them can be available as VST at a time. There are essentially four options:
1. Make compcert / VST for different architectures mutually exclusive in opam
2. Have different root names for different platforms, say VST_X86_32, VST_X84_64, VST_ARM_32, VST_ARM_64 - the same for CompCert
3. Use the same root name for different platforms (VST) and do some -Q / symlink tricks to link "the" VST to the desired folders
4. Have one variant readily accessible as VST and require -Q options for all others.
Since one might want to verify the same code for different platforms, I would think that option 1 and 2 are not very practical. 1.) would require to constantly reinstall VST and CompCert - something opam is not very efficient in - and 2.) would require to adjust the package names in the Coq sources.
4.) is the status quo for CompCert and the opam packages I suggested to @andrew-appel (attached as zip to this issues) and agreeable but raises the question which one should be "the" VST - Xavier recently said that if there is the "CompCert" in opam, it should be x86 64, not 32 as is.
If we agree on option 3.), I would propose the following mechanism(s):
- have specific opam packages, say VST_X86_32, VST_X86_64, VST_ARM_64 and put these into special locations (as is done already for coq-vst-64) where Coq usually does not find them. All of these packages can be installed in parallel. The folder structure is <special_package_root>/VST_<arch>_<bitsize>/VST so that when <special_package_root>/VST_<arch>_<bitsize> is linked in with (just one) -Q option, VST is still known as VST. Which VST it is, depends on the -Q option.
- have selection opam packages, which depend on the specific packages and symlink one of them to the default location and root path VST. The selection packages are mutually exclusive, but can be uninstalled / installed very fast since they just create a folder symlink (a few more for CompCert). This should hardly take a second.
This gives the VST user the following choices:
- install just one selection package (which automatically installs the specific package) and use VST without -Q. Possibly switch between selection packages when switching between platforms.
- Install several specific packages and use VST with -Q options to point to the specific packages.
- point with -Q options to the root of the special package folder and use long qualified names (something like Require Import VST_X86_64.VST.xyz). This would allow to create single proofs which involve several platforms, but it would take some thinking to make sure the respective VSTs find the respective CompCerts.
The current status of CompCert and the currently proposed VST opam packages is that VST X86 32 installs as "VST" in the default location and everything else installs in special locations. So one can use VST X86 32 without -Q but needs -Q for all other platforms.
| 1.0 | Create new opam packages for VST - This issue is intended as a discussion platform for the desired structure of opam packages for VST (and also CompCert).
What I am currently thinking about is how to handle different platforms (say 32 and 64 bit or x86 and ARM). Obviously only one of them can be available as VST at a time. There are essentially four options:
1. Make compcert / VST for different architectures mutually exclusive in opam
2. Have different root names for different platforms, say VST_X86_32, VST_X84_64, VST_ARM_32, VST_ARM_64 - the same for CompCert
3. Use the same root name for different platforms (VST) and do some -Q / symlink tricks to link "the" VST to the desired folders
4. Have one variant readily accessible as VST and require -Q options for all others.
Since one might want to verify the same code for different platforms, I would think that option 1 and 2 are not very practical. 1.) would require to constantly reinstall VST and CompCert - something opam is not very efficient in - and 2.) would require to adjust the package names in the Coq sources.
4.) is the status quo for CompCert and the opam packages I suggested to @andrew-appel (attached as zip to this issues) and agreeable but raises the question which one should be "the" VST - Xavier recently said that if there is the "CompCert" in opam, it should be x86 64, not 32 as is.
If we agree on option 3.), I would propose the following mechanism(s):
- have specific opam packages, say VST_X86_32, VST_X86_64, VST_ARM_64 and put these into special locations (as is done already for coq-vst-64) where Coq usually does not find them. All of these packages can be installed in parallel. The folder structure is <special_package_root>/VST_<arch>_<bitsize>/VST so that when <special_package_root>/VST_<arch>_<bitsize> is linked in with (just one) -Q option, VST is still known as VST. Which VST it is, depends on the -Q option.
- have selection opam packages, which depend on the specific packages and symlink one of them to the default location and root path VST. The selection packages are mutually exclusive, but can be uninstalled / installed very fast since they just create a folder symlink (a few more for CompCert). This should hardly take a second.
This gives the VST user the following choices:
- install just one selection package (which automatically installs the specific package) and use VST without -Q. Possibly switch between selection packages when switching between platforms.
- Install several specific packages and use VST with -Q options to point to the specific packages.
- point with -Q options to the root of the special package folder and use long qualified names (something like Require Import VST_X86_64.VST.xyz). This would allow to create single proofs which involve several platforms, but it would take some thinking to make sure the respective VSTs find the respective CompCerts.
The current status of CompCert and the currently proposed VST opam packages is that VST X86 32 installs as "VST" in the default location and everything else installs in special locations. So one can use VST X86 32 without -Q but needs -Q for all other platforms.
| infrastructure | create new opam packages for vst this issue is intended as a discussion platform for the desired structure of opam packages for vst and also compcert what i am currently thinking about is how to handle different platforms say and bit or and arm obviously only one of them can be available as vst at a time there are essentially four options make compcert vst for different architectures mutually exclusive in opam have different root names for different platforms say vst vst vst arm vst arm the same for compcert use the same root name for different platforms vst and do some q symlink tricks to link the vst to the desired folders have one variant readily accessible as vst and require q options for all others since one might want to verify the same code for different platforms i would think that option and are not very practical would require to constantly reinstall vst and compcert something opam is not very efficient in and would require to adjust the package names in the coq sources is the status quo for compcert and the opam packages i suggested to andrew appel attached as zip to this issues and agreeable but raises the question which one should be the vst xavier recently said that if there is the compcert in opam it should be not as is if we agree on option i would propose the following mechanism s have specific opam packages say vst vst vst arm and put these into special locations as is done already for coq vst where coq usually does not find them all of these packages can be installed in parallel the folder structure is vst vst so that when vst is linked in with just one q option vst is still known as vst which vst it is depends on the q option have selection opam packages which depend on the specific packages and symlink one of them to the default location and root path vst the selection packages are mutually exclusive but can be uninstalled installed very fast since they just create a folder symlink a few more for compcert this should hardly take a second this gives the vst user the following choices install just one selection package which automatically installs the specific package and use vst without q possibly switch between selection packages when switching between platforms install several specific packages and use vst with q options to point to the specific packages point with q options to the root of the special package folder and use long qualified names something like require import vst vst xyz this would allow to create single proofs which involve several platforms but it would take some thinking to make sure the respective vsts find the respective compcerts the current status of compcert and the currently proposed vst opam packages is that vst installs as vst in the default location and everything else installs in special locations so one can use vst without q but needs q for all other platforms | 1 |
24,069 | 16,818,924,701 | IssuesEvent | 2021-06-17 10:42:49 | hzi-braunschweig/SORMAS-Project | https://api.github.com/repos/hzi-braunschweig/SORMAS-Project | closed | country.name does not consider all deposited formats deposited in country infrastructure data | backend bug critical important infrastructure refine | <!--
If you've never submitted an issue to the SORMAS repository before or this is your first time using this template, please read the Contributing guidelines (https://github.com/hzi-braunschweig/SORMAS-Project/blob/development/docs/CONTRIBUTING.md) for an explanation of the information we need you to provide. You don't have to remove this comment or any other comment from this issue as they will automatically be hidden.
-->
### Bug Description
<!-- Mandatory -->
when defining a country.name in the properties, only specific formats can be read. This is a problem when countries are missing in the standard import (cf. https://github.com/hzi-braunschweig/SORMAS-Project/issues/4782#issuecomment-801263814) or were generally added to the list. These countries, to count as the server country, need to be set according to the deposited value. However, the properties file does not allow spaces, quotations marks, apostrophes or special characters. This leads to country names having to be adjusted in undesired ways in order to allow importing of districts.
### Steps to Reproduce
<!-- Optional; please add more steps if necessary -->
1. Add "Côte d'Ivoire" as a country in configurations
2. Set country.name="Côte d'Ivoire"
2. Import regions and districts. (Only the district import should through an error saying that the region is not in server country.)
3. Change the country name to "Cote_dIvoire" in configurations
4. Set country.name=Cote_dIvoire
5. Import districts again
### Expected Behavior
<!-- Optional -->
Any deposited country should be able to be set as country.name and still maintain its proper caption
### Screenshots
<!-- Optional -->
<img width="599" alt="IvoryCoastProperties" src="https://user-images.githubusercontent.com/70317594/120790990-e7545600-c533-11eb-951f-e250a0954f49.PNG">
### System Details
<!-- Mandatory; you only have to specify the Server URL if the error appeared on a publicly available test server -->
* Device:
* SORMAS version: 1.58.3/1.60
* Android version/Browser: firefox
* Server URL: https://test-inhp-ci.sormas.netzlink.com/
* User Role: admin, national user
### Additional Information
<!-- Optional -->
tested country.name options
|country.name|result|
|:--------------|:------|
"Côte d'Ivoire"|fail
Côte d'Ivoire|fail
Ivory Coast|fail
Ivory_Coast|success
Côte_d'Ivoire|fail
Côte_dIvoire|fail
Cote_dIvoire|success
"Ivory Coast"|fail
error report:
[sormas_import_error_ivorycoast(1).txt](https://github.com/hzi-braunschweig/SORMAS-Project/files/6597996/sormas_import_error_ivorycoast.1.txt)
district import template:
[sormas_import_district_template_ivoryCoast(1).txt](https://github.com/hzi-braunschweig/SORMAS-Project/files/6598051/sormas_import_district_template_ivoryCoast.1.txt)
### Possible solutions
[These should merely be suggestions with the limited knowledge I have about the technical details]
- Allow text in between "" to be read in the properties file
- Add country references to lower hierarchy infrastructure (might also have the advantages that these hierarchies can be imported at all for other countries then set in country.name)
- restructure infrastructure so that each line has its own value independent of the name which then will be used as a caption. E.g. when creating an entry for Côte d'Ivoire, the entry produces a value that conforms to the needed format COTE_DIVOIRE and would then be referenced in the properties file.
| 1.0 | country.name does not consider all deposited formats deposited in country infrastructure data - <!--
If you've never submitted an issue to the SORMAS repository before or this is your first time using this template, please read the Contributing guidelines (https://github.com/hzi-braunschweig/SORMAS-Project/blob/development/docs/CONTRIBUTING.md) for an explanation of the information we need you to provide. You don't have to remove this comment or any other comment from this issue as they will automatically be hidden.
-->
### Bug Description
<!-- Mandatory -->
when defining a country.name in the properties, only specific formats can be read. This is a problem when countries are missing in the standard import (cf. https://github.com/hzi-braunschweig/SORMAS-Project/issues/4782#issuecomment-801263814) or were generally added to the list. These countries, to count as the server country, need to be set according to the deposited value. However, the properties file does not allow spaces, quotations marks, apostrophes or special characters. This leads to country names having to be adjusted in undesired ways in order to allow importing of districts.
### Steps to Reproduce
<!-- Optional; please add more steps if necessary -->
1. Add "Côte d'Ivoire" as a country in configurations
2. Set country.name="Côte d'Ivoire"
2. Import regions and districts. (Only the district import should through an error saying that the region is not in server country.)
3. Change the country name to "Cote_dIvoire" in configurations
4. Set country.name=Cote_dIvoire
5. Import districts again
### Expected Behavior
<!-- Optional -->
Any deposited country should be able to be set as country.name and still maintain its proper caption
### Screenshots
<!-- Optional -->
<img width="599" alt="IvoryCoastProperties" src="https://user-images.githubusercontent.com/70317594/120790990-e7545600-c533-11eb-951f-e250a0954f49.PNG">
### System Details
<!-- Mandatory; you only have to specify the Server URL if the error appeared on a publicly available test server -->
* Device:
* SORMAS version: 1.58.3/1.60
* Android version/Browser: firefox
* Server URL: https://test-inhp-ci.sormas.netzlink.com/
* User Role: admin, national user
### Additional Information
<!-- Optional -->
tested country.name options
|country.name|result|
|:--------------|:------|
"Côte d'Ivoire"|fail
Côte d'Ivoire|fail
Ivory Coast|fail
Ivory_Coast|success
Côte_d'Ivoire|fail
Côte_dIvoire|fail
Cote_dIvoire|success
"Ivory Coast"|fail
error report:
[sormas_import_error_ivorycoast(1).txt](https://github.com/hzi-braunschweig/SORMAS-Project/files/6597996/sormas_import_error_ivorycoast.1.txt)
district import template:
[sormas_import_district_template_ivoryCoast(1).txt](https://github.com/hzi-braunschweig/SORMAS-Project/files/6598051/sormas_import_district_template_ivoryCoast.1.txt)
### Possible solutions
[These should merely be suggestions with the limited knowledge I have about the technical details]
- Allow text in between "" to be read in the properties file
- Add country references to lower hierarchy infrastructure (might also have the advantages that these hierarchies can be imported at all for other countries then set in country.name)
- restructure infrastructure so that each line has its own value independent of the name which then will be used as a caption. E.g. when creating an entry for Côte d'Ivoire, the entry produces a value that conforms to the needed format COTE_DIVOIRE and would then be referenced in the properties file.
| infrastructure | country name does not consider all deposited formats deposited in country infrastructure data if you ve never submitted an issue to the sormas repository before or this is your first time using this template please read the contributing guidelines for an explanation of the information we need you to provide you don t have to remove this comment or any other comment from this issue as they will automatically be hidden bug description when defining a country name in the properties only specific formats can be read this is a problem when countries are missing in the standard import cf or were generally added to the list these countries to count as the server country need to be set according to the deposited value however the properties file does not allow spaces quotations marks apostrophes or special characters this leads to country names having to be adjusted in undesired ways in order to allow importing of districts steps to reproduce add côte d ivoire as a country in configurations set country name côte d ivoire import regions and districts only the district import should through an error saying that the region is not in server country change the country name to cote divoire in configurations set country name cote divoire import districts again expected behavior any deposited country should be able to be set as country name and still maintain its proper caption screenshots img width alt ivorycoastproperties src system details device sormas version android version browser firefox server url user role admin national user additional information tested country name options country name result côte d ivoire fail côte d ivoire fail ivory coast fail ivory coast success côte d ivoire fail côte divoire fail cote divoire success ivory coast fail error report district import template possible solutions allow text in between to be read in the properties file add country references to lower hierarchy infrastructure might also have the advantages that these hierarchies can be imported at all for other countries then set in country name restructure infrastructure so that each line has its own value independent of the name which then will be used as a caption e g when creating an entry for côte d ivoire the entry produces a value that conforms to the needed format cote divoire and would then be referenced in the properties file | 1 |
5,835 | 6,008,382,426 | IssuesEvent | 2017-06-06 07:40:29 | vmware/docker-volume-vsphere | https://api.github.com/repos/vmware/docker-volume-vsphere | opened | Turn off unnecessary logs from cleanup routines | component/test-infrastructure P1 | `make clean-all` spits out following lines which is at no use and can be discarded.
```
dpkg-query: no packages found matching docker-volume-vsphere
Error response from daemon: plugin "vsphere:latest" not found
```
Identify which lines are leftout and added redirection `> /dev/null` | 1.0 | Turn off unnecessary logs from cleanup routines - `make clean-all` spits out following lines which is at no use and can be discarded.
```
dpkg-query: no packages found matching docker-volume-vsphere
Error response from daemon: plugin "vsphere:latest" not found
```
Identify which lines are leftout and added redirection `> /dev/null` | infrastructure | turn off unnecessary logs from cleanup routines make clean all spits out following lines which is at no use and can be discarded dpkg query no packages found matching docker volume vsphere error response from daemon plugin vsphere latest not found identify which lines are leftout and added redirection dev null | 1 |
113,121 | 17,116,003,324 | IssuesEvent | 2021-07-11 11:14:14 | theHinneh/ridge-condos- | https://api.github.com/repos/theHinneh/ridge-condos- | closed | CVE-2020-11023 (Medium) detected in jquery-1.7.1.min.js, jquery-3.4.1.slim.min.js | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.7.1.min.js</b>, <b>jquery-3.4.1.slim.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.7.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js</a></p>
<p>Path to dependency file: ridge-condos-/node_modules/sockjs/examples/multiplex/index.html</p>
<p>Path to vulnerable library: ridge-condos-/node_modules/sockjs/examples/multiplex/index.html,ridge-condos-/node_modules/sockjs/examples/express-3.x/index.html,ridge-condos-/node_modules/sockjs/examples/express/index.html,ridge-condos-/node_modules/sockjs/examples/hapi/html/index.html,ridge-condos-/node_modules/sockjs/examples/echo/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.4.1.slim.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.4.1/jquery.slim.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.4.1/jquery.slim.min.js</a></p>
<p>Path to dependency file: ridge-condos-/src/index.html</p>
<p>Path to vulnerable library: ridge-condos-/src/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.4.1.slim.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/theHinneh/ridge-condos-/commit/7c1e7fe6dd1bbeac6fe80f7baf08a8f793d23222">7c1e7fe6dd1bbeac6fe80f7baf08a8f793d23222</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11023 (Medium) detected in jquery-1.7.1.min.js, jquery-3.4.1.slim.min.js - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.7.1.min.js</b>, <b>jquery-3.4.1.slim.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.7.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js</a></p>
<p>Path to dependency file: ridge-condos-/node_modules/sockjs/examples/multiplex/index.html</p>
<p>Path to vulnerable library: ridge-condos-/node_modules/sockjs/examples/multiplex/index.html,ridge-condos-/node_modules/sockjs/examples/express-3.x/index.html,ridge-condos-/node_modules/sockjs/examples/express/index.html,ridge-condos-/node_modules/sockjs/examples/hapi/html/index.html,ridge-condos-/node_modules/sockjs/examples/echo/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.4.1.slim.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.4.1/jquery.slim.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.4.1/jquery.slim.min.js</a></p>
<p>Path to dependency file: ridge-condos-/src/index.html</p>
<p>Path to vulnerable library: ridge-condos-/src/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.4.1.slim.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/theHinneh/ridge-condos-/commit/7c1e7fe6dd1bbeac6fe80f7baf08a8f793d23222">7c1e7fe6dd1bbeac6fe80f7baf08a8f793d23222</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve medium detected in jquery min js jquery slim min js cve medium severity vulnerability vulnerable libraries jquery min js jquery slim min js jquery min js javascript library for dom operations library home page a href path to dependency file ridge condos node modules sockjs examples multiplex index html path to vulnerable library ridge condos node modules sockjs examples multiplex index html ridge condos node modules sockjs examples express x index html ridge condos node modules sockjs examples express index html ridge condos node modules sockjs examples hapi html index html ridge condos node modules sockjs examples echo index html dependency hierarchy x jquery min js vulnerable library jquery slim min js javascript library for dom operations library home page a href path to dependency file ridge condos src index html path to vulnerable library ridge condos src index html dependency hierarchy x jquery slim min js vulnerable library found in head commit a href found in base branch master vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
8,154 | 7,253,944,915 | IssuesEvent | 2018-02-16 08:56:12 | dzhw/metadatamanagement | https://api.github.com/repos/dzhw/metadatamanagement | closed | Edit / Create Page for Surveys | category:surveymanagement points:20 prio:1 scope:project infrastructure status:testing type:backlog item | We will implement a edit / create surveys page without attachment. | 1.0 | Edit / Create Page for Surveys - We will implement a edit / create surveys page without attachment. | infrastructure | edit create page for surveys we will implement a edit create surveys page without attachment | 1 |
462,620 | 13,250,259,703 | IssuesEvent | 2020-08-19 22:33:12 | CredentialEngine/CredentialRegistry | https://api.github.com/repos/CredentialEngine/CredentialRegistry | reopened | Attempt to update a registry document is flagged as not changed when content has changed. | High Priority | The credential: "CyberSAFE (Securing Assets for End-Users) Exam CBS-210" has been set the status of deprecated. The current envelope/graph is:
https://credentialengineregistry.org/ce-registry/envelopes/bd6c0223-311d-4bd2-9adb-9ef558950b1f
https://credentialengineregistry.org/graph/ce-d80e6f22-1cbb-4b8f-97ab-25b255274b92
The json from the following gist has several differences, including the new status and owner:
https://gist.github.com/mparsons-ce/bca7225457c075a06eddee0968cab0ba
When trying to publish the latter JSON document I get the not changed condition.
The latter is only supposed to occur if the payload being uploaded is the same as that in the current envelope.
First, I would like to know why this is occurring.
Second, regardless of the answer to the latter, it may be useful to have an option to bypass the process that compares the update with the current content and force an update.
| 1.0 | Attempt to update a registry document is flagged as not changed when content has changed. - The credential: "CyberSAFE (Securing Assets for End-Users) Exam CBS-210" has been set the status of deprecated. The current envelope/graph is:
https://credentialengineregistry.org/ce-registry/envelopes/bd6c0223-311d-4bd2-9adb-9ef558950b1f
https://credentialengineregistry.org/graph/ce-d80e6f22-1cbb-4b8f-97ab-25b255274b92
The json from the following gist has several differences, including the new status and owner:
https://gist.github.com/mparsons-ce/bca7225457c075a06eddee0968cab0ba
When trying to publish the latter JSON document I get the not changed condition.
The latter is only supposed to occur if the payload being uploaded is the same as that in the current envelope.
First, I would like to know why this is occurring.
Second, regardless of the answer to the latter, it may be useful to have an option to bypass the process that compares the update with the current content and force an update.
| non_infrastructure | attempt to update a registry document is flagged as not changed when content has changed the credential cybersafe securing assets for end users exam cbs has been set the status of deprecated the current envelope graph is the json from the following gist has several differences including the new status and owner when trying to publish the latter json document i get the not changed condition the latter is only supposed to occur if the payload being uploaded is the same as that in the current envelope first i would like to know why this is occurring second regardless of the answer to the latter it may be useful to have an option to bypass the process that compares the update with the current content and force an update | 0 |
34,394 | 29,797,598,547 | IssuesEvent | 2023-06-16 04:50:23 | BCACTF/arcs-issues | https://api.github.com/repos/BCACTF/arcs-issues | opened | Webhook notifications for first bloods on challenges | Infrastructure Feature Suggestion | Having web hook send out more notifications to Discord mid-ctf would be nice and would give it more of a purpose. | 1.0 | Webhook notifications for first bloods on challenges - Having web hook send out more notifications to Discord mid-ctf would be nice and would give it more of a purpose. | infrastructure | webhook notifications for first bloods on challenges having web hook send out more notifications to discord mid ctf would be nice and would give it more of a purpose | 1 |
288,711 | 21,718,418,849 | IssuesEvent | 2022-05-10 20:28:40 | cagov/odi-engineering | https://api.github.com/repos/cagov/odi-engineering | closed | Create documentation for ODI Publishing system. | Documentation p1 | Where does our documentation live? What is the cadence of updates?
Suggestions from Jared:
- "First aid" documentation (wiki) (contact information) - (if any of our third party services
- Internal documentation (who to contact in ODI) | 1.0 | Create documentation for ODI Publishing system. - Where does our documentation live? What is the cadence of updates?
Suggestions from Jared:
- "First aid" documentation (wiki) (contact information) - (if any of our third party services
- Internal documentation (who to contact in ODI) | non_infrastructure | create documentation for odi publishing system where does our documentation live what is the cadence of updates suggestions from jared first aid documentation wiki contact information if any of our third party services internal documentation who to contact in odi | 0 |
18,767 | 13,097,362,647 | IssuesEvent | 2020-08-03 17:19:19 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Switch to label.N form for pre-release label | area-Infrastructure-coreclr | In order to facilitate better preview sorting, switch to label.N form for the pre-release label.
Requires a recent version of arcade, so filing an issue rather than opening a PR. See https://github.com/dotnet/windowsdesktop/pull/104 for an example of how this is done. | 1.0 | Switch to label.N form for pre-release label - In order to facilitate better preview sorting, switch to label.N form for the pre-release label.
Requires a recent version of arcade, so filing an issue rather than opening a PR. See https://github.com/dotnet/windowsdesktop/pull/104 for an example of how this is done. | infrastructure | switch to label n form for pre release label in order to facilitate better preview sorting switch to label n form for the pre release label requires a recent version of arcade so filing an issue rather than opening a pr see for an example of how this is done | 1 |
13,309 | 10,197,709,358 | IssuesEvent | 2019-08-13 01:42:47 | askmench/mench-web-app | https://api.github.com/repos/askmench/mench-web-app | closed | Stop/Terminate Intention V1 | DB/Server/Infrastructure Mined Intelligence | As part of #2526 this would allow the Action Plan intent to be terminated if any stop intent has been marked as complete. | 1.0 | Stop/Terminate Intention V1 - As part of #2526 this would allow the Action Plan intent to be terminated if any stop intent has been marked as complete. | infrastructure | stop terminate intention as part of this would allow the action plan intent to be terminated if any stop intent has been marked as complete | 1 |
18,659 | 13,063,465,768 | IssuesEvent | 2020-07-30 16:34:30 | bradyrx/climpred | https://api.github.com/repos/bradyrx/climpred | reopened | get rid of the sources of warnings in tests | infrastructure | You are encouraged to add information about all relevant sections, but not required to submit an issue.
#### Code Sample, a copy-pastable example if possible
- just fix them
- see https://github.com/pydata/xarray/issues/3266 they have a few good suggestions
#### Problem description
This should explain **why** the current behaviour is a problem and why the expected output is a better solution.
#### Expected Output
#### Output of `climpred.show_versions()`
<details>
# Paste the output here xr.show_versions() here
</details>
| 1.0 | get rid of the sources of warnings in tests - You are encouraged to add information about all relevant sections, but not required to submit an issue.
#### Code Sample, a copy-pastable example if possible
- just fix them
- see https://github.com/pydata/xarray/issues/3266 they have a few good suggestions
#### Problem description
This should explain **why** the current behaviour is a problem and why the expected output is a better solution.
#### Expected Output
#### Output of `climpred.show_versions()`
<details>
# Paste the output here xr.show_versions() here
</details>
| infrastructure | get rid of the sources of warnings in tests you are encouraged to add information about all relevant sections but not required to submit an issue code sample a copy pastable example if possible just fix them see they have a few good suggestions problem description this should explain why the current behaviour is a problem and why the expected output is a better solution expected output output of climpred show versions paste the output here xr show versions here | 1 |
19,102 | 13,187,580,313 | IssuesEvent | 2020-08-13 03:52:58 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | closed | HitSpool interface: report running component (Trac #944) | Migrated from Trac enhancement infrastructure | The cronjob installed on expcont for doing an hourly:
fab hs_status
that reports running or not running comonents to i3live is still not working properly.
<details>
<summary><em>Migrated from https://code.icecube.wisc.edu/ticket/944
, reported by dheereman and owned by dheereman</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-08-10T22:35:05",
"description": "The cronjob installed on expcont for doing an hourly:\n\nfab hs_status\n\nthat reports running or not running comonents to i3live is still not working properly. ",
"reporter": "dheereman",
"cc": "dheereman",
"resolution": "wontfix",
"_ts": "1439246105293024",
"component": "infrastructure",
"summary": "HitSpool interface: report running component",
"priority": "normal",
"keywords": "hitspool",
"time": "2015-04-21T09:52:00",
"milestone": "",
"owner": "dheereman",
"type": "enhancement"
}
```
</p>
</details>
| 1.0 | HitSpool interface: report running component (Trac #944) - The cronjob installed on expcont for doing an hourly:
fab hs_status
that reports running or not running comonents to i3live is still not working properly.
<details>
<summary><em>Migrated from https://code.icecube.wisc.edu/ticket/944
, reported by dheereman and owned by dheereman</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-08-10T22:35:05",
"description": "The cronjob installed on expcont for doing an hourly:\n\nfab hs_status\n\nthat reports running or not running comonents to i3live is still not working properly. ",
"reporter": "dheereman",
"cc": "dheereman",
"resolution": "wontfix",
"_ts": "1439246105293024",
"component": "infrastructure",
"summary": "HitSpool interface: report running component",
"priority": "normal",
"keywords": "hitspool",
"time": "2015-04-21T09:52:00",
"milestone": "",
"owner": "dheereman",
"type": "enhancement"
}
```
</p>
</details>
| infrastructure | hitspool interface report running component trac the cronjob installed on expcont for doing an hourly fab hs status that reports running or not running comonents to is still not working properly migrated from reported by dheereman and owned by dheereman json status closed changetime description the cronjob installed on expcont for doing an hourly n nfab hs status n nthat reports running or not running comonents to is still not working properly reporter dheereman cc dheereman resolution wontfix ts component infrastructure summary hitspool interface report running component priority normal keywords hitspool time milestone owner dheereman type enhancement | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.