Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
391,526 | 26,896,663,212 | IssuesEvent | 2023-02-06 12:57:22 | cloudflare/cloudflare-docs | https://api.github.com/repos/cloudflare/cloudflare-docs | opened | Add guidance when creating Domain lists via API | documentation content:edit | ### Which Cloudflare product does this pertain to?
Zero Trust
### Existing documentation URL(s)
https://developers.cloudflare.com/cloudflare-one/policies/filtering/lists/
### Section that requires update
[](https://developers.cloudflare.com/cloudflare-one/policies/filtering/lists/#create-a-list-from-a-csv-file)
Create a list from a CSV file
### What needs to change?
The conditions doesn't detail what happens when using duplicate hostnames for a "Domain" list.
The API would simply return 409 with the message "A resource with this identifier already exists." and code 1204.
This is potentially misleading if it's the List name or a List item.
### How should it change?
Mention that all hostnames in a list are:
- converted from IDN to Punycode
- checked against existing duplicate hostname in Punycode format.
### Additional information
for e.g, passing a list with these two entries will fail with 1204 error because they're duplicate (though not obvious until you convert to Punycode):
www.españa.com
www.xn--espaa-rta.com | 1.0 | Add guidance when creating Domain lists via API - ### Which Cloudflare product does this pertain to?
Zero Trust
### Existing documentation URL(s)
https://developers.cloudflare.com/cloudflare-one/policies/filtering/lists/
### Section that requires update
[](https://developers.cloudflare.com/cloudflare-one/policies/filtering/lists/#create-a-list-from-a-csv-file)
Create a list from a CSV file
### What needs to change?
The conditions doesn't detail what happens when using duplicate hostnames for a "Domain" list.
The API would simply return 409 with the message "A resource with this identifier already exists." and code 1204.
This is potentially misleading if it's the List name or a List item.
### How should it change?
Mention that all hostnames in a list are:
- converted from IDN to Punycode
- checked against existing duplicate hostname in Punycode format.
### Additional information
for e.g, passing a list with these two entries will fail with 1204 error because they're duplicate (though not obvious until you convert to Punycode):
www.españa.com
www.xn--espaa-rta.com | non_priority | add guidance when creating domain lists via api which cloudflare product does this pertain to zero trust existing documentation url s section that requires update create a list from a csv file what needs to change the conditions doesn t detail what happens when using duplicate hostnames for a domain list the api would simply return with the message a resource with this identifier already exists and code this is potentially misleading if it s the list name or a list item how should it change mention that all hostnames in a list are converted from idn to punycode checked against existing duplicate hostname in punycode format additional information for e g passing a list with these two entries will fail with error because they re duplicate though not obvious until you convert to punycode | 0 |
108,162 | 9,284,628,455 | IssuesEvent | 2019-03-21 02:38:31 | mritd/dockerfile | https://api.github.com/repos/mritd/dockerfile | closed | 能提供一个安卓kcp示例吗 | Need test | 服务端
```
docker run -dt --name ssserver -p 6443:6443 -p 6500:6500/udp mritd/shadowsocks -m "ss-server" -s "-s 0.0.0.0 -p 6443 -m chacha20 -k test123 --fast-open" -x -e "kcpserver" -k "-t 127.0.0.1:6443 -l :6500 -mode fast2"
```
客户端
```
docker run -dt --name ssclient -p 1080:1080 mritd/shadowsocks -m "ss-local" -s "-s 127.0.0.1 -p 6500 -b 0.0.0.0 -l 1080 -m chacha20 -k test123 --fast-open" -x -e "kcpclient" -k "-r SSSERVER_IP:6500 -
l :6500 -mode fast2"
```
在电脑上是可以连接上的,但是到了安卓上就不知道怎么做了。


配置
```
key=;crypt=none;mode=fast2;mtu=1350;sndwnd=128;rcvwnd=512;datashard=10;parityshard=3;dscp=0;nocomp;quiet
```
请问配置哪里有问题了,求助。
| 1.0 | 能提供一个安卓kcp示例吗 - 服务端
```
docker run -dt --name ssserver -p 6443:6443 -p 6500:6500/udp mritd/shadowsocks -m "ss-server" -s "-s 0.0.0.0 -p 6443 -m chacha20 -k test123 --fast-open" -x -e "kcpserver" -k "-t 127.0.0.1:6443 -l :6500 -mode fast2"
```
客户端
```
docker run -dt --name ssclient -p 1080:1080 mritd/shadowsocks -m "ss-local" -s "-s 127.0.0.1 -p 6500 -b 0.0.0.0 -l 1080 -m chacha20 -k test123 --fast-open" -x -e "kcpclient" -k "-r SSSERVER_IP:6500 -
l :6500 -mode fast2"
```
在电脑上是可以连接上的,但是到了安卓上就不知道怎么做了。


配置
```
key=;crypt=none;mode=fast2;mtu=1350;sndwnd=128;rcvwnd=512;datashard=10;parityshard=3;dscp=0;nocomp;quiet
```
请问配置哪里有问题了,求助。
| non_priority | 能提供一个安卓kcp示例吗 服务端 docker run dt name ssserver p p udp mritd shadowsocks m ss server s s p m k fast open x e kcpserver k t l mode 客户端 docker run dt name ssclient p mritd shadowsocks m ss local s s p b l m k fast open x e kcpclient k r ssserver ip l mode 在电脑上是可以连接上的,但是到了安卓上就不知道怎么做了。 配置 key crypt none mode mtu sndwnd rcvwnd datashard parityshard dscp nocomp quiet 请问配置哪里有问题了,求助。 | 0 |
369,651 | 25,861,842,130 | IssuesEvent | 2022-12-13 17:31:00 | jgauchia/IceNav-v3 | https://api.github.com/repos/jgauchia/IceNav-v3 | closed | [doc] request for map documentation | documentation | ## Overview
Great project. I want contribute with the project. My first goal will be try to run a minimal version on T-Display board with my GPS and maybe with the minimal resources files into the user partition flash. For that, is possible describe the procedure to have the map or a basic guide of the map files generation? | 1.0 | [doc] request for map documentation - ## Overview
Great project. I want contribute with the project. My first goal will be try to run a minimal version on T-Display board with my GPS and maybe with the minimal resources files into the user partition flash. For that, is possible describe the procedure to have the map or a basic guide of the map files generation? | non_priority | request for map documentation overview great project i want contribute with the project my first goal will be try to run a minimal version on t display board with my gps and maybe with the minimal resources files into the user partition flash for that is possible describe the procedure to have the map or a basic guide of the map files generation | 0 |
61,141 | 14,939,146,842 | IssuesEvent | 2021-01-25 16:35:53 | EIDSS/EIDSS7 | https://api.github.com/repos/EIDSS/EIDSS7 | closed | LAB: Region does not display and report ID does not populate, unable to register new samples | Build 77.0 Critical bug | **Summary**
Region does not display and report ID does not populate unable to register new samples in the laboratory module
**To Reproduce**
Steps to reproduce the behavior:
1. Log in as mollyrue
2. Go to step #6 >Region: does not populate>Report ID>no report ID generated>Report ID does not populate
2. Click on '.#6>Region>Kakheti (not in drop down)>Report ID does not populate>>> unable to enter subsequent steps
**Expected behavior**
A clear and concise description of what you expected to happen.
Screenshots**
If applicable, add screenshots to help explain your problem.
**Additional details:**
- Build: 77
- Script title (enter ad hoc if not script-based): LAB06
**Issue severity**: Critical
**Additional context**
Add any other context about the problem here.
| 1.0 | LAB: Region does not display and report ID does not populate, unable to register new samples - **Summary**
Region does not display and report ID does not populate unable to register new samples in the laboratory module
**To Reproduce**
Steps to reproduce the behavior:
1. Log in as mollyrue
2. Go to step #6 >Region: does not populate>Report ID>no report ID generated>Report ID does not populate
2. Click on '.#6>Region>Kakheti (not in drop down)>Report ID does not populate>>> unable to enter subsequent steps
**Expected behavior**
A clear and concise description of what you expected to happen.
Screenshots**
If applicable, add screenshots to help explain your problem.
**Additional details:**
- Build: 77
- Script title (enter ad hoc if not script-based): LAB06
**Issue severity**: Critical
**Additional context**
Add any other context about the problem here.
| non_priority | lab region does not display and report id does not populate unable to register new samples summary region does not display and report id does not populate unable to register new samples in the laboratory module to reproduce steps to reproduce the behavior log in as mollyrue go to step region does not populate report id no report id generated report id does not populate click on region kakheti not in drop down report id does not populate unable to enter subsequent steps expected behavior a clear and concise description of what you expected to happen screenshots if applicable add screenshots to help explain your problem additional details build script title enter ad hoc if not script based issue severity critical additional context add any other context about the problem here | 0 |
70,410 | 7,187,823,771 | IssuesEvent | 2018-02-02 07:36:01 | vipshop/Saturn | https://api.github.com/repos/vipshop/Saturn | closed | Job cannot be scheduled within 1 second when executor and zk not located in same data center | done enhancement review done tested | 在executor与zk非同机房的情况下,秒级作业调度不能做到1秒内执行完毕 | 1.0 | Job cannot be scheduled within 1 second when executor and zk not located in same data center - 在executor与zk非同机房的情况下,秒级作业调度不能做到1秒内执行完毕 | non_priority | job cannot be scheduled within second when executor and zk not located in same data center 在executor与zk非同机房的情况下, | 0 |
141,472 | 21,526,115,673 | IssuesEvent | 2022-04-28 18:37:37 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | [Design] Adjust the UI for cancelled Appointments | design ux HCE-Checkin | ## User Story
I click a pre-check-in link for an appointment that has been cancelled.
## Related Documentation
- [MVP Product Outline](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/products/health-care/checkin/product/product-outline.md)
## Description
A wireframes set for [feature name] will be delivered with the technical specifications needed for engineering to implement said feature.
## Tasks
> this is a list of design tasks that are needed for this ticket
- [ ] Finalize detailed mockup and callouts of [feature name](link to prototype)
- [ ] Decide: Should a content and accessibility review be part of this ticket or separate tickets due to scope?
- [ ] %Add any additional Tasks%
## Acceptance Criteria
> when is the ticket done
- [ ] UI review meeting with product/UX team for feature capabilities
- [ ] UI review meeting with engineering for layout and callouts (can be the same meeting as above)
- [ ] Wireframe available on Sketch Cloud
- [ ] If the wireframes applies to an error state or text message, then update the [GitHub source of truth](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/products/health-care/checkin/design/text-and-error-messages.md) documentation.
- [ ] %Add any additional Acceptance Criteria%
| 1.0 | [Design] Adjust the UI for cancelled Appointments - ## User Story
I click a pre-check-in link for an appointment that has been cancelled.
## Related Documentation
- [MVP Product Outline](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/products/health-care/checkin/product/product-outline.md)
## Description
A wireframes set for [feature name] will be delivered with the technical specifications needed for engineering to implement said feature.
## Tasks
> this is a list of design tasks that are needed for this ticket
- [ ] Finalize detailed mockup and callouts of [feature name](link to prototype)
- [ ] Decide: Should a content and accessibility review be part of this ticket or separate tickets due to scope?
- [ ] %Add any additional Tasks%
## Acceptance Criteria
> when is the ticket done
- [ ] UI review meeting with product/UX team for feature capabilities
- [ ] UI review meeting with engineering for layout and callouts (can be the same meeting as above)
- [ ] Wireframe available on Sketch Cloud
- [ ] If the wireframes applies to an error state or text message, then update the [GitHub source of truth](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/products/health-care/checkin/design/text-and-error-messages.md) documentation.
- [ ] %Add any additional Acceptance Criteria%
| non_priority | adjust the ui for cancelled appointments user story i click a pre check in link for an appointment that has been cancelled related documentation description a wireframes set for will be delivered with the technical specifications needed for engineering to implement said feature tasks this is a list of design tasks that are needed for this ticket finalize detailed mockup and callouts of link to prototype decide should a content and accessibility review be part of this ticket or separate tickets due to scope add any additional tasks acceptance criteria when is the ticket done ui review meeting with product ux team for feature capabilities ui review meeting with engineering for layout and callouts can be the same meeting as above wireframe available on sketch cloud if the wireframes applies to an error state or text message then update the documentation add any additional acceptance criteria | 0 |
43,964 | 5,578,851,055 | IssuesEvent | 2017-03-28 13:25:33 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | opened | End to end test for bazel rules are hard to write | category: misc > testing Customer impact | In Bazel we use //src/test/shell to do end to end tests, those tests are in shell so hard to maintain and we do not expose that framework for rules writer.
We could:
- Clean-up our e2e support
- Expose it in @bazel_tools
- Expose the bazel binary as a dependency so we can write those tests.
/cc @steren @or-shachar | 1.0 | End to end test for bazel rules are hard to write - In Bazel we use //src/test/shell to do end to end tests, those tests are in shell so hard to maintain and we do not expose that framework for rules writer.
We could:
- Clean-up our e2e support
- Expose it in @bazel_tools
- Expose the bazel binary as a dependency so we can write those tests.
/cc @steren @or-shachar | non_priority | end to end test for bazel rules are hard to write in bazel we use src test shell to do end to end tests those tests are in shell so hard to maintain and we do not expose that framework for rules writer we could clean up our support expose it in bazel tools expose the bazel binary as a dependency so we can write those tests cc steren or shachar | 0 |
71,003 | 18,389,021,040 | IssuesEvent | 2021-10-12 01:20:36 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | Building failure of libtensorflowlite_gpu_delegate.so | stat:awaiting tensorflower type:build/install subtype: ubuntu/linux 2.6.0 |
**System information**
- OS Platform and Distribution: Ubuntu 20.04
- TensorFlow installed from (source or binary): source
- TensorFlow version: 2.6.0
- Bazel version (if compiling from source): 3.7.2
- GCC/Compiler version (if compiling from source): 9.3.0
**Describe the problem**
Building libtensorflowlite_gpu_delegate.so fails complaining about `absl::Status`.
However building libtensorflowlite_c.so works well (using `bazel build -c opt tensorflow/lite/c:libtensorflowlite_c.so`)
Using lastest or v2.5.0 also fails.
**Provide the exact sequence of commands / steps that you executed before running into the problem**
```
git clone https://github.com/tensorflow/tensorflow -b v2.6.0
cd tensorflow
bazel build -c opt tensorflow/lite/delegates/gpu:libtensorflowlite_gpu_delegate.so
```
**Any other info / logs**
```
INFO: Options provided by the client:
Inherited 'common' options: --isatty=1 --terminal_columns=201
INFO: Reading rc options for 'build' from /home/michel/gin-tflite/tensorflow/.bazelrc:
Inherited 'common' options: --experimental_repo_remote_exec
INFO: Reading rc options for 'build' from /home/michel/gin-tflite/tensorflow/.bazelrc:
'build' options: --define framework_shared_object=true --java_toolchain=@tf_toolchains//toolchains/java:tf_java_toolchain --host_java_toolchain=@tf_toolchains//toolchains/java:tf_java_toolchain --define=use_fast_cpp_protos=true --define=allow_oversize_protos=true --spawn_strategy=standalone -c opt --announce_rc --define=grpc_no_ares=true --noincompatible_remove_legacy_whole_archive --enable_platform_specific_config --define=with_xla_support=true --config=short_logs --config=v2 --define=no_aws_support=true --define=no_hdfs_support=true
INFO: Found applicable config definition build:short_logs in file /home/michel/gin-tflite/tensorflow/.bazelrc: --output_filter=DONT_MATCH_ANYTHING
INFO: Found applicable config definition build:v2 in file /home/michel/gin-tflite/tensorflow/.bazelrc: --define=tf_api_version=2 --action_env=TF2_BEHAVIOR=1
INFO: Found applicable config definition build:linux in file /home/michel/gin-tflite/tensorflow/.bazelrc: --copt=-w --host_copt=-w --define=PREFIX=/usr --define=LIBDIR=$(PREFIX)/lib --define=INCLUDEDIR=$(PREFIX)/include --define=PROTOBUF_INCLUDE_PATH=$(PREFIX)/include --cxxopt=-std=c++14 --host_cxxopt=-std=c++14 --config=dynamic_kernels --distinct_host_configuration=false
INFO: Found applicable config definition build:dynamic_kernels in file /home/michel/gin-tflite/tensorflow/.bazelrc: --define=dynamic_loaded_kernels=true --copt=-DAUTOLOAD_DYNAMIC_KERNELS
DEBUG: /home/michel/.cache/bazel/_bazel_michel/2729c94059558bc79129827a71924973/external/tf_runtime/third_party/cuda/dependencies.bzl:51:10: The following command will download NVIDIA proprietary software. By using the software you agree to comply with the terms of the license agreement that accompanies the software. If you do not agree to the terms of the license agreement, do not use the software.
DEBUG: Rule 'io_bazel_rules_docker' indicated that a canonical reproducible form can be obtained by modifying arguments shallow_since = "1556410077 -0400"
DEBUG: Repository io_bazel_rules_docker instantiated at:
/home/michel/gin-tflite/tensorflow/WORKSPACE:23:14: in <toplevel>
/home/michel/gin-tflite/tensorflow/tensorflow/workspace0.bzl:108:34: in workspace
/home/michel/.cache/bazel/_bazel_michel/2729c94059558bc79129827a71924973/external/bazel_toolchains/repositories/repositories.bzl:37:23: in repositories
Repository rule git_repository defined at:
/home/michel/.cache/bazel/_bazel_michel/2729c94059558bc79129827a71924973/external/bazel_tools/tools/build_defs/repo/git.bzl:199:33: in <toplevel>
INFO: Analyzed target //tensorflow/lite/delegates/gpu:libtensorflowlite_gpu_delegate.so (0 packages loaded, 0 targets configured).
INFO: Found 1 target...
ERROR: /home/michel/gin-tflite/tensorflow/tensorflow/lite/delegates/gpu/gl/BUILD:48:11: C++ compilation of rule '//tensorflow/lite/delegates/gpu/gl:api2' failed (Exit 1): gcc failed: error executing command /usr/bin/gcc -U_FORTIFY_SOURCE -fstack-protector -Wall -Wunused-but-set-parameter -Wno-free-nonheap-object -fno-omit-frame-pointer -g0 -O2 '-D_FORTIFY_SOURCE=1' -DNDEBUG -ffunction-sections ... (remaining 43 argument(s) skipped)
In file included from external/opencl_headers/CL/cl.h:32,
from ./tensorflow/lite/delegates/gpu/api.h:42,
from ./tensorflow/lite/delegates/gpu/gl/api2.h:23,
from tensorflow/lite/delegates/gpu/gl/api2.cc:16:
external/opencl_headers/CL/cl_version.h:34:104: note: #pragma message: cl_version.h: CL_TARGET_OPENCL_VERSION is not defined. Defaulting to 220 (OpenCL 2.2)
34 | #pragma message("cl_version.h: CL_TARGET_OPENCL_VERSION is not defined. Defaulting to 220 (OpenCL 2.2)")
| ^
In file included from /usr/include/EGL/eglplatform.h:128,
from /usr/include/EGL/egl.h:39,
from ./tensorflow/lite/delegates/gpu/gl/portable_gl31.h:21,
from ./tensorflow/lite/delegates/gpu/api.h:50,
from ./tensorflow/lite/delegates/gpu/gl/api2.h:23,
from tensorflow/lite/delegates/gpu/gl/api2.cc:16:
./tensorflow/lite/delegates/gpu/api.h:261:17: error: expected unqualified-id before 'int'
261 | virtual absl::Status SetInputShape(int index,
| ^~~~~~
./tensorflow/lite/delegates/gpu/api.h:271:17: error: expected unqualified-id before 'int'
271 | virtual absl::Status SetInputObjectDef(int index, ObjectDef def) = 0;
| ^~~~~~
./tensorflow/lite/delegates/gpu/api.h:272:17: error: expected unqualified-id before 'int'
272 | virtual absl::Status SetOutputObjectDef(int index, ObjectDef def) = 0;
| ^~~~~~
./tensorflow/lite/delegates/gpu/api.h:273:17: error: expected unqualified-id before 'int'
273 | virtual absl::Status SetAllInputObjectDefsTo(ObjectDef def) {
| ^~~~~~
```
| 1.0 | Building failure of libtensorflowlite_gpu_delegate.so -
**System information**
- OS Platform and Distribution: Ubuntu 20.04
- TensorFlow installed from (source or binary): source
- TensorFlow version: 2.6.0
- Bazel version (if compiling from source): 3.7.2
- GCC/Compiler version (if compiling from source): 9.3.0
**Describe the problem**
Building libtensorflowlite_gpu_delegate.so fails complaining about `absl::Status`.
However building libtensorflowlite_c.so works well (using `bazel build -c opt tensorflow/lite/c:libtensorflowlite_c.so`)
Using lastest or v2.5.0 also fails.
**Provide the exact sequence of commands / steps that you executed before running into the problem**
```
git clone https://github.com/tensorflow/tensorflow -b v2.6.0
cd tensorflow
bazel build -c opt tensorflow/lite/delegates/gpu:libtensorflowlite_gpu_delegate.so
```
**Any other info / logs**
```
INFO: Options provided by the client:
Inherited 'common' options: --isatty=1 --terminal_columns=201
INFO: Reading rc options for 'build' from /home/michel/gin-tflite/tensorflow/.bazelrc:
Inherited 'common' options: --experimental_repo_remote_exec
INFO: Reading rc options for 'build' from /home/michel/gin-tflite/tensorflow/.bazelrc:
'build' options: --define framework_shared_object=true --java_toolchain=@tf_toolchains//toolchains/java:tf_java_toolchain --host_java_toolchain=@tf_toolchains//toolchains/java:tf_java_toolchain --define=use_fast_cpp_protos=true --define=allow_oversize_protos=true --spawn_strategy=standalone -c opt --announce_rc --define=grpc_no_ares=true --noincompatible_remove_legacy_whole_archive --enable_platform_specific_config --define=with_xla_support=true --config=short_logs --config=v2 --define=no_aws_support=true --define=no_hdfs_support=true
INFO: Found applicable config definition build:short_logs in file /home/michel/gin-tflite/tensorflow/.bazelrc: --output_filter=DONT_MATCH_ANYTHING
INFO: Found applicable config definition build:v2 in file /home/michel/gin-tflite/tensorflow/.bazelrc: --define=tf_api_version=2 --action_env=TF2_BEHAVIOR=1
INFO: Found applicable config definition build:linux in file /home/michel/gin-tflite/tensorflow/.bazelrc: --copt=-w --host_copt=-w --define=PREFIX=/usr --define=LIBDIR=$(PREFIX)/lib --define=INCLUDEDIR=$(PREFIX)/include --define=PROTOBUF_INCLUDE_PATH=$(PREFIX)/include --cxxopt=-std=c++14 --host_cxxopt=-std=c++14 --config=dynamic_kernels --distinct_host_configuration=false
INFO: Found applicable config definition build:dynamic_kernels in file /home/michel/gin-tflite/tensorflow/.bazelrc: --define=dynamic_loaded_kernels=true --copt=-DAUTOLOAD_DYNAMIC_KERNELS
DEBUG: /home/michel/.cache/bazel/_bazel_michel/2729c94059558bc79129827a71924973/external/tf_runtime/third_party/cuda/dependencies.bzl:51:10: The following command will download NVIDIA proprietary software. By using the software you agree to comply with the terms of the license agreement that accompanies the software. If you do not agree to the terms of the license agreement, do not use the software.
DEBUG: Rule 'io_bazel_rules_docker' indicated that a canonical reproducible form can be obtained by modifying arguments shallow_since = "1556410077 -0400"
DEBUG: Repository io_bazel_rules_docker instantiated at:
/home/michel/gin-tflite/tensorflow/WORKSPACE:23:14: in <toplevel>
/home/michel/gin-tflite/tensorflow/tensorflow/workspace0.bzl:108:34: in workspace
/home/michel/.cache/bazel/_bazel_michel/2729c94059558bc79129827a71924973/external/bazel_toolchains/repositories/repositories.bzl:37:23: in repositories
Repository rule git_repository defined at:
/home/michel/.cache/bazel/_bazel_michel/2729c94059558bc79129827a71924973/external/bazel_tools/tools/build_defs/repo/git.bzl:199:33: in <toplevel>
INFO: Analyzed target //tensorflow/lite/delegates/gpu:libtensorflowlite_gpu_delegate.so (0 packages loaded, 0 targets configured).
INFO: Found 1 target...
ERROR: /home/michel/gin-tflite/tensorflow/tensorflow/lite/delegates/gpu/gl/BUILD:48:11: C++ compilation of rule '//tensorflow/lite/delegates/gpu/gl:api2' failed (Exit 1): gcc failed: error executing command /usr/bin/gcc -U_FORTIFY_SOURCE -fstack-protector -Wall -Wunused-but-set-parameter -Wno-free-nonheap-object -fno-omit-frame-pointer -g0 -O2 '-D_FORTIFY_SOURCE=1' -DNDEBUG -ffunction-sections ... (remaining 43 argument(s) skipped)
In file included from external/opencl_headers/CL/cl.h:32,
from ./tensorflow/lite/delegates/gpu/api.h:42,
from ./tensorflow/lite/delegates/gpu/gl/api2.h:23,
from tensorflow/lite/delegates/gpu/gl/api2.cc:16:
external/opencl_headers/CL/cl_version.h:34:104: note: #pragma message: cl_version.h: CL_TARGET_OPENCL_VERSION is not defined. Defaulting to 220 (OpenCL 2.2)
34 | #pragma message("cl_version.h: CL_TARGET_OPENCL_VERSION is not defined. Defaulting to 220 (OpenCL 2.2)")
| ^
In file included from /usr/include/EGL/eglplatform.h:128,
from /usr/include/EGL/egl.h:39,
from ./tensorflow/lite/delegates/gpu/gl/portable_gl31.h:21,
from ./tensorflow/lite/delegates/gpu/api.h:50,
from ./tensorflow/lite/delegates/gpu/gl/api2.h:23,
from tensorflow/lite/delegates/gpu/gl/api2.cc:16:
./tensorflow/lite/delegates/gpu/api.h:261:17: error: expected unqualified-id before 'int'
261 | virtual absl::Status SetInputShape(int index,
| ^~~~~~
./tensorflow/lite/delegates/gpu/api.h:271:17: error: expected unqualified-id before 'int'
271 | virtual absl::Status SetInputObjectDef(int index, ObjectDef def) = 0;
| ^~~~~~
./tensorflow/lite/delegates/gpu/api.h:272:17: error: expected unqualified-id before 'int'
272 | virtual absl::Status SetOutputObjectDef(int index, ObjectDef def) = 0;
| ^~~~~~
./tensorflow/lite/delegates/gpu/api.h:273:17: error: expected unqualified-id before 'int'
273 | virtual absl::Status SetAllInputObjectDefsTo(ObjectDef def) {
| ^~~~~~
```
| non_priority | building failure of libtensorflowlite gpu delegate so system information os platform and distribution ubuntu tensorflow installed from source or binary source tensorflow version bazel version if compiling from source gcc compiler version if compiling from source describe the problem building libtensorflowlite gpu delegate so fails complaining about absl status however building libtensorflowlite c so works well using bazel build c opt tensorflow lite c libtensorflowlite c so using lastest or also fails provide the exact sequence of commands steps that you executed before running into the problem git clone b cd tensorflow bazel build c opt tensorflow lite delegates gpu libtensorflowlite gpu delegate so any other info logs info options provided by the client inherited common options isatty terminal columns info reading rc options for build from home michel gin tflite tensorflow bazelrc inherited common options experimental repo remote exec info reading rc options for build from home michel gin tflite tensorflow bazelrc build options define framework shared object true java toolchain tf toolchains toolchains java tf java toolchain host java toolchain tf toolchains toolchains java tf java toolchain define use fast cpp protos true define allow oversize protos true spawn strategy standalone c opt announce rc define grpc no ares true noincompatible remove legacy whole archive enable platform specific config define with xla support true config short logs config define no aws support true define no hdfs support true info found applicable config definition build short logs in file home michel gin tflite tensorflow bazelrc output filter dont match anything info found applicable config definition build in file home michel gin tflite tensorflow bazelrc define tf api version action env behavior info found applicable config definition build linux in file home michel gin tflite tensorflow bazelrc copt w host copt w define prefix usr define libdir prefix lib define includedir prefix include define protobuf include path prefix include cxxopt std c host cxxopt std c config dynamic kernels distinct host configuration false info found applicable config definition build dynamic kernels in file home michel gin tflite tensorflow bazelrc define dynamic loaded kernels true copt dautoload dynamic kernels debug home michel cache bazel bazel michel external tf runtime third party cuda dependencies bzl the following command will download nvidia proprietary software by using the software you agree to comply with the terms of the license agreement that accompanies the software if you do not agree to the terms of the license agreement do not use the software debug rule io bazel rules docker indicated that a canonical reproducible form can be obtained by modifying arguments shallow since debug repository io bazel rules docker instantiated at home michel gin tflite tensorflow workspace in home michel gin tflite tensorflow tensorflow bzl in workspace home michel cache bazel bazel michel external bazel toolchains repositories repositories bzl in repositories repository rule git repository defined at home michel cache bazel bazel michel external bazel tools tools build defs repo git bzl in info analyzed target tensorflow lite delegates gpu libtensorflowlite gpu delegate so packages loaded targets configured info found target error home michel gin tflite tensorflow tensorflow lite delegates gpu gl build c compilation of rule tensorflow lite delegates gpu gl failed exit gcc failed error executing command usr bin gcc u fortify source fstack protector wall wunused but set parameter wno free nonheap object fno omit frame pointer d fortify source dndebug ffunction sections remaining argument s skipped in file included from external opencl headers cl cl h from tensorflow lite delegates gpu api h from tensorflow lite delegates gpu gl h from tensorflow lite delegates gpu gl cc external opencl headers cl cl version h note pragma message cl version h cl target opencl version is not defined defaulting to opencl pragma message cl version h cl target opencl version is not defined defaulting to opencl in file included from usr include egl eglplatform h from usr include egl egl h from tensorflow lite delegates gpu gl portable h from tensorflow lite delegates gpu api h from tensorflow lite delegates gpu gl h from tensorflow lite delegates gpu gl cc tensorflow lite delegates gpu api h error expected unqualified id before int virtual absl status setinputshape int index tensorflow lite delegates gpu api h error expected unqualified id before int virtual absl status setinputobjectdef int index objectdef def tensorflow lite delegates gpu api h error expected unqualified id before int virtual absl status setoutputobjectdef int index objectdef def tensorflow lite delegates gpu api h error expected unqualified id before int virtual absl status setallinputobjectdefsto objectdef def | 0 |
121,521 | 25,982,777,738 | IssuesEvent | 2022-12-19 20:28:57 | Clueless-Community/seamless-ui | https://api.github.com/repos/Clueless-Community/seamless-ui | closed | Create a Dashboard Navigation component | codepeak 22 | One need to make this component using `HTML` and `Tailwind CSS`. I would suggest to use [Tailwind Playgrounds](https://play.tailwindcss.com/) to make things faster and quicker.
Here is a reference to the component.
<img width="854" alt="Screenshot 2022-12-20 at 12 27 33 AM" src="https://user-images.githubusercontent.com/107763774/208499652-eba535d3-c191-4cbe-9d4a-74cee0bb468c.png">
After building the component please raise a PR with a screenshot of the component and add the component in `path of the file`.
If you need to use any icon please use it from [Hero Icons](https://heroicons.com/)
Good luck.
| 1.0 | Create a Dashboard Navigation component - One need to make this component using `HTML` and `Tailwind CSS`. I would suggest to use [Tailwind Playgrounds](https://play.tailwindcss.com/) to make things faster and quicker.
Here is a reference to the component.
<img width="854" alt="Screenshot 2022-12-20 at 12 27 33 AM" src="https://user-images.githubusercontent.com/107763774/208499652-eba535d3-c191-4cbe-9d4a-74cee0bb468c.png">
After building the component please raise a PR with a screenshot of the component and add the component in `path of the file`.
If you need to use any icon please use it from [Hero Icons](https://heroicons.com/)
Good luck.
| non_priority | create a dashboard navigation component one need to make this component using html and tailwind css i would suggest to use to make things faster and quicker here is a reference to the component img width alt screenshot at am src after building the component please raise a pr with a screenshot of the component and add the component in path of the file if you need to use any icon please use it from good luck | 0 |
176,882 | 21,443,107,652 | IssuesEvent | 2022-04-25 01:10:45 | ghuangsnl/spring-boot | https://api.github.com/repos/ghuangsnl/spring-boot | closed | CVE-2022-0265 (High) detected in hazelcast-4.0.1.jar, hazelcast-3.12.8.jar - autoclosed | security vulnerability | ## CVE-2022-0265 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>hazelcast-4.0.1.jar</b>, <b>hazelcast-3.12.8.jar</b></p></summary>
<p>
<details><summary><b>hazelcast-4.0.1.jar</b></p></summary>
<p>Core Hazelcast Module</p>
<p>Library home page: <a href="http://www.hazelcast.com/">http://www.hazelcast.com/</a></p>
<p>Path to dependency file: /spring-boot-tests/spring-boot-smoke-tests/spring-boot-smoke-test-hazelcast4/build.gradle</p>
<p>Path to vulnerable library: /canner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/4.0.1/426b4f661f66df46f2c023eb96ce9e02529007d4/hazelcast-4.0.1.jar,/canner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/4.0.1/426b4f661f66df46f2c023eb96ce9e02529007d4/hazelcast-4.0.1.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/4.0.1/426b4f661f66df46f2c023eb96ce9e02529007d4/hazelcast-4.0.1.jar</p>
<p>
Dependency Hierarchy:
</details>
<details><summary><b>hazelcast-3.12.8.jar</b></p></summary>
<p>Core Hazelcast Module</p>
<p>Library home page: <a href="http://www.hazelcast.com/">http://www.hazelcast.com/</a></p>
<p>Path to dependency file: /spring-boot-project/spring-boot-actuator-autoconfigure/build.gradle</p>
<p>Path to vulnerable library: /canner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/3.12.8/c92dd8dd1bdd8ed0733aa6e0827761acec46cb6/hazelcast-3.12.8.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/3.12.8/c92dd8dd1bdd8ed0733aa6e0827761acec46cb6/hazelcast-3.12.8.jar,/canner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/3.12.8/c92dd8dd1bdd8ed0733aa6e0827761acec46cb6/hazelcast-3.12.8.jar</p>
<p>
Dependency Hierarchy:
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Improper Restriction of XML External Entity Reference in GitHub repository hazelcast/hazelcast in 5.1-BETA-1.
<p>Publish Date: 2022-03-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0265>CVE-2022-0265</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-99wh-973f-779p">https://github.com/advisories/GHSA-99wh-973f-779p</a></p>
<p>Release Date: 2022-03-03</p>
<p>Fix Resolution: com.hazelcast:hazelcast:5.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-0265 (High) detected in hazelcast-4.0.1.jar, hazelcast-3.12.8.jar - autoclosed - ## CVE-2022-0265 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>hazelcast-4.0.1.jar</b>, <b>hazelcast-3.12.8.jar</b></p></summary>
<p>
<details><summary><b>hazelcast-4.0.1.jar</b></p></summary>
<p>Core Hazelcast Module</p>
<p>Library home page: <a href="http://www.hazelcast.com/">http://www.hazelcast.com/</a></p>
<p>Path to dependency file: /spring-boot-tests/spring-boot-smoke-tests/spring-boot-smoke-test-hazelcast4/build.gradle</p>
<p>Path to vulnerable library: /canner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/4.0.1/426b4f661f66df46f2c023eb96ce9e02529007d4/hazelcast-4.0.1.jar,/canner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/4.0.1/426b4f661f66df46f2c023eb96ce9e02529007d4/hazelcast-4.0.1.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/4.0.1/426b4f661f66df46f2c023eb96ce9e02529007d4/hazelcast-4.0.1.jar</p>
<p>
Dependency Hierarchy:
</details>
<details><summary><b>hazelcast-3.12.8.jar</b></p></summary>
<p>Core Hazelcast Module</p>
<p>Library home page: <a href="http://www.hazelcast.com/">http://www.hazelcast.com/</a></p>
<p>Path to dependency file: /spring-boot-project/spring-boot-actuator-autoconfigure/build.gradle</p>
<p>Path to vulnerable library: /canner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/3.12.8/c92dd8dd1bdd8ed0733aa6e0827761acec46cb6/hazelcast-3.12.8.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/3.12.8/c92dd8dd1bdd8ed0733aa6e0827761acec46cb6/hazelcast-3.12.8.jar,/canner/.gradle/caches/modules-2/files-2.1/com.hazelcast/hazelcast/3.12.8/c92dd8dd1bdd8ed0733aa6e0827761acec46cb6/hazelcast-3.12.8.jar</p>
<p>
Dependency Hierarchy:
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Improper Restriction of XML External Entity Reference in GitHub repository hazelcast/hazelcast in 5.1-BETA-1.
<p>Publish Date: 2022-03-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0265>CVE-2022-0265</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-99wh-973f-779p">https://github.com/advisories/GHSA-99wh-973f-779p</a></p>
<p>Release Date: 2022-03-03</p>
<p>Fix Resolution: com.hazelcast:hazelcast:5.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in hazelcast jar hazelcast jar autoclosed cve high severity vulnerability vulnerable libraries hazelcast jar hazelcast jar hazelcast jar core hazelcast module library home page a href path to dependency file spring boot tests spring boot smoke tests spring boot smoke test build gradle path to vulnerable library canner gradle caches modules files com hazelcast hazelcast hazelcast jar canner gradle caches modules files com hazelcast hazelcast hazelcast jar home wss scanner gradle caches modules files com hazelcast hazelcast hazelcast jar dependency hierarchy hazelcast jar core hazelcast module library home page a href path to dependency file spring boot project spring boot actuator autoconfigure build gradle path to vulnerable library canner gradle caches modules files com hazelcast hazelcast hazelcast jar home wss scanner gradle caches modules files com hazelcast hazelcast hazelcast jar canner gradle caches modules files com hazelcast hazelcast hazelcast jar dependency hierarchy vulnerability details improper restriction of xml external entity reference in github repository hazelcast hazelcast in beta publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com hazelcast hazelcast step up your open source security game with whitesource | 0 |
142,014 | 19,012,454,770 | IssuesEvent | 2021-11-23 10:47:52 | Yann-dv/_Pekocko | https://api.github.com/repos/Yann-dv/_Pekocko | opened | CVE-2018-20822 (Medium) detected in node-sass-4.9.3.tgz, opennmsopennms-source-26.0.0-1 | security vulnerability | ## CVE-2018-20822 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.9.3.tgz</b>, <b>opennmsopennms-source-26.0.0-1</b></p></summary>
<p>
<details><summary><b>node-sass-4.9.3.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.9.3.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.9.3.tgz</a></p>
<p>
Dependency Hierarchy:
- build-angular-0.10.2.tgz (Root Library)
- :x: **node-sass-4.9.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Yann-dv/_Pekocko/commit/29a980e4dad903d391a0354b9cb7c71642e2c2fe">29a980e4dad903d391a0354b9cb7c71642e2c2fe</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
LibSass 3.5.4 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Complex_Selector::perform in ast.hpp and Sass::Inspect::operator in inspect.cpp).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20822>CVE-2018-20822</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.5.5">https://github.com/sass/libsass/releases/tag/3.5.5</a></p>
<p>Release Date: 2019-04-23</p>
<p>Fix Resolution: libsass - 3.5.5;node-sass - 4.14.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-20822 (Medium) detected in node-sass-4.9.3.tgz, opennmsopennms-source-26.0.0-1 - ## CVE-2018-20822 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.9.3.tgz</b>, <b>opennmsopennms-source-26.0.0-1</b></p></summary>
<p>
<details><summary><b>node-sass-4.9.3.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.9.3.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.9.3.tgz</a></p>
<p>
Dependency Hierarchy:
- build-angular-0.10.2.tgz (Root Library)
- :x: **node-sass-4.9.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Yann-dv/_Pekocko/commit/29a980e4dad903d391a0354b9cb7c71642e2c2fe">29a980e4dad903d391a0354b9cb7c71642e2c2fe</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
LibSass 3.5.4 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Complex_Selector::perform in ast.hpp and Sass::Inspect::operator in inspect.cpp).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20822>CVE-2018-20822</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.5.5">https://github.com/sass/libsass/releases/tag/3.5.5</a></p>
<p>Release Date: 2019-04-23</p>
<p>Fix Resolution: libsass - 3.5.5;node-sass - 4.14.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node sass tgz opennmsopennms source cve medium severity vulnerability vulnerable libraries node sass tgz opennmsopennms source node sass tgz wrapper around libsass library home page a href dependency hierarchy build angular tgz root library x node sass tgz vulnerable library found in head commit a href found in base branch main vulnerability details libsass allows attackers to cause a denial of service uncontrolled recursion in sass complex selector perform in ast hpp and sass inspect operator in inspect cpp publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass node sass step up your open source security game with whitesource | 0 |
75,736 | 9,310,730,658 | IssuesEvent | 2019-03-25 19:31:56 | aspnet/AspNetCore | https://api.github.com/repos/aspnet/AspNetCore | closed | What should HubConnection.StopAsync cancellation token do? | PRI: 3 - Optional area-signalr cost: M enhancement needs design release-3.0 | https://github.com/aspnet/SignalR/pull/2000#discussion_r181334729
> Not sure yet. Need to look deeper. Maybe we need to pass it to DisposeAsync or use it from the outside to cancel dispose. But we can just not support it for now. File an issue. | 1.0 | What should HubConnection.StopAsync cancellation token do? - https://github.com/aspnet/SignalR/pull/2000#discussion_r181334729
> Not sure yet. Need to look deeper. Maybe we need to pass it to DisposeAsync or use it from the outside to cancel dispose. But we can just not support it for now. File an issue. | non_priority | what should hubconnection stopasync cancellation token do not sure yet need to look deeper maybe we need to pass it to disposeasync or use it from the outside to cancel dispose but we can just not support it for now file an issue | 0 |
385,732 | 26,651,069,778 | IssuesEvent | 2023-01-25 13:44:23 | kedro-org/kedro | https://api.github.com/repos/kedro-org/kedro | closed | Add documentation explaining how to load credentials from environment variables using OmegaConfLoader | Component: Documentation 📄 | ## Description
In #2178 we are adding the ability to load credentials from environment variables via `OmegaConfLoader`. We should add documentation that helps our users find this feature and use it.
## Context
This is a much-requested and very useful feature, so we should help users discover it as easily as possible.
| 1.0 | Add documentation explaining how to load credentials from environment variables using OmegaConfLoader - ## Description
In #2178 we are adding the ability to load credentials from environment variables via `OmegaConfLoader`. We should add documentation that helps our users find this feature and use it.
## Context
This is a much-requested and very useful feature, so we should help users discover it as easily as possible.
| non_priority | add documentation explaining how to load credentials from environment variables using omegaconfloader description in we are adding the ability to load credentials from environment variables via omegaconfloader we should add documentation that helps our users find this feature and use it context this is a much requested and very useful feature so we should help users discover it as easily as possible | 0 |
190,934 | 22,192,231,899 | IssuesEvent | 2022-06-07 01:05:18 | Seagate/cortx-test | https://api.github.com/repos/Seagate/cortx-test | closed | CVE-2022-29361 (High) detected in Werkzeug-1.0.1-py2.py3-none-any.whl - autoclosed | security vulnerability | ## CVE-2022-29361 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Werkzeug-1.0.1-py2.py3-none-any.whl</b></p></summary>
<p>The comprehensive WSGI web application library.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/cc/94/5f7079a0e00bd6863ef8f1da638721e9da21e5bacee597595b318f71d62e/Werkzeug-1.0.1-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/cc/94/5f7079a0e00bd6863ef8f1da638721e9da21e5bacee597595b318f71d62e/Werkzeug-1.0.1-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt,/libs/csm/csm,/requirements.txt,/switch</p>
<p>
Dependency Hierarchy:
- :x: **Werkzeug-1.0.1-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Seagate/cortx-test/commit/2a86195797b4352c780fa88a5a2cf3dfea63af99">2a86195797b4352c780fa88a5a2cf3dfea63af99</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** Improper parsing of HTTP requests in Pallets Werkzeug v2.1.0 and below allows attackers to perform HTTP Request Smuggling using a crafted HTTP request with multiple requests included inside the body. NOTE: the vendor's position is that this behavior can only occur in unsupported configurations involving development mode and an HTTP server from outside the Werkzeug project.
<p>Publish Date: 2022-05-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29361>CVE-2022-29361</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29361">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29361</a></p>
<p>Release Date: 2022-05-25</p>
<p>Fix Resolution: Werkzeug - 2.1.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"Werkzeug","packageVersion":"1.0.1","packageFilePaths":["/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"Werkzeug:1.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"Werkzeug - 2.1.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2022-29361","vulnerabilityDetails":"** DISPUTED ** Improper parsing of HTTP requests in Pallets Werkzeug v2.1.0 and below allows attackers to perform HTTP Request Smuggling using a crafted HTTP request with multiple requests included inside the body. NOTE: the vendor\u0027s position is that this behavior can only occur in unsupported configurations involving development mode and an HTTP server from outside the Werkzeug project.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29361","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2022-29361 (High) detected in Werkzeug-1.0.1-py2.py3-none-any.whl - autoclosed - ## CVE-2022-29361 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Werkzeug-1.0.1-py2.py3-none-any.whl</b></p></summary>
<p>The comprehensive WSGI web application library.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/cc/94/5f7079a0e00bd6863ef8f1da638721e9da21e5bacee597595b318f71d62e/Werkzeug-1.0.1-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/cc/94/5f7079a0e00bd6863ef8f1da638721e9da21e5bacee597595b318f71d62e/Werkzeug-1.0.1-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt,/libs/csm/csm,/requirements.txt,/switch</p>
<p>
Dependency Hierarchy:
- :x: **Werkzeug-1.0.1-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Seagate/cortx-test/commit/2a86195797b4352c780fa88a5a2cf3dfea63af99">2a86195797b4352c780fa88a5a2cf3dfea63af99</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** Improper parsing of HTTP requests in Pallets Werkzeug v2.1.0 and below allows attackers to perform HTTP Request Smuggling using a crafted HTTP request with multiple requests included inside the body. NOTE: the vendor's position is that this behavior can only occur in unsupported configurations involving development mode and an HTTP server from outside the Werkzeug project.
<p>Publish Date: 2022-05-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29361>CVE-2022-29361</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29361">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29361</a></p>
<p>Release Date: 2022-05-25</p>
<p>Fix Resolution: Werkzeug - 2.1.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"Werkzeug","packageVersion":"1.0.1","packageFilePaths":["/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"Werkzeug:1.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"Werkzeug - 2.1.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2022-29361","vulnerabilityDetails":"** DISPUTED ** Improper parsing of HTTP requests in Pallets Werkzeug v2.1.0 and below allows attackers to perform HTTP Request Smuggling using a crafted HTTP request with multiple requests included inside the body. NOTE: the vendor\u0027s position is that this behavior can only occur in unsupported configurations involving development mode and an HTTP server from outside the Werkzeug project.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29361","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in werkzeug none any whl autoclosed cve high severity vulnerability vulnerable library werkzeug none any whl the comprehensive wsgi web application library library home page a href path to dependency file requirements txt path to vulnerable library requirements txt libs csm csm requirements txt switch dependency hierarchy x werkzeug none any whl vulnerable library found in head commit a href found in base branch main vulnerability details disputed improper parsing of http requests in pallets werkzeug and below allows attackers to perform http request smuggling using a crafted http request with multiple requests included inside the body note the vendor s position is that this behavior can only occur in unsupported configurations involving development mode and an http server from outside the werkzeug project publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution werkzeug rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree werkzeug isminimumfixversionavailable true minimumfixversion werkzeug isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails disputed improper parsing of http requests in pallets werkzeug and below allows attackers to perform http request smuggling using a crafted http request with multiple requests included inside the body note the vendor position is that this behavior can only occur in unsupported configurations involving development mode and an http server from outside the werkzeug project vulnerabilityurl | 0 |
165,409 | 20,574,563,959 | IssuesEvent | 2022-03-04 02:10:41 | Nivaskumark/kernel_v4.19.72 | https://api.github.com/repos/Nivaskumark/kernel_v4.19.72 | opened | CVE-2022-25375 (Medium) detected in linux-yoctov5.4.51 | security vulnerability | ## CVE-2022-25375 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/gadget/function/rndis.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/gadget/function/rndis.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in drivers/usb/gadget/function/rndis.c in the Linux kernel before 5.16.10. The RNDIS USB gadget lacks validation of the size of the RNDIS_MSG_SET command. Attackers can obtain sensitive information from kernel memory.
<p>Publish Date: 2022-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25375>CVE-2022-25375</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25375">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25375</a></p>
<p>Release Date: 2022-02-20</p>
<p>Fix Resolution: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25375</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-25375 (Medium) detected in linux-yoctov5.4.51 - ## CVE-2022-25375 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/gadget/function/rndis.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/gadget/function/rndis.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in drivers/usb/gadget/function/rndis.c in the Linux kernel before 5.16.10. The RNDIS USB gadget lacks validation of the size of the RNDIS_MSG_SET command. Attackers can obtain sensitive information from kernel memory.
<p>Publish Date: 2022-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25375>CVE-2022-25375</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25375">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25375</a></p>
<p>Release Date: 2022-02-20</p>
<p>Fix Resolution: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25375</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in base branch master vulnerable source files drivers usb gadget function rndis c drivers usb gadget function rndis c vulnerability details an issue was discovered in drivers usb gadget function rndis c in the linux kernel before the rndis usb gadget lacks validation of the size of the rndis msg set command attackers can obtain sensitive information from kernel memory publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
240,982 | 18,410,899,744 | IssuesEvent | 2021-10-13 05:34:01 | dohooo/react-native-reanimated-carousel | https://api.github.com/repos/dohooo/react-native-reanimated-carousel | closed | Provide a snack | documentation | I think it's always great to provide a snack at https://snack.expo.dev/
It's always better to get a feel instead of only showcasing a video/gif.
Would also love to know, if this library works on web. I've inspected the code a little bit and you're using PanGestureHandler, I am very confident that this library should work with react-native-web out of the box. Also things we could test, if provided a Snack :) | 1.0 | Provide a snack - I think it's always great to provide a snack at https://snack.expo.dev/
It's always better to get a feel instead of only showcasing a video/gif.
Would also love to know, if this library works on web. I've inspected the code a little bit and you're using PanGestureHandler, I am very confident that this library should work with react-native-web out of the box. Also things we could test, if provided a Snack :) | non_priority | provide a snack i think it s always great to provide a snack at it s always better to get a feel instead of only showcasing a video gif would also love to know if this library works on web i ve inspected the code a little bit and you re using pangesturehandler i am very confident that this library should work with react native web out of the box also things we could test if provided a snack | 0 |
62,482 | 15,268,965,725 | IssuesEvent | 2021-02-22 12:08:25 | sandboxie-plus/Sandboxie | https://api.github.com/repos/sandboxie-plus/Sandboxie | closed | [v0.7.0/5.48.0] Free Download Manager | fixed in next build workaround | Just for your information: If someone wants to use the "Free Download Manager" with version 0.7.0/5.48.0, it will only work after adding the following setting.
```
RpcMgmtSetComTimeout=fdm.exe,y
```
Without this setting, the user interface will not appear. | 1.0 | [v0.7.0/5.48.0] Free Download Manager - Just for your information: If someone wants to use the "Free Download Manager" with version 0.7.0/5.48.0, it will only work after adding the following setting.
```
RpcMgmtSetComTimeout=fdm.exe,y
```
Without this setting, the user interface will not appear. | non_priority | free download manager just for your information if someone wants to use the free download manager with version it will only work after adding the following setting rpcmgmtsetcomtimeout fdm exe y without this setting the user interface will not appear | 0 |
24,053 | 5,019,233,976 | IssuesEvent | 2016-12-14 11:01:54 | Lakion/SyliusCmsBundle | https://api.github.com/repos/Lakion/SyliusCmsBundle | closed | Initial documentation & README | Documentation | * README
* Installation
* References to appropriate resource/grid bundle docs | 1.0 | Initial documentation & README - * README
* Installation
* References to appropriate resource/grid bundle docs | non_priority | initial documentation readme readme installation references to appropriate resource grid bundle docs | 0 |
275,788 | 20,958,237,708 | IssuesEvent | 2022-03-27 12:10:59 | raquelmolinare/TFG | https://api.github.com/repos/raquelmolinare/TFG | opened | Completar Estado del arte en la memoria. | documentation task | Esta tarea pertenece a la HU #4
El Estado del arte incluye:
- Situación actual del ámbito investigado.
- Antecedentes teóricos y teorías existentes. | 1.0 | Completar Estado del arte en la memoria. - Esta tarea pertenece a la HU #4
El Estado del arte incluye:
- Situación actual del ámbito investigado.
- Antecedentes teóricos y teorías existentes. | non_priority | completar estado del arte en la memoria esta tarea pertenece a la hu el estado del arte incluye situación actual del ámbito investigado antecedentes teóricos y teorías existentes | 0 |
15,515 | 8,949,873,267 | IssuesEvent | 2019-01-25 09:09:20 | surveyjs/editor | https://api.github.com/repos/surveyjs/editor | opened | Select a question in a survey that has many questions and large matrices take a lot of time | performance issue | We should move the setup expression editor on a later stage to solve this performance issue. | True | Select a question in a survey that has many questions and large matrices take a lot of time - We should move the setup expression editor on a later stage to solve this performance issue. | non_priority | select a question in a survey that has many questions and large matrices take a lot of time we should move the setup expression editor on a later stage to solve this performance issue | 0 |
44,369 | 9,574,157,931 | IssuesEvent | 2019-05-07 00:25:48 | desktop/desktop | https://api.github.com/repos/desktop/desktop | closed | diff flickering when cursoring up/down with only one file | codemirror enhancement | ### Description
When there is one file in the changes list, or one file in the commit details, you can up/down in the list and make the diff flicker due to re-rendering.
### Version
**GitHub Desktop version:** 1.0.0-beta0
**OS version:** macOS Sierra (also reproducible on Windows 10)
### Steps to Reproduce
1. Take an existing repository
1. Modify one file so it appears in the changes list
1. Select that file in the changes list
1. Press up/down
Alternatively
1. Take an existing repository
1. Find a commit that changes exactly one file
1. Select that file in the commit file list
1. Press up/down
**Expected behavior:** no change to file selection, no unnecessary re-rendering of the diff
**Actual behavior:** file diff is re-rendered, appearing as flickering to the naked eye
**Reproduces how often:** 100%
| 1.0 | diff flickering when cursoring up/down with only one file - ### Description
When there is one file in the changes list, or one file in the commit details, you can up/down in the list and make the diff flicker due to re-rendering.
### Version
**GitHub Desktop version:** 1.0.0-beta0
**OS version:** macOS Sierra (also reproducible on Windows 10)
### Steps to Reproduce
1. Take an existing repository
1. Modify one file so it appears in the changes list
1. Select that file in the changes list
1. Press up/down
Alternatively
1. Take an existing repository
1. Find a commit that changes exactly one file
1. Select that file in the commit file list
1. Press up/down
**Expected behavior:** no change to file selection, no unnecessary re-rendering of the diff
**Actual behavior:** file diff is re-rendered, appearing as flickering to the naked eye
**Reproduces how often:** 100%
| non_priority | diff flickering when cursoring up down with only one file description when there is one file in the changes list or one file in the commit details you can up down in the list and make the diff flicker due to re rendering version github desktop version os version macos sierra also reproducible on windows steps to reproduce take an existing repository modify one file so it appears in the changes list select that file in the changes list press up down alternatively take an existing repository find a commit that changes exactly one file select that file in the commit file list press up down expected behavior no change to file selection no unnecessary re rendering of the diff actual behavior file diff is re rendered appearing as flickering to the naked eye reproduces how often | 0 |
79,317 | 15,586,128,243 | IssuesEvent | 2021-03-18 01:14:10 | revfactory/task-api | https://api.github.com/repos/revfactory/task-api | opened | CVE-2020-14061 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2020-14061 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: task-api/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.3.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.3.RELEASE.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to oracle.jms.AQjmsQueueConnectionFactory, oracle.jms.AQjmsXATopicConnectionFactory, oracle.jms.AQjmsTopicConnectionFactory, oracle.jms.AQjmsXAQueueConnectionFactory, and oracle.jms.AQjmsXAConnectionFactory (aka weblogic/oracle-aqjms).
<p>Publish Date: 2020-06-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14061>CVE-2020-14061</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14061">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14061</a></p>
<p>Release Date: 2020-06-14</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-14061 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2020-14061 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: task-api/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.3.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.3.RELEASE.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to oracle.jms.AQjmsQueueConnectionFactory, oracle.jms.AQjmsXATopicConnectionFactory, oracle.jms.AQjmsTopicConnectionFactory, oracle.jms.AQjmsXAQueueConnectionFactory, and oracle.jms.AQjmsXAConnectionFactory (aka weblogic/oracle-aqjms).
<p>Publish Date: 2020-06-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14061>CVE-2020-14061</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14061">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14061</a></p>
<p>Release Date: 2020-06-14</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file task api build gradle path to vulnerable library root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library spring boot starter json release jar x jackson databind jar vulnerable library vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to oracle jms aqjmsqueueconnectionfactory oracle jms aqjmsxatopicconnectionfactory oracle jms aqjmstopicconnectionfactory oracle jms aqjmsxaqueueconnectionfactory and oracle jms aqjmsxaconnectionfactory aka weblogic oracle aqjms publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
287,064 | 31,814,219,295 | IssuesEvent | 2023-09-13 19:08:38 | tuanductran/fullstackradio.com | https://api.github.com/repos/tuanductran/fullstackradio.com | closed | next-9.5.3-canary.17.tgz: 23 vulnerabilities (highest severity is: 9.8) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>next-9.5.3-canary.17.tgz</b></p></summary>
<p>The React Framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz">https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz</a></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (next version) | Remediation Possible** |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-37601](https://www.mend.io/vulnerability-database/CVE-2022-37601) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | detected in multiple dependencies | Transitive | 12.0.9-canary.1 | ❌ |
| [CVE-2020-15256](https://www.mend.io/vulnerability-database/CVE-2020-15256) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | object-path-0.11.4.tgz | Transitive | 9.5.6-canary.9 | ❌ |
| [CVE-2021-42740](https://www.mend.io/vulnerability-database/CVE-2021-42740) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | shell-quote-1.7.2.tgz | Transitive | 11.1.1-canary.12 | ❌ |
| [CVE-2020-7774](https://www.mend.io/vulnerability-database/CVE-2020-7774) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | y18n-4.0.0.tgz | Transitive | 9.5.3-canary.18 | ❌ |
| [CVE-2021-23434](https://www.mend.io/vulnerability-database/CVE-2021-23434) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.6 | object-path-0.11.4.tgz | Transitive | 9.5.6-canary.9 | ❌ |
| [CVE-2022-25858](https://www.mend.io/vulnerability-database/CVE-2022-25858) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | terser-4.8.0.tgz | Transitive | 9.5.6-canary.10 | ❌ |
| [CVE-2021-3807](https://www.mend.io/vulnerability-database/CVE-2021-3807) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | ansi-regex-5.0.0.tgz | Transitive | 9.5.3-canary.18 | ❌ |
| [CVE-2020-28469](https://www.mend.io/vulnerability-database/CVE-2020-28469) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | 10.0.6-canary.1 | ❌ |
| [CVE-2022-37599](https://www.mend.io/vulnerability-database/CVE-2022-37599) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | loader-utils-2.0.0.tgz | Transitive | 10.0.6-canary.2 | ❌ |
| [CVE-2022-3517](https://www.mend.io/vulnerability-database/CVE-2022-3517) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | minimatch-3.0.4.tgz | Transitive | N/A* | ❌ |
| [CVE-2021-27290](https://www.mend.io/vulnerability-database/CVE-2021-27290) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | 9.5.3-canary.18 | ❌ |
| [CVE-2022-38900](https://www.mend.io/vulnerability-database/CVE-2022-38900) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | decode-uri-component-0.2.0.tgz | Transitive | 9.5.3-canary.18 | ❌ |
| [CVE-2022-37603](https://www.mend.io/vulnerability-database/CVE-2022-37603) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | 12.0.9-canary.1 | ❌ |
| [CVE-2021-23382](https://www.mend.io/vulnerability-database/CVE-2021-23382) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | postcss-7.0.21.tgz | Transitive | 10.0.7-canary.7 | ❌ |
| [CVE-2022-25883](https://www.mend.io/vulnerability-database/CVE-2022-25883) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | semver-7.0.0.tgz | Transitive | 12.0.8-canary.11 | ❌ |
| [CVE-2021-43803](https://www.mend.io/vulnerability-database/CVE-2021-43803) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | next-9.5.3-canary.17.tgz | Direct | 11.1.2-canary.0 | ❌ |
| [CVE-2021-3805](https://www.mend.io/vulnerability-database/CVE-2021-3805) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | object-path-0.11.4.tgz | Transitive | 9.5.6-canary.9 | ❌ |
| [CVE-2020-28498](https://www.mend.io/vulnerability-database/CVE-2020-28498) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.8 | elliptic-6.5.3.tgz | Transitive | 9.5.3-canary.18 | ❌ |
| [CVE-2021-37699](https://www.mend.io/vulnerability-database/CVE-2021-37699) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | next-9.5.3-canary.17.tgz | Direct | 11.0.1-canary.0 | ❌ |
| [CVE-2022-0235](https://www.mend.io/vulnerability-database/CVE-2022-0235) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | node-fetch-2.6.0.tgz | Transitive | 11.1.4 | ❌ |
| [CVE-2020-15168](https://www.mend.io/vulnerability-database/CVE-2020-15168) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | node-fetch-2.6.0.tgz | Transitive | 10.0.4-canary.2 | ❌ |
| [CVE-2021-23364](https://www.mend.io/vulnerability-database/CVE-2021-23364) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | browserslist-4.13.0.tgz | Transitive | 10.2.1-canary.9 | ❌ |
| [CVE-2021-23368](https://www.mend.io/vulnerability-database/CVE-2021-23368) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | postcss-7.0.21.tgz | Transitive | 10.0.7-canary.7 | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p><p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2022-37601</summary>
### Vulnerable Libraries - <b>loader-utils-1.2.3.tgz</b>, <b>loader-utils-1.4.0.tgz</b>, <b>loader-utils-2.0.0.tgz</b></p>
<p>
### <b>loader-utils-1.2.3.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.2.3.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.2.3.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- :x: **loader-utils-1.2.3.tgz** (Vulnerable Library)
### <b>loader-utils-1.4.0.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- sass-loader-8.0.2.tgz
- :x: **loader-utils-1.4.0.tgz** (Vulnerable Library)
### <b>loader-utils-2.0.0.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- :x: **loader-utils-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype pollution vulnerability in function parseQuery in parseQuery.js in webpack loader-utils 2.0.0 via the name variable in parseQuery.js.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-37601>CVE-2022-37601</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-76p3-8jx3-jpfq">https://github.com/advisories/GHSA-76p3-8jx3-jpfq</a></p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution (loader-utils): 1.4.1</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p><p>Fix Resolution (loader-utils): 1.4.1</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p><p>Fix Resolution (loader-utils): 1.4.1</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-15256</summary>
### Vulnerable Library - <b>object-path-0.11.4.tgz</b></p>
<p>Access deep object properties using a path</p>
<p>Library home page: <a href="https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz">https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- adjust-sourcemap-loader-2.0.0.tgz
- :x: **object-path-0.11.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A prototype pollution vulnerability has been found in `object-path` <= 0.11.4 affecting the `set()` method. The vulnerability is limited to the `includeInheritedProps` mode (if version >= 0.11.0 is used), which has to be explicitly enabled by creating a new instance of `object-path` and setting the option `includeInheritedProps: true`, or by using the default `withInheritedProps` instance. The default operating mode is not affected by the vulnerability if version >= 0.11.0 is used. Any usage of `set()` in versions < 0.11.0 is vulnerable. The issue is fixed in object-path version 0.11.5 As a workaround, don't use the `includeInheritedProps: true` options or the `withInheritedProps` instance if using a version >= 0.11.0.
<p>Publish Date: 2020-10-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15256>CVE-2020-15256</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mariocasciaro/object-path/security/advisories/GHSA-cwx2-736x-mf6w">https://github.com/mariocasciaro/object-path/security/advisories/GHSA-cwx2-736x-mf6w</a></p>
<p>Release Date: 2020-10-19</p>
<p>Fix Resolution (object-path): 0.11.5</p>
<p>Direct dependency fix Resolution (next): 9.5.6-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2021-42740</summary>
### Vulnerable Library - <b>shell-quote-1.7.2.tgz</b></p>
<p>quote and parse shell commands</p>
<p>Library home page: <a href="https://registry.npmjs.org/shell-quote/-/shell-quote-1.7.2.tgz">https://registry.npmjs.org/shell-quote/-/shell-quote-1.7.2.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- react-dev-overlay-9.5.3-canary.17.tgz
- :x: **shell-quote-1.7.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The shell-quote package before 1.7.3 for Node.js allows command injection. An attacker can inject unescaped shell metacharacters through a regex designed to support Windows drive letters. If the output of this package is passed to a real shell as a quoted argument to a command with exec(), an attacker can inject arbitrary commands. This is because the Windows drive letter regex character class is {A-z] instead of the correct {A-Za-z]. Several shell metacharacters exist in the space between capital letter Z and lower case letter a, such as the backtick character.
<p>Publish Date: 2021-10-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-42740>CVE-2021-42740</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740</a></p>
<p>Release Date: 2021-10-21</p>
<p>Fix Resolution (shell-quote): 1.7.3</p>
<p>Direct dependency fix Resolution (next): 11.1.1-canary.12</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-7774</summary>
### Vulnerable Library - <b>y18n-4.0.0.tgz</b></p>
<p>the bare-bones internationalization library used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz">https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- webpack-4.44.1.tgz
- terser-webpack-plugin-1.4.5.tgz
- cacache-12.0.4.tgz
- :x: **y18n-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package y18n before 3.2.2, 4.0.1 and 5.0.5, is vulnerable to Prototype Pollution.
<p>Publish Date: 2020-11-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7774>CVE-2020-7774</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1654">https://www.npmjs.com/advisories/1654</a></p>
<p>Release Date: 2020-11-17</p>
<p>Fix Resolution (y18n): 4.0.1</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-23434</summary>
### Vulnerable Library - <b>object-path-0.11.4.tgz</b></p>
<p>Access deep object properties using a path</p>
<p>Library home page: <a href="https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz">https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- adjust-sourcemap-loader-2.0.0.tgz
- :x: **object-path-0.11.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package object-path before 0.11.6. A type confusion vulnerability can lead to a bypass of CVE-2020-15256 when the path components used in the path parameter are arrays. In particular, the condition currentPath === '__proto__' returns false if currentPath is ['__proto__']. This is because the === operator returns always false when the type of the operands is different.
<p>Publish Date: 2021-08-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23434>CVE-2021-23434</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23434">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23434</a></p>
<p>Release Date: 2021-08-27</p>
<p>Fix Resolution (object-path): 0.11.6</p>
<p>Direct dependency fix Resolution (next): 9.5.6-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-25858</summary>
### Vulnerable Library - <b>terser-4.8.0.tgz</b></p>
<p>JavaScript parser, mangler/compressor and beautifier toolkit for ES6+</p>
<p>Library home page: <a href="https://registry.npmjs.org/terser/-/terser-4.8.0.tgz">https://registry.npmjs.org/terser/-/terser-4.8.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- webpack-4.44.1.tgz
- terser-webpack-plugin-1.4.5.tgz
- :x: **terser-4.8.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package terser before 4.8.1, from 5.0.0 and before 5.14.2 are vulnerable to Regular Expression Denial of Service (ReDoS) due to insecure usage of regular expressions.
<p>Publish Date: 2022-07-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25858>CVE-2022-25858</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25858">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25858</a></p>
<p>Release Date: 2022-07-15</p>
<p>Fix Resolution (terser): 4.8.1</p>
<p>Direct dependency fix Resolution (next): 9.5.6-canary.10</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-3807</summary>
### Vulnerable Library - <b>ansi-regex-5.0.0.tgz</b></p>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- react-dev-overlay-9.5.3-canary.17.tgz
- strip-ansi-6.0.0.tgz
- :x: **ansi-regex-5.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ansi-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3807>CVE-2021-3807</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/">https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution (ansi-regex): 5.0.1</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-28469</summary>
### Vulnerable Libraries - <b>glob-parent-3.1.0.tgz</b>, <b>glob-parent-5.1.1.tgz</b></p>
<p>
### <b>glob-parent-3.1.0.tgz</b></p>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
### <b>glob-parent-5.1.1.tgz</b></p>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- webpack-4.44.1.tgz
- watchpack-1.7.4.tgz
- chokidar-3.4.2.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (next): 10.0.6-canary.1</p><p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (next): 10.0.6-canary.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-37599</summary>
### Vulnerable Library - <b>loader-utils-2.0.0.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- :x: **loader-utils-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the resourcePath variable in interpolateName.js.
<p>Publish Date: 2022-10-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-37599>CVE-2022-37599</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-hhq3-ff78-jv3g">https://github.com/advisories/GHSA-hhq3-ff78-jv3g</a></p>
<p>Release Date: 2022-10-11</p>
<p>Fix Resolution (loader-utils): 2.0.3</p>
<p>Direct dependency fix Resolution (next): 10.0.6-canary.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-3517</summary>
### Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- cacache-13.0.1.tgz
- glob-7.1.6.tgz
- :x: **minimatch-3.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service.
<p>Publish Date: 2022-10-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3517>CVE-2022-3517</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-17</p>
<p>Fix Resolution: minimatch - 3.0.5</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-27290</summary>
### Vulnerable Libraries - <b>ssri-6.0.1.tgz</b>, <b>ssri-7.1.0.tgz</b></p>
<p>
### <b>ssri-6.0.1.tgz</b></p>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and verifies integrity metadata according to the SRI spec.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz">https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- webpack-4.44.1.tgz
- terser-webpack-plugin-1.4.5.tgz
- cacache-12.0.4.tgz
- :x: **ssri-6.0.1.tgz** (Vulnerable Library)
### <b>ssri-7.1.0.tgz</b></p>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and verifies integrity metadata according to the SRI spec.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ssri/-/ssri-7.1.0.tgz">https://registry.npmjs.org/ssri/-/ssri-7.1.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- cacache-13.0.1.tgz
- :x: **ssri-7.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ssri 5.2.2-8.0.0, fixed in 8.0.1, processes SRIs using a regular expression which is vulnerable to a denial of service. Malicious SRIs could take an extremely long time to process, leading to denial of service. This issue only affects consumers using the strict option.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-27290>CVE-2021-27290</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-vx3p-948g-6vhq">https://github.com/advisories/GHSA-vx3p-948g-6vhq</a></p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution (ssri): 6.0.2</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p><p>Fix Resolution (ssri): 6.0.2</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-38900</summary>
### Vulnerable Library - <b>decode-uri-component-0.2.0.tgz</b></p>
<p>A better decodeURIComponent</p>
<p>Library home page: <a href="https://registry.npmjs.org/decode-uri-component/-/decode-uri-component-0.2.0.tgz">https://registry.npmjs.org/decode-uri-component/-/decode-uri-component-0.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- rework-1.0.1.tgz
- css-2.2.4.tgz
- source-map-resolve-0.5.3.tgz
- :x: **decode-uri-component-0.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
decode-uri-component 0.2.0 is vulnerable to Improper Input Validation resulting in DoS.
<p>Publish Date: 2022-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38900>CVE-2022-38900</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-w573-4hg7-7wgq">https://github.com/advisories/GHSA-w573-4hg7-7wgq</a></p>
<p>Release Date: 2022-11-28</p>
<p>Fix Resolution (decode-uri-component): 0.2.1</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-37603</summary>
### Vulnerable Libraries - <b>loader-utils-1.2.3.tgz</b>, <b>loader-utils-1.4.0.tgz</b>, <b>loader-utils-2.0.0.tgz</b></p>
<p>
### <b>loader-utils-1.2.3.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.2.3.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.2.3.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- :x: **loader-utils-1.2.3.tgz** (Vulnerable Library)
### <b>loader-utils-1.4.0.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- sass-loader-8.0.2.tgz
- :x: **loader-utils-1.4.0.tgz** (Vulnerable Library)
### <b>loader-utils-2.0.0.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- :x: **loader-utils-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the url variable in interpolateName.js.
<p>Publish Date: 2022-10-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-37603>CVE-2022-37603</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-3rfm-jhwj-7488">https://github.com/advisories/GHSA-3rfm-jhwj-7488</a></p>
<p>Release Date: 2022-10-14</p>
<p>Fix Resolution (loader-utils): 1.4.2</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p><p>Fix Resolution (loader-utils): 1.4.2</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p><p>Fix Resolution (loader-utils): 1.4.2</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-23382</summary>
### Vulnerable Library - <b>postcss-7.0.21.tgz</b></p>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- :x: **postcss-7.0.21.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package postcss before 8.2.13 are vulnerable to Regular Expression Denial of Service (ReDoS) via getAnnotationURL() and loadAnnotation() in lib/previous-map.js. The vulnerable regexes are caused mainly by the sub-pattern \/\*\s* sourceMappingURL=(.*).
<p>Publish Date: 2021-04-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23382>CVE-2021-23382</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23382">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23382</a></p>
<p>Release Date: 2021-04-26</p>
<p>Fix Resolution (postcss): 7.0.36</p>
<p>Direct dependency fix Resolution (next): 10.0.7-canary.7</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-25883</summary>
### Vulnerable Library - <b>semver-7.0.0.tgz</b></p>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-7.0.0.tgz">https://registry.npmjs.org/semver/-/semver-7.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- preset-env-7.9.6.tgz
- core-js-compat-3.6.5.tgz
- :x: **semver-7.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of the package semver before 7.5.2 are vulnerable to Regular Expression Denial of Service (ReDoS) via the function new Range, when untrusted user data is provided as a range.
<p>Publish Date: 2023-06-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25883>CVE-2022-25883</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-c2qf-rxjj-qqgw">https://github.com/advisories/GHSA-c2qf-rxjj-qqgw</a></p>
<p>Release Date: 2023-06-21</p>
<p>Fix Resolution (semver): 7.5.2</p>
<p>Direct dependency fix Resolution (next): 12.0.8-canary.11</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-43803</summary>
### Vulnerable Library - <b>next-9.5.3-canary.17.tgz</b></p>
<p>The React Framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz">https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **next-9.5.3-canary.17.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Next.js is a React framework. In versions of Next.js prior to 12.0.5 or 11.1.3, invalid or malformed URLs could lead to a server crash. In order to be affected by this issue, the deployment must use Next.js versions above 11.1.0 and below 12.0.5, Node.js above 15.0.0, and next start or a custom server. Deployments on Vercel are not affected, along with similar environments where invalid requests are filtered before reaching Next.js. Versions 12.0.5 and 11.1.3 contain patches for this issue.
<p>Publish Date: 2021-12-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43803>CVE-2021-43803</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/vercel/next.js/security/advisories/GHSA-25mp-g6fv-mqxx">https://github.com/vercel/next.js/security/advisories/GHSA-25mp-g6fv-mqxx</a></p>
<p>Release Date: 2021-12-10</p>
<p>Fix Resolution: 11.1.2-canary.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-3805</summary>
### Vulnerable Library - <b>object-path-0.11.4.tgz</b></p>
<p>Access deep object properties using a path</p>
<p>Library home page: <a href="https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz">https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- adjust-sourcemap-loader-2.0.0.tgz
- :x: **object-path-0.11.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
object-path is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3805>CVE-2021-3805</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/571e3baf-7c46-46e3-9003-ba7e4e623053/">https://huntr.dev/bounties/571e3baf-7c46-46e3-9003-ba7e4e623053/</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution (object-path): 0.11.8</p>
<p>Direct dependency fix Resolution (next): 9.5.6-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-28498</summary>
### Vulnerable Library - <b>elliptic-6.5.3.tgz</b></p>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.3.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.3.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.2.1.tgz
- :x: **elliptic-6.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package elliptic before 6.5.4 are vulnerable to Cryptographic Issues via the secp256k1 implementation in elliptic/ec/key.js. There is no check to confirm that the public key point passed into the derive function actually exists on the secp256k1 curve. This results in the potential for the private key used in this implementation to be revealed after a number of ECDH operations are performed.
<p>Publish Date: 2021-02-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28498>CVE-2020-28498</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498</a></p>
<p>Release Date: 2021-02-02</p>
<p>Fix Resolution (elliptic): 6.5.4</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-37699</summary>
### Vulnerable Library - <b>next-9.5.3-canary.17.tgz</b></p>
<p>The React Framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz">https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **next-9.5.3-canary.17.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Next.js is an open source website development framework to be used with the React library. In affected versions specially encoded paths could be used when pages/_error.js was statically generated allowing an open redirect to occur to an external site. In general, this redirect does not directly harm users although can allow for phishing attacks by redirecting to an attacker's domain from a trusted domain. We recommend everyone to upgrade regardless of whether you can reproduce the issue or not. The issue has been patched in release 11.1.0.
<p>Publish Date: 2021-08-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-37699>CVE-2021-37699</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/vercel/next.js/security/advisories/GHSA-vxf5-wxwp-m7g9">https://github.com/vercel/next.js/security/advisories/GHSA-vxf5-wxwp-m7g9</a></p>
<p>Release Date: 2021-08-12</p>
<p>Fix Resolution: 11.0.1-canary.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-0235</summary>
### Vulnerable Library - <b>node-fetch-2.6.0.tgz</b></p>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- toolbox-optimizer-2.6.0.tgz
- :x: **node-fetch-2.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor
<p>Publish Date: 2022-01-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0235>CVE-2022-0235</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-r683-j2x4-v87g">https://github.com/advisories/GHSA-r683-j2x4-v87g</a></p>
<p>Release Date: 2022-01-16</p>
<p>Fix Resolution (node-fetch): 2.6.7</p>
<p>Direct dependency fix Resolution (next): 11.1.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-15168</summary>
### Vulnerable Library - <b>node-fetch-2.6.0.tgz</b></p>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- toolbox-optimizer-2.6.0.tgz
- :x: **node-fetch-2.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
node-fetch before versions 2.6.1 and 3.0.0-beta.9 did not honor the size option after following a redirect, which means that when a content size was over the limit, a FetchError would never get thrown and the process would end without failure. For most people, this fix will have a little or no impact. However, if you are relying on node-fetch to gate files above a size, the impact could be significant, for example: If you don't double-check the size of the data after fetch() has completed, your JS thread could get tied up doing work on a large file (DoS) and/or cost you money in computing.
<p>Publish Date: 2020-09-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15168>CVE-2020-15168</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r">https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r</a></p>
<p>Release Date: 2020-09-17</p>
<p>Fix Resolution (node-fetch): 2.6.1</p>
<p>Direct dependency fix Resolution (next): 10.0.4-canary.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-23364</summary>
### Vulnerable Library - <b>browserslist-4.13.0.tgz</b></p>
<p>Share target browsers between different front-end tools, like Autoprefixer, Stylelint and babel-env-preset</p>
<p>Library home page: <a href="https://registry.npmjs.org/browserslist/-/browserslist-4.13.0.tgz">https://registry.npmjs.org/browserslist/-/browserslist-4.13.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- :x: **browserslist-4.13.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package browserslist from 4.0.0 and before 4.16.5 are vulnerable to Regular Expression Denial of Service (ReDoS) during parsing of queries.
<p>Publish Date: 2021-04-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23364>CVE-2021-23364</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23364">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23364</a></p>
<p>Release Date: 2021-04-28</p>
<p>Fix Resolution (browserslist): 4.16.5</p>
<p>Direct dependency fix Resolution (next): 10.2.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-23368</summary>
### Vulnerable Library - <b>postcss-7.0.21.tgz</b></p>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- :x: **postcss-7.0.21.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package postcss from 7.0.0 and before 8.2.10 are vulnerable to Regular Expression Denial of Service (ReDoS) during source map parsing.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23368>CVE-2021-23368</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution (postcss): 7.0.36</p>
<p>Direct dependency fix Resolution (next): 10.0.7-canary.7</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | next-9.5.3-canary.17.tgz: 23 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>next-9.5.3-canary.17.tgz</b></p></summary>
<p>The React Framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz">https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz</a></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (next version) | Remediation Possible** |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-37601](https://www.mend.io/vulnerability-database/CVE-2022-37601) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | detected in multiple dependencies | Transitive | 12.0.9-canary.1 | ❌ |
| [CVE-2020-15256](https://www.mend.io/vulnerability-database/CVE-2020-15256) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | object-path-0.11.4.tgz | Transitive | 9.5.6-canary.9 | ❌ |
| [CVE-2021-42740](https://www.mend.io/vulnerability-database/CVE-2021-42740) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | shell-quote-1.7.2.tgz | Transitive | 11.1.1-canary.12 | ❌ |
| [CVE-2020-7774](https://www.mend.io/vulnerability-database/CVE-2020-7774) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | y18n-4.0.0.tgz | Transitive | 9.5.3-canary.18 | ❌ |
| [CVE-2021-23434](https://www.mend.io/vulnerability-database/CVE-2021-23434) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.6 | object-path-0.11.4.tgz | Transitive | 9.5.6-canary.9 | ❌ |
| [CVE-2022-25858](https://www.mend.io/vulnerability-database/CVE-2022-25858) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | terser-4.8.0.tgz | Transitive | 9.5.6-canary.10 | ❌ |
| [CVE-2021-3807](https://www.mend.io/vulnerability-database/CVE-2021-3807) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | ansi-regex-5.0.0.tgz | Transitive | 9.5.3-canary.18 | ❌ |
| [CVE-2020-28469](https://www.mend.io/vulnerability-database/CVE-2020-28469) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | 10.0.6-canary.1 | ❌ |
| [CVE-2022-37599](https://www.mend.io/vulnerability-database/CVE-2022-37599) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | loader-utils-2.0.0.tgz | Transitive | 10.0.6-canary.2 | ❌ |
| [CVE-2022-3517](https://www.mend.io/vulnerability-database/CVE-2022-3517) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | minimatch-3.0.4.tgz | Transitive | N/A* | ❌ |
| [CVE-2021-27290](https://www.mend.io/vulnerability-database/CVE-2021-27290) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | 9.5.3-canary.18 | ❌ |
| [CVE-2022-38900](https://www.mend.io/vulnerability-database/CVE-2022-38900) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | decode-uri-component-0.2.0.tgz | Transitive | 9.5.3-canary.18 | ❌ |
| [CVE-2022-37603](https://www.mend.io/vulnerability-database/CVE-2022-37603) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | 12.0.9-canary.1 | ❌ |
| [CVE-2021-23382](https://www.mend.io/vulnerability-database/CVE-2021-23382) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | postcss-7.0.21.tgz | Transitive | 10.0.7-canary.7 | ❌ |
| [CVE-2022-25883](https://www.mend.io/vulnerability-database/CVE-2022-25883) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | semver-7.0.0.tgz | Transitive | 12.0.8-canary.11 | ❌ |
| [CVE-2021-43803](https://www.mend.io/vulnerability-database/CVE-2021-43803) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | next-9.5.3-canary.17.tgz | Direct | 11.1.2-canary.0 | ❌ |
| [CVE-2021-3805](https://www.mend.io/vulnerability-database/CVE-2021-3805) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | object-path-0.11.4.tgz | Transitive | 9.5.6-canary.9 | ❌ |
| [CVE-2020-28498](https://www.mend.io/vulnerability-database/CVE-2020-28498) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.8 | elliptic-6.5.3.tgz | Transitive | 9.5.3-canary.18 | ❌ |
| [CVE-2021-37699](https://www.mend.io/vulnerability-database/CVE-2021-37699) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | next-9.5.3-canary.17.tgz | Direct | 11.0.1-canary.0 | ❌ |
| [CVE-2022-0235](https://www.mend.io/vulnerability-database/CVE-2022-0235) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | node-fetch-2.6.0.tgz | Transitive | 11.1.4 | ❌ |
| [CVE-2020-15168](https://www.mend.io/vulnerability-database/CVE-2020-15168) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | node-fetch-2.6.0.tgz | Transitive | 10.0.4-canary.2 | ❌ |
| [CVE-2021-23364](https://www.mend.io/vulnerability-database/CVE-2021-23364) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | browserslist-4.13.0.tgz | Transitive | 10.2.1-canary.9 | ❌ |
| [CVE-2021-23368](https://www.mend.io/vulnerability-database/CVE-2021-23368) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | postcss-7.0.21.tgz | Transitive | 10.0.7-canary.7 | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p><p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2022-37601</summary>
### Vulnerable Libraries - <b>loader-utils-1.2.3.tgz</b>, <b>loader-utils-1.4.0.tgz</b>, <b>loader-utils-2.0.0.tgz</b></p>
<p>
### <b>loader-utils-1.2.3.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.2.3.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.2.3.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- :x: **loader-utils-1.2.3.tgz** (Vulnerable Library)
### <b>loader-utils-1.4.0.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- sass-loader-8.0.2.tgz
- :x: **loader-utils-1.4.0.tgz** (Vulnerable Library)
### <b>loader-utils-2.0.0.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- :x: **loader-utils-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype pollution vulnerability in function parseQuery in parseQuery.js in webpack loader-utils 2.0.0 via the name variable in parseQuery.js.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-37601>CVE-2022-37601</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-76p3-8jx3-jpfq">https://github.com/advisories/GHSA-76p3-8jx3-jpfq</a></p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution (loader-utils): 1.4.1</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p><p>Fix Resolution (loader-utils): 1.4.1</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p><p>Fix Resolution (loader-utils): 1.4.1</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-15256</summary>
### Vulnerable Library - <b>object-path-0.11.4.tgz</b></p>
<p>Access deep object properties using a path</p>
<p>Library home page: <a href="https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz">https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- adjust-sourcemap-loader-2.0.0.tgz
- :x: **object-path-0.11.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A prototype pollution vulnerability has been found in `object-path` <= 0.11.4 affecting the `set()` method. The vulnerability is limited to the `includeInheritedProps` mode (if version >= 0.11.0 is used), which has to be explicitly enabled by creating a new instance of `object-path` and setting the option `includeInheritedProps: true`, or by using the default `withInheritedProps` instance. The default operating mode is not affected by the vulnerability if version >= 0.11.0 is used. Any usage of `set()` in versions < 0.11.0 is vulnerable. The issue is fixed in object-path version 0.11.5 As a workaround, don't use the `includeInheritedProps: true` options or the `withInheritedProps` instance if using a version >= 0.11.0.
<p>Publish Date: 2020-10-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15256>CVE-2020-15256</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mariocasciaro/object-path/security/advisories/GHSA-cwx2-736x-mf6w">https://github.com/mariocasciaro/object-path/security/advisories/GHSA-cwx2-736x-mf6w</a></p>
<p>Release Date: 2020-10-19</p>
<p>Fix Resolution (object-path): 0.11.5</p>
<p>Direct dependency fix Resolution (next): 9.5.6-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2021-42740</summary>
### Vulnerable Library - <b>shell-quote-1.7.2.tgz</b></p>
<p>quote and parse shell commands</p>
<p>Library home page: <a href="https://registry.npmjs.org/shell-quote/-/shell-quote-1.7.2.tgz">https://registry.npmjs.org/shell-quote/-/shell-quote-1.7.2.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- react-dev-overlay-9.5.3-canary.17.tgz
- :x: **shell-quote-1.7.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The shell-quote package before 1.7.3 for Node.js allows command injection. An attacker can inject unescaped shell metacharacters through a regex designed to support Windows drive letters. If the output of this package is passed to a real shell as a quoted argument to a command with exec(), an attacker can inject arbitrary commands. This is because the Windows drive letter regex character class is {A-z] instead of the correct {A-Za-z]. Several shell metacharacters exist in the space between capital letter Z and lower case letter a, such as the backtick character.
<p>Publish Date: 2021-10-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-42740>CVE-2021-42740</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740</a></p>
<p>Release Date: 2021-10-21</p>
<p>Fix Resolution (shell-quote): 1.7.3</p>
<p>Direct dependency fix Resolution (next): 11.1.1-canary.12</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-7774</summary>
### Vulnerable Library - <b>y18n-4.0.0.tgz</b></p>
<p>the bare-bones internationalization library used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz">https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- webpack-4.44.1.tgz
- terser-webpack-plugin-1.4.5.tgz
- cacache-12.0.4.tgz
- :x: **y18n-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package y18n before 3.2.2, 4.0.1 and 5.0.5, is vulnerable to Prototype Pollution.
<p>Publish Date: 2020-11-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7774>CVE-2020-7774</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1654">https://www.npmjs.com/advisories/1654</a></p>
<p>Release Date: 2020-11-17</p>
<p>Fix Resolution (y18n): 4.0.1</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-23434</summary>
### Vulnerable Library - <b>object-path-0.11.4.tgz</b></p>
<p>Access deep object properties using a path</p>
<p>Library home page: <a href="https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz">https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- adjust-sourcemap-loader-2.0.0.tgz
- :x: **object-path-0.11.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package object-path before 0.11.6. A type confusion vulnerability can lead to a bypass of CVE-2020-15256 when the path components used in the path parameter are arrays. In particular, the condition currentPath === '__proto__' returns false if currentPath is ['__proto__']. This is because the === operator returns always false when the type of the operands is different.
<p>Publish Date: 2021-08-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23434>CVE-2021-23434</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23434">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23434</a></p>
<p>Release Date: 2021-08-27</p>
<p>Fix Resolution (object-path): 0.11.6</p>
<p>Direct dependency fix Resolution (next): 9.5.6-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-25858</summary>
### Vulnerable Library - <b>terser-4.8.0.tgz</b></p>
<p>JavaScript parser, mangler/compressor and beautifier toolkit for ES6+</p>
<p>Library home page: <a href="https://registry.npmjs.org/terser/-/terser-4.8.0.tgz">https://registry.npmjs.org/terser/-/terser-4.8.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- webpack-4.44.1.tgz
- terser-webpack-plugin-1.4.5.tgz
- :x: **terser-4.8.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package terser before 4.8.1, from 5.0.0 and before 5.14.2 are vulnerable to Regular Expression Denial of Service (ReDoS) due to insecure usage of regular expressions.
<p>Publish Date: 2022-07-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25858>CVE-2022-25858</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25858">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25858</a></p>
<p>Release Date: 2022-07-15</p>
<p>Fix Resolution (terser): 4.8.1</p>
<p>Direct dependency fix Resolution (next): 9.5.6-canary.10</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-3807</summary>
### Vulnerable Library - <b>ansi-regex-5.0.0.tgz</b></p>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- react-dev-overlay-9.5.3-canary.17.tgz
- strip-ansi-6.0.0.tgz
- :x: **ansi-regex-5.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ansi-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3807>CVE-2021-3807</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/">https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution (ansi-regex): 5.0.1</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-28469</summary>
### Vulnerable Libraries - <b>glob-parent-3.1.0.tgz</b>, <b>glob-parent-5.1.1.tgz</b></p>
<p>
### <b>glob-parent-3.1.0.tgz</b></p>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
### <b>glob-parent-5.1.1.tgz</b></p>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- webpack-4.44.1.tgz
- watchpack-1.7.4.tgz
- chokidar-3.4.2.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (next): 10.0.6-canary.1</p><p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (next): 10.0.6-canary.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-37599</summary>
### Vulnerable Library - <b>loader-utils-2.0.0.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- :x: **loader-utils-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the resourcePath variable in interpolateName.js.
<p>Publish Date: 2022-10-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-37599>CVE-2022-37599</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-hhq3-ff78-jv3g">https://github.com/advisories/GHSA-hhq3-ff78-jv3g</a></p>
<p>Release Date: 2022-10-11</p>
<p>Fix Resolution (loader-utils): 2.0.3</p>
<p>Direct dependency fix Resolution (next): 10.0.6-canary.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-3517</summary>
### Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- cacache-13.0.1.tgz
- glob-7.1.6.tgz
- :x: **minimatch-3.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service.
<p>Publish Date: 2022-10-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3517>CVE-2022-3517</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-17</p>
<p>Fix Resolution: minimatch - 3.0.5</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-27290</summary>
### Vulnerable Libraries - <b>ssri-6.0.1.tgz</b>, <b>ssri-7.1.0.tgz</b></p>
<p>
### <b>ssri-6.0.1.tgz</b></p>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and verifies integrity metadata according to the SRI spec.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz">https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- webpack-4.44.1.tgz
- terser-webpack-plugin-1.4.5.tgz
- cacache-12.0.4.tgz
- :x: **ssri-6.0.1.tgz** (Vulnerable Library)
### <b>ssri-7.1.0.tgz</b></p>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and verifies integrity metadata according to the SRI spec.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ssri/-/ssri-7.1.0.tgz">https://registry.npmjs.org/ssri/-/ssri-7.1.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- cacache-13.0.1.tgz
- :x: **ssri-7.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ssri 5.2.2-8.0.0, fixed in 8.0.1, processes SRIs using a regular expression which is vulnerable to a denial of service. Malicious SRIs could take an extremely long time to process, leading to denial of service. This issue only affects consumers using the strict option.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-27290>CVE-2021-27290</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-vx3p-948g-6vhq">https://github.com/advisories/GHSA-vx3p-948g-6vhq</a></p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution (ssri): 6.0.2</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p><p>Fix Resolution (ssri): 6.0.2</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-38900</summary>
### Vulnerable Library - <b>decode-uri-component-0.2.0.tgz</b></p>
<p>A better decodeURIComponent</p>
<p>Library home page: <a href="https://registry.npmjs.org/decode-uri-component/-/decode-uri-component-0.2.0.tgz">https://registry.npmjs.org/decode-uri-component/-/decode-uri-component-0.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- rework-1.0.1.tgz
- css-2.2.4.tgz
- source-map-resolve-0.5.3.tgz
- :x: **decode-uri-component-0.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
decode-uri-component 0.2.0 is vulnerable to Improper Input Validation resulting in DoS.
<p>Publish Date: 2022-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38900>CVE-2022-38900</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-w573-4hg7-7wgq">https://github.com/advisories/GHSA-w573-4hg7-7wgq</a></p>
<p>Release Date: 2022-11-28</p>
<p>Fix Resolution (decode-uri-component): 0.2.1</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-37603</summary>
### Vulnerable Libraries - <b>loader-utils-1.2.3.tgz</b>, <b>loader-utils-1.4.0.tgz</b>, <b>loader-utils-2.0.0.tgz</b></p>
<p>
### <b>loader-utils-1.2.3.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.2.3.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.2.3.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- :x: **loader-utils-1.2.3.tgz** (Vulnerable Library)
### <b>loader-utils-1.4.0.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- sass-loader-8.0.2.tgz
- :x: **loader-utils-1.4.0.tgz** (Vulnerable Library)
### <b>loader-utils-2.0.0.tgz</b></p>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- :x: **loader-utils-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the url variable in interpolateName.js.
<p>Publish Date: 2022-10-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-37603>CVE-2022-37603</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-3rfm-jhwj-7488">https://github.com/advisories/GHSA-3rfm-jhwj-7488</a></p>
<p>Release Date: 2022-10-14</p>
<p>Fix Resolution (loader-utils): 1.4.2</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p><p>Fix Resolution (loader-utils): 1.4.2</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p><p>Fix Resolution (loader-utils): 1.4.2</p>
<p>Direct dependency fix Resolution (next): 12.0.9-canary.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-23382</summary>
### Vulnerable Library - <b>postcss-7.0.21.tgz</b></p>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- :x: **postcss-7.0.21.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package postcss before 8.2.13 are vulnerable to Regular Expression Denial of Service (ReDoS) via getAnnotationURL() and loadAnnotation() in lib/previous-map.js. The vulnerable regexes are caused mainly by the sub-pattern \/\*\s* sourceMappingURL=(.*).
<p>Publish Date: 2021-04-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23382>CVE-2021-23382</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23382">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23382</a></p>
<p>Release Date: 2021-04-26</p>
<p>Fix Resolution (postcss): 7.0.36</p>
<p>Direct dependency fix Resolution (next): 10.0.7-canary.7</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-25883</summary>
### Vulnerable Library - <b>semver-7.0.0.tgz</b></p>
<p>The semantic version parser used by npm.</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver/-/semver-7.0.0.tgz">https://registry.npmjs.org/semver/-/semver-7.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- preset-env-7.9.6.tgz
- core-js-compat-3.6.5.tgz
- :x: **semver-7.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of the package semver before 7.5.2 are vulnerable to Regular Expression Denial of Service (ReDoS) via the function new Range, when untrusted user data is provided as a range.
<p>Publish Date: 2023-06-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25883>CVE-2022-25883</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-c2qf-rxjj-qqgw">https://github.com/advisories/GHSA-c2qf-rxjj-qqgw</a></p>
<p>Release Date: 2023-06-21</p>
<p>Fix Resolution (semver): 7.5.2</p>
<p>Direct dependency fix Resolution (next): 12.0.8-canary.11</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-43803</summary>
### Vulnerable Library - <b>next-9.5.3-canary.17.tgz</b></p>
<p>The React Framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz">https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **next-9.5.3-canary.17.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Next.js is a React framework. In versions of Next.js prior to 12.0.5 or 11.1.3, invalid or malformed URLs could lead to a server crash. In order to be affected by this issue, the deployment must use Next.js versions above 11.1.0 and below 12.0.5, Node.js above 15.0.0, and next start or a custom server. Deployments on Vercel are not affected, along with similar environments where invalid requests are filtered before reaching Next.js. Versions 12.0.5 and 11.1.3 contain patches for this issue.
<p>Publish Date: 2021-12-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43803>CVE-2021-43803</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/vercel/next.js/security/advisories/GHSA-25mp-g6fv-mqxx">https://github.com/vercel/next.js/security/advisories/GHSA-25mp-g6fv-mqxx</a></p>
<p>Release Date: 2021-12-10</p>
<p>Fix Resolution: 11.1.2-canary.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-3805</summary>
### Vulnerable Library - <b>object-path-0.11.4.tgz</b></p>
<p>Access deep object properties using a path</p>
<p>Library home page: <a href="https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz">https://registry.npmjs.org/object-path/-/object-path-0.11.4.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- adjust-sourcemap-loader-2.0.0.tgz
- :x: **object-path-0.11.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
object-path is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3805>CVE-2021-3805</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/571e3baf-7c46-46e3-9003-ba7e4e623053/">https://huntr.dev/bounties/571e3baf-7c46-46e3-9003-ba7e4e623053/</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution (object-path): 0.11.8</p>
<p>Direct dependency fix Resolution (next): 9.5.6-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-28498</summary>
### Vulnerable Library - <b>elliptic-6.5.3.tgz</b></p>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.3.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.3.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.2.1.tgz
- :x: **elliptic-6.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package elliptic before 6.5.4 are vulnerable to Cryptographic Issues via the secp256k1 implementation in elliptic/ec/key.js. There is no check to confirm that the public key point passed into the derive function actually exists on the secp256k1 curve. This results in the potential for the private key used in this implementation to be revealed after a number of ECDH operations are performed.
<p>Publish Date: 2021-02-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28498>CVE-2020-28498</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498</a></p>
<p>Release Date: 2021-02-02</p>
<p>Fix Resolution (elliptic): 6.5.4</p>
<p>Direct dependency fix Resolution (next): 9.5.3-canary.18</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-37699</summary>
### Vulnerable Library - <b>next-9.5.3-canary.17.tgz</b></p>
<p>The React Framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz">https://registry.npmjs.org/next/-/next-9.5.3-canary.17.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **next-9.5.3-canary.17.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Next.js is an open source website development framework to be used with the React library. In affected versions specially encoded paths could be used when pages/_error.js was statically generated allowing an open redirect to occur to an external site. In general, this redirect does not directly harm users although can allow for phishing attacks by redirecting to an attacker's domain from a trusted domain. We recommend everyone to upgrade regardless of whether you can reproduce the issue or not. The issue has been patched in release 11.1.0.
<p>Publish Date: 2021-08-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-37699>CVE-2021-37699</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/vercel/next.js/security/advisories/GHSA-vxf5-wxwp-m7g9">https://github.com/vercel/next.js/security/advisories/GHSA-vxf5-wxwp-m7g9</a></p>
<p>Release Date: 2021-08-12</p>
<p>Fix Resolution: 11.0.1-canary.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-0235</summary>
### Vulnerable Library - <b>node-fetch-2.6.0.tgz</b></p>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- toolbox-optimizer-2.6.0.tgz
- :x: **node-fetch-2.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor
<p>Publish Date: 2022-01-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0235>CVE-2022-0235</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-r683-j2x4-v87g">https://github.com/advisories/GHSA-r683-j2x4-v87g</a></p>
<p>Release Date: 2022-01-16</p>
<p>Fix Resolution (node-fetch): 2.6.7</p>
<p>Direct dependency fix Resolution (next): 11.1.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-15168</summary>
### Vulnerable Library - <b>node-fetch-2.6.0.tgz</b></p>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- toolbox-optimizer-2.6.0.tgz
- :x: **node-fetch-2.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
node-fetch before versions 2.6.1 and 3.0.0-beta.9 did not honor the size option after following a redirect, which means that when a content size was over the limit, a FetchError would never get thrown and the process would end without failure. For most people, this fix will have a little or no impact. However, if you are relying on node-fetch to gate files above a size, the impact could be significant, for example: If you don't double-check the size of the data after fetch() has completed, your JS thread could get tied up doing work on a large file (DoS) and/or cost you money in computing.
<p>Publish Date: 2020-09-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15168>CVE-2020-15168</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r">https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r</a></p>
<p>Release Date: 2020-09-17</p>
<p>Fix Resolution (node-fetch): 2.6.1</p>
<p>Direct dependency fix Resolution (next): 10.0.4-canary.2</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-23364</summary>
### Vulnerable Library - <b>browserslist-4.13.0.tgz</b></p>
<p>Share target browsers between different front-end tools, like Autoprefixer, Stylelint and babel-env-preset</p>
<p>Library home page: <a href="https://registry.npmjs.org/browserslist/-/browserslist-4.13.0.tgz">https://registry.npmjs.org/browserslist/-/browserslist-4.13.0.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- :x: **browserslist-4.13.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package browserslist from 4.0.0 and before 4.16.5 are vulnerable to Regular Expression Denial of Service (ReDoS) during parsing of queries.
<p>Publish Date: 2021-04-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23364>CVE-2021-23364</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23364">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23364</a></p>
<p>Release Date: 2021-04-28</p>
<p>Fix Resolution (browserslist): 4.16.5</p>
<p>Direct dependency fix Resolution (next): 10.2.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-23368</summary>
### Vulnerable Library - <b>postcss-7.0.21.tgz</b></p>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz</a></p>
<p>
Dependency Hierarchy:
- next-9.5.3-canary.17.tgz (Root Library)
- resolve-url-loader-3.1.1.tgz
- :x: **postcss-7.0.21.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanductran/fullstackradio.com/commit/de48655e50c844671347f795aaaf626836826e8e">de48655e50c844671347f795aaaf626836826e8e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package postcss from 7.0.0 and before 8.2.10 are vulnerable to Regular Expression Denial of Service (ReDoS) during source map parsing.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23368>CVE-2021-23368</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution (postcss): 7.0.36</p>
<p>Direct dependency fix Resolution (next): 10.0.7-canary.7</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_priority | next canary tgz vulnerabilities highest severity is vulnerable library next canary tgz the react framework library home page a href found in head commit a href vulnerabilities cve severity cvss dependency type fixed in next version remediation possible critical detected in multiple dependencies transitive canary critical object path tgz transitive canary critical shell quote tgz transitive canary critical tgz transitive canary high object path tgz transitive canary high terser tgz transitive canary high ansi regex tgz transitive canary high detected in multiple dependencies transitive canary high loader utils tgz transitive canary high minimatch tgz transitive n a high detected in multiple dependencies transitive canary high decode uri component tgz transitive canary high detected in multiple dependencies transitive canary high postcss tgz transitive canary high semver tgz transitive canary high next canary tgz direct canary high object path tgz transitive canary medium elliptic tgz transitive canary medium next canary tgz direct canary medium node fetch tgz transitive medium node fetch tgz transitive canary medium browserslist tgz transitive canary medium postcss tgz transitive canary for some transitive vulnerabilities there is no version of direct dependency with a fix check the details section below to see if there is a version of transitive dependency where vulnerability is fixed in some cases remediation pr cannot be created automatically for a vulnerability despite the availability of remediation details cve vulnerable libraries loader utils tgz loader utils tgz loader utils tgz loader utils tgz utils for webpack loaders library home page a href dependency hierarchy next canary tgz root library resolve url loader tgz x loader utils tgz vulnerable library loader utils tgz utils for webpack loaders library home page a href dependency hierarchy next canary tgz root library sass loader tgz x loader utils tgz vulnerable library loader utils tgz utils for webpack loaders library home page a href dependency hierarchy next canary tgz root library x loader utils tgz vulnerable library found in head commit a href found in base branch master vulnerability details prototype pollution vulnerability in function parsequery in parsequery js in webpack loader utils via the name variable in parsequery js publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution loader utils direct dependency fix resolution next canary fix resolution loader utils direct dependency fix resolution next canary fix resolution loader utils direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library object path tgz access deep object properties using a path library home page a href dependency hierarchy next canary tgz root library resolve url loader tgz adjust sourcemap loader tgz x object path tgz vulnerable library found in head commit a href found in base branch master vulnerability details a prototype pollution vulnerability has been found in object path is used which has to be explicitly enabled by creating a new instance of object path and setting the option includeinheritedprops true or by using the default withinheritedprops instance the default operating mode is not affected by the vulnerability if version is used any usage of set in versions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution object path direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library shell quote tgz quote and parse shell commands library home page a href dependency hierarchy next canary tgz root library react dev overlay canary tgz x shell quote tgz vulnerable library found in head commit a href found in base branch master vulnerability details the shell quote package before for node js allows command injection an attacker can inject unescaped shell metacharacters through a regex designed to support windows drive letters if the output of this package is passed to a real shell as a quoted argument to a command with exec an attacker can inject arbitrary commands this is because the windows drive letter regex character class is a z instead of the correct a za z several shell metacharacters exist in the space between capital letter z and lower case letter a such as the backtick character publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution shell quote direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library tgz the bare bones internationalization library used by yargs library home page a href dependency hierarchy next canary tgz root library webpack tgz terser webpack plugin tgz cacache tgz x tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package before and is vulnerable to prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library object path tgz access deep object properties using a path library home page a href dependency hierarchy next canary tgz root library resolve url loader tgz adjust sourcemap loader tgz x object path tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package object path before a type confusion vulnerability can lead to a bypass of cve when the path components used in the path parameter are arrays in particular the condition currentpath proto returns false if currentpath is this is because the operator returns always false when the type of the operands is different publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution object path direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library terser tgz javascript parser mangler compressor and beautifier toolkit for library home page a href dependency hierarchy next canary tgz root library webpack tgz terser webpack plugin tgz x terser tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package terser before from and before are vulnerable to regular expression denial of service redos due to insecure usage of regular expressions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution terser direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library ansi regex tgz regular expression for matching ansi escape codes library home page a href dependency hierarchy next canary tgz root library react dev overlay canary tgz strip ansi tgz x ansi regex tgz vulnerable library found in head commit a href found in base branch master vulnerability details ansi regex is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ansi regex direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable libraries glob parent tgz glob parent tgz glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href dependency hierarchy next canary tgz root library chokidar tgz x glob parent tgz vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href dependency hierarchy next canary tgz root library webpack tgz watchpack tgz chokidar tgz x glob parent tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent direct dependency fix resolution next canary fix resolution glob parent direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library loader utils tgz utils for webpack loaders library home page a href dependency hierarchy next canary tgz root library x loader utils tgz vulnerable library found in head commit a href found in base branch master vulnerability details a regular expression denial of service redos flaw was found in function interpolatename in interpolatename js in webpack loader utils via the resourcepath variable in interpolatename js publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution loader utils direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library minimatch tgz a glob matcher in javascript library home page a href dependency hierarchy next canary tgz root library cacache tgz glob tgz x minimatch tgz vulnerable library found in head commit a href found in base branch master vulnerability details a vulnerability was found in the minimatch package this flaw allows a regular expression denial of service redos when calling the braceexpand function with specific arguments resulting in a denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution minimatch step up your open source security game with mend cve vulnerable libraries ssri tgz ssri tgz ssri tgz standard subresource integrity library parses serializes generates and verifies integrity metadata according to the sri spec library home page a href dependency hierarchy next canary tgz root library webpack tgz terser webpack plugin tgz cacache tgz x ssri tgz vulnerable library ssri tgz standard subresource integrity library parses serializes generates and verifies integrity metadata according to the sri spec library home page a href dependency hierarchy next canary tgz root library cacache tgz x ssri tgz vulnerable library found in head commit a href found in base branch master vulnerability details ssri fixed in processes sris using a regular expression which is vulnerable to a denial of service malicious sris could take an extremely long time to process leading to denial of service this issue only affects consumers using the strict option publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ssri direct dependency fix resolution next canary fix resolution ssri direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library decode uri component tgz a better decodeuricomponent library home page a href dependency hierarchy next canary tgz root library resolve url loader tgz rework tgz css tgz source map resolve tgz x decode uri component tgz vulnerable library found in head commit a href found in base branch master vulnerability details decode uri component is vulnerable to improper input validation resulting in dos publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution decode uri component direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable libraries loader utils tgz loader utils tgz loader utils tgz loader utils tgz utils for webpack loaders library home page a href dependency hierarchy next canary tgz root library resolve url loader tgz x loader utils tgz vulnerable library loader utils tgz utils for webpack loaders library home page a href dependency hierarchy next canary tgz root library sass loader tgz x loader utils tgz vulnerable library loader utils tgz utils for webpack loaders library home page a href dependency hierarchy next canary tgz root library x loader utils tgz vulnerable library found in head commit a href found in base branch master vulnerability details a regular expression denial of service redos flaw was found in function interpolatename in interpolatename js in webpack loader utils via the url variable in interpolatename js publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution loader utils direct dependency fix resolution next canary fix resolution loader utils direct dependency fix resolution next canary fix resolution loader utils direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library postcss tgz tool for transforming styles with js plugins library home page a href dependency hierarchy next canary tgz root library resolve url loader tgz x postcss tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package postcss before are vulnerable to regular expression denial of service redos via getannotationurl and loadannotation in lib previous map js the vulnerable regexes are caused mainly by the sub pattern s sourcemappingurl publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution postcss direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library semver tgz the semantic version parser used by npm library home page a href dependency hierarchy next canary tgz root library preset env tgz core js compat tgz x semver tgz vulnerable library found in head commit a href found in base branch master vulnerability details versions of the package semver before are vulnerable to regular expression denial of service redos via the function new range when untrusted user data is provided as a range publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution semver direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library next canary tgz the react framework library home page a href dependency hierarchy x next canary tgz vulnerable library found in head commit a href found in base branch master vulnerability details next js is a react framework in versions of next js prior to or invalid or malformed urls could lead to a server crash in order to be affected by this issue the deployment must use next js versions above and below node js above and next start or a custom server deployments on vercel are not affected along with similar environments where invalid requests are filtered before reaching next js versions and contain patches for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution canary step up your open source security game with mend cve vulnerable library object path tgz access deep object properties using a path library home page a href dependency hierarchy next canary tgz root library resolve url loader tgz adjust sourcemap loader tgz x object path tgz vulnerable library found in head commit a href found in base branch master vulnerability details object path is vulnerable to improperly controlled modification of object prototype attributes prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution object path direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library elliptic tgz ec cryptography library home page a href dependency hierarchy next canary tgz root library crypto browserify tgz browserify sign tgz x elliptic tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package elliptic before are vulnerable to cryptographic issues via the implementation in elliptic ec key js there is no check to confirm that the public key point passed into the derive function actually exists on the curve this results in the potential for the private key used in this implementation to be revealed after a number of ecdh operations are performed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution elliptic direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library next canary tgz the react framework library home page a href dependency hierarchy x next canary tgz vulnerable library found in head commit a href found in base branch master vulnerability details next js is an open source website development framework to be used with the react library in affected versions specially encoded paths could be used when pages error js was statically generated allowing an open redirect to occur to an external site in general this redirect does not directly harm users although can allow for phishing attacks by redirecting to an attacker s domain from a trusted domain we recommend everyone to upgrade regardless of whether you can reproduce the issue or not the issue has been patched in release publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution canary step up your open source security game with mend cve vulnerable library node fetch tgz a light weight module that brings window fetch to node js library home page a href dependency hierarchy next canary tgz root library toolbox optimizer tgz x node fetch tgz vulnerable library found in head commit a href found in base branch master vulnerability details node fetch is vulnerable to exposure of sensitive information to an unauthorized actor publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node fetch direct dependency fix resolution next step up your open source security game with mend cve vulnerable library node fetch tgz a light weight module that brings window fetch to node js library home page a href dependency hierarchy next canary tgz root library toolbox optimizer tgz x node fetch tgz vulnerable library found in head commit a href found in base branch master vulnerability details node fetch before versions and beta did not honor the size option after following a redirect which means that when a content size was over the limit a fetcherror would never get thrown and the process would end without failure for most people this fix will have a little or no impact however if you are relying on node fetch to gate files above a size the impact could be significant for example if you don t double check the size of the data after fetch has completed your js thread could get tied up doing work on a large file dos and or cost you money in computing publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node fetch direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library browserslist tgz share target browsers between different front end tools like autoprefixer stylelint and babel env preset library home page a href dependency hierarchy next canary tgz root library x browserslist tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package browserslist from and before are vulnerable to regular expression denial of service redos during parsing of queries publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution browserslist direct dependency fix resolution next canary step up your open source security game with mend cve vulnerable library postcss tgz tool for transforming styles with js plugins library home page a href dependency hierarchy next canary tgz root library resolve url loader tgz x postcss tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package postcss from and before are vulnerable to regular expression denial of service redos during source map parsing publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution postcss direct dependency fix resolution next canary step up your open source security game with mend | 0 |
84,876 | 15,728,361,947 | IssuesEvent | 2021-03-29 13:44:29 | ssobue/bean-injection-demo | https://api.github.com/repos/ssobue/bean-injection-demo | closed | CVE-2021-24122 (Medium) detected in tomcat-embed-core-8.5.32.jar | security vulnerability | ## CVE-2021-24122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.32.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: /bean-injection-demo/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.32/tomcat-embed-core-8.5.32.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.4.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.0.4.RELEASE.jar
- :x: **tomcat-embed-core-8.5.32.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.
<p>Publish Date: 2021-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122>CVE-2021-24122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122</a></p>
<p>Release Date: 2021-01-14</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-24122 (Medium) detected in tomcat-embed-core-8.5.32.jar - ## CVE-2021-24122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.32.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: /bean-injection-demo/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.32/tomcat-embed-core-8.5.32.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.4.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.0.4.RELEASE.jar
- :x: **tomcat-embed-core-8.5.32.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.
<p>Publish Date: 2021-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122>CVE-2021-24122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122</a></p>
<p>Release Date: 2021-01-14</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tomcat embed core jar cve medium severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file bean injection demo pom xml path to vulnerable library root repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library vulnerability details when serving resources from a network location using the ntfs file system apache tomcat versions to to to and to were susceptible to jsp source code disclosure in some configurations the root cause was the unexpected behaviour of the jre api file getcanonicalpath which in turn was caused by the inconsistent behaviour of the windows api findfirstfilew in some circumstances publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina step up your open source security game with whitesource | 0 |
382,999 | 26,528,082,624 | IssuesEvent | 2023-01-19 10:18:23 | UTokyo-FieldPhenomics-Lab/EasyIDP | https://api.github.com/repos/UTokyo-FieldPhenomics-Lab/EasyIDP | closed | Provide small demo docs for each function | documentation | Current single demo involves too many functions, splited them to small docs, focusing on simple function and its example | 1.0 | Provide small demo docs for each function - Current single demo involves too many functions, splited them to small docs, focusing on simple function and its example | non_priority | provide small demo docs for each function current single demo involves too many functions splited them to small docs focusing on simple function and its example | 0 |
52,768 | 27,764,620,183 | IssuesEvent | 2023-03-16 10:36:58 | enso-org/enso | https://api.github.com/repos/enso-org/enso | closed | GraalVM updater attempts to install component multiple times | -compiler --low-performance -project-manager | Clean installation on Windows 10:
```
[debug] [2023-02-23T10:29:42.666Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Loading Graal runtime [C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1].
[debug] [2023-02-23T10:29:42.667Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Installing GraalVM components [GraalVM 22.3.1-java11, Windows].
[trace] [2023-02-23T10:29:42.668Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd { exists=true, executable=true }
[debug] [2023-02-23T10:29:42.668Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] Executing: JAVA_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 GRRAALVM_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd list -v
[trace] [2023-02-23T10:29:43.023Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] ID : graalvm
Name : GraalVM Core
Version : 22.3.1
GraalVM : n/a
Stability: Supported
Origin :
ID : js
Name : Graal.js
Version : 22.3.1
GraalVM : 22.3.1
Stability: Supported
Origin : https://github.com/oracle/graaljs/releases/download/vm-22.3.1/js-installable-svm-java11-windows-amd64-22.3.1.jar
ID : native-image
Name : Native Image
Version : 22.3.1
GraalVM : 22.3.1
Stability: Early adopter
Origin : https://github.com/graalvm/graalvm-ce-builds/releases/download/vm-22.3.1/native-image-installable-svm-java11-windows-amd64-22.3.1.jar
[debug] [2023-02-23T10:29:43.023Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Available GraalVM components: [Vector(GraalVMComponent(graalvm), GraalVMComponent(js), GraalVMComponent(native-image))].
[trace] [2023-02-23T10:29:43.023Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd { exists=true, executable=true }
[debug] [2023-02-23T10:29:43.023Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] Executing: JAVA_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 GRRAALVM_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd install python R
[trace] [2023-02-23T10:29:44.098Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] [stderr] Error: Component "python" is not available in catalog.
[warn] [2023-02-23T10:29:44.118Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Failed to install required components on the existing [GraalVM 22.3.1-java11]. Some language features may be unavailable. Nonzero exit code: 3
[trace] [2023-02-23T10:29:44.118Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Installed engines (1):
- Enso 2023.1.1-nightly.2023.2.22 [runtime: GraalVM 22.3.1-java11] [location: ***\2023.1.1-nightly.2023.2.22]
Installed runtimes (1):
- GraalVM 22.3.1-java11 [location: ***\graalvm-ce-java11-22.3.1]
[info] [2023-02-23T10:29:44.119Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] The engine [2023.1.1-nightly.2023.2.22] found.
[debug] [2023-02-23T10:29:44.119Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Loading Graal runtime [C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1].
[debug] [2023-02-23T10:29:44.12Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Installing GraalVM components [GraalVM 22.3.1-java11, Windows].
[trace] [2023-02-23T10:29:44.12Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd { exists=true, executable=true }
[debug] [2023-02-23T10:29:44.12Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] Executing: JAVA_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 GRRAALVM_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd list -v
[trace] [2023-02-23T10:29:44.493Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] ID : graalvm
Name : GraalVM Core
Version : 22.3.1
GraalVM : n/a
Stability: Supported
Origin :
ID : js
Name : Graal.js
Version : 22.3.1
GraalVM : 22.3.1
Stability: Supported
Origin : https://github.com/oracle/graaljs/releases/download/vm-22.3.1/js-installable-svm-java11-windows-amd64-22.3.1.jar
ID : native-image
Name : Native Image
Version : 22.3.1
GraalVM : 22.3.1
Stability: Early adopter
Origin : https://github.com/graalvm/graalvm-ce-builds/releases/download/vm-22.3.1/native-image-installable-svm-java11-windows-amd64-22.3.1.jar
[debug] [2023-02-23T10:29:44.493Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Available GraalVM components: [Vector(GraalVMComponent(graalvm), GraalVMComponent(js), GraalVMComponent(native-image))].
[trace] [2023-02-23T10:29:44.493Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd { exists=true, executable=true }
[debug] [2023-02-23T10:29:44.493Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] Executing: JAVA_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 GRRAALVM_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd install python R
[trace] [2023-02-23T10:29:45.636Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] [stderr] Error: Component "python" is not available in catalog.
[warn] [2023-02-23T10:29:45.656Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Failed to install required components on the existing [GraalVM 22.3.1-java11]. Some language features may be unavailable. Nonzero exit code: 3
```
is attempted 4 times before giving up.
I can understand that we may want to retry the process on failure, but this one is clearly not recoverable.
This can and has led to timeouts during handling of the `ProjectCreate` request which led to IDE just appearing to hang. | True | GraalVM updater attempts to install component multiple times - Clean installation on Windows 10:
```
[debug] [2023-02-23T10:29:42.666Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Loading Graal runtime [C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1].
[debug] [2023-02-23T10:29:42.667Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Installing GraalVM components [GraalVM 22.3.1-java11, Windows].
[trace] [2023-02-23T10:29:42.668Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd { exists=true, executable=true }
[debug] [2023-02-23T10:29:42.668Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] Executing: JAVA_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 GRRAALVM_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd list -v
[trace] [2023-02-23T10:29:43.023Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] ID : graalvm
Name : GraalVM Core
Version : 22.3.1
GraalVM : n/a
Stability: Supported
Origin :
ID : js
Name : Graal.js
Version : 22.3.1
GraalVM : 22.3.1
Stability: Supported
Origin : https://github.com/oracle/graaljs/releases/download/vm-22.3.1/js-installable-svm-java11-windows-amd64-22.3.1.jar
ID : native-image
Name : Native Image
Version : 22.3.1
GraalVM : 22.3.1
Stability: Early adopter
Origin : https://github.com/graalvm/graalvm-ce-builds/releases/download/vm-22.3.1/native-image-installable-svm-java11-windows-amd64-22.3.1.jar
[debug] [2023-02-23T10:29:43.023Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Available GraalVM components: [Vector(GraalVMComponent(graalvm), GraalVMComponent(js), GraalVMComponent(native-image))].
[trace] [2023-02-23T10:29:43.023Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd { exists=true, executable=true }
[debug] [2023-02-23T10:29:43.023Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] Executing: JAVA_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 GRRAALVM_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd install python R
[trace] [2023-02-23T10:29:44.098Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] [stderr] Error: Component "python" is not available in catalog.
[warn] [2023-02-23T10:29:44.118Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Failed to install required components on the existing [GraalVM 22.3.1-java11]. Some language features may be unavailable. Nonzero exit code: 3
[trace] [2023-02-23T10:29:44.118Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Installed engines (1):
- Enso 2023.1.1-nightly.2023.2.22 [runtime: GraalVM 22.3.1-java11] [location: ***\2023.1.1-nightly.2023.2.22]
Installed runtimes (1):
- GraalVM 22.3.1-java11 [location: ***\graalvm-ce-java11-22.3.1]
[info] [2023-02-23T10:29:44.119Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] The engine [2023.1.1-nightly.2023.2.22] found.
[debug] [2023-02-23T10:29:44.119Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Loading Graal runtime [C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1].
[debug] [2023-02-23T10:29:44.12Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Installing GraalVM components [GraalVM 22.3.1-java11, Windows].
[trace] [2023-02-23T10:29:44.12Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd { exists=true, executable=true }
[debug] [2023-02-23T10:29:44.12Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] Executing: JAVA_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 GRRAALVM_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd list -v
[trace] [2023-02-23T10:29:44.493Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] ID : graalvm
Name : GraalVM Core
Version : 22.3.1
GraalVM : n/a
Stability: Supported
Origin :
ID : js
Name : Graal.js
Version : 22.3.1
GraalVM : 22.3.1
Stability: Supported
Origin : https://github.com/oracle/graaljs/releases/download/vm-22.3.1/js-installable-svm-java11-windows-amd64-22.3.1.jar
ID : native-image
Name : Native Image
Version : 22.3.1
GraalVM : 22.3.1
Stability: Early adopter
Origin : https://github.com/graalvm/graalvm-ce-builds/releases/download/vm-22.3.1/native-image-installable-svm-java11-windows-amd64-22.3.1.jar
[debug] [2023-02-23T10:29:44.493Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Available GraalVM components: [Vector(GraalVMComponent(graalvm), GraalVMComponent(js), GraalVMComponent(native-image))].
[trace] [2023-02-23T10:29:44.493Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd { exists=true, executable=true }
[debug] [2023-02-23T10:29:44.493Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] Executing: JAVA_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 GRRAALVM_HOME=C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1 C:\Users\...\AppData\Local\Programs\enso\resources\enso\runtime\graalvm-ce-java11-22.3.1\bin\gu.cmd install python R
[trace] [2023-02-23T10:29:45.636Z] [org.enso.runtimeversionmanager.components.GraalVMComponentUpdater] [stderr] Error: Component "python" is not available in catalog.
[warn] [2023-02-23T10:29:45.656Z] [org.enso.runtimeversionmanager.components.RuntimeVersionManager] Failed to install required components on the existing [GraalVM 22.3.1-java11]. Some language features may be unavailable. Nonzero exit code: 3
```
is attempted 4 times before giving up.
I can understand that we may want to retry the process on failure, but this one is clearly not recoverable.
This can and has led to timeouts during handling of the `ProjectCreate` request which led to IDE just appearing to hang. | non_priority | graalvm updater attempts to install component multiple times clean installation on windows loading graal runtime installing graalvm components c users appdata local programs enso resources enso runtime graalvm ce bin gu cmd exists true executable true executing java home c users appdata local programs enso resources enso runtime graalvm ce grraalvm home c users appdata local programs enso resources enso runtime graalvm ce c users appdata local programs enso resources enso runtime graalvm ce bin gu cmd list v id graalvm name graalvm core version graalvm n a stability supported origin id js name graal js version graalvm stability supported origin id native image name native image version graalvm stability early adopter origin available graalvm components c users appdata local programs enso resources enso runtime graalvm ce bin gu cmd exists true executable true executing java home c users appdata local programs enso resources enso runtime graalvm ce grraalvm home c users appdata local programs enso resources enso runtime graalvm ce c users appdata local programs enso resources enso runtime graalvm ce bin gu cmd install python r error component python is not available in catalog failed to install required components on the existing some language features may be unavailable nonzero exit code installed engines enso nightly installed runtimes graalvm the engine found loading graal runtime installing graalvm components c users appdata local programs enso resources enso runtime graalvm ce bin gu cmd exists true executable true executing java home c users appdata local programs enso resources enso runtime graalvm ce grraalvm home c users appdata local programs enso resources enso runtime graalvm ce c users appdata local programs enso resources enso runtime graalvm ce bin gu cmd list v id graalvm name graalvm core version graalvm n a stability supported origin id js name graal js version graalvm stability supported origin id native image name native image version graalvm stability early adopter origin available graalvm components c users appdata local programs enso resources enso runtime graalvm ce bin gu cmd exists true executable true executing java home c users appdata local programs enso resources enso runtime graalvm ce grraalvm home c users appdata local programs enso resources enso runtime graalvm ce c users appdata local programs enso resources enso runtime graalvm ce bin gu cmd install python r error component python is not available in catalog failed to install required components on the existing some language features may be unavailable nonzero exit code is attempted times before giving up i can understand that we may want to retry the process on failure but this one is clearly not recoverable this can and has led to timeouts during handling of the projectcreate request which led to ide just appearing to hang | 0 |
92,268 | 26,633,087,044 | IssuesEvent | 2023-01-24 19:26:57 | AcademySoftwareFoundation/OpenRV | https://api.github.com/repos/AcademySoftwareFoundation/OpenRV | closed | [Linux] Various errors when building | build | Hello there,
_Just mention that I have no knowledge of programming and these workaround may cause more problems than fixes. I'm reporting those so anyone with experience can deal with it._
I'm using a fully updated Arch Linux.
```
/home/adro/Applications/3D/OpenRV/src/pub/LibRaw/internal/dcraw_common.cpp:6395:64: error: call of overloaded ‘powf64(int, int)’ is ambiguous
6395 | 10*(table_buf[iLensData+9]>>2) * powf64(4, (table_buf[iLensData+9] & 0x03)-2);
| ~~~~~~^~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
In file included from /usr/include/c++/12.2.1/cmath:45,
from /usr/include/c++/12.2.1/math.h:36,
from /home/adro/Applications/3D/OpenRV/src/pub/LibRaw/internal/dcraw_common.cpp:24:
```
A workaround i found is to delete the lines 6392-6395 as mentioned [here](https://github.com/ofnode/of/issues/15#issuecomment-395387638)
Another error I found:
```
/home/adro/Applications/3D/OpenRV/src/lib/app/RvCommon/RvApplication.cpp:855:27: error: ‘sleep_for’ is not a member of ‘std::this_thread’
855 | std::this_thread::sleep_for(std::chrono::milliseconds(1));
| ^~~~~~~~~
```
```
/home/adro/Applications/3D/OpenRV/src/bin/apps/rv/main.cpp:431:27: error: ‘sleep_for’ is not a member of ‘std::this_thread’
431 | std::this_thread::sleep_for( std::chrono::seconds( sleepTime ) );
|
```
As well as the previous one, deleting the line works.
After all this workarounds, I succesfully built OpenRV. | 1.0 | [Linux] Various errors when building - Hello there,
_Just mention that I have no knowledge of programming and these workaround may cause more problems than fixes. I'm reporting those so anyone with experience can deal with it._
I'm using a fully updated Arch Linux.
```
/home/adro/Applications/3D/OpenRV/src/pub/LibRaw/internal/dcraw_common.cpp:6395:64: error: call of overloaded ‘powf64(int, int)’ is ambiguous
6395 | 10*(table_buf[iLensData+9]>>2) * powf64(4, (table_buf[iLensData+9] & 0x03)-2);
| ~~~~~~^~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
In file included from /usr/include/c++/12.2.1/cmath:45,
from /usr/include/c++/12.2.1/math.h:36,
from /home/adro/Applications/3D/OpenRV/src/pub/LibRaw/internal/dcraw_common.cpp:24:
```
A workaround i found is to delete the lines 6392-6395 as mentioned [here](https://github.com/ofnode/of/issues/15#issuecomment-395387638)
Another error I found:
```
/home/adro/Applications/3D/OpenRV/src/lib/app/RvCommon/RvApplication.cpp:855:27: error: ‘sleep_for’ is not a member of ‘std::this_thread’
855 | std::this_thread::sleep_for(std::chrono::milliseconds(1));
| ^~~~~~~~~
```
```
/home/adro/Applications/3D/OpenRV/src/bin/apps/rv/main.cpp:431:27: error: ‘sleep_for’ is not a member of ‘std::this_thread’
431 | std::this_thread::sleep_for( std::chrono::seconds( sleepTime ) );
|
```
As well as the previous one, deleting the line works.
After all this workarounds, I succesfully built OpenRV. | non_priority | various errors when building hello there just mention that i have no knowledge of programming and these workaround may cause more problems than fixes i m reporting those so anyone with experience can deal with it i m using a fully updated arch linux home adro applications openrv src pub libraw internal dcraw common cpp error call of overloaded ‘ int int ’ is ambiguous table buf table buf in file included from usr include c cmath from usr include c math h from home adro applications openrv src pub libraw internal dcraw common cpp a workaround i found is to delete the lines as mentioned another error i found home adro applications openrv src lib app rvcommon rvapplication cpp error ‘sleep for’ is not a member of ‘std this thread’ std this thread sleep for std chrono milliseconds home adro applications openrv src bin apps rv main cpp error ‘sleep for’ is not a member of ‘std this thread’ std this thread sleep for std chrono seconds sleeptime as well as the previous one deleting the line works after all this workarounds i succesfully built openrv | 0 |
444,413 | 31,048,077,271 | IssuesEvent | 2023-08-11 03:04:03 | CSC207-2023Y-UofT/course-project-ancient-brawlers-1 | https://api.github.com/repos/CSC207-2023Y-UofT/course-project-ancient-brawlers-1 | closed | Revise documentations | documentation | Fill in missing documentations, edit existing ones for clarity and general grammar and spelling. | 1.0 | Revise documentations - Fill in missing documentations, edit existing ones for clarity and general grammar and spelling. | non_priority | revise documentations fill in missing documentations edit existing ones for clarity and general grammar and spelling | 0 |
81,098 | 7,767,726,502 | IssuesEvent | 2018-06-03 10:06:30 | NucleusPowered/Nucleus | https://api.github.com/repos/NucleusPowered/Nucleus | closed | Unable to delete nucleus-created world | needs testing pending information | Hello,
I recently created a world via /world create that I would now like to delete. When I attempt to unload it, which is necessary for deletion according to /world delete, using /world unload it gives the following output:
```
[18:01:21] [Server thread/INFO]: Attempting to unload world mining.
[18:01:21] [Server thread/INFO]: Unable to unload the world mining.
```
This happens even after a fresh server start with no players online. There should be no chunks force-loaded in the world. How can I unload and delete this world?
Thank you.
Versioning Information:
/nucleus info: http://paste.ubuntu.com/26030773/
Modpack: FTB Direwolf20 1.12 pack version 1.1.0
SpongeForge version: 1.12.2-2529-7.0.0-BETA-2730
OS: Ubuntu Server 16.04 LTS x64
Java: Oracle Java version 8 in ppa:webupd8team/java | 1.0 | Unable to delete nucleus-created world - Hello,
I recently created a world via /world create that I would now like to delete. When I attempt to unload it, which is necessary for deletion according to /world delete, using /world unload it gives the following output:
```
[18:01:21] [Server thread/INFO]: Attempting to unload world mining.
[18:01:21] [Server thread/INFO]: Unable to unload the world mining.
```
This happens even after a fresh server start with no players online. There should be no chunks force-loaded in the world. How can I unload and delete this world?
Thank you.
Versioning Information:
/nucleus info: http://paste.ubuntu.com/26030773/
Modpack: FTB Direwolf20 1.12 pack version 1.1.0
SpongeForge version: 1.12.2-2529-7.0.0-BETA-2730
OS: Ubuntu Server 16.04 LTS x64
Java: Oracle Java version 8 in ppa:webupd8team/java | non_priority | unable to delete nucleus created world hello i recently created a world via world create that i would now like to delete when i attempt to unload it which is necessary for deletion according to world delete using world unload it gives the following output attempting to unload world mining unable to unload the world mining this happens even after a fresh server start with no players online there should be no chunks force loaded in the world how can i unload and delete this world thank you versioning information nucleus info modpack ftb pack version spongeforge version beta os ubuntu server lts java oracle java version in ppa java | 0 |
259,192 | 27,621,718,837 | IssuesEvent | 2023-03-10 01:06:28 | michaeldotson/home-inventory | https://api.github.com/repos/michaeldotson/home-inventory | opened | CVE-2022-44570 (High) detected in rack-2.0.7.gem | Mend: dependency security vulnerability | ## CVE-2022-44570 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rack-2.0.7.gem</b></p></summary>
<p>Rack provides a minimal, modular and adaptable interface for developing
web applications in Ruby. By wrapping HTTP requests and responses in
the simplest way possible, it unifies and distills the API for web
servers, web frameworks, and software in between (the so-called
middleware) into a single method call.
Also see https://rack.github.io/.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rack-2.0.7.gem">https://rubygems.org/gems/rack-2.0.7.gem</a></p>
<p>Path to dependency file: /home-inventory/Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.3.0/cache/rack-2.0.7.gem</p>
<p>
Dependency Hierarchy:
- web-console-3.7.0.gem (Root Library)
- railties-5.2.2.1.gem
- actionpack-5.2.2.1.gem
- :x: **rack-2.0.7.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A denial of service vulnerability in the Range header parsing component of Rack >= 1.5.0. A Carefully crafted input can cause the Range header parsing component in Rack to take an unexpected amount of time, possibly resulting in a denial of service attack vector. Any applications that deal with Range requests (such as streaming applications, or applications that serve files) may be impacted.
<p>Publish Date: 2023-02-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-44570>CVE-2022-44570</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-65f5-mfpf-vfhj">https://github.com/advisories/GHSA-65f5-mfpf-vfhj</a></p>
<p>Release Date: 2023-02-09</p>
<p>Fix Resolution: rack - 2.0.9.2,2.1.4.2,2.2.6.2,3.0.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-44570 (High) detected in rack-2.0.7.gem - ## CVE-2022-44570 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rack-2.0.7.gem</b></p></summary>
<p>Rack provides a minimal, modular and adaptable interface for developing
web applications in Ruby. By wrapping HTTP requests and responses in
the simplest way possible, it unifies and distills the API for web
servers, web frameworks, and software in between (the so-called
middleware) into a single method call.
Also see https://rack.github.io/.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rack-2.0.7.gem">https://rubygems.org/gems/rack-2.0.7.gem</a></p>
<p>Path to dependency file: /home-inventory/Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.3.0/cache/rack-2.0.7.gem</p>
<p>
Dependency Hierarchy:
- web-console-3.7.0.gem (Root Library)
- railties-5.2.2.1.gem
- actionpack-5.2.2.1.gem
- :x: **rack-2.0.7.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A denial of service vulnerability in the Range header parsing component of Rack >= 1.5.0. A Carefully crafted input can cause the Range header parsing component in Rack to take an unexpected amount of time, possibly resulting in a denial of service attack vector. Any applications that deal with Range requests (such as streaming applications, or applications that serve files) may be impacted.
<p>Publish Date: 2023-02-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-44570>CVE-2022-44570</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-65f5-mfpf-vfhj">https://github.com/advisories/GHSA-65f5-mfpf-vfhj</a></p>
<p>Release Date: 2023-02-09</p>
<p>Fix Resolution: rack - 2.0.9.2,2.1.4.2,2.2.6.2,3.0.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in rack gem cve high severity vulnerability vulnerable library rack gem rack provides a minimal modular and adaptable interface for developing web applications in ruby by wrapping http requests and responses in the simplest way possible it unifies and distills the api for web servers web frameworks and software in between the so called middleware into a single method call also see library home page a href path to dependency file home inventory gemfile lock path to vulnerable library var lib gems cache rack gem dependency hierarchy web console gem root library railties gem actionpack gem x rack gem vulnerable library vulnerability details a denial of service vulnerability in the range header parsing component of rack a carefully crafted input can cause the range header parsing component in rack to take an unexpected amount of time possibly resulting in a denial of service attack vector any applications that deal with range requests such as streaming applications or applications that serve files may be impacted publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rack step up your open source security game with mend | 0 |
90,748 | 26,181,154,807 | IssuesEvent | 2023-01-02 15:46:10 | CGNS/CGNS | https://api.github.com/repos/CGNS/CGNS | closed | [CGNS-146] Can't compile using MSVC & IVF on windows (MSVS 14) | bug Done Build Blocker |
> This issue has been imported from JIRA. Read the [original ticket here](https://cgnsorg.atlassian.net/browse/CGNS-146).
- _**Created at:**_ Sat, 15 Sep 2018 15:24:01 -0500
- _**Resolved at:**_ Mon, 4 Mar 2019 10:41:29 -0600
<p>A requirement of a project I am working on is to statically link against CGNS on windows, including the Fortran interfaces.</p>
<p>I have tried to compile on Windows 10, using the CMake files and using the "Visual Studio 14 2015 Win64" generator. The C compiler is the default MSVC compiler, and the fortran compiler is Intel IVF 18.0.3.</p>
<p>I have tried setting the CMake configuration according to both the "Building on Windows" section of the FAQ, and the configure options being passed to CMake in the AppVeyor CI testing in the main CGNS repository.</p>
<p>I have downloaded the v3.3.1 release from the github releases page.</p>
<p><b>UPDATE: A work around has been identified</b></p>
<p>The work around is to explicitly set the linker language to C for `cgns_static`</p>
<div class="code panel" style="border-width: 1px;"><div class="codeContent panelContent">
<pre class="code-none">
set_property(TARGET cgns_static PROPERTY LINKER_LANGUAGE C)
</pre>
</div></div>
| 1.0 | [CGNS-146] Can't compile using MSVC & IVF on windows (MSVS 14) -
> This issue has been imported from JIRA. Read the [original ticket here](https://cgnsorg.atlassian.net/browse/CGNS-146).
- _**Created at:**_ Sat, 15 Sep 2018 15:24:01 -0500
- _**Resolved at:**_ Mon, 4 Mar 2019 10:41:29 -0600
<p>A requirement of a project I am working on is to statically link against CGNS on windows, including the Fortran interfaces.</p>
<p>I have tried to compile on Windows 10, using the CMake files and using the "Visual Studio 14 2015 Win64" generator. The C compiler is the default MSVC compiler, and the fortran compiler is Intel IVF 18.0.3.</p>
<p>I have tried setting the CMake configuration according to both the "Building on Windows" section of the FAQ, and the configure options being passed to CMake in the AppVeyor CI testing in the main CGNS repository.</p>
<p>I have downloaded the v3.3.1 release from the github releases page.</p>
<p><b>UPDATE: A work around has been identified</b></p>
<p>The work around is to explicitly set the linker language to C for `cgns_static`</p>
<div class="code panel" style="border-width: 1px;"><div class="codeContent panelContent">
<pre class="code-none">
set_property(TARGET cgns_static PROPERTY LINKER_LANGUAGE C)
</pre>
</div></div>
| non_priority | can t compile using msvc ivf on windows msvs this issue has been imported from jira read the created at sat sep resolved at mon mar a requirement of a project i am working on is to statically link against cgns on windows including the fortran interfaces i have tried to compile on windows using the cmake files and using the visual studio generator the c compiler is the default msvc compiler and the fortran compiler is intel ivf i have tried setting the cmake configuration according to both the building on windows section of the faq and the configure options being passed to cmake in the appveyor ci testing in the main cgns repository i have downloaded the release from the github releases page update a work around has been identified the work around is to explicitly set the linker language to c for cgns static set property target cgns static property linker language c | 0 |
46,020 | 24,322,935,715 | IssuesEvent | 2022-09-30 12:28:45 | raethkcj/RatingBuster | https://api.github.com/repos/raethkcj/RatingBuster | closed | Intense frame lag when hovering over items with Stat Summary enabled | performance | If you hover over an item on your character sheet while the Stat Summary feature is enabled, your game freezes for half a second. Disabling the Stat Summary feature fixes this problem. | True | Intense frame lag when hovering over items with Stat Summary enabled - If you hover over an item on your character sheet while the Stat Summary feature is enabled, your game freezes for half a second. Disabling the Stat Summary feature fixes this problem. | non_priority | intense frame lag when hovering over items with stat summary enabled if you hover over an item on your character sheet while the stat summary feature is enabled your game freezes for half a second disabling the stat summary feature fixes this problem | 0 |
350,759 | 31,932,294,372 | IssuesEvent | 2023-09-19 08:15:35 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | opened | Fix non_linear_activations.test_jax_sigmoid | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6201859588"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6201859588"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6201859588"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6201859588"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6201859588"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix non_linear_activations.test_jax_sigmoid - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6201859588"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6201859588"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6201859588"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6201859588"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6201859588"><img src=https://img.shields.io/badge/-success-success></a>
| non_priority | fix non linear activations test jax sigmoid numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src | 0 |
41,638 | 21,801,384,779 | IssuesEvent | 2022-05-16 05:52:14 | statamic/cms | https://api.github.com/repos/statamic/cms | closed | Significantly worse loading times / TTFB on 3.3 and Larvel 9 | performance | ### Bug description
Not a bug, but still a huge problem I'm facing after upgrading a site to 3.3 and I'm wondering if I'm alone with these observations and/or it there's something that can be done about it.
I'm not an an expert in any (devops, webperf, php) of this, but I've received reports from clients/users about slow performance on a site running Statamic 3.3.
So I started digging and found out this site has a local TTFB of almost one second with a completely empty frontend. My other local Statamic sites are somewhere around 150-350 ms.
So I looked for the differences in those sites and disabled addons and the only difference standing out to me was that the slower site was running Statamic 3.3 and Laravel 9.
So I rolled back to Statamic 3.2 on both Laravel 8 and 9 and took the same measurement for loading the empty document (the bulk of which was time to first byte)
Statamic 3.3.4 / Laravel 9: 940ms
Statamic 3.3.34 / Laravel 8: 581ms
Statamic 3.2.39 / Laravel 8: 355ms
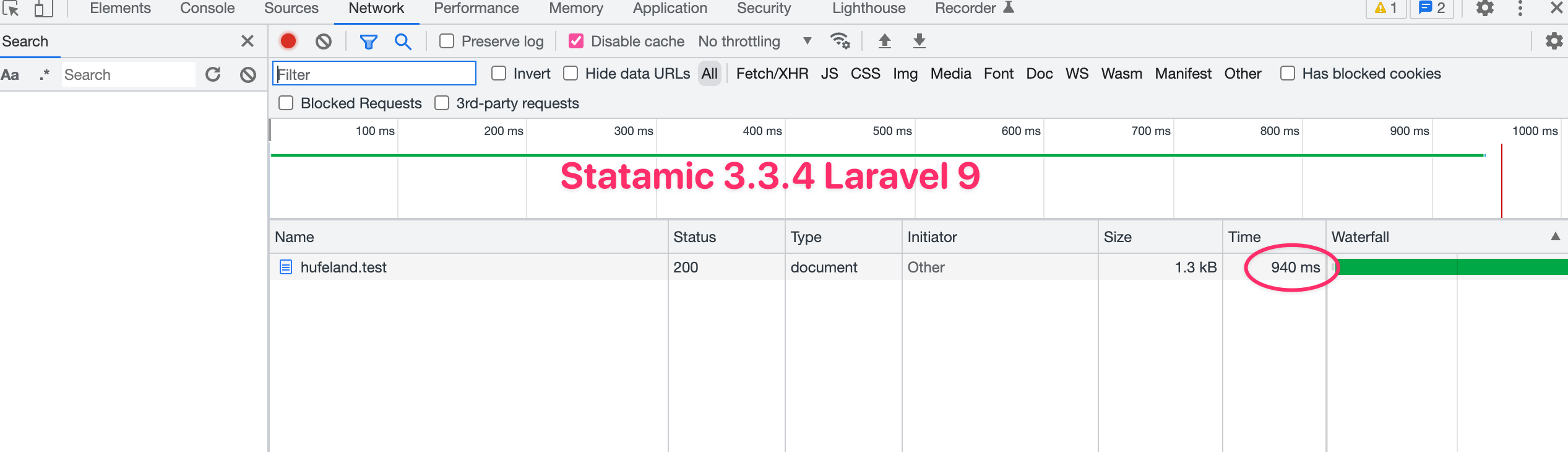
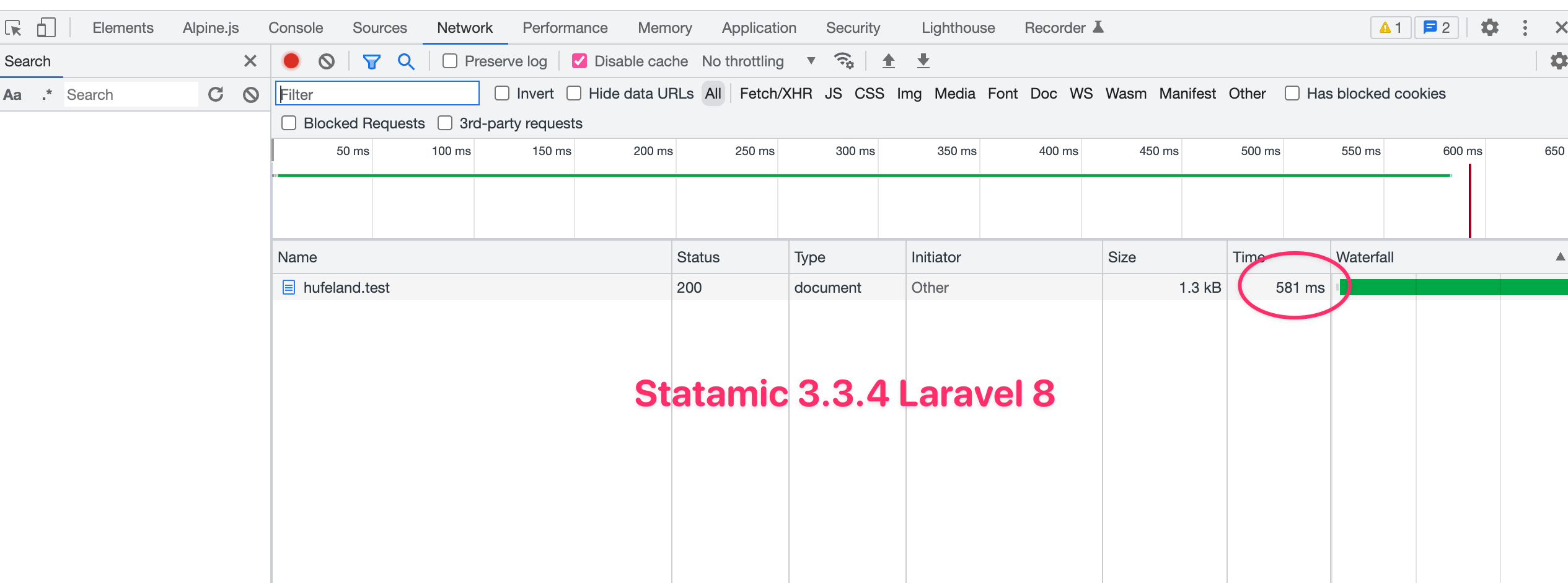
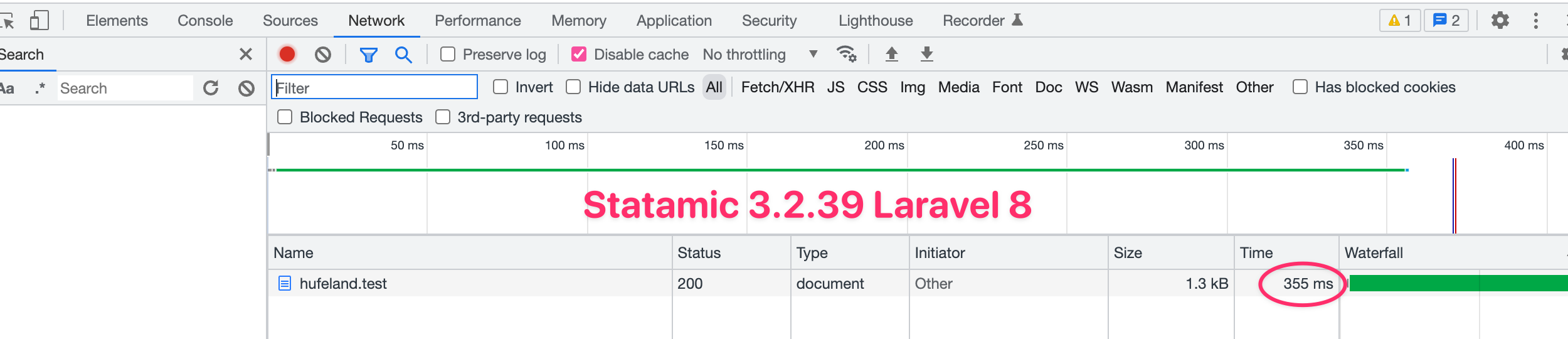
### How to reproduce
Compare the same site's loading time for a blank page before and after upgrading it to Statamic 3.3 and optionally Laravel 9
### Logs
_No response_
### Versions
Statamic 3.3.4 Pro
Laravel 9.6.0
PHP 8.0.16
---
Statamic 3.3.4 Pro
Laravel 8.83.6
PHP 8.0.16
---
Statamic 3.2.39 Pro
Laravel 8.79.0
PHP 8.0.16
### Installation
Starter Kit using via CLI
### Antlers Parser
regex (default)
### Additional details
- All measures were done locally with Valet and PHP 8.0 (but are also observable and even worse on a remote server)
- All measures were done with a completely blank layout.antlers.php, so no static assets influence results
- Addons were disabled
- No static caching
- No new antlers parser | True | Significantly worse loading times / TTFB on 3.3 and Larvel 9 - ### Bug description
Not a bug, but still a huge problem I'm facing after upgrading a site to 3.3 and I'm wondering if I'm alone with these observations and/or it there's something that can be done about it.
I'm not an an expert in any (devops, webperf, php) of this, but I've received reports from clients/users about slow performance on a site running Statamic 3.3.
So I started digging and found out this site has a local TTFB of almost one second with a completely empty frontend. My other local Statamic sites are somewhere around 150-350 ms.
So I looked for the differences in those sites and disabled addons and the only difference standing out to me was that the slower site was running Statamic 3.3 and Laravel 9.
So I rolled back to Statamic 3.2 on both Laravel 8 and 9 and took the same measurement for loading the empty document (the bulk of which was time to first byte)
Statamic 3.3.4 / Laravel 9: 940ms
Statamic 3.3.34 / Laravel 8: 581ms
Statamic 3.2.39 / Laravel 8: 355ms
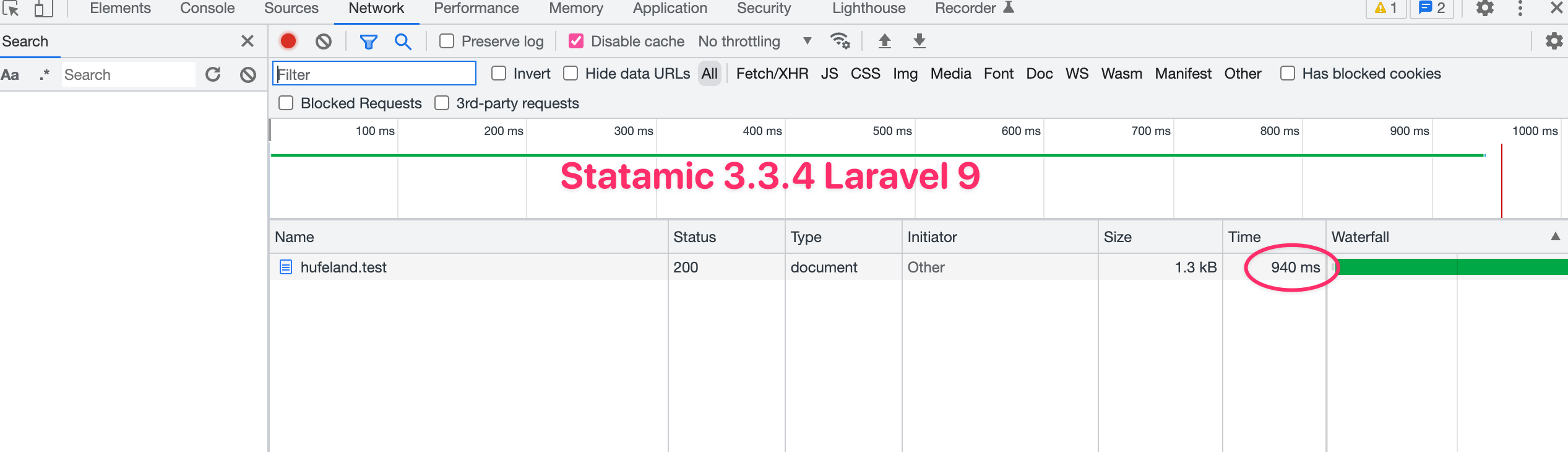
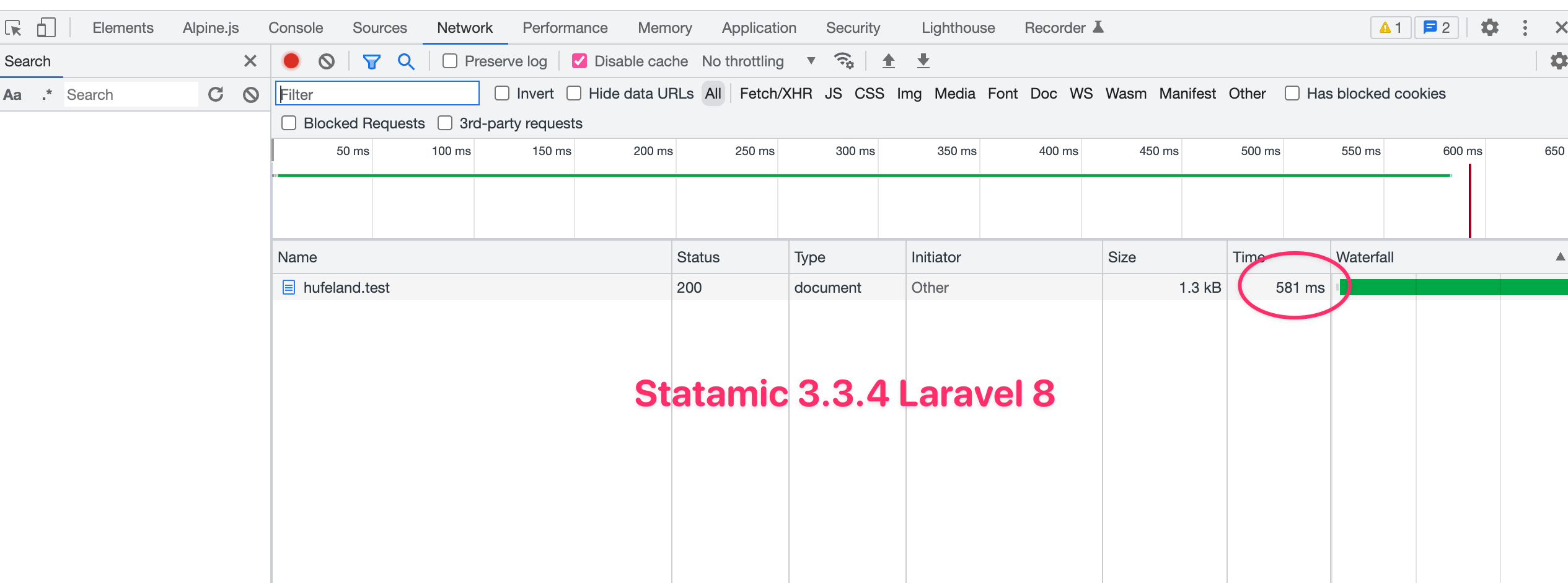
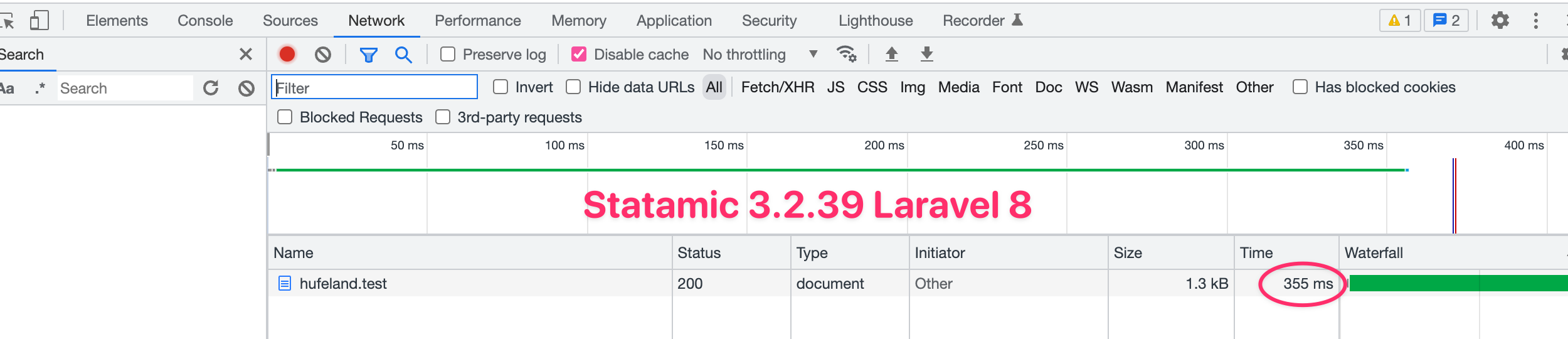
### How to reproduce
Compare the same site's loading time for a blank page before and after upgrading it to Statamic 3.3 and optionally Laravel 9
### Logs
_No response_
### Versions
Statamic 3.3.4 Pro
Laravel 9.6.0
PHP 8.0.16
---
Statamic 3.3.4 Pro
Laravel 8.83.6
PHP 8.0.16
---
Statamic 3.2.39 Pro
Laravel 8.79.0
PHP 8.0.16
### Installation
Starter Kit using via CLI
### Antlers Parser
regex (default)
### Additional details
- All measures were done locally with Valet and PHP 8.0 (but are also observable and even worse on a remote server)
- All measures were done with a completely blank layout.antlers.php, so no static assets influence results
- Addons were disabled
- No static caching
- No new antlers parser | non_priority | significantly worse loading times ttfb on and larvel bug description not a bug but still a huge problem i m facing after upgrading a site to and i m wondering if i m alone with these observations and or it there s something that can be done about it i m not an an expert in any devops webperf php of this but i ve received reports from clients users about slow performance on a site running statamic so i started digging and found out this site has a local ttfb of almost one second with a completely empty frontend my other local statamic sites are somewhere around ms so i looked for the differences in those sites and disabled addons and the only difference standing out to me was that the slower site was running statamic and laravel so i rolled back to statamic on both laravel and and took the same measurement for loading the empty document the bulk of which was time to first byte statamic laravel statamic laravel statamic laravel how to reproduce compare the same site s loading time for a blank page before and after upgrading it to statamic and optionally laravel logs no response versions statamic pro laravel php statamic pro laravel php statamic pro laravel php installation starter kit using via cli antlers parser regex default additional details all measures were done locally with valet and php but are also observable and even worse on a remote server all measures were done with a completely blank layout antlers php so no static assets influence results addons were disabled no static caching no new antlers parser | 0 |
132,016 | 12,496,825,129 | IssuesEvent | 2020-06-01 15:27:59 | gren236/m3u-proxifier | https://api.github.com/repos/gren236/m3u-proxifier | closed | Install and usage documentation | documentation | Write documentation for installation process and describe some usage tips | 1.0 | Install and usage documentation - Write documentation for installation process and describe some usage tips | non_priority | install and usage documentation write documentation for installation process and describe some usage tips | 0 |
349,480 | 31,807,774,536 | IssuesEvent | 2023-09-13 14:54:07 | eclipse-openj9/openj9 | https://api.github.com/repos/eclipse-openj9/openj9 | opened | cmdLineTester_jvmtitests ith001 timeout | test failure | https://openj9-jenkins.osuosl.org/job/Test_openjdk8_j9_sanity.functional_ppc64_aix_Nightly/614
cmdLineTester_jvmtitests_5
No diagnostic files captured.
```
Testing: ith001
Test start time: 2023/09/13 03:06:24 Coordinated Universal Time
Running command: "/home/jenkins/workspace/Test_openjdk8_j9_sanity.functional_ppc64_aix_Nightly_testList_1/openjdkbinary/j2sdk-image/bin/java" -Xgcpolicy:metronome -Xcompressedrefs -Xdump -agentlib:jvmtitest=test:ith001 -cp "/home/jenkins/workspace/Test_openjdk8_j9_sanity.functional_ppc64_aix_Nightly_testList_1/aqa-tests/TKG/../../jvmtest/functional/cmdLineTests/jvmtitests/jvmtitest.jar" com.ibm.jvmti.tests.util.TestRunner
Time spent starting: 18 milliseconds
***[TEST INFO 2023/09/13 03:10:24] ProcessKiller detected a timeout after 240000 milliseconds!***
INFO: The current OS is 'AIX'. 'Debug on timeout' is currently only supported on Linux.
***[TEST INFO 2023/09/13 03:10:24] executing kill -ABRT 23789970***
***[TEST INFO 2023/09/13 03:10:24] kill -ABRT signal sent***
***[TEST INFO 2023/09/13 03:15:25] ABRT timed out***
***[TEST INFO 2023/09/13 03:15:25] executing kill -9 23789970***
***[TEST INFO 2023/09/13 03:15:25] kill -9 signal sent***
Output from test:
[OUT] *** Testing [1/4]: testHeapIteration
Time spent executing: 540177 milliseconds
Test result: FAILED
Output from test:
```
Changes from last build
https://github.com/eclipse-openj9/openj9/compare/5bf1ff4e80b...1f58a610b37 | 1.0 | cmdLineTester_jvmtitests ith001 timeout - https://openj9-jenkins.osuosl.org/job/Test_openjdk8_j9_sanity.functional_ppc64_aix_Nightly/614
cmdLineTester_jvmtitests_5
No diagnostic files captured.
```
Testing: ith001
Test start time: 2023/09/13 03:06:24 Coordinated Universal Time
Running command: "/home/jenkins/workspace/Test_openjdk8_j9_sanity.functional_ppc64_aix_Nightly_testList_1/openjdkbinary/j2sdk-image/bin/java" -Xgcpolicy:metronome -Xcompressedrefs -Xdump -agentlib:jvmtitest=test:ith001 -cp "/home/jenkins/workspace/Test_openjdk8_j9_sanity.functional_ppc64_aix_Nightly_testList_1/aqa-tests/TKG/../../jvmtest/functional/cmdLineTests/jvmtitests/jvmtitest.jar" com.ibm.jvmti.tests.util.TestRunner
Time spent starting: 18 milliseconds
***[TEST INFO 2023/09/13 03:10:24] ProcessKiller detected a timeout after 240000 milliseconds!***
INFO: The current OS is 'AIX'. 'Debug on timeout' is currently only supported on Linux.
***[TEST INFO 2023/09/13 03:10:24] executing kill -ABRT 23789970***
***[TEST INFO 2023/09/13 03:10:24] kill -ABRT signal sent***
***[TEST INFO 2023/09/13 03:15:25] ABRT timed out***
***[TEST INFO 2023/09/13 03:15:25] executing kill -9 23789970***
***[TEST INFO 2023/09/13 03:15:25] kill -9 signal sent***
Output from test:
[OUT] *** Testing [1/4]: testHeapIteration
Time spent executing: 540177 milliseconds
Test result: FAILED
Output from test:
```
Changes from last build
https://github.com/eclipse-openj9/openj9/compare/5bf1ff4e80b...1f58a610b37 | non_priority | cmdlinetester jvmtitests timeout cmdlinetester jvmtitests no diagnostic files captured testing test start time coordinated universal time running command home jenkins workspace test sanity functional aix nightly testlist openjdkbinary image bin java xgcpolicy metronome xcompressedrefs xdump agentlib jvmtitest test cp home jenkins workspace test sanity functional aix nightly testlist aqa tests tkg jvmtest functional cmdlinetests jvmtitests jvmtitest jar com ibm jvmti tests util testrunner time spent starting milliseconds processkiller detected a timeout after milliseconds info the current os is aix debug on timeout is currently only supported on linux executing kill abrt kill abrt signal sent abrt timed out executing kill kill signal sent output from test testing testheapiteration time spent executing milliseconds test result failed output from test changes from last build | 0 |
1,458 | 2,853,318,781 | IssuesEvent | 2015-06-01 17:58:23 | sandstorm-io/sandstorm | https://api.github.com/repos/sandstorm-io/sandstorm | opened | Error message when enabling non-configured service is not clear | bite-size usability | > Failure!
>
> The google service is not configured, and so cannot be enabled.
> The github service is not configured, and so cannot be enabled.
>
> See <install-location>/var/log/sandstorm.log for details.
This wording apparently does not make it clear to users that their next action should be to click "configure" next to the service.
We should:
* Change the wording to "You must configure the google service before you can enable it. Click the "configure" link."
* Do not suggest that `sandstorm.log` has more details when we don't know this to be the case. We could say that it _might_ have more details, but the current wording says that it _does_, and users duly go there looking for details. IMO, though, we should remove this line entirely, and display any details directly. If that's not easily possible, then we should only suggest looking at `sandstorm.log` in error cases that we know are likely to put details there.
* Ideally, clicking on the check box next to Google or Github would automatically open the configure dialog if they aren't already configured, so user never see an error. | True | Error message when enabling non-configured service is not clear - > Failure!
>
> The google service is not configured, and so cannot be enabled.
> The github service is not configured, and so cannot be enabled.
>
> See <install-location>/var/log/sandstorm.log for details.
This wording apparently does not make it clear to users that their next action should be to click "configure" next to the service.
We should:
* Change the wording to "You must configure the google service before you can enable it. Click the "configure" link."
* Do not suggest that `sandstorm.log` has more details when we don't know this to be the case. We could say that it _might_ have more details, but the current wording says that it _does_, and users duly go there looking for details. IMO, though, we should remove this line entirely, and display any details directly. If that's not easily possible, then we should only suggest looking at `sandstorm.log` in error cases that we know are likely to put details there.
* Ideally, clicking on the check box next to Google or Github would automatically open the configure dialog if they aren't already configured, so user never see an error. | non_priority | error message when enabling non configured service is not clear failure the google service is not configured and so cannot be enabled the github service is not configured and so cannot be enabled see var log sandstorm log for details this wording apparently does not make it clear to users that their next action should be to click configure next to the service we should change the wording to you must configure the google service before you can enable it click the configure link do not suggest that sandstorm log has more details when we don t know this to be the case we could say that it might have more details but the current wording says that it does and users duly go there looking for details imo though we should remove this line entirely and display any details directly if that s not easily possible then we should only suggest looking at sandstorm log in error cases that we know are likely to put details there ideally clicking on the check box next to google or github would automatically open the configure dialog if they aren t already configured so user never see an error | 0 |
48,444 | 13,068,534,945 | IssuesEvent | 2020-07-31 03:53:19 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | Regeneration of BackgroundI3MCTree from RNG State (Trac #2403) | Migrated from Trac combo simulation defect | Currently Polyplopia is configured to use the standard RNG and the state is not saved in the frame.
In order to support this, we have a couple of options.
1. Have Polyplopia manually configure the name of the RNG state in the frame for background events separately. Support would also be needed in the regeneration scripts.
2. Combine events prior to propagating through PROPOSAL. In this case you don't have both a background and signal trees but just a combined tree.
The advantage of combining events later in the simulation is that it is easier to determine what the background vs. signal contribution is. In reality many of the events that have multiple coincidences only have significan contribution from one of the tracks.
Migrated from https://code.icecube.wisc.edu/ticket/2403
```json
{
"status": "closed",
"changetime": "2020-01-28T20:09:23",
"description": "Currently Polyplopia is configured to use the standard RNG and the state is not saved in the frame. \n\nIn order to support this, we have a couple of options.\n\n1. Have Polyplopia manually configure the name of the RNG state in the frame for background events separately. Support would also be needed in the regeneration scripts.\n\n2. Combine events prior to propagating through PROPOSAL. In this case you don't have both a background and signal trees but just a combined tree. \n\nThe advantage of combining events later in the simulation is that it is easier to determine what the background vs. signal contribution is. In reality many of the events that have multiple coincidences only have significan contribution from one of the tracks.\n\n",
"reporter": "juancarlos",
"cc": "",
"resolution": "fixed",
"_ts": "1580242163108345",
"component": "combo simulation",
"summary": "Regeneration of BackgroundI3MCTree from RNG State",
"priority": "normal",
"keywords": "polyplopia, PROPOSAL",
"time": "2020-01-24T17:27:51",
"milestone": "",
"owner": "juancarlos",
"type": "defect"
}
```
| 1.0 | Regeneration of BackgroundI3MCTree from RNG State (Trac #2403) - Currently Polyplopia is configured to use the standard RNG and the state is not saved in the frame.
In order to support this, we have a couple of options.
1. Have Polyplopia manually configure the name of the RNG state in the frame for background events separately. Support would also be needed in the regeneration scripts.
2. Combine events prior to propagating through PROPOSAL. In this case you don't have both a background and signal trees but just a combined tree.
The advantage of combining events later in the simulation is that it is easier to determine what the background vs. signal contribution is. In reality many of the events that have multiple coincidences only have significan contribution from one of the tracks.
Migrated from https://code.icecube.wisc.edu/ticket/2403
```json
{
"status": "closed",
"changetime": "2020-01-28T20:09:23",
"description": "Currently Polyplopia is configured to use the standard RNG and the state is not saved in the frame. \n\nIn order to support this, we have a couple of options.\n\n1. Have Polyplopia manually configure the name of the RNG state in the frame for background events separately. Support would also be needed in the regeneration scripts.\n\n2. Combine events prior to propagating through PROPOSAL. In this case you don't have both a background and signal trees but just a combined tree. \n\nThe advantage of combining events later in the simulation is that it is easier to determine what the background vs. signal contribution is. In reality many of the events that have multiple coincidences only have significan contribution from one of the tracks.\n\n",
"reporter": "juancarlos",
"cc": "",
"resolution": "fixed",
"_ts": "1580242163108345",
"component": "combo simulation",
"summary": "Regeneration of BackgroundI3MCTree from RNG State",
"priority": "normal",
"keywords": "polyplopia, PROPOSAL",
"time": "2020-01-24T17:27:51",
"milestone": "",
"owner": "juancarlos",
"type": "defect"
}
```
| non_priority | regeneration of from rng state trac currently polyplopia is configured to use the standard rng and the state is not saved in the frame in order to support this we have a couple of options have polyplopia manually configure the name of the rng state in the frame for background events separately support would also be needed in the regeneration scripts combine events prior to propagating through proposal in this case you don t have both a background and signal trees but just a combined tree the advantage of combining events later in the simulation is that it is easier to determine what the background vs signal contribution is in reality many of the events that have multiple coincidences only have significan contribution from one of the tracks migrated from json status closed changetime description currently polyplopia is configured to use the standard rng and the state is not saved in the frame n nin order to support this we have a couple of options n have polyplopia manually configure the name of the rng state in the frame for background events separately support would also be needed in the regeneration scripts n combine events prior to propagating through proposal in this case you don t have both a background and signal trees but just a combined tree n nthe advantage of combining events later in the simulation is that it is easier to determine what the background vs signal contribution is in reality many of the events that have multiple coincidences only have significan contribution from one of the tracks n n reporter juancarlos cc resolution fixed ts component combo simulation summary regeneration of from rng state priority normal keywords polyplopia proposal time milestone owner juancarlos type defect | 0 |
262,042 | 22,787,558,753 | IssuesEvent | 2022-07-09 13:49:41 | Uuvana-Studios/longvinter-windows-client | https://api.github.com/repos/Uuvana-Studios/longvinter-windows-client | closed | impossible de rejoindre un serveur, cela charge en boucle puis me ramène au menu principal, je viens pourtant tout juste d'installer le jeux, je ne sais pas quoi faire. | Bug Not Tested | bug | 1.0 | impossible de rejoindre un serveur, cela charge en boucle puis me ramène au menu principal, je viens pourtant tout juste d'installer le jeux, je ne sais pas quoi faire. - bug | non_priority | impossible de rejoindre un serveur cela charge en boucle puis me ramène au menu principal je viens pourtant tout juste d installer le jeux je ne sais pas quoi faire bug | 0 |
136,673 | 19,909,748,222 | IssuesEvent | 2022-01-25 16:03:56 | ParabolInc/parabol | https://api.github.com/repos/ParabolInc/parabol | closed | Link Parabol task with already existing GitHub / Jira issue | enhancement design | ## Issue - Enhancement
Currently, we can only create new GitHub / Jira issues. There should be a way to link Parabol task with the already existing GitHub / Jira issue.
Related conversation: https://parabol.slack.com/archives/C836NA350/p1634140455441800
### Acceptance Criteria (optional)
- [ ] User can link Parabol task with existing GitHub / Jira issue
### Estimated effort
- 4 hrs for design explorations | 1.0 | Link Parabol task with already existing GitHub / Jira issue - ## Issue - Enhancement
Currently, we can only create new GitHub / Jira issues. There should be a way to link Parabol task with the already existing GitHub / Jira issue.
Related conversation: https://parabol.slack.com/archives/C836NA350/p1634140455441800
### Acceptance Criteria (optional)
- [ ] User can link Parabol task with existing GitHub / Jira issue
### Estimated effort
- 4 hrs for design explorations | non_priority | link parabol task with already existing github jira issue issue enhancement currently we can only create new github jira issues there should be a way to link parabol task with the already existing github jira issue related conversation acceptance criteria optional user can link parabol task with existing github jira issue estimated effort hrs for design explorations | 0 |
342,539 | 24,747,528,946 | IssuesEvent | 2022-10-21 10:59:50 | GQDeltex/ft_transcendence | https://api.github.com/repos/GQDeltex/ft_transcendence | closed | Export graphql schema to file for documentation | documentation backend | There is an option to export the code-first GraphQL endpoints to a graphql file. This would be useful for documentation purposes.
Inspiration: @Madasanya @Kromolux | 1.0 | Export graphql schema to file for documentation - There is an option to export the code-first GraphQL endpoints to a graphql file. This would be useful for documentation purposes.
Inspiration: @Madasanya @Kromolux | non_priority | export graphql schema to file for documentation there is an option to export the code first graphql endpoints to a graphql file this would be useful for documentation purposes inspiration madasanya kromolux | 0 |
65,036 | 8,785,454,088 | IssuesEvent | 2018-12-20 13:03:31 | andr9528/ComputerScienceFinalProject | https://api.github.com/repos/andr9528/ComputerScienceFinalProject | closed | (4/4)Updating proces section of report | documentation | - [ ] Proper grammar
- [ ] Proper spelling
- [ ] Contains everything needed
- [ ] No contradictions
The proces section needs to be updated to reflect how we planned the proces, with sprint dokumentation explaining what changed and why.
Task will add:
- A new start to the section
- A subsection to SCRUM about Sprint Planning
- A subsection to SCRUM about Sprint Retrospective | 1.0 | (4/4)Updating proces section of report - - [ ] Proper grammar
- [ ] Proper spelling
- [ ] Contains everything needed
- [ ] No contradictions
The proces section needs to be updated to reflect how we planned the proces, with sprint dokumentation explaining what changed and why.
Task will add:
- A new start to the section
- A subsection to SCRUM about Sprint Planning
- A subsection to SCRUM about Sprint Retrospective | non_priority | updating proces section of report proper grammar proper spelling contains everything needed no contradictions the proces section needs to be updated to reflect how we planned the proces with sprint dokumentation explaining what changed and why task will add a new start to the section a subsection to scrum about sprint planning a subsection to scrum about sprint retrospective | 0 |
291,998 | 21,945,826,831 | IssuesEvent | 2022-05-24 00:22:21 | MSURoboCats/website | https://api.github.com/repos/MSURoboCats/website | closed | Create a youtube introduction | documentation enhancement | If someone has good editing powers it would be neet to have an introduction portion of the video. | 1.0 | Create a youtube introduction - If someone has good editing powers it would be neet to have an introduction portion of the video. | non_priority | create a youtube introduction if someone has good editing powers it would be neet to have an introduction portion of the video | 0 |
98,771 | 11,095,664,816 | IssuesEvent | 2019-12-16 09:34:49 | telerik/kendo-angular | https://api.github.com/repos/telerik/kendo-angular | opened | ASP.NET Web API example with server-side paging, filtering and sorting | Documentation Enhancement pkg:grid | **Describe the issue**
The documentation lacks an example for implementing server-side operations with ASP.NET Web API. This is a supported platform that sees [substantial use](https://insights.stackoverflow.com/trends?tags=asp.net-web-api%2Casp.net-core) today.
**Additional context**
* The scenario is covered in the UI for ASP.NET MVC [documentation](https://docs.telerik.com/aspnet-mvc/helpers/data-management/grid/editing/webapi-editing) and [examples](https://demos.telerik.com/aspnet-mvc/grid/webapi).
* The documentation includes a sample for server-side operations with ASP.NET Core - [Integration with UI for ASP.NET Core](https://www.telerik.com/kendo-angular-ui/components/dataquery/mvc-integration/).
| 1.0 | ASP.NET Web API example with server-side paging, filtering and sorting - **Describe the issue**
The documentation lacks an example for implementing server-side operations with ASP.NET Web API. This is a supported platform that sees [substantial use](https://insights.stackoverflow.com/trends?tags=asp.net-web-api%2Casp.net-core) today.
**Additional context**
* The scenario is covered in the UI for ASP.NET MVC [documentation](https://docs.telerik.com/aspnet-mvc/helpers/data-management/grid/editing/webapi-editing) and [examples](https://demos.telerik.com/aspnet-mvc/grid/webapi).
* The documentation includes a sample for server-side operations with ASP.NET Core - [Integration with UI for ASP.NET Core](https://www.telerik.com/kendo-angular-ui/components/dataquery/mvc-integration/).
| non_priority | asp net web api example with server side paging filtering and sorting describe the issue the documentation lacks an example for implementing server side operations with asp net web api this is a supported platform that sees today additional context the scenario is covered in the ui for asp net mvc and the documentation includes a sample for server side operations with asp net core | 0 |
53,964 | 7,867,708,174 | IssuesEvent | 2018-06-23 12:21:08 | e107inc/e107 | https://api.github.com/repos/e107inc/e107 | closed | e107::css(), e107::js(), etc. in myplugin_menu.php not working | documentation invalid | ```
<?php
if (!defined('e107_INIT')) { exit; }
e107::css('inline','div { background-color:#000000; }');
e107::js('inline','window.alert("Hello World");');
$ns = e107::getRender();
$caption = '<h2>Some caption</h2>';
$text = '<div>Some text</div>';
$ns->tablerender($caption, $text, 'myplugin_menu');
?>
```
AFAIK: This should render all div on the page with a black background and give an Hello World alert popup. | 1.0 | e107::css(), e107::js(), etc. in myplugin_menu.php not working - ```
<?php
if (!defined('e107_INIT')) { exit; }
e107::css('inline','div { background-color:#000000; }');
e107::js('inline','window.alert("Hello World");');
$ns = e107::getRender();
$caption = '<h2>Some caption</h2>';
$text = '<div>Some text</div>';
$ns->tablerender($caption, $text, 'myplugin_menu');
?>
```
AFAIK: This should render all div on the page with a black background and give an Hello World alert popup. | non_priority | css js etc in myplugin menu php not working php if defined init exit css inline div background color js inline window alert hello world ns getrender caption some caption text some text ns tablerender caption text myplugin menu afaik this should render all div on the page with a black background and give an hello world alert popup | 0 |
146,434 | 11,735,204,724 | IssuesEvent | 2020-03-11 10:42:12 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: tpccbench/nodes=9/cpu=4/multi-region failed | C-test-failure O-roachtest O-robot branch-provisional_202001281357_v19.2.3 release-blocker | [(roachtest).tpccbench/nodes=9/cpu=4/multi-region failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1717645&tab=buildLog) on [provisional_202001281357_v19.2.3@3a68f146d8c59060761b1f525801b1e1b6e22fe8](https://github.com/cockroachdb/cockroach/commits/3a68f146d8c59060761b1f525801b1e1b6e22fe8):
```
183.0s 0 4.0 5.6 419.4 453.0 453.0 453.0 orderStatus
183.0s 0 90.0 53.5 2281.7 18253.6 47244.6 51539.6 payment
183.0s 0 5.0 5.3 159.4 704.6 704.6 704.6 stockLevel
184.0s 0 4.0 5.6 2952.8 8321.5 8321.5 8321.5 delivery
184.0s 0 51.0 49.5 3489.7 10200.5 11274.3 13958.6 newOrder
184.0s 0 5.0 5.6 335.5 637.5 637.5 637.5 orderStatus
184.0s 0 48.0 53.5 2415.9 28991.0 60129.5 60129.5 payment
184.0s 0 1.0 5.3 2684.4 2684.4 2684.4 2684.4 stockLevel
_elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
185.0s 0 9.0 5.7 2281.7 3623.9 3623.9 3623.9 delivery
185.0s 0 43.0 49.4 3758.1 8321.5 15032.4 15032.4 newOrder
185.0s 0 10.0 5.6 209.7 973.1 973.1 973.1 orderStatus
185.0s 0 45.0 53.5 2415.9 16643.0 40802.2 40802.2 payment
185.0s 0 7.0 5.3 805.3 2147.5 2147.5 2147.5 stockLevel
186.0s 0 3.0 5.7 3892.3 4295.0 4295.0 4295.0 delivery
186.0s 0 72.9 49.5 3623.9 8053.1 10737.4 11274.3 newOrder
186.0s 0 5.0 5.6 302.0 536.9 536.9 536.9 orderStatus
186.0s 0 102.9 53.7 2818.6 25769.8 32212.3 57982.1 payment
186.0s 0 5.0 5.3 503.3 4160.7 4160.7 4160.7 stockLevel
187.0s 0 1.0 5.6 2281.7 2281.7 2281.7 2281.7 delivery
187.0s 0 43.1 49.5 3221.2 9663.7 25769.8 25769.8 newOrder
187.0s 0 1.0 5.6 251.7 251.7 251.7 251.7 orderStatus
187.0s 0 29.1 53.6 2281.7 30064.8 55834.6 55834.6 payment
187.0s 0 6.0 5.3 536.9 1006.6 1006.6 1006.6 stockLevel
188.0s 0 2.0 5.6 1006.6 1946.2 1946.2 1946.2 delivery
188.0s 0 70.9 49.6 3892.3 9663.7 15569.3 15569.3 newOrder
188.0s 0 5.0 5.6 369.1 671.1 671.1 671.1 orderStatus
188.0s 0 30.0 53.5 2952.8 7516.2 22548.6 22548.6 payment
188.0s 0 7.0 5.3 302.0 2147.5 2147.5 2147.5 stockLevel
_elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
189.0s 0 10.0 5.6 1275.1 3221.2 3221.2 3221.2 delivery
189.0s 0 85.9 49.8 4160.7 11274.3 15032.4 15569.3 newOrder
189.0s 0 4.0 5.6 192.9 486.5 486.5 486.5 orderStatus
189.0s 0 89.9 53.7 2684.4 8321.5 34359.7 64424.5 payment
189.0s 0 8.0 5.4 402.7 3355.4 3355.4 3355.4 stockLevel
190.0s 0 5.0 5.6 2550.1 13958.6 13958.6 13958.6 delivery
190.0s 0 26.0 49.7 4026.5 10200.5 13421.8 13421.8 newOrder
190.0s 0 2.0 5.5 385.9 469.8 469.8 469.8 orderStatus
190.0s 0 81.1 53.8 5100.3 30064.8 45097.2 47244.6 payment
190.0s 0 3.0 5.3 469.8 771.8 771.8 771.8 stockLevel:
- context canceled
error running tpcc load generator
main.runTPCCBench.func3.1
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:818
main.(*monitor).Go.func1
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2344
github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup.(*Group).Go.func1
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:57
runtime.goexit
/usr/local/go/src/runtime/asm_amd64.s:1357
```
<details><summary>More</summary><p>
Artifacts: [/tpccbench/nodes=9/cpu=4/multi-region](https://teamcity.cockroachdb.com/viewLog.html?buildId=1717645&tab=artifacts#/tpccbench/nodes=9/cpu=4/multi-region)
Related:
- #44302 roachtest: tpccbench/nodes=9/cpu=4/multi-region failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-19.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-19.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #41876 roachtest: tpccbench/nodes=9/cpu=4/multi-region failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Atpccbench%2Fnodes%3D9%2Fcpu%3D4%2Fmulti-region.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: tpccbench/nodes=9/cpu=4/multi-region failed - [(roachtest).tpccbench/nodes=9/cpu=4/multi-region failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1717645&tab=buildLog) on [provisional_202001281357_v19.2.3@3a68f146d8c59060761b1f525801b1e1b6e22fe8](https://github.com/cockroachdb/cockroach/commits/3a68f146d8c59060761b1f525801b1e1b6e22fe8):
```
183.0s 0 4.0 5.6 419.4 453.0 453.0 453.0 orderStatus
183.0s 0 90.0 53.5 2281.7 18253.6 47244.6 51539.6 payment
183.0s 0 5.0 5.3 159.4 704.6 704.6 704.6 stockLevel
184.0s 0 4.0 5.6 2952.8 8321.5 8321.5 8321.5 delivery
184.0s 0 51.0 49.5 3489.7 10200.5 11274.3 13958.6 newOrder
184.0s 0 5.0 5.6 335.5 637.5 637.5 637.5 orderStatus
184.0s 0 48.0 53.5 2415.9 28991.0 60129.5 60129.5 payment
184.0s 0 1.0 5.3 2684.4 2684.4 2684.4 2684.4 stockLevel
_elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
185.0s 0 9.0 5.7 2281.7 3623.9 3623.9 3623.9 delivery
185.0s 0 43.0 49.4 3758.1 8321.5 15032.4 15032.4 newOrder
185.0s 0 10.0 5.6 209.7 973.1 973.1 973.1 orderStatus
185.0s 0 45.0 53.5 2415.9 16643.0 40802.2 40802.2 payment
185.0s 0 7.0 5.3 805.3 2147.5 2147.5 2147.5 stockLevel
186.0s 0 3.0 5.7 3892.3 4295.0 4295.0 4295.0 delivery
186.0s 0 72.9 49.5 3623.9 8053.1 10737.4 11274.3 newOrder
186.0s 0 5.0 5.6 302.0 536.9 536.9 536.9 orderStatus
186.0s 0 102.9 53.7 2818.6 25769.8 32212.3 57982.1 payment
186.0s 0 5.0 5.3 503.3 4160.7 4160.7 4160.7 stockLevel
187.0s 0 1.0 5.6 2281.7 2281.7 2281.7 2281.7 delivery
187.0s 0 43.1 49.5 3221.2 9663.7 25769.8 25769.8 newOrder
187.0s 0 1.0 5.6 251.7 251.7 251.7 251.7 orderStatus
187.0s 0 29.1 53.6 2281.7 30064.8 55834.6 55834.6 payment
187.0s 0 6.0 5.3 536.9 1006.6 1006.6 1006.6 stockLevel
188.0s 0 2.0 5.6 1006.6 1946.2 1946.2 1946.2 delivery
188.0s 0 70.9 49.6 3892.3 9663.7 15569.3 15569.3 newOrder
188.0s 0 5.0 5.6 369.1 671.1 671.1 671.1 orderStatus
188.0s 0 30.0 53.5 2952.8 7516.2 22548.6 22548.6 payment
188.0s 0 7.0 5.3 302.0 2147.5 2147.5 2147.5 stockLevel
_elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
189.0s 0 10.0 5.6 1275.1 3221.2 3221.2 3221.2 delivery
189.0s 0 85.9 49.8 4160.7 11274.3 15032.4 15569.3 newOrder
189.0s 0 4.0 5.6 192.9 486.5 486.5 486.5 orderStatus
189.0s 0 89.9 53.7 2684.4 8321.5 34359.7 64424.5 payment
189.0s 0 8.0 5.4 402.7 3355.4 3355.4 3355.4 stockLevel
190.0s 0 5.0 5.6 2550.1 13958.6 13958.6 13958.6 delivery
190.0s 0 26.0 49.7 4026.5 10200.5 13421.8 13421.8 newOrder
190.0s 0 2.0 5.5 385.9 469.8 469.8 469.8 orderStatus
190.0s 0 81.1 53.8 5100.3 30064.8 45097.2 47244.6 payment
190.0s 0 3.0 5.3 469.8 771.8 771.8 771.8 stockLevel:
- context canceled
error running tpcc load generator
main.runTPCCBench.func3.1
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:818
main.(*monitor).Go.func1
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2344
github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup.(*Group).Go.func1
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:57
runtime.goexit
/usr/local/go/src/runtime/asm_amd64.s:1357
```
<details><summary>More</summary><p>
Artifacts: [/tpccbench/nodes=9/cpu=4/multi-region](https://teamcity.cockroachdb.com/viewLog.html?buildId=1717645&tab=artifacts#/tpccbench/nodes=9/cpu=4/multi-region)
Related:
- #44302 roachtest: tpccbench/nodes=9/cpu=4/multi-region failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-19.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-19.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #41876 roachtest: tpccbench/nodes=9/cpu=4/multi-region failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Atpccbench%2Fnodes%3D9%2Fcpu%3D4%2Fmulti-region.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| non_priority | roachtest tpccbench nodes cpu multi region failed on orderstatus payment stocklevel delivery neworder orderstatus payment stocklevel elapsed errors ops sec inst ops sec cum ms ms ms pmax ms delivery neworder orderstatus payment stocklevel delivery neworder orderstatus payment stocklevel delivery neworder orderstatus payment stocklevel delivery neworder orderstatus payment stocklevel elapsed errors ops sec inst ops sec cum ms ms ms pmax ms delivery neworder orderstatus payment stocklevel delivery neworder orderstatus payment stocklevel context canceled error running tpcc load generator main runtpccbench home agent work go src github com cockroachdb cockroach pkg cmd roachtest tpcc go main monitor go home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go github com cockroachdb cockroach vendor golang org x sync errgroup group go home agent work go src github com cockroachdb cockroach vendor golang org x sync errgroup errgroup go runtime goexit usr local go src runtime asm s more artifacts related roachtest tpccbench nodes cpu multi region failed roachtest tpccbench nodes cpu multi region failed powered by | 0 |
130,135 | 10,597,649,696 | IssuesEvent | 2019-10-10 01:32:34 | Princeton-CDH/mep-django | https://api.github.com/repos/Princeton-CDH/mep-django | closed | style changes from "notes on website design" | awaiting testing | # testing notes
this issue aggregates a bunch of small things from josh's notes (see link below).
- check that the size of the logotype (the main title and subtitle) on the homepage are slightly larger (you can compare [test](https://test-shakespeareandco.cdh.princeton.edu/) with [production](https://shakespeareandco.princeton.edu/) - the difference might be more visible on smaller screen sizes)
- open the main menu and check the taglines under the links (see notes below)
- open the main menu and check the order of the links (see below)
- check the order of the links in the footer (see below)
- go to the [members search page](https://test-shakespeareandco.cdh.princeton.edu/members/) (you might be prompted to log in) and check that "birth year" comes before "membership dates" in the filters
- check that the words Birth Year are capitalized
- go to [hemingway's page](https://test-shakespeareandco.cdh.princeton.edu/members/224/) and check that there is a link that says "Wikipedia" (instead of "more info")
# dev notes
[link to Josh's notes](https://drive.google.com/open?id=1VFMkKe3J6gCb4X5vrv2V42jvrGhOJn9x0ocWC6f0JCM)
- [x] change the size of the homepage title text and the subtitle text for desktop (based on the new homepage screen for desktop on Zeplin) - the sizes have increased a bit for this page and for desktop only
- [x] change the menu taglines for members: Explore the lending library membership
for books: Explore the lending library holdings
for lending library cards: Explore the extant lending library cards
- [x] change the order of links in footer to: members, books, cards, analysis, sources, about
- [x] change the order (and naming) of links in main nav to: members, books, cards, etc...
- [x] swap the order of the "birth year" and "membership dates" filters on members search
- [x] capitalize "Birth Year" on members search
- [x] if the member's reference is a Wikipedia link, make the text of the link "Wikipedia"
<s>create "demographics" dropdown on members search and move birth year/gender into it</s>
<s>add a disabled "books" dropdown on members search</s>
see #287 - not implementing until November release | 1.0 | style changes from "notes on website design" - # testing notes
this issue aggregates a bunch of small things from josh's notes (see link below).
- check that the size of the logotype (the main title and subtitle) on the homepage are slightly larger (you can compare [test](https://test-shakespeareandco.cdh.princeton.edu/) with [production](https://shakespeareandco.princeton.edu/) - the difference might be more visible on smaller screen sizes)
- open the main menu and check the taglines under the links (see notes below)
- open the main menu and check the order of the links (see below)
- check the order of the links in the footer (see below)
- go to the [members search page](https://test-shakespeareandco.cdh.princeton.edu/members/) (you might be prompted to log in) and check that "birth year" comes before "membership dates" in the filters
- check that the words Birth Year are capitalized
- go to [hemingway's page](https://test-shakespeareandco.cdh.princeton.edu/members/224/) and check that there is a link that says "Wikipedia" (instead of "more info")
# dev notes
[link to Josh's notes](https://drive.google.com/open?id=1VFMkKe3J6gCb4X5vrv2V42jvrGhOJn9x0ocWC6f0JCM)
- [x] change the size of the homepage title text and the subtitle text for desktop (based on the new homepage screen for desktop on Zeplin) - the sizes have increased a bit for this page and for desktop only
- [x] change the menu taglines for members: Explore the lending library membership
for books: Explore the lending library holdings
for lending library cards: Explore the extant lending library cards
- [x] change the order of links in footer to: members, books, cards, analysis, sources, about
- [x] change the order (and naming) of links in main nav to: members, books, cards, etc...
- [x] swap the order of the "birth year" and "membership dates" filters on members search
- [x] capitalize "Birth Year" on members search
- [x] if the member's reference is a Wikipedia link, make the text of the link "Wikipedia"
<s>create "demographics" dropdown on members search and move birth year/gender into it</s>
<s>add a disabled "books" dropdown on members search</s>
see #287 - not implementing until November release | non_priority | style changes from notes on website design testing notes this issue aggregates a bunch of small things from josh s notes see link below check that the size of the logotype the main title and subtitle on the homepage are slightly larger you can compare with the difference might be more visible on smaller screen sizes open the main menu and check the taglines under the links see notes below open the main menu and check the order of the links see below check the order of the links in the footer see below go to the you might be prompted to log in and check that birth year comes before membership dates in the filters check that the words birth year are capitalized go to and check that there is a link that says wikipedia instead of more info dev notes change the size of the homepage title text and the subtitle text for desktop based on the new homepage screen for desktop on zeplin the sizes have increased a bit for this page and for desktop only change the menu taglines for members explore the lending library membership for books explore the lending library holdings for lending library cards explore the extant lending library cards change the order of links in footer to members books cards analysis sources about change the order and naming of links in main nav to members books cards etc swap the order of the birth year and membership dates filters on members search capitalize birth year on members search if the member s reference is a wikipedia link make the text of the link wikipedia create demographics dropdown on members search and move birth year gender into it add a disabled books dropdown on members search see not implementing until november release | 0 |
45,312 | 7,177,489,933 | IssuesEvent | 2018-01-31 13:49:34 | ViacomInc/data-point | https://api.github.com/repos/ViacomInc/data-point | opened | Remove the term TransformOptions from the readme | type:documentation | **Problem description**:
In the readme, we refer to a `TransformOptions` type that does not exist in the code:
`dataPoint.resolve(reducer:Reducer, input:*, options:TransformOptions):Promise(output:*)`
This is confusing, because it makes it seem like `TransformOptions` is a class.
**Suggested solution**:
Replace the term `TransformOptions` with `Object`.
| 1.0 | Remove the term TransformOptions from the readme - **Problem description**:
In the readme, we refer to a `TransformOptions` type that does not exist in the code:
`dataPoint.resolve(reducer:Reducer, input:*, options:TransformOptions):Promise(output:*)`
This is confusing, because it makes it seem like `TransformOptions` is a class.
**Suggested solution**:
Replace the term `TransformOptions` with `Object`.
| non_priority | remove the term transformoptions from the readme problem description in the readme we refer to a transformoptions type that does not exist in the code datapoint resolve reducer reducer input options transformoptions promise output this is confusing because it makes it seem like transformoptions is a class suggested solution replace the term transformoptions with object | 0 |
168,792 | 13,103,229,860 | IssuesEvent | 2020-08-04 08:12:31 | WoWManiaUK/Redemption | https://api.github.com/repos/WoWManiaUK/Redemption | closed | [quest] Medallion of Faith | Fix - Tester Confirmed | **Links:**
https://classic.wowhead.com/quest=5122/the-medallion-of-faith
**What is Happening:**
The quest opens with no text and no objectives.
**What Should happen:**
The window should contain the text of the quest listing its objectives.
| 1.0 | [quest] Medallion of Faith - **Links:**
https://classic.wowhead.com/quest=5122/the-medallion-of-faith
**What is Happening:**
The quest opens with no text and no objectives.
**What Should happen:**
The window should contain the text of the quest listing its objectives.
| non_priority | medallion of faith links what is happening the quest opens with no text and no objectives what should happen the window should contain the text of the quest listing its objectives | 0 |
269,395 | 20,381,293,676 | IssuesEvent | 2022-02-21 22:16:12 | Interlisp/medley | https://api.github.com/repos/Interlisp/medley | reopened | Online should be clearer about Interlisp vs. Common Lisp in startup | documentation enhancement help wanted config online | **Font related functions missing**
Some functions that are explained in medley-primer.pdf like FONTSET, FONTPROFILE, CREATEW, PP are missing
**To Reproduce**
Steps to reproduce the behavior:
1. type (FONTSET 'BIGGER)
2. system responds with undefined car of form FONT....
3. similar results with CREATEW/PP etc.
**Expected behavior**
I thought the medley-primer has basic functions which will work as is. Infact i see the definitions in the sources.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Context (please complete the following information):**
- OS: Linux/online docker
- OS Version: Linux Debian 11 for local install/ Chrome on Windows 10 for online setup
- Host arch: x86_64/dont know for online
- Maiko version: [maiko-220117-5eba2c3a](https://github.com/Interlisp/maiko/releases/tag/maiko-220117-5eba2c3a) for local setup
- IL:MAKESYSDATE: [ "19-Feb-2022 04:38:48" for local setupdate /"11-Feb-2022 23:06-42" for online version ]
**Additional context**
None
| 1.0 | Online should be clearer about Interlisp vs. Common Lisp in startup - **Font related functions missing**
Some functions that are explained in medley-primer.pdf like FONTSET, FONTPROFILE, CREATEW, PP are missing
**To Reproduce**
Steps to reproduce the behavior:
1. type (FONTSET 'BIGGER)
2. system responds with undefined car of form FONT....
3. similar results with CREATEW/PP etc.
**Expected behavior**
I thought the medley-primer has basic functions which will work as is. Infact i see the definitions in the sources.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Context (please complete the following information):**
- OS: Linux/online docker
- OS Version: Linux Debian 11 for local install/ Chrome on Windows 10 for online setup
- Host arch: x86_64/dont know for online
- Maiko version: [maiko-220117-5eba2c3a](https://github.com/Interlisp/maiko/releases/tag/maiko-220117-5eba2c3a) for local setup
- IL:MAKESYSDATE: [ "19-Feb-2022 04:38:48" for local setupdate /"11-Feb-2022 23:06-42" for online version ]
**Additional context**
None
| non_priority | online should be clearer about interlisp vs common lisp in startup font related functions missing some functions that are explained in medley primer pdf like fontset fontprofile createw pp are missing to reproduce steps to reproduce the behavior type fontset bigger system responds with undefined car of form font similar results with createw pp etc expected behavior i thought the medley primer has basic functions which will work as is infact i see the definitions in the sources screenshots if applicable add screenshots to help explain your problem context please complete the following information os linux online docker os version linux debian for local install chrome on windows for online setup host arch dont know for online maiko version for local setup il makesysdate additional context none | 0 |
49,110 | 6,009,563,796 | IssuesEvent | 2017-06-06 10:52:02 | DMPRoadmap/roadmap | https://api.github.com/repos/DMPRoadmap/roadmap | opened | Questions mis-ordered on DMPTuuli | DMPTuuli MVP-v0.3 plans testing | Questions are displaying in the wrong order on Tuuli. Again, I assume this is a config issue as not occuring on DMPonline test.
Tekes template on live

Tekes template on test

| 1.0 | Questions mis-ordered on DMPTuuli - Questions are displaying in the wrong order on Tuuli. Again, I assume this is a config issue as not occuring on DMPonline test.
Tekes template on live

Tekes template on test

| non_priority | questions mis ordered on dmptuuli questions are displaying in the wrong order on tuuli again i assume this is a config issue as not occuring on dmponline test tekes template on live tekes template on test | 0 |
241,133 | 26,256,651,886 | IssuesEvent | 2023-01-06 01:45:09 | arielorn/goalert | https://api.github.com/repos/arielorn/goalert | opened | CVE-2021-27292 (High) detected in ua-parser-js-0.7.20.tgz | security vulnerability | ## CVE-2021-27292 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ua-parser-js-0.7.20.tgz</b></p></summary>
<p>Lightweight JavaScript-based user-agent string parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.20.tgz">https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.20.tgz</a></p>
<p>Path to dependency file: /web/src/package.json</p>
<p>Path to vulnerable library: /web/src/node_modules/ua-parser-js/package.json</p>
<p>
Dependency Hierarchy:
- react-swipeable-views-0.13.3.tgz (Root Library)
- react-swipeable-views-utils-0.13.3.tgz
- fbjs-0.8.17.tgz
- :x: **ua-parser-js-0.7.20.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ua-parser-js >= 0.7.14, fixed in 0.7.24, uses a regular expression which is vulnerable to denial of service. If an attacker sends a malicious User-Agent header, ua-parser-js will get stuck processing it for an extended period of time.
<p>Publish Date: 2021-03-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-27292>CVE-2021-27292</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-03-17</p>
<p>Fix Resolution (ua-parser-js): 0.7.24</p>
<p>Direct dependency fix Resolution (react-swipeable-views): 0.13.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-27292 (High) detected in ua-parser-js-0.7.20.tgz - ## CVE-2021-27292 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ua-parser-js-0.7.20.tgz</b></p></summary>
<p>Lightweight JavaScript-based user-agent string parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.20.tgz">https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.20.tgz</a></p>
<p>Path to dependency file: /web/src/package.json</p>
<p>Path to vulnerable library: /web/src/node_modules/ua-parser-js/package.json</p>
<p>
Dependency Hierarchy:
- react-swipeable-views-0.13.3.tgz (Root Library)
- react-swipeable-views-utils-0.13.3.tgz
- fbjs-0.8.17.tgz
- :x: **ua-parser-js-0.7.20.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ua-parser-js >= 0.7.14, fixed in 0.7.24, uses a regular expression which is vulnerable to denial of service. If an attacker sends a malicious User-Agent header, ua-parser-js will get stuck processing it for an extended period of time.
<p>Publish Date: 2021-03-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-27292>CVE-2021-27292</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-03-17</p>
<p>Fix Resolution (ua-parser-js): 0.7.24</p>
<p>Direct dependency fix Resolution (react-swipeable-views): 0.13.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in ua parser js tgz cve high severity vulnerability vulnerable library ua parser js tgz lightweight javascript based user agent string parser library home page a href path to dependency file web src package json path to vulnerable library web src node modules ua parser js package json dependency hierarchy react swipeable views tgz root library react swipeable views utils tgz fbjs tgz x ua parser js tgz vulnerable library vulnerability details ua parser js fixed in uses a regular expression which is vulnerable to denial of service if an attacker sends a malicious user agent header ua parser js will get stuck processing it for an extended period of time publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution ua parser js direct dependency fix resolution react swipeable views step up your open source security game with mend | 0 |
90,150 | 8,229,510,779 | IssuesEvent | 2018-09-07 09:36:47 | istio/istio | https://api.github.com/repos/istio/istio | closed | Helm Charts: BookInfo Application example not working with mixer disabled | area/test and release community/help wanted | **Describe the bug**
<sub><sup> As per the istio documentation the istio can work with minimal components(https://istio.io/docs/concepts/policies-and-telemetry/). Trying to test the BookInfo Application deploying istio with disabling mixer . It is giving connection refused error.
(Tested the BookInfo application deploying istio with all the components it works fine.)
Have used Helm for installation of istio in both cases.
</sup></sub>
**Expected behavior**
<sub><sup>The BookInfo Application should work fine with mixer disabled</sup></sub>
**Steps to reproduce the bug**
<sub><sup>
1) Install istio with mixer diabled.
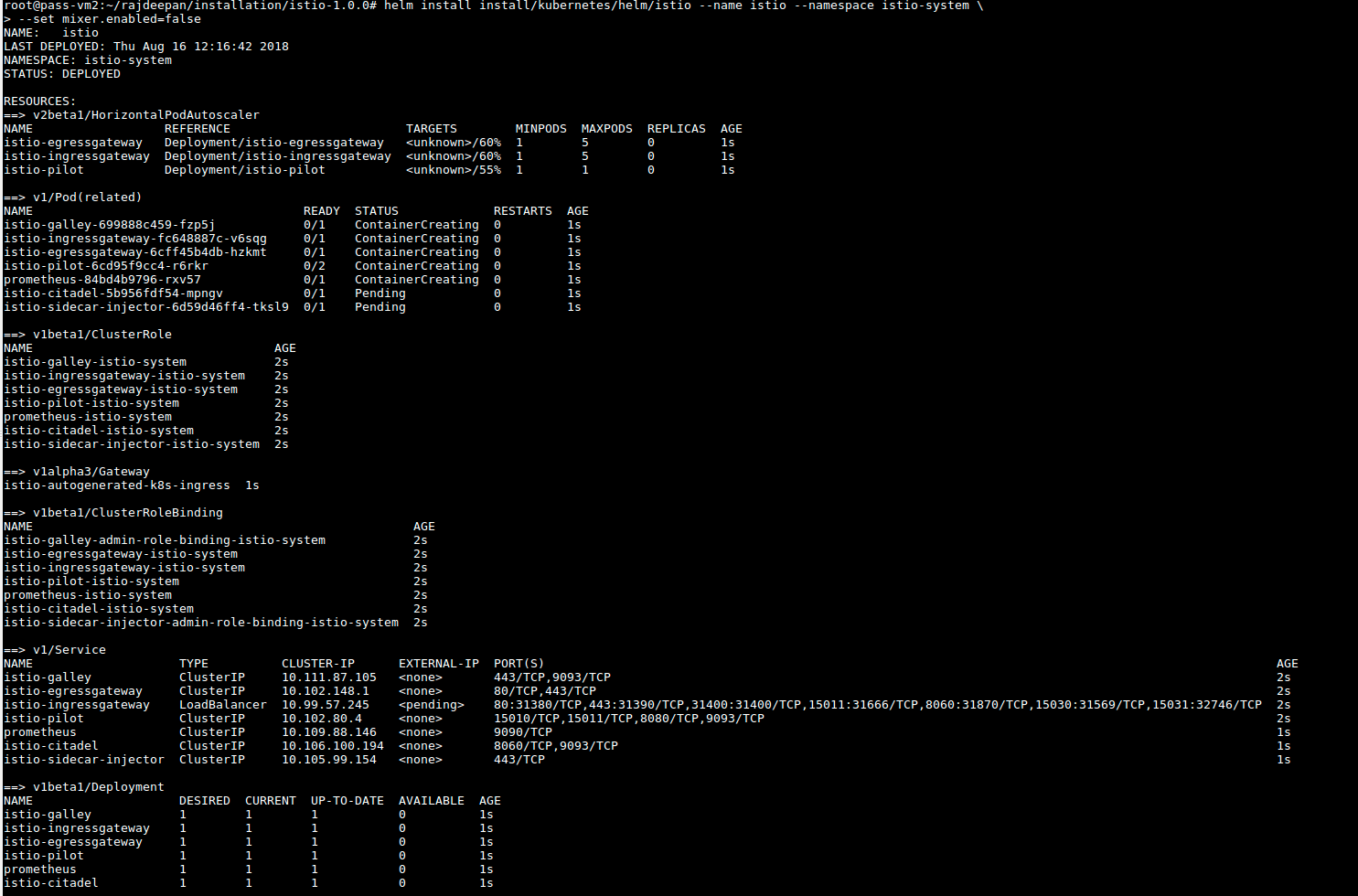
In the istio system namespace all the istio components are running except mixer components
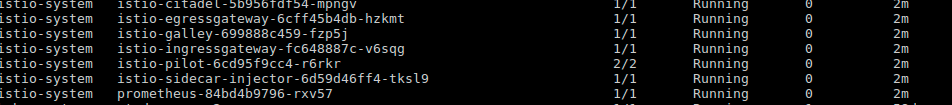
<sub><sup>
2) Deploy the Book Application example as shown below
<sub><sup>

All the pods are running
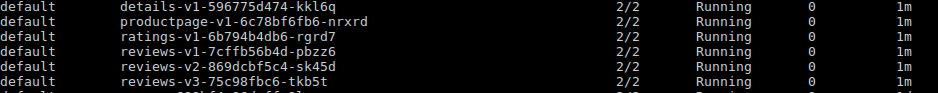
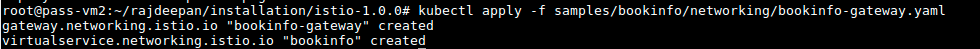
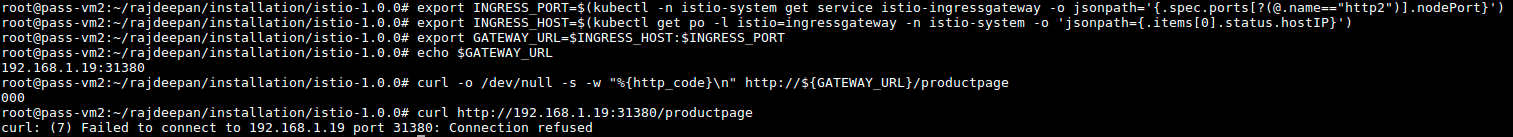
*Connection refused error is getting show when trying to access the application.*
</sup></sub>
### Observation:
<sub><sup>
The egress and ingress pods in the istio-system get restarted and the logs shows
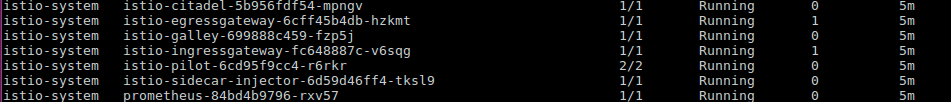
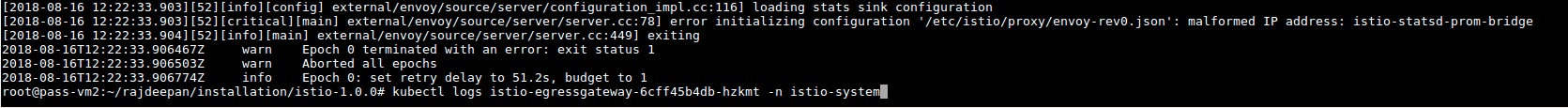
</sup></sub>
**Version**
<sub><sup> istio version : 1.0.0
kubectl version : v1.10.4
</sup></sub>
**Is Istio Auth enabled or not?**
<sub><sup>Disabled </sup></sub>
**Environment**
<sub><sup>Ubuntu

</sup></sub>
| 1.0 | Helm Charts: BookInfo Application example not working with mixer disabled - **Describe the bug**
<sub><sup> As per the istio documentation the istio can work with minimal components(https://istio.io/docs/concepts/policies-and-telemetry/). Trying to test the BookInfo Application deploying istio with disabling mixer . It is giving connection refused error.
(Tested the BookInfo application deploying istio with all the components it works fine.)
Have used Helm for installation of istio in both cases.
</sup></sub>
**Expected behavior**
<sub><sup>The BookInfo Application should work fine with mixer disabled</sup></sub>
**Steps to reproduce the bug**
<sub><sup>
1) Install istio with mixer diabled.
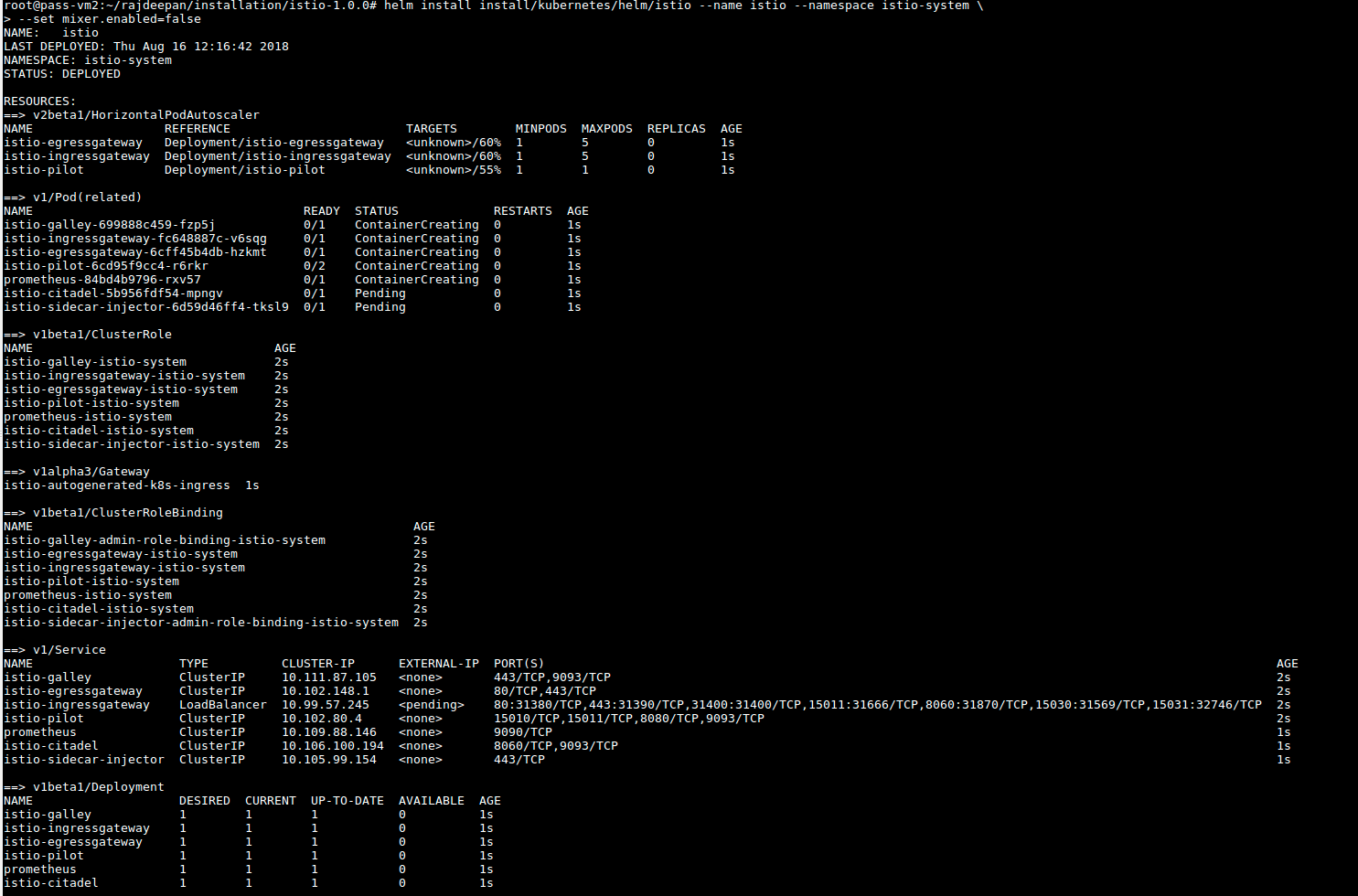
In the istio system namespace all the istio components are running except mixer components
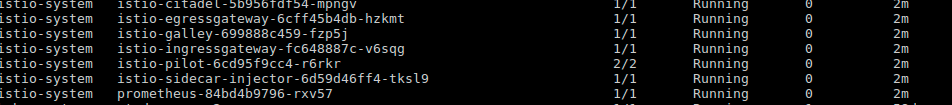
<sub><sup>
2) Deploy the Book Application example as shown below
<sub><sup>

All the pods are running
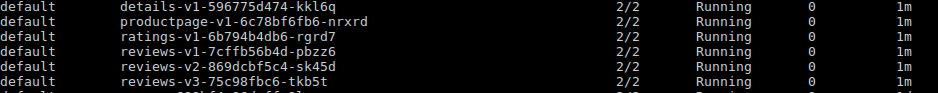
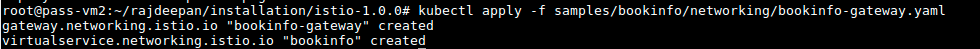
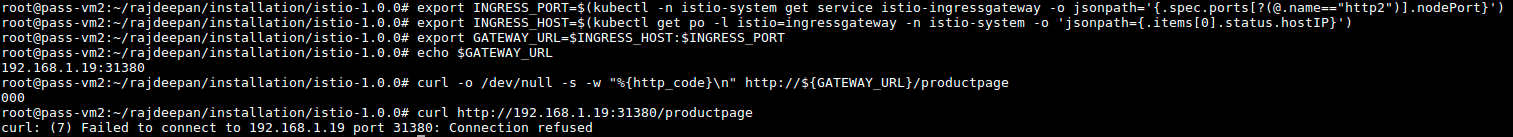
*Connection refused error is getting show when trying to access the application.*
</sup></sub>
### Observation:
<sub><sup>
The egress and ingress pods in the istio-system get restarted and the logs shows
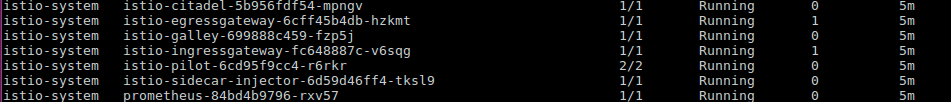
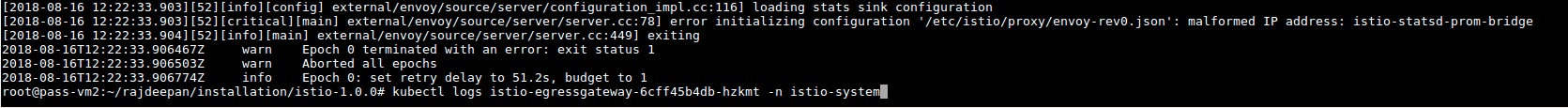
</sup></sub>
**Version**
<sub><sup> istio version : 1.0.0
kubectl version : v1.10.4
</sup></sub>
**Is Istio Auth enabled or not?**
<sub><sup>Disabled </sup></sub>
**Environment**
<sub><sup>Ubuntu

</sup></sub>
| non_priority | helm charts bookinfo application example not working with mixer disabled describe the bug as per the istio documentation the istio can work with minimal components trying to test the bookinfo application deploying istio with disabling mixer it is giving connection refused error tested the bookinfo application deploying istio with all the components it works fine have used helm for installation of istio in both cases expected behavior the bookinfo application should work fine with mixer disabled steps to reproduce the bug install istio with mixer diabled in the istio system namespace all the istio components are running except mixer components deploy the book application example as shown below all the pods are running connection refused error is getting show when trying to access the application observation the egress and ingress pods in the istio system get restarted and the logs shows version istio version kubectl version is istio auth enabled or not disabled environment ubuntu | 0 |
303,114 | 22,954,148,556 | IssuesEvent | 2022-07-19 10:00:21 | phukiendienthoaigiare/Qua-Tang-Doanh-Nghiep-4-trong-1 | https://api.github.com/repos/phukiendienthoaigiare/Qua-Tang-Doanh-Nghiep-4-trong-1 | opened | 7 Ý Tưởng Quà Tặng Doanh Nghiệp Đối Tác Hiện Đại | documentation help wanted good first issue question | <p>Gốc rễ của công ty phát triển nhờ sự thống nhất và sự thống nhất đó bắt đầu từ các đối tác kinh doanh. Bất kể tỷ lệ sở hữu mà họ nắm giữ trong doanh nghiệp là bao nhiêu, làm việc cùng nhau và giữ cho mọi người hạnh phúc là mục tiêu cuối cùng. Duy trì mối quan hệ kinh doanh lành mạnh với các đối tác kinh doanh của bạn là chìa khóa để đạt được thành công và những tầm cao lớn hơn. Một trong những cách tốt nhất để làm như vậy là gửi quà tặng doanh nghiệp đối tác kinh doanh cho dù họ ở đâu.</p>
<p>Để giúp bạn tìm được những món quà tặng doanh nghiệp tốt nhất, chúng tôi đã liệt kê một số món quà tặng doanh nghiệp sẽ hoàn hảo để giới thiệu cho các đối tác kinh doanh của bạn trong những dịp khác nhau.</p>
<h2 id="h-mẹo-chọn-qua-tặng-dối-tac-giup-doanh-nghiệp-gắn-kết">Mẹo chọn quà tặng đối tác giúp doanh nghiệp gắn kết</h2>
<p>Các mối quan hệ có thể được củng cố bằng cách gửi quà tặng. Tuy nhiên, có thể khó khăn để chọn món quà phù hợp với từng đối tác của bạn.</p>
<div class="wp-block-image"><figure class="aligncenter size-large"><img width="1024" height="684" src="https://phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-1024x684.jpg" alt="" class="wp-image-19207" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-1024x684.jpg 1024w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-300x200.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-768x513.jpg 768w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-990x661.jpg 990w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-441x294.jpg 441w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-600x401.jpg 600w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-150x100.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai.jpg 1200w" sizes="(max-width: 1024px) 100vw, 1024px" /><figcaption>Quà tặng đối tác – nền tảng phát triển doanh nghiệp</figcaption></figure></div>
<p>Bạn muốn đảm bảo rằng món quà bạn chọn được xem là hữu ích và có thể áp dụng cho sứ mệnh của doanh nghiệp?</p>
<p>Hãy xem các mẹo của chúng tôi để giúp hành trình chọn quà của bạn dễ dàng hơn rất nhiều.</p>
<h3 id="h-mẹo-số-1-cung-cấp-một-mon-qua-thực-sự-hữu-ich">Mẹo số 1: Cung cấp một món quà thực sự hữu ích</h3>
<p>Lựa chọn quà tặng hữu ích cho cuộc sống sẽ giúp món quà của bạn trở thành cách tinh tế nhất để gắn kết mối quan hệ.</p>
<p>Ví dụ: hãy xem xét cung cấp một chiếc tai nghe Bluetooth để có thể dùng nghe điện thoại khi lái xe… Hoặc một chiếc loa nghe nhạc mini nhỏ gọn để mang theo khi đi du lịch, picnic…</p>
<h3 id="h-mẹo-số-2-tặng-qua-ca-nhan-hoa">Mẹo số 2: Tặng quà cá nhân hóa</h3>
<p>Quà tặng cá nhân hóa là một trong những loại quà tặng không thể quên được. Một món quà tùy chỉnh có in logo hoặc tên của công ty sẽ tạo nên một giá trị tuyệt vời.</p>
<div class="wp-block-image"><figure class="aligncenter size-full"><img width="1000" height="1000" src="https://phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1.jpg" alt="" class="wp-image-19208" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1.jpg 1000w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-300x300.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-150x150.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-768x768.jpg 768w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-900x900.jpg 900w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-990x990.jpg 990w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-441x441.jpg 441w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-600x600.jpg 600w" sizes="(max-width: 1000px) 100vw, 1000px" /><figcaption><em>Một món quà thể hiện cá tính luôn mang lại cảm giác ấn tượng tuyệt vời.</em></figcaption></figure></div>
<h3 id="h-mẹo-số-3-xem-xet-vấn-dề-chất-lượng">Mẹo số 3: Xem xét vấn đề chất lượng</h3>
<p>Bạn cũng nên suy nghĩ về chất lượng của món quà, độ bền sau thời gian sử dụng và lợi ích của nó. Hãy chọn món quà nào đó thật sự đáng giá và ý nghĩa phù hợp với người nhận.</p>
<h3 id="h-mẹo-số-4-it-hơn-chinh-la-nhiều-hơn">Mẹo số 4: Ít hơn chính là nhiều hơn</h3>
<ul><li>Hành động được đánh giá cao phải thật sự tế nhị, thẳng thắn, ân cần và trung thực.</li><li>Bạn không cần phải đi quá đà để thể hiện lòng biết ơn của mình.</li><li>Tặng quà và gửi thiệp chúc mừng là một chiến lược tiếp thị sẽ giúp bạn xây dựng sự công nhận thương hiệu của mình.</li></ul>
<h2 id="h-top-qua-tặng-y-nghia-danh-cho-dối-tac">Top quà tặng ý nghĩa dành cho đối tác</h2>
<p>Dưới đây là một số gợi ý về những món quà tặng doanh nghiệp đối tác chất lượng cao, giúp bạn xây dựng một chiến dịch tặng quà hoàn hảo. Thông qua bộ quà tặng, bạn sẽ dễ dàng kết nối và duy trì mối quan hệ với các đối tác của mình. Tạo tiền đề giúp doanh nghiệp phát triển bền vững.</p>
<h3 id="h-pin-sạc-dự-phong">Pin sạc dự phòng</h3>
<p>Chắc chắn là một trong những sản phẩm quà tặng doanh nghiệp đối tác hữu ích nằm trong top quà tặng ý nghĩa. Bộ sạc di động sẽ giúp các đối tác kinh doanh chủ động hơn trong các cuộc họp và khi đi du lịch. Đó là một rắc rối mà nhiều người phải đối mặt khi pin điện thoại hoặc máy tính xách tay bị cạn kiệt và một số nội dung quan trọng đang chờ xử lý. Bộ sạc di động sẽ rất hữu ích trong những lúc như vậy.</p>
<div class="wp-block-image"><figure class="aligncenter size-full"><img width="600" height="600" src="https://phukiendienthoaigiare.com/wp-content/uploads/2022/06/Pin-Sac-Du-Phong-5000mAh-PB0504-1.jpg" alt="" class="wp-image-18754" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2022/06/Pin-Sac-Du-Phong-5000mAh-PB0504-1.jpg 600w, //phukiendienthoaigiare.com/wp-content/uploads/2022/06/Pin-Sac-Du-Phong-5000mAh-PB0504-1-300x300.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2022/06/Pin-Sac-Du-Phong-5000mAh-PB0504-1-150x150.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2022/06/Pin-Sac-Du-Phong-5000mAh-PB0504-1-441x441.jpg 441w" sizes="(max-width: 600px) 100vw, 600px" /><figcaption>Quà tặng pin sạc dự phòng</figcaption></figure></div>
<p>Những dòng sạc di động được rất nhiều người ưa chuộng và lựa chọn làm quà tặng cho đối tác điển hình nhất là:</p>
<ul><li>Pin Sạc Dự Phòng 10000mAh Recci RPB-P09 Sạc Nhanh 22.5W: <em><strong><a href="https://phukiendienthoaigiare.com/product/pin-sac-du-phong-10000mah-recci-rpb-p09-sac-nhanh-22-5w-chuan-pd-qc3-0/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></strong></em></li><li>Pin Sạc Dự Phòng 5000mAh PB0504 – Logo Led Phát Sáng: <em><strong><a href="https://phukiendienthoaigiare.com/product/pin-sac-du-phong-5000mah-pb0504-logo-led-phat-sang-khi-su-dung/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></strong></em></li><li>Pin Sạc Dự Phòng Polymer 10000mAh Type C 18W PD QC3.0 Recci P01: <strong><em><a href="https://phukiendienthoaigiare.com/product/pin-sac-du-phong-polymer-10000mah-type-c-18w-pd-qc3-0-recci-p01/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></em></strong></li><li>Pin Sạc Dự Phòng 10000 mAh Recci N16: <strong><em><a href="https://phukiendienthoaigiare.com/product/pin-sac-du-phong-10000-mah-recci-n16-sac-nhieu-thiet-bi/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></em></strong></li></ul>
<p><a href="https://phukiendienthoaigiare.com/product-category/pin-sac-du-phong/" target="_blank" rel="noreferrer noopener">Tìm hiểu thêm</a></p>
<h3 id="h-theo-doi-sức-khỏe">Theo dõi sức khỏe</h3>
<p>Các đối tác kinh doanh của bạn luôn bận rộn với công việc và có thể không có đủ thời gian để kiểm tra sức khỏe của họ. Hãy mua cho họ một chiếc đồng hồ thông minh hoặc vòng đeo tay thông minh sẽ hiển thị tất cả dữ liệu thời gian thực vì nó đi kèm với tính năng theo dõi nhịp tim, theo dõi giấc ngủ, theo dõi số bước, … Ngoài ra, còn có nhiều tính năng khác như kết nối di động, trung tâm hiển thị tin nhắn, cuộc gọi…</p>
<div class="wp-block-image"><figure class="aligncenter size-large"><img width="1024" height="982" src="https://phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-1024x982.jpg" alt="" class="wp-image-12753" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-1024x982.jpg 1024w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-300x288.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-768x737.jpg 768w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-990x950.jpg 990w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-441x423.jpg 441w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-600x576.jpg 600w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-150x144.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19.jpg 1351w" sizes="(max-width: 1024px) 100vw, 1024px" /><figcaption>Quà tặng đồng hồ thông minh</figcaption></figure></div>
<ul><li>Đồng Hồ Thông Minh V19 đo nhịp tim đo huyết áp đo spo2: <em><strong><a href="https://phukiendienthoaigiare.com/product/dong-ho-thong-minh-v19-huyet-ap-nhip-tim-spo2/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></strong></em></li><li>Đồng Hồ Thông Minh T19 đo nhịp tim đo huyết áp đo spo2: <em><strong><a href="https://phukiendienthoaigiare.com/product/dong-ho-thong-minh-t19-huyet-ap-nhip-tim-spo2/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></strong></em></li><li>Vòng Đeo Tay Thông Minh V20: <strong><em><a href="https://phukiendienthoaigiare.com/product/vong-deo-tay-thong-minh-v20/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></em></strong></li><li>Vòng Đeo Tay Thông Minh V18: <strong><em><a href="https://phukiendienthoaigiare.com/product/vong-deo-tay-thong-minh-v18/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></em></strong></li></ul>
<p><a href="https://phukiendienthoaigiare.com/product-category/theo-doi-suc-khoe/" target="_blank" rel="noreferrer noopener">Tìm hiểu thêm</a></p>
<h3 id="h-tai-nghe-khong-day">Tai nghe không dây</h3>
<p>Tai nghe không dây cũng là một thành viên của nhóm quà tặng hữu ích dành cho đối tác. Mặc dù tai nghe không dây đã có từ lâu, nhưng sự phổ biến của chúng đã tăng vọt cùng với sự ra đời của điện thoại thông minh.</p>
<p>Những tiện ích này cho phép chúng truy cập nhiều hơn vào phương tiện khi đang di chuyển, vì vậy tạo ra những món quà tuyệt vời.</p>
<div class="wp-block-image"><figure class="aligncenter size-full"><img width="920" height="613" src="https://phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8.jpg" alt="" class="wp-image-18657" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8.jpg 920w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8-300x200.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8-768x512.jpg 768w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8-441x294.jpg 441w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8-600x400.jpg 600w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8-150x100.jpg 150w" sizes="(max-width: 920px) 100vw, 920px" /><figcaption>Tai nghe không dây Bluetooth</figcaption></figure></div>
<p>Bây giờ, việc sử dụng tai nghe không dây là một điều cần thiết vì chúng rất linh hoạt và dễ nghe. Người nhận của bạn sẽ cảm ơn bạn vì bất kỳ ai cũng có thể sử dụng vật phẩm này tại văn phòng, trong cuộc họp, tại phòng tập thể dục để nghe nhạc hoặc podcast hoặc thậm chí khi họ chỉ muốn thư giãn.</p>
<ul><li>Tai Nghe Nhét Tai In-Ear Bluetooth TWS 5.0 Jacqueline APP (cực xịn): <strong><em><a href="https://phukiendienthoaigiare.com/product/tai-nghe-nhet-tai-in-ear-bluetooth-tws-5-0-jacqueline-app-mien-phi-in-logo-doanh-nghiep/" target="_blank" rel="noreferrer noopener">XEM THÊM</a></em></strong></li><li>Tai Nghe Không Dây TWS EF006 Phong Cách Retro: <strong><em><a href="https://phukiendienthoaigiare.com/product/tai-nghe-khong-day-tws-ef006-phong-cach-retro/" target="_blank" rel="noreferrer noopener">XEM THÊM</a></em></strong></li><li>Tai Nghe Bluetooh 5.0 Âm Thanh 6D TWS08: <em><strong><a href="https://phukiendienthoaigiare.com/product/tai-nghe-bluetooh-5-0-am-thanh-6d-tws08/" target="_blank" rel="noreferrer noopener">XEM THÊM</a></strong></em></li></ul>
<p><a href="https://phukiendienthoaigiare.com/product-category/tai-nghe-nhac/" target="_blank" rel="noreferrer noopener">Tìm hiểu thêm</a></p>
<h3 id="h-dồng-hồ-dể-ban-tich-hợp-sạc-khong-day">Đồng hồ để bàn tích hợp sạc không dây</h3>
<p>Đồng hồ để bàn sạc không dây cực kỳ độc đáo và tiện ích. Bạn có thể vừa kiểm tra thời gian vừa có thể sạc điện thoại mà không cần dây cáp rắc rối. Một thiết bị cực kỳ tiện ích tích hợp 2 trong 1.</p>
<div class="wp-block-image"><figure class="aligncenter size-full"><img width="600" height="600" src="https://phukiendienthoaigiare.com/wp-content/uploads/2022/05/Sac-Khong-Day-15W-Kiem-Dong-Ho-Bao-Thuc-WCT002.jpg" alt="" class="wp-image-18718" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2022/05/Sac-Khong-Day-15W-Kiem-Dong-Ho-Bao-Thuc-WCT002.jpg 600w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Sac-Khong-Day-15W-Kiem-Dong-Ho-Bao-Thuc-WCT002-300x300.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Sac-Khong-Day-15W-Kiem-Dong-Ho-Bao-Thuc-WCT002-150x150.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Sac-Khong-Day-15W-Kiem-Dong-Ho-Bao-Thuc-WCT002-441x441.jpg 441w" sizes="(max-width: 600px) 100vw, 600px" /><figcaption>Quà tặng doanh nghiệp đồng hồ để bàn tích hợp sạc không dây</figcaption></figure></div>
<p>Bạn có thể giữ nó ngay trên bàn làm việc hoặc để ở Tab đầu giường…</p>
<ul><li>Sạc Không Dây 15W Kiêm Đồng Hồ Báo Thức WCT002: <em><strong><a href="https://phukiendienthoaigiare.com/product/sac-khong-day-15w-kiem-dong-ho-bao-thuc-qua-tang-in-logo/" target="_blank" rel="noreferrer noopener">XEM THÊM</a></strong></em></li><li>Đồng Hồ Báo Thức Kiêm Sạc Không Dây 15W WCT001: <em><strong><a href="https://phukiendienthoaigiare.com/product/dong-ho-bao-thuc-kiem-sac-khong-day-15w-in-logo-theo-yeu-cau/" target="_blank" rel="noreferrer noopener">XEM THÊM</a></strong></em></li></ul>
<h3 id="h-sạc-khong-day">Sạc không dây</h3>
<p>Đây được coi là món quà tặng doanh nghiệp đối tác phù hợp với bất kỳ ai. Từ chủ doanh nghiệp nhỏ đến đại lý…</p>
<div class="wp-block-image"><figure class="aligncenter size-full"><img width="800" height="800" src="https://phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm.jpg" alt="đế sạc không dây đa năng chuẩn qi sạc nhanh 10w quà tặng đối tác in logo doanh nghiệp" class="wp-image-15931" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm.jpg 800w, //phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm-300x300.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm-150x150.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm-768x768.jpg 768w, //phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm-441x441.jpg 441w, //phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm-600x600.jpg 600w" sizes="(max-width: 800px) 100vw, 800px" /><figcaption>Đế sạc không dây tiện ích</figcaption></figure></div>
<p>Các lợi ích của sạc không dây bao gồm:</p>
<ul><li>Đó là một phương pháp sạc điện thoại an toàn</li><li>Nó làm giảm áp lực lên cổng sạc điện thoại của bạn</li><li>Sạc không dây đang được lắp đặt ở các vị trí khác nhau, cho phép bạn sạc điện thoại ngay cả khi hết năng lượng và không có cáp.</li></ul>
<p><strong><strong><a href="https://phukiendienthoaigiare.com/product-category/sac-khong-day/" target="_blank" rel="noreferrer noopener">Tìm hiểu thêm</a></strong></strong></p>
<h2 id="h-dặt-mua-qua-tặng-dối-tac-gia-rẻ-miễn-phi-in-logo-thương-hiệu">Đặt mua quà tặng đối tác giá rẻ – miễn phí in logo thương hiệu</h2>
<p>Bạn cảm thấy hứng thú với các tệp quà tặng doanh nghiệp đối tác ở trên và muốn tìm nơi để đặt mua? Một gợi ý cực kỳ tuyệt vời để bạn tiết kiệm chi phí và sở hữu được những món quà mang cá tính riêng của thương hiệu đó là đặt mua tại Phụ Kiện Điện Thoại Giá Rẻ</p>
<p>Chúng tôi có rất nhiều dòng sản phẩm quà tặng công nghệ hữu ích và phổ biến hiện nay. Bạn sẽ không thể không hài lòng khi kiểm duyệt sản phẩm và xem bảng báo giá hấp dẫn khi đặt theo số lượng.</p>
<p>Hiện tại, kho quà tặng doanh nghiệp đối tác của Phụ Kiện Điện Thoại Giá Rẻ đang cập nhật nhiều mẫu sản phẩm cực mới và cực hot theo xu hướng. Hãy đặt mua ngay để mang đến những bộ quà tặng hấp dẫn và khác biệt nhé!</p>
<p>The post <a rel="nofollow" href="https://phukiendienthoaigiare.com/7-y-tuong-qua-tang-doanh-nghiep-doi-tac-hien-dai/">7 Ý Tưởng Quà Tặng Doanh Nghiệp Đối Tác Hiện Đại</a> appeared first on <a rel="nofollow" href="https://phukiendienthoaigiare.com">Phụ kiện điện thoại</a>.</p> | 1.0 | 7 Ý Tưởng Quà Tặng Doanh Nghiệp Đối Tác Hiện Đại - <p>Gốc rễ của công ty phát triển nhờ sự thống nhất và sự thống nhất đó bắt đầu từ các đối tác kinh doanh. Bất kể tỷ lệ sở hữu mà họ nắm giữ trong doanh nghiệp là bao nhiêu, làm việc cùng nhau và giữ cho mọi người hạnh phúc là mục tiêu cuối cùng. Duy trì mối quan hệ kinh doanh lành mạnh với các đối tác kinh doanh của bạn là chìa khóa để đạt được thành công và những tầm cao lớn hơn. Một trong những cách tốt nhất để làm như vậy là gửi quà tặng doanh nghiệp đối tác kinh doanh cho dù họ ở đâu.</p>
<p>Để giúp bạn tìm được những món quà tặng doanh nghiệp tốt nhất, chúng tôi đã liệt kê một số món quà tặng doanh nghiệp sẽ hoàn hảo để giới thiệu cho các đối tác kinh doanh của bạn trong những dịp khác nhau.</p>
<h2 id="h-mẹo-chọn-qua-tặng-dối-tac-giup-doanh-nghiệp-gắn-kết">Mẹo chọn quà tặng đối tác giúp doanh nghiệp gắn kết</h2>
<p>Các mối quan hệ có thể được củng cố bằng cách gửi quà tặng. Tuy nhiên, có thể khó khăn để chọn món quà phù hợp với từng đối tác của bạn.</p>
<div class="wp-block-image"><figure class="aligncenter size-large"><img width="1024" height="684" src="https://phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-1024x684.jpg" alt="" class="wp-image-19207" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-1024x684.jpg 1024w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-300x200.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-768x513.jpg 768w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-990x661.jpg 990w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-441x294.jpg 441w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-600x401.jpg 600w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai-150x100.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai.jpg 1200w" sizes="(max-width: 1024px) 100vw, 1024px" /><figcaption>Quà tặng đối tác – nền tảng phát triển doanh nghiệp</figcaption></figure></div>
<p>Bạn muốn đảm bảo rằng món quà bạn chọn được xem là hữu ích và có thể áp dụng cho sứ mệnh của doanh nghiệp?</p>
<p>Hãy xem các mẹo của chúng tôi để giúp hành trình chọn quà của bạn dễ dàng hơn rất nhiều.</p>
<h3 id="h-mẹo-số-1-cung-cấp-một-mon-qua-thực-sự-hữu-ich">Mẹo số 1: Cung cấp một món quà thực sự hữu ích</h3>
<p>Lựa chọn quà tặng hữu ích cho cuộc sống sẽ giúp món quà của bạn trở thành cách tinh tế nhất để gắn kết mối quan hệ.</p>
<p>Ví dụ: hãy xem xét cung cấp một chiếc tai nghe Bluetooth để có thể dùng nghe điện thoại khi lái xe… Hoặc một chiếc loa nghe nhạc mini nhỏ gọn để mang theo khi đi du lịch, picnic…</p>
<h3 id="h-mẹo-số-2-tặng-qua-ca-nhan-hoa">Mẹo số 2: Tặng quà cá nhân hóa</h3>
<p>Quà tặng cá nhân hóa là một trong những loại quà tặng không thể quên được. Một món quà tùy chỉnh có in logo hoặc tên của công ty sẽ tạo nên một giá trị tuyệt vời.</p>
<div class="wp-block-image"><figure class="aligncenter size-full"><img width="1000" height="1000" src="https://phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1.jpg" alt="" class="wp-image-19208" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1.jpg 1000w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-300x300.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-150x150.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-768x768.jpg 768w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-900x900.jpg 900w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-990x990.jpg 990w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-441x441.jpg 441w, //phukiendienthoaigiare.com/wp-content/uploads/2022/07/7-Y-Tuong-Qua-Tang-Doanh-Nghiep-Doi-Tac-Hien-Dai1-600x600.jpg 600w" sizes="(max-width: 1000px) 100vw, 1000px" /><figcaption><em>Một món quà thể hiện cá tính luôn mang lại cảm giác ấn tượng tuyệt vời.</em></figcaption></figure></div>
<h3 id="h-mẹo-số-3-xem-xet-vấn-dề-chất-lượng">Mẹo số 3: Xem xét vấn đề chất lượng</h3>
<p>Bạn cũng nên suy nghĩ về chất lượng của món quà, độ bền sau thời gian sử dụng và lợi ích của nó. Hãy chọn món quà nào đó thật sự đáng giá và ý nghĩa phù hợp với người nhận.</p>
<h3 id="h-mẹo-số-4-it-hơn-chinh-la-nhiều-hơn">Mẹo số 4: Ít hơn chính là nhiều hơn</h3>
<ul><li>Hành động được đánh giá cao phải thật sự tế nhị, thẳng thắn, ân cần và trung thực.</li><li>Bạn không cần phải đi quá đà để thể hiện lòng biết ơn của mình.</li><li>Tặng quà và gửi thiệp chúc mừng là một chiến lược tiếp thị sẽ giúp bạn xây dựng sự công nhận thương hiệu của mình.</li></ul>
<h2 id="h-top-qua-tặng-y-nghia-danh-cho-dối-tac">Top quà tặng ý nghĩa dành cho đối tác</h2>
<p>Dưới đây là một số gợi ý về những món quà tặng doanh nghiệp đối tác chất lượng cao, giúp bạn xây dựng một chiến dịch tặng quà hoàn hảo. Thông qua bộ quà tặng, bạn sẽ dễ dàng kết nối và duy trì mối quan hệ với các đối tác của mình. Tạo tiền đề giúp doanh nghiệp phát triển bền vững.</p>
<h3 id="h-pin-sạc-dự-phong">Pin sạc dự phòng</h3>
<p>Chắc chắn là một trong những sản phẩm quà tặng doanh nghiệp đối tác hữu ích nằm trong top quà tặng ý nghĩa. Bộ sạc di động sẽ giúp các đối tác kinh doanh chủ động hơn trong các cuộc họp và khi đi du lịch. Đó là một rắc rối mà nhiều người phải đối mặt khi pin điện thoại hoặc máy tính xách tay bị cạn kiệt và một số nội dung quan trọng đang chờ xử lý. Bộ sạc di động sẽ rất hữu ích trong những lúc như vậy.</p>
<div class="wp-block-image"><figure class="aligncenter size-full"><img width="600" height="600" src="https://phukiendienthoaigiare.com/wp-content/uploads/2022/06/Pin-Sac-Du-Phong-5000mAh-PB0504-1.jpg" alt="" class="wp-image-18754" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2022/06/Pin-Sac-Du-Phong-5000mAh-PB0504-1.jpg 600w, //phukiendienthoaigiare.com/wp-content/uploads/2022/06/Pin-Sac-Du-Phong-5000mAh-PB0504-1-300x300.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2022/06/Pin-Sac-Du-Phong-5000mAh-PB0504-1-150x150.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2022/06/Pin-Sac-Du-Phong-5000mAh-PB0504-1-441x441.jpg 441w" sizes="(max-width: 600px) 100vw, 600px" /><figcaption>Quà tặng pin sạc dự phòng</figcaption></figure></div>
<p>Những dòng sạc di động được rất nhiều người ưa chuộng và lựa chọn làm quà tặng cho đối tác điển hình nhất là:</p>
<ul><li>Pin Sạc Dự Phòng 10000mAh Recci RPB-P09 Sạc Nhanh 22.5W: <em><strong><a href="https://phukiendienthoaigiare.com/product/pin-sac-du-phong-10000mah-recci-rpb-p09-sac-nhanh-22-5w-chuan-pd-qc3-0/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></strong></em></li><li>Pin Sạc Dự Phòng 5000mAh PB0504 – Logo Led Phát Sáng: <em><strong><a href="https://phukiendienthoaigiare.com/product/pin-sac-du-phong-5000mah-pb0504-logo-led-phat-sang-khi-su-dung/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></strong></em></li><li>Pin Sạc Dự Phòng Polymer 10000mAh Type C 18W PD QC3.0 Recci P01: <strong><em><a href="https://phukiendienthoaigiare.com/product/pin-sac-du-phong-polymer-10000mah-type-c-18w-pd-qc3-0-recci-p01/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></em></strong></li><li>Pin Sạc Dự Phòng 10000 mAh Recci N16: <strong><em><a href="https://phukiendienthoaigiare.com/product/pin-sac-du-phong-10000-mah-recci-n16-sac-nhieu-thiet-bi/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></em></strong></li></ul>
<p><a href="https://phukiendienthoaigiare.com/product-category/pin-sac-du-phong/" target="_blank" rel="noreferrer noopener">Tìm hiểu thêm</a></p>
<h3 id="h-theo-doi-sức-khỏe">Theo dõi sức khỏe</h3>
<p>Các đối tác kinh doanh của bạn luôn bận rộn với công việc và có thể không có đủ thời gian để kiểm tra sức khỏe của họ. Hãy mua cho họ một chiếc đồng hồ thông minh hoặc vòng đeo tay thông minh sẽ hiển thị tất cả dữ liệu thời gian thực vì nó đi kèm với tính năng theo dõi nhịp tim, theo dõi giấc ngủ, theo dõi số bước, … Ngoài ra, còn có nhiều tính năng khác như kết nối di động, trung tâm hiển thị tin nhắn, cuộc gọi…</p>
<div class="wp-block-image"><figure class="aligncenter size-large"><img width="1024" height="982" src="https://phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-1024x982.jpg" alt="" class="wp-image-12753" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-1024x982.jpg 1024w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-300x288.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-768x737.jpg 768w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-990x950.jpg 990w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-441x423.jpg 441w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-600x576.jpg 600w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19-150x144.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2021/11/Danh-Gia-Dong-Ho-Thong-Minh-Theo-Doi-Suc-Khoe-V19-19.jpg 1351w" sizes="(max-width: 1024px) 100vw, 1024px" /><figcaption>Quà tặng đồng hồ thông minh</figcaption></figure></div>
<ul><li>Đồng Hồ Thông Minh V19 đo nhịp tim đo huyết áp đo spo2: <em><strong><a href="https://phukiendienthoaigiare.com/product/dong-ho-thong-minh-v19-huyet-ap-nhip-tim-spo2/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></strong></em></li><li>Đồng Hồ Thông Minh T19 đo nhịp tim đo huyết áp đo spo2: <em><strong><a href="https://phukiendienthoaigiare.com/product/dong-ho-thong-minh-t19-huyet-ap-nhip-tim-spo2/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></strong></em></li><li>Vòng Đeo Tay Thông Minh V20: <strong><em><a href="https://phukiendienthoaigiare.com/product/vong-deo-tay-thong-minh-v20/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></em></strong></li><li>Vòng Đeo Tay Thông Minh V18: <strong><em><a href="https://phukiendienthoaigiare.com/product/vong-deo-tay-thong-minh-v18/" target="_blank" rel="noreferrer noopener">XEM GIÁ</a></em></strong></li></ul>
<p><a href="https://phukiendienthoaigiare.com/product-category/theo-doi-suc-khoe/" target="_blank" rel="noreferrer noopener">Tìm hiểu thêm</a></p>
<h3 id="h-tai-nghe-khong-day">Tai nghe không dây</h3>
<p>Tai nghe không dây cũng là một thành viên của nhóm quà tặng hữu ích dành cho đối tác. Mặc dù tai nghe không dây đã có từ lâu, nhưng sự phổ biến của chúng đã tăng vọt cùng với sự ra đời của điện thoại thông minh.</p>
<p>Những tiện ích này cho phép chúng truy cập nhiều hơn vào phương tiện khi đang di chuyển, vì vậy tạo ra những món quà tuyệt vời.</p>
<div class="wp-block-image"><figure class="aligncenter size-full"><img width="920" height="613" src="https://phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8.jpg" alt="" class="wp-image-18657" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8.jpg 920w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8-300x200.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8-768x512.jpg 768w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8-441x294.jpg 441w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8-600x400.jpg 600w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Tai-Nghe-Airpods-Pro-Huilian-A8-150x100.jpg 150w" sizes="(max-width: 920px) 100vw, 920px" /><figcaption>Tai nghe không dây Bluetooth</figcaption></figure></div>
<p>Bây giờ, việc sử dụng tai nghe không dây là một điều cần thiết vì chúng rất linh hoạt và dễ nghe. Người nhận của bạn sẽ cảm ơn bạn vì bất kỳ ai cũng có thể sử dụng vật phẩm này tại văn phòng, trong cuộc họp, tại phòng tập thể dục để nghe nhạc hoặc podcast hoặc thậm chí khi họ chỉ muốn thư giãn.</p>
<ul><li>Tai Nghe Nhét Tai In-Ear Bluetooth TWS 5.0 Jacqueline APP (cực xịn): <strong><em><a href="https://phukiendienthoaigiare.com/product/tai-nghe-nhet-tai-in-ear-bluetooth-tws-5-0-jacqueline-app-mien-phi-in-logo-doanh-nghiep/" target="_blank" rel="noreferrer noopener">XEM THÊM</a></em></strong></li><li>Tai Nghe Không Dây TWS EF006 Phong Cách Retro: <strong><em><a href="https://phukiendienthoaigiare.com/product/tai-nghe-khong-day-tws-ef006-phong-cach-retro/" target="_blank" rel="noreferrer noopener">XEM THÊM</a></em></strong></li><li>Tai Nghe Bluetooh 5.0 Âm Thanh 6D TWS08: <em><strong><a href="https://phukiendienthoaigiare.com/product/tai-nghe-bluetooh-5-0-am-thanh-6d-tws08/" target="_blank" rel="noreferrer noopener">XEM THÊM</a></strong></em></li></ul>
<p><a href="https://phukiendienthoaigiare.com/product-category/tai-nghe-nhac/" target="_blank" rel="noreferrer noopener">Tìm hiểu thêm</a></p>
<h3 id="h-dồng-hồ-dể-ban-tich-hợp-sạc-khong-day">Đồng hồ để bàn tích hợp sạc không dây</h3>
<p>Đồng hồ để bàn sạc không dây cực kỳ độc đáo và tiện ích. Bạn có thể vừa kiểm tra thời gian vừa có thể sạc điện thoại mà không cần dây cáp rắc rối. Một thiết bị cực kỳ tiện ích tích hợp 2 trong 1.</p>
<div class="wp-block-image"><figure class="aligncenter size-full"><img width="600" height="600" src="https://phukiendienthoaigiare.com/wp-content/uploads/2022/05/Sac-Khong-Day-15W-Kiem-Dong-Ho-Bao-Thuc-WCT002.jpg" alt="" class="wp-image-18718" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2022/05/Sac-Khong-Day-15W-Kiem-Dong-Ho-Bao-Thuc-WCT002.jpg 600w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Sac-Khong-Day-15W-Kiem-Dong-Ho-Bao-Thuc-WCT002-300x300.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Sac-Khong-Day-15W-Kiem-Dong-Ho-Bao-Thuc-WCT002-150x150.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2022/05/Sac-Khong-Day-15W-Kiem-Dong-Ho-Bao-Thuc-WCT002-441x441.jpg 441w" sizes="(max-width: 600px) 100vw, 600px" /><figcaption>Quà tặng doanh nghiệp đồng hồ để bàn tích hợp sạc không dây</figcaption></figure></div>
<p>Bạn có thể giữ nó ngay trên bàn làm việc hoặc để ở Tab đầu giường…</p>
<ul><li>Sạc Không Dây 15W Kiêm Đồng Hồ Báo Thức WCT002: <em><strong><a href="https://phukiendienthoaigiare.com/product/sac-khong-day-15w-kiem-dong-ho-bao-thuc-qua-tang-in-logo/" target="_blank" rel="noreferrer noopener">XEM THÊM</a></strong></em></li><li>Đồng Hồ Báo Thức Kiêm Sạc Không Dây 15W WCT001: <em><strong><a href="https://phukiendienthoaigiare.com/product/dong-ho-bao-thuc-kiem-sac-khong-day-15w-in-logo-theo-yeu-cau/" target="_blank" rel="noreferrer noopener">XEM THÊM</a></strong></em></li></ul>
<h3 id="h-sạc-khong-day">Sạc không dây</h3>
<p>Đây được coi là món quà tặng doanh nghiệp đối tác phù hợp với bất kỳ ai. Từ chủ doanh nghiệp nhỏ đến đại lý…</p>
<div class="wp-block-image"><figure class="aligncenter size-full"><img width="800" height="800" src="https://phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm.jpg" alt="đế sạc không dây đa năng chuẩn qi sạc nhanh 10w quà tặng đối tác in logo doanh nghiệp" class="wp-image-15931" srcset="//phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm.jpg 800w, //phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm-300x300.jpg 300w, //phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm-150x150.jpg 150w, //phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm-768x768.jpg 768w, //phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm-441x441.jpg 441w, //phukiendienthoaigiare.com/wp-content/uploads/2021/12/de-sac-nhanh-khong-day-tuong-thich-nhieu-thiet-bi-in-logo-doanh-nghiep-tphcm-600x600.jpg 600w" sizes="(max-width: 800px) 100vw, 800px" /><figcaption>Đế sạc không dây tiện ích</figcaption></figure></div>
<p>Các lợi ích của sạc không dây bao gồm:</p>
<ul><li>Đó là một phương pháp sạc điện thoại an toàn</li><li>Nó làm giảm áp lực lên cổng sạc điện thoại của bạn</li><li>Sạc không dây đang được lắp đặt ở các vị trí khác nhau, cho phép bạn sạc điện thoại ngay cả khi hết năng lượng và không có cáp.</li></ul>
<p><strong><strong><a href="https://phukiendienthoaigiare.com/product-category/sac-khong-day/" target="_blank" rel="noreferrer noopener">Tìm hiểu thêm</a></strong></strong></p>
<h2 id="h-dặt-mua-qua-tặng-dối-tac-gia-rẻ-miễn-phi-in-logo-thương-hiệu">Đặt mua quà tặng đối tác giá rẻ – miễn phí in logo thương hiệu</h2>
<p>Bạn cảm thấy hứng thú với các tệp quà tặng doanh nghiệp đối tác ở trên và muốn tìm nơi để đặt mua? Một gợi ý cực kỳ tuyệt vời để bạn tiết kiệm chi phí và sở hữu được những món quà mang cá tính riêng của thương hiệu đó là đặt mua tại Phụ Kiện Điện Thoại Giá Rẻ</p>
<p>Chúng tôi có rất nhiều dòng sản phẩm quà tặng công nghệ hữu ích và phổ biến hiện nay. Bạn sẽ không thể không hài lòng khi kiểm duyệt sản phẩm và xem bảng báo giá hấp dẫn khi đặt theo số lượng.</p>
<p>Hiện tại, kho quà tặng doanh nghiệp đối tác của Phụ Kiện Điện Thoại Giá Rẻ đang cập nhật nhiều mẫu sản phẩm cực mới và cực hot theo xu hướng. Hãy đặt mua ngay để mang đến những bộ quà tặng hấp dẫn và khác biệt nhé!</p>
<p>The post <a rel="nofollow" href="https://phukiendienthoaigiare.com/7-y-tuong-qua-tang-doanh-nghiep-doi-tac-hien-dai/">7 Ý Tưởng Quà Tặng Doanh Nghiệp Đối Tác Hiện Đại</a> appeared first on <a rel="nofollow" href="https://phukiendienthoaigiare.com">Phụ kiện điện thoại</a>.</p> | non_priority | ý tưởng quà tặng doanh nghiệp đối tác hiện đại gốc rễ của công ty phát triển nhờ sự thống nhất và sự thống nhất đó bắt đầu từ các đối tác kinh doanh bất kể tỷ lệ sở hữu mà họ nắm giữ trong doanh nghiệp là bao nhiêu làm việc cùng nhau và giữ cho mọi người hạnh phúc là mục tiêu cuối cùng duy trì mối quan hệ kinh doanh lành mạnh với các đối tác kinh doanh của bạn là chìa khóa để đạt được thành công và những tầm cao lớn hơn một trong những cách tốt nhất để làm như vậy là gửi quà tặng doanh nghiệp đối tác kinh doanh cho dù họ ở đâu để giúp bạn tìm được những món quà tặng doanh nghiệp tốt nhất chúng tôi đã liệt kê một số món quà tặng doanh nghiệp sẽ hoàn hảo để giới thiệu cho các đối tác kinh doanh của bạn trong những dịp khác nhau mẹo chọn quà tặng đối tác giúp doanh nghiệp gắn kết các mối quan hệ có thể được củng cố bằng cách gửi quà tặng tuy nhiên có thể khó khăn để chọn món quà phù hợp với từng đối tác của bạn quà tặng đối tác – nền tảng phát triển doanh nghiệp bạn muốn đảm bảo rằng món quà bạn chọn được xem là hữu ích và có thể áp dụng cho sứ mệnh của doanh nghiệp hãy xem các mẹo của chúng tôi để giúp hành trình chọn quà của bạn dễ dàng hơn rất nhiều mẹo số cung cấp một món quà thực sự hữu ích lựa chọn quà tặng hữu ích cho cuộc sống sẽ giúp món quà của bạn trở thành cách tinh tế nhất để gắn kết mối quan hệ ví dụ hãy xem xét cung cấp một chiếc tai nghe bluetooth để có thể dùng nghe điện thoại khi lái xe… hoặc một chiếc loa nghe nhạc mini nhỏ gọn để mang theo khi đi du lịch picnic… mẹo số tặng quà cá nhân hóa quà tặng cá nhân hóa là một trong những loại quà tặng không thể quên được một món quà tùy chỉnh có in logo hoặc tên của công ty sẽ tạo nên một giá trị tuyệt vời một món quà thể hiện cá tính luôn mang lại cảm giác ấn tượng tuyệt vời mẹo số xem xét vấn đề chất lượng bạn cũng nên suy nghĩ về chất lượng của món quà độ bền sau thời gian sử dụng và lợi ích của nó hãy chọn món quà nào đó thật sự đáng giá và ý nghĩa phù hợp với người nhận mẹo số ít hơn chính là nhiều hơn hành động được đánh giá cao phải thật sự tế nhị thẳng thắn ân cần và trung thực bạn không cần phải đi quá đà để thể hiện lòng biết ơn của mình tặng quà và gửi thiệp chúc mừng là một chiến lược tiếp thị sẽ giúp bạn xây dựng sự công nhận thương hiệu của mình top quà tặng ý nghĩa dành cho đối tác dưới đây là một số gợi ý về những món quà tặng doanh nghiệp đối tác chất lượng cao giúp bạn xây dựng một chiến dịch tặng quà hoàn hảo thông qua bộ quà tặng bạn sẽ dễ dàng kết nối và duy trì mối quan hệ với các đối tác của mình tạo tiền đề giúp doanh nghiệp phát triển bền vững pin sạc dự phòng chắc chắn là một trong những sản phẩm quà tặng doanh nghiệp đối tác hữu ích nằm trong top quà tặng ý nghĩa bộ sạc di động sẽ giúp các đối tác kinh doanh chủ động hơn trong các cuộc họp và khi đi du lịch đó là một rắc rối mà nhiều người phải đối mặt khi pin điện thoại hoặc máy tính xách tay bị cạn kiệt và một số nội dung quan trọng đang chờ xử lý bộ sạc di động sẽ rất hữu ích trong những lúc như vậy quà tặng pin sạc dự phòng những dòng sạc di động được rất nhiều người ưa chuộng và lựa chọn làm quà tặng cho đối tác điển hình nhất là pin sạc dự phòng recci rpb sạc nhanh xem giá pin sạc dự phòng – logo led phát sáng xem giá pin sạc dự phòng polymer type c pd recci xem giá pin sạc dự phòng mah recci xem giá tìm hiểu thêm theo dõi sức khỏe các đối tác kinh doanh của bạn luôn bận rộn với công việc và có thể không có đủ thời gian để kiểm tra sức khỏe của họ hãy mua cho họ một chiếc đồng hồ thông minh hoặc vòng đeo tay thông minh sẽ hiển thị tất cả dữ liệu thời gian thực vì nó đi kèm với tính năng theo dõi nhịp tim theo dõi giấc ngủ theo dõi số bước … ngoài ra còn có nhiều tính năng khác như kết nối di động trung tâm hiển thị tin nhắn cuộc gọi… quà tặng đồng hồ thông minh đồng hồ thông minh đo nhịp tim đo huyết áp đo xem giá đồng hồ thông minh đo nhịp tim đo huyết áp đo xem giá vòng đeo tay thông minh xem giá vòng đeo tay thông minh xem giá tìm hiểu thêm tai nghe không dây tai nghe không dây cũng là một thành viên của nhóm quà tặng hữu ích dành cho đối tác mặc dù tai nghe không dây đã có từ lâu nhưng sự phổ biến của chúng đã tăng vọt cùng với sự ra đời của điện thoại thông minh những tiện ích này cho phép chúng truy cập nhiều hơn vào phương tiện khi đang di chuyển vì vậy tạo ra những món quà tuyệt vời tai nghe không dây bluetooth bây giờ việc sử dụng tai nghe không dây là một điều cần thiết vì chúng rất linh hoạt và dễ nghe người nhận của bạn sẽ cảm ơn bạn vì bất kỳ ai cũng có thể sử dụng vật phẩm này tại văn phòng trong cuộc họp tại phòng tập thể dục để nghe nhạc hoặc podcast hoặc thậm chí khi họ chỉ muốn thư giãn tai nghe nhét tai in ear bluetooth tws jacqueline app cực xịn xem thêm tai nghe không dây tws phong cách retro xem thêm tai nghe bluetooh âm thanh xem thêm tìm hiểu thêm đồng hồ để bàn tích hợp sạc không dây đồng hồ để bàn sạc không dây cực kỳ độc đáo và tiện ích bạn có thể vừa kiểm tra thời gian vừa có thể sạc điện thoại mà không cần dây cáp rắc rối một thiết bị cực kỳ tiện ích tích hợp trong quà tặng doanh nghiệp đồng hồ để bàn tích hợp sạc không dây bạn có thể giữ nó ngay trên bàn làm việc hoặc để ở tab đầu giường… sạc không dây kiêm đồng hồ báo thức xem thêm đồng hồ báo thức kiêm sạc không dây xem thêm sạc không dây đây được coi là món quà tặng doanh nghiệp đối tác phù hợp với bất kỳ ai từ chủ doanh nghiệp nhỏ đến đại lý… đế sạc không dây tiện ích các lợi ích của sạc không dây bao gồm đó là một phương pháp sạc điện thoại an toàn nó làm giảm áp lực lên cổng sạc điện thoại của bạn sạc không dây đang được lắp đặt ở các vị trí khác nhau cho phép bạn sạc điện thoại ngay cả khi hết năng lượng và không có cáp tìm hiểu thêm đặt mua quà tặng đối tác giá rẻ – miễn phí in logo thương hiệu bạn cảm thấy hứng thú với các tệp quà tặng doanh nghiệp đối tác ở trên và muốn tìm nơi để đặt mua một gợi ý cực kỳ tuyệt vời để bạn tiết kiệm chi phí và sở hữu được những món quà mang cá tính riêng của thương hiệu đó là đặt mua tại phụ kiện điện thoại giá rẻ chúng tôi có rất nhiều dòng sản phẩm quà tặng công nghệ hữu ích và phổ biến hiện nay bạn sẽ không thể không hài lòng khi kiểm duyệt sản phẩm và xem bảng báo giá hấp dẫn khi đặt theo số lượng hiện tại kho quà tặng doanh nghiệp đối tác của phụ kiện điện thoại giá rẻ đang cập nhật nhiều mẫu sản phẩm cực mới và cực hot theo xu hướng hãy đặt mua ngay để mang đến những bộ quà tặng hấp dẫn và khác biệt nhé the post appeared first on | 0 |
3,508 | 13,885,265,418 | IssuesEvent | 2020-10-18 19:17:22 | GoodDollar/GoodDAPP | https://api.github.com/repos/GoodDollar/GoodDAPP | closed | [BUG] Redirect to the https://support.gooddollar.org/?transitioned=1 page in cypress-tests by clicking on the "Help & Feedback" menu item | automation | preconditions:
reproduces in a cypress environment.
"userAgent": "Mozilla/5.0 (X11; Linux x86_64; Cypress) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/78.0.3904.108 Safari/537.36"
steps:
go to https://gooddev.netlify.app/
login with exist acc
click on the "Help & Feedback" menu item
pay attention to the opened page
video: https://www.screencast.com/t/ln5lJR7dmB
 | 1.0 | [BUG] Redirect to the https://support.gooddollar.org/?transitioned=1 page in cypress-tests by clicking on the "Help & Feedback" menu item - preconditions:
reproduces in a cypress environment.
"userAgent": "Mozilla/5.0 (X11; Linux x86_64; Cypress) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/78.0.3904.108 Safari/537.36"
steps:
go to https://gooddev.netlify.app/
login with exist acc
click on the "Help & Feedback" menu item
pay attention to the opened page
video: https://www.screencast.com/t/ln5lJR7dmB
 | non_priority | redirect to the page in cypress tests by clicking on the help feedback menu item preconditions reproduces in a cypress environment useragent mozilla linux cypress applewebkit khtml like gecko chrome safari steps go to login with exist acc click on the help feedback menu item pay attention to the opened page video | 0 |
337,479 | 30,248,325,996 | IssuesEvent | 2023-07-06 18:18:43 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | opened | Fix jax_lax_operators.test_jax_shift_right_logical | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5478319447"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5477523919"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5473310115"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5474480955"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix jax_lax_operators.test_jax_shift_right_logical - | | |
|---|---|
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5478319447"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5477523919"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5473310115"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5474480955"><img src=https://img.shields.io/badge/-success-success></a>
| non_priority | fix jax lax operators test jax shift right logical paddle a href src numpy a href src jax a href src tensorflow a href src | 0 |
84,186 | 16,468,714,010 | IssuesEvent | 2021-05-23 00:42:29 | DIT112-V21/group-17 | https://api.github.com/repos/DIT112-V21/group-17 | closed | Check messages (mailman) | Android Design Java code Sprint4 | As a mailman, I want to be able to check messages that I receiived from the receivers so I know when they confirm a pickup. | 1.0 | Check messages (mailman) - As a mailman, I want to be able to check messages that I receiived from the receivers so I know when they confirm a pickup. | non_priority | check messages mailman as a mailman i want to be able to check messages that i receiived from the receivers so i know when they confirm a pickup | 0 |
266,218 | 23,226,663,925 | IssuesEvent | 2022-08-03 01:24:15 | MPMG-DCC-UFMG/F01 | https://api.github.com/repos/MPMG-DCC-UFMG/F01 | closed | Teste de generalizacao para a tag Servidores - Relatório mensal da despesa com pessoal - Mata Verde | generalization test development template-Síntese tecnologia informatica subtag-Relatórios Despesas com Pessoal tag-Servidores | DoD: Realizar o teste de Generalização do validador da tag Servidores - Relatório mensal da despesa com pessoal para o Município de Mata Verde. | 1.0 | Teste de generalizacao para a tag Servidores - Relatório mensal da despesa com pessoal - Mata Verde - DoD: Realizar o teste de Generalização do validador da tag Servidores - Relatório mensal da despesa com pessoal para o Município de Mata Verde. | non_priority | teste de generalizacao para a tag servidores relatório mensal da despesa com pessoal mata verde dod realizar o teste de generalização do validador da tag servidores relatório mensal da despesa com pessoal para o município de mata verde | 0 |
270,925 | 20,614,958,299 | IssuesEvent | 2022-03-07 12:20:01 | kubernetes-sigs/cluster-api | https://api.github.com/repos/kubernetes-sigs/cluster-api | closed | Document the release process for v1beta1 | kind/documentation kind/feature lifecycle/rotten |
**User Story**
As a developer I would like to understand all the actions that are taken in a major version change for Cluster API.
**Detailed Description**
While we're moving from v1alpha4 to v1beta1 we should do our best to document all the work items that need to be done, and the decisions that need to be made in making such a release. It might be a good idea to use a specific label (area/release is there and looks underused) to mark all of the work items. This can then be consolidated into a fuller release guide down the line.
The current release guide at https://github.com/kubernetes-sigs/cluster-api/blob/master/docs/developer/releasing.md is only really concerned with Github and docker image releases. There are a number of other pieces of work documented in the book https://cluster-api.sigs.k8s.io/contributing?search=release
It would be great to end up with a single higher-level how to release a cluster API release doc after the v1beta1 process is complete.
/kind documentation
/kind feature
| 1.0 | Document the release process for v1beta1 -
**User Story**
As a developer I would like to understand all the actions that are taken in a major version change for Cluster API.
**Detailed Description**
While we're moving from v1alpha4 to v1beta1 we should do our best to document all the work items that need to be done, and the decisions that need to be made in making such a release. It might be a good idea to use a specific label (area/release is there and looks underused) to mark all of the work items. This can then be consolidated into a fuller release guide down the line.
The current release guide at https://github.com/kubernetes-sigs/cluster-api/blob/master/docs/developer/releasing.md is only really concerned with Github and docker image releases. There are a number of other pieces of work documented in the book https://cluster-api.sigs.k8s.io/contributing?search=release
It would be great to end up with a single higher-level how to release a cluster API release doc after the v1beta1 process is complete.
/kind documentation
/kind feature
| non_priority | document the release process for user story as a developer i would like to understand all the actions that are taken in a major version change for cluster api detailed description while we re moving from to we should do our best to document all the work items that need to be done and the decisions that need to be made in making such a release it might be a good idea to use a specific label area release is there and looks underused to mark all of the work items this can then be consolidated into a fuller release guide down the line the current release guide at is only really concerned with github and docker image releases there are a number of other pieces of work documented in the book it would be great to end up with a single higher level how to release a cluster api release doc after the process is complete kind documentation kind feature | 0 |
40,482 | 10,019,212,943 | IssuesEvent | 2019-07-16 09:35:28 | contao/contao | https://api.github.com/repos/contao/contao | closed | Punycode in backend meta title | defect | **Affected version(s)**
Contao 4.7.6
**Description**
Die Meta-Title im Backend zeigen ja nun die Domain an. Es wäre schön, wenn hier bei Umlaut-Domains nicht der Punycode angezeigt werden würde, also "köstlichfein.de" stat "xn--kstlichfein-rfb.de".
**How to reproduce**
Backend unter einer Umlaut-Domain aufrufen. | 1.0 | Punycode in backend meta title - **Affected version(s)**
Contao 4.7.6
**Description**
Die Meta-Title im Backend zeigen ja nun die Domain an. Es wäre schön, wenn hier bei Umlaut-Domains nicht der Punycode angezeigt werden würde, also "köstlichfein.de" stat "xn--kstlichfein-rfb.de".
**How to reproduce**
Backend unter einer Umlaut-Domain aufrufen. | non_priority | punycode in backend meta title affected version s contao description die meta title im backend zeigen ja nun die domain an es wäre schön wenn hier bei umlaut domains nicht der punycode angezeigt werden würde also köstlichfein de stat xn kstlichfein rfb de how to reproduce backend unter einer umlaut domain aufrufen | 0 |
61,479 | 12,191,426,608 | IssuesEvent | 2020-04-29 11:06:50 | kwk/test-llvm-bz-import-5 | https://api.github.com/repos/kwk/test-llvm-bz-import-5 | closed | clang/llvm expands memcpy thus making the resulting code big | BZ-BUG-STATUS: RESOLVED BZ-RESOLUTION: FIXED dummy import from bugzilla libraries/Common Code Generator Code | This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=6623. | 2.0 | clang/llvm expands memcpy thus making the resulting code big - This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=6623. | non_priority | clang llvm expands memcpy thus making the resulting code big this issue was imported from bugzilla | 0 |
141,374 | 21,485,747,282 | IssuesEvent | 2022-04-26 23:06:40 | endojs/endo | https://api.github.com/repos/endojs/endo | closed | Divergence when bundling `yarn install --production` | bug design endo | I have checked that `dev` mode is disabled, but https://github.com/Agoric/agoric-sdk/tree/mfig-bundle-divergence/dev-vs-prod-bundle.sh reveals a difference between bundling in the two different `yarn install` situations.
TODO: More details
| 1.0 | Divergence when bundling `yarn install --production` - I have checked that `dev` mode is disabled, but https://github.com/Agoric/agoric-sdk/tree/mfig-bundle-divergence/dev-vs-prod-bundle.sh reveals a difference between bundling in the two different `yarn install` situations.
TODO: More details
| non_priority | divergence when bundling yarn install production i have checked that dev mode is disabled but reveals a difference between bundling in the two different yarn install situations todo more details | 0 |
315,308 | 23,550,812,802 | IssuesEvent | 2022-08-21 20:02:13 | FreshRSS/FreshRSS | https://api.github.com/repos/FreshRSS/FreshRSS | closed | Trying to get in touch regarding a security issue | Documentation :books: Security :shield: | Hi there,
I couldn't find a `SECURITY.md` in your repository and am not sure how to best contact you privately to disclose a security issue.
Can you add a `SECURITY.md` file with an e-mail to your repository, so that our system can send you the vulnerability details? GitHub suggests that a [security policy](https://docs.github.com/en/code-security/getting-started/adding-a-security-policy-to-your-repository) is the best way to make sure security issues are responsibly disclosed.
Once you've done that, you should receive an e-mail within the next hour with more info.
Thanks! (cc @huntr-helper) | 1.0 | Trying to get in touch regarding a security issue - Hi there,
I couldn't find a `SECURITY.md` in your repository and am not sure how to best contact you privately to disclose a security issue.
Can you add a `SECURITY.md` file with an e-mail to your repository, so that our system can send you the vulnerability details? GitHub suggests that a [security policy](https://docs.github.com/en/code-security/getting-started/adding-a-security-policy-to-your-repository) is the best way to make sure security issues are responsibly disclosed.
Once you've done that, you should receive an e-mail within the next hour with more info.
Thanks! (cc @huntr-helper) | non_priority | trying to get in touch regarding a security issue hi there i couldn t find a security md in your repository and am not sure how to best contact you privately to disclose a security issue can you add a security md file with an e mail to your repository so that our system can send you the vulnerability details github suggests that a is the best way to make sure security issues are responsibly disclosed once you ve done that you should receive an e mail within the next hour with more info thanks cc huntr helper | 0 |
1,819 | 4,402,263,561 | IssuesEvent | 2016-08-11 00:04:57 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | reopened | No error for array index passed by ref | Area-Compilers Bug New Language Feature - Ref Locals and Returns Resolution-Won't Fix Tenet-Compatibility | No error reported for `a[ref i]` below:
```
class C
{
static object F(object[] a, int i)
{
return a[ref i];
}
}
``` | True | No error for array index passed by ref - No error reported for `a[ref i]` below:
```
class C
{
static object F(object[] a, int i)
{
return a[ref i];
}
}
``` | non_priority | no error for array index passed by ref no error reported for a below class c static object f object a int i return a | 0 |
12,797 | 8,109,535,618 | IssuesEvent | 2018-08-14 07:56:02 | zaproxy/zaproxy | https://api.github.com/repos/zaproxy/zaproxy | closed | User-Agent changes from configured value | Usability bug | When using the ZAP gui I found that in certain circumstances the default user agent defined in tools-options-connection was not used. Instead an older user agent was used.
To reproduce, set value to 'Firefox 39.0 Win8.1 64-bit' and attack a URL.
Expected behaviour is that all pages will be attacked with the same user agent that has been set as above.
Request for alert "Content-Security-Policy (CSP) Header Not Set":
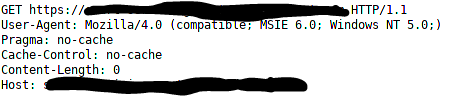
Response - note CSP is set. I believe the X-CSP header is set as a result of the IE6 user agent as it normally appears as CSP without the X:
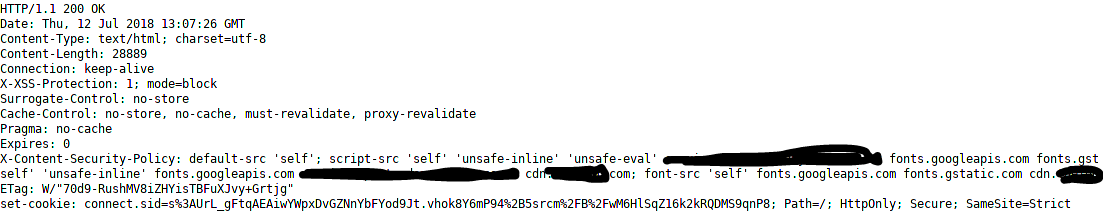
Request for alert "Timestamp Disclosure - Unix":

OWASP ZAP Version 2.7.0 on Linux (Kali) and Windows 10 64-bit
| True | User-Agent changes from configured value - When using the ZAP gui I found that in certain circumstances the default user agent defined in tools-options-connection was not used. Instead an older user agent was used.
To reproduce, set value to 'Firefox 39.0 Win8.1 64-bit' and attack a URL.
Expected behaviour is that all pages will be attacked with the same user agent that has been set as above.
Request for alert "Content-Security-Policy (CSP) Header Not Set":
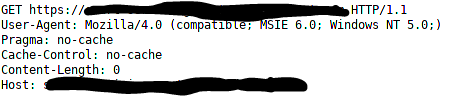
Response - note CSP is set. I believe the X-CSP header is set as a result of the IE6 user agent as it normally appears as CSP without the X:
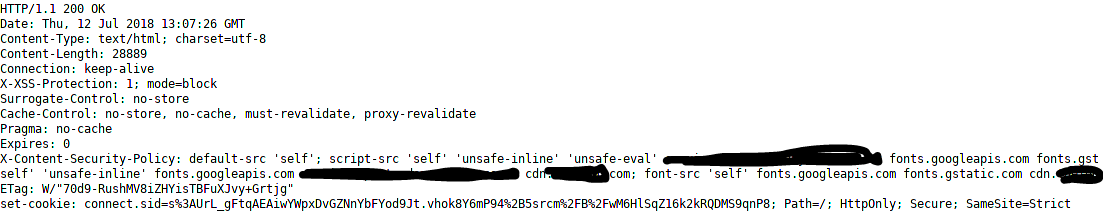
Request for alert "Timestamp Disclosure - Unix":

OWASP ZAP Version 2.7.0 on Linux (Kali) and Windows 10 64-bit
| non_priority | user agent changes from configured value when using the zap gui i found that in certain circumstances the default user agent defined in tools options connection was not used instead an older user agent was used to reproduce set value to firefox bit and attack a url expected behaviour is that all pages will be attacked with the same user agent that has been set as above request for alert content security policy csp header not set response note csp is set i believe the x csp header is set as a result of the user agent as it normally appears as csp without the x request for alert timestamp disclosure unix owasp zap version on linux kali and windows bit | 0 |
151,347 | 19,648,814,900 | IssuesEvent | 2022-01-10 02:36:48 | chiq2045/my-diary | https://api.github.com/repos/chiq2045/my-diary | opened | CVE-2022-0122 (Medium) detected in node-forge-0.9.0.tgz | security vulnerability | ## CVE-2022-0122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.9.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- webpack-dev-server-3.11.0.tgz (Root Library)
- selfsigned-1.10.7.tgz
- :x: **node-forge-0.9.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
forge is vulnerable to URL Redirection to Untrusted Site
<p>Publish Date: 2022-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0122>CVE-2022-0122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/41852c50-3c6d-4703-8c55-4db27164a4ae/">https://huntr.dev/bounties/41852c50-3c6d-4703-8c55-4db27164a4ae/</a></p>
<p>Release Date: 2022-01-06</p>
<p>Fix Resolution: forge - v1.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-0122 (Medium) detected in node-forge-0.9.0.tgz - ## CVE-2022-0122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.9.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- webpack-dev-server-3.11.0.tgz (Root Library)
- selfsigned-1.10.7.tgz
- :x: **node-forge-0.9.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
forge is vulnerable to URL Redirection to Untrusted Site
<p>Publish Date: 2022-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0122>CVE-2022-0122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/41852c50-3c6d-4703-8c55-4db27164a4ae/">https://huntr.dev/bounties/41852c50-3c6d-4703-8c55-4db27164a4ae/</a></p>
<p>Release Date: 2022-01-06</p>
<p>Fix Resolution: forge - v1.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node forge tgz cve medium severity vulnerability vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules node forge package json dependency hierarchy webpack dev server tgz root library selfsigned tgz x node forge tgz vulnerable library vulnerability details forge is vulnerable to url redirection to untrusted site publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution forge step up your open source security game with whitesource | 0 |
78,847 | 22,469,556,381 | IssuesEvent | 2022-06-22 06:50:21 | TortugaResearch/Chain | https://api.github.com/repos/TortugaResearch/Chain | closed | PostgreSQL GetTableApproximateCount returns -1 for empty tables | PostgreSQL Command Builders | If the table has never had any rows, GetTableApproximateCount will return -1 instead of 0. | 1.0 | PostgreSQL GetTableApproximateCount returns -1 for empty tables - If the table has never had any rows, GetTableApproximateCount will return -1 instead of 0. | non_priority | postgresql gettableapproximatecount returns for empty tables if the table has never had any rows gettableapproximatecount will return instead of | 0 |
289,525 | 21,785,841,832 | IssuesEvent | 2022-05-14 05:32:20 | renpy/renpy | https://api.github.com/repos/renpy/renpy | closed | unexpected behavior of after_load label and callbacks | documentation | ```py
default test1 = 0
default test2 = Test(10)
init python:
class Test():
def __init__(self, v=0):
self.v = v
def inc(self):
self.v += 1
def after_load():
global test1
test1 += 1
test2.inc()
config.after_load_callbacks.append(after_load)
label after_load:
$ test1 += 1
$ test2.inc()
return
label main_menu:
return
label start:
while True:
"[test1], [test2.v]"
```
a changed object within label or callback doesn't retain its value after rolling back prior the loading point. (clean 7.4.11.2266)
is this an undocumented change in 7.4.x compared to 7.3.x?
it basically takes away the ability to update stuff for new versions or you have to block rolling back. | 1.0 | unexpected behavior of after_load label and callbacks - ```py
default test1 = 0
default test2 = Test(10)
init python:
class Test():
def __init__(self, v=0):
self.v = v
def inc(self):
self.v += 1
def after_load():
global test1
test1 += 1
test2.inc()
config.after_load_callbacks.append(after_load)
label after_load:
$ test1 += 1
$ test2.inc()
return
label main_menu:
return
label start:
while True:
"[test1], [test2.v]"
```
a changed object within label or callback doesn't retain its value after rolling back prior the loading point. (clean 7.4.11.2266)
is this an undocumented change in 7.4.x compared to 7.3.x?
it basically takes away the ability to update stuff for new versions or you have to block rolling back. | non_priority | unexpected behavior of after load label and callbacks py default default test init python class test def init self v self v v def inc self self v def after load global inc config after load callbacks append after load label after load inc return label main menu return label start while true a changed object within label or callback doesn t retain its value after rolling back prior the loading point clean is this an undocumented change in x compared to x it basically takes away the ability to update stuff for new versions or you have to block rolling back | 0 |
20,235 | 26,840,348,278 | IssuesEvent | 2023-02-02 23:37:34 | hackforla/peopledepot | https://api.github.com/repos/hackforla/peopledepot | closed | CONTRIBUTING.md: modify instructions and env file so non-interactive | role: back end size: 1pt Feature: Process Improvement | ### Overview
Current instructions for Docker require the person deploying to enter in a username, email, and password for creating the superuser. This article https://docs.djangoproject.com/en/3.0/ref/django-admin/#django-admin-createsuperuser explains how to automatically create superuser using env variables without requiring any interactive entry. To do this in People Depot, the .env.dev.example file and CONTRIBUTING.md need to be modified. | 1.0 | CONTRIBUTING.md: modify instructions and env file so non-interactive - ### Overview
Current instructions for Docker require the person deploying to enter in a username, email, and password for creating the superuser. This article https://docs.djangoproject.com/en/3.0/ref/django-admin/#django-admin-createsuperuser explains how to automatically create superuser using env variables without requiring any interactive entry. To do this in People Depot, the .env.dev.example file and CONTRIBUTING.md need to be modified. | non_priority | contributing md modify instructions and env file so non interactive overview current instructions for docker require the person deploying to enter in a username email and password for creating the superuser this article explains how to automatically create superuser using env variables without requiring any interactive entry to do this in people depot the env dev example file and contributing md need to be modified | 0 |
43,595 | 9,465,973,251 | IssuesEvent | 2019-04-18 02:12:41 | AaronTraas/Clash-Royale-Clan-Tools | https://api.github.com/repos/AaronTraas/Clash-Royale-Clan-Tools | closed | refactor process_* functions, test coverage | code quality | Refactor process_member(), process_clan(), process_warlog() to be simpler and clearer.
Get to near 100% code coverage of resulting code. | 1.0 | refactor process_* functions, test coverage - Refactor process_member(), process_clan(), process_warlog() to be simpler and clearer.
Get to near 100% code coverage of resulting code. | non_priority | refactor process functions test coverage refactor process member process clan process warlog to be simpler and clearer get to near code coverage of resulting code | 0 |
20,543 | 15,681,150,784 | IssuesEvent | 2021-03-25 04:39:19 | microsoft/win32metadata | https://api.github.com/repos/microsoft/win32metadata | closed | WindowsCreateString PCNZWCH not represented as String | usability | This should be a Pointer to a WCHAR-style string, rather than a `ushort *`.
The [WindowsCreateString](https://docs.microsoft.com/en-us/windows/win32/api/winstring/nf-winstring-windowscreatestring) documentation is unclear whether this should be treated as null-terminated or not. In the _Parameters_ section, it says:
> A null-terminated string to use as the source for the new `HSTRING`.
but later, it says:
> If `sourceString` has embedded null characters, the `WindowsCreateString` function copies all characters to the terminating null character.
This latter statement is hard to interpret -- is the terminating null character the one that ends the string, or the first null character it finds?
So, I don't know exactly how it should be represented without reading the source code or further experimenting, but one way or another it should be a string. | True | WindowsCreateString PCNZWCH not represented as String - This should be a Pointer to a WCHAR-style string, rather than a `ushort *`.
The [WindowsCreateString](https://docs.microsoft.com/en-us/windows/win32/api/winstring/nf-winstring-windowscreatestring) documentation is unclear whether this should be treated as null-terminated or not. In the _Parameters_ section, it says:
> A null-terminated string to use as the source for the new `HSTRING`.
but later, it says:
> If `sourceString` has embedded null characters, the `WindowsCreateString` function copies all characters to the terminating null character.
This latter statement is hard to interpret -- is the terminating null character the one that ends the string, or the first null character it finds?
So, I don't know exactly how it should be represented without reading the source code or further experimenting, but one way or another it should be a string. | non_priority | windowscreatestring pcnzwch not represented as string this should be a pointer to a wchar style string rather than a ushort the documentation is unclear whether this should be treated as null terminated or not in the parameters section it says a null terminated string to use as the source for the new hstring but later it says if sourcestring has embedded null characters the windowscreatestring function copies all characters to the terminating null character this latter statement is hard to interpret is the terminating null character the one that ends the string or the first null character it finds so i don t know exactly how it should be represented without reading the source code or further experimenting but one way or another it should be a string | 0 |
28,425 | 4,104,697,003 | IssuesEvent | 2016-06-05 15:07:13 | JuliaLang/julia | https://api.github.com/repos/JuliaLang/julia | opened | 2-arg A_mul_B! should be consistent, or not exist | design linear algebra | Example methods are here: https://github.com/JuliaLang/julia/blob/643bdbec6aeca8053e33a242df86e2de2327f815/base/linalg/triangular.jl#L402-L403 where these clearly follow the BLAS `trmm` convention of mutating whichever argument is full. So `A_mul_B!(A, B)` might mutate A, or it might mutate B, depending on their types. This is the case for several other combinations of input types as well, and I think it's bad for generic programming. Ref discussion at https://github.com/JuliaLang/julia/pull/16615#discussion_r65652965
If we can't apply a consistent rule here, "always mutates the second argument" (or the first?), then we shouldn't define this method. Better to favor the more explicit `A_mul_B!(C, A, B)` method where the output is a separate argument. Some combinations of types will allow one of `A_mul_B!(A, A, B)` or `A_mul_B!(B, A, B)` to work, but writing code that does that will be inherently non-generic. The individual methods of `A_mul_B!` should be responsible for checking whether the inputs are `===` (and possibly more complicated forms of alias checks if we have more view types in common use) and only allowing the specific combinations that are expected to work.
This issue is still present for all the in-place multiplication methods even if #6837 renames all 7 (or 9 if you count possible combinations we don't define right now, ref #5332) variants to methods of `mul!`. I think this is an explicitly post-0.5 cleanup to make though since we don't have time to deal with it right now. | 1.0 | 2-arg A_mul_B! should be consistent, or not exist - Example methods are here: https://github.com/JuliaLang/julia/blob/643bdbec6aeca8053e33a242df86e2de2327f815/base/linalg/triangular.jl#L402-L403 where these clearly follow the BLAS `trmm` convention of mutating whichever argument is full. So `A_mul_B!(A, B)` might mutate A, or it might mutate B, depending on their types. This is the case for several other combinations of input types as well, and I think it's bad for generic programming. Ref discussion at https://github.com/JuliaLang/julia/pull/16615#discussion_r65652965
If we can't apply a consistent rule here, "always mutates the second argument" (or the first?), then we shouldn't define this method. Better to favor the more explicit `A_mul_B!(C, A, B)` method where the output is a separate argument. Some combinations of types will allow one of `A_mul_B!(A, A, B)` or `A_mul_B!(B, A, B)` to work, but writing code that does that will be inherently non-generic. The individual methods of `A_mul_B!` should be responsible for checking whether the inputs are `===` (and possibly more complicated forms of alias checks if we have more view types in common use) and only allowing the specific combinations that are expected to work.
This issue is still present for all the in-place multiplication methods even if #6837 renames all 7 (or 9 if you count possible combinations we don't define right now, ref #5332) variants to methods of `mul!`. I think this is an explicitly post-0.5 cleanup to make though since we don't have time to deal with it right now. | non_priority | arg a mul b should be consistent or not exist example methods are here where these clearly follow the blas trmm convention of mutating whichever argument is full so a mul b a b might mutate a or it might mutate b depending on their types this is the case for several other combinations of input types as well and i think it s bad for generic programming ref discussion at if we can t apply a consistent rule here always mutates the second argument or the first then we shouldn t define this method better to favor the more explicit a mul b c a b method where the output is a separate argument some combinations of types will allow one of a mul b a a b or a mul b b a b to work but writing code that does that will be inherently non generic the individual methods of a mul b should be responsible for checking whether the inputs are and possibly more complicated forms of alias checks if we have more view types in common use and only allowing the specific combinations that are expected to work this issue is still present for all the in place multiplication methods even if renames all or if you count possible combinations we don t define right now ref variants to methods of mul i think this is an explicitly post cleanup to make though since we don t have time to deal with it right now | 0 |
23,022 | 4,864,876,509 | IssuesEvent | 2016-11-14 19:14:43 | miguelgrinberg/python-socketio | https://api.github.com/repos/miguelgrinberg/python-socketio | opened | Add note in documentation regarding class-based namespaces being singletons | documentation | Applications cannot store client data in them. | 1.0 | Add note in documentation regarding class-based namespaces being singletons - Applications cannot store client data in them. | non_priority | add note in documentation regarding class based namespaces being singletons applications cannot store client data in them | 0 |
22,213 | 30,763,203,604 | IssuesEvent | 2023-07-30 00:47:45 | danrleypereira/verzel-pleno-prova | https://api.github.com/repos/danrleypereira/verzel-pleno-prova | opened | Autenticar usuário - FrontEnd | feature Processo Seletivo | Como parte do nosso esforço contínuo para melhorar a segurança e a experiência do usuário, precisamos implementar a autenticação de usuário no frontend da aplicação. Isso inclui:
- [ ] Implementar o formulário de registro de usuário (precisamos coletar: nome de usuário, email e senha)
- [ ] Implementar a lógica de autenticação no frontend que irá comunicar-se com o backend
- [ ] Implementar a lógica para salvar o JWT token em um reducer
- [ ] Implementar um método para incluir o token JWT nas futuras solicitações que necessitem de autenticação
- [ ] Proteger rotas no frontend com autenticação (apenas usuários autenticados devem ter acesso)
- [ ] Implementar lógica para lidar com tokens JWT expirados
- [ ] Testar todos os aspectos do fluxo de autenticação
Nota: É importante garantir que todas as informações do usuário sejam transmitidas de forma segura. | 1.0 | Autenticar usuário - FrontEnd - Como parte do nosso esforço contínuo para melhorar a segurança e a experiência do usuário, precisamos implementar a autenticação de usuário no frontend da aplicação. Isso inclui:
- [ ] Implementar o formulário de registro de usuário (precisamos coletar: nome de usuário, email e senha)
- [ ] Implementar a lógica de autenticação no frontend que irá comunicar-se com o backend
- [ ] Implementar a lógica para salvar o JWT token em um reducer
- [ ] Implementar um método para incluir o token JWT nas futuras solicitações que necessitem de autenticação
- [ ] Proteger rotas no frontend com autenticação (apenas usuários autenticados devem ter acesso)
- [ ] Implementar lógica para lidar com tokens JWT expirados
- [ ] Testar todos os aspectos do fluxo de autenticação
Nota: É importante garantir que todas as informações do usuário sejam transmitidas de forma segura. | non_priority | autenticar usuário frontend como parte do nosso esforço contínuo para melhorar a segurança e a experiência do usuário precisamos implementar a autenticação de usuário no frontend da aplicação isso inclui implementar o formulário de registro de usuário precisamos coletar nome de usuário email e senha implementar a lógica de autenticação no frontend que irá comunicar se com o backend implementar a lógica para salvar o jwt token em um reducer implementar um método para incluir o token jwt nas futuras solicitações que necessitem de autenticação proteger rotas no frontend com autenticação apenas usuários autenticados devem ter acesso implementar lógica para lidar com tokens jwt expirados testar todos os aspectos do fluxo de autenticação nota é importante garantir que todas as informações do usuário sejam transmitidas de forma segura | 0 |
18,987 | 13,530,849,134 | IssuesEvent | 2020-09-15 20:35:54 | emanuelen5/NEXA-910-codec | https://api.github.com/repos/emanuelen5/NEXA-910-codec | closed | Move source code into `src` folder | refactor usability | Structure up the Repo: move all of the functions except for the main entry point to a `src` folder | True | Move source code into `src` folder - Structure up the Repo: move all of the functions except for the main entry point to a `src` folder | non_priority | move source code into src folder structure up the repo move all of the functions except for the main entry point to a src folder | 0 |
361,537 | 25,343,092,073 | IssuesEvent | 2022-11-19 00:25:52 | amzn/selling-partner-api-docs | https://api.github.com/repos/amzn/selling-partner-api-docs | closed | [BUG] Rate Limit Change for Amazon Fulfilled Shipments Data Report? | bug Documentation closing soon | CaseID: 9185839181
**Describe the bug**
Until recently, we could create and download this report by staying within the rate limit of 0.0167 per second and ensuring we do not request the same report more than once every 30 mins as stated in documentation:
SP API: reports - POST /reports/2020-09-04/reports
Operation: createReport
reportType: GET_AMAZON_FULFILLED_SHIPMENTS_DATA_GENERAL
But we are suddenly getting quota exceeded error messages:
Response body: { "errors": [ { "code": "QuotaExceeded", "message": "You exceeded your quota for the requested resource."
Has there been a change to the rate limit? Can you update the documentation?
**URL of the content on GitHub**
Please provide the GitHub URL for the documentation where you see the bug.
**Description of what the documentation currently says**
Please describe the section/paragraph of the documentation where you see the bug.
**Description of what the documentation should say**
A clear and concise description of the guidance you expected to see in the documentation.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Additional context**
Add any other context about the problem here.
| 1.0 | [BUG] Rate Limit Change for Amazon Fulfilled Shipments Data Report? - CaseID: 9185839181
**Describe the bug**
Until recently, we could create and download this report by staying within the rate limit of 0.0167 per second and ensuring we do not request the same report more than once every 30 mins as stated in documentation:
SP API: reports - POST /reports/2020-09-04/reports
Operation: createReport
reportType: GET_AMAZON_FULFILLED_SHIPMENTS_DATA_GENERAL
But we are suddenly getting quota exceeded error messages:
Response body: { "errors": [ { "code": "QuotaExceeded", "message": "You exceeded your quota for the requested resource."
Has there been a change to the rate limit? Can you update the documentation?
**URL of the content on GitHub**
Please provide the GitHub URL for the documentation where you see the bug.
**Description of what the documentation currently says**
Please describe the section/paragraph of the documentation where you see the bug.
**Description of what the documentation should say**
A clear and concise description of the guidance you expected to see in the documentation.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Additional context**
Add any other context about the problem here.
| non_priority | rate limit change for amazon fulfilled shipments data report caseid describe the bug until recently we could create and download this report by staying within the rate limit of per second and ensuring we do not request the same report more than once every mins as stated in documentation sp api reports post reports reports operation createreport reporttype get amazon fulfilled shipments data general but we are suddenly getting quota exceeded error messages response body errors code quotaexceeded message you exceeded your quota for the requested resource has there been a change to the rate limit can you update the documentation url of the content on github please provide the github url for the documentation where you see the bug description of what the documentation currently says please describe the section paragraph of the documentation where you see the bug description of what the documentation should say a clear and concise description of the guidance you expected to see in the documentation screenshots if applicable add screenshots to help explain your problem additional context add any other context about the problem here | 0 |
88,841 | 10,581,106,211 | IssuesEvent | 2019-10-08 08:29:48 | packit-service/requre | https://api.github.com/repos/packit-service/requre | opened | Document format of filters passed to `upgrade_import_system()` | documentation | I'm just looking at the function and the only documentation is
```
list of filters, for examples see: tests/test_import_system.py
```
There are examples like these:
```
HANDLE_MODULE_LIST = [
(
"^tempfile$",
{"who_name": SELECTOR},
{"": [ReplaceType.REPLACE_MODULE, TempFile]},
)
]
```
I can guess what some arguments mean, but without proper documentation it's just a guessing game: please provide complete, precise documentation for each of the fields. | 1.0 | Document format of filters passed to `upgrade_import_system()` - I'm just looking at the function and the only documentation is
```
list of filters, for examples see: tests/test_import_system.py
```
There are examples like these:
```
HANDLE_MODULE_LIST = [
(
"^tempfile$",
{"who_name": SELECTOR},
{"": [ReplaceType.REPLACE_MODULE, TempFile]},
)
]
```
I can guess what some arguments mean, but without proper documentation it's just a guessing game: please provide complete, precise documentation for each of the fields. | non_priority | document format of filters passed to upgrade import system i m just looking at the function and the only documentation is list of filters for examples see tests test import system py there are examples like these handle module list tempfile who name selector i can guess what some arguments mean but without proper documentation it s just a guessing game please provide complete precise documentation for each of the fields | 0 |
180,763 | 30,564,076,726 | IssuesEvent | 2023-07-20 16:25:31 | department-of-veterans-affairs/abd-vro | https://api.github.com/repos/department-of-veterans-affairs/abd-vro | opened | Chats with VRO engineers | Design research | **User Story**
As a designer/researcher, I want to talk to VRO engineers about working with CFT teams, so that I can better understand the support needed.
**Acceptance Criteria**
1. The first round of chats will start with Mason & Teja, since they have been or will be acting as point-of-contact for CFT teams
| 1.0 | Chats with VRO engineers - **User Story**
As a designer/researcher, I want to talk to VRO engineers about working with CFT teams, so that I can better understand the support needed.
**Acceptance Criteria**
1. The first round of chats will start with Mason & Teja, since they have been or will be acting as point-of-contact for CFT teams
| non_priority | chats with vro engineers user story as a designer researcher i want to talk to vro engineers about working with cft teams so that i can better understand the support needed acceptance criteria the first round of chats will start with mason teja since they have been or will be acting as point of contact for cft teams | 0 |
60,852 | 6,716,704,651 | IssuesEvent | 2017-10-14 12:08:43 | brave/browser-laptop | https://api.github.com/repos/brave/browser-laptop | reopened | Update enabledContent.js to our modified BEM style | feature/about-pages polish QA/test-plan-specified refactoring/aphrodite release-notes/exclude | ## Test plan
https://github.com/brave/browser-laptop/pull/10238#issue-247151904
----
**Describe the issue you encountered:** update enabledContent.js to our modified BEM style (ref: https://github.com/brave/browser-laptop/blob/master/docs/style.md#defining-our-blocks-elements-and-modifiers).
- Brave Version (revision SHA): master
- Extra QA steps:
1. Open about:preferences#payments
2. Enable Payments
3. Make sure the page is loaded without breaking styles
- Any related issues:
| 1.0 | Update enabledContent.js to our modified BEM style - ## Test plan
https://github.com/brave/browser-laptop/pull/10238#issue-247151904
----
**Describe the issue you encountered:** update enabledContent.js to our modified BEM style (ref: https://github.com/brave/browser-laptop/blob/master/docs/style.md#defining-our-blocks-elements-and-modifiers).
- Brave Version (revision SHA): master
- Extra QA steps:
1. Open about:preferences#payments
2. Enable Payments
3. Make sure the page is loaded without breaking styles
- Any related issues:
| non_priority | update enabledcontent js to our modified bem style test plan describe the issue you encountered update enabledcontent js to our modified bem style ref brave version revision sha master extra qa steps open about preferences payments enable payments make sure the page is loaded without breaking styles any related issues | 0 |
63,834 | 7,746,571,756 | IssuesEvent | 2018-05-29 22:16:10 | metabase/metabase | https://api.github.com/repos/metabase/metabase | closed | We should list deactivated SSO-created accounts and let admins restore them from the UI | Auth Designs UX | I'm too scared to try this on any of our actual Google-auth-created accounts, but I think it might be the case that if you use the `remove` action on an account created via Google Auth that there's no way to restore that account, and thus that user can never log into metabase with that Google account again.
If I'm right about that, I'm going to change this issue to be a more general proposal about creating a system to display "deactivated" SSO-created accounts (be they Google, LDAP, Okta in the future, etc.), and have a way to restore accounts from that list. I mentioned this in https://github.com/metabase/metabase/pull/4340 and just wanted to have a place to discuss this specific problem.
⬇️ **Please click the 👍 reaction instead of leaving a `+1` or 👍 comment** | 1.0 | We should list deactivated SSO-created accounts and let admins restore them from the UI - I'm too scared to try this on any of our actual Google-auth-created accounts, but I think it might be the case that if you use the `remove` action on an account created via Google Auth that there's no way to restore that account, and thus that user can never log into metabase with that Google account again.
If I'm right about that, I'm going to change this issue to be a more general proposal about creating a system to display "deactivated" SSO-created accounts (be they Google, LDAP, Okta in the future, etc.), and have a way to restore accounts from that list. I mentioned this in https://github.com/metabase/metabase/pull/4340 and just wanted to have a place to discuss this specific problem.
⬇️ **Please click the 👍 reaction instead of leaving a `+1` or 👍 comment** | non_priority | we should list deactivated sso created accounts and let admins restore them from the ui i m too scared to try this on any of our actual google auth created accounts but i think it might be the case that if you use the remove action on an account created via google auth that there s no way to restore that account and thus that user can never log into metabase with that google account again if i m right about that i m going to change this issue to be a more general proposal about creating a system to display deactivated sso created accounts be they google ldap okta in the future etc and have a way to restore accounts from that list i mentioned this in and just wanted to have a place to discuss this specific problem ⬇️ please click the 👍 reaction instead of leaving a or 👍 comment | 0 |
5,830 | 13,201,736,296 | IssuesEvent | 2020-08-14 10:45:45 | dotnet/docs | https://api.github.com/repos/dotnet/docs | closed | GetAll function | :book: guide - .NET Microservices :books: Area - .NET Architecture Guide product-question | How would the GetAll() function be used in a real example?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: d118f070-8743-e905-2d08-dc725a4e8b5f
* Version Independent ID: fae35cbd-75ae-4448-f066-7c91ccc35779
* Content: [Using Enumeration classes instead of enum types](https://docs.microsoft.com/en-us/dotnet/architecture/microservices/microservice-ddd-cqrs-patterns/enumeration-classes-over-enum-types#feedback)
* Content Source: [docs/architecture/microservices/microservice-ddd-cqrs-patterns/enumeration-classes-over-enum-types.md](https://github.com/dotnet/docs/blob/master/docs/architecture/microservices/microservice-ddd-cqrs-patterns/enumeration-classes-over-enum-types.md)
* Product: **dotnet-architecture**
* Technology: **microservices**
* GitHub Login: @nishanil
* Microsoft Alias: **nanil** | 1.0 | GetAll function - How would the GetAll() function be used in a real example?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: d118f070-8743-e905-2d08-dc725a4e8b5f
* Version Independent ID: fae35cbd-75ae-4448-f066-7c91ccc35779
* Content: [Using Enumeration classes instead of enum types](https://docs.microsoft.com/en-us/dotnet/architecture/microservices/microservice-ddd-cqrs-patterns/enumeration-classes-over-enum-types#feedback)
* Content Source: [docs/architecture/microservices/microservice-ddd-cqrs-patterns/enumeration-classes-over-enum-types.md](https://github.com/dotnet/docs/blob/master/docs/architecture/microservices/microservice-ddd-cqrs-patterns/enumeration-classes-over-enum-types.md)
* Product: **dotnet-architecture**
* Technology: **microservices**
* GitHub Login: @nishanil
* Microsoft Alias: **nanil** | non_priority | getall function how would the getall function be used in a real example document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product dotnet architecture technology microservices github login nishanil microsoft alias nanil | 0 |
226,694 | 18,043,888,854 | IssuesEvent | 2021-09-18 14:41:12 | logicmoo/logicmoo_workspace | https://api.github.com/repos/logicmoo/logicmoo_workspace | opened | logicmoo.pfc.test.sanity_base.FC_01R JUnit | Test_9999 logicmoo.pfc.test.sanity_base unit_test FC_01R | (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)
GH_MASTER_ISSUE_FINFO=
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R
GITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc
Latest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/
This Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc
```
%
%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))
%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))
%~ make_dynamic_here(header_sane,a11)
%~ make_dynamic_here(header_sane,b11)
%~ mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)
Call: (68) [header_sane] header_sane:a11
Fail: (68) [header_sane] header_sane:a11
^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)
^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)
failure=info((why_was_true(header_sane:(\+a11)),rtrace(header_sane:a11)))
no_proof_for(\+a11).
no_proof_for(\+a11).
no_proof_for(\+a11).
sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))
%~ FIlE: * https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27
(0)$[system] '$c_call_prolog'. no(clause)
(2)$[system] catch('$toplevel':initialise_prolog,A,'$toplevel':initialise_error(A)). % init.pl:546:
(3)[$toplevel] initialise_prolog. % toplevel.pl:495:
(4)<*>$[$toplevel] load_associated_files('<garbage_collected>'). % toplevel.pl:450:
(8)$[system] '$load_file'('fc_01r.pfc',user,'<garbage_collected>'). % init.pl:2353:
(11)$[system]# '$sig_atomic'(setup_call_cleanup(with_mutex('$load_file','$mt_start_load'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',<clause>(0x5636aaced800),[expand(false)])),'$mt_do_load'(<clause>(0x5636aaced800),'fc_01r.pfc','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',user,[expand(false)]),'$mt_end_load'(<clause>(0x5636aaced800)))). no(clause)
(12)$[system] '$c_call_prolog'. no(clause)
(14)$[system]# setup_call_catcher_cleanup(system:with_mutex('$load_file','$mt_start_load'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',<clause>(0x5636aaced800),[expand(false)])),system:'$mt_do_load'(<clause>(0x5636aaced800),'fc_01r.pfc','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',user,[expand(false)]),A,system:'$mt_end_load'(<clause>(0x5636aaced800))). % init.pl:646:
(16)$[system]# '$qdo_load_file'('fc_01r.pfc','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',user,[expand(false)]). % init.pl:2546:
(19)<*>$[system]# '$do_load_file_2'('fc_01r.pfc','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',user,compiled,[expand(false)]). % init.pl:2592:
(23)$[system]# setup_call_catcher_cleanup(system:'$start_consult'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',1631494506.892328),system:'$load_file'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',A,[expand(false)]),B,system:'$end_consult'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',lexstate(202,swi),user)). % init.pl:646:
(24)<*>$[system]# '$load_file'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',A,[expand(false)]). % init.pl:3007:
(25)$[system]# '$compile_term'((:-mpred_test(a11)),A,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '). % init.pl:3074:
(26)$[system]# '$compile_term'((:-mpred_test(a11)),A,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',-). % init.pl:3084:
(27)$[system]# '$execute_directive'(mpred_test(a11),'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '). % init.pl:3549:
(28)$[system]# '$execute_directive_2'(mpred_test(a11),'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '). % init.pl:3571:
(29)<*>$[system] '$execute_directive_3'(mpred_test(a11)). % init.pl:3574:
(30)$[system] catch(header_sane:mpred_test(a11),error(A,B),system:'$exception_in_directive'(error(A,B))). % init.pl:546:
(31)[pfc_test] pfc_test:mpred_test(header_sane:a11). % pfc_test.pl:63:
(32)<*>$[pfc_test] pfc_test:mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11). % pfc_test.pl:82:
(33)$[pfc_test] pfc_test:mpred_test_fok("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11). % pfc_test.pl:85:
(34)$[locally_each]# locally_each:locally(t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane"),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1))). % redo_locally.pl:149:
(35)$[locally_each]# locally_each:wtl(t_l,mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane"),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),pfc_test:ecc). % redo_locally.pl:199:
(36)$[locally_each]# locally_each:wtl(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane"),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),pfc_test:ecc). % redo_locally.pl:204:
(37)$[locally_each]# locally_each:wtl_how(pfc_test:ecc,locally_each:clause_true(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),locally_each:key_erase(t_l)). % redo_locally.pl:217:
(38)$[each_call_cleanup]# each_call_cleanup:each_call_cleanup(locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),locally_each:key_erase(t_l)). % each_call.pl:147:
(39)$[each_call_cleanup]# each_call_cleanup:trusted_redo_call_cleanup(locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),locally_each:key_erase(t_l)). % each_call.pl:116:
(40)$[system]# setup_call_cleanup(locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),each_call_cleanup:((pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),deterministic(B)),(notrace(B==true)->!;mquietly(locally_each:key_erase(t_l)),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),true));locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),locally_each:key_erase(t_l))),notrace(fail))),each_call_cleanup:mquietly(locally_each:key_erase(t_l))). % init.pl:650:
(41)$[system]# setup_call_catcher_cleanup(locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),each_call_cleanup:((pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),deterministic(B)),(notrace(B==true)->!;mquietly(locally_each:key_erase(t_l)),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),true));locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),locally_each:key_erase(t_l))),notrace(fail))),C,each_call_cleanup:mquietly(locally_each:key_erase(t_l))). % init.pl:646:
(42)$[each_call_cleanup]# '<meta-call>'(each_call_cleanup:((pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),deterministic(B)),(notrace(B==true)->!;mquietly(locally_each:key_erase(t_l)),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),true));locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),locally_each:key_erase(t_l))),notrace(fail)))). no(clause)
(43)<*>[system]# ignore(pfc_test:(nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))). % init.pl:528:
(44)$[pfc_test]# '<meta-call>'(pfc_test:(nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))). no(clause)
(45)[ucatch]# ucatch:pfc_test:(get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee)))). % ucatch.pl:1756:
(46)$[ucatch]# ucatch:call_each(must_det_u,pfc_test:(get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))). % ucatch.pl:1769:
(47)$[ucatch]# ucatch:call_each(must_det_u,pfc_test:(0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))). % ucatch.pl:1769:
(48)$[ucatch]# ucatch:call_each(must_det_u,pfc_test:(add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))). % ucatch.pl:1769:
(53)[ucatch]# ucatch:call_each(must_det_u,pfc_test:ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee)))). % ucatch.pl:1771:
(54)$[ucatch]# ucatch:p_call(must_det_u,pfc_test:ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee)))). % ucatch.pl:1777:
(55)$[ucatch]# ucatch:pfc_test:ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))). % ucatch.pl:1725:
(56)<*>$[must_sanity]# must_sanity:pfc_test:ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))). % must_sanity.pl:65:
(57)<*>$[system]# ignore(pfc_test:(getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))). % init.pl:528:
(62)[ucatch] ucatch:call_each(must_det_u,pfc_test:(save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))). % ucatch.pl:1769:
(63)$[ucatch] ucatch:call_each(must_det_u,pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")). % ucatch.pl:1771:
(64)$[ucatch] ucatch:p_call(must_det_u,pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")). % ucatch.pl:1777:
(65)$[ucatch]# ucatch:pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"). % ucatch.pl:1725:
(67)[must_sanity]# must_sanity:pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"). % must_sanity.pl:66:
(71)[locally_each] locally_each:wtl_how(locally_each:trusted_redo_call_cleanup,locally_each:(false==true),must_sanity:set_prolog_flag(debug_on_error,false),must_sanity:(catch(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),A,xnotrace((dumpST_error(sHOW_MUST_go_on_xI__xI__xI__xI__xI_(A,pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))))*->true;xnotrace(dumpST_error(sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),must_sanity:set_prolog_flag(debug_on_error,true)). % redo_locally.pl:217:
(74)$[system] setup_call_catcher_cleanup(must_sanity:set_prolog_flag(debug_on_error,false),each_call_cleanup:((must_sanity:(catch(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),A,xnotrace((dumpST_error(sHOW_MUST_go_on_xI__xI__xI__xI__xI_(A,pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))))*->true;xnotrace(dumpST_error(sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),deterministic(B)),(notrace(B==true)->!;mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),notrace(nb_setarg(1,mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),true));must_sanity:set_prolog_flag(debug_on_error,false),notrace(nb_setarg(1,mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),must_sanity:set_prolog_flag(debug_on_error,true))),notrace(fail))),C,each_call_cleanup:mquietly(must_sanity:set_prolog_flag(debug_on_error,true))). % init.pl:646:
(75)$[each_call_cleanup] '<meta-call>'(each_call_cleanup:((must_sanity:(catch(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),A,xnotrace((dumpST_error(sHOW_MUST_go_on_xI__xI__xI__xI__xI_(A,pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))))*->true;xnotrace(dumpST_error(sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),deterministic(B)),(notrace(B==true)->!;mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),notrace(nb_setarg(1,mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),true));must_sanity:set_prolog_flag(debug_on_error,false),notrace(nb_setarg(1,mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),must_sanity:set_prolog_flag(debug_on_error,true))),notrace(fail)))). no(clause)
(76)$[must_sanity] must_sanity:xnotrace(dumpST_error(sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))). % must_sanity.pl:172:
(78)$[must_sanity] notrace((ddmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),dumpST,wdmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))))). no(clause)
(79)$[system] '$c_call_prolog'. no(clause)
(80)[system] must_sanity:ddmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),must_sanity:(dumpST,wdmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))). % init.pl:382:
(81)$[system] '<meta-call>'((must_sanity:ddmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),must_sanity:(dumpST,wdmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))))). no(clause)
(84)[butterfly] butterfly:in_bfly(f,must_sanity:zotrace(with_all_dmsg((b_setval('$dump_frame',1242),dumpST1)))). % butterfly_console.pl:226:
%~ error( sHOW_MUST_go_on_failed_F__A__I__L_( pfc_test : save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))
^ Call: (82) [pfc_test] save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")
^ Unify: (82) [pfc_test] save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")
^ Call: (86) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Unify: (86) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Exit: (86) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Call: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Unify: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Exit: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Call: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Unify: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Exit: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Call: (87) [locally_each] locally_each:clause_true(t_l, t_l:dont_shrink)
^ Unify: (87) [locally_each] locally_each:clause_true(t_l, t_l:dont_shrink)
Call: (88) [system] copy_term(t_l:dont_shrink, _37086)
Exit: (88) [system] copy_term(t_l:dont_shrink, t_l:dont_shrink)
^ Call: (88) [t_l] clause(t_l:dont_shrink, true)
^ Fail: (88) [t_l] clause(t_l:dont_shrink, true)
^ Fail: (87) [locally_each] locally_each:clause_true(t_l, t_l:dont_shrink)
^ Call: (93) [locally_each] locally_each:key_asserta(t_l, t_l:dont_shrink)
^ Unify: (93) [locally_each] locally_each:key_asserta(t_l, t_l:dont_shrink)
^ Call: (94) [t_l] asserta(t_l:dont_shrink, _41540)
^ Exit: (94) [t_l] asserta(t_l:dont_shrink, <clause>(0x5636aa6850e0))
Call: (94) [system] nb_current('$w_tl_e', _42778)
Exit: (94) [system] nb_current('$w_tl_e', [<clause>(0x5636aa723290)])
Call: (94) [system] nb_linkval('$w_tl_e', [<clause>(0x5636aa6850e0), <clause>(0x5636aa723290)])
Exit: (94) [system] nb_linkval('$w_tl_e', [<clause>(0x5636aa6850e0), <clause>(0x5636aa723290)])
^ Exit: (93) [locally_each] locally_each:key_asserta(t_l, t_l:dont_shrink)
^ Call: (92) [pfc_test] save_single_testcase_shrink("Test_0001_Line_0027__A11_in_header_sane", _28776)
^ Unify: (92) [pfc_test] save_single_testcase_shrink("Test_0001_Line_0027__A11_in_header_sane", _28776)
^ Call: (95) [pfc_test] writeln('<?xml version="1.0" encoding="utf-8"?>'), j_u:junit_prop(testsuite, file, _47170), writeln(" <testsuites>"), (getenv('JUNIT_SUITE', _47206);_47206=_47170), !, get_suite_attribs(_47228), format(" <testsuite name=\"~w\" ~w>\n", [_47206|...]), show_junit_testcase(_47170, "Test_0001_Line_0027__A11_in_header_sane"), writeln(...), writeln(...)
^ Unify: (95) [system] pfc_test:writeln('<?xml version="1.0" encoding="utf-8"?>'), pfc_test:(j_u:junit_prop(testsuite, file, _47170), writeln(" <testsuites>"), (getenv('JUNIT_SUITE', _47206);_47206=_47170), !, get_suite_attribs(_47228), format(" <testsuite name=\"~w\" ~w>\n", [...|...]), show_junit_testcase(..., ...), ..., ...)
Call: (97) [system] writeln('<?xml version="1.0" encoding="utf-8"?>')
Exit: (97) [system] writeln('<?xml version="1.0" encoding="utf-8"?>')
Call: (97) [j_u] j_u:junit_prop(testsuite, file, _47170)
Fail: (97) [j_u] j_u:junit_prop(testsuite, file, _47170)
^ Fail: (95) [system] pfc_test:writeln('<?xml version="1.0" encoding="utf-8"?>'), pfc_test:(j_u:junit_prop(testsuite, file, _47170), writeln(" <testsuites>"), (getenv('JUNIT_SUITE', _47206);_47206=_47170), !, get_suite_attribs(_47228), format(" <testsuite name=\"~w\" ~w>\n", [...|...]), show_junit_testcase(..., ...), ..., ...)
^ Fail: (92) [pfc_test] save_single_testcase_shrink("Test_0001_Line_0027__A11_in_header_sane", _28776)
^ Call: (93) [locally_each] locally_each:key_erase(t_l)
^ Unify: (93) [locally_each] locally_each:key_erase(t_l)
Call: (94) [system] nb_current('$w_tl_e', [_53522|_53524])
Exit: (94) [system] nb_current('$w_tl_e', [<clause>(0x5636aa6850e0), <clause>(0x5636aa723290)])
Call: (94) [system] nb_linkval('$w_tl_e', [<clause>(0x5636aa723290)])
Exit: (94) [system] nb_linkval('$w_tl_e', [<clause>(0x5636aa723290)])
Call: (95) [system] erase(<clause>(0x5636aa6850e0))
Exit: (95) [system] erase(<clause>(0x5636aa6850e0))
Call: (94) [system] true
Exit: (94) [system] true
Call: (94) [system] true
Exit: (94) [system] true
^ Exit: (93) [locally_each] locally_each:key_erase(t_l)
^ Fail: (82) [pfc_test] save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")
^ Call: (82) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)
^ Unify: (82) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)
%~ FILE: * https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27
```
totalTime=10
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R
GITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc
Latest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/
This Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc
FAILED: /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-junit-minor -k fc_01r.pfc (returned 137)
| 3.0 | logicmoo.pfc.test.sanity_base.FC_01R JUnit - (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)
GH_MASTER_ISSUE_FINFO=
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R
GITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc
Latest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/
This Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc
```
%
%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))
%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))
%~ make_dynamic_here(header_sane,a11)
%~ make_dynamic_here(header_sane,b11)
%~ mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)
Call: (68) [header_sane] header_sane:a11
Fail: (68) [header_sane] header_sane:a11
^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)
^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)
failure=info((why_was_true(header_sane:(\+a11)),rtrace(header_sane:a11)))
no_proof_for(\+a11).
no_proof_for(\+a11).
no_proof_for(\+a11).
sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))
%~ FIlE: * https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27
(0)$[system] '$c_call_prolog'. no(clause)
(2)$[system] catch('$toplevel':initialise_prolog,A,'$toplevel':initialise_error(A)). % init.pl:546:
(3)[$toplevel] initialise_prolog. % toplevel.pl:495:
(4)<*>$[$toplevel] load_associated_files('<garbage_collected>'). % toplevel.pl:450:
(8)$[system] '$load_file'('fc_01r.pfc',user,'<garbage_collected>'). % init.pl:2353:
(11)$[system]# '$sig_atomic'(setup_call_cleanup(with_mutex('$load_file','$mt_start_load'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',<clause>(0x5636aaced800),[expand(false)])),'$mt_do_load'(<clause>(0x5636aaced800),'fc_01r.pfc','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',user,[expand(false)]),'$mt_end_load'(<clause>(0x5636aaced800)))). no(clause)
(12)$[system] '$c_call_prolog'. no(clause)
(14)$[system]# setup_call_catcher_cleanup(system:with_mutex('$load_file','$mt_start_load'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',<clause>(0x5636aaced800),[expand(false)])),system:'$mt_do_load'(<clause>(0x5636aaced800),'fc_01r.pfc','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',user,[expand(false)]),A,system:'$mt_end_load'(<clause>(0x5636aaced800))). % init.pl:646:
(16)$[system]# '$qdo_load_file'('fc_01r.pfc','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',user,[expand(false)]). % init.pl:2546:
(19)<*>$[system]# '$do_load_file_2'('fc_01r.pfc','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',user,compiled,[expand(false)]). % init.pl:2592:
(23)$[system]# setup_call_catcher_cleanup(system:'$start_consult'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',1631494506.892328),system:'$load_file'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',A,[expand(false)]),B,system:'$end_consult'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',lexstate(202,swi),user)). % init.pl:646:
(24)<*>$[system]# '$load_file'('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',A,[expand(false)]). % init.pl:3007:
(25)$[system]# '$compile_term'((:-mpred_test(a11)),A,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '). % init.pl:3074:
(26)$[system]# '$compile_term'((:-mpred_test(a11)),A,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',-). % init.pl:3084:
(27)$[system]# '$execute_directive'(mpred_test(a11),'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '). % init.pl:3549:
(28)$[system]# '$execute_directive_2'(mpred_test(a11),'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '). % init.pl:3571:
(29)<*>$[system] '$execute_directive_3'(mpred_test(a11)). % init.pl:3574:
(30)$[system] catch(header_sane:mpred_test(a11),error(A,B),system:'$exception_in_directive'(error(A,B))). % init.pl:546:
(31)[pfc_test] pfc_test:mpred_test(header_sane:a11). % pfc_test.pl:63:
(32)<*>$[pfc_test] pfc_test:mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11). % pfc_test.pl:82:
(33)$[pfc_test] pfc_test:mpred_test_fok("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11). % pfc_test.pl:85:
(34)$[locally_each]# locally_each:locally(t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane"),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1))). % redo_locally.pl:149:
(35)$[locally_each]# locally_each:wtl(t_l,mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane"),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),pfc_test:ecc). % redo_locally.pl:199:
(36)$[locally_each]# locally_each:wtl(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane"),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),pfc_test:ecc). % redo_locally.pl:204:
(37)$[locally_each]# locally_each:wtl_how(pfc_test:ecc,locally_each:clause_true(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),locally_each:key_erase(t_l)). % redo_locally.pl:217:
(38)$[each_call_cleanup]# each_call_cleanup:each_call_cleanup(locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),locally_each:key_erase(t_l)). % each_call.pl:147:
(39)$[each_call_cleanup]# each_call_cleanup:trusted_redo_call_cleanup(locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),locally_each:key_erase(t_l)). % each_call.pl:116:
(40)$[system]# setup_call_cleanup(locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),each_call_cleanup:((pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),deterministic(B)),(notrace(B==true)->!;mquietly(locally_each:key_erase(t_l)),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),true));locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),locally_each:key_erase(t_l))),notrace(fail))),each_call_cleanup:mquietly(locally_each:key_erase(t_l))). % init.pl:650:
(41)$[system]# setup_call_catcher_cleanup(locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),each_call_cleanup:((pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),deterministic(B)),(notrace(B==true)->!;mquietly(locally_each:key_erase(t_l)),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),true));locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),locally_each:key_erase(t_l))),notrace(fail))),C,each_call_cleanup:mquietly(locally_each:key_erase(t_l))). % init.pl:646:
(42)$[each_call_cleanup]# '<meta-call>'(each_call_cleanup:((pfc_test:((wdmsg(mpred_test("Test_0001_Line_0027__A11_in_header_sane",header_sane:a11)),add_test_info("Test_0001_Line_0027__A11_in_header_sane",goal,header_sane:a11),ignore((source_location('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27),atom('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc '),add_test_info("Test_0001_Line_0027__A11_in_header_sane",src,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27 '),sformat("/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27",'~w#L~w',['* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc ',27]),replace_in_string(["/opt/logicmoo_workspace"="https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master"],"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27","/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"),add_test_info("Test_0001_Line_0027__A11_in_header_sane",url,"/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27"))),get_time(1631976060.5277061)),nb(0)=nb(0),catch((call_u_hook(header_sane:a11)*->failure=passed;failure=failure),A,failure=error(A)),ignore((nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))),(failure=error(A)->throw(A);true),nb_setarg(1,nb(0),1)),deterministic(B)),(notrace(B==true)->!;mquietly(locally_each:key_erase(t_l)),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),true));locally_each:key_asserta(t_l,t_l:mpred_current_testcase("Test_0001_Line_0027__A11_in_header_sane")),notrace(nb_setarg(1,mquietly(locally_each:key_erase(t_l)),locally_each:key_erase(t_l))),notrace(fail)))). no(clause)
(43)<*>[system]# ignore(pfc_test:(nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))). % init.pl:528:
(44)$[pfc_test]# '<meta-call>'(pfc_test:(nb(0)=nb(0),get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))). no(clause)
(45)[ucatch]# ucatch:pfc_test:(get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee)))). % ucatch.pl:1756:
(46)$[ucatch]# ucatch:call_each(must_det_u,pfc_test:(get_time(1631976060.5278394),0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))). % ucatch.pl:1769:
(47)$[ucatch]# ucatch:call_each(must_det_u,pfc_test:(0.00013327598571777344 is 1631976060.5278394-1631976060.5277061,add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))). % ucatch.pl:1769:
(48)$[ucatch]# ucatch:call_each(must_det_u,pfc_test:(add_test_info("Test_0001_Line_0027__A11_in_header_sane",time,0.00013327598571777344),process_test_result(failure,header_sane:a11),failure=..[failure],add_test_info("Test_0001_Line_0027__A11_in_header_sane",failure,[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",result,failure),ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))))). % ucatch.pl:1769:
(53)[ucatch]# ucatch:call_each(must_det_u,pfc_test:ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee)))). % ucatch.pl:1771:
(54)$[ucatch]# ucatch:p_call(must_det_u,pfc_test:ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee)))). % ucatch.pl:1777:
(55)$[ucatch]# ucatch:pfc_test:ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))). % ucatch.pl:1725:
(56)<*>$[must_sanity]# must_sanity:pfc_test:ignore((getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))). % must_sanity.pl:65:
(57)<*>$[system]# ignore(pfc_test:(getenv('TEE_FILE','* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '),read_file_to_string('* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/test_results/jenkins/CMD_LAST.ansi '," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n",[]),add_test_info("Test_0001_Line_0027__A11_in_header_sane",out," (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif fc_01r.pfc)\n\nGH_MASTER_ISSUE_FINFO=\n\nISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R \nGITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \nLatest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nThis Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/ \nGITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae \n https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc \n\n\n```\n%\n%~ make_dynamic_here(header_sane,'$nt'(test_header_include,_3534,_3536))\n%~ make_dynamic_here(header_sane,genlPreds(kb_shared,_9354))\n%~ make_dynamic_here(header_sane,a11)\n%~ make_dynamic_here(header_sane,b11)\n%~ mpred_test(\"Test_0001_Line_0027__A11_in_header_sane\",header_sane:a11)\n Call: (68) [header_sane] header_sane:a11\n Fail: (68) [header_sane] header_sane:a11\n^ Call: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\n^ Unify: (68) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)\nfailure=info((why_was_true(header_sane:(\\+a11)),rtrace(header_sane:a11)))\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\nno_proof_for(\\+a11).\n\n"),save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))). % init.pl:528:
(62)[ucatch] ucatch:call_each(must_det_u,pfc_test:(save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),nop(kill_junit_tee))). % ucatch.pl:1769:
(63)$[ucatch] ucatch:call_each(must_det_u,pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")). % ucatch.pl:1771:
(64)$[ucatch] ucatch:p_call(must_det_u,pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")). % ucatch.pl:1777:
(65)$[ucatch]# ucatch:pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"). % ucatch.pl:1725:
(67)[must_sanity]# must_sanity:pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"). % must_sanity.pl:66:
(71)[locally_each] locally_each:wtl_how(locally_each:trusted_redo_call_cleanup,locally_each:(false==true),must_sanity:set_prolog_flag(debug_on_error,false),must_sanity:(catch(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),A,xnotrace((dumpST_error(sHOW_MUST_go_on_xI__xI__xI__xI__xI_(A,pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))))*->true;xnotrace(dumpST_error(sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),must_sanity:set_prolog_flag(debug_on_error,true)). % redo_locally.pl:217:
(74)$[system] setup_call_catcher_cleanup(must_sanity:set_prolog_flag(debug_on_error,false),each_call_cleanup:((must_sanity:(catch(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),A,xnotrace((dumpST_error(sHOW_MUST_go_on_xI__xI__xI__xI__xI_(A,pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))))*->true;xnotrace(dumpST_error(sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),deterministic(B)),(notrace(B==true)->!;mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),notrace(nb_setarg(1,mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),true));must_sanity:set_prolog_flag(debug_on_error,false),notrace(nb_setarg(1,mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),must_sanity:set_prolog_flag(debug_on_error,true))),notrace(fail))),C,each_call_cleanup:mquietly(must_sanity:set_prolog_flag(debug_on_error,true))). % init.pl:646:
(75)$[each_call_cleanup] '<meta-call>'(each_call_cleanup:((must_sanity:(catch(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"),A,xnotrace((dumpST_error(sHOW_MUST_go_on_xI__xI__xI__xI__xI_(A,pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))))*->true;xnotrace(dumpST_error(sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))),ignore(rtrace(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),badfood(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),deterministic(B)),(notrace(B==true)->!;mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),notrace(nb_setarg(1,mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),true));must_sanity:set_prolog_flag(debug_on_error,false),notrace(nb_setarg(1,mquietly(must_sanity:set_prolog_flag(debug_on_error,true)),must_sanity:set_prolog_flag(debug_on_error,true))),notrace(fail)))). no(clause)
(76)$[must_sanity] must_sanity:xnotrace(dumpST_error(sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))). % must_sanity.pl:172:
(78)$[must_sanity] notrace((ddmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),dumpST,wdmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))))). no(clause)
(79)$[system] '$c_call_prolog'. no(clause)
(80)[system] must_sanity:ddmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),must_sanity:(dumpST,wdmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))). % init.pl:382:
(81)$[system] '<meta-call>'((must_sanity:ddmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane"))),must_sanity:(dumpST,wdmsg(error,sHOW_MUST_go_on_failed_F__A__I__L_(pfc_test:save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))))). no(clause)
(84)[butterfly] butterfly:in_bfly(f,must_sanity:zotrace(with_all_dmsg((b_setval('$dump_frame',1242),dumpST1)))). % butterfly_console.pl:226:
%~ error( sHOW_MUST_go_on_failed_F__A__I__L_( pfc_test : save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")))
^ Call: (82) [pfc_test] save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")
^ Unify: (82) [pfc_test] save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")
^ Call: (86) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Unify: (86) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Exit: (86) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Call: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Unify: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Exit: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Call: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Unify: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Exit: (87) [must_sanity] must_sanity:mquietly_if(false, rtrace:tAt_rtrace)
^ Call: (87) [locally_each] locally_each:clause_true(t_l, t_l:dont_shrink)
^ Unify: (87) [locally_each] locally_each:clause_true(t_l, t_l:dont_shrink)
Call: (88) [system] copy_term(t_l:dont_shrink, _37086)
Exit: (88) [system] copy_term(t_l:dont_shrink, t_l:dont_shrink)
^ Call: (88) [t_l] clause(t_l:dont_shrink, true)
^ Fail: (88) [t_l] clause(t_l:dont_shrink, true)
^ Fail: (87) [locally_each] locally_each:clause_true(t_l, t_l:dont_shrink)
^ Call: (93) [locally_each] locally_each:key_asserta(t_l, t_l:dont_shrink)
^ Unify: (93) [locally_each] locally_each:key_asserta(t_l, t_l:dont_shrink)
^ Call: (94) [t_l] asserta(t_l:dont_shrink, _41540)
^ Exit: (94) [t_l] asserta(t_l:dont_shrink, <clause>(0x5636aa6850e0))
Call: (94) [system] nb_current('$w_tl_e', _42778)
Exit: (94) [system] nb_current('$w_tl_e', [<clause>(0x5636aa723290)])
Call: (94) [system] nb_linkval('$w_tl_e', [<clause>(0x5636aa6850e0), <clause>(0x5636aa723290)])
Exit: (94) [system] nb_linkval('$w_tl_e', [<clause>(0x5636aa6850e0), <clause>(0x5636aa723290)])
^ Exit: (93) [locally_each] locally_each:key_asserta(t_l, t_l:dont_shrink)
^ Call: (92) [pfc_test] save_single_testcase_shrink("Test_0001_Line_0027__A11_in_header_sane", _28776)
^ Unify: (92) [pfc_test] save_single_testcase_shrink("Test_0001_Line_0027__A11_in_header_sane", _28776)
^ Call: (95) [pfc_test] writeln('<?xml version="1.0" encoding="utf-8"?>'), j_u:junit_prop(testsuite, file, _47170), writeln(" <testsuites>"), (getenv('JUNIT_SUITE', _47206);_47206=_47170), !, get_suite_attribs(_47228), format(" <testsuite name=\"~w\" ~w>\n", [_47206|...]), show_junit_testcase(_47170, "Test_0001_Line_0027__A11_in_header_sane"), writeln(...), writeln(...)
^ Unify: (95) [system] pfc_test:writeln('<?xml version="1.0" encoding="utf-8"?>'), pfc_test:(j_u:junit_prop(testsuite, file, _47170), writeln(" <testsuites>"), (getenv('JUNIT_SUITE', _47206);_47206=_47170), !, get_suite_attribs(_47228), format(" <testsuite name=\"~w\" ~w>\n", [...|...]), show_junit_testcase(..., ...), ..., ...)
Call: (97) [system] writeln('<?xml version="1.0" encoding="utf-8"?>')
Exit: (97) [system] writeln('<?xml version="1.0" encoding="utf-8"?>')
Call: (97) [j_u] j_u:junit_prop(testsuite, file, _47170)
Fail: (97) [j_u] j_u:junit_prop(testsuite, file, _47170)
^ Fail: (95) [system] pfc_test:writeln('<?xml version="1.0" encoding="utf-8"?>'), pfc_test:(j_u:junit_prop(testsuite, file, _47170), writeln(" <testsuites>"), (getenv('JUNIT_SUITE', _47206);_47206=_47170), !, get_suite_attribs(_47228), format(" <testsuite name=\"~w\" ~w>\n", [...|...]), show_junit_testcase(..., ...), ..., ...)
^ Fail: (92) [pfc_test] save_single_testcase_shrink("Test_0001_Line_0027__A11_in_header_sane", _28776)
^ Call: (93) [locally_each] locally_each:key_erase(t_l)
^ Unify: (93) [locally_each] locally_each:key_erase(t_l)
Call: (94) [system] nb_current('$w_tl_e', [_53522|_53524])
Exit: (94) [system] nb_current('$w_tl_e', [<clause>(0x5636aa6850e0), <clause>(0x5636aa723290)])
Call: (94) [system] nb_linkval('$w_tl_e', [<clause>(0x5636aa723290)])
Exit: (94) [system] nb_linkval('$w_tl_e', [<clause>(0x5636aa723290)])
Call: (95) [system] erase(<clause>(0x5636aa6850e0))
Exit: (95) [system] erase(<clause>(0x5636aa6850e0))
Call: (94) [system] true
Exit: (94) [system] true
Call: (94) [system] true
Exit: (94) [system] true
^ Exit: (93) [locally_each] locally_each:key_erase(t_l)
^ Fail: (82) [pfc_test] save_single_testcase("Test_0001_Line_0027__A11_in_header_sane")
^ Call: (82) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)
^ Unify: (82) [must_sanity] must_sanity:mquietly_if(true, rtrace:tAt_normal)
%~ FILE: * https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/fc_01r.pfc#L27
```
totalTime=10
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AFC_01R
GITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc
Latest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/
This Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/FC_01R/logicmoo_pfc_test_sanity_base_FC_01R_JUnit/
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/fc_01r.pfc
FAILED: /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-junit-minor -k fc_01r.pfc (returned 137)
| non_priority | logicmoo pfc test sanity base fc junit cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc gh master issue finfo issue search gitlab latest this build github make dynamic here header sane nt test header include make dynamic here header sane genlpreds kb shared make dynamic here header sane make dynamic here header sane mpred test test line in header sane header sane call header sane fail header sane call must sanity mquietly if true rtrace tat normal unify must sanity mquietly if true rtrace tat normal failure info why was true header sane rtrace header sane no proof for no proof for no proof for show must go on failed f a i l pfc test save single testcase test line in header sane file c call prolog no clause catch toplevel initialise prolog a toplevel initialise error a init pl initialise prolog toplevel pl load associated files toplevel pl load file fc pfc user init pl sig atomic setup call cleanup with mutex load file mt start load mt do load fc pfc user mt end load no clause c call prolog no clause setup call catcher cleanup system with mutex load file mt start load system mt do load fc pfc user a system mt end load init pl qdo load file fc pfc user init pl do load file fc pfc user compiled init pl setup call catcher cleanup system start consult system load file a b system end consult lexstate swi user init pl load file a init pl compile term mpred test a init pl compile term mpred test a init pl execute directive mpred test init pl execute directive mpred test init pl execute directive mpred test init pl catch header sane mpred test error a b system exception in directive error a b init pl pfc test mpred test header sane pfc test pl pfc test mpred test test line in header sane header sane pfc test pl pfc test mpred test fok test line in header sane header sane pfc test pl locally each locally t l mpred current testcase test line in header sane pfc test wdmsg mpred test test line in header sane header sane add test info test line in header sane goal header sane ignore source location atom add test info test line in header sane src sformat var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc w l w replace in string var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc add test info test line in header sane url var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc get time nb nb catch call u hook header sane failure passed failure failure a failure error a ignore nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee failure error a throw a true nb setarg nb redo locally pl locally each wtl t l mpred current testcase test line in header sane pfc test wdmsg mpred test test line in header sane header sane add test info test line in header sane goal header sane ignore source location atom add test info test line in header sane src sformat var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc w l w replace in string var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc add test info test line in header sane url var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc get time nb nb catch call u hook header sane failure passed failure failure a failure error a ignore nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee failure error a throw a true nb setarg nb pfc test ecc redo locally pl locally each wtl t l t l mpred current testcase test line in header sane pfc test wdmsg mpred test test line in header sane header sane add test info test line in header sane goal header sane ignore source location atom add test info test line in header sane src sformat var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc w l w replace in string var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc add test info test line in header sane url var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc get time nb nb catch call u hook header sane failure passed failure failure a failure error a ignore nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee failure error a throw a true nb setarg nb pfc test ecc redo locally pl locally each wtl how pfc test ecc locally each clause true t l t l mpred current testcase test line in header sane locally each key asserta t l t l mpred current testcase test line in header sane pfc test wdmsg mpred test test line in header sane header sane add test info test line in header sane goal header sane ignore source location atom add test info test line in header sane src sformat var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc w l w replace in string var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc add test info test line in header sane url var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc get time nb nb catch call u hook header sane failure passed failure failure a failure error a ignore nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee failure error a throw a true nb setarg nb locally each key erase t l redo locally pl each call cleanup each call cleanup locally each key asserta t l t l mpred current testcase test line in header sane pfc test wdmsg mpred test test line in header sane header sane add test info test line in header sane goal header sane ignore source location atom add test info test line in header sane src sformat var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc w l w replace in string var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc add test info test line in header sane url var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc get time nb nb catch call u hook header sane failure passed failure failure a failure error a ignore nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee failure error a throw a true nb setarg nb locally each key erase t l each call pl each call cleanup trusted redo call cleanup locally each key asserta t l t l mpred current testcase test line in header sane pfc test wdmsg mpred test test line in header sane header sane add test info test line in header sane goal header sane ignore source location atom add test info test line in header sane src sformat var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc w l w replace in string var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc add test info test line in header sane url var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc get time nb nb catch call u hook header sane failure passed failure failure a failure error a ignore nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee failure error a throw a true nb setarg nb locally each key erase t l each call pl setup call cleanup locally each key asserta t l t l mpred current testcase test line in header sane each call cleanup pfc test wdmsg mpred test test line in header sane header sane add test info test line in header sane goal header sane ignore source location atom add test info test line in header sane src sformat var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc w l w replace in string var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc add test info test line in header sane url var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc get time nb nb catch call u hook header sane failure passed failure failure a failure error a ignore nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee failure error a throw a true nb setarg nb deterministic b notrace b true mquietly locally each key erase t l notrace nb setarg mquietly locally each key erase t l true locally each key asserta t l t l mpred current testcase test line in header sane notrace nb setarg mquietly locally each key erase t l locally each key erase t l notrace fail each call cleanup mquietly locally each key erase t l init pl setup call catcher cleanup locally each key asserta t l t l mpred current testcase test line in header sane each call cleanup pfc test wdmsg mpred test test line in header sane header sane add test info test line in header sane goal header sane ignore source location atom add test info test line in header sane src sformat var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc w l w replace in string var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc add test info test line in header sane url var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc get time nb nb catch call u hook header sane failure passed failure failure a failure error a ignore nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee failure error a throw a true nb setarg nb deterministic b notrace b true mquietly locally each key erase t l notrace nb setarg mquietly locally each key erase t l true locally each key asserta t l t l mpred current testcase test line in header sane notrace nb setarg mquietly locally each key erase t l locally each key erase t l notrace fail c each call cleanup mquietly locally each key erase t l init pl each call cleanup pfc test wdmsg mpred test test line in header sane header sane add test info test line in header sane goal header sane ignore source location atom add test info test line in header sane src sformat var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc w l w replace in string var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc add test info test line in header sane url var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base fc pfc get time nb nb catch call u hook header sane failure passed failure failure a failure error a ignore nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee failure error a throw a true nb setarg nb deterministic b notrace b true mquietly locally each key erase t l notrace nb setarg mquietly locally each key erase t l true locally each key asserta t l t l mpred current testcase test line in header sane notrace nb setarg mquietly locally each key erase t l locally each key erase t l notrace fail no clause ignore pfc test nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee init pl pfc test nb nb get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee no clause ucatch pfc test get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee ucatch pl ucatch call each must det u pfc test get time is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee ucatch pl ucatch call each must det u pfc test is add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee ucatch pl ucatch call each must det u pfc test add test info test line in header sane time process test result failure header sane failure add test info test line in header sane failure add test info test line in header sane result failure ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee ucatch pl ucatch call each must det u pfc test ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee ucatch pl ucatch p call must det u pfc test ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee ucatch pl ucatch pfc test ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee ucatch pl must sanity pfc test ignore getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee must sanity pl ignore pfc test getenv tee file read file to string cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n add test info test line in header sane out cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif fc pfc n ngh master issue finfo n nissue search ngitlab n nlatest nthis build ngithub n n n n n n make dynamic here header sane nt test header include n make dynamic here header sane genlpreds kb shared n make dynamic here header sane n make dynamic here header sane n mpred test test line in header sane header sane n call header sane n fail header sane n call must sanity mquietly if true rtrace tat normal n unify must sanity mquietly if true rtrace tat normal nfailure info why was true header sane rtrace header sane nno proof for n nno proof for n nno proof for n n save single testcase test line in header sane nop kill junit tee init pl ucatch call each must det u pfc test save single testcase test line in header sane nop kill junit tee ucatch pl ucatch call each must det u pfc test save single testcase test line in header sane ucatch pl ucatch p call must det u pfc test save single testcase test line in header sane ucatch pl ucatch pfc test save single testcase test line in header sane ucatch pl must sanity pfc test save single testcase test line in header sane must sanity pl locally each wtl how locally each trusted redo call cleanup locally each false true must sanity set prolog flag debug on error false must sanity catch pfc test save single testcase test line in header sane a xnotrace dumpst error show must go on xi xi xi xi xi a pfc test save single testcase test line in header sane ignore rtrace pfc test save single testcase test line in header sane badfood pfc test save single testcase test line in header sane true xnotrace dumpst error show must go on failed f a i l pfc test save single testcase test line in header sane ignore rtrace pfc test save single testcase test line in header sane badfood pfc test save single testcase test line in header sane must sanity set prolog flag debug on error true redo locally pl setup call catcher cleanup must sanity set prolog flag debug on error false each call cleanup must sanity catch pfc test save single testcase test line in header sane a xnotrace dumpst error show must go on xi xi xi xi xi a pfc test save single testcase test line in header sane ignore rtrace pfc test save single testcase test line in header sane badfood pfc test save single testcase test line in header sane true xnotrace dumpst error show must go on failed f a i l pfc test save single testcase test line in header sane ignore rtrace pfc test save single testcase test line in header sane badfood pfc test save single testcase test line in header sane deterministic b notrace b true mquietly must sanity set prolog flag debug on error true notrace nb setarg mquietly must sanity set prolog flag debug on error true true must sanity set prolog flag debug on error false notrace nb setarg mquietly must sanity set prolog flag debug on error true must sanity set prolog flag debug on error true notrace fail c each call cleanup mquietly must sanity set prolog flag debug on error true init pl each call cleanup must sanity catch pfc test save single testcase test line in header sane a xnotrace dumpst error show must go on xi xi xi xi xi a pfc test save single testcase test line in header sane ignore rtrace pfc test save single testcase test line in header sane badfood pfc test save single testcase test line in header sane true xnotrace dumpst error show must go on failed f a i l pfc test save single testcase test line in header sane ignore rtrace pfc test save single testcase test line in header sane badfood pfc test save single testcase test line in header sane deterministic b notrace b true mquietly must sanity set prolog flag debug on error true notrace nb setarg mquietly must sanity set prolog flag debug on error true true must sanity set prolog flag debug on error false notrace nb setarg mquietly must sanity set prolog flag debug on error true must sanity set prolog flag debug on error true notrace fail no clause must sanity xnotrace dumpst error show must go on failed f a i l pfc test save single testcase test line in header sane must sanity pl notrace ddmsg error show must go on failed f a i l pfc test save single testcase test line in header sane dumpst wdmsg error show must go on failed f a i l pfc test save single testcase test line in header sane no clause c call prolog no clause must sanity ddmsg error show must go on failed f a i l pfc test save single testcase test line in header sane must sanity dumpst wdmsg error show must go on failed f a i l pfc test save single testcase test line in header sane init pl must sanity ddmsg error show must go on failed f a i l pfc test save single testcase test line in header sane must sanity dumpst wdmsg error show must go on failed f a i l pfc test save single testcase test line in header sane no clause butterfly in bfly f must sanity zotrace with all dmsg b setval dump frame butterfly console pl error show must go on failed f a i l pfc test save single testcase test line in header sane call save single testcase test line in header sane unify save single testcase test line in header sane call must sanity mquietly if false rtrace tat rtrace unify must sanity mquietly if false rtrace tat rtrace exit must sanity mquietly if false rtrace tat rtrace call must sanity mquietly if false rtrace tat rtrace unify must sanity mquietly if false rtrace tat rtrace exit must sanity mquietly if false rtrace tat rtrace call must sanity mquietly if false rtrace tat rtrace unify must sanity mquietly if false rtrace tat rtrace exit must sanity mquietly if false rtrace tat rtrace call locally each clause true t l t l dont shrink unify locally each clause true t l t l dont shrink call copy term t l dont shrink exit copy term t l dont shrink t l dont shrink call clause t l dont shrink true fail clause t l dont shrink true fail locally each clause true t l t l dont shrink call locally each key asserta t l t l dont shrink unify locally each key asserta t l t l dont shrink call asserta t l dont shrink exit asserta t l dont shrink call nb current w tl e exit nb current w tl e call nb linkval w tl e exit nb linkval w tl e exit locally each key asserta t l t l dont shrink call save single testcase shrink test line in header sane unify save single testcase shrink test line in header sane call writeln j u junit prop testsuite file writeln getenv junit suite get suite attribs format n show junit testcase test line in header sane writeln writeln unify pfc test writeln pfc test j u junit prop testsuite file writeln getenv junit suite get suite attribs format n show junit testcase call writeln exit writeln call j u junit prop testsuite file fail j u junit prop testsuite file fail pfc test writeln pfc test j u junit prop testsuite file writeln getenv junit suite get suite attribs format n show junit testcase fail save single testcase shrink test line in header sane call locally each key erase t l unify locally each key erase t l call nb current w tl e exit nb current w tl e call nb linkval w tl e exit nb linkval w tl e call erase exit erase call true exit true call true exit true exit locally each key erase t l fail save single testcase test line in header sane call must sanity mquietly if true rtrace tat normal unify must sanity mquietly if true rtrace tat normal file totaltime issue search gitlab latest this build github failed var lib jenkins workspace logicmoo workspace bin lmoo junit minor k fc pfc returned | 0 |
27,373 | 12,546,810,833 | IssuesEvent | 2020-06-05 21:26:47 | Azure/azure-sdk-for-net | https://api.github.com/repos/Azure/azure-sdk-for-net | opened | Update service version | Client Cognitive Services FormRecognizer | When the service releases their GA version, and we consume it, we need to update our docs/samples to match service version | 1.0 | Update service version - When the service releases their GA version, and we consume it, we need to update our docs/samples to match service version | non_priority | update service version when the service releases their ga version and we consume it we need to update our docs samples to match service version | 0 |
69,126 | 14,970,075,920 | IssuesEvent | 2021-01-27 19:04:31 | jgeraigery/experian-java | https://api.github.com/repos/jgeraigery/experian-java | closed | CVE-2020-14195 (High) detected in jackson-databind-2.9.2.jar - autoclosed | security vulnerability | ## CVE-2020-14195 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: experian-java/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.2/jackson-databind-2.9.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/experian-java/commit/e2b236143990842a0d83d97532011829192916a7">e2b236143990842a0d83d97532011829192916a7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).
<p>Publish Date: 2020-06-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195>CVE-2020-14195</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195</a></p>
<p>Release Date: 2020-06-16</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.2","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.5"}],"vulnerabilityIdentifier":"CVE-2020-14195","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-14195 (High) detected in jackson-databind-2.9.2.jar - autoclosed - ## CVE-2020-14195 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: experian-java/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.2/jackson-databind-2.9.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/experian-java/commit/e2b236143990842a0d83d97532011829192916a7">e2b236143990842a0d83d97532011829192916a7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).
<p>Publish Date: 2020-06-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195>CVE-2020-14195</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195</a></p>
<p>Release Date: 2020-06-16</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.2","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.5"}],"vulnerabilityIdentifier":"CVE-2020-14195","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file experian java mavenworkspace bis services lib bis services base pom xml path to vulnerable library canner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org jsecurity realm jndi jndirealmfactory aka org jsecurity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org jsecurity realm jndi jndirealmfactory aka org jsecurity vulnerabilityurl | 0 |
243,790 | 20,573,950,881 | IssuesEvent | 2022-03-04 01:04:28 | Blade1996/repoTest | https://api.github.com/repos/Blade1996/repoTest | opened | I:[2](PRODUCT) - Registro y validacion de product | repoTest issue | **Topic**
_**Required.** Link to this issue's "Topic" on GitHub, if applicable. If the
issue doesn't belong to a Topic, "N/A" should be added to this section._
**Description**
_**Required.**_
**Acceptance Test**
_**Required.**_
**Implementation Notes**
_**Required.** Write "none" if you think that there are not implementation notes._
**Subtasks**
_**Required.** Write "N/A" if there are not subtasks._
**Planning Estimate**
_**Required.** Write "TBD" if the
estimate is not yet ready and add the `needs-estimate` label._
**References**
_**Required.**_
**Latest Assets**
_**Required.** If there are
no assets, "N/A" should be added to this section._
| 1.0 | I:[2](PRODUCT) - Registro y validacion de product - **Topic**
_**Required.** Link to this issue's "Topic" on GitHub, if applicable. If the
issue doesn't belong to a Topic, "N/A" should be added to this section._
**Description**
_**Required.**_
**Acceptance Test**
_**Required.**_
**Implementation Notes**
_**Required.** Write "none" if you think that there are not implementation notes._
**Subtasks**
_**Required.** Write "N/A" if there are not subtasks._
**Planning Estimate**
_**Required.** Write "TBD" if the
estimate is not yet ready and add the `needs-estimate` label._
**References**
_**Required.**_
**Latest Assets**
_**Required.** If there are
no assets, "N/A" should be added to this section._
| non_priority | i product registro y validacion de product topic required link to this issue s topic on github if applicable if the issue doesn t belong to a topic n a should be added to this section description required acceptance test required implementation notes required write none if you think that there are not implementation notes subtasks required write n a if there are not subtasks planning estimate required write tbd if the estimate is not yet ready and add the needs estimate label references required latest assets required if there are no assets n a should be added to this section | 0 |
422,911 | 28,486,899,319 | IssuesEvent | 2023-04-18 08:30:00 | mullvad/mullvad-browser | https://api.github.com/repos/mullvad/mullvad-browser | opened | How many buckets of users from Operating Systems? | documentation fingerprinting | > It is mentioned that "Mullvad Browser is specifically engineered to have a nearly identical (we're not perfect!) fingerprint across its users per operating system." Does this mean that Mullvad Browser users are placed into 3 possible OS fingerprinting buckets (Windows, macOS, Linux) depending on the OS ("per operating system")? | 1.0 | How many buckets of users from Operating Systems? - > It is mentioned that "Mullvad Browser is specifically engineered to have a nearly identical (we're not perfect!) fingerprint across its users per operating system." Does this mean that Mullvad Browser users are placed into 3 possible OS fingerprinting buckets (Windows, macOS, Linux) depending on the OS ("per operating system")? | non_priority | how many buckets of users from operating systems it is mentioned that mullvad browser is specifically engineered to have a nearly identical we re not perfect fingerprint across its users per operating system does this mean that mullvad browser users are placed into possible os fingerprinting buckets windows macos linux depending on the os per operating system | 0 |
73,734 | 15,281,602,022 | IssuesEvent | 2021-02-23 08:22:57 | pwc-technology-be/eu-captcha | https://api.github.com/repos/pwc-technology-be/eu-captcha | closed | CVE-2020-8908 (Low) detected in guava-29.0-jre.jar | security vulnerability | ## CVE-2020-8908 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>guava-29.0-jre.jar</b></p></summary>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.</p>
<p>Library home page: <a href="https://github.com/google/guava">https://github.com/google/guava</a></p>
<p>Path to dependency file: eu-captcha/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/google/guava/guava/29.0-jre/guava-29.0-jre.jar,eu-captcha/target/EuCaptcha/WEB-INF/lib/guava-29.0-jre.jar</p>
<p>
Dependency Hierarchy:
- :x: **guava-29.0-jre.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A temp directory creation vulnerability exists in all versions of Guava, allowing an attacker with access to the machine to potentially access data in a temporary directory created by the Guava API com.google.common.io.Files.createTempDir(). By default, on unix-like systems, the created directory is world-readable (readable by an attacker with access to the system). The method in question has been marked @Deprecated in versions 30.0 and later and should not be used. For Android developers, we recommend choosing a temporary directory API provided by Android, such as context.getCacheDir(). For other Java developers, we recommend migrating to the Java 7 API java.nio.file.Files.createTempDirectory() which explicitly configures permissions of 700, or configuring the Java runtime's java.io.tmpdir system property to point to a location whose permissions are appropriately configured.
<p>Publish Date: 2020-12-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8908>CVE-2020-8908</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908</a></p>
<p>Release Date: 2020-12-10</p>
<p>Fix Resolution: v30.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-8908 (Low) detected in guava-29.0-jre.jar - ## CVE-2020-8908 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>guava-29.0-jre.jar</b></p></summary>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.</p>
<p>Library home page: <a href="https://github.com/google/guava">https://github.com/google/guava</a></p>
<p>Path to dependency file: eu-captcha/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/google/guava/guava/29.0-jre/guava-29.0-jre.jar,eu-captcha/target/EuCaptcha/WEB-INF/lib/guava-29.0-jre.jar</p>
<p>
Dependency Hierarchy:
- :x: **guava-29.0-jre.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A temp directory creation vulnerability exists in all versions of Guava, allowing an attacker with access to the machine to potentially access data in a temporary directory created by the Guava API com.google.common.io.Files.createTempDir(). By default, on unix-like systems, the created directory is world-readable (readable by an attacker with access to the system). The method in question has been marked @Deprecated in versions 30.0 and later and should not be used. For Android developers, we recommend choosing a temporary directory API provided by Android, such as context.getCacheDir(). For other Java developers, we recommend migrating to the Java 7 API java.nio.file.Files.createTempDirectory() which explicitly configures permissions of 700, or configuring the Java runtime's java.io.tmpdir system property to point to a location whose permissions are appropriately configured.
<p>Publish Date: 2020-12-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8908>CVE-2020-8908</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908</a></p>
<p>Release Date: 2020-12-10</p>
<p>Fix Resolution: v30.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve low detected in guava jre jar cve low severity vulnerability vulnerable library guava jre jar guava is a suite of core and expanded libraries that include utility classes google s collections io classes and much much more library home page a href path to dependency file eu captcha pom xml path to vulnerable library canner repository com google guava guava jre guava jre jar eu captcha target eucaptcha web inf lib guava jre jar dependency hierarchy x guava jre jar vulnerable library vulnerability details a temp directory creation vulnerability exists in all versions of guava allowing an attacker with access to the machine to potentially access data in a temporary directory created by the guava api com google common io files createtempdir by default on unix like systems the created directory is world readable readable by an attacker with access to the system the method in question has been marked deprecated in versions and later and should not be used for android developers we recommend choosing a temporary directory api provided by android such as context getcachedir for other java developers we recommend migrating to the java api java nio file files createtempdirectory which explicitly configures permissions of or configuring the java runtime s java io tmpdir system property to point to a location whose permissions are appropriately configured publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
256,920 | 22,111,657,649 | IssuesEvent | 2022-06-01 21:50:53 | apache/accumulo | https://api.github.com/repos/apache/accumulo | closed | Broken or Flaky test: PermissionsIT | bug test | PermissionsIT test methods are failing after merging #2707
| 1.0 | Broken or Flaky test: PermissionsIT - PermissionsIT test methods are failing after merging #2707
| non_priority | broken or flaky test permissionsit permissionsit test methods are failing after merging | 0 |
66,605 | 7,008,323,652 | IssuesEvent | 2017-12-19 15:23:39 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | Test: randomValueOtherThan confusing with nulls | bug test | `ESTestCase#randomValueOtherThan` ignores nulls. This is it now:
```
/**
* helper to get a random value in a certain range that's different from the input
*/
public static <T> T randomValueOtherThan(T input, Supplier<T> randomSupplier) {
if (input != null) {
return randomValueOtherThanMany(input::equals, randomSupplier);
}
return(randomSupplier.get());
}
```
So if you pass in `null` it'll just run the supplier one time. I think this is confusing - if you pass in null it shouldn't return null. I think something like:
```
/**
* helper to get a random value in a certain range that's different from the input
*/
public static <T> T randomValueOtherThan(T input, Supplier<T> randomSupplier) {
return randomValueOtherThanMany(v -> Object.equals(input, v), randomSupplier);
}
```
Would be better. Discuss? | 1.0 | Test: randomValueOtherThan confusing with nulls - `ESTestCase#randomValueOtherThan` ignores nulls. This is it now:
```
/**
* helper to get a random value in a certain range that's different from the input
*/
public static <T> T randomValueOtherThan(T input, Supplier<T> randomSupplier) {
if (input != null) {
return randomValueOtherThanMany(input::equals, randomSupplier);
}
return(randomSupplier.get());
}
```
So if you pass in `null` it'll just run the supplier one time. I think this is confusing - if you pass in null it shouldn't return null. I think something like:
```
/**
* helper to get a random value in a certain range that's different from the input
*/
public static <T> T randomValueOtherThan(T input, Supplier<T> randomSupplier) {
return randomValueOtherThanMany(v -> Object.equals(input, v), randomSupplier);
}
```
Would be better. Discuss? | non_priority | test randomvalueotherthan confusing with nulls estestcase randomvalueotherthan ignores nulls this is it now helper to get a random value in a certain range that s different from the input public static t randomvalueotherthan t input supplier randomsupplier if input null return randomvalueotherthanmany input equals randomsupplier return randomsupplier get so if you pass in null it ll just run the supplier one time i think this is confusing if you pass in null it shouldn t return null i think something like helper to get a random value in a certain range that s different from the input public static t randomvalueotherthan t input supplier randomsupplier return randomvalueotherthanmany v object equals input v randomsupplier would be better discuss | 0 |
102,240 | 31,879,868,436 | IssuesEvent | 2023-09-16 08:34:44 | python/cpython | https://api.github.com/repos/python/cpython | closed | Compile warning in `_testcapi/dict.c` on macos | type-bug build | # Bug report
When you compile CPython on macos, you get:
```
gcc -fno-strict-overflow -Wsign-compare -g -Og -Wall -I/Library/Developer/CommandLineTools/SDKs/MacOSX.sdk/usr/include -I/Library/Developer/CommandLineTools/SDKs/MacOSX.sdk/usr/include -std=c11 -Wextra -Wno-unused-parameter -Wno-missing-field-initializers -Wstrict-prototypes -Werror=implicit-function-declaration -fvisibility=hidden -I./Include/internal -I. -I./Include -I/opt/homebrew/opt/openssl/include -I/opt/homebrew/opt/openssl/include -c ./Modules/_testcapi/dict.c -o Modules/_testcapi/dict.o
./Modules/_testcapi/dict.c:289:16: warning: result of comparison against a string literal is unspecified (use an explicit string comparison function instead) [-Wstring-compare]
assert(key == UNINITIALIZED_PTR);
^ ~~~~~~~~~~~~~~~~~
/Library/Developer/CommandLineTools/SDKs/MacOSX.sdk/usr/include/assert.h:99:25: note: expanded from macro 'assert'
(__builtin_expect(!(e), 0) ? __assert_rtn(__func__, __ASSERT_FILE_NAME, __LINE__, #e) : (void)0)
^
./Modules/_testcapi/dict.c:290:18: warning: result of comparison against a string literal is unspecified (use an explicit string comparison function instead) [-Wstring-compare]
assert(value == UNINITIALIZED_PTR);
^ ~~~~~~~~~~~~~~~~~
/Library/Developer/CommandLineTools/SDKs/MacOSX.sdk/usr/include/assert.h:99:25: note: expanded from macro 'assert'
(__builtin_expect(!(e), 0) ? __assert_rtn(__func__, __ASSERT_FILE_NAME, __LINE__, #e) : (void)0)
^
2 warnings generated.
```
It is defined as:
```c
/* Marker to check that pointer value was set. */
#define UNINITIALIZED_PTR ((void *)"uninitialized")
``` | 1.0 | Compile warning in `_testcapi/dict.c` on macos - # Bug report
When you compile CPython on macos, you get:
```
gcc -fno-strict-overflow -Wsign-compare -g -Og -Wall -I/Library/Developer/CommandLineTools/SDKs/MacOSX.sdk/usr/include -I/Library/Developer/CommandLineTools/SDKs/MacOSX.sdk/usr/include -std=c11 -Wextra -Wno-unused-parameter -Wno-missing-field-initializers -Wstrict-prototypes -Werror=implicit-function-declaration -fvisibility=hidden -I./Include/internal -I. -I./Include -I/opt/homebrew/opt/openssl/include -I/opt/homebrew/opt/openssl/include -c ./Modules/_testcapi/dict.c -o Modules/_testcapi/dict.o
./Modules/_testcapi/dict.c:289:16: warning: result of comparison against a string literal is unspecified (use an explicit string comparison function instead) [-Wstring-compare]
assert(key == UNINITIALIZED_PTR);
^ ~~~~~~~~~~~~~~~~~
/Library/Developer/CommandLineTools/SDKs/MacOSX.sdk/usr/include/assert.h:99:25: note: expanded from macro 'assert'
(__builtin_expect(!(e), 0) ? __assert_rtn(__func__, __ASSERT_FILE_NAME, __LINE__, #e) : (void)0)
^
./Modules/_testcapi/dict.c:290:18: warning: result of comparison against a string literal is unspecified (use an explicit string comparison function instead) [-Wstring-compare]
assert(value == UNINITIALIZED_PTR);
^ ~~~~~~~~~~~~~~~~~
/Library/Developer/CommandLineTools/SDKs/MacOSX.sdk/usr/include/assert.h:99:25: note: expanded from macro 'assert'
(__builtin_expect(!(e), 0) ? __assert_rtn(__func__, __ASSERT_FILE_NAME, __LINE__, #e) : (void)0)
^
2 warnings generated.
```
It is defined as:
```c
/* Marker to check that pointer value was set. */
#define UNINITIALIZED_PTR ((void *)"uninitialized")
``` | non_priority | compile warning in testcapi dict c on macos bug report when you compile cpython on macos you get gcc fno strict overflow wsign compare g og wall i library developer commandlinetools sdks macosx sdk usr include i library developer commandlinetools sdks macosx sdk usr include std wextra wno unused parameter wno missing field initializers wstrict prototypes werror implicit function declaration fvisibility hidden i include internal i i include i opt homebrew opt openssl include i opt homebrew opt openssl include c modules testcapi dict c o modules testcapi dict o modules testcapi dict c warning result of comparison against a string literal is unspecified use an explicit string comparison function instead assert key uninitialized ptr library developer commandlinetools sdks macosx sdk usr include assert h note expanded from macro assert builtin expect e assert rtn func assert file name line e void modules testcapi dict c warning result of comparison against a string literal is unspecified use an explicit string comparison function instead assert value uninitialized ptr library developer commandlinetools sdks macosx sdk usr include assert h note expanded from macro assert builtin expect e assert rtn func assert file name line e void warnings generated it is defined as c marker to check that pointer value was set define uninitialized ptr void uninitialized | 0 |
27,688 | 11,551,318,735 | IssuesEvent | 2020-02-19 01:05:07 | doc-ai/react-native-animatable | https://api.github.com/repos/doc-ai/react-native-animatable | opened | WS-2019-0332 (Medium) detected in handlebars-4.1.2.tgz | security vulnerability | ## WS-2019-0332 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /react-native-animatable/package.json</p>
<p>Path to vulnerable library: /tmp/git/react-native-animatable/node_modules/handlebars/package.json,/tmp/git/react-native-animatable/node_modules/handlebars/package.json,/tmp/git/react-native-animatable/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- jest-22.3.0.tgz (Root Library)
- jest-cli-22.4.4.tgz
- istanbul-api-1.3.7.tgz
- istanbul-reports-1.5.1.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability found in handlebars before 4.5.3. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.It is due to an incomplete fix for a WS-2019-0331.
<p>Publish Date: 2019-12-05
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/198887808780bbef9dba67a8af68ece091d5baa7>WS-2019-0332</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1324">https://www.npmjs.com/advisories/1324</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"handlebars","packageVersion":"4.1.2","isTransitiveDependency":true,"dependencyTree":"jest:22.3.0;jest-cli:22.4.4;istanbul-api:1.3.7;istanbul-reports:1.5.1;handlebars:4.1.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"handlebars - 4.5.3"}],"vulnerabilityIdentifier":"WS-2019-0332","vulnerabilityDetails":"Arbitrary Code Execution vulnerability found in handlebars before 4.5.3. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.It is due to an incomplete fix for a WS-2019-0331.","vulnerabilityUrl":"https://github.com/wycats/handlebars.js/commit/198887808780bbef9dba67a8af68ece091d5baa7","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}</REMEDIATE> --> | True | WS-2019-0332 (Medium) detected in handlebars-4.1.2.tgz - ## WS-2019-0332 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /react-native-animatable/package.json</p>
<p>Path to vulnerable library: /tmp/git/react-native-animatable/node_modules/handlebars/package.json,/tmp/git/react-native-animatable/node_modules/handlebars/package.json,/tmp/git/react-native-animatable/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- jest-22.3.0.tgz (Root Library)
- jest-cli-22.4.4.tgz
- istanbul-api-1.3.7.tgz
- istanbul-reports-1.5.1.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability found in handlebars before 4.5.3. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.It is due to an incomplete fix for a WS-2019-0331.
<p>Publish Date: 2019-12-05
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/198887808780bbef9dba67a8af68ece091d5baa7>WS-2019-0332</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1324">https://www.npmjs.com/advisories/1324</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"handlebars","packageVersion":"4.1.2","isTransitiveDependency":true,"dependencyTree":"jest:22.3.0;jest-cli:22.4.4;istanbul-api:1.3.7;istanbul-reports:1.5.1;handlebars:4.1.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"handlebars - 4.5.3"}],"vulnerabilityIdentifier":"WS-2019-0332","vulnerabilityDetails":"Arbitrary Code Execution vulnerability found in handlebars before 4.5.3. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.It is due to an incomplete fix for a WS-2019-0331.","vulnerabilityUrl":"https://github.com/wycats/handlebars.js/commit/198887808780bbef9dba67a8af68ece091d5baa7","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in handlebars tgz ws medium severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file react native animatable package json path to vulnerable library tmp git react native animatable node modules handlebars package json tmp git react native animatable node modules handlebars package json tmp git react native animatable node modules handlebars package json dependency hierarchy jest tgz root library jest cli tgz istanbul api tgz istanbul reports tgz x handlebars tgz vulnerable library vulnerability details arbitrary code execution vulnerability found in handlebars before lookup helper fails to validate templates attack may submit templates that execute arbitrary javascript in the system it is due to an incomplete fix for a ws publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution handlebars isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails arbitrary code execution vulnerability found in handlebars before lookup helper fails to validate templates attack may submit templates that execute arbitrary javascript in the system it is due to an incomplete fix for a ws vulnerabilityurl | 0 |
23,702 | 7,370,069,822 | IssuesEvent | 2018-03-13 06:45:06 | ShaikASK/Testing | https://api.github.com/repos/ShaikASK/Testing | closed | Email_templates::Edit Email Template - Unable to remove the uploaded files | Build Version #09 Defect P2 SumFive Team | Steps To Replicate :
1. Launch the url
2. Login with Admin credentials
3. Navigate to "Settings" menu
4. Select "Email templates" tab
5. Create a new Email template [with uploading a file]
6. Navigate to the above created 'Email template' >> select Edit option
7. Navigate to "Attachment" section
8. click on (x) symbol displayed in 'Attachment' section right after the file name
Experienced Behavior : Observed that upon clicking (X) icon nothing is happening
Expected Behavior : Ensure that the uploaded file should get deleted once the user clicks on (X) symbol.
| 1.0 | Email_templates::Edit Email Template - Unable to remove the uploaded files - Steps To Replicate :
1. Launch the url
2. Login with Admin credentials
3. Navigate to "Settings" menu
4. Select "Email templates" tab
5. Create a new Email template [with uploading a file]
6. Navigate to the above created 'Email template' >> select Edit option
7. Navigate to "Attachment" section
8. click on (x) symbol displayed in 'Attachment' section right after the file name
Experienced Behavior : Observed that upon clicking (X) icon nothing is happening
Expected Behavior : Ensure that the uploaded file should get deleted once the user clicks on (X) symbol.
| non_priority | email templates edit email template unable to remove the uploaded files steps to replicate launch the url login with admin credentials navigate to settings menu select email templates tab create a new email template navigate to the above created email template select edit option navigate to attachment section click on x symbol displayed in attachment section right after the file name experienced behavior observed that upon clicking x icon nothing is happening expected behavior ensure that the uploaded file should get deleted once the user clicks on x symbol | 0 |
56,485 | 23,794,781,764 | IssuesEvent | 2022-09-02 18:16:34 | microsoft/BotFramework-WebChat | https://api.github.com/repos/microsoft/BotFramework-WebChat | closed | SendBoxDisable dialogue tag displaying text on canvas. | bug customer-reported Bot Services customer-replied-to area-skylight | ### Is it an issue related to Adaptive Cards?
- [ ] Yes, this is an Adaptive Card issue but it is specific to Web Chat.
### Do you have any screenshots?
Activity looks like this :
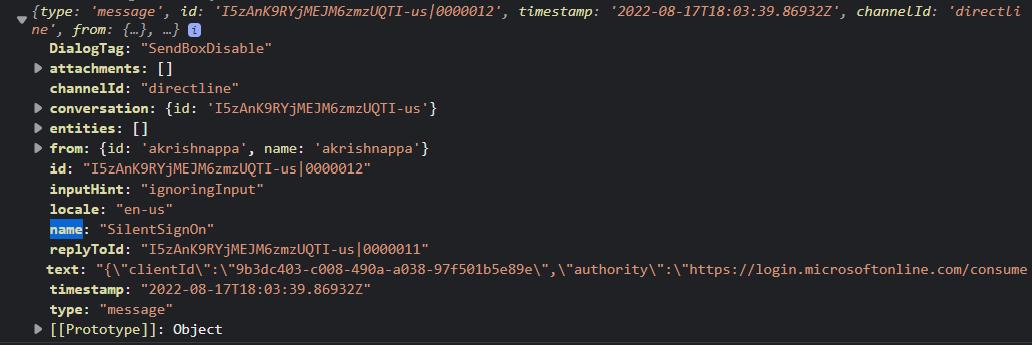
This is how it is displayed on canvas :

If I make this activity.textHidden = true
it is sending this activity 4 times :
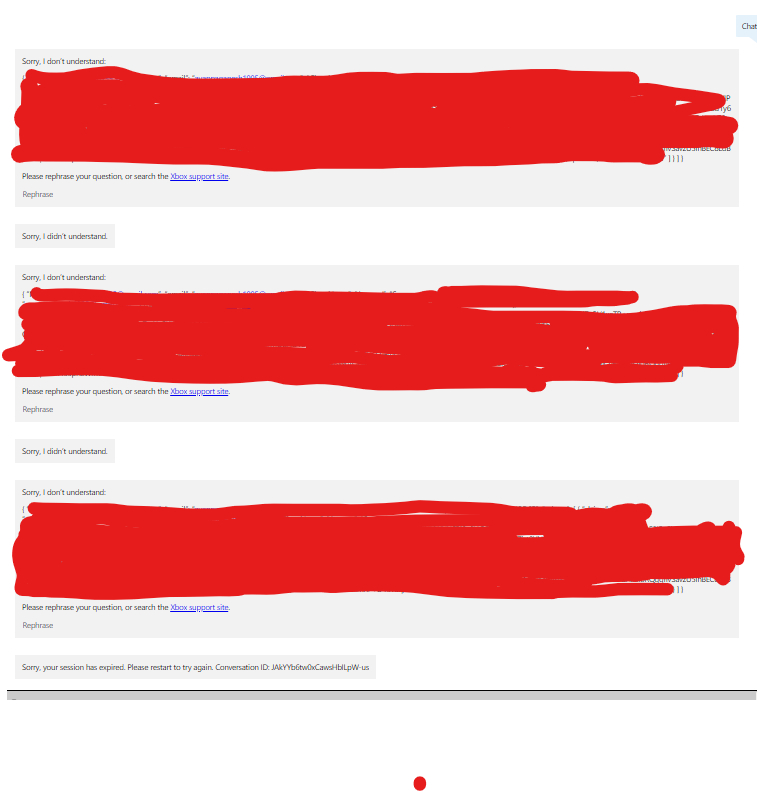
### What version of Web Chat are you using?
Latest production
### Which distribution are you using Web Chat from?
NPM
### Which hosting environment does this issue primarily affect?
Web apps
### Which browsers and platforms do the issue happened?
Browser: Edge (latest), Browser: Chrome (latest)
### Which area does this issue affect?
Send box
### Is this an accessibility issue?
- [ ] Yes, this is an accessibility issue.
### Please describe the bug
I see this issue when we I send an activity with text and dialogue tag - SendBoxDisable
it is displaying text on the canvas, before this was not the case.
When I added a property to activity - texthidden = true
it wasnt showing the text on canvas but this activity is processed 4 times.
Which was not the problem with older version.
previous version - 4.14.1 (no issues)
latest version - 4.15 (above issue)
### Do you see any errors in console log?
no
### How to reproduce the issue?
- upgrade it to latest version
- send an activity with following properties:
- test
- DialogueTag= SendBoxDisable
- other scenario to test adding extra property
- textHidden = true
### What is the expected and actual behavior?
Expected:
Shouldn't show text message on canvas.
Actual:
Shows text message on canvas
### Adaptive Card JSON
_No response_
### Additional context
_No response_ | 1.0 | SendBoxDisable dialogue tag displaying text on canvas. - ### Is it an issue related to Adaptive Cards?
- [ ] Yes, this is an Adaptive Card issue but it is specific to Web Chat.
### Do you have any screenshots?
Activity looks like this :
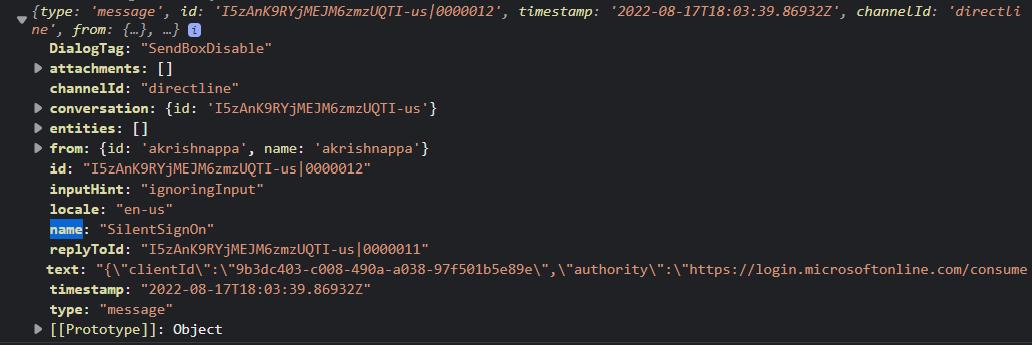
This is how it is displayed on canvas :

If I make this activity.textHidden = true
it is sending this activity 4 times :
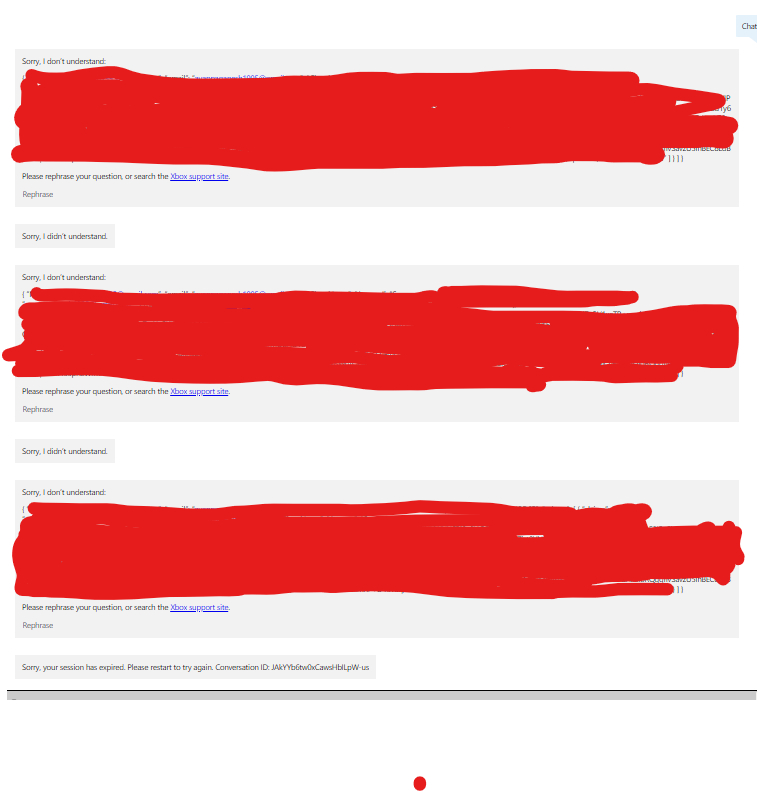
### What version of Web Chat are you using?
Latest production
### Which distribution are you using Web Chat from?
NPM
### Which hosting environment does this issue primarily affect?
Web apps
### Which browsers and platforms do the issue happened?
Browser: Edge (latest), Browser: Chrome (latest)
### Which area does this issue affect?
Send box
### Is this an accessibility issue?
- [ ] Yes, this is an accessibility issue.
### Please describe the bug
I see this issue when we I send an activity with text and dialogue tag - SendBoxDisable
it is displaying text on the canvas, before this was not the case.
When I added a property to activity - texthidden = true
it wasnt showing the text on canvas but this activity is processed 4 times.
Which was not the problem with older version.
previous version - 4.14.1 (no issues)
latest version - 4.15 (above issue)
### Do you see any errors in console log?
no
### How to reproduce the issue?
- upgrade it to latest version
- send an activity with following properties:
- test
- DialogueTag= SendBoxDisable
- other scenario to test adding extra property
- textHidden = true
### What is the expected and actual behavior?
Expected:
Shouldn't show text message on canvas.
Actual:
Shows text message on canvas
### Adaptive Card JSON
_No response_
### Additional context
_No response_ | non_priority | sendboxdisable dialogue tag displaying text on canvas is it an issue related to adaptive cards yes this is an adaptive card issue but it is specific to web chat do you have any screenshots activity looks like this this is how it is displayed on canvas if i make this activity texthidden true it is sending this activity times what version of web chat are you using latest production which distribution are you using web chat from npm which hosting environment does this issue primarily affect web apps which browsers and platforms do the issue happened browser edge latest browser chrome latest which area does this issue affect send box is this an accessibility issue yes this is an accessibility issue please describe the bug i see this issue when we i send an activity with text and dialogue tag sendboxdisable it is displaying text on the canvas before this was not the case when i added a property to activity texthidden true it wasnt showing the text on canvas but this activity is processed times which was not the problem with older version previous version no issues latest version above issue do you see any errors in console log no how to reproduce the issue upgrade it to latest version send an activity with following properties test dialoguetag sendboxdisable other scenario to test adding extra property texthidden true what is the expected and actual behavior expected shouldn t show text message on canvas actual shows text message on canvas adaptive card json no response additional context no response | 0 |
40,868 | 10,198,166,270 | IssuesEvent | 2019-08-13 03:54:34 | IBM/CAST | https://api.github.com/repos/IBM/CAST | closed | bbtools $controller variable is no longer being defined | Comp: Burst Buffer PhaseFound: Customer Sev: 2 Status: Closed Type: Defect | Refactor of the bbtools.pm environment variables has left the $controller variable undefined. So code that uses it to determine if it is operating in a CSM environment is not activated.
| 1.0 | bbtools $controller variable is no longer being defined - Refactor of the bbtools.pm environment variables has left the $controller variable undefined. So code that uses it to determine if it is operating in a CSM environment is not activated.
| non_priority | bbtools controller variable is no longer being defined refactor of the bbtools pm environment variables has left the controller variable undefined so code that uses it to determine if it is operating in a csm environment is not activated | 0 |
226,405 | 17,349,863,872 | IssuesEvent | 2021-07-29 07:18:21 | kyverno/website | https://api.github.com/repos/kyverno/website | closed | Document existence of `request.roles` and `request.clusterRoles` | documentation | Document `request.roles` as a pre-defined variable to access the Roles held by the given user. An example of this might be `["foo:chip"]`. Document `request.clusterRoles` for ClusterRoles, an example of which might return `["chip-admin","system:basic-user","system:discovery","system:public-info-viewer"]`. Also note that one or the other will be substituted, not both. Variables which fail to substitute will cause the rule to be skipped currently.
```log
E0707 22:45:13.875060 1 validation.go:131] EngineValidate "msg"="failed to substitute variables, skip current rule" "error"="NotFoundVariableErr, variable request.roles not resolved at path /validate/message" "kind"="Pod" "name"="asd-foo-bar-baz" "namespace"="foo" "policy"="restrict-namespace-image-registries" "rule"="deny-statement" "rule name"="deny-statement"
``` | 1.0 | Document existence of `request.roles` and `request.clusterRoles` - Document `request.roles` as a pre-defined variable to access the Roles held by the given user. An example of this might be `["foo:chip"]`. Document `request.clusterRoles` for ClusterRoles, an example of which might return `["chip-admin","system:basic-user","system:discovery","system:public-info-viewer"]`. Also note that one or the other will be substituted, not both. Variables which fail to substitute will cause the rule to be skipped currently.
```log
E0707 22:45:13.875060 1 validation.go:131] EngineValidate "msg"="failed to substitute variables, skip current rule" "error"="NotFoundVariableErr, variable request.roles not resolved at path /validate/message" "kind"="Pod" "name"="asd-foo-bar-baz" "namespace"="foo" "policy"="restrict-namespace-image-registries" "rule"="deny-statement" "rule name"="deny-statement"
``` | non_priority | document existence of request roles and request clusterroles document request roles as a pre defined variable to access the roles held by the given user an example of this might be document request clusterroles for clusterroles an example of which might return also note that one or the other will be substituted not both variables which fail to substitute will cause the rule to be skipped currently log validation go enginevalidate msg failed to substitute variables skip current rule error notfoundvariableerr variable request roles not resolved at path validate message kind pod name asd foo bar baz namespace foo policy restrict namespace image registries rule deny statement rule name deny statement | 0 |
112,521 | 17,090,987,027 | IssuesEvent | 2021-07-08 17:25:13 | globeandmail/sophi-for-wordpress | https://api.github.com/repos/globeandmail/sophi-for-wordpress | opened | CVE-2021-33587 (High) detected in css-what-3.4.2.tgz, css-what-4.0.0.tgz | security vulnerability | ## CVE-2021-33587 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>css-what-3.4.2.tgz</b>, <b>css-what-4.0.0.tgz</b></p></summary>
<p>
<details><summary><b>css-what-3.4.2.tgz</b></p></summary>
<p>a CSS selector parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/css-what/-/css-what-3.4.2.tgz">https://registry.npmjs.org/css-what/-/css-what-3.4.2.tgz</a></p>
<p>Path to dependency file: sophi-for-wordpress/package.json</p>
<p>Path to vulnerable library: sophi-for-wordpress/node_modules/css-what/package.json</p>
<p>
Dependency Hierarchy:
- scripts-1.3.1.tgz (Root Library)
- webpack-5.5.0.tgz
- plugin-svgo-5.5.0.tgz
- svgo-1.3.2.tgz
- css-select-2.1.0.tgz
- :x: **css-what-3.4.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>css-what-4.0.0.tgz</b></p></summary>
<p>a CSS selector parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/css-what/-/css-what-4.0.0.tgz">https://registry.npmjs.org/css-what/-/css-what-4.0.0.tgz</a></p>
<p>Path to dependency file: sophi-for-wordpress/package.json</p>
<p>Path to vulnerable library: sophi-for-wordpress/node_modules/cheerio-select-tmp/node_modules/css-what/package.json</p>
<p>
Dependency Hierarchy:
- scripts-1.3.1.tgz (Root Library)
- jest-preset-default-7.0.1.tgz
- enzyme-3.11.0.tgz
- cheerio-1.0.0-rc.5.tgz
- cheerio-select-tmp-0.1.1.tgz
- :x: **css-what-4.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/globeandmail/sophi-for-wordpress/commit/f53708b0035f054189b00c3ec0de1de8c8799b41">f53708b0035f054189b00c3ec0de1de8c8799b41</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The css-what package 4.0.0 through 5.0.0 for Node.js does not ensure that attribute parsing has Linear Time Complexity relative to the size of the input.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33587>CVE-2021-33587</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33587">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33587</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: css-what - 5.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-33587 (High) detected in css-what-3.4.2.tgz, css-what-4.0.0.tgz - ## CVE-2021-33587 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>css-what-3.4.2.tgz</b>, <b>css-what-4.0.0.tgz</b></p></summary>
<p>
<details><summary><b>css-what-3.4.2.tgz</b></p></summary>
<p>a CSS selector parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/css-what/-/css-what-3.4.2.tgz">https://registry.npmjs.org/css-what/-/css-what-3.4.2.tgz</a></p>
<p>Path to dependency file: sophi-for-wordpress/package.json</p>
<p>Path to vulnerable library: sophi-for-wordpress/node_modules/css-what/package.json</p>
<p>
Dependency Hierarchy:
- scripts-1.3.1.tgz (Root Library)
- webpack-5.5.0.tgz
- plugin-svgo-5.5.0.tgz
- svgo-1.3.2.tgz
- css-select-2.1.0.tgz
- :x: **css-what-3.4.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>css-what-4.0.0.tgz</b></p></summary>
<p>a CSS selector parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/css-what/-/css-what-4.0.0.tgz">https://registry.npmjs.org/css-what/-/css-what-4.0.0.tgz</a></p>
<p>Path to dependency file: sophi-for-wordpress/package.json</p>
<p>Path to vulnerable library: sophi-for-wordpress/node_modules/cheerio-select-tmp/node_modules/css-what/package.json</p>
<p>
Dependency Hierarchy:
- scripts-1.3.1.tgz (Root Library)
- jest-preset-default-7.0.1.tgz
- enzyme-3.11.0.tgz
- cheerio-1.0.0-rc.5.tgz
- cheerio-select-tmp-0.1.1.tgz
- :x: **css-what-4.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/globeandmail/sophi-for-wordpress/commit/f53708b0035f054189b00c3ec0de1de8c8799b41">f53708b0035f054189b00c3ec0de1de8c8799b41</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The css-what package 4.0.0 through 5.0.0 for Node.js does not ensure that attribute parsing has Linear Time Complexity relative to the size of the input.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33587>CVE-2021-33587</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33587">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33587</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: css-what - 5.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in css what tgz css what tgz cve high severity vulnerability vulnerable libraries css what tgz css what tgz css what tgz a css selector parser library home page a href path to dependency file sophi for wordpress package json path to vulnerable library sophi for wordpress node modules css what package json dependency hierarchy scripts tgz root library webpack tgz plugin svgo tgz svgo tgz css select tgz x css what tgz vulnerable library css what tgz a css selector parser library home page a href path to dependency file sophi for wordpress package json path to vulnerable library sophi for wordpress node modules cheerio select tmp node modules css what package json dependency hierarchy scripts tgz root library jest preset default tgz enzyme tgz cheerio rc tgz cheerio select tmp tgz x css what tgz vulnerable library found in head commit a href found in base branch develop vulnerability details the css what package through for node js does not ensure that attribute parsing has linear time complexity relative to the size of the input publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution css what step up your open source security game with whitesource | 0 |
231,874 | 17,759,864,885 | IssuesEvent | 2021-08-29 13:43:41 | scipy/scipy | https://api.github.com/repos/scipy/scipy | closed | BUG: not enough values to unpack (expected 6, got 5) in linregress | scipy.stats Documentation | ### Reproducing Code Example
```python
from scipy.stats import linregress
slope, intercept, rvalue, pvalue, stderr, intercept_stderr = linregress([1,2],[1,2])
```
### Error message
```shell
---------------------------------------------------------------------------
ValueError Traceback (most recent call last)
<ipython-input-19-f8c8c3600141> in <module>
----> 1 slope, intercept, rvalue, pvalue, stderr, intercept_stderr = linregress([1,2],[1,2])
ValueError: not enough values to unpack (expected 6, got 5)
```
### SciPy/NumPy/Python version information
1.7.1, 1.20.3, 3.9.6 | 1.0 | BUG: not enough values to unpack (expected 6, got 5) in linregress - ### Reproducing Code Example
```python
from scipy.stats import linregress
slope, intercept, rvalue, pvalue, stderr, intercept_stderr = linregress([1,2],[1,2])
```
### Error message
```shell
---------------------------------------------------------------------------
ValueError Traceback (most recent call last)
<ipython-input-19-f8c8c3600141> in <module>
----> 1 slope, intercept, rvalue, pvalue, stderr, intercept_stderr = linregress([1,2],[1,2])
ValueError: not enough values to unpack (expected 6, got 5)
```
### SciPy/NumPy/Python version information
1.7.1, 1.20.3, 3.9.6 | non_priority | bug not enough values to unpack expected got in linregress reproducing code example python from scipy stats import linregress slope intercept rvalue pvalue stderr intercept stderr linregress error message shell valueerror traceback most recent call last in slope intercept rvalue pvalue stderr intercept stderr linregress valueerror not enough values to unpack expected got scipy numpy python version information | 0 |
208,435 | 15,890,039,576 | IssuesEvent | 2021-04-10 13:59:11 | Programming-Engineering-Pmi-33/ProjectReporter | https://api.github.com/repos/Programming-Engineering-Pmi-33/ProjectReporter | opened | [Backend] UsersApi dependencies in Unit Tests | backend help wanted invalid tests | ### Опис
У завданні #12 потрібно було реалізувати юніт тести для `UsersApi`, що не вдалось реалізувати.
Коментар -
Зробити моки на:
- [ ] `SignInManager`
- [ ] `UserManager`
Реалізувати:
- [ ] Юніт тести | 1.0 | [Backend] UsersApi dependencies in Unit Tests - ### Опис
У завданні #12 потрібно було реалізувати юніт тести для `UsersApi`, що не вдалось реалізувати.
Коментар -
Зробити моки на:
- [ ] `SignInManager`
- [ ] `UserManager`
Реалізувати:
- [ ] Юніт тести | non_priority | usersapi dependencies in unit tests опис у завданні потрібно було реалізувати юніт тести для usersapi що не вдалось реалізувати коментар зробити моки на signinmanager usermanager реалізувати юніт тести | 0 |
9,543 | 6,362,318,138 | IssuesEvent | 2017-07-31 14:45:24 | Scirra/Construct-3-bugs | https://api.github.com/repos/Scirra/Construct-3-bugs | closed | Tooltips obscured by "rendering sprites" and other System messages | usability wontfix | ## Problem description
Trying to read tooltips in the bottom left corner of the screen (eg, for behaviour parameters), but when saving or rendering spritesheets, tooltips are hidden behind the message
## Attach a .c3p
None needed
## Steps to reproduce
1. Save file / wait for spritesheets to render / export file
2. Click on something in the properties window (like a behaviour parameter) and try to read the tooltip at the bottom left corner of the screen.
## Observed result
System message (eg Rendering spritesheets) obscuring tooltips in bottom left corner of the screen.
## Expected result
Unobscured tooltips
## Affected browsers
* Chrome: yes
* Opera: yes
## System details
*If you see a crash report dialog, please copy and paste it to where it says "PASTE HERE" below. Otherwise please go to **Menu** -> **About** -> **Platform information** and paste that information there instead.*
<details><summary>View details</summary>
No crash
</details>
| True | Tooltips obscured by "rendering sprites" and other System messages - ## Problem description
Trying to read tooltips in the bottom left corner of the screen (eg, for behaviour parameters), but when saving or rendering spritesheets, tooltips are hidden behind the message
## Attach a .c3p
None needed
## Steps to reproduce
1. Save file / wait for spritesheets to render / export file
2. Click on something in the properties window (like a behaviour parameter) and try to read the tooltip at the bottom left corner of the screen.
## Observed result
System message (eg Rendering spritesheets) obscuring tooltips in bottom left corner of the screen.
## Expected result
Unobscured tooltips
## Affected browsers
* Chrome: yes
* Opera: yes
## System details
*If you see a crash report dialog, please copy and paste it to where it says "PASTE HERE" below. Otherwise please go to **Menu** -> **About** -> **Platform information** and paste that information there instead.*
<details><summary>View details</summary>
No crash
</details>
| non_priority | tooltips obscured by rendering sprites and other system messages problem description trying to read tooltips in the bottom left corner of the screen eg for behaviour parameters but when saving or rendering spritesheets tooltips are hidden behind the message attach a none needed steps to reproduce save file wait for spritesheets to render export file click on something in the properties window like a behaviour parameter and try to read the tooltip at the bottom left corner of the screen observed result system message eg rendering spritesheets obscuring tooltips in bottom left corner of the screen expected result unobscured tooltips affected browsers chrome yes opera yes system details if you see a crash report dialog please copy and paste it to where it says paste here below otherwise please go to menu about platform information and paste that information there instead view details no crash | 0 |
147,653 | 11,800,349,558 | IssuesEvent | 2020-03-18 17:23:23 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | When display k3s node args and environment variables, use ******** for omitted values | [zube]: To Test area/import-k3s | See: https://github.com/rancher/k3s/issues/1524
This issue is just to make sure we check this out in the Rancher UI and it looks good
This is waiting for a *K3s RC* of 1.17.4 | 1.0 | When display k3s node args and environment variables, use ******** for omitted values - See: https://github.com/rancher/k3s/issues/1524
This issue is just to make sure we check this out in the Rancher UI and it looks good
This is waiting for a *K3s RC* of 1.17.4 | non_priority | when display node args and environment variables use for omitted values see this issue is just to make sure we check this out in the rancher ui and it looks good this is waiting for a rc of | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.