Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
19,524 | 6,733,510,341 | IssuesEvent | 2017-10-18 15:01:56 | eclipse/omr | https://api.github.com/repos/eclipse/omr | opened | PROPOSAL: Add semantic versioning to JitBuilder API | enhancement jitbuilder | In preparation to record JitBuilder IL (JBIL) under Issue #1818, I would like to start versioning the JitBuilder API so that the version can be written out as part of a JBIL record. With an embedded semantic version (see [http://semver.org/](http://semver.org/)) , any particular JitBuilder library should be able to sel... | 1.0 | PROPOSAL: Add semantic versioning to JitBuilder API - In preparation to record JitBuilder IL (JBIL) under Issue #1818, I would like to start versioning the JitBuilder API so that the version can be written out as part of a JBIL record. With an embedded semantic version (see [http://semver.org/](http://semver.org/)) , a... | non_priority | proposal add semantic versioning to jitbuilder api in preparation to record jitbuilder il jbil under issue i would like to start versioning the jitbuilder api so that the version can be written out as part of a jbil record with an embedded semantic version see any particular jitbuilder library should b... | 0 |
166,131 | 14,020,365,616 | IssuesEvent | 2020-10-29 19:34:27 | shreyanshchordia/Graph_Algorithms | https://api.github.com/repos/shreyanshchordia/Graph_Algorithms | closed | HACKTOBER FEST | DSA | Graphs 🔥🔥 | bug digital ocean documentation enhancement good first issue hacktoberfest hacktoberfest-accepted hacktoberfest2020 | 1. **Star** the Repository
2. **Fork** it
3. **Contribute** your code
4. Issue a **PULL REQUEST**
Contribution of new code to this repository needs to be done in a specific manner otherwise your Pull Requests will be invalid. Kindly check README.md file to understand how exactly contribution can be done to ... | 1.0 | HACKTOBER FEST | DSA | Graphs 🔥🔥 - 1. **Star** the Repository
2. **Fork** it
3. **Contribute** your code
4. Issue a **PULL REQUEST**
Contribution of new code to this repository needs to be done in a specific manner otherwise your Pull Requests will be invalid. Kindly check README.md file to understand how... | non_priority | hacktober fest dsa graphs 🔥🔥 star the repository fork it contribute your code issue a pull request contribution of new code to this repository needs to be done in a specific manner otherwise your pull requests will be invalid kindly check readme md file to understand how... | 0 |
75,394 | 15,397,649,338 | IssuesEvent | 2021-03-03 22:30:25 | OpenLiberty/open-liberty | https://api.github.com/repos/OpenLiberty/open-liberty | opened | authFilter element is missing from generated feature docs and has incorrect descriptions | bug in:Security | **Describe the bug**
The Open LIberty autogenerated docs for the `authFilter` element, which is generated from [this metatype.properties file](https://github.com/OpenLiberty/open-liberty/blob/integration/dev/com.ibm.ws.security.authentication.filter/resources/OSGI-INF/l10n/metatype.properties) (and other files in the ... | True | authFilter element is missing from generated feature docs and has incorrect descriptions - **Describe the bug**
The Open LIberty autogenerated docs for the `authFilter` element, which is generated from [this metatype.properties file](https://github.com/OpenLiberty/open-liberty/blob/integration/dev/com.ibm.ws.security.... | non_priority | authfilter element is missing from generated feature docs and has incorrect descriptions describe the bug the open liberty autogenerated docs for the authfilter element which is generated from and other files in the has two issues the autogen is not pulling in the attribute descriptions from ... | 0 |
98,005 | 12,281,069,629 | IssuesEvent | 2020-05-08 15:12:06 | f8upd8/Product503 | https://api.github.com/repos/f8upd8/Product503 | closed | Иконки | design | Нужны все иконки с дизайна сайта в формате .svg или в формате проекта иллюстратора. На крайняк - в .png не меньше чем 2048x2048 с прозрачностью. Пока делаю без них. | 1.0 | Иконки - Нужны все иконки с дизайна сайта в формате .svg или в формате проекта иллюстратора. На крайняк - в .png не меньше чем 2048x2048 с прозрачностью. Пока делаю без них. | non_priority | иконки нужны все иконки с дизайна сайта в формате svg или в формате проекта иллюстратора на крайняк в png не меньше чем с прозрачностью пока делаю без них | 0 |
1,891 | 6,577,533,420 | IssuesEvent | 2017-09-12 01:34:41 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | Docker pull: always and state: reloaded no longer ignores unnamed containers | affects_1.9 bug_report cloud docker waiting_on_maintainer | ##### Issue Type:
- Bug Report
##### Plugin Name:
Docker
##### Ansible Version:
**Worked:**
```
ansible 1.9.4
configured module search path = None
```
**Broken:**
```
ansible 2.0.0.1
config file = /Users/mmorris/Work/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### Ansible ... | True | Docker pull: always and state: reloaded no longer ignores unnamed containers - ##### Issue Type:
- Bug Report
##### Plugin Name:
Docker
##### Ansible Version:
**Worked:**
```
ansible 1.9.4
configured module search path = None
```
**Broken:**
```
ansible 2.0.0.1
config file = /Users/mmorris/Work/ansible/ansible... | non_priority | docker pull always and state reloaded no longer ignores unnamed containers issue type bug report plugin name docker ansible version worked ansible configured module search path none broken ansible config file users mmorris work ansible ansible... | 0 |
67,479 | 12,964,623,687 | IssuesEvent | 2020-07-20 20:48:59 | vshaxe/vshaxe | https://api.github.com/repos/vshaxe/vshaxe | closed | Code Action to create non-existant methods | blocked-haxe code-actions code-generation enhancement | I'd like to have a code action like this in vshaxe as well:
https://twitter.com/mayakwd/status/1001825619557191680
This requires some info from the compiler, such as what the inferred argument types are and what our current context is (static vs instance). Probably has to wait until diagnostics have been transiti... | 2.0 | Code Action to create non-existant methods - I'd like to have a code action like this in vshaxe as well:
https://twitter.com/mayakwd/status/1001825619557191680
This requires some info from the compiler, such as what the inferred argument types are and what our current context is (static vs instance). Probably has... | non_priority | code action to create non existant methods i d like to have a code action like this in vshaxe as well this requires some info from the compiler such as what the inferred argument types are and what our current context is static vs instance probably has to wait until diagnostics have been transitioned ove... | 0 |
257,781 | 19,531,566,972 | IssuesEvent | 2021-12-30 17:53:53 | woodpecker-ci/woodpecker | https://api.github.com/repos/woodpecker-ci/woodpecker | closed | create a matrix room for chat/support | documentation | currently when clicking on questions and support it redirects you to discord.
i created a temp account, but it required my phone number, for just creating an empty account.
i suggest creating a matrix room like codeberg with a bridge to discord.
so we users don't have to deal with discord bad privacy. | 1.0 | create a matrix room for chat/support - currently when clicking on questions and support it redirects you to discord.
i created a temp account, but it required my phone number, for just creating an empty account.
i suggest creating a matrix room like codeberg with a bridge to discord.
so we users don't have to d... | non_priority | create a matrix room for chat support currently when clicking on questions and support it redirects you to discord i created a temp account but it required my phone number for just creating an empty account i suggest creating a matrix room like codeberg with a bridge to discord so we users don t have to d... | 0 |
7,055 | 10,348,139,414 | IssuesEvent | 2019-09-04 19:03:53 | openopps/openopps-platform | https://api.github.com/repos/openopps/openopps-platform | opened | Sitewide User: Add agency to manage users | Admin Requirements Ready | Who: Sitewide admin
What: Add Agency to manage users
Why: In order to facilitate user support
Acceptance Criteria:
Admin --> Sitewide --> Users --> Manage
- Add "Agency" after the Name field in manager users | 1.0 | Sitewide User: Add agency to manage users - Who: Sitewide admin
What: Add Agency to manage users
Why: In order to facilitate user support
Acceptance Criteria:
Admin --> Sitewide --> Users --> Manage
- Add "Agency" after the Name field in manager users | non_priority | sitewide user add agency to manage users who sitewide admin what add agency to manage users why in order to facilitate user support acceptance criteria admin sitewide users manage add agency after the name field in manager users | 0 |
130,743 | 18,170,276,599 | IssuesEvent | 2021-09-27 19:08:14 | snowdensb/job-dsl-plugin | https://api.github.com/repos/snowdensb/job-dsl-plugin | opened | CVE-2015-4852 (High) detected in commons-collections-3.2.jar | security vulnerability | ## CVE-2015-4852 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-collections-3.2.jar</b></p></summary>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>L... | True | CVE-2015-4852 (High) detected in commons-collections-3.2.jar - ## CVE-2015-4852 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-collections-3.2.jar</b></p></summary>
<p>Types t... | non_priority | cve high detected in commons collections jar cve high severity vulnerability vulnerable library commons collections jar types that extend and augment the java collections framework library home page a href path to dependency file job dsl plugin job dsl plugin build gradle ... | 0 |
140,749 | 32,055,732,365 | IssuesEvent | 2023-09-24 03:46:21 | pulumi/pulumi | https://api.github.com/repos/pulumi/pulumi | opened | Improve user experience when running `pulumi policy publish` | kind/enhancement impact/usability area/policy-as-code needs-triage | ## Hello!
<!-- Please leave this section as-is, it's designed to help others in the community know how to interact with our GitHub issues. -->
- Vote on this issue by adding a 👍 reaction
- If you want to implement this feature, comment to let us know (we'll work with you on design, scheduling, etc.)
## Issue d... | 1.0 | Improve user experience when running `pulumi policy publish` - ## Hello!
<!-- Please leave this section as-is, it's designed to help others in the community know how to interact with our GitHub issues. -->
- Vote on this issue by adding a 👍 reaction
- If you want to implement this feature, comment to let us know ... | non_priority | improve user experience when running pulumi policy publish hello vote on this issue by adding a 👍 reaction if you want to implement this feature comment to let us know we ll work with you on design scheduling etc issue details when running pulumi policy publish without an org name ... | 0 |
155,359 | 24,452,361,572 | IssuesEvent | 2022-10-07 01:10:54 | ubyssey/ubyssey.ca | https://api.github.com/repos/ubyssey/ubyssey.ca | closed | Design for /contribute | design feature | Design /contribute page to be more than just a block of text.
| 1.0 | Design for /contribute - Design /contribute page to be more than just a block of text.
| non_priority | design for contribute design contribute page to be more than just a block of text | 0 |
212,991 | 16,492,272,019 | IssuesEvent | 2021-05-25 06:15:57 | amazeeio/lagoon | https://api.github.com/repos/amazeeio/lagoon | closed | MariaDB image ship with functions not available in AWS RDS Aurora | 6-images-testing | **Describe the bug**
At the moment, Alpine Linux 3.11 ships with [MariaDB 10.4.13-r0](https://pkgs.alpinelinux.org/package/v3.11/main/x86/mariadb).
MariaDB introduced a new function `REGEXP_SUBSTR` in [10.0.5](https://mariadb.com/kb/en/regexp_substr/) (around 2013).
This function is available in MySQL 8.0. Ho... | 1.0 | MariaDB image ship with functions not available in AWS RDS Aurora - **Describe the bug**
At the moment, Alpine Linux 3.11 ships with [MariaDB 10.4.13-r0](https://pkgs.alpinelinux.org/package/v3.11/main/x86/mariadb).
MariaDB introduced a new function `REGEXP_SUBSTR` in [10.0.5](https://mariadb.com/kb/en/regexp_su... | non_priority | mariadb image ship with functions not available in aws rds aurora describe the bug at the moment alpine linux ships with mariadb introduced a new function regexp substr in around this function is available in mysql however is your lagoon cluster is backed with aws aurora rds th... | 0 |
225,586 | 24,873,823,663 | IssuesEvent | 2022-10-27 17:17:50 | hashicorp/nomad | https://api.github.com/repos/hashicorp/nomad | closed | Nomad Event Stream Subscriber Using ACL Token with TTL Receive Updates Until Garbage Collected | type/bug theme/security | Bulletin ID: HCSEC-2022-26
Bulletin Title: Nomad Event Stream Subscriber Using ACL Token with TTL Receive Updates Until Garbage Collected
Publication Date: October 27, 2022
Affected Products / Versions: Nomad and Nomad Enterprise 1.4.0 up to 1.4.1; fixed in 1.4.2.
Summary:
A vulnerability was identified in ... | True | Nomad Event Stream Subscriber Using ACL Token with TTL Receive Updates Until Garbage Collected - Bulletin ID: HCSEC-2022-26
Bulletin Title: Nomad Event Stream Subscriber Using ACL Token with TTL Receive Updates Until Garbage Collected
Publication Date: October 27, 2022
Affected Products / Versions: Nomad and Nom... | non_priority | nomad event stream subscriber using acl token with ttl receive updates until garbage collected bulletin id hcsec bulletin title nomad event stream subscriber using acl token with ttl receive updates until garbage collected publication date october affected products versions nomad and nomad enter... | 0 |
128,364 | 12,370,919,948 | IssuesEvent | 2020-05-18 17:38:21 | National-COVID-Cohort-Collaborative/Phenotype_Data_Acquisition | https://api.github.com/repos/National-COVID-Cohort-Collaborative/Phenotype_Data_Acquisition | closed | Add assumptions to OMOP documentation | documentation | Kristin noted a couple of assumptions for OMOP on the Colorado call: Updating vocab regularly and using ERA tables. Can you add these and any others to the OMOP documentation please? | 1.0 | Add assumptions to OMOP documentation - Kristin noted a couple of assumptions for OMOP on the Colorado call: Updating vocab regularly and using ERA tables. Can you add these and any others to the OMOP documentation please? | non_priority | add assumptions to omop documentation kristin noted a couple of assumptions for omop on the colorado call updating vocab regularly and using era tables can you add these and any others to the omop documentation please | 0 |
438,944 | 30,670,689,455 | IssuesEvent | 2023-07-25 22:10:43 | apache/openwhisk | https://api.github.com/repos/apache/openwhisk | closed | add documentation for typescript function runtime and update runtimes | help wanted documentation good first issue | The typescript runtime was recently added to openwhisk but we do not yet have docs for the runtime and it is missing from runtimes.json.
We need a doc like https://github.com/apache/incubator-openwhisk/blob/master/docs/actions-nodejs.md for typescript functions.
Adding the runtime to the runtime manifest can be d... | 1.0 | add documentation for typescript function runtime and update runtimes - The typescript runtime was recently added to openwhisk but we do not yet have docs for the runtime and it is missing from runtimes.json.
We need a doc like https://github.com/apache/incubator-openwhisk/blob/master/docs/actions-nodejs.md for type... | non_priority | add documentation for typescript function runtime and update runtimes the typescript runtime was recently added to openwhisk but we do not yet have docs for the runtime and it is missing from runtimes json we need a doc like for typescript functions adding the runtime to the runtime manifest can be done per... | 0 |
7,002 | 3,073,062,927 | IssuesEvent | 2015-08-19 20:02:26 | NETponents/octoduino | https://api.github.com/repos/NETponents/octoduino | opened | Expose SPI library API over PB | c++ documentation enhancement hard help wanted octoduino_core parser | Could port over SD and LCD libraries over to PB since they both depend on SPI. | 1.0 | Expose SPI library API over PB - Could port over SD and LCD libraries over to PB since they both depend on SPI. | non_priority | expose spi library api over pb could port over sd and lcd libraries over to pb since they both depend on spi | 0 |
48,900 | 7,463,455,190 | IssuesEvent | 2018-04-01 05:34:55 | ThomGeG/Tom-Talk | https://api.github.com/repos/ThomGeG/Tom-Talk | opened | No README.md | documentation enhancement | The project lacks even a basic README. The sooner one is produced the better.
### Fundamental Sections:
- Title & Description
- Installation/Deployment guide
- Relevant additional resources | 1.0 | No README.md - The project lacks even a basic README. The sooner one is produced the better.
### Fundamental Sections:
- Title & Description
- Installation/Deployment guide
- Relevant additional resources | non_priority | no readme md the project lacks even a basic readme the sooner one is produced the better fundamental sections title description installation deployment guide relevant additional resources | 0 |
129,454 | 27,496,579,454 | IssuesEvent | 2023-03-05 07:44:36 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Non-SEF urls still remains in Article's Link A parameter | No Code Attached Yet bug | Go to edit article mode > Images and Links
Add non-SEF url in Link A parameter:
<img width="1637" alt="Снимок экрана 2023-02-21 в 22 41 46" src="https://user-images.githubusercontent.com/3432048/220442849-5e19573d-585d-41ab-afea-22be02458221.png">
`/index.php?option=com_content&view=article&id=1&catid... | 1.0 | Non-SEF urls still remains in Article's Link A parameter - Go to edit article mode > Images and Links
Add non-SEF url in Link A parameter:
<img width="1637" alt="Снимок экрана 2023-02-21 в 22 41 46" src="https://user-images.githubusercontent.com/3432048/220442849-5e19573d-585d-41ab-afea-22be02458221.png">
`/index... | non_priority | non sef urls still remains in article s link a parameter go to edit article mode images and links add non sef url in link a parameter img width alt снимок экрана в src index php option com content amp view article amp id amp catid and this non sef url still remains on the fron... | 0 |
339,230 | 30,352,941,792 | IssuesEvent | 2023-07-11 20:31:27 | kopia/kopia | https://api.github.com/repos/kopia/kopia | closed | Test Log File Max Total Size failure: corner case for log size | help wanted good first issue test-failure keep-open | ```
logfile_test.go:193:
Error Trace: D:/a/kopia/kopia/internal/logfile/logfile_test.go:193
Error: "19600" is not less than "19600"
Test: TestLogFileMaxTotalSize/content-logs
=== FAIL: internal/logfile TestLogFileMaxTotalSize (31.97s)
``` | 1.0 | Test Log File Max Total Size failure: corner case for log size - ```
logfile_test.go:193:
Error Trace: D:/a/kopia/kopia/internal/logfile/logfile_test.go:193
Error: "19600" is not less than "19600"
Test: TestLogFileMaxTotalSize/content-logs
=== FAIL: internal/logfile T... | non_priority | test log file max total size failure corner case for log size logfile test go error trace d a kopia kopia internal logfile logfile test go error is not less than test testlogfilemaxtotalsize content logs fail internal logfile testlogfilema... | 0 |
165,399 | 14,000,901,286 | IssuesEvent | 2020-10-28 12:58:58 | futurewei-cloud/zeta | https://api.github.com/repos/futurewei-cloud/zeta | opened | Zeta Target Deployment | documentation enhancement | **User Story**
As a developer, I want a consistent deployment mechanism so that I can easily test/deploy Zeta services on AWS cloud, Lab Servers and localhost
**Is your feature request related to a problem? Please describe.**
I'm always frustrated when test or integrate Zeta on different environments, the setting ... | 1.0 | Zeta Target Deployment - **User Story**
As a developer, I want a consistent deployment mechanism so that I can easily test/deploy Zeta services on AWS cloud, Lab Servers and localhost
**Is your feature request related to a problem? Please describe.**
I'm always frustrated when test or integrate Zeta on different e... | non_priority | zeta target deployment user story as a developer i want a consistent deployment mechanism so that i can easily test deploy zeta services on aws cloud lab servers and localhost is your feature request related to a problem please describe i m always frustrated when test or integrate zeta on different e... | 0 |
266,795 | 20,164,808,362 | IssuesEvent | 2022-02-10 02:25:41 | opengeospatial/ogc-geosparql | https://api.github.com/repos/opengeospatial/ogc-geosparql | closed | GeoSPARQL and Common Query language CQL | documentation | The common query language (CQL) (http://docs.opengeospatial.org/DRAFTS/19-079.html#simple-cql_filter-expression) is used in many geospatial web services (WFS) and in the currently in OGC API features to filter geospatial featurecollections.
In one of our research projects we developed a "semanticwfs" (https://github... | 1.0 | GeoSPARQL and Common Query language CQL - The common query language (CQL) (http://docs.opengeospatial.org/DRAFTS/19-079.html#simple-cql_filter-expression) is used in many geospatial web services (WFS) and in the currently in OGC API features to filter geospatial featurecollections.
In one of our research projects we... | non_priority | geosparql and common query language cql the common query language cql is used in many geospatial web services wfs and in the currently in ogc api features to filter geospatial featurecollections in one of our research projects we developed a semanticwfs i e a wfs ogc api features compatible webservic... | 0 |
37,771 | 15,370,716,098 | IssuesEvent | 2021-03-02 09:09:08 | GovernIB/portafib | https://api.github.com/repos/GovernIB/portafib | closed | Evitar ús de thread locals amb classes pròpies de l'aplicació o netejar-los | Estimació: S Lloc:WebServices | Quan es crea un `ThreadLocal` amb una classe pròpia de l'aplicació, i per tant que s'ha carregat amb el classloader quan aquesta s'ha iniciat, i no es neteja aquesta referència, el thread manté una referència a una classe carregada amb el classloader de l'aplicació. Quan es fa `undeploy` de l'aplicació, aquesta referèn... | 1.0 | Evitar ús de thread locals amb classes pròpies de l'aplicació o netejar-los - Quan es crea un `ThreadLocal` amb una classe pròpia de l'aplicació, i per tant que s'ha carregat amb el classloader quan aquesta s'ha iniciat, i no es neteja aquesta referència, el thread manté una referència a una classe carregada amb el cla... | non_priority | evitar ús de thread locals amb classes pròpies de l aplicació o netejar los quan es crea un threadlocal amb una classe pròpia de l aplicació i per tant que s ha carregat amb el classloader quan aquesta s ha iniciat i no es neteja aquesta referència el thread manté una referència a una classe carregada amb el cla... | 0 |
261,618 | 22,758,058,231 | IssuesEvent | 2022-07-07 18:23:02 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | System.Net.Requests.Tests failure in checked coreclr Linux x64 Release | area-System.Net test-failure | Hit in this unrelated infra change: https://github.com/dotnet/runtime/pull/71770/checks?check_run_id=7238923095
The [log](https://helixre107v0xdeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-pull-71770-merge-8e7d0a4ddc254d5489/System.Net.Requests.Tests/1/console.dd07ba3f.log?helixlogtype=result) says:
```
... | 1.0 | System.Net.Requests.Tests failure in checked coreclr Linux x64 Release - Hit in this unrelated infra change: https://github.com/dotnet/runtime/pull/71770/checks?check_run_id=7238923095
The [log](https://helixre107v0xdeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-pull-71770-merge-8e7d0a4ddc254d5489/System.Net... | non_priority | system net requests tests failure in checked coreclr linux release hit in this unrelated infra change the says exit code means sigsegv illegal memory access deref invalid pointer overrunning buffer stack overflow etc core dumped net threadpool segfault at ip sp error in... | 0 |
30,036 | 4,545,645,794 | IssuesEvent | 2016-09-11 11:03:01 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | stress: failed test in cockroach/storage/storage.test: TestAcceptsUnsplitRanges | Robot test-failure | Binary: cockroach/static-tests.tar.gz sha: https://github.com/cockroachdb/cockroach/commits/860d5044234abcda41ca45990e3f0f2cebabf454
Stress build found a failed test:
```
=== RUN TestAcceptsUnsplitRanges
I160911 04:32:11.934913 1090 gossip/gossip.go:230 initial resolvers: []
W160911 04:32:11.934938 1090 gossip/gos... | 1.0 | stress: failed test in cockroach/storage/storage.test: TestAcceptsUnsplitRanges - Binary: cockroach/static-tests.tar.gz sha: https://github.com/cockroachdb/cockroach/commits/860d5044234abcda41ca45990e3f0f2cebabf454
Stress build found a failed test:
```
=== RUN TestAcceptsUnsplitRanges
I160911 04:32:11.934913 1090 g... | non_priority | stress failed test in cockroach storage storage test testacceptsunsplitranges binary cockroach static tests tar gz sha stress build found a failed test run testacceptsunsplitranges gossip gossip go initial resolvers gossip gossip go no resolvers found use join to... | 0 |
345,585 | 24,866,306,316 | IssuesEvent | 2022-10-27 12:14:26 | keptn/lifecycle-controller | https://api.github.com/repos/keptn/lifecycle-controller | opened | Implementi the documentation structure | documentation | ### Discussed in https://github.com/keptn/lifecycle-controller/discussions/141
<div type='discussions-op-text'>
<sup>Originally posted by **oleg-nenashev** October 11, 2022</sup>
Hello,
I propose to rework the documentation structure in the following way
* README files - top level overviews and quick-start... | 1.0 | Implementi the documentation structure - ### Discussed in https://github.com/keptn/lifecycle-controller/discussions/141
<div type='discussions-op-text'>
<sup>Originally posted by **oleg-nenashev** October 11, 2022</sup>
Hello,
I propose to rework the documentation structure in the following way
* README fi... | non_priority | implementi the documentation structure discussed in originally posted by oleg nenashev october hello i propose to rework the documentation structure in the following way readme files top level overviews and quick start bits the rest will go to special pages under “ doc” see belo... | 0 |
394,116 | 27,021,207,744 | IssuesEvent | 2023-02-11 02:41:46 | JustBrandonLim/ICT2106_P2_Project | https://api.github.com/repos/JustBrandonLim/ICT2106_P2_Project | closed | 1.2 Team Class Diagram Start: 10/01/23 | End: 27/01/23 | documentation | Start: 10/01/23 | End: 27/01/23
- Creation of Team Class Diagram
- Linking of Class Diagram with other Teams | 1.0 | 1.2 Team Class Diagram Start: 10/01/23 | End: 27/01/23 - Start: 10/01/23 | End: 27/01/23
- Creation of Team Class Diagram
- Linking of Class Diagram with other Teams | non_priority | team class diagram start end start end creation of team class diagram linking of class diagram with other teams | 0 |
87,541 | 25,142,314,074 | IssuesEvent | 2022-11-10 00:37:42 | microsoft/onnxruntime | https://api.github.com/repos/microsoft/onnxruntime | closed | [Build] cmake error: list sub-command REMOVE_ITEM requires two or more arguments | build | ### Describe the issue
building on windows with cmake 3.19 fails with `list sub-command REMOVE_ITEM requires two or more arguments`
This is due to a cmake "bug" in 3.19 and lower with the `list(REMOVE_ITEM...)` command.
Seen in other projects like https://github.com/microsoft/vcpkg/pull/23410
Easy fix in forthcomin... | 1.0 | [Build] cmake error: list sub-command REMOVE_ITEM requires two or more arguments - ### Describe the issue
building on windows with cmake 3.19 fails with `list sub-command REMOVE_ITEM requires two or more arguments`
This is due to a cmake "bug" in 3.19 and lower with the `list(REMOVE_ITEM...)` command.
Seen in other ... | non_priority | cmake error list sub command remove item requires two or more arguments describe the issue building on windows with cmake fails with list sub command remove item requires two or more arguments this is due to a cmake bug in and lower with the list remove item command seen in other projects... | 0 |
158,647 | 13,744,594,583 | IssuesEvent | 2020-10-06 00:24:45 | TesseractCoding/NeoAlgo | https://api.github.com/repos/TesseractCoding/NeoAlgo | closed | [TAKEN] Add Selection Sort Algorithm | documentation enhancement good first issue no-issue-activity | **Algorithm: Selection Sort **
**DS:**
**Languages Supported: C, C++, Java, JavaScript, etc.**
| 1.0 | [TAKEN] Add Selection Sort Algorithm - **Algorithm: Selection Sort **
**DS:**
**Languages Supported: C, C++, Java, JavaScript, etc.**
| non_priority | add selection sort algorithm algorithm selection sort ds languages supported c c java javascript etc | 0 |
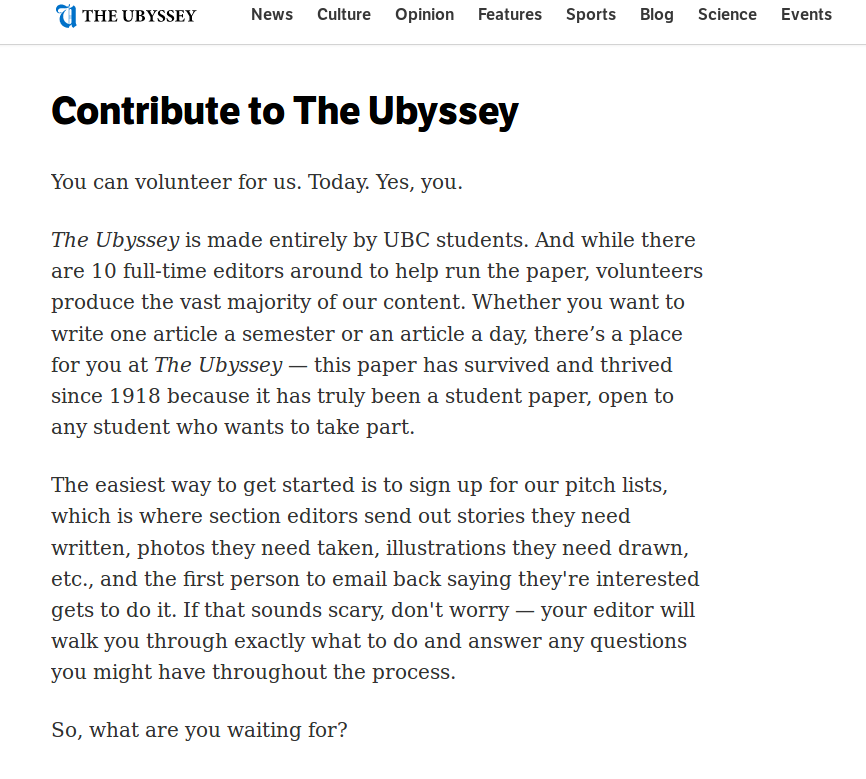
204,582 | 23,257,001,110 | IssuesEvent | 2022-08-04 10:08:16 | GoldenSoftwareLtd/gedemin | https://api.github.com/repos/GoldenSoftwareLtd/gedemin | closed | Общие. В свойства объекта добавить отображение IP-адреса (Q) | Security | _**Запись по документу → Контекстное меню → Свойства... → Общие.**_
@ShlTanya , пожалуйста, для реквизитов **Кто создал**, **Кто изменил** добавь отображение IP-адреса:
| True | Общие. В свойства объекта добавить отображение IP-адреса (Q) - _**Запись по документу → Контекстное меню → Свойства... → Общие.**_
@ShlTanya , пожалуйста, для реквизитов **Кто создал**, **Кто изменил** добавь отображение IP-адреса:
.
I'd like to add my personal fork (which already exists) to the local clone without having to... | 1.0 | Add `gh repo remote add [forkname] <org|user> [-- [flags]]` - ### Describe the feature or problem you’d like to solve
I have a clone (this can come from anything, e.g. `homebrew`, or `gh repo clone`, or `git clone`, or some random script from some other thing that gives me a clone).
I'd like to add my personal fo... | non_priority | add gh repo remote add describe the feature or problem you’d like to solve i have a clone this can come from anything e g homebrew or gh repo clone or git clone or some random script from some other thing that gives me a clone i d like to add my personal fork which already exists to... | 0 |
69,761 | 13,337,951,971 | IssuesEvent | 2020-08-28 10:07:50 | fac20/Week7-DEKN | https://api.github.com/repos/fac20/Week7-DEKN | closed | Deployed | Code review Complement | You've successfully deployed on Heroku. We did lots of testing there and got GET /, POST /signup and POST /posts working | 1.0 | Deployed - You've successfully deployed on Heroku. We did lots of testing there and got GET /, POST /signup and POST /posts working | non_priority | deployed you ve successfully deployed on heroku we did lots of testing there and got get post signup and post posts working | 0 |
143,679 | 13,079,590,275 | IssuesEvent | 2020-08-01 03:58:44 | emerson-matos/financasapi | https://api.github.com/repos/emerson-matos/financasapi | closed | [docs] Make api documentation | documentation enhancement | **Is your feature request related to a problem? Please describe.**
We should teach our client how we are organized, information about our endpoints and our requests contracts should be public to make easier to consume of potentials clients
**Describe the solution you'd like**
We should implement some auto document... | 1.0 | [docs] Make api documentation - **Is your feature request related to a problem? Please describe.**
We should teach our client how we are organized, information about our endpoints and our requests contracts should be public to make easier to consume of potentials clients
**Describe the solution you'd like**
We sho... | non_priority | make api documentation is your feature request related to a problem please describe we should teach our client how we are organized information about our endpoints and our requests contracts should be public to make easier to consume of potentials clients describe the solution you d like we should i... | 0 |
202,156 | 23,059,260,439 | IssuesEvent | 2022-07-25 08:26:48 | elastic/beats | https://api.github.com/repos/elastic/beats | closed | Auditbeat: Propagate output backpressure in socket dataset | enhancement Auditbeat Team:Security-External Integrations | **Describe the enhancement:**
The socket dataset tracks network flows to/from processes on a Linux system using kprobe tracepoints on the kernel's TCP/IP stack.
Currently, an unbounded linked list is used to store flows ready to be reported to the output. A system with a lot of network I/O can generate events fas... | True | Auditbeat: Propagate output backpressure in socket dataset - **Describe the enhancement:**
The socket dataset tracks network flows to/from processes on a Linux system using kprobe tracepoints on the kernel's TCP/IP stack.
Currently, an unbounded linked list is used to store flows ready to be reported to the outpu... | non_priority | auditbeat propagate output backpressure in socket dataset describe the enhancement the socket dataset tracks network flows to from processes on a linux system using kprobe tracepoints on the kernel s tcp ip stack currently an unbounded linked list is used to store flows ready to be reported to the outpu... | 0 |
218,222 | 16,977,702,096 | IssuesEvent | 2021-06-30 03:10:17 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: Creates and activates a new custom rule with override option - Detection rules, override Creates and activates a new custom rule with override option | Team: SecuritySolution Team:Detections and Resp Team:SIEM blocker failed-test skipped-test v7.11.0 v8.0.0 | A test failed on a tracked branch
```
SyntaxError: The following error originated from your application code, not from Cypress.
> Unexpected end of JSON input
When Cypress detects uncaught errors originating from your application it will automatically fail the current test.
This behavior is configurable, and you ... | 2.0 | Failing test: Creates and activates a new custom rule with override option - Detection rules, override Creates and activates a new custom rule with override option - A test failed on a tracked branch
```
SyntaxError: The following error originated from your application code, not from Cypress.
> Unexpected end of JS... | non_priority | failing test creates and activates a new custom rule with override option detection rules override creates and activates a new custom rule with override option a test failed on a tracked branch syntaxerror the following error originated from your application code not from cypress unexpected end of js... | 0 |
65,498 | 27,120,499,790 | IssuesEvent | 2023-02-15 22:23:47 | microsoft/BotFramework-Composer | https://api.github.com/repos/microsoft/BotFramework-Composer | closed | does not match memory scopes error in bot composer with multiturn implementation | customer-reported Bot Services customer-replied-to | Getting an error message does not match memory scopes error in bot composer with multiturn implementation. Multiturn is working but getting this error each time the dialog executes. Please let me know how to handle this error in bot composer.
| 1.0 | does not match memory scopes error in bot composer with multiturn implementation - Getting an error message does not match memory scopes error in bot composer with multiturn implementation. Multiturn is working but getting this error each time the dialog executes. Please let me know how to handle this error in bot comp... | non_priority | does not match memory scopes error in bot composer with multiturn implementation getting an error message does not match memory scopes error in bot composer with multiturn implementation multiturn is working but getting this error each time the dialog executes please let me know how to handle this error in bot comp... | 0 |
66,304 | 20,146,365,263 | IssuesEvent | 2022-02-09 07:59:30 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | PrimeNG Calendar (p-calendar) Loses alignment when positioned at the top of the input and the user clicks in the year/month | defect | **I'm submitting a ...** (check one with "x")
```
[x] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request h... | 1.0 | PrimeNG Calendar (p-calendar) Loses alignment when positioned at the top of the input and the user clicks in the year/month - **I'm submitting a ...** (check one with "x")
```
[x] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roa... | non_priority | primeng calendar p calendar loses alignment when positioned at the top of the input and the user clicks in the year month i m submitting a check one with x bug report search github for a similar issue or pr before submitting feature request please check if request is not on the roadmap... | 0 |
224,481 | 17,190,074,056 | IssuesEvent | 2021-07-16 09:39:22 | ita-social-projects/dokazovi-requirements | https://api.github.com/repos/ita-social-projects/dokazovi-requirements | opened | [Test for Change request #241] | documentation test case | **Story link**
[#241 Story]
### Status:
Not executed
### Title:
Verify if all writings on the Authors Page are remain readable after disabling the images.
### Description:
### Pre-conditions:
You are launched https://dokazovi-fe.herokuapp.com
Click the 'Authors' tab
Step № | Test Steps | Test data ... | 1.0 | [Test for Change request #241] - **Story link**
[#241 Story]
### Status:
Not executed
### Title:
Verify if all writings on the Authors Page are remain readable after disabling the images.
### Description:
### Pre-conditions:
You are launched https://dokazovi-fe.herokuapp.com
Click the 'Authors' tab
... | non_priority | story link status not executed title verify if all writings on the authors page are remain readable after disabling the images description pre conditions you are launched click the authors tab step № test steps test data expected result status pass fail n... | 0 |
233,265 | 25,758,332,519 | IssuesEvent | 2022-12-08 18:12:08 | whitesource-ps/ws-bulk-report-generator | https://api.github.com/repos/whitesource-ps/ws-bulk-report-generator | opened | certifi-2022.6.15-py3-none-any.whl: 1 vulnerabilities (highest severity is: 6.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>certifi-2022.6.15-py3-none-any.whl</b></p></summary>
<p>Python package for providing Mozilla's CA Bundle.</p>
<p>Library home page: <a href="https://files.pythonhoste... | True | certifi-2022.6.15-py3-none-any.whl: 1 vulnerabilities (highest severity is: 6.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>certifi-2022.6.15-py3-none-any.whl</b></p></summary>
<p>Python package for providin... | non_priority | certifi none any whl vulnerabilities highest severity is vulnerable library certifi none any whl python package for providing mozilla s ca bundle library home page a href path to dependency file tmp ws scm ws bulk report generator path to vulnerable library tmp ws ... | 0 |
100,415 | 11,194,840,587 | IssuesEvent | 2020-01-03 03:13:26 | gatsbyjs/gatsby-pt-BR | https://api.github.com/repos/gatsbyjs/gatsby-pt-BR | closed | Translation Progress (Batch #1) - Finished | documentation | ## --------------------- ! UPDATE IMPORTANTE ! ------------------
Todos os arquivos já foram designados, futuramente abriremos novos para tradução!
## Maintainers: NUNCA mergem uma PR com somente uma aprovação!
### Revisores Oficiais
- @jessescn
- @rafaeelaudibert
- @Dennissiq
- @jay-jlm
- @iaurg
- @mjr... | 1.0 | Translation Progress (Batch #1) - Finished - ## --------------------- ! UPDATE IMPORTANTE ! ------------------
Todos os arquivos já foram designados, futuramente abriremos novos para tradução!
## Maintainers: NUNCA mergem uma PR com somente uma aprovação!
### Revisores Oficiais
- @jessescn
- @rafaeelaudibert ... | non_priority | translation progress batch finished update importante todos os arquivos já foram designados futuramente abriremos novos para tradução maintainers nunca mergem uma pr com somente uma aprovação revisores oficiais jessescn rafaeelaudibert ... | 0 |
44,635 | 12,303,170,548 | IssuesEvent | 2020-05-11 18:13:27 | cakephp/cakephp | https://api.github.com/repos/cakephp/cakephp | closed | Serialize issue on ResultSet | defect | This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: master / 4.x
### What you did
Upgraded from 3.x:
```php
$this->loadModel('Data.States');
$states = $this->States->find('all');
$this->set(compact('states'));
$this->set('_serialize', ['st... | 1.0 | Serialize issue on ResultSet - This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: master / 4.x
### What you did
Upgraded from 3.x:
```php
$this->loadModel('Data.States');
$states = $this->States->find('all');
$this->set(compact('states'));
... | non_priority | serialize issue on resultset this is a multiple allowed bug enhancement feature discussion rfc cakephp version master x what you did upgraded from x php this loadmodel data states states this states find all this set compact states thi... | 0 |
98,019 | 16,342,884,048 | IssuesEvent | 2021-05-13 01:21:48 | joaonetoo/saaddeploy | https://api.github.com/repos/joaonetoo/saaddeploy | opened | CVE-2021-29509 (High) detected in puma-3.6.0.gem | security vulnerability | ## CVE-2021-29509 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>puma-3.6.0.gem</b></p></summary>
<p>Puma is a simple, fast, threaded, and highly concurrent HTTP 1.1 server for Ruby/R... | True | CVE-2021-29509 (High) detected in puma-3.6.0.gem - ## CVE-2021-29509 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>puma-3.6.0.gem</b></p></summary>
<p>Puma is a simple, fast, threade... | non_priority | cve high detected in puma gem cve high severity vulnerability vulnerable library puma gem puma is a simple fast threaded and highly concurrent http server for ruby rack applications puma is intended for use in both development and production environments in order to get... | 0 |
10,725 | 9,081,589,725 | IssuesEvent | 2019-02-17 03:02:30 | AlwaysBeCrafting/Mysticell | https://api.github.com/repos/AlwaysBeCrafting/Mysticell | opened | Migrate to React v16.8 / React Hooks | enhancement service-web | ## Summary
React has released Hooks as a way to write stateful components as plain functions, and describes them as a new path forward for the framework. The intent of Hooks aligns well with our code style. We should migrate the existing class components now while it's still a small task.
[API reference](https://re... | 1.0 | Migrate to React v16.8 / React Hooks - ## Summary
React has released Hooks as a way to write stateful components as plain functions, and describes them as a new path forward for the framework. The intent of Hooks aligns well with our code style. We should migrate the existing class components now while it's still a sm... | non_priority | migrate to react react hooks summary react has released hooks as a way to write stateful components as plain functions and describes them as a new path forward for the framework the intent of hooks aligns well with our code style we should migrate the existing class components now while it s still a smal... | 0 |
284,978 | 31,019,477,310 | IssuesEvent | 2023-08-10 03:16:13 | Grunet/cloud-native-honeypot | https://api.github.com/repos/Grunet/cloud-native-honeypot | closed | Don't Leave pipx Usage in CI Unpinned | security | Check the version that comes pre-installed on the runner and fail CI otherwise to make sure the update is legitimate | True | Don't Leave pipx Usage in CI Unpinned - Check the version that comes pre-installed on the runner and fail CI otherwise to make sure the update is legitimate | non_priority | don t leave pipx usage in ci unpinned check the version that comes pre installed on the runner and fail ci otherwise to make sure the update is legitimate | 0 |
42,964 | 23,057,881,784 | IssuesEvent | 2022-07-25 07:10:49 | qbittorrent/qBittorrent | https://api.github.com/repos/qbittorrent/qBittorrent | closed | High ram usage and disabling the OS cache cripple my download speed | Performance Libtorrent | **Please provide the following information**
### qBittorrent version and Operating System
4.0.4 on Windows 10
### What is the problem
i have a very high ram usage after a while, up to a point, where my system just freezes, and i have to force shutdown. no error message but i can see that my memory is at 99% (it... | True | High ram usage and disabling the OS cache cripple my download speed - **Please provide the following information**
### qBittorrent version and Operating System
4.0.4 on Windows 10
### What is the problem
i have a very high ram usage after a while, up to a point, where my system just freezes, and i have to force... | non_priority | high ram usage and disabling the os cache cripple my download speed please provide the following information qbittorrent version and operating system on windows what is the problem i have a very high ram usage after a while up to a point where my system just freezes and i have to force ... | 0 |
255,644 | 21,941,721,732 | IssuesEvent | 2022-05-23 18:51:38 | gonmarfer2/Acme-Toolkits | https://api.github.com/repos/gonmarfer2/Acme-Toolkits | closed | Task-097/T: Operations by patrons on patronages (8) | testing D04 | Create both positive and negative tests for the following operations:
- [ ] Create patronages.
- [ ] Update patronages, as long as they're not published.
- [ ] Delete patronages, as long as they're not published.
- [ ] Publish patronages | 1.0 | Task-097/T: Operations by patrons on patronages (8) - Create both positive and negative tests for the following operations:
- [ ] Create patronages.
- [ ] Update patronages, as long as they're not published.
- [ ] Delete patronages, as long as they're not published.
- [ ] Publish patronages | non_priority | task t operations by patrons on patronages create both positive and negative tests for the following operations create patronages update patronages as long as they re not published delete patronages as long as they re not published publish patronages | 0 |
231,261 | 17,671,623,288 | IssuesEvent | 2021-08-23 07:05:46 | apache/skywalking | https://api.github.com/repos/apache/skywalking | opened | Cut the current java-agent/readme into different documents | documentation | We should cut the document into several small documents and update the menu. | 1.0 | Cut the current java-agent/readme into different documents - We should cut the document into several small documents and update the menu. | non_priority | cut the current java agent readme into different documents we should cut the document into several small documents and update the menu | 0 |
220,731 | 24,566,022,258 | IssuesEvent | 2022-10-13 03:08:56 | nexmo-community/client-sdk-tutorials | https://api.github.com/repos/nexmo-community/client-sdk-tutorials | opened | lint-gradle-27.2.1.jar: 18 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lint-gradle-27.2.1.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /app-to-app-java/app-to-app/app/build.gradle</p>
<p>Path to vulnerable library: /home/wss... | True | lint-gradle-27.2.1.jar: 18 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lint-gradle-27.2.1.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /app-to-app-java/... | non_priority | lint gradle jar vulnerabilities highest severity is vulnerable library lint gradle jar path to dependency file app to app java app to app app build gradle path to vulnerable library home wss scanner gradle caches modules files com google guava guava jre guava ... | 0 |
112,443 | 24,271,433,591 | IssuesEvent | 2022-09-28 10:35:29 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | If you host via the in game buttons and the server takes too long to load, you will get disconnected from it | Bug Code Networking | - [X] I have searched the issue tracker to check if the issue has already been reported.
**Description**
Looks like for a few selected people, they get disconnected from the in game server before the server can fully load, making it impossible to host using the in game buttons.
**Steps To Reproduce**
1) Host a ... | 1.0 | If you host via the in game buttons and the server takes too long to load, you will get disconnected from it - - [X] I have searched the issue tracker to check if the issue has already been reported.
**Description**
Looks like for a few selected people, they get disconnected from the in game server before the serve... | non_priority | if you host via the in game buttons and the server takes too long to load you will get disconnected from it i have searched the issue tracker to check if the issue has already been reported description looks like for a few selected people they get disconnected from the in game server before the server ... | 0 |
137,130 | 30,630,979,792 | IssuesEvent | 2023-07-24 14:31:33 | Son1kXDev/5opkagame2d | https://api.github.com/repos/Son1kXDev/5opkagame2d | opened | Параллакс эффект | Code World | Сделай его более гибким (чтобы не было фиксированного количество фонов - просто создать лист для них. Скорость движения фона, относительно игрока, будет зависеть от положения в листе) | 1.0 | Параллакс эффект - Сделай его более гибким (чтобы не было фиксированного количество фонов - просто создать лист для них. Скорость движения фона, относительно игрока, будет зависеть от положения в листе) | non_priority | параллакс эффект сделай его более гибким чтобы не было фиксированного количество фонов просто создать лист для них скорость движения фона относительно игрока будет зависеть от положения в листе | 0 |
17,618 | 10,098,143,100 | IssuesEvent | 2019-07-28 12:46:46 | Shuunen/bergerac-roads | https://api.github.com/repos/Shuunen/bergerac-roads | closed | CVE-2018-19797 Low Severity Vulnerability detected by WhiteSource | security vulnerability | ## CVE-2018-19797 - Low Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.9.4</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a hr... | True | CVE-2018-19797 Low Severity Vulnerability detected by WhiteSource - ## CVE-2018-19797 - Low Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.9.4</b></p></summary>
<p>
<p>:... | non_priority | cve low severity vulnerability detected by whitesource cve low severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href library source files the source files were matched to this source library based on ... | 0 |
268,420 | 28,565,968,629 | IssuesEvent | 2023-04-21 02:08:57 | andygonzalez2010/store | https://api.github.com/repos/andygonzalez2010/store | closed | CVE-2021-3805 (High) detected in object-path-0.9.2.tgz - autoclosed | Mend: dependency security vulnerability | ## CVE-2021-3805 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>object-path-0.9.2.tgz</b></p></summary>
<p>Access deep properties using a path</p>
<p>Library home page: <a href="https... | True | CVE-2021-3805 (High) detected in object-path-0.9.2.tgz - autoclosed - ## CVE-2021-3805 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>object-path-0.9.2.tgz</b></p></summary>
<p>Access... | non_priority | cve high detected in object path tgz autoclosed cve high severity vulnerability vulnerable library object path tgz access deep properties using a path library home page a href path to dependency file package json path to vulnerable library node modules object pat... | 0 |
26,988 | 6,812,976,446 | IssuesEvent | 2017-11-06 07:02:09 | BTDF/DeploymentFramework | https://api.github.com/repos/BTDF/DeploymentFramework | closed | Fix issue where test for existing service instances was skipped | bug CodePlexMigrationInitiated General Impact: High Release 5.0 | Fix issue where test for existing service instances was skipped
#### This work item was migrated from CodePlex
CodePlex work item ID: '6500'
Assigned to: 'tfabraham'
Vote count: '0'
| 1.0 | Fix issue where test for existing service instances was skipped - Fix issue where test for existing service instances was skipped
#### This work item was migrated from CodePlex
CodePlex work item ID: '6500'
Assigned to: 'tfabraham'
Vote count: '0'
| non_priority | fix issue where test for existing service instances was skipped fix issue where test for existing service instances was skipped this work item was migrated from codeplex codeplex work item id assigned to tfabraham vote count | 0 |
49,022 | 10,315,171,163 | IssuesEvent | 2019-08-30 06:43:33 | intellij-rust/intellij-rust | https://api.github.com/repos/intellij-rust/intellij-rust | closed | "Implement members" ignores arbitrary self types. | bug code insight | ## Environment
* **IntelliJ Rust plugin version:** 0.2.102.2682-192-nightly
## Problem description
`self` is inserted as `Self` instead of one of a few new self types stabilized recently on the way to arbitrary self types.
## Steps to reproduce
Code:
```rust
trait X {
fn x(self: Pin<&mut Self>);
... | 1.0 | "Implement members" ignores arbitrary self types. - ## Environment
* **IntelliJ Rust plugin version:** 0.2.102.2682-192-nightly
## Problem description
`self` is inserted as `Self` instead of one of a few new self types stabilized recently on the way to arbitrary self types.
## Steps to reproduce
Code:
`... | non_priority | implement members ignores arbitrary self types environment intellij rust plugin version nightly problem description self is inserted as self instead of one of a few new self types stabilized recently on the way to arbitrary self types steps to reproduce code rust ... | 0 |
103,706 | 16,604,665,088 | IssuesEvent | 2021-06-02 01:16:28 | greenetx/jenkins2-course-spring-boot | https://api.github.com/repos/greenetx/jenkins2-course-spring-boot | opened | CVE-2019-14888 (High) detected in undertow-core-1.3.23.Final.jar | security vulnerability | ## CVE-2019-14888 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>undertow-core-1.3.23.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Library home page: <a href="http://www.jboss.org/"... | True | CVE-2019-14888 (High) detected in undertow-core-1.3.23.Final.jar - ## CVE-2019-14888 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>undertow-core-1.3.23.Final.jar</b></p></summary>
<p... | non_priority | cve high detected in undertow core final jar cve high severity vulnerability vulnerable library undertow core final jar undertow library home page a href path to dependency file course spring boot spring boot autoconfigure pom xml path to vulnerable library root ... | 0 |
158,314 | 12,412,289,353 | IssuesEvent | 2020-05-22 10:15:20 | aliasrobotics/RVD | https://api.github.com/repos/aliasrobotics/RVD | opened | 938] | bug cppcheck static analysis testing triage | ```yaml
{
"id": 1,
"title": "938]",
"type": "bug",
"description": "[src/opencv3/3rdparty/libjpeg/jmemmgr.c:983] -> [src/opencv3/3rdparty/libjpeg/jmemmgr.c:938]: (warning) Either the condition 'pool_id>=2' is redundant or the array 'mem->small_list[2]' is accessed at index 2, which is out of bounds.",
... | 1.0 | 938] - ```yaml
{
"id": 1,
"title": "938]",
"type": "bug",
"description": "[src/opencv3/3rdparty/libjpeg/jmemmgr.c:983] -> [src/opencv3/3rdparty/libjpeg/jmemmgr.c:938]: (warning) Either the condition 'pool_id>=2' is redundant or the array 'mem->small_list[2]' is accessed at index 2, which is out of bound... | non_priority | yaml id title type bug description warning either the condition pool id is redundant or the array mem small list is accessed at index which is out of bounds cwe none cve none keywords cppcheck st... | 0 |
275,227 | 20,913,462,959 | IssuesEvent | 2022-03-24 11:21:25 | firebase/flutterfire | https://api.github.com/repos/firebase/flutterfire | closed | [📚] google_sign_in docs ref is heading to 404 page | type: bug type: documentation good first issue | When I'm going through the [usage part of CLI](https://firebase.flutter.dev/docs/cli/#usage), There I saw `google_sign_in` manual installation references. When I click on that it goes [here](https://firebase.flutter.dev/docs/cli/auth/social#google)(404 page) | 1.0 | [📚] google_sign_in docs ref is heading to 404 page - When I'm going through the [usage part of CLI](https://firebase.flutter.dev/docs/cli/#usage), There I saw `google_sign_in` manual installation references. When I click on that it goes [here](https://firebase.flutter.dev/docs/cli/auth/social#google)(404 page) | non_priority | google sign in docs ref is heading to page when i m going through the there i saw google sign in manual installation references when i click on that it goes page | 0 |
98,639 | 11,091,798,432 | IssuesEvent | 2019-12-15 14:49:27 | TDAmeritrade/stumpy | https://api.github.com/repos/TDAmeritrade/stumpy | opened | Check for "dimensioanl" typos | documentation enhancement | There are some typos in the docstrings where "dimensional" is mis-spelled as "dimensioanl". We need to check if any other ones exist. | 1.0 | Check for "dimensioanl" typos - There are some typos in the docstrings where "dimensional" is mis-spelled as "dimensioanl". We need to check if any other ones exist. | non_priority | check for dimensioanl typos there are some typos in the docstrings where dimensional is mis spelled as dimensioanl we need to check if any other ones exist | 0 |
138,697 | 12,826,982,987 | IssuesEvent | 2020-07-06 17:34:56 | rstudio/rstudio | https://api.github.com/repos/rstudio/rstudio | opened | Update Terminal support article for 1.3 | documentation terminal | The Terminal pane in RStudio 1.3 now supports custom shells for Windows (previously only available on Mac/Linux).
Should update support article to mention that, and show an example for hooking up RTools4 as a terminal per #6810.
Also a quick skim for other helpful updates since this article was written for RStudi... | 1.0 | Update Terminal support article for 1.3 - The Terminal pane in RStudio 1.3 now supports custom shells for Windows (previously only available on Mac/Linux).
Should update support article to mention that, and show an example for hooking up RTools4 as a terminal per #6810.
Also a quick skim for other helpful updates... | non_priority | update terminal support article for the terminal pane in rstudio now supports custom shells for windows previously only available on mac linux should update support article to mention that and show an example for hooking up as a terminal per also a quick skim for other helpful updates since th... | 0 |
10,216 | 4,021,481,812 | IssuesEvent | 2016-05-16 22:08:08 | buckte/buckte | https://api.github.com/repos/buckte/buckte | closed | Fix "Insecure Dependency" issue in Gemfile.lock | codeclimate | Nested attributes rejection proc bypass in Active Record
https://codeclimate.com/github/buckte/buckte/Gemfile.lock#issue_573a287e737f7500019ec40e | 1.0 | Fix "Insecure Dependency" issue in Gemfile.lock - Nested attributes rejection proc bypass in Active Record
https://codeclimate.com/github/buckte/buckte/Gemfile.lock#issue_573a287e737f7500019ec40e | non_priority | fix insecure dependency issue in gemfile lock nested attributes rejection proc bypass in active record | 0 |
312,011 | 23,413,287,134 | IssuesEvent | 2022-08-12 20:10:34 | mikyurkev/Most_to_Coast_v2 | https://api.github.com/repos/mikyurkev/Most_to_Coast_v2 | opened | Front-end: Accessibility: Better Dark/Light background contrast. | documentation enhancement | - Improve accessibility by better-contrasted background for people with disability. | 1.0 | Front-end: Accessibility: Better Dark/Light background contrast. - - Improve accessibility by better-contrasted background for people with disability. | non_priority | front end accessibility better dark light background contrast improve accessibility by better contrasted background for people with disability | 0 |
110,871 | 24,023,818,630 | IssuesEvent | 2022-09-15 09:47:59 | gitpod-io/gitpod | https://api.github.com/repos/gitpod-io/gitpod | closed | embed service status of Gitpod into Gitpod | type: feature request user experience component: dashboard editor: code (browser) meta: never-stale operations: observability | Here are the configuration options:
<img width="488" alt="2021-05-06_19-30-03" src="https://user-images.githubusercontent.com/127353/117275565-80df0800-aea1-11eb-83b2-e75bf6a9cd03.png">
Here is the JavaScript embed
```javascript
<script src="https://2wkvzfyrpv0h.statuspage.io/embed/script.js"></script>
```
... | 1.0 | embed service status of Gitpod into Gitpod - Here are the configuration options:
<img width="488" alt="2021-05-06_19-30-03" src="https://user-images.githubusercontent.com/127353/117275565-80df0800-aea1-11eb-83b2-e75bf6a9cd03.png">
Here is the JavaScript embed
```javascript
<script src="https://2wkvzfyrpv0h.st... | non_priority | embed service status of gitpod into gitpod here are the configuration options img width alt src here is the javascript embed javascript script src alternatively we could build our own img width alt src | 0 |
114,561 | 14,597,443,871 | IssuesEvent | 2020-12-20 20:09:28 | coding-circle/charades | https://api.github.com/repos/coding-circle/charades | opened | Add edit score feature to host settings panel. | client design restAPI server | Occasionally the score can get messed up by someone clicking the wrong buttons following a turn. The goal of this is to add fields to adjust the score for each team.
Should coordinate with @anderspollack on designs, but open to creating your own designs and taking feedback.
**Requirements**
- Edit restAPI docu... | 1.0 | Add edit score feature to host settings panel. - Occasionally the score can get messed up by someone clicking the wrong buttons following a turn. The goal of this is to add fields to adjust the score for each team.
Should coordinate with @anderspollack on designs, but open to creating your own designs and taking fe... | non_priority | add edit score feature to host settings panel occasionally the score can get messed up by someone clicking the wrong buttons following a turn the goal of this is to add fields to adjust the score for each team should coordinate with anderspollack on designs but open to creating your own designs and taking fe... | 0 |
110,909 | 17,009,627,099 | IssuesEvent | 2021-07-02 00:57:39 | Chiencc/angular | https://api.github.com/repos/Chiencc/angular | opened | CVE-2017-16024 (Medium) detected in sync-exec-0.6.2.tgz | security vulnerability | ## CVE-2017-16024 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sync-exec-0.6.2.tgz</b></p></summary>
<p>Synchronous exec with status code support. Requires no external dependencie... | True | CVE-2017-16024 (Medium) detected in sync-exec-0.6.2.tgz - ## CVE-2017-16024 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sync-exec-0.6.2.tgz</b></p></summary>
<p>Synchronous exec ... | non_priority | cve medium detected in sync exec tgz cve medium severity vulnerability vulnerable library sync exec tgz synchronous exec with status code support requires no external dependencies no need for node gyp compilations etc library home page a href path to dependency file ... | 0 |
8,108 | 20,968,779,721 | IssuesEvent | 2022-03-28 09:23:00 | MicrosoftDocs/architecture-center | https://api.github.com/repos/MicrosoftDocs/architecture-center | closed | Error regarding blob name | cxp triaged product-question architecture-center/svc Pri2 azure-guide/subsvc |
[I want to read a csv file located in the blob storage. However, I am getting error that specified blob does not exist. I am confused what should be the blob name. I gave LOCALFILENAME as my csv file name seen in the blob container]
---
#### Document Details
⚠ *Do not edit this section. It is required for do... | 1.0 | Error regarding blob name -
[I want to read a csv file located in the blob storage. However, I am getting error that specified blob does not exist. I am confused what should be the blob name. I gave LOCALFILENAME as my csv file name seen in the blob container]
---
#### Document Details
⚠ *Do not edit this se... | non_priority | error regarding blob name document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service architecture center sub service azure guide ... | 0 |
331,960 | 29,174,921,041 | IssuesEvent | 2023-05-19 07:03:52 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | opened | Fix dtype.test_as_native_dtype | Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5020544812/jobs/9002105988" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5020544812/jobs/9002105988" rel="noopener ... | 1.0 | Fix dtype.test_as_native_dtype - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5020544812/jobs/9002105988" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/502054481... | non_priority | fix dtype test as native dtype tensorflow img src torch img src numpy img src jax img src paddle img src failed ivy tests test ivy test functional test core test dtype py test as native dtype e keyerror cpu e e... | 0 |
205,295 | 23,322,381,748 | IssuesEvent | 2022-08-08 17:38:32 | jgeraigery/sol003-lifecycle-driver | https://api.github.com/repos/jgeraigery/sol003-lifecycle-driver | opened | logstash-logback-encoder-5.1.jar: 1 vulnerabilities (highest severity is: 6.6) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>logstash-logback-encoder-5.1.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/ch... | True | logstash-logback-encoder-5.1.jar: 1 vulnerabilities (highest severity is: 6.6) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>logstash-logback-encoder-5.1.jar</b></p></summary>
<p></p>
<p>Path to dependency file... | non_priority | logstash logback encoder jar vulnerabilities highest severity is vulnerable library logstash logback encoder jar path to dependency file pom xml path to vulnerable library home wss scanner repository ch qos logback logback core logback core jar found in head... | 0 |
271,314 | 23,595,401,038 | IssuesEvent | 2022-08-23 18:44:37 | sandialabs/Albany | https://api.github.com/repos/sandialabs/Albany | closed | Broken tests on Weaver | Testing | A bunch of the nightly tests on Weaver started failing:
https://sems-cdash-son.sandia.gov/cdash/test/2685897
```
[weaver3:23006:0:23006] Caught signal 11 (Segmentation fault: address not mapped to object at address 0x2000bf9cfa80)
[weaver3:23004:0:23004] Caught signal 11 (Segmentation fault: address not mapped ... | 1.0 | Broken tests on Weaver - A bunch of the nightly tests on Weaver started failing:
https://sems-cdash-son.sandia.gov/cdash/test/2685897
```
[weaver3:23006:0:23006] Caught signal 11 (Segmentation fault: address not mapped to object at address 0x2000bf9cfa80)
[weaver3:23004:0:23004] Caught signal 11 (Segmentation f... | non_priority | broken tests on weaver a bunch of the nightly tests on weaver started failing caught signal segmentation fault address not mapped to object at address caught signal segmentation fault address not mapped to object at address caught signal segmentation fault address not mapped to... | 0 |
111,757 | 11,741,492,049 | IssuesEvent | 2020-03-11 21:52:57 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | flutter create template creates configureFlutter engine in MainActivity - leading to plugins registered twice | d: wiki documentation engine framework p: framework plugin ▣ platform-android | Creating a new project with flutter create the main activity has code to configure the flutter engine.
e.g.
```java
public class MainActivity extends FlutterActivity {
@Override
public void configureFlutterEngine(@NonNull FlutterEngine flutterEngine) {
GeneratedPluginRegistrant.registerWith(flutterEngine... | 1.0 | flutter create template creates configureFlutter engine in MainActivity - leading to plugins registered twice - Creating a new project with flutter create the main activity has code to configure the flutter engine.
e.g.
```java
public class MainActivity extends FlutterActivity {
@Override
public void configur... | non_priority | flutter create template creates configureflutter engine in mainactivity leading to plugins registered twice creating a new project with flutter create the main activity has code to configure the flutter engine e g java public class mainactivity extends flutteractivity override public void configur... | 0 |
357,545 | 25,176,402,852 | IssuesEvent | 2022-11-11 09:38:57 | zacchaeuschok/pe | https://api.github.com/repos/zacchaeuschok/pe | opened | Formatting error | type.DocumentationBug severity.Low | Two colons in a single bullet point.
Usually best to break them up.
<!--session: 1668153124908-ed46472a-a5a9-4d62-acf6-e12362aef54f-->
<!--Version: Web v3.4.4--> | 1.0 | Formatting error - Two colons in a single bullet point.
Usually best to break them up.
<!--session: 1668153124908-ed46472a-a5a9-4d62-acf6-e12362aef54f-->
<!--Version: Web v3.4.4--> | non_priority | formatting error two colons in a single bullet point usually best to break them up | 0 |
160,710 | 20,117,438,121 | IssuesEvent | 2022-02-07 21:09:16 | Toposware/hash | https://api.github.com/repos/Toposware/hash | opened | Rescue-Prime impl is not constant-time | security | While the underlying arithmetic in Cheetah is made constant-time, the current implementation of Rescue-Prime for the two different sets of parameters is not constant-time. This can be an issue for applications hashing sensitive data, which is *currently* not the case. | True | Rescue-Prime impl is not constant-time - While the underlying arithmetic in Cheetah is made constant-time, the current implementation of Rescue-Prime for the two different sets of parameters is not constant-time. This can be an issue for applications hashing sensitive data, which is *currently* not the case. | non_priority | rescue prime impl is not constant time while the underlying arithmetic in cheetah is made constant time the current implementation of rescue prime for the two different sets of parameters is not constant time this can be an issue for applications hashing sensitive data which is currently not the case | 0 |
49,388 | 10,344,553,857 | IssuesEvent | 2019-09-04 11:31:11 | Genymobile/scrcpy | https://api.github.com/repos/Genymobile/scrcpy | closed | Special (Accent) characters missing | input events unicode | Hy rom1v!
First of all, you are a special man! I love your program :D
I followed the progression of the application for a long time, and I seen that you have started to add support for special characters too.
But there are still some missing.
Űű : WARN: Could not inject char u+170, u+171
Őő : WARN: Could not i... | 1.0 | Special (Accent) characters missing - Hy rom1v!
First of all, you are a special man! I love your program :D
I followed the progression of the application for a long time, and I seen that you have started to add support for special characters too.
But there are still some missing.
Űű : WARN: Could not inject cha... | non_priority | special accent characters missing hy first of all you are a special man i love your program d i followed the progression of the application for a long time and i seen that you have started to add support for special characters too but there are still some missing űű warn could not inject char u ... | 0 |
51,620 | 6,537,621,893 | IssuesEvent | 2017-08-31 23:40:14 | unfoldcollective/Apprentice-of-Okolicne | https://api.github.com/repos/unfoldcollective/Apprentice-of-Okolicne | closed | save & gallery & composition view: implement redesigned composition titles | design development p-must-have | we figured out that the current way of titling the compositions ({initial} from {town}) leads to problems in Slovak, because {town} should be inflected (e.g. Amsterdam -> Amsterdamu)
We are not going to solve that thorny i18n grammar issue automatically in the app, so here's a new idea:
- the user just signs with ... | 1.0 | save & gallery & composition view: implement redesigned composition titles - we figured out that the current way of titling the compositions ({initial} from {town}) leads to problems in Slovak, because {town} should be inflected (e.g. Amsterdam -> Amsterdamu)
We are not going to solve that thorny i18n grammar issue ... | non_priority | save gallery composition view implement redesigned composition titles we figured out that the current way of titling the compositions initial from town leads to problems in slovak because town should be inflected e g amsterdam amsterdamu we are not going to solve that thorny grammar issue aut... | 0 |
183,300 | 31,276,614,946 | IssuesEvent | 2023-08-22 06:48:45 | flowforge/flowforge | https://api.github.com/repos/flowforge/flowforge | opened | Image Rebranding | task design artwork | ### Related Issue
CtrlX Project
### Description
Rebranding "FlowForge" -> "FlowFuse":

| 1.0 | Image Rebranding - ### Related Issue
CtrlX Project
### Description
Rebranding "FlowForge" -> "FlowFuse":

| non_priority | image rebranding related issue ctrlx project description rebranding flowforge flowfuse | 0 |
114,784 | 24,663,234,644 | IssuesEvent | 2022-10-18 08:23:34 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | new ugcId logic in master 0.19 matches when both are none | Bug Code Modding Unstable | ### Disclaimers
- [X] I have searched the issue tracker to check if the issue has already been reported.
- [X] My issue happened while using mods.
### What happened?
Originally the content path logic matches `%ModDir:xxx%` first with workshop id (ignores if not present, `workshopid==0`), then package name then alt-n... | 1.0 | new ugcId logic in master 0.19 matches when both are none - ### Disclaimers
- [X] I have searched the issue tracker to check if the issue has already been reported.
- [X] My issue happened while using mods.
### What happened?
Originally the content path logic matches `%ModDir:xxx%` first with workshop id (ignores if... | non_priority | new ugcid logic in master matches when both are none disclaimers i have searched the issue tracker to check if the issue has already been reported my issue happened while using mods what happened originally the content path logic matches moddir xxx first with workshop id ignores if not ... | 0 |
200,140 | 15,790,701,118 | IssuesEvent | 2021-04-02 02:16:08 | open-contracting/standard | https://api.github.com/repos/open-contracting/standard | opened | Check whether some csv-table-no-translate should be csv-table | Focus - Documentation | Only codelists are translated by Transifex. The rest should likely be csv-table. Right now, only two tables use `csv-table`. To find the other tables, regex-search for `:file: (?!\.\./\.\./build/current_lang/.*csv)`. | 1.0 | Check whether some csv-table-no-translate should be csv-table - Only codelists are translated by Transifex. The rest should likely be csv-table. Right now, only two tables use `csv-table`. To find the other tables, regex-search for `:file: (?!\.\./\.\./build/current_lang/.*csv)`. | non_priority | check whether some csv table no translate should be csv table only codelists are translated by transifex the rest should likely be csv table right now only two tables use csv table to find the other tables regex search for file build current lang csv | 0 |
18,323 | 10,927,663,856 | IssuesEvent | 2019-11-22 17:11:08 | mozilla/fxa | https://api.github.com/repos/mozilla/fxa | closed | Load test / tune | fxa-email-service | We haven't done anything to analyse (or optimise) performance in this repo. If train 125 looks stable there should be some time to spend on this. | 1.0 | Load test / tune - We haven't done anything to analyse (or optimise) performance in this repo. If train 125 looks stable there should be some time to spend on this. | non_priority | load test tune we haven t done anything to analyse or optimise performance in this repo if train looks stable there should be some time to spend on this | 0 |
13,887 | 16,654,864,392 | IssuesEvent | 2021-06-05 10:36:08 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | [PM] Responsive issue > UI is broken for toaster messages | Bug P2 Participant manager Process: Fixed Process: Tested QA Process: Tested dev | UI is broken for all the toaster messages
[Note: Issue should be fixed for all the toaster messages]
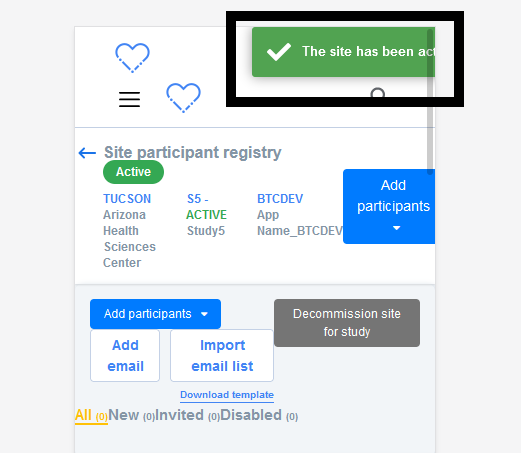
| 3.0 | [PM] Responsive issue > UI is broken for toaster messages - UI is broken for all the toaster messages
[Note: Issue should be fixed for all the toaster messages]
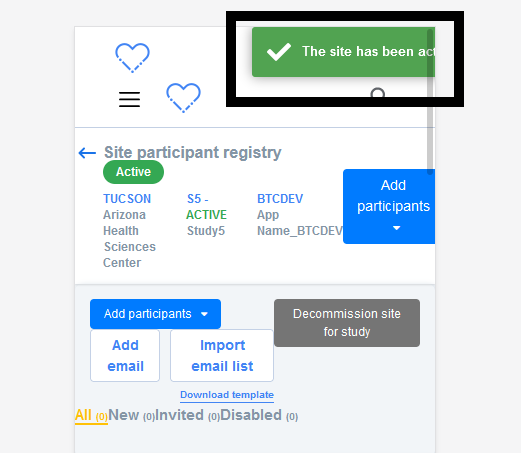
| non_priority | responsive issue ui is broken for toaster messages ui is broken for all the toaster messages | 0 |
239,709 | 18,281,469,469 | IssuesEvent | 2021-10-05 04:21:53 | GowthamGoush/Amazing_Sites | https://api.github.com/repos/GowthamGoush/Amazing_Sites | closed | Submarine Cable System | documentation hacktoberfest | This site gives us an interactive and regularly updated map of world's major submarine cable systems and landing stations. | 1.0 | Submarine Cable System - This site gives us an interactive and regularly updated map of world's major submarine cable systems and landing stations. | non_priority | submarine cable system this site gives us an interactive and regularly updated map of world s major submarine cable systems and landing stations | 0 |
222,688 | 17,468,225,664 | IssuesEvent | 2021-08-06 20:25:14 | sylabs/singularity | https://api.github.com/repos/sylabs/singularity | closed | e2e remote test failing after #217 | bug ci:e2e testing | **Version of Singularity**
master
**Describe the bug**
#217 changed usage strings on the remote sub-commands, without me realizing they were checked in the e2e tests. Since no e2e test code or go.mod modifications were made, the e2e tests were not triggered in CI. They are now failing in PRs in which they are ... | 1.0 | e2e remote test failing after #217 - **Version of Singularity**
master
**Describe the bug**
#217 changed usage strings on the remote sub-commands, without me realizing they were checked in the e2e tests. Since no e2e test code or go.mod modifications were made, the e2e tests were not triggered in CI. They are ... | non_priority | remote test failing after version of singularity master describe the bug changed usage strings on the remote sub commands without me realizing they were checked in the tests since no test code or go mod modifications were made the tests were not triggered in ci they are now failing ... | 0 |
67,953 | 14,894,262,300 | IssuesEvent | 2021-01-21 07:12:57 | murthy1979/hackazon | https://api.github.com/repos/murthy1979/hackazon | opened | CVE-2016-4055 (Medium) detected in moment-2.8.3.min.js | security vulnerability | ## CVE-2016-4055 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>moment-2.8.3.min.js</b></p></summary>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a ... | True | CVE-2016-4055 (Medium) detected in moment-2.8.3.min.js - ## CVE-2016-4055 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>moment-2.8.3.min.js</b></p></summary>
<p>Parse, validate, ma... | non_priority | cve medium detected in moment min js cve medium severity vulnerability vulnerable library moment min js parse validate manipulate and display dates library home page a href path to vulnerable library hackazon web js moment min js dependency hierarchy x m... | 0 |
52,757 | 10,925,130,032 | IssuesEvent | 2019-11-22 11:45:25 | eclipse-theia/theia | https://api.github.com/repos/eclipse-theia/theia | closed | [vscode] webview does not have proper styles | bug plug-in system vscode webviews | ### Description
Theia

VSCode

### Reproduction Steps
Download vscode plugin REST Client(... | 1.0 | [vscode] webview does not have proper styles - ### Description
Theia

VSCode

### Reprodu... | non_priority | webview does not have proper styles description theia vscode reproduction steps download vscode plugin rest client humao rest client create a new http file send request look response the response is there but text is not highlighted properly i e black text on black background ... | 0 |
87,631 | 10,934,131,801 | IssuesEvent | 2019-11-24 09:07:14 | GospelAid/badiup | https://api.github.com/repos/GospelAid/badiup | opened | Selected indication needed in gallery page | bug P0 design | Need the design for showing selected images in the gallery page. The current design shows all images unselected. Please update the design with some of the images selected.

| 1.0 | Selected indication needed in gallery page - Need the design for showing selected images in the gallery page. The current design shows all images unselected. Please update the design with some of the images selected.
 | service/s3 needs-triage | I get this error when running TF 1.1.6 and these versions
Installing hashicorp/random v3.1.0...
Installing hashicorp/external v2.2.0...
Installing hashicorp/aws v4.2.0...
Error: error creating S3 Lifecycle Configuration for bucket (test-master-deadletters): MalformedXML: The XML you provided was not well-fo... | 1.0 | MalformedXML: The XML you provided was not well-formed or did not validate against our published schema (aws_s3_bucket_lifecycle_configuration) - I get this error when running TF 1.1.6 and these versions
Installing hashicorp/random v3.1.0...
Installing hashicorp/external v2.2.0...
Installing hashicorp/aws v4.2.0..... | non_priority | malformedxml the xml you provided was not well formed or did not validate against our published schema aws bucket lifecycle configuration i get this error when running tf and these versions installing hashicorp random installing hashicorp external installing hashicorp aws ... | 0 |
418,374 | 28,114,578,408 | IssuesEvent | 2023-03-31 09:45:45 | Kalipo-BV/kalipo-core | https://api.github.com/repos/Kalipo-BV/kalipo-core | opened | As a developer I would like to have STAR documentations of every review, retrospective and planning so that we can find ways to improve as a team. | Documentation User Story | ## User story specification
As a developer I would like to have STAR documentations of every review, retrospective and planning so that we can find ways to improve as a team.
## Acceptance criteria
### Functionals
- [ ] STAR review sprint 3
- [ ] STAR retro sprint 3
- [ ] STAR planning sprint 3
- [ ] STAR rev... | 1.0 | As a developer I would like to have STAR documentations of every review, retrospective and planning so that we can find ways to improve as a team. - ## User story specification
As a developer I would like to have STAR documentations of every review, retrospective and planning so that we can find ways to improve as a ... | non_priority | as a developer i would like to have star documentations of every review retrospective and planning so that we can find ways to improve as a team user story specification as a developer i would like to have star documentations of every review retrospective and planning so that we can find ways to improve as a ... | 0 |
171,107 | 20,920,870,737 | IssuesEvent | 2022-03-24 17:16:05 | webmachinelearning/webnn | https://api.github.com/repos/webmachinelearning/webnn | closed | op metadata that helps avoid implementation mistakes | security-tracker | Some way to help implementors validate that data is being passed correctly between nodes in the computation graph, has the expected sizes, etc.
Perhaps a little language which describes the required sizes/shapes and can be used to create checks that can be enforced as a graph is constructed, and as a graph is execut... | True | op metadata that helps avoid implementation mistakes - Some way to help implementors validate that data is being passed correctly between nodes in the computation graph, has the expected sizes, etc.
Perhaps a little language which describes the required sizes/shapes and can be used to create checks that can be enfor... | non_priority | op metadata that helps avoid implementation mistakes some way to help implementors validate that data is being passed correctly between nodes in the computation graph has the expected sizes etc perhaps a little language which describes the required sizes shapes and can be used to create checks that can be enfor... | 0 |
323,771 | 27,750,892,989 | IssuesEvent | 2023-03-15 20:38:42 | golang/go | https://api.github.com/repos/golang/go | opened | cmd/go: `go clean --fuzzcache` failure in TestScript/test_fuzz_limit_dup_entry | Testing NeedsFix GoCommand | ```
#!watchflakes
post <- pkg == "cmd/go" && `go clean --fuzzcache: exit status`
```
Pulled out from https://github.com/golang/go/issues/55311#issuecomment-1469087280.
I think the fix is to set `env GOCACHE=$WORK/cache` or similar explicitly in script tests that need a clean fuzzcache. | 1.0 | cmd/go: `go clean --fuzzcache` failure in TestScript/test_fuzz_limit_dup_entry - ```
#!watchflakes
post <- pkg == "cmd/go" && `go clean --fuzzcache: exit status`
```
Pulled out from https://github.com/golang/go/issues/55311#issuecomment-1469087280.
I think the fix is to set `env GOCACHE=$WORK/cache` or similar... | non_priority | cmd go go clean fuzzcache failure in testscript test fuzz limit dup entry watchflakes post pkg cmd go go clean fuzzcache exit status pulled out from i think the fix is to set env gocache work cache or similar explicitly in script tests that need a clean fuzzcache | 0 |
112,496 | 11,770,415,015 | IssuesEvent | 2020-03-15 19:08:09 | contributing-to-kubernetes/cool-kubernetes | https://api.github.com/repos/contributing-to-kubernetes/cool-kubernetes | closed | Document PR #85968 (Fix bug in apiserver service cidr split) | documentation | **PR:**
https://github.com/kubernetes/kubernetes/pull/85968
**ISSUE:**
bug
**SIG LABELS:**
sig/api-machinery
sig/network | 1.0 | Document PR #85968 (Fix bug in apiserver service cidr split) - **PR:**
https://github.com/kubernetes/kubernetes/pull/85968
**ISSUE:**
bug
**SIG LABELS:**
sig/api-machinery
sig/network | non_priority | document pr fix bug in apiserver service cidr split pr issue bug sig labels sig api machinery sig network | 0 |
204,342 | 15,897,254,386 | IssuesEvent | 2021-04-11 20:21:30 | Retro-Cartoons/Tom | https://api.github.com/repos/Retro-Cartoons/Tom | closed | documents-for-functions-and-properties | documentation enhancement | - Add document with 'option + command + slash' to essential and complex properties and functions
- No need for insignificant function and properties | 1.0 | documents-for-functions-and-properties - - Add document with 'option + command + slash' to essential and complex properties and functions
- No need for insignificant function and properties | non_priority | documents for functions and properties add document with option command slash to essential and complex properties and functions no need for insignificant function and properties | 0 |
237,587 | 19,660,122,566 | IssuesEvent | 2022-01-10 16:13:11 | aaronangxz/Carouhell | https://api.github.com/repos/aaronangxz/Carouhell | reopened | [FEATURE#82] DeleteListings - Move deleted listings to archive table | enhancement merged to test | Instead of just deleting listings, move it to archive_tab to preserve data
- [x] Create listings_archive_tab in `test`
- [x] Create listings_archive_tab in `live`
- [x] Add INSERT query in `DeleteListing` | 1.0 | [FEATURE#82] DeleteListings - Move deleted listings to archive table - Instead of just deleting listings, move it to archive_tab to preserve data
- [x] Create listings_archive_tab in `test`
- [x] Create listings_archive_tab in `live`
- [x] Add INSERT query in `DeleteListing` | non_priority | deletelistings move deleted listings to archive table instead of just deleting listings move it to archive tab to preserve data create listings archive tab in test create listings archive tab in live add insert query in deletelisting | 0 |
14,160 | 8,491,761,790 | IssuesEvent | 2018-10-27 16:14:19 | chreden/trview | https://api.github.com/repos/chreden/trview | opened | Minimap is always being re-rendered | bug performance | Turns out it was always redrawing - wasn't resetting the force redraw flag.
| True | Minimap is always being re-rendered - Turns out it was always redrawing - wasn't resetting the force redraw flag.
| non_priority | minimap is always being re rendered turns out it was always redrawing wasn t resetting the force redraw flag | 0 |
251,758 | 27,208,395,258 | IssuesEvent | 2023-02-20 14:45:02 | scm-automation-project/vsix-nuget-simple-project | https://api.github.com/repos/scm-automation-project/vsix-nuget-simple-project | opened | microsoft.chakracore.1.8.0.nupkg: 162 vulnerabilities (highest severity is: 9.8) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>microsoft.chakracore.1.8.0.nupkg</b></p></summary>
<p>ChakraCore is the core part of the Chakra Javascript engine that powers Microsoft Edge.</p>
<p>Library home page... | True | microsoft.chakracore.1.8.0.nupkg: 162 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>microsoft.chakracore.1.8.0.nupkg</b></p></summary>
<p>ChakraCore is the core part o... | non_priority | microsoft chakracore nupkg vulnerabilities highest severity is vulnerable library microsoft chakracore nupkg chakracore is the core part of the chakra javascript engine that powers microsoft edge library home page a href path to dependency file nuget vsix project nuget vsi... | 0 |
1,174 | 3,414,436,837 | IssuesEvent | 2015-12-07 06:37:44 | daemonraco/toobasic | https://api.github.com/repos/daemonraco/toobasic | closed | Routes for Services | Core Logic enhancement Services | ## What to do
Add a mechanism to allow and analyze routes (clean urls) for servicies. | 1.0 | Routes for Services - ## What to do
Add a mechanism to allow and analyze routes (clean urls) for servicies. | non_priority | routes for services what to do add a mechanism to allow and analyze routes clean urls for servicies | 0 |
258,676 | 22,338,821,471 | IssuesEvent | 2022-06-14 21:28:53 | GoogleForCreators/web-stories-wp | https://api.github.com/repos/GoogleForCreators/web-stories-wp | opened | Page Attachment clashing with Shopping Attachment | Type: Bug P1 Needs Tests Pod: WP Group: Page Attachment Group: Shopping | <!--
NOTE: For help requests, support questions, or general feedback,
please use the WordPress.org forums instead: https://wordpress.org/support/plugin/web-stories/
-->
## Bug Description
<!-- A clear and concise description of what the bug is. -->
There's a couple of conflicts between the page attachment (... | 1.0 | Page Attachment clashing with Shopping Attachment - <!--
NOTE: For help requests, support questions, or general feedback,
please use the WordPress.org forums instead: https://wordpress.org/support/plugin/web-stories/
-->
## Bug Description
<!-- A clear and concise description of what the bug is. -->
There's... | non_priority | page attachment clashing with shopping attachment note for help requests support questions or general feedback please use the wordpress org forums instead bug description there s a couple of conflicts between the page attachment aka outlink and the shopping attachment most notably ... | 0 |
23,623 | 10,926,954,709 | IssuesEvent | 2019-11-22 15:43:17 | finnessyj/mage-android-sdk | https://api.github.com/repos/finnessyj/mage-android-sdk | opened | CVE-2018-12023 (High) detected in jackson-databind-2.9.5.jar | security vulnerability | ## CVE-2018-12023 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2018-12023 (High) detected in jackson-databind-2.9.5.jar - ## CVE-2018-12023 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm mage android sdk sd... | 0 |
85,239 | 24,545,628,121 | IssuesEvent | 2022-10-12 08:34:40 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | [VAPT] [SB] Studies > UI Issue in the 'Filter by apps' dropdown | Bug P2 Study builder Process: Fixed Process: Tested QA Process: Tested dev | Studies > UI Issue in the 'Filter by apps' dropdown i.e., There is no outline border getting displayed in the dropdown and also no separtaion of all apps and app values
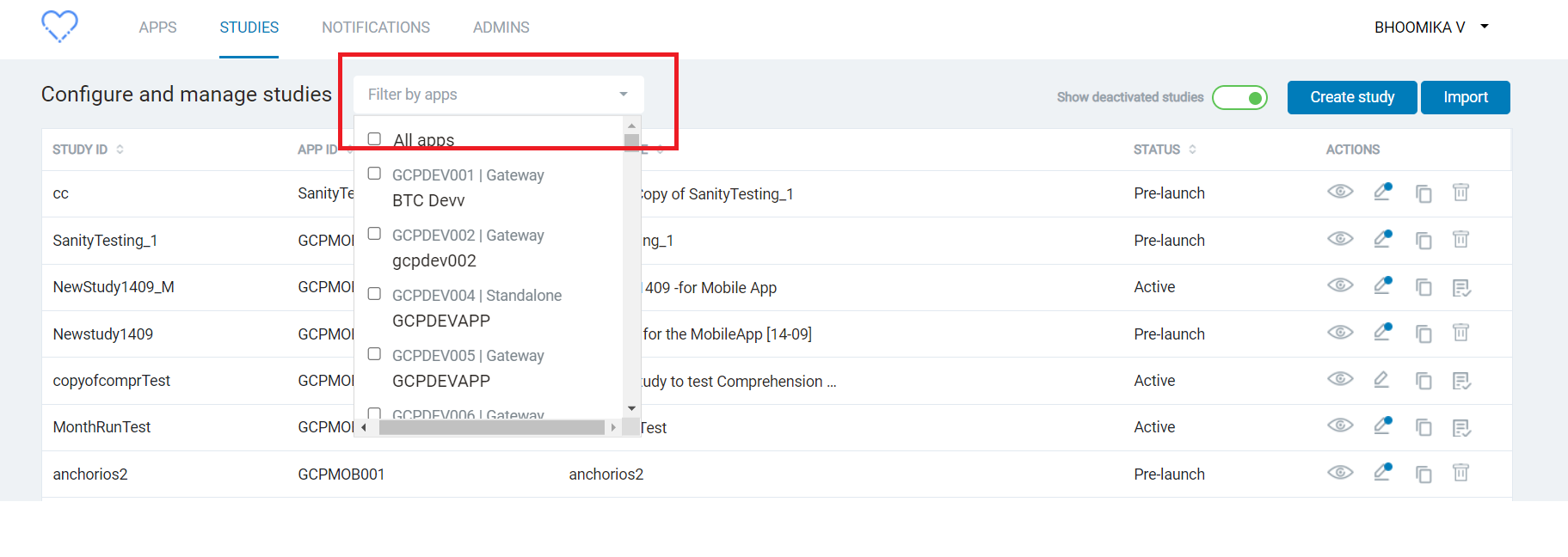
| 1.0 | [VAPT] [SB] Studies > UI Issue in the 'Filter by apps' dropdown - Studies > UI Issue in the 'Filter by apps' dropdown i.e., There is no outline border getting displayed in the dropdown and also no separtaion of all apps and app values

It would be great if the labels could be renamed.
Thanks | 1.0 | OSX -> macOS - OSX was renamed to macOS. (Or you can say: OSXI)
It would be great if the labels could be renamed.
Thanks | non_priority | osx macos osx was renamed to macos or you can say osxi it would be great if the labels could be renamed thanks | 0 |
61,354 | 8,514,980,736 | IssuesEvent | 2018-10-31 20:10:39 | aws-amplify/amplify-js | https://api.github.com/repos/aws-amplify/amplify-js | closed | Small issue in your documentation with the Jekyll Page Generator. | documentation | BUG
Small issue in your documentation with the Jekyll Page Generator.
AWS Amplify Authentication module exposes set of APIs to be used in any JavaScript framework. Please check [AWS Amplify API Reference]({%if jekyll.environment == 'production'%}{{site.amplify.baseurl}}{%endif%}/api/classes/authclass.html) for fu... | 1.0 | Small issue in your documentation with the Jekyll Page Generator. - BUG
Small issue in your documentation with the Jekyll Page Generator.
AWS Amplify Authentication module exposes set of APIs to be used in any JavaScript framework. Please check [AWS Amplify API Reference]({%if jekyll.environment == 'production'%}... | non_priority | small issue in your documentation with the jekyll page generator bug small issue in your documentation with the jekyll page generator aws amplify authentication module exposes set of apis to be used in any javascript framework please check if jekyll environment production site amplify baseurl ... | 0 |
163,061 | 25,746,490,486 | IssuesEvent | 2022-12-08 10:11:07 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | closed | Modified files not showing in source control tab | git *as-designed new release | Type: <b>Bug</b>
_Actual_:
Modified files are no longer listed in the 'Source Control Repositories' tab. Git extension is active and all other aspects working as expected (e.g. markers M/D/U in the 'Explorer' tab). The header in the 'SCR' tab is also showing the number of modified files in the current branch. Hitt... | 1.0 | Modified files not showing in source control tab - Type: <b>Bug</b>
_Actual_:
Modified files are no longer listed in the 'Source Control Repositories' tab. Git extension is active and all other aspects working as expected (e.g. markers M/D/U in the 'Explorer' tab). The header in the 'SCR' tab is also showing the n... | non_priority | modified files not showing in source control tab type bug actual modified files are no longer listed in the source control repositories tab git extension is active and all other aspects working as expected e g markers m d u in the explorer tab the header in the scr tab is also showing the number... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.