Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
81,084 | 30,703,447,125 | IssuesEvent | 2023-07-27 02:53:02 | vector-im/element-desktop | https://api.github.com/repos/vector-im/element-desktop | opened | Notifications are not shown in desktop notification list despite popping up as a desktop notification | T-Defect | ### Steps to reproduce
1. Receive a notification
2. observe that notification is shown
3. observe that notification is not put into desktop notification list/history
### Outcome
#### What did you expect?
I expect notifications to be put into notification history. Discord does the same, for example.
#### Wh... | 1.0 | Notifications are not shown in desktop notification list despite popping up as a desktop notification - ### Steps to reproduce
1. Receive a notification
2. observe that notification is shown
3. observe that notification is not put into desktop notification list/history
### Outcome
#### What did you expect?
I ... | non_priority | notifications are not shown in desktop notification list despite popping up as a desktop notification steps to reproduce receive a notification observe that notification is shown observe that notification is not put into desktop notification list history outcome what did you expect i ... | 0 |
20,316 | 6,024,288,027 | IssuesEvent | 2017-06-08 04:18:39 | darknite12/rms | https://api.github.com/repos/darknite12/rms | opened | Create first GUI for Person | code todo ui | This UI may consist of multiple pages to view/create/modify/remove a Person from the database | 1.0 | Create first GUI for Person - This UI may consist of multiple pages to view/create/modify/remove a Person from the database | non_priority | create first gui for person this ui may consist of multiple pages to view create modify remove a person from the database | 0 |
314,001 | 23,501,552,660 | IssuesEvent | 2022-08-18 08:52:20 | ali2210/WizDwarf | https://api.github.com/repos/ali2210/WizDwarf | closed | Registries Keygen encryption | documentation enhancement | **Is your feature request related to a problem? Please describe.**
Yes, Many application have third parties registries keygen which is used for different purpose. Like Database connection, third parties application etc. Programmer will use different method to protect application credentials . One way function, key rot... | 1.0 | Registries Keygen encryption - **Is your feature request related to a problem? Please describe.**
Yes, Many application have third parties registries keygen which is used for different purpose. Like Database connection, third parties application etc. Programmer will use different method to protect application credenti... | non_priority | registries keygen encryption is your feature request related to a problem please describe yes many application have third parties registries keygen which is used for different purpose like database connection third parties application etc programmer will use different method to protect application credenti... | 0 |
279,746 | 21,182,444,571 | IssuesEvent | 2022-04-08 09:17:08 | Avaiga/taipy-doc | https://api.github.com/repos/Avaiga/taipy-doc | closed | Ubuntu deployment | devops documentation | * Taipy version: 1.0.0
* Python version: Python3.8+
* Operating System: Ubuntu
### Description
Add documentation on how to deploy on Ubuntu.
| 1.0 | Ubuntu deployment - * Taipy version: 1.0.0
* Python version: Python3.8+
* Operating System: Ubuntu
### Description
Add documentation on how to deploy on Ubuntu.
| non_priority | ubuntu deployment taipy version python version operating system ubuntu description add documentation on how to deploy on ubuntu | 0 |
264,959 | 23,145,082,232 | IssuesEvent | 2022-07-28 23:14:22 | MPMG-DCC-UFMG/F01 | https://api.github.com/repos/MPMG-DCC-UFMG/F01 | closed | Teste de generalizacao para a tag Seridores - Registro por lotação - Coluna | generalization test development template-Síntese tecnologia informatica tag-Servidores subtag-Registro por lotação | DoD: Realizar o teste de Generalização do validador da tag Seridores - Registro por lotação para o Município de Coluna. | 1.0 | Teste de generalizacao para a tag Seridores - Registro por lotação - Coluna - DoD: Realizar o teste de Generalização do validador da tag Seridores - Registro por lotação para o Município de Coluna. | non_priority | teste de generalizacao para a tag seridores registro por lotação coluna dod realizar o teste de generalização do validador da tag seridores registro por lotação para o município de coluna | 0 |
241,433 | 18,454,655,556 | IssuesEvent | 2021-10-15 14:58:14 | CMPUT301F21T13/FungalFunhouse | https://api.github.com/repos/CMPUT301F21T13/FungalFunhouse | closed | Draft UI-prototype and mockup storyboard sequences for general UI flow | documentation | Diagram the layout of your main user interface and major dialogs, with comments describing the important elements. Also, diagram storyboard sequences of using your application, with transitions between different states of the user interface, caused by the user manipulating the controls or providing input. Within the di... | 1.0 | Draft UI-prototype and mockup storyboard sequences for general UI flow - Diagram the layout of your main user interface and major dialogs, with comments describing the important elements. Also, diagram storyboard sequences of using your application, with transitions between different states of the user interface, cause... | non_priority | draft ui prototype and mockup storyboard sequences for general ui flow diagram the layout of your main user interface and major dialogs with comments describing the important elements also diagram storyboard sequences of using your application with transitions between different states of the user interface cause... | 0 |
276,780 | 21,000,096,970 | IssuesEvent | 2022-03-29 16:36:07 | jrenjq/PainAssessment | https://api.github.com/repos/jrenjq/PainAssessment | closed | D2: Updated User Requirements | documentation | - [x] update calculate weightage to save checklist
- [x] add details on save checklist user feature | 1.0 | D2: Updated User Requirements - - [x] update calculate weightage to save checklist
- [x] add details on save checklist user feature | non_priority | updated user requirements update calculate weightage to save checklist add details on save checklist user feature | 0 |
64,451 | 26,744,198,353 | IssuesEvent | 2023-01-30 14:58:28 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | Bus Stop Scoring Tool | Workgroup: TED Type: New Application Impact: 2-Major Service: Dev Service: Product Need: 2-Should Have | <!-- Email -->
<!-- caitlin.d'alton@austintexas.gov -->
> Name
2022 Bus Stop Analysis and Map
> What application are you using?
Other / Not Sure
> Describe the problem.
ATD has an existing tool (https://capmetro.atxvisionzero.xyz/) that we (ATD and CapMetro) use to identify bus stops that should be evaluated for ... | 2.0 | Bus Stop Scoring Tool - <!-- Email -->
<!-- caitlin.d'alton@austintexas.gov -->
> Name
2022 Bus Stop Analysis and Map
> What application are you using?
Other / Not Sure
> Describe the problem.
ATD has an existing tool (https://capmetro.atxvisionzero.xyz/) that we (ATD and CapMetro) use to identify bus stops that ... | non_priority | bus stop scoring tool name bus stop analysis and map what application are you using other not sure describe the problem atd has an existing tool that we atd and capmetro use to identify bus stops that should be evaluated for improvement relocation or closure in order to improve bus operati... | 0 |
158,828 | 12,426,283,731 | IssuesEvent | 2020-05-24 20:23:40 | phetsims/circuit-construction-kit-common | https://api.github.com/repos/phetsims/circuit-construction-kit-common | closed | CT Cannot read property disposeCircuitElement of null | type:automated-testing | Occurs in multiple CCK sims
```
circuit-construction-kit-dc-virtual-lab : interactive-description-fuzzBoard : built : run
https://bayes.colorado.edu/continuous-testing/snapshot-1584591344628/circuit-construction-kit-dc-virtual-lab/build/phet/circuit-construction-kit-dc-virtual-lab_en_phet.html?postMessageOnLoad&post... | 1.0 | CT Cannot read property disposeCircuitElement of null - Occurs in multiple CCK sims
```
circuit-construction-kit-dc-virtual-lab : interactive-description-fuzzBoard : built : run
https://bayes.colorado.edu/continuous-testing/snapshot-1584591344628/circuit-construction-kit-dc-virtual-lab/build/phet/circuit-constructio... | non_priority | ct cannot read property disposecircuitelement of null occurs in multiple cck sims circuit construction kit dc virtual lab interactive description fuzzboard built run query fuzzboard supportsdescriptions memorylimit uncaught typeerror cannot read property disposecircuitelement of null typeerror... | 0 |
87,899 | 17,391,876,145 | IssuesEvent | 2021-08-02 08:28:21 | ministryofjustice/modernisation-platform | https://api.github.com/repos/ministryofjustice/modernisation-platform | closed | Investigate Terraform linters | code quality documentation enhancement | We should investigate using a Terraform linter such as [tflint](/terraform-linters/tflint) to ensure we remain consistent and in-line with best practice with the code we're writing. | 1.0 | Investigate Terraform linters - We should investigate using a Terraform linter such as [tflint](/terraform-linters/tflint) to ensure we remain consistent and in-line with best practice with the code we're writing. | non_priority | investigate terraform linters we should investigate using a terraform linter such as terraform linters tflint to ensure we remain consistent and in line with best practice with the code we re writing | 0 |
401,027 | 27,312,943,111 | IssuesEvent | 2023-02-24 13:39:52 | mcuee/libusb-win32 | https://api.github.com/repos/mcuee/libusb-win32 | opened | libusb0.sys filter driver may not work with some USB devices (please report issues here) | documentation | Take note there is no gurantee that libusb0.sys device filter (which functions as a upper filter) will work for all the USB devices.
Please report issues here. | 1.0 | libusb0.sys filter driver may not work with some USB devices (please report issues here) - Take note there is no gurantee that libusb0.sys device filter (which functions as a upper filter) will work for all the USB devices.
Please report issues here. | non_priority | sys filter driver may not work with some usb devices please report issues here take note there is no gurantee that sys device filter which functions as a upper filter will work for all the usb devices please report issues here | 0 |
130,533 | 18,090,858,211 | IssuesEvent | 2021-09-22 01:22:07 | carbon-design-system/carbon-addons-iot-react | https://api.github.com/repos/carbon-design-system/carbon-addons-iot-react | closed | [Icon content switcher] Styling enhancement | type: enhancement :bulb: val: 2 status: needs design :art: design reconciliation | Looking to update the icon content switcher styling slightly to match what Carbon has for their [content switcher](https://react.carbondesignsystem.com/?path=/story/contentswitcher--content-switcher-playground)
Updates:
- Update color of hover and selected states to match Carbon's content switcher
- remove stroke ... | 2.0 | [Icon content switcher] Styling enhancement - Looking to update the icon content switcher styling slightly to match what Carbon has for their [content switcher](https://react.carbondesignsystem.com/?path=/story/contentswitcher--content-switcher-playground)
Updates:
- Update color of hover and selected states to mat... | non_priority | styling enhancement looking to update the icon content switcher styling slightly to match what carbon has for their updates update color of hover and selected states to match carbon s content switcher remove stroke around default state although that is in design on the pal site but i m not seeing it ... | 0 |
96,108 | 27,750,707,435 | IssuesEvent | 2023-03-15 20:29:21 | PowerShell/vscode-powershell | https://api.github.com/repos/PowerShell/vscode-powershell | closed | Adopt the pre-release extension feature | Issue-Enhancement Area-Build & Release | ### Prerequisites
- [X] I have written a descriptive issue title.
- [X] I have searched all [issues](https://github.com/PowerShell/vscode-powershell/issues?q=is%3Aissue) to ensure it has not already been reported.
### Summary
Refs: https://github.com/microsoft/vscode/issues/15756
VS Code now supports pre-release ... | 1.0 | Adopt the pre-release extension feature - ### Prerequisites
- [X] I have written a descriptive issue title.
- [X] I have searched all [issues](https://github.com/PowerShell/vscode-powershell/issues?q=is%3Aissue) to ensure it has not already been reported.
### Summary
Refs: https://github.com/microsoft/vscode/issues/... | non_priority | adopt the pre release extension feature prerequisites i have written a descriptive issue title i have searched all to ensure it has not already been reported summary refs vs code now supports pre release extensions docs that should help i know powershell has a separate powershell... | 0 |
53,605 | 28,309,581,441 | IssuesEvent | 2023-04-10 14:16:19 | apache/arrow-datafusion | https://api.github.com/repos/apache/arrow-datafusion | opened | Fuse grouped aggregate and filter operators for improved performance | enhancement performance | ### Is your feature request related to a problem or challenge?
When we perform a grouped aggregate on a filtered input (such as with TPC-H q1), the filter operator performs two main tasks:
- Evaluate the filter predicate (usually very fast)
- Create new batches and copy over the filtered data (very slow if the fil... | True | Fuse grouped aggregate and filter operators for improved performance - ### Is your feature request related to a problem or challenge?
When we perform a grouped aggregate on a filtered input (such as with TPC-H q1), the filter operator performs two main tasks:
- Evaluate the filter predicate (usually very fast)
- C... | non_priority | fuse grouped aggregate and filter operators for improved performance is your feature request related to a problem or challenge when we perform a grouped aggregate on a filtered input such as with tpc h the filter operator performs two main tasks evaluate the filter predicate usually very fast cr... | 0 |
168,780 | 14,172,806,514 | IssuesEvent | 2020-11-12 17:26:10 | dsm-cefet-rj/trabalho-integrado-2020-1-grupo-2 | https://api.github.com/repos/dsm-cefet-rj/trabalho-integrado-2020-1-grupo-2 | closed | Criação do Kanban - aba Projects [8h] | documentation enhancement | :man_pilot: Estruturar todas as colunas com os cartões de tarefas a serem executadas pelas equipes de PSW e Teste de Software | 1.0 | Criação do Kanban - aba Projects [8h] - :man_pilot: Estruturar todas as colunas com os cartões de tarefas a serem executadas pelas equipes de PSW e Teste de Software | non_priority | criação do kanban aba projects man pilot estruturar todas as colunas com os cartões de tarefas a serem executadas pelas equipes de psw e teste de software | 0 |
427,680 | 29,832,419,267 | IssuesEvent | 2023-06-18 12:42:13 | keironchaudhry/june-pride-hackathon-2023 | https://api.github.com/repos/keironchaudhry/june-pride-hackathon-2023 | closed | User Story: History archive | documentation frontend | As a **user**, I want **to be able to view historical information** so that **I can learn and appreciate LGBTQ+ history**.
| 1.0 | User Story: History archive - As a **user**, I want **to be able to view historical information** so that **I can learn and appreciate LGBTQ+ history**.
| non_priority | user story history archive as a user i want to be able to view historical information so that i can learn and appreciate lgbtq history | 0 |
247,294 | 20,971,007,919 | IssuesEvent | 2022-03-28 11:22:11 | opencurve/curve | https://api.github.com/repos/opencurve/curve | closed | curvefs_tool create-fs failed, error is CREATE_PARTITION_ERROR | bug need test | **Describe the bug (描述bug)**
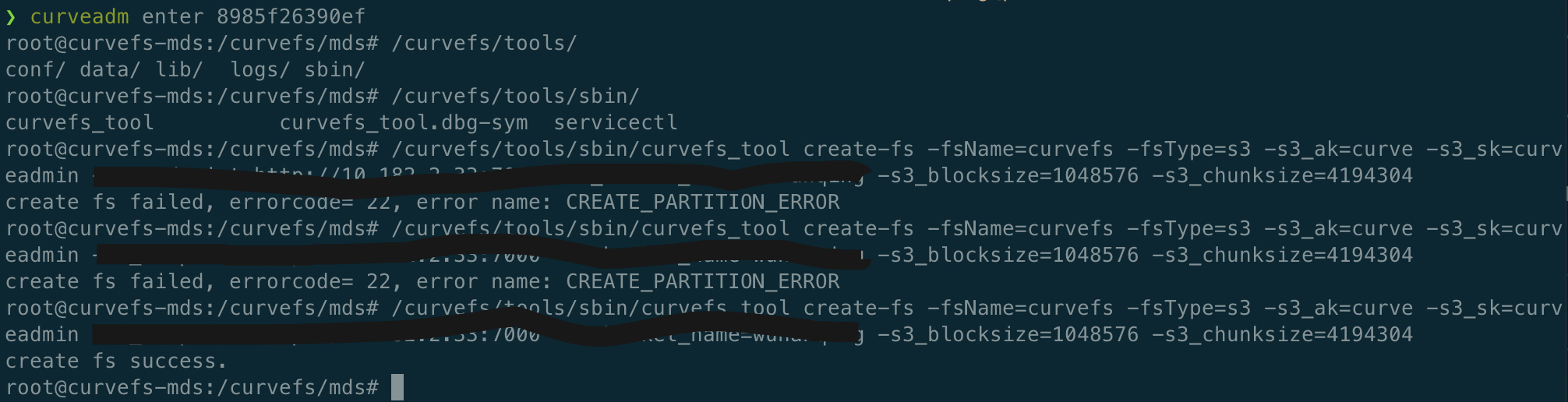
**To Reproduce (复现方法)**
use CurveAdm deploy a cluster with three etcd/mds/metaserver, and after deploy succeed, use curvefs_tool create a filesystem.
**Expected behavi... | 1.0 | curvefs_tool create-fs failed, error is CREATE_PARTITION_ERROR - **Describe the bug (描述bug)**
**To Reproduce (复现方法)**
use CurveAdm deploy a cluster with three etcd/mds/metaserver, and after deploy su... | non_priority | curvefs tool create fs failed error is create partition error describe the bug 描述bug to reproduce 复现方法 use curveadm deploy a cluster with three etcd mds metaserver and after deploy succeed use curvefs tool create a filesystem expected behavior 期望行为 versions 各种版本 fs ... | 0 |
143,999 | 19,268,469,681 | IssuesEvent | 2021-12-10 00:49:54 | leanswift/bob-frontend | https://api.github.com/repos/leanswift/bob-frontend | opened | CVE-2021-23424 (High) detected in ansi-html-0.0.7.tgz | security vulnerability | ## CVE-2021-23424 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansi-html-0.0.7.tgz</b></p></summary>
<p>An elegant lib that converts the chalked (ANSI) text to HTML.</p>
<p>Library ... | True | CVE-2021-23424 (High) detected in ansi-html-0.0.7.tgz - ## CVE-2021-23424 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansi-html-0.0.7.tgz</b></p></summary>
<p>An elegant lib that c... | non_priority | cve high detected in ansi html tgz cve high severity vulnerability vulnerable library ansi html tgz an elegant lib that converts the chalked ansi text to html library home page a href path to dependency file bob frontend package json path to vulnerable library bob... | 0 |
91,265 | 15,856,386,602 | IssuesEvent | 2021-04-08 02:13:23 | n-devs/NodeJSControUI | https://api.github.com/repos/n-devs/NodeJSControUI | opened | CVE-2021-23337 (High) detected in lodash-4.17.5.tgz | security vulnerability | ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.5.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.n... | True | CVE-2021-23337 (High) detected in lodash-4.17.5.tgz - ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.5.tgz</b></p></summary>
<p>Lodash modular utilities.... | non_priority | cve high detected in lodash tgz cve high severity vulnerability vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file nodejscontroui package json path to vulnerable library nodejscontroui node modules lodash package... | 0 |
294,870 | 25,410,976,091 | IssuesEvent | 2022-11-22 18:56:57 | USEPA/haztrak | https://api.github.com/repos/USEPA/haztrak | opened | Tsdf Search API endpoint | enhancement good first issue django test | # 🚀 Feature Request
Add a generic API view that allows the client to POST search criteria to http server and return an array of Handler that are TSDFs and meet the search criteria.
This should be similar to #168 and should be relatively easy to implement. | 1.0 | Tsdf Search API endpoint - # 🚀 Feature Request
Add a generic API view that allows the client to POST search criteria to http server and return an array of Handler that are TSDFs and meet the search criteria.
This should be similar to #168 and should be relatively easy to implement. | non_priority | tsdf search api endpoint 🚀 feature request add a generic api view that allows the client to post search criteria to http server and return an array of handler that are tsdfs and meet the search criteria this should be similar to and should be relatively easy to implement | 0 |
19,869 | 4,448,611,708 | IssuesEvent | 2016-08-22 00:53:11 | BergFulton/metropolitan | https://api.github.com/repos/BergFulton/metropolitan | opened | Verify black and white paint job | History/Documentation | Was my car originally the black and white it claims to be (I think yes). But will seek verification. | 1.0 | Verify black and white paint job - Was my car originally the black and white it claims to be (I think yes). But will seek verification. | non_priority | verify black and white paint job was my car originally the black and white it claims to be i think yes but will seek verification | 0 |
31,713 | 4,287,152,798 | IssuesEvent | 2016-07-16 15:34:18 | StockSharp/StockSharp | https://api.github.com/repos/StockSharp/StockSharp | closed | Could not load file or assembly 'DevExpress.Xpf.Core | by design | While I was running my app based on stocksharp 4.3.14.1 referenced from NuGet, I got the following error:
```
Exception thrown: 'System.Windows.Markup.XamlParseException' in PresentationFramework.dll
Additional information: Could not load file or assembly 'DevExpress.Xpf.Core.v15.2, PublicKeyToken=b88d1754d700e4... | 1.0 | Could not load file or assembly 'DevExpress.Xpf.Core - While I was running my app based on stocksharp 4.3.14.1 referenced from NuGet, I got the following error:
```
Exception thrown: 'System.Windows.Markup.XamlParseException' in PresentationFramework.dll
Additional information: Could not load file or assembly 'D... | non_priority | could not load file or assembly devexpress xpf core while i was running my app based on stocksharp referenced from nuget i got the following error exception thrown system windows markup xamlparseexception in presentationframework dll additional information could not load file or assembly de... | 0 |
375,683 | 26,172,746,639 | IssuesEvent | 2023-01-02 04:07:50 | dokku/dokku | https://api.github.com/repos/dokku/dokku | closed | Documentation Issue | type: documentation merge-level: patch difficulty: easy status: has plan plugin: nginx | ### Description of problem
I have a specific Dokku app which I use to catch all HTTP traffic to my server. This is what I would refer to as my "default app". On this same server, there are other deployed Dokku apps, each of which has one or more domain assigned to it. All HTTP requests which to not match any of the do... | 1.0 | Documentation Issue - ### Description of problem
I have a specific Dokku app which I use to catch all HTTP traffic to my server. This is what I would refer to as my "default app". On this same server, there are other deployed Dokku apps, each of which has one or more domain assigned to it. All HTTP requests which to n... | non_priority | documentation issue description of problem i have a specific dokku app which i use to catch all http traffic to my server this is what i would refer to as my default app on this same server there are other deployed dokku apps each of which has one or more domain assigned to it all http requests which to n... | 0 |
71,672 | 30,914,170,900 | IssuesEvent | 2023-08-05 04:11:52 | Zahlungsmittel/Zahlungsmittel | https://api.github.com/repos/Zahlungsmittel/Zahlungsmittel | opened | [CLOSED] feat: Test Apollo Provider in Frontend | epic service: wallet frontend feature devops test service: admin frontend imported | <a href="https://github.com/Mogge"><img src="https://avatars.githubusercontent.com/u/15882241?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [Mogge](https://github.com/Mogge)**
_Tuesday Dec 07, 2021 at 17:45 GMT_
_Originally opened as https://github.com/gradido/gradido/pull/1161_
----
## �... | 2.0 | [CLOSED] feat: Test Apollo Provider in Frontend - <a href="https://github.com/Mogge"><img src="https://avatars.githubusercontent.com/u/15882241?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [Mogge](https://github.com/Mogge)**
_Tuesday Dec 07, 2021 at 17:45 GMT_
_Originally opened as https:/... | non_priority | feat test apollo provider in frontend issue by tuesday dec at gmt originally opened as 🍰 pullrequest test the middleware of the apollo provider in the frontend issues fixes fixes included the following code | 0 |
155,498 | 19,802,891,111 | IssuesEvent | 2022-01-19 01:08:58 | susanstwss/SecurityShepherd | https://api.github.com/repos/susanstwss/SecurityShepherd | opened | CVE-2022-23302 (High) detected in log4j-1.2.7.jar | security vulnerability | ## CVE-2022-23302 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.7.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /tor... | True | CVE-2022-23302 (High) detected in log4j-1.2.7.jar - ## CVE-2022-23302 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.7.jar</b></p></summary>
<p></p>
<p>Path to dependency fi... | non_priority | cve high detected in jar cve high severity vulnerability vulnerable library jar path to dependency file pom xml path to vulnerable library tory jar dependency hierarchy x jar vulnerable library found in base branch dev ... | 0 |
91,787 | 26,486,715,102 | IssuesEvent | 2023-01-17 18:40:29 | golang/go | https://api.github.com/repos/golang/go | opened | x/build: use cloud build to deploy x/build services | Builders NeedsInvestigation | We should automate the building and deployment of infrastructure binaries. The components of the infrastructure should be built in a central environment.
@golang/release | 1.0 | x/build: use cloud build to deploy x/build services - We should automate the building and deployment of infrastructure binaries. The components of the infrastructure should be built in a central environment.
@golang/release | non_priority | x build use cloud build to deploy x build services we should automate the building and deployment of infrastructure binaries the components of the infrastructure should be built in a central environment golang release | 0 |
280,311 | 24,293,579,487 | IssuesEvent | 2022-09-29 08:18:19 | valory-xyz/open-autonomy | https://api.github.com/repos/valory-xyz/open-autonomy | closed | Containers need more time to start on CI from `contracts-amm` image | test | ### Subject of the issue
Some tests are flaky because containers fail to start on time on CI. Specifically, this happened on [Merge pull request #1395 from valory-xyz/feat/autoupdate-packagelist main_workflow #5418](https://github.com/valory-xyz/open-autonomy/actions/runs/3133747181/jobs/5087596544) for some tests tha... | 1.0 | Containers need more time to start on CI from `contracts-amm` image - ### Subject of the issue
Some tests are flaky because containers fail to start on time on CI. Specifically, this happened on [Merge pull request #1395 from valory-xyz/feat/autoupdate-packagelist main_workflow #5418](https://github.com/valory-xyz/ope... | non_priority | containers need more time to start on ci from contracts amm image subject of the issue some tests are flaky because containers fail to start on time on ci specifically this happened on for some tests that use the contracts amm image we could try increasing the max attempts e g from to here ... | 0 |
227,399 | 25,070,088,718 | IssuesEvent | 2022-11-07 11:24:48 | Watemlifts/Platform-Integration | https://api.github.com/repos/Watemlifts/Platform-Integration | opened | CVE-2020-14343 (High) detected in PyYAML-5.1.1.tar.gz | security vulnerability | ## CVE-2020-14343 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>PyYAML-5.1.1.tar.gz</b></p></summary>
<p>YAML parser and emitter for Python</p>
<p>Library home page: <a href="https:/... | True | CVE-2020-14343 (High) detected in PyYAML-5.1.1.tar.gz - ## CVE-2020-14343 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>PyYAML-5.1.1.tar.gz</b></p></summary>
<p>YAML parser and emitt... | non_priority | cve high detected in pyyaml tar gz cve high severity vulnerability vulnerable library pyyaml tar gz yaml parser and emitter for python library home page a href path to dependency file homeassistant path to vulnerable library homeassistant homeassistant components ... | 0 |
105,228 | 16,624,753,868 | IssuesEvent | 2021-06-03 08:10:08 | tabac-ws-demo/js-demo | https://api.github.com/repos/tabac-ws-demo/js-demo | opened | CVE-2020-7598 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b>, <b>minimist-0.0.10.tgz</b></p></summary>
<p>
<details><summary><... | True | CVE-2020-7598 (Medium) detected in multiple libraries - ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b>, <b>minimi... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries minimist tgz minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file js demo package json ... | 0 |
134,094 | 18,421,773,587 | IssuesEvent | 2021-10-13 16:54:17 | daniel-brown-ws-test/verademo | https://api.github.com/repos/daniel-brown-ws-test/verademo | closed | CVE-2020-5421 (Medium) detected in spring-web-5.2.7.RELEASE.jar | security vulnerability IaC violation | ## CVE-2020-5421 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-5.2.7.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/sp... | True | CVE-2020-5421 (Medium) detected in spring-web-5.2.7.RELEASE.jar - ## CVE-2020-5421 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-5.2.7.RELEASE.jar</b></p></summary>
<p>S... | non_priority | cve medium detected in spring web release jar cve medium severity vulnerability vulnerable library spring web release jar spring web library home page a href path to dependency file verademo app pom xml path to vulnerable library home wss scanner repository org s... | 0 |
101,814 | 31,683,149,037 | IssuesEvent | 2023-09-08 02:49:17 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | [wasm][debugger] CheckInspectLocalsAtBreakpointSite | blocking-clean-ci Known Build Error | ## Build Information
Build: https://dev.azure.com/dnceng-public/cbb18261-c48f-4abb-8651-8cdcb5474649/_build/results?buildId=398924
Build error leg or test failing: chrome-DebuggerTests.GetPropertiesTests.WorkItemExecution
Pull request: https://github.com/dotnet/runtime/pull/91759
<!-- Error message template -->
#... | 1.0 | [wasm][debugger] CheckInspectLocalsAtBreakpointSite - ## Build Information
Build: https://dev.azure.com/dnceng-public/cbb18261-c48f-4abb-8651-8cdcb5474649/_build/results?buildId=398924
Build error leg or test failing: chrome-DebuggerTests.GetPropertiesTests.WorkItemExecution
Pull request: https://github.com/dotnet/... | non_priority | checkinspectlocalsatbreakpointsite build information build build error leg or test failing chrome debuggertests getpropertiestests workitemexecution pull request error message fill the error message using json errormessage checkinspectlocalsatbreakpointsite er... | 0 |
103,933 | 16,613,263,775 | IssuesEvent | 2021-06-02 13:58:26 | Thanraj/linux-4.1.15 | https://api.github.com/repos/Thanraj/linux-4.1.15 | opened | CVE-2019-19966 (Medium) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2019-19966 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home p... | True | CVE-2019-19966 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2019-19966 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia C... | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source f... | 0 |
347,974 | 24,905,251,326 | IssuesEvent | 2022-10-29 06:36:35 | aws-actions/amazon-ecr-login | https://api.github.com/repos/aws-actions/amazon-ecr-login | closed | Possible to just use and deploy containers for my github aciton environment from aws (NOT TO PUSH, IF NOT PULL) | documentation | Hi community!
I would like to ask for a feature (or in case of me missing this feature please help me to see how to proceed), when deploying actions in github CI.
**Basically I dont find any info about how to pull containers from aws and deploy them in CI github actions during the job execution**
```
jobs:
... | 1.0 | Possible to just use and deploy containers for my github aciton environment from aws (NOT TO PUSH, IF NOT PULL) - Hi community!
I would like to ask for a feature (or in case of me missing this feature please help me to see how to proceed), when deploying actions in github CI.
**Basically I dont find any info abou... | non_priority | possible to just use and deploy containers for my github aciton environment from aws not to push if not pull hi community i would like to ask for a feature or in case of me missing this feature please help me to see how to proceed when deploying actions in github ci basically i dont find any info abou... | 0 |
65,559 | 12,620,375,627 | IssuesEvent | 2020-06-13 06:21:01 | fabianschuiki/moore | https://api.github.com/repos/fabianschuiki/moore | opened | Canonicalize param env before codegen | A-codegen C-enhancement L-vlog | Codegen currently uses the `ParamEnv` to determine if two modules have the same parametrization. However, since most parameters are indirectly bound, i.e., they depend on outer parameters, these param envs look distinct in many cases, even though they will resolve to the exact same parametrization. To fix this, codegen... | 1.0 | Canonicalize param env before codegen - Codegen currently uses the `ParamEnv` to determine if two modules have the same parametrization. However, since most parameters are indirectly bound, i.e., they depend on outer parameters, these param envs look distinct in many cases, even though they will resolve to the exact sa... | non_priority | canonicalize param env before codegen codegen currently uses the paramenv to determine if two modules have the same parametrization however since most parameters are indirectly bound i e they depend on outer parameters these param envs look distinct in many cases even though they will resolve to the exact sa... | 0 |
69,773 | 17,851,584,532 | IssuesEvent | 2021-09-04 06:46:52 | spack/spack | https://api.github.com/repos/spack/spack | opened | Installation issue: motif | build-error | ### Steps to reproduce the issue
```console
spack install motif
```
### Information on your system
Ubuntu 20.04 LTS (x86_64)
* **Spack:** 0.16.2-4144-536121cadf
* **Python:** 3.8.10
* **Platform:** linux-ubuntu20.04-skylake
* **Concretizer:** original
### Additional information
cc main authors of the packa... | 1.0 | Installation issue: motif - ### Steps to reproduce the issue
```console
spack install motif
```
### Information on your system
Ubuntu 20.04 LTS (x86_64)
* **Spack:** 0.16.2-4144-536121cadf
* **Python:** 3.8.10
* **Platform:** linux-ubuntu20.04-skylake
* **Concretizer:** original
### Additional information
... | non_priority | installation issue motif steps to reproduce the issue console spack install motif information on your system ubuntu lts spack python platform linux skylake concretizer original additional information cc main authors of the pack... | 0 |
139,662 | 12,877,676,761 | IssuesEvent | 2020-07-11 12:31:04 | toolisticon/jgiven-addons | https://api.github.com/repos/toolisticon/jgiven-addons | opened | provide better docs | documentation | The readme should provide information how to use the library (include coordinates for both gradle and maven) | 1.0 | provide better docs - The readme should provide information how to use the library (include coordinates for both gradle and maven) | non_priority | provide better docs the readme should provide information how to use the library include coordinates for both gradle and maven | 0 |
337,644 | 30,252,882,090 | IssuesEvent | 2023-07-06 22:21:10 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | jobs: TestJobInfoUpgradeRegressionTests failed | C-test-failure O-robot branch-master T-disaster-recovery T-jobs | jobs.TestJobInfoUpgradeRegressionTests [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Ci_TestsAwsLinuxArm64_UnitTests/10810911?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Ci_TestsAwsLinuxArm64_UnitTests/10810911?buildTab=artifacts#/) on master @ [... | 1.0 | jobs: TestJobInfoUpgradeRegressionTests failed - jobs.TestJobInfoUpgradeRegressionTests [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Ci_TestsAwsLinuxArm64_UnitTests/10810911?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Ci_TestsAwsLinuxArm64_UnitT... | non_priority | jobs testjobinfoupgraderegressiontests failed jobs testjobinfoupgraderegressiontests with on master upgrade upgradecluster cluster go executing bump cluster version fence on nodes n server migration go active cluster version setting is now f... | 0 |
296,716 | 25,571,714,966 | IssuesEvent | 2022-11-30 18:14:39 | MD-Anderson-Bioinformatics/NG-CHM | https://api.github.com/repos/MD-Anderson-Bioinformatics/NG-CHM | closed | Expand pane doesn't take pane resizes while collapsed into account when redrawing expanded pane. | bug ready-for-testing 2.23.0 | To recreate:
Open map with two default panes.
Below left pane open new pane.
Set new pane to detail map.
Collapse new pane.
Grab resize bar in middle of screen and drag it left.
Expand hidden pane.
New pane will overwrite area of right pane by amount the resize bar was moved.
` to `httpsMockWebServer.start()` in the mock ... | 1.0 | Three OkHttpOpenRosaServerClientProviderTest fail under some circumstances - There are 4 `OkHttpOpenRosaServerClientProviderTest` that use `MockWebServer`. Three of them fail for some configurations. I can get them to fail when running `./gradlew testDebugUnitTest` but not when running from Android Studio.
Changing ... | non_priority | three okhttpopenrosaserverclientprovidertest fail under some circumstances there are okhttpopenrosaserverclientprovidertest that use mockwebserver three of them fail for some configurations i can get them to fail when running gradlew testdebugunittest but not when running from android studio changing ... | 0 |
64,192 | 26,641,161,902 | IssuesEvent | 2023-01-25 05:03:56 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | Flaky bug: error waiting for DynamoDB PITR update: unexpected state 'DISABLED', wanted target 'ENABLED' | bug service/dynamodb | ### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant n... | 1.0 | Flaky bug: error waiting for DynamoDB PITR update: unexpected state 'DISABLED', wanted target 'ENABLED' - ### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and ma... | non_priority | flaky bug error waiting for dynamodb pitr update unexpected state disabled wanted target enabled community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or other comments that do not add... | 0 |
92,917 | 8,388,194,666 | IssuesEvent | 2018-10-09 05:02:22 | TerriaJS/aremi-natmap | https://api.github.com/repos/TerriaJS/aremi-natmap | closed | AREMI v2018-09-28 Pre-Release Test - Error accessing catalogue item #13 | GA-testing | Layer: Topography/Elevation/LIDAR 25m DEM
Error: Request has failed - Status code: 503
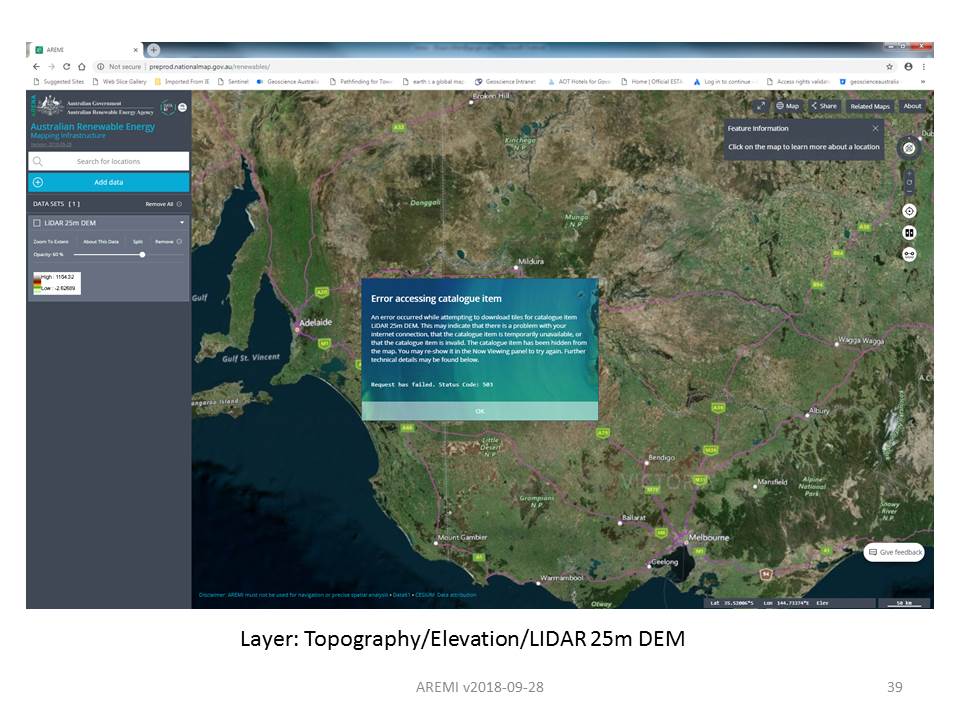
| 1.0 | AREMI v2018-09-28 Pre-Release Test - Error accessing catalogue item #13 - Layer: Topography/Elevation/LIDAR 25m DEM
Error: Request has failed - Status code: 503
| non_priority | aremi pre release test error accessing catalogue item layer topography elevation lidar dem error request has failed status code | 0 |
25,089 | 12,217,681,904 | IssuesEvent | 2020-05-01 17:42:51 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | AWS Sqs Queue not setting visibility_timeout_seconds = 0 on create | bug service/sqs stale | _This issue was originally opened by @scottharrisaus as hashicorp/terraform#14300. It was migrated here as part of the [provider split](https://www.hashicorp.com/blog/upcoming-provider-changes-in-terraform-0-10/). The original body of the issue is below._
<hr>
When creating a sqs queue and setting visibility_time... | 1.0 | AWS Sqs Queue not setting visibility_timeout_seconds = 0 on create - _This issue was originally opened by @scottharrisaus as hashicorp/terraform#14300. It was migrated here as part of the [provider split](https://www.hashicorp.com/blog/upcoming-provider-changes-in-terraform-0-10/). The original body of the issue is bel... | non_priority | aws sqs queue not setting visibility timeout seconds on create this issue was originally opened by scottharrisaus as hashicorp terraform it was migrated here as part of the the original body of the issue is below when creating a sqs queue and setting visibility timeout seconds the queue get... | 0 |
30,941 | 14,704,327,640 | IssuesEvent | 2021-01-04 16:20:08 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | opened | Poor performance of IS NULL / IS NOT NULL queries against table with allow_nullable_key | performance | ```sql
CREATE TABLE test_nullable_key.test
(
`n` Nullable(UInt8)
)
ENGINE = MergeTree
ORDER BY n
SETTINGS allow_nullable_key = 1, index_granularity = 8192;
insert into test select * from numbers_mt(1000000000);
optimize table test;
```
Here PK is used:
```
echo 'select count() from test_nullabl... | True | Poor performance of IS NULL / IS NOT NULL queries against table with allow_nullable_key - ```sql
CREATE TABLE test_nullable_key.test
(
`n` Nullable(UInt8)
)
ENGINE = MergeTree
ORDER BY n
SETTINGS allow_nullable_key = 1, index_granularity = 8192;
insert into test select * from numbers_mt(1000000000);
op... | non_priority | poor performance of is null is not null queries against table with allow nullable key sql create table test nullable key test n nullable engine mergetree order by n settings allow nullable key index granularity insert into test select from numbers mt optimize table tes... | 0 |
336,560 | 30,201,958,712 | IssuesEvent | 2023-07-05 06:44:22 | snu-quiqcl/artiq-proxy | https://api.github.com/repos/snu-quiqcl/artiq-proxy | closed | Unit tests for the implemented functions | test | ### Feature you want to implement
What is the feature you want to implement?
### How the feature is implemented
ex) Add *B* method to *A* class, Upgrade *C* model
### Additional context
Add any other context or screenshots about the feature here.
| 1.0 | Unit tests for the implemented functions - ### Feature you want to implement
What is the feature you want to implement?
### How the feature is implemented
ex) Add *B* method to *A* class, Upgrade *C* model
### Additional context
Add any other context or screenshots about the feature here.
| non_priority | unit tests for the implemented functions feature you want to implement what is the feature you want to implement how the feature is implemented ex add b method to a class upgrade c model additional context add any other context or screenshots about the feature here | 0 |
32,989 | 14,000,579,743 | IssuesEvent | 2020-10-28 12:32:01 | aws/aws-controllers-k8s | https://api.github.com/repos/aws/aws-controllers-k8s | closed | ECR service controller | ECR Service Controller | ## ACK service controller
Support for Amazon ECR.
### Checklist for Dev Preview
- [x] Code generation (`make build-controller`)
- [x] End-to-end test (`make kind-test`)
- [x] Docs are updated, at least:
- [x] [testing](https://aws.github.io/aws-controllers-k8s/dev-docs/testing/)
- [x] [svc controller li... | 1.0 | ECR service controller - ## ACK service controller
Support for Amazon ECR.
### Checklist for Dev Preview
- [x] Code generation (`make build-controller`)
- [x] End-to-end test (`make kind-test`)
- [x] Docs are updated, at least:
- [x] [testing](https://aws.github.io/aws-controllers-k8s/dev-docs/testing/)
... | non_priority | ecr service controller ack service controller support for amazon ecr checklist for dev preview code generation make build controller end to end test make kind test docs are updated at least | 0 |
32,595 | 4,381,876,385 | IssuesEvent | 2016-08-06 14:38:40 | hoburg/gpkit | https://api.github.com/repos/hoburg/gpkit | closed | Model.__getitem__ should return highest-level varkey | design discussion | list of varkeys all with the same name should be in `.byname`. Also there could be a fuzzy search, `.search("W wing")` which would get all of `W_wing`, `W with model=['wing']`, `W descr="wing weight"` and return a list sorted by relevance (or just the most relevant) | 1.0 | Model.__getitem__ should return highest-level varkey - list of varkeys all with the same name should be in `.byname`. Also there could be a fuzzy search, `.search("W wing")` which would get all of `W_wing`, `W with model=['wing']`, `W descr="wing weight"` and return a list sorted by relevance (or just the most relevant... | non_priority | model getitem should return highest level varkey list of varkeys all with the same name should be in byname also there could be a fuzzy search search w wing which would get all of w wing w with model w descr wing weight and return a list sorted by relevance or just the most relevant | 0 |
108,331 | 23,592,958,270 | IssuesEvent | 2022-08-23 16:40:49 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | Disabled PC-relative calls for object allocations | area-vm type-performance vm-aot-code-size | The change in 91ed53413990eab8a0410e8c88f00f7a4007330c has disabled PC-relative calls for allocation stubs. The corresponding code was commented out:
```diff
diff --git a/runtime/vm/compiler/stub_code_compiler_arm64.cc b/runtime/vm/compiler/stub_code_compiler_arm64.cc
index db103f75f2f..afc9b109efa 100644
--- a/run... | 1.0 | Disabled PC-relative calls for object allocations - The change in 91ed53413990eab8a0410e8c88f00f7a4007330c has disabled PC-relative calls for allocation stubs. The corresponding code was commented out:
```diff
diff --git a/runtime/vm/compiler/stub_code_compiler_arm64.cc b/runtime/vm/compiler/stub_code_compiler_arm64.... | non_priority | disabled pc relative calls for object allocations the change in has disabled pc relative calls for allocation stubs the corresponding code was commented out diff diff git a runtime vm compiler stub code compiler cc b runtime vm compiler stub code compiler cc index a runtime vm compiler stu... | 0 |
266,187 | 23,226,658,329 | IssuesEvent | 2022-08-03 01:23:42 | MPMG-DCC-UFMG/F01 | https://api.github.com/repos/MPMG-DCC-UFMG/F01 | closed | Teste de generalizacao para a tag Servidores - Relatório mensal da despesa com pessoal - Felício dos Santos | generalization test development template-Síntese tecnologia informatica subtag-Relatórios Despesas com Pessoal tag-Servidores | DoD: Realizar o teste de Generalização do validador da tag Servidores - Relatório mensal da despesa com pessoal para o Município de Felício dos Santos. | 1.0 | Teste de generalizacao para a tag Servidores - Relatório mensal da despesa com pessoal - Felício dos Santos - DoD: Realizar o teste de Generalização do validador da tag Servidores - Relatório mensal da despesa com pessoal para o Município de Felício dos Santos. | non_priority | teste de generalizacao para a tag servidores relatório mensal da despesa com pessoal felício dos santos dod realizar o teste de generalização do validador da tag servidores relatório mensal da despesa com pessoal para o município de felício dos santos | 0 |
297,445 | 25,732,020,513 | IssuesEvent | 2022-12-07 21:06:02 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Doesn't work with Windows 11 VHD | devtest-lab/svc triaged in-progress assigned-to-author doc-enhancement Pri2 |
Hello,
Thanks for the wonderful examples here and on the Azure pages, many have been very helpful. We have been using this example script almost verbatim for a while now with Windows 10 and it works beautifully. We just created our first Windows 11 vhd and the script generates a custom image without error, howev... | 1.0 | Doesn't work with Windows 11 VHD -
Hello,
Thanks for the wonderful examples here and on the Azure pages, many have been very helpful. We have been using this example script almost verbatim for a while now with Windows 10 and it works beautifully. We just created our first Windows 11 vhd and the script generates ... | non_priority | doesn t work with windows vhd hello thanks for the wonderful examples here and on the azure pages many have been very helpful we have been using this example script almost verbatim for a while now with windows and it works beautifully we just created our first windows vhd and the script generates a c... | 0 |
132,547 | 10,758,972,403 | IssuesEvent | 2019-10-31 15:50:21 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | FATA: Only support with English System Locale | [zube]: To Test area/windows kind/bug team/cn | Rancher version: 2.3.0.0-rc8
I had Rancher 2.3.0.0-rc3/4 was working.
When adding a windows node i get the error message: FATA: Only support with English System Locale . ( Screenshot: https://imgur.com/a/xGXKgcp )
First of all its hard to know what this means? (Im work mostly with windows). Is it complaining ab... | 1.0 | FATA: Only support with English System Locale - Rancher version: 2.3.0.0-rc8
I had Rancher 2.3.0.0-rc3/4 was working.
When adding a windows node i get the error message: FATA: Only support with English System Locale . ( Screenshot: https://imgur.com/a/xGXKgcp )
First of all its hard to know what this means? (Im... | non_priority | fata only support with english system locale rancher version i had rancher was working when adding a windows node i get the error message fata only support with english system locale screenshot first of all its hard to know what this means im work mostly with windows is... | 0 |
239,647 | 19,905,866,454 | IssuesEvent | 2022-01-25 12:44:31 | vector-im/element-android | https://api.github.com/repos/vector-im/element-android | opened | Threads: Turning Threads on doesn't move messages into a Thread | T-Enhancement A-Threads Z-ThreadsP0 Z-ThreadsInternalTesting | ### Your use case
Found during testing on January 20, 2022
- Turned threads off
- Used "reply" to respond to a thread message
- Turned threads back on
- Reply was not in the thread, but still on the timeline
@daniellekirkwood to add a screenshot
### Have you considered any alternatives?
_No response_
###... | 1.0 | Threads: Turning Threads on doesn't move messages into a Thread - ### Your use case
Found during testing on January 20, 2022
- Turned threads off
- Used "reply" to respond to a thread message
- Turned threads back on
- Reply was not in the thread, but still on the timeline
@daniellekirkwood to add a screensho... | non_priority | threads turning threads on doesn t move messages into a thread your use case found during testing on january turned threads off used reply to respond to a thread message turned threads back on reply was not in the thread but still on the timeline daniellekirkwood to add a screenshot ... | 0 |
28,384 | 5,246,676,846 | IssuesEvent | 2017-02-01 10:23:56 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | opened | NullPointerException in LockServiceImpl | Team: Core Type: Defect | We can produce a NPE in `LockServiceImpl` by creating one map with a quorum configuration (which activates the `QuorumServiceImpl` for all `QuorumAware` operations) and then call an `QuorumAware` operation on another data structure without a quorum configuration:
```
java.lang.NullPointerException
at java.util.conc... | 1.0 | NullPointerException in LockServiceImpl - We can produce a NPE in `LockServiceImpl` by creating one map with a quorum configuration (which activates the `QuorumServiceImpl` for all `QuorumAware` operations) and then call an `QuorumAware` operation on another data structure without a quorum configuration:
```
java.lan... | non_priority | nullpointerexception in lockserviceimpl we can produce a npe in lockserviceimpl by creating one map with a quorum configuration which activates the quorumserviceimpl for all quorumaware operations and then call an quorumaware operation on another data structure without a quorum configuration java lan... | 0 |
258,990 | 19,581,313,103 | IssuesEvent | 2022-01-04 21:45:38 | napari/napari | https://api.github.com/repos/napari/napari | closed | Better autogenerated docs | documentation | ## 📚 Documentation
we currently use `sphinx-apidoc` to autogenerate docs, but it leaves a little to be desired in the way of organization... but it also doesn't provide a ton of options (beyond templates) to configure it. This issue is just to remind us to look into autogenerating our own API docs to look just as ... | 1.0 | Better autogenerated docs - ## 📚 Documentation
we currently use `sphinx-apidoc` to autogenerate docs, but it leaves a little to be desired in the way of organization... but it also doesn't provide a ton of options (beyond templates) to configure it. This issue is just to remind us to look into autogenerating our o... | non_priority | better autogenerated docs 📚 documentation we currently use sphinx apidoc to autogenerate docs but it leaves a little to be desired in the way of organization but it also doesn t provide a ton of options beyond templates to configure it this issue is just to remind us to look into autogenerating our o... | 0 |
33,144 | 7,660,415,297 | IssuesEvent | 2018-05-11 10:26:09 | rust-community/content-o-tron | https://api.github.com/repos/rust-community/content-o-tron | closed | Create a new content-o-tron task issue template | mozsprint no code work-in-progress | Should include various fields we require to have a task that someone can help out on. Also add a create new link at the top of the template. | 1.0 | Create a new content-o-tron task issue template - Should include various fields we require to have a task that someone can help out on. Also add a create new link at the top of the template. | non_priority | create a new content o tron task issue template should include various fields we require to have a task that someone can help out on also add a create new link at the top of the template | 0 |
304,174 | 23,052,160,210 | IssuesEvent | 2022-07-24 19:50:13 | P2JN/doit | https://api.github.com/repos/P2JN/doit | closed | doc - inicio, plan y diseño | documentation | ## descripcion
revisar la documentación de las fases iniciales del proyecto y pasarlas a la memoria, haciendo uso de la wiki y la memoria
## to-do
- [ ] comprobar usabilidad de formato markdown en latex
- [x] documentar el Inicio
- [ ] documentar la Planificación
- [ ] documentar el Diseño
## recursos
- memo... | 1.0 | doc - inicio, plan y diseño - ## descripcion
revisar la documentación de las fases iniciales del proyecto y pasarlas a la memoria, haciendo uso de la wiki y la memoria
## to-do
- [ ] comprobar usabilidad de formato markdown en latex
- [x] documentar el Inicio
- [ ] documentar la Planificación
- [ ] documentar el... | non_priority | doc inicio plan y diseño descripcion revisar la documentación de las fases iniciales del proyecto y pasarlas a la memoria haciendo uso de la wiki y la memoria to do comprobar usabilidad de formato markdown en latex documentar el inicio documentar la planificación documentar el diseño ... | 0 |
46,274 | 13,153,311,384 | IssuesEvent | 2020-08-10 02:49:24 | WKHAllen/NorseBooks | https://api.github.com/repos/WKHAllen/NorseBooks | closed | Improve security on user contact info modal | backend bug frontend security | Make user info available through an API endpoint. Access the endpoint and set results in the modal's inner text accordingly. **Do not pass contact info values to the view.** | True | Improve security on user contact info modal - Make user info available through an API endpoint. Access the endpoint and set results in the modal's inner text accordingly. **Do not pass contact info values to the view.** | non_priority | improve security on user contact info modal make user info available through an api endpoint access the endpoint and set results in the modal s inner text accordingly do not pass contact info values to the view | 0 |
63,972 | 7,756,507,858 | IssuesEvent | 2018-05-31 13:49:30 | Threespot/aldf-wp | https://api.github.com/repos/Threespot/aldf-wp | closed | Article: Increase title block subtitle font size | Design Issue 🎨 | Increase subtitle to match subtitles on issue and case pages
* Font-size: 22px
* Line-height: 29px
Dev
Issue subtitle

Issue subtitle
)
- [ ] Import wallet learn more links to MM help page.([#6103](https://github.com/brave/brave-browser/issues/6103))
- [ ] JSON file import help links to MM help p... | 1.0 | Manual test run on Linux for Ethereum Remote Client 1.0.16 - ## Per release specialty tests
- [ ] Add reset data / delete account option to Crypto Wallets.([#5741](https://github.com/brave/brave-browser/issues/5741))
- [ ] Import wallet learn more links to MM help page.([#6103](https://github.com/brave/brave-browser/... | non_priority | manual test run on linux for ethereum remote client per release specialty tests add reset data delete account option to crypto wallets import wallet learn more links to mm help page json file import help links to mm help page allowing dapp sites to install opens a blank b... | 0 |
13,740 | 3,355,460,874 | IssuesEvent | 2015-11-18 16:30:50 | mozilla/webmaker-core | https://api.github.com/repos/mozilla/webmaker-core | closed | Webmaker 1.5 Android Viewing Project | Quality test | * [x] Open the app and tap the Discover tab, which opens the Discover view
**Discover View**
* [x] In the Discover view you see a list of projects. Each projects includes...
* [x] a title
* [x] a preview image
* [x] an author (indicated in blue)
* [x] scroll up and down to view additional projects
* [x] ... | 1.0 | Webmaker 1.5 Android Viewing Project - * [x] Open the app and tap the Discover tab, which opens the Discover view
**Discover View**
* [x] In the Discover view you see a list of projects. Each projects includes...
* [x] a title
* [x] a preview image
* [x] an author (indicated in blue)
* [x] scroll up and d... | non_priority | webmaker android viewing project open the app and tap the discover tab which opens the discover view discover view in the discover view you see a list of projects each projects includes a title a preview image an author indicated in blue scroll up and down to view ... | 0 |
289,575 | 24,998,641,694 | IssuesEvent | 2022-11-03 04:48:53 | csssbot/testing | https://api.github.com/repos/csssbot/testing | closed | New review for CPSC 100 by Test | octokit test | > Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugi... | 1.0 | New review for CPSC 100 by Test - > Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Duis aute irure dolor in reprehenderit in voluptat... | non_priority | new review for cpsc by test lorem ipsum dolor sit amet consectetur adipiscing elit sed do eiusmod tempor incididunt ut labore et dolore magna aliqua ut enim ad minim veniam quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat duis aute irure dolor in reprehenderit in voluptate ... | 0 |
79,441 | 15,586,151,952 | IssuesEvent | 2021-03-18 01:17:25 | logicalguru/WG | https://api.github.com/repos/logicalguru/WG | opened | CVE-2020-8908 (Low) detected in guava-18.0.jar | security vulnerability | ## CVE-2020-8908 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>guava-18.0.jar</b></p></summary>
<p>Guava is a suite of core and expanded libraries that include
utility classes, go... | True | CVE-2020-8908 (Low) detected in guava-18.0.jar - ## CVE-2020-8908 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>guava-18.0.jar</b></p></summary>
<p>Guava is a suite of core and expand... | non_priority | cve low detected in guava jar cve low severity vulnerability vulnerable library guava jar guava is a suite of core and expanded libraries that include utility classes google s collections io classes and much much more guava has only one code dependency javax annot... | 0 |
273,405 | 29,820,297,847 | IssuesEvent | 2023-06-17 01:23:23 | Nivaskumark/CVE-2020-0074-frameworks_base_after | https://api.github.com/repos/Nivaskumark/CVE-2020-0074-frameworks_base_after | closed | CVE-2023-20919 (High) detected in baseandroid-11.0.0_r39 - autoclosed | Mend: dependency security vulnerability | ## CVE-2023-20919 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-11.0.0_r39</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a hr... | True | CVE-2023-20919 (High) detected in baseandroid-11.0.0_r39 - autoclosed - ## CVE-2023-20919 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-11.0.0_r39</b></p></summary>
<p>
<... | non_priority | cve high detected in baseandroid autoclosed cve high severity vulnerability vulnerable library baseandroid android framework classes and services library home page a href found in head commit a href found in base branch master vulnerable sourc... | 0 |
480 | 3,454,483,835 | IssuesEvent | 2015-12-17 16:06:05 | softlayer/sl-ember-components | https://api.github.com/repos/softlayer/sl-ember-components | opened | Refactor to align with updated style guide | architecture changetype:6 internal ready refactor sl-select | https://github.com/softlayer/ember-style-guide#defining-functions-to-be-called-when-events-are-triggered
* `willClearRender()` - https://github.com/softlayer/sl-ember-components/blob/v0.11.0/addon/components/sl-select.js#L104
* `didInsertElement()` - https://github.com/softlayer/sl-ember-components/blob/v0.11.0/ad... | 1.0 | Refactor to align with updated style guide - https://github.com/softlayer/ember-style-guide#defining-functions-to-be-called-when-events-are-triggered
* `willClearRender()` - https://github.com/softlayer/sl-ember-components/blob/v0.11.0/addon/components/sl-select.js#L104
* `didInsertElement()` - https://github.com/... | non_priority | refactor to align with updated style guide willclearrender didinsertelement | 0 |
89,437 | 10,599,562,914 | IssuesEvent | 2019-10-10 08:14:42 | gotson/komga | https://api.github.com/repos/gotson/komga | closed | Unclear OS compatibility information, no CUI/GUI on Fat Jar execution | documentation | I first want to thank you for what you are attempting/executing.I have followed other's work on the creation of comic servers namely Tachiyomi-Server (only a client, actually), ubooqity, HappyPanda-X (Most Detailed Metadata+Search), ComicRack. It is awesome to see someone finally adding this func. to Tachiyomi
Even ... | 1.0 | Unclear OS compatibility information, no CUI/GUI on Fat Jar execution - I first want to thank you for what you are attempting/executing.I have followed other's work on the creation of comic servers namely Tachiyomi-Server (only a client, actually), ubooqity, HappyPanda-X (Most Detailed Metadata+Search), ComicRack. It i... | non_priority | unclear os compatibility information no cui gui on fat jar execution i first want to thank you for what you are attempting executing i have followed other s work on the creation of comic servers namely tachiyomi server only a client actually ubooqity happypanda x most detailed metadata search comicrack it i... | 0 |
98,562 | 12,339,406,776 | IssuesEvent | 2020-05-14 18:04:26 | unicode-org/icu4x | https://api.github.com/repos/unicode-org/icu4x | closed | How should we build static data? | A-design C-data T-enhancement backlog | When we don't want to perform file or network I/O, it may be necessary to build the data into a binary format that can be built into the Rust static memory space.
We can use a solution like [CBOR](https://github.com/pyfisch/cbor) or [bincode](https://crates.io/crates/bincode).
However, these solutions require par... | 1.0 | How should we build static data? - When we don't want to perform file or network I/O, it may be necessary to build the data into a binary format that can be built into the Rust static memory space.
We can use a solution like [CBOR](https://github.com/pyfisch/cbor) or [bincode](https://crates.io/crates/bincode).
H... | non_priority | how should we build static data when we don t want to perform file or network i o it may be necessary to build the data into a binary format that can be built into the rust static memory space we can use a solution like or however these solutions require parsing the data structure into rust objects ... | 0 |
120,202 | 10,109,714,448 | IssuesEvent | 2019-07-30 08:40:00 | khartec/waltz | https://api.github.com/repos/khartec/waltz | closed | Support for licence as an entity in Waltz | DDL change fixed (test & close) noteworthy | Table definition:
```
id | name | description | external_id | created_by / at | last_updated_by / at | provenance
```
Page to view licence definition, which should also include an `approval status` assessment. Bookmarks to be able to reference a destination URL. Also, include the ability to associate applicat... | 1.0 | Support for licence as an entity in Waltz - Table definition:
```
id | name | description | external_id | created_by / at | last_updated_by / at | provenance
```
Page to view licence definition, which should also include an `approval status` assessment. Bookmarks to be able to reference a destination URL. Als... | non_priority | support for licence as an entity in waltz table definition id name description external id created by at last updated by at provenance page to view licence definition which should also include an approval status assessment bookmarks to be able to reference a destination url als... | 0 |
348,103 | 24,906,764,573 | IssuesEvent | 2022-10-29 10:54:47 | Azure/terraform-azurerm-caf-enterprise-scale | https://api.github.com/repos/Azure/terraform-azurerm-caf-enterprise-scale | closed | Error received when running custom network connectivity deployment | documentation | <h3 id=communitynote>Community Note </h3>
<ul>
<li>Please vote on this issue by adding a 👍 <a href="https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/">reaction</a> to the original issue to help the community and maintainers prioritize this request </li>
<li>Please do not lea... | 1.0 | Error received when running custom network connectivity deployment - <h3 id=communitynote>Community Note </h3>
<ul>
<li>Please vote on this issue by adding a 👍 <a href="https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/">reaction</a> to the original issue to help the communit... | non_priority | error received when running custom network connectivity deployment community note please vote on this issue by adding a please do not leave quot quot or quot me too quot comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in work... | 0 |
49,924 | 20,978,796,529 | IssuesEvent | 2022-03-28 17:43:04 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | Clean up Dockerfile and docker-compose yml files | BE autonomous deploys platform-team-focus Console-Services | Clean up dockerfile, getting it “k8s ready”. Refactor docker-compose setup so it doesn’t suck.
## AC
- [ ] Dockerfile is K8s Ready (we may need two Dockerfiles)
- [ ] Development doesn't require rebuilding docker image when files change
- [ ] Dockerfile is compatible with GitHub Actions
- [ ] [Sidekiq workers TS... | 1.0 | Clean up Dockerfile and docker-compose yml files - Clean up dockerfile, getting it “k8s ready”. Refactor docker-compose setup so it doesn’t suck.
## AC
- [ ] Dockerfile is K8s Ready (we may need two Dockerfiles)
- [ ] Development doesn't require rebuilding docker image when files change
- [ ] Dockerfile is compat... | non_priority | clean up dockerfile and docker compose yml files clean up dockerfile getting it “ ready” refactor docker compose setup so it doesn’t suck ac dockerfile is ready we may need two dockerfiles development doesn t require rebuilding docker image when files change dockerfile is compatible with ... | 0 |
56,592 | 8,101,379,315 | IssuesEvent | 2018-08-12 13:04:47 | salaros/vtwsclib-php | https://api.github.com/repos/salaros/vtwsclib-php | closed | Update Sales Order, removes Items | bug documentation | When I update an existing Sales order it remove all items from sales order.
Below you can find my code. Please help me to find issue.
I developed my code in 2 styles and every 2 styles has this issue :
1-
function update_sales_order($id)
{
$client = new WSClient(VTIGER_URL, VTIGER_API_USER, VTIGER_API_KEY);
$Upd... | 1.0 | Update Sales Order, removes Items - When I update an existing Sales order it remove all items from sales order.
Below you can find my code. Please help me to find issue.
I developed my code in 2 styles and every 2 styles has this issue :
1-
function update_sales_order($id)
{
$client = new WSClient(VTIGER_URL, VT... | non_priority | update sales order removes items when i update an existing sales order it remove all items from sales order below you can find my code please help me to find issue i developed my code in styles and every styles has this issue function update sales order id client new wsclient vtiger url vt... | 0 |
44,197 | 12,037,294,693 | IssuesEvent | 2020-04-13 21:31:25 | madchap/deleteme_ghtest | https://api.github.com/repos/madchap/deleteme_ghtest | opened | CVE-2011-3389 - Libgnutls30-3.5.8-5+deb9u4(dpkg) | defectdojo security / medium | *CVE-2011-3389 - Libgnutls30-3.5.8-5+deb9u4(dpkg)*
*Severity:* Medium
*Cve:* CVE-2011-3389
*Product/Engagement:* _ghtest / AdHoc Import - Mon, 13 Apr 2020 21:23:11
*Systems*:
*Description*:
Image hash: sha256:xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
Package: libgnutls30-3.5.8-5+deb9u4
... | 1.0 | CVE-2011-3389 - Libgnutls30-3.5.8-5+deb9u4(dpkg) - *CVE-2011-3389 - Libgnutls30-3.5.8-5+deb9u4(dpkg)*
*Severity:* Medium
*Cve:* CVE-2011-3389
*Product/Engagement:* _ghtest / AdHoc Import - Mon, 13 Apr 2020 21:23:11
*Systems*:
*Description*:
Image hash: sha256:xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx... | non_priority | cve dpkg cve dpkg severity medium cve cve product engagement ghtest adhoc import mon apr systems description image hash xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx package package path none ... | 0 |
93,037 | 26,844,581,845 | IssuesEvent | 2023-02-03 05:22:22 | open-telemetry/opentelemetry-cpp | https://api.github.com/repos/open-telemetry/opentelemetry-cpp | closed | [BUILD] OTLP HTTP Exporter has build warnings in maintainer mode | bug build and test | Build the OTLP HTTP exporter in maintainer mode:
```
/home/malff/CODE/MY_GITHUB/opentelemetry-cpp/exporters/otlp/src/otlp_metric_utils.cc:269:34: error: unused parameter 'instrument_type' [-Werror,-Wunused-parameter]
sdk::metrics::InstrumentType instrument_type) noexcept
```
To fix:
* fix the relevant b... | 1.0 | [BUILD] OTLP HTTP Exporter has build warnings in maintainer mode - Build the OTLP HTTP exporter in maintainer mode:
```
/home/malff/CODE/MY_GITHUB/opentelemetry-cpp/exporters/otlp/src/otlp_metric_utils.cc:269:34: error: unused parameter 'instrument_type' [-Werror,-Wunused-parameter]
sdk::metrics::InstrumentTy... | non_priority | otlp http exporter has build warnings in maintainer mode build the otlp http exporter in maintainer mode home malff code my github opentelemetry cpp exporters otlp src otlp metric utils cc error unused parameter instrument type sdk metrics instrumenttype instrument type noexcept ... | 0 |
59,821 | 14,478,901,472 | IssuesEvent | 2020-12-10 09:05:10 | olivialancaster/amplify-cli | https://api.github.com/repos/olivialancaster/amplify-cli | opened | CVE-2018-21270 (High) detected in stringstream-0.0.5.tgz | security vulnerability | ## CVE-2018-21270 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>stringstream-0.0.5.tgz</b></p></summary>
<p>Encode and decode streams into string streams</p>
<p>Library home page: <a... | True | CVE-2018-21270 (High) detected in stringstream-0.0.5.tgz - ## CVE-2018-21270 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>stringstream-0.0.5.tgz</b></p></summary>
<p>Encode and deco... | non_priority | cve high detected in stringstream tgz cve high severity vulnerability vulnerable library stringstream tgz encode and decode streams into string streams library home page a href path to dependency file amplify cli packages amplify category interactions package json pat... | 0 |
17,315 | 23,138,122,761 | IssuesEvent | 2022-07-28 15:51:01 | ORNL-AMO/AMO-Tools-Desktop | https://api.github.com/repos/ORNL-AMO/AMO-Tools-Desktop | closed | Add Hydrogen to "Other Fuels" for carbon | Process Heating important CO2 Emissions | Add Hydrogen to teh list of "Other Fuels" for carbon / CO2 calcs.
It has a value of 0 CO2/MMBTU, but the work around for using it is a bit of a pain, so would be better if it had an entry. | 1.0 | Add Hydrogen to "Other Fuels" for carbon - Add Hydrogen to teh list of "Other Fuels" for carbon / CO2 calcs.
It has a value of 0 CO2/MMBTU, but the work around for using it is a bit of a pain, so would be better if it had an entry. | non_priority | add hydrogen to other fuels for carbon add hydrogen to teh list of other fuels for carbon calcs it has a value of mmbtu but the work around for using it is a bit of a pain so would be better if it had an entry | 0 |
181,083 | 21,645,530,556 | IssuesEvent | 2022-05-06 01:03:39 | renfei/start | https://api.github.com/repos/renfei/start | opened | CVE-2022-25647 (High) detected in gson-2.8.6.jar | security vulnerability | ## CVE-2022-25647 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>gson-2.8.6.jar</b></p></summary>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gso... | True | CVE-2022-25647 (High) detected in gson-2.8.6.jar - ## CVE-2022-25647 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>gson-2.8.6.jar</b></p></summary>
<p>Gson JSON library</p>
<p>Librar... | non_priority | cve high detected in gson jar cve high severity vulnerability vulnerable library gson jar gson json library library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com google code gson gson gson ... | 0 |
241,278 | 18,440,723,088 | IssuesEvent | 2021-10-14 17:45:01 | dmtzs/NierWorldsWeaponManager | https://api.github.com/repos/dmtzs/NierWorldsWeaponManager | opened | Specifications migration | documentation | Migrate to the README file to the documentation part in the wiki, in specifications should be only the technologies used in this project, not commands or other stuffs like that.
That should be in the documentation. | 1.0 | Specifications migration - Migrate to the README file to the documentation part in the wiki, in specifications should be only the technologies used in this project, not commands or other stuffs like that.
That should be in the documentation. | non_priority | specifications migration migrate to the readme file to the documentation part in the wiki in specifications should be only the technologies used in this project not commands or other stuffs like that that should be in the documentation | 0 |
7,509 | 6,925,167,809 | IssuesEvent | 2017-11-30 15:10:36 | OpenLiberty/open-liberty | https://api.github.com/repos/OpenLiberty/open-liberty | closed | Update the metatype description for LdapRegistry to clarify the context pool timeout | in:Security team:Wendigo East | Follow up on fixing a problem with the context pool timeout. The code change is in, updating the context pool timeout description in the metatype for LdapRegistry. | True | Update the metatype description for LdapRegistry to clarify the context pool timeout - Follow up on fixing a problem with the context pool timeout. The code change is in, updating the context pool timeout description in the metatype for LdapRegistry. | non_priority | update the metatype description for ldapregistry to clarify the context pool timeout follow up on fixing a problem with the context pool timeout the code change is in updating the context pool timeout description in the metatype for ldapregistry | 0 |
307,410 | 26,529,824,018 | IssuesEvent | 2023-01-19 11:36:01 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix math.test_tensorflow_argmax | TensorFlow Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/3951396504/jobs/6765195651" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/3951396504/jobs/6765195651" rel="noopener ... | 1.0 | Fix math.test_tensorflow_argmax - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/3951396504/jobs/6765195651" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/39513965... | non_priority | fix math test tensorflow argmax tensorflow img src torch img src numpy img src jax img src failed ivy tests test ivy test frontends test tensorflow test math py test tensorflow argmax e ivy exceptions ivyexception cannot convert to pytorch dty... | 0 |
81,069 | 15,603,034,725 | IssuesEvent | 2021-03-19 01:03:21 | k8s-team/asynql | https://api.github.com/repos/k8s-team/asynql | opened | CVE-2021-27291 (Medium) detected in Pygments-2.4.2-py2.py3-none-any.whl | security vulnerability | ## CVE-2021-27291 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pygments-2.4.2-py2.py3-none-any.whl</b></p></summary>
<p>Pygments is a syntax highlighting package written in Python... | True | CVE-2021-27291 (Medium) detected in Pygments-2.4.2-py2.py3-none-any.whl - ## CVE-2021-27291 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pygments-2.4.2-py2.py3-none-any.whl</b></p>... | non_priority | cve medium detected in pygments none any whl cve medium severity vulnerability vulnerable library pygments none any whl pygments is a syntax highlighting package written in python library home page a href path to dependency file asynql docs requirements txt ... | 0 |
44,506 | 7,111,979,450 | IssuesEvent | 2018-01-17 15:45:04 | thayerAlshaabi/DeepEye | https://api.github.com/repos/thayerAlshaabi/DeepEye | opened | CHAPTER 4: RESULTS | documentation | (5-7 pages)
User Interface Design
----
Design details of your project. This section can include various visualizations (e.g., user interfaces, screenshots) that depict your final project implementation.
Architecture
------
Statement and descriptions of systems and structures (e.g., data structures) used in th... | 1.0 | CHAPTER 4: RESULTS - (5-7 pages)
User Interface Design
----
Design details of your project. This section can include various visualizations (e.g., user interfaces, screenshots) that depict your final project implementation.
Architecture
------
Statement and descriptions of systems and structures (e.g., data ... | non_priority | chapter results pages user interface design design details of your project this section can include various visualizations e g user interfaces screenshots that depict your final project implementation architecture statement and descriptions of systems and structures e g data ... | 0 |
190,038 | 14,531,399,105 | IssuesEvent | 2020-12-14 20:43:39 | mswinkels09/finalcapstone | https://api.github.com/repos/mswinkels09/finalcapstone | closed | User can update listed items when item is sold | TEST postman | When user fills out the `"shipping_cost", "shipping_paid", "item_paid", "final_value_fee", "sold_date"` the item is then considered a sold item.
All fields must be filled out to be considered sold.
| 1.0 | User can update listed items when item is sold - When user fills out the `"shipping_cost", "shipping_paid", "item_paid", "final_value_fee", "sold_date"` the item is then considered a sold item.
All fields must be filled out to be considered sold.
| non_priority | user can update listed items when item is sold when user fills out the shipping cost shipping paid item paid final value fee sold date the item is then considered a sold item all fields must be filled out to be considered sold | 0 |
134,771 | 30,182,304,299 | IssuesEvent | 2023-07-04 09:40:54 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | Character reset (removed when dead on round end) | Bug Need more info Code Severe | ### Disclaimers
- [X] I have searched the issue tracker to check if the issue has already been reported.
- [X] My issue happened while using mods.
### What happened?
The character of one of the players in our host's campaign had died and got removed from the save file completely on round end. The player spawn... | 1.0 | Character reset (removed when dead on round end) - ### Disclaimers
- [X] I have searched the issue tracker to check if the issue has already been reported.
- [X] My issue happened while using mods.
### What happened?
The character of one of the players in our host's campaign had died and got removed from the ... | non_priority | character reset removed when dead on round end disclaimers i have searched the issue tracker to check if the issue has already been reported my issue happened while using mods what happened the character of one of the players in our host s campaign had died and got removed from the save... | 0 |
186,289 | 21,922,862,062 | IssuesEvent | 2022-05-22 20:47:53 | AlexRogalskiy/object-mappers-playground | https://api.github.com/repos/AlexRogalskiy/object-mappers-playground | closed | CVE-2020-14338 (Medium) detected in xercesImpl-2.9.1.jar - autoclosed | security vulnerability | ## CVE-2020-14338 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xercesImpl-2.9.1.jar</b></p></summary>
<p>Xerces2 is the next generation of high performance, fully compliant XML pa... | True | CVE-2020-14338 (Medium) detected in xercesImpl-2.9.1.jar - autoclosed - ## CVE-2020-14338 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xercesImpl-2.9.1.jar</b></p></summary>
<p>Xe... | non_priority | cve medium detected in xercesimpl jar autoclosed cve medium severity vulnerability vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces nati... | 0 |
336,707 | 30,217,337,629 | IssuesEvent | 2023-07-05 16:30:20 | BoBAdministration/QA-Bug-Reports | https://api.github.com/repos/BoBAdministration/QA-Bug-Reports | closed | Acro doesnt have its idle animation in its emote wheel | Fixed-PendingTesting | **Describe the Bug**
Acro doesnt have its idle animation in the emote wheel
**To Reproduce**
1. log into tester server
2. spawn in as acro
3. open emote menu
**Expected behavior**
emote menu has idle anim
**Actual behavior**
emote menu does not have idle anim
**Screenshots & Video**
: ExecuteProcessRequest { argv: ["python", "./pytest-with-requirements.pex", "pants_test/backend/jvm/tasks/test_scope_runtime_integration.py"], env: {"LANG": "en_US.UTF-8", "LC_ALL": "en_US.UTF-8", "PATH": "... | 1.0 | Remoting: Request had invalid authentication credentials - E.g.
```
<snip>
Computing MultiPlatformExecuteProcess(MultiPlatformExecuteProcessRequest({(None, None): ExecuteProcessRequest { argv: ["python", "./pytest-with-requirements.pex", "pants_test/backend/jvm/tasks/test_scope_runtime_integration.py"], env:... | non_priority | remoting request had invalid authentication credentials e g computing multiplatformexecuteprocess multiplatformexecuteprocessrequest none none executeprocessrequest argv env lang en us utf lc all en us utf path opt pyenv versions bin opt pyenv libexec opt p... | 0 |
102,633 | 16,576,205,217 | IssuesEvent | 2021-05-31 05:24:01 | AlexRogalskiy/github-action-file-size | https://api.github.com/repos/AlexRogalskiy/github-action-file-size | opened | CVE-2021-33502 (High) detected in normalize-url-6.0.0.tgz | security vulnerability | ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>normalize-url-6.0.0.tgz</b></p></summary>
<p>Normalize a URL</p>
<p>Library home page: <a href="https://registry.npmjs... | True | CVE-2021-33502 (High) detected in normalize-url-6.0.0.tgz - ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>normalize-url-6.0.0.tgz</b></p></summary>
<p>Normalize a U... | non_priority | cve high detected in normalize url tgz cve high severity vulnerability vulnerable library normalize url tgz normalize a url library home page a href path to dependency file github action file size package json path to vulnerable library github action file size node m... | 0 |
132,981 | 12,528,778,693 | IssuesEvent | 2020-06-04 10:08:45 | saidfathalla/Science-knowledge-graph-ontologies | https://api.github.com/repos/saidfathalla/Science-knowledge-graph-ontologies | closed | [Improvement] for ModSci ontology | documentation enhancement | **Is your feature request related to a problem? Please describe.**
no.
For ModSci ontology:
I'd suggest integrating several existing taxonomies of research fields, such as Field of Research (FoR) by ANZSRC and Dewey Decimal Classification scheme. | 1.0 | [Improvement] for ModSci ontology - **Is your feature request related to a problem? Please describe.**
no.
For ModSci ontology:
I'd suggest integrating several existing taxonomies of research fields, such as Field of Research (FoR) by ANZSRC and Dewey Decimal Classification scheme. | non_priority | for modsci ontology is your feature request related to a problem please describe no for modsci ontology i d suggest integrating several existing taxonomies of research fields such as field of research for by anzsrc and dewey decimal classification scheme | 0 |
7,636 | 3,105,830,633 | IssuesEvent | 2015-08-31 23:14:23 | rackerlabs/encore-ui | https://api.github.com/repos/rackerlabs/encore-ui | closed | Add something about distributed LESS files to styleguide | documentation | Once https://github.com/rackerlabs/encore-ui/pull/901 gets merged in, we need to think about how to address this in the style guide. | 1.0 | Add something about distributed LESS files to styleguide - Once https://github.com/rackerlabs/encore-ui/pull/901 gets merged in, we need to think about how to address this in the style guide. | non_priority | add something about distributed less files to styleguide once gets merged in we need to think about how to address this in the style guide | 0 |
171,303 | 20,961,350,967 | IssuesEvent | 2022-03-27 21:00:20 | jmservera/videochat-webapp | https://api.github.com/repos/jmservera/videochat-webapp | opened | CVE-2020-7788 (High) detected in ini-1.3.5.tgz | security vulnerability | ## CVE-2020-7788 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ini-1.3.5.tgz</b></p></summary>
<p>An ini encoder/decoder for node</p>
<p>Library home page: <a href="https://registry.... | True | CVE-2020-7788 (High) detected in ini-1.3.5.tgz - ## CVE-2020-7788 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ini-1.3.5.tgz</b></p></summary>
<p>An ini encoder/decoder for node</p>... | non_priority | cve high detected in ini tgz cve high severity vulnerability vulnerable library ini tgz an ini encoder decoder for node library home page a href path to dependency file package json path to vulnerable library node modules ini package json dependency hierarchy ... | 0 |
18,205 | 5,607,139,051 | IssuesEvent | 2017-04-01 02:21:08 | mcsheaj/SPEasyForms | https://api.github.com/repos/mcsheaj/SPEasyForms | closed | Changing the height of SuiteBar Nav causes Overlap Issues with the Settings Page | bug codeplex | **This issue was imported from [CodePlex](http://SPEasyForms.codeplex.com/workitem/23)**
**[mcsheaj](http://www.codeplex.com/site/users/view/mcsheaj)** wrote 2015-02-06 at 18:18
This isn't actually a problem specific to the SuiteBar Nav, changing the height of any part of the header would yield the same results. Th... | 1.0 | Changing the height of SuiteBar Nav causes Overlap Issues with the Settings Page - **This issue was imported from [CodePlex](http://SPEasyForms.codeplex.com/workitem/23)**
**[mcsheaj](http://www.codeplex.com/site/users/view/mcsheaj)** wrote 2015-02-06 at 18:18
This isn't actually a problem specific to the SuiteBar ... | non_priority | changing the height of suitebar nav causes overlap issues with the settings page this issue was imported from wrote at this isn t actually a problem specific to the suitebar nav changing the height of any part of the header would yield the same results the worst of the results is that the ... | 0 |
170,752 | 14,269,053,188 | IssuesEvent | 2020-11-21 00:03:43 | zio/zio-redis | https://api.github.com/repos/zio/zio-redis | opened | Document hashes API | documentation good first issue zio-hackathon | The current hashes API (see `zio.redis.api.Hashes`) exposes functions with argument names that are generic and meaningless. I propose to rename those to match those used in the [official documentation](https://redis.io/commands). Additionally, it would be great to provide a small, single-sentence scaladoc for them. | 1.0 | Document hashes API - The current hashes API (see `zio.redis.api.Hashes`) exposes functions with argument names that are generic and meaningless. I propose to rename those to match those used in the [official documentation](https://redis.io/commands). Additionally, it would be great to provide a small, single-sentence ... | non_priority | document hashes api the current hashes api see zio redis api hashes exposes functions with argument names that are generic and meaningless i propose to rename those to match those used in the additionally it would be great to provide a small single sentence scaladoc for them | 0 |
334,805 | 29,992,309,688 | IssuesEvent | 2023-06-26 00:00:50 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix general_functions.test_tensorflow_ones | TensorFlow Frontend Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5372121654/jobs/9745312844"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5372121654/jobs/9745312844"><img src=https://img.shields.io/badge/-success-success><... | 1.0 | Fix general_functions.test_tensorflow_ones - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5372121654/jobs/9745312844"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5372121654/jobs/9745312844"><img src=ht... | non_priority | fix general functions test tensorflow ones numpy a href src tensorflow a href src jax a href src torch a href src paddle a href src | 0 |
29,868 | 7,127,404,540 | IssuesEvent | 2018-01-20 21:17:48 | elves/elvish | https://api.github.com/repos/elves/elvish | opened | Do not abuse panic for errors | better-code | Currently the Elvish codebase abuses panics for returning errors in the runtime (the `eval` package). This has turned out to cause more problems than it solves. Let's switch to the typical Go style of returning an `error` to indicate an error. | 1.0 | Do not abuse panic for errors - Currently the Elvish codebase abuses panics for returning errors in the runtime (the `eval` package). This has turned out to cause more problems than it solves. Let's switch to the typical Go style of returning an `error` to indicate an error. | non_priority | do not abuse panic for errors currently the elvish codebase abuses panics for returning errors in the runtime the eval package this has turned out to cause more problems than it solves let s switch to the typical go style of returning an error to indicate an error | 0 |
413,433 | 27,952,043,985 | IssuesEvent | 2023-03-24 09:36:17 | jle1001/AI-Music | https://api.github.com/repos/jle1001/AI-Music | opened | documentation: TensorFlow model | documentation | The purpose of this issue is to add the implementation process of the TensorFlow model to the documentation. | 1.0 | documentation: TensorFlow model - The purpose of this issue is to add the implementation process of the TensorFlow model to the documentation. | non_priority | documentation tensorflow model the purpose of this issue is to add the implementation process of the tensorflow model to the documentation | 0 |
307 | 2,571,518,732 | IssuesEvent | 2015-02-10 16:56:59 | Graylog2/graylog2-web-interface | https://api.github.com/repos/Graylog2/graylog2-web-interface | closed | Newlines in message property values not displayed as pre on message detail page. | papercut usability | In the stream view newlines are shown as pre for message property values in the message detail panel in the sidebar. When navigating to a message detail page the newlines are not handled as pre. The div in the sidebar message detail with class `message-detail` gives the nested detail dl -> dd the following css properti... | True | Newlines in message property values not displayed as pre on message detail page. - In the stream view newlines are shown as pre for message property values in the message detail panel in the sidebar. When navigating to a message detail page the newlines are not handled as pre. The div in the sidebar message detail wit... | non_priority | newlines in message property values not displayed as pre on message detail page in the stream view newlines are shown as pre for message property values in the message detail panel in the sidebar when navigating to a message detail page the newlines are not handled as pre the div in the sidebar message detail wit... | 0 |
280,914 | 24,344,539,604 | IssuesEvent | 2022-10-02 05:52:06 | hoppscotch/hoppscotch | https://api.github.com/repos/hoppscotch/hoppscotch | closed | [bug]: delete request in the collection is invalid | bug need testing | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current behavior
The prompt delete was successful, but it actually exists
### Steps to reproduce
1. click collection button
2. Prompts for deletion
3. click "ok"
4.Check the request and find that it has not been deleted
###... | 1.0 | [bug]: delete request in the collection is invalid - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current behavior
The prompt delete was successful, but it actually exists
### Steps to reproduce
1. click collection button
2. Prompts for deletion
3. click "ok"
4.Check t... | non_priority | delete request in the collection is invalid is there an existing issue for this i have searched the existing issues current behavior the prompt delete was successful but it actually exists steps to reproduce click collection button prompts for deletion click ok check the req... | 0 |
234,952 | 18,023,935,231 | IssuesEvent | 2021-09-17 00:12:32 | timescale/docs | https://api.github.com/repos/timescale/docs | opened | [Site Bug] Issue with the page: /timescaledb/latest/getting-started/create-hypertable/ | bug documentation | _Use this template for reporting bugs in the docs._
# Describe the bug
Overall I think the Timescale documentation is excellent, and I really appreciate it. This page is useful. That said, I am technical user but I didn't find the TIP on this page to be helpful:
> TIP
For technically interested readers, th... | 1.0 | [Site Bug] Issue with the page: /timescaledb/latest/getting-started/create-hypertable/ - _Use this template for reporting bugs in the docs._
# Describe the bug
Overall I think the Timescale documentation is excellent, and I really appreciate it. This page is useful. That said, I am technical user but I didn't ... | non_priority | issue with the page timescaledb latest getting started create hypertable use this template for reporting bugs in the docs describe the bug overall i think the timescale documentation is excellent and i really appreciate it this page is useful that said i am technical user but i didn t find the ... | 0 |
73,683 | 19,760,954,775 | IssuesEvent | 2022-01-16 12:06:13 | Stupid4You/Digit | https://api.github.com/repos/Stupid4You/Digit | opened | Change from the beginning and not when we edit the file. | Easier Build | We now just change the 0000 in the checker then we have lesser code.
if len(str(num)) == 2:
num0 = "00"
if len(str(num)) == 3:
num0 = "0"
if len(str(num)) == 4:
num0 = ""
if num >= 9999:
done = 1 | 1.0 | Change from the beginning and not when we edit the file. - We now just change the 0000 in the checker then we have lesser code.
if len(str(num)) == 2:
num0 = "00"
if len(str(num)) == 3:
num0 = "0"
if len(str(num)) == 4:
num0 = ""
if num >= 9999:
done = 1 | non_priority | change from the beginning and not when we edit the file we now just change the in the checker then we have lesser code if len str num if len str num if len str num if num done | 0 |
185,631 | 15,027,156,241 | IssuesEvent | 2021-02-02 00:09:27 | spring-projects/spring-boot | https://api.github.com/repos/spring-projects/spring-boot | closed | Improve usage description for BufferedApplicationStartup | type: documentation | I was trying the nice new Spring Boot startup tracking feature and used `BufferedApplicationStartup` to collect initialization data. I found that the collected data is drained from the buffer after each request. In particular, it took me a moment to recognize that the most important data is lost after the first request... | 1.0 | Improve usage description for BufferedApplicationStartup - I was trying the nice new Spring Boot startup tracking feature and used `BufferedApplicationStartup` to collect initialization data. I found that the collected data is drained from the buffer after each request. In particular, it took me a moment to recognize t... | non_priority | improve usage description for bufferedapplicationstartup i was trying the nice new spring boot startup tracking feature and used bufferedapplicationstartup to collect initialization data i found that the collected data is drained from the buffer after each request in particular it took me a moment to recognize t... | 0 |
15,383 | 3,955,096,993 | IssuesEvent | 2016-04-29 19:31:54 | facebook/hhvm | https://api.github.com/repos/facebook/hhvm | closed | HHVM-3.3.0 Core dumped: Aborted - stack trace | crash documentation duplicate | We've been running HHVM in production for a few weeks to great effect. Unfortunately it randomly crashed this morning with the line "Core dumped: Aborted". The PHP function it crashed on is a simple text parsing/printing function, called frequently.
The stack trace message mentions "increasing Eval.JitASize, Eval.Ji... | 1.0 | HHVM-3.3.0 Core dumped: Aborted - stack trace - We've been running HHVM in production for a few weeks to great effect. Unfortunately it randomly crashed this morning with the line "Core dumped: Aborted". The PHP function it crashed on is a simple text parsing/printing function, called frequently.
The stack trace mes... | non_priority | hhvm core dumped aborted stack trace we ve been running hhvm in production for a few weeks to great effect unfortunately it randomly crashed this morning with the line core dumped aborted the php function it crashed on is a simple text parsing printing function called frequently the stack trace mes... | 0 |
233,944 | 25,784,580,187 | IssuesEvent | 2022-12-09 19:03:59 | MatBenfield/news | https://api.github.com/repos/MatBenfield/news | closed | [SecurityWeek] WAFs of Several Major Vendors Bypassed With Generic Attack Method | SecurityWeek Stale |
**Researchers at industrial and IoT cybersecurity firm Claroty have identified a generic method for bypassing the web application firewalls (WAFs) of several major vendors.**
[read more](https://www.securityweek.com/wafs-several-major-vendors-bypassed-generic-attack-method)
<https://www.securityweek.com/wafs-seve... | True | [SecurityWeek] WAFs of Several Major Vendors Bypassed With Generic Attack Method -
**Researchers at industrial and IoT cybersecurity firm Claroty have identified a generic method for bypassing the web application firewalls (WAFs) of several major vendors.**
[read more](https://www.securityweek.com/wafs-several-major... | non_priority | wafs of several major vendors bypassed with generic attack method researchers at industrial and iot cybersecurity firm claroty have identified a generic method for bypassing the web application firewalls wafs of several major vendors | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.