Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3
values | title stringlengths 1 744 | labels stringlengths 4 574 | body stringlengths 9 211k | index stringclasses 10
values | text_combine stringlengths 96 211k | label stringclasses 2
values | text stringlengths 96 188k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
21,585 | 11,660,443,594 | IssuesEvent | 2020-03-03 03:21:39 | cityofaustin/atd-knack-data-tracker | https://api.github.com/repos/cityofaustin/atd-knack-data-tracker | closed | Work Scheduling page - Job Calendar | Product: AMD Tracker Service: Apps Type: Enhancement Workgroup: AMD | Description: Would like to use Job Calendar on Data Tracker, but develop it like the existing schedule spreadsheet that the AMD supervisors use.
Request Date: 2018-08-22 09:34:00
Request ID: DTS18-100975
Status: Backlog
Customer Priority: 4
Level of Effort: Large Project
DTS URL: https://atd.knack.com/dts#servic... | 1.0 | Work Scheduling page - Job Calendar - Description: Would like to use Job Calendar on Data Tracker, but develop it like the existing schedule spreadsheet that the AMD supervisors use.
Request Date: 2018-08-22 09:34:00
Request ID: DTS18-100975
Status: Backlog
Customer Priority: 4
Level of Effort: Large Project
DT... | non_process | work scheduling page job calendar description would like to use job calendar on data tracker but develop it like the existing schedule spreadsheet that the amd supervisors use request date request id status backlog customer priority level of effort large project dts url | 0 |
5,993 | 8,805,375,049 | IssuesEvent | 2018-12-26 19:14:09 | dita-ot/dita-ot | https://api.github.com/repos/dita-ot/dita-ot | closed | Keyref resolution fails if input path contains ../ | bug preprocess/keyref stale | 2.2.3 and `develop`.
If you do e.g. `dita -i ../docsrc/userguide.ditamap -f pdf`, keyref resolution fails:
```
[keyref] file:/tmp/docsrc/index.dita:6:55: [DOTJ047I][INFO] Unable to find key definition for key reference "release" in root scope. The href attribute may be used as fallback if it exists
```
If you do `di... | 1.0 | Keyref resolution fails if input path contains ../ - 2.2.3 and `develop`.
If you do e.g. `dita -i ../docsrc/userguide.ditamap -f pdf`, keyref resolution fails:
```
[keyref] file:/tmp/docsrc/index.dita:6:55: [DOTJ047I][INFO] Unable to find key definition for key reference "release" in root scope. The href attribute ma... | process | keyref resolution fails if input path contains and develop if you do e g dita i docsrc userguide ditamap f pdf keyref resolution fails file tmp docsrc index dita unable to find key definition for key reference release in root scope the href attribute may be used as fallback ... | 1 |
16,860 | 22,142,364,059 | IssuesEvent | 2022-06-03 08:17:48 | camunda/zeebe | https://api.github.com/repos/camunda/zeebe | closed | Reduce test pipeline time | kind/toil team/distributed team/process-automation area/test | **Description**
I have the feeling that our pipeline takes to long and it seems to be increasing over time.
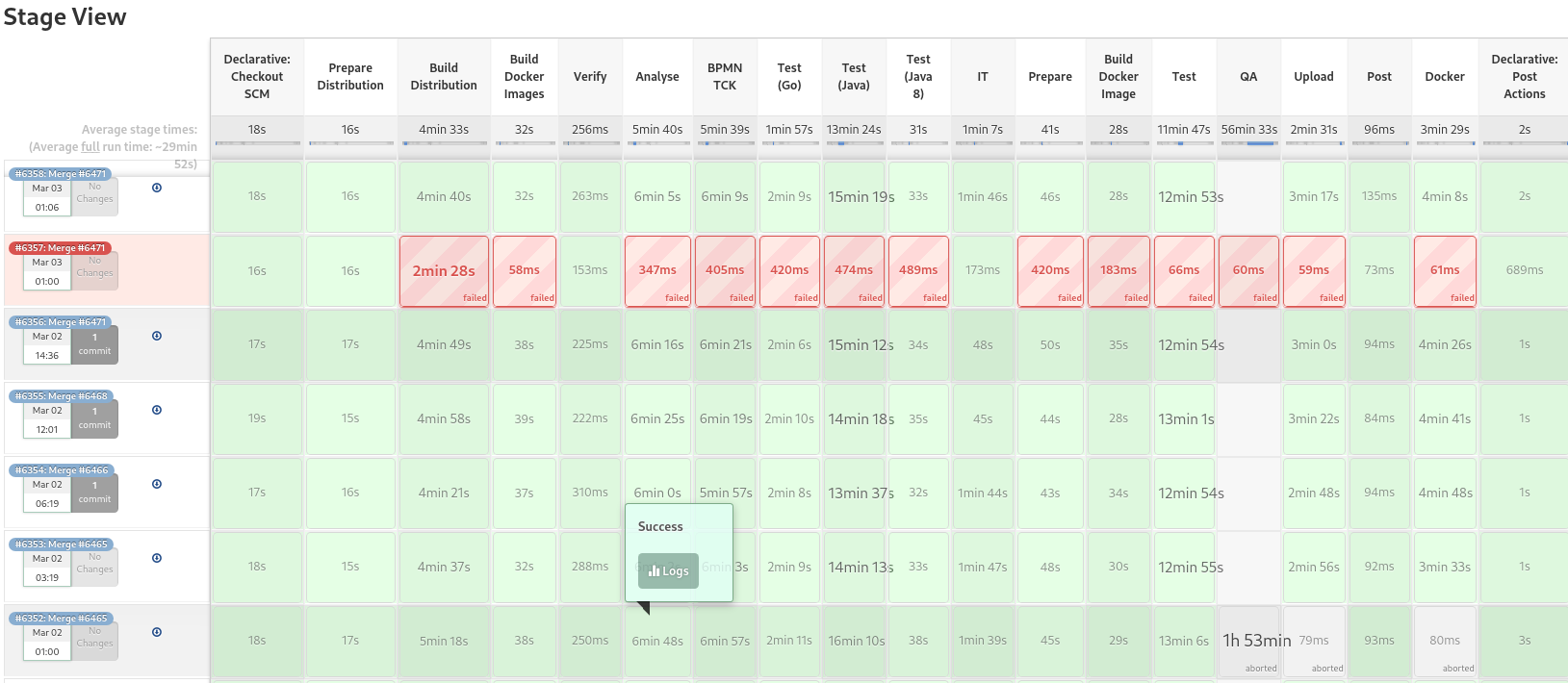
If we take a look at the avg. it is around 29 min. If we add QA then it is even more. I wou... | 1.0 | Reduce test pipeline time - **Description**
I have the feeling that our pipeline takes to long and it seems to be increasing over time.
If we take a look at the avg. it is around 29 min. If we add QA... | process | reduce test pipeline time description i have the feeling that our pipeline takes to long and it seems to be increasing over time if we take a look at the avg it is around min if we add qa then it is even more i would like to see us in improving the pipeline again that we get faster feedback f... | 1 |
275,911 | 8,582,152,520 | IssuesEvent | 2018-11-13 16:18:48 | HewlettPackard/oneview-redfish-toolkit | https://api.github.com/repos/HewlettPackard/oneview-redfish-toolkit | reopened | Apply concept DRY to share API classes with same Schema | Low priority enhancement | Currently, we have some case of API classes implementing a same Redfish Schema, building a similar JSONs, but replicating the code to do that.
So, it would good if we could reuse that classes, applying so the DRY concept.
The files (or classes) with same Schema:
- `api/computer_system.py` = `api/resource_block_co... | 1.0 | Apply concept DRY to share API classes with same Schema - Currently, we have some case of API classes implementing a same Redfish Schema, building a similar JSONs, but replicating the code to do that.
So, it would good if we could reuse that classes, applying so the DRY concept.
The files (or classes) with same Sch... | non_process | apply concept dry to share api classes with same schema currently we have some case of api classes implementing a same redfish schema building a similar jsons but replicating the code to do that so it would good if we could reuse that classes applying so the dry concept the files or classes with same sch... | 0 |
10,476 | 13,248,908,776 | IssuesEvent | 2020-08-19 19:49:57 | googleapis/python-firestore | https://api.github.com/repos/googleapis/python-firestore | closed | Synth loses import of `google.api_core.path_template` | api: firestore type: process | See PRs #141, #142, #143.
@busunkim96 thinks that we need to update `synth.py` to re-add the import, just as we add the actual helpers which use it. | 1.0 | Synth loses import of `google.api_core.path_template` - See PRs #141, #142, #143.
@busunkim96 thinks that we need to update `synth.py` to re-add the import, just as we add the actual helpers which use it. | process | synth loses import of google api core path template see prs thinks that we need to update synth py to re add the import just as we add the actual helpers which use it | 1 |
684,474 | 23,419,323,302 | IssuesEvent | 2022-08-13 12:52:36 | Derpius/VisTrace | https://api.github.com/repos/Derpius/VisTrace | closed | [bug] Add font fallbacks to extension badge | bug good first issue low-priority | **Describe the bug**
While Windows has the Franklin Gothic font used by the VisTrace logo bundled in most cases, Mac/iOS/iPadOS and possibly other operating systems do not, causing it to fall back to Times New Roman
**Expected behaviour**
The font should fall back through a Verdana font stack.
Additionally a fo... | 1.0 | [bug] Add font fallbacks to extension badge - **Describe the bug**
While Windows has the Franklin Gothic font used by the VisTrace logo bundled in most cases, Mac/iOS/iPadOS and possibly other operating systems do not, causing it to fall back to Times New Roman
**Expected behaviour**
The font should fall back thro... | non_process | add font fallbacks to extension badge describe the bug while windows has the franklin gothic font used by the vistrace logo bundled in most cases mac ios ipados and possibly other operating systems do not causing it to fall back to times new roman expected behaviour the font should fall back through ... | 0 |
818,712 | 30,701,236,120 | IssuesEvent | 2023-07-26 23:45:18 | marbl/HG002-issues | https://api.github.com/repos/marbl/HG002-issues | closed | Issue: chr7_MATERNAL:4504368-4504369 | priority element_evidence trio_based trioassembly_plus_element geno_12 onso_evidence mendel_filter correction_applied | ### Assembly Region
chr7_MATERNAL:4504368-4504369
### Assembly Version
v0.7
### DeepVariant Call
chr7_MATERNAL 4504368 . CA C 44.7 PASS AC=2;AN=2 GT:GQ:DP:AD:VAF:PL 1/1:.:.:0,1:.:. | 1.0 | Issue: chr7_MATERNAL:4504368-4504369 - ### Assembly Region
chr7_MATERNAL:4504368-4504369
### Assembly Version
v0.7
### DeepVariant Call
chr7_MATERNAL 4504368 . CA C 44.7 PASS AC=2;AN=2 GT:GQ:DP:AD:VAF:PL 1/1:.:.:0,1:.:. | non_process | issue maternal assembly region maternal assembly version deepvariant call maternal ca c pass ac an gt gq dp ad vaf pl | 0 |
15,929 | 10,417,901,206 | IssuesEvent | 2019-09-15 02:55:50 | penrose/penrose | https://api.github.com/repos/penrose/penrose | closed | Request to be able to edit Domain and Style program in IDE | ide usability | @keenancrane and I are testing the user/developer in the experience in the IDE and think it would be really helpful to be able to edit the Domain and Style programs there. It would also be helpful for demoing the system to people. | True | Request to be able to edit Domain and Style program in IDE - @keenancrane and I are testing the user/developer in the experience in the IDE and think it would be really helpful to be able to edit the Domain and Style programs there. It would also be helpful for demoing the system to people. | non_process | request to be able to edit domain and style program in ide keenancrane and i are testing the user developer in the experience in the ide and think it would be really helpful to be able to edit the domain and style programs there it would also be helpful for demoing the system to people | 0 |
7,366 | 10,511,144,235 | IssuesEvent | 2019-09-27 14:51:08 | spring-projects/spring-hateoas | https://api.github.com/repos/spring-projects/spring-hateoas | closed | NPE when generating a link to POST method without RequestBody parameter | process: waiting for feedback type: bug | ### New in 1.0.0.M1
I've written an endpoint that updates an object based on a provided ID (path parameter), and some variables (request parameters):
```
@PostMapping("entity/{id}")
public ResponseEntity<Void> update(@PathVariable UUID id, @RequestParam String variable)
```
When I try to generate a HATEOAS link... | 1.0 | NPE when generating a link to POST method without RequestBody parameter - ### New in 1.0.0.M1
I've written an endpoint that updates an object based on a provided ID (path parameter), and some variables (request parameters):
```
@PostMapping("entity/{id}")
public ResponseEntity<Void> update(@PathVariable UUID id, @R... | process | npe when generating a link to post method without requestbody parameter new in i ve written an endpoint that updates an object based on a provided id path parameter and some variables request parameters postmapping entity id public responseentity update pathvariable uuid id request... | 1 |
3,870 | 6,808,647,762 | IssuesEvent | 2017-11-04 06:10:16 | Great-Hill-Corporation/quickBlocks | https://api.github.com/repos/Great-Hill-Corporation/quickBlocks | reopened | Should do better switch statements in generated code from grabABI/makeClass | apps-grabABI status-inprocess type-enhancement | In the code generated by grabABI, it should check the first character of the topic and do a switch as it does in the code for getFieldValueByName to avoid testing every string.
From https://github.com/Great-Hill-Corporation/ethslurp/issues/138 | 1.0 | Should do better switch statements in generated code from grabABI/makeClass - In the code generated by grabABI, it should check the first character of the topic and do a switch as it does in the code for getFieldValueByName to avoid testing every string.
From https://github.com/Great-Hill-Corporation/ethslurp/issues... | process | should do better switch statements in generated code from grababi makeclass in the code generated by grababi it should check the first character of the topic and do a switch as it does in the code for getfieldvaluebyname to avoid testing every string from | 1 |
27,846 | 2,696,614,435 | IssuesEvent | 2015-04-02 15:05:48 | OCHA-DAP/hdx-ckan | https://api.github.com/repos/OCHA-DAP/hdx-ckan | opened | Custom org page: admin menu is always displayed | bug Custom org page Priority-High | Admin menu should be displayed only for users that have the right to see it.

| 1.0 | Custom org page: admin menu is always displayed - Admin menu should be displayed only for users that have the right to see it.

| non_process | custom org page admin menu is always displayed admin menu should be displayed only for users that have the right to see it | 0 |
111,732 | 17,033,433,733 | IssuesEvent | 2021-07-05 01:15:43 | ervin210/ApplicationInsights-Home | https://api.github.com/repos/ervin210/ApplicationInsights-Home | opened | CVE-2018-14042 (Medium) detected in bootstrap-3.0.0.js | security vulnerability | ## CVE-2018-14042 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.0.0.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first... | True | CVE-2018-14042 (Medium) detected in bootstrap-3.0.0.js - ## CVE-2018-14042 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.0.0.js</b></p></summary>
<p>The most popular fr... | non_process | cve medium detected in bootstrap js cve medium severity vulnerability vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library applicationinsight... | 0 |
370,142 | 25,890,438,281 | IssuesEvent | 2022-12-14 17:29:32 | KinsonDigital/Velaptor | https://api.github.com/repos/KinsonDigital/Velaptor | opened | 🚧Fix small grammar issue in contributing document | high priority preview 📝documentation/product | ### Complete The Item Below
- [X] I have updated the title without removing the 🚧 emoji.
### Description
Make a small change in the _**CONTRIBUTING.md**_ document.
The change will involve making the sentence more specific as to prevent confusion or misinterpretation in the future.
**Change To Implement:**
... | 1.0 | 🚧Fix small grammar issue in contributing document - ### Complete The Item Below
- [X] I have updated the title without removing the 🚧 emoji.
### Description
Make a small change in the _**CONTRIBUTING.md**_ document.
The change will involve making the sentence more specific as to prevent confusion or misinterpre... | non_process | 🚧fix small grammar issue in contributing document complete the item below i have updated the title without removing the 🚧 emoji description make a small change in the contributing md document the change will involve making the sentence more specific as to prevent confusion or misinterpreta... | 0 |
315,324 | 9,612,110,550 | IssuesEvent | 2019-05-13 08:07:13 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.amazon.de - see bug description | browser-firefox-mobile engine-gecko priority-critical | <!-- @browser: Firefox Mobile 66.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:66.0) Gecko/66.0 Firefox/66.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://www.amazon.de/Musclealive-Fitnessstudio-Bodybuilding-Trainieren-Baumwolle/dp/B01IT1PPVK/ref=pd_aw_sim_193_2/260-2039301-6875619?_enc... | 1.0 | www.amazon.de - see bug description - <!-- @browser: Firefox Mobile 66.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:66.0) Gecko/66.0 Firefox/66.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://www.amazon.de/Musclealive-Fitnessstudio-Bodybuilding-Trainieren-Baumwolle/dp/B01IT1PPVK/ref=pd... | non_process | see bug description url browser version firefox mobile operating system android tested another browser no problem type something else description pics cannot be viewed steps to reproduce product photos cannot be viewed browser configuration ... | 0 |
87,992 | 8,128,920,606 | IssuesEvent | 2018-08-17 13:33:44 | IEEEKeralaSection/rescuekerala | https://api.github.com/repos/IEEEKeralaSection/rescuekerala | closed | IMP: Tweak CF CDN and fix redirects for speed | Tested low merge-now | **Issue 1: HTML is not cached**
fetching HTML doc alone take ~1s (location SG) and it is because CF cache by default contents with extensions like .html.
<img width="775" alt="screen shot 2018-08-17 at 11 54 08 am" src="https://user-images.githubusercontent.com/5820155/44247181-1d09e200-a215-11e8-9f9b-9e6d508ce4ee.... | 1.0 | IMP: Tweak CF CDN and fix redirects for speed - **Issue 1: HTML is not cached**
fetching HTML doc alone take ~1s (location SG) and it is because CF cache by default contents with extensions like .html.
<img width="775" alt="screen shot 2018-08-17 at 11 54 08 am" src="https://user-images.githubusercontent.com/582015... | non_process | imp tweak cf cdn and fix redirects for speed issue html is not cached fetching html doc alone take location sg and it is because cf cache by default contents with extensions like html img width alt screen shot at am src fix create page rule to cache everything follow ... | 0 |
12,805 | 15,181,985,047 | IssuesEvent | 2021-02-15 05:13:39 | hashgraph/hedera-mirror-node | https://api.github.com/repos/hashgraph/hedera-mirror-node | closed | Add Scheduled Transactions Acceptance Tests | P1 enhancement process test | **Problem**
Acceptance Tests do not currently have Schedule Transactions support.
**Solution**
Add support for Schedule transactions scenarios
**Alternatives**
A clear and concise description of any alternative solutions or features you've considered.
**Additional Context**
v2 SDK seems to have most suppor... | 1.0 | Add Scheduled Transactions Acceptance Tests - **Problem**
Acceptance Tests do not currently have Schedule Transactions support.
**Solution**
Add support for Schedule transactions scenarios
**Alternatives**
A clear and concise description of any alternative solutions or features you've considered.
**Addition... | process | add scheduled transactions acceptance tests problem acceptance tests do not currently have schedule transactions support solution add support for schedule transactions scenarios alternatives a clear and concise description of any alternative solutions or features you ve considered addition... | 1 |
66,722 | 27,559,399,822 | IssuesEvent | 2023-03-07 20:37:21 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Unable to verify TLS bootstrapping in an AKS cluster | container-service/svc triaged assigned-to-author product-question Pri2 | The [instructions](https://docs.microsoft.com/en-us/azure/aks/certificate-rotation#certificate-auto-rotation) on MS's site read as follows:
To verify if TLS Bootstrapping is enabled on your cluster browse to the following paths:
On a Linux node: /var/lib/kubelet/bootstrap-kubeconfig
This directory does not exist... | 1.0 | Unable to verify TLS bootstrapping in an AKS cluster - The [instructions](https://docs.microsoft.com/en-us/azure/aks/certificate-rotation#certificate-auto-rotation) on MS's site read as follows:
To verify if TLS Bootstrapping is enabled on your cluster browse to the following paths:
On a Linux node: /var/lib/kubele... | non_process | unable to verify tls bootstrapping in an aks cluster the on ms s site read as follows to verify if tls bootstrapping is enabled on your cluster browse to the following paths on a linux node var lib kubelet bootstrap kubeconfig this directory does not exist on any of my cluster nodes and these clusters... | 0 |
10,388 | 13,196,701,089 | IssuesEvent | 2020-08-13 21:12:32 | pacificclimate/osprey | https://api.github.com/repos/pacificclimate/osprey | closed | wps_convolution config builder | enhancement process | RVIC 1.1.0.post1 runs based only on config files, which degrades the user-friendliness of the software. Therefore, a `config_builder` program, which takes user inputs to create config files, is needed for each process.
For `RVIC convolution`, refer to the [document](https://rvic.readthedocs.io/en/latest/user-guide/... | 1.0 | wps_convolution config builder - RVIC 1.1.0.post1 runs based only on config files, which degrades the user-friendliness of the software. Therefore, a `config_builder` program, which takes user inputs to create config files, is needed for each process.
For `RVIC convolution`, refer to the [document](https://rvic.rea... | process | wps convolution config builder rvic runs based only on config files which degrades the user friendliness of the software therefore a config builder program which takes user inputs to create config files is needed for each process for rvic convolution refer to the page to see what contents s... | 1 |
14,437 | 17,485,242,529 | IssuesEvent | 2021-08-09 10:08:26 | Raveesh1505/EDA | https://api.github.com/repos/Raveesh1505/EDA | opened | Olympics EDA | Under Process | # Exploratory Data Analysis on Olympics
An Exploratory Data Analysis on dataset provided by [**Kaggle on olympics history**](https://www.kaggle.com).
*Data available from 1896 Greek Olympics to 2016 Rio Olympics*
___
## Expected tools to be used
| | | |
| --- | --- | --- |
| SQL| Python | Jupiter Note... | 1.0 | Olympics EDA - # Exploratory Data Analysis on Olympics
An Exploratory Data Analysis on dataset provided by [**Kaggle on olympics history**](https://www.kaggle.com).
*Data available from 1896 Greek Olympics to 2016 Rio Olympics*
___
## Expected tools to be used
| | | |
| --- | --- | --- |
| SQL| Python... | process | olympics eda exploratory data analysis on olympics an exploratory data analysis on dataset provided by data available from greek olympics to rio olympics expected tools to be used sql python jupiter notebooks expected packages to be ... | 1 |
80,755 | 30,521,505,778 | IssuesEvent | 2023-07-19 08:24:13 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | new invites don't appear when filtered | T-Defect A-Room-List | i filtered on Foo, got invited to a room called Foo, and it didn't show unless i unfiltered | 1.0 | new invites don't appear when filtered - i filtered on Foo, got invited to a room called Foo, and it didn't show unless i unfiltered | non_process | new invites don t appear when filtered i filtered on foo got invited to a room called foo and it didn t show unless i unfiltered | 0 |
102,952 | 4,163,327,256 | IssuesEvent | 2016-06-18 01:52:15 | gravityview/GravityView | https://api.github.com/repos/gravityview/GravityView | opened | Updating an entry which in turns remove this entry from that view makes the entry unreachable | Core: Edit Entry Priority: Low | It's hard to describe this in the title, here's what one of our users have to say:
```
We are using the gravityview plugin as part of an internal crm-type solution. Recently we have run into the following issue:
There is 1 form. There are several views, one that lists form entries which are new (based on the value... | 1.0 | Updating an entry which in turns remove this entry from that view makes the entry unreachable - It's hard to describe this in the title, here's what one of our users have to say:
```
We are using the gravityview plugin as part of an internal crm-type solution. Recently we have run into the following issue:
There ... | non_process | updating an entry which in turns remove this entry from that view makes the entry unreachable it s hard to describe this in the title here s what one of our users have to say we are using the gravityview plugin as part of an internal crm type solution recently we have run into the following issue there ... | 0 |
8,659 | 11,798,046,378 | IssuesEvent | 2020-03-18 13:47:19 | qgis/QGIS-Documentation | https://api.github.com/repos/qgis/QGIS-Documentation | closed | [FEATURE][processing] New parameter type for datetime (or date, or time) values | 3.14 Automatic new feature Processing | Original commit: https://github.com/qgis/QGIS/commit/0efc6f531c26b0157e45c91b968b019d0cdee9e6 by nyalldawson
Adds a new parameter type QgsProcessingParameterDateTime for handling
date/datetime/time values | 1.0 | [FEATURE][processing] New parameter type for datetime (or date, or time) values - Original commit: https://github.com/qgis/QGIS/commit/0efc6f531c26b0157e45c91b968b019d0cdee9e6 by nyalldawson
Adds a new parameter type QgsProcessingParameterDateTime for handling
date/datetime/time values | process | new parameter type for datetime or date or time values original commit by nyalldawson adds a new parameter type qgsprocessingparameterdatetime for handling date datetime time values | 1 |
112,313 | 9,560,244,017 | IssuesEvent | 2019-05-03 19:01:25 | saltstack/salt | https://api.github.com/repos/saltstack/salt | closed | Fedora tests are hanging | 2017.7 2017.7.9 2019.2 2019.2.1 Blocker Fixed Pending Verification Test Failure develop | ### Description of Issue/Question
The fedora test run is not completing and hanging on this test: `test_present_when_stage_associating_to_new_deployment_errored_on_resource_creation`
https://jenkinsci.saltstack.com/job/2017.7.9/job/salt-fedora-28-py2/15/console
also affects fedora 29
```
17:57:54 test... | 1.0 | Fedora tests are hanging - ### Description of Issue/Question
The fedora test run is not completing and hanging on this test: `test_present_when_stage_associating_to_new_deployment_errored_on_resource_creation`
https://jenkinsci.saltstack.com/job/2017.7.9/job/salt-fedora-28-py2/15/console
also affects fedora 29
... | non_process | fedora tests are hanging description of issue question the fedora test run is not completing and hanging on this test test present when stage associating to new deployment errored on resource creation also affects fedora test present when stage associating to new deployment erro... | 0 |
47,643 | 19,686,238,780 | IssuesEvent | 2022-01-11 22:34:22 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | Feature Request: AppStream support | new-resource service/appstream | ### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra no... | 1.0 | Feature Request: AppStream support - ### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me ... | non_process | feature request appstream support community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the req... | 0 |
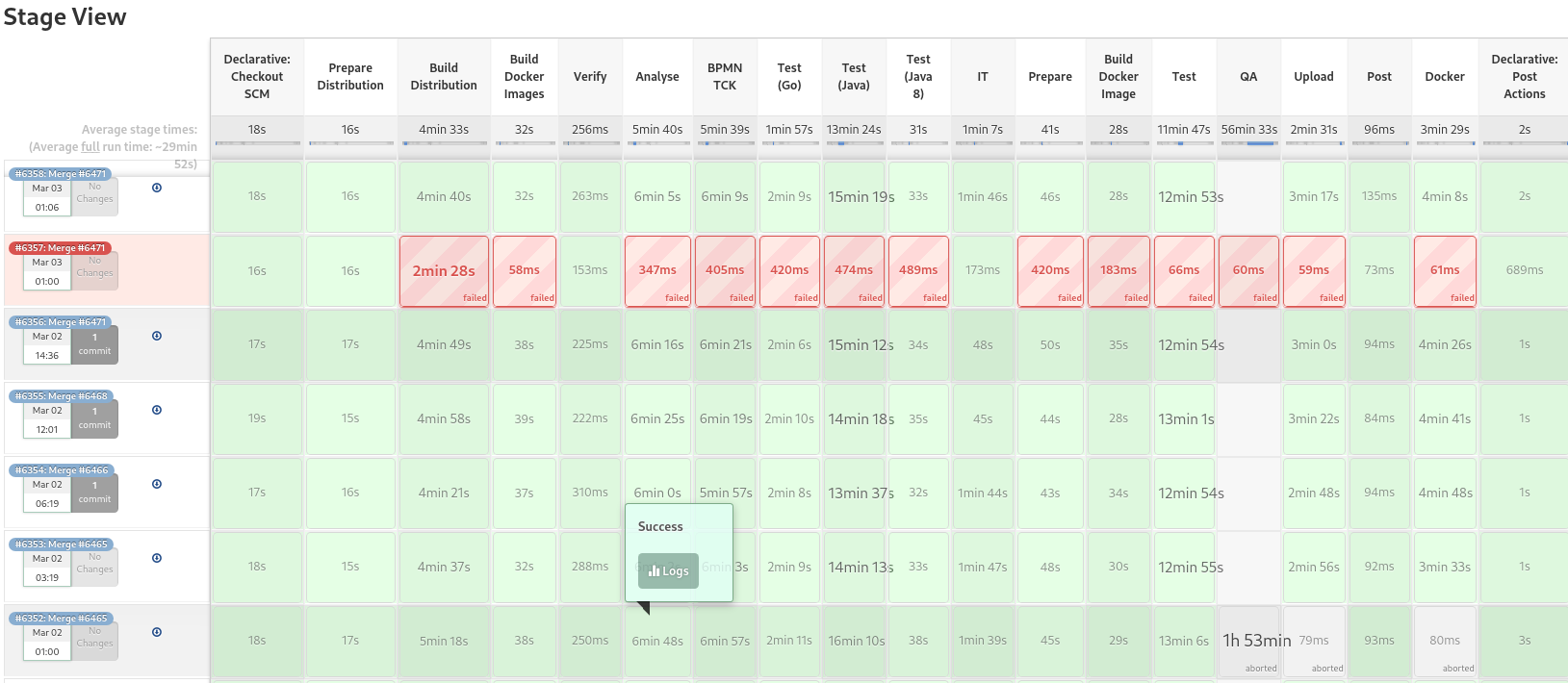
678,933 | 23,216,154,337 | IssuesEvent | 2022-08-02 14:14:09 | status-im/status-desktop | https://api.github.com/repos/status-im/status-desktop | closed | Update Help & Glossary to the new design | ui Profile feature priority F3: nice to have | ### Description
~~design: https://www.figma.com/file/idUoxN7OIW2Jpp3PMJ1Rl8/%E2%9A%99%EF%B8%8F-Settings-%7C-Desktop?node-id=1511%3A137592~~ Design needs to be updated
| 1.0 | Update Help & Glossary to the new design - ### Description
~~design: https://www.figma.com/file/idUoxN7OIW2Jpp3PMJ1Rl8/%E2%9A%99%EF%B8%8F-Settings-%7C-Desktop?node-id=1511%3A137592~~ Design needs to be updated

- [ ] Tech used
- [ ] Contact
| 1.0 | Updating project details - Project info need more details:
- [ ] Project presentation and pitch
- [ ] Contribution rules
- [ ] App's prototype GIFs
- [ ] App features ( needs details on what's to be built)
- [ ] Tech used
- [ ] Contact
| non_process | updating project details project info need more details project presentation and pitch contribution rules app s prototype gifs app features needs details on what s to be built tech used contact | 0 |
161,071 | 12,530,291,993 | IssuesEvent | 2020-06-04 12:51:00 | sebuaa2020/Team208 | https://api.github.com/repos/sebuaa2020/Team208 | closed | Test-Basic | test | - [ ] `RobotMove`
- [ ] `RobotAvoidance`
## RobotMove
该模块介绍与运行方法参考`robot2077_basic`包中`README`文件。
由于该模块没有与用户直接交互的接口,所以主要测试为:
- [x] 单元测试
- [ ] 节点测试
测试方法:
- 单元测试:构造测试样例,向函数`move_listen`输入测试样例,然后检测`vel_temp`的变化。
需保证:`vel_temp`中的速度始终没有超过设定最大速度,并需覆盖`check_vel`函数中的所有分支。
- 节点测试:使用黑箱测试,向`RobotMove`节点... | 1.0 | Test-Basic - - [ ] `RobotMove`
- [ ] `RobotAvoidance`
## RobotMove
该模块介绍与运行方法参考`robot2077_basic`包中`README`文件。
由于该模块没有与用户直接交互的接口,所以主要测试为:
- [x] 单元测试
- [ ] 节点测试
测试方法:
- 单元测试:构造测试样例,向函数`move_listen`输入测试样例,然后检测`vel_temp`的变化。
需保证:`vel_temp`中的速度始终没有超过设定最大速度,并需覆盖`check_vel`函数中的所有分支。
- 节点测试:使用黑箱测试,向... | non_process | test basic robotmove robotavoidance robotmove 该模块介绍与运行方法参考 basic 包中 readme 文件。 由于该模块没有与用户直接交互的接口,所以主要测试为: 单元测试 节点测试 测试方法: 单元测试:构造测试样例,向函数 move listen 输入测试样例,然后检测 vel temp 的变化。 需保证: vel temp 中的速度始终没有超过设定最大速度,并需覆盖 check vel 函数中的所有分支。 节点测试:使用黑箱测试,向 robotmove 节点发送 ... | 0 |
814,832 | 30,523,887,164 | IssuesEvent | 2023-07-19 09:53:24 | Weiver-project/Weiver | https://api.github.com/repos/Weiver-project/Weiver | closed | BE_[Feat]: 배우 정보 조회 | ✨feat 🟡 Priority: Medium | ## 📃To do List
- [x] 오늘의 배우 조회
- 랜덤으로 배우ID 통해서 정보[배우 이미지, 이름, 출연작(10개)] 가져오기
- [x] 배우 상세 페이지에서 배우 정보 조회
- 배우ID 통해 정보[이름, 프로필 사진, 작품 포스터] 가져오기
- [x] 뮤지컬 상세 페이지에서 배우 정보 조회
- 조회한 뮤지컬에 따라 배우 매칭 정보를 기반으로 [프로필 사진, 이름, 배역] 가져오기
| 1.0 | BE_[Feat]: 배우 정보 조회 - ## 📃To do List
- [x] 오늘의 배우 조회
- 랜덤으로 배우ID 통해서 정보[배우 이미지, 이름, 출연작(10개)] 가져오기
- [x] 배우 상세 페이지에서 배우 정보 조회
- 배우ID 통해 정보[이름, 프로필 사진, 작품 포스터] 가져오기
- [x] 뮤지컬 상세 페이지에서 배우 정보 조회
- 조회한 뮤지컬에 따라 배우 매칭 정보를 기반으로 [프로필 사진, 이름, 배역] 가져오기
| non_process | be 배우 정보 조회 📃to do list 오늘의 배우 조회 랜덤으로 배우id 통해서 정보 가져오기 배우 상세 페이지에서 배우 정보 조회 배우id 통해 정보 가져오기 뮤지컬 상세 페이지에서 배우 정보 조회 조회한 뮤지컬에 따라 배우 매칭 정보를 기반으로 가져오기 | 0 |
15,270 | 19,250,065,884 | IssuesEvent | 2021-12-09 03:22:58 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | opened | DISABLED test_fd_pool (__main__.TestMultiprocessing) | module: multiprocessing module: flaky-tests | This test has been determined flaky through reruns in CI and its instances are reported in our flaky_tests table here https://metrics.pytorch.org/d/L0r6ErGnk/github-status?orgId=1&from=1636426818307&to=1639018818307&viewPanel=57.
It is our second flakiest test in the last 15 days with 28 failed instances.
```
==... | 1.0 | DISABLED test_fd_pool (__main__.TestMultiprocessing) - This test has been determined flaky through reruns in CI and its instances are reported in our flaky_tests table here https://metrics.pytorch.org/d/L0r6ErGnk/github-status?orgId=1&from=1636426818307&to=1639018818307&viewPanel=57.
It is our second flakiest test i... | process | disabled test fd pool main testmultiprocessing this test has been determined flaky through reruns in ci and its instances are reported in our flaky tests table here it is our second flakiest test in the last days with failed instances ... | 1 |
267,110 | 28,497,428,001 | IssuesEvent | 2023-04-18 15:04:18 | lukebrogan-mend/vulnerable-node | https://api.github.com/repos/lukebrogan-mend/vulnerable-node | opened | bootstrap-3.3.6.min.js: 6 vulnerabilities (highest severity is: 6.1) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page... | True | bootstrap-3.3.6.min.js: 6 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p></summary>
<p>The most popular front-end framework for developing... | non_process | bootstrap min js vulnerabilities highest severity is vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library public js bootstrap min js fo... | 0 |
611,871 | 18,983,669,081 | IssuesEvent | 2021-11-21 10:44:27 | 26F-Studio/Techmino | https://api.github.com/repos/26F-Studio/Techmino | opened | Disconnecting a controller on the fly leaves phantom held keys | bug low priority | Screenshot with unintended behaviors (*Image(s) Here*):
If you can reproduce it, write the steps here. If you can't, try to describe the exactly time the game crash, like pressing which key or which button (*Details Here*):
- Connect a controller.
- Open a mode, and hold left key (or whatever this action is mapp... | 1.0 | Disconnecting a controller on the fly leaves phantom held keys - Screenshot with unintended behaviors (*Image(s) Here*):
If you can reproduce it, write the steps here. If you can't, try to describe the exactly time the game crash, like pressing which key or which button (*Details Here*):
- Connect a controller.
... | non_process | disconnecting a controller on the fly leaves phantom held keys screenshot with unintended behaviors image s here if you can reproduce it write the steps here if you can t try to describe the exactly time the game crash like pressing which key or which button details here connect a controller ... | 0 |
20,184 | 26,745,213,931 | IssuesEvent | 2023-01-30 15:33:21 | Open-EO/openeo-processes | https://api.github.com/repos/Open-EO/openeo-processes | closed | Vector data cubes + processes | help wanted new process breaking minor platform vector | We basically ignored vector data cubes and related processes until now and will need to add more related processes in 1.0, which will be a major work package!
We also need to update existing processes, which currently only support raster-cubes and add vector-cube support to processes that currently only allow geojso... | 1.0 | Vector data cubes + processes - We basically ignored vector data cubes and related processes until now and will need to add more related processes in 1.0, which will be a major work package!
We also need to update existing processes, which currently only support raster-cubes and add vector-cube support to processes ... | process | vector data cubes processes we basically ignored vector data cubes and related processes until now and will need to add more related processes in which will be a major work package we also need to update existing processes which currently only support raster cubes and add vector cube support to processes ... | 1 |
16,053 | 20,194,739,296 | IssuesEvent | 2022-02-11 09:37:21 | PPHubApp/PPHub-Feedback | https://api.github.com/repos/PPHubApp/PPHub-Feedback | closed | v2.4.7 - “文本转换为UTF8编码时失败”
当代码... | Enhancement💯 Processing 👨🏻💻🚧 | “文本转换为UTF8编码时失败”
当代码中含有中文的时候,无法查看线上代码;虽然提供了前往网页查看的功能,但是如果是自己私有仓库的话需要登录才能查看;会略显不方便。
能否支持UTF8编码的解析功能?
运行环境: iPhone11 - iOS13.5.1 - v2.4.7(180) | 1.0 | v2.4.7 - “文本转换为UTF8编码时失败”
当代码... - “文本转换为UTF8编码时失败”
当代码中含有中文的时候,无法查看线上代码;虽然提供了前往网页查看的功能,但是如果是自己私有仓库的话需要登录才能查看;会略显不方便。
能否支持UTF8编码的解析功能?
运行环境: iPhone11 - iOS13.5.1 - v2.4.7(180) | process | “ ” 当代码 “ ” 当代码中含有中文的时候,无法查看线上代码;虽然提供了前往网页查看的功能,但是如果是自己私有仓库的话需要登录才能查看;会略显不方便。 ? 运行环境 | 1 |
2,368 | 5,167,535,875 | IssuesEvent | 2017-01-17 19:06:11 | w3c/mediacapture-record | https://api.github.com/repos/w3c/mediacapture-record | closed | Convert mediacapture-record spec to bikeshed | process/infra | I propose moving this Spec to bikeshed in the spirit of w3c/mediacapture-image#139. Like in this issue, the only blocker is the WG boilerplate in tabatkins/bikeshed#890. Otherwise, I _love_ being able to fold those `<a href="https://www.w3.org/TR/FileAPI/#blob"><code>Blob</code></a>` into just `{{Blob}}`, and add a l... | 1.0 | Convert mediacapture-record spec to bikeshed - I propose moving this Spec to bikeshed in the spirit of w3c/mediacapture-image#139. Like in this issue, the only blocker is the WG boilerplate in tabatkins/bikeshed#890. Otherwise, I _love_ being able to fold those `<a href="https://www.w3.org/TR/FileAPI/#blob"><code>Blo... | process | convert mediacapture record spec to bikeshed i propose moving this spec to bikeshed in the spirit of mediacapture image like in this issue the only blocker is the wg boilerplate in tabatkins bikeshed otherwise i love being able to fold those a href into just blob and add a lot of direct link... | 1 |
52,563 | 6,260,920,409 | IssuesEvent | 2017-07-14 22:02:32 | geoffhumphrey/brewcompetitiononlineentry | https://api.github.com/repos/geoffhumphrey/brewcompetitiononlineentry | closed | Pay pal not updating some paid users | enhancement in latest master commit v2.1.10 | Not exactly sure why, but a good amount of users don't get updated when the pay with paypal. Not sure how to replicate, but might be good to look at. Thanks | 1.0 | Pay pal not updating some paid users - Not exactly sure why, but a good amount of users don't get updated when the pay with paypal. Not sure how to replicate, but might be good to look at. Thanks | non_process | pay pal not updating some paid users not exactly sure why but a good amount of users don t get updated when the pay with paypal not sure how to replicate but might be good to look at thanks | 0 |
224,691 | 7,472,053,471 | IssuesEvent | 2018-04-03 11:20:51 | salesagility/SuiteCRM | https://api.github.com/repos/salesagility/SuiteCRM | closed | Problem exporting account when filter is applied | Fix Proposed Medium Priority Resolved: Next Release bug | Hi everybody:
I've found a problem, maybe a bug, when I tried to export an accounts list after applied a filter by campaign name.
I haven't found any topic on forum about this and the help in forum haven't solve the problem.
This is the way to reproduce the problem:
1. Add the field 'campaign_name' to the av... | 1.0 | Problem exporting account when filter is applied - Hi everybody:
I've found a problem, maybe a bug, when I tried to export an accounts list after applied a filter by campaign name.
I haven't found any topic on forum about this and the help in forum haven't solve the problem.
This is the way to reproduce the pro... | non_process | problem exporting account when filter is applied hi everybody i ve found a problem maybe a bug when i tried to export an accounts list after applied a filter by campaign name i haven t found any topic on forum about this and the help in forum haven t solve the problem this is the way to reproduce the pro... | 0 |
17,897 | 23,872,820,085 | IssuesEvent | 2022-09-07 16:09:20 | GregTechCEu/gt-ideas | https://api.github.com/repos/GregTechCEu/gt-ideas | opened | The Mond Process | processing chain | ## Details
The Mond Process produces Nickel and a Cobalt byproduct from Garnierite.
## Products
Main Product: Nickel
Side Product(s): Cobalt
## Steps
2 Garnierite (s) + 2 Hydrogen (g) -> Impure Nickel (s) + Steam (g)
`NiO (s) + 2H (g) -> Ni (s) + H2O (g)`
This step is performend at 473K.
Impure Nickel (... | 1.0 | The Mond Process - ## Details
The Mond Process produces Nickel and a Cobalt byproduct from Garnierite.
## Products
Main Product: Nickel
Side Product(s): Cobalt
## Steps
2 Garnierite (s) + 2 Hydrogen (g) -> Impure Nickel (s) + Steam (g)
`NiO (s) + 2H (g) -> Ni (s) + H2O (g)`
This step is performend at 473K.... | process | the mond process details the mond process produces nickel and a cobalt byproduct from garnierite products main product nickel side product s cobalt steps garnierite s hydrogen g impure nickel s steam g nio s g ni s g this step is performend at im... | 1 |
80,981 | 30,640,639,410 | IssuesEvent | 2023-07-24 21:37:36 | NREL/EnergyPlus | https://api.github.com/repos/NREL/EnergyPlus | closed | EnergyPlus fail to run when IDF file path has special character | Defect | Issue overview
--------------
EnergyPlus fail to run calculation when I have accented character in the path of the IDF file. For example, I have an IDF file in the folder "D:\térmica Oficinas". When I run simulation with EPLaunch, I get the following error:
key.GetValue(String.Empty);
```
Where we cast the value to string no matter what is the type of that value.
On netcoreapp we do:
```cs
string value = key.GetValue(string.Empty) as string;
if (string.IsNullOrEmpty(value))
... | 1.0 | [Netfx bug]: ProcessStartInfo.Verbs throws InvalidCastException when an int value is present in the RegistryKey - On netfx we try to do this when getting the verbs:
```cs
string value = (string)key.GetValue(String.Empty);
```
Where we cast the value to string no matter what is the type of that value.
On netcor... | process | processstartinfo verbs throws invalidcastexception when an int value is present in the registrykey on netfx we try to do this when getting the verbs cs string value string key getvalue string empty where we cast the value to string no matter what is the type of that value on netcoreapp we do... | 1 |
16,892 | 22,194,885,007 | IssuesEvent | 2022-06-07 05:37:02 | camunda/zeebe | https://api.github.com/repos/camunda/zeebe | closed | Expand Elastic Search exporter for ProcessInstanceCreation record | team/process-automation | Specifically, we'll need to expand the [template of ProcessInstanceCreation record](https://github.com/camunda/zeebe/blob/main/exporters/elasticsearch-exporter/src/main/resources/zeebe-record-process-instance-creation-template.json)) with the start instructions.
Blocked by #9388 | 1.0 | Expand Elastic Search exporter for ProcessInstanceCreation record - Specifically, we'll need to expand the [template of ProcessInstanceCreation record](https://github.com/camunda/zeebe/blob/main/exporters/elasticsearch-exporter/src/main/resources/zeebe-record-process-instance-creation-template.json)) with the start ins... | process | expand elastic search exporter for processinstancecreation record specifically we ll need to expand the with the start instructions blocked by | 1 |
743,966 | 25,921,575,837 | IssuesEvent | 2022-12-15 22:34:12 | rokwire/illinois-app | https://api.github.com/repos/rokwire/illinois-app | closed | [FEATURE] Please add link to Video Tutorials in Campus Guide. | Type: Feature Request Priority: High | [[ @vburgett - Would you please review this and assign it to Mark when it's OK? (thanks, joe) ]]
So that we can make new videos available within the app as they are created, we would like to add new videos via Campus Guide.
Please confirm with JP, but he asked to have a landing page for Video Tutorials in Campus... | 1.0 | [FEATURE] Please add link to Video Tutorials in Campus Guide. - [[ @vburgett - Would you please review this and assign it to Mark when it's OK? (thanks, joe) ]]
So that we can make new videos available within the app as they are created, we would like to add new videos via Campus Guide.
Please confirm with JP, b... | non_process | please add link to video tutorials in campus guide so that we can make new videos available within the app as they are created we would like to add new videos via campus guide please confirm with jp but he asked to have a landing page for video tutorials in campus guide that could be linked from browse... | 0 |
164,001 | 6,218,077,105 | IssuesEvent | 2017-07-08 21:12:43 | Tamaized/VoidCraft | https://api.github.com/repos/Tamaized/VoidCraft | closed | Xia generation problems | Bug Priority | In the most recent version of voidcraft (1.12-0.22.1) the Xia dimension doesn't generate right. none of the voidbrick blocks generate, nor do most of the holes in reality and the voidcraft:blocknobreak. I've tried in three different worlds (two of which were only voidcraft and TamModized | 1.0 | Xia generation problems - In the most recent version of voidcraft (1.12-0.22.1) the Xia dimension doesn't generate right. none of the voidbrick blocks generate, nor do most of the holes in reality and the voidcraft:blocknobreak. I've tried in three different worlds (two of which were only voidcraft and TamModized | non_process | xia generation problems in the most recent version of voidcraft the xia dimension doesn t generate right none of the voidbrick blocks generate nor do most of the holes in reality and the voidcraft blocknobreak i ve tried in three different worlds two of which were only voidcraft and tammodized | 0 |
286,710 | 31,757,803,037 | IssuesEvent | 2023-09-12 01:02:18 | Pio1006/envoy | https://api.github.com/repos/Pio1006/envoy | opened | CVE-2022-41721 (High) detected in github.com/golang/net-v0.0.0-20190403144856-b630fd6fe46b, github.com/golang/net-v0.0.0-20200301022130-244492dfa37a | Mend: dependency security vulnerability | ## CVE-2022-41721 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>github.com/golang/net-v0.0.0-20190403144856-b630fd6fe46b</b>, <b>github.com/golang/net-v0.0.0-20200301022130-244492df... | True | CVE-2022-41721 (High) detected in github.com/golang/net-v0.0.0-20190403144856-b630fd6fe46b, github.com/golang/net-v0.0.0-20200301022130-244492dfa37a - ## CVE-2022-41721 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 hei... | non_process | cve high detected in github com golang net github com golang net cve high severity vulnerability vulnerable libraries github com golang net github com golang net github com golang net go supplementary network libraries libra... | 0 |
17,454 | 23,272,673,263 | IssuesEvent | 2022-08-05 02:06:02 | MicrosoftDocs/azure-devops-docs | https://api.github.com/repos/MicrosoftDocs/azure-devops-docs | closed | Extract Year and Month from Date | devops/prod support-request cba Pri1 devops-cicd-process/tech | I need to get into Azure yaml file a variable that would consist of only year and month from the current date. How do I accomplish this?
I've already tried:
```
$(Year:yyyy).$(Month).$(Build.BuildNumber)
datetime_part("year", $(date)).datetime_part("month", $(date)).$(Build.BuildNumber)
format_datetime($(date... | 1.0 | Extract Year and Month from Date - I need to get into Azure yaml file a variable that would consist of only year and month from the current date. How do I accomplish this?
I've already tried:
```
$(Year:yyyy).$(Month).$(Build.BuildNumber)
datetime_part("year", $(date)).datetime_part("month", $(date)).$(Build.B... | process | extract year and month from date i need to get into azure yaml file a variable that would consist of only year and month from the current date how do i accomplish this i ve already tried year yyyy month build buildnumber datetime part year date datetime part month date build b... | 1 |
22,555 | 31,765,418,058 | IssuesEvent | 2023-09-12 08:28:57 | ppy/osu-web | https://api.github.com/repos/ppy/osu-web | closed | The mode field is null on beatmap object if mode_int is unknown. | type:api area:beatmap-processing external component | Current docs shows that mode is not nullable: https://osu.ppy.sh/docs/index.html#beatmapcompact
Rather than putting a PR in the documentation, I'm adding this as an issue because I think there's a better way to handle it.
/api/v2/beatmaps/1482781
```js
{
"beatmapset_id": 700402,
"difficulty_rating": 4.53,
... | 1.0 | The mode field is null on beatmap object if mode_int is unknown. - Current docs shows that mode is not nullable: https://osu.ppy.sh/docs/index.html#beatmapcompact
Rather than putting a PR in the documentation, I'm adding this as an issue because I think there's a better way to handle it.
/api/v2/beatmaps/1482781
`... | process | the mode field is null on beatmap object if mode int is unknown current docs shows that mode is not nullable rather than putting a pr in the documentation i m adding this as an issue because i think there s a better way to handle it api beatmaps js beatmapset id difficulty rating ... | 1 |
219,801 | 17,112,320,325 | IssuesEvent | 2021-07-10 15:30:59 | mreidt/gf-app | https://api.github.com/repos/mreidt/gf-app | closed | Test operations management endpoints | enhancement operations tests | - [ ] Test create operation
- [ ] Test edit operation
- [ ] Test remove operation
- [ ] Test list operations | 1.0 | Test operations management endpoints - - [ ] Test create operation
- [ ] Test edit operation
- [ ] Test remove operation
- [ ] Test list operations | non_process | test operations management endpoints test create operation test edit operation test remove operation test list operations | 0 |
21,394 | 29,202,232,376 | IssuesEvent | 2023-05-21 00:37:45 | devssa/onde-codar-em-salvador | https://api.github.com/repos/devssa/onde-codar-em-salvador | closed | [Remoto] Fullstack Developer na Coodesh | SALVADOR BACK-END FRONT-END PJ BANCO DE DADOS JAVASCRIPT FULL-STACK MVC HTML SQL GIT REST JSON REACT AWS REQUISITOS REMOTO ASP.NET PROCESSOS INOVAÇÃO GITHUB E-COMMERCE IONIC UMA TFS C R APIs METODOLOGIAS ÁGEIS SAAS MANUTENÇÃO AUTOMAÇÃO DE PROCESSOS Stale | ## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com](https://coodesh.com/vagas/pessoa-desenvolvedora-fullstack-11592... | 2.0 | [Remoto] Fullstack Developer na Coodesh - ## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com](https://coodesh.com/v... | process | fullstack developer na coodesh descrição da vaga esta é uma vaga de um parceiro da plataforma coodesh ao candidatar se você terá acesso as informações completas sobre a empresa e benefícios fique atento ao redirecionamento que vai te levar para uma url com o pop up personalizado de candidatura 👋 ... | 1 |
118,293 | 4,734,054,789 | IssuesEvent | 2016-10-19 13:13:45 | dmwm/PHEDEX | https://api.github.com/repos/dmwm/PHEDEX | closed | PerfMonitor agent: slow t_status_block_dest query | Category: Agents Priority 4: High Status: Fixed | The PerfMonitor agent had performance issues recently:
https://ggus.eu/?mode=ticket_info&ticket_id=124312
Tracked down to the following SQL used to update the t_status_block_dest table:
https://github.com/dmwm/PHEDEX/blob/4ffa9024e63948b6c6ac6b49a5bf50cb0f15130d/perl_lib/PHEDEX/Monitoring/PerfMonitor/Agent.pm#... | 1.0 | PerfMonitor agent: slow t_status_block_dest query - The PerfMonitor agent had performance issues recently:
https://ggus.eu/?mode=ticket_info&ticket_id=124312
Tracked down to the following SQL used to update the t_status_block_dest table:
https://github.com/dmwm/PHEDEX/blob/4ffa9024e63948b6c6ac6b49a5bf50cb0f151... | non_process | perfmonitor agent slow t status block dest query the perfmonitor agent had performance issues recently tracked down to the following sql used to update the t status block dest table the problem is the join to t dps file in this case the same information is also available in t dps block fix comm... | 0 |
123,362 | 17,772,214,505 | IssuesEvent | 2021-08-30 14:51:43 | kapseliboi/RDocumentation-app | https://api.github.com/repos/kapseliboi/RDocumentation-app | opened | CVE-2019-14939 (Medium) detected in mysql-2.15.0.tgz | security vulnerability | ## CVE-2019-14939 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-2.15.0.tgz</b></p></summary>
<p>A node.js driver for mysql. It is written in JavaScript, does not require comp... | True | CVE-2019-14939 (Medium) detected in mysql-2.15.0.tgz - ## CVE-2019-14939 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-2.15.0.tgz</b></p></summary>
<p>A node.js driver for my... | non_process | cve medium detected in mysql tgz cve medium severity vulnerability vulnerable library mysql tgz a node js driver for mysql it is written in javascript does not require compiling and is mit licensed library home page a href path to dependency file rdocumentation a... | 0 |
117,513 | 25,135,220,889 | IssuesEvent | 2022-11-09 18:02:00 | trezor/trezor-suite | https://api.github.com/repos/trezor/trezor-suite | closed | Specify the calculation of the service fee | account code bitcoin | - [x] Count only UTXOs with lower then desired anonymity level
- [x] Remove UTXOs with amount lower than `plebsDontPayThreshold` (1M sats)
- [x] Remove previously coinjoined UTXOs (direct and indirect)
- [x] Direct remix is an UTXO that is an output of a coinjoin transaction.
- [x] ~~Indirect remix is an UT... | 1.0 | Specify the calculation of the service fee - - [x] Count only UTXOs with lower then desired anonymity level
- [x] Remove UTXOs with amount lower than `plebsDontPayThreshold` (1M sats)
- [x] Remove previously coinjoined UTXOs (direct and indirect)
- [x] Direct remix is an UTXO that is an output of a coinjoin tran... | non_process | specify the calculation of the service fee count only utxos with lower then desired anonymity level remove utxos with amount lower than plebsdontpaythreshold sats remove previously coinjoined utxos direct and indirect direct remix is an utxo that is an output of a coinjoin transaction ... | 0 |
16,556 | 3,537,973,602 | IssuesEvent | 2016-01-18 06:54:21 | FreeCodeCamp/FreeCodeCamp | https://api.github.com/repos/FreeCodeCamp/FreeCodeCamp | closed | Bonfire Friendly Date Ranges Test Inconsistencies | confirmed Discussing tests | Challenge http://freecodecamp.com/challenges/bonfire-friendly-date-ranges has an issue. Please describe how to reproduce it, and include links to screenshots if possible.
I know this has been debated before, and I understand that if the dates are within 11 months it can be inferred that it is the following year, but... | 1.0 | Bonfire Friendly Date Ranges Test Inconsistencies - Challenge http://freecodecamp.com/challenges/bonfire-friendly-date-ranges has an issue. Please describe how to reproduce it, and include links to screenshots if possible.
I know this has been debated before, and I understand that if the dates are within 11 months i... | non_process | bonfire friendly date ranges test inconsistencies challenge has an issue please describe how to reproduce it and include links to screenshots if possible i know this has been debated before and i understand that if the dates are within months it can be inferred that it is the following year but test be... | 0 |
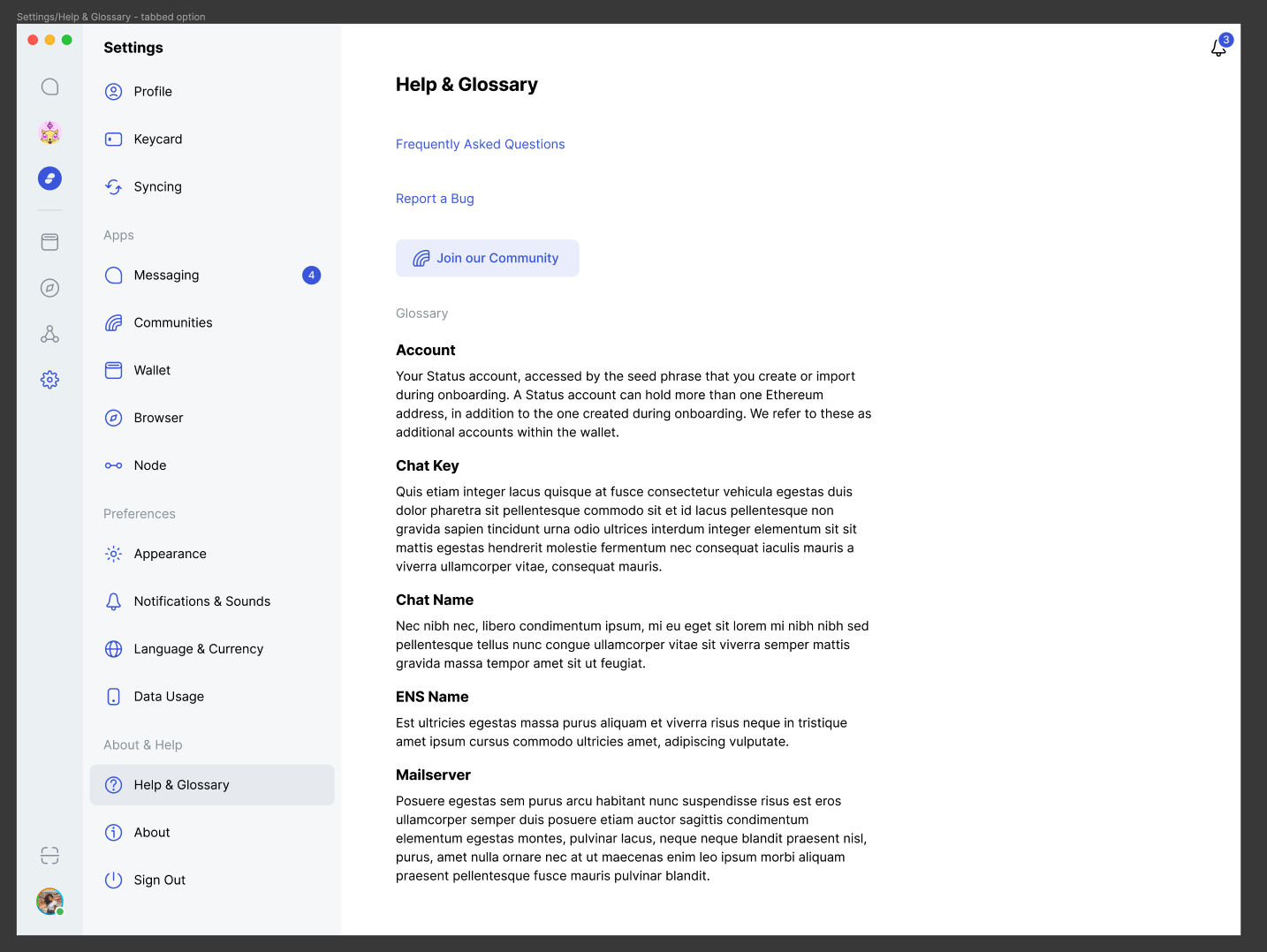
588,475 | 17,661,116,846 | IssuesEvent | 2021-08-21 14:24:22 | francheska-vicente/cssweng | https://api.github.com/repos/francheska-vicente/cssweng | closed | Booking button on click visual error | bug priority: high issue: front-end severity: medium | ### Summary:
Booking button turns white after clicking
### Steps to Reproduce:
1. Log in
2. Go to reservation
3. Click booking
### Visual Proof:
### Expected Results:
Booking button remains the... | 1.0 | Booking button on click visual error - ### Summary:
Booking button turns white after clicking
### Steps to Reproduce:
1. Log in
2. Go to reservation
3. Click booking
### Visual Proof:
### Expect... | non_process | booking button on click visual error summary booking button turns white after clicking steps to reproduce log in go to reservation click booking visual proof expected results booking button remains the same color after clicking actual results booking button tu... | 0 |
6,395 | 9,477,782,621 | IssuesEvent | 2019-04-19 19:56:04 | arxiv-vanity/engrafo | https://api.github.com/repos/arxiv-vanity/engrafo | closed | Match more arXiv ID forms | area/postprocessor good first issue help wanted type/enhancement | We currently convert URLs that look a bit like `arxiv:1234.5678` into arxiv.org URLs. I expect there are many more things in papers that could be converted to URLs - stuff without `arxiv:` and old style IDs.
We need to find more examples of these and make them linked.
- This has lots of fun stuff (cmd-f "arxiv"):... | 1.0 | Match more arXiv ID forms - We currently convert URLs that look a bit like `arxiv:1234.5678` into arxiv.org URLs. I expect there are many more things in papers that could be converted to URLs - stuff without `arxiv:` and old style IDs.
We need to find more examples of these and make them linked.
- This has lots o... | process | match more arxiv id forms we currently convert urls that look a bit like arxiv into arxiv org urls i expect there are many more things in papers that could be converted to urls stuff without arxiv and old style ids we need to find more examples of these and make them linked this has lots of fun ... | 1 |
4,869 | 7,751,842,611 | IssuesEvent | 2018-05-30 18:21:58 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | .Net Core Process.Start on Linux | area-System.Diagnostics.Process os-linux question | I am facing the following issue when running my .Net Core 2.0 application on Linux as a SCD.
I am attempting to start another .Net Core project (Console Application) though the Aspnet Core project.
The exception below is thrown when I call `Start()`.
The permissions on the file and folders have been set to `777` ... | 1.0 | .Net Core Process.Start on Linux - I am facing the following issue when running my .Net Core 2.0 application on Linux as a SCD.
I am attempting to start another .Net Core project (Console Application) though the Aspnet Core project.
The exception below is thrown when I call `Start()`.
The permissions on the file ... | process | net core process start on linux i am facing the following issue when running my net core application on linux as a scd i am attempting to start another net core project console application though the aspnet core project the exception below is thrown when i call start the permissions on the file ... | 1 |
15,725 | 19,898,018,202 | IssuesEvent | 2022-01-25 02:50:33 | djcurill/two-wheels | https://api.github.com/repos/djcurill/two-wheels | opened | Post Scrape Data Processing | utility data processing | Create functions for cleaning & formatting data after scraping from the internet. We will need the following:
1. Extract price and convert to CAD
2. Extract brand from title and format
3. Extract model from title and format
4. Extract front travel and convert to number
5. Extract rear travel and convert to number
... | 1.0 | Post Scrape Data Processing - Create functions for cleaning & formatting data after scraping from the internet. We will need the following:
1. Extract price and convert to CAD
2. Extract brand from title and format
3. Extract model from title and format
4. Extract front travel and convert to number
5. Extract rear... | process | post scrape data processing create functions for cleaning formatting data after scraping from the internet we will need the following extract price and convert to cad extract brand from title and format extract model from title and format extract front travel and convert to number extract rear... | 1 |
149,802 | 13,302,709,245 | IssuesEvent | 2020-08-25 14:36:07 | FirebaseExtended/flutterfire | https://api.github.com/repos/FirebaseExtended/flutterfire | closed | [firebase_storage] Add notes on installing firebase to every firebase package | blocked: customer-response plugin: auth resolution: needs-repro type: documentation | I was trying to install firebase via the firebase_storage package and had difficulties, later i found following the instructions at https://pub.dartlang.org/packages/firebase_auth in order to properly install it.
Apologies if this issue isn't made at the right repo, but I'd like to suggest we add notes to each fireb... | 1.0 | [firebase_storage] Add notes on installing firebase to every firebase package - I was trying to install firebase via the firebase_storage package and had difficulties, later i found following the instructions at https://pub.dartlang.org/packages/firebase_auth in order to properly install it.
Apologies if this issue ... | non_process | add notes on installing firebase to every firebase package i was trying to install firebase via the firebase storage package and had difficulties later i found following the instructions at in order to properly install it apologies if this issue isn t made at the right repo but i d like to suggest we add no... | 0 |
3,483 | 6,554,787,837 | IssuesEvent | 2017-09-06 07:45:06 | threefoldfoundation/app_backend | https://api.github.com/repos/threefoldfoundation/app_backend | closed | Need a final description for the payment wallet | process_wontfix state_question | The description (markdown) is shown when the user creates the wallet. The full page (mobile) is available.
Right now, we configured this as description
# ThreeFold Token
### Our backed, safe digital currency funds a neutral green Internet
| 1.0 | Need a final description for the payment wallet - The description (markdown) is shown when the user creates the wallet. The full page (mobile) is available.
Right now, we configured this as description
# ThreeFold Token
### Our backed, safe digital currency funds a neutral green Internet
| process | need a final description for the payment wallet the description markdown is shown when the user creates the wallet the full page mobile is available right now we configured this as description threefold token our backed safe digital currency funds a neutral green internet | 1 |
11,680 | 14,539,653,884 | IssuesEvent | 2020-12-15 12:12:15 | prisma/e2e-tests | https://api.github.com/repos/prisma/e2e-tests | closed | Test community generators | kind/feature process/candidate team/support-engineering | - Input on generators to test: https://app.redash.io/prismaio/queries/476639
- Make tests optional or fyi, separate workflow so build status is separate
- (Nexus Plugin Prisma test can also be part of this "fyi" test suite for example) | 1.0 | Test community generators - - Input on generators to test: https://app.redash.io/prismaio/queries/476639
- Make tests optional or fyi, separate workflow so build status is separate
- (Nexus Plugin Prisma test can also be part of this "fyi" test suite for example) | process | test community generators input on generators to test make tests optional or fyi separate workflow so build status is separate nexus plugin prisma test can also be part of this fyi test suite for example | 1 |
5,954 | 8,780,382,173 | IssuesEvent | 2018-12-19 17:09:14 | GoogleCloudPlatform/google-cloud-cpp | https://api.github.com/repos/GoogleCloudPlatform/google-cloud-cpp | closed | Create a configuration flag to disable tests. | good first issue type: process | Our users, and package maintainers, may not be interested in compiling and running the tests. Their workflows are faster if they can disable the tests for our code.
| 1.0 | Create a configuration flag to disable tests. - Our users, and package maintainers, may not be interested in compiling and running the tests. Their workflows are faster if they can disable the tests for our code.
| process | create a configuration flag to disable tests our users and package maintainers may not be interested in compiling and running the tests their workflows are faster if they can disable the tests for our code | 1 |
7,730 | 10,852,889,318 | IssuesEvent | 2019-11-13 13:43:24 | NationalSecurityAgency/ghidra | https://api.github.com/repos/NationalSecurityAgency/ghidra | closed | MCS-96: Can't read language spec | Feature: Processor/Other Type: Bug | **Describe the bug**
I cannot load files with the MCS-96 processor.
**To Reproduce**
Steps to reproduce the behavior:
1. Import a new file
2. Choose MCS-96 as the processor
3. Hit Ok
**Expected behavior**
The file should be imported. Instead I get lots of exceptions.
**Screenshots**
,timerange:(from:%272019-08-28T11:00:00.000Z%27,kind:absolute,to:%272019-08-28T13:59:59.999Z%27)),timeline:(linkTo:!(global),timerange:(from:%272019-... | 2.0 | Failing test: redirects from a $ip$ with a null query - ml conditional links redirects from a $ip$ with a null query - A test failed on a tracked branch
```
AssertionError: Timed out retrying: expected 'http://localhost:6111/app/security/network/flows?timerange=(global:(linkTo:!(timeline),timerange:(from:%272019-08-28... | non_process | failing test redirects from a ip with a null query ml conditional links redirects from a ip with a null query a test failed on a tracked branch assertionerror timed out retrying expected to include app security network flows sourcerer default timerange global linkto timeline timera... | 0 |
22,371 | 31,141,282,959 | IssuesEvent | 2023-08-16 00:21:17 | googleapis/python-firestore | https://api.github.com/repos/googleapis/python-firestore | closed | Add autospec or manual spec to async unit testing | api: firestore type: process | As we create our own `AsyncMock` class, extending `MagicMock`, we cannot use `create_autospec` to create mocks in async unit tests. We should investigate creating a `create_autospec` counterpart for async, or alternatively manually spec classes that are tested.
https://github.com/googleapis/python-firestore/pull/123... | 1.0 | Add autospec or manual spec to async unit testing - As we create our own `AsyncMock` class, extending `MagicMock`, we cannot use `create_autospec` to create mocks in async unit tests. We should investigate creating a `create_autospec` counterpart for async, or alternatively manually spec classes that are tested.
htt... | process | add autospec or manual spec to async unit testing as we create our own asyncmock class extending magicmock we cannot use create autospec to create mocks in async unit tests we should investigate creating a create autospec counterpart for async or alternatively manually spec classes that are tested | 1 |
615,465 | 19,255,649,182 | IssuesEvent | 2021-12-09 10:58:41 | bounswe/2021SpringGroup6 | https://api.github.com/repos/bounswe/2021SpringGroup6 | opened | Create an Endpoint to give badges to other users. | Type: Feature Status: Not Yet Started Platform: Back-end Priority: High | | path | type | functionality | parameters | exampl... | 1.0 | Create an Endpoint to give badges to other users. - | path | type | functionality | parameters ... | non_process | create an endpoint to give badges to other users path type functionality parameters ... | 0 |
4,185 | 7,123,577,200 | IssuesEvent | 2018-01-19 15:51:05 | facebook/osquery | https://api.github.com/repos/facebook/osquery | closed | linux: Audit redesign merge criteria | Linux process auditing | From what I can see by running the daemon:
- The ^D event is not handled quickly. The daemon or shell still takes a few moments before stopping. Is there any way to make this respond quicker?
- The implementation is still taking way more resources at idle that master. After a minute the redesign is +20 seconds of sys... | 1.0 | linux: Audit redesign merge criteria - From what I can see by running the daemon:
- The ^D event is not handled quickly. The daemon or shell still takes a few moments before stopping. Is there any way to make this respond quicker?
- The implementation is still taking way more resources at idle that master. After a mi... | process | linux audit redesign merge criteria from what i can see by running the daemon the d event is not handled quickly the daemon or shell still takes a few moments before stopping is there any way to make this respond quicker the implementation is still taking way more resources at idle that master after a mi... | 1 |
322,046 | 9,812,021,998 | IssuesEvent | 2019-06-13 02:30:55 | wevote/WebApp | https://api.github.com/repos/wevote/WebApp | opened | Issue popover: X positioning wrong, and popover centering instead of being at bottom | Difficulty: Medium Priority: 1 | When you click an Issue under a candidate:
<img width="303" alt="Screen Shot 2019-06-12 at 7 25 42 PM" src="https://user-images.githubusercontent.com/7756031/59399274-4b2e5480-8d48-11e9-85e9-51432cdec538.png">
The popover opens with two problems:
<img width="309" alt="Screen Shot 2019-06-12 at 7 25 33 PM" src="htt... | 1.0 | Issue popover: X positioning wrong, and popover centering instead of being at bottom - When you click an Issue under a candidate:
<img width="303" alt="Screen Shot 2019-06-12 at 7 25 42 PM" src="https://user-images.githubusercontent.com/7756031/59399274-4b2e5480-8d48-11e9-85e9-51432cdec538.png">
The popover opens w... | non_process | issue popover x positioning wrong and popover centering instead of being at bottom when you click an issue under a candidate img width alt screen shot at pm src the popover opens with two problems img width alt screen shot at pm src the x to close the pop... | 0 |
2,187 | 5,036,974,488 | IssuesEvent | 2016-12-17 11:29:48 | fujaba/org.fujaba.graphengine | https://api.github.com/repos/fujaba/org.fujaba.graphengine | opened | implement requested changes from meeting 5 | bug high priority improvement in process | 
- [ ] use "..."-parameter where useful
- [ ] fix null-pointer exception bug in IsomorphismHandlerCSP.java
- [ ] implement BridgeTest/RoadWork/RoadBlocking example
- [ ] possibly improve visualiz... | 1.0 | implement requested changes from meeting 5 - 
- [ ] use "..."-parameter where useful
- [ ] fix null-pointer exception bug in IsomorphismHandlerCSP.java
- [ ] implement BridgeTest/RoadWork/RoadBloc... | process | implement requested changes from meeting use parameter where useful fix null pointer exception bug in isomorphismhandlercsp java implement bridgetest roadwork roadblocking example possibly improve visualization maybe with alchemy js instead of sigma js | 1 |
150,508 | 13,348,280,265 | IssuesEvent | 2020-08-29 17:42:51 | mand2/mand2_blog | https://api.github.com/repos/mand2/mand2_blog | closed | upload old contents: TIL | documentation enhancement | replace the blog theme **jekyll** to **hugo** 👉 `day 4`
upload old contents again, the topic is TIL. | 1.0 | upload old contents: TIL - replace the blog theme **jekyll** to **hugo** 👉 `day 4`
upload old contents again, the topic is TIL. | non_process | upload old contents til replace the blog theme jekyll to hugo 👉 day upload old contents again the topic is til | 0 |
151,382 | 19,648,841,366 | IssuesEvent | 2022-01-10 02:40:48 | jinuem/Shopping-Cart-POC | https://api.github.com/repos/jinuem/Shopping-Cart-POC | opened | CVE-2022-0122 (Medium) detected in node-forge-0.7.5.tgz | security vulnerability | ## CVE-2022-0122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.7.5.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PK... | True | CVE-2022-0122 (Medium) detected in node-forge-0.7.5.tgz - ## CVE-2022-0122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.7.5.tgz</b></p></summary>
<p>JavaScript implem... | non_process | cve medium detected in node forge tgz cve medium severity vulnerability vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency fil... | 0 |
648,057 | 21,163,992,586 | IssuesEvent | 2022-04-07 12:02:28 | kubernetes/website | https://api.github.com/repos/kubernetes/website | closed | Localize "Runtime Class" page to Italian | priority/important-longterm lifecycle/rotten language/it | I would like to have the "Runtime Class" page to be translated into Italian
page https://kubernetes.io/docs/concepts/containers/runtime-class/
/language it
/priority important-soon | 1.0 | Localize "Runtime Class" page to Italian - I would like to have the "Runtime Class" page to be translated into Italian
page https://kubernetes.io/docs/concepts/containers/runtime-class/
/language it
/priority important-soon | non_process | localize runtime class page to italian i would like to have the runtime class page to be translated into italian page language it priority important soon | 0 |
20,516 | 27,174,869,499 | IssuesEvent | 2023-02-17 23:46:35 | 0xPolygonMiden/miden-vm | https://api.github.com/repos/0xPolygonMiden/miden-vm | closed | Potential optimization for loading values from memory | enhancement assembly processor on hold | Currently, at the VM level we have a single [loadw](https://github.com/maticnetwork/miden/blob/next/core/src/operations/mod.rs#L297) operation which is used to load data from memory onto the stack. This operation is used as the basis for `loadw.mem` and `pushw.mem` assembly instructions. Specifically, `loadw.mem` trans... | 1.0 | Potential optimization for loading values from memory - Currently, at the VM level we have a single [loadw](https://github.com/maticnetwork/miden/blob/next/core/src/operations/mod.rs#L297) operation which is used to load data from memory onto the stack. This operation is used as the basis for `loadw.mem` and `pushw.mem... | process | potential optimization for loading values from memory currently at the vm level we have a single operation which is used to load data from memory onto the stack this operation is used as the basis for loadw mem and pushw mem assembly instructions specifically loadw mem translates directly to loadw ope... | 1 |
304,312 | 26,266,646,179 | IssuesEvent | 2023-01-06 13:11:40 | Kuadrant/testsuite | https://api.github.com/repos/Kuadrant/testsuite | opened | improve HF agents configuration from testsuite | test-case | **Summary**
Currently are HF agents configured automatically from test-specific fixtures. In some cases, it is needed to add extra options for agents. The goal of this issue is to extend current behavior to contain also extra agents options.
**Documentation**
Similar implementation as used in 3scale tests -> h... | 1.0 | improve HF agents configuration from testsuite - **Summary**
Currently are HF agents configured automatically from test-specific fixtures. In some cases, it is needed to add extra options for agents. The goal of this issue is to extend current behavior to contain also extra agents options.
**Documentation**
Si... | non_process | improve hf agents configuration from testsuite summary currently are hf agents configured automatically from test specific fixtures in some cases it is needed to add extra options for agents the goal of this issue is to extend current behavior to contain also extra agents options documentation si... | 0 |
19,876 | 26,289,810,336 | IssuesEvent | 2023-01-08 09:04:18 | googleapis/google-cloud-python | https://api.github.com/repos/googleapis/google-cloud-python | opened | Your .repo-metadata.json files have a problem 🤒 | type: process repo-metadata: lint | You have a problem with your .repo-metadata.json files:
Result of scan 📈:
* api_shortname 'apiName' invalid in containers/python-bootstrap-container/.repo-metadata.json
* api_shortname 'type' invalid in packages/google-apps-script-type/.repo-metadata.json
* api_shortname 'routing' invalid in packages/google-maps-r... | 1.0 | Your .repo-metadata.json files have a problem 🤒 - You have a problem with your .repo-metadata.json files:
Result of scan 📈:
* api_shortname 'apiName' invalid in containers/python-bootstrap-container/.repo-metadata.json
* api_shortname 'type' invalid in packages/google-apps-script-type/.repo-metadata.json
* api_sh... | process | your repo metadata json files have a problem 🤒 you have a problem with your repo metadata json files result of scan 📈 api shortname apiname invalid in containers python bootstrap container repo metadata json api shortname type invalid in packages google apps script type repo metadata json api sh... | 1 |
25,729 | 11,208,797,705 | IssuesEvent | 2020-01-06 08:55:01 | MichaelAharon/Noche | https://api.github.com/repos/MichaelAharon/Noche | opened | CVE-2015-4852 (High) detected in commons-collections-3.2.1.jar | security vulnerability | ## CVE-2015-4852 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-collections-3.2.1.jar</b></p></summary>
<p>Types that extend and augment the Java Collections Framework.</p>
<p... | True | CVE-2015-4852 (High) detected in commons-collections-3.2.1.jar - ## CVE-2015-4852 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-collections-3.2.1.jar</b></p></summary>
<p>Typ... | non_process | cve high detected in commons collections jar cve high severity vulnerability vulnerable library commons collections jar types that extend and augment the java collections framework library home page a href path to dependency file tmp ws scm noche pom xml path to vul... | 0 |
36,174 | 5,038,106,446 | IssuesEvent | 2016-12-18 02:28:14 | d3athrow/vgstation13 | https://api.github.com/repos/d3athrow/vgstation13 | closed | Weird pressure value | Bug / Fix Needs Moar Testing ⚠️ OH GOD IT'S LOOSE ⚠️ | This happened after I screwed up the TEG, reset it and put CO2 on each loop.

| 1.0 | Weird pressure value - This happened after I screwed up the TEG, reset it and put CO2 on each loop.

| non_process | weird pressure value this happened after i screwed up the teg reset it and put on each loop | 0 |
11,990 | 14,737,202,668 | IssuesEvent | 2021-01-07 01:09:38 | kdjstudios/SABillingGitlab | https://api.github.com/repos/kdjstudios/SABillingGitlab | closed | Allentown Getting Something Went Wrong Message While Applying Usage For Billing ` | anc-ops anc-process anp-important ant-bug ant-support | In GitLab by @kdjstudios on Apr 23, 2018, 10:33
**Submitted by:** "Tobey McInally" <tobey.mcinally@answernet.com>
**Helpdesk:** http://www.servicedesk.answernet.com/profiles/ticket/2018-04-23-34624/conversation
**Server:** Internal
**Client/Site:** Allentown
**Account:** NA
**Issue:**
Site: 061
Challenge: som... | 1.0 | Allentown Getting Something Went Wrong Message While Applying Usage For Billing ` - In GitLab by @kdjstudios on Apr 23, 2018, 10:33
**Submitted by:** "Tobey McInally" <tobey.mcinally@answernet.com>
**Helpdesk:** http://www.servicedesk.answernet.com/profiles/ticket/2018-04-23-34624/conversation
**Server:** Internal
... | process | allentown getting something went wrong message while applying usage for billing in gitlab by kdjstudios on apr submitted by tobey mcinally helpdesk server internal client site allentown account na issue site challenge something went wrong message while ap... | 1 |
260,709 | 22,642,165,330 | IssuesEvent | 2022-07-01 04:04:15 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | opened | DISABLED test_chain_iterable_style_dataset (__main__.TestDataLoaderPersistentWorkers) | module: flaky-tests skipped module: unknown | Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_chain_iterable_style_dataset&suite=TestDataLoaderPersistentWorkers&file=test_dataloader.py) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/7141678531... | 1.0 | DISABLED test_chain_iterable_style_dataset (__main__.TestDataLoaderPersistentWorkers) - Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_chain_iterable_style_dataset&suite=TestDataLoaderPersistentWorkers&file=test_dataloader.py) and ... | non_process | disabled test chain iterable style dataset main testdataloaderpersistentworkers platforms linux this test was disabled because it is failing in ci see and the most recent trunk over the past hours it has been determined flaky in workflow s with red and green | 0 |
12,093 | 14,740,081,591 | IssuesEvent | 2021-01-07 08:29:04 | kdjstudios/SABillingGitlab | https://api.github.com/repos/kdjstudios/SABillingGitlab | closed | Atlanta - SA Billing - Late Fee Account List | anc-process anp-important ant-bug has attachment | In GitLab by @kdjstudios on Oct 3, 2018, 11:09
[Atlanta.xlsx](/uploads/efbbfb141893f5b2abbb8b52ea0c24e0/Atlanta.xlsx)
HD: http://www.servicedesk.answernet.com/profiles/ticket/2018-10-03-52748 | 1.0 | Atlanta - SA Billing - Late Fee Account List - In GitLab by @kdjstudios on Oct 3, 2018, 11:09
[Atlanta.xlsx](/uploads/efbbfb141893f5b2abbb8b52ea0c24e0/Atlanta.xlsx)
HD: http://www.servicedesk.answernet.com/profiles/ticket/2018-10-03-52748 | process | atlanta sa billing late fee account list in gitlab by kdjstudios on oct uploads atlanta xlsx hd | 1 |
4,662 | 7,496,846,628 | IssuesEvent | 2018-04-08 13:54:01 | allinurl/goaccess | https://api.github.com/repos/allinurl/goaccess | closed | Unknown 4xx client error codes | log-processing question | Hi! I installed the latest goaccess code from the master branch but my stats have a lot of "Unknown" "4xx Client Error". I know for sure that most of them are 429 error codes, why are they not listed? I attached a sceenshot in case it helps.
Thanks!
<img width="567" alt="screen shot 2018-04-05 at 13 52 10" src="h... | 1.0 | Unknown 4xx client error codes - Hi! I installed the latest goaccess code from the master branch but my stats have a lot of "Unknown" "4xx Client Error". I know for sure that most of them are 429 error codes, why are they not listed? I attached a sceenshot in case it helps.
Thanks!
<img width="567" alt="screen sh... | process | unknown client error codes hi i installed the latest goaccess code from the master branch but my stats have a lot of unknown client error i know for sure that most of them are error codes why are they not listed i attached a sceenshot in case it helps thanks img width alt screen shot ... | 1 |
12,902 | 2,725,858,921 | IssuesEvent | 2015-04-15 05:25:34 | jmcgeheeiv/pyfakefs | https://api.github.com/repos/jmcgeheeiv/pyfakefs | closed | Please host the documentation for pyfakefs | auto-migrated Priority-Medium Type-Defect | ```
It is very difficult to browse through the documentation in source. Kindly
upload it to pythonhosted or readthedocs.
```
Original issue reported on code.google.com by `pratika...@gmail.com` on 21 Jan 2014 at 4:08 | 1.0 | Please host the documentation for pyfakefs - ```
It is very difficult to browse through the documentation in source. Kindly
upload it to pythonhosted or readthedocs.
```
Original issue reported on code.google.com by `pratika...@gmail.com` on 21 Jan 2014 at 4:08 | non_process | please host the documentation for pyfakefs it is very difficult to browse through the documentation in source kindly upload it to pythonhosted or readthedocs original issue reported on code google com by pratika gmail com on jan at | 0 |
5,076 | 7,870,366,447 | IssuesEvent | 2018-06-25 00:56:26 | nodejs/node | https://api.github.com/repos/nodejs/node | closed | IPC can freeze the process | child_process libuv windows | Since we upgraded our app from 0.10.38 to v6, we experienced a lot of problem with IPC messaging.
Essentially, we have a web application with a few workers to handle all the requests. The workers contains caches to speed up the request and theses caches are synchronized between process with IPC messaging. We were al... | 1.0 | IPC can freeze the process - Since we upgraded our app from 0.10.38 to v6, we experienced a lot of problem with IPC messaging.
Essentially, we have a web application with a few workers to handle all the requests. The workers contains caches to speed up the request and theses caches are synchronized between process wi... | process | ipc can freeze the process since we upgraded our app from to we experienced a lot of problem with ipc messaging essentially we have a web application with a few workers to handle all the requests the workers contains caches to speed up the request and theses caches are synchronized between process with ... | 1 |
6,369 | 9,419,112,386 | IssuesEvent | 2019-04-10 21:00:13 | googlegenomics/gcp-variant-transforms | https://api.github.com/repos/googlegenomics/gcp-variant-transforms | closed | Find a solution for multiple BigQuery versions | P2 process | In our integration tests, we rely on `google-cloud-bigquery>0.25`, however, Beam needs BigQuery [`google-cloud-bigquery==0.25`](https://github.com/apache/beam/blob/8d854d4ce0365a8e201b388618d7732f000c65b9/sdks/python/setup.py#L130). Even though the two code paths don't currently connect, we should find some way to han... | 1.0 | Find a solution for multiple BigQuery versions - In our integration tests, we rely on `google-cloud-bigquery>0.25`, however, Beam needs BigQuery [`google-cloud-bigquery==0.25`](https://github.com/apache/beam/blob/8d854d4ce0365a8e201b388618d7732f000c65b9/sdks/python/setup.py#L130). Even though the two code paths don't... | process | find a solution for multiple bigquery versions in our integration tests we rely on google cloud bigquery however beam needs bigquery even though the two code paths don t currently connect we should find some way to handle both versions we currently have an target in our setup py to handle this ca... | 1 |
132,829 | 18,272,146,115 | IssuesEvent | 2021-10-04 14:48:42 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | log: include crdb version into metadata envelope for logging events | C-enhancement A-logging T-server-and-security | **Is your feature request related to a problem? Please describe.**
This was raised by @knz from a conversation around handling/consuming different versions of logs on different versions of crdb
**Describe the solution you'd like**
We'd like to add the crdb version into the envelope for log events so that that meta... | True | log: include crdb version into metadata envelope for logging events - **Is your feature request related to a problem? Please describe.**
This was raised by @knz from a conversation around handling/consuming different versions of logs on different versions of crdb
**Describe the solution you'd like**
We'd like to a... | non_process | log include crdb version into metadata envelope for logging events is your feature request related to a problem please describe this was raised by knz from a conversation around handling consuming different versions of logs on different versions of crdb describe the solution you d like we d like to a... | 0 |
40,965 | 5,328,410,737 | IssuesEvent | 2017-02-15 11:59:51 | owncloud/QA | https://api.github.com/repos/owncloud/QA | closed | Use separate skeleton dir for integration tests | enhancement Integration tests | The current integration tests will directly write files into the source code folder "core/skeleton". This requires appropriate permissions and isn't good practice.
We should rather use "occ config:set" to set the "skeletondirectory" config.php value to a folder inside "build/integration/skeleton" that already contai... | 1.0 | Use separate skeleton dir for integration tests - The current integration tests will directly write files into the source code folder "core/skeleton". This requires appropriate permissions and isn't good practice.
We should rather use "occ config:set" to set the "skeletondirectory" config.php value to a folder insid... | non_process | use separate skeleton dir for integration tests the current integration tests will directly write files into the source code folder core skeleton this requires appropriate permissions and isn t good practice we should rather use occ config set to set the skeletondirectory config php value to a folder insid... | 0 |
6,920 | 10,077,806,964 | IssuesEvent | 2019-07-24 19:39:41 | tc39/proposal-promise-any | https://api.github.com/repos/tc39/proposal-promise-any | closed | Advance to stage 2 | process | Criteria taken from [the TC39 process document](https://tc39.github.io/process-document/) minus those from previous stages:
> - [x] Initial spec text
https://github.com/tc39/proposal-promise-any#specification | 1.0 | Advance to stage 2 - Criteria taken from [the TC39 process document](https://tc39.github.io/process-document/) minus those from previous stages:
> - [x] Initial spec text
https://github.com/tc39/proposal-promise-any#specification | process | advance to stage criteria taken from minus those from previous stages initial spec text | 1 |
236,551 | 19,559,111,429 | IssuesEvent | 2022-01-03 13:56:28 | wazuh/wazuh-qa | https://api.github.com/repos/wazuh/wazuh-qa | opened | Fix `check_files` script | type/bug subteam/qa-thunder test/check-files | Something is not working as expected due to this script. This behavior has been detected in this issue: https://github.com/wazuh/wazuh-qa/issues/2312.
In some cases, it is logging a directory's content but not that directory. For example, `/` and `/tmp` are not being logged sometimes. | 1.0 | Fix `check_files` script - Something is not working as expected due to this script. This behavior has been detected in this issue: https://github.com/wazuh/wazuh-qa/issues/2312.
In some cases, it is logging a directory's content but not that directory. For example, `/` and `/tmp` are not being logged sometimes. | non_process | fix check files script something is not working as expected due to this script this behavior has been detected in this issue in some cases it is logging a directory s content but not that directory for example and tmp are not being logged sometimes | 0 |
16,887 | 22,173,382,893 | IssuesEvent | 2022-06-06 05:09:43 | amor71/LiuAlgoTrader | https://api.github.com/repos/amor71/LiuAlgoTrader | closed | ModuleNotFoundError: No module named 'liualgotrader.trading.tradier' when running backtester | in-process | Hi! I think I might have found a bug (probably fell between versions)
`liualgotrader.backtester ` tries to `liualgotrader.trading.tradier import TradierTrader` but that is currently missing from the package.
**To Reproduce**
Steps to reproduce the behavior:
1. install liualgotrader
2. download sample data
**... | 1.0 | ModuleNotFoundError: No module named 'liualgotrader.trading.tradier' when running backtester - Hi! I think I might have found a bug (probably fell between versions)
`liualgotrader.backtester ` tries to `liualgotrader.trading.tradier import TradierTrader` but that is currently missing from the package.
**To Reprodu... | process | modulenotfounderror no module named liualgotrader trading tradier when running backtester hi i think i might have found a bug probably fell between versions liualgotrader backtester tries to liualgotrader trading tradier import tradiertrader but that is currently missing from the package to reprodu... | 1 |
432,176 | 12,490,183,136 | IssuesEvent | 2020-05-31 22:37:50 | Tschipp/BuildersBag | https://api.github.com/repos/Tschipp/BuildersBag | closed | [Feature] Bag Cache | added in next release feature - base mod priority: high | **Description of the Feature in as much detail as possible**
Bag Caching System for the Client Side | 1.0 | [Feature] Bag Cache - **Description of the Feature in as much detail as possible**
Bag Caching System for the Client Side | non_process | bag cache description of the feature in as much detail as possible bag caching system for the client side | 0 |
6,292 | 9,301,198,843 | IssuesEvent | 2019-03-23 19:52:11 | juanmait/seedjs | https://api.github.com/repos/juanmait/seedjs | opened | seed-process: add and configure nodemon | seed-process | - would be nice to have [nodemon] running with [babel-node] for development
[nodemon]: https://github.com/remy/nodemon/
[babel-node]: https://babeljs.io/docs/en/babel-node | 1.0 | seed-process: add and configure nodemon - - would be nice to have [nodemon] running with [babel-node] for development
[nodemon]: https://github.com/remy/nodemon/
[babel-node]: https://babeljs.io/docs/en/babel-node | process | seed process add and configure nodemon would be nice to have running with for development | 1 |
5,142 | 7,923,554,888 | IssuesEvent | 2018-07-05 14:23:27 | Open-EO/openeo-api | https://api.github.com/repos/Open-EO/openeo-api | closed | Type definitions for process arguments | process discovery work in progress | At the moment the process definition is typeless, arguments only have a human-readable description and no type definition. This is a problem for usability, since in different languages there are native equivalents for spatial types; users are very likely to already have their data in the native type and would want the ... | 1.0 | Type definitions for process arguments - At the moment the process definition is typeless, arguments only have a human-readable description and no type definition. This is a problem for usability, since in different languages there are native equivalents for spatial types; users are very likely to already have their da... | process | type definitions for process arguments at the moment the process definition is typeless arguments only have a human readable description and no type definition this is a problem for usability since in different languages there are native equivalents for spatial types users are very likely to already have their da... | 1 |
36,903 | 12,428,257,231 | IssuesEvent | 2020-05-25 05:38:42 | varora1406/is-number | https://api.github.com/repos/varora1406/is-number | opened | WS-2020-0070 (High) detected in lodash-1.3.1.tgz, lodash-4.17.15.tgz | security vulnerability | ## WS-2020-0070 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-1.3.1.tgz</b>, <b>lodash-4.17.15.tgz</b></p></summary>
<p>
<details><summary><b>lodash-1.3.1.tgz</b></p></summa... | True | WS-2020-0070 (High) detected in lodash-1.3.1.tgz, lodash-4.17.15.tgz - ## WS-2020-0070 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-1.3.1.tgz</b>, <b>lodash-4.17.15.tgz</b><... | non_process | ws high detected in lodash tgz lodash tgz ws high severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz a utility library delivering consistency customization performance and extras library home page a href path t... | 0 |
13,186 | 15,612,959,534 | IssuesEvent | 2021-03-19 15:53:42 | googleapis/google-cloud-cpp | https://api.github.com/repos/googleapis/google-cloud-cpp | closed | ABI/API checker doesn't match overloads properly | external type: process | This build failed the ABI/API check, but it shouldn't have - the actual changes were adding `const` to a non-const method, which is always safe. It does this correctly in some cases, but the 3 at the top match one overload against another and claims the parameters change (which is a breaking change).
[log](https://... | 1.0 | ABI/API checker doesn't match overloads properly - This build failed the ABI/API check, but it shouldn't have - the actual changes were adding `const` to a non-const method, which is always safe. It does this correctly in some cases, but the 3 at the top match one overload against another and claims the parameters cha... | process | abi api checker doesn t match overloads properly this build failed the abi api check but it shouldn t have the actual changes were adding const to a non const method which is always safe it does this correctly in some cases but the at the top match one overload against another and claims the parameters cha... | 1 |
11,585 | 14,445,283,453 | IssuesEvent | 2020-12-07 22:40:53 | bisq-network/bisq | https://api.github.com/repos/bisq-network/bisq | closed | BHHZ34I - Cannot Accept Proposed Resolution due to Deposit TX ID = N/A | a:bug in:trade-process | <!--
SUPPORT REQUESTS: This is for reporting bugs in the Bisq app.
If you have a support request, please join #support on Bisq's
Keybase team at https://keybase.io/team/Bisq
-->
BHHZ34I - Cannot Accept Proposed Resolution due to Deposit TX ID = N/A
Leo816 is the mediator, and suggested a resolution due... | 1.0 | BHHZ34I - Cannot Accept Proposed Resolution due to Deposit TX ID = N/A - <!--
SUPPORT REQUESTS: This is for reporting bugs in the Bisq app.
If you have a support request, please join #support on Bisq's
Keybase team at https://keybase.io/team/Bisq
-->
BHHZ34I - Cannot Accept Proposed Resolution due to De... | process | cannot accept proposed resolution due to deposit tx id n a support requests this is for reporting bugs in the bisq app if you have a support request please join support on bisq s keybase team at cannot accept proposed resolution due to deposit tx id n a is the mediator a... | 1 |
5,401 | 2,773,440,946 | IssuesEvent | 2015-05-03 16:50:00 | medic/medic-webapp | https://api.github.com/repos/medic/medic-webapp | closed | Concierge: Force regeneration of couchdb-lucene indexes at startup, in addition to ordinary views | 3 - Acceptance testing Feature Request Performance | The first load of the `Reports` view takes a long time if there's substantial data preloaded, as there is with the demo dataset. If there's an easy way to prime `/_fti` like we do the map/reduce views, we should take advantage of it. | 1.0 | Concierge: Force regeneration of couchdb-lucene indexes at startup, in addition to ordinary views - The first load of the `Reports` view takes a long time if there's substantial data preloaded, as there is with the demo dataset. If there's an easy way to prime `/_fti` like we do the map/reduce views, we should take adv... | non_process | concierge force regeneration of couchdb lucene indexes at startup in addition to ordinary views the first load of the reports view takes a long time if there s substantial data preloaded as there is with the demo dataset if there s an easy way to prime fti like we do the map reduce views we should take adv... | 0 |
22,191 | 30,746,170,326 | IssuesEvent | 2023-07-28 15:13:17 | Kumar-laxmi/Algorithms | https://api.github.com/repos/Kumar-laxmi/Algorithms | closed | Implement Canny Edge Detection Algorithm for Image Processing | C C++ Python Java SSOC23 SSOC-INTERMEDIATE Image Processing | **Is your feature request related to a problem? Please describe.**
The Canny edge detection algorithm is a widely used technique for detecting edges in digital images, known for its effectiveness in accurately detecting edges while suppressing noise.
**Describe the solution you'd like**
I would like to implement t... | 1.0 | Implement Canny Edge Detection Algorithm for Image Processing - **Is your feature request related to a problem? Please describe.**
The Canny edge detection algorithm is a widely used technique for detecting edges in digital images, known for its effectiveness in accurately detecting edges while suppressing noise.
... | process | implement canny edge detection algorithm for image processing is your feature request related to a problem please describe the canny edge detection algorithm is a widely used technique for detecting edges in digital images known for its effectiveness in accurately detecting edges while suppressing noise ... | 1 |
12,739 | 15,105,640,054 | IssuesEvent | 2021-02-08 13:19:23 | pystatgen/sgkit | https://api.github.com/repos/pystatgen/sgkit | closed | Disable scheduled build/windows and validation CI on forks | process + tools | Right now some of our CI workflows are unnecessarily being run on the forks, this include:
* validation workflow
* scheduled build and windows
This is unnecessary (consumes resources etc), and can be confusing. | 1.0 | Disable scheduled build/windows and validation CI on forks - Right now some of our CI workflows are unnecessarily being run on the forks, this include:
* validation workflow
* scheduled build and windows
This is unnecessary (consumes resources etc), and can be confusing. | process | disable scheduled build windows and validation ci on forks right now some of our ci workflows are unnecessarily being run on the forks this include validation workflow scheduled build and windows this is unnecessary consumes resources etc and can be confusing | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.