Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3 values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17 values | text_combine stringlengths 95 262k | label stringclasses 2 values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
271,182 | 23,588,169,598 | IssuesEvent | 2022-08-23 13:18:33 | streamnative/pulsar | https://api.github.com/repos/streamnative/pulsar | opened | ISSUE-17219: Flaky-test: PersistentSubscriptionMessageDispatchStreamingDispatcherThrottlingTest.testBytesRateLimitingReceiveAllMessagesAfterThrottling | component/test flaky-tests help-wanted | Original Issue: apache/pulsar#17219
---
### Search before asking
- [X] I searched in the [issues](https://github.com/apache/pulsar/issues) and found nothing similar.
### Example failure
https://github.com/apache/pulsar/runs/7964639300?check_suite_focus=true
### Exception stacktrace
Error: Tests run: 53, Failures: 1, Errors: 0, Skipped: 38, Time elapsed: 91.764 s <<< FAILURE! - in org.apache.pulsar.broker.service.persistent.PersistentSubscriptionMessageDispatchStreamingDispatcherThrottlingTest
Error: testBytesRateLimitingReceiveAllMessagesAfterThrottling(org.apache.pulsar.broker.service.persistent.PersistentSubscriptionMessageDispatchStreamingDispatcherThrottlingTest) Time elapsed: 1.156 s <<< FAILURE!
java.lang.AssertionError: expected [true] but found [false]
at org.testng.Assert.fail(Assert.java:99)
at org.testng.Assert.failNotEquals(Assert.java:1037)
at org.testng.Assert.assertTrue(Assert.java:45)
at org.testng.Assert.assertTrue(Assert.java:55)
at org.apache.pulsar.client.api.SubscriptionMessageDispatchThrottlingTest.testBytesRateLimitingReceiveAllMessagesAfterThrottling(SubscriptionMessageDispatchThrottlingTest.java:307)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:568)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:132)
at org.testng.internal.InvokeMethodRunnable.runOne(InvokeMethodRunnable.java:45)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:73)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:11)
at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1136)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:635)
at java.base/java.lang.Thread.run(Thread.java:833)
### Are you willing to submit a PR?
- [ ] I'm willing to submit a PR! | 2.0 | ISSUE-17219: Flaky-test: PersistentSubscriptionMessageDispatchStreamingDispatcherThrottlingTest.testBytesRateLimitingReceiveAllMessagesAfterThrottling - Original Issue: apache/pulsar#17219
---
### Search before asking
- [X] I searched in the [issues](https://github.com/apache/pulsar/issues) and found nothing similar.
### Example failure
https://github.com/apache/pulsar/runs/7964639300?check_suite_focus=true
### Exception stacktrace
Error: Tests run: 53, Failures: 1, Errors: 0, Skipped: 38, Time elapsed: 91.764 s <<< FAILURE! - in org.apache.pulsar.broker.service.persistent.PersistentSubscriptionMessageDispatchStreamingDispatcherThrottlingTest
Error: testBytesRateLimitingReceiveAllMessagesAfterThrottling(org.apache.pulsar.broker.service.persistent.PersistentSubscriptionMessageDispatchStreamingDispatcherThrottlingTest) Time elapsed: 1.156 s <<< FAILURE!
java.lang.AssertionError: expected [true] but found [false]
at org.testng.Assert.fail(Assert.java:99)
at org.testng.Assert.failNotEquals(Assert.java:1037)
at org.testng.Assert.assertTrue(Assert.java:45)
at org.testng.Assert.assertTrue(Assert.java:55)
at org.apache.pulsar.client.api.SubscriptionMessageDispatchThrottlingTest.testBytesRateLimitingReceiveAllMessagesAfterThrottling(SubscriptionMessageDispatchThrottlingTest.java:307)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:568)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:132)
at org.testng.internal.InvokeMethodRunnable.runOne(InvokeMethodRunnable.java:45)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:73)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:11)
at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1136)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:635)
at java.base/java.lang.Thread.run(Thread.java:833)
### Are you willing to submit a PR?
- [ ] I'm willing to submit a PR! | test | issue flaky test persistentsubscriptionmessagedispatchstreamingdispatcherthrottlingtest testbytesratelimitingreceiveallmessagesafterthrottling original issue apache pulsar search before asking i searched in the and found nothing similar example failure exception stacktrace error tests run failures errors skipped time elapsed s failure in org apache pulsar broker service persistent persistentsubscriptionmessagedispatchstreamingdispatcherthrottlingtest error testbytesratelimitingreceiveallmessagesafterthrottling org apache pulsar broker service persistent persistentsubscriptionmessagedispatchstreamingdispatcherthrottlingtest time elapsed s failure java lang assertionerror expected but found at org testng assert fail assert java at org testng assert failnotequals assert java at org testng assert asserttrue assert java at org testng assert asserttrue assert java at org apache pulsar client api subscriptionmessagedispatchthrottlingtest testbytesratelimitingreceiveallmessagesafterthrottling subscriptionmessagedispatchthrottlingtest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org testng internal methodinvocationhelper invokemethod methodinvocationhelper java at org testng internal invokemethodrunnable runone invokemethodrunnable java at org testng internal invokemethodrunnable call invokemethodrunnable java at org testng internal invokemethodrunnable call invokemethodrunnable java at java base java util concurrent futuretask run futuretask java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java base java lang thread run thread java are you willing to submit a pr i m willing to submit a pr | 1 |
269,759 | 23,463,698,502 | IssuesEvent | 2022-08-16 14:59:41 | ImagingDataCommons/IDC-WebApp | https://api.github.com/repos/ImagingDataCommons/IDC-WebApp | closed | Add SamplesPerPixel to Original Data attributes | enhancement merged:dev testing needed testing passed | This would allow users to more easily filter for HTAN data (so is part of v10 data release, or after it).
This may be stored as a String in dicom_metadata; if so it will need to be added to the curation table. @bcli4d @fedorov Can you let me know if this needs to be done, and if so when it has been. (If not I can immediately move to add the field name to my various query builders for ETL.) | 2.0 | Add SamplesPerPixel to Original Data attributes - This would allow users to more easily filter for HTAN data (so is part of v10 data release, or after it).
This may be stored as a String in dicom_metadata; if so it will need to be added to the curation table. @bcli4d @fedorov Can you let me know if this needs to be done, and if so when it has been. (If not I can immediately move to add the field name to my various query builders for ETL.) | test | add samplesperpixel to original data attributes this would allow users to more easily filter for htan data so is part of data release or after it this may be stored as a string in dicom metadata if so it will need to be added to the curation table fedorov can you let me know if this needs to be done and if so when it has been if not i can immediately move to add the field name to my various query builders for etl | 1 |
152,500 | 5,848,187,710 | IssuesEvent | 2017-05-10 20:18:20 | samsung-cnct/k2 | https://api.github.com/repos/samsung-cnct/k2 | closed | investigate nginx as external loadbalancer for kubernetes | bare-metal K2 priority-p1 research spike | what are we going to use for our baremetal load balancer. Nginx? Envoy? HAProxy? Other? | 1.0 | investigate nginx as external loadbalancer for kubernetes - what are we going to use for our baremetal load balancer. Nginx? Envoy? HAProxy? Other? | non_test | investigate nginx as external loadbalancer for kubernetes what are we going to use for our baremetal load balancer nginx envoy haproxy other | 0 |
307,697 | 26,553,345,614 | IssuesEvent | 2023-01-20 09:51:46 | EddieHubCommunity/LinkFree | https://api.github.com/repos/EddieHubCommunity/LinkFree | closed | New Testimonial for Eddie Jaoude | testimonial | ### Name
eddiejaoude
### Title
Best Guru to learn about GitHub
### Description
Your Youtube Videos helps me a lot to learn about GitHub. Thanks for making such excellent videos. | 1.0 | New Testimonial for Eddie Jaoude - ### Name
eddiejaoude
### Title
Best Guru to learn about GitHub
### Description
Your Youtube Videos helps me a lot to learn about GitHub. Thanks for making such excellent videos. | test | new testimonial for eddie jaoude name eddiejaoude title best guru to learn about github description your youtube videos helps me a lot to learn about github thanks for making such excellent videos | 1 |
194,077 | 15,396,728,244 | IssuesEvent | 2021-03-03 21:03:53 | coredns/coredns | https://api.github.com/repos/coredns/coredns | closed | [WIP] Document PTR reverse records via template | documentation plugin/reverse thinking | As the reverse plugin was removed and the suggestion was it's possible doing with template, I did my best to take a stab at it. It's currently still a WIP so as I don't handle subnets yet.
Also I assume that I'm missing something here. Feels too manual for reverse lookups even with template.
One can also use 0.8.e.f.ip6.arpa 127.in-addr.arpa (sidenote: fe80::/10 doesn't fully map to 0.8.e.f.ip6.arpa)
Full template example for reverse zone records.
```
127.0.0.0/8 fe80::/10 {
template IN SOA arpa {
answer "{{ .Name }} 86400 IN SOA ns.example.com. domains.example.com. 2019072302 300 300 604800 43200"
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
template IN PTR in-addr.arpa {
# 1.0.0.127.in-addr.arpa
match "^(?P<a>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<b>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<c>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<d>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.]in-addr[.]arpa[.]$"
answer "{{ .Name }} 86400 IN PTR {{ .Group.d }}-{{ .Group.c }}-{{ .Group.b }}-{{ .Group.a }}.net.example.com"
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
fallthrough
}
template IN PTR ip6.arpa {
# 0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.8.e.f.ip6.arpa
match "^(?P<aa>[0-9a-f])[.](?P<ab>[0-9a-f])[.](?P<ac>[0-9a-f])[.](?P<ad>[0-9a-f])[.](?P<ae>[0-9a-f])[.](?P<af>[0-9a-f])[.](?P<ag>[0-9a-f])[.](?P<ah>[0-9a-f])[.](?P<ai>[0-9a-f])[.](?P<aj>[0-9a-f])[.](?P<ak>[0-9a-f])[.](?P<al>[0-9a-f])[.](?P<am>[0-9a-f])[.](?P<an>[0-9a-f])[.](?P<ao>[0-9a-f])[.](?P<ap>[0-9a-f])[.](?P<aq>[0-9a-f])[.](?P<ar>[0-9a-f])[.](?P<as>[0-9a-f])[.](?P<at>[0-9a-f])[.](?P<au>[0-9a-f])[.](?P<av>[0-9a-f])[.](?P<aw>[0-9a-f])[.](?P<ax>[0-9a-f])[.](?P<ay>[0-9a-f])[.](?P<az>[0-9a-f])[.](?P<ba>[0-9a-f])[.](?P<bb>[0-9a-f])[.](?P<bc>[0-9a-f])[.](?P<bd>[0-9a-f])[.](?P<be>[0-9a-f])[.](?P<bf>[0-9a-f])[.]ip6[.]arpa[.]$"
answer "{{ .Name }} 86400 IN PTR {{ .Group.bf }}-{{ .Group.be }}-{{ .Group.bd }}-{{ .Group.bc }}-{{ .Group.bb }}-{{ .Group.ba }}-{{ .Group.az }}-{{ .Group.ay }}-{{ .Group.ax }}-{{ .Group.aw }}-{{ .Group.av }}-{{ .Group.au }}-{{ .Group.at }}-{{ .Group.as }}-{{ .Group.ar }}-{{ .Group.aq }}-{{ .Group.ap }}-{{ .Group.ao }}-{{ .Group.an }}-{{ .Group.am }}-{{ .Group.al }}-{{ .Group.ak }}-{{ .Group.aj }}-{{ .Group.ai }}-{{ .Group.ah }}-{{ .Group.ag }}-{{ .Group.af }}-{{ .Group.ae }}-{{ .Group.ad }}-{{ .Group.ac }}-{{ .Group.ab }}-{{ .Group.aa }}.net.example.com."
additional "{{ .Name }} 86400 IN PTR {{ .Group.bf }}{{ .Group.be }}{{ .Group.bd }}{{ .Group.bc }}-{{ .Group.bb }}{{ .Group.ba }}{{ .Group.az }}{{ .Group.ay }}-{{ .Group.ax }}{{ .Group.aw }}{{ .Group.av }}{{ .Group.au }}-{{ .Group.at }}{{ .Group.as }}{{ .Group.ar }}{{ .Group.aq }}-{{ .Group.ap }}{{ .Group.ao }}{{ .Group.an }}{{ .Group.am }}-{{ .Group.al }}{{ .Group.ak }}{{ .Group.aj }}{{ .Group.ai }}-{{ .Group.ah }}{{ .Group.ag }}{{ .Group.af }}{{ .Group.ae }}-{{ .Group.ad }}{{ .Group.ac }}{{ .Group.ab }}{{ .Group.aa }}.net.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
template IN NS in-addr.arpa {
answer "{{ .Name }} 86400 IN NS ns.example.com."
answer "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
fallthrough
}
template IN NS ip6.arpa {
answer "{{ .Name }} 86400 IN NS ns.example.com."
answer "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
}
net.example.com {
template IN SOA net.example.com {
answer "{{ .Name }} 86400 IN SOA ns.example.com. domains.example.com. 2019072302 300 300 604800 43200"
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
template IN A net.example.com {
# ip-127-0-0-1.net.example.com
match "^ip-(?P<a>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<b>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<c>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<d>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.]net[.]example[.]com[.]$"
# 127-0-0-1.net.example.com
match "^(?P<a>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<b>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<c>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<d>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.]net[.]example[.]com[.]$"
# 127.0.0.1.net.example.com
match "^(?P<a>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<b>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<c>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<d>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.]net[.]example[.]com[.]$"
answer "{{ .Name }} 86400 IN A {{ .Group.a }}.{{ .Group.b }}.{{ .Group.c }}.{{ .Group.d }}"
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
fallthrough
}
template IN AAAA net.example.com {
# ip-f-e-8-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0.net.example.com
match "^ip-(?P<aa>[0-9a-f])-(?P<ab>[0-9a-f])-(?P<ac>[0-9a-f])-(?P<ad>[0-9a-f])-(?P<ae>[0-9a-f])-(?P<af>[0-9a-f])-(?P<ag>[0-9a-f])-(?P<ah>[0-9a-f])-(?P<ai>[0-9a-f])-(?P<aj>[0-9a-f])-(?P<ak>[0-9a-f])-(?P<al>[0-9a-f])-(?P<am>[0-9a-f])-(?P<an>[0-9a-f])-(?P<ao>[0-9a-f])-(?P<ap>[0-9a-f])-(?P<aq>[0-9a-f])-(?P<ar>[0-9a-f])-(?P<as>[0-9a-f])-(?P<at>[0-9a-f])-(?P<au>[0-9a-f])-(?P<av>[0-9a-f])-(?P<aw>[0-9a-f])-(?P<ax>[0-9a-f])-(?P<ay>[0-9a-f])-(?P<az>[0-9a-f])-(?P<ba>[0-9a-f])-(?P<bb>[0-9a-f])-(?P<bc>[0-9a-f])-(?P<bd>[0-9a-f])-(?P<be>[0-9a-f])-(?P<bf>[0-9a-f])[.]net[.]example[.]com[.]$"
# f-e-8-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0.net.example.com
match "^(?P<aa>[0-9a-f])-(?P<ab>[0-9a-f])-(?P<ac>[0-9a-f])-(?P<ad>[0-9a-f])-(?P<ae>[0-9a-f])-(?P<af>[0-9a-f])-(?P<ag>[0-9a-f])-(?P<ah>[0-9a-f])-(?P<ai>[0-9a-f])-(?P<aj>[0-9a-f])-(?P<ak>[0-9a-f])-(?P<al>[0-9a-f])-(?P<am>[0-9a-f])-(?P<an>[0-9a-f])-(?P<ao>[0-9a-f])-(?P<ap>[0-9a-f])-(?P<aq>[0-9a-f])-(?P<ar>[0-9a-f])-(?P<as>[0-9a-f])-(?P<at>[0-9a-f])-(?P<au>[0-9a-f])-(?P<av>[0-9a-f])-(?P<aw>[0-9a-f])-(?P<ax>[0-9a-f])-(?P<ay>[0-9a-f])-(?P<az>[0-9a-f])-(?P<ba>[0-9a-f])-(?P<bb>[0-9a-f])-(?P<bc>[0-9a-f])-(?P<bd>[0-9a-f])-(?P<be>[0-9a-f])-(?P<bf>[0-9a-f])[.]net[.]example[.]com[.]$"
# f.e.8.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.net.example.com
match "^(?P<aa>[0-9a-f])[.](?P<ab>[0-9a-f])[.](?P<ac>[0-9a-f])[.](?P<ad>[0-9a-f])[.](?P<ae>[0-9a-f])[.](?P<af>[0-9a-f])[.](?P<ag>[0-9a-f])[.](?P<ah>[0-9a-f])[.](?P<ai>[0-9a-f])[.](?P<aj>[0-9a-f])[.](?P<ak>[0-9a-f])[.](?P<al>[0-9a-f])[.](?P<am>[0-9a-f])[.](?P<an>[0-9a-f])[.](?P<ao>[0-9a-f])[.](?P<ap>[0-9a-f])[.](?P<aq>[0-9a-f])[.](?P<ar>[0-9a-f])[.](?P<as>[0-9a-f])[.](?P<at>[0-9a-f])[.](?P<au>[0-9a-f])[.](?P<av>[0-9a-f])[.](?P<aw>[0-9a-f])[.](?P<ax>[0-9a-f])[.](?P<ay>[0-9a-f])[.](?P<az>[0-9a-f])[.](?P<ba>[0-9a-f])[.](?P<bb>[0-9a-f])[.](?P<bc>[0-9a-f])[.](?P<bd>[0-9a-f])[.](?P<be>[0-9a-f])[.](?P<bf>[0-9a-f])[.]net[.]example[.]com[.]$"
answer "{{ .Name }} 86400 IN AAAA {{ .Group.aa }}{{ .Group.ab }}{{ .Group.ac }}{{ .Group.ad }}:{{ .Group.ae }}{{ .Group.af }}{{ .Group.ag }}{{ .Group.ah }}:{{ .Group.ai }}{{ .Group.aj }}{{ .Group.ak }}{{ .Group.al }}:{{ .Group.am }}{{ .Group.an }}{{ .Group.ao }}{{ .Group.ap }}:{{ .Group.aq }}{{ .Group.ar }}{{ .Group.as }}{{ .Group.at }}:{{ .Group.au }}{{ .Group.av }}{{ .Group.aw }}{{ .Group.ax }}:{{ .Group.ay }}{{ .Group.az }}{{ .Group.ba }}{{ .Group.bb }}:{{ .Group.bc }}{{ .Group.bd }}{{ .Group.be }}{{ .Group.bf }}"
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
template IN NS net.example.com {
answer "{{ .Name }} 86400 IN NS ns.example.com."
answer "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
}
``` | 1.0 | [WIP] Document PTR reverse records via template - As the reverse plugin was removed and the suggestion was it's possible doing with template, I did my best to take a stab at it. It's currently still a WIP so as I don't handle subnets yet.
Also I assume that I'm missing something here. Feels too manual for reverse lookups even with template.
One can also use 0.8.e.f.ip6.arpa 127.in-addr.arpa (sidenote: fe80::/10 doesn't fully map to 0.8.e.f.ip6.arpa)
Full template example for reverse zone records.
```
127.0.0.0/8 fe80::/10 {
template IN SOA arpa {
answer "{{ .Name }} 86400 IN SOA ns.example.com. domains.example.com. 2019072302 300 300 604800 43200"
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
template IN PTR in-addr.arpa {
# 1.0.0.127.in-addr.arpa
match "^(?P<a>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<b>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<c>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<d>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.]in-addr[.]arpa[.]$"
answer "{{ .Name }} 86400 IN PTR {{ .Group.d }}-{{ .Group.c }}-{{ .Group.b }}-{{ .Group.a }}.net.example.com"
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
fallthrough
}
template IN PTR ip6.arpa {
# 0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.8.e.f.ip6.arpa
match "^(?P<aa>[0-9a-f])[.](?P<ab>[0-9a-f])[.](?P<ac>[0-9a-f])[.](?P<ad>[0-9a-f])[.](?P<ae>[0-9a-f])[.](?P<af>[0-9a-f])[.](?P<ag>[0-9a-f])[.](?P<ah>[0-9a-f])[.](?P<ai>[0-9a-f])[.](?P<aj>[0-9a-f])[.](?P<ak>[0-9a-f])[.](?P<al>[0-9a-f])[.](?P<am>[0-9a-f])[.](?P<an>[0-9a-f])[.](?P<ao>[0-9a-f])[.](?P<ap>[0-9a-f])[.](?P<aq>[0-9a-f])[.](?P<ar>[0-9a-f])[.](?P<as>[0-9a-f])[.](?P<at>[0-9a-f])[.](?P<au>[0-9a-f])[.](?P<av>[0-9a-f])[.](?P<aw>[0-9a-f])[.](?P<ax>[0-9a-f])[.](?P<ay>[0-9a-f])[.](?P<az>[0-9a-f])[.](?P<ba>[0-9a-f])[.](?P<bb>[0-9a-f])[.](?P<bc>[0-9a-f])[.](?P<bd>[0-9a-f])[.](?P<be>[0-9a-f])[.](?P<bf>[0-9a-f])[.]ip6[.]arpa[.]$"
answer "{{ .Name }} 86400 IN PTR {{ .Group.bf }}-{{ .Group.be }}-{{ .Group.bd }}-{{ .Group.bc }}-{{ .Group.bb }}-{{ .Group.ba }}-{{ .Group.az }}-{{ .Group.ay }}-{{ .Group.ax }}-{{ .Group.aw }}-{{ .Group.av }}-{{ .Group.au }}-{{ .Group.at }}-{{ .Group.as }}-{{ .Group.ar }}-{{ .Group.aq }}-{{ .Group.ap }}-{{ .Group.ao }}-{{ .Group.an }}-{{ .Group.am }}-{{ .Group.al }}-{{ .Group.ak }}-{{ .Group.aj }}-{{ .Group.ai }}-{{ .Group.ah }}-{{ .Group.ag }}-{{ .Group.af }}-{{ .Group.ae }}-{{ .Group.ad }}-{{ .Group.ac }}-{{ .Group.ab }}-{{ .Group.aa }}.net.example.com."
additional "{{ .Name }} 86400 IN PTR {{ .Group.bf }}{{ .Group.be }}{{ .Group.bd }}{{ .Group.bc }}-{{ .Group.bb }}{{ .Group.ba }}{{ .Group.az }}{{ .Group.ay }}-{{ .Group.ax }}{{ .Group.aw }}{{ .Group.av }}{{ .Group.au }}-{{ .Group.at }}{{ .Group.as }}{{ .Group.ar }}{{ .Group.aq }}-{{ .Group.ap }}{{ .Group.ao }}{{ .Group.an }}{{ .Group.am }}-{{ .Group.al }}{{ .Group.ak }}{{ .Group.aj }}{{ .Group.ai }}-{{ .Group.ah }}{{ .Group.ag }}{{ .Group.af }}{{ .Group.ae }}-{{ .Group.ad }}{{ .Group.ac }}{{ .Group.ab }}{{ .Group.aa }}.net.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
template IN NS in-addr.arpa {
answer "{{ .Name }} 86400 IN NS ns.example.com."
answer "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
fallthrough
}
template IN NS ip6.arpa {
answer "{{ .Name }} 86400 IN NS ns.example.com."
answer "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
}
net.example.com {
template IN SOA net.example.com {
answer "{{ .Name }} 86400 IN SOA ns.example.com. domains.example.com. 2019072302 300 300 604800 43200"
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
template IN A net.example.com {
# ip-127-0-0-1.net.example.com
match "^ip-(?P<a>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<b>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<c>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<d>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.]net[.]example[.]com[.]$"
# 127-0-0-1.net.example.com
match "^(?P<a>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<b>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<c>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])-(?P<d>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.]net[.]example[.]com[.]$"
# 127.0.0.1.net.example.com
match "^(?P<a>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<b>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<c>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.](?P<d>[0-9]|[1-9][0-9]|1[0-9][0-9]|2[0-4][0-9]|25[0-5])[.]net[.]example[.]com[.]$"
answer "{{ .Name }} 86400 IN A {{ .Group.a }}.{{ .Group.b }}.{{ .Group.c }}.{{ .Group.d }}"
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
fallthrough
}
template IN AAAA net.example.com {
# ip-f-e-8-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0.net.example.com
match "^ip-(?P<aa>[0-9a-f])-(?P<ab>[0-9a-f])-(?P<ac>[0-9a-f])-(?P<ad>[0-9a-f])-(?P<ae>[0-9a-f])-(?P<af>[0-9a-f])-(?P<ag>[0-9a-f])-(?P<ah>[0-9a-f])-(?P<ai>[0-9a-f])-(?P<aj>[0-9a-f])-(?P<ak>[0-9a-f])-(?P<al>[0-9a-f])-(?P<am>[0-9a-f])-(?P<an>[0-9a-f])-(?P<ao>[0-9a-f])-(?P<ap>[0-9a-f])-(?P<aq>[0-9a-f])-(?P<ar>[0-9a-f])-(?P<as>[0-9a-f])-(?P<at>[0-9a-f])-(?P<au>[0-9a-f])-(?P<av>[0-9a-f])-(?P<aw>[0-9a-f])-(?P<ax>[0-9a-f])-(?P<ay>[0-9a-f])-(?P<az>[0-9a-f])-(?P<ba>[0-9a-f])-(?P<bb>[0-9a-f])-(?P<bc>[0-9a-f])-(?P<bd>[0-9a-f])-(?P<be>[0-9a-f])-(?P<bf>[0-9a-f])[.]net[.]example[.]com[.]$"
# f-e-8-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0-0.net.example.com
match "^(?P<aa>[0-9a-f])-(?P<ab>[0-9a-f])-(?P<ac>[0-9a-f])-(?P<ad>[0-9a-f])-(?P<ae>[0-9a-f])-(?P<af>[0-9a-f])-(?P<ag>[0-9a-f])-(?P<ah>[0-9a-f])-(?P<ai>[0-9a-f])-(?P<aj>[0-9a-f])-(?P<ak>[0-9a-f])-(?P<al>[0-9a-f])-(?P<am>[0-9a-f])-(?P<an>[0-9a-f])-(?P<ao>[0-9a-f])-(?P<ap>[0-9a-f])-(?P<aq>[0-9a-f])-(?P<ar>[0-9a-f])-(?P<as>[0-9a-f])-(?P<at>[0-9a-f])-(?P<au>[0-9a-f])-(?P<av>[0-9a-f])-(?P<aw>[0-9a-f])-(?P<ax>[0-9a-f])-(?P<ay>[0-9a-f])-(?P<az>[0-9a-f])-(?P<ba>[0-9a-f])-(?P<bb>[0-9a-f])-(?P<bc>[0-9a-f])-(?P<bd>[0-9a-f])-(?P<be>[0-9a-f])-(?P<bf>[0-9a-f])[.]net[.]example[.]com[.]$"
# f.e.8.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.net.example.com
match "^(?P<aa>[0-9a-f])[.](?P<ab>[0-9a-f])[.](?P<ac>[0-9a-f])[.](?P<ad>[0-9a-f])[.](?P<ae>[0-9a-f])[.](?P<af>[0-9a-f])[.](?P<ag>[0-9a-f])[.](?P<ah>[0-9a-f])[.](?P<ai>[0-9a-f])[.](?P<aj>[0-9a-f])[.](?P<ak>[0-9a-f])[.](?P<al>[0-9a-f])[.](?P<am>[0-9a-f])[.](?P<an>[0-9a-f])[.](?P<ao>[0-9a-f])[.](?P<ap>[0-9a-f])[.](?P<aq>[0-9a-f])[.](?P<ar>[0-9a-f])[.](?P<as>[0-9a-f])[.](?P<at>[0-9a-f])[.](?P<au>[0-9a-f])[.](?P<av>[0-9a-f])[.](?P<aw>[0-9a-f])[.](?P<ax>[0-9a-f])[.](?P<ay>[0-9a-f])[.](?P<az>[0-9a-f])[.](?P<ba>[0-9a-f])[.](?P<bb>[0-9a-f])[.](?P<bc>[0-9a-f])[.](?P<bd>[0-9a-f])[.](?P<be>[0-9a-f])[.](?P<bf>[0-9a-f])[.]net[.]example[.]com[.]$"
answer "{{ .Name }} 86400 IN AAAA {{ .Group.aa }}{{ .Group.ab }}{{ .Group.ac }}{{ .Group.ad }}:{{ .Group.ae }}{{ .Group.af }}{{ .Group.ag }}{{ .Group.ah }}:{{ .Group.ai }}{{ .Group.aj }}{{ .Group.ak }}{{ .Group.al }}:{{ .Group.am }}{{ .Group.an }}{{ .Group.ao }}{{ .Group.ap }}:{{ .Group.aq }}{{ .Group.ar }}{{ .Group.as }}{{ .Group.at }}:{{ .Group.au }}{{ .Group.av }}{{ .Group.aw }}{{ .Group.ax }}:{{ .Group.ay }}{{ .Group.az }}{{ .Group.ba }}{{ .Group.bb }}:{{ .Group.bc }}{{ .Group.bd }}{{ .Group.be }}{{ .Group.bf }}"
authority "{{ .Name }} 86400 IN NS ns.example.com."
authority "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
template IN NS net.example.com {
answer "{{ .Name }} 86400 IN NS ns.example.com."
answer "{{ .Name }} 86400 IN NS ns.example.net."
additional "ns.example.com. 86400 IN A 127.0.0.2"
additional "ns.example.net. 86400 IN A 127.0.0.3"
additional "ns.example.com. 86400 IN AAAA fe80:0000:2::1"
additional "ns.example.net. 86400 IN AAAA fe80:0000:3::1"
fallthrough
}
}
``` | non_test | document ptr reverse records via template as the reverse plugin was removed and the suggestion was it s possible doing with template i did my best to take a stab at it it s currently still a wip so as i don t handle subnets yet also i assume that i m missing something here feels too manual for reverse lookups even with template one can also use e f arpa in addr arpa sidenote doesn t fully map to e f arpa full template example for reverse zone records template in soa arpa answer name in soa ns example com domains example com authority name in ns ns example com authority name in ns ns example net additional ns example com in a additional ns example net in a additional ns example com in aaaa additional ns example net in aaaa fallthrough template in ptr in addr arpa in addr arpa match p p p p in addr arpa answer name in ptr group d group c group b group a net example com authority name in ns ns example com authority name in ns ns example net additional ns example com in a additional ns example net in a fallthrough template in ptr arpa e f arpa match p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p arpa answer name in ptr group bf group be group bd group bc group bb group ba group az group ay group ax group aw group av group au group at group as group ar group aq group ap group ao group an group am group al group ak group aj group ai group ah group ag group af group ae group ad group ac group ab group aa net example com additional name in ptr group bf group be group bd group bc group bb group ba group az group ay group ax group aw group av group au group at group as group ar group aq group ap group ao group an group am group al group ak group aj group ai group ah group ag group af group ae group ad group ac group ab group aa net example com authority name in ns ns example com authority name in ns ns example net additional ns example com in aaaa additional ns example net in aaaa fallthrough template in ns in addr arpa answer name in ns ns example com answer name in ns ns example net additional ns example com in a additional ns example net in a fallthrough template in ns arpa answer name in ns ns example com answer name in ns ns example net additional ns example com in aaaa additional ns example net in aaaa fallthrough net example com template in soa net example com answer name in soa ns example com domains example com authority name in ns ns example com authority name in ns ns example net additional ns example com in a additional ns example net in a additional ns example com in aaaa additional ns example net in aaaa fallthrough template in a net example com ip net example com match ip p p p p net example com net example com match p p p p net example com net example com match p p p p net example com answer name in a group a group b group c group d authority name in ns ns example com authority name in ns ns example net additional ns example com in a additional ns example net in a fallthrough template in aaaa net example com ip f e net example com match ip p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p net example com f e net example com match p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p net example com f e net example com match p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p p net example com answer name in aaaa group aa group ab group ac group ad group ae group af group ag group ah group ai group aj group ak group al group am group an group ao group ap group aq group ar group as group at group au group av group aw group ax group ay group az group ba group bb group bc group bd group be group bf authority name in ns ns example com authority name in ns ns example net additional ns example com in aaaa additional ns example net in aaaa fallthrough template in ns net example com answer name in ns ns example com answer name in ns ns example net additional ns example com in a additional ns example net in a additional ns example com in aaaa additional ns example net in aaaa fallthrough | 0 |
187,728 | 22,045,872,257 | IssuesEvent | 2022-05-30 01:35:16 | Nivaskumark/kernel_v4.1.15 | https://api.github.com/repos/Nivaskumark/kernel_v4.1.15 | closed | WS-2021-0517 (Medium) detected in linuxlinux-4.6 - autoclosed | security vulnerability | ## WS-2021-0517 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Nivaskumark/kernel_v4.1.15/commit/00db4e8795bcbec692fb60b19160bdd763ad42e3">00db4e8795bcbec692fb60b19160bdd763ad42e3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/proc/vmcore.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/proc/vmcore.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Linux/Kernel is vulnerable to user buffer by properly using clear_user() in fs/proc/vmcore.c. The fix versions are v4.4.294, v4.9.292, v4.14.258, v4.19.219, v5.4.163, v5.10.83, v5.15.6, v5.16-rc3.
<p>Publish Date: 2021-12-01
<p>URL: <a href=https://github.com/gregkh/linux/commit/7b3a34f08d11e7f05cd00b8e09adaa15192f0ad1>WS-2021-0517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://osv.dev/vulnerability/GSD-2021-1002530">https://osv.dev/vulnerability/GSD-2021-1002530</a></p>
<p>Release Date: 2021-12-01</p>
<p>Fix Resolution: Linux/Kernel - v4.4.294, v4.9.292, v4.14.258, v4.19.219, v5.4.163, v5.10.83, v5.15.6, v5.16-rc3
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2021-0517 (Medium) detected in linuxlinux-4.6 - autoclosed - ## WS-2021-0517 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Nivaskumark/kernel_v4.1.15/commit/00db4e8795bcbec692fb60b19160bdd763ad42e3">00db4e8795bcbec692fb60b19160bdd763ad42e3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/proc/vmcore.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/proc/vmcore.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Linux/Kernel is vulnerable to user buffer by properly using clear_user() in fs/proc/vmcore.c. The fix versions are v4.4.294, v4.9.292, v4.14.258, v4.19.219, v5.4.163, v5.10.83, v5.15.6, v5.16-rc3.
<p>Publish Date: 2021-12-01
<p>URL: <a href=https://github.com/gregkh/linux/commit/7b3a34f08d11e7f05cd00b8e09adaa15192f0ad1>WS-2021-0517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://osv.dev/vulnerability/GSD-2021-1002530">https://osv.dev/vulnerability/GSD-2021-1002530</a></p>
<p>Release Date: 2021-12-01</p>
<p>Fix Resolution: Linux/Kernel - v4.4.294, v4.9.292, v4.14.258, v4.19.219, v5.4.163, v5.10.83, v5.15.6, v5.16-rc3
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | ws medium detected in linuxlinux autoclosed ws medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files fs proc vmcore c fs proc vmcore c vulnerability details in linux kernel is vulnerable to user buffer by properly using clear user in fs proc vmcore c the fix versions are publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution linux kernel step up your open source security game with whitesource | 0 |
495,416 | 14,281,384,698 | IssuesEvent | 2020-11-23 07:58:46 | space-wizards/space-station-14 | https://api.github.com/repos/space-wizards/space-station-14 | opened | Need a volume slider | Priority: 2-medium Type: Feature | At least having a master volume for now would be useful, then later on when someone feels like it SFX / ambience etc.
There's already a placeholder area for it on the options menu. | 1.0 | Need a volume slider - At least having a master volume for now would be useful, then later on when someone feels like it SFX / ambience etc.
There's already a placeholder area for it on the options menu. | non_test | need a volume slider at least having a master volume for now would be useful then later on when someone feels like it sfx ambience etc there s already a placeholder area for it on the options menu | 0 |
248,768 | 21,056,461,024 | IssuesEvent | 2022-04-01 04:10:30 | pingcap/tidb | https://api.github.com/repos/pingcap/tidb | closed | DATA RACE in the ```setDDLLabelForTopSQL``` | type/bug component/test severity/minor | ## Bug Report
Please answer these questions before submitting your issue. Thanks!
### 1. Minimal reproduce step (Required)
```
==================
WARNING: DATA RACE
Write at 0x00c0222501b0 by goroutine 252:
github.com/pingcap/tidb/ddl.(*jobContext).setDDLLabelForTopSQL()
/go/tidb/ddl/ddl_worker.go:523 +0x36c
github.com/pingcap/tidb/ddl.(*worker).handleDDLJobQueue.func1()
/go/tidb/ddl/ddl_worker.go:583 +0x25c
github.com/pingcap/tidb/kv.RunInNewTxn()
/go/tidb/kv/txn.go:49 +0x155
github.com/pingcap/tidb/ddl.(*worker).handleDDLJobQueue()
/go/tidb/ddl/ddl_worker.go:564 +0x1cf
github.com/pingcap/tidb/ddl.(*worker).start()
/go/tidb/ddl/ddl_worker.go:204 +0x64f
github.com/pingcap/tidb/ddl.(*ddl).Start.func3()
/go/tidb/ddl/ddl.go:401 +0x47
Previous write at 0x00c0222501b0 by goroutine 195:
github.com/pingcap/tidb/ddl.(*jobContext).setDDLLabelForTopSQL()
/go/tidb/ddl/ddl_worker.go:523 +0x36c
github.com/pingcap/tidb/ddl.(*backfillWorker).run()
/go/tidb/ddl/backfilling.go:305 +0x2d1
github.com/pingcap/tidb/ddl.(*worker).writePhysicalTableRecord.func2()
/go/tidb/ddl/backfilling.go:648 +0x71
Goroutine 252 (running) created at:
github.com/pingcap/tidb/ddl.(*ddl).Start()
/go/tidb/ddl/ddl.go:401 +0x9f1
github.com/pingcap/tidb/domain.(*Domain).Init()
/go/tidb/domain/domain.go:855 +0x11d6
github.com/pingcap/tidb/session.(*domainMap).Get.func1()
/go/tidb/session/tidb.go:83 +0x664
github.com/pingcap/tidb/util.RunWithRetry()
/go/tidb/util/misc.go:65 +0x93
github.com/pingcap/tidb/session.(*domainMap).Get()
/go/tidb/session/tidb.go:71 +0x38b
github.com/pingcap/tidb/session.createSessionWithOpt()
/go/tidb/session/session.go:2942 +0x75
github.com/pingcap/tidb/session.createSession()
/go/tidb/session/session.go:2938 +0x84
github.com/pingcap/tidb/session.createSessions()
/go/tidb/session/session.go:2927 +0x6e
github.com/pingcap/tidb/session.BootstrapSession()
/go/tidb/session/session.go:2810 +0x297
github.com/pingcap/tidb/ddl_test.(*stateChangeSuite).SetupSuite()
/go/tidb/ddl/db_change_test.go:73 +0x1f9
github.com/stretchr/testify/suite.Run()
/home/prow/go/pkg/mod/github.com/stretchr/testify@v1.7.0/suite/suite.go:118 +0x597
github.com/pingcap/tidb/ddl_test.TestStateChange()
/go/tidb/ddl/db_change_test.go:63 +0x44
testing.tRunner()
/usr/local/go/src/testing/testing.go:1439 +0x213
testing.(*T).Run.func1()
/usr/local/go/src/testing/testing.go:1486 +0x47
Goroutine 195 (running) created at:
github.com/pingcap/tidb/ddl.(*worker).writePhysicalTableRecord()
/go/tidb/ddl/backfilling.go:648 +0x2059
github.com/pingcap/tidb/ddl.(*worker).addPhysicalTableIndex()
/go/tidb/ddl/index.go:1353 +0x284
github.com/pingcap/tidb/ddl.(*worker).addTableIndex()
/go/tidb/ddl/index.go:1376 +0xcc
github.com/pingcap/tidb/ddl.(*worker).updateColumnAndIndexes()
/go/tidb/ddl/column.go:1192 +0xef5
github.com/pingcap/tidb/ddl.(*worker).doModifyColumnTypeWithData.func1()
/go/tidb/ddl/column.go:1032 +0x314
github.com/pingcap/tidb/ddl.(*worker).runReorgJob.func1()
/go/tidb/ddl/reorg.go:227 +0x88
==================
==================
WARNING: DATA RACE
Write at 0x00c022250180 by goroutine 252:
github.com/pingcap/tidb/ddl.(*jobContext).setDDLLabelForTopSQL()
/go/tidb/ddl/ddl_worker.go:524 +0x3bd
github.com/pingcap/tidb/ddl.(*worker).handleDDLJobQueue.func1()
/go/tidb/ddl/ddl_worker.go:583 +0x25c
github.com/pingcap/tidb/kv.RunInNewTxn()
/go/tidb/kv/txn.go:49 +0x155
github.com/pingcap/tidb/ddl.(*worker).handleDDLJobQueue()
/go/tidb/ddl/ddl_worker.go:564 +0x1cf
github.com/pingcap/tidb/ddl.(*worker).start()
/go/tidb/ddl/ddl_worker.go:204 +0x64f
github.com/pingcap/tidb/ddl.(*ddl).Start.func3()
/go/tidb/ddl/ddl.go:401 +0x47
Previous write at 0x00c022250180 by goroutine 195:
github.com/pingcap/tidb/ddl.(*jobContext).setDDLLabelForTopSQL()
/go/tidb/ddl/ddl_worker.go:524 +0x3bd
github.com/pingcap/tidb/ddl.(*backfillWorker).run()
/go/tidb/ddl/backfilling.go:305 +0x2d1
github.com/pingcap/tidb/ddl.(*worker).writePhysicalTableRecord.func2()
/go/tidb/ddl/backfilling.go:648 +0x71
Goroutine 252 (running) created at:
github.com/pingcap/tidb/ddl.(*ddl).Start()
/go/tidb/ddl/ddl.go:401 +0x9f1
github.com/pingcap/tidb/domain.(*Domain).Init()
/go/tidb/domain/domain.go:855 +0x11d6
github.com/pingcap/tidb/session.(*domainMap).Get.func1()
/go/tidb/session/tidb.go:83 +0x664
github.com/pingcap/tidb/util.RunWithRetry()
/go/tidb/util/misc.go:65 +0x93
github.com/pingcap/tidb/session.(*domainMap).Get()
/go/tidb/session/tidb.go:71 +0x38b
github.com/pingcap/tidb/session.createSessionWithOpt()
/go/tidb/session/session.go:2942 +0x75
github.com/pingcap/tidb/session.createSession()
/go/tidb/session/session.go:2938 +0x84
github.com/pingcap/tidb/session.createSessions()
/go/tidb/session/session.go:2927 +0x6e
github.com/pingcap/tidb/session.BootstrapSession()
/go/tidb/session/session.go:2810 +0x297
github.com/pingcap/tidb/ddl_test.(*stateChangeSuite).SetupSuite()
/go/tidb/ddl/db_change_test.go:73 +0x1f9
github.com/stretchr/testify/suite.Run()
/home/prow/go/pkg/mod/github.com/stretchr/testify@v1.7.0/suite/suite.go:118 +0x597
github.com/pingcap/tidb/ddl_test.TestStateChange()
/go/tidb/ddl/db_change_test.go:63 +0x44
testing.tRunner()
/usr/local/go/src/testing/testing.go:1439 +0x213
testing.(*T).Run.func1()
/usr/local/go/src/testing/testing.go:1486 +0x47
Goroutine 195 (running) created at:
github.com/pingcap/tidb/ddl.(*worker).writePhysicalTableRecord()
/go/tidb/ddl/backfilling.go:648 +0x2059
github.com/pingcap/tidb/ddl.(*worker).addPhysicalTableIndex()
/go/tidb/ddl/index.go:1353 +0x284
github.com/pingcap/tidb/ddl.(*worker).addTableIndex()
/go/tidb/ddl/index.go:1376 +0xcc
github.com/pingcap/tidb/ddl.(*worker).updateColumnAndIndexes()
/go/tidb/ddl/column.go:1192 +0xef5
github.com/pingcap/tidb/ddl.(*worker).doModifyColumnTypeWithData.func1()
/go/tidb/ddl/column.go:1032 +0x314
github.com/pingcap/tidb/ddl.(*worker).runReorgJob.func1()
/go/tidb/ddl/reorg.go:227 +0x88
==================
```
<!-- a step by step guide for reproducing the bug. -->
### 2. What did you expect to see? (Required)
### 3. What did you see instead (Required)
### 4. What is your TiDB version? (Required)
<!-- Paste the output of SELECT tidb_version() -->
| 1.0 | DATA RACE in the ```setDDLLabelForTopSQL``` - ## Bug Report
Please answer these questions before submitting your issue. Thanks!
### 1. Minimal reproduce step (Required)
```
==================
WARNING: DATA RACE
Write at 0x00c0222501b0 by goroutine 252:
github.com/pingcap/tidb/ddl.(*jobContext).setDDLLabelForTopSQL()
/go/tidb/ddl/ddl_worker.go:523 +0x36c
github.com/pingcap/tidb/ddl.(*worker).handleDDLJobQueue.func1()
/go/tidb/ddl/ddl_worker.go:583 +0x25c
github.com/pingcap/tidb/kv.RunInNewTxn()
/go/tidb/kv/txn.go:49 +0x155
github.com/pingcap/tidb/ddl.(*worker).handleDDLJobQueue()
/go/tidb/ddl/ddl_worker.go:564 +0x1cf
github.com/pingcap/tidb/ddl.(*worker).start()
/go/tidb/ddl/ddl_worker.go:204 +0x64f
github.com/pingcap/tidb/ddl.(*ddl).Start.func3()
/go/tidb/ddl/ddl.go:401 +0x47
Previous write at 0x00c0222501b0 by goroutine 195:
github.com/pingcap/tidb/ddl.(*jobContext).setDDLLabelForTopSQL()
/go/tidb/ddl/ddl_worker.go:523 +0x36c
github.com/pingcap/tidb/ddl.(*backfillWorker).run()
/go/tidb/ddl/backfilling.go:305 +0x2d1
github.com/pingcap/tidb/ddl.(*worker).writePhysicalTableRecord.func2()
/go/tidb/ddl/backfilling.go:648 +0x71
Goroutine 252 (running) created at:
github.com/pingcap/tidb/ddl.(*ddl).Start()
/go/tidb/ddl/ddl.go:401 +0x9f1
github.com/pingcap/tidb/domain.(*Domain).Init()
/go/tidb/domain/domain.go:855 +0x11d6
github.com/pingcap/tidb/session.(*domainMap).Get.func1()
/go/tidb/session/tidb.go:83 +0x664
github.com/pingcap/tidb/util.RunWithRetry()
/go/tidb/util/misc.go:65 +0x93
github.com/pingcap/tidb/session.(*domainMap).Get()
/go/tidb/session/tidb.go:71 +0x38b
github.com/pingcap/tidb/session.createSessionWithOpt()
/go/tidb/session/session.go:2942 +0x75
github.com/pingcap/tidb/session.createSession()
/go/tidb/session/session.go:2938 +0x84
github.com/pingcap/tidb/session.createSessions()
/go/tidb/session/session.go:2927 +0x6e
github.com/pingcap/tidb/session.BootstrapSession()
/go/tidb/session/session.go:2810 +0x297
github.com/pingcap/tidb/ddl_test.(*stateChangeSuite).SetupSuite()
/go/tidb/ddl/db_change_test.go:73 +0x1f9
github.com/stretchr/testify/suite.Run()
/home/prow/go/pkg/mod/github.com/stretchr/testify@v1.7.0/suite/suite.go:118 +0x597
github.com/pingcap/tidb/ddl_test.TestStateChange()
/go/tidb/ddl/db_change_test.go:63 +0x44
testing.tRunner()
/usr/local/go/src/testing/testing.go:1439 +0x213
testing.(*T).Run.func1()
/usr/local/go/src/testing/testing.go:1486 +0x47
Goroutine 195 (running) created at:
github.com/pingcap/tidb/ddl.(*worker).writePhysicalTableRecord()
/go/tidb/ddl/backfilling.go:648 +0x2059
github.com/pingcap/tidb/ddl.(*worker).addPhysicalTableIndex()
/go/tidb/ddl/index.go:1353 +0x284
github.com/pingcap/tidb/ddl.(*worker).addTableIndex()
/go/tidb/ddl/index.go:1376 +0xcc
github.com/pingcap/tidb/ddl.(*worker).updateColumnAndIndexes()
/go/tidb/ddl/column.go:1192 +0xef5
github.com/pingcap/tidb/ddl.(*worker).doModifyColumnTypeWithData.func1()
/go/tidb/ddl/column.go:1032 +0x314
github.com/pingcap/tidb/ddl.(*worker).runReorgJob.func1()
/go/tidb/ddl/reorg.go:227 +0x88
==================
==================
WARNING: DATA RACE
Write at 0x00c022250180 by goroutine 252:
github.com/pingcap/tidb/ddl.(*jobContext).setDDLLabelForTopSQL()
/go/tidb/ddl/ddl_worker.go:524 +0x3bd
github.com/pingcap/tidb/ddl.(*worker).handleDDLJobQueue.func1()
/go/tidb/ddl/ddl_worker.go:583 +0x25c
github.com/pingcap/tidb/kv.RunInNewTxn()
/go/tidb/kv/txn.go:49 +0x155
github.com/pingcap/tidb/ddl.(*worker).handleDDLJobQueue()
/go/tidb/ddl/ddl_worker.go:564 +0x1cf
github.com/pingcap/tidb/ddl.(*worker).start()
/go/tidb/ddl/ddl_worker.go:204 +0x64f
github.com/pingcap/tidb/ddl.(*ddl).Start.func3()
/go/tidb/ddl/ddl.go:401 +0x47
Previous write at 0x00c022250180 by goroutine 195:
github.com/pingcap/tidb/ddl.(*jobContext).setDDLLabelForTopSQL()
/go/tidb/ddl/ddl_worker.go:524 +0x3bd
github.com/pingcap/tidb/ddl.(*backfillWorker).run()
/go/tidb/ddl/backfilling.go:305 +0x2d1
github.com/pingcap/tidb/ddl.(*worker).writePhysicalTableRecord.func2()
/go/tidb/ddl/backfilling.go:648 +0x71
Goroutine 252 (running) created at:
github.com/pingcap/tidb/ddl.(*ddl).Start()
/go/tidb/ddl/ddl.go:401 +0x9f1
github.com/pingcap/tidb/domain.(*Domain).Init()
/go/tidb/domain/domain.go:855 +0x11d6
github.com/pingcap/tidb/session.(*domainMap).Get.func1()
/go/tidb/session/tidb.go:83 +0x664
github.com/pingcap/tidb/util.RunWithRetry()
/go/tidb/util/misc.go:65 +0x93
github.com/pingcap/tidb/session.(*domainMap).Get()
/go/tidb/session/tidb.go:71 +0x38b
github.com/pingcap/tidb/session.createSessionWithOpt()
/go/tidb/session/session.go:2942 +0x75
github.com/pingcap/tidb/session.createSession()
/go/tidb/session/session.go:2938 +0x84
github.com/pingcap/tidb/session.createSessions()
/go/tidb/session/session.go:2927 +0x6e
github.com/pingcap/tidb/session.BootstrapSession()
/go/tidb/session/session.go:2810 +0x297
github.com/pingcap/tidb/ddl_test.(*stateChangeSuite).SetupSuite()
/go/tidb/ddl/db_change_test.go:73 +0x1f9
github.com/stretchr/testify/suite.Run()
/home/prow/go/pkg/mod/github.com/stretchr/testify@v1.7.0/suite/suite.go:118 +0x597
github.com/pingcap/tidb/ddl_test.TestStateChange()
/go/tidb/ddl/db_change_test.go:63 +0x44
testing.tRunner()
/usr/local/go/src/testing/testing.go:1439 +0x213
testing.(*T).Run.func1()
/usr/local/go/src/testing/testing.go:1486 +0x47
Goroutine 195 (running) created at:
github.com/pingcap/tidb/ddl.(*worker).writePhysicalTableRecord()
/go/tidb/ddl/backfilling.go:648 +0x2059
github.com/pingcap/tidb/ddl.(*worker).addPhysicalTableIndex()
/go/tidb/ddl/index.go:1353 +0x284
github.com/pingcap/tidb/ddl.(*worker).addTableIndex()
/go/tidb/ddl/index.go:1376 +0xcc
github.com/pingcap/tidb/ddl.(*worker).updateColumnAndIndexes()
/go/tidb/ddl/column.go:1192 +0xef5
github.com/pingcap/tidb/ddl.(*worker).doModifyColumnTypeWithData.func1()
/go/tidb/ddl/column.go:1032 +0x314
github.com/pingcap/tidb/ddl.(*worker).runReorgJob.func1()
/go/tidb/ddl/reorg.go:227 +0x88
==================
```
<!-- a step by step guide for reproducing the bug. -->
### 2. What did you expect to see? (Required)
### 3. What did you see instead (Required)
### 4. What is your TiDB version? (Required)
<!-- Paste the output of SELECT tidb_version() -->
| test | data race in the setddllabelfortopsql bug report please answer these questions before submitting your issue thanks minimal reproduce step required warning data race write at by goroutine github com pingcap tidb ddl jobcontext setddllabelfortopsql go tidb ddl ddl worker go github com pingcap tidb ddl worker handleddljobqueue go tidb ddl ddl worker go github com pingcap tidb kv runinnewtxn go tidb kv txn go github com pingcap tidb ddl worker handleddljobqueue go tidb ddl ddl worker go github com pingcap tidb ddl worker start go tidb ddl ddl worker go github com pingcap tidb ddl ddl start go tidb ddl ddl go previous write at by goroutine github com pingcap tidb ddl jobcontext setddllabelfortopsql go tidb ddl ddl worker go github com pingcap tidb ddl backfillworker run go tidb ddl backfilling go github com pingcap tidb ddl worker writephysicaltablerecord go tidb ddl backfilling go goroutine running created at github com pingcap tidb ddl ddl start go tidb ddl ddl go github com pingcap tidb domain domain init go tidb domain domain go github com pingcap tidb session domainmap get go tidb session tidb go github com pingcap tidb util runwithretry go tidb util misc go github com pingcap tidb session domainmap get go tidb session tidb go github com pingcap tidb session createsessionwithopt go tidb session session go github com pingcap tidb session createsession go tidb session session go github com pingcap tidb session createsessions go tidb session session go github com pingcap tidb session bootstrapsession go tidb session session go github com pingcap tidb ddl test statechangesuite setupsuite go tidb ddl db change test go github com stretchr testify suite run home prow go pkg mod github com stretchr testify suite suite go github com pingcap tidb ddl test teststatechange go tidb ddl db change test go testing trunner usr local go src testing testing go testing t run usr local go src testing testing go goroutine running created at github com pingcap tidb ddl worker writephysicaltablerecord go tidb ddl backfilling go github com pingcap tidb ddl worker addphysicaltableindex go tidb ddl index go github com pingcap tidb ddl worker addtableindex go tidb ddl index go github com pingcap tidb ddl worker updatecolumnandindexes go tidb ddl column go github com pingcap tidb ddl worker domodifycolumntypewithdata go tidb ddl column go github com pingcap tidb ddl worker runreorgjob go tidb ddl reorg go warning data race write at by goroutine github com pingcap tidb ddl jobcontext setddllabelfortopsql go tidb ddl ddl worker go github com pingcap tidb ddl worker handleddljobqueue go tidb ddl ddl worker go github com pingcap tidb kv runinnewtxn go tidb kv txn go github com pingcap tidb ddl worker handleddljobqueue go tidb ddl ddl worker go github com pingcap tidb ddl worker start go tidb ddl ddl worker go github com pingcap tidb ddl ddl start go tidb ddl ddl go previous write at by goroutine github com pingcap tidb ddl jobcontext setddllabelfortopsql go tidb ddl ddl worker go github com pingcap tidb ddl backfillworker run go tidb ddl backfilling go github com pingcap tidb ddl worker writephysicaltablerecord go tidb ddl backfilling go goroutine running created at github com pingcap tidb ddl ddl start go tidb ddl ddl go github com pingcap tidb domain domain init go tidb domain domain go github com pingcap tidb session domainmap get go tidb session tidb go github com pingcap tidb util runwithretry go tidb util misc go github com pingcap tidb session domainmap get go tidb session tidb go github com pingcap tidb session createsessionwithopt go tidb session session go github com pingcap tidb session createsession go tidb session session go github com pingcap tidb session createsessions go tidb session session go github com pingcap tidb session bootstrapsession go tidb session session go github com pingcap tidb ddl test statechangesuite setupsuite go tidb ddl db change test go github com stretchr testify suite run home prow go pkg mod github com stretchr testify suite suite go github com pingcap tidb ddl test teststatechange go tidb ddl db change test go testing trunner usr local go src testing testing go testing t run usr local go src testing testing go goroutine running created at github com pingcap tidb ddl worker writephysicaltablerecord go tidb ddl backfilling go github com pingcap tidb ddl worker addphysicaltableindex go tidb ddl index go github com pingcap tidb ddl worker addtableindex go tidb ddl index go github com pingcap tidb ddl worker updatecolumnandindexes go tidb ddl column go github com pingcap tidb ddl worker domodifycolumntypewithdata go tidb ddl column go github com pingcap tidb ddl worker runreorgjob go tidb ddl reorg go what did you expect to see required what did you see instead required what is your tidb version required | 1 |
346,065 | 30,864,057,315 | IssuesEvent | 2023-08-03 06:40:43 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | opened | DISABLED test_fn_fwgrad_bwgrad_linalg_lu_cuda_float64 (__main__.TestFwdGradientsCUDA) | module: flaky-tests skipped module: unknown | Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_fn_fwgrad_bwgrad_linalg_lu_cuda_float64&suite=TestFwdGradientsCUDA) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/15574308086).
Over the past 3 hours, it has been determined flaky in 2 workflow(s) with 7 failures and 2 successes.
**Debugging instructions (after clicking on the recent samples link):**
DO NOT ASSUME THINGS ARE OKAY IF THE CI IS GREEN. We now shield flaky tests from developers so CI will thus be green but it will be harder to parse the logs.
To find relevant log snippets:
1. Click on the workflow logs linked above
2. Click on the Test step of the job so that it is expanded. Otherwise, the grepping will not work.
3. Grep for `test_fn_fwgrad_bwgrad_linalg_lu_cuda_float64`
4. There should be several instances run (as flaky tests are rerun in CI) from which you can study the logs.
Test file path: `test_ops_fwd_gradients.py` | 1.0 | DISABLED test_fn_fwgrad_bwgrad_linalg_lu_cuda_float64 (__main__.TestFwdGradientsCUDA) - Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_fn_fwgrad_bwgrad_linalg_lu_cuda_float64&suite=TestFwdGradientsCUDA) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/15574308086).
Over the past 3 hours, it has been determined flaky in 2 workflow(s) with 7 failures and 2 successes.
**Debugging instructions (after clicking on the recent samples link):**
DO NOT ASSUME THINGS ARE OKAY IF THE CI IS GREEN. We now shield flaky tests from developers so CI will thus be green but it will be harder to parse the logs.
To find relevant log snippets:
1. Click on the workflow logs linked above
2. Click on the Test step of the job so that it is expanded. Otherwise, the grepping will not work.
3. Grep for `test_fn_fwgrad_bwgrad_linalg_lu_cuda_float64`
4. There should be several instances run (as flaky tests are rerun in CI) from which you can study the logs.
Test file path: `test_ops_fwd_gradients.py` | test | disabled test fn fwgrad bwgrad linalg lu cuda main testfwdgradientscuda platforms linux this test was disabled because it is failing in ci see and the most recent trunk over the past hours it has been determined flaky in workflow s with failures and successes debugging instructions after clicking on the recent samples link do not assume things are okay if the ci is green we now shield flaky tests from developers so ci will thus be green but it will be harder to parse the logs to find relevant log snippets click on the workflow logs linked above click on the test step of the job so that it is expanded otherwise the grepping will not work grep for test fn fwgrad bwgrad linalg lu cuda there should be several instances run as flaky tests are rerun in ci from which you can study the logs test file path test ops fwd gradients py | 1 |
179,255 | 13,853,388,018 | IssuesEvent | 2020-10-15 08:03:42 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: decommission/randomized failed | C-test-failure O-roachtest O-robot branch-master release-blocker | [(roachtest).decommission/randomized failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2366018&tab=buildLog) on [master@80e7127197f76ef35c1f6ec3984c4d49d4afde7f](https://github.com/cockroachdb/cockroach/commits/80e7127197f76ef35c1f6ec3984c4d49d4afde7f):
```
| | main.main
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1839
| | runtime.main
| | /usr/local/go/src/runtime/proc.go:203
| | runtime.goexit
| | /usr/local/go/src/runtime/asm_amd64.s:1357
| Wraps: (2) 1: dead
| Error types: (1) *withstack.withStack (2) *errutil.leafError
Wraps: (4) secondary error attachment
| 4: dead
| (1) attached stack trace
| -- stack trace:
| | main.glob..func14
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1143
| | main.wrap.func1
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:267
| | github.com/spf13/cobra.(*Command).execute
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:830
| | github.com/spf13/cobra.(*Command).ExecuteC
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:914
| | github.com/spf13/cobra.(*Command).Execute
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:864
| | main.main
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1839
| | runtime.main
| | /usr/local/go/src/runtime/proc.go:203
| | runtime.goexit
| | /usr/local/go/src/runtime/asm_amd64.s:1357
| Wraps: (2) 4: dead
| Error types: (1) *withstack.withStack (2) *errutil.leafError
Wraps: (5) attached stack trace
-- stack trace:
| main.glob..func14
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1143
| main.wrap.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:267
| github.com/spf13/cobra.(*Command).execute
| /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:830
| github.com/spf13/cobra.(*Command).ExecuteC
| /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:914
| github.com/spf13/cobra.(*Command).Execute
| /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:864
| main.main
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1839
| runtime.main
| /usr/local/go/src/runtime/proc.go:203
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (6) 3: dead
Error types: (1) errors.Unclassified (2) *secondary.withSecondaryError (3) *secondary.withSecondaryError (4) *secondary.withSecondaryError (5) *withstack.withStack (6) *errutil.leafError
```
<details><summary>More</summary><p>
Artifacts: [/decommission/randomized](https://teamcity.cockroachdb.com/viewLog.html?buildId=2366018&tab=artifacts#/decommission/randomized)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Adecommission%2Frandomized.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: decommission/randomized failed - [(roachtest).decommission/randomized failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2366018&tab=buildLog) on [master@80e7127197f76ef35c1f6ec3984c4d49d4afde7f](https://github.com/cockroachdb/cockroach/commits/80e7127197f76ef35c1f6ec3984c4d49d4afde7f):
```
| | main.main
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1839
| | runtime.main
| | /usr/local/go/src/runtime/proc.go:203
| | runtime.goexit
| | /usr/local/go/src/runtime/asm_amd64.s:1357
| Wraps: (2) 1: dead
| Error types: (1) *withstack.withStack (2) *errutil.leafError
Wraps: (4) secondary error attachment
| 4: dead
| (1) attached stack trace
| -- stack trace:
| | main.glob..func14
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1143
| | main.wrap.func1
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:267
| | github.com/spf13/cobra.(*Command).execute
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:830
| | github.com/spf13/cobra.(*Command).ExecuteC
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:914
| | github.com/spf13/cobra.(*Command).Execute
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:864
| | main.main
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1839
| | runtime.main
| | /usr/local/go/src/runtime/proc.go:203
| | runtime.goexit
| | /usr/local/go/src/runtime/asm_amd64.s:1357
| Wraps: (2) 4: dead
| Error types: (1) *withstack.withStack (2) *errutil.leafError
Wraps: (5) attached stack trace
-- stack trace:
| main.glob..func14
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1143
| main.wrap.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:267
| github.com/spf13/cobra.(*Command).execute
| /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:830
| github.com/spf13/cobra.(*Command).ExecuteC
| /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:914
| github.com/spf13/cobra.(*Command).Execute
| /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:864
| main.main
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1839
| runtime.main
| /usr/local/go/src/runtime/proc.go:203
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (6) 3: dead
Error types: (1) errors.Unclassified (2) *secondary.withSecondaryError (3) *secondary.withSecondaryError (4) *secondary.withSecondaryError (5) *withstack.withStack (6) *errutil.leafError
```
<details><summary>More</summary><p>
Artifacts: [/decommission/randomized](https://teamcity.cockroachdb.com/viewLog.html?buildId=2366018&tab=artifacts#/decommission/randomized)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Adecommission%2Frandomized.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| test | roachtest decommission randomized failed on main main home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go runtime main usr local go src runtime proc go runtime goexit usr local go src runtime asm s wraps dead error types withstack withstack errutil leaferror wraps secondary error attachment dead attached stack trace stack trace main glob home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go main wrap home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go github com cobra command execute home agent work go pkg mod github com cobra command go github com cobra command executec home agent work go pkg mod github com cobra command go github com cobra command execute home agent work go pkg mod github com cobra command go main main home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go runtime main usr local go src runtime proc go runtime goexit usr local go src runtime asm s wraps dead error types withstack withstack errutil leaferror wraps attached stack trace stack trace main glob home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go main wrap home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go github com cobra command execute home agent work go pkg mod github com cobra command go github com cobra command executec home agent work go pkg mod github com cobra command go github com cobra command execute home agent work go pkg mod github com cobra command go main main home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go runtime main usr local go src runtime proc go runtime goexit usr local go src runtime asm s wraps dead error types errors unclassified secondary withsecondaryerror secondary withsecondaryerror secondary withsecondaryerror withstack withstack errutil leaferror more artifacts powered by | 1 |
67,583 | 7,054,426,617 | IssuesEvent | 2018-01-04 00:39:43 | Automattic/jetpack | https://api.github.com/repos/Automattic/jetpack | opened | Tests: test_register_post_types_callback_error() fatals under PHP 5.2 despite a version check | Unit Tests | `test_register_post_types_callback_error()` fatals under PHP 5.2 despite a version check.
See https://travis-ci.org/Automattic/jetpack/jobs/324450213#L614 and #8447. | 1.0 | Tests: test_register_post_types_callback_error() fatals under PHP 5.2 despite a version check - `test_register_post_types_callback_error()` fatals under PHP 5.2 despite a version check.
See https://travis-ci.org/Automattic/jetpack/jobs/324450213#L614 and #8447. | test | tests test register post types callback error fatals under php despite a version check test register post types callback error fatals under php despite a version check see and | 1 |
78,095 | 10,039,627,272 | IssuesEvent | 2019-07-18 17:51:46 | google/go-cloud | https://api.github.com/repos/google/go-cloud | closed | doc: add website guide for server | documentation process | With #1598 we now have a minimal sample for using the CDK's `server` in `samples/server`. @zombiezen suggests "we should add a guide in the website tutorials to promote discoverability." | 1.0 | doc: add website guide for server - With #1598 we now have a minimal sample for using the CDK's `server` in `samples/server`. @zombiezen suggests "we should add a guide in the website tutorials to promote discoverability." | non_test | doc add website guide for server with we now have a minimal sample for using the cdk s server in samples server zombiezen suggests we should add a guide in the website tutorials to promote discoverability | 0 |
135,132 | 5,242,727,798 | IssuesEvent | 2017-01-31 18:49:55 | nextgis/nextgisweb_compulink | https://api.github.com/repos/nextgis/nextgisweb_compulink | closed | Название полей в таблице ОС | enhancement High Priority | Добавить к наименованию двух полей «Начало/Окончание сдачи заказчику»
следующий текст «в эксплуатацию» в нижней панели:

| 1.0 | Название полей в таблице ОС - Добавить к наименованию двух полей «Начало/Окончание сдачи заказчику»
следующий текст «в эксплуатацию» в нижней панели:

| non_test | название полей в таблице ос добавить к наименованию двух полей «начало окончание сдачи заказчику» следующий текст «в эксплуатацию» в нижней панели | 0 |
285,404 | 31,154,521,933 | IssuesEvent | 2023-08-16 12:18:59 | Trinadh465/linux-4.1.15_CVE-2018-5873 | https://api.github.com/repos/Trinadh465/linux-4.1.15_CVE-2018-5873 | opened | CVE-2016-3135 (High) detected in linuxlinux-4.1.52 | Mend: dependency security vulnerability | ## CVE-2016-3135 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.52</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2018-5873/commit/32145daf0c96b012284199f23418243e0168269f">32145daf0c96b012284199f23418243e0168269f</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/netfilter/x_tables.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/netfilter/x_tables.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Integer overflow in the xt_alloc_table_info function in net/netfilter/x_tables.c in the Linux kernel through 4.5.2 on 32-bit platforms allows local users to gain privileges or cause a denial of service (heap memory corruption) via an IPT_SO_SET_REPLACE setsockopt call.
<p>Publish Date: 2016-04-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3135>CVE-2016-3135</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-3135">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-3135</a></p>
<p>Release Date: 2016-04-27</p>
<p>Fix Resolution: v4.6-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-3135 (High) detected in linuxlinux-4.1.52 - ## CVE-2016-3135 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.52</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2018-5873/commit/32145daf0c96b012284199f23418243e0168269f">32145daf0c96b012284199f23418243e0168269f</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/netfilter/x_tables.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/netfilter/x_tables.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Integer overflow in the xt_alloc_table_info function in net/netfilter/x_tables.c in the Linux kernel through 4.5.2 on 32-bit platforms allows local users to gain privileges or cause a denial of service (heap memory corruption) via an IPT_SO_SET_REPLACE setsockopt call.
<p>Publish Date: 2016-04-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3135>CVE-2016-3135</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-3135">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-3135</a></p>
<p>Release Date: 2016-04-27</p>
<p>Fix Resolution: v4.6-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files net netfilter x tables c net netfilter x tables c vulnerability details integer overflow in the xt alloc table info function in net netfilter x tables c in the linux kernel through on bit platforms allows local users to gain privileges or cause a denial of service heap memory corruption via an ipt so set replace setsockopt call publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
229,865 | 18,446,689,822 | IssuesEvent | 2021-10-15 03:37:49 | mozilla-mobile/focus-ios | https://api.github.com/repos/mozilla-mobile/focus-ios | opened | Light Theme: Background colour of Settings background and table list should be reversed | eng:ui-test eng:automation | ## Steps to reproduce
- Go to ⚙️ Settings
- Observe background colour of modal sheet and table list elements
### Expected behavior
Background colour of modal sheet should be **darker** than table list.
<img width="375" alt="iPhone - Settings - Light@2x" src="https://user-images.githubusercontent.com/51007/137428474-37f6bf9c-29de-46c6-ba48-1fb3175ec145.png">
I think swapping the two colour values would give us the right appearance?
### Actual behavior
Background colour of modal sheet is **lighter** than table list.
<img width="320" src="https://user-images.githubusercontent.com/51007/137428394-4e3e82ac-25a8-403b-8b3a-8cc394c5d9b8.jpeg"> | 1.0 | Light Theme: Background colour of Settings background and table list should be reversed - ## Steps to reproduce
- Go to ⚙️ Settings
- Observe background colour of modal sheet and table list elements
### Expected behavior
Background colour of modal sheet should be **darker** than table list.
<img width="375" alt="iPhone - Settings - Light@2x" src="https://user-images.githubusercontent.com/51007/137428474-37f6bf9c-29de-46c6-ba48-1fb3175ec145.png">
I think swapping the two colour values would give us the right appearance?
### Actual behavior
Background colour of modal sheet is **lighter** than table list.
<img width="320" src="https://user-images.githubusercontent.com/51007/137428394-4e3e82ac-25a8-403b-8b3a-8cc394c5d9b8.jpeg"> | test | light theme background colour of settings background and table list should be reversed steps to reproduce go to ⚙️ settings observe background colour of modal sheet and table list elements expected behavior background colour of modal sheet should be darker than table list img width alt iphone settings light src i think swapping the two colour values would give us the right appearance actual behavior background colour of modal sheet is lighter than table list img width src | 1 |
504,898 | 14,623,435,353 | IssuesEvent | 2020-12-23 03:20:38 | ChrisNZL/Tallowmere2 | https://api.github.com/repos/ChrisNZL/Tallowmere2 | closed | Add emergency mechanisms to warp out-of-bound players to room entrance | ⚛ physics ⚠ priority++ 🌐 online 🪓 weapons | For 0.2.0 – all game modes: Single-player, Couch Co-op, Online Co-op....
While it's more appropriate to fix the root cause of bugs, it's also not fun if you're playing and a run encounters a show-stopping bug.
Regarding weird bugs where players are outside of room bounds, would probably be feasible for clients to detect if a player is out of bounds incorrectly, and tell the server to correct the issue, rather than remaining "stuck".
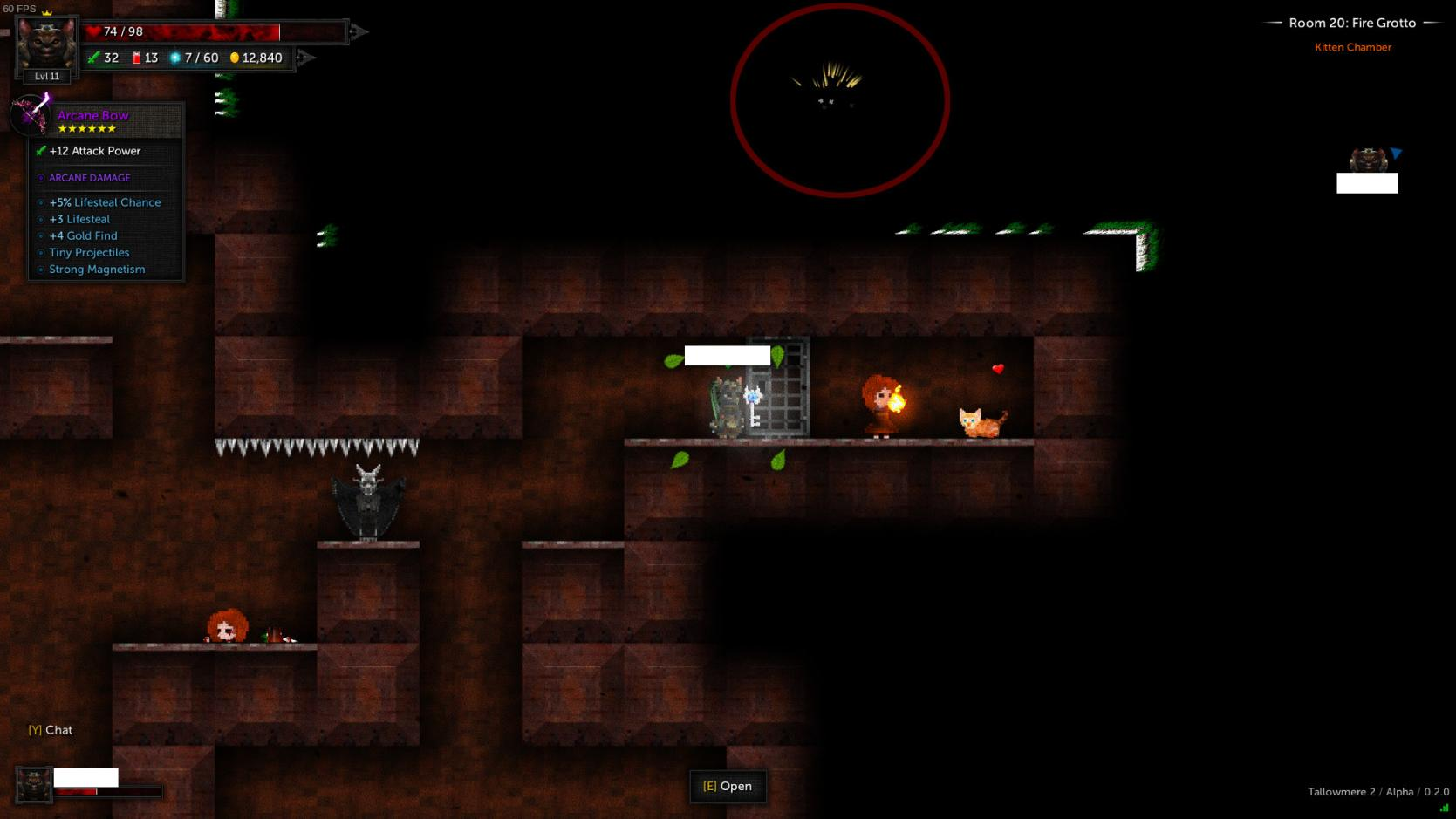
Related:
- issue #538
- issue #487
---
Report from 0.2.1 also saying they were stuck in a block and unable to continue, single-player, was using the katana, saved, exited, resumed, stuck in the wall.
- Feedback ID: 20201213-KVCBK
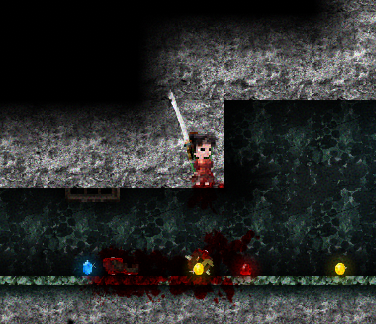
| 1.0 | Add emergency mechanisms to warp out-of-bound players to room entrance - For 0.2.0 – all game modes: Single-player, Couch Co-op, Online Co-op....
While it's more appropriate to fix the root cause of bugs, it's also not fun if you're playing and a run encounters a show-stopping bug.
Regarding weird bugs where players are outside of room bounds, would probably be feasible for clients to detect if a player is out of bounds incorrectly, and tell the server to correct the issue, rather than remaining "stuck".
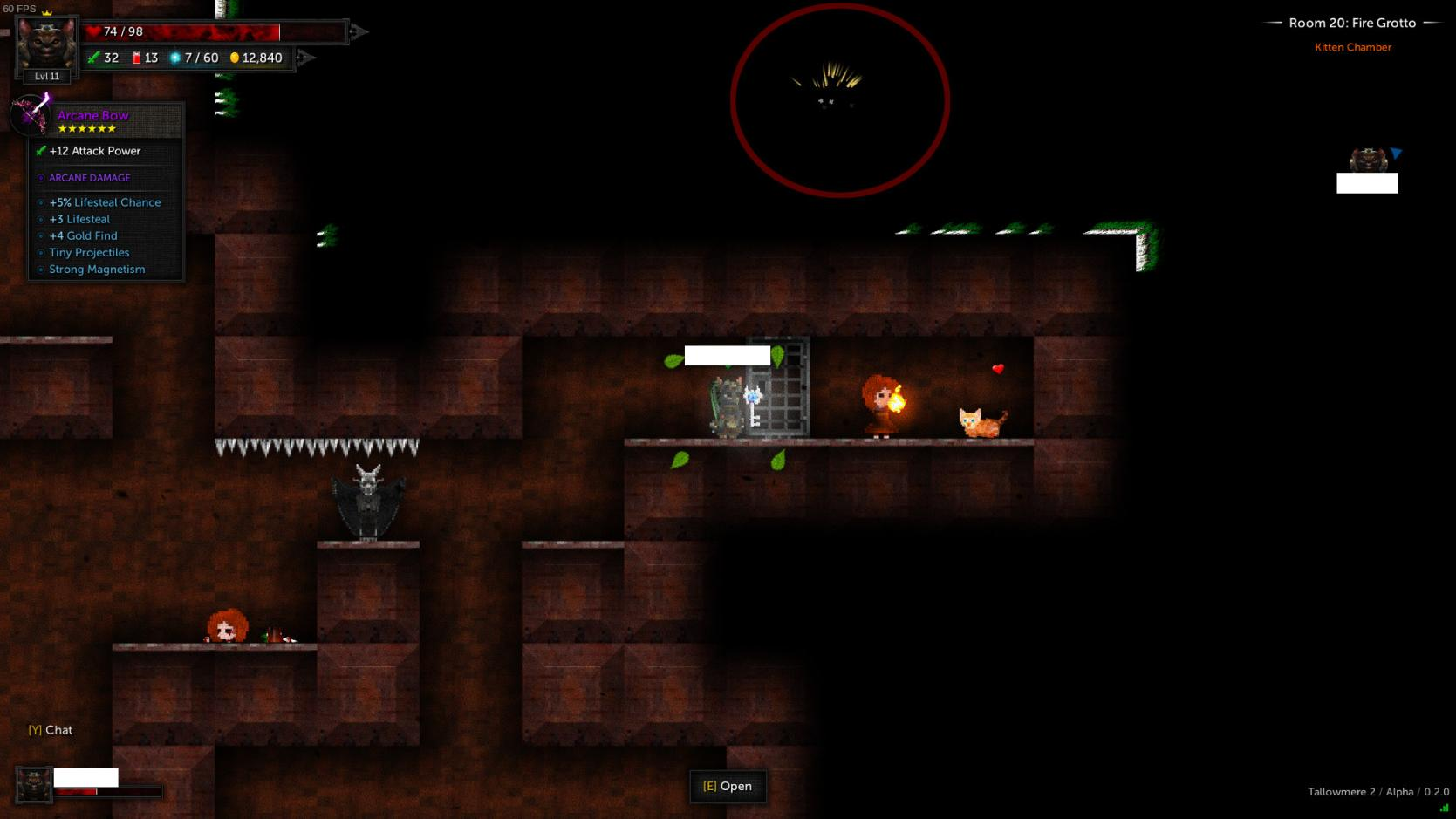
Related:
- issue #538
- issue #487
---
Report from 0.2.1 also saying they were stuck in a block and unable to continue, single-player, was using the katana, saved, exited, resumed, stuck in the wall.
- Feedback ID: 20201213-KVCBK
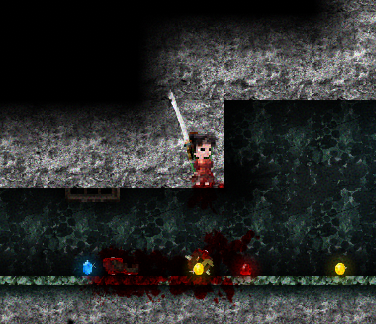
| non_test | add emergency mechanisms to warp out of bound players to room entrance for – all game modes single player couch co op online co op while it s more appropriate to fix the root cause of bugs it s also not fun if you re playing and a run encounters a show stopping bug regarding weird bugs where players are outside of room bounds would probably be feasible for clients to detect if a player is out of bounds incorrectly and tell the server to correct the issue rather than remaining stuck related issue issue report from also saying they were stuck in a block and unable to continue single player was using the katana saved exited resumed stuck in the wall feedback id kvcbk | 0 |
312,232 | 26,850,584,272 | IssuesEvent | 2023-02-03 10:42:24 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | sql/pgwire: TestParseClientProvidedSessionParameters failed | C-test-failure O-robot branch-master | sql/pgwire.TestParseClientProvidedSessionParameters [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8570786?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8570786?buildTab=artifacts#/) on master @ [cebffa1eb4127c2ae9bd362b462956167c732a18](https://github.com/cockroachdb/cockroach/commits/cebffa1eb4127c2ae9bd362b462956167c732a18):
```
=== RUN TestParseClientProvidedSessionParameters
test_log_scope.go:161: test logs captured to: /artifacts/tmp/_tmp/28616e575ae934b92eba220441c7ca42/logTestParseClientProvidedSessionParameters795899212
test_log_scope.go:79: use -show-logs to present logs inline
=== CONT TestParseClientProvidedSessionParameters
conn_test.go:1603: -- test log scope end --
conn_test.go:1603: Leaked goroutine: goroutine 9211248 [IO wait]:
internal/poll.runtime_pollWait(0x7f1bab75aa88, 0x72)
GOROOT/src/runtime/netpoll.go:305 +0x89
internal/poll.(*pollDesc).wait(0xc01d85c000?, 0xc01dca6030?, 0x0)
GOROOT/src/internal/poll/fd_poll_runtime.go:84 +0x32
internal/poll.(*pollDesc).waitRead(...)
GOROOT/src/internal/poll/fd_poll_runtime.go:89
internal/poll.(*FD).Read(0xc01d85c000, {0xc01dca6030, 0x10, 0x10})
GOROOT/src/internal/poll/fd_unix.go:167 +0x25a
net.(*netFD).Read(0xc01d85c000, {0xc01dca6030?, 0xc0142d5e48?, 0x47d5f2?})
GOROOT/src/net/fd_posix.go:55 +0x29
net.(*conn).Read(0xc01a58a000, {0xc01dca6030?, 0xc01dcc01e0?, 0xc01dcc01e0?})
GOROOT/src/net/net.go:183 +0x45
github.com/jackc/pgconn.(*PgConn).CancelRequest(0xc005cfe160, {0x623bc78?, 0xc01dcc01e0})
github.com/jackc/pgconn/external/com_github_jackc_pgconn/pgconn.go:934 +0x3db
github.com/jackc/pgconn.(*PgConn).asyncClose.func1()
github.com/jackc/pgconn/external/com_github_jackc_pgconn/pgconn.go:667 +0x10f
created by github.com/jackc/pgconn.(*PgConn).asyncClose
github.com/jackc/pgconn/external/com_github_jackc_pgconn/pgconn.go:658 +0x65
Leaked goroutine: goroutine 9211311 [select]:
github.com/jackc/pgconn/internal/ctxwatch.(*ContextWatcher).Watch.func1()
github.com/jackc/pgconn/internal/ctxwatch/external/com_github_jackc_pgconn/internal/ctxwatch/context_watcher.go:47 +0x6c
created by github.com/jackc/pgconn/internal/ctxwatch.(*ContextWatcher).Watch
github.com/jackc/pgconn/internal/ctxwatch/external/com_github_jackc_pgconn/internal/ctxwatch/context_watcher.go:46 +0x12c
--- FAIL: TestParseClientProvidedSessionParameters (7.49s)
```
<p>Parameters: <code>TAGS=bazel,gss,deadlock</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
/cc @cockroachdb/sql-sessions @cockroachdb/server
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestParseClientProvidedSessionParameters.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 1.0 | sql/pgwire: TestParseClientProvidedSessionParameters failed - sql/pgwire.TestParseClientProvidedSessionParameters [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8570786?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8570786?buildTab=artifacts#/) on master @ [cebffa1eb4127c2ae9bd362b462956167c732a18](https://github.com/cockroachdb/cockroach/commits/cebffa1eb4127c2ae9bd362b462956167c732a18):
```
=== RUN TestParseClientProvidedSessionParameters
test_log_scope.go:161: test logs captured to: /artifacts/tmp/_tmp/28616e575ae934b92eba220441c7ca42/logTestParseClientProvidedSessionParameters795899212
test_log_scope.go:79: use -show-logs to present logs inline
=== CONT TestParseClientProvidedSessionParameters
conn_test.go:1603: -- test log scope end --
conn_test.go:1603: Leaked goroutine: goroutine 9211248 [IO wait]:
internal/poll.runtime_pollWait(0x7f1bab75aa88, 0x72)
GOROOT/src/runtime/netpoll.go:305 +0x89
internal/poll.(*pollDesc).wait(0xc01d85c000?, 0xc01dca6030?, 0x0)
GOROOT/src/internal/poll/fd_poll_runtime.go:84 +0x32
internal/poll.(*pollDesc).waitRead(...)
GOROOT/src/internal/poll/fd_poll_runtime.go:89
internal/poll.(*FD).Read(0xc01d85c000, {0xc01dca6030, 0x10, 0x10})
GOROOT/src/internal/poll/fd_unix.go:167 +0x25a
net.(*netFD).Read(0xc01d85c000, {0xc01dca6030?, 0xc0142d5e48?, 0x47d5f2?})
GOROOT/src/net/fd_posix.go:55 +0x29
net.(*conn).Read(0xc01a58a000, {0xc01dca6030?, 0xc01dcc01e0?, 0xc01dcc01e0?})
GOROOT/src/net/net.go:183 +0x45
github.com/jackc/pgconn.(*PgConn).CancelRequest(0xc005cfe160, {0x623bc78?, 0xc01dcc01e0})
github.com/jackc/pgconn/external/com_github_jackc_pgconn/pgconn.go:934 +0x3db
github.com/jackc/pgconn.(*PgConn).asyncClose.func1()
github.com/jackc/pgconn/external/com_github_jackc_pgconn/pgconn.go:667 +0x10f
created by github.com/jackc/pgconn.(*PgConn).asyncClose
github.com/jackc/pgconn/external/com_github_jackc_pgconn/pgconn.go:658 +0x65
Leaked goroutine: goroutine 9211311 [select]:
github.com/jackc/pgconn/internal/ctxwatch.(*ContextWatcher).Watch.func1()
github.com/jackc/pgconn/internal/ctxwatch/external/com_github_jackc_pgconn/internal/ctxwatch/context_watcher.go:47 +0x6c
created by github.com/jackc/pgconn/internal/ctxwatch.(*ContextWatcher).Watch
github.com/jackc/pgconn/internal/ctxwatch/external/com_github_jackc_pgconn/internal/ctxwatch/context_watcher.go:46 +0x12c
--- FAIL: TestParseClientProvidedSessionParameters (7.49s)
```
<p>Parameters: <code>TAGS=bazel,gss,deadlock</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
/cc @cockroachdb/sql-sessions @cockroachdb/server
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestParseClientProvidedSessionParameters.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| test | sql pgwire testparseclientprovidedsessionparameters failed sql pgwire testparseclientprovidedsessionparameters with on master run testparseclientprovidedsessionparameters test log scope go test logs captured to artifacts tmp tmp test log scope go use show logs to present logs inline cont testparseclientprovidedsessionparameters conn test go test log scope end conn test go leaked goroutine goroutine internal poll runtime pollwait goroot src runtime netpoll go internal poll polldesc wait goroot src internal poll fd poll runtime go internal poll polldesc waitread goroot src internal poll fd poll runtime go internal poll fd read goroot src internal poll fd unix go net netfd read goroot src net fd posix go net conn read goroot src net net go github com jackc pgconn pgconn cancelrequest github com jackc pgconn external com github jackc pgconn pgconn go github com jackc pgconn pgconn asyncclose github com jackc pgconn external com github jackc pgconn pgconn go created by github com jackc pgconn pgconn asyncclose github com jackc pgconn external com github jackc pgconn pgconn go leaked goroutine goroutine github com jackc pgconn internal ctxwatch contextwatcher watch github com jackc pgconn internal ctxwatch external com github jackc pgconn internal ctxwatch context watcher go created by github com jackc pgconn internal ctxwatch contextwatcher watch github com jackc pgconn internal ctxwatch external com github jackc pgconn internal ctxwatch context watcher go fail testparseclientprovidedsessionparameters parameters tags bazel gss deadlock help see also cc cockroachdb sql sessions cockroachdb server | 1 |
169,131 | 20,828,053,990 | IssuesEvent | 2022-03-19 01:26:32 | gms-ws-sandbox/dev-example-places | https://api.github.com/repos/gms-ws-sandbox/dev-example-places | opened | CVE-2021-44906 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2021-44906 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-1.2.0.tgz</b>, <b>minimist-0.0.10.tgz</b>, <b>minimist-0.0.8.tgz</b></p></summary>
<p>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /client/package.json</p>
<p>Path to vulnerable library: /client/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.2.0.tgz (Root Library)
- core-7.6.0.tgz
- json5-2.1.1.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /client/package.json</p>
<p>Path to vulnerable library: /client/node_modules/optimist/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.2.0.tgz (Root Library)
- jest-24.9.0.tgz
- jest-cli-24.9.0.tgz
- core-24.9.0.tgz
- reporters-24.9.0.tgz
- istanbul-reports-2.2.6.tgz
- handlebars-4.5.1.tgz
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /client/package.json</p>
<p>Path to vulnerable library: /client/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.2.0.tgz (Root Library)
- babel-loader-8.0.6.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-44906">https://nvd.nist.gov/vuln/detail/CVE-2021-44906</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"1.2.0","packageFilePaths":["/client/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-scripts:3.2.0;@babel/core:7.6.0;json5:2.1.1;minimist:1.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105","isBinary":false},{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.10","packageFilePaths":["/client/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-scripts:3.2.0;jest:24.9.0;jest-cli:24.9.0;@jest/core:24.9.0;@jest/reporters:24.9.0;istanbul-reports:2.2.6;handlebars:4.5.1;optimist:0.6.1;minimist:0.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105","isBinary":false},{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.8","packageFilePaths":["/client/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-scripts:3.2.0;babel-loader:8.0.6;mkdirp:0.5.1;minimist:0.0.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44906","vulnerabilityDetails":"Minimist \u003c\u003d1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-44906 (Medium) detected in multiple libraries - ## CVE-2021-44906 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-1.2.0.tgz</b>, <b>minimist-0.0.10.tgz</b>, <b>minimist-0.0.8.tgz</b></p></summary>
<p>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /client/package.json</p>
<p>Path to vulnerable library: /client/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.2.0.tgz (Root Library)
- core-7.6.0.tgz
- json5-2.1.1.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /client/package.json</p>
<p>Path to vulnerable library: /client/node_modules/optimist/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.2.0.tgz (Root Library)
- jest-24.9.0.tgz
- jest-cli-24.9.0.tgz
- core-24.9.0.tgz
- reporters-24.9.0.tgz
- istanbul-reports-2.2.6.tgz
- handlebars-4.5.1.tgz
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /client/package.json</p>
<p>Path to vulnerable library: /client/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.2.0.tgz (Root Library)
- babel-loader-8.0.6.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-44906">https://nvd.nist.gov/vuln/detail/CVE-2021-44906</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"1.2.0","packageFilePaths":["/client/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-scripts:3.2.0;@babel/core:7.6.0;json5:2.1.1;minimist:1.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105","isBinary":false},{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.10","packageFilePaths":["/client/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-scripts:3.2.0;jest:24.9.0;jest-cli:24.9.0;@jest/core:24.9.0;@jest/reporters:24.9.0;istanbul-reports:2.2.6;handlebars:4.5.1;optimist:0.6.1;minimist:0.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105","isBinary":false},{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.8","packageFilePaths":["/client/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-scripts:3.2.0;babel-loader:8.0.6;mkdirp:0.5.1;minimist:0.0.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44906","vulnerabilityDetails":"Minimist \u003c\u003d1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | non_test | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries minimist tgz minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file client package json path to vulnerable library client node modules minimist package json dependency hierarchy react scripts tgz root library core tgz tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file client package json path to vulnerable library client node modules optimist node modules minimist package json dependency hierarchy react scripts tgz root library jest tgz jest cli tgz core tgz reporters tgz istanbul reports tgz handlebars tgz optimist tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file client package json path to vulnerable library client node modules mkdirp node modules minimist package json dependency hierarchy react scripts tgz root library babel loader tgz mkdirp tgz x minimist tgz vulnerable library found in base branch master vulnerability details minimist is vulnerable to prototype pollution via file index js function setkey lines publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bumperlane public service contracts prerelease cloudscribe templates virteom tenant mobile bluetooth prerelease showingvault dotnet sdk prerelease envisia dotnet templates yarnpkg yarn virteom tenant mobile framework uwp prerelease virteom tenant mobile framework ios prerelease bumperlane public api clientmodule prerelease vuejs netcore dianoga virteom tenant mobile bluetooth ios prerelease virteom public utilities prerelease indianadavy vuejswebapitemplate csharp nordron angulartemplate virteom tenant mobile framework prerelease virteom tenant mobile bluetooth android prerelease dotnet scaffold raml parser corevuewebtest dotnetng template sitecoremaster truedynamicplaceholders virteom tenant mobile framework android prerelease fable template elmish react blazorpolyfill build fable snowpack template bumperlane public api client prerelease yarn msbuild blazor tailwindcss bunit bridge aws tslint safe template gr pagerender razor midiator webclient isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree react scripts babel core minimist isminimumfixversionavailable true minimumfixversion bumperlane public service contracts prerelease cloudscribe templates virteom tenant mobile bluetooth prerelease showingvault dotnet sdk prerelease envisia dotnet templates yarnpkg yarn virteom tenant mobile framework uwp prerelease virteom tenant mobile framework ios prerelease bumperlane public api clientmodule prerelease vuejs netcore dianoga virteom tenant mobile bluetooth ios prerelease virteom public utilities prerelease indianadavy vuejswebapitemplate csharp nordron angulartemplate virteom tenant mobile framework prerelease virteom tenant mobile bluetooth android prerelease dotnet scaffold raml parser corevuewebtest dotnetng template sitecoremaster truedynamicplaceholders virteom tenant mobile framework android prerelease fable template elmish react blazorpolyfill build fable snowpack template bumperlane public api client prerelease yarn msbuild blazor tailwindcss bunit bridge aws tslint safe template gr pagerender razor midiator webclient isbinary false packagetype javascript node js packagename minimist packageversion packagefilepaths istransitivedependency true dependencytree react scripts jest jest cli jest core jest reporters istanbul reports handlebars optimist minimist isminimumfixversionavailable true minimumfixversion bumperlane public service contracts prerelease cloudscribe templates virteom tenant mobile bluetooth prerelease showingvault dotnet sdk prerelease envisia dotnet templates yarnpkg yarn virteom tenant mobile framework uwp prerelease virteom tenant mobile framework ios prerelease bumperlane public api clientmodule prerelease vuejs netcore dianoga virteom tenant mobile bluetooth ios prerelease virteom public utilities prerelease indianadavy vuejswebapitemplate csharp nordron angulartemplate virteom tenant mobile framework prerelease virteom tenant mobile bluetooth android prerelease dotnet scaffold raml parser corevuewebtest dotnetng template sitecoremaster truedynamicplaceholders virteom tenant mobile framework android prerelease fable template elmish react blazorpolyfill build fable snowpack template bumperlane public api client prerelease yarn msbuild blazor tailwindcss bunit bridge aws tslint safe template gr pagerender razor midiator webclient isbinary false packagetype javascript node js packagename minimist packageversion packagefilepaths istransitivedependency true dependencytree react scripts babel loader mkdirp minimist isminimumfixversionavailable true minimumfixversion bumperlane public service contracts prerelease cloudscribe templates virteom tenant mobile bluetooth prerelease showingvault dotnet sdk prerelease envisia dotnet templates yarnpkg yarn virteom tenant mobile framework uwp prerelease virteom tenant mobile framework ios prerelease bumperlane public api clientmodule prerelease vuejs netcore dianoga virteom tenant mobile bluetooth ios prerelease virteom public utilities prerelease indianadavy vuejswebapitemplate csharp nordron angulartemplate virteom tenant mobile framework prerelease virteom tenant mobile bluetooth android prerelease dotnet scaffold raml parser corevuewebtest dotnetng template sitecoremaster truedynamicplaceholders virteom tenant mobile framework android prerelease fable template elmish react blazorpolyfill build fable snowpack template bumperlane public api client prerelease yarn msbuild blazor tailwindcss bunit bridge aws tslint safe template gr pagerender razor midiator webclient isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails minimist is vulnerable to prototype pollution via file index js function setkey lines vulnerabilityurl | 0 |
19,596 | 3,475,562,272 | IssuesEvent | 2015-12-25 20:07:40 | WikiEducationFoundation/WikiEduDashboard | https://api.github.com/repos/WikiEducationFoundation/WikiEduDashboard | closed | training quiz question font is too small | bug needs design | Eryk makes this suggestion: Increase the size of the question text to match the answer text, but add bold formatting to the question text.
cc @bmathews | 1.0 | training quiz question font is too small - Eryk makes this suggestion: Increase the size of the question text to match the answer text, but add bold formatting to the question text.
cc @bmathews | non_test | training quiz question font is too small eryk makes this suggestion increase the size of the question text to match the answer text but add bold formatting to the question text cc bmathews | 0 |
221,964 | 17,379,505,907 | IssuesEvent | 2021-07-31 11:54:13 | practicalli/data-science-content | https://api.github.com/repos/practicalli/data-science-content | opened | Defining the scope of the initial version of the Clojure Data Science guide | nextjournal notebooks notespace oz project tablecloth testing | The first release of the Clojure Data Scienc would start with common Clojure tools and code and through a series of practical step by step tutorials show how to apply and adopt the more specific Clojure data science tools like tablecloth, etc.
One aim is to provide a smooth transition for existing Clojure developers to move into data science projects.
The initial sections would include
- installing Clojure and data inspection tooling (Clojure CLI, practicalli/clojure-deps-edn for Rebel Readline, Portal, Reveal and general tooling for Clojure projects)
- data wrangling with the clojure.data tools and the basics of tablecloth - including some idea when to use each of these
- REPL driven development in Clojure data science
- using the REPL, data inspectors (Portal, Reveal, Cider inspect) to help with data wrangling
- using notespace and NextJournal to create a visual notebook for a data science project
- visualising the results with asciigraph, Oz and perhaps Hanami too (and if so, some suggestions as to when to use Oz or Hanami)
- testing, CI, collaborative coding, packaging and deployment of Clojure Data Science projects
Ideally the guide would consist of 2-3 practical step by step tutorials. Each tutorial would either build on a previous one or cover a different aspect of data science (although probably not anything too deep into the science). This would complement much of the work that has been done in the Clojure data science hand book and perhaps enable more people to contribute to that handbook in the long run. | 1.0 | Defining the scope of the initial version of the Clojure Data Science guide - The first release of the Clojure Data Scienc would start with common Clojure tools and code and through a series of practical step by step tutorials show how to apply and adopt the more specific Clojure data science tools like tablecloth, etc.
One aim is to provide a smooth transition for existing Clojure developers to move into data science projects.
The initial sections would include
- installing Clojure and data inspection tooling (Clojure CLI, practicalli/clojure-deps-edn for Rebel Readline, Portal, Reveal and general tooling for Clojure projects)
- data wrangling with the clojure.data tools and the basics of tablecloth - including some idea when to use each of these
- REPL driven development in Clojure data science
- using the REPL, data inspectors (Portal, Reveal, Cider inspect) to help with data wrangling
- using notespace and NextJournal to create a visual notebook for a data science project
- visualising the results with asciigraph, Oz and perhaps Hanami too (and if so, some suggestions as to when to use Oz or Hanami)
- testing, CI, collaborative coding, packaging and deployment of Clojure Data Science projects
Ideally the guide would consist of 2-3 practical step by step tutorials. Each tutorial would either build on a previous one or cover a different aspect of data science (although probably not anything too deep into the science). This would complement much of the work that has been done in the Clojure data science hand book and perhaps enable more people to contribute to that handbook in the long run. | test | defining the scope of the initial version of the clojure data science guide the first release of the clojure data scienc would start with common clojure tools and code and through a series of practical step by step tutorials show how to apply and adopt the more specific clojure data science tools like tablecloth etc one aim is to provide a smooth transition for existing clojure developers to move into data science projects the initial sections would include installing clojure and data inspection tooling clojure cli practicalli clojure deps edn for rebel readline portal reveal and general tooling for clojure projects data wrangling with the clojure data tools and the basics of tablecloth including some idea when to use each of these repl driven development in clojure data science using the repl data inspectors portal reveal cider inspect to help with data wrangling using notespace and nextjournal to create a visual notebook for a data science project visualising the results with asciigraph oz and perhaps hanami too and if so some suggestions as to when to use oz or hanami testing ci collaborative coding packaging and deployment of clojure data science projects ideally the guide would consist of practical step by step tutorials each tutorial would either build on a previous one or cover a different aspect of data science although probably not anything too deep into the science this would complement much of the work that has been done in the clojure data science hand book and perhaps enable more people to contribute to that handbook in the long run | 1 |
37,527 | 5,118,676,430 | IssuesEvent | 2017-01-08 09:15:09 | imixs/imixs-workflow | https://api.github.com/repos/imixs/imixs-workflow | closed | ReportRestService - sort result | bug testing | provide parameters for pageindex, pagesize, sortorder and sortdirection | 1.0 | ReportRestService - sort result - provide parameters for pageindex, pagesize, sortorder and sortdirection | test | reportrestservice sort result provide parameters for pageindex pagesize sortorder and sortdirection | 1 |
62,089 | 14,656,431,972 | IssuesEvent | 2020-12-28 13:24:46 | fu1771695yongxie/angular.js | https://api.github.com/repos/fu1771695yongxie/angular.js | opened | CVE-2017-18077 (High) detected in brace-expansion-1.1.6.tgz | security vulnerability | ## CVE-2017-18077 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>brace-expansion-1.1.6.tgz</b></p></summary>
<p>Brace expansion as known from sh/bash</p>
<p>Library home page: <a href="https://registry.npmjs.org/brace-expansion/-/brace-expansion-1.1.6.tgz">https://registry.npmjs.org/brace-expansion/-/brace-expansion-1.1.6.tgz</a></p>
<p>Path to dependency file: angular.js/yarn.lock</p>
<p>Path to vulnerable library: angular.js/yarn.lock</p>
<p>
Dependency Hierarchy:
- glob-6.0.4.tgz (Root Library)
- minimatch-3.0.3.tgz
- :x: **brace-expansion-1.1.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/angular.js/commit/1b1b50185bc6258e96ba849a00be9ba44d9ac05c">1b1b50185bc6258e96ba849a00be9ba44d9ac05c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
index.js in brace-expansion before 1.1.7 is vulnerable to Regular Expression Denial of Service (ReDoS) attacks, as demonstrated by an expand argument containing many comma characters.
<p>Publish Date: 2018-01-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18077>CVE-2017-18077</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-18077">https://nvd.nist.gov/vuln/detail/CVE-2017-18077</a></p>
<p>Release Date: 2018-01-27</p>
<p>Fix Resolution: 1.1.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-18077 (High) detected in brace-expansion-1.1.6.tgz - ## CVE-2017-18077 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>brace-expansion-1.1.6.tgz</b></p></summary>
<p>Brace expansion as known from sh/bash</p>
<p>Library home page: <a href="https://registry.npmjs.org/brace-expansion/-/brace-expansion-1.1.6.tgz">https://registry.npmjs.org/brace-expansion/-/brace-expansion-1.1.6.tgz</a></p>
<p>Path to dependency file: angular.js/yarn.lock</p>
<p>Path to vulnerable library: angular.js/yarn.lock</p>
<p>
Dependency Hierarchy:
- glob-6.0.4.tgz (Root Library)
- minimatch-3.0.3.tgz
- :x: **brace-expansion-1.1.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/angular.js/commit/1b1b50185bc6258e96ba849a00be9ba44d9ac05c">1b1b50185bc6258e96ba849a00be9ba44d9ac05c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
index.js in brace-expansion before 1.1.7 is vulnerable to Regular Expression Denial of Service (ReDoS) attacks, as demonstrated by an expand argument containing many comma characters.
<p>Publish Date: 2018-01-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18077>CVE-2017-18077</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-18077">https://nvd.nist.gov/vuln/detail/CVE-2017-18077</a></p>
<p>Release Date: 2018-01-27</p>
<p>Fix Resolution: 1.1.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in brace expansion tgz cve high severity vulnerability vulnerable library brace expansion tgz brace expansion as known from sh bash library home page a href path to dependency file angular js yarn lock path to vulnerable library angular js yarn lock dependency hierarchy glob tgz root library minimatch tgz x brace expansion tgz vulnerable library found in head commit a href found in base branch master vulnerability details index js in brace expansion before is vulnerable to regular expression denial of service redos attacks as demonstrated by an expand argument containing many comma characters publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
337,059 | 30,237,344,144 | IssuesEvent | 2023-07-06 11:11:04 | ESMValGroup/ESMValCore | https://api.github.com/repos/ESMValGroup/ESMValCore | closed | [Github Actions] Compress all bash shell setters into one default option per workflow | testing | @bouweandela rightly suggested doing that so the workflow files are a bit more readable, and supplied and [example](https://github.com/dask/dask/blob/11f2b83ee034aea7837691f9a0d4ede6309d6194/.github/workflows/conda.yml#L18-L21) how that's done - cheers, bud! I'll do this as soon as possible :+1: | 1.0 | [Github Actions] Compress all bash shell setters into one default option per workflow - @bouweandela rightly suggested doing that so the workflow files are a bit more readable, and supplied and [example](https://github.com/dask/dask/blob/11f2b83ee034aea7837691f9a0d4ede6309d6194/.github/workflows/conda.yml#L18-L21) how that's done - cheers, bud! I'll do this as soon as possible :+1: | test | compress all bash shell setters into one default option per workflow bouweandela rightly suggested doing that so the workflow files are a bit more readable and supplied and how that s done cheers bud i ll do this as soon as possible | 1 |
136,292 | 30,516,586,842 | IssuesEvent | 2023-07-19 03:54:31 | SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0 | https://api.github.com/repos/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0 | opened | Code Security Report: 30 high severity findings, 56 total findings | Mend: code security findings | # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-07-19 03:53am
**Total Findings:** 56 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 1
**Detected Programming Languages:** 1 (Java*)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
### Most Relevant Findings
> The below list presents the 10 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend SAST Application](https://dev.whitesourcesoftware.com/sast/#/scans/59ae87e1-e13d-40ad-a2b0-1b890c93ee09/details).
<table role='table'><thead><tr><th>Severity</th><th>Vulnerability Type</th><th>CWE</th><th>File</th><th>Data Flows</th><th>Date</th></tr></thead><tbody><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:1813](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1813)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1808-L1813
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1795
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1798
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1798
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1802
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1802
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1802
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1813
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1813
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:172](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L172)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L167-L172
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L166
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L172
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L172
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L172
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:199](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L199)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L194-L199
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L188
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L199
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L199
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L199
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:696](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L696)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L691-L696
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L685
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:721](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L721)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L716-L721
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L714
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:1183](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1183)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1178-L1183
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1163
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1167
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1167
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1167
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1179
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1179
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1179
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1183
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:744](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L744)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L739-L744
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L738
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:1230](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1230)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1225-L1230
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1215
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1219
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1219
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1219
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1225
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1225
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1225
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1230
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[60Findings.java:301](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L301)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L296-L301
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L288
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L289
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L292
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L294
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L301
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[60Findings.java:1271](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1271)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1266-L1271
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1260
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1264
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1264
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1264
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1266
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1271
</details>
</details>
</td></tr></details></td></tr></tbody></table>
### Findings Overview
| Severity | Vulnerability Type | CWE | Language | Count |
|-|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Deserialization of Untrusted Data|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Java*|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Cross-Site Scripting|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|SQL Injection|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Command Injection|[CWE-78](https://cwe.mitre.org/data/definitions/78.html)|Java*|9|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Expression Language Injection|[CWE-917](https://cwe.mitre.org/data/definitions/917.html)|Java*|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Path/Directory Traversal|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Java*|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Unsafe Format String|[CWE-134](https://cwe.mitre.org/data/definitions/134.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Improper Verification of JWT Signature|[CWE-347](https://cwe.mitre.org/data/definitions/347.html)|Java*|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|LDAP Injection|[CWE-90](https://cwe.mitre.org/data/definitions/90.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Insecure Cryptographic Algorithm|[CWE-327](https://cwe.mitre.org/data/definitions/327.html)|Java*|7|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Trust Boundary Violation|[CWE-501](https://cwe.mitre.org/data/definitions/501.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Hardcoded Password/Credentials|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Java*|7|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Error Messages Information Exposure|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|HTTP Header Injection|[CWE-113](https://cwe.mitre.org/data/definitions/113.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Weak Hash Strength|[CWE-328](https://cwe.mitre.org/data/definitions/328.html)|Java*|2|
| 1.0 | Code Security Report: 30 high severity findings, 56 total findings - # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-07-19 03:53am
**Total Findings:** 56 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 1
**Detected Programming Languages:** 1 (Java*)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
### Most Relevant Findings
> The below list presents the 10 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend SAST Application](https://dev.whitesourcesoftware.com/sast/#/scans/59ae87e1-e13d-40ad-a2b0-1b890c93ee09/details).
<table role='table'><thead><tr><th>Severity</th><th>Vulnerability Type</th><th>CWE</th><th>File</th><th>Data Flows</th><th>Date</th></tr></thead><tbody><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:1813](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1813)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1808-L1813
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1795
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1798
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1798
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1802
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1802
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1802
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1813
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1813
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:172](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L172)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L167-L172
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L166
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L172
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L172
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L172
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:199](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L199)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L194-L199
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L188
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L199
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L199
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L199
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:696](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L696)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L691-L696
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L685
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:721](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L721)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L716-L721
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L714
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:1183](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1183)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1178-L1183
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1163
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1167
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1167
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1167
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1179
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1179
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1179
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1183
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:744](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L744)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L739-L744
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L738
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[60Findings.java:1230](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1230)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1225-L1230
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1215
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1219
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1219
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1219
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1225
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1225
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1225
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1230
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[60Findings.java:301](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L301)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L296-L301
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L288
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L289
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L292
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L294
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L301
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[60Findings.java:1271](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1271)
</td><td>1</td><td>2023-07-19 03:54am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1266-L1271
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1260
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1264
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1264
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1264
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1266
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-c9f0deea-14c8-4d72-bec7-936e23e700a0/blob/b1cc27d2ba3c28d6a6d23c5083e76f7fb50003be/60Findings.java#L1271
</details>
</details>
</td></tr></details></td></tr></tbody></table>
### Findings Overview
| Severity | Vulnerability Type | CWE | Language | Count |
|-|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Deserialization of Untrusted Data|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Java*|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Cross-Site Scripting|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|SQL Injection|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Command Injection|[CWE-78](https://cwe.mitre.org/data/definitions/78.html)|Java*|9|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Expression Language Injection|[CWE-917](https://cwe.mitre.org/data/definitions/917.html)|Java*|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Path/Directory Traversal|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Java*|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Unsafe Format String|[CWE-134](https://cwe.mitre.org/data/definitions/134.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Improper Verification of JWT Signature|[CWE-347](https://cwe.mitre.org/data/definitions/347.html)|Java*|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|LDAP Injection|[CWE-90](https://cwe.mitre.org/data/definitions/90.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Insecure Cryptographic Algorithm|[CWE-327](https://cwe.mitre.org/data/definitions/327.html)|Java*|7|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Trust Boundary Violation|[CWE-501](https://cwe.mitre.org/data/definitions/501.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Hardcoded Password/Credentials|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Java*|7|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Error Messages Information Exposure|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|HTTP Header Injection|[CWE-113](https://cwe.mitre.org/data/definitions/113.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Weak Hash Strength|[CWE-328](https://cwe.mitre.org/data/definitions/328.html)|Java*|2|
| non_test | code security report high severity findings total findings code security report scan metadata latest scan total findings new findings resolved findings tested project files detected programming languages java check this box to manually trigger a scan most relevant findings the below list presents the most relevant findings that need your attention to view information on the remaining findings navigate to the severity vulnerability type cwe file data flows date high command injection more info data flow s detected view data flow high command injection more info data flow s detected view data flow high command injection more info data flow s detected view data flow high command injection more info data flow s detected view data flow high command injection more info data flow s detected view data flow high command injection more info data flow s detected view data flow high command injection more info data flow s detected view data flow high command injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow findings overview severity vulnerability type cwe language count high deserialization of untrusted data high cross site scripting high sql injection high command injection high expression language injection high path directory traversal high unsafe format string medium improper verification of jwt signature medium ldap injection medium insecure cryptographic algorithm medium trust boundary violation medium hardcoded password credentials medium error messages information exposure low http header injection low weak hash strength | 0 |
179,457 | 13,881,761,961 | IssuesEvent | 2020-10-18 02:28:21 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | closed | ICE: unexpected predicate TraitPredicate on opaque type | A-traits C-bug E-needs-test F-trait_alias I-ICE ICEBreaker-Cleanup-Crew P-medium T-compiler glacier requires-nightly | Found in the `pr-75180` crater run:
````
git clone https://github.com/PaulGrandperrin/playground/
cd playground
git checkout 572ff41ccdfa72771a37fd9ab89f37e9b5451041
cargo check
````
ICEs:
````
error: internal compiler error: unexpected predicate TraitPredicate(<<std::rc::Rc<impl non_volatile::object::any_rc_object::Object> as std::convert::TryFrom<non_volatile::object::any_rc_object::AnyRcObject>>::Error as std::fmt::Debug>) on opaque type
--> src/non_volatile/object/any_rc_object.rs:34:52
|
34 | <Rc<Self> as TryFrom<AnyRcObject>>::Error: Debug;
| ^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
error: internal compiler error: unexpected predicate TraitPredicate(<std::rc::Rc<impl non_volatile::object::any_rc_object::Object> as std::convert::TryFrom<non_volatile::object::any_rc_object::AnyRcObject>>) on opaque type
--> src/non_volatile/object/any_rc_object.rs:33:19
|
33 | Rc<Self>: TryFrom<AnyRcObject>,
| ^^^^^^^^^^^^^^^^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
error: internal compiler error: unexpected predicate TraitPredicate(<std::rc::Rc<impl non_volatile::object::any_rc_object::Object> as std::marker::Sized>) on opaque type
--> /home/matthias/.rustup/toolchains/nightly-x86_64-unknown-linux-gnu/lib/rustlib/src/rust/library/core/src/convert/mod.rs:494:23
|
494 | pub trait TryFrom<T>: Sized {
| ^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
error: internal compiler error: unexpected predicate TraitPredicate(<non_volatile::object::any_rc_object::AnyRcObject as std::convert::From<std::rc::Rc<impl non_volatile::object::any_rc_object::Object>>>) on opaque type
--> src/non_volatile/object/any_rc_object.rs:32:22
|
32 | AnyRcObject: From<Rc<Self>>,
| ^^^^^^^^^^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
error: internal compiler error: unexpected predicate TraitPredicate(<non_volatile::object::any_rc_object::AnyRcObject as std::marker::Sized>) on opaque type
--> /home/matthias/.rustup/toolchains/nightly-x86_64-unknown-linux-gnu/lib/rustlib/src/rust/library/core/src/convert/mod.rs:386:20
|
386 | pub trait From<T>: Sized {
| ^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
error: internal compiler error: unexpected predicate TraitPredicate(<non_volatile::object::any_rc_object::AnyRcObject as std::convert::From<impl non_volatile::object::any_rc_object::Object>>) on opaque type
--> src/non_volatile/object/any_rc_object.rs:31:77
|
31 | pub trait Object = Serializable + ConstObjType + Default where AnyRcObject: From<Self>,
| ^^^^^^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
thread 'rustc' panicked at 'no errors encountered even though `delay_span_bug` issued', src/librustc_errors/lib.rs:369:17
stack backtrace:
0: std::panicking::begin_panic
1: <rustc_errors::HandlerInner as core::ops::drop::Drop>::drop
2: core::ptr::drop_in_place
3: <alloc::rc::Rc<T> as core::ops::drop::Drop>::drop
4: core::ptr::drop_in_place
5: rustc_span::with_source_map
6: rustc_interface::interface::create_compiler_and_run
7: scoped_tls::ScopedKey<T>::set
note: Some details are omitted, run with `RUST_BACKTRACE=full` for a verbose backtrace.
error: internal compiler error: unexpected panic
note: the compiler unexpectedly panicked. this is a bug.
note: we would appreciate a bug report: https://github.com/rust-lang/rust/issues/new?labels=C-bug%2C+I-ICE%2C+T-compiler&template=ice.md
note: rustc 1.47.0-nightly (2d8a3b918 2020-08-26) running on x86_64-unknown-linux-gnu
note: compiler flags: -C embed-bitcode=no -C debuginfo=2 -C incremental -C target-cpu=native --crate-type bin
note: some of the compiler flags provided by cargo are hidden
query stack during panic:
end of query stack
error: could not compile `playground`.
To learn more, run the command again with --verbose.
````
This ICE happens on:
`rustc 1.47.0-beta.1 (0f91f5c28 2020-08-25)`
`rustc 1.47.0-nightly (2d8a3b918 2020-08-26)`
but rustc `1.45.2 (d3fb005a3 2020-07-31)` builds fine. | 1.0 | ICE: unexpected predicate TraitPredicate on opaque type - Found in the `pr-75180` crater run:
````
git clone https://github.com/PaulGrandperrin/playground/
cd playground
git checkout 572ff41ccdfa72771a37fd9ab89f37e9b5451041
cargo check
````
ICEs:
````
error: internal compiler error: unexpected predicate TraitPredicate(<<std::rc::Rc<impl non_volatile::object::any_rc_object::Object> as std::convert::TryFrom<non_volatile::object::any_rc_object::AnyRcObject>>::Error as std::fmt::Debug>) on opaque type
--> src/non_volatile/object/any_rc_object.rs:34:52
|
34 | <Rc<Self> as TryFrom<AnyRcObject>>::Error: Debug;
| ^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
error: internal compiler error: unexpected predicate TraitPredicate(<std::rc::Rc<impl non_volatile::object::any_rc_object::Object> as std::convert::TryFrom<non_volatile::object::any_rc_object::AnyRcObject>>) on opaque type
--> src/non_volatile/object/any_rc_object.rs:33:19
|
33 | Rc<Self>: TryFrom<AnyRcObject>,
| ^^^^^^^^^^^^^^^^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
error: internal compiler error: unexpected predicate TraitPredicate(<std::rc::Rc<impl non_volatile::object::any_rc_object::Object> as std::marker::Sized>) on opaque type
--> /home/matthias/.rustup/toolchains/nightly-x86_64-unknown-linux-gnu/lib/rustlib/src/rust/library/core/src/convert/mod.rs:494:23
|
494 | pub trait TryFrom<T>: Sized {
| ^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
error: internal compiler error: unexpected predicate TraitPredicate(<non_volatile::object::any_rc_object::AnyRcObject as std::convert::From<std::rc::Rc<impl non_volatile::object::any_rc_object::Object>>>) on opaque type
--> src/non_volatile/object/any_rc_object.rs:32:22
|
32 | AnyRcObject: From<Rc<Self>>,
| ^^^^^^^^^^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
error: internal compiler error: unexpected predicate TraitPredicate(<non_volatile::object::any_rc_object::AnyRcObject as std::marker::Sized>) on opaque type
--> /home/matthias/.rustup/toolchains/nightly-x86_64-unknown-linux-gnu/lib/rustlib/src/rust/library/core/src/convert/mod.rs:386:20
|
386 | pub trait From<T>: Sized {
| ^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
error: internal compiler error: unexpected predicate TraitPredicate(<non_volatile::object::any_rc_object::AnyRcObject as std::convert::From<impl non_volatile::object::any_rc_object::Object>>) on opaque type
--> src/non_volatile/object/any_rc_object.rs:31:77
|
31 | pub trait Object = Serializable + ConstObjType + Default where AnyRcObject: From<Self>,
| ^^^^^^^^^^
|
= note: delayed at src/librustc_ty/ty.rs:480:18
thread 'rustc' panicked at 'no errors encountered even though `delay_span_bug` issued', src/librustc_errors/lib.rs:369:17
stack backtrace:
0: std::panicking::begin_panic
1: <rustc_errors::HandlerInner as core::ops::drop::Drop>::drop
2: core::ptr::drop_in_place
3: <alloc::rc::Rc<T> as core::ops::drop::Drop>::drop
4: core::ptr::drop_in_place
5: rustc_span::with_source_map
6: rustc_interface::interface::create_compiler_and_run
7: scoped_tls::ScopedKey<T>::set
note: Some details are omitted, run with `RUST_BACKTRACE=full` for a verbose backtrace.
error: internal compiler error: unexpected panic
note: the compiler unexpectedly panicked. this is a bug.
note: we would appreciate a bug report: https://github.com/rust-lang/rust/issues/new?labels=C-bug%2C+I-ICE%2C+T-compiler&template=ice.md
note: rustc 1.47.0-nightly (2d8a3b918 2020-08-26) running on x86_64-unknown-linux-gnu
note: compiler flags: -C embed-bitcode=no -C debuginfo=2 -C incremental -C target-cpu=native --crate-type bin
note: some of the compiler flags provided by cargo are hidden
query stack during panic:
end of query stack
error: could not compile `playground`.
To learn more, run the command again with --verbose.
````
This ICE happens on:
`rustc 1.47.0-beta.1 (0f91f5c28 2020-08-25)`
`rustc 1.47.0-nightly (2d8a3b918 2020-08-26)`
but rustc `1.45.2 (d3fb005a3 2020-07-31)` builds fine. | test | ice unexpected predicate traitpredicate on opaque type found in the pr crater run git clone cd playground git checkout cargo check ices error internal compiler error unexpected predicate traitpredicate as std convert tryfrom error as std fmt debug on opaque type src non volatile object any rc object rs as tryfrom error debug note delayed at src librustc ty ty rs error internal compiler error unexpected predicate traitpredicate as std convert tryfrom on opaque type src non volatile object any rc object rs rc tryfrom note delayed at src librustc ty ty rs error internal compiler error unexpected predicate traitpredicate as std marker sized on opaque type home matthias rustup toolchains nightly unknown linux gnu lib rustlib src rust library core src convert mod rs pub trait tryfrom sized note delayed at src librustc ty ty rs error internal compiler error unexpected predicate traitpredicate on opaque type src non volatile object any rc object rs anyrcobject from note delayed at src librustc ty ty rs error internal compiler error unexpected predicate traitpredicate on opaque type home matthias rustup toolchains nightly unknown linux gnu lib rustlib src rust library core src convert mod rs pub trait from sized note delayed at src librustc ty ty rs error internal compiler error unexpected predicate traitpredicate on opaque type src non volatile object any rc object rs pub trait object serializable constobjtype default where anyrcobject from note delayed at src librustc ty ty rs thread rustc panicked at no errors encountered even though delay span bug issued src librustc errors lib rs stack backtrace std panicking begin panic drop core ptr drop in place as core ops drop drop drop core ptr drop in place rustc span with source map rustc interface interface create compiler and run scoped tls scopedkey set note some details are omitted run with rust backtrace full for a verbose backtrace error internal compiler error unexpected panic note the compiler unexpectedly panicked this is a bug note we would appreciate a bug report note rustc nightly running on unknown linux gnu note compiler flags c embed bitcode no c debuginfo c incremental c target cpu native crate type bin note some of the compiler flags provided by cargo are hidden query stack during panic end of query stack error could not compile playground to learn more run the command again with verbose this ice happens on rustc beta rustc nightly but rustc builds fine | 1 |
64,272 | 15,838,106,596 | IssuesEvent | 2021-04-06 21:51:45 | dxx-rebirth/dxx-rebirth | https://api.github.com/repos/dxx-rebirth/dxx-rebirth | opened | Build failure: | build-failure | Hetig already commented on the commit and identified the problem. I did the same thing once, a very long time ago, and the comment wasn't noticed. As a result, I'm just opening the report with his comment.
[ddb9e8e](https://github.com/dxx-rebirth/dxx-rebirth/commit/ddb9e8e774f1a7ff187079d7a551f6ca02748cc1#commitcomment-49094909) | 1.0 | Build failure: - Hetig already commented on the commit and identified the problem. I did the same thing once, a very long time ago, and the comment wasn't noticed. As a result, I'm just opening the report with his comment.
[ddb9e8e](https://github.com/dxx-rebirth/dxx-rebirth/commit/ddb9e8e774f1a7ff187079d7a551f6ca02748cc1#commitcomment-49094909) | non_test | build failure hetig already commented on the commit and identified the problem i did the same thing once a very long time ago and the comment wasn t noticed as a result i m just opening the report with his comment | 0 |
205,984 | 15,703,281,323 | IssuesEvent | 2021-03-26 13:41:50 | ansible/awx | https://api.github.com/repos/ansible/awx | closed | [ui_next] Unable to add multiple custom credential type's credential to job template | component:ui flag:community priority:high qe:escape state:needs_test type:bug | <!-- Issues are for **concrete, actionable bugs and feature requests** only - if you're just asking for debugging help or technical support, please use:
- http://webchat.freenode.net/?channels=ansible-awx
- https://groups.google.com/forum/#!forum/awx-project
We have to limit this because of limited volunteer time to respond to issues! -->
##### ISSUE TYPE
- Bug Report
##### SUMMARY
<!-- Briefly describe the problem. -->
New UI Unable to add multiple custom credential to a job template.
steps involved
##### ENVIRONMENT
* AWX version: AWX 16.0.0
* AWX install method: Kubernetes
* Ansible version: 2.9.15
* Operating System: Centos 8
* Web Browser: Chrome
##### STEPS TO REPRODUCE
<!-- Please describe exactly how to reproduce the problem. -->
- Select custom credential type A in job template
- Select custom credential type B in job template - custom credential type A is replaced by type B
##### EXPECTED RESULTS
<!-- What did you expect to happen when running the steps above? -->
Both custom credentials are added to job template
##### ACTUAL RESULTS
only latest selected credential is added
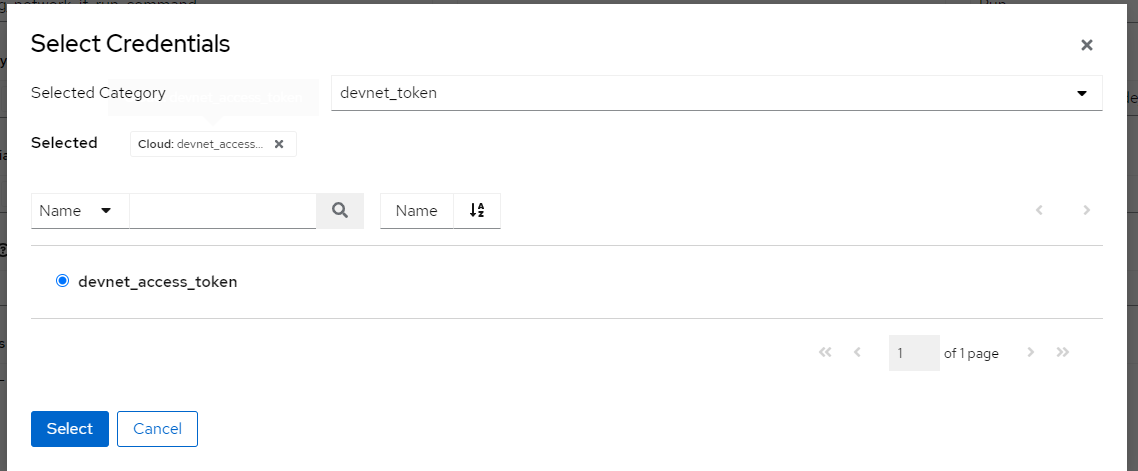
<!-- What actually happened? -->
##### ADDITIONAL INFORMATION
<!-- Include any links to sosreport, database dumps, screenshots or other
information. -->
| 1.0 | [ui_next] Unable to add multiple custom credential type's credential to job template - <!-- Issues are for **concrete, actionable bugs and feature requests** only - if you're just asking for debugging help or technical support, please use:
- http://webchat.freenode.net/?channels=ansible-awx
- https://groups.google.com/forum/#!forum/awx-project
We have to limit this because of limited volunteer time to respond to issues! -->
##### ISSUE TYPE
- Bug Report
##### SUMMARY
<!-- Briefly describe the problem. -->
New UI Unable to add multiple custom credential to a job template.
steps involved
##### ENVIRONMENT
* AWX version: AWX 16.0.0
* AWX install method: Kubernetes
* Ansible version: 2.9.15
* Operating System: Centos 8
* Web Browser: Chrome
##### STEPS TO REPRODUCE
<!-- Please describe exactly how to reproduce the problem. -->
- Select custom credential type A in job template
- Select custom credential type B in job template - custom credential type A is replaced by type B
##### EXPECTED RESULTS
<!-- What did you expect to happen when running the steps above? -->
Both custom credentials are added to job template
##### ACTUAL RESULTS
only latest selected credential is added
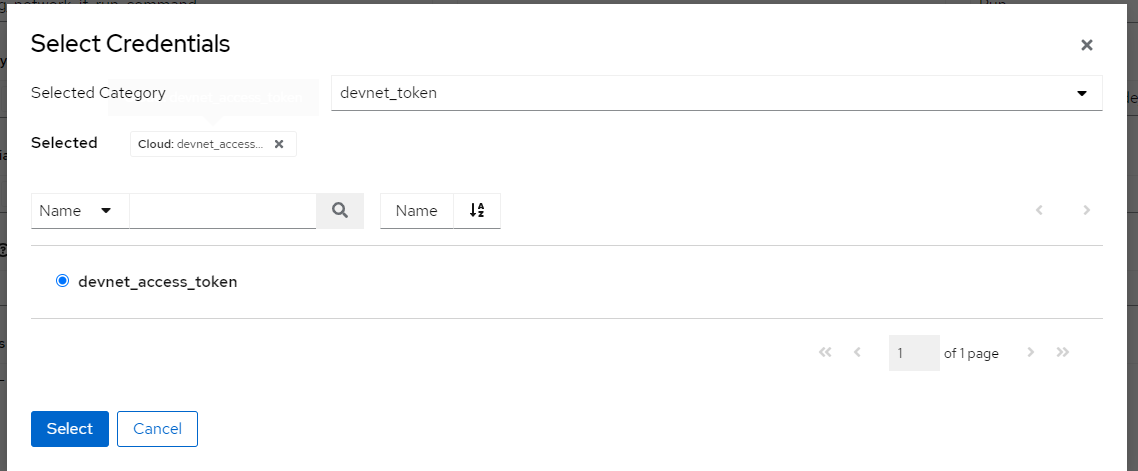
<!-- What actually happened? -->
##### ADDITIONAL INFORMATION
<!-- Include any links to sosreport, database dumps, screenshots or other
information. -->
| test | unable to add multiple custom credential type s credential to job template issues are for concrete actionable bugs and feature requests only if you re just asking for debugging help or technical support please use we have to limit this because of limited volunteer time to respond to issues issue type bug report summary new ui unable to add multiple custom credential to a job template steps involved environment awx version awx awx install method kubernetes ansible version operating system centos web browser chrome steps to reproduce select custom credential type a in job template select custom credential type b in job template custom credential type a is replaced by type b expected results both custom credentials are added to job template actual results only latest selected credential is added additional information include any links to sosreport database dumps screenshots or other information | 1 |
253,383 | 27,300,572,192 | IssuesEvent | 2023-02-24 01:19:57 | panasalap/linux-4.19.72_1 | https://api.github.com/repos/panasalap/linux-4.19.72_1 | opened | CVE-2021-45095 (Medium) detected in linux-yoctov5.4.51 | security vulnerability | ## CVE-2021-45095 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/phonet/pep.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/phonet/pep.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
pep_sock_accept in net/phonet/pep.c in the Linux kernel through 5.15.8 has a refcount leak.
<p>Publish Date: 2021-12-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-45095>CVE-2021-45095</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-12-16</p>
<p>Fix Resolution: v5.16-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-45095 (Medium) detected in linux-yoctov5.4.51 - ## CVE-2021-45095 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/phonet/pep.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/phonet/pep.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
pep_sock_accept in net/phonet/pep.c in the Linux kernel through 5.15.8 has a refcount leak.
<p>Publish Date: 2021-12-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-45095>CVE-2021-45095</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-12-16</p>
<p>Fix Resolution: v5.16-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in linux cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in base branch master vulnerable source files net phonet pep c net phonet pep c vulnerability details pep sock accept in net phonet pep c in the linux kernel through has a refcount leak publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend | 0 |
394,304 | 11,634,767,105 | IssuesEvent | 2020-02-28 11:01:39 | GoogleContainerTools/kaniko | https://api.github.com/repos/GoogleContainerTools/kaniko | closed | Copy From with Chown on Multistage does not chown | area/dockerfile-command cmd/copy kind/bug priority/p1 | **Actual behavior**
When I use a multi stage build which copies from the first stage to the second with a `--chown`, the directories are not actually `chowned`.
**Expected behavior**
The chown on a `copy` should actually chown to the selected user.
**To Reproduce**
Steps to reproduce the behavior:
1. Use this simple NodeJS DockerFile with any node project.
```
FROM node:10.11.0 as builder
WORKDIR /home/node
COPY . .
RUN npm install --only=production --verbose
FROM node:10.11.0-alpine as runner
ENV NPM_CONFIG_LOGLEVEL=info \
NODE_ENV=production
WORKDIR /home/node
COPY --from=builder --chown=node:node /home/node .
EXPOSE 3500
USER node
RUN mkdir -p logs
CMD [ "npm", "start" ]
```
2. When you build this with docker, everything works. When built with kaniko, the line with `RUN mkdir -p logs` will fail with permission denied and the whole `/home/node` dir is owned by root still.
**Additional Information**
Here is what I had to do to the Dockerfile to make it work in the mean time:
```
FROM node:10.11.0 as builder
WORKDIR /home/node
COPY . .
RUN npm install --only=production --verbose
FROM node:10.11.0-alpine as runner
ENV NPM_CONFIG_LOGLEVEL=info \
NODE_ENV=production
WORKDIR /home/node
COPY --from=builder --chown=node:node /home/node .
EXPOSE 3500
RUN chown -R node:node /home/node && \
mkdir -p logs
USER node
CMD [ "npm", "start" ]
``` | 1.0 | Copy From with Chown on Multistage does not chown - **Actual behavior**
When I use a multi stage build which copies from the first stage to the second with a `--chown`, the directories are not actually `chowned`.
**Expected behavior**
The chown on a `copy` should actually chown to the selected user.
**To Reproduce**
Steps to reproduce the behavior:
1. Use this simple NodeJS DockerFile with any node project.
```
FROM node:10.11.0 as builder
WORKDIR /home/node
COPY . .
RUN npm install --only=production --verbose
FROM node:10.11.0-alpine as runner
ENV NPM_CONFIG_LOGLEVEL=info \
NODE_ENV=production
WORKDIR /home/node
COPY --from=builder --chown=node:node /home/node .
EXPOSE 3500
USER node
RUN mkdir -p logs
CMD [ "npm", "start" ]
```
2. When you build this with docker, everything works. When built with kaniko, the line with `RUN mkdir -p logs` will fail with permission denied and the whole `/home/node` dir is owned by root still.
**Additional Information**
Here is what I had to do to the Dockerfile to make it work in the mean time:
```
FROM node:10.11.0 as builder
WORKDIR /home/node
COPY . .
RUN npm install --only=production --verbose
FROM node:10.11.0-alpine as runner
ENV NPM_CONFIG_LOGLEVEL=info \
NODE_ENV=production
WORKDIR /home/node
COPY --from=builder --chown=node:node /home/node .
EXPOSE 3500
RUN chown -R node:node /home/node && \
mkdir -p logs
USER node
CMD [ "npm", "start" ]
``` | non_test | copy from with chown on multistage does not chown actual behavior when i use a multi stage build which copies from the first stage to the second with a chown the directories are not actually chowned expected behavior the chown on a copy should actually chown to the selected user to reproduce steps to reproduce the behavior use this simple nodejs dockerfile with any node project from node as builder workdir home node copy run npm install only production verbose from node alpine as runner env npm config loglevel info node env production workdir home node copy from builder chown node node home node expose user node run mkdir p logs cmd when you build this with docker everything works when built with kaniko the line with run mkdir p logs will fail with permission denied and the whole home node dir is owned by root still additional information here is what i had to do to the dockerfile to make it work in the mean time from node as builder workdir home node copy run npm install only production verbose from node alpine as runner env npm config loglevel info node env production workdir home node copy from builder chown node node home node expose run chown r node node home node mkdir p logs user node cmd | 0 |
294,079 | 25,344,092,760 | IssuesEvent | 2022-11-19 02:31:18 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed | kernel: tests: Evaluate "platform_allow" usage in kernel tests. | Enhancement area: Tests | **Problem**
Platform_allow lists in kernel's testcase.yamls are incorrectly blocking testing scope.
**Describe the solution you'd like**
Every test scenario under tests/kernel which defines platform_allow has to be evaluated. Platform_allow lists should be replaced with other filtration means. To limit the CI execution scope one can use integration_platforms which will also enforce such test execution in the CI (skips are turned to errors in the CI for integration_platforms). Platform_allow lists should only be allowed for cases where there is no other means of filtration or tests are not portable (e.g. ones which require dedicated overlays for each platform).
**Describe alternatives you've considered**
I don't see other approach to fix the issue.
**Additional context**
IMO it is more a bug than an enhancement but due to the scope I put it under "enhancement". This problem is also not limited to kernel tests, but due to the scope I believe evaluation of platform_allow abuse can be limited to kernel tests in this task and we will continue solving the issue in following tasks.
Platform_allow is abused and used incorrectly. Looking at examples it seems it was often added just to limit the CI execution scope. Or because a developer only tested the solution on certain boards and didn't care about other platforms. Platform_allow is a hard filter preventing testing on anything outside of it. It also makes tests hard to maintain, since it needs constant updating with new boards being added (which is not happening in most cases...).
This evaluation is especially important in context of on-target testing and selecting "tier 1" boards. Kernel tests will be crucial for such boards. However, it seems there might be quite many artificial skips due to platform_allow misuse.
An example showing the problem: https://github.com/zephyrproject-rtos/zephyr/blob/main/tests/kernel/gen_isr_table/testcase.yaml#L11
The platforms in platform_allow seem totally arbitrarily selected and blocks testing on vast majority of platforms. | 1.0 | kernel: tests: Evaluate "platform_allow" usage in kernel tests. - **Problem**
Platform_allow lists in kernel's testcase.yamls are incorrectly blocking testing scope.
**Describe the solution you'd like**
Every test scenario under tests/kernel which defines platform_allow has to be evaluated. Platform_allow lists should be replaced with other filtration means. To limit the CI execution scope one can use integration_platforms which will also enforce such test execution in the CI (skips are turned to errors in the CI for integration_platforms). Platform_allow lists should only be allowed for cases where there is no other means of filtration or tests are not portable (e.g. ones which require dedicated overlays for each platform).
**Describe alternatives you've considered**
I don't see other approach to fix the issue.
**Additional context**
IMO it is more a bug than an enhancement but due to the scope I put it under "enhancement". This problem is also not limited to kernel tests, but due to the scope I believe evaluation of platform_allow abuse can be limited to kernel tests in this task and we will continue solving the issue in following tasks.
Platform_allow is abused and used incorrectly. Looking at examples it seems it was often added just to limit the CI execution scope. Or because a developer only tested the solution on certain boards and didn't care about other platforms. Platform_allow is a hard filter preventing testing on anything outside of it. It also makes tests hard to maintain, since it needs constant updating with new boards being added (which is not happening in most cases...).
This evaluation is especially important in context of on-target testing and selecting "tier 1" boards. Kernel tests will be crucial for such boards. However, it seems there might be quite many artificial skips due to platform_allow misuse.
An example showing the problem: https://github.com/zephyrproject-rtos/zephyr/blob/main/tests/kernel/gen_isr_table/testcase.yaml#L11
The platforms in platform_allow seem totally arbitrarily selected and blocks testing on vast majority of platforms. | test | kernel tests evaluate platform allow usage in kernel tests problem platform allow lists in kernel s testcase yamls are incorrectly blocking testing scope describe the solution you d like every test scenario under tests kernel which defines platform allow has to be evaluated platform allow lists should be replaced with other filtration means to limit the ci execution scope one can use integration platforms which will also enforce such test execution in the ci skips are turned to errors in the ci for integration platforms platform allow lists should only be allowed for cases where there is no other means of filtration or tests are not portable e g ones which require dedicated overlays for each platform describe alternatives you ve considered i don t see other approach to fix the issue additional context imo it is more a bug than an enhancement but due to the scope i put it under enhancement this problem is also not limited to kernel tests but due to the scope i believe evaluation of platform allow abuse can be limited to kernel tests in this task and we will continue solving the issue in following tasks platform allow is abused and used incorrectly looking at examples it seems it was often added just to limit the ci execution scope or because a developer only tested the solution on certain boards and didn t care about other platforms platform allow is a hard filter preventing testing on anything outside of it it also makes tests hard to maintain since it needs constant updating with new boards being added which is not happening in most cases this evaluation is especially important in context of on target testing and selecting tier boards kernel tests will be crucial for such boards however it seems there might be quite many artificial skips due to platform allow misuse an example showing the problem the platforms in platform allow seem totally arbitrarily selected and blocks testing on vast majority of platforms | 1 |
248,227 | 21,003,609,348 | IssuesEvent | 2022-03-29 20:00:44 | nih-cfde/dashboard | https://api.github.com/repos/nih-cfde/dashboard | opened | Dashboard interactive chart resizing | testing | The dashboard chart is acting extremely weird. It seems like HMP, procca, and SPARC all make the chart get smaller, but only if they are selected with specific other DCCs. I don't know how to best explain it so I made a video
https://user-images.githubusercontent.com/1719360/160696827-7ca98fe3-a481-47bc-b33b-a7c2b440ecbb.mov
| 1.0 | Dashboard interactive chart resizing - The dashboard chart is acting extremely weird. It seems like HMP, procca, and SPARC all make the chart get smaller, but only if they are selected with specific other DCCs. I don't know how to best explain it so I made a video
https://user-images.githubusercontent.com/1719360/160696827-7ca98fe3-a481-47bc-b33b-a7c2b440ecbb.mov
| test | dashboard interactive chart resizing the dashboard chart is acting extremely weird it seems like hmp procca and sparc all make the chart get smaller but only if they are selected with specific other dccs i don t know how to best explain it so i made a video | 1 |
20,712 | 10,548,283,289 | IssuesEvent | 2019-10-03 05:05:14 | uniquelyparticular/sync-stripe-to-zendesk | https://api.github.com/repos/uniquelyparticular/sync-stripe-to-zendesk | opened | CVE-2015-9251 (Medium) detected in jquery-1.8.1.min.js | security vulnerability | ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/sync-stripe-to-zendesk/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: /sync-stripe-to-zendesk/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uniquelyparticular/sync-stripe-to-zendesk/commit/9e27cb6f56b78a2b53b3671a65fdd9b080d89b7f">9e27cb6f56b78a2b53b3671a65fdd9b080d89b7f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2015-9251 (Medium) detected in jquery-1.8.1.min.js - ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/sync-stripe-to-zendesk/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: /sync-stripe-to-zendesk/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uniquelyparticular/sync-stripe-to-zendesk/commit/9e27cb6f56b78a2b53b3671a65fdd9b080d89b7f">9e27cb6f56b78a2b53b3671a65fdd9b080d89b7f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file tmp ws scm sync stripe to zendesk node modules redeyed examples browser index html path to vulnerable library sync stripe to zendesk node modules redeyed examples browser index html dependency hierarchy x jquery min js vulnerable library found in head commit a href vulnerability details jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
207,565 | 7,131,158,069 | IssuesEvent | 2018-01-22 09:58:57 | arquillian/smart-testing | https://api.github.com/repos/arquillian/smart-testing | closed | Categorized - support categorization for test methods | Component: Selection Priority: High Type: Feature train/ginger | ##### Issue Overview
Currently, only the categories of the whole test classes are retrieved. The goal of this task is to categorize also the test methods.
By default, this feature should be enabled, but the configuration should support disabling categorization of the test methods and keep only for test classes.
| 1.0 | Categorized - support categorization for test methods - ##### Issue Overview
Currently, only the categories of the whole test classes are retrieved. The goal of this task is to categorize also the test methods.
By default, this feature should be enabled, but the configuration should support disabling categorization of the test methods and keep only for test classes.
| non_test | categorized support categorization for test methods issue overview currently only the categories of the whole test classes are retrieved the goal of this task is to categorize also the test methods by default this feature should be enabled but the configuration should support disabling categorization of the test methods and keep only for test classes | 0 |
34,095 | 4,891,131,987 | IssuesEvent | 2016-11-18 15:52:18 | red/red | https://api.github.com/repos/red/red | closed | make path! <block> gives path! in stead of path value | status.built status.tested type.bug | ```
red>> make path! [a b]
== path! ; expected a/b
```
Goes also for `lit-path!` etc | 1.0 | make path! <block> gives path! in stead of path value - ```
red>> make path! [a b]
== path! ; expected a/b
```
Goes also for `lit-path!` etc | test | make path gives path in stead of path value red make path path expected a b goes also for lit path etc | 1 |
334,317 | 29,830,776,206 | IssuesEvent | 2023-06-18 08:40:47 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix exponents_and_logarithms.test_numpy_exp2 | NumPy Frontend Sub Task Failing Test | | | |
|---|---|
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5302452748/jobs/9597384630"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5302452748/jobs/9597384630"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5302452748/jobs/9597384630"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5302452748/jobs/9597384630"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5302452748/jobs/9597384630"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix exponents_and_logarithms.test_numpy_exp2 - | | |
|---|---|
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5302452748/jobs/9597384630"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5302452748/jobs/9597384630"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5302452748/jobs/9597384630"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5302452748/jobs/9597384630"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5302452748/jobs/9597384630"><img src=https://img.shields.io/badge/-failure-red></a>
| test | fix exponents and logarithms test numpy torch a href src tensorflow a href src numpy a href src jax a href src paddle a href src | 1 |
193,586 | 6,886,225,725 | IssuesEvent | 2017-11-21 18:42:27 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | image.noelshack.com - see bug description | browser-firefox-mobile priority-normal status-needsinfo | <!-- @browser: Firefox Mobile 58.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:58.0) Gecko/58.0 Firefox/58.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: http://image.noelshack.com/fichiers/2015/50/1450023383-albert-dupontel.jpg
**Browser / Version**: Firefox Mobile 58.0
**Operating System**: Android 6.0.1
**Tested Another Browser**: Yes
**Problem type**: Something else
**Description**: Impossible to share an image with whatsapp. The API shares the image link only
**Steps to Reproduce**:
[](https://webcompat.com/uploads/2017/11/61e2d6ff-2a11-42fd-996f-481e73b6eb47.jpeg)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | image.noelshack.com - see bug description - <!-- @browser: Firefox Mobile 58.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:58.0) Gecko/58.0 Firefox/58.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: http://image.noelshack.com/fichiers/2015/50/1450023383-albert-dupontel.jpg
**Browser / Version**: Firefox Mobile 58.0
**Operating System**: Android 6.0.1
**Tested Another Browser**: Yes
**Problem type**: Something else
**Description**: Impossible to share an image with whatsapp. The API shares the image link only
**Steps to Reproduce**:
[](https://webcompat.com/uploads/2017/11/61e2d6ff-2a11-42fd-996f-481e73b6eb47.jpeg)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_test | image noelshack com see bug description url browser version firefox mobile operating system android tested another browser yes problem type something else description impossible to share an image with whatsapp the api shares the image link only steps to reproduce from with ❤️ | 0 |
457,653 | 13,159,777,341 | IssuesEvent | 2020-08-10 16:24:13 | NuGet/Home | https://api.github.com/repos/NuGet/Home | closed | Modifying VS Project Properties Page for Readme Support | Functionality:Pack Partner:Project-System Priority:2 Type:Feature | Add the ability to include a Readme file and property to a project through the Project Properties page. | 1.0 | Modifying VS Project Properties Page for Readme Support - Add the ability to include a Readme file and property to a project through the Project Properties page. | non_test | modifying vs project properties page for readme support add the ability to include a readme file and property to a project through the project properties page | 0 |
327,850 | 28,085,236,491 | IssuesEvent | 2023-03-30 09:20:06 | ntop/ntopng | https://api.github.com/repos/ntop/ntopng | closed | Missing Link for Jumping to SNMP Pages | Feature Request Ready to Test | As shown below, there are only links for filtering into the alerts page, but no icons (or similar as for instance in flows) for jumping into the SNMP host/interface. This ticket is to request to add such icons
<img width="1155" alt="image" src="https://user-images.githubusercontent.com/4493366/224006070-0c4c424f-08fa-463e-8fa8-4e961547dc1c.png"> | 1.0 | Missing Link for Jumping to SNMP Pages - As shown below, there are only links for filtering into the alerts page, but no icons (or similar as for instance in flows) for jumping into the SNMP host/interface. This ticket is to request to add such icons
<img width="1155" alt="image" src="https://user-images.githubusercontent.com/4493366/224006070-0c4c424f-08fa-463e-8fa8-4e961547dc1c.png"> | test | missing link for jumping to snmp pages as shown below there are only links for filtering into the alerts page but no icons or similar as for instance in flows for jumping into the snmp host interface this ticket is to request to add such icons img width alt image src | 1 |
243,050 | 20,360,306,420 | IssuesEvent | 2022-02-20 15:38:46 | mennaelkashef/eShop | https://api.github.com/repos/mennaelkashef/eShop | opened | No description entered by the user. | Hello! RULE-GOT-APPLIED DOES-NOT-CONTAIN-STRING Rule-works-on-convert-to-bug test instabug | # :clipboard: Bug Details
>No description entered by the user.
key | value
--|--
Reported At | 2022-02-20 15:37:58 UTC
Categories | Report a bug
Tags | test, Hello!, RULE-GOT-APPLIED, DOES-NOT-CONTAIN-STRING, Rule-works-on-convert-to-bug, instabug
App Version | 1.1 (1)
Session Duration | 76
Device | Google AOSP on IA Emulator, OS Level 28
Display | 1080x2160 (xhdpi)
Location | Giza, Egypt (en)
## :point_right: [View Full Bug Report on Instabug](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8492?utm_source=github&utm_medium=integrations) :point_left:
___
# :iphone: View Hierarchy
This bug was reported from **com.example.app.main.MainFragment**
Find its interactive view hierarchy with all its subviews here: :point_right: **[Check View Hierarchy](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8492?show-hierarchy-view=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :chart_with_downwards_trend: Session Profiler
Here is what the app was doing right before the bug was reported:
Key | Value
--|--
Used Memory | 54.6% - 0.8/1.46 GB
Used Storage | 8.9% - 0.52/5.81 GB
Connectivity | LTE - Android
Battery | 100% - unplugged
Orientation | portrait
Find all the changes that happened in the parameters mentioned above during the last 60 seconds before the bug was reported here: :point_right: **[View Full Session Profiler](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8492?show-session-profiler=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :bust_in_silhouette: User Info
### User Attributes
```
key_name 1595009626: key value bla bla bla la
key_name 2001182420: key value bla bla bla la
```
___
# :mag_right: Logs
### User Steps
Here are the last 10 steps done by the user right before the bug was reported:
```
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.crash.CrashFragment was paused.
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.crash.CrashFragment was stopped.
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was created.
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was started.
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.crash.CrashFragment was detached.
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was resumed.
15:37:57 Tap in "androidx.constraintlayout.widget.ConstraintLayout" in "com.example.app.main.MainActivity"
15:37:57 com.example.app.main.MainActivity was paused.
15:37:57 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was paused.
15:37:58 Tap in "androidx.constraintlayout.widget.ConstraintLayout" in "com.example.app.main.MainActivity"
```
Find all the user steps done by the user throughout the session here: :point_right: **[View All User Steps](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8492?show-logs=user_steps&utm_source=github&utm_medium=integrations)** :point_left:
### Console Log
Here are the last 10 console logs logged right before the bug was reported:
```
15:37:59 D/IB-ActivityViewInspectorTask( 2853): bug ! null,converting>json ended
15:37:59 D/IB-ActivityViewInspectorTask( 2853): bug ! null,set inspection state
15:37:59 D/IB-BaseReportingPresenter( 2853): receive a view hierarchy inspection action, action value: COMPLETED
15:37:59 D/IB-BaseReportingPresenter( 2853): receive a view hierarchy inspection action, action value: COMPLETED
15:38:01 D/EGL_emulation( 2853): eglMakeCurrent: 0xdd7ae980: ver 3 0 (tinfo 0xdd8143a0)
15:38:01 D/EGL_emulation( 2853): eglMakeCurrent: 0xdd7ae980: ver 3 0 (tinfo 0xdd8143a0)
15:38:02 D/LeakCanary( 2853): Watching instance of android.widget.LinearLayout (android.widget.LinearLayout received View#onDetachedFromWindow() callback) with key 46afd8fa-0683-440b-a4c2-371de17b1a7a
15:38:02 D/IB-BaseReportingPresenter( 2853): checkUserEmailValid :empty-email
15:38:02 D/IB-ActionsOrchestrator( 2853): runAction
15:38:02 D/IB-AttachmentsUtility( 2853): encryptAttachments
```
Find all the logged console logs throughout the session here: :point_right: **[View All Console Log](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8492?show-logs=console_log&utm_source=github&utm_medium=integrations)** :point_left:
___
# :camera: Images
[](https://d38gnqwzxziyyy.cloudfront.net/attachments/bugs/17892190/54eac708dcdc96a5340bfc397448d4e7_original/25100482/bug_1645371477122_.jpg?Expires=4801045124&Signature=cT3bDZaTP2PYBbVk0~WbKp-84ZbBL5cMz3Uh3wuLDoalUlrdV3~FOTa9i9z~fHpnyLZKc5tzJPQEygAcrVqcnBF5MKfsiRF8fvWsuKhbPp6xe34tVnJCNCXx2Q6-G~aeH5GEiWNfAQXcpE3AusQLbZeSJUOpegTxVRfUD8W1icAt2eFFXjmC-Hs7mcraOE0dd0wDU10U3Y4w6RMpaI-Ol3qTm7IPJylmoDwb9WR6q~tRSjFWiyAmCr4MDFO-~M8XjQ3FyNb7hi1WNaA9Ms7lofEqNhG-StctignyQV83tlgOUQaNOcKBWcb5OCMEsghl9PODgYF83i68hsD~wpB6Cg__&Key-Pair-Id=APKAIXAG65U6UUX7JAQQ)
___
# :warning: Looking for More Details?
1. **Network Log**: we are unable to capture your network requests automatically. If you are using HttpUrlConnection or Okhttp requests, [**check the details mentioned here**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations#section-network-logs).
2. **User Events**: start capturing custom User Events to send them along with each report. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations).
3. **Instabug Log**: start adding Instabug logs to see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations). | 1.0 | No description entered by the user. - # :clipboard: Bug Details
>No description entered by the user.
key | value
--|--
Reported At | 2022-02-20 15:37:58 UTC
Categories | Report a bug
Tags | test, Hello!, RULE-GOT-APPLIED, DOES-NOT-CONTAIN-STRING, Rule-works-on-convert-to-bug, instabug
App Version | 1.1 (1)
Session Duration | 76
Device | Google AOSP on IA Emulator, OS Level 28
Display | 1080x2160 (xhdpi)
Location | Giza, Egypt (en)
## :point_right: [View Full Bug Report on Instabug](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8492?utm_source=github&utm_medium=integrations) :point_left:
___
# :iphone: View Hierarchy
This bug was reported from **com.example.app.main.MainFragment**
Find its interactive view hierarchy with all its subviews here: :point_right: **[Check View Hierarchy](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8492?show-hierarchy-view=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :chart_with_downwards_trend: Session Profiler
Here is what the app was doing right before the bug was reported:
Key | Value
--|--
Used Memory | 54.6% - 0.8/1.46 GB
Used Storage | 8.9% - 0.52/5.81 GB
Connectivity | LTE - Android
Battery | 100% - unplugged
Orientation | portrait
Find all the changes that happened in the parameters mentioned above during the last 60 seconds before the bug was reported here: :point_right: **[View Full Session Profiler](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8492?show-session-profiler=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :bust_in_silhouette: User Info
### User Attributes
```
key_name 1595009626: key value bla bla bla la
key_name 2001182420: key value bla bla bla la
```
___
# :mag_right: Logs
### User Steps
Here are the last 10 steps done by the user right before the bug was reported:
```
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.crash.CrashFragment was paused.
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.crash.CrashFragment was stopped.
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was created.
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was started.
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.crash.CrashFragment was detached.
15:37:09 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was resumed.
15:37:57 Tap in "androidx.constraintlayout.widget.ConstraintLayout" in "com.example.app.main.MainActivity"
15:37:57 com.example.app.main.MainActivity was paused.
15:37:57 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was paused.
15:37:58 Tap in "androidx.constraintlayout.widget.ConstraintLayout" in "com.example.app.main.MainActivity"
```
Find all the user steps done by the user throughout the session here: :point_right: **[View All User Steps](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8492?show-logs=user_steps&utm_source=github&utm_medium=integrations)** :point_left:
### Console Log
Here are the last 10 console logs logged right before the bug was reported:
```
15:37:59 D/IB-ActivityViewInspectorTask( 2853): bug ! null,converting>json ended
15:37:59 D/IB-ActivityViewInspectorTask( 2853): bug ! null,set inspection state
15:37:59 D/IB-BaseReportingPresenter( 2853): receive a view hierarchy inspection action, action value: COMPLETED
15:37:59 D/IB-BaseReportingPresenter( 2853): receive a view hierarchy inspection action, action value: COMPLETED
15:38:01 D/EGL_emulation( 2853): eglMakeCurrent: 0xdd7ae980: ver 3 0 (tinfo 0xdd8143a0)
15:38:01 D/EGL_emulation( 2853): eglMakeCurrent: 0xdd7ae980: ver 3 0 (tinfo 0xdd8143a0)
15:38:02 D/LeakCanary( 2853): Watching instance of android.widget.LinearLayout (android.widget.LinearLayout received View#onDetachedFromWindow() callback) with key 46afd8fa-0683-440b-a4c2-371de17b1a7a
15:38:02 D/IB-BaseReportingPresenter( 2853): checkUserEmailValid :empty-email
15:38:02 D/IB-ActionsOrchestrator( 2853): runAction
15:38:02 D/IB-AttachmentsUtility( 2853): encryptAttachments
```
Find all the logged console logs throughout the session here: :point_right: **[View All Console Log](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8492?show-logs=console_log&utm_source=github&utm_medium=integrations)** :point_left:
___
# :camera: Images
[](https://d38gnqwzxziyyy.cloudfront.net/attachments/bugs/17892190/54eac708dcdc96a5340bfc397448d4e7_original/25100482/bug_1645371477122_.jpg?Expires=4801045124&Signature=cT3bDZaTP2PYBbVk0~WbKp-84ZbBL5cMz3Uh3wuLDoalUlrdV3~FOTa9i9z~fHpnyLZKc5tzJPQEygAcrVqcnBF5MKfsiRF8fvWsuKhbPp6xe34tVnJCNCXx2Q6-G~aeH5GEiWNfAQXcpE3AusQLbZeSJUOpegTxVRfUD8W1icAt2eFFXjmC-Hs7mcraOE0dd0wDU10U3Y4w6RMpaI-Ol3qTm7IPJylmoDwb9WR6q~tRSjFWiyAmCr4MDFO-~M8XjQ3FyNb7hi1WNaA9Ms7lofEqNhG-StctignyQV83tlgOUQaNOcKBWcb5OCMEsghl9PODgYF83i68hsD~wpB6Cg__&Key-Pair-Id=APKAIXAG65U6UUX7JAQQ)
___
# :warning: Looking for More Details?
1. **Network Log**: we are unable to capture your network requests automatically. If you are using HttpUrlConnection or Okhttp requests, [**check the details mentioned here**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations#section-network-logs).
2. **User Events**: start capturing custom User Events to send them along with each report. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations).
3. **Instabug Log**: start adding Instabug logs to see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations). | test | no description entered by the user clipboard bug details no description entered by the user key value reported at utc categories report a bug tags test hello rule got applied does not contain string rule works on convert to bug instabug app version session duration device google aosp on ia emulator os level display xhdpi location giza egypt en point right point left iphone view hierarchy this bug was reported from com example app main mainfragment find its interactive view hierarchy with all its subviews here point right point left chart with downwards trend session profiler here is what the app was doing right before the bug was reported key value used memory gb used storage gb connectivity lte android battery unplugged orientation portrait find all the changes that happened in the parameters mentioned above during the last seconds before the bug was reported here point right point left bust in silhouette user info user attributes key name key value bla bla bla la key name key value bla bla bla la mag right logs user steps here are the last steps done by the user right before the bug was reported in activity com example app main mainactivity fragment com example app crash crashfragment was paused in activity com example app main mainactivity fragment com example app crash crashfragment was stopped in activity com example app main mainactivity fragment com example app main mainfragment was created in activity com example app main mainactivity fragment com example app main mainfragment was started in activity com example app main mainactivity fragment com example app crash crashfragment was detached in activity com example app main mainactivity fragment com example app main mainfragment was resumed tap in androidx constraintlayout widget constraintlayout in com example app main mainactivity com example app main mainactivity was paused in activity com example app main mainactivity fragment com example app main mainfragment was paused tap in androidx constraintlayout widget constraintlayout in com example app main mainactivity find all the user steps done by the user throughout the session here point right point left console log here are the last console logs logged right before the bug was reported d ib activityviewinspectortask bug null converting json ended d ib activityviewinspectortask bug null set inspection state d ib basereportingpresenter receive a view hierarchy inspection action action value completed d ib basereportingpresenter receive a view hierarchy inspection action action value completed d egl emulation eglmakecurrent ver tinfo d egl emulation eglmakecurrent ver tinfo d leakcanary watching instance of android widget linearlayout android widget linearlayout received view ondetachedfromwindow callback with key d ib basereportingpresenter checkuseremailvalid empty email d ib actionsorchestrator runaction d ib attachmentsutility encryptattachments find all the logged console logs throughout the session here point right point left camera images warning looking for more details network log we are unable to capture your network requests automatically if you are using httpurlconnection or okhttp requests user events start capturing custom user events to send them along with each report instabug log start adding instabug logs to see them right inside each report you receive | 1 |
253,221 | 21,664,255,533 | IssuesEvent | 2022-05-07 00:47:52 | expertiza/expertiza | https://api.github.com/repos/expertiza/expertiza | closed | Test cases for AdvertiseForPartnerController are failing | testing needs manual testing rails5 | Some of the test cases for AdvertiseForPartnerController are failing.
Failed examples:
```rspec ./spec/controllers/advertise_for_partner_controller_spec.rb:33 # AdvertiseForPartnerController action allowed method performs access check when called before check if update method can be called by the user
rspec ./spec/controllers/advertise_for_partner_controller_spec.rb:24 # AdvertiseForPartnerController action allowed method performs access check when called before checks if create method can be called by the user
rspec ./spec/controllers/advertise_for_partner_controller_spec.rb:42 # AdvertiseForPartnerController action allowed method performs access check when called before check if edit method can be called by the user
```
The common reason being
```expect(result.status).to eq 302
expected: 302
got: 200
``` | 2.0 | Test cases for AdvertiseForPartnerController are failing - Some of the test cases for AdvertiseForPartnerController are failing.
Failed examples:
```rspec ./spec/controllers/advertise_for_partner_controller_spec.rb:33 # AdvertiseForPartnerController action allowed method performs access check when called before check if update method can be called by the user
rspec ./spec/controllers/advertise_for_partner_controller_spec.rb:24 # AdvertiseForPartnerController action allowed method performs access check when called before checks if create method can be called by the user
rspec ./spec/controllers/advertise_for_partner_controller_spec.rb:42 # AdvertiseForPartnerController action allowed method performs access check when called before check if edit method can be called by the user
```
The common reason being
```expect(result.status).to eq 302
expected: 302
got: 200
``` | test | test cases for advertiseforpartnercontroller are failing some of the test cases for advertiseforpartnercontroller are failing failed examples rspec spec controllers advertise for partner controller spec rb advertiseforpartnercontroller action allowed method performs access check when called before check if update method can be called by the user rspec spec controllers advertise for partner controller spec rb advertiseforpartnercontroller action allowed method performs access check when called before checks if create method can be called by the user rspec spec controllers advertise for partner controller spec rb advertiseforpartnercontroller action allowed method performs access check when called before check if edit method can be called by the user the common reason being expect result status to eq expected got | 1 |
316,165 | 9,637,655,971 | IssuesEvent | 2019-05-16 09:17:55 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | oo.blue.fedex.com - site is not usable | browser-focus-geckoview engine-gecko priority-important | <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:68.0) Gecko/68.0 Firefox/68.0 -->
<!-- @reported_with: -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: http://oo.blue.fedex.com/
**Browser / Version**: Firefox Mobile 68.0
**Operating System**: Android
**Tested Another Browser**: Yes
**Problem type**: Site is not usable
**Description**: sure won't load
**Steps to Reproduce**:
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | oo.blue.fedex.com - site is not usable - <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:68.0) Gecko/68.0 Firefox/68.0 -->
<!-- @reported_with: -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: http://oo.blue.fedex.com/
**Browser / Version**: Firefox Mobile 68.0
**Operating System**: Android
**Tested Another Browser**: Yes
**Problem type**: Site is not usable
**Description**: sure won't load
**Steps to Reproduce**:
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_test | oo blue fedex com site is not usable url browser version firefox mobile operating system android tested another browser yes problem type site is not usable description sure won t load steps to reproduce browser configuration none from with ❤️ | 0 |
636,427 | 20,600,023,694 | IssuesEvent | 2022-03-06 04:54:34 | AY2122S2-CS2103T-T13-4/tp | https://api.github.com/repos/AY2122S2-CS2103T-T13-4/tp | opened | As an organized student, I want to be able to sort my contacts | priority.MEDIUM | so I can organize ModuleMateFinder in a manner suitable to my needs. | 1.0 | As an organized student, I want to be able to sort my contacts - so I can organize ModuleMateFinder in a manner suitable to my needs. | non_test | as an organized student i want to be able to sort my contacts so i can organize modulematefinder in a manner suitable to my needs | 0 |
173,884 | 13,448,559,699 | IssuesEvent | 2020-09-08 15:37:45 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: schemachange/index/tpcc/w=1000 failed | C-test-failure O-roachtest O-robot branch-release-19.2 release-blocker | [(roachtest).schemachange/index/tpcc/w=1000 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2231098&tab=buildLog) on [release-19.2@92a6f699c625fe08fcec978000b5e84be5a76d06](https://github.com/cockroachdb/cockroach/commits/92a6f699c625fe08fcec978000b5e84be5a76d06):
```
| 177.0s 0 570.4 539.2 771.8 1409.3 1476.4 1946.2 payment
| 177.0s 0 67.0 54.1 159.4 536.9 704.6 738.2 stockLevel
| 178.0s 0 64.0 53.7 838.9 1208.0 1275.1 1677.7 delivery
| 178.0s 0 535.3 538.0 939.5 1677.7 1879.0 2281.7 newOrder
| 178.0s 0 54.0 54.1 39.8 243.3 302.0 352.3 orderStatus
| 178.0s 0 486.3 538.9 838.9 1409.3 1677.7 2013.3 payment
| 178.0s 0 37.0 54.0 125.8 536.9 604.0 604.0 stockLevel
| 179.0s 0 59.0 53.8 704.6 1140.9 1275.1 1275.1 delivery
| 179.0s 0 498.0 537.8 973.1 1677.7 2013.3 2281.7 newOrder
| 179.0s 0 58.0 54.1 46.1 184.5 218.1 637.5 orderStatus
| 179.0s 0 635.0 539.4 805.3 1476.4 1677.7 1744.8 payment
| 179.0s 0 53.0 54.0 142.6 570.4 704.6 771.8 stockLevel
Wraps: (4) secondary error attachment
| signal: killed
| (1) signal: killed
| Error types: (1) *exec.ExitError
Wraps: (5) context canceled
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *main.withCommandDetails (4) *secondary.withSecondaryError (5) *errors.errorString
cluster.go:2613,tpcc.go:187,schemachange.go:302,test_runner.go:754: monitor failure: monitor task failed: t.Fatal() was called
(1) attached stack trace
-- stack trace:
| main.(*monitor).WaitE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2601
| main.(*monitor).Wait
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2609
| main.runTPCC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:187
| main.makeIndexAddTpccTest.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/schemachange.go:302
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:754
Wraps: (2) monitor failure
Wraps: (3) attached stack trace
-- stack trace:
| main.(*monitor).wait.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2657
Wraps: (4) monitor task failed
Wraps: (5) attached stack trace
-- stack trace:
| main.init
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2571
| runtime.doInit
| /usr/local/go/src/runtime/proc.go:5228
| runtime.main
| /usr/local/go/src/runtime/proc.go:190
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (6) t.Fatal() was called
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *withstack.withStack (4) *errutil.withPrefix (5) *withstack.withStack (6) *errutil.leafError
```
<details><summary>More</summary><p>
Artifacts: [/schemachange/index/tpcc/w=1000](https://teamcity.cockroachdb.com/viewLog.html?buildId=2231098&tab=artifacts#/schemachange/index/tpcc/w=1000)
Related:
- #51224 roachtest: schemachange/index/tpcc/w=1000 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202007081918_v20.2.0-alpha.2](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202007081918_v20.2.0-alpha.2) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47559 roachtest: schemachange/index/tpcc/w=1000 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-20.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-20.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #44071 roachtest: schemachange/index/tpcc/w=1000 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Aschemachange%2Findex%2Ftpcc%2Fw%3D1000.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: schemachange/index/tpcc/w=1000 failed - [(roachtest).schemachange/index/tpcc/w=1000 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2231098&tab=buildLog) on [release-19.2@92a6f699c625fe08fcec978000b5e84be5a76d06](https://github.com/cockroachdb/cockroach/commits/92a6f699c625fe08fcec978000b5e84be5a76d06):
```
| 177.0s 0 570.4 539.2 771.8 1409.3 1476.4 1946.2 payment
| 177.0s 0 67.0 54.1 159.4 536.9 704.6 738.2 stockLevel
| 178.0s 0 64.0 53.7 838.9 1208.0 1275.1 1677.7 delivery
| 178.0s 0 535.3 538.0 939.5 1677.7 1879.0 2281.7 newOrder
| 178.0s 0 54.0 54.1 39.8 243.3 302.0 352.3 orderStatus
| 178.0s 0 486.3 538.9 838.9 1409.3 1677.7 2013.3 payment
| 178.0s 0 37.0 54.0 125.8 536.9 604.0 604.0 stockLevel
| 179.0s 0 59.0 53.8 704.6 1140.9 1275.1 1275.1 delivery
| 179.0s 0 498.0 537.8 973.1 1677.7 2013.3 2281.7 newOrder
| 179.0s 0 58.0 54.1 46.1 184.5 218.1 637.5 orderStatus
| 179.0s 0 635.0 539.4 805.3 1476.4 1677.7 1744.8 payment
| 179.0s 0 53.0 54.0 142.6 570.4 704.6 771.8 stockLevel
Wraps: (4) secondary error attachment
| signal: killed
| (1) signal: killed
| Error types: (1) *exec.ExitError
Wraps: (5) context canceled
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *main.withCommandDetails (4) *secondary.withSecondaryError (5) *errors.errorString
cluster.go:2613,tpcc.go:187,schemachange.go:302,test_runner.go:754: monitor failure: monitor task failed: t.Fatal() was called
(1) attached stack trace
-- stack trace:
| main.(*monitor).WaitE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2601
| main.(*monitor).Wait
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2609
| main.runTPCC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:187
| main.makeIndexAddTpccTest.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/schemachange.go:302
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:754
Wraps: (2) monitor failure
Wraps: (3) attached stack trace
-- stack trace:
| main.(*monitor).wait.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2657
Wraps: (4) monitor task failed
Wraps: (5) attached stack trace
-- stack trace:
| main.init
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2571
| runtime.doInit
| /usr/local/go/src/runtime/proc.go:5228
| runtime.main
| /usr/local/go/src/runtime/proc.go:190
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (6) t.Fatal() was called
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *withstack.withStack (4) *errutil.withPrefix (5) *withstack.withStack (6) *errutil.leafError
```
<details><summary>More</summary><p>
Artifacts: [/schemachange/index/tpcc/w=1000](https://teamcity.cockroachdb.com/viewLog.html?buildId=2231098&tab=artifacts#/schemachange/index/tpcc/w=1000)
Related:
- #51224 roachtest: schemachange/index/tpcc/w=1000 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202007081918_v20.2.0-alpha.2](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202007081918_v20.2.0-alpha.2) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47559 roachtest: schemachange/index/tpcc/w=1000 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-20.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-20.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #44071 roachtest: schemachange/index/tpcc/w=1000 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Aschemachange%2Findex%2Ftpcc%2Fw%3D1000.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| test | roachtest schemachange index tpcc w failed on payment stocklevel delivery neworder orderstatus payment stocklevel delivery neworder orderstatus payment stocklevel wraps secondary error attachment signal killed signal killed error types exec exiterror wraps context canceled error types withstack withstack errutil withprefix main withcommanddetails secondary withsecondaryerror errors errorstring cluster go tpcc go schemachange go test runner go monitor failure monitor task failed t fatal was called attached stack trace stack trace main monitor waite home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main monitor wait home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main runtpcc home agent work go src github com cockroachdb cockroach pkg cmd roachtest tpcc go main makeindexaddtpcctest home agent work go src github com cockroachdb cockroach pkg cmd roachtest schemachange go main testrunner runtest home agent work go src github com cockroachdb cockroach pkg cmd roachtest test runner go wraps monitor failure wraps attached stack trace stack trace main monitor wait home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go wraps monitor task failed wraps attached stack trace stack trace main init home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go runtime doinit usr local go src runtime proc go runtime main usr local go src runtime proc go runtime goexit usr local go src runtime asm s wraps t fatal was called error types withstack withstack errutil withprefix withstack withstack errutil withprefix withstack withstack errutil leaferror more artifacts related roachtest schemachange index tpcc w failed roachtest schemachange index tpcc w failed roachtest schemachange index tpcc w failed powered by | 1 |
66,101 | 6,988,824,109 | IssuesEvent | 2017-12-14 14:19:32 | rhpit/manageiq-cli | https://api.github.com/repos/rhpit/manageiq-cli | opened | Unit tests to validate the command line structure | nice to have tests | The command line structure design mirrors the available ManageIQ REST API collections. The command line has commands **collections** which have sub-commands **collection actions**. @tvieira brought up a nice point of how can we validate these commands. How can we know if our commands are compatible with the REST API collections. The goal here is to validate all our commands are valid commands on ManageIQ.
I.e. A future release of ManageIQ could depreciate certain collections, add collections, change collection name or even add new actions to collections. How would we easily know about this: users report bugs, we see it in release notes, etc. It would be nice to have an automated way that we could tell if our command line structure is valid or not.
The idea here is to create tests to verify all the command line commands are valid commands with ManageIQ. This could be an integration test requiring ManageIQ server to be running and fetch the collections/actions to compare.
For release 1.0 the command line structure is inline with the current collections [1] provided by ManageIQ.
[1] http://manageiq.org/docs/reference/latest/api/reference/collections
| 1.0 | Unit tests to validate the command line structure - The command line structure design mirrors the available ManageIQ REST API collections. The command line has commands **collections** which have sub-commands **collection actions**. @tvieira brought up a nice point of how can we validate these commands. How can we know if our commands are compatible with the REST API collections. The goal here is to validate all our commands are valid commands on ManageIQ.
I.e. A future release of ManageIQ could depreciate certain collections, add collections, change collection name or even add new actions to collections. How would we easily know about this: users report bugs, we see it in release notes, etc. It would be nice to have an automated way that we could tell if our command line structure is valid or not.
The idea here is to create tests to verify all the command line commands are valid commands with ManageIQ. This could be an integration test requiring ManageIQ server to be running and fetch the collections/actions to compare.
For release 1.0 the command line structure is inline with the current collections [1] provided by ManageIQ.
[1] http://manageiq.org/docs/reference/latest/api/reference/collections
| test | unit tests to validate the command line structure the command line structure design mirrors the available manageiq rest api collections the command line has commands collections which have sub commands collection actions tvieira brought up a nice point of how can we validate these commands how can we know if our commands are compatible with the rest api collections the goal here is to validate all our commands are valid commands on manageiq i e a future release of manageiq could depreciate certain collections add collections change collection name or even add new actions to collections how would we easily know about this users report bugs we see it in release notes etc it would be nice to have an automated way that we could tell if our command line structure is valid or not the idea here is to create tests to verify all the command line commands are valid commands with manageiq this could be an integration test requiring manageiq server to be running and fetch the collections actions to compare for release the command line structure is inline with the current collections provided by manageiq | 1 |
162,801 | 12,691,656,759 | IssuesEvent | 2020-06-21 18:10:36 | victorbucutea/parking-space | https://api.github.com/repos/victorbucutea/parking-space | closed | United States of America este duplicat | bug fixed - to retest | 1.Acceseaza https://go-park-staging.herokuapp.com/app/index.html#!/register
2.Click pe butonul alege tara si deruleaza pana la USA
Observat
United States of America este duplicat, iar dand click pe primul USA din lista, apare in campul telefon doar "e.g."
Asteptat
Doar un rezultat de USA ar trebui sa apara in lista, iar pe campul telefon ar trebui sa apara "e.g. 201 555 1234"
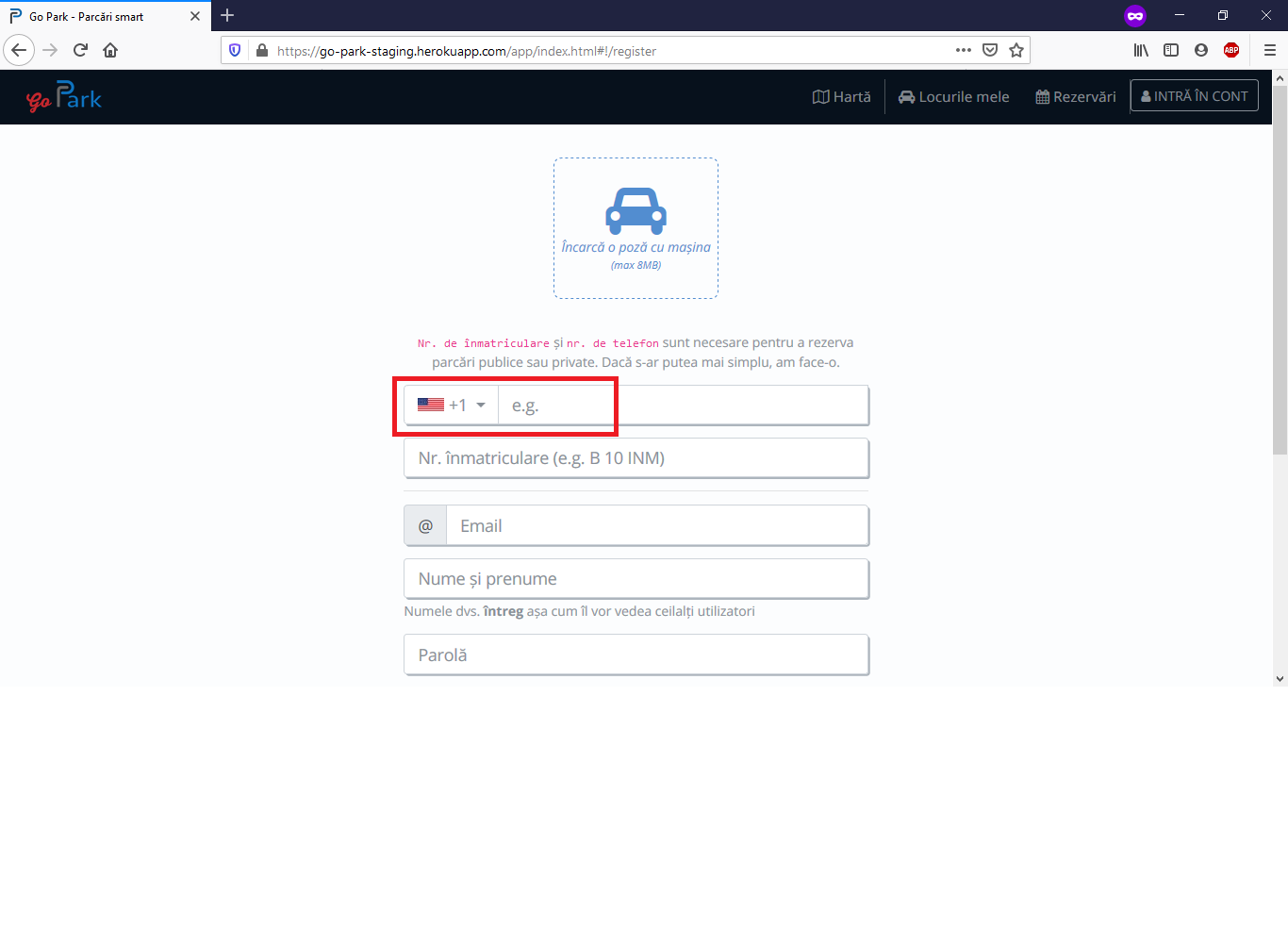
| 1.0 | United States of America este duplicat - 1.Acceseaza https://go-park-staging.herokuapp.com/app/index.html#!/register
2.Click pe butonul alege tara si deruleaza pana la USA
Observat
United States of America este duplicat, iar dand click pe primul USA din lista, apare in campul telefon doar "e.g."
Asteptat
Doar un rezultat de USA ar trebui sa apara in lista, iar pe campul telefon ar trebui sa apara "e.g. 201 555 1234"
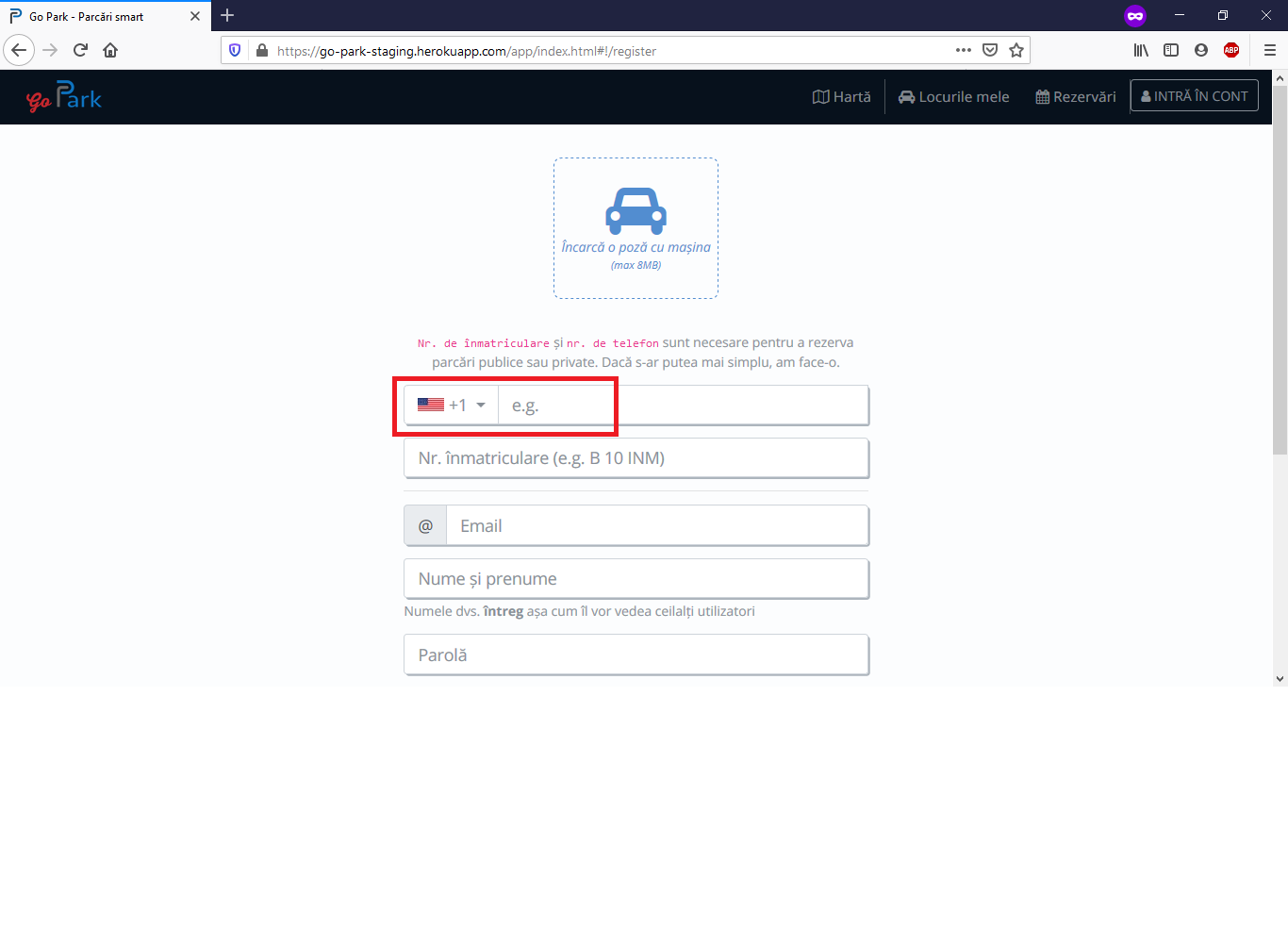
| test | united states of america este duplicat acceseaza click pe butonul alege tara si deruleaza pana la usa observat united states of america este duplicat iar dand click pe primul usa din lista apare in campul telefon doar e g asteptat doar un rezultat de usa ar trebui sa apara in lista iar pe campul telefon ar trebui sa apara e g | 1 |
190,337 | 14,542,743,116 | IssuesEvent | 2020-12-15 16:03:41 | LazeMSS/OctoPrint-UICustomizer | https://api.github.com/repos/LazeMSS/OctoPrint-UICustomizer | closed | Webcam stuck on 'loading' | awaitingtest bug fixedinnext question | I've got two all-but identical OctoPrint systems, both running on Pi4s. On one, the webcam tab and side bar works fine. On the other, the webcam just hangs with a constant 'loading' sign. I also can't view the webcam on my Pi octodash screen. The cam worked fine on this system before I installed UI Customiser. I never noticed the issue before as the problem system is the one I used less often. Is is possible/likely that the UI plugin is the problem?
**Plugins installed:**
- BetterHeaterTimeout
- DisplayLayerProgress
- GcodeEditor
- IFTTT
- PrintTimeGenius
- PrinterAlerts
- PrusaLevelingGuide
- action_command_notification
- action_command_prompt
- announcements
- backup
- backupscheduler
- bedlevelvisualizer
- cancelobject
- costestimation
- dashboard
- discovery
- enclosure
- errortracking
- excluderegion
- filamentmanager
- floatingnavbar
- gcodeviewer
- navbartemp
- pi_support
- pluginmanager
- preheat
- printoid
- prusaslicerthumbnails
- simpleemergencystop
- softwareupdate
- uicustomizer
- virtual_printer
**Software versions:**
- OctoPrint 1.5.2
- Python 2.7.16
- OctoPi 0.17.0 | 1.0 | Webcam stuck on 'loading' - I've got two all-but identical OctoPrint systems, both running on Pi4s. On one, the webcam tab and side bar works fine. On the other, the webcam just hangs with a constant 'loading' sign. I also can't view the webcam on my Pi octodash screen. The cam worked fine on this system before I installed UI Customiser. I never noticed the issue before as the problem system is the one I used less often. Is is possible/likely that the UI plugin is the problem?
**Plugins installed:**
- BetterHeaterTimeout
- DisplayLayerProgress
- GcodeEditor
- IFTTT
- PrintTimeGenius
- PrinterAlerts
- PrusaLevelingGuide
- action_command_notification
- action_command_prompt
- announcements
- backup
- backupscheduler
- bedlevelvisualizer
- cancelobject
- costestimation
- dashboard
- discovery
- enclosure
- errortracking
- excluderegion
- filamentmanager
- floatingnavbar
- gcodeviewer
- navbartemp
- pi_support
- pluginmanager
- preheat
- printoid
- prusaslicerthumbnails
- simpleemergencystop
- softwareupdate
- uicustomizer
- virtual_printer
**Software versions:**
- OctoPrint 1.5.2
- Python 2.7.16
- OctoPi 0.17.0 | test | webcam stuck on loading i ve got two all but identical octoprint systems both running on on one the webcam tab and side bar works fine on the other the webcam just hangs with a constant loading sign i also can t view the webcam on my pi octodash screen the cam worked fine on this system before i installed ui customiser i never noticed the issue before as the problem system is the one i used less often is is possible likely that the ui plugin is the problem plugins installed betterheatertimeout displaylayerprogress gcodeeditor ifttt printtimegenius printeralerts prusalevelingguide action command notification action command prompt announcements backup backupscheduler bedlevelvisualizer cancelobject costestimation dashboard discovery enclosure errortracking excluderegion filamentmanager floatingnavbar gcodeviewer navbartemp pi support pluginmanager preheat printoid prusaslicerthumbnails simpleemergencystop softwareupdate uicustomizer virtual printer software versions octoprint python octopi | 1 |
60,865 | 8,470,248,196 | IssuesEvent | 2018-10-24 03:13:21 | bcit-ci/CodeIgniter4 | https://api.github.com/repos/bcit-ci/CodeIgniter4 | closed | Error in user guide for session config | bug documentation | The user guide (libraries/sessions) still describes the CI3 style of configuration (i.e. $sessionDriver = "files" instead of $sessionDriver = 'CodeIgniter\Session\Handlers\FileHandler';
Needs fixing :-/ | 1.0 | Error in user guide for session config - The user guide (libraries/sessions) still describes the CI3 style of configuration (i.e. $sessionDriver = "files" instead of $sessionDriver = 'CodeIgniter\Session\Handlers\FileHandler';
Needs fixing :-/ | non_test | error in user guide for session config the user guide libraries sessions still describes the style of configuration i e sessiondriver files instead of sessiondriver codeigniter session handlers filehandler needs fixing | 0 |
260,084 | 22,590,146,614 | IssuesEvent | 2022-06-28 19:00:06 | gradle/gradle | https://api.github.com/repos/gradle/gradle | closed | JVM Test Suite Plugin for integrationTest, how to add all test dependencies to integrationTest task in multi module project | a:feature in:test-suites | I am trying to use new JVM Test Suite Plugin (Gradle version 7.3+).
I have difficulty to add all `test` dependencies to `integrationTest` task at top level in a multi-module project.
please advise if there is a clean way set it in root project that apply to all sub projects in https://github.com/xmlking/micro-apps
my env: Gradle v7.4
New
```kotlin
testing {
suites {
val test by getting(JvmTestSuite::class) {
useJUnitJupiter()
targets {
all {
testTask.configure {
useJUnitPlatform {
excludeTags("slow", "integration")
}
filter {
isFailOnNoMatchingTests = false
}
// maxParallelForks = Runtime.getRuntime().availableProcessors() // FIXME: port conflict for quarkus
testLogging {
exceptionFormat = FULL
showExceptions = true
showStandardStreams = true
events(PASSED, FAILED, SKIPPED, STANDARD_OUT, STANDARD_ERROR)
}
finalizedBy("jacocoTestReport")
}
}
}
}
val integrationTest by registering(JvmTestSuite::class) {
sources {
java {
setSrcDirs(listOf("src/test/kotlin", "src/test/java"))
}
resources {
setSrcDirs(listOf("src/test/resources"))
}
}
dependencies {
implementation(project)
//testImplementation(project(path = ":ontrack-extension-casc", configuration = "tests"))
implementation(project(":apps:classifier-pipeline"){ configurations { "testRuntime" } })
// implementation("org.assertj:assertj-core:3.22.0")
}
targets {
all {
testTask.configure {
useJUnitPlatform {
includeTags("integration", "e2e")
}
filter {
isFailOnNoMatchingTests = false
}
testLogging {
exceptionFormat = FULL
showExceptions = true
showStandardStreams = true
events(PASSED, FAILED, SKIPPED, STANDARD_OUT, STANDARD_ERROR)
}
shouldRunAfter(test)
finalizedBy("jacocoTestReport")
}
}
}
}
}
}
```
Old
```kotlin
test {
useJUnitPlatform {
excludeTags("slow", "integration")
}
filter {
isFailOnNoMatchingTests = false
}
// maxParallelForks = Runtime.getRuntime().availableProcessors() // FIXME: port conflict for quarkus
testLogging {
exceptionFormat = FULL
showExceptions = true
showStandardStreams = true
events(PASSED, FAILED, SKIPPED, STANDARD_OUT, STANDARD_ERROR)
}
finalizedBy("jacocoTestReport")
}
register<Test>("integrationTest") {
useJUnitPlatform {
includeTags("integration", "e2e")
}
filter {
isFailOnNoMatchingTests = false
}
testLogging {
exceptionFormat = FULL
showExceptions = true
showStandardStreams = true
events(PASSED, FAILED, SKIPPED, STANDARD_OUT, STANDARD_ERROR)
}
shouldRunAfter(test)
finalizedBy("jacocoTestReport")
}
``` | 1.0 | JVM Test Suite Plugin for integrationTest, how to add all test dependencies to integrationTest task in multi module project - I am trying to use new JVM Test Suite Plugin (Gradle version 7.3+).
I have difficulty to add all `test` dependencies to `integrationTest` task at top level in a multi-module project.
please advise if there is a clean way set it in root project that apply to all sub projects in https://github.com/xmlking/micro-apps
my env: Gradle v7.4
New
```kotlin
testing {
suites {
val test by getting(JvmTestSuite::class) {
useJUnitJupiter()
targets {
all {
testTask.configure {
useJUnitPlatform {
excludeTags("slow", "integration")
}
filter {
isFailOnNoMatchingTests = false
}
// maxParallelForks = Runtime.getRuntime().availableProcessors() // FIXME: port conflict for quarkus
testLogging {
exceptionFormat = FULL
showExceptions = true
showStandardStreams = true
events(PASSED, FAILED, SKIPPED, STANDARD_OUT, STANDARD_ERROR)
}
finalizedBy("jacocoTestReport")
}
}
}
}
val integrationTest by registering(JvmTestSuite::class) {
sources {
java {
setSrcDirs(listOf("src/test/kotlin", "src/test/java"))
}
resources {
setSrcDirs(listOf("src/test/resources"))
}
}
dependencies {
implementation(project)
//testImplementation(project(path = ":ontrack-extension-casc", configuration = "tests"))
implementation(project(":apps:classifier-pipeline"){ configurations { "testRuntime" } })
// implementation("org.assertj:assertj-core:3.22.0")
}
targets {
all {
testTask.configure {
useJUnitPlatform {
includeTags("integration", "e2e")
}
filter {
isFailOnNoMatchingTests = false
}
testLogging {
exceptionFormat = FULL
showExceptions = true
showStandardStreams = true
events(PASSED, FAILED, SKIPPED, STANDARD_OUT, STANDARD_ERROR)
}
shouldRunAfter(test)
finalizedBy("jacocoTestReport")
}
}
}
}
}
}
```
Old
```kotlin
test {
useJUnitPlatform {
excludeTags("slow", "integration")
}
filter {
isFailOnNoMatchingTests = false
}
// maxParallelForks = Runtime.getRuntime().availableProcessors() // FIXME: port conflict for quarkus
testLogging {
exceptionFormat = FULL
showExceptions = true
showStandardStreams = true
events(PASSED, FAILED, SKIPPED, STANDARD_OUT, STANDARD_ERROR)
}
finalizedBy("jacocoTestReport")
}
register<Test>("integrationTest") {
useJUnitPlatform {
includeTags("integration", "e2e")
}
filter {
isFailOnNoMatchingTests = false
}
testLogging {
exceptionFormat = FULL
showExceptions = true
showStandardStreams = true
events(PASSED, FAILED, SKIPPED, STANDARD_OUT, STANDARD_ERROR)
}
shouldRunAfter(test)
finalizedBy("jacocoTestReport")
}
``` | test | jvm test suite plugin for integrationtest how to add all test dependencies to integrationtest task in multi module project i am trying to use new jvm test suite plugin gradle version i have difficulty to add all test dependencies to integrationtest task at top level in a multi module project please advise if there is a clean way set it in root project that apply to all sub projects in my env gradle new kotlin testing suites val test by getting jvmtestsuite class usejunitjupiter targets all testtask configure usejunitplatform excludetags slow integration filter isfailonnomatchingtests false maxparallelforks runtime getruntime availableprocessors fixme port conflict for quarkus testlogging exceptionformat full showexceptions true showstandardstreams true events passed failed skipped standard out standard error finalizedby jacocotestreport val integrationtest by registering jvmtestsuite class sources java setsrcdirs listof src test kotlin src test java resources setsrcdirs listof src test resources dependencies implementation project testimplementation project path ontrack extension casc configuration tests implementation project apps classifier pipeline configurations testruntime implementation org assertj assertj core targets all testtask configure usejunitplatform includetags integration filter isfailonnomatchingtests false testlogging exceptionformat full showexceptions true showstandardstreams true events passed failed skipped standard out standard error shouldrunafter test finalizedby jacocotestreport old kotlin test usejunitplatform excludetags slow integration filter isfailonnomatchingtests false maxparallelforks runtime getruntime availableprocessors fixme port conflict for quarkus testlogging exceptionformat full showexceptions true showstandardstreams true events passed failed skipped standard out standard error finalizedby jacocotestreport register integrationtest usejunitplatform includetags integration filter isfailonnomatchingtests false testlogging exceptionformat full showexceptions true showstandardstreams true events passed failed skipped standard out standard error shouldrunafter test finalizedby jacocotestreport | 1 |
77,402 | 7,573,550,342 | IssuesEvent | 2018-04-23 18:07:13 | Microsoft/AzureStorageExplorer | https://api.github.com/repos/Microsoft/AzureStorageExplorer | closed | The background of the selected items don't theme under HC-modes | testing | **Storage Explorer Version:** master/20180419.2
**OS Version:** Windows 10/Mac/Linux
**Regression:** Works well on 1.0.0 release
**Steps to Reproduce:**
1. Launch Storage Explorer and expand Storage Accounts.
2. Change the theme to HC-Black/White.
3. Open one container and check the background of the selected items.
**Expected Experience:**
The background of the selected items is themed.
**Actual Experience:**
The background of the selected items isn't themed.

| 1.0 | The background of the selected items don't theme under HC-modes - **Storage Explorer Version:** master/20180419.2
**OS Version:** Windows 10/Mac/Linux
**Regression:** Works well on 1.0.0 release
**Steps to Reproduce:**
1. Launch Storage Explorer and expand Storage Accounts.
2. Change the theme to HC-Black/White.
3. Open one container and check the background of the selected items.
**Expected Experience:**
The background of the selected items is themed.
**Actual Experience:**
The background of the selected items isn't themed.

| test | the background of the selected items don t theme under hc modes storage explorer version master os version windows mac linux regression works well on release steps to reproduce launch storage explorer and expand storage accounts change the theme to hc black white open one container and check the background of the selected items expected experience the background of the selected items is themed actual experience the background of the selected items isn t themed | 1 |
212,396 | 16,447,059,030 | IssuesEvent | 2021-05-20 20:58:09 | apple/servicetalk | https://api.github.com/repos/apple/servicetalk | opened | Flaky test: PublisherBufferConcurrencyTest.executorIsPreserved | flaky tests | https://github.com/apple/servicetalk/runs/2633917236?check_suite_focus=true
```
java.util.concurrent.TimeoutException: executorIsPreserved() timed out after 30 seconds
at org.junit.jupiter.engine.extension.TimeoutInvocation.createTimeoutException(TimeoutInvocation.java:70)
at org.junit.jupiter.engine.extension.TimeoutInvocation.proceed(TimeoutInvocation.java:59)
at org.junit.jupiter.engine.extension.TimeoutExtension.intercept(TimeoutExtension.java:149)
at org.junit.jupiter.engine.extension.TimeoutExtension.interceptTestableMethod(TimeoutExtension.java:140)
at org.junit.jupiter.engine.extension.TimeoutExtension.interceptTestMethod(TimeoutExtension.java:84)
at org.junit.jupiter.engine.execution.ExecutableInvoker$ReflectiveInterceptorCall.lambda$ofVoidMethod$0(ExecutableInvoker.java:115)
at org.junit.jupiter.engine.execution.ExecutableInvoker.lambda$invoke$0(ExecutableInvoker.java:105)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain$InterceptedInvocation.proceed(InvocationInterceptorChain.java:106)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.proceed(InvocationInterceptorChain.java:64)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.chainAndInvoke(InvocationInterceptorChain.java:45)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.invoke(InvocationInterceptorChain.java:37)
at org.junit.jupiter.engine.execution.ExecutableInvoker.invoke(ExecutableInvoker.java:104)
at org.junit.jupiter.engine.execution.ExecutableInvoker.invoke(ExecutableInvoker.java:98)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.lambda$invokeTestMethod$6(TestMethodTestDescriptor.java:210)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.invokeTestMethod(TestMethodTestDescriptor.java:206)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:131)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:65)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:139)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:129)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:137)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:127)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:126)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:84)
at java.util.ArrayList.forEach(ArrayList.java:1259)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:143)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:129)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:137)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:127)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:126)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:84)
at java.util.ArrayList.forEach(ArrayList.java:1259)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:143)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:129)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:137)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:127)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:126)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:84)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.submit(SameThreadHierarchicalTestExecutorService.java:32)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestExecutor.execute(HierarchicalTestExecutor.java:57)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestEngine.execute(HierarchicalTestEngine.java:51)
at org.junit.platform.launcher.core.EngineExecutionOrchestrator.execute(EngineExecutionOrchestrator.java:108)
at org.junit.platform.launcher.core.EngineExecutionOrchestrator.execute(EngineExecutionOrchestrator.java:88)
at org.junit.platform.launcher.core.EngineExecutionOrchestrator.lambda$execute$0(EngineExecutionOrchestrator.java:54)
at org.junit.platform.launcher.core.EngineExecutionOrchestrator.withInterceptedStreams(EngineExecutionOrchestrator.java:67)
at org.junit.platform.launcher.core.EngineExecutionOrchestrator.execute(EngineExecutionOrchestrator.java:52)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:96)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:75)
at org.gradle.api.internal.tasks.testing.junitplatform.JUnitPlatformTestClassProcessor$CollectAllTestClassesExecutor.processAllTestClasses(JUnitPlatformTestClassProcessor.java:99)
at org.gradle.api.internal.tasks.testing.junitplatform.JUnitPlatformTestClassProcessor$CollectAllTestClassesExecutor.access$000(JUnitPlatformTestClassProcessor.java:79)
at org.gradle.api.internal.tasks.testing.junitplatform.JUnitPlatformTestClassProcessor.stop(JUnitPlatformTestClassProcessor.java:75)
at org.gradle.api.internal.tasks.testing.SuiteTestClassProcessor.stop(SuiteTestClassProcessor.java:61)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:36)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:24)
at org.gradle.internal.dispatch.ContextClassLoaderDispatch.dispatch(ContextClassLoaderDispatch.java:33)
at org.gradle.internal.dispatch.ProxyDispatchAdapter$DispatchingInvocationHandler.invoke(ProxyDispatchAdapter.java:94)
at com.sun.proxy.$Proxy2.stop(Unknown Source)
at org.gradle.api.internal.tasks.testing.worker.TestWorker.stop(TestWorker.java:133)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:36)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:24)
at org.gradle.internal.remote.internal.hub.MessageHubBackedObjectConnection$DispatchWrapper.dispatch(MessageHubBackedObjectConnection.java:182)
at org.gradle.internal.remote.internal.hub.MessageHubBackedObjectConnection$DispatchWrapper.dispatch(MessageHubBackedObjectConnection.java:164)
at org.gradle.internal.remote.internal.hub.MessageHub$Handler.run(MessageHub.java:414)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.lang.Thread.run(Thread.java:748)
Suppressed: java.lang.InterruptedException
at java.util.concurrent.locks.AbstractQueuedSynchronizer.doAcquireSharedInterruptibly(AbstractQueuedSynchronizer.java:998)
at java.util.concurrent.locks.AbstractQueuedSynchronizer.acquireSharedInterruptibly(AbstractQueuedSynchronizer.java:1304)
at java.util.concurrent.CountDownLatch.await(CountDownLatch.java:231)
at io.servicetalk.concurrent.api.SourceToFuture.get(SourceToFuture.java:91)
at io.servicetalk.concurrent.api.PublisherBufferConcurrencyTest.runTest(PublisherBufferConcurrencyTest.java:168)
at io.servicetalk.concurrent.api.PublisherBufferConcurrencyTest.executorIsPreserved(PublisherBufferConcurrencyTest.java:59)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.platform.commons.util.ReflectionUtils.invokeMethod(ReflectionUtils.java:688)
at org.junit.jupiter.engine.execution.MethodInvocation.proceed(MethodInvocation.java:60)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain$ValidatingInvocation.proceed(InvocationInterceptorChain.java:131)
at org.junit.jupiter.engine.extension.TimeoutInvocation.proceed(TimeoutInvocation.java:46)
... 83 more
``` | 1.0 | Flaky test: PublisherBufferConcurrencyTest.executorIsPreserved - https://github.com/apple/servicetalk/runs/2633917236?check_suite_focus=true
```
java.util.concurrent.TimeoutException: executorIsPreserved() timed out after 30 seconds
at org.junit.jupiter.engine.extension.TimeoutInvocation.createTimeoutException(TimeoutInvocation.java:70)
at org.junit.jupiter.engine.extension.TimeoutInvocation.proceed(TimeoutInvocation.java:59)
at org.junit.jupiter.engine.extension.TimeoutExtension.intercept(TimeoutExtension.java:149)
at org.junit.jupiter.engine.extension.TimeoutExtension.interceptTestableMethod(TimeoutExtension.java:140)
at org.junit.jupiter.engine.extension.TimeoutExtension.interceptTestMethod(TimeoutExtension.java:84)
at org.junit.jupiter.engine.execution.ExecutableInvoker$ReflectiveInterceptorCall.lambda$ofVoidMethod$0(ExecutableInvoker.java:115)
at org.junit.jupiter.engine.execution.ExecutableInvoker.lambda$invoke$0(ExecutableInvoker.java:105)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain$InterceptedInvocation.proceed(InvocationInterceptorChain.java:106)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.proceed(InvocationInterceptorChain.java:64)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.chainAndInvoke(InvocationInterceptorChain.java:45)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain.invoke(InvocationInterceptorChain.java:37)
at org.junit.jupiter.engine.execution.ExecutableInvoker.invoke(ExecutableInvoker.java:104)
at org.junit.jupiter.engine.execution.ExecutableInvoker.invoke(ExecutableInvoker.java:98)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.lambda$invokeTestMethod$6(TestMethodTestDescriptor.java:210)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.invokeTestMethod(TestMethodTestDescriptor.java:206)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:131)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:65)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:139)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:129)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:137)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:127)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:126)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:84)
at java.util.ArrayList.forEach(ArrayList.java:1259)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:143)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:129)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:137)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:127)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:126)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:84)
at java.util.ArrayList.forEach(ArrayList.java:1259)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:143)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:129)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:137)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:127)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:126)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:84)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.submit(SameThreadHierarchicalTestExecutorService.java:32)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestExecutor.execute(HierarchicalTestExecutor.java:57)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestEngine.execute(HierarchicalTestEngine.java:51)
at org.junit.platform.launcher.core.EngineExecutionOrchestrator.execute(EngineExecutionOrchestrator.java:108)
at org.junit.platform.launcher.core.EngineExecutionOrchestrator.execute(EngineExecutionOrchestrator.java:88)
at org.junit.platform.launcher.core.EngineExecutionOrchestrator.lambda$execute$0(EngineExecutionOrchestrator.java:54)
at org.junit.platform.launcher.core.EngineExecutionOrchestrator.withInterceptedStreams(EngineExecutionOrchestrator.java:67)
at org.junit.platform.launcher.core.EngineExecutionOrchestrator.execute(EngineExecutionOrchestrator.java:52)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:96)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:75)
at org.gradle.api.internal.tasks.testing.junitplatform.JUnitPlatformTestClassProcessor$CollectAllTestClassesExecutor.processAllTestClasses(JUnitPlatformTestClassProcessor.java:99)
at org.gradle.api.internal.tasks.testing.junitplatform.JUnitPlatformTestClassProcessor$CollectAllTestClassesExecutor.access$000(JUnitPlatformTestClassProcessor.java:79)
at org.gradle.api.internal.tasks.testing.junitplatform.JUnitPlatformTestClassProcessor.stop(JUnitPlatformTestClassProcessor.java:75)
at org.gradle.api.internal.tasks.testing.SuiteTestClassProcessor.stop(SuiteTestClassProcessor.java:61)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:36)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:24)
at org.gradle.internal.dispatch.ContextClassLoaderDispatch.dispatch(ContextClassLoaderDispatch.java:33)
at org.gradle.internal.dispatch.ProxyDispatchAdapter$DispatchingInvocationHandler.invoke(ProxyDispatchAdapter.java:94)
at com.sun.proxy.$Proxy2.stop(Unknown Source)
at org.gradle.api.internal.tasks.testing.worker.TestWorker.stop(TestWorker.java:133)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:36)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:24)
at org.gradle.internal.remote.internal.hub.MessageHubBackedObjectConnection$DispatchWrapper.dispatch(MessageHubBackedObjectConnection.java:182)
at org.gradle.internal.remote.internal.hub.MessageHubBackedObjectConnection$DispatchWrapper.dispatch(MessageHubBackedObjectConnection.java:164)
at org.gradle.internal.remote.internal.hub.MessageHub$Handler.run(MessageHub.java:414)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.lang.Thread.run(Thread.java:748)
Suppressed: java.lang.InterruptedException
at java.util.concurrent.locks.AbstractQueuedSynchronizer.doAcquireSharedInterruptibly(AbstractQueuedSynchronizer.java:998)
at java.util.concurrent.locks.AbstractQueuedSynchronizer.acquireSharedInterruptibly(AbstractQueuedSynchronizer.java:1304)
at java.util.concurrent.CountDownLatch.await(CountDownLatch.java:231)
at io.servicetalk.concurrent.api.SourceToFuture.get(SourceToFuture.java:91)
at io.servicetalk.concurrent.api.PublisherBufferConcurrencyTest.runTest(PublisherBufferConcurrencyTest.java:168)
at io.servicetalk.concurrent.api.PublisherBufferConcurrencyTest.executorIsPreserved(PublisherBufferConcurrencyTest.java:59)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.platform.commons.util.ReflectionUtils.invokeMethod(ReflectionUtils.java:688)
at org.junit.jupiter.engine.execution.MethodInvocation.proceed(MethodInvocation.java:60)
at org.junit.jupiter.engine.execution.InvocationInterceptorChain$ValidatingInvocation.proceed(InvocationInterceptorChain.java:131)
at org.junit.jupiter.engine.extension.TimeoutInvocation.proceed(TimeoutInvocation.java:46)
... 83 more
``` | test | flaky test publisherbufferconcurrencytest executorispreserved java util concurrent timeoutexception executorispreserved timed out after seconds at org junit jupiter engine extension timeoutinvocation createtimeoutexception timeoutinvocation java at org junit jupiter engine extension timeoutinvocation proceed timeoutinvocation java at org junit jupiter engine extension timeoutextension intercept timeoutextension java at org junit jupiter engine extension timeoutextension intercepttestablemethod timeoutextension java at org junit jupiter engine extension timeoutextension intercepttestmethod timeoutextension java at org junit jupiter engine execution executableinvoker reflectiveinterceptorcall lambda ofvoidmethod executableinvoker java at org junit jupiter engine execution executableinvoker lambda invoke executableinvoker java at org junit jupiter engine execution invocationinterceptorchain interceptedinvocation proceed invocationinterceptorchain java at org junit jupiter engine execution invocationinterceptorchain proceed invocationinterceptorchain java at org junit jupiter engine execution invocationinterceptorchain chainandinvoke invocationinterceptorchain java at org junit jupiter engine execution invocationinterceptorchain invoke invocationinterceptorchain java at org junit jupiter engine execution executableinvoker invoke executableinvoker java at org junit jupiter engine execution executableinvoker invoke executableinvoker java at org junit jupiter engine descriptor testmethodtestdescriptor lambda invoketestmethod testmethodtestdescriptor java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit jupiter engine descriptor testmethodtestdescriptor invoketestmethod testmethodtestdescriptor java at org junit jupiter engine descriptor testmethodtestdescriptor execute testmethodtestdescriptor java at org junit jupiter engine descriptor testmethodtestdescriptor execute testmethodtestdescriptor java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical node around node java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask executerecursively nodetesttask java at org junit platform engine support hierarchical nodetesttask execute nodetesttask java at java util arraylist foreach arraylist java at org junit platform engine support hierarchical samethreadhierarchicaltestexecutorservice invokeall samethreadhierarchicaltestexecutorservice java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical node around node java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask executerecursively nodetesttask java at org junit platform engine support hierarchical nodetesttask execute nodetesttask java at java util arraylist foreach arraylist java at org junit platform engine support hierarchical samethreadhierarchicaltestexecutorservice invokeall samethreadhierarchicaltestexecutorservice java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical node around node java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask executerecursively nodetesttask java at org junit platform engine support hierarchical nodetesttask execute nodetesttask java at org junit platform engine support hierarchical samethreadhierarchicaltestexecutorservice submit samethreadhierarchicaltestexecutorservice java at org junit platform engine support hierarchical hierarchicaltestexecutor execute hierarchicaltestexecutor java at org junit platform engine support hierarchical hierarchicaltestengine execute hierarchicaltestengine java at org junit platform launcher core engineexecutionorchestrator execute engineexecutionorchestrator java at org junit platform launcher core engineexecutionorchestrator execute engineexecutionorchestrator java at org junit platform launcher core engineexecutionorchestrator lambda execute engineexecutionorchestrator java at org junit platform launcher core engineexecutionorchestrator withinterceptedstreams engineexecutionorchestrator java at org junit platform launcher core engineexecutionorchestrator execute engineexecutionorchestrator java at org junit platform launcher core defaultlauncher execute defaultlauncher java at org junit platform launcher core defaultlauncher execute defaultlauncher java at org gradle api internal tasks testing junitplatform junitplatformtestclassprocessor collectalltestclassesexecutor processalltestclasses junitplatformtestclassprocessor java at org gradle api internal tasks testing junitplatform junitplatformtestclassprocessor collectalltestclassesexecutor access junitplatformtestclassprocessor java at org gradle api internal tasks testing junitplatform junitplatformtestclassprocessor stop junitplatformtestclassprocessor java at org gradle api internal tasks testing suitetestclassprocessor stop suitetestclassprocessor java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org gradle internal dispatch reflectiondispatch dispatch reflectiondispatch java at org gradle internal dispatch reflectiondispatch dispatch reflectiondispatch java at org gradle internal dispatch contextclassloaderdispatch dispatch contextclassloaderdispatch java at org gradle internal dispatch proxydispatchadapter dispatchinginvocationhandler invoke proxydispatchadapter java at com sun proxy stop unknown source at org gradle api internal tasks testing worker testworker stop testworker java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org gradle internal dispatch reflectiondispatch dispatch reflectiondispatch java at org gradle internal dispatch reflectiondispatch dispatch reflectiondispatch java at org gradle internal remote internal hub messagehubbackedobjectconnection dispatchwrapper dispatch messagehubbackedobjectconnection java at org gradle internal remote internal hub messagehubbackedobjectconnection dispatchwrapper dispatch messagehubbackedobjectconnection java at org gradle internal remote internal hub messagehub handler run messagehub java at org gradle internal concurrent executorpolicy catchandrecordfailures onexecute executorpolicy java at org gradle internal concurrent managedexecutorimpl run managedexecutorimpl java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at org gradle internal concurrent threadfactoryimpl managedthreadrunnable run threadfactoryimpl java at java lang thread run thread java suppressed java lang interruptedexception at java util concurrent locks abstractqueuedsynchronizer doacquiresharedinterruptibly abstractqueuedsynchronizer java at java util concurrent locks abstractqueuedsynchronizer acquiresharedinterruptibly abstractqueuedsynchronizer java at java util concurrent countdownlatch await countdownlatch java at io servicetalk concurrent api sourcetofuture get sourcetofuture java at io servicetalk concurrent api publisherbufferconcurrencytest runtest publisherbufferconcurrencytest java at io servicetalk concurrent api publisherbufferconcurrencytest executorispreserved publisherbufferconcurrencytest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org junit platform commons util reflectionutils invokemethod reflectionutils java at org junit jupiter engine execution methodinvocation proceed methodinvocation java at org junit jupiter engine execution invocationinterceptorchain validatinginvocation proceed invocationinterceptorchain java at org junit jupiter engine extension timeoutinvocation proceed timeoutinvocation java more | 1 |
346,578 | 30,958,150,311 | IssuesEvent | 2023-08-08 00:02:46 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | [Flaky Test] can be created by selecting text and clicking Link | [Status] Stale [Type] Flaky Test | <!-- __META_DATA__:{} -->
**Flaky test detected. This is an auto-generated issue by GitHub Actions. Please do NOT edit this manually.**
## Test title
can be created by selecting text and clicking Link
## Test path
`specs/editor/various/links.test.js`
## Errors
<!-- __TEST_RESULTS_LIST__ -->
<!-- __TEST_RESULT__ --><time datetime="2023-03-07T12:01:33.170Z"><code>[2023-03-07T12:01:33.170Z]</code></time> Test passed after 2 failed attempts on <a href="https://github.com/WordPress/gutenberg/actions/runs/4353563197"><code>try/dedicated-block-controls-filter</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><details>
<summary>
<time datetime="2023-07-06T10:12:31.200Z"><code>[2023-07-06T10:12:31.200Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/5473758534"><code>try/iframe-without-asset-parsing</code></a>.
</summary>
```
● Links › can be created by selecting text and clicking Link
No node found for selector: button[aria-label="Link"]
76 |
77 | // Click on the Link button.
> 78 | await page.click( 'button[aria-label="Link"]' );
| ^
79 |
80 | // Wait for the URL field to auto-focus.
81 | await waitForURLFieldAutoFocus();
at assert (../../node_modules/puppeteer-core/src/common/assert.ts:23:21)
at DOMWorld.click (../../node_modules/puppeteer-core/src/common/DOMWorld.ts:461:11)
at runMicrotasks (<anonymous>)
at Object.<anonymous> (specs/editor/various/links.test.js:78:3)
```
</details><!-- /__TEST_RESULT__ -->
<!-- /__TEST_RESULTS_LIST__ -->
| 1.0 | [Flaky Test] can be created by selecting text and clicking Link - <!-- __META_DATA__:{} -->
**Flaky test detected. This is an auto-generated issue by GitHub Actions. Please do NOT edit this manually.**
## Test title
can be created by selecting text and clicking Link
## Test path
`specs/editor/various/links.test.js`
## Errors
<!-- __TEST_RESULTS_LIST__ -->
<!-- __TEST_RESULT__ --><time datetime="2023-03-07T12:01:33.170Z"><code>[2023-03-07T12:01:33.170Z]</code></time> Test passed after 2 failed attempts on <a href="https://github.com/WordPress/gutenberg/actions/runs/4353563197"><code>try/dedicated-block-controls-filter</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><details>
<summary>
<time datetime="2023-07-06T10:12:31.200Z"><code>[2023-07-06T10:12:31.200Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/5473758534"><code>try/iframe-without-asset-parsing</code></a>.
</summary>
```
● Links › can be created by selecting text and clicking Link
No node found for selector: button[aria-label="Link"]
76 |
77 | // Click on the Link button.
> 78 | await page.click( 'button[aria-label="Link"]' );
| ^
79 |
80 | // Wait for the URL field to auto-focus.
81 | await waitForURLFieldAutoFocus();
at assert (../../node_modules/puppeteer-core/src/common/assert.ts:23:21)
at DOMWorld.click (../../node_modules/puppeteer-core/src/common/DOMWorld.ts:461:11)
at runMicrotasks (<anonymous>)
at Object.<anonymous> (specs/editor/various/links.test.js:78:3)
```
</details><!-- /__TEST_RESULT__ -->
<!-- /__TEST_RESULTS_LIST__ -->
| test | can be created by selecting text and clicking link flaky test detected this is an auto generated issue by github actions please do not edit this manually test title can be created by selecting text and clicking link test path specs editor various links test js errors test passed after failed attempts on test passed after failed attempt on a href ● links › can be created by selecting text and clicking link no node found for selector button click on the link button await page click button wait for the url field to auto focus await waitforurlfieldautofocus at assert node modules puppeteer core src common assert ts at domworld click node modules puppeteer core src common domworld ts at runmicrotasks at object specs editor various links test js | 1 |
54,925 | 6,417,751,140 | IssuesEvent | 2017-08-08 17:26:55 | sonarwhal/sonar | https://api.github.com/repos/sonarwhal/sonar | reopened | Support `https` and `http` requests simultaneously in the test-server | type:new-feature type:testing | The current `test-server` after https://github.com/sonarwhal/sonar/pull/370 is merged supports creating a server that serves EITHER `http` or `https` pages ONLY, but doesn't have support for listening to `http` and `https` requests simultaneously in the same rule test, which is needed to add tests for rule `strict transport security` (https://github.com/sonarwhal/sonar/pull/370) if we want to support testing `http` site first, and then test the same site with `https` protocol if it doesn't redirect itself, as suggested by @alrra . | 1.0 | Support `https` and `http` requests simultaneously in the test-server - The current `test-server` after https://github.com/sonarwhal/sonar/pull/370 is merged supports creating a server that serves EITHER `http` or `https` pages ONLY, but doesn't have support for listening to `http` and `https` requests simultaneously in the same rule test, which is needed to add tests for rule `strict transport security` (https://github.com/sonarwhal/sonar/pull/370) if we want to support testing `http` site first, and then test the same site with `https` protocol if it doesn't redirect itself, as suggested by @alrra . | test | support https and http requests simultaneously in the test server the current test server after is merged supports creating a server that serves either http or https pages only but doesn t have support for listening to http and https requests simultaneously in the same rule test which is needed to add tests for rule strict transport security if we want to support testing http site first and then test the same site with https protocol if it doesn t redirect itself as suggested by alrra | 1 |
344,742 | 30,756,946,624 | IssuesEvent | 2023-07-29 07:00:13 | nazrinharris/pecunia | https://api.github.com/repos/nazrinharris/pecunia | closed | Create tests for `provider`s/`controller`s | testing | I'm fairly sure this will be done after #47 is completed.
So basically, I want to make tests for the `usecases` in `transactions`. (and possibly `accounts` and `auth` as well). But what exactly am I trying to test? | 1.0 | Create tests for `provider`s/`controller`s - I'm fairly sure this will be done after #47 is completed.
So basically, I want to make tests for the `usecases` in `transactions`. (and possibly `accounts` and `auth` as well). But what exactly am I trying to test? | test | create tests for provider s controller s i m fairly sure this will be done after is completed so basically i want to make tests for the usecases in transactions and possibly accounts and auth as well but what exactly am i trying to test | 1 |
217,920 | 16,891,515,248 | IssuesEvent | 2021-06-23 09:48:43 | hakehuang/zephyr | https://api.github.com/repos/hakehuang/zephyr | opened |
tests-ci :kernel.memory_protection.syscalls.user_string_copy : zephyr-v2.6.0-286-g46029914a7ac: mimxrt1015_evk: test Flash error
| area: Tests bug |
**Describe the bug**
kernel.memory_protection.syscalls.user_string_copy test is Flash error on zephyr-v2.6.0-286-g46029914a7ac on mimxrt1015_evk
see logs for details
**To Reproduce**
1.
```
scripts/twister --device-testing --device-serial /dev/ttyACM0 -p mimxrt1015_evk --testcase-root tests --sub-test kernel.memory_protection
```
2. See error
**Expected behavior**
test pass
**Impact**
**Logs and console output**
```
None
```
**Environment (please complete the following information):**
- OS: (e.g. Linux )
- Toolchain (e.g Zephyr SDK)
- Commit SHA or Version used: zephyr-v2.6.0-286-g46029914a7ac
| 1.0 |
tests-ci :kernel.memory_protection.syscalls.user_string_copy : zephyr-v2.6.0-286-g46029914a7ac: mimxrt1015_evk: test Flash error
-
**Describe the bug**
kernel.memory_protection.syscalls.user_string_copy test is Flash error on zephyr-v2.6.0-286-g46029914a7ac on mimxrt1015_evk
see logs for details
**To Reproduce**
1.
```
scripts/twister --device-testing --device-serial /dev/ttyACM0 -p mimxrt1015_evk --testcase-root tests --sub-test kernel.memory_protection
```
2. See error
**Expected behavior**
test pass
**Impact**
**Logs and console output**
```
None
```
**Environment (please complete the following information):**
- OS: (e.g. Linux )
- Toolchain (e.g Zephyr SDK)
- Commit SHA or Version used: zephyr-v2.6.0-286-g46029914a7ac
| test | tests ci kernel memory protection syscalls user string copy zephyr evk test flash error describe the bug kernel memory protection syscalls user string copy test is flash error on zephyr on evk see logs for details to reproduce scripts twister device testing device serial dev p evk testcase root tests sub test kernel memory protection see error expected behavior test pass impact logs and console output none environment please complete the following information os e g linux toolchain e g zephyr sdk commit sha or version used zephyr | 1 |
274,017 | 23,803,367,873 | IssuesEvent | 2022-09-03 16:52:34 | tempesta-tech/tempesta | https://api.github.com/repos/tempesta-tech/tempesta | closed | Test for synchronous sockets | test | ~~Current tests for synchronous sockets in `tempesta_fw/t/sync_sockets/` are outdated. They must be moved to unit or functional test suite. The must be updated to accurately cover all SS code, preferably with `ss_skb.c`. Kernel/kernel, kenel-client/user-space-server and user-space-client/kernel-server modes must be tested. Pay attention to lock-free ring buffer usage as a transport, so develop tests for the ring buffer and close backlog testing.~~
Initially the task was created during long debugging of #692, however SS code is too integrated with Linux TCP/IP stack and I doubt that the original bug could be caught by the kserver/kclient unit test. Actually all our functional tests use and test SS code, so there is no need in the unit test and `tempesta_fw/t/sync_sockets/` should be just deleted. However, we have `t/functional/tcp_connection` functional tests using `t/functional/helpers/analyzer.py` and the tests are the right way for accurate testing of SS.
So in context of the issue, please develop tests for #873. | 1.0 | Test for synchronous sockets - ~~Current tests for synchronous sockets in `tempesta_fw/t/sync_sockets/` are outdated. They must be moved to unit or functional test suite. The must be updated to accurately cover all SS code, preferably with `ss_skb.c`. Kernel/kernel, kenel-client/user-space-server and user-space-client/kernel-server modes must be tested. Pay attention to lock-free ring buffer usage as a transport, so develop tests for the ring buffer and close backlog testing.~~
Initially the task was created during long debugging of #692, however SS code is too integrated with Linux TCP/IP stack and I doubt that the original bug could be caught by the kserver/kclient unit test. Actually all our functional tests use and test SS code, so there is no need in the unit test and `tempesta_fw/t/sync_sockets/` should be just deleted. However, we have `t/functional/tcp_connection` functional tests using `t/functional/helpers/analyzer.py` and the tests are the right way for accurate testing of SS.
So in context of the issue, please develop tests for #873. | test | test for synchronous sockets current tests for synchronous sockets in tempesta fw t sync sockets are outdated they must be moved to unit or functional test suite the must be updated to accurately cover all ss code preferably with ss skb c kernel kernel kenel client user space server and user space client kernel server modes must be tested pay attention to lock free ring buffer usage as a transport so develop tests for the ring buffer and close backlog testing initially the task was created during long debugging of however ss code is too integrated with linux tcp ip stack and i doubt that the original bug could be caught by the kserver kclient unit test actually all our functional tests use and test ss code so there is no need in the unit test and tempesta fw t sync sockets should be just deleted however we have t functional tcp connection functional tests using t functional helpers analyzer py and the tests are the right way for accurate testing of ss so in context of the issue please develop tests for | 1 |
198,311 | 14,972,474,944 | IssuesEvent | 2021-01-27 22:55:59 | correctcomputation/checkedc-clang | https://api.github.com/repos/correctcomputation/checkedc-clang | opened | Should we use Csmith (+ CReduce) to test 3c for seg-faults? | testing | @mwhicks1 Do you think this is a good idea to check for some stuff that we don't handle? | 1.0 | Should we use Csmith (+ CReduce) to test 3c for seg-faults? - @mwhicks1 Do you think this is a good idea to check for some stuff that we don't handle? | test | should we use csmith creduce to test for seg faults do you think this is a good idea to check for some stuff that we don t handle | 1 |
42,285 | 5,431,374,530 | IssuesEvent | 2017-03-04 00:32:31 | gnieboer/GNURadio_Windows_Build_Scripts | https://api.github.com/repos/gnieboer/GNURadio_Windows_Build_Scripts | closed | libpng version out of date, fails build script | in test | getPackage in Setup.ps1 fails when trying to fetch libpng-1.6.21, current version hosted is 1.6.28. Updating the path worked when running the script. | 1.0 | libpng version out of date, fails build script - getPackage in Setup.ps1 fails when trying to fetch libpng-1.6.21, current version hosted is 1.6.28. Updating the path worked when running the script. | test | libpng version out of date fails build script getpackage in setup fails when trying to fetch libpng current version hosted is updating the path worked when running the script | 1 |
126,498 | 10,425,432,818 | IssuesEvent | 2019-09-16 15:24:44 | astropy/astropy | https://api.github.com/repos/astropy/astropy | closed | Move flake8 test to circleCI | Refactoring testing | As they should never be skipped. Maybe add them as the first step in the docs testing job? I suppose that job will be the one run most frequently as the only way to skip it is with `[skip ci]`, while in the current setup the flake8 tests don't run with `[skip travis]` or with `[docs only]`.
(e.g. to avoid failures like the ones in https://github.com/astropy/astropy/pull/9177 that also sneaked into the backport branch). | 1.0 | Move flake8 test to circleCI - As they should never be skipped. Maybe add them as the first step in the docs testing job? I suppose that job will be the one run most frequently as the only way to skip it is with `[skip ci]`, while in the current setup the flake8 tests don't run with `[skip travis]` or with `[docs only]`.
(e.g. to avoid failures like the ones in https://github.com/astropy/astropy/pull/9177 that also sneaked into the backport branch). | test | move test to circleci as they should never be skipped maybe add them as the first step in the docs testing job i suppose that job will be the one run most frequently as the only way to skip it is with while in the current setup the tests don t run with or with e g to avoid failures like the ones in that also sneaked into the backport branch | 1 |
68,365 | 21,649,297,415 | IssuesEvent | 2022-05-06 07:37:13 | vector-im/element-ios | https://api.github.com/repos/vector-im/element-ios | closed | Location sharing: Stop button is not working in timeline cell | T-Defect Z-Labs A-Location-Sharing | Nothing happen when you hit the "stop" button in the live location cell.
Check cell reuse and that delegate is not gone in `RoomTimelineLocationView`. | 1.0 | Location sharing: Stop button is not working in timeline cell - Nothing happen when you hit the "stop" button in the live location cell.
Check cell reuse and that delegate is not gone in `RoomTimelineLocationView`. | non_test | location sharing stop button is not working in timeline cell nothing happen when you hit the stop button in the live location cell check cell reuse and that delegate is not gone in roomtimelinelocationview | 0 |
306,430 | 9,393,117,993 | IssuesEvent | 2019-04-07 08:40:14 | BentoBoxWorld/BentoBox | https://api.github.com/repos/BentoBoxWorld/BentoBox | closed | Toggle whether "blank lines" in translations should be sent in the chat or not | Priority: Low Status: Declined Type: Enhancement | ### Description
#### Is your feature request related to a problem?
<!-- A clear and concise description of the problem you're encountering, if any. -->
<!-- Please type below this line. -->
This has been requested on Discord quite a while ago.
#### Describe the solution you'd like us to implement.
<!-- A clear and concise description of what you want us to do to resolve your problem. -->
<!-- Please type below this line. -->
Add an option in the configuration to toggle whether "blank lines" (= lines that contains nothing) should be printed in the chat or not.
#### Describe alternatives you've considered.
<!-- A clear and concise description of any alternative solutions or features you've considered. -->
<!-- Please type below this line. -->
None.
### Additional context
<!-- Add any other context or screenshots about the feature request here. -->
<!-- Please type below this line. -->
None. | 1.0 | Toggle whether "blank lines" in translations should be sent in the chat or not - ### Description
#### Is your feature request related to a problem?
<!-- A clear and concise description of the problem you're encountering, if any. -->
<!-- Please type below this line. -->
This has been requested on Discord quite a while ago.
#### Describe the solution you'd like us to implement.
<!-- A clear and concise description of what you want us to do to resolve your problem. -->
<!-- Please type below this line. -->
Add an option in the configuration to toggle whether "blank lines" (= lines that contains nothing) should be printed in the chat or not.
#### Describe alternatives you've considered.
<!-- A clear and concise description of any alternative solutions or features you've considered. -->
<!-- Please type below this line. -->
None.
### Additional context
<!-- Add any other context or screenshots about the feature request here. -->
<!-- Please type below this line. -->
None. | non_test | toggle whether blank lines in translations should be sent in the chat or not description is your feature request related to a problem this has been requested on discord quite a while ago describe the solution you d like us to implement add an option in the configuration to toggle whether blank lines lines that contains nothing should be printed in the chat or not describe alternatives you ve considered none additional context none | 0 |
300,440 | 22,678,317,330 | IssuesEvent | 2022-07-04 07:35:38 | ut-issl/s2e-core | https://api.github.com/repos/ut-issl/s2e-core | opened | Add rule for file path | documentation | ## Overview
Add specific rule for file path of config or data.
## Details
Currently, no rule for (config/data) file path.
Some file paths are embed in user's code and it looks like `../../data/SampleSat/ini/SampleSimBase.ini`.
It causes lack of portability.
So, we must be make default file path strategy.
## Conditions for close
When xxx is complete.
## Supplement
Write additional comments if you need.
## Note
- If there are related Projects, tie them together.
- Set `priority` label if possible.
- Assignees should be set if possible.
- Write a conclusion when closing the issue.
| 1.0 | Add rule for file path - ## Overview
Add specific rule for file path of config or data.
## Details
Currently, no rule for (config/data) file path.
Some file paths are embed in user's code and it looks like `../../data/SampleSat/ini/SampleSimBase.ini`.
It causes lack of portability.
So, we must be make default file path strategy.
## Conditions for close
When xxx is complete.
## Supplement
Write additional comments if you need.
## Note
- If there are related Projects, tie them together.
- Set `priority` label if possible.
- Assignees should be set if possible.
- Write a conclusion when closing the issue.
| non_test | add rule for file path overview add specific rule for file path of config or data details currently no rule for config data file path some file paths are embed in user s code and it looks like data samplesat ini samplesimbase ini it causes lack of portability so we must be make default file path strategy conditions for close when xxx is complete supplement write additional comments if you need note if there are related projects tie them together set priority label if possible assignees should be set if possible write a conclusion when closing the issue | 0 |
340,509 | 30,521,872,405 | IssuesEvent | 2023-07-19 08:38:19 | kyma-project/kyma | https://api.github.com/repos/kyma-project/kyma | closed | Logging tests are frequently failing | kind/bug area/logging kind/failing-test | **Description**
The logging tests are frequently failing on [`kyma-upgrade-gardener-kyma2-to-main-reconciler-main`](https://status.build.kyma-project.io/job-history/gs/kyma-prow-logs/logs/kyma-upgrade-gardener-kyma2-to-main-reconciler-main) and [`kyma-upgrade-k3d-kyma2-to-main`](https://status.build.kyma-project.io/job-history/gs/kyma-prow-logs/logs/kyma-upgrade-k3d-kyma2-to-main) prowjobs.
**Expected result**
The tests are passing
**Actual result**
```
1) Upgrade test tests
Logging Tests:
Istio Access Logs tests
Should query Loki and verify format of Istio Access Logs:
TypeError: Cannot read property 'values' of undefined
at Object.verifyIstioAccessLogFormat (logging/loki.js:58:48)
at processTicksAndRejections (internal/process/task_queues.js:95:5)
at async Context.<anonymous> (logging/index.js:45:7)
```
**See also**
- https://status.build.kyma-project.io/view/gs/kyma-prow-logs/logs/kyma-upgrade-k3d-kyma2-to-main/1663968646646468608
- https://status.build.kyma-project.io/view/gs/kyma-prow-logs/logs/kyma-upgrade-k3d-kyma2-to-main/1663908248077471744
- https://status.build.kyma-project.io/view/gs/kyma-prow-logs/logs/kyma-upgrade-k3d-kyma2-to-main/1664331099871907840
- https://status.build.kyma-project.io/view/gs/kyma-prow-logs/logs/kyma-upgrade-gardener-kyma2-to-main-reconciler-main/1664300838761271296
- https://status.build.kyma-project.io/view/gs/kyma-prow-logs/logs/kyma-upgrade-gardener-kyma2-to-main-reconciler-main/1664270639537590272
| 1.0 | Logging tests are frequently failing - **Description**
The logging tests are frequently failing on [`kyma-upgrade-gardener-kyma2-to-main-reconciler-main`](https://status.build.kyma-project.io/job-history/gs/kyma-prow-logs/logs/kyma-upgrade-gardener-kyma2-to-main-reconciler-main) and [`kyma-upgrade-k3d-kyma2-to-main`](https://status.build.kyma-project.io/job-history/gs/kyma-prow-logs/logs/kyma-upgrade-k3d-kyma2-to-main) prowjobs.
**Expected result**
The tests are passing
**Actual result**
```
1) Upgrade test tests
Logging Tests:
Istio Access Logs tests
Should query Loki and verify format of Istio Access Logs:
TypeError: Cannot read property 'values' of undefined
at Object.verifyIstioAccessLogFormat (logging/loki.js:58:48)
at processTicksAndRejections (internal/process/task_queues.js:95:5)
at async Context.<anonymous> (logging/index.js:45:7)
```
**See also**
- https://status.build.kyma-project.io/view/gs/kyma-prow-logs/logs/kyma-upgrade-k3d-kyma2-to-main/1663968646646468608
- https://status.build.kyma-project.io/view/gs/kyma-prow-logs/logs/kyma-upgrade-k3d-kyma2-to-main/1663908248077471744
- https://status.build.kyma-project.io/view/gs/kyma-prow-logs/logs/kyma-upgrade-k3d-kyma2-to-main/1664331099871907840
- https://status.build.kyma-project.io/view/gs/kyma-prow-logs/logs/kyma-upgrade-gardener-kyma2-to-main-reconciler-main/1664300838761271296
- https://status.build.kyma-project.io/view/gs/kyma-prow-logs/logs/kyma-upgrade-gardener-kyma2-to-main-reconciler-main/1664270639537590272
| test | logging tests are frequently failing description the logging tests are frequently failing on and prowjobs expected result the tests are passing actual result upgrade test tests logging tests istio access logs tests should query loki and verify format of istio access logs typeerror cannot read property values of undefined at object verifyistioaccesslogformat logging loki js at processticksandrejections internal process task queues js at async context logging index js see also | 1 |
192,726 | 14,628,326,959 | IssuesEvent | 2020-12-23 13:58:29 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | cisco-ie/pipeline-gnmi: xport_udp_test.go; 39 LoC | fresh small test |
Found a possible issue in [cisco-ie/pipeline-gnmi](https://www.github.com/cisco-ie/pipeline-gnmi) at [xport_udp_test.go](https://github.com/cisco-ie/pipeline-gnmi/blob/d931496b9d70a8d9a14c047a9f94b6081469ed21/xport_udp_test.go#L208-L246)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call at line 221 may store a reference to subt
[Click here to see the code in its original context.](https://github.com/cisco-ie/pipeline-gnmi/blob/d931496b9d70a8d9a14c047a9f94b6081469ed21/xport_udp_test.go#L208-L246)
<details>
<summary>Click here to show the 39 line(s) of Go which triggered the analyzer.</summary>
```go
for _, subt := range subtests {
subt.lock = &udpTestContextLock{}
tb.Run(
fmt.Sprint(subt.name),
func(tb *testing.T) {
subt.tDone = make(chan struct{})
subt.conn = outConn
subt.dataChan = dataChan
subt.lock.Add(2)
go udpTestHandleMessages(&subt)
time.Sleep(time.Millisecond * 500)
go udpTestSendMessages(&subt)
ticker := time.NewTicker(time.Second * 2)
old_handled := 0
for range ticker.C {
subt.lock.Lock()
if subt.handled >= subt.max {
ticker.Stop()
break
}
if subt.handled == old_handled {
//
// stopped making progress
ticker.Stop()
tb.Fatalf("Progress stalled: handled %d, sent %d, max %d",
subt.handled, subt.send, subt.max)
}
old_handled = subt.handled
subt.lock.Unlock()
}
close(subt.tDone)
subt.lock.Wait()
})
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: d931496b9d70a8d9a14c047a9f94b6081469ed21
| 1.0 | cisco-ie/pipeline-gnmi: xport_udp_test.go; 39 LoC -
Found a possible issue in [cisco-ie/pipeline-gnmi](https://www.github.com/cisco-ie/pipeline-gnmi) at [xport_udp_test.go](https://github.com/cisco-ie/pipeline-gnmi/blob/d931496b9d70a8d9a14c047a9f94b6081469ed21/xport_udp_test.go#L208-L246)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call at line 221 may store a reference to subt
[Click here to see the code in its original context.](https://github.com/cisco-ie/pipeline-gnmi/blob/d931496b9d70a8d9a14c047a9f94b6081469ed21/xport_udp_test.go#L208-L246)
<details>
<summary>Click here to show the 39 line(s) of Go which triggered the analyzer.</summary>
```go
for _, subt := range subtests {
subt.lock = &udpTestContextLock{}
tb.Run(
fmt.Sprint(subt.name),
func(tb *testing.T) {
subt.tDone = make(chan struct{})
subt.conn = outConn
subt.dataChan = dataChan
subt.lock.Add(2)
go udpTestHandleMessages(&subt)
time.Sleep(time.Millisecond * 500)
go udpTestSendMessages(&subt)
ticker := time.NewTicker(time.Second * 2)
old_handled := 0
for range ticker.C {
subt.lock.Lock()
if subt.handled >= subt.max {
ticker.Stop()
break
}
if subt.handled == old_handled {
//
// stopped making progress
ticker.Stop()
tb.Fatalf("Progress stalled: handled %d, sent %d, max %d",
subt.handled, subt.send, subt.max)
}
old_handled = subt.handled
subt.lock.Unlock()
}
close(subt.tDone)
subt.lock.Wait()
})
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: d931496b9d70a8d9a14c047a9f94b6081469ed21
| test | cisco ie pipeline gnmi xport udp test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call at line may store a reference to subt click here to show the line s of go which triggered the analyzer go for subt range subtests subt lock udptestcontextlock tb run fmt sprint subt name func tb testing t subt tdone make chan struct subt conn outconn subt datachan datachan subt lock add go udptesthandlemessages subt time sleep time millisecond go udptestsendmessages subt ticker time newticker time second old handled for range ticker c subt lock lock if subt handled subt max ticker stop break if subt handled old handled stopped making progress ticker stop tb fatalf progress stalled handled d sent d max d subt handled subt send subt max old handled subt handled subt lock unlock close subt tdone subt lock wait leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
8,815 | 3,220,029,527 | IssuesEvent | 2015-10-08 13:08:42 | structuremap/structuremap | https://api.github.com/repos/structuremap/structuremap | opened | New little topic on working with primitive type dependencies | Documentation | Hit the rules and how defaults work now | 1.0 | New little topic on working with primitive type dependencies - Hit the rules and how defaults work now | non_test | new little topic on working with primitive type dependencies hit the rules and how defaults work now | 0 |
343,786 | 30,689,222,799 | IssuesEvent | 2023-07-26 14:13:12 | sarahsporck/Migration-Test-Repository | https://api.github.com/repos/sarahsporck/Migration-Test-Repository | closed | IGAPP-722: Recursively set paths in ts-config to shorten imports | Web Native Test API-Client |
# sarahsporck - 2.8.2021, 10:28:52
In the ts-config update to recursive paths so intelliJ always finds the shortest imports.
paths: <
"api-client/*": [
"api-client/*"
>
Maybe also check-out how we could shorten the path to the testing directories.
**Environment**: -
**Linked issues:**
| 1.0 | IGAPP-722: Recursively set paths in ts-config to shorten imports -
# sarahsporck - 2.8.2021, 10:28:52
In the ts-config update to recursive paths so intelliJ always finds the shortest imports.
paths: <
"api-client/*": [
"api-client/*"
>
Maybe also check-out how we could shorten the path to the testing directories.
**Environment**: -
**Linked issues:**
| test | igapp recursively set paths in ts config to shorten imports sarahsporck in the ts config update to recursive paths so intellij always finds the shortest imports paths api client api client maybe also check out how we could shorten the path to the testing directories environment linked issues | 1 |
33,456 | 6,205,445,751 | IssuesEvent | 2017-07-06 16:09:18 | vertexproject/synapse | https://api.github.com/repos/vertexproject/synapse | closed | CertDir: functions should only have one possible return type | documentation enhancement | Most of the functions in `CertDir` currently return a value or None.
- The functions which currently return a path or None should return a path or an empty string.
- The functions which currently return a certificate object or None should return the certificate or raise a Synapse exception. | 1.0 | CertDir: functions should only have one possible return type - Most of the functions in `CertDir` currently return a value or None.
- The functions which currently return a path or None should return a path or an empty string.
- The functions which currently return a certificate object or None should return the certificate or raise a Synapse exception. | non_test | certdir functions should only have one possible return type most of the functions in certdir currently return a value or none the functions which currently return a path or none should return a path or an empty string the functions which currently return a certificate object or none should return the certificate or raise a synapse exception | 0 |
188,897 | 14,478,878,942 | IssuesEvent | 2020-12-10 09:03:14 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | endurio/ndrw: wtxmgr/query_test.go; 3 LoC | fresh test tiny |
Found a possible issue in [endurio/ndrw](https://www.github.com/endurio/ndrw) at [wtxmgr/query_test.go](https://github.com/endurio/ndrw/blob/7f13f22e3fce63f83320d90d7ea74f94d7712970/wtxmgr/query_test.go#L653-L655)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to tst at line 654 may start a goroutine
[Click here to see the code in its original context.](https://github.com/endurio/ndrw/blob/7f13f22e3fce63f83320d90d7ea74f94d7712970/wtxmgr/query_test.go#L653-L655)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, tst := range tests {
runTest(ns, &tst)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 7f13f22e3fce63f83320d90d7ea74f94d7712970
| 1.0 | endurio/ndrw: wtxmgr/query_test.go; 3 LoC -
Found a possible issue in [endurio/ndrw](https://www.github.com/endurio/ndrw) at [wtxmgr/query_test.go](https://github.com/endurio/ndrw/blob/7f13f22e3fce63f83320d90d7ea74f94d7712970/wtxmgr/query_test.go#L653-L655)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to tst at line 654 may start a goroutine
[Click here to see the code in its original context.](https://github.com/endurio/ndrw/blob/7f13f22e3fce63f83320d90d7ea74f94d7712970/wtxmgr/query_test.go#L653-L655)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, tst := range tests {
runTest(ns, &tst)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 7f13f22e3fce63f83320d90d7ea74f94d7712970
| test | endurio ndrw wtxmgr query test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to tst at line may start a goroutine click here to show the line s of go which triggered the analyzer go for tst range tests runtest ns tst leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
162,787 | 12,691,220,174 | IssuesEvent | 2020-06-21 15:57:58 | Vachok/ftpplus | https://api.github.com/repos/Vachok/ftpplus | closed | testWhatSrvNeed | TestQuality bug | Execute SshActsCTRLTest::testWhatSrvNeed**testWhatSrvNeed**
*SshActsCTRLTest*
*srv-git.eatmeat.ru expected [true] but found [false]*
*java.lang.AssertionError* | 1.0 | testWhatSrvNeed - Execute SshActsCTRLTest::testWhatSrvNeed**testWhatSrvNeed**
*SshActsCTRLTest*
*srv-git.eatmeat.ru expected [true] but found [false]*
*java.lang.AssertionError* | test | testwhatsrvneed execute sshactsctrltest testwhatsrvneed testwhatsrvneed sshactsctrltest srv git eatmeat ru expected but found java lang assertionerror | 1 |
261,875 | 22,777,602,012 | IssuesEvent | 2022-07-08 15:54:35 | Hamlib/Hamlib | https://api.github.com/repos/Hamlib/Hamlib | closed | Kenwood TS-480 issues: split frequency not set (always sets VFOA) and RFPOWER not working | bug needs test critical | Kenwood TS-480 issues:
* Setting split frequency always sets VFOA frequency
* RFPOWER setting not working anymore
I'm looking into these issues, hopefully fixing them this week.
| 1.0 | Kenwood TS-480 issues: split frequency not set (always sets VFOA) and RFPOWER not working - Kenwood TS-480 issues:
* Setting split frequency always sets VFOA frequency
* RFPOWER setting not working anymore
I'm looking into these issues, hopefully fixing them this week.
| test | kenwood ts issues split frequency not set always sets vfoa and rfpower not working kenwood ts issues setting split frequency always sets vfoa frequency rfpower setting not working anymore i m looking into these issues hopefully fixing them this week | 1 |
11,000 | 3,155,226,738 | IssuesEvent | 2015-09-17 07:26:02 | obspy/obspy | https://api.github.com/repos/obspy/obspy | opened | Shapefile tests do not work with GDAL 2.0.0 | testing | This came up in #1121 and those tests were changed to be skipped when running with GDAL 2.0.0. They should probably be updated to work correctly in all cases.
Only the `.dbf` files have been changed, and I suspect there is some version field that has been updated. | 1.0 | Shapefile tests do not work with GDAL 2.0.0 - This came up in #1121 and those tests were changed to be skipped when running with GDAL 2.0.0. They should probably be updated to work correctly in all cases.
Only the `.dbf` files have been changed, and I suspect there is some version field that has been updated. | test | shapefile tests do not work with gdal this came up in and those tests were changed to be skipped when running with gdal they should probably be updated to work correctly in all cases only the dbf files have been changed and i suspect there is some version field that has been updated | 1 |
91,121 | 26,278,051,846 | IssuesEvent | 2023-01-07 01:51:03 | dotnet/arcade | https://api.github.com/repos/dotnet/arcade | opened | Build failed: dotnet-arcade-validation-official/main #20230106.4 | Build Failed | Build [#20230106.4](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_build/results?buildId=2081814) partiallySucceeded
## :warning: : internal / dotnet-arcade-validation-official partiallySucceeded
### Summary
**Finished** - Sat, 07 Jan 2023 01:50:48 GMT
**Duration** - 107 minutes
**Requested for** - Microsoft.VisualStudio.Services.TFS
**Reason** - schedule
### Details
#### Promote Arcade to '.NET Eng - Latest' channel
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2081814/logs/354) - The latest build on 'main' branch for the 'runtime' repository was not successful.
### Changes
- [7b009712](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/7b00971258da02ff296c06e73eb626095ea17b38) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20230106.2 (#3599)
- [75338439](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/753384396e9f9ec33507cba29eeb5d427ce5ec15) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20230106.1 (#3598)
- [79af63ff](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/79af63ffd23db2f6b52d25d67a7ec43f75b866d5) - dotnet-maestro[bot] - [main] Update dependencies from dotnet/arcade (#3597)
| 1.0 | Build failed: dotnet-arcade-validation-official/main #20230106.4 - Build [#20230106.4](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_build/results?buildId=2081814) partiallySucceeded
## :warning: : internal / dotnet-arcade-validation-official partiallySucceeded
### Summary
**Finished** - Sat, 07 Jan 2023 01:50:48 GMT
**Duration** - 107 minutes
**Requested for** - Microsoft.VisualStudio.Services.TFS
**Reason** - schedule
### Details
#### Promote Arcade to '.NET Eng - Latest' channel
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2081814/logs/354) - The latest build on 'main' branch for the 'runtime' repository was not successful.
### Changes
- [7b009712](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/7b00971258da02ff296c06e73eb626095ea17b38) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20230106.2 (#3599)
- [75338439](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/753384396e9f9ec33507cba29eeb5d427ce5ec15) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20230106.1 (#3598)
- [79af63ff](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/79af63ffd23db2f6b52d25d67a7ec43f75b866d5) - dotnet-maestro[bot] - [main] Update dependencies from dotnet/arcade (#3597)
| non_test | build failed dotnet arcade validation official main build partiallysucceeded warning internal dotnet arcade validation official partiallysucceeded summary finished sat jan gmt duration minutes requested for microsoft visualstudio services tfs reason schedule details promote arcade to net eng latest channel warning the latest build on main branch for the runtime repository was not successful changes dotnet maestro update dependencies from build dotnet maestro update dependencies from build dotnet maestro update dependencies from dotnet arcade | 0 |
220,336 | 16,938,106,883 | IssuesEvent | 2021-06-27 00:44:12 | kouta0530/my-portfolio | https://api.github.com/repos/kouta0530/my-portfolio | closed | feat(components): 所持スキル一覧を可視化する | documentation | # 3. スキルコンポーネントの作成
* 単体
- [x] スキル名を表示することができる
- [x] Propに対応する数のスターアイコンを表示することができる
* 複数
- [x] カテゴリごとにスキルを表示することができる
## models
* 新規
/models/SkillParameter.ts
```
skillLabel: string
skilledStars: number
type: string
```
/models/SkillGroupParameter.ts
```
skillTypesKey: string
skillInformationMatchTypesKey: SkillParameter[]
```
## api
* 新規
/api/portfolioSkillsAPI.ts
| methods | url |
|---|---|
| getPortfolioSkillList():Promise<SkillParameter[]> | GET /v1/skills |
| getPortfolioSkill(id:number):Promise<SkillParameter> | GET /v1/skills/:id |
| getPortfolioSkillTypeList():Promise<string[]> | GET /v1/skills/type |
## components・pages
/components/PortfolioSkill.tsx
```
skillInformation: SkillParameter
```
/components/PortfolioSkillGroup.tsx
```
skillTypes: string[]
skillInformationLists: SkillParameter[]
``` | 1.0 | feat(components): 所持スキル一覧を可視化する - # 3. スキルコンポーネントの作成
* 単体
- [x] スキル名を表示することができる
- [x] Propに対応する数のスターアイコンを表示することができる
* 複数
- [x] カテゴリごとにスキルを表示することができる
## models
* 新規
/models/SkillParameter.ts
```
skillLabel: string
skilledStars: number
type: string
```
/models/SkillGroupParameter.ts
```
skillTypesKey: string
skillInformationMatchTypesKey: SkillParameter[]
```
## api
* 新規
/api/portfolioSkillsAPI.ts
| methods | url |
|---|---|
| getPortfolioSkillList():Promise<SkillParameter[]> | GET /v1/skills |
| getPortfolioSkill(id:number):Promise<SkillParameter> | GET /v1/skills/:id |
| getPortfolioSkillTypeList():Promise<string[]> | GET /v1/skills/type |
## components・pages
/components/PortfolioSkill.tsx
```
skillInformation: SkillParameter
```
/components/PortfolioSkillGroup.tsx
```
skillTypes: string[]
skillInformationLists: SkillParameter[]
``` | non_test | feat components 所持スキル一覧を可視化する スキルコンポーネントの作成 単体 スキル名を表示することができる propに対応する数のスターアイコンを表示することができる 複数 カテゴリごとにスキルを表示することができる models 新規 models skillparameter ts skilllabel string skilledstars number type string models skillgroupparameter ts skilltypeskey string skillinformationmatchtypeskey skillparameter api 新規 api portfolioskillsapi ts methods url getportfolioskilllist promise get skills getportfolioskill id number promise get skills id getportfolioskilltypelist promise get skills type components・pages components portfolioskill tsx skillinformation skillparameter components portfolioskillgroup tsx skilltypes string skillinformationlists skillparameter | 0 |
667,882 | 22,513,856,918 | IssuesEvent | 2022-06-24 00:01:54 | kubernetes-sigs/kind | https://api.github.com/repos/kubernetes-sigs/kind | closed | Please update containerd to 1.6.6 | kind/feature priority/important-soon lifecycle/active | **What would you like to be added**:
I would like containerd to be bumped to 1.6.6.
**Why is this needed**:
1.6.4 broke Weave support (see https://github.com/weaveworks/weave/issues/3942); this was fixed in containerd 1.6.5 (https://github.com/containerd/containerd/issues/6921, included in https://github.com/containerd/containerd/releases/tag/v1.6.5).
Additionally, 1.6.6 fixes [a memory exhaustion issue](https://github.com/containerd/containerd/security/advisories/GHSA-5ffw-gxpp-mxpf). | 1.0 | Please update containerd to 1.6.6 - **What would you like to be added**:
I would like containerd to be bumped to 1.6.6.
**Why is this needed**:
1.6.4 broke Weave support (see https://github.com/weaveworks/weave/issues/3942); this was fixed in containerd 1.6.5 (https://github.com/containerd/containerd/issues/6921, included in https://github.com/containerd/containerd/releases/tag/v1.6.5).
Additionally, 1.6.6 fixes [a memory exhaustion issue](https://github.com/containerd/containerd/security/advisories/GHSA-5ffw-gxpp-mxpf). | non_test | please update containerd to what would you like to be added i would like containerd to be bumped to why is this needed broke weave support see this was fixed in containerd included in additionally fixes | 0 |
363,067 | 25,407,078,678 | IssuesEvent | 2022-11-22 16:01:27 | foundryvtt/foundryvtt | https://api.github.com/repos/foundryvtt/foundryvtt | closed | Unable to select multiple map notes with the note select tool | documentation | Originally reported by Aedif#7268 https://discord.com/channels/170995199584108546/956306859491471420/1032693272772087860
**ALL MODULES DISABLED?** true
**OS, Hosting, Browser (if applicable):** n/a
**Short Description of bug:** Not able to select multiple notes using 'The Select Notes' tool. The select tool added in v10 and documented in an article here (https://foundryvtt.com/article/map-notes/) does not work as intended.
**Simple steps to reproduce the bug:** Place multiple notes on the scene, enable 'The Select Notes' tool, and attempt to drag a square or click on notes to select them.
**Screenshots and/or console errors:**
`canvas.getLayerByEmbeddedName("Note").options.controllableObjects === false` | 1.0 | Unable to select multiple map notes with the note select tool - Originally reported by Aedif#7268 https://discord.com/channels/170995199584108546/956306859491471420/1032693272772087860
**ALL MODULES DISABLED?** true
**OS, Hosting, Browser (if applicable):** n/a
**Short Description of bug:** Not able to select multiple notes using 'The Select Notes' tool. The select tool added in v10 and documented in an article here (https://foundryvtt.com/article/map-notes/) does not work as intended.
**Simple steps to reproduce the bug:** Place multiple notes on the scene, enable 'The Select Notes' tool, and attempt to drag a square or click on notes to select them.
**Screenshots and/or console errors:**
`canvas.getLayerByEmbeddedName("Note").options.controllableObjects === false` | non_test | unable to select multiple map notes with the note select tool originally reported by aedif all modules disabled true os hosting browser if applicable n a short description of bug not able to select multiple notes using the select notes tool the select tool added in and documented in an article here does not work as intended simple steps to reproduce the bug place multiple notes on the scene enable the select notes tool and attempt to drag a square or click on notes to select them screenshots and or console errors canvas getlayerbyembeddedname note options controllableobjects false | 0 |
245,608 | 20,781,167,592 | IssuesEvent | 2022-03-16 14:54:22 | scylladb/scylla | https://api.github.com/repos/scylladb/scylla | closed | test_periodic_commitlog fails with Could not retrieve CDC streams with timestamp {2020/11/13 02:20:56} upon gossip event | bug dtest CDC backport 4.2 backport 4.3 | Seen in https://jenkins.scylladb.com/job/scylla-master/job/dtest-release/654/testReport/commitlog_test/TestCommitLog/test_periodic_commitlog/
Scylla version 5b123758421fa4d3611cb69915b9bf833a3c6527
(includes 78649c2322c63f3156440d86bdecb1c16ddb2efe)
```
Traceback (most recent call last):
File "/usr/lib64/python3.7/unittest/case.py", line 60, in testPartExecutor
yield
File "/usr/lib64/python3.7/unittest/case.py", line 648, in run
self.tearDown()
File "/jenkins/workspace/scylla-master/dtest-release/scylla-dtest/commitlog_test.py", line 38, in tearDown
super(TestCommitLog, self).tearDown()
File "/jenkins/workspace/scylla-master/dtest-release/scylla-dtest/dtest.py", line 1118, in tearDown
self.cleanUpCluster()
File "/jenkins/workspace/scylla-master/dtest-release/scylla-dtest/dtest.py", line 1164, in cleanUpCluster
raise AssertionError('Unexpected errors found: {}'.format(found_errors))
AssertionError: Unexpected errors found: [('node1', ['ERROR 2020-11-13 02:20:35,033 [shard 0] cdc - Could not retrieve CDC streams with timestamp {2020/11/13 02:20:56} upon gossip event. Reason: "std::runtime_error (Could not find CDC generation with timestamp 2020/11/13 02:20:56 in distributed system tables (current time: 2020/11/13 02:20:35), even though some node gossiped about it.)". Action: not retrying.'])]
``` | 1.0 | test_periodic_commitlog fails with Could not retrieve CDC streams with timestamp {2020/11/13 02:20:56} upon gossip event - Seen in https://jenkins.scylladb.com/job/scylla-master/job/dtest-release/654/testReport/commitlog_test/TestCommitLog/test_periodic_commitlog/
Scylla version 5b123758421fa4d3611cb69915b9bf833a3c6527
(includes 78649c2322c63f3156440d86bdecb1c16ddb2efe)
```
Traceback (most recent call last):
File "/usr/lib64/python3.7/unittest/case.py", line 60, in testPartExecutor
yield
File "/usr/lib64/python3.7/unittest/case.py", line 648, in run
self.tearDown()
File "/jenkins/workspace/scylla-master/dtest-release/scylla-dtest/commitlog_test.py", line 38, in tearDown
super(TestCommitLog, self).tearDown()
File "/jenkins/workspace/scylla-master/dtest-release/scylla-dtest/dtest.py", line 1118, in tearDown
self.cleanUpCluster()
File "/jenkins/workspace/scylla-master/dtest-release/scylla-dtest/dtest.py", line 1164, in cleanUpCluster
raise AssertionError('Unexpected errors found: {}'.format(found_errors))
AssertionError: Unexpected errors found: [('node1', ['ERROR 2020-11-13 02:20:35,033 [shard 0] cdc - Could not retrieve CDC streams with timestamp {2020/11/13 02:20:56} upon gossip event. Reason: "std::runtime_error (Could not find CDC generation with timestamp 2020/11/13 02:20:56 in distributed system tables (current time: 2020/11/13 02:20:35), even though some node gossiped about it.)". Action: not retrying.'])]
``` | test | test periodic commitlog fails with could not retrieve cdc streams with timestamp upon gossip event seen in scylla version includes traceback most recent call last file usr unittest case py line in testpartexecutor yield file usr unittest case py line in run self teardown file jenkins workspace scylla master dtest release scylla dtest commitlog test py line in teardown super testcommitlog self teardown file jenkins workspace scylla master dtest release scylla dtest dtest py line in teardown self cleanupcluster file jenkins workspace scylla master dtest release scylla dtest dtest py line in cleanupcluster raise assertionerror unexpected errors found format found errors assertionerror unexpected errors found cdc could not retrieve cdc streams with timestamp upon gossip event reason std runtime error could not find cdc generation with timestamp in distributed system tables current time even though some node gossiped about it action not retrying | 1 |
92,586 | 11,685,356,955 | IssuesEvent | 2020-03-05 08:56:47 | Geonovum/KP-APIs | https://api.github.com/repos/Geonovum/KP-APIs | closed | Paragraaf 4.4 | fix in current version API design rules | Opmerking via review-formulier:
OpenAPI is enkel voor technische documentatie. Er dient ook context documentatie te zijn die hier buiten valt.
| 1.0 | Paragraaf 4.4 - Opmerking via review-formulier:
OpenAPI is enkel voor technische documentatie. Er dient ook context documentatie te zijn die hier buiten valt.
| non_test | paragraaf opmerking via review formulier openapi is enkel voor technische documentatie er dient ook context documentatie te zijn die hier buiten valt | 0 |
118,736 | 10,001,475,918 | IssuesEvent | 2019-07-12 15:43:02 | GetTerminus/terminus-ui | https://api.github.com/repos/GetTerminus/terminus-ui | closed | Toggle: Deprecate existing change output and add replacement | Focus: component Goal: Library Stabilization Target: latest Type: chore | Custom components should not have event emitters whose names can collide with native methods. Listeners subscribed to an output with such a name will also be invoked when the native event is raised.
### Describe the solution you'd like.
- [x] Add a new emitter named `selectionChange` that functions exactly as the existing `change` emitter does
- [x] Deprecate the `change` emitter with an `@deprecated` JSDoc comment. (Let's not callout specifically which version will remove it as lately we've had to move our changes around.)
- [ ] Test the new emitter
- [x] Update JSDoc and usage docs
| 1.0 | Toggle: Deprecate existing change output and add replacement - Custom components should not have event emitters whose names can collide with native methods. Listeners subscribed to an output with such a name will also be invoked when the native event is raised.
### Describe the solution you'd like.
- [x] Add a new emitter named `selectionChange` that functions exactly as the existing `change` emitter does
- [x] Deprecate the `change` emitter with an `@deprecated` JSDoc comment. (Let's not callout specifically which version will remove it as lately we've had to move our changes around.)
- [ ] Test the new emitter
- [x] Update JSDoc and usage docs
| test | toggle deprecate existing change output and add replacement custom components should not have event emitters whose names can collide with native methods listeners subscribed to an output with such a name will also be invoked when the native event is raised describe the solution you d like add a new emitter named selectionchange that functions exactly as the existing change emitter does deprecate the change emitter with an deprecated jsdoc comment let s not callout specifically which version will remove it as lately we ve had to move our changes around test the new emitter update jsdoc and usage docs | 1 |
311,153 | 26,771,773,045 | IssuesEvent | 2023-01-31 14:35:20 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed |
tests-ci : net: mqtt_sn: client test No Console Output(Timeout)
| bug priority: low platform: NXP area: Tests |
**Describe the bug**
client test is No Console Output(Timeout) on zephyr-v3.2.0-2490-ga1b4896efe46 on mimxrt1170_evk_cm7
see logs for details
**To Reproduce**
1.
```
scripts/twister --device-testing --device-serial /dev/ttyACM0 -p mimxrt1170_evk_cm7 --sub-test net.mqtt_sn
```
2. See error
**Expected behavior**
test pass
**Impact**
**Logs and console output**
```
D: ethernet@40424000 MAC 02:04:9f:00:00:00
D: (main): Priority 90
D: (main): Allocating 14 RX (896 bytes), 14 TX (896 bytes), 0 RX data (0 bytes) and 0 TX data (0 bytes) buffers
D: (main): Allocated 8 routing entries (576 bytes)
D: (main): Allocated 8 nexthop entries (224 bytes)
D: (main): Network L3 init done
D: (main):
D: (main): No TX thread created
D: (main): On iface 0x800014cc
D: (main): Initializing Ethernet L2 0x80003004 for iface 0x800014cc
D: (main): iface 0x800014cc, oper state DOWN admin DOWN carrier OFF dormant OFF
D: (main): min_reachable:15000 max_reachable:45000
E: ***** USAGE FAULT *****
E: Illegal use of the EPSR
E: r0/a1: 0x00000000 r1/a2: 0xfffffff0 r2/a3: 0x00000001
E: r3/a4: 0x00000001 r12/ip: 0x00000008 r14/lr: 0x3001ba01
E: xpsr: 0x60000000
E: Faulting instruction address (r15/pc): 0x30015894
E: >>> ZEPHYR FATAL ERROR 0: CPU exception on CPU 0
E: Current thread: 0x80002770 (main)
E: Halting system
```
**Environment (please complete the following information):**
- OS: (e.g. Linux )
- Toolchain (e.g Zephyr SDK)
- Commit SHA or Version used: zephyr-v3.2.0-2490-ga1b4896efe46
| 1.0 |
tests-ci : net: mqtt_sn: client test No Console Output(Timeout)
-
**Describe the bug**
client test is No Console Output(Timeout) on zephyr-v3.2.0-2490-ga1b4896efe46 on mimxrt1170_evk_cm7
see logs for details
**To Reproduce**
1.
```
scripts/twister --device-testing --device-serial /dev/ttyACM0 -p mimxrt1170_evk_cm7 --sub-test net.mqtt_sn
```
2. See error
**Expected behavior**
test pass
**Impact**
**Logs and console output**
```
D: ethernet@40424000 MAC 02:04:9f:00:00:00
D: (main): Priority 90
D: (main): Allocating 14 RX (896 bytes), 14 TX (896 bytes), 0 RX data (0 bytes) and 0 TX data (0 bytes) buffers
D: (main): Allocated 8 routing entries (576 bytes)
D: (main): Allocated 8 nexthop entries (224 bytes)
D: (main): Network L3 init done
D: (main):
D: (main): No TX thread created
D: (main): On iface 0x800014cc
D: (main): Initializing Ethernet L2 0x80003004 for iface 0x800014cc
D: (main): iface 0x800014cc, oper state DOWN admin DOWN carrier OFF dormant OFF
D: (main): min_reachable:15000 max_reachable:45000
E: ***** USAGE FAULT *****
E: Illegal use of the EPSR
E: r0/a1: 0x00000000 r1/a2: 0xfffffff0 r2/a3: 0x00000001
E: r3/a4: 0x00000001 r12/ip: 0x00000008 r14/lr: 0x3001ba01
E: xpsr: 0x60000000
E: Faulting instruction address (r15/pc): 0x30015894
E: >>> ZEPHYR FATAL ERROR 0: CPU exception on CPU 0
E: Current thread: 0x80002770 (main)
E: Halting system
```
**Environment (please complete the following information):**
- OS: (e.g. Linux )
- Toolchain (e.g Zephyr SDK)
- Commit SHA or Version used: zephyr-v3.2.0-2490-ga1b4896efe46
| test | tests ci net mqtt sn client test no console output timeout describe the bug client test is no console output timeout on zephyr on evk see logs for details to reproduce scripts twister device testing device serial dev p evk sub test net mqtt sn see error expected behavior test pass impact logs and console output d ethernet mac d main priority d main allocating rx bytes tx bytes rx data bytes and tx data bytes buffers d main allocated routing entries bytes d main allocated nexthop entries bytes d main network init done d main d main no tx thread created d main on iface d main initializing ethernet for iface d main iface oper state down admin down carrier off dormant off d main min reachable max reachable e usage fault e illegal use of the epsr e e ip lr e xpsr e faulting instruction address pc e zephyr fatal error cpu exception on cpu e current thread main e halting system environment please complete the following information os e g linux toolchain e g zephyr sdk commit sha or version used zephyr | 1 |
122,113 | 26,088,552,630 | IssuesEvent | 2022-12-26 07:51:00 | sebastianbergmann/phpunit | https://api.github.com/repos/sebastianbergmann/phpunit | closed | Fatal error instead of PHPUnit warning when no code coverage driver is available | feature/test-runner feature/code-coverage | ```
An error occurred inside PHPUnit.
Message: No code coverage driver available
Location: /usr/local/src/php-code-coverage/src/Driver/Selector.php:41
#0 /usr/local/src/php-code-coverage/vendor/phpunit/phpunit/src/Runner/CodeCoverage.php(51): SebastianBergmann\CodeCoverage\Driver\Selector->forLineCoverage()
#1 /usr/local/src/php-code-coverage/vendor/phpunit/phpunit/src/TextUI/TestRunner.php(319): PHPUnit\Runner\CodeCoverage::activate()
#2 /usr/local/src/php-code-coverage/vendor/phpunit/phpunit/src/TextUI/Application.php(107): PHPUnit\TextUI\TestRunner->run()
#3 /usr/local/src/php-code-coverage/vendor/phpunit/phpunit/src/TextUI/Application.php(78): PHPUnit\TextUI\Application->run()
#4 /usr/local/src/php-code-coverage/vendor/phpunit/phpunit/phpunit(90): PHPUnit\TextUI\Application::main()
#5 /usr/local/src/php-code-coverage/vendor/bin/phpunit(123): include('...')
#6 {main}
``` | 1.0 | Fatal error instead of PHPUnit warning when no code coverage driver is available - ```
An error occurred inside PHPUnit.
Message: No code coverage driver available
Location: /usr/local/src/php-code-coverage/src/Driver/Selector.php:41
#0 /usr/local/src/php-code-coverage/vendor/phpunit/phpunit/src/Runner/CodeCoverage.php(51): SebastianBergmann\CodeCoverage\Driver\Selector->forLineCoverage()
#1 /usr/local/src/php-code-coverage/vendor/phpunit/phpunit/src/TextUI/TestRunner.php(319): PHPUnit\Runner\CodeCoverage::activate()
#2 /usr/local/src/php-code-coverage/vendor/phpunit/phpunit/src/TextUI/Application.php(107): PHPUnit\TextUI\TestRunner->run()
#3 /usr/local/src/php-code-coverage/vendor/phpunit/phpunit/src/TextUI/Application.php(78): PHPUnit\TextUI\Application->run()
#4 /usr/local/src/php-code-coverage/vendor/phpunit/phpunit/phpunit(90): PHPUnit\TextUI\Application::main()
#5 /usr/local/src/php-code-coverage/vendor/bin/phpunit(123): include('...')
#6 {main}
``` | non_test | fatal error instead of phpunit warning when no code coverage driver is available an error occurred inside phpunit message no code coverage driver available location usr local src php code coverage src driver selector php usr local src php code coverage vendor phpunit phpunit src runner codecoverage php sebastianbergmann codecoverage driver selector forlinecoverage usr local src php code coverage vendor phpunit phpunit src textui testrunner php phpunit runner codecoverage activate usr local src php code coverage vendor phpunit phpunit src textui application php phpunit textui testrunner run usr local src php code coverage vendor phpunit phpunit src textui application php phpunit textui application run usr local src php code coverage vendor phpunit phpunit phpunit phpunit textui application main usr local src php code coverage vendor bin phpunit include main | 0 |
88,383 | 17,572,383,392 | IssuesEvent | 2021-08-15 00:33:48 | hackuci/eventbot | https://api.github.com/repos/hackuci/eventbot | closed | Create a message table component | Code Improvement | /scheduleMessage and /editMessage both have a table that displays a list of messages with the option to edit and delete.
These are extremely similar and should use a shared component. Main difference between the two is the action for edit/delete and the fact that scheduleMessage had an ID column | 1.0 | Create a message table component - /scheduleMessage and /editMessage both have a table that displays a list of messages with the option to edit and delete.
These are extremely similar and should use a shared component. Main difference between the two is the action for edit/delete and the fact that scheduleMessage had an ID column | non_test | create a message table component schedulemessage and editmessage both have a table that displays a list of messages with the option to edit and delete these are extremely similar and should use a shared component main difference between the two is the action for edit delete and the fact that schedulemessage had an id column | 0 |
646,357 | 21,045,873,737 | IssuesEvent | 2022-03-31 15:57:39 | SAP/xsk | https://api.github.com/repos/SAP/xsk | opened | All dependancies version should come from the parent pom as a property | core priority-medium effort-low Improvement | Check all POMs and make sure that all versions are from the parent POM | 1.0 | All dependancies version should come from the parent pom as a property - Check all POMs and make sure that all versions are from the parent POM | non_test | all dependancies version should come from the parent pom as a property check all poms and make sure that all versions are from the parent pom | 0 |
161,121 | 25,288,425,900 | IssuesEvent | 2022-11-16 21:27:54 | harvard-lts/CURIOSity | https://api.github.com/repos/harvard-lts/CURIOSity | closed | Design refinements: Feature and About pages (sidebar and widget styling) | Front End Design Epic | ## Sidebar (left nav)
- [x] Prevent menu items from shifting position between active and non-active states (currently they shift slightly, [see menu here as an example](https://localhost:21407/demo/feature/feature-page-examples))
- [x] About sidebar: Left nav menu items should be all upper case like parent items on Curated Features left nav
## Standard Widgets
See [Standard Widgets](https://localhost:21407/demo/feature/standard-widgets) page for examples of all widgets in use
- [x] Quote widget - update styling to [match quote styling on this page](https://harvard-library-web-team.gitlab.io/Harvard-Patterns/?p=molecules-rich-text)
- [x] Horizontal Rule widget - update styling to [match bottom horizontal rule style of the quote](https://harvard-library-web-team.gitlab.io/Harvard-Patterns/?p=molecules-rich-text)
- [x] We have a border for borders (#afafaf) so I tried that first as it's less harsh than the black line
- [x] I also increased the margin above and below to give each section more spacing
- [x] Uploaded Item Row widget - Remove border line, update caption text to [match style on this page](https://harvard-library-web-team.gitlab.io/Harvard-Patterns/?p=molecules-rich-text) (do not include the camera icon), [use this button style for View Larger button](https://harvard-library-web-team.gitlab.io/Harvard-Patterns/?p=atoms-button-as-outline), in the View Larger viewer remove gray boarder and match HL styling if exists.
- [x] [In edit mode](https://staging-harvard-curiosity.notch8.cloud/spotlight/exhibit3/feature/standard-widgets/edit), for the Uploaded Item Row widget, either decrease the font size of the word 'Remove' or increase its container so the 'e' does not wrap [see screenshot](https://user-images.githubusercontent.com/60190174/176684729-e81336c0-e0f5-466c-8e31-4929dce2eb2f.png). This happens with many other [exhibit widgets](https://localhost:21407/demo/feature/exhibit-item-widgets/edit) as well.
- [x] Maura made the width of the remove container larger and decrease font-size
## Exhibit Widgets
See [Exhibit Widgets](https://localhost:21407/demo/feature/exhibit-item-widgets) page for examples of all widgets in use
- [x] For the Browse Categories, Browse Group Categories, Saved Searches, and Pages widgets use the same card styling as on the collections landing and Browse pages.
- [x] Item Row widget
- [x] Remove the border line.
- [x] Slide carousel widget
- [x] Use same styling for slide caption as used for title hover in masonry view.
- [x] Item Slideshow widget - Update nav styling to match theme. Recommendations on other styling improvements? | 1.0 | Design refinements: Feature and About pages (sidebar and widget styling) - ## Sidebar (left nav)
- [x] Prevent menu items from shifting position between active and non-active states (currently they shift slightly, [see menu here as an example](https://localhost:21407/demo/feature/feature-page-examples))
- [x] About sidebar: Left nav menu items should be all upper case like parent items on Curated Features left nav
## Standard Widgets
See [Standard Widgets](https://localhost:21407/demo/feature/standard-widgets) page for examples of all widgets in use
- [x] Quote widget - update styling to [match quote styling on this page](https://harvard-library-web-team.gitlab.io/Harvard-Patterns/?p=molecules-rich-text)
- [x] Horizontal Rule widget - update styling to [match bottom horizontal rule style of the quote](https://harvard-library-web-team.gitlab.io/Harvard-Patterns/?p=molecules-rich-text)
- [x] We have a border for borders (#afafaf) so I tried that first as it's less harsh than the black line
- [x] I also increased the margin above and below to give each section more spacing
- [x] Uploaded Item Row widget - Remove border line, update caption text to [match style on this page](https://harvard-library-web-team.gitlab.io/Harvard-Patterns/?p=molecules-rich-text) (do not include the camera icon), [use this button style for View Larger button](https://harvard-library-web-team.gitlab.io/Harvard-Patterns/?p=atoms-button-as-outline), in the View Larger viewer remove gray boarder and match HL styling if exists.
- [x] [In edit mode](https://staging-harvard-curiosity.notch8.cloud/spotlight/exhibit3/feature/standard-widgets/edit), for the Uploaded Item Row widget, either decrease the font size of the word 'Remove' or increase its container so the 'e' does not wrap [see screenshot](https://user-images.githubusercontent.com/60190174/176684729-e81336c0-e0f5-466c-8e31-4929dce2eb2f.png). This happens with many other [exhibit widgets](https://localhost:21407/demo/feature/exhibit-item-widgets/edit) as well.
- [x] Maura made the width of the remove container larger and decrease font-size
## Exhibit Widgets
See [Exhibit Widgets](https://localhost:21407/demo/feature/exhibit-item-widgets) page for examples of all widgets in use
- [x] For the Browse Categories, Browse Group Categories, Saved Searches, and Pages widgets use the same card styling as on the collections landing and Browse pages.
- [x] Item Row widget
- [x] Remove the border line.
- [x] Slide carousel widget
- [x] Use same styling for slide caption as used for title hover in masonry view.
- [x] Item Slideshow widget - Update nav styling to match theme. Recommendations on other styling improvements? | non_test | design refinements feature and about pages sidebar and widget styling sidebar left nav prevent menu items from shifting position between active and non active states currently they shift slightly about sidebar left nav menu items should be all upper case like parent items on curated features left nav standard widgets see page for examples of all widgets in use quote widget update styling to horizontal rule widget update styling to we have a border for borders afafaf so i tried that first as it s less harsh than the black line i also increased the margin above and below to give each section more spacing uploaded item row widget remove border line update caption text to do not include the camera icon in the view larger viewer remove gray boarder and match hl styling if exists for the uploaded item row widget either decrease the font size of the word remove or increase its container so the e does not wrap this happens with many other as well maura made the width of the remove container larger and decrease font size exhibit widgets see page for examples of all widgets in use for the browse categories browse group categories saved searches and pages widgets use the same card styling as on the collections landing and browse pages item row widget remove the border line slide carousel widget use same styling for slide caption as used for title hover in masonry view item slideshow widget update nav styling to match theme recommendations on other styling improvements | 0 |
72,344 | 7,294,564,940 | IssuesEvent | 2018-02-26 00:52:39 | NorthBridge/nexus-community | https://api.github.com/repos/NorthBridge/nexus-community | closed | Everyone on the team can see the language switcher. | North Stars acceptance criteria ready to test | Make sure everyone on the team has a valid account in Nexus Web Meet in DEV. | 1.0 | Everyone on the team can see the language switcher. - Make sure everyone on the team has a valid account in Nexus Web Meet in DEV. | test | everyone on the team can see the language switcher make sure everyone on the team has a valid account in nexus web meet in dev | 1 |
161,720 | 12,559,524,449 | IssuesEvent | 2020-06-07 19:13:25 | kotest/kotest | https://api.github.com/repos/kotest/kotest | closed | Arb.flatMap is broken | bug property-testing | Arbs by their nature are infinite, so flatMap { a -> a.flatMap { arbB } } doesn't work because the inner arb never expires to then request a value from the outer arb. | 1.0 | Arb.flatMap is broken - Arbs by their nature are infinite, so flatMap { a -> a.flatMap { arbB } } doesn't work because the inner arb never expires to then request a value from the outer arb. | test | arb flatmap is broken arbs by their nature are infinite so flatmap a a flatmap arbb doesn t work because the inner arb never expires to then request a value from the outer arb | 1 |
4,796 | 2,874,199,274 | IssuesEvent | 2015-06-08 21:08:00 | xray7224/PyPump | https://api.github.com/repos/xray7224/PyPump | opened | ssl modules for py 2 not mentioned in pypump.org docs | documentation | recommended install of additional modules for SSL/SNI support in Py2 (see https://github.com/xray7224/PyPump#installation) is not mentioned in pypump.org docs, we should add it to install section | 1.0 | ssl modules for py 2 not mentioned in pypump.org docs - recommended install of additional modules for SSL/SNI support in Py2 (see https://github.com/xray7224/PyPump#installation) is not mentioned in pypump.org docs, we should add it to install section | non_test | ssl modules for py not mentioned in pypump org docs recommended install of additional modules for ssl sni support in see is not mentioned in pypump org docs we should add it to install section | 0 |
385,020 | 26,612,440,918 | IssuesEvent | 2023-01-24 02:03:30 | hashgraph/guardian | https://api.github.com/repos/hashgraph/guardian | closed | Policy Differentiation Feature | documentation enhancement Epic research | ### Problem description
Different Standard Registries (SRs) can be managing policies of varying degree of compatibility, issuing tokens as a result. Policies could be essentially the same and vary in version, or differ in various parts including accounting methods. SRs themselves can be of different degree of 'trustworthiness' and reputation. Participants in the ecological market currently have no way of establishing the relative status of policies issued by different or the same SR at different stages.
### Requirements
Introduce the functionality to 'diff' policies, where policies can be compared against each other in the following dimensions
- blocks
- transitions between blocks
- roles/actors
As the result of the diff operation the system should produce a numerical score (e.g. saying 'these policies are 68% compatible') as well as the list of all differences.
### Definition of done
Guardian users can determine the difference in policies, via UI and through the API.
### Acceptance criteria
- The comparison is deterministic, i.e. re-running the comparison for the same 2 policies should result in exactly the same score and the list of incompatibilities
- Elements of the policy are considered 'the same' if they are semantically equivalent (e.g. the same json block but with re-ordered entries should be viewed as the same).
- At this stage there is no requirement to produce a verifiable record of the comparison results.
| 1.0 | Policy Differentiation Feature - ### Problem description
Different Standard Registries (SRs) can be managing policies of varying degree of compatibility, issuing tokens as a result. Policies could be essentially the same and vary in version, or differ in various parts including accounting methods. SRs themselves can be of different degree of 'trustworthiness' and reputation. Participants in the ecological market currently have no way of establishing the relative status of policies issued by different or the same SR at different stages.
### Requirements
Introduce the functionality to 'diff' policies, where policies can be compared against each other in the following dimensions
- blocks
- transitions between blocks
- roles/actors
As the result of the diff operation the system should produce a numerical score (e.g. saying 'these policies are 68% compatible') as well as the list of all differences.
### Definition of done
Guardian users can determine the difference in policies, via UI and through the API.
### Acceptance criteria
- The comparison is deterministic, i.e. re-running the comparison for the same 2 policies should result in exactly the same score and the list of incompatibilities
- Elements of the policy are considered 'the same' if they are semantically equivalent (e.g. the same json block but with re-ordered entries should be viewed as the same).
- At this stage there is no requirement to produce a verifiable record of the comparison results.
| non_test | policy differentiation feature problem description different standard registries srs can be managing policies of varying degree of compatibility issuing tokens as a result policies could be essentially the same and vary in version or differ in various parts including accounting methods srs themselves can be of different degree of trustworthiness and reputation participants in the ecological market currently have no way of establishing the relative status of policies issued by different or the same sr at different stages requirements introduce the functionality to diff policies where policies can be compared against each other in the following dimensions blocks transitions between blocks roles actors as the result of the diff operation the system should produce a numerical score e g saying these policies are compatible as well as the list of all differences definition of done guardian users can determine the difference in policies via ui and through the api acceptance criteria the comparison is deterministic i e re running the comparison for the same policies should result in exactly the same score and the list of incompatibilities elements of the policy are considered the same if they are semantically equivalent e g the same json block but with re ordered entries should be viewed as the same at this stage there is no requirement to produce a verifiable record of the comparison results | 0 |
198,433 | 6,972,968,707 | IssuesEvent | 2017-12-11 18:51:02 | DavidAlt/VATumorBoard | https://api.github.com/repos/DavidAlt/VATumorBoard | opened | FReq: HIPAA-compliant messaging | Care Coordination high priority | "The system shall support secure/HIPAA-compliant messaging."
_Requirement added after discussion at 11/30/17 meeting._
This includes both data exchange with other IT systems as well as automated notifications to providers. | 1.0 | FReq: HIPAA-compliant messaging - "The system shall support secure/HIPAA-compliant messaging."
_Requirement added after discussion at 11/30/17 meeting._
This includes both data exchange with other IT systems as well as automated notifications to providers. | non_test | freq hipaa compliant messaging the system shall support secure hipaa compliant messaging requirement added after discussion at meeting this includes both data exchange with other it systems as well as automated notifications to providers | 0 |
61,363 | 3,144,911,086 | IssuesEvent | 2015-09-14 15:31:36 | theodi/member-directory | https://api.github.com/repos/theodi/member-directory | closed | Change membership contact email for NHS England | bug capsulecrm priority: high | @jordelver - Please manually add emma.doyle2@nhs.net as main membership account holder, cheers! | 1.0 | Change membership contact email for NHS England - @jordelver - Please manually add emma.doyle2@nhs.net as main membership account holder, cheers! | non_test | change membership contact email for nhs england jordelver please manually add emma nhs net as main membership account holder cheers | 0 |
552,989 | 16,332,554,820 | IssuesEvent | 2021-05-12 11:03:52 | ntop/ntopng | https://api.github.com/repos/ntop/ntopng | closed | InfluxDB monitor (or RRD ) | low-priority bug | Hy. I cannot seem to find the page where you can see the size of the influxDB database or RRD database. It seems that the script for influxdb monitor is active but it doesn't work. The influxdb is configured and it works but cannot see size. Thanks.
ntopng Enterprise L v.4.3.210511

| 1.0 | InfluxDB monitor (or RRD ) - Hy. I cannot seem to find the page where you can see the size of the influxDB database or RRD database. It seems that the script for influxdb monitor is active but it doesn't work. The influxdb is configured and it works but cannot see size. Thanks.
ntopng Enterprise L v.4.3.210511

| non_test | influxdb monitor or rrd hy i cannot seem to find the page where you can see the size of the influxdb database or rrd database it seems that the script for influxdb monitor is active but it doesn t work the influxdb is configured and it works but cannot see size thanks ntopng enterprise l v | 0 |
103,301 | 16,602,467,112 | IssuesEvent | 2021-06-01 21:38:06 | gms-ws-sandbox/nibrs | https://api.github.com/repos/gms-ws-sandbox/nibrs | opened | CVE-2018-1000180 (High) detected in bcprov-jdk15on-1.54.jar | security vulnerability | ## CVE-2018-1000180 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.54.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: nibrs/web/nibrs-web/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar</p>
<p>
Dependency Hierarchy:
- :x: **bcprov-jdk15on-1.54.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs/commit/dba6b0930aa319c568021490e9259f5cae89b6c5">dba6b0930aa319c568021490e9259f5cae89b6c5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Bouncy Castle BC 1.54 - 1.59, BC-FJA 1.0.0, BC-FJA 1.0.1 and earlier have a flaw in the Low-level interface to RSA key pair generator, specifically RSA Key Pairs generated in low-level API with added certainty may have less M-R tests than expected. This appears to be fixed in versions BC 1.60 beta 4 and later, BC-FJA 1.0.2 and later.
<p>Publish Date: 2018-06-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000180>CVE-2018-1000180</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180</a></p>
<p>Release Date: 2018-06-05</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk15on:1.60,org.bouncycastle:bcprov-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk15on:1.60</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.bouncycastle","packageName":"bcprov-jdk15on","packageVersion":"1.54","packageFilePaths":["/web/nibrs-web/pom.xml","/tools/nibrs-validation/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-common/pom.xml","/tools/nibrs-validate-common/pom.xml","/tools/nibrs-summary-report-common/pom.xml","/tools/nibrs-flatfile/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-staging-data/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.bouncycastle:bcprov-jdk15on:1.54","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.bouncycastle:bcprov-jdk15on:1.60,org.bouncycastle:bcprov-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk15on:1.60"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-1000180","vulnerabilityDetails":"Bouncy Castle BC 1.54 - 1.59, BC-FJA 1.0.0, BC-FJA 1.0.1 and earlier have a flaw in the Low-level interface to RSA key pair generator, specifically RSA Key Pairs generated in low-level API with added certainty may have less M-R tests than expected. This appears to be fixed in versions BC 1.60 beta 4 and later, BC-FJA 1.0.2 and later.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000180","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-1000180 (High) detected in bcprov-jdk15on-1.54.jar - ## CVE-2018-1000180 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.54.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: nibrs/web/nibrs-web/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar,/home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.54/bcprov-jdk15on-1.54.jar</p>
<p>
Dependency Hierarchy:
- :x: **bcprov-jdk15on-1.54.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs/commit/dba6b0930aa319c568021490e9259f5cae89b6c5">dba6b0930aa319c568021490e9259f5cae89b6c5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Bouncy Castle BC 1.54 - 1.59, BC-FJA 1.0.0, BC-FJA 1.0.1 and earlier have a flaw in the Low-level interface to RSA key pair generator, specifically RSA Key Pairs generated in low-level API with added certainty may have less M-R tests than expected. This appears to be fixed in versions BC 1.60 beta 4 and later, BC-FJA 1.0.2 and later.
<p>Publish Date: 2018-06-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000180>CVE-2018-1000180</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180</a></p>
<p>Release Date: 2018-06-05</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk15on:1.60,org.bouncycastle:bcprov-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk15on:1.60</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.bouncycastle","packageName":"bcprov-jdk15on","packageVersion":"1.54","packageFilePaths":["/web/nibrs-web/pom.xml","/tools/nibrs-validation/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-common/pom.xml","/tools/nibrs-validate-common/pom.xml","/tools/nibrs-summary-report-common/pom.xml","/tools/nibrs-flatfile/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-staging-data/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.bouncycastle:bcprov-jdk15on:1.54","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.bouncycastle:bcprov-jdk15on:1.60,org.bouncycastle:bcprov-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk15on:1.60"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-1000180","vulnerabilityDetails":"Bouncy Castle BC 1.54 - 1.59, BC-FJA 1.0.0, BC-FJA 1.0.1 and earlier have a flaw in the Low-level interface to RSA key pair generator, specifically RSA Key Pairs generated in low-level API with added certainty may have less M-R tests than expected. This appears to be fixed in versions BC 1.60 beta 4 and later, BC-FJA 1.0.2 and later.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000180","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_test | cve high detected in bcprov jar cve high severity vulnerability vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk to jdk library home page a href path to dependency file nibrs web nibrs web pom xml path to vulnerable library home wss scanner repository org bouncycastle bcprov bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar nibrs web nibrs web target nibrs web web inf lib bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar home wss scanner repository org bouncycastle bcprov bcprov jar dependency hierarchy x bcprov jar vulnerable library found in head commit a href found in base branch master vulnerability details bouncy castle bc bc fja bc fja and earlier have a flaw in the low level interface to rsa key pair generator specifically rsa key pairs generated in low level api with added certainty may have less m r tests than expected this appears to be fixed in versions bc beta and later bc fja and later publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org bouncycastle bcprov org bouncycastle bcprov org bouncycastle bcprov ext org bouncycastle bcprov ext rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org bouncycastle bcprov isminimumfixversionavailable true minimumfixversion org bouncycastle bcprov org bouncycastle bcprov org bouncycastle bcprov ext org bouncycastle bcprov ext basebranches vulnerabilityidentifier cve vulnerabilitydetails bouncy castle bc bc fja bc fja and earlier have a flaw in the low level interface to rsa key pair generator specifically rsa key pairs generated in low level api with added certainty may have less m r tests than expected this appears to be fixed in versions bc beta and later bc fja and later vulnerabilityurl | 0 |
115,432 | 4,668,812,456 | IssuesEvent | 2016-10-06 05:05:02 | badili/erpnext | https://api.github.com/repos/badili/erpnext | closed | Price List to be Obtained from uploaded Quotation File | top priority | For the moment, the Price List is not updated from the uploaded Quotation File, or doesn't create a new price list based on the quotation. The problem here is that we cannot use the main Item Price List, because there might be different prices quoted in different quotations for the same Item Number. | 1.0 | Price List to be Obtained from uploaded Quotation File - For the moment, the Price List is not updated from the uploaded Quotation File, or doesn't create a new price list based on the quotation. The problem here is that we cannot use the main Item Price List, because there might be different prices quoted in different quotations for the same Item Number. | non_test | price list to be obtained from uploaded quotation file for the moment the price list is not updated from the uploaded quotation file or doesn t create a new price list based on the quotation the problem here is that we cannot use the main item price list because there might be different prices quoted in different quotations for the same item number | 0 |
219,480 | 17,093,742,054 | IssuesEvent | 2021-07-08 21:24:57 | TauCetiStation/TauCetiClassic | https://api.github.com/repos/TauCetiStation/TauCetiClassic | closed | нету панели мафии | Bug Test Feedback |
#### Подробное описание проблемы
нету панельки с голосованием,ролями и прочим в мафии.
#### Что должно было произойти
панель есть
#### Что произошло на самом деле
панели нету,даже екшн кнопки
#### Как повторить
зайти в мафию
#### Дополнительная информация:
раунд 42720 | 1.0 | нету панели мафии -
#### Подробное описание проблемы
нету панельки с голосованием,ролями и прочим в мафии.
#### Что должно было произойти
панель есть
#### Что произошло на самом деле
панели нету,даже екшн кнопки
#### Как повторить
зайти в мафию
#### Дополнительная информация:
раунд 42720 | test | нету панели мафии подробное описание проблемы нету панельки с голосованием ролями и прочим в мафии что должно было произойти панель есть что произошло на самом деле панели нету даже екшн кнопки как повторить зайти в мафию дополнительная информация раунд | 1 |
71,221 | 7,237,723,551 | IssuesEvent | 2018-02-13 12:07:05 | dzhw/zofar | https://api.github.com/repos/dzhw/zofar | closed | Attached Open | et: 16 prio: 1 status: testing type: backlog.task | To Do:
- [x] Test Infrastructure
- [x] Formulate Test Cases
- [x] Write Unit Tests
Used Time : 1
Sprint 3 Used Time: 16 | 1.0 | Attached Open - To Do:
- [x] Test Infrastructure
- [x] Formulate Test Cases
- [x] Write Unit Tests
Used Time : 1
Sprint 3 Used Time: 16 | test | attached open to do test infrastructure formulate test cases write unit tests used time sprint used time | 1 |
288,290 | 24,896,587,788 | IssuesEvent | 2022-10-28 16:22:41 | dotnet/machinelearning-modelbuilder | https://api.github.com/repos/dotnet/machinelearning-modelbuilder | closed | Sometimes cannot detect Data path on Train page after data setting. | Priority:1 Reported by: Test Multiple Requests Stale | **System Information (please complete the following information):**
- Model Builder Version (available in Manage Extensions dialog): 16.9.1.2156701 (Main)
- Microsoft Visual Studio Enterprise 2019: 16.11.7
**Describe the bug**
- On which step of the process did you run into an issue: Data is empty on Train page
- Clear description of the problem: have already input the data source, and set the columns settings, but Data is empty on Train page. This problem does not occur frequently, but I met it on different scenarios currently.
**To Reproduce**
Steps to reproduce the behavior:
1. Select Create a new project from the Visual Studio 2019 start window;
2. Choose the C# Console App (.NET Core) project template with .Net 5.0;
3. Add model builder by right click on the project;
4. Select Recommendation scenario;
5. Input the data source, and set the columns settings;
6. Navigate to Train page, click Start training, prompt Model Builder Error said that: "Value cannot be nulll. Parameter name: fileName".
7. Close the error dialog, expand the Training setup summary, find that: Data is empty.
**Expected behavior**
Can detect the Data path on Train page after Data setting.
**Screenshots**
If applicable, add screenshots to help explain your problem.
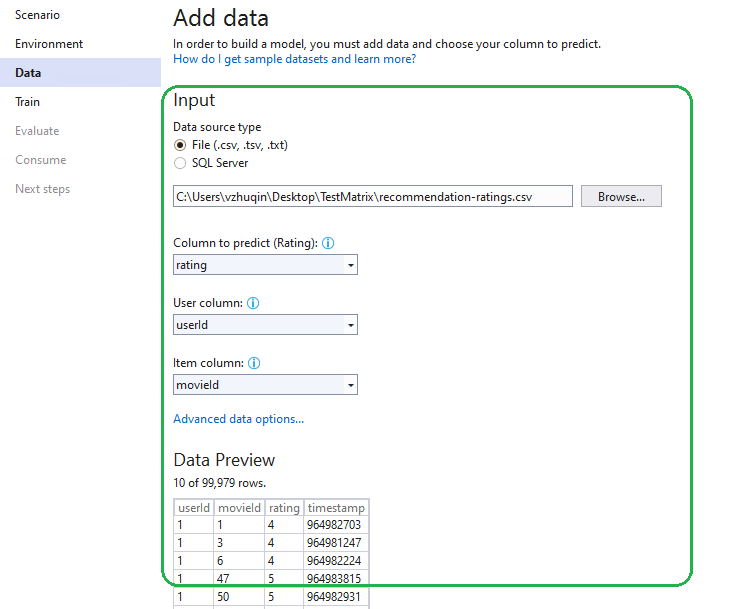
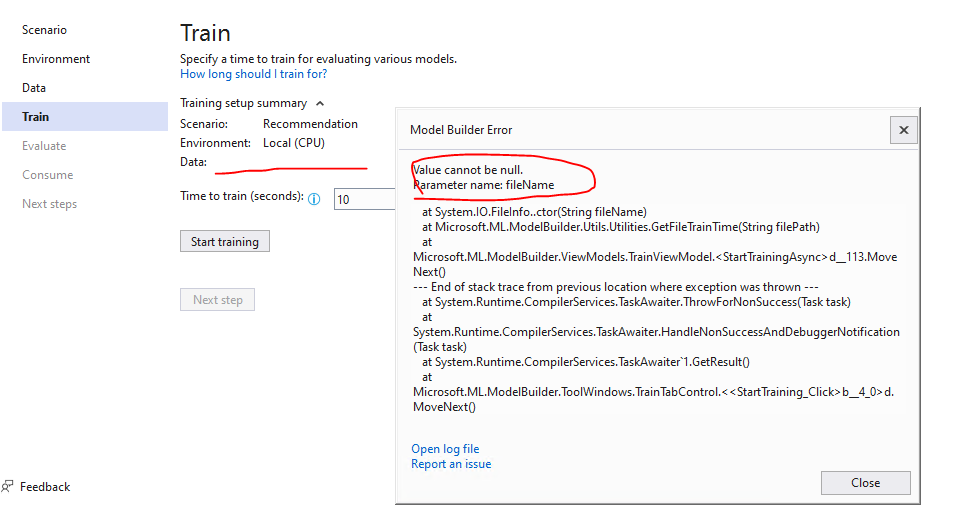
**Additional context**
Reload the mbconfig file, re-input the Data source, can detect the data path on Train page.
| 1.0 | Sometimes cannot detect Data path on Train page after data setting. - **System Information (please complete the following information):**
- Model Builder Version (available in Manage Extensions dialog): 16.9.1.2156701 (Main)
- Microsoft Visual Studio Enterprise 2019: 16.11.7
**Describe the bug**
- On which step of the process did you run into an issue: Data is empty on Train page
- Clear description of the problem: have already input the data source, and set the columns settings, but Data is empty on Train page. This problem does not occur frequently, but I met it on different scenarios currently.
**To Reproduce**
Steps to reproduce the behavior:
1. Select Create a new project from the Visual Studio 2019 start window;
2. Choose the C# Console App (.NET Core) project template with .Net 5.0;
3. Add model builder by right click on the project;
4. Select Recommendation scenario;
5. Input the data source, and set the columns settings;
6. Navigate to Train page, click Start training, prompt Model Builder Error said that: "Value cannot be nulll. Parameter name: fileName".
7. Close the error dialog, expand the Training setup summary, find that: Data is empty.
**Expected behavior**
Can detect the Data path on Train page after Data setting.
**Screenshots**
If applicable, add screenshots to help explain your problem.
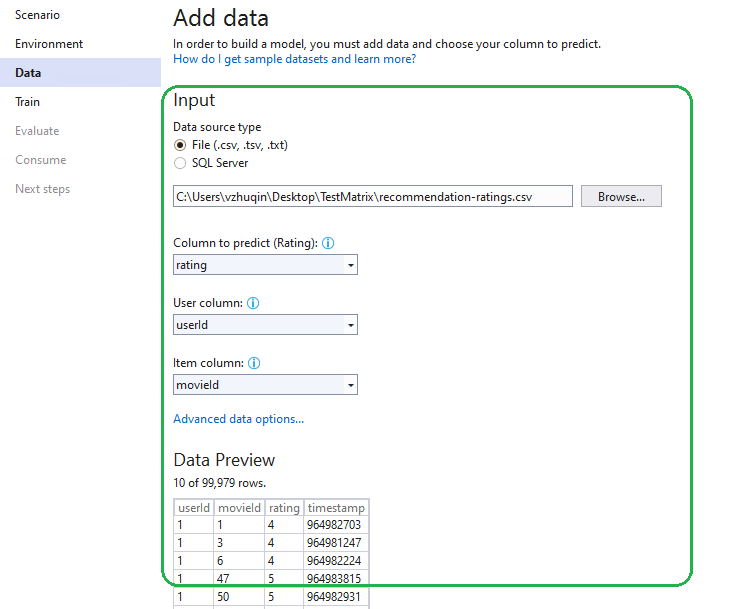
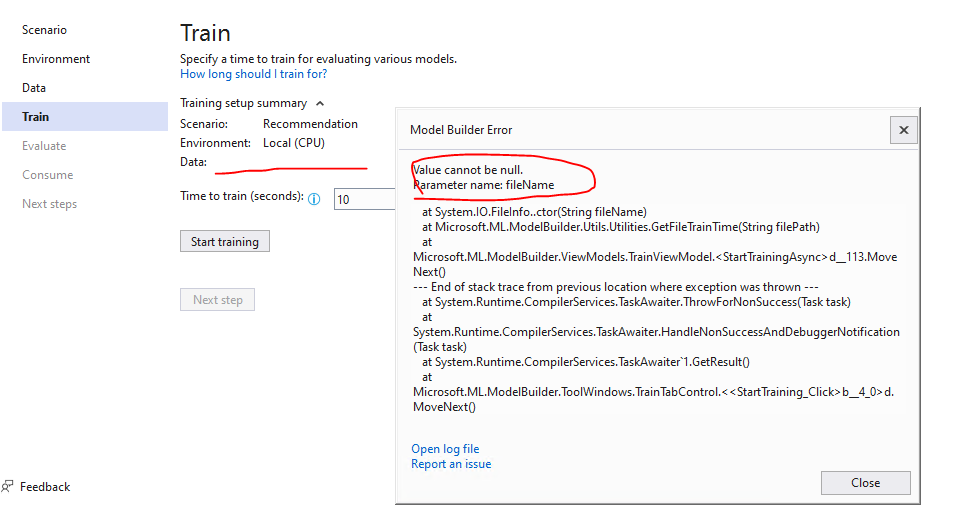
**Additional context**
Reload the mbconfig file, re-input the Data source, can detect the data path on Train page.
| test | sometimes cannot detect data path on train page after data setting system information please complete the following information model builder version available in manage extensions dialog main microsoft visual studio enterprise describe the bug on which step of the process did you run into an issue data is empty on train page clear description of the problem have already input the data source and set the columns settings but data is empty on train page this problem does not occur frequently but i met it on different scenarios currently to reproduce steps to reproduce the behavior select create a new project from the visual studio start window choose the c console app net core project template with net add model builder by right click on the project select recommendation scenario input the data source and set the columns settings navigate to train page click start training prompt model builder error said that value cannot be nulll parameter name filename close the error dialog expand the training setup summary find that data is empty expected behavior can detect the data path on train page after data setting screenshots if applicable add screenshots to help explain your problem additional context reload the mbconfig file re input the data source can detect the data path on train page | 1 |
369,233 | 10,894,230,826 | IssuesEvent | 2019-11-19 08:11:40 | threefoldtech/jumpscaleX_core | https://api.github.com/repos/threefoldtech/jumpscaleX_core | opened | release Jumpscale 10.1 | priority_critical type_feature |
- [ ] make sure there are no branches left which are not on stories in home
- [ ] make sure all branches for 10.1 are merged into development
- [ ] run the autotests we have on development
- [ ] use jsx threebotbuilder ... to see if it works (builds)
- [ ] stories which cannot be finished in 10.1 should be discussed with stakeholders & moved to 10.2
- [ ] once tests done -> development -> master so we are ready for new development branch for 10.2
| 1.0 | release Jumpscale 10.1 -
- [ ] make sure there are no branches left which are not on stories in home
- [ ] make sure all branches for 10.1 are merged into development
- [ ] run the autotests we have on development
- [ ] use jsx threebotbuilder ... to see if it works (builds)
- [ ] stories which cannot be finished in 10.1 should be discussed with stakeholders & moved to 10.2
- [ ] once tests done -> development -> master so we are ready for new development branch for 10.2
| non_test | release jumpscale make sure there are no branches left which are not on stories in home make sure all branches for are merged into development run the autotests we have on development use jsx threebotbuilder to see if it works builds stories which cannot be finished in should be discussed with stakeholders moved to once tests done development master so we are ready for new development branch for | 0 |
55,103 | 14,218,349,826 | IssuesEvent | 2020-11-17 11:40:47 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Add missing documentation about throwing of DataDefinitionException in relevant API | C: Documentation E: All Editions P: Medium T: Defect | The interpreter logic throws `DataDefinitionException` in methods like `DSLContext.meta(String...)`. This is currently not documented as usual, in Javadoc | 1.0 | Add missing documentation about throwing of DataDefinitionException in relevant API - The interpreter logic throws `DataDefinitionException` in methods like `DSLContext.meta(String...)`. This is currently not documented as usual, in Javadoc | non_test | add missing documentation about throwing of datadefinitionexception in relevant api the interpreter logic throws datadefinitionexception in methods like dslcontext meta string this is currently not documented as usual in javadoc | 0 |
16,424 | 2,615,064,739 | IssuesEvent | 2015-03-01 04:08:37 | chrsmith/google-api-java-client | https://api.github.com/repos/chrsmith/google-api-java-client | opened | CustomSearch API Java | auto-migrated Priority-Medium Type-Sample | ```
Which Google API and version ? CustomSearch API in Java
http://code.google.com/p/google-api-java-client/wiki/APIs#CustomSearch_API
```
Original issue reported on code.google.com by `guy...@gmail.com` on 15 Mar 2012 at 4:25 | 1.0 | CustomSearch API Java - ```
Which Google API and version ? CustomSearch API in Java
http://code.google.com/p/google-api-java-client/wiki/APIs#CustomSearch_API
```
Original issue reported on code.google.com by `guy...@gmail.com` on 15 Mar 2012 at 4:25 | non_test | customsearch api java which google api and version customsearch api in java original issue reported on code google com by guy gmail com on mar at | 0 |
190,216 | 22,047,323,997 | IssuesEvent | 2022-05-30 04:17:31 | pazhanivel07/linux-4.19.72 | https://api.github.com/repos/pazhanivel07/linux-4.19.72 | closed | CVE-2019-19080 (Medium) detected in linuxlinux-4.19.83 - autoclosed | security vulnerability | ## CVE-2019-19080 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.83</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/linux-4.19.72/commit/ce28e4f7a922d93d9b737061ae46827305c8c30a">ce28e4f7a922d93d9b737061ae46827305c8c30a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Four memory leaks in the nfp_flower_spawn_phy_reprs() function in drivers/net/ethernet/netronome/nfp/flower/main.c in the Linux kernel before 5.3.4 allow attackers to cause a denial of service (memory consumption), aka CID-8572cea1461a.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19080>CVE-2019-19080</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19080">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19080</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution: v5.4-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-19080 (Medium) detected in linuxlinux-4.19.83 - autoclosed - ## CVE-2019-19080 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.83</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/linux-4.19.72/commit/ce28e4f7a922d93d9b737061ae46827305c8c30a">ce28e4f7a922d93d9b737061ae46827305c8c30a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Four memory leaks in the nfp_flower_spawn_phy_reprs() function in drivers/net/ethernet/netronome/nfp/flower/main.c in the Linux kernel before 5.3.4 allow attackers to cause a denial of service (memory consumption), aka CID-8572cea1461a.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19080>CVE-2019-19080</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19080">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19080</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution: v5.4-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in linuxlinux autoclosed cve medium severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details four memory leaks in the nfp flower spawn phy reprs function in drivers net ethernet netronome nfp flower main c in the linux kernel before allow attackers to cause a denial of service memory consumption aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
163,400 | 12,728,002,957 | IssuesEvent | 2020-06-25 01:05:21 | mapbox/mapbox-navigation-android | https://api.github.com/repos/mapbox/mapbox-navigation-android | opened | The feedback screenshot's puck location in the InstructionViewActivity example is away from where it should be. | UI SDK v1+ navigation-ui test app | <!--
Hello and thanks for contributing! To help us diagnose your problem quickly, please:
- Include a minimal demonstration of the bug, including code, logs, and screenshots.
- Ensure you can reproduce the bug using the latest release.
- Only post to report a bug or request a feature; direct all other questions to: https://stackoverflow.com/questions/tagged/mapbox
-->
**Android API:** Any
**Mapbox Navigation SDK version:** UI SDK 1.0
### Steps to trigger behavior
1. Launch `example` app
2. Run `InstructionViewActivity`
3. Submit `Feedback`
### Expected behavior
The puck location in the feedback screenshot should match where when the user presses the FeedbackButton
### Actual behavior
The puck location is away from where it should be, because the screenshot is taken at the end of the whole Feedback flow.
| 1.0 | The feedback screenshot's puck location in the InstructionViewActivity example is away from where it should be. - <!--
Hello and thanks for contributing! To help us diagnose your problem quickly, please:
- Include a minimal demonstration of the bug, including code, logs, and screenshots.
- Ensure you can reproduce the bug using the latest release.
- Only post to report a bug or request a feature; direct all other questions to: https://stackoverflow.com/questions/tagged/mapbox
-->
**Android API:** Any
**Mapbox Navigation SDK version:** UI SDK 1.0
### Steps to trigger behavior
1. Launch `example` app
2. Run `InstructionViewActivity`
3. Submit `Feedback`
### Expected behavior
The puck location in the feedback screenshot should match where when the user presses the FeedbackButton
### Actual behavior
The puck location is away from where it should be, because the screenshot is taken at the end of the whole Feedback flow.
| test | the feedback screenshot s puck location in the instructionviewactivity example is away from where it should be hello and thanks for contributing to help us diagnose your problem quickly please include a minimal demonstration of the bug including code logs and screenshots ensure you can reproduce the bug using the latest release only post to report a bug or request a feature direct all other questions to android api any mapbox navigation sdk version ui sdk steps to trigger behavior launch example app run instructionviewactivity submit feedback expected behavior the puck location in the feedback screenshot should match where when the user presses the feedbackbutton actual behavior the puck location is away from where it should be because the screenshot is taken at the end of the whole feedback flow | 1 |
40,626 | 20,996,191,538 | IssuesEvent | 2022-03-29 13:41:39 | getsentry/sentry-dart | https://api.github.com/repos/getsentry/sentry-dart | opened | `SentryEnvelopeItem.fromMethods` should always use `_CachedItem` to do it async in case users don't await for the Future to be completed | performance | https://github.com/getsentry/sentry-dart/pull/810/files#r837490293 | True | `SentryEnvelopeItem.fromMethods` should always use `_CachedItem` to do it async in case users don't await for the Future to be completed - https://github.com/getsentry/sentry-dart/pull/810/files#r837490293 | non_test | sentryenvelopeitem frommethods should always use cacheditem to do it async in case users don t await for the future to be completed | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.